Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
45,093 | 12,541,488,676 | IssuesEvent | 2020-06-05 12:26:48 | NREL/EnergyPlus | https://api.github.com/repos/NREL/EnergyPlus | closed | Surface Convection Algorithm AdaptiveModelSelections is not truncatable. | Defect | Issue overview
--------------
The SurfaceConvectionAlgorithm:(Inside/Outside):AdaptiveModelSelections algorithm selection cannot be truncated even though all the inputs have a default defined in the idd. The expected behavior here would be that the user can input:
" SurfaceConvectionAlgorithm:Inside:AdaptiveModelSelections,
Default Algorithm; !- Name"
into their idf and expect to get all default algorithm selections. However, a ',' must be input for each field for this object in order to get default values.
### Details
- Platform: All
- Version of EnergyPlus: 9.3
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [ ] Defect file added (list location of defect file here)
- [ ] Ticket added to Pivotal for defect (development team task)
- [ ] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect)
| 1.0 | Surface Convection Algorithm AdaptiveModelSelections is not truncatable. - Issue overview
--------------
The SurfaceConvectionAlgorithm:(Inside/Outside):AdaptiveModelSelections algorithm selection cannot be truncated even though all the inputs have a default defined in the idd. The expected behavior here would be that the user can input:
" SurfaceConvectionAlgorithm:Inside:AdaptiveModelSelections,
Default Algorithm; !- Name"
into their idf and expect to get all default algorithm selections. However, a ',' must be input for each field for this object in order to get default values.
### Details
- Platform: All
- Version of EnergyPlus: 9.3
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [ ] Defect file added (list location of defect file here)
- [ ] Ticket added to Pivotal for defect (development team task)
- [ ] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect)
| non_priority | surface convection algorithm adaptivemodelselections is not truncatable issue overview the surfaceconvectionalgorithm inside outside adaptivemodelselections algorithm selection cannot be truncated even though all the inputs have a default defined in the idd the expected behavior here would be that the user can input surfaceconvectionalgorithm inside adaptivemodelselections default algorithm name into their idf and expect to get all default algorithm selections however a must be input for each field for this object in order to get default values details platform all version of energyplus checklist add to this list or remove from it as applicable this is a simple templated set of guidelines defect file added list location of defect file here ticket added to pivotal for defect development team task pull request created the pull request will have additional tasks related to reviewing changes that fix this defect | 0 |
27,473 | 7,968,752,817 | IssuesEvent | 2018-07-16 05:48:10 | hashicorp/packer | https://api.github.com/repos/hashicorp/packer | closed | vmware-iso: ESXi - ssh times out | builder/vmware-esxi need-more-info question waiting-reply | Hi Team,
While using the packer to convert OVA to AMI it stuck always at below "opening new ssh session"(this is happening on the latest version of packer). The same script used to work for a long time and started failing suddenly on a few occurrences(When running the old packer version).
debug level logs:
https://gist.github.com/harshchauhan1988/c1ba804aef94874f8af2654b58818907
Script used:
https://gist.github.com/harshchauhan1988/2e53a62ad741290bed640cd21976ff0b
Can you please take a look by simulating this issue? This is hampering build automation for a long time.
| 1.0 | vmware-iso: ESXi - ssh times out - Hi Team,
While using the packer to convert OVA to AMI it stuck always at below "opening new ssh session"(this is happening on the latest version of packer). The same script used to work for a long time and started failing suddenly on a few occurrences(When running the old packer version).
debug level logs:
https://gist.github.com/harshchauhan1988/c1ba804aef94874f8af2654b58818907
Script used:
https://gist.github.com/harshchauhan1988/2e53a62ad741290bed640cd21976ff0b
Can you please take a look by simulating this issue? This is hampering build automation for a long time.
| non_priority | vmware iso esxi ssh times out hi team while using the packer to convert ova to ami it stuck always at below opening new ssh session this is happening on the latest version of packer the same script used to work for a long time and started failing suddenly on a few occurrences when running the old packer version debug level logs script used can you please take a look by simulating this issue this is hampering build automation for a long time | 0 |
180,217 | 14,742,322,467 | IssuesEvent | 2021-01-07 12:05:37 | eclipse/capella | https://api.github.com/repos/eclipse/capella | closed | Add release note and update some sections in the documentation | documentation normal | Add release note and update some sections in the documentation
`🆔 ECLIPSE-564346` `👷 minh.tu.ton.that` `📅 2020-06-16` `🔎 1.4.1` | 1.0 | Add release note and update some sections in the documentation - Add release note and update some sections in the documentation
`🆔 ECLIPSE-564346` `👷 minh.tu.ton.that` `📅 2020-06-16` `🔎 1.4.1` | non_priority | add release note and update some sections in the documentation add release note and update some sections in the documentation 🆔 eclipse 👷 minh tu ton that 📅 🔎 | 0 |
111,381 | 11,731,062,952 | IssuesEvent | 2020-03-10 22:56:47 | admin341/INSTA341 | https://api.github.com/repos/admin341/INSTA341 | opened | Rewrite acceptance tests for Core + Additional features | documentation | Made format error in sprint #3 and need acceptance tests for additional features for the final fourth sprint. | 1.0 | Rewrite acceptance tests for Core + Additional features - Made format error in sprint #3 and need acceptance tests for additional features for the final fourth sprint. | non_priority | rewrite acceptance tests for core additional features made format error in sprint and need acceptance tests for additional features for the final fourth sprint | 0 |
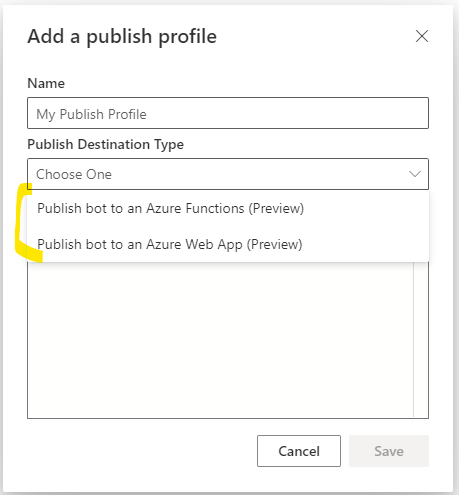
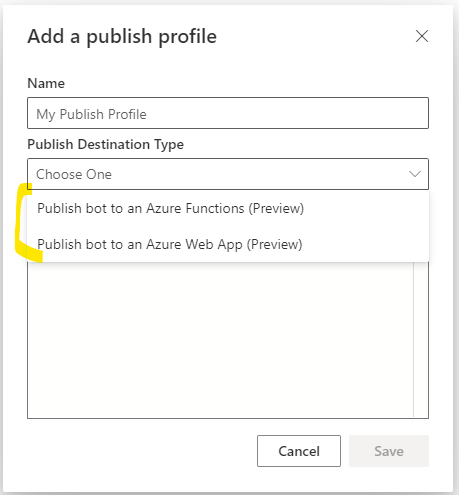
133,126 | 12,532,668,424 | IssuesEvent | 2020-06-04 16:18:00 | microsoft/BotFramework-Composer | https://api.github.com/repos/microsoft/BotFramework-Composer | closed | Docs: Publish to Azure Functions | Needs-triage Type: Documentation Type: Enhancement | The [docs pages on how to publish a bot to Azure](https://docs.microsoft.com/en-us/composer/how-to-publish-bot#create-azure-resources) are well written, but mostly with only Azure Web App publishing in mind. Please include in the docs pages that parameter `-customArmTemplate` with value `DeploymentTemplates/function-template-with-preexisting-rg.json` is required in the 'node provisionComposer.js' command to deploy the bot to Azure Functions.
Since the Composer UI still allows to create a publishing profile to publish to Azure Functions (even though the node provisionComposer.js, as listed in the docs, deployed the Azure WebApp Services), it took me quite some time to figure out why I was not seeing an Azure Function appear in Azure after publishing via the Azure Functions publishing profile.
Ultimately the option to create a publishing profile should be related to the type of Azure Services deployed via the node command, and it should not allow me to choose a publishing profile that doesn't match the Azure Services deployed.
Better even would be if the publishing profile could run the node provisionComposer.js automatically from within Composer. That way the correct Azure Services would be deployed based on the user's choice in the Composer UI.
| 1.0 | Docs: Publish to Azure Functions - The [docs pages on how to publish a bot to Azure](https://docs.microsoft.com/en-us/composer/how-to-publish-bot#create-azure-resources) are well written, but mostly with only Azure Web App publishing in mind. Please include in the docs pages that parameter `-customArmTemplate` with value `DeploymentTemplates/function-template-with-preexisting-rg.json` is required in the 'node provisionComposer.js' command to deploy the bot to Azure Functions.
Since the Composer UI still allows to create a publishing profile to publish to Azure Functions (even though the node provisionComposer.js, as listed in the docs, deployed the Azure WebApp Services), it took me quite some time to figure out why I was not seeing an Azure Function appear in Azure after publishing via the Azure Functions publishing profile.
Ultimately the option to create a publishing profile should be related to the type of Azure Services deployed via the node command, and it should not allow me to choose a publishing profile that doesn't match the Azure Services deployed.
Better even would be if the publishing profile could run the node provisionComposer.js automatically from within Composer. That way the correct Azure Services would be deployed based on the user's choice in the Composer UI.
| non_priority | docs publish to azure functions the are well written but mostly with only azure web app publishing in mind please include in the docs pages that parameter customarmtemplate with value deploymenttemplates function template with preexisting rg json is required in the node provisioncomposer js command to deploy the bot to azure functions since the composer ui still allows to create a publishing profile to publish to azure functions even though the node provisioncomposer js as listed in the docs deployed the azure webapp services it took me quite some time to figure out why i was not seeing an azure function appear in azure after publishing via the azure functions publishing profile ultimately the option to create a publishing profile should be related to the type of azure services deployed via the node command and it should not allow me to choose a publishing profile that doesn t match the azure services deployed better even would be if the publishing profile could run the node provisioncomposer js automatically from within composer that way the correct azure services would be deployed based on the user s choice in the composer ui | 0 |
143,388 | 13,062,206,593 | IssuesEvent | 2020-07-30 14:52:36 | r-lib/gh | https://api.github.com/repos/r-lib/gh | closed | Link to the new docs location | documentation | I will do this in the remaining places that need it after #121 gets merged, which makes a start on this. | 1.0 | Link to the new docs location - I will do this in the remaining places that need it after #121 gets merged, which makes a start on this. | non_priority | link to the new docs location i will do this in the remaining places that need it after gets merged which makes a start on this | 0 |
14,663 | 11,044,933,025 | IssuesEvent | 2019-12-09 14:15:17 | jhu-sheridan-libraries/jhuda-general-issues | https://api.github.com/repos/jhu-sheridan-libraries/jhuda-general-issues | closed | investigate and propose a specific messaging technology | infrastructure | the technologies mentioned include: ActiveMQ, Kafka, Microsoft Azure Messaging Service
Please make a recommendation based on known restrictions/conditions of JHU and Data Archive specific infrastructure.
part of ticket #13 | 1.0 | investigate and propose a specific messaging technology - the technologies mentioned include: ActiveMQ, Kafka, Microsoft Azure Messaging Service
Please make a recommendation based on known restrictions/conditions of JHU and Data Archive specific infrastructure.
part of ticket #13 | non_priority | investigate and propose a specific messaging technology the technologies mentioned include activemq kafka microsoft azure messaging service please make a recommendation based on known restrictions conditions of jhu and data archive specific infrastructure part of ticket | 0 |
430,473 | 30,186,356,883 | IssuesEvent | 2023-07-04 12:23:52 | NetAppDocs/ontap-systems-switches | https://api.github.com/repos/NetAppDocs/ontap-systems-switches | closed | Add a section for source switch CN1610 and destination switch NVIDIA SN2100 | documentation | ### Page URL
https://docs.netapp.com/us-en/ontap-systems-switches/switch-nvidia-sn2100/migrate-cisco-sn2100-cluster-switch.html
### Page title
Migrate from a Cisco cluster switch to a NVIDIA SN2100 cluster switch
### Summary
We have a significant number of CN1610 switches in the field. I have used this procedure to migrate from CN1610's to Cisco 9336 switches successfully.
Customer's a hesitant to use the procedure, since we are not calling out the CN1610 in our documentation.
Please a section for CN1610 to Cisco 9336, and section for CN1610 to NVIDIA SN2100
### Public issues must not contain sensitive information
- [X] This issue contains no sensitive information. | 1.0 | Add a section for source switch CN1610 and destination switch NVIDIA SN2100 - ### Page URL
https://docs.netapp.com/us-en/ontap-systems-switches/switch-nvidia-sn2100/migrate-cisco-sn2100-cluster-switch.html
### Page title
Migrate from a Cisco cluster switch to a NVIDIA SN2100 cluster switch
### Summary
We have a significant number of CN1610 switches in the field. I have used this procedure to migrate from CN1610's to Cisco 9336 switches successfully.
Customer's a hesitant to use the procedure, since we are not calling out the CN1610 in our documentation.
Please a section for CN1610 to Cisco 9336, and section for CN1610 to NVIDIA SN2100
### Public issues must not contain sensitive information
- [X] This issue contains no sensitive information. | non_priority | add a section for source switch and destination switch nvidia page url page title migrate from a cisco cluster switch to a nvidia cluster switch summary we have a significant number of switches in the field i have used this procedure to migrate from s to cisco switches successfully customer s a hesitant to use the procedure since we are not calling out the in our documentation please a section for to cisco and section for to nvidia public issues must not contain sensitive information this issue contains no sensitive information | 0 |
225,768 | 24,881,305,732 | IssuesEvent | 2022-10-28 01:32:13 | easycv/easycv | https://api.github.com/repos/easycv/easycv | opened | CVE-2022-39286 (High) detected in jupyter_core-4.7.1-py3-none-any.whl | security vulnerability | ## CVE-2022-39286 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jupyter_core-4.7.1-py3-none-any.whl</b></p></summary>
<p>Jupyter core package. A base package on which Jupyter projects rely.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/53/40/5af36bffa0af3ac71d3a6fc6709de10e4f6ff7c01745b8bc4715372189c9/jupyter_core-4.7.1-py3-none-any.whl">https://files.pythonhosted.org/packages/53/40/5af36bffa0af3ac71d3a6fc6709de10e4f6ff7c01745b8bc4715372189c9/jupyter_core-4.7.1-py3-none-any.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/easycv</p>
<p>Path to vulnerable library: /easycv</p>
<p>
Dependency Hierarchy:
- :x: **jupyter_core-4.7.1-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Jupyter Core is a package for the core common functionality of Jupyter projects. Jupyter Core prior to version 4.11.2 contains an arbitrary code execution vulnerability in `jupyter_core` that stems from `jupyter_core` executing untrusted files in CWD. This vulnerability allows one user to run code as another. Version 4.11.2 contains a patch for this issue. There are no known workarounds.
<p>Publish Date: 2022-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-39286>CVE-2022-39286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3363">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3363</a></p>
<p>Release Date: 2022-10-26</p>
<p>Fix Resolution: jupyter-core - 4.11.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-39286 (High) detected in jupyter_core-4.7.1-py3-none-any.whl - ## CVE-2022-39286 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jupyter_core-4.7.1-py3-none-any.whl</b></p></summary>
<p>Jupyter core package. A base package on which Jupyter projects rely.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/53/40/5af36bffa0af3ac71d3a6fc6709de10e4f6ff7c01745b8bc4715372189c9/jupyter_core-4.7.1-py3-none-any.whl">https://files.pythonhosted.org/packages/53/40/5af36bffa0af3ac71d3a6fc6709de10e4f6ff7c01745b8bc4715372189c9/jupyter_core-4.7.1-py3-none-any.whl</a></p>
<p>Path to dependency file: /tmp/ws-scm/easycv</p>
<p>Path to vulnerable library: /easycv</p>
<p>
Dependency Hierarchy:
- :x: **jupyter_core-4.7.1-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Jupyter Core is a package for the core common functionality of Jupyter projects. Jupyter Core prior to version 4.11.2 contains an arbitrary code execution vulnerability in `jupyter_core` that stems from `jupyter_core` executing untrusted files in CWD. This vulnerability allows one user to run code as another. Version 4.11.2 contains a patch for this issue. There are no known workarounds.
<p>Publish Date: 2022-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-39286>CVE-2022-39286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3363">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-3363</a></p>
<p>Release Date: 2022-10-26</p>
<p>Fix Resolution: jupyter-core - 4.11.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jupyter core none any whl cve high severity vulnerability vulnerable library jupyter core none any whl jupyter core package a base package on which jupyter projects rely library home page a href path to dependency file tmp ws scm easycv path to vulnerable library easycv dependency hierarchy x jupyter core none any whl vulnerable library found in base branch master vulnerability details jupyter core is a package for the core common functionality of jupyter projects jupyter core prior to version contains an arbitrary code execution vulnerability in jupyter core that stems from jupyter core executing untrusted files in cwd this vulnerability allows one user to run code as another version contains a patch for this issue there are no known workarounds publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jupyter core step up your open source security game with mend | 0 |
183,889 | 14,961,723,837 | IssuesEvent | 2021-01-27 08:14:31 | smithtalk/Warehouse-Management | https://api.github.com/repos/smithtalk/Warehouse-Management | opened | Make SQL Commands to integrated database to this Software | bug documentation enhancement prior:high question | Here the Checklist :
- [ ] Create the Database
- [ ] Create the Table | 1.0 | Make SQL Commands to integrated database to this Software - Here the Checklist :
- [ ] Create the Database
- [ ] Create the Table | non_priority | make sql commands to integrated database to this software here the checklist create the database create the table | 0 |
169,665 | 26,838,818,542 | IssuesEvent | 2023-02-02 21:59:46 | sandboxnu/graduatenu | https://api.github.com/repos/sandboxnu/graduatenu | closed | Design: UX Mockups For Add Course Modal | Design | Some work has already been done. The mockups need to be finalized and moved to the handoff page. | 1.0 | Design: UX Mockups For Add Course Modal - Some work has already been done. The mockups need to be finalized and moved to the handoff page. | non_priority | design ux mockups for add course modal some work has already been done the mockups need to be finalized and moved to the handoff page | 0 |
11,245 | 9,292,002,811 | IssuesEvent | 2019-03-22 00:58:16 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | opened | [Service Bus] Renaming as per API review feedback | Client Service Bus | _From API review notes in #1481_
- `getReceiver` -> `createReceiver` + throw error when an open receiver already exists
- `getSender` -> `createSender` + throw error when an open sender already exists
- `getSessionReceiver` -> `createSessionReceiver`
- `messageCount` -> `maxMessageCount` in peek() functions
- `Namespace` -> `ServiceBusClient`
- `SqlExpression` need not be exported, use string instead in `RuleDescription` | 1.0 | [Service Bus] Renaming as per API review feedback - _From API review notes in #1481_
- `getReceiver` -> `createReceiver` + throw error when an open receiver already exists
- `getSender` -> `createSender` + throw error when an open sender already exists
- `getSessionReceiver` -> `createSessionReceiver`
- `messageCount` -> `maxMessageCount` in peek() functions
- `Namespace` -> `ServiceBusClient`
- `SqlExpression` need not be exported, use string instead in `RuleDescription` | non_priority | renaming as per api review feedback from api review notes in getreceiver createreceiver throw error when an open receiver already exists getsender createsender throw error when an open sender already exists getsessionreceiver createsessionreceiver messagecount maxmessagecount in peek functions namespace servicebusclient sqlexpression need not be exported use string instead in ruledescription | 0 |
26,302 | 11,297,125,352 | IssuesEvent | 2020-01-17 04:41:39 | drakeg/drakeweb.org | https://api.github.com/repos/drakeg/drakeweb.org | opened | CVE-2014-10064 (High) detected in qs-0.5.6.tgz, qs-0.6.6.tgz | security vulnerability | ## CVE-2014-10064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-0.5.6.tgz</b>, <b>qs-0.6.6.tgz</b></p></summary>
<p>
<details><summary><b>qs-0.5.6.tgz</b></p></summary>
<p>querystring parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-0.5.6.tgz">https://registry.npmjs.org/qs/-/qs-0.5.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/qs/package.json,/tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- tiny-lr-fork-0.0.5.tgz
- :x: **qs-0.5.6.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-0.6.6.tgz</b></p></summary>
<p>querystring parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-0.6.6.tgz">https://registry.npmjs.org/qs/-/qs-0.6.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/drakeweb.org/wp-content/themes/decode/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/drakeweb.org/wp-content/themes/decode/node_modules/request/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- grunt-modernizr-0.5.2.tgz (Root Library)
- request-2.27.0.tgz
- :x: **qs-0.6.6.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/drakeg/drakeweb.org/commit/3759e4bc84151f770a6f4cc54da1c6232f666a6e">3759e4bc84151f770a6f4cc54da1c6232f666a6e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The qs module before 1.0.0 does not have an option or default for specifying object depth and when parsing a string representing a deeply nested object will block the event loop for long periods of time. An attacker could leverage this to cause a temporary denial-of-service condition, for example, in a web application, other requests would not be processed while this blocking is occurring.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-10064>CVE-2014-10064</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/28">https://nodesecurity.io/advisories/28</a></p>
<p>Release Date: 2014-08-06</p>
<p>Fix Resolution: Update to version 1.0.0 or later</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2014-10064 (High) detected in qs-0.5.6.tgz, qs-0.6.6.tgz - ## CVE-2014-10064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-0.5.6.tgz</b>, <b>qs-0.6.6.tgz</b></p></summary>
<p>
<details><summary><b>qs-0.5.6.tgz</b></p></summary>
<p>querystring parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-0.5.6.tgz">https://registry.npmjs.org/qs/-/qs-0.5.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/qs/package.json,/tmp/ws-scm/drakeweb.org/wp-content/plugins/press-this/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- grunt-contrib-watch-0.6.1.tgz (Root Library)
- tiny-lr-fork-0.0.5.tgz
- :x: **qs-0.5.6.tgz** (Vulnerable Library)
</details>
<details><summary><b>qs-0.6.6.tgz</b></p></summary>
<p>querystring parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-0.6.6.tgz">https://registry.npmjs.org/qs/-/qs-0.6.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/drakeweb.org/wp-content/themes/decode/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/drakeweb.org/wp-content/themes/decode/node_modules/request/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- grunt-modernizr-0.5.2.tgz (Root Library)
- request-2.27.0.tgz
- :x: **qs-0.6.6.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/drakeg/drakeweb.org/commit/3759e4bc84151f770a6f4cc54da1c6232f666a6e">3759e4bc84151f770a6f4cc54da1c6232f666a6e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The qs module before 1.0.0 does not have an option or default for specifying object depth and when parsing a string representing a deeply nested object will block the event loop for long periods of time. An attacker could leverage this to cause a temporary denial-of-service condition, for example, in a web application, other requests would not be processed while this blocking is occurring.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-10064>CVE-2014-10064</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/28">https://nodesecurity.io/advisories/28</a></p>
<p>Release Date: 2014-08-06</p>
<p>Fix Resolution: Update to version 1.0.0 or later</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in qs tgz qs tgz cve high severity vulnerability vulnerable libraries qs tgz qs tgz qs tgz querystring parser library home page a href path to dependency file tmp ws scm drakeweb org wp content plugins press this package json path to vulnerable library tmp ws scm drakeweb org wp content plugins press this node modules qs package json tmp ws scm drakeweb org wp content plugins press this node modules qs package json dependency hierarchy grunt contrib watch tgz root library tiny lr fork tgz x qs tgz vulnerable library qs tgz querystring parser library home page a href path to dependency file tmp ws scm drakeweb org wp content themes decode package json path to vulnerable library tmp ws scm drakeweb org wp content themes decode node modules request node modules qs package json dependency hierarchy grunt modernizr tgz root library request tgz x qs tgz vulnerable library found in head commit a href vulnerability details the qs module before does not have an option or default for specifying object depth and when parsing a string representing a deeply nested object will block the event loop for long periods of time an attacker could leverage this to cause a temporary denial of service condition for example in a web application other requests would not be processed while this blocking is occurring publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution update to version or later step up your open source security game with whitesource | 0 |
65,776 | 14,761,896,382 | IssuesEvent | 2021-01-09 00:53:51 | olivialancaster/angular | https://api.github.com/repos/olivialancaster/angular | opened | WS-2020-0218 (High) detected in juice-shopjuice-shop-10.1.0_node13_linux_x64 | security vulnerability | ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>juice-shopjuice-shop-10.1.0_node13_linux_x64</b></p></summary>
<p>
<p>Probably the most modern and sophisticated insecure web application</p>
<p>Library home page: <a href=https://sourceforge.net/projects/juice-shop/>https://sourceforge.net/projects/juice-shop/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/olivialancaster/angular/commit/3319152594d134df0af4a78d3036722911934182">3319152594d134df0af4a78d3036722911934182</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>angular/bower_components/polymer/bower_components/web-component-tester/node_modules/merge/merge.min.js</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>angular/bower_components/polymer/bower_components/web-component-tester/node_modules/merge/merge.min.js</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
| True | WS-2020-0218 (High) detected in juice-shopjuice-shop-10.1.0_node13_linux_x64 - ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>juice-shopjuice-shop-10.1.0_node13_linux_x64</b></p></summary>
<p>
<p>Probably the most modern and sophisticated insecure web application</p>
<p>Library home page: <a href=https://sourceforge.net/projects/juice-shop/>https://sourceforge.net/projects/juice-shop/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/olivialancaster/angular/commit/3319152594d134df0af4a78d3036722911934182">3319152594d134df0af4a78d3036722911934182</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>angular/bower_components/polymer/bower_components/web-component-tester/node_modules/merge/merge.min.js</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>angular/bower_components/polymer/bower_components/web-component-tester/node_modules/merge/merge.min.js</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Prototype Pollution vulnerability was found in merge before 2.1.0 via the merge.recursive function. It can be tricked into adding or modifying properties of the Object prototype. These properties will be present on all objects.
<p>Publish Date: 2020-10-09
<p>URL: <a href=https://github.com/yeikos/js.merge/pull/38>WS-2020-0218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/yeikos/js.merge/pull/38">https://github.com/yeikos/js.merge/pull/38</a></p>
<p>Release Date: 2020-10-09</p>
<p>Fix Resolution: merge - 2.1.0</p>
</p>
</details>
<p></p>
| non_priority | ws high detected in juice shopjuice shop linux ws high severity vulnerability vulnerable library juice shopjuice shop linux probably the most modern and sophisticated insecure web application library home page a href found in head commit a href vulnerable source files angular bower components polymer bower components web component tester node modules merge merge min js angular bower components polymer bower components web component tester node modules merge merge min js vulnerability details a prototype pollution vulnerability was found in merge before via the merge recursive function it can be tricked into adding or modifying properties of the object prototype these properties will be present on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution merge | 0 |
8,128 | 2,868,982,488 | IssuesEvent | 2015-06-05 22:21:52 | dart-lang/pub | https://api.github.com/repos/dart-lang/pub | closed | Pub seems to get constraints of semantic versions wrong | AsDesigned bug | <a href="https://github.com/mkustermann"><img src="https://avatars.githubusercontent.com/u/5757092?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [mkustermann](https://github.com/mkustermann)**
_Originally opened as dart-lang/sdk#20404_
----
A package "foobar" with version "0.0.3-dev" satisfies the following version constraint:
dependencies:
foobar: '>=0.0.3-dev <0.0.3'
according to semantic versioning, see the specification here: http://semver.org/
But pub seems to complain that there is no suitable version for "foobar" -- could be because the constraints are parsed incorrectly or because the ordering implementation is wrong?
Error message:
$ pub get
Resolving dependencies...
Package foobar has no versions that match >=0.0.3-dev <0.0.3 derived from:
- mypackage 0.1.0-dev depends on version >=0.0.3-dev <0.0.3
| 1.0 | Pub seems to get constraints of semantic versions wrong - <a href="https://github.com/mkustermann"><img src="https://avatars.githubusercontent.com/u/5757092?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [mkustermann](https://github.com/mkustermann)**
_Originally opened as dart-lang/sdk#20404_
----
A package "foobar" with version "0.0.3-dev" satisfies the following version constraint:
dependencies:
foobar: '>=0.0.3-dev <0.0.3'
according to semantic versioning, see the specification here: http://semver.org/
But pub seems to complain that there is no suitable version for "foobar" -- could be because the constraints are parsed incorrectly or because the ordering implementation is wrong?
Error message:
$ pub get
Resolving dependencies...
Package foobar has no versions that match >=0.0.3-dev <0.0.3 derived from:
- mypackage 0.1.0-dev depends on version >=0.0.3-dev <0.0.3
| non_priority | pub seems to get constraints of semantic versions wrong issue by originally opened as dart lang sdk a package quot foobar quot with version quot dev quot satisfies the following version constraint dependencies nbsp nbsp foobar gt dev lt according to semantic versioning see the specification here but pub seems to complain that there is no suitable version for quot foobar quot could be because the constraints are parsed incorrectly or because the ordering implementation is wrong error message pub get resolving dependencies package foobar has no versions that match gt dev lt derived from mypackage dev depends on version gt dev lt | 0 |
201,943 | 23,046,609,686 | IssuesEvent | 2022-07-24 01:36:19 | temporalio/graphql | https://api.github.com/repos/temporalio/graphql | opened | graphql-cli-common-2.9.0.tgz: 2 vulnerabilities (highest severity is: 8.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>graphql-cli-common-2.9.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@graphql-inspector/graphql-cli-common/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/github-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/url-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/apollo-engine-loader/node_modules/node-fetch/package.json</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-23326](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23326) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | git-loader-6.2.4.tgz | Transitive | N/A | ❌ |
| [CVE-2022-0235](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.1.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23326</summary>
### Vulnerable Library - <b>git-loader-6.2.4.tgz</b></p>
<p>A set of utils for faster development of GraphQL tools</p>
<p>Library home page: <a href="https://registry.npmjs.org/@graphql-tools/git-loader/-/git-loader-6.2.4.tgz">https://registry.npmjs.org/@graphql-tools/git-loader/-/git-loader-6.2.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@graphql-inspector/graphql-cli-common/node_modules/@graphql-tools/git-loader/package.json</p>
<p>
Dependency Hierarchy:
- graphql-cli-common-2.9.0.tgz (Root Library)
- loaders-4.1.0.tgz
- :x: **git-loader-6.2.4.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package @graphql-tools/git-loader before 6.2.6. The use of exec and execSync in packages/loaders/git/src/load-git.ts allows arbitrary command injection.
<p>Publish Date: 2021-01-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23326>CVE-2021-23326</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-20</p>
<p>Fix Resolution: @graphql-tools/git-loader - 6.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.1.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@graphql-inspector/graphql-cli-common/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/github-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/url-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/apollo-engine-loader/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- graphql-cli-common-2.9.0.tgz (Root Library)
- loaders-4.1.0.tgz
- github-loader-6.2.4.tgz
- cross-fetch-3.0.6.tgz
- :x: **node-fetch-2.6.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution: node-fetch - 2.6.7,3.1.1</p>
</p>
<p></p>
</details> | True | graphql-cli-common-2.9.0.tgz: 2 vulnerabilities (highest severity is: 8.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>graphql-cli-common-2.9.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@graphql-inspector/graphql-cli-common/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/github-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/url-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/apollo-engine-loader/node_modules/node-fetch/package.json</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-23326](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23326) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | git-loader-6.2.4.tgz | Transitive | N/A | ❌ |
| [CVE-2022-0235](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | node-fetch-2.6.1.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23326</summary>
### Vulnerable Library - <b>git-loader-6.2.4.tgz</b></p>
<p>A set of utils for faster development of GraphQL tools</p>
<p>Library home page: <a href="https://registry.npmjs.org/@graphql-tools/git-loader/-/git-loader-6.2.4.tgz">https://registry.npmjs.org/@graphql-tools/git-loader/-/git-loader-6.2.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@graphql-inspector/graphql-cli-common/node_modules/@graphql-tools/git-loader/package.json</p>
<p>
Dependency Hierarchy:
- graphql-cli-common-2.9.0.tgz (Root Library)
- loaders-4.1.0.tgz
- :x: **git-loader-6.2.4.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package @graphql-tools/git-loader before 6.2.6. The use of exec and execSync in packages/loaders/git/src/load-git.ts allows arbitrary command injection.
<p>Publish Date: 2021-01-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23326>CVE-2021-23326</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-01-20</p>
<p>Fix Resolution: @graphql-tools/git-loader - 6.2.6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-0235</summary>
### Vulnerable Library - <b>node-fetch-2.6.1.tgz</b></p>
<p>A light-weight module that brings window.fetch to node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz">https://registry.npmjs.org/node-fetch/-/node-fetch-2.6.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/@graphql-inspector/graphql-cli-common/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/github-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/url-loader/node_modules/node-fetch/package.json,/node_modules/@graphql-tools/apollo-engine-loader/node_modules/node-fetch/package.json</p>
<p>
Dependency Hierarchy:
- graphql-cli-common-2.9.0.tgz (Root Library)
- loaders-4.1.0.tgz
- github-loader-6.2.4.tgz
- cross-fetch-3.0.6.tgz
- :x: **node-fetch-2.6.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
node-fetch is vulnerable to Exposure of Sensitive Information to an Unauthorized Actor
<p>Publish Date: 2022-01-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0235>CVE-2022-0235</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-r683-j2x4-v87g">https://github.com/advisories/GHSA-r683-j2x4-v87g</a></p>
<p>Release Date: 2022-01-16</p>
<p>Fix Resolution: node-fetch - 2.6.7,3.1.1</p>
</p>
<p></p>
</details> | non_priority | graphql cli common tgz vulnerabilities highest severity is vulnerable library graphql cli common tgz path to dependency file package json path to vulnerable library node modules graphql inspector graphql cli common node modules node fetch package json node modules graphql tools github loader node modules node fetch package json node modules graphql tools url loader node modules node fetch package json node modules graphql tools apollo engine loader node modules node fetch package json vulnerabilities cve severity cvss dependency type fixed in remediation available high git loader tgz transitive n a medium node fetch tgz transitive n a details cve vulnerable library git loader tgz a set of utils for faster development of graphql tools library home page a href path to dependency file package json path to vulnerable library node modules graphql inspector graphql cli common node modules graphql tools git loader package json dependency hierarchy graphql cli common tgz root library loaders tgz x git loader tgz vulnerable library found in base branch main vulnerability details this affects the package graphql tools git loader before the use of exec and execsync in packages loaders git src load git ts allows arbitrary command injection publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution graphql tools git loader cve vulnerable library node fetch tgz a light weight module that brings window fetch to node js library home page a href path to dependency file package json path to vulnerable library node modules graphql inspector graphql cli common node modules node fetch package json node modules graphql tools github loader node modules node fetch package json node modules graphql tools url loader node modules node fetch package json node modules graphql tools apollo engine loader node modules node fetch package json dependency hierarchy graphql cli common tgz root library loaders tgz github loader tgz cross fetch tgz x node fetch tgz vulnerable library found in base branch main vulnerability details node fetch is vulnerable to exposure of sensitive information to an unauthorized actor publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution node fetch | 0 |
28,458 | 8,148,448,952 | IssuesEvent | 2018-08-22 05:53:58 | ApolloAuto/apollo | https://api.github.com/repos/ApolloAuto/apollo | closed | Faild to build_velodyne | Module: Build Module: Driver | Hi!
When I try "bash apollo.sh build_velodyne", it shows follows:
......
-- Up-to-date: /home/tmp/ros/share/velodyne/launch/start_velodyne_16.launch
-- Installing: /home/tmp/ros/share/velodyne/scripts
-- Up-to-date: /home/tmp/ros/share/velodyne/scripts/start_velodyne.sh
CMake Error at gtest/cmake_install.cmake:42 (FILE):
file INSTALL cannot find
"/apollo/modules/build_isolated/velodyne/gtest/libgtest.so".
