Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
186,167 | 21,920,062,559 | IssuesEvent | 2022-05-22 12:39:03 | turkdevops/sourcegraph | https://api.github.com/repos/turkdevops/sourcegraph | closed | CVE-2018-20190 (Medium) detected in node-sass-4.14.1.tgz - autoclosed | security vulnerability | ## CVE-2018-20190 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/sourcegraph/commit/5a4a7def9ddff6354e22069c494feb0f30196e36">5a4a7def9ddff6354e22069c494feb0f30196e36</a></p>
<p>Found in base branch: <b>dev/seed-tool</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Eval::operator()(Sass::Supports_Operator*) in eval.cpp may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20190>CVE-2018-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.6.0">https://github.com/sass/libsass/releases/tag/3.6.0</a></p>
<p>Release Date: 2018-12-17</p>
<p>Fix Resolution: 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-20190 (Medium) detected in node-sass-4.14.1.tgz - autoclosed - ## CVE-2018-20190 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.14.1.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.14.1.tgz</a></p>
<p>
Dependency Hierarchy:
- :x: **node-sass-4.14.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/sourcegraph/commit/5a4a7def9ddff6354e22069c494feb0f30196e36">5a4a7def9ddff6354e22069c494feb0f30196e36</a></p>
<p>Found in base branch: <b>dev/seed-tool</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Eval::operator()(Sass::Supports_Operator*) in eval.cpp may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20190>CVE-2018-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sass/libsass/releases/tag/3.6.0">https://github.com/sass/libsass/releases/tag/3.6.0</a></p>
<p>Release Date: 2018-12-17</p>
<p>Fix Resolution: 5.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz autoclosed cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href dependency hierarchy x node sass tgz vulnerable library found in head commit a href found in base branch dev seed tool vulnerability details in libsass a null pointer dereference in the function sass eval operator sass supports operator in eval cpp may cause a denial of service application crash via a crafted sass input file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
153,710 | 13,523,847,376 | IssuesEvent | 2020-09-15 10:35:36 | paritytech/parity-signer | https://api.github.com/repos/paritytech/parity-signer | closed | Remove or replace recommended command to install NDK | F5-documentation | In https://github.com/paritytech/parity-signer/blob/master/create-ndk-standalone.sh#L23 we recommend that the user installs NDK using Homebrew, however this installs the latest version of NDK that may not work with Parity Signer instead of the version r13b that has been tested to actually work with Parity Signer.
Also it deceptively prints a message that appears to be the users command prompt and the command, rather than differentiating itself as an actually message to the user | 1.0 | Remove or replace recommended command to install NDK - In https://github.com/paritytech/parity-signer/blob/master/create-ndk-standalone.sh#L23 we recommend that the user installs NDK using Homebrew, however this installs the latest version of NDK that may not work with Parity Signer instead of the version r13b that has been tested to actually work with Parity Signer.
Also it deceptively prints a message that appears to be the users command prompt and the command, rather than differentiating itself as an actually message to the user | non_priority | remove or replace recommended command to install ndk in we recommend that the user installs ndk using homebrew however this installs the latest version of ndk that may not work with parity signer instead of the version that has been tested to actually work with parity signer also it deceptively prints a message that appears to be the users command prompt and the command rather than differentiating itself as an actually message to the user | 0 |
81,227 | 30,760,095,859 | IssuesEvent | 2023-07-29 15:28:25 | amyjko/bookish | https://api.github.com/repos/amyjko/bookish | closed | Horizontal rule has much more spacing in read mode than in editor | defect writing reading | Example rule in editor:

Same rule in reader:

Setup: My usual: recent chrome on Win11 home
Theme: I use the "Bookish" theme. I played around with adding the following custom CSS and did not see a difference:
hr { margin: 10px 0 10px 0; }
Thoughts:
- The spacing in the editor is satisfactory for me. If we can get the same spacing in the reader, that would be perfect
- If it requires custom CSS, I'm happy to add custom CSS, but I would need some advice on which spacing values I need to customize
| 1.0 | Horizontal rule has much more spacing in read mode than in editor - Example rule in editor:

Same rule in reader:

Setup: My usual: recent chrome on Win11 home
Theme: I use the "Bookish" theme. I played around with adding the following custom CSS and did not see a difference:
hr { margin: 10px 0 10px 0; }
Thoughts:
- The spacing in the editor is satisfactory for me. If we can get the same spacing in the reader, that would be perfect
- If it requires custom CSS, I'm happy to add custom CSS, but I would need some advice on which spacing values I need to customize
| non_priority | horizontal rule has much more spacing in read mode than in editor example rule in editor same rule in reader setup my usual recent chrome on home theme i use the bookish theme i played around with adding the following custom css and did not see a difference hr margin thoughts the spacing in the editor is satisfactory for me if we can get the same spacing in the reader that would be perfect if it requires custom css i m happy to add custom css but i would need some advice on which spacing values i need to customize | 0 |
12,845 | 3,655,879,771 | IssuesEvent | 2016-02-17 17:46:57 | ExcaliburZero/tempconvert-c | https://api.github.com/repos/ExcaliburZero/tempconvert-c | closed | Add reporting bugs section to manual file | documentation | A section should be added to the manual file with information on how to report bugs.
See `man ls` for an example. | 1.0 | Add reporting bugs section to manual file - A section should be added to the manual file with information on how to report bugs.
See `man ls` for an example. | non_priority | add reporting bugs section to manual file a section should be added to the manual file with information on how to report bugs see man ls for an example | 0 |
113,471 | 14,441,132,811 | IssuesEvent | 2020-12-07 16:24:36 | ParabolInc/parabol | https://api.github.com/repos/ParabolInc/parabol | closed | Comments should be able to be promoted to tasks | design stale | When I've mistakenly entered a commend I wished instead to be a task, I want an affordance for me to be able to change the comment into a task, so that I don't have to copy the comment text, paste into a new task, and delete the old commend (that's too cumbersome!)
AC:
- A medium-fi design for the above
EE:
- 6 hours
| 1.0 | Comments should be able to be promoted to tasks - When I've mistakenly entered a commend I wished instead to be a task, I want an affordance for me to be able to change the comment into a task, so that I don't have to copy the comment text, paste into a new task, and delete the old commend (that's too cumbersome!)
AC:
- A medium-fi design for the above
EE:
- 6 hours
| non_priority | comments should be able to be promoted to tasks when i ve mistakenly entered a commend i wished instead to be a task i want an affordance for me to be able to change the comment into a task so that i don t have to copy the comment text paste into a new task and delete the old commend that s too cumbersome ac a medium fi design for the above ee hours | 0 |
115,441 | 17,313,987,177 | IssuesEvent | 2021-07-27 01:40:45 | bsbtd/Teste | https://api.github.com/repos/bsbtd/Teste | opened | CVE-2021-34552 (High) detected in Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-34552 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/e0/50/8e78e6f62ffa50d6ca95c281d5a2819bef66d023ac1b723e253de5bda9c5/Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/e0/50/8e78e6f62ffa50d6ca95c281d5a2819bef66d023ac1b723e253de5bda9c5/Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: Teste/pytorch-metric-learning</p>
<p>Path to vulnerable library: Teste/pytorch-metric-learning</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pillow through 8.2.0 and PIL (aka Python Imaging Library) through 1.1.7 allow an attacker to pass controlled parameters directly into a convert function to trigger a buffer overflow in Convert.c.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-34552>CVE-2021-34552</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pillow.readthedocs.io/en/stable/releasenotes/8.3.0.html#buffer-overflow">https://pillow.readthedocs.io/en/stable/releasenotes/8.3.0.html#buffer-overflow</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: Pillow-8.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-34552 (High) detected in Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl - ## CVE-2021-34552 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/e0/50/8e78e6f62ffa50d6ca95c281d5a2819bef66d023ac1b723e253de5bda9c5/Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/e0/50/8e78e6f62ffa50d6ca95c281d5a2819bef66d023ac1b723e253de5bda9c5/Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: Teste/pytorch-metric-learning</p>
<p>Path to vulnerable library: Teste/pytorch-metric-learning</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-7.1.2-cp36-cp36m-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pillow through 8.2.0 and PIL (aka Python Imaging Library) through 1.1.7 allow an attacker to pass controlled parameters directly into a convert function to trigger a buffer overflow in Convert.c.
<p>Publish Date: 2021-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-34552>CVE-2021-34552</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://pillow.readthedocs.io/en/stable/releasenotes/8.3.0.html#buffer-overflow">https://pillow.readthedocs.io/en/stable/releasenotes/8.3.0.html#buffer-overflow</a></p>
<p>Release Date: 2021-07-13</p>
<p>Fix Resolution: Pillow-8.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in pillow whl cve high severity vulnerability vulnerable library pillow whl python imaging library fork library home page a href path to dependency file teste pytorch metric learning path to vulnerable library teste pytorch metric learning dependency hierarchy x pillow whl vulnerable library vulnerability details pillow through and pil aka python imaging library through allow an attacker to pass controlled parameters directly into a convert function to trigger a buffer overflow in convert c publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pillow step up your open source security game with whitesource | 0 |
353,433 | 25,118,358,652 | IssuesEvent | 2022-11-09 05:20:42 | WSUCptSCapstone-Fall2022Spring2023/remi-hpcstochpy | https://api.github.com/repos/WSUCptSCapstone-Fall2022Spring2023/remi-hpcstochpy | closed | Update Project Description Document to Include Testing and Acceptance Plans | documentation | Update the git repo to contain the newest version of the project description. | 1.0 | Update Project Description Document to Include Testing and Acceptance Plans - Update the git repo to contain the newest version of the project description. | non_priority | update project description document to include testing and acceptance plans update the git repo to contain the newest version of the project description | 0 |
271,602 | 23,617,259,162 | IssuesEvent | 2022-08-24 16:58:12 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | ccl/multitenantccl/tenantcostclient: TestConsumption failed | C-test-failure O-robot branch-master release-blocker branch-release-22.2 | ccl/multitenantccl/tenantcostclient.TestConsumption [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/5695797?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/5695797?buildTab=artifacts#/) on master @ [54b4fcaa231abd16260fb09722ed291dbd6a4900](https://github.com/cockroachdb/cockroach/commits/54b4fcaa231abd16260fb09722ed291dbd6a4900):
```
=== RUN TestConsumption
test_log_scope.go:79: test logs captured to: /artifacts/tmp/_tmp/8c8c3ac7e6f376e55ddb65c834857f3f/logTestConsumption2162408875
test_log_scope.go:80: use -show-logs to present logs inline
tenant_side_test.go:886: usage after write: r_u:9.999999000000344 sql_pods_cpu_seconds:0.03000000000000025
tenant_side_test.go:910: -- test log scope end --
--- FAIL: TestConsumption (2.36s)
```
<p>Parameters: <code>TAGS=bazel,gss,deadlock</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/multi-tenant
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestConsumption.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-17467 | 1.0 | ccl/multitenantccl/tenantcostclient: TestConsumption failed - ccl/multitenantccl/tenantcostclient.TestConsumption [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/5695797?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/5695797?buildTab=artifacts#/) on master @ [54b4fcaa231abd16260fb09722ed291dbd6a4900](https://github.com/cockroachdb/cockroach/commits/54b4fcaa231abd16260fb09722ed291dbd6a4900):
```
=== RUN TestConsumption
test_log_scope.go:79: test logs captured to: /artifacts/tmp/_tmp/8c8c3ac7e6f376e55ddb65c834857f3f/logTestConsumption2162408875
test_log_scope.go:80: use -show-logs to present logs inline
tenant_side_test.go:886: usage after write: r_u:9.999999000000344 sql_pods_cpu_seconds:0.03000000000000025
tenant_side_test.go:910: -- test log scope end --
--- FAIL: TestConsumption (2.36s)
```
<p>Parameters: <code>TAGS=bazel,gss,deadlock</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/multi-tenant
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestConsumption.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-17467 | non_priority | ccl multitenantccl tenantcostclient testconsumption failed ccl multitenantccl tenantcostclient testconsumption with on master run testconsumption test log scope go test logs captured to artifacts tmp tmp test log scope go use show logs to present logs inline tenant side test go usage after write r u sql pods cpu seconds tenant side test go test log scope end fail testconsumption parameters tags bazel gss deadlock help see also cc cockroachdb multi tenant jira issue crdb | 0 |
170,668 | 20,883,817,841 | IssuesEvent | 2022-03-23 01:16:16 | chaitanya00/aem-wknd | https://api.github.com/repos/chaitanya00/aem-wknd | opened | CVE-2021-44906 (Medium) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz | security vulnerability | ## CVE-2021-44906 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /.scannerwork/css-bundle/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-11.1.5.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /.scannerwork/css-bundle/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- browserify-13.3.0.tgz (Root Library)
- subarg-1.0.0.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-44906 (Medium) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz - ## CVE-2021-44906 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /.scannerwork/css-bundle/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- tap-11.1.5.tgz (Root Library)
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /.scannerwork/css-bundle/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- browserify-13.3.0.tgz (Root Library)
- subarg-1.0.0.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Minimist <=1.2.5 is vulnerable to Prototype Pollution via file index.js, function setKey() (lines 69-95).
<p>Publish Date: 2022-03-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44906>CVE-2021-44906</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-44906">https://nvd.nist.gov/vuln/detail/CVE-2021-44906</a></p>
<p>Release Date: 2022-03-17</p>
<p>Fix Resolution: BumperLane.Public.Service.Contracts - 0.23.35.214-prerelease;cloudscribe.templates - 5.2.0;Virteom.Tenant.Mobile.Bluetooth - 0.21.29.159-prerelease;ShowingVault.DotNet.Sdk - 0.13.41.190-prerelease;Envisia.DotNet.Templates - 3.0.1;Yarnpkg.Yarn - 0.26.1;Virteom.Tenant.Mobile.Framework.UWP - 0.20.41.103-prerelease;Virteom.Tenant.Mobile.Framework.iOS - 0.20.41.103-prerelease;BumperLane.Public.Api.V2.ClientModule - 0.23.35.214-prerelease;VueJS.NetCore - 1.1.1;Dianoga - 4.0.0,3.0.0-RC02;Virteom.Tenant.Mobile.Bluetooth.iOS - 0.20.41.103-prerelease;Virteom.Public.Utilities - 0.23.37.212-prerelease;Indianadavy.VueJsWebAPITemplate.CSharp - 1.0.1;NorDroN.AngularTemplate - 0.1.6;Virteom.Tenant.Mobile.Framework - 0.21.29.159-prerelease;Virteom.Tenant.Mobile.Bluetooth.Android - 0.20.41.103-prerelease;z4a-dotnet-scaffold - 1.0.0.2;Raml.Parser - 1.0.7;CoreVueWebTest - 3.0.101;dotnetng.template - 1.0.0.4;SitecoreMaster.TrueDynamicPlaceholders - 1.0.3;Virteom.Tenant.Mobile.Framework.Android - 0.20.41.103-prerelease;Fable.Template.Elmish.React - 0.1.6;BlazorPolyfill.Build - 6.0.100.2;Fable.Snowpack.Template - 2.1.0;BumperLane.Public.Api.Client - 0.23.35.214-prerelease;Yarn.MSBuild - 0.22.0,0.24.6;Blazor.TailwindCSS.BUnit - 1.0.2;Bridge.AWS - 0.3.30.36;tslint - 5.6.0;SAFE.Template - 3.0.1;GR.PageRender.Razor - 1.8.0;MIDIator.WebClient - 1.0.105</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in minimist tgz minimist tgz cve medium severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library scannerwork css bundle node modules mkdirp node modules minimist package json dependency hierarchy tap tgz root library mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file package json path to vulnerable library scannerwork css bundle node modules minimist package json dependency hierarchy browserify tgz root library subarg tgz x minimist tgz vulnerable library found in base branch master vulnerability details minimist is vulnerable to prototype pollution via file index js function setkey lines publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bumperlane public service contracts prerelease cloudscribe templates virteom tenant mobile bluetooth prerelease showingvault dotnet sdk prerelease envisia dotnet templates yarnpkg yarn virteom tenant mobile framework uwp prerelease virteom tenant mobile framework ios prerelease bumperlane public api clientmodule prerelease vuejs netcore dianoga virteom tenant mobile bluetooth ios prerelease virteom public utilities prerelease indianadavy vuejswebapitemplate csharp nordron angulartemplate virteom tenant mobile framework prerelease virteom tenant mobile bluetooth android prerelease dotnet scaffold raml parser corevuewebtest dotnetng template sitecoremaster truedynamicplaceholders virteom tenant mobile framework android prerelease fable template elmish react blazorpolyfill build fable snowpack template bumperlane public api client prerelease yarn msbuild blazor tailwindcss bunit bridge aws tslint safe template gr pagerender razor midiator webclient step up your open source security game with whitesource | 0 |
442,681 | 30,850,658,425 | IssuesEvent | 2023-08-02 16:28:54 | re-organization-sandbox/sandbox-repo | https://api.github.com/repos/re-organization-sandbox/sandbox-repo | closed | Welcome to sandbox-repo Discussions! | bug documentation duplicate | ### Discussed in https://github.com/re-organization-sandbox/sandbox-repo/discussions/3
<div type='discussions-op-text'>
<sup>Originally posted by **SkPhilipp** August 2, 2023</sup>
Please don't share your ideas here because this is a repository meant to record GitHub events, I definitely won't be reading any of this.</div>
This seems important | 1.0 | Welcome to sandbox-repo Discussions! - ### Discussed in https://github.com/re-organization-sandbox/sandbox-repo/discussions/3
<div type='discussions-op-text'>
<sup>Originally posted by **SkPhilipp** August 2, 2023</sup>
Please don't share your ideas here because this is a repository meant to record GitHub events, I definitely won't be reading any of this.</div>
This seems important | non_priority | welcome to sandbox repo discussions discussed in originally posted by skphilipp august please don t share your ideas here because this is a repository meant to record github events i definitely won t be reading any of this this seems important | 0 |
450,957 | 32,000,740,953 | IssuesEvent | 2023-09-21 12:08:20 | aws/sagemaker-python-sdk | https://api.github.com/repos/aws/sagemaker-python-sdk | closed | [DOC]sphinx_rtd_theme PackagesNotFoundError | type: documentation | **Describe the bug**
Got the following error when attempting to build the docs locally.
PackagesNotFoundError: The following packages are not available from current channels:
- sphinx_rtd_theme=0.5.0
**To reproduce**
Run the following:
# conda
conda create -n sagemaker python=3.7
conda activate sagemaker
conda install sphinx=3.1.1 sphinx_rtd_theme=0.5.0
# pip
pip install -r doc/requirements.txt
**Expected behavior**
Expect the package to download and update.
**System information**
A description of your system. Please provide:
Trying to build through terminal on Mac running Mojave.
| 1.0 | [DOC]sphinx_rtd_theme PackagesNotFoundError - **Describe the bug**
Got the following error when attempting to build the docs locally.
PackagesNotFoundError: The following packages are not available from current channels:
- sphinx_rtd_theme=0.5.0
**To reproduce**
Run the following:
# conda
conda create -n sagemaker python=3.7
conda activate sagemaker
conda install sphinx=3.1.1 sphinx_rtd_theme=0.5.0
# pip
pip install -r doc/requirements.txt
**Expected behavior**
Expect the package to download and update.
**System information**
A description of your system. Please provide:
Trying to build through terminal on Mac running Mojave.
| non_priority | sphinx rtd theme packagesnotfounderror describe the bug got the following error when attempting to build the docs locally packagesnotfounderror the following packages are not available from current channels sphinx rtd theme to reproduce run the following conda conda create n sagemaker python conda activate sagemaker conda install sphinx sphinx rtd theme pip pip install r doc requirements txt expected behavior expect the package to download and update system information a description of your system please provide trying to build through terminal on mac running mojave | 0 |
255,048 | 21,896,969,855 | IssuesEvent | 2022-05-20 09:33:55 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | opened | [CI] ActiveDirectoryGroupsResolverTests testResolveSubTree failing | >test-failure :Security/Authentication Team:Security | **Build scan:**
https://gradle-enterprise.elastic.co/s/lbk5ynxsss7ym/tests/:x-pack:qa:third-party:active-directory:test/org.elasticsearch.xpack.security.authc.ldap.ActiveDirectoryGroupsResolverTests/testResolveSubTree
**Reproduction line:**
`./gradlew ':x-pack:qa:third-party:active-directory:test' --tests "org.elasticsearch.xpack.security.authc.ldap.ActiveDirectoryGroupsResolverTests.testResolveSubTree" -Dtests.seed=B75C7A14E63A1ABB -Dtests.locale=is-IS -Dtests.timezone=Australia/Adelaide -Druntime.java=18`
**Applicable branches:**
master
**Reproduces locally?:**
Didn't try
**Failure history:**
https://gradle-enterprise.elastic.co/scans/tests?tests.container=org.elasticsearch.xpack.security.authc.ldap.ActiveDirectoryGroupsResolverTests&tests.test=testResolveSubTree
**Failure excerpt:**
```
com.unboundid.ldap.sdk.LDAPException: A client-side timeout was encountered while waiting 5005ms for a response to simple bind request with message ID 1 for user 'cn=Bruce Banner,CN=Users,DC=ad,DC=test,DC=elasticsearch,DC=com' from server localhost:49182.
at __randomizedtesting.SeedInfo.seed([B75C7A14E63A1ABB:3CE0D99C8300612D]:0)
at com.unboundid.ldap.sdk.SimpleBindRequest.handleResponse(SimpleBindRequest.java:738)
at com.unboundid.ldap.sdk.SimpleBindRequest.process(SimpleBindRequest.java:619)
at com.unboundid.ldap.sdk.LDAPConnection.processBindOperation(LDAPConnection.java:4560)
at com.unboundid.ldap.sdk.LDAPConnection.bind(LDAPConnection.java:2393)
at com.unboundid.ldap.sdk.LDAPConnection.<init>(LDAPConnection.java:700)
at org.elasticsearch.xpack.security.authc.ldap.LdapTestUtils.lambda$openConnection$0(LdapTestUtils.java:60)
at java.security.AccessController.doPrivileged(AccessController.java:569)
at org.elasticsearch.xpack.security.authc.ldap.support.LdapUtils.privilegedConnect(LdapUtils.java:76)
at org.elasticsearch.xpack.security.authc.ldap.LdapTestUtils.openConnection(LdapTestUtils.java:55)
at org.elasticsearch.xpack.security.authc.ldap.GroupsResolverTestCase.setUpLdapConnection(GroupsResolverTestCase.java:58)
at jdk.internal.reflect.DirectMethodHandleAccessor.invoke(DirectMethodHandleAccessor.java:104)
at java.lang.reflect.Method.invoke(Method.java:577)
at com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
at com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:980)
at com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.tests.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:44)
at org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
at org.apache.lucene.tests.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:45)
at org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
at org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:824)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:475)
at com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
at com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
at com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
at com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
at org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.tests.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:38)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.tests.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
at org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
at org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
at org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
at org.apache.lucene.tests.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:47)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:831)
at java.lang.Thread.run(Thread.java:833)
``` | 1.0 | [CI] ActiveDirectoryGroupsResolverTests testResolveSubTree failing - **Build scan:**
https://gradle-enterprise.elastic.co/s/lbk5ynxsss7ym/tests/:x-pack:qa:third-party:active-directory:test/org.elasticsearch.xpack.security.authc.ldap.ActiveDirectoryGroupsResolverTests/testResolveSubTree
**Reproduction line:**
`./gradlew ':x-pack:qa:third-party:active-directory:test' --tests "org.elasticsearch.xpack.security.authc.ldap.ActiveDirectoryGroupsResolverTests.testResolveSubTree" -Dtests.seed=B75C7A14E63A1ABB -Dtests.locale=is-IS -Dtests.timezone=Australia/Adelaide -Druntime.java=18`
**Applicable branches:**
master
**Reproduces locally?:**
Didn't try
**Failure history:**
https://gradle-enterprise.elastic.co/scans/tests?tests.container=org.elasticsearch.xpack.security.authc.ldap.ActiveDirectoryGroupsResolverTests&tests.test=testResolveSubTree
**Failure excerpt:**
```
com.unboundid.ldap.sdk.LDAPException: A client-side timeout was encountered while waiting 5005ms for a response to simple bind request with message ID 1 for user 'cn=Bruce Banner,CN=Users,DC=ad,DC=test,DC=elasticsearch,DC=com' from server localhost:49182.
at __randomizedtesting.SeedInfo.seed([B75C7A14E63A1ABB:3CE0D99C8300612D]:0)
at com.unboundid.ldap.sdk.SimpleBindRequest.handleResponse(SimpleBindRequest.java:738)
at com.unboundid.ldap.sdk.SimpleBindRequest.process(SimpleBindRequest.java:619)
at com.unboundid.ldap.sdk.LDAPConnection.processBindOperation(LDAPConnection.java:4560)
at com.unboundid.ldap.sdk.LDAPConnection.bind(LDAPConnection.java:2393)
at com.unboundid.ldap.sdk.LDAPConnection.<init>(LDAPConnection.java:700)
at org.elasticsearch.xpack.security.authc.ldap.LdapTestUtils.lambda$openConnection$0(LdapTestUtils.java:60)
at java.security.AccessController.doPrivileged(AccessController.java:569)
at org.elasticsearch.xpack.security.authc.ldap.support.LdapUtils.privilegedConnect(LdapUtils.java:76)
at org.elasticsearch.xpack.security.authc.ldap.LdapTestUtils.openConnection(LdapTestUtils.java:55)
at org.elasticsearch.xpack.security.authc.ldap.GroupsResolverTestCase.setUpLdapConnection(GroupsResolverTestCase.java:58)
at jdk.internal.reflect.DirectMethodHandleAccessor.invoke(DirectMethodHandleAccessor.java:104)
at java.lang.reflect.Method.invoke(Method.java:577)
at com.carrotsearch.randomizedtesting.RandomizedRunner.invoke(RandomizedRunner.java:1758)
at com.carrotsearch.randomizedtesting.RandomizedRunner$9.evaluate(RandomizedRunner.java:980)
at com.carrotsearch.randomizedtesting.RandomizedRunner$10.evaluate(RandomizedRunner.java:996)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.tests.util.TestRuleSetupTeardownChained$1.evaluate(TestRuleSetupTeardownChained.java:44)
at org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
at org.apache.lucene.tests.util.TestRuleThreadAndTestName$1.evaluate(TestRuleThreadAndTestName.java:45)
at org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
at org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.forkTimeoutingTask(ThreadLeakControl.java:824)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$3.evaluate(ThreadLeakControl.java:475)
at com.carrotsearch.randomizedtesting.RandomizedRunner.runSingleTest(RandomizedRunner.java:955)
at com.carrotsearch.randomizedtesting.RandomizedRunner$5.evaluate(RandomizedRunner.java:840)
at com.carrotsearch.randomizedtesting.RandomizedRunner$6.evaluate(RandomizedRunner.java:891)
at com.carrotsearch.randomizedtesting.RandomizedRunner$7.evaluate(RandomizedRunner.java:902)
at org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.tests.util.TestRuleStoreClassName$1.evaluate(TestRuleStoreClassName.java:38)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.NoShadowingOrOverridesOnMethodsRule$1.evaluate(NoShadowingOrOverridesOnMethodsRule.java:40)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at org.apache.lucene.tests.util.TestRuleAssertionsRequired$1.evaluate(TestRuleAssertionsRequired.java:53)
at org.apache.lucene.tests.util.AbstractBeforeAfterRule$1.evaluate(AbstractBeforeAfterRule.java:43)
at org.apache.lucene.tests.util.TestRuleMarkFailure$1.evaluate(TestRuleMarkFailure.java:44)
at org.apache.lucene.tests.util.TestRuleIgnoreAfterMaxFailures$1.evaluate(TestRuleIgnoreAfterMaxFailures.java:60)
at org.apache.lucene.tests.util.TestRuleIgnoreTestSuites$1.evaluate(TestRuleIgnoreTestSuites.java:47)
at com.carrotsearch.randomizedtesting.rules.StatementAdapter.evaluate(StatementAdapter.java:36)
at com.carrotsearch.randomizedtesting.ThreadLeakControl$StatementRunner.run(ThreadLeakControl.java:375)
at com.carrotsearch.randomizedtesting.ThreadLeakControl.lambda$forkTimeoutingTask$0(ThreadLeakControl.java:831)
at java.lang.Thread.run(Thread.java:833)
``` | non_priority | activedirectorygroupsresolvertests testresolvesubtree failing build scan reproduction line gradlew x pack qa third party active directory test tests org elasticsearch xpack security authc ldap activedirectorygroupsresolvertests testresolvesubtree dtests seed dtests locale is is dtests timezone australia adelaide druntime java applicable branches master reproduces locally didn t try failure history failure excerpt com unboundid ldap sdk ldapexception a client side timeout was encountered while waiting for a response to simple bind request with message id for user cn bruce banner cn users dc ad dc test dc elasticsearch dc com from server localhost at randomizedtesting seedinfo seed at com unboundid ldap sdk simplebindrequest handleresponse simplebindrequest java at com unboundid ldap sdk simplebindrequest process simplebindrequest java at com unboundid ldap sdk ldapconnection processbindoperation ldapconnection java at com unboundid ldap sdk ldapconnection bind ldapconnection java at com unboundid ldap sdk ldapconnection ldapconnection java at org elasticsearch xpack security authc ldap ldaptestutils lambda openconnection ldaptestutils java at java security accesscontroller doprivileged accesscontroller java at org elasticsearch xpack security authc ldap support ldaputils privilegedconnect ldaputils java at org elasticsearch xpack security authc ldap ldaptestutils openconnection ldaptestutils java at org elasticsearch xpack security authc ldap groupsresolvertestcase setupldapconnection groupsresolvertestcase java at jdk internal reflect directmethodhandleaccessor invoke directmethodhandleaccessor java at java lang reflect method invoke method java at com carrotsearch randomizedtesting randomizedrunner invoke randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene tests util testrulesetupteardownchained evaluate testrulesetupteardownchained java at org apache lucene tests util abstractbeforeafterrule evaluate abstractbeforeafterrule java at org apache lucene tests util testrulethreadandtestname evaluate testrulethreadandtestname java at org apache lucene tests util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at org apache lucene tests util testrulemarkfailure evaluate testrulemarkfailure java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at com carrotsearch randomizedtesting threadleakcontrol forktimeoutingtask threadleakcontrol java at com carrotsearch randomizedtesting threadleakcontrol evaluate threadleakcontrol java at com carrotsearch randomizedtesting randomizedrunner runsingletest randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at com carrotsearch randomizedtesting randomizedrunner evaluate randomizedrunner java at org apache lucene tests util abstractbeforeafterrule evaluate abstractbeforeafterrule java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene tests util testrulestoreclassname evaluate testrulestoreclassname java at com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at com carrotsearch randomizedtesting rules noshadowingoroverridesonmethodsrule evaluate noshadowingoroverridesonmethodsrule java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at org apache lucene tests util testruleassertionsrequired evaluate testruleassertionsrequired java at org apache lucene tests util abstractbeforeafterrule evaluate abstractbeforeafterrule java at org apache lucene tests util testrulemarkfailure evaluate testrulemarkfailure java at org apache lucene tests util testruleignoreaftermaxfailures evaluate testruleignoreaftermaxfailures java at org apache lucene tests util testruleignoretestsuites evaluate testruleignoretestsuites java at com carrotsearch randomizedtesting rules statementadapter evaluate statementadapter java at com carrotsearch randomizedtesting threadleakcontrol statementrunner run threadleakcontrol java at com carrotsearch randomizedtesting threadleakcontrol lambda forktimeoutingtask threadleakcontrol java at java lang thread run thread java | 0 |
142,454 | 21,768,736,998 | IssuesEvent | 2022-05-13 06:46:43 | iFixit/react-commerce | https://api.github.com/repos/iFixit/react-commerce | closed | Excessive whitespace in mobile product list | design | On mobile, the product list view has a lot of whitespace.
| Amazon | ebay | Alibaba | iFixit collection |
| ------------- | ------------- | ------------- | ------------- |
| 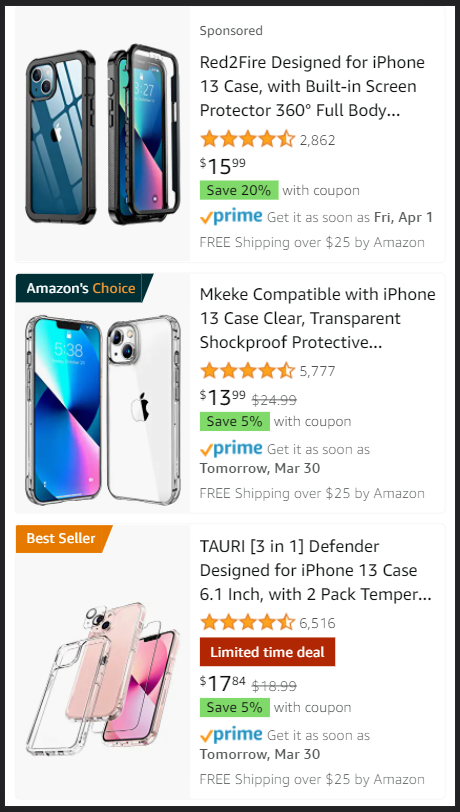 | 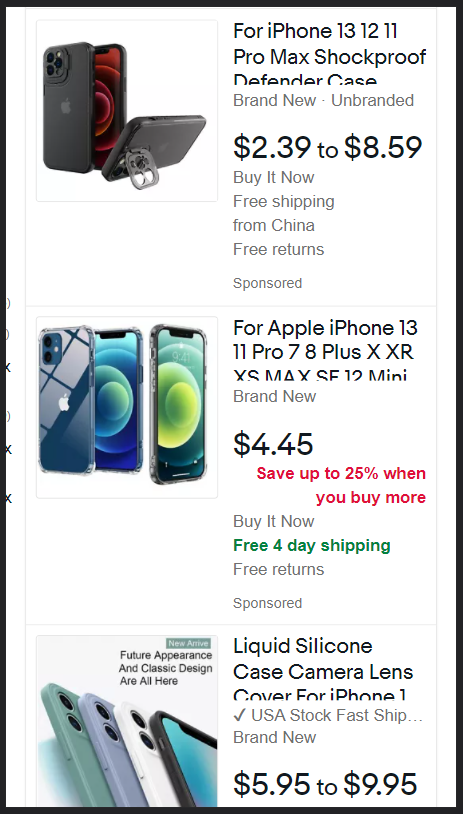 | 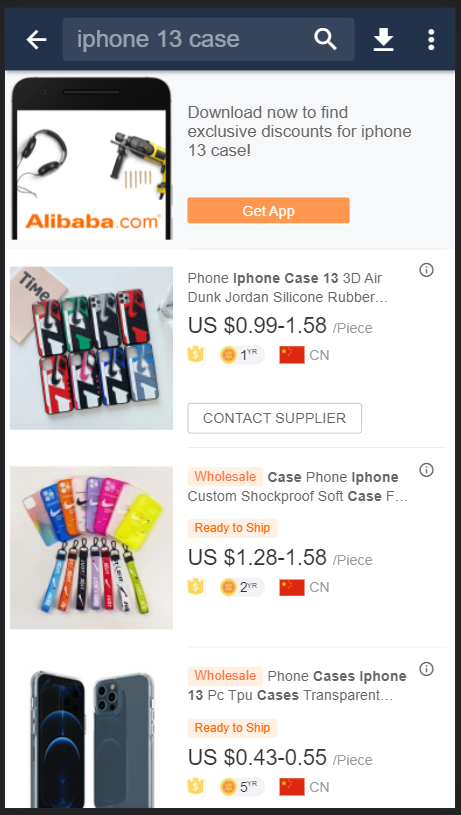 | 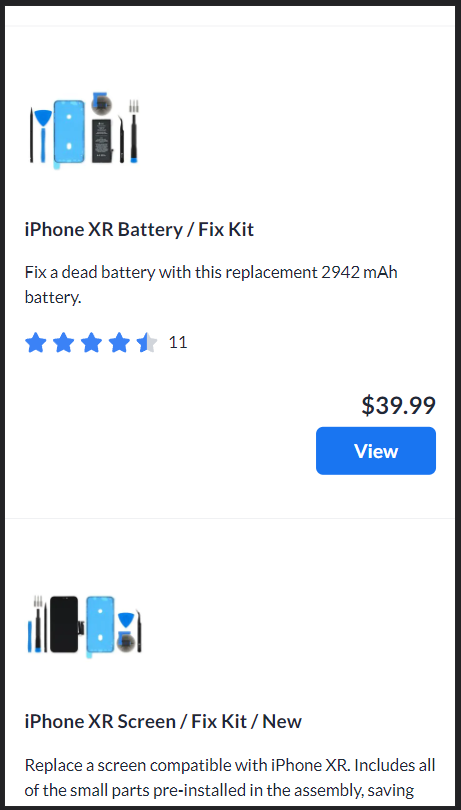 |
| 1.0 | Excessive whitespace in mobile product list - On mobile, the product list view has a lot of whitespace.
| Amazon | ebay | Alibaba | iFixit collection |
| ------------- | ------------- | ------------- | ------------- |
| 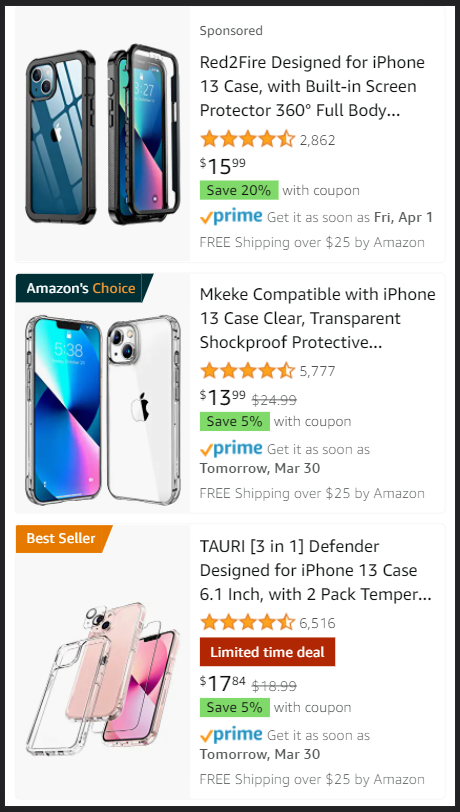 | 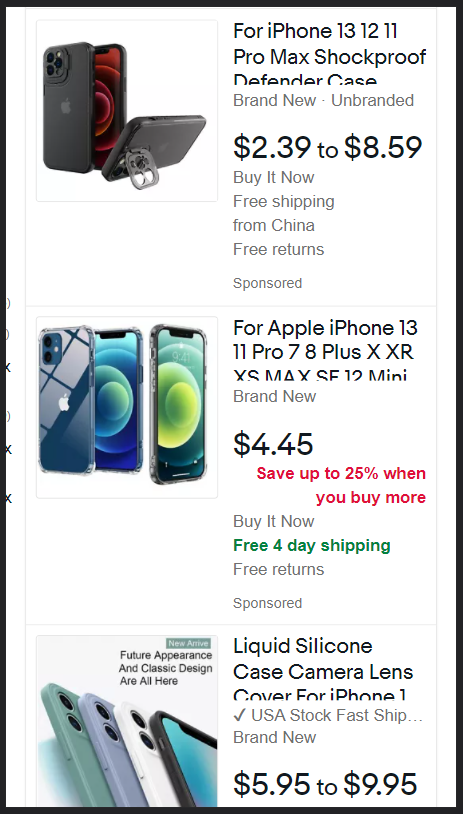 |  |  |
| non_priority | excessive whitespace in mobile product list on mobile the product list view has a lot of whitespace amazon ebay alibaba ifixit collection | 0 |
19,702 | 14,475,725,580 | IssuesEvent | 2020-12-10 02:20:04 | NCAR/VAPOR | https://api.github.com/repos/NCAR/VAPOR | closed | Flow: Gridded seed distribution gives unexpected results | High Usability | The gridded seed distribution does not seem to do what is expected.
