Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
10,100 | 2,930,326,413 | IssuesEvent | 2015-06-29 02:19:06 | geetsisbac/WCVVENIXYFVIRBXH3BYTI6TE | https://api.github.com/repos/geetsisbac/WCVVENIXYFVIRBXH3BYTI6TE | closed | SZjz1Zc+B9Qs86aU+J7Zz8kgjOY4+d+76xpTNy1HoMrPFJonwhtaFZK/wXF4UZgXytBT+Yph7TWfqOxizafqMTi/1D9D597PhsddRI/gCp3lqt1dOjObWjwQAWfNT+nX7vtxROkKMA4SmRLveWDR7Q2iv+xLzV4FE+Ct9mgdzH0= | design | UTzYVAuoY5ragE0pRo0Uj3zcj7v139wxZYvaIew2t7Rj56q6/xnqU+ij+ecBEkWnApDPMz96TtQzQ2Ls+Y7pNNwa6IQPF8dy9ih9e/WMChu10G6uveiUOIaasmy8lFthvRbO9/0C3dVF+Q8oYMwd5yhctDRJ2JNzIZkMcakiJD9fWCoisEwA3zhs6mmoejzPZiHRdIV/Si2kaKq5Wm24S+NjNIPImnzyTFsBz/bzecZA+cppJtrjVIaYtVnHQGXllq68vZU2AgFcBLal6qk3y/zprvMefjQiRh89DlqEoh5tJTvMSJGMOuVz6r9Y5Wm7ZG0oHXu0V6CrKg96L0Wzxj6K9V1dYwUcdxptpGZ6fFz4O4CIM8h6YJa5oD4saHiIrZGb3+mUzj2RslM6lgImmBHrpRTkypd8eMY+TrPjagKSXahJ7MKUrUFlLrZPOAYB85a0UihQ5vqkL7TgXTvDn+qL4PmrqL+Q+UXxkPwvHL9Pi3CXhw02SzWJK/u1iDlwUeQitLMv4Tf8YjmCyOBWn/YucHlxnct67jI8W1uSxzJlsNqOnv+//7ZsXxbumTMCKkv2gFXf5ix+AVtzRdL7LPtWbj1cdQaOiXAtCMSKVAbo12+P7EzsaQ+0SBmNO/NwFsmHBZCtseXW1dHM5k3iqSKLi6TShsK2//BVBrTWfDHUJhX0hWlTWkz4Op6mGlHQcr8VT/r1LHlPudYH2+pSDai7ubL1nMInVrbDqE3vx5FHqPWU+FuS3splyp5fZUicAHFjS6WstsRqfPFqtMuAG4hqxDDYDa8FA1jEQybhsO497Rnr/dG8e0zMXgsYUCK0Eyar2UZJN7bpKVVSduY22saN7VGh4BZ2cEqSiKidEIdhg+YFklQ1fK8wzWvPqa/RvWtbPsD+Gb9Ui197Bk5uBcs/AOR7eCIkDNYtEZm4rAynHk85cyF8vlvMLqpqHbjHqH5pbHw3K97l4HLzhdzAdAj78lCm6QLTlv0D0JHedEwmx0nmubp2HBDQlVUC953kVKhL1RzsfEDaVsvs6WUjNMuEPnVUz4+Xb/fh9IfxxTjfDt+nwbemeaJWpSU5uqtfVerhYq7hTvu5RoyO1uxeqYNvo/QXiLrjUrlWtF0Qat2LisnHYUGBzW1Y+zDepf7ViuKZatw0czsiEFyNDFBTyLUY65/5orV82R2+7eopyK6LN9Mv1wDBW2+KZHFgtaB//TG+WkBI5U+CP3TIL9/8jjEi6DZM4DltjivYM8tEzF8Bs07aL88Asb9EcIrHVxmPyEb3fS+I+303yeHG/c/Z7WRuuN2eZ4erZuH0GjIcLrZlCcLXfXVSMeC1m7mUiy6sb7Fe18bGh/mABsnHY3NA7dFm2cu0m5s5qqOne0Iss3MfzTXwI/ciXKFT4tbWrstAr9HSimaS2n/KOPQhCf4EIi4g/XV4Y+7lFDSgjy9GiO5UbUuOaLqrSqfcsgHsoFAWP/VgGDR/5pbTrKp+Px2x8DImMpUyoIWWxHGBtaJF0Ou9nnRCe2UETSw9gAYHRk5QyeDKt9atTx5TLgRjOyASNvZlYr06uRrvckajl3q1cxIOMXIzHJ43iVWFmxFAPls8MT7tMYMv3+x+bwsvWDgjdC7rg7WL4icbINebcDPzvOw5d+f9GsFu03eJ/xwcy4Sysw5UDWba8O7QpgHVw+LXG89yDKLrcWQRqcxIpSsGSIUE5Hjolh/wyy4XPR/yZIgGjDY30n70r3Feir9zYxhTcw== | 1.0 | SZjz1Zc+B9Qs86aU+J7Zz8kgjOY4+d+76xpTNy1HoMrPFJonwhtaFZK/wXF4UZgXytBT+Yph7TWfqOxizafqMTi/1D9D597PhsddRI/gCp3lqt1dOjObWjwQAWfNT+nX7vtxROkKMA4SmRLveWDR7Q2iv+xLzV4FE+Ct9mgdzH0= - UTzYVAuoY5ragE0pRo0Uj3zcj7v139wxZYvaIew2t7Rj56q6/xnqU+ij+ecBEkWnApDPMz96TtQzQ2Ls+Y7pNNwa6IQPF8dy9ih9e/WMChu10G6uveiUOIaasmy8lFthvRbO9/0C3dVF+Q8oYMwd5yhctDRJ2JNzIZkMcakiJD9fWCoisEwA3zhs6mmoejzPZiHRdIV/Si2kaKq5Wm24S+NjNIPImnzyTFsBz/bzecZA+cppJtrjVIaYtVnHQGXllq68vZU2AgFcBLal6qk3y/zprvMefjQiRh89DlqEoh5tJTvMSJGMOuVz6r9Y5Wm7ZG0oHXu0V6CrKg96L0Wzxj6K9V1dYwUcdxptpGZ6fFz4O4CIM8h6YJa5oD4saHiIrZGb3+mUzj2RslM6lgImmBHrpRTkypd8eMY+TrPjagKSXahJ7MKUrUFlLrZPOAYB85a0UihQ5vqkL7TgXTvDn+qL4PmrqL+Q+UXxkPwvHL9Pi3CXhw02SzWJK/u1iDlwUeQitLMv4Tf8YjmCyOBWn/YucHlxnct67jI8W1uSxzJlsNqOnv+//7ZsXxbumTMCKkv2gFXf5ix+AVtzRdL7LPtWbj1cdQaOiXAtCMSKVAbo12+P7EzsaQ+0SBmNO/NwFsmHBZCtseXW1dHM5k3iqSKLi6TShsK2//BVBrTWfDHUJhX0hWlTWkz4Op6mGlHQcr8VT/r1LHlPudYH2+pSDai7ubL1nMInVrbDqE3vx5FHqPWU+FuS3splyp5fZUicAHFjS6WstsRqfPFqtMuAG4hqxDDYDa8FA1jEQybhsO497Rnr/dG8e0zMXgsYUCK0Eyar2UZJN7bpKVVSduY22saN7VGh4BZ2cEqSiKidEIdhg+YFklQ1fK8wzWvPqa/RvWtbPsD+Gb9Ui197Bk5uBcs/AOR7eCIkDNYtEZm4rAynHk85cyF8vlvMLqpqHbjHqH5pbHw3K97l4HLzhdzAdAj78lCm6QLTlv0D0JHedEwmx0nmubp2HBDQlVUC953kVKhL1RzsfEDaVsvs6WUjNMuEPnVUz4+Xb/fh9IfxxTjfDt+nwbemeaJWpSU5uqtfVerhYq7hTvu5RoyO1uxeqYNvo/QXiLrjUrlWtF0Qat2LisnHYUGBzW1Y+zDepf7ViuKZatw0czsiEFyNDFBTyLUY65/5orV82R2+7eopyK6LN9Mv1wDBW2+KZHFgtaB//TG+WkBI5U+CP3TIL9/8jjEi6DZM4DltjivYM8tEzF8Bs07aL88Asb9EcIrHVxmPyEb3fS+I+303yeHG/c/Z7WRuuN2eZ4erZuH0GjIcLrZlCcLXfXVSMeC1m7mUiy6sb7Fe18bGh/mABsnHY3NA7dFm2cu0m5s5qqOne0Iss3MfzTXwI/ciXKFT4tbWrstAr9HSimaS2n/KOPQhCf4EIi4g/XV4Y+7lFDSgjy9GiO5UbUuOaLqrSqfcsgHsoFAWP/VgGDR/5pbTrKp+Px2x8DImMpUyoIWWxHGBtaJF0Ou9nnRCe2UETSw9gAYHRk5QyeDKt9atTx5TLgRjOyASNvZlYr06uRrvckajl3q1cxIOMXIzHJ43iVWFmxFAPls8MT7tMYMv3+x+bwsvWDgjdC7rg7WL4icbINebcDPzvOw5d+f9GsFu03eJ/xwcy4Sysw5UDWba8O7QpgHVw+LXG89yDKLrcWQRqcxIpSsGSIUE5Hjolh/wyy4XPR/yZIgGjDY30n70r3Feir9zYxhTcw== | non_priority | d xnqu ij njnipimnzytfsbz bzecza q rvwtbpsd xb kzhfgtab tg i c vggdr x | 0 |
53,239 | 11,030,444,917 | IssuesEvent | 2019-12-06 15:45:59 | bee-travels/bee-travels | https://api.github.com/repos/bee-travels/bee-travels | opened | Currency Exchange UBI on OpenShift 4 | Code Pattern Currency Exchange Service v1 | Create a Python 3 version of the Currency Exchange service that runs on OpenShift 4 | 1.0 | Currency Exchange UBI on OpenShift 4 - Create a Python 3 version of the Currency Exchange service that runs on OpenShift 4 | non_priority | currency exchange ubi on openshift create a python version of the currency exchange service that runs on openshift | 0 |
26,122 | 12,856,006,275 | IssuesEvent | 2020-07-09 06:45:08 | polsys/ennemi | https://api.github.com/repos/polsys/ennemi | closed | Do another profiling round | performance | I'm especially interested in seeing if the unconditional MI case can be improved. | True | Do another profiling round - I'm especially interested in seeing if the unconditional MI case can be improved. | non_priority | do another profiling round i m especially interested in seeing if the unconditional mi case can be improved | 0 |
94,295 | 8,483,531,071 | IssuesEvent | 2018-10-25 21:54:59 | buttplugio/buttplug-csharp | https://api.github.com/repos/buttplugio/buttplug-csharp | closed | Clean up vorze device tests | testing | Move to separate fixtures that inherit a base Vorze test class, versus the weird for-loop thing we have right now. | 1.0 | Clean up vorze device tests - Move to separate fixtures that inherit a base Vorze test class, versus the weird for-loop thing we have right now. | non_priority | clean up vorze device tests move to separate fixtures that inherit a base vorze test class versus the weird for loop thing we have right now | 0 |
148,941 | 23,405,068,878 | IssuesEvent | 2022-08-12 12:01:03 | kubermatic/dashboard | https://api.github.com/repos/kubermatic/dashboard | closed | Make it clear what proxy mode will be configured when creating a new cluster if user makes no choice | kind/design sig/ui | With the addition of Cilium and "None" CNIs, it's become more confusing than ever which proxy mode will be used if the user doesn't pick one specifically. Please somehow indicate which one is the default, either by pre-filling the drop down (like you do for the CNI version) or by adding something like `[default]` to the according option in the dropdown (which should of course change when a different CNI plugin is chosen. | 1.0 | Make it clear what proxy mode will be configured when creating a new cluster if user makes no choice - With the addition of Cilium and "None" CNIs, it's become more confusing than ever which proxy mode will be used if the user doesn't pick one specifically. Please somehow indicate which one is the default, either by pre-filling the drop down (like you do for the CNI version) or by adding something like `[default]` to the according option in the dropdown (which should of course change when a different CNI plugin is chosen. | non_priority | make it clear what proxy mode will be configured when creating a new cluster if user makes no choice with the addition of cilium and none cnis it s become more confusing than ever which proxy mode will be used if the user doesn t pick one specifically please somehow indicate which one is the default either by pre filling the drop down like you do for the cni version or by adding something like to the according option in the dropdown which should of course change when a different cni plugin is chosen | 0 |
55,891 | 14,072,610,847 | IssuesEvent | 2020-11-04 02:20:24 | junghanlee/juice-shop | https://api.github.com/repos/junghanlee/juice-shop | opened | CVE-2018-16487 (Medium) detected in lodash-2.4.2.tgz | security vulnerability | ## CVE-2018-16487 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: juice-shop/package.json</p>
<p>Path to vulnerable library: juice-shop/node_modules/sanitize-html/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- sanitize-html-1.4.2.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/junghanlee/juice-shop/commit/765fa79934265f7322f82b9e91a33ec80e92457d">765fa79934265f7322f82b9e91a33ec80e92457d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-16487 (Medium) detected in lodash-2.4.2.tgz - ## CVE-2018-16487 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: juice-shop/package.json</p>
<p>Path to vulnerable library: juice-shop/node_modules/sanitize-html/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- sanitize-html-1.4.2.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/junghanlee/juice-shop/commit/765fa79934265f7322f82b9e91a33ec80e92457d">765fa79934265f7322f82b9e91a33ec80e92457d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A prototype pollution vulnerability was found in lodash <4.17.11 where the functions merge, mergeWith, and defaultsDeep can be tricked into adding or modifying properties of Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16487>CVE-2018-16487</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487">https://bugzilla.redhat.com/show_bug.cgi?id=CVE-2018-16487</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file juice shop package json path to vulnerable library juice shop node modules sanitize html node modules lodash package json dependency hierarchy sanitize html tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details a prototype pollution vulnerability was found in lodash where the functions merge mergewith and defaultsdeep can be tricked into adding or modifying properties of object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
51,656 | 10,708,244,202 | IssuesEvent | 2019-10-24 19:15:27 | polsys/cle | https://api.github.com/repos/polsys/cle | opened | Tail call optimization | area-CodeGen area-Optimization type-Feature | If a method ends in a (native) call and returns the result verbatim, convert the call to a jump instead. In the Intel optimization manual, this is a "low impact, low generality" recommendation, but if the caller and callee happen to be the same method, this will have very high impact.
Could this be implemented in the peephole optimizer, or does this need a separate LIR pass? Might affect some assumptions in the register allocator.
Full tail call optimization can probably be improved further (no need to reinitialize everything), but at least implement the general case. | 1.0 | Tail call optimization - If a method ends in a (native) call and returns the result verbatim, convert the call to a jump instead. In the Intel optimization manual, this is a "low impact, low generality" recommendation, but if the caller and callee happen to be the same method, this will have very high impact.
Could this be implemented in the peephole optimizer, or does this need a separate LIR pass? Might affect some assumptions in the register allocator.
Full tail call optimization can probably be improved further (no need to reinitialize everything), but at least implement the general case. | non_priority | tail call optimization if a method ends in a native call and returns the result verbatim convert the call to a jump instead in the intel optimization manual this is a low impact low generality recommendation but if the caller and callee happen to be the same method this will have very high impact could this be implemented in the peephole optimizer or does this need a separate lir pass might affect some assumptions in the register allocator full tail call optimization can probably be improved further no need to reinitialize everything but at least implement the general case | 0 |
238,277 | 19,707,464,516 | IssuesEvent | 2022-01-13 00:10:23 | redwoodjs/redwood | https://api.github.com/repos/redwoodjs/redwood | closed | `mockCurrentUser` returns null `currentUser` on web side | topic/auth topic/testing next-release/update-docs | **What is happening?**
My expectation was: immediately after the `mockCurrentUser` call, the given component should render the mocked user from the first render, but it first renders null, then sets mocked user after.
**Background on how currently auth works on the web side**
As soon as the page loads or the whole page refreshes, then Auth context provider (React context) triggers the GraphQL call for `currentUser` and update the context with the result. And since auth provider is at the root level, this process only happens when the app loads, not when sub-tree/components are swapped.
**Why is this happening?**
In web unit tests, we mock the auth context in each `render` call which means the initial value of `currentUser` is always `null` in the first render. Then, it triggers a GraphQL call which will return mocked user in the second render. So if test `expect` is immediately after `mockCurrentUser`, it’ll fail.
**Can I not just use `waitFor`?**
The component may be behind some private route, so it is practical to think that component doesn’t need to handle the `null` case for `currentUser` because the router is checking that for us. And expect to force the mock from the first render.
**Possible next steps:**
Even though we can override the auth context for `mockCurentUser` but since these are unit tests, I am inclined towards keeping this behaviour as is - without caring about router behaviour. That means component should handle null `currentUser`. Also, we can update the documentation to explain this behaviour, and we clearly say that we must use `waitFor` (or anything that waits) expected user or derivative values with `mockCurrentUser`.
@dac09 What do you think? | 1.0 | `mockCurrentUser` returns null `currentUser` on web side - **What is happening?**
My expectation was: immediately after the `mockCurrentUser` call, the given component should render the mocked user from the first render, but it first renders null, then sets mocked user after.
**Background on how currently auth works on the web side**
As soon as the page loads or the whole page refreshes, then Auth context provider (React context) triggers the GraphQL call for `currentUser` and update the context with the result. And since auth provider is at the root level, this process only happens when the app loads, not when sub-tree/components are swapped.
**Why is this happening?**
In web unit tests, we mock the auth context in each `render` call which means the initial value of `currentUser` is always `null` in the first render. Then, it triggers a GraphQL call which will return mocked user in the second render. So if test `expect` is immediately after `mockCurrentUser`, it’ll fail.
**Can I not just use `waitFor`?**
The component may be behind some private route, so it is practical to think that component doesn’t need to handle the `null` case for `currentUser` because the router is checking that for us. And expect to force the mock from the first render.
**Possible next steps:**
Even though we can override the auth context for `mockCurentUser` but since these are unit tests, I am inclined towards keeping this behaviour as is - without caring about router behaviour. That means component should handle null `currentUser`. Also, we can update the documentation to explain this behaviour, and we clearly say that we must use `waitFor` (or anything that waits) expected user or derivative values with `mockCurrentUser`.
@dac09 What do you think? | non_priority | mockcurrentuser returns null currentuser on web side what is happening my expectation was immediately after the mockcurrentuser call the given component should render the mocked user from the first render but it first renders null then sets mocked user after background on how currently auth works on the web side as soon as the page loads or the whole page refreshes then auth context provider react context triggers the graphql call for currentuser and update the context with the result and since auth provider is at the root level this process only happens when the app loads not when sub tree components are swapped why is this happening in web unit tests we mock the auth context in each render call which means the initial value of currentuser is always null in the first render then it triggers a graphql call which will return mocked user in the second render so if test expect is immediately after mockcurrentuser it’ll fail can i not just use waitfor the component may be behind some private route so it is practical to think that component doesn’t need to handle the null case for currentuser because the router is checking that for us and expect to force the mock from the first render possible next steps even though we can override the auth context for mockcurentuser but since these are unit tests i am inclined towards keeping this behaviour as is without caring about router behaviour that means component should handle null currentuser also we can update the documentation to explain this behaviour and we clearly say that we must use waitfor or anything that waits expected user or derivative values with mockcurrentuser what do you think | 0 |
346,579 | 30,958,262,719 | IssuesEvent | 2023-08-08 00:12:09 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/canvas/datasource·ts - Canvas Canvas app datasource "before all" hook in "datasource" | failed-test | A test failed on a tracked branch
```
Error: retry.tryForTime timeout: Error: retry.try timeout: Error: App failed to load: canvas in 10000ms appUrl=http://localhost:5620/app/canvas#/ currentUrl=http://localhost:5620/app/canvas/
at common_page.ts:294:17
at processTicksAndRejections (node:internal/process/task_queues:95:5)
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.try (retry.ts:31:12)
at common_page.ts:252:21
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.tryForTime (retry.ts:22:12)
at CommonPageObject.navigateToApp (common_page.ts:251:5)
at Context.<anonymous> (datasource.ts:38:7)
at Object.apply (wrap_function.js:73:16)
at onFailure (retry_for_success.ts:17:9)
at retryForSuccess (retry_for_success.ts:59:13)
at RetryService.try (retry.ts:31:12)
at common_page.ts:252:21
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.tryForTime (retry.ts:22:12)
at CommonPageObject.navigateToApp (common_page.ts:251:5)
at Context.<anonymous> (datasource.ts:38:7)
at Object.apply (wrap_function.js:73:16)
at onFailure (retry_for_success.ts:17:9)
at retryForSuccess (retry_for_success.ts:59:13)
at RetryService.tryForTime (retry.ts:22:12)
at CommonPageObject.navigateToApp (common_page.ts:251:5)
at Context.<anonymous> (datasource.ts:38:7)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/33654#0189d24e-7760-4a83-92ec-db780d1df900)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/canvas/datasource·ts","test.name":"Canvas Canvas app datasource \"before all\" hook in \"datasource\"","test.failCount":1}} --> | 1.0 | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/canvas/datasource·ts - Canvas Canvas app datasource "before all" hook in "datasource" - A test failed on a tracked branch
```
Error: retry.tryForTime timeout: Error: retry.try timeout: Error: App failed to load: canvas in 10000ms appUrl=http://localhost:5620/app/canvas#/ currentUrl=http://localhost:5620/app/canvas/
at common_page.ts:294:17
at processTicksAndRejections (node:internal/process/task_queues:95:5)
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.try (retry.ts:31:12)
at common_page.ts:252:21
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.tryForTime (retry.ts:22:12)
at CommonPageObject.navigateToApp (common_page.ts:251:5)
at Context.<anonymous> (datasource.ts:38:7)
at Object.apply (wrap_function.js:73:16)
at onFailure (retry_for_success.ts:17:9)
at retryForSuccess (retry_for_success.ts:59:13)
at RetryService.try (retry.ts:31:12)
at common_page.ts:252:21
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.tryForTime (retry.ts:22:12)
at CommonPageObject.navigateToApp (common_page.ts:251:5)
at Context.<anonymous> (datasource.ts:38:7)
at Object.apply (wrap_function.js:73:16)
at onFailure (retry_for_success.ts:17:9)
at retryForSuccess (retry_for_success.ts:59:13)
at RetryService.tryForTime (retry.ts:22:12)
at CommonPageObject.navigateToApp (common_page.ts:251:5)
at Context.<anonymous> (datasource.ts:38:7)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/33654#0189d24e-7760-4a83-92ec-db780d1df900)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/canvas/datasource·ts","test.name":"Canvas Canvas app datasource \"before all\" hook in \"datasource\"","test.failCount":1}} --> | non_priority | failing test chrome x pack ui functional tests x pack test functional apps canvas datasource·ts canvas canvas app datasource before all hook in datasource a test failed on a tracked branch error retry tryfortime timeout error retry try timeout error app failed to load canvas in appurl currenturl at common page ts at processticksandrejections node internal process task queues at runattempt retry for success ts at retryforsuccess retry for success ts at retryservice try retry ts at common page ts at runattempt retry for success ts at retryforsuccess retry for success ts at retryservice tryfortime retry ts at commonpageobject navigatetoapp common page ts at context datasource ts at object apply wrap function js at onfailure retry for success ts at retryforsuccess retry for success ts at retryservice try retry ts at common page ts at runattempt retry for success ts at retryforsuccess retry for success ts at retryservice tryfortime retry ts at commonpageobject navigatetoapp common page ts at context datasource ts at object apply wrap function js at onfailure retry for success ts at retryforsuccess retry for success ts at retryservice tryfortime retry ts at commonpageobject navigatetoapp common page ts at context datasource ts at object apply wrap function js first failure | 0 |
267,805 | 28,509,231,325 | IssuesEvent | 2023-04-19 01:46:51 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | closed | CVE-2020-8992 (Medium) detected in linuxv3.0 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-8992 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/ext4/block_validity.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ext4_protect_reserved_inode in fs/ext4/block_validity.c in the Linux kernel through 5.5.3 allows attackers to cause a denial of service (soft lockup) via a crafted journal size.
<p>Publish Date: 2020-02-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8992>CVE-2020-8992</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-8992">https://www.linuxkernelcves.com/cves/CVE-2020-8992</a></p>
<p>Release Date: 2020-02-14</p>
<p>Fix Resolution: v5.6-rc2,v5.4.21,v5.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-8992 (Medium) detected in linuxv3.0 - autoclosed - ## CVE-2020-8992 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/ext4/block_validity.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
ext4_protect_reserved_inode in fs/ext4/block_validity.c in the Linux kernel through 5.5.3 allows attackers to cause a denial of service (soft lockup) via a crafted journal size.
<p>Publish Date: 2020-02-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8992>CVE-2020-8992</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2020-8992">https://www.linuxkernelcves.com/cves/CVE-2020-8992</a></p>
<p>Release Date: 2020-02-14</p>
<p>Fix Resolution: v5.6-rc2,v5.4.21,v5.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files fs block validity c vulnerability details protect reserved inode in fs block validity c in the linux kernel through allows attackers to cause a denial of service soft lockup via a crafted journal size publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
229,827 | 18,440,433,242 | IssuesEvent | 2021-10-14 17:23:13 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Functional test for saved objects import/export UI | test Feature:Saved Objects | Tests for testing export/import using saved objects UI:
For 7.x to 8.x import:
Data set:
sample dashboards and all the beats dashboards viz .ndjson
Tests:
1. To empty Kibana - import the file with related objects and make sure import works fine.
2. To empty Kibana - import the file without related objects and make sure import works fine.
3. Load esarchive with one index pattern - import a file with just one saved object and ensure Kibana lets us associate the saved object with the index pattern which we loaded and verify its accuracy.
4. Export a dashboard with related objects - change the id of a saved object inside the dashboard - import it back -ensure Kibana behaves accurately
Technical challenges to work through:
- [ ] Can import beats dashboards without enabling migration: true in beats.xml
- [ ] Need to figure out a place to store saved objects json file
- [x] understand related objects
| 1.0 | Functional test for saved objects import/export UI - Tests for testing export/import using saved objects UI:
For 7.x to 8.x import:
Data set:
sample dashboards and all the beats dashboards viz .ndjson
Tests:
1. To empty Kibana - import the file with related objects and make sure import works fine.
2. To empty Kibana - import the file without related objects and make sure import works fine.
3. Load esarchive with one index pattern - import a file with just one saved object and ensure Kibana lets us associate the saved object with the index pattern which we loaded and verify its accuracy.
4. Export a dashboard with related objects - change the id of a saved object inside the dashboard - import it back -ensure Kibana behaves accurately
Technical challenges to work through:
- [ ] Can import beats dashboards without enabling migration: true in beats.xml
- [ ] Need to figure out a place to store saved objects json file
- [x] understand related objects
| non_priority | functional test for saved objects import export ui tests for testing export import using saved objects ui for x to x import data set sample dashboards and all the beats dashboards viz ndjson tests to empty kibana import the file with related objects and make sure import works fine to empty kibana import the file without related objects and make sure import works fine load esarchive with one index pattern import a file with just one saved object and ensure kibana lets us associate the saved object with the index pattern which we loaded and verify its accuracy export a dashboard with related objects change the id of a saved object inside the dashboard import it back ensure kibana behaves accurately technical challenges to work through can import beats dashboards without enabling migration true in beats xml need to figure out a place to store saved objects json file understand related objects | 0 |
3,853 | 6,047,146,369 | IssuesEvent | 2017-06-12 13:51:27 | Microsoft/visualfsharp | https://api.github.com/repos/Microsoft/visualfsharp | closed | Compiler error causes VS2017 to crash | Area-IDE Language Service regression Urgency-Now | Visual Studio crash caused by the F# compiler services.
I have a suspicion that it's related to fetch intellisense for a property on a type from another assembly (C#) where the property's type is in a third unreferenced assembly.
I'm running VS2017 with nighties. Initially saw the crash with a build from a few days ago, updated to test latest and still occuring, now running version 15.4.1.17060101
Stack trace:
```
at Microsoft.FSharp.Compiler.ErrorLogger.ErrorLoggerExtensions.ErrorLogger.Error[b](ErrorLogger x, Exception exn)
at Microsoft.FSharp.Compiler.Import.ImportTypeRefData(ImportMap env, range m, ILScopeRef scoref, String[] path, String typeName)
at Microsoft.FSharp.Compiler.Import.ImportILTypeRefUncached(ImportMap env, range m, ILTypeRef tref)
at Microsoft.FSharp.Compiler.Import.ImportILTypeRef(ImportMap env, range m, ILTypeRef tref)
at Microsoft.FSharp.Compiler.Import.ImportILType(ImportMap env, range m, FSharpList`1 tinst, ILType typ)
at Microsoft.FSharp.Compiler.Infos.itys@137-3.Invoke(ILType ity)
at Microsoft.FSharp.Primitives.Basics.List.choose[T,TResult](FSharpFunc`2 f, FSharpList`1 xs)
at Microsoft.FSharp.Compiler.Infos.GetImmediateInterfacesOfType(SkipUnrefInterfaces skipUnref, TcGlobals g, ImportMap amap, range m, TType typ)
at Microsoft.FSharp.Compiler.Infos.loop@162-45[a](Boolean followInterfaces, AllowMultiIntfInstantiations allowMultiIntfInst, SkipUnrefInterfaces skipUnref, FSharpFunc`2 visitor, TcGlobals g, ImportMap amap, range m, Int32 ndeep, TType typ, Tuple`3 tupledArg)
at Microsoft.FSharp.Compiler.Infos.FoldHierarchyOfTypeAux[a](Boolean followInterfaces, AllowMultiIntfInstantiations allowMultiIntfInst, SkipUnrefInterfaces skipUnref, FSharpFunc`2 visitor, TcGlobals g, ImportMap amap, range m, TType typ, a acc)
at Microsoft.FSharp.Compiler.InfoReader.InfoReader.GetIntrinsicRecdOrClassFieldInfosUncached[a](Tuple`2 _arg5, range m, TType typ)
at Microsoft.FSharp.Compiler.InfoReader.-ctor@345-32.Invoke(Tuple`3 tupledArg)
at Microsoft.FSharp.Compiler.AbstractIL.Internal.Library.f@1-3[T,U](MemoizationTable`2 t, T x, Unit unitVar0)
at Microsoft.FSharp.Compiler.AbstractIL.Internal.Library.MemoizationTable`2.Apply(T x)
at Microsoft.FSharp.Compiler.NameResolution.ResolveCompletionsInType(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets completionTargets, range m, AccessorDomain ad, Boolean statics, TType typ)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentInType(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets isApplicableMeth, range m, AccessorDomain ad, Boolean statics, FSharpList`1 plid, TType typ)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentInType@3610-2.Invoke(PropInfo pinfo)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentInType(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets isApplicableMeth, range m, AccessorDomain ad, Boolean statics, FSharpList`1 plid, TType typ)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentPrim(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets isApplicableMeth, FullyQualifiedFlag fullyQualified, range m, AccessorDomain ad, FSharpList`1 plid, Boolean allowObsolete)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetEnvironmentLookupResolutions(NameResolutionEnv nenv, AccessorDomain ad, range m, FSharpList`1 plid, TypeNameResolutionFlag filterCtors, Boolean showObsolete)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetDeclaredItems[a](FSharpOption`1 parseResultsOpt, String lineStr, FSharpOption`1 origLongIdentOpt, Int32 colAtEndOfNamesAndResidue, FSharpOption`1 residueOpt, Int32 line, Int32 loc, TypeNameResolutionFlag filterCtors, ResolveOverloads resolveOverloads, FSharpFunc`2 hasTextChangedSinceLastTypecheck, Boolean isInRangeOperator, FSharpFunc`2 allSymbols)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetDeclItemsForNamesAtPosition(CompilationThreadToken ctok, FSharpOption`1 parseResultsOpt, FSharpOption`1 origLongIdentOpt, FSharpOption`1 residueOpt, Int32 line, String lineStr, Int32 colAtEndOfNamesAndResidue, TypeNameResolutionFlag filterCtors, ResolveOverloads resolveOverloads, FSharpFunc`2 getAllSymbols, FSharpFunc`2 hasTextChangedSinceLastTypecheck)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetSymbolUseAtLocation(CompilationThreadToken ctok, Int32 line, String lineStr, Int32 colAtEndOfNames, FSharpList`1 names)
at <StartupCode$FSharp-Compiler-Private>.$Service.GetSymbolUseAtLocation@1826-2.Invoke(CompilationThreadToken ctok, TypeCheckInfo scope)
at <StartupCode$FSharp-Compiler-Private>.$Service.clo@1760-246.Invoke(CompilationThreadToken ctok)
at <StartupCode$FSharp-Compiler-Private>.$Reactor.EnqueueAndAwaitOpAsync@153-2.Invoke(CompilationThreadToken ctok)
at System.Runtime.CompilerServices.TaskAwaiter.ThrowForNonSuccess(Task task)
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.CodeAnalysis.Editor.Implementation.ReferenceHighlighting.ReferenceHighlightingViewTaggerProvider.<ProduceTagsAsync>d__12.MoveNext()
at System.Runtime.CompilerServices.TaskAwaiter.ThrowForNonSuccess(Task task)
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.CodeAnalysis.Editor.Tagging.AbstractAsynchronousTaggerProvider`1.TagSource.<RecomputeTagsAsync>d__83.MoveNext()
```
#### Repro steps
See comment below
####
* Operating system - Win7
* VS2017
| 1.0 | Compiler error causes VS2017 to crash - Visual Studio crash caused by the F# compiler services.
I have a suspicion that it's related to fetch intellisense for a property on a type from another assembly (C#) where the property's type is in a third unreferenced assembly.
