Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
34,931 | 4,593,335,581 | IssuesEvent | 2016-09-21 00:27:17 | TeamPorcupine/ProjectPorcupine | https://api.github.com/repos/TeamPorcupine/ProjectPorcupine | closed | Floor tile idea- Keep track of how often it is stepped on | discussion enhancement game design | I've stated I don't like the floor tile. One thought I just had was to keep track of how often a tile is walked on, and change accordingly. If a tile is heavily used, it will start to look more worn after a while. It seems easy enough to do, and could be a cool effect. Thoughts? | 1.0 | Floor tile idea- Keep track of how often it is stepped on - I've stated I don't like the floor tile. One thought I just had was to keep track of how often a tile is walked on, and change accordingly. If a tile is heavily used, it will start to look more worn after a while. It seems easy enough to do, and could be a cool effect. Thoughts? | non_priority | floor tile idea keep track of how often it is stepped on i ve stated i don t like the floor tile one thought i just had was to keep track of how often a tile is walked on and change accordingly if a tile is heavily used it will start to look more worn after a while it seems easy enough to do and could be a cool effect thoughts | 0 |
207,069 | 23,419,037,307 | IssuesEvent | 2022-08-13 12:03:28 | nexmo-community/vonage-php-sdk-drupal-9 | https://api.github.com/repos/nexmo-community/vonage-php-sdk-drupal-9 | closed | core9.4.1: 1 vulnerabilities (highest severity is: 6.1) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>core9.4.1</b></p></summary>
<p>
<p>Subtree split of drupal's /core directory</p>
<p>Library home page: <a href=https://github.com/drupal/core.git>https://github.com/drupal/core.git</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/web/core/assets/vendor/jquery.ui/ui/widgets/checkboxradio.js</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-31160](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31160) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | core9.4.1 | Direct | jquery-ui - 1.13.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-31160</summary>
### Vulnerable Library - <b>core9.4.1</b></p>
<p>
<p>Subtree split of drupal's /core directory</p>
<p>Library home page: <a href=https://github.com/drupal/core.git>https://github.com/drupal/core.git</a></p>
<p>Found in base branch: <b>main</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/web/core/assets/vendor/jquery.ui/ui/widgets/checkboxradio.js</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery UI is a curated set of user interface interactions, effects, widgets, and themes built on top of jQuery. Versions prior to 1.13.2 are potentially vulnerable to cross-site scripting. Initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label. Calling `.checkboxradio( "refresh" )` on such a widget and the initial HTML contained encoded HTML entities will make them erroneously get decoded. This can lead to potentially executing JavaScript code. The bug has been patched in jQuery UI 1.13.2. To remediate the issue, someone who can change the initial HTML can wrap all the non-input contents of the `label` in a `span`.
<p>Publish Date: 2022-07-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31160>CVE-2022-31160</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160</a></p>
<p>Release Date: 2022-07-20</p>
<p>Fix Resolution: jquery-ui - 1.13.2</p>
</p>
<p></p>
</details> | True | core9.4.1: 1 vulnerabilities (highest severity is: 6.1) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>core9.4.1</b></p></summary>
<p>
<p>Subtree split of drupal's /core directory</p>
<p>Library home page: <a href=https://github.com/drupal/core.git>https://github.com/drupal/core.git</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/web/core/assets/vendor/jquery.ui/ui/widgets/checkboxradio.js</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2022-31160](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31160) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | core9.4.1 | Direct | jquery-ui - 1.13.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-31160</summary>
### Vulnerable Library - <b>core9.4.1</b></p>
<p>
<p>Subtree split of drupal's /core directory</p>
<p>Library home page: <a href=https://github.com/drupal/core.git>https://github.com/drupal/core.git</a></p>
<p>Found in base branch: <b>main</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/web/core/assets/vendor/jquery.ui/ui/widgets/checkboxradio.js</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery UI is a curated set of user interface interactions, effects, widgets, and themes built on top of jQuery. Versions prior to 1.13.2 are potentially vulnerable to cross-site scripting. Initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label. Calling `.checkboxradio( "refresh" )` on such a widget and the initial HTML contained encoded HTML entities will make them erroneously get decoded. This can lead to potentially executing JavaScript code. The bug has been patched in jQuery UI 1.13.2. To remediate the issue, someone who can change the initial HTML can wrap all the non-input contents of the `label` in a `span`.
<p>Publish Date: 2022-07-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31160>CVE-2022-31160</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160</a></p>
<p>Release Date: 2022-07-20</p>
<p>Fix Resolution: jquery-ui - 1.13.2</p>
</p>
<p></p>
</details> | non_priority | vulnerabilities highest severity is autoclosed vulnerable library subtree split of drupal s core directory library home page a href vulnerable source files web core assets vendor jquery ui ui widgets checkboxradio js vulnerabilities cve severity cvss dependency type fixed in remediation available medium direct jquery ui details cve vulnerable library subtree split of drupal s core directory library home page a href found in base branch main vulnerable source files web core assets vendor jquery ui ui widgets checkboxradio js vulnerability details jquery ui is a curated set of user interface interactions effects widgets and themes built on top of jquery versions prior to are potentially vulnerable to cross site scripting initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label calling checkboxradio refresh on such a widget and the initial html contained encoded html entities will make them erroneously get decoded this can lead to potentially executing javascript code the bug has been patched in jquery ui to remediate the issue someone who can change the initial html can wrap all the non input contents of the label in a span publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery ui | 0 |
70,836 | 30,748,544,826 | IssuesEvent | 2023-07-28 17:01:50 | hashicorp/terraform-provider-azurerm | https://api.github.com/repos/hashicorp/terraform-provider-azurerm | closed | Unable to create new azurerm_app_configuration_key | bug service/app-configuration v/2.x (legacy) | ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
### Terraform (and AzureRM Provider) Version
Version: 2.75.0
```
Terraform v1.0.6
on linux_amd64
+ provider registry.terraform.io/hashicorp/azurerm v2.75.0
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* `azurerm_app_configuration_key`
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
resource "azurerm_app_configuration" "config-use" {
name = "some-config"
resource_group_name = azurerm_resource_group.some-rg.name
location = azurerm_resource_group.some-rg.location
sku = "free"
tags = {
"Environment" = local.environment,
}
}
resource "azurerm_app_configuration_key" "test" {
configuration_store_id = azurerm_app_configuration.config-use.id
key = "test"
value = "1"
}
```
### Debug Output
Debug output contains sensible data... and it's too big to be sure I'm not leaking any secret, so here only the classic logs
```
Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with the following symbols:
+ create
Terraform will perform the following actions:
# azurerm_app_configuration_key.test will be created
+ resource "azurerm_app_configuration_key" "test" {
+ configuration_store_id = "/subscriptions/00000000-0000-0000-0000-000000000000/resourceGroups/some-rg/providers/Microsoft.AppConfiguration/configurationStores/some-config"
+ content_type = (known after apply)
+ etag = (known after apply)
+ id = (known after apply)
+ key = "test"
+ locked = false
+ type = "kv"
+ value = "1"
}
Plan: 1 to add, 0 to change, 0 to destroy.
Do you want to perform these actions?
Terraform will perform the actions described above.
Only 'yes' will be accepted to approve.
Enter a value: yes
azurerm_app_configuration_key.test: Creating...
╷
│ Error: while checking for key's "test" existence: appconfiguration.BaseClient#GetKeyValues: Failure responding to request: StatusCode=403 -- Original Error: autorest/azure: error response cannot be parsed: "" error: EOF
│
│ with azurerm_app_configuration_key.test,
│ on app_config.tf line 153, in resource "azurerm_app_configuration_key" "test":
│ 153: resource "azurerm_app_configuration_key" "test" {
│
│ while checking for key's "test" existence: appconfiguration.BaseClient#GetKeyValues: Failure responding to request: StatusCode=403 -- Original Error: autorest/azure: error response cannot be parsed: "" error: EOF
╵
```
### Expected Behaviour
It create a new error
### Actual Behaviour
It crash
### Steps to Reproduce
`terraform apply`
### Important Factoids
- The command `az appconfig kv set -n some-config --key test --value abc` is working so I have the correct access. Terraform is displaying a 403 error.
- Azure US East
| 1.0 | Unable to create new azurerm_app_configuration_key - ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
### Terraform (and AzureRM Provider) Version
Version: 2.75.0
```
Terraform v1.0.6
on linux_amd64
+ provider registry.terraform.io/hashicorp/azurerm v2.75.0
```
### Affected Resource(s)
<!--- Please list the affected resources and data sources. --->
* `azurerm_app_configuration_key`
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
```hcl
resource "azurerm_app_configuration" "config-use" {
name = "some-config"
resource_group_name = azurerm_resource_group.some-rg.name
location = azurerm_resource_group.some-rg.location
sku = "free"
tags = {
"Environment" = local.environment,
}
}
resource "azurerm_app_configuration_key" "test" {
configuration_store_id = azurerm_app_configuration.config-use.id
key = "test"
value = "1"
}
```
### Debug Output
Debug output contains sensible data... and it's too big to be sure I'm not leaking any secret, so here only the classic logs
```
Terraform used the selected providers to generate the following execution plan. Resource actions are indicated with the following symbols:
+ create
Terraform will perform the following actions:
# azurerm_app_configuration_key.test will be created
+ resource "azurerm_app_configuration_key" "test" {
+ configuration_store_id = "/subscriptions/00000000-0000-0000-0000-000000000000/resourceGroups/some-rg/providers/Microsoft.AppConfiguration/configurationStores/some-config"
+ content_type = (known after apply)
+ etag = (known after apply)
+ id = (known after apply)
+ key = "test"
+ locked = false
+ type = "kv"
+ value = "1"
}
Plan: 1 to add, 0 to change, 0 to destroy.
Do you want to perform these actions?
Terraform will perform the actions described above.
Only 'yes' will be accepted to approve.
Enter a value: yes
azurerm_app_configuration_key.test: Creating...
╷
│ Error: while checking for key's "test" existence: appconfiguration.BaseClient#GetKeyValues: Failure responding to request: StatusCode=403 -- Original Error: autorest/azure: error response cannot be parsed: "" error: EOF
│
│ with azurerm_app_configuration_key.test,
│ on app_config.tf line 153, in resource "azurerm_app_configuration_key" "test":
│ 153: resource "azurerm_app_configuration_key" "test" {
│
│ while checking for key's "test" existence: appconfiguration.BaseClient#GetKeyValues: Failure responding to request: StatusCode=403 -- Original Error: autorest/azure: error response cannot be parsed: "" error: EOF
╵
```
### Expected Behaviour
It create a new error
### Actual Behaviour
It crash
### Steps to Reproduce
`terraform apply`
### Important Factoids
- The command `az appconfig kv set -n some-config --key test --value abc` is working so I have the correct access. Terraform is displaying a 403 error.
- Azure US East
| non_priority | unable to create new azurerm app configuration key community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform and azurerm provider version version terraform on linux provider registry terraform io hashicorp azurerm affected resource s azurerm app configuration key terraform configuration files hcl resource azurerm app configuration config use name some config resource group name azurerm resource group some rg name location azurerm resource group some rg location sku free tags environment local environment resource azurerm app configuration key test configuration store id azurerm app configuration config use id key test value debug output debug output contains sensible data and it s too big to be sure i m not leaking any secret so here only the classic logs terraform used the selected providers to generate the following execution plan resource actions are indicated with the following symbols create terraform will perform the following actions azurerm app configuration key test will be created resource azurerm app configuration key test configuration store id subscriptions resourcegroups some rg providers microsoft appconfiguration configurationstores some config content type known after apply etag known after apply id known after apply key test locked false type kv value plan to add to change to destroy do you want to perform these actions terraform will perform the actions described above only yes will be accepted to approve enter a value yes azurerm app configuration key test creating ╷ │ error while checking for key s test existence appconfiguration baseclient getkeyvalues failure responding to request statuscode original error autorest azure error response cannot be parsed error eof │ │ with azurerm app configuration key test │ on app config tf line in resource azurerm app configuration key test │ resource azurerm app configuration key test │ │ while checking for key s test existence appconfiguration baseclient getkeyvalues failure responding to request statuscode original error autorest azure error response cannot be parsed error eof ╵ expected behaviour it create a new error actual behaviour it crash steps to reproduce terraform apply important factoids the command az appconfig kv set n some config key test value abc is working so i have the correct access terraform is displaying a error azure us east | 0 |
273,245 | 23,740,544,288 | IssuesEvent | 2022-08-31 12:04:05 | pseewald/fprettify | https://api.github.com/repos/pseewald/fprettify | closed | Re-enable automatic tests | testing urgent | - Travis CI no longer free of charge and automatic testing is not working at the moment
- Find another CI service (github actions?) and set up automatic tests by adapting https://github.com/pseewald/fprettify/blob/master/.travis.yml | 1.0 | Re-enable automatic tests - - Travis CI no longer free of charge and automatic testing is not working at the moment
- Find another CI service (github actions?) and set up automatic tests by adapting https://github.com/pseewald/fprettify/blob/master/.travis.yml | non_priority | re enable automatic tests travis ci no longer free of charge and automatic testing is not working at the moment find another ci service github actions and set up automatic tests by adapting | 0 |
51,290 | 13,207,409,573 | IssuesEvent | 2020-08-14 22:59:48 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | ROOTSYS in `make tarball` tarball (Trac #149) | Incomplete Migration Migrated from Trac cmake defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/149">https://code.icecube.wisc.edu/projects/icecube/ticket/149</a>, reported by troyand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2011-04-14T19:21:48",
"_ts": "1302808908000000",
"description": "root under some circumstances rummages through various directories under ROOTSYS. What are they, does the 'make tarball' step need to copy more stuff under I3_BUILD/CMAKE_INSTALL_PREFIX/lib/?\n\n",
"reporter": "troy",
"cc": "",
"resolution": "fixed",
"time": "2008-11-18T14:04:08",
"component": "cmake",
"summary": "ROOTSYS in `make tarball` tarball",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
| 1.0 | ROOTSYS in `make tarball` tarball (Trac #149) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/149">https://code.icecube.wisc.edu/projects/icecube/ticket/149</a>, reported by troyand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2011-04-14T19:21:48",
"_ts": "1302808908000000",
"description": "root under some circumstances rummages through various directories under ROOTSYS. What are they, does the 'make tarball' step need to copy more stuff under I3_BUILD/CMAKE_INSTALL_PREFIX/lib/?\n\n",
"reporter": "troy",
"cc": "",
"resolution": "fixed",
"time": "2008-11-18T14:04:08",
"component": "cmake",
"summary": "ROOTSYS in `make tarball` tarball",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
| non_priority | rootsys in make tarball tarball trac migrated from json status closed changetime ts description root under some circumstances rummages through various directories under rootsys what are they does the make tarball step need to copy more stuff under build cmake install prefix lib n n reporter troy cc resolution fixed time component cmake summary rootsys in make tarball tarball priority normal keywords milestone owner troy type defect | 0 |
23,228 | 3,829,422,557 | IssuesEvent | 2016-03-31 10:36:02 | cgeo/cgeo | https://api.github.com/repos/cgeo/cgeo | closed | Have Send button in system information in a new line | Field test Frontend Design | ##### Detailed steps causing the problem:
- Open Menu - About c:geo - System
##### Actual behavior after performing these steps:
"Send" button is clatched right next to "Copy to Clipboard".
This looks strange and in some languages we might run out of the screen.

##### Expected behavior after performing these steps:
Have a separate button in the line below "Copy to Clipboard"
##### Version of c:geo used:
2016.03.29-NB
##### Is the problem reproducible for you?
Yes
| 1.0 | Have Send button in system information in a new line - ##### Detailed steps causing the problem:
- Open Menu - About c:geo - System
##### Actual behavior after performing these steps:
"Send" button is clatched right next to "Copy to Clipboard".
This looks strange and in some languages we might run out of the screen.

##### Expected behavior after performing these steps:
Have a separate button in the line below "Copy to Clipboard"
##### Version of c:geo used:
2016.03.29-NB
##### Is the problem reproducible for you?
Yes
| non_priority | have send button in system information in a new line detailed steps causing the problem open menu about c geo system actual behavior after performing these steps send button is clatched right next to copy to clipboard this looks strange and in some languages we might run out of the screen expected behavior after performing these steps have a separate button in the line below copy to clipboard version of c geo used nb is the problem reproducible for you yes | 0 |
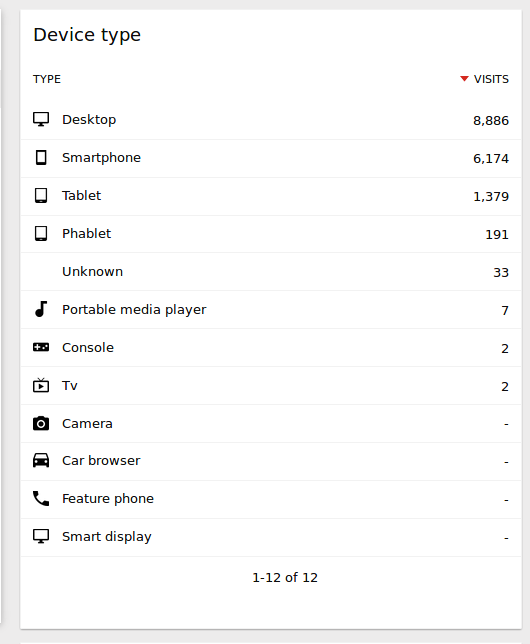
10,652 | 6,835,947,012 | IssuesEvent | 2017-11-10 04:29:06 | piwik/piwik | https://api.github.com/repos/piwik/piwik | opened | Device Type report: hide device type without visits | c: Usability | For consistency and clarity, let's remove rows that don't have "visits" in the Device Type report. The report currently looks like this:
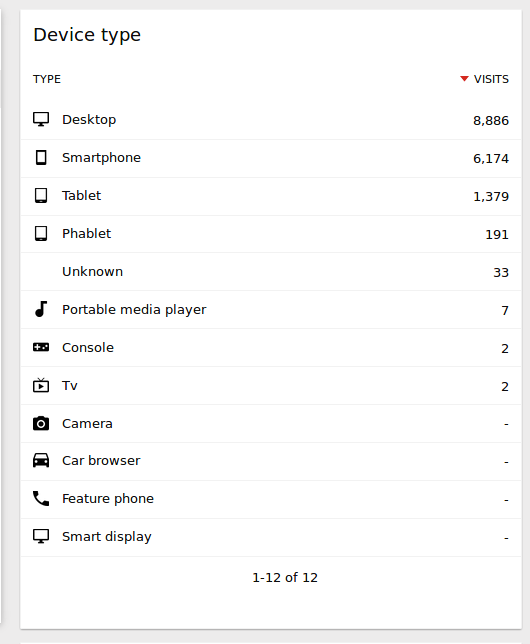
The rows Camera/Car browser/Feature phone/Smart display should be hidden. | True | Device Type report: hide device type without visits - For consistency and clarity, let's remove rows that don't have "visits" in the Device Type report. The report currently looks like this:
The rows Camera/Car browser/Feature phone/Smart display should be hidden. | non_priority | device type report hide device type without visits for consistency and clarity let s remove rows that don t have visits in the device type report the report currently looks like this the rows camera car browser feature phone smart display should be hidden | 0 |
318,948 | 23,748,555,283 | IssuesEvent | 2022-08-31 18:17:03 | rkd103/Group-11 | https://api.github.com/repos/rkd103/Group-11 | opened | Complete User Story D | documentation | Construct a user story for the following functionality: "like, comment, and share the status/timeline post of their friends."
The addition should occur on the 'User Story' wiki page. | 1.0 | Complete User Story D - Construct a user story for the following functionality: "like, comment, and share the status/timeline post of their friends."
The addition should occur on the 'User Story' wiki page. | non_priority | complete user story d construct a user story for the following functionality like comment and share the status timeline post of their friends the addition should occur on the user story wiki page | 0 |
10,974 | 4,859,482,854 | IssuesEvent | 2016-11-13 17:37:20 | bitcoin/bitcoin | https://api.github.com/repos/bitcoin/bitcoin | closed | Failed to run on-target setarch | Build system | I use this manual
https://github.com/bitcoin/bitcoin/blob/master/doc/gitian-building.md
https://github.com/bitcoin/bitcoin/blob/master/doc/release-process.md#fetch-and-create-inputs-first-time-or-when-dependency-versions-change
How can I solve the problem?
```
Creating build script (var/build-script)
Running build script (log in var/build.log)
./bin/gbuild:21:in `system!': failed to run on-target setarch x86_64 bash -x < var/build-script > var/build.log 2>&1 (RuntimeError)
from ./bin/gbuild:149:in `build_one_configuration'
from ./bin/gbuild:285:in `block (2 levels) in <main>'
from ./bin/gbuild:280:in `each'
from ./bin/gbuild:280:in `block in <main>'
from ./bin/gbuild:278:in `each'
from ./bin/gbuild:278:in `<main>'
```
tail -f var/build.log
```
libtool: install: /usr/bin/install -c .libs/libprotoc.a /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: strip --strip-debug /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: chmod 644 /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: ranlib /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: warning: remember to run `libtool --finish /home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib'
/bin/mkdir -p '/home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_p
``` | 1.0 | Failed to run on-target setarch - I use this manual
https://github.com/bitcoin/bitcoin/blob/master/doc/gitian-building.md
https://github.com/bitcoin/bitcoin/blob/master/doc/release-process.md#fetch-and-create-inputs-first-time-or-when-dependency-versions-change
How can I solve the problem?
```
Creating build script (var/build-script)
Running build script (log in var/build.log)
./bin/gbuild:21:in `system!': failed to run on-target setarch x86_64 bash -x < var/build-script > var/build.log 2>&1 (RuntimeError)
from ./bin/gbuild:149:in `build_one_configuration'
from ./bin/gbuild:285:in `block (2 levels) in <main>'
from ./bin/gbuild:280:in `each'
from ./bin/gbuild:280:in `block in <main>'
from ./bin/gbuild:278:in `each'
from ./bin/gbuild:278:in `<main>'
```
tail -f var/build.log
```
libtool: install: /usr/bin/install -c .libs/libprotoc.a /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: strip --strip-debug /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: chmod 644 /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: ranlib /home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_protobuf/2.6.1-70c104d3b77/home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib/libprotoc.a
libtool: install: warning: remember to run `libtool --finish /home/ubuntu/build/bitcoin/depends/arm-linux-gnueabihf/native/lib'
/bin/mkdir -p '/home/ubuntu/build/bitcoin/depends/work/staging/arm-linux-gnueabihf/native_p
``` | non_priority | failed to run on target setarch i use this manual how can i solve the problem creating build script var build script running build script log in var build log bin gbuild in system failed to run on target setarch bash x var build log runtimeerror from bin gbuild in build one configuration from bin gbuild in block levels in from bin gbuild in each from bin gbuild in block in from bin gbuild in each from bin gbuild in tail f var build log libtool install usr bin install c libs libprotoc a home ubuntu build bitcoin depends work staging arm linux gnueabihf native protobuf home ubuntu build bitcoin depends arm linux gnueabihf native lib libprotoc a libtool install strip strip debug home ubuntu build bitcoin depends work staging arm linux gnueabihf native protobuf home ubuntu build bitcoin depends arm linux gnueabihf native lib libprotoc a libtool install chmod home ubuntu build bitcoin depends work staging arm linux gnueabihf native protobuf home ubuntu build bitcoin depends arm linux gnueabihf native lib libprotoc a libtool install ranlib home ubuntu build bitcoin depends work staging arm linux gnueabihf native protobuf home ubuntu build bitcoin depends arm linux gnueabihf native lib libprotoc a libtool install warning remember to run libtool finish home ubuntu build bitcoin depends arm linux gnueabihf native lib bin mkdir p home ubuntu build bitcoin depends work staging arm linux gnueabihf native p | 0 |
243,353 | 20,381,112,818 | IssuesEvent | 2022-02-21 21:59:07 | red-hat-storage/ocs-ci | https://api.github.com/repos/red-hat-storage/ocs-ci | closed | test_clone_pvc failing | bug TestCase failing ui_automation | ```
> pvc_ui_obj.pvc_clone_ui(
project_name=project_name,
pvc_name=pvc_name,
clone_name=clone_pvc_name,
clone_access_mode=clone_access_mode,
)
E TypeError: pvc_clone_ui() got an unexpected keyword argument 'clone_name'
tests/ui/test_pvc_ui.py:260: TypeError
``` | 1.0 | test_clone_pvc failing - ```
> pvc_ui_obj.pvc_clone_ui(
project_name=project_name,
pvc_name=pvc_name,
clone_name=clone_pvc_name,
clone_access_mode=clone_access_mode,
)
E TypeError: pvc_clone_ui() got an unexpected keyword argument 'clone_name'
tests/ui/test_pvc_ui.py:260: TypeError
``` | non_priority | test clone pvc failing pvc ui obj pvc clone ui project name project name pvc name pvc name clone name clone pvc name clone access mode clone access mode e typeerror pvc clone ui got an unexpected keyword argument clone name tests ui test pvc ui py typeerror | 0 |
161,744 | 20,155,324,492 | IssuesEvent | 2022-02-09 15:58:07 | kapseliboi/Node-Data | https://api.github.com/repos/kapseliboi/Node-Data | opened | CVE-2016-10539 (High) detected in negotiator-0.5.3.tgz | security vulnerability | ## CVE-2016-10539 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>negotiator-0.5.3.tgz</b></p></summary>
<p>HTTP content negotiation</p>
<p>Library home page: <a href="https://registry.npmjs.org/negotiator/-/negotiator-0.5.3.tgz">https://registry.npmjs.org/negotiator/-/negotiator-0.5.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/negotiator/package.json</p>
<p>
Dependency Hierarchy:
- express-4.13.3.tgz (Root Library)
- accepts-1.2.13.tgz
- :x: **negotiator-0.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/Node-Data/commit/289c77565fc637d4c0e4bf4a9a1e81df96cd190a">289c77565fc637d4c0e4bf4a9a1e81df96cd190a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
negotiator is an HTTP content negotiator for Node.js and is used by many modules and frameworks including Express and Koa. The header for "Accept-Language", when parsed by negotiator 0.6.0 and earlier is vulnerable to Regular Expression Denial of Service via a specially crafted string.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10539>CVE-2016-10539</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/106">https://www.npmjs.com/advisories/106</a></p>
<p>Release Date: 2018-05-31</p>
<p>Fix Resolution (negotiator): 0.6.1</p>
<p>Direct dependency fix Resolution (express): 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-10539 (High) detected in negotiator-0.5.3.tgz - ## CVE-2016-10539 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>negotiator-0.5.3.tgz</b></p></summary>
<p>HTTP content negotiation</p>
<p>Library home page: <a href="https://registry.npmjs.org/negotiator/-/negotiator-0.5.3.tgz">https://registry.npmjs.org/negotiator/-/negotiator-0.5.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/negotiator/package.json</p>
<p>
Dependency Hierarchy:
- express-4.13.3.tgz (Root Library)
- accepts-1.2.13.tgz
- :x: **negotiator-0.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/Node-Data/commit/289c77565fc637d4c0e4bf4a9a1e81df96cd190a">289c77565fc637d4c0e4bf4a9a1e81df96cd190a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
negotiator is an HTTP content negotiator for Node.js and is used by many modules and frameworks including Express and Koa. The header for "Accept-Language", when parsed by negotiator 0.6.0 and earlier is vulnerable to Regular Expression Denial of Service via a specially crafted string.
<p>Publish Date: 2018-05-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10539>CVE-2016-10539</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/106">https://www.npmjs.com/advisories/106</a></p>
<p>Release Date: 2018-05-31</p>
<p>Fix Resolution (negotiator): 0.6.1</p>
<p>Direct dependency fix Resolution (express): 4.14.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in negotiator tgz cve high severity vulnerability vulnerable library negotiator tgz http content negotiation library home page a href path to dependency file package json path to vulnerable library node modules negotiator package json dependency hierarchy express tgz root library accepts tgz x negotiator tgz vulnerable library found in head commit a href found in base branch master vulnerability details negotiator is an http content negotiator for node js and is used by many modules and frameworks including express and koa the header for accept language when parsed by negotiator and earlier is vulnerable to regular expression denial of service via a specially crafted string publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution negotiator direct dependency fix resolution express step up your open source security game with whitesource | 0 |
141,430 | 11,418,690,510 | IssuesEvent | 2020-02-03 05:36:59 | webcompat/webcompat.com | https://api.github.com/repos/webcompat/webcompat.com | opened | [test] Create a test topsite db for testing webhooks | lang: Python type: testing | Some tests have a dependency on getting the right labels.
If a test makes a query to a populated sites.db, the test will return a different set of labels.
There are two options:
1. mocking everywhere we request the labels.
2. Create a db when we are running tests with the right information in it.
Option 2 seems a better choice.
We could rationalize it to a couple of controlled domains for our tests.
* [ ] Create a fake db in unittests levels
* [ ] Make sure the tests are using the right domains for this to be effective
* [ ] Remove the mocking of `extract_priority_label` if it still exists
This mainly impacts [webhooks tests](https://github.com/webcompat/webcompat.com/blob/master/tests/unit/test_webhook.py)
| 1.0 | [test] Create a test topsite db for testing webhooks - Some tests have a dependency on getting the right labels.
If a test makes a query to a populated sites.db, the test will return a different set of labels.
There are two options:
1. mocking everywhere we request the labels.
2. Create a db when we are running tests with the right information in it.
Option 2 seems a better choice.
We could rationalize it to a couple of controlled domains for our tests.
* [ ] Create a fake db in unittests levels
* [ ] Make sure the tests are using the right domains for this to be effective
* [ ] Remove the mocking of `extract_priority_label` if it still exists
This mainly impacts [webhooks tests](https://github.com/webcompat/webcompat.com/blob/master/tests/unit/test_webhook.py)
| non_priority | create a test topsite db for testing webhooks some tests have a dependency on getting the right labels if a test makes a query to a populated sites db the test will return a different set of labels there are two options mocking everywhere we request the labels create a db when we are running tests with the right information in it option seems a better choice we could rationalize it to a couple of controlled domains for our tests create a fake db in unittests levels make sure the tests are using the right domains for this to be effective remove the mocking of extract priority label if it still exists this mainly impacts | 0 |
86,671 | 15,755,811,562 | IssuesEvent | 2021-03-31 02:25:53 | clazdo/WebGoat | https://api.github.com/repos/clazdo/WebGoat | opened | CVE-2020-11023 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.2.3.js</b>, <b>jquery-3.3.1.min.js</b>, <b>jquery-2.1.4.min.js</b>, <b>jquery-1.10.2.min.js</b>, <b>jquery-2.2.4.min.js</b>, <b>jquery-3.3.1.tgz</b></p></summary>
<p>
<details><summary><b>jquery-2.2.3.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.3/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.3/jquery.js</a></p>
<p>Path to dependency file: WebGoat/docs/node_modules/jquery.easing/example/demo.html</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/jquery.easing/example/demo.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.3.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.3.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js</a></p>
<p>Path to dependency file: WebGoat/docs/index.html</p>
<p>Path to vulnerable library: WebGoat/docs/vendor/jquery/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to dependency file: WebGoat/docs/node_modules/jquery.easing/example/example.html</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/jquery.easing/example/example.html,WebGoat/docs/node_modules/js-base64/test/index.html,WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.10.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-1.10.2.min.js,WebGoat/webgoat-container/src/main/resources/static/js/jquery/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.2.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-2.2.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.3.1.tgz</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz">https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz</a></p>
<p>Path to dependency file: WebGoat/docs/package.json</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/jquery/package.json</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11023 (Medium) detected in multiple libraries - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-2.2.3.js</b>, <b>jquery-3.3.1.min.js</b>, <b>jquery-2.1.4.min.js</b>, <b>jquery-1.10.2.min.js</b>, <b>jquery-2.2.4.min.js</b>, <b>jquery-3.3.1.tgz</b></p></summary>
<p>
<details><summary><b>jquery-2.2.3.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.3/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.3/jquery.js</a></p>
<p>Path to dependency file: WebGoat/docs/node_modules/jquery.easing/example/demo.html</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/jquery.easing/example/demo.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.3.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.3.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js</a></p>
<p>Path to dependency file: WebGoat/docs/index.html</p>
<p>Path to vulnerable library: WebGoat/docs/vendor/jquery/jquery.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>Path to dependency file: WebGoat/docs/node_modules/jquery.easing/example/example.html</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/jquery.easing/example/example.html,WebGoat/docs/node_modules/js-base64/test/index.html,WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-2.1.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.10.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.10.2/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-1.10.2.min.js,WebGoat/webgoat-container/src/main/resources/static/js/jquery/jquery-1.10.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.10.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.2.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.2.4/jquery.min.js</a></p>
<p>Path to vulnerable library: WebGoat/webgoat-container/src/main/resources/static/js/libs/jquery-2.2.4.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.2.4.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-3.3.1.tgz</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz">https://registry.npmjs.org/jquery/-/jquery-3.3.1.tgz</a></p>
<p>Path to dependency file: WebGoat/docs/package.json</p>
<p>Path to vulnerable library: WebGoat/docs/node_modules/jquery/package.json</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.tgz** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11023</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries jquery js jquery min js jquery min js jquery min js jquery min js jquery tgz jquery js javascript library for dom operations library home page a href path to dependency file webgoat docs node modules jquery easing example demo html path to vulnerable library webgoat docs node modules jquery easing example demo html dependency hierarchy x jquery js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file webgoat docs index html path to vulnerable library webgoat docs vendor jquery jquery min js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file webgoat docs node modules jquery easing example example html path to vulnerable library webgoat docs node modules jquery easing example example html webgoat docs node modules js test index html webgoat webgoat container src main resources static js libs jquery min js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library webgoat webgoat container src main resources static js libs jquery min js webgoat webgoat container src main resources static js jquery jquery min js dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library webgoat webgoat container src main resources static js libs jquery min js dependency hierarchy x jquery min js vulnerable library jquery tgz javascript library for dom operations library home page a href path to dependency file webgoat docs package json path to vulnerable library webgoat docs node modules jquery package json dependency hierarchy x jquery tgz vulnerable library vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
395,343 | 27,066,247,292 | IssuesEvent | 2023-02-14 00:50:01 | statelesscode/nerd_dice | https://api.github.com/repos/statelesscode/nerd_dice | closed | Fix README to use relative links | documentation | Instead of having links in the README hardcoded, use relative links. See commit [b6100f3](https://github.com/statelesscode/nerd_dice_dot_com/commit/b6100f3179826d6256485775ffb4f9cf1575a741) on the [NerdDice.com](https://github.com/statelesscode/nerd_dice_dot_com) repo for an example. | 1.0 | Fix README to use relative links - Instead of having links in the README hardcoded, use relative links. See commit [b6100f3](https://github.com/statelesscode/nerd_dice_dot_com/commit/b6100f3179826d6256485775ffb4f9cf1575a741) on the [NerdDice.com](https://github.com/statelesscode/nerd_dice_dot_com) repo for an example. | non_priority | fix readme to use relative links instead of having links in the readme hardcoded use relative links see commit on the repo for an example | 0 |
24,946 | 11,114,461,332 | IssuesEvent | 2019-12-18 08:43:41 | Hi-Fi/remotesikulilibrary | https://api.github.com/repos/Hi-Fi/remotesikulilibrary | opened | CVE-2011-4461 (Medium) detected in jetty-server-7.6.3.v20120416.jar | security vulnerability | ## CVE-2011-4461 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-server-7.6.3.v20120416.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty/jetty-server">http://www.eclipse.org/jetty/jetty-server</a></p>
<p>Path to dependency file: /tmp/ws-scm/remotesikulilibrary/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/eclipse/jetty/jetty-server/7.6.3.v20120416/jetty-server-7.6.3.v20120416.jar</p>
<p>
Dependency Hierarchy:
- jrobotremoteserver-3.0.jar (Root Library)
- jetty-servlet-7.6.3.v20120416.jar
- jetty-security-7.6.3.v20120416.jar
- :x: **jetty-server-7.6.3.v20120416.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Hi-Fi/remotesikulilibrary/commit/8d8753ec3a9b63366b607fac3f3b5a9fdd1d3097">8d8753ec3a9b63366b607fac3f3b5a9fdd1d3097</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Jetty 8.1.0.RC2 and earlier computes hash values for form parameters without restricting the ability to trigger hash collisions predictably, which allows remote attackers to cause a denial of service (CPU consumption) by sending many crafted parameters.
<p>Publish Date: 2011-12-30
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-4461>CVE-2011-4461</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-4461">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-4461</a></p>
<p>Release Date: 2011-12-30</p>
<p>Fix Resolution: 8.1.0.RC4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2011-4461 (Medium) detected in jetty-server-7.6.3.v20120416.jar - ## CVE-2011-4461 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-server-7.6.3.v20120416.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty/jetty-server">http://www.eclipse.org/jetty/jetty-server</a></p>
<p>Path to dependency file: /tmp/ws-scm/remotesikulilibrary/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/org/eclipse/jetty/jetty-server/7.6.3.v20120416/jetty-server-7.6.3.v20120416.jar</p>
<p>
Dependency Hierarchy:
- jrobotremoteserver-3.0.jar (Root Library)
- jetty-servlet-7.6.3.v20120416.jar
- jetty-security-7.6.3.v20120416.jar
- :x: **jetty-server-7.6.3.v20120416.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Hi-Fi/remotesikulilibrary/commit/8d8753ec3a9b63366b607fac3f3b5a9fdd1d3097">8d8753ec3a9b63366b607fac3f3b5a9fdd1d3097</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Jetty 8.1.0.RC2 and earlier computes hash values for form parameters without restricting the ability to trigger hash collisions predictably, which allows remote attackers to cause a denial of service (CPU consumption) by sending many crafted parameters.