With the default configuration for 3D data (a 5 x 5 x 5 grid) I'd
expect to see 125 stream/path lines. What you see is something less.
This is more obvious if you define an even coarser grid, for example
2 x 2 x 2. For some data sets nothing may be drawn. I suspect the
problem is because the seeding grid is aligned to the domain extents.
This is probably not what the user wants. Calculating the sample locations,
Si, as follows would give more useful and intuitive results:
Si = min + (0.5*delta) + (i*delta) : 0<i<nSamples
where:
delta = (max-min) / (nSamples)
min and max are the domain extents
nSamples are the number of samples
To reproduce:
1. Load CM1/Orf/24Maycontrol
2. Enable the flow renderer
3. Change the grid to 2x2x2. Only one streamline is drawn and it's in a
corner
| True | Flow: Gridded seed distribution gives unexpected results - The gridded seed distribution does not seem to do what is expected.
With the default configuration for 3D data (a 5 x 5 x 5 grid) I'd
expect to see 125 stream/path lines. What you see is something less.
This is more obvious if you define an even coarser grid, for example
2 x 2 x 2. For some data sets nothing may be drawn. I suspect the
problem is because the seeding grid is aligned to the domain extents.
This is probably not what the user wants. Calculating the sample locations,
Si, as follows would give more useful and intuitive results:
Si = min + (0.5*delta) + (i*delta) : 0<i<nSamples
where:
delta = (max-min) / (nSamples)
min and max are the domain extents
nSamples are the number of samples
To reproduce:
1. Load CM1/Orf/24Maycontrol
2. Enable the flow renderer
3. Change the grid to 2x2x2. Only one streamline is drawn and it's in a
corner
| non_priority | flow gridded seed distribution gives unexpected results the gridded seed distribution does not seem to do what is expected with the default configuration for data a x x grid i d expect to see stream path lines what you see is something less this is more obvious if you define an even coarser grid for example x x for some data sets nothing may be drawn i suspect the problem is because the seeding grid is aligned to the domain extents this is probably not what the user wants calculating the sample locations si as follows would give more useful and intuitive results si min delta i delta i nsamples where delta max min nsamples min and max are the domain extents nsamples are the number of samples to reproduce load orf enable the flow renderer change the grid to only one streamline is drawn and it s in a corner | 0 |
451,105 | 32,008,451,779 | IssuesEvent | 2023-09-21 16:15:58 | mantidproject/mantid | https://api.github.com/repos/mantidproject/mantid | opened | Add Documentation for MagnetismReflectometryReduction | Reflectometry Documentation Maintenance | **Describe the outcome that is desired.**
A documentation page should be available for the algorithm so the ? button doesn't redirect to a 404 page.
**Describe any solutions you are considering**
None
**Additional context**
| 1.0 | Add Documentation for MagnetismReflectometryReduction - **Describe the outcome that is desired.**
A documentation page should be available for the algorithm so the ? button doesn't redirect to a 404 page.
**Describe any solutions you are considering**
None
**Additional context**
| non_priority | add documentation for magnetismreflectometryreduction describe the outcome that is desired a documentation page should be available for the algorithm so the button doesn t redirect to a page describe any solutions you are considering none additional context | 0 |
64,992 | 19,006,969,575 | IssuesEvent | 2021-11-23 02:06:08 | vector-im/element-ios | https://api.github.com/repos/vector-im/element-ios | opened | Value of type 'MXSDKOptions' has no member 'clientPermalinkBaseUrl' | T-Defect | ### Steps to reproduce
keep running into error :// Value of type 'MXSDKOptions' has no member 'clientPermalinkBaseUrl'
### Outcome
no idea how to fix
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
Yes | 1.0 | Value of type 'MXSDKOptions' has no member 'clientPermalinkBaseUrl' - ### Steps to reproduce
keep running into error :// Value of type 'MXSDKOptions' has no member 'clientPermalinkBaseUrl'
### Outcome
no idea how to fix
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
_No response_
### Homeserver
_No response_
### Will you send logs?
Yes | non_priority | value of type mxsdkoptions has no member clientpermalinkbaseurl steps to reproduce keep running into error value of type mxsdkoptions has no member clientpermalinkbaseurl outcome no idea how to fix your phone model no response operating system version no response application version no response homeserver no response will you send logs yes | 0 |
113,431 | 11,802,508,181 | IssuesEvent | 2020-03-18 21:43:00 | rsmp-nordic/rsmp_sxl_traffic_lights | https://api.github.com/repos/rsmp-nordic/rsmp_sxl_traffic_lights | opened | S0205 uses comma-separated list, not colon-separated? | documentation | Documentation states that the vehicle count list in S0205 is a list of integers separated by colons. I think it shoould say commas?
https://github.com/rsmp-nordic/rsmp_sxl_traffic_lights/blob/master/sxl_traffic_controller.md#s0205 | 1.0 | S0205 uses comma-separated list, not colon-separated? - Documentation states that the vehicle count list in S0205 is a list of integers separated by colons. I think it shoould say commas?
https://github.com/rsmp-nordic/rsmp_sxl_traffic_lights/blob/master/sxl_traffic_controller.md#s0205 | non_priority | uses comma separated list not colon separated documentation states that the vehicle count list in is a list of integers separated by colons i think it shoould say commas | 0 |
138,229 | 11,195,282,664 | IssuesEvent | 2020-01-03 05:40:55 | nwjs/nw.js | https://api.github.com/repos/nwjs/nw.js | closed | NW2: Event navigation get not fired | nw2 test-todo | NWJS Version : v0.43.3
Operating System : Windows 10
### Expected behavior
When I navigate to another page, the event should be triggered and the call should be prevented.
For example when clicking on a Link like google.
### Actual behavior
Event is not triggered.
If I add "chromium-args": "--disable-features=nw2" in package.json, the Event is triggered.
### How to reproduce
main.js
> nw.Window.open('index.html', {}, function(win) {
> win.on('navigation', function (frame, url, policy) {
> console.log("navigation called: " + url);
> policy.ignore();
> });
> });
index.html
`<a href="https://www.google.de">Click</a>`
| 1.0 | NW2: Event navigation get not fired - NWJS Version : v0.43.3
Operating System : Windows 10
### Expected behavior
When I navigate to another page, the event should be triggered and the call should be prevented.
For example when clicking on a Link like google.
### Actual behavior
Event is not triggered.
If I add "chromium-args": "--disable-features=nw2" in package.json, the Event is triggered.
### How to reproduce
main.js
> nw.Window.open('index.html', {}, function(win) {
> win.on('navigation', function (frame, url, policy) {
> console.log("navigation called: " + url);
> policy.ignore();
> });
> });
index.html
`<a href="https://www.google.de">Click</a>`
| non_priority | event navigation get not fired nwjs version operating system windows expected behavior when i navigate to another page the event should be triggered and the call should be prevented for example when clicking on a link like google actual behavior event is not triggered if i add chromium args disable features in package json the event is triggered how to reproduce main js nw window open index html function win win on navigation function frame url policy console log navigation called url policy ignore index html a href | 0 |
84,210 | 7,894,584,751 | IssuesEvent | 2018-06-28 22:05:20 | envoyproxy/envoy | https://api.github.com/repos/envoyproxy/envoy | closed | hotrestart_test flakes in spdlog with TSAN (and other sanitizers) | test flakes | Occasionally we've observed in CI that `hotrestart_test` flakes during early spdlog use in `ValidationClusterManager`. Something isn't quite right here, since we should be doing the kind of verbose logging that would trigger it. Previous investigations by @mattklein123 and myself point to possible validation init not doing the right setup for logging.
We should figure this one out.
```
[2018-03-15 21:06:45.658][20070][info][main] external/envoy/source/server/server.cc:275] runtime symlink: /build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data/current
[2018-03-15 21:06:45.658][20070][info][main] external/envoy/source/server/server.cc:276] runtime subdirectory: envoy
[2018-03-15 21:06:45.658][20070][info][main] external/envoy/source/server/server.cc:280] runtime override subdirectory: envoy_override/cluster
[2018-03-15 21:06:45.659][20070][debug][file] external/envoy/source/common/filesystem/inotify/watcher_impl.cc:48] added watch for directory: '/build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data' file: 'current' fd: 1
[2018-03-15 21:06:45.659][20070][debug][runtime] external/envoy/source/common/runtime/runtime_impl.cc:196] walking directory: /build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data/current/envoy
[2018-03-15 21:06:45.659][20070][debug][runtime] external/envoy/source/common/runtime/runtime_impl.cc:167] error creating runtime snapshot: unable to open directory: /build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data/current/envoy
[2018-03-15 21:06:45.673][20152][debug][grpc] external/envoy/source/common/grpc/google_async_client_impl.cc:34] completionThread running
==================
WARNING: ThreadSanitizer: data race (pid=20070)
Write of size 8 at 0x7b9000006000 by main thread:
#0 memcpy ??:? (envoy-static+0x54755c)
#1 std::basic_streambuf<char, std::char_traits<char> >::xsputn(char const*, long) ??:? (envoy-static+0x1b255da)
#2 spdlog::logger::_sink_it(spdlog::details::log_msg&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:321 (envoy-static+0x5d09cc)
#3 void spdlog::logger::log<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > >(spdlog::level::level_enum, char const*, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > const&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:74 (envoy-static+0x6b542a)
#4 void spdlog::logger::debug<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> >>(char const*, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > const&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:139 (envoy-static+0x69eedd)
#5 ThreadLocalClusterManagerImpl /proc/self/cwd/external/envoy/source/common/upstream/cluster_manager_impl.cc:573 (envoy-static+0x9b60ac)
#6 void __gnu_cxx::new_allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>::construct<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl*, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/ext/new_allocator.h:120 (envoy-static+0x9d7fd4)
#7 void std::allocator_traits<std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> >::construct<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>&, Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl*, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/alloc_traits.h:530 (envoy-static+0x9d7c20)
#8 _Sp_counted_ptr_inplace<Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr_base.h:522 (envoy-static+0x9d76d9)
#9 __shared_count<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr_base.h:617 (envoy-static+0x9d733d)
#10 __shared_ptr<std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr_base.h:1096 (envoy-static+0x9d711a)
#11 shared_ptr<std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr.h:319 (envoy-static+0x9d7010)
#12 std::shared_ptr<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> std::allocate_shared<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> const&, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr.h:619 (envoy-static+0x9d6e74)
#13 std::shared_ptr<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> std::make_shared<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr.h:635 (envoy-static+0x9d6cf0)
#14 operator() /proc/self/cwd/external/envoy/source/common/upstream/cluster_manager_impl.cc:255 (envoy-static+0x9bbb91)
#15 std::_Function_handler<std::shared_ptr<Envoy::ThreadLocal::ThreadLocalObject> (Envoy::Event::Dispatcher&), Envoy::Upstream::ClusterManagerImpl::ClusterManagerImpl(envoy::config::bootstrap::v2::Bootstrap const&, Envoy::Upstream::ClusterManagerFactory&, Envoy::Stats::Store&, Envoy::ThreadLocal::Instance&, Envoy::Runtime::Loader&, Envoy::Runtime::RandomGenerator&, Envoy::LocalInfo::LocalInfo const&, Envoy::AccessLog::AccessLogManager&, Envoy::Event::Dispatcher&)::$_5>::_M_invoke(std::_Any_data const&, Envoy::Event::Dispatcher&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:1856 (envoy-static+0x9bb811)
#16 std::function<std::shared_ptr<Envoy::ThreadLocal::ThreadLocalObject> (Envoy::Event::Dispatcher&)>::operator()(Envoy::Event::Dispatcher&) const /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:2267 (envoy-static+0x8b2b69)
#17 Envoy::ThreadLocal::InstanceImpl::SlotImpl::set(std::function<std::shared_ptr<Envoy::ThreadLocal::ThreadLocalObject> (Envoy::Event::Dispatcher&)>) /proc/self/cwd/external/envoy/source/common/thread_local/thread_local_impl.cc:104 (envoy-static+0x8af854)
#18 ClusterManagerImpl /proc/self/cwd/external/envoy/source/common/upstream/cluster_manager_impl.cc:253 (envoy-static+0x9b04f3)
#19 ValidationClusterManager /proc/self/cwd/external/envoy/source/server/config_validation/cluster_manager.cc:36 (envoy-static+0x8a40e0)
#20 Envoy::Upstream::ValidationClusterManagerFactory::clusterManagerFromProto(envoy::config::bootstrap::v2::Bootstrap const&, Envoy::Stats::Store&, Envoy::ThreadLocal::Instance&, Envoy::Runtime::Loader&, Envoy::Runtime::RandomGenerator&, Envoy::LocalInfo::LocalInfo const&, Envoy::AccessLog::AccessLogManager&) /proc/self/cwd/external/envoy/source/server/config_validation/cluster_manager.cc:18 (envoy-static+0x8a3e99)
#21 Envoy::Server::Configuration::MainImpl::initialize(envoy::config::bootstrap::v2::Bootstrap const&, Envoy::Server::Instance&, Envoy::Upstream::ClusterManagerFactory&) /proc/self/cwd/external/envoy/source/server/configuration_impl.cc:48 (envoy-static+0x10bb950)
#22 Envoy::Server::ValidationInstance::initialize(Envoy::Server::Options&, std::shared_ptr<Envoy::Network::Address::Instance const>, Envoy::Server::ComponentFactory&) /proc/self/cwd/external/envoy/source/server/config_validation/server.cc:88 (envoy-static+0x87c097)
#23 ValidationInstance /proc/self/cwd/external/envoy/source/server/config_validation/server.cc:45 (envoy-static+0x87b57e)
#24 Envoy::Server::validateConfig(Envoy::Server::Options&, std::shared_ptr<Envoy::Network::Address::Instance const>, Envoy::Server::ComponentFactory&) /proc/self/cwd/external/envoy/source/server/config_validation/server.cc:24 (envoy-static+0x87ad4f)
#25 Envoy::MainCommonBase::run() /proc/self/cwd/external/envoy/source/exe/main_common.cc:83 (envoy-static+0x600752)
#26 Envoy::MainCommon::run() /proc/self/cwd/bazel-out/k8-dbg/bin/external/envoy/source/exe/_virtual_includes/envoy_main_common_lib/exe/main_common.h:43 (envoy-static+0x5d05bf)
#27 main /proc/self/cwd/external/envoy/source/exe/main.cc:36 (envoy-static+0x5cec4d)
Previous write of size 8 at 0x7b9000006000 by thread T3:
#0 memcpy ??:? (envoy-static+0x54755c)
#1 std::basic_streambuf<char, std::char_traits<char> >::xsputn(char const*, long) ??:? (envoy-static+0x1b255da)
#2 spdlog::logger::_sink_it(spdlog::details::log_msg&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:321 (envoy-static+0x5d09cc)
#3 void spdlog::logger::log<>(spdlog::level::level_enum, char const*) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:95 (envoy-static+0x718c8c)
#4 void spdlog::logger::debug<char [91]>(char const (&) [91]) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:176 (envoy-static+0xa759fd)
#5 Envoy::Grpc::GoogleAsyncClientThreadLocal::completionThread() /proc/self/cwd/external/envoy/source/common/grpc/google_async_client_impl.cc:34 (envoy-static+0xa6e991)
#6 operator() /proc/self/cwd/external/envoy/source/common/grpc/google_async_client_impl.cc:10 (envoy-static+0xa74d88)
#7 std::_Function_handler<void (), Envoy::Grpc::GoogleAsyncClientThreadLocal::GoogleAsyncClientThreadLocal()::$_0>::_M_invoke(std::_Any_data const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:1871 (envoy-static+0xa74b1a)
#8 std::function<void ()>::operator()() const /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:2267 (envoy-static+0x6c079e)
#9 operator() /proc/self/cwd/external/envoy/source/common/common/thread.cc:20 (envoy-static+0x14480d4)
#10 __invoke /proc/self/cwd/external/envoy/source/common/common/thread.cc:19 (envoy-static+0x1448068)
``` | 1.0 | hotrestart_test flakes in spdlog with TSAN (and other sanitizers) - Occasionally we've observed in CI that `hotrestart_test` flakes during early spdlog use in `ValidationClusterManager`. Something isn't quite right here, since we should be doing the kind of verbose logging that would trigger it. Previous investigations by @mattklein123 and myself point to possible validation init not doing the right setup for logging.
We should figure this one out.
```
[2018-03-15 21:06:45.658][20070][info][main] external/envoy/source/server/server.cc:275] runtime symlink: /build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data/current
[2018-03-15 21:06:45.658][20070][info][main] external/envoy/source/server/server.cc:276] runtime subdirectory: envoy
[2018-03-15 21:06:45.658][20070][info][main] external/envoy/source/server/server.cc:280] runtime override subdirectory: envoy_override/cluster
[2018-03-15 21:06:45.659][20070][debug][file] external/envoy/source/common/filesystem/inotify/watcher_impl.cc:48] added watch for directory: '/build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data' file: 'current' fd: 1
[2018-03-15 21:06:45.659][20070][debug][runtime] external/envoy/source/common/runtime/runtime_impl.cc:196] walking directory: /build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data/current/envoy
[2018-03-15 21:06:45.659][20070][debug][runtime] external/envoy/source/common/runtime/runtime_impl.cc:167] error creating runtime snapshot: unable to open directory: /build/tmp/_bazel_bazel/400406edc57d332f0b9b805d2b8e33a1/execroot/envoy/bazel-out/k8-dbg/bin/external/envoy/test/integration/hotrestart_test.runfiles/envoy/test/common/runtime/test_data/current/envoy
[2018-03-15 21:06:45.673][20152][debug][grpc] external/envoy/source/common/grpc/google_async_client_impl.cc:34] completionThread running
==================
WARNING: ThreadSanitizer: data race (pid=20070)
Write of size 8 at 0x7b9000006000 by main thread:
#0 memcpy ??:? (envoy-static+0x54755c)
#1 std::basic_streambuf<char, std::char_traits<char> >::xsputn(char const*, long) ??:? (envoy-static+0x1b255da)
#2 spdlog::logger::_sink_it(spdlog::details::log_msg&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:321 (envoy-static+0x5d09cc)
#3 void spdlog::logger::log<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > >(spdlog::level::level_enum, char const*, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > const&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:74 (envoy-static+0x6b542a)
#4 void spdlog::logger::debug<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> >>(char const*, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > const&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:139 (envoy-static+0x69eedd)
#5 ThreadLocalClusterManagerImpl /proc/self/cwd/external/envoy/source/common/upstream/cluster_manager_impl.cc:573 (envoy-static+0x9b60ac)
#6 void __gnu_cxx::new_allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>::construct<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl*, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/ext/new_allocator.h:120 (envoy-static+0x9d7fd4)
#7 void std::allocator_traits<std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> >::construct<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>&, Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl*, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/alloc_traits.h:530 (envoy-static+0x9d7c20)
#8 _Sp_counted_ptr_inplace<Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr_base.h:522 (envoy-static+0x9d76d9)
#9 __shared_count<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr_base.h:617 (envoy-static+0x9d733d)
#10 __shared_ptr<std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr_base.h:1096 (envoy-static+0x9d711a)
#11 shared_ptr<std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl &, Envoy::Event::Dispatcher &, const Envoy::Optional<std::__cxx11::basic_string<char> > &> /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr.h:319 (envoy-static+0x9d7010)
#12 std::shared_ptr<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> std::allocate_shared<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl>, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(std::allocator<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> const&, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr.h:619 (envoy-static+0x9d6e74)
#13 std::shared_ptr<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl> std::make_shared<Envoy::Upstream::ClusterManagerImpl::ThreadLocalClusterManagerImpl, Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&>(Envoy::Upstream::ClusterManagerImpl&, Envoy::Event::Dispatcher&, Envoy::Optional<std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > > const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/bits/shared_ptr.h:635 (envoy-static+0x9d6cf0)
#14 operator() /proc/self/cwd/external/envoy/source/common/upstream/cluster_manager_impl.cc:255 (envoy-static+0x9bbb91)
#15 std::_Function_handler<std::shared_ptr<Envoy::ThreadLocal::ThreadLocalObject> (Envoy::Event::Dispatcher&), Envoy::Upstream::ClusterManagerImpl::ClusterManagerImpl(envoy::config::bootstrap::v2::Bootstrap const&, Envoy::Upstream::ClusterManagerFactory&, Envoy::Stats::Store&, Envoy::ThreadLocal::Instance&, Envoy::Runtime::Loader&, Envoy::Runtime::RandomGenerator&, Envoy::LocalInfo::LocalInfo const&, Envoy::AccessLog::AccessLogManager&, Envoy::Event::Dispatcher&)::$_5>::_M_invoke(std::_Any_data const&, Envoy::Event::Dispatcher&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:1856 (envoy-static+0x9bb811)
#16 std::function<std::shared_ptr<Envoy::ThreadLocal::ThreadLocalObject> (Envoy::Event::Dispatcher&)>::operator()(Envoy::Event::Dispatcher&) const /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:2267 (envoy-static+0x8b2b69)
#17 Envoy::ThreadLocal::InstanceImpl::SlotImpl::set(std::function<std::shared_ptr<Envoy::ThreadLocal::ThreadLocalObject> (Envoy::Event::Dispatcher&)>) /proc/self/cwd/external/envoy/source/common/thread_local/thread_local_impl.cc:104 (envoy-static+0x8af854)
#18 ClusterManagerImpl /proc/self/cwd/external/envoy/source/common/upstream/cluster_manager_impl.cc:253 (envoy-static+0x9b04f3)
#19 ValidationClusterManager /proc/self/cwd/external/envoy/source/server/config_validation/cluster_manager.cc:36 (envoy-static+0x8a40e0)
#20 Envoy::Upstream::ValidationClusterManagerFactory::clusterManagerFromProto(envoy::config::bootstrap::v2::Bootstrap const&, Envoy::Stats::Store&, Envoy::ThreadLocal::Instance&, Envoy::Runtime::Loader&, Envoy::Runtime::RandomGenerator&, Envoy::LocalInfo::LocalInfo const&, Envoy::AccessLog::AccessLogManager&) /proc/self/cwd/external/envoy/source/server/config_validation/cluster_manager.cc:18 (envoy-static+0x8a3e99)
#21 Envoy::Server::Configuration::MainImpl::initialize(envoy::config::bootstrap::v2::Bootstrap const&, Envoy::Server::Instance&, Envoy::Upstream::ClusterManagerFactory&) /proc/self/cwd/external/envoy/source/server/configuration_impl.cc:48 (envoy-static+0x10bb950)
#22 Envoy::Server::ValidationInstance::initialize(Envoy::Server::Options&, std::shared_ptr<Envoy::Network::Address::Instance const>, Envoy::Server::ComponentFactory&) /proc/self/cwd/external/envoy/source/server/config_validation/server.cc:88 (envoy-static+0x87c097)
#23 ValidationInstance /proc/self/cwd/external/envoy/source/server/config_validation/server.cc:45 (envoy-static+0x87b57e)
#24 Envoy::Server::validateConfig(Envoy::Server::Options&, std::shared_ptr<Envoy::Network::Address::Instance const>, Envoy::Server::ComponentFactory&) /proc/self/cwd/external/envoy/source/server/config_validation/server.cc:24 (envoy-static+0x87ad4f)
#25 Envoy::MainCommonBase::run() /proc/self/cwd/external/envoy/source/exe/main_common.cc:83 (envoy-static+0x600752)
#26 Envoy::MainCommon::run() /proc/self/cwd/bazel-out/k8-dbg/bin/external/envoy/source/exe/_virtual_includes/envoy_main_common_lib/exe/main_common.h:43 (envoy-static+0x5d05bf)
#27 main /proc/self/cwd/external/envoy/source/exe/main.cc:36 (envoy-static+0x5cec4d)
Previous write of size 8 at 0x7b9000006000 by thread T3:
#0 memcpy ??:? (envoy-static+0x54755c)
#1 std::basic_streambuf<char, std::char_traits<char> >::xsputn(char const*, long) ??:? (envoy-static+0x1b255da)
#2 spdlog::logger::_sink_it(spdlog::details::log_msg&) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:321 (envoy-static+0x5d09cc)
#3 void spdlog::logger::log<>(spdlog::level::level_enum, char const*) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:95 (envoy-static+0x718c8c)
#4 void spdlog::logger::debug<char [91]>(char const (&) [91]) /proc/self/cwd/external/com_github_gabime_spdlog/include/spdlog/details/logger_impl.h:176 (envoy-static+0xa759fd)
#5 Envoy::Grpc::GoogleAsyncClientThreadLocal::completionThread() /proc/self/cwd/external/envoy/source/common/grpc/google_async_client_impl.cc:34 (envoy-static+0xa6e991)
#6 operator() /proc/self/cwd/external/envoy/source/common/grpc/google_async_client_impl.cc:10 (envoy-static+0xa74d88)
#7 std::_Function_handler<void (), Envoy::Grpc::GoogleAsyncClientThreadLocal::GoogleAsyncClientThreadLocal()::$_0>::_M_invoke(std::_Any_data const&) /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:1871 (envoy-static+0xa74b1a)
#8 std::function<void ()>::operator()() const /usr/bin/../lib/gcc/x86_64-linux-gnu/5.4.0/../../../../include/c++/5.4.0/functional:2267 (envoy-static+0x6c079e)
#9 operator() /proc/self/cwd/external/envoy/source/common/common/thread.cc:20 (envoy-static+0x14480d4)
#10 __invoke /proc/self/cwd/external/envoy/source/common/common/thread.cc:19 (envoy-static+0x1448068)
``` | non_priority | hotrestart test flakes in spdlog with tsan and other sanitizers occasionally we ve observed in ci that hotrestart test flakes during early spdlog use in validationclustermanager something isn t quite right here since we should be doing the kind of verbose logging that would trigger it previous investigations by and myself point to possible validation init not doing the right setup for logging we should figure this one out external envoy source server server cc runtime symlink build tmp bazel bazel execroot envoy bazel out dbg bin external envoy test integration hotrestart test runfiles envoy test common runtime test data current external envoy source server server cc runtime subdirectory envoy external envoy source server server cc runtime override subdirectory envoy override cluster external envoy source common filesystem inotify watcher impl cc added watch for directory build tmp bazel bazel execroot envoy bazel out dbg bin external envoy test integration hotrestart test runfiles envoy test common runtime test data file current fd external envoy source common runtime runtime impl cc walking directory build tmp bazel bazel execroot envoy bazel out dbg bin external envoy test integration hotrestart test runfiles envoy test common runtime test data current envoy external envoy source common runtime runtime impl cc error creating runtime snapshot unable to open directory build tmp bazel bazel execroot envoy bazel out dbg bin external envoy test integration hotrestart test runfiles envoy test common runtime test data current envoy external envoy source common grpc google async client impl cc completionthread running warning threadsanitizer data race pid write of size at by main thread memcpy envoy static std basic streambuf xsputn char const long envoy static spdlog logger sink it spdlog details log msg proc self cwd external com github gabime spdlog include spdlog details logger impl h envoy static void spdlog logger log std allocator spdlog level level enum char const std basic string std allocator const proc self cwd external com github gabime spdlog include spdlog details logger impl h envoy static void spdlog logger debug std allocator char const std basic string std allocator const proc self cwd external com github gabime spdlog include spdlog details logger impl h envoy static threadlocalclustermanagerimpl proc self cwd external envoy source common upstream cluster manager impl cc envoy static void gnu cxx new allocator construct std allocator const envoy upstream clustermanagerimpl threadlocalclustermanagerimpl envoy upstream clustermanagerimpl envoy event dispatcher envoy optional std allocator const usr bin lib gcc linux gnu include c ext new allocator h envoy static void std allocator traits construct std allocator const std allocator envoy upstream clustermanagerimpl threadlocalclustermanagerimpl envoy upstream clustermanagerimpl envoy event dispatcher envoy optional std allocator const usr bin lib gcc linux gnu include c bits alloc traits h envoy static sp counted ptr inplace usr bin lib gcc linux gnu include c bits shared ptr base h envoy static shared count envoy upstream clustermanagerimpl envoy event dispatcher const envoy optional usr bin lib gcc linux gnu include c bits shared ptr base h envoy static shared ptr envoy upstream clustermanagerimpl envoy event dispatcher const envoy optional usr bin lib gcc linux gnu include c bits shared ptr base h envoy static shared ptr envoy upstream clustermanagerimpl envoy event dispatcher const envoy optional usr bin lib gcc linux gnu include c bits shared ptr h envoy static std shared ptr std allocate shared envoy upstream clustermanagerimpl envoy event dispatcher envoy optional std allocator const std allocator const envoy upstream clustermanagerimpl envoy event dispatcher envoy optional std allocator const usr bin lib gcc linux gnu include c bits shared ptr h envoy static std shared ptr std make shared std allocator const envoy upstream clustermanagerimpl envoy event dispatcher envoy optional std allocator const usr bin lib gcc linux gnu include c bits shared ptr h envoy static operator proc self cwd external envoy source common upstream cluster manager impl cc envoy static std function handler envoy event dispatcher envoy upstream clustermanagerimpl clustermanagerimpl envoy config bootstrap bootstrap const envoy upstream clustermanagerfactory envoy stats store envoy threadlocal instance envoy runtime loader envoy runtime randomgenerator envoy localinfo localinfo const envoy accesslog accesslogmanager envoy event dispatcher m invoke std any data const envoy event dispatcher usr bin lib gcc linux gnu include c functional envoy static std function envoy event dispatcher operator envoy event dispatcher const usr bin lib gcc linux gnu include c functional envoy static envoy threadlocal instanceimpl slotimpl set std function envoy event dispatcher proc self cwd external envoy source common thread local thread local impl cc envoy static clustermanagerimpl proc self cwd external envoy source common upstream cluster manager impl cc envoy static validationclustermanager proc self cwd external envoy source server config validation cluster manager cc envoy static envoy upstream validationclustermanagerfactory clustermanagerfromproto envoy config bootstrap bootstrap const envoy stats store envoy threadlocal instance envoy runtime loader envoy runtime randomgenerator envoy localinfo localinfo const envoy accesslog accesslogmanager proc self cwd external envoy source server config validation cluster manager cc envoy static envoy server configuration mainimpl initialize envoy config bootstrap bootstrap const envoy server instance envoy upstream clustermanagerfactory proc self cwd external envoy source server configuration impl cc envoy static envoy server validationinstance initialize envoy server options std shared ptr envoy server componentfactory proc self cwd external envoy source server config validation server cc envoy static validationinstance proc self cwd external envoy source server config validation server cc envoy static envoy server validateconfig envoy server options std shared ptr envoy server componentfactory proc self cwd external envoy source server config validation server cc envoy static envoy maincommonbase run proc self cwd external envoy source exe main common cc envoy static envoy maincommon run proc self cwd bazel out dbg bin external envoy source exe virtual includes envoy main common lib exe main common h envoy static main proc self cwd external envoy source exe main cc envoy static previous write of size at by thread memcpy envoy static std basic streambuf xsputn char const long envoy static spdlog logger sink it spdlog details log msg proc self cwd external com github gabime spdlog include spdlog details logger impl h envoy static void spdlog logger log spdlog level level enum char const proc self cwd external com github gabime spdlog include spdlog details logger impl h envoy static void spdlog logger debug char const proc self cwd external com github gabime spdlog include spdlog details logger impl h envoy static envoy grpc googleasyncclientthreadlocal completionthread proc self cwd external envoy source common grpc google async client impl cc envoy static operator proc self cwd external envoy source common grpc google async client impl cc envoy static std function handler m invoke std any data const usr bin lib gcc linux gnu include c functional envoy static std function operator const usr bin lib gcc linux gnu include c functional envoy static operator proc self cwd external envoy source common common thread cc envoy static invoke proc self cwd external envoy source common common thread cc envoy static | 0 |
2,017 | 2,869,582,584 | IssuesEvent | 2015-06-06 09:50:47 | zikula/core | https://api.github.com/repos/zikula/core | reopened | composer no longer installing zikula-modules in /modules | Bug CI Build | composer no longer installing zikula-modules (legal/profile/breakit) correctly at least not on `composer update`
Composer version 1.0-dev (e64470c987fdd6bff03b85eed823eb4b865a4152) 2015-05-28 14:52:12
it copies repos to `/vendors` and not `/modules | 1.0 | composer no longer installing zikula-modules in /modules - composer no longer installing zikula-modules (legal/profile/breakit) correctly at least not on `composer update`
Composer version 1.0-dev (e64470c987fdd6bff03b85eed823eb4b865a4152) 2015-05-28 14:52:12
it copies repos to `/vendors` and not `/modules | non_priority | composer no longer installing zikula modules in modules composer no longer installing zikula modules legal profile breakit correctly at least not on composer update composer version dev it copies repos to vendors and not modules | 0 |
233,543 | 25,765,567,937 | IssuesEvent | 2022-12-09 01:20:33 | gabriel-milan/comp-soc | https://api.github.com/repos/gabriel-milan/comp-soc | opened | python_telegram_bot-13.12-py3-none-any.whl: 1 vulnerabilities (highest severity is: 6.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>python_telegram_bot-13.12-py3-none-any.whl</b></p></summary>
<p></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (python_telegram_bot version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-23491](https://www.mend.io/vulnerability-database/CVE-2022-23491) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.8 | certifi-2022.5.18.1-py3-none-any.whl | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23491</summary>
### Vulnerable Library - <b>certifi-2022.5.18.1-py3-none-any.whl</b></p>
<p>Python package for providing Mozilla's CA Bundle.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/11/dd/e015f3780f42dd9af62cf0107b44ea1298926627ecd70c17b0e484e95bcd/certifi-2022.5.18.1-py3-none-any.whl">https://files.pythonhosted.org/packages/11/dd/e015f3780f42dd9af62cf0107b44ea1298926627ecd70c17b0e484e95bcd/certifi-2022.5.18.1-py3-none-any.whl</a></p>
<p>
Dependency Hierarchy:
- python_telegram_bot-13.12-py3-none-any.whl (Root Library)
- :x: **certifi-2022.5.18.1-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Certifi is a curated collection of Root Certificates for validating the trustworthiness of SSL certificates while verifying the identity of TLS hosts. Certifi 2022.12.07 removes root certificates from "TrustCor" from the root store. These are in the process of being removed from Mozilla's trust store. TrustCor's root certificates are being removed pursuant to an investigation prompted by media reporting that TrustCor's ownership also operated a business that produced spyware. Conclusions of Mozilla's investigation can be found in the linked google group discussion.