I'm running VS2017 with nighties. Initially saw the crash with a build from a few days ago, updated to test latest and still occuring, now running version 15.4.1.17060101
Stack trace:
```
at Microsoft.FSharp.Compiler.ErrorLogger.ErrorLoggerExtensions.ErrorLogger.Error[b](ErrorLogger x, Exception exn)
at Microsoft.FSharp.Compiler.Import.ImportTypeRefData(ImportMap env, range m, ILScopeRef scoref, String[] path, String typeName)
at Microsoft.FSharp.Compiler.Import.ImportILTypeRefUncached(ImportMap env, range m, ILTypeRef tref)
at Microsoft.FSharp.Compiler.Import.ImportILTypeRef(ImportMap env, range m, ILTypeRef tref)
at Microsoft.FSharp.Compiler.Import.ImportILType(ImportMap env, range m, FSharpList`1 tinst, ILType typ)
at Microsoft.FSharp.Compiler.Infos.itys@137-3.Invoke(ILType ity)
at Microsoft.FSharp.Primitives.Basics.List.choose[T,TResult](FSharpFunc`2 f, FSharpList`1 xs)
at Microsoft.FSharp.Compiler.Infos.GetImmediateInterfacesOfType(SkipUnrefInterfaces skipUnref, TcGlobals g, ImportMap amap, range m, TType typ)
at Microsoft.FSharp.Compiler.Infos.loop@162-45[a](Boolean followInterfaces, AllowMultiIntfInstantiations allowMultiIntfInst, SkipUnrefInterfaces skipUnref, FSharpFunc`2 visitor, TcGlobals g, ImportMap amap, range m, Int32 ndeep, TType typ, Tuple`3 tupledArg)
at Microsoft.FSharp.Compiler.Infos.FoldHierarchyOfTypeAux[a](Boolean followInterfaces, AllowMultiIntfInstantiations allowMultiIntfInst, SkipUnrefInterfaces skipUnref, FSharpFunc`2 visitor, TcGlobals g, ImportMap amap, range m, TType typ, a acc)
at Microsoft.FSharp.Compiler.InfoReader.InfoReader.GetIntrinsicRecdOrClassFieldInfosUncached[a](Tuple`2 _arg5, range m, TType typ)
at Microsoft.FSharp.Compiler.InfoReader.-ctor@345-32.Invoke(Tuple`3 tupledArg)
at Microsoft.FSharp.Compiler.AbstractIL.Internal.Library.f@1-3[T,U](MemoizationTable`2 t, T x, Unit unitVar0)
at Microsoft.FSharp.Compiler.AbstractIL.Internal.Library.MemoizationTable`2.Apply(T x)
at Microsoft.FSharp.Compiler.NameResolution.ResolveCompletionsInType(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets completionTargets, range m, AccessorDomain ad, Boolean statics, TType typ)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentInType(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets isApplicableMeth, range m, AccessorDomain ad, Boolean statics, FSharpList`1 plid, TType typ)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentInType@3610-2.Invoke(PropInfo pinfo)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentInType(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets isApplicableMeth, range m, AccessorDomain ad, Boolean statics, FSharpList`1 plid, TType typ)
at Microsoft.FSharp.Compiler.NameResolution.ResolvePartialLongIdentPrim(NameResolver ncenv, NameResolutionEnv nenv, ResolveCompletionTargets isApplicableMeth, FullyQualifiedFlag fullyQualified, range m, AccessorDomain ad, FSharpList`1 plid, Boolean allowObsolete)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetEnvironmentLookupResolutions(NameResolutionEnv nenv, AccessorDomain ad, range m, FSharpList`1 plid, TypeNameResolutionFlag filterCtors, Boolean showObsolete)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetDeclaredItems[a](FSharpOption`1 parseResultsOpt, String lineStr, FSharpOption`1 origLongIdentOpt, Int32 colAtEndOfNamesAndResidue, FSharpOption`1 residueOpt, Int32 line, Int32 loc, TypeNameResolutionFlag filterCtors, ResolveOverloads resolveOverloads, FSharpFunc`2 hasTextChangedSinceLastTypecheck, Boolean isInRangeOperator, FSharpFunc`2 allSymbols)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetDeclItemsForNamesAtPosition(CompilationThreadToken ctok, FSharpOption`1 parseResultsOpt, FSharpOption`1 origLongIdentOpt, FSharpOption`1 residueOpt, Int32 line, String lineStr, Int32 colAtEndOfNamesAndResidue, TypeNameResolutionFlag filterCtors, ResolveOverloads resolveOverloads, FSharpFunc`2 getAllSymbols, FSharpFunc`2 hasTextChangedSinceLastTypecheck)
at Microsoft.FSharp.Compiler.SourceCodeServices.TypeCheckInfo.GetSymbolUseAtLocation(CompilationThreadToken ctok, Int32 line, String lineStr, Int32 colAtEndOfNames, FSharpList`1 names)
at <StartupCode$FSharp-Compiler-Private>.$Service.GetSymbolUseAtLocation@1826-2.Invoke(CompilationThreadToken ctok, TypeCheckInfo scope)
at <StartupCode$FSharp-Compiler-Private>.$Service.clo@1760-246.Invoke(CompilationThreadToken ctok)
at <StartupCode$FSharp-Compiler-Private>.$Reactor.EnqueueAndAwaitOpAsync@153-2.Invoke(CompilationThreadToken ctok)
at System.Runtime.CompilerServices.TaskAwaiter.ThrowForNonSuccess(Task task)
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.CodeAnalysis.Editor.Implementation.ReferenceHighlighting.ReferenceHighlightingViewTaggerProvider.<ProduceTagsAsync>d__12.MoveNext()
at System.Runtime.CompilerServices.TaskAwaiter.ThrowForNonSuccess(Task task)
at System.Runtime.CompilerServices.TaskAwaiter.HandleNonSuccessAndDebuggerNotification(Task task)
at Microsoft.CodeAnalysis.Editor.Tagging.AbstractAsynchronousTaggerProvider`1.TagSource.<RecomputeTagsAsync>d__83.MoveNext()
```
#### Repro steps
See comment below
####
* Operating system - Win7
* VS2017
| non_priority | compiler error causes to crash visual studio crash caused by the f compiler services i have a suspicion that it s related to fetch intellisense for a property on a type from another assembly c where the property s type is in a third unreferenced assembly i m running with nighties initially saw the crash with a build from a few days ago updated to test latest and still occuring now running version stack trace at microsoft fsharp compiler errorlogger errorloggerextensions errorlogger error errorlogger x exception exn at microsoft fsharp compiler import importtyperefdata importmap env range m ilscoperef scoref string path string typename at microsoft fsharp compiler import importiltyperefuncached importmap env range m iltyperef tref at microsoft fsharp compiler import importiltyperef importmap env range m iltyperef tref at microsoft fsharp compiler import importiltype importmap env range m fsharplist tinst iltype typ at microsoft fsharp compiler infos itys invoke iltype ity at microsoft fsharp primitives basics list choose fsharpfunc f fsharplist xs at microsoft fsharp compiler infos getimmediateinterfacesoftype skipunrefinterfaces skipunref tcglobals g importmap amap range m ttype typ at microsoft fsharp compiler infos loop boolean followinterfaces allowmultiintfinstantiations allowmultiintfinst skipunrefinterfaces skipunref fsharpfunc visitor tcglobals g importmap amap range m ndeep ttype typ tuple tupledarg at microsoft fsharp compiler infos foldhierarchyoftypeaux boolean followinterfaces allowmultiintfinstantiations allowmultiintfinst skipunrefinterfaces skipunref fsharpfunc visitor tcglobals g importmap amap range m ttype typ a acc at microsoft fsharp compiler inforeader inforeader getintrinsicrecdorclassfieldinfosuncached tuple range m ttype typ at microsoft fsharp compiler inforeader ctor invoke tuple tupledarg at microsoft fsharp compiler abstractil internal library f memoizationtable t t x unit at microsoft fsharp compiler abstractil internal library memoizationtable apply t x at microsoft fsharp compiler nameresolution resolvecompletionsintype nameresolver ncenv nameresolutionenv nenv resolvecompletiontargets completiontargets range m accessordomain ad boolean statics ttype typ at microsoft fsharp compiler nameresolution resolvepartiallongidentintype nameresolver ncenv nameresolutionenv nenv resolvecompletiontargets isapplicablemeth range m accessordomain ad boolean statics fsharplist plid ttype typ at microsoft fsharp compiler nameresolution resolvepartiallongidentintype invoke propinfo pinfo at microsoft fsharp compiler nameresolution resolvepartiallongidentintype nameresolver ncenv nameresolutionenv nenv resolvecompletiontargets isapplicablemeth range m accessordomain ad boolean statics fsharplist plid ttype typ at microsoft fsharp compiler nameresolution resolvepartiallongidentprim nameresolver ncenv nameresolutionenv nenv resolvecompletiontargets isapplicablemeth fullyqualifiedflag fullyqualified range m accessordomain ad fsharplist plid boolean allowobsolete at microsoft fsharp compiler sourcecodeservices typecheckinfo getenvironmentlookupresolutions nameresolutionenv nenv accessordomain ad range m fsharplist plid typenameresolutionflag filterctors boolean showobsolete at microsoft fsharp compiler sourcecodeservices typecheckinfo getdeclareditems fsharpoption parseresultsopt string linestr fsharpoption origlongidentopt colatendofnamesandresidue fsharpoption residueopt line loc typenameresolutionflag filterctors resolveoverloads resolveoverloads fsharpfunc hastextchangedsincelasttypecheck boolean isinrangeoperator fsharpfunc allsymbols at microsoft fsharp compiler sourcecodeservices typecheckinfo getdeclitemsfornamesatposition compilationthreadtoken ctok fsharpoption parseresultsopt fsharpoption origlongidentopt fsharpoption residueopt line string linestr colatendofnamesandresidue typenameresolutionflag filterctors resolveoverloads resolveoverloads fsharpfunc getallsymbols fsharpfunc hastextchangedsincelasttypecheck at microsoft fsharp compiler sourcecodeservices typecheckinfo getsymboluseatlocation compilationthreadtoken ctok line string linestr colatendofnames fsharplist names at service getsymboluseatlocation invoke compilationthreadtoken ctok typecheckinfo scope at service clo invoke compilationthreadtoken ctok at reactor enqueueandawaitopasync invoke compilationthreadtoken ctok at system runtime compilerservices taskawaiter throwfornonsuccess task task at system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task at microsoft codeanalysis editor implementation referencehighlighting referencehighlightingviewtaggerprovider d movenext at system runtime compilerservices taskawaiter throwfornonsuccess task task at system runtime compilerservices taskawaiter handlenonsuccessanddebuggernotification task task at microsoft codeanalysis editor tagging abstractasynchronoustaggerprovider tagsource d movenext repro steps see comment below operating system | 0 |
11,393 | 8,380,328,672 | IssuesEvent | 2018-10-07 13:42:05 | symfony/symfony | https://api.github.com/repos/symfony/symfony | closed | [Security][Factory] use ArrayNodeDefinition instead of NodeDefinition | SecurityBundle | | Q | A
| ---------------- | -----
| Bug report? | no
| Feature request? | no
| BC Break report? | yes
| RFC? | no
| Symfony version | 2.1
``NodeDefinition`` does not have ``children`` or ``fixXmlConfig`` methods.
But the ``ArrayNodeDefinition`` have those methods.
This could throw errors with a linter.
Is it normal? | True | [Security][Factory] use ArrayNodeDefinition instead of NodeDefinition - | Q | A
| ---------------- | -----
| Bug report? | no
| Feature request? | no
| BC Break report? | yes
| RFC? | no
| Symfony version | 2.1
``NodeDefinition`` does not have ``children`` or ``fixXmlConfig`` methods.
But the ``ArrayNodeDefinition`` have those methods.
This could throw errors with a linter.
Is it normal? | non_priority | use arraynodedefinition instead of nodedefinition q a bug report no feature request no bc break report yes rfc no symfony version nodedefinition does not have children or fixxmlconfig methods but the arraynodedefinition have those methods this could throw errors with a linter is it normal | 0 |
96,054 | 12,092,409,404 | IssuesEvent | 2020-04-19 15:32:22 | ekzyis/physicsbot | https://api.github.com/repos/ekzyis/physicsbot | opened | No date in log outputs | design enhancement | ```
3|physicsb | 14:42:40.754 [BOT] ROLE_ADD: derOMSIfahrer#8206, Höhere Mathematik II
3|physicsb | 14:42:41.195 [BOT] REACTION_ADD: derOMSIfahrer#8206, hoema3, 513534396524134420
3|physicsb | 14:42:41.373 [BOT] ROLE_ADD: derOMSIfahrer#8206, Höhere Mathematik III
3|physicsb | 17:19:10.903 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 11:20:52.012 [BOT] SEND_MSG: Physik Heidelberg@allgemein: <@700287933189455893>
3|physicsb | 17:29:00.873 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 19:12:56.865 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 19:13:11.304 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 20:58:02.943 [BOT] REACTION_ADD: CAT#8652, physik, 513534396524134420
3|physicsb | 20:58:03.321 [BOT] ROLE_ADD: CAT#8652, Physik
3|physicsb | 21:07:53.045 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 12:23:50.901 [BOT] REACTION_ADD: sbalint98#8597, theo2, 513534396524134420
3|physicsb | 12:23:51.140 [BOT] ROLE_ADD: sbalint98#8597, Theoretische Physik II
3|physicsb | 12:42:06.813 [BOT] REACTION_ADD: mwjk03#3004, num, 513534396524134420
3|physicsb | 12:42:07.004 [BOT] ROLE_ADD: mwjk03#3004, Numerik
```
Well. A date and not only the time would be nice to have. Maybe pm2 has an option? | 1.0 | No date in log outputs - ```
3|physicsb | 14:42:40.754 [BOT] ROLE_ADD: derOMSIfahrer#8206, Höhere Mathematik II
3|physicsb | 14:42:41.195 [BOT] REACTION_ADD: derOMSIfahrer#8206, hoema3, 513534396524134420
3|physicsb | 14:42:41.373 [BOT] ROLE_ADD: derOMSIfahrer#8206, Höhere Mathematik III
3|physicsb | 17:19:10.903 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 11:20:52.012 [BOT] SEND_MSG: Physik Heidelberg@allgemein: <@700287933189455893>
3|physicsb | 17:29:00.873 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 19:12:56.865 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 19:13:11.304 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 20:58:02.943 [BOT] REACTION_ADD: CAT#8652, physik, 513534396524134420
3|physicsb | 20:58:03.321 [BOT] ROLE_ADD: CAT#8652, Physik
3|physicsb | 21:07:53.045 [STARTUP] PhysicsBot#2569 is now logged in! Mode: production
3|physicsb | 12:23:50.901 [BOT] REACTION_ADD: sbalint98#8597, theo2, 513534396524134420
3|physicsb | 12:23:51.140 [BOT] ROLE_ADD: sbalint98#8597, Theoretische Physik II
3|physicsb | 12:42:06.813 [BOT] REACTION_ADD: mwjk03#3004, num, 513534396524134420
3|physicsb | 12:42:07.004 [BOT] ROLE_ADD: mwjk03#3004, Numerik
```
Well. A date and not only the time would be nice to have. Maybe pm2 has an option? | non_priority | no date in log outputs physicsb role add deromsifahrer höhere mathematik ii physicsb reaction add deromsifahrer physicsb role add deromsifahrer höhere mathematik iii physicsb physicsbot is now logged in mode production physicsb send msg physik heidelberg allgemein physicsb physicsbot is now logged in mode production physicsb physicsbot is now logged in mode production physicsb physicsbot is now logged in mode production physicsb reaction add cat physik physicsb role add cat physik physicsb physicsbot is now logged in mode production physicsb reaction add physicsb role add theoretische physik ii physicsb reaction add num physicsb role add numerik well a date and not only the time would be nice to have maybe has an option | 0 |
75,233 | 9,214,850,816 | IssuesEvent | 2019-03-10 23:10:28 | ServiceInnovationLab/PresenceChecker | https://api.github.com/repos/ServiceInnovationLab/PresenceChecker | closed | Presentation on call-outs / implications of the current solution | design development review | As the citizenship team
We want to be able to put together a presentation that calls out any implications with the process and the demo data that we've reviewed.
A / C
- [x] Should show any implications, pain points of the current process
- [x] Should show analysis of demo data
requires #62 | 1.0 | Presentation on call-outs / implications of the current solution - As the citizenship team
We want to be able to put together a presentation that calls out any implications with the process and the demo data that we've reviewed.
A / C
- [x] Should show any implications, pain points of the current process
- [x] Should show analysis of demo data
requires #62 | non_priority | presentation on call outs implications of the current solution as the citizenship team we want to be able to put together a presentation that calls out any implications with the process and the demo data that we ve reviewed a c should show any implications pain points of the current process should show analysis of demo data requires | 0 |
316,620 | 27,170,749,118 | IssuesEvent | 2023-02-17 19:10:44 | US-EPA-CAMD/easey-ui | https://api.github.com/repos/US-EPA-CAMD/easey-ui | closed | MP Performance Testing During 11.5 - I&P sprint | Emissioners Testing | ## Context
Conduct performance testing on MP Module | 1.0 | MP Performance Testing During 11.5 - I&P sprint - ## Context
Conduct performance testing on MP Module | non_priority | mp performance testing during i p sprint context conduct performance testing on mp module | 0 |
123,390 | 17,772,222,315 | IssuesEvent | 2021-08-30 14:52:11 | kapseliboi/RDocumentation-app | https://api.github.com/repos/kapseliboi/RDocumentation-app | opened | WS-2019-0333 (High) detected in handlebars-4.0.11.tgz | security vulnerability | ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.11.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz</a></p>
<p>Path to dependency file: RDocumentation-app/package.json</p>
<p>Path to vulnerable library: RDocumentation-app/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- sails-0.12.11.tgz (Root Library)
- express-handlebars-3.0.0.tgz
- :x: **handlebars-4.0.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/RDocumentation-app/commit/ea1d4334329f74384d2d1b67f98e875da0b95310">ea1d4334329f74384d2d1b67f98e875da0b95310</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it's possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08>WS-2019-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1325">https://www.npmjs.com/advisories/1325</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0333 (High) detected in handlebars-4.0.11.tgz - ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.11.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.11.tgz</a></p>
<p>Path to dependency file: RDocumentation-app/package.json</p>
<p>Path to vulnerable library: RDocumentation-app/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- sails-0.12.11.tgz (Root Library)
- express-handlebars-3.0.0.tgz
- :x: **handlebars-4.0.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/RDocumentation-app/commit/ea1d4334329f74384d2d1b67f98e875da0b95310">ea1d4334329f74384d2d1b67f98e875da0b95310</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In handlebars, versions prior to v4.5.3 are vulnerable to prototype pollution. Using a malicious template it's possbile to add or modify properties to the Object prototype. This can also lead to DOS and RCE in certain conditions.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://github.com/wycats/handlebars.js/commit/f7f05d7558e674856686b62a00cde5758f3b7a08>WS-2019-0333</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1325">https://www.npmjs.com/advisories/1325</a></p>
<p>Release Date: 2019-12-05</p>
<p>Fix Resolution: handlebars - 4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in handlebars tgz ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file rdocumentation app package json path to vulnerable library rdocumentation app node modules handlebars package json dependency hierarchy sails tgz root library express handlebars tgz x handlebars tgz vulnerable library found in head commit a href found in base branch master vulnerability details in handlebars versions prior to are vulnerable to prototype pollution using a malicious template it s possbile to add or modify properties to the object prototype this can also lead to dos and rce in certain conditions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars step up your open source security game with whitesource | 0 |
73,180 | 7,328,871,922 | IssuesEvent | 2018-03-05 00:54:29 | easydigitaldownloads/easy-digital-downloads | https://api.github.com/repos/easydigitaldownloads/easy-digital-downloads | closed | Upgrade to latest version of Chosen | Enhancement Has PR Needs Testing | EDD core uses Chosen 1.1.0 whereas the latest released on 5 Sep 2017 is **1.8.2**.
If we upgrade Chosen to the latest version, this may also fix #4662.
Note: testing would need to be done it doesn't break any extensions that are using Chosen (namely FES and CFM). | 1.0 | Upgrade to latest version of Chosen - EDD core uses Chosen 1.1.0 whereas the latest released on 5 Sep 2017 is **1.8.2**.
If we upgrade Chosen to the latest version, this may also fix #4662.
Note: testing would need to be done it doesn't break any extensions that are using Chosen (namely FES and CFM). | non_priority | upgrade to latest version of chosen edd core uses chosen whereas the latest released on sep is if we upgrade chosen to the latest version this may also fix note testing would need to be done it doesn t break any extensions that are using chosen namely fes and cfm | 0 |
69,119 | 13,210,792,215 | IssuesEvent | 2020-08-15 18:53:17 | DS-13-Dev-Team/DS13 | https://api.github.com/repos/DS-13-Dev-Team/DS13 | closed | [Suggestion] Move the "Join the Discord" verb to the top with the wiki, forum, etc. | Code Suggestion | <!--
For the title make sure to put the words, 'Suggestion:' or 'Bug:' before the actual title of your issue, it helps with sorting!
If a specific field doesn't apply, remove it!
Anything inside tags like these is a comment and will not be displayed in the final issue.
Be careful not to write inside them!
Joke or spammed issues can and will result in punishment.
PUT YOUR ANSWERS ON THE BLANK LINES BELOW THE HEADERS
(The lines with four #'s)
Don't edit them or delete them it's part of the formatting
-->
<!--
<!--
The next two lines are for Suggestions, delete these if you aren't making a suggestion.
-->
#### Suggestion:
Move the "Join the Discord" verb out of OOC and to the top of the window with the wiki, forum, etc. I can do this myself but I'd like to know if @JakeDaBoss is okay with it.
#### What do you think it'd add:
I believe doing this would make it easier for people to find the discord verb and not ask for it in OOC. | 1.0 | [Suggestion] Move the "Join the Discord" verb to the top with the wiki, forum, etc. - <!--
For the title make sure to put the words, 'Suggestion:' or 'Bug:' before the actual title of your issue, it helps with sorting!
If a specific field doesn't apply, remove it!
Anything inside tags like these is a comment and will not be displayed in the final issue.
Be careful not to write inside them!
Joke or spammed issues can and will result in punishment.
PUT YOUR ANSWERS ON THE BLANK LINES BELOW THE HEADERS
(The lines with four #'s)
Don't edit them or delete them it's part of the formatting
-->
<!--
<!--
The next two lines are for Suggestions, delete these if you aren't making a suggestion.
-->
#### Suggestion:
Move the "Join the Discord" verb out of OOC and to the top of the window with the wiki, forum, etc. I can do this myself but I'd like to know if @JakeDaBoss is okay with it.
#### What do you think it'd add:
I believe doing this would make it easier for people to find the discord verb and not ask for it in OOC. | non_priority | move the join the discord verb to the top with the wiki forum etc for the title make sure to put the words suggestion or bug before the actual title of your issue it helps with sorting if a specific field doesn t apply remove it anything inside tags like these is a comment and will not be displayed in the final issue be careful not to write inside them joke or spammed issues can and will result in punishment put your answers on the blank lines below the headers the lines with four s don t edit them or delete them it s part of the formatting the next two lines are for suggestions delete these if you aren t making a suggestion suggestion move the join the discord verb out of ooc and to the top of the window with the wiki forum etc i can do this myself but i d like to know if jakedaboss is okay with it what do you think it d add i believe doing this would make it easier for people to find the discord verb and not ask for it in ooc | 0 |
151,963 | 19,670,318,189 | IssuesEvent | 2022-01-11 06:13:17 | ChoeMinji/godot | https://api.github.com/repos/ChoeMinji/godot | opened | CVE-2021-23362 (Medium) detected in hosted-git-info-2.8.8.tgz | security vulnerability | ## CVE-2021-23362 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hosted-git-info-2.8.8.tgz</b></p></summary>
<p>Provides metadata and conversions from repository urls for Github, Bitbucket and Gitlab</p>
<p>Library home page: <a href="https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz">https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz</a></p>
<p>Path to dependency file: /platform/javascript/package.json</p>
<p>Path to vulnerable library: /platform/javascript/node_modules/hosted-git-info/package.json</p>
<p>
Dependency Hierarchy:
- eslint-plugin-import-2.22.0.tgz (Root Library)
- read-pkg-up-2.0.0.tgz
- read-pkg-2.0.0.tgz
- normalize-package-data-2.5.0.tgz
- :x: **hosted-git-info-2.8.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/godot/commit/620ad7ae3fef04e165cbc3f2776d3e3bf6cfdc4d">620ad7ae3fef04e165cbc3f2776d3e3bf6cfdc4d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362>CVE-2021-23362</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-43f8-2h32-f4cj">https://github.com/advisories/GHSA-43f8-2h32-f4cj</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: hosted-git-info - 2.8.9,3.0.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23362 (Medium) detected in hosted-git-info-2.8.8.tgz - ## CVE-2021-23362 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hosted-git-info-2.8.8.tgz</b></p></summary>
<p>Provides metadata and conversions from repository urls for Github, Bitbucket and Gitlab</p>
<p>Library home page: <a href="https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz">https://registry.npmjs.org/hosted-git-info/-/hosted-git-info-2.8.8.tgz</a></p>
<p>Path to dependency file: /platform/javascript/package.json</p>
<p>Path to vulnerable library: /platform/javascript/node_modules/hosted-git-info/package.json</p>
<p>
Dependency Hierarchy:
- eslint-plugin-import-2.22.0.tgz (Root Library)
- read-pkg-up-2.0.0.tgz
- read-pkg-2.0.0.tgz
- normalize-package-data-2.5.0.tgz
- :x: **hosted-git-info-2.8.8.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ChoeMinji/godot/commit/620ad7ae3fef04e165cbc3f2776d3e3bf6cfdc4d">620ad7ae3fef04e165cbc3f2776d3e3bf6cfdc4d</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-03-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362>CVE-2021-23362</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-43f8-2h32-f4cj">https://github.com/advisories/GHSA-43f8-2h32-f4cj</a></p>
<p>Release Date: 2021-03-23</p>
<p>Fix Resolution: hosted-git-info - 2.8.9,3.0.8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in hosted git info tgz cve medium severity vulnerability vulnerable library hosted git info tgz provides metadata and conversions from repository urls for github bitbucket and gitlab library home page a href path to dependency file platform javascript package json path to vulnerable library platform javascript node modules hosted git info package json dependency hierarchy eslint plugin import tgz root library read pkg up tgz read pkg tgz normalize package data tgz x hosted git info tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package hosted git info before are vulnerable to regular expression denial of service redos via regular expression shortcutmatch in the fromurl function in index js the affected regular expression exhibits polynomial worst case time complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution hosted git info step up your open source security game with whitesource | 0 |
218,593 | 16,997,827,942 | IssuesEvent | 2021-07-01 08:47:27 | gradle/gradle | https://api.github.com/repos/gradle/gradle | closed | Let Gradle test a specific package but ignoring/without the sub-package(s) | a:feature closed:not-fixed in:testing | Considering that exists the following packages and classes in `src/test/java`
com.something.one
AlphaTest
BetaTest
DeltaTest
com.something.one.more
OmicronTest
ZuluTest
With any of the two following commands:
```
./gradlew :module-name:test --tests "com.something.one*"
./gradlew :module-name:test --tests "com.something.one.*" // observe it ends now with .*
```
The `com.something.one` and `com.something.one.more` packages were executed. Until here it is expected.
But, what if is need it to test _only_ the `com.something.one` package and **not** the `com.something.one.more` sub-package?
So:
I have already read:
* [Testing in Java & JVM projects - Test filtering](https://docs.gradle.org/current/userguide/java_testing.html#test_filtering)
But _'seems'_ is not possible. The option to change the sub-package name to other different than the parent package is not always an option. Of course - if exists the option, should be indicated in the documentation - therefore, currently it is missing
If not exists, please consider to add that feature, perhaps with a new parameter such as `--no-subpackages`, therefore
```
./gradlew :module-name:test --tests "com.something.one*" --no-subpackages
./gradlew :module-name:test --tests "com.something.one.*" --no-subpackages
```
Thanks for your understanding
| 1.0 | Let Gradle test a specific package but ignoring/without the sub-package(s) - Considering that exists the following packages and classes in `src/test/java`
com.something.one
AlphaTest
BetaTest
DeltaTest
com.something.one.more
OmicronTest
ZuluTest
With any of the two following commands:
```
./gradlew :module-name:test --tests "com.something.one*"
./gradlew :module-name:test --tests "com.something.one.*" // observe it ends now with .*
```
The `com.something.one` and `com.something.one.more` packages were executed. Until here it is expected.
But, what if is need it to test _only_ the `com.something.one` package and **not** the `com.something.one.more` sub-package?
So:
I have already read:
* [Testing in Java & JVM projects - Test filtering](https://docs.gradle.org/current/userguide/java_testing.html#test_filtering)
But _'seems'_ is not possible. The option to change the sub-package name to other different than the parent package is not always an option. Of course - if exists the option, should be indicated in the documentation - therefore, currently it is missing
If not exists, please consider to add that feature, perhaps with a new parameter such as `--no-subpackages`, therefore
```
./gradlew :module-name:test --tests "com.something.one*" --no-subpackages
./gradlew :module-name:test --tests "com.something.one.*" --no-subpackages
```
Thanks for your understanding
| non_priority | let gradle test a specific package but ignoring without the sub package s considering that exists the following packages and classes in src test java com something one alphatest betatest deltatest com something one more omicrontest zulutest with any of the two following commands gradlew module name test tests com something one gradlew module name test tests com something one observe it ends now with the com something one and com something one more packages were executed until here it is expected but what if is need it to test only the com something one package and not the com something one more sub package so i have already read but seems is not possible the option to change the sub package name to other different than the parent package is not always an option of course if exists the option should be indicated in the documentation therefore currently it is missing if not exists please consider to add that feature perhaps with a new parameter such as no subpackages therefore gradlew module name test tests com something one no subpackages gradlew module name test tests com something one no subpackages thanks for your understanding | 0 |
247,775 | 20,988,159,068 | IssuesEvent | 2022-03-29 06:40:40 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: sstable-corruption/table failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.sstable-corruption/table [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4713654&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4713654&tab=artifacts#/sstable-corruption/table) on master @ [29716850b181718594663889ddb5f479fef7a305](https://github.com/cockroachdb/cockroach/commits/29716850b181718594663889ddb5f479fef7a305):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /artifacts/sstable-corruption/table/run_1
cluster.go:1868,sstable_corruption.go:37,sstable_corruption.go:158,test_runner.go:875: one or more parallel execution failure
(1) attached stack trace
-- stack trace:
| github.com/cockroachdb/cockroach/pkg/roachprod/install.(*SyncedCluster).ParallelE
| github.com/cockroachdb/cockroach/pkg/roachprod/install/cluster_synced.go:2042
| github.com/cockroachdb/cockroach/pkg/roachprod/install.(*SyncedCluster).Parallel
| github.com/cockroachdb/cockroach/pkg/roachprod/install/cluster_synced.go:1923
| github.com/cockroachdb/cockroach/pkg/roachprod/install.(*SyncedCluster).Start
| github.com/cockroachdb/cockroach/pkg/roachprod/install/cockroach.go:167
| github.com/cockroachdb/cockroach/pkg/roachprod.Start
| github.com/cockroachdb/cockroach/pkg/roachprod/roachprod.go:660
| main.(*clusterImpl).StartE
| main/pkg/cmd/roachtest/cluster.go:1826
| main.(*clusterImpl).Start
| main/pkg/cmd/roachtest/cluster.go:1867
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runSSTableCorruption
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/sstable_corruption.go:37
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.registerSSTableCorruption.func1
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/sstable_corruption.go:158
| main.(*testRunner).runTest.func2
| main/pkg/cmd/roachtest/test_runner.go:875
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1581
Wraps: (2) one or more parallel execution failure
Error types: (1) *withstack.withStack (2) *errutil.leafError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #78121 roachtest: sstable-corruption/table failed [C-test-failure O-roachtest O-robot T-storage branch-release-22.1]
</p>
</details>
/cc @cockroachdb/storage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sstable-corruption/table.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: sstable-corruption/table failed - roachtest.sstable-corruption/table [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4713654&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4713654&tab=artifacts#/sstable-corruption/table) on master @ [29716850b181718594663889ddb5f479fef7a305](https://github.com/cockroachdb/cockroach/commits/29716850b181718594663889ddb5f479fef7a305):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /artifacts/sstable-corruption/table/run_1
cluster.go:1868,sstable_corruption.go:37,sstable_corruption.go:158,test_runner.go:875: one or more parallel execution failure
(1) attached stack trace
-- stack trace:
| github.com/cockroachdb/cockroach/pkg/roachprod/install.(*SyncedCluster).ParallelE
| github.com/cockroachdb/cockroach/pkg/roachprod/install/cluster_synced.go:2042
| github.com/cockroachdb/cockroach/pkg/roachprod/install.(*SyncedCluster).Parallel
| github.com/cockroachdb/cockroach/pkg/roachprod/install/cluster_synced.go:1923
| github.com/cockroachdb/cockroach/pkg/roachprod/install.(*SyncedCluster).Start
| github.com/cockroachdb/cockroach/pkg/roachprod/install/cockroach.go:167
| github.com/cockroachdb/cockroach/pkg/roachprod.Start
| github.com/cockroachdb/cockroach/pkg/roachprod/roachprod.go:660
| main.(*clusterImpl).StartE
| main/pkg/cmd/roachtest/cluster.go:1826
| main.(*clusterImpl).Start
| main/pkg/cmd/roachtest/cluster.go:1867
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runSSTableCorruption
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/sstable_corruption.go:37
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.registerSSTableCorruption.func1
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/sstable_corruption.go:158
| main.(*testRunner).runTest.func2
| main/pkg/cmd/roachtest/test_runner.go:875
| runtime.goexit
| GOROOT/src/runtime/asm_amd64.s:1581
Wraps: (2) one or more parallel execution failure
Error types: (1) *withstack.withStack (2) *errutil.leafError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #78121 roachtest: sstable-corruption/table failed [C-test-failure O-roachtest O-robot T-storage branch-release-22.1]
</p>
</details>
/cc @cockroachdb/storage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*sstable-corruption/table.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest sstable corruption table failed roachtest sstable corruption table with on master the test failed on branch master cloud gce test artifacts and logs in artifacts sstable corruption table run cluster go sstable corruption go sstable corruption go test runner go one or more parallel execution failure attached stack trace stack trace github com cockroachdb cockroach pkg roachprod install syncedcluster parallele github com cockroachdb cockroach pkg roachprod install cluster synced go github com cockroachdb cockroach pkg roachprod install syncedcluster parallel github com cockroachdb cockroach pkg roachprod install cluster synced go github com cockroachdb cockroach pkg roachprod install syncedcluster start github com cockroachdb cockroach pkg roachprod install cockroach go github com cockroachdb cockroach pkg roachprod start github com cockroachdb cockroach pkg roachprod roachprod go main clusterimpl starte main pkg cmd roachtest cluster go main clusterimpl start main pkg cmd roachtest cluster go github com cockroachdb cockroach pkg cmd roachtest tests runsstablecorruption github com cockroachdb cockroach pkg cmd roachtest tests sstable corruption go github com cockroachdb cockroach pkg cmd roachtest tests registersstablecorruption github com cockroachdb cockroach pkg cmd roachtest tests sstable corruption go main testrunner runtest main pkg cmd roachtest test runner go runtime goexit goroot src runtime asm s wraps one or more parallel execution failure error types withstack withstack errutil leaferror help see see same failure on other branches roachtest sstable corruption table failed cc cockroachdb storage | 0 |
155,843 | 19,803,069,274 | IssuesEvent | 2022-01-19 01:25:44 | developerone12/WebGoat-WhiteSource-Bolt | https://api.github.com/repos/developerone12/WebGoat-WhiteSource-Bolt | opened | CVE-2020-9488 (Low) detected in log4j-1.2.17.jar | security vulnerability | ## CVE-2020-9488 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /4j/log4j/1.2.17/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.
