Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
340,548 | 30,524,814,246 | IssuesEvent | 2023-07-19 10:28:53 | DeveloperAcademy-POSTECH/MC3-Team1-SixTech | https://api.github.com/repos/DeveloperAcademy-POSTECH/MC3-Team1-SixTech | closed | [Test] Test engagement code communication functionality | 🎈 Test | ### 📝 작업할 내용 요약
Test engagement code communication functionality
<!-- 설명 -->
---
### 🛠️ Tasks
* [x] GameKit, CloundKit Test
* [x] 진행시켜 고만해 ~
| 1.0 | [Test] Test engagement code communication functionality - ### 📝 작업할 내용 요약
Test engagement code communication functionality
<!-- 설명 -->
---
### 🛠️ Tasks
* [x] GameKit, CloundKit Test
* [x] 진행시켜 고만해 ~
| non_priority | test engagement code communication functionality 📝 작업할 내용 요약 test engagement code communication functionality 🛠️ tasks gamekit cloundkit test 진행시켜 고만해 | 0 |
234,775 | 25,886,404,952 | IssuesEvent | 2022-12-14 14:51:07 | ghga-de/datameta | https://api.github.com/repos/ghga-de/datameta | closed | Add OTP 2FA | Enhancement Security | We need to have the ability to require 2FA for interactive logins.
A wide spread Python lib for doing OTP seems to be https://github.com/pyauth/pyotp. | True | Add OTP 2FA - We need to have the ability to require 2FA for interactive logins.
A wide spread Python lib for doing OTP seems to be https://github.com/pyauth/pyotp. | non_priority | add otp we need to have the ability to require for interactive logins a wide spread python lib for doing otp seems to be | 0 |
95,229 | 10,868,653,580 | IssuesEvent | 2019-11-15 04:41:10 | atharvjoshi/pe | https://api.github.com/repos/atharvjoshi/pe | opened | Undocumented behaviour for edit command - editing choices | severity.Medium type.DocumentationBug | Undocumented behaviour - apparently I can only edit choices as long as at least one of the new choices matches the answer. This is not specified in the user guide.
| 1.0 | Undocumented behaviour for edit command - editing choices - Undocumented behaviour - apparently I can only edit choices as long as at least one of the new choices matches the answer. This is not specified in the user guide.
| non_priority | undocumented behaviour for edit command editing choices undocumented behaviour apparently i can only edit choices as long as at least one of the new choices matches the answer this is not specified in the user guide | 0 |
106,126 | 11,471,878,742 | IssuesEvent | 2020-02-09 14:04:56 | ComputeCanada/magic_castle | https://api.github.com/repos/ComputeCanada/magic_castle | closed | Add DNS configuration to main documentation | documentation | Move DNS configuration documentation from README.md to docs/README.md | 1.0 | Add DNS configuration to main documentation - Move DNS configuration documentation from README.md to docs/README.md | non_priority | add dns configuration to main documentation move dns configuration documentation from readme md to docs readme md | 0 |
16,023 | 3,493,364,113 | IssuesEvent | 2016-01-05 01:27:45 | mapbox/mapbox-gl-native | https://api.github.com/repos/mapbox/mapbox-gl-native | closed | Storage.HTTPCancelMultiple test occasionally fails | tests | https://travis-ci.org/mapbox/mapbox-gl-native/jobs/94300803#L1439
```
../../test/storage/http_cancel.cpp:43: Failure
Value of: res.error
Actual: 8-byte object <60-43 24-01 00-00 00-00>
Expected: nullptr
Which is: 8-byte object <00-00 00-00 00-00 00-00>
../../test/storage/http_cancel.cpp:45: Failure
Value of: res.data.get()
Actual: false
Expected: true
``` | 1.0 | Storage.HTTPCancelMultiple test occasionally fails - https://travis-ci.org/mapbox/mapbox-gl-native/jobs/94300803#L1439
```
../../test/storage/http_cancel.cpp:43: Failure
Value of: res.error
Actual: 8-byte object <60-43 24-01 00-00 00-00>
Expected: nullptr
Which is: 8-byte object <00-00 00-00 00-00 00-00>
../../test/storage/http_cancel.cpp:45: Failure
Value of: res.data.get()
Actual: false
Expected: true
``` | non_priority | storage httpcancelmultiple test occasionally fails test storage http cancel cpp failure value of res error actual byte object expected nullptr which is byte object test storage http cancel cpp failure value of res data get actual false expected true | 0 |
224,322 | 17,172,532,136 | IssuesEvent | 2021-07-15 07:18:28 | kimuson13/cafe-api-application | https://api.github.com/repos/kimuson13/cafe-api-application | closed | ユーザーエンドポイントの作成 | documentation | # やること
- [x] ユーザーエンドポイントのテストの作成
- [x] ユーザーエンドポイントの作成
- [x] ユーザーエンドポイントのトークンのテストの作成
- [x] ユーザーエンドポイントのトークンの作成
- [x] ユーザーエンドポイントの編集部分のテストの作成
- [x] ユーザーエンドポイントの編集部分の作成
- [x] ブラウザで動作確認 | 1.0 | ユーザーエンドポイントの作成 - # やること
- [x] ユーザーエンドポイントのテストの作成
- [x] ユーザーエンドポイントの作成
- [x] ユーザーエンドポイントのトークンのテストの作成
- [x] ユーザーエンドポイントのトークンの作成
- [x] ユーザーエンドポイントの編集部分のテストの作成
- [x] ユーザーエンドポイントの編集部分の作成
- [x] ブラウザで動作確認 | non_priority | ユーザーエンドポイントの作成 やること ユーザーエンドポイントのテストの作成 ユーザーエンドポイントの作成 ユーザーエンドポイントのトークンのテストの作成 ユーザーエンドポイントのトークンの作成 ユーザーエンドポイントの編集部分のテストの作成 ユーザーエンドポイントの編集部分の作成 ブラウザで動作確認 | 0 |
3,197 | 2,671,036,907 | IssuesEvent | 2015-03-24 01:19:13 | louie55/tfdb | https://api.github.com/repos/louie55/tfdb | closed | Fix Navbar CSS so that the whole button area is a hotspot | Design Enhancement | The top site Navbar buttons should be able to be clicked anywhere in order to make the link work. Right now only the text can be clicked. Check the CSS for the Calamus Lodge website to see how to do this. I believe you use display: block on the <a> tag to make it the size of the button, but I'm not sure. | 1.0 | Fix Navbar CSS so that the whole button area is a hotspot - The top site Navbar buttons should be able to be clicked anywhere in order to make the link work. Right now only the text can be clicked. Check the CSS for the Calamus Lodge website to see how to do this. I believe you use display: block on the <a> tag to make it the size of the button, but I'm not sure. | non_priority | fix navbar css so that the whole button area is a hotspot the top site navbar buttons should be able to be clicked anywhere in order to make the link work right now only the text can be clicked check the css for the calamus lodge website to see how to do this i believe you use display block on the tag to make it the size of the button but i m not sure | 0 |
267,607 | 28,509,130,250 | IssuesEvent | 2023-04-19 01:37:51 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | closed | CVE-2020-0305 (Medium) detected in linuxv3.0 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-0305 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/char_dev.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/char_dev.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/char_dev.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In cdev_get of char_dev.c, there is a possible use-after-free due to a race condition. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-153467744
<p>Publish Date: 2020-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0305>CVE-2020-0305</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-08-21</p>
<p>Fix Resolution: v5.5-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-0305 (Medium) detected in linuxv3.0 - autoclosed - ## CVE-2020-0305 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0</b></p></summary>
<p>
<p>Linux kernel source tree</p>
<p>Library home page: <a href=https://github.com/verygreen/linux.git>https://github.com/verygreen/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/char_dev.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/char_dev.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/char_dev.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In cdev_get of char_dev.c, there is a possible use-after-free due to a race condition. This could lead to local escalation of privilege with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-153467744
<p>Publish Date: 2020-07-17
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0305>CVE-2020-0305</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-08-21</p>
<p>Fix Resolution: v5.5-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel source tree library home page a href found in head commit a href found in base branch master vulnerable source files fs char dev c fs char dev c fs char dev c vulnerability details in cdev get of char dev c there is a possible use after free due to a race condition this could lead to local escalation of privilege with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend | 0 |
91,889 | 10,730,915,741 | IssuesEvent | 2019-10-28 18:23:56 | pulibrary/plantain | https://api.github.com/repos/pulibrary/plantain | opened | Provide development instructions for the installation and testing of the Aeon request service | documentation | (James will need to find and link to the ArcLight issue in which sdellis outlined this process locally). | 1.0 | Provide development instructions for the installation and testing of the Aeon request service - (James will need to find and link to the ArcLight issue in which sdellis outlined this process locally). | non_priority | provide development instructions for the installation and testing of the aeon request service james will need to find and link to the arclight issue in which sdellis outlined this process locally | 0 |
264,825 | 23,141,628,242 | IssuesEvent | 2022-07-28 19:05:38 | Moonshine-IDE/Moonshine-IDE | https://api.github.com/repos/Moonshine-IDE/Moonshine-IDE | closed | [Windows] Compilation of Royale Project breaks when Apache Royale SDK path contains whitespaces | bug windows test ready | Test scenario:
1. Move Apache SDK to a location containing a whitespace, e.g.: `C:\Moonshine SDKs\Royale_SDK\apache-royale-0.9.8-bin-js`
2. Adjust the path in Moonshine IDE settings
3. After Build & Run Moonshine IDE fails with: `'C:\Moonshine' is not recognized as an internal or external command`
Content of the `C:\%USERNAME%\Roaming\com.moonshine-ide\Local Store\setLocalEnvironment.cmd`:
```
@echo off
set JAVA_HOME=C:\Program Files\OpenJDK\jdk-15
set ANT_HOME=C:\ProgramData\chocolatey\lib\ant\tools\apache-ant-1.10.8
set GIT_HOME=C:\Moonshine SDKs\Git\git-2.20.1
set ROYALE_HOME=C:\Moonshine SDKs\Royale_SDK\apache-royale-0.9.8-bin-js\royale-asjs
set PATH=%JAVA_HOME%\bin;%ANT_HOME%\bin;%ROYALE_HOME%\bin;%PATH%
"%GIT_HOME%\bin\git" config --global http.sslCAInfo "%GIT_HOME%\mingw64\ssl\cert.pem"
"C:\Program Files (x86)\HCL\Notes/nsd.exe" -version
```
This issue is related to: https://github.com/prominic/Moonshine-IDE/issues/739#issuecomment-706063869 | 1.0 | [Windows] Compilation of Royale Project breaks when Apache Royale SDK path contains whitespaces - Test scenario:
1. Move Apache SDK to a location containing a whitespace, e.g.: `C:\Moonshine SDKs\Royale_SDK\apache-royale-0.9.8-bin-js`
2. Adjust the path in Moonshine IDE settings
3. After Build & Run Moonshine IDE fails with: `'C:\Moonshine' is not recognized as an internal or external command`
Content of the `C:\%USERNAME%\Roaming\com.moonshine-ide\Local Store\setLocalEnvironment.cmd`:
```
@echo off
set JAVA_HOME=C:\Program Files\OpenJDK\jdk-15
set ANT_HOME=C:\ProgramData\chocolatey\lib\ant\tools\apache-ant-1.10.8
set GIT_HOME=C:\Moonshine SDKs\Git\git-2.20.1
set ROYALE_HOME=C:\Moonshine SDKs\Royale_SDK\apache-royale-0.9.8-bin-js\royale-asjs
set PATH=%JAVA_HOME%\bin;%ANT_HOME%\bin;%ROYALE_HOME%\bin;%PATH%
"%GIT_HOME%\bin\git" config --global http.sslCAInfo "%GIT_HOME%\mingw64\ssl\cert.pem"
"C:\Program Files (x86)\HCL\Notes/nsd.exe" -version
```
This issue is related to: https://github.com/prominic/Moonshine-IDE/issues/739#issuecomment-706063869 | non_priority | compilation of royale project breaks when apache royale sdk path contains whitespaces test scenario move apache sdk to a location containing a whitespace e g c moonshine sdks royale sdk apache royale bin js adjust the path in moonshine ide settings after build run moonshine ide fails with c moonshine is not recognized as an internal or external command content of the c username roaming com moonshine ide local store setlocalenvironment cmd echo off set java home c program files openjdk jdk set ant home c programdata chocolatey lib ant tools apache ant set git home c moonshine sdks git git set royale home c moonshine sdks royale sdk apache royale bin js royale asjs set path java home bin ant home bin royale home bin path git home bin git config global http sslcainfo git home ssl cert pem c program files hcl notes nsd exe version this issue is related to | 0 |
22,030 | 3,770,009,666 | IssuesEvent | 2016-03-16 13:08:55 | pydata/pandas | https://api.github.com/repos/pydata/pandas | opened | API: why are we importing pandas.tseries.period.pnow into the pd namespace? | API Design Period | from ``pandas.tseries.api``
if someone can take a look and see when this was added?
