Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
428,555 | 29,997,969,337 | IssuesEvent | 2023-06-26 07:18:44 | pharmaverse/admiralvaccine | https://api.github.com/repos/pharmaverse/admiralvaccine | opened | Update full form for all acronyms | documentation final review | ### Please select a category the issue is focused on?
_No response_
### Let us know where something needs a refresh or put your idea here!
Eg: Update full for CBER | 1.0 | Update full form for all acronyms - ### Please select a category the issue is focused on?
_No response_
### Let us know where something needs a refresh or put your idea here!
Eg: Update full for CBER | non_priority | update full form for all acronyms please select a category the issue is focused on no response let us know where something needs a refresh or put your idea here eg update full for cber | 0 |
77,813 | 21,965,607,186 | IssuesEvent | 2022-05-24 19:57:49 | GaloisInc/cryptol | https://api.github.com/repos/GaloisInc/cryptol | closed | Windows installer includes too many files? | windows build system | The Windows `.msi` installer we produce for releases is 4x the size of the corresponding tarball. It may partly be using less powerful compression, but I'm suspicious that it might include multiple copies of the binaries, in different locations. | 1.0 | Windows installer includes too many files? - The Windows `.msi` installer we produce for releases is 4x the size of the corresponding tarball. It may partly be using less powerful compression, but I'm suspicious that it might include multiple copies of the binaries, in different locations. | non_priority | windows installer includes too many files the windows msi installer we produce for releases is the size of the corresponding tarball it may partly be using less powerful compression but i m suspicious that it might include multiple copies of the binaries in different locations | 0 |
451 | 2,858,527,722 | IssuesEvent | 2015-06-03 03:25:49 | uqfoundation/dill | https://api.github.com/repos/uqfoundation/dill | closed | Unpicklable objects defined in doctests interfere with serialization of lambdas | compatibility | I found another example where Dill fails to pickle objects when running under doctest. This is a one-line addition to my test-case in #18.
I'm using Python 2.7.6 and Dill eb122e6eb00dcfa9704ffa692fc7a14850867185.
/cc @distobj
```python
import dill as pickle
import doctest
pickle.dill._trace(1)
class SomeUnreferencedUnpicklableClass(object):
def __reduce__(self):
raise Exception
unpicklable = SomeUnreferencedUnpicklableClass()
# This works fine outside of Doctest:
serialized = pickle.dumps(lambda x: x)
# This fails because it tries to pickle the unpicklable object:
def tests():
"""
>>> unpicklable = SomeUnreferencedUnpicklableClass() # <-- Added since #18
>>> serialized = pickle.dumps(lambda x: x)
"""
return
print "\n\nRunning Doctest:"
doctest.testmod()
```
Output:
```
F1: <function <lambda> at 0x101f8f848>
F2: <function _create_function at 0x101c96d70>
Co: <code object <lambda> at 0x100474ab0, file "dillbugtwo.py", line 13>
F2: <function _unmarshal at 0x101c96c08>
D1: <dict object at 0x10031ba20>
D2: <dict object at 0x101da9de0>
Running Doctest:
F1: <function <lambda> at 0x101f8f938>
F2: <function _create_function at 0x101c96d70>
Co: <code object <lambda> at 0x101f369b0, file "<doctest __main__.tests[1]>", line 1>
F2: <function _unmarshal at 0x101c96c08>
D2: <dict object at 0x102206120>
F1: <function tests at 0x101f8f848>
Co: <code object tests at 0x100474e30, file "dillbugtwo.py", line 16>
D1: <dict object at 0x10031ba20>
D2: <dict object at 0x10222e940>
**********************************************************************
File "dillbugtwo.py", line 19, in __main__.tests
Failed example:
serialized = pickle.dumps(lambda x: x)
Exception raised:
Traceback (most recent call last):
File "/Users/joshrosen/anaconda/lib/python2.7/doctest.py", line 1289, in __run
compileflags, 1) in test.globs
File "<doctest __main__.tests[1]>", line 1, in <module>
serialized = pickle.dumps(lambda x: x)
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 165, in dumps
dump(obj, file, protocol, byref)
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 158, in dump
pik.dump(obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 224, in dump
self.save(obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 286, in save
f(self, obj) # Call unbound method with explicit self
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 506, in save_function
obj.__dict__), obj=obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 401, in save_reduce
save(args)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 286, in save
f(self, obj) # Call unbound method with explicit self
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 562, in save_tuple
save(element)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 286, in save
f(self, obj) # Call unbound method with explicit self
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 538, in save_module_dict
StockPickler.save_dict(pickler, obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 649, in save_dict
self._batch_setitems(obj.iteritems())
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 681, in _batch_setitems
save(v)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 306, in save
rv = reduce(self.proto)
File "dillbugtwo.py", line 8, in __reduce__
raise Exception
Exception
**********************************************************************
1 items had failures:
1 of 2 in __main__.tests
***Test Failed*** 1 failures.
``` | True | Unpicklable objects defined in doctests interfere with serialization of lambdas - I found another example where Dill fails to pickle objects when running under doctest. This is a one-line addition to my test-case in #18.
I'm using Python 2.7.6 and Dill eb122e6eb00dcfa9704ffa692fc7a14850867185.
/cc @distobj
```python
import dill as pickle
import doctest
pickle.dill._trace(1)
class SomeUnreferencedUnpicklableClass(object):
def __reduce__(self):
raise Exception
unpicklable = SomeUnreferencedUnpicklableClass()
# This works fine outside of Doctest:
serialized = pickle.dumps(lambda x: x)
# This fails because it tries to pickle the unpicklable object:
def tests():
"""
>>> unpicklable = SomeUnreferencedUnpicklableClass() # <-- Added since #18
>>> serialized = pickle.dumps(lambda x: x)
"""
return
print "\n\nRunning Doctest:"
doctest.testmod()
```
Output:
```
F1: <function <lambda> at 0x101f8f848>
F2: <function _create_function at 0x101c96d70>
Co: <code object <lambda> at 0x100474ab0, file "dillbugtwo.py", line 13>
F2: <function _unmarshal at 0x101c96c08>
D1: <dict object at 0x10031ba20>
D2: <dict object at 0x101da9de0>
Running Doctest:
F1: <function <lambda> at 0x101f8f938>
F2: <function _create_function at 0x101c96d70>
Co: <code object <lambda> at 0x101f369b0, file "<doctest __main__.tests[1]>", line 1>
F2: <function _unmarshal at 0x101c96c08>
D2: <dict object at 0x102206120>
F1: <function tests at 0x101f8f848>
Co: <code object tests at 0x100474e30, file "dillbugtwo.py", line 16>
D1: <dict object at 0x10031ba20>
D2: <dict object at 0x10222e940>
**********************************************************************
File "dillbugtwo.py", line 19, in __main__.tests
Failed example:
serialized = pickle.dumps(lambda x: x)
Exception raised:
Traceback (most recent call last):
File "/Users/joshrosen/anaconda/lib/python2.7/doctest.py", line 1289, in __run
compileflags, 1) in test.globs
File "<doctest __main__.tests[1]>", line 1, in <module>
serialized = pickle.dumps(lambda x: x)
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 165, in dumps
dump(obj, file, protocol, byref)
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 158, in dump
pik.dump(obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 224, in dump
self.save(obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 286, in save
f(self, obj) # Call unbound method with explicit self
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 506, in save_function
obj.__dict__), obj=obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 401, in save_reduce
save(args)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 286, in save
f(self, obj) # Call unbound method with explicit self
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 562, in save_tuple
save(element)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 286, in save
f(self, obj) # Call unbound method with explicit self
File "/Users/joshrosen/anaconda/lib/python2.7/site-packages/dill-0.2.2.dev-py2.7.egg/dill/dill.py", line 538, in save_module_dict
StockPickler.save_dict(pickler, obj)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 649, in save_dict
self._batch_setitems(obj.iteritems())
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 681, in _batch_setitems
save(v)
File "/Users/joshrosen/anaconda/lib/python2.7/pickle.py", line 306, in save
rv = reduce(self.proto)
File "dillbugtwo.py", line 8, in __reduce__
raise Exception
Exception
**********************************************************************
1 items had failures:
1 of 2 in __main__.tests
***Test Failed*** 1 failures.
``` | non_priority | unpicklable objects defined in doctests interfere with serialization of lambdas i found another example where dill fails to pickle objects when running under doctest this is a one line addition to my test case in i m using python and dill cc distobj python import dill as pickle import doctest pickle dill trace class someunreferencedunpicklableclass object def reduce self raise exception unpicklable someunreferencedunpicklableclass this works fine outside of doctest serialized pickle dumps lambda x x this fails because it tries to pickle the unpicklable object def tests unpicklable someunreferencedunpicklableclass added since serialized pickle dumps lambda x x return print n nrunning doctest doctest testmod output at co at file dillbugtwo py line running doctest at co at file line co file dillbugtwo py line in main tests failed example serialized pickle dumps lambda x x exception raised traceback most recent call last file users joshrosen anaconda lib doctest py line in run compileflags in test globs file line in serialized pickle dumps lambda x x file users joshrosen anaconda lib site packages dill dev egg dill dill py line in dumps dump obj file protocol byref file users joshrosen anaconda lib site packages dill dev egg dill dill py line in dump pik dump obj file users joshrosen anaconda lib pickle py line in dump self save obj file users joshrosen anaconda lib pickle py line in save f self obj call unbound method with explicit self file users joshrosen anaconda lib site packages dill dev egg dill dill py line in save function obj dict obj obj file users joshrosen anaconda lib pickle py line in save reduce save args file users joshrosen anaconda lib pickle py line in save f self obj call unbound method with explicit self file users joshrosen anaconda lib pickle py line in save tuple save element file users joshrosen anaconda lib pickle py line in save f self obj call unbound method with explicit self file users joshrosen anaconda lib site packages dill dev egg dill dill py line in save module dict stockpickler save dict pickler obj file users joshrosen anaconda lib pickle py line in save dict self batch setitems obj iteritems file users joshrosen anaconda lib pickle py line in batch setitems save v file users joshrosen anaconda lib pickle py line in save rv reduce self proto file dillbugtwo py line in reduce raise exception exception items had failures of in main tests test failed failures | 0 |
280,001 | 30,792,334,796 | IssuesEvent | 2023-07-31 17:06:16 | KDWSS/openedr | https://api.github.com/repos/KDWSS/openedr | closed | CVE-2021-23840 (High) detected in multiple libraries - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-23840 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opensslOpenSSL_1_1_1b</b>, <b>opensslOpenSSL_1_1_1b</b>, <b>opensslOpenSSL_1_1_1b</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Calls to EVP_CipherUpdate, EVP_EncryptUpdate and EVP_DecryptUpdate may overflow the output length argument in some cases where the input length is close to the maximum permissable length for an integer on the platform. In such cases the return value from the function call will be 1 (indicating success), but the output length value will be negative. This could cause applications to behave incorrectly or crash. OpenSSL versions 1.1.1i and below are affected by this issue. Users of these versions should upgrade to OpenSSL 1.1.1j. OpenSSL versions 1.0.2x and below are affected by this issue. However OpenSSL 1.0.2 is out of support and no longer receiving public updates. Premium support customers of OpenSSL 1.0.2 should upgrade to 1.0.2y. Other users should upgrade to 1.1.1j. Fixed in OpenSSL 1.1.1j (Affected 1.1.1-1.1.1i). Fixed in OpenSSL 1.0.2y (Affected 1.0.2-1.0.2x).
<p>Publish Date: 2021-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23840>CVE-2021-23840</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23840">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23840</a></p>
<p>Release Date: 2021-02-16</p>
<p>Fix Resolution: OpenSSL_1_1_1j; openssl-src -111.14.0+1.1.1j</p>
</p>
</details>
<p></p>
| True | CVE-2021-23840 (High) detected in multiple libraries - autoclosed - ## CVE-2021-23840 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opensslOpenSSL_1_1_1b</b>, <b>opensslOpenSSL_1_1_1b</b>, <b>opensslOpenSSL_1_1_1b</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
Calls to EVP_CipherUpdate, EVP_EncryptUpdate and EVP_DecryptUpdate may overflow the output length argument in some cases where the input length is close to the maximum permissable length for an integer on the platform. In such cases the return value from the function call will be 1 (indicating success), but the output length value will be negative. This could cause applications to behave incorrectly or crash. OpenSSL versions 1.1.1i and below are affected by this issue. Users of these versions should upgrade to OpenSSL 1.1.1j. OpenSSL versions 1.0.2x and below are affected by this issue. However OpenSSL 1.0.2 is out of support and no longer receiving public updates. Premium support customers of OpenSSL 1.0.2 should upgrade to 1.0.2y. Other users should upgrade to 1.1.1j. Fixed in OpenSSL 1.1.1j (Affected 1.1.1-1.1.1i). Fixed in OpenSSL 1.0.2y (Affected 1.0.2-1.0.2x).
<p>Publish Date: 2021-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23840>CVE-2021-23840</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23840">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23840</a></p>
<p>Release Date: 2021-02-16</p>
<p>Fix Resolution: OpenSSL_1_1_1j; openssl-src -111.14.0+1.1.1j</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in multiple libraries autoclosed cve high severity vulnerability vulnerable libraries opensslopenssl opensslopenssl opensslopenssl vulnerability details calls to evp cipherupdate evp encryptupdate and evp decryptupdate may overflow the output length argument in some cases where the input length is close to the maximum permissable length for an integer on the platform in such cases the return value from the function call will be indicating success but the output length value will be negative this could cause applications to behave incorrectly or crash openssl versions and below are affected by this issue users of these versions should upgrade to openssl openssl versions and below are affected by this issue however openssl is out of support and no longer receiving public updates premium support customers of openssl should upgrade to other users should upgrade to fixed in openssl affected fixed in openssl affected publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution openssl openssl src | 0 |
15,861 | 5,192,252,882 | IssuesEvent | 2017-01-22 06:17:36 | ClinGen/clincoded | https://api.github.com/repos/ClinGen/clincoded | closed | Travis/Sauce Lab connection -- decrease sporadic connection problems | bug code testing release ready | We are getting Sauce Labs failures with some frequency. This is *not* due to errors related to actual BDD test errors, but appears to be related to the client/browser not being ready on the Sauce Labs end.
Restarting just the browser test half of the test on Travis fixes problem of the test failing. Multiple restarts may be required on some days. Each restart means an additional 6 minutes of waiting (for instance if you are waiting for a PR to be completed)
Possible things to try:
- upgrade sauce connect package in our local Travis config... we have `4.3.11` and the current one is `4.4.2` (possibly this has better connection capabilities)
- Upgrade pytest-splinter to `1.8.0` (or whatever is the latest)
- Upgrade splinter
- Add an explicit wait after the Sauce tunnel is created. Possibly there is a lag before Sauce is ready on their end to begin the test. This is likely because as far as Sauce is concerned the test _never even_ was run as evidenced by the absence of the failing BDD test suite on https://saucelabs.com/u/clincoded | 1.0 | Travis/Sauce Lab connection -- decrease sporadic connection problems - We are getting Sauce Labs failures with some frequency. This is *not* due to errors related to actual BDD test errors, but appears to be related to the client/browser not being ready on the Sauce Labs end.
Restarting just the browser test half of the test on Travis fixes problem of the test failing. Multiple restarts may be required on some days. Each restart means an additional 6 minutes of waiting (for instance if you are waiting for a PR to be completed)
Possible things to try:
- upgrade sauce connect package in our local Travis config... we have `4.3.11` and the current one is `4.4.2` (possibly this has better connection capabilities)
- Upgrade pytest-splinter to `1.8.0` (or whatever is the latest)
- Upgrade splinter
- Add an explicit wait after the Sauce tunnel is created. Possibly there is a lag before Sauce is ready on their end to begin the test. This is likely because as far as Sauce is concerned the test _never even_ was run as evidenced by the absence of the failing BDD test suite on https://saucelabs.com/u/clincoded | non_priority | travis sauce lab connection decrease sporadic connection problems we are getting sauce labs failures with some frequency this is not due to errors related to actual bdd test errors but appears to be related to the client browser not being ready on the sauce labs end restarting just the browser test half of the test on travis fixes problem of the test failing multiple restarts may be required on some days each restart means an additional minutes of waiting for instance if you are waiting for a pr to be completed possible things to try upgrade sauce connect package in our local travis config we have and the current one is possibly this has better connection capabilities upgrade pytest splinter to or whatever is the latest upgrade splinter add an explicit wait after the sauce tunnel is created possibly there is a lag before sauce is ready on their end to begin the test this is likely because as far as sauce is concerned the test never even was run as evidenced by the absence of the failing bdd test suite on | 0 |
10,001 | 25,972,920,052 | IssuesEvent | 2022-12-19 12:45:35 | facebook/react-native | https://api.github.com/repos/facebook/react-native | closed | Codegen for TurboModules does not allow for Events to be Emitted | Type: New Architecture Resolution: Answered | ### Description
I am working on an app that requires a native module to be able to emit random events. In my case I am building a pedometer and steps can come from the native part of the application at random times. I can't use simple method calls because of this behaviour. I also want to use a BLE heart rate monitor which again requires the ability to use random events because the sensor data comes in at random times.
I tried to use `DirectEventHandler` in my Codegen file and the codegen compiler just shows errors. My interface code looks like this:
```
import type { TurboModule } from 'react-native';
import { TurboModuleRegistry } from 'react-native';
import type {
DirectEventHandler,
Int32,
} from 'react-native/Libraries/Types/CodegenTypes';
export interface Spec extends TurboModule {
multiply(a: number, b: number): number;
add(a: number, b: number): number;
randomEvent: DirectEventHandler<{ data: Int32 }>;
}
export default TurboModuleRegistry.getEnforcing<Spec>('RtmPedometer');
```
If I comment out the randomEvent code then Codegen works perfectly fine and I have no issues. This seems to be the only type in the documentation we have for event emitting unless I am missing something. This issue is especially frustrating because this was easy to do with the old arch and is really well documented. See: https://reactnative.dev/docs/native-modules-android#sending-events-to-javascript . This bug with `DirectEventHandler` is integral to how TurboModules should work and I feel like it should be a pretty high priority fix.
### Version
0.70.5
### Output of `npx react-native info`
```
System:
OS: macOS 12.5
CPU: (10) arm64 Apple M1 Pro
Memory: 149.16 MB / 16.00 GB
Shell: 5.8.1 - /bin/zsh
Binaries:
Node: 16.17.0 - /usr/local/bin/node
Yarn: 1.22.19 - /usr/local/bin/yarn
npm: 8.15.0 - /usr/local/bin/npm
Watchman: Not Found
Managers:
CocoaPods: 1.11.3 - /Users/danielfriyia/.rvm/gems/ruby-3.0.0/bin/pod
SDKs:
iOS SDK:
Platforms: DriverKit 21.4, iOS 16.0, macOS 12.3, tvOS 16.0, watchOS 9.0
Android SDK: Not Found
IDEs:
Android Studio: 2021.2 AI-212.5712.43.2112.8815526
Xcode: 14.0/14A309 - /usr/bin/xcodebuild
Languages:
Java: 11.0.16 - /usr/bin/javac
npmPackages:
@react-native-community/cli: Not Found
react: 18.1.0 => 18.1.0
react-native: 0.70.5 => 0.70.5
react-native-macos: Not Found
npmGlobalPackages:
*react-native*: Not Found
```
### Steps to reproduce
Clone the Reproducer Repo:
https://github.com/friyiajr/EventBugReproducer
Run the command
`yarn bootstrap`
At this point you will see it fail. If you want it to succeed comment out the `randomEvent` line along with its import statements.
### Snack, code example, screenshot, or link to a repository
https://github.com/friyiajr/EventBugReproducer | 1.0 | Codegen for TurboModules does not allow for Events to be Emitted - ### Description
I am working on an app that requires a native module to be able to emit random events. In my case I am building a pedometer and steps can come from the native part of the application at random times. I can't use simple method calls because of this behaviour. I also want to use a BLE heart rate monitor which again requires the ability to use random events because the sensor data comes in at random times.
I tried to use `DirectEventHandler` in my Codegen file and the codegen compiler just shows errors. My interface code looks like this:
```
import type { TurboModule } from 'react-native';
import { TurboModuleRegistry } from 'react-native';
import type {
DirectEventHandler,
Int32,
} from 'react-native/Libraries/Types/CodegenTypes';
export interface Spec extends TurboModule {
multiply(a: number, b: number): number;
add(a: number, b: number): number;
randomEvent: DirectEventHandler<{ data: Int32 }>;
}
export default TurboModuleRegistry.getEnforcing<Spec>('RtmPedometer');
```
If I comment out the randomEvent code then Codegen works perfectly fine and I have no issues. This seems to be the only type in the documentation we have for event emitting unless I am missing something. This issue is especially frustrating because this was easy to do with the old arch and is really well documented. See: https://reactnative.dev/docs/native-modules-android#sending-events-to-javascript . This bug with `DirectEventHandler` is integral to how TurboModules should work and I feel like it should be a pretty high priority fix.
### Version
0.70.5
### Output of `npx react-native info`
```
System:
OS: macOS 12.5
CPU: (10) arm64 Apple M1 Pro
Memory: 149.16 MB / 16.00 GB
Shell: 5.8.1 - /bin/zsh
Binaries:
Node: 16.17.0 - /usr/local/bin/node
Yarn: 1.22.19 - /usr/local/bin/yarn
npm: 8.15.0 - /usr/local/bin/npm
Watchman: Not Found
Managers:
CocoaPods: 1.11.3 - /Users/danielfriyia/.rvm/gems/ruby-3.0.0/bin/pod
SDKs:
iOS SDK:
Platforms: DriverKit 21.4, iOS 16.0, macOS 12.3, tvOS 16.0, watchOS 9.0
Android SDK: Not Found
IDEs:
Android Studio: 2021.2 AI-212.5712.43.2112.8815526
Xcode: 14.0/14A309 - /usr/bin/xcodebuild
Languages:
Java: 11.0.16 - /usr/bin/javac
npmPackages:
@react-native-community/cli: Not Found
react: 18.1.0 => 18.1.0
react-native: 0.70.5 => 0.70.5
react-native-macos: Not Found
npmGlobalPackages:
*react-native*: Not Found
```
### Steps to reproduce
Clone the Reproducer Repo:
https://github.com/friyiajr/EventBugReproducer
Run the command
`yarn bootstrap`
At this point you will see it fail. If you want it to succeed comment out the `randomEvent` line along with its import statements.
### Snack, code example, screenshot, or link to a repository
https://github.com/friyiajr/EventBugReproducer | non_priority | codegen for turbomodules does not allow for events to be emitted description i am working on an app that requires a native module to be able to emit random events in my case i am building a pedometer and steps can come from the native part of the application at random times i can t use simple method calls because of this behaviour i also want to use a ble heart rate monitor which again requires the ability to use random events because the sensor data comes in at random times i tried to use directeventhandler in my codegen file and the codegen compiler just shows errors my interface code looks like this import type turbomodule from react native import turbomoduleregistry from react native import type directeventhandler from react native libraries types codegentypes export interface spec extends turbomodule multiply a number b number number add a number b number number randomevent directeventhandler export default turbomoduleregistry getenforcing rtmpedometer if i comment out the randomevent code then codegen works perfectly fine and i have no issues this seems to be the only type in the documentation we have for event emitting unless i am missing something this issue is especially frustrating because this was easy to do with the old arch and is really well documented see this bug with directeventhandler is integral to how turbomodules should work and i feel like it should be a pretty high priority fix version output of npx react native info system os macos cpu apple pro memory mb gb shell bin zsh binaries node usr local bin node yarn usr local bin yarn npm usr local bin npm watchman not found managers cocoapods users danielfriyia rvm gems ruby bin pod sdks ios sdk platforms driverkit ios macos tvos watchos android sdk not found ides android studio ai xcode usr bin xcodebuild languages java usr bin javac npmpackages react native community cli not found react react native react native macos not found npmglobalpackages react native not found steps to reproduce clone the reproducer repo run the command yarn bootstrap at this point you will see it fail if you want it to succeed comment out the randomevent line along with its import statements snack code example screenshot or link to a repository | 0 |
20,455 | 6,889,973,020 | IssuesEvent | 2017-11-22 12:21:35 | spack/spack | https://api.github.com/repos/spack/spack | closed | Failure to install RHEL6 hpctoolkit | build-error | I get an error in the install phase. Log file attached
[speck.zip](https://github.com/LLNL/spack/files/622925/speck.zip)
| 1.0 | Failure to install RHEL6 hpctoolkit - I get an error in the install phase. Log file attached
[speck.zip](https://github.com/LLNL/spack/files/622925/speck.zip)
| non_priority | failure to install hpctoolkit i get an error in the install phase log file attached | 0 |
7,649 | 9,917,261,654 | IssuesEvent | 2019-06-28 23:17:19 | sisbell/tor-android-service | https://api.github.com/repos/sisbell/tor-android-service | opened | Change to Toolbar Notification Text | Orbit Compatibility | Don't show any text on toolbar notification, just icon
https://github.com/guardianproject/orbot/commit/56917567cd21a734a35f3bee0e56ba23793b6887 | True | Change to Toolbar Notification Text - Don't show any text on toolbar notification, just icon
https://github.com/guardianproject/orbot/commit/56917567cd21a734a35f3bee0e56ba23793b6887 | non_priority | change to toolbar notification text don t show any text on toolbar notification just icon | 0 |
350,643 | 24,994,665,702 | IssuesEvent | 2022-11-02 22:20:53 | PlasmoHQ/plasmo | https://api.github.com/repos/PlasmoHQ/plasmo | opened | EXP | with-tailwindcss dark mode not working | documentation | ### What is the example you wish to see?
In the `with-tailwindcss` example the content.tsx uses `dark:` classes.
In my experiments, can't get tailwind to recognise dark mode of the current page.
Neither if `<html class="dark"...` is set nor if `<html data-color-mode="dark"` with the suggested `darkMode: ['class', '[data-color-mode="dark"]']` tailwind config setup.
### Is there any context that might help us understand?
Debugging context so far:
https://discord.com/channels/946290204443025438/1035409196218331238/1037474596192014446
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
- [X] I checked the [current issues](https://github.com/PlasmoHQ/plasmo/issues) for duplicate problems. | 1.0 | EXP | with-tailwindcss dark mode not working - ### What is the example you wish to see?
In the `with-tailwindcss` example the content.tsx uses `dark:` classes.
In my experiments, can't get tailwind to recognise dark mode of the current page.
Neither if `<html class="dark"...` is set nor if `<html data-color-mode="dark"` with the suggested `darkMode: ['class', '[data-color-mode="dark"]']` tailwind config setup.
### Is there any context that might help us understand?
Debugging context so far:
https://discord.com/channels/946290204443025438/1035409196218331238/1037474596192014446
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
- [X] I checked the [current issues](https://github.com/PlasmoHQ/plasmo/issues) for duplicate problems. | non_priority | exp with tailwindcss dark mode not working what is the example you wish to see in the with tailwindcss example the content tsx uses dark classes in my experiments can t get tailwind to recognise dark mode of the current page neither if html class dark is set nor if html data color mode dark with the suggested darkmode tailwind config setup is there any context that might help us understand debugging context so far code of conduct i agree to follow this project s code of conduct i checked the for duplicate problems | 0 |
4,032 | 6,969,020,272 | IssuesEvent | 2017-12-11 02:13:35 | triplea-game/triplea | https://api.github.com/repos/triplea-game/triplea | closed | Remove Codacy? | category: dev & admin process close pending confirmation discussion | At question: remove codacy branch builds? Codacy is reading zero issues, did we zero that out thanks to the checkstyle? If so, then codacy is seeming a bit redundant.
 | 1.0 | Remove Codacy? - At question: remove codacy branch builds? Codacy is reading zero issues, did we zero that out thanks to the checkstyle? If so, then codacy is seeming a bit redundant.
 | non_priority | remove codacy at question remove codacy branch builds codacy is reading zero issues did we zero that out thanks to the checkstyle if so then codacy is seeming a bit redundant | 0 |
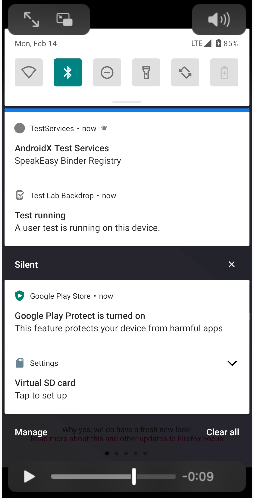
242,886 | 20,270,749,248 | IssuesEvent | 2022-02-15 15:59:08 | mozilla-mobile/focus-android | https://api.github.com/repos/mozilla-mobile/focus-android | closed | Intermittent UI test failure - <notificationOpenButtonTest> | eng:ui-test eng:intermittent-test | https://console.firebase.google.com/u/0/project/moz-focus-android/testlab/histories/bh.2189b040bbce6d5a/matrices/5933786035319020532
```Kotlin
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:86)
at org.junit.Assert.assertTrue(Assert.java:41)
at org.junit.Assert.assertTrue(Assert.java:52)
at org.mozilla.focus.activity.robots.NotificationRobot.verifySystemNotificationExists(NotificationRobot.kt:49)
at org.mozilla.focus.activity.SwitchContextTest$notificationOpenButtonTest$3.invoke(SwitchContextTest.kt:97)
at org.mozilla.focus.activity.SwitchContextTest$notificationOpenButtonTest$3.invoke(SwitchContextTest.kt:96)
at org.mozilla.focus.activity.robots.NotificationRobotKt.notificationTray(NotificationRobot.kt:94)
at org.mozilla.focus.activity.SwitchContextTest.notificationOpenButtonTest(SwitchContextTest.kt:96)
```
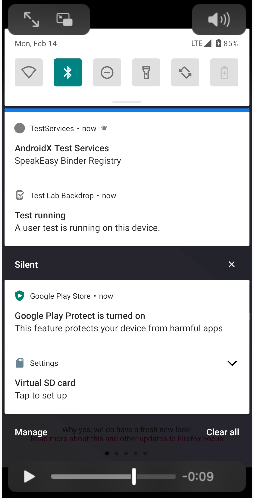
@AndiAJ It looks like there are more default notifications completely filling up the Firebase Pixel 3 device all of a sudden. Clear all is supposed to clear the silent notifications which is called in the `setup`, but it didn't do anything here. Can you see if you can reproduce locally by filling up notifications and seeing why clear all isn't working here? | 2.0 | Intermittent UI test failure - <notificationOpenButtonTest> - https://console.firebase.google.com/u/0/project/moz-focus-android/testlab/histories/bh.2189b040bbce6d5a/matrices/5933786035319020532
```Kotlin
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:86)
at org.junit.Assert.assertTrue(Assert.java:41)
at org.junit.Assert.assertTrue(Assert.java:52)
at org.mozilla.focus.activity.robots.NotificationRobot.verifySystemNotificationExists(NotificationRobot.kt:49)
at org.mozilla.focus.activity.SwitchContextTest$notificationOpenButtonTest$3.invoke(SwitchContextTest.kt:97)
at org.mozilla.focus.activity.SwitchContextTest$notificationOpenButtonTest$3.invoke(SwitchContextTest.kt:96)
at org.mozilla.focus.activity.robots.NotificationRobotKt.notificationTray(NotificationRobot.kt:94)
at org.mozilla.focus.activity.SwitchContextTest.notificationOpenButtonTest(SwitchContextTest.kt:96)
```
@AndiAJ It looks like there are more default notifications completely filling up the Firebase Pixel 3 device all of a sudden. Clear all is supposed to clear the silent notifications which is called in the `setup`, but it didn't do anything here. Can you see if you can reproduce locally by filling up notifications and seeing why clear all isn't working here? | non_priority | intermittent ui test failure kotlin java lang assertionerror at org junit assert fail assert java at org junit assert asserttrue assert java at org junit assert asserttrue assert java at org mozilla focus activity robots notificationrobot verifysystemnotificationexists notificationrobot kt at org mozilla focus activity switchcontexttest notificationopenbuttontest invoke switchcontexttest kt at org mozilla focus activity switchcontexttest notificationopenbuttontest invoke switchcontexttest kt at org mozilla focus activity robots notificationrobotkt notificationtray notificationrobot kt at org mozilla focus activity switchcontexttest notificationopenbuttontest switchcontexttest kt andiaj it looks like there are more default notifications completely filling up the firebase pixel device all of a sudden clear all is supposed to clear the silent notifications which is called in the setup but it didn t do anything here can you see if you can reproduce locally by filling up notifications and seeing why clear all isn t working here | 0 |
17,521 | 6,468,753,681 | IssuesEvent | 2017-08-17 02:28:10 | istio/istio | https://api.github.com/repos/istio/istio | closed | pre submit keeps failing: investigate why it takes minutes for pod to be ready some times | bug build-cop debuggability e2e & integration | see #533 and many build failures after > 2mins of retry
| 1.0 | pre submit keeps failing: investigate why it takes minutes for pod to be ready some times - see #533 and many build failures after > 2mins of retry
| non_priority | pre submit keeps failing investigate why it takes minutes for pod to be ready some times see and many build failures after of retry | 0 |
405,291 | 27,511,854,841 | IssuesEvent | 2023-03-06 09:22:05 | keptn/lifecycle-toolkit | https://api.github.com/repos/keptn/lifecycle-toolkit | opened | Add Markdownlint-rule Max 1 Sentence Per Line | documentation enhancement question | ## Description
Having a consistent style for Markdown files helps contributors and maintainers.
Currently, we're only checking for line length, but that doesn't mean it is easy to work with the documentation, moving around sentences etc. is hard with punctuation in the middle of a line, etc.
## Issue
There is a markdown-lint rule, which limits the amount of sentences to max one per line - https://github.com/aepfli/markdownlint-rule-max-one-sentence-per-line
as an example:
```markdown
This is a markdown example where we are working with a certain line limit,
specially with our currently configured one.
This line limit is set to 120 and allows us for a limited line length.
If this is suitabl or not is questionable,
as we can easily use `soft-wrap` which is supported by any kind of tool.
Hence that, why not focus more on one sentence per line.
```
and
```markdown
This is a markdown example where we are working with a certain line limit,
specially with our currently configured one. This line limit is set to 120 and
allows us for a limited line-length. If this is suitabl or not is questionable,
as we can easily use `soft-wrap` which is supported by any kind of tool. Hence
that, why not focus more on one sentence per line.
```
are both the same when rendered. But the first one is easier to maintain, as you can rearrange the sentences easier.
Note this rule those not enforce one sentence per line, it is maximum one sentence per line, which allows more specific breaking if needed and depending on the contributor.
## Proposal
Usage of https://github.com/aepfli/markdownlint-rule-max-one-sentence-per-line
### Problems
There is only one docker image containing this rule out of the box and it is within davidanson/markdownlint-cli2-rules:next hence that we would need to swap also to markdownlint-cli2 instead of markdownlint-cli.
#### Possible problems with IDE Integrations
It might be that eg. the VS code extension for markdownlint, does not like the new kind of configuration, because of the missing rule (it is in the docker image but not within the project)
We should provide a functionality or a guide within our readme on how to handle this.
- [ ] lets discuss this approach
- [ ] how do we want to handle IDE integration, or do we want to do this afterwards?
| 1.0 | Add Markdownlint-rule Max 1 Sentence Per Line - ## Description
Having a consistent style for Markdown files helps contributors and maintainers.
Currently, we're only checking for line length, but that doesn't mean it is easy to work with the documentation, moving around sentences etc. is hard with punctuation in the middle of a line, etc.
## Issue
There is a markdown-lint rule, which limits the amount of sentences to max one per line - https://github.com/aepfli/markdownlint-rule-max-one-sentence-per-line
as an example:
```markdown
This is a markdown example where we are working with a certain line limit,
specially with our currently configured one.
This line limit is set to 120 and allows us for a limited line length.
If this is suitabl or not is questionable,
as we can easily use `soft-wrap` which is supported by any kind of tool.
Hence that, why not focus more on one sentence per line.