<p>Publish Date: 2020-04-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488>CVE-2020-9488</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/LOG4J2-2819">https://issues.apache.org/jira/browse/LOG4J2-2819</a></p>
<p>Release Date: 2020-04-27</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.13.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-9488 (Low) detected in log4j-1.2.17.jar - ## CVE-2020-9488 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /4j/log4j/1.2.17/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper validation of certificate with host mismatch in Apache Log4j SMTP appender. This could allow an SMTPS connection to be intercepted by a man-in-the-middle attack which could leak any log messages sent through that appender.
<p>Publish Date: 2020-04-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9488>CVE-2020-9488</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/LOG4J2-2819">https://issues.apache.org/jira/browse/LOG4J2-2819</a></p>
<p>Release Date: 2020-04-27</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.13.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve low detected in jar cve low severity vulnerability vulnerable library jar apache path to dependency file pom xml path to vulnerable library jar dependency hierarchy x jar vulnerable library found in base branch master vulnerability details improper validation of certificate with host mismatch in apache smtp appender this could allow an smtps connection to be intercepted by a man in the middle attack which could leak any log messages sent through that appender publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core step up your open source security game with whitesource | 0 |
110,262 | 9,441,367,693 | IssuesEvent | 2019-04-15 01:08:04 | QubesOS/updates-status | https://api.github.com/repos/QubesOS/updates-status | closed | mgmt-salt v4.0.17 (r4.0) | buggy r4.0-buster-cur-test r4.0-centos7-cur-test r4.0-dom0-cur-test r4.0-fc27-cur-test r4.0-fc28-cur-test r4.0-fc29-cur-test r4.0-fc30-cur-test r4.0-jessie-cur-test r4.0-stretch-cur-test | Update of mgmt-salt to v4.0.17 for Qubes r4.0, see comments below for details.
Built from: https://github.com/QubesOS/qubes-mgmt-salt/commit/f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d
[Changes since previous version](https://github.com/QubesOS/qubes-mgmt-salt/compare/v4.0.16...v4.0.17):
QubesOS/qubes-mgmt-salt@f74c7b7 version 4.0.17
QubesOS/qubes-mgmt-salt@d91aee0 travis: update Fedora,Debian versions, switch to xenial
QubesOS/qubes-mgmt-salt@0d19550 Make ssh-wrapper python3 script
QubesOS/qubes-mgmt-salt@076aa5b Make qubesctl explicit python2
Referenced issues:
QubesOS/qubes-issues#4613
QubesOS/qubes-issues#4845
If you're release manager, you can issue GPG-inline signed command:
* `Upload mgmt-salt f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d r4.0 current repo` (available 7 days from now)
* `Upload mgmt-salt f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d r4.0 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload mgmt-salt f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d r4.0 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| 9.0 | mgmt-salt v4.0.17 (r4.0) - Update of mgmt-salt to v4.0.17 for Qubes r4.0, see comments below for details.
Built from: https://github.com/QubesOS/qubes-mgmt-salt/commit/f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d
[Changes since previous version](https://github.com/QubesOS/qubes-mgmt-salt/compare/v4.0.16...v4.0.17):
QubesOS/qubes-mgmt-salt@f74c7b7 version 4.0.17
QubesOS/qubes-mgmt-salt@d91aee0 travis: update Fedora,Debian versions, switch to xenial
QubesOS/qubes-mgmt-salt@0d19550 Make ssh-wrapper python3 script
QubesOS/qubes-mgmt-salt@076aa5b Make qubesctl explicit python2
Referenced issues:
QubesOS/qubes-issues#4613
QubesOS/qubes-issues#4845
If you're release manager, you can issue GPG-inline signed command:
* `Upload mgmt-salt f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d r4.0 current repo` (available 7 days from now)
* `Upload mgmt-salt f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d r4.0 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload mgmt-salt f74c7b7174a2d89f921c67e5fddcc7fac3f5c50d r4.0 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| non_priority | mgmt salt update of mgmt salt to for qubes see comments below for details built from qubesos qubes mgmt salt version qubesos qubes mgmt salt travis update fedora debian versions switch to xenial qubesos qubes mgmt salt make ssh wrapper script qubesos qubes mgmt salt make qubesctl explicit referenced issues qubesos qubes issues qubesos qubes issues if you re release manager you can issue gpg inline signed command upload mgmt salt current repo available days from now upload mgmt salt current dists repo you can choose subset of distributions like vm vm available days from now upload mgmt salt security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it | 0 |
137,739 | 30,744,211,460 | IssuesEvent | 2023-07-28 13:51:17 | SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b | https://api.github.com/repos/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b | opened | Code Security Report: 24 high severity findings, 38 total findings | Mend: code security findings | # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-28 01:47pm
**Total Findings:** 38 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 422
**Detected Programming Languages:** 2 (Java*, JavaScript / Node.js)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend Application](https://dev.whitesourcesoftware.com/app/orgs/QA%20SAST%20Only/scans/7c8b84d2-36ec-4c85-93a7-c47c61bfc9bd/sast?project=6114370e-4d32-468b-a1af-9ab07725c586).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson3.java:65](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson2.java:62](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L55
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L59
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson10.java:63](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson6a.java:67](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67)
</td><td>3</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L62-L67
<details>
<summary>3 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidation.java#L48
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidation.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L51
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L48
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L53
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson4.java:63](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Servers.java:72](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L67-L72
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L68
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5a.java:62](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L53
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Assignment5.java:59](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L51
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson9.java:66](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61-L66
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L55
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L59
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L65
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L128
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L65
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5b.java:71](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L66-L71
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L51
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L55
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|DOM Based Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|JavaScript / Node.js|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|6|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|14|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|XML External Entity (XXE) Injection|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java*|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|JavaScript / Node.js|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Log Forging|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|System Properties Disclosure|[CWE-497](https://cwe.mitre.org/data/definitions/497.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|1|
| 1.0 | Code Security Report: 24 high severity findings, 38 total findings - # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-28 01:47pm
**Total Findings:** 38 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 422
**Detected Programming Languages:** 2 (Java*, JavaScript / Node.js)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend Application](https://dev.whitesourcesoftware.com/app/orgs/QA%20SAST%20Only/scans/7c8b84d2-36ec-4c85-93a7-c47c61bfc9bd/sast?project=6114370e-4d32-468b-a1af-9ab07725c586).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson3.java:65](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60-L65
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L57
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson3.java#L65
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson2.java:62](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L55
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L59
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson2.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson10.java:63](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L53
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L58
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson10.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson6a.java:67](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67)
</td><td>3</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L62-L67
<details>
<summary>3 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidation.java#L48
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidation.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L51
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67
</details>
<details>
<summary>View Data Flow 3</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L48
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L49
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/SqlOnlyInputValidationOnKeywords.java#L53
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/advanced/SqlInjectionLesson6a.java#L67
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson4.java:63](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L58-L63
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L57
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson4.java#L63
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Servers.java:72](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L67-L72
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L68
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/mitigation/Servers.java#L72
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5a.java:62](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57-L62
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L53
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L54
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L57
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L60
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5a.java#L62
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[Assignment5.java:59](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L54-L59
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L51
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/challenges/challenge5/Assignment5.java#L59
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson9.java:66](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61-L66
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L55
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L59
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L61
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L65
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson8.java#L128
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L65
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson9.java#L66
</details>
</details>
</td></tr></details></td></tr><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[SqlInjectionLesson5b.java:71](https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71)
</td><td>1</td><td>2023-07-28 01:50pm</td></tr><tr><td colspan='6'><details><summary>More info</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L66-L71
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L51
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L52
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L55
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L56
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L58
https://github.com/SAST-UP-DEV/SAST-Test-Repo-84dfeafa-3a5d-4e0f-ac07-add55c9ddf2b/blob/c07ad06a9a3dab0a71af12e6f3f0157778bfa07c/src/main/java/org/owasp/webgoat/lessons/sql_injection/introduction/SqlInjectionLesson5b.java#L71
</details>
</details>
</td></tr></details></td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|DOM Based Cross-Site Scripting|[CWE-79](https://cwe.mitre.org/data/definitions/79.html)|JavaScript / Node.js|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|6|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|14|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|XML External Entity (XXE) Injection|[CWE-611](https://cwe.mitre.org/data/definitions/611.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Error Messages Information Exposure|[CWE-209](https://cwe.mitre.org/data/definitions/209.html)|Java*|5|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Weak Pseudo-Random|[CWE-338](https://cwe.mitre.org/data/definitions/338.html)|JavaScript / Node.js|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Log Forging|[CWE-117](https://cwe.mitre.org/data/definitions/117.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|System Properties Disclosure|[CWE-497](https://cwe.mitre.org/data/definitions/497.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|1|
| non_priority | code security report high severity findings total findings code security report scan metadata latest scan total findings new findings resolved findings tested project files detected programming languages java javascript node js check this box to manually trigger a scan most relevant findings the below list presents the most relevant findings that need your attention to view information on the remaining findings navigate to the severity vulnerability type cwe file data flows date high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow view data flow view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow high sql injection more info data flow s detected view data flow findings overview severity vulnerability type cwe language count high dom based cross site scripting node js high path directory traversal high deserialization of untrusted data high sql injection high server side request forgery medium xml external entity xxe injection medium hardcoded password credentials medium error messages information exposure medium weak pseudo random node js low log forging low system properties disclosure low weak hash strength | 0 |
79,107 | 27,992,382,401 | IssuesEvent | 2023-03-27 05:32:19 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | opened | `Cake\Log\Log` is not a PSR-3 compatible provider | defect | ### Description
👋 I noticed that CakePHP's Composer manifest was [recently updated](https://github.com/cakephp/cakephp/pull/17059) to identify it as being a provider a number of PSRs, including PSR-3 `psr/log-implementation`. Great to see! 👏
However, it doesn't appear [`Cake\Log\Log`](https://github.com/cakephp/cakephp/blob/4.x/src/Log/Log.php) is actually PSR-3 compatible at present. Although it has the correct methods, many of them are *static*, which is incompatible with [the standard](https://www.php-fig.org/psr/psr-3/#3-psrlogloggerinterface). The standard expects `log()`, `debug()`, `info()`, `notice()`, `warning()`, `error()`, `critical()`, `alert()` and `emergency()` to not be static.
As it is, a library that might consume `Cake\Log\Log` anticipating it speaks PSR-3 would throw exceptions due to the missing methods.
### CakePHP Version
4.4.12
### PHP Version
8.1 | 1.0 | `Cake\Log\Log` is not a PSR-3 compatible provider - ### Description
👋 I noticed that CakePHP's Composer manifest was [recently updated](https://github.com/cakephp/cakephp/pull/17059) to identify it as being a provider a number of PSRs, including PSR-3 `psr/log-implementation`. Great to see! 👏
However, it doesn't appear [`Cake\Log\Log`](https://github.com/cakephp/cakephp/blob/4.x/src/Log/Log.php) is actually PSR-3 compatible at present. Although it has the correct methods, many of them are *static*, which is incompatible with [the standard](https://www.php-fig.org/psr/psr-3/#3-psrlogloggerinterface). The standard expects `log()`, `debug()`, `info()`, `notice()`, `warning()`, `error()`, `critical()`, `alert()` and `emergency()` to not be static.
As it is, a library that might consume `Cake\Log\Log` anticipating it speaks PSR-3 would throw exceptions due to the missing methods.
### CakePHP Version
4.4.12
### PHP Version
8.1 | non_priority | cake log log is not a psr compatible provider description 👋 i noticed that cakephp s composer manifest was to identify it as being a provider a number of psrs including psr psr log implementation great to see 👏 however it doesn t appear is actually psr compatible at present although it has the correct methods many of them are static which is incompatible with the standard expects log debug info notice warning error critical alert and emergency to not be static as it is a library that might consume cake log log anticipating it speaks psr would throw exceptions due to the missing methods cakephp version php version | 0 |
42,781 | 11,072,285,016 | IssuesEvent | 2019-12-12 09:59:54 | vector-im/riot-web | https://api.github.com/repos/vector-im/riot-web | opened | Automate building of debian repo | new-build-process | Script to take the deb that electron-builder spits out and package it into a debian repo | 1.0 | Automate building of debian repo - Script to take the deb that electron-builder spits out and package it into a debian repo | non_priority | automate building of debian repo script to take the deb that electron builder spits out and package it into a debian repo | 0 |
246,153 | 26,597,778,473 | IssuesEvent | 2023-01-23 13:45:30 | uriel-naor/UrielTest | https://api.github.com/repos/uriel-naor/UrielTest | reopened | spring-web-2.5.6.jar: 8 vulnerabilities (highest severity is: 7.3) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-2.5.6.jar</b></p></summary>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (spring-web version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2010-1622](https://www.mend.io/vulnerability-database/CVE-2010-1622) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | spring-beans-2.5.6.jar | Transitive | 2.5.6.SEC01 | ✅ |
| [CVE-2011-2730](https://www.mend.io/vulnerability-database/CVE-2011-2730) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2013-6430](https://www.mend.io/vulnerability-database/CVE-2013-6430) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.4 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2013-6429](https://www.mend.io/vulnerability-database/CVE-2013-6429) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2018-1199](https://www.mend.io/vulnerability-database/CVE-2018-1199) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-core-2.5.6.jar | Transitive | N/A* | ❌ |
| [CVE-2014-0054](https://www.mend.io/vulnerability-database/CVE-2014-0054) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2014-3578](https://www.mend.io/vulnerability-database/CVE-2014-3578) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-core-2.5.6.jar | Transitive | 2.5.6.SEC01 | ✅ |
| [CVE-2009-1190](https://www.mend.io/vulnerability-database/CVE-2009-1190) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | detected in multiple dependencies | Transitive | 2.5.6.SEC01 | ✅ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2010-1622</summary>
### Vulnerable Library - <b>spring-beans-2.5.6.jar</b></p>
<p>Spring Framework: Beans</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-beans/2.5.6/spring-beans-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-beans-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SpringSource Spring Framework 2.5.x before 2.5.6.SEC02, 2.5.7 before 2.5.7.SR01, and 3.0.x before 3.0.3 allows remote attackers to execute arbitrary code via an HTTP request containing class.classLoader.URLs[0]=jar: followed by a URL of a crafted .jar file.
<p>Publish Date: 2010-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2010-1622>CVE-2010-1622</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-1622">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-1622</a></p>
<p>Release Date: 2010-06-21</p>
<p>Fix Resolution (spring-beans): 3.0.3.RELEASE,2.5.6.SEC02</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2011-2730</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
VMware SpringSource Spring Framework before 2.5.6.SEC03, 2.5.7.SR023, and 3.x before 3.0.6, when a container supports Expression Language (EL), evaluates EL expressions in tags twice, which allows remote attackers to obtain sensitive information via a (1) name attribute in a (a) spring:hasBindErrors tag; (2) path attribute in a (b) spring:bind or (c) spring:nestedpath tag; (3) arguments, (4) code, (5) text, (6) var, (7) scope, or (8) message attribute in a (d) spring:message or (e) spring:theme tag; or (9) var, (10) scope, or (11) value attribute in a (f) spring:transform tag, aka "Expression Language Injection."
<p>Publish Date: 2012-12-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2011-2730>CVE-2011-2730</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2011-2730">https://nvd.nist.gov/vuln/detail/CVE-2011-2730</a></p>
<p>Release Date: 2012-12-05</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-6430</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The JavaScriptUtils.javaScriptEscape method in web/util/JavaScriptUtils.java in Spring MVC in Spring Framework before 3.2.2 does not properly escape certain characters, which allows remote attackers to conduct cross-site scripting (XSS) attacks via a (1) line separator or (2) paragraph separator Unicode character or (3) left or (4) right angle bracket.
<p>Publish Date: 2020-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-6430>CVE-2013-6430</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-6430">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-6430</a></p>
<p>Release Date: 2020-01-10</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-6429</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The SourceHttpMessageConverter in Spring MVC in Spring Framework before 3.2.5 and 4.0.0.M1 through 4.0.0.RC1 does not disable external entity resolution, which allows remote attackers to read arbitrary files, cause a denial of service, and conduct CSRF attacks via crafted XML, aka an XML External Entity (XXE) issue, and a different vulnerability than CVE-2013-4152 and CVE-2013-7315.
<p>Publish Date: 2014-01-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-6429>CVE-2013-6429</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-6429">https://nvd.nist.gov/vuln/detail/CVE-2013-6429</a></p>
<p>Release Date: 2014-01-26</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-1199</summary>
### Vulnerable Library - <b>spring-core-2.5.6.jar</b></p>
<p>Spring Framework: Core</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-core/2.5.6/spring-core-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-core-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security (Spring Security 4.1.x before 4.1.5, 4.2.x before 4.2.4, and 5.0.x before 5.0.1; and Spring Framework 4.3.x before 4.3.14 and 5.0.x before 5.0.3) does not consider URL path parameters when processing security constraints. By adding a URL path parameter with special encodings, an attacker may be able to bypass a security constraint. The root cause of this issue is a lack of clarity regarding the handling of path parameters in the Servlet Specification. Some Servlet containers include path parameters in the value returned for getPathInfo() and some do not. Spring Security uses the value returned by getPathInfo() as part of the process of mapping requests to security constraints. In this particular attack, different character encodings used in path parameters allows secured Spring MVC static resource URLs to be bypassed.
<p>Publish Date: 2018-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1199>CVE-2018-1199</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1199">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1199</a></p>
<p>Release Date: 2018-03-16</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:4.1.5.RELEASE,4.2.4.RELEASE,5.0.1.RELEASE;org.springframework.security:spring-security-config:4.1.5.RELEASE,4.2.4.RELEASE,5.0.1.RELEASE;org.springframework:spring-core:4.3.14.RELEASE,5.0.3.RELEASE</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2014-0054</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Jaxb2RootElementHttpMessageConverter in Spring MVC in Spring Framework before 3.2.8 and 4.0.0 before 4.0.2 does not disable external entity resolution, which allows remote attackers to read arbitrary files, cause a denial of service, and conduct CSRF attacks via crafted XML, aka an XML External Entity (XXE) issue. NOTE: this vulnerability exists because of an incomplete fix for CVE-2013-4152, CVE-2013-7315, and CVE-2013-6429.
<p>Publish Date: 2014-04-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0054>CVE-2014-0054</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-0054">https://nvd.nist.gov/vuln/detail/CVE-2014-0054</a></p>
<p>Release Date: 2014-04-17</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2014-3578</summary>
### Vulnerable Library - <b>spring-core-2.5.6.jar</b></p>
<p>Spring Framework: Core</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-core/2.5.6/spring-core-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-core-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Directory traversal vulnerability in Pivotal Spring Framework 3.x before 3.2.9 and 4.0 before 4.0.5 allows remote attackers to read arbitrary files via a crafted URL.
<p>Publish Date: 2015-02-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-3578>CVE-2014-3578</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-3578">https://nvd.nist.gov/vuln/detail/CVE-2014-3578</a></p>
<p>Release Date: 2015-02-19</p>
<p>Fix Resolution (spring-core): 3.2.9,4.0.5</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2009-1190</summary>
### Vulnerable Libraries - <b>spring-context-2.5.6.jar</b>, <b>spring-core-2.5.6.jar</b>, <b>spring-beans-2.5.6.jar</b></p>
<p>
### <b>spring-context-2.5.6.jar</b></p>
<p>Spring Framework: Context</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-context/2.5.6/spring-context-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-context-2.5.6.jar** (Vulnerable Library)
### <b>spring-core-2.5.6.jar</b></p>
<p>Spring Framework: Core</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-core/2.5.6/spring-core-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-core-2.5.6.jar** (Vulnerable Library)
### <b>spring-beans-2.5.6.jar</b></p>
<p>Spring Framework: Beans</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-beans/2.5.6/spring-beans-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-beans-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Algorithmic complexity vulnerability in the java.util.regex.Pattern.compile method in Sun Java Development Kit (JDK) before 1.6, when used with spring.jar in SpringSource Spring Framework 1.1.0 through 2.5.6 and 3.0.0.M1 through 3.0.0.M2 and dm Server 1.0.0 through 1.0.2, allows remote attackers to cause a denial of service (CPU consumption) via serializable data with a long regex string containing multiple optional groups, a related issue to CVE-2004-2540.
<p>Publish Date: 2009-04-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2009-1190>CVE-2009-1190</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2009-1190">https://nvd.nist.gov/vuln/detail/CVE-2009-1190</a></p>
<p>Release Date: 2009-04-28</p>
<p>Fix Resolution (spring-context): 1.6</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p><p>Fix Resolution (spring-core): 1.6</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p><p>Fix Resolution (spring-beans): 1.6</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | spring-web-2.5.6.jar: 8 vulnerabilities (highest severity is: 7.3) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-2.5.6.jar</b></p></summary>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (spring-web version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2010-1622](https://www.mend.io/vulnerability-database/CVE-2010-1622) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | spring-beans-2.5.6.jar | Transitive | 2.5.6.SEC01 | ✅ |
| [CVE-2011-2730](https://www.mend.io/vulnerability-database/CVE-2011-2730) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2013-6430](https://www.mend.io/vulnerability-database/CVE-2013-6430) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.4 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2013-6429](https://www.mend.io/vulnerability-database/CVE-2013-6429) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2018-1199](https://www.mend.io/vulnerability-database/CVE-2018-1199) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-core-2.5.6.jar | Transitive | N/A* | ❌ |
| [CVE-2014-0054](https://www.mend.io/vulnerability-database/CVE-2014-0054) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-web-2.5.6.jar | Direct | 2.5.6.SEC01 | ✅ |
| [CVE-2014-3578](https://www.mend.io/vulnerability-database/CVE-2014-3578) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | spring-core-2.5.6.jar | Transitive | 2.5.6.SEC01 | ✅ |
| [CVE-2009-1190](https://www.mend.io/vulnerability-database/CVE-2009-1190) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.7 | detected in multiple dependencies | Transitive | 2.5.6.SEC01 | ✅ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2010-1622</summary>
### Vulnerable Library - <b>spring-beans-2.5.6.jar</b></p>
<p>Spring Framework: Beans</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-beans/2.5.6/spring-beans-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-beans-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SpringSource Spring Framework 2.5.x before 2.5.6.SEC02, 2.5.7 before 2.5.7.SR01, and 3.0.x before 3.0.3 allows remote attackers to execute arbitrary code via an HTTP request containing class.classLoader.URLs[0]=jar: followed by a URL of a crafted .jar file.
<p>Publish Date: 2010-06-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2010-1622>CVE-2010-1622</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-1622">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-1622</a></p>
<p>Release Date: 2010-06-21</p>
<p>Fix Resolution (spring-beans): 3.0.3.RELEASE,2.5.6.SEC02</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2011-2730</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
VMware SpringSource Spring Framework before 2.5.6.SEC03, 2.5.7.SR023, and 3.x before 3.0.6, when a container supports Expression Language (EL), evaluates EL expressions in tags twice, which allows remote attackers to obtain sensitive information via a (1) name attribute in a (a) spring:hasBindErrors tag; (2) path attribute in a (b) spring:bind or (c) spring:nestedpath tag; (3) arguments, (4) code, (5) text, (6) var, (7) scope, or (8) message attribute in a (d) spring:message or (e) spring:theme tag; or (9) var, (10) scope, or (11) value attribute in a (f) spring:transform tag, aka "Expression Language Injection."
<p>Publish Date: 2012-12-05
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2011-2730>CVE-2011-2730</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2011-2730">https://nvd.nist.gov/vuln/detail/CVE-2011-2730</a></p>
<p>Release Date: 2012-12-05</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-6430</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The JavaScriptUtils.javaScriptEscape method in web/util/JavaScriptUtils.java in Spring MVC in Spring Framework before 3.2.2 does not properly escape certain characters, which allows remote attackers to conduct cross-site scripting (XSS) attacks via a (1) line separator or (2) paragraph separator Unicode character or (3) left or (4) right angle bracket.
<p>Publish Date: 2020-01-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-6430>CVE-2013-6430</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.4</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-6430">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-6430</a></p>
<p>Release Date: 2020-01-10</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-6429</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The SourceHttpMessageConverter in Spring MVC in Spring Framework before 3.2.5 and 4.0.0.M1 through 4.0.0.RC1 does not disable external entity resolution, which allows remote attackers to read arbitrary files, cause a denial of service, and conduct CSRF attacks via crafted XML, aka an XML External Entity (XXE) issue, and a different vulnerability than CVE-2013-4152 and CVE-2013-7315.
<p>Publish Date: 2014-01-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-6429>CVE-2013-6429</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-6429">https://nvd.nist.gov/vuln/detail/CVE-2013-6429</a></p>
<p>Release Date: 2014-01-26</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-1199</summary>
### Vulnerable Library - <b>spring-core-2.5.6.jar</b></p>
<p>Spring Framework: Core</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-core/2.5.6/spring-core-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-core-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Spring Security (Spring Security 4.1.x before 4.1.5, 4.2.x before 4.2.4, and 5.0.x before 5.0.1; and Spring Framework 4.3.x before 4.3.14 and 5.0.x before 5.0.3) does not consider URL path parameters when processing security constraints. By adding a URL path parameter with special encodings, an attacker may be able to bypass a security constraint. The root cause of this issue is a lack of clarity regarding the handling of path parameters in the Servlet Specification. Some Servlet containers include path parameters in the value returned for getPathInfo() and some do not. Spring Security uses the value returned by getPathInfo() as part of the process of mapping requests to security constraints. In this particular attack, different character encodings used in path parameters allows secured Spring MVC static resource URLs to be bypassed.
<p>Publish Date: 2018-03-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-1199>CVE-2018-1199</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1199">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1199</a></p>
<p>Release Date: 2018-03-16</p>
<p>Fix Resolution: org.springframework.security:spring-security-web:4.1.5.RELEASE,4.2.4.RELEASE,5.0.1.RELEASE;org.springframework.security:spring-security-config:4.1.5.RELEASE,4.2.4.RELEASE,5.0.1.RELEASE;org.springframework:spring-core:4.3.14.RELEASE,5.0.3.RELEASE</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2014-0054</summary>
### Vulnerable Library - <b>spring-web-2.5.6.jar</b></p>
<p>Spring Framework: Web</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /spring-web/2.5.6/spring-web-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Jaxb2RootElementHttpMessageConverter in Spring MVC in Spring Framework before 3.2.8 and 4.0.0 before 4.0.2 does not disable external entity resolution, which allows remote attackers to read arbitrary files, cause a denial of service, and conduct CSRF attacks via crafted XML, aka an XML External Entity (XXE) issue. NOTE: this vulnerability exists because of an incomplete fix for CVE-2013-4152, CVE-2013-7315, and CVE-2013-6429.
<p>Publish Date: 2014-04-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0054>CVE-2014-0054</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-0054">https://nvd.nist.gov/vuln/detail/CVE-2014-0054</a></p>
<p>Release Date: 2014-04-17</p>
<p>Fix Resolution: 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2014-3578</summary>
### Vulnerable Library - <b>spring-core-2.5.6.jar</b></p>
<p>Spring Framework: Core</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-core/2.5.6/spring-core-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-core-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Directory traversal vulnerability in Pivotal Spring Framework 3.x before 3.2.9 and 4.0 before 4.0.5 allows remote attackers to read arbitrary files via a crafted URL.
<p>Publish Date: 2015-02-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-3578>CVE-2014-3578</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2014-3578">https://nvd.nist.gov/vuln/detail/CVE-2014-3578</a></p>
<p>Release Date: 2015-02-19</p>
<p>Fix Resolution (spring-core): 3.2.9,4.0.5</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2009-1190</summary>
### Vulnerable Libraries - <b>spring-context-2.5.6.jar</b>, <b>spring-core-2.5.6.jar</b>, <b>spring-beans-2.5.6.jar</b></p>
<p>
### <b>spring-context-2.5.6.jar</b></p>
<p>Spring Framework: Context</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-context/2.5.6/spring-context-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-context-2.5.6.jar** (Vulnerable Library)
### <b>spring-core-2.5.6.jar</b></p>
<p>Spring Framework: Core</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-core/2.5.6/spring-core-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-core-2.5.6.jar** (Vulnerable Library)
### <b>spring-beans-2.5.6.jar</b></p>
<p>Spring Framework: Beans</p>
<p>Library home page: <a href="http://www.springframework.org">http://www.springframework.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /C:/Users/UrielNaor/.m2/repository/org/springframework/spring-beans/2.5.6/spring-beans-2.5.6.jar</p>
<p>
Dependency Hierarchy:
- spring-web-2.5.6.jar (Root Library)
- :x: **spring-beans-2.5.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uriel-naor/UrielTest/commit/66d32d98d2d772169e36a121fbcf3cc747cd8ec2">66d32d98d2d772169e36a121fbcf3cc747cd8ec2</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Algorithmic complexity vulnerability in the java.util.regex.Pattern.compile method in Sun Java Development Kit (JDK) before 1.6, when used with spring.jar in SpringSource Spring Framework 1.1.0 through 2.5.6 and 3.0.0.M1 through 3.0.0.M2 and dm Server 1.0.0 through 1.0.2, allows remote attackers to cause a denial of service (CPU consumption) via serializable data with a long regex string containing multiple optional groups, a related issue to CVE-2004-2540.
<p>Publish Date: 2009-04-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2009-1190>CVE-2009-1190</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.7</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2009-1190">https://nvd.nist.gov/vuln/detail/CVE-2009-1190</a></p>
<p>Release Date: 2009-04-28</p>
<p>Fix Resolution (spring-context): 1.6</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p><p>Fix Resolution (spring-core): 1.6</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p><p>Fix Resolution (spring-beans): 1.6</p>
<p>Direct dependency fix Resolution (org.springframework:spring-web): 2.5.6.SEC01</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | spring web jar vulnerabilities highest severity is vulnerable library spring web jar spring framework web library home page a href path to dependency file pom xml path to vulnerable library spring web spring web jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in spring web version remediation available high spring beans jar transitive high spring web jar direct medium spring web jar direct medium spring web jar direct medium spring core jar transitive n a medium spring web jar direct medium spring core jar transitive low detected in multiple dependencies transitive for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library spring beans jar spring framework beans library home page a href path to dependency file pom xml path to vulnerable library c users urielnaor repository org springframework spring beans spring beans jar dependency hierarchy spring web jar root library x spring beans jar vulnerable library found in head commit a href found in base branch main vulnerability details springsource spring framework x before before and x before allows remote attackers to execute arbitrary code via an http request containing class classloader urls jar followed by a url of a crafted jar file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution spring beans release direct dependency fix resolution org springframework spring web rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring web jar spring framework web library home page a href path to dependency file pom xml path to vulnerable library spring web spring web jar dependency hierarchy x spring web jar vulnerable library found in head commit a href found in base branch main vulnerability details vmware springsource spring framework before and x before when a container supports expression language el evaluates el expressions in tags twice which allows remote attackers to obtain sensitive information via a name attribute in a a spring hasbinderrors tag path attribute in a b spring bind or c spring nestedpath tag arguments code text var scope or message attribute in a d spring message or e spring theme tag or var scope or value attribute in a f spring transform tag aka expression language injection publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring web jar spring framework web library home page a href path to dependency file pom xml path to vulnerable library spring web spring web jar dependency hierarchy x spring web jar vulnerable library found in head commit a href found in base branch main vulnerability details the javascriptutils javascriptescape method in web util javascriptutils java in spring mvc in spring framework before does not properly escape certain characters which allows remote attackers to conduct cross site scripting xss attacks via a line separator or paragraph separator unicode character or left or right angle bracket publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring web jar spring framework web library home page a href path to dependency file pom xml path to vulnerable library spring web spring web jar dependency hierarchy x spring web jar vulnerable library found in head commit a href found in base branch main vulnerability details the sourcehttpmessageconverter in spring mvc in spring framework before and through does not disable external entity resolution which allows remote attackers to read arbitrary files cause a denial of service and conduct csrf attacks via crafted xml aka an xml external entity xxe issue and a different vulnerability than cve and cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring core jar spring framework core library home page a href path to dependency file pom xml path to vulnerable library c users urielnaor repository org springframework spring core spring core jar dependency hierarchy spring web jar root library x spring core jar vulnerable library found in head commit a href found in base branch main vulnerability details spring security spring security x before x before and x before and spring framework x before and x before does not consider url path parameters when processing security constraints by adding a url path parameter with special encodings an attacker may be able to bypass a security constraint the root cause of this issue is a lack of clarity regarding the handling of path parameters in the servlet specification some servlet containers include path parameters in the value returned for getpathinfo and some do not spring security uses the value returned by getpathinfo as part of the process of mapping requests to security constraints in this particular attack different character encodings used in path parameters allows secured spring mvc static resource urls to be bypassed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework security spring security web release release release org springframework security spring security config release release release org springframework spring core release release cve vulnerable library spring web jar spring framework web library home page a href path to dependency file pom xml path to vulnerable library spring web spring web jar dependency hierarchy x spring web jar vulnerable library found in head commit a href found in base branch main vulnerability details the in spring mvc in spring framework before and before does not disable external entity resolution which allows remote attackers to read arbitrary files cause a denial of service and conduct csrf attacks via crafted xml aka an xml external entity xxe issue note this vulnerability exists because of an incomplete fix for cve cve and cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library spring core jar spring framework core library home page a href path to dependency file pom xml path to vulnerable library c users urielnaor repository org springframework spring core spring core jar dependency hierarchy spring web jar root library x spring core jar vulnerable library found in head commit a href found in base branch main vulnerability details directory traversal vulnerability in pivotal spring framework x before and before allows remote attackers to read arbitrary files via a crafted url publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution spring core direct dependency fix resolution org springframework spring web rescue worker helmet automatic remediation is available for this issue cve vulnerable libraries spring context jar spring core jar spring beans jar spring context jar spring framework context library home page a href path to dependency file pom xml path to vulnerable library c users urielnaor repository org springframework spring context spring context jar dependency hierarchy spring web jar root library x spring context jar vulnerable library spring core jar spring framework core library home page a href path to dependency file pom xml path to vulnerable library c users urielnaor repository org springframework spring core spring core jar dependency hierarchy spring web jar root library x spring core jar vulnerable library spring beans jar spring framework beans library home page a href path to dependency file pom xml path to vulnerable library c users urielnaor repository org springframework spring beans spring beans jar dependency hierarchy spring web jar root library x spring beans jar vulnerable library found in head commit a href found in base branch main vulnerability details algorithmic complexity vulnerability in the java util regex pattern compile method in sun java development kit jdk before when used with spring jar in springsource spring framework through and through and dm server through allows remote attackers to cause a denial of service cpu consumption via serializable data with a long regex string containing multiple optional groups a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution spring context direct dependency fix resolution org springframework spring web fix resolution spring core direct dependency fix resolution org springframework spring web fix resolution spring beans direct dependency fix resolution org springframework spring web rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
44,247 | 13,049,810,697 | IssuesEvent | 2020-07-29 14:36:30 | ThomasRuemmler/openspaceplanner | https://api.github.com/repos/ThomasRuemmler/openspaceplanner | opened | CVE-2020-7693 (Medium) detected in sockjs-0.3.19.tgz | security vulnerability | ## CVE-2020-7693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sockjs-0.3.19.tgz</b></p></summary>
<p>SockJS-node is a server counterpart of SockJS-client a JavaScript library that provides a WebSocket-like object in the browser. SockJS gives you a coherent, cross-browser, Javascript API which creates a low latency, full duplex, cross-domain communication</p>
<p>Library home page: <a href="https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz">https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/openspaceplanner/Web/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/openspaceplanner/Web/node_modules/sockjs/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.803.20.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- :x: **sockjs-0.3.19.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ThomasRuemmler/openspaceplanner/commit/f6c2c84ced43eeee592037f4035255d8f6a450bc">f6c2c84ced43eeee592037f4035255d8f6a450bc</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693>CVE-2020-7693</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sockjs/sockjs-node/pull/265">https://github.com/sockjs/sockjs-node/pull/265</a></p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution: sockjs - 0.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7693 (Medium) detected in sockjs-0.3.19.tgz - ## CVE-2020-7693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sockjs-0.3.19.tgz</b></p></summary>
<p>SockJS-node is a server counterpart of SockJS-client a JavaScript library that provides a WebSocket-like object in the browser. SockJS gives you a coherent, cross-browser, Javascript API which creates a low latency, full duplex, cross-domain communication</p>
<p>Library home page: <a href="https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz">https://registry.npmjs.org/sockjs/-/sockjs-0.3.19.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/openspaceplanner/Web/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/openspaceplanner/Web/node_modules/sockjs/package.json</p>
<p>
Dependency Hierarchy:
- build-angular-0.803.20.tgz (Root Library)
- webpack-dev-server-3.9.0.tgz
- :x: **sockjs-0.3.19.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ThomasRuemmler/openspaceplanner/commit/f6c2c84ced43eeee592037f4035255d8f6a450bc">f6c2c84ced43eeee592037f4035255d8f6a450bc</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Incorrect handling of Upgrade header with the value websocket leads in crashing of containers hosting sockjs apps. This affects the package sockjs before 0.3.20.