I don't think this is useful at all. Let's just deprecate and remove this function entirely. Could always add a ``Period.now()``. | 1.0 | API: why are we importing pandas.tseries.period.pnow into the pd namespace? - from ``pandas.tseries.api``
if someone can take a look and see when this was added?
I don't think this is useful at all. Let's just deprecate and remove this function entirely. Could always add a ``Period.now()``. | non_priority | api why are we importing pandas tseries period pnow into the pd namespace from pandas tseries api if someone can take a look and see when this was added i don t think this is useful at all let s just deprecate and remove this function entirely could always add a period now | 0 |
146,679 | 19,457,134,463 | IssuesEvent | 2021-12-23 01:11:42 | inmar/actions-dpn-python-version-check | https://api.github.com/repos/inmar/actions-dpn-python-version-check | opened | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz | security vulnerability | ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>Path to dependency file: actions-dpn-python-version-check/package.json</p>
<p>Path to vulnerable library: actions-dpn-python-version-check/node_modules/json-schema/package.json</p>
<p>
Dependency Hierarchy:
- request-2.88.0.tgz (Root Library)
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution: json-schema - 0.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"json-schema","packageVersion":"0.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"request:2.88.0;http-signature:1.2.0;jsprim:1.4.1;json-schema:0.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"json-schema - 0.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-3918","vulnerabilityDetails":"json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (\u0027Prototype Pollution\u0027)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-3918 (High) detected in json-schema-0.2.3.tgz - ## CVE-2021-3918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p></summary>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>Path to dependency file: actions-dpn-python-version-check/package.json</p>
<p>Path to vulnerable library: actions-dpn-python-version-check/node_modules/json-schema/package.json</p>
<p>
Dependency Hierarchy:
- request-2.88.0.tgz (Root Library)
- http-signature-1.2.0.tgz
- jsprim-1.4.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution: json-schema - 0.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"json-schema","packageVersion":"0.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"request:2.88.0;http-signature:1.2.0;jsprim:1.4.1;json-schema:0.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"json-schema - 0.4.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-3918","vulnerabilityDetails":"json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (\u0027Prototype Pollution\u0027)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in json schema tgz cve high severity vulnerability vulnerable library json schema tgz json schema validation and specifications library home page a href path to dependency file actions dpn python version check package json path to vulnerable library actions dpn python version check node modules json schema package json dependency hierarchy request tgz root library http signature tgz jsprim tgz x json schema tgz vulnerable library found in base branch master vulnerability details json schema is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution json schema isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree request http signature jsprim json schema isminimumfixversionavailable true minimumfixversion json schema isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails json schema is vulnerable to improperly controlled modification of object prototype attributes pollution vulnerabilityurl | 0 |
307,528 | 23,202,830,000 | IssuesEvent | 2022-08-02 00:06:02 | fga-eps-mds/2022-1-OiaAMoeda | https://api.github.com/repos/fga-eps-mds/2022-1-OiaAMoeda | closed | Sprint 7 - Revisar o termo de abertura | documentation | # Descrição
O termo de abertura do projeto está faltando o preço do projeto.
# Tarefas
- [x] Colocar a estimativa de preço do projeto.
- [x] Revisar a escrita geral do projeto.
# Critérios de aceitação
- [ ] Documento revisado. | 1.0 | Sprint 7 - Revisar o termo de abertura - # Descrição
O termo de abertura do projeto está faltando o preço do projeto.
# Tarefas
- [x] Colocar a estimativa de preço do projeto.
- [x] Revisar a escrita geral do projeto.
# Critérios de aceitação
- [ ] Documento revisado. | non_priority | sprint revisar o termo de abertura descrição o termo de abertura do projeto está faltando o preço do projeto tarefas colocar a estimativa de preço do projeto revisar a escrita geral do projeto critérios de aceitação documento revisado | 0 |
86,897 | 17,099,584,452 | IssuesEvent | 2021-07-09 09:18:56 | qiskit-community/qiskit-textbook | https://api.github.com/repos/qiskit-community/qiskit-textbook | closed | [4.1.3] QAOA notebook has wrong cost computation function | code bug | ## Describe the Issue
In the following notebook: https://qiskit.org/textbook/ch-applications/qaoa.html `cost_function_C` function computes the MaxCut cost for a sample. The sample is created in the following line, [link to the notebook section](https://qiskit.org/textbook/ch-applications/qaoa.html#Evaluate-the-date-from-the-simulation):
```
x = [int(num) for num in list(sample)]
```
The samples are in little endian format, i.e. applying `x[0]` on a 4-qubit circuit will results in a sample string `0001`. The qubits, however are stored in reversed order
## Expected Solution
Reverse the label of the sample:
#499
## Anything else we should know?
The graph used in the example is symmetric with respect to relabeling of qubits `0...n -> n..0`. Maybe the issue would be spotted if another graph was used. I used a square with one diagonal, adjacency matrix:
```
[[0. 1. 0. 1.]
[1. 0. 1. 1.]
[0. 1. 0. 1.]
[1. 1. 1. 0.]]
``` | 1.0 | [4.1.3] QAOA notebook has wrong cost computation function - ## Describe the Issue
In the following notebook: https://qiskit.org/textbook/ch-applications/qaoa.html `cost_function_C` function computes the MaxCut cost for a sample. The sample is created in the following line, [link to the notebook section](https://qiskit.org/textbook/ch-applications/qaoa.html#Evaluate-the-date-from-the-simulation):
```
x = [int(num) for num in list(sample)]
```
The samples are in little endian format, i.e. applying `x[0]` on a 4-qubit circuit will results in a sample string `0001`. The qubits, however are stored in reversed order
## Expected Solution
Reverse the label of the sample:
#499
## Anything else we should know?
The graph used in the example is symmetric with respect to relabeling of qubits `0...n -> n..0`. Maybe the issue would be spotted if another graph was used. I used a square with one diagonal, adjacency matrix:
```
[[0. 1. 0. 1.]
[1. 0. 1. 1.]
[0. 1. 0. 1.]
[1. 1. 1. 0.]]
``` | non_priority | qaoa notebook has wrong cost computation function describe the issue in the following notebook cost function c function computes the maxcut cost for a sample the sample is created in the following line x the samples are in little endian format i e applying x on a qubit circuit will results in a sample string the qubits however are stored in reversed order expected solution reverse the label of the sample anything else we should know the graph used in the example is symmetric with respect to relabeling of qubits n n maybe the issue would be spotted if another graph was used i used a square with one diagonal adjacency matrix | 0 |
70,576 | 9,423,240,153 | IssuesEvent | 2019-04-11 11:21:34 | valtech/aem-easy-content-upgrade | https://api.github.com/repos/valtech/aem-easy-content-upgrade | closed | Uninstalling bundle package does not remove content properly | documentation | If you uninstall the bundle package, the sources are not getting removed from the instance. If you install the groovy console and aecu.ui.apps package separately, it is possible to remove all sources by uninstalling the related packages. | 1.0 | Uninstalling bundle package does not remove content properly - If you uninstall the bundle package, the sources are not getting removed from the instance. If you install the groovy console and aecu.ui.apps package separately, it is possible to remove all sources by uninstalling the related packages. | non_priority | uninstalling bundle package does not remove content properly if you uninstall the bundle package the sources are not getting removed from the instance if you install the groovy console and aecu ui apps package separately it is possible to remove all sources by uninstalling the related packages | 0 |
20,088 | 10,595,687,849 | IssuesEvent | 2019-10-09 19:32:59 | keras-team/keras | https://api.github.com/repos/keras-team/keras | closed | tf.keras works, tf.python.keras doesn't | backend:tensorflow type:bug/performance | **DOESN'T WORK**:
```python
from tensorflow.python.keras.layers import Input, Dense
from tensorflow.python.keras.models import Model
from tensorflow.python.keras.optimizers import Nadam
ipt = Input(shape=(4,))
out = Dense(1, activation='sigmoid')(ipt)
model = Model(ipt, out)
model.compile(optimizer=Nadam(lr=1e-4), loss='binary_crossentropy')
X = np.random.randn(32,4)
Y = np.random.randint(0,2,(32,1))
model.train_on_batch(X,Y)
```
**WORKS**: remove `.python` from above's imports. Above's error trace below.
Keras 2.3.0 and TensorFlow 2.0.0 freshly-installed via Anaconda, older versions uninstalled. Why the difference?
<hr>
```python
File "<ipython-input-7-1e86d21d8fc4>", line 13, in <module>
model.train_on_batch(X,Y)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\engine\training.py", line 1017, in train_on_batch
self._make_train_function()
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\engine\training.py", line 2116, in _make_train_function
params=self._collected_trainable_weights, loss=self.total_loss)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\optimizers.py", line 653, in get_updates
grads = self.get_gradients(loss, params)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\optimizers.py", line 92, in get_gradients
if None in grads:
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\ops\math_ops.py", line 1336, in tensor_equals
return gen_math_ops.equal(self, other)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\ops\gen_math_ops.py", line 3627, in equal
name=name)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\framework\op_def_library.py", line 545, in _apply_op_helper
(input_name, err))
ValueError: Tried to convert 'y' to a tensor and failed. Error: None values not supported.
```
<hr>
**UPDATE:** Debugging the two side-by-side, while both use the [same files](https://github.com/tensorflow/tensorflow/blob/master/tensorflow/python/keras/engine/training.py#L1008), execution diverges fairly quickly:
```python
# .\tensorflow_core\python\keras\engine\training.py
### TF.KERAS
if self._experimental_run_tf_function: # TRUE
### TF.PYTHON.KERAS
if self._experimental_run_tf_function: # FALSE
```
Former proceeds to call `training_v2_utils.train_on_batch(...)` and returns thereafter, latter `self._standardize_user_data(...)` and others before ultimately failing.
One difference I noted between linked file and mine is, latter's short by ~100 lines - though I installed TF 2 via pip after the file's last update 12 days ago according to Github. | True | tf.keras works, tf.python.keras doesn't - **DOESN'T WORK**:
```python
from tensorflow.python.keras.layers import Input, Dense
from tensorflow.python.keras.models import Model
from tensorflow.python.keras.optimizers import Nadam
ipt = Input(shape=(4,))
out = Dense(1, activation='sigmoid')(ipt)
model = Model(ipt, out)
model.compile(optimizer=Nadam(lr=1e-4), loss='binary_crossentropy')
X = np.random.randn(32,4)
Y = np.random.randint(0,2,(32,1))
model.train_on_batch(X,Y)
```
**WORKS**: remove `.python` from above's imports. Above's error trace below.
Keras 2.3.0 and TensorFlow 2.0.0 freshly-installed via Anaconda, older versions uninstalled. Why the difference?
<hr>
```python
File "<ipython-input-7-1e86d21d8fc4>", line 13, in <module>
model.train_on_batch(X,Y)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\engine\training.py", line 1017, in train_on_batch
self._make_train_function()
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\engine\training.py", line 2116, in _make_train_function
params=self._collected_trainable_weights, loss=self.total_loss)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\optimizers.py", line 653, in get_updates
grads = self.get_gradients(loss, params)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\keras\optimizers.py", line 92, in get_gradients
if None in grads:
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\ops\math_ops.py", line 1336, in tensor_equals
return gen_math_ops.equal(self, other)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\ops\gen_math_ops.py", line 3627, in equal
name=name)
File "D:\Anaconda\envs\tf2_env\lib\site-packages\tensorflow_core\python\framework\op_def_library.py", line 545, in _apply_op_helper
(input_name, err))
ValueError: Tried to convert 'y' to a tensor and failed. Error: None values not supported.