<p>Publish Date: 2022-12-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23491>CVE-2022-23491</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-23491">https://www.cve.org/CVERecord?id=CVE-2022-23491</a></p>
<p>Release Date: 2022-12-07</p>
<p>Fix Resolution: certifi - 2022.12.07</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | python_telegram_bot-13.12-py3-none-any.whl: 1 vulnerabilities (highest severity is: 6.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>python_telegram_bot-13.12-py3-none-any.whl</b></p></summary>
<p></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (python_telegram_bot version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-23491](https://www.mend.io/vulnerability-database/CVE-2022-23491) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.8 | certifi-2022.5.18.1-py3-none-any.whl | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23491</summary>
### Vulnerable Library - <b>certifi-2022.5.18.1-py3-none-any.whl</b></p>
<p>Python package for providing Mozilla's CA Bundle.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/11/dd/e015f3780f42dd9af62cf0107b44ea1298926627ecd70c17b0e484e95bcd/certifi-2022.5.18.1-py3-none-any.whl">https://files.pythonhosted.org/packages/11/dd/e015f3780f42dd9af62cf0107b44ea1298926627ecd70c17b0e484e95bcd/certifi-2022.5.18.1-py3-none-any.whl</a></p>
<p>
Dependency Hierarchy:
- python_telegram_bot-13.12-py3-none-any.whl (Root Library)
- :x: **certifi-2022.5.18.1-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Certifi is a curated collection of Root Certificates for validating the trustworthiness of SSL certificates while verifying the identity of TLS hosts. Certifi 2022.12.07 removes root certificates from "TrustCor" from the root store. These are in the process of being removed from Mozilla's trust store. TrustCor's root certificates are being removed pursuant to an investigation prompted by media reporting that TrustCor's ownership also operated a business that produced spyware. Conclusions of Mozilla's investigation can be found in the linked google group discussion.
<p>Publish Date: 2022-12-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23491>CVE-2022-23491</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-23491">https://www.cve.org/CVERecord?id=CVE-2022-23491</a></p>
<p>Release Date: 2022-12-07</p>
<p>Fix Resolution: certifi - 2022.12.07</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | python telegram bot none any whl vulnerabilities highest severity is vulnerable library python telegram bot none any whl vulnerabilities cve severity cvss dependency type fixed in python telegram bot version remediation available medium certifi none any whl transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library certifi none any whl python package for providing mozilla s ca bundle library home page a href dependency hierarchy python telegram bot none any whl root library x certifi none any whl vulnerable library found in base branch master vulnerability details certifi is a curated collection of root certificates for validating the trustworthiness of ssl certificates while verifying the identity of tls hosts certifi removes root certificates from trustcor from the root store these are in the process of being removed from mozilla s trust store trustcor s root certificates are being removed pursuant to an investigation prompted by media reporting that trustcor s ownership also operated a business that produced spyware conclusions of mozilla s investigation can be found in the linked google group discussion publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope changed impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution certifi step up your open source security game with mend | 0 |
96,074 | 19,896,435,746 | IssuesEvent | 2022-01-25 00:01:29 | detiuaveiro/RacingGame- | https://api.github.com/repos/detiuaveiro/RacingGame- | closed | Script para o Sol rodar à volta da cena | Code CV | Script para emular o movimento do sol relativo ao quarto. | 1.0 | Script para o Sol rodar à volta da cena - Script para emular o movimento do sol relativo ao quarto. | non_priority | script para o sol rodar à volta da cena script para emular o movimento do sol relativo ao quarto | 0 |
8,984 | 3,244,233,404 | IssuesEvent | 2015-10-16 00:20:26 | pyqg/pyqg | https://api.github.com/repos/pyqg/pyqg | opened | Add documentation for diagnostics in two-layer model | documentation | Why do we take the negative sign of the diagnostics before plotting?
http://pyqg.readthedocs.org/en/stable/examples/two-layer.html#plot-diagnostics | 1.0 | Add documentation for diagnostics in two-layer model - Why do we take the negative sign of the diagnostics before plotting?
http://pyqg.readthedocs.org/en/stable/examples/two-layer.html#plot-diagnostics | non_priority | add documentation for diagnostics in two layer model why do we take the negative sign of the diagnostics before plotting | 0 |
106,285 | 11,474,403,539 | IssuesEvent | 2020-02-10 04:07:33 | microsoft/vscode-docs | https://api.github.com/repos/microsoft/vscode-docs | closed | API page doesn't list the important bits | API documentation doc-enhancement extensibility | The [API](https://code.visualstudio.com/docs/extensionAPI/vscode-api)-page list the namespaces only but doesn't list any of the actual types in the page TOC. That make it hard to read/discover things.
| 1.0 | API page doesn't list the important bits - The [API](https://code.visualstudio.com/docs/extensionAPI/vscode-api)-page list the namespaces only but doesn't list any of the actual types in the page TOC. That make it hard to read/discover things.
| non_priority | api page doesn t list the important bits the list the namespaces only but doesn t list any of the actual types in the page toc that make it hard to read discover things | 0 |
318,582 | 27,316,473,318 | IssuesEvent | 2023-02-24 16:05:01 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix math.test_tensorflow_erfcinv | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4054925606/jobs/6977404251" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4011265503/jobs/6888662116" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4054925606/jobs/6977409309" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4011265503/jobs/6888662116" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_math.py::test_tensorflow_erfcinv[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-26T00:55:36.2494480Z E AssertionError: 0.5426817005919033 != inf
2023-01-26T00:55:36.2494907Z E Falsifying example: test_tensorflow_erfcinv(
2023-01-26T00:55:36.2495435Z E dtype_and_x=(['float64'], [array(-1.)]),
2023-01-26T00:55:36.2496271Z E test_flags=num_positional_args=0. with_out=False. inplace=False. native_arrays=[False]. as_variable=[False]. ,
2023-01-26T00:55:36.2496983Z E fn_tree='ivy.functional.frontends.tensorflow.math.erfcinv',
2023-01-26T00:55:36.2497530Z E frontend='tensorflow',
2023-01-26T00:55:36.2497945Z E on_device='cpu',
2023-01-26T00:55:36.2498441Z E )
2023-01-26T00:55:36.2498757Z E
2023-01-26T00:55:36.2499494Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AXicY2AAAkYGCADTAAAkAAM=') as a decorator on your test case
</details>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_math.py::test_tensorflow_erfcinv[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-26T00:55:36.2494480Z E AssertionError: 0.5426817005919033 != inf
2023-01-26T00:55:36.2494907Z E Falsifying example: test_tensorflow_erfcinv(
2023-01-26T00:55:36.2495435Z E dtype_and_x=(['float64'], [array(-1.)]),
2023-01-26T00:55:36.2496271Z E test_flags=num_positional_args=0. with_out=False. inplace=False. native_arrays=[False]. as_variable=[False]. ,
2023-01-26T00:55:36.2496983Z E fn_tree='ivy.functional.frontends.tensorflow.math.erfcinv',
2023-01-26T00:55:36.2497530Z E frontend='tensorflow',
2023-01-26T00:55:36.2497945Z E on_device='cpu',
2023-01-26T00:55:36.2498441Z E )
2023-01-26T00:55:36.2498757Z E
2023-01-26T00:55:36.2499494Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AXicY2AAAkYGCADTAAAkAAM=') as a decorator on your test case
</details>
| 1.0 | Fix math.test_tensorflow_erfcinv - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4054925606/jobs/6977404251" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4011265503/jobs/6888662116" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4054925606/jobs/6977409309" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4011265503/jobs/6888662116" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_math.py::test_tensorflow_erfcinv[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-26T00:55:36.2494480Z E AssertionError: 0.5426817005919033 != inf
2023-01-26T00:55:36.2494907Z E Falsifying example: test_tensorflow_erfcinv(
2023-01-26T00:55:36.2495435Z E dtype_and_x=(['float64'], [array(-1.)]),
2023-01-26T00:55:36.2496271Z E test_flags=num_positional_args=0. with_out=False. inplace=False. native_arrays=[False]. as_variable=[False]. ,
2023-01-26T00:55:36.2496983Z E fn_tree='ivy.functional.frontends.tensorflow.math.erfcinv',
2023-01-26T00:55:36.2497530Z E frontend='tensorflow',
2023-01-26T00:55:36.2497945Z E on_device='cpu',
2023-01-26T00:55:36.2498441Z E )
2023-01-26T00:55:36.2498757Z E
2023-01-26T00:55:36.2499494Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AXicY2AAAkYGCADTAAAkAAM=') as a decorator on your test case
</details>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>FAILED ivy_tests/test_ivy/test_frontends/test_tensorflow/test_math.py::test_tensorflow_erfcinv[cpu-ivy.functional.backends.jax-False-False]</summary>
2023-01-26T00:55:36.2494480Z E AssertionError: 0.5426817005919033 != inf
2023-01-26T00:55:36.2494907Z E Falsifying example: test_tensorflow_erfcinv(
2023-01-26T00:55:36.2495435Z E dtype_and_x=(['float64'], [array(-1.)]),
2023-01-26T00:55:36.2496271Z E test_flags=num_positional_args=0. with_out=False. inplace=False. native_arrays=[False]. as_variable=[False]. ,
2023-01-26T00:55:36.2496983Z E fn_tree='ivy.functional.frontends.tensorflow.math.erfcinv',
2023-01-26T00:55:36.2497530Z E frontend='tensorflow',
2023-01-26T00:55:36.2497945Z E on_device='cpu',
2023-01-26T00:55:36.2498441Z E )
2023-01-26T00:55:36.2498757Z E
2023-01-26T00:55:36.2499494Z E You can reproduce this example by temporarily adding @reproduce_failure('6.55.0', b'AXicY2AAAkYGCADTAAAkAAM=') as a decorator on your test case
</details>
| non_priority | fix math test tensorflow erfcinv tensorflow img src torch img src numpy img src jax img src not found not found failed ivy tests test ivy test frontends test tensorflow test math py test tensorflow erfcinv e assertionerror inf e falsifying example test tensorflow erfcinv e dtype and x e test flags num positional args with out false inplace false native arrays as variable e fn tree ivy functional frontends tensorflow math erfcinv e frontend tensorflow e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b as a decorator on your test case not found not found failed ivy tests test ivy test frontends test tensorflow test math py test tensorflow erfcinv e assertionerror inf e falsifying example test tensorflow erfcinv e dtype and x e test flags num positional args with out false inplace false native arrays as variable e fn tree ivy functional frontends tensorflow math erfcinv e frontend tensorflow e on device cpu e e e you can reproduce this example by temporarily adding reproduce failure b as a decorator on your test case | 0 |
314,008 | 26,969,690,454 | IssuesEvent | 2023-02-09 02:59:38 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | [wasm] Runtime test `simpleprovidervalidation.sh` failing on CI | arch-wasm blocking-clean-ci in-pr test-failure | [Rolling build](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164624&view=logs&j=3e93a48f-6568-53f2-76b3-1285c183c39d), and [log](https://helixre107v0xdeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-heads-main-c5375adeae8e4f48a4/PayloadGroup0/1/console.74f02e35.log?helixlogtype=result):
```
Starting: tracing.eventpipe.XUnitWrapper (parallel test collections = on, max threads = 2)
tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation/simpleprovidervalidation.sh [FAIL]
{"name":"ExitStatus","message":"Program terminated with exit(-1)","status":-1}
Return code: 1
Raw output file: /datadisks/disk1/work/B644095B/w/B577098C/uploads/Reports/tracing.eventpipe/simpleprovidervalidation/simpleprovidervalidation/simpleprovidervalidation.output.txt
Raw output:
BEGIN EXECUTION
MSBuild version 17.5.0-preview-23056-01+d89d4bc91 for .NET
AppDir: /datadisks/disk1/work/B644095B/w/B577098C/e/tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation/WasmApp/
TestBinDir: /datadisks/disk1/work/B644095B/w/B577098C/e/tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation
ArtifactsBinDir:
/datadisks/disk1/work/B644095B/p/build/WasmApp.targets(412,5): warning WASM0004: Loading assembly reference 'Microsoft.Diagnostics.Tools.RuntimeClient, Version=1.0.4.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35' for 'common, Version=0.0.0.0, Culture=neutral, PublicKeyToken=null' failed: Could not find assembly 'Microsoft.Diagnostics.Tools.RuntimeClient, Version=1.0.4.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35'. Either explicitly load this assembly using a method such as LoadFromAssemblyPath() or use a MetadataAssemblyResolver that returns a valid assembly. Skipping. [/datadisks/disk1/work/B644095B/p/wasm-test-runner/WasmTestRunner.proj]
Generated app bundle at /datadisks/disk1/work/B644095B/w/B577098C/e/tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation/WasmApp/
Incoming arguments: --run simpleprovidervalidation.dll
Application arguments: --run simpleprovidervalidation.dll
console.info: Initializing dotnet version 8.0.0-ci commit hash 0304f1f5157a8280fa093bdfc7cfb8d9f62e016f
0.0s: ==TEST STARTING==
0.1s: System.PlatformNotSupportedException: System.Diagnostics.Process is not supported on this platform.
at System.Diagnostics.Process.GetProcesses()
at Tracing.Tests.Common.IpcTraceTest.<>c.<EnsureCleanEnvironment>b__10_0()
at Tracing.Tests.Common.IpcTraceTest.EnsureCleanEnvironment()
at Tracing.Tests.Common.IpcTraceTest.Validate(Boolean enableRundownProvider)
at Tracing.Tests.Common.IpcTraceTest.RunAndValidateEventCounts(Dictionary`2 expectedEventCounts, Action eventGeneratingAction, List`1 providers, Int32 circularBufferMB, Func`2 optionalTraceValidator, Boolean enableRundownProvider)
0.1s: ==TEST FINISHED: FAILED!==
WASM EXIT -1
Expected: 100
Actual: 255
END EXECUTION - FAILED
```
This change was merged in https://github.com/dotnet/runtime/pull/80382 . The test did fail was on the PR, but it got merged on red.
cc @LakshanF
<!-- Error message template -->
### Known Issue Error Message
Fill the error message using [known issues guidance](https://github.com/dotnet/arcade/blob/main/Documentation/Projects/Build%20Analysis/KnownIssues.md#how-to-fill-out-a-known-issue-error-section).
```json
{
"ErrorPattern": ".*warning WASM0004: Loading assembly reference 'Microsoft.Diagnostics.Tools.RuntimeClient.*",
"BuildRetry": false
}
```
<!--Known issue error report start -->
### Report
|Build|Definition|Test|Pull Request|
|---|---|---|---|
|[164331](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164331)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164331&view=ms.vss-test-web.build-test-results-tab&runId=3355952&resultId=103655)|dotnet/runtime#81831|
|[164665](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164665)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164665&view=ms.vss-test-web.build-test-results-tab&runId=3351536&resultId=103655)|dotnet/runtime#81843|
|[164636](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164636)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164636&view=ms.vss-test-web.build-test-results-tab&runId=3351013&resultId=103655)|dotnet/runtime#79544|
|[164618](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164618)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164618&view=ms.vss-test-web.build-test-results-tab&runId=3350586&resultId=103655)|dotnet/runtime#81827|
|[164573](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164573)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164573&view=ms.vss-test-web.build-test-results-tab&runId=3350081&resultId=103655)|dotnet/runtime#78852|
|[164555](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164555)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164555&view=ms.vss-test-web.build-test-results-tab&runId=3349848&resultId=103655)|dotnet/runtime#81407|
|[164522](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164522)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164522&view=ms.vss-test-web.build-test-results-tab&runId=3349564&resultId=103655)|dotnet/runtime#81836|
|[164512](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164512)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164512&view=ms.vss-test-web.build-test-results-tab&runId=3349425&resultId=103655)|dotnet/runtime#81480|
|[163901](https://dev.azure.com/dnceng-public/public/_build/results?buildId=163901)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=163901&view=ms.vss-test-web.build-test-results-tab&runId=3341456&resultId=103654)|dotnet/runtime#80382|
#### Summary
|24-Hour Hit Count|7-Day Hit Count|1-Month Count|
|---|---|---|
|9|9|9|
<!--Known issue error report end --> | 1.0 | [wasm] Runtime test `simpleprovidervalidation.sh` failing on CI - [Rolling build](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164624&view=logs&j=3e93a48f-6568-53f2-76b3-1285c183c39d), and [log](https://helixre107v0xdeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-heads-main-c5375adeae8e4f48a4/PayloadGroup0/1/console.74f02e35.log?helixlogtype=result):
```
Starting: tracing.eventpipe.XUnitWrapper (parallel test collections = on, max threads = 2)
tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation/simpleprovidervalidation.sh [FAIL]
{"name":"ExitStatus","message":"Program terminated with exit(-1)","status":-1}
Return code: 1
Raw output file: /datadisks/disk1/work/B644095B/w/B577098C/uploads/Reports/tracing.eventpipe/simpleprovidervalidation/simpleprovidervalidation/simpleprovidervalidation.output.txt
Raw output:
BEGIN EXECUTION
MSBuild version 17.5.0-preview-23056-01+d89d4bc91 for .NET
AppDir: /datadisks/disk1/work/B644095B/w/B577098C/e/tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation/WasmApp/
TestBinDir: /datadisks/disk1/work/B644095B/w/B577098C/e/tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation
ArtifactsBinDir:
/datadisks/disk1/work/B644095B/p/build/WasmApp.targets(412,5): warning WASM0004: Loading assembly reference 'Microsoft.Diagnostics.Tools.RuntimeClient, Version=1.0.4.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35' for 'common, Version=0.0.0.0, Culture=neutral, PublicKeyToken=null' failed: Could not find assembly 'Microsoft.Diagnostics.Tools.RuntimeClient, Version=1.0.4.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35'. Either explicitly load this assembly using a method such as LoadFromAssemblyPath() or use a MetadataAssemblyResolver that returns a valid assembly. Skipping. [/datadisks/disk1/work/B644095B/p/wasm-test-runner/WasmTestRunner.proj]
Generated app bundle at /datadisks/disk1/work/B644095B/w/B577098C/e/tracing/eventpipe/simpleprovidervalidation/simpleprovidervalidation/WasmApp/
Incoming arguments: --run simpleprovidervalidation.dll
Application arguments: --run simpleprovidervalidation.dll
console.info: Initializing dotnet version 8.0.0-ci commit hash 0304f1f5157a8280fa093bdfc7cfb8d9f62e016f
0.0s: ==TEST STARTING==
0.1s: System.PlatformNotSupportedException: System.Diagnostics.Process is not supported on this platform.
at System.Diagnostics.Process.GetProcesses()
at Tracing.Tests.Common.IpcTraceTest.<>c.<EnsureCleanEnvironment>b__10_0()
at Tracing.Tests.Common.IpcTraceTest.EnsureCleanEnvironment()
at Tracing.Tests.Common.IpcTraceTest.Validate(Boolean enableRundownProvider)
at Tracing.Tests.Common.IpcTraceTest.RunAndValidateEventCounts(Dictionary`2 expectedEventCounts, Action eventGeneratingAction, List`1 providers, Int32 circularBufferMB, Func`2 optionalTraceValidator, Boolean enableRundownProvider)
0.1s: ==TEST FINISHED: FAILED!==
WASM EXIT -1
Expected: 100
Actual: 255
END EXECUTION - FAILED
```
This change was merged in https://github.com/dotnet/runtime/pull/80382 . The test did fail was on the PR, but it got merged on red.
cc @LakshanF
<!-- Error message template -->
### Known Issue Error Message
Fill the error message using [known issues guidance](https://github.com/dotnet/arcade/blob/main/Documentation/Projects/Build%20Analysis/KnownIssues.md#how-to-fill-out-a-known-issue-error-section).
```json
{
"ErrorPattern": ".*warning WASM0004: Loading assembly reference 'Microsoft.Diagnostics.Tools.RuntimeClient.*",
"BuildRetry": false
}
```
<!--Known issue error report start -->
### Report
|Build|Definition|Test|Pull Request|
|---|---|---|---|
|[164331](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164331)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164331&view=ms.vss-test-web.build-test-results-tab&runId=3355952&resultId=103655)|dotnet/runtime#81831|
|[164665](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164665)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164665&view=ms.vss-test-web.build-test-results-tab&runId=3351536&resultId=103655)|dotnet/runtime#81843|
|[164636](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164636)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164636&view=ms.vss-test-web.build-test-results-tab&runId=3351013&resultId=103655)|dotnet/runtime#79544|
|[164618](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164618)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164618&view=ms.vss-test-web.build-test-results-tab&runId=3350586&resultId=103655)|dotnet/runtime#81827|
|[164573](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164573)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164573&view=ms.vss-test-web.build-test-results-tab&runId=3350081&resultId=103655)|dotnet/runtime#78852|
|[164555](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164555)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164555&view=ms.vss-test-web.build-test-results-tab&runId=3349848&resultId=103655)|dotnet/runtime#81407|
|[164522](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164522)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164522&view=ms.vss-test-web.build-test-results-tab&runId=3349564&resultId=103655)|dotnet/runtime#81836|
|[164512](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164512)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=164512&view=ms.vss-test-web.build-test-results-tab&runId=3349425&resultId=103655)|dotnet/runtime#81480|
|[163901](https://dev.azure.com/dnceng-public/public/_build/results?buildId=163901)|dotnet/runtime|[PayloadGroup0.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=163901&view=ms.vss-test-web.build-test-results-tab&runId=3341456&resultId=103654)|dotnet/runtime#80382|
#### Summary
|24-Hour Hit Count|7-Day Hit Count|1-Month Count|
|---|---|---|
|9|9|9|
<!--Known issue error report end --> | non_priority | runtime test simpleprovidervalidation sh failing on ci and starting tracing eventpipe xunitwrapper parallel test collections on max threads tracing eventpipe simpleprovidervalidation simpleprovidervalidation simpleprovidervalidation sh name exitstatus message program terminated with exit status return code raw output file datadisks work w uploads reports tracing eventpipe simpleprovidervalidation simpleprovidervalidation simpleprovidervalidation output txt raw output begin execution msbuild version preview for net appdir datadisks work w e tracing eventpipe simpleprovidervalidation simpleprovidervalidation wasmapp testbindir datadisks work w e tracing eventpipe simpleprovidervalidation simpleprovidervalidation artifactsbindir datadisks work p build wasmapp targets warning loading assembly reference microsoft diagnostics tools runtimeclient version culture neutral publickeytoken for common version culture neutral publickeytoken null failed could not find assembly microsoft diagnostics tools runtimeclient version culture neutral publickeytoken either explicitly load this assembly using a method such as loadfromassemblypath or use a metadataassemblyresolver that returns a valid assembly skipping generated app bundle at datadisks work w e tracing eventpipe simpleprovidervalidation simpleprovidervalidation wasmapp incoming arguments run simpleprovidervalidation dll application arguments run simpleprovidervalidation dll console info initializing dotnet version ci commit hash test starting system platformnotsupportedexception system diagnostics process is not supported on this platform at system diagnostics process getprocesses at tracing tests common ipctracetest c b at tracing tests common ipctracetest ensurecleanenvironment at tracing tests common ipctracetest validate boolean enablerundownprovider at tracing tests common ipctracetest runandvalidateeventcounts dictionary expectedeventcounts action eventgeneratingaction list providers circularbuffermb func optionaltracevalidator boolean enablerundownprovider test finished failed wasm exit expected actual end execution failed this change was merged in the test did fail was on the pr but it got merged on red cc lakshanf known issue error message fill the error message using json errorpattern warning loading assembly reference microsoft diagnostics tools runtimeclient buildretry false report build definition test pull request summary hour hit count day hit count month count | 0 |
418,503 | 28,117,931,299 | IssuesEvent | 2023-03-31 12:15:16 | biaslab/ReactiveMP.jl | https://api.github.com/repos/biaslab/ReactiveMP.jl | opened | The CVI re-use optimiser at each prod call, and this behaviour can be not suitable for some optimisers | bug documentation enhancement | Imagine you have an optimizer that has an inner state and somehow changes its parameters with each iteration (e.g., Adam).
If you will try to use it in several optimization tasks with a shared state: the convergence of each following task is not granted.
So if CVI used in several consequent products with such optimizer it can start brake from some point.
The following code starts to find a bad approximation from some point:
```julia
using ReactiveMP
using StableRNGs
using Distributions
using Flux
n1 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n2 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n_analytical = prod(ProdAnalytical(), n1, n2)
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info n_analytical
@info prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info isapprox(cvi_result, n_analytical, atol = 0.1)
for i in 1:10000
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
if !isapprox(cvi_result, n_analytical, atol = 0.1)
@info "broken at $(i) iteration"
end
end
```
This code works fine:
```julia
n1 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n2 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n_analytical = prod(ProdAnalytical(), n1, n2)
rng = StableRNG(42)
cvi = CVI(rng, 1, 1000, Flux.Adam(0.007), ForwardDiffGrad(), 10, Val(true), true)
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info n_analytical
@info prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info isapprox(cvi_result, n_analytical, atol = 0.1)
for i in 1:10000
cvi = CVI(rng, 1, 1000, Flux.Adam(0.007), ForwardDiffGrad(), 10, Val(true), true)
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
if !isapprox(cvi_result, n_analytical, atol = 0.1)
@info "broken at $(i) iteration"
end
end
```
Should we give a user an ability to reset an optimizer between iterations?
| 1.0 | The CVI re-use optimiser at each prod call, and this behaviour can be not suitable for some optimisers - Imagine you have an optimizer that has an inner state and somehow changes its parameters with each iteration (e.g., Adam).
If you will try to use it in several optimization tasks with a shared state: the convergence of each following task is not granted.
So if CVI used in several consequent products with such optimizer it can start brake from some point.
The following code starts to find a bad approximation from some point:
```julia
using ReactiveMP
using StableRNGs
using Distributions
using Flux
n1 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n2 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n_analytical = prod(ProdAnalytical(), n1, n2)
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info n_analytical
@info prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info isapprox(cvi_result, n_analytical, atol = 0.1)
for i in 1:10000
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
if !isapprox(cvi_result, n_analytical, atol = 0.1)
@info "broken at $(i) iteration"
end
end
```
This code works fine:
```julia
n1 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n2 = NormalMeanVariance(10 * randn(rng), 10 * rand(rng))
n_analytical = prod(ProdAnalytical(), n1, n2)
rng = StableRNG(42)
cvi = CVI(rng, 1, 1000, Flux.Adam(0.007), ForwardDiffGrad(), 10, Val(true), true)
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info n_analytical
@info prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
@info isapprox(cvi_result, n_analytical, atol = 0.1)
for i in 1:10000
cvi = CVI(rng, 1, 1000, Flux.Adam(0.007), ForwardDiffGrad(), 10, Val(true), true)
cvi_result = prod(cvi, ContinuousUnivariateLogPdf((x) -> logpdf(n1, x)), n2)
if !isapprox(cvi_result, n_analytical, atol = 0.1)
@info "broken at $(i) iteration"
end
end
```
Should we give a user an ability to reset an optimizer between iterations?
| non_priority | the cvi re use optimiser at each prod call and this behaviour can be not suitable for some optimisers imagine you have an optimizer that has an inner state and somehow changes its parameters with each iteration e g adam if you will try to use it in several optimization tasks with a shared state the convergence of each following task is not granted so if cvi used in several consequent products with such optimizer it can start brake from some point the following code starts to find a bad approximation from some point julia using reactivemp using stablerngs using distributions using flux normalmeanvariance randn rng rand rng normalmeanvariance randn rng rand rng n analytical prod prodanalytical cvi result prod cvi continuousunivariatelogpdf x logpdf x info n analytical info prod cvi continuousunivariatelogpdf x logpdf x info isapprox cvi result n analytical atol for i in cvi result prod cvi continuousunivariatelogpdf x logpdf x if isapprox cvi result n analytical atol info broken at i iteration end end this code works fine julia normalmeanvariance randn rng rand rng normalmeanvariance randn rng rand rng n analytical prod prodanalytical rng stablerng cvi cvi rng flux adam forwarddiffgrad val true true cvi result prod cvi continuousunivariatelogpdf x logpdf x info n analytical info prod cvi continuousunivariatelogpdf x logpdf x info isapprox cvi result n analytical atol for i in cvi cvi rng flux adam forwarddiffgrad val true true cvi result prod cvi continuousunivariatelogpdf x logpdf x if isapprox cvi result n analytical atol info broken at i iteration end end should we give a user an ability to reset an optimizer between iterations | 0 |
288,370 | 24,901,350,914 | IssuesEvent | 2022-10-28 21:17:58 | Merck/gsDesign2 | https://api.github.com/repos/Merck/gsDesign2 | closed | Add tests of AHR related functions | tests | The functions to be tested include:
- `AHR.R`
- `gs_design_ahr.R`
- `gs_info_ahr`
- `gs_power_ahr`
To test the above functions, please copy the test files from the following two `testthat` folders.
- https://github.com/Merck/gsdmvn/tree/main/tests/testthat
- https://github.com/Merck/gsDesign2/tree/7538aac9fa2f0d818114f71ca20c0de32f5fd1bb/tests/testthat | 1.0 | Add tests of AHR related functions - The functions to be tested include:
- `AHR.R`
- `gs_design_ahr.R`
- `gs_info_ahr`
- `gs_power_ahr`
To test the above functions, please copy the test files from the following two `testthat` folders.
- https://github.com/Merck/gsdmvn/tree/main/tests/testthat
- https://github.com/Merck/gsDesign2/tree/7538aac9fa2f0d818114f71ca20c0de32f5fd1bb/tests/testthat | non_priority | add tests of ahr related functions the functions to be tested include ahr r gs design ahr r gs info ahr gs power ahr to test the above functions please copy the test files from the following two testthat folders | 0 |
135,032 | 12,651,661,103 | IssuesEvent | 2020-06-17 01:04:23 | ProjectEvergreen/greenwood | https://api.github.com/repos/ProjectEvergreen/greenwood | opened | expose unified presets through greenwood configuration | CLI documentation enhancement | ## Type of Change
- [x] New Feature Request
- [ ] Documentation / Website
- [ ] Improvement / Suggestion
- [ ] Bug
- [ ] Other (please clarify below)
## Summary
In addition to the principal web languages (HTML, CSS, JavaScript) Greenwood should also support markdown out of the box. In particular, being able to take advantage of passing [**unified**](https://unifiedjs.com/) compatible presets to [**wc-markdown-loader**](https://github.com/hutchgrant/wc-markdown-loader#unified-presets).
## Details
1. Add a configuration option called `unified` that should take an object with `settings` and `presets` keys
1. It should "forward" that config to **wc-markdown-loader**
1. Add documentation to [Docs -> Markdown](https://www.greenwoodjs.io/docs/markdown) section detailing unified support and best practices / tips for how to use this in the context of the loader
1. Add unit tests | 1.0 | expose unified presets through greenwood configuration - ## Type of Change
- [x] New Feature Request
- [ ] Documentation / Website
- [ ] Improvement / Suggestion
- [ ] Bug
- [ ] Other (please clarify below)
## Summary
In addition to the principal web languages (HTML, CSS, JavaScript) Greenwood should also support markdown out of the box. In particular, being able to take advantage of passing [**unified**](https://unifiedjs.com/) compatible presets to [**wc-markdown-loader**](https://github.com/hutchgrant/wc-markdown-loader#unified-presets).
## Details
1. Add a configuration option called `unified` that should take an object with `settings` and `presets` keys
1. It should "forward" that config to **wc-markdown-loader**
1. Add documentation to [Docs -> Markdown](https://www.greenwoodjs.io/docs/markdown) section detailing unified support and best practices / tips for how to use this in the context of the loader
1. Add unit tests | non_priority | expose unified presets through greenwood configuration type of change new feature request documentation website improvement suggestion bug other please clarify below summary in addition to the principal web languages html css javascript greenwood should also support markdown out of the box in particular being able to take advantage of passing compatible presets to details add a configuration option called unified that should take an object with settings and presets keys it should forward that config to wc markdown loader add documentation to section detailing unified support and best practices tips for how to use this in the context of the loader add unit tests | 0 |
271,118 | 29,269,905,267 | IssuesEvent | 2023-05-24 01:06:56 | cniweb/cniweb-demo | https://api.github.com/repos/cniweb/cniweb-demo | opened | CVE-2019-17573 (Medium) detected in cxf-rt-transports-http-3.1.12.jar | Mend: dependency security vulnerability | ## CVE-2019-17573 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cxf-rt-transports-http-3.1.12.jar</b></p></summary>
<p>Apache CXF Runtime HTTP Transport</p>
<p>Library home page: <a href="http://cxf.apache.org">http://cxf.apache.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/cxf/cxf-rt-transports-http/3.1.12/cxf-rt-transports-http-3.1.12.jar</p>
<p>
Dependency Hierarchy:
- cxf-spring-boot-starter-jaxrs-3.1.12.jar (Root Library)
- :x: **cxf-rt-transports-http-3.1.12.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
By default, Apache CXF creates a /services page containing a listing of the available endpoint names and addresses. This webpage is vulnerable to a reflected Cross-Site Scripting (XSS) attack, which allows a malicious actor to inject javascript into the web page. Please note that the attack exploits a feature which is not typically not present in modern browsers, who remove dot segments before sending the request. However, Mobile applications may be vulnerable.
<p>Publish Date: 2020-01-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17573>CVE-2019-17573</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/3h62d52yw0y9hzsj5nn3wwl0gqrhbd92">https://lists.apache.org/thread/3h62d52yw0y9hzsj5nn3wwl0gqrhbd92</a></p>
<p>Release Date: 2020-01-16</p>
<p>Fix Resolution (org.apache.cxf:cxf-rt-transports-http): 3.2.12</p>
<p>Direct dependency fix Resolution (org.apache.cxf:cxf-spring-boot-starter-jaxrs): 3.2.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-17573 (Medium) detected in cxf-rt-transports-http-3.1.12.jar - ## CVE-2019-17573 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cxf-rt-transports-http-3.1.12.jar</b></p></summary>
<p>Apache CXF Runtime HTTP Transport</p>
<p>Library home page: <a href="http://cxf.apache.org">http://cxf.apache.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/cxf/cxf-rt-transports-http/3.1.12/cxf-rt-transports-http-3.1.12.jar</p>
<p>
Dependency Hierarchy:
- cxf-spring-boot-starter-jaxrs-3.1.12.jar (Root Library)
- :x: **cxf-rt-transports-http-3.1.12.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
By default, Apache CXF creates a /services page containing a listing of the available endpoint names and addresses. This webpage is vulnerable to a reflected Cross-Site Scripting (XSS) attack, which allows a malicious actor to inject javascript into the web page. Please note that the attack exploits a feature which is not typically not present in modern browsers, who remove dot segments before sending the request. However, Mobile applications may be vulnerable.
<p>Publish Date: 2020-01-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-17573>CVE-2019-17573</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/3h62d52yw0y9hzsj5nn3wwl0gqrhbd92">https://lists.apache.org/thread/3h62d52yw0y9hzsj5nn3wwl0gqrhbd92</a></p>
<p>Release Date: 2020-01-16</p>
<p>Fix Resolution (org.apache.cxf:cxf-rt-transports-http): 3.2.12</p>
<p>Direct dependency fix Resolution (org.apache.cxf:cxf-spring-boot-starter-jaxrs): 3.2.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cxf rt transports http jar cve medium severity vulnerability vulnerable library cxf rt transports http jar apache cxf runtime http transport library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache cxf cxf rt transports http cxf rt transports http jar dependency hierarchy cxf spring boot starter jaxrs jar root library x cxf rt transports http jar vulnerable library found in base branch master vulnerability details by default apache cxf creates a services page containing a listing of the available endpoint names and addresses this webpage is vulnerable to a reflected cross site scripting xss attack which allows a malicious actor to inject javascript into the web page please note that the attack exploits a feature which is not typically not present in modern browsers who remove dot segments before sending the request however mobile applications may be vulnerable publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache cxf cxf rt transports http direct dependency fix resolution org apache cxf cxf spring boot starter jaxrs step up your open source security game with mend | 0 |
50,472 | 7,605,579,158 | IssuesEvent | 2018-04-30 09:36:42 | NateWr/restaurant-reservations | https://api.github.com/repos/NateWr/restaurant-reservations | closed | Add more information to docs about email deliverability | documentation | There's a bit more detail in this support request:
https://wordpress.org/support/topic/e-mails-not-being-send?replies=6#post-8716463
And a more simple breakdown here:
https://wordpress.org/support/topic/confirmation-booking-notification-doesnt-work/#post-8328133
| 1.0 | Add more information to docs about email deliverability - There's a bit more detail in this support request:
https://wordpress.org/support/topic/e-mails-not-being-send?replies=6#post-8716463
And a more simple breakdown here:
https://wordpress.org/support/topic/confirmation-booking-notification-doesnt-work/#post-8328133
| non_priority | add more information to docs about email deliverability there s a bit more detail in this support request and a more simple breakdown here | 0 |
52,538 | 6,260,826,570 | IssuesEvent | 2017-07-14 21:44:36 | rook/rook | https://api.github.com/repos/rook/rook | closed | Improve integration test logging | test | switch to capnslog from Test.Log() which doesn't output to stdout in real-time.
Also, improve logging on existing tests. | 1.0 | Improve integration test logging - switch to capnslog from Test.Log() which doesn't output to stdout in real-time.
Also, improve logging on existing tests. | non_priority | improve integration test logging switch to capnslog from test log which doesn t output to stdout in real time also improve logging on existing tests | 0 |
110,730 | 13,934,117,090 | IssuesEvent | 2020-10-22 09:35:51 | radicle-dev/radicle-upstream | https://api.github.com/repos/radicle-dev/radicle-upstream | closed | Improve seed node input in setting | design improvement ui | As experienced in the integration party there's a need to improve the seed node input. There's an old commit lying around somewhere where it was implemented in a better way. Let's see if we can revert it to that or else I think we still have the designs somewhere.
This is what it is about:
<img width="1151" alt="Screenshot 2020-10-13 at 20 36 16" src="https://user-images.githubusercontent.com/2326909/95901512-c1efbd80-0d93-11eb-90d2-b587c69ea239.png">
| 1.0 | Improve seed node input in setting - As experienced in the integration party there's a need to improve the seed node input. There's an old commit lying around somewhere where it was implemented in a better way. Let's see if we can revert it to that or else I think we still have the designs somewhere.