<p>Publish Date: 2020-07-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7693>CVE-2020-7693</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sockjs/sockjs-node/pull/265">https://github.com/sockjs/sockjs-node/pull/265</a></p>
<p>Release Date: 2020-07-09</p>
<p>Fix Resolution: sockjs - 0.3.20</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in sockjs tgz cve medium severity vulnerability vulnerable library sockjs tgz sockjs node is a server counterpart of sockjs client a javascript library that provides a websocket like object in the browser sockjs gives you a coherent cross browser javascript api which creates a low latency full duplex cross domain communication library home page a href path to dependency file tmp ws scm openspaceplanner web package json path to vulnerable library tmp ws scm openspaceplanner web node modules sockjs package json dependency hierarchy build angular tgz root library webpack dev server tgz x sockjs tgz vulnerable library found in head commit a href vulnerability details incorrect handling of upgrade header with the value websocket leads in crashing of containers hosting sockjs apps this affects the package sockjs before publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution sockjs step up your open source security game with whitesource | 0 |
111,952 | 17,063,642,081 | IssuesEvent | 2021-07-07 02:52:44 | atlslscsrv-app/didactic-guacamole | https://api.github.com/repos/atlslscsrv-app/didactic-guacamole | opened | WS-2021-0153 (High) detected in ejs-2.5.9.tgz | security vulnerability | ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.5.9.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.5.9.tgz">https://registry.npmjs.org/ejs/-/ejs-2.5.9.tgz</a></p>
<p>Path to dependency file: didactic-guacamole/dist/resources/app/package.json</p>
<p>Path to vulnerable library: didactic-guacamole/dist/resources/app/node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- spectron-5.0.0.tgz (Root Library)
- webdriverio-4.14.4.tgz
- :x: **ejs-2.5.9.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/atlslscsrv-app/didactic-guacamole/commit/7827e0d645ca2322b7556800b2ede9f474836f86">7827e0d645ca2322b7556800b2ede9f474836f86</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2021-0153 (High) detected in ejs-2.5.9.tgz - ## WS-2021-0153 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.5.9.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.5.9.tgz">https://registry.npmjs.org/ejs/-/ejs-2.5.9.tgz</a></p>
<p>Path to dependency file: didactic-guacamole/dist/resources/app/package.json</p>
<p>Path to vulnerable library: didactic-guacamole/dist/resources/app/node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- spectron-5.0.0.tgz (Root Library)
- webdriverio-4.14.4.tgz
- :x: **ejs-2.5.9.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/atlslscsrv-app/didactic-guacamole/commit/7827e0d645ca2322b7556800b2ede9f474836f86">7827e0d645ca2322b7556800b2ede9f474836f86</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Arbitrary Code Injection vulnerability was found in ejs before 3.1.6. Caused by filename which isn't sanitized for display.
<p>Publish Date: 2021-01-22
<p>URL: <a href=https://github.com/mde/ejs/commit/abaee2be937236b1b8da9a1f55096c17dda905fd>WS-2021-0153</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mde/ejs/issues/571">https://github.com/mde/ejs/issues/571</a></p>
<p>Release Date: 2021-01-22</p>
<p>Fix Resolution: ejs - 3.1.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in ejs tgz ws high severity vulnerability vulnerable library ejs tgz embedded javascript templates library home page a href path to dependency file didactic guacamole dist resources app package json path to vulnerable library didactic guacamole dist resources app node modules ejs package json dependency hierarchy spectron tgz root library webdriverio tgz x ejs tgz vulnerable library found in head commit a href found in base branch master vulnerability details arbitrary code injection vulnerability was found in ejs before caused by filename which isn t sanitized for display publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution ejs step up your open source security game with whitesource | 0 |
73,738 | 24,782,382,093 | IssuesEvent | 2022-10-24 06:50:24 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | Cannot persistently clear unread messages in rooms containing threads | T-Defect S-Major O-Uncommon A-Threads Z-Labs Z-ThreadsNotifications | ### Steps to reproduce
Load my account in our test server. See this
<img width="380" alt="Screenshot 2022-02-17 at 13 19 10" src="https://user-images.githubusercontent.com/57377/154489855-a049b003-3811-4e57-bb71-fda2ac9a5243.png">
Click on all of the rooms in the room list to clear unread
<img width="315" alt="Screenshot 2022-02-17 at 13 19 29" src="https://user-images.githubusercontent.com/57377/154489945-31b206f1-fa46-47a4-b090-bb1537e803e9.png">
Reload the page and the unreads are back
<img width="310" alt="Screenshot 2022-02-17 at 13 20 02" src="https://user-images.githubusercontent.com/57377/154489982-d7163242-f5b4-46d0-95fd-567fcea98ab5.png">
### Outcome
#### What did you expect?
For the unread markers and badges to not return after they were cleared
#### What happened instead?
They came back
### Operating system
OS X
### Browser information
Chrome
### URL for webapp
develop.element.io
### Application version
Element version: ba55473a0e4e-react-c19aa957b655-js-74d24f38f742 Olm version: 3.2.8
### Homeserver
threads-dev.lab.element.dev
### Will you send logs?
No | 1.0 | Cannot persistently clear unread messages in rooms containing threads - ### Steps to reproduce
Load my account in our test server. See this
<img width="380" alt="Screenshot 2022-02-17 at 13 19 10" src="https://user-images.githubusercontent.com/57377/154489855-a049b003-3811-4e57-bb71-fda2ac9a5243.png">
Click on all of the rooms in the room list to clear unread
<img width="315" alt="Screenshot 2022-02-17 at 13 19 29" src="https://user-images.githubusercontent.com/57377/154489945-31b206f1-fa46-47a4-b090-bb1537e803e9.png">
Reload the page and the unreads are back
<img width="310" alt="Screenshot 2022-02-17 at 13 20 02" src="https://user-images.githubusercontent.com/57377/154489982-d7163242-f5b4-46d0-95fd-567fcea98ab5.png">
### Outcome
#### What did you expect?
For the unread markers and badges to not return after they were cleared
#### What happened instead?
They came back
### Operating system
OS X
### Browser information
Chrome
### URL for webapp
develop.element.io
### Application version
Element version: ba55473a0e4e-react-c19aa957b655-js-74d24f38f742 Olm version: 3.2.8
### Homeserver
threads-dev.lab.element.dev
### Will you send logs?
No | non_priority | cannot persistently clear unread messages in rooms containing threads steps to reproduce load my account in our test server see this img width alt screenshot at src click on all of the rooms in the room list to clear unread img width alt screenshot at src reload the page and the unreads are back img width alt screenshot at src outcome what did you expect for the unread markers and badges to not return after they were cleared what happened instead they came back operating system os x browser information chrome url for webapp develop element io application version element version react js olm version homeserver threads dev lab element dev will you send logs no | 0 |
337,983 | 30,275,354,081 | IssuesEvent | 2023-07-07 19:04:03 | BNAndras/pyret-test-runner | https://api.github.com/repos/BNAndras/pyret-test-runner | closed | Sanitize file paths in test output | x:knowledge/none x:size/tiny x:module/test-runner | pyret takes in relative file paths, but the test output returns absolute file paths (see below). As a result, we'd need to remove the folder path for each test file so we can compare `results.json` to `expected_results.json`.
```
pyret -q tests/example-all-fail/example-all-fail-test.arr
**file:///Users/anagy/Documents/pyret-test-runner/tests/example-all-fail/**example-all-fail-test.arr:3:0-5:3: year not divisible by 4 in common year (0/1)
line 4, column 2: failed because:
Values not equal "foo" true
**file:///Users/anagy/Documents/pyret-test-runner/tests/example-all-fail/**example-all-fail-test.arr:7:0-9:3: year divisible by 2, not divisible by 4 in common year (0/1)
line 8, column 2: failed because:
Values not equal "foo" true
Passed: 0; Failed: 2; Ended in Error: 0; Total: 2
``` | 1.0 | Sanitize file paths in test output - pyret takes in relative file paths, but the test output returns absolute file paths (see below). As a result, we'd need to remove the folder path for each test file so we can compare `results.json` to `expected_results.json`.
```
pyret -q tests/example-all-fail/example-all-fail-test.arr
**file:///Users/anagy/Documents/pyret-test-runner/tests/example-all-fail/**example-all-fail-test.arr:3:0-5:3: year not divisible by 4 in common year (0/1)
line 4, column 2: failed because:
Values not equal "foo" true
**file:///Users/anagy/Documents/pyret-test-runner/tests/example-all-fail/**example-all-fail-test.arr:7:0-9:3: year divisible by 2, not divisible by 4 in common year (0/1)
line 8, column 2: failed because:
Values not equal "foo" true
Passed: 0; Failed: 2; Ended in Error: 0; Total: 2
``` | non_priority | sanitize file paths in test output pyret takes in relative file paths but the test output returns absolute file paths see below as a result we d need to remove the folder path for each test file so we can compare results json to expected results json pyret q tests example all fail example all fail test arr file users anagy documents pyret test runner tests example all fail example all fail test arr year not divisible by in common year line column failed because values not equal foo true file users anagy documents pyret test runner tests example all fail example all fail test arr year divisible by not divisible by in common year line column failed because values not equal foo true passed failed ended in error total | 0 |
35,888 | 17,330,067,085 | IssuesEvent | 2021-07-28 00:03:23 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachperf: bulk jobs not reporting perf artifacts | A-bulkio C-performance T-bulkio | It looks like bulk jobs have not been reporting progress metrics. This likely regressed in .https://github.com/cockroachdb/cockroach/pull/67380 | True | roachperf: bulk jobs not reporting perf artifacts - It looks like bulk jobs have not been reporting progress metrics. This likely regressed in .https://github.com/cockroachdb/cockroach/pull/67380 | non_priority | roachperf bulk jobs not reporting perf artifacts it looks like bulk jobs have not been reporting progress metrics this likely regressed in | 0 |
69,134 | 7,125,659,737 | IssuesEvent | 2018-01-20 00:28:32 | log2timeline/plaso | https://api.github.com/repos/log2timeline/plaso | closed | Improve psort and analysis end-to-end testing | testing | The following command yields the following error:
`psort.py -d --analysis tagging --tagging-file tag_Windows7.txt -w NEW_2016_Tagged.csv -o l2tcsv -z UTC NEW.dump "date > '2016-01-01 00:00:00'" --logfile /NEW_2016_Tagged.log`
> Traceback (most recent call last):
> File "/usr/lib64/python2.7/multiprocessing/queues.py", line 266, in _feed
> send(obj)
> IOError: [Errno 32] Broken pipe
> Report generated from: tagging
> Generated on: 2016-02-19T17:08:13+00:00
> Filter String: date > '2016-01-01 00:00:00'
>
> Report text:
> Tagging plugin produced 0 tags.
>
> Processing completed.
Tail of the logfile has the following:
> ...
> "[DEBUG] Returned state to INITIAL
> [DEBUG] Storing state 'INITIAL'
> [DEBUG] Storing attribute 'timestamp_desc'
> [DEBUG] Storing operator 'contains'
> [DEBUG] Storing state 'ARG'
> [DEBUG] Returned state to ARG
> [DEBUG] Storing argument: Printed
> [DEBUG] Adding ['data_type', 'metadata:hachoir']
> [DEBUG] Adding ['data_type', 'olecf:summary_info']
> [DEBUG] Adding [<plaso.lib.objectfilter.Equals object at 0x7f11c6e73550>, <plaso.lib.objectfilter.Equals object at 0x7f11c6e73710>]
> [DEBUG] Adding ['timestamp_desc', 'Printed']
> [DEBUG] Adding [<plaso.lib.objectfilter.OrFilter object at 0x7f11c6e736d0>, <plaso.lib.objectfilter.Contains object at 0x7f11c6e737d0>]
> [INFO] Starting analysis plugins.
> [INFO] Plugin: [tagging] started.
> [INFO] Analysis plugins running
> [DEBUG] ConsumeItems exiting with exception <class 'plaso.lib.errors.QueueEmpty'>.
> [INFO] Processing data from analysis plugins.
> [INFO] Waiting for analysis plugin: tagging to complete.
> [INFO] Plugin tagging has completed.
> [INFO] All analysis plugins are now completed.
> [DEBUG] ConsumeItems exiting with exception <class 'plaso.lib.errors.QueueEmpty'>.
> [DEBUG] [Storage] Closing the storage, number of events added: 0"
Nothing useful in dmesg.
I re-ran the above command without the tagging plugin (sans the `--analysis tagging --tagging-file <file>`) to rule out a general psort error and it completed successfully.
| 1.0 | Improve psort and analysis end-to-end testing - The following command yields the following error:
`psort.py -d --analysis tagging --tagging-file tag_Windows7.txt -w NEW_2016_Tagged.csv -o l2tcsv -z UTC NEW.dump "date > '2016-01-01 00:00:00'" --logfile /NEW_2016_Tagged.log`
> Traceback (most recent call last):
> File "/usr/lib64/python2.7/multiprocessing/queues.py", line 266, in _feed
> send(obj)
> IOError: [Errno 32] Broken pipe
> Report generated from: tagging
> Generated on: 2016-02-19T17:08:13+00:00
> Filter String: date > '2016-01-01 00:00:00'
>
> Report text:
> Tagging plugin produced 0 tags.
>
> Processing completed.
Tail of the logfile has the following:
> ...
> "[DEBUG] Returned state to INITIAL
> [DEBUG] Storing state 'INITIAL'
> [DEBUG] Storing attribute 'timestamp_desc'
> [DEBUG] Storing operator 'contains'
> [DEBUG] Storing state 'ARG'
> [DEBUG] Returned state to ARG
> [DEBUG] Storing argument: Printed
> [DEBUG] Adding ['data_type', 'metadata:hachoir']
> [DEBUG] Adding ['data_type', 'olecf:summary_info']
> [DEBUG] Adding [<plaso.lib.objectfilter.Equals object at 0x7f11c6e73550>, <plaso.lib.objectfilter.Equals object at 0x7f11c6e73710>]
> [DEBUG] Adding ['timestamp_desc', 'Printed']
> [DEBUG] Adding [<plaso.lib.objectfilter.OrFilter object at 0x7f11c6e736d0>, <plaso.lib.objectfilter.Contains object at 0x7f11c6e737d0>]
> [INFO] Starting analysis plugins.
> [INFO] Plugin: [tagging] started.
> [INFO] Analysis plugins running
> [DEBUG] ConsumeItems exiting with exception <class 'plaso.lib.errors.QueueEmpty'>.
> [INFO] Processing data from analysis plugins.
> [INFO] Waiting for analysis plugin: tagging to complete.
> [INFO] Plugin tagging has completed.
> [INFO] All analysis plugins are now completed.
> [DEBUG] ConsumeItems exiting with exception <class 'plaso.lib.errors.QueueEmpty'>.
> [DEBUG] [Storage] Closing the storage, number of events added: 0"
Nothing useful in dmesg.
I re-ran the above command without the tagging plugin (sans the `--analysis tagging --tagging-file <file>`) to rule out a general psort error and it completed successfully.
| non_priority | improve psort and analysis end to end testing the following command yields the following error psort py d analysis tagging tagging file tag txt w new tagged csv o z utc new dump date logfile new tagged log traceback most recent call last file usr multiprocessing queues py line in feed send obj ioerror broken pipe report generated from tagging generated on filter string date report text tagging plugin produced tags processing completed tail of the logfile has the following returned state to initial storing state initial storing attribute timestamp desc storing operator contains storing state arg returned state to arg storing argument printed adding adding adding adding adding starting analysis plugins plugin started analysis plugins running consumeitems exiting with exception processing data from analysis plugins waiting for analysis plugin tagging to complete plugin tagging has completed all analysis plugins are now completed consumeitems exiting with exception closing the storage number of events added nothing useful in dmesg i re ran the above command without the tagging plugin sans the analysis tagging tagging file to rule out a general psort error and it completed successfully | 0 |
137,251 | 30,659,991,111 | IssuesEvent | 2023-07-25 14:26:46 | kiwiproject/kiwi | https://api.github.com/repos/kiwiproject/kiwi | closed | Fix tests that breaks in Jackson 2.15.x and higher | code cleanup | Errors:
```
Error: JsonHelperBasicsTest.shouldCreateNewDropwizardJsonHelper:147
expected: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.018Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.018, localDateTime=2023-07-24T19:26:19.018, zonedDateTime=2023-07-24T19:26:19.018Z[UTC], duration=PT1M)
but was: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.018Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.018, localDateTime=2023-07-24T19:26:19.018, zonedDateTime=2023-07-24T19:26:19.018Z, duration=PT1M)
Error: JsonHelperBasicsTest.shouldCreateNewDropwizardObjectMapper:136
expected: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.238Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.238, localDateTime=2023-07-24T19:26:19.238, zonedDateTime=2023-07-24T19:26:19.238Z[UTC], duration=PT1M)
but was: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.238Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.238, localDateTime=2023-07-24T19:26:19.238, zonedDateTime=2023-07-24T19:26:19.238Z, duration=PT1M)
```
I am pretty sure these relate to the time zone discrepancy that I also had to fix in registry-aware-jersey-client. See https://github.com/kiwiproject/kiwi-bom/pull/655#issuecomment-1529095832 | 1.0 | Fix tests that breaks in Jackson 2.15.x and higher - Errors:
```
Error: JsonHelperBasicsTest.shouldCreateNewDropwizardJsonHelper:147
expected: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.018Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.018, localDateTime=2023-07-24T19:26:19.018, zonedDateTime=2023-07-24T19:26:19.018Z[UTC], duration=PT1M)
but was: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.018Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.018, localDateTime=2023-07-24T19:26:19.018, zonedDateTime=2023-07-24T19:26:19.018Z, duration=PT1M)
Error: JsonHelperBasicsTest.shouldCreateNewDropwizardObjectMapper:136
expected: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.238Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.238, localDateTime=2023-07-24T19:26:19.238, zonedDateTime=2023-07-24T19:26:19.238Z[UTC], duration=PT1M)
but was: JsonHelperBasicsTest.Foo(instant=2023-07-24T19:26:19.238Z, date=Mon Jul 24 19:26:19 UTC 2023, timestamp=2023-07-24 19:26:19.238, localDateTime=2023-07-24T19:26:19.238, zonedDateTime=2023-07-24T19:26:19.238Z, duration=PT1M)
```
I am pretty sure these relate to the time zone discrepancy that I also had to fix in registry-aware-jersey-client. See https://github.com/kiwiproject/kiwi-bom/pull/655#issuecomment-1529095832 | non_priority | fix tests that breaks in jackson x and higher errors error jsonhelperbasicstest shouldcreatenewdropwizardjsonhelper expected jsonhelperbasicstest foo instant date mon jul utc timestamp localdatetime zoneddatetime duration but was jsonhelperbasicstest foo instant date mon jul utc timestamp localdatetime zoneddatetime duration error jsonhelperbasicstest shouldcreatenewdropwizardobjectmapper expected jsonhelperbasicstest foo instant date mon jul utc timestamp localdatetime zoneddatetime duration but was jsonhelperbasicstest foo instant date mon jul utc timestamp localdatetime zoneddatetime duration i am pretty sure these relate to the time zone discrepancy that i also had to fix in registry aware jersey client see | 0 |
104,992 | 9,013,701,856 | IssuesEvent | 2019-02-05 20:13:49 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | jepsen: bank/majority-ring failed with `wrong-total` | O-roachtest O-robot | SHA: https://github.com/cockroachdb/cockroach/commits/e10fb557b11b5ff1b8609aa963da23c37a1143c8
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
stdbuf -oL -eL \
make stressrace TESTS=jepsen-batch1/bank/majority-ring PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1113854&tab=buildLog
```
The test failed on master:
test.go:743,jepsen.go:247,jepsen.go:308: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-1113854-jepsen-batch1:6 -- bash -e -c "\
cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
~/lein run test \
--tarball file://${PWD}/cockroach.tgz \
--username ${USER} \
--ssh-private-key ~/.ssh/id_rsa \
--os ubuntu \
--time-limit 300 \
--concurrency 30 \
--recovery-time 25 \
--test-count 1 \
-n 10.128.0.70 -n 10.128.0.92 -n 10.128.0.78 -n 10.128.0.29 -n 10.128.0.88 \
--test bank --nemesis majority-ring \
> invoke.log 2>&1 \
" returned:
stderr:
stdout:
Error: exit status 1
: exit status 1
``` | 1.0 | jepsen: bank/majority-ring failed with `wrong-total` - SHA: https://github.com/cockroachdb/cockroach/commits/e10fb557b11b5ff1b8609aa963da23c37a1143c8
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
stdbuf -oL -eL \
make stressrace TESTS=jepsen-batch1/bank/majority-ring PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1113854&tab=buildLog
```
The test failed on master:
test.go:743,jepsen.go:247,jepsen.go:308: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-1113854-jepsen-batch1:6 -- bash -e -c "\
cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
~/lein run test \
--tarball file://${PWD}/cockroach.tgz \
--username ${USER} \
--ssh-private-key ~/.ssh/id_rsa \
--os ubuntu \
--time-limit 300 \
--concurrency 30 \
--recovery-time 25 \
--test-count 1 \
-n 10.128.0.70 -n 10.128.0.92 -n 10.128.0.78 -n 10.128.0.29 -n 10.128.0.88 \
--test bank --nemesis majority-ring \
> invoke.log 2>&1 \
" returned:
stderr:
stdout:
Error: exit status 1
: exit status 1
``` | non_priority | jepsen bank majority ring failed with wrong total sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which controls concurrency scripts gceworker sh start scripts gceworker sh mosh cd go src github com cockroachdb cockroach stdbuf ol el make stressrace tests jepsen bank majority ring pkg roachtest testtimeout stressflags maxtime timeout tee tmp stress log failed test the test failed on master test go jepsen go jepsen go home agent work go src github com cockroachdb cockroach bin roachprod run teamcity jepsen bash e c cd mnt jepsen cockroachdb set eo pipefail lein run test tarball file pwd cockroach tgz username user ssh private key ssh id rsa os ubuntu time limit concurrency recovery time test count n n n n n test bank nemesis majority ring invoke log returned stderr stdout error exit status exit status | 0 |
53,291 | 6,307,840,901 | IssuesEvent | 2017-07-22 05:41:31 | MDAnalysis/mdanalysis | https://api.github.com/repos/MDAnalysis/mdanalysis | closed | Make Python 3.6 official development version | Python3 testing | Once #1524 is merged we will support py3 as it must pass for changes to be accepted, however we should move to working around 3.6.
For this, the coverage, minimal and linter builds should be moved to using 3.6 as the default python version
| 1.0 | Make Python 3.6 official development version - Once #1524 is merged we will support py3 as it must pass for changes to be accepted, however we should move to working around 3.6.
For this, the coverage, minimal and linter builds should be moved to using 3.6 as the default python version
| non_priority | make python official development version once is merged we will support as it must pass for changes to be accepted however we should move to working around for this the coverage minimal and linter builds should be moved to using as the default python version | 0 |
161,813 | 13,878,496,234 | IssuesEvent | 2020-10-17 09:52:27 | kadamQ/project-templates-spring-react | https://api.github.com/repos/kadamQ/project-templates-spring-react | closed | SRS dokumentáció kiegészítése / adatstruktúrák leírása | documentation | Ki kellene egészíteni az SRS dokumentumot, hogy mit logoljunk róla, mit kell lementeni, mit adjon vissza, ezek milyen adattípusoka lesznek és hogyan is fog kinézni a formátum.
Fontos, hogy ne adatbázis legyen, csak leírás, amelyben az adatszerkezet körvonalazódik.
AC:
-le van írva miket adjon vissza különböző kérésekre
| 1.0 | SRS dokumentáció kiegészítése / adatstruktúrák leírása - Ki kellene egészíteni az SRS dokumentumot, hogy mit logoljunk róla, mit kell lementeni, mit adjon vissza, ezek milyen adattípusoka lesznek és hogyan is fog kinézni a formátum.
Fontos, hogy ne adatbázis legyen, csak leírás, amelyben az adatszerkezet körvonalazódik.
AC:
-le van írva miket adjon vissza különböző kérésekre
| non_priority | srs dokumentáció kiegészítése adatstruktúrák leírása ki kellene egészíteni az srs dokumentumot hogy mit logoljunk róla mit kell lementeni mit adjon vissza ezek milyen adattípusoka lesznek és hogyan is fog kinézni a formátum fontos hogy ne adatbázis legyen csak leírás amelyben az adatszerkezet körvonalazódik ac le van írva miket adjon vissza különböző kérésekre | 0 |
51,412 | 13,635,119,905 | IssuesEvent | 2020-09-25 01:57:18 | nasifimtiazohi/openmrs-module-htmlformentryui-1.10.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-htmlformentryui-1.10.0 | opened | CVE-2013-0334 (Medium) detected in bundler-1.1.4.gem | security vulnerability | ## CVE-2013-0334 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bundler-1.1.4.gem</b></p></summary>
<p>Bundler manages an application's dependencies through its entire life, across many machines, systematically and repeatably</p>
<p>Library home page: <a href="https://rubygems.org/gems/bundler-1.1.4.gem">https://rubygems.org/gems/bundler-1.1.4.gem</a></p>
<p>Path to vulnerable library: rmentryui-1.10.0/omod/.rubygems-provided/cache/bundler-1.1.4.gem</p>
<p>
Dependency Hierarchy:
- :x: **bundler-1.1.4.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-htmlformentryui-1.10.0/commit/cd8c929d7267e19fadc5f2e066491ce0f871f8d6">cd8c929d7267e19fadc5f2e066491ce0f871f8d6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bundler before 1.7, when multiple top-level source lines are used, allows remote attackers to install arbitrary gems by creating a gem with the same name as another gem in a different source.
<p>Publish Date: 2014-10-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0334>CVE-2013-0334</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0334">https://nvd.nist.gov/vuln/detail/CVE-2013-0334</a></p>
<p>Release Date: 2014-10-31</p>
<p>Fix Resolution: 1.7.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2013-0334 (Medium) detected in bundler-1.1.4.gem - ## CVE-2013-0334 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bundler-1.1.4.gem</b></p></summary>
<p>Bundler manages an application's dependencies through its entire life, across many machines, systematically and repeatably</p>
<p>Library home page: <a href="https://rubygems.org/gems/bundler-1.1.4.gem">https://rubygems.org/gems/bundler-1.1.4.gem</a></p>
<p>Path to vulnerable library: rmentryui-1.10.0/omod/.rubygems-provided/cache/bundler-1.1.4.gem</p>
<p>
Dependency Hierarchy:
- :x: **bundler-1.1.4.gem** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-htmlformentryui-1.10.0/commit/cd8c929d7267e19fadc5f2e066491ce0f871f8d6">cd8c929d7267e19fadc5f2e066491ce0f871f8d6</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bundler before 1.7, when multiple top-level source lines are used, allows remote attackers to install arbitrary gems by creating a gem with the same name as another gem in a different source.
<p>Publish Date: 2014-10-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-0334>CVE-2013-0334</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2013-0334">https://nvd.nist.gov/vuln/detail/CVE-2013-0334</a></p>
<p>Release Date: 2014-10-31</p>
<p>Fix Resolution: 1.7.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bundler gem cve medium severity vulnerability vulnerable library bundler gem bundler manages an application s dependencies through its entire life across many machines systematically and repeatably library home page a href path to vulnerable library rmentryui omod rubygems provided cache bundler gem dependency hierarchy x bundler gem vulnerable library found in head commit a href found in base branch master vulnerability details bundler before when multiple top level source lines are used allows remote attackers to install arbitrary gems by creating a gem with the same name as another gem in a different source publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
80,227 | 10,165,843,755 | IssuesEvent | 2019-08-07 14:40:02 | niceonionslice/react-sandbox | https://api.github.com/repos/niceonionslice/react-sandbox | closed | stateとイベントハンドリング | documentation | 実用的なアプリケーションを作成するために「何が入力されているか」、「何を表示するべきか」といった状態を管理する必要がある。
Reactでは状態を管理するためにstateという仕組みが用意されている。 | 1.0 | stateとイベントハンドリング - 実用的なアプリケーションを作成するために「何が入力されているか」、「何を表示するべきか」といった状態を管理する必要がある。
Reactでは状態を管理するためにstateという仕組みが用意されている。 | non_priority | stateとイベントハンドリング 実用的なアプリケーションを作成するために「何が入力されているか」、「何を表示するべきか」といった状態を管理する必要がある。 reactでは状態を管理するためにstateという仕組みが用意されている。 | 0 |
134,027 | 18,408,125,442 | IssuesEvent | 2021-10-12 23:56:32 | t1dmlgus/springSecurityEx | https://api.github.com/repos/t1dmlgus/springSecurityEx | opened | [Security] User, admin 로그인 구현 | security BE | ### Subject
Security 프레임워크를 이용하여 User, Admin 로그인하여 페이지를 호출한다.
### Detail | True | [Security] User, admin 로그인 구현 - ### Subject
Security 프레임워크를 이용하여 User, Admin 로그인하여 페이지를 호출한다.
### Detail | non_priority | user admin 로그인 구현 subject security 프레임워크를 이용하여 user admin 로그인하여 페이지를 호출한다 detail | 0 |
289,612 | 21,787,866,427 | IssuesEvent | 2022-05-14 12:34:24 | Nitcbase/nitcbase-documentation-v2-code | https://api.github.com/repos/Nitcbase/nitcbase-documentation-v2-code | closed | renameAttr/renameRel in Schema layer do not check for E_INVALID | bug documentation Done for now (Review Remaining) | A check for E_INVALID must be included before the check for E_RELOPEN since the catalogs are always open. | 1.0 | renameAttr/renameRel in Schema layer do not check for E_INVALID - A check for E_INVALID must be included before the check for E_RELOPEN since the catalogs are always open. | non_priority | renameattr renamerel in schema layer do not check for e invalid a check for e invalid must be included before the check for e relopen since the catalogs are always open | 0 |
23,978 | 4,055,077,997 | IssuesEvent | 2016-05-24 14:28:15 | Microsoft/vscode | https://api.github.com/repos/Microsoft/vscode | closed | Test: language server protocol trace option | testplan-item | From https://github.com/Microsoft/vscode-languageserver-node/issues/39
- [x] Windows | OS X | Linux - **@aeschli**
Steps:
- install eslint or tslint
- enable tracing via the setting:
```json
"eslint.trace.server":"messages"
```
or
```json
"tslint.trace.server":"messages"
```
- open output window and switch to the tslint / eslint channel
- open a ts / js file and ensure that the communication between client and server is logged.