```
<hr>
**UPDATE:** Debugging the two side-by-side, while both use the [same files](https://github.com/tensorflow/tensorflow/blob/master/tensorflow/python/keras/engine/training.py#L1008), execution diverges fairly quickly:
```python
# .\tensorflow_core\python\keras\engine\training.py
### TF.KERAS
if self._experimental_run_tf_function: # TRUE
### TF.PYTHON.KERAS
if self._experimental_run_tf_function: # FALSE
```
Former proceeds to call `training_v2_utils.train_on_batch(...)` and returns thereafter, latter `self._standardize_user_data(...)` and others before ultimately failing.
One difference I noted between linked file and mine is, latter's short by ~100 lines - though I installed TF 2 via pip after the file's last update 12 days ago according to Github. | non_priority | tf keras works tf python keras doesn t doesn t work python from tensorflow python keras layers import input dense from tensorflow python keras models import model from tensorflow python keras optimizers import nadam ipt input shape out dense activation sigmoid ipt model model ipt out model compile optimizer nadam lr loss binary crossentropy x np random randn y np random randint model train on batch x y works remove python from above s imports above s error trace below keras and tensorflow freshly installed via anaconda older versions uninstalled why the difference python file line in model train on batch x y file d anaconda envs env lib site packages tensorflow core python keras engine training py line in train on batch self make train function file d anaconda envs env lib site packages tensorflow core python keras engine training py line in make train function params self collected trainable weights loss self total loss file d anaconda envs env lib site packages tensorflow core python keras optimizers py line in get updates grads self get gradients loss params file d anaconda envs env lib site packages tensorflow core python keras optimizers py line in get gradients if none in grads file d anaconda envs env lib site packages tensorflow core python ops math ops py line in tensor equals return gen math ops equal self other file d anaconda envs env lib site packages tensorflow core python ops gen math ops py line in equal name name file d anaconda envs env lib site packages tensorflow core python framework op def library py line in apply op helper input name err valueerror tried to convert y to a tensor and failed error none values not supported update debugging the two side by side while both use the execution diverges fairly quickly python tensorflow core python keras engine training py tf keras if self experimental run tf function true tf python keras if self experimental run tf function false former proceeds to call training utils train on batch and returns thereafter latter self standardize user data and others before ultimately failing one difference i noted between linked file and mine is latter s short by lines though i installed tf via pip after the file s last update days ago according to github | 0 |
391,058 | 26,879,147,915 | IssuesEvent | 2023-02-05 12:23:38 | DucTran999/small-project | https://api.github.com/repos/DucTran999/small-project | closed | Guessing number | documentation | - Add docstrings to help code readable.
- Add a brief document to describe the code. | 1.0 | Guessing number - - Add docstrings to help code readable.
- Add a brief document to describe the code. | non_priority | guessing number add docstrings to help code readable add a brief document to describe the code | 0 |
11,949 | 4,323,259,763 | IssuesEvent | 2016-07-25 16:26:00 | phetsims/energy-skate-park-basics | https://api.github.com/repos/phetsims/energy-skate-park-basics | closed | EnergySkateParkBasicsScreenView should mix PropertySet once that is available | dev:code-review sim:For 1.1+ | I see usages like:
```js
this.availableModelBounds = this.modelViewTransform.viewToModelBounds( this.availableViewBounds );
this.availableModelBoundsProperty.value = this.availableModelBounds;
```
that would be better handled. | 1.0 | EnergySkateParkBasicsScreenView should mix PropertySet once that is available - I see usages like:
```js
this.availableModelBounds = this.modelViewTransform.viewToModelBounds( this.availableViewBounds );
this.availableModelBoundsProperty.value = this.availableModelBounds;
```
that would be better handled. | non_priority | energyskateparkbasicsscreenview should mix propertyset once that is available i see usages like js this availablemodelbounds this modelviewtransform viewtomodelbounds this availableviewbounds this availablemodelboundsproperty value this availablemodelbounds that would be better handled | 0 |
192,220 | 22,215,917,271 | IssuesEvent | 2022-06-08 01:36:54 | AlexRogalskiy/github-action-node-dependency | https://api.github.com/repos/AlexRogalskiy/github-action-node-dependency | closed | CVE-2012-6708 (Medium) detected in jquery-1.8.1.min.js - autoclosed | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: github-action-node-dependency/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: github-action-node-dependency/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-node-dependency/commit/856c28e2689dd54cb1335a960165ae66275b404e">856c28e2689dd54cb1335a960165ae66275b404e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2012-6708 (Medium) detected in jquery-1.8.1.min.js - autoclosed - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.8.1.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.8.1/jquery.min.js</a></p>
<p>Path to dependency file: github-action-node-dependency/node_modules/redeyed/examples/browser/index.html</p>
<p>Path to vulnerable library: github-action-node-dependency/node_modules/redeyed/examples/browser/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.8.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/github-action-node-dependency/commit/856c28e2689dd54cb1335a960165ae66275b404e">856c28e2689dd54cb1335a960165ae66275b404e</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
jQuery before 1.9.0 is vulnerable to Cross-site Scripting (XSS) attacks. The jQuery(strInput) function does not differentiate selectors from HTML in a reliable fashion. In vulnerable versions, jQuery determined whether the input was HTML by looking for the '<' character anywhere in the string, giving attackers more flexibility when attempting to construct a malicious payload. In fixed versions, jQuery only deems the input to be HTML if it explicitly starts with the '<' character, limiting exploitability only to attackers who can control the beginning of a string, which is far less common.
<p>Publish Date: 2018-01-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2012-6708>CVE-2012-6708</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-6708">https://nvd.nist.gov/vuln/detail/CVE-2012-6708</a></p>
<p>Release Date: 2018-01-18</p>
<p>Fix Resolution: jQuery - v1.9.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js autoclosed cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file github action node dependency node modules redeyed examples browser index html path to vulnerable library github action node dependency node modules redeyed examples browser index html dependency hierarchy x jquery min js vulnerable library found in head commit a href vulnerability details jquery before is vulnerable to cross site scripting xss attacks the jquery strinput function does not differentiate selectors from html in a reliable fashion in vulnerable versions jquery determined whether the input was html by looking for the character anywhere in the string giving attackers more flexibility when attempting to construct a malicious payload in fixed versions jquery only deems the input to be html if it explicitly starts with the character limiting exploitability only to attackers who can control the beginning of a string which is far less common publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
235,858 | 18,062,322,708 | IssuesEvent | 2021-09-20 15:09:33 | girlscript/winter-of-contributing | https://api.github.com/repos/girlscript/winter-of-contributing | closed | MERN_React: 2.6 Using eventListenrs in JSX | documentation GWOC21 MERN | # Instructions
## Project directory
Branch MERN>MERN/Topic/Frontend/React/
Please read the [contributing guidelines](https://github.com/girlscript/winter-of-contributing/blob/MERN/Web_Development/MERN/Contributing.md) to get started
## Using eventListeners in JSX
# Task
- [ ] Documentation
## Domain of contribution
- [X] MERN
| 1.0 | MERN_React: 2.6 Using eventListenrs in JSX - # Instructions
## Project directory
Branch MERN>MERN/Topic/Frontend/React/
Please read the [contributing guidelines](https://github.com/girlscript/winter-of-contributing/blob/MERN/Web_Development/MERN/Contributing.md) to get started
## Using eventListeners in JSX
# Task
- [ ] Documentation
## Domain of contribution
- [X] MERN
| non_priority | mern react using eventlistenrs in jsx instructions project directory branch mern mern topic frontend react please read the to get started using eventlisteners in jsx task documentation domain of contribution mern | 0 |
69,033 | 14,970,040,737 | IssuesEvent | 2021-01-27 19:01:22 | jgeraigery/SilverKing | https://api.github.com/repos/jgeraigery/SilverKing | opened | CVE-2018-19362 (High) detected in jackson-databind-2.6.7.1.jar | security vulnerability | ## CVE-2018-19362 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: SilverKing/lib/aws-java-sdk-1.11.333/third-party/lib/jackson-databind-2.6.7.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.7.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/SilverKing/commit/8ba31a514d374422e5f4712cf554ef10ac674e5a">8ba31a514d374422e5f4712cf554ef10ac674e5a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the jboss-common-core class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19362>CVE-2018-19362</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.8</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.7.1","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.9.8"}],"vulnerabilityIdentifier":"CVE-2018-19362","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the jboss-common-core class from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19362","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-19362 (High) detected in jackson-databind-2.6.7.1.jar - ## CVE-2018-19362 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: SilverKing/lib/aws-java-sdk-1.11.333/third-party/lib/jackson-databind-2.6.7.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.6.7.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/SilverKing/commit/8ba31a514d374422e5f4712cf554ef10ac674e5a">8ba31a514d374422e5f4712cf554ef10ac674e5a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the jboss-common-core class from polymorphic deserialization.
<p>Publish Date: 2019-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19362>CVE-2018-19362</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19362</a></p>
<p>Release Date: 2019-01-02</p>
<p>Fix Resolution: 2.9.8</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.6.7.1","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.6.7.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.9.8"}],"vulnerabilityIdentifier":"CVE-2018-19362","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.8 might allow attackers to have unspecified impact by leveraging failure to block the jboss-common-core class from polymorphic deserialization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19362","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library silverking lib aws java sdk third party lib jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the jboss common core class from polymorphic deserialization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before might allow attackers to have unspecified impact by leveraging failure to block the jboss common core class from polymorphic deserialization vulnerabilityurl | 0 |
379,094 | 26,352,984,048 | IssuesEvent | 2023-01-11 07:18:10 | zhinst/laboneq | https://api.github.com/repos/zhinst/laboneq | closed | [BUG] - Output simulator | bug documentation fix commited | **Describe the bug**
A clear and concise description of what the bug is.
I was just checking the example notebook.
The new simulator does not give the same results as the old simulator. Please see the following file.
1. For SHFSG there is not Q signal existed.
2. I would assume if the oscillator modulation type is Hardware, the waveform is the envelop, if it is software, the waveform is the envelop together with oscillator frequency. Correct me if it is wrong.
3. Based on the assumption on 2, for measure line, it should be a constant envelop with frequency 1e8 Hz. However, the result shows a waveform with frequency 1e6 Hz.
4. All the devices in the descriptor has sample rate 2GHz, however all the results are showing points with sample rate 20MHz. This may also the cause of problem no.3
**To Reproduce**
Steps to reproduce the behavior:
1. Define pulse sequence...
6. Execute on hardware / in emulation ...
7. Do additional steps...
8. See error
run the following notebook
[simulator_error.zip](https://github.com/zhinst/laboneq/files/10196820/simulator_error.zip)
**Expected behavior**
A clear and concise description of what you expected to happen.
**Code & Screenshots**
If possible, add example code or serialized LabOne Q data objects, like the Experiment and DeviceSetup, that allow us to reproduce the behavior.
If applicable, add screenshots to help explain your problem.
**Versions used:**
- laboneq 1.4
- zhinst-core 22.8
- others
**Context**
- [ ] Do you know a workaround for the issue? If yes, please provide a short description.
- [ ] Does the issue block your experiments? | 1.0 | [BUG] - Output simulator - **Describe the bug**
A clear and concise description of what the bug is.
I was just checking the example notebook.
The new simulator does not give the same results as the old simulator. Please see the following file.
1. For SHFSG there is not Q signal existed.
2. I would assume if the oscillator modulation type is Hardware, the waveform is the envelop, if it is software, the waveform is the envelop together with oscillator frequency. Correct me if it is wrong.
3. Based on the assumption on 2, for measure line, it should be a constant envelop with frequency 1e8 Hz. However, the result shows a waveform with frequency 1e6 Hz.