This is what it is about:
<img width="1151" alt="Screenshot 2020-10-13 at 20 36 16" src="https://user-images.githubusercontent.com/2326909/95901512-c1efbd80-0d93-11eb-90d2-b587c69ea239.png">
| non_priority | improve seed node input in setting as experienced in the integration party there s a need to improve the seed node input there s an old commit lying around somewhere where it was implemented in a better way let s see if we can revert it to that or else i think we still have the designs somewhere this is what it is about img width alt screenshot at src | 0 |
122,891 | 17,771,616,589 | IssuesEvent | 2021-08-30 14:16:14 | Tim-sandbox/barista | https://api.github.com/repos/Tim-sandbox/barista | opened | CVE-2017-18342 (High) detected in PyYAML-3.12.tar.gz | security vulnerability | ## CVE-2017-18342 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyYAML-3.12.tar.gz</b></p></summary>
<p>YAML parser and emitter for Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/4a/85/db5a2df477072b2902b0eb892feb37d88ac635d36245a72a6a69b23b383a/PyYAML-3.12.tar.gz">https://files.pythonhosted.org/packages/4a/85/db5a2df477072b2902b0eb892feb37d88ac635d36245a72a6a69b23b383a/PyYAML-3.12.tar.gz</a></p>
<p>Path to vulnerable library: barista-scan/tools/scancode-toolkit/thirdparty/PyYAML-3.12.tar.gz</p>
<p>
Dependency Hierarchy:
- :x: **PyYAML-3.12.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Tim-sandbox/barista/commit/2b8e77b2ff0d688bfd2ffb44061287e82fa71967">2b8e77b2ff0d688bfd2ffb44061287e82fa71967</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In PyYAML before 5.1, the yaml.load() API could execute arbitrary code if used with untrusted data. The load() function has been deprecated in version 5.1 and the 'UnsafeLoader' has been introduced for backward compatibility with the function.
<p>Publish Date: 2018-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18342>CVE-2017-18342</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18342">https://nvd.nist.gov/vuln/detail/CVE-2017-18342</a></p>
<p>Release Date: 2018-06-27</p>
<p>Fix Resolution: PyYAML - 5.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"PyYAML","packageVersion":"3.12","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"PyYAML:3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"PyYAML - 5.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-18342","vulnerabilityDetails":"In PyYAML before 5.1, the yaml.load() API could execute arbitrary code if used with untrusted data. The load() function has been deprecated in version 5.1 and the \u0027UnsafeLoader\u0027 has been introduced for backward compatibility with the function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18342","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-18342 (High) detected in PyYAML-3.12.tar.gz - ## CVE-2017-18342 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>PyYAML-3.12.tar.gz</b></p></summary>
<p>YAML parser and emitter for Python</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/4a/85/db5a2df477072b2902b0eb892feb37d88ac635d36245a72a6a69b23b383a/PyYAML-3.12.tar.gz">https://files.pythonhosted.org/packages/4a/85/db5a2df477072b2902b0eb892feb37d88ac635d36245a72a6a69b23b383a/PyYAML-3.12.tar.gz</a></p>
<p>Path to vulnerable library: barista-scan/tools/scancode-toolkit/thirdparty/PyYAML-3.12.tar.gz</p>
<p>
Dependency Hierarchy:
- :x: **PyYAML-3.12.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Tim-sandbox/barista/commit/2b8e77b2ff0d688bfd2ffb44061287e82fa71967">2b8e77b2ff0d688bfd2ffb44061287e82fa71967</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In PyYAML before 5.1, the yaml.load() API could execute arbitrary code if used with untrusted data. The load() function has been deprecated in version 5.1 and the 'UnsafeLoader' has been introduced for backward compatibility with the function.
<p>Publish Date: 2018-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18342>CVE-2017-18342</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-18342">https://nvd.nist.gov/vuln/detail/CVE-2017-18342</a></p>
<p>Release Date: 2018-06-27</p>
<p>Fix Resolution: PyYAML - 5.1</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"PyYAML","packageVersion":"3.12","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"PyYAML:3.12","isMinimumFixVersionAvailable":true,"minimumFixVersion":"PyYAML - 5.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-18342","vulnerabilityDetails":"In PyYAML before 5.1, the yaml.load() API could execute arbitrary code if used with untrusted data. The load() function has been deprecated in version 5.1 and the \u0027UnsafeLoader\u0027 has been introduced for backward compatibility with the function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18342","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in pyyaml tar gz cve high severity vulnerability vulnerable library pyyaml tar gz yaml parser and emitter for python library home page a href path to vulnerable library barista scan tools scancode toolkit thirdparty pyyaml tar gz dependency hierarchy x pyyaml tar gz vulnerable library found in head commit a href found in base branch master vulnerability details in pyyaml before the yaml load api could execute arbitrary code if used with untrusted data the load function has been deprecated in version and the unsafeloader has been introduced for backward compatibility with the function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution pyyaml rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree pyyaml isminimumfixversionavailable true minimumfixversion pyyaml basebranches vulnerabilityidentifier cve vulnerabilitydetails in pyyaml before the yaml load api could execute arbitrary code if used with untrusted data the load function has been deprecated in version and the has been introduced for backward compatibility with the function vulnerabilityurl | 0 |
71,106 | 23,447,399,558 | IssuesEvent | 2022-08-15 21:10:52 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | VA Forms System Core [Component]: Multiple screens - Step 1, 6, 7, 8 - Radio buttons and checkboxes need fieldsets and legends | 508/Accessibility 508-defect-1 | ### Point of contact
Angela Fowler
### Severity level
1, Launchblocker. Critical. Must be fixed before launch.
### Details
On Step 1, 6, 7, 8, several of the radio button and checkbox components aren't contained in fieldsets.
For example, when navigating to the "relationship to deceased" radio button, the question isn't read. Similar issues occur on other steps as well.
### Reproduction steps
1. Go to one of the steps listed.
2. Inspect HTML.
3. Note that the radio button and checkbox question lack fieldsets.
### Proposed solution or next steps
Add the radio button and checkbox question to fieldsets. Like:
```html
<fieldset>
<lenged>Question text</legend>
…radio buttons…
</fieldset>
```
A bigger question? Is this not the default container for this component in the design system? Is that something we could make work out of the box when teams use radio button or checkbox components?
### References, articles, or WCAG support
WCAG 1.3.1 Info and Relationships
### Type of issue
- [X] Screenreader
- [ ] Keyboard
- [ ] Focus
- [ ] Headings
- [ ] Color
- [ ] Zoom
- [ ] Semantics
- [ ] Axe-core
- [ ] Something else | 1.0 | VA Forms System Core [Component]: Multiple screens - Step 1, 6, 7, 8 - Radio buttons and checkboxes need fieldsets and legends - ### Point of contact
Angela Fowler
### Severity level
1, Launchblocker. Critical. Must be fixed before launch.
### Details
On Step 1, 6, 7, 8, several of the radio button and checkbox components aren't contained in fieldsets.
For example, when navigating to the "relationship to deceased" radio button, the question isn't read. Similar issues occur on other steps as well.
### Reproduction steps
1. Go to one of the steps listed.
2. Inspect HTML.
3. Note that the radio button and checkbox question lack fieldsets.
### Proposed solution or next steps
Add the radio button and checkbox question to fieldsets. Like:
```html
<fieldset>
<lenged>Question text</legend>
…radio buttons…
</fieldset>
```
A bigger question? Is this not the default container for this component in the design system? Is that something we could make work out of the box when teams use radio button or checkbox components?
### References, articles, or WCAG support
WCAG 1.3.1 Info and Relationships
### Type of issue
- [X] Screenreader
- [ ] Keyboard
- [ ] Focus
- [ ] Headings
- [ ] Color
- [ ] Zoom
- [ ] Semantics
- [ ] Axe-core
- [ ] Something else | non_priority | va forms system core multiple screens step radio buttons and checkboxes need fieldsets and legends point of contact angela fowler severity level launchblocker critical must be fixed before launch details on step several of the radio button and checkbox components aren t contained in fieldsets for example when navigating to the relationship to deceased radio button the question isn t read similar issues occur on other steps as well reproduction steps go to one of the steps listed inspect html note that the radio button and checkbox question lack fieldsets proposed solution or next steps add the radio button and checkbox question to fieldsets like html question text …radio buttons… a bigger question is this not the default container for this component in the design system is that something we could make work out of the box when teams use radio button or checkbox components references articles or wcag support wcag info and relationships type of issue screenreader keyboard focus headings color zoom semantics axe core something else | 0 |
143,272 | 13,057,817,981 | IssuesEvent | 2020-07-30 08:01:49 | ggirmay/Top-Shop-e-commerce | https://api.github.com/repos/ggirmay/Top-Shop-e-commerce | closed | Construct Package Structure | documentation enhancement good first issue | Selecting architectures (hexagonal and command query architecture) and construct the packages. | 1.0 | Construct Package Structure - Selecting architectures (hexagonal and command query architecture) and construct the packages. | non_priority | construct package structure selecting architectures hexagonal and command query architecture and construct the packages | 0 |
228,169 | 18,162,996,464 | IssuesEvent | 2021-09-27 11:50:42 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | opened | [CI] SearchableSnapshotEnableAllocationDeciderIntegTests testAllocationDisabled failing | :Distributed/Snapshot/Restore >test-failure | **Build scan:**
https://gradle-enterprise.elastic.co/s/iesmgw5two4y6/tests/:x-pack:plugin:searchable-snapshots:internalClusterTest/org.elasticsearch.xpack.searchablesnapshots.allocation.SearchableSnapshotEnableAllocationDeciderIntegTests/testAllocationDisabled
**Reproduction line:**
`./gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.allocation.SearchableSnapshotEnableAllocationDeciderIntegTests.testAllocationDisabled" -Dtests.seed=B37144B9F5C71BEC -Dtests.locale=de-AT -Dtests.timezone=America/Kentucky/Monticello -Druntime.java=11`
**Applicable branches:**
master
**Reproduces locally?:**
No
**Failure history:**
https://gradle-enterprise.elastic.co/scans/tests?tests.container=org.elasticsearch.xpack.searchablesnapshots.allocation.SearchableSnapshotEnableAllocationDeciderIntegTests&tests.test=testAllocationDisabled
**Failure excerpt:**
```
com.carrotsearch.randomizedtesting.UncaughtExceptionError: Captured an uncaught exception in thread: Thread[id=875, name=elasticsearch[node_t0][generic][T#6], state=RUNNABLE, group=TGRP-SearchableSnapshotEnableAllocationDeciderIntegTests]
at __randomizedtesting.SeedInfo.seed([B37144B9F5C71BEC:5311FC9EB41E488A]:0)
Caused by: java.lang.AssertionError: no previous metadata found for [wvbksxreci/gtSvVp42R9CmXLKQ-Sz8pQ]
at __randomizedtesting.SeedInfo.seed([B37144B9F5C71BEC]:0)
at org.elasticsearch.xpack.searchablesnapshots.cache.blob.BlobStoreCacheMaintenanceService$MaintenanceTask.doRun(BlobStoreCacheMaintenanceService.java:146)
at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingAbstractRunnable.doRun(ThreadContext.java:737)
at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:26)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.lang.Thread.run(Thread.java:834)
``` | 1.0 | [CI] SearchableSnapshotEnableAllocationDeciderIntegTests testAllocationDisabled failing - **Build scan:**
https://gradle-enterprise.elastic.co/s/iesmgw5two4y6/tests/:x-pack:plugin:searchable-snapshots:internalClusterTest/org.elasticsearch.xpack.searchablesnapshots.allocation.SearchableSnapshotEnableAllocationDeciderIntegTests/testAllocationDisabled
**Reproduction line:**
`./gradlew ':x-pack:plugin:searchable-snapshots:internalClusterTest' --tests "org.elasticsearch.xpack.searchablesnapshots.allocation.SearchableSnapshotEnableAllocationDeciderIntegTests.testAllocationDisabled" -Dtests.seed=B37144B9F5C71BEC -Dtests.locale=de-AT -Dtests.timezone=America/Kentucky/Monticello -Druntime.java=11`
**Applicable branches:**
master
**Reproduces locally?:**
No
**Failure history:**
https://gradle-enterprise.elastic.co/scans/tests?tests.container=org.elasticsearch.xpack.searchablesnapshots.allocation.SearchableSnapshotEnableAllocationDeciderIntegTests&tests.test=testAllocationDisabled
**Failure excerpt:**
```
com.carrotsearch.randomizedtesting.UncaughtExceptionError: Captured an uncaught exception in thread: Thread[id=875, name=elasticsearch[node_t0][generic][T#6], state=RUNNABLE, group=TGRP-SearchableSnapshotEnableAllocationDeciderIntegTests]
at __randomizedtesting.SeedInfo.seed([B37144B9F5C71BEC:5311FC9EB41E488A]:0)
Caused by: java.lang.AssertionError: no previous metadata found for [wvbksxreci/gtSvVp42R9CmXLKQ-Sz8pQ]
at __randomizedtesting.SeedInfo.seed([B37144B9F5C71BEC]:0)
at org.elasticsearch.xpack.searchablesnapshots.cache.blob.BlobStoreCacheMaintenanceService$MaintenanceTask.doRun(BlobStoreCacheMaintenanceService.java:146)
at org.elasticsearch.common.util.concurrent.ThreadContext$ContextPreservingAbstractRunnable.doRun(ThreadContext.java:737)
at org.elasticsearch.common.util.concurrent.AbstractRunnable.run(AbstractRunnable.java:26)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.lang.Thread.run(Thread.java:834)
``` | non_priority | searchablesnapshotenableallocationdeciderintegtests testallocationdisabled failing build scan reproduction line gradlew x pack plugin searchable snapshots internalclustertest tests org elasticsearch xpack searchablesnapshots allocation searchablesnapshotenableallocationdeciderintegtests testallocationdisabled dtests seed dtests locale de at dtests timezone america kentucky monticello druntime java applicable branches master reproduces locally no failure history failure excerpt com carrotsearch randomizedtesting uncaughtexceptionerror captured an uncaught exception in thread thread state runnable group tgrp searchablesnapshotenableallocationdeciderintegtests at randomizedtesting seedinfo seed caused by java lang assertionerror no previous metadata found for at randomizedtesting seedinfo seed at org elasticsearch xpack searchablesnapshots cache blob blobstorecachemaintenanceservice maintenancetask dorun blobstorecachemaintenanceservice java at org elasticsearch common util concurrent threadcontext contextpreservingabstractrunnable dorun threadcontext java at org elasticsearch common util concurrent abstractrunnable run abstractrunnable java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java | 0 |
345,552 | 30,822,580,239 | IssuesEvent | 2023-08-01 17:26:25 | coder/coder | https://api.github.com/repos/coder/coder | closed | bug: improve performance of GetAuthorizedWorkspaces query | scaletest bug | # Problem:
GET `/api/v2/workspaces` can take a long time to load with a number of active workspaces.
See the following trace for more information: https://console.cloud.google.com/traces/list?project=v2-loadtest&tid=18cccfc446a9f8550aebf0656b8f26b4
(Partial screenshot below)

Essentially it looks like the `GetAuthorizedWorkspaces` query is having to call `GetWorkspaceByID` on every workspace.
This is going to kill performance in the long run. | 1.0 | bug: improve performance of GetAuthorizedWorkspaces query - # Problem:
GET `/api/v2/workspaces` can take a long time to load with a number of active workspaces.
See the following trace for more information: https://console.cloud.google.com/traces/list?project=v2-loadtest&tid=18cccfc446a9f8550aebf0656b8f26b4
(Partial screenshot below)

Essentially it looks like the `GetAuthorizedWorkspaces` query is having to call `GetWorkspaceByID` on every workspace.
This is going to kill performance in the long run. | non_priority | bug improve performance of getauthorizedworkspaces query problem get api workspaces can take a long time to load with a number of active workspaces see the following trace for more information partial screenshot below essentially it looks like the getauthorizedworkspaces query is having to call getworkspacebyid on every workspace this is going to kill performance in the long run | 0 |
6,321 | 5,375,282,514 | IssuesEvent | 2017-02-23 03:56:31 | Microsoft/WinObjC | https://api.github.com/repos/Microsoft/WinObjC | opened | Trim size of UIKit.dll if possible | Area-User Experience Performance Task | We should investigate why UIKit.dll is ~13MB, and trim that down if possible. | True | Trim size of UIKit.dll if possible - We should investigate why UIKit.dll is ~13MB, and trim that down if possible. | non_priority | trim size of uikit dll if possible we should investigate why uikit dll is and trim that down if possible | 0 |
293,940 | 25,334,835,996 | IssuesEvent | 2022-11-18 15:59:12 | WASdev/websphere-liberty-operator | https://api.github.com/repos/WASdev/websphere-liberty-operator | opened | License test failure in OCP | test | Build [719](https://cloud.ibm.com/devops/pipelines/tekton/c3b2797d-c8ad-4dab-9660-2ec8c0643a76/runs/eb70f36d-51a6-44fd-a6f3-54449ae615ec/deploy-acceptance-tests/run-stage?env_id=ibm:yp:us-south)
License e2e/kuttl test failed in OCP. It passed in Kind/minikube test though. Could it be a timing issue? or is it checking wrong Pod?
```
Name: license
State: fail
Errors:
resource Pod:wlo-test-719/: .metadata.annotations.productChargedContainers: value mismatch, expected: app != actual: ALL
``` | 1.0 | License test failure in OCP - Build [719](https://cloud.ibm.com/devops/pipelines/tekton/c3b2797d-c8ad-4dab-9660-2ec8c0643a76/runs/eb70f36d-51a6-44fd-a6f3-54449ae615ec/deploy-acceptance-tests/run-stage?env_id=ibm:yp:us-south)
License e2e/kuttl test failed in OCP. It passed in Kind/minikube test though. Could it be a timing issue? or is it checking wrong Pod?
```
Name: license
State: fail
Errors:
resource Pod:wlo-test-719/: .metadata.annotations.productChargedContainers: value mismatch, expected: app != actual: ALL
``` | non_priority | license test failure in ocp build license kuttl test failed in ocp it passed in kind minikube test though could it be a timing issue or is it checking wrong pod name license state fail errors resource pod wlo test metadata annotations productchargedcontainers value mismatch expected app actual all | 0 |
5,830 | 7,346,549,693 | IssuesEvent | 2018-03-07 21:06:41 | Microsoft/vscode-cpptools | https://api.github.com/repos/Microsoft/vscode-cpptools | closed | VSCode C/C++ Extension(ms-vscode.cpptools) can be cached? | Language Service bug | As my usage, I usually open 2 or more Linux Kernel Source projects in vscode, it's very huge.
When I open vscode, ms-vscode.cpptools will auto start preparation of C/C++ IntelliSense, such as symbol search ing, goto defination and so on.
But as I say, the project of kernel source code is very huge and ms-vscode.cpptools will take a lot of time to finish. Every time I open vscode, this preparation job will run again and take a lot of time.
I'm thinking that ms-vscode.cpptools should add cache support for a project. | 1.0 | VSCode C/C++ Extension(ms-vscode.cpptools) can be cached? - As my usage, I usually open 2 or more Linux Kernel Source projects in vscode, it's very huge.
When I open vscode, ms-vscode.cpptools will auto start preparation of C/C++ IntelliSense, such as symbol search ing, goto defination and so on.
But as I say, the project of kernel source code is very huge and ms-vscode.cpptools will take a lot of time to finish. Every time I open vscode, this preparation job will run again and take a lot of time.
I'm thinking that ms-vscode.cpptools should add cache support for a project. | non_priority | vscode c c extension ms vscode cpptools can be cached as my usage i usually open or more linux kernel source projects in vscode it s very huge when i open vscode ms vscode cpptools will auto start preparation of c c intellisense such as symbol search ing goto defination and so on but as i say the project of kernel source code is very huge and ms vscode cpptools will take a lot of time to finish every time i open vscode this preparation job will run again and take a lot of time i m thinking that ms vscode cpptools should add cache support for a project | 0 |
274,371 | 23,834,930,619 | IssuesEvent | 2022-09-06 04:17:59 | Automattic/woocommerce-payments | https://api.github.com/repos/Automattic/woocommerce-payments | opened | Failing Internal E2E Test | type: bug component: deposits component: tests | ### Describe the bug
TBC
### To Reproduce
<!-- Describe the steps to reproduce the behavior. -->
1. Go to '…'
2. Click on '…'
3. Scroll down to …'
4. See error
### Actual behavior
<!-- A clear and concise description of what actually happens. -->
### Screenshots
<!-- If applicable, add screenshots to help explain your problem. -->
### Expected behavior
<!-- A clear and concise description of what you expected to happen. -->
### Desktop (please complete the following information):
* OS: [e.g. iOS]
* Browser [e.g. chrome, safari]
* Version [e.g. 22]
### Smartphone (please complete the following information):
* Device: [e.g. iPhone6]
* OS: [e.g. iOS8.1]
* Browser [e.g. stock browser, safari]
* Version [e.g. 22]
### Additional context
<!-- Any additional context or details you think might be helpful. -->
<!-- Ticket numbers/links, plugin versions, system statuses etc. -->
| 1.0 | Failing Internal E2E Test - ### Describe the bug
TBC
### To Reproduce
<!-- Describe the steps to reproduce the behavior. -->
1. Go to '…'
2. Click on '…'
3. Scroll down to …'
4. See error
### Actual behavior
<!-- A clear and concise description of what actually happens. -->
### Screenshots
<!-- If applicable, add screenshots to help explain your problem. -->
### Expected behavior
<!-- A clear and concise description of what you expected to happen. -->
### Desktop (please complete the following information):
* OS: [e.g. iOS]
* Browser [e.g. chrome, safari]
* Version [e.g. 22]
### Smartphone (please complete the following information):
* Device: [e.g. iPhone6]
* OS: [e.g. iOS8.1]
* Browser [e.g. stock browser, safari]
* Version [e.g. 22]
### Additional context
<!-- Any additional context or details you think might be helpful. -->
<!-- Ticket numbers/links, plugin versions, system statuses etc. -->
| non_priority | failing internal test describe the bug tbc to reproduce go to … click on … scroll down to … see error actual behavior screenshots expected behavior desktop please complete the following information os browser version smartphone please complete the following information device os browser version additional context | 0 |
17,779 | 12,551,770,971 | IssuesEvent | 2020-06-06 15:52:41 | javahippie/clj-test-containers | https://api.github.com/repos/javahippie/clj-test-containers | closed | Set up clojars deployment | infrastructure | The library should be published on clojars, so other users can include it in their build pipeline. | 1.0 | Set up clojars deployment - The library should be published on clojars, so other users can include it in their build pipeline. | non_priority | set up clojars deployment the library should be published on clojars so other users can include it in their build pipeline | 0 |
113,201 | 24,378,500,468 | IssuesEvent | 2022-10-04 05:00:12 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug] Check for stale datasource connection before execution for Mysql plugin. | Bug Backend Datasources Critical community BE Coders Pod Project | ## Description
1. Check for stale datasource connection before execution for the Mysql plugin.
2. Return stale connection exception.
## Context
Currently, stale connection is not checked for, and hence an exception occurs during execution which gets returned to UI as it is. With a stale connection, the new action implementation class catches this exception and takes corrective action.
### Steps to reproduce the behavior:
1. Create MySQL datasource.
2. Restart MySQL to invalidate connection.
3. Run MySQL query.
### Important Details
- Version: Any
- OS: Any
- Browser: Any
| 1.0 | [Bug] Check for stale datasource connection before execution for Mysql plugin. - ## Description
1. Check for stale datasource connection before execution for the Mysql plugin.
2. Return stale connection exception.
## Context
Currently, stale connection is not checked for, and hence an exception occurs during execution which gets returned to UI as it is. With a stale connection, the new action implementation class catches this exception and takes corrective action.
### Steps to reproduce the behavior:
1. Create MySQL datasource.
2. Restart MySQL to invalidate connection.
3. Run MySQL query.
### Important Details
- Version: Any
- OS: Any
- Browser: Any
| non_priority | check for stale datasource connection before execution for mysql plugin description check for stale datasource connection before execution for the mysql plugin return stale connection exception context currently stale connection is not checked for and hence an exception occurs during execution which gets returned to ui as it is with a stale connection the new action implementation class catches this exception and takes corrective action steps to reproduce the behavior create mysql datasource restart mysql to invalidate connection run mysql query important details version any os any browser any | 0 |
272,135 | 20,734,397,633 | IssuesEvent | 2022-03-14 12:27:44 | RasmusDahlJensen/testrepo | https://api.github.com/repos/RasmusDahlJensen/testrepo | closed | Opdater README med fiktiv CV første entry | documentation | Opdater README med et fiktivt CV der indeholder en beskrivelse af et fiktivt arbejde | 1.0 | Opdater README med fiktiv CV første entry - Opdater README med et fiktivt CV der indeholder en beskrivelse af et fiktivt arbejde | non_priority | opdater readme med fiktiv cv første entry opdater readme med et fiktivt cv der indeholder en beskrivelse af et fiktivt arbejde | 0 |
87,890 | 25,241,502,982 | IssuesEvent | 2022-11-15 07:53:13 | onlydustxyz/kaaper | https://api.github.com/repos/onlydustxyz/kaaper | closed | Publish kaaper on npm | Type: build Context: isolated Duration: under a day State: open Techno: js Difficulty: easy | Publish kaaper on npm upon new release (tag `v*`), using github action.
Here is an example:
https://github.com/onlydustxyz/backoffice-wallet-link/blob/main/.github/workflows/deployment.yml
| 1.0 | Publish kaaper on npm - Publish kaaper on npm upon new release (tag `v*`), using github action.
Here is an example:
https://github.com/onlydustxyz/backoffice-wallet-link/blob/main/.github/workflows/deployment.yml
| non_priority | publish kaaper on npm publish kaaper on npm upon new release tag v using github action here is an example | 0 |
448,074 | 31,765,486,448 | IssuesEvent | 2023-09-12 08:31:19 | MobileReality/react-native-select-pro | https://api.github.com/repos/MobileReality/react-native-select-pro | closed | [BUG] SelectModalProvider not working in IOS | bug documentation | **Describe the bug**
A clear and concise description of what the bug is when you open modal and click the list but do not select anything and click any where in the screen to close the select list and then try to Hide modal in **IOS**.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to your Modal provider link `https://themobilereality.com/react-native-select-pro-docs`
2. Just open your own example in expo.
3. open the list and just close it by clicking anywhere and just **click hide modal** you will see the **BUG**
**Expected behavior**
Modal will close.
**Environment (please complete the following information):**
- OS: [iOS/Android]
- OS Version: [eq. iOS 14]
- React Native Version
- Device on which issue is presented
**Additional context**
https://github.com/MobileReality/react-native-select-pro/assets/132438054/c598d348-06df-4362-a480-a1b59c86bee0
| 1.0 | [BUG] SelectModalProvider not working in IOS - **Describe the bug**
A clear and concise description of what the bug is when you open modal and click the list but do not select anything and click any where in the screen to close the select list and then try to Hide modal in **IOS**.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to your Modal provider link `https://themobilereality.com/react-native-select-pro-docs`
2. Just open your own example in expo.
3. open the list and just close it by clicking anywhere and just **click hide modal** you will see the **BUG**
**Expected behavior**
Modal will close.
**Environment (please complete the following information):**
- OS: [iOS/Android]
- OS Version: [eq. iOS 14]
- React Native Version
- Device on which issue is presented
**Additional context**
https://github.com/MobileReality/react-native-select-pro/assets/132438054/c598d348-06df-4362-a480-a1b59c86bee0
| non_priority | selectmodalprovider not working in ios describe the bug a clear and concise description of what the bug is when you open modal and click the list but do not select anything and click any where in the screen to close the select list and then try to hide modal in ios to reproduce steps to reproduce the behavior go to your modal provider link just open your own example in expo open the list and just close it by clicking anywhere and just click hide modal you will see the bug expected behavior modal will close environment please complete the following information os os version react native version device on which issue is presented additional context | 0 |
32,805 | 4,790,798,175 | IssuesEvent | 2016-10-31 10:05:33 | muller89/ubix | https://api.github.com/repos/muller89/ubix | opened | [P#:['98181284']] Implement Modified Policy Evaluation for MDP-based agents in AC | agentframework rl test | Pivotal Issue: https://www.pivotaltracker.com/story/show/98181284
See Russel & Norvig Chap 17 on Policy Iteration. | 1.0 | [P#:['98181284']] Implement Modified Policy Evaluation for MDP-based agents in AC - Pivotal Issue: https://www.pivotaltracker.com/story/show/98181284
See Russel & Norvig Chap 17 on Policy Iteration. | non_priority | implement modified policy evaluation for mdp based agents in ac pivotal issue see russel norvig chap on policy iteration | 0 |
13,425 | 5,359,045,537 | IssuesEvent | 2017-02-21 01:05:02 | SEED-platform/seed | https://api.github.com/repos/SEED-platform/seed | closed | Settings not saved on Detail View | Building Detail P-1 | instance: seeddev
SHA: 514e883
See this doc
https://drive.google.com/open?id=1bjJdnl5UIZFIFQ5MspH34saNCj-2LQqTZR_GIiD5G2k
I have only tested this on Property Detail Settings, so please test on Tax Lot Detail Settings when this is fixed.
| 1.0 | Settings not saved on Detail View - instance: seeddev
SHA: 514e883
See this doc
https://drive.google.com/open?id=1bjJdnl5UIZFIFQ5MspH34saNCj-2LQqTZR_GIiD5G2k
I have only tested this on Property Detail Settings, so please test on Tax Lot Detail Settings when this is fixed.
| non_priority | settings not saved on detail view instance seeddev sha see this doc i have only tested this on property detail settings so please test on tax lot detail settings when this is fixed | 0 |
4,682 | 7,299,572,205 | IssuesEvent | 2018-02-26 20:34:29 | LLK/scratch-vm | https://api.github.com/repos/LLK/scratch-vm | closed | Errors when no sprites are in loaded Scratch 2.0 project | bug compatibility | > Uncaught TypeError: Cannot read property 'blocks' of undefined
Presumably, I've made an assumption somewhere that there would be a stage and a first sprite. However this is not always the case: https://llk.github.io/scratch-vm/#125571490
The project functions fine as far as execution, but the blocks loading fails; must be something about setting the editing target. | True | Errors when no sprites are in loaded Scratch 2.0 project - > Uncaught TypeError: Cannot read property 'blocks' of undefined
Presumably, I've made an assumption somewhere that there would be a stage and a first sprite. However this is not always the case: https://llk.github.io/scratch-vm/#125571490
The project functions fine as far as execution, but the blocks loading fails; must be something about setting the editing target. | non_priority | errors when no sprites are in loaded scratch project uncaught typeerror cannot read property blocks of undefined presumably i ve made an assumption somewhere that there would be a stage and a first sprite however this is not always the case the project functions fine as far as execution but the blocks loading fails must be something about setting the editing target | 0 |
155,958 | 13,637,750,421 | IssuesEvent | 2020-09-25 08:20:03 | tejanc/StocksApp | https://api.github.com/repos/tejanc/StocksApp | closed | AWS S3 Bucket redirection error | documentation | 404 Key not found
See below for fix:
https://stackoverflow.com/questions/51218979/react-router-doesnt-work-in-aws-s3-bucket
Use 'index.html' in the error document | 1.0 | AWS S3 Bucket redirection error - 404 Key not found
See below for fix:
https://stackoverflow.com/questions/51218979/react-router-doesnt-work-in-aws-s3-bucket
Use 'index.html' in the error document | non_priority | aws bucket redirection error key not found see below for fix use index html in the error document | 0 |
326,667 | 28,010,422,894 | IssuesEvent | 2023-03-27 18:11:44 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: X-Pack EPM API Integration Tests.x-pack/test/fleet_api_integration/apis/epm/install_prerelease·ts - Fleet Endpoints EPM Endpoints installs package that has a prerelease version should bulk install the GA packages when prerelease is not set | failed-test skipped-test Team:Fleet v8.7.0 v8.8.0 | A test failed on a tracked branch
```
Error: expected undefined to equal '8.6.1'
at Assertion.assert (expect.js:100:11)
at Assertion.equal (expect.js:227:8)
at Context.<anonymous> (install_prerelease.ts:99:46)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/26462#0186272d-d5c7-40c7-868d-9a4f03982386)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack EPM API Integration Tests.x-pack/test/fleet_api_integration/apis/epm/install_prerelease·ts","test.name":"Fleet Endpoints EPM Endpoints installs package that has a prerelease version should bulk install the GA packages when prerelease is not set","test.failCount":9}} --> | 2.0 | Failing test: X-Pack EPM API Integration Tests.x-pack/test/fleet_api_integration/apis/epm/install_prerelease·ts - Fleet Endpoints EPM Endpoints installs package that has a prerelease version should bulk install the GA packages when prerelease is not set - A test failed on a tracked branch
```
Error: expected undefined to equal '8.6.1'
at Assertion.assert (expect.js:100:11)
at Assertion.equal (expect.js:227:8)
at Context.<anonymous> (install_prerelease.ts:99:46)
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/26462#0186272d-d5c7-40c7-868d-9a4f03982386)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack EPM API Integration Tests.x-pack/test/fleet_api_integration/apis/epm/install_prerelease·ts","test.name":"Fleet Endpoints EPM Endpoints installs package that has a prerelease version should bulk install the GA packages when prerelease is not set","test.failCount":9}} --> | non_priority | failing test x pack epm api integration tests x pack test fleet api integration apis epm install prerelease·ts fleet endpoints epm endpoints installs package that has a prerelease version should bulk install the ga packages when prerelease is not set a test failed on a tracked branch error expected undefined to equal at assertion assert expect js at assertion equal expect js at context install prerelease ts at runmicrotasks at processticksandrejections node internal process task queues at object apply wrap function js first failure | 0 |
74,569 | 9,086,690,900 | IssuesEvent | 2019-02-18 11:39:06 | IBM-Blockchain/blockchain-vscode-extension | https://api.github.com/repos/IBM-Blockchain/blockchain-vscode-extension | closed | As a developer I can create a contract through the ui | design phase 2 user story | Currently there is no way to create a smart contract through the ui only a command | 1.0 | As a developer I can create a contract through the ui - Currently there is no way to create a smart contract through the ui only a command | non_priority | as a developer i can create a contract through the ui currently there is no way to create a smart contract through the ui only a command | 0 |
158,684 | 20,028,877,460 | IssuesEvent | 2022-02-02 01:25:04 | manishshanker/numericRangeInput | https://api.github.com/repos/manishshanker/numericRangeInput | opened | CVE-2020-11022 (Medium) detected in jquery-1.9.1.js | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.9.1.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js</a></p>
<p>Path to dependency file: /numericRangeInput/code/index.html</p>
<p>Path to vulnerable library: /numericRangeInput/code/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.1.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11022 (Medium) detected in jquery-1.9.1.js - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.9.1.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.9.1/jquery.js</a></p>
<p>Path to dependency file: /numericRangeInput/code/index.html</p>
<p>Path to vulnerable library: /numericRangeInput/code/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.9.1.js** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery js cve medium severity vulnerability vulnerable library jquery js javascript library for dom operations library home page a href path to dependency file numericrangeinput code index html path to vulnerable library numericrangeinput code index html dependency hierarchy x jquery js vulnerable library vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
119,675 | 12,036,834,257 | IssuesEvent | 2020-04-13 20:34:51 | golang/go | https://api.github.com/repos/golang/go | closed | errors: example code for errors.As has extraneous code | Documentation NeedsInvestigation | The example code for `errors.As` (viewed at https://pkg.go.dev/errors?tab=doc#As) is the [entire contents of the `wrap_test.go` file](https://github.com/golang/go/blob/go1.14.1/src/errors/wrap_test.go). It should be just `func ExampleAs() { ... }` I presume.
In talking this over with @FiloSottile, this may be a more systemic issue which can be improved in `godoc`. For example, we have the same issue with the [chacha20poly1305.NewX](https://pkg.go.dev/golang.org/x/crypto/chacha20poly1305?tab=doc#NewX) example code. However, perhaps we should fix the example for the errors package for now either way.
While we're in there, perhaps we should check if there are any improvements to the documentation for errors as tracked in https://github.com/golang/go/issues/31716.
/cc @jba @mpvl | 1.0 | errors: example code for errors.As has extraneous code - The example code for `errors.As` (viewed at https://pkg.go.dev/errors?tab=doc#As) is the [entire contents of the `wrap_test.go` file](https://github.com/golang/go/blob/go1.14.1/src/errors/wrap_test.go). It should be just `func ExampleAs() { ... }` I presume.
In talking this over with @FiloSottile, this may be a more systemic issue which can be improved in `godoc`. For example, we have the same issue with the [chacha20poly1305.NewX](https://pkg.go.dev/golang.org/x/crypto/chacha20poly1305?tab=doc#NewX) example code. However, perhaps we should fix the example for the errors package for now either way.
While we're in there, perhaps we should check if there are any improvements to the documentation for errors as tracked in https://github.com/golang/go/issues/31716.
/cc @jba @mpvl | non_priority | errors example code for errors as has extraneous code the example code for errors as viewed at is the it should be just func exampleas i presume in talking this over with filosottile this may be a more systemic issue which can be improved in godoc for example we have the same issue with the example code however perhaps we should fix the example for the errors package for now either way while we re in there perhaps we should check if there are any improvements to the documentation for errors as tracked in cc jba mpvl | 0 |
88,997 | 10,585,761,096 | IssuesEvent | 2019-10-08 18:13:44 | spotify/heroic | https://api.github.com/repos/spotify/heroic | closed | Document aggregations of resource identifiers | note:accepted type:documentation | When talking various squads the use case for this is as follows. Alerts are typically a max/avg within a given region. When an alert fires the on-call person will often change the aggregation from region -> instance.