- change the setting to: "verbose"
- ensure that you get a verbose log
- change the setting to "off"
- ensure that tracing stops. | 1.0 | Test: language server protocol trace option - From https://github.com/Microsoft/vscode-languageserver-node/issues/39
- [x] Windows | OS X | Linux - **@aeschli**
Steps:
- install eslint or tslint
- enable tracing via the setting:
```json
"eslint.trace.server":"messages"
```
or
```json
"tslint.trace.server":"messages"
```
- open output window and switch to the tslint / eslint channel
- open a ts / js file and ensure that the communication between client and server is logged.
- change the setting to: "verbose"
- ensure that you get a verbose log
- change the setting to "off"
- ensure that tracing stops. | non_priority | test language server protocol trace option from windows os x linux aeschli steps install eslint or tslint enable tracing via the setting json eslint trace server messages or json tslint trace server messages open output window and switch to the tslint eslint channel open a ts js file and ensure that the communication between client and server is logged change the setting to verbose ensure that you get a verbose log change the setting to off ensure that tracing stops | 0 |
68,475 | 14,924,711,719 | IssuesEvent | 2021-01-24 01:32:44 | yaeljacobs67/fs-agent | https://api.github.com/repos/yaeljacobs67/fs-agent | opened | CVE-2020-36182 (Medium) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2020-36182 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /fs-agent/pom.xml</p>
<p>Path to vulnerable library: 2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182>CVE-2020-36182</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2020-36182","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.cpdsadapter.DriverAdapterCPDS.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | True | CVE-2020-36182 (Medium) detected in jackson-databind-2.9.8.jar - ## CVE-2020-36182 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /fs-agent/pom.xml</p>
<p>Path to vulnerable library: 2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182>CVE-2020-36182</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2020-36182","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.tomcat.dbcp.dbcp2.cpdsadapter.DriverAdapterCPDS.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file fs agent pom xml path to vulnerable library repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp cpdsadapter driveradaptercpds publish date url a href cvss score details base score metrics not available isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache tomcat dbcp cpdsadapter driveradaptercpds vulnerabilityurl | 0 |
39,071 | 10,291,075,018 | IssuesEvent | 2019-08-27 13:37:57 | nielsbasjes/yauaa | https://api.github.com/repos/nielsbasjes/yauaa | closed | Relocated shaded dependencies are still transitive. | Build system bug | As reported by @kirilkalchev here https://github.com/nielsbasjes/yauaa/pull/170 the downstream users of the Yauaa analyzer still get all the transitive dependencies that have already been shaded/relocated into the jar file.
Problem seems related to https://issues.apache.org/jira/browse/MSHADE-36
We need to have the "dependency-reduced-pom.xml" being used in the final jar instead of what we have now.
| 1.0 | Relocated shaded dependencies are still transitive. - As reported by @kirilkalchev here https://github.com/nielsbasjes/yauaa/pull/170 the downstream users of the Yauaa analyzer still get all the transitive dependencies that have already been shaded/relocated into the jar file.
Problem seems related to https://issues.apache.org/jira/browse/MSHADE-36
We need to have the "dependency-reduced-pom.xml" being used in the final jar instead of what we have now.
| non_priority | relocated shaded dependencies are still transitive as reported by kirilkalchev here the downstream users of the yauaa analyzer still get all the transitive dependencies that have already been shaded relocated into the jar file problem seems related to we need to have the dependency reduced pom xml being used in the final jar instead of what we have now | 0 |
132,945 | 28,439,968,036 | IssuesEvent | 2023-04-15 19:43:40 | advaithsrao/694Team14Dbms2023 | https://api.github.com/repos/advaithsrao/694Team14Dbms2023 | closed | Relational Database Scripts | enhancement code task 2 | - [x] Outline the architecture for our database
- [x] Create tables
- [x] Prepare data for push
- [x] Script .py to create/push the data to pg
- [x] Script .sh for /setup | 1.0 | Relational Database Scripts - - [x] Outline the architecture for our database
- [x] Create tables
- [x] Prepare data for push
- [x] Script .py to create/push the data to pg
- [x] Script .sh for /setup | non_priority | relational database scripts outline the architecture for our database create tables prepare data for push script py to create push the data to pg script sh for setup | 0 |
20,918 | 10,560,042,544 | IssuesEvent | 2019-10-04 13:04:25 | uniquelyparticular/import-moltin-to-algolia | https://api.github.com/repos/uniquelyparticular/import-moltin-to-algolia | opened | CVE-2015-9251 (Medium) detected in jquery-1.8.1.min.js | security vulnerability | ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/import-moltin-to-algolia/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /import-moltin-to-algolia/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uniquelyparticular/import-moltin-to-algolia/commit/f550e94cbfcf37a6144b7c53435f62ef8157f9eb">f550e94cbfcf37a6144b7c53435f62ef8157f9eb</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2015-9251 (Medium) detected in jquery-1.8.1.min.js - ## CVE-2015-9251 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/import-moltin-to-algolia/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: /import-moltin-to-algolia/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/uniquelyparticular/import-moltin-to-algolia/commit/f550e94cbfcf37a6144b7c53435f62ef8157f9eb">f550e94cbfcf37a6144b7c53435f62ef8157f9eb</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 3.0.0 is vulnerable to Cross-site Scripting (XSS) attacks when a cross-domain Ajax request is performed without the dataType option, causing text/javascript responses to be executed.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-9251>CVE-2015-9251</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2015-9251">https://nvd.nist.gov/vuln/detail/CVE-2015-9251</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v3.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm import moltin to algolia node modules redeyed examples browser index html path to vulnerable library import moltin to algolia node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before is vulnerable to cross site scripting xss attacks when a cross domain ajax request is performed without the datatype option causing text javascript responses to be executed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
107,685 | 9,220,884,415 | IssuesEvent | 2019-03-11 18:34:10 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Commit on shift+enter fails for async completion | 4 - In Review Area-IDE Disabled Test Integration-Test Regression | **Version Used**: 2773f5e
Caught by integration test `CommitOnShiftEnter`.
| 2.0 | Commit on shift+enter fails for async completion - **Version Used**: 2773f5e
Caught by integration test `CommitOnShiftEnter`.
| non_priority | commit on shift enter fails for async completion version used caught by integration test commitonshiftenter | 0 |
151,568 | 23,842,857,876 | IssuesEvent | 2022-09-06 11:49:37 | mui/mui-toolpad | https://api.github.com/repos/mui/mui-toolpad | opened | Landing page v2 | design: ui website | ### Duplicates
- [X] I have searched the existing issues
### Latest version
- [X] I have tested the latest version
### Summary 💡
1. Add online demo for the public app shown in the video.
2. Link docs from landing page (later to be moved to MUI -> Docs)
3. Link GitHub issues from docs
4. Showcase features
5.
Stretch:
1. Update video (record with new UI)
### Examples 🌈
_No response_
### Motivation 🔦
_No response_ | 1.0 | Landing page v2 - ### Duplicates
- [X] I have searched the existing issues
### Latest version
- [X] I have tested the latest version
### Summary 💡
1. Add online demo for the public app shown in the video.
2. Link docs from landing page (later to be moved to MUI -> Docs)
3. Link GitHub issues from docs
4. Showcase features
5.
Stretch:
1. Update video (record with new UI)
### Examples 🌈
_No response_
### Motivation 🔦
_No response_ | non_priority | landing page duplicates i have searched the existing issues latest version i have tested the latest version summary 💡 add online demo for the public app shown in the video link docs from landing page later to be moved to mui docs link github issues from docs showcase features stretch update video record with new ui examples 🌈 no response motivation 🔦 no response | 0 |
34,875 | 4,567,608,460 | IssuesEvent | 2016-09-15 11:49:47 | vizorvr/vizor | https://api.github.com/repos/vizorvr/vizor | closed | avatars on project tiles | Design in progress site ui UI | - looking at self
- looking at someone else’s avatar
- “v”’s (360) avatar
- looking at missing avatar
- looking at self among other tiles (e.g. explore)
- missing avatar among other tiles
also related #1716 | 1.0 | avatars on project tiles - - looking at self
- looking at someone else’s avatar
- “v”’s (360) avatar
- looking at missing avatar
- looking at self among other tiles (e.g. explore)
- missing avatar among other tiles
also related #1716 | non_priority | avatars on project tiles looking at self looking at someone else’s avatar “v”’s avatar looking at missing avatar looking at self among other tiles e g explore missing avatar among other tiles also related | 0 |
32,424 | 12,126,074,380 | IssuesEvent | 2020-04-22 16:27:06 | mixcore/mix.core | https://api.github.com/repos/mixcore/mix.core | closed | CVE-2020-7598 (High) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz | security vulnerability | ## CVE-2020-7598 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/node_modules/mkdirp/node_modules/minimist/package.json,/tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- grpc-1.24.2.tgz (Root Library)
- node-pre-gyp-0.14.0.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /tmp/archiveExtraction_bb4808c9-7037-4ccf-93f9-7941fe2420c4/20200323173539_18923/ws-scm_depth_0/mix.core/src/Mix.Cms.Service.Gprc/grpc-dotnet-examples-Browser-Server/wwwroot/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/node_modules/grpc/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- grpc-1.24.2.tgz (Root Library)
- node-pre-gyp-0.14.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/mixcore/mix.core/commit/69fabf4e15a0035f78d1a219cf5cfceb08d0fd3c">69fabf4e15a0035f78d1a219cf5cfceb08d0fd3c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7598 (High) detected in minimist-0.0.8.tgz, minimist-1.2.0.tgz - ## CVE-2020-7598 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimist-0.0.8.tgz</b>, <b>minimist-1.2.0.tgz</b></p></summary>
<p>
<details><summary><b>minimist-0.0.8.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz">https://registry.npmjs.org/minimist/-/minimist-0.0.8.tgz</a></p>
<p>Path to dependency file: /tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/node_modules/mkdirp/node_modules/minimist/package.json,/tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/node_modules/mkdirp/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- grpc-1.24.2.tgz (Root Library)
- node-pre-gyp-0.14.0.tgz
- mkdirp-0.5.1.tgz
- :x: **minimist-0.0.8.tgz** (Vulnerable Library)
</details>
<details><summary><b>minimist-1.2.0.tgz</b></p></summary>
<p>parse argument options</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz">https://registry.npmjs.org/minimist/-/minimist-1.2.0.tgz</a></p>
<p>Path to dependency file: /tmp/archiveExtraction_bb4808c9-7037-4ccf-93f9-7941fe2420c4/20200323173539_18923/ws-scm_depth_0/mix.core/src/Mix.Cms.Service.Gprc/grpc-dotnet-examples-Browser-Server/wwwroot/package.json</p>
<p>Path to vulnerable library: /tmp/ws-scm/mix.core/src/Mix.Cms.Service.Gprc/wwwroot/node_modules/grpc/node_modules/minimist/package.json</p>
<p>
Dependency Hierarchy:
- grpc-1.24.2.tgz (Root Library)
- node-pre-gyp-0.14.0.tgz
- rc-1.2.8.tgz
- :x: **minimist-1.2.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/mixcore/mix.core/commit/69fabf4e15a0035f78d1a219cf5cfceb08d0fd3c">69fabf4e15a0035f78d1a219cf5cfceb08d0fd3c</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
minimist before 1.2.2 could be tricked into adding or modifying properties of Object.prototype using a "constructor" or "__proto__" payload.
<p>Publish Date: 2020-03-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7598>CVE-2020-7598</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94">https://github.com/substack/minimist/commit/63e7ed05aa4b1889ec2f3b196426db4500cbda94</a></p>
<p>Release Date: 2020-03-11</p>
<p>Fix Resolution: minimist - 0.2.1,1.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in minimist tgz minimist tgz cve high severity vulnerability vulnerable libraries minimist tgz minimist tgz minimist tgz parse argument options library home page a href path to dependency file tmp ws scm mix core src mix cms service gprc wwwroot package json path to vulnerable library tmp ws scm mix core src mix cms service gprc wwwroot node modules mkdirp node modules minimist package json tmp ws scm mix core src mix cms service gprc wwwroot node modules mkdirp node modules minimist package json dependency hierarchy grpc tgz root library node pre gyp tgz mkdirp tgz x minimist tgz vulnerable library minimist tgz parse argument options library home page a href path to dependency file tmp archiveextraction ws scm depth mix core src mix cms service gprc grpc dotnet examples browser server wwwroot package json path to vulnerable library tmp ws scm mix core src mix cms service gprc wwwroot node modules grpc node modules minimist package json dependency hierarchy grpc tgz root library node pre gyp tgz rc tgz x minimist tgz vulnerable library found in head commit a href vulnerability details minimist before could be tricked into adding or modifying properties of object prototype using a constructor or proto payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution minimist step up your open source security game with whitesource | 0 |
70,532 | 15,086,171,483 | IssuesEvent | 2021-02-05 19:53:04 | kadirselcuk/vscode | https://api.github.com/repos/kadirselcuk/vscode | opened | WS-2018-0625 (High) detected in xmlbuilder-9.0.4.tgz | security vulnerability | ## WS-2018-0625 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlbuilder-9.0.4.tgz</b></p></summary>
<p>An XML builder for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlbuilder/-/xmlbuilder-9.0.4.tgz">https://registry.npmjs.org/xmlbuilder/-/xmlbuilder-9.0.4.tgz</a></p>
<p>Path to dependency file: vscode/yarn.lock</p>
<p>Path to vulnerable library: vscode/yarn.lock</p>
<p>
Dependency Hierarchy:
- vscode-nls-dev-3.3.1.tgz (Root Library)
- xml2js-0.4.19.tgz
- :x: **xmlbuilder-9.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kadirselcuk/vscode/commit/5776d2e8d59da04e822e24902e046617721dfefa">5776d2e8d59da04e822e24902e046617721dfefa</a></p>
<p>Found in base branch: <b>webview-views</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package xmlbuilder-js before 9.0.5 is vulnerable to denial of service due to a regular expression issue.
<p>Publish Date: 2018-02-08
<p>URL: <a href=https://github.com/oozcitak/xmlbuilder-js/commit/bbf929a8a54f0d012bdc44cbe622fdeda2509230>WS-2018-0625</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/oozcitak/xmlbuilder-js/commit/bbf929a8a54f0d012bdc44cbe622fdeda2509230">https://github.com/oozcitak/xmlbuilder-js/commit/bbf929a8a54f0d012bdc44cbe622fdeda2509230</a></p>
<p>Release Date: 2020-03-23</p>
<p>Fix Resolution: 9.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2018-0625 (High) detected in xmlbuilder-9.0.4.tgz - ## WS-2018-0625 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xmlbuilder-9.0.4.tgz</b></p></summary>
<p>An XML builder for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/xmlbuilder/-/xmlbuilder-9.0.4.tgz">https://registry.npmjs.org/xmlbuilder/-/xmlbuilder-9.0.4.tgz</a></p>
<p>Path to dependency file: vscode/yarn.lock</p>
<p>Path to vulnerable library: vscode/yarn.lock</p>
<p>
Dependency Hierarchy:
- vscode-nls-dev-3.3.1.tgz (Root Library)
- xml2js-0.4.19.tgz
- :x: **xmlbuilder-9.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kadirselcuk/vscode/commit/5776d2e8d59da04e822e24902e046617721dfefa">5776d2e8d59da04e822e24902e046617721dfefa</a></p>
<p>Found in base branch: <b>webview-views</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package xmlbuilder-js before 9.0.5 is vulnerable to denial of service due to a regular expression issue.
<p>Publish Date: 2018-02-08
<p>URL: <a href=https://github.com/oozcitak/xmlbuilder-js/commit/bbf929a8a54f0d012bdc44cbe622fdeda2509230>WS-2018-0625</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/oozcitak/xmlbuilder-js/commit/bbf929a8a54f0d012bdc44cbe622fdeda2509230">https://github.com/oozcitak/xmlbuilder-js/commit/bbf929a8a54f0d012bdc44cbe622fdeda2509230</a></p>
<p>Release Date: 2020-03-23</p>
<p>Fix Resolution: 9.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws high detected in xmlbuilder tgz ws high severity vulnerability vulnerable library xmlbuilder tgz an xml builder for node js library home page a href path to dependency file vscode yarn lock path to vulnerable library vscode yarn lock dependency hierarchy vscode nls dev tgz root library tgz x xmlbuilder tgz vulnerable library found in head commit a href found in base branch webview views vulnerability details the package xmlbuilder js before is vulnerable to denial of service due to a regular expression issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
232,219 | 25,565,444,560 | IssuesEvent | 2022-11-30 13:59:55 | hygieia/api-audit | https://api.github.com/repos/hygieia/api-audit | closed | CVE-2017-18640 (High) detected in snakeyaml-1.17.jar - autoclosed | security vulnerability | ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.17.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.17/snakeyaml-1.17.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.22.RELEASE.jar (Root Library)
- spring-boot-starter-1.5.22.RELEASE.jar
- :x: **snakeyaml-1.17.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/api-audit/commit/9c627a3dee72bf43b46a7cc41b8c073efba5cfab">9c627a3dee72bf43b46a7cc41b8c073efba5cfab</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Alias feature in SnakeYAML before 1.26 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution (org.yaml:snakeyaml): 1.26</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.3.0.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-18640 (High) detected in snakeyaml-1.17.jar - autoclosed - ## CVE-2017-18640 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.17.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="http://www.snakeyaml.org">http://www.snakeyaml.org</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/yaml/snakeyaml/1.17/snakeyaml-1.17.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.22.RELEASE.jar (Root Library)
- spring-boot-starter-1.5.22.RELEASE.jar
- :x: **snakeyaml-1.17.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/hygieia/api-audit/commit/9c627a3dee72bf43b46a7cc41b8c073efba5cfab">9c627a3dee72bf43b46a7cc41b8c073efba5cfab</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Alias feature in SnakeYAML before 1.26 allows entity expansion during a load operation, a related issue to CVE-2003-1564.
<p>Publish Date: 2019-12-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18640>CVE-2017-18640</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-18640</a></p>
<p>Release Date: 2019-12-12</p>
<p>Fix Resolution (org.yaml:snakeyaml): 1.26</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.3.0.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in snakeyaml jar autoclosed cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org yaml snakeyaml snakeyaml jar dependency hierarchy spring boot starter web release jar root library spring boot starter release jar x snakeyaml jar vulnerable library found in head commit a href found in base branch master vulnerability details the alias feature in snakeyaml before allows entity expansion during a load operation a related issue to cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org yaml snakeyaml direct dependency fix resolution org springframework boot spring boot starter web release step up your open source security game with mend | 0 |
88,998 | 17,770,197,134 | IssuesEvent | 2021-08-30 12:49:52 | husterlf/blog-comments | https://api.github.com/repos/husterlf/blog-comments | opened | 给 Mac 添加右键菜单「使用 VSCode 打开」 — Flavio的博客 | gitment /2020/10/28/add-vscode-to-right-click/ | https://blog.ictlf.xyz/2020/10/28/add-vscode-to-right-click/
最终的实现效果是在文件 / 文件夹上右击时,会出现菜单项「用 VSCode 打开」,点击后会启动 Visual Studio Code 打开对应的文件 / 文件夹。 | 1.0 | 给 Mac 添加右键菜单「使用 VSCode 打开」 — Flavio的博客 - https://blog.ictlf.xyz/2020/10/28/add-vscode-to-right-click/
最终的实现效果是在文件 / 文件夹上右击时,会出现菜单项「用 VSCode 打开」,点击后会启动 Visual Studio Code 打开对应的文件 / 文件夹。 | non_priority | 给 mac 添加右键菜单「使用 vscode 打开」 — flavio的博客 最终的实现效果是在文件 文件夹上右击时,会出现菜单项「用 vscode 打开」,点击后会启动 visual studio code 打开对应的文件 文件夹。 | 0 |
434,033 | 30,440,774,946 | IssuesEvent | 2023-07-15 03:18:15 | keptn/lifecycle-toolkit | https://api.github.com/repos/keptn/lifecycle-toolkit | closed | Integrate KLT | documentation stale | * Must define ingress (such as nginx) for cluster
* Create namespace for KLT, apply manifest or Helm Chart. Include info about how to modify the manifest or Helm Chart, perhaps to increase or decrease the size
* Label/annotate deployment with Keptn workload, version
* What goes into what namespace? I think KLT, nginx, KeptnApp must all be in same namespace. What else must be in that namespace and what else could be in that namespace?
Part of https://github.com/keptn/lifecycle-toolkit/issues/970 | 1.0 | Integrate KLT - * Must define ingress (such as nginx) for cluster
* Create namespace for KLT, apply manifest or Helm Chart. Include info about how to modify the manifest or Helm Chart, perhaps to increase or decrease the size
* Label/annotate deployment with Keptn workload, version
* What goes into what namespace? I think KLT, nginx, KeptnApp must all be in same namespace. What else must be in that namespace and what else could be in that namespace?
Part of https://github.com/keptn/lifecycle-toolkit/issues/970 | non_priority | integrate klt must define ingress such as nginx for cluster create namespace for klt apply manifest or helm chart include info about how to modify the manifest or helm chart perhaps to increase or decrease the size label annotate deployment with keptn workload version what goes into what namespace i think klt nginx keptnapp must all be in same namespace what else must be in that namespace and what else could be in that namespace part of | 0 |
183,798 | 21,784,709,028 | IssuesEvent | 2022-05-14 01:03:28 | dmyers87/camunda-message-streaming | https://api.github.com/repos/dmyers87/camunda-message-streaming | opened | CVE-2022-22970 (Medium) detected in spring-beans-5.2.4.RELEASE.jar, spring-core-5.2.4.RELEASE.jar | security vulnerability | ## CVE-2022-22970 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-beans-5.2.4.RELEASE.jar</b>, <b>spring-core-5.2.4.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-beans-5.2.4.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /messaging-kafka/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.4.RELEASE/spring-beans-5.2.4.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.4.RELEASE/spring-beans-5.2.4.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.4.RELEASE/spring-beans-5.2.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- camunda-engine-7.12.0.jar (Root Library)
- :x: **spring-beans-5.2.4.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-core-5.2.4.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /webapp/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/5.2.4.RELEASE/spring-core-5.2.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-2.2.5.RELEASE.jar (Root Library)
- :x: **spring-core-5.2.4.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/camunda-message-streaming/commit/41e27a1fe9f0949f331a284bafd06fdaefba62e0">41e27a1fe9f0949f331a284bafd06fdaefba62e0</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22970>CVE-2022-22970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22970">https://tanzu.vmware.com/security/cve-2022-22970</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-beans","packageVersion":"5.2.4.RELEASE","packageFilePaths":["/messaging-kafka/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.camunda.bpm:camunda-engine:7.12.0;org.springframework:spring-beans:5.2.4.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20","isBinary":false},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-core","packageVersion":"5.2.4.RELEASE","packageFilePaths":["/webapp/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter:2.2.5.RELEASE;org.springframework:spring-core:5.2.4.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2022-22970","vulnerabilityDetails":"In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22970","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-22970 (Medium) detected in spring-beans-5.2.4.RELEASE.jar, spring-core-5.2.4.RELEASE.jar - ## CVE-2022-22970 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-beans-5.2.4.RELEASE.jar</b>, <b>spring-core-5.2.4.RELEASE.jar</b></p></summary>
<p>
<details><summary><b>spring-beans-5.2.4.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /messaging-kafka/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.4.RELEASE/spring-beans-5.2.4.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.4.RELEASE/spring-beans-5.2.4.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.4.RELEASE/spring-beans-5.2.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- camunda-engine-7.12.0.jar (Root Library)
- :x: **spring-beans-5.2.4.RELEASE.jar** (Vulnerable Library)
</details>
<details><summary><b>spring-core-5.2.4.RELEASE.jar</b></p></summary>
<p>Spring Core</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /webapp/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-core/5.2.4.RELEASE/spring-core-5.2.4.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-2.2.5.RELEASE.jar (Root Library)
- :x: **spring-core-5.2.4.RELEASE.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/dmyers87/camunda-message-streaming/commit/41e27a1fe9f0949f331a284bafd06fdaefba62e0">41e27a1fe9f0949f331a284bafd06fdaefba62e0</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.
<p>Publish Date: 2022-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22970>CVE-2022-22970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22970">https://tanzu.vmware.com/security/cve-2022-22970</a></p>
<p>Release Date: 2022-05-12</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-beans","packageVersion":"5.2.4.RELEASE","packageFilePaths":["/messaging-kafka/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.camunda.bpm:camunda-engine:7.12.0;org.springframework:spring-beans:5.2.4.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20","isBinary":false},{"packageType":"Java","groupId":"org.springframework","packageName":"spring-core","packageVersion":"5.2.4.RELEASE","packageFilePaths":["/webapp/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter:2.2.5.RELEASE;org.springframework:spring-core:5.2.4.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.22,5.3.20;org.springframework:spring-core:5.2.22,5.3.20","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2022-22970","vulnerabilityDetails":"In spring framework versions prior to 5.3.20+ , 5.2.22+ and old unsupported versions, applications that handle file uploads are vulnerable to DoS attack if they rely on data binding to set a MultipartFile or javax.servlet.Part to a field in a model object.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22970","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in spring beans release jar spring core release jar cve medium severity vulnerability vulnerable libraries spring beans release jar spring core release jar spring beans release jar spring beans library home page a href path to dependency file messaging kafka pom xml path to vulnerable library home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar dependency hierarchy camunda engine jar root library x spring beans release jar vulnerable library spring core release jar spring core library home page a href path to dependency file webapp pom xml path to vulnerable library home wss scanner repository org springframework spring core release spring core release jar dependency hierarchy spring boot starter release jar root library x spring core release jar vulnerable library found in head commit a href found in base branch develop vulnerability details in spring framework versions prior to and old unsupported versions applications that handle file uploads are vulnerable to dos attack if they rely on data binding to set a multipartfile or javax servlet part to a field in a model object publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans org springframework spring core isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org camunda bpm camunda engine org springframework spring beans release isminimumfixversionavailable true minimumfixversion org springframework spring beans org springframework spring core isbinary false packagetype java groupid org springframework packagename spring core packageversion release packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter release org springframework spring core release isminimumfixversionavailable true minimumfixversion org springframework spring beans org springframework spring core isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in spring framework versions prior to and old unsupported versions applications that handle file uploads are vulnerable to dos attack if they rely on data binding to set a multipartfile or javax servlet part to a field in a model object vulnerabilityurl | 0 |
44,974 | 9,662,219,034 | IssuesEvent | 2019-05-20 20:13:41 | pb866/pyp | https://api.github.com/repos/pb866/pyp | opened | Improve constructor for PlotData | code revision update | Use inner and out constructors to construct `PlotData` and check that data is consistent for plotting. | 1.0 | Improve constructor for PlotData - Use inner and out constructors to construct `PlotData` and check that data is consistent for plotting. | non_priority | improve constructor for plotdata use inner and out constructors to construct plotdata and check that data is consistent for plotting | 0 |
21,554 | 4,724,607,917 | IssuesEvent | 2016-10-18 01:23:09 | syl20bnr/spacemacs | https://api.github.com/repos/syl20bnr/spacemacs | closed | Describe scss-lint setup in the html layer documentation. | - Bug tracker - Documentation ✏ Fixed in develop Web | [The HTML layer](https://github.com/syl20bnr/spacemacs/tree/develop/layers/%2Blang/html) provides `flycheck-mode` hook for `scss-mode` and it uses [scss-lint](https://github.com/brigade/scss-lint). I managed to setup it, but it was kinda tricky and I'm not sure this is the right way so it might be beneficent for those who came after us to say something, in the layer's docs, about `scss-lint` and how to use it.
I had to install required ruby gems directly from the github since [rubygems.org doesn't have a compitable version with flycheck](https://rubygems.org/gems/scss-lint/versions) - I think it requires at least [`SCSS-Lint 0.43.0`](https://github.com/brigade/scss-lint/releases/tag/v0.43.0)
This is my way:
```sh
gem install specific_install
gem specific_install https://github.com/brigade/scss-lint.git
gem specific_install https://github.com/Sweetchuck/scss_lint_reporter_checkstyle.git
```
Not sure if the best one. | 1.0 | Describe scss-lint setup in the html layer documentation. - [The HTML layer](https://github.com/syl20bnr/spacemacs/tree/develop/layers/%2Blang/html) provides `flycheck-mode` hook for `scss-mode` and it uses [scss-lint](https://github.com/brigade/scss-lint). I managed to setup it, but it was kinda tricky and I'm not sure this is the right way so it might be beneficent for those who came after us to say something, in the layer's docs, about `scss-lint` and how to use it.
I had to install required ruby gems directly from the github since [rubygems.org doesn't have a compitable version with flycheck](https://rubygems.org/gems/scss-lint/versions) - I think it requires at least [`SCSS-Lint 0.43.0`](https://github.com/brigade/scss-lint/releases/tag/v0.43.0)
This is my way:
```sh
gem install specific_install
gem specific_install https://github.com/brigade/scss-lint.git
gem specific_install https://github.com/Sweetchuck/scss_lint_reporter_checkstyle.git
```
Not sure if the best one. | non_priority | describe scss lint setup in the html layer documentation provides flycheck mode hook for scss mode and it uses i managed to setup it but it was kinda tricky and i m not sure this is the right way so it might be beneficent for those who came after us to say something in the layer s docs about scss lint and how to use it i had to install required ruby gems directly from the github since i think it requires at least this is my way sh gem install specific install gem specific install gem specific install not sure if the best one | 0 |
132,984 | 12,528,919,958 | IssuesEvent | 2020-06-04 10:23:32 | code4moldova/covid19md-voluntari-server | https://api.github.com/repos/code4moldova/covid19md-voluntari-server | opened | clean beneficary implementation | documentation help wanted | - delete BeneficiaryAPI(MethodView) class and imported classes
- add swagger information about endpoints
- delete comments and add function description | 1.0 | clean beneficary implementation - - delete BeneficiaryAPI(MethodView) class and imported classes
- add swagger information about endpoints
- delete comments and add function description | non_priority | clean beneficary implementation delete beneficiaryapi methodview class and imported classes add swagger information about endpoints delete comments and add function description | 0 |
279,099 | 21,111,320,596 | IssuesEvent | 2022-04-05 02:09:38 | seanpm2001/SNU_2D_ProgrammingTools_IDE_MoonScript | https://api.github.com/repos/seanpm2001/SNU_2D_ProgrammingTools_IDE_MoonScript | opened | Contributor attribution thread | documentation enhancement good first issue | ***
### /SNU/2D/ProgrammingTools/IDE/MoonScript/ Contributor attribution
If you are a contributor on this project, you will be credited in this thread. @all-contributors will be helping out here.
***
| 1.0 | Contributor attribution thread - ***
### /SNU/2D/ProgrammingTools/IDE/MoonScript/ Contributor attribution
If you are a contributor on this project, you will be credited in this thread. @all-contributors will be helping out here.
***
| non_priority | contributor attribution thread snu programmingtools ide moonscript contributor attribution if you are a contributor on this project you will be credited in this thread all contributors will be helping out here | 0 |
191,932 | 22,215,870,798 | IssuesEvent | 2022-06-08 01:32:05 | ShaikUsaf/linux-3.0.35 | https://api.github.com/repos/ShaikUsaf/linux-3.0.35 | opened | CVE-2013-4514 (Medium) detected in kvmarmv3.0.43 | security vulnerability | ## CVE-2013-4514 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kvmarmv3.0.43</b></p></summary>
<p>
<p>ARM KVM group's fork of linux.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/kvmarm/kvmarm.git>https://git.kernel.org/pub/scm/linux/kernel/git/kvmarm/kvmarm.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/wlags49_h2/wl_priv.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/wlags49_h2/wl_priv.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Multiple buffer overflows in drivers/staging/wlags49_h2/wl_priv.c in the Linux kernel before 3.12 allow local users to cause a denial of service or possibly have unspecified other impact by leveraging the CAP_NET_ADMIN capability and providing a long station-name string, related to the (1) wvlan_uil_put_info and (2) wvlan_set_station_nickname functions.
<p>Publish Date: 2013-11-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4514>CVE-2013-4514</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4514">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4514</a></p>
<p>Release Date: 2013-11-12</p>
<p>Fix Resolution: v3.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2013-4514 (Medium) detected in kvmarmv3.0.43 - ## CVE-2013-4514 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>kvmarmv3.0.43</b></p></summary>
<p>
<p>ARM KVM group's fork of linux.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/kvmarm/kvmarm.git>https://git.kernel.org/pub/scm/linux/kernel/git/kvmarm/kvmarm.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/wlags49_h2/wl_priv.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/staging/wlags49_h2/wl_priv.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Multiple buffer overflows in drivers/staging/wlags49_h2/wl_priv.c in the Linux kernel before 3.12 allow local users to cause a denial of service or possibly have unspecified other impact by leveraging the CAP_NET_ADMIN capability and providing a long station-name string, related to the (1) wvlan_uil_put_info and (2) wvlan_set_station_nickname functions.
<p>Publish Date: 2013-11-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-4514>CVE-2013-4514</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4514">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4514</a></p>
<p>Release Date: 2013-11-12</p>
<p>Fix Resolution: v3.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in cve medium severity vulnerability vulnerable library arm kvm group s fork of linux git library home page a href found in base branch master vulnerable source files drivers staging wl priv c drivers staging wl priv c vulnerability details multiple buffer overflows in drivers staging wl priv c in the linux kernel before allow local users to cause a denial of service or possibly have unspecified other impact by leveraging the cap net admin capability and providing a long station name string related to the wvlan uil put info and wvlan set station nickname functions publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
121,174 | 10,152,515,014 | IssuesEvent | 2019-08-06 00:06:51 | letsencrypt/boulder | https://api.github.com/repos/letsencrypt/boulder | closed | tests: Find a better way to spot dangling transactions | area/sa kind/tests | In https://github.com/letsencrypt/boulder/pull/4336, we fixed a bug where an error condition could lead to a transaction that was left open indefinitely. When this happens, we pile up resources on both the SA and the database and eventually start serving errors. We've fixed a similar bug at least once before.
We should find an automated way to catch these earlier during the development / test phase. Maybe a lint tool that looks for functions that are either called with something that is likely to be a transaction, or that have `.Begin` in them, and flags `return ... err` in those without a `Rollback` call? Or maybe we can find some way to put the Rollback in a defer without making things too messy. Or maybe attach rollbacking to the context's Done event somehow? I wonder what happens if you try to rollback a completed transaction. | 1.0 | tests: Find a better way to spot dangling transactions - In https://github.com/letsencrypt/boulder/pull/4336, we fixed a bug where an error condition could lead to a transaction that was left open indefinitely. When this happens, we pile up resources on both the SA and the database and eventually start serving errors. We've fixed a similar bug at least once before.