Call Stack (most recent call first):
cmake_install.cmake:142 (INCLUDE)
make: *** [install] Error 1
<== Failed to process package 'velodyne':
Command '['make', 'install']' returned non-zero exit status 2
Reproduce this error by running:
==> cd /apollo/modules/build_isolated/velodyne && make install
It seems like that I don`t have the require file.
I will be very appreciate if anyone help me!
Thank you very much!
| 1.0 | Faild to build_velodyne - Hi!
When I try "bash apollo.sh build_velodyne", it shows follows:
......
-- Up-to-date: /home/tmp/ros/share/velodyne/launch/start_velodyne_16.launch
-- Installing: /home/tmp/ros/share/velodyne/scripts
-- Up-to-date: /home/tmp/ros/share/velodyne/scripts/start_velodyne.sh
CMake Error at gtest/cmake_install.cmake:42 (FILE):
file INSTALL cannot find
"/apollo/modules/build_isolated/velodyne/gtest/libgtest.so".
Call Stack (most recent call first):
cmake_install.cmake:142 (INCLUDE)
make: *** [install] Error 1
<== Failed to process package 'velodyne':
Command '['make', 'install']' returned non-zero exit status 2
Reproduce this error by running:
==> cd /apollo/modules/build_isolated/velodyne && make install
It seems like that I don`t have the require file.
I will be very appreciate if anyone help me!
Thank you very much!
| non_priority | faild to build velodyne hi when i try bash apollo sh build velodyne it shows follows up to date home tmp ros share velodyne launch start velodyne launch installing home tmp ros share velodyne scripts up to date home tmp ros share velodyne scripts start velodyne sh cmake error at gtest cmake install cmake file file install cannot find apollo modules build isolated velodyne gtest libgtest so call stack most recent call first cmake install cmake include make error failed to process package velodyne command returned non zero exit status reproduce this error by running cd apollo modules build isolated velodyne make install it seems like that i don t have the require file i will be very appreciate if anyone help me thank you very much | 0 |
12,794 | 8,109,441,785 | IssuesEvent | 2018-08-14 07:34:45 | accordproject/ergo | https://api.github.com/repos/accordproject/ergo | closed | Add native support for DateTime operators | enhancement semantics usability | Currently DateTime operators can only be evaluated when compiling to JavaScript. We should provide a native implementation for those operators either in Coq or OCaml for the extracted code. This can then be used for the reference interpreter (See #4) or the REPL (See #25). | True | Add native support for DateTime operators - Currently DateTime operators can only be evaluated when compiling to JavaScript. We should provide a native implementation for those operators either in Coq or OCaml for the extracted code. This can then be used for the reference interpreter (See #4) or the REPL (See #25). | non_priority | add native support for datetime operators currently datetime operators can only be evaluated when compiling to javascript we should provide a native implementation for those operators either in coq or ocaml for the extracted code this can then be used for the reference interpreter see or the repl see | 0 |
124,071 | 16,569,394,223 | IssuesEvent | 2021-05-30 04:31:51 | m48483/SocializerRepo | https://api.github.com/repos/m48483/SocializerRepo | closed | 2021.05.16 [이승민] | delay design manage-folder | 📢 마감일 : 5월 23일
◾ 4회차 회의 시간에 정리했던 구조도 형식으로 폴더 관리
◾ 기획자의 기획서 세분화가 완료되면 폴더 정리 후 기획서도 함께 push
| 1.0 | 2021.05.16 [이승민] - 📢 마감일 : 5월 23일
◾ 4회차 회의 시간에 정리했던 구조도 형식으로 폴더 관리
◾ 기획자의 기획서 세분화가 완료되면 폴더 정리 후 기획서도 함께 push
| non_priority | 📢 마감일 ◾ 회의 시간에 정리했던 구조도 형식으로 폴더 관리 ◾ 기획자의 기획서 세분화가 완료되면 폴더 정리 후 기획서도 함께 push | 0 |
4,996 | 2,894,378,325 | IssuesEvent | 2015-06-15 23:15:10 | elastic/elasticsearch-py | https://api.github.com/repos/elastic/elasticsearch-py | closed | Should 'fields' be a list or a string? | Documentation | The client args for the `fields` param says `A comma-separated list of fields to return as part of a hit`. That's not super clear, but suggests to me that it expects a string (since specifying the delimiter implies a pseudo-list encoded as a string. However, this argument seems passed-through to Elasticsearch and appears to work if I send a list here (`'fields': ['first_name', 'last_name']`), but not if I send a string (`'fields': "first_name,last_name"`).
Either way I think we'll have a change to make in haystack to support this feature because it's currently assuming the client wants a string containing a space-delimited list of fields [1]. I figured I'd confirm the expectations here before issuing a pull request over there. Thanks!
[1] https://github.com/toastdriven/django-haystack/blob/master/haystack/backends/elasticsearch_backend.py#L275 | 1.0 | Should 'fields' be a list or a string? - The client args for the `fields` param says `A comma-separated list of fields to return as part of a hit`. That's not super clear, but suggests to me that it expects a string (since specifying the delimiter implies a pseudo-list encoded as a string. However, this argument seems passed-through to Elasticsearch and appears to work if I send a list here (`'fields': ['first_name', 'last_name']`), but not if I send a string (`'fields': "first_name,last_name"`).
Either way I think we'll have a change to make in haystack to support this feature because it's currently assuming the client wants a string containing a space-delimited list of fields [1]. I figured I'd confirm the expectations here before issuing a pull request over there. Thanks!
[1] https://github.com/toastdriven/django-haystack/blob/master/haystack/backends/elasticsearch_backend.py#L275 | non_priority | should fields be a list or a string the client args for the fields param says a comma separated list of fields to return as part of a hit that s not super clear but suggests to me that it expects a string since specifying the delimiter implies a pseudo list encoded as a string however this argument seems passed through to elasticsearch and appears to work if i send a list here fields but not if i send a string fields first name last name either way i think we ll have a change to make in haystack to support this feature because it s currently assuming the client wants a string containing a space delimited list of fields i figured i d confirm the expectations here before issuing a pull request over there thanks | 0 |
209,375 | 16,018,386,320 | IssuesEvent | 2021-04-20 19:03:21 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | ccl/importccl: TestImportComputed failed | C-test-failure O-robot branch-master | ccl/importccl.TestImportComputed [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2900755&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=2900755&tab=artifacts#/) on master @ [f451dd080c95fa73f7d796e1dc8bd6dd33eba09b](https://github.com/cockroachdb/cockroach/commits/f451dd080c95fa73f7d796e1dc8bd6dd33eba09b):
```
Previous write at 0x00c0074df910 by goroutine 1025:
github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr.(*nameResolver).addColumn()
/go/src/github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr/expr.go:265 +0x1d4
github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr.MakeComputedExprs()
/go/src/github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr/computed_column.go:285 +0x8e6
github.com/cockroachdb/cockroach/pkg/sql/row.NewDatumRowConverter()
/go/src/github.com/cockroachdb/cockroach/pkg/sql/row/row_converter.go:435 +0x1550
github.com/cockroachdb/cockroach/pkg/ccl/importccl.makeDatumConverter()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:449 +0x18c
github.com/cockroachdb/cockroach/pkg/ccl/importccl.(*parallelImporter).importWorker()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:653 +0x7c
github.com/cockroachdb/cockroach/pkg/ccl/importccl.runParallelImport.func1.1()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:553 +0xae
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.GroupWorkers.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:175 +0x5d
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:166 +0x4e
golang.org/x/sync/errgroup.(*Group).Go.func1()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x94
Goroutine 558 (running) created at:
golang.org/x/sync/errgroup.(*Group).Go()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:54 +0x73
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:165 +0xe4
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.GroupWorkers()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:175 +0xaa
github.com/cockroachdb/cockroach/pkg/ccl/importccl.runParallelImport.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:552 +0x2f1
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:166 +0x4e
golang.org/x/sync/errgroup.(*Group).Go.func1()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x94
Goroutine 1025 (finished) created at:
golang.org/x/sync/errgroup.(*Group).Go()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:54 +0x73
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:165 +0xe4
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.GroupWorkers()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:175 +0xaa
github.com/cockroachdb/cockroach/pkg/ccl/importccl.runParallelImport.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:552 +0x2f1
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:166 +0x4e
golang.org/x/sync/errgroup.(*Group).Go.func1()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x94
==================
testing.go:1038: race detected during execution of test
--- FAIL: TestImportComputed/import-table-avro (1.39s)
```
<details><summary>Reproduce</summary>
<p>
<p>To reproduce, try:
```bash
make stressrace TESTS=TestImportComputed PKG=./pkg/ccl/importccl TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
</p>
<p>Parameters in this failure:
- GOFLAGS=-race -parallel=4
</p>
</p>
</details>
/cc @Anzoteh96
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestImportComputed.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 1.0 | ccl/importccl: TestImportComputed failed - ccl/importccl.TestImportComputed [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2900755&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=2900755&tab=artifacts#/) on master @ [f451dd080c95fa73f7d796e1dc8bd6dd33eba09b](https://github.com/cockroachdb/cockroach/commits/f451dd080c95fa73f7d796e1dc8bd6dd33eba09b):
```
Previous write at 0x00c0074df910 by goroutine 1025:
github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr.(*nameResolver).addColumn()
/go/src/github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr/expr.go:265 +0x1d4
github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr.MakeComputedExprs()
/go/src/github.com/cockroachdb/cockroach/pkg/sql/catalog/schemaexpr/computed_column.go:285 +0x8e6
github.com/cockroachdb/cockroach/pkg/sql/row.NewDatumRowConverter()
/go/src/github.com/cockroachdb/cockroach/pkg/sql/row/row_converter.go:435 +0x1550
github.com/cockroachdb/cockroach/pkg/ccl/importccl.makeDatumConverter()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:449 +0x18c
github.com/cockroachdb/cockroach/pkg/ccl/importccl.(*parallelImporter).importWorker()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:653 +0x7c
github.com/cockroachdb/cockroach/pkg/ccl/importccl.runParallelImport.func1.1()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:553 +0xae
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.GroupWorkers.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:175 +0x5d
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:166 +0x4e
golang.org/x/sync/errgroup.(*Group).Go.func1()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x94
Goroutine 558 (running) created at:
golang.org/x/sync/errgroup.(*Group).Go()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:54 +0x73
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:165 +0xe4
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.GroupWorkers()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:175 +0xaa
github.com/cockroachdb/cockroach/pkg/ccl/importccl.runParallelImport.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:552 +0x2f1
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:166 +0x4e
golang.org/x/sync/errgroup.(*Group).Go.func1()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x94
Goroutine 1025 (finished) created at:
golang.org/x/sync/errgroup.(*Group).Go()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:54 +0x73
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:165 +0xe4
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.GroupWorkers()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:175 +0xaa
github.com/cockroachdb/cockroach/pkg/ccl/importccl.runParallelImport.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/ccl/importccl/read_import_base.go:552 +0x2f1
github.com/cockroachdb/cockroach/pkg/util/ctxgroup.Group.GoCtx.func1()
/go/src/github.com/cockroachdb/cockroach/pkg/util/ctxgroup/ctxgroup.go:166 +0x4e
golang.org/x/sync/errgroup.(*Group).Go.func1()
/go/src/github.com/cockroachdb/cockroach/vendor/golang.org/x/sync/errgroup/errgroup.go:57 +0x94
==================
testing.go:1038: race detected during execution of test
--- FAIL: TestImportComputed/import-table-avro (1.39s)
```
<details><summary>Reproduce</summary>
<p>
<p>To reproduce, try:
```bash
make stressrace TESTS=TestImportComputed PKG=./pkg/ccl/importccl TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
</p>
<p>Parameters in this failure:
- GOFLAGS=-race -parallel=4
</p>
</p>
</details>
/cc @Anzoteh96
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestImportComputed.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | ccl importccl testimportcomputed failed ccl importccl testimportcomputed with on master previous write at by goroutine github com cockroachdb cockroach pkg sql catalog schemaexpr nameresolver addcolumn go src github com cockroachdb cockroach pkg sql catalog schemaexpr expr go github com cockroachdb cockroach pkg sql catalog schemaexpr makecomputedexprs go src github com cockroachdb cockroach pkg sql catalog schemaexpr computed column go github com cockroachdb cockroach pkg sql row newdatumrowconverter go src github com cockroachdb cockroach pkg sql row row converter go github com cockroachdb cockroach pkg ccl importccl makedatumconverter go src github com cockroachdb cockroach pkg ccl importccl read import base go github com cockroachdb cockroach pkg ccl importccl parallelimporter importworker go src github com cockroachdb cockroach pkg ccl importccl read import base go github com cockroachdb cockroach pkg ccl importccl runparallelimport go src github com cockroachdb cockroach pkg ccl importccl read import base go github com cockroachdb cockroach pkg util ctxgroup groupworkers go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go github com cockroachdb cockroach pkg util ctxgroup group goctx go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go golang org x sync errgroup group go go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go goroutine running created at golang org x sync errgroup group go go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go github com cockroachdb cockroach pkg util ctxgroup group goctx go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go github com cockroachdb cockroach pkg util ctxgroup groupworkers go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go github com cockroachdb cockroach pkg ccl importccl runparallelimport go src github com cockroachdb cockroach pkg ccl importccl read import base go github com cockroachdb cockroach pkg util ctxgroup group goctx go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go golang org x sync errgroup group go go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go goroutine finished created at golang org x sync errgroup group go go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go github com cockroachdb cockroach pkg util ctxgroup group goctx go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go github com cockroachdb cockroach pkg util ctxgroup groupworkers go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go github com cockroachdb cockroach pkg ccl importccl runparallelimport go src github com cockroachdb cockroach pkg ccl importccl read import base go github com cockroachdb cockroach pkg util ctxgroup group goctx go src github com cockroachdb cockroach pkg util ctxgroup ctxgroup go golang org x sync errgroup group go go src github com cockroachdb cockroach vendor golang org x sync errgroup errgroup go testing go race detected during execution of test fail testimportcomputed import table avro reproduce to reproduce try bash make stressrace tests testimportcomputed pkg pkg ccl importccl testtimeout stressflags timeout parameters in this failure goflags race parallel cc | 0 |
65,191 | 16,132,443,363 | IssuesEvent | 2021-04-29 07:29:51 | spring-projects/spring-session | https://api.github.com/repos/spring-projects/spring-session | closed | docs.af.pivotal.io->docs-ip.spring.io | in: build type: bug | The host for deploying the docs has changed to docs-ip.spring.io | 1.0 | docs.af.pivotal.io->docs-ip.spring.io - The host for deploying the docs has changed to docs-ip.spring.io | non_priority | docs af pivotal io docs ip spring io the host for deploying the docs has changed to docs ip spring io | 0 |
155,259 | 19,771,278,003 | IssuesEvent | 2022-01-17 10:17:25 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | Vulnerability roundup 110: archivy-1.6.1: 1 advisory [4.3] | 1.severity: security | [search](https://search.nix.gsc.io/?q=archivy&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=archivy+in%3Apath&type=Code)
* [ ] [CVE-2021-4162](https://nvd.nist.gov/vuln/detail/CVE-2021-4162) CVSSv3=4.3 (nixos-unstable)
## CVE details
### CVE-2021-4162
archivy is vulnerable to Cross-Site Request Forgery (CSRF)
-----
Scanned versions: nixos-unstable: 5aaed40d22f.
Cc @siraben
| True | Vulnerability roundup 110: archivy-1.6.1: 1 advisory [4.3] - [search](https://search.nix.gsc.io/?q=archivy&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=archivy+in%3Apath&type=Code)
* [ ] [CVE-2021-4162](https://nvd.nist.gov/vuln/detail/CVE-2021-4162) CVSSv3=4.3 (nixos-unstable)
## CVE details
### CVE-2021-4162
archivy is vulnerable to Cross-Site Request Forgery (CSRF)
-----
Scanned versions: nixos-unstable: 5aaed40d22f.
Cc @siraben
| non_priority | vulnerability roundup archivy advisory nixos unstable cve details cve archivy is vulnerable to cross site request forgery csrf scanned versions nixos unstable cc siraben | 0 |
73,058 | 31,844,409,404 | IssuesEvent | 2023-09-14 18:44:46 | AmplicaLabs/content-publishing-service | https://api.github.com/repos/AmplicaLabs/content-publishing-service | opened | File upload limitation | content-publishing-service | Think about how to do streaming for assets instead of storing everything in memory which allow for bigger size assets | 1.0 | File upload limitation - Think about how to do streaming for assets instead of storing everything in memory which allow for bigger size assets | non_priority | file upload limitation think about how to do streaming for assets instead of storing everything in memory which allow for bigger size assets | 0 |
237,260 | 19,605,062,935 | IssuesEvent | 2022-01-06 08:23:01 | IntellectualSites/PlotSquared | https://api.github.com/repos/IntellectualSites/PlotSquared | opened | Negative max-tiles value bugs world and spams log | Requires Testing | ### Server Implementation
Paper
### Server Version
1.17.1
### Describe the bug
Setting a negative value for `max-tiles` in the chunk processor causes a massive amount of console spam and seems to delete all tile entities in loaded chunks.
### To Reproduce
1. Place some chests in a chunk
2. Enable chunk processor and set `max-tiles` to `-1`
3. Restart server and join
4. Chests are gone and massive console spam
### Expected behaviour
At the very least, not spam the console and not delete blocks.
### Screenshots / Videos
_No response_
### Error log (if applicable)
https://paste.gg/p/anonymous/fe62defc051e457e95f59f5c29e9bef1
### Plot Debugpaste
https://athion.net/ISPaster/paste/view/e45b3c123ebb475c80f7f18063589926
### PlotSquared Version
6.2.3-SNAPSHOT
### Checklist
- [X] I have included a Plot debugpaste.
- [X] I am using the newest build from https://www.spigotmc.org/resources/77506/ and the issue still persists.
### Anything else?
Scared the crap out of me and I terminated the server as soon as I saw it so that none of the chunks would save in this state. This also happened on version 6.1.5, which I updated to the latest version (6.2.3) and tested again for this report. Results were the same. The provided error log is just the single error, as far as I can tell this is the only one but it spammed thousands of lines per second. I anticipated this would disable the check for tile entities in the chunk processor. I am using a different plugin (Insights) for block entity limits, which I disabled, so it is not interfering with PS and didn't cause this bug. If negative values simply can't be supported, it would be at least be nice if doing so anyway wouldn't delete blocks and just disable the processor. I really think that it should be supported as an "uncapped" limit though, as I want to use the `max-entities` limit but have an uncapped `max-tiles` limit. I am unsure if any value below 1 would have the same result, I just know that `-1` does. | 1.0 | Negative max-tiles value bugs world and spams log - ### Server Implementation
Paper
### Server Version
1.17.1
### Describe the bug
Setting a negative value for `max-tiles` in the chunk processor causes a massive amount of console spam and seems to delete all tile entities in loaded chunks.
### To Reproduce
1. Place some chests in a chunk
2. Enable chunk processor and set `max-tiles` to `-1`
3. Restart server and join
4. Chests are gone and massive console spam
### Expected behaviour
At the very least, not spam the console and not delete blocks.
### Screenshots / Videos
_No response_
### Error log (if applicable)
https://paste.gg/p/anonymous/fe62defc051e457e95f59f5c29e9bef1
### Plot Debugpaste
https://athion.net/ISPaster/paste/view/e45b3c123ebb475c80f7f18063589926
### PlotSquared Version
6.2.3-SNAPSHOT
### Checklist
- [X] I have included a Plot debugpaste.
- [X] I am using the newest build from https://www.spigotmc.org/resources/77506/ and the issue still persists.
### Anything else?
Scared the crap out of me and I terminated the server as soon as I saw it so that none of the chunks would save in this state. This also happened on version 6.1.5, which I updated to the latest version (6.2.3) and tested again for this report. Results were the same. The provided error log is just the single error, as far as I can tell this is the only one but it spammed thousands of lines per second. I anticipated this would disable the check for tile entities in the chunk processor. I am using a different plugin (Insights) for block entity limits, which I disabled, so it is not interfering with PS and didn't cause this bug. If negative values simply can't be supported, it would be at least be nice if doing so anyway wouldn't delete blocks and just disable the processor. I really think that it should be supported as an "uncapped" limit though, as I want to use the `max-entities` limit but have an uncapped `max-tiles` limit. I am unsure if any value below 1 would have the same result, I just know that `-1` does. | non_priority | negative max tiles value bugs world and spams log server implementation paper server version describe the bug setting a negative value for max tiles in the chunk processor causes a massive amount of console spam and seems to delete all tile entities in loaded chunks to reproduce place some chests in a chunk enable chunk processor and set max tiles to restart server and join chests are gone and massive console spam expected behaviour at the very least not spam the console and not delete blocks screenshots videos no response error log if applicable plot debugpaste plotsquared version snapshot checklist i have included a plot debugpaste i am using the newest build from and the issue still persists anything else scared the crap out of me and i terminated the server as soon as i saw it so that none of the chunks would save in this state this also happened on version which i updated to the latest version and tested again for this report results were the same the provided error log is just the single error as far as i can tell this is the only one but it spammed thousands of lines per second i anticipated this would disable the check for tile entities in the chunk processor i am using a different plugin insights for block entity limits which i disabled so it is not interfering with ps and didn t cause this bug if negative values simply can t be supported it would be at least be nice if doing so anyway wouldn t delete blocks and just disable the processor i really think that it should be supported as an uncapped limit though as i want to use the max entities limit but have an uncapped max tiles limit i am unsure if any value below would have the same result i just know that does | 0 |
293,176 | 25,275,299,834 | IssuesEvent | 2022-11-16 12:13:20 | epiphany-platform/epiphany | https://api.github.com/repos/epiphany-platform/epiphany | closed | [FEATURE REQUEST] Add Molecule execution into test pipelines | area/testing | **Is your feature request related to a problem? Please describe.**
We started to create Molecule tests that at the moment exist for PostgreSQL. The idea is to include them into existing test pipelines in Azure DevOps.
**Describe the solution you'd like**
Add an additional step. It runs in Docker containers, so some adjusment may be needed.
**Describe alternatives you've considered**
No.
**Additional context**
Consider [pytest-molecule](https://pypi.org/project/pytest-molecule/) to run scenarios in parallel.
---
**DoD checklist**
- Changelog
- [ ] updated
- [ ] not needed
- COMPONENTS.md
- [ ] updated
- [ ] not needed
- Schema
- [ ] updated
- [ ] not needed
- Backport tasks
- [ ] created
- [ ] not needed
- Documentation
- [ ] added
- [ ] updated
- [ ] not needed
- [ ] Feature has automated tests
- [ ] Automated tests passed (QA pipelines)
- [ ] apply
- [ ] upgrade
- [ ] backup/restore
- [ ] Idempotency tested
- [ ] All conversations in PR resolved
- [ ] Solution meets requirements and is done according to design doc
- [ ] Usage compliant with license | 1.0 | [FEATURE REQUEST] Add Molecule execution into test pipelines - **Is your feature request related to a problem? Please describe.**
We started to create Molecule tests that at the moment exist for PostgreSQL. The idea is to include them into existing test pipelines in Azure DevOps.
**Describe the solution you'd like**
Add an additional step. It runs in Docker containers, so some adjusment may be needed.
**Describe alternatives you've considered**
No.
**Additional context**
Consider [pytest-molecule](https://pypi.org/project/pytest-molecule/) to run scenarios in parallel.
---
**DoD checklist**
- Changelog
- [ ] updated
- [ ] not needed
- COMPONENTS.md
- [ ] updated
- [ ] not needed
- Schema
- [ ] updated
- [ ] not needed
- Backport tasks
- [ ] created
- [ ] not needed
- Documentation
- [ ] added
- [ ] updated
- [ ] not needed
- [ ] Feature has automated tests
- [ ] Automated tests passed (QA pipelines)
- [ ] apply
- [ ] upgrade
- [ ] backup/restore
- [ ] Idempotency tested
- [ ] All conversations in PR resolved
- [ ] Solution meets requirements and is done according to design doc
- [ ] Usage compliant with license | non_priority | add molecule execution into test pipelines is your feature request related to a problem please describe we started to create molecule tests that at the moment exist for postgresql the idea is to include them into existing test pipelines in azure devops describe the solution you d like add an additional step it runs in docker containers so some adjusment may be needed describe alternatives you ve considered no additional context consider to run scenarios in parallel dod checklist changelog updated not needed components md updated not needed schema updated not needed backport tasks created not needed documentation added updated not needed feature has automated tests automated tests passed qa pipelines apply upgrade backup restore idempotency tested all conversations in pr resolved solution meets requirements and is done according to design doc usage compliant with license | 0 |
127,567 | 10,475,278,860 | IssuesEvent | 2019-09-23 16:00:27 | kcigeospatial/Fred_Co_Land-Management | https://api.github.com/repos/kcigeospatial/Fred_Co_Land-Management | closed | Building - Capacity - Permit Issued Notification | Ready for Test Env. Retest | The approved and issued Capacity notification is sending at the wrong time. The notification should be sent after the Admin Review/Pending Certificate milestone.
| 2.0 | Building - Capacity - Permit Issued Notification - The approved and issued Capacity notification is sending at the wrong time. The notification should be sent after the Admin Review/Pending Certificate milestone.
| non_priority | building capacity permit issued notification the approved and issued capacity notification is sending at the wrong time the notification should be sent after the admin review pending certificate milestone | 0 |
136,486 | 12,716,749,641 | IssuesEvent | 2020-06-24 02:55:08 | RonAsis/Wsep202 | https://api.github.com/repos/RonAsis/Wsep202 | closed | Make GUI requirements testable | documentation | for example: 40. Use text that is not too small for elderly / visually impaired users. What is "not too small", use % of the screen to define it. | 1.0 | Make GUI requirements testable - for example: 40. Use text that is not too small for elderly / visually impaired users. What is "not too small", use % of the screen to define it. | non_priority | make gui requirements testable for example use text that is not too small for elderly visually impaired users what is not too small use of the screen to define it | 0 |
288,635 | 31,861,525,908 | IssuesEvent | 2023-09-15 11:17:07 | nidhi7598/linux-v4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564 | opened | WS-2021-0468 (High) detected in linuxlinux-4.19.294 | Mend: dependency security vulnerability | ## WS-2021-0468 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In Linux/Kernel is vulnerable to injected vht mcs/nss in ieee80211_parse_tx_radiotap in net/mac80211/tx.c
<p>Publish Date: 2021-11-29
<p>URL: <a href=https://github.com/gregkh/linux/commit/997ee230e4f5285cd98445c102d9033c7ec4814b>WS-2021-0468</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1001723">https://osv.dev/vulnerability/UVI-2021-1001723</a></p>
<p>Release Date: 2021-11-29</p>
<p>Fix Resolution: Linux/Kernel -v4.9.285, v4.14.249, v4.19.209, v5.4.151, v5.10.71, v5.14.10, v5.15-rc4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0468 (High) detected in linuxlinux-4.19.294 - ## WS-2021-0468 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In Linux/Kernel is vulnerable to injected vht mcs/nss in ieee80211_parse_tx_radiotap in net/mac80211/tx.c
<p>Publish Date: 2021-11-29
<p>URL: <a href=https://github.com/gregkh/linux/commit/997ee230e4f5285cd98445c102d9033c7ec4814b>WS-2021-0468</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://osv.dev/vulnerability/UVI-2021-1001723">https://osv.dev/vulnerability/UVI-2021-1001723</a></p>
<p>Release Date: 2021-11-29</p>
<p>Fix Resolution: Linux/Kernel -v4.9.285, v4.14.249, v4.19.209, v5.4.151, v5.10.71, v5.14.10, v5.15-rc4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in linuxlinux ws high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files vulnerability details in linux kernel is vulnerable to injected vht mcs nss in parse tx radiotap in net tx c publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux kernel step up your open source security game with mend | 0 |
300,521 | 22,684,260,766 | IssuesEvent | 2022-07-04 12:44:51 | Justicea83/Expensify | https://api.github.com/repos/Justicea83/Expensify | reopened | [Chore] Graduate Attendees for interview on 2022-03-30 -werw059458477 | bug documentation duplicate enhancement good first issue GraduateInterview | Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aenean commodo ligula eget dolor. Aenean massa. Cum sociis natoque penatibus et magnis dis parturient montes, nascetur ridiculus mus. Donec quam felis, ultricies nec, pellentesque eu, pretium quis, sem. Nulla consequat massa quis enim. Donec pede justo, fringilla vel, aliquet nec, vulputate eget, arcu. In enim justo, rhoncus ut, imperdiet a, venenatis vitae, justo. Nullam dictum felis eu pede mollis pretium. Integer tincidunt. Cras dapibus. Vivamus elementum semper nisi. Aenean vulputate eleifend tellus. Aenean leo ligula, porttitor eu, consequat vitae, eleifend ac, enim. Aliquam lorem ante, dapibus in, viverra quis, feugiat a, tellus. Phasellus viverra nulla ut metus varius laoreet. Quisque rutrum. Aenean imperdiet. Etiam ultricies nisi vel augue. Curabitur ullamcorper ultricies nisi. Nam eget dui. Etiam rhoncus. Maecenas tempus, tellus eget condimentum rhoncus, sem quam semper libero, sit amet adipiscing sem neque sed ipsum. Nam quam nunc, blandit vel, luctus pulvinar, hendrerit id, lorem. Maecenas nec odio et ante tincidunt tempus. Donec vitae sapien ut libero venenatis faucibus. Nullam quis ante. Etiam sit amet orci eget eros faucibus tincidunt. Duis leo. Sed fringilla mauris sit amet nibh. Donec sodales sagittis magna. Sed consequat, leo eget bibendum sodales, augue velit cursus nunc,
| 1.0 | [Chore] Graduate Attendees for interview on 2022-03-30 -werw059458477 - Lorem ipsum dolor sit amet, consectetuer adipiscing elit. Aenean commodo ligula eget dolor. Aenean massa. Cum sociis natoque penatibus et magnis dis parturient montes, nascetur ridiculus mus. Donec quam felis, ultricies nec, pellentesque eu, pretium quis, sem. Nulla consequat massa quis enim. Donec pede justo, fringilla vel, aliquet nec, vulputate eget, arcu. In enim justo, rhoncus ut, imperdiet a, venenatis vitae, justo. Nullam dictum felis eu pede mollis pretium. Integer tincidunt. Cras dapibus. Vivamus elementum semper nisi. Aenean vulputate eleifend tellus. Aenean leo ligula, porttitor eu, consequat vitae, eleifend ac, enim. Aliquam lorem ante, dapibus in, viverra quis, feugiat a, tellus. Phasellus viverra nulla ut metus varius laoreet. Quisque rutrum. Aenean imperdiet. Etiam ultricies nisi vel augue. Curabitur ullamcorper ultricies nisi. Nam eget dui. Etiam rhoncus. Maecenas tempus, tellus eget condimentum rhoncus, sem quam semper libero, sit amet adipiscing sem neque sed ipsum. Nam quam nunc, blandit vel, luctus pulvinar, hendrerit id, lorem. Maecenas nec odio et ante tincidunt tempus. Donec vitae sapien ut libero venenatis faucibus. Nullam quis ante. Etiam sit amet orci eget eros faucibus tincidunt. Duis leo. Sed fringilla mauris sit amet nibh. Donec sodales sagittis magna. Sed consequat, leo eget bibendum sodales, augue velit cursus nunc,
| non_priority | graduate attendees for interview on lorem ipsum dolor sit amet consectetuer adipiscing elit aenean commodo ligula eget dolor aenean massa cum sociis natoque penatibus et magnis dis parturient montes nascetur ridiculus mus donec quam felis ultricies nec pellentesque eu pretium quis sem nulla consequat massa quis enim donec pede justo fringilla vel aliquet nec vulputate eget arcu in enim justo rhoncus ut imperdiet a venenatis vitae justo nullam dictum felis eu pede mollis pretium integer tincidunt cras dapibus vivamus elementum semper nisi aenean vulputate eleifend tellus aenean leo ligula porttitor eu consequat vitae eleifend ac enim aliquam lorem ante dapibus in viverra quis feugiat a tellus phasellus viverra nulla ut metus varius laoreet quisque rutrum aenean imperdiet etiam ultricies nisi vel augue curabitur ullamcorper ultricies nisi nam eget dui etiam rhoncus maecenas tempus tellus eget condimentum rhoncus sem quam semper libero sit amet adipiscing sem neque sed ipsum nam quam nunc blandit vel luctus pulvinar hendrerit id lorem maecenas nec odio et ante tincidunt tempus donec vitae sapien ut libero venenatis faucibus nullam quis ante etiam sit amet orci eget eros faucibus tincidunt duis leo sed fringilla mauris sit amet nibh donec sodales sagittis magna sed consequat leo eget bibendum sodales augue velit cursus nunc | 0 |
6,301 | 4,216,724,871 | IssuesEvent | 2016-06-30 10:17:18 | ff36/halo-gui | https://api.github.com/repos/ff36/halo-gui | closed | Opening property modal reloads table | bug urgent usability ux | If you open a property modal with a filter applied to the table, the table clears the filter and reloads. This should not happen. I also noticed that you cannot select the filter text. | True | Opening property modal reloads table - If you open a property modal with a filter applied to the table, the table clears the filter and reloads. This should not happen. I also noticed that you cannot select the filter text. | non_priority | opening property modal reloads table if you open a property modal with a filter applied to the table the table clears the filter and reloads this should not happen i also noticed that you cannot select the filter text | 0 |
248,418 | 26,785,157,169 | IssuesEvent | 2023-02-01 01:44:36 | raindigi/site-landing | https://api.github.com/repos/raindigi/site-landing | opened | CVE-2020-7768 (High) detected in grpc-1.16.1.tgz | security vulnerability | ## CVE-2020-7768 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grpc-1.16.1.tgz</b></p></summary>
<p>gRPC Library for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/grpc/-/grpc-1.16.1.tgz">https://registry.npmjs.org/grpc/-/grpc-1.16.1.tgz</a></p>
<p>Path to dependency file: /site-landing/package.json</p>
<p>Path to vulnerable library: /node_modules/@firebase/firestore/node_modules/grpc/package.json</p>
<p>
Dependency Hierarchy:
- firestore-0.9.3.tgz (Root Library)
- :x: **grpc-1.16.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package grpc before 1.24.4; the package @grpc/grpc-js before 1.1.8 are vulnerable to Prototype Pollution via loadPackageDefinition.
<p>Publish Date: 2020-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7768>CVE-2020-7768</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768</a></p>
<p>Release Date: 2020-11-11</p>
<p>Fix Resolution (grpc): 1.24.4</p>
<p>Direct dependency fix Resolution (@firebase/firestore): 1.3.1-canary.4771184</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7768 (High) detected in grpc-1.16.1.tgz - ## CVE-2020-7768 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grpc-1.16.1.tgz</b></p></summary>
<p>gRPC Library for Node</p>
<p>Library home page: <a href="https://registry.npmjs.org/grpc/-/grpc-1.16.1.tgz">https://registry.npmjs.org/grpc/-/grpc-1.16.1.tgz</a></p>
<p>Path to dependency file: /site-landing/package.json</p>
<p>Path to vulnerable library: /node_modules/@firebase/firestore/node_modules/grpc/package.json</p>
<p>
Dependency Hierarchy:
- firestore-0.9.3.tgz (Root Library)
- :x: **grpc-1.16.1.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package grpc before 1.24.4; the package @grpc/grpc-js before 1.1.8 are vulnerable to Prototype Pollution via loadPackageDefinition.