With kubernetes, instance is now becoming podname which is not in the suggest index. With Grafana, it should be documented that resource identifiers can be added free-form even though they won't show up as suggestions.
Also for a nicer UX perhaps we can have a fixed list of RI's or get the list of RI's returned by the query to populate the dropdown.
| 1.0 | Document aggregations of resource identifiers - When talking various squads the use case for this is as follows. Alerts are typically a max/avg within a given region. When an alert fires the on-call person will often change the aggregation from region -> instance.
With kubernetes, instance is now becoming podname which is not in the suggest index. With Grafana, it should be documented that resource identifiers can be added free-form even though they won't show up as suggestions.
Also for a nicer UX perhaps we can have a fixed list of RI's or get the list of RI's returned by the query to populate the dropdown.
| non_priority | document aggregations of resource identifiers when talking various squads the use case for this is as follows alerts are typically a max avg within a given region when an alert fires the on call person will often change the aggregation from region instance with kubernetes instance is now becoming podname which is not in the suggest index with grafana it should be documented that resource identifiers can be added free form even though they won t show up as suggestions also for a nicer ux perhaps we can have a fixed list of ri s or get the list of ri s returned by the query to populate the dropdown | 0 |
182,570 | 14,142,489,451 | IssuesEvent | 2020-11-10 14:07:44 | deathlyrage/pot-demo-bugs | https://api.github.com/repos/deathlyrage/pot-demo-bugs | closed | [Demo Public Test] Secondly used attack type is stucked | bug needs testing public-test | ## Expected Behavior
All attacks can be used in any order.
## Current Behavior
After changing attack type, the one which is used in second time is stucked, the first one cannot be used (i.e. it makes no harm) anymore.
E.g., if firstly bitten (also more then once), then slapped, then only slap works afterwards.
If firstly slapped, then bite is used, then only bite harms afterwards.
## Reproduction Steps
Log in (SP or MP), and try attack any prey with Sucho, Spino or Conca (i.e. which has currently secondary attack enabled).
## Evidence (Screenshots & Videos)
Bitten (harms), then slapped (harms), then bite doesn't harm anymore:
https://www.youtube.com/watch?v=jj2sdX0F1YQ
Slapped (harms), then bitten (harms), thereafter slap is not harming anymore:
https://www.youtube.com/watch?v=zzxV17PCcSo
## Crash Logs
(If Applicable. No logs needed if there is no crash.)
## Build Information
**Game Version:** 0.0.0.10043
Operating System & Version: Win10 Education N (1909)
Alderon Games ID: 735-756-627 | 2.0 | [Demo Public Test] Secondly used attack type is stucked - ## Expected Behavior
All attacks can be used in any order.
## Current Behavior
After changing attack type, the one which is used in second time is stucked, the first one cannot be used (i.e. it makes no harm) anymore.
E.g., if firstly bitten (also more then once), then slapped, then only slap works afterwards.
If firstly slapped, then bite is used, then only bite harms afterwards.
## Reproduction Steps
Log in (SP or MP), and try attack any prey with Sucho, Spino or Conca (i.e. which has currently secondary attack enabled).
## Evidence (Screenshots & Videos)
Bitten (harms), then slapped (harms), then bite doesn't harm anymore:
https://www.youtube.com/watch?v=jj2sdX0F1YQ
Slapped (harms), then bitten (harms), thereafter slap is not harming anymore:
https://www.youtube.com/watch?v=zzxV17PCcSo
## Crash Logs
(If Applicable. No logs needed if there is no crash.)
## Build Information
**Game Version:** 0.0.0.10043
Operating System & Version: Win10 Education N (1909)
Alderon Games ID: 735-756-627 | non_priority | secondly used attack type is stucked expected behavior all attacks can be used in any order current behavior after changing attack type the one which is used in second time is stucked the first one cannot be used i e it makes no harm anymore e g if firstly bitten also more then once then slapped then only slap works afterwards if firstly slapped then bite is used then only bite harms afterwards reproduction steps log in sp or mp and try attack any prey with sucho spino or conca i e which has currently secondary attack enabled evidence screenshots videos bitten harms then slapped harms then bite doesn t harm anymore slapped harms then bitten harms thereafter slap is not harming anymore crash logs if applicable no logs needed if there is no crash build information game version operating system version education n alderon games id | 0 |
56,247 | 23,730,008,529 | IssuesEvent | 2022-08-31 00:16:56 | dockstore/dockstore | https://api.github.com/repos/dockstore/dockstore | closed | Collections endpoint not indicating verified entries | bug web-service review | **Describe the bug**
The collections endpoint indicates verified is false for all entries, even if they are verified.
**To Reproduce**
1.
```
curl 'https://dev.dockstore.net/api/organizations/bdcatalyst/collections/TOPMedworkflows/name' -H 'Accept: application/json' | jq '.'
...
"entryPath": "github.com/DataBiosphere/topmed-workflows/UM_aligner_wdl",
"entryType": "workflow",
"id": 5817,
"labels": [
"u-of-michigan",
"datastage",
"topmed",
"datacommons"
],
"verified": false,
...
```
2. Go to https://dev.dockstore.net/workflows/github.com/DataBiosphere/topmed-workflows/UM_aligner_wdl:1.32.0?tab=info. See how the entry is verified in the UI (checkmark at the top)
**Expected behavior**
The API should indicate the entry is verified. This will have the effect of altering the UI as well, as we [display the done icon](https://github.com/dockstore/dockstore-ui2/blob/133fd1b20c6a59a2ee520455b25f454d27cc0103/src/app/organizations/collection/collection.component.html#L143) if verified is true.
**Additional context**
[Webservice](https://github.com/dockstore/dockstore/commits/6d891ef) - 6d891ef
[UI](https://github.com/dockstore/dockstore-ui2/commits/97af6aee) - 2.8.4-107-g97af6aee
[Compose Setup](https://github.com/dockstore/compose_setup/commits/5454f4a) - 5454f4a
[Deploy](https://github.com/dockstore/dockstore-deploy/commits/b5fc8b9) - 1.11.2-106-gb5fc8b9
galaxyParsingLambdaVersion: 0.0.6
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-2027)
┆fixVersions: Dockstore 1.13
┆friendlyId: DOCK-2027
┆sprint: 92- T
┆taskType: Story
| 1.0 | Collections endpoint not indicating verified entries - **Describe the bug**
The collections endpoint indicates verified is false for all entries, even if they are verified.
**To Reproduce**
1.
```
curl 'https://dev.dockstore.net/api/organizations/bdcatalyst/collections/TOPMedworkflows/name' -H 'Accept: application/json' | jq '.'
...
"entryPath": "github.com/DataBiosphere/topmed-workflows/UM_aligner_wdl",
"entryType": "workflow",
"id": 5817,
"labels": [
"u-of-michigan",
"datastage",
"topmed",
"datacommons"
],
"verified": false,
...
```
2. Go to https://dev.dockstore.net/workflows/github.com/DataBiosphere/topmed-workflows/UM_aligner_wdl:1.32.0?tab=info. See how the entry is verified in the UI (checkmark at the top)
**Expected behavior**
The API should indicate the entry is verified. This will have the effect of altering the UI as well, as we [display the done icon](https://github.com/dockstore/dockstore-ui2/blob/133fd1b20c6a59a2ee520455b25f454d27cc0103/src/app/organizations/collection/collection.component.html#L143) if verified is true.
**Additional context**
[Webservice](https://github.com/dockstore/dockstore/commits/6d891ef) - 6d891ef
[UI](https://github.com/dockstore/dockstore-ui2/commits/97af6aee) - 2.8.4-107-g97af6aee
[Compose Setup](https://github.com/dockstore/compose_setup/commits/5454f4a) - 5454f4a
[Deploy](https://github.com/dockstore/dockstore-deploy/commits/b5fc8b9) - 1.11.2-106-gb5fc8b9
galaxyParsingLambdaVersion: 0.0.6
┆Issue is synchronized with this [Jira Story](https://ucsc-cgl.atlassian.net/browse/DOCK-2027)
┆fixVersions: Dockstore 1.13
┆friendlyId: DOCK-2027
┆sprint: 92- T
┆taskType: Story
| non_priority | collections endpoint not indicating verified entries describe the bug the collections endpoint indicates verified is false for all entries even if they are verified to reproduce curl h accept application json jq entrypath github com databiosphere topmed workflows um aligner wdl entrytype workflow id labels u of michigan datastage topmed datacommons verified false go to see how the entry is verified in the ui checkmark at the top expected behavior the api should indicate the entry is verified this will have the effect of altering the ui as well as we if verified is true additional context galaxyparsinglambdaversion ┆issue is synchronized with this ┆fixversions dockstore ┆friendlyid dock ┆sprint t ┆tasktype story | 0 |
11,429 | 14,248,198,428 | IssuesEvent | 2020-11-19 12:35:47 | tikv/tikv | https://api.github.com/repos/tikv/tikv | closed | UCP: Migrate scalar function `User` from TiDB | challenge-program difficulty/easy sig/coprocessor |
## Description
Port the scalar function `User` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @lonng
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
| 1.0 | UCP: Migrate scalar function `User` from TiDB -
## Description
Port the scalar function `User` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @lonng
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
| non_priority | ucp migrate scalar function user from tidb description port the scalar function user from tidb to coprocessor score mentor s lonng recommended skills rust programming learning materials already implemented expressions ported from tidb | 0 |
10,612 | 13,437,423,364 | IssuesEvent | 2020-09-07 15:54:28 | timberio/vector | https://api.github.com/repos/timberio/vector | opened | Add support for parsing and normalizing time units in the remap sytnax | domain: processing type: feature | With log data, especially after parsing, it's common for numbers to contain units in string format.
## Example
For example, this common Elixir log contains time units (`5.4ms`):
```
17:42:51.469 [info] GET /17:42:51.469 [info] Sent 200 in 5.4ms
```
But the unit can change depending on the duration (`167µs`):
```
17:42:51.469 [info] GET /17:42:51.469 [info] Sent 200 in 167µs
```
In addition to the changing unit, you'll notice we went from floats to integers.
## Proposal
In the same vein that we have `int` and `float` functions, I propose that we add a `duration` function that handles parsing and normalizing. For example, when parsing this log:
```
17:42:51.469 [info] GET /17:42:51.469 [info] Sent 200 in 5.4ms
```
You'll likely end up with a `duration` (or whatever name they want) field:
```js
{
// ...
"duration": "5.4ms",
// ...
}
```
And in order parse this into a normalized unit, I would recommend the user use the remap syntax to do the following:
```
.duration_seconds = duration(.duration, "s")
del(duration)
```
This would result in:
```js
{
// ...
"duration_seconds": 0.0054,
// ...
}
```
The `duration` function handles all of the intricacies to normalize any value passed to it to seconds. This means:
* Handling unit suffixes.
* Converting units between each other.
## Requirements
- [ ] Recognize [valid time units](https://en.wikipedia.org/wiki/Orders_of_magnitude_(time)#Less_than_one_second) for our use case: `µs` (microsecond), `ns` (nanosecond), `ms` (millisecond), `s` (second), `m` (minute), `h` (hour), `d` (day).
- [ ] Be forgiving with parsing: `10ms` or `10 ms`.
- [ ] Convert and normalized units to the specified unit. | 1.0 | Add support for parsing and normalizing time units in the remap sytnax - With log data, especially after parsing, it's common for numbers to contain units in string format.
## Example
For example, this common Elixir log contains time units (`5.4ms`):
```
17:42:51.469 [info] GET /17:42:51.469 [info] Sent 200 in 5.4ms
```
But the unit can change depending on the duration (`167µs`):
```
17:42:51.469 [info] GET /17:42:51.469 [info] Sent 200 in 167µs
```
In addition to the changing unit, you'll notice we went from floats to integers.
## Proposal
In the same vein that we have `int` and `float` functions, I propose that we add a `duration` function that handles parsing and normalizing. For example, when parsing this log:
```
17:42:51.469 [info] GET /17:42:51.469 [info] Sent 200 in 5.4ms
```
You'll likely end up with a `duration` (or whatever name they want) field:
```js
{
// ...
"duration": "5.4ms",
// ...
}
```
And in order parse this into a normalized unit, I would recommend the user use the remap syntax to do the following:
```
.duration_seconds = duration(.duration, "s")
del(duration)
```
This would result in:
```js
{
// ...
"duration_seconds": 0.0054,
// ...
}
```
The `duration` function handles all of the intricacies to normalize any value passed to it to seconds. This means:
* Handling unit suffixes.
* Converting units between each other.
## Requirements
- [ ] Recognize [valid time units](https://en.wikipedia.org/wiki/Orders_of_magnitude_(time)#Less_than_one_second) for our use case: `µs` (microsecond), `ns` (nanosecond), `ms` (millisecond), `s` (second), `m` (minute), `h` (hour), `d` (day).
- [ ] Be forgiving with parsing: `10ms` or `10 ms`.
- [ ] Convert and normalized units to the specified unit. | non_priority | add support for parsing and normalizing time units in the remap sytnax with log data especially after parsing it s common for numbers to contain units in string format example for example this common elixir log contains time units get sent in but the unit can change depending on the duration get sent in in addition to the changing unit you ll notice we went from floats to integers proposal in the same vein that we have int and float functions i propose that we add a duration function that handles parsing and normalizing for example when parsing this log get sent in you ll likely end up with a duration or whatever name they want field js duration and in order parse this into a normalized unit i would recommend the user use the remap syntax to do the following duration seconds duration duration s del duration this would result in js duration seconds the duration function handles all of the intricacies to normalize any value passed to it to seconds this means handling unit suffixes converting units between each other requirements recognize for our use case µs microsecond ns nanosecond ms millisecond s second m minute h hour d day be forgiving with parsing or ms convert and normalized units to the specified unit | 0 |
154,083 | 12,192,471,331 | IssuesEvent | 2020-04-29 13:00:35 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | v8.0.0-RC1: Image block sits outside of perceived conatiner in editor (Twenty Twenty theme) | Needs Testing [Block] Image | **Describe the bug**
In v8.0.0-RC1 and the Twenty Twenty theme enabled, within the editor the image block sits outside of the central 'container' of the page.
This issue is related to #21885 and #21911 (but this issue is about when no alignment is set).
It looks like this is to do with the change in https://github.com/WordPress/gutenberg/pull/21822 where the wrapper `div` was removed from the Image block in the editor. This change means that the [following styling in the Twenty Twenty theme](https://core.trac.wordpress.org/browser/trunk/src/wp-content/themes/twentytwenty/assets/css/editor-style-block.css#L366) now overrides the margins that should centre the block:
```css
.editor-styles-wrapper figure {
margin: 0;
}
```
Whereas if you disable the plugin, then the wrapper div element is targeted by
```
.edit-post-visual-editor .block-editor-block-list__block {
```
This particular selector was removed in https://github.com/WordPress/gutenberg/pull/20951 at [this line](https://github.com/WordPress/gutenberg/pull/20951/files#diff-947e2eca7278f9a543620b68d7187d09L40). A solution to this issue could be either to fix this in Twenty Twenty, or add back in the div wrapper to the Image block to mitigate the specificity issue.
**To reproduce**
Steps to reproduce the behavior:
1. Activate the Twenty Twenty theme on your site
2. Add an Image block and select any image and set it to left aligned
3. Instead of the image block being centered within the perceived container of the page, the image is left aligned outside of that 'container'.
**Expected behavior**
The image block to sit within the perceived 'container' of the page in Twenty Twenty as it does on the front end.
**Screenshots**
### Before (WordPress 5.4, plugin disabled)

### After (WordPress 5.4, plugin v8.0.0-RC1 enabled)

**Editor version (please complete the following information):**
- WordPress version: 5.4, Gutenberg v8.0.0-RC1
**Desktop (please complete the following information):**
- OS: MacOS
- Browser: Chrome 81
| 1.0 | v8.0.0-RC1: Image block sits outside of perceived conatiner in editor (Twenty Twenty theme) - **Describe the bug**
In v8.0.0-RC1 and the Twenty Twenty theme enabled, within the editor the image block sits outside of the central 'container' of the page.
This issue is related to #21885 and #21911 (but this issue is about when no alignment is set).
It looks like this is to do with the change in https://github.com/WordPress/gutenberg/pull/21822 where the wrapper `div` was removed from the Image block in the editor. This change means that the [following styling in the Twenty Twenty theme](https://core.trac.wordpress.org/browser/trunk/src/wp-content/themes/twentytwenty/assets/css/editor-style-block.css#L366) now overrides the margins that should centre the block:
```css
.editor-styles-wrapper figure {
margin: 0;
}
```
Whereas if you disable the plugin, then the wrapper div element is targeted by
```
.edit-post-visual-editor .block-editor-block-list__block {
```
This particular selector was removed in https://github.com/WordPress/gutenberg/pull/20951 at [this line](https://github.com/WordPress/gutenberg/pull/20951/files#diff-947e2eca7278f9a543620b68d7187d09L40). A solution to this issue could be either to fix this in Twenty Twenty, or add back in the div wrapper to the Image block to mitigate the specificity issue.
**To reproduce**
Steps to reproduce the behavior:
1. Activate the Twenty Twenty theme on your site
2. Add an Image block and select any image and set it to left aligned
3. Instead of the image block being centered within the perceived container of the page, the image is left aligned outside of that 'container'.
**Expected behavior**
The image block to sit within the perceived 'container' of the page in Twenty Twenty as it does on the front end.
**Screenshots**
### Before (WordPress 5.4, plugin disabled)

### After (WordPress 5.4, plugin v8.0.0-RC1 enabled)

**Editor version (please complete the following information):**
- WordPress version: 5.4, Gutenberg v8.0.0-RC1
**Desktop (please complete the following information):**
- OS: MacOS
- Browser: Chrome 81
| non_priority | image block sits outside of perceived conatiner in editor twenty twenty theme describe the bug in and the twenty twenty theme enabled within the editor the image block sits outside of the central container of the page this issue is related to and but this issue is about when no alignment is set it looks like this is to do with the change in where the wrapper div was removed from the image block in the editor this change means that the now overrides the margins that should centre the block css editor styles wrapper figure margin whereas if you disable the plugin then the wrapper div element is targeted by edit post visual editor block editor block list block this particular selector was removed in at a solution to this issue could be either to fix this in twenty twenty or add back in the div wrapper to the image block to mitigate the specificity issue to reproduce steps to reproduce the behavior activate the twenty twenty theme on your site add an image block and select any image and set it to left aligned instead of the image block being centered within the perceived container of the page the image is left aligned outside of that container expected behavior the image block to sit within the perceived container of the page in twenty twenty as it does on the front end screenshots before wordpress plugin disabled after wordpress plugin enabled editor version please complete the following information wordpress version gutenberg desktop please complete the following information os macos browser chrome | 0 |
147,391 | 13,207,103,124 | IssuesEvent | 2020-08-14 21:58:13 | airctic/mantisshrimp | https://api.github.com/repos/airctic/mantisshrimp | opened | Add an example on backbones usage for Faster RCNN | documentation example request good first issue help wanted | ## 📓 New <Tutorial/Example>
**Is this a request for a tutorial or for an example?**
This is an example on how to use the different backbones that Mantisshrimp offer for the Faster RCNN model
**What is the task?**
Object detection
**Is this example for a specific model?**
FasterRCNN
**Is this example for a specific dataset?**
Either the Raccoon or the Fridge Objects datasets.
---
**Don't remove**
Main issue for examples: #39
| 1.0 | Add an example on backbones usage for Faster RCNN - ## 📓 New <Tutorial/Example>
**Is this a request for a tutorial or for an example?**
This is an example on how to use the different backbones that Mantisshrimp offer for the Faster RCNN model
**What is the task?**
Object detection
**Is this example for a specific model?**
FasterRCNN
**Is this example for a specific dataset?**
Either the Raccoon or the Fridge Objects datasets.
---
**Don't remove**
Main issue for examples: #39
| non_priority | add an example on backbones usage for faster rcnn 📓 new is this a request for a tutorial or for an example this is an example on how to use the different backbones that mantisshrimp offer for the faster rcnn model what is the task object detection is this example for a specific model fasterrcnn is this example for a specific dataset either the raccoon or the fridge objects datasets don t remove main issue for examples | 0 |
250,084 | 21,259,254,121 | IssuesEvent | 2022-04-13 01:02:10 | RamiMustafa/WAF_Sec_Test | https://api.github.com/repos/RamiMustafa/WAF_Sec_Test | opened | Provide guidance for either platform managed keys (PMK) or customer managed keys (CMK), based on security or compliance requirements of this workload | WARP-Import WAF_Sec_Test Security Operational Procedures Configuration & Secrets Management | <a href="https://docs.microsoft.com/azure/security/fundamentals/encryption-models">Provide guidance for either platform managed keys (PMK) or customer managed keys (CMK), based on security or compliance requirements of this workload</a>
<p><b>Why Consider This?</b></p>
Different approaches can be used by the workload team. Decisions are often driven by security, compliance and specific data classification requirements. Understanding these requirements is important to determine which key types are best suitable (Platform-Managed Keys, Customer-Managed Keys or Bring Your Own Key(BYOK)).
<p><b>Context</b></p>
<p><b>Suggested Actions</b></p>
<p><span>Provide guidance for either platform managed keys (PMK) or customer managed keys (CMK), based on security or compliance requirements of this workload</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/security/fundamentals/encryption-models" target="_blank"><span>https://docs.microsoft.com/en-us/azure/security/fundamentals/encryption-models</span></a><span /></p><p><a href="https://docs.microsoft.com/en-us/azure/compliance" target="_blank"><span>Azure compliance documentation</span></a><span /></p> | 1.0 | Provide guidance for either platform managed keys (PMK) or customer managed keys (CMK), based on security or compliance requirements of this workload - <a href="https://docs.microsoft.com/azure/security/fundamentals/encryption-models">Provide guidance for either platform managed keys (PMK) or customer managed keys (CMK), based on security or compliance requirements of this workload</a>
<p><b>Why Consider This?</b></p>
Different approaches can be used by the workload team. Decisions are often driven by security, compliance and specific data classification requirements. Understanding these requirements is important to determine which key types are best suitable (Platform-Managed Keys, Customer-Managed Keys or Bring Your Own Key(BYOK)).
<p><b>Context</b></p>
<p><b>Suggested Actions</b></p>
<p><span>Provide guidance for either platform managed keys (PMK) or customer managed keys (CMK), based on security or compliance requirements of this workload</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/security/fundamentals/encryption-models" target="_blank"><span>https://docs.microsoft.com/en-us/azure/security/fundamentals/encryption-models</span></a><span /></p><p><a href="https://docs.microsoft.com/en-us/azure/compliance" target="_blank"><span>Azure compliance documentation</span></a><span /></p> | non_priority | provide guidance for either platform managed keys pmk or customer managed keys cmk based on security or compliance requirements of this workload why consider this different approaches can be used by the workload team decisions are often driven by security compliance and specific data classification requirements understanding these requirements is important to determine which key types are best suitable platform managed keys customer managed keys or bring your own key byok context suggested actions provide guidance for either platform managed keys pmk or customer managed keys cmk based on security or compliance requirements of this workload learn more azure compliance documentation | 0 |
37,595 | 6,623,050,181 | IssuesEvent | 2017-09-22 04:24:22 | YaleDecisionNeuro/PsychTaskFramework | https://api.github.com/repos/YaleDecisionNeuro/PsychTaskFramework | closed | Sphinx code documentation | documentation | Doxygen is annoying; [Sphinx](http://www.sphinx-doc.org/en/stable/tutorial.html) with [matlabdomain](https://pypi.python.org/pypi/sphinxcontrib-matlabdomain) seems like a good way to _sort of_ do the standard MathWorks thing while maintaining a good external resource (e.g. with [ReadTheDocs](https://docs.readthedocs.io/en/latest/getting_started.html)).
It's a good way to integrate the cookbook (#62) with code details, too. | 1.0 | Sphinx code documentation - Doxygen is annoying; [Sphinx](http://www.sphinx-doc.org/en/stable/tutorial.html) with [matlabdomain](https://pypi.python.org/pypi/sphinxcontrib-matlabdomain) seems like a good way to _sort of_ do the standard MathWorks thing while maintaining a good external resource (e.g. with [ReadTheDocs](https://docs.readthedocs.io/en/latest/getting_started.html)).
It's a good way to integrate the cookbook (#62) with code details, too. | non_priority | sphinx code documentation doxygen is annoying with seems like a good way to sort of do the standard mathworks thing while maintaining a good external resource e g with it s a good way to integrate the cookbook with code details too | 0 |
3,032 | 8,743,165,896 | IssuesEvent | 2018-12-12 18:21:57 | dotnet/dotnet-api-docs | https://api.github.com/repos/dotnet/dotnet-api-docs | opened | Ensure return values conform to standard pattern | :bookmark_tabs: Information Architecture up-for-grabs | ## Ensure return values conform to standard pattern
OPS displays return value information as follows:
The only authored content is the description itself, which should describe the return value, optimally without repeating the return type.
In many case, the return value description doesn't conform to this pattern. The most egregious violation of it, and one that we should eliminate, is:
> "return-type-as-authored-content"
> "return value description, usually including return type as well"
This duplicates (and sometimes even triples) the return type. We should identify and modify these instances to that they conform to the standard pattern.
| 1.0 | Ensure return values conform to standard pattern - ## Ensure return values conform to standard pattern
OPS displays return value information as follows:
The only authored content is the description itself, which should describe the return value, optimally without repeating the return type.
In many case, the return value description doesn't conform to this pattern. The most egregious violation of it, and one that we should eliminate, is:
> "return-type-as-authored-content"
> "return value description, usually including return type as well"
This duplicates (and sometimes even triples) the return type. We should identify and modify these instances to that they conform to the standard pattern.
| non_priority | ensure return values conform to standard pattern ensure return values conform to standard pattern ops displays return value information as follows the only authored content is the description itself which should describe the return value optimally without repeating the return type in many case the return value description doesn t conform to this pattern the most egregious violation of it and one that we should eliminate is return type as authored content return value description usually including return type as well this duplicates and sometimes even triples the return type we should identify and modify these instances to that they conform to the standard pattern | 0 |
64,301 | 7,783,414,870 | IssuesEvent | 2018-06-06 09:49:03 | openebs/openebs | https://api.github.com/repos/openebs/openebs | closed | OpenEBS components deployment strategy / tracker | Epic area/maya kind/design solution/dedicated solution/hyperconverged summerhack | This will act as a common placeholder to discuss & debate about deployment, maintenance, upgrade, rollback strategies of various OpenEBS components.
We should have clarity to questions like:
- Should OpenEBS components rely on systemd ?
- Should OpenEBS components run as containers & managed by some tool similar to kubelet ?
- Should OpenEBS components runs as containers or standalone binaries & managed by Nomad ?
- *Here Nomad is being referred as tool for deployment & management of OpenEBS components*
- What happens if container runtime require an upgrade ?
- Can multiple versions of container runtime (*e.g. dockerd, rkt engine*) be used across hosts ?
- What happens if orchestrator engine requires an upgrade ?
- Can multiple versions of orchestrator engine be used across hosts ?
### Alternatively:
```yaml
- Can we just use tried & tested tools like Ansible:
- https://github.com/openshift/openshift-ansible
- https://www.ansible.com/tower
- https://github.com/ansible-semaphore/semaphore
- https://github.com/purpleidea/mgmt
- https://github.com/dmsimard/ara
```
### Alternative:
```yaml
- http://operable.io/
```
### References:
- https://www.infoq.com/news/2017/02/common-kubernetes-fail-reasons
- [Lets find why deployment failed](https://github.com/rosskukulinski/k8s-scripts/blob/master/bin/debug-deployment) | 1.0 | OpenEBS components deployment strategy / tracker - This will act as a common placeholder to discuss & debate about deployment, maintenance, upgrade, rollback strategies of various OpenEBS components.
We should have clarity to questions like:
- Should OpenEBS components rely on systemd ?
- Should OpenEBS components run as containers & managed by some tool similar to kubelet ?
- Should OpenEBS components runs as containers or standalone binaries & managed by Nomad ?
- *Here Nomad is being referred as tool for deployment & management of OpenEBS components*
- What happens if container runtime require an upgrade ?
- Can multiple versions of container runtime (*e.g. dockerd, rkt engine*) be used across hosts ?
- What happens if orchestrator engine requires an upgrade ?
- Can multiple versions of orchestrator engine be used across hosts ?
### Alternatively:
```yaml
- Can we just use tried & tested tools like Ansible:
- https://github.com/openshift/openshift-ansible
- https://www.ansible.com/tower
- https://github.com/ansible-semaphore/semaphore
- https://github.com/purpleidea/mgmt
- https://github.com/dmsimard/ara
```
### Alternative:
```yaml
- http://operable.io/
```
### References:
- https://www.infoq.com/news/2017/02/common-kubernetes-fail-reasons
- [Lets find why deployment failed](https://github.com/rosskukulinski/k8s-scripts/blob/master/bin/debug-deployment) | non_priority | openebs components deployment strategy tracker this will act as a common placeholder to discuss debate about deployment maintenance upgrade rollback strategies of various openebs components we should have clarity to questions like should openebs components rely on systemd should openebs components run as containers managed by some tool similar to kubelet should openebs components runs as containers or standalone binaries managed by nomad here nomad is being referred as tool for deployment management of openebs components what happens if container runtime require an upgrade can multiple versions of container runtime e g dockerd rkt engine be used across hosts what happens if orchestrator engine requires an upgrade can multiple versions of orchestrator engine be used across hosts alternatively yaml can we just use tried tested tools like ansible alternative yaml references | 0 |
55,004 | 23,381,167,501 | IssuesEvent | 2022-08-11 09:35:43 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [Reporting] Allow sharing reports to different users in Kibana | enhancement Feature:Reporting loe:week Team:AppServicesSv impact:low Team:Reporting Services EnableJiraSync | **Describe the feature:**
Currently (Kibana 7.3.0) users can only see the reports that they created, but it would be great if users can mark reports as 'public' or 'shared' to allow other users to access them.
A UI to do this withing Kibana would be ideal but it should be fine if it can be done programmatically by modifying the 'created_by' field to some specific value.
**Describe a specific use case for the feature:**
Kibana users that need to share generated reports with other users without needing for each to generate their own. | 2.0 | [Reporting] Allow sharing reports to different users in Kibana - **Describe the feature:**
Currently (Kibana 7.3.0) users can only see the reports that they created, but it would be great if users can mark reports as 'public' or 'shared' to allow other users to access them.
A UI to do this withing Kibana would be ideal but it should be fine if it can be done programmatically by modifying the 'created_by' field to some specific value.
**Describe a specific use case for the feature:**
Kibana users that need to share generated reports with other users without needing for each to generate their own. | non_priority | allow sharing reports to different users in kibana describe the feature currently kibana users can only see the reports that they created but it would be great if users can mark reports as public or shared to allow other users to access them a ui to do this withing kibana would be ideal but it should be fine if it can be done programmatically by modifying the created by field to some specific value describe a specific use case for the feature kibana users that need to share generated reports with other users without needing for each to generate their own | 0 |
260,569 | 27,784,573,414 | IssuesEvent | 2023-03-17 01:19:03 | iworkforthem/ts-screenshot | https://api.github.com/repos/iworkforthem/ts-screenshot | opened | CVE-2023-28155 (Medium) detected in request-2.88.2.tgz | Mend: dependency security vulnerability | ## CVE-2023-28155 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>request-2.88.2.tgz</b></p></summary>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.88.2.tgz">https://registry.npmjs.org/request/-/request-2.88.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- jest-26.6.3.tgz (Root Library)
- core-26.6.3.tgz
- jest-config-26.6.3.tgz
- jest-environment-jsdom-26.6.2.tgz
- jsdom-16.4.0.tgz
- :x: **request-2.88.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/iworkforthem/ts-screenshot/commit/797a6cdc19b4e999d2f8fcc15cea4b7c6b0fc2e6">797a6cdc19b4e999d2f8fcc15cea4b7c6b0fc2e6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** UNSUPPORTED WHEN ASSIGNED ** The Request package through 2.88.1 for Node.js allows a bypass of SSRF mitigations via an attacker-controller server that does a cross-protocol redirect (HTTP to HTTPS, or HTTPS to HTTP). NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
<p>Publish Date: 2023-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28155>CVE-2023-28155</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-28155 (Medium) detected in request-2.88.2.tgz - ## CVE-2023-28155 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>request-2.88.2.tgz</b></p></summary>
<p>Simplified HTTP request client.</p>
<p>Library home page: <a href="https://registry.npmjs.org/request/-/request-2.88.2.tgz">https://registry.npmjs.org/request/-/request-2.88.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/request/package.json</p>
<p>
Dependency Hierarchy:
- jest-26.6.3.tgz (Root Library)
- core-26.6.3.tgz
- jest-config-26.6.3.tgz
- jest-environment-jsdom-26.6.2.tgz
- jsdom-16.4.0.tgz
- :x: **request-2.88.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/iworkforthem/ts-screenshot/commit/797a6cdc19b4e999d2f8fcc15cea4b7c6b0fc2e6">797a6cdc19b4e999d2f8fcc15cea4b7c6b0fc2e6</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** UNSUPPORTED WHEN ASSIGNED ** The Request package through 2.88.1 for Node.js allows a bypass of SSRF mitigations via an attacker-controller server that does a cross-protocol redirect (HTTP to HTTPS, or HTTPS to HTTP). NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
<p>Publish Date: 2023-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28155>CVE-2023-28155</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in request tgz cve medium severity vulnerability vulnerable library request tgz simplified http request client library home page a href path to dependency file package json path to vulnerable library node modules request package json dependency hierarchy jest tgz root library core tgz jest config tgz jest environment jsdom tgz jsdom tgz x request tgz vulnerable library found in head commit a href found in base branch main vulnerability details unsupported when assigned the request package through for node js allows a bypass of ssrf mitigations via an attacker controller server that does a cross protocol redirect http to https or https to http note this vulnerability only affects products that are no longer supported by the maintainer publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
345,043 | 30,783,108,603 | IssuesEvent | 2023-07-31 11:26:28 | cosmos/ibc-go | https://api.github.com/repos/cosmos/ibc-go | closed | GetValsAtHeight should account for current uncommitted height | testing | <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberation
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Summary
https://github.com/cosmos/ibc-go/commit/57777235f6c1cb33a67de300414b9b824b050f29
`GetValsAtHeight` should account for the current uncommitted height. A comment should be added explaining this reasoning and it should be looked into if we can remove the if statement [here](https://github.com/cosmos/ibc-go/blob/main/testing/chain.go#L428)
When the latest committed height == trusted height (happens when testing misbehaviour), this will fail. The validator set associated with a trusted height is the next validator set for that height. When the next height is uncommitted the correct validator set cannot be obtained through historical information and must be returned from the `TestChain` struct
Note: the print statement was accidentally committed, it should not be included
____
#### For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate contributors tagged/assigned
| 1.0 | GetValsAtHeight should account for current uncommitted height - <!-- < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < < ☺
v ✰ Thanks for opening an issue! ✰
v Before smashing the submit button please review the template.