We should find an automated way to catch these earlier during the development / test phase. Maybe a lint tool that looks for functions that are either called with something that is likely to be a transaction, or that have `.Begin` in them, and flags `return ... err` in those without a `Rollback` call? Or maybe we can find some way to put the Rollback in a defer without making things too messy. Or maybe attach rollbacking to the context's Done event somehow? I wonder what happens if you try to rollback a completed transaction. | non_priority | tests find a better way to spot dangling transactions in we fixed a bug where an error condition could lead to a transaction that was left open indefinitely when this happens we pile up resources on both the sa and the database and eventually start serving errors we ve fixed a similar bug at least once before we should find an automated way to catch these earlier during the development test phase maybe a lint tool that looks for functions that are either called with something that is likely to be a transaction or that have begin in them and flags return err in those without a rollback call or maybe we can find some way to put the rollback in a defer without making things too messy or maybe attach rollbacking to the context s done event somehow i wonder what happens if you try to rollback a completed transaction | 0 |
259,698 | 27,716,591,296 | IssuesEvent | 2023-03-14 17:20:40 | snowdensb/job-dsl-plugin | https://api.github.com/repos/snowdensb/job-dsl-plugin | opened | CVE-2019-20922 (High) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2019-20922 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.2.js</b>, <b>handlebars-4.0.2.min.js</b>, <b>handlebars-4.0.2.jar</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.2.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.js</a></p>
<p>Path to vulnerable library: /job-dsl-api-viewer/build/webjars/handlebars/4.0.2/handlebars.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.2.js** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.2.min.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.min.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.min.js</a></p>
<p>Path to vulnerable library: /job-dsl-api-viewer/build/webjars/handlebars/4.0.2/handlebars.min.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.2.jar</b></p></summary>
<p>WebJar for Handlebars</p>
<p>Library home page: <a href="http://webjars.org">http://webjars.org</a></p>
<p>Path to dependency file: /job-dsl-api-viewer/build.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.webjars/handlebars/4.0.2/259c7e47df1d59761c33f3d4a77a0b9673153af4/handlebars-4.0.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.2.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20922>CVE-2019-20922</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1300">https://www.npmjs.com/advisories/1300</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: handlebars - 4.4.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2019-20922 (High) detected in multiple libraries - ## CVE-2019-20922 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.2.js</b>, <b>handlebars-4.0.2.min.js</b>, <b>handlebars-4.0.2.jar</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.2.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.js</a></p>
<p>Path to vulnerable library: /job-dsl-api-viewer/build/webjars/handlebars/4.0.2/handlebars.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.2.js** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.2.min.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.min.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.2/handlebars.min.js</a></p>
<p>Path to vulnerable library: /job-dsl-api-viewer/build/webjars/handlebars/4.0.2/handlebars.min.js</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>handlebars-4.0.2.jar</b></p></summary>
<p>WebJar for Handlebars</p>
<p>Library home page: <a href="http://webjars.org">http://webjars.org</a></p>
<p>Path to dependency file: /job-dsl-api-viewer/build.gradle</p>
<p>Path to vulnerable library: /caches/modules-2/files-2.1/org.webjars/handlebars/4.0.2/259c7e47df1d59761c33f3d4a77a0b9673153af4/handlebars-4.0.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **handlebars-4.0.2.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20922>CVE-2019-20922</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1300">https://www.npmjs.com/advisories/1300</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: handlebars - 4.4.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries handlebars js handlebars min js handlebars jar handlebars js handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to vulnerable library job dsl api viewer build webjars handlebars handlebars js dependency hierarchy x handlebars js vulnerable library handlebars min js handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to vulnerable library job dsl api viewer build webjars handlebars handlebars min js dependency hierarchy x handlebars min js vulnerable library handlebars jar webjar for handlebars library home page a href path to dependency file job dsl api viewer build gradle path to vulnerable library caches modules files org webjars handlebars handlebars jar dependency hierarchy x handlebars jar vulnerable library found in base branch master vulnerability details handlebars before allows regular expression denial of service redos because of eager matching the parser may be forced into an endless loop while processing crafted templates this may allow attackers to exhaust system resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution handlebars rescue worker helmet automatic remediation is available for this issue | 0 |
148,441 | 11,852,401,754 | IssuesEvent | 2020-03-24 19:52:00 | hashicorp/consul | https://api.github.com/repos/hashicorp/consul | opened | flaky test: api TestAPI_AgentMonitor | theme/flaky-tests | I saw this test fail twice, and pass the third time. One failure is [here](https://app.circleci.com/pipelines/github/hashicorp/consul/7963/workflows/ae8ce3de-6438-4fcf-b7af-cf48f7baffbf/jobs/144171).
There are lots of log messages, but the relevant failure line seems to be:
```
agent_test.go:1196: failed to get a log message
```
| 1.0 | flaky test: api TestAPI_AgentMonitor - I saw this test fail twice, and pass the third time. One failure is [here](https://app.circleci.com/pipelines/github/hashicorp/consul/7963/workflows/ae8ce3de-6438-4fcf-b7af-cf48f7baffbf/jobs/144171).
There are lots of log messages, but the relevant failure line seems to be:
```
agent_test.go:1196: failed to get a log message
```
| non_priority | flaky test api testapi agentmonitor i saw this test fail twice and pass the third time one failure is there are lots of log messages but the relevant failure line seems to be agent test go failed to get a log message | 0 |
110,641 | 13,923,748,633 | IssuesEvent | 2020-10-21 14:46:23 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | [DESIGN] MyVA Dashboard: Revisit Direction/Wireframe explorations (1 week) | design my-va-dashboard needs-grooming vsa-authenticated-exp | ## Background
We are taking the first week of this sprint (S33) to revisit the direction of the MyVA dashboard redesign and explore different options and decide upon the approach going forward. The focus should be on sketches/low-fi wireframes not on detailed visual design.
My VA goals: Get users to personalized information and tasks as quickly as possible. The page should be personalized, actionable, and scalable.
## Tasks
- [ ] Wireframe explorations
- [ ] Sketches/low-fi wireframes
- [ ] Meet and review with Samara/Ryan/Matt
- [ ] Decide on direction going forward
| 1.0 | [DESIGN] MyVA Dashboard: Revisit Direction/Wireframe explorations (1 week) - ## Background
We are taking the first week of this sprint (S33) to revisit the direction of the MyVA dashboard redesign and explore different options and decide upon the approach going forward. The focus should be on sketches/low-fi wireframes not on detailed visual design.
My VA goals: Get users to personalized information and tasks as quickly as possible. The page should be personalized, actionable, and scalable.
## Tasks
- [ ] Wireframe explorations
- [ ] Sketches/low-fi wireframes
- [ ] Meet and review with Samara/Ryan/Matt
- [ ] Decide on direction going forward
| non_priority | myva dashboard revisit direction wireframe explorations week background we are taking the first week of this sprint to revisit the direction of the myva dashboard redesign and explore different options and decide upon the approach going forward the focus should be on sketches low fi wireframes not on detailed visual design my va goals get users to personalized information and tasks as quickly as possible the page should be personalized actionable and scalable tasks wireframe explorations sketches low fi wireframes meet and review with samara ryan matt decide on direction going forward | 0 |
67,164 | 8,081,949,290 | IssuesEvent | 2018-08-08 06:37:46 | cosmos/voyager | https://api.github.com/repos/cosmos/voyager | opened | user experience improvement: eventual consistency. | design discuss feature | UI Version: 0.9.3
Description: The block times for `gaia-7005` average around 10 seconds. This is a long time for users to wait to receive feedback. Users may wonder if anything is happening after they send some tokens or delegate some steak.
Solution: We need to improve the responsiveness of Voyager by implementing elements of [optimistic UIs](https://uxplanet.org/optimistic-1000-34d9eefe4c05).
In short, the UI should not lock up after a user bonds atoms to a validator. Instead, we should instantly update the interface to show that the atoms have bonded and remove the atoms from the user's wallet. We can have a loading icon somewhere in the app to show that the bonding event in happening in the background. Once the bonding event finishes, we notify the user that it's complete.
The same for sending tokens. Once a user hits "Send", the tokens should be removed from his wallet. The transaction history should show that the tokens have been sent. Somewhere in the transaction card, there should be a loading icon showing that the transaction is in progress. It can change to a green checkmark when the transaction is verified on the network.
This sort of optimistic behavior makes the UI feel much faster and more responsive even with slower block times. | 1.0 | user experience improvement: eventual consistency. - UI Version: 0.9.3
Description: The block times for `gaia-7005` average around 10 seconds. This is a long time for users to wait to receive feedback. Users may wonder if anything is happening after they send some tokens or delegate some steak.
Solution: We need to improve the responsiveness of Voyager by implementing elements of [optimistic UIs](https://uxplanet.org/optimistic-1000-34d9eefe4c05).
In short, the UI should not lock up after a user bonds atoms to a validator. Instead, we should instantly update the interface to show that the atoms have bonded and remove the atoms from the user's wallet. We can have a loading icon somewhere in the app to show that the bonding event in happening in the background. Once the bonding event finishes, we notify the user that it's complete.
The same for sending tokens. Once a user hits "Send", the tokens should be removed from his wallet. The transaction history should show that the tokens have been sent. Somewhere in the transaction card, there should be a loading icon showing that the transaction is in progress. It can change to a green checkmark when the transaction is verified on the network.
This sort of optimistic behavior makes the UI feel much faster and more responsive even with slower block times. | non_priority | user experience improvement eventual consistency ui version description the block times for gaia average around seconds this is a long time for users to wait to receive feedback users may wonder if anything is happening after they send some tokens or delegate some steak solution we need to improve the responsiveness of voyager by implementing elements of in short the ui should not lock up after a user bonds atoms to a validator instead we should instantly update the interface to show that the atoms have bonded and remove the atoms from the user s wallet we can have a loading icon somewhere in the app to show that the bonding event in happening in the background once the bonding event finishes we notify the user that it s complete the same for sending tokens once a user hits send the tokens should be removed from his wallet the transaction history should show that the tokens have been sent somewhere in the transaction card there should be a loading icon showing that the transaction is in progress it can change to a green checkmark when the transaction is verified on the network this sort of optimistic behavior makes the ui feel much faster and more responsive even with slower block times | 0 |
118,284 | 25,287,992,590 | IssuesEvent | 2022-11-16 21:04:12 | rkd103/Group-11 | https://api.github.com/repos/rkd103/Group-11 | closed | Implement Additional Feature #1 - Add Support for Messaging Friends | enhancement code | _Notes_:
- Add support for sending and receiving direct messages from friends. Messages are text-only.
- Add a direct messages page which displays a list of friends. When a particular friend is clicked, the user's messaging history with that friend will be displayed. A button should also be clickable to send a new message to that friend.
- User Story Points: 2 | 1.0 | Implement Additional Feature #1 - Add Support for Messaging Friends - _Notes_:
- Add support for sending and receiving direct messages from friends. Messages are text-only.
- Add a direct messages page which displays a list of friends. When a particular friend is clicked, the user's messaging history with that friend will be displayed. A button should also be clickable to send a new message to that friend.
- User Story Points: 2 | non_priority | implement additional feature add support for messaging friends notes add support for sending and receiving direct messages from friends messages are text only add a direct messages page which displays a list of friends when a particular friend is clicked the user s messaging history with that friend will be displayed a button should also be clickable to send a new message to that friend user story points | 0 |
44,803 | 12,393,017,163 | IssuesEvent | 2020-05-20 14:49:30 | telemundo/jira-sync | https://api.github.com/repos/telemundo/jira-sync | closed | GST-44 Testing Sri | BOT DEFECT | ## This ticket is to test big header.
### I would like to test small header.
**_As a QA Engineer i would test bold description.This is for testing only_ .**
### QA Checklist.
- [x] QA Tested on Chrome.
- [x] QA tested on forefox.
- [x] QA tested on Safari.
- [ ] QA tested on IE.
### Min items to be uploaded.
- Sample Urls.
- Any Images available.
- References.
### Below Information if available.
1. High level smoke tests.
2. Any use case from product.
3. Different elements to be tested.
> 
`$element_id = '#' . $this->getSession()->getPage()->find('xpath', '//*[@name="' . $ftype['field_name'] . '"]/preceding-sibling::a')->getAttribute('id');`
[telemundo](https://staging.newsapp.telemundo.com/noticias)
| 1.0 | GST-44 Testing Sri - ## This ticket is to test big header.
### I would like to test small header.
**_As a QA Engineer i would test bold description.This is for testing only_ .**
### QA Checklist.
- [x] QA Tested on Chrome.
- [x] QA tested on forefox.
- [x] QA tested on Safari.
- [ ] QA tested on IE.
### Min items to be uploaded.
- Sample Urls.
- Any Images available.
- References.
### Below Information if available.
1. High level smoke tests.
2. Any use case from product.
3. Different elements to be tested.
> 
`$element_id = '#' . $this->getSession()->getPage()->find('xpath', '//*[@name="' . $ftype['field_name'] . '"]/preceding-sibling::a')->getAttribute('id');`
[telemundo](https://staging.newsapp.telemundo.com/noticias)
| non_priority | gst testing sri this ticket is to test big header i would like to test small header as a qa engineer i would test bold description this is for testing only qa checklist qa tested on chrome qa tested on forefox qa tested on safari qa tested on ie min items to be uploaded sample urls any images available references below information if available high level smoke tests any use case from product different elements to be tested element id this getsession getpage find xpath preceding sibling a getattribute id | 0 |
18,847 | 10,242,092,210 | IssuesEvent | 2019-08-20 03:20:39 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | closed | Performance Issues Adding Items To List Is Slower in Core 3 than Core 2.2 | area-System.Collections tenet-performance | Below are the benchmark results, using BenchmarkDotnet, to test adding items to a List<> collection. As you can see, while .NET Core 3 is faster than the Clr, it seems the performance is slower when compared to .NET Core 2.2.

Below is the code for the benchmark test:
```
[Benchmark(Description = "COLLECTION CREATION: Using List<> & Add()")]
public List<FakePerson> TestAddingItemsToCollections01()
{
var collection = new List<FakePerson>();
for (var count = 0; count < this.CollectionCount; count++)
{
collection.Add(this._fakePersonFixedCollection[count]);
}
return collection;
}
``` | True | Performance Issues Adding Items To List Is Slower in Core 3 than Core 2.2 - Below are the benchmark results, using BenchmarkDotnet, to test adding items to a List<> collection. As you can see, while .NET Core 3 is faster than the Clr, it seems the performance is slower when compared to .NET Core 2.2.

Below is the code for the benchmark test:
```
[Benchmark(Description = "COLLECTION CREATION: Using List<> & Add()")]
public List<FakePerson> TestAddingItemsToCollections01()
{
var collection = new List<FakePerson>();
for (var count = 0; count < this.CollectionCount; count++)
{
collection.Add(this._fakePersonFixedCollection[count]);
}
return collection;
}
``` | non_priority | performance issues adding items to list is slower in core than core below are the benchmark results using benchmarkdotnet to test adding items to a list collection as you can see while net core is faster than the clr it seems the performance is slower when compared to net core below is the code for the benchmark test public list var collection new list for var count count this collectioncount count collection add this fakepersonfixedcollection return collection | 0 |
325,165 | 24,037,672,764 | IssuesEvent | 2022-09-15 20:50:15 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | TripleDES Encryption in .NET 6 failure | documentation area-System.Security | _This issue has been moved from [a ticket on Developer Community](https://developercommunity.visualstudio.com/t/TripleDES-Encryption-in-NET-6-failure/1649343)._
---
[severity:Other]
I followed this TripleDES url by Copying the code. However, I get a bad result. The Url:
https://docs.microsoft.com/en-us/dotnet/api/system.security.cryptography.tripledes.create?view=net-6.0
I'm working with the EncryptTextToMemory example. My code:
```
TripleDES tripleDes = TripleDES.Create("TripleDES");
string sData = "Here is some data to encrypt.";
byte[] bytes = Encrypt(sData, tripleDes.Key, tripleDes.IV);
string final = Decrypt(bytes, tripleDes.Key, tripleDes.IV);
// here I have 32 bytes
byte[] fromEncrypt = new byte[data.Length];
// here it outputs 24 valid bytes with the remaining with value 0
csDecrypt.Read(fromEncrypt, 0, fromEncrypt.Length);
```
The value found in my "final" variable is "Here is some data to enc\0\0\0\0\0\0\0\0".
How do I get this to return the entire string? Thanks, Joel
---
### Original Comments
#### Feedback Bot on 1/28/2022, 08:21 AM:
(private comment, text removed)
#### jlpm on 1/28/2022, 04:29 PM:
(private comment, text removed)
#### David Lowndes on 3/1/2022, 08:06 PM:
(private comment, text removed)
#### jlpm on 3/1/2022, 08:10 PM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 00:10 AM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 10:42 AM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 00:18 PM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 00:53 PM:
(private comment, text removed)
#### jlpm on 3/2/2022, 04:32 PM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 04:40 PM:
(private comment, text removed)
#### Feedback Bot on 5/7/2022, 11:07 AM:
(private comment, text removed)
#### David Lowndes on 5/7/2022, 03:28 PM:
(private comment, text removed)
#### jlpm on 5/9/2022, 05:00 PM:
(private comment, text removed)
#### David Lowndes on 5/9/2022, 05:47 PM:
(private comment, text removed)
#### jlpm on 5/9/2022, 05:52 PM:
(private comment, text removed)
#### David Lowndes on 5/9/2022, 06:22 PM:
(private comment, text removed)
#### jlpm on 5/9/2022, 07:00 PM:
(private comment, text removed)
#### David Lowndes on 5/9/2022, 09:57 PM:
(private comment, text removed)
---
### Original Solutions
(no solutions) | 1.0 | TripleDES Encryption in .NET 6 failure - _This issue has been moved from [a ticket on Developer Community](https://developercommunity.visualstudio.com/t/TripleDES-Encryption-in-NET-6-failure/1649343)._
---
[severity:Other]
I followed this TripleDES url by Copying the code. However, I get a bad result. The Url:
https://docs.microsoft.com/en-us/dotnet/api/system.security.cryptography.tripledes.create?view=net-6.0
I'm working with the EncryptTextToMemory example. My code:
```
TripleDES tripleDes = TripleDES.Create("TripleDES");
string sData = "Here is some data to encrypt.";
byte[] bytes = Encrypt(sData, tripleDes.Key, tripleDes.IV);
string final = Decrypt(bytes, tripleDes.Key, tripleDes.IV);
// here I have 32 bytes
byte[] fromEncrypt = new byte[data.Length];
// here it outputs 24 valid bytes with the remaining with value 0
csDecrypt.Read(fromEncrypt, 0, fromEncrypt.Length);
```
The value found in my "final" variable is "Here is some data to enc\0\0\0\0\0\0\0\0".
How do I get this to return the entire string? Thanks, Joel
---
### Original Comments
#### Feedback Bot on 1/28/2022, 08:21 AM:
(private comment, text removed)
#### jlpm on 1/28/2022, 04:29 PM:
(private comment, text removed)
#### David Lowndes on 3/1/2022, 08:06 PM:
(private comment, text removed)
#### jlpm on 3/1/2022, 08:10 PM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 00:10 AM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 10:42 AM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 00:18 PM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 00:53 PM:
(private comment, text removed)
#### jlpm on 3/2/2022, 04:32 PM:
(private comment, text removed)
#### David Lowndes on 3/2/2022, 04:40 PM:
(private comment, text removed)
#### Feedback Bot on 5/7/2022, 11:07 AM:
(private comment, text removed)
#### David Lowndes on 5/7/2022, 03:28 PM:
(private comment, text removed)
#### jlpm on 5/9/2022, 05:00 PM:
(private comment, text removed)
#### David Lowndes on 5/9/2022, 05:47 PM:
(private comment, text removed)
#### jlpm on 5/9/2022, 05:52 PM:
(private comment, text removed)
#### David Lowndes on 5/9/2022, 06:22 PM:
(private comment, text removed)
#### jlpm on 5/9/2022, 07:00 PM:
(private comment, text removed)
#### David Lowndes on 5/9/2022, 09:57 PM:
(private comment, text removed)
---
### Original Solutions
(no solutions) | non_priority | tripledes encryption in net failure this issue has been moved from i followed this tripledes url by copying the code however i get a bad result the url i m working with the encrypttexttomemory example my code tripledes tripledes tripledes create tripledes string sdata here is some data to encrypt byte bytes encrypt sdata tripledes key tripledes iv string final decrypt bytes tripledes key tripledes iv here i have bytes byte fromencrypt new byte here it outputs valid bytes with the remaining with value csdecrypt read fromencrypt fromencrypt length the value found in my final variable is here is some data to enc how do i get this to return the entire string thanks joel original comments feedback bot on am private comment text removed jlpm on pm private comment text removed david lowndes on pm private comment text removed jlpm on pm private comment text removed david lowndes on am private comment text removed david lowndes on am private comment text removed david lowndes on pm private comment text removed david lowndes on pm private comment text removed jlpm on pm private comment text removed david lowndes on pm private comment text removed feedback bot on am private comment text removed david lowndes on pm private comment text removed jlpm on pm private comment text removed david lowndes on pm private comment text removed jlpm on pm private comment text removed david lowndes on pm private comment text removed jlpm on pm private comment text removed david lowndes on pm private comment text removed original solutions no solutions | 0 |
101,160 | 8,780,203,192 | IssuesEvent | 2018-12-19 16:41:03 | SME-Issues/issues | https://api.github.com/repos/SME-Issues/issues | closed | Test Summary - 19/12/2018 - 5004 Gold | NLP Api PETEDEV pulse_tests | ### Canonical
- Query Balance Tests Canonical (1): **100%** pass (1), 0 failed understood (-)
Url: http://13.80.119.239:5004/pulse?g=
| 1.0 | Test Summary - 19/12/2018 - 5004 Gold - ### Canonical
- Query Balance Tests Canonical (1): **100%** pass (1), 0 failed understood (-)
Url: http://13.80.119.239:5004/pulse?g=
| non_priority | test summary gold canonical query balance tests canonical pass failed understood url | 0 |
63,157 | 8,663,939,015 | IssuesEvent | 2018-11-28 18:43:46 | fga-eps-mds/2018.2-GamesBI | https://api.github.com/repos/fga-eps-mds/2018.2-GamesBI | opened | Corrigir a metrica de Velocity | 0 - Scrum Master 2 - Bug 2 - Documentation 4 - Question | ## Descrição
<!--- Describe the reason of the issue, what is the problem you want to solve, the bug you want to fix, etc -->
Foi identificado durante a apresentação da R2 que a metrica Velocity estava calculada errada.
## Tarefas
- [ ] Corrigir atributo velocity
- [ ] Atualizar documentação
## Critérios de aceitação
<!--- describe what needs to be done so this issue can be closed -->
Calculo correto: Somatorio de x PontosConcluido por Sprint/ x
| 1.0 | Corrigir a metrica de Velocity - ## Descrição
<!--- Describe the reason of the issue, what is the problem you want to solve, the bug you want to fix, etc -->
Foi identificado durante a apresentação da R2 que a metrica Velocity estava calculada errada.
## Tarefas
- [ ] Corrigir atributo velocity
- [ ] Atualizar documentação
## Critérios de aceitação
<!--- describe what needs to be done so this issue can be closed -->
Calculo correto: Somatorio de x PontosConcluido por Sprint/ x
| non_priority | corrigir a metrica de velocity descrição foi identificado durante a apresentação da que a metrica velocity estava calculada errada tarefas corrigir atributo velocity atualizar documentação critérios de aceitação calculo correto somatorio de x pontosconcluido por sprint x | 0 |
186,437 | 21,933,229,670 | IssuesEvent | 2022-05-23 11:39:37 | onokatio/blog.katio.net | https://api.github.com/repos/onokatio/blog.katio.net | closed | CVE-2022-21681 (High) detected in marked-0.7.0.tgz | security vulnerability | ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.7.0.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.7.0.tgz">https://registry.npmjs.org/marked/-/marked-0.7.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.7.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Marked is a markdown parser and compiler. Prior to version 4.0.10, the regular expression `inline.reflinkSearch` may cause catastrophic backtracking against some strings and lead to a denial of service (DoS). Anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected. This issue is patched in version 4.0.10. As a workaround, avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21681>CVE-2022-21681</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5v2h-r2cx-5xgj">https://github.com/advisories/GHSA-5v2h-r2cx-5xgj</a></p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution: 4.0.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-21681 (High) detected in marked-0.7.0.tgz - ## CVE-2022-21681 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>marked-0.7.0.tgz</b></p></summary>
<p>A markdown parser built for speed</p>
<p>Library home page: <a href="https://registry.npmjs.org/marked/-/marked-0.7.0.tgz">https://registry.npmjs.org/marked/-/marked-0.7.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/marked/package.json</p>
<p>
Dependency Hierarchy:
- :x: **marked-0.7.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Marked is a markdown parser and compiler. Prior to version 4.0.10, the regular expression `inline.reflinkSearch` may cause catastrophic backtracking against some strings and lead to a denial of service (DoS). Anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected. This issue is patched in version 4.0.10. As a workaround, avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources.
<p>Publish Date: 2022-01-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21681>CVE-2022-21681</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-5v2h-r2cx-5xgj">https://github.com/advisories/GHSA-5v2h-r2cx-5xgj</a></p>
<p>Release Date: 2022-01-14</p>
<p>Fix Resolution: 4.0.10</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in marked tgz cve high severity vulnerability vulnerable library marked tgz a markdown parser built for speed library home page a href path to dependency file package json path to vulnerable library node modules marked package json dependency hierarchy x marked tgz vulnerable library found in base branch master vulnerability details marked is a markdown parser and compiler prior to version the regular expression inline reflinksearch may cause catastrophic backtracking against some strings and lead to a denial of service dos anyone who runs untrusted markdown through a vulnerable version of marked and does not use a worker with a time limit may be affected this issue is patched in version as a workaround avoid running untrusted markdown through marked or run marked on a worker thread and set a reasonable time limit to prevent draining resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
22,497 | 4,807,683,044 | IssuesEvent | 2016-11-02 22:14:17 | minio/minio | https://api.github.com/repos/minio/minio | closed | [doc] File is wrapped in FormData boundary when using presigned http put in browser | community documentation faq | When uploading using a presigned using form data ajax as described in the [docs
](https://docs.minio.io/docs/upload-files-from-browser-using-pre-signed-urls) the form data metadata is retained in the stored file. Happens in the edge and stable builds.
## Expected Behavior
File is stored as given by the client
## Current Behavior
File is wrapped in the the form data
```
------WebKitFormBoundary9hhme0TSqEoakTEU
Content-Disposition: form-data; name="tmp.txt"; filename="tmp.txt"
Content-Type: text/plain
File Content
------WebKitFormBoundary9hhme0TSqEoakTEU--
```
## Steps to Reproduce
1. Generate Presigned PUT url
2. Use FormData ajax to upload the file ( either plain xhr or jquery as used in the [docs
](https://docs.minio.io/docs/upload-files-from-browser-using-pre-signed-urls))
```
<input type="file" id="selector" multiple>
<button onclick="upload()">Upload</button>
<div id="status">No uploads</div>
<script src="https://code.jquery.com/jquery-3.1.0.min.js"></script>
<script type="text/javascript">
function upload() {
var files = $('#selector')[0].files
var file = files[0];
let data = new FormData()
data.append(file.name, file)
$.ajax({
url: "https://play.minio.io:9000/blamoo/test.txt?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=Q3AM3UQ867SPQQA43P2F%2F20161101%2Fus-east-1%2Fs3%2Faws4_request&X-Amz-Date=20161101T144030Z&X-Amz-Expires=259200&X-Amz-SignedHeaders=host&X-Amz-Signature=454206c4c1ef0aaca9f0f892a46fb9e3190758469396ae38de0343ee323bad9c",
method: 'PUT',
success: () => {
$('#status').text(`Uploaded ${file.name}.`)
},
processData: false,
contentType: false,
data
})
}
</script>
```
## Your Environment
minio stable build
minio java-client 2.0.4
Chrome & Firefox
| 1.0 | [doc] File is wrapped in FormData boundary when using presigned http put in browser - When uploading using a presigned using form data ajax as described in the [docs
](https://docs.minio.io/docs/upload-files-from-browser-using-pre-signed-urls) the form data metadata is retained in the stored file. Happens in the edge and stable builds.
## Expected Behavior
File is stored as given by the client
## Current Behavior
File is wrapped in the the form data
```
------WebKitFormBoundary9hhme0TSqEoakTEU
Content-Disposition: form-data; name="tmp.txt"; filename="tmp.txt"
Content-Type: text/plain
File Content
------WebKitFormBoundary9hhme0TSqEoakTEU--
```
## Steps to Reproduce
1. Generate Presigned PUT url
2. Use FormData ajax to upload the file ( either plain xhr or jquery as used in the [docs
](https://docs.minio.io/docs/upload-files-from-browser-using-pre-signed-urls))
```
<input type="file" id="selector" multiple>
<button onclick="upload()">Upload</button>
<div id="status">No uploads</div>
<script src="https://code.jquery.com/jquery-3.1.0.min.js"></script>
<script type="text/javascript">
function upload() {
var files = $('#selector')[0].files
var file = files[0];
let data = new FormData()
data.append(file.name, file)
$.ajax({
url: "https://play.minio.io:9000/blamoo/test.txt?X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=Q3AM3UQ867SPQQA43P2F%2F20161101%2Fus-east-1%2Fs3%2Faws4_request&X-Amz-Date=20161101T144030Z&X-Amz-Expires=259200&X-Amz-SignedHeaders=host&X-Amz-Signature=454206c4c1ef0aaca9f0f892a46fb9e3190758469396ae38de0343ee323bad9c",
method: 'PUT',
success: () => {
$('#status').text(`Uploaded ${file.name}.`)
},
processData: false,
contentType: false,
data
})
}
</script>
```
## Your Environment
minio stable build
minio java-client 2.0.4
Chrome & Firefox
| non_priority | file is wrapped in formdata boundary when using presigned http put in browser when uploading using a presigned using form data ajax as described in the docs the form data metadata is retained in the stored file happens in the edge and stable builds expected behavior file is stored as given by the client current behavior file is wrapped in the the form data content disposition form data name tmp txt filename tmp txt content type text plain file content steps to reproduce generate presigned put url use formdata ajax to upload the file either plain xhr or jquery as used in the docs upload no uploads script src function upload var files selector files var file files let data new formdata data append file name file ajax url method put success status text uploaded file name processdata false contenttype false data your environment minio stable build minio java client chrome firefox | 0 |
119,974 | 17,644,003,986 | IssuesEvent | 2021-08-20 01:26:21 | AkshayMukkavilli/Tensorflow | https://api.github.com/repos/AkshayMukkavilli/Tensorflow | opened | CVE-2020-26266 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2020-26266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /Tensorflow/src/requirements.txt</p>
<p>Path to vulnerable library: teSource-ArchiveExtractor_5ea86033-7612-4210-97f3-8edb65806ddf/20190525011619_2843/20190525011537_depth_0/2/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In affected versions of TensorFlow under certain cases a saved model can trigger use of uninitialized values during code execution. This is caused by having tensor buffers be filled with the default value of the type but forgetting to default initialize the quantized floating point types in Eigen. This is fixed in versions 1.15.5, 2.0.4, 2.1.3, 2.2.2, 2.3.2, and 2.4.0.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26266>CVE-2020-26266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-qhxx-j73r-qpm2">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-qhxx-j73r-qpm2</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: tensorflow-1.15.5, 2.0.4, 2.1.3, 2.2.2, 2.3.2, 2.4.0,tensorflow-cpu-2.1.3, 2.2.2, 2.3.2, 2.4.0,tensorflow-gpu-1.15.5, 2.0.4, 2.1.3, 2.2.2, 2.3.2, 2.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-26266 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2020-26266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /Tensorflow/src/requirements.txt</p>
<p>Path to vulnerable library: teSource-ArchiveExtractor_5ea86033-7612-4210-97f3-8edb65806ddf/20190525011619_2843/20190525011537_depth_0/2/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In affected versions of TensorFlow under certain cases a saved model can trigger use of uninitialized values during code execution. This is caused by having tensor buffers be filled with the default value of the type but forgetting to default initialize the quantized floating point types in Eigen. This is fixed in versions 1.15.5, 2.0.4, 2.1.3, 2.2.2, 2.3.2, and 2.4.0.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-26266>CVE-2020-26266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-qhxx-j73r-qpm2">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-qhxx-j73r-qpm2</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: tensorflow-1.15.5, 2.0.4, 2.1.3, 2.2.2, 2.3.2, 2.4.0,tensorflow-cpu-2.1.3, 2.2.2, 2.3.2, 2.4.0,tensorflow-gpu-1.15.5, 2.0.4, 2.1.3, 2.2.2, 2.3.2, 2.4.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file tensorflow src requirements txt path to vulnerable library tesource archiveextractor depth tensorflow tensorflow data purelib tensorflow dependency hierarchy x tensorflow whl vulnerable library vulnerability details in affected versions of tensorflow under certain cases a saved model can trigger use of uninitialized values during code execution this is caused by having tensor buffers be filled with the default value of the type but forgetting to default initialize the quantized floating point types in eigen this is fixed in versions and publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with whitesource | 0 |
79,477 | 22,777,854,456 | IssuesEvent | 2022-07-08 16:09:00 | dotnet/arcade | https://api.github.com/repos/dotnet/arcade | closed | Build failed: arcade-services-internal-ci/main #20220707.2 | Build Failed | Build [#20220707.2](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=1866085) failed
## :x: : internal / arcade-services-internal-ci failed
### Summary
**Finished** - Fri, 08 Jul 2022 04:02:02 GMT
**Duration** - 65 minutes
**Requested for** - Ricardo Arenas
**Reason** - manual
### Details
#### Deploy
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/207) - Error: Failed to update deployment history. Error: Conflict (CODE: 409)
#### Validate deployment
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Test Run Failed.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Vstest failed with error. Check logs for failures. There might be failed tests.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Error: The process 'D:\a\_work\_tasks\VSTest_ef087383-ee5e-42c7-9a53-ab56c98420f9\2.205.0\Modules\DTAExecutionHost.exe' failed with exit code 1
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Vstest failed with error. Check logs for failures. There might be failed tests.