4. All the devices in the descriptor has sample rate 2GHz, however all the results are showing points with sample rate 20MHz. This may also the cause of problem no.3
**To Reproduce**
Steps to reproduce the behavior:
1. Define pulse sequence...
6. Execute on hardware / in emulation ...
7. Do additional steps...
8. See error
run the following notebook
[simulator_error.zip](https://github.com/zhinst/laboneq/files/10196820/simulator_error.zip)
**Expected behavior**
A clear and concise description of what you expected to happen.
**Code & Screenshots**
If possible, add example code or serialized LabOne Q data objects, like the Experiment and DeviceSetup, that allow us to reproduce the behavior.
If applicable, add screenshots to help explain your problem.
**Versions used:**
- laboneq 1.4
- zhinst-core 22.8
- others
**Context**
- [ ] Do you know a workaround for the issue? If yes, please provide a short description.
- [ ] Does the issue block your experiments? | non_priority | output simulator describe the bug a clear and concise description of what the bug is i was just checking the example notebook the new simulator does not give the same results as the old simulator please see the following file for shfsg there is not q signal existed i would assume if the oscillator modulation type is hardware the waveform is the envelop if it is software the waveform is the envelop together with oscillator frequency correct me if it is wrong based on the assumption on for measure line it should be a constant envelop with frequency hz however the result shows a waveform with frequency hz all the devices in the descriptor has sample rate however all the results are showing points with sample rate this may also the cause of problem no to reproduce steps to reproduce the behavior define pulse sequence execute on hardware in emulation do additional steps see error run the following notebook expected behavior a clear and concise description of what you expected to happen code screenshots if possible add example code or serialized labone q data objects like the experiment and devicesetup that allow us to reproduce the behavior if applicable add screenshots to help explain your problem versions used laboneq zhinst core others context do you know a workaround for the issue if yes please provide a short description does the issue block your experiments | 0 |
326,178 | 27,979,175,612 | IssuesEvent | 2023-03-26 00:03:43 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix general.test_gather | Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4476610484/jobs/7867148931" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4463025763/jobs/7837951858" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4476610484/jobs/7867148931" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4476610484/jobs/7867148587" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix general.test_gather - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4476610484/jobs/7867148931" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4463025763/jobs/7837951858" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4476610484/jobs/7867148931" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4476610484/jobs/7867148587" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
| non_priority | fix general test gather tensorflow img src torch img src numpy img src jax img src | 0 |
168,620 | 13,097,716,757 | IssuesEvent | 2020-08-03 18:00:20 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | acceptance: TestDockerCLI failed | C-test-failure O-robot branch-master | [(acceptance).TestDockerCLI failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2021716&tab=buildLog) on [master@a523cf3564e00275d990fbf14f49e84c0d6be400](https://github.com/cockroachdb/cockroach/commits/a523cf3564e00275d990fbf14f49e84c0d6be400):
```
=== RUN TestDockerCLI
--- FAIL: TestDockerCLI (319.76s)
test_log_scope.go:77: test logs captured to: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/acceptance/logTestDockerCLI453901509
test_log_scope.go:58: use -show-logs to present logs inline
=== RUN TestDockerCLI/test_demo_partitioning.tcl
--- FAIL: TestDockerCLI/test_demo_partitioning.tcl (43.85s)
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestDockerCLI PKG=./pkg/acceptance TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestDockerCLI.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 1.0 | acceptance: TestDockerCLI failed - [(acceptance).TestDockerCLI failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2021716&tab=buildLog) on [master@a523cf3564e00275d990fbf14f49e84c0d6be400](https://github.com/cockroachdb/cockroach/commits/a523cf3564e00275d990fbf14f49e84c0d6be400):
```
=== RUN TestDockerCLI
--- FAIL: TestDockerCLI (319.76s)
test_log_scope.go:77: test logs captured to: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/acceptance/logTestDockerCLI453901509
test_log_scope.go:58: use -show-logs to present logs inline
=== RUN TestDockerCLI/test_demo_partitioning.tcl
--- FAIL: TestDockerCLI/test_demo_partitioning.tcl (43.85s)
```
<details><summary>More</summary><p>
Parameters:
- GOFLAGS=-json
```
make stressrace TESTS=TestDockerCLI PKG=./pkg/acceptance TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestDockerCLI.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| non_priority | acceptance testdockercli failed on run testdockercli fail testdockercli test log scope go test logs captured to home agent work go src github com cockroachdb cockroach artifacts acceptance test log scope go use show logs to present logs inline run testdockercli test demo partitioning tcl fail testdockercli test demo partitioning tcl more parameters goflags json make stressrace tests testdockercli pkg pkg acceptance testtimeout stressflags timeout powered by | 0 |
403,914 | 27,441,280,977 | IssuesEvent | 2023-03-02 11:10:51 | threefoldtech/gridify | https://api.github.com/repos/threefoldtech/gridify | closed | readme | documentation | we need to add readme with:
- overview
- how to use and install
- how to test
- how to release using a workflow (check goreleaser)
| 1.0 | readme - we need to add readme with:
- overview
- how to use and install
- how to test
- how to release using a workflow (check goreleaser)
| non_priority | readme we need to add readme with overview how to use and install how to test how to release using a workflow check goreleaser | 0 |
3,036 | 5,939,701,187 | IssuesEvent | 2017-05-25 06:28:37 | OpenCubicChunks/CubicChunks | https://api.github.com/repos/OpenCubicChunks/CubicChunks | opened | Patch PackerBuffer to make writing BlockPos work | Compatibility | This is a bit questionable as it may break network compatibility.
One way to avoid breaking compat:
In vanilla a few bits of the long value written are unused. They could be used as a flag to say "there are more bits" and read them too. | True | Patch PackerBuffer to make writing BlockPos work - This is a bit questionable as it may break network compatibility.
One way to avoid breaking compat:
In vanilla a few bits of the long value written are unused. They could be used as a flag to say "there are more bits" and read them too. | non_priority | patch packerbuffer to make writing blockpos work this is a bit questionable as it may break network compatibility one way to avoid breaking compat in vanilla a few bits of the long value written are unused they could be used as a flag to say there are more bits and read them too | 0 |
22,520 | 15,238,281,381 | IssuesEvent | 2021-02-19 01:32:25 | dlang/projects | https://api.github.com/repos/dlang/projects | opened | Write an LLDB plugin for dlang | core infrastructure gsoc2021 | ## Description
LLDB is the LLVM debugger. It's the main debugger on Mac OSX and available on other platforms.
Currently, support for LLDB is rather poor. While GDB support has been implemented years ago by @ibuclaw (), LLDB still doesn't know much about D.
Support for language is implemented via [Plugins](https://github.com/llvm/llvm-project/tree/main/lldb/source/Plugins/Language). The goal of this project is to write such a plugin, and to upstream it.
## What are rough milestones of this project?
1. Get familiar with the capability of plugins, what is possible / isn't;
2. Get a basic plugin architecture in place, which is called when dlang is detected;
3. Implement demangling of D symbols, most likely integrating the same code as GDB;
4. Recognize D-specific data structures, such as arrays, associative arrays, typeinfo...
5. Implement support for parsing D expressions, e.g. the ability to do `"foo"[0 .. 2] in myAA`;
## How does this project help the D community?
Currently, one of the biggest obstacle in D adoption is the tool support. Notable, the debugging experience is miles behind other established languages.
## Recommended skills
Knowledge of Linux and how binaries are generated.
Experience with debugging in other native languages, such as C / C++.
DWARF or LLVM knowledge is a plus.
## What can students expect to get out of doing this project?
Deep knowledge of how debugging works at the core.
Participation in not just one, but two open source projects.
## Point of Contact
@Geod24
## References
The DWARF standard: http://www.dwarfstd.org/
DMD debug info generator: https://github.com/dlang/dmd/blob/master/src/dmd/backend/dwarfdbginf.d
LDC debug info generator: https://github.com/ldc-developers/ldc/blob/master/gen/dibuilder.cpp
Example of a simple D-related contribution: https://reviews.llvm.org/D79559
Previous attempt limited to demangling: https://reviews.llvm.org/D44321
Associated discussion: https://lists.llvm.org/pipermail/lldb-dev/2016-September/011321.html | 1.0 | Write an LLDB plugin for dlang - ## Description
LLDB is the LLVM debugger. It's the main debugger on Mac OSX and available on other platforms.
Currently, support for LLDB is rather poor. While GDB support has been implemented years ago by @ibuclaw (), LLDB still doesn't know much about D.
Support for language is implemented via [Plugins](https://github.com/llvm/llvm-project/tree/main/lldb/source/Plugins/Language). The goal of this project is to write such a plugin, and to upstream it.
## What are rough milestones of this project?
1. Get familiar with the capability of plugins, what is possible / isn't;
2. Get a basic plugin architecture in place, which is called when dlang is detected;
3. Implement demangling of D symbols, most likely integrating the same code as GDB;
4. Recognize D-specific data structures, such as arrays, associative arrays, typeinfo...
5. Implement support for parsing D expressions, e.g. the ability to do `"foo"[0 .. 2] in myAA`;
## How does this project help the D community?
Currently, one of the biggest obstacle in D adoption is the tool support. Notable, the debugging experience is miles behind other established languages.
## Recommended skills
Knowledge of Linux and how binaries are generated.
Experience with debugging in other native languages, such as C / C++.
DWARF or LLVM knowledge is a plus.
## What can students expect to get out of doing this project?
Deep knowledge of how debugging works at the core.
Participation in not just one, but two open source projects.