v Word of caution: poorly thought-out proposals may be rejected
v without deliberation
☺ > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > > -->
## Summary
https://github.com/cosmos/ibc-go/commit/57777235f6c1cb33a67de300414b9b824b050f29
`GetValsAtHeight` should account for the current uncommitted height. A comment should be added explaining this reasoning and it should be looked into if we can remove the if statement [here](https://github.com/cosmos/ibc-go/blob/main/testing/chain.go#L428)
When the latest committed height == trusted height (happens when testing misbehaviour), this will fail. The validator set associated with a trusted height is the next validator set for that height. When the next height is uncommitted the correct validator set cannot be obtained through historical information and must be returned from the `TestChain` struct
Note: the print statement was accidentally committed, it should not be included
____
#### For Admin Use
- [ ] Not duplicate issue
- [ ] Appropriate labels applied
- [ ] Appropriate contributors tagged/assigned
| non_priority | getvalsatheight should account for current uncommitted height ☺ v ✰ thanks for opening an issue ✰ v before smashing the submit button please review the template v word of caution poorly thought out proposals may be rejected v without deliberation ☺ summary getvalsatheight should account for the current uncommitted height a comment should be added explaining this reasoning and it should be looked into if we can remove the if statement when the latest committed height trusted height happens when testing misbehaviour this will fail the validator set associated with a trusted height is the next validator set for that height when the next height is uncommitted the correct validator set cannot be obtained through historical information and must be returned from the testchain struct note the print statement was accidentally committed it should not be included for admin use not duplicate issue appropriate labels applied appropriate contributors tagged assigned | 0 |
34,228 | 28,808,114,878 | IssuesEvent | 2023-05-03 00:41:05 | grafana/agent | https://api.github.com/repos/grafana/agent | closed | integrations/process_exporter scrape read_bytes_total counter / write_bytes_total counter value always 0 | type/infrastructure | hello
I use integrations/process_exporter
and find out there always 0 in scrape read_bytes_total counter / write_bytes_total counter
when I install process-exporter can see value change
OS: ubuntu 22.04
agent version:
```
agent, version v0.32.1 (branch: HEAD, revision: f48e41a9)
build user: root@ce4f3c31cd6b
build date: 2023-03-06T19:07:00Z
go version: go1.20
platform: linux/amd64
```
agent config:
```
server:
log_level: warn
metrics:
global:
scrape_interval: 15s
external_labels:
node_name: 'sample_node'
remote_write:
- url: https://XXXXX:XXX/api/v1/push
tls_config:
insecure_skip_verify: true
headers:
X-Scope-OrgID: prometheus
basic_auth:
username: "mimirwrite"
password: "mimirwrite"
wal_directory: '/var/lib/grafana-agent'
wal_cleanup_age: "12h"
configs:
- name: local
host_filter: false
scrape_configs:
- job_name: 'process-exporter'
# https://www.rabbitmq.com/prometheus.html
static_configs:
- targets: ['127.0.0.1:9256']
integrations:
agent:
enabled: true
node_exporter:
enabled: true
include_exporter_metrics: true
process_exporter:
enabled: true
process_names:
- name: "{{.Comm}}"
cmdline:
- '.+'
```
grafana explore
[Imgur](https://imgur.com/AaPYegx)
| 1.0 | integrations/process_exporter scrape read_bytes_total counter / write_bytes_total counter value always 0 - hello
I use integrations/process_exporter
and find out there always 0 in scrape read_bytes_total counter / write_bytes_total counter
when I install process-exporter can see value change
OS: ubuntu 22.04
agent version:
```
agent, version v0.32.1 (branch: HEAD, revision: f48e41a9)
build user: root@ce4f3c31cd6b
build date: 2023-03-06T19:07:00Z
go version: go1.20
platform: linux/amd64
```
agent config:
```
server:
log_level: warn
metrics:
global:
scrape_interval: 15s
external_labels:
node_name: 'sample_node'
remote_write:
- url: https://XXXXX:XXX/api/v1/push
tls_config:
insecure_skip_verify: true
headers:
X-Scope-OrgID: prometheus
basic_auth:
username: "mimirwrite"
password: "mimirwrite"
wal_directory: '/var/lib/grafana-agent'
wal_cleanup_age: "12h"
configs:
- name: local
host_filter: false
scrape_configs:
- job_name: 'process-exporter'
# https://www.rabbitmq.com/prometheus.html
static_configs:
- targets: ['127.0.0.1:9256']
integrations:
agent:
enabled: true
node_exporter:
enabled: true
include_exporter_metrics: true
process_exporter:
enabled: true
process_names:
- name: "{{.Comm}}"
cmdline:
- '.+'
```
grafana explore
[Imgur](https://imgur.com/AaPYegx)
| non_priority | integrations process exporter scrape read bytes total counter write bytes total counter value always hello i use integrations process exporter and find out there always in scrape read bytes total counter write bytes total counter when i install process exporter can see value change os ubuntu agent version agent version branch head revision build user root build date go version platform linux agent config server log level warn metrics global scrape interval external labels node name sample node remote write url tls config insecure skip verify true headers x scope orgid prometheus basic auth username mimirwrite password mimirwrite wal directory var lib grafana agent wal cleanup age configs name local host filter false scrape configs job name process exporter static configs targets integrations agent enabled true node exporter enabled true include exporter metrics true process exporter enabled true process names name comm cmdline grafana explore | 0 |
183,380 | 31,394,479,793 | IssuesEvent | 2023-08-26 19:01:03 | activist-org/activist | https://api.github.com/repos/activist-org/activist | closed | Create base MediaVideo component | help wanted good first issue design | ### Terms
- [X] I have searched [open and closed design issues](https://github.com/activist-org/activist/issues?q=is%3Aissue+label%3Adesign)
- [X] I agree to follow activist's [Code of Conduct](https://github.com/activist-org/activist/blob/main/.github/CODE_OF_CONDUCT.md)
### Description
This issue would create a baseline file for the `MediaVideo` component that could be used to either show a video on a page or link in to a video call if the event is online. This component is generally defined in the designs with the other [Page Media components](https://www.figma.com/file/I9McFfaLu1RiiWp5IP3YjE/activist_public_designs?type=design&node-id=2673%3A20111&mode=design&t=hJRakNbmbK83mZ9P-1) that are then created in the [components/media](https://github.com/activist-org/activist/tree/main/frontend/components/media) directory :) We do not need a full implementation for this task, but more a component that:
- Has a required `link` prop
- Is sized similar to other components in the [components/media](https://github.com/activist-org/activist/tree/main/frontend/components/media) directory
- Follows coloration as set out in [tailwind.config.ts](https://github.com/activist-org/activist/blob/main/frontend/tailwind.config.ts)
Later on we can add to this component where video links would lead to a popover or video links would direct the user to the call. An example of the basis we want for now is:

### Contribution
Happy to support someone on this issue or work on it myself :) | 1.0 | Create base MediaVideo component - ### Terms
- [X] I have searched [open and closed design issues](https://github.com/activist-org/activist/issues?q=is%3Aissue+label%3Adesign)
- [X] I agree to follow activist's [Code of Conduct](https://github.com/activist-org/activist/blob/main/.github/CODE_OF_CONDUCT.md)
### Description
This issue would create a baseline file for the `MediaVideo` component that could be used to either show a video on a page or link in to a video call if the event is online. This component is generally defined in the designs with the other [Page Media components](https://www.figma.com/file/I9McFfaLu1RiiWp5IP3YjE/activist_public_designs?type=design&node-id=2673%3A20111&mode=design&t=hJRakNbmbK83mZ9P-1) that are then created in the [components/media](https://github.com/activist-org/activist/tree/main/frontend/components/media) directory :) We do not need a full implementation for this task, but more a component that:
- Has a required `link` prop
- Is sized similar to other components in the [components/media](https://github.com/activist-org/activist/tree/main/frontend/components/media) directory
- Follows coloration as set out in [tailwind.config.ts](https://github.com/activist-org/activist/blob/main/frontend/tailwind.config.ts)
Later on we can add to this component where video links would lead to a popover or video links would direct the user to the call. An example of the basis we want for now is:

### Contribution
Happy to support someone on this issue or work on it myself :) | non_priority | create base mediavideo component terms i have searched i agree to follow activist s description this issue would create a baseline file for the mediavideo component that could be used to either show a video on a page or link in to a video call if the event is online this component is generally defined in the designs with the other that are then created in the directory we do not need a full implementation for this task but more a component that has a required link prop is sized similar to other components in the directory follows coloration as set out in later on we can add to this component where video links would lead to a popover or video links would direct the user to the call an example of the basis we want for now is contribution happy to support someone on this issue or work on it myself | 0 |
144,290 | 19,286,134,892 | IssuesEvent | 2021-12-11 01:45:02 | samq-wsdemo/struts-demo | https://api.github.com/repos/samq-wsdemo/struts-demo | opened | WS-2016-7112 (Medium) detected in spring-context-3.0.5.RELEASE.jar | security vulnerability | ## WS-2016-7112 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-context-3.0.5.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: struts-demo/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/3.0.5.RELEASE/spring-context-3.0.5.RELEASE.jar,struts-demo/target/struts2-showcase/WEB-INF/lib/spring-context-3.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- struts2-spring-plugin-2.3.20.jar (Root Library)
- :x: **spring-context-3.0.5.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.
<p>Publish Date: 2021-09-23
<p>URL: <a href=https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9>WS-2016-7112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1">https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1</a></p>
<p>Release Date: 2016-07-14</p>
<p>Fix Resolution: org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-context","packageVersion":"3.0.5.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.struts:struts2-spring-plugin:2.3.20;org.springframework:spring-context:3.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2016-7112","vulnerabilityDetails":"In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.","vulnerabilityUrl":"https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9","cvss3Severity":"medium","cvss3Score":"4.9","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | True | WS-2016-7112 (Medium) detected in spring-context-3.0.5.RELEASE.jar - ## WS-2016-7112 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-context-3.0.5.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: struts-demo/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/3.0.5.RELEASE/spring-context-3.0.5.RELEASE.jar,struts-demo/target/struts2-showcase/WEB-INF/lib/spring-context-3.0.5.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- struts2-spring-plugin-2.3.20.jar (Root Library)
- :x: **spring-context-3.0.5.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.
<p>Publish Date: 2021-09-23
<p>URL: <a href=https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9>WS-2016-7112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1">https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1</a></p>
<p>Release Date: 2016-07-14</p>
<p>Fix Resolution: org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-context","packageVersion":"3.0.5.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.struts:struts2-spring-plugin:2.3.20;org.springframework:spring-context:3.0.5.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2016-7112","vulnerabilityDetails":"In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.","vulnerabilityUrl":"https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9","cvss3Severity":"medium","cvss3Score":"4.9","cvss3Metrics":{"A":"N/A","AC":"N/A","PR":"N/A","S":"N/A","C":"N/A","UI":"N/A","AV":"N/A","I":"N/A"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in spring context release jar ws medium severity vulnerability vulnerable library spring context release jar spring framework parent path to dependency file struts demo pom xml path to vulnerable library home wss scanner repository org springframework spring context release spring context release jar struts demo target showcase web inf lib spring context release jar dependency hierarchy spring plugin jar root library x spring context release jar vulnerable library found in base branch master vulnerability details in spring framework versions release through release release through release and release through release are vulnerable to stack based buffer overflow which allows an authenticated attacker to crash the application when giving cronsequencegenerator a reversed range in the “minutes” or “hours” fields publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring context release release release release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache struts spring plugin org springframework spring context release isminimumfixversionavailable true minimumfixversion org springframework spring context release release release release isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails in spring framework versions release through release release through release and release through release are vulnerable to stack based buffer overflow which allows an authenticated attacker to crash the application when giving cronsequencegenerator a reversed range in the “minutes” or “hours” fields vulnerabilityurl | 0 |
74,987 | 25,468,743,880 | IssuesEvent | 2022-11-25 08:11:48 | matrix-org/matrix-hookshot | https://api.github.com/repos/matrix-org/matrix-hookshot | opened | Empty admin rooms should be discarded or unused | T-Defect Admin Room S-Minor javascript | If a user leaves their admin room, Hookshot continues to use it for posting URLs generated by `!hookshot webhook`. Since admin rooms are typically invite-only DMs, the user will never be able rejoin the room after leaving it, and will never be able to see those messages.
To prevent posting messages in inaccessible admin rooms, Hookshot should either leave empty admin rooms (on startup or in response to the user leaving), or should invite the user back to an admin room when posting a new message in it. My preference is the former, because it prevents Hookshot's room list from slowly growing larger and larger. | 1.0 | Empty admin rooms should be discarded or unused - If a user leaves their admin room, Hookshot continues to use it for posting URLs generated by `!hookshot webhook`. Since admin rooms are typically invite-only DMs, the user will never be able rejoin the room after leaving it, and will never be able to see those messages.
To prevent posting messages in inaccessible admin rooms, Hookshot should either leave empty admin rooms (on startup or in response to the user leaving), or should invite the user back to an admin room when posting a new message in it. My preference is the former, because it prevents Hookshot's room list from slowly growing larger and larger. | non_priority | empty admin rooms should be discarded or unused if a user leaves their admin room hookshot continues to use it for posting urls generated by hookshot webhook since admin rooms are typically invite only dms the user will never be able rejoin the room after leaving it and will never be able to see those messages to prevent posting messages in inaccessible admin rooms hookshot should either leave empty admin rooms on startup or in response to the user leaving or should invite the user back to an admin room when posting a new message in it my preference is the former because it prevents hookshot s room list from slowly growing larger and larger | 0 |
63,468 | 7,723,338,031 | IssuesEvent | 2018-05-24 12:10:10 | status-im/status-react | https://api.github.com/repos/status-im/status-react | opened | Add indicator of unread messages (navigation bar) | :eyes: design-input-required desktop feature | ### User Story
As a user, I want to see so that that I have unread messages in app
### Description
*Type*: Feature
*Summary*: add the red badge of unread messages, like

Not implemented in mobile.
| 1.0 | Add indicator of unread messages (navigation bar) - ### User Story
As a user, I want to see so that that I have unread messages in app
### Description
*Type*: Feature
*Summary*: add the red badge of unread messages, like

Not implemented in mobile.
| non_priority | add indicator of unread messages navigation bar user story as a user i want to see so that that i have unread messages in app description type feature summary add the red badge of unread messages like not implemented in mobile | 0 |
54,163 | 23,184,402,143 | IssuesEvent | 2022-08-01 07:03:00 | filecoin-project/venus | https://api.github.com/repos/filecoin-project/venus | closed | venus-messager存在内存泄漏问题, 存在持续的内存增长的情况 | P2 BU-chain-service | ### Checklist
- [X] This is **not** a new feature or an enhancement to the Filecoin protocol. If it is, please open an [FIP issue](https://github.com/filecoin-project/FIPs/blob/master/FIPS/fip-0001.md).
- [X] This is **not** a new feature request. If it is, please file a [feature request](https://github.com/filecoin-project/venus/issues/new?assignees=&labels=need%2Ftriage%2Ckind%2Ffeature&template=feature_request.yml) instead.
- [X] This is **not** brainstorming ideas. If you have an idea you'd like to discuss, please open a new discussion on [the venus forum](https://github.com/filecoin-project/venus/discussions/categories/ideas) and select the category as `Ideas`.
- [X] I **have** a specific, actionable, and well motivated improvement to propose.
### Venus component
- [ ] venus daemon - [chain service] chain sync
- [ ] venus auth - [chain service] authentication
- [X] venus messager - [chain service] message management (mpool)
- [ ] venus gateway - [chain service] gateway
- [ ] venus miner - [chain service] mining and block production
- [ ] venus sealer/worker - sealing
- [ ] venus sealer - proving (WindowPoSt)
- [ ] venus market - storage deal
- [ ] venus market - retrieval deal
- [ ] venus market - data transfer
- [ ] venus light-weight client
- [ ] venus JSON-RPC API
- [ ] Other
### Improvement Suggestion
当venus-messager运行一段时间后,占用的内存越来越大,且不会主动释放资源,参考下图
<img width="1746" alt="image" src="https://user-images.githubusercontent.com/43364105/176819679-ceeea0cf-8ccf-44e6-b38f-93f8cb3a72aa.png">
| 1.0 | venus-messager存在内存泄漏问题, 存在持续的内存增长的情况 - ### Checklist
- [X] This is **not** a new feature or an enhancement to the Filecoin protocol. If it is, please open an [FIP issue](https://github.com/filecoin-project/FIPs/blob/master/FIPS/fip-0001.md).
- [X] This is **not** a new feature request. If it is, please file a [feature request](https://github.com/filecoin-project/venus/issues/new?assignees=&labels=need%2Ftriage%2Ckind%2Ffeature&template=feature_request.yml) instead.
- [X] This is **not** brainstorming ideas. If you have an idea you'd like to discuss, please open a new discussion on [the venus forum](https://github.com/filecoin-project/venus/discussions/categories/ideas) and select the category as `Ideas`.
- [X] I **have** a specific, actionable, and well motivated improvement to propose.
### Venus component
- [ ] venus daemon - [chain service] chain sync
- [ ] venus auth - [chain service] authentication
- [X] venus messager - [chain service] message management (mpool)
- [ ] venus gateway - [chain service] gateway
- [ ] venus miner - [chain service] mining and block production
- [ ] venus sealer/worker - sealing
- [ ] venus sealer - proving (WindowPoSt)
- [ ] venus market - storage deal
- [ ] venus market - retrieval deal
- [ ] venus market - data transfer
- [ ] venus light-weight client
- [ ] venus JSON-RPC API
- [ ] Other
### Improvement Suggestion
当venus-messager运行一段时间后,占用的内存越来越大,且不会主动释放资源,参考下图
<img width="1746" alt="image" src="https://user-images.githubusercontent.com/43364105/176819679-ceeea0cf-8ccf-44e6-b38f-93f8cb3a72aa.png">
| non_priority | venus messager存在内存泄漏问题, 存在持续的内存增长的情况 checklist this is not a new feature or an enhancement to the filecoin protocol if it is please open an this is not a new feature request if it is please file a instead this is not brainstorming ideas if you have an idea you d like to discuss please open a new discussion on and select the category as ideas i have a specific actionable and well motivated improvement to propose venus component venus daemon chain sync venus auth authentication venus messager message management mpool venus gateway gateway venus miner mining and block production venus sealer worker sealing venus sealer proving windowpost venus market storage deal venus market retrieval deal venus market data transfer venus light weight client venus json rpc api other improvement suggestion 当venus messager运行一段时间后,占用的内存越来越大,且不会主动释放资源,参考下图 img width alt image src | 0 |
70,171 | 13,434,284,428 | IssuesEvent | 2020-09-07 11:07:24 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Repeatable outpost event | Bug Code | - [ Yes] I have searched the issue tracker to check if the issue has already been reported.
**Description**
The 'Bug station crew' outpost event is repeatable and grants full 2k marks reward each time completed. We replicated this 4 times in a row.
**Steps To Reproduce**
Find a military outpost that grants the above event, complete the event, undock from station and redock, each time you redock the event triggers with the crew chief requested a representative to meet them.
**Version**
0.10.4.0 - Windows 10
| 1.0 | Repeatable outpost event - - [ Yes] I have searched the issue tracker to check if the issue has already been reported.
**Description**
The 'Bug station crew' outpost event is repeatable and grants full 2k marks reward each time completed. We replicated this 4 times in a row.
**Steps To Reproduce**
Find a military outpost that grants the above event, complete the event, undock from station and redock, each time you redock the event triggers with the crew chief requested a representative to meet them.
**Version**
0.10.4.0 - Windows 10
| non_priority | repeatable outpost event i have searched the issue tracker to check if the issue has already been reported description the bug station crew outpost event is repeatable and grants full marks reward each time completed we replicated this times in a row steps to reproduce find a military outpost that grants the above event complete the event undock from station and redock each time you redock the event triggers with the crew chief requested a representative to meet them version windows | 0 |
146,198 | 13,173,620,744 | IssuesEvent | 2020-08-11 20:40:53 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Migrate Sidekiq setup instrux to -sensitive | content-ia-team documentation documentation-support | This doc: https://github.com/department-of-veterans-affairs/vets.gov-team/blob/master/Products/Platform/Vets-API/Sidekiq%20Enterprise%20Setup.md
Should be migrated to `va.gov-team-sensitive`
And the link to it should be updated here: https://github.com/department-of-veterans-affairs/vets-api/#sidekiq-enterprise | 2.0 | Migrate Sidekiq setup instrux to -sensitive - This doc: https://github.com/department-of-veterans-affairs/vets.gov-team/blob/master/Products/Platform/Vets-API/Sidekiq%20Enterprise%20Setup.md
Should be migrated to `va.gov-team-sensitive`
And the link to it should be updated here: https://github.com/department-of-veterans-affairs/vets-api/#sidekiq-enterprise | non_priority | migrate sidekiq setup instrux to sensitive this doc should be migrated to va gov team sensitive and the link to it should be updated here | 0 |
48,220 | 6,084,080,115 | IssuesEvent | 2017-06-17 00:24:27 | 18F/crime-data-explorer | https://api.github.com/repos/18F/crime-data-explorer | closed | Need to make label for agency bar chart dynamic based on data type | bug workflow: design-review | Currently the label for the agency bar chart says the data is derived from NIBRS regardless of the agency's reporting type. The label should update based on what data type that state and or agency reports | 1.0 | Need to make label for agency bar chart dynamic based on data type - Currently the label for the agency bar chart says the data is derived from NIBRS regardless of the agency's reporting type. The label should update based on what data type that state and or agency reports | non_priority | need to make label for agency bar chart dynamic based on data type currently the label for the agency bar chart says the data is derived from nibrs regardless of the agency s reporting type the label should update based on what data type that state and or agency reports | 0 |
71,127 | 9,480,252,191 | IssuesEvent | 2019-04-20 16:12:38 | kubernetes/kops | https://api.github.com/repos/kubernetes/kops | closed | Help with creating dns-free cluster | area/documentation good-starter-issue lifecycle/rotten | 1. kops version 1.9.1
2. kubectl client version 1.11.0
3. aws
4. I was following the tutorial on how to use kops in aws-china, but in us-west-2 (I just wanted a dns-free cluster). Everything went smooth until I reached the `kops validate cluster` part.
5.
```Using cluster from kubectl context: xxxxxxxxx-example.k8s.local
Validating cluster xxxxxxxxx-example.k8s.local
unexpected error during validation: error listing nodes: Get https://internal-api-xxxxxxxxx-exam-6vnila-578615394.us-west-2.elb.amazonaws.com/api/v1/nodes: dial tcp xxx.xx.xx.xx:443: i/o timeout
```
6. I expected everything to work like in the tutorial/
7. cluster manifest:
```apiVersion: kops/v1alpha2
kind: Cluster
metadata:
creationTimestamp: 2018-07-05T11:29:14Z
name: xxxxxxxxx-example.k8s.local
spec:
api:
loadBalancer:
type: Internal
authorization:
rbac: {}
channel: stable
cloudProvider: aws
configBase: s3://xxxxxxxxx-example-com-state-store/xxxxxxxxx-example.k8s.local
etcdClusters:
- etcdMembers:
- instanceGroup: master-us-west-2a
name: a
name: main
- etcdMembers:
- instanceGroup: master-us-west-2a
name: a
name: events
iam:
allowContainerRegistry: true
legacy: false
kubernetesApiAccess:
- 0.0.0.0/0
kubernetesVersion: 1.9.6
masterPublicName: api.xxxxxxxxx-example.k8s.local
networkCIDR: 172.20.0.0/16
networking:
weave:
mtu: 8912
nonMasqueradeCIDR: 100.64.0.0/10
sshAccess:
- 0.0.0.0/0
subnets:
- cidr: 172.20.32.0/19
name: us-west-2a
type: Private
zone: us-west-2a
- cidr: 172.20.0.0/22
name: utility-us-west-2a
type: Utility
zone: us-west-2a
topology:
dns:
type: Public
masters: private
nodes: private
---
apiVersion: kops/v1alpha2
kind: InstanceGroup
metadata:
creationTimestamp: 2018-07-05T11:29:15Z
labels:
kops.k8s.io/cluster: xxxxxxxxx-example.k8s.local
name: master-us-west-2a
spec:
associatePublicIp: false
image: kope.io/k8s-1.9-debian-jessie-amd64-hvm-ebs-2018-03-11
machineType: m3.medium
maxSize: 1
minSize: 1
nodeLabels:
kops.k8s.io/instancegroup: master-us-west-2a
role: Master
subnets:
- us-west-2a
---
apiVersion: kops/v1alpha2
kind: InstanceGroup
metadata:
creationTimestamp: 2018-07-05T11:29:16Z
labels:
kops.k8s.io/cluster: xxxxxxxxx-example.k8s.local
name: nodes
spec:
associatePublicIp: false
image: kope.io/k8s-1.9-debian-jessie-amd64-hvm-ebs-2018-03-11
machineType: t2.medium
maxSize: 2
minSize: 2
nodeLabels:
kops.k8s.io/instancegroup: nodes
role: Node
subnets:
- us-west-2a``` | 1.0 | Help with creating dns-free cluster - 1. kops version 1.9.1
2. kubectl client version 1.11.0
3. aws
4. I was following the tutorial on how to use kops in aws-china, but in us-west-2 (I just wanted a dns-free cluster). Everything went smooth until I reached the `kops validate cluster` part.
5.
```Using cluster from kubectl context: xxxxxxxxx-example.k8s.local
Validating cluster xxxxxxxxx-example.k8s.local
unexpected error during validation: error listing nodes: Get https://internal-api-xxxxxxxxx-exam-6vnila-578615394.us-west-2.elb.amazonaws.com/api/v1/nodes: dial tcp xxx.xx.xx.xx:443: i/o timeout
```
6. I expected everything to work like in the tutorial/
7. cluster manifest:
```apiVersion: kops/v1alpha2
kind: Cluster
metadata:
creationTimestamp: 2018-07-05T11:29:14Z
name: xxxxxxxxx-example.k8s.local
spec:
api:
loadBalancer:
type: Internal
authorization:
rbac: {}
channel: stable
cloudProvider: aws
configBase: s3://xxxxxxxxx-example-com-state-store/xxxxxxxxx-example.k8s.local
etcdClusters:
- etcdMembers:
- instanceGroup: master-us-west-2a
name: a
name: main
- etcdMembers:
- instanceGroup: master-us-west-2a
name: a
name: events
iam:
allowContainerRegistry: true
legacy: false
kubernetesApiAccess:
- 0.0.0.0/0
kubernetesVersion: 1.9.6
masterPublicName: api.xxxxxxxxx-example.k8s.local
networkCIDR: 172.20.0.0/16
networking:
weave:
mtu: 8912
nonMasqueradeCIDR: 100.64.0.0/10
sshAccess:
- 0.0.0.0/0
subnets:
- cidr: 172.20.32.0/19
name: us-west-2a
type: Private
zone: us-west-2a
- cidr: 172.20.0.0/22
name: utility-us-west-2a
type: Utility
zone: us-west-2a
topology:
dns:
type: Public
masters: private
nodes: private
---
apiVersion: kops/v1alpha2
kind: InstanceGroup
metadata:
creationTimestamp: 2018-07-05T11:29:15Z
labels:
kops.k8s.io/cluster: xxxxxxxxx-example.k8s.local
name: master-us-west-2a
spec:
associatePublicIp: false
image: kope.io/k8s-1.9-debian-jessie-amd64-hvm-ebs-2018-03-11
machineType: m3.medium
maxSize: 1
minSize: 1
nodeLabels:
kops.k8s.io/instancegroup: master-us-west-2a
role: Master
subnets:
- us-west-2a
---
apiVersion: kops/v1alpha2
kind: InstanceGroup
metadata:
creationTimestamp: 2018-07-05T11:29:16Z
labels:
kops.k8s.io/cluster: xxxxxxxxx-example.k8s.local
name: nodes
spec:
associatePublicIp: false
image: kope.io/k8s-1.9-debian-jessie-amd64-hvm-ebs-2018-03-11
machineType: t2.medium
maxSize: 2
minSize: 2
nodeLabels:
kops.k8s.io/instancegroup: nodes
role: Node
subnets:
- us-west-2a``` | non_priority | help with creating dns free cluster kops version kubectl client version aws i was following the tutorial on how to use kops in aws china but in us west i just wanted a dns free cluster everything went smooth until i reached the kops validate cluster part using cluster from kubectl context xxxxxxxxx example local validating cluster xxxxxxxxx example local unexpected error during validation error listing nodes get dial tcp xxx xx xx xx i o timeout i expected everything to work like in the tutorial cluster manifest apiversion kops kind cluster metadata creationtimestamp name xxxxxxxxx example local spec api loadbalancer type internal authorization rbac channel stable cloudprovider aws configbase xxxxxxxxx example com state store xxxxxxxxx example local etcdclusters etcdmembers instancegroup master us west name a name main etcdmembers instancegroup master us west name a name events iam allowcontainerregistry true legacy false kubernetesapiaccess kubernetesversion masterpublicname api xxxxxxxxx example local networkcidr networking weave mtu nonmasqueradecidr sshaccess subnets cidr name us west type private zone us west cidr name utility us west type utility zone us west topology dns type public masters private nodes private apiversion kops kind instancegroup metadata creationtimestamp labels kops io cluster xxxxxxxxx example local name master us west spec associatepublicip false image kope io debian jessie hvm ebs machinetype medium maxsize minsize nodelabels kops io instancegroup master us west role master subnets us west apiversion kops kind instancegroup metadata creationtimestamp labels kops io cluster xxxxxxxxx example local name nodes spec associatepublicip false image kope io debian jessie hvm ebs machinetype medium maxsize minsize nodelabels kops io instancegroup nodes role node subnets us west | 0 |
154,459 | 12,215,184,162 | IssuesEvent | 2020-05-01 12:12:00 | Students-of-the-city-of-Kostroma/trpo_automation | https://api.github.com/repos/Students-of-the-city-of-Kostroma/trpo_automation | closed | Создание экземпляров класса Letter | Sprint 6 Sprint 7 Testing | Доделать экземпляры писем после каждой из функций
Создать экземпляры класса Letter для тестирования системы.
- 10 экземпляров на вход;
- 1-2 экземпляра, прошедшие обработку после каждой функции, заданной глобально; | 1.0 | Создание экземпляров класса Letter - Доделать экземпляры писем после каждой из функций
Создать экземпляры класса Letter для тестирования системы.
- 10 экземпляров на вход;
- 1-2 экземпляра, прошедшие обработку после каждой функции, заданной глобально; | non_priority | создание экземпляров класса letter доделать экземпляры писем после каждой из функций создать экземпляры класса letter для тестирования системы экземпляров на вход экземпляра прошедшие обработку после каждой функции заданной глобально | 0 |
101,423 | 12,683,314,471 | IssuesEvent | 2020-06-19 19:27:04 | pythonindia/inpycon2020 | https://api.github.com/repos/pythonindia/inpycon2020 | closed | Make the website responsive | design dev responsive | There are few areas that clearly needs more attention right now:
- [x] Banner section
- [x] The dates for devsprint, workshop, etc (might need to adjust the padding and margins)
- [x] Navbar
cc @aavrug | 1.0 | Make the website responsive - There are few areas that clearly needs more attention right now:
- [x] Banner section
- [x] The dates for devsprint, workshop, etc (might need to adjust the padding and margins)
- [x] Navbar
cc @aavrug | non_priority | make the website responsive there are few areas that clearly needs more attention right now banner section the dates for devsprint workshop etc might need to adjust the padding and margins navbar cc aavrug | 0 |
23,480 | 3,830,401,655 | IssuesEvent | 2016-03-31 14:29:07 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | NPE in DataTableRenderer when sorting AND grouping is used | defect | The NPE happens only when both sorting AND grouping is used, and when the sorted column actually contains data. See PullRequest #1286 for a fix. | 1.0 | NPE in DataTableRenderer when sorting AND grouping is used - The NPE happens only when both sorting AND grouping is used, and when the sorted column actually contains data. See PullRequest #1286 for a fix. | non_priority | npe in datatablerenderer when sorting and grouping is used the npe happens only when both sorting and grouping is used and when the sorted column actually contains data see pullrequest for a fix | 0 |
222,486 | 24,708,979,234 | IssuesEvent | 2022-10-19 21:54:33 | lukebrogan-mend/railsgoat | https://api.github.com/repos/lukebrogan-mend/railsgoat | closed | CVE-2022-23634 (Medium) detected in actionpack-6.0.0.gem - autoclosed | security vulnerability | ## CVE-2022-23634 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionpack-6.0.0.gem</b></p></summary>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>
Dependency Hierarchy:
- sassc-rails-2.1.2.gem (Root Library)
- railties-6.0.0.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/railsgoat/commit/d94b554e8b55637d1bbc827a129348c0c2562d12">d94b554e8b55637d1bbc827a129348c0c2562d12</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Puma is a Ruby/Rack web server built for parallelism. Prior to `puma` version `5.6.2`, `puma` may not always call `close` on the response body. Rails, prior to version `7.0.2.2`, depended on the response body being closed in order for its `CurrentAttributes` implementation to work correctly. The combination of these two behaviors (Puma not closing the body + Rails' Executor implementation) causes information leakage. This problem is fixed in Puma versions 5.6.2 and 4.3.11. This problem is fixed in Rails versions 7.02.2, 6.1.4.6, 6.0.4.6, and 5.2.6.2. Upgrading to a patched Rails _or_ Puma version fixes the vulnerability.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23634>CVE-2022-23634</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9">https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: puma - 4.3.11, 5.6.2; actionpack - 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2</p>
</p>
</details>
<p></p>
| True | CVE-2022-23634 (Medium) detected in actionpack-6.0.0.gem - autoclosed - ## CVE-2022-23634 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionpack-6.0.0.gem</b></p></summary>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-6.0.0.gem">https://rubygems.org/gems/actionpack-6.0.0.gem</a></p>
<p>
Dependency Hierarchy:
- sassc-rails-2.1.2.gem (Root Library)
- railties-6.0.0.gem
- :x: **actionpack-6.0.0.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/railsgoat/commit/d94b554e8b55637d1bbc827a129348c0c2562d12">d94b554e8b55637d1bbc827a129348c0c2562d12</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Puma is a Ruby/Rack web server built for parallelism. Prior to `puma` version `5.6.2`, `puma` may not always call `close` on the response body. Rails, prior to version `7.0.2.2`, depended on the response body being closed in order for its `CurrentAttributes` implementation to work correctly. The combination of these two behaviors (Puma not closing the body + Rails' Executor implementation) causes information leakage. This problem is fixed in Puma versions 5.6.2 and 4.3.11. This problem is fixed in Rails versions 7.02.2, 6.1.4.6, 6.0.4.6, and 5.2.6.2. Upgrading to a patched Rails _or_ Puma version fixes the vulnerability.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-23634>CVE-2022-23634</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9">https://github.com/puma/puma/security/advisories/GHSA-rmj8-8hhh-gv5h,https://github.com/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: puma - 4.3.11, 5.6.2; actionpack - 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in actionpack gem autoclosed cve medium severity vulnerability vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href dependency hierarchy sassc rails gem root library railties gem x actionpack gem vulnerable library found in head commit a href found in base branch master vulnerability details puma is a ruby rack web server built for parallelism prior to puma version puma may not always call close on the response body rails prior to version depended on the response body being closed in order for its currentattributes implementation to work correctly the combination of these two behaviors puma not closing the body rails executor implementation causes information leakage this problem is fixed in puma versions and this problem is fixed in rails versions and upgrading to a patched rails or puma version fixes the vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution puma actionpack | 0 |
6,784 | 2,860,030,835 | IssuesEvent | 2015-06-03 14:04:06 | davidyell/CakePHP3-Proffer | https://api.github.com/repos/davidyell/CakePHP3-Proffer | closed | Test for multiple uploads on one model | testing | Need to create tests to ensure that you can properly upload more than one file on a single table.
Such as,
```php
$config = [
'photo' => [
'dir' => 'photo_dir',
'thumbnailSizes' => [
'square' => ['w' => 200, 'h' => 200, 'crop' => true],
'portrait' => ['w' => 100, 'h' => 300],
]
],
'profile_image' => [
'dir' => 'profile_image_dir',
'thumbnailSizes' => [
'square' => ['w' => 200, 'h' => 200, 'crop' => true],
'portrait' => ['w' => 100, 'h' => 300],
]
]
]
``` | 1.0 | Test for multiple uploads on one model - Need to create tests to ensure that you can properly upload more than one file on a single table.
Such as,
```php
$config = [
'photo' => [
'dir' => 'photo_dir',
'thumbnailSizes' => [
'square' => ['w' => 200, 'h' => 200, 'crop' => true],
'portrait' => ['w' => 100, 'h' => 300],
]
],
'profile_image' => [
'dir' => 'profile_image_dir',
'thumbnailSizes' => [
'square' => ['w' => 200, 'h' => 200, 'crop' => true],
'portrait' => ['w' => 100, 'h' => 300],
]
]
]
``` | non_priority | test for multiple uploads on one model need to create tests to ensure that you can properly upload more than one file on a single table such as php config photo dir photo dir thumbnailsizes square portrait profile image dir profile image dir thumbnailsizes square portrait | 0 |
172,301 | 21,043,344,112 | IssuesEvent | 2022-03-31 14:06:19 | jgeraigery/dynatrace-service-broker | https://api.github.com/repos/jgeraigery/dynatrace-service-broker | opened | WS-2016-7112 (Medium) detected in spring-context-4.0.8.RELEASE.jar | security vulnerability | ## WS-2016-7112 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-context-4.0.8.RELEASE.jar</b></p></summary>
<p>Spring Context</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/4.0.8.RELEASE/spring-context-4.0.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-security-1.1.9.RELEASE.jar (Root Library)
- :x: **spring-context-4.0.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/dynatrace-service-broker/commit/075c652078643180fb05751cdbc793df371d6844">075c652078643180fb05751cdbc793df371d6844</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.
<p>Publish Date: 2021-09-23
<p>URL: <a href=https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9>WS-2016-7112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1">https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1</a></p>
<p>Release Date: 2016-07-14</p>
<p>Fix Resolution: org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-context","packageVersion":"4.0.8.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-security:1.1.9.RELEASE;org.springframework:spring-context:4.0.8.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2016-7112","vulnerabilityDetails":"In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.","vulnerabilityUrl":"https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9","cvss3Severity":"medium","cvss3Score":"4.9","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2016-7112 (Medium) detected in spring-context-4.0.8.RELEASE.jar - ## WS-2016-7112 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-context-4.0.8.RELEASE.jar</b></p></summary>
<p>Spring Context</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/4.0.8.RELEASE/spring-context-4.0.8.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-security-1.1.9.RELEASE.jar (Root Library)
- :x: **spring-context-4.0.8.RELEASE.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/dynatrace-service-broker/commit/075c652078643180fb05751cdbc793df371d6844">075c652078643180fb05751cdbc793df371d6844</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.