```
and
```markdown
This is a markdown example where we are working with a certain line limit,
specially with our currently configured one. This line limit is set to 120 and
allows us for a limited line-length. If this is suitabl or not is questionable,
as we can easily use `soft-wrap` which is supported by any kind of tool. Hence
that, why not focus more on one sentence per line.
```
are both the same when rendered. But the first one is easier to maintain, as you can rearrange the sentences easier.
Note this rule those not enforce one sentence per line, it is maximum one sentence per line, which allows more specific breaking if needed and depending on the contributor.
## Proposal
Usage of https://github.com/aepfli/markdownlint-rule-max-one-sentence-per-line
### Problems
There is only one docker image containing this rule out of the box and it is within davidanson/markdownlint-cli2-rules:next hence that we would need to swap also to markdownlint-cli2 instead of markdownlint-cli.
#### Possible problems with IDE Integrations
It might be that eg. the VS code extension for markdownlint, does not like the new kind of configuration, because of the missing rule (it is in the docker image but not within the project)
We should provide a functionality or a guide within our readme on how to handle this.
- [ ] lets discuss this approach
- [ ] how do we want to handle IDE integration, or do we want to do this afterwards?
| non_priority | add markdownlint rule max sentence per line description having a consistent style for markdown files helps contributors and maintainers currently we re only checking for line length but that doesn t mean it is easy to work with the documentation moving around sentences etc is hard with punctuation in the middle of a line etc issue there is a markdown lint rule which limits the amount of sentences to max one per line as an example markdown this is a markdown example where we are working with a certain line limit specially with our currently configured one this line limit is set to and allows us for a limited line length if this is suitabl or not is questionable as we can easily use soft wrap which is supported by any kind of tool hence that why not focus more on one sentence per line and markdown this is a markdown example where we are working with a certain line limit specially with our currently configured one this line limit is set to and allows us for a limited line length if this is suitabl or not is questionable as we can easily use soft wrap which is supported by any kind of tool hence that why not focus more on one sentence per line are both the same when rendered but the first one is easier to maintain as you can rearrange the sentences easier note this rule those not enforce one sentence per line it is maximum one sentence per line which allows more specific breaking if needed and depending on the contributor proposal usage of problems there is only one docker image containing this rule out of the box and it is within davidanson markdownlint rules next hence that we would need to swap also to markdownlint instead of markdownlint cli possible problems with ide integrations it might be that eg the vs code extension for markdownlint does not like the new kind of configuration because of the missing rule it is in the docker image but not within the project we should provide a functionality or a guide within our readme on how to handle this lets discuss this approach how do we want to handle ide integration or do we want to do this afterwards | 0 |
11,011 | 13,795,713,609 | IssuesEvent | 2020-10-09 18:30:35 | unicode-org/icu4x | https://api.github.com/repos/unicode-org/icu4x | closed | Where to save generated data | C-process T-task | I would like to save the output of the data exporter tool (#200) such that the CLDR source files are not required when using ICU4X.
Putting this directly into the ICU4X repo has some advantages: fewer moving parts, easy to make synchronous updates to code and data, etc. However, if we put it into the ICU4X repo, but that would mean a deep directory structure with volatile, generated data.
I was thinking that a separate, independently versioned repo, called icu4x-data, might be more appropriate. In addition to keeping ICU4X as a pristine source of truth (without auto-generated clutter), it would make it easier to check in multiple types of generated data (e.g., JSON and Bincode for multiple CLDR versions).
We could also use a branch of the ICU4X repo.
Thoughts? | 1.0 | Where to save generated data - I would like to save the output of the data exporter tool (#200) such that the CLDR source files are not required when using ICU4X.
Putting this directly into the ICU4X repo has some advantages: fewer moving parts, easy to make synchronous updates to code and data, etc. However, if we put it into the ICU4X repo, but that would mean a deep directory structure with volatile, generated data.
I was thinking that a separate, independently versioned repo, called icu4x-data, might be more appropriate. In addition to keeping ICU4X as a pristine source of truth (without auto-generated clutter), it would make it easier to check in multiple types of generated data (e.g., JSON and Bincode for multiple CLDR versions).
We could also use a branch of the ICU4X repo.
Thoughts? | non_priority | where to save generated data i would like to save the output of the data exporter tool such that the cldr source files are not required when using putting this directly into the repo has some advantages fewer moving parts easy to make synchronous updates to code and data etc however if we put it into the repo but that would mean a deep directory structure with volatile generated data i was thinking that a separate independently versioned repo called data might be more appropriate in addition to keeping as a pristine source of truth without auto generated clutter it would make it easier to check in multiple types of generated data e g json and bincode for multiple cldr versions we could also use a branch of the repo thoughts | 0 |
8,508 | 8,336,410,218 | IssuesEvent | 2018-09-28 07:42:54 | kyma-project/kyma | https://api.github.com/repos/kyma-project/kyma | closed | [Remote Environment Broker] Issue Relist Request when EM is created/removed | area/service-catalog bug | **Description**
In case of Remote Environment Broker working as a namespace broker, we should issue Relist request on creation/removal of Environment Mapping.
Currently, we relist request only on changes to Remote Environments, what was ok in case of Cluster Service Broker.
**Steps to reproduce**
1. Ensure that REB is working as a namespace broker
2. Create 2 Remote Environments
3. In the `testing` namespace, create 2 Environment Mapping to 2 RE created in the previous step, but do it with some time gap between registering EM
**Expected result**
4. Classes from both RE are visible in the namespace
**Actual result**
4. Classes only from the first RE are visible in the namespace. To see classes from the second RE, we have to manually increase RelistRequest for the ServiceBroker.
| 1.0 | [Remote Environment Broker] Issue Relist Request when EM is created/removed - **Description**
In case of Remote Environment Broker working as a namespace broker, we should issue Relist request on creation/removal of Environment Mapping.
Currently, we relist request only on changes to Remote Environments, what was ok in case of Cluster Service Broker.
**Steps to reproduce**
1. Ensure that REB is working as a namespace broker
2. Create 2 Remote Environments
3. In the `testing` namespace, create 2 Environment Mapping to 2 RE created in the previous step, but do it with some time gap between registering EM
**Expected result**
4. Classes from both RE are visible in the namespace
**Actual result**
4. Classes only from the first RE are visible in the namespace. To see classes from the second RE, we have to manually increase RelistRequest for the ServiceBroker.
| non_priority | issue relist request when em is created removed description in case of remote environment broker working as a namespace broker we should issue relist request on creation removal of environment mapping currently we relist request only on changes to remote environments what was ok in case of cluster service broker steps to reproduce ensure that reb is working as a namespace broker create remote environments in the testing namespace create environment mapping to re created in the previous step but do it with some time gap between registering em expected result classes from both re are visible in the namespace actual result classes only from the first re are visible in the namespace to see classes from the second re we have to manually increase relistrequest for the servicebroker | 0 |
27,653 | 11,525,095,997 | IssuesEvent | 2020-02-15 05:35:26 | TrapTeamCCNZ/website | https://api.github.com/repos/TrapTeamCCNZ/website | opened | CVE-2019-11358 (Medium) detected in jquery-3.3.1.min.js | security vulnerability | ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.3.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/website/about.html</p>
<p>Path to vulnerable library: /website/about.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TrapTeamCCNZ/website/commit/df4cd067502ec4dc965766214531392cfeb2fa89">df4cd067502ec4dc965766214531392cfeb2fa89</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-11358 (Medium) detected in jquery-3.3.1.min.js - ## CVE-2019-11358 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-3.3.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/3.3.1/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/website/about.html</p>
<p>Path to vulnerable library: /website/about.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-3.3.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/TrapTeamCCNZ/website/commit/df4cd067502ec4dc965766214531392cfeb2fa89">df4cd067502ec4dc965766214531392cfeb2fa89</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.4.0, as used in Drupal, Backdrop CMS, and other products, mishandles jQuery.extend(true, {}, ...) because of Object.prototype pollution. If an unsanitized source object contained an enumerable __proto__ property, it could extend the native Object.prototype.
<p>Publish Date: 2019-04-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11358>CVE-2019-11358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11358</a></p>
<p>Release Date: 2019-04-20</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm website about html path to vulnerable library website about html dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before as used in drupal backdrop cms and other products mishandles jquery extend true because of object prototype pollution if an unsanitized source object contained an enumerable proto property it could extend the native object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
4,923 | 3,479,632,981 | IssuesEvent | 2015-12-28 21:49:58 | AlexIIL/Buildcraft_1.8_Issues | https://api.github.com/repos/AlexIIL/Buildcraft_1.8_Issues | closed | Crash when breaking block without breaking particle icon with a filler (probably a builder too) | help wanted not buildcraft | http://paste.ee/p/cW89A
To reproduce, remove a chest with a filler | 1.0 | Crash when breaking block without breaking particle icon with a filler (probably a builder too) - http://paste.ee/p/cW89A
To reproduce, remove a chest with a filler | non_priority | crash when breaking block without breaking particle icon with a filler probably a builder too to reproduce remove a chest with a filler | 0 |
25,347 | 6,654,061,014 | IssuesEvent | 2017-09-29 11:04:37 | Porucznik/Nexia-Home | https://api.github.com/repos/Porucznik/Nexia-Home | closed | Correct code formating | code refactor | We should correct code formating, in current state is too illegible (lines are too long).
Maybe use PEP-8 code guilde (80 lines for code, 72 comments, tabs as spaces, 4 spaces long).
| 1.0 | Correct code formating - We should correct code formating, in current state is too illegible (lines are too long).
Maybe use PEP-8 code guilde (80 lines for code, 72 comments, tabs as spaces, 4 spaces long).
| non_priority | correct code formating we should correct code formating in current state is too illegible lines are too long maybe use pep code guilde lines for code comments tabs as spaces spaces long | 0 |
241,273 | 18,440,285,864 | IssuesEvent | 2021-10-14 17:12:56 | ICEI-PUC-Minas-PMV-ADS/pmv-ads-2021-2-e1-proj-web-t4-projeto-mundo-sem-fronteiras | https://api.github.com/repos/ICEI-PUC-Minas-PMV-ADS/pmv-ads-2021-2-e1-proj-web-t4-projeto-mundo-sem-fronteiras | closed | Especificação do Projeto - Personas e Histórias de Usuários | documentation | Identificação do grupo de pessoas a qual o sistema será útil e quais desejos os usuários têm em relação a solução que será prestada. | 1.0 | Especificação do Projeto - Personas e Histórias de Usuários - Identificação do grupo de pessoas a qual o sistema será útil e quais desejos os usuários têm em relação a solução que será prestada. | non_priority | especificação do projeto personas e histórias de usuários identificação do grupo de pessoas a qual o sistema será útil e quais desejos os usuários têm em relação a solução que será prestada | 0 |
453,002 | 32,077,781,131 | IssuesEvent | 2023-09-25 12:11:12 | kyma-project/community | https://api.github.com/repos/kyma-project/community | reopened | Review and update /docs/guidelines/releases-guidelines | area/documentation area/tooling | **Description**
After enabling Markdown Link Check GitHub Action, some links in the [release guidelines](https://github.com/kyma-project/community/tree/main/docs/guidelines/releases-guidelines), occurred to break. Investigating broken links proved that in order to fix the links, the documents in the directory require review and update first.
TWs and Neighbors, let's join forces and update the release documentation.
**Area**
- infrastructure
- documentation
**Reasons**
<!-- Explain why we should improve the document. -->
**Assignees**
@kyma-project/technical-writers
**Attachments**
<!-- Attach any files, links, code samples, or screenshots that will convince us to your idea. --> | 1.0 | Review and update /docs/guidelines/releases-guidelines - **Description**
After enabling Markdown Link Check GitHub Action, some links in the [release guidelines](https://github.com/kyma-project/community/tree/main/docs/guidelines/releases-guidelines), occurred to break. Investigating broken links proved that in order to fix the links, the documents in the directory require review and update first.
TWs and Neighbors, let's join forces and update the release documentation.
**Area**
- infrastructure
- documentation
**Reasons**
<!-- Explain why we should improve the document. -->
**Assignees**
@kyma-project/technical-writers
**Attachments**
<!-- Attach any files, links, code samples, or screenshots that will convince us to your idea. --> | non_priority | review and update docs guidelines releases guidelines description after enabling markdown link check github action some links in the occurred to break investigating broken links proved that in order to fix the links the documents in the directory require review and update first tws and neighbors let s join forces and update the release documentation area infrastructure documentation reasons assignees kyma project technical writers attachments | 0 |
5,976 | 6,076,747,133 | IssuesEvent | 2017-06-16 00:31:43 | sindresorhus/refined-github | https://api.github.com/repos/sindresorhus/refined-github | opened | Use Promised `browser.*` APIs | firefox infrastructure under discussion | Firefox copied Chrome's extensions API, renamed `chrome.*` to `browser.*` and made them Promised.
Do you think it's worthwhile to use a `browser.*` polyfill like [mozilla/webextension-polyfill](https://github.com/mozilla/webextension-polyfill) so we can leave callback APIs (and the awful `chrome.runtime.lastError`) in the dust? I'm guessing that the polyfill also works with unsupported APIs like `chrome.permissions.*` | 1.0 | Use Promised `browser.*` APIs - Firefox copied Chrome's extensions API, renamed `chrome.*` to `browser.*` and made them Promised.
Do you think it's worthwhile to use a `browser.*` polyfill like [mozilla/webextension-polyfill](https://github.com/mozilla/webextension-polyfill) so we can leave callback APIs (and the awful `chrome.runtime.lastError`) in the dust? I'm guessing that the polyfill also works with unsupported APIs like `chrome.permissions.*` | non_priority | use promised browser apis firefox copied chrome s extensions api renamed chrome to browser and made them promised do you think it s worthwhile to use a browser polyfill like so we can leave callback apis and the awful chrome runtime lasterror in the dust i m guessing that the polyfill also works with unsupported apis like chrome permissions | 0 |
2,078 | 11,355,895,328 | IssuesEvent | 2020-01-24 21:11:41 | kedacore/keda-scaler-durable-functions | https://api.github.com/repos/kedacore/keda-scaler-durable-functions | opened | Update Azure Functions Core Tools | Need to investigate automation enhancement | As a developer, I'd like to update Azure Functions Core Tools template.
Currently, the `func kubernetes` command doesn't generate correct YAML file. Once this project is approved, It should be updated to fit this project.
## Success Criteria
- [ ] Azure Functions Core Tools https://github.com/Azure/azure-functions-core-tools behavior should be updated for using this project
- [ ] Document is property updated for Azure Functions Core Tools repo
- [ ] Document (Getting Started) is property updated. | 1.0 | Update Azure Functions Core Tools - As a developer, I'd like to update Azure Functions Core Tools template.
Currently, the `func kubernetes` command doesn't generate correct YAML file. Once this project is approved, It should be updated to fit this project.
## Success Criteria
- [ ] Azure Functions Core Tools https://github.com/Azure/azure-functions-core-tools behavior should be updated for using this project
- [ ] Document is property updated for Azure Functions Core Tools repo
- [ ] Document (Getting Started) is property updated. | non_priority | update azure functions core tools as a developer i d like to update azure functions core tools template currently the func kubernetes command doesn t generate correct yaml file once this project is approved it should be updated to fit this project success criteria azure functions core tools behavior should be updated for using this project document is property updated for azure functions core tools repo document getting started is property updated | 0 |
158,742 | 24,890,394,873 | IssuesEvent | 2022-10-28 11:28:38 | react-hook-form/react-hook-form | https://api.github.com/repos/react-hook-form/react-hook-form | closed | issue: FieldErrors can't handle union type | duplicated design limitation | ### Version Number
7.38.0
### Codesandbox/Expo snack
https://codesandbox.io/s/nostalgic-butterfly-j84vtt?file=/src/App.tsx
### Steps to reproduce
1. Create a form with a union type. The types used in the union should have a property not in common
2. When trying to access to errors.property, typescript is not happy
### Expected behaviour
The errors object should have the same shape as the FormValues, so in case of union type, we could use a type predicate to correctly infer the type
With
```
type Foo = {
id: 1;
foo: string;
};
type Bar = {
id: 2;
bar: string;
}
type Form = Foo | Bar;
```
We should be able to do:
```
function isFoo(foobar: Foo | Bar): foobar is Foo {
return foobar.foo !== undefined;
}
if (isFoo(errors)) {
errors.foo // OK
}
```
### What browsers are you seeing the problem on?
Chrome
### Relevant log output
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | issue: FieldErrors can't handle union type - ### Version Number
7.38.0
### Codesandbox/Expo snack
https://codesandbox.io/s/nostalgic-butterfly-j84vtt?file=/src/App.tsx
### Steps to reproduce
1. Create a form with a union type. The types used in the union should have a property not in common
2. When trying to access to errors.property, typescript is not happy
### Expected behaviour
The errors object should have the same shape as the FormValues, so in case of union type, we could use a type predicate to correctly infer the type
With
```
type Foo = {
id: 1;
foo: string;
};
type Bar = {
id: 2;
bar: string;
}
type Form = Foo | Bar;
```
We should be able to do:
```
function isFoo(foobar: Foo | Bar): foobar is Foo {
return foobar.foo !== undefined;
}
if (isFoo(errors)) {
errors.foo // OK
}
```
### What browsers are you seeing the problem on?
Chrome
### Relevant log output
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | non_priority | issue fielderrors can t handle union type version number codesandbox expo snack steps to reproduce create a form with a union type the types used in the union should have a property not in common when trying to access to errors property typescript is not happy expected behaviour the errors object should have the same shape as the formvalues so in case of union type we could use a type predicate to correctly infer the type with type foo id foo string type bar id bar string type form foo bar we should be able to do function isfoo foobar foo bar foobar is foo return foobar foo undefined if isfoo errors errors foo ok what browsers are you seeing the problem on chrome relevant log output no response code of conduct i agree to follow this project s code of conduct | 0 |
277,510 | 30,659,279,463 | IssuesEvent | 2023-07-25 14:04:33 | rsoreq/zenbot | https://api.github.com/repos/rsoreq/zenbot | closed | CVE-2020-13822 (High) detected in elliptic-6.5.0.tgz - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-13822 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.0.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.0.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- webpack-4.44.1.tgz (Root Library)
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- create-ecdh-4.0.3.tgz
- :x: **elliptic-6.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7a24c0d7b98ee76e6bac827974cff490a7694378">7a24c0d7b98ee76e6bac827974cff490a7694378</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Elliptic package 6.5.2 for Node.js allows ECDSA signature malleability via variations in encoding, leading '\0' bytes, or integer overflows. This could conceivably have a security-relevant impact if an application relied on a single canonical signature.
<p>Publish Date: 2020-06-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13822>CVE-2020-13822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution (elliptic): 6.5.3</p>
<p>Direct dependency fix Resolution (webpack): 4.44.2</p>
</p>
</details>
<p></p>
| True | CVE-2020-13822 (High) detected in elliptic-6.5.0.tgz - autoclosed - ## CVE-2020-13822 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.0.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.0.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.0.tgz</a></p>
<p>
Dependency Hierarchy:
- webpack-4.44.1.tgz (Root Library)
- node-libs-browser-2.2.1.tgz
- crypto-browserify-3.12.0.tgz
- create-ecdh-4.0.3.tgz
- :x: **elliptic-6.5.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rsoreq/zenbot/commit/7a24c0d7b98ee76e6bac827974cff490a7694378">7a24c0d7b98ee76e6bac827974cff490a7694378</a></p>
<p>Found in base branch: <b>unstable</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The Elliptic package 6.5.2 for Node.js allows ECDSA signature malleability via variations in encoding, leading '\0' bytes, or integer overflows. This could conceivably have a security-relevant impact if an application relied on a single canonical signature.
<p>Publish Date: 2020-06-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-13822>CVE-2020-13822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution (elliptic): 6.5.3</p>
<p>Direct dependency fix Resolution (webpack): 4.44.2</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in elliptic tgz autoclosed cve high severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href dependency hierarchy webpack tgz root library node libs browser tgz crypto browserify tgz create ecdh tgz x elliptic tgz vulnerable library found in head commit a href found in base branch unstable vulnerability details the elliptic package for node js allows ecdsa signature malleability via variations in encoding leading bytes or integer overflows this could conceivably have a security relevant impact if an application relied on a single canonical signature publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution elliptic direct dependency fix resolution webpack | 0 |
86,727 | 10,791,130,782 | IssuesEvent | 2019-11-05 16:07:12 | aragon/aragon | https://api.github.com/repos/aragon/aragon | closed | Interpreting custom radspec for intent baskets / accumulators | abandoned design: request ux | ## Context
In instances where we are able to use calls scripts to do multiple actions, e.g. upgrade an entire organization's applications to their latest versions, we often need to use custom radspec descriptors to make the final intent clear and understandable for users.
For the 0.7 single-transaction upgrade, we've gone with the following descriptors:
*Client (short) description*:
<img width="302" alt="Screen Shot 2019-04-17 at 7 58 05 PM" src="https://user-images.githubusercontent.com/4166642/56310256-b9410b80-614b-11e9-8d40-901cf8373d9c.png">
*Voting app (full) description*:
<img width="400" alt="Screen Shot 2019-04-17 at 7 58 10 PM" src="https://user-images.githubusercontent.com/4166642/56310258-bba36580-614b-11e9-8c67-4207b6eaa9c9.png">
--------------
**However**, it would be nice if we used the same description across all areas of the app. One idea is to make these descriptions expandable, so that we could always use the short description but on hover (like a tooltip) or click it displays the full, literal description. | 1.0 | Interpreting custom radspec for intent baskets / accumulators - ## Context
In instances where we are able to use calls scripts to do multiple actions, e.g. upgrade an entire organization's applications to their latest versions, we often need to use custom radspec descriptors to make the final intent clear and understandable for users.
For the 0.7 single-transaction upgrade, we've gone with the following descriptors:
*Client (short) description*:
<img width="302" alt="Screen Shot 2019-04-17 at 7 58 05 PM" src="https://user-images.githubusercontent.com/4166642/56310256-b9410b80-614b-11e9-8d40-901cf8373d9c.png">
*Voting app (full) description*:
<img width="400" alt="Screen Shot 2019-04-17 at 7 58 10 PM" src="https://user-images.githubusercontent.com/4166642/56310258-bba36580-614b-11e9-8c67-4207b6eaa9c9.png">
--------------
**However**, it would be nice if we used the same description across all areas of the app. One idea is to make these descriptions expandable, so that we could always use the short description but on hover (like a tooltip) or click it displays the full, literal description. | non_priority | interpreting custom radspec for intent baskets accumulators context in instances where we are able to use calls scripts to do multiple actions e g upgrade an entire organization s applications to their latest versions we often need to use custom radspec descriptors to make the final intent clear and understandable for users for the single transaction upgrade we ve gone with the following descriptors client short description img width alt screen shot at pm src voting app full description img width alt screen shot at pm src however it would be nice if we used the same description across all areas of the app one idea is to make these descriptions expandable so that we could always use the short description but on hover like a tooltip or click it displays the full literal description | 0 |
327,842 | 28,084,791,601 | IssuesEvent | 2023-03-30 09:04:07 | ansible/ansible | https://api.github.com/repos/ansible/ansible | closed | ansible-test sanity expects all modules to be licensed under the GPLv3 | python3 test support:core bug affects_2.9 bot_closed | ##### SUMMARY
Running `ansible-test sanity --test validate-modules` in a collection that is not licensed under the GPLv3 produces the following error:
```
Running sanity test 'validate-modules' with Python 3.7
ERROR: Found 1 validate-modules issue(s) which need to be resolved:
ERROR: plugins/modules/marker.py:0:0: missing-gplv3-license: GPLv3 license header not found in the first 20 lines of the module
See documentation for help: https://docs.ansible.com/ansible/2.9/dev_guide/testing/sanity/validate-modules.html
ERROR: The 1 sanity test(s) listed below (out of 1) failed. See error output above for details.
validate-modules
```
##### ISSUE TYPE
- ~Bug Report~
- Feature Idea
##### COMPONENT NAME
ansible-test
##### ANSIBLE VERSION
<!--- Paste verbatim output from "ansible --version" between quotes -->
```paste below
ansible 2.9.4
config file = /etc/ansible/ansible.cfg
configured module search path = ['/home/tadej/.ansible/plugins/modules', '/usr/share/ansible/plugins/modules']
ansible python module location = /home/tadej/xlab/steampunk/circleci/venv/lib64/python3.7/site-packages/ansible
executable location = /home/tadej/xlab/steampunk/circleci/venv/bin/ansible
python version = 3.7.6 (default, Dec 19 2019, 22:52:49) [GCC 9.2.1 20190827 (Red Hat 9.2.1-1)]
```
##### CONFIGURATION
<!--- Paste verbatim output from "ansible-config dump --only-changed" between quotes -->
```paste below
COLLECTIONS_PATHS(env: ANSIBLE_COLLECTIONS_PATHS) = ['/home/tadej/xlab/steampunk/circleci/molecule-tests']
```
##### OS / ENVIRONMENT
<!--- Provide all relevant information below, e.g. target OS versions, network device firmware, etc. -->
Commands are being executed on latest stable Fedora (31).
##### STEPS TO REPRODUCE
<!--- Describe exactly how to reproduce the problem, using a minimal test-case -->
Just run the `ansible-test sanity --test validate-modules` command against the module that does not have a GPLv3 header (but it does have another valid license header).
##### WORKAROUND
Placing the `plugins/modules validate-modules:missing-gplv3-license` line into the *tests/sanity/ignore-2.9.txt* silences this check. | 1.0 | ansible-test sanity expects all modules to be licensed under the GPLv3 - ##### SUMMARY
Running `ansible-test sanity --test validate-modules` in a collection that is not licensed under the GPLv3 produces the following error:
```
Running sanity test 'validate-modules' with Python 3.7
ERROR: Found 1 validate-modules issue(s) which need to be resolved:
ERROR: plugins/modules/marker.py:0:0: missing-gplv3-license: GPLv3 license header not found in the first 20 lines of the module
See documentation for help: https://docs.ansible.com/ansible/2.9/dev_guide/testing/sanity/validate-modules.html
ERROR: The 1 sanity test(s) listed below (out of 1) failed. See error output above for details.
validate-modules
```
##### ISSUE TYPE
- ~Bug Report~
- Feature Idea
##### COMPONENT NAME
ansible-test
##### ANSIBLE VERSION
<!--- Paste verbatim output from "ansible --version" between quotes -->
```paste below
ansible 2.9.4
config file = /etc/ansible/ansible.cfg
configured module search path = ['/home/tadej/.ansible/plugins/modules', '/usr/share/ansible/plugins/modules']
ansible python module location = /home/tadej/xlab/steampunk/circleci/venv/lib64/python3.7/site-packages/ansible
executable location = /home/tadej/xlab/steampunk/circleci/venv/bin/ansible
python version = 3.7.6 (default, Dec 19 2019, 22:52:49) [GCC 9.2.1 20190827 (Red Hat 9.2.1-1)]
```
##### CONFIGURATION
<!--- Paste verbatim output from "ansible-config dump --only-changed" between quotes -->
```paste below
COLLECTIONS_PATHS(env: ANSIBLE_COLLECTIONS_PATHS) = ['/home/tadej/xlab/steampunk/circleci/molecule-tests']
```
##### OS / ENVIRONMENT
<!--- Provide all relevant information below, e.g. target OS versions, network device firmware, etc. -->
Commands are being executed on latest stable Fedora (31).
##### STEPS TO REPRODUCE
<!--- Describe exactly how to reproduce the problem, using a minimal test-case -->
Just run the `ansible-test sanity --test validate-modules` command against the module that does not have a GPLv3 header (but it does have another valid license header).
##### WORKAROUND
Placing the `plugins/modules validate-modules:missing-gplv3-license` line into the *tests/sanity/ignore-2.9.txt* silences this check. | non_priority | ansible test sanity expects all modules to be licensed under the summary running ansible test sanity test validate modules in a collection that is not licensed under the produces the following error running sanity test validate modules with python error found validate modules issue s which need to be resolved error plugins modules marker py missing license license header not found in the first lines of the module see documentation for help error the sanity test s listed below out of failed see error output above for details validate modules issue type bug report feature idea component name ansible test ansible version paste below ansible config file etc ansible ansible cfg configured module search path ansible python module location home tadej xlab steampunk circleci venv site packages ansible executable location home tadej xlab steampunk circleci venv bin ansible python version default dec configuration paste below collections paths env ansible collections paths os environment commands are being executed on latest stable fedora steps to reproduce just run the ansible test sanity test validate modules command against the module that does not have a header but it does have another valid license header workaround placing the plugins modules validate modules missing license line into the tests sanity ignore txt silences this check | 0 |
4,855 | 3,897,123,431 | IssuesEvent | 2016-04-16 07:02:03 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 15885970: The location of the "next keyboard" button is inconsistent | classification:usability reproducible:always status:open | #### Description
Summary:
The “next keyboard“ button on the Emoji keyboard is located in the lower left corner, but on the English or German iOS keyboard the "123" button is located at this point and the "next keyboard" button moved to the right of it (I don't know if the location of the "next keyboard" button differs on any other than the Emoji keyboard, but I guess most of us use that one often enough to get confused). This behavior leads to unwanted touches of the "123" keyboard, especially because the button switches to the last or most recently used keyboard and thus the order of the keyboards changes and you can only guess if the Emoji or another keyboard is going to show up. As this button is in need on every iOS keyboard, it should stay at the same point to provide maximum usability.
Steps to Reproduce:
Use minimum one standard and the Emoji keyboard.
Change the keyboards with the "next keyboard" button in the lower left corner.
Get confused when you want to change the keyboard back and the button moved to the right of the "123" button.
Expected Results:
I would like the "next keyboard" button to stay in place.
Actual Results:
The "next keyboard" button moves to the right of the "123" button on the Emoji keyboard.
Version:
iOS 7
-
Product Version: 7
Created: 2014-01-22T23:35:51.453971
Originated: 2014-01-23T00:00:00
Open Radar Link: http://www.openradar.me/15885970 | True | 15885970: The location of the "next keyboard" button is inconsistent - #### Description
Summary:
The “next keyboard“ button on the Emoji keyboard is located in the lower left corner, but on the English or German iOS keyboard the "123" button is located at this point and the "next keyboard" button moved to the right of it (I don't know if the location of the "next keyboard" button differs on any other than the Emoji keyboard, but I guess most of us use that one often enough to get confused). This behavior leads to unwanted touches of the "123" keyboard, especially because the button switches to the last or most recently used keyboard and thus the order of the keyboards changes and you can only guess if the Emoji or another keyboard is going to show up. As this button is in need on every iOS keyboard, it should stay at the same point to provide maximum usability.
Steps to Reproduce:
Use minimum one standard and the Emoji keyboard.
Change the keyboards with the "next keyboard" button in the lower left corner.
Get confused when you want to change the keyboard back and the button moved to the right of the "123" button.
Expected Results:
I would like the "next keyboard" button to stay in place.
Actual Results:
The "next keyboard" button moves to the right of the "123" button on the Emoji keyboard.
Version:
iOS 7
-
Product Version: 7
Created: 2014-01-22T23:35:51.453971
Originated: 2014-01-23T00:00:00
Open Radar Link: http://www.openradar.me/15885970 | non_priority | the location of the next keyboard button is inconsistent description summary the “next keyboard“ button on the emoji keyboard is located in the lower left corner but on the english or german ios keyboard the button is located at this point and the next keyboard button moved to the right of it i don t know if the location of the next keyboard button differs on any other than the emoji keyboard but i guess most of us use that one often enough to get confused this behavior leads to unwanted touches of the keyboard especially because the button switches to the last or most recently used keyboard and thus the order of the keyboards changes and you can only guess if the emoji or another keyboard is going to show up as this button is in need on every ios keyboard it should stay at the same point to provide maximum usability steps to reproduce use minimum one standard and the emoji keyboard change the keyboards with the next keyboard button in the lower left corner get confused when you want to change the keyboard back and the button moved to the right of the button expected results i would like the next keyboard button to stay in place actual results the next keyboard button moves to the right of the button on the emoji keyboard version ios product version created originated open radar link | 0 |
12,997 | 8,758,386,284 | IssuesEvent | 2018-12-15 03:14:18 | GillesCrebassa/FinancialManager | https://api.github.com/repos/GillesCrebassa/FinancialManager | opened | CVE-2015-8860 High Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2015-8860 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-0.1.20.tgz</b></p></summary>
<p>tar for node</p>
<p>path: /tmp/git/FinancialManager/web/assets/vendors/morris.js/node_modules/tar/package.json,/FinancialManager/web/assets/vendors/switchery/node_modules/tar/package.json</p>
<p>
<p>Library home page: <a href=http://registry.npmjs.org/tar/-/tar-0.1.20.tgz>http://registry.npmjs.org/tar/-/tar-0.1.20.tgz</a></p>
Dependency Hierarchy:
- :x: **tar-0.1.20.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The tar package before 2.0.0 for Node.js allows remote attackers to write to arbitrary files via a symlink attack in an archive.
<p>Publish Date: 2017-01-23
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-8860>CVE-2015-8860</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/npm/node-tar/commit/a5337a6cd58a2d800fc03b3781a25751cf459f28">https://github.com/npm/node-tar/commit/a5337a6cd58a2d800fc03b3781a25751cf459f28</a></p>
<p>Release Date: 2015-03-27</p>
<p>Fix Resolution: Replace or update the following files: extract.js, dir-normalization.tar, dir-normalization.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-8860 High Severity Vulnerability detected by WhiteSource - ## CVE-2015-8860 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-0.1.20.tgz</b></p></summary>
<p>tar for node</p>
<p>path: /tmp/git/FinancialManager/web/assets/vendors/morris.js/node_modules/tar/package.json,/FinancialManager/web/assets/vendors/switchery/node_modules/tar/package.json</p>
<p>
<p>Library home page: <a href=http://registry.npmjs.org/tar/-/tar-0.1.20.tgz>http://registry.npmjs.org/tar/-/tar-0.1.20.tgz</a></p>
Dependency Hierarchy:
- :x: **tar-0.1.20.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The tar package before 2.0.0 for Node.js allows remote attackers to write to arbitrary files via a symlink attack in an archive.
<p>Publish Date: 2017-01-23
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-8860>CVE-2015-8860</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/npm/node-tar/commit/a5337a6cd58a2d800fc03b3781a25751cf459f28">https://github.com/npm/node-tar/commit/a5337a6cd58a2d800fc03b3781a25751cf459f28</a></p>
<p>Release Date: 2015-03-27</p>
<p>Fix Resolution: Replace or update the following files: extract.js, dir-normalization.tar, dir-normalization.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library tar tgz tar for node path tmp git financialmanager web assets vendors morris js node modules tar package json financialmanager web assets vendors switchery node modules tar package json library home page a href dependency hierarchy x tar tgz vulnerable library vulnerability details the tar package before for node js allows remote attackers to write to arbitrary files via a symlink attack in an archive publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following files extract js dir normalization tar dir normalization js step up your open source security game with whitesource | 0 |
4,779 | 3,081,460,343 | IssuesEvent | 2015-08-22 19:01:54 | PSMGGamesSS2015/PSMG_SS_2015_RTS_GameGroup | https://api.github.com/repos/PSMGGamesSS2015/PSMG_SS_2015_RTS_GameGroup | closed | Einsammeln von Objekten Fade-Out | code Product Backlog Normal Prio unity | z.B. Blinken von Icon, +-Symbol oder weiches Fade-Out bei verschwinden der Objekte | 1.0 | Einsammeln von Objekten Fade-Out - z.B. Blinken von Icon, +-Symbol oder weiches Fade-Out bei verschwinden der Objekte | non_priority | einsammeln von objekten fade out z b blinken von icon symbol oder weiches fade out bei verschwinden der objekte | 0 |
12,827 | 9,793,569,927 | IssuesEvent | 2019-06-10 20:17:50 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | Include ability to request headers with ses_identity_notification_topic | enhancement service/ses | [ses_identity_notification_topic](https://www.terraform.io/docs/providers/aws/r/ses_identity_notification_topic.html) does not appear to offer the ability to request headers with notifications.