## Point of Contact
@Geod24
## References
The DWARF standard: http://www.dwarfstd.org/
DMD debug info generator: https://github.com/dlang/dmd/blob/master/src/dmd/backend/dwarfdbginf.d
LDC debug info generator: https://github.com/ldc-developers/ldc/blob/master/gen/dibuilder.cpp
Example of a simple D-related contribution: https://reviews.llvm.org/D79559
Previous attempt limited to demangling: https://reviews.llvm.org/D44321
Associated discussion: https://lists.llvm.org/pipermail/lldb-dev/2016-September/011321.html | non_priority | write an lldb plugin for dlang description lldb is the llvm debugger it s the main debugger on mac osx and available on other platforms currently support for lldb is rather poor while gdb support has been implemented years ago by ibuclaw lldb still doesn t know much about d support for language is implemented via the goal of this project is to write such a plugin and to upstream it what are rough milestones of this project get familiar with the capability of plugins what is possible isn t get a basic plugin architecture in place which is called when dlang is detected implement demangling of d symbols most likely integrating the same code as gdb recognize d specific data structures such as arrays associative arrays typeinfo implement support for parsing d expressions e g the ability to do foo in myaa how does this project help the d community currently one of the biggest obstacle in d adoption is the tool support notable the debugging experience is miles behind other established languages recommended skills knowledge of linux and how binaries are generated experience with debugging in other native languages such as c c dwarf or llvm knowledge is a plus what can students expect to get out of doing this project deep knowledge of how debugging works at the core participation in not just one but two open source projects point of contact references the dwarf standard dmd debug info generator ldc debug info generator example of a simple d related contribution previous attempt limited to demangling associated discussion | 0 |
49,387 | 12,337,312,691 | IssuesEvent | 2020-05-14 14:49:25 | grafana/grafana | https://api.github.com/repos/grafana/grafana | closed | Signing: manifest should allow missing files | type/build-packaging | Our current manifest check verifies that everything in the manifest exists, and fails if a file does not exist. In order to better support platform specific bundles, we should allow removing files from the bundle, but still having the signature work. For example:
```
{
"plugin": "grafana-googlesheets-datasource",
"version": "1.0.0-dev",
"files": {
"LICENSE": "7df059597099bb7dcf25d2a9aedfaf4465f72d8d",
"README.md": "08ec6d704b6115bef57710f6d7e866c050cb50ee",
"gfx_sheets_darwin_amd64": "1b8ae92c6e80e502bb0bf2d0ae9d7223805993ab",
"gfx_sheets_linux_amd64": "f39e0cc7344d3186b1052e6d356eecaf54d75b49",
"gfx_sheets_windows_amd64.exe": "c8825dfec512c1c235244f7998ee95182f9968de",
"module.js": "aaec6f51a995b7b843b843cd14041925274d960d",
"module.js.LICENSE.txt": "7f822fe9341af8f82ad1b0c69aba957822a377cf",
"module.js.map": "c5a524f5c4237f6ed6a016d43cd46938efeadb45",
"plugin.json": "55556b845e91935cc48fae3aa67baf0f22694c3f"
},
"time": 1586817677115,
"keyId": "7e4d0c6a708866e7"
}
```
Should not need the three binary copies (each 18MB)
This should be a simple change to:
https://github.com/grafana/grafana/blob/2661054fe8009704c55646c551e3bca7ed6ea6fe/pkg/plugins/manifest.go#L105
| 1.0 | Signing: manifest should allow missing files - Our current manifest check verifies that everything in the manifest exists, and fails if a file does not exist. In order to better support platform specific bundles, we should allow removing files from the bundle, but still having the signature work. For example:
```
{
"plugin": "grafana-googlesheets-datasource",
"version": "1.0.0-dev",
"files": {
"LICENSE": "7df059597099bb7dcf25d2a9aedfaf4465f72d8d",
"README.md": "08ec6d704b6115bef57710f6d7e866c050cb50ee",
"gfx_sheets_darwin_amd64": "1b8ae92c6e80e502bb0bf2d0ae9d7223805993ab",
"gfx_sheets_linux_amd64": "f39e0cc7344d3186b1052e6d356eecaf54d75b49",
"gfx_sheets_windows_amd64.exe": "c8825dfec512c1c235244f7998ee95182f9968de",
"module.js": "aaec6f51a995b7b843b843cd14041925274d960d",
"module.js.LICENSE.txt": "7f822fe9341af8f82ad1b0c69aba957822a377cf",
"module.js.map": "c5a524f5c4237f6ed6a016d43cd46938efeadb45",
"plugin.json": "55556b845e91935cc48fae3aa67baf0f22694c3f"
},
"time": 1586817677115,
"keyId": "7e4d0c6a708866e7"
}
```
Should not need the three binary copies (each 18MB)
This should be a simple change to:
https://github.com/grafana/grafana/blob/2661054fe8009704c55646c551e3bca7ed6ea6fe/pkg/plugins/manifest.go#L105
| non_priority | signing manifest should allow missing files our current manifest check verifies that everything in the manifest exists and fails if a file does not exist in order to better support platform specific bundles we should allow removing files from the bundle but still having the signature work for example plugin grafana googlesheets datasource version dev files license readme md gfx sheets darwin gfx sheets linux gfx sheets windows exe module js module js license txt module js map plugin json time keyid should not need the three binary copies each this should be a simple change to | 0 |
10,230 | 6,643,220,429 | IssuesEvent | 2017-09-27 10:25:12 | TheTorProject/ooniprobe-ios | https://api.github.com/repos/TheTorProject/ooniprobe-ios | closed | About page shows wrong version number | bug usability | In the about page I see the version without the suffix `-rc.xx` or whatnot. | True | About page shows wrong version number - In the about page I see the version without the suffix `-rc.xx` or whatnot. | non_priority | about page shows wrong version number in the about page i see the version without the suffix rc xx or whatnot | 0 |
41,943 | 5,410,794,601 | IssuesEvent | 2017-03-01 09:48:43 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | When navigating to the targets tab, I see a flash of the "no analytics modules configured" message | 4 - Acceptance Testing Bug | This happens every time when logged in as a restricted user on lg.dev (2.10.0-beta.6). I'm seeing it when logged in via a browser on my laptop, but it's much worse on a Tecno Y4 because the message is visible for longer. | 1.0 | When navigating to the targets tab, I see a flash of the "no analytics modules configured" message - This happens every time when logged in as a restricted user on lg.dev (2.10.0-beta.6). I'm seeing it when logged in via a browser on my laptop, but it's much worse on a Tecno Y4 because the message is visible for longer. | non_priority | when navigating to the targets tab i see a flash of the no analytics modules configured message this happens every time when logged in as a restricted user on lg dev beta i m seeing it when logged in via a browser on my laptop but it s much worse on a tecno because the message is visible for longer | 0 |
4,364 | 5,008,412,753 | IssuesEvent | 2016-12-12 19:26:40 | MasterLemon2016/LeanMood | https://api.github.com/repos/MasterLemon2016/LeanMood | closed | Create two configurations for karma: one including coverage the other not | infrastructure | Code coverage support slows down build and debugging processes, we should only call it when needed.
The easiest way to achieve this is to add a copy of the karma.conf.js, include the coverage thing and then create a script in the package.json, something like (pseudocode)
test-coverage: 'karma karma.conf.cov.js ...'
We should fin a better way to do this (take as base the original karma conf and extend it), I have seen this in grunt plugins, maybe we can find something. | 1.0 | Create two configurations for karma: one including coverage the other not - Code coverage support slows down build and debugging processes, we should only call it when needed.
The easiest way to achieve this is to add a copy of the karma.conf.js, include the coverage thing and then create a script in the package.json, something like (pseudocode)
test-coverage: 'karma karma.conf.cov.js ...'
We should fin a better way to do this (take as base the original karma conf and extend it), I have seen this in grunt plugins, maybe we can find something. | non_priority | create two configurations for karma one including coverage the other not code coverage support slows down build and debugging processes we should only call it when needed the easiest way to achieve this is to add a copy of the karma conf js include the coverage thing and then create a script in the package json something like pseudocode test coverage karma karma conf cov js we should fin a better way to do this take as base the original karma conf and extend it i have seen this in grunt plugins maybe we can find something | 0 |
63,862 | 18,022,024,876 | IssuesEvent | 2021-09-16 20:47:25 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | closed | [TESTING]: OMB Info - Unit tests MUST run axe checks with the modal open for better code coverage | pattern-update 508-defect-3 accessibility testing vsp-design-system-team | @1Copenut commented on [Wed Jun 03 2020](https://github.com/department-of-veterans-affairs/va.gov-team/issues/9816)
## [508-defect-3](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-3)
<!--
Enter an issue title using the format [ERROR TYPE]: Brief description of the problem
---
[SCREENREADER]: Edit buttons need aria-label for context
[KEYBOARD]: Add another user link will not receive keyboard focus
[AXE-CORE]: Heading levels should increase by one
[COGNITION]: Error messages should be more specific
[COLOR]: Blue button on blue background does not have sufficient contrast ratio
---
-->
<!-- It's okay to delete the instructions above, but leave the link to the 508 defect severity level for your issue. -->
**Feedback framework**
- **❗️ Must** for if the feedback must be applied
- **⚠️ Should** if the feedback is best practice
- **✔️ Consider** for suggestions/enhancements
## Description
<!-- This is a detailed description of the issue. It should include a restatement of the title, and provide more background information. -->
The OMB Info component includes a modal window of legal text. The unit tests don't run an axe check on this modal. The component depends on this modal, so it must include an axe check with the modal open. This looks like it can be passed as a prop easily in the `OMBInfo.unit.spec.jsx` file.
## Point of Contact
<!-- If this issue is being opened by a VFS team member, please add a point of contact. Usually this is the same person who enters the issue ticket.
-->
**VFS Point of Contact:** _Trevor_
## Acceptance Criteria
<!-- As a keyboard user, I want to open the Level of Coverage widget by pressing Spacebar or pressing Enter. These keypress actions should not interfere with the mouse click event also opening the widget. -->
- [ ] Unit test file includes an axe check with the modal window open
- [ ] Axe checks return 0 violations
## Environment
* https://department-of-veterans-affairs.github.io/veteran-facing-services-tools/visual-design/components/ombinfo/
| 1.0 | [TESTING]: OMB Info - Unit tests MUST run axe checks with the modal open for better code coverage - @1Copenut commented on [Wed Jun 03 2020](https://github.com/department-of-veterans-affairs/va.gov-team/issues/9816)
## [508-defect-3](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/platform/accessibility/guidance/defect-severity-rubric.md#508-defect-3)
<!--
Enter an issue title using the format [ERROR TYPE]: Brief description of the problem
---
[SCREENREADER]: Edit buttons need aria-label for context
[KEYBOARD]: Add another user link will not receive keyboard focus
[AXE-CORE]: Heading levels should increase by one
[COGNITION]: Error messages should be more specific
[COLOR]: Blue button on blue background does not have sufficient contrast ratio
---
-->
<!-- It's okay to delete the instructions above, but leave the link to the 508 defect severity level for your issue. -->
**Feedback framework**
- **❗️ Must** for if the feedback must be applied
- **⚠️ Should** if the feedback is best practice
- **✔️ Consider** for suggestions/enhancements
## Description
<!-- This is a detailed description of the issue. It should include a restatement of the title, and provide more background information. -->
The OMB Info component includes a modal window of legal text. The unit tests don't run an axe check on this modal. The component depends on this modal, so it must include an axe check with the modal open. This looks like it can be passed as a prop easily in the `OMBInfo.unit.spec.jsx` file.
## Point of Contact
<!-- If this issue is being opened by a VFS team member, please add a point of contact. Usually this is the same person who enters the issue ticket.
-->
**VFS Point of Contact:** _Trevor_
## Acceptance Criteria
<!-- As a keyboard user, I want to open the Level of Coverage widget by pressing Spacebar or pressing Enter. These keypress actions should not interfere with the mouse click event also opening the widget. -->
- [ ] Unit test file includes an axe check with the modal window open
- [ ] Axe checks return 0 violations
## Environment
* https://department-of-veterans-affairs.github.io/veteran-facing-services-tools/visual-design/components/ombinfo/
| non_priority | omb info unit tests must run axe checks with the modal open for better code coverage commented on enter an issue title using the format brief description of the problem edit buttons need aria label for context add another user link will not receive keyboard focus heading levels should increase by one error messages should be more specific blue button on blue background does not have sufficient contrast ratio feedback framework ❗️ must for if the feedback must be applied ⚠️ should if the feedback is best practice ✔️ consider for suggestions enhancements description the omb info component includes a modal window of legal text the unit tests don t run an axe check on this modal the component depends on this modal so it must include an axe check with the modal open this looks like it can be passed as a prop easily in the ombinfo unit spec jsx file point of contact if this issue is being opened by a vfs team member please add a point of contact usually this is the same person who enters the issue ticket vfs point of contact trevor acceptance criteria unit test file includes an axe check with the modal window open axe checks return violations environment | 0 |
124,931 | 10,330,442,184 | IssuesEvent | 2019-09-02 14:41:20 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] S3BlobStoreRepositoryTests.testSnapshotAndRestore fails in master and 7.x | :Distributed/Snapshot/Restore >test-failure | Following looks like the cause:
```
Caused by: com.amazonaws.services.s3.model.AmazonS3Exception: Internal Server Error (Service: Amazon S3; Status Code: 500; Error Code: 500 Internal Server Error; Request ID: 8e933e55-d3b7-51d7-9290-2950875e6c63; S3 Extended Request ID: null)
```
Example failures:
[7.x](https://gradle-enterprise.elastic.co/s/qotlstic456vk/tests/gharp3fr6cqle-6yehmjhn3mkmc?openStackTraces=WzBd)
[master](https://gradle-enterprise.elastic.co/s/obmf7q6gfmbjw/console-log?task=:plugins:repository-s3:test#L24)
`testMultipleSnapshotAndRollback` also fails with 500 error from AWS, will open separate issue and link to this.
Was not able to reproduce on master using:
```
./gradlew :plugins:repository-s3:test --tests "org.elasticsearch.repositories.s3.S3BlobStoreRepositoryTests.testSnapshotAndRestore" -Dtests.seed=5240E29A131A5AB2 -Dtests.security.manager=true -Dtests.locale=fil -Dtests.timezone=America/Costa_Rica -Dcompiler.java=12 -Druntime.java=11
```
Looks like these started failing more frequently on August 31st. | 1.0 | [CI] S3BlobStoreRepositoryTests.testSnapshotAndRestore fails in master and 7.x - Following looks like the cause:
```
Caused by: com.amazonaws.services.s3.model.AmazonS3Exception: Internal Server Error (Service: Amazon S3; Status Code: 500; Error Code: 500 Internal Server Error; Request ID: 8e933e55-d3b7-51d7-9290-2950875e6c63; S3 Extended Request ID: null)
```
Example failures:
[7.x](https://gradle-enterprise.elastic.co/s/qotlstic456vk/tests/gharp3fr6cqle-6yehmjhn3mkmc?openStackTraces=WzBd)
[master](https://gradle-enterprise.elastic.co/s/obmf7q6gfmbjw/console-log?task=:plugins:repository-s3:test#L24)
`testMultipleSnapshotAndRollback` also fails with 500 error from AWS, will open separate issue and link to this.