<p>Publish Date: 2020-11-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-7768>CVE-2020-7768</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7768</a></p>
<p>Release Date: 2020-11-11</p>
<p>Fix Resolution (grpc): 1.24.4</p>
<p>Direct dependency fix Resolution (@firebase/firestore): 1.3.1-canary.4771184</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in grpc tgz cve high severity vulnerability vulnerable library grpc tgz grpc library for node library home page a href path to dependency file site landing package json path to vulnerable library node modules firebase firestore node modules grpc package json dependency hierarchy firestore tgz root library x grpc tgz vulnerable library found in base branch master vulnerability details the package grpc before the package grpc grpc js before are vulnerable to prototype pollution via loadpackagedefinition publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution grpc direct dependency fix resolution firebase firestore canary step up your open source security game with mend | 0 |
63,426 | 12,321,868,158 | IssuesEvent | 2020-05-13 09:24:30 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Spawnsub command not working | Bug Code | - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Im not being able to use the "spawnsub" command, i always get a kinda object not set to reference or something. At first i thought i was putting the name incorrectly but it seems to not be the problem,
**Version**
Stable Windows 10 (Windows/Linux/Mac).
| 1.0 | Spawnsub command not working - - [X] I have searched the issue tracker to check if the issue has already been reported.
**Description**
Im not being able to use the "spawnsub" command, i always get a kinda object not set to reference or something. At first i thought i was putting the name incorrectly but it seems to not be the problem,
**Version**
Stable Windows 10 (Windows/Linux/Mac).
| non_priority | spawnsub command not working i have searched the issue tracker to check if the issue has already been reported description im not being able to use the spawnsub command i always get a kinda object not set to reference or something at first i thought i was putting the name incorrectly but it seems to not be the problem version stable windows windows linux mac | 0 |
49,968 | 10,436,734,704 | IssuesEvent | 2019-09-17 20:15:10 | MicrosoftDocs/visualstudio-docs | https://api.github.com/repos/MicrosoftDocs/visualstudio-docs | closed | Add documentation for new Performance rule CA1825 (AvoidZeroLengthArrayAllocations) in FxCop analyzers | Pri2 doc-idea visual-studio-windows/prod vs-ide-code-analysis/tech | 1. Does not exist in legacy FxCop
2. Rule Implementation: https://github.com/dotnet/roslyn-analyzers/blob/32d8f1e397439035f0ecb5f61a9e672225f0ecdb/src/Microsoft.NetCore.Analyzers/Core/Runtime/AvoidZeroLengthArrayAllocations.cs#L14
3. Rule message and description: https://github.com/dotnet/roslyn-analyzers/blob/760b9c9188cf95ec6ab8cbadb75a1d129d15442f/src/Microsoft.NetCore.Analyzers/Core/Runtime/SystemRuntimeAnalyzersResources.resx#L270-L275
```
<data name="AvoidZeroLengthArrayAllocationsTitle" xml:space="preserve">
<value>Avoid zero-length array allocations.</value>
</data>
<data name="AvoidZeroLengthArrayAllocationsMessage" xml:space="preserve">
<value>Avoid unnecessary zero-length array allocations. Use {0} instead.</value>
</data>
```
4. Unit tests: https://github.com/dotnet/roslyn-analyzers/blob/9c08642f76abffb8cce34aa1971a046e69ce710d/src/Microsoft.NetCore.Analyzers/UnitTests/Runtime/AvoidZeroLengthArrayAllocationsTests.cs#L18
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: a6821238-fc59-9229-824a-c7ddc6d6e98b
* Version Independent ID: 518e70a1-9dc2-be79-76f7-13689ebacaea
* Content: [Performance Warnings - Visual Studio](https://docs.microsoft.com/en-us/visualstudio/code-quality/performance-warnings?view=vs-2019)
* Content Source: [docs/code-quality/performance-warnings.md](https://github.com/MicrosoftDocs/visualstudio-docs/blob/master/docs/code-quality/performance-warnings.md)
* Product: **visual-studio-windows**
* Technology: **vs-ide-code-analysis**
* GitHub Login: @gewarren
* Microsoft Alias: **gewarren** | 1.0 | Add documentation for new Performance rule CA1825 (AvoidZeroLengthArrayAllocations) in FxCop analyzers - 1. Does not exist in legacy FxCop
2. Rule Implementation: https://github.com/dotnet/roslyn-analyzers/blob/32d8f1e397439035f0ecb5f61a9e672225f0ecdb/src/Microsoft.NetCore.Analyzers/Core/Runtime/AvoidZeroLengthArrayAllocations.cs#L14
3. Rule message and description: https://github.com/dotnet/roslyn-analyzers/blob/760b9c9188cf95ec6ab8cbadb75a1d129d15442f/src/Microsoft.NetCore.Analyzers/Core/Runtime/SystemRuntimeAnalyzersResources.resx#L270-L275
```
<data name="AvoidZeroLengthArrayAllocationsTitle" xml:space="preserve">
<value>Avoid zero-length array allocations.</value>
</data>
<data name="AvoidZeroLengthArrayAllocationsMessage" xml:space="preserve">
<value>Avoid unnecessary zero-length array allocations. Use {0} instead.</value>
</data>
```
4. Unit tests: https://github.com/dotnet/roslyn-analyzers/blob/9c08642f76abffb8cce34aa1971a046e69ce710d/src/Microsoft.NetCore.Analyzers/UnitTests/Runtime/AvoidZeroLengthArrayAllocationsTests.cs#L18
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: a6821238-fc59-9229-824a-c7ddc6d6e98b
* Version Independent ID: 518e70a1-9dc2-be79-76f7-13689ebacaea
* Content: [Performance Warnings - Visual Studio](https://docs.microsoft.com/en-us/visualstudio/code-quality/performance-warnings?view=vs-2019)
* Content Source: [docs/code-quality/performance-warnings.md](https://github.com/MicrosoftDocs/visualstudio-docs/blob/master/docs/code-quality/performance-warnings.md)
* Product: **visual-studio-windows**
* Technology: **vs-ide-code-analysis**
* GitHub Login: @gewarren
* Microsoft Alias: **gewarren** | non_priority | add documentation for new performance rule avoidzerolengtharrayallocations in fxcop analyzers does not exist in legacy fxcop rule implementation rule message and description lt data name avoidzerolengtharrayallocationstitle xml space preserve gt lt value gt avoid zero length array allocations lt value gt lt data gt lt data name avoidzerolengtharrayallocationsmessage xml space preserve gt lt value gt avoid unnecessary zero length array allocations use instead lt value gt lt data gt unit tests document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product visual studio windows technology vs ide code analysis github login gewarren microsoft alias gewarren | 0 |
61,785 | 12,195,649,171 | IssuesEvent | 2020-04-29 17:43:48 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | opened | [PATCH] Fix wint_t for Solaris, fix Linux wint_t test, fix Linux wint_t stdint.h | BZ-BUG-STATUS: NEW clang/LLVM Codegen dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=9772. | 1.0 | [PATCH] Fix wint_t for Solaris, fix Linux wint_t test, fix Linux wint_t stdint.h - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=9772. | non_priority | fix wint t for solaris fix linux wint t test fix linux wint t stdint h this issue was imported from bugzilla | 0 |
133,325 | 18,858,228,110 | IssuesEvent | 2021-11-12 09:31:41 | Andrey-1992/quick-news-ui | https://api.github.com/repos/Andrey-1992/quick-news-ui | closed | Test accessibility with LightHouse | enhancement Design & Layout Css Styling Deployment Accessibility Accessibility Test | As a developer, I should be able to test and pass the accessibility standards with Lighthouse. | 1.0 | Test accessibility with LightHouse - As a developer, I should be able to test and pass the accessibility standards with Lighthouse. | non_priority | test accessibility with lighthouse as a developer i should be able to test and pass the accessibility standards with lighthouse | 0 |
219,763 | 16,850,658,941 | IssuesEvent | 2021-06-20 12:45:29 | amzn/selling-partner-api-docs | https://api.github.com/repos/amzn/selling-partner-api-docs | opened | How to generate the PHP code from java library downloaded | documentation enhancement request | I was able to generate the php code for selling-partner-api-models/models/authorization-api-model/authorization.json using command
java -jar /app/swagger-codegen-cli.jar generate -i /app/selling-partner-api-models/models/authorization-api-model/authorization.json -l php -o /var/tmp/php_api_client_ani
Now I want to generate the php files for -
https://github.com/amzn/selling-partner-api-models/tree/main/clients/sellingpartner-api-documents-helper-java
but there is no .json file in that folder, so how can we generate the php files?
Any idea? if this is missing or any way to generate it without json file? | 1.0 | How to generate the PHP code from java library downloaded - I was able to generate the php code for selling-partner-api-models/models/authorization-api-model/authorization.json using command
java -jar /app/swagger-codegen-cli.jar generate -i /app/selling-partner-api-models/models/authorization-api-model/authorization.json -l php -o /var/tmp/php_api_client_ani
Now I want to generate the php files for -
https://github.com/amzn/selling-partner-api-models/tree/main/clients/sellingpartner-api-documents-helper-java
but there is no .json file in that folder, so how can we generate the php files?
Any idea? if this is missing or any way to generate it without json file? | non_priority | how to generate the php code from java library downloaded i was able to generate the php code for selling partner api models models authorization api model authorization json using command java jar app swagger codegen cli jar generate i app selling partner api models models authorization api model authorization json l php o var tmp php api client ani now i want to generate the php files for but there is no json file in that folder so how can we generate the php files any idea if this is missing or any way to generate it without json file | 0 |
268,240 | 23,352,928,353 | IssuesEvent | 2022-08-10 03:16:51 | Tencent/bk-ci | https://api.github.com/repos/Tencent/bk-ci | closed | bug: go agent定时日志切割重试逻辑不生效 | kind/bug for gray for test area/ci/backend grayed streams/tested streams/for test streams/for gray streams/done | go agent中的定时日志切割的逻辑因为 break loop 使用错误导致管道一旦关闭就无法重新切割日志
<img width="1243" alt="image" src="https://user-images.githubusercontent.com/33863729/181181561-713d0237-0e7d-46fd-a98c-25111820fa26.png">
| 3.0 | bug: go agent定时日志切割重试逻辑不生效 - go agent中的定时日志切割的逻辑因为 break loop 使用错误导致管道一旦关闭就无法重新切割日志
<img width="1243" alt="image" src="https://user-images.githubusercontent.com/33863729/181181561-713d0237-0e7d-46fd-a98c-25111820fa26.png">
| non_priority | bug go agent定时日志切割重试逻辑不生效 go agent中的定时日志切割的逻辑因为 break loop 使用错误导致管道一旦关闭就无法重新切割日志 img width alt image src | 0 |
198,053 | 15,699,472,066 | IssuesEvent | 2021-03-26 08:32:17 | proofit404/stories | https://api.github.com/repos/proofit404/stories | reopened | Document expected application exception pattern. | documentation | #### Approach
Exception arguments aren't necessary. We have `state` object accessible.
See https://github.com/proofit404/stories/issues/627#issuecomment-803674101
#### HTTP Status codes
HTTP codes does not match to domain errors well.
If we respond with 400 HTTP status code, but expect our application to have 12 variants of different behavior.
For example,
```
Администратор просматривает запрос на отчёт, который запросил человек
не имеющий права в конкретном данном случае работать с тем подразделением,
которое присутствует в данных для отчёта. Мы не можем отдать ему 403 код,
потому что у него есть право на работу с данным запросом.
И самое важное, что в данном случае мы бы хотели предложить ему выдать
права доступа инициатору запроса или же перевести отчёт в статус отклонённых
с уведомлением инициатора.
``` | 1.0 | Document expected application exception pattern. - #### Approach
Exception arguments aren't necessary. We have `state` object accessible.
See https://github.com/proofit404/stories/issues/627#issuecomment-803674101
#### HTTP Status codes
HTTP codes does not match to domain errors well.
If we respond with 400 HTTP status code, but expect our application to have 12 variants of different behavior.
For example,
```
Администратор просматривает запрос на отчёт, который запросил человек
не имеющий права в конкретном данном случае работать с тем подразделением,
которое присутствует в данных для отчёта. Мы не можем отдать ему 403 код,
потому что у него есть право на работу с данным запросом.
И самое важное, что в данном случае мы бы хотели предложить ему выдать
права доступа инициатору запроса или же перевести отчёт в статус отклонённых
с уведомлением инициатора.
``` | non_priority | document expected application exception pattern approach exception arguments aren t necessary we have state object accessible see http status codes http codes does not match to domain errors well if we respond with http status code but expect our application to have variants of different behavior for example администратор просматривает запрос на отчёт который запросил человек не имеющий права в конкретном данном случае работать с тем подразделением которое присутствует в данных для отчёта мы не можем отдать ему код потому что у него есть право на работу с данным запросом и самое важное что в данном случае мы бы хотели предложить ему выдать права доступа инициатору запроса или же перевести отчёт в статус отклонённых с уведомлением инициатора | 0 |
7,664 | 9,921,631,778 | IssuesEvent | 2019-06-30 19:58:17 | sisbell/tor-android-service | https://api.github.com/repos/sisbell/tor-android-service | closed | Tor Install Changes | Orbit Compatibility |
- TOR_VERSION field has changed
- Change preference value on new install
https://github.com/guardianproject/orbot/commit/455757726d519ac56cd53eaed29c3abef25707d4 | True | Tor Install Changes -
- TOR_VERSION field has changed
- Change preference value on new install
https://github.com/guardianproject/orbot/commit/455757726d519ac56cd53eaed29c3abef25707d4 | non_priority | tor install changes tor version field has changed change preference value on new install | 0 |
258,803 | 19,574,069,098 | IssuesEvent | 2022-01-04 13:32:23 | bank2ynab/bank2ynab | https://api.github.com/repos/bank2ynab/bank2ynab | closed | More helpful API error messages | enhancement documentation help wanted user support | **Is your feature request related to a problem? Please describe.**
The API error messages are rather generic and I think we can improve them - in particular the error 401 `API access token missing, invalid, revoked, or expired` ([link to code line](https://github.com/bank2ynab/bank2ynab/blob/develop/bank2ynab.py#L883)) because users are very likely to encounter this error on their first try of the new API-enabled bank2ynab.
**Describe the solution you'd like**
The error messages should be longer. In particular, they should not only describe the problem but also describe possible solutions and/or link to our wiki and/or the YNAB (API?) help pages for details.
**Describe alternatives you've considered**
A first step is to provide a little guidance right in the error message.
**Additional context**
Relevant link for the 401 error: https://api.youneedabudget.com/#personal-access-tokens
I prefer to link directly to YNAB pages because then we don't have to maintain our own wiki page and run the risk of it being outdated. OTOH a wiki page can contain anything we want! | 1.0 | More helpful API error messages - **Is your feature request related to a problem? Please describe.**
The API error messages are rather generic and I think we can improve them - in particular the error 401 `API access token missing, invalid, revoked, or expired` ([link to code line](https://github.com/bank2ynab/bank2ynab/blob/develop/bank2ynab.py#L883)) because users are very likely to encounter this error on their first try of the new API-enabled bank2ynab.
**Describe the solution you'd like**
The error messages should be longer. In particular, they should not only describe the problem but also describe possible solutions and/or link to our wiki and/or the YNAB (API?) help pages for details.
**Describe alternatives you've considered**
A first step is to provide a little guidance right in the error message.
**Additional context**
Relevant link for the 401 error: https://api.youneedabudget.com/#personal-access-tokens
I prefer to link directly to YNAB pages because then we don't have to maintain our own wiki page and run the risk of it being outdated. OTOH a wiki page can contain anything we want! | non_priority | more helpful api error messages is your feature request related to a problem please describe the api error messages are rather generic and i think we can improve them in particular the error api access token missing invalid revoked or expired because users are very likely to encounter this error on their first try of the new api enabled describe the solution you d like the error messages should be longer in particular they should not only describe the problem but also describe possible solutions and or link to our wiki and or the ynab api help pages for details describe alternatives you ve considered a first step is to provide a little guidance right in the error message additional context relevant link for the error i prefer to link directly to ynab pages because then we don t have to maintain our own wiki page and run the risk of it being outdated otoh a wiki page can contain anything we want | 0 |
173,283 | 21,155,258,879 | IssuesEvent | 2022-04-07 02:02:12 | Aivolt1/u-i-u-x-volt-ai | https://api.github.com/repos/Aivolt1/u-i-u-x-volt-ai | reopened | CVE-2022-0355 (High) detected in simple-get-3.1.0.tgz | security vulnerability | ## CVE-2022-0355 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>simple-get-3.1.0.tgz</b></p></summary>
<p>Simplest way to make http get requests. Supports HTTPS, redirects, gzip/deflate, streams in < 100 lines.</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-get/-/simple-get-3.1.0.tgz">https://registry.npmjs.org/simple-get/-/simple-get-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/simple-get</p>
<p>
Dependency Hierarchy:
- gatsby-plugin-manifest-3.9.0.tgz (Root Library)
- sharp-0.28.3.tgz
- :x: **simple-get-3.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM simple-get prior to 4.0.1.
<p>Publish Date: 2022-01-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0355>CVE-2022-0355</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355</a></p>
<p>Release Date: 2022-01-26</p>
<p>Fix Resolution: simple-get - 4.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0355 (High) detected in simple-get-3.1.0.tgz - ## CVE-2022-0355 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>simple-get-3.1.0.tgz</b></p></summary>
<p>Simplest way to make http get requests. Supports HTTPS, redirects, gzip/deflate, streams in < 100 lines.</p>
<p>Library home page: <a href="https://registry.npmjs.org/simple-get/-/simple-get-3.1.0.tgz">https://registry.npmjs.org/simple-get/-/simple-get-3.1.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/simple-get</p>
<p>
Dependency Hierarchy:
- gatsby-plugin-manifest-3.9.0.tgz (Root Library)
- sharp-0.28.3.tgz
- :x: **simple-get-3.1.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Exposure of Sensitive Information to an Unauthorized Actor in NPM simple-get prior to 4.0.1.
<p>Publish Date: 2022-01-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0355>CVE-2022-0355</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0355</a></p>
<p>Release Date: 2022-01-26</p>
<p>Fix Resolution: simple-get - 4.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in simple get tgz cve high severity vulnerability vulnerable library simple get tgz simplest way to make http get requests supports https redirects gzip deflate streams in library home page a href path to dependency file package json path to vulnerable library node modules simple get dependency hierarchy gatsby plugin manifest tgz root library sharp tgz x simple get tgz vulnerable library found in base branch master vulnerability details exposure of sensitive information to an unauthorized actor in npm simple get prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution simple get step up your open source security game with whitesource | 0 |
46,684 | 13,055,959,279 | IssuesEvent | 2020-07-30 03:14:20 | icecube-trac/tix2 | https://api.github.com/repos/icecube-trac/tix2 | opened | [steamshovel] ipdf I3DOMLikelihoodArtist causes shovelart to segfault on exit (Trac #1711) | Incomplete Migration Migrated from Trac combo reconstruction defect | Migrated from https://code.icecube.wisc.edu/ticket/1711
```json
{
"status": "closed",
"changetime": "2019-02-13T14:14:55",
"description": "Simply loading `icecube.ipdf.artists` causes `shovelart.so` to segfault on exit. It is not clear why this is happening. This code was disabled in r146010/IceCube, but the issue still needs to be fixed. \n\nThis segfault was causing the doc build to segfault and fail even though the docs build correctly. See the complete stacktrace at http://builds.icecube.wisc.edu/builders/docs/builds/59/steps/compile_2/logs/stdio",
"reporter": "kjmeagher",
"cc": "nega",
"resolution": "fixed",
"_ts": "1550067295757382",
"component": "combo reconstruction",
"summary": "[steamshovel] ipdf I3DOMLikelihoodArtist causes shovelart to segfault on exit",
"priority": "normal",
"keywords": "",
"time": "2016-05-18T09:12:15",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| 1.0 | [steamshovel] ipdf I3DOMLikelihoodArtist causes shovelart to segfault on exit (Trac #1711) - Migrated from https://code.icecube.wisc.edu/ticket/1711
```json
{
"status": "closed",
"changetime": "2019-02-13T14:14:55",
"description": "Simply loading `icecube.ipdf.artists` causes `shovelart.so` to segfault on exit. It is not clear why this is happening. This code was disabled in r146010/IceCube, but the issue still needs to be fixed. \n\nThis segfault was causing the doc build to segfault and fail even though the docs build correctly. See the complete stacktrace at http://builds.icecube.wisc.edu/builders/docs/builds/59/steps/compile_2/logs/stdio",
"reporter": "kjmeagher",
"cc": "nega",
"resolution": "fixed",
"_ts": "1550067295757382",
"component": "combo reconstruction",
"summary": "[steamshovel] ipdf I3DOMLikelihoodArtist causes shovelart to segfault on exit",
"priority": "normal",
"keywords": "",
"time": "2016-05-18T09:12:15",
"milestone": "",
"owner": "hdembinski",
"type": "defect"
}
```
| non_priority | ipdf causes shovelart to segfault on exit trac migrated from json status closed changetime description simply loading icecube ipdf artists causes shovelart so to segfault on exit it is not clear why this is happening this code was disabled in icecube but the issue still needs to be fixed n nthis segfault was causing the doc build to segfault and fail even though the docs build correctly see the complete stacktrace at reporter kjmeagher cc nega resolution fixed ts component combo reconstruction summary ipdf causes shovelart to segfault on exit priority normal keywords time milestone owner hdembinski type defect | 0 |
17,252 | 10,675,526,732 | IssuesEvent | 2019-10-21 11:54:10 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | [UWP6.0] Rect and Size in System.Runtime.WindowsRuntime has different exception thrown for size validation | area-System.Runtime.InteropServices bug os-windows-uwp | As suggested in #21658 - disabling tests against this issue.
```
Windows.Foundation.Tests.SizeTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(51,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(51,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(91,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass7_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(91,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass7_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(43,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(43,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(71,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass5_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(71,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass5_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(66,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(66,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(188,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass16_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(188,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass16_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(58,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(58,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(171,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass14_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(171,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass14_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
`` | 1.0 | [UWP6.0] Rect and Size in System.Runtime.WindowsRuntime has different exception thrown for size validation - As suggested in #21658 - disabling tests against this issue.
```
Windows.Foundation.Tests.SizeTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(51,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(51,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(91,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass7_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(91,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass7_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(43,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(43,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(71,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass5_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.SizeTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\SizeTests.cs(71,0): at Windows.Foundation.Tests.SizeTests.<>c__DisplayClass5_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(66,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(66,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass3_0.<Ctor_NegativeHeight_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(188,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass16_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Height_SetNegative_ThrowsArgumentOutOfRangeException(height: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(188,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass16_0.<Height_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(58,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(58,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass2_0.<Ctor_NegativeWidth_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -1) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(171,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass14_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
Windows.Foundation.Tests.RectTests.Width_SetNegative_ThrowsArgumentOutOfRangeException(width: -ì) [FAIL]
Assert.Throws() Failure
Expected: typeof(System.ArgumentOutOfRangeException)
Actual: typeof(System.ArgumentException): Value does not fall within the expected range.
Stack Trace:
D:\repos\corefxCopy\corefx\src\System.Runtime.WindowsRuntime\tests\Windows\Foundation\RectTests.cs(171,0): at Windows.Foundation.Tests.RectTests.<>c__DisplayClass14_0.<Width_SetNegative_ThrowsArgumentOutOfRangeException>b__0()
`` | non_priority | rect and size in system runtime windowsruntime has different exception thrown for size validation as suggested in disabling tests against this issue windows foundation tests sizetests ctor negativeheight throwsargumentoutofrangeexception height assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests ctor negativeheight throwsargumentoutofrangeexception height ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests height setnegative throwsargumentoutofrangeexception height assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests height setnegative throwsargumentoutofrangeexception height ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests ctor negativewidth throwsargumentoutofrangeexception width assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests ctor negativewidth throwsargumentoutofrangeexception width ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests width setnegative throwsargumentoutofrangeexception width assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests sizetests width setnegative throwsargumentoutofrangeexception width ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation sizetests cs at windows foundation tests sizetests c b windows foundation tests recttests ctor negativeheight throwsargumentoutofrangeexception height assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests ctor negativeheight throwsargumentoutofrangeexception height ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests height setnegative throwsargumentoutofrangeexception height assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests height setnegative throwsargumentoutofrangeexception height ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests ctor negativewidth throwsargumentoutofrangeexception width assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests ctor negativewidth throwsargumentoutofrangeexception width ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests width setnegative throwsargumentoutofrangeexception width assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b windows foundation tests recttests width setnegative throwsargumentoutofrangeexception width ì assert throws failure expected typeof system argumentoutofrangeexception actual typeof system argumentexception value does not fall within the expected range stack trace d repos corefxcopy corefx src system runtime windowsruntime tests windows foundation recttests cs at windows foundation tests recttests c b | 0 |
4,467 | 7,332,724,583 | IssuesEvent | 2018-03-05 17:06:51 | cedardevs/psi | https://api.github.com/repos/cedardevs/psi | closed | IsoLite parsing happens in script-wrapper | EPIC: PSI DSCOVR datastream psi-processor ready script-wrapper | Instead of a topic container IsoLite and a service to transform those messages into the OS ES json payload, we want all of that to happen in one service. | 1.0 | IsoLite parsing happens in script-wrapper - Instead of a topic container IsoLite and a service to transform those messages into the OS ES json payload, we want all of that to happen in one service. | non_priority | isolite parsing happens in script wrapper instead of a topic container isolite and a service to transform those messages into the os es json payload we want all of that to happen in one service | 0 |
42,219 | 9,188,147,235 | IssuesEvent | 2019-03-06 06:17:53 | electrumsv/electrumsv | https://api.github.com/repos/electrumsv/electrumsv | opened | Test running with missing hardware libs works fine | code quality | Made fixes so Trezor and Keepkey are fine. Need others to check ledger / DBB
| 1.0 | Test running with missing hardware libs works fine - Made fixes so Trezor and Keepkey are fine. Need others to check ledger / DBB
| non_priority | test running with missing hardware libs works fine made fixes so trezor and keepkey are fine need others to check ledger dbb | 0 |
56,455 | 11,584,170,194 | IssuesEvent | 2020-02-22 15:47:35 | WarEmu/WarBugs | https://api.github.com/repos/WarEmu/WarBugs | closed | [NPC] Greenskin chapter 9: Quest giver "Ugra" is missing his quest giver symbol | NPC Sourcecode | The quest giver "Ugra" in the ch 9 Greenskin camp has no quest giver symbol above his 'ead like usual.

| 1.0 | [NPC] Greenskin chapter 9: Quest giver "Ugra" is missing his quest giver symbol - The quest giver "Ugra" in the ch 9 Greenskin camp has no quest giver symbol above his 'ead like usual.

| non_priority | greenskin chapter quest giver ugra is missing his quest giver symbol the quest giver ugra in the ch greenskin camp has no quest giver symbol above his ead like usual | 0 |
140,886 | 18,927,136,418 | IssuesEvent | 2021-11-17 10:43:32 | sultanabubaker/Rem_Ren_Test | https://api.github.com/repos/sultanabubaker/Rem_Ren_Test | opened | CVE-2019-10744 (High) detected in lodash-4.17.4.tgz | security vulnerability | ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.4.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz</a></p>
<p>Path to dependency file: Rem_Ren_Test/package.json</p>
<p>Path to vulnerable library: /node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.17.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/Rem_Ren_Test/commit/8bb0a94bd7adff96ab95fdccc13c0009d2c7a789">8bb0a94bd7adff96ab95fdccc13c0009d2c7a789</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.4","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.17.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-10744","vulnerabilityDetails":"Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-10744 (High) detected in lodash-4.17.4.tgz - ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.4.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz</a></p>
<p>Path to dependency file: Rem_Ren_Test/package.json</p>
<p>Path to vulnerable library: /node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- :x: **lodash-4.17.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sultanabubaker/Rem_Ren_Test/commit/8bb0a94bd7adff96ab95fdccc13c0009d2c7a789">8bb0a94bd7adff96ab95fdccc13c0009d2c7a789</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.4","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"lodash:4.17.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0"}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-10744","vulnerabilityDetails":"Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in lodash tgz cve high severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file rem ren test package json path to vulnerable library node modules lodash package json dependency hierarchy x lodash tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree lodash isminimumfixversionavailable true minimumfixversion lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload vulnerabilityurl | 0 |
47,325 | 7,315,398,891 | IssuesEvent | 2018-03-01 10:54:22 | MarcioJales/Sperf | https://api.github.com/repos/MarcioJales/Sperf | closed | sperf_thrnum? | documentation question | @VitorRamos Vi que a documentção ainda refere-se a `sperf_thrnum`, mas não vejo mais essa função como opção em `sperfops.h` | 1.0 | sperf_thrnum? - @VitorRamos Vi que a documentção ainda refere-se a `sperf_thrnum`, mas não vejo mais essa função como opção em `sperfops.h` | non_priority | sperf thrnum vitorramos vi que a documentção ainda refere se a sperf thrnum mas não vejo mais essa função como opção em sperfops h | 0 |
38,118 | 15,527,978,258 | IssuesEvent | 2021-03-13 08:47:48 | aws-controllers-k8s/community | https://api.github.com/repos/aws-controllers-k8s/community | opened | AWS Organisations service controller | Service Controller | ## New ACK Service Controller
Support for AWS Organisations API
### List of API resources
List the API resources in order of importance to you:
1) CreateAccount
1) DescribeAccountStatus
1) ListAccountsForParent
1) DescribeAccount
1) InviteAccountToOrganisation
1) [the rest]
| 1.0 | AWS Organisations service controller - ## New ACK Service Controller
Support for AWS Organisations API
### List of API resources
List the API resources in order of importance to you:
1) CreateAccount
1) DescribeAccountStatus
1) ListAccountsForParent
1) DescribeAccount
1) InviteAccountToOrganisation
1) [the rest]
| non_priority | aws organisations service controller new ack service controller support for aws organisations api list of api resources list the api resources in order of importance to you createaccount describeaccountstatus listaccountsforparent describeaccount inviteaccounttoorganisation | 0 |
12,812 | 8,717,744,671 | IssuesEvent | 2018-12-07 18:08:07 | jowein/forever | https://api.github.com/repos/jowein/forever | closed | CVE-2008-6218 High Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2008-6218 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>libpngv1.2.2</b></p></summary>
<p>
<p>LIBPNG: Portable Network Graphics support, official libpng repository</p>
<p>Library home page: <a href=https://github.com/hunter-packages/libpng.git>https://github.com/hunter-packages/libpng.git</a></p>
<p>Found in commit: <a href="https://github.com/jowein/forever/commit/3f2a6b067e42d7858dce5bf690808a2abdb20d6d">3f2a6b067e42d7858dce5bf690808a2abdb20d6d</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (4)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /forever/pngset.c
- /forever/pngrio.c
- /forever/pngrtran.c
- /forever/pngrutil.c
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Memory leak in the png_handle_tEXt function in pngrutil.c in libpng before 1.2.33 rc02 and 1.4.0 beta36 allows context-dependent attackers to cause a denial of service (memory exhaustion) via a crafted PNG file.
<p>Publish Date: 2009-02-20
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-6218>CVE-2008-6218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://security.gentoo.org/glsa/glsa-200903-28.xml">http://security.gentoo.org/glsa/glsa-200903-28.xml</a></p>
<p>Release Date: 2009-03-14</p>
<p>Fix Resolution: All libpng users should upgrade to the latest version >= libpng-1.2.35
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2008-6218 High Severity Vulnerability detected by WhiteSource - ## CVE-2008-6218 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>libpngv1.2.2</b></p></summary>
<p>
<p>LIBPNG: Portable Network Graphics support, official libpng repository</p>
<p>Library home page: <a href=https://github.com/hunter-packages/libpng.git>https://github.com/hunter-packages/libpng.git</a></p>
<p>Found in commit: <a href="https://github.com/jowein/forever/commit/3f2a6b067e42d7858dce5bf690808a2abdb20d6d">3f2a6b067e42d7858dce5bf690808a2abdb20d6d</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (4)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /forever/pngset.c
- /forever/pngrio.c
- /forever/pngrtran.c
- /forever/pngrutil.c
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Memory leak in the png_handle_tEXt function in pngrutil.c in libpng before 1.2.33 rc02 and 1.4.0 beta36 allows context-dependent attackers to cause a denial of service (memory exhaustion) via a crafted PNG file.
<p>Publish Date: 2009-02-20
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-6218>CVE-2008-6218</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://security.gentoo.org/glsa/glsa-200903-28.xml">http://security.gentoo.org/glsa/glsa-200903-28.xml</a></p>
<p>Release Date: 2009-03-14</p>
<p>Fix Resolution: All libpng users should upgrade to the latest version >= libpng-1.2.35
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library libpng portable network graphics support official libpng repository library home page a href found in commit a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries forever pngset c forever pngrio c forever pngrtran c forever pngrutil c vulnerability details memory leak in the png handle text function in pngrutil c in libpng before and allows context dependent attackers to cause a denial of service memory exhaustion via a crafted png file publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution all libpng users should upgrade to the latest version libpng step up your open source security game with whitesource | 0 |
10,524 | 7,203,444,419 | IssuesEvent | 2018-02-06 09:14:27 | gnocchixyz/gnocchi | https://api.github.com/repos/gnocchixyz/gnocchi | closed | keepalive won't work with our uwsgi config | performance | It's not clear why yet, but with uwsgi http keepalive doesn't work with Gnocchi.
even if we use http11-socket or, http-keepalive and add-header="Connection: Keep-Alive".
The current workaround is to set `--add-header "Connection: close"`. | True | keepalive won't work with our uwsgi config - It's not clear why yet, but with uwsgi http keepalive doesn't work with Gnocchi.
even if we use http11-socket or, http-keepalive and add-header="Connection: Keep-Alive".
The current workaround is to set `--add-header "Connection: close"`. | non_priority | keepalive won t work with our uwsgi config it s not clear why yet but with uwsgi http keepalive doesn t work with gnocchi even if we use socket or http keepalive and add header connection keep alive the current workaround is to set add header connection close | 0 |
115,968 | 24,834,939,944 | IssuesEvent | 2022-10-26 08:05:56 | microsoft/vsmarketplace | https://api.github.com/repos/microsoft/vsmarketplace | closed | failed to install python extension in Jetson agx orin | vscode | Type: <b>Bug</b>
I tried to install **python extension** in **Jetson agx orin**, but always failed, bug report below:
```
error 10:20:22.42: Failed to install Python Extension via Kernel Picker command
warn 10:20:22.45: DataScience Error [Error: Failed to install the Python Extension.
at _.installPythonExtensionViaKernelPicker (/home/orin/.vscode-server-insiders/extensions/ms-toolsai.jupyter-2022.8.1002431052/out/extension.node.js:2:2407793)
at async a._executeContributedCommand (/home/orin/.vscode-server-insiders/bin/da76f93349a72022ca4670c1b84860304616aaa2/out/vs/workbench/api/node/extensionHostProcess.js:85:63914)]
```
VS Code version: Code - Insiders 1.70.0-insider (da76f93349a72022ca4670c1b84860304616aaa2, 2022-08-03T05:53:23.899Z)
OS version: Windows_NT x64 10.0.19044
Modes:
Remote OS version: Linux arm64 5.10.65-tegra
Remote OS version: Linux x64 4.15.0-176-generic
<!-- generated by issue reporter --> | 1.0 | failed to install python extension in Jetson agx orin - Type: <b>Bug</b>
I tried to install **python extension** in **Jetson agx orin**, but always failed, bug report below:
```
error 10:20:22.42: Failed to install Python Extension via Kernel Picker command
warn 10:20:22.45: DataScience Error [Error: Failed to install the Python Extension.
at _.installPythonExtensionViaKernelPicker (/home/orin/.vscode-server-insiders/extensions/ms-toolsai.jupyter-2022.8.1002431052/out/extension.node.js:2:2407793)
at async a._executeContributedCommand (/home/orin/.vscode-server-insiders/bin/da76f93349a72022ca4670c1b84860304616aaa2/out/vs/workbench/api/node/extensionHostProcess.js:85:63914)]
```
VS Code version: Code - Insiders 1.70.0-insider (da76f93349a72022ca4670c1b84860304616aaa2, 2022-08-03T05:53:23.899Z)
OS version: Windows_NT x64 10.0.19044
Modes:
Remote OS version: Linux arm64 5.10.65-tegra
Remote OS version: Linux x64 4.15.0-176-generic
<!-- generated by issue reporter --> | non_priority | failed to install python extension in jetson agx orin type bug i tried to install python extension in jetson agx orin but always failed bug report below error failed to install python extension via kernel picker command warn datascience error error failed to install the python extension at installpythonextensionviakernelpicker home orin vscode server insiders extensions ms toolsai jupyter out extension node js at async a executecontributedcommand home orin vscode server insiders bin out vs workbench api node extensionhostprocess js vs code version code insiders insider os version windows nt modes remote os version linux tegra remote os version linux generic | 0 |
282,223 | 30,889,230,097 | IssuesEvent | 2023-08-04 02:25:39 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | reopened | CVE-2019-19037 (Medium) detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2019-19037 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/ext4/namei.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/ext4/namei.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
ext4_empty_dir in fs/ext4/namei.c in the Linux kernel through 5.3.12 allows a NULL pointer dereference because ext4_read_dirblock(inode,0,DIRENT_HTREE) can be zero.