This functionality is presented in the web console as:
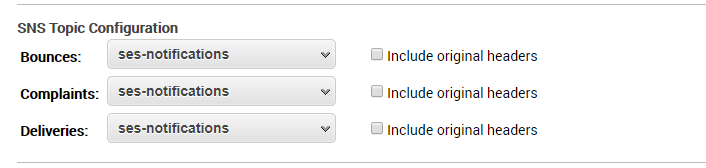
And is available via the AWS cli command [`aws ses set-identity-headers-in-notifications-enabled`](https://docs.aws.amazon.com/cli/latest/reference/ses/set-identity-headers-in-notifications-enabled.html) (unfortunately it's not part of [`set-identity-notification-topic`](https://docs.aws.amazon.com/cli/latest/reference/ses/set-identity-notification-topic.html) which might be why it didn't make it into Terraform!)
Is this possible? | 1.0 | Include ability to request headers with ses_identity_notification_topic - [ses_identity_notification_topic](https://www.terraform.io/docs/providers/aws/r/ses_identity_notification_topic.html) does not appear to offer the ability to request headers with notifications.
This functionality is presented in the web console as:
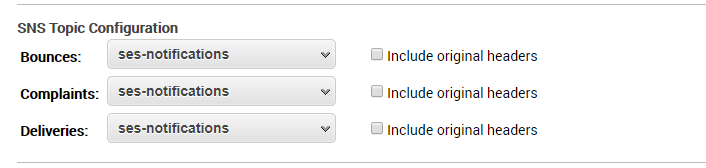
And is available via the AWS cli command [`aws ses set-identity-headers-in-notifications-enabled`](https://docs.aws.amazon.com/cli/latest/reference/ses/set-identity-headers-in-notifications-enabled.html) (unfortunately it's not part of [`set-identity-notification-topic`](https://docs.aws.amazon.com/cli/latest/reference/ses/set-identity-notification-topic.html) which might be why it didn't make it into Terraform!)
Is this possible? | non_priority | include ability to request headers with ses identity notification topic does not appear to offer the ability to request headers with notifications this functionality is presented in the web console as and is available via the aws cli command unfortunately it s not part of which might be why it didn t make it into terraform is this possible | 0 |
8,963 | 12,069,463,017 | IssuesEvent | 2020-04-16 16:05:58 | ORNL-AMO/AMO-Tools-Desktop | https://api.github.com/repos/ORNL-AMO/AMO-Tools-Desktop | closed | Explore Opps + Report | Fans Process Heating Pumps Steam enhancement | Need to report which “Assessment” modifications are checked, and echo the input parameters for each modification, i.e. “Install VFD”, “more efficient fan”, etc. - koa - @rmroot can we do this? what about assessments made in expert view? if we do it here we should do with with other assessments also
Could we use something like the Select Scenario page + the checkboxes from Explore Opps?
 | 1.0 | Explore Opps + Report - Need to report which “Assessment” modifications are checked, and echo the input parameters for each modification, i.e. “Install VFD”, “more efficient fan”, etc. - koa - @rmroot can we do this? what about assessments made in expert view? if we do it here we should do with with other assessments also
Could we use something like the Select Scenario page + the checkboxes from Explore Opps?
 | non_priority | explore opps report need to report which “assessment” modifications are checked and echo the input parameters for each modification i e “install vfd” “more efficient fan” etc koa rmroot can we do this what about assessments made in expert view if we do it here we should do with with other assessments also could we use something like the select scenario page the checkboxes from explore opps | 0 |
178,800 | 14,679,590,200 | IssuesEvent | 2020-12-31 07:25:34 | rasatmaja/links-barnacle | https://api.github.com/repos/rasatmaja/links-barnacle | closed | Add logging on repository, cors, and server | documentation | # **Add logging on repository, cors, and server**
**Issue type** :
- [x] 🤴 Code style update (formatting, renaming)
- [x] 🏇🏼 Refactoring (no functional changes, no api changes) | 1.0 | Add logging on repository, cors, and server - # **Add logging on repository, cors, and server**
**Issue type** :
- [x] 🤴 Code style update (formatting, renaming)
- [x] 🏇🏼 Refactoring (no functional changes, no api changes) | non_priority | add logging on repository cors and server add logging on repository cors and server issue type 🤴 code style update formatting renaming 🏇🏼 refactoring no functional changes no api changes | 0 |
390,261 | 26,855,675,996 | IssuesEvent | 2023-02-03 14:27:12 | geta-org/sex-adapt-backend | https://api.github.com/repos/geta-org/sex-adapt-backend | closed | Backend | Documento com as informações sobre o deploy | documentation question | Top 5 plataformas e seus custo beneficios | 1.0 | Backend | Documento com as informações sobre o deploy - Top 5 plataformas e seus custo beneficios | non_priority | backend documento com as informações sobre o deploy top plataformas e seus custo beneficios | 0 |
183,909 | 14,962,622,006 | IssuesEvent | 2021-01-27 09:30:52 | cqfn/diKTat | https://api.github.com/repos/cqfn/diKTat | closed | Add warning to suggest to use inline classes when a class has single property | documentation enhancement | https://kotlinlang.org/docs/reference/inline-classes.html
However, only since 1.3. Maybe needs some more considerations. | 1.0 | Add warning to suggest to use inline classes when a class has single property - https://kotlinlang.org/docs/reference/inline-classes.html
However, only since 1.3. Maybe needs some more considerations. | non_priority | add warning to suggest to use inline classes when a class has single property however only since maybe needs some more considerations | 0 |
223,846 | 17,142,489,674 | IssuesEvent | 2021-07-13 11:12:25 | oladhari/e-commerce | https://api.github.com/repos/oladhari/e-commerce | opened | RoadMap: ecommerce | documentation | TODO before deployment:
## frontend
- [ ] add page Product list with categories
- [ ] add a category page
- [ ] add the cart page
- [ ] add the payment page
## backend
- [ ] add the models related to products, and cart
- [ ] create a related API
- [ ] connect the API with the fronted
## deployment
- [ ] dockerize the whole application
- [ ] use Kubernetes for containers
- [ ] connect media and static files to cloud storage (Google or Amazon)
- [ ] deploy to google cloud or AWS (check the free options)
| 1.0 | RoadMap: ecommerce - TODO before deployment:
## frontend
- [ ] add page Product list with categories
- [ ] add a category page
- [ ] add the cart page
- [ ] add the payment page
## backend
- [ ] add the models related to products, and cart
- [ ] create a related API
- [ ] connect the API with the fronted
## deployment
- [ ] dockerize the whole application
- [ ] use Kubernetes for containers
- [ ] connect media and static files to cloud storage (Google or Amazon)
- [ ] deploy to google cloud or AWS (check the free options)
| non_priority | roadmap ecommerce todo before deployment frontend add page product list with categories add a category page add the cart page add the payment page backend add the models related to products and cart create a related api connect the api with the fronted deployment dockerize the whole application use kubernetes for containers connect media and static files to cloud storage google or amazon deploy to google cloud or aws check the free options | 0 |
304,264 | 23,057,556,291 | IssuesEvent | 2022-07-25 06:50:09 | scalameta/metals | https://api.github.com/repos/scalameta/metals | closed | Add a section to the docs that show all code actions | documentation | There isn't currently a great way to know what code actions exist in Metals apart from looking in the source. I think it'd be a great idea to have a small section in the docs highlighting the code actions that Metals supports. As we continue to add in more refactoring related actions, it may be wise to have a centralized place to show those. It seems to be a somewhat common questions asked of Metals, _What refactoring support does Metals have?_
| 1.0 | Add a section to the docs that show all code actions - There isn't currently a great way to know what code actions exist in Metals apart from looking in the source. I think it'd be a great idea to have a small section in the docs highlighting the code actions that Metals supports. As we continue to add in more refactoring related actions, it may be wise to have a centralized place to show those. It seems to be a somewhat common questions asked of Metals, _What refactoring support does Metals have?_
| non_priority | add a section to the docs that show all code actions there isn t currently a great way to know what code actions exist in metals apart from looking in the source i think it d be a great idea to have a small section in the docs highlighting the code actions that metals supports as we continue to add in more refactoring related actions it may be wise to have a centralized place to show those it seems to be a somewhat common questions asked of metals what refactoring support does metals have | 0 |
57,575 | 7,079,080,331 | IssuesEvent | 2018-01-10 08:03:06 | BSData/wh40k | https://api.github.com/repos/BSData/wh40k | closed | [Anon] Bug report: Imperium - Adeptus Mechanicus.catz | Bug - text/rule/profile Imperium - Adeptus Mechanicus Resolution - by design | **File:** Imperium - Adeptus Mechanicus.catz
**BattleScribe version:** 2.01.13
**Platform:** Android
**Dropbox:** No
**Description:** In v23 admech of v1.1.11 of wh40k the onegar dunecrawler will only show 1 cognise stubber if it's selected in addition to the neutron laser / stubber combo. It should show HEAVY 6 for the weapon type not HEAVY 3. | 1.0 | [Anon] Bug report: Imperium - Adeptus Mechanicus.catz - **File:** Imperium - Adeptus Mechanicus.catz
**BattleScribe version:** 2.01.13
**Platform:** Android
**Dropbox:** No
**Description:** In v23 admech of v1.1.11 of wh40k the onegar dunecrawler will only show 1 cognise stubber if it's selected in addition to the neutron laser / stubber combo. It should show HEAVY 6 for the weapon type not HEAVY 3. | non_priority | bug report imperium adeptus mechanicus catz file imperium adeptus mechanicus catz battlescribe version platform android dropbox no description in admech of of the onegar dunecrawler will only show cognise stubber if it s selected in addition to the neutron laser stubber combo it should show heavy for the weapon type not heavy | 0 |
30,217 | 11,801,271,778 | IssuesEvent | 2020-03-18 19:07:14 | jgeraigery/blueocean-environments | https://api.github.com/repos/jgeraigery/blueocean-environments | opened | CVE-2015-8858 (High) detected in uglify-js-2.2.5.tgz, uglify-js-2.3.6.tgz | security vulnerability | ## CVE-2015-8858 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>uglify-js-2.2.5.tgz</b>, <b>uglify-js-2.3.6.tgz</b></p></summary>
<p>
<details><summary><b>uglify-js-2.2.5.tgz</b></p></summary>
<p>JavaScript parser, mangler/compressor and beautifier toolkit</p>
<p>Library home page: <a href="https://registry.npmjs.org/uglify-js/-/uglify-js-2.2.5.tgz">https://registry.npmjs.org/uglify-js/-/uglify-js-2.2.5.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/blueocean-environments/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/blueocean-environments/node_modules/transformers/node_modules/uglify-js/package.json</p>
<p>
Dependency Hierarchy:
- js-builder-0.0.62.tgz (Root Library)
- transform-1.1.2.tgz
- transformers-2.1.0.tgz
- :x: **uglify-js-2.2.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>uglify-js-2.3.6.tgz</b></p></summary>
<p>JavaScript parser, mangler/compressor and beautifier toolkit</p>
<p>Library home page: <a href="https://registry.npmjs.org/uglify-js/-/uglify-js-2.3.6.tgz">https://registry.npmjs.org/uglify-js/-/uglify-js-2.3.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/blueocean-environments/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/blueocean-environments/node_modules/uglify-js/package.json</p>
<p>
Dependency Hierarchy:
- js-builder-0.0.62.tgz (Root Library)
- handlebars-3.0.3.tgz
- :x: **uglify-js-2.3.6.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/blueocean-environments/commit/906df1e2c2b1353a7f809ef51960f8980d6cec13">906df1e2c2b1353a7f809ef51960f8980d6cec13</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The uglify-js package before 2.6.0 for Node.js allows attackers to cause a denial of service (CPU consumption) via crafted input in a parse call, aka a "regular expression denial of service (ReDoS)."
<p>Publish Date: 2017-01-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-8858>CVE-2015-8858</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-8858">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-8858</a></p>
<p>Release Date: 2018-12-15</p>
<p>Fix Resolution: v2.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"uglify-js","packageVersion":"2.2.5","isTransitiveDependency":true,"dependencyTree":"@jenkins-cd/js-builder:0.0.62;transform:1.1.2;transformers:2.1.0;uglify-js:2.2.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.6.0"},{"packageType":"javascript/Node.js","packageName":"uglify-js","packageVersion":"2.3.6","isTransitiveDependency":true,"dependencyTree":"@jenkins-cd/js-builder:0.0.62;handlebars:3.0.3;uglify-js:2.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.6.0"}],"vulnerabilityIdentifier":"CVE-2015-8858","vulnerabilityDetails":"The uglify-js package before 2.6.0 for Node.js allows attackers to cause a denial of service (CPU consumption) via crafted input in a parse call, aka a \"regular expression denial of service (ReDoS).\"","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-8858","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2015-8858 (High) detected in uglify-js-2.2.5.tgz, uglify-js-2.3.6.tgz - ## CVE-2015-8858 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>uglify-js-2.2.5.tgz</b>, <b>uglify-js-2.3.6.tgz</b></p></summary>
<p>
<details><summary><b>uglify-js-2.2.5.tgz</b></p></summary>
<p>JavaScript parser, mangler/compressor and beautifier toolkit</p>
<p>Library home page: <a href="https://registry.npmjs.org/uglify-js/-/uglify-js-2.2.5.tgz">https://registry.npmjs.org/uglify-js/-/uglify-js-2.2.5.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/blueocean-environments/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/blueocean-environments/node_modules/transformers/node_modules/uglify-js/package.json</p>
<p>
Dependency Hierarchy:
- js-builder-0.0.62.tgz (Root Library)
- transform-1.1.2.tgz
- transformers-2.1.0.tgz
- :x: **uglify-js-2.2.5.tgz** (Vulnerable Library)
</details>
<details><summary><b>uglify-js-2.3.6.tgz</b></p></summary>
<p>JavaScript parser, mangler/compressor and beautifier toolkit</p>
<p>Library home page: <a href="https://registry.npmjs.org/uglify-js/-/uglify-js-2.3.6.tgz">https://registry.npmjs.org/uglify-js/-/uglify-js-2.3.6.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/blueocean-environments/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/blueocean-environments/node_modules/uglify-js/package.json</p>
<p>
Dependency Hierarchy:
- js-builder-0.0.62.tgz (Root Library)
- handlebars-3.0.3.tgz
- :x: **uglify-js-2.3.6.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/blueocean-environments/commit/906df1e2c2b1353a7f809ef51960f8980d6cec13">906df1e2c2b1353a7f809ef51960f8980d6cec13</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The uglify-js package before 2.6.0 for Node.js allows attackers to cause a denial of service (CPU consumption) via crafted input in a parse call, aka a "regular expression denial of service (ReDoS)."
<p>Publish Date: 2017-01-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-8858>CVE-2015-8858</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-8858">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-8858</a></p>
<p>Release Date: 2018-12-15</p>
<p>Fix Resolution: v2.6.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"uglify-js","packageVersion":"2.2.5","isTransitiveDependency":true,"dependencyTree":"@jenkins-cd/js-builder:0.0.62;transform:1.1.2;transformers:2.1.0;uglify-js:2.2.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.6.0"},{"packageType":"javascript/Node.js","packageName":"uglify-js","packageVersion":"2.3.6","isTransitiveDependency":true,"dependencyTree":"@jenkins-cd/js-builder:0.0.62;handlebars:3.0.3;uglify-js:2.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.6.0"}],"vulnerabilityIdentifier":"CVE-2015-8858","vulnerabilityDetails":"The uglify-js package before 2.6.0 for Node.js allows attackers to cause a denial of service (CPU consumption) via crafted input in a parse call, aka a \"regular expression denial of service (ReDoS).\"","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-8858","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in uglify js tgz uglify js tgz cve high severity vulnerability vulnerable libraries uglify js tgz uglify js tgz uglify js tgz javascript parser mangler compressor and beautifier toolkit library home page a href path to dependency file tmp ws scm blueocean environments package json path to vulnerable library tmp ws scm blueocean environments node modules transformers node modules uglify js package json dependency hierarchy js builder tgz root library transform tgz transformers tgz x uglify js tgz vulnerable library uglify js tgz javascript parser mangler compressor and beautifier toolkit library home page a href path to dependency file tmp ws scm blueocean environments package json path to vulnerable library tmp ws scm blueocean environments node modules uglify js package json dependency hierarchy js builder tgz root library handlebars tgz x uglify js tgz vulnerable library found in head commit a href vulnerability details the uglify js package before for node js allows attackers to cause a denial of service cpu consumption via crafted input in a parse call aka a regular expression denial of service redos publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails the uglify js package before for node js allows attackers to cause a denial of service cpu consumption via crafted input in a parse call aka a regular expression denial of service redos vulnerabilityurl | 0 |
217,509 | 16,719,300,188 | IssuesEvent | 2021-06-10 04:22:13 | IoTReady/iotready.github.io | https://api.github.com/repos/IoTReady/iotready.github.io | opened | Blog on Building a Websockets Client | documentation | - WS fundamentals - link to previous blog post
- State diagram of a WS client or a flowchart - whatever is easier to understand
- Code blocks with description
- Why and how are we able to connect from a browser to a local server?
- Limitations
- Possibilities | 1.0 | Blog on Building a Websockets Client - - WS fundamentals - link to previous blog post
- State diagram of a WS client or a flowchart - whatever is easier to understand
- Code blocks with description
- Why and how are we able to connect from a browser to a local server?
- Limitations
- Possibilities | non_priority | blog on building a websockets client ws fundamentals link to previous blog post state diagram of a ws client or a flowchart whatever is easier to understand code blocks with description why and how are we able to connect from a browser to a local server limitations possibilities | 0 |
243,856 | 20,593,554,336 | IssuesEvent | 2022-03-05 05:53:36 | Uuvana-Studios/longvinter-windows-client | https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client | opened | 17 digit code to connect gives no password prompt | bug Not Tested | **Describe the bug**
When you use the 17 digit code to connect to a server, if that server is password protected there is no prompt to input a password. The server disconnects you automatically with an incorrect password.
This makes it more so difficult for server hosts that must use this to connect to a local server that they are unable to see in the server browser.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
**Expected behavior**
Enter code, prompted with password input to connect.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version [e.g. 1.0]
- Steam Version [e.g. 1.0]
**Additional context**
Add any other context about the problem here.
| 1.0 | 17 digit code to connect gives no password prompt - **Describe the bug**
When you use the 17 digit code to connect to a server, if that server is password protected there is no prompt to input a password. The server disconnects you automatically with an incorrect password.
This makes it more so difficult for server hosts that must use this to connect to a local server that they are unable to see in the server browser.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
**Expected behavior**
Enter code, prompted with password input to connect.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version [e.g. 1.0]
- Steam Version [e.g. 1.0]
**Additional context**
Add any other context about the problem here.
| non_priority | digit code to connect gives no password prompt describe the bug when you use the digit code to connect to a server if that server is password protected there is no prompt to input a password the server disconnects you automatically with an incorrect password this makes it more so difficult for server hosts that must use this to connect to a local server that they are unable to see in the server browser to reproduce steps to reproduce the behavior go to click on scroll down to see error expected behavior enter code prompted with password input to connect screenshots if applicable add screenshots to help explain your problem desktop please complete the following information os game version steam version additional context add any other context about the problem here | 0 |
103,202 | 11,349,107,529 | IssuesEvent | 2020-01-24 03:15:36 | irods/irods | https://api.github.com/repos/irods/irods | opened | document cannot specify dbsalt during upgrade | consortium-member documentation | `dbsalt` was a compile-time option for 4.1.x and before - it is not something that can be changed after upgrade.
document this behavior and reasoning in the upgrade section of the docs. | 1.0 | document cannot specify dbsalt during upgrade - `dbsalt` was a compile-time option for 4.1.x and before - it is not something that can be changed after upgrade.
document this behavior and reasoning in the upgrade section of the docs. | non_priority | document cannot specify dbsalt during upgrade dbsalt was a compile time option for x and before it is not something that can be changed after upgrade document this behavior and reasoning in the upgrade section of the docs | 0 |
275,420 | 23,914,263,646 | IssuesEvent | 2022-09-09 11:09:10 | xmos/lib_i2s | https://api.github.com/repos/xmos/lib_i2s | opened | Backpressure test for <32b data widths needs refining | type:testing size:S | In particular, a 24b data width takes significantly longer to process than the current tests allow; I suspect all non-power-of-2 cases take longer than their power-of-2 counterparts. Either the implementation needs tightening to give some breathing space or the test needs loosening in these cases. | 1.0 | Backpressure test for <32b data widths needs refining - In particular, a 24b data width takes significantly longer to process than the current tests allow; I suspect all non-power-of-2 cases take longer than their power-of-2 counterparts. Either the implementation needs tightening to give some breathing space or the test needs loosening in these cases. | non_priority | backpressure test for data widths needs refining in particular a data width takes significantly longer to process than the current tests allow i suspect all non power of cases take longer than their power of counterparts either the implementation needs tightening to give some breathing space or the test needs loosening in these cases | 0 |
325,939 | 24,066,786,371 | IssuesEvent | 2022-09-17 15:59:14 | illBeRoy/taskipy | https://api.github.com/repos/illBeRoy/taskipy | closed | Backport and use a changelog | documentation | It would be nice if the project had some sort of changelog so users of the package would know what is changing with each release and, if the package has a major version bump, what breaking changes may have occurred.
For ideas, I like the [Keep a Changelog](https://keepachangelog.com/en/1.0.0/) format personally. | 1.0 | Backport and use a changelog - It would be nice if the project had some sort of changelog so users of the package would know what is changing with each release and, if the package has a major version bump, what breaking changes may have occurred.
For ideas, I like the [Keep a Changelog](https://keepachangelog.com/en/1.0.0/) format personally. | non_priority | backport and use a changelog it would be nice if the project had some sort of changelog so users of the package would know what is changing with each release and if the package has a major version bump what breaking changes may have occurred for ideas i like the format personally | 0 |
311,777 | 23,404,549,023 | IssuesEvent | 2022-08-12 11:28:03 | UnBArqDsw2022-1/2022_1_G5_SerFit | https://api.github.com/repos/UnBArqDsw2022-1/2022_1_G5_SerFit | closed | GOF Criacional - Builder | documentation | ### Contact Details (optional)
_No response_
### Summary
Documetar Builder
### Motivation
Entrega 3
### Alternatives
_No response_
### Additional Context
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | GOF Criacional - Builder - ### Contact Details (optional)
_No response_
### Summary
Documetar Builder
### Motivation
Entrega 3
### Alternatives
_No response_
### Additional Context
_No response_
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | non_priority | gof criacional builder contact details optional no response summary documetar builder motivation entrega alternatives no response additional context no response code of conduct i agree to follow this project s code of conduct | 0 |
275,974 | 20,962,284,229 | IssuesEvent | 2022-03-28 00:02:06 | unstructuredstudio/zubhub | https://api.github.com/repos/unstructuredstudio/zubhub | opened | Generate improved and conscise ZubHub documentation | documentation enhancement good first issue | Current developer documentation for ZubHub resides in multiple places
- https://github.com/unstructuredstudio/zubhub/tree/master/zubhub_backend/zubhub/docs as well as
- https://github.com/unstructuredstudio/zubhub#development
- https://github.com/unstructuredstudio/zubhub/tree/master/single_vm_deployment
We currently need a way to bring all the documentation in one place which is concise and easy to use. New documentation should make lives of developers and newcomers to the project more easy than it is now. We have decided for now to being working on the existing markdown documentation we have and integrate it into a statically generated doc using `mkdocs`. We will be using the mkdocs-material project (https://squidfunk.github.io/mkdocs-material/) to build this new documentation. The tasks involved in this work are as follows:
- [ ] Consolidate all markdown files and create a proper documentation structure. Get inspired from https://beta.reactjs.org/learn and https://squidfunk.github.io/mkdocs-material/reference/ themselves
- [ ] Convert all the documentation in structure the mkdocs understands and ensure that the documentation builds
- [ ] Use current ERD diagram generator mechanism as part of the build
- [ ] Create a Github Sction to build the docs and push them to github pages
| 1.0 | Generate improved and conscise ZubHub documentation - Current developer documentation for ZubHub resides in multiple places
- https://github.com/unstructuredstudio/zubhub/tree/master/zubhub_backend/zubhub/docs as well as
- https://github.com/unstructuredstudio/zubhub#development
- https://github.com/unstructuredstudio/zubhub/tree/master/single_vm_deployment
We currently need a way to bring all the documentation in one place which is concise and easy to use. New documentation should make lives of developers and newcomers to the project more easy than it is now. We have decided for now to being working on the existing markdown documentation we have and integrate it into a statically generated doc using `mkdocs`. We will be using the mkdocs-material project (https://squidfunk.github.io/mkdocs-material/) to build this new documentation. The tasks involved in this work are as follows:
- [ ] Consolidate all markdown files and create a proper documentation structure. Get inspired from https://beta.reactjs.org/learn and https://squidfunk.github.io/mkdocs-material/reference/ themselves
- [ ] Convert all the documentation in structure the mkdocs understands and ensure that the documentation builds
- [ ] Use current ERD diagram generator mechanism as part of the build
- [ ] Create a Github Sction to build the docs and push them to github pages
| non_priority | generate improved and conscise zubhub documentation current developer documentation for zubhub resides in multiple places as well as we currently need a way to bring all the documentation in one place which is concise and easy to use new documentation should make lives of developers and newcomers to the project more easy than it is now we have decided for now to being working on the existing markdown documentation we have and integrate it into a statically generated doc using mkdocs we will be using the mkdocs material project to build this new documentation the tasks involved in this work are as follows consolidate all markdown files and create a proper documentation structure get inspired from and themselves convert all the documentation in structure the mkdocs understands and ensure that the documentation builds use current erd diagram generator mechanism as part of the build create a github sction to build the docs and push them to github pages | 0 |
26,724 | 20,608,632,650 | IssuesEvent | 2022-03-07 05:23:17 | WordPress/performance | https://api.github.com/repos/WordPress/performance | closed | Provide admin pointer informing about the plugin's admin screen | [Type] Enhancement Infrastructure Needs Review | For WordPress plugins that don't add their own top-level menu item to the WordPress admin menu it has been notoriously hard to be noticeable after plugin activation. The "Performance Lab" plugin adds a new submenu item "Settings > Performance", but that's obviously hard to find since it's under the existing "Settings" top-level menu item.
Displaying a WP admin pointer was suggested in https://github.com/WordPress/performance/issues/61#issuecomment-1012844968, and this issue is focused on implementing that.
Related is #192 which also adds an alternative way to discover the plugin's admin screen.
My suggestion for the admin pointer copy would be a simple text like this:
* Title: _Performance Lab_
* Content: _You can now test upcoming WordPress performance features. Open Settings > Performance to individually toggle the performance features included in the plugin._
* The _Settings > Performance_ part could be a link to the admin screen.
cc @JustinyAhin | 1.0 | Provide admin pointer informing about the plugin's admin screen - For WordPress plugins that don't add their own top-level menu item to the WordPress admin menu it has been notoriously hard to be noticeable after plugin activation. The "Performance Lab" plugin adds a new submenu item "Settings > Performance", but that's obviously hard to find since it's under the existing "Settings" top-level menu item.
Displaying a WP admin pointer was suggested in https://github.com/WordPress/performance/issues/61#issuecomment-1012844968, and this issue is focused on implementing that.
Related is #192 which also adds an alternative way to discover the plugin's admin screen.
My suggestion for the admin pointer copy would be a simple text like this:
* Title: _Performance Lab_
* Content: _You can now test upcoming WordPress performance features. Open Settings > Performance to individually toggle the performance features included in the plugin._
* The _Settings > Performance_ part could be a link to the admin screen.
cc @JustinyAhin | non_priority | provide admin pointer informing about the plugin s admin screen for wordpress plugins that don t add their own top level menu item to the wordpress admin menu it has been notoriously hard to be noticeable after plugin activation the performance lab plugin adds a new submenu item settings performance but that s obviously hard to find since it s under the existing settings top level menu item displaying a wp admin pointer was suggested in and this issue is focused on implementing that related is which also adds an alternative way to discover the plugin s admin screen my suggestion for the admin pointer copy would be a simple text like this title performance lab content you can now test upcoming wordpress performance features open settings performance to individually toggle the performance features included in the plugin the settings performance part could be a link to the admin screen cc justinyahin | 0 |
119,251 | 10,036,008,682 | IssuesEvent | 2019-07-18 09:38:52 | certbot/certbot | https://api.github.com/repos/certbot/certbot | closed | Integration tests for CLI < -- > plugin interactions | area: testing needs-update | Unit testing of cli.py's responses to various types of misconfigured plugins is quite an intricate task, because the plugins are not present when unit tests are run, and because mocking out the relevant bits of disco and plugins while keeping the tests meaningful is a very elaborate process.
Instead, we should use integration tests where the plugins are actually available, and we can mock up things like broken Apache and Nginx configurations.
| 1.0 | Integration tests for CLI < -- > plugin interactions - Unit testing of cli.py's responses to various types of misconfigured plugins is quite an intricate task, because the plugins are not present when unit tests are run, and because mocking out the relevant bits of disco and plugins while keeping the tests meaningful is a very elaborate process.
Instead, we should use integration tests where the plugins are actually available, and we can mock up things like broken Apache and Nginx configurations.
| non_priority | integration tests for cli plugin interactions unit testing of cli py s responses to various types of misconfigured plugins is quite an intricate task because the plugins are not present when unit tests are run and because mocking out the relevant bits of disco and plugins while keeping the tests meaningful is a very elaborate process instead we should use integration tests where the plugins are actually available and we can mock up things like broken apache and nginx configurations | 0 |
28,419 | 8,140,095,651 | IssuesEvent | 2018-08-20 19:55:35 | cpbills/openpa_migrate | https://api.github.com/repos/cpbills/openpa_migrate | opened | Release tarball for V1.0.4 is missing the GCC ARM header for primitives | C: build system P: blocker bug | **Reported by michael forstner on 19 Sep 2013 11:20 UTC**
Release tarball for V1.0.4 is missing the GCC ARM header for primitives.
I've downloaded the header from the current trunk and successfully compiled and tested the release on a nVidia Tegra2 system. | 1.0 | Release tarball for V1.0.4 is missing the GCC ARM header for primitives - **Reported by michael forstner on 19 Sep 2013 11:20 UTC**
Release tarball for V1.0.4 is missing the GCC ARM header for primitives.
I've downloaded the header from the current trunk and successfully compiled and tested the release on a nVidia Tegra2 system. | non_priority | release tarball for is missing the gcc arm header for primitives reported by michael forstner on sep utc release tarball for is missing the gcc arm header for primitives i ve downloaded the header from the current trunk and successfully compiled and tested the release on a nvidia system | 0 |
59,021 | 6,626,338,702 | IssuesEvent | 2017-09-22 19:06:49 | Princeton-CDH/cdh-web | https://api.github.com/repos/Princeton-CDH/cdh-web | closed | As a user, I want to view previous events by semester so that I can get a sense of event and workshop offerings. | awaiting testing | ## Notes for testing
- links to archive are not styled yet, but logic should be working | 1.0 | As a user, I want to view previous events by semester so that I can get a sense of event and workshop offerings. - ## Notes for testing
- links to archive are not styled yet, but logic should be working | non_priority | as a user i want to view previous events by semester so that i can get a sense of event and workshop offerings notes for testing links to archive are not styled yet but logic should be working | 0 |
119,252 | 15,439,055,880 | IssuesEvent | 2021-03-07 22:43:57 | civictechindex/CTI-website-frontend | https://api.github.com/repos/civictechindex/CTI-website-frontend | closed | Fix Breadcrumbs color issues | bug feature: design system feature: header role: front end | ### Overview
Per Figma, breadcrumb links should be our standard light on dark, or dark on light, but not purple like they are now, nor other colors.
These are typical problems:
<img width="439" alt="Screen Shot 2021-02-16 at 11 41 07 AM" src="https://user-images.githubusercontent.com/1218844/108113127-ef9f8880-704b-11eb-9756-d494df8d886e.png">
<img width="439" alt="Screen Shot 2021-02-16 at 11 40 45 AM" src="https://user-images.githubusercontent.com/1218844/108113135-f201e280-704b-11eb-888f-4ff445de73a9.png">
### Action
Refactor NavBreadcrumbs.js accordingly.
| 1.0 | Fix Breadcrumbs color issues - ### Overview
Per Figma, breadcrumb links should be our standard light on dark, or dark on light, but not purple like they are now, nor other colors.
These are typical problems:
<img width="439" alt="Screen Shot 2021-02-16 at 11 41 07 AM" src="https://user-images.githubusercontent.com/1218844/108113127-ef9f8880-704b-11eb-9756-d494df8d886e.png">
<img width="439" alt="Screen Shot 2021-02-16 at 11 40 45 AM" src="https://user-images.githubusercontent.com/1218844/108113135-f201e280-704b-11eb-888f-4ff445de73a9.png">
### Action
Refactor NavBreadcrumbs.js accordingly.
| non_priority | fix breadcrumbs color issues overview per figma breadcrumb links should be our standard light on dark or dark on light but not purple like they are now nor other colors these are typical problems img width alt screen shot at am src img width alt screen shot at am src action refactor navbreadcrumbs js accordingly | 0 |
12,729 | 20,825,035,661 | IssuesEvent | 2022-03-18 19:41:33 | rltsystems/Group5_CST438_Project02 | https://api.github.com/repos/rltsystems/Group5_CST438_Project02 | closed | User Story: Create Account | Core Requirement Back-End Complete | As a user, I want to be able to create an account, so I can make use of the website | 1.0 | User Story: Create Account - As a user, I want to be able to create an account, so I can make use of the website | non_priority | user story create account as a user i want to be able to create an account so i can make use of the website | 0 |
237,109 | 26,078,803,532 | IssuesEvent | 2022-12-25 01:16:48 | Nivaskumark/CVE-2020-0114-frameworks_base11 | https://api.github.com/repos/Nivaskumark/CVE-2020-0114-frameworks_base11 | opened | CVE-2022-20504 (Medium) detected in baseandroid-10.0.0_r14 | security vulnerability | ## CVE-2022-20504 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r14</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/SystemUI/src/com/android/systemui/Somnambulator.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In multiple locations of DreamManagerService.java, there is a missing permission check. This could lead to local escalation of privilege and dismissal of system dialogs with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-13Android ID: A-225878553
<p>Publish Date: 2022-12-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20504>CVE-2022-20504</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/base/+/74c52366701debed5f39c629ab85906fd3965605">https://android.googlesource.com/platform/frameworks/base/+/74c52366701debed5f39c629ab85906fd3965605</a></p>
<p>Release Date: 2022-12-16</p>
<p>Fix Resolution: android-13.0.0_r16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-20504 (Medium) detected in baseandroid-10.0.0_r14 - ## CVE-2022-20504 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r14</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a href=https://android.googlesource.com/platform/frameworks/base>https://android.googlesource.com/platform/frameworks/base</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/SystemUI/src/com/android/systemui/Somnambulator.java</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In multiple locations of DreamManagerService.java, there is a missing permission check. This could lead to local escalation of privilege and dismissal of system dialogs with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-13Android ID: A-225878553
<p>Publish Date: 2022-12-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-20504>CVE-2022-20504</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/base/+/74c52366701debed5f39c629ab85906fd3965605">https://android.googlesource.com/platform/frameworks/base/+/74c52366701debed5f39c629ab85906fd3965605</a></p>
<p>Release Date: 2022-12-16</p>
<p>Fix Resolution: android-13.0.0_r16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in baseandroid cve medium severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in base branch master vulnerable source files systemui src com android systemui somnambulator java vulnerability details in multiple locations of dreammanagerservice java there is a missing permission check this could lead to local escalation of privilege and dismissal of system dialogs with user execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with mend | 0 |
246,476 | 26,611,721,861 | IssuesEvent | 2023-01-24 01:06:47 | MohamedElashri/snibox-1 | https://api.github.com/repos/MohamedElashri/snibox-1 | opened | CVE-2022-23633 (Medium) detected in actionpack-5.2.3.gem | security vulnerability | ## CVE-2022-23633 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionpack-5.2.3.gem</b></p></summary>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-5.2.3.gem">https://rubygems.org/gems/actionpack-5.2.3.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-5.2.3.gem</p>
<p>
Dependency Hierarchy:
- rails-5.2.3.gem (Root Library)
- :x: **actionpack-5.2.3.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Action Pack is a framework for handling and responding to web requests. Under certain circumstances response bodies will not be closed. In the event a response is *not* notified of a `close`, `ActionDispatch::Executor` will not know to reset thread local state for the next request. This can lead to data being leaked to subsequent requests.This has been fixed in Rails 7.0.2.1, 6.1.4.5, 6.0.4.5, and 5.2.6.1. Upgrading is highly recommended, but to work around this problem a middleware described in GHSA-wh98-p28r-vrc9 can be used.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23633>CVE-2022-23633</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9">https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-23633 (Medium) detected in actionpack-5.2.3.gem - ## CVE-2022-23633 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>actionpack-5.2.3.gem</b></p></summary>
<p>Web apps on Rails. Simple, battle-tested conventions for building and testing MVC web applications. Works with any Rack-compatible server.</p>
<p>Library home page: <a href="https://rubygems.org/gems/actionpack-5.2.3.gem">https://rubygems.org/gems/actionpack-5.2.3.gem</a></p>
<p>Path to dependency file: /Gemfile.lock</p>
<p>Path to vulnerable library: /home/wss-scanner/.gem/ruby/2.7.0/cache/actionpack-5.2.3.gem</p>
<p>
Dependency Hierarchy:
- rails-5.2.3.gem (Root Library)
- :x: **actionpack-5.2.3.gem** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Action Pack is a framework for handling and responding to web requests. Under certain circumstances response bodies will not be closed. In the event a response is *not* notified of a `close`, `ActionDispatch::Executor` will not know to reset thread local state for the next request. This can lead to data being leaked to subsequent requests.This has been fixed in Rails 7.0.2.1, 6.1.4.5, 6.0.4.5, and 5.2.6.1. Upgrading is highly recommended, but to work around this problem a middleware described in GHSA-wh98-p28r-vrc9 can be used.