<p>Publish Date: 2021-09-23
<p>URL: <a href=https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9>WS-2016-7112</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1">https://github.com/spring-projects/spring-framework/releases/tag/v5.0.0.M1</a></p>
<p>Release Date: 2016-07-14</p>
<p>Fix Resolution: org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-context","packageVersion":"4.0.8.RELEASE","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-security:1.1.9.RELEASE;org.springframework:spring-context:4.0.8.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-context:3.2.18.RELEASE,4.2.8.RELEASE,4.3.2.RELEASE,5.0.0.RELEASE","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"WS-2016-7112","vulnerabilityDetails":"In Spring Framework, versions 3.0.0.RELEASE through 3.2.17.RELEASE, 4.0.0.RELEASE through 4.2.7.RELEASE and 4.3.0.RELEASE through 4.3.1.RELEASE are vulnerable to Stack-based Buffer Overflow, which allows an authenticated attacker to crash the application when giving CronSequenceGenerator a reversed range in the “minutes” or “hours” fields.","vulnerabilityUrl":"https://github.com/spring-projects/spring-framework/commit/e431624e8472b3b53d1a0c4528bf736c612f1fd9","cvss3Severity":"medium","cvss3Score":"4.9","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in spring context release jar ws medium severity vulnerability vulnerable library spring context release jar spring context library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring context release spring context release jar dependency hierarchy spring boot starter security release jar root library x spring context release jar vulnerable library found in head commit a href found in base branch master vulnerability details in spring framework versions release through release release through release and release through release are vulnerable to stack based buffer overflow which allows an authenticated attacker to crash the application when giving cronsequencegenerator a reversed range in the “minutes” or “hours” fields publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring context release release release release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter security release org springframework spring context release isminimumfixversionavailable true minimumfixversion org springframework spring context release release release release isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails in spring framework versions release through release release through release and release through release are vulnerable to stack based buffer overflow which allows an authenticated attacker to crash the application when giving cronsequencegenerator a reversed range in the “minutes” or “hours” fields vulnerabilityurl | 0 |
41,917 | 10,824,823,972 | IssuesEvent | 2019-11-09 12:02:51 | dpa99c/cordova-plugin-firebasex | https://api.github.com/repos/dpa99c/cordova-plugin-firebasex | closed | Cannot install plugin - Failed to install 'cordova-plugin-firebasex': undefined | build issue documentation investigate ios | # Bug report
**Current behavior:**
Fails on installation
**Expected behavior:**
Should install sucsessfully
**Steps to reproduce:**
cordova plugin add cordova-plugin-firebasex@6.0.6
**Environment information**
<!-- Please supply full details of your development environment including: -->
- Cordova CLI version
- `9.0.0 (cordova-lib@9.0.1)`
- Cordova platform version
- `ios 5.0.0`
- Plugins & versions installed in project (including this plugin)
- `cordova-plugin-add-swift-support 2.0.2 "AddSwiftSupport"
cordova-plugin-advanced-http 2.1.1 "Advanced HTTP plugin"
cordova-plugin-androidx 1.0.2 "cordova-plugin-androidx"
cordova-plugin-androidx-adapter 1.1.0 "cordova-plugin-androidx-adapter"
cordova-plugin-camera 4.1.0 "Camera"
cordova-plugin-chooser 1.2.5 "Chooser"
cordova-plugin-crop 0.3.1 "CropPlugin"
cordova-plugin-device 2.0.3 "Device"
cordova-plugin-file 6.0.2 "File"
cordova-plugin-file-transfer 1.7.1 "File Transfer"
cordova-plugin-filepath 1.5.6 "cordova-plugin-filepath"
cordova-plugin-firebasex 6.0.6 "Google Firebase Plugin"
cordova-plugin-ionic-keyboard 2.1.3 "cordova-plugin-ionic-keyboard"
cordova-plugin-ionic-webview 3.1.2 "cordova-plugin-ionic-webview"
cordova-plugin-nativestorage 2.3.2 "NativeStorage"
cordova-plugin-splashscreen 5.0.3 "Splashscreen"
cordova-plugin-statusbar 2.4.3 "StatusBar"
cordova-plugin-whitelist 1.3.4 "Whitelist"`
- Dev machine OS and version, e.g.
- OSX
- `ProductName: Mac OS X
ProductVersion: 10.14.6
BuildVersion: 18G87`
**Console output**
<details>
<summary>Installing "cordova-plugin-firebasex" for ios
Installing "cordova-plugin-androidx" for ios
Installing "cordova-plugin-androidx-adapter" for ios
Failed to install 'cordova-plugin-firebasex': undefined
CordovaError: Promise rejected with non-error: 'Version should contain only numbers and dots'
at cli.catch.err (/usr/local/lib/node_modules/cordova/bin/cordova:29:15)
at process._tickCallback (internal/process/next_tick.js:68:7)
[ERROR] An error occurred while running subprocess cordova.</summary>
``` | 1.0 | Cannot install plugin - Failed to install 'cordova-plugin-firebasex': undefined - # Bug report
**Current behavior:**
Fails on installation
**Expected behavior:**
Should install sucsessfully
**Steps to reproduce:**
cordova plugin add cordova-plugin-firebasex@6.0.6
**Environment information**
<!-- Please supply full details of your development environment including: -->
- Cordova CLI version
- `9.0.0 (cordova-lib@9.0.1)`
- Cordova platform version
- `ios 5.0.0`
- Plugins & versions installed in project (including this plugin)
- `cordova-plugin-add-swift-support 2.0.2 "AddSwiftSupport"
cordova-plugin-advanced-http 2.1.1 "Advanced HTTP plugin"
cordova-plugin-androidx 1.0.2 "cordova-plugin-androidx"
cordova-plugin-androidx-adapter 1.1.0 "cordova-plugin-androidx-adapter"
cordova-plugin-camera 4.1.0 "Camera"
cordova-plugin-chooser 1.2.5 "Chooser"
cordova-plugin-crop 0.3.1 "CropPlugin"
cordova-plugin-device 2.0.3 "Device"
cordova-plugin-file 6.0.2 "File"
cordova-plugin-file-transfer 1.7.1 "File Transfer"
cordova-plugin-filepath 1.5.6 "cordova-plugin-filepath"
cordova-plugin-firebasex 6.0.6 "Google Firebase Plugin"
cordova-plugin-ionic-keyboard 2.1.3 "cordova-plugin-ionic-keyboard"
cordova-plugin-ionic-webview 3.1.2 "cordova-plugin-ionic-webview"
cordova-plugin-nativestorage 2.3.2 "NativeStorage"
cordova-plugin-splashscreen 5.0.3 "Splashscreen"
cordova-plugin-statusbar 2.4.3 "StatusBar"
cordova-plugin-whitelist 1.3.4 "Whitelist"`
- Dev machine OS and version, e.g.
- OSX
- `ProductName: Mac OS X
ProductVersion: 10.14.6
BuildVersion: 18G87`
**Console output**
<details>
<summary>Installing "cordova-plugin-firebasex" for ios
Installing "cordova-plugin-androidx" for ios
Installing "cordova-plugin-androidx-adapter" for ios
Failed to install 'cordova-plugin-firebasex': undefined
CordovaError: Promise rejected with non-error: 'Version should contain only numbers and dots'
at cli.catch.err (/usr/local/lib/node_modules/cordova/bin/cordova:29:15)
at process._tickCallback (internal/process/next_tick.js:68:7)
[ERROR] An error occurred while running subprocess cordova.</summary>
``` | non_priority | cannot install plugin failed to install cordova plugin firebasex undefined bug report current behavior fails on installation expected behavior should install sucsessfully steps to reproduce cordova plugin add cordova plugin firebasex environment information cordova cli version cordova lib cordova platform version ios plugins versions installed in project including this plugin cordova plugin add swift support addswiftsupport cordova plugin advanced http advanced http plugin cordova plugin androidx cordova plugin androidx cordova plugin androidx adapter cordova plugin androidx adapter cordova plugin camera camera cordova plugin chooser chooser cordova plugin crop cropplugin cordova plugin device device cordova plugin file file cordova plugin file transfer file transfer cordova plugin filepath cordova plugin filepath cordova plugin firebasex google firebase plugin cordova plugin ionic keyboard cordova plugin ionic keyboard cordova plugin ionic webview cordova plugin ionic webview cordova plugin nativestorage nativestorage cordova plugin splashscreen splashscreen cordova plugin statusbar statusbar cordova plugin whitelist whitelist dev machine os and version e g osx productname mac os x productversion buildversion console output installing cordova plugin firebasex for ios installing cordova plugin androidx for ios installing cordova plugin androidx adapter for ios failed to install cordova plugin firebasex undefined cordovaerror promise rejected with non error version should contain only numbers and dots at cli catch err usr local lib node modules cordova bin cordova at process tickcallback internal process next tick js an error occurred while running subprocess cordova | 0 |
16,571 | 22,612,229,776 | IssuesEvent | 2022-06-29 18:14:26 | uqfoundation/pyina | https://api.github.com/repos/uqfoundation/pyina | opened | remove dead code blocks from unsupported python versions | compatibility | Can remove dead code blocks for python < 3.7. | True | remove dead code blocks from unsupported python versions - Can remove dead code blocks for python < 3.7. | non_priority | remove dead code blocks from unsupported python versions can remove dead code blocks for python | 0 |
89,051 | 8,188,579,311 | IssuesEvent | 2018-08-30 02:44:32 | rtfd/readthedocs.org | https://api.github.com/repos/rtfd/readthedocs.org | closed | Add better tests for regex file search | Needed: tests | We fixed the regex search issue in #4584, test coverage is still required though. The PR was hotfixed in. | 1.0 | Add better tests for regex file search - We fixed the regex search issue in #4584, test coverage is still required though. The PR was hotfixed in. | non_priority | add better tests for regex file search we fixed the regex search issue in test coverage is still required though the pr was hotfixed in | 0 |
283,865 | 21,335,785,055 | IssuesEvent | 2022-04-18 14:25:17 | ifgi/optimetaPortal | https://api.github.com/repos/ifgi/optimetaPortal | opened | OpenAPI docs for the API | documentation enhancement | Possible starting point: https://dev.to/errietta/documenting-a-django-api-with-openapi-and-dataclasses-1p6h
OpenAPI docs should be automatically generated from the code and served at `/docs`. | 1.0 | OpenAPI docs for the API - Possible starting point: https://dev.to/errietta/documenting-a-django-api-with-openapi-and-dataclasses-1p6h
OpenAPI docs should be automatically generated from the code and served at `/docs`. | non_priority | openapi docs for the api possible starting point openapi docs should be automatically generated from the code and served at docs | 0 |
282,374 | 21,315,485,240 | IssuesEvent | 2022-04-16 07:38:01 | AAlghrairy/pe | https://api.github.com/repos/AAlghrairy/pe | opened | Inaccurate information about resetting passwords | type.DocumentationBug severity.Medium | The User guide has the following diagram in the Getting Started section:
However, the FAQ states that you cannot reset passwords:
<!--session: 1650088430122-d7db7cda-41bb-4a35-974d-cbeb28fb6dc7-->
<!--Version: Web v3.4.2--> | 1.0 | Inaccurate information about resetting passwords - The User guide has the following diagram in the Getting Started section:
However, the FAQ states that you cannot reset passwords:
<!--session: 1650088430122-d7db7cda-41bb-4a35-974d-cbeb28fb6dc7-->
<!--Version: Web v3.4.2--> | non_priority | inaccurate information about resetting passwords the user guide has the following diagram in the getting started section however the faq states that you cannot reset passwords | 0 |
252,668 | 21,609,531,884 | IssuesEvent | 2022-05-04 08:39:54 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | opened | Fix failing regression e2e testcases | testing task e2e-tests | <!--
If you've never submitted an issue to the SORMAS repository before or this is your first time using this template, please read the Contributing guidelines (https://github.com/hzi-braunschweig/SORMAS-Project/blob/development/docs/CONTRIBUTING.md) for an explanation of the information we need you to provide. You don't have to remove this comment or any other comment from this issue as they will automatically be hidden.
-->
**Tests that have a success rate of 25% or lower and need fixing**
- Check reference definition for cases - fails at the same step
- Fill the case person tab - fails at the same step
- Refine the update mechanism between case outcome and person other cause date - fails at different step every time flaky test
- Check checkboxes filters on Case directory page for DE specific - fails at the same step
- Testing bulk edit of Events - fails at the same step
- Test Inactive Destrict Feauture for Travel Entries - fails at the same step
- Edit existent person - fails at the same step
| 2.0 | Fix failing regression e2e testcases - <!--
If you've never submitted an issue to the SORMAS repository before or this is your first time using this template, please read the Contributing guidelines (https://github.com/hzi-braunschweig/SORMAS-Project/blob/development/docs/CONTRIBUTING.md) for an explanation of the information we need you to provide. You don't have to remove this comment or any other comment from this issue as they will automatically be hidden.
-->
**Tests that have a success rate of 25% or lower and need fixing**
- Check reference definition for cases - fails at the same step
- Fill the case person tab - fails at the same step
- Refine the update mechanism between case outcome and person other cause date - fails at different step every time flaky test
- Check checkboxes filters on Case directory page for DE specific - fails at the same step
- Testing bulk edit of Events - fails at the same step
- Test Inactive Destrict Feauture for Travel Entries - fails at the same step
- Edit existent person - fails at the same step
| non_priority | fix failing regression testcases if you ve never submitted an issue to the sormas repository before or this is your first time using this template please read the contributing guidelines for an explanation of the information we need you to provide you don t have to remove this comment or any other comment from this issue as they will automatically be hidden tests that have a success rate of or lower and need fixing check reference definition for cases fails at the same step fill the case person tab fails at the same step refine the update mechanism between case outcome and person other cause date fails at different step every time flaky test check checkboxes filters on case directory page for de specific fails at the same step testing bulk edit of events fails at the same step test inactive destrict feauture for travel entries fails at the same step edit existent person fails at the same step | 0 |
172,936 | 21,083,976,668 | IssuesEvent | 2022-04-03 10:29:48 | AlexRogalskiy/java-patterns | https://api.github.com/repos/AlexRogalskiy/java-patterns | opened | CVE-2018-1000620 (High) detected in cryptiles-2.0.5.tgz | security vulnerability | ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json,/node_modules/npmi/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- gitbook-cli-2.3.2.tgz (Root Library)
- npm-5.1.0.tgz
- request-2.81.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/java-patterns/commit/293ab07ba323c57f39a3e1d9c3bc0f2e7ecf9e11">293ab07ba323c57f39a3e1d9c3bc0f2e7ecf9e11</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-1000620 (High) detected in cryptiles-2.0.5.tgz - ## CVE-2018-1000620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>cryptiles-2.0.5.tgz</b></p></summary>
<p>General purpose crypto utilities</p>
<p>Library home page: <a href="https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz">https://registry.npmjs.org/cryptiles/-/cryptiles-2.0.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json,/node_modules/npmi/node_modules/npm/node_modules/request/node_modules/hawk/node_modules/cryptiles/package.json</p>
<p>
Dependency Hierarchy:
- gitbook-cli-2.3.2.tgz (Root Library)
- npm-5.1.0.tgz
- request-2.81.0.tgz
- hawk-3.1.3.tgz
- :x: **cryptiles-2.0.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/java-patterns/commit/293ab07ba323c57f39a3e1d9c3bc0f2e7ecf9e11">293ab07ba323c57f39a3e1d9c3bc0f2e7ecf9e11</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Eran Hammer cryptiles version 4.1.1 earlier contains a CWE-331: Insufficient Entropy vulnerability in randomDigits() method that can result in An attacker is more likely to be able to brute force something that was supposed to be random.. This attack appear to be exploitable via Depends upon the calling application.. This vulnerability appears to have been fixed in 4.1.2.
<p>Publish Date: 2018-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000620>CVE-2018-1000620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2018-1000620</a></p>
<p>Release Date: 2018-07-09</p>
<p>Fix Resolution: v4.1.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in cryptiles tgz cve high severity vulnerability vulnerable library cryptiles tgz general purpose crypto utilities library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules hawk node modules cryptiles package json node modules npmi node modules npm node modules request node modules hawk node modules cryptiles package json dependency hierarchy gitbook cli tgz root library npm tgz request tgz hawk tgz x cryptiles tgz vulnerable library found in head commit a href found in base branch master vulnerability details eran hammer cryptiles version earlier contains a cwe insufficient entropy vulnerability in randomdigits method that can result in an attacker is more likely to be able to brute force something that was supposed to be random this attack appear to be exploitable via depends upon the calling application this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
114,941 | 14,666,652,880 | IssuesEvent | 2020-12-29 16:46:03 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | opened | UriHelper.BuildAbsolute: opportunity for performance improvement | design-proposal | ## Summary
`UriHelper.BuildAbsolute` creates an intermediary string for the combined path that is used only for concatenating with the other components to create the final URL.
It also uses a non-pooled `StringBuilder` that is instantiated on every invocation. Although optimized in size, it is a heap allocation with an intermediary buffer.
```csharp
public static string BuildAbsolute(
string scheme,
HostString host,
PathString pathBase = new PathString(),
PathString path = new PathString(),
QueryString query = new QueryString(),
FragmentString fragment = new FragmentString())
{
if (scheme == null)
{
throw new ArgumentNullException(nameof(scheme));
}
var combinedPath = (pathBase.HasValue || path.HasValue) ? (pathBase + path).ToString() : "/";
var encodedHost = host.ToString();
var encodedQuery = query.ToString();
var encodedFragment = fragment.ToString();
// PERF: Calculate string length to allocate correct buffer size for StringBuilder.
var length = scheme.Length + SchemeDelimiter.Length + encodedHost.Length
+ combinedPath.Length + encodedQuery.Length + encodedFragment.Length;
return new StringBuilder(length)
.Append(scheme)
.Append(SchemeDelimiter)
.Append(encodedHost)
.Append(combinedPath)
.Append(encodedQuery)
.Append(encodedFragment)
.ToString();
}
```
## Motivation and goals
This method is frequently use in hot paths like redirect and rewrite rules.
# Detailed design
## StringBuilder_WithoutCombinedPathGeneration
Just by not generating the intermediary `combinePath`, there are memory usage improvements in the when the number of components is highier. There are also time improvements in those cases, but it's wrost in the other cases.
## String_Concat_WithArrayArgument
Given that the final URL is composed of more than 4 parts, the use of `string.Concat` incurs in an array allocation.
But it still always performs better in terms of time and memory usage that using a `StringBuilder`.
## String_Create
`string.Create` excels here in comparison to all the other options. It was created exactly for these use cases.
# Benchmarks
``` ini
BenchmarkDotNet=v0.12.1, OS=Windows 10.0.21277
Intel Core i7-8650U CPU 1.90GHz (Kaby Lake R), 1 CPU, 8 logical and 4 physical cores
.NET Core SDK=5.0.200-preview.20614.14
[Host] : .NET Core 5.0.1 (CoreCLR 5.0.120.57516, CoreFX 5.0.120.57516), X64 RyuJIT
DefaultJob : .NET Core 5.0.1 (CoreCLR 5.0.120.57516, CoreFX 5.0.120.57516), X64 RyuJIT
```
| Method | host | pathBase | path | query | fragment | Mean | Error | StdDev | Median | Ratio | RatioSD | Gen 0 | Gen 1 | Gen 2 | Allocated |
|-------------------------------------------- |----------------- |----------- |-------------------- |------------------------------------------- |---------- |---------:|---------:|---------:|---------:|------:|--------:|-------:|------:|------:|----------:|
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | | | **201.1 ns** | **9.05 ns** | **25.52 ns** | **191.8 ns** | **1.00** | **0.00** | **0.0477** | **-** | **-** | **200 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | | | 189.3 ns | 5.81 ns | 15.91 ns | 188.4 ns | 0.96 | 0.16 | 0.0477 | - | - | 200 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | | | 142.8 ns | 2.91 ns | 4.70 ns | 141.6 ns | 0.74 | 0.10 | 0.0381 | - | - | 160 B |
| String_Create | cname.domain.tld | | | | | 129.9 ns | 3.74 ns | 10.96 ns | 129.0 ns | 0.66 | 0.10 | 0.0172 | - | - | 72 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | | **#fragment** | **170.9 ns** | **4.67 ns** | **13.54 ns** | **168.8 ns** | **1.00** | **0.00** | **0.0572** | **-** | **-** | **240 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | | #fragment | 181.8 ns | 6.66 ns | 19.22 ns | 179.5 ns | 1.07 | 0.15 | 0.0572 | - | - | 240 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | | #fragment | 151.2 ns | 3.09 ns | 4.24 ns | 150.2 ns | 0.86 | 0.08 | 0.0420 | - | - | 176 B |
| String_Create | cname.domain.tld | | | | #fragment | 111.3 ns | 2.26 ns | 2.32 ns | 111.2 ns | 0.65 | 0.05 | 0.0229 | - | - | 96 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | **?param1=value1&param2=value2&param3=value3** | | **236.3 ns** | **3.59 ns** | **3.35 ns** | **235.6 ns** | **1.00** | **0.00** | **0.0877** | **-** | **-** | **368 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | | 247.0 ns | 5.05 ns | 4.72 ns | 247.5 ns | 1.05 | 0.03 | 0.0877 | - | - | 368 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | | 227.2 ns | 4.64 ns | 9.47 ns | 225.7 ns | 0.99 | 0.04 | 0.0572 | - | - | 240 B |
| String_Create | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | | 189.4 ns | 3.90 ns | 8.22 ns | 185.9 ns | 0.82 | 0.04 | 0.0381 | - | - | 160 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **246.6 ns** | **5.04 ns** | **8.15 ns** | **244.2 ns** | **1.00** | **0.00** | **0.0954** | **-** | **-** | **400 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | #fragment | 252.3 ns | 5.12 ns | 10.35 ns | 250.2 ns | 1.03 | 0.06 | 0.0954 | - | - | 400 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | #fragment | 224.9 ns | 2.22 ns | 1.74 ns | 225.3 ns | 0.92 | 0.03 | 0.0610 | - | - | 256 B |
| String_Create | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | #fragment | 192.0 ns | 3.62 ns | 5.08 ns | 192.2 ns | 0.78 | 0.04 | 0.0420 | - | - | 176 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | | | **309.4 ns** | **3.35 ns** | **2.97 ns** | **309.7 ns** | **1.00** | **0.00** | **0.0648** | **-** | **-** | **272 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | | | 321.7 ns | 4.44 ns | 3.93 ns | 321.1 ns | 1.04 | 0.01 | 0.0648 | - | - | 272 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | | | 300.6 ns | 5.86 ns | 12.74 ns | 296.0 ns | 1.01 | 0.04 | 0.0477 | - | - | 200 B |
| String_Create | cname.domain.tld | | /path/one/two/three | | | 247.0 ns | 5.06 ns | 7.25 ns | 244.7 ns | 0.81 | 0.03 | 0.0267 | - | - | 112 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | | **#fragment** | **319.5 ns** | **4.68 ns** | **4.15 ns** | **318.9 ns** | **1.00** | **0.00** | **0.0725** | **-** | **-** | **304 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | | #fragment | 307.3 ns | 4.89 ns | 4.58 ns | 306.4 ns | 0.96 | 0.02 | 0.0725 | - | - | 304 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | | #fragment | 302.8 ns | 6.11 ns | 8.77 ns | 300.1 ns | 0.95 | 0.04 | 0.0515 | - | - | 216 B |
| String_Create | cname.domain.tld | | /path/one/two/three | | #fragment | 253.0 ns | 5.12 ns | 8.13 ns | 251.5 ns | 0.79 | 0.03 | 0.0305 | - | - | 128 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | | **421.7 ns** | **8.49 ns** | **15.09 ns** | **418.3 ns** | **1.00** | **0.00** | **0.1049** | **-** | **-** | **440 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 395.9 ns | 4.71 ns | 4.18 ns | 395.1 ns | 0.94 | 0.02 | 0.1049 | - | - | 440 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 372.2 ns | 6.86 ns | 5.73 ns | 370.3 ns | 0.88 | 0.03 | 0.0687 | - | - | 288 B |
| String_Create | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 325.6 ns | 6.51 ns | 6.69 ns | 323.5 ns | 0.78 | 0.02 | 0.0458 | - | - | 192 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **396.1 ns** | **7.65 ns** | **7.16 ns** | **395.3 ns** | **1.00** | **0.00** | **0.1144** | **-** | **-** | **480 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 394.3 ns | 3.10 ns | 2.42 ns | 393.8 ns | 0.99 | 0.02 | 0.1144 | - | - | 480 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 377.6 ns | 4.22 ns | 3.74 ns | 377.8 ns | 0.95 | 0.02 | 0.0725 | - | - | 304 B |
| String_Create | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 329.2 ns | 6.29 ns | 6.46 ns | 327.9 ns | 0.83 | 0.02 | 0.0515 | - | - | 216 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | | | **241.0 ns** | **2.40 ns** | **2.25 ns** | **241.4 ns** | **1.00** | **0.00** | **0.0572** | **-** | **-** | **240 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | | | 245.4 ns | 4.99 ns | 4.66 ns | 245.3 ns | 1.02 | 0.02 | 0.0572 | - | - | 240 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | | | 215.0 ns | 2.70 ns | 2.11 ns | 214.9 ns | 0.89 | 0.01 | 0.0439 | - | - | 184 B |
| String_Create | cname.domain.tld | /base-path | | | | 164.7 ns | 1.27 ns | 1.19 ns | 164.8 ns | 0.68 | 0.01 | 0.0229 | - | - | 96 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | | **#fragment** | **243.2 ns** | **4.56 ns** | **11.85 ns** | **240.1 ns** | **1.00** | **0.00** | **0.0648** | **-** | **-** | **272 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | | #fragment | 236.3 ns | 4.75 ns | 6.66 ns | 234.3 ns | 0.96 | 0.05 | 0.0648 | - | - | 272 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | | #fragment | 233.3 ns | 3.86 ns | 3.22 ns | 233.0 ns | 0.95 | 0.05 | 0.0477 | - | - | 200 B |
| String_Create | cname.domain.tld | /base-path | | | #fragment | 171.6 ns | 2.93 ns | 2.88 ns | 170.8 ns | 0.70 | 0.04 | 0.0267 | - | - | 112 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | **?param1=value1&param2=value2&param3=value3** | | **324.3 ns** | **6.38 ns** | **7.59 ns** | **322.2 ns** | **1.00** | **0.00** | **0.0954** | **-** | **-** | **400 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | | 324.8 ns | 6.06 ns | 5.37 ns | 323.4 ns | 1.00 | 0.03 | 0.0954 | - | - | 400 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | | 298.9 ns | 5.48 ns | 4.58 ns | 298.2 ns | 0.92 | 0.03 | 0.0629 | - | - | 264 B |
| String_Create | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | | 252.5 ns | 5.12 ns | 8.26 ns | 250.9 ns | 0.78 | 0.03 | 0.0420 | - | - | 176 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **319.1 ns** | **4.57 ns** | **4.06 ns** | **318.7 ns** | **1.00** | **0.00** | **0.1049** | **-** | **-** | **440 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | #fragment | 320.0 ns | 4.47 ns | 4.18 ns | 319.2 ns | 1.00 | 0.02 | 0.1049 | - | - | 440 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | #fragment | 320.8 ns | 6.39 ns | 11.19 ns | 315.0 ns | 1.02 | 0.05 | 0.0687 | - | - | 288 B |
| String_Create | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | #fragment | 249.8 ns | 5.07 ns | 5.21 ns | 250.2 ns | 0.78 | 0.02 | 0.0458 | - | - | 192 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | | | **421.9 ns** | **6.69 ns** | **6.25 ns** | **419.6 ns** | **1.00** | **0.00** | **0.0935** | **-** | **-** | **392 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | | | 389.2 ns | 6.62 ns | 7.08 ns | 387.0 ns | 0.92 | 0.02 | 0.0744 | - | - | 312 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | | | 362.6 ns | 6.17 ns | 6.85 ns | 361.0 ns | 0.86 | 0.02 | 0.0534 | - | - | 224 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | | | 318.4 ns | 6.41 ns | 8.56 ns | 315.5 ns | 0.76 | 0.03 | 0.0305 | - | - | 128 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | | **#fragment** | **412.6 ns** | **4.19 ns** | **3.72 ns** | **412.5 ns** | **1.00** | **0.00** | **0.1030** | **-** | **-** | **432 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | | #fragment | 390.0 ns | 7.68 ns | 18.84 ns | 381.2 ns | 0.94 | 0.04 | 0.0839 | - | - | 352 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | | #fragment | 360.9 ns | 5.15 ns | 4.30 ns | 359.0 ns | 0.87 | 0.01 | 0.0572 | - | - | 240 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | | #fragment | 322.3 ns | 5.97 ns | 5.30 ns | 320.7 ns | 0.78 | 0.01 | 0.0362 | - | - | 152 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | | **488.9 ns** | **6.15 ns** | **5.75 ns** | **490.3 ns** | **1.00** | **0.00** | **0.1335** | **-** | **-** | **560 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 476.3 ns | 9.62 ns | 15.81 ns | 470.6 ns | 0.98 | 0.04 | 0.1144 | - | - | 480 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 439.7 ns | 7.73 ns | 7.23 ns | 438.8 ns | 0.90 | 0.02 | 0.0725 | - | - | 304 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 396.9 ns | 7.76 ns | 7.62 ns | 393.0 ns | 0.81 | 0.02 | 0.0515 | - | - | 216 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **496.5 ns** | **9.76 ns** | **13.68 ns** | **494.4 ns** | **1.00** | **0.00** | **0.1411** | **-** | **-** | **592 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 525.1 ns | 16.74 ns | 49.10 ns | 517.1 ns | 1.01 | 0.08 | 0.1221 | - | - | 512 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 449.7 ns | 8.55 ns | 9.50 ns | 447.6 ns | 0.90 | 0.03 | 0.0763 | - | - | 320 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 398.3 ns | 6.32 ns | 5.60 ns | 397.2 ns | 0.79 | 0.02 | 0.0553 | - | - | 232 B |
## Code
```csharp
[MemoryDiagnoser]
public class BuildAbsoluteBenchmark
{
public IEnumerable<object[]> Data() => TestData.HostPathBasePathQueryFragment();
[Benchmark(Baseline = true)]
[ArgumentsSource(nameof(Data))]
public string UriHelper_BuildRelative(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
=> UriHelper.BuildAbsolute("https", host, pathBase, path, query, fragment);
[Benchmark]
[ArgumentsSource(nameof(Data))]
public string StringBuilder_WithoutCombinedPathGeneration(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
{
var scheme = "https";
var SchemeDelimiter = Uri.SchemeDelimiter;
var encodedHost = host.ToUriComponent();
var encodedPathBase = pathBase.ToUriComponent();
var encodedPath = path.ToUriComponent();
var encodedQuery = query.ToUriComponent();
var encodedFragment = fragment.ToUriComponent();
// PERF: Calculate string length to allocate correct buffer size for StringBuilder.
var length =
scheme.Length +
SchemeDelimiter.Length +
encodedHost.Length +
encodedPathBase.Length +
encodedPath.Length +
encodedQuery.Length +
encodedFragment.Length;
if (!pathBase.HasValue && !path.HasValue)
{
length++;
}
var builder = new StringBuilder(length)
.Append(scheme)
.Append(SchemeDelimiter)
.Append(encodedHost);
if (!pathBase.HasValue && !path.HasValue)
{
builder.Append("/");
}
else
{
builder
.Append(encodedPathBase)
.Append(encodedPath);
}
return builder
.Append(encodedQuery)
.Append(encodedFragment)
.ToString();
}
[Benchmark]
[ArgumentsSource(nameof(Data))]
public string String_Concat_WithArrayArgument(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
{
var scheme = "https";
var SchemeDelimiter = Uri.SchemeDelimiter;
if (!pathBase.HasValue && !path.HasValue)
{
return scheme + SchemeDelimiter + "/" + host.ToUriComponent() + "/" + query.ToUriComponent() + fragment.ToUriComponent();
}
else
{
return scheme + SchemeDelimiter + pathBase.ToUriComponent() + path.ToUriComponent() + host.ToUriComponent() + "/" + query.ToUriComponent() + fragment.ToUriComponent();
}
}
private static readonly SpanAction<char, (string scheme, string host, string pathBase, string path, string query, string fragment)> InitializeStringAction = new(InitializeString);
[Benchmark]
[ArgumentsSource(nameof(Data))]
public string String_Create(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
{
var uriParts = (
scheme: "https",
host: host.ToUriComponent(),
pathBase: pathBase.ToUriComponent(),
path: path.ToUriComponent(),
query: query.ToUriComponent(),
fragment: fragment.ToUriComponent());
// PERF: Calculate string length to allocate correct buffer size for StringBuilder.
var length =
uriParts.scheme.Length +
Uri.SchemeDelimiter.Length +
uriParts.host.Length +
uriParts.pathBase.Length +
uriParts.path.Length +
uriParts.query.Length +
uriParts.fragment.Length;
if (!pathBase.HasValue && !path.HasValue)
{
uriParts.path = "/";
length++;
}
return string.Create(length, uriParts, InitializeStringAction);
}
private static void InitializeString(Span<char> buffer, (string scheme, string host, string pathBase, string path, string query, string fragment) uriParts)
{
var index = 0;
index = Copy(buffer, index, uriParts.scheme);
index = Copy(buffer, index, Uri.SchemeDelimiter);
index = Copy(buffer, index, uriParts.host);
index = Copy(buffer, index, uriParts.pathBase);
index = Copy(buffer, index, uriParts.path);
index = Copy(buffer, index, uriParts.query);
_ = Copy(buffer, index, uriParts.fragment);
[MethodImpl(MethodImplOptions.AggressiveInlining)]
static int Copy(Span<char> buffer, int index, string text)
{
if (!string.IsNullOrEmpty(text))
{
var span = text.AsSpan();
span.CopyTo(buffer.Slice(index, span.Length));
return index + span.Length;
}
return index;
}
}
}
public static class TestData
{
private static readonly string[] hosts = new[] { "cname.domain.tld" };
private static readonly string[] basePaths = new[] { "", "/base-path", };
private static readonly string[] paths = new[] { "", "/path/one/two/three", };
private static readonly string[] queries = new[] { "", "?param1=value1¶m2=value2¶m3=value3", };
private static readonly string[] fragments = new[] { "", "#fragment", };
public static IEnumerable<object[]> HostPathBasePathQueryFragment()
{
foreach (var host in hosts)
{
foreach (var basePath in basePaths)
{
foreach (var path in paths)
{
foreach (var query in queries)
{
foreach (var fragment in fragments)
{
yield return new object[] { new HostString(host), new PathString(basePath), new PathString(path), new QueryString(query), new FragmentString(fragment), };
}
}
}
}
}
}
}
```
| 1.0 | UriHelper.BuildAbsolute: opportunity for performance improvement - ## Summary
`UriHelper.BuildAbsolute` creates an intermediary string for the combined path that is used only for concatenating with the other components to create the final URL.
It also uses a non-pooled `StringBuilder` that is instantiated on every invocation. Although optimized in size, it is a heap allocation with an intermediary buffer.
```csharp
public static string BuildAbsolute(
string scheme,
HostString host,
PathString pathBase = new PathString(),
PathString path = new PathString(),
QueryString query = new QueryString(),
FragmentString fragment = new FragmentString())
{
if (scheme == null)
{
throw new ArgumentNullException(nameof(scheme));
}
var combinedPath = (pathBase.HasValue || path.HasValue) ? (pathBase + path).ToString() : "/";
var encodedHost = host.ToString();
var encodedQuery = query.ToString();
var encodedFragment = fragment.ToString();
// PERF: Calculate string length to allocate correct buffer size for StringBuilder.
var length = scheme.Length + SchemeDelimiter.Length + encodedHost.Length
+ combinedPath.Length + encodedQuery.Length + encodedFragment.Length;
return new StringBuilder(length)
.Append(scheme)
.Append(SchemeDelimiter)
.Append(encodedHost)
.Append(combinedPath)
.Append(encodedQuery)
.Append(encodedFragment)
.ToString();
}
```
## Motivation and goals
This method is frequently use in hot paths like redirect and rewrite rules.
# Detailed design
## StringBuilder_WithoutCombinedPathGeneration
Just by not generating the intermediary `combinePath`, there are memory usage improvements in the when the number of components is highier. There are also time improvements in those cases, but it's wrost in the other cases.
## String_Concat_WithArrayArgument
Given that the final URL is composed of more than 4 parts, the use of `string.Concat` incurs in an array allocation.
But it still always performs better in terms of time and memory usage that using a `StringBuilder`.
## String_Create
`string.Create` excels here in comparison to all the other options. It was created exactly for these use cases.