<p>Publish Date: 2011-12-30
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-4461>CVE-2011-4461</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-4461">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2011-4461</a></p>
<p>Release Date: 2011-12-30</p>
<p>Fix Resolution: 8.1.0.RC4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jetty server jar cve medium severity vulnerability vulnerable library jetty server jar the core jetty server artifact library home page a href path to dependency file tmp ws scm remotesikulilibrary pom xml path to vulnerable library root repository org eclipse jetty jetty server jetty server jar dependency hierarchy jrobotremoteserver jar root library jetty servlet jar jetty security jar x jetty server jar vulnerable library found in head commit a href vulnerability details jetty and earlier computes hash values for form parameters without restricting the ability to trigger hash collisions predictably which allows remote attackers to cause a denial of service cpu consumption by sending many crafted parameters publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
18,668 | 4,294,627,524 | IssuesEvent | 2016-07-19 01:24:39 | KyleJHarper/stupidbashtard | https://api.github.com/repos/KyleJHarper/stupidbashtard | closed | Namespace hierarchy should be clearer | documentation | Namespace dependency might be a concern to others. A diagram or note in the README should make it clear.
Only core.sh is ever (and always) a prerequisite to other modules. | 1.0 | Namespace hierarchy should be clearer - Namespace dependency might be a concern to others. A diagram or note in the README should make it clear.
Only core.sh is ever (and always) a prerequisite to other modules. | non_priority | namespace hierarchy should be clearer namespace dependency might be a concern to others a diagram or note in the readme should make it clear only core sh is ever and always a prerequisite to other modules | 0 |
142,143 | 13,017,055,413 | IssuesEvent | 2020-07-26 10:17:53 | slothsoft/eclipse-maven-view | https://api.github.com/repos/slothsoft/eclipse-maven-view | closed | Link Release Documentation | documentation | After [#3 Document Release of Plug-ins](https://github.com/slothsoft/eclipse-update-site/issues/3), link the release documentation so I'll find it again the next time I want to release. | 1.0 | Link Release Documentation - After [#3 Document Release of Plug-ins](https://github.com/slothsoft/eclipse-update-site/issues/3), link the release documentation so I'll find it again the next time I want to release. | non_priority | link release documentation after link the release documentation so i ll find it again the next time i want to release | 0 |
414,516 | 27,990,603,815 | IssuesEvent | 2023-03-27 03:07:11 | PalisadoesFoundation/talawa-docs | https://api.github.com/repos/PalisadoesFoundation/talawa-docs | closed | Streamline Talawa-Docs Content | bug documentation unapproved | The Talawa Docs content is vague in these areas:
1. Getting started with Outreachy
2. The rationale for the technologies we use
3. Explications of the Palisadoes Foundation main focus areas
4. Introductions to our repositories
5. Overviews of our architecture.
We need to improve this to make sure we have a better user experience when reading our documentation site. | 1.0 | Streamline Talawa-Docs Content - The Talawa Docs content is vague in these areas:
1. Getting started with Outreachy
2. The rationale for the technologies we use
3. Explications of the Palisadoes Foundation main focus areas
4. Introductions to our repositories
5. Overviews of our architecture.
We need to improve this to make sure we have a better user experience when reading our documentation site. | non_priority | streamline talawa docs content the talawa docs content is vague in these areas getting started with outreachy the rationale for the technologies we use explications of the palisadoes foundation main focus areas introductions to our repositories overviews of our architecture we need to improve this to make sure we have a better user experience when reading our documentation site | 0 |
316,721 | 23,644,987,504 | IssuesEvent | 2022-08-25 21:00:42 | seyyidibrahimgulec/yasozluk | https://api.github.com/repos/seyyidibrahimgulec/yasozluk | closed | Software requirements specification | documentation | - Functional Requirements
- System requirements
- Software requirements
- Design | 1.0 | Software requirements specification - - Functional Requirements
- System requirements
- Software requirements
- Design | non_priority | software requirements specification functional requirements system requirements software requirements design | 0 |
156,845 | 12,339,562,754 | IssuesEvent | 2020-05-14 18:20:38 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | [Test Failure] integration.runners.test_state.StateRunnerTest.test_orchestrate_target_does_not_exist | Bug Test Failure | integration.runners.test_state.StateRunnerTest.test_orchestrate_target_does_not_exist | 1.0 | [Test Failure] integration.runners.test_state.StateRunnerTest.test_orchestrate_target_does_not_exist - integration.runners.test_state.StateRunnerTest.test_orchestrate_target_does_not_exist | non_priority | integration runners test state staterunnertest test orchestrate target does not exist integration runners test state staterunnertest test orchestrate target does not exist | 0 |
166,480 | 12,958,268,439 | IssuesEvent | 2020-07-20 11:05:09 | Automattic/jetpack | https://api.github.com/repos/Automattic/jetpack | closed | Block Categories Updates | Gutenberg [Block] GIF [Block] Image Compare [Block] Latest Instagram Posts [Block] Slideshow [Block] Tiled Gallery [Pri] Normal [Size] S [Type] Enhancement | The [following new categories](https://github.com/WordPress/gutenberg/pull/19279#issuecomment-621322775) are set to be coming to Gutenberg shortly. There are mappings in place, so all blocks would end up somewhere. However, it'd be worth to look at registering things like Tiled Galleries or Slideshow in the Media group. (I'd imagine Jetpack would need to retain older categories as well for previous versions of Gutenberg / WP.) | 1.0 | Block Categories Updates - The [following new categories](https://github.com/WordPress/gutenberg/pull/19279#issuecomment-621322775) are set to be coming to Gutenberg shortly. There are mappings in place, so all blocks would end up somewhere. However, it'd be worth to look at registering things like Tiled Galleries or Slideshow in the Media group. (I'd imagine Jetpack would need to retain older categories as well for previous versions of Gutenberg / WP.) | non_priority | block categories updates the are set to be coming to gutenberg shortly there are mappings in place so all blocks would end up somewhere however it d be worth to look at registering things like tiled galleries or slideshow in the media group i d imagine jetpack would need to retain older categories as well for previous versions of gutenberg wp | 0 |
396,109 | 27,102,240,273 | IssuesEvent | 2023-02-15 09:31:35 | WordPress/Documentation-Issue-Tracker | https://api.github.com/repos/WordPress/Documentation-Issue-Tracker | closed | Team roles - new Documentation team handbook page | new document contributor documentation | ## What is the new page you are requesting?
The page that will hold description and responsibility for each team role in WordPress Documentation team.
## How will this new page help you?
It will give clear(er) insight to all documentation contributors about the roles they can take on and ways to contribute to WordPress documentation.
- [ ] Update landing handbook page with link to this page when published - https://make.wordpress.org/docs/handbook/#:~:text=team%20roles
| 1.0 | Team roles - new Documentation team handbook page - ## What is the new page you are requesting?
The page that will hold description and responsibility for each team role in WordPress Documentation team.
## How will this new page help you?
It will give clear(er) insight to all documentation contributors about the roles they can take on and ways to contribute to WordPress documentation.
- [ ] Update landing handbook page with link to this page when published - https://make.wordpress.org/docs/handbook/#:~:text=team%20roles
| non_priority | team roles new documentation team handbook page what is the new page you are requesting the page that will hold description and responsibility for each team role in wordpress documentation team how will this new page help you it will give clear er insight to all documentation contributors about the roles they can take on and ways to contribute to wordpress documentation update landing handbook page with link to this page when published | 0 |
132,849 | 10,771,528,489 | IssuesEvent | 2019-11-02 08:27:43 | Skycoin-cp/skycoin | https://api.github.com/repos/Skycoin-cp/skycoin | opened | [Hardware Wallet][e2e] update/create automatic GUI tests after hardware wallet integration | tests wallet-hw | some e2e already exist. we will need to update them once the hardware wallet features will be integrated | 1.0 | [Hardware Wallet][e2e] update/create automatic GUI tests after hardware wallet integration - some e2e already exist. we will need to update them once the hardware wallet features will be integrated | non_priority | update create automatic gui tests after hardware wallet integration some already exist we will need to update them once the hardware wallet features will be integrated | 0 |
63,871 | 6,886,692,708 | IssuesEvent | 2017-11-21 20:25:27 | atlasmap/atlasmap | https://api.github.com/repos/atlasmap/atlasmap | closed | Element IDs on mapping details | module/tests module/ui | |<img src="https://avatars0.githubusercontent.com/u/5637792?v=4" valign="middle" width="22px"></img> @dsimansk | [2017-11-01](https://github.com/atlasmap/atlasmap-ui/issues/119) | test |
|-|-|-|
@igarashitm
Hi Tomo, we'd like to enhance the UI a bit and create IDs to specifically select elements like Action dropdwon, input fields, etc.
Matej @mmelko wanted to look into it, but if you happen to have a plan for it already don't hesitate to comment :)
| 1.0 | Element IDs on mapping details - |<img src="https://avatars0.githubusercontent.com/u/5637792?v=4" valign="middle" width="22px"></img> @dsimansk | [2017-11-01](https://github.com/atlasmap/atlasmap-ui/issues/119) | test |
|-|-|-|
@igarashitm
Hi Tomo, we'd like to enhance the UI a bit and create IDs to specifically select elements like Action dropdwon, input fields, etc.
Matej @mmelko wanted to look into it, but if you happen to have a plan for it already don't hesitate to comment :)
| non_priority | element ids on mapping details dsimansk test igarashitm hi tomo we d like to enhance the ui a bit and create ids to specifically select elements like action dropdwon input fields etc matej mmelko wanted to look into it but if you happen to have a plan for it already don t hesitate to comment | 0 |
51,437 | 13,635,123,661 | IssuesEvent | 2020-09-25 01:57:59 | nasifimtiazohi/openmrs-module-atlas-2.2 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-atlas-2.2 | opened | CVE-2015-9251 (Medium) detected in jquery-1.11.1.min.js | security vulnerability | ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to vulnerable library: openmrs-module-atlas-2.2/omod/target/classes/web/module/resources/scripts/jquery-1.11.1.min.js,openmrs-module-atlas-2.2/omod/src/main/webapp/resources/scripts/jquery-1.11.1.min.js,openmrs-module-atlas-2.2/omod/target/atlas-omod-2.2/web/module/resources/scripts/jquery-1.11.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-atlas-2.2/commit/523414ffdb00236d7acc3b69ef1c13366235fb3e">523414ffdb00236d7acc3b69ef1c13366235fb3e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-9251 (Medium) detected in jquery-1.11.1.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.11.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.11.1/jquery.min.js</a></p>
<p>Path to vulnerable library: openmrs-module-atlas-2.2/omod/target/classes/web/module/resources/scripts/jquery-1.11.1.min.js,openmrs-module-atlas-2.2/omod/src/main/webapp/resources/scripts/jquery-1.11.1.min.js,openmrs-module-atlas-2.2/omod/target/atlas-omod-2.2/web/module/resources/scripts/jquery-1.11.1.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.11.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-atlas-2.2/commit/523414ffdb00236d7acc3b69ef1c13366235fb3e">523414ffdb00236d7acc3b69ef1c13366235fb3e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library openmrs module atlas omod target classes web module resources scripts jquery min js openmrs module atlas omod src main webapp resources scripts jquery min js openmrs module atlas omod target atlas omod web module resources scripts jquery min js dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
124,261 | 17,772,514,651 | IssuesEvent | 2021-08-30 15:09:07 | kapseliboi/evergreen | https://api.github.com/repos/kapseliboi/evergreen | opened | WS-2020-0042 (High) detected in acorn-6.0.2.tgz, acorn-5.7.3.tgz | security vulnerability | ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>acorn-6.0.2.tgz</b>, <b>acorn-5.7.3.tgz</b></p></summary>
<p>
<details><summary><b>acorn-6.0.2.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-6.0.2.tgz">https://registry.npmjs.org/acorn/-/acorn-6.0.2.tgz</a></p>
<p>Path to dependency file: evergreen/distribution/client/package.json</p>
<p>Path to vulnerable library: evergreen/distribution/client/node_modules/acorn-globals/node_modules/acorn/package.json,evergreen/services/node_modules/acorn-globals/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- jest-23.6.0.tgz (Root Library)
- jest-cli-23.6.0.tgz
- jest-environment-jsdom-23.4.0.tgz
- jsdom-11.12.0.tgz
- acorn-globals-4.3.0.tgz
- :x: **acorn-6.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>acorn-5.7.3.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz</a></p>
<p>Path to dependency file: evergreen/services/package.json</p>
<p>Path to vulnerable library: evergreen/services/node_modules/acorn/package.json,evergreen/distribution/client/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- eslint-4.19.1.tgz (Root Library)
- espree-3.5.4.tgz
- :x: **acorn-5.7.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/evergreen/commit/13675096220f0e986aa94cafc5f57de6b38e38cd">13675096220f0e986aa94cafc5f57de6b38e38cd</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 7.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0042 (High) detected in acorn-6.0.2.tgz, acorn-5.7.3.tgz - ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>acorn-6.0.2.tgz</b>, <b>acorn-5.7.3.tgz</b></p></summary>
<p>
<details><summary><b>acorn-6.0.2.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-6.0.2.tgz">https://registry.npmjs.org/acorn/-/acorn-6.0.2.tgz</a></p>
<p>Path to dependency file: evergreen/distribution/client/package.json</p>
<p>Path to vulnerable library: evergreen/distribution/client/node_modules/acorn-globals/node_modules/acorn/package.json,evergreen/services/node_modules/acorn-globals/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- jest-23.6.0.tgz (Root Library)
- jest-cli-23.6.0.tgz
- jest-environment-jsdom-23.4.0.tgz
- jsdom-11.12.0.tgz
- acorn-globals-4.3.0.tgz
- :x: **acorn-6.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>acorn-5.7.3.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.3.tgz</a></p>
<p>Path to dependency file: evergreen/services/package.json</p>
<p>Path to vulnerable library: evergreen/services/node_modules/acorn/package.json,evergreen/distribution/client/node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- eslint-4.19.1.tgz (Root Library)
- espree-3.5.4.tgz
- :x: **acorn-5.7.3.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/evergreen/commit/13675096220f0e986aa94cafc5f57de6b38e38cd">13675096220f0e986aa94cafc5f57de6b38e38cd</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-08</p>
<p>Fix Resolution: 7.1.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in acorn tgz acorn tgz ws high severity vulnerability vulnerable libraries acorn tgz acorn tgz acorn tgz ecmascript parser library home page a href path to dependency file evergreen distribution client package json path to vulnerable library evergreen distribution client node modules acorn globals node modules acorn package json evergreen services node modules acorn globals node modules acorn package json dependency hierarchy jest tgz root library jest cli tgz jest environment jsdom tgz jsdom tgz acorn globals tgz x acorn tgz vulnerable library acorn tgz ecmascript parser library home page a href path to dependency file evergreen services package json path to vulnerable library evergreen services node modules acorn package json evergreen distribution client node modules acorn package json dependency hierarchy eslint tgz root library espree tgz x acorn tgz vulnerable library found in head commit a href found in base branch master vulnerability details acorn is vulnerable to regex dos a regex of the form u causes the parser to enter an infinite loop attackers may leverage the vulnerability leading to a denial of service since the string is not valid and it results in it being sanitized before reaching the parser publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
176,739 | 28,146,760,880 | IssuesEvent | 2023-04-02 15:18:48 | dotnet/winforms | https://api.github.com/repos/dotnet/winforms | opened | Still issue with layouts missing on toolbox and not rendering on designer. | area: VS designer untriaged | ### Environment
Microsoft Visual Studio Community 2022
Version 17.4.2
VisualStudio.17.Release/17.4.2+33122.133
### .NET version
.Net 7
### Did this work in a previous version of Visual Studio and/or previous .NET release?
It still works in .Net Framework, but I would like to assumed that it have never worked in core and then .net 5+ version.
### Issue description
I managed to find this issue that was made for 3 years ago: https://github.com/dotnet/winforms/issues/2842
and I do not think that tablelayoutpanel or flowlayoutpanel has been available for core or .net 5+ version, and I could not find any more information for why they haven't been available when it was expected that they should have been available for today's designer.
The fact that it still is same issue today after three years in newer version (especially) is concerning. So I hope it is acceptable that I am reporting that this is still an on-going issue and brought to the winform designer team's attention.
So at least that they are being aware of it, even if they have many things on their plate.
### Steps to reproduce
Create empty winfroms project in .net 7 version. Do not choose the framework one.
Try to find TableLayoutPanel or Flowtablelayout in toolbox window.
### Diagnostics
_No response_ | 1.0 | Still issue with layouts missing on toolbox and not rendering on designer. - ### Environment
Microsoft Visual Studio Community 2022
Version 17.4.2
VisualStudio.17.Release/17.4.2+33122.133
### .NET version
.Net 7
### Did this work in a previous version of Visual Studio and/or previous .NET release?
It still works in .Net Framework, but I would like to assumed that it have never worked in core and then .net 5+ version.
### Issue description
I managed to find this issue that was made for 3 years ago: https://github.com/dotnet/winforms/issues/2842
and I do not think that tablelayoutpanel or flowlayoutpanel has been available for core or .net 5+ version, and I could not find any more information for why they haven't been available when it was expected that they should have been available for today's designer.
The fact that it still is same issue today after three years in newer version (especially) is concerning. So I hope it is acceptable that I am reporting that this is still an on-going issue and brought to the winform designer team's attention.
So at least that they are being aware of it, even if they have many things on their plate.
### Steps to reproduce
Create empty winfroms project in .net 7 version. Do not choose the framework one.
Try to find TableLayoutPanel or Flowtablelayout in toolbox window.
### Diagnostics
_No response_ | non_priority | still issue with layouts missing on toolbox and not rendering on designer environment microsoft visual studio community version visualstudio release net version net did this work in a previous version of visual studio and or previous net release it still works in net framework but i would like to assumed that it have never worked in core and then net version issue description i managed to find this issue that was made for years ago and i do not think that tablelayoutpanel or flowlayoutpanel has been available for core or net version and i could not find any more information for why they haven t been available when it was expected that they should have been available for today s designer the fact that it still is same issue today after three years in newer version especially is concerning so i hope it is acceptable that i am reporting that this is still an on going issue and brought to the winform designer team s attention so at least that they are being aware of it even if they have many things on their plate steps to reproduce create empty winfroms project in net version do not choose the framework one try to find tablelayoutpanel or flowtablelayout in toolbox window diagnostics no response | 0 |
16,131 | 9,694,949,379 | IssuesEvent | 2019-05-24 20:34:39 | GetSimpleCMS/GetSimpleCMS | https://api.github.com/repos/GetSimpleCMS/GetSimpleCMS | reopened | Cross Site Scripting Vulnerability in Latest Release 3.3.13 | SECURITY | Hi, I would like to report Cross Site Scripting vulnerability in latest release.
## Description:
Cross-site scripting (XSS) vulnerability in uploadify flash file might allow remote attackers to inject arbitrary web script or HTML via the multiple parameters.
## Steps To Reproduce:
1. Open below URL in browser which supports flash.
``http://[URL]GetSimpleCMS-3.3.13/admin/template/js/uploadify/uploadify.swf?movieName="])}catche(e){alert("xss")}//``
## Fix:
Update uploadify version.
## Release Info:
3.3.13 | True | Cross Site Scripting Vulnerability in Latest Release 3.3.13 - Hi, I would like to report Cross Site Scripting vulnerability in latest release.
## Description:
Cross-site scripting (XSS) vulnerability in uploadify flash file might allow remote attackers to inject arbitrary web script or HTML via the multiple parameters.
## Steps To Reproduce:
1. Open below URL in browser which supports flash.
``http://[URL]GetSimpleCMS-3.3.13/admin/template/js/uploadify/uploadify.swf?movieName="])}catche(e){alert("xss")}//``
## Fix:
Update uploadify version.
## Release Info:
3.3.13 | non_priority | cross site scripting vulnerability in latest release hi i would like to report cross site scripting vulnerability in latest release description cross site scripting xss vulnerability in uploadify flash file might allow remote attackers to inject arbitrary web script or html via the multiple parameters steps to reproduce open below url in browser which supports flash http getsimplecms admin template js uploadify uploadify swf moviename catche e alert xss fix update uploadify version release info | 0 |
269,939 | 28,960,348,701 | IssuesEvent | 2023-05-10 01:34:37 | praneethpanasala/linux | https://api.github.com/repos/praneethpanasala/linux | reopened | CVE-2019-9213 (Medium) detected in linuxv4.19 | Mend: dependency security vulnerability | ## CVE-2019-9213 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel before 4.20.14, expand_downwards in mm/mmap.c lacks a check for the mmap minimum address, which makes it easier for attackers to exploit kernel NULL pointer dereferences on non-SMAP platforms. This is related to a capability check for the wrong task.
<p>Publish Date: 2019-03-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-9213>CVE-2019-9213</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.securityfocus.com/bid/107296">https://www.securityfocus.com/bid/107296</a></p>
<p>Release Date: 2019-06-17</p>
<p>Fix Resolution: v5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-9213 (Medium) detected in linuxv4.19 - ## CVE-2019-9213 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv4.19</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/torvalds/linux.git>https://github.com/torvalds/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://api.github.com/repos/praneethpanasala/linux/commits/d80c4f847c91020292cb280132b15e2ea147f1a3">d80c4f847c91020292cb280132b15e2ea147f1a3</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel before 4.20.14, expand_downwards in mm/mmap.c lacks a check for the mmap minimum address, which makes it easier for attackers to exploit kernel NULL pointer dereferences on non-SMAP platforms. This is related to a capability check for the wrong task.
<p>Publish Date: 2019-03-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-9213>CVE-2019-9213</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.securityfocus.com/bid/107296">https://www.securityfocus.com/bid/107296</a></p>
<p>Release Date: 2019-06-17</p>
<p>Fix Resolution: v5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details in the linux kernel before expand downwards in mm mmap c lacks a check for the mmap minimum address which makes it easier for attackers to exploit kernel null pointer dereferences on non smap platforms this is related to a capability check for the wrong task publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
25,716 | 6,700,192,822 | IssuesEvent | 2017-10-11 03:00:02 | Tat5ato/Phantasmic-Mind | https://api.github.com/repos/Tat5ato/Phantasmic-Mind | opened | Graphics/CSS/HTML for our Subreddit | Art Can Wait Code Marketing Please send help. | We need someone who is good at web design and CSS to design our Subreddit. I'd do it myself but someone could probably do it better.
Subreddit: https://www.reddit.com/r/PhantasmicMind/
if anyone is interested DM me and i'll make you mod | 1.0 | Graphics/CSS/HTML for our Subreddit - We need someone who is good at web design and CSS to design our Subreddit. I'd do it myself but someone could probably do it better.
Subreddit: https://www.reddit.com/r/PhantasmicMind/
if anyone is interested DM me and i'll make you mod | non_priority | graphics css html for our subreddit we need someone who is good at web design and css to design our subreddit i d do it myself but someone could probably do it better subreddit if anyone is interested dm me and i ll make you mod | 0 |
178,049 | 29,490,165,156 | IssuesEvent | 2023-06-02 12:55:11 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | opened | PasswordValidator - why does IsUpper and IsLower nethods checks only latin characters | design-proposal | <!--
This template is useful to build consensus about whether work should be done, and if so, the high-level shape of how it should be approached. Use this before fixating on a particular implementation.
-->
## Summary
When checking if password contains upper/lower characters it only checks for ['A-Z'/'a-z'](https://github.com/dotnet/aspnetcore/blob/d919168952ac4da33be8532c6980547a783a7389/src/Identity/Extensions.Core/src/PasswordValidator.cs#LL107C25-L107C32). It's not useful as other non-latin characters can be used in password.
## Motivation and goals
Imporve PasswordValidator usage with non-latin symbols
## Risks / unknowns
It's a breaking change
# Detailed design
`IsUpper` method should use `Char.IsUpper` method, and IsLower should use `Char.IsLower` methods
| 1.0 | PasswordValidator - why does IsUpper and IsLower nethods checks only latin characters - <!--
This template is useful to build consensus about whether work should be done, and if so, the high-level shape of how it should be approached. Use this before fixating on a particular implementation.
-->
## Summary
When checking if password contains upper/lower characters it only checks for ['A-Z'/'a-z'](https://github.com/dotnet/aspnetcore/blob/d919168952ac4da33be8532c6980547a783a7389/src/Identity/Extensions.Core/src/PasswordValidator.cs#LL107C25-L107C32). It's not useful as other non-latin characters can be used in password.
## Motivation and goals
Imporve PasswordValidator usage with non-latin symbols
## Risks / unknowns
It's a breaking change
# Detailed design
`IsUpper` method should use `Char.IsUpper` method, and IsLower should use `Char.IsLower` methods
| non_priority | passwordvalidator why does isupper and islower nethods checks only latin characters this template is useful to build consensus about whether work should be done and if so the high level shape of how it should be approached use this before fixating on a particular implementation summary when checking if password contains upper lower characters it only checks for it s not useful as other non latin characters can be used in password motivation and goals imporve passwordvalidator usage with non latin symbols risks unknowns it s a breaking change detailed design isupper method should use char isupper method and islower should use char islower methods | 0 |
124,032 | 26,385,511,001 | IssuesEvent | 2023-01-12 11:58:21 | llvm/llvm-project | https://api.github.com/repos/llvm/llvm-project | closed | Sema/SemaConcept.cpp:1348:19: warning: unused variable 'FD1' [-Wunused-variable | clang:frontend code-quality | ```console
/optimized_clang/stage-0/clang/lib/Sema/SemaConcept.cpp: In member function 'bool clang::Sema::IsAtLeastAsConstrained(clang::NamedDecl*, llvm::MutableArrayRef<const clang::Expr*>, clang::NamedDecl*, llvm::MutableArrayRef<const clang::Expr*>, bool&)':
/optimized_clang/stage-0/clang/lib/Sema/SemaConcept.cpp:1348:19: warning: unused variable 'FD1' [-Wunused-variable]
1348 | if (const auto *FD1 = dyn_cast<FunctionDecl>(D1)) {
| ^~~
``` | 1.0 | Sema/SemaConcept.cpp:1348:19: warning: unused variable 'FD1' [-Wunused-variable - ```console
/optimized_clang/stage-0/clang/lib/Sema/SemaConcept.cpp: In member function 'bool clang::Sema::IsAtLeastAsConstrained(clang::NamedDecl*, llvm::MutableArrayRef<const clang::Expr*>, clang::NamedDecl*, llvm::MutableArrayRef<const clang::Expr*>, bool&)':
/optimized_clang/stage-0/clang/lib/Sema/SemaConcept.cpp:1348:19: warning: unused variable 'FD1' [-Wunused-variable]
1348 | if (const auto *FD1 = dyn_cast<FunctionDecl>(D1)) {
| ^~~
``` | non_priority | sema semaconcept cpp warning unused variable wunused variable console optimized clang stage clang lib sema semaconcept cpp in member function bool clang sema isatleastasconstrained clang nameddecl llvm mutablearrayref clang nameddecl llvm mutablearrayref bool optimized clang stage clang lib sema semaconcept cpp warning unused variable if const auto dyn cast | 0 |
16,489 | 22,329,531,687 | IssuesEvent | 2022-06-14 13:31:04 | ankidroid/Anki-Android | https://api.github.com/repos/ankidroid/Anki-Android | closed | Saved searches are deleted during synchronization | Bug Needs Triage Anki Ecosystem Compatibility Keep Open Card Browser Sync | ###### Research
*Enter an [ x ] character to confirm the points below:*
[ x ] I have read the [support page](https://ankidroid.org/docs/help.html) and am reporting a bug or enhancement request specific to AnkiDroid
[ x ] I have checked the [manual](https://ankidroid.org/docs/manual.html) and the [FAQ](https://github.com/ankidroid/Anki-Android/wiki/FAQ) and could not find a solution to my issue
[ x ] I have searched for similar existing issues here and on the user forum
----
Hi,
I use Anki computer version + Anki Android + cloud sync.
Some monthes ago I found a bug related to saved searches. Unfortunatelly, It's still here.
This bug on Anki PC: [link](https://anki.tenderapp.com/discussions/ankidesktop/26296-saved-searches-are-deleted-during-synchronization)
Anki PC developer's comment:
> Anki is marking the collection data as modified when the filter is saved, so the only reason it would disappear is if when syncing AnkiDroid, the collection is marked as more recently modified in AnkiDroid. If AnkiDroid was in sync prior to syncing the computer and you made no changes on AnkiDroid it sounds like a bug in AnkiDroid - please report the issue to the developers.
###### Reproduction Steps
1. In Anki PC
1. Open browser, do any search
1. Click heart icon and enter search name
1. (Can see the saved search in browser)
1. Synchronize with the cloud
1. (Still can see the saved search in browser)
1. In Anki Android:
1. Synchronize
1. In Anki PC
1. Synchronize
1. The saved search is absent. Expect to see the saved search in browser.
###### Expected Result
The saved search is absent in Anki PC.
###### Actual Result
The saved search is present in Anki PC.
###### Debug info
AnkiDroid Version = 2.8.3
Android Version = 7.1.1
ACRA UUID = 4f1a71fd-0b4e-40c9-9dfa-afb7cd3e5803
Anki computer version:
Version 2.0.32 (Linux)
Qt 4.8.7 PyQt 4.11.4
| True | Saved searches are deleted during synchronization - ###### Research
*Enter an [ x ] character to confirm the points below:*
[ x ] I have read the [support page](https://ankidroid.org/docs/help.html) and am reporting a bug or enhancement request specific to AnkiDroid
[ x ] I have checked the [manual](https://ankidroid.org/docs/manual.html) and the [FAQ](https://github.com/ankidroid/Anki-Android/wiki/FAQ) and could not find a solution to my issue
[ x ] I have searched for similar existing issues here and on the user forum
----
Hi,
I use Anki computer version + Anki Android + cloud sync.
Some monthes ago I found a bug related to saved searches. Unfortunatelly, It's still here.
This bug on Anki PC: [link](https://anki.tenderapp.com/discussions/ankidesktop/26296-saved-searches-are-deleted-during-synchronization)
Anki PC developer's comment:
> Anki is marking the collection data as modified when the filter is saved, so the only reason it would disappear is if when syncing AnkiDroid, the collection is marked as more recently modified in AnkiDroid. If AnkiDroid was in sync prior to syncing the computer and you made no changes on AnkiDroid it sounds like a bug in AnkiDroid - please report the issue to the developers.
###### Reproduction Steps
1. In Anki PC
1. Open browser, do any search
1. Click heart icon and enter search name
1. (Can see the saved search in browser)
1. Synchronize with the cloud
1. (Still can see the saved search in browser)
1. In Anki Android:
1. Synchronize
1. In Anki PC
1. Synchronize
1. The saved search is absent. Expect to see the saved search in browser.
###### Expected Result
The saved search is absent in Anki PC.
###### Actual Result
The saved search is present in Anki PC.
###### Debug info
AnkiDroid Version = 2.8.3
Android Version = 7.1.1
ACRA UUID = 4f1a71fd-0b4e-40c9-9dfa-afb7cd3e5803
Anki computer version:
Version 2.0.32 (Linux)
Qt 4.8.7 PyQt 4.11.4
| non_priority | saved searches are deleted during synchronization research enter an character to confirm the points below i have read the and am reporting a bug or enhancement request specific to ankidroid i have checked the and the and could not find a solution to my issue i have searched for similar existing issues here and on the user forum hi i use anki computer version anki android cloud sync some monthes ago i found a bug related to saved searches unfortunatelly it s still here this bug on anki pc anki pc developer s comment anki is marking the collection data as modified when the filter is saved so the only reason it would disappear is if when syncing ankidroid the collection is marked as more recently modified in ankidroid if ankidroid was in sync prior to syncing the computer and you made no changes on ankidroid it sounds like a bug in ankidroid please report the issue to the developers reproduction steps in anki pc open browser do any search click heart icon and enter search name can see the saved search in browser synchronize with the cloud still can see the saved search in browser in anki android synchronize in anki pc synchronize the saved search is absent expect to see the saved search in browser expected result the saved search is absent in anki pc actual result the saved search is present in anki pc debug info ankidroid version android version acra uuid anki computer version version linux qt pyqt | 0 |
9,594 | 8,042,419,910 | IssuesEvent | 2018-07-31 08:05:25 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | closed | Restructure directory hierarchy based on process | hackathon infrastructure refactoring stale | Ideally there would be:
- browser: For the main process code (Most of this code is inside ./app right now)
- stores
- ...
- renderer: For the renderer process code (Most of this code is inside of ./js right now)
- components
- stores
- ...
- common: Code used by both processes
- constants
- ...
| 1.0 | Restructure directory hierarchy based on process - Ideally there would be:
- browser: For the main process code (Most of this code is inside ./app right now)
- stores
- ...
- renderer: For the renderer process code (Most of this code is inside of ./js right now)
- components
- stores
- ...
- common: Code used by both processes
- constants
- ...
| non_priority | restructure directory hierarchy based on process ideally there would be browser for the main process code most of this code is inside app right now stores renderer for the renderer process code most of this code is inside of js right now components stores common code used by both processes constants | 0 |
95,947 | 8,581,672,827 | IssuesEvent | 2018-11-13 15:15:05 | ubtue/DatenProbleme | https://api.github.com/repos/ubtue/DatenProbleme | closed | CUP ISSN 2163-3088 THE NEW GENEALOGY OF RELIGIOUS FREEDOM Tag 936 | Zotero_AUTO Zotero_Server back to IT ready for testing | Es fehlt $e, $h, $j - Heft, Jahr, Seitenangabe
Vgl. #43 | 1.0 | CUP ISSN 2163-3088 THE NEW GENEALOGY OF RELIGIOUS FREEDOM Tag 936 - Es fehlt $e, $h, $j - Heft, Jahr, Seitenangabe
Vgl. #43 | non_priority | cup issn the new genealogy of religious freedom tag es fehlt e h j heft jahr seitenangabe vgl | 0 |
1,151 | 3,633,939,081 | IssuesEvent | 2016-02-11 16:18:19 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | NTR: cellular response to pulsatile (and: oscillatory) fluid shear stress | BHF-UCL miRNA New term request pending RNA processes | Dear Biocurators,
I am writing to request a new GO term, which arose whilst annotating paper PMID: 21768538 (Wu et al., 2011).
It is demonstrated in Figures 3 and 4 in this paper that the type of fluid shear stress, which endothelial cells are exposed to, affects the expression of miR-92a and, consequently, its target: the transcription factor Kru¨ppel-like factor 2 (KLF2).
I was able to capture the data presented in Figure 3 using term GO:0071499: ‘cellular response to laminar fluid shear stress’.
I order to capture the information from Figure 4, I wish to request two sibling terms:
1) ‘cellular response to pulsatile fluid shear stress’
2) ‘cellular response to oscillatory fluid shear stress’
Like their existing sibling, these terms would be is_a child terms to two parents:
GO:0071498: ‘cellular response to fluid shear stress’; and
GO:0034616: ‘response to laminar fluid shear stress’.
DbxREFs: GOC:BHF, GOC:BHF_miRNA, GOC:bc
I will look forward to hearing from you with regard to my request.
Thank you,
Barbara
cc: @RLovering
cc: @rachhuntley
| 1.0 | NTR: cellular response to pulsatile (and: oscillatory) fluid shear stress - Dear Biocurators,
I am writing to request a new GO term, which arose whilst annotating paper PMID: 21768538 (Wu et al., 2011).
It is demonstrated in Figures 3 and 4 in this paper that the type of fluid shear stress, which endothelial cells are exposed to, affects the expression of miR-92a and, consequently, its target: the transcription factor Kru¨ppel-like factor 2 (KLF2).
I was able to capture the data presented in Figure 3 using term GO:0071499: ‘cellular response to laminar fluid shear stress’.
I order to capture the information from Figure 4, I wish to request two sibling terms:
1) ‘cellular response to pulsatile fluid shear stress’
2) ‘cellular response to oscillatory fluid shear stress’
Like their existing sibling, these terms would be is_a child terms to two parents:
GO:0071498: ‘cellular response to fluid shear stress’; and
GO:0034616: ‘response to laminar fluid shear stress’.
DbxREFs: GOC:BHF, GOC:BHF_miRNA, GOC:bc
I will look forward to hearing from you with regard to my request.
Thank you,
Barbara
cc: @RLovering
cc: @rachhuntley
| non_priority | ntr cellular response to pulsatile and oscillatory fluid shear stress dear biocurators i am writing to request a new go term which arose whilst annotating paper pmid wu et al it is demonstrated in figures and in this paper that the type of fluid shear stress which endothelial cells are exposed to affects the expression of mir and consequently its target the transcription factor kru¨ppel like factor i was able to capture the data presented in figure using term go ‘cellular response to laminar fluid shear stress’ i order to capture the information from figure i wish to request two sibling terms ‘cellular response to pulsatile fluid shear stress’ ‘cellular response to oscillatory fluid shear stress’ like their existing sibling these terms would be is a child terms to two parents go ‘cellular response to fluid shear stress’ and go ‘response to laminar fluid shear stress’ dbxrefs goc bhf goc bhf mirna goc bc i will look forward to hearing from you with regard to my request thank you barbara cc rlovering cc rachhuntley | 0 |
48,532 | 20,170,889,028 | IssuesEvent | 2022-02-10 10:17:57 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | [APM] Service groups: Add `EuiTour` steps for assisting users in creating their first service group and provide guidance on the navigation changes | Team:apm v8.2.0 apm:service-groups | # Summary
Awaiting [design](https://github.com/elastic/observability-design/issues/168) so to be treated as a placeholder for the moment. | 1.0 | [APM] Service groups: Add `EuiTour` steps for assisting users in creating their first service group and provide guidance on the navigation changes - # Summary
Awaiting [design](https://github.com/elastic/observability-design/issues/168) so to be treated as a placeholder for the moment. | non_priority | service groups add euitour steps for assisting users in creating their first service group and provide guidance on the navigation changes summary awaiting so to be treated as a placeholder for the moment | 0 |
60,767 | 12,133,442,310 | IssuesEvent | 2020-04-23 09:02:33 | ciampo/offbeat-appetite | https://api.github.com/repos/ciampo/offbeat-appetite | closed | Advanced social sharing | Code P0 | Have a look at https://warfareplugins.com/
- [x] facebook
- [x] twitter
- [x] pocket
- [x] pinterest
- [x] whatsapp
- [x] email
- [x] native web sharing | 1.0 | Advanced social sharing - Have a look at https://warfareplugins.com/
- [x] facebook
- [x] twitter
- [x] pocket
- [x] pinterest
- [x] whatsapp
- [x] email
- [x] native web sharing | non_priority | advanced social sharing have a look at facebook twitter pocket pinterest whatsapp email native web sharing | 0 |
174,972 | 21,300,617,476 | IssuesEvent | 2022-04-15 02:15:50 | fasttrack-solutions/jQuery-QueryBuilder | https://api.github.com/repos/fasttrack-solutions/jQuery-QueryBuilder | opened | CVE-2022-0436 (High) detected in grunt-1.0.4.tgz | security vulnerability | ## CVE-2022-0436 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-1.0.4.tgz</b></p></summary>
<p>The JavaScript Task Runner</p>
<p>Library home page: <a href="https://registry.npmjs.org/grunt/-/grunt-1.0.4.tgz">https://registry.npmjs.org/grunt/-/grunt-1.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt/package.json</p>
<p>
Dependency Hierarchy:
- :x: **grunt-1.0.4.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Path Traversal in GitHub repository gruntjs/grunt prior to 1.5.2.