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23633>CVE-2022-23633</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9">https://github.com/rails/rails/security/advisories/GHSA-wh98-p28r-vrc9</a></p>
<p>Release Date: 2022-02-11</p>
<p>Fix Resolution: 5.2.6.2, 6.0.4.6, 6.1.4.6, 7.0.2.2
</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in actionpack gem cve medium severity vulnerability vulnerable library actionpack gem web apps on rails simple battle tested conventions for building and testing mvc web applications works with any rack compatible server library home page a href path to dependency file gemfile lock path to vulnerable library home wss scanner gem ruby cache actionpack gem dependency hierarchy rails gem root library x actionpack gem vulnerable library found in base branch master vulnerability details action pack is a framework for handling and responding to web requests under certain circumstances response bodies will not be closed in the event a response is not notified of a close actiondispatch executor will not know to reset thread local state for the next request this can lead to data being leaked to subsequent requests this has been fixed in rails and upgrading is highly recommended but to work around this problem a middleware described in ghsa can be used publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
62,316 | 6,793,677,574 | IssuesEvent | 2017-11-01 08:47:30 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | Test: Quicklook for source files supported by Code | testplan-item | Tests #25843
Complexity: 1
- [ ] macOS - @roblourens
[File types supported by Code](https://github.com/Microsoft/vscode/blob/master/build/gulpfile.vscode.js#L140) should now be able to be displayed as source code when using the <kbd>Space</kbd> key in Finder: their source should be readable. | 1.0 | Test: Quicklook for source files supported by Code - Tests #25843
Complexity: 1
- [ ] macOS - @roblourens
[File types supported by Code](https://github.com/Microsoft/vscode/blob/master/build/gulpfile.vscode.js#L140) should now be able to be displayed as source code when using the <kbd>Space</kbd> key in Finder: their source should be readable. | non_priority | test quicklook for source files supported by code tests complexity macos roblourens should now be able to be displayed as source code when using the space key in finder their source should be readable | 0 |
65,887 | 8,852,603,746 | IssuesEvent | 2019-01-08 18:50:03 | open-oni/open-oni | https://api.github.com/repos/open-oni/open-oni | opened | Document how MARC fields are used | documentation metadata type_tech | We need to create documentation that says which marc fields are used for what database / solr features. This would be very helpful in debugging features of issue and title displays. | 1.0 | Document how MARC fields are used - We need to create documentation that says which marc fields are used for what database / solr features. This would be very helpful in debugging features of issue and title displays. | non_priority | document how marc fields are used we need to create documentation that says which marc fields are used for what database solr features this would be very helpful in debugging features of issue and title displays | 0 |
128,265 | 27,223,875,182 | IssuesEvent | 2023-02-21 08:16:13 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] Add support search ID in articles and modules managers in search field admin panel. | No Code Attached Yet | ### Steps to reproduce the issue
For a very large number of 1500 articles and a large number of 100 modules .
It is very inconvenient to search by sorting materials.
For example, among 1500 materials, it is extremely difficult to find a material with ID 525.
At the same time, we know that searching for material by ID is a very common task.
.
You also need to add a filter for several categories, several types , and several positions for modules in the module Manager. | 1.0 | [4.0] Add support search ID in articles and modules managers in search field admin panel. - ### Steps to reproduce the issue
For a very large number of 1500 articles and a large number of 100 modules .
It is very inconvenient to search by sorting materials.
For example, among 1500 materials, it is extremely difficult to find a material with ID 525.
At the same time, we know that searching for material by ID is a very common task.
.
You also need to add a filter for several categories, several types , and several positions for modules in the module Manager. | non_priority | add support search id in articles and modules managers in search field admin panel steps to reproduce the issue for a very large number of articles and a large number of modules it is very inconvenient to search by sorting materials for example among materials it is extremely difficult to find a material with id at the same time we know that searching for material by id is a very common task you also need to add a filter for several categories several types and several positions for modules in the module manager | 0 |
13,180 | 3,690,337,316 | IssuesEvent | 2016-02-25 19:37:59 | scikit-image/scikit-image | https://api.github.com/repos/scikit-image/scikit-image | opened | Clarify difference between filled_area, area, and convex_hull_area in regionprops | documentation | Update the regionprops docstring to clarify the above. | 1.0 | Clarify difference between filled_area, area, and convex_hull_area in regionprops - Update the regionprops docstring to clarify the above. | non_priority | clarify difference between filled area area and convex hull area in regionprops update the regionprops docstring to clarify the above | 0 |
259,255 | 27,621,778,937 | IssuesEvent | 2023-03-10 01:11:01 | artsking/linux-4.1.15 | https://api.github.com/repos/artsking/linux-4.1.15 | opened | CVE-2023-1078 (High) detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2023-1078 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.1.15/commit/b1c15f7dc4cfe553aeed8332e46f285ee92b5756">b1c15f7dc4cfe553aeed8332e46f285ee92b5756</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This CVE was marked as RESERVED by NVD. This means that the CVE-ID is reserved for future use by the CVE Numbering Authority (CNA) or a security researcher. Still, the CVE details were not included in the CVE entry. This is because the original requester of the CVE ID assignment has not sent an update to MITRE with the information needed to populate the CVE entry.
This page will reflect the classification results once they are available through NVD
<p>Publish Date: 2023-02-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1078>CVE-2023-1078</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-1078">https://www.linuxkernelcves.com/cves/CVE-2023-1078</a></p>
<p>Release Date: 2023-02-28</p>
<p>Fix Resolution: v4.19.273,v5.4.232,v5.10.168,v5.15.94,v6.1.12,v6.2-rc8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2023-1078 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2023-1078 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.1.15/commit/b1c15f7dc4cfe553aeed8332e46f285ee92b5756">b1c15f7dc4cfe553aeed8332e46f285ee92b5756</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This CVE was marked as RESERVED by NVD. This means that the CVE-ID is reserved for future use by the CVE Numbering Authority (CNA) or a security researcher. Still, the CVE details were not included in the CVE entry. This is because the original requester of the CVE ID assignment has not sent an update to MITRE with the information needed to populate the CVE entry.
This page will reflect the classification results once they are available through NVD
<p>Publish Date: 2023-02-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-1078>CVE-2023-1078</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2023-1078">https://www.linuxkernelcves.com/cves/CVE-2023-1078</a></p>
<p>Release Date: 2023-02-28</p>
<p>Fix Resolution: v4.19.273,v5.4.232,v5.10.168,v5.15.94,v6.1.12,v6.2-rc8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details this cve was marked as reserved by nvd this means that the cve id is reserved for future use by the cve numbering authority cna or a security researcher still the cve details were not included in the cve entry this is because the original requester of the cve id assignment has not sent an update to mitre with the information needed to populate the cve entry this page will reflect the classification results once they are available through nvd publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
125,082 | 12,246,814,054 | IssuesEvent | 2020-05-05 14:59:26 | Yuki2Kisaragi/github-slideshow | https://api.github.com/repos/Yuki2Kisaragi/github-slideshow | closed | Your first contribution | documentation good first issue question | ### GitHubフローの紹介
さてイシューに慣れてきたところで、このイシューを使ってあなたの初めてのコントリビュートの道筋をたどってみましょう。
プロジェクトによってコントリビュートのフローは異なりますが、GitHub上で最もシンプルで最も効率的なコントリビュートのやり方はGitHubフローです。
:tv: [ビデオ:GitHubフローを理解する](https://www.youtube.com/watch?v=PBI2Rz-ZOxU)
<hr>
<h3 align="center">以下を読み進めて、次のステップに移りましょう</h3>
| 1.0 | Your first contribution - ### GitHubフローの紹介
さてイシューに慣れてきたところで、このイシューを使ってあなたの初めてのコントリビュートの道筋をたどってみましょう。
プロジェクトによってコントリビュートのフローは異なりますが、GitHub上で最もシンプルで最も効率的なコントリビュートのやり方はGitHubフローです。
:tv: [ビデオ:GitHubフローを理解する](https://www.youtube.com/watch?v=PBI2Rz-ZOxU)
<hr>
<h3 align="center">以下を読み進めて、次のステップに移りましょう</h3>
| non_priority | your first contribution githubフローの紹介 さてイシューに慣れてきたところで、このイシューを使ってあなたの初めてのコントリビュートの道筋をたどってみましょう。 プロジェクトによってコントリビュートのフローは異なりますが、github上で最もシンプルで最も効率的なコントリビュートのやり方はgithubフローです。 tv 以下を読み進めて、次のステップに移りましょう | 0 |
368,238 | 25,783,531,212 | IssuesEvent | 2022-12-09 18:05:35 | webdataset/webdataset | https://api.github.com/repos/webdataset/webdataset | closed | WebDataset no longer has a length argument (documentation) | documentation | In the docs, it's mentioned that "you can specify an explicit size using the `length=` argument to WebDataset"
https://github.com/webdataset/webdataset/blob/2eaa96e6a266ad0ae1a1433e86eb6c2d3b7c50f8/docs/sharding/index.html#L177-L179
This is no longer true, as there is no `length=` argument to WebDataset.
https://github.com/webdataset/webdataset/blob/45724cdfcc0935c63ac6952c5f6b0ada9fa44f37/webdataset/dataset.py#L29-L39
I'm not sure if the documentation is out of date in mentioning a removed parameter, or if the parameter should be there, but got removed accidentally. | 1.0 | WebDataset no longer has a length argument (documentation) - In the docs, it's mentioned that "you can specify an explicit size using the `length=` argument to WebDataset"
https://github.com/webdataset/webdataset/blob/2eaa96e6a266ad0ae1a1433e86eb6c2d3b7c50f8/docs/sharding/index.html#L177-L179
This is no longer true, as there is no `length=` argument to WebDataset.
https://github.com/webdataset/webdataset/blob/45724cdfcc0935c63ac6952c5f6b0ada9fa44f37/webdataset/dataset.py#L29-L39
I'm not sure if the documentation is out of date in mentioning a removed parameter, or if the parameter should be there, but got removed accidentally. | non_priority | webdataset no longer has a length argument documentation in the docs it s mentioned that you can specify an explicit size using the length argument to webdataset this is no longer true as there is no length argument to webdataset i m not sure if the documentation is out of date in mentioning a removed parameter or if the parameter should be there but got removed accidentally | 0 |
187,732 | 15,106,711,595 | IssuesEvent | 2021-02-08 14:37:15 | phantom08266/TIL | https://api.github.com/repos/phantom08266/TIL | closed | JSP 웹 프로그래밍 | documentation | 최범균의 JSP2.3 웹 프로그래밍 학습하기.
- [x] 1장
- [x] 2장
- [x] 3장
- [x] 4장
- [x] 9장
- [x] 10장
- [x] 17장
- [x] 18장
- [x] 19장
- [x] 20장
1 ~ 4, 9, 10, 17 ~ 20 학습할 것. | 1.0 | JSP 웹 프로그래밍 - 최범균의 JSP2.3 웹 프로그래밍 학습하기.
- [x] 1장
- [x] 2장
- [x] 3장
- [x] 4장
- [x] 9장
- [x] 10장
- [x] 17장
- [x] 18장
- [x] 19장
- [x] 20장
1 ~ 4, 9, 10, 17 ~ 20 학습할 것. | non_priority | jsp 웹 프로그래밍 최범균의 웹 프로그래밍 학습하기 학습할 것 | 0 |
267,792 | 28,509,224,469 | IssuesEvent | 2023-04-19 01:46:13 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | closed | CVE-2013-2889 (Medium) detected in linuxv3.0 - autoclosed | Mend: dependency security vulnerability | ## CVE-2013-2889 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-zpff.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-zpff.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-zpff.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/hid/hid-zpff.c in the Human Interface Device (HID) subsystem in the Linux kernel through 3.11, when CONFIG_HID_ZEROPLUS is enabled, allows physically proximate attackers to cause a denial of service (heap-based out-of-bounds write) via a crafted device.
<p>Publish Date: 2013-09-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-2889>CVE-2013-2889</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2889">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2889</a></p>
<p>Release Date: 2013-09-16</p>
<p>Fix Resolution: v3.12-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2013-2889 (Medium) detected in linuxv3.0 - autoclosed - ## CVE-2013-2889 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-zpff.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-zpff.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/hid/hid-zpff.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/hid/hid-zpff.c in the Human Interface Device (HID) subsystem in the Linux kernel through 3.11, when CONFIG_HID_ZEROPLUS is enabled, allows physically proximate attackers to cause a denial of service (heap-based out-of-bounds write) via a crafted device.
<p>Publish Date: 2013-09-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-2889>CVE-2013-2889</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2889">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2889</a></p>
<p>Release Date: 2013-09-16</p>
<p>Fix Resolution: v3.12-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files drivers hid hid zpff c drivers hid hid zpff c drivers hid hid zpff c vulnerability details drivers hid hid zpff c in the human interface device hid subsystem in the linux kernel through when config hid zeroplus is enabled allows physically proximate attackers to cause a denial of service heap based out of bounds write via a crafted device publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
25,259 | 12,532,611,873 | IssuesEvent | 2020-06-04 16:12:50 | intellij-rust/intellij-rust | https://api.github.com/repos/intellij-rust/intellij-rust | closed | Half minute to minute long freezes on versions > 0.2.120.2202-201 due to getOwnedDirectory | performance | <!--
Hello and thank you for the issue!
If you would like to report a bug, we have added some points below that you can fill out.
Feel free to remove all the irrelevant text to request a new feature.
-->
## Environment
* 0.2.123.3132-201
* rustc 1.45.0-nightly (769d12eec 2020-05-12)
* IntelliJ Ultimate Edition 2020.1.2
* macOS 10.15.4
## Problem description
In order to prevent 10s of seconds to almost a minute long pauses when making changes in https://github.com/lumen/lumen, I've had to downgrade from the latest release to 0.2.120.2202-201.
A lot of the longest pauses seem attributed to `getOwnedDirectory` from the `threadDumps-freeze` directories.
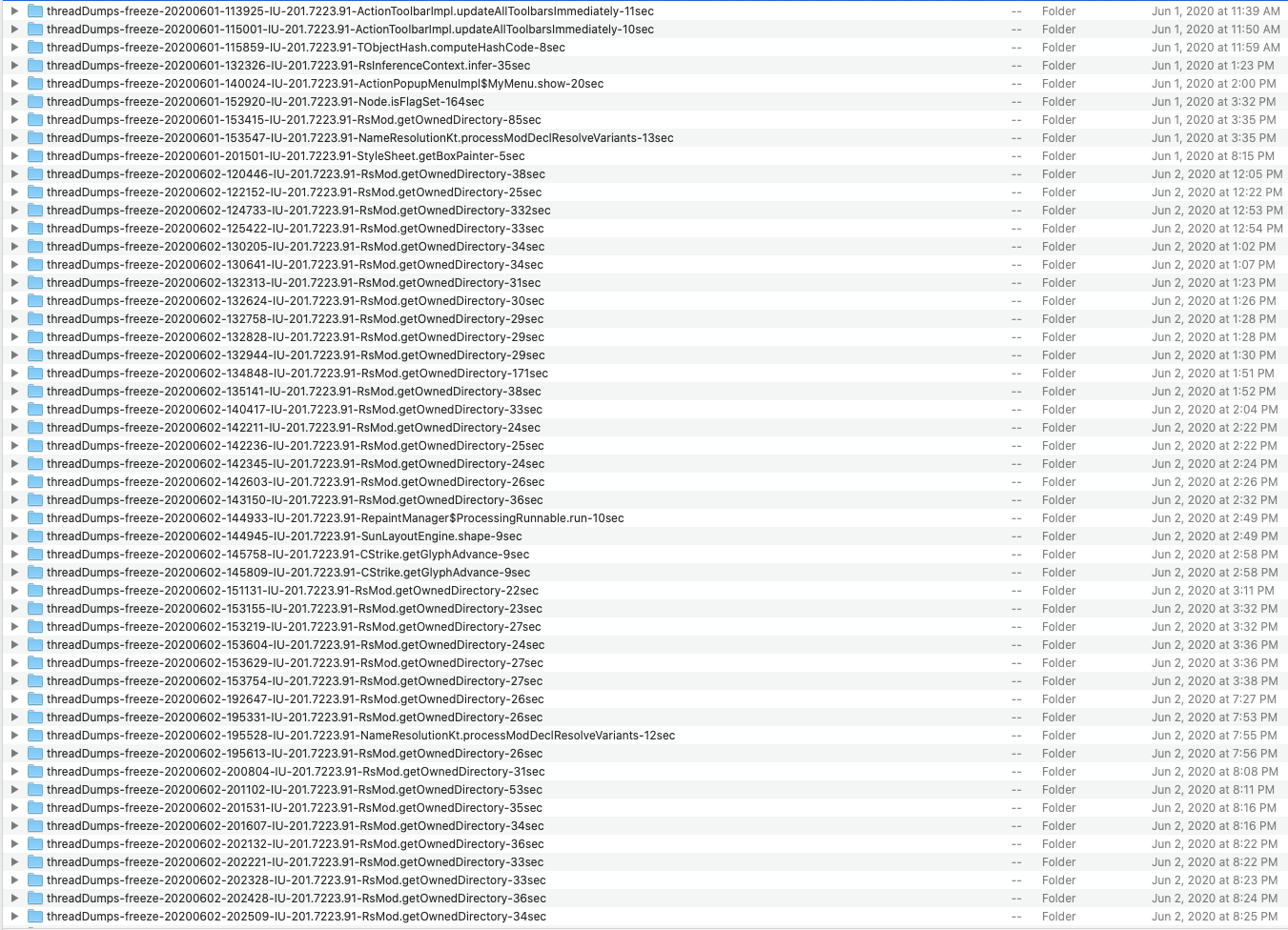
All the `threadDumps-freeze` directories that appear associated with the plugin are attached in this zip: [Archive.zip](https://github.com/intellij-rust/intellij-rust/files/4730110/Archive.zip)
## Steps to reproduce
1. `git clone git@github.com:lumen/lumen.git lumen/lumen`
2. `cd lumen/lumen`
3. `git checkout otp-runtime-selection`
3. Open the repository in the IDE.
4. Try to edit a file, such as adding an if inside a function in `liblumen_alloc/src/erts/process.rs`
5. Get a long freeze if plugin > 0.2.120.2202-201
| True | Half minute to minute long freezes on versions > 0.2.120.2202-201 due to getOwnedDirectory - <!--
Hello and thank you for the issue!
If you would like to report a bug, we have added some points below that you can fill out.
Feel free to remove all the irrelevant text to request a new feature.
-->
## Environment
* 0.2.123.3132-201
* rustc 1.45.0-nightly (769d12eec 2020-05-12)
* IntelliJ Ultimate Edition 2020.1.2
* macOS 10.15.4
## Problem description
In order to prevent 10s of seconds to almost a minute long pauses when making changes in https://github.com/lumen/lumen, I've had to downgrade from the latest release to 0.2.120.2202-201.
A lot of the longest pauses seem attributed to `getOwnedDirectory` from the `threadDumps-freeze` directories.
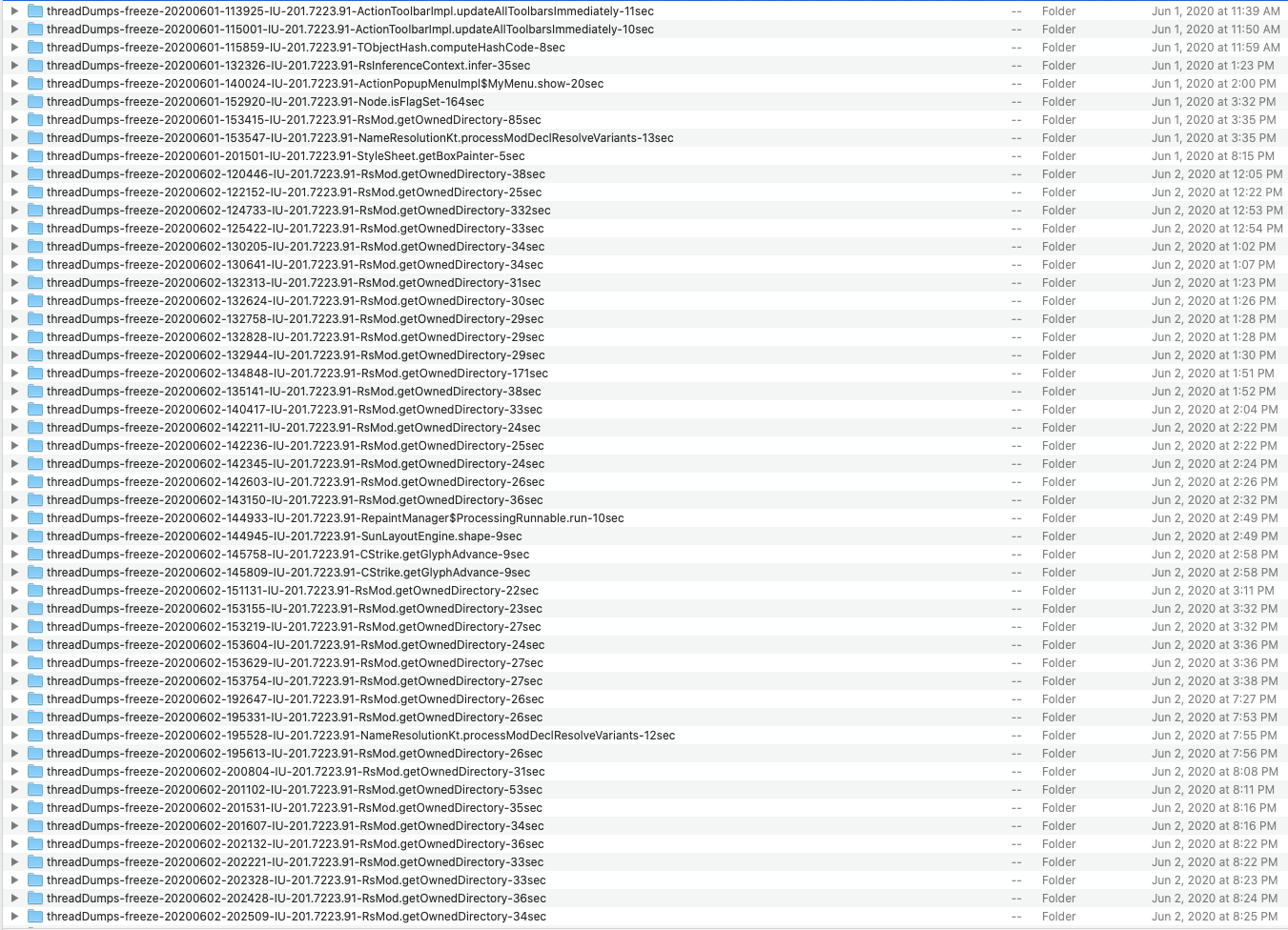
All the `threadDumps-freeze` directories that appear associated with the plugin are attached in this zip: [Archive.zip](https://github.com/intellij-rust/intellij-rust/files/4730110/Archive.zip)
## Steps to reproduce
1. `git clone git@github.com:lumen/lumen.git lumen/lumen`
2. `cd lumen/lumen`
3. `git checkout otp-runtime-selection`
3. Open the repository in the IDE.
4. Try to edit a file, such as adding an if inside a function in `liblumen_alloc/src/erts/process.rs`
5. Get a long freeze if plugin > 0.2.120.2202-201
| non_priority | half minute to minute long freezes on versions due to getowneddirectory hello and thank you for the issue if you would like to report a bug we have added some points below that you can fill out feel free to remove all the irrelevant text to request a new feature environment rustc nightly intellij ultimate edition macos problem description in order to prevent of seconds to almost a minute long pauses when making changes in i ve had to downgrade from the latest release to a lot of the longest pauses seem attributed to getowneddirectory from the threaddumps freeze directories all the threaddumps freeze directories that appear associated with the plugin are attached in this zip steps to reproduce git clone git github com lumen lumen git lumen lumen cd lumen lumen git checkout otp runtime selection open the repository in the ide try to edit a file such as adding an if inside a function in liblumen alloc src erts process rs get a long freeze if plugin | 0 |
235,278 | 18,046,019,361 | IssuesEvent | 2021-09-18 22:56:27 | exoscoriae/eXoDOS | https://api.github.com/repos/exoscoriae/eXoDOS | closed | Wing Commander (1990) | documentation | There's a German fan patch for Wing Commander 1 and Secret Missions 1:
[CG-Board (Traxx Amiga EP](https://cgboard.raysworld.ch/showthread.php?tid=26961)
- Install english WC (I used 3*3,5" floppies)
- Install english Secret Missions (I used 2*3,5" floppies)
- copy the files from the patch WC folder to the installation folder (WING)
- copy the files from the patch WC_SM1 folder to the installation folder (WING)
- copy the INTRO.DAT from PROT\WC1 SM1 folder to the installation folder (WING) (it's a "special" copy protection solution ;-) )
- copy the WINGCMDR.CFG from the patch folder to the installation folder (WING)
(I also modified the WINGCMDR.CFG for MT32 and added it as a startup option)
Now the game is German 👍 | 1.0 | Wing Commander (1990) - There's a German fan patch for Wing Commander 1 and Secret Missions 1:
[CG-Board (Traxx Amiga EP](https://cgboard.raysworld.ch/showthread.php?tid=26961)
- Install english WC (I used 3*3,5" floppies)
- Install english Secret Missions (I used 2*3,5" floppies)
- copy the files from the patch WC folder to the installation folder (WING)
- copy the files from the patch WC_SM1 folder to the installation folder (WING)
- copy the INTRO.DAT from PROT\WC1 SM1 folder to the installation folder (WING) (it's a "special" copy protection solution ;-) )
- copy the WINGCMDR.CFG from the patch folder to the installation folder (WING)
(I also modified the WINGCMDR.CFG for MT32 and added it as a startup option)
Now the game is German 👍 | non_priority | wing commander there s a german fan patch for wing commander and secret missions install english wc i used floppies install english secret missions i used floppies copy the files from the patch wc folder to the installation folder wing copy the files from the patch wc folder to the installation folder wing copy the intro dat from prot folder to the installation folder wing it s a special copy protection solution copy the wingcmdr cfg from the patch folder to the installation folder wing i also modified the wingcmdr cfg for and added it as a startup option now the game is german 👍 | 0 |
242,876 | 20,269,541,996 | IssuesEvent | 2022-02-15 15:05:07 | microsoft/playwright | https://api.github.com/repos/microsoft/playwright | closed | Hide/remove Elements from Screenshots | feature-visual-regression-testing v1.20 | ### Discussed in https://github.com/microsoft/playwright/discussions/5068
<div type='discussions-op-text'>
<sup>Originally posted by **rollin-cogers** January 20, 2021</sup>
Hey everyone! I've been very excited to use this tool for testing, as I've previously been using protractor for all my testing.
In the past I've used modules like webdriver-image-comparison that allow for options like [hiding and removing elements](https://github.com/wswebcreation/webdriver-image-comparison/blob/master/docs/OPTIONS.md#hideelements-5) from a screenshot by adding `visibility: hidden` or `display: none` to the styling for the passed elements.
Is this a feature that we might see in the future with playwright? Would anyone else benefit from the ability to exclude elements from screenshots?
I would love to see something like this:
```javascript
page.screenshot({fullpage: true, hideElements: ['div.dynamic_content', 'div#profilePicture']})
```</div> | 1.0 | Hide/remove Elements from Screenshots - ### Discussed in https://github.com/microsoft/playwright/discussions/5068
<div type='discussions-op-text'>
<sup>Originally posted by **rollin-cogers** January 20, 2021</sup>
Hey everyone! I've been very excited to use this tool for testing, as I've previously been using protractor for all my testing.
In the past I've used modules like webdriver-image-comparison that allow for options like [hiding and removing elements](https://github.com/wswebcreation/webdriver-image-comparison/blob/master/docs/OPTIONS.md#hideelements-5) from a screenshot by adding `visibility: hidden` or `display: none` to the styling for the passed elements.
Is this a feature that we might see in the future with playwright? Would anyone else benefit from the ability to exclude elements from screenshots?
I would love to see something like this:
```javascript
page.screenshot({fullpage: true, hideElements: ['div.dynamic_content', 'div#profilePicture']})
```</div> | non_priority | hide remove elements from screenshots discussed in originally posted by rollin cogers january hey everyone i ve been very excited to use this tool for testing as i ve previously been using protractor for all my testing in the past i ve used modules like webdriver image comparison that allow for options like from a screenshot by adding visibility hidden or display none to the styling for the passed elements is this a feature that we might see in the future with playwright would anyone else benefit from the ability to exclude elements from screenshots i would love to see something like this javascript page screenshot fullpage true hideelements | 0 |
12,549 | 3,281,800,760 | IssuesEvent | 2015-10-28 00:28:10 | d3athrow/vgstation13 | https://api.github.com/repos/d3athrow/vgstation13 | closed | BLINDED BY MY HATE FOR OXYGEN-BREATHERS | Bug Needs Moar Testing | AFTER BEING BOMBED BY AN OXYGEN BREATHER I WAS CLONED. DURING THE TIME I WAS BEING CLONED I BECAME BLINDED BY MY HATE FOR THOSE WHO BREATHE TOXINS
OFF THE O2
 | 1.0 | BLINDED BY MY HATE FOR OXYGEN-BREATHERS - AFTER BEING BOMBED BY AN OXYGEN BREATHER I WAS CLONED. DURING THE TIME I WAS BEING CLONED I BECAME BLINDED BY MY HATE FOR THOSE WHO BREATHE TOXINS
OFF THE O2
 | non_priority | blinded by my hate for oxygen breathers after being bombed by an oxygen breather i was cloned during the time i was being cloned i became blinded by my hate for those who breathe toxins off the | 0 |
211,441 | 23,826,148,690 | IssuesEvent | 2022-09-05 15:01:24 | sast-automation-dev/easybuggy-12 | https://api.github.com/repos/sast-automation-dev/easybuggy-12 | opened | esapi-2.1.0.1.jar: 14 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2016-1000031](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000031) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2016-2510](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2510) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | bsh-core-2.0b4.jar | Transitive | N/A | ❌ |
| [CVE-2016-3092](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3092) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2012-0881](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-0881) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xercesImpl-2.8.0.jar | Transitive | N/A | ❌ |
| [WS-2014-0034](https://commons.apache.org/proper/commons-fileupload/changes-report.html) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2014-0107](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0107) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | xalan-2.7.0.jar | Transitive | 2.5.0.0 | ✅ |
| [CVE-2019-10086](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2014-0114](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | N/A | ❌ |
| [CVE-2016-10006](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10006) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2017-14735](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-14735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2013-4002](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4002) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | xercesImpl-2.8.0.jar | Transitive | N/A | ❌ |
| [CVE-2009-2625](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | xercesImpl-2.8.0.jar | Transitive | N/A | ❌ |
| [CVE-2012-5783](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-5783) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-httpclient-3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2021-29425](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-io-2.2.jar | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1000031</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons FileUpload before 1.3.3 DiskFileItem File Manipulation Remote Code Execution
<p>Publish Date: 2016-10-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000031>CVE-2016-1000031</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031</a></p>
<p>Release Date: 2016-10-25</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.1-jenkins-1</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2510</summary>
### Vulnerable Library - <b>bsh-core-2.0b4.jar</b></p>
<p>BeanShell core</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/beanshell/bsh-core/2.0b4/bsh-core-2.0b4.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **bsh-core-2.0b4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
BeanShell (bsh) before 2.0b6, when included on the classpath by an application that uses Java serialization or XStream, allows remote attackers to execute arbitrary code via crafted serialized data, related to XThis.Handler.
<p>Publish Date: 2016-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2510>CVE-2016-2510</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2510">https://nvd.nist.gov/vuln/detail/CVE-2016-2510</a></p>
<p>Release Date: 2016-04-07</p>
<p>Fix Resolution: 2.0b6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-3092</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MultipartStream class in Apache Commons Fileupload before 1.3.2, as used in Apache Tomcat 7.x before 7.0.70, 8.x before 8.0.36, 8.5.x before 8.5.3, and 9.x before 9.0.0.M7 and other products, allows remote attackers to cause a denial of service (CPU consumption) via a long boundary string.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3092>CVE-2016-3092</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.1-jenkins-1</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-0881</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Xerces2 Java Parser before 2.12.0 allows remote attackers to cause a denial of service (CPU consumption) via a crafted message to an XML service, which triggers hash table collisions.
<p>Publish Date: 2017-10-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-0881>CVE-2012-0881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881</a></p>
<p>Release Date: 2017-10-30</p>
<p>Fix Resolution: 2.12.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2014-0034</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The class FileUploadBase in Apache Commons Fileupload before 1.4 has potential resource leak - InputStream not closed on exception.
<p>Publish Date: 2014-02-17
<p>URL: <a href=https://commons.apache.org/proper/commons-fileupload/changes-report.html>WS-2014-0034</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2014-02-17</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.1-jenkins-1</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0107</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The TransformerFactory in Apache Xalan-Java before 2.7.2 does not properly restrict access to certain properties when FEATURE_SECURE_PROCESSING is enabled, which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted (1) xalan:content-header, (2) xalan:entities, (3) xslt:content-header, or (4) xslt:entities property, or a Java property that is bound to the XSLT 1.0 system-property function.
<p>Publish Date: 2014-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0107>CVE-2014-0107</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107</a></p>
<p>Release Date: 2014-04-15</p>
<p>Fix Resolution (xalan:xalan): 2.7.1-NODEP</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.5.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10086</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p>The Apache Software Foundation provides support for the Apache community of open-source software projects.
The Apache projects are characterized by a collaborative, consensus based development process, an open and
pragmatic software license, and a desire to create high quality software that leads the way in its field.