Mend Note: After conducting further research, Mend has determined that versions v2.6.30-rc1-v4.9.207, v4.10-rc1-v4.14.160, v4.15-rc1--v4.19.91, v5.0-rc1--v5.4.6 and v5.5-rc1--v5.5-rc2 of Linux Kernel are vulnerable to CVE-2019-19037.
<p>Publish Date: 2019-11-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19037>CVE-2019-19037</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2019-19037">https://www.linuxkernelcves.com/cves/CVE-2019-19037</a></p>
<p>Release Date: 2019-11-21</p>
<p>Fix Resolution: v4.9.208, v4.14.161, v4.19.92, v5.4.7, v5.5-rc3,</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19037 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2019-19037 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/ext4/namei.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/ext4/namei.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
ext4_empty_dir in fs/ext4/namei.c in the Linux kernel through 5.3.12 allows a NULL pointer dereference because ext4_read_dirblock(inode,0,DIRENT_HTREE) can be zero.
Mend Note: After conducting further research, Mend has determined that versions v2.6.30-rc1-v4.9.207, v4.10-rc1-v4.14.160, v4.15-rc1--v4.19.91, v5.0-rc1--v5.4.6 and v5.5-rc1--v5.5-rc2 of Linux Kernel are vulnerable to CVE-2019-19037.
<p>Publish Date: 2019-11-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-19037>CVE-2019-19037</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2019-19037">https://www.linuxkernelcves.com/cves/CVE-2019-19037</a></p>
<p>Release Date: 2019-11-21</p>
<p>Fix Resolution: v4.9.208, v4.14.161, v4.19.92, v5.4.7, v5.5-rc3,</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files fs namei c fs namei c vulnerability details empty dir in fs namei c in the linux kernel through allows a null pointer dereference because read dirblock inode dirent htree can be zero mend note after conducting further research mend has determined that versions and of linux kernel are vulnerable to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
146,173 | 23,018,145,382 | IssuesEvent | 2022-07-22 00:18:57 | opensearch-project/geospatial | https://api.github.com/repos/opensearch-project/geospatial | closed | [Proposal]: Low Level Implementation Details for Geo Shape Aggregation and future Geo related Features | enhancement Design | ## Introduction
This proposal talks about the low level implementation details for the Geo Shape aggregations. We will be covering what are the components/classes/interfaces required for the Geo Shape aggregations and *what should be the right place to put those components.*
In whole proposal we will be using components, classes, interfaces terms interchangeably. As we will be focusing on the low level implementation details it is expected that reader is already aware that how indexing and query works on GeoShape in OpenSearch, what is a doc value and how it is used in the aggregation framework.
## Goal
Goal of proposal is to answer the following questions.
_Note: Module here refer to the different [libs](https://github.com/opensearch-project/OpenSearch/tree/main/libs), [modules](https://github.com/opensearch-project/OpenSearch/tree/main/modules) folders provided in the OpenSearch core repo._
### P0
1. Which module we should use to write the Geo Shape Aggregation level interfaces? or should we directly go with the Geo-Spatial repo?
2. Which module we should use to write the Value Source boiler plate code for converting Doc Values back to specific classes for GeoShape, as they have some dependency between classes already present like [CoreValueSourceType](https://github.com/opensearch-project/OpenSearch/blob/main/server/src/main/java/org/opensearch/search/aggregations/support/CoreValuesSourceType.java) etc?
### P1
1. What should be the long term vision of Geo team around what is the right place to put the code related to Geo space? The code involves Geo FieldMapper(Geo Point and Geo Shape) used for indexing and querying, Geo Aggregations(both older and newer geo aggregations both on Point and Shape) and Value Source boiler plate code for converting Doc Values back to specific classes.
2. How we should do the migration of the code mentioned in `#1` to the module we decide to move?
### Assumptions
1. The XYPoint and XY shape related features will be added in the [Geo-Spatial](https://github.com/opensearch-project/geospatial) repo and it will be keep on happening.
### Why we need to answer the questions above?
The answer to these questions will help us do the following:
1. As there will be a lot of common code between the aggregations and we will be abstracting that logic out, hence we need to make sure that we are abstracting them in the right place so that this is not a throw away work.
2. With the release of XY Point and XY shape in the Geo-Spatial plugin, we need to deicide in long term where we want to put all our Geo related features(in a backward compatible fashion), how we want to provide them to customers.
3. It will help us provide better estimate on the timelines, efforts for the launch of Geo Shape aggregations and the other features in the future like(GeoLineAggregation, GeoHexAggregations, Aggregations on XY Point and XY Shape).
## Current Architecture
As of version 2.1 of OpenSearch the Geo related aggregations(which contains only GeoPoint aggregations) are present in the OpenSearch core repo. There are no aggregations present on the Geo Shape. The Field mapper which init the GeoShape mapper is initialized via the [Geo module](https://github.com/opensearch-project/OpenSearch/blob/main/modules/geo/src/main/java/org/opensearch/geo/GeoPlugin.java) present in the OpenSearch repo.
We have created a new repo named [Geo-Spatial](https://github.com/opensearch-project/geospatial) which host GeoJson related features. The XY Point and XY shape indexing and querying functionalities are getting developed and will be released as part of 2.3 release(tentative). The intent of that repo was to provide and encapsulate all the geo-related features via that
## New Aggregations which we are building
In the current roadmap we have [4 different aggregations](https://github.com/opensearch-project/geospatial/issues/84) that we will be implementing on the Geo Shape. Below are those aggregations.
1. GeoBounds
2. GeoCentroid
3. GeoTile
4. GeoHashGrid
To provide more context these aggregations are already implemented for the GeoPoint field. We are also working on planning on implementing the Geo Line Aggregation, GeoHex Gird(customer has already reached out for this) which are already supported in Elastic Search.
## Proposed Solution
The solution is to move the Aggregations, Indexing and Query for both Geo Point and GeoShape to the Geo-Spatial plugin provided via [Geo-Spatial Repo](https://github.com/opensearch-project/geospatial). As this is breaking changes, hence we are proposing a phased approach, which make sure that we are incrementally progressing to the final goal.
### Phase 1
**Step1: One by one move aggregation(4 different classes for aggregations + Tests) to the Geo modules folder in the OpenSearch core. The aggregation that we will move will be the one which we are developing over the GeoShape.**
**Why we need this? Or what is the Pros about it?**
The code between the aggregations for GeoPoint and GeoShape is same and we can abstract common logic between GeoPoint and GeoShape rather than duplicating them.
**Will there be customer Impact?**
No, there will be no customer impact, as these classes are directly build with the OpenSearch core min distribution.
**What will happen if we don’t do this?**
We either need to copy the same code/logic from GeoPoint Aggregations to GeoShape aggregations or we will be creating more interfaces in the server folder of OpenSearch which will needs to be migrated later on.
**Step2: Abstract out the common logic for the GeoShape and GeoPoint aggregation. Allow both the aggregation to depend on this logic.**
**Why we need this? Or what is the Pros about it?**
This will abstract out the common logic and we can reuse the logic across aggregations
**Will there be customer Impact?**
No, as the aggregations will still be built in min distribution of OpenSearch.
Repeat the above 2 steps for each Aggregation that we are launching for GeoShape. This will make sure that we are moving towards right abstraction.
**Step3: Move the FieldMappers, Queries and ValueSource related code(Both GeoShape and GeoPoint), Integration Tests etc. to the Geo module once all the Aggregations have moved to the Geo Module.**
**Why we need this? Or what is the Pros about it?**
This will abstract out the common logic and we can reuse the logic across aggregations
**Will there be customer Impact?**
No, as the aggregations will still be built in min distribution of OpenSearch.
### Phase 2
**Step1: Build the proposal to move the Geo Module to Geo-Spatial Repo as a separate plugin or under a GeoSpatial Plugin. Analyze the impact and community feedback around what is the best way to provide the backward compatibly and seamless migration.**
**Why we need this? or what we want to achieve on this?**
This will provide us the insights around what community wants and what extra support will be required from our side for the seamless upgrade.
**Step2: Move the actual code from the Geo Module to Geo-Spatial Repo and release it via OpenSearch major version(exact version depends on various factors) release cycle as a breaking change.**
On a high level this will be a simple movement of code from Geo Module to Geo-Spatial plugin. The complexity will arise around how customer will migrate. Given that this will be done in major release of OpenSearch(given that it is breaking change), we will use the feedbacks provided in step-1 to give customer all the tools for doing backward compatibility. Example:
1. We can release a distribution of open search with Geo-spatial plugin already installed.
2. We can build on top of the Extensions framework which is currently being worked upon OpenSearch.[Issue](https://github.com/opensearch-project/OpenSearch/issues/2447)
Below are the pros and cons of the above solution:
**Pros:**
1. No change for customers till we go the phase-2 of the solution.
2. No confusion in customer around from which version they need the GeoSpatial plugin for the geo based aggregations and when they will get the aggregations out of the box from OpenSearch min distribution.
3. Code remains in 1 single repo always which provides easier debugging, development experience and release experience.
**Cons:**
1. Till we have moved the aggregations to the Geo-Spatial repo we need to depend on the OpenSearch Core infrastructure, PR reviewers etc, which can increase the development time, as it is a fast moving repo. Seeing that we have many new aggregations to build this can have large overall impact on development timeline.
2. Difficulties in back-port as the main and 2.x version of repo has breaking changes as compared to Geo-Spatial repo which has less or no breaking changes.
## Alternatives
### Alternative 1
Provide Aggregations on GeoShape as a part of Open search min distribution by directly implementing the GeoShape aggregations in the OpenSearch core itself.(Don’t move aggregations to even geo module in the core repo).
**Pros:**
1. Code remains in 1 single repo always which provides easier debugging and development experience.
2. No upgrade required for customers till phase-1.
3. Customers will start to get out of box aggregations support on geo-shape. Plus they will have proper upgrade paths and SOP when we move the code to plugin.
**Cons:**
1. Difficulties in back-port as the main and 2.x version of repo has breaking changes as compared to Geo-Spatial repo which has less or no breaking changes.
2. We need to depend on the OpenSearch Core infrastructure, PR reviewers etc, which can increase the development time, as it is a fast moving repo. Seeing that we have many new aggregations to build this can have larger impact on development timeline.
3. There can be potential changes required when we start implementing the aggregations over XY shape and Point.
The cons provided here can be removed working with the OpenSearch team to discuss on the dedicated reviewers and bandwidth for PRs. Also, as we move towards moving the code to geo-module we will have zero to no conflicts as apart from geo-spatial team no one will be working on that in best case. On con #3 as of now we don’t have any plan and customer use-case. Even if we do have that we can still use the common interfaces that we have created in the Geo module.
Overall the solution do have some cons which can create some delays and delayed launches but this is the most customer obsessed way.
### Alternative 2
Create the new aggregations for GeoShape directly in the Geo Spatial repo, do all the refactoring required in core OpenSearch repo to avoid code duplication. As a backlog task move the Aggregations(Geo Point) to new repo and keep adding new features on Geo to the Geo-Spatial repo only.
**Pros:**
1. **Easy Upgrade:** As fewer customers will be there who won’t have installed the Geo-Spatial plugin when we move all our aggregations to Geo-Spatial plugin.
2. Easy to back-port and release the patch versions.
3. Faster release cycles, reduction in PR review time, merges and lesser merge conflicts etc.
**Cons:**
1. **Customer Confusion:** It can cause confusion to the customer to understand as the aggregations are divided in the plugins and core repo.
2. We can end up modifying the code in core repo more often than not to support the new features and interfaces that we want to build in Geo-Spatial repo. Even small changes can end up touching more than 1 repo, which will create problems of backward compatibility, testing, developer frustration.
3. As of now, we have no input from community whether we should move the aggregations to Geo-Spatial repo or keep them in the OpenSearch core.
### Alternative 3
Create the new aggregations for GeoShape directly in the Geo Spatial repo, do all the refactoring required in core OpenSearch repo to avoid code duplication. Keep adding new features on the Geo Spatial repo only.
**Pros:**
1. No upgrade required and no confusion as customer who wants to use new aggregations just need to install the right plugin.
2. Easy to back-port and release for the patch versions.
3. Faster release cycles, reduction in PR review time, merges and lesser merge conflicts etc.
**Cons:**
1. We can end up modifying the code in core repo more often to support the new features and interfaces that we want to build in Geo-Spatial repo. Even small changes can end up touching more than 1 repo, which will increase the developer frustration for release.
## Feedback Required
The above sections provide Phased Approach as the proposed solution, but we really want to focus on the Alternative-2 as well. It would be great to know community thinks about the Alternative-2 and should we do that instead of phased approach which is long and time consuming.
## Appendix
### Frequently Asked Question
*Q: If after step 1 of phase 2 we found out that community doesn’t want yet another plugin for Geo related indexing and querying then will phase 1 effort be in vain?*
No it won’t be in vain as we would have developed the interfaces that can be used in the XY aggregations, we would have carved out the geo related code to module which can evolve of its own, even when it is with the Core repo.
### Useful Links:
1. https://github.com/opensearch-project/OpenSearch/
2. https://github.com/opensearch-project/geospatial/
3. https://github.com/opensearch-project/geospatial/issues/84 | 1.0 | [Proposal]: Low Level Implementation Details for Geo Shape Aggregation and future Geo related Features - ## Introduction
This proposal talks about the low level implementation details for the Geo Shape aggregations. We will be covering what are the components/classes/interfaces required for the Geo Shape aggregations and *what should be the right place to put those components.*
In whole proposal we will be using components, classes, interfaces terms interchangeably. As we will be focusing on the low level implementation details it is expected that reader is already aware that how indexing and query works on GeoShape in OpenSearch, what is a doc value and how it is used in the aggregation framework.
## Goal
Goal of proposal is to answer the following questions.
_Note: Module here refer to the different [libs](https://github.com/opensearch-project/OpenSearch/tree/main/libs), [modules](https://github.com/opensearch-project/OpenSearch/tree/main/modules) folders provided in the OpenSearch core repo._
### P0
1. Which module we should use to write the Geo Shape Aggregation level interfaces? or should we directly go with the Geo-Spatial repo?
2. Which module we should use to write the Value Source boiler plate code for converting Doc Values back to specific classes for GeoShape, as they have some dependency between classes already present like [CoreValueSourceType](https://github.com/opensearch-project/OpenSearch/blob/main/server/src/main/java/org/opensearch/search/aggregations/support/CoreValuesSourceType.java) etc?
### P1
1. What should be the long term vision of Geo team around what is the right place to put the code related to Geo space? The code involves Geo FieldMapper(Geo Point and Geo Shape) used for indexing and querying, Geo Aggregations(both older and newer geo aggregations both on Point and Shape) and Value Source boiler plate code for converting Doc Values back to specific classes.
2. How we should do the migration of the code mentioned in `#1` to the module we decide to move?
### Assumptions
1. The XYPoint and XY shape related features will be added in the [Geo-Spatial](https://github.com/opensearch-project/geospatial) repo and it will be keep on happening.
### Why we need to answer the questions above?
The answer to these questions will help us do the following:
1. As there will be a lot of common code between the aggregations and we will be abstracting that logic out, hence we need to make sure that we are abstracting them in the right place so that this is not a throw away work.
2. With the release of XY Point and XY shape in the Geo-Spatial plugin, we need to deicide in long term where we want to put all our Geo related features(in a backward compatible fashion), how we want to provide them to customers.
3. It will help us provide better estimate on the timelines, efforts for the launch of Geo Shape aggregations and the other features in the future like(GeoLineAggregation, GeoHexAggregations, Aggregations on XY Point and XY Shape).
## Current Architecture
As of version 2.1 of OpenSearch the Geo related aggregations(which contains only GeoPoint aggregations) are present in the OpenSearch core repo. There are no aggregations present on the Geo Shape. The Field mapper which init the GeoShape mapper is initialized via the [Geo module](https://github.com/opensearch-project/OpenSearch/blob/main/modules/geo/src/main/java/org/opensearch/geo/GeoPlugin.java) present in the OpenSearch repo.
We have created a new repo named [Geo-Spatial](https://github.com/opensearch-project/geospatial) which host GeoJson related features. The XY Point and XY shape indexing and querying functionalities are getting developed and will be released as part of 2.3 release(tentative). The intent of that repo was to provide and encapsulate all the geo-related features via that
## New Aggregations which we are building
In the current roadmap we have [4 different aggregations](https://github.com/opensearch-project/geospatial/issues/84) that we will be implementing on the Geo Shape. Below are those aggregations.
1. GeoBounds
2. GeoCentroid
3. GeoTile
4. GeoHashGrid
To provide more context these aggregations are already implemented for the GeoPoint field. We are also working on planning on implementing the Geo Line Aggregation, GeoHex Gird(customer has already reached out for this) which are already supported in Elastic Search.
## Proposed Solution
The solution is to move the Aggregations, Indexing and Query for both Geo Point and GeoShape to the Geo-Spatial plugin provided via [Geo-Spatial Repo](https://github.com/opensearch-project/geospatial). As this is breaking changes, hence we are proposing a phased approach, which make sure that we are incrementally progressing to the final goal.
### Phase 1
**Step1: One by one move aggregation(4 different classes for aggregations + Tests) to the Geo modules folder in the OpenSearch core. The aggregation that we will move will be the one which we are developing over the GeoShape.**
**Why we need this? Or what is the Pros about it?**
The code between the aggregations for GeoPoint and GeoShape is same and we can abstract common logic between GeoPoint and GeoShape rather than duplicating them.
**Will there be customer Impact?**
No, there will be no customer impact, as these classes are directly build with the OpenSearch core min distribution.
**What will happen if we don’t do this?**
We either need to copy the same code/logic from GeoPoint Aggregations to GeoShape aggregations or we will be creating more interfaces in the server folder of OpenSearch which will needs to be migrated later on.
**Step2: Abstract out the common logic for the GeoShape and GeoPoint aggregation. Allow both the aggregation to depend on this logic.**
**Why we need this? Or what is the Pros about it?**
This will abstract out the common logic and we can reuse the logic across aggregations
**Will there be customer Impact?**
No, as the aggregations will still be built in min distribution of OpenSearch.
Repeat the above 2 steps for each Aggregation that we are launching for GeoShape. This will make sure that we are moving towards right abstraction.
**Step3: Move the FieldMappers, Queries and ValueSource related code(Both GeoShape and GeoPoint), Integration Tests etc. to the Geo module once all the Aggregations have moved to the Geo Module.**
**Why we need this? Or what is the Pros about it?**
This will abstract out the common logic and we can reuse the logic across aggregations
**Will there be customer Impact?**
No, as the aggregations will still be built in min distribution of OpenSearch.
### Phase 2
**Step1: Build the proposal to move the Geo Module to Geo-Spatial Repo as a separate plugin or under a GeoSpatial Plugin. Analyze the impact and community feedback around what is the best way to provide the backward compatibly and seamless migration.**
**Why we need this? or what we want to achieve on this?**
This will provide us the insights around what community wants and what extra support will be required from our side for the seamless upgrade.
**Step2: Move the actual code from the Geo Module to Geo-Spatial Repo and release it via OpenSearch major version(exact version depends on various factors) release cycle as a breaking change.**
On a high level this will be a simple movement of code from Geo Module to Geo-Spatial plugin. The complexity will arise around how customer will migrate. Given that this will be done in major release of OpenSearch(given that it is breaking change), we will use the feedbacks provided in step-1 to give customer all the tools for doing backward compatibility. Example:
1. We can release a distribution of open search with Geo-spatial plugin already installed.
2. We can build on top of the Extensions framework which is currently being worked upon OpenSearch.[Issue](https://github.com/opensearch-project/OpenSearch/issues/2447)
Below are the pros and cons of the above solution:
**Pros:**
1. No change for customers till we go the phase-2 of the solution.
2. No confusion in customer around from which version they need the GeoSpatial plugin for the geo based aggregations and when they will get the aggregations out of the box from OpenSearch min distribution.
3. Code remains in 1 single repo always which provides easier debugging, development experience and release experience.
**Cons:**
1. Till we have moved the aggregations to the Geo-Spatial repo we need to depend on the OpenSearch Core infrastructure, PR reviewers etc, which can increase the development time, as it is a fast moving repo. Seeing that we have many new aggregations to build this can have large overall impact on development timeline.
2. Difficulties in back-port as the main and 2.x version of repo has breaking changes as compared to Geo-Spatial repo which has less or no breaking changes.
## Alternatives
### Alternative 1
Provide Aggregations on GeoShape as a part of Open search min distribution by directly implementing the GeoShape aggregations in the OpenSearch core itself.(Don’t move aggregations to even geo module in the core repo).
**Pros:**
1. Code remains in 1 single repo always which provides easier debugging and development experience.
2. No upgrade required for customers till phase-1.
3. Customers will start to get out of box aggregations support on geo-shape. Plus they will have proper upgrade paths and SOP when we move the code to plugin.
**Cons:**
1. Difficulties in back-port as the main and 2.x version of repo has breaking changes as compared to Geo-Spatial repo which has less or no breaking changes.
2. We need to depend on the OpenSearch Core infrastructure, PR reviewers etc, which can increase the development time, as it is a fast moving repo. Seeing that we have many new aggregations to build this can have larger impact on development timeline.
3. There can be potential changes required when we start implementing the aggregations over XY shape and Point.
The cons provided here can be removed working with the OpenSearch team to discuss on the dedicated reviewers and bandwidth for PRs. Also, as we move towards moving the code to geo-module we will have zero to no conflicts as apart from geo-spatial team no one will be working on that in best case. On con #3 as of now we don’t have any plan and customer use-case. Even if we do have that we can still use the common interfaces that we have created in the Geo module.
Overall the solution do have some cons which can create some delays and delayed launches but this is the most customer obsessed way.
### Alternative 2
Create the new aggregations for GeoShape directly in the Geo Spatial repo, do all the refactoring required in core OpenSearch repo to avoid code duplication. As a backlog task move the Aggregations(Geo Point) to new repo and keep adding new features on Geo to the Geo-Spatial repo only.
**Pros:**
1. **Easy Upgrade:** As fewer customers will be there who won’t have installed the Geo-Spatial plugin when we move all our aggregations to Geo-Spatial plugin.
2. Easy to back-port and release the patch versions.
3. Faster release cycles, reduction in PR review time, merges and lesser merge conflicts etc.
**Cons:**
1. **Customer Confusion:** It can cause confusion to the customer to understand as the aggregations are divided in the plugins and core repo.
2. We can end up modifying the code in core repo more often than not to support the new features and interfaces that we want to build in Geo-Spatial repo. Even small changes can end up touching more than 1 repo, which will create problems of backward compatibility, testing, developer frustration.
3. As of now, we have no input from community whether we should move the aggregations to Geo-Spatial repo or keep them in the OpenSearch core.
### Alternative 3
Create the new aggregations for GeoShape directly in the Geo Spatial repo, do all the refactoring required in core OpenSearch repo to avoid code duplication. Keep adding new features on the Geo Spatial repo only.
**Pros:**
1. No upgrade required and no confusion as customer who wants to use new aggregations just need to install the right plugin.
2. Easy to back-port and release for the patch versions.
3. Faster release cycles, reduction in PR review time, merges and lesser merge conflicts etc.
**Cons:**
1. We can end up modifying the code in core repo more often to support the new features and interfaces that we want to build in Geo-Spatial repo. Even small changes can end up touching more than 1 repo, which will increase the developer frustration for release.
## Feedback Required
The above sections provide Phased Approach as the proposed solution, but we really want to focus on the Alternative-2 as well. It would be great to know community thinks about the Alternative-2 and should we do that instead of phased approach which is long and time consuming.
## Appendix
### Frequently Asked Question
*Q: If after step 1 of phase 2 we found out that community doesn’t want yet another plugin for Geo related indexing and querying then will phase 1 effort be in vain?*
No it won’t be in vain as we would have developed the interfaces that can be used in the XY aggregations, we would have carved out the geo related code to module which can evolve of its own, even when it is with the Core repo.
### Useful Links:
1. https://github.com/opensearch-project/OpenSearch/
2. https://github.com/opensearch-project/geospatial/
3. https://github.com/opensearch-project/geospatial/issues/84 | non_priority | low level implementation details for geo shape aggregation and future geo related features introduction this proposal talks about the low level implementation details for the geo shape aggregations we will be covering what are the components classes interfaces required for the geo shape aggregations and what should be the right place to put those components in whole proposal we will be using components classes interfaces terms interchangeably as we will be focusing on the low level implementation details it is expected that reader is already aware that how indexing and query works on geoshape in opensearch what is a doc value and how it is used in the aggregation framework goal goal of proposal is to answer the following questions note module here refer to the different folders provided in the opensearch core repo which module we should use to write the geo shape aggregation level interfaces or should we directly go with the geo spatial repo which module we should use to write the value source boiler plate code for converting doc values back to specific classes for geoshape as they have some dependency between classes already present like etc what should be the long term vision of geo team around what is the right place to put the code related to geo space the code involves geo fieldmapper geo point and geo shape used for indexing and querying geo aggregations both older and newer geo aggregations both on point and shape and value source boiler plate code for converting doc values back to specific classes how we should do the migration of the code mentioned in to the module we decide to move assumptions the xypoint and xy shape related features will be added in the repo and it will be keep on happening why we need to answer the questions above the answer to these questions will help us do the following as there will be a lot of common code between the aggregations and we will be abstracting that logic out hence we need to make sure that we are abstracting them in the right place so that this is not a throw away work with the release of xy point and xy shape in the geo spatial plugin we need to deicide in long term where we want to put all our geo related features in a backward compatible fashion how we want to provide them to customers it will help us provide better estimate on the timelines efforts for the launch of geo shape aggregations and the other features in the future like geolineaggregation geohexaggregations aggregations on xy point and xy shape current architecture as of version of opensearch the geo related aggregations which contains only geopoint aggregations are present in the opensearch core repo there are no aggregations present on the geo shape the field mapper which init the geoshape mapper is initialized via the present in the opensearch repo we have created a new repo named which host geojson related features the xy point and xy shape indexing and querying functionalities are getting developed and will be released as part of release tentative the intent of that repo was to provide and encapsulate all the geo related features via that new aggregations which we are building in the current roadmap we have that we will be implementing on the geo shape below are those aggregations geobounds geocentroid geotile geohashgrid to provide more context these aggregations are already implemented for the geopoint field we are also working on planning on implementing the geo line aggregation geohex gird customer has already reached out for this which are already supported in elastic search proposed solution the solution is to move the aggregations indexing and query for both geo point and geoshape to the geo spatial plugin provided via as this is breaking changes hence we are proposing a phased approach which make sure that we are incrementally progressing to the final goal phase one by one move aggregation different classes for aggregations tests to the geo modules folder in the opensearch core the aggregation that we will move will be the one which we are developing over the geoshape why we need this or what is the pros about it the code between the aggregations for geopoint and geoshape is same and we can abstract common logic between geopoint and geoshape rather than duplicating them will there be customer impact no there will be no customer impact as these classes are directly build with the opensearch core min distribution what will happen if we don’t do this we either need to copy the same code logic from geopoint aggregations to geoshape aggregations or we will be creating more interfaces in the server folder of opensearch which will needs to be migrated later on abstract out the common logic for the geoshape and geopoint aggregation allow both the aggregation to depend on this logic why we need this or what is the pros about it this will abstract out the common logic and we can reuse the logic across aggregations will there be customer impact no as the aggregations will still be built in min distribution of opensearch repeat the above steps for each aggregation that we are launching for geoshape this will make sure that we are moving towards right abstraction move the fieldmappers queries and valuesource related code both geoshape and geopoint integration tests etc to the geo module once all the aggregations have moved to the geo module why we need this or what is the pros about it this will abstract out the common logic and we can reuse the logic across aggregations will there be customer impact no as the aggregations will still be built in min distribution of opensearch phase build the proposal to move the geo module to geo spatial repo as a separate plugin or under a geospatial plugin analyze the impact and community feedback around what is the best way to provide the backward compatibly and seamless migration why we need this or what we want to achieve on this this will provide us the insights around what community wants and what extra support will be required from our side for the seamless upgrade move the actual code from the geo module to geo spatial repo and release it via opensearch major version exact version depends on various factors release cycle as a breaking change on a high level this will be a simple movement of code from geo module to geo spatial plugin the complexity will arise around how customer will migrate given that this will be done in major release of opensearch given that it is breaking change we will use the feedbacks provided in step to give customer all the tools for doing backward compatibility example we can release a distribution of open search with geo spatial plugin already installed we can build on top of the extensions framework which is currently being worked upon opensearch below are the pros and cons of the above solution pros no change for customers till we go the phase of the solution no confusion in customer around from which version they need the geospatial plugin for the geo based aggregations and when they will get the aggregations out of the box from opensearch min distribution code remains in single repo always which provides easier debugging development experience and release experience cons till we have moved the aggregations to the geo spatial repo we need to depend on the opensearch core infrastructure pr reviewers etc which can increase the development time as it is a fast moving repo seeing that we have many new aggregations to build this can have large overall impact on development timeline difficulties in back port as the main and x version of repo has breaking changes as compared to geo spatial repo which has less or no breaking changes alternatives alternative provide aggregations on geoshape as a part of open search min distribution by directly implementing the geoshape aggregations in the opensearch core itself don’t move aggregations to even geo module in the core repo pros code remains in single repo always which provides easier debugging and development experience no upgrade required for customers till phase customers will start to get out of box aggregations support on geo shape plus they will have proper upgrade paths and sop when we move the code to plugin cons difficulties in back port as the main and x version of repo has breaking changes as compared to geo spatial repo which has less or no breaking changes we need to depend on the opensearch core infrastructure pr reviewers etc which can increase the development time as it is a fast moving repo seeing that we have many new aggregations to build this can have larger impact on development timeline there can be potential changes required when we start implementing the aggregations over xy shape and point the cons provided here can be removed working with the opensearch team to discuss on the dedicated reviewers and bandwidth for prs also as we move towards moving the code to geo module we will have zero to no conflicts as apart from geo spatial team no one will be working on that in best case on con as of now we don’t have any plan and customer use case even if we do have that we can still use the common interfaces that we have created in the geo module overall the solution do have some cons which can create some delays and delayed launches but this is the most customer obsessed way alternative create the new aggregations for geoshape directly in the geo spatial repo do all the refactoring required in core opensearch repo to avoid code duplication as a backlog task move the aggregations geo point to new repo and keep adding new features on geo to the geo spatial repo only pros easy upgrade as fewer customers will be there who won’t have installed the geo spatial plugin when we move all our aggregations to geo spatial plugin easy to back port and release the patch versions faster release cycles reduction in pr review time merges and lesser merge conflicts etc cons customer confusion it can cause confusion to the customer to understand as the aggregations are divided in the plugins and core repo we can end up modifying the code in core repo more often than not to support the new features and interfaces that we want to build in geo spatial repo even small changes can end up touching more than repo which will create problems of backward compatibility testing developer frustration as of now we have no input from community whether we should move the aggregations to geo spatial repo or keep them in the opensearch core alternative create the new aggregations for geoshape directly in the geo spatial repo do all the refactoring required in core opensearch repo to avoid code duplication keep adding new features on the geo spatial repo only pros no upgrade required and no confusion as customer who wants to use new aggregations just need to install the right plugin easy to back port and release for the patch versions faster release cycles reduction in pr review time merges and lesser merge conflicts etc cons we can end up modifying the code in core repo more often to support the new features and interfaces that we want to build in geo spatial repo even small changes can end up touching more than repo which will increase the developer frustration for release feedback required the above sections provide phased approach as the proposed solution but we really want to focus on the alternative as well it would be great to know community thinks about the alternative and should we do that instead of phased approach which is long and time consuming appendix frequently asked question q if after step of phase we found out that community doesn’t want yet another plugin for geo related indexing and querying then will phase effort be in vain no it won’t be in vain as we would have developed the interfaces that can be used in the xy aggregations we would have carved out the geo related code to module which can evolve of its own even when it is with the core repo useful links | 0 |
405,433 | 27,518,977,994 | IssuesEvent | 2023-03-06 13:55:02 | devvsakib/power-the-web | https://api.github.com/repos/devvsakib/power-the-web | closed | Fix Typo mistake | documentation good first issue EddieHub:good-first-issue | **Describe the bug**
There are a project folder typo mistake in PROJECTS folder
**To Reproduce**
Steps to reproduce the behavior:
tribute -> tribute
**Screenshots**
added
| 1.0 | Fix Typo mistake - **Describe the bug**
There are a project folder typo mistake in PROJECTS folder
**To Reproduce**
Steps to reproduce the behavior:
tribute -> tribute
**Screenshots**
added
| non_priority | fix typo mistake describe the bug there are a project folder typo mistake in projects folder to reproduce steps to reproduce the behavior tribute tribute screenshots added | 0 |
199,911 | 22,715,381,120 | IssuesEvent | 2022-07-06 01:10:11 | RG4421/openedr | https://api.github.com/repos/RG4421/openedr | reopened | CVE-2020-8286 (High) detected in curlcurl-7_63_0 | security vulnerability | ## CVE-2020-8286 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>curlcurl-7_63_0</b></p></summary>
<p>
<p>A command line tool and library for transferring data with URL syntax, supporting HTTP, HTTPS, FTP, FTPS, GOPHER, TFTP, SCP, SFTP, SMB, TELNET, DICT, LDAP, LDAPS, FILE, IMAP, SMTP, POP3, RTSP and RTMP. libcurl offers a myriad of powerful features</p>
<p>Library home page: <a href=https://github.com/curl/curl.git>https://github.com/curl/curl.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/RG4421/openedr/commit/f991dbd97bf34917a1d61c43ef4b41832708779c">f991dbd97bf34917a1d61c43ef4b41832708779c</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/edrav2/eprj/curl/lib/vtls/openssl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/edrav2/eprj/curl/lib/vtls/openssl.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
curl 7.41.0 through 7.73.0 is vulnerable to an improper check for certificate revocation due to insufficient verification of the OCSP response.
<p>Publish Date: 2020-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8286>CVE-2020-8286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8286">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8286</a></p>
<p>Release Date: 2020-12-14</p>
<p>Fix Resolution: 7.74.0</p>
</p>
</details>
<p></p>
| True | CVE-2020-8286 (High) detected in curlcurl-7_63_0 - ## CVE-2020-8286 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>curlcurl-7_63_0</b></p></summary>
<p>
<p>A command line tool and library for transferring data with URL syntax, supporting HTTP, HTTPS, FTP, FTPS, GOPHER, TFTP, SCP, SFTP, SMB, TELNET, DICT, LDAP, LDAPS, FILE, IMAP, SMTP, POP3, RTSP and RTMP. libcurl offers a myriad of powerful features</p>
<p>Library home page: <a href=https://github.com/curl/curl.git>https://github.com/curl/curl.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/RG4421/openedr/commit/f991dbd97bf34917a1d61c43ef4b41832708779c">f991dbd97bf34917a1d61c43ef4b41832708779c</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/edrav2/eprj/curl/lib/vtls/openssl.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/edrav2/eprj/curl/lib/vtls/openssl.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
curl 7.41.0 through 7.73.0 is vulnerable to an improper check for certificate revocation due to insufficient verification of the OCSP response.