<p>Publish Date: 2022-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0436>CVE-2022-0436</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0436">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0436</a></p>
<p>Release Date: 2022-04-12</p>
<p>Fix Resolution: grunt - 1.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0436 (High) detected in grunt-1.0.4.tgz - ## CVE-2022-0436 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-1.0.4.tgz</b></p></summary>
<p>The JavaScript Task Runner</p>
<p>Library home page: <a href="https://registry.npmjs.org/grunt/-/grunt-1.0.4.tgz">https://registry.npmjs.org/grunt/-/grunt-1.0.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/grunt/package.json</p>
<p>
Dependency Hierarchy:
- :x: **grunt-1.0.4.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Path Traversal in GitHub repository gruntjs/grunt prior to 1.5.2.
<p>Publish Date: 2022-04-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0436>CVE-2022-0436</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0436">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0436</a></p>
<p>Release Date: 2022-04-12</p>
<p>Fix Resolution: grunt - 1.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in grunt tgz cve high severity vulnerability vulnerable library grunt tgz the javascript task runner library home page a href path to dependency file package json path to vulnerable library node modules grunt package json dependency hierarchy x grunt tgz vulnerable library found in base branch dev vulnerability details path traversal in github repository gruntjs grunt prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution grunt step up your open source security game with whitesource | 0 |
148,526 | 11,855,140,353 | IssuesEvent | 2020-03-25 03:13:53 | RGPosadas/WayFinder | https://api.github.com/repos/RGPosadas/WayFinder | opened | AT-2: | acceptance tests | ### Issue Tracking
This acceptance test is for #15.
### User Flow Acceptance Test
* All SGW buildings/annexes are present
* All Loyola building/annexes are present | 1.0 | AT-2: - ### Issue Tracking
This acceptance test is for #15.
### User Flow Acceptance Test
* All SGW buildings/annexes are present
* All Loyola building/annexes are present | non_priority | at issue tracking this acceptance test is for user flow acceptance test all sgw buildings annexes are present all loyola building annexes are present | 0 |
333,388 | 29,580,137,281 | IssuesEvent | 2023-06-07 04:44:53 | TWOGATH3R/twogather-web-backend | https://api.github.com/repos/TWOGATH3R/twogather-web-backend | closed | 가게 등록 api 하나로 합치기 | feature test | ## Description
- 기존 가게 등록 api는 다음과 같이 진행되었다
- 1. 가게 등록 api호출 후 가게 등록 id를 발급받는다
- 2. 발급받은 id로 영업시간정보나 메뉴 등 부가적인 정보를 세팅한다
- 하지만 위의 작업은 중간에 실패하게 되는경우 롤백관련 문제가 생길뿐더러 프론트쪽에서 보통 비동기통신을 하기때문에
- 가게 등록 api를 하나로 합치기로 결정했다
## To-Do List
- [x] 가게 등록 api 하나로 합쳐서 새로운 api 개발
- [x] 개발된 api test
## Etc
| 1.0 | 가게 등록 api 하나로 합치기 - ## Description
- 기존 가게 등록 api는 다음과 같이 진행되었다
- 1. 가게 등록 api호출 후 가게 등록 id를 발급받는다
- 2. 발급받은 id로 영업시간정보나 메뉴 등 부가적인 정보를 세팅한다
- 하지만 위의 작업은 중간에 실패하게 되는경우 롤백관련 문제가 생길뿐더러 프론트쪽에서 보통 비동기통신을 하기때문에
- 가게 등록 api를 하나로 합치기로 결정했다
## To-Do List
- [x] 가게 등록 api 하나로 합쳐서 새로운 api 개발
- [x] 개발된 api test
## Etc
| non_priority | 가게 등록 api 하나로 합치기 description 기존 가게 등록 api는 다음과 같이 진행되었다 가게 등록 api호출 후 가게 등록 id를 발급받는다 발급받은 id로 영업시간정보나 메뉴 등 부가적인 정보를 세팅한다 하지만 위의 작업은 중간에 실패하게 되는경우 롤백관련 문제가 생길뿐더러 프론트쪽에서 보통 비동기통신을 하기때문에 가게 등록 api를 하나로 합치기로 결정했다 to do list 가게 등록 api 하나로 합쳐서 새로운 api 개발 개발된 api test etc | 0 |
226,428 | 17,350,822,481 | IssuesEvent | 2021-07-29 08:30:43 | timoast/signac | https://api.github.com/repos/timoast/signac | opened | Off-by-one coordinates in blacklist_hg38 | documentation | <!-- A clear description of what content at https://satijalab.org/signac or in the Signac function man pages is an issue. -->
Hi,
I exported the blacklist_hg38 object with `rtracklayer::export.bed` for use with a command line tool (to make sure I was using the exact same version as within Signac), and I realised that the resulting file contains negative coordinates.
```
[lingsim@node-head1a]$ head blacklist_hg38.bed
chr10 -1 45700 . 0 .
chr10 38481299 38596500 . 0 .
chr10 38782599 38967900 . 0 .
chr10 39901299 41712900 . 0 .
chr10 41838899 42107300 . 0 .
chr10 42279399 42322500 . 0 .
chr10 126946299 126953400 . 0 .
chr10 133625799 133797400 . 0 .
chr11 -1 194500 . 0 .
chr11 518899 520700 . 0 .
```
This is probably because `rtracklayer::export.bed` converts GRanges coordinates (conventionally 1-based, end coordinate included in the range) to 0-based BED format (also half-open, end coordinate excluded from the range). It looks like the coordinates in the provided blacklist_hg38 object are exactly the same as those in the source data (https://github.com/Boyle-Lab/Blacklist), rather than having been converted to 1-based to match the GenomicRanges conventions. So, I have a couple of questions:
* does this also affect the other provided blacklists?
* does this also affect e.g. peak coordinates in ChromatinAssay objects? I.e., does Signac treat all genomic coordinates as 0-based instead of 1-based?
There's no real need for a fix for this as such, I know that I can modify the start coordinates and export, or export with `write.table(as.data.frame(blacklist_hg38))` (and off-by-one-base errors are probably not going to be a big issue for this type of analysis), but it would be good to have some clarity about the conventions used within Signac included in the documentation for these objects.
<details>
<summary>sessionInfo:</summary>
```r
R version 4.0.3 (2020-10-10)
Platform: x86_64-apple-darwin17.0 (64-bit)
Running under: macOS Mojave 10.14.6
Matrix products: default
BLAS: /System/Library/Frameworks/Accelerate.framework/Versions/A/Frameworks/vecLib.framework/Versions/A/libBLAS.dylib
LAPACK: /Library/Frameworks/R.framework/Versions/4.0/Resources/lib/libRlapack.dylib
locale:
[1] en_GB.UTF-8/en_GB.UTF-8/en_GB.UTF-8/C/en_GB.UTF-8/en_GB.UTF-8
attached base packages:
[1] stats graphics grDevices utils datasets methods base
other attached packages:
[1] Signac_1.2.1 SeuratObject_4.0.2 Seurat_4.0.3
loaded via a namespace (and not attached):
[1] drat_0.1.8 Rtsne_0.15 colorspace_2.0-1 deldir_0.2-10 ellipsis_0.3.2
[6] ggridges_0.5.3 lsa_0.73.2 XVector_0.28.0 GenomicRanges_1.40.0 rstudioapi_0.13
[11] spatstat.data_2.0-0 farver_2.1.0 leiden_0.3.7 listenv_0.8.0 SnowballC_0.7.0
[16] ggrepel_0.9.1 fansi_0.5.0 codetools_0.2-18 splines_4.0.3 docopt_0.7.1
[21] RcppRoll_0.3.0 polyclip_1.10-0 jsonlite_1.7.2 Rsamtools_2.4.0 ica_1.0-2
[26] cluster_2.1.1 png_0.1-7 uwot_0.1.10 ggforce_0.3.3 shiny_1.6.0
[31] sctransform_0.3.2 spatstat.sparse_1.2-1 compiler_4.0.3 httr_1.4.2 assertthat_0.2.1
[36] Matrix_1.3-4 fastmap_1.1.0 lazyeval_0.2.2 tweenr_1.0.1 later_1.1.0.1
[41] htmltools_0.5.1.1 tools_4.0.3 igraph_1.2.6 gtable_0.3.0 glue_1.4.2
[46] GenomeInfoDbData_1.2.3 RANN_2.6.1 reshape2_1.4.4 dplyr_1.0.5 fastmatch_1.1-0
[51] Rcpp_1.0.6 slam_0.1-48 scattermore_0.7 Biostrings_2.56.0 vctrs_0.3.8
[56] nlme_3.1-152 ggseqlogo_0.1 lmtest_0.9-38 stringr_1.4.0 globals_0.14.0
[61] mime_0.10 miniUI_0.1.1.1 lifecycle_1.0.0 irlba_2.3.3 goftest_1.2-2
[66] future_1.21.0 MASS_7.3-53.1 zlibbioc_1.34.0 zoo_1.8-9 scales_1.1.1
[71] spatstat.core_1.65-5 promises_1.2.0.1 spatstat.utils_2.0-0 parallel_4.0.3 RColorBrewer_1.1-2
[76] reticulate_1.18 pbapply_1.4-3 gridExtra_2.3 ggplot2_3.3.3 rpart_4.1-15
[81] stringi_1.5.3 S4Vectors_0.26.1 BiocGenerics_0.34.0 BiocParallel_1.22.0 GenomeInfoDb_1.24.2
[86] rlang_0.4.11 pkgconfig_2.0.3 matrixStats_0.59.0 bitops_1.0-7 qlcMatrix_0.9.7
[91] lattice_0.20-41 ROCR_1.0-11 purrr_0.3.4 tensor_1.5 patchwork_1.1.1
[96] htmlwidgets_1.5.3 cowplot_1.1.1 tidyselect_1.1.0 parallelly_1.24.0 RcppAnnoy_0.0.18
[101] plyr_1.8.6 magrittr_2.0.1 R6_2.5.0 IRanges_2.22.2 generics_0.1.0
[106] DBI_1.1.1 pillar_1.6.1 mgcv_1.8-34 fitdistrplus_1.1-3 survival_3.2-9
[111] abind_1.4-5 RCurl_1.98-1.2 tibble_3.1.2 future.apply_1.7.0 crayon_1.4.1
[116] KernSmooth_2.23-18 utf8_1.2.1 spatstat.geom_1.65-5 plotly_4.9.3 grid_4.0.3
[121] data.table_1.14.0 sparsesvd_0.2 digest_0.6.27 xtable_1.8-4 tidyr_1.1.3
[126] httpuv_1.5.5 stats4_4.0.3 munsell_0.5.0 viridisLite_0.4.0
```
</details> | 1.0 | Off-by-one coordinates in blacklist_hg38 - <!-- A clear description of what content at https://satijalab.org/signac or in the Signac function man pages is an issue. -->
Hi,
I exported the blacklist_hg38 object with `rtracklayer::export.bed` for use with a command line tool (to make sure I was using the exact same version as within Signac), and I realised that the resulting file contains negative coordinates.
```
[lingsim@node-head1a]$ head blacklist_hg38.bed
chr10 -1 45700 . 0 .
chr10 38481299 38596500 . 0 .
chr10 38782599 38967900 . 0 .
chr10 39901299 41712900 . 0 .
chr10 41838899 42107300 . 0 .
chr10 42279399 42322500 . 0 .
chr10 126946299 126953400 . 0 .
chr10 133625799 133797400 . 0 .
chr11 -1 194500 . 0 .
chr11 518899 520700 . 0 .
```
This is probably because `rtracklayer::export.bed` converts GRanges coordinates (conventionally 1-based, end coordinate included in the range) to 0-based BED format (also half-open, end coordinate excluded from the range). It looks like the coordinates in the provided blacklist_hg38 object are exactly the same as those in the source data (https://github.com/Boyle-Lab/Blacklist), rather than having been converted to 1-based to match the GenomicRanges conventions. So, I have a couple of questions:
* does this also affect the other provided blacklists?
* does this also affect e.g. peak coordinates in ChromatinAssay objects? I.e., does Signac treat all genomic coordinates as 0-based instead of 1-based?
There's no real need for a fix for this as such, I know that I can modify the start coordinates and export, or export with `write.table(as.data.frame(blacklist_hg38))` (and off-by-one-base errors are probably not going to be a big issue for this type of analysis), but it would be good to have some clarity about the conventions used within Signac included in the documentation for these objects.
<details>
<summary>sessionInfo:</summary>
```r
R version 4.0.3 (2020-10-10)
Platform: x86_64-apple-darwin17.0 (64-bit)
Running under: macOS Mojave 10.14.6
Matrix products: default
BLAS: /System/Library/Frameworks/Accelerate.framework/Versions/A/Frameworks/vecLib.framework/Versions/A/libBLAS.dylib
LAPACK: /Library/Frameworks/R.framework/Versions/4.0/Resources/lib/libRlapack.dylib
locale:
[1] en_GB.UTF-8/en_GB.UTF-8/en_GB.UTF-8/C/en_GB.UTF-8/en_GB.UTF-8
attached base packages:
[1] stats graphics grDevices utils datasets methods base
other attached packages:
[1] Signac_1.2.1 SeuratObject_4.0.2 Seurat_4.0.3
loaded via a namespace (and not attached):
[1] drat_0.1.8 Rtsne_0.15 colorspace_2.0-1 deldir_0.2-10 ellipsis_0.3.2
[6] ggridges_0.5.3 lsa_0.73.2 XVector_0.28.0 GenomicRanges_1.40.0 rstudioapi_0.13
[11] spatstat.data_2.0-0 farver_2.1.0 leiden_0.3.7 listenv_0.8.0 SnowballC_0.7.0
[16] ggrepel_0.9.1 fansi_0.5.0 codetools_0.2-18 splines_4.0.3 docopt_0.7.1
[21] RcppRoll_0.3.0 polyclip_1.10-0 jsonlite_1.7.2 Rsamtools_2.4.0 ica_1.0-2
[26] cluster_2.1.1 png_0.1-7 uwot_0.1.10 ggforce_0.3.3 shiny_1.6.0
[31] sctransform_0.3.2 spatstat.sparse_1.2-1 compiler_4.0.3 httr_1.4.2 assertthat_0.2.1
[36] Matrix_1.3-4 fastmap_1.1.0 lazyeval_0.2.2 tweenr_1.0.1 later_1.1.0.1
[41] htmltools_0.5.1.1 tools_4.0.3 igraph_1.2.6 gtable_0.3.0 glue_1.4.2
[46] GenomeInfoDbData_1.2.3 RANN_2.6.1 reshape2_1.4.4 dplyr_1.0.5 fastmatch_1.1-0
[51] Rcpp_1.0.6 slam_0.1-48 scattermore_0.7 Biostrings_2.56.0 vctrs_0.3.8
[56] nlme_3.1-152 ggseqlogo_0.1 lmtest_0.9-38 stringr_1.4.0 globals_0.14.0
[61] mime_0.10 miniUI_0.1.1.1 lifecycle_1.0.0 irlba_2.3.3 goftest_1.2-2
[66] future_1.21.0 MASS_7.3-53.1 zlibbioc_1.34.0 zoo_1.8-9 scales_1.1.1
[71] spatstat.core_1.65-5 promises_1.2.0.1 spatstat.utils_2.0-0 parallel_4.0.3 RColorBrewer_1.1-2
[76] reticulate_1.18 pbapply_1.4-3 gridExtra_2.3 ggplot2_3.3.3 rpart_4.1-15
[81] stringi_1.5.3 S4Vectors_0.26.1 BiocGenerics_0.34.0 BiocParallel_1.22.0 GenomeInfoDb_1.24.2
[86] rlang_0.4.11 pkgconfig_2.0.3 matrixStats_0.59.0 bitops_1.0-7 qlcMatrix_0.9.7
[91] lattice_0.20-41 ROCR_1.0-11 purrr_0.3.4 tensor_1.5 patchwork_1.1.1
[96] htmlwidgets_1.5.3 cowplot_1.1.1 tidyselect_1.1.0 parallelly_1.24.0 RcppAnnoy_0.0.18
[101] plyr_1.8.6 magrittr_2.0.1 R6_2.5.0 IRanges_2.22.2 generics_0.1.0
[106] DBI_1.1.1 pillar_1.6.1 mgcv_1.8-34 fitdistrplus_1.1-3 survival_3.2-9
[111] abind_1.4-5 RCurl_1.98-1.2 tibble_3.1.2 future.apply_1.7.0 crayon_1.4.1
[116] KernSmooth_2.23-18 utf8_1.2.1 spatstat.geom_1.65-5 plotly_4.9.3 grid_4.0.3
[121] data.table_1.14.0 sparsesvd_0.2 digest_0.6.27 xtable_1.8-4 tidyr_1.1.3
[126] httpuv_1.5.5 stats4_4.0.3 munsell_0.5.0 viridisLite_0.4.0
```
</details> | non_priority | off by one coordinates in blacklist hi i exported the blacklist object with rtracklayer export bed for use with a command line tool to make sure i was using the exact same version as within signac and i realised that the resulting file contains negative coordinates head blacklist bed this is probably because rtracklayer export bed converts granges coordinates conventionally based end coordinate included in the range to based bed format also half open end coordinate excluded from the range it looks like the coordinates in the provided blacklist object are exactly the same as those in the source data rather than having been converted to based to match the genomicranges conventions so i have a couple of questions does this also affect the other provided blacklists does this also affect e g peak coordinates in chromatinassay objects i e does signac treat all genomic coordinates as based instead of based there s no real need for a fix for this as such i know that i can modify the start coordinates and export or export with write table as data frame blacklist and off by one base errors are probably not going to be a big issue for this type of analysis but it would be good to have some clarity about the conventions used within signac included in the documentation for these objects sessioninfo r r version platform apple bit running under macos mojave matrix products default blas system library frameworks accelerate framework versions a frameworks veclib framework versions a libblas dylib lapack library frameworks r framework versions resources lib librlapack dylib locale en gb utf en gb utf en gb utf c en gb utf en gb utf attached base packages stats graphics grdevices utils datasets methods base other attached packages signac seuratobject seurat loaded via a namespace and not attached drat rtsne colorspace deldir ellipsis ggridges lsa xvector genomicranges rstudioapi spatstat data farver leiden listenv snowballc ggrepel fansi codetools splines docopt rcpproll polyclip jsonlite rsamtools ica cluster png uwot ggforce shiny sctransform spatstat sparse compiler httr assertthat matrix fastmap lazyeval tweenr later htmltools tools igraph gtable glue genomeinfodbdata rann dplyr fastmatch rcpp slam scattermore biostrings vctrs nlme ggseqlogo lmtest stringr globals mime miniui lifecycle irlba goftest future mass zlibbioc zoo scales spatstat core promises spatstat utils parallel rcolorbrewer reticulate pbapply gridextra rpart stringi biocgenerics biocparallel genomeinfodb rlang pkgconfig matrixstats bitops qlcmatrix lattice rocr purrr tensor patchwork htmlwidgets cowplot tidyselect parallelly rcppannoy plyr magrittr iranges generics dbi pillar mgcv fitdistrplus survival abind rcurl tibble future apply crayon kernsmooth spatstat geom plotly grid data table sparsesvd digest xtable tidyr httpuv munsell viridislite | 0 |
262,153 | 19,762,294,581 | IssuesEvent | 2022-01-16 15:59:57 | Texnoit-com/Microbit | https://api.github.com/repos/Texnoit-com/Microbit | opened | Устройства вывода: Сверхяркий светодиод | documentation enhancement good first issue | Описание класса и методов работы с модулем "Сверхяркий светодиод
" | 1.0 | Устройства вывода: Сверхяркий светодиод - Описание класса и методов работы с модулем "Сверхяркий светодиод
" | non_priority | устройства вывода сверхяркий светодиод описание класса и методов работы с модулем сверхяркий светодиод | 0 |
31,937 | 7,468,536,567 | IssuesEvent | 2018-04-02 19:20:50 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [CodeMirror] Syntax don't work if 2 editor on page | No Code Attached Yet | If you display two or more editors on the page, the syntax of the first one will be applied to all
XML for test
```
<form>
<field name="html" type="editor" filter="JComponentHelper::filterText"/>
<field name="css" type="editor" filter="raw" editor="codemirror|none" syntax="css"/>
<field name="js" type="editor" filter="raw" editor="codemirror|none" syntax="js"/>
</form>
```
Perhaps there are others there are also problems if you display several CodeMirror.
| 1.0 | [CodeMirror] Syntax don't work if 2 editor on page - If you display two or more editors on the page, the syntax of the first one will be applied to all
XML for test
```
<form>
<field name="html" type="editor" filter="JComponentHelper::filterText"/>
<field name="css" type="editor" filter="raw" editor="codemirror|none" syntax="css"/>
<field name="js" type="editor" filter="raw" editor="codemirror|none" syntax="js"/>
</form>
```
Perhaps there are others there are also problems if you display several CodeMirror.
| non_priority | syntax don t work if editor on page if you display two or more editors on the page the syntax of the first one will be applied to all xml for test perhaps there are others there are also problems if you display several codemirror | 0 |
32,624 | 4,779,253,692 | IssuesEvent | 2016-10-27 21:50:29 | MusikAnimal/pageviews | https://api.github.com/repos/MusikAnimal/pageviews | closed | View for 60 / 90 days not working | Needs test case | Hi, thanks for the tool, better than http://stats.grok.se, especially the possibility to compare several articles. ONLY THING I MISS: to call the 50 (or 100) most viewed pages per month / week of a specified wikipedia.
PROBLEM TO REPORT: I use it for swwiki. 30-day-view is fine. Switching to 60 or 90 days gives a flat line after the first dates.
Example our starter page Mwanzo gets
Totals: 25.692 in 30-day-view, but only
Totals: 13.169 in 60-day-view - cuts off on March 20 (my uplook is on May 7)
Totals: 39.890 in 90-day-view - cuts off again on March 20 | 1.0 | View for 60 / 90 days not working - Hi, thanks for the tool, better than http://stats.grok.se, especially the possibility to compare several articles. ONLY THING I MISS: to call the 50 (or 100) most viewed pages per month / week of a specified wikipedia.
PROBLEM TO REPORT: I use it for swwiki. 30-day-view is fine. Switching to 60 or 90 days gives a flat line after the first dates.
Example our starter page Mwanzo gets
Totals: 25.692 in 30-day-view, but only
Totals: 13.169 in 60-day-view - cuts off on March 20 (my uplook is on May 7)
Totals: 39.890 in 90-day-view - cuts off again on March 20 | non_priority | view for days not working hi thanks for the tool better than especially the possibility to compare several articles only thing i miss to call the or most viewed pages per month week of a specified wikipedia problem to report i use it for swwiki day view is fine switching to or days gives a flat line after the first dates example our starter page mwanzo gets totals in day view but only totals in day view cuts off on march my uplook is on may totals in day view cuts off again on march | 0 |
166,350 | 12,950,186,279 | IssuesEvent | 2020-07-19 12:14:07 | RolandJansen/intermix | https://api.github.com/repos/RolandJansen/intermix | opened | Refactor SeqPart | refactoring tests | Sequencer parts have gone through drastical changes in 0.5.0. Lots of the structure is redundant while new code is still not under test. Read the code and improve things. | 1.0 | Refactor SeqPart - Sequencer parts have gone through drastical changes in 0.5.0. Lots of the structure is redundant while new code is still not under test. Read the code and improve things. | non_priority | refactor seqpart sequencer parts have gone through drastical changes in lots of the structure is redundant while new code is still not under test read the code and improve things | 0 |
376,954 | 26,225,246,155 | IssuesEvent | 2023-01-04 18:03:35 | Cusymint/cusymint | https://api.github.com/repos/Cusymint/cusymint | closed | Installation guide | documentation devops engine front | Guide should contain:
- [x] `engine` installation using Docker
- [ ] `client` Windows installation using `.msi`
- [ ] `client` Android installation using `.apk`
- [ ] `client` Linux installation using `snap`
- [ ] `client` Web installation using Docker | 1.0 | Installation guide - Guide should contain:
- [x] `engine` installation using Docker
- [ ] `client` Windows installation using `.msi`
- [ ] `client` Android installation using `.apk`
- [ ] `client` Linux installation using `snap`
- [ ] `client` Web installation using Docker | non_priority | installation guide guide should contain engine installation using docker client windows installation using msi client android installation using apk client linux installation using snap client web installation using docker | 0 |
128,442 | 12,372,868,269 | IssuesEvent | 2020-05-18 21:15:21 | tauri-apps/tauri-docs | https://api.github.com/repos/tauri-apps/tauri-docs | closed | Retrieve docs from the Wiki | documentation | All docs from the current Wiki should be moved to the website. Also, we need to ensure that every links are updated.
Contents may have to be updated, reworked and detailed. | 1.0 | Retrieve docs from the Wiki - All docs from the current Wiki should be moved to the website. Also, we need to ensure that every links are updated.
Contents may have to be updated, reworked and detailed. | non_priority | retrieve docs from the wiki all docs from the current wiki should be moved to the website also we need to ensure that every links are updated contents may have to be updated reworked and detailed | 0 |
72,537 | 24,169,317,662 | IssuesEvent | 2022-09-22 17:41:48 | scipy/scipy | https://api.github.com/repos/scipy/scipy | opened | BUG: Can't import rel_entr from scipy.special | defect | ### Describe your issue.
Import statement `from scipy.special import rel_entr` fails
### Reproducing Code Example
```python
from scipy.special import rel_entr
```
### Error message
```shell
---------------------------------------------------------------------------
ImportError Traceback (most recent call last)
<ipython-input-1-36fe78ea68ea> in <module>
----> 1 from scipy.special import rel_entr
ImportError: cannot import name 'rel_entr' from 'scipy.special' (unknown location)
```
### SciPy/NumPy/Python version information
1.9.1 1.22.4 sys.version_info(major=3, minor=8, micro=8, releaselevel='final', serial=0) | 1.0 | BUG: Can't import rel_entr from scipy.special - ### Describe your issue.
Import statement `from scipy.special import rel_entr` fails
### Reproducing Code Example
```python
from scipy.special import rel_entr
```
### Error message
```shell
---------------------------------------------------------------------------
ImportError Traceback (most recent call last)
<ipython-input-1-36fe78ea68ea> in <module>
----> 1 from scipy.special import rel_entr
ImportError: cannot import name 'rel_entr' from 'scipy.special' (unknown location)
```
### SciPy/NumPy/Python version information
1.9.1 1.22.4 sys.version_info(major=3, minor=8, micro=8, releaselevel='final', serial=0) | non_priority | bug can t import rel entr from scipy special describe your issue import statement from scipy special import rel entr fails reproducing code example python from scipy special import rel entr error message shell importerror traceback most recent call last in from scipy special import rel entr importerror cannot import name rel entr from scipy special unknown location scipy numpy python version information sys version info major minor micro releaselevel final serial | 0 |
133,404 | 18,297,457,787 | IssuesEvent | 2021-10-05 21:59:38 | ghc-dev/Jennifer-Poole | https://api.github.com/repos/ghc-dev/Jennifer-Poole | opened | CVE-2015-9251 (Medium) detected in jquery-1.8.1.min.js, jquery-1.7.2.min.js | security vulnerability | ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.8.1.min.js</b>, <b>jquery-1.7.2.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: Jennifer-Poole/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to dependency file: Jennifer-Poole/node_modules/js-base64/test/index.html</p>
<p>Path to vulnerable library: /node_modules/js-base64/test/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Jennifer-Poole/commit/a42e1f276b13ba57ab48e60289e7f00c2858fab6">a42e1f276b13ba57ab48e60289e7f00c2858fab6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.8.1","packageFilePaths":["/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.8.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v3.0.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.7.2","packageFilePaths":["/node_modules/js-base64/test/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.7.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v3.0.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-9251","vulnerabilityDetails":"jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2015-9251 (Medium) detected in jquery-1.8.1.min.js, jquery-1.7.2.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.8.1.min.js</b>, <b>jquery-1.7.2.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: Jennifer-Poole/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to dependency file: Jennifer-Poole/node_modules/js-base64/test/index.html</p>
<p>Path to vulnerable library: /node_modules/js-base64/test/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Jennifer-Poole/commit/a42e1f276b13ba57ab48e60289e7f00c2858fab6">a42e1f276b13ba57ab48e60289e7f00c2858fab6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.8.1","packageFilePaths":["/node_modules/bower/lib/node_modules/redeyed/examples/browser/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.8.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v3.0.0"},{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.7.2","packageFilePaths":["/node_modules/js-base64/test/index.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:1.7.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jQuery - v3.0.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-9251","vulnerabilityDetails":"jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-9251","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js jquery min js cve medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations library home page a href path to dependency file jennifer poole node modules bower lib node modules redeyed examples browser index html path to vulnerable library node modules bower lib node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file jennifer poole node modules js test index html path to vulnerable library node modules js test index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery packagetype javascript packagename jquery packageversion packagefilepaths istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery basebranches vulnerabilityidentifier cve vulnerabilitydetails jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed vulnerabilityurl | 0 |
19,653 | 27,293,414,625 | IssuesEvent | 2023-02-23 18:16:16 | elementor/elementor | https://api.github.com/repos/elementor/elementor | closed | ⛔ 🐞 Bug Report: Elementor-created shop page defaults back to WooCommerce standard shop page after assigning it in the Settings. After the page is assigned, I’m unable to edit the page using Elementor | bug compatibility/3rd_party product/pro component/woocommerce type/dynamic-content type/templates | ### Prerequisites
- [X] I have searched for similar issues in both open and closed tickets and cannot find a duplicate.
- [X] The issue still exists against the latest stable version of Elementor.
### Description
When exactly did you first notice the problem?
- I noticed this problem today when I finished modifying the Shop All page and navigated to the WooCommerce Settings to assign this page as a WooCommerce Shop Page
Have any updates been applied to your website recently?
- Updated the woocommerce templates that required an update
Have you changed themes or made design changes?
- No theme changes
Have you installed any new plugins?
- Yes, but I disabled and uninstalled it. (Royal Addons)
Can the issue be replicated on multiple devices?
- Yes, shop page shows incorrectly all devices
Is your problem happening in one browser or all of them?
- all of them
Do you see a specific error message? Take a screenshot.
- yes, when I attempt to edit the page after assigning it to WooCommerce I get the message: The Preview could not be loaded.
### Steps to reproduce
1. Created a Shop Page with Elementor
2. Navigate to the WooCommerce Settings to assign this page as a WooCommerce Shop Page
3. Navigate back to the page from the Pages menu
4. Click the Edit with Elementor link
5. Get an error The Preview Could Not Be Loaded
<img width="1393" alt="Screen Shot 2023-02-21 at 10 59 35 PM" src="https://user-images.githubusercontent.com/57504763/220518797-e13f501b-4ffa-44ec-aaa9-7fa1b5fe463d.png">
<img width="1299" alt="Screen Shot 2023-02-21 at 11 00 11 PM" src="https://user-images.githubusercontent.com/57504763/220518801-ff8d9985-b888-43ec-bc5b-b46bc04ec662.png">
<img width="587" alt="Screen Shot 2023-02-21 at 11 00 51 PM" src="https://user-images.githubusercontent.com/57504763/220518803-e31a3ada-b3dc-4b16-b5e3-3fa38db7a01c.png">
### Isolating the problem
- [ ] This bug happens with only Elementor plugin active (and Elementor Pro).
- [ ] This bug happens with a Blank WordPress theme active ([Hello theme](https://wordpress.org/themes/hello-elementor/)).
- [ ] I can reproduce this bug consistently following the steps above.
### System Info
<details>
<summary>System Info</summary>
````txt
== Server Environment ==
Operating System: Linux
Software: LiteSpeed
MySQL version: MariaDB Server v10.3.34
PHP Version: 7.4.29
PHP Memory Limit: 256M
PHP Max Input Vars: 5000
PHP Max Post Size: 1024M
GD Installed: Yes
ZIP Installed: Yes
Write Permissions: All right
Elementor Library: Connected
== WordPress Environment ==
Version: 6.1.1
Site URL: https://www.silkresse.com
Home URL: https://www.silkresse.com
WP Multisite: No
Max Upload Size: 512 MB
Memory limit: 40M
Max Memory limit: 256M
Permalink Structure: /blog/%postname%/
Language: en-US
Timezone: 0
Admin Email: silkresse@gmail.com
Debug Mode: Inactive
== Theme ==
Name: Blocksy Child
Version:
Author: Creative Themes
Child Theme: Yes
Parent Theme Name: Blocksy
Parent Theme Version: 1.8.42
Parent Theme Author: CreativeThemes
== User ==
Role: administrator
WP Profile lang: en_US
User Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36
== Active Plugins ==
Advanced Product Fields for WooCommerce
Version: 1.5.9
Author: StudioWombat
Blocksy Companion
Version: 1.8.75
Author: CreativeThemes
CoDesigner
Version: 3.9
Author: Codexpert
Elementor
Version: 3.12.0-dev4
Author: Elementor.com
Elementor Beta (Developer Edition)
Version: 1.1.1
Author: Elementor.com
ElementsKit Lite
Version: 2.8.1
Author: Wpmet
Essential Addons for Elementor
Version: 5.5.4
Author: WPDeveloper
Spotlight - Social Media Feeds
Version: 1.4.4
Author: RebelCode
WooCommerce
Version: 7.4.0
Author: Automattic
WPForms Lite
Version: 1.8.0.1
Author: WPForms
== Elementor Experiments ==
Optimized DOM Output: Active by default
Improved Asset Loading: Active by default
Improved CSS Loading: Active by default
Inline Font Icons: Active by default
Accessibility Improvements: Active by default
Additional Custom Breakpoints: Active by default
admin_menu_rearrangement: Inactive by default
Flexbox Container: Active
Upgrade Swiper Library: Active by default
Editor V2: Inactive by default
Landing Pages: Active by default
Nested Elements: Active by default
Lazy Load Background Images: Inactive by default
Save as Default: Active by default
== Log ==
JS: showing 17 of 17JS: 2022-07-12 18:06:59 [error X 75][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.6.7:3:475108] Cannot read properties of undefined (reading \'parent\')
JS: 2022-07-16 15:21:36 [error X 28][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:185947] Cannot read properties of undefined (reading \'data\')
JS: 2022-07-20 16:33:37 [error X 6][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:610510] Cannot read properties of null (reading \'getBoundingClientRect\')
JS: 2022-08-12 21:59:03 [error X 8][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:614960] Cannot read properties of undefined (reading \'toLowerCase\')
JS: 2022-08-16 02:01:16 [error X 34][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:615467] Cannot read properties of undefined (reading \'localized\')
JS: 2022-09-12 01:10:55 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/container-converter.min.js?ver=3.7.0-dev10:2:10719] elementor is not defined
JS: 2022-11-09 01:26:51 [error X 13][https://www.silkresse.com/wp-admin/load-scripts.php?c=1&loadchunk_0=jquery-core,jquery-migrate,regenerator-runtime,wp-polyfill,underscore,shortcode,utils,backbone,wp-util,wp-backbone,media-models,&loadchunk_1=moxiejs,plupload,wp-plupload,jquery-ui-core,jquery-ui-mouse,jquery-ui-sortable&ver=6.1:2:51824] Cannot read properties of undefined (reading \'replace\')
JS: 2022-11-09 02:35:21 [error X 36][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/frontend.min.js?ver=3.10.0-dev1:2:32848] elementorFrontendConfig is not defined
JS: 2022-11-09 03:20:43 [error X 2][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.10.0-dev1:3:811312] Cannot convert undefined or null to object
JS: 2022-11-17 22:00:07 [error X 4][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/frontend.min.js?ver=3.10.0-dev1:2:32871] Can\'t find variable: elementorFrontendConfig
JS: 2023-01-10 04:51:46 [error X 69][https://www.silkresse.com/wp-admin/load-scripts.php?c=1&loadchunk_0=jquery-core,jquery-migrate,regenerator-runtime,wp-polyfill,jquery-ui-core,jquery-ui-mouse,underscore,backbone,wp-api-request,wp-&loadchunk_1=hooks&ver=6.1.1:2:51824] Cannot read properties of undefined (reading 'replace')
JS: 2023-01-11 15:19:35 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.11.0-dev3:3:583495] Cannot read properties of null (reading 'id')
JS: 2023-01-11 17:27:40 [error X 3][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.11.0-dev3:3:782318] Cannot read properties of undefined (reading 'toLowerCase')
JS: 2023-01-18 02:51:41 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/web-cli.min.js?ver=3.11.0-dev3:3:105230] Routes: `library/templates` not found.
JS: 2023-01-19 04:31:23 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/web-cli.min.js?ver=3.11.0-dev3:3:105230] Routes: `library/blocks` not found.
JS: 2023-01-19 04:31:26 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/web-cli.min.js?ver=3.11.0-dev3:3:105230] Routes: `library/pages` not found.