We consider ourselves not simply a group of projects sharing a server, but rather a community of developers
and users.</p>
<p>Library home page: <a href="http://commons.apache.org/beanutils/">http://commons.apache.org/beanutils/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons Beanutils 1.9.2, a special BeanIntrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all Java objects. We, however were not using this by default characteristic of the PropertyUtilsBean.
<p>Publish Date: 2019-08-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10086>CVE-2019-10086</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-20</p>
<p>Fix Resolution (commons-beanutils:commons-beanutils-core): 1.8.3-SONATYPE</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0114</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p>The Apache Software Foundation provides support for the Apache community of open-source software projects.
The Apache projects are characterized by a collaborative, consensus based development process, an open and
pragmatic software license, and a desire to create high quality software that leads the way in its field.
We consider ourselves not simply a group of projects sharing a server, but rather a community of developers
and users.</p>
<p>Library home page: <a href="http://commons.apache.org/beanutils/">http://commons.apache.org/beanutils/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10006</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In OWASP AntiSamy before 1.5.5, by submitting a specially crafted input (a tag that supports style with active content), you could bypass the library protections and supply executable code. The impact is XSS.
<p>Publish Date: 2016-12-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10006>CVE-2016-10006</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006</a></p>
<p>Release Date: 2016-12-24</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.5</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-14735</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.5.7 allows XSS via HTML5 entities, as demonstrated by use of : to construct a javascript: URL.
<p>Publish Date: 2017-09-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-14735>CVE-2017-14735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735</a></p>
<p>Release Date: 2017-09-25</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.7</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-4002</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLscanner.java in Apache Xerces2 Java Parser before 2.12.0, as used in the Java Runtime Environment (JRE) in IBM Java 5.0 before 5.0 SR16-FP3, 6 before 6 SR14, 6.0.1 before 6.0.1 SR6, and 7 before 7 SR5 as well as Oracle Java SE 7u40 and earlier, Java SE 6u60 and earlier, Java SE 5.0u51 and earlier, JRockit R28.2.8 and earlier, JRockit R27.7.6 and earlier, Java SE Embedded 7u40 and earlier, and possibly other products allows remote attackers to cause a denial of service via vectors related to XML attribute names.
<p>Publish Date: 2013-07-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4002>CVE-2013-4002</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002</a></p>
<p>Release Date: 2013-07-23</p>
<p>Fix Resolution: xerces:xercesImpl:Xerces-J_2_12_0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2009-2625</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.
<p>Publish Date: 2009-08-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625>CVE-2009-2625</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2009-2625">https://nvd.nist.gov/vuln/detail/CVE-2009-2625</a></p>
<p>Release Date: 2009-08-06</p>
<p>Fix Resolution: apache-xerces:xercesImpl - 2.9.1;xerces:xercesImpl - 2.9.1-NODEP,2.3.0,2.9.0;org.apache.servicemix.bundles:org.apache.servicemix.bundles.xerces - 2.10.0_1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-5783</summary>
### Vulnerable Library - <b>commons-httpclient-3.1.jar</b></p>
<p>The HttpClient component supports the client-side of RFC 1945 (HTTP/1.0) and RFC 2616 (HTTP/1.1) , several related specifications (RFC 2109 (Cookies) , RFC 2617 (HTTP Authentication) , etc.), and provides a framework by which new request types (methods) or HTTP extensions can be created easily.</p>
<p>Library home page: <a href="http://jakarta.apache.org/httpcomponents/httpclient-3.x/">http://jakarta.apache.org/httpcomponents/httpclient-3.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-httpclient/commons-httpclient/3.1/commons-httpclient-3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- antisamy-1.5.3.jar
- :x: **commons-httpclient-3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons HttpClient 3.x, as used in Amazon Flexible Payments Service (FPS) merchant Java SDK and other products, does not verify that the server hostname matches a domain name in the subject's Common Name (CN) or subjectAltName field of the X.509 certificate, which allows man-in-the-middle attackers to spoof SSL servers via an arbitrary valid certificate.
<p>Publish Date: 2012-11-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-5783>CVE-2012-5783</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-5783">https://nvd.nist.gov/vuln/detail/CVE-2012-5783</a></p>
<p>Release Date: 2012-11-04</p>
<p>Fix Resolution (commons-httpclient:commons-httpclient): 3.1-HTTPCLIENT-1265</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-29425</summary>
### Vulnerable Library - <b>commons-io-2.2.jar</b></p>
<p>The Commons IO library contains utility classes, stream implementations, file filters,
file comparators, endian transformation classes, and much more.</p>
<p>Library home page: <a href="http://commons.apache.org/io/">http://commons.apache.org/io/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-io/commons-io/2.2/commons-io-2.2.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- commons-fileupload-1.3.1.jar
- :x: **commons-io-2.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons IO before 2.7, When invoking the method FileNameUtils.normalize with an improper input string, like "//../foo", or "\\..\foo", the result would be the same value, thus possibly providing access to files in the parent directory, but not further above (thus "limited" path traversal), if the calling code would use the result to construct a path value.
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29425>CVE-2021-29425</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425</a></p>
<p>Release Date: 2021-04-13</p>
<p>Fix Resolution: commons-io:commons-io:2.7</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | esapi-2.1.0.1.jar: 14 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2016-1000031](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000031) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2016-2510](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2510) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | bsh-core-2.0b4.jar | Transitive | N/A | ❌ |
| [CVE-2016-3092](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3092) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2012-0881](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-0881) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xercesImpl-2.8.0.jar | Transitive | N/A | ❌ |
| [WS-2014-0034](https://commons.apache.org/proper/commons-fileupload/changes-report.html) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2014-0107](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0107) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | xalan-2.7.0.jar | Transitive | 2.5.0.0 | ✅ |
| [CVE-2019-10086](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2014-0114](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | N/A | ❌ |
| [CVE-2016-10006](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10006) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2017-14735](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-14735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2013-4002](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4002) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | xercesImpl-2.8.0.jar | Transitive | N/A | ❌ |
| [CVE-2009-2625](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | xercesImpl-2.8.0.jar | Transitive | N/A | ❌ |
| [CVE-2012-5783](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-5783) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-httpclient-3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2021-29425](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-io-2.2.jar | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1000031</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons FileUpload before 1.3.3 DiskFileItem File Manipulation Remote Code Execution
<p>Publish Date: 2016-10-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000031>CVE-2016-1000031</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031</a></p>
<p>Release Date: 2016-10-25</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.1-jenkins-1</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2510</summary>
### Vulnerable Library - <b>bsh-core-2.0b4.jar</b></p>
<p>BeanShell core</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/beanshell/bsh-core/2.0b4/bsh-core-2.0b4.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **bsh-core-2.0b4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
BeanShell (bsh) before 2.0b6, when included on the classpath by an application that uses Java serialization or XStream, allows remote attackers to execute arbitrary code via crafted serialized data, related to XThis.Handler.
<p>Publish Date: 2016-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2510>CVE-2016-2510</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2510">https://nvd.nist.gov/vuln/detail/CVE-2016-2510</a></p>
<p>Release Date: 2016-04-07</p>
<p>Fix Resolution: 2.0b6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-3092</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MultipartStream class in Apache Commons Fileupload before 1.3.2, as used in Apache Tomcat 7.x before 7.0.70, 8.x before 8.0.36, 8.5.x before 8.5.3, and 9.x before 9.0.0.M7 and other products, allows remote attackers to cause a denial of service (CPU consumption) via a long boundary string.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-3092>CVE-2016-3092</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.1-jenkins-1</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-0881</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Xerces2 Java Parser before 2.12.0 allows remote attackers to cause a denial of service (CPU consumption) via a crafted message to an XML service, which triggers hash table collisions.
<p>Publish Date: 2017-10-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-0881>CVE-2012-0881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881</a></p>
<p>Release Date: 2017-10-30</p>
<p>Fix Resolution: 2.12.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2014-0034</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Library home page: <a href="http://commons.apache.org/proper/commons-fileupload/">http://commons.apache.org/proper/commons-fileupload/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The class FileUploadBase in Apache Commons Fileupload before 1.4 has potential resource leak - InputStream not closed on exception.
<p>Publish Date: 2014-02-17
<p>URL: <a href=https://commons.apache.org/proper/commons-fileupload/changes-report.html>WS-2014-0034</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2014-02-17</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.1-jenkins-1</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0107</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The TransformerFactory in Apache Xalan-Java before 2.7.2 does not properly restrict access to certain properties when FEATURE_SECURE_PROCESSING is enabled, which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted (1) xalan:content-header, (2) xalan:entities, (3) xslt:content-header, or (4) xslt:entities property, or a Java property that is bound to the XSLT 1.0 system-property function.
<p>Publish Date: 2014-04-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0107>CVE-2014-0107</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107</a></p>
<p>Release Date: 2014-04-15</p>
<p>Fix Resolution (xalan:xalan): 2.7.1-NODEP</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.5.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10086</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p>The Apache Software Foundation provides support for the Apache community of open-source software projects.
The Apache projects are characterized by a collaborative, consensus based development process, an open and
pragmatic software license, and a desire to create high quality software that leads the way in its field.
We consider ourselves not simply a group of projects sharing a server, but rather a community of developers
and users.</p>
<p>Library home page: <a href="http://commons.apache.org/beanutils/">http://commons.apache.org/beanutils/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons Beanutils 1.9.2, a special BeanIntrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all Java objects. We, however were not using this by default characteristic of the PropertyUtilsBean.
<p>Publish Date: 2019-08-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10086>CVE-2019-10086</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-20</p>
<p>Fix Resolution (commons-beanutils:commons-beanutils-core): 1.8.3-SONATYPE</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0114</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p>The Apache Software Foundation provides support for the Apache community of open-source software projects.
The Apache projects are characterized by a collaborative, consensus based development process, an open and
pragmatic software license, and a desire to create high quality software that leads the way in its field.
We consider ourselves not simply a group of projects sharing a server, but rather a community of developers
and users.</p>
<p>Library home page: <a href="http://commons.apache.org/beanutils/">http://commons.apache.org/beanutils/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10006</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In OWASP AntiSamy before 1.5.5, by submitting a specially crafted input (a tag that supports style with active content), you could bypass the library protections and supply executable code. The impact is XSS.
<p>Publish Date: 2016-12-24
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10006>CVE-2016-10006</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006</a></p>
<p>Release Date: 2016-12-24</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.5</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-14735</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.5.7 allows XSS via HTML5 entities, as demonstrated by use of : to construct a javascript: URL.
<p>Publish Date: 2017-09-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-14735>CVE-2017-14735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735</a></p>
<p>Release Date: 2017-09-25</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.7</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-4002</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLscanner.java in Apache Xerces2 Java Parser before 2.12.0, as used in the Java Runtime Environment (JRE) in IBM Java 5.0 before 5.0 SR16-FP3, 6 before 6 SR14, 6.0.1 before 6.0.1 SR6, and 7 before 7 SR5 as well as Oracle Java SE 7u40 and earlier, Java SE 6u60 and earlier, Java SE 5.0u51 and earlier, JRockit R28.2.8 and earlier, JRockit R27.7.6 and earlier, Java SE Embedded 7u40 and earlier, and possibly other products allows remote attackers to cause a denial of service via vectors related to XML attribute names.
<p>Publish Date: 2013-07-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4002>CVE-2013-4002</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002</a></p>
<p>Release Date: 2013-07-23</p>
<p>Fix Resolution: xerces:xercesImpl:Xerces-J_2_12_0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2009-2625</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.
<p>Publish Date: 2009-08-06
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2009-2625>CVE-2009-2625</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2009-2625">https://nvd.nist.gov/vuln/detail/CVE-2009-2625</a></p>
<p>Release Date: 2009-08-06</p>
<p>Fix Resolution: apache-xerces:xercesImpl - 2.9.1;xerces:xercesImpl - 2.9.1-NODEP,2.3.0,2.9.0;org.apache.servicemix.bundles:org.apache.servicemix.bundles.xerces - 2.10.0_1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-5783</summary>
### Vulnerable Library - <b>commons-httpclient-3.1.jar</b></p>
<p>The HttpClient component supports the client-side of RFC 1945 (HTTP/1.0) and RFC 2616 (HTTP/1.1) , several related specifications (RFC 2109 (Cookies) , RFC 2617 (HTTP Authentication) , etc.), and provides a framework by which new request types (methods) or HTTP extensions can be created easily.</p>
<p>Library home page: <a href="http://jakarta.apache.org/httpcomponents/httpclient-3.x/">http://jakarta.apache.org/httpcomponents/httpclient-3.x/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-httpclient/commons-httpclient/3.1/commons-httpclient-3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- antisamy-1.5.3.jar
- :x: **commons-httpclient-3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons HttpClient 3.x, as used in Amazon Flexible Payments Service (FPS) merchant Java SDK and other products, does not verify that the server hostname matches a domain name in the subject's Common Name (CN) or subjectAltName field of the X.509 certificate, which allows man-in-the-middle attackers to spoof SSL servers via an arbitrary valid certificate.
<p>Publish Date: 2012-11-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-5783>CVE-2012-5783</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-5783">https://nvd.nist.gov/vuln/detail/CVE-2012-5783</a></p>
<p>Release Date: 2012-11-04</p>
<p>Fix Resolution (commons-httpclient:commons-httpclient): 3.1-HTTPCLIENT-1265</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-29425</summary>
### Vulnerable Library - <b>commons-io-2.2.jar</b></p>
<p>The Commons IO library contains utility classes, stream implementations, file filters,
file comparators, endian transformation classes, and much more.</p>
<p>Library home page: <a href="http://commons.apache.org/io/">http://commons.apache.org/io/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-io/commons-io/2.2/commons-io-2.2.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- commons-fileupload-1.3.1.jar
- :x: **commons-io-2.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/sast-automation-dev/easybuggy-12/commit/f73b332cff4b14eaedb777ef34c136f17639810b">f73b332cff4b14eaedb777ef34c136f17639810b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons IO before 2.7, When invoking the method FileNameUtils.normalize with an improper input string, like "//../foo", or "\\..\foo", the result would be the same value, thus possibly providing access to files in the parent directory, but not further above (thus "limited" path traversal), if the calling code would use the result to construct a path value.
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29425>CVE-2021-29425</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425</a></p>
<p>Release Date: 2021-04-13</p>
<p>Fix Resolution: commons-io:commons-io:2.7</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | esapi jar vulnerabilities highest severity is vulnerable library esapi jar path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high commons fileupload jar transitive high bsh core jar transitive n a high commons fileupload jar transitive high xercesimpl jar transitive n a high commons fileupload jar transitive high xalan jar transitive high commons beanutils core jar transitive high commons beanutils core jar transitive n a medium antisamy jar transitive medium antisamy jar transitive medium xercesimpl jar transitive n a medium xercesimpl jar transitive n a medium commons httpclient jar transitive medium commons io jar transitive n a details cve vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy esapi jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons fileupload before diskfileitem file manipulation remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons fileupload commons fileupload jenkins direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library bsh core jar beanshell core path to dependency file pom xml path to vulnerable library home wss scanner repository org beanshell bsh core bsh core jar dependency hierarchy esapi jar root library x bsh core jar vulnerable library found in head commit a href found in base branch master vulnerability details beanshell bsh before when included on the classpath by an application that uses java serialization or xstream allows remote attackers to execute arbitrary code via crafted serialized data related to xthis handler publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy esapi jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch master vulnerability details the multipartstream class in apache commons fileupload before as used in apache tomcat x before x before x before and x before and other products allows remote attackers to cause a denial of service cpu consumption via a long boundary string publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons fileupload commons fileupload jenkins direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details apache java parser before allows remote attackers to cause a denial of service cpu consumption via a crafted message to an xml service which triggers hash table collisions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ws vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy esapi jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch master vulnerability details the class fileuploadbase in apache commons fileupload before has potential resource leak inputstream not closed on exception publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution commons fileupload commons fileupload jenkins direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library xalan jar path to dependency file pom xml path to vulnerable library home wss scanner repository xalan xalan xalan jar dependency hierarchy esapi jar root library xom jar x xalan jar vulnerable library found in head commit a href found in base branch master vulnerability details the transformerfactory in apache xalan java before does not properly restrict access to certain properties when feature secure processing is enabled which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted xalan content header xalan entities xslt content header or xslt entities property or a java property that is bound to the xslt system property function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xalan xalan nodep direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library commons beanutils core jar the apache software foundation provides support for the apache community of open source software projects the apache projects are characterized by a collaborative consensus based development process an open and pragmatic software license and a desire to create high quality software that leads the way in its field we consider ourselves not simply a group of projects sharing a server but rather a community of developers and users library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils core commons beanutils core jar dependency hierarchy esapi jar root library x commons beanutils core jar vulnerable library found in head commit a href found in base branch master vulnerability details in apache commons beanutils a special beanintrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all java objects we however were not using this by default characteristic of the propertyutilsbean publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution commons beanutils commons beanutils core sonatype direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library commons beanutils core jar the apache software foundation provides support for the apache community of open source software projects the apache projects are characterized by a collaborative consensus based development process an open and pragmatic software license and a desire to create high quality software that leads the way in its field we consider ourselves not simply a group of projects sharing a server but rather a community of developers and users library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils core commons beanutils core jar dependency hierarchy esapi jar root library x commons beanutils core jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons beanutils as distributed in lib commons beanutils jar in apache struts x through and in other products requiring commons beanutils through does not suppress the class property which allows remote attackers to manipulate the classloader and execute arbitrary code via the class parameter as demonstrated by the passing of this parameter to the getclass method of the actionform object in struts publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons beanutils commons beanutils org apache struts core cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details in owasp antisamy before by submitting a specially crafted input a tag that supports style with active content you could bypass the library protections and supply executable code the impact is xss publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details owasp antisamy before allows xss via entities as demonstrated by use of colon to construct a javascript url publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details xmlscanner java in apache java parser before as used in the java runtime environment jre in ibm java before before before and before as well as oracle java se and earlier java se and earlier java se and earlier jrockit and earlier jrockit and earlier java se embedded and earlier and possibly other products allows remote attackers to cause a denial of service via vectors related to xml attribute names publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl xerces j cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details xmlscanner java in apache java as used in sun java runtime environment jre in jdk and jre before update and jdk and jre before update and in other products allows remote attackers to cause a denial of service infinite loop and application hang via malformed xml input as demonstrated by the codenomicon xml fuzzing framework publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution apache xerces xercesimpl xerces xercesimpl nodep org apache servicemix bundles org apache servicemix bundles xerces cve vulnerable library commons httpclient jar the httpclient component supports the client side of rfc http and rfc http several related specifications rfc cookies rfc http authentication etc and provides a framework by which new request types methods or http extensions can be created easily library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons httpclient commons httpclient commons httpclient jar dependency hierarchy esapi jar root library antisamy jar x commons httpclient jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons httpclient x as used in amazon flexible payments service fps merchant java sdk and other products does not verify that the server hostname matches a domain name in the subject s common name cn or subjectaltname field of the x certificate which allows man in the middle attackers to spoof ssl servers via an arbitrary valid certificate publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons httpclient commons httpclient httpclient direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library commons io jar the commons io library contains utility classes stream implementations file filters file comparators endian transformation classes and much more library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository commons io commons io commons io jar dependency hierarchy esapi jar root library commons fileupload jar x commons io jar vulnerable library found in head commit a href found in base branch master vulnerability details in apache commons io before when invoking the method filenameutils normalize with an improper input string like foo or foo the result would be the same value thus possibly providing access to files in the parent directory but not further above thus limited path traversal if the calling code would use the result to construct a path value publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons io commons io rescue worker helmet automatic remediation is available for this issue | 0 |
95,618 | 10,883,868,999 | IssuesEvent | 2019-11-18 06:36:27 | patriciadevina/this-is-a-test-repo | https://api.github.com/repos/patriciadevina/this-is-a-test-repo | opened | Issue for | bug documentation duplicate enhancement good first issue help wanted | Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
TEST NOV 18
151115111511151115111511151115111511151115111511 | 1.0 | Issue for - Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
Issue for
TEST NOV 18
151115111511151115111511151115111511151115111511 | non_priority | issue for issue for issue for issue for issue for issue for issue for issue for issue for issue for issue for issue for test nov | 0 |
3,711 | 10,041,266,044 | IssuesEvent | 2019-07-18 22:14:29 | Azure/azure-sdk | https://api.github.com/repos/Azure/azure-sdk | closed | Change Request: define "progressive concept disclosure" for all languages | architecture | ## The Basics
* Which design guideline is affected?
The "Approachable" design principle [here](https://github.com/Azure/azure-sdk/blob/b31d1ae11ab1739344d5ab2991ded7fc3d370776/docs/design/general/DesignPrinciples.mdk#L24)
* Which target languages are affected?
All
* Describe the change:
Add a definition (or a link) for "progressive concept disclosure".
## Reasoning
This is not a standard enough term to simply use it without explaining it. People reading the design guidelines will almost certainly need additional context here. | 1.0 | Change Request: define "progressive concept disclosure" for all languages - ## The Basics
* Which design guideline is affected?
The "Approachable" design principle [here](https://github.com/Azure/azure-sdk/blob/b31d1ae11ab1739344d5ab2991ded7fc3d370776/docs/design/general/DesignPrinciples.mdk#L24)
* Which target languages are affected?
All
* Describe the change:
Add a definition (or a link) for "progressive concept disclosure".
## Reasoning
This is not a standard enough term to simply use it without explaining it. People reading the design guidelines will almost certainly need additional context here. | non_priority | change request define progressive concept disclosure for all languages the basics which design guideline is affected the approachable design principle which target languages are affected all describe the change add a definition or a link for progressive concept disclosure reasoning this is not a standard enough term to simply use it without explaining it people reading the design guidelines will almost certainly need additional context here | 0 |
216,683 | 16,795,224,917 | IssuesEvent | 2021-06-16 01:52:44 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: dump roachtest goroutine stacks on SIGINT | A-testing C-enhancement X-stale no-issue-activity | Roachtest currently intercepts `SIGINT` and uses it to attempt to fail and cleanup running tests. For debugging roachtest itself, we should extend this to dumping the stacktraces of all running goroutines at the time `SIGINT` is received (i.e. before the cleanup is performed). | 1.0 | roachtest: dump roachtest goroutine stacks on SIGINT - Roachtest currently intercepts `SIGINT` and uses it to attempt to fail and cleanup running tests. For debugging roachtest itself, we should extend this to dumping the stacktraces of all running goroutines at the time `SIGINT` is received (i.e. before the cleanup is performed). | non_priority | roachtest dump roachtest goroutine stacks on sigint roachtest currently intercepts sigint and uses it to attempt to fail and cleanup running tests for debugging roachtest itself we should extend this to dumping the stacktraces of all running goroutines at the time sigint is received i e before the cleanup is performed | 0 |
201,789 | 23,039,651,929 | IssuesEvent | 2022-07-23 01:08:31 | turkdevops/snyk | https://api.github.com/repos/turkdevops/snyk | opened | CVE-2022-31090 (Medium) detected in guzzlehttp/guzzle-6.3.0 | security vulnerability | ## CVE-2022-31090 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guzzlehttp/guzzle-6.3.0</b></p></summary>
<p>Guzzle, an extensible PHP HTTP client</p>
<p>
Dependency Hierarchy:
- aws/aws-sdk-php-3.0.0 (Root Library)
- :x: **guzzlehttp/guzzle-6.3.0** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/snyk/commit/9505f4ca92405cc9273dc3726c2d274ce28a4407">9505f4ca92405cc9273dc3726c2d274ce28a4407</a></p>
<p>Found in base branch: <b>ALL_HANDS/major-secrets</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Guzzle, an extensible PHP HTTP client. `Authorization` headers on requests are sensitive information. In affected versions when using our Curl handler, it is possible to use the `CURLOPT_HTTPAUTH` option to specify an `Authorization` header. On making a request which responds with a redirect to a URI with a different origin (change in host, scheme or port), if we choose to follow it, we should remove the `CURLOPT_HTTPAUTH` option before continuing, stopping curl from appending the `Authorization` header to the new request. Affected Guzzle 7 users should upgrade to Guzzle 7.4.5 as soon as possible. Affected users using any earlier series of Guzzle should upgrade to Guzzle 6.5.8 or 7.4.5. Note that a partial fix was implemented in Guzzle 7.4.2, where a change in host would trigger removal of the curl-added Authorization header, however this earlier fix did not cover change in scheme or change in port. If you do not require or expect redirects to be followed, one should simply disable redirects all together. Alternatively, one can specify to use the Guzzle steam handler backend, rather than curl.
<p>Publish Date: 2022-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31090>CVE-2022-31090</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/guzzle/guzzle/security/advisories/GHSA-25mq-v84q-4j7r">https://github.com/guzzle/guzzle/security/advisories/GHSA-25mq-v84q-4j7r</a></p>
<p>Release Date: 2022-05-19</p>
<p>Fix Resolution: 6.5.8,7.4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-31090 (Medium) detected in guzzlehttp/guzzle-6.3.0 - ## CVE-2022-31090 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guzzlehttp/guzzle-6.3.0</b></p></summary>
<p>Guzzle, an extensible PHP HTTP client</p>
<p>
Dependency Hierarchy:
- aws/aws-sdk-php-3.0.0 (Root Library)
- :x: **guzzlehttp/guzzle-6.3.0** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/snyk/commit/9505f4ca92405cc9273dc3726c2d274ce28a4407">9505f4ca92405cc9273dc3726c2d274ce28a4407</a></p>
<p>Found in base branch: <b>ALL_HANDS/major-secrets</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Guzzle, an extensible PHP HTTP client. `Authorization` headers on requests are sensitive information. In affected versions when using our Curl handler, it is possible to use the `CURLOPT_HTTPAUTH` option to specify an `Authorization` header. On making a request which responds with a redirect to a URI with a different origin (change in host, scheme or port), if we choose to follow it, we should remove the `CURLOPT_HTTPAUTH` option before continuing, stopping curl from appending the `Authorization` header to the new request. Affected Guzzle 7 users should upgrade to Guzzle 7.4.5 as soon as possible. Affected users using any earlier series of Guzzle should upgrade to Guzzle 6.5.8 or 7.4.5. Note that a partial fix was implemented in Guzzle 7.4.2, where a change in host would trigger removal of the curl-added Authorization header, however this earlier fix did not cover change in scheme or change in port. If you do not require or expect redirects to be followed, one should simply disable redirects all together. Alternatively, one can specify to use the Guzzle steam handler backend, rather than curl.
<p>Publish Date: 2022-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-31090>CVE-2022-31090</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/guzzle/guzzle/security/advisories/GHSA-25mq-v84q-4j7r">https://github.com/guzzle/guzzle/security/advisories/GHSA-25mq-v84q-4j7r</a></p>
<p>Release Date: 2022-05-19</p>
<p>Fix Resolution: 6.5.8,7.4.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in guzzlehttp guzzle cve medium severity vulnerability vulnerable library guzzlehttp guzzle guzzle an extensible php http client dependency hierarchy aws aws sdk php root library x guzzlehttp guzzle vulnerable library found in head commit a href found in base branch all hands major secrets vulnerability details guzzle an extensible php http client authorization headers on requests are sensitive information in affected versions when using our curl handler it is possible to use the curlopt httpauth option to specify an authorization header on making a request which responds with a redirect to a uri with a different origin change in host scheme or port if we choose to follow it we should remove the curlopt httpauth option before continuing stopping curl from appending the authorization header to the new request affected guzzle users should upgrade to guzzle as soon as possible affected users using any earlier series of guzzle should upgrade to guzzle or note that a partial fix was implemented in guzzle where a change in host would trigger removal of the curl added authorization header however this earlier fix did not cover change in scheme or change in port if you do not require or expect redirects to be followed one should simply disable redirects all together alternatively one can specify to use the guzzle steam handler backend rather than curl publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
71,596 | 30,913,709,156 | IssuesEvent | 2023-08-05 02:41:13 | Zahlungsmittel/Zahlungsmittel | https://api.github.com/repos/Zahlungsmittel/Zahlungsmittel | opened | [CLOSED] change getCustomRepository to createUser function | bug service: backend service: database imported | <a href="https://github.com/ogerly"><img src="https://avatars.githubusercontent.com/u/1324583?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ogerly](https://github.com/ogerly)**
_Tuesday Oct 26, 2021 at 15:49 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/1046_
----
## 🍰 Pullrequest
wenn ich einen neuen user anlege im localen bereich, wird dieser nach dem speichern nicht richtig übergeben.
ich habe auf zeile 148 folgendes eingefügt
> const userRepository = getCustomRepository(UserRepository)
und auf zeile 149 folgendes geändert
> userRepository.save(dbuser).catch(() => {
----
_**[ogerly](https://github.com/ogerly)** included the following code: https://github.com/gradido/gradido/pull/1046/commits_
| 2.0 | [CLOSED] change getCustomRepository to createUser function - <a href="https://github.com/ogerly"><img src="https://avatars.githubusercontent.com/u/1324583?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ogerly](https://github.com/ogerly)**
_Tuesday Oct 26, 2021 at 15:49 GMT_
_Originally opened as https://github.com/gradido/gradido/pull/1046_
----
## 🍰 Pullrequest
wenn ich einen neuen user anlege im localen bereich, wird dieser nach dem speichern nicht richtig übergeben.
ich habe auf zeile 148 folgendes eingefügt
> const userRepository = getCustomRepository(UserRepository)
und auf zeile 149 folgendes geändert
> userRepository.save(dbuser).catch(() => {
----
_**[ogerly](https://github.com/ogerly)** included the following code: https://github.com/gradido/gradido/pull/1046/commits_
| non_priority | change getcustomrepository to createuser function issue by tuesday oct at gmt originally opened as 🍰 pullrequest wenn ich einen neuen user anlege im localen bereich wird dieser nach dem speichern nicht richtig übergeben ich habe auf zeile folgendes eingefügt const userrepository getcustomrepository userrepository und auf zeile folgendes geändert userrepository save dbuser catch included the following code | 0 |
42,960 | 23,057,096,173 | IssuesEvent | 2022-07-25 06:17:45 | PavelBlend/blender-xray | https://api.github.com/repos/PavelBlend/blender-xray | opened | Выдавать предупреждения, если файлы и папки в настройках некорректны | convenience performance | Это нужно для того, что пользователь знал, что параметр `export path` и путь к текстурам может быть некорректным. | True | Выдавать предупреждения, если файлы и папки в настройках некорректны - Это нужно для того, что пользователь знал, что параметр `export path` и путь к текстурам может быть некорректным. | non_priority | выдавать предупреждения если файлы и папки в настройках некорректны это нужно для того что пользователь знал что параметр export path и путь к текстурам может быть некорректным | 0 |
133,333 | 12,536,753,251 | IssuesEvent | 2020-06-05 01:08:28 | MLH-Fellowship/0.0.1-API-Parser | https://api.github.com/repos/MLH-Fellowship/0.0.1-API-Parser | closed | Compare Repology API packages vs HomeBrew API packages | bug documentation help wanted | Compare the Repology packages to the HomeBrew packages.
If Repology Version Number > HomeBrew Version Number then we will make that into a new .json file.
The new .json file will allow us to see what packages on HomeBrew are outdated. | 1.0 | Compare Repology API packages vs HomeBrew API packages - Compare the Repology packages to the HomeBrew packages.
If Repology Version Number > HomeBrew Version Number then we will make that into a new .json file.
The new .json file will allow us to see what packages on HomeBrew are outdated. | non_priority | compare repology api packages vs homebrew api packages compare the repology packages to the homebrew packages if repology version number homebrew version number then we will make that into a new json file the new json file will allow us to see what packages on homebrew are outdated | 0 |
47,119 | 13,204,167,923 | IssuesEvent | 2020-08-14 15:24:56 | xinYG/bootstrap-timepicker | https://api.github.com/repos/xinYG/bootstrap-timepicker | opened | WS-2019-0064 (High) detected in handlebars-4.0.10.min.js, handlebars-4.0.10.js | security vulnerability | ## WS-2019-0064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.10.min.js</b>, <b>handlebars-4.0.10.js</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.10.min.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js</a></p>
<p>Path to vulnerable library: /bootstrap-timepicker/node_modules/bower/lib/node_modules/handlebars/dist/handlebars.min.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.10.min.js** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.10.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js</a></p>
<p>Path to vulnerable library: /bootstrap-timepicker/node_modules/bower/lib/node_modules/handlebars/dist/handlebars.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.10.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/xinYG/bootstrap-timepicker/commit/b011a55ee3bfce5d2fedf4fd780e4196d446c504">b011a55ee3bfce5d2fedf4fd780e4196d446c504</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of handlebars prior to 4.0.14 are vulnerable to Prototype Pollution. Templates may alter an Objects' prototype, thus allowing an attacker to execute arbitrary code on the server.
<p>Publish Date: 2019-01-30
<p>URL: <a href=https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2>WS-2019-0064</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/755/versions">https://www.npmjs.com/advisories/755/versions</a></p>
<p>Release Date: 2019-04-30</p>
<p>Fix Resolution: 1.0.6-2,4.0.14,4.1.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","isTransitiveDependency":false,"dependencyTree":"handlebars.js:4.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.6-2,4.0.14,4.1.2"},{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","isTransitiveDependency":false,"dependencyTree":"handlebars.js:4.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.6-2,4.0.14,4.1.2"}],"vulnerabilityIdentifier":"WS-2019-0064","vulnerabilityDetails":"Versions of handlebars prior to 4.0.14 are vulnerable to Prototype Pollution. Templates may alter an Objects\u0027 prototype, thus allowing an attacker to execute arbitrary code on the server.","vulnerabilityUrl":"https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2","cvss2Severity":"high","cvss2Score":"8.0","extraData":{}}</REMEDIATE> --> | True | WS-2019-0064 (High) detected in handlebars-4.0.10.min.js, handlebars-4.0.10.js - ## WS-2019-0064 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.10.min.js</b>, <b>handlebars-4.0.10.js</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.10.min.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js</a></p>
<p>Path to vulnerable library: /bootstrap-timepicker/node_modules/bower/lib/node_modules/handlebars/dist/handlebars.min.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.10.min.js** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.10.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js</a></p>
<p>Path to vulnerable library: /bootstrap-timepicker/node_modules/bower/lib/node_modules/handlebars/dist/handlebars.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.10.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/xinYG/bootstrap-timepicker/commit/b011a55ee3bfce5d2fedf4fd780e4196d446c504">b011a55ee3bfce5d2fedf4fd780e4196d446c504</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of handlebars prior to 4.0.14 are vulnerable to Prototype Pollution. Templates may alter an Objects' prototype, thus allowing an attacker to execute arbitrary code on the server.