<p>Publish Date: 2020-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8286>CVE-2020-8286</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8286">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8286</a></p>
<p>Release Date: 2020-12-14</p>
<p>Fix Resolution: 7.74.0</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in curlcurl cve high severity vulnerability vulnerable library curlcurl a command line tool and library for transferring data with url syntax supporting http https ftp ftps gopher tftp scp sftp smb telnet dict ldap ldaps file imap smtp rtsp and rtmp libcurl offers a myriad of powerful features library home page a href found in head commit a href found in base branch main vulnerable source files eprj curl lib vtls openssl c eprj curl lib vtls openssl c vulnerability details curl through is vulnerable to an improper check for certificate revocation due to insufficient verification of the ocsp response publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
77,273 | 21,718,102,084 | IssuesEvent | 2022-05-10 20:08:18 | bazelbuild/bazel-buildfarm | https://api.github.com/repos/bazelbuild/bazel-buildfarm | closed | Remote build stuck on caching empty file | Build Failure | We start buildfarm and it looks like working (we use it to build our production builds and test execution).
But if rule generates empty output file (zero bytes size) then action is stuck in build queue forever. I don't see anything strange in the logs.
For reproducing this issue:
- I simply create empty `WORKSPACE` and `BUILD`-file with content:
```
genrule(
name = "foo",
srcs = [],
outs = ["foo.txt"],
cmd = "echo -n > \"$@\"",
)
```
After that I call:
```
bazel --bazelrc=/dev/null clean && bazel --bazelrc=/dev/null build --remote_executor=grpcs://buildfarm.example.net :foo
```
This rule stuck with bazel output like:
```
INFO: Invocation ID: 6fbe2fc2-3486-4235-8f55-b0fe7a15260c
INFO: Starting clean (this may take a while). Consider using --async if the clean takes more than several minutes.
INFO: Invocation ID: e823a16f-bb10-4872-a9e0-3a7b4cb94c47
INFO: Analyzed target //:foo (5 packages loaded, 7 targets configured).
INFO: Found 1 target...
[1 / 2] Executing genrule //:foo; 40s remote
```
If I rewrite rule to write non-empty output - it's works correctly...
Bazel version: 5.1.1
Buildfarm version: 0.13.0
| 1.0 | Remote build stuck on caching empty file - We start buildfarm and it looks like working (we use it to build our production builds and test execution).
But if rule generates empty output file (zero bytes size) then action is stuck in build queue forever. I don't see anything strange in the logs.
For reproducing this issue:
- I simply create empty `WORKSPACE` and `BUILD`-file with content:
```
genrule(
name = "foo",
srcs = [],
outs = ["foo.txt"],
cmd = "echo -n > \"$@\"",
)
```
After that I call:
```
bazel --bazelrc=/dev/null clean && bazel --bazelrc=/dev/null build --remote_executor=grpcs://buildfarm.example.net :foo
```
This rule stuck with bazel output like:
```
INFO: Invocation ID: 6fbe2fc2-3486-4235-8f55-b0fe7a15260c
INFO: Starting clean (this may take a while). Consider using --async if the clean takes more than several minutes.
INFO: Invocation ID: e823a16f-bb10-4872-a9e0-3a7b4cb94c47
INFO: Analyzed target //:foo (5 packages loaded, 7 targets configured).
INFO: Found 1 target...
[1 / 2] Executing genrule //:foo; 40s remote
```
If I rewrite rule to write non-empty output - it's works correctly...
Bazel version: 5.1.1
Buildfarm version: 0.13.0
| non_priority | remote build stuck on caching empty file we start buildfarm and it looks like working we use it to build our production builds and test execution but if rule generates empty output file zero bytes size then action is stuck in build queue forever i don t see anything strange in the logs for reproducing this issue i simply create empty workspace and build file with content genrule name foo srcs outs cmd echo n after that i call bazel bazelrc dev null clean bazel bazelrc dev null build remote executor grpcs buildfarm example net foo this rule stuck with bazel output like info invocation id info starting clean this may take a while consider using async if the clean takes more than several minutes info invocation id info analyzed target foo packages loaded targets configured info found target executing genrule foo remote if i rewrite rule to write non empty output it s works correctly bazel version buildfarm version | 0 |
308,757 | 23,265,734,288 | IssuesEvent | 2022-08-04 17:11:01 | blendthink/value_class.dart | https://api.github.com/repos/blendthink/value_class.dart | closed | Add to Usage how to use it in combination with freezed and json_seriarizable | documentation enhancement value_class | ## Overview
This package can be used in combination with freezed and json_seriarizable. | 1.0 | Add to Usage how to use it in combination with freezed and json_seriarizable - ## Overview
This package can be used in combination with freezed and json_seriarizable. | non_priority | add to usage how to use it in combination with freezed and json seriarizable overview this package can be used in combination with freezed and json seriarizable | 0 |
235,484 | 19,348,892,749 | IssuesEvent | 2021-12-15 13:48:50 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | kv/kvserver: TestStoreRecoverFromEngine failed | C-test-failure O-robot branch-master | kv/kvserver.TestStoreRecoverFromEngine [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3288590&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3288590&tab=artifacts#/) on master @ [26ebecb9b9d3631a3c7c5dde21e1e1d39b05285d](https://github.com/cockroachdb/cockroach/commits/26ebecb9b9d3631a3c7c5dde21e1e1d39b05285d):
```
=== RUN TestStoreRecoverFromEngine
test_log_scope.go:73: test logs captured to: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStoreRecoverFromEngine261765857
test_log_scope.go:74: use -show-logs to present logs inline
client_raft_test.go:167:
Error Trace: client_raft_test.go:167
Error: Received unexpected error:
listen tcp 127.0.0.1:44157: bind: address already in use
Test: TestStoreRecoverFromEngine
panic.go:613: -- test log scope end --
test logs left over in: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStoreRecoverFromEngine261765857
--- FAIL: TestStoreRecoverFromEngine (0.77s)
```
<details><summary>Reproduce</summary>
<p>
To reproduce, try:
```bash
make stressrace TESTS=TestStoreRecoverFromEngine PKG=./pkg/kv/kvserver TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
Parameters in this failure:
- GOFLAGS=-json
</p>
</details>
/cc @cockroachdb/kv bdarnell
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestStoreRecoverFromEngine.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 1.0 | kv/kvserver: TestStoreRecoverFromEngine failed - kv/kvserver.TestStoreRecoverFromEngine [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3288590&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3288590&tab=artifacts#/) on master @ [26ebecb9b9d3631a3c7c5dde21e1e1d39b05285d](https://github.com/cockroachdb/cockroach/commits/26ebecb9b9d3631a3c7c5dde21e1e1d39b05285d):
```
=== RUN TestStoreRecoverFromEngine
test_log_scope.go:73: test logs captured to: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStoreRecoverFromEngine261765857
test_log_scope.go:74: use -show-logs to present logs inline
client_raft_test.go:167:
Error Trace: client_raft_test.go:167
Error: Received unexpected error:
listen tcp 127.0.0.1:44157: bind: address already in use
Test: TestStoreRecoverFromEngine
panic.go:613: -- test log scope end --
test logs left over in: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStoreRecoverFromEngine261765857
--- FAIL: TestStoreRecoverFromEngine (0.77s)
```
<details><summary>Reproduce</summary>
<p>
To reproduce, try:
```bash
make stressrace TESTS=TestStoreRecoverFromEngine PKG=./pkg/kv/kvserver TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
Parameters in this failure:
- GOFLAGS=-json
</p>
</details>
/cc @cockroachdb/kv bdarnell
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestStoreRecoverFromEngine.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | kv kvserver teststorerecoverfromengine failed kv kvserver teststorerecoverfromengine with on master run teststorerecoverfromengine test log scope go test logs captured to go src github com cockroachdb cockroach artifacts test log scope go use show logs to present logs inline client raft test go error trace client raft test go error received unexpected error listen tcp bind address already in use test teststorerecoverfromengine panic go test log scope end test logs left over in go src github com cockroachdb cockroach artifacts fail teststorerecoverfromengine reproduce to reproduce try bash make stressrace tests teststorerecoverfromengine pkg pkg kv kvserver testtimeout stressflags timeout parameters in this failure goflags json cc cockroachdb kv bdarnell | 0 |
116,665 | 17,384,162,184 | IssuesEvent | 2021-08-01 09:34:52 | TEAMMATES/teammates | https://api.github.com/repos/TEAMMATES/teammates | closed | Remove HTML sanitization in EntityAttributes classes | a-Security committers only p.Medium | Since we are using JDO to store and retrieve data from the database, by right, SQL injection should never happen and there is no need to sanitize before saving data. So we can safely remove sanitizeForSaving() function from all classes extended from `EntityAttributes`.
Those classes are:
AccountAttributes
AdminEmailAttributes
CommentAttributes
CourseAttributes
FeedbackQuestionAttributes
FeedbackResponseAttributes
FeedbackResponseCommentAttributes
FeedbackSessionAttributes
InstructorAttributes **(Ongoing)**
:white_check_mark: StudentAttributes
StudentProfileAttributes
While removing sanitizeForSaving(), we also have to apply sanitization in the frontend (JSP/JSTL), where the attribute is used, as well. From now, I will create small issues to work on those classes one by one.
| True | Remove HTML sanitization in EntityAttributes classes - Since we are using JDO to store and retrieve data from the database, by right, SQL injection should never happen and there is no need to sanitize before saving data. So we can safely remove sanitizeForSaving() function from all classes extended from `EntityAttributes`.
Those classes are:
AccountAttributes
AdminEmailAttributes
CommentAttributes
CourseAttributes
FeedbackQuestionAttributes
FeedbackResponseAttributes
FeedbackResponseCommentAttributes
FeedbackSessionAttributes
InstructorAttributes **(Ongoing)**
:white_check_mark: StudentAttributes
StudentProfileAttributes
While removing sanitizeForSaving(), we also have to apply sanitization in the frontend (JSP/JSTL), where the attribute is used, as well. From now, I will create small issues to work on those classes one by one.
| non_priority | remove html sanitization in entityattributes classes since we are using jdo to store and retrieve data from the database by right sql injection should never happen and there is no need to sanitize before saving data so we can safely remove sanitizeforsaving function from all classes extended from entityattributes those classes are accountattributes adminemailattributes commentattributes courseattributes feedbackquestionattributes feedbackresponseattributes feedbackresponsecommentattributes feedbacksessionattributes instructorattributes ongoing white check mark studentattributes studentprofileattributes while removing sanitizeforsaving we also have to apply sanitization in the frontend jsp jstl where the attribute is used as well from now i will create small issues to work on those classes one by one | 0 |
172,205 | 21,041,571,243 | IssuesEvent | 2022-03-31 12:48:24 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Respond to TLS certificate/key changes without requiring a restart | Team:Security enhancement loe:hours impact:low EnableJiraSync | Kibana maintains a number of different TLS configuration settings:
- Kibana's own HTTP server
- Kibana's connection to Elasticsearch
- Kibana's connection to the monitoring cluster (when Stack Monitoring is in use)
- Kibana's connection to the Enterprise Search service
- Kibana Alerting (TODO)
TLS certificates and keys are generally stored on disk, read once on startup, and used for the lifetime of the process. Changes to these files will not be picked up until Kibana is restarted.
Elasticsearch has long supported reloading this configuration from disk -- we should explore the feasibility of similar support within Kibana, so that we can accept updated certificates/keys without a restart.
Support for this would greatly simplify certificate rotation in managed environments such as ESS and ECE | True | Respond to TLS certificate/key changes without requiring a restart - Kibana maintains a number of different TLS configuration settings:
- Kibana's own HTTP server
- Kibana's connection to Elasticsearch
- Kibana's connection to the monitoring cluster (when Stack Monitoring is in use)
- Kibana's connection to the Enterprise Search service
- Kibana Alerting (TODO)
TLS certificates and keys are generally stored on disk, read once on startup, and used for the lifetime of the process. Changes to these files will not be picked up until Kibana is restarted.
Elasticsearch has long supported reloading this configuration from disk -- we should explore the feasibility of similar support within Kibana, so that we can accept updated certificates/keys without a restart.
Support for this would greatly simplify certificate rotation in managed environments such as ESS and ECE | non_priority | respond to tls certificate key changes without requiring a restart kibana maintains a number of different tls configuration settings kibana s own http server kibana s connection to elasticsearch kibana s connection to the monitoring cluster when stack monitoring is in use kibana s connection to the enterprise search service kibana alerting todo tls certificates and keys are generally stored on disk read once on startup and used for the lifetime of the process changes to these files will not be picked up until kibana is restarted elasticsearch has long supported reloading this configuration from disk we should explore the feasibility of similar support within kibana so that we can accept updated certificates keys without a restart support for this would greatly simplify certificate rotation in managed environments such as ess and ece | 0 |
92,687 | 18,922,848,103 | IssuesEvent | 2021-11-17 05:20:33 | okjuan/music-lib-bot | https://api.github.com/repos/okjuan/music-lib-bot | opened | Encapsulate UI formatting in `ui` module | code-style | Calls to `ui.tell_user` shouldn't contain "\n", "\t" characters because that's a low-level detail about the UI. Instead, the `ConsoleUI` class should handle that. Maybe it needs to expose functions like `ui.show_menu` for more complicated formatting scenarios. | 1.0 | Encapsulate UI formatting in `ui` module - Calls to `ui.tell_user` shouldn't contain "\n", "\t" characters because that's a low-level detail about the UI. Instead, the `ConsoleUI` class should handle that. Maybe it needs to expose functions like `ui.show_menu` for more complicated formatting scenarios. | non_priority | encapsulate ui formatting in ui module calls to ui tell user shouldn t contain n t characters because that s a low level detail about the ui instead the consoleui class should handle that maybe it needs to expose functions like ui show menu for more complicated formatting scenarios | 0 |
36,333 | 17,615,583,330 | IssuesEvent | 2021-08-18 09:17:56 | turms-im/turms | https://api.github.com/repos/turms-im/turms | opened | Remove Spring-WebFlux and only uses reactor-netty | enhancement performance | Remove Spring-WebFlux and only uses reactor-netty | True | Remove Spring-WebFlux and only uses reactor-netty - Remove Spring-WebFlux and only uses reactor-netty | non_priority | remove spring webflux and only uses reactor netty remove spring webflux and only uses reactor netty | 0 |
437,559 | 30,603,711,074 | IssuesEvent | 2023-07-22 18:20:04 | BenWestgate/Bails | https://api.github.com/repos/BenWestgate/Bails | closed | in bails-wallet entering a share with spaces is rejected | bug documentation enhancement | If the user enters the spaces exactly like it was displayed by `display_confirm` then the share should be accepted. Spaces anywhere else including a trailing space will throw the non-alphanumeric character error.
in order to prevent copy and paste from the display dialog to the entry dialog, a different whitespace character than space will be used and perhaps other invisible characters that throw a warning when detected to not copy and paste and to write the share down. | 1.0 | in bails-wallet entering a share with spaces is rejected - If the user enters the spaces exactly like it was displayed by `display_confirm` then the share should be accepted. Spaces anywhere else including a trailing space will throw the non-alphanumeric character error.
in order to prevent copy and paste from the display dialog to the entry dialog, a different whitespace character than space will be used and perhaps other invisible characters that throw a warning when detected to not copy and paste and to write the share down. | non_priority | in bails wallet entering a share with spaces is rejected if the user enters the spaces exactly like it was displayed by display confirm then the share should be accepted spaces anywhere else including a trailing space will throw the non alphanumeric character error in order to prevent copy and paste from the display dialog to the entry dialog a different whitespace character than space will be used and perhaps other invisible characters that throw a warning when detected to not copy and paste and to write the share down | 0 |
16,968 | 23,377,188,194 | IssuesEvent | 2022-08-11 05:19:48 | WPChill/modula-lite | https://api.github.com/repos/WPChill/modula-lite | opened | test all modulas with new version of elementor and elementor pro (3.7.3) | compatibility |
Hi, Since I have updated Elementor 3.7 & Elementor Pro 3.7.3, there is a conflict with all of the Modula Pro plugins I have setup. It is causing the Elementor page builder to be constantly on a grey loading screen, but when I deactivate your plugins it works again.
| True | test all modulas with new version of elementor and elementor pro (3.7.3) -
Hi, Since I have updated Elementor 3.7 & Elementor Pro 3.7.3, there is a conflict with all of the Modula Pro plugins I have setup. It is causing the Elementor page builder to be constantly on a grey loading screen, but when I deactivate your plugins it works again.
| non_priority | test all modulas with new version of elementor and elementor pro hi since i have updated elementor elementor pro there is a conflict with all of the modula pro plugins i have setup it is causing the elementor page builder to be constantly on a grey loading screen but when i deactivate your plugins it works again | 0 |
303,896 | 23,043,745,343 | IssuesEvent | 2022-07-23 15:09:26 | adam-rms/website | https://api.github.com/repos/adam-rms/website | opened | [DOCS] Update public site documentation | documentation | ### What would you like the training to cover?
Update public site documentation
### Is this already partially covered elsewhere?
_No response_
### Anything else?
_No response_ | 1.0 | [DOCS] Update public site documentation - ### What would you like the training to cover?
Update public site documentation
### Is this already partially covered elsewhere?
_No response_
### Anything else?
_No response_ | non_priority | update public site documentation what would you like the training to cover update public site documentation is this already partially covered elsewhere no response anything else no response | 0 |
107,913 | 16,762,607,163 | IssuesEvent | 2021-06-14 02:36:15 | gms-ws-demo/nibrs-pr-test | https://api.github.com/repos/gms-ws-demo/nibrs-pr-test | opened | CVE-2019-10212 (High) detected in undertow-core-1.4.20.Final.jar, undertow-core-1.4.25.Final.jar | security vulnerability | ## CVE-2019-10212 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>undertow-core-1.4.20.Final.jar</b>, <b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>
<details><summary><b>undertow-core-1.4.20.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.20.Final/undertow-core-1.4.20.Final.jar,nibrs-pr-test/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/undertow-core-1.4.20.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.20.Final.jar** (Vulnerable Library)
</details>
<details><summary><b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-route/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.25.Final/undertow-core-1.4.25.Final.jar,nibrs-pr-test/tools/nibrs-route/target/nibrs-route-1.0.0/WEB-INF/lib/undertow-core-1.4.25.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.25.Final.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs-pr-test/commit/860cc22f54e17594e32e303f0716fb065202fff5">860cc22f54e17594e32e303f0716fb065202fff5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in, all under 2.0.20, in the Undertow DEBUG log for io.undertow.request.security. If enabled, an attacker could abuse this flaw to obtain the user's credentials from the log files.
<p>Publish Date: 2019-10-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10212>CVE-2019-10212</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2019-10212">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2019-10212</a></p>
<p>Release Date: 2019-10-02</p>
<p>Fix Resolution: 2.0.27.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.20.Final","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.20.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.0.27.Final"},{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.25.Final","packageFilePaths":["/tools/nibrs-route/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.25.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.0.27.Final"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-10212","vulnerabilityDetails":"A flaw was found in, all under 2.0.20, in the Undertow DEBUG log for io.undertow.request.security. If enabled, an attacker could abuse this flaw to obtain the user\u0027s credentials from the log files.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10212","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-10212 (High) detected in undertow-core-1.4.20.Final.jar, undertow-core-1.4.25.Final.jar - ## CVE-2019-10212 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>undertow-core-1.4.20.Final.jar</b>, <b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>
<details><summary><b>undertow-core-1.4.20.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.20.Final/undertow-core-1.4.20.Final.jar,nibrs-pr-test/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/undertow-core-1.4.20.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.20.Final.jar** (Vulnerable Library)
</details>
<details><summary><b>undertow-core-1.4.25.Final.jar</b></p></summary>
<p>Undertow</p>
<p>Library home page: <a href="http://www.jboss.org/">http://www.jboss.org/</a></p>
<p>Path to dependency file: nibrs-pr-test/tools/nibrs-route/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/io/undertow/undertow-core/1.4.25.Final/undertow-core-1.4.25.Final.jar,nibrs-pr-test/tools/nibrs-route/target/nibrs-route-1.0.0/WEB-INF/lib/undertow-core-1.4.25.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **undertow-core-1.4.25.Final.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/gms-ws-demo/nibrs-pr-test/commit/860cc22f54e17594e32e303f0716fb065202fff5">860cc22f54e17594e32e303f0716fb065202fff5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in, all under 2.0.20, in the Undertow DEBUG log for io.undertow.request.security. If enabled, an attacker could abuse this flaw to obtain the user's credentials from the log files.
<p>Publish Date: 2019-10-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10212>CVE-2019-10212</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2019-10212">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2019-10212</a></p>
<p>Release Date: 2019-10-02</p>
<p>Fix Resolution: 2.0.27.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.20.Final","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.20.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.0.27.Final"},{"packageType":"Java","groupId":"io.undertow","packageName":"undertow-core","packageVersion":"1.4.25.Final","packageFilePaths":["/tools/nibrs-route/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"io.undertow:undertow-core:1.4.25.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.0.27.Final"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-10212","vulnerabilityDetails":"A flaw was found in, all under 2.0.20, in the Undertow DEBUG log for io.undertow.request.security. If enabled, an attacker could abuse this flaw to obtain the user\u0027s credentials from the log files.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10212","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in undertow core final jar undertow core final jar cve high severity vulnerability vulnerable libraries undertow core final jar undertow core final jar undertow core final jar undertow library home page a href path to dependency file nibrs pr test tools nibrs fbi service pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar nibrs pr test tools nibrs fbi service target nibrs fbi service web inf lib undertow core final jar dependency hierarchy x undertow core final jar vulnerable library undertow core final jar undertow library home page a href path to dependency file nibrs pr test tools nibrs route pom xml path to vulnerable library home wss scanner repository io undertow undertow core final undertow core final jar nibrs pr test tools nibrs route target nibrs route web inf lib undertow core final jar dependency hierarchy x undertow core final jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was found in all under in the undertow debug log for io undertow request security if enabled an attacker could abuse this flaw to obtain the user s credentials from the log files publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution final isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree io undertow undertow core final isminimumfixversionavailable true minimumfixversion final packagetype java groupid io undertow packagename undertow core packageversion final packagefilepaths istransitivedependency false dependencytree io undertow undertow core final isminimumfixversionavailable true minimumfixversion final basebranches vulnerabilityidentifier cve vulnerabilitydetails a flaw was found in all under in the undertow debug log for io undertow request security if enabled an attacker could abuse this flaw to obtain the user credentials from the log files vulnerabilityurl | 0 |
193,326 | 22,216,131,418 | IssuesEvent | 2022-06-08 01:59:11 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2016-10044 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2016-10044 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/aio.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The aio_mount function in fs/aio.c in the Linux kernel before 4.7.7 does not properly restrict execute access, which makes it easier for local users to bypass intended SELinux W^X policy restrictions, and consequently gain privileges, via an io_setup system call.
<p>Publish Date: 2017-02-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10044>CVE-2016-10044</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-10044">https://nvd.nist.gov/vuln/detail/CVE-2016-10044</a></p>
<p>Release Date: 2017-02-07</p>
<p>Fix Resolution: 4.7.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-10044 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2016-10044 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/aio.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The aio_mount function in fs/aio.c in the Linux kernel before 4.7.7 does not properly restrict execute access, which makes it easier for local users to bypass intended SELinux W^X policy restrictions, and consequently gain privileges, via an io_setup system call.
<p>Publish Date: 2017-02-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10044>CVE-2016-10044</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-10044">https://nvd.nist.gov/vuln/detail/CVE-2016-10044</a></p>
<p>Release Date: 2017-02-07</p>
<p>Fix Resolution: 4.7.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files fs aio c vulnerability details the aio mount function in fs aio c in the linux kernel before does not properly restrict execute access which makes it easier for local users to bypass intended selinux w x policy restrictions and consequently gain privileges via an io setup system call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
117,411 | 9,934,631,175 | IssuesEvent | 2019-07-02 14:51:03 | packit-service/sandcastle | https://api.github.com/repos/packit-service/sandcastle | opened | Some tests freeze quite often | bug testing | Tests quite often freeze on this:
```
/usr/lib/python3.7/site-packages/kubernetes/stream/ws_client.py:256:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
self = <kubernetes.stream.ws_client.WSClient object at 0x7f00787005f8>, timeout = None
def run_forever(self, timeout=None):
"""Wait till connection is closed or timeout reached. Buffer any input
received during this time."""
if timeout:
start = time.time()
while self.is_open() and time.time() - start < timeout:
self.update(timeout=(timeout - time.time() + start))
else:
while self.is_open():
> self.update(timeout=None)
/usr/lib/python3.7/site-packages/kubernetes/stream/ws_client.py:206:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
self = <kubernetes.stream.ws_client.WSClient object at 0x7f00787005f8>, timeout = None
def update(self, timeout=0):
"""Update channel buffers with at most one complete frame of input."""
if not self.is_open():
return
if not self.sock.connected:
self._connected = False
return
r, _, _ = select.select(
> (self.sock.sock, ), (), (), timeout)
E KeyboardInterrupt
```
Stack trace:
```
sandcastle/api.py:502: in exec
self._copy_path_to_pod(self.mapped_dir.local_dir, unique_dir)
sandcastle/api.py:579: in _copy_path_to_pod
self._do_exec(["rm", "-rf", remote_tmp_dir])
sandcastle/api.py:439: in _do_exec
_preload_content=preload_content, # <<< we need a client object
/usr/lib/python3.7/site-packages/kubernetes/stream/stream.py:36: in stream
return func(*args, **kwargs)
/usr/lib/python3.7/site-packages/kubernetes/client/apis/core_v1_api.py:835: in connect_get_namespaced_pod_exec
(data) = self.connect_get_namespaced_pod_exec_with_http_info(name, namespace, **kwargs)
/usr/lib/python3.7/site-packages/kubernetes/client/apis/core_v1_api.py:935: in connect_get_namespaced_pod_exec_with_http_info
collection_formats=collection_formats)
/usr/lib/python3.7/site-packages/kubernetes/client/api_client.py:321: in call_api
_return_http_data_only, collection_formats, _preload_content, _request_timeout)
/usr/lib/python3.7/site-packages/kubernetes/client/api_client.py:155: in __call_api
_request_timeout=_request_timeout)
/usr/lib/python3.7/site-packages/kubernetes/stream/stream.py:31: in _intercept_request_call
return ws_client.websocket_call(config, *args, **kwargs)
```
No idea if this is a client or server problem. | 1.0 | Some tests freeze quite often - Tests quite often freeze on this:
```
/usr/lib/python3.7/site-packages/kubernetes/stream/ws_client.py:256:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
self = <kubernetes.stream.ws_client.WSClient object at 0x7f00787005f8>, timeout = None
def run_forever(self, timeout=None):
"""Wait till connection is closed or timeout reached. Buffer any input
received during this time."""
if timeout:
start = time.time()
while self.is_open() and time.time() - start < timeout:
self.update(timeout=(timeout - time.time() + start))
else:
while self.is_open():
> self.update(timeout=None)
/usr/lib/python3.7/site-packages/kubernetes/stream/ws_client.py:206:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
self = <kubernetes.stream.ws_client.WSClient object at 0x7f00787005f8>, timeout = None
def update(self, timeout=0):
"""Update channel buffers with at most one complete frame of input."""
if not self.is_open():
return
if not self.sock.connected:
self._connected = False
return
r, _, _ = select.select(
> (self.sock.sock, ), (), (), timeout)
E KeyboardInterrupt
```
Stack trace:
```
sandcastle/api.py:502: in exec
self._copy_path_to_pod(self.mapped_dir.local_dir, unique_dir)
sandcastle/api.py:579: in _copy_path_to_pod
self._do_exec(["rm", "-rf", remote_tmp_dir])
sandcastle/api.py:439: in _do_exec
_preload_content=preload_content, # <<< we need a client object
/usr/lib/python3.7/site-packages/kubernetes/stream/stream.py:36: in stream
return func(*args, **kwargs)
/usr/lib/python3.7/site-packages/kubernetes/client/apis/core_v1_api.py:835: in connect_get_namespaced_pod_exec
(data) = self.connect_get_namespaced_pod_exec_with_http_info(name, namespace, **kwargs)
/usr/lib/python3.7/site-packages/kubernetes/client/apis/core_v1_api.py:935: in connect_get_namespaced_pod_exec_with_http_info
collection_formats=collection_formats)
/usr/lib/python3.7/site-packages/kubernetes/client/api_client.py:321: in call_api
_return_http_data_only, collection_formats, _preload_content, _request_timeout)
/usr/lib/python3.7/site-packages/kubernetes/client/api_client.py:155: in __call_api
_request_timeout=_request_timeout)
/usr/lib/python3.7/site-packages/kubernetes/stream/stream.py:31: in _intercept_request_call
return ws_client.websocket_call(config, *args, **kwargs)
```
No idea if this is a client or server problem. | non_priority | some tests freeze quite often tests quite often freeze on this usr lib site packages kubernetes stream ws client py self timeout none def run forever self timeout none wait till connection is closed or timeout reached buffer any input received during this time if timeout start time time while self is open and time time start timeout self update timeout timeout time time start else while self is open self update timeout none usr lib site packages kubernetes stream ws client py self timeout none def update self timeout update channel buffers with at most one complete frame of input if not self is open return if not self sock connected self connected false return r select select self sock sock timeout e keyboardinterrupt stack trace sandcastle api py in exec self copy path to pod self mapped dir local dir unique dir sandcastle api py in copy path to pod self do exec sandcastle api py in do exec preload content preload content we need a client object usr lib site packages kubernetes stream stream py in stream return func args kwargs usr lib site packages kubernetes client apis core api py in connect get namespaced pod exec data self connect get namespaced pod exec with http info name namespace kwargs usr lib site packages kubernetes client apis core api py in connect get namespaced pod exec with http info collection formats collection formats usr lib site packages kubernetes client api client py in call api return http data only collection formats preload content request timeout usr lib site packages kubernetes client api client py in call api request timeout request timeout usr lib site packages kubernetes stream stream py in intercept request call return ws client websocket call config args kwargs no idea if this is a client or server problem | 0 |
144 | 2,551,571,467 | IssuesEvent | 2015-02-02 10:47:56 | LinDA-tools/LindaWorkbench | https://api.github.com/repos/LinDA-tools/LindaWorkbench | closed | Support and provide deployment options for the Transformation Engine on a local platform. Provide interfaces for management of the tools and execution options. | Requirement from D1.2 Deliverable Transformation tool | Support and provide deployment options for the Transformation Engine on a local platform. Provide interfaces for management of the tools and execution options.
| 1.0 | Support and provide deployment options for the Transformation Engine on a local platform. Provide interfaces for management of the tools and execution options. - Support and provide deployment options for the Transformation Engine on a local platform. Provide interfaces for management of the tools and execution options.