JS: 2023-02-20 16:19:44 [error X 14][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.12.0-dev4:3:794636] Cannot read properties of undefined (reading 'localized')
PHP: showing 5 of 5PHP: 2022-07-12 20:02:17 [notice X 120][/home/silkress/public_html/wp-content/plugins/elementor/modules/dev-tools/deprecation.php::301] The $finder_category_name argument is deprecated since version 3.5.0! [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2022-07-12 20:05:38 [notice X 5][/home/silkress/public_html/wp-content/plugins/elementor/includes/widgets/traits/button-trait.php::553] Undefined index: icon [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2022-09-12 19:12:19 [notice X 1][/home/silkress/public_html/wp-content/plugins/elementor/core/common/modules/ajax/module.php::171] Undefined index: data [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2023-01-18 02:53:19 [notice X 2][/home/silkress/public_html/wp-content/plugins/elementor/core/page-assets/data-managers/font-icon-svg/font-awesome.php::50] Trying to access array offset on value of type null [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2023-02-20 04:56:40 [notice X 21][/home/silkress/public_html/wp-content/plugins/elementor/includes/managers/image.php::108] Trying to access array offset on value of type bool [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
Log: showing 20 of 202022-07-16 14:45:12 [info] elementor::elementor_updater Started
2022-07-16 14:45:12 [info] Elementor/Upgrades - _on_each_version Start
2022-07-16 14:45:12 [info] Elementor/Upgrades - _on_each_version Finished
2022-07-16 14:45:12 [info] Elementor/Upgrades - _v_3_7_0_remove_old_elements_usage Start
2022-07-16 14:45:12 [info] Elementor/Upgrades - _v_3_7_0_remove_old_elements_usage Finished
2022-07-16 14:45:12 [info] Elementor data updater process has been completed. [array (
'plugin' => 'Elementor',
'from' => '3.6.7',
'to' => '3.7.0-dev10',
)]
2022-07-16 14:45:12 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.6.7',
'to' => '3.7.0-dev10',
)]
2022-11-09 02:20:27 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.7.0-dev10',
'to' => '3.10.0-dev1',
)]
2022-11-09 02:20:27 [info] elementor::elementor_updater Started
2022-11-09 02:20:27 [info] Elementor/Upgrades - _on_each_version Start
2022-11-09 02:20:27 [info] Elementor/Upgrades - _on_each_version Finished
2022-11-09 02:20:27 [info] Elementor/Upgrades - _v_3_8_0_fix_php8_image_custom_size Start
2022-11-09 02:20:27 [info] Elementor/Upgrades - _v_3_8_0_fix_php8_image_custom_size Finished
2022-11-09 02:20:27 [info] Elementor data updater process has been completed. [array (
'plugin' => 'Elementor',
'from' => '3.7.0-dev10',
'to' => '3.10.0-dev1',
)]
2022-12-14 01:22:22 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.10.0-dev1',
'to' => '3.11.0-dev1',
)]
2022-12-14 01:22:22 [info] elementor::elementor_updater Started
2022-12-14 01:22:22 [info] Elementor/Upgrades - _on_each_version Start
2022-12-14 01:22:22 [info] Elementor/Upgrades - _on_each_version Finished
2022-12-14 01:22:22 [info] Elementor data updater process has been completed. [array (
'plugin' => 'Elementor',
'from' => '3.10.0-dev1',
'to' => '3.11.0-dev1',
)]
2022-12-14 01:22:23 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.10.0-dev1',
'to' => '3.11.0-dev1',
)]
== Elementor - Compatibility Tag ==
Essential Addons for Elementor: Incompatible
````
</details> | True | ⛔ 🐞 Bug Report: Elementor-created shop page defaults back to WooCommerce standard shop page after assigning it in the Settings. After the page is assigned, I’m unable to edit the page using Elementor - ### Prerequisites
- [X] I have searched for similar issues in both open and closed tickets and cannot find a duplicate.
- [X] The issue still exists against the latest stable version of Elementor.
### Description
When exactly did you first notice the problem?
- I noticed this problem today when I finished modifying the Shop All page and navigated to the WooCommerce Settings to assign this page as a WooCommerce Shop Page
Have any updates been applied to your website recently?
- Updated the woocommerce templates that required an update
Have you changed themes or made design changes?
- No theme changes
Have you installed any new plugins?
- Yes, but I disabled and uninstalled it. (Royal Addons)
Can the issue be replicated on multiple devices?
- Yes, shop page shows incorrectly all devices
Is your problem happening in one browser or all of them?
- all of them
Do you see a specific error message? Take a screenshot.
- yes, when I attempt to edit the page after assigning it to WooCommerce I get the message: The Preview could not be loaded.
### Steps to reproduce
1. Created a Shop Page with Elementor
2. Navigate to the WooCommerce Settings to assign this page as a WooCommerce Shop Page
3. Navigate back to the page from the Pages menu
4. Click the Edit with Elementor link
5. Get an error The Preview Could Not Be Loaded
<img width="1393" alt="Screen Shot 2023-02-21 at 10 59 35 PM" src="https://user-images.githubusercontent.com/57504763/220518797-e13f501b-4ffa-44ec-aaa9-7fa1b5fe463d.png">
<img width="1299" alt="Screen Shot 2023-02-21 at 11 00 11 PM" src="https://user-images.githubusercontent.com/57504763/220518801-ff8d9985-b888-43ec-bc5b-b46bc04ec662.png">
<img width="587" alt="Screen Shot 2023-02-21 at 11 00 51 PM" src="https://user-images.githubusercontent.com/57504763/220518803-e31a3ada-b3dc-4b16-b5e3-3fa38db7a01c.png">
### Isolating the problem
- [ ] This bug happens with only Elementor plugin active (and Elementor Pro).
- [ ] This bug happens with a Blank WordPress theme active ([Hello theme](https://wordpress.org/themes/hello-elementor/)).
- [ ] I can reproduce this bug consistently following the steps above.
### System Info
<details>
<summary>System Info</summary>
````txt
== Server Environment ==
Operating System: Linux
Software: LiteSpeed
MySQL version: MariaDB Server v10.3.34
PHP Version: 7.4.29
PHP Memory Limit: 256M
PHP Max Input Vars: 5000
PHP Max Post Size: 1024M
GD Installed: Yes
ZIP Installed: Yes
Write Permissions: All right
Elementor Library: Connected
== WordPress Environment ==
Version: 6.1.1
Site URL: https://www.silkresse.com
Home URL: https://www.silkresse.com
WP Multisite: No
Max Upload Size: 512 MB
Memory limit: 40M
Max Memory limit: 256M
Permalink Structure: /blog/%postname%/
Language: en-US
Timezone: 0
Admin Email: silkresse@gmail.com
Debug Mode: Inactive
== Theme ==
Name: Blocksy Child
Version:
Author: Creative Themes
Child Theme: Yes
Parent Theme Name: Blocksy
Parent Theme Version: 1.8.42
Parent Theme Author: CreativeThemes
== User ==
Role: administrator
WP Profile lang: en_US
User Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36
== Active Plugins ==
Advanced Product Fields for WooCommerce
Version: 1.5.9
Author: StudioWombat
Blocksy Companion
Version: 1.8.75
Author: CreativeThemes
CoDesigner
Version: 3.9
Author: Codexpert
Elementor
Version: 3.12.0-dev4
Author: Elementor.com
Elementor Beta (Developer Edition)
Version: 1.1.1
Author: Elementor.com
ElementsKit Lite
Version: 2.8.1
Author: Wpmet
Essential Addons for Elementor
Version: 5.5.4
Author: WPDeveloper
Spotlight - Social Media Feeds
Version: 1.4.4
Author: RebelCode
WooCommerce
Version: 7.4.0
Author: Automattic
WPForms Lite
Version: 1.8.0.1
Author: WPForms
== Elementor Experiments ==
Optimized DOM Output: Active by default
Improved Asset Loading: Active by default
Improved CSS Loading: Active by default
Inline Font Icons: Active by default
Accessibility Improvements: Active by default
Additional Custom Breakpoints: Active by default
admin_menu_rearrangement: Inactive by default
Flexbox Container: Active
Upgrade Swiper Library: Active by default
Editor V2: Inactive by default
Landing Pages: Active by default
Nested Elements: Active by default
Lazy Load Background Images: Inactive by default
Save as Default: Active by default
== Log ==
JS: showing 17 of 17JS: 2022-07-12 18:06:59 [error X 75][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.6.7:3:475108] Cannot read properties of undefined (reading \'parent\')
JS: 2022-07-16 15:21:36 [error X 28][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:185947] Cannot read properties of undefined (reading \'data\')
JS: 2022-07-20 16:33:37 [error X 6][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:610510] Cannot read properties of null (reading \'getBoundingClientRect\')
JS: 2022-08-12 21:59:03 [error X 8][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:614960] Cannot read properties of undefined (reading \'toLowerCase\')
JS: 2022-08-16 02:01:16 [error X 34][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.7.0-dev10:2:615467] Cannot read properties of undefined (reading \'localized\')
JS: 2022-09-12 01:10:55 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/container-converter.min.js?ver=3.7.0-dev10:2:10719] elementor is not defined
JS: 2022-11-09 01:26:51 [error X 13][https://www.silkresse.com/wp-admin/load-scripts.php?c=1&loadchunk_0=jquery-core,jquery-migrate,regenerator-runtime,wp-polyfill,underscore,shortcode,utils,backbone,wp-util,wp-backbone,media-models,&loadchunk_1=moxiejs,plupload,wp-plupload,jquery-ui-core,jquery-ui-mouse,jquery-ui-sortable&ver=6.1:2:51824] Cannot read properties of undefined (reading \'replace\')
JS: 2022-11-09 02:35:21 [error X 36][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/frontend.min.js?ver=3.10.0-dev1:2:32848] elementorFrontendConfig is not defined
JS: 2022-11-09 03:20:43 [error X 2][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.10.0-dev1:3:811312] Cannot convert undefined or null to object
JS: 2022-11-17 22:00:07 [error X 4][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/frontend.min.js?ver=3.10.0-dev1:2:32871] Can\'t find variable: elementorFrontendConfig
JS: 2023-01-10 04:51:46 [error X 69][https://www.silkresse.com/wp-admin/load-scripts.php?c=1&loadchunk_0=jquery-core,jquery-migrate,regenerator-runtime,wp-polyfill,jquery-ui-core,jquery-ui-mouse,underscore,backbone,wp-api-request,wp-&loadchunk_1=hooks&ver=6.1.1:2:51824] Cannot read properties of undefined (reading 'replace')
JS: 2023-01-11 15:19:35 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.11.0-dev3:3:583495] Cannot read properties of null (reading 'id')
JS: 2023-01-11 17:27:40 [error X 3][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.11.0-dev3:3:782318] Cannot read properties of undefined (reading 'toLowerCase')
JS: 2023-01-18 02:51:41 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/web-cli.min.js?ver=3.11.0-dev3:3:105230] Routes: `library/templates` not found.
JS: 2023-01-19 04:31:23 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/web-cli.min.js?ver=3.11.0-dev3:3:105230] Routes: `library/blocks` not found.
JS: 2023-01-19 04:31:26 [error X 1][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/web-cli.min.js?ver=3.11.0-dev3:3:105230] Routes: `library/pages` not found.
JS: 2023-02-20 16:19:44 [error X 14][https://www.silkresse.com/wp-content/plugins/elementor/assets/js/editor.min.js?ver=3.12.0-dev4:3:794636] Cannot read properties of undefined (reading 'localized')
PHP: showing 5 of 5PHP: 2022-07-12 20:02:17 [notice X 120][/home/silkress/public_html/wp-content/plugins/elementor/modules/dev-tools/deprecation.php::301] The $finder_category_name argument is deprecated since version 3.5.0! [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2022-07-12 20:05:38 [notice X 5][/home/silkress/public_html/wp-content/plugins/elementor/includes/widgets/traits/button-trait.php::553] Undefined index: icon [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2022-09-12 19:12:19 [notice X 1][/home/silkress/public_html/wp-content/plugins/elementor/core/common/modules/ajax/module.php::171] Undefined index: data [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2023-01-18 02:53:19 [notice X 2][/home/silkress/public_html/wp-content/plugins/elementor/core/page-assets/data-managers/font-icon-svg/font-awesome.php::50] Trying to access array offset on value of type null [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
PHP: 2023-02-20 04:56:40 [notice X 21][/home/silkress/public_html/wp-content/plugins/elementor/includes/managers/image.php::108] Trying to access array offset on value of type bool [array (
'trace' => '
#0: Elementor\Core\Logger\Manager -> shutdown()
',
)]
Log: showing 20 of 202022-07-16 14:45:12 [info] elementor::elementor_updater Started
2022-07-16 14:45:12 [info] Elementor/Upgrades - _on_each_version Start
2022-07-16 14:45:12 [info] Elementor/Upgrades - _on_each_version Finished
2022-07-16 14:45:12 [info] Elementor/Upgrades - _v_3_7_0_remove_old_elements_usage Start
2022-07-16 14:45:12 [info] Elementor/Upgrades - _v_3_7_0_remove_old_elements_usage Finished
2022-07-16 14:45:12 [info] Elementor data updater process has been completed. [array (
'plugin' => 'Elementor',
'from' => '3.6.7',
'to' => '3.7.0-dev10',
)]
2022-07-16 14:45:12 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.6.7',
'to' => '3.7.0-dev10',
)]
2022-11-09 02:20:27 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.7.0-dev10',
'to' => '3.10.0-dev1',
)]
2022-11-09 02:20:27 [info] elementor::elementor_updater Started
2022-11-09 02:20:27 [info] Elementor/Upgrades - _on_each_version Start
2022-11-09 02:20:27 [info] Elementor/Upgrades - _on_each_version Finished
2022-11-09 02:20:27 [info] Elementor/Upgrades - _v_3_8_0_fix_php8_image_custom_size Start
2022-11-09 02:20:27 [info] Elementor/Upgrades - _v_3_8_0_fix_php8_image_custom_size Finished
2022-11-09 02:20:27 [info] Elementor data updater process has been completed. [array (
'plugin' => 'Elementor',
'from' => '3.7.0-dev10',
'to' => '3.10.0-dev1',
)]
2022-12-14 01:22:22 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.10.0-dev1',
'to' => '3.11.0-dev1',
)]
2022-12-14 01:22:22 [info] elementor::elementor_updater Started
2022-12-14 01:22:22 [info] Elementor/Upgrades - _on_each_version Start
2022-12-14 01:22:22 [info] Elementor/Upgrades - _on_each_version Finished
2022-12-14 01:22:22 [info] Elementor data updater process has been completed. [array (
'plugin' => 'Elementor',
'from' => '3.10.0-dev1',
'to' => '3.11.0-dev1',
)]
2022-12-14 01:22:23 [info] Elementor data updater process has been queued. [array (
'plugin' => 'Elementor',
'from' => '3.10.0-dev1',
'to' => '3.11.0-dev1',
)]
== Elementor - Compatibility Tag ==
Essential Addons for Elementor: Incompatible
````
</details> | non_priority | ⛔ 🐞 bug report elementor created shop page defaults back to woocommerce standard shop page after assigning it in the settings after the page is assigned i’m unable to edit the page using elementor prerequisites i have searched for similar issues in both open and closed tickets and cannot find a duplicate the issue still exists against the latest stable version of elementor description when exactly did you first notice the problem i noticed this problem today when i finished modifying the shop all page and navigated to the woocommerce settings to assign this page as a woocommerce shop page have any updates been applied to your website recently updated the woocommerce templates that required an update have you changed themes or made design changes no theme changes have you installed any new plugins yes but i disabled and uninstalled it royal addons can the issue be replicated on multiple devices yes shop page shows incorrectly all devices is your problem happening in one browser or all of them all of them do you see a specific error message take a screenshot yes when i attempt to edit the page after assigning it to woocommerce i get the message the preview could not be loaded steps to reproduce created a shop page with elementor navigate to the woocommerce settings to assign this page as a woocommerce shop page navigate back to the page from the pages menu click the edit with elementor link get an error the preview could not be loaded img width alt screen shot at pm src img width alt screen shot at pm src img width alt screen shot at pm src isolating the problem this bug happens with only elementor plugin active and elementor pro this bug happens with a blank wordpress theme active i can reproduce this bug consistently following the steps above system info system info txt server environment operating system linux software litespeed mysql version mariadb server php version php memory limit php max input vars php max post size gd installed yes zip installed yes write permissions all right elementor library connected wordpress environment version site url home url wp multisite no max upload size mb memory limit max memory limit permalink structure blog postname language en us timezone admin email silkresse gmail com debug mode inactive theme name blocksy child version author creative themes child theme yes parent theme name blocksy parent theme version parent theme author creativethemes user role administrator wp profile lang en us user agent mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari active plugins advanced product fields for woocommerce version author studiowombat blocksy companion version author creativethemes codesigner version author codexpert elementor version author elementor com elementor beta developer edition version author elementor com elementskit lite version author wpmet essential addons for elementor version author wpdeveloper spotlight social media feeds version author rebelcode woocommerce version author automattic wpforms lite version author wpforms elementor experiments optimized dom output active by default improved asset loading active by default improved css loading active by default inline font icons active by default accessibility improvements active by default additional custom breakpoints active by default admin menu rearrangement inactive by default flexbox container active upgrade swiper library active by default editor inactive by default landing pages active by default nested elements active by default lazy load background images inactive by default save as default active by default log js showing of cannot read properties of undefined reading parent js cannot read properties of undefined reading data js cannot read properties of null reading getboundingclientrect js cannot read properties of undefined reading tolowercase js cannot read properties of undefined reading localized js elementor is not defined js cannot read properties of undefined reading replace js elementorfrontendconfig is not defined js cannot convert undefined or null to object js can t find variable elementorfrontendconfig js cannot read properties of undefined reading replace js cannot read properties of null reading id js cannot read properties of undefined reading tolowercase js routes library templates not found js routes library blocks not found js routes library pages not found js cannot read properties of undefined reading localized php showing of the finder category name argument is deprecated since version array trace elementor core logger manager shutdown php undefined index icon array trace elementor core logger manager shutdown php undefined index data array trace elementor core logger manager shutdown php trying to access array offset on value of type null array trace elementor core logger manager shutdown php trying to access array offset on value of type bool array trace elementor core logger manager shutdown log showing of elementor elementor updater started elementor upgrades on each version start elementor upgrades on each version finished elementor upgrades v remove old elements usage start elementor upgrades v remove old elements usage finished elementor data updater process has been completed array plugin elementor from to elementor data updater process has been queued array plugin elementor from to elementor data updater process has been queued array plugin elementor from to elementor elementor updater started elementor upgrades on each version start elementor upgrades on each version finished elementor upgrades v fix image custom size start elementor upgrades v fix image custom size finished elementor data updater process has been completed array plugin elementor from to elementor data updater process has been queued array plugin elementor from to elementor elementor updater started elementor upgrades on each version start elementor upgrades on each version finished elementor data updater process has been completed array plugin elementor from to elementor data updater process has been queued array plugin elementor from to elementor compatibility tag essential addons for elementor incompatible | 0 |
178,463 | 29,830,846,117 | IssuesEvent | 2023-06-18 08:52:31 | Trendyol/codex | https://api.github.com/repos/Trendyol/codex | closed | Add congrats popup | type: feature app: client type: design | We should find a way to celebrate the top ranking teams on discussion lobby | 1.0 | Add congrats popup - We should find a way to celebrate the top ranking teams on discussion lobby | non_priority | add congrats popup we should find a way to celebrate the top ranking teams on discussion lobby | 0 |
272,948 | 23,715,850,285 | IssuesEvent | 2022-08-30 11:43:05 | jupyterlab/jupyterlab | https://api.github.com/repos/jupyterlab/jupyterlab | closed | Provide galata support for logging in to a JupyterLab session | enhancement tag:Testing | Jupyter notebook and JupyterLab defaults encourage the use of authentication to access the server. However, the galata test framework expects to run against a server that is wide open / no authentication.
For users in education, at least, galata may be attractive for:
- testing student deployments;
- generating videos of various interactions.
However, the test environments are likely to require authentication.
It would be useful if galata could be extended to optionally allow testing to start with the passing of credentials via the Jupyter authentication page.
Related: https://discourse.jupyter.org/t/using-galata-jupyterlab-ui-test-framework-with-token-password-enabled-sites/15106 | 1.0 | Provide galata support for logging in to a JupyterLab session - Jupyter notebook and JupyterLab defaults encourage the use of authentication to access the server. However, the galata test framework expects to run against a server that is wide open / no authentication.
For users in education, at least, galata may be attractive for:
- testing student deployments;
- generating videos of various interactions.
However, the test environments are likely to require authentication.
It would be useful if galata could be extended to optionally allow testing to start with the passing of credentials via the Jupyter authentication page.
Related: https://discourse.jupyter.org/t/using-galata-jupyterlab-ui-test-framework-with-token-password-enabled-sites/15106 | non_priority | provide galata support for logging in to a jupyterlab session jupyter notebook and jupyterlab defaults encourage the use of authentication to access the server however the galata test framework expects to run against a server that is wide open no authentication for users in education at least galata may be attractive for testing student deployments generating videos of various interactions however the test environments are likely to require authentication it would be useful if galata could be extended to optionally allow testing to start with the passing of credentials via the jupyter authentication page related | 0 |
63,200 | 26,277,909,886 | IssuesEvent | 2023-01-07 01:28:34 | hashicorp/terraform-provider-aws | https://api.github.com/repos/hashicorp/terraform-provider-aws | closed | aws_eks_node_group desired_size config does not update aws | service/eks | ### Terraform CLI and Terraform AWS Provider Version
Confirmed in terraform 1.0.10 and 0.14.11
aws provider 3.63.0
### Affected Resource(s)
* aws_eks_node_group
### Terraform Configuration Files
Just use the example from the docs.
https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/eks_node_group
### Debug Output
n/a
### Panic Output
n/a
### Expected Behavior
When you change the desired_size, it should actually update that config in aws and not just in terraform state.
### Actual Behavior
Terraform state updates, but if you go look in aws console the configuration did not change. This causes additional problems if you try to increase min size and desired size, terraform will fail indicating that desired size is lower then min size. To update this configuration requires manually updating the console and then making terraform match afterword (which defeats the purpose).
### Steps to Reproduce
1. `terraform apply`
2. update the desired_size to a value higher
3. `terraform apply`
4. run `terraform plan` and verify that no changes are required
5. check aws console to see if desired_size has been updated
### Important Factoids
We have observed this behavior with ASGs as well, this could be an AWS API or SDK issue.
### References
None that I could see.
| 1.0 | aws_eks_node_group desired_size config does not update aws - ### Terraform CLI and Terraform AWS Provider Version
Confirmed in terraform 1.0.10 and 0.14.11
aws provider 3.63.0
### Affected Resource(s)
* aws_eks_node_group
### Terraform Configuration Files
Just use the example from the docs.
https://registry.terraform.io/providers/hashicorp/aws/latest/docs/resources/eks_node_group
### Debug Output
n/a
### Panic Output
n/a
### Expected Behavior
When you change the desired_size, it should actually update that config in aws and not just in terraform state.
### Actual Behavior
Terraform state updates, but if you go look in aws console the configuration did not change. This causes additional problems if you try to increase min size and desired size, terraform will fail indicating that desired size is lower then min size. To update this configuration requires manually updating the console and then making terraform match afterword (which defeats the purpose).
### Steps to Reproduce
1. `terraform apply`
2. update the desired_size to a value higher
3. `terraform apply`
4. run `terraform plan` and verify that no changes are required
5. check aws console to see if desired_size has been updated
### Important Factoids
We have observed this behavior with ASGs as well, this could be an AWS API or SDK issue.
### References
None that I could see.
| non_priority | aws eks node group desired size config does not update aws terraform cli and terraform aws provider version confirmed in terraform and aws provider affected resource s aws eks node group terraform configuration files just use the example from the docs debug output n a panic output n a expected behavior when you change the desired size it should actually update that config in aws and not just in terraform state actual behavior terraform state updates but if you go look in aws console the configuration did not change this causes additional problems if you try to increase min size and desired size terraform will fail indicating that desired size is lower then min size to update this configuration requires manually updating the console and then making terraform match afterword which defeats the purpose steps to reproduce terraform apply update the desired size to a value higher terraform apply run terraform plan and verify that no changes are required check aws console to see if desired size has been updated important factoids we have observed this behavior with asgs as well this could be an aws api or sdk issue references none that i could see | 0 |
81,870 | 10,263,320,759 | IssuesEvent | 2019-08-22 14:09:00 | angristan/openvpn-install | https://api.github.com/repos/angristan/openvpn-install | closed | Need "#security-and-encryption" section in README.md | documentation | Hello,
```
Do you want to customize encryption settings?
Unless you know what you're doing, you should stick with the default parameters provided by the script.
Note that whatever you choose, all the choices presented in the script are safe. (Unlike OpenVPN's defaults)
See https://github.com/angristan/openvpn-install#security-and-encryption to learn more.
```
Link: https://github.com/angristan/openvpn-install#security-and-encryption
At: https://github.com/angristan/openvpn-install/blob/master/README.md
Best,
Max Base | 1.0 | Need "#security-and-encryption" section in README.md - Hello,
```
Do you want to customize encryption settings?
Unless you know what you're doing, you should stick with the default parameters provided by the script.
Note that whatever you choose, all the choices presented in the script are safe. (Unlike OpenVPN's defaults)
See https://github.com/angristan/openvpn-install#security-and-encryption to learn more.
```
Link: https://github.com/angristan/openvpn-install#security-and-encryption
At: https://github.com/angristan/openvpn-install/blob/master/README.md
Best,
Max Base | non_priority | need security and encryption section in readme md hello do you want to customize encryption settings unless you know what you re doing you should stick with the default parameters provided by the script note that whatever you choose all the choices presented in the script are safe unlike openvpn s defaults see to learn more link at best max base | 0 |
34,223 | 12,258,179,941 | IssuesEvent | 2020-05-06 14:45:19 | kids-first/kf-portal-ui | https://api.github.com/repos/kids-first/kf-portal-ui | closed | Arrange Component Upgrade | Security arranger | We have currently 2 high risk vulnerabilities in the portal injected by arranger component.
First step will be to upgrade our version to see if it fix the issues
Then, fix arranger component if the warning is still present

| True | Arrange Component Upgrade - We have currently 2 high risk vulnerabilities in the portal injected by arranger component.
First step will be to upgrade our version to see if it fix the issues
Then, fix arranger component if the warning is still present

| non_priority | arrange component upgrade we have currently high risk vulnerabilities in the portal injected by arranger component first step will be to upgrade our version to see if it fix the issues then fix arranger component if the warning is still present | 0 |
91,598 | 8,309,999,581 | IssuesEvent | 2018-09-24 09:08:11 | tschottdorf/cockroach | https://api.github.com/repos/tschottdorf/cockroach | closed | teamcity: failed test: TestImportPgDump | C-test-failure O-robot | The following tests appear to have failed on release-banana: test/TestImportPgDump
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+TestImportPgDump).
[#864629](https://teamcity.cockroachdb.com/viewLog.html?buildId=864629):
```
test/TestImportPgDump
...1:54.113657 51850 storage/replica_proposal.go:210 [n3,s3,r25/2:/Table/53/2/"\x{15\x8…-c0\t\…}] new range lease repl=(n3,s3):2 seq=3 start=1535402514.112607829,0 epo=1 pro=1535402514.112610518,0 following repl=(n1,s1):1 seq=2 start=1535402512.768597075,0 exp=1535402521.769064687,0 pro=1535402512.769088099,0
I180827 20:41:54.117098 52757 storage/replica_command.go:298 [n1,s1,r26/1:/{Table/53/2/"…-Max}] initiating a split of this range at key /Table/53/3/";π,\\✅✅ᐿπ✅,�a\r<\nπᐿॹ;π\\,✅\nᐿॹ✅�,\r�\r\r\r,;\r;ᐿ,\n\nᐿaπ\r,,✅\na,a\\<✅\"✅\\,,a\"π\r\n�✅π\"ॹπ;\nπ;<,<\n;<\n\tॹ\rπ\r,a\\\t�\n\r\\ᐿ<\t,\n\\ᐿa\t\t\n\nπ\t\\\n\\πa;π\r\rᐿ\",a<\"\n�\r\ta\r\t�\r\t✅\t;ᐿᐿ��\nᐿᐿ\\,ᐿᐿ\na\"ᐿ\"\"aa\n;✅π\nॹ\\\"\"�✅ॹॹ\\\nॹ\t\nॹ✅,\n\"πᐿ\n\n;<<;\r\tᐿ�,,\\\n\n\n\n\nπ�;\n;,\"✅\r;a\n\\;aa\n\n\n;\n\n<<ॹ�\nπa�πॹaॹ\r\n;✅✅,;ᐿ\n;π\"\\πᐿ\n\"\n\\a\\aπ✅ᐿ\n<\",\tॹ\r<;\";\nππ\"�\n\n\t,π\\\\<\\\t;ॹπ\\,;�✅ॹ,\r<\n✅�;ᐿ\",;✅\n\nॹॹ\r\n✅\n<<\n\"\",a\t\r\r,ॹ\t�;�,π\\\t,;\\\"✅\t\n\n\nᐿ\n<\\\rᐿ,;�\nπ\r\\<ᐿᐿ\n<✅ᐿaॹ�✅\n\t,π\"\r<<\n\nπ\tπ✅\n<\\πॹaᐿ\t;�ॹॹ,\"\n\\a\n,\"πॹ,\r,ॹॹ\\\";�\n\\π✅\n\"ππ\n✅�πॹ,\r✅\n;π;ᐿ\"\nᐿ✅\rॹ;;\n\"ॹ\"�\"a\n\rπ\n<\n\t\"aπ\t;\\\n\";\"π,\ta\t\n\nᐿ<,;�<ᐿ\"\\ᐿᐿa,\n;;ॹॹ\tॹπa�ᐿ\ra,π<✅\tᐿᐿ\n,✅\ra�\"\r\r\",;π�<;\n<;ᐿ\"�;ᐿ;�;✅\t\\<\\<;πa✅\rॹ\\\\\\ᐿ\n;\r\t\n\\\r\"✅\n\tπ✅\"\"<\r\rπ\r<,\n,\\✅ᐿᐿ�\t�,ππ;ᐿ\t�\"\\ππ\"ॹ,πa<\n\n<��\rॹॹ\t,\r\"ॹ✅✅\n\n;\\ॹ;π<\"�\t�<\"ᐿॹॹ;\n<\n\r\na\t�ॹᐿa\n,\"\t\r\"\n,\r<,\"\tᐿ\\\n<,;<\"\t\n\nᐿ,ᐿ\tπ✅\n,\r,\n\t<,�\\;<\\a\nπ\t,\t�ॹ\t\n�a✅\n✅\nॹ\";\r\t✅<\tᐿ\n\tᐿॹ✅\"\r\rॹ✅π\n\n,\t\\\t\\;\"a\t,ॹॹ\"aॹ\n,\n✅�\t\nॹᐿ\n\r✅<πॹ\n✅\tॹ\"ॹ\"�\r\\;\\✅;ॹπ;\n\nᐿ<\r<\"ॹ\n,\n;π\nॹ\ta✅\n�;ᐿ\"a�✅π\r✅ॹ,\n\n\",✅\nᐿ\n<�\r\nπᐿ\"πॹᐿ\r�\n<,✅a\\ॹ\r✅<;πᐿ✅ॹ<\"<✅\"π,\\\rπ\\<\"<\"π\n✅<;\\�\tॹ\n\n\r<\n\rᐿ\nᐿaॹaॹ\\\r<<\n\r\n�\ta,\nॹॹᐿ\n,π✅<;\\\nπॹπᐿॹ<;\"a\r<;\t\t<,;�π\n<✅ॹॹ\tᐿ\rᐿaaaॹ\t\\,ᐿ✅\n\\ॹ<\"π\t\r\"\tᐿ\n\ta\t,<ππ;\n\\\r�\n,\n\n\\ᐿa\nॹᐿa\n\t\n\t\n✅\"ᐿ\"\r\n\n\"�\r\n\n<<π\ra✅\\<ᐿ�\n\n✅�a✅�"/105 [r27]
I180827 20:41:54.137397 52716 storage/store_snapshot.go:615 [raftsnapshot,n3,s3,r25/2:/Table/53/2/"\x{15\x8…-c0\t\…}] sending Raft snapshot 547ab8d0 at applied index 21
I180827 20:41:54.140430 52716 storage/store_snapshot.go:657 [raftsnapshot,n3,s3,r25/2:/Table/53/2/"\x{15\x8…-c0\t\…}] streamed snapshot to (n2,s2):3: kv pairs: 14, log entries: 2, rate-limit: 8.0 MiB/sec, 22ms
I180827 20:41:54.140860 52705 storage/replica_raftstorage.go:784 [n2,s2,r25/3:/Table/53/2/"\x{15\x8…-c0\t\…}] applying Raft snapshot at index 21 (id=547ab8d0, encoded size=31270, 1 rocksdb batches, 2 log entries)
I180827 20:41:54.162696 52705 storage/replica_raftstorage.go:790 [n2,s2,r25/3:/Table/53/2/"\x{15\x8…-c0\t\…}] applied Raft snapshot in 22ms [clear=0ms batch=0ms entries=21ms commit=0ms]
I180827 20:41:54.166103 52791 storage/replica_range_lease.go:554 [n1,s1,r26/1:/Table/53/{2/"\xc0…-3/";π,…}] transferring lease to s3
I180827 20:41:54.167118 51903 storage/replica_proposal.go:210 [n3,s3,r26/2:/Table/53/{2/"\xc0…-3/";π,…}] new range lease repl=(n3,s3):2 seq=3 start=1535402514.166156675,0 epo=1 pro=1535402514.166159831,0 following repl=(n1,s1):1 seq=2 start=1535402512.768597075,0 exp=1535402521.769064687,0 pro=1535402512.769088099,0
I180827 20:41:54.167216 52791 storage/replica_range_lease.go:617 [n1,s1,r26/1:/Table/53/{2/"\xc0…-3/";π,…}] done transferring lease to s3: <nil>
I180827 20:41:54.172711 52589 storage/replica_command.go:298 [n1,s1,r27/1:/{Table/53/3/"…-Max}] initiating a split of this range at key /Table/54 [r28]
I180827 20:41:54.182740 52807 storage/replica_range_lease.go:554 [n1,s1,r27/1:/Table/5{3/3/";π…-4}] transferring lease to s2
I180827 20:41:54.183947 52807 storage/replica_range_lease.go:617 [n1,s1,r27/1:/Table/5{3/3/";π…-4}] done transferring lease to s2: <nil>
I180827 20:41:54.184954 51646 storage/replica_proposal.go:210 [n2,s2,r27/3:/Table/5{3/3/";π…-4}] new range lease repl=(n2,s2):3 seq=3 start=1535402514.182761052,0 epo=1 pro=1535402514.182764040,0 following repl=(n1,s1):1 seq=2 start=1535402512.768597075,0 exp=1535402521.769064687,0 pro=1535402512.769088099,0
test/TestImportPgDump
...inutes]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*ccResolverWrapper).watcher(0xc424cbeb40)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/resolver_conn_wrapper.go:109 +0x182
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*ccResolverWrapper).start
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/resolver_conn_wrapper.go:95 +0x3f
goroutine 51615 [semacquire]:
sync.runtime_notifyListWait(0xc4216f3ed0, 0x1174)
/usr/local/go/src/runtime/sema.go:510 +0x10b
sync.(*Cond).Wait(0xc4216f3ec0)
/usr/local/go/src/sync/cond.go:56 +0x80
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc420966480, 0x2eb2080, 0xc4226d3aa0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:197 +0x7c
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x2eb2080, 0xc4226d3aa0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:166 +0x3e
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42035d2a0, 0xc4215a8cf0, 0xc42035d290)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
goroutine 51491 [select, 4 minutes]:
github.com/cockroachdb/cockroach/pkg/sql.(*DistSQLPlanner).initRunners.func1(0x2eb2080, 0xc42144c0f0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:88 +0x151
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4251cf610, 0xc4215a8cf0, 0xc4251cf5f0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
goroutine 50899 [chan receive, 7 minutes]:
github.com/cockroachdb/cockroach/pkg/util/log.(*loggingT).gcDaemon(0xc4204fc780)
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/clog.go:1230 +0x68
created by github.com/cockroachdb/cockroach/pkg/util/log.NewSecondaryLogger
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/secondary_log.go:80 +0x288
goroutine 51583 [chan receive]:
github.com/cockroachdb/cockroach/pkg/storage/closedts/provider.(*Provider).Notify.func1(0x2eb2080, 0xc421ec4570)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/closedts/provider/provider.go:204 +0x148
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038a0c0, 0xc42539e1b0, 0xc420310540)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
goroutine 51971 [select, 7 minutes]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.newClientStream.func5(0xc4216da000, 0xc42337d780, 0x2eb2080, 0xc420e695c0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:321 +0xfe
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.newClientStream
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:320 +0xa76
goroutine 50888 [select, 7 minutes]:
github.com/cockroachdb/cockroach/pkg/sql.(*DistSQLPlanner).initRunners.func1(0x2eb2080, 0xc4209be000)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:88 +0x151
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42055d1f0, 0xc42539e1b0, 0xc42055d1e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
I180827 20:41:04.554200 1 rand.go:75 Random seed: 2144118708575765637
test/TestImportPgDump
...ptive snapshot 0df534b1 at applied index 21
I180827 20:41:53.711657 52485 storage/store_snapshot.go:657 [replicate,n1,s1,r8/1:/Table/1{1-2}] streamed snapshot to (n2,s2):?: kv pairs: 10, log entries: 11, rate-limit: 8.0 MiB/sec, 3ms
I180827 20:41:53.712336 52431 storage/replica_raftstorage.go:784 [n2,s2,r8/?:{-}] applying preemptive snapshot at index 21 (id=0df534b1, encoded size=5384, 1 rocksdb batches, 11 log entries)
I180827 20:41:53.712589 52431 storage/replica_raftstorage.go:790 [n2,s2,r8/?:/Table/1{1-2}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180827 20:41:53.712941 52485 storage/replica_command.go:812 [replicate,n1,s1,r8/1:/Table/1{1-2}] change replicas (ADD_REPLICA (n2,s2):3): read existing descriptor r8:/Table/1{1-2} [(n1,s1):1, (n3,s3):2, next=3, gen=1]
I180827 20:41:53.716662 52485 storage/replica.go:3743 [n1,s1,r8/1:/Table/1{1-2}] proposing ADD_REPLICA((n2,s2):3): updated=[(n1,s1):1 (n3,s3):2 (n2,s2):3] next=4
I180827 20:41:53.716741 50862 testutils/testcluster/testcluster.go:536 [n1,s1] has 3 underreplicated ranges
I180827 20:41:53.719005 52448 storage/store_snapshot.go:615 [replicate,n1,s1,r22/1:/{Table/51-Max}] sending preemptive snapshot 67476018 at applied index 15
I180827 20:41:53.719195 52448 storage/store_snapshot.go:657 [replicate,n1,s1,r22/1:/{Table/51-Max}] streamed snapshot to (n2,s2):?: kv pairs: 8, log entries: 5, rate-limit: 8.0 MiB/sec, 1ms
I180827 20:41:53.719598 52470 storage/replica_raftstorage.go:784 [n2,s2,r22/?:{-}] applying preemptive snapshot at index 15 (id=67476018, encoded size=1418, 1 rocksdb batches, 5 log entries)
I180827 20:41:53.719793 52470 storage/replica_raftstorage.go:790 [n2,s2,r22/?:/{Table/51-Max}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180827 20:41:53.720252 52448 storage/replica_command.go:812 [replicate,n1,s1,r22/1:/{Table/51-Max}] change replicas (ADD_REPLICA (n2,s2):3): read existing descriptor r22:/{Table/51-Max} [(n1,s1):1, (n3,s3):2, next=3, gen=0]
I180827 20:41:53.724721 52448 storage/replica.go:3743 [n1,s1,r22/1:/{Table/51-Max}] proposing ADD_REPLICA((n2,s2):3): updated=[(n1,s1):1 (n3,s3):2 (n2,s2):3] next=4
I180827 20:41:53.726370 52456 storage/store_snapshot.go:615 [replicate,n1,s1,r21/1:/Table/5{0-1}] sending preemptive snapshot 57d2d847 at applied index 21
I180827 20:41:53.726577 52456 storage/store_snapshot.go:657 [replicate,n1,s1,r21/1:/Table/5{0-1}] streamed snapshot to (n2,s2):?: kv pairs: 9, log entries: 11, rate-limit: 8.0 MiB/sec, 1ms
I180827 20:41:53.726928 52460 storage/replica_raftstorage.go:784 [n2,s2,r21/?:{-}] applying preemptive snapshot at index 21 (id=57d2d847, encoded size=3678, 1 rocksdb batches, 11 log entries)
I180827 20:41:53.727126 52460 storage/replica_raftstorage.go:790 [n2,s2,r21/?:/Table/5{0-1}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180827 20:41:53.727433 52456 storage/replica_command.go:812 [replicate,n1,s1,r21/1:/Table/5{0-1}] change replicas (ADD_REPLICA (n2,s2):3): read existing descriptor r21:/Table/5{0-1} [(n1,s1):1, (n3,s3):2, next=3, gen=1]
I180827 20:41:53.732265 52456 storage/replica.go:3743 [n1,s1,r21/1:/Table/5{0-1}] proposing ADD_REPLICA((n2,s2):3): updated=[(n1,s1):1 (n3,s3):2 (n2,s2):3] next=4
I180827 20:41:53.798848 52462 rpc/nodedialer/nodedialer.go:92 [consistencyChecker,n1,s1,r1/1:/{Min-System/}] connection to n1 established
I180827 20:41:53.959825 52553 sql/event_log.go:126 [n1,client=127.0.0.1:57092,user=root] Event: "set_cluster_setting", target: 0, info: {SettingName:kv.import.batch_size Value:10KB User:root}
I180827 20:41:53.969828 52553 sql/event_log.go:126 [n1,client=127.0.0.1:57092,user=root] Event: "create_database", target: 52, info: {DatabaseName:foo Statement:CREATE DATABASE foo User:root}
I180827 20:41:53.970454 52505 storage/replica_command.go:298 [split,n1,s1,r22/1:/{Table/51-Max}] initiating a split of this range at key /Table/52 [r23]
```
Please assign, take a look and update the issue accordingly.
| 1.0 | teamcity: failed test: TestImportPgDump - The following tests appear to have failed on release-banana: test/TestImportPgDump
You may want to check [for open issues](https://github.com/cockroachdb/cockroach/issues?q=is%3Aissue+is%3Aopen+TestImportPgDump).