<p>Publish Date: 2019-01-30
<p>URL: <a href=https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2>WS-2019-0064</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/755/versions">https://www.npmjs.com/advisories/755/versions</a></p>
<p>Release Date: 2019-04-30</p>
<p>Fix Resolution: 1.0.6-2,4.0.14,4.1.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","isTransitiveDependency":false,"dependencyTree":"handlebars.js:4.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.6-2,4.0.14,4.1.2"},{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","isTransitiveDependency":false,"dependencyTree":"handlebars.js:4.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.6-2,4.0.14,4.1.2"}],"vulnerabilityIdentifier":"WS-2019-0064","vulnerabilityDetails":"Versions of handlebars prior to 4.0.14 are vulnerable to Prototype Pollution. Templates may alter an Objects\u0027 prototype, thus allowing an attacker to execute arbitrary code on the server.","vulnerabilityUrl":"https://github.com/wycats/handlebars.js/compare/v4.1.1...v4.1.2","cvss2Severity":"high","cvss2Score":"8.0","extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in handlebars min js handlebars js ws high severity vulnerability vulnerable libraries handlebars min js handlebars js handlebars min js handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to vulnerable library bootstrap timepicker node modules bower lib node modules handlebars dist handlebars min js dependency hierarchy x handlebars min js vulnerable library handlebars js handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to vulnerable library bootstrap timepicker node modules bower lib node modules handlebars dist handlebars js dependency hierarchy x handlebars js vulnerable library found in head commit a href vulnerability details versions of handlebars prior to are vulnerable to prototype pollution templates may alter an objects prototype thus allowing an attacker to execute arbitrary code on the server publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails versions of handlebars prior to are vulnerable to prototype pollution templates may alter an objects prototype thus allowing an attacker to execute arbitrary code on the server vulnerabilityurl | 0 |
346,852 | 31,029,080,771 | IssuesEvent | 2023-08-10 11:11:41 | status-im/status-mobile | https://api.github.com/repos/status-im/status-mobile | opened | e2e builds: can't invite user to closed community | e2e test blocker E:Mobile Bug MVP E:Mobile Communities MVP | # Bug Report
## Problem
We need an ability to create communities on mobile for e2e tests. Currently we can't test closed community properly. That's not reproducible in https://github.com/status-im/status-mobile/pull/16806 where this feature was presented
#### Expected behavior
Community is shared
#### Actual behavior
[259719671-f04ea1b9-520a-4851-8521-cb6e34719bc7.webm](https://github.com/status-im/status-mobile/assets/29711298/10ee8399-9f1b-4f1e-9722-66a443c7965f)
### Reproduction
1. Create closed community
2. Click Invite people from contact list or Share community
3. Select contacts to invite
4. Click Invite button
### Additional Information
- Status version: nightly e2e (x86)
- Operating System: Android
[comment]: # (Please, add logs/notes if necessary)
| 1.0 | e2e builds: can't invite user to closed community - # Bug Report
## Problem
We need an ability to create communities on mobile for e2e tests. Currently we can't test closed community properly. That's not reproducible in https://github.com/status-im/status-mobile/pull/16806 where this feature was presented
#### Expected behavior
Community is shared
#### Actual behavior
[259719671-f04ea1b9-520a-4851-8521-cb6e34719bc7.webm](https://github.com/status-im/status-mobile/assets/29711298/10ee8399-9f1b-4f1e-9722-66a443c7965f)
### Reproduction
1. Create closed community
2. Click Invite people from contact list or Share community
3. Select contacts to invite
4. Click Invite button
### Additional Information
- Status version: nightly e2e (x86)
- Operating System: Android
[comment]: # (Please, add logs/notes if necessary)
| non_priority | builds can t invite user to closed community bug report problem we need an ability to create communities on mobile for tests currently we can t test closed community properly that s not reproducible in where this feature was presented expected behavior community is shared actual behavior reproduction create closed community click invite people from contact list or share community select contacts to invite click invite button additional information status version nightly operating system android please add logs notes if necessary | 0 |
13,980 | 3,371,153,051 | IssuesEvent | 2015-11-23 17:53:08 | mozilla/123done | https://api.github.com/repos/mozilla/123done | closed | sign in button never shown if cookies are disabled | needs testcase waffle:backlog ★★★★ | Just reporting this "for the record". I was checking an issue for 'requires cookies' screen in dialog and disabled cookies and loaded 123done.org. The sign in button stays as a spinner forever.
This is obviously not a huge deal, since if the sign in were shown, clicking it would just say "you must enable cookies". | 1.0 | sign in button never shown if cookies are disabled - Just reporting this "for the record". I was checking an issue for 'requires cookies' screen in dialog and disabled cookies and loaded 123done.org. The sign in button stays as a spinner forever.
This is obviously not a huge deal, since if the sign in were shown, clicking it would just say "you must enable cookies". | non_priority | sign in button never shown if cookies are disabled just reporting this for the record i was checking an issue for requires cookies screen in dialog and disabled cookies and loaded org the sign in button stays as a spinner forever this is obviously not a huge deal since if the sign in were shown clicking it would just say you must enable cookies | 0 |
167,411 | 14,112,171,662 | IssuesEvent | 2020-11-07 03:42:10 | AY2021S1-CS2103T-T09-1/tp | https://api.github.com/repos/AY2021S1-CS2103T-T09-1/tp | closed | DG: Tags feature | documentation type.Task | - Explain how tags work now with the new classes/implementations
- Explain how `add`, `edit`, and `delete` now work with these new things
- Maybe can explain how `tags` command lists all tags | 1.0 | DG: Tags feature - - Explain how tags work now with the new classes/implementations
- Explain how `add`, `edit`, and `delete` now work with these new things
- Maybe can explain how `tags` command lists all tags | non_priority | dg tags feature explain how tags work now with the new classes implementations explain how add edit and delete now work with these new things maybe can explain how tags command lists all tags | 0 |
340,060 | 30,492,727,980 | IssuesEvent | 2023-07-18 08:48:12 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: kv/contention/nodes=4 failed | C-test-failure O-robot O-roachtest branch-master release-blocker T-kv | roachtest.kv/contention/nodes=4 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10950435?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10950435?buildTab=artifacts#/kv/contention/nodes=4) on master @ [7675ca4998134028f0623e04737b5cb69fcc33a9](https://github.com/cockroachdb/cockroach/commits/7675ca4998134028f0623e04737b5cb69fcc33a9):
```
(cluster.go:2180).Start: ~ COCKROACH_CONNECT_TIMEOUT=1200 ./cockroach sql --url 'postgres://root@localhost:26257?sslmode=disable' -e "CREATE SCHEDULE IF NOT EXISTS test_only_backup FOR BACKUP INTO 'gs://cockroach-backup-testing-private/roachprod-scheduled-backups/teamcity-10950435-1689659335-28-n5cpu4/1689664870831906498?AUTH=implicit' RECURRING '*/15 * * * *' FULL BACKUP '@hourly' WITH SCHEDULE OPTIONS first_run = 'now'"
ERROR: unexpected error occurred when checking for existing backups in gs://cockroach-backup-testing-private/roachprod-scheduled-backups/teamcity-10950435-1689659335-28-n5cpu4/1689664870831906498?AUTH=implicit: unable to list files in gcs bucket: googleapi: Error 403: 21965078311-compute@developer.gserviceaccount.com does not have storage.objects.list access to the Google Cloud Storage bucket. Permission 'storage.objects.list' denied on resource (or it may not exist).
SQLSTATE: 58030
Failed running "sql": COMMAND_PROBLEM: exit status 1
test artifacts and logs in: /artifacts/kv/contention/nodes=4/run_1
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*kv/contention/nodes=4.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-29853 | 2.0 | roachtest: kv/contention/nodes=4 failed - roachtest.kv/contention/nodes=4 [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10950435?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10950435?buildTab=artifacts#/kv/contention/nodes=4) on master @ [7675ca4998134028f0623e04737b5cb69fcc33a9](https://github.com/cockroachdb/cockroach/commits/7675ca4998134028f0623e04737b5cb69fcc33a9):
```
(cluster.go:2180).Start: ~ COCKROACH_CONNECT_TIMEOUT=1200 ./cockroach sql --url 'postgres://root@localhost:26257?sslmode=disable' -e "CREATE SCHEDULE IF NOT EXISTS test_only_backup FOR BACKUP INTO 'gs://cockroach-backup-testing-private/roachprod-scheduled-backups/teamcity-10950435-1689659335-28-n5cpu4/1689664870831906498?AUTH=implicit' RECURRING '*/15 * * * *' FULL BACKUP '@hourly' WITH SCHEDULE OPTIONS first_run = 'now'"
ERROR: unexpected error occurred when checking for existing backups in gs://cockroach-backup-testing-private/roachprod-scheduled-backups/teamcity-10950435-1689659335-28-n5cpu4/1689664870831906498?AUTH=implicit: unable to list files in gcs bucket: googleapi: Error 403: 21965078311-compute@developer.gserviceaccount.com does not have storage.objects.list access to the Google Cloud Storage bucket. Permission 'storage.objects.list' denied on resource (or it may not exist).
SQLSTATE: 58030
Failed running "sql": COMMAND_PROBLEM: exit status 1
test artifacts and logs in: /artifacts/kv/contention/nodes=4/run_1
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*kv/contention/nodes=4.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-29853 | non_priority | roachtest kv contention nodes failed roachtest kv contention nodes with on master cluster go start cockroach connect timeout cockroach sql url postgres root localhost sslmode disable e create schedule if not exists test only backup for backup into gs cockroach backup testing private roachprod scheduled backups teamcity auth implicit recurring full backup hourly with schedule options first run now error unexpected error occurred when checking for existing backups in gs cockroach backup testing private roachprod scheduled backups teamcity auth implicit unable to list files in gcs bucket googleapi error compute developer gserviceaccount com does not have storage objects list access to the google cloud storage bucket permission storage objects list denied on resource or it may not exist sqlstate failed running sql command problem exit status test artifacts and logs in artifacts kv contention nodes run parameters roachtest arch roachtest cloud gce roachtest cpu roachtest encrypted false roachtest ssd help see see cc cockroachdb kv triage jira issue crdb | 0 |
17,016 | 23,445,012,481 | IssuesEvent | 2022-08-15 18:40:34 | Luke100000/minecraft-comes-alive | https://api.github.com/repos/Luke100000/minecraft-comes-alive | closed | Villager Names are Not Names | mod compatibility | Short Issue, I'm not sure how to fix this but all the villagers in my villages spawn with names like this
entity.mca.female_villager_cleric
Any way to fix this? | True | Villager Names are Not Names - Short Issue, I'm not sure how to fix this but all the villagers in my villages spawn with names like this
entity.mca.female_villager_cleric
Any way to fix this? | non_priority | villager names are not names short issue i m not sure how to fix this but all the villagers in my villages spawn with names like this entity mca female villager cleric any way to fix this | 0 |
57,952 | 11,810,581,735 | IssuesEvent | 2020-03-19 16:43:08 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Prefer sizeof over Marshal.SizeOf | api-suggestion area-System.Runtime.InteropServices code-analyzer | `sizeof` is much more efficient than `Marshal.SizeOf`. In cases where they'll produce the same answer, the former should be preferred (it'll generally require using `unsafe`, though, so this should only fire if `unsafe` is allowed in the project).
**Category**: Performance | 1.0 | Prefer sizeof over Marshal.SizeOf - `sizeof` is much more efficient than `Marshal.SizeOf`. In cases where they'll produce the same answer, the former should be preferred (it'll generally require using `unsafe`, though, so this should only fire if `unsafe` is allowed in the project).
**Category**: Performance | non_priority | prefer sizeof over marshal sizeof sizeof is much more efficient than marshal sizeof in cases where they ll produce the same answer the former should be preferred it ll generally require using unsafe though so this should only fire if unsafe is allowed in the project category performance | 0 |
255,201 | 21,911,742,810 | IssuesEvent | 2022-05-21 06:34:22 | hyperledger/iroha | https://api.github.com/repos/hyperledger/iroha | reopened | Fix Flaky tests | iroha2 CI Tests | Cargo nextest is the more permanent solution to flaky tests, specifically it has a method of remembering and re-running tests that have failed previously.
https://nexte.st/index.html
We should move to use it in our CI image, and potentially generate test coverage and run tests in one go. | 1.0 | Fix Flaky tests - Cargo nextest is the more permanent solution to flaky tests, specifically it has a method of remembering and re-running tests that have failed previously.
https://nexte.st/index.html
We should move to use it in our CI image, and potentially generate test coverage and run tests in one go. | non_priority | fix flaky tests cargo nextest is the more permanent solution to flaky tests specifically it has a method of remembering and re running tests that have failed previously we should move to use it in our ci image and potentially generate test coverage and run tests in one go | 0 |
229,595 | 25,362,287,429 | IssuesEvent | 2022-11-21 01:03:43 | AkshayMukkavilli/Tensorflow | https://api.github.com/repos/AkshayMukkavilli/Tensorflow | opened | CVE-2022-41891 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2022-41891 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /Tensorflow/src/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_5ea86033-7612-4210-97f3-8edb65806ddf/20190525011619_2843/20190525011537_depth_0/2/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. If `tf.raw_ops.TensorListConcat` is given `element_shape=[]`, it results segmentation fault which can be used to trigger a denial of service attack. We have patched the issue in GitHub commit fc33f3dc4c14051a83eec6535b608abe1d355fde. The fix will be included in TensorFlow 2.11. We will also cherrypick this commit on TensorFlow 2.10.1, 2.9.3, and TensorFlow 2.8.4, as these are also affected and still in supported range.
<p>Publish Date: 2022-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41891>CVE-2022-41891</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-41891">https://www.cve.org/CVERecord?id=CVE-2022-41891</a></p>
<p>Release Date: 2022-11-18</p>
<p>Fix Resolution: tensorflow - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-cpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-gpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-41891 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2022-41891 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /Tensorflow/src/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_5ea86033-7612-4210-97f3-8edb65806ddf/20190525011619_2843/20190525011537_depth_0/2/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an open source platform for machine learning. If `tf.raw_ops.TensorListConcat` is given `element_shape=[]`, it results segmentation fault which can be used to trigger a denial of service attack. We have patched the issue in GitHub commit fc33f3dc4c14051a83eec6535b608abe1d355fde. The fix will be included in TensorFlow 2.11. We will also cherrypick this commit on TensorFlow 2.10.1, 2.9.3, and TensorFlow 2.8.4, as these are also affected and still in supported range.
<p>Publish Date: 2022-11-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-41891>CVE-2022-41891</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-41891">https://www.cve.org/CVERecord?id=CVE-2022-41891</a></p>
<p>Release Date: 2022-11-18</p>
<p>Fix Resolution: tensorflow - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-cpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0, tensorflow-gpu - 2.8.4, 2.9.3, 2.10.1, 2.11.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file tensorflow src requirements txt path to vulnerable library tesource archiveextractor depth tensorflow tensorflow data purelib tensorflow dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an open source platform for machine learning if tf raw ops tensorlistconcat is given element shape it results segmentation fault which can be used to trigger a denial of service attack we have patched the issue in github commit the fix will be included in tensorflow we will also cherrypick this commit on tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with mend | 0 |
84,053 | 15,720,825,607 | IssuesEvent | 2021-03-29 01:19:56 | jmacwhitesource/cloud-pipeline | https://api.github.com/repos/jmacwhitesource/cloud-pipeline | opened | CVE-2021-24122 (Medium) detected in tomcat-embed-core-8.5.31.jar, tomcat-embed-core-8.5.11.jar | security vulnerability | ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tomcat-embed-core-8.5.31.jar</b>, <b>tomcat-embed-core-8.5.11.jar</b></p></summary>
<p>
<details><summary><b>tomcat-embed-core-8.5.31.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: cloud-pipeline/billing-report-agent/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.31/f5adf7ed8c34aa005b22b6a2dc7b6796e10e9c79/tomcat-embed-core-8.5.31.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.2.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.0.2.RELEASE.jar
- tomcat-embed-websocket-8.5.31.jar
- :x: **tomcat-embed-core-8.5.31.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-8.5.11.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: cloud-pipeline/docker-comp-scan/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.11/72761f51fc7cef3ee19d4aafc7adc605df9f611f/tomcat-embed-core-8.5.11.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.2.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.2.RELEASE.jar
- :x: **tomcat-embed-core-8.5.11.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.31","packageFilePaths":["/billing-report-agent/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.0.2.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.0.2.RELEASE;org.apache.tomcat.embed:tomcat-embed-websocket:8.5.31;org.apache.tomcat.embed:tomcat-embed-core:8.5.31","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.11","packageFilePaths":["/docker-comp-scan/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.2.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.2.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-24122","vulnerabilityDetails":"When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-24122 (Medium) detected in tomcat-embed-core-8.5.31.jar, tomcat-embed-core-8.5.11.jar - ## CVE-2021-24122 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tomcat-embed-core-8.5.31.jar</b>, <b>tomcat-embed-core-8.5.11.jar</b></p></summary>
<p>
<details><summary><b>tomcat-embed-core-8.5.31.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: cloud-pipeline/billing-report-agent/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.31/f5adf7ed8c34aa005b22b6a2dc7b6796e10e9c79/tomcat-embed-core-8.5.31.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.2.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-2.0.2.RELEASE.jar
- tomcat-embed-websocket-8.5.31.jar
- :x: **tomcat-embed-core-8.5.31.jar** (Vulnerable Library)
</details>
<details><summary><b>tomcat-embed-core-8.5.11.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="http://tomcat.apache.org/">http://tomcat.apache.org/</a></p>
<p>Path to dependency file: cloud-pipeline/docker-comp-scan/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/8.5.11/72761f51fc7cef3ee19d4aafc7adc605df9f611f/tomcat-embed-core-8.5.11.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.2.RELEASE.jar (Root Library)
- spring-boot-starter-tomcat-1.5.2.RELEASE.jar
- :x: **tomcat-embed-core-8.5.11.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.
<p>Publish Date: 2021-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122>CVE-2021-24122</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-24122</a></p>
<p>Release Date: 2021-01-14</p>
<p>Fix Resolution: org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.31","packageFilePaths":["/billing-report-agent/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.0.2.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:2.0.2.RELEASE;org.apache.tomcat.embed:tomcat-embed-websocket:8.5.31;org.apache.tomcat.embed:tomcat-embed-core:8.5.31","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10"},{"packageType":"Java","groupId":"org.apache.tomcat.embed","packageName":"tomcat-embed-core","packageVersion":"8.5.11","packageFilePaths":["/docker-comp-scan/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.2.RELEASE;org.springframework.boot:spring-boot-starter-tomcat:1.5.2.RELEASE;org.apache.tomcat.embed:tomcat-embed-core:8.5.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.apache.tomcat.embed:tomcat-embed-core:7.0.107,8.5.60,9.0.40,10.0.0-M10;org.apache.tomcat:tomcat-catalina:7.0.107,8.5.60,9.0.40,10.0.0-M10"}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2021-24122","vulnerabilityDetails":"When serving resources from a network location using the NTFS file system, Apache Tomcat versions 10.0.0-M1 to 10.0.0-M9, 9.0.0.M1 to 9.0.39, 8.5.0 to 8.5.59 and 7.0.0 to 7.0.106 were susceptible to JSP source code disclosure in some configurations. The root cause was the unexpected behaviour of the JRE API File.getCanonicalPath() which in turn was caused by the inconsistent behaviour of the Windows API (FindFirstFileW) in some circumstances.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24122","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"None","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in tomcat embed core jar tomcat embed core jar cve medium severity vulnerability vulnerable libraries tomcat embed core jar tomcat embed core jar tomcat embed core jar core tomcat implementation library home page a href path to dependency file cloud pipeline billing report agent build gradle path to vulnerable library home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar tomcat embed websocket jar x tomcat embed core jar vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file cloud pipeline docker comp scan build gradle path to vulnerable library home wss scanner gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web release jar root library spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in base branch develop vulnerability details when serving resources from a network location using the ntfs file system apache tomcat versions to to to and to were susceptible to jsp source code disclosure in some configurations the root cause was the unexpected behaviour of the jre api file getcanonicalpath which in turn was caused by the inconsistent behaviour of the windows api findfirstfilew in some circumstances publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed websocket org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina packagetype java groupid org apache tomcat embed packagename tomcat embed core packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter tomcat release org apache tomcat embed tomcat embed core isminimumfixversionavailable true minimumfixversion org apache tomcat embed tomcat embed core org apache tomcat tomcat catalina basebranches vulnerabilityidentifier cve vulnerabilitydetails when serving resources from a network location using the ntfs file system apache tomcat versions to to to and to were susceptible to jsp source code disclosure in some configurations the root cause was the unexpected behaviour of the jre api file getcanonicalpath which in turn was caused by the inconsistent behaviour of the windows api findfirstfilew in some circumstances vulnerabilityurl | 0 |
350,714 | 31,931,970,593 | IssuesEvent | 2023-09-19 08:03:27 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix raw_ops.test_tensorflow_Angle | TensorFlow Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix raw_ops.test_tensorflow_Angle - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6221908008/job/16884781805"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix raw ops test tensorflow angle numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
169,198 | 26,760,487,486 | IssuesEvent | 2023-01-31 06:15:56 | codestates-seb/seb41_main_028 | https://api.github.com/repos/codestates-seb/seb41_main_028 | closed | [FE] design: 버튼 한국어 패치 | FE Design | ## To do List
<!--해당 Issue를 해결하기 위해 수행해야 할 To do list를 작성해주세요.-->
- [x] 버튼 한국어 패치
- [ ]
- [ ]
- [ ]
## Deadline
<!--작업 완료 기한을 입력해주세요. (e.g. 221219 / 15:00)-->
## Issue Checklist
아래 체크리스트를 확인해주세요.
- [ ] Issue Title을 다음 예시와 같이 작성했습니다. (e.g. [FE] Feat: 회원가입 기능 구현 )
- [ ] 우측의 Assignees, Labels, Projects, Milestone을 적절하게 선택했습니다.
| 1.0 | [FE] design: 버튼 한국어 패치 - ## To do List
<!--해당 Issue를 해결하기 위해 수행해야 할 To do list를 작성해주세요.-->
- [x] 버튼 한국어 패치
- [ ]
- [ ]
- [ ]
## Deadline
<!--작업 완료 기한을 입력해주세요. (e.g. 221219 / 15:00)-->
## Issue Checklist
아래 체크리스트를 확인해주세요.
- [ ] Issue Title을 다음 예시와 같이 작성했습니다. (e.g. [FE] Feat: 회원가입 기능 구현 )
- [ ] 우측의 Assignees, Labels, Projects, Milestone을 적절하게 선택했습니다.
| non_priority | design 버튼 한국어 패치 to do list 버튼 한국어 패치 deadline issue checklist 아래 체크리스트를 확인해주세요 issue title을 다음 예시와 같이 작성했습니다 e g feat 회원가입 기능 구현 우측의 assignees labels projects milestone을 적절하게 선택했습니다 | 0 |
147,036 | 13,199,999,831 | IssuesEvent | 2020-08-14 07:18:50 | DLR-RM/stable-baselines3 | https://api.github.com/repos/DLR-RM/stable-baselines3 | closed | Pre_Train in Stablebaselines3 | documentation duplicate question | Is there a `pre_train` function in PPO of stablebaselines3? There is one in stablebaseline. If not, how to pretrain? | 1.0 | Pre_Train in Stablebaselines3 - Is there a `pre_train` function in PPO of stablebaselines3? There is one in stablebaseline. If not, how to pretrain? | non_priority | pre train in is there a pre train function in ppo of there is one in stablebaseline if not how to pretrain | 0 |
190,389 | 15,229,491,647 | IssuesEvent | 2021-02-18 12:59:09 | MozNeurons/ML-Workshop | https://api.github.com/repos/MozNeurons/ML-Workshop | closed | [Addition] SVM Documentation | documentation enhancement good first issue | Add documentation along with explanation and examples for Support Vector Machines(SVM). | 1.0 | [Addition] SVM Documentation - Add documentation along with explanation and examples for Support Vector Machines(SVM). | non_priority | svm documentation add documentation along with explanation and examples for support vector machines svm | 0 |
155,405 | 12,254,419,634 | IssuesEvent | 2020-05-06 08:27:25 | microsoft/PTVS | https://api.github.com/repos/microsoft/PTVS | closed | When debugged a second time, VS loses its response and restarts. | area:Debugger area:Debugger (VSC) area:Test Adapter bug regression upstream: vs |
**Steps to Reproduce**
1.Add unit test test_1.py in python application
2.Typing code in test_1.py
import unittest
class Test_test_1(unittest.TestCase):
def test_A(self):
self.assertEqual(1,1)
if __name__ == '__main__':
unittest.main()
3.Set bk in the code
4.In TE, select the test and right-click to select Debug Selected tests
5.After the first successful debug, debug the current test again.
**Expected behavior**
The test can be debugged successfully
**Actual behavior**
When debugged a second time, VS loses its response and restarts.
**Debug Adapter Host Log**
```
1> DebugAdapterHost version: 16.7.40413.2 commit:b7937c15e33a949e648926944d211d657e3684f0
1> [DebugAdapter] <-- E (output): {"seq": 1, "type": "event", "event": "output", "body": {"category": "telemetry", "output": "ptvsd", "data": {"packageVersion": "1.0.0b5"}}}
1> [DebugAdapter] --> C (initialize-1): {"type":"request","command":"initialize","arguments":{"pathFormat":"path","clientID":"visualstudio","clientName":"Visual Studio","adapterID":null,"locale":"en-US","linesStartAt1":true,"columnsStartAt1":true,"supportsVariableType":true,"supportsRunInTerminalRequest":true,"supportsMemoryReferences":true,"supportsProgressReporting":true,"supportsHandshakeRequest":true},"seq":1}
1> [DebugAdapter] <-- E (output): {"seq": 2, "type": "event", "event": "output", "body": {"category": "telemetry", "output": "debugpy", "data": {"packageVersion": "1.0.0b5"}}}
1> [DebugAdapter] <-- R (initialize-1) [167 ms]: {"seq": 3, "type": "response", "request_seq": 1, "success": true, "command": "initialize", "body": {"supportsCompletionsRequest": true, "supportsConditionalBreakpoints": true, "supportsConfigurationDoneRequest": true, "supportsDebuggerProperties": true, "supportsDelayedStackTraceLoading": true, "supportsEvaluateForHovers": true, "supportsExceptionInfoRequest": true, "supportsExceptionOptions": true, "supportsHitConditionalBreakpoints": true, "supportsLogPoints": true, "supportsModulesRequest": true, "supportsSetExpression": true, "supportsSetVariable": true, "supportsValueFormattingOptions": true, "supportsTerminateDebuggee": true, "supportsGotoTargetsRequest": true, "exceptionBreakpointFilters": [{"filter": "raised", "label": "Raised Exceptions", "default": false}, {"filter": "uncaught", "label": "Uncaught Exceptions", "default": true}]}}
1> [DebugAdapter] --> C (attach-2): {"type":"request","command":"attach","arguments":{"host":"localhost","port":52468,"stopOnEntry":true,"promptBeforeRunningWithBuildError":true,"redirectOutput":true,"waitOnAbnormalExit":true,"waitOnNormalExit":true,"breakOnSystemExitZero":false,"debugStdLib":false,"showReturnValue":true,"rules":[{"path":"c:\\program files (x86)\\microsoft visual studio\\2019\\preview\\common7\\ide\\extensions\\microsoft\\python\\core\\","include":false}]},"seq":2}
1> [DebugAdapter] <-- E (debugpyWaitingForServer): {"seq": 4, "type": "event", "event": "debugpyWaitingForServer", "body": {"host": "127.0.0.1", "port": 52521}}
1> WARNING: No handler registered for event of type 'debugpyWaitingForServer'!
1> [DebugAdapter] <-- E (initialized): {"seq": 5, "type": "event", "event": "initialized"}
1> [DebugAdapter] --> C (debugpySystemInfo-3): {"type":"request","command":"debugpySystemInfo","arguments":{},"seq":3}
1> [DebugAdapter] <-- R (debugpySystemInfo-3) [16 ms]: {"seq": 6, "type": "response", "request_seq": 3, "success": true, "command": "debugpySystemInfo", "body": {"debugpy": {"version": "1.0.0b5"}, "python": {"version": "3.7.7final0", "implementation": {"name": "cpython", "version": "3.7.7final0", "description": "CPython"}}, "platform": {"name": "win32"}, "process": {"pid": 4668, "ppid": 6728, "executable": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\python.exe", "bitness": 64}, "pydevd": {"usingCython": false, "usingFrameEval": false}}}
1> [DebugAdapter] --> C (setDebuggerProperty-4): {"type":"request","command":"setDebuggerProperty","arguments":{"AllowOutOfProcessSymbols":1},"seq":4}
1> [DebugAdapter] --> C (setDebuggerProperty-5): {"type":"request","command":"setDebuggerProperty","arguments":{"DisableJITOptimization":0},"seq":5}
1> [DebugAdapter] --> C (setDebuggerProperty-6): {"type":"request","command":"setDebuggerProperty","arguments":{"EnableFastEvaluate":1},"seq":6}
1> [DebugAdapter] --> C (setDebuggerProperty-7): {"type":"request","command":"setDebuggerProperty","arguments":{"InterpreterOptions":1},"seq":7}
1> [DebugAdapter] --> C (setDebuggerProperty-8): {"type":"request","command":"setDebuggerProperty","arguments":{"JustMyCodeStepping":1},"seq":8}
1> [DebugAdapter] --> C (setDebuggerProperty-9): {"type":"request","command":"setDebuggerProperty","arguments":{"StopOnExceptionCrossingManagedBoundary":0},"seq":9}
1> [DebugAdapter] --> C (setDebuggerProperty-10): {"type":"request","command":"setDebuggerProperty","arguments":{"WarnIfNoUserCodeOnLaunch":1},"seq":10}
1> [DebugAdapter] --> C (setDebuggerProperty-11): {"type":"request","command":"setDebuggerProperty","arguments":{"EnableStepFiltering":true},"seq":11}
1> [DebugAdapter] <-- R (setDebuggerProperty-4) [6 ms]: {"seq": 7, "type": "response", "request_seq": 4, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-5) [6 ms]: {"seq": 8, "type": "response", "request_seq": 5, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-6) [6 ms]: {"seq": 9, "type": "response", "request_seq": 6, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-7) [7 ms]: {"seq": 10, "type": "response", "request_seq": 7, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-8) [7 ms]: {"seq": 11, "type": "response", "request_seq": 8, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-9) [8 ms]: {"seq": 12, "type": "response", "request_seq": 9, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-10) [9 ms]: {"seq": 13, "type": "response", "request_seq": 10, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-11) [10 ms]: {"seq": 14, "type": "response", "request_seq": 11, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] --> C (setBreakpoints-12): {"type":"request","command":"setBreakpoints","arguments":{"source":{"path":"c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_ut.py","sources":[],"checksums":[]},"breakpoints":[{"line":8,"column":1}],"lines":[8]},"seq":12}
1> [DebugAdapter] --> C (setBreakpoints-13): {"type":"request","command":"setBreakpoints","arguments":{"source":{"path":"c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_pta.py","sources":[],"checksums":[]},"breakpoints":[{"line":5,"column":1}],"lines":[5]},"seq":13}
1> [DebugAdapter] --> C (setBreakpoints-14): {"type":"request","command":"setBreakpoints","arguments":{"source":{"path":"c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py","sources":[],"checksums":[]},"breakpoints":[{"line":5,"column":1}],"lines":[5]},"seq":14}
1> [DebugAdapter] <-- R (setBreakpoints-12) [35 ms]: {"seq": 15, "type": "response", "request_seq": 12, "success": true, "command": "setBreakpoints", "body": {"breakpoints": [{"verified": true, "id": 0, "source": {"path": "c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_ut.py", "sources": [], "checksums": []}, "line": 8}]}}
1> [DebugAdapter] <-- R (setBreakpoints-13) [28 ms]: {"seq": 16, "type": "response", "request_seq": 13, "success": true, "command": "setBreakpoints", "body": {"breakpoints": [{"verified": true, "id": 1, "source": {"path": "c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_pta.py", "sources": [], "checksums": []}, "line": 5}]}}
1> [DebugAdapter] <-- R (setBreakpoints-14) [29 ms]: {"seq": 17, "type": "response", "request_seq": 14, "success": true, "command": "setBreakpoints", "body": {"breakpoints": [{"verified": true, "id": 2, "source": {"path": "c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sources": [], "checksums": []}, "line": 5}]}}
1> [DebugAdapter] --> C (setExceptionBreakpoints-15): {"type":"request","command":"setExceptionBreakpoints","arguments":{"filters":[],"exceptionOptions":[{"breakMode":"userUnhandled","path":[{"names":["Python Exceptions"]}]},{"breakMode":"unhandled","path":[{"names":["Python Exceptions"]},{"names":["GeneratorExit","IndexError","StopIteration","AttributeError","KeyError"]}]}]},"seq":15}
1> [DebugAdapter] <-- R (setExceptionBreakpoints-15) [20 ms]: {"seq": 18, "type": "response", "request_seq": 15, "success": true, "command": "setExceptionBreakpoints"}
1> [DebugAdapter] --> C (configurationDone-16): {"type":"request","command":"configurationDone","arguments":{},"seq":16}
1> [DebugAdapter] <-- R (configurationDone-16) [5 ms]: {"seq": 19, "type": "response", "request_seq": 16, "success": true, "command": "configurationDone"}
1> [DebugAdapter] <-- R (attach-2) [376 ms]: {"seq": 20, "type": "response", "request_seq": 2, "success": true, "command": "attach"}
1> [DebugAdapter] <-- E (process): {"seq": 21, "type": "event", "event": "process", "body": {"name": "C:\\PROGRAM FILES (X86)\\MICROSOFT VISUAL STUDIO\\2019\\PREVIEW\\COMMON7\\IDE\\EXTENSIONS\\MICROSOFT\\PYTHON\\CORE\\testlauncher.py", "systemProcessId": 4668, "isLocalProcess": true, "startMethod": "attach"}}
1> [DebugAdapter] <-- E (thread): {"seq": 22, "type": "event", "event": "thread", "body": {"reason": "started", "threadId": 1}}
1> [DebugAdapter] <-- E (output): {"seq": 23, "type": "event", "event": "output", "body": {"output": "============================= test session starts =============================", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 24, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 25, "type": "event", "event": "output", "body": {"output": "platform win32 -- Python 3.7.7, pytest-5.4.1, py-1.8.1, pluggy-0.13.1", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 26, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 27, "type": "event", "event": "output", "body": {"output": "rootdir: C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 28, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 29, "type": "event", "event": "output", "body": {"output": "collected 1 item", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 30, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 31, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 32, "type": "event", "event": "output", "body": {"output": "test_1.py ", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (stopped): {"seq": 33, "type": "event", "event": "stopped", "body": {"reason": "breakpoint", "threadId": 1, "preserveFocusHint": false, "allThreadsStopped": true}}
1> [DebugAdapter] --> C (threads-17): {"type":"request","command":"threads","arguments":{},"seq":17}
1> [DebugAdapter] <-- R (threads-17) [3 ms]: {"seq": 34, "type": "response", "request_seq": 17, "success": true, "command": "threads", "body": {"threads": [{"id": 1, "name": "MainThread"}]}}
1> [DebugAdapter] --> C (stackTrace-18): {"type":"request","command":"stackTrace","arguments":{"threadId":1,"startFrame":0,"levels":1,"format":{"includeAll":true}},"seq":18}
1> [DebugAdapter] <-- R (stackTrace-18) [18 ms]: {"seq": 35, "type": "response", "request_seq": 18, "success": true, "command": "stackTrace", "body": {"stackFrames": [{"id": 2, "name": "test_A", "line": 5, "column": 1, "source": {"path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sourceReference": 0}}], "totalFrames": 1}}
1> [DebugAdapter] <-- E (module): {"seq": 36, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 0, "name": "test_1", "path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py"}}}
1> [DebugAdapter] --> C (stackTrace-19): {"type":"request","command":"stackTrace","arguments":{"threadId":1,"startFrame":0,"levels":1000,"format":{"parameters":true,"parameterTypes":true,"parameterNames":true,"line":true,"module":true}},"seq":19}
1> [DebugAdapter] <-- E (module): {"seq": 37, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 1, "name": "_pytest.python", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\python.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 38, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 2, "name": "pluggy.callers", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\pluggy\\callers.py", "package": "pluggy"}}}
1> [DebugAdapter] <-- E (module): {"seq": 39, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 3, "name": "pluggy.manager", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\pluggy\\manager.py", "package": "pluggy"}}}
1> [DebugAdapter] <-- E (module): {"seq": 40, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 4, "name": "pluggy.hooks", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\pluggy\\hooks.py", "package": "pluggy"}}}
1> [DebugAdapter] <-- E (module): {"seq": 41, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 5, "name": "_pytest.unittest", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\unittest.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 42, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 6, "name": "unittest.case", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\unittest\\case.py", "package": "unittest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 43, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 7, "name": "_pytest.runner", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\runner.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 44, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 8, "name": "_pytest.main", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\main.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 45, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 9, "name": "_pytest.config", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\config\\__init__.py", "package": "_pytest.config"}}}
1> [DebugAdapter] <-- E (module): {"seq": 46, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 10, "name": "__main__", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\2019\\Preview\\Common7\\IDE\\Extensions\\Microsoft\\Python\\Core\\testlauncher.py", "package": "None"}}}
1> [DebugAdapter] <-- R (stackTrace-19) [7 ms]: {"seq": 47, "type": "response", "request_seq": 19, "success": true, "command": "stackTrace", "body": {"stackFrames": [{"id": 2, "name": "test_1.test_A : 5", "line": 5, "column": 1, "source": {"path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sourceReference": 0}}], "totalFrames": 1}}
1> [DebugAdapter] --> C (stackTrace-20): {"type":"request","command":"stackTrace","arguments":{"threadId":1,"startFrame":0,"levels":1,"format":{"includeAll":true}},"seq":20}
1> [DebugAdapter] <-- R (stackTrace-20) [2 ms]: {"seq": 48, "type": "response", "request_seq": 20, "success": true, "command": "stackTrace", "body": {"stackFrames": [{"id": 2, "name": "test_A", "line": 5, "column": 1, "source": {"path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sourceReference": 0}}], "totalFrames": 1}}
1> [DebugAdapter] --> C (evaluate-21): {"type":"request","command":"evaluate","arguments":{"context":"hover","expression":"test_A","frameId":2,"noSideEffects":true,"timeout":5000},"seq":21}
1> [DebugAdapter] --> C (evaluate-22): {"type":"request","command":"evaluate","arguments":{"context":"hover","expression":"Test_test_1","frameId":2,"noSideEffects":true,"timeout":5000},"seq":22}
1> [DebugAdapter] --> C (evaluate-23): {"type":"request","command":"evaluate","arguments":{"context":"hover","expression":"unittest.TestCase","frameId":2,"noSideEffects":true,"timeout":5000},"seq":23}
1> [DebugAdapter] <-- R (evaluate-21) [42 ms]: {"seq": 49, "type": "response", "request_seq": 21, "success": false, "command": "evaluate", "message": "Exception occurred during evaluation."}
1> [DebugAdapter] <-- R (evaluate-22) [45 ms]: {"seq": 50, "type": "response", "request_seq": 22, "success": true, "command": "evaluate", "body": {"result": "<class 'test_1.Test_test_1'>", "variablesReference": 3, "type": "type", "presentationHint": {}}}
1> [DebugAdapter] <-- R (evaluate-23) [32 ms]: {"seq": 51, "type": "response", "request_seq": 23, "success": true, "command": "evaluate", "body": {"result": "<class 'unittest.case.TestCase'>", "variablesReference": 4, "type": "type", "presentationHint": {}}}
1> [DebugAdapter] --> C (next-24): {"type":"request","command":"next","arguments":{"threadId":1},"seq":24}
1> [DebugAdapter] <-- R (next-24) [4 ms]: {"seq": 52, "type": "response", "request_seq": 24, "success": true, "command": "next"}
1> [DebugAdapter] <-- E (output): {"seq": 53, "type": "event", "event": "output", "body": {"output": ".", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 54, "type": "event", "event": "output", "body": {"output": " [100%]", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 55, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 56, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 57, "type": "event", "event": "output", "body": {"output": "- generated xml file: C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\TestResults\\junitresults_96063626-8e02-4a76-b063-c1d220785f39.xml -", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 58, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 59, "type": "event", "event": "output", "body": {"output": "============================== 1 passed in 1.43s ==============================", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 60, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (thread): {"seq": 61, "type": "event", "event": "thread", "body": {"reason": "exited", "threadId": 1}}
1> [DebugAdapter] <-- E (terminated): {"seq": 62, "type": "event", "event": "terminated"}
1> [DebugAdapter] --> C (disconnect-25): {"type":"request","command":"disconnect","arguments":{},"seq":25}
1> [DebugAdapter] <-- R (disconnect-25) [6 ms]: {"seq": 63, "type": "response", "request_seq": 25, "success": true, "command": "disconnect"}
1> Debug adapter process exited.