| non_priority | support and provide deployment options for the transformation engine on a local platform provide interfaces for management of the tools and execution options support and provide deployment options for the transformation engine on a local platform provide interfaces for management of the tools and execution options | 0 |
244,585 | 26,434,906,898 | IssuesEvent | 2023-01-15 09:02:54 | aayant-mend/onboardtraining | https://api.github.com/repos/aayant-mend/onboardtraining | opened | slack-spring-boot-starter-2.0.0.jar: 60 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>slack-spring-boot-starter-2.0.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-io/commons-io/2.6/815893df5f31da2ece4040fe0a12fd44b577afaf/commons-io-2.6.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-io/commons-io/2.6/815893df5f31da2ece4040fe0a12fd44b577afaf/commons-io-2.6.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (slack-spring-boot-starter version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-14540](https://www.mend.io/vulnerability-database/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-17531](https://www.mend.io/vulnerability-database/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-16335](https://www.mend.io/vulnerability-database/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-17267](https://www.mend.io/vulnerability-database/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-16942](https://www.mend.io/vulnerability-database/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-8840](https://www.mend.io/vulnerability-database/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-16943](https://www.mend.io/vulnerability-database/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-10202](https://www.mend.io/vulnerability-database/CVE-2019-10202) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.8.jar | Transitive | N/A* | ❌ |
| [CVE-2019-14893](https://www.mend.io/vulnerability-database/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-14892](https://www.mend.io/vulnerability-database/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-9546](https://www.mend.io/vulnerability-database/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-14379](https://www.mend.io/vulnerability-database/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-9547](https://www.mend.io/vulnerability-database/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-9548](https://www.mend.io/vulnerability-database/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-20330](https://www.mend.io/vulnerability-database/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10968](https://www.mend.io/vulnerability-database/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10969](https://www.mend.io/vulnerability-database/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11111](https://www.mend.io/vulnerability-database/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11113](https://www.mend.io/vulnerability-database/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11112](https://www.mend.io/vulnerability-database/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10672](https://www.mend.io/vulnerability-database/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10673](https://www.mend.io/vulnerability-database/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11619](https://www.mend.io/vulnerability-database/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-35728](https://www.mend.io/vulnerability-database/CVE-2020-35728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36189](https://www.mend.io/vulnerability-database/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36188](https://www.mend.io/vulnerability-database/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11620](https://www.mend.io/vulnerability-database/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10650](https://www.mend.io/vulnerability-database/CVE-2020-10650) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36181](https://www.mend.io/vulnerability-database/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36180](https://www.mend.io/vulnerability-database/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36183](https://www.mend.io/vulnerability-database/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-35490](https://www.mend.io/vulnerability-database/CVE-2020-35490) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36182](https://www.mend.io/vulnerability-database/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36185](https://www.mend.io/vulnerability-database/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-35491](https://www.mend.io/vulnerability-database/CVE-2020-35491) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36184](https://www.mend.io/vulnerability-database/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36187](https://www.mend.io/vulnerability-database/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36186](https://www.mend.io/vulnerability-database/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-20190](https://www.mend.io/vulnerability-database/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36179](https://www.mend.io/vulnerability-database/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-24616](https://www.mend.io/vulnerability-database/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14060](https://www.mend.io/vulnerability-database/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14061](https://www.mend.io/vulnerability-database/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14062](https://www.mend.io/vulnerability-database/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-24750](https://www.mend.io/vulnerability-database/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14195](https://www.mend.io/vulnerability-database/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-27772](https://www.mend.io/vulnerability-database/CVE-2022-27772) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | spring-boot-2.1.3.RELEASE.jar | Transitive | N/A* | ❌ |
| [CVE-2019-12086](https://www.mend.io/vulnerability-database/CVE-2019-12086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.8.jar | Transitive | N/A* | ❌ |
| [CVE-2020-25649](https://www.mend.io/vulnerability-database/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-14439](https://www.mend.io/vulnerability-database/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [WS-2019-0379](https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-codec-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2019-12814](https://www.mend.io/vulnerability-database/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-12384](https://www.mend.io/vulnerability-database/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-22970](https://www.mend.io/vulnerability-database/CVE-2022-22970) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-core-5.1.5.RELEASE.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13956](https://www.mend.io/vulnerability-database/CVE-2020-13956) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | httpclient-4.5.9.jar | Transitive | N/A* | ❌ |
| [CVE-2021-29425](https://www.mend.io/vulnerability-database/CVE-2021-29425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-io-2.6.jar | Transitive | N/A* | ❌ |
| [CVE-2021-22096](https://www.mend.io/vulnerability-database/CVE-2021-22096) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.3 | spring-core-5.1.5.RELEASE.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (15 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10202</summary>
### Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A series of deserialization vulnerabilities have been discovered in Codehaus 1.9.x implemented in EAP 7. This CVE fixes CVE-2017-17485, CVE-2017-7525, CVE-2017-15095, CVE-2018-5968, CVE-2018-7489, CVE-2018-1000873, CVE-2019-12086 reported for FasterXML jackson-databind by implementing a whitelist approach that will mitigate these vulnerabilities and future ones alike.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10202>CVE-2019-10202</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://access.redhat.com/errata/RHSA-2019:2938">https://access.redhat.com/errata/RHSA-2019:2938</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: org.codehaus.jackson:jackson-mapper-asl-7.2.4;com.fasterxml.jackson.core:jackson-databind-2.9.9</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-09-04</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.6,2.9.10.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20330</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.5,2.9.10.2</p>
</p>
<p></p>
</details> | True | slack-spring-boot-starter-2.0.0.jar: 60 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>slack-spring-boot-starter-2.0.0.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-io/commons-io/2.6/815893df5f31da2ece4040fe0a12fd44b577afaf/commons-io-2.6.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-io/commons-io/2.6/815893df5f31da2ece4040fe0a12fd44b577afaf/commons-io-2.6.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (slack-spring-boot-starter version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-14540](https://www.mend.io/vulnerability-database/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-17531](https://www.mend.io/vulnerability-database/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-16335](https://www.mend.io/vulnerability-database/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-17267](https://www.mend.io/vulnerability-database/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-16942](https://www.mend.io/vulnerability-database/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-8840](https://www.mend.io/vulnerability-database/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-16943](https://www.mend.io/vulnerability-database/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-10202](https://www.mend.io/vulnerability-database/CVE-2019-10202) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.8.jar | Transitive | N/A* | ❌ |
| [CVE-2019-14893](https://www.mend.io/vulnerability-database/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-14892](https://www.mend.io/vulnerability-database/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-9546](https://www.mend.io/vulnerability-database/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-14379](https://www.mend.io/vulnerability-database/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-9547](https://www.mend.io/vulnerability-database/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-9548](https://www.mend.io/vulnerability-database/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-20330](https://www.mend.io/vulnerability-database/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10968](https://www.mend.io/vulnerability-database/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10969](https://www.mend.io/vulnerability-database/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11111](https://www.mend.io/vulnerability-database/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11113](https://www.mend.io/vulnerability-database/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11112](https://www.mend.io/vulnerability-database/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10672](https://www.mend.io/vulnerability-database/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10673](https://www.mend.io/vulnerability-database/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11619](https://www.mend.io/vulnerability-database/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-35728](https://www.mend.io/vulnerability-database/CVE-2020-35728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36189](https://www.mend.io/vulnerability-database/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36188](https://www.mend.io/vulnerability-database/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-11620](https://www.mend.io/vulnerability-database/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-10650](https://www.mend.io/vulnerability-database/CVE-2020-10650) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36181](https://www.mend.io/vulnerability-database/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36180](https://www.mend.io/vulnerability-database/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36183](https://www.mend.io/vulnerability-database/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-35490](https://www.mend.io/vulnerability-database/CVE-2020-35490) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36182](https://www.mend.io/vulnerability-database/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36185](https://www.mend.io/vulnerability-database/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-35491](https://www.mend.io/vulnerability-database/CVE-2020-35491) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36184](https://www.mend.io/vulnerability-database/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36187](https://www.mend.io/vulnerability-database/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36186](https://www.mend.io/vulnerability-database/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2021-20190](https://www.mend.io/vulnerability-database/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36179](https://www.mend.io/vulnerability-database/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-24616](https://www.mend.io/vulnerability-database/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14060](https://www.mend.io/vulnerability-database/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14061](https://www.mend.io/vulnerability-database/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14062](https://www.mend.io/vulnerability-database/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-24750](https://www.mend.io/vulnerability-database/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-14195](https://www.mend.io/vulnerability-database/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-27772](https://www.mend.io/vulnerability-database/CVE-2022-27772) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | spring-boot-2.1.3.RELEASE.jar | Transitive | N/A* | ❌ |
| [CVE-2019-12086](https://www.mend.io/vulnerability-database/CVE-2019-12086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.8.jar | Transitive | N/A* | ❌ |
| [CVE-2020-25649](https://www.mend.io/vulnerability-database/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-14439](https://www.mend.io/vulnerability-database/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-42004](https://www.mend.io/vulnerability-database/CVE-2022-42004) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-42003](https://www.mend.io/vulnerability-database/CVE-2022-42003) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2020-36518](https://www.mend.io/vulnerability-database/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [WS-2019-0379](https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | commons-codec-1.12.jar | Transitive | N/A* | ❌ |
| [CVE-2019-12814](https://www.mend.io/vulnerability-database/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2019-12384](https://www.mend.io/vulnerability-database/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | detected in multiple dependencies | Transitive | N/A* | ❌ |
| [CVE-2022-22970](https://www.mend.io/vulnerability-database/CVE-2022-22970) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-core-5.1.5.RELEASE.jar | Transitive | N/A* | ❌ |
| [CVE-2020-13956](https://www.mend.io/vulnerability-database/CVE-2020-13956) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | httpclient-4.5.9.jar | Transitive | N/A* | ❌ |
| [CVE-2021-29425](https://www.mend.io/vulnerability-database/CVE-2021-29425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-io-2.6.jar | Transitive | N/A* | ❌ |
| [CVE-2021-22096](https://www.mend.io/vulnerability-database/CVE-2021-22096) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.3 | spring-core-5.1.5.RELEASE.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
> Partial details (15 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10202</summary>
### Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A series of deserialization vulnerabilities have been discovered in Codehaus 1.9.x implemented in EAP 7. This CVE fixes CVE-2017-17485, CVE-2017-7525, CVE-2017-15095, CVE-2018-5968, CVE-2018-7489, CVE-2018-1000873, CVE-2019-12086 reported for FasterXML jackson-databind by implementing a whitelist approach that will mitigate these vulnerabilities and future ones alike.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10202>CVE-2019-10202</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://access.redhat.com/errata/RHSA-2019:2938">https://access.redhat.com/errata/RHSA-2019:2938</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: org.codehaus.jackson:jackson-mapper-asl-7.2.4;com.fasterxml.jackson.core:jackson-databind-2.9.9</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-09-04</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.9.jar</b></p>
<p>
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.6,2.9.10.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20330</summary>
### Vulnerable Libraries - <b>jackson-databind-2.9.9.jar</b>, <b>jackson-databind-2.9.8.jar</b></p>
<p>
### <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.9/d6eb9817d9c7289a91f043ac5ee02a6b3cc86238/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.9.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
### <b>jackson-databind-2.9.8.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /Java/Gradle/kotlin-build-1/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.8/11283f21cc480aa86c4df7a0a3243ec508372ed2/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- slack-spring-boot-starter-2.0.0.jar (Root Library)
- jackson-module-kotlin-2.9.8.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/aayant-mend/onboardtraining/commit/4839f6588961e746880b27503fdce27cafb1e42e">4839f6588961e746880b27503fdce27cafb1e42e</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.7.9.7,2.8.11.5,2.9.10.2</p>
</p>
<p></p>
</details> | non_priority | slack spring boot starter jar vulnerabilities highest severity is vulnerable library slack spring boot starter jar path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files commons io commons io commons io jar home wss scanner gradle caches modules files commons io commons io commons io jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in slack spring boot starter version remediation available high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high jackson databind jar transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high spring boot release jar transitive n a high jackson databind jar transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a high detected in multiple dependencies transitive n a medium commons codec jar transitive n a medium detected in multiple dependencies transitive n a medium detected in multiple dependencies transitive n a medium spring core release jar transitive n a medium httpclient jar transitive n a medium commons io jar transitive n a medium spring core release jar transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the apache extra version x jar in the classpath and an attacker can provide a jndi service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to net sf ehcache hibernate ehcachejtatransactionmanagerlookup publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the commons dbcp jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of org apache commons dbcp datasources sharedpooldatasource and org apache commons dbcp datasources peruserpooldatasource mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind through lacks certain xbean reflect jndi blocking as demonstrated by org apache xbean propertyeditor jndiconverter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of com engine spy mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a series of deserialization vulnerabilities have been discovered in codehaus x implemented in eap this cve fixes cve cve cve cve cve cve cve reported for fasterxml jackson databind by implementing a whitelist approach that will mitigate these vulnerabilities and future ones alike publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org codehaus jackson jackson mapper asl com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a flaw was discovered in fasterxml jackson databind in all versions before and where it would permit polymorphic deserialization of malicious objects using the xalan jndi gadget when used in conjunction with polymorphic type handling methods such as enabledefaulttyping or when jsontypeinfo is using id class or id minimal class or in any other way which objectmapper readvalue might instantiate objects from unsafe sources an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details a flaw was discovered in jackson databind in versions before and where it would permit polymorphic deserialization of a malicious object using commons configuration and jndi classes an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details subtypevalidator java in fasterxml jackson databind before mishandles default typing when ehcache is used because of net sf ehcache transaction manager defaulttransactionmanagerlookup leading to remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com ibatis sqlmap engine transaction jta jtatransactionconfig aka ibatis sqlmap publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to br com anteros dbcp anterosdbcpconfig aka anteros core publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind cve vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file java gradle kotlin build build gradle kts path to vulnerable library home wss scanner gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy slack spring boot starter jar root library jackson module kotlin jar x jackson databind jar vulnerable library found in head commit a href found in base branch main vulnerability details fasterxml jackson databind x before lacks certain net sf ehcache blocking publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution com fasterxml jackson core jackson databind | 0 |
17,057 | 11,612,089,191 | IssuesEvent | 2020-02-26 08:14:42 | stancl/tenancy | https://api.github.com/repos/stancl/tenancy | closed | Make asset() tenancy optional | feature usability | Hi,
I am having somewhat issues including Horizon and the documentation is not quite clear. What I have done is installed Horizon and added the "universal" middleware on config/horizon.php. But when I try to load /horizon the js and css assets are referenced to the tenant instead of globally.
`http://hostaname/tenancy/assets/vendor/horizon/app.js?id=f41217b645f8cd9ffacc`
The [Horizon blade layout is using asset() helper](https://github.com/laravel/horizon/blob/3.0/resources/views/layout.blade.php#L14) so shouldn't it call it from the /vendor/horizon instead of the tenancy assets? | True | Make asset() tenancy optional - Hi,
I am having somewhat issues including Horizon and the documentation is not quite clear. What I have done is installed Horizon and added the "universal" middleware on config/horizon.php. But when I try to load /horizon the js and css assets are referenced to the tenant instead of globally.
`http://hostaname/tenancy/assets/vendor/horizon/app.js?id=f41217b645f8cd9ffacc`
The [Horizon blade layout is using asset() helper](https://github.com/laravel/horizon/blob/3.0/resources/views/layout.blade.php#L14) so shouldn't it call it from the /vendor/horizon instead of the tenancy assets? | non_priority | make asset tenancy optional hi i am having somewhat issues including horizon and the documentation is not quite clear what i have done is installed horizon and added the universal middleware on config horizon php but when i try to load horizon the js and css assets are referenced to the tenant instead of globally the so shouldn t it call it from the vendor horizon instead of the tenancy assets | 0 |
93,828 | 15,946,420,176 | IssuesEvent | 2021-04-15 01:01:37 | jgeraigery/core | https://api.github.com/repos/jgeraigery/core | opened | CVE-2018-14721 (High) detected in jackson-databind-2.9.6.jar | security vulnerability | ## CVE-2018-14721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: core/nimbus-entity-dsl/pom.xml</p>
<p>Path to vulnerable library: core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-config-2.0.0.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721>CVE-2018-14721</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","packageFilePaths":["/nimbus-entity-dsl/pom.xml","/nimbus-core/pom.xml","/nimbus-test/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.cloud:spring-cloud-starter-config:2.0.0.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-14721","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-14721 (High) detected in jackson-databind-2.9.6.jar - ## CVE-2018-14721 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: core/nimbus-entity-dsl/pom.xml</p>
<p>Path to vulnerable library: core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-config-2.0.0.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721>CVE-2018-14721</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","packageFilePaths":["/nimbus-entity-dsl/pom.xml","/nimbus-core/pom.xml","/nimbus-test/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.cloud:spring-cloud-starter-config:2.0.0.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-14721","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14721","cvss3Severity":"high","cvss3Score":"10.0","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Changed","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file core nimbus entity dsl pom xml path to vulnerable library core jackson databind jackson databind jar core jackson databind jackson databind jar core jackson databind jackson databind jar dependency hierarchy spring cloud starter config release jar root library x jackson databind jar vulnerable library found in base branch master vulnerability details fasterxml jackson databind x before might allow remote attackers to conduct server side request forgery ssrf attacks by leveraging failure to block the jaxws class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework cloud spring cloud starter config release com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before might allow remote attackers to conduct server side request forgery ssrf attacks by leveraging failure to block the jaxws class from polymorphic deserialization vulnerabilityurl | 0 |
217,755 | 16,887,341,227 | IssuesEvent | 2021-06-23 03:15:29 | crypto-org-chain/chain-main | https://api.github.com/repos/crypto-org-chain/chain-main | closed | Problem: nix function called with an unexpected argument | test | https://github.com/crypto-org-chain/chain-main/runs/2881839518#step:8:1
```
error: anonymous function at /home/runner/work/chain-main/chain-main/pystarport/default.nix:1:1 called with unexpected argument 'chaind', at /home/runner/work/chain-main/chain-main/default.nix:72:16
19
(use '--show-trace' to show detailed location information)
``` | 1.0 | Problem: nix function called with an unexpected argument - https://github.com/crypto-org-chain/chain-main/runs/2881839518#step:8:1
```
error: anonymous function at /home/runner/work/chain-main/chain-main/pystarport/default.nix:1:1 called with unexpected argument 'chaind', at /home/runner/work/chain-main/chain-main/default.nix:72:16
19
(use '--show-trace' to show detailed location information)
``` | non_priority | problem nix function called with an unexpected argument error anonymous function at home runner work chain main chain main pystarport default nix called with unexpected argument chaind at home runner work chain main chain main default nix use show trace to show detailed location information | 0 |
44,298 | 13,051,312,691 | IssuesEvent | 2020-07-29 16:53:00 | kenferrara/hadoop-crypto | https://api.github.com/repos/kenferrara/hadoop-crypto | opened | CVE-2014-3488 (Medium) detected in netty-3.7.0.Final.jar | security vulnerability | ## CVE-2014-3488 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-3.7.0.Final.jar</b></p></summary>
<p>The Netty project is an effort to provide an asynchronous event-driven
network application framework and tools for rapid development of
maintainable high performance and high scalability protocol servers and
clients. In other words, Netty is a NIO client server framework which
enables quick and easy development of network applications such as protocol
servers and clients. It greatly simplifies and streamlines network
programming such as TCP and UDP socket server.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /tmp/ws-scm/hadoop-crypto/hadoop-crypto/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.netty/netty/3.7.0.Final/7a8c35599c68c0bf383df74469aa3e03d9aca87/netty-3.7.0.Final.jar,canner/.gradle/caches/modules-2/files-2.1/io.netty/netty/3.7.0.Final/7a8c35599c68c0bf383df74469aa3e03d9aca87/netty-3.7.0.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-3.7.0.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kenferrara/hadoop-crypto/commit/c87ffc6b57551c0ce1c2ffa481dbff77be9b0e38">c87ffc6b57551c0ce1c2ffa481dbff77be9b0e38</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The SslHandler in Netty before 3.9.2 allows remote attackers to cause a denial of service (infinite loop and CPU consumption) via a crafted SSLv2Hello message.
<p>Publish Date: 2014-07-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3488>CVE-2014-3488</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3488">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3488</a></p>
<p>Release Date: 2014-07-31</p>
<p>Fix Resolution: 3.9.2.Final</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty","packageVersion":"3.7.0.Final","isTransitiveDependency":false,"dependencyTree":"io.netty:netty:3.7.0.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.9.2.Final"}],"vulnerabilityIdentifier":"CVE-2014-3488","vulnerabilityDetails":"The SslHandler in Netty before 3.9.2 allows remote attackers to cause a denial of service (infinite loop and CPU consumption) via a crafted SSLv2Hello message.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3488","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | True | CVE-2014-3488 (Medium) detected in netty-3.7.0.Final.jar - ## CVE-2014-3488 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-3.7.0.Final.jar</b></p></summary>
<p>The Netty project is an effort to provide an asynchronous event-driven
network application framework and tools for rapid development of
maintainable high performance and high scalability protocol servers and
clients. In other words, Netty is a NIO client server framework which
enables quick and easy development of network applications such as protocol
servers and clients. It greatly simplifies and streamlines network
programming such as TCP and UDP socket server.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /tmp/ws-scm/hadoop-crypto/hadoop-crypto/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/io.netty/netty/3.7.0.Final/7a8c35599c68c0bf383df74469aa3e03d9aca87/netty-3.7.0.Final.jar,canner/.gradle/caches/modules-2/files-2.1/io.netty/netty/3.7.0.Final/7a8c35599c68c0bf383df74469aa3e03d9aca87/netty-3.7.0.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-3.7.0.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kenferrara/hadoop-crypto/commit/c87ffc6b57551c0ce1c2ffa481dbff77be9b0e38">c87ffc6b57551c0ce1c2ffa481dbff77be9b0e38</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The SslHandler in Netty before 3.9.2 allows remote attackers to cause a denial of service (infinite loop and CPU consumption) via a crafted SSLv2Hello message.
<p>Publish Date: 2014-07-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3488>CVE-2014-3488</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3488">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3488</a></p>
<p>Release Date: 2014-07-31</p>
<p>Fix Resolution: 3.9.2.Final</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty","packageVersion":"3.7.0.Final","isTransitiveDependency":false,"dependencyTree":"io.netty:netty:3.7.0.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.9.2.Final"}],"vulnerabilityIdentifier":"CVE-2014-3488","vulnerabilityDetails":"The SslHandler in Netty before 3.9.2 allows remote attackers to cause a denial of service (infinite loop and CPU consumption) via a crafted SSLv2Hello message.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-3488","cvss2Severity":"medium","cvss2Score":"5.0","extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in netty final jar cve medium severity vulnerability vulnerable library netty final jar the netty project is an effort to provide an asynchronous event driven network application framework and tools for rapid development of maintainable high performance and high scalability protocol servers and clients in other words netty is a nio client server framework which enables quick and easy development of network applications such as protocol servers and clients it greatly simplifies and streamlines network programming such as tcp and udp socket server library home page a href path to dependency file tmp ws scm hadoop crypto hadoop crypto build gradle path to vulnerable library home wss scanner gradle caches modules files io netty netty final netty final jar canner gradle caches modules files io netty netty final netty final jar dependency hierarchy x netty final jar vulnerable library found in head commit a href vulnerability details the sslhandler in netty before allows remote attackers to cause a denial of service infinite loop and cpu consumption via a crafted message publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution final check this box to open an automated fix pr isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails the sslhandler in netty before allows remote attackers to cause a denial of service infinite loop and cpu consumption via a crafted message vulnerabilityurl | 0 |
44,382 | 12,124,470,731 | IssuesEvent | 2020-04-22 14:13:48 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | the mistake that No database selected appears when dslContext.resultQuery(sql) | T: Defect | String sql = String.format("select * from workorder where workorder.id in ");
sql=sql+idString;
resultQuery = dslContext.resultQuery(sql).fetchInto(Workorder.class);
mistake :
"jOOQ; uncategorized SQLException for SQL [select * from workorder where workorder.id in ('1')]; SQL state [3D000]; error code [1046]; No database selected; nested exception is java.sql.SQLException: No database selected", | 1.0 | the mistake that No database selected appears when dslContext.resultQuery(sql) - String sql = String.format("select * from workorder where workorder.id in ");
sql=sql+idString;
resultQuery = dslContext.resultQuery(sql).fetchInto(Workorder.class);
mistake :
"jOOQ; uncategorized SQLException for SQL [select * from workorder where workorder.id in ('1')]; SQL state [3D000]; error code [1046]; No database selected; nested exception is java.sql.SQLException: No database selected", | non_priority | the mistake that no database selected appears when dslcontext resultquery sql string sql string format select from workorder where workorder id in sql sql idstring resultquery dslcontext resultquery sql fetchinto workorder class mistake jooq uncategorized sqlexception for sql sql state error code no database selected nested exception is java sql sqlexception no database selected | 0 |
384,998 | 26,611,030,625 | IssuesEvent | 2023-01-24 00:14:51 | foundryvtt/foundryvtt | https://api.github.com/repos/foundryvtt/foundryvtt | opened | createScrollingText incorrectly(?) references text originating from ObjectHUD container | documentation api | From `@Mana#4176
The text originates from a Point on the canvas, not whatever weird the documentation says.
Ref: https://foundryvtt.com/api/classes/client.InterfaceCanvasGroup.html#createScrollingText | 1.0 | createScrollingText incorrectly(?) references text originating from ObjectHUD container - From `@Mana#4176
The text originates from a Point on the canvas, not whatever weird the documentation says.
Ref: https://foundryvtt.com/api/classes/client.InterfaceCanvasGroup.html#createScrollingText | non_priority | createscrollingtext incorrectly references text originating from objecthud container from mana the text originates from a point on the canvas not whatever weird the documentation says ref | 0 |
268,022 | 20,255,119,171 | IssuesEvent | 2022-02-14 22:10:55 | nf-core/rnaseq | https://api.github.com/repos/nf-core/rnaseq | closed | Set STAR align option 'limitSjdbInsertNsj' | documentation | With certain RNA datasets I have an error from STAR align telling me to increase the value of option 'limitSjdbInsertNsj':
`Fatal LIMIT error: the number of junctions to be inserted on the fly =1043854 is larger than the limitSjdbInsertNsj=1000000
SOLUTION: re-run with at least --limitSjdbInsertNsj 1043854`
I've tried looking for a way to set this STAR align option in config. I saw this commit 6f3d33059966d52947bde86f81ee0571ba851ae7 allowed parsing of STAR options in the config file, but do not see it implemented in the release versions.
Is there a current way to change this option in the pipeline? | 1.0 | Set STAR align option 'limitSjdbInsertNsj' - With certain RNA datasets I have an error from STAR align telling me to increase the value of option 'limitSjdbInsertNsj':
`Fatal LIMIT error: the number of junctions to be inserted on the fly =1043854 is larger than the limitSjdbInsertNsj=1000000
SOLUTION: re-run with at least --limitSjdbInsertNsj 1043854`
I've tried looking for a way to set this STAR align option in config. I saw this commit 6f3d33059966d52947bde86f81ee0571ba851ae7 allowed parsing of STAR options in the config file, but do not see it implemented in the release versions.
Is there a current way to change this option in the pipeline? | non_priority | set star align option limitsjdbinsertnsj with certain rna datasets i have an error from star align telling me to increase the value of option limitsjdbinsertnsj fatal limit error the number of junctions to be inserted on the fly is larger than the limitsjdbinsertnsj solution re run with at least limitsjdbinsertnsj i ve tried looking for a way to set this star align option in config i saw this commit allowed parsing of star options in the config file but do not see it implemented in the release versions is there a current way to change this option in the pipeline | 0 |
260,252 | 27,781,257,465 | IssuesEvent | 2023-03-16 21:17:01 | TIBCOSoftware/lmi-azure-ec | https://api.github.com/repos/TIBCOSoftware/lmi-azure-ec | opened | CVE-2023-28155 (Medium) detected in request-2.88.0.tgz | Mend: dependency security vulnerability | ## CVE-2023-28155 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>request-2.88.0.tgz</b></p></summary>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.88.0.tgz">https://registry.npmjs.org/request/-/request-2.88.0.tgz</a></p>
<p>Path to dependency file: /lmi-azure-ec/azure-windows-forwarder/package.json</p>
<p>Path to vulnerable library: /azure-windows-forwarder/node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- azure-storage-2.10.3.tgz (Root Library)
- :x: **request-2.88.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** UNSUPPORTED WHEN ASSIGNED ** The Request package through 2.88.1 for Node.js allows a bypass of SSRF mitigations via an attacker-controller server that does a cross-protocol redirect (HTTP to HTTPS, or HTTPS to HTTP). NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
<p>Publish Date: 2023-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28155>CVE-2023-28155</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| True | CVE-2023-28155 (Medium) detected in request-2.88.0.tgz - ## CVE-2023-28155 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>request-2.88.0.tgz</b></p></summary>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.88.0.tgz">https://registry.npmjs.org/request/-/request-2.88.0.tgz</a></p>
<p>Path to dependency file: /lmi-azure-ec/azure-windows-forwarder/package.json</p>
<p>Path to vulnerable library: /azure-windows-forwarder/node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- azure-storage-2.10.3.tgz (Root Library)
- :x: **request-2.88.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** UNSUPPORTED WHEN ASSIGNED ** The Request package through 2.88.1 for Node.js allows a bypass of SSRF mitigations via an attacker-controller server that does a cross-protocol redirect (HTTP to HTTPS, or HTTPS to HTTP). NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
<p>Publish Date: 2023-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28155>CVE-2023-28155</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| non_priority | cve medium detected in request tgz cve medium severity vulnerability vulnerable library request tgz simplified http request client library home page a href path to dependency file lmi azure ec azure windows forwarder package json path to vulnerable library azure windows forwarder node modules request package json dependency hierarchy azure storage tgz root library x request tgz vulnerable library found in base branch master vulnerability details unsupported when assigned the request package through for node js allows a bypass of ssrf mitigations via an attacker controller server that does a cross protocol redirect http to https or https to http note this vulnerability only affects products that are no longer supported by the maintainer publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href | 0 |
309,036 | 23,280,867,465 | IssuesEvent | 2022-08-05 11:57:17 | vegaprotocol/vega | https://api.github.com/repos/vegaprotocol/vega | closed | Fix JSON generation | documentation | Generating the JSON bundle required for documentation has been removed from all pipelines, but still exists in `generate_json.sh`. However it fails to create the file [we need](https://github.com/vegaprotocol/documentation/blob/main/scripts/build.sh):
```
INFO[0000] Generating JSON-schema for MESSAGE jsonschema_filename=GetRiskFactorsRequest.json msg_name=GetRiskFactorsRequest proto_filename=trading_data.proto
INFO[0000] Generating JSON-schema for MESSAGE jsonschema_filename=GetRiskFactorsResponse.json msg_name=GetRiskFactorsResponse proto_filename=trading_data.proto
data-node/api/v2/trading_data.proto: This file contains proto3 optional fields, but --experimental_allow_proto3_optional was not set.
```
Helpfully. it includes a suggested fix. | 1.0 | Fix JSON generation - Generating the JSON bundle required for documentation has been removed from all pipelines, but still exists in `generate_json.sh`. However it fails to create the file [we need](https://github.com/vegaprotocol/documentation/blob/main/scripts/build.sh):
```
INFO[0000] Generating JSON-schema for MESSAGE jsonschema_filename=GetRiskFactorsRequest.json msg_name=GetRiskFactorsRequest proto_filename=trading_data.proto
INFO[0000] Generating JSON-schema for MESSAGE jsonschema_filename=GetRiskFactorsResponse.json msg_name=GetRiskFactorsResponse proto_filename=trading_data.proto
data-node/api/v2/trading_data.proto: This file contains proto3 optional fields, but --experimental_allow_proto3_optional was not set.
```
Helpfully. it includes a suggested fix. | non_priority | fix json generation generating the json bundle required for documentation has been removed from all pipelines but still exists in generate json sh however it fails to create the file info generating json schema for message jsonschema filename getriskfactorsrequest json msg name getriskfactorsrequest proto filename trading data proto info generating json schema for message jsonschema filename getriskfactorsresponse json msg name getriskfactorsresponse proto filename trading data proto data node api trading data proto this file contains optional fields but experimental allow optional was not set helpfully it includes a suggested fix | 0 |
15,469 | 3,961,942,485 | IssuesEvent | 2016-05-02 15:01:17 | cloudant/python-cloudant | https://api.github.com/repos/cloudant/python-cloudant | opened | Update readthedocs link in README.rst | bug documentation | The current link to the library documentation in the README.rst is set to `http://python-cloudant.readthedocs.org`. This resolves to `http://python-cloudant.readthedocs.org/index.html` which is actually our index module documentation. When a user clicks this link we want it to go to the documentation home page which is currently `default.html`. We may want to consider either changing the link to specifically point to `http://python-cloudant.readthedocs.org/default.html` or renaming index.html to something different and renaming default.html to index.html.
| 1.0 | Update readthedocs link in README.rst - The current link to the library documentation in the README.rst is set to `http://python-cloudant.readthedocs.org`. This resolves to `http://python-cloudant.readthedocs.org/index.html` which is actually our index module documentation. When a user clicks this link we want it to go to the documentation home page which is currently `default.html`. We may want to consider either changing the link to specifically point to `http://python-cloudant.readthedocs.org/default.html` or renaming index.html to something different and renaming default.html to index.html.
| non_priority | update readthedocs link in readme rst the current link to the library documentation in the readme rst is set to this resolves to which is actually our index module documentation when a user clicks this link we want it to go to the documentation home page which is currently default html we may want to consider either changing the link to specifically point to or renaming index html to something different and renaming default html to index html | 0 |
122,023 | 10,210,311,826 | IssuesEvent | 2019-08-14 14:33:20 | kettanaito/react-advanced-form | https://api.github.com/repos/kettanaito/react-advanced-form | closed | Each Field triggers the render method of the Form Component on load | needs:testing question | # Environment
* **react-advanaced-form:** 1.6.7
# What
## Current behavior
On the initial page load of a form with fields, the render method of the form is triggered once for each field registration.
## Expected behavior
Collect field registrations somehow and update the state in one go.
# Why
I realize this is probably by design, because the field registration needs to update the state of the form to add the field to the state. However, the side effect of this is the render method being called for every single field in the form.
# How
Steps to reproduce the issue (ideally, link to the repository/sandbox).
1. Add a Form element with multiple fields.
2. Add a sub component to the form that returns a list of fields.
3. Add a console.log("sub component") inside the render method of the sub component.
4. Note the number of times the console.log() line will be called will be a factor of the number of fields in your form. | 1.0 | Each Field triggers the render method of the Form Component on load - # Environment
* **react-advanaced-form:** 1.6.7
# What
## Current behavior
On the initial page load of a form with fields, the render method of the form is triggered once for each field registration.
## Expected behavior
Collect field registrations somehow and update the state in one go.
# Why
I realize this is probably by design, because the field registration needs to update the state of the form to add the field to the state. However, the side effect of this is the render method being called for every single field in the form.
# How
Steps to reproduce the issue (ideally, link to the repository/sandbox).
1. Add a Form element with multiple fields.
2. Add a sub component to the form that returns a list of fields.
3. Add a console.log("sub component") inside the render method of the sub component.
4. Note the number of times the console.log() line will be called will be a factor of the number of fields in your form. | non_priority | each field triggers the render method of the form component on load environment react advanaced form what current behavior on the initial page load of a form with fields the render method of the form is triggered once for each field registration expected behavior collect field registrations somehow and update the state in one go why i realize this is probably by design because the field registration needs to update the state of the form to add the field to the state however the side effect of this is the render method being called for every single field in the form how steps to reproduce the issue ideally link to the repository sandbox add a form element with multiple fields add a sub component to the form that returns a list of fields add a console log sub component inside the render method of the sub component note the number of times the console log line will be called will be a factor of the number of fields in your form | 0 |
161,228 | 20,122,344,087 | IssuesEvent | 2022-02-08 04:40:35 | samq-ghdemo/JS-Demo | https://api.github.com/repos/samq-ghdemo/JS-Demo | closed | grunt-retire-0.3.12.tgz: 13 vulnerabilities (highest severity is: 9.8) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-retire-0.3.12.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/cryptiles/package.json,/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-23807](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jsonpointer-4.0.1.tgz | Transitive | 1.0.0 | ✅ |
| [WS-2020-0344](https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | is-my-json-valid-2.19.0.tgz | Transitive | 1.0.0 | ✅ |
| [CVE-2018-1000620](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | cryptiles-2.0.5.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2018-3728](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | hoek-2.16.3.tgz | Transitive | 1.0.7 | ✅ |
| [WS-2020-0345](https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.2 | jsonpointer-4.0.1.tgz | Transitive | 1.0.0 | ✅ |
| [CVE-2017-15010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | tough-cookie-2.2.2.tgz | Transitive | 1.0.7 | ✅ |
| [WS-2020-0342](https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | is-my-json-valid-2.19.0.tgz | Transitive | 1.0.0 | ✅ |
| [CVE-2017-1000048](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-5.2.1.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2021-23358](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | underscore-1.8.3.tgz | Transitive | 1.0.2 | ✅ |
| [CVE-2020-8244](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | bl-1.0.3.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2017-16026](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | request-2.67.0.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2016-1000232](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | tough-cookie-2.2.2.tgz | Transitive | 1.0.7 | ✅ |
| [WS-2018-0076](https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.1 | tunnel-agent-0.4.3.tgz | Transitive | 1.0.7 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23807</summary>
### Vulnerable Library - <b>jsonpointer-4.0.1.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.19.0.tgz
- :x: **jsonpointer-4.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.
<p>Publish Date: 2021-11-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807>CVE-2021-23807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution (jsonpointer): 5.0.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0344</summary>
### Vulnerable Library - <b>is-my-json-valid-2.19.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.19.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.
<p>Publish Date: 2020-06-09
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d>WS-2020-0344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-09</p>
<p>Fix Resolution (is-my-json-valid): 2.20.3</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000620</summary>
### Vulnerable Library - <b>cryptiles-2.0.5.tgz</b></p>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/cryptiles/package.json,/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution (cryptiles): 4.1.2</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-3728</summary>
### Vulnerable Library - <b>hoek-2.16.3.tgz</b></p>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz">https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hoek/package.json,/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- hawk-3.1.3.tgz
- :x: **hoek-2.16.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via 'merge' and 'applyToDefaults' functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728>CVE-2018-3728</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082</a></p>
<p>Release Date: 2018-03-30</p>
<p>Fix Resolution (hoek): 4.2.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0345</summary>
### Vulnerable Library - <b>jsonpointer-4.0.1.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.19.0.tgz
- :x: **jsonpointer-4.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.
<p>Publish Date: 2020-07-03
<p>URL: <a href=https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34>WS-2020-0345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0">https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0</a></p>
<p>Release Date: 2020-07-03</p>
<p>Fix Resolution (jsonpointer): 4.1.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-15010</summary>
### Vulnerable Library - <b>tough-cookie-2.2.2.tgz</b></p>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tough-cookie-2.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.
<p>Publish Date: 2017-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010>CVE-2017-15010</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15010">https://nvd.nist.gov/vuln/detail/CVE-2017-15010</a></p>
<p>Release Date: 2017-10-04</p>
<p>Fix Resolution (tough-cookie): 2.3.3</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0342</summary>
### Vulnerable Library - <b>is-my-json-valid-2.19.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.19.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular Expression Denial of Service (ReDoS) vulnerability was found in is-my-json-valid before 2.20.2 via the style format.
<p>Publish Date: 2020-06-27
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb>WS-2020-0342</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-27</p>
<p>Fix Resolution (is-my-json-valid): 2.20.2</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-1000048</summary>
### Vulnerable Library - <b>qs-5.2.1.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-5.2.1.tgz">https://registry.npmjs.org/qs/-/qs-5.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **qs-5.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution (qs): 6.0.4</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23358</summary>
### Vulnerable Library - <b>underscore-1.8.3.tgz</b></p>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.8.3.tgz">https://registry.npmjs.org/underscore/-/underscore-1.8.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/retire/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- retire-1.1.6.tgz
- :x: **underscore-1.8.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution (underscore): 1.12.1</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.2</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8244</summary>
### Vulnerable Library - <b>bl-1.0.3.tgz</b></p>
<p>Buffer List: collect buffers and access with a standard readable Buffer interface, streamable too!</p>
<p>Library home page: <a href="https://registry.npmjs.org/bl/-/bl-1.0.3.tgz">https://registry.npmjs.org/bl/-/bl-1.0.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/bl/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **bl-1.0.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A buffer over-read vulnerability exists in bl <4.0.3, <3.0.1, <2.2.1, and <1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.