### Changes
- [a0dd8439](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/a0dd843946da6c63452215b885e36d6886d5c230) - Matt Galbraith - Suppress CodeQL warning about local SQLExpress usage (#1941)
- [6fd1531e](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/6fd1531e210f0daea3c0d81c965f9482da3539c5) - Jon Fortescue - Upgrade RolloutScorerAzureFunction to work with net6.0 (#1940)
| 1.0 | Build failed: arcade-services-internal-ci/main #20220707.2 - Build [#20220707.2](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_build/results?buildId=1866085) failed
## :x: : internal / arcade-services-internal-ci failed
### Summary
**Finished** - Fri, 08 Jul 2022 04:02:02 GMT
**Duration** - 65 minutes
**Requested for** - Ricardo Arenas
**Reason** - manual
### Details
#### Deploy
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/207) - Error: Failed to update deployment history. Error: Conflict (CODE: 409)
#### Validate deployment
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Test Run Failed.
- :warning: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Vstest failed with error. Check logs for failures. There might be failed tests.
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Error: The process 'D:\a\_work\_tasks\VSTest_ef087383-ee5e-42c7-9a53-ab56c98420f9\2.205.0\Modules\DTAExecutionHost.exe' failed with exit code 1
- :x: - [[Log]](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_apis/build/builds/1866085/logs/485) - Vstest failed with error. Check logs for failures. There might be failed tests.
### Changes
- [a0dd8439](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/a0dd843946da6c63452215b885e36d6886d5c230) - Matt Galbraith - Suppress CodeQL warning about local SQLExpress usage (#1941)
- [6fd1531e](https://dev.azure.com/dnceng/7ea9116e-9fac-403d-b258-b31fcf1bb293/_git/ec29e881-6ad7-4427-832d-ce639ccba518/commit/6fd1531e210f0daea3c0d81c965f9482da3539c5) - Jon Fortescue - Upgrade RolloutScorerAzureFunction to work with net6.0 (#1940)
| non_priority | build failed arcade services internal ci main build failed x internal arcade services internal ci failed summary finished fri jul gmt duration minutes requested for ricardo arenas reason manual details deploy warning error failed to update deployment history error conflict code validate deployment x test run failed warning vstest failed with error check logs for failures there might be failed tests x error the process d a work tasks vstest modules dtaexecutionhost exe failed with exit code x vstest failed with error check logs for failures there might be failed tests changes matt galbraith suppress codeql warning about local sqlexpress usage jon fortescue upgrade rolloutscorerazurefunction to work with | 0 |
17,265 | 23,046,129,758 | IssuesEvent | 2022-07-23 23:27:37 | tokio-rs/tokio | https://api.github.com/repos/tokio-rs/tokio | closed | process: fix tokio process abort issues on windows | C-bug M-process | Unfortunately, as a result of https://github.com/rust-lang/rust/pull/95469, we can no longer use `tokio::process` to communicate with child processes which are themselves rust binaries using std or tokio for stdio. Doing so may result in the child process being aborted.
This was the cause of https://github.com/tokio-rs/tokio/issues/4801.
Unfortunately, this doesn't have an easy solution. What we probably need to do is either have the normal stdio stuff use mio, or have the child process stdio use the blocking pool. The latter is very much the better option since we don't want to risk causing issues by setting stdin/stdout to be nonblocking on windows. | 1.0 | process: fix tokio process abort issues on windows - Unfortunately, as a result of https://github.com/rust-lang/rust/pull/95469, we can no longer use `tokio::process` to communicate with child processes which are themselves rust binaries using std or tokio for stdio. Doing so may result in the child process being aborted.
This was the cause of https://github.com/tokio-rs/tokio/issues/4801.
Unfortunately, this doesn't have an easy solution. What we probably need to do is either have the normal stdio stuff use mio, or have the child process stdio use the blocking pool. The latter is very much the better option since we don't want to risk causing issues by setting stdin/stdout to be nonblocking on windows. | non_priority | process fix tokio process abort issues on windows unfortunately as a result of we can no longer use tokio process to communicate with child processes which are themselves rust binaries using std or tokio for stdio doing so may result in the child process being aborted this was the cause of unfortunately this doesn t have an easy solution what we probably need to do is either have the normal stdio stuff use mio or have the child process stdio use the blocking pool the latter is very much the better option since we don t want to risk causing issues by setting stdin stdout to be nonblocking on windows | 0 |
60,057 | 14,699,245,888 | IssuesEvent | 2021-01-04 08:13:05 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | opened | [SB] UI > Forgot Password page > Placeholder text turns grey on mouse hover of 'Back to sign in' link | P2 Study builder UI | Steps:
1. Open SB signin page
2. Click on forgot passowrd
3. Mouse hover on 'Back to sign in' link
4. Observe the colour
Actual: Placeholder text turns grey on mouse hover of 'Back to sign in' link
Expected: When mouse hovered on the link, more visible colour should be displayed to user
| 1.0 | [SB] UI > Forgot Password page > Placeholder text turns grey on mouse hover of 'Back to sign in' link - Steps:
1. Open SB signin page
2. Click on forgot passowrd
3. Mouse hover on 'Back to sign in' link
4. Observe the colour
Actual: Placeholder text turns grey on mouse hover of 'Back to sign in' link
Expected: When mouse hovered on the link, more visible colour should be displayed to user
| non_priority | ui forgot password page placeholder text turns grey on mouse hover of back to sign in link steps open sb signin page click on forgot passowrd mouse hover on back to sign in link observe the colour actual placeholder text turns grey on mouse hover of back to sign in link expected when mouse hovered on the link more visible colour should be displayed to user | 0 |
443,923 | 30,987,668,970 | IssuesEvent | 2023-08-09 00:01:31 | myoung34/docker-github-actions-runner | https://api.github.com/repos/myoung34/docker-github-actions-runner | closed | Doubt about app_token.sh | documentation help wanted good first issue | I've not found anything in documentation about the GitHub App permissions needed to be able to register a runner for a given repo/org/enterprise.
I've read the needed PAT permission here
https://github.com/myoung34/docker-github-actions-runner/wiki/Usage#token-scope
but the mapping to App permission is not trivial. Can you help me? | 1.0 | Doubt about app_token.sh - I've not found anything in documentation about the GitHub App permissions needed to be able to register a runner for a given repo/org/enterprise.
I've read the needed PAT permission here
https://github.com/myoung34/docker-github-actions-runner/wiki/Usage#token-scope
but the mapping to App permission is not trivial. Can you help me? | non_priority | doubt about app token sh i ve not found anything in documentation about the github app permissions needed to be able to register a runner for a given repo org enterprise i ve read the needed pat permission here but the mapping to app permission is not trivial can you help me | 0 |
299,101 | 25,881,750,816 | IssuesEvent | 2022-12-14 11:46:17 | openBackhaul/ApplicationLayerTopology | https://api.github.com/repos/openBackhaul/ApplicationLayerTopology | opened | Add testcase for topology-change-information notified to network-control-domain of ALT | testsuite_to_be_changed | In version 1.0.0, forwarding the topology-change-information of ALT control-construct to ALT itself was like posting redundant data since, ALT's config data is also present inside network-control-domain of ALT.
In version 2.0.0, the application-data (network-control-domain) is segregated from config-data and placed in an external ElasticSearch database. So, now the topology-change-information should be updated to ES client, to maintain synchronized data.
As a result of this, we need to write testcases for checking is the forwarding is happening for any topology-updates.
This testcases should be added for the following:
- Update LTP notified?
- [ ] /v1/bequeath-your-data-and-die
- [ ] /v1/regard-application
- Delete LTP and dependents notified?
- [ ] /v1/disregard-application
- Update FC notified?
- [ ] /v1/regard-application
- Delete FC port notified?
- [ ] /v1/end-subscription | 1.0 | Add testcase for topology-change-information notified to network-control-domain of ALT - In version 1.0.0, forwarding the topology-change-information of ALT control-construct to ALT itself was like posting redundant data since, ALT's config data is also present inside network-control-domain of ALT.
In version 2.0.0, the application-data (network-control-domain) is segregated from config-data and placed in an external ElasticSearch database. So, now the topology-change-information should be updated to ES client, to maintain synchronized data.
As a result of this, we need to write testcases for checking is the forwarding is happening for any topology-updates.
This testcases should be added for the following:
- Update LTP notified?
- [ ] /v1/bequeath-your-data-and-die
- [ ] /v1/regard-application
- Delete LTP and dependents notified?
- [ ] /v1/disregard-application
- Update FC notified?
- [ ] /v1/regard-application
- Delete FC port notified?
- [ ] /v1/end-subscription | non_priority | add testcase for topology change information notified to network control domain of alt in version forwarding the topology change information of alt control construct to alt itself was like posting redundant data since alt s config data is also present inside network control domain of alt in version the application data network control domain is segregated from config data and placed in an external elasticsearch database so now the topology change information should be updated to es client to maintain synchronized data as a result of this we need to write testcases for checking is the forwarding is happening for any topology updates this testcases should be added for the following update ltp notified bequeath your data and die regard application delete ltp and dependents notified disregard application update fc notified regard application delete fc port notified end subscription | 0 |
49,233 | 6,018,220,861 | IssuesEvent | 2017-06-07 11:45:57 | red/red | https://api.github.com/repos/red/red | closed | float and percent value can be divided by tuple, but result makes no sense | status.built status.tested type.review | ```
>> 1.0 / 2.3.4
== 2.3.4
>> 100% / 2.3.4
== 2.3.4
```
This would better be treated as error, like with integer divided by tuple (see previous issue) | 1.0 | float and percent value can be divided by tuple, but result makes no sense - ```
>> 1.0 / 2.3.4
== 2.3.4
>> 100% / 2.3.4
== 2.3.4
```
This would better be treated as error, like with integer divided by tuple (see previous issue) | non_priority | float and percent value can be divided by tuple but result makes no sense this would better be treated as error like with integer divided by tuple see previous issue | 0 |
212,126 | 16,473,617,671 | IssuesEvent | 2021-05-23 22:29:15 | ytmytm/geos | https://api.github.com/repos/ytmytm/geos | opened | Disk caches / RAM disk | documentation enhancement |
# design
There is enough RAM for:
- 1541 disk cache (3 banks, 256 pages each) and RAM disk (4 banks, 256 pages each), needs $0d80 bytes for disk driver swap space (end of cache bank 3 is enough)
- 1541 disk cache for 2 drives, no RAM disk
- 1571 disk cache (6 banks, 256 pages each), last bank unused
- RAM disk (7 banks, 256 pages each)
First and second option seems most useful - maybe this should be automatically decided upon boot - if drive #9 exists?
Large RAM disk is easy but without battery backup it would have to be filled manually on every boot.
# implementation
## disk cache
Reuse existing code for REU shadowing. Read/Write/Verify operations are needed, with common register setup.
## RAM disk
Completely new disk driver based on my old RAMDrives code,
`SetDevice` needs to be changed to support new disk driver swapper.
| 1.0 | Disk caches / RAM disk -
# design
There is enough RAM for:
- 1541 disk cache (3 banks, 256 pages each) and RAM disk (4 banks, 256 pages each), needs $0d80 bytes for disk driver swap space (end of cache bank 3 is enough)
- 1541 disk cache for 2 drives, no RAM disk
- 1571 disk cache (6 banks, 256 pages each), last bank unused
- RAM disk (7 banks, 256 pages each)
First and second option seems most useful - maybe this should be automatically decided upon boot - if drive #9 exists?
Large RAM disk is easy but without battery backup it would have to be filled manually on every boot.
# implementation
## disk cache
Reuse existing code for REU shadowing. Read/Write/Verify operations are needed, with common register setup.
## RAM disk
Completely new disk driver based on my old RAMDrives code,
`SetDevice` needs to be changed to support new disk driver swapper.
| non_priority | disk caches ram disk design there is enough ram for disk cache banks pages each and ram disk banks pages each needs bytes for disk driver swap space end of cache bank is enough disk cache for drives no ram disk disk cache banks pages each last bank unused ram disk banks pages each first and second option seems most useful maybe this should be automatically decided upon boot if drive exists large ram disk is easy but without battery backup it would have to be filled manually on every boot implementation disk cache reuse existing code for reu shadowing read write verify operations are needed with common register setup ram disk completely new disk driver based on my old ramdrives code setdevice needs to be changed to support new disk driver swapper | 0 |
19,752 | 3,252,444,490 | IssuesEvent | 2015-10-19 14:54:15 | idaholab/moose | https://api.github.com/repos/idaholab/moose | opened | Solution vectors are not restored when solve fails in sub-apps while doing Picard iterations | C: MOOSE P: normal T: defect | When running BISON (master) and RELAP-7 (sub-app), it can happen that RELAP-7 gets into a non-physical region which results in a NaN in the solution vector. MOOSE correctly cuts the time step in a half and tries to resolve, however, the initial vector on RELAP-7 side still has a NaN, so the solve aborts immediately, time steps gets cut again and so on until we reach dt_min. | 1.0 | Solution vectors are not restored when solve fails in sub-apps while doing Picard iterations - When running BISON (master) and RELAP-7 (sub-app), it can happen that RELAP-7 gets into a non-physical region which results in a NaN in the solution vector. MOOSE correctly cuts the time step in a half and tries to resolve, however, the initial vector on RELAP-7 side still has a NaN, so the solve aborts immediately, time steps gets cut again and so on until we reach dt_min. | non_priority | solution vectors are not restored when solve fails in sub apps while doing picard iterations when running bison master and relap sub app it can happen that relap gets into a non physical region which results in a nan in the solution vector moose correctly cuts the time step in a half and tries to resolve however the initial vector on relap side still has a nan so the solve aborts immediately time steps gets cut again and so on until we reach dt min | 0 |
128,268 | 18,042,580,321 | IssuesEvent | 2021-09-18 09:45:10 | alguerre/TrackEditorWeb | https://api.github.com/repos/alguerre/TrackEditorWeb | closed | Use github secrets for sensitive information | security | Passwords are exposed in settings.py and github action. They should be store under github secrets. | True | Use github secrets for sensitive information - Passwords are exposed in settings.py and github action. They should be store under github secrets. | non_priority | use github secrets for sensitive information passwords are exposed in settings py and github action they should be store under github secrets | 0 |
44,452 | 9,596,216,511 | IssuesEvent | 2019-05-09 18:01:44 | microsoft/calculator | https://api.github.com/repos/microsoft/calculator | closed | Remove Serialize/Deserialize functions never used in StandardCalculatorViewModel, UnitConverter and UnitConverterViewModel | Bug Codebase Quality Pri: 3 in code review triage approved | **Describe the change requested**
`StandardCalculatorViewModel` as well as `UnitConverterViewModel` and `UnitConverter` contain custom binary serializers and deserializers never used by the application. I suspect they were used a long time ago when the app lifecycle model was more restricted (Windows Phone 8/8.1?).
These unused functions make it harder to add features or refactor these 3 classes, especially due to the format used (custom binary serialization).
A big part of the information saved by `UnitConverter` for example is not relevant or is redundant:
- `CurrentCategory` is already saved in `LocalSettings` by `MainPage`
- `FromType` and `ToType` are already saved by the function `UnitConverter::SaveUserPreferences` (in file) as well as by `UnitConverterViewModel::SaveUserPreferences()` (in LocalSettings)
- `ratioMapTokens` is based on static data (for unit conversion) or data already backed up by `CurrencyDataLoader`
**Prerequisite**
Be sure Microsoft doesn't use these functions in tools or code not in the git repository (integration tests, tools used by QA, etc..)
**Functions no longer used we can remove**
- CalculatorManager::SerializeCommands
- CalculatorManager::DeSerializeCommands
- UnitConverter::StringToCategory
- UnitConverter::StringToConversionData
- UnitConverter::ConversionDataToString
- UnitConverter::Serialize
- UnitConverter::DeSerialize
- StandardCalculatorViewModel::Serialize
- StandardCalculatorViewModel::Deserialize
- UnitConverterViewModel::Serialize
- UnitConverterViewModel::Deserialize | 2.0 | Remove Serialize/Deserialize functions never used in StandardCalculatorViewModel, UnitConverter and UnitConverterViewModel - **Describe the change requested**
`StandardCalculatorViewModel` as well as `UnitConverterViewModel` and `UnitConverter` contain custom binary serializers and deserializers never used by the application. I suspect they were used a long time ago when the app lifecycle model was more restricted (Windows Phone 8/8.1?).
These unused functions make it harder to add features or refactor these 3 classes, especially due to the format used (custom binary serialization).
A big part of the information saved by `UnitConverter` for example is not relevant or is redundant:
- `CurrentCategory` is already saved in `LocalSettings` by `MainPage`
- `FromType` and `ToType` are already saved by the function `UnitConverter::SaveUserPreferences` (in file) as well as by `UnitConverterViewModel::SaveUserPreferences()` (in LocalSettings)
- `ratioMapTokens` is based on static data (for unit conversion) or data already backed up by `CurrencyDataLoader`
**Prerequisite**
Be sure Microsoft doesn't use these functions in tools or code not in the git repository (integration tests, tools used by QA, etc..)
**Functions no longer used we can remove**
- CalculatorManager::SerializeCommands
- CalculatorManager::DeSerializeCommands
- UnitConverter::StringToCategory
- UnitConverter::StringToConversionData
- UnitConverter::ConversionDataToString
- UnitConverter::Serialize
- UnitConverter::DeSerialize
- StandardCalculatorViewModel::Serialize
- StandardCalculatorViewModel::Deserialize
- UnitConverterViewModel::Serialize
- UnitConverterViewModel::Deserialize | non_priority | remove serialize deserialize functions never used in standardcalculatorviewmodel unitconverter and unitconverterviewmodel describe the change requested standardcalculatorviewmodel as well as unitconverterviewmodel and unitconverter contain custom binary serializers and deserializers never used by the application i suspect they were used a long time ago when the app lifecycle model was more restricted windows phone these unused functions make it harder to add features or refactor these classes especially due to the format used custom binary serialization a big part of the information saved by unitconverter for example is not relevant or is redundant currentcategory is already saved in localsettings by mainpage fromtype and totype are already saved by the function unitconverter saveuserpreferences in file as well as by unitconverterviewmodel saveuserpreferences in localsettings ratiomaptokens is based on static data for unit conversion or data already backed up by currencydataloader prerequisite be sure microsoft doesn t use these functions in tools or code not in the git repository integration tests tools used by qa etc functions no longer used we can remove calculatormanager serializecommands calculatormanager deserializecommands unitconverter stringtocategory unitconverter stringtoconversiondata unitconverter conversiondatatostring unitconverter serialize unitconverter deserialize standardcalculatorviewmodel serialize standardcalculatorviewmodel deserialize unitconverterviewmodel serialize unitconverterviewmodel deserialize | 0 |
239,445 | 18,273,753,055 | IssuesEvent | 2021-10-04 16:18:51 | CarsOk/proyecto-formativo-cinyuje | https://api.github.com/repos/CarsOk/proyecto-formativo-cinyuje | opened | Introduction and purpose of the SRS | documentation | Attach the introduction and purpose information of the SRS | 1.0 | Introduction and purpose of the SRS - Attach the introduction and purpose information of the SRS | non_priority | introduction and purpose of the srs attach the introduction and purpose information of the srs | 0 |
100,365 | 30,682,875,996 | IssuesEvent | 2023-07-26 10:18:37 | ToolJet/ToolJet | https://api.github.com/repos/ToolJet/ToolJet | opened | Folders in query manager | feature request appbuilder App Execution Engine Query Manager | ### Is your proposal related to a problem?
Query manager does not support organising queries under folders at the moment
### Describe the solution you'd like
As a developer, I should be able to:
1. Add folders on to the queries section of the query manager
2. Delete folders
3. Rename folder
4. Move existing queries in and out of folders
5. Add new queries directly on to selected folders
6. If a query `myQuery` is moved inside folder `myFolder`, then the query should be accessible as `queries.myFolder.myQuery`
Constraints on folders:
1. Nesting is not allowed, that is, folders are only there in the top level, we cannot add a folder inside another folder
2. Folder naming:
1. Unique ( Cannot share name with another folder or query )
2. Alphanumeric
3. No special characters or white spaces
4. Cannot start with a number
5. A minimum of 1 character and maximum of 32 characters
| 1.0 | Folders in query manager - ### Is your proposal related to a problem?
Query manager does not support organising queries under folders at the moment
### Describe the solution you'd like
As a developer, I should be able to:
1. Add folders on to the queries section of the query manager
2. Delete folders
3. Rename folder
4. Move existing queries in and out of folders
5. Add new queries directly on to selected folders
6. If a query `myQuery` is moved inside folder `myFolder`, then the query should be accessible as `queries.myFolder.myQuery`
Constraints on folders:
1. Nesting is not allowed, that is, folders are only there in the top level, we cannot add a folder inside another folder
2. Folder naming:
1. Unique ( Cannot share name with another folder or query )
2. Alphanumeric
3. No special characters or white spaces
4. Cannot start with a number
5. A minimum of 1 character and maximum of 32 characters
| non_priority | folders in query manager is your proposal related to a problem query manager does not support organising queries under folders at the moment describe the solution you d like as a developer i should be able to add folders on to the queries section of the query manager delete folders rename folder move existing queries in and out of folders add new queries directly on to selected folders if a query myquery is moved inside folder myfolder then the query should be accessible as queries myfolder myquery constraints on folders nesting is not allowed that is folders are only there in the top level we cannot add a folder inside another folder folder naming unique cannot share name with another folder or query alphanumeric no special characters or white spaces cannot start with a number a minimum of character and maximum of characters | 0 |
147,349 | 19,515,748,519 | IssuesEvent | 2021-12-29 09:55:44 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | [Security Solution]REMOVE and CHANGE button are not case sensitive | bug triage_needed Team: SecuritySolution | **Describe the bug**
`REMOVE` and `CHANGE ` button are not case sensitive
**Build Details**
```
Version:8.0.0-SNAPSHOT
Commit:4a1d5698fb0a452e2eebb91483d584334eeeeb59
Build:48876
```
**Steps**
- Login to Kibana version 8.0.0-SNAPSHOT
- Navigate to Alert Page and create few of the custom runtime fields
- Now navigate to Data view
- search for the created fields
- click on pencil icon to edit and change the existing name of the fields
- Observed that in `CHANGE` is mentioned however user can still process with small case change
- Observed the same for the `REMOVE` for removing the data view
**Screen-Shoot**
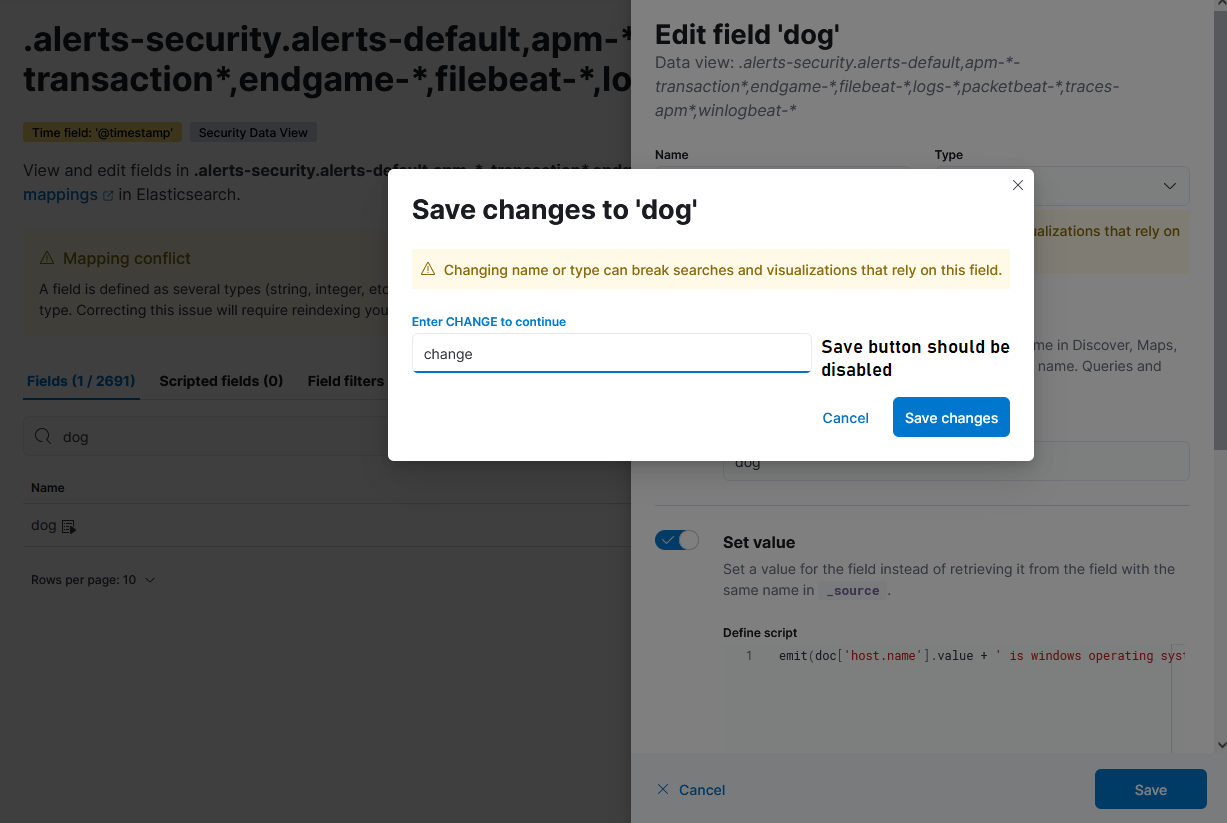
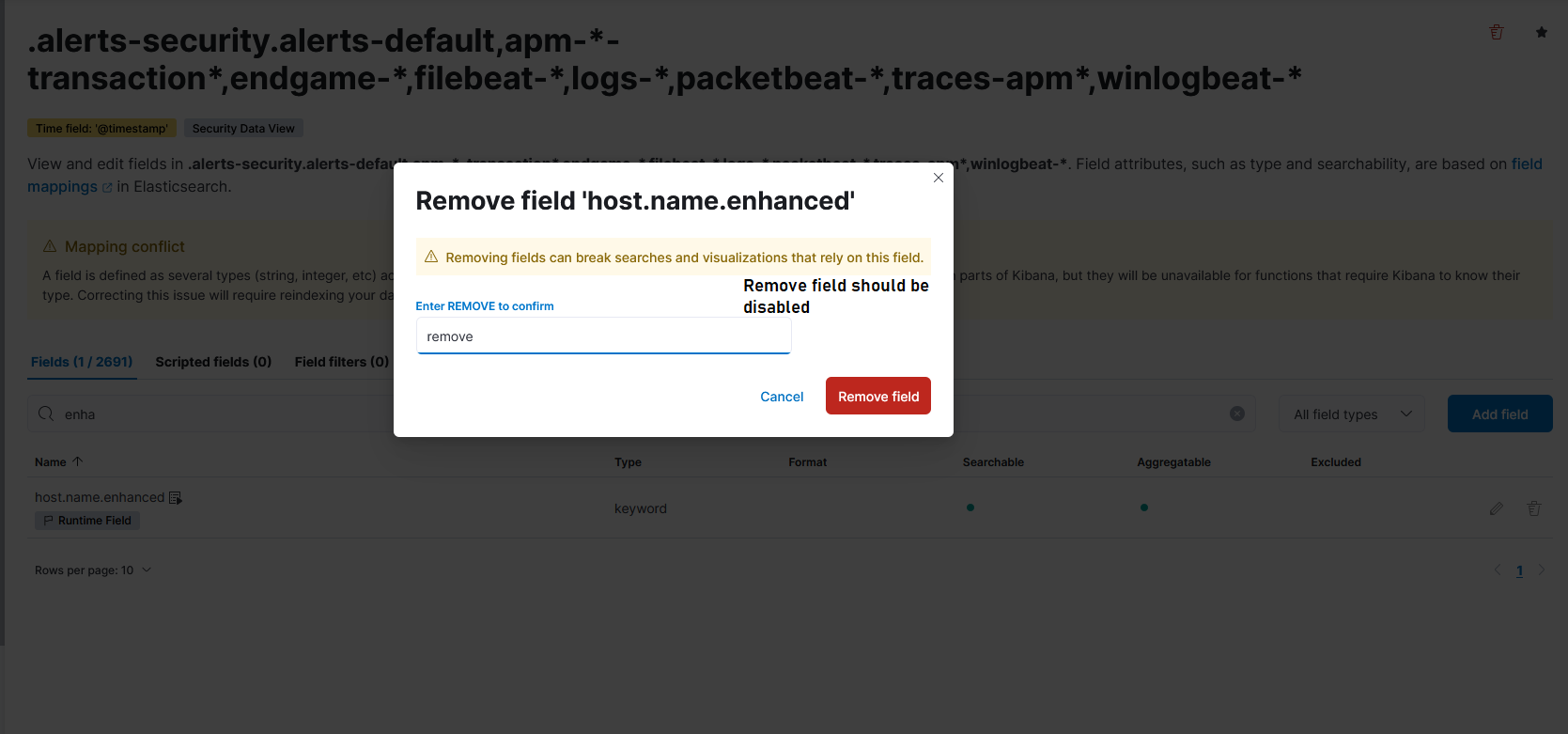
| True | [Security Solution]REMOVE and CHANGE button are not case sensitive - **Describe the bug**
`REMOVE` and `CHANGE ` button are not case sensitive
**Build Details**
```
Version:8.0.0-SNAPSHOT
Commit:4a1d5698fb0a452e2eebb91483d584334eeeeb59
Build:48876
```
**Steps**
- Login to Kibana version 8.0.0-SNAPSHOT
- Navigate to Alert Page and create few of the custom runtime fields
- Now navigate to Data view
- search for the created fields
- click on pencil icon to edit and change the existing name of the fields
- Observed that in `CHANGE` is mentioned however user can still process with small case change
- Observed the same for the `REMOVE` for removing the data view
**Screen-Shoot**
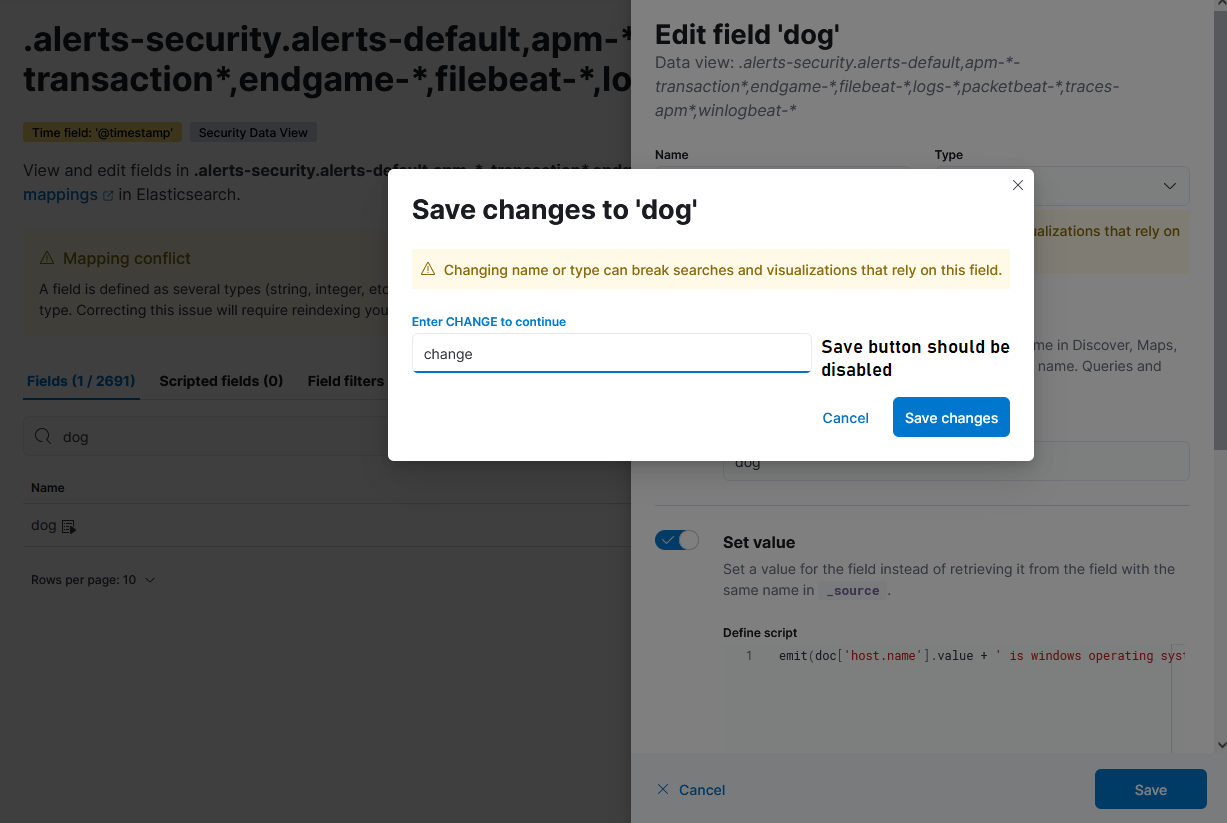
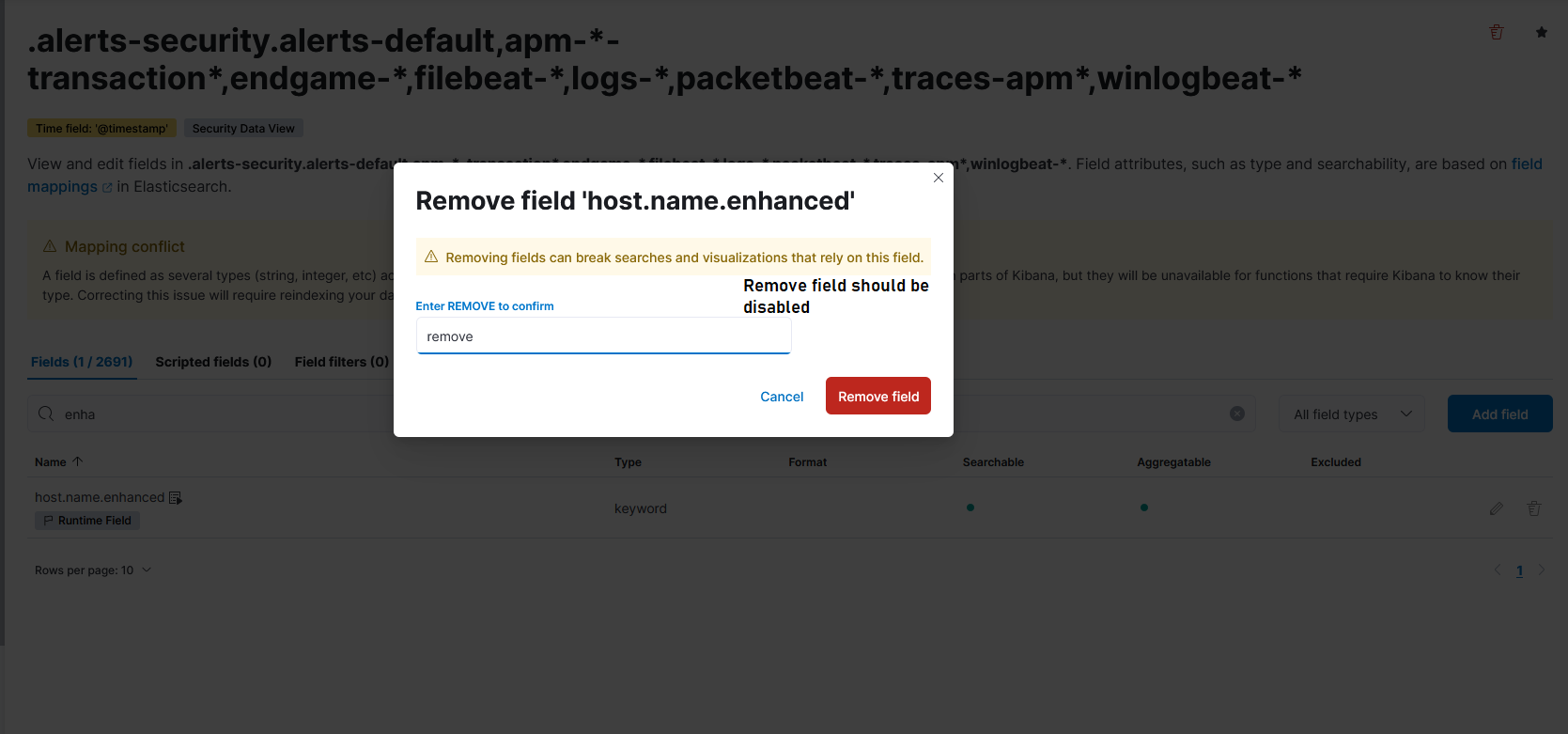
| non_priority | remove and change button are not case sensitive describe the bug remove and change button are not case sensitive build details version snapshot commit build steps login to kibana version snapshot navigate to alert page and create few of the custom runtime fields now navigate to data view search for the created fields click on pencil icon to edit and change the existing name of the fields observed that in change is mentioned however user can still process with small case change observed the same for the remove for removing the data view screen shoot | 0 |
29,613 | 4,175,207,869 | IssuesEvent | 2016-06-21 16:09:15 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | Tooltip under "Not available for Firefox" text is not working when hovering over it | redesign style refresh wont fix | Prerequisites:
Build identifier: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:47.0) Gecko/20100101 Firefox/47.0
Step to reproduce:
1.Go to any addons listing page where we have an incompatible addon (ie. see first addon from https://addons-dev.allizom.org/en-US/firefox/search/?q=evernote&cat=1%2C0&appver=47.0&platform=windows )
2.Hover over the addon and observe the Tooltip under "Not available for Firefox" text
3.Hover over the tooltip
Expected results:
Tooltip text is automatically displayed when hovering over it
Actual results:
Nothing happens
Please see video for this bug :
 | 1.0 | Tooltip under "Not available for Firefox" text is not working when hovering over it - Prerequisites:
Build identifier: Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:47.0) Gecko/20100101 Firefox/47.0
Step to reproduce:
1.Go to any addons listing page where we have an incompatible addon (ie. see first addon from https://addons-dev.allizom.org/en-US/firefox/search/?q=evernote&cat=1%2C0&appver=47.0&platform=windows )
2.Hover over the addon and observe the Tooltip under "Not available for Firefox" text
3.Hover over the tooltip
Expected results:
Tooltip text is automatically displayed when hovering over it
Actual results:
Nothing happens
Please see video for this bug :
 | non_priority | tooltip under not available for firefox text is not working when hovering over it prerequisites build identifier mozilla windows nt rv gecko firefox step to reproduce go to any addons listing page where we have an incompatible addon ie see first addon from hover over the addon and observe the tooltip under not available for firefox text hover over the tooltip expected results tooltip text is automatically displayed when hovering over it actual results nothing happens please see video for this bug | 0 |
134,449 | 10,916,454,298 | IssuesEvent | 2019-11-21 13:24:06 | imbitdhbwma/brillianplatform | https://api.github.com/repos/imbitdhbwma/brillianplatform | closed | CUR: Inhalte fehlen | Projektmanagement Testing | Im Curriculum fehlen auf einigen Seiten links Inhalte.