Was not able to reproduce on master using:
```
./gradlew :plugins:repository-s3:test --tests "org.elasticsearch.repositories.s3.S3BlobStoreRepositoryTests.testSnapshotAndRestore" -Dtests.seed=5240E29A131A5AB2 -Dtests.security.manager=true -Dtests.locale=fil -Dtests.timezone=America/Costa_Rica -Dcompiler.java=12 -Druntime.java=11
```
Looks like these started failing more frequently on August 31st. | non_priority | testsnapshotandrestore fails in master and x following looks like the cause caused by com amazonaws services model internal server error service amazon status code error code internal server error request id extended request id null example failures testmultiplesnapshotandrollback also fails with error from aws will open separate issue and link to this was not able to reproduce on master using gradlew plugins repository test tests org elasticsearch repositories testsnapshotandrestore dtests seed dtests security manager true dtests locale fil dtests timezone america costa rica dcompiler java druntime java looks like these started failing more frequently on august | 0 |
65,490 | 6,965,067,523 | IssuesEvent | 2017-12-09 01:27:16 | tschottdorf/cockroach | https://api.github.com/repos/tschottdorf/cockroach | closed | Test failure in CI build 428 | test-failure | The following test appears to have failed:
[#428](https://circleci.com/gh/tschottdorf/cockroach/428):
```
I0331 16:39:38.036788 79 multiraft.go:448] node 1: group 1 got message 6->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036815 79 multiraft.go:448] node 1: group 1 got message 8->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036856 79 multiraft.go:448] node 1: group 1 got message 10->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036884 79 multiraft.go:448] node 1: group 1 got message 3->1 MsgHeartbeatResp Term:6 Log:0/0
E0331 16:39:39.022641 79 heartbeat_test.go:52] timeout when reading from intercept channel
panic: test timed out after 30s
goroutine 427 [running]:
testing.func·008()
/usr/src/go/src/testing/testing.go:681 +0x12f
created by time.goFunc
/usr/src/go/src/time/sleep.go:129 +0x4b
goroutine 1 [chan receive]:
testing.RunTests(0x9aa860, 0xb12340, 0x7, 0x7, 0xc207ffc301)
/usr/src/go/src/testing/testing.go:556 +0xad6
--
goroutine 392 [select]:
github.com/cockroachdb/cockroach/multiraft.func·009()
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:51 +0x3fc
created by github.com/cockroachdb/cockroach/multiraft.(*eventDemux).start
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:72 +0x8c
FAIL github.com/cockroachdb/cockroach/multiraft 30.012s
=== RUN TestMemoryStorage
--- PASS: TestMemoryStorage (0.00s)
PASS
ok github.com/cockroachdb/cockroach/multiraft/storagetest 0.004s
=== RUN TestClientCmdIDIsEmpty
--- PASS: TestClientCmdIDIsEmpty (0.00s)
=== RUN TestResponseHeaderSetGoError
--- PASS: TestResponseHeaderSetGoError (0.00s)
=== RUN TestResponseHeaderNilError
--- PASS: TestResponseHeaderNilError (0.00s)
I0331 16:39:38.036788 79 multiraft.go:448] node 1: group 1 got message 6->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036815 79 multiraft.go:448] node 1: group 1 got message 8->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036856 79 multiraft.go:448] node 1: group 1 got message 10->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036884 79 multiraft.go:448] node 1: group 1 got message 3->1 MsgHeartbeatResp Term:6 Log:0/0
E0331 16:39:39.022641 79 heartbeat_test.go:52] timeout when reading from intercept channel
panic: test timed out after 30s
goroutine 427 [running]:
testing.func·008()
/usr/src/go/src/testing/testing.go:681 +0x12f
created by time.goFunc
/usr/src/go/src/time/sleep.go:129 +0x4b
goroutine 1 [chan receive]:
testing.RunTests(0x9aa860, 0xb12340, 0x7, 0x7, 0xc207ffc301)
/usr/src/go/src/testing/testing.go:556 +0xad6
--
goroutine 392 [select]:
github.com/cockroachdb/cockroach/multiraft.func·009()
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:51 +0x3fc
created by github.com/cockroachdb/cockroach/multiraft.(*eventDemux).start
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:72 +0x8c
FAIL github.com/cockroachdb/cockroach/multiraft 30.012s
=== RUN TestMemoryStorage
--- PASS: TestMemoryStorage (0.00s)
PASS
ok github.com/cockroachdb/cockroach/multiraft/storagetest 0.004s
=== RUN TestClientCmdIDIsEmpty
--- PASS: TestClientCmdIDIsEmpty (0.00s)
=== RUN TestResponseHeaderSetGoError
--- PASS: TestResponseHeaderSetGoError (0.00s)
=== RUN TestResponseHeaderNilError
--- PASS: TestResponseHeaderNilError (0.00s)
```
Please assign, take a look and update the issue accordingly.
| 1.0 | Test failure in CI build 428 - The following test appears to have failed:
[#428](https://circleci.com/gh/tschottdorf/cockroach/428):
```
I0331 16:39:38.036788 79 multiraft.go:448] node 1: group 1 got message 6->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036815 79 multiraft.go:448] node 1: group 1 got message 8->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036856 79 multiraft.go:448] node 1: group 1 got message 10->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036884 79 multiraft.go:448] node 1: group 1 got message 3->1 MsgHeartbeatResp Term:6 Log:0/0
E0331 16:39:39.022641 79 heartbeat_test.go:52] timeout when reading from intercept channel
panic: test timed out after 30s
goroutine 427 [running]:
testing.func·008()
/usr/src/go/src/testing/testing.go:681 +0x12f
created by time.goFunc
/usr/src/go/src/time/sleep.go:129 +0x4b
goroutine 1 [chan receive]:
testing.RunTests(0x9aa860, 0xb12340, 0x7, 0x7, 0xc207ffc301)
/usr/src/go/src/testing/testing.go:556 +0xad6
--
goroutine 392 [select]:
github.com/cockroachdb/cockroach/multiraft.func·009()
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:51 +0x3fc
created by github.com/cockroachdb/cockroach/multiraft.(*eventDemux).start
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:72 +0x8c
FAIL github.com/cockroachdb/cockroach/multiraft 30.012s
=== RUN TestMemoryStorage
--- PASS: TestMemoryStorage (0.00s)
PASS
ok github.com/cockroachdb/cockroach/multiraft/storagetest 0.004s
=== RUN TestClientCmdIDIsEmpty
--- PASS: TestClientCmdIDIsEmpty (0.00s)
=== RUN TestResponseHeaderSetGoError
--- PASS: TestResponseHeaderSetGoError (0.00s)
=== RUN TestResponseHeaderNilError
--- PASS: TestResponseHeaderNilError (0.00s)
I0331 16:39:38.036788 79 multiraft.go:448] node 1: group 1 got message 6->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036815 79 multiraft.go:448] node 1: group 1 got message 8->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036856 79 multiraft.go:448] node 1: group 1 got message 10->1 MsgHeartbeatResp Term:6 Log:0/0
I0331 16:39:38.036884 79 multiraft.go:448] node 1: group 1 got message 3->1 MsgHeartbeatResp Term:6 Log:0/0
E0331 16:39:39.022641 79 heartbeat_test.go:52] timeout when reading from intercept channel
panic: test timed out after 30s
goroutine 427 [running]:
testing.func·008()
/usr/src/go/src/testing/testing.go:681 +0x12f
created by time.goFunc
/usr/src/go/src/time/sleep.go:129 +0x4b
goroutine 1 [chan receive]:
testing.RunTests(0x9aa860, 0xb12340, 0x7, 0x7, 0xc207ffc301)
/usr/src/go/src/testing/testing.go:556 +0xad6
--
goroutine 392 [select]:
github.com/cockroachdb/cockroach/multiraft.func·009()
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:51 +0x3fc
created by github.com/cockroachdb/cockroach/multiraft.(*eventDemux).start
/go/src/github.com/cockroachdb/cockroach/multiraft/events_test.go:72 +0x8c
FAIL github.com/cockroachdb/cockroach/multiraft 30.012s
=== RUN TestMemoryStorage
--- PASS: TestMemoryStorage (0.00s)
PASS
ok github.com/cockroachdb/cockroach/multiraft/storagetest 0.004s
=== RUN TestClientCmdIDIsEmpty
--- PASS: TestClientCmdIDIsEmpty (0.00s)
=== RUN TestResponseHeaderSetGoError
--- PASS: TestResponseHeaderSetGoError (0.00s)
=== RUN TestResponseHeaderNilError
--- PASS: TestResponseHeaderNilError (0.00s)
```
Please assign, take a look and update the issue accordingly.
| non_priority | test failure in ci build the following test appears to have failed multiraft go node group got message msgheartbeatresp term log multiraft go node group got message msgheartbeatresp term log multiraft go node group got message msgheartbeatresp term log multiraft go node group got message msgheartbeatresp term log heartbeat test go timeout when reading from intercept channel panic test timed out after goroutine testing func· usr src go src testing testing go created by time gofunc usr src go src time sleep go goroutine testing runtests usr src go src testing testing go goroutine github com cockroachdb cockroach multiraft func· go src github com cockroachdb cockroach multiraft events test go created by github com cockroachdb cockroach multiraft eventdemux start go src github com cockroachdb cockroach multiraft events test go fail github com cockroachdb cockroach multiraft run testmemorystorage pass testmemorystorage pass ok github com cockroachdb cockroach multiraft storagetest run testclientcmdidisempty pass testclientcmdidisempty run testresponseheadersetgoerror pass testresponseheadersetgoerror run testresponseheadernilerror pass testresponseheadernilerror multiraft go node group got message msgheartbeatresp term log multiraft go node group got message msgheartbeatresp term log multiraft go node group got message msgheartbeatresp term log multiraft go node group got message msgheartbeatresp term log heartbeat test go timeout when reading from intercept channel panic test timed out after goroutine testing func· usr src go src testing testing go created by time gofunc usr src go src time sleep go goroutine testing runtests usr src go src testing testing go goroutine github com cockroachdb cockroach multiraft func· go src github com cockroachdb cockroach multiraft events test go created by github com cockroachdb cockroach multiraft eventdemux start go src github com cockroachdb cockroach multiraft events test go fail github com cockroachdb cockroach multiraft run testmemorystorage pass testmemorystorage pass ok github com cockroachdb cockroach multiraft storagetest run testclientcmdidisempty pass testclientcmdidisempty run testresponseheadersetgoerror pass testresponseheadersetgoerror run testresponseheadernilerror pass testresponseheadernilerror please assign take a look and update the issue accordingly | 0 |
218,165 | 24,351,804,926 | IssuesEvent | 2022-10-03 01:21:15 | susanstwss/JavaLive | https://api.github.com/repos/susanstwss/JavaLive | opened | CVE-2022-42003 (Medium) detected in jackson-databind-2.9.9.3.jar | security vulnerability | ## CVE-2022-42003 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9.3/jackson-databind-2.9.9.3.jar</p>
<p>
Dependency Hierarchy:
- solr-velocity-8.3.1.jar (Root Library)
- :x: **jackson-databind-2.9.9.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/susanstwss/JavaLive/commit/bada63441522c15b923cde8a080ad10d787106e1">bada63441522c15b923cde8a080ad10d787106e1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| True | CVE-2022-42003 (Medium) detected in jackson-databind-2.9.9.3.jar - ## CVE-2022-42003 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9.3/jackson-databind-2.9.9.3.jar</p>
<p>
Dependency Hierarchy:
- solr-velocity-8.3.1.jar (Root Library)
- :x: **jackson-databind-2.9.9.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/susanstwss/JavaLive/commit/bada63441522c15b923cde8a080ad10d787106e1">bada63441522c15b923cde8a080ad10d787106e1</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In FasterXML jackson-databind before 2.14.0-rc1, resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting, when the UNWRAP_SINGLE_VALUE_ARRAYS feature is enabled.