<p>Publish Date: 2020-08-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244>CVE-2020-8244</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pp7h-53gx-mx7r">https://github.com/advisories/GHSA-pp7h-53gx-mx7r</a></p>
<p>Release Date: 2020-08-30</p>
<p>Fix Resolution (bl): 1.2.3</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16026</summary>
### Vulnerable Library - <b>request-2.67.0.tgz</b></p>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.67.0.tgz">https://registry.npmjs.org/request/-/request-2.67.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- :x: **request-2.67.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request >=2.2.6 <2.47.0 || >2.51.0 <=2.67.0.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026>CVE-2017-16026</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16026">https://nvd.nist.gov/vuln/detail/CVE-2017-16026</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution (request): 2.68.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-1000232</summary>
### Vulnerable Library - <b>tough-cookie-2.2.2.tgz</b></p>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tough-cookie-2.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.
<p>Publish Date: 2018-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232>CVE-2016-1000232</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/130">https://www.npmjs.com/advisories/130</a></p>
<p>Release Date: 2018-09-05</p>
<p>Fix Resolution (tough-cookie): 2.3.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2018-0076</summary>
### Vulnerable Library - <b>tunnel-agent-0.4.3.tgz</b></p>
<p>HTTP proxy tunneling agent. Formerly part of mikeal/request, now a standalone module.</p>
<p>Library home page: <a href="https://registry.npmjs.org/tunnel-agent/-/tunnel-agent-0.4.3.tgz">https://registry.npmjs.org/tunnel-agent/-/tunnel-agent-0.4.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/tunnel-agent/package.json,/node_modules/tunnel-agent/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tunnel-agent-0.4.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of tunnel-agent before 0.6.0 are vulnerable to memory exposure. This is exploitable if user supplied input is provided to the auth value and is a number.
<p>Publish Date: 2017-03-05
<p>URL: <a href=https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0>WS-2018-0076</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/598">https://nodesecurity.io/advisories/598</a></p>
<p>Release Date: 2017-03-05</p>
<p>Fix Resolution (tunnel-agent): 0.6.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23807","vulnerabilityDetails":"This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0344","vulnerabilityDetails":"Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-1000620","vulnerabilityDetails":"Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-3728","vulnerabilityDetails":"hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via \u0027merge\u0027 and \u0027applyToDefaults\u0027 functions, which allows a malicious user to modify the prototype of \"Object\" via __proto__, causing the addition or modification of an existing property that will exist on all objects.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0345","vulnerabilityDetails":"Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.","vulnerabilityUrl":"https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34","cvss3Severity":"high","cvss3Score":"8.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-15010","vulnerabilityDetails":"A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0342","vulnerabilityDetails":"Regular Expression Denial of Service (ReDoS) vulnerability was found in is-my-json-valid before 2.20.2 via the style format.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-1000048","vulnerabilityDetails":"the web framework using ljharb\u0027s qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23358","vulnerabilityDetails":"The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-8244","vulnerabilityDetails":"A buffer over-read vulnerability exists in bl \u003c4.0.3, \u003c3.0.1, \u003c2.2.1, and \u003c1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16026","vulnerabilityDetails":"Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request \u003e\u003d2.2.6 \u003c2.47.0 || \u003e2.51.0 \u003c\u003d2.67.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-1000232","vulnerabilityDetails":"NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0076","vulnerabilityDetails":"Versions of tunnel-agent before 0.6.0 are vulnerable to memory exposure. This is exploitable if user supplied input is provided to the auth value and is a number.","vulnerabilityUrl":"https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0","cvss3Severity":"medium","cvss3Score":"5.1","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | grunt-retire-0.3.12.tgz: 13 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-retire-0.3.12.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/cryptiles/package.json,/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-23807](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jsonpointer-4.0.1.tgz | Transitive | 1.0.0 | ✅ |
| [WS-2020-0344](https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | is-my-json-valid-2.19.0.tgz | Transitive | 1.0.0 | ✅ |
| [CVE-2018-1000620](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | cryptiles-2.0.5.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2018-3728](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | hoek-2.16.3.tgz | Transitive | 1.0.7 | ✅ |
| [WS-2020-0345](https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.2 | jsonpointer-4.0.1.tgz | Transitive | 1.0.0 | ✅ |
| [CVE-2017-15010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | tough-cookie-2.2.2.tgz | Transitive | 1.0.7 | ✅ |
| [WS-2020-0342](https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | is-my-json-valid-2.19.0.tgz | Transitive | 1.0.0 | ✅ |
| [CVE-2017-1000048](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-5.2.1.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2021-23358](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.2 | underscore-1.8.3.tgz | Transitive | 1.0.2 | ✅ |
| [CVE-2020-8244](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | bl-1.0.3.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2017-16026](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | request-2.67.0.tgz | Transitive | 1.0.7 | ✅ |
| [CVE-2016-1000232](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | tough-cookie-2.2.2.tgz | Transitive | 1.0.7 | ✅ |
| [WS-2018-0076](https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.1 | tunnel-agent-0.4.3.tgz | Transitive | 1.0.7 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23807</summary>
### Vulnerable Library - <b>jsonpointer-4.0.1.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.19.0.tgz
- :x: **jsonpointer-4.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.
<p>Publish Date: 2021-11-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807>CVE-2021-23807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution (jsonpointer): 5.0.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0344</summary>
### Vulnerable Library - <b>is-my-json-valid-2.19.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.19.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.
<p>Publish Date: 2020-06-09
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d>WS-2020-0344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-09</p>
<p>Fix Resolution (is-my-json-valid): 2.20.3</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-1000620</summary>
### Vulnerable Library - <b>cryptiles-2.0.5.tgz</b></p>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/cryptiles/package.json,/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution (cryptiles): 4.1.2</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-3728</summary>
### Vulnerable Library - <b>hoek-2.16.3.tgz</b></p>
<p>General purpose node utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz">https://registry.npmjs.org/hoek/-/hoek-2.16.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/hoek/package.json,/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/hoek/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- hawk-3.1.3.tgz
- :x: **hoek-2.16.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via 'merge' and 'applyToDefaults' functions, which allows a malicious user to modify the prototype of "Object" via __proto__, causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2018-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728>CVE-2018-3728</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082</a></p>
<p>Release Date: 2018-03-30</p>
<p>Fix Resolution (hoek): 4.2.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0345</summary>
### Vulnerable Library - <b>jsonpointer-4.0.1.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.19.0.tgz
- :x: **jsonpointer-4.0.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.
<p>Publish Date: 2020-07-03
<p>URL: <a href=https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34>WS-2020-0345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0">https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0</a></p>
<p>Release Date: 2020-07-03</p>
<p>Fix Resolution (jsonpointer): 4.1.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-15010</summary>
### Vulnerable Library - <b>tough-cookie-2.2.2.tgz</b></p>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tough-cookie-2.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.
<p>Publish Date: 2017-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010>CVE-2017-15010</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15010">https://nvd.nist.gov/vuln/detail/CVE-2017-15010</a></p>
<p>Release Date: 2017-10-04</p>
<p>Fix Resolution (tough-cookie): 2.3.3</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0342</summary>
### Vulnerable Library - <b>is-my-json-valid-2.19.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.19.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.19.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Regular Expression Denial of Service (ReDoS) vulnerability was found in is-my-json-valid before 2.20.2 via the style format.
<p>Publish Date: 2020-06-27
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb>WS-2020-0342</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-27</p>
<p>Fix Resolution (is-my-json-valid): 2.20.2</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.0</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-1000048</summary>
### Vulnerable Library - <b>qs-5.2.1.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-5.2.1.tgz">https://registry.npmjs.org/qs/-/qs-5.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **qs-5.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
the web framework using ljharb's qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.
<p>Publish Date: 2017-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048>CVE-2017-1000048</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000048</a></p>
<p>Release Date: 2017-07-17</p>
<p>Fix Resolution (qs): 6.0.4</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23358</summary>
### Vulnerable Library - <b>underscore-1.8.3.tgz</b></p>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.8.3.tgz">https://registry.npmjs.org/underscore/-/underscore-1.8.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/retire/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- retire-1.1.6.tgz
- :x: **underscore-1.8.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution (underscore): 1.12.1</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.2</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2020-8244</summary>
### Vulnerable Library - <b>bl-1.0.3.tgz</b></p>
<p>Buffer List: collect buffers and access with a standard readable Buffer interface, streamable too!</p>
<p>Library home page: <a href="https://registry.npmjs.org/bl/-/bl-1.0.3.tgz">https://registry.npmjs.org/bl/-/bl-1.0.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/bl/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **bl-1.0.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A buffer over-read vulnerability exists in bl <4.0.3, <3.0.1, <2.2.1, and <1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.
<p>Publish Date: 2020-08-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244>CVE-2020-8244</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pp7h-53gx-mx7r">https://github.com/advisories/GHSA-pp7h-53gx-mx7r</a></p>
<p>Release Date: 2020-08-30</p>
<p>Fix Resolution (bl): 1.2.3</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-16026</summary>
### Vulnerable Library - <b>request-2.67.0.tgz</b></p>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.67.0.tgz">https://registry.npmjs.org/request/-/request-2.67.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- :x: **request-2.67.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request >=2.2.6 <2.47.0 || >2.51.0 <=2.67.0.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026>CVE-2017-16026</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16026">https://nvd.nist.gov/vuln/detail/CVE-2017-16026</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution (request): 2.68.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-1000232</summary>
### Vulnerable Library - <b>tough-cookie-2.2.2.tgz</b></p>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt-retire/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tough-cookie-2.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.
<p>Publish Date: 2018-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232>CVE-2016-1000232</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/130">https://www.npmjs.com/advisories/130</a></p>
<p>Release Date: 2018-09-05</p>
<p>Fix Resolution (tough-cookie): 2.3.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> WS-2018-0076</summary>
### Vulnerable Library - <b>tunnel-agent-0.4.3.tgz</b></p>
<p>HTTP proxy tunneling agent. Formerly part of mikeal/request, now a standalone module.</p>
<p>Library home page: <a href="https://registry.npmjs.org/tunnel-agent/-/tunnel-agent-0.4.3.tgz">https://registry.npmjs.org/tunnel-agent/-/tunnel-agent-0.4.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/tunnel-agent/package.json,/node_modules/tunnel-agent/package.json</p>
<p>
Dependency Hierarchy:
- grunt-retire-0.3.12.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tunnel-agent-0.4.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/33cd7775cefbf105dc51f3d5f5d136e529948d6f">33cd7775cefbf105dc51f3d5f5d136e529948d6f</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of tunnel-agent before 0.6.0 are vulnerable to memory exposure. This is exploitable if user supplied input is provided to the auth value and is a number.
<p>Publish Date: 2017-03-05
<p>URL: <a href=https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0>WS-2018-0076</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/598">https://nodesecurity.io/advisories/598</a></p>
<p>Release Date: 2017-03-05</p>
<p>Fix Resolution (tunnel-agent): 0.6.0</p>
<p>Direct dependency fix Resolution (grunt-retire): 1.0.7</p>
</p>
<p></p>
<p>In order to enable automatic remediation, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
</details>
***
<p>In order to enable automatic remediation for this issue, please create <a target="_blank" href="https://whitesource.atlassian.net/wiki/spaces/WD/pages/697696422/WhiteSource+for+GitHub.com#Remediate-Settings-(remediateSettings)">workflow rules</a></p>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23807","vulnerabilityDetails":"This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0344","vulnerabilityDetails":"Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-1000620","vulnerabilityDetails":"Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-3728","vulnerabilityDetails":"hoek node module before 4.2.0 and 5.0.x before 5.0.3 suffers from a Modification of Assumed-Immutable Data (MAID) vulnerability via \u0027merge\u0027 and \u0027applyToDefaults\u0027 functions, which allows a malicious user to modify the prototype of \"Object\" via __proto__, causing the addition or modification of an existing property that will exist on all objects.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3728","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0345","vulnerabilityDetails":"Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.","vulnerabilityUrl":"https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34","cvss3Severity":"high","cvss3Score":"8.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-15010","vulnerabilityDetails":"A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0342","vulnerabilityDetails":"Regular Expression Denial of Service (ReDoS) vulnerability was found in is-my-json-valid before 2.20.2 via the style format.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-1000048","vulnerabilityDetails":"the web framework using ljharb\u0027s qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23358","vulnerabilityDetails":"The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-8244","vulnerabilityDetails":"A buffer over-read vulnerability exists in bl \u003c4.0.3, \u003c3.0.1, \u003c2.2.1, and \u003c1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16026","vulnerabilityDetails":"Request is an http client. If a request is made using ```multipart```, and the body type is a ```number```, then the specified number of non-zero memory is passed in the body. This affects Request \u003e\u003d2.2.6 \u003c2.47.0 || \u003e2.51.0 \u003c\u003d2.67.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16026","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-1000232","vulnerabilityDetails":"NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"grunt-retire","packageVersion":"0.3.12","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"grunt-retire:0.3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0076","vulnerabilityDetails":"Versions of tunnel-agent before 0.6.0 are vulnerable to memory exposure. This is exploitable if user supplied input is provided to the auth value and is a number.","vulnerabilityUrl":"https://github.com/request/tunnel-agent/commit/9ca95ec7219daface8a6fc2674000653de0922c0","cvss3Severity":"medium","cvss3Score":"5.1","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_priority | grunt retire tgz vulnerabilities highest severity is autoclosed vulnerable library grunt retire tgz path to dependency file package json path to vulnerable library node modules cryptiles package json node modules npm node modules request node modules hawk node modules cryptiles package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high jsonpointer tgz transitive ✅ high is my json valid tgz transitive ✅ high cryptiles tgz transitive ✅ high hoek tgz transitive ✅ high jsonpointer tgz transitive ✅ high tough cookie tgz transitive ✅ high is my json valid tgz transitive ✅ high qs tgz transitive ✅ high underscore tgz transitive ✅ medium bl tgz transitive ✅ medium request tgz transitive ✅ medium tough cookie tgz transitive ✅ medium tunnel agent tgz transitive ✅ details cve vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file package json path to vulnerable library node modules jsonpointer package json dependency hierarchy grunt retire tgz root library request tgz har validator tgz is my json valid tgz x jsonpointer tgz vulnerable library found in head commit a href found in base branch main vulnerability details this affects the package jsonpointer before a type confusion vulnerability can lead to a bypass of a previous prototype pollution fix when the pointer components are arrays publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jsonpointer direct dependency fix resolution grunt retire in order to enable automatic remediation please create ws vulnerable library is my json valid tgz a jsonschema validator that uses code generation to be extremely fast library home page a href path to dependency file package json path to vulnerable library node modules is my json valid package json dependency hierarchy grunt retire tgz root library request tgz har validator tgz x is my json valid tgz vulnerable library found in head commit a href found in base branch main vulnerability details arbitrary code execution vulnerability was found in is my json valid before via the fromatname function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution is my json valid direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library cryptiles tgz general purpose crypto utilities library home page a href path to dependency file package json path to vulnerable library node modules cryptiles package json node modules npm node modules request node modules hawk node modules cryptiles package json dependency hierarchy grunt retire tgz root library request tgz hawk tgz x cryptiles tgz vulnerable library found in head commit a href found in base branch main vulnerability details eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cryptiles direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library hoek tgz general purpose node utilities library home page a href path to dependency file package json path to vulnerable library node modules hoek package json node modules npm node modules request node modules hawk node modules hoek package json dependency hierarchy grunt retire tgz root library request tgz hawk tgz x hoek tgz vulnerable library found in head commit a href found in base branch main vulnerability details hoek node module before and x before suffers from a modification of assumed immutable data maid vulnerability via merge and applytodefaults functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hoek direct dependency fix resolution grunt retire in order to enable automatic remediation please create ws vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file package json path to vulnerable library node modules jsonpointer package json dependency hierarchy grunt retire tgz root library request tgz har validator tgz is my json valid tgz x jsonpointer tgz vulnerable library found in head commit a href found in base branch main vulnerability details prototype pollution vulnerability was found in jsonpointer before via the set function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jsonpointer direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library tough cookie tgz cookies and cookie jar for node js library home page a href path to dependency file package json path to vulnerable library node modules grunt retire node modules tough cookie package json dependency hierarchy grunt retire tgz root library request tgz x tough cookie tgz vulnerable library found in head commit a href found in base branch main vulnerability details a redos regular expression denial of service flaw was found in the tough cookie module before for node js an attacker that is able to make an http request using a specially crafted cookie may cause the application to consume an excessive amount of cpu publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tough cookie direct dependency fix resolution grunt retire in order to enable automatic remediation please create ws vulnerable library is my json valid tgz a jsonschema validator that uses code generation to be extremely fast library home page a href path to dependency file package json path to vulnerable library node modules is my json valid package json dependency hierarchy grunt retire tgz root library request tgz har validator tgz x is my json valid tgz vulnerable library found in head commit a href found in base branch main vulnerability details regular expression denial of service redos vulnerability was found in is my json valid before via the style format publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution is my json valid direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file package json path to vulnerable library node modules grunt retire node modules qs package json dependency hierarchy grunt retire tgz root library request tgz x qs tgz vulnerable library found in head commit a href found in base branch main vulnerability details the web framework using ljharb s qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution qs direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file package json path to vulnerable library node modules retire node modules underscore package json dependency hierarchy grunt retire tgz root library retire tgz x underscore tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library bl tgz buffer list collect buffers and access with a standard readable buffer interface streamable too library home page a href path to dependency file package json path to vulnerable library node modules bl package json dependency hierarchy grunt retire tgz root library request tgz x bl tgz vulnerable library found in head commit a href found in base branch main vulnerability details a buffer over read vulnerability exists in bl and which could allow an attacker to supply user input even typed that if it ends up in consume argument and can become negative the bufferlist state can be corrupted tricking it into exposing uninitialized memory via regular slice calls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bl direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library request tgz simplified http request client library home page a href path to dependency file package json path to vulnerable library node modules grunt retire node modules request package json dependency hierarchy grunt retire tgz root library x request tgz vulnerable library found in head commit a href found in base branch main vulnerability details request is an http client if a request is made using multipart and the body type is a number then the specified number of non zero memory is passed in the body this affects request publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution request direct dependency fix resolution grunt retire in order to enable automatic remediation please create cve vulnerable library tough cookie tgz cookies and cookie jar for node js library home page a href path to dependency file package json path to vulnerable library node modules grunt retire node modules tough cookie package json dependency hierarchy grunt retire tgz root library request tgz x tough cookie tgz vulnerable library found in head commit a href found in base branch main vulnerability details nodejs tough cookie version contains a regular expression parsing vulnerability in http request cookie header parsing that can result in denial of service this attack appear to be exploitable via custom http header passed by client this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tough cookie direct dependency fix resolution grunt retire in order to enable automatic remediation please create ws vulnerable library tunnel agent tgz http proxy tunneling agent formerly part of mikeal request now a standalone module library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules tunnel agent package json node modules tunnel agent package json dependency hierarchy grunt retire tgz root library request tgz x tunnel agent tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of tunnel agent before are vulnerable to memory exposure this is exploitable if user supplied input is provided to the auth value and is a number publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tunnel agent direct dependency fix resolution grunt retire in order to enable automatic remediation please create in order to enable automatic remediation for this issue please create istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package jsonpointer before a type confusion vulnerability can lead to a bypass of a previous prototype pollution fix when the pointer components are arrays vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails arbitrary code execution vulnerability was found in is my json valid before via the fromatname function vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails hoek node module before and x before suffers from a modification of assumed immutable data maid vulnerability via and functions which allows a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails prototype pollution vulnerability was found in jsonpointer before via the set function vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a redos regular expression denial of service flaw was found in the tough cookie module before for node js an attacker that is able to make an http request using a specially crafted cookie may cause the application to consume an excessive amount of cpu vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails regular expression denial of service redos vulnerability was found in is my json valid before via the style format vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the web framework using ljharb qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a buffer over read vulnerability exists in bl and which could allow an attacker to supply user input even typed that if it ends up in consume argument and can become negative the bufferlist state can be corrupted tricking it into exposing uninitialized memory via regular slice calls vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails request is an http client if a request is made using multipart and the body type is a number then the specified number of non zero memory is passed in the body this affects request vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails nodejs tough cookie version contains a regular expression parsing vulnerability in http request cookie header parsing that can result in denial of service this attack appear to be exploitable via custom http header passed by client this vulnerability appears to have been fixed in vulnerabilityurl istransitivedependency false dependencytree grunt retire isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails versions of tunnel agent before are vulnerable to memory exposure this is exploitable if user supplied input is provided to the auth value and is a number vulnerabilityurl | 0 |
60,255 | 12,086,144,434 | IssuesEvent | 2020-04-18 08:25:29 | Tcdian/keep | https://api.github.com/repos/Tcdian/keep | closed | 1292. Maximum Side Length of a Square with Sum Less than or Equal to Threshold | LeetCode | ## [1292. Maximum Side Length of a Square with Sum Less than or Equal to Threshold](https://leetcode.com/problems/maximum-side-length-of-a-square-with-sum-less-than-or-equal-to-threshold/)
给你一个大小为 m x n 的矩阵 mat 和一个整数阈值 threshold。
请你返回元素总和小于或等于阈值的正方形区域的最大边长;如果没有这样的正方形区域,则返回 0 。
#### Example 1
<img src="https://assets.leetcode.com/uploads/2019/12/05/e1.png" />
```text
Input: mat = [[1,1,3,2,4,3,2],[1,1,3,2,4,3,2],[1,1,3,2,4,3,2]], threshold = 4
Output: 2
Explanation: The maximum side length of square with sum less than 4 is 2 as shown.
```
#### Example 2
```text
Input: mat = [[2,2,2,2,2],[2,2,2,2,2],[2,2,2,2,2],[2,2,2,2,2],[2,2,2,2,2]], threshold = 1
Output: 0
```
#### Example 3
```text
Input: mat = [[1,1,1,1],[1,0,0,0],[1,0,0,0],[1,0,0,0]], threshold = 6
Output: 3
```
#### Example 4
```text
Input: mat = [[18,70],[61,1],[25,85],[14,40],[11,96],[97,96],[63,45]], threshold = 40184
Output: 2
```
#### Constraints
- `1 <= m, n <= 300`
- `m == mat.length`
- `n == mat[i].length`
- `0 <= mat[i][j] <= 10000`
- `0 <= threshold <= 10^5`
| 1.0 | 1292. Maximum Side Length of a Square with Sum Less than or Equal to Threshold - ## [1292. Maximum Side Length of a Square with Sum Less than or Equal to Threshold](https://leetcode.com/problems/maximum-side-length-of-a-square-with-sum-less-than-or-equal-to-threshold/)
给你一个大小为 m x n 的矩阵 mat 和一个整数阈值 threshold。
请你返回元素总和小于或等于阈值的正方形区域的最大边长;如果没有这样的正方形区域,则返回 0 。
#### Example 1
<img src="https://assets.leetcode.com/uploads/2019/12/05/e1.png" />
```text
Input: mat = [[1,1,3,2,4,3,2],[1,1,3,2,4,3,2],[1,1,3,2,4,3,2]], threshold = 4
Output: 2
Explanation: The maximum side length of square with sum less than 4 is 2 as shown.
```
#### Example 2
```text
Input: mat = [[2,2,2,2,2],[2,2,2,2,2],[2,2,2,2,2],[2,2,2,2,2],[2,2,2,2,2]], threshold = 1
Output: 0
```
#### Example 3
```text
Input: mat = [[1,1,1,1],[1,0,0,0],[1,0,0,0],[1,0,0,0]], threshold = 6
Output: 3
```
#### Example 4
```text
Input: mat = [[18,70],[61,1],[25,85],[14,40],[11,96],[97,96],[63,45]], threshold = 40184
Output: 2
```
#### Constraints
- `1 <= m, n <= 300`
- `m == mat.length`
- `n == mat[i].length`
- `0 <= mat[i][j] <= 10000`
- `0 <= threshold <= 10^5`
| non_priority | maximum side length of a square with sum less than or equal to threshold 给你一个大小为 m x n 的矩阵 mat 和一个整数阈值 threshold。 请你返回元素总和小于或等于阈值的正方形区域的最大边长;如果没有这样的正方形区域,则返回 。 example text input mat threshold output explanation the maximum side length of square with sum less than is as shown example text input mat threshold output example text input mat threshold output example text input mat threshold output constraints m n m mat length n mat length mat threshold | 0 |
443,453 | 30,913,140,137 | IssuesEvent | 2023-08-05 01:10:40 | open-metadata/OpenMetadata | https://api.github.com/repos/open-metadata/OpenMetadata | closed | Configuration file details | documentation | **Is some content missing, wrong or not clear?**
A clear and concise description of what the problem is and the source URL. Ex. Page [...] is not clear.
**Describe the solution you'd like**
Let us know what could help us improve the docs.
**Additional context**
As shown in the figure, whether deletion is required in the configuration.
How to configure specifically?
**Urgent, urgent, urgent.**
Add any other context or screenshots about the feature request here.
<img width="793" alt="image" src="https://github.com/open-metadata/OpenMetadata/assets/122763218/0580a717-1d3c-46cd-98ca-3248099fc2dd">
| 1.0 | Configuration file details - **Is some content missing, wrong or not clear?**
A clear and concise description of what the problem is and the source URL. Ex. Page [...] is not clear.
**Describe the solution you'd like**
Let us know what could help us improve the docs.
**Additional context**
As shown in the figure, whether deletion is required in the configuration.
How to configure specifically?
**Urgent, urgent, urgent.**
Add any other context or screenshots about the feature request here.
<img width="793" alt="image" src="https://github.com/open-metadata/OpenMetadata/assets/122763218/0580a717-1d3c-46cd-98ca-3248099fc2dd">
| non_priority | configuration file details is some content missing wrong or not clear a clear and concise description of what the problem is and the source url ex page is not clear describe the solution you d like let us know what could help us improve the docs additional context as shown in the figure whether deletion is required in the configuration how to configure specifically urgent urgent urgent add any other context or screenshots about the feature request here img width alt image src | 0 |
70,600 | 13,502,609,934 | IssuesEvent | 2020-09-13 09:23:32 | EKA2L1/Compatibility-List | https://api.github.com/repos/EKA2L1/Compatibility-List | opened | Sega Rally Championship | - Game Genre: Racing Graphical Issues Menus N-Gage Name Issues Unimplemented Opcode | # App summary
- App name: Sega Rally Championship
# EKA2L1 info
- Build name: B4439326
# Test environment summary
- OS: Windows
- CPU: AMD
- GPU: NVIDIA
- RAM: 8 GB
# Issues
it's showing up under the name 6R12. Broken graphics make in it impossible to start a new game
# Screenshots
# Log
[EKA2L1.log](https://github.com/EKA2L1/Compatibility-List/files/5185840/EKA2L1.log) | 1.0 | Sega Rally Championship - # App summary
- App name: Sega Rally Championship
# EKA2L1 info
- Build name: B4439326
# Test environment summary
- OS: Windows
- CPU: AMD
- GPU: NVIDIA
- RAM: 8 GB
# Issues
it's showing up under the name 6R12. Broken graphics make in it impossible to start a new game
# Screenshots
# Log
[EKA2L1.log](https://github.com/EKA2L1/Compatibility-List/files/5185840/EKA2L1.log) | non_priority | sega rally championship app summary app name sega rally championship info build name test environment summary os windows cpu amd gpu nvidia ram gb issues it s showing up under the name broken graphics make in it impossible to start a new game screenshots log | 0 |
33,324 | 4,822,541,824 | IssuesEvent | 2016-11-05 22:21:21 | camilosampedro/Aton | https://api.github.com/repos/camilosampedro/Aton | closed | Create unit test for LaboratoryController (LaboratoryControllerSpec) | bitesize hacktoberfest help wanted test up-for-grabs | Create a unit test for `controllers.LaboratoryController` controller. It might be pretty similar to [`ComputerControllerSpec`](https://github.com/camilosampedro/Aton/blob/master/test/controllers/admin/ComputerControllerSpec.scala):
- You would need to mock the dependencies of LaboratoryController (Add a return value to the needed methods without executing anything, they are not intended to be tested here).
- Check the return HTTP code of the methods (Firstly as you would expect them to be).
Don't worry if you don't know something about the functionality of this class, it will be a pleasure to me to answer your questions.
| 1.0 | Create unit test for LaboratoryController (LaboratoryControllerSpec) - Create a unit test for `controllers.LaboratoryController` controller. It might be pretty similar to [`ComputerControllerSpec`](https://github.com/camilosampedro/Aton/blob/master/test/controllers/admin/ComputerControllerSpec.scala):
- You would need to mock the dependencies of LaboratoryController (Add a return value to the needed methods without executing anything, they are not intended to be tested here).
- Check the return HTTP code of the methods (Firstly as you would expect them to be).
Don't worry if you don't know something about the functionality of this class, it will be a pleasure to me to answer your questions.
| non_priority | create unit test for laboratorycontroller laboratorycontrollerspec create a unit test for controllers laboratorycontroller controller it might be pretty similar to you would need to mock the dependencies of laboratorycontroller add a return value to the needed methods without executing anything they are not intended to be tested here check the return http code of the methods firstly as you would expect them to be don t worry if you don t know something about the functionality of this class it will be a pleasure to me to answer your questions | 0 |
268,887 | 20,363,699,413 | IssuesEvent | 2022-02-21 01:17:30 | nelsopet/landscape_of_change | https://api.github.com/repos/nelsopet/landscape_of_change | closed | Define how we assign values, terms, etc. - add to Rmd | documentation | Add this info into a write up in the Rmd for future reference. | 1.0 | Define how we assign values, terms, etc. - add to Rmd - Add this info into a write up in the Rmd for future reference. | non_priority | define how we assign values terms etc add to rmd add this info into a write up in the rmd for future reference | 0 |
90,362 | 18,127,261,443 | IssuesEvent | 2021-09-24 00:52:07 | 4GeeksAcademy/About-4Geeks-Academy | https://api.github.com/repos/4GeeksAcademy/About-4Geeks-Academy | closed | Fix function to replicate same timeslots in all academies | bug :star: P1 backend breathecode D2 (😌 average) | If I try to replicate timeslots among all academies I get an error:
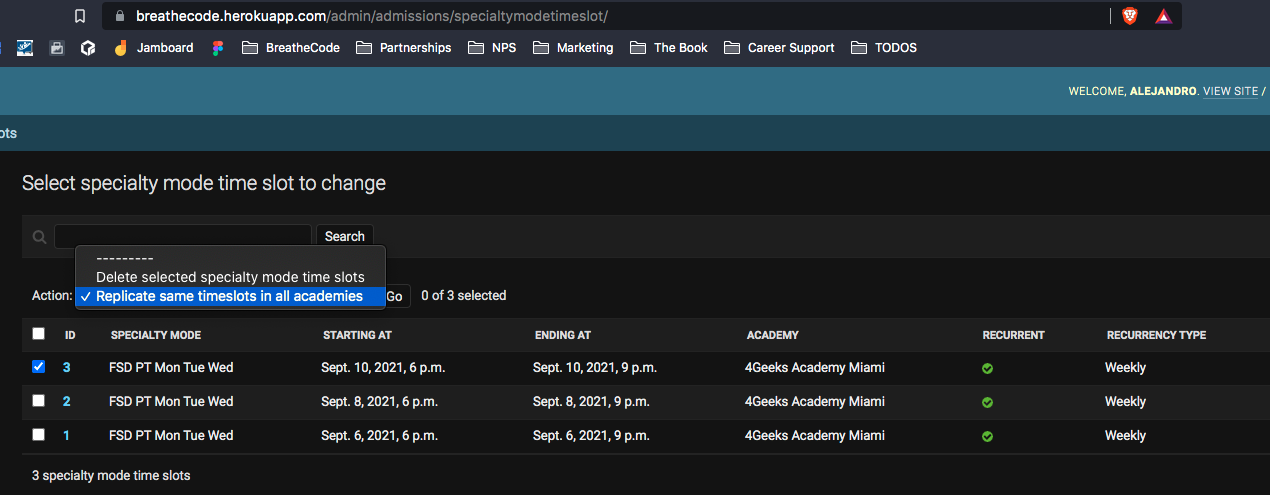
This is probably because the table certificate does not exist anymore, the function code must be fix to comply with the new database struture.
```
def replicate_in_all(modeladmin, request, queryset):
cert_timeslot = queryset.all()
academies = Academy.objects.all()
for a in academies:
to_filter = {}
for c in cert_timeslot:
# delete all timeslots for that academy and certificate ONLY the first time
if c.certificate.slug not in to_filter:
SpecialtyModeTimeSlot.objects.filter(certificate=c.certificate, academy=a).delete()
to_filter[c.certificate.slug] = True
# and then re add the timeslots one by one
new_timeslot = SpecialtyModeTimeSlot(recurrent=c.recurrent,
starting_at=c.starting_at,
ending_at=c.ending_at,
certificate=c.certificate,
academy=a)
new_timeslot.save()
``` | 1.0 | Fix function to replicate same timeslots in all academies - If I try to replicate timeslots among all academies I get an error:
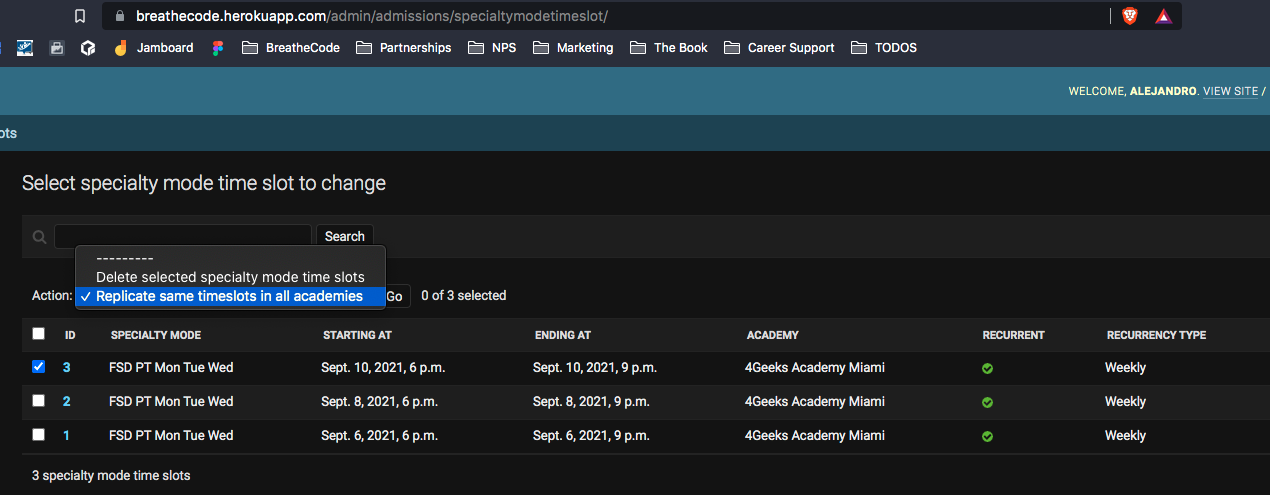
This is probably because the table certificate does not exist anymore, the function code must be fix to comply with the new database struture.