Explizit genannt wurden in der Analyse die Schlüsselqualifikationen (II und III), Global Project Management und Dienstleistungsmanagement. Aber es gibt auch noch andere Seiten auf denen nur ein oder zwei Einträge vorhanden sind, vielleicht sollte man da auch noch was hinzufügen.
| 1.0 | CUR: Inhalte fehlen - Im Curriculum fehlen auf einigen Seiten links Inhalte.
Explizit genannt wurden in der Analyse die Schlüsselqualifikationen (II und III), Global Project Management und Dienstleistungsmanagement. Aber es gibt auch noch andere Seiten auf denen nur ein oder zwei Einträge vorhanden sind, vielleicht sollte man da auch noch was hinzufügen.
| non_priority | cur inhalte fehlen im curriculum fehlen auf einigen seiten links inhalte explizit genannt wurden in der analyse die schlüsselqualifikationen ii und iii global project management und dienstleistungsmanagement aber es gibt auch noch andere seiten auf denen nur ein oder zwei einträge vorhanden sind vielleicht sollte man da auch noch was hinzufügen | 0 |
59,582 | 24,825,054,686 | IssuesEvent | 2022-10-25 19:51:21 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Please improve the documentation for the OIDC Issuer feature | container-service/svc triaged assigned-to-author doc-enhancement product-question Pri1 | I came to this page from the AKS release notes, saying that "OIDC Issuer is now Generally Available". However, the docs here don't help me at all to understand what this feature is all about.
> OIDC Issuer
>
> This enables an OIDC Issuer URL of the provider which allows the API server to discover public signing keys.
What does this mean? What provider? What do I do with an OIDC Issuer URL? Why and how would I use this feature?
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: e1e42fdb-aa59-786b-ba0d-659f67db3cf3
* Version Independent ID: cc199e1d-6737-5f52-f2a2-b6c0b603dbdc
* Content: [Cluster configuration in Azure Kubernetes Services (AKS) - Azure Kubernetes Service](https://learn.microsoft.com/en-us/azure/aks/cluster-configuration#oidc-issuer)
* Content Source: [articles/aks/cluster-configuration.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/aks/cluster-configuration.md)
* Service: **container-service**
* GitHub Login: @MGoedtel
* Microsoft Alias: **magoedte** | 1.0 | Please improve the documentation for the OIDC Issuer feature - I came to this page from the AKS release notes, saying that "OIDC Issuer is now Generally Available". However, the docs here don't help me at all to understand what this feature is all about.
> OIDC Issuer
>
> This enables an OIDC Issuer URL of the provider which allows the API server to discover public signing keys.
What does this mean? What provider? What do I do with an OIDC Issuer URL? Why and how would I use this feature?
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: e1e42fdb-aa59-786b-ba0d-659f67db3cf3
* Version Independent ID: cc199e1d-6737-5f52-f2a2-b6c0b603dbdc
* Content: [Cluster configuration in Azure Kubernetes Services (AKS) - Azure Kubernetes Service](https://learn.microsoft.com/en-us/azure/aks/cluster-configuration#oidc-issuer)
* Content Source: [articles/aks/cluster-configuration.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/aks/cluster-configuration.md)
* Service: **container-service**
* GitHub Login: @MGoedtel
* Microsoft Alias: **magoedte** | non_priority | please improve the documentation for the oidc issuer feature i came to this page from the aks release notes saying that oidc issuer is now generally available however the docs here don t help me at all to understand what this feature is all about oidc issuer this enables an oidc issuer url of the provider which allows the api server to discover public signing keys what does this mean what provider what do i do with an oidc issuer url why and how would i use this feature document details ⚠ do not edit this section it is required for learn microsoft com ➟ github issue linking id version independent id content content source service container service github login mgoedtel microsoft alias magoedte | 0 |
328,236 | 28,107,242,474 | IssuesEvent | 2023-03-31 02:29:05 | DevelopLife/reviewtwits_backend | https://api.github.com/repos/DevelopLife/reviewtwits_backend | closed | [refactor] EC2 서버에 저장되던 파일을 S3로 옮겨 저장하기 | feat test | # 🛠 Issue
파일을 EC2 서버에 저장하게 되면, EC2를 여러 개 사용하여 LoadBalancing 할 때 파일들이 각자 다른 EC2 서버에 저장되게 되는 이슈가 생긴다.
파일을 S3에 일괄적으로 저장하여, 서로 다른 EC2 서버에 요청이 분산되더라도 파일을 잘 줄 수 있도록 만들자.
# 📝 Todo
1. AWS S3 를 활용하여 파일 저장, 파일 가지고 오기 기능 만들기
2. 기존의 FileStoreService 에 해당 기능을 접목시켜 붙이기
3. S3 로 저장되어도 잘 통과할 수 있게 테스트 내용 고치기 | 1.0 | [refactor] EC2 서버에 저장되던 파일을 S3로 옮겨 저장하기 - # 🛠 Issue
파일을 EC2 서버에 저장하게 되면, EC2를 여러 개 사용하여 LoadBalancing 할 때 파일들이 각자 다른 EC2 서버에 저장되게 되는 이슈가 생긴다.
파일을 S3에 일괄적으로 저장하여, 서로 다른 EC2 서버에 요청이 분산되더라도 파일을 잘 줄 수 있도록 만들자.
# 📝 Todo
1. AWS S3 를 활용하여 파일 저장, 파일 가지고 오기 기능 만들기
2. 기존의 FileStoreService 에 해당 기능을 접목시켜 붙이기
3. S3 로 저장되어도 잘 통과할 수 있게 테스트 내용 고치기 | non_priority | 서버에 저장되던 파일을 옮겨 저장하기 🛠 issue 파일을 서버에 저장하게 되면 여러 개 사용하여 loadbalancing 할 때 파일들이 각자 다른 서버에 저장되게 되는 이슈가 생긴다 파일을 일괄적으로 저장하여 서로 다른 서버에 요청이 분산되더라도 파일을 잘 줄 수 있도록 만들자 📝 todo aws 를 활용하여 파일 저장 파일 가지고 오기 기능 만들기 기존의 filestoreservice 에 해당 기능을 접목시켜 붙이기 로 저장되어도 잘 통과할 수 있게 테스트 내용 고치기 | 0 |
198,447 | 15,709,850,469 | IssuesEvent | 2021-03-26 23:38:53 | PlayPickUp/pickup-ui | https://api.github.com/repos/PlayPickUp/pickup-ui | opened | Update / Create UI Docs | documentation 📝 enhancement ✨ | The docs at https://ui.playpickup.com (storybook) are not up to date and need to be updated ASAP for a better developer experience. | 1.0 | Update / Create UI Docs - The docs at https://ui.playpickup.com (storybook) are not up to date and need to be updated ASAP for a better developer experience. | non_priority | update create ui docs the docs at storybook are not up to date and need to be updated asap for a better developer experience | 0 |
1,372 | 5,949,202,693 | IssuesEvent | 2017-05-26 13:42:50 | MDAnalysis/mdanalysis | https://api.github.com/repos/MDAnalysis/mdanalysis | closed | Inconsistent behavior of align functions | Component-Analysis maintainability question refactoring usability | In #714 the rmsd functions default behavior is changed and I looked if this would affect potential uses of it in `align.py`. I found that the functions/classes in there to alignment all slightly differently.
1. **mass_weighted**
`rotation_matrix` and `rmsd` use weights relative to the mean weight for calculations. In eg `alignto` it
means we use the center_of_mass for translational centering AND the mass as additional fit weights.
2. **rms_fit_trj**
This function is only using the center of mass for centering. Weights are optionally given to the
alignment function `CalcRMSDRotationalMatrix`.
3. **CalcRMSDRotationalMatrix**
This is used directly in functions that work on AtomGroups in `align.py` and `rms.py` instead of
the wrapper functions `rmsd` and `rotation_matrix`. Only Exception `alignto`.
All of this can be fixed when we port the alignment to the new `BaseAnalysis` class. The questions is what unified behavior should they have (similar/same keywords should have the same effect in different functions).
| True | Inconsistent behavior of align functions - In #714 the rmsd functions default behavior is changed and I looked if this would affect potential uses of it in `align.py`. I found that the functions/classes in there to alignment all slightly differently.
1. **mass_weighted**
`rotation_matrix` and `rmsd` use weights relative to the mean weight for calculations. In eg `alignto` it
means we use the center_of_mass for translational centering AND the mass as additional fit weights.
2. **rms_fit_trj**
This function is only using the center of mass for centering. Weights are optionally given to the
alignment function `CalcRMSDRotationalMatrix`.
3. **CalcRMSDRotationalMatrix**
This is used directly in functions that work on AtomGroups in `align.py` and `rms.py` instead of
the wrapper functions `rmsd` and `rotation_matrix`. Only Exception `alignto`.
All of this can be fixed when we port the alignment to the new `BaseAnalysis` class. The questions is what unified behavior should they have (similar/same keywords should have the same effect in different functions).
| non_priority | inconsistent behavior of align functions in the rmsd functions default behavior is changed and i looked if this would affect potential uses of it in align py i found that the functions classes in there to alignment all slightly differently mass weighted rotation matrix and rmsd use weights relative to the mean weight for calculations in eg alignto it means we use the center of mass for translational centering and the mass as additional fit weights rms fit trj this function is only using the center of mass for centering weights are optionally given to the alignment function calcrmsdrotationalmatrix calcrmsdrotationalmatrix this is used directly in functions that work on atomgroups in align py and rms py instead of the wrapper functions rmsd and rotation matrix only exception alignto all of this can be fixed when we port the alignment to the new baseanalysis class the questions is what unified behavior should they have similar same keywords should have the same effect in different functions | 0 |
119,191 | 17,604,122,741 | IssuesEvent | 2021-08-17 15:03:25 | ghc-dev/Jason-Mcbride | https://api.github.com/repos/ghc-dev/Jason-Mcbride | opened | CVE-2021-3533 (Low) detected in ansible-2.9.9.tar.gz | security vulnerability | ## CVE-2021-3533 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: Jason-Mcbride/requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Jason-Mcbride/commit/2ecec95f645c09f7a2384dcbd90766ee1417fb5e">2ecec95f645c09f7a2384dcbd90766ee1417fb5e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Vulnerability in ansible when ANSIBLE_ASYNC_DIR defaults to ~/.ansible_async/ but is settable by the user. It can be set by the ansible user to a subdirectory of a world writable directory, for instance ANSIBLE_ASYNC_DIR=/tmp/username-ansible-async/. When this occurs, there is a race condition on the managed machine. A malicious, low privileged account on the remote machine can pre-create /tmp/username-ansible-async and then use various attacks to access the async result data.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3533>CVE-2021-3533</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>2.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ansible","packageVersion":"2.9.9","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"ansible:2.9.9","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-3533","vulnerabilityDetails":"Vulnerability in ansible when ANSIBLE_ASYNC_DIR defaults to ~/.ansible_async/ but is settable by the user. It can be set by the ansible user to a subdirectory of a world writable directory, for instance ANSIBLE_ASYNC_DIR\u003d/tmp/username-ansible-async/. When this occurs, there is a race condition on the managed machine. A malicious, low privileged account on the remote machine can pre-create /tmp/username-ansible-async and then use various attacks to access the async result data.\n","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3533","cvss3Severity":"low","cvss3Score":"2.5","cvss3Metrics":{"A":"None","AC":"High","PR":"Low","S":"Unchanged","C":"Low","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-3533 (Low) detected in ansible-2.9.9.tar.gz - ## CVE-2021-3533 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ansible-2.9.9.tar.gz</b></p></summary>
<p>Radically simple IT automation</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz">https://files.pythonhosted.org/packages/00/5d/e10b83e0e6056dbd5b4809b451a191395175a57e3175ce04e35d9c5fc2a0/ansible-2.9.9.tar.gz</a></p>
<p>Path to dependency file: Jason-Mcbride/requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **ansible-2.9.9.tar.gz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Jason-Mcbride/commit/2ecec95f645c09f7a2384dcbd90766ee1417fb5e">2ecec95f645c09f7a2384dcbd90766ee1417fb5e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Vulnerability in ansible when ANSIBLE_ASYNC_DIR defaults to ~/.ansible_async/ but is settable by the user. It can be set by the ansible user to a subdirectory of a world writable directory, for instance ANSIBLE_ASYNC_DIR=/tmp/username-ansible-async/. When this occurs, there is a race condition on the managed machine. A malicious, low privileged account on the remote machine can pre-create /tmp/username-ansible-async and then use various attacks to access the async result data.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3533>CVE-2021-3533</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>2.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Python","packageName":"ansible","packageVersion":"2.9.9","packageFilePaths":["/requirements.txt"],"isTransitiveDependency":false,"dependencyTree":"ansible:2.9.9","isMinimumFixVersionAvailable":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-3533","vulnerabilityDetails":"Vulnerability in ansible when ANSIBLE_ASYNC_DIR defaults to ~/.ansible_async/ but is settable by the user. It can be set by the ansible user to a subdirectory of a world writable directory, for instance ANSIBLE_ASYNC_DIR\u003d/tmp/username-ansible-async/. When this occurs, there is a race condition on the managed machine. A malicious, low privileged account on the remote machine can pre-create /tmp/username-ansible-async and then use various attacks to access the async result data.\n","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3533","cvss3Severity":"low","cvss3Score":"2.5","cvss3Metrics":{"A":"None","AC":"High","PR":"Low","S":"Unchanged","C":"Low","UI":"None","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve low detected in ansible tar gz cve low severity vulnerability vulnerable library ansible tar gz radically simple it automation library home page a href path to dependency file jason mcbride requirements txt path to vulnerable library requirements txt dependency hierarchy x ansible tar gz vulnerable library found in head commit a href found in base branch master vulnerability details vulnerability in ansible when ansible async dir defaults to ansible async but is settable by the user it can be set by the ansible user to a subdirectory of a world writable directory for instance ansible async dir tmp username ansible async when this occurs there is a race condition on the managed machine a malicious low privileged account on the remote machine can pre create tmp username ansible async and then use various attacks to access the async result data publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree ansible isminimumfixversionavailable false basebranches vulnerabilityidentifier cve vulnerabilitydetails vulnerability in ansible when ansible async dir defaults to ansible async but is settable by the user it can be set by the ansible user to a subdirectory of a world writable directory for instance ansible async dir tmp username ansible async when this occurs there is a race condition on the managed machine a malicious low privileged account on the remote machine can pre create tmp username ansible async and then use various attacks to access the async result data n vulnerabilityurl | 0 |
44,524 | 5,843,256,345 | IssuesEvent | 2017-05-10 08:43:17 | canonical-ols/build.snapcraft.io | https://api.github.com/repos/canonical-ols/build.snapcraft.io | opened | Match snapcraft and the dashboard's use of publish and release | Design: Required | It [was raised in the forum](https://forum.snapcraft.io/t/publish-or-release/518/11) that "publish" should be used when we speak about an ISV offering their applications and "release" for the action of making a version available (i.e. releasing into a channel).
If you disagree, by all means follow up on the forum thread. Otherwise, can we update the spec? | 1.0 | Match snapcraft and the dashboard's use of publish and release - It [was raised in the forum](https://forum.snapcraft.io/t/publish-or-release/518/11) that "publish" should be used when we speak about an ISV offering their applications and "release" for the action of making a version available (i.e. releasing into a channel).
If you disagree, by all means follow up on the forum thread. Otherwise, can we update the spec? | non_priority | match snapcraft and the dashboard s use of publish and release it that publish should be used when we speak about an isv offering their applications and release for the action of making a version available i e releasing into a channel if you disagree by all means follow up on the forum thread otherwise can we update the spec | 0 |
255,899 | 27,517,635,801 | IssuesEvent | 2023-03-06 13:05:00 | 389ds/389-ds-base | https://api.github.com/repos/389ds/389-ds-base | closed | UI - sensitive information disclosure | security cockpit | **Issue Description**
When editing credentials for replication agreement, password is passed as an argument to dsconf in clear text. This can be seen in the console log and by technically by running "ps -ef" whiel the command is still running.
Also the password hash can be seen by a non-privileged user (using pspy64) when searching the database from the UI | True | UI - sensitive information disclosure - **Issue Description**
When editing credentials for replication agreement, password is passed as an argument to dsconf in clear text. This can be seen in the console log and by technically by running "ps -ef" whiel the command is still running.
Also the password hash can be seen by a non-privileged user (using pspy64) when searching the database from the UI | non_priority | ui sensitive information disclosure issue description when editing credentials for replication agreement password is passed as an argument to dsconf in clear text this can be seen in the console log and by technically by running ps ef whiel the command is still running also the password hash can be seen by a non privileged user using when searching the database from the ui | 0 |
75,196 | 20,719,406,457 | IssuesEvent | 2022-03-13 06:05:05 | JuliaLang/julia | https://api.github.com/repos/JuliaLang/julia | closed | build error/crash using out-of-tree build option | build | The files usually installed in JULIA_HOME/../share/julia/base using the default (in-tree?) build are installed in JULIA_HOME/../../base during an out-of-tree build.
The misplaced base directory results in crashes when julia attempts to access the files:
MichaelHatherly/Docile.jl#165
@MichaelHatherly
| 1.0 | build error/crash using out-of-tree build option - The files usually installed in JULIA_HOME/../share/julia/base using the default (in-tree?) build are installed in JULIA_HOME/../../base during an out-of-tree build.
The misplaced base directory results in crashes when julia attempts to access the files:
MichaelHatherly/Docile.jl#165
@MichaelHatherly
| non_priority | build error crash using out of tree build option the files usually installed in julia home share julia base using the default in tree build are installed in julia home base during an out of tree build the misplaced base directory results in crashes when julia attempts to access the files michaelhatherly docile jl michaelhatherly | 0 |
761 | 10,198,705,944 | IssuesEvent | 2019-08-13 06:25:23 | wahern/cqueues | https://api.github.com/repos/wahern/cqueues | closed | "This rockspec for cqueues does not support platforms." on openresty:alpine-fat. | packaging/portability | Hi, William
When I tryed to distribute docker image on alpine, cqueues was an error like title.
Do you know something what happened?
Dockerfile:
```
FROM openresty/openresty:alpine-fat
ARG GATEWAY_BASE_URL
ENV GATEWAY_BASE_URL ${GATEWAY_BASE_URL:-https://"mysite.com" }
COPY ./nginx/lua/md5sum /usr/bin
RUN apk add --no-cache autoconf openssl-dev build-base bsd-compat-headers dnsmasq
RUN /usr/local/openresty/luajit/bin/luarocks --verbose install cqueues
RUN /usr/local/openresty/luajit/bin/luarocks install http \
&& /usr/local/openresty/luajit/bin/luarocks install lua-resty-template \
&& /usr/local/openresty/luajit/bin/luarocks install lua-resty-http \
&& echo 'nameserver 127.0.0.1' >> /etc/resolv.conf \
&& addgroup -g 1000 nginx \
&& adduser -u 1000 -H -D -G nginx nginx
COPY ./nginx/lua /usr/local/openresty/nginx/lua
COPY ./nginx/conf.d /etc/nginx/conf.d
COPY ./nginx/nginx.conf /usr/local/openresty/nginx/conf/nginx.conf
COPY ./nginx/html/heartbeat/ /usr/local/openresty/nginx/html/heartbeat/
COPY ./nginx/html/health/ /usr/local/openresty/nginx/html/health/
COPY ./nginx/html/loader/ /usr/local/openresty/nginx/html/loader/
```
Errored:
```
> docker build -t proxy ./
Sending build context to Docker daemon 143.9kB
Step 1/13 : FROM openresty/openresty:alpine-fat
---> 741e0c64e7b5
Step 2/13 : ARG GATEWAY_BASE_URL
---> Using cache
---> 7c2da32b3d7a
Step 3/13 : ENV GATEWAY_BASE_URL ${GATEWAY_BASE_URL:-https://gateway.dmm.com}
---> Using cache
---> 9637666acb0b
Step 4/13 : COPY ./nginx/lua/md5sum /usr/bin
---> Using cache
---> 9a841512af85
Step 5/13 : RUN apk add --no-cache autoconf openssl-dev build-base bsd-compat-headers dnsmasq
---> Using cache
---> a4a31009a6bf
Step 6/13 : RUN /usr/local/openresty/luajit/bin/luarocks --verbose install cqueues
---> Running in c6c364697808
os.execute: cd '/' && test '-d' '//./.luarocks'
Results: 3
1 (nil): nil
2 (string): exit
3 (number): 1
...(snip)
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/include/openssl/crypto.h'
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/lib/libcrypto.a'
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/local/include/openssl/ssl.h'
Results: 3
1 (nil): nil
2 (string): exit
3 (number): 1
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/local/include/openssl/ssl.h'
Results: 3
1 (nil): nil
2 (string): exit
3 (number): 1
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/include/openssl/ssl.h'
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/lib/libssl.a'
Error: This rockspec for cqueues does not support platforms.
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
...(snip)
The command '/bin/sh -c /usr/local/openresty/luajit/bin/luarocks --verbose install cqueues' returned a non-zero code: 1
``` | True | "This rockspec for cqueues does not support platforms." on openresty:alpine-fat. - Hi, William
When I tryed to distribute docker image on alpine, cqueues was an error like title.
Do you know something what happened?
Dockerfile:
```
FROM openresty/openresty:alpine-fat
ARG GATEWAY_BASE_URL
ENV GATEWAY_BASE_URL ${GATEWAY_BASE_URL:-https://"mysite.com" }
COPY ./nginx/lua/md5sum /usr/bin
RUN apk add --no-cache autoconf openssl-dev build-base bsd-compat-headers dnsmasq
RUN /usr/local/openresty/luajit/bin/luarocks --verbose install cqueues
RUN /usr/local/openresty/luajit/bin/luarocks install http \
&& /usr/local/openresty/luajit/bin/luarocks install lua-resty-template \
&& /usr/local/openresty/luajit/bin/luarocks install lua-resty-http \
&& echo 'nameserver 127.0.0.1' >> /etc/resolv.conf \
&& addgroup -g 1000 nginx \
&& adduser -u 1000 -H -D -G nginx nginx
COPY ./nginx/lua /usr/local/openresty/nginx/lua
COPY ./nginx/conf.d /etc/nginx/conf.d
COPY ./nginx/nginx.conf /usr/local/openresty/nginx/conf/nginx.conf
COPY ./nginx/html/heartbeat/ /usr/local/openresty/nginx/html/heartbeat/
COPY ./nginx/html/health/ /usr/local/openresty/nginx/html/health/
COPY ./nginx/html/loader/ /usr/local/openresty/nginx/html/loader/
```
Errored:
```
> docker build -t proxy ./
Sending build context to Docker daemon 143.9kB
Step 1/13 : FROM openresty/openresty:alpine-fat
---> 741e0c64e7b5
Step 2/13 : ARG GATEWAY_BASE_URL
---> Using cache
---> 7c2da32b3d7a
Step 3/13 : ENV GATEWAY_BASE_URL ${GATEWAY_BASE_URL:-https://gateway.dmm.com}
---> Using cache
---> 9637666acb0b
Step 4/13 : COPY ./nginx/lua/md5sum /usr/bin
---> Using cache
---> 9a841512af85
Step 5/13 : RUN apk add --no-cache autoconf openssl-dev build-base bsd-compat-headers dnsmasq
---> Using cache
---> a4a31009a6bf
Step 6/13 : RUN /usr/local/openresty/luajit/bin/luarocks --verbose install cqueues
---> Running in c6c364697808
os.execute: cd '/' && test '-d' '//./.luarocks'
Results: 3
1 (nil): nil
2 (string): exit
3 (number): 1
...(snip)
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/include/openssl/crypto.h'
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/lib/libcrypto.a'
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/local/include/openssl/ssl.h'
Results: 3
1 (nil): nil
2 (string): exit
3 (number): 1
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/local/include/openssl/ssl.h'
Results: 3
1 (nil): nil
2 (string): exit
3 (number): 1
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/include/openssl/ssl.h'
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
os.execute: cd '/tmp/luarocks_cqueues-20171014.51-0-MeoDgj' && test '-f' '/usr/lib/libssl.a'
Error: This rockspec for cqueues does not support platforms.
Results: 3
1 (boolean): true
2 (string): exit
3 (number): 0
...(snip)
The command '/bin/sh -c /usr/local/openresty/luajit/bin/luarocks --verbose install cqueues' returned a non-zero code: 1
``` | non_priority | this rockspec for cqueues does not support platforms on openresty alpine fat hi william when i tryed to distribute docker image on alpine cqueues was an error like title do you know something what happened dockerfile from openresty openresty alpine fat arg gateway base url env gateway base url gateway base url copy nginx lua usr bin run apk add no cache autoconf openssl dev build base bsd compat headers dnsmasq run usr local openresty luajit bin luarocks verbose install cqueues run usr local openresty luajit bin luarocks install http usr local openresty luajit bin luarocks install lua resty template usr local openresty luajit bin luarocks install lua resty http echo nameserver etc resolv conf addgroup g nginx adduser u h d g nginx nginx copy nginx lua usr local openresty nginx lua copy nginx conf d etc nginx conf d copy nginx nginx conf usr local openresty nginx conf nginx conf copy nginx html heartbeat usr local openresty nginx html heartbeat copy nginx html health usr local openresty nginx html health copy nginx html loader usr local openresty nginx html loader errored docker build t proxy sending build context to docker daemon step from openresty openresty alpine fat step arg gateway base url using cache step env gateway base url gateway base url using cache step copy nginx lua usr bin using cache step run apk add no cache autoconf openssl dev build base bsd compat headers dnsmasq using cache step run usr local openresty luajit bin luarocks verbose install cqueues running in os execute cd test d luarocks results nil nil string exit number snip os execute cd tmp luarocks cqueues meodgj test f usr include openssl crypto h results boolean true string exit number os execute cd tmp luarocks cqueues meodgj test f usr lib libcrypto a results boolean true string exit number os execute cd tmp luarocks cqueues meodgj test f usr local include openssl ssl h results nil nil string exit number os execute cd tmp luarocks cqueues meodgj test f usr local include openssl ssl h results nil nil string exit number os execute cd tmp luarocks cqueues meodgj test f usr include openssl ssl h results boolean true string exit number os execute cd tmp luarocks cqueues meodgj test f usr lib libssl a error this rockspec for cqueues does not support platforms results boolean true string exit number snip the command bin sh c usr local openresty luajit bin luarocks verbose install cqueues returned a non zero code | 0 |
39,727 | 12,698,870,103 | IssuesEvent | 2020-06-22 14:04:05 | mahonec/WebGoat-Legacy | https://api.github.com/repos/mahonec/WebGoat-Legacy | opened | WS-2018-0021 (Medium) detected in bootstrap-3.1.1.min.js | security vulnerability | ## WS-2018-0021 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /WebGoat-Legacy/target/WebGoat-6.0.1/plugins/bootstrap/js/bootstrap.min.js,/WebGoat-Legacy/src/main/webapp/plugins/bootstrap/js/bootstrap.min.js,/WebGoat-Legacy/newDesign/assets/plugins/bootstrap/js/bootstrap.min.js,/WebGoat-Legacy/newDesign/assets/plugins/bootstrap/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mahonec/WebGoat-Legacy/commit/9b9155ac6645ae2fcb5f2195a346a9a39d3137e7">9b9155ac6645ae2fcb5f2195a346a9a39d3137e7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XSS in data-target in bootstrap (3.3.7 and before)
<p>Publish Date: 2017-09-29
<p>URL: <a href=https://github.com/twbs/bootstrap/issues/20184>WS-2018-0021</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-06-12</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.1.1","isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"vulnerabilityIdentifier":"WS-2018-0021","vulnerabilityDetails":"XSS in data-target in bootstrap (3.3.7 and before)","vulnerabilityUrl":"https://github.com/twbs/bootstrap/issues/20184","cvss2Severity":"medium","cvss2Score":"6.5","extraData":{}}</REMEDIATE> --> | True | WS-2018-0021 (Medium) detected in bootstrap-3.1.1.min.js - ## WS-2018-0021 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: /WebGoat-Legacy/target/WebGoat-6.0.1/plugins/bootstrap/js/bootstrap.min.js,/WebGoat-Legacy/src/main/webapp/plugins/bootstrap/js/bootstrap.min.js,/WebGoat-Legacy/newDesign/assets/plugins/bootstrap/js/bootstrap.min.js,/WebGoat-Legacy/newDesign/assets/plugins/bootstrap/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mahonec/WebGoat-Legacy/commit/9b9155ac6645ae2fcb5f2195a346a9a39d3137e7">9b9155ac6645ae2fcb5f2195a346a9a39d3137e7</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
XSS in data-target in bootstrap (3.3.7 and before)
<p>Publish Date: 2017-09-29
<p>URL: <a href=https://github.com/twbs/bootstrap/issues/20184>WS-2018-0021</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-06-12</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.1.1","isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"vulnerabilityIdentifier":"WS-2018-0021","vulnerabilityDetails":"XSS in data-target in bootstrap (3.3.7 and before)","vulnerabilityUrl":"https://github.com/twbs/bootstrap/issues/20184","cvss2Severity":"medium","cvss2Score":"6.5","extraData":{}}</REMEDIATE> --> | non_priority | ws medium detected in bootstrap min js ws medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library webgoat legacy target webgoat plugins bootstrap js bootstrap min js webgoat legacy src main webapp plugins bootstrap js bootstrap min js webgoat legacy newdesign assets plugins bootstrap js bootstrap min js webgoat legacy newdesign assets plugins bootstrap js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href vulnerability details xss in data target in bootstrap and before publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails xss in data target in bootstrap and before vulnerabilityurl | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.