<p>Publish Date: 2022-10-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-42003>CVE-2022-42003</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
| non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy solr velocity jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details in fasterxml jackson databind before resource exhaustion can occur because of a lack of a check in primitive value deserializers to avoid deep wrapper array nesting when the unwrap single value arrays feature is enabled publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href | 0 |
126,687 | 10,431,988,545 | IssuesEvent | 2019-09-17 10:14:41 | MangopearUK/European-Boating-Association--Theme | https://api.github.com/repos/MangopearUK/European-Boating-Association--Theme | reopened | Test & audit group: SBU | Testing | Page URL: https://eba.eu.com/membership/groups/sbu/
## Table of contents
- [ ] **Task 1:** Perform automated audits _(10 tasks)_
- [ ] **Task 2:** Manual standards & accessibility tests _(61 tasks)_
- [ ] **Task 3:** Breakpoint testing _(15 tasks)_
- [ ] **Task 4:** Re-run automated audits _(10 tasks)_
## 1: Perform automated audits _(10 tasks)_
### Lighthouse:
- [ ] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [ ] Run "Performance" audit in lighthouse _(using incognito tab)_
- [ ] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [ ] Run "SEO" audit in lighthouse _(using incognito tab)_
- [ ] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [ ] Run full audit of the the page's performance in Pingdom
### Browser's console
- [ ] Check Chrome's console for errors
### Log results of audits
- [ ] Screenshot snapshot of the lighthouse audits
- [ ] Upload PDF of detailed lighthouse reports
- [ ] Provide a screenshot of any console errors
## 2: Manual standards & accessibility tests _(61 tasks)_
### Forms
- [ ] Give all form elements permanently visible labels
- [ ] Place labels above form elements
- [ ] Mark invalid fields clearly and provide associated error messages
- [ ] Make forms as short as possible; offer shortcuts like autocompleting the address using the postcode
- [ ] Ensure all form fields have the correct requried state
- [ ] Provide status and error messages as WAI-ARIA live regions
### Readability of content
- [ ] Ensure page has good grammar
- [ ] Ensure page content has been spell-checked
- [ ] Make sure headings are in logical order
- [ ] Ensure the same content is available across different devices and platforms
- [ ] Begin long, multi-section documents with a table of contents
### Presentation
- [ ] Make sure all content is formatted correctly
- [ ] Avoid all-caps text
- [ ] Make sure data tables wider than their container can be scrolled horizontally
- [ ] Use the same design patterns to solve the same problems
- [ ] Do not mark up subheadings/straplines with separate heading elements
### Links & buttons
#### Links
- [ ] Check all links to ensure they work
- [ ] Check all links to third party websites use `rel="noopener"`
- [ ] Make sure the purpose of a link is clearly described: "read more" vs. "read more about accessibility"
- [ ] Provide a skip link if necessary
- [ ] Underline links — at least in body copy
- [ ] Warn users of links that have unusual behaviors, like linking off-site, or loading a new tab (i.e. aria-label)
#### Buttons
- [ ] Ensure primary calls to action are easy to recognize and reach
- [ ] Provide clear, unambiguous focus styles
- [ ] Ensure states (pressed, expanded, invalid, etc) are communicated to assistive software
- [ ] Ensure disabled controls are not focusable
- [ ] Make sure controls within hidden content are not focusable
- [ ] Provide large touch "targets" for interactive elements
- [ ] Make controls look like controls; give them strong perceived affordance
- [ ] Use well-established, therefore recognizable, icons and symbols
### Assistive technology
- [ ] Ensure content is not obscured through zooming
- [ ] Support Windows high contrast mode (use images, not background images)
- [ ] Provide alternative text for salient images
- [ ] Make scrollable elements focusable for keyboard users
- [ ] Ensure keyboard focus order is logical regarding visual layout
- [ ] Match semantics to behavior for assistive technology users
- [ ] Provide a default language and use lang="[ISO code]" for subsections in different languages
- [ ] Inform the user when there are important changes to the application state
- [ ] Do not hijack standard scrolling behavior
- [ ] Do not instate "infinite scroll" by default; provide buttons to load more items
### General accessibility
- [ ] Make sure text and background colors contrast sufficiently
- [ ] Do not rely on color for differentiation of visual elements
- [ ] Avoid images of text — text that cannot be translated, selected, or understood by assistive tech
- [ ] Provide a print stylesheet
- [ ] Honour requests to remove animation via the prefers-reduced-motion media query
### SEO
- [ ] Ensure all pages have appropriate title
- [ ] Ensure all pages have meta descriptions
- [ ] Make content easier to find and improve search results with structured data [Read more](https://developers.google.com/search/docs/guides/prototype)
- [ ] Check whether page should be appearing in sitemap
- [ ] Make sure page has Facebook and Twitter large image previews set correctly
- [ ] Check canonical links for page
- [ ] Mark as cornerstone content?
### Performance
- [ ] Ensure all CSS assets are minified and concatenated
- [ ] Ensure all JS assets are minified and concatenated
- [ ] Ensure all images are compressed
- [ ] Where possible, remove redundant code
- [ ] Ensure all SVG assets have been optimised
- [ ] Make sure styles and scripts are not render blocking
- [ ] Ensure large image assets are lazy loaded
### Other
- [ ] Make sure all content belongs to a landmark element
- [ ] Provide a manifest.json file for identifiable homescreen entries
## 3: Breakpoint testing _(15 tasks)_
### Desktop
- [ ] Provide a full screenshot of **1920px** wide page
- [ ] Provide a full screenshot of **1500px** wide page
- [ ] Provide a full screenshot of **1280px** wide page
- [ ] Provide a full screenshot of **1024px** wide page
### Tablet
- [ ] Provide a full screenshot of **960px** wide page
- [ ] Provide a full screenshot of **800px** wide page
- [ ] Provide a full screenshot of **760px** wide page
- [ ] Provide a full screenshot of **650px** wide page
### Mobile
- [ ] Provide a full screenshot of **600px** wide page
- [ ] Provide a full screenshot of **500px** wide page
- [ ] Provide a full screenshot of **450px** wide page
- [ ] Provide a full screenshot of **380px** wide page
- [ ] Provide a full screenshot of **320px** wide page
- [ ] Provide a full screenshot of **280px** wide page
- [ ] Provide a full screenshot of **250px** wide page
## 4: Re-run automated audits _(10 tasks)_
### Lighthouse:
- [ ] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [ ] Run "Performance" audit in lighthouse _(using incognito tab)_
- [ ] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [ ] Run "SEO" audit in lighthouse _(using incognito tab)_
- [ ] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [ ] Run full audit of the the page's performance in Pingdom
### Browser's console
- [ ] Check Chrome's console for errors
### Log results of audits
- [ ] Screenshot snapshot of the lighthouse audits
- [ ] Upload PDF of detailed lighthouse reports
- [ ] Provide a screenshot of any console errors | 1.0 | Test & audit group: SBU - Page URL: https://eba.eu.com/membership/groups/sbu/
## Table of contents
- [ ] **Task 1:** Perform automated audits _(10 tasks)_
- [ ] **Task 2:** Manual standards & accessibility tests _(61 tasks)_
- [ ] **Task 3:** Breakpoint testing _(15 tasks)_
- [ ] **Task 4:** Re-run automated audits _(10 tasks)_
## 1: Perform automated audits _(10 tasks)_
### Lighthouse:
- [ ] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [ ] Run "Performance" audit in lighthouse _(using incognito tab)_
- [ ] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [ ] Run "SEO" audit in lighthouse _(using incognito tab)_
- [ ] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [ ] Run full audit of the the page's performance in Pingdom
### Browser's console
- [ ] Check Chrome's console for errors
### Log results of audits
- [ ] Screenshot snapshot of the lighthouse audits
- [ ] Upload PDF of detailed lighthouse reports
- [ ] Provide a screenshot of any console errors
## 2: Manual standards & accessibility tests _(61 tasks)_
### Forms
- [ ] Give all form elements permanently visible labels
- [ ] Place labels above form elements
- [ ] Mark invalid fields clearly and provide associated error messages
- [ ] Make forms as short as possible; offer shortcuts like autocompleting the address using the postcode
- [ ] Ensure all form fields have the correct requried state
- [ ] Provide status and error messages as WAI-ARIA live regions
### Readability of content
- [ ] Ensure page has good grammar
- [ ] Ensure page content has been spell-checked
- [ ] Make sure headings are in logical order
- [ ] Ensure the same content is available across different devices and platforms
- [ ] Begin long, multi-section documents with a table of contents
### Presentation
- [ ] Make sure all content is formatted correctly
- [ ] Avoid all-caps text
- [ ] Make sure data tables wider than their container can be scrolled horizontally
- [ ] Use the same design patterns to solve the same problems
- [ ] Do not mark up subheadings/straplines with separate heading elements
### Links & buttons
#### Links
- [ ] Check all links to ensure they work
- [ ] Check all links to third party websites use `rel="noopener"`
- [ ] Make sure the purpose of a link is clearly described: "read more" vs. "read more about accessibility"
- [ ] Provide a skip link if necessary
- [ ] Underline links — at least in body copy
- [ ] Warn users of links that have unusual behaviors, like linking off-site, or loading a new tab (i.e. aria-label)
#### Buttons
- [ ] Ensure primary calls to action are easy to recognize and reach
- [ ] Provide clear, unambiguous focus styles
- [ ] Ensure states (pressed, expanded, invalid, etc) are communicated to assistive software
- [ ] Ensure disabled controls are not focusable
- [ ] Make sure controls within hidden content are not focusable
- [ ] Provide large touch "targets" for interactive elements
- [ ] Make controls look like controls; give them strong perceived affordance
- [ ] Use well-established, therefore recognizable, icons and symbols
### Assistive technology
- [ ] Ensure content is not obscured through zooming
- [ ] Support Windows high contrast mode (use images, not background images)
- [ ] Provide alternative text for salient images
- [ ] Make scrollable elements focusable for keyboard users
- [ ] Ensure keyboard focus order is logical regarding visual layout
- [ ] Match semantics to behavior for assistive technology users
- [ ] Provide a default language and use lang="[ISO code]" for subsections in different languages
- [ ] Inform the user when there are important changes to the application state
- [ ] Do not hijack standard scrolling behavior
- [ ] Do not instate "infinite scroll" by default; provide buttons to load more items
### General accessibility
- [ ] Make sure text and background colors contrast sufficiently
- [ ] Do not rely on color for differentiation of visual elements
- [ ] Avoid images of text — text that cannot be translated, selected, or understood by assistive tech
- [ ] Provide a print stylesheet
- [ ] Honour requests to remove animation via the prefers-reduced-motion media query
### SEO
- [ ] Ensure all pages have appropriate title
- [ ] Ensure all pages have meta descriptions
- [ ] Make content easier to find and improve search results with structured data [Read more](https://developers.google.com/search/docs/guides/prototype)
- [ ] Check whether page should be appearing in sitemap
- [ ] Make sure page has Facebook and Twitter large image previews set correctly
- [ ] Check canonical links for page
- [ ] Mark as cornerstone content?