[#864629](https://teamcity.cockroachdb.com/viewLog.html?buildId=864629):
```
test/TestImportPgDump
...1:54.113657 51850 storage/replica_proposal.go:210 [n3,s3,r25/2:/Table/53/2/"\x{15\x8…-c0\t\…}] new range lease repl=(n3,s3):2 seq=3 start=1535402514.112607829,0 epo=1 pro=1535402514.112610518,0 following repl=(n1,s1):1 seq=2 start=1535402512.768597075,0 exp=1535402521.769064687,0 pro=1535402512.769088099,0
I180827 20:41:54.117098 52757 storage/replica_command.go:298 [n1,s1,r26/1:/{Table/53/2/"…-Max}] initiating a split of this range at key /Table/53/3/";π,\\✅✅ᐿπ✅,�a\r<\nπᐿॹ;π\\,✅\nᐿॹ✅�,\r�\r\r\r,;\r;ᐿ,\n\nᐿaπ\r,,✅\na,a\\<✅\"✅\\,,a\"π\r\n�✅π\"ॹπ;\nπ;<,<\n;<\n\tॹ\rπ\r,a\\\t�\n\r\\ᐿ<\t,\n\\ᐿa\t\t\n\nπ\t\\\n\\πa;π\r\rᐿ\",a<\"\n�\r\ta\r\t�\r\t✅\t;ᐿᐿ��\nᐿᐿ\\,ᐿᐿ\na\"ᐿ\"\"aa\n;✅π\nॹ\\\"\"�✅ॹॹ\\\nॹ\t\nॹ✅,\n\"πᐿ\n\n;<<;\r\tᐿ�,,\\\n\n\n\n\nπ�;\n;,\"✅\r;a\n\\;aa\n\n\n;\n\n<<ॹ�\nπa�πॹaॹ\r\n;✅✅,;ᐿ\n;π\"\\πᐿ\n\"\n\\a\\aπ✅ᐿ\n<\",\tॹ\r<;\";\nππ\"�\n\n\t,π\\\\<\\\t;ॹπ\\,;�✅ॹ,\r<\n✅�;ᐿ\",;✅\n\nॹॹ\r\n✅\n<<\n\"\",a\t\r\r,ॹ\t�;�,π\\\t,;\\\"✅\t\n\n\nᐿ\n<\\\rᐿ,;�\nπ\r\\<ᐿᐿ\n<✅ᐿaॹ�✅\n\t,π\"\r<<\n\nπ\tπ✅\n<\\πॹaᐿ\t;�ॹॹ,\"\n\\a\n,\"πॹ,\r,ॹॹ\\\";�\n\\π✅\n\"ππ\n✅�πॹ,\r✅\n;π;ᐿ\"\nᐿ✅\rॹ;;\n\"ॹ\"�\"a\n\rπ\n<\n\t\"aπ\t;\\\n\";\"π,\ta\t\n\nᐿ<,;�<ᐿ\"\\ᐿᐿa,\n;;ॹॹ\tॹπa�ᐿ\ra,π<✅\tᐿᐿ\n,✅\ra�\"\r\r\",;π�<;\n<;ᐿ\"�;ᐿ;�;✅\t\\<\\<;πa✅\rॹ\\\\\\ᐿ\n;\r\t\n\\\r\"✅\n\tπ✅\"\"<\r\rπ\r<,\n,\\✅ᐿᐿ�\t�,ππ;ᐿ\t�\"\\ππ\"ॹ,πa<\n\n<��\rॹॹ\t,\r\"ॹ✅✅\n\n;\\ॹ;π<\"�\t�<\"ᐿॹॹ;\n<\n\r\na\t�ॹᐿa\n,\"\t\r\"\n,\r<,\"\tᐿ\\\n<,;<\"\t\n\nᐿ,ᐿ\tπ✅\n,\r,\n\t<,�\\;<\\a\nπ\t,\t�ॹ\t\n�a✅\n✅\nॹ\";\r\t✅<\tᐿ\n\tᐿॹ✅\"\r\rॹ✅π\n\n,\t\\\t\\;\"a\t,ॹॹ\"aॹ\n,\n✅�\t\nॹᐿ\n\r✅<πॹ\n✅\tॹ\"ॹ\"�\r\\;\\✅;ॹπ;\n\nᐿ<\r<\"ॹ\n,\n;π\nॹ\ta✅\n�;ᐿ\"a�✅π\r✅ॹ,\n\n\",✅\nᐿ\n<�\r\nπᐿ\"πॹᐿ\r�\n<,✅a\\ॹ\r✅<;πᐿ✅ॹ<\"<✅\"π,\\\rπ\\<\"<\"π\n✅<;\\�\tॹ\n\n\r<\n\rᐿ\nᐿaॹaॹ\\\r<<\n\r\n�\ta,\nॹॹᐿ\n,π✅<;\\\nπॹπᐿॹ<;\"a\r<;\t\t<,;�π\n<✅ॹॹ\tᐿ\rᐿaaaॹ\t\\,ᐿ✅\n\\ॹ<\"π\t\r\"\tᐿ\n\ta\t,<ππ;\n\\\r�\n,\n\n\\ᐿa\nॹᐿa\n\t\n\t\n✅\"ᐿ\"\r\n\n\"�\r\n\n<<π\ra✅\\<ᐿ�\n\n✅�a✅�"/105 [r27]
I180827 20:41:54.137397 52716 storage/store_snapshot.go:615 [raftsnapshot,n3,s3,r25/2:/Table/53/2/"\x{15\x8…-c0\t\…}] sending Raft snapshot 547ab8d0 at applied index 21
I180827 20:41:54.140430 52716 storage/store_snapshot.go:657 [raftsnapshot,n3,s3,r25/2:/Table/53/2/"\x{15\x8…-c0\t\…}] streamed snapshot to (n2,s2):3: kv pairs: 14, log entries: 2, rate-limit: 8.0 MiB/sec, 22ms
I180827 20:41:54.140860 52705 storage/replica_raftstorage.go:784 [n2,s2,r25/3:/Table/53/2/"\x{15\x8…-c0\t\…}] applying Raft snapshot at index 21 (id=547ab8d0, encoded size=31270, 1 rocksdb batches, 2 log entries)
I180827 20:41:54.162696 52705 storage/replica_raftstorage.go:790 [n2,s2,r25/3:/Table/53/2/"\x{15\x8…-c0\t\…}] applied Raft snapshot in 22ms [clear=0ms batch=0ms entries=21ms commit=0ms]
I180827 20:41:54.166103 52791 storage/replica_range_lease.go:554 [n1,s1,r26/1:/Table/53/{2/"\xc0…-3/";π,…}] transferring lease to s3
I180827 20:41:54.167118 51903 storage/replica_proposal.go:210 [n3,s3,r26/2:/Table/53/{2/"\xc0…-3/";π,…}] new range lease repl=(n3,s3):2 seq=3 start=1535402514.166156675,0 epo=1 pro=1535402514.166159831,0 following repl=(n1,s1):1 seq=2 start=1535402512.768597075,0 exp=1535402521.769064687,0 pro=1535402512.769088099,0
I180827 20:41:54.167216 52791 storage/replica_range_lease.go:617 [n1,s1,r26/1:/Table/53/{2/"\xc0…-3/";π,…}] done transferring lease to s3: <nil>
I180827 20:41:54.172711 52589 storage/replica_command.go:298 [n1,s1,r27/1:/{Table/53/3/"…-Max}] initiating a split of this range at key /Table/54 [r28]
I180827 20:41:54.182740 52807 storage/replica_range_lease.go:554 [n1,s1,r27/1:/Table/5{3/3/";π…-4}] transferring lease to s2
I180827 20:41:54.183947 52807 storage/replica_range_lease.go:617 [n1,s1,r27/1:/Table/5{3/3/";π…-4}] done transferring lease to s2: <nil>
I180827 20:41:54.184954 51646 storage/replica_proposal.go:210 [n2,s2,r27/3:/Table/5{3/3/";π…-4}] new range lease repl=(n2,s2):3 seq=3 start=1535402514.182761052,0 epo=1 pro=1535402514.182764040,0 following repl=(n1,s1):1 seq=2 start=1535402512.768597075,0 exp=1535402521.769064687,0 pro=1535402512.769088099,0
test/TestImportPgDump
...inutes]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*ccResolverWrapper).watcher(0xc424cbeb40)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/resolver_conn_wrapper.go:109 +0x182
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.(*ccResolverWrapper).start
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/resolver_conn_wrapper.go:95 +0x3f
goroutine 51615 [semacquire]:
sync.runtime_notifyListWait(0xc4216f3ed0, 0x1174)
/usr/local/go/src/runtime/sema.go:510 +0x10b
sync.(*Cond).Wait(0xc4216f3ec0)
/usr/local/go/src/sync/cond.go:56 +0x80
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).worker(0xc420966480, 0x2eb2080, 0xc4226d3aa0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:197 +0x7c
github.com/cockroachdb/cockroach/pkg/storage.(*raftScheduler).Start.func2(0x2eb2080, 0xc4226d3aa0)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/scheduler.go:166 +0x3e
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42035d2a0, 0xc4215a8cf0, 0xc42035d290)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
goroutine 51491 [select, 4 minutes]:
github.com/cockroachdb/cockroach/pkg/sql.(*DistSQLPlanner).initRunners.func1(0x2eb2080, 0xc42144c0f0)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:88 +0x151
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc4251cf610, 0xc4215a8cf0, 0xc4251cf5f0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
goroutine 50899 [chan receive, 7 minutes]:
github.com/cockroachdb/cockroach/pkg/util/log.(*loggingT).gcDaemon(0xc4204fc780)
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/clog.go:1230 +0x68
created by github.com/cockroachdb/cockroach/pkg/util/log.NewSecondaryLogger
/go/src/github.com/cockroachdb/cockroach/pkg/util/log/secondary_log.go:80 +0x288
goroutine 51583 [chan receive]:
github.com/cockroachdb/cockroach/pkg/storage/closedts/provider.(*Provider).Notify.func1(0x2eb2080, 0xc421ec4570)
/go/src/github.com/cockroachdb/cockroach/pkg/storage/closedts/provider/provider.go:204 +0x148
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42038a0c0, 0xc42539e1b0, 0xc420310540)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
goroutine 51971 [select, 7 minutes]:
github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.newClientStream.func5(0xc4216da000, 0xc42337d780, 0x2eb2080, 0xc420e695c0)
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:321 +0xfe
created by github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc.newClientStream
/go/src/github.com/cockroachdb/cockroach/vendor/google.golang.org/grpc/stream.go:320 +0xa76
goroutine 50888 [select, 7 minutes]:
github.com/cockroachdb/cockroach/pkg/sql.(*DistSQLPlanner).initRunners.func1(0x2eb2080, 0xc4209be000)
/go/src/github.com/cockroachdb/cockroach/pkg/sql/distsql_running.go:88 +0x151
github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker.func1(0xc42055d1f0, 0xc42539e1b0, 0xc42055d1e0)
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:199 +0xe9
created by github.com/cockroachdb/cockroach/pkg/util/stop.(*Stopper).RunWorker
/go/src/github.com/cockroachdb/cockroach/pkg/util/stop/stopper.go:192 +0xad
I180827 20:41:04.554200 1 rand.go:75 Random seed: 2144118708575765637
test/TestImportPgDump
...ptive snapshot 0df534b1 at applied index 21
I180827 20:41:53.711657 52485 storage/store_snapshot.go:657 [replicate,n1,s1,r8/1:/Table/1{1-2}] streamed snapshot to (n2,s2):?: kv pairs: 10, log entries: 11, rate-limit: 8.0 MiB/sec, 3ms
I180827 20:41:53.712336 52431 storage/replica_raftstorage.go:784 [n2,s2,r8/?:{-}] applying preemptive snapshot at index 21 (id=0df534b1, encoded size=5384, 1 rocksdb batches, 11 log entries)
I180827 20:41:53.712589 52431 storage/replica_raftstorage.go:790 [n2,s2,r8/?:/Table/1{1-2}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180827 20:41:53.712941 52485 storage/replica_command.go:812 [replicate,n1,s1,r8/1:/Table/1{1-2}] change replicas (ADD_REPLICA (n2,s2):3): read existing descriptor r8:/Table/1{1-2} [(n1,s1):1, (n3,s3):2, next=3, gen=1]
I180827 20:41:53.716662 52485 storage/replica.go:3743 [n1,s1,r8/1:/Table/1{1-2}] proposing ADD_REPLICA((n2,s2):3): updated=[(n1,s1):1 (n3,s3):2 (n2,s2):3] next=4
I180827 20:41:53.716741 50862 testutils/testcluster/testcluster.go:536 [n1,s1] has 3 underreplicated ranges
I180827 20:41:53.719005 52448 storage/store_snapshot.go:615 [replicate,n1,s1,r22/1:/{Table/51-Max}] sending preemptive snapshot 67476018 at applied index 15
I180827 20:41:53.719195 52448 storage/store_snapshot.go:657 [replicate,n1,s1,r22/1:/{Table/51-Max}] streamed snapshot to (n2,s2):?: kv pairs: 8, log entries: 5, rate-limit: 8.0 MiB/sec, 1ms
I180827 20:41:53.719598 52470 storage/replica_raftstorage.go:784 [n2,s2,r22/?:{-}] applying preemptive snapshot at index 15 (id=67476018, encoded size=1418, 1 rocksdb batches, 5 log entries)
I180827 20:41:53.719793 52470 storage/replica_raftstorage.go:790 [n2,s2,r22/?:/{Table/51-Max}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180827 20:41:53.720252 52448 storage/replica_command.go:812 [replicate,n1,s1,r22/1:/{Table/51-Max}] change replicas (ADD_REPLICA (n2,s2):3): read existing descriptor r22:/{Table/51-Max} [(n1,s1):1, (n3,s3):2, next=3, gen=0]
I180827 20:41:53.724721 52448 storage/replica.go:3743 [n1,s1,r22/1:/{Table/51-Max}] proposing ADD_REPLICA((n2,s2):3): updated=[(n1,s1):1 (n3,s3):2 (n2,s2):3] next=4
I180827 20:41:53.726370 52456 storage/store_snapshot.go:615 [replicate,n1,s1,r21/1:/Table/5{0-1}] sending preemptive snapshot 57d2d847 at applied index 21
I180827 20:41:53.726577 52456 storage/store_snapshot.go:657 [replicate,n1,s1,r21/1:/Table/5{0-1}] streamed snapshot to (n2,s2):?: kv pairs: 9, log entries: 11, rate-limit: 8.0 MiB/sec, 1ms
I180827 20:41:53.726928 52460 storage/replica_raftstorage.go:784 [n2,s2,r21/?:{-}] applying preemptive snapshot at index 21 (id=57d2d847, encoded size=3678, 1 rocksdb batches, 11 log entries)
I180827 20:41:53.727126 52460 storage/replica_raftstorage.go:790 [n2,s2,r21/?:/Table/5{0-1}] applied preemptive snapshot in 0ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I180827 20:41:53.727433 52456 storage/replica_command.go:812 [replicate,n1,s1,r21/1:/Table/5{0-1}] change replicas (ADD_REPLICA (n2,s2):3): read existing descriptor r21:/Table/5{0-1} [(n1,s1):1, (n3,s3):2, next=3, gen=1]
I180827 20:41:53.732265 52456 storage/replica.go:3743 [n1,s1,r21/1:/Table/5{0-1}] proposing ADD_REPLICA((n2,s2):3): updated=[(n1,s1):1 (n3,s3):2 (n2,s2):3] next=4
I180827 20:41:53.798848 52462 rpc/nodedialer/nodedialer.go:92 [consistencyChecker,n1,s1,r1/1:/{Min-System/}] connection to n1 established
I180827 20:41:53.959825 52553 sql/event_log.go:126 [n1,client=127.0.0.1:57092,user=root] Event: "set_cluster_setting", target: 0, info: {SettingName:kv.import.batch_size Value:10KB User:root}
I180827 20:41:53.969828 52553 sql/event_log.go:126 [n1,client=127.0.0.1:57092,user=root] Event: "create_database", target: 52, info: {DatabaseName:foo Statement:CREATE DATABASE foo User:root}
I180827 20:41:53.970454 52505 storage/replica_command.go:298 [split,n1,s1,r22/1:/{Table/51-Max}] initiating a split of this range at key /Table/52 [r23]
```
Please assign, take a look and update the issue accordingly.
| non_priority | teamcity failed test testimportpgdump the following tests appear to have failed on release banana test testimportpgdump you may want to check test testimportpgdump storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica command go initiating a split of this range at key table π ✅✅ᐿπ✅ �a r nπᐿॹ π ✅ nᐿॹ✅� r� r r r r ᐿ n nᐿaπ r ✅ na a ✅ ✅ a π r n�✅π ॹπ nπ n n tॹ rπ r a t� n r ᐿ t n ᐿa t t n nπ t n πa π r rᐿ a n� r ta r t� r t✅ t ᐿᐿ�� nᐿᐿ ᐿᐿ na ᐿ aa n ✅π nॹ �✅ॹॹ nॹ t nॹ✅ n πᐿ n n r tᐿ� n n n n nπ� n ✅ r a n aa n n n n n ॹ� nπa�πॹaॹ r n ✅✅ ᐿ n π πᐿ n n a aπ✅ᐿ n tॹ r nππ � n n t π t ॹπ �✅ॹ r n✅� ᐿ ✅ n nॹॹ r n✅ n n a t r r ॹ t� � π t ✅ t n n nᐿ n rᐿ � nπ r ᐿᐿ n ✅ᐿaॹ�✅ n t π r n nπ tπ✅ n πॹaᐿ t �ॹॹ n a n πॹ r ॹॹ � n π✅ n ππ n✅�πॹ r✅ n π ᐿ nᐿ✅ rॹ n ॹ � a n rπ n n t aπ t n π ta t n nᐿ � ᐿ ᐿᐿa n ॹॹ tॹπa�ᐿ ra π ✅ tᐿᐿ n ✅ ra� r r π� n ᐿ � ᐿ � ✅ t πa✅ rॹ ᐿ n r t n r ✅ n tπ✅ r rπ r n ✅ᐿᐿ� t� ππ ᐿ t� ππ ॹ πa n n �� rॹॹ t r ॹ✅✅ n n ॹ π � t� ᐿॹॹ n n r na t�ॹᐿa n t r n r tᐿ n t n nᐿ ᐿ tπ✅ n r n t � a nπ t t�ॹ t n�a✅ n✅ nॹ r t✅ tᐿ n tᐿॹ✅ r rॹ✅π n n t t a t ॹॹ aॹ n n✅� t nॹᐿ n r✅ πॹ n✅ tॹ ॹ � r ✅ ॹπ n nᐿ r ॹ n n π nॹ ta✅ n� ᐿ a�✅π r✅ॹ n n ✅ nᐿ n � r nπᐿ πॹᐿ r� n ✅a ॹ r✅ πᐿ✅ॹ ✅ π rπ π n✅ � tॹ n n r n rᐿ nᐿaॹaॹ r n r n� ta nॹॹᐿ n π✅ nπॹπᐿॹ a r t t �π n ✅ॹॹ tᐿ rᐿaaaॹ t ᐿ✅ n ॹ π t r tᐿ n ta t ππ n r� n n n ᐿa nॹᐿa n t n t n✅ ᐿ r n n � r n n π ra✅ ᐿ� n n✅�a✅� storage store snapshot go sending raft snapshot at applied index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying raft snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied raft snapshot in storage replica range lease go transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro storage replica range lease go done transferring lease to storage replica command go initiating a split of this range at key table storage replica range lease go transferring lease to storage replica range lease go done transferring lease to storage replica proposal go new range lease repl seq start epo pro following repl seq start exp pro test testimportpgdump inutes github com cockroachdb cockroach vendor google golang org grpc ccresolverwrapper watcher go src github com cockroachdb cockroach vendor google golang org grpc resolver conn wrapper go created by github com cockroachdb cockroach vendor google golang org grpc ccresolverwrapper start go src github com cockroachdb cockroach vendor google golang org grpc resolver conn wrapper go goroutine sync runtime notifylistwait usr local go src runtime sema go sync cond wait usr local go src sync cond go github com cockroachdb cockroach pkg storage raftscheduler worker go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg storage raftscheduler start go src github com cockroachdb cockroach pkg storage scheduler go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach pkg util log loggingt gcdaemon go src github com cockroachdb cockroach pkg util log clog go created by github com cockroachdb cockroach pkg util log newsecondarylogger go src github com cockroachdb cockroach pkg util log secondary log go goroutine github com cockroachdb cockroach pkg storage closedts provider provider notify go src github com cockroachdb cockroach pkg storage closedts provider provider go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go goroutine github com cockroachdb cockroach vendor google golang org grpc newclientstream go src github com cockroachdb cockroach vendor google golang org grpc stream go created by github com cockroachdb cockroach vendor google golang org grpc newclientstream go src github com cockroachdb cockroach vendor google golang org grpc stream go goroutine github com cockroachdb cockroach pkg sql distsqlplanner initrunners go src github com cockroachdb cockroach pkg sql distsql running go github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go created by github com cockroachdb cockroach pkg util stop stopper runworker go src github com cockroachdb cockroach pkg util stop stopper go rand go random seed test testimportpgdump ptive snapshot at applied index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next testutils testcluster testcluster go has underreplicated ranges storage store snapshot go sending preemptive snapshot at applied index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table max storage replica go proposing add replica updated next storage store snapshot go sending preemptive snapshot at applied index storage store snapshot go streamed snapshot to kv pairs log entries rate limit mib sec storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas add replica read existing descriptor table storage replica go proposing add replica updated next rpc nodedialer nodedialer go connection to established sql event log go event set cluster setting target info settingname kv import batch size value user root sql event log go event create database target info databasename foo statement create database foo user root storage replica command go initiating a split of this range at key table please assign take a look and update the issue accordingly | 0 |
224,813 | 24,793,177,483 | IssuesEvent | 2022-10-24 15:09:45 | sast-automation-dev/BenchmarkJava-44 | https://api.github.com/repos/sast-automation-dev/BenchmarkJava-44 | opened | bootstrap-3.3.4.min.js: 6 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | True | bootstrap-3.3.4.min.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.min.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.min.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.min.js</a></p>
<p>Path to dependency file: /scorecard/Benchmark_v1.1_Scorecard_for_SAST-05.html</p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.min.js,/scorecard/content/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/BenchmarkJava-44/commit/75c0595188732cd4fe579e9679057929e0d315d7">75c0595188732cd4fe579e9679057929e0d315d7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | non_priority | bootstrap min js vulnerabilities highest severity is vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in bootstrap version remediation available medium bootstrap min js direct bootstrap bootstrap sass medium bootstrap min js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap min js direct bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter medium bootstrap min js direct bootstrap medium bootstrap min js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap min js direct details cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution bootstrap bootstrap sass cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file scorecard benchmark scorecard for sast html path to vulnerable library scorecard content js bootstrap min js scorecard content js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution | 0 |
36,983 | 12,462,398,384 | IssuesEvent | 2020-05-28 08:50:11 | eclipse/vorto | https://api.github.com/repos/eclipse/vorto | closed | Upgrade AngularJS to latest stable | Compliance UI blocker security | A new issue impacting the currently in use version of AngularJS (impacting angular-sanitize 1.3.13) has been discovered - see sonatype-2018-0005 and advisory [here](https://github.com/angular/angular.js/blob/master/CHANGELOG.md#169-fiery-basilisk-2018-02-02).
We need to explore the upgrade path for now.
The ultimate idea is to replace the whole UI with a non-obsoleting framework, but this is the medium-term solution (provided that upgrading is not overly complicated and the relevant CQ is processed and approved before we actually switch frameworks, which is not necessarily a given). | True | Upgrade AngularJS to latest stable - A new issue impacting the currently in use version of AngularJS (impacting angular-sanitize 1.3.13) has been discovered - see sonatype-2018-0005 and advisory [here](https://github.com/angular/angular.js/blob/master/CHANGELOG.md#169-fiery-basilisk-2018-02-02).
We need to explore the upgrade path for now.
The ultimate idea is to replace the whole UI with a non-obsoleting framework, but this is the medium-term solution (provided that upgrading is not overly complicated and the relevant CQ is processed and approved before we actually switch frameworks, which is not necessarily a given). | non_priority | upgrade angularjs to latest stable a new issue impacting the currently in use version of angularjs impacting angular sanitize has been discovered see sonatype and advisory we need to explore the upgrade path for now the ultimate idea is to replace the whole ui with a non obsoleting framework but this is the medium term solution provided that upgrading is not overly complicated and the relevant cq is processed and approved before we actually switch frameworks which is not necessarily a given | 0 |
51,743 | 6,195,420,734 | IssuesEvent | 2017-07-05 12:35:25 | Fourdee/DietPi | https://api.github.com/repos/Fourdee/DietPi | reopened | Image Request | Native PC x86_64: eg Intel NUC or Gigabyte Brix | Image Request Testing/testers required | First of all thank you for making DietPi, it is fantastic and makes life much easier dealing with single board computers. So much so, I'm wondering if I can use it with x86 barebones like https://www.gigabyte.com/Mini-PcBarebone Brix?
I especially like the ability to just flash an image onto a disk and have it auto resize the partition and set everything else up automatically on first login. | 2.0 | Image Request | Native PC x86_64: eg Intel NUC or Gigabyte Brix - First of all thank you for making DietPi, it is fantastic and makes life much easier dealing with single board computers. So much so, I'm wondering if I can use it with x86 barebones like https://www.gigabyte.com/Mini-PcBarebone Brix?
I especially like the ability to just flash an image onto a disk and have it auto resize the partition and set everything else up automatically on first login. | non_priority | image request native pc eg intel nuc or gigabyte brix first of all thank you for making dietpi it is fantastic and makes life much easier dealing with single board computers so much so i m wondering if i can use it with barebones like brix i especially like the ability to just flash an image onto a disk and have it auto resize the partition and set everything else up automatically on first login | 0 |
61,988 | 25,821,556,229 | IssuesEvent | 2022-12-12 09:57:10 | hashicorp/terraform-provider-azurerm | https://api.github.com/repos/hashicorp/terraform-provider-azurerm | closed | [WAF] Terraform not support "Action" parameter on Managed rules | bug enhancement service/firewall | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform Version
1.2.6
### AzureRM Provider Version
3.30.0
### Affected Resource(s)/Data Source(s)
azurerm_web_application_firewall_policy
### Terraform Configuration Files
```hcl
main.tf
resource "azurerm_web_application_firewall_policy" "this" {
name = "XXXX"
resource_group_name = "XXXX"
location = "XXXX"
policy_settings {
enabled = true
mode = "Detection"
request_body_check = true
file_upload_limit_in_mb = 100
max_request_body_size_in_kb = 128
}
dynamic custom_rules {
for_each = local.xxx_custom_rules
content {
name = custom_rules.value.name
priority = custom_rules.value.priority
rule_type = custom_rules.value.rule_type
action = custom_rules.value.action
dynamic match_conditions {
for_each = custom_rules.value.match_conditions
content {
match_values = match_conditions.value.match_values
operator = match_conditions.value.operator
dynamic match_variables {
for_each = match_conditions.value.match_variables
content {
variable_name = match_variables.value.variable_name
selector = match_variables.value.selector
}
}
}
}
}
}
managed_rules {
dynamic exclusion {
for_each = local.xxx_waf_exclusions
content {
match_variable = exclusion.value.match_variable
selector = exclusion.value.selector
selector_match_operator = exclusion.value.selector_match_operator
dynamic excluded_rule_set {
for_each = exclusion.value.excluded_rule_set
content {
type = "OWASP"
version = "3.2"
dynamic rule_group {
for_each = excluded_rule_set.value.rule_group
content {
rule_group_name = rule_group.value.rule_group_name
excluded_rules = rule_group.value.excluded_rules
}
}
}
}
}
}
managed_rule_set {
type = "OWASP"
version = "3.2"
dynamic rule_group_override {
for_each = local.xxx_disabled_rule_group
content {
rule_group_name = rule_group_override.value.rule_group_name
disabled_rules = rule_group_override.value.rules
}
}
}
managed_rule_set {
type = "Microsoft_BotManagerRuleSet"
version = "0.1"
}
}
}
locals.tf
xxx_disabled_rule_group = {
General = {
rule_group_name = "General"
rules = [200003]
}
REQUEST-920-PROTOCOL-ENFORCEMENT = {
rule_group_name = "REQUEST-920-PROTOCOL-ENFORCEMENT"
rules = [920300, 920230, 920320]
}
}
```
### Debug Output/Panic Output
```shell
~ managed_rule_set {
# (2 unchanged attributes hidden)
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-931-APPLICATION-ATTACK-RFI" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-942-APPLICATION-ATTACK-SQLI" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-911-METHOD-ENFORCEMENT" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-913-SCANNER-DETECTION" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-921-PROTOCOL-ATTACK" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-930-APPLICATION-ATTACK-LFI" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-932-APPLICATION-ATTACK-RCE" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-933-APPLICATION-ATTACK-PHP" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-941-APPLICATION-ATTACK-XSS" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-943-APPLICATION-ATTACK-SESSION-FIXATION" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-944-APPLICATION-ATTACK-JAVA" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "Known-CVEs" -> null
}
# (2 unchanged blocks hidden)
}
```
### Expected Behaviour
No change
### Actual Behaviour
TF seems to set by default rules action to "Anomaly Score". I want set it to "Block".
When I set manually on Azure rule action to Block, Terraform delete my change and set "Anomaly Score"
### Steps to Reproduce
_No response_
### Important Factoids
_No response_
### References
_No response_ | 1.0 | [WAF] Terraform not support "Action" parameter on Managed rules - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Community Note
<!--- Please keep this note for the community --->
* Please vote on this issue by adding a :thumbsup: [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
<!--- Thank you for keeping this note for the community --->
### Terraform Version
1.2.6
### AzureRM Provider Version
3.30.0
### Affected Resource(s)/Data Source(s)
azurerm_web_application_firewall_policy
### Terraform Configuration Files
```hcl
main.tf
resource "azurerm_web_application_firewall_policy" "this" {
name = "XXXX"
resource_group_name = "XXXX"
location = "XXXX"
policy_settings {
enabled = true
mode = "Detection"
request_body_check = true
file_upload_limit_in_mb = 100
max_request_body_size_in_kb = 128
}
dynamic custom_rules {
for_each = local.xxx_custom_rules
content {
name = custom_rules.value.name
priority = custom_rules.value.priority
rule_type = custom_rules.value.rule_type
action = custom_rules.value.action
dynamic match_conditions {
for_each = custom_rules.value.match_conditions
content {
match_values = match_conditions.value.match_values
operator = match_conditions.value.operator
dynamic match_variables {
for_each = match_conditions.value.match_variables
content {
variable_name = match_variables.value.variable_name
selector = match_variables.value.selector
}
}
}
}
}
}
managed_rules {
dynamic exclusion {
for_each = local.xxx_waf_exclusions
content {
match_variable = exclusion.value.match_variable
selector = exclusion.value.selector
selector_match_operator = exclusion.value.selector_match_operator
dynamic excluded_rule_set {
for_each = exclusion.value.excluded_rule_set
content {
type = "OWASP"
version = "3.2"
dynamic rule_group {
for_each = excluded_rule_set.value.rule_group
content {
rule_group_name = rule_group.value.rule_group_name
excluded_rules = rule_group.value.excluded_rules
}
}
}
}
}
}
managed_rule_set {
type = "OWASP"
version = "3.2"
dynamic rule_group_override {
for_each = local.xxx_disabled_rule_group
content {
rule_group_name = rule_group_override.value.rule_group_name
disabled_rules = rule_group_override.value.rules
}
}
}
managed_rule_set {
type = "Microsoft_BotManagerRuleSet"
version = "0.1"
}
}
}
locals.tf
xxx_disabled_rule_group = {
General = {
rule_group_name = "General"
rules = [200003]
}
REQUEST-920-PROTOCOL-ENFORCEMENT = {
rule_group_name = "REQUEST-920-PROTOCOL-ENFORCEMENT"
rules = [920300, 920230, 920320]
}
}
```
### Debug Output/Panic Output
```shell
~ managed_rule_set {
# (2 unchanged attributes hidden)
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-931-APPLICATION-ATTACK-RFI" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-942-APPLICATION-ATTACK-SQLI" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-911-METHOD-ENFORCEMENT" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-913-SCANNER-DETECTION" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-921-PROTOCOL-ATTACK" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-930-APPLICATION-ATTACK-LFI" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-932-APPLICATION-ATTACK-RCE" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-933-APPLICATION-ATTACK-PHP" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-941-APPLICATION-ATTACK-XSS" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-943-APPLICATION-ATTACK-SESSION-FIXATION" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "REQUEST-944-APPLICATION-ATTACK-JAVA" -> null
}
- rule_group_override {
- disabled_rules = [] -> null
- rule_group_name = "Known-CVEs" -> null
}
# (2 unchanged blocks hidden)
}
```
### Expected Behaviour
No change
### Actual Behaviour
TF seems to set by default rules action to "Anomaly Score". I want set it to "Block".