# Benchmarks
``` ini
BenchmarkDotNet=v0.12.1, OS=Windows 10.0.21277
Intel Core i7-8650U CPU 1.90GHz (Kaby Lake R), 1 CPU, 8 logical and 4 physical cores
.NET Core SDK=5.0.200-preview.20614.14
[Host] : .NET Core 5.0.1 (CoreCLR 5.0.120.57516, CoreFX 5.0.120.57516), X64 RyuJIT
DefaultJob : .NET Core 5.0.1 (CoreCLR 5.0.120.57516, CoreFX 5.0.120.57516), X64 RyuJIT
```
| Method | host | pathBase | path | query | fragment | Mean | Error | StdDev | Median | Ratio | RatioSD | Gen 0 | Gen 1 | Gen 2 | Allocated |
|-------------------------------------------- |----------------- |----------- |-------------------- |------------------------------------------- |---------- |---------:|---------:|---------:|---------:|------:|--------:|-------:|------:|------:|----------:|
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | | | **201.1 ns** | **9.05 ns** | **25.52 ns** | **191.8 ns** | **1.00** | **0.00** | **0.0477** | **-** | **-** | **200 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | | | 189.3 ns | 5.81 ns | 15.91 ns | 188.4 ns | 0.96 | 0.16 | 0.0477 | - | - | 200 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | | | 142.8 ns | 2.91 ns | 4.70 ns | 141.6 ns | 0.74 | 0.10 | 0.0381 | - | - | 160 B |
| String_Create | cname.domain.tld | | | | | 129.9 ns | 3.74 ns | 10.96 ns | 129.0 ns | 0.66 | 0.10 | 0.0172 | - | - | 72 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | | **#fragment** | **170.9 ns** | **4.67 ns** | **13.54 ns** | **168.8 ns** | **1.00** | **0.00** | **0.0572** | **-** | **-** | **240 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | | #fragment | 181.8 ns | 6.66 ns | 19.22 ns | 179.5 ns | 1.07 | 0.15 | 0.0572 | - | - | 240 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | | #fragment | 151.2 ns | 3.09 ns | 4.24 ns | 150.2 ns | 0.86 | 0.08 | 0.0420 | - | - | 176 B |
| String_Create | cname.domain.tld | | | | #fragment | 111.3 ns | 2.26 ns | 2.32 ns | 111.2 ns | 0.65 | 0.05 | 0.0229 | - | - | 96 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | **?param1=value1&param2=value2&param3=value3** | | **236.3 ns** | **3.59 ns** | **3.35 ns** | **235.6 ns** | **1.00** | **0.00** | **0.0877** | **-** | **-** | **368 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | | 247.0 ns | 5.05 ns | 4.72 ns | 247.5 ns | 1.05 | 0.03 | 0.0877 | - | - | 368 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | | 227.2 ns | 4.64 ns | 9.47 ns | 225.7 ns | 0.99 | 0.04 | 0.0572 | - | - | 240 B |
| String_Create | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | | 189.4 ns | 3.90 ns | 8.22 ns | 185.9 ns | 0.82 | 0.04 | 0.0381 | - | - | 160 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **246.6 ns** | **5.04 ns** | **8.15 ns** | **244.2 ns** | **1.00** | **0.00** | **0.0954** | **-** | **-** | **400 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | #fragment | 252.3 ns | 5.12 ns | 10.35 ns | 250.2 ns | 1.03 | 0.06 | 0.0954 | - | - | 400 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | #fragment | 224.9 ns | 2.22 ns | 1.74 ns | 225.3 ns | 0.92 | 0.03 | 0.0610 | - | - | 256 B |
| String_Create | cname.domain.tld | | | ?param1=value1&param2=value2&param3=value3 | #fragment | 192.0 ns | 3.62 ns | 5.08 ns | 192.2 ns | 0.78 | 0.04 | 0.0420 | - | - | 176 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | | | **309.4 ns** | **3.35 ns** | **2.97 ns** | **309.7 ns** | **1.00** | **0.00** | **0.0648** | **-** | **-** | **272 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | | | 321.7 ns | 4.44 ns | 3.93 ns | 321.1 ns | 1.04 | 0.01 | 0.0648 | - | - | 272 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | | | 300.6 ns | 5.86 ns | 12.74 ns | 296.0 ns | 1.01 | 0.04 | 0.0477 | - | - | 200 B |
| String_Create | cname.domain.tld | | /path/one/two/three | | | 247.0 ns | 5.06 ns | 7.25 ns | 244.7 ns | 0.81 | 0.03 | 0.0267 | - | - | 112 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | | **#fragment** | **319.5 ns** | **4.68 ns** | **4.15 ns** | **318.9 ns** | **1.00** | **0.00** | **0.0725** | **-** | **-** | **304 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | | #fragment | 307.3 ns | 4.89 ns | 4.58 ns | 306.4 ns | 0.96 | 0.02 | 0.0725 | - | - | 304 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | | #fragment | 302.8 ns | 6.11 ns | 8.77 ns | 300.1 ns | 0.95 | 0.04 | 0.0515 | - | - | 216 B |
| String_Create | cname.domain.tld | | /path/one/two/three | | #fragment | 253.0 ns | 5.12 ns | 8.13 ns | 251.5 ns | 0.79 | 0.03 | 0.0305 | - | - | 128 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | | **421.7 ns** | **8.49 ns** | **15.09 ns** | **418.3 ns** | **1.00** | **0.00** | **0.1049** | **-** | **-** | **440 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 395.9 ns | 4.71 ns | 4.18 ns | 395.1 ns | 0.94 | 0.02 | 0.1049 | - | - | 440 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 372.2 ns | 6.86 ns | 5.73 ns | 370.3 ns | 0.88 | 0.03 | 0.0687 | - | - | 288 B |
| String_Create | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 325.6 ns | 6.51 ns | 6.69 ns | 323.5 ns | 0.78 | 0.02 | 0.0458 | - | - | 192 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **396.1 ns** | **7.65 ns** | **7.16 ns** | **395.3 ns** | **1.00** | **0.00** | **0.1144** | **-** | **-** | **480 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 394.3 ns | 3.10 ns | 2.42 ns | 393.8 ns | 0.99 | 0.02 | 0.1144 | - | - | 480 B |
| String_Concat_WithArrayArgument | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 377.6 ns | 4.22 ns | 3.74 ns | 377.8 ns | 0.95 | 0.02 | 0.0725 | - | - | 304 B |
| String_Create | cname.domain.tld | | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 329.2 ns | 6.29 ns | 6.46 ns | 327.9 ns | 0.83 | 0.02 | 0.0515 | - | - | 216 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | | | **241.0 ns** | **2.40 ns** | **2.25 ns** | **241.4 ns** | **1.00** | **0.00** | **0.0572** | **-** | **-** | **240 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | | | 245.4 ns | 4.99 ns | 4.66 ns | 245.3 ns | 1.02 | 0.02 | 0.0572 | - | - | 240 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | | | 215.0 ns | 2.70 ns | 2.11 ns | 214.9 ns | 0.89 | 0.01 | 0.0439 | - | - | 184 B |
| String_Create | cname.domain.tld | /base-path | | | | 164.7 ns | 1.27 ns | 1.19 ns | 164.8 ns | 0.68 | 0.01 | 0.0229 | - | - | 96 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | | **#fragment** | **243.2 ns** | **4.56 ns** | **11.85 ns** | **240.1 ns** | **1.00** | **0.00** | **0.0648** | **-** | **-** | **272 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | | #fragment | 236.3 ns | 4.75 ns | 6.66 ns | 234.3 ns | 0.96 | 0.05 | 0.0648 | - | - | 272 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | | #fragment | 233.3 ns | 3.86 ns | 3.22 ns | 233.0 ns | 0.95 | 0.05 | 0.0477 | - | - | 200 B |
| String_Create | cname.domain.tld | /base-path | | | #fragment | 171.6 ns | 2.93 ns | 2.88 ns | 170.8 ns | 0.70 | 0.04 | 0.0267 | - | - | 112 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | **?param1=value1&param2=value2&param3=value3** | | **324.3 ns** | **6.38 ns** | **7.59 ns** | **322.2 ns** | **1.00** | **0.00** | **0.0954** | **-** | **-** | **400 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | | 324.8 ns | 6.06 ns | 5.37 ns | 323.4 ns | 1.00 | 0.03 | 0.0954 | - | - | 400 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | | 298.9 ns | 5.48 ns | 4.58 ns | 298.2 ns | 0.92 | 0.03 | 0.0629 | - | - | 264 B |
| String_Create | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | | 252.5 ns | 5.12 ns | 8.26 ns | 250.9 ns | 0.78 | 0.03 | 0.0420 | - | - | 176 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **319.1 ns** | **4.57 ns** | **4.06 ns** | **318.7 ns** | **1.00** | **0.00** | **0.1049** | **-** | **-** | **440 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | #fragment | 320.0 ns | 4.47 ns | 4.18 ns | 319.2 ns | 1.00 | 0.02 | 0.1049 | - | - | 440 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | #fragment | 320.8 ns | 6.39 ns | 11.19 ns | 315.0 ns | 1.02 | 0.05 | 0.0687 | - | - | 288 B |
| String_Create | cname.domain.tld | /base-path | | ?param1=value1&param2=value2&param3=value3 | #fragment | 249.8 ns | 5.07 ns | 5.21 ns | 250.2 ns | 0.78 | 0.02 | 0.0458 | - | - | 192 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | | | **421.9 ns** | **6.69 ns** | **6.25 ns** | **419.6 ns** | **1.00** | **0.00** | **0.0935** | **-** | **-** | **392 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | | | 389.2 ns | 6.62 ns | 7.08 ns | 387.0 ns | 0.92 | 0.02 | 0.0744 | - | - | 312 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | | | 362.6 ns | 6.17 ns | 6.85 ns | 361.0 ns | 0.86 | 0.02 | 0.0534 | - | - | 224 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | | | 318.4 ns | 6.41 ns | 8.56 ns | 315.5 ns | 0.76 | 0.03 | 0.0305 | - | - | 128 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | | **#fragment** | **412.6 ns** | **4.19 ns** | **3.72 ns** | **412.5 ns** | **1.00** | **0.00** | **0.1030** | **-** | **-** | **432 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | | #fragment | 390.0 ns | 7.68 ns | 18.84 ns | 381.2 ns | 0.94 | 0.04 | 0.0839 | - | - | 352 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | | #fragment | 360.9 ns | 5.15 ns | 4.30 ns | 359.0 ns | 0.87 | 0.01 | 0.0572 | - | - | 240 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | | #fragment | 322.3 ns | 5.97 ns | 5.30 ns | 320.7 ns | 0.78 | 0.01 | 0.0362 | - | - | 152 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | | **488.9 ns** | **6.15 ns** | **5.75 ns** | **490.3 ns** | **1.00** | **0.00** | **0.1335** | **-** | **-** | **560 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 476.3 ns | 9.62 ns | 15.81 ns | 470.6 ns | 0.98 | 0.04 | 0.1144 | - | - | 480 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 439.7 ns | 7.73 ns | 7.23 ns | 438.8 ns | 0.90 | 0.02 | 0.0725 | - | - | 304 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | | 396.9 ns | 7.76 ns | 7.62 ns | 393.0 ns | 0.81 | 0.02 | 0.0515 | - | - | 216 B |
| | | | | | | | | | | | | | | | |
| **UriHelper_BuildRelative** | **cname.domain.tld** | **/base-path** | **/path/one/two/three** | **?param1=value1&param2=value2&param3=value3** | **#fragment** | **496.5 ns** | **9.76 ns** | **13.68 ns** | **494.4 ns** | **1.00** | **0.00** | **0.1411** | **-** | **-** | **592 B** |
| StringBuilder_WithoutCombinedPathGeneration | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 525.1 ns | 16.74 ns | 49.10 ns | 517.1 ns | 1.01 | 0.08 | 0.1221 | - | - | 512 B |
| String_Concat_WithArrayArgument | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 449.7 ns | 8.55 ns | 9.50 ns | 447.6 ns | 0.90 | 0.03 | 0.0763 | - | - | 320 B |
| String_Create | cname.domain.tld | /base-path | /path/one/two/three | ?param1=value1&param2=value2&param3=value3 | #fragment | 398.3 ns | 6.32 ns | 5.60 ns | 397.2 ns | 0.79 | 0.02 | 0.0553 | - | - | 232 B |
## Code
```csharp
[MemoryDiagnoser]
public class BuildAbsoluteBenchmark
{
public IEnumerable<object[]> Data() => TestData.HostPathBasePathQueryFragment();
[Benchmark(Baseline = true)]
[ArgumentsSource(nameof(Data))]
public string UriHelper_BuildRelative(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
=> UriHelper.BuildAbsolute("https", host, pathBase, path, query, fragment);
[Benchmark]
[ArgumentsSource(nameof(Data))]
public string StringBuilder_WithoutCombinedPathGeneration(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
{
var scheme = "https";
var SchemeDelimiter = Uri.SchemeDelimiter;
var encodedHost = host.ToUriComponent();
var encodedPathBase = pathBase.ToUriComponent();
var encodedPath = path.ToUriComponent();
var encodedQuery = query.ToUriComponent();
var encodedFragment = fragment.ToUriComponent();
// PERF: Calculate string length to allocate correct buffer size for StringBuilder.
var length =
scheme.Length +
SchemeDelimiter.Length +
encodedHost.Length +
encodedPathBase.Length +
encodedPath.Length +
encodedQuery.Length +
encodedFragment.Length;
if (!pathBase.HasValue && !path.HasValue)
{
length++;
}
var builder = new StringBuilder(length)
.Append(scheme)
.Append(SchemeDelimiter)
.Append(encodedHost);
if (!pathBase.HasValue && !path.HasValue)
{
builder.Append("/");
}
else
{
builder
.Append(encodedPathBase)
.Append(encodedPath);
}
return builder
.Append(encodedQuery)
.Append(encodedFragment)
.ToString();
}
[Benchmark]
[ArgumentsSource(nameof(Data))]
public string String_Concat_WithArrayArgument(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
{
var scheme = "https";
var SchemeDelimiter = Uri.SchemeDelimiter;
if (!pathBase.HasValue && !path.HasValue)
{
return scheme + SchemeDelimiter + "/" + host.ToUriComponent() + "/" + query.ToUriComponent() + fragment.ToUriComponent();
}
else
{
return scheme + SchemeDelimiter + pathBase.ToUriComponent() + path.ToUriComponent() + host.ToUriComponent() + "/" + query.ToUriComponent() + fragment.ToUriComponent();
}
}
private static readonly SpanAction<char, (string scheme, string host, string pathBase, string path, string query, string fragment)> InitializeStringAction = new(InitializeString);
[Benchmark]
[ArgumentsSource(nameof(Data))]
public string String_Create(HostString host, PathString pathBase, PathString path, QueryString query, FragmentString fragment)
{
var uriParts = (
scheme: "https",
host: host.ToUriComponent(),
pathBase: pathBase.ToUriComponent(),
path: path.ToUriComponent(),
query: query.ToUriComponent(),
fragment: fragment.ToUriComponent());
// PERF: Calculate string length to allocate correct buffer size for StringBuilder.
var length =
uriParts.scheme.Length +
Uri.SchemeDelimiter.Length +
uriParts.host.Length +
uriParts.pathBase.Length +
uriParts.path.Length +
uriParts.query.Length +
uriParts.fragment.Length;
if (!pathBase.HasValue && !path.HasValue)
{
uriParts.path = "/";
length++;
}
return string.Create(length, uriParts, InitializeStringAction);
}
private static void InitializeString(Span<char> buffer, (string scheme, string host, string pathBase, string path, string query, string fragment) uriParts)
{
var index = 0;
index = Copy(buffer, index, uriParts.scheme);
index = Copy(buffer, index, Uri.SchemeDelimiter);
index = Copy(buffer, index, uriParts.host);
index = Copy(buffer, index, uriParts.pathBase);
index = Copy(buffer, index, uriParts.path);
index = Copy(buffer, index, uriParts.query);
_ = Copy(buffer, index, uriParts.fragment);
[MethodImpl(MethodImplOptions.AggressiveInlining)]
static int Copy(Span<char> buffer, int index, string text)
{
if (!string.IsNullOrEmpty(text))
{
var span = text.AsSpan();
span.CopyTo(buffer.Slice(index, span.Length));
return index + span.Length;
}
return index;
}
}
}
public static class TestData
{
private static readonly string[] hosts = new[] { "cname.domain.tld" };
private static readonly string[] basePaths = new[] { "", "/base-path", };
private static readonly string[] paths = new[] { "", "/path/one/two/three", };
private static readonly string[] queries = new[] { "", "?param1=value1¶m2=value2¶m3=value3", };
private static readonly string[] fragments = new[] { "", "#fragment", };
public static IEnumerable<object[]> HostPathBasePathQueryFragment()
{
foreach (var host in hosts)
{
foreach (var basePath in basePaths)
{
foreach (var path in paths)
{
foreach (var query in queries)
{
foreach (var fragment in fragments)
{
yield return new object[] { new HostString(host), new PathString(basePath), new PathString(path), new QueryString(query), new FragmentString(fragment), };
}
}
}
}
}
}
}
```
| non_priority | urihelper buildabsolute opportunity for performance improvement summary urihelper buildabsolute creates an intermediary string for the combined path that is used only for concatenating with the other components to create the final url it also uses a non pooled stringbuilder that is instantiated on every invocation although optimized in size it is a heap allocation with an intermediary buffer csharp public static string buildabsolute string scheme hoststring host pathstring pathbase new pathstring pathstring path new pathstring querystring query new querystring fragmentstring fragment new fragmentstring if scheme null throw new argumentnullexception nameof scheme var combinedpath pathbase hasvalue path hasvalue pathbase path tostring var encodedhost host tostring var encodedquery query tostring var encodedfragment fragment tostring perf calculate string length to allocate correct buffer size for stringbuilder var length scheme length schemedelimiter length encodedhost length combinedpath length encodedquery length encodedfragment length return new stringbuilder length append scheme append schemedelimiter append encodedhost append combinedpath append encodedquery append encodedfragment tostring motivation and goals this method is frequently use in hot paths like redirect and rewrite rules detailed design stringbuilder withoutcombinedpathgeneration just by not generating the intermediary combinepath there are memory usage improvements in the when the number of components is highier there are also time improvements in those cases but it s wrost in the other cases string concat witharrayargument given that the final url is composed of more than parts the use of string concat incurs in an array allocation but it still always performs better in terms of time and memory usage that using a stringbuilder string create string create excels here in comparison to all the other options it was created exactly for these use cases benchmarks ini benchmarkdotnet os windows intel core cpu kaby lake r cpu logical and physical cores net core sdk preview net core coreclr corefx ryujit defaultjob net core coreclr corefx ryujit method host pathbase path query fragment mean error stddev median ratio ratiosd gen gen gen allocated urihelper buildrelative cname domain tld ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld ns ns ns ns b string concat witharrayargument cname domain tld ns ns ns ns b string create cname domain tld ns ns ns ns b urihelper buildrelative cname domain tld fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld fragment ns ns ns ns b string concat witharrayargument cname domain tld fragment ns ns ns ns b string create cname domain tld fragment ns ns ns ns b urihelper buildrelative cname domain tld amp amp ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld amp amp ns ns ns ns b string concat witharrayargument cname domain tld amp amp ns ns ns ns b string create cname domain tld amp amp ns ns ns ns b urihelper buildrelative cname domain tld amp amp fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld amp amp fragment ns ns ns ns b string concat witharrayargument cname domain tld amp amp fragment ns ns ns ns b string create cname domain tld amp amp fragment ns ns ns ns b urihelper buildrelative cname domain tld path one two three ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld path one two three ns ns ns ns b string concat witharrayargument cname domain tld path one two three ns ns ns ns b string create cname domain tld path one two three ns ns ns ns b urihelper buildrelative cname domain tld path one two three fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld path one two three fragment ns ns ns ns b string concat witharrayargument cname domain tld path one two three fragment ns ns ns ns b string create cname domain tld path one two three fragment ns ns ns ns b urihelper buildrelative cname domain tld path one two three amp amp ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld path one two three amp amp ns ns ns ns b string concat witharrayargument cname domain tld path one two three amp amp ns ns ns ns b string create cname domain tld path one two three amp amp ns ns ns ns b urihelper buildrelative cname domain tld path one two three amp amp fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld path one two three amp amp fragment ns ns ns ns b string concat witharrayargument cname domain tld path one two three amp amp fragment ns ns ns ns b string create cname domain tld path one two three amp amp fragment ns ns ns ns b urihelper buildrelative cname domain tld base path ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path ns ns ns ns b string concat witharrayargument cname domain tld base path ns ns ns ns b string create cname domain tld base path ns ns ns ns b urihelper buildrelative cname domain tld base path fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path fragment ns ns ns ns b string concat witharrayargument cname domain tld base path fragment ns ns ns ns b string create cname domain tld base path fragment ns ns ns ns b urihelper buildrelative cname domain tld base path amp amp ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path amp amp ns ns ns ns b string concat witharrayargument cname domain tld base path amp amp ns ns ns ns b string create cname domain tld base path amp amp ns ns ns ns b urihelper buildrelative cname domain tld base path amp amp fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path amp amp fragment ns ns ns ns b string concat witharrayargument cname domain tld base path amp amp fragment ns ns ns ns b string create cname domain tld base path amp amp fragment ns ns ns ns b urihelper buildrelative cname domain tld base path path one two three ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path path one two three ns ns ns ns b string concat witharrayargument cname domain tld base path path one two three ns ns ns ns b string create cname domain tld base path path one two three ns ns ns ns b urihelper buildrelative cname domain tld base path path one two three fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path path one two three fragment ns ns ns ns b string concat witharrayargument cname domain tld base path path one two three fragment ns ns ns ns b string create cname domain tld base path path one two three fragment ns ns ns ns b urihelper buildrelative cname domain tld base path path one two three amp amp ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path path one two three amp amp ns ns ns ns b string concat witharrayargument cname domain tld base path path one two three amp amp ns ns ns ns b string create cname domain tld base path path one two three amp amp ns ns ns ns b urihelper buildrelative cname domain tld base path path one two three amp amp fragment ns ns ns ns b stringbuilder withoutcombinedpathgeneration cname domain tld base path path one two three amp amp fragment ns ns ns ns b string concat witharrayargument cname domain tld base path path one two three amp amp fragment ns ns ns ns b string create cname domain tld base path path one two three amp amp fragment ns ns ns ns b code csharp public class buildabsolutebenchmark public ienumerable data testdata hostpathbasepathqueryfragment public string urihelper buildrelative hoststring host pathstring pathbase pathstring path querystring query fragmentstring fragment urihelper buildabsolute https host pathbase path query fragment public string stringbuilder withoutcombinedpathgeneration hoststring host pathstring pathbase pathstring path querystring query fragmentstring fragment var scheme https var schemedelimiter uri schemedelimiter var encodedhost host touricomponent var encodedpathbase pathbase touricomponent var encodedpath path touricomponent var encodedquery query touricomponent var encodedfragment fragment touricomponent perf calculate string length to allocate correct buffer size for stringbuilder var length scheme length schemedelimiter length encodedhost length encodedpathbase length encodedpath length encodedquery length encodedfragment length if pathbase hasvalue path hasvalue length var builder new stringbuilder length append scheme append schemedelimiter append encodedhost if pathbase hasvalue path hasvalue builder append else builder append encodedpathbase append encodedpath return builder append encodedquery append encodedfragment tostring public string string concat witharrayargument hoststring host pathstring pathbase pathstring path querystring query fragmentstring fragment var scheme https var schemedelimiter uri schemedelimiter if pathbase hasvalue path hasvalue return scheme schemedelimiter host touricomponent query touricomponent fragment touricomponent else return scheme schemedelimiter pathbase touricomponent path touricomponent host touricomponent query touricomponent fragment touricomponent private static readonly spanaction initializestringaction new initializestring public string string create hoststring host pathstring pathbase pathstring path querystring query fragmentstring fragment var uriparts scheme https host host touricomponent pathbase pathbase touricomponent path path touricomponent query query touricomponent fragment fragment touricomponent perf calculate string length to allocate correct buffer size for stringbuilder var length uriparts scheme length uri schemedelimiter length uriparts host length uriparts pathbase length uriparts path length uriparts query length uriparts fragment length if pathbase hasvalue path hasvalue uriparts path length return string create length uriparts initializestringaction private static void initializestring span buffer string scheme string host string pathbase string path string query string fragment uriparts var index index copy buffer index uriparts scheme index copy buffer index uri schemedelimiter index copy buffer index uriparts host index copy buffer index uriparts pathbase index copy buffer index uriparts path index copy buffer index uriparts query copy buffer index uriparts fragment static int copy span buffer int index string text if string isnullorempty text var span text asspan span copyto buffer slice index span length return index span length return index public static class testdata private static readonly string hosts new cname domain tld private static readonly string basepaths new base path private static readonly string paths new path one two three private static readonly string queries new private static readonly string fragments new fragment public static ienumerable hostpathbasepathqueryfragment foreach var host in hosts foreach var basepath in basepaths foreach var path in paths foreach var query in queries foreach var fragment in fragments yield return new object new hoststring host new pathstring basepath new pathstring path new querystring query new fragmentstring fragment | 0 |
223,152 | 17,105,238,143 | IssuesEvent | 2021-07-09 16:39:32 | BB-33/multiplication-website | https://api.github.com/repos/BB-33/multiplication-website | opened | Make a project board | documentation | Define a scope and set of goals that I want the project to have:
What am I going to teach?
How am I going to do it?
What are the different stages to teaching this?
Lay out some broad strokes goals for this. | 1.0 | Make a project board - Define a scope and set of goals that I want the project to have:
What am I going to teach?
How am I going to do it?
What are the different stages to teaching this?
Lay out some broad strokes goals for this. | non_priority | make a project board define a scope and set of goals that i want the project to have what am i going to teach how am i going to do it what are the different stages to teaching this lay out some broad strokes goals for this | 0 |
242,501 | 20,251,331,870 | IssuesEvent | 2022-02-14 18:11:15 | metaplex-foundation/metaplex | https://api.github.com/repos/metaplex-foundation/metaplex | closed | [Bug]: Cannot withdraw funds of candy machine on mainnet-beta | needs tests bug needs more information | ### Which package is this bug report for?
candy machine cli
### Issue description
Hello, I have been retrying for one hour and still can't get the candymachine withdrawed... Always getting this error
### Command
```shell
ts-node ./~/metaplex/js/packages/cli/src/candy-machine-v2-cli.ts withdraw -e mainnet-beta -k ./~/.config/AFC4FpBPaBFzx1DyQbh6cJQEXe7Ga6CQbLMhwgjj4KYR.json
```
### Relevant log output
```shell
wallet public key: AFC4FpBPaBFzx1DyQbh6cJQEXe7Ga6CQbLMhwgjj4KYR
Total Number of Candy Machine Config Accounts to drain 1
1.67640648 SOL locked up in configs
WARNING: This command will drain ALL of the Candy Machine config accounts that are owned by your current KeyPair, this will break your Candy Machine if its still in use
Rejecting for timeout...
Timeout Error caught { timeout: true }
Withdraw has failed for config account 2va6XAGAZGur2TuWU2vEpXSKvypi6SLhLRYUNL1mEbkd Error: Timed out awaiting confirmation on transaction
Congratulations, 0 config accounts have been successfully drained.
Now you kinda rich, please consider supporting Open Source developers.
```
### Operating system
Windows 10
### Priority this issue should have
Medium (should be fixed soon)
### Check the Docs First
- [X] I have checked the docs and it didn't solve my issue | 1.0 | [Bug]: Cannot withdraw funds of candy machine on mainnet-beta - ### Which package is this bug report for?
candy machine cli
### Issue description
Hello, I have been retrying for one hour and still can't get the candymachine withdrawed... Always getting this error
### Command
```shell
ts-node ./~/metaplex/js/packages/cli/src/candy-machine-v2-cli.ts withdraw -e mainnet-beta -k ./~/.config/AFC4FpBPaBFzx1DyQbh6cJQEXe7Ga6CQbLMhwgjj4KYR.json
```
### Relevant log output
```shell
wallet public key: AFC4FpBPaBFzx1DyQbh6cJQEXe7Ga6CQbLMhwgjj4KYR
Total Number of Candy Machine Config Accounts to drain 1
1.67640648 SOL locked up in configs
WARNING: This command will drain ALL of the Candy Machine config accounts that are owned by your current KeyPair, this will break your Candy Machine if its still in use
Rejecting for timeout...
Timeout Error caught { timeout: true }
Withdraw has failed for config account 2va6XAGAZGur2TuWU2vEpXSKvypi6SLhLRYUNL1mEbkd Error: Timed out awaiting confirmation on transaction
Congratulations, 0 config accounts have been successfully drained.
Now you kinda rich, please consider supporting Open Source developers.
```
### Operating system
Windows 10
### Priority this issue should have
Medium (should be fixed soon)
### Check the Docs First
- [X] I have checked the docs and it didn't solve my issue | non_priority | cannot withdraw funds of candy machine on mainnet beta which package is this bug report for candy machine cli issue description hello i have been retrying for one hour and still can t get the candymachine withdrawed always getting this error command shell ts node metaplex js packages cli src candy machine cli ts withdraw e mainnet beta k config json relevant log output shell wallet public key total number of candy machine config accounts to drain sol locked up in configs warning this command will drain all of the candy machine config accounts that are owned by your current keypair this will break your candy machine if its still in use rejecting for timeout timeout error caught timeout true withdraw has failed for config account error timed out awaiting confirmation on transaction congratulations config accounts have been successfully drained now you kinda rich please consider supporting open source developers operating system windows priority this issue should have medium should be fixed soon check the docs first i have checked the docs and it didn t solve my issue | 0 |
27,951 | 22,635,740,979 | IssuesEvent | 2022-06-30 18:47:21 | google/site-kit-wp | https://api.github.com/repos/google/site-kit-wp | closed | Fix broken stories for Gathering Data | P1 Type: Infrastructure | ## Bug Description
The `DashboardOverallPageMetricsWidget` stories for gathering data states are no longer showing properly. This is due to an invalid report being received in Storybook.
## Steps to reproduce
https://google.github.io/site-kit-wp/storybook/main/?path=/story/modules-analytics-widgets-dashboardoverallpagemetricswidget--gathering-data-zero-data-states
## Screenshots
<img width="916" alt="image" src="https://user-images.githubusercontent.com/1621608/174874299-2c3f940f-2398-4a11-aa15-82271d28ebff.png">
---------------
_Do not alter or remove anything below. The following sections will be managed by moderators only._
## Acceptance criteria
* All "gathering data" stories should show a gathering data state
## Implementation Brief
* Update use of `receiveGetReport` in `DashboardOverallPageMetricsWidget` to receive an empty array instead of an empty object
* No other improper uses found when reviewing calls to `receiveGetReport`
* Merge #5405
### Test Coverage
* No changes
## QA Brief
* This change only affects Storybook, no changes to production code have been made
* Once merged, the fix should be verifiable in Storybook here: https://google.github.io/site-kit-wp/storybook/develop/?path=/story/modules-analytics-widgets-dashboardoverallpagemetricswidget--gathering-data-zero-data-states
## Changelog entry
* N/A
| 1.0 | Fix broken stories for Gathering Data - ## Bug Description
The `DashboardOverallPageMetricsWidget` stories for gathering data states are no longer showing properly. This is due to an invalid report being received in Storybook.
## Steps to reproduce
https://google.github.io/site-kit-wp/storybook/main/?path=/story/modules-analytics-widgets-dashboardoverallpagemetricswidget--gathering-data-zero-data-states
## Screenshots
<img width="916" alt="image" src="https://user-images.githubusercontent.com/1621608/174874299-2c3f940f-2398-4a11-aa15-82271d28ebff.png">
---------------
_Do not alter or remove anything below. The following sections will be managed by moderators only._
## Acceptance criteria
* All "gathering data" stories should show a gathering data state
## Implementation Brief
* Update use of `receiveGetReport` in `DashboardOverallPageMetricsWidget` to receive an empty array instead of an empty object
* No other improper uses found when reviewing calls to `receiveGetReport`
* Merge #5405
### Test Coverage
* No changes
## QA Brief
* This change only affects Storybook, no changes to production code have been made
* Once merged, the fix should be verifiable in Storybook here: https://google.github.io/site-kit-wp/storybook/develop/?path=/story/modules-analytics-widgets-dashboardoverallpagemetricswidget--gathering-data-zero-data-states
## Changelog entry
* N/A
| non_priority | fix broken stories for gathering data bug description the dashboardoverallpagemetricswidget stories for gathering data states are no longer showing properly this is due to an invalid report being received in storybook steps to reproduce screenshots img width alt image src do not alter or remove anything below the following sections will be managed by moderators only acceptance criteria all gathering data stories should show a gathering data state implementation brief update use of receivegetreport in dashboardoverallpagemetricswidget to receive an empty array instead of an empty object no other improper uses found when reviewing calls to receivegetreport merge test coverage no changes qa brief this change only affects storybook no changes to production code have been made once merged the fix should be verifiable in storybook here changelog entry n a | 0 |
2,680 | 3,801,423,072 | IssuesEvent | 2016-03-23 22:51:22 | MozillaFoundation/plan | https://api.github.com/repos/MozillaFoundation/plan | closed | Science site refresh: homepage comps + programs wireframes | Convening Learning Membership MLN Infrastructure p1 production Size: large | We have enough agreement about IA, homepage wireframes, and copy to complete the following:
- [ ] [Homepage comps](https://github.com/mozillascience/site/issues/101)
- [x] [Wireframes for Programs and Events](https://github.com/mozillascience/site/issues/100)
- [x] [Determine urls](https://github.com/mozillascience/site/issues/99) | 1.0 | Science site refresh: homepage comps + programs wireframes - We have enough agreement about IA, homepage wireframes, and copy to complete the following:
- [ ] [Homepage comps](https://github.com/mozillascience/site/issues/101)
- [x] [Wireframes for Programs and Events](https://github.com/mozillascience/site/issues/100)
- [x] [Determine urls](https://github.com/mozillascience/site/issues/99) | non_priority | science site refresh homepage comps programs wireframes we have enough agreement about ia homepage wireframes and copy to complete the following | 0 |
6,365 | 3,014,850,182 | IssuesEvent | 2015-07-29 16:41:12 | Cardshifter/Cardshifter | https://api.github.com/repos/Cardshifter/Cardshifter | closed | Add @example JavaDoc tag | documentation | I will be using an `@example` keyword throughout API and perhaps other documentation. If possible please have it added to the pom or Gradle so that it is recognized as a valid JavaDoc tag.
Example usage:
/**
* Constructor.
* @param username the incoming user name passed from client to server, not null
* @example Message: <code>{ "command":"login","username":"JohnDoe" }</code>
* @example Response: <code>{"command":"loginresponse","status":200,"userId":6,"message":"OK"}</code>
*/
public LoginMessage(String username) {
super("login");
this.username = username;
} | 1.0 | Add @example JavaDoc tag - I will be using an `@example` keyword throughout API and perhaps other documentation. If possible please have it added to the pom or Gradle so that it is recognized as a valid JavaDoc tag.
Example usage:
/**
* Constructor.
* @param username the incoming user name passed from client to server, not null
* @example Message: <code>{ "command":"login","username":"JohnDoe" }</code>
* @example Response: <code>{"command":"loginresponse","status":200,"userId":6,"message":"OK"}</code>
*/
public LoginMessage(String username) {
super("login");
this.username = username;
} | non_priority | add example javadoc tag i will be using an example keyword throughout api and perhaps other documentation if possible please have it added to the pom or gradle so that it is recognized as a valid javadoc tag example usage constructor param username the incoming user name passed from client to server not null example message command login username johndoe example response command loginresponse status userid message ok public loginmessage string username super login this username username | 0 |
409,678 | 27,748,312,979 | IssuesEvent | 2023-03-15 18:38:55 | rak3rman/rakerman-status | https://api.github.com/repos/rak3rman/rakerman-status | opened | Create README.md | documentation enhancement | Create a new README.md document describing how to use and deploy this project. Should contain all documentation. | 1.0 | Create README.md - Create a new README.md document describing how to use and deploy this project. Should contain all documentation. | non_priority | create readme md create a new readme md document describing how to use and deploy this project should contain all documentation | 0 |
120,326 | 17,644,088,539 | IssuesEvent | 2021-08-20 01:39:43 | DavidSpek/pipelines | https://api.github.com/repos/DavidSpek/pipelines | opened | CVE-2021-29616 (High) detected in tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl | security vulnerability | ## CVE-2021-29616 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/ec/98/f968caf5f65759e78873b900cbf0ae20b1699fb11268ecc0f892186419a7/tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/ec/98/f968caf5f65759e78873b900cbf0ae20b1699fb11268ecc0f892186419a7/tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: pipelines/contrib/components/openvino/ovms-deployer/containers/requirements.txt</p>
<p>Path to vulnerable library: pipelines/contrib/components/openvino/ovms-deployer/containers/requirements.txt,pipelines/samples/core/ai_platform/training</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. The implementation of TrySimplify(https://github.com/tensorflow/tensorflow/blob/c22d88d6ff33031aa113e48aa3fc9aa74ed79595/tensorflow/core/grappler/optimizers/arithmetic_optimizer.cc#L390-L401) has undefined behavior due to dereferencing a null pointer in corner cases that result in optimizing a node with no inputs. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29616>CVE-2021-29616</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-4hvv-7x94-7vq8">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-4hvv-7x94-7vq8</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-29616 (High) detected in tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl - ## CVE-2021-29616 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/ec/98/f968caf5f65759e78873b900cbf0ae20b1699fb11268ecc0f892186419a7/tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl">https://files.pythonhosted.org/packages/ec/98/f968caf5f65759e78873b900cbf0ae20b1699fb11268ecc0f892186419a7/tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl</a></p>
<p>Path to dependency file: pipelines/contrib/components/openvino/ovms-deployer/containers/requirements.txt</p>
<p>Path to vulnerable library: pipelines/contrib/components/openvino/ovms-deployer/containers/requirements.txt,pipelines/samples/core/ai_platform/training</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.15.0-cp27-cp27mu-manylinux2010_x86_64.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. The implementation of TrySimplify(https://github.com/tensorflow/tensorflow/blob/c22d88d6ff33031aa113e48aa3fc9aa74ed79595/tensorflow/core/grappler/optimizers/arithmetic_optimizer.cc#L390-L401) has undefined behavior due to dereferencing a null pointer in corner cases that result in optimizing a node with no inputs. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29616>CVE-2021-29616</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-4hvv-7x94-7vq8">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-4hvv-7x94-7vq8</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file pipelines contrib components openvino ovms deployer containers requirements txt path to vulnerable library pipelines contrib components openvino ovms deployer containers requirements txt pipelines samples core ai platform training dependency hierarchy x tensorflow whl vulnerable library found in base branch master vulnerability details tensorflow is an end to end open source platform for machine learning the implementation of trysimplify has undefined behavior due to dereferencing a null pointer in corner cases that result in optimizing a node with no inputs the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with whitesource | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.