1> WARNING: Stopping due to fatal error: AggregateException: One or more errors occurred.
1> ERROR: Unexpected error
AggregateException: One or more errors occurred.
System.Threading.Tasks.Task.ThrowIfExceptional(Boolean includeTaskCanceledExceptions)
System.Threading.Tasks.Task`1.GetResultCore(Boolean waitCompletionNotification)
System.Threading.Tasks.Task`1.get_Result()
Microsoft.VisualStudio.Shared.VSCodeDebugProtocol.Protocol.DebugProtocol.ReaderThreadProc()
Aggregate exception:
IOException: Unable to read data from the transport connection: A blocking operation was interrupted by a call to WSACancelBlockingCall.
Inner Exception:
SocketException: A blocking operation was interrupted by a call to WSACancelBlockingCall
Inner Exception:
IOException: Unable to read data from the transport connection: A blocking operation was interrupted by a call to WSACancelBlockingCall.
System.Net.Sockets.NetworkStream.Read(Byte[] buffer, Int32 offset, Int32 size)
Microsoft.PythonTools.Debugger.DebugRemoteAdapterProcessStream.Read(Byte[] buffer, Int32 offset, Int32 count)
System.IO.Stream.<>c.<BeginReadInternal>b__39_0(Object <p0>)
System.Threading.Tasks.Task`1.InnerInvoke()
System.Threading.Tasks.Task.Execute()
--- End of stack trace from previous location where exception was thrown ---
System.Runtime.CompilerServices.TaskAwaiter.ThrowForNonSuccess(Task task)
System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
System.IO.Stream.EndRead(IAsyncResult asyncResult)
System.IO.Stream.<>c.<BeginEndReadAsync>b__43_1(Stream stream, IAsyncResult asyncResult)
System.Threading.Tasks.TaskFactory`1.FromAsyncTrimPromise`1.Complete(TInstance thisRef, Func`3 endMethod, IAsyncResult asyncResult, Boolean requiresSynchronization)
Inner Exception:
SocketException: A blocking operation was interrupted by a call to WSACancelBlockingCall
System.Net.Sockets.Socket.Receive(Byte[] buffer, Int32 offset, Int32 size, SocketFlags socketFlags)
System.Net.Sockets.NetworkStream.Read(Byte[] buffer, Int32 offset, Int32 size)
1> ERROR: One or more errors occurred.
Unable to read data from the transport connection: A blocking operation was interrupted by a call to WSACancelBlockingCall.
A blocking operation was interrupted by a call to WSACancelBlockingCall
1> ERROR: Exception while reporting error.
NullReferenceException: Object reference not set to an instance of an object.
Microsoft.VisualStudio.Debugger.VSCodeDebuggerHost.AD7.Implementation.EngineCallback.Send(IAD7DebugEvent eventObject, IDebugThread2 thread)
Microsoft.VisualStudio.Debugger.VSCodeDebuggerHost.AD7.Implementation.EngineCallback.OnError(String errorMessage)
``` | 1.0 | When debugged a second time, VS loses its response and restarts. -
**Steps to Reproduce**
1.Add unit test test_1.py in python application
2.Typing code in test_1.py
import unittest
class Test_test_1(unittest.TestCase):
def test_A(self):
self.assertEqual(1,1)
if __name__ == '__main__':
unittest.main()
3.Set bk in the code
4.In TE, select the test and right-click to select Debug Selected tests
5.After the first successful debug, debug the current test again.
**Expected behavior**
The test can be debugged successfully
**Actual behavior**
When debugged a second time, VS loses its response and restarts.
**Debug Adapter Host Log**
```
1> DebugAdapterHost version: 16.7.40413.2 commit:b7937c15e33a949e648926944d211d657e3684f0
1> [DebugAdapter] <-- E (output): {"seq": 1, "type": "event", "event": "output", "body": {"category": "telemetry", "output": "ptvsd", "data": {"packageVersion": "1.0.0b5"}}}
1> [DebugAdapter] --> C (initialize-1): {"type":"request","command":"initialize","arguments":{"pathFormat":"path","clientID":"visualstudio","clientName":"Visual Studio","adapterID":null,"locale":"en-US","linesStartAt1":true,"columnsStartAt1":true,"supportsVariableType":true,"supportsRunInTerminalRequest":true,"supportsMemoryReferences":true,"supportsProgressReporting":true,"supportsHandshakeRequest":true},"seq":1}
1> [DebugAdapter] <-- E (output): {"seq": 2, "type": "event", "event": "output", "body": {"category": "telemetry", "output": "debugpy", "data": {"packageVersion": "1.0.0b5"}}}
1> [DebugAdapter] <-- R (initialize-1) [167 ms]: {"seq": 3, "type": "response", "request_seq": 1, "success": true, "command": "initialize", "body": {"supportsCompletionsRequest": true, "supportsConditionalBreakpoints": true, "supportsConfigurationDoneRequest": true, "supportsDebuggerProperties": true, "supportsDelayedStackTraceLoading": true, "supportsEvaluateForHovers": true, "supportsExceptionInfoRequest": true, "supportsExceptionOptions": true, "supportsHitConditionalBreakpoints": true, "supportsLogPoints": true, "supportsModulesRequest": true, "supportsSetExpression": true, "supportsSetVariable": true, "supportsValueFormattingOptions": true, "supportsTerminateDebuggee": true, "supportsGotoTargetsRequest": true, "exceptionBreakpointFilters": [{"filter": "raised", "label": "Raised Exceptions", "default": false}, {"filter": "uncaught", "label": "Uncaught Exceptions", "default": true}]}}
1> [DebugAdapter] --> C (attach-2): {"type":"request","command":"attach","arguments":{"host":"localhost","port":52468,"stopOnEntry":true,"promptBeforeRunningWithBuildError":true,"redirectOutput":true,"waitOnAbnormalExit":true,"waitOnNormalExit":true,"breakOnSystemExitZero":false,"debugStdLib":false,"showReturnValue":true,"rules":[{"path":"c:\\program files (x86)\\microsoft visual studio\\2019\\preview\\common7\\ide\\extensions\\microsoft\\python\\core\\","include":false}]},"seq":2}
1> [DebugAdapter] <-- E (debugpyWaitingForServer): {"seq": 4, "type": "event", "event": "debugpyWaitingForServer", "body": {"host": "127.0.0.1", "port": 52521}}
1> WARNING: No handler registered for event of type 'debugpyWaitingForServer'!
1> [DebugAdapter] <-- E (initialized): {"seq": 5, "type": "event", "event": "initialized"}
1> [DebugAdapter] --> C (debugpySystemInfo-3): {"type":"request","command":"debugpySystemInfo","arguments":{},"seq":3}
1> [DebugAdapter] <-- R (debugpySystemInfo-3) [16 ms]: {"seq": 6, "type": "response", "request_seq": 3, "success": true, "command": "debugpySystemInfo", "body": {"debugpy": {"version": "1.0.0b5"}, "python": {"version": "3.7.7final0", "implementation": {"name": "cpython", "version": "3.7.7final0", "description": "CPython"}}, "platform": {"name": "win32"}, "process": {"pid": 4668, "ppid": 6728, "executable": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\python.exe", "bitness": 64}, "pydevd": {"usingCython": false, "usingFrameEval": false}}}
1> [DebugAdapter] --> C (setDebuggerProperty-4): {"type":"request","command":"setDebuggerProperty","arguments":{"AllowOutOfProcessSymbols":1},"seq":4}
1> [DebugAdapter] --> C (setDebuggerProperty-5): {"type":"request","command":"setDebuggerProperty","arguments":{"DisableJITOptimization":0},"seq":5}
1> [DebugAdapter] --> C (setDebuggerProperty-6): {"type":"request","command":"setDebuggerProperty","arguments":{"EnableFastEvaluate":1},"seq":6}
1> [DebugAdapter] --> C (setDebuggerProperty-7): {"type":"request","command":"setDebuggerProperty","arguments":{"InterpreterOptions":1},"seq":7}
1> [DebugAdapter] --> C (setDebuggerProperty-8): {"type":"request","command":"setDebuggerProperty","arguments":{"JustMyCodeStepping":1},"seq":8}
1> [DebugAdapter] --> C (setDebuggerProperty-9): {"type":"request","command":"setDebuggerProperty","arguments":{"StopOnExceptionCrossingManagedBoundary":0},"seq":9}
1> [DebugAdapter] --> C (setDebuggerProperty-10): {"type":"request","command":"setDebuggerProperty","arguments":{"WarnIfNoUserCodeOnLaunch":1},"seq":10}
1> [DebugAdapter] --> C (setDebuggerProperty-11): {"type":"request","command":"setDebuggerProperty","arguments":{"EnableStepFiltering":true},"seq":11}
1> [DebugAdapter] <-- R (setDebuggerProperty-4) [6 ms]: {"seq": 7, "type": "response", "request_seq": 4, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-5) [6 ms]: {"seq": 8, "type": "response", "request_seq": 5, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-6) [6 ms]: {"seq": 9, "type": "response", "request_seq": 6, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-7) [7 ms]: {"seq": 10, "type": "response", "request_seq": 7, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-8) [7 ms]: {"seq": 11, "type": "response", "request_seq": 8, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-9) [8 ms]: {"seq": 12, "type": "response", "request_seq": 9, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-10) [9 ms]: {"seq": 13, "type": "response", "request_seq": 10, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] <-- R (setDebuggerProperty-11) [10 ms]: {"seq": 14, "type": "response", "request_seq": 11, "success": true, "command": "setDebuggerProperty"}
1> [DebugAdapter] --> C (setBreakpoints-12): {"type":"request","command":"setBreakpoints","arguments":{"source":{"path":"c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_ut.py","sources":[],"checksums":[]},"breakpoints":[{"line":8,"column":1}],"lines":[8]},"seq":12}
1> [DebugAdapter] --> C (setBreakpoints-13): {"type":"request","command":"setBreakpoints","arguments":{"source":{"path":"c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_pta.py","sources":[],"checksums":[]},"breakpoints":[{"line":5,"column":1}],"lines":[5]},"seq":13}
1> [DebugAdapter] --> C (setBreakpoints-14): {"type":"request","command":"setBreakpoints","arguments":{"source":{"path":"c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py","sources":[],"checksums":[]},"breakpoints":[{"line":5,"column":1}],"lines":[5]},"seq":14}
1> [DebugAdapter] <-- R (setBreakpoints-12) [35 ms]: {"seq": 15, "type": "response", "request_seq": 12, "success": true, "command": "setBreakpoints", "body": {"breakpoints": [{"verified": true, "id": 0, "source": {"path": "c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_ut.py", "sources": [], "checksums": []}, "line": 8}]}}
1> [DebugAdapter] <-- R (setBreakpoints-13) [28 ms]: {"seq": 16, "type": "response", "request_seq": 13, "success": true, "command": "setBreakpoints", "body": {"breakpoints": [{"verified": true, "id": 1, "source": {"path": "c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\Test_a\\test_pta.py", "sources": [], "checksums": []}, "line": 5}]}}
1> [DebugAdapter] <-- R (setBreakpoints-14) [29 ms]: {"seq": 17, "type": "response", "request_seq": 14, "success": true, "command": "setBreakpoints", "body": {"breakpoints": [{"verified": true, "id": 2, "source": {"path": "c:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sources": [], "checksums": []}, "line": 5}]}}
1> [DebugAdapter] --> C (setExceptionBreakpoints-15): {"type":"request","command":"setExceptionBreakpoints","arguments":{"filters":[],"exceptionOptions":[{"breakMode":"userUnhandled","path":[{"names":["Python Exceptions"]}]},{"breakMode":"unhandled","path":[{"names":["Python Exceptions"]},{"names":["GeneratorExit","IndexError","StopIteration","AttributeError","KeyError"]}]}]},"seq":15}
1> [DebugAdapter] <-- R (setExceptionBreakpoints-15) [20 ms]: {"seq": 18, "type": "response", "request_seq": 15, "success": true, "command": "setExceptionBreakpoints"}
1> [DebugAdapter] --> C (configurationDone-16): {"type":"request","command":"configurationDone","arguments":{},"seq":16}
1> [DebugAdapter] <-- R (configurationDone-16) [5 ms]: {"seq": 19, "type": "response", "request_seq": 16, "success": true, "command": "configurationDone"}
1> [DebugAdapter] <-- R (attach-2) [376 ms]: {"seq": 20, "type": "response", "request_seq": 2, "success": true, "command": "attach"}
1> [DebugAdapter] <-- E (process): {"seq": 21, "type": "event", "event": "process", "body": {"name": "C:\\PROGRAM FILES (X86)\\MICROSOFT VISUAL STUDIO\\2019\\PREVIEW\\COMMON7\\IDE\\EXTENSIONS\\MICROSOFT\\PYTHON\\CORE\\testlauncher.py", "systemProcessId": 4668, "isLocalProcess": true, "startMethod": "attach"}}
1> [DebugAdapter] <-- E (thread): {"seq": 22, "type": "event", "event": "thread", "body": {"reason": "started", "threadId": 1}}
1> [DebugAdapter] <-- E (output): {"seq": 23, "type": "event", "event": "output", "body": {"output": "============================= test session starts =============================", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 24, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 25, "type": "event", "event": "output", "body": {"output": "platform win32 -- Python 3.7.7, pytest-5.4.1, py-1.8.1, pluggy-0.13.1", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 26, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 27, "type": "event", "event": "output", "body": {"output": "rootdir: C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 28, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 29, "type": "event", "event": "output", "body": {"output": "collected 1 item", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 30, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 31, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 32, "type": "event", "event": "output", "body": {"output": "test_1.py ", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (stopped): {"seq": 33, "type": "event", "event": "stopped", "body": {"reason": "breakpoint", "threadId": 1, "preserveFocusHint": false, "allThreadsStopped": true}}
1> [DebugAdapter] --> C (threads-17): {"type":"request","command":"threads","arguments":{},"seq":17}
1> [DebugAdapter] <-- R (threads-17) [3 ms]: {"seq": 34, "type": "response", "request_seq": 17, "success": true, "command": "threads", "body": {"threads": [{"id": 1, "name": "MainThread"}]}}
1> [DebugAdapter] --> C (stackTrace-18): {"type":"request","command":"stackTrace","arguments":{"threadId":1,"startFrame":0,"levels":1,"format":{"includeAll":true}},"seq":18}
1> [DebugAdapter] <-- R (stackTrace-18) [18 ms]: {"seq": 35, "type": "response", "request_seq": 18, "success": true, "command": "stackTrace", "body": {"stackFrames": [{"id": 2, "name": "test_A", "line": 5, "column": 1, "source": {"path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sourceReference": 0}}], "totalFrames": 1}}
1> [DebugAdapter] <-- E (module): {"seq": 36, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 0, "name": "test_1", "path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py"}}}
1> [DebugAdapter] --> C (stackTrace-19): {"type":"request","command":"stackTrace","arguments":{"threadId":1,"startFrame":0,"levels":1000,"format":{"parameters":true,"parameterTypes":true,"parameterNames":true,"line":true,"module":true}},"seq":19}
1> [DebugAdapter] <-- E (module): {"seq": 37, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 1, "name": "_pytest.python", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\python.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 38, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 2, "name": "pluggy.callers", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\pluggy\\callers.py", "package": "pluggy"}}}
1> [DebugAdapter] <-- E (module): {"seq": 39, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 3, "name": "pluggy.manager", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\pluggy\\manager.py", "package": "pluggy"}}}
1> [DebugAdapter] <-- E (module): {"seq": 40, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 4, "name": "pluggy.hooks", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\pluggy\\hooks.py", "package": "pluggy"}}}
1> [DebugAdapter] <-- E (module): {"seq": 41, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 5, "name": "_pytest.unittest", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\unittest.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 42, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 6, "name": "unittest.case", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\unittest\\case.py", "package": "unittest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 43, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 7, "name": "_pytest.runner", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\runner.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 44, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 8, "name": "_pytest.main", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\main.py", "package": "_pytest"}}}
1> [DebugAdapter] <-- E (module): {"seq": 45, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 9, "name": "_pytest.config", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\Shared\\Python37_64\\Lib\\site-packages\\_pytest\\config\\__init__.py", "package": "_pytest.config"}}}
1> [DebugAdapter] <-- E (module): {"seq": 46, "type": "event", "event": "module", "body": {"reason": "new", "module": {"id": 10, "name": "__main__", "path": "C:\\Program Files (x86)\\Microsoft Visual Studio\\2019\\Preview\\Common7\\IDE\\Extensions\\Microsoft\\Python\\Core\\testlauncher.py", "package": "None"}}}
1> [DebugAdapter] <-- R (stackTrace-19) [7 ms]: {"seq": 47, "type": "response", "request_seq": 19, "success": true, "command": "stackTrace", "body": {"stackFrames": [{"id": 2, "name": "test_1.test_A : 5", "line": 5, "column": 1, "source": {"path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sourceReference": 0}}], "totalFrames": 1}}
1> [DebugAdapter] --> C (stackTrace-20): {"type":"request","command":"stackTrace","arguments":{"threadId":1,"startFrame":0,"levels":1,"format":{"includeAll":true}},"seq":20}
1> [DebugAdapter] <-- R (stackTrace-20) [2 ms]: {"seq": 48, "type": "response", "request_seq": 20, "success": true, "command": "stackTrace", "body": {"stackFrames": [{"id": 2, "name": "test_A", "line": 5, "column": 1, "source": {"path": "C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\PythonApplication1\\test_1.py", "sourceReference": 0}}], "totalFrames": 1}}
1> [DebugAdapter] --> C (evaluate-21): {"type":"request","command":"evaluate","arguments":{"context":"hover","expression":"test_A","frameId":2,"noSideEffects":true,"timeout":5000},"seq":21}
1> [DebugAdapter] --> C (evaluate-22): {"type":"request","command":"evaluate","arguments":{"context":"hover","expression":"Test_test_1","frameId":2,"noSideEffects":true,"timeout":5000},"seq":22}
1> [DebugAdapter] --> C (evaluate-23): {"type":"request","command":"evaluate","arguments":{"context":"hover","expression":"unittest.TestCase","frameId":2,"noSideEffects":true,"timeout":5000},"seq":23}
1> [DebugAdapter] <-- R (evaluate-21) [42 ms]: {"seq": 49, "type": "response", "request_seq": 21, "success": false, "command": "evaluate", "message": "Exception occurred during evaluation."}
1> [DebugAdapter] <-- R (evaluate-22) [45 ms]: {"seq": 50, "type": "response", "request_seq": 22, "success": true, "command": "evaluate", "body": {"result": "<class 'test_1.Test_test_1'>", "variablesReference": 3, "type": "type", "presentationHint": {}}}
1> [DebugAdapter] <-- R (evaluate-23) [32 ms]: {"seq": 51, "type": "response", "request_seq": 23, "success": true, "command": "evaluate", "body": {"result": "<class 'unittest.case.TestCase'>", "variablesReference": 4, "type": "type", "presentationHint": {}}}
1> [DebugAdapter] --> C (next-24): {"type":"request","command":"next","arguments":{"threadId":1},"seq":24}
1> [DebugAdapter] <-- R (next-24) [4 ms]: {"seq": 52, "type": "response", "request_seq": 24, "success": true, "command": "next"}
1> [DebugAdapter] <-- E (output): {"seq": 53, "type": "event", "event": "output", "body": {"output": ".", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 54, "type": "event", "event": "output", "body": {"output": " [100%]", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 55, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 56, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 57, "type": "event", "event": "output", "body": {"output": "- generated xml file: C:\\Users\\vwazho\\source\\repos\\PythonApplication1\\TestResults\\junitresults_96063626-8e02-4a76-b063-c1d220785f39.xml -", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 58, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 59, "type": "event", "event": "output", "body": {"output": "============================== 1 passed in 1.43s ==============================", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (output): {"seq": 60, "type": "event", "event": "output", "body": {"output": "\n", "category": "stdout", "source": {}}}
1> [DebugAdapter] <-- E (thread): {"seq": 61, "type": "event", "event": "thread", "body": {"reason": "exited", "threadId": 1}}
1> [DebugAdapter] <-- E (terminated): {"seq": 62, "type": "event", "event": "terminated"}
1> [DebugAdapter] --> C (disconnect-25): {"type":"request","command":"disconnect","arguments":{},"seq":25}
1> [DebugAdapter] <-- R (disconnect-25) [6 ms]: {"seq": 63, "type": "response", "request_seq": 25, "success": true, "command": "disconnect"}
1> Debug adapter process exited.
1> WARNING: Stopping due to fatal error: AggregateException: One or more errors occurred.
1> ERROR: Unexpected error
AggregateException: One or more errors occurred.
System.Threading.Tasks.Task.ThrowIfExceptional(Boolean includeTaskCanceledExceptions)
System.Threading.Tasks.Task`1.GetResultCore(Boolean waitCompletionNotification)
System.Threading.Tasks.Task`1.get_Result()
Microsoft.VisualStudio.Shared.VSCodeDebugProtocol.Protocol.DebugProtocol.ReaderThreadProc()
Aggregate exception:
IOException: Unable to read data from the transport connection: A blocking operation was interrupted by a call to WSACancelBlockingCall.
Inner Exception:
SocketException: A blocking operation was interrupted by a call to WSACancelBlockingCall
Inner Exception:
IOException: Unable to read data from the transport connection: A blocking operation was interrupted by a call to WSACancelBlockingCall.
System.Net.Sockets.NetworkStream.Read(Byte[] buffer, Int32 offset, Int32 size)
Microsoft.PythonTools.Debugger.DebugRemoteAdapterProcessStream.Read(Byte[] buffer, Int32 offset, Int32 count)
System.IO.Stream.<>c.<BeginReadInternal>b__39_0(Object <p0>)
System.Threading.Tasks.Task`1.InnerInvoke()
System.Threading.Tasks.Task.Execute()
--- End of stack trace from previous location where exception was thrown ---
System.Runtime.CompilerServices.TaskAwaiter.ThrowForNonSuccess(Task task)
System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
System.IO.Stream.EndRead(IAsyncResult asyncResult)
System.IO.Stream.<>c.<BeginEndReadAsync>b__43_1(Stream stream, IAsyncResult asyncResult)
System.Threading.Tasks.TaskFactory`1.FromAsyncTrimPromise`1.Complete(TInstance thisRef, Func`3 endMethod, IAsyncResult asyncResult, Boolean requiresSynchronization)
Inner Exception:
SocketException: A blocking operation was interrupted by a call to WSACancelBlockingCall
System.Net.Sockets.Socket.Receive(Byte[] buffer, Int32 offset, Int32 size, SocketFlags socketFlags)
System.Net.Sockets.NetworkStream.Read(Byte[] buffer, Int32 offset, Int32 size)
1> ERROR: One or more errors occurred.
Unable to read data from the transport connection: A blocking operation was interrupted by a call to WSACancelBlockingCall.
A blocking operation was interrupted by a call to WSACancelBlockingCall
1> ERROR: Exception while reporting error.
NullReferenceException: Object reference not set to an instance of an object.
Microsoft.VisualStudio.Debugger.VSCodeDebuggerHost.AD7.Implementation.EngineCallback.Send(IAD7DebugEvent eventObject, IDebugThread2 thread)
Microsoft.VisualStudio.Debugger.VSCodeDebuggerHost.AD7.Implementation.EngineCallback.OnError(String errorMessage)
``` | non_priority | when debugged a second time vs loses its response and restarts steps to reproduce add unit test test py in python application typing code in test py import unittest class test test unittest testcase def test a self self assertequal if name main unittest main set bk in the code in te select the test and right click to select debug selected tests after the first successful debug debug the current test again expected behavior the test can be debugged successfully actual behavior when debugged a second time vs loses its response and restarts debug adapter host log debugadapterhost version commit e output seq type event event output body category telemetry output ptvsd data packageversion c initialize type request command initialize arguments pathformat path clientid visualstudio clientname visual studio adapterid null locale en us true true supportsvariabletype true supportsruninterminalrequest true supportsmemoryreferences true supportsprogressreporting true supportshandshakerequest true seq e output seq type event event output body category telemetry output debugpy data packageversion r initialize seq type response request seq success true command initialize body supportscompletionsrequest true supportsconditionalbreakpoints true supportsconfigurationdonerequest true supportsdebuggerproperties true supportsdelayedstacktraceloading true supportsevaluateforhovers true supportsexceptioninforequest true supportsexceptionoptions true supportshitconditionalbreakpoints true supportslogpoints true supportsmodulesrequest true supportssetexpression true supportssetvariable true supportsvalueformattingoptions true supportsterminatedebuggee true supportsgototargetsrequest true exceptionbreakpointfilters c attach type request command attach arguments host localhost port stoponentry true promptbeforerunningwithbuilderror true redirectoutput true waitonabnormalexit true waitonnormalexit true breakonsystemexitzero false debugstdlib false showreturnvalue true rules seq e debugpywaitingforserver seq type event event debugpywaitingforserver body host port warning no handler registered for event of type debugpywaitingforserver e initialized seq type event event initialized c debugpysysteminfo type request command debugpysysteminfo arguments seq r debugpysysteminfo seq type response request seq success true command debugpysysteminfo body debugpy version python version implementation name cpython version description cpython platform name process pid ppid executable c program files microsoft visual studio shared python exe bitness pydevd usingcython false usingframeeval false c setdebuggerproperty type request command setdebuggerproperty arguments allowoutofprocesssymbols seq c setdebuggerproperty type request command setdebuggerproperty arguments disablejitoptimization seq c setdebuggerproperty type request command setdebuggerproperty arguments enablefastevaluate seq c setdebuggerproperty type request command setdebuggerproperty arguments interpreteroptions seq c setdebuggerproperty type request command setdebuggerproperty arguments justmycodestepping seq c setdebuggerproperty type request command setdebuggerproperty arguments stoponexceptioncrossingmanagedboundary seq c setdebuggerproperty type request command setdebuggerproperty arguments warnifnousercodeonlaunch seq c setdebuggerproperty type request command setdebuggerproperty arguments enablestepfiltering true seq r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty r setdebuggerproperty seq type response request seq success true command setdebuggerproperty c setbreakpoints type request command setbreakpoints arguments source path c users vwazho source repos test a test ut py sources checksums breakpoints lines seq c setbreakpoints type request command setbreakpoints arguments source path c users vwazho source repos test a test pta py sources checksums breakpoints lines seq c setbreakpoints type request command setbreakpoints arguments source path c users vwazho source repos test py sources checksums breakpoints lines seq r setbreakpoints seq type response request seq success true command setbreakpoints body breakpoints checksums line r setbreakpoints seq type response request seq success true command setbreakpoints body breakpoints checksums line r setbreakpoints seq type response request seq success true command setbreakpoints body breakpoints checksums line c setexceptionbreakpoints type request command setexceptionbreakpoints arguments filters exceptionoptions breakmode unhandled path names seq r setexceptionbreakpoints seq type response request seq success true command setexceptionbreakpoints c configurationdone type request command configurationdone arguments seq r configurationdone seq type response request seq success true command configurationdone r attach seq type response request seq success true command attach e process seq type event event process body name c program files microsoft visual studio preview ide extensions microsoft python core testlauncher py systemprocessid islocalprocess true startmethod attach e thread seq type event event thread body reason started threadid e output seq type event event output body output test session starts category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output platform python pytest py pluggy category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output rootdir c users vwazho source repos category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output collected item category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output test py category stdout source e stopped seq type event event stopped body reason breakpoint threadid preservefocushint false allthreadsstopped true c threads type request command threads arguments seq r threads seq type response request seq success true command threads body threads c stacktrace type request command stacktrace arguments threadid startframe levels format includeall true seq r stacktrace seq type response request seq success true command stacktrace body stackframes totalframes e module seq type event event module body reason new module id name test path c users vwazho source repos test py c stacktrace type request command stacktrace arguments threadid startframe levels format parameters true parametertypes true parameternames true line true module true seq e module seq type event event module body reason new module id name pytest python path c program files microsoft visual studio shared lib site packages pytest python py package pytest e module seq type event event module body reason new module id name pluggy callers path c program files microsoft visual studio shared lib site packages pluggy callers py package pluggy e module seq type event event module body reason new module id name pluggy manager path c program files microsoft visual studio shared lib site packages pluggy manager py package pluggy e module seq type event event module body reason new module id name pluggy hooks path c program files microsoft visual studio shared lib site packages pluggy hooks py package pluggy e module seq type event event module body reason new module id name pytest unittest path c program files microsoft visual studio shared lib site packages pytest unittest py package pytest e module seq type event event module body reason new module id name unittest case path c program files microsoft visual studio shared lib unittest case py package unittest e module seq type event event module body reason new module id name pytest runner path c program files microsoft visual studio shared lib site packages pytest runner py package pytest e module seq type event event module body reason new module id name pytest main path c program files microsoft visual studio shared lib site packages pytest main py package pytest e module seq type event event module body reason new module id name pytest config path c program files microsoft visual studio shared lib site packages pytest config init py package pytest config e module seq type event event module body reason new module id name main path c program files microsoft visual studio preview ide extensions microsoft python core testlauncher py package none r stacktrace seq type response request seq success true command stacktrace body stackframes totalframes c stacktrace type request command stacktrace arguments threadid startframe levels format includeall true seq r stacktrace seq type response request seq success true command stacktrace body stackframes totalframes c evaluate type request command evaluate arguments context hover expression test a frameid nosideeffects true timeout seq c evaluate type request command evaluate arguments context hover expression test test frameid nosideeffects true timeout seq c evaluate type request command evaluate arguments context hover expression unittest testcase frameid nosideeffects true timeout seq r evaluate seq type response request seq success false command evaluate message exception occurred during evaluation variablesreference type type presentationhint variablesreference type type presentationhint c next type request command next arguments threadid seq r next seq type response request seq success true command next e output seq type event event output body output category stdout source e output seq type event event output body output category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output generated xml file c users vwazho source repos testresults junitresults xml category stdout source e output seq type event event output body output n category stdout source e output seq type event event output body output passed in category stdout source e output seq type event event output body output n category stdout source e thread seq type event event thread body reason exited threadid e terminated seq type event event terminated c disconnect type request command disconnect arguments seq r disconnect seq type response request seq success true command disconnect debug adapter process exited warning stopping due to fatal error aggregateexception one or more errors occurred error unexpected error aggregateexception one or more errors occurred system threading tasks task throwifexceptional boolean includetaskcanceledexceptions system threading tasks task getresultcore boolean waitcompletionnotification system threading tasks task get result microsoft visualstudio shared vscodedebugprotocol protocol debugprotocol readerthreadproc aggregate exception ioexception unable to read data from the transport connection a blocking operation was interrupted by a call to wsacancelblockingcall inner exception socketexception a blocking operation was interrupted by a call to wsacancelblockingcall inner exception ioexception unable to read data from the transport connection a blocking operation was interrupted by a call to wsacancelblockingcall system net sockets networkstream read byte buffer offset size microsoft pythontools debugger debugremoteadapterprocessstream read byte buffer offset count system io stream c b object system threading tasks task innerinvoke system threading tasks task execute end of stack trace from previous location where exception was thrown system runtime compilerservices taskawaiter throwfornonsuccess task task system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task system io stream endread iasyncresult asyncresult system io stream c b stream stream iasyncresult asyncresult system threading tasks taskfactory fromasynctrimpromise complete tinstance thisref func endmethod iasyncresult asyncresult boolean requiressynchronization inner exception socketexception a blocking operation was interrupted by a call to wsacancelblockingcall system net sockets socket receive byte buffer offset size socketflags socketflags system net sockets networkstream read byte buffer offset size error one or more errors occurred unable to read data from the transport connection a blocking operation was interrupted by a call to wsacancelblockingcall a blocking operation was interrupted by a call to wsacancelblockingcall error exception while reporting error nullreferenceexception object reference not set to an instance of an object microsoft visualstudio debugger vscodedebuggerhost implementation enginecallback send eventobject thread microsoft visualstudio debugger vscodedebuggerhost implementation enginecallback onerror string errormessage | 0 |
41,733 | 5,394,875,451 | IssuesEvent | 2017-02-27 06:00:20 | OpenDICOMweb/sdk | https://api.github.com/repos/OpenDICOMweb/sdk | closed | Test Tag Validators in tag/tag.dart | dictionary P0 Urgent Test - unit | isValidValues
isValidLength
isValidWidth
isValidVFLength
isValidPrivateDataTag
| 1.0 | Test Tag Validators in tag/tag.dart - isValidValues
isValidLength
isValidWidth
isValidVFLength
isValidPrivateDataTag
| non_priority | test tag validators in tag tag dart isvalidvalues isvalidlength isvalidwidth isvalidvflength isvalidprivatedatatag | 0 |
330,034 | 24,243,852,494 | IssuesEvent | 2022-09-27 08:58:35 | spring-projects/spring-data-commons | https://api.github.com/repos/spring-projects/spring-data-commons | closed | Prefer Java configuration over XML | type: documentation | While XML configuration is still supported for the time being, we typically don't add new features to it.