When I set manually on Azure rule action to Block, Terraform delete my change and set "Anomaly Score"
### Steps to Reproduce
_No response_
### Important Factoids
_No response_
### References
_No response_ | non_priority | terraform not support action parameter on managed rules is there an existing issue for this i have searched the existing issues community note please vote on this issue by adding a thumbsup to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform version azurerm provider version affected resource s data source s azurerm web application firewall policy terraform configuration files hcl main tf resource azurerm web application firewall policy this name xxxx resource group name xxxx location xxxx policy settings enabled true mode detection request body check true file upload limit in mb max request body size in kb dynamic custom rules for each local xxx custom rules content name custom rules value name priority custom rules value priority rule type custom rules value rule type action custom rules value action dynamic match conditions for each custom rules value match conditions content match values match conditions value match values operator match conditions value operator dynamic match variables for each match conditions value match variables content variable name match variables value variable name selector match variables value selector managed rules dynamic exclusion for each local xxx waf exclusions content match variable exclusion value match variable selector exclusion value selector selector match operator exclusion value selector match operator dynamic excluded rule set for each exclusion value excluded rule set content type owasp version dynamic rule group for each excluded rule set value rule group content rule group name rule group value rule group name excluded rules rule group value excluded rules managed rule set type owasp version dynamic rule group override for each local xxx disabled rule group content rule group name rule group override value rule group name disabled rules rule group override value rules managed rule set type microsoft botmanagerruleset version locals tf xxx disabled rule group general rule group name general rules request protocol enforcement rule group name request protocol enforcement rules debug output panic output shell managed rule set unchanged attributes hidden rule group override disabled rules null rule group name request application attack rfi null rule group override disabled rules null rule group name request application attack sqli null rule group override disabled rules null rule group name request method enforcement null rule group override disabled rules null rule group name request scanner detection null rule group override disabled rules null rule group name request protocol attack null rule group override disabled rules null rule group name request application attack lfi null rule group override disabled rules null rule group name request application attack rce null rule group override disabled rules null rule group name request application attack php null rule group override disabled rules null rule group name request application attack xss null rule group override disabled rules null rule group name request application attack session fixation null rule group override disabled rules null rule group name request application attack java null rule group override disabled rules null rule group name known cves null unchanged blocks hidden expected behaviour no change actual behaviour tf seems to set by default rules action to anomaly score i want set it to block when i set manually on azure rule action to block terraform delete my change and set anomaly score steps to reproduce no response important factoids no response references no response | 0 |
104,916 | 9,012,421,387 | IssuesEvent | 2019-02-05 16:51:05 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | opened | Fix rare timing issue in metatype provider tests | test bug | On rare occasions the metatype provider tests in com.ibm.ws.config_fat can run into an issue where configurations have not been removed from config admin before the test runs.
The ideal solution to this problem would be to hook configuration updates that result from removal of a metatype provider into the runtime update framework. However, given that we do not currently have official support for metatype providers, there is little advantage to doing that. Instead, I'm going to add some trace log messages for the tests to wait on. | 1.0 | Fix rare timing issue in metatype provider tests - On rare occasions the metatype provider tests in com.ibm.ws.config_fat can run into an issue where configurations have not been removed from config admin before the test runs.
The ideal solution to this problem would be to hook configuration updates that result from removal of a metatype provider into the runtime update framework. However, given that we do not currently have official support for metatype providers, there is little advantage to doing that. Instead, I'm going to add some trace log messages for the tests to wait on. | non_priority | fix rare timing issue in metatype provider tests on rare occasions the metatype provider tests in com ibm ws config fat can run into an issue where configurations have not been removed from config admin before the test runs the ideal solution to this problem would be to hook configuration updates that result from removal of a metatype provider into the runtime update framework however given that we do not currently have official support for metatype providers there is little advantage to doing that instead i m going to add some trace log messages for the tests to wait on | 0 |
139,330 | 12,853,899,785 | IssuesEvent | 2020-07-09 00:09:53 | seanpm2001/horsin-around-in-the-barn | https://api.github.com/repos/seanpm2001/horsin-around-in-the-barn | opened | Google sites edition can't be imported | documentation enhancement help wanted question |
***
### Google sites edition can't be imported
I can't import the Google Sites edition of this site, as it was written in the "new" Google Sites, and doesn't appear as an option on Google Takeout. I have tried using a website ripper [HTTrack (NON-HTTPS LINK WARNING)](http://www.httrack.com/) and I get most of the files, with the cons of:
> Many files don't get ripped (such as videos and images)
> All files redirect back to Google sites, instead of opening locally
If anyone knows how to rip the new Google Sites, please let me know. It will be greatly appreciated, and I will award you for it.
***
| 1.0 | Google sites edition can't be imported -
***
### Google sites edition can't be imported
I can't import the Google Sites edition of this site, as it was written in the "new" Google Sites, and doesn't appear as an option on Google Takeout. I have tried using a website ripper [HTTrack (NON-HTTPS LINK WARNING)](http://www.httrack.com/) and I get most of the files, with the cons of:
> Many files don't get ripped (such as videos and images)
> All files redirect back to Google sites, instead of opening locally
If anyone knows how to rip the new Google Sites, please let me know. It will be greatly appreciated, and I will award you for it.
***
| non_priority | google sites edition can t be imported google sites edition can t be imported i can t import the google sites edition of this site as it was written in the new google sites and doesn t appear as an option on google takeout i have tried using a website ripper and i get most of the files with the cons of many files don t get ripped such as videos and images all files redirect back to google sites instead of opening locally if anyone knows how to rip the new google sites please let me know it will be greatly appreciated and i will award you for it | 0 |
363,505 | 25,454,635,636 | IssuesEvent | 2022-11-24 13:14:33 | kubeshop/tracetest | https://api.github.com/repos/kubeshop/tracetest | opened | [docs] Write a dedicated config file reference page for Tracetest CLI commands | documentation | The docs need a dedicated page with a full reference for all possible configuration possibilities for the Tracetest CLI. All available commands need to be referenced and explained in detail.
| 1.0 | [docs] Write a dedicated config file reference page for Tracetest CLI commands - The docs need a dedicated page with a full reference for all possible configuration possibilities for the Tracetest CLI. All available commands need to be referenced and explained in detail.
| non_priority | write a dedicated config file reference page for tracetest cli commands the docs need a dedicated page with a full reference for all possible configuration possibilities for the tracetest cli all available commands need to be referenced and explained in detail | 0 |
340,196 | 24,644,858,688 | IssuesEvent | 2022-10-17 14:12:43 | coq/coq | https://api.github.com/repos/coq/coq | closed | Format Notation needs documentation | kind: documentation | Note: the issue was created automatically with bugzilla2github tool
Original bug ID: BZ#5534
From: @psteckler
Reported version: 8.6
CC: @ejgallego
| 1.0 | Format Notation needs documentation - Note: the issue was created automatically with bugzilla2github tool
Original bug ID: BZ#5534
From: @psteckler
Reported version: 8.6
CC: @ejgallego
| non_priority | format notation needs documentation note the issue was created automatically with tool original bug id bz from psteckler reported version cc ejgallego | 0 |
177,254 | 21,468,988,072 | IssuesEvent | 2022-04-26 07:47:25 | Shai-SAST/Easybuggy | https://api.github.com/repos/Shai-SAST/Easybuggy | closed | CVE-2020-11023 (Medium) detected in jquery-3.1.1.min.js - autoclosed | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js</a></p>
<p>Path to dependency file: /src/main/webapp/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: /src/main/webapp/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Shai-SAST/Easybuggy/commit/e1c337cc723ebc1cc88779690db3dea63e3489bf">e1c337cc723ebc1cc88779690db3dea63e3489bf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"3.1.1","packageFilePaths":["/src/main/webapp/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11023 (Medium) detected in jquery-3.1.1.min.js - autoclosed - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.1.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.1.1/jquery.min.js</a></p>
<p>Path to dependency file: /src/main/webapp/dfi/style_bootstrap.html</p>
<p>Path to vulnerable library: /src/main/webapp/dfi/style_bootstrap.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Shai-SAST/Easybuggy/commit/e1c337cc723ebc1cc88779690db3dea63e3489bf">e1c337cc723ebc1cc88779690db3dea63e3489bf</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"3.1.1","packageFilePaths":["/src/main/webapp/dfi/style_bootstrap.html"],"isTransitiveDependency":false,"dependencyTree":"jquery:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js autoclosed cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file src main webapp dfi style bootstrap html path to vulnerable library src main webapp dfi style bootstrap html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery jquery rails isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery jquery rails isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl | 0 |
27,217 | 6,821,962,842 | IssuesEvent | 2017-11-07 18:26:50 | Daniel-Svensson/test2 | https://api.github.com/repos/Daniel-Svensson/test2 | closed | Fluent API | CodePlex | <b>ColinBlair[CodePlex]</b> <br />Open RIA Services needs to move to a Fluent API as the default configuration method.
| 1.0 | Fluent API - <b>ColinBlair[CodePlex]</b> <br />Open RIA Services needs to move to a Fluent API as the default configuration method.
| non_priority | fluent api colinblair open ria services needs to move to a fluent api as the default configuration method | 0 |
342,356 | 30,616,700,047 | IssuesEvent | 2023-07-24 04:16:49 | opensearch-project/cross-cluster-replication | https://api.github.com/repos/opensearch-project/cross-cluster-replication | closed | [AUTOCUT] Integration Test failed for cross-cluster-replication: 2.9.0 rpm distribution | untriaged autocut integ-test-failure v2.9.0 | The integration test failed at distribution level for component cross-cluster-replication<br>Version: 2.9.0<br>Distribution: rpm<br>Architecture: arm64<br>Platform: linux<br><br>Please check the logs: https://build.ci.opensearch.org/job/integ-test/5349/display/redirect<br><br> * Steps to reproduce: See https://github.com/opensearch-project/opensearch-build/tree/main/src/test_workflow#integration-tests<br>* Access components yml file:<br> - [With security](https://ci.opensearch.org/ci/dbc/integ-test/2.9.0/8184/linux/arm64/rpm/test-results/5349/integ-test/cross-cluster-replication/with-security/cross-cluster-replication.yml) (if applicable)<br> - [Without security](https://ci.opensearch.org/ci/dbc/integ-test/2.9.0/8184/linux/arm64/rpm/test-results/5349/integ-test/cross-cluster-replication/without-security/cross-cluster-replication.yml) (if applicable)<br><br> _Note: All in one test report manifest with all the details coming soon. See https://github.com/opensearch-project/opensearch-build/issues/1274_ | 1.0 | [AUTOCUT] Integration Test failed for cross-cluster-replication: 2.9.0 rpm distribution - The integration test failed at distribution level for component cross-cluster-replication<br>Version: 2.9.0<br>Distribution: rpm<br>Architecture: arm64<br>Platform: linux<br><br>Please check the logs: https://build.ci.opensearch.org/job/integ-test/5349/display/redirect<br><br> * Steps to reproduce: See https://github.com/opensearch-project/opensearch-build/tree/main/src/test_workflow#integration-tests<br>* Access components yml file:<br> - [With security](https://ci.opensearch.org/ci/dbc/integ-test/2.9.0/8184/linux/arm64/rpm/test-results/5349/integ-test/cross-cluster-replication/with-security/cross-cluster-replication.yml) (if applicable)<br> - [Without security](https://ci.opensearch.org/ci/dbc/integ-test/2.9.0/8184/linux/arm64/rpm/test-results/5349/integ-test/cross-cluster-replication/without-security/cross-cluster-replication.yml) (if applicable)<br><br> _Note: All in one test report manifest with all the details coming soon. See https://github.com/opensearch-project/opensearch-build/issues/1274_ | non_priority | integration test failed for cross cluster replication rpm distribution the integration test failed at distribution level for component cross cluster replication version distribution rpm architecture platform linux please check the logs steps to reproduce see access components yml file if applicable if applicable note all in one test report manifest with all the details coming soon see | 0 |
186,835 | 21,992,925,977 | IssuesEvent | 2022-05-26 01:11:33 | rvvergara/rails-api | https://api.github.com/repos/rvvergara/rails-api | opened | CVE-2022-29181 (High) detected in nokogiri-1.10.10.gem | security vulnerability | ## CVE-2022-29181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.10.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.10.gem">https://rubygems.org/gems/nokogiri-1.10.10.gem</a></p>
<p>
Dependency Hierarchy:
- sass-rails-5.0.7.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-5.2.2.gem
- rails-dom-testing-2.0.3.gem
- :x: **nokogiri-1.10.10.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is an open source XML and HTML library for Ruby. Nokogiri prior to version 1.13.6 does not type-check all inputs into the XML and HTML4 SAX parsers, allowing specially crafted untrusted inputs to cause illegal memory access errors (segfault) or reads from unrelated memory. Version 1.13.6 contains a patch for this issue. As a workaround, ensure the untrusted input is a `String` by calling `#to_s` or equivalent.
<p>Publish Date: 2022-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29181>CVE-2022-29181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181</a></p>
<p>Release Date: 2022-05-20</p>
<p>Fix Resolution: nokogiri - 1.13.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-29181 (High) detected in nokogiri-1.10.10.gem - ## CVE-2022-29181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>nokogiri-1.10.10.gem</b></p></summary>
<p>Nokogiri (鋸) is an HTML, XML, SAX, and Reader parser. Among
Nokogiri's many features is the ability to search documents via XPath
or CSS3 selectors.</p>
<p>Library home page: <a href="https://rubygems.org/gems/nokogiri-1.10.10.gem">https://rubygems.org/gems/nokogiri-1.10.10.gem</a></p>
<p>
Dependency Hierarchy:
- sass-rails-5.0.7.gem (Root Library)
- sprockets-rails-3.2.1.gem
- actionpack-5.2.2.gem
- rails-dom-testing-2.0.3.gem
- :x: **nokogiri-1.10.10.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Nokogiri is an open source XML and HTML library for Ruby. Nokogiri prior to version 1.13.6 does not type-check all inputs into the XML and HTML4 SAX parsers, allowing specially crafted untrusted inputs to cause illegal memory access errors (segfault) or reads from unrelated memory. Version 1.13.6 contains a patch for this issue. As a workaround, ensure the untrusted input is a `String` by calling `#to_s` or equivalent.
<p>Publish Date: 2022-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29181>CVE-2022-29181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29181</a></p>
<p>Release Date: 2022-05-20</p>
<p>Fix Resolution: nokogiri - 1.13.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in nokogiri gem cve high severity vulnerability vulnerable library nokogiri gem nokogiri 鋸 is an html xml sax and reader parser among nokogiri s many features is the ability to search documents via xpath or selectors library home page a href dependency hierarchy sass rails gem root library sprockets rails gem actionpack gem rails dom testing gem x nokogiri gem vulnerable library found in base branch master vulnerability details nokogiri is an open source xml and html library for ruby nokogiri prior to version does not type check all inputs into the xml and sax parsers allowing specially crafted untrusted inputs to cause illegal memory access errors segfault or reads from unrelated memory version contains a patch for this issue as a workaround ensure the untrusted input is a string by calling to s or equivalent publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution nokogiri step up your open source security game with whitesource | 0 |
109,551 | 23,785,088,474 | IssuesEvent | 2022-09-02 09:20:11 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | Search aggregation insights URL improvements | webapp team/code-insights insights-search-aggregation-4.0 | - `&groupBy=PATH` – our URL parameters are always lowercase, should be `&groupBy=path`
- `&groupByUI=sidebar`, `&groupByUI=searchPage` this makes the URL very verbose for every search use, even when aggregations are not desired. "searchPage" is also a bit of a misnomer because the sidebar is part of the search page too. Instead of an "enum", can we make it a single boolean parameter `&expanded` that only gets added when expand is clicked, and removed when collapse is clicked?
/cc @joelkw @felixfbecker @vovakulikov @unclejustin | 1.0 | Search aggregation insights URL improvements - - `&groupBy=PATH` – our URL parameters are always lowercase, should be `&groupBy=path`
- `&groupByUI=sidebar`, `&groupByUI=searchPage` this makes the URL very verbose for every search use, even when aggregations are not desired. "searchPage" is also a bit of a misnomer because the sidebar is part of the search page too. Instead of an "enum", can we make it a single boolean parameter `&expanded` that only gets added when expand is clicked, and removed when collapse is clicked?
/cc @joelkw @felixfbecker @vovakulikov @unclejustin | non_priority | search aggregation insights url improvements groupby path – our url parameters are always lowercase should be groupby path groupbyui sidebar groupbyui searchpage this makes the url very verbose for every search use even when aggregations are not desired searchpage is also a bit of a misnomer because the sidebar is part of the search page too instead of an enum can we make it a single boolean parameter expanded that only gets added when expand is clicked and removed when collapse is clicked cc joelkw felixfbecker vovakulikov unclejustin | 0 |
11,347 | 3,487,153,340 | IssuesEvent | 2016-01-01 15:31:52 | aurelia-ui-toolkits/aurelia-kendoui-plugin | https://api.github.com/repos/aurelia-ui-toolkits/aurelia-kendoui-plugin | closed | All code needs to be a lot better commented | documentation plugin | I used to like how Angular team does this - even if one can say that they went overboard - ratio of code versus comment is less than 1/10
Perhaps **[this](https://github.com/aurelia/templating/blob/master/src/composition-engine.js)** should be the minimum although I think the comments in this file are written to be able to automatically extract api docs - which is of no interest to us.
In general code comments are written to simplify the life of the next guy | 1.0 | All code needs to be a lot better commented - I used to like how Angular team does this - even if one can say that they went overboard - ratio of code versus comment is less than 1/10
Perhaps **[this](https://github.com/aurelia/templating/blob/master/src/composition-engine.js)** should be the minimum although I think the comments in this file are written to be able to automatically extract api docs - which is of no interest to us.
In general code comments are written to simplify the life of the next guy | non_priority | all code needs to be a lot better commented i used to like how angular team does this even if one can say that they went overboard ratio of code versus comment is less than perhaps should be the minimum although i think the comments in this file are written to be able to automatically extract api docs which is of no interest to us in general code comments are written to simplify the life of the next guy | 0 |
118,091 | 15,222,823,693 | IssuesEvent | 2021-02-18 01:11:35 | ibm-brand/center-import-test | https://api.github.com/repos/ibm-brand/center-import-test | opened | [BC] Add creative partners page | Design Epic High | _mjabbink created the following on Jul 02:_
Photography > illustration > Animation > Design > Strategy > Etc.
Pages should include images where relevant, links to their personal site/agent/reps sites, instagram, etc.
Let’s start with Illustrators (Mike has running list), Photographers (Emily Keegin has new list and categorized in US, Europe, Asia), Animators (i.e. Buck TV ,etc.)
_Original issue: https://github.ibm.com/brand/center/issues/809_ | 1.0 | [BC] Add creative partners page - _mjabbink created the following on Jul 02:_
Photography > illustration > Animation > Design > Strategy > Etc.
Pages should include images where relevant, links to their personal site/agent/reps sites, instagram, etc.
Let’s start with Illustrators (Mike has running list), Photographers (Emily Keegin has new list and categorized in US, Europe, Asia), Animators (i.e. Buck TV ,etc.)
_Original issue: https://github.ibm.com/brand/center/issues/809_ | non_priority | add creative partners page mjabbink created the following on jul photography illustration animation design strategy etc pages should include images where relevant links to their personal site agent reps sites instagram etc let’s start with illustrators mike has running list photographers emily keegin has new list and categorized in us europe asia animators i e buck tv etc original issue | 0 |
383,895 | 26,567,981,847 | IssuesEvent | 2023-01-20 22:29:19 | gbowne1/reactsocialnetwork | https://api.github.com/repos/gbowne1/reactsocialnetwork | opened | Contrast issues | bug documentation enhancement help wanted good first issue question | **Describe the bug**
[Accessibility]
Contrast issues with the text [text leaf] which describes each panel component.
**To Reproduce**
Steps to reproduce the behavior:
Run the dev server with npm start in the root dir. After the app loads in browser,
Press Ctrl Shift J or otherwise load the browser console.
1. Go to 'Accessiblity'
2. Click on 'All issues' button next to "Check for issues:"
3. See errors which include Contrast for the text which labels each panel
**Expected behavior**
No focus styling issues with icons in navbar. Consider using focus visible and aria labeling.
**Desktop (please complete the following information):**
- OS: [e.g. iOS]
Linux, 64bit
- Browser [e.g. chrome, safari]
Firefox
- Version [e.g. 22]
107
**Additional context**
This is an accessibility issue.
| 1.0 | Contrast issues - **Describe the bug**
[Accessibility]
Contrast issues with the text [text leaf] which describes each panel component.
**To Reproduce**
Steps to reproduce the behavior:
Run the dev server with npm start in the root dir. After the app loads in browser,
Press Ctrl Shift J or otherwise load the browser console.
1. Go to 'Accessiblity'
2. Click on 'All issues' button next to "Check for issues:"
3. See errors which include Contrast for the text which labels each panel
**Expected behavior**
No focus styling issues with icons in navbar. Consider using focus visible and aria labeling.
**Desktop (please complete the following information):**
- OS: [e.g. iOS]
Linux, 64bit
- Browser [e.g. chrome, safari]
Firefox
- Version [e.g. 22]
107
**Additional context**
This is an accessibility issue.
| non_priority | contrast issues describe the bug contrast issues with the text which describes each panel component to reproduce steps to reproduce the behavior run the dev server with npm start in the root dir after the app loads in browser press ctrl shift j or otherwise load the browser console go to accessiblity click on all issues button next to check for issues see errors which include contrast for the text which labels each panel expected behavior no focus styling issues with icons in navbar consider using focus visible and aria labeling desktop please complete the following information os linux browser firefox version additional context this is an accessibility issue | 0 |
167,435 | 26,501,810,345 | IssuesEvent | 2023-01-18 10:50:52 | kodadot/nft-gallery | https://api.github.com/repos/kodadot/nft-gallery | closed | Move the login box to be drop-down under connect menu | p3 redesign design-request | We should probably move the select box to be drop-down under connect menu
@exezbcz will drop designs
Suggested look would be to have sliding sidebar
_Originally posted by @yangwao in https://github.com/kodadot/nft-gallery/issues/4222#issuecomment-1310659662_
| 2.0 | Move the login box to be drop-down under connect menu - We should probably move the select box to be drop-down under connect menu
@exezbcz will drop designs
Suggested look would be to have sliding sidebar
_Originally posted by @yangwao in https://github.com/kodadot/nft-gallery/issues/4222#issuecomment-1310659662_
| non_priority | move the login box to be drop down under connect menu we should probably move the select box to be drop down under connect menu exezbcz will drop designs suggested look would be to have sliding sidebar originally posted by yangwao in | 0 |
31,341 | 4,257,796,369 | IssuesEvent | 2016-07-11 01:29:49 | geetsisbac/YE7GLKCP77LP3XTRJGXDSBHN | https://api.github.com/repos/geetsisbac/YE7GLKCP77LP3XTRJGXDSBHN | closed | FBNeBls4BCG/ItYKnHLWRsSW8A8P7GzoaJXY5DtlFnHyaNCmx60K3hYs09q69Iwi0PXcnPdHBsjC63TyM6p1zEY5VrFl3f5vbJK+lHYb9+YxjK6w+MucSV5IkdhFrgwHikVPLjU+RaR9gfnxFZTJ/3DOsOK4otFOuR54PXRy68M= | design | EKv1xJYwKLgzDqRGJy2JHC48bQPLVC8YxI9nrDEdPJBQHk9M7E4ckVWykmIUTQJ3VaHwqWbuIUU7+ifavIKetDPLaUW0bok3dEV4WLauWll6KBnmRUYxqt50oTnNpso9BRRBphFDy9lx5J2QZXm+5BrwaWlEHPR8cyhgwweZDy67z7HsYuGIX0Jo9ckbezaRCTZR5STk0UTDJAH4HPebijxY6eNha7R4an5EjoKIoR3CnQ46rpIyZnznnGdmni4+NVG8QSCldp7skWllkDpn5PaRabymQYO9hhyOT+rajUdXUCRoIbxcNXhIY/bzMLMKFlgGaFmbdNI4+7zxsPB1ADVRvEEgpXae7JFpZZA6Z+ThwcZntyGd1BByGiBRUN31siRkHDQFWSYTU+GpJmE8hGgNZilJ1FEOANiGkK/GYxiWq/d5yg8Y8kk9zvcZpp0gPtOzngdyxPgj3sSG2O6dQjVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkg0f9QLRlluAoICZwju3L7xVs6a0ADWYLQ7xMyk+xs1Q1UbxBIKV2nuyRaWWQOmfk+PofopURPcwdjQeOyy0J9rX75QXvkXhgE378C+w36EFjLlBBxx2dFOCUI6HMQvs0NVG8QSCldp7skWllkDpn5MD6rGld7Lp27UF+NyZUJIkPuBzN6V/XWv+7fa0gwZEfGzH0syU+wMNwWHK5knQJFJa14QHX/UjK80iTsGkVHdqmPjPu3PL7TZOCoD45rLWqbcCtjmb6yClet/CkVM0c4B/tWDeimkzJF7UGbvpRTq41UbxBIKV2nuyRaWWQOmfkkyY2XmQGP284F27jR6i1DZOj2RqC0ftUmmYnBxesswCyxLNoXnjLlomzuxTw9+1+RP9/3gTu4DL0/0KYN3BfL5yz7zzqo1RNFen/5xCXZ/DiCjGuXx2j+UnZkKdlNsA4VFCvrxQENz2wVz460GXuoTVRvEEgpXae7JFpZZA6Z+QRmeWVHMgnXWVu8VGDdNbtV24R8W26htuPnnMttAhJuXlN8WRkRf8SCtBTTZu1Afa7FFY0B5nHzaCjtR/mq9sgVAg4lhlLCWk+OOh/UnEGvnndsMuvq83pTBR9aGa+c/o1UbxBIKV2nuyRaWWQOmfkmYcjwjgHYLgNl0S4kWNGjq3eoDSmJskUAxJgEkqmW6PGk8hVh+8AW2AmVNc4auHdUXedCJ7MHXQMkE/2i2ggs09U6bb5n20GhXFrrVWXLZ67z7HsYuGIX0Jo9ckbezaRhvELaVLagScbOSWP2a11lXSlI9BsK9M+heRbJRZaxVN+XvlaedHUCc3xpPut8CEtbrDbXSFJMoikUAhnatWimz1QN3yNOyeWtc79zssiRSs1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5GXqJ6FNN/1LznG/HyHGQ+jL/6aLS8p4EtvVnT2TVNMp1kXId4txrNzW6ywWYxjar4JEQ+2wJvPofTALk/nPyGt56PnLO0ENUTYHyobXWWxKNnfxuMcuNkPE1+YF2obpX29FiXYQmoev8fwPjPQ4ql3DVkxT81VdynGb0Q+/cYYpN5r5lf3o2ZxRHDQil4B5ONYpuj7hvYA5feZSbsbXqHGZeq0nThbWgJ3RXl3BW6oINVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+RbbTE9AAqu4sgBR7lYHwTPrSnZo941NXITtI5jS3NBXmlPrJK+XPonaDuamPLA655PZz8krvOxyzTBgGaiZ25Yp3gnhxTtjXA+3MT6mDhI91pWnHm7RGQDSKuq8X0UqPm6o3RmfmVdoi7QZ9u1tVjaNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+SyXZxAE2W5wLfprK8aXwYOzI/JmfdKOI4cgdvYlRIP1TVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkaYZt0hrMfYgrnjVDFlMhhTm8y0JUBW+ellkYhY8GombvzUmxVeZ9fl9qv1nONqsONVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+TOpLCl7dcAOUAx5Qv3g4WMyTXlnIPXYHORWNr/WvlQnTVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkpX/0flrUQo5DKAGAflfH9KxMlD8FeKeqBAq4cU0wnHIICrP+zYmbcIKLVNO+3k5nNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+TMgRgQT/HpA9q0igF8Ji/3MW2QkWMmeitL1yZqvsJDQjVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkkSa1RA9ypYMFPPGFHTrzZNeojh/Vb+HI0T+/BX4RP7xEqTD+qAb524mRBvpdDA6dNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+QL/nAfXhHuAf96V8Obzp1N06Pr8LVjKRrvyAG5IVFopevbw40equ99CsgT4/QzMiY1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5FK0tY95XmqJD3BUIcNxP6yA/l3D2N/lyX+EH6MYw2JBNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+QqPbcTiIknZW47xfyfHul6QxUTJeC+cECAzzo0DF2kGVNWFF2ZM1rCUF/9nBzlwMs1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5ONFvrIMESPTxcM7N38pqmqEpr/1CnwpcZ06PGepK7bFNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+TxWO8pVoG+OvWi7xbIWGq0z1EG+MM07F6Z3yAmqe+0gUOOeeM0oF5MaEbssC+hxqc1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5B4zbEeTU7HcyeSNhxwR+d7mSTkq5iCVHFv0y2V5oVITNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+Qrkf5FWwiAknOWl42ezoUA+97afm+Ko2Xj1TsGXM2vfTutl258K0rqJ5ffUvNu++k1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5N+PYylIBSIZuiCajMlnnR6jCiW61tltOzVKQmoO+4AxKJmLlSvY8XTCRQk1xqPQGhOabpiEaA3juIq9r/vEmoIGx3WR3IU8ExMpR/DU2ldHuhO2o6OM1N0UNcW3ANvI6KiQKyBkaUd7IYGTnfffMbDq9yI8eSVX0OU3RLsVJwRG | 1.0 | FBNeBls4BCG/ItYKnHLWRsSW8A8P7GzoaJXY5DtlFnHyaNCmx60K3hYs09q69Iwi0PXcnPdHBsjC63TyM6p1zEY5VrFl3f5vbJK+lHYb9+YxjK6w+MucSV5IkdhFrgwHikVPLjU+RaR9gfnxFZTJ/3DOsOK4otFOuR54PXRy68M= - EKv1xJYwKLgzDqRGJy2JHC48bQPLVC8YxI9nrDEdPJBQHk9M7E4ckVWykmIUTQJ3VaHwqWbuIUU7+ifavIKetDPLaUW0bok3dEV4WLauWll6KBnmRUYxqt50oTnNpso9BRRBphFDy9lx5J2QZXm+5BrwaWlEHPR8cyhgwweZDy67z7HsYuGIX0Jo9ckbezaRCTZR5STk0UTDJAH4HPebijxY6eNha7R4an5EjoKIoR3CnQ46rpIyZnznnGdmni4+NVG8QSCldp7skWllkDpn5PaRabymQYO9hhyOT+rajUdXUCRoIbxcNXhIY/bzMLMKFlgGaFmbdNI4+7zxsPB1ADVRvEEgpXae7JFpZZA6Z+ThwcZntyGd1BByGiBRUN31siRkHDQFWSYTU+GpJmE8hGgNZilJ1FEOANiGkK/GYxiWq/d5yg8Y8kk9zvcZpp0gPtOzngdyxPgj3sSG2O6dQjVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkg0f9QLRlluAoICZwju3L7xVs6a0ADWYLQ7xMyk+xs1Q1UbxBIKV2nuyRaWWQOmfk+PofopURPcwdjQeOyy0J9rX75QXvkXhgE378C+w36EFjLlBBxx2dFOCUI6HMQvs0NVG8QSCldp7skWllkDpn5MD6rGld7Lp27UF+NyZUJIkPuBzN6V/XWv+7fa0gwZEfGzH0syU+wMNwWHK5knQJFJa14QHX/UjK80iTsGkVHdqmPjPu3PL7TZOCoD45rLWqbcCtjmb6yClet/CkVM0c4B/tWDeimkzJF7UGbvpRTq41UbxBIKV2nuyRaWWQOmfkkyY2XmQGP284F27jR6i1DZOj2RqC0ftUmmYnBxesswCyxLNoXnjLlomzuxTw9+1+RP9/3gTu4DL0/0KYN3BfL5yz7zzqo1RNFen/5xCXZ/DiCjGuXx2j+UnZkKdlNsA4VFCvrxQENz2wVz460GXuoTVRvEEgpXae7JFpZZA6Z+QRmeWVHMgnXWVu8VGDdNbtV24R8W26htuPnnMttAhJuXlN8WRkRf8SCtBTTZu1Afa7FFY0B5nHzaCjtR/mq9sgVAg4lhlLCWk+OOh/UnEGvnndsMuvq83pTBR9aGa+c/o1UbxBIKV2nuyRaWWQOmfkmYcjwjgHYLgNl0S4kWNGjq3eoDSmJskUAxJgEkqmW6PGk8hVh+8AW2AmVNc4auHdUXedCJ7MHXQMkE/2i2ggs09U6bb5n20GhXFrrVWXLZ67z7HsYuGIX0Jo9ckbezaRhvELaVLagScbOSWP2a11lXSlI9BsK9M+heRbJRZaxVN+XvlaedHUCc3xpPut8CEtbrDbXSFJMoikUAhnatWimz1QN3yNOyeWtc79zssiRSs1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5GXqJ6FNN/1LznG/HyHGQ+jL/6aLS8p4EtvVnT2TVNMp1kXId4txrNzW6ywWYxjar4JEQ+2wJvPofTALk/nPyGt56PnLO0ENUTYHyobXWWxKNnfxuMcuNkPE1+YF2obpX29FiXYQmoev8fwPjPQ4ql3DVkxT81VdynGb0Q+/cYYpN5r5lf3o2ZxRHDQil4B5ONYpuj7hvYA5feZSbsbXqHGZeq0nThbWgJ3RXl3BW6oINVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+RbbTE9AAqu4sgBR7lYHwTPrSnZo941NXITtI5jS3NBXmlPrJK+XPonaDuamPLA655PZz8krvOxyzTBgGaiZ25Yp3gnhxTtjXA+3MT6mDhI91pWnHm7RGQDSKuq8X0UqPm6o3RmfmVdoi7QZ9u1tVjaNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+SyXZxAE2W5wLfprK8aXwYOzI/JmfdKOI4cgdvYlRIP1TVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkaYZt0hrMfYgrnjVDFlMhhTm8y0JUBW+ellkYhY8GombvzUmxVeZ9fl9qv1nONqsONVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+TOpLCl7dcAOUAx5Qv3g4WMyTXlnIPXYHORWNr/WvlQnTVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkpX/0flrUQo5DKAGAflfH9KxMlD8FeKeqBAq4cU0wnHIICrP+zYmbcIKLVNO+3k5nNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+TMgRgQT/HpA9q0igF8Ji/3MW2QkWMmeitL1yZqvsJDQjVRvEEgpXae7JFpZZA6Z+Q1UbxBIKV2nuyRaWWQOmfkkSa1RA9ypYMFPPGFHTrzZNeojh/Vb+HI0T+/BX4RP7xEqTD+qAb524mRBvpdDA6dNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+QL/nAfXhHuAf96V8Obzp1N06Pr8LVjKRrvyAG5IVFopevbw40equ99CsgT4/QzMiY1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5FK0tY95XmqJD3BUIcNxP6yA/l3D2N/lyX+EH6MYw2JBNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+QqPbcTiIknZW47xfyfHul6QxUTJeC+cECAzzo0DF2kGVNWFF2ZM1rCUF/9nBzlwMs1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5ONFvrIMESPTxcM7N38pqmqEpr/1CnwpcZ06PGepK7bFNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+TxWO8pVoG+OvWi7xbIWGq0z1EG+MM07F6Z3yAmqe+0gUOOeeM0oF5MaEbssC+hxqc1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5B4zbEeTU7HcyeSNhxwR+d7mSTkq5iCVHFv0y2V5oVITNVG8QSCldp7skWllkDpn5DVRvEEgpXae7JFpZZA6Z+Qrkf5FWwiAknOWl42ezoUA+97afm+Ko2Xj1TsGXM2vfTutl258K0rqJ5ffUvNu++k1UbxBIKV2nuyRaWWQOmfkNVG8QSCldp7skWllkDpn5N+PYylIBSIZuiCajMlnnR6jCiW61tltOzVKQmoO+4AxKJmLlSvY8XTCRQk1xqPQGhOabpiEaA3juIq9r/vEmoIGx3WR3IU8ExMpR/DU2ldHuhO2o6OM1N0UNcW3ANvI6KiQKyBkaUd7IYGTnfffMbDq9yI8eSVX0OU3RLsVJwRG | non_priority | rajudxucroibxcnxhiy gyxiwq xwv ooh c herbjrzaxvn hyhgq jl zymbciklvno tmgrgqt vb ql lyx | 0 |
19,146 | 3,146,363,481 | IssuesEvent | 2015-09-14 22:35:46 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | opened | VM service: pause() doesn't do anything when no code is running | Area-Observatory Type-Defect | When an isolate is alive but no code is running, the `pause` RPC doesn't have any effect. This makes it hard to write code that works correctly in different contexts; for example, code that pauses an isolate and waits for a pause event to fire can deadlock.
Ideally, calling `pause` in this state would fire a `PauseInterrupted` event and set the Isolate's `pauseEvent`. But if that's not possible, it should at least throw an error indicating that the pause couldn't be completed. | 1.0 | VM service: pause() doesn't do anything when no code is running - When an isolate is alive but no code is running, the `pause` RPC doesn't have any effect. This makes it hard to write code that works correctly in different contexts; for example, code that pauses an isolate and waits for a pause event to fire can deadlock.
Ideally, calling `pause` in this state would fire a `PauseInterrupted` event and set the Isolate's `pauseEvent`. But if that's not possible, it should at least throw an error indicating that the pause couldn't be completed. | non_priority | vm service pause doesn t do anything when no code is running when an isolate is alive but no code is running the pause rpc doesn t have any effect this makes it hard to write code that works correctly in different contexts for example code that pauses an isolate and waits for a pause event to fire can deadlock ideally calling pause in this state would fire a pauseinterrupted event and set the isolate s pauseevent but if that s not possible it should at least throw an error indicating that the pause couldn t be completed | 0 |
215,236 | 24,151,181,229 | IssuesEvent | 2022-09-22 01:03:32 | swagger-api/swagger-codegen | https://api.github.com/repos/swagger-api/swagger-codegen | opened | CVE-2022-40149 (High) detected in jettison-1.1.jar | security vulnerability | ## CVE-2022-40149 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.1.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /samples/client/petstore/scala/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar</p>
<p>
Dependency Hierarchy:
- jersey-ahc-client-1.0.5.jar (Root Library)
- jersey-json-1.14.jar
- :x: **jettison-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/swagger-api/swagger-codegen/commit/4b7a8d7d7384aa6a27d6309c35ade0916edae7ed">4b7a8d7d7384aa6a27d6309c35ade0916edae7ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40149>CVE-2022-40149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| True | CVE-2022-40149 (High) detected in jettison-1.1.jar - ## CVE-2022-40149 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.1.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /samples/client/petstore/scala/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar</p>
<p>
Dependency Hierarchy:
- jersey-ahc-client-1.0.5.jar (Root Library)
- jersey-json-1.14.jar
- :x: **jettison-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/swagger-api/swagger-codegen/commit/4b7a8d7d7384aa6a27d6309c35ade0916edae7ed">4b7a8d7d7384aa6a27d6309c35ade0916edae7ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Those using Jettison to parse untrusted XML or JSON data may be vulnerable to Denial of Service attacks (DOS). If the parser is running on user supplied input, an attacker may supply content that causes the parser to crash by stackoverflow. This effect may support a denial of service attack.