```
def replicate_in_all(modeladmin, request, queryset):
cert_timeslot = queryset.all()
academies = Academy.objects.all()
for a in academies:
to_filter = {}
for c in cert_timeslot:
# delete all timeslots for that academy and certificate ONLY the first time
if c.certificate.slug not in to_filter:
SpecialtyModeTimeSlot.objects.filter(certificate=c.certificate, academy=a).delete()
to_filter[c.certificate.slug] = True
# and then re add the timeslots one by one
new_timeslot = SpecialtyModeTimeSlot(recurrent=c.recurrent,
starting_at=c.starting_at,
ending_at=c.ending_at,
certificate=c.certificate,
academy=a)
new_timeslot.save()
``` | non_priority | fix function to replicate same timeslots in all academies if i try to replicate timeslots among all academies i get an error this is probably because the table certificate does not exist anymore the function code must be fix to comply with the new database struture def replicate in all modeladmin request queryset cert timeslot queryset all academies academy objects all for a in academies to filter for c in cert timeslot delete all timeslots for that academy and certificate only the first time if c certificate slug not in to filter specialtymodetimeslot objects filter certificate c certificate academy a delete to filter true and then re add the timeslots one by one new timeslot specialtymodetimeslot recurrent c recurrent starting at c starting at ending at c ending at certificate c certificate academy a new timeslot save | 0 |
13,909 | 4,787,872,415 | IssuesEvent | 2016-10-30 08:05:51 | DotSpatial/DotSpatial | https://api.github.com/repos/DotSpatial/DotSpatial | closed | DotSpatial.Positioning FormatException and Gobi 2000 GPS Devices | CodePlex DS.Positioning | **This issue was imported from [CodePlex](http://dotspatial.codeplex.com/workitem/63594)**
**[ClevelandRaymond](http://www.codeplex.com/site/users/view/ClevelandRaymond)** wrote 2015-08-15 at 21:44
I'm the Sr. Software Engineer for an oil and gas company, and we use the DotSpatial.Positioning library to read GPS data from the Qualcomm Gobi 2000 (HP un2420) card built into our Panasonic CF-19 Toughbook laptops. We were getting FormatException(s) from
DotSpatial.Positioning when parsing VTG sentences. So, I incorporated the source code into our solution and debugged the code.
I found that the Qualcomm Gobi 2000 (HP un2420) GPS device is returning a VTG sentence with the longitude and speed set to "nan" in the actual sentence read from the COM port. Because the DotSpatial.Positioning library v2.0 uses the double.Parse()
method to convert the strings into doubles, the FormatException(s) are being thrown when encountering the "nan" string values.
Although the library handles these exceptions, I've fixed the issue within our copy of the source code and we are no longer getting these exceptions. I'm not sure how the DotSpatial team wants to handle this, but I made the following changes to the source code:
In file NmeaSentence.cs at line 43, we can change the access modifier for _isValid to protected:
protected bool _isValid;
or we could stay within best practices and change the property IsValid to have a protected set accessor, but then the IsValid property of the NmeaSentence and Packet base class would have to be modified:
Packet.cs:
public abstract bool IsValid { get; protected set; }
NmeaSentence.cs:
public override bool IsValid
{
<pre><code>get
{
return _isValid;
}
protected set
{
_isValid = value;
}</code></pre>
}
Either way will work, but we have to be able to set IsValid within the OnSentenceChanged method of the derived GpvtgSentence class. Then, in the OnSentenceChanged method located in the file GpvtgSentence.cs at line 77, we test for invalid strings by using double.TryParse
as follows:
protected override void OnSentenceChanged()
{
<pre><code>// First, process the basic info for the sentence
base.OnSentenceChanged();
// Cache the sentence words
string[] words = Words;
int wordCount = words.Length;
// Even if we get a valid VTG sentence, we can have invalid values
if (words != null)
{
double result = 0;
// Check the Longitude - third word of the sentence
if (wordCount > 2 && double.TryParse(words[2], out result) == false)
{
_isValid = false;
return;
}
// Check the Speed - fifth word of the sentence
if (wordCount > 4 && double.TryParse(words[4], out result) == false)
{
_isValid = false;
return;
}
}
</code></pre>
...
}
I've also found some mistakes when testing the wordCount to make sure we are not accessing elements of the words string array that do not exist:
protected override void OnSentenceChanged()
{
<pre><code>// First, process the basic info for the sentence
base.OnSentenceChanged();
</code></pre>
....
<pre><code>#region Bearing
if (wordCount >= 1 && words[0].Length != 0)
_bearing = Azimuth.Parse(words[0], NmeaCultureInfo);
else
_bearing = Azimuth.Invalid;
#endregion Bearing
#region Magnetic Variation
// This is ok because we are testing wordCount >= 3
// but we could've just tested using wordCount > 2
if (wordCount >= 3 && words[2].Length != 0)
{
_magneticVariation = new Longitude(double.Parse(words[2], NmeaCultureInfo) -
_bearing.DecimalDegrees);
}
else
{
_magneticVariation = Longitude.Invalid;
}
#endregion Magnetic Variation
#region Speed
/* Speed is reported as both knots and KM/H. We can parse either of the values.
* First, try to parse knots. If that fails, parse KM/h.
*/
// This should be testing for wordCount >=5 or just wordCount > 4
if (wordCount > 5 && words[4].Length != 0)
{
_speed = new Speed(
// Parse the numeric portion
double.Parse(words[4], NmeaCultureInfo),
// Use knots
SpeedUnit.Knots);
}
// This should be testing for wordCount >=7 or just wordCount > 6
else if (wordCount > 7 && words[6].Length != 0)
{
_speed = new Speed(
// Parse the numeric portion
double.Parse(words[6], NmeaCultureInfo),
// Use knots
SpeedUnit.KilometersPerHour);
}
else
{
// Invalid speed
_speed = Speed.Invalid;
}
#endregion Speed</code></pre>
}
I added comments about changing the if statements to use the proper testing of the wordCount, but I don't think this is causing any issues because the word count is longer than 7. However, I did make the changes to our version of the code. Now that the OnSentenceChanged
method of the GpvtgSentence class is fixed, we can add the last piece of code that checks the sentence's IsValid property and prevents processing invalid sentences. In the OnReadPacket method located in the file NmeaInterpreter.cs at line 279, we need to add
a check for the sentence's IsValid property:
protected override void OnReadPacket()
{
<pre><code>// Read a sentence from the underlying stream
NmeaSentence sentence = _stream.ReadTypedSentence();
// Don't process invalid sentences
if (sentence.IsValid == false)
{
return;
}
</code></pre>
...
}
There are probably other places in the DotSpatial.Positioning library where this improvement could be made but, since we only use the NmeaInterpreter to read GPS data from our GoBi cards, the above fix is all we needed to resolve the issue.
I have attached the GPS device stream as read by a third party application called VisualGPS that shows the $GPSVTG sentence containing "nan" for the values:
$GPVTG,nan,T,nan,M,0.0,N,0.0,K,A<em>23
$GPRMC,205238.3,A,3512.585528,N,09725.570975,W,0.0,,100815,,,A</em>50
$GPGSA,A,3,02,05,06,12,17,,,,,,,,5.1,2.2,4.6<em>30
$GPGSV,4,1,16,06,57,032,35,05,25,178,30,12,52,309,28,02,71,279,25</em>7C
$GPGSV,4,2,16,17,27,084,24,09,,,,10,50,108,,24,19,244,*49
$GPGSV,4,3,16,25,15,319,,08,,,,32,,,,31,,,*4A
$GPGSV,4,4,16,30,,,,29,,,,27,,,,26,,,<em>77
$GPGGA,205239.3,3512.585528,N,09725.570975,W,1,05,2.2,336.2,M,-27.0,M,,<em>69
$PQXFI,205239.3,3512.585528,N,09725.570975,W,336.2,13.08,20.44,2.08</em>75
$GPVTG,nan,T,nan,M,0.0,N,0.0,K,A</em>23
Thank you for writing such a wonderful piece of software. I hope that my analysis will be useful to your team and anyone else who has experienced this issue.
Cleveland E. Raymond | 1.0 | DotSpatial.Positioning FormatException and Gobi 2000 GPS Devices - **This issue was imported from [CodePlex](http://dotspatial.codeplex.com/workitem/63594)**
**[ClevelandRaymond](http://www.codeplex.com/site/users/view/ClevelandRaymond)** wrote 2015-08-15 at 21:44
I'm the Sr. Software Engineer for an oil and gas company, and we use the DotSpatial.Positioning library to read GPS data from the Qualcomm Gobi 2000 (HP un2420) card built into our Panasonic CF-19 Toughbook laptops. We were getting FormatException(s) from
DotSpatial.Positioning when parsing VTG sentences. So, I incorporated the source code into our solution and debugged the code.
I found that the Qualcomm Gobi 2000 (HP un2420) GPS device is returning a VTG sentence with the longitude and speed set to "nan" in the actual sentence read from the COM port. Because the DotSpatial.Positioning library v2.0 uses the double.Parse()
method to convert the strings into doubles, the FormatException(s) are being thrown when encountering the "nan" string values.
Although the library handles these exceptions, I've fixed the issue within our copy of the source code and we are no longer getting these exceptions. I'm not sure how the DotSpatial team wants to handle this, but I made the following changes to the source code:
In file NmeaSentence.cs at line 43, we can change the access modifier for _isValid to protected:
protected bool _isValid;
or we could stay within best practices and change the property IsValid to have a protected set accessor, but then the IsValid property of the NmeaSentence and Packet base class would have to be modified:
Packet.cs:
public abstract bool IsValid { get; protected set; }
NmeaSentence.cs:
public override bool IsValid
{
<pre><code>get
{
return _isValid;
}
protected set
{
_isValid = value;
}</code></pre>
}
Either way will work, but we have to be able to set IsValid within the OnSentenceChanged method of the derived GpvtgSentence class. Then, in the OnSentenceChanged method located in the file GpvtgSentence.cs at line 77, we test for invalid strings by using double.TryParse
as follows:
protected override void OnSentenceChanged()
{
<pre><code>// First, process the basic info for the sentence
base.OnSentenceChanged();
// Cache the sentence words
string[] words = Words;
int wordCount = words.Length;
// Even if we get a valid VTG sentence, we can have invalid values
if (words != null)
{
double result = 0;
// Check the Longitude - third word of the sentence
if (wordCount > 2 && double.TryParse(words[2], out result) == false)
{
_isValid = false;
return;
}
// Check the Speed - fifth word of the sentence
if (wordCount > 4 && double.TryParse(words[4], out result) == false)
{
_isValid = false;
return;
}
}
</code></pre>
...
}
I've also found some mistakes when testing the wordCount to make sure we are not accessing elements of the words string array that do not exist:
protected override void OnSentenceChanged()
{
<pre><code>// First, process the basic info for the sentence
base.OnSentenceChanged();
</code></pre>
....
<pre><code>#region Bearing
if (wordCount >= 1 && words[0].Length != 0)
_bearing = Azimuth.Parse(words[0], NmeaCultureInfo);
else
_bearing = Azimuth.Invalid;
#endregion Bearing
#region Magnetic Variation
// This is ok because we are testing wordCount >= 3
// but we could've just tested using wordCount > 2
if (wordCount >= 3 && words[2].Length != 0)
{
_magneticVariation = new Longitude(double.Parse(words[2], NmeaCultureInfo) -
_bearing.DecimalDegrees);
}
else
{
_magneticVariation = Longitude.Invalid;
}
#endregion Magnetic Variation
#region Speed
/* Speed is reported as both knots and KM/H. We can parse either of the values.
* First, try to parse knots. If that fails, parse KM/h.
*/
// This should be testing for wordCount >=5 or just wordCount > 4
if (wordCount > 5 && words[4].Length != 0)
{
_speed = new Speed(
// Parse the numeric portion
double.Parse(words[4], NmeaCultureInfo),
// Use knots
SpeedUnit.Knots);
}
// This should be testing for wordCount >=7 or just wordCount > 6
else if (wordCount > 7 && words[6].Length != 0)
{
_speed = new Speed(
// Parse the numeric portion
double.Parse(words[6], NmeaCultureInfo),
// Use knots
SpeedUnit.KilometersPerHour);
}
else
{
// Invalid speed
_speed = Speed.Invalid;
}
#endregion Speed</code></pre>
}
I added comments about changing the if statements to use the proper testing of the wordCount, but I don't think this is causing any issues because the word count is longer than 7. However, I did make the changes to our version of the code. Now that the OnSentenceChanged
method of the GpvtgSentence class is fixed, we can add the last piece of code that checks the sentence's IsValid property and prevents processing invalid sentences. In the OnReadPacket method located in the file NmeaInterpreter.cs at line 279, we need to add
a check for the sentence's IsValid property:
protected override void OnReadPacket()
{
<pre><code>// Read a sentence from the underlying stream
NmeaSentence sentence = _stream.ReadTypedSentence();
// Don't process invalid sentences
if (sentence.IsValid == false)
{
return;
}
</code></pre>
...
}
There are probably other places in the DotSpatial.Positioning library where this improvement could be made but, since we only use the NmeaInterpreter to read GPS data from our GoBi cards, the above fix is all we needed to resolve the issue.
I have attached the GPS device stream as read by a third party application called VisualGPS that shows the $GPSVTG sentence containing "nan" for the values:
$GPVTG,nan,T,nan,M,0.0,N,0.0,K,A<em>23
$GPRMC,205238.3,A,3512.585528,N,09725.570975,W,0.0,,100815,,,A</em>50
$GPGSA,A,3,02,05,06,12,17,,,,,,,,5.1,2.2,4.6<em>30
$GPGSV,4,1,16,06,57,032,35,05,25,178,30,12,52,309,28,02,71,279,25</em>7C
$GPGSV,4,2,16,17,27,084,24,09,,,,10,50,108,,24,19,244,*49
$GPGSV,4,3,16,25,15,319,,08,,,,32,,,,31,,,*4A
$GPGSV,4,4,16,30,,,,29,,,,27,,,,26,,,<em>77
$GPGGA,205239.3,3512.585528,N,09725.570975,W,1,05,2.2,336.2,M,-27.0,M,,<em>69
$PQXFI,205239.3,3512.585528,N,09725.570975,W,336.2,13.08,20.44,2.08</em>75
$GPVTG,nan,T,nan,M,0.0,N,0.0,K,A</em>23
Thank you for writing such a wonderful piece of software. I hope that my analysis will be useful to your team and anyone else who has experienced this issue.
Cleveland E. Raymond | non_priority | dotspatial positioning formatexception and gobi gps devices this issue was imported from wrote at i m the sr software engineer for an oil and gas company and we use the dotspatial positioning library to read gps data from the qualcomm gobi hp card built into our panasonic cf toughbook laptops we were getting formatexception s from dotspatial positioning when parsing vtg sentences so i incorporated the source code into our solution and debugged the code i found that the qualcomm gobi hp gps device is returning a vtg sentence with the longitude and speed set to nan in the actual sentence read from the com port because the dotspatial positioning library uses the double parse method to convert the strings into doubles the formatexception s are being thrown when encountering the nan string values although the library handles these exceptions i ve fixed the issue within our copy of the source code and we are no longer getting these exceptions i m not sure how the dotspatial team wants to handle this but i made the following changes to the source code in file nmeasentence cs at line we can change the access modifier for isvalid to protected protected bool isvalid or we could stay within best practices and change the property isvalid to have a protected set accessor but then the isvalid property of the nmeasentence and packet base class would have to be modified packet cs public abstract bool isvalid get protected set nmeasentence cs public override bool isvalid get return isvalid protected set isvalid value either way will work but we have to be able to set isvalid within the onsentencechanged method of the derived gpvtgsentence class then in the onsentencechanged method located in the file gpvtgsentence cs at line we test for invalid strings by using double tryparse as follows protected override void onsentencechanged first process the basic info for the sentence base onsentencechanged cache the sentence words string words words int wordcount words length even if we get a valid vtg sentence we can have invalid values if words null double result check the longitude third word of the sentence if wordcount double tryparse words out result false isvalid false return check the speed fifth word of the sentence if wordcount double tryparse words out result false isvalid false return i ve also found some mistakes when testing the wordcount to make sure we are not accessing elements of the words string array that do not exist protected override void onsentencechanged first process the basic info for the sentence base onsentencechanged region bearing if wordcount words length bearing azimuth parse words nmeacultureinfo else bearing azimuth invalid endregion bearing region magnetic variation this is ok because we are testing wordcount but we could ve just tested using wordcount if wordcount words length magneticvariation new longitude double parse words nmeacultureinfo bearing decimaldegrees else magneticvariation longitude invalid endregion magnetic variation region speed speed is reported as both knots and km h we can parse either of the values first try to parse knots if that fails parse km h this should be testing for wordcount or just wordcount if wordcount words length speed new speed parse the numeric portion double parse words nmeacultureinfo use knots speedunit knots this should be testing for wordcount or just wordcount else if wordcount words length speed new speed parse the numeric portion double parse words nmeacultureinfo use knots speedunit kilometersperhour else invalid speed speed speed invalid endregion speed i added comments about changing the if statements to use the proper testing of the wordcount but i don t think this is causing any issues because the word count is longer than however i did make the changes to our version of the code now that the onsentencechanged method of the gpvtgsentence class is fixed we can add the last piece of code that checks the sentence s isvalid property and prevents processing invalid sentences in the onreadpacket method located in the file nmeainterpreter cs at line we need to add a check for the sentence s isvalid property protected override void onreadpacket read a sentence from the underlying stream nmeasentence sentence stream readtypedsentence don t process invalid sentences if sentence isvalid false return there are probably other places in the dotspatial positioning library where this improvement could be made but since we only use the nmeainterpreter to read gps data from our gobi cards the above fix is all we needed to resolve the issue i have attached the gps device stream as read by a third party application called visualgps that shows the gpsvtg sentence containing nan for the values gpvtg nan t nan m n k a gprmc a n w a gpgsa a gpgsv gpgsv gpgsv gpgsv gpgga n w m m pqxfi n w gpvtg nan t nan m n k a thank you for writing such a wonderful piece of software i hope that my analysis will be useful to your team and anyone else who has experienced this issue cleveland e raymond | 0 |
28,762 | 11,688,510,844 | IssuesEvent | 2020-03-05 14:39:25 | Ryan-Oneil/oneil-industries-website | https://api.github.com/repos/Ryan-Oneil/oneil-industries-website | closed | CVE-2020-9546 (Medium) detected in jackson-databind-2.9.10.3.jar | security vulnerability | ## CVE-2020-9546 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/oneil-industries-website/backend/pom.xml</p>
<p>Path to vulnerable library: downloadResource_fef68085-5450-4b7d-ab3e-a02e26e07811/20200305121424/jackson-databind-2.9.10.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Ryan-Oneil/oneil-industries-website/commit/920764ef724c8d13dd83a8b562b08c635d2694d3">920764ef724c8d13dd83a8b562b08c635d2694d3</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-9546 (Medium) detected in jackson-databind-2.9.10.3.jar - ## CVE-2020-9546 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/oneil-industries-website/backend/pom.xml</p>
<p>Path to vulnerable library: downloadResource_fef68085-5450-4b7d-ab3e-a02e26e07811/20200305121424/jackson-databind-2.9.10.3.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Ryan-Oneil/oneil-industries-website/commit/920764ef724c8d13dd83a8b562b08c635d2694d3">920764ef724c8d13dd83a8b562b08c635d2694d3</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm oneil industries website backend pom xml path to vulnerable library downloadresource jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
23,607 | 12,036,001,906 | IssuesEvent | 2020-04-13 18:57:20 | sciencehistory/scihist_digicoll | https://api.github.com/repos/sciencehistory/scihist_digicoll | opened | Rename all source code files related to audio/oral history | developer tools maintenance/performance | We originally named them without referring to oral history, as if they were just for "audio". And we weren't very consistent even there, sometimes `show_audio`, sometimes `show_with_audio`, sometimes `audio_work`, etc.
But this set of views became really customized for oral history specifically. We should rename them to be clear about that. But `oral_history` is a lot to type. Maybe all based on `oh_audio`, all beginning with that? And we should change the logic in the controller to only activate this special view if the thing is genre oral histories **and** has audio.
Some of the files:
* show_audio.scss
* audio_work_show_decorator.rb
* show_audio.scss
* audio_front_end_spec.rb
* show_with_audio.html.erb
There may be more.
Or is this maybe not really worth it? | True | Rename all source code files related to audio/oral history - We originally named them without referring to oral history, as if they were just for "audio". And we weren't very consistent even there, sometimes `show_audio`, sometimes `show_with_audio`, sometimes `audio_work`, etc.
But this set of views became really customized for oral history specifically. We should rename them to be clear about that. But `oral_history` is a lot to type. Maybe all based on `oh_audio`, all beginning with that? And we should change the logic in the controller to only activate this special view if the thing is genre oral histories **and** has audio.
Some of the files:
* show_audio.scss
* audio_work_show_decorator.rb
* show_audio.scss
* audio_front_end_spec.rb
* show_with_audio.html.erb
There may be more.
Or is this maybe not really worth it? | non_priority | rename all source code files related to audio oral history we originally named them without referring to oral history as if they were just for audio and we weren t very consistent even there sometimes show audio sometimes show with audio sometimes audio work etc but this set of views became really customized for oral history specifically we should rename them to be clear about that but oral history is a lot to type maybe all based on oh audio all beginning with that and we should change the logic in the controller to only activate this special view if the thing is genre oral histories and has audio some of the files show audio scss audio work show decorator rb show audio scss audio front end spec rb show with audio html erb there may be more or is this maybe not really worth it | 0 |
271,340 | 29,477,316,387 | IssuesEvent | 2023-06-02 00:09:44 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Dart internal builds always use main recipes | team: security | Dart internal builds are not using their release candidate branch of recipes. | True | Dart internal builds always use main recipes - Dart internal builds are not using their release candidate branch of recipes. | non_priority | dart internal builds always use main recipes dart internal builds are not using their release candidate branch of recipes | 0 |
35,596 | 7,786,135,582 | IssuesEvent | 2018-06-06 17:58:24 | telus/tds-core | https://api.github.com/repos/telus/tds-core | closed | [StepTracker] - Mobile view - "Step x of y" is hardcoded and displayed only in English | defect in development status: core team | ## Description
- On the step tracker for mobile view, copy "Step x of y" is displayed in English for French
## Reproduction Steps
- https://www.wcstage.telus.com/my-account/payment/preauthorized/account/ye_rZFV2bLYlFedcXxDH5w/debit
- Login: ssffh4@telusinternal.com / Passw0rd - BAN: 603163163s
## Reproduction Percentage (if applicable)
- 10/10 times
## Version Number of TDS
- [0.19] Include version of TDS this is occuring on
*note attach screenshots whenever possible*
 | 1.0 | [StepTracker] - Mobile view - "Step x of y" is hardcoded and displayed only in English - ## Description
- On the step tracker for mobile view, copy "Step x of y" is displayed in English for French
## Reproduction Steps
- https://www.wcstage.telus.com/my-account/payment/preauthorized/account/ye_rZFV2bLYlFedcXxDH5w/debit
- Login: ssffh4@telusinternal.com / Passw0rd - BAN: 603163163s
## Reproduction Percentage (if applicable)
- 10/10 times
## Version Number of TDS
- [0.19] Include version of TDS this is occuring on
*note attach screenshots whenever possible*
 | non_priority | mobile view step x of y is hardcoded and displayed only in english description on the step tracker for mobile view copy step x of y is displayed in english for french reproduction steps login telusinternal com ban reproduction percentage if applicable times version number of tds include version of tds this is occuring on note attach screenshots whenever possible | 0 |
110,261 | 16,977,092,098 | IssuesEvent | 2021-06-30 01:43:25 | AlekEagle/sharex-vue-docs | https://api.github.com/repos/AlekEagle/sharex-vue-docs | opened | CVE-2021-32723 (High) detected in prismjs-1.22.0.tgz | security vulnerability | ## CVE-2021-32723 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>prismjs-1.22.0.tgz</b></p></summary>
<p>Lightweight, robust, elegant syntax highlighting. A spin-off project from Dabblet.</p>
<p>Library home page: <a href="https://registry.npmjs.org/prismjs/-/prismjs-1.22.0.tgz">https://registry.npmjs.org/prismjs/-/prismjs-1.22.0.tgz</a></p>
<p>Path to dependency file: sharex-vue-docs/package.json</p>
<p>Path to vulnerable library: sharex-vue-docs/node_modules/prismjs/package.json</p>
<p>
Dependency Hierarchy:
- vuepress-1.7.1.tgz (Root Library)
- core-1.7.1.tgz
- markdown-1.7.1.tgz
- :x: **prismjs-1.22.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prism is a syntax highlighting library. Some languages before 1.24.0 are vulnerable to Regular Expression Denial of Service (ReDoS). When Prism is used to highlight untrusted (user-given) text, an attacker can craft a string that will take a very very long time to highlight. This problem has been fixed in Prism v1.24. As a workaround, do not use ASCIIDoc or ERB to highlight untrusted text. Other languages are not affected and can be used to highlight untrusted text.
<p>Publish Date: 2021-06-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32723>CVE-2021-32723</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/PrismJS/prism/security/advisories/GHSA-gj77-59wh-66hg">https://github.com/PrismJS/prism/security/advisories/GHSA-gj77-59wh-66hg</a></p>
<p>Release Date: 2021-06-28</p>
<p>Fix Resolution: prismjs - 1.24.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-32723 (High) detected in prismjs-1.22.0.tgz - ## CVE-2021-32723 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>prismjs-1.22.0.tgz</b></p></summary>
<p>Lightweight, robust, elegant syntax highlighting. A spin-off project from Dabblet.</p>
<p>Library home page: <a href="https://registry.npmjs.org/prismjs/-/prismjs-1.22.0.tgz">https://registry.npmjs.org/prismjs/-/prismjs-1.22.0.tgz</a></p>
<p>Path to dependency file: sharex-vue-docs/package.json</p>
<p>Path to vulnerable library: sharex-vue-docs/node_modules/prismjs/package.json</p>
<p>
Dependency Hierarchy:
- vuepress-1.7.1.tgz (Root Library)
- core-1.7.1.tgz
- markdown-1.7.1.tgz
- :x: **prismjs-1.22.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prism is a syntax highlighting library. Some languages before 1.24.0 are vulnerable to Regular Expression Denial of Service (ReDoS). When Prism is used to highlight untrusted (user-given) text, an attacker can craft a string that will take a very very long time to highlight. This problem has been fixed in Prism v1.24. As a workaround, do not use ASCIIDoc or ERB to highlight untrusted text. Other languages are not affected and can be used to highlight untrusted text.
<p>Publish Date: 2021-06-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32723>CVE-2021-32723</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/PrismJS/prism/security/advisories/GHSA-gj77-59wh-66hg">https://github.com/PrismJS/prism/security/advisories/GHSA-gj77-59wh-66hg</a></p>
<p>Release Date: 2021-06-28</p>
<p>Fix Resolution: prismjs - 1.24.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in prismjs tgz cve high severity vulnerability vulnerable library prismjs tgz lightweight robust elegant syntax highlighting a spin off project from dabblet library home page a href path to dependency file sharex vue docs package json path to vulnerable library sharex vue docs node modules prismjs package json dependency hierarchy vuepress tgz root library core tgz markdown tgz x prismjs tgz vulnerable library found in base branch master vulnerability details prism is a syntax highlighting library some languages before are vulnerable to regular expression denial of service redos when prism is used to highlight untrusted user given text an attacker can craft a string that will take a very very long time to highlight this problem has been fixed in prism as a workaround do not use asciidoc or erb to highlight untrusted text other languages are not affected and can be used to highlight untrusted text publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution prismjs step up your open source security game with whitesource | 0 |
4,616 | 7,247,806,762 | IssuesEvent | 2018-02-15 05:52:29 | PrinceOfAmber/Cyclic | https://api.github.com/repos/PrinceOfAmber/Cyclic | closed | cyclicmagic.fake_player.sapling_regrowth wakes up Weirding Gadget chunk loader | bug: lag done [pending release] mod compatibility | Minecraft version & Mod Version:
Forge 2615
1.12.2
Cyclic-1.12.2-1.11.2
Latest Weirding Gadget
Single player or Server:
Server
Cyclic cyclicmagic.fake_player.sapling_regrowth triggers Weirding Gadget chunk loader. Excerpt from log:
`[10:36:09] [Server thread/INFO] [weirdinggadget]: Waking up Chunk Loader at BlockPos{x=2577, y=66, z=1175} because cyclicmagic.fake_player.sapling_regrowth placed/interacted with it` | True | cyclicmagic.fake_player.sapling_regrowth wakes up Weirding Gadget chunk loader - Minecraft version & Mod Version:
Forge 2615
1.12.2
Cyclic-1.12.2-1.11.2
Latest Weirding Gadget
Single player or Server:
Server
Cyclic cyclicmagic.fake_player.sapling_regrowth triggers Weirding Gadget chunk loader. Excerpt from log:
`[10:36:09] [Server thread/INFO] [weirdinggadget]: Waking up Chunk Loader at BlockPos{x=2577, y=66, z=1175} because cyclicmagic.fake_player.sapling_regrowth placed/interacted with it` | non_priority | cyclicmagic fake player sapling regrowth wakes up weirding gadget chunk loader minecraft version mod version forge cyclic latest weirding gadget single player or server server cyclic cyclicmagic fake player sapling regrowth triggers weirding gadget chunk loader excerpt from log waking up chunk loader at blockpos x y z because cyclicmagic fake player sapling regrowth placed interacted with it | 0 |
8,811 | 3,791,017,086 | IssuesEvent | 2016-03-22 00:04:17 | WayofTime/BloodMagic | https://api.github.com/repos/WayofTime/BloodMagic | closed | Crash while launching game. (1.9) | 1.9 bug code complete | #### Issue Description:
Note: If this bug occurs in a modpack, please report this to the modpack author. Otherwise, delete this line and add your description here. If this is a feature request, this template does not apply to you. Just delete everything.
#### What happens: While loading, the game crashed with this crash report:
http://pastebin.com/hkXCApgc
#### What you expected to happen: Game should open.
#### Steps to reproduce:
1. I pressed ''play''
2. Game started loading.
3. Crash happened.
...
____
#### Affected Versions (Do *not* use "latest"):
- BloodMagic: 1.9- 2.0.0-21
- Minecraft: 1.9
- Forge: 1.9-12.16.0.1782-1.9 | 1.0 | Crash while launching game. (1.9) - #### Issue Description:
Note: If this bug occurs in a modpack, please report this to the modpack author. Otherwise, delete this line and add your description here. If this is a feature request, this template does not apply to you. Just delete everything.
#### What happens: While loading, the game crashed with this crash report:
http://pastebin.com/hkXCApgc
#### What you expected to happen: Game should open.
#### Steps to reproduce:
1. I pressed ''play''
2. Game started loading.
3. Crash happened.
...
____
#### Affected Versions (Do *not* use "latest"):
- BloodMagic: 1.9- 2.0.0-21
- Minecraft: 1.9
- Forge: 1.9-12.16.0.1782-1.9 | non_priority | crash while launching game issue description note if this bug occurs in a modpack please report this to the modpack author otherwise delete this line and add your description here if this is a feature request this template does not apply to you just delete everything what happens while loading the game crashed with this crash report what you expected to happen game should open steps to reproduce i pressed play game started loading crash happened affected versions do not use latest bloodmagic minecraft forge | 0 |
271,275 | 29,368,851,996 | IssuesEvent | 2023-05-29 01:08:36 | vlaship/bank-api | https://api.github.com/repos/vlaship/bank-api | opened | CVE-2023-24998 (High) detected in tomcat-embed-core-9.0.30.jar | Mend: dependency security vulnerability | ## CVE-2023-24998 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.30.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.30/ad32909314fe2ba02cec036434c0addd19bcc580/tomcat-embed-core-9.0.30.jar,/root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.30/ad32909314fe2ba02cec036434c0addd19bcc580/tomcat-embed-core-9.0.30.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.4.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.2.4.RELEASE.jar
- :x: **tomcat-embed-core-9.0.30.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Commons FileUpload before 1.5 does not limit the number of request parts to be processed resulting in the possibility of an attacker triggering a DoS with a malicious upload or series of uploads.
Note that, like all of the file upload limits, the
new configuration option (FileUploadBase#setFileCountMax) is not
enabled by default and must be explicitly configured.
<p>Publish Date: 2023-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24998>CVE-2023-24998</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tomcat.apache.org/security-10.html">https://tomcat.apache.org/security-10.html</a></p>
<p>Release Date: 2023-02-20</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.71</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.5.15</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-24998 (High) detected in tomcat-embed-core-9.0.30.jar - ## CVE-2023-24998 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.30.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.30/ad32909314fe2ba02cec036434c0addd19bcc580/tomcat-embed-core-9.0.30.jar,/root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.30/ad32909314fe2ba02cec036434c0addd19bcc580/tomcat-embed-core-9.0.30.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.2.4.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.2.4.RELEASE.jar
- :x: **tomcat-embed-core-9.0.30.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Commons FileUpload before 1.5 does not limit the number of request parts to be processed resulting in the possibility of an attacker triggering a DoS with a malicious upload or series of uploads.
Note that, like all of the file upload limits, the
new configuration option (FileUploadBase#setFileCountMax) is not
enabled by default and must be explicitly configured.
<p>Publish Date: 2023-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-24998>CVE-2023-24998</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tomcat.apache.org/security-10.html">https://tomcat.apache.org/security-10.html</a></p>
<p>Release Date: 2023-02-20</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.71</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.5.15</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file build gradle path to vulnerable library root gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar root gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library vulnerability details apache commons fileupload before does not limit the number of request parts to be processed resulting in the possibility of an attacker triggering a dos with a malicious upload or series of uploads note that like all of the file upload limits the new configuration option fileuploadbase setfilecountmax is not enabled by default and must be explicitly configured publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core direct dependency fix resolution org springframework boot spring boot starter web step up your open source security game with mend | 0 |
130,528 | 27,717,350,118 | IssuesEvent | 2023-03-14 17:50:00 | informalsystems/hermes | https://api.github.com/repos/informalsystems/hermes | closed | Improve packet forward tests by submitting transaction within Rust | O: code-hygiene | ## Proposal
<!-- Describe your proposal for how the process of Hermes should be improved -->
<!-- Apply relevant labels to indicate:
- (WHY) The purpose or objective of this proposal with "O" labels
- (WHICH) The part of the system this proposal relates to (use "E" for external or "I" for internal levels)
- (HOW) If any administrative considerations should be taken into account (use "A" labels)
This will help us prioritize and categorize your proposal more effectively
-->
Following https://github.com/informalsystems/hermes/pull/3032#discussion_r1085311988 the method used to test packet forwarding should be updated to submit the transaction without using the chain binary CLI.
This requires `ibc-proto-rs` to have the `memo` field.
____
## For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate milestone (priority) applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
| 1.0 | Improve packet forward tests by submitting transaction within Rust - ## Proposal
<!-- Describe your proposal for how the process of Hermes should be improved -->
<!-- Apply relevant labels to indicate:
- (WHY) The purpose or objective of this proposal with "O" labels
- (WHICH) The part of the system this proposal relates to (use "E" for external or "I" for internal levels)
- (HOW) If any administrative considerations should be taken into account (use "A" labels)
This will help us prioritize and categorize your proposal more effectively
-->
Following https://github.com/informalsystems/hermes/pull/3032#discussion_r1085311988 the method used to test packet forwarding should be updated to submit the transaction without using the chain binary CLI.
This requires `ibc-proto-rs` to have the `memo` field.
____
## For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate milestone (priority) applied
- [ ] Appropriate contributors tagged
- [ ] Contributor assigned/self-assigned
| non_priority | improve packet forward tests by submitting transaction within rust proposal apply relevant labels to indicate why the purpose or objective of this proposal with o labels which the part of the system this proposal relates to use e for external or i for internal levels how if any administrative considerations should be taken into account use a labels this will help us prioritize and categorize your proposal more effectively following the method used to test packet forwarding should be updated to submit the transaction without using the chain binary cli this requires ibc proto rs to have the memo field for admin use not duplicate issue appropriate labels applied appropriate milestone priority applied appropriate contributors tagged contributor assigned self assigned | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.