We should reflect that in the documentation by:
* Adding Java configuration variants where XML is used.
* Allow for toggling between Java and XML where we have samples for both.
* Default to showing the Java variant. | 1.0 | Prefer Java configuration over XML - While XML configuration is still supported for the time being, we typically don't add new features to it.
We should reflect that in the documentation by:
* Adding Java configuration variants where XML is used.
* Allow for toggling between Java and XML where we have samples for both.
* Default to showing the Java variant. | non_priority | prefer java configuration over xml while xml configuration is still supported for the time being we typically don t add new features to it we should reflect that in the documentation by adding java configuration variants where xml is used allow for toggling between java and xml where we have samples for both default to showing the java variant | 0 |
134,595 | 30,085,429,326 | IssuesEvent | 2023-06-29 08:17:01 | raycast/extensions | https://api.github.com/repos/raycast/extensions | closed | [Visual Studio Code] Issue to open with VSCode Insiders | bug extension extension: visual-studio-code | ### Extension
https://www.raycast.com/thomas/visual-studio-code
### Description
#### Error:
```
Error: The database does not exist
Z6:index.tsx:30:30
---
27: import { getBuildScheme } from "./lib/vscode"
### Steps To Reproduce
I use only VSCode Insiders, and I haven't access to all features of the extensions.
For instance, I can't use "Search Recent Projects" and "Open with Visual Studio Code".
### Current Behaviour
Error page
### Expected Behaviour
Do the expected things in VSCode Insiders | 1.0 | [Visual Studio Code] Issue to open with VSCode Insiders - ### Extension
https://www.raycast.com/thomas/visual-studio-code
### Description
#### Error:
```
Error: The database does not exist
Z6:index.tsx:30:30
---
27: import { getBuildScheme } from "./lib/vscode"
### Steps To Reproduce
I use only VSCode Insiders, and I haven't access to all features of the extensions.
For instance, I can't use "Search Recent Projects" and "Open with Visual Studio Code".
### Current Behaviour
Error page
### Expected Behaviour
Do the expected things in VSCode Insiders | non_priority | issue to open with vscode insiders extension description error error the database does not exist index tsx import getbuildscheme from lib vscode steps to reproduce i use only vscode insiders and i haven t access to all features of the extensions for instance i can t use search recent projects and open with visual studio code current behaviour error page expected behaviour do the expected things in vscode insiders | 0 |
308,683 | 23,261,222,714 | IssuesEvent | 2022-08-04 13:39:42 | MarketSquare/robotframework-tidy | https://api.github.com/repos/MarketSquare/robotframework-tidy | closed | Doc typo: NormalizeSeparators page - Ignored sections example typo | bug documentation | Doc uses '**sections**' but example incorrectly uses '**section**':
### Ignored sections
You can decide which sections should be transformed by configuring
**sections** = comments,settings,variables,keywords,testcases param:
robotidy --configure NormalizeSeparators:**section**=variables src
.....................................................................^^^^
| 1.0 | Doc typo: NormalizeSeparators page - Ignored sections example typo - Doc uses '**sections**' but example incorrectly uses '**section**':
### Ignored sections
You can decide which sections should be transformed by configuring
**sections** = comments,settings,variables,keywords,testcases param:
robotidy --configure NormalizeSeparators:**section**=variables src
.....................................................................^^^^
| non_priority | doc typo normalizeseparators page ignored sections example typo doc uses sections but example incorrectly uses section ignored sections you can decide which sections should be transformed by configuring sections comments settings variables keywords testcases param robotidy configure normalizeseparators section variables src | 0 |
157,016 | 19,911,683,548 | IssuesEvent | 2022-01-25 17:47:47 | vlaship/case-coding-test | https://api.github.com/repos/vlaship/case-coding-test | opened | CVE-2021-23463 (High) detected in h2-1.4.200.jar | security vulnerability | ## CVE-2021-23463 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>h2-1.4.200.jar</b></p></summary>
<p>H2 Database Engine</p>
<p>Library home page: <a href="https://h2database.com">https://h2database.com</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /ches/modules-2/files-2.1/com.h2database/h2/1.4.200/f7533fe7cb8e99c87a43d325a77b4b678ad9031a/h2-1.4.200.jar</p>
<p>
Dependency Hierarchy:
- :x: **h2-1.4.200.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vlaship/case-coding-test/commit/b3c9d839b725e3d71d46642e2f32e7b11a28f87b">b3c9d839b725e3d71d46642e2f32e7b11a28f87b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package com.h2database:h2 from 1.4.198 and before 2.0.202 are vulnerable to XML External Entity (XXE) Injection via the org.h2.jdbc.JdbcSQLXML class object, when it receives parsed string data from org.h2.jdbc.JdbcResultSet.getSQLXML() method. If it executes the getSource() method when the parameter is DOMSource.class it will trigger the vulnerability.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23463>CVE-2021-23463</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-23463">https://nvd.nist.gov/vuln/detail/CVE-2021-23463</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: com.h2database:h2:2.0.202</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23463 (High) detected in h2-1.4.200.jar - ## CVE-2021-23463 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>h2-1.4.200.jar</b></p></summary>
<p>H2 Database Engine</p>
<p>Library home page: <a href="https://h2database.com">https://h2database.com</a></p>
<p>Path to dependency file: /build.gradle</p>
<p>Path to vulnerable library: /ches/modules-2/files-2.1/com.h2database/h2/1.4.200/f7533fe7cb8e99c87a43d325a77b4b678ad9031a/h2-1.4.200.jar</p>
<p>
Dependency Hierarchy:
- :x: **h2-1.4.200.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vlaship/case-coding-test/commit/b3c9d839b725e3d71d46642e2f32e7b11a28f87b">b3c9d839b725e3d71d46642e2f32e7b11a28f87b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package com.h2database:h2 from 1.4.198 and before 2.0.202 are vulnerable to XML External Entity (XXE) Injection via the org.h2.jdbc.JdbcSQLXML class object, when it receives parsed string data from org.h2.jdbc.JdbcResultSet.getSQLXML() method. If it executes the getSource() method when the parameter is DOMSource.class it will trigger the vulnerability.
<p>Publish Date: 2021-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23463>CVE-2021-23463</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-23463">https://nvd.nist.gov/vuln/detail/CVE-2021-23463</a></p>
<p>Release Date: 2021-12-10</p>
<p>Fix Resolution: com.h2database:h2:2.0.202</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jar cve high severity vulnerability vulnerable library jar database engine library home page a href path to dependency file build gradle path to vulnerable library ches modules files com jar dependency hierarchy x jar vulnerable library found in head commit a href found in base branch master vulnerability details the package com from and before are vulnerable to xml external entity xxe injection via the org jdbc jdbcsqlxml class object when it receives parsed string data from org jdbc jdbcresultset getsqlxml method if it executes the getsource method when the parameter is domsource class it will trigger the vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com step up your open source security game with whitesource | 0 |
143,108 | 19,142,910,241 | IssuesEvent | 2021-12-02 02:19:07 | arohablue/BlockDockServer | https://api.github.com/repos/arohablue/BlockDockServer | opened | CVE-2021-22096 (Medium) detected in spring-web-4.3.9.RELEASE.jar | security vulnerability | ## CVE-2021-22096 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.3.9.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /BlockDockServer/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/4.3.9.RELEASE/91dae64c4280093ad5fb4736a10913c9233479c1/spring-web-4.3.9.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- grails-core-3.3.0.jar (Root Library)
- grails-spring-3.3.0.jar
- :x: **spring-web-4.3.9.RELEASE.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework versions 5.3.0 - 5.3.10, 5.2.0 - 5.2.17, and older unsupported versions, it is possible for a user to provide malicious input to cause the insertion of additional log entries.
<p>Publish Date: 2021-10-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22096>CVE-2021-22096</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22096">https://tanzu.vmware.com/security/cve-2021-22096</a></p>
<p>Release Date: 2021-10-28</p>
<p>Fix Resolution: org.springframework:spring:5.2.18.RELEASE,5.3.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-22096 (Medium) detected in spring-web-4.3.9.RELEASE.jar - ## CVE-2021-22096 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-4.3.9.RELEASE.jar</b></p></summary>
<p>Spring Web</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /BlockDockServer/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.springframework/spring-web/4.3.9.RELEASE/91dae64c4280093ad5fb4736a10913c9233479c1/spring-web-4.3.9.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- grails-core-3.3.0.jar (Root Library)
- grails-spring-3.3.0.jar
- :x: **spring-web-4.3.9.RELEASE.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework versions 5.3.0 - 5.3.10, 5.2.0 - 5.2.17, and older unsupported versions, it is possible for a user to provide malicious input to cause the insertion of additional log entries.
<p>Publish Date: 2021-10-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-22096>CVE-2021-22096</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2021-22096">https://tanzu.vmware.com/security/cve-2021-22096</a></p>
<p>Release Date: 2021-10-28</p>
<p>Fix Resolution: org.springframework:spring:5.2.18.RELEASE,5.3.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in spring web release jar cve medium severity vulnerability vulnerable library spring web release jar spring web library home page a href path to dependency file blockdockserver build gradle path to vulnerable library root gradle caches modules files org springframework spring web release spring web release jar dependency hierarchy grails core jar root library grails spring jar x spring web release jar vulnerable library vulnerability details in spring framework versions and older unsupported versions it is possible for a user to provide malicious input to cause the insertion of additional log entries publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring release step up your open source security game with whitesource | 0 |
44,499 | 23,655,793,114 | IssuesEvent | 2022-08-26 11:05:08 | datafuselabs/databend | https://api.github.com/repos/datafuselabs/databend | opened | performance: subquery is slow | C-performance | **Summary**
query:
```
sql:
WITH
-- latest 6hours
latest AS
(
SELECT min(number)
FROM blocks
WHERE timestamp >
(
SELECT subtract_hours(to_datetime(timestamp), 6)
FROM blocks
ORDER BY timestamp DESC limit 1 ))
SELECT token_address,
count(*) AS c
FROM token_transfers
WHERE block_number>
(
SELECT *
FROM latest)
GROUP BY token_address
ORDER BY c desc;
```
explain:
```
Project: [token_address (#39),c (#48)]
└── Sort: [c (#48) DESC]
└── EvalScalar: [COUNT(*) (#50)]
└── Aggregate(Final): group items: [token_transfers.token_address (#39)], aggregate functions: [COUNT(*)]
└── Aggregate(Partial): group items: [token_transfers.token_address (#39)], aggregate functions: [COUNT(*)]
└── Filter: [token_transfers.block_number (#47) > scalar_subquery_37 (#37)]
└── HashJoin: SINGLE, build keys: [], probe keys: [], join filters: []
├── Scan: default.eth.token_transfers, filters: []
└── Project: [min(number) (#37)]
└── EvalScalar: [min(number) (#38)]
└── Aggregate(Final): group items: [], aggregate functions: [min(number)]
└── Aggregate(Partial): group items: [], aggregate functions: [min(number)]
└── Filter: [blocks.timestamp (#15) > scalar_subquery_36 (#36)]
└── HashJoin: SINGLE, build keys: [], probe keys: [], join filters: []
├── Scan: default.eth.blocks, filters: []
└── Limit: [1], Offset: [0]
└── Project: [subtract_hours(to_datetime(timestamp), 6) (#36)]
└── EvalScalar: [subtract_hours(to_datetime(blocks.timestamp (#33)), 6)]
└── Sort: [timestamp (#33) DESC]
└── Scan: default.eth.blocks, filters: []
```
The query is very slow, it looks like do a full table scan:

The subquery result is `15388455`:
```
SELECT min(number)
FROM blocks
WHERE timestamp >
(
SELECT subtract_hours(to_datetime(timestamp), 6)
FROM blocks
ORDER BY timestamp DESC limit 1 ))
```
Rewrite the query to the follow is very fast:
```
SELECT token_address,
count(*) AS c
FROM token_transfers
WHERE block_number>15388455
GROUP BY token_address
ORDER BY c desc;
```
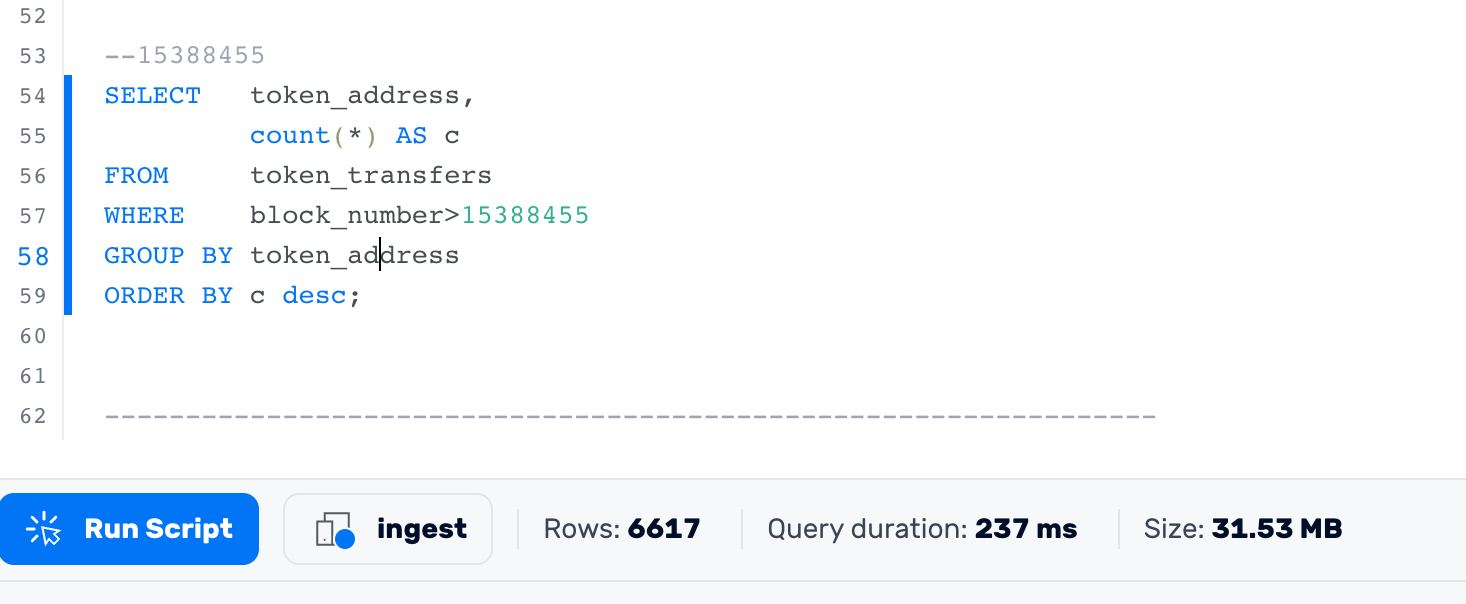
| True | performance: subquery is slow - **Summary**
query:
```
sql:
WITH
-- latest 6hours
latest AS
(
SELECT min(number)
FROM blocks
WHERE timestamp >
(
SELECT subtract_hours(to_datetime(timestamp), 6)
FROM blocks
ORDER BY timestamp DESC limit 1 ))
SELECT token_address,
count(*) AS c
FROM token_transfers
WHERE block_number>
(
SELECT *
FROM latest)
GROUP BY token_address
ORDER BY c desc;
```
explain:
```
Project: [token_address (#39),c (#48)]
└── Sort: [c (#48) DESC]
└── EvalScalar: [COUNT(*) (#50)]
└── Aggregate(Final): group items: [token_transfers.token_address (#39)], aggregate functions: [COUNT(*)]
└── Aggregate(Partial): group items: [token_transfers.token_address (#39)], aggregate functions: [COUNT(*)]
└── Filter: [token_transfers.block_number (#47) > scalar_subquery_37 (#37)]
└── HashJoin: SINGLE, build keys: [], probe keys: [], join filters: []
├── Scan: default.eth.token_transfers, filters: []
└── Project: [min(number) (#37)]
└── EvalScalar: [min(number) (#38)]
└── Aggregate(Final): group items: [], aggregate functions: [min(number)]
└── Aggregate(Partial): group items: [], aggregate functions: [min(number)]
└── Filter: [blocks.timestamp (#15) > scalar_subquery_36 (#36)]
└── HashJoin: SINGLE, build keys: [], probe keys: [], join filters: []
├── Scan: default.eth.blocks, filters: []
└── Limit: [1], Offset: [0]
└── Project: [subtract_hours(to_datetime(timestamp), 6) (#36)]
└── EvalScalar: [subtract_hours(to_datetime(blocks.timestamp (#33)), 6)]
└── Sort: [timestamp (#33) DESC]
└── Scan: default.eth.blocks, filters: []
```
The query is very slow, it looks like do a full table scan:

The subquery result is `15388455`:
```
SELECT min(number)
FROM blocks
WHERE timestamp >
(
SELECT subtract_hours(to_datetime(timestamp), 6)
FROM blocks
ORDER BY timestamp DESC limit 1 ))
```
Rewrite the query to the follow is very fast:
```
SELECT token_address,
count(*) AS c
FROM token_transfers
WHERE block_number>15388455
GROUP BY token_address
ORDER BY c desc;
```
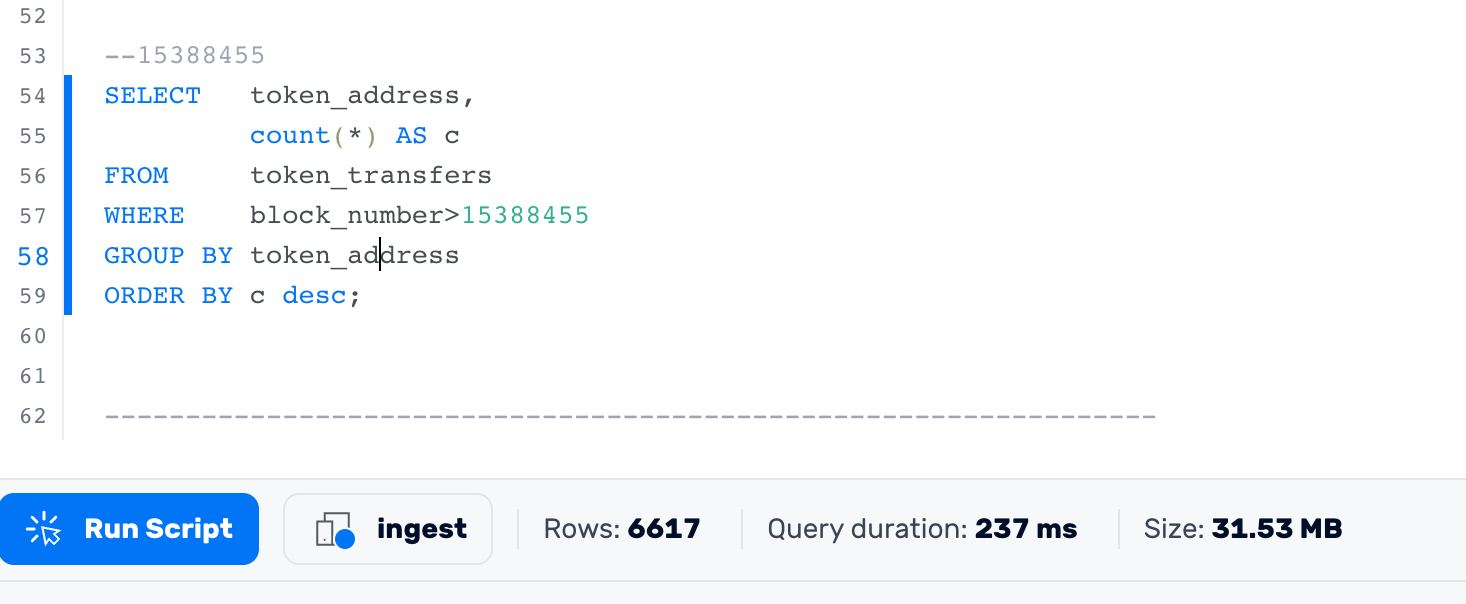
| non_priority | performance subquery is slow summary query sql with latest latest as select min number from blocks where timestamp select subtract hours to datetime timestamp from blocks order by timestamp desc limit select token address count as c from token transfers where block number select from latest group by token address order by c desc explain project └── sort └── evalscalar └── aggregate final group items aggregate functions └── aggregate partial group items aggregate functions └── filter └── hashjoin single build keys probe keys join filters ├── scan default eth token transfers filters └── project └── evalscalar └── aggregate final group items aggregate functions └── aggregate partial group items aggregate functions └── filter └── hashjoin single build keys probe keys join filters ├── scan default eth blocks filters └── limit offset └── project └── evalscalar └── sort └── scan default eth blocks filters the query is very slow it looks like do a full table scan the subquery result is select min number from blocks where timestamp select subtract hours to datetime timestamp from blocks order by timestamp desc limit rewrite the query to the follow is very fast select token address count as c from token transfers where block number group by token address order by c desc | 0 |
311,433 | 26,791,769,224 | IssuesEvent | 2023-02-01 09:03:35 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | kv/kvserver: TestSnapshotAfterTruncation failed | C-test-failure O-robot branch-master | kv/kvserver.TestSnapshotAfterTruncation [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8536064?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8536064?buildTab=artifacts#/) on master @ [da247ff22039f4579e2b043656ba561e71876115](https://github.com/cockroachdb/cockroach/commits/da247ff22039f4579e2b043656ba561e71876115):
```
=== RUN TestSnapshotAfterTruncation/differentTerm
client_raft_test.go:757:
Error Trace: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2900/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/kv/kvserver/kvserver_test_/kvserver_test.runfiles/com_github_cockroachdb_cockroach/pkg/kv/kvserver/client_raft_test.go:757
Error: Received unexpected error:
migration-job-find-already-completed: unexpected value: raw_bytes:"N\022n\316\n" timestamp:<wall_time:1675240624532525057 >
(1) attached stack trace
-- stack trace:
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).execInternal.func1.1
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:844
| github.com/cockroachdb/cockroach/pkg/sql.(*rowsIterator).Next.func1
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:424
| github.com/cockroachdb/cockroach/pkg/sql.(*rowsIterator).Next
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:475
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).queryInternalBuffered
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:585
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).QueryRowExWithCols
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:637
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).QueryRowEx
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:623
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).QueryRow
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:607
| github.com/cockroachdb/cockroach/pkg/upgrade/migrationstable.CheckIfMigrationCompleted
| github.com/cockroachdb/cockroach/pkg/upgrade/migrationstable/migrations_table.go:118
| github.com/cockroachdb/cockroach/pkg/upgrade/upgrademanager.(*Manager).RunPermanentUpgrades
| github.com/cockroachdb/cockroach/pkg/upgrade/upgrademanager/manager.go:210
| github.com/cockroachdb/cockroach/pkg/server.(*SQLServer).preStart
| github.com/cockroachdb/cockroach/pkg/server/server_sql.go:1515
| github.com/cockroachdb/cockroach/pkg/server.(*Server).PreStart
| github.com/cockroachdb/cockroach/pkg/server/server.go:1833
| github.com/cockroachdb/cockroach/pkg/server.(*Server).Start
| github.com/cockroachdb/cockroach/pkg/server/server.go:1186
| github.com/cockroachdb/cockroach/pkg/server.(*TestServer).Start
| github.com/cockroachdb/cockroach/pkg/server/testserver.go:598
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster.(*TestCluster).RestartServerWithInspect.func1
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster/testcluster.go:1594
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster.(*TestCluster).RestartServerWithInspect
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster/testcluster.go:1605
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster.(*TestCluster).RestartServer
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster/testcluster.go:1535
| github.com/cockroachdb/cockroach/pkg/kv/kvserver_test.TestSnapshotAfterTruncation.func1
| github.com/cockroachdb/cockroach/pkg/kv/kvserver_test/pkg/kv/kvserver/client_raft_test.go:757
| testing.tRunner
| GOROOT/src/testing/testing.go:1446
| runtime.goexit
| src/runtime/asm_amd64.s:1594
Wraps: (2) migration-job-find-already-completed
Wraps: (3) unexpected value: raw_bytes:"N\022n\316\n" timestamp:<wall_time:1675240624532525057 >
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *roachpb.ConditionFailedError
Test: TestSnapshotAfterTruncation/differentTerm
--- FAIL: TestSnapshotAfterTruncation/differentTerm (9.17s)
```
<p>Parameters: <code>TAGS=bazel,gss,race</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/replication
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestSnapshotAfterTruncation.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 1.0 | kv/kvserver: TestSnapshotAfterTruncation failed - kv/kvserver.TestSnapshotAfterTruncation [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8536064?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/8536064?buildTab=artifacts#/) on master @ [da247ff22039f4579e2b043656ba561e71876115](https://github.com/cockroachdb/cockroach/commits/da247ff22039f4579e2b043656ba561e71876115):
```
=== RUN TestSnapshotAfterTruncation/differentTerm
client_raft_test.go:757:
Error Trace: /home/roach/.cache/bazel/_bazel_roach/c5a4e7d36696d9cd970af2045211a7df/sandbox/processwrapper-sandbox/2900/execroot/com_github_cockroachdb_cockroach/bazel-out/k8-fastbuild/bin/pkg/kv/kvserver/kvserver_test_/kvserver_test.runfiles/com_github_cockroachdb_cockroach/pkg/kv/kvserver/client_raft_test.go:757
Error: Received unexpected error:
migration-job-find-already-completed: unexpected value: raw_bytes:"N\022n\316\n" timestamp:<wall_time:1675240624532525057 >
(1) attached stack trace
-- stack trace:
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).execInternal.func1.1
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:844
| github.com/cockroachdb/cockroach/pkg/sql.(*rowsIterator).Next.func1
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:424
| github.com/cockroachdb/cockroach/pkg/sql.(*rowsIterator).Next
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:475
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).queryInternalBuffered
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:585
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).QueryRowExWithCols
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:637
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).QueryRowEx
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:623
| github.com/cockroachdb/cockroach/pkg/sql.(*InternalExecutor).QueryRow
| github.com/cockroachdb/cockroach/pkg/sql/internal.go:607
| github.com/cockroachdb/cockroach/pkg/upgrade/migrationstable.CheckIfMigrationCompleted
| github.com/cockroachdb/cockroach/pkg/upgrade/migrationstable/migrations_table.go:118
| github.com/cockroachdb/cockroach/pkg/upgrade/upgrademanager.(*Manager).RunPermanentUpgrades
| github.com/cockroachdb/cockroach/pkg/upgrade/upgrademanager/manager.go:210
| github.com/cockroachdb/cockroach/pkg/server.(*SQLServer).preStart
| github.com/cockroachdb/cockroach/pkg/server/server_sql.go:1515
| github.com/cockroachdb/cockroach/pkg/server.(*Server).PreStart
| github.com/cockroachdb/cockroach/pkg/server/server.go:1833
| github.com/cockroachdb/cockroach/pkg/server.(*Server).Start
| github.com/cockroachdb/cockroach/pkg/server/server.go:1186
| github.com/cockroachdb/cockroach/pkg/server.(*TestServer).Start
| github.com/cockroachdb/cockroach/pkg/server/testserver.go:598
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster.(*TestCluster).RestartServerWithInspect.func1
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster/testcluster.go:1594
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster.(*TestCluster).RestartServerWithInspect
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster/testcluster.go:1605
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster.(*TestCluster).RestartServer
| github.com/cockroachdb/cockroach/pkg/testutils/testcluster/testcluster.go:1535
| github.com/cockroachdb/cockroach/pkg/kv/kvserver_test.TestSnapshotAfterTruncation.func1
| github.com/cockroachdb/cockroach/pkg/kv/kvserver_test/pkg/kv/kvserver/client_raft_test.go:757
| testing.tRunner
| GOROOT/src/testing/testing.go:1446
| runtime.goexit
| src/runtime/asm_amd64.s:1594
Wraps: (2) migration-job-find-already-completed
Wraps: (3) unexpected value: raw_bytes:"N\022n\316\n" timestamp:<wall_time:1675240624532525057 >
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *roachpb.ConditionFailedError
Test: TestSnapshotAfterTruncation/differentTerm
--- FAIL: TestSnapshotAfterTruncation/differentTerm (9.17s)
```
<p>Parameters: <code>TAGS=bazel,gss,race</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
/cc @cockroachdb/replication
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestSnapshotAfterTruncation.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | kv kvserver testsnapshotaftertruncation failed kv kvserver testsnapshotaftertruncation with on master run testsnapshotaftertruncation differentterm client raft test go error trace home roach cache bazel bazel roach sandbox processwrapper sandbox execroot com github cockroachdb cockroach bazel out fastbuild bin pkg kv kvserver kvserver test kvserver test runfiles com github cockroachdb cockroach pkg kv kvserver client raft test go error received unexpected error migration job find already completed unexpected value raw bytes n n timestamp attached stack trace stack trace github com cockroachdb cockroach pkg sql internalexecutor execinternal github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg sql rowsiterator next github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg sql rowsiterator next github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg sql internalexecutor queryinternalbuffered github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg sql internalexecutor queryrowexwithcols github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg sql internalexecutor queryrowex github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg sql internalexecutor queryrow github com cockroachdb cockroach pkg sql internal go github com cockroachdb cockroach pkg upgrade migrationstable checkifmigrationcompleted github com cockroachdb cockroach pkg upgrade migrationstable migrations table go github com cockroachdb cockroach pkg upgrade upgrademanager manager runpermanentupgrades github com cockroachdb cockroach pkg upgrade upgrademanager manager go github com cockroachdb cockroach pkg server sqlserver prestart github com cockroachdb cockroach pkg server server sql go github com cockroachdb cockroach pkg server server prestart github com cockroachdb cockroach pkg server server go github com cockroachdb cockroach pkg server server start github com cockroachdb cockroach pkg server server go github com cockroachdb cockroach pkg server testserver start github com cockroachdb cockroach pkg server testserver go github com cockroachdb cockroach pkg testutils testcluster testcluster restartserverwithinspect github com cockroachdb cockroach pkg testutils testcluster testcluster go github com cockroachdb cockroach pkg testutils testcluster testcluster restartserverwithinspect github com cockroachdb cockroach pkg testutils testcluster testcluster go github com cockroachdb cockroach pkg testutils testcluster testcluster restartserver github com cockroachdb cockroach pkg testutils testcluster testcluster go github com cockroachdb cockroach pkg kv kvserver test testsnapshotaftertruncation github com cockroachdb cockroach pkg kv kvserver test pkg kv kvserver client raft test go testing trunner goroot src testing testing go runtime goexit src runtime asm s wraps migration job find already completed wraps unexpected value raw bytes n n timestamp error types withstack withstack errutil withprefix roachpb conditionfailederror test testsnapshotaftertruncation differentterm fail testsnapshotaftertruncation differentterm parameters tags bazel gss race help see also cc cockroachdb replication | 0 |
417,437 | 28,110,487,846 | IssuesEvent | 2023-03-31 06:43:28 | NoyaRoeT/ped | https://api.github.com/repos/NoyaRoeT/ped | opened | Explanation of filter command is a bit brief | type.DocumentationBug severity.Low | It seems that when filtering by tags, the matching of tags is case-sensitive.
Perhaps it would be better to explain these sort of details.
<!--session: 1680242665641-1b491de0-615b-40bf-af0d-409ed132ea12-->
<!--Version: Web v3.4.7--> | 1.0 | Explanation of filter command is a bit brief - It seems that when filtering by tags, the matching of tags is case-sensitive.
Perhaps it would be better to explain these sort of details.
<!--session: 1680242665641-1b491de0-615b-40bf-af0d-409ed132ea12-->
<!--Version: Web v3.4.7--> | non_priority | explanation of filter command is a bit brief it seems that when filtering by tags the matching of tags is case sensitive perhaps it would be better to explain these sort of details | 0 |
112,389 | 9,564,143,384 | IssuesEvent | 2019-05-05 00:22:09 | KingAkeem/TorBotApp | https://api.github.com/repos/KingAkeem/TorBotApp | opened | Design method of testing GetLinks and GetEmails functions | enhancement test added test improvement | I'm not sure how to accurately test these methods since we have to be able to generate HTML that can be parsed by the [HTML parsing library](https://godoc.org/golang.org/x/net/html) being used. | 2.0 | Design method of testing GetLinks and GetEmails functions - I'm not sure how to accurately test these methods since we have to be able to generate HTML that can be parsed by the [HTML parsing library](https://godoc.org/golang.org/x/net/html) being used. | non_priority | design method of testing getlinks and getemails functions i m not sure how to accurately test these methods since we have to be able to generate html that can be parsed by the being used | 0 |
14,330 | 3,828,050,744 | IssuesEvent | 2016-03-31 02:37:58 | studentinsights/studentinsights | https://api.github.com/repos/studentinsights/studentinsights | closed | 3/29 Code for Boston agenda | documentation | Last week: #208 (comment).
**Review priorities (umbrella issues):**
* current: finish Student profile improvements
* ???
* next: Productionize visualizations of STAR academic progress
* after: SPED referral form
**Help finish what's in progress:**
* Finish any work-in-progress you own
* Help anyone else with work-in-progress if you can (keeping in mind that sometimes piling on more people doesn't help)
* Check out work that's left over from last week.
* Check open pull requests
* Umbrella issues - see if there's a clear piece you can get done on one of the open issues
**Start some new work:**
* Fix an Open bug
* Start on a help wanted issue
* Start a brand new feature
* Talk it out with Kevin if you have questions or if you're stuck
**Help new folks pitch in:**
* Coordinating tonight: @erose
* Talk about any questions from the project overview
* Help them set up development environment
* Show them the agenda issue and our workflow | 1.0 | 3/29 Code for Boston agenda - Last week: #208 (comment).
**Review priorities (umbrella issues):**
* current: finish Student profile improvements
* ???
* next: Productionize visualizations of STAR academic progress
* after: SPED referral form
**Help finish what's in progress:**
* Finish any work-in-progress you own
* Help anyone else with work-in-progress if you can (keeping in mind that sometimes piling on more people doesn't help)
* Check out work that's left over from last week.
* Check open pull requests
* Umbrella issues - see if there's a clear piece you can get done on one of the open issues
**Start some new work:**
* Fix an Open bug
* Start on a help wanted issue
* Start a brand new feature
* Talk it out with Kevin if you have questions or if you're stuck
**Help new folks pitch in:**
* Coordinating tonight: @erose
* Talk about any questions from the project overview
* Help them set up development environment
* Show them the agenda issue and our workflow | non_priority | code for boston agenda last week comment review priorities umbrella issues current finish student profile improvements next productionize visualizations of star academic progress after sped referral form help finish what s in progress finish any work in progress you own help anyone else with work in progress if you can keeping in mind that sometimes piling on more people doesn t help check out work that s left over from last week check open pull requests umbrella issues see if there s a clear piece you can get done on one of the open issues start some new work fix an open bug start on a help wanted issue start a brand new feature talk it out with kevin if you have questions or if you re stuck help new folks pitch in coordinating tonight erose talk about any questions from the project overview help them set up development environment show them the agenda issue and our workflow | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.