<p>Publish Date: 2022-09-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-40149>CVE-2022-40149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| non_priority | cve high detected in jettison jar cve high severity vulnerability vulnerable library jettison jar a stax implementation for json path to dependency file samples client petstore scala build gradle path to vulnerable library home wss scanner gradle caches modules files org codehaus jettison jettison jettison jar home wss scanner gradle caches modules files org codehaus jettison jettison jettison jar dependency hierarchy jersey ahc client jar root library jersey json jar x jettison jar vulnerable library found in head commit a href found in base branch master vulnerability details those using jettison to parse untrusted xml or json data may be vulnerable to denial of service attacks dos if the parser is running on user supplied input an attacker may supply content that causes the parser to crash by stackoverflow this effect may support a denial of service attack publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href | 0 |
51,182 | 13,207,388,563 | IssuesEvent | 2020-08-14 22:55:04 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | java path to libzip.so not in env-shell.sh environment (Trac #3) | Incomplete Migration Migrated from Trac cmake defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/3">https://code.icecube.wisc.edu/projects/icecube/ticket/3</a>, reported by troyand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T03:51:18",
"_ts": "1194753078000000",
"description": "",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"time": "2007-06-03T16:02:10",
"component": "cmake",
"summary": "java path to libzip.so not in env-shell.sh environment",
"priority": "minor",
"keywords": "",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
| 1.0 | java path to libzip.so not in env-shell.sh environment (Trac #3) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/3">https://code.icecube.wisc.edu/projects/icecube/ticket/3</a>, reported by troyand owned by troy</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2007-11-11T03:51:18",
"_ts": "1194753078000000",
"description": "",
"reporter": "troy",
"cc": "",
"resolution": "duplicate",
"time": "2007-06-03T16:02:10",
"component": "cmake",
"summary": "java path to libzip.so not in env-shell.sh environment",
"priority": "minor",
"keywords": "",
"milestone": "",
"owner": "troy",
"type": "defect"
}
```
</p>
</details>
| non_priority | java path to libzip so not in env shell sh environment trac migrated from json status closed changetime ts description reporter troy cc resolution duplicate time component cmake summary java path to libzip so not in env shell sh environment priority minor keywords milestone owner troy type defect | 0 |
9,105 | 8,518,999,579 | IssuesEvent | 2018-11-01 13:32:03 | cityofaustin/techstack | https://api.github.com/repos/cityofaustin/techstack | closed | Refine next round of ARR Service page drafts | Content type: Service Page Department: Resource Recovery Epic Site Content Size: S Team: Content | - [x] Send 4 pages to ARR team for review (URO, change trash cart size, apt. recycling, and donate items)
- [ ] Make edits | 1.0 | Refine next round of ARR Service page drafts - - [x] Send 4 pages to ARR team for review (URO, change trash cart size, apt. recycling, and donate items)
- [ ] Make edits | non_priority | refine next round of arr service page drafts send pages to arr team for review uro change trash cart size apt recycling and donate items make edits | 0 |
53,862 | 28,933,197,012 | IssuesEvent | 2023-05-09 02:24:56 | UIUC-PPL/charm | https://api.github.com/repos/UIUC-PPL/charm | opened | Pool small messages inside the runtime | enhancement Performance Converse | The runtime should pool small messages under a tunable size threshold to minimize memory allocation costs. This is especially important for applications (like Spectre) that use parameter marshalling, since the message object is hidden inside the runtime and can't be pooled by the application. This could be as simple as keeping a free list of fixed size messages on each PE. AMPI already does this with its AmpiMsgPool. Charm in fact already does this for some messages allocated via CkAllocSysMsg(), but that's only effective for a very limited set of messages. | True | Pool small messages inside the runtime - The runtime should pool small messages under a tunable size threshold to minimize memory allocation costs. This is especially important for applications (like Spectre) that use parameter marshalling, since the message object is hidden inside the runtime and can't be pooled by the application. This could be as simple as keeping a free list of fixed size messages on each PE. AMPI already does this with its AmpiMsgPool. Charm in fact already does this for some messages allocated via CkAllocSysMsg(), but that's only effective for a very limited set of messages. | non_priority | pool small messages inside the runtime the runtime should pool small messages under a tunable size threshold to minimize memory allocation costs this is especially important for applications like spectre that use parameter marshalling since the message object is hidden inside the runtime and can t be pooled by the application this could be as simple as keeping a free list of fixed size messages on each pe ampi already does this with its ampimsgpool charm in fact already does this for some messages allocated via ckallocsysmsg but that s only effective for a very limited set of messages | 0 |
289,345 | 21,780,017,435 | IssuesEvent | 2022-05-13 17:45:27 | vulkano-rs/vulkano | https://api.github.com/repos/vulkano-rs/vulkano | closed | Mention GPU boost in timestamp queries documentation | status: blocked type: documentation | Once timestamp queries are implemented, mention this in the docs.
https://developer.nvidia.com/setstablepowerstateexe-%20disabling%20-gpu-boost-windows-10-getting-more-deterministic-timestamp-queries
| 1.0 | Mention GPU boost in timestamp queries documentation - Once timestamp queries are implemented, mention this in the docs.
https://developer.nvidia.com/setstablepowerstateexe-%20disabling%20-gpu-boost-windows-10-getting-more-deterministic-timestamp-queries
| non_priority | mention gpu boost in timestamp queries documentation once timestamp queries are implemented mention this in the docs | 0 |
188,163 | 22,046,186,450 | IssuesEvent | 2022-05-30 02:10:11 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | closed | CVE-2016-9685 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed | security vulnerability | ## CVE-2016-9685 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/xfs/xfs_attr_list.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Multiple memory leaks in error paths in fs/xfs/xfs_attr_list.c in the Linux kernel before 4.5.1 allow local users to cause a denial of service (memory consumption) via crafted XFS filesystem operations.
<p>Publish Date: 2016-12-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-9685>CVE-2016-9685</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9685">https://nvd.nist.gov/vuln/detail/CVE-2016-9685</a></p>
<p>Release Date: 2016-12-28</p>
<p>Fix Resolution: 4.5.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-9685 (Medium) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2016-9685 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/xfs/xfs_attr_list.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Multiple memory leaks in error paths in fs/xfs/xfs_attr_list.c in the Linux kernel before 4.5.1 allow local users to cause a denial of service (memory consumption) via crafted XFS filesystem operations.
<p>Publish Date: 2016-12-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-9685>CVE-2016-9685</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9685">https://nvd.nist.gov/vuln/detail/CVE-2016-9685</a></p>
<p>Release Date: 2016-12-28</p>
<p>Fix Resolution: 4.5.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files fs xfs xfs attr list c vulnerability details multiple memory leaks in error paths in fs xfs xfs attr list c in the linux kernel before allow local users to cause a denial of service memory consumption via crafted xfs filesystem operations publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
126,412 | 17,028,788,235 | IssuesEvent | 2021-07-04 05:32:21 | b1017173/Hometoku | https://api.github.com/repos/b1017173/Hometoku | closed | gifとテキストの変更 | Python design enhancement | **作ろうとしている機能の詳細**
ゴール: 撮影したgifを使い,テキストも変更する
プロセス:
1. gifのURLをプログラムに書き込む
2. gifにあったようなテキストに変更する
3. ホメられ度によって表示する内容を変化させる
**完成の定義**
バグの精査(入り込みそうなバグ):
1. gif,テキストが表示されない
2. ホメられ度による条件分岐ができていない
**見積もり**
120 m/人
**その他**
***作業ブランチ***
main - develop - issue51
***特筆事項***
****タスク作成者への注意事項****
1. タグ管理をしっかりやってほしいです。上のタスクを例にとると:"優先度B", "feat(or 機能)", "search(or 検索)", "form(or 入力フォーム)"くらいは最低限つけてほしい。
2. このカードの存在を忘れないで(T . T)
作ったタスクは移動すべきタイミングでカラムを移動し、最後まで見守りましょう。
3. 作業ブランチを切って,ブランチ名はイシュー名にする.
ex)issue23 , issue33 とか
| 1.0 | gifとテキストの変更 - **作ろうとしている機能の詳細**
ゴール: 撮影したgifを使い,テキストも変更する
プロセス:
1. gifのURLをプログラムに書き込む
2. gifにあったようなテキストに変更する
3. ホメられ度によって表示する内容を変化させる
**完成の定義**
バグの精査(入り込みそうなバグ):
1. gif,テキストが表示されない
2. ホメられ度による条件分岐ができていない
**見積もり**
120 m/人
**その他**
***作業ブランチ***
main - develop - issue51
***特筆事項***
****タスク作成者への注意事項****
1. タグ管理をしっかりやってほしいです。上のタスクを例にとると:"優先度B", "feat(or 機能)", "search(or 検索)", "form(or 入力フォーム)"くらいは最低限つけてほしい。
2. このカードの存在を忘れないで(T . T)
作ったタスクは移動すべきタイミングでカラムを移動し、最後まで見守りましょう。
3. 作業ブランチを切って,ブランチ名はイシュー名にする.
ex)issue23 , issue33 とか
| non_priority | gifとテキストの変更 作ろうとしている機能の詳細 ゴール: 撮影したgifを使い,テキストも変更する プロセス: gifのurlをプログラムに書き込む gifにあったようなテキストに変更する ホメられ度によって表示する内容を変化させる 完成の定義 バグの精査 入り込みそうなバグ : gif,テキストが表示されない ホメられ度による条件分岐ができていない 見積もり m 人 その他 作業ブランチ main develop 特筆事項 タスク作成者への注意事項 タグ管理をしっかりやってほしいです。上のタスクを例にとると: 優先度b feat or 機能 search or 検索 form or 入力フォーム くらいは最低限つけてほしい。 このカードの存在を忘れないで t t 作ったタスクは移動すべきタイミングでカラムを移動し、最後まで見守りましょう。 作業ブランチを切って,ブランチ名はイシュー名にする. ex とか | 0 |
248,732 | 21,054,508,304 | IssuesEvent | 2022-04-01 00:49:00 | dotnet/winforms | https://api.github.com/repos/dotnet/winforms | closed | Flaky test: Splitter_OnSplitterMoved_Invoke_CallsSplitterMoved | test-bug | <!-- runfo report start -->
Runfo Tracking Issue: [system.windows.forms.tests.splittertests.splitter_onsplittermoved_invoke_callssplittermoved](https://runfo.azurewebsites.net/tracking/issue/315)
|Build|Definition|Kind|Run Name|
|---|---|---|---|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_arm64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_arm64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
Build Result Summary
|Day Hit Count|Week Hit Count|Month Hit Count|
|---|---|---|
|0|1|1|
<!-- runfo report end -->
| 1.0 | Flaky test: Splitter_OnSplitterMoved_Invoke_CallsSplitterMoved - <!-- runfo report start -->
Runfo Tracking Issue: [system.windows.forms.tests.splittertests.splitter_onsplittermoved_invoke_callssplittermoved](https://runfo.azurewebsites.net/tracking/issue/315)
|Build|Definition|Kind|Run Name|
|---|---|---|---|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_arm64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_arm64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x64-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
|[1687371](https://dev.azure.com/dnceng/public/_build/results?buildId=1687371)|[dotnet-winforms CI](https://dnceng.visualstudio.com/public/_build?definitionId=267)|[PR 6904](https://github.com/dotnet/winforms/pull/6904)|Windows_x86-xunit|
Build Result Summary
|Day Hit Count|Week Hit Count|Month Hit Count|
|---|---|---|
|0|1|1|
<!-- runfo report end -->
| non_priority | flaky test splitter onsplittermoved invoke callssplittermoved runfo tracking issue build definition kind run name build result summary day hit count week hit count month hit count | 0 |
138,962 | 31,150,286,560 | IssuesEvent | 2023-08-16 09:28:47 | AntaresSimulatorTeam/Antares_Simulator | https://api.github.com/repos/AntaresSimulatorTeam/Antares_Simulator | opened | Class Area : remove data member "enabled" | enhancement code | Class **Area** data member **enabled** does not seem of great use.
By the way it is initialized only in one of three **Area**'s constructor, which is strange could lead to undefined behavior. | 1.0 | Class Area : remove data member "enabled" - Class **Area** data member **enabled** does not seem of great use.
By the way it is initialized only in one of three **Area**'s constructor, which is strange could lead to undefined behavior. | non_priority | class area remove data member enabled class area data member enabled does not seem of great use by the way it is initialized only in one of three area s constructor which is strange could lead to undefined behavior | 0 |
96,525 | 20,027,286,703 | IssuesEvent | 2022-02-01 23:01:29 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.1] Child Templates - content templates | No Code Attached Yet | When you create a child template an html/tinymce folder is not created.
As a result when you go to set the folder in tinymce it only shows the availability to set the parent template. Its not obvious that if you create the folder in the child template it will then be displayed as an available location. | 1.0 | [4.1] Child Templates - content templates - When you create a child template an html/tinymce folder is not created.
As a result when you go to set the folder in tinymce it only shows the availability to set the parent template. Its not obvious that if you create the folder in the child template it will then be displayed as an available location. | non_priority | child templates content templates when you create a child template an html tinymce folder is not created as a result when you go to set the folder in tinymce it only shows the availability to set the parent template its not obvious that if you create the folder in the child template it will then be displayed as an available location | 0 |
99,880 | 11,165,661,886 | IssuesEvent | 2019-12-27 10:11:10 | alexdevteam/LUINT | https://api.github.com/repos/alexdevteam/LUINT | closed | Update the Processing Unit interface | documentation | It is not correct. push_signal should be just "push", and pull_signal should be just "pull".
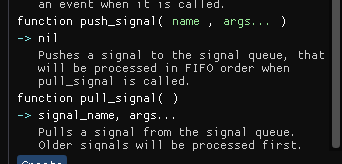
| 1.0 | Update the Processing Unit interface - It is not correct. push_signal should be just "push", and pull_signal should be just "pull".
| non_priority | update the processing unit interface it is not correct push signal should be just push and pull signal should be just pull | 0 |
66,631 | 27,529,387,787 | IssuesEvent | 2023-03-06 20:42:58 | microsoft/vscode-cpptools | https://api.github.com/repos/microsoft/vscode-cpptools | closed | "C_Cpp.default.___" properties no longer inherited by other workspace folders since v1.14.3 | Language Service more info needed | ### Environment
- OS and Version:
- VS Code Version:
- C/C++ Extension Version:
- If using SSH remote, specify OS of remote machine:
### Bug Summary and Steps to Reproduce
Create a multi-folder workspace e.g. "main.code-workspace" with two folders, in this case the main workspace folder and a separate folder called "module":
"folders": [
{
"path": "../"
},
{
"path": "../../../../module"
}
],
Add a "default" property so that intellisense inherits the property value when editing files within the modules folder e.g.:
"C_Cpp.default.defines": [
"EXAMPLE_DEFINE",
],
Since version v1.14.3, with the workspace open, intellisense will fail to find the definition "EXAMPLE_DEFINE" for files within the "modules" folder. This applies also to "C_Cpp.default.includePath" values.
Here is an example with some include files, they exist within the directories specified within "C_Cpp.default.includePath" but are no longer found by intellisense when working on the "subscriber.c", they were found on previous versions of the extension:


### Configuration and Logs
```shell
c_cpp_properties.json (sensitive files removed):
{
"configurations": [
{
"name": "Win32",
"includePath": [
".",
"../../../sdk/SDK_2_12_1_EVK-MCIMX7ULP/rtos/freertos/freertos_kernel/include/**",
"../../../sdk/SDK_2_12_1_EVK-MCIMX7ULP/rtos/freertos/freertos_kernel/portable/GCC/ARM_CM4F",
],
"defines": [
"EXAMPLE_DEFINE",
],
"windowsSdkVersion": "10.0.18362.0",
"compilerPath": "${env:ARMGCC_DIR}/bin/arm-none-eabi-gcc.exe",
"cStandard": "c17",
"cppStandard": "c++17",
"intelliSenseMode": "gcc-arm"
}
],
"version": 4
}
```
### Other Extensions
Plastic SCM (issue still occurs without use of this extension)
### Additional context
_No response_ | 1.0 | "C_Cpp.default.___" properties no longer inherited by other workspace folders since v1.14.3 - ### Environment
- OS and Version:
- VS Code Version:
- C/C++ Extension Version:
- If using SSH remote, specify OS of remote machine:
### Bug Summary and Steps to Reproduce
Create a multi-folder workspace e.g. "main.code-workspace" with two folders, in this case the main workspace folder and a separate folder called "module":
"folders": [
{
"path": "../"
},
{
"path": "../../../../module"
}
],
Add a "default" property so that intellisense inherits the property value when editing files within the modules folder e.g.:
"C_Cpp.default.defines": [
"EXAMPLE_DEFINE",
],
Since version v1.14.3, with the workspace open, intellisense will fail to find the definition "EXAMPLE_DEFINE" for files within the "modules" folder. This applies also to "C_Cpp.default.includePath" values.
Here is an example with some include files, they exist within the directories specified within "C_Cpp.default.includePath" but are no longer found by intellisense when working on the "subscriber.c", they were found on previous versions of the extension:


### Configuration and Logs
```shell
c_cpp_properties.json (sensitive files removed):
{
"configurations": [
{
"name": "Win32",
"includePath": [
".",
"../../../sdk/SDK_2_12_1_EVK-MCIMX7ULP/rtos/freertos/freertos_kernel/include/**",
"../../../sdk/SDK_2_12_1_EVK-MCIMX7ULP/rtos/freertos/freertos_kernel/portable/GCC/ARM_CM4F",
],
"defines": [
"EXAMPLE_DEFINE",
],
"windowsSdkVersion": "10.0.18362.0",
"compilerPath": "${env:ARMGCC_DIR}/bin/arm-none-eabi-gcc.exe",
"cStandard": "c17",
"cppStandard": "c++17",
"intelliSenseMode": "gcc-arm"
}
],
"version": 4
}
```
### Other Extensions
Plastic SCM (issue still occurs without use of this extension)
### Additional context
_No response_ | non_priority | c cpp default properties no longer inherited by other workspace folders since environment os and version vs code version c c extension version if using ssh remote specify os of remote machine bug summary and steps to reproduce create a multi folder workspace e g main code workspace with two folders in this case the main workspace folder and a separate folder called module folders path path module add a default property so that intellisense inherits the property value when editing files within the modules folder e g c cpp default defines example define since version with the workspace open intellisense will fail to find the definition example define for files within the modules folder this applies also to c cpp default includepath values here is an example with some include files they exist within the directories specified within c cpp default includepath but are no longer found by intellisense when working on the subscriber c they were found on previous versions of the extension configuration and logs shell c cpp properties json sensitive files removed configurations name includepath sdk sdk evk rtos freertos freertos kernel include sdk sdk evk rtos freertos freertos kernel portable gcc arm defines example define windowssdkversion compilerpath env armgcc dir bin arm none eabi gcc exe cstandard cppstandard c intellisensemode gcc arm version other extensions plastic scm issue still occurs without use of this extension additional context no response | 0 |
15,715 | 9,024,001,457 | IssuesEvent | 2019-02-07 09:20:10 | symfony/symfony | https://api.github.com/repos/symfony/symfony | closed | prefixed routes for localization bring slow performance in dev and prod | Performance Routing Status: Waiting feedback | Hi,
I migrated a project from Symfony 3.4 to Symfony 4.2 with prefixed routes for localization purposes and experienced that every time I change some code in a controller, the first time a page is loaded it takes more than 30s, when It was about 1-2 seconds before.
In Symfony 3.4 I used the third party component: be_simple_i18n.
In Symfony 4.2 I use the symfony's routing component that works about the same way (not using be_simple_i18n anymore).
Here you are a short code from a yaml conf file:
```yaml
frontend_yaml_i18n_routes:
resource: "../../src/K2K/Resources/config/routing/routing_frontend.yml"
prefix:
default: "/"
es: "/es"
es_ES: "/"
en_ES: "/en-es"
```
Thanks!
| True | prefixed routes for localization bring slow performance in dev and prod - Hi,
I migrated a project from Symfony 3.4 to Symfony 4.2 with prefixed routes for localization purposes and experienced that every time I change some code in a controller, the first time a page is loaded it takes more than 30s, when It was about 1-2 seconds before.
In Symfony 3.4 I used the third party component: be_simple_i18n.
In Symfony 4.2 I use the symfony's routing component that works about the same way (not using be_simple_i18n anymore).
Here you are a short code from a yaml conf file:
```yaml
frontend_yaml_i18n_routes:
resource: "../../src/K2K/Resources/config/routing/routing_frontend.yml"
prefix:
default: "/"
es: "/es"
es_ES: "/"
en_ES: "/en-es"
```
Thanks!
| non_priority | prefixed routes for localization bring slow performance in dev and prod hi i migrated a project from symfony to symfony with prefixed routes for localization purposes and experienced that every time i change some code in a controller the first time a page is loaded it takes more than when it was about seconds before in symfony i used the third party component be simple in symfony i use the symfony s routing component that works about the same way not using be simple anymore here you are a short code from a yaml conf file yaml frontend yaml routes resource src resources config routing routing frontend yml prefix default es es es es en es en es thanks | 0 |
183,499 | 14,234,399,912 | IssuesEvent | 2020-11-18 13:32:54 | SAPDocuments/Tutorials | https://api.github.com/repos/SAPDocuments/Tutorials | closed | Set Up Account for Document Information Extraction | Low-Prio SCPTest-2010A SCPTest-docinfo SCPTest-trial1 SCPTest-trial2 | Tutorial URL: https://developers.sap.com/tutorials/cp-aibus-dox-service-instance-booster.html
Please specify the step you are referring to : Step 2: Get service key
Step 4: Screenshot should be updated for service key info with new UI. Also step can be added to view the service key in SAP CP although we are downloading the service key after Booster creation.
This screenshot need to update in Tutorial 2(Step1) and Tutorial 3(Step1) as well.
Expected result:
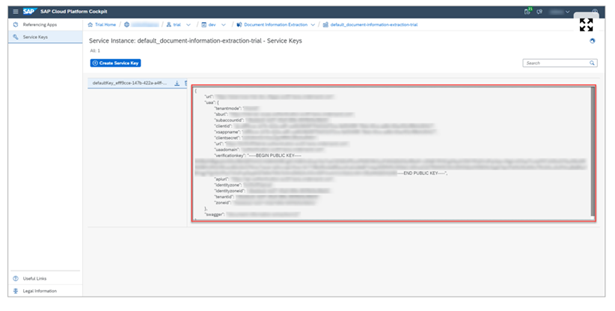
Actual result:
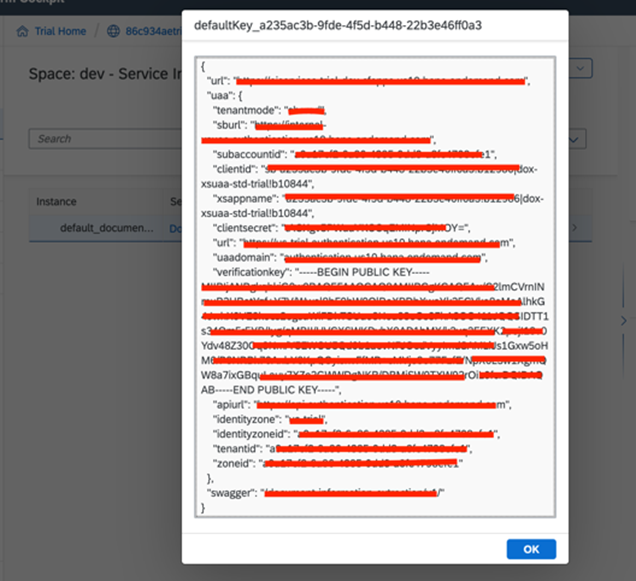
Labels to be added:
Landscape label: trail1, trial2
Scenario label: SCPTest-docinfo
| 4.0 | Set Up Account for Document Information Extraction - Tutorial URL: https://developers.sap.com/tutorials/cp-aibus-dox-service-instance-booster.html
Please specify the step you are referring to : Step 2: Get service key
Step 4: Screenshot should be updated for service key info with new UI. Also step can be added to view the service key in SAP CP although we are downloading the service key after Booster creation.
This screenshot need to update in Tutorial 2(Step1) and Tutorial 3(Step1) as well.
Expected result:
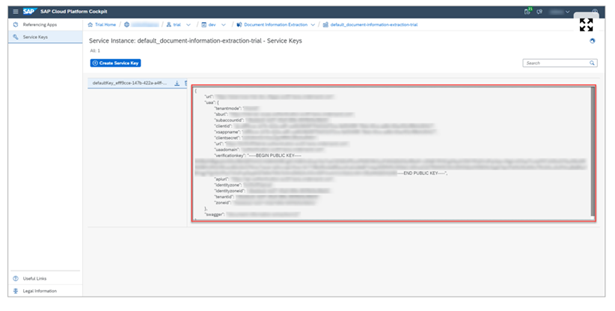
Actual result:
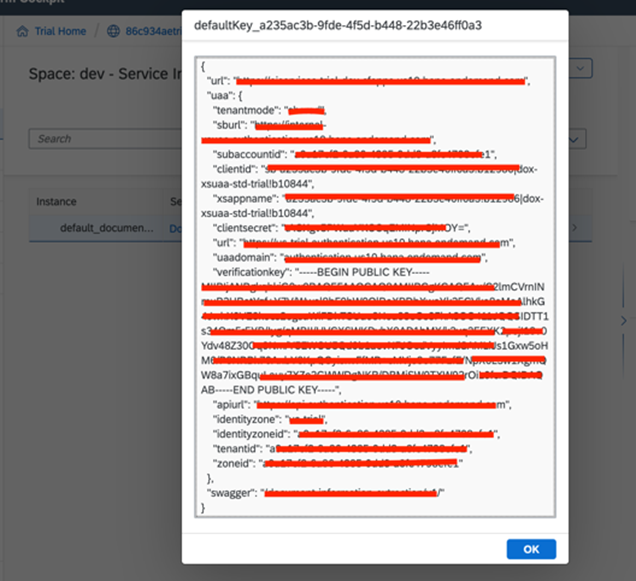
Labels to be added:
Landscape label: trail1, trial2
Scenario label: SCPTest-docinfo
| non_priority | set up account for document information extraction tutorial url please specify the step you are referring to step get service key step screenshot should be updated for service key info with new ui also step can be added to view the service key in sap cp although we are downloading the service key after booster creation this screenshot need to update in tutorial and tutorial as well expected result actual result labels to be added landscape label scenario label scptest docinfo | 0 |
303,299 | 22,969,365,679 | IssuesEvent | 2022-07-20 00:27:41 | wdika/mridc | https://api.github.com/repos/wdika/mridc | closed | The center_fractions argument can be confusing for non cartesian masking | bug documentation enhancement Stale | **Describe the bug**
Not precisely a bug, but [this](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/projects/reconstruction/model_zoo/conf/base_cirim_train.yaml#L65) argument should be generalized among different masking functions.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to [MaskFunc](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/mridc/collections/reconstruction/data/subsample.py#L76).
2. See how it acts for [random cartesian](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/mridc/collections/reconstruction/data/subsample.py#L130) masking and how for [gaussian](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/mridc/collections/reconstruction/data/subsample.py#L357) masking.
**Expected behavior**
For example, in gaussian masking, this argument acts as FWHM. This should be clearly formalized.
| 1.0 | The center_fractions argument can be confusing for non cartesian masking - **Describe the bug**
Not precisely a bug, but [this](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/projects/reconstruction/model_zoo/conf/base_cirim_train.yaml#L65) argument should be generalized among different masking functions.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to [MaskFunc](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/mridc/collections/reconstruction/data/subsample.py#L76).
2. See how it acts for [random cartesian](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/mridc/collections/reconstruction/data/subsample.py#L130) masking and how for [gaussian](https://github.com/wdika/mridc/blob/d859550a8d9b394b00dc815313a6805c0c59cd29/mridc/collections/reconstruction/data/subsample.py#L357) masking.
**Expected behavior**
For example, in gaussian masking, this argument acts as FWHM. This should be clearly formalized.
| non_priority | the center fractions argument can be confusing for non cartesian masking describe the bug not precisely a bug but argument should be generalized among different masking functions to reproduce steps to reproduce the behavior go to see how it acts for masking and how for masking expected behavior for example in gaussian masking this argument acts as fwhm this should be clearly formalized | 0 |
21,163 | 10,578,029,231 | IssuesEvent | 2019-10-07 21:29:46 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | opened | Crypto DecryptEnvelopedEmptyOctetString test crashes on CI | area-System.Security | Configuration: `netfx-Windows_NT-Release-x86-Windows.10.Amd64.ClientRS5.Open`
Dump is available: https://helix.dot.net/api/2019-06-17/jobs/948bbfd1-1a8d-4f80-98c7-87f70a914f20/workitems/System.Security.Cryptography.Pkcs.Tests/files/xunit.console.exe.6212.dmp
```
C:\dotnetbuild\work\948bbfd1-1a8d-4f80-98c7-87f70a914f20\Work\cf8fae2e-31fb-4c36-bc96-bc2f3e1ee396\Exec>xunit.console.exe System.Security.Cryptography.Pkcs.Tests.dll -xml testResults.xml -nologo -nocolor -notrait category=nonnetfxtests -notrait category=nonwindowstests -notrait category=IgnoreForCI -notrait category=OuterLoop -notrait category=failing
Discovering: System.Security.Cryptography.Pkcs.Tests (app domain = on [no shadow copy], method display = ClassAndMethod, method display options = None)
Discovered: System.Security.Cryptography.Pkcs.Tests (found 309 of 378 test cases)
Starting: System.Security.Cryptography.Pkcs.Tests (parallel test collections = on, max threads = 2)
System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.KeyTransRecipientInfoRsaOaepCertTests.TestKeyTransEncryptKey_RsaOaepCertificate_NoPlatformSupport_Throws [SKIP]
Condition(s) not met: "DoesNotSupportRsaOaepCerts"
System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.KeyAgreeRecipientInfoTests.TestKeyAgreement_PlatformNotSupported [SKIP]
Condition(s) not met: "DoesNotSupportDiffieHellman"
Unhandled Exception: System.Reflection.TargetInvocationException: Exception has been thrown by the target of an invocation. ---> System.AccessViolationException: Attempted to read or write protected memory. This is often an indication that other memory is corrupt.
at System.Security.Cryptography.X509Certificates.X509Utils._LoadCertFromBlob(Byte[] rawData, IntPtr password, UInt32 dwFlags, Boolean persistKeySet, SafeCertContextHandle& pCertCtx)
at System.Security.Cryptography.X509Certificates.X509Utils.LoadCertFromBlob(Byte[] rawData, IntPtr password, UInt32 dwFlags, Boolean persistKeySet, SafeCertContextHandle pCertCtx)
at System.Security.Cryptography.X509Certificates.X509Certificate.LoadCertificateFromBlob(Byte[] rawData, Object password, X509KeyStorageFlags keyStorageFlags)
at System.Security.Cryptography.X509Certificates.X509Certificate2..ctor(Byte[] rawData, String password, X509KeyStorageFlags keyStorageFlags)
at Test.Cryptography.CertLoader.TryGetCertificateWithPrivateKey(Boolean exportable) in /_/src/System.Security.Cryptography.Pkcs/tests/CertLoader.cs:line 86
at System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.DecryptTests.VerifySimpleDecrypt(Byte[] encodedMessage, CertLoader certLoader, ContentInfo expectedContent) in /_/src/System.Security.Cryptography.Pkcs/tests/EnvelopedCms/DecryptTests.cs:line 834
at System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.DecryptTests.TestSimpleDecrypt_RoundTrip(CertLoader certLoader, ContentInfo contentInfo, String algorithmOidValue, SubjectIdentifierType type, ContentInfo expectedContentInfo) in /_/src/System.Security.Cryptography.Pkcs/tests/EnvelopedCms/DecryptTests.cs:line 827
at System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.DecryptTests.DecryptEnvelopedEmptyOctetString() in /_/src/System.Security.Cryptography.Pkcs/tests/EnvelopedCms/DecryptTests.cs:line 755
--- End of inner exception stack trace ---
at System.RuntimeMethodHandle.InvokeMethod(Object target, Object[] arguments, Signature sig, Boolean constructor)
at System.Reflection.RuntimeMethodInfo.UnsafeInvokeInternal(Object obj, Object[] parameters, Object[] arguments)
at System.Reflection.RuntimeMethodInfo.Invoke(Object obj, BindingFlags invokeAttr, Binder binder, Object[] parameters, CultureInfo culture)
at Xunit.Sdk.TestInvoker`1.CallTestMethod(Object testClassInstance) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 150
at Xunit.Sdk.TestInvoker`1.<>c__DisplayClass48_1.<<InvokeTestMethodAsync>b__1>d.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 257
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestInvoker`1.<>c__DisplayClass48_1.<InvokeTestMethodAsync>b__1()
at Xunit.Sdk.ExecutionTimer.<AggregateAsync>d__4.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\ExecutionTimer.cs:line 48
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExecutionTimer.AggregateAsync(Func`1 asyncAction)
at Xunit.Sdk.ExceptionAggregator.<RunAsync>d__9.MoveNext() in C:\Dev\xunit\xunit\src\xunit.core\Sdk\ExceptionAggregator.cs:line 90
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExceptionAggregator.RunAsync(Func`1 code)
at Xunit.Sdk.TestInvoker`1.<InvokeTestMethodAsync>d__48.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 239
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestInvoker`1.InvokeTestMethodAsync(Object testClassInstance)
at Xunit.Sdk.TestInvoker`1.<<RunAsync>b__47_0>d.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 206
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestInvoker`1.<RunAsync>b__47_0()
at Xunit.Sdk.ExceptionAggregator.<RunAsync>d__10`1.MoveNext() in C:\Dev\xunit\xunit\src\xunit.core\Sdk\ExceptionAggregator.cs:line 107
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExceptionAggregator.RunAsync[T](Func`1 code)
at Xunit.Sdk.XunitTestRunner.<InvokeTestAsync>d__4.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\XunitTestRunner.cs:line 67
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.XunitTestRunner.InvokeTestAsync(ExceptionAggregator aggregator)
at Xunit.Sdk.ExceptionAggregator.<RunAsync>d__10`1.MoveNext()
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExceptionAggregator.RunAsync[T](Func`1 code)
at Xunit.Sdk.TestRunner`1.<RunAsync>d__43.MoveNext()
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestRunner`1.RunAsync()
at Xunit.Sdk.TestCaseRunner`1.<RunAsync>d__19.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestCaseRunner.cs:line 82
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestCaseRunner`1.RunAsync()
at Xunit.Sdk.XunitTestMethodRunner.RunTestCaseAsync(IXunitTestCase testCase) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\XunitTestMethodRunner.cs:line 45
at Xunit.Sdk.TestMethodRunner`1.<RunTestCasesAsync>d__32.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestMethodRunner.cs:line 136
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestMethodRunner`1.RunTestCasesAsync()
at Xunit.Sdk.TestMethodRunner`1.<RunAsync>d__31.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestMethodRunner.cs:line 106
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestMethodRunner`1.RunAsync()
at Xunit.Sdk.TestClassRunner`1.<RunTestMethodsAsync>d__38.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestClassRunner.cs:line 213
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestClassRunner`1.RunTestMethodsAsync()
at Xunit.Sdk.TestClassRunner`1.<RunAsync>d__37.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestClassRunner.cs:line 171
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestClassRunner`1.RunAsync()
at Xunit.Sdk.TestCollectionRunner`1.<RunTestClassesAsync>d__28.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestCollectionRunner.cs:line 130
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestCollectionRunner`1.RunTestClassesAsync()
at Xunit.Sdk.TestCollectionRunner`1.<RunAsync>d__27.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestCollectionRunner.cs:line 101
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestCollectionRunner`1.RunAsync()
at Xunit.Sdk.XunitTestAssemblyRunner.<>c__DisplayClass14_2.<RunTestCollectionsAsync>b__2() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\XunitTestAssemblyRunner.cs:line 184
at System.Threading.Tasks.Task`1.InnerInvoke()
at System.Threading.Tasks.Task.Execute()
at System.Threading.ExecutionContext.RunInternal(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.Tasks.Task.ExecuteWithThreadLocal(Task& currentTaskSlot)
at System.Threading.Tasks.Task.ExecuteEntry(Boolean bPreventDoubleExecution)
at Xunit.Sdk.MaxConcurrencySyncContext.RunOnSyncContext(SendOrPostCallback callback, Object state) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\MaxConcurrencySyncContext.cs:line 107
at System.Threading.ExecutionContext.RunInternal(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state)
at Xunit.Sdk.ExecutionContextHelper.Run(Object context, Action`1 action) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Utility\ExecutionContextHelper.cs:line 22
at Xunit.Sdk.MaxConcurrencySyncContext.WorkerThreadProc() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\MaxConcurrencySyncContext.cs:line 89
at System.Threading.ExecutionContext.RunInternal(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state)
at System.Threading.ThreadHelper.ThreadStart(Object obj)
----- end Mon 10/07/2019 20:21:24.52 ----- exit code -532462766 ----------------------------------------------------------
```
cc @bartonjs @krwq @GrabYourPitchforks | True | Crypto DecryptEnvelopedEmptyOctetString test crashes on CI - Configuration: `netfx-Windows_NT-Release-x86-Windows.10.Amd64.ClientRS5.Open`
Dump is available: https://helix.dot.net/api/2019-06-17/jobs/948bbfd1-1a8d-4f80-98c7-87f70a914f20/workitems/System.Security.Cryptography.Pkcs.Tests/files/xunit.console.exe.6212.dmp
```
C:\dotnetbuild\work\948bbfd1-1a8d-4f80-98c7-87f70a914f20\Work\cf8fae2e-31fb-4c36-bc96-bc2f3e1ee396\Exec>xunit.console.exe System.Security.Cryptography.Pkcs.Tests.dll -xml testResults.xml -nologo -nocolor -notrait category=nonnetfxtests -notrait category=nonwindowstests -notrait category=IgnoreForCI -notrait category=OuterLoop -notrait category=failing
Discovering: System.Security.Cryptography.Pkcs.Tests (app domain = on [no shadow copy], method display = ClassAndMethod, method display options = None)
Discovered: System.Security.Cryptography.Pkcs.Tests (found 309 of 378 test cases)
Starting: System.Security.Cryptography.Pkcs.Tests (parallel test collections = on, max threads = 2)
System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.KeyTransRecipientInfoRsaOaepCertTests.TestKeyTransEncryptKey_RsaOaepCertificate_NoPlatformSupport_Throws [SKIP]
Condition(s) not met: "DoesNotSupportRsaOaepCerts"
System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.KeyAgreeRecipientInfoTests.TestKeyAgreement_PlatformNotSupported [SKIP]
Condition(s) not met: "DoesNotSupportDiffieHellman"
Unhandled Exception: System.Reflection.TargetInvocationException: Exception has been thrown by the target of an invocation. ---> System.AccessViolationException: Attempted to read or write protected memory. This is often an indication that other memory is corrupt.
at System.Security.Cryptography.X509Certificates.X509Utils._LoadCertFromBlob(Byte[] rawData, IntPtr password, UInt32 dwFlags, Boolean persistKeySet, SafeCertContextHandle& pCertCtx)
at System.Security.Cryptography.X509Certificates.X509Utils.LoadCertFromBlob(Byte[] rawData, IntPtr password, UInt32 dwFlags, Boolean persistKeySet, SafeCertContextHandle pCertCtx)
at System.Security.Cryptography.X509Certificates.X509Certificate.LoadCertificateFromBlob(Byte[] rawData, Object password, X509KeyStorageFlags keyStorageFlags)
at System.Security.Cryptography.X509Certificates.X509Certificate2..ctor(Byte[] rawData, String password, X509KeyStorageFlags keyStorageFlags)
at Test.Cryptography.CertLoader.TryGetCertificateWithPrivateKey(Boolean exportable) in /_/src/System.Security.Cryptography.Pkcs/tests/CertLoader.cs:line 86
at System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.DecryptTests.VerifySimpleDecrypt(Byte[] encodedMessage, CertLoader certLoader, ContentInfo expectedContent) in /_/src/System.Security.Cryptography.Pkcs/tests/EnvelopedCms/DecryptTests.cs:line 834
at System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.DecryptTests.TestSimpleDecrypt_RoundTrip(CertLoader certLoader, ContentInfo contentInfo, String algorithmOidValue, SubjectIdentifierType type, ContentInfo expectedContentInfo) in /_/src/System.Security.Cryptography.Pkcs/tests/EnvelopedCms/DecryptTests.cs:line 827
at System.Security.Cryptography.Pkcs.EnvelopedCmsTests.Tests.DecryptTests.DecryptEnvelopedEmptyOctetString() in /_/src/System.Security.Cryptography.Pkcs/tests/EnvelopedCms/DecryptTests.cs:line 755
--- End of inner exception stack trace ---
at System.RuntimeMethodHandle.InvokeMethod(Object target, Object[] arguments, Signature sig, Boolean constructor)
at System.Reflection.RuntimeMethodInfo.UnsafeInvokeInternal(Object obj, Object[] parameters, Object[] arguments)
at System.Reflection.RuntimeMethodInfo.Invoke(Object obj, BindingFlags invokeAttr, Binder binder, Object[] parameters, CultureInfo culture)
at Xunit.Sdk.TestInvoker`1.CallTestMethod(Object testClassInstance) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 150
at Xunit.Sdk.TestInvoker`1.<>c__DisplayClass48_1.<<InvokeTestMethodAsync>b__1>d.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 257
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestInvoker`1.<>c__DisplayClass48_1.<InvokeTestMethodAsync>b__1()
at Xunit.Sdk.ExecutionTimer.<AggregateAsync>d__4.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\ExecutionTimer.cs:line 48
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExecutionTimer.AggregateAsync(Func`1 asyncAction)
at Xunit.Sdk.ExceptionAggregator.<RunAsync>d__9.MoveNext() in C:\Dev\xunit\xunit\src\xunit.core\Sdk\ExceptionAggregator.cs:line 90
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExceptionAggregator.RunAsync(Func`1 code)
at Xunit.Sdk.TestInvoker`1.<InvokeTestMethodAsync>d__48.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 239
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestInvoker`1.InvokeTestMethodAsync(Object testClassInstance)
at Xunit.Sdk.TestInvoker`1.<<RunAsync>b__47_0>d.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestInvoker.cs:line 206
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestInvoker`1.<RunAsync>b__47_0()
at Xunit.Sdk.ExceptionAggregator.<RunAsync>d__10`1.MoveNext() in C:\Dev\xunit\xunit\src\xunit.core\Sdk\ExceptionAggregator.cs:line 107
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExceptionAggregator.RunAsync[T](Func`1 code)
at Xunit.Sdk.XunitTestRunner.<InvokeTestAsync>d__4.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\XunitTestRunner.cs:line 67
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.XunitTestRunner.InvokeTestAsync(ExceptionAggregator aggregator)
at Xunit.Sdk.ExceptionAggregator.<RunAsync>d__10`1.MoveNext()
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.ExceptionAggregator.RunAsync[T](Func`1 code)
at Xunit.Sdk.TestRunner`1.<RunAsync>d__43.MoveNext()
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestRunner`1.RunAsync()
at Xunit.Sdk.TestCaseRunner`1.<RunAsync>d__19.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestCaseRunner.cs:line 82
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestCaseRunner`1.RunAsync()
at Xunit.Sdk.XunitTestMethodRunner.RunTestCaseAsync(IXunitTestCase testCase) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\XunitTestMethodRunner.cs:line 45
at Xunit.Sdk.TestMethodRunner`1.<RunTestCasesAsync>d__32.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestMethodRunner.cs:line 136
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestMethodRunner`1.RunTestCasesAsync()
at Xunit.Sdk.TestMethodRunner`1.<RunAsync>d__31.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestMethodRunner.cs:line 106
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestMethodRunner`1.RunAsync()
at Xunit.Sdk.TestClassRunner`1.<RunTestMethodsAsync>d__38.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestClassRunner.cs:line 213
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestClassRunner`1.RunTestMethodsAsync()
at Xunit.Sdk.TestClassRunner`1.<RunAsync>d__37.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestClassRunner.cs:line 171
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestClassRunner`1.RunAsync()
at Xunit.Sdk.TestCollectionRunner`1.<RunTestClassesAsync>d__28.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestCollectionRunner.cs:line 130
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestCollectionRunner`1.RunTestClassesAsync()
at Xunit.Sdk.TestCollectionRunner`1.<RunAsync>d__27.MoveNext() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\TestCollectionRunner.cs:line 101
at System.Runtime.CompilerServices.AsyncTaskMethodBuilder`1.Start[TStateMachine](TStateMachine& stateMachine)
at Xunit.Sdk.TestCollectionRunner`1.RunAsync()
at Xunit.Sdk.XunitTestAssemblyRunner.<>c__DisplayClass14_2.<RunTestCollectionsAsync>b__2() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Frameworks\Runners\XunitTestAssemblyRunner.cs:line 184
at System.Threading.Tasks.Task`1.InnerInvoke()
at System.Threading.Tasks.Task.Execute()
at System.Threading.ExecutionContext.RunInternal(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.Tasks.Task.ExecuteWithThreadLocal(Task& currentTaskSlot)
at System.Threading.Tasks.Task.ExecuteEntry(Boolean bPreventDoubleExecution)
at Xunit.Sdk.MaxConcurrencySyncContext.RunOnSyncContext(SendOrPostCallback callback, Object state) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\MaxConcurrencySyncContext.cs:line 107
at System.Threading.ExecutionContext.RunInternal(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state)
at Xunit.Sdk.ExecutionContextHelper.Run(Object context, Action`1 action) in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\Utility\ExecutionContextHelper.cs:line 22
at Xunit.Sdk.MaxConcurrencySyncContext.WorkerThreadProc() in C:\Dev\xunit\xunit\src\xunit.execution\Sdk\MaxConcurrencySyncContext.cs:line 89
at System.Threading.ExecutionContext.RunInternal(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state, Boolean preserveSyncCtx)
at System.Threading.ExecutionContext.Run(ExecutionContext executionContext, ContextCallback callback, Object state)
at System.Threading.ThreadHelper.ThreadStart(Object obj)
----- end Mon 10/07/2019 20:21:24.52 ----- exit code -532462766 ----------------------------------------------------------
```
cc @bartonjs @krwq @GrabYourPitchforks | non_priority | crypto decryptenvelopedemptyoctetstring test crashes on ci configuration netfx windows nt release windows open dump is available c dotnetbuild work work exec xunit console exe system security cryptography pkcs tests dll xml testresults xml nologo nocolor notrait category nonnetfxtests notrait category nonwindowstests notrait category ignoreforci notrait category outerloop notrait category failing discovering system security cryptography pkcs tests app domain on method display classandmethod method display options none discovered system security cryptography pkcs tests found of test cases starting system security cryptography pkcs tests parallel test collections on max threads system security cryptography pkcs envelopedcmstests tests keytransrecipientinforsaoaepcerttests testkeytransencryptkey rsaoaepcertificate noplatformsupport throws condition s not met doesnotsupportrsaoaepcerts system security cryptography pkcs envelopedcmstests tests keyagreerecipientinfotests testkeyagreement platformnotsupported condition s not met doesnotsupportdiffiehellman unhandled exception system reflection targetinvocationexception exception has been thrown by the target of an invocation system accessviolationexception attempted to read or write protected memory this is often an indication that other memory is corrupt at system security cryptography loadcertfromblob byte rawdata intptr password dwflags boolean persistkeyset safecertcontexthandle pcertctx at system security cryptography loadcertfromblob byte rawdata intptr password dwflags boolean persistkeyset safecertcontexthandle pcertctx at system security cryptography loadcertificatefromblob byte rawdata object password keystorageflags at system security cryptography ctor byte rawdata string password keystorageflags at test cryptography certloader trygetcertificatewithprivatekey boolean exportable in src system security cryptography pkcs tests certloader cs line at system security cryptography pkcs envelopedcmstests tests decrypttests verifysimpledecrypt byte encodedmessage certloader certloader contentinfo expectedcontent in src system security cryptography pkcs tests envelopedcms decrypttests cs line at system security cryptography pkcs envelopedcmstests tests decrypttests testsimpledecrypt roundtrip certloader certloader contentinfo contentinfo string algorithmoidvalue subjectidentifiertype type contentinfo expectedcontentinfo in src system security cryptography pkcs tests envelopedcms decrypttests cs line at system security cryptography pkcs envelopedcmstests tests decrypttests decryptenvelopedemptyoctetstring in src system security cryptography pkcs tests envelopedcms decrypttests cs line end of inner exception stack trace at system runtimemethodhandle invokemethod object target object arguments signature sig boolean constructor at system reflection runtimemethodinfo unsafeinvokeinternal object obj object parameters object arguments at system reflection runtimemethodinfo invoke object obj bindingflags invokeattr binder binder object parameters cultureinfo culture at xunit sdk testinvoker calltestmethod object testclassinstance in c dev xunit xunit src xunit execution sdk frameworks runners testinvoker cs line at xunit sdk testinvoker c b d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testinvoker cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testinvoker c b at xunit sdk executiontimer d movenext in c dev xunit xunit src xunit execution sdk frameworks executiontimer cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk executiontimer aggregateasync func asyncaction at xunit sdk exceptionaggregator d movenext in c dev xunit xunit src xunit core sdk exceptionaggregator cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk exceptionaggregator runasync func code at xunit sdk testinvoker d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testinvoker cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testinvoker invoketestmethodasync object testclassinstance at xunit sdk testinvoker b d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testinvoker cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testinvoker b at xunit sdk exceptionaggregator d movenext in c dev xunit xunit src xunit core sdk exceptionaggregator cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk exceptionaggregator runasync func code at xunit sdk xunittestrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners xunittestrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk xunittestrunner invoketestasync exceptionaggregator aggregator at xunit sdk exceptionaggregator d movenext at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk exceptionaggregator runasync func code at xunit sdk testrunner d movenext at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testrunner runasync at xunit sdk testcaserunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testcaserunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testcaserunner runasync at xunit sdk xunittestmethodrunner runtestcaseasync ixunittestcase testcase in c dev xunit xunit src xunit execution sdk frameworks runners xunittestmethodrunner cs line at xunit sdk testmethodrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testmethodrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testmethodrunner runtestcasesasync at xunit sdk testmethodrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testmethodrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testmethodrunner runasync at xunit sdk testclassrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testclassrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testclassrunner runtestmethodsasync at xunit sdk testclassrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testclassrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testclassrunner runasync at xunit sdk testcollectionrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testcollectionrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testcollectionrunner runtestclassesasync at xunit sdk testcollectionrunner d movenext in c dev xunit xunit src xunit execution sdk frameworks runners testcollectionrunner cs line at system runtime compilerservices asynctaskmethodbuilder start tstatemachine statemachine at xunit sdk testcollectionrunner runasync at xunit sdk xunittestassemblyrunner c b in c dev xunit xunit src xunit execution sdk frameworks runners xunittestassemblyrunner cs line at system threading tasks task innerinvoke at system threading tasks task execute at system threading executioncontext runinternal executioncontext executioncontext contextcallback callback object state boolean preservesyncctx at system threading executioncontext run executioncontext executioncontext contextcallback callback object state boolean preservesyncctx at system threading tasks task executewiththreadlocal task currenttaskslot at system threading tasks task executeentry boolean bpreventdoubleexecution at xunit sdk maxconcurrencysynccontext runonsynccontext sendorpostcallback callback object state in c dev xunit xunit src xunit execution sdk maxconcurrencysynccontext cs line at system threading executioncontext runinternal executioncontext executioncontext contextcallback callback object state boolean preservesyncctx at system threading executioncontext run executioncontext executioncontext contextcallback callback object state boolean preservesyncctx at system threading executioncontext run executioncontext executioncontext contextcallback callback object state at xunit sdk executioncontexthelper run object context action action in c dev xunit xunit src xunit execution sdk utility executioncontexthelper cs line at xunit sdk maxconcurrencysynccontext workerthreadproc in c dev xunit xunit src xunit execution sdk maxconcurrencysynccontext cs line at system threading executioncontext runinternal executioncontext executioncontext contextcallback callback object state boolean preservesyncctx at system threading executioncontext run executioncontext executioncontext contextcallback callback object state boolean preservesyncctx at system threading executioncontext run executioncontext executioncontext contextcallback callback object state at system threading threadhelper threadstart object obj end mon exit code cc bartonjs krwq grabyourpitchforks | 0 |
93,925 | 27,075,164,907 | IssuesEvent | 2023-02-14 10:04:18 | home-assistant/operating-system | https://api.github.com/repos/home-assistant/operating-system | closed | HAOS compile failed with git dubious ownership | bug build | ### Describe the issue you are experiencing
I try to follow the instruction at https://developers.home-assistant.io/docs/operating-system/getting-started, and it failed to build containerd with `fatal: detected dubious ownership in repository at '/build'`
This failed with both podman on my home Arch linux machine and docker version 20.10.17 on AWS EC2 Ubuntu
The last output is this:
```
>>> containerd 1.6.8 Building
cd /build/output/build/containerd-1.6.8; GO111MODULE=on GOFLAGS=-mod=vendor GOROOT="/build/output/host/lib/go" GOPATH="/build/output/host/usr/share/go-path" GOCACHE="/build/output/host/usr/share/go-cache" GOMODCACHE="/build/output/host/usr/share/go-path/pkg/mod" GOPROXY=off PATH="/build/output/host/bin:/build/output/host/sbin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" GOBIN= CGO_ENABLED=1 GOOS="linux" GOARCH=arm64 CC="/build/output/host/bin/aarch64-buildroot-linux-gnu-gcc" CXX="/build/output/host/bin/aarch64-buildroot-linux-gnu-g++" CGO_CFLAGS="-D_LARGEFILE_SOURCE -D_LARGEFILE64_SOURCE -D_FILE_OFFSET_BITS=64 -O2 -g0 -D_FORTIFY_SOURCE=1" CGO_CXXFLAGS="-D_LARGEFILE_SOURCE -D_LARGEFILE64_SOURCE -D_FILE_OFFSET_BITS=64 -O2 -g0 -D_FORTIFY_SOURCE=1" CGO_LDFLAGS="" GOTOOLDIR="/build/output/host/lib/go/pkg/tool/linux_arm64" /build/output/host/bin/go build -v -ldflags "-X github.com/containerd/containerd/version.Version=1.6.8" -modcacherw -tags "apparmor no_btrfs" -trimpath -p 33 -o /build/output/build/containerd-1.6.8/bin/containerd github.com/containerd/containerd/cmd/containerd
# cd /build; git status --porcelain
fatal: detected dubious ownership in repository at '/build'
To add an exception for this directory, call:
git config --global --add safe.directory /build
error obtaining VCS status: exit status 128
Use -buildvcs=false to disable VCS stamping.
make[1]: *** [package/pkg-generic.mk:293: /build/output/build/containerd-1.6.8/.stamp_built] Error 1
make[1]: Leaving directory '/build/buildroot'
make: *** [Makefile:39: rpi4_64] Error 2
```
### What operating system image do you use?
rpi4-64 (Raspberry Pi 4/400 64-bit OS)
### What version of Home Assistant Operating System is installed?
dev
### Did you upgrade the Operating System.
Yes
### Steps to reproduce the issue
1. Follow the instruction at https://developers.home-assistant.io/docs/operating-system/getting-started#prepare-development-environment to clone HAOS
2. Follow the instruction at https://developers.home-assistant.io/docs/operating-system/getting-started#build-images-using-build-container
3. Let it run for a while
4. Build failed with `fatal: detected dubious ownership in repository at '/build'`
...
### Anything in the Supervisor logs that might be useful for us?
```txt
There's no supervisor log, as I can't even compile the OS
```
### Anything in the Host logs that might be useful for us?
```txt
There's no host log, as I can't even compile the OS
```
### System information
_No response_
### Additional information
_No response_ | 1.0 | HAOS compile failed with git dubious ownership - ### Describe the issue you are experiencing
I try to follow the instruction at https://developers.home-assistant.io/docs/operating-system/getting-started, and it failed to build containerd with `fatal: detected dubious ownership in repository at '/build'`
This failed with both podman on my home Arch linux machine and docker version 20.10.17 on AWS EC2 Ubuntu
The last output is this:
```
>>> containerd 1.6.8 Building
cd /build/output/build/containerd-1.6.8; GO111MODULE=on GOFLAGS=-mod=vendor GOROOT="/build/output/host/lib/go" GOPATH="/build/output/host/usr/share/go-path" GOCACHE="/build/output/host/usr/share/go-cache" GOMODCACHE="/build/output/host/usr/share/go-path/pkg/mod" GOPROXY=off PATH="/build/output/host/bin:/build/output/host/sbin:/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin" GOBIN= CGO_ENABLED=1 GOOS="linux" GOARCH=arm64 CC="/build/output/host/bin/aarch64-buildroot-linux-gnu-gcc" CXX="/build/output/host/bin/aarch64-buildroot-linux-gnu-g++" CGO_CFLAGS="-D_LARGEFILE_SOURCE -D_LARGEFILE64_SOURCE -D_FILE_OFFSET_BITS=64 -O2 -g0 -D_FORTIFY_SOURCE=1" CGO_CXXFLAGS="-D_LARGEFILE_SOURCE -D_LARGEFILE64_SOURCE -D_FILE_OFFSET_BITS=64 -O2 -g0 -D_FORTIFY_SOURCE=1" CGO_LDFLAGS="" GOTOOLDIR="/build/output/host/lib/go/pkg/tool/linux_arm64" /build/output/host/bin/go build -v -ldflags "-X github.com/containerd/containerd/version.Version=1.6.8" -modcacherw -tags "apparmor no_btrfs" -trimpath -p 33 -o /build/output/build/containerd-1.6.8/bin/containerd github.com/containerd/containerd/cmd/containerd
# cd /build; git status --porcelain
fatal: detected dubious ownership in repository at '/build'
To add an exception for this directory, call:
git config --global --add safe.directory /build
error obtaining VCS status: exit status 128
Use -buildvcs=false to disable VCS stamping.
make[1]: *** [package/pkg-generic.mk:293: /build/output/build/containerd-1.6.8/.stamp_built] Error 1
make[1]: Leaving directory '/build/buildroot'
make: *** [Makefile:39: rpi4_64] Error 2
```
### What operating system image do you use?
rpi4-64 (Raspberry Pi 4/400 64-bit OS)
### What version of Home Assistant Operating System is installed?
dev
### Did you upgrade the Operating System.
Yes
### Steps to reproduce the issue
1. Follow the instruction at https://developers.home-assistant.io/docs/operating-system/getting-started#prepare-development-environment to clone HAOS
2. Follow the instruction at https://developers.home-assistant.io/docs/operating-system/getting-started#build-images-using-build-container
3. Let it run for a while
4. Build failed with `fatal: detected dubious ownership in repository at '/build'`
...
### Anything in the Supervisor logs that might be useful for us?
```txt
There's no supervisor log, as I can't even compile the OS
```
### Anything in the Host logs that might be useful for us?
```txt
There's no host log, as I can't even compile the OS
```
### System information
_No response_
### Additional information
_No response_ | non_priority | haos compile failed with git dubious ownership describe the issue you are experiencing i try to follow the instruction at and it failed to build containerd with fatal detected dubious ownership in repository at build this failed with both podman on my home arch linux machine and docker version on aws ubuntu the last output is this containerd building cd build output build containerd on goflags mod vendor goroot build output host lib go gopath build output host usr share go path gocache build output host usr share go cache gomodcache build output host usr share go path pkg mod goproxy off path build output host bin build output host sbin usr local sbin usr local bin usr sbin usr bin sbin bin gobin cgo enabled goos linux goarch cc build output host bin buildroot linux gnu gcc cxx build output host bin buildroot linux gnu g cgo cflags d largefile source d source d file offset bits d fortify source cgo cxxflags d largefile source d source d file offset bits d fortify source cgo ldflags gotooldir build output host lib go pkg tool linux build output host bin go build v ldflags x github com containerd containerd version version modcacherw tags apparmor no btrfs trimpath p o build output build containerd bin containerd github com containerd containerd cmd containerd cd build git status porcelain fatal detected dubious ownership in repository at build to add an exception for this directory call git config global add safe directory build error obtaining vcs status exit status use buildvcs false to disable vcs stamping make error make leaving directory build buildroot make error what operating system image do you use raspberry pi bit os what version of home assistant operating system is installed dev did you upgrade the operating system yes steps to reproduce the issue follow the instruction at to clone haos follow the instruction at let it run for a while build failed with fatal detected dubious ownership in repository at build anything in the supervisor logs that might be useful for us txt there s no supervisor log as i can t even compile the os anything in the host logs that might be useful for us txt there s no host log as i can t even compile the os system information no response additional information no response | 0 |
26,822 | 7,873,070,469 | IssuesEvent | 2018-06-25 13:18:25 | Microsoft/WindowsTemplateStudio | https://api.github.com/repos/Microsoft/WindowsTemplateStudio | closed | Build dev.templates.tests.wack_20180619.6 failed | bug vsts-build | ## Build dev.templates.tests.wack_20180619.6
- **Build result:** `failed`
- **Build queued:** 6/19/2018 2:57:04 PM
- **Build duration:** 343.37 minutes
### Details
Build [dev.templates.tests.wack_20180619.6](https://winappstudio.visualstudio.com/web/build.aspx?pcguid=a4ef43be-68ce-4195-a619-079b4d9834c2&builduri=vstfs%3a%2f%2f%2fBuild%2fBuild%2f25898) failed
+ Process completed with exit code 5.
+ There is not enough space on the disk
+ There is not enough space on the disk
Find detailed information in the [build log files](https://uwpctdiags.blob.core.windows.net/buildlogs/dev.templates.tests.wack_20180619.6_logs.zip)
| 1.0 | Build dev.templates.tests.wack_20180619.6 failed - ## Build dev.templates.tests.wack_20180619.6
- **Build result:** `failed`
- **Build queued:** 6/19/2018 2:57:04 PM
- **Build duration:** 343.37 minutes
### Details
Build [dev.templates.tests.wack_20180619.6](https://winappstudio.visualstudio.com/web/build.aspx?pcguid=a4ef43be-68ce-4195-a619-079b4d9834c2&builduri=vstfs%3a%2f%2f%2fBuild%2fBuild%2f25898) failed
+ Process completed with exit code 5.
+ There is not enough space on the disk
+ There is not enough space on the disk
Find detailed information in the [build log files](https://uwpctdiags.blob.core.windows.net/buildlogs/dev.templates.tests.wack_20180619.6_logs.zip)
| non_priority | build dev templates tests wack failed build dev templates tests wack build result failed build queued pm build duration minutes details build failed process completed with exit code there is not enough space on the disk there is not enough space on the disk find detailed information in the | 0 |
150,632 | 13,349,617,949 | IssuesEvent | 2020-08-30 02:12:25 | WhiteFox-Lugh/sdvx-difficulty-table | https://api.github.com/repos/WhiteFox-Lugh/sdvx-difficulty-table | opened | 曲データの管理 | documentation | レベルごとに管理するとわかりやすいけど、曲の ID はデータを入れる際に入れ替わってはいけないので、新曲が入ったときは末尾にどんどん加えていくことを気を付けなければいけない | 1.0 | 曲データの管理 - レベルごとに管理するとわかりやすいけど、曲の ID はデータを入れる際に入れ替わってはいけないので、新曲が入ったときは末尾にどんどん加えていくことを気を付けなければいけない | non_priority | 曲データの管理 レベルごとに管理するとわかりやすいけど、曲の id はデータを入れる際に入れ替わってはいけないので、新曲が入ったときは末尾にどんどん加えていくことを気を付けなければいけない | 0 |
53,160 | 11,013,850,324 | IssuesEvent | 2019-12-04 21:23:12 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | [iOS] AppStore: ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. | t: xcode tool ⌺ platform-ios |
ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. If method names in your source code match the private Apple APIs listed above, altering your method names will help prevent this app from being flagged in future submissions. In addition, note that one or more of the above APIs may be located in a static library that was included with your app. If so, they must be removed. For further information, visit the Technical Support Information at http://developer.apple.com/support/technical/Though you are not required to fix the following issues, we wanted to make you aware of them:ITMS-90809: Deprecated API Usage - Apple will stop accepting submissions of apps that use UIWebView APIs . See https://developer.apple.com/documentation/uikit/uiwebview for more information. | ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. If method names in your source code match the private Apple APIs listed above, altering your method names will help prevent this app from being flagged in future submissions. In addition, note that one or more of the above APIs may be located in a static library that was included with your app. If so, they must be removed. For further information, visit the Technical Support Information at http://developer.apple.com/support/technical/Though you are not required to fix the following issues, we wanted to make you aware of them:ITMS-90809: Deprecated API Usage - Apple will stop accepting submissions of apps that use UIWebView APIs . See https://developer.apple.com/documentation/uikit/uiwebview for more information.
-- | --
ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. If method names in your source code match the private Apple APIs listed above, altering your method names will help prevent this app from being flagged in future submissions. In addition, note that one or more of the above APIs may be located in a static library that was included with your app. If so, they must be removed. For further information, visit the Technical Support Information at http://developer.apple.com/support/technical/Though you are not required to fix the following issues, we wanted to make you aware of them:ITMS-90809: Deprecated API Usage - Apple will stop accepting submissions of apps that use UIWebView APIs . See https://developer.apple.com/documentation/uikit/uiwebview for more information.
i have submitted release build but by default it takes debug build
| 1.0 | [iOS] AppStore: ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. -
ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. If method names in your source code match the private Apple APIs listed above, altering your method names will help prevent this app from being flagged in future submissions. In addition, note that one or more of the above APIs may be located in a static library that was included with your app. If so, they must be removed. For further information, visit the Technical Support Information at http://developer.apple.com/support/technical/Though you are not required to fix the following issues, we wanted to make you aware of them:ITMS-90809: Deprecated API Usage - Apple will stop accepting submissions of apps that use UIWebView APIs . See https://developer.apple.com/documentation/uikit/uiwebview for more information. | ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. If method names in your source code match the private Apple APIs listed above, altering your method names will help prevent this app from being flagged in future submissions. In addition, note that one or more of the above APIs may be located in a static library that was included with your app. If so, they must be removed. For further information, visit the Technical Support Information at http://developer.apple.com/support/technical/Though you are not required to fix the following issues, we wanted to make you aware of them:ITMS-90809: Deprecated API Usage - Apple will stop accepting submissions of apps that use UIWebView APIs . See https://developer.apple.com/documentation/uikit/uiwebview for more information.
-- | --
ITMS-90338: Non-public API usage - The app references non-public symbols in Frameworks/Flutter.framework/Flutter: _ptrace. If method names in your source code match the private Apple APIs listed above, altering your method names will help prevent this app from being flagged in future submissions. In addition, note that one or more of the above APIs may be located in a static library that was included with your app. If so, they must be removed. For further information, visit the Technical Support Information at http://developer.apple.com/support/technical/Though you are not required to fix the following issues, we wanted to make you aware of them:ITMS-90809: Deprecated API Usage - Apple will stop accepting submissions of apps that use UIWebView APIs . See https://developer.apple.com/documentation/uikit/uiwebview for more information.
i have submitted release build but by default it takes debug build
| non_priority | appstore itms non public api usage the app references non public symbols in frameworks flutter framework flutter ptrace itms non public api usage the app references non public symbols in frameworks flutter framework flutter ptrace if method names in your source code match the private apple apis listed above altering your method names will help prevent this app from being flagged in future submissions in addition note that one or more of the above apis may be located in a static library that was included with your app if so they must be removed for further information visit the technical support information at you are not required to fix the following issues we wanted to make you aware of them itms deprecated api usage apple will stop accepting submissions of apps that use uiwebview apis see for more information itms non public api usage the app references non public symbols in frameworks flutter framework flutter ptrace if method names in your source code match the private apple apis listed above altering your method names will help prevent this app from being flagged in future submissions in addition note that one or more of the above apis may be located in a static library that was included with your app if so they must be removed for further information visit the technical support information at you are not required to fix the following issues we wanted to make you aware of them itms deprecated api usage apple will stop accepting submissions of apps that use uiwebview apis see for more information itms non public api usage the app references non public symbols in frameworks flutter framework flutter ptrace if method names in your source code match the private apple apis listed above altering your method names will help prevent this app from being flagged in future submissions in addition note that one or more of the above apis may be located in a static library that was included with your app if so they must be removed for further information visit the technical support information at you are not required to fix the following issues we wanted to make you aware of them itms deprecated api usage apple will stop accepting submissions of apps that use uiwebview apis see for more information i have submitted release build but by default it takes debug build | 0 |
136,751 | 11,082,262,152 | IssuesEvent | 2019-12-13 11:40:37 | Twonki/Hopinosis | https://api.github.com/repos/Twonki/Hopinosis | opened | QuickCheck-Tests | Idea Test | Quickcheck can be used to have a nice check of some of the properties of my graph.
**Proposed Solution**
Write some quickcheck-tests for
- graph being monoid
- graphs being distinct after parsing (no nodes duplicated)
- values being monoid
run them with the normal cabal build.
**Possible Problems:**
There are maybe problems with running both quickcheck and hunit.
Maybe creating arbitrary instances of the types will turn out bad.
**Additional Context:**
The arbitrary instances can be perfectly used for manual testing as well.
This means there is a huge value in just being able to generate random graphs,nodes and paths.
| 1.0 | QuickCheck-Tests - Quickcheck can be used to have a nice check of some of the properties of my graph.
**Proposed Solution**
Write some quickcheck-tests for
- graph being monoid
- graphs being distinct after parsing (no nodes duplicated)
- values being monoid
run them with the normal cabal build.
**Possible Problems:**
There are maybe problems with running both quickcheck and hunit.
Maybe creating arbitrary instances of the types will turn out bad.
**Additional Context:**
The arbitrary instances can be perfectly used for manual testing as well.
This means there is a huge value in just being able to generate random graphs,nodes and paths.
| non_priority | quickcheck tests quickcheck can be used to have a nice check of some of the properties of my graph proposed solution write some quickcheck tests for graph being monoid graphs being distinct after parsing no nodes duplicated values being monoid run them with the normal cabal build possible problems there are maybe problems with running both quickcheck and hunit maybe creating arbitrary instances of the types will turn out bad additional context the arbitrary instances can be perfectly used for manual testing as well this means there is a huge value in just being able to generate random graphs nodes and paths | 0 |
853 | 16,110,672,549 | IssuesEvent | 2021-04-27 20:43:31 | restincode/restincode | https://api.github.com/repos/restincode/restincode | opened | Veruus | Add Person Needs Review People | Please fill out as much information as you can. No fields are required, but the more you can provide the better.
**General Info**
* First name:
* Last name:
* Handle: Veruus
* Birth Year:
* Death Year:
* Link to Obituary:
* Group Affiliations:
* URL to main photo (or attach to Issue):
* Description of person and/or activities:
* Facebook memorial group URL:
**Social Media Links**
* Twitter: https://twitter.com/veruus
* Github:
* LinkedIn:
* Facebook:
* Other:
**Contributions**
DEFCON goon (swag)
* Project name:
* Project URL:
* Project Description:
**Photo Gallery**
* URL(s) to additional photos:
| 1.0 | Veruus - Please fill out as much information as you can. No fields are required, but the more you can provide the better.
**General Info**
* First name:
* Last name:
* Handle: Veruus
* Birth Year:
* Death Year:
* Link to Obituary:
* Group Affiliations:
* URL to main photo (or attach to Issue):
* Description of person and/or activities:
* Facebook memorial group URL:
**Social Media Links**
* Twitter: https://twitter.com/veruus
* Github:
* LinkedIn:
* Facebook:
* Other:
**Contributions**
DEFCON goon (swag)
* Project name:
* Project URL:
* Project Description:
**Photo Gallery**
* URL(s) to additional photos:
| non_priority | veruus please fill out as much information as you can no fields are required but the more you can provide the better general info first name last name handle veruus birth year death year link to obituary group affiliations url to main photo or attach to issue description of person and or activities facebook memorial group url social media links twitter github linkedin facebook other contributions defcon goon swag project name project url project description photo gallery url s to additional photos | 0 |
47,661 | 7,341,811,122 | IssuesEvent | 2018-03-07 04:15:15 | Microsoft/ApplicationInsights-dotnet-logging | https://api.github.com/repos/Microsoft/ApplicationInsights-dotnet-logging | closed | Web.config transformation is not applied correctly when using configSource | discussion documentation | When you install the TraceListener package, it adds the trace listener to the `system.diagnostics` section in the web.config file. However, we're using the `configSource` attribute to configure trace listeners and sources in a separate file. When I install the package, it results in the following:
```
<system.diagnostics configSource="trace.config">
<trace autoflush="true" indentsize="0">
<listeners>
<add name="myAppInsightsListener" type="Microsoft.ApplicationInsights.TraceListener.ApplicationInsightsTraceListener, Microsoft.ApplicationInsights.TraceListener" />
</listeners>
</trace>
</system.diagnostics>
```
I am not very familiar with the internals of the configuration, but I believe the `configSource` overrides web.config in this case. If there is a `configSource` present, I think it should modify the `configSource` file, or at the very least not modify the web.config incorrectly. | 1.0 | Web.config transformation is not applied correctly when using configSource - When you install the TraceListener package, it adds the trace listener to the `system.diagnostics` section in the web.config file. However, we're using the `configSource` attribute to configure trace listeners and sources in a separate file. When I install the package, it results in the following:
```
<system.diagnostics configSource="trace.config">
<trace autoflush="true" indentsize="0">
<listeners>
<add name="myAppInsightsListener" type="Microsoft.ApplicationInsights.TraceListener.ApplicationInsightsTraceListener, Microsoft.ApplicationInsights.TraceListener" />
</listeners>
</trace>
</system.diagnostics>
```
I am not very familiar with the internals of the configuration, but I believe the `configSource` overrides web.config in this case. If there is a `configSource` present, I think it should modify the `configSource` file, or at the very least not modify the web.config incorrectly. | non_priority | web config transformation is not applied correctly when using configsource when you install the tracelistener package it adds the trace listener to the system diagnostics section in the web config file however we re using the configsource attribute to configure trace listeners and sources in a separate file when i install the package it results in the following i am not very familiar with the internals of the configuration but i believe the configsource overrides web config in this case if there is a configsource present i think it should modify the configsource file or at the very least not modify the web config incorrectly | 0 |
52,885 | 22,495,283,651 | IssuesEvent | 2022-06-23 06:58:40 | kyma-project/control-plane | https://api.github.com/repos/kyma-project/control-plane | opened | Remove ORY oathkeeper | area/service-mesh area/security 2023-Q2 | <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
Remove ORY oathkeeper component from control plane. Charts should be cleaned along with any configuration. ORY oathkeeper component (helm release) should be removed from dev, stage and prod cluster (managed kyma) also with configuration (overrides). Corresponding resources (CRDs, CRs) should be removed from charts and from clusters. Documentation update if needed.
**Reasons**
Dropping dependency to ORY oathkeeper
**Attachments**
Depends on: https://github.com/kyma-project/control-plane/issues/1732
Part of: https://github.com/kyma-project/control-plane/issues/1540
| 1.0 | Remove ORY oathkeeper - <!-- Thank you for your contribution. Before you submit the issue:
1. Search open and closed issues for duplicates.
2. Read the contributing guidelines.
-->
**Description**
Remove ORY oathkeeper component from control plane. Charts should be cleaned along with any configuration. ORY oathkeeper component (helm release) should be removed from dev, stage and prod cluster (managed kyma) also with configuration (overrides). Corresponding resources (CRDs, CRs) should be removed from charts and from clusters. Documentation update if needed.
**Reasons**
Dropping dependency to ORY oathkeeper
**Attachments**
Depends on: https://github.com/kyma-project/control-plane/issues/1732
Part of: https://github.com/kyma-project/control-plane/issues/1540
| non_priority | remove ory oathkeeper thank you for your contribution before you submit the issue search open and closed issues for duplicates read the contributing guidelines description remove ory oathkeeper component from control plane charts should be cleaned along with any configuration ory oathkeeper component helm release should be removed from dev stage and prod cluster managed kyma also with configuration overrides corresponding resources crds crs should be removed from charts and from clusters documentation update if needed reasons dropping dependency to ory oathkeeper attachments depends on part of | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.