### Performance
- [ ] Ensure all CSS assets are minified and concatenated
- [ ] Ensure all JS assets are minified and concatenated
- [ ] Ensure all images are compressed
- [ ] Where possible, remove redundant code
- [ ] Ensure all SVG assets have been optimised
- [ ] Make sure styles and scripts are not render blocking
- [ ] Ensure large image assets are lazy loaded
### Other
- [ ] Make sure all content belongs to a landmark element
- [ ] Provide a manifest.json file for identifiable homescreen entries
## 3: Breakpoint testing _(15 tasks)_
### Desktop
- [ ] Provide a full screenshot of **1920px** wide page
- [ ] Provide a full screenshot of **1500px** wide page
- [ ] Provide a full screenshot of **1280px** wide page
- [ ] Provide a full screenshot of **1024px** wide page
### Tablet
- [ ] Provide a full screenshot of **960px** wide page
- [ ] Provide a full screenshot of **800px** wide page
- [ ] Provide a full screenshot of **760px** wide page
- [ ] Provide a full screenshot of **650px** wide page
### Mobile
- [ ] Provide a full screenshot of **600px** wide page
- [ ] Provide a full screenshot of **500px** wide page
- [ ] Provide a full screenshot of **450px** wide page
- [ ] Provide a full screenshot of **380px** wide page
- [ ] Provide a full screenshot of **320px** wide page
- [ ] Provide a full screenshot of **280px** wide page
- [ ] Provide a full screenshot of **250px** wide page
## 4: Re-run automated audits _(10 tasks)_
### Lighthouse:
- [ ] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [ ] Run "Performance" audit in lighthouse _(using incognito tab)_
- [ ] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [ ] Run "SEO" audit in lighthouse _(using incognito tab)_
- [ ] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [ ] Run full audit of the the page's performance in Pingdom
### Browser's console
- [ ] Check Chrome's console for errors
### Log results of audits
- [ ] Screenshot snapshot of the lighthouse audits
- [ ] Upload PDF of detailed lighthouse reports
- [ ] Provide a screenshot of any console errors | non_priority | test audit group sbu page url table of contents task perform automated audits tasks task manual standards accessibility tests tasks task breakpoint testing tasks task re run automated audits tasks perform automated audits tasks lighthouse run accessibility audit in lighthouse using incognito tab run performance audit in lighthouse using incognito tab run best practices audit in lighthouse using incognito tab run seo audit in lighthouse using incognito tab run pwa audit in lighthouse using incognito tab pingdom run full audit of the the page s performance in pingdom browser s console check chrome s console for errors log results of audits screenshot snapshot of the lighthouse audits upload pdf of detailed lighthouse reports provide a screenshot of any console errors manual standards accessibility tests tasks forms give all form elements permanently visible labels place labels above form elements mark invalid fields clearly and provide associated error messages make forms as short as possible offer shortcuts like autocompleting the address using the postcode ensure all form fields have the correct requried state provide status and error messages as wai aria live regions readability of content ensure page has good grammar ensure page content has been spell checked make sure headings are in logical order ensure the same content is available across different devices and platforms begin long multi section documents with a table of contents presentation make sure all content is formatted correctly avoid all caps text make sure data tables wider than their container can be scrolled horizontally use the same design patterns to solve the same problems do not mark up subheadings straplines with separate heading elements links buttons links check all links to ensure they work check all links to third party websites use rel noopener make sure the purpose of a link is clearly described read more vs read more about accessibility provide a skip link if necessary underline links — at least in body copy warn users of links that have unusual behaviors like linking off site or loading a new tab i e aria label buttons ensure primary calls to action are easy to recognize and reach provide clear unambiguous focus styles ensure states pressed expanded invalid etc are communicated to assistive software ensure disabled controls are not focusable make sure controls within hidden content are not focusable provide large touch targets for interactive elements make controls look like controls give them strong perceived affordance use well established therefore recognizable icons and symbols assistive technology ensure content is not obscured through zooming support windows high contrast mode use images not background images provide alternative text for salient images make scrollable elements focusable for keyboard users ensure keyboard focus order is logical regarding visual layout match semantics to behavior for assistive technology users provide a default language and use lang for subsections in different languages inform the user when there are important changes to the application state do not hijack standard scrolling behavior do not instate infinite scroll by default provide buttons to load more items general accessibility make sure text and background colors contrast sufficiently do not rely on color for differentiation of visual elements avoid images of text — text that cannot be translated selected or understood by assistive tech provide a print stylesheet honour requests to remove animation via the prefers reduced motion media query seo ensure all pages have appropriate title ensure all pages have meta descriptions make content easier to find and improve search results with structured data check whether page should be appearing in sitemap make sure page has facebook and twitter large image previews set correctly check canonical links for page mark as cornerstone content performance ensure all css assets are minified and concatenated ensure all js assets are minified and concatenated ensure all images are compressed where possible remove redundant code ensure all svg assets have been optimised make sure styles and scripts are not render blocking ensure large image assets are lazy loaded other make sure all content belongs to a landmark element provide a manifest json file for identifiable homescreen entries breakpoint testing tasks desktop provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page tablet provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page mobile provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page re run automated audits tasks lighthouse run accessibility audit in lighthouse using incognito tab run performance audit in lighthouse using incognito tab run best practices audit in lighthouse using incognito tab run seo audit in lighthouse using incognito tab run pwa audit in lighthouse using incognito tab pingdom run full audit of the the page s performance in pingdom browser s console check chrome s console for errors log results of audits screenshot snapshot of the lighthouse audits upload pdf of detailed lighthouse reports provide a screenshot of any console errors | 0 |
5,719 | 2,791,323,296 | IssuesEvent | 2015-05-10 01:29:27 | red/red | https://api.github.com/repos/red/red | closed | Interpreter: Foreach doesn't allow block returned from function as its series argument | Red status.built status.tested type.bug | ##### EXAMPLE 1
```rebol
f: function [
/l
][
b: []
if l [return b]
append b 1
]
f f f
foreach a f/l [print a]
```
returns:
```
*** Script error: foreach does not allow word for its series argument
*** Where: foreach
```
while this code:
```rebol
f: function [
/l
][
b: []
if l [return b]
append b 1
]
f f f
foreach a head f/l [print a]
```
correctly returns:
```
1
1
1
```
##### EXAMPLE 2
```rebol
f: function [
/l
][
b: []
if l [return b]
append b [1 2]
]
f f f
foreach [a b] f/l [print [a b]]
```
returns:
```
(nothing)
```
while this code:
```rebol
f: function [
/l
][
b: []
if l [return b]
append b [1 2]
]
f f f
foreach [a b] head f/l [print [a b]]
```
correctly returns:
```
1 2
1 2
1 2
```
| 1.0 | Interpreter: Foreach doesn't allow block returned from function as its series argument - ##### EXAMPLE 1
```rebol
f: function [
/l
][
b: []
if l [return b]
append b 1
]
f f f
foreach a f/l [print a]
```
returns:
```
*** Script error: foreach does not allow word for its series argument
*** Where: foreach
```
while this code:
```rebol
f: function [
/l
][
b: []
if l [return b]
append b 1
]
f f f
foreach a head f/l [print a]
```
correctly returns:
```
1
1
1
```
##### EXAMPLE 2
```rebol
f: function [
/l
][
b: []
if l [return b]
append b [1 2]
]
f f f
foreach [a b] f/l [print [a b]]
```
returns:
```
(nothing)
```
while this code:
```rebol
f: function [
/l
][
b: []
if l [return b]
append b [1 2]
]
f f f
foreach [a b] head f/l [print [a b]]
```
correctly returns:
```
1 2
1 2
1 2
```
| non_priority | interpreter foreach doesn t allow block returned from function as its series argument example rebol f function l b if l append b f f f foreach a f l returns script error foreach does not allow word for its series argument where foreach while this code rebol f function l b if l append b f f f foreach a head f l correctly returns example rebol f function l b if l append b f f f foreach f l returns nothing while this code rebol f function l b if l append b f f f foreach head f l correctly returns | 0 |
277,003 | 24,039,666,383 | IssuesEvent | 2022-09-15 23:26:48 | rancher/dashboard | https://api.github.com/repos/rancher/dashboard | closed | Improve the User Profile page's 'Formatting' Section | [zube]: To Test QA/XS kind/enhancement good-first-issue team/area2 | **Is your feature request related to a problem? Please describe.**
This came out of the discussion in https://github.com/rancher/dashboard/issues/6614. I've created a new issue to remove any confusion with the request in it's description.
**Describe the solution you'd like**
1. `Formatting` title --> `Display Settings`
2. Add a description underneath the title (styled the same as the `You can change...` description underneath `Login Landing Page`
```
Change the way information is displayed in <product name>
```
Note - product name i think is just {product} in the translation file. It should be clear that this only applies to the UI.
3. Move the `Table Rows per Page` onto the same row as `Number of clusters to show in side menu`
| 1.0 | Improve the User Profile page's 'Formatting' Section - **Is your feature request related to a problem? Please describe.**
This came out of the discussion in https://github.com/rancher/dashboard/issues/6614. I've created a new issue to remove any confusion with the request in it's description.
**Describe the solution you'd like**
1. `Formatting` title --> `Display Settings`
2. Add a description underneath the title (styled the same as the `You can change...` description underneath `Login Landing Page`
```
Change the way information is displayed in <product name>
```
Note - product name i think is just {product} in the translation file. It should be clear that this only applies to the UI.
3. Move the `Table Rows per Page` onto the same row as `Number of clusters to show in side menu`
| non_priority | improve the user profile page s formatting section is your feature request related to a problem please describe this came out of the discussion in i ve created a new issue to remove any confusion with the request in it s description describe the solution you d like formatting title display settings add a description underneath the title styled the same as the you can change description underneath login landing page change the way information is displayed in note product name i think is just product in the translation file it should be clear that this only applies to the ui move the table rows per page onto the same row as number of clusters to show in side menu | 0 |
56,936 | 7,017,880,880 | IssuesEvent | 2017-12-21 11:21:54 | RyuuSukeChan/ProjectDungeon | https://api.github.com/repos/RyuuSukeChan/ProjectDungeon | opened | Gameplay Screen - Apply Sounds | Audio Game Design | Apply a total of 10 sound to the gameplay to give feedback of what's going on.
**EXPECTED RESULT:**
_10 files named X.x_ | 1.0 | Gameplay Screen - Apply Sounds - Apply a total of 10 sound to the gameplay to give feedback of what's going on.
**EXPECTED RESULT:**
_10 files named X.x_ | non_priority | gameplay screen apply sounds apply a total of sound to the gameplay to give feedback of what s going on expected result files named x x | 0 |
74,614 | 9,794,093,116 | IssuesEvent | 2019-06-10 21:42:14 | BodeSpezial/Stimmungstracker | https://api.github.com/repos/BodeSpezial/Stimmungstracker | opened | Add more languages | documentation enhancement | Add a file system, that lets easily adding new langauage files. Maybe with some XML-Code or similar. | 1.0 | Add more languages - Add a file system, that lets easily adding new langauage files. Maybe with some XML-Code or similar. | non_priority | add more languages add a file system that lets easily adding new langauage files maybe with some xml code or similar | 0 |
164,184 | 20,364,356,210 | IssuesEvent | 2022-02-21 02:37:37 | turkdevops/headless-recorder | https://api.github.com/repos/turkdevops/headless-recorder | opened | CVE-2022-0512 (High) detected in url-parse-1.5.3.tgz | security vulnerability | ## CVE-2022-0512 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>
Dependency Hierarchy:
- cli-service-4.5.0.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- sockjs-client-1.5.1.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.6.
<p>Publish Date: 2022-02-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512>CVE-2022-0512</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512</a></p>
<p>Release Date: 2022-02-14</p>
<p>Fix Resolution: url-parse - 1.5.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-0512 (High) detected in url-parse-1.5.3.tgz - ## CVE-2022-0512 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.5.3.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser environments</p>
<p>Library home page: <a href="https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz">https://registry.npmjs.org/url-parse/-/url-parse-1.5.3.tgz</a></p>
<p>
Dependency Hierarchy:
- cli-service-4.5.0.tgz (Root Library)
- webpack-dev-server-3.11.2.tgz
- sockjs-client-1.5.1.tgz
- :x: **url-parse-1.5.3.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Authorization Bypass Through User-Controlled Key in NPM url-parse prior to 1.5.6.
<p>Publish Date: 2022-02-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-0512>CVE-2022-0512</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-0512</a></p>
<p>Release Date: 2022-02-14</p>
<p>Fix Resolution: url-parse - 1.5.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in url parse tgz cve high severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href dependency hierarchy cli service tgz root library webpack dev server tgz sockjs client tgz x url parse tgz vulnerable library found in base branch master vulnerability details authorization bypass through user controlled key in npm url parse prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution url parse step up your open source security game with whitesource | 0 |
269,066 | 23,416,334,938 | IssuesEvent | 2022-08-13 02:36:29 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Fleet Accessibility Tests | Team:QA test_ui_functional test_xpack_functional release_note:skip Feature:Fleet backport:skip Feature:Functional Testing v8.4.0 | This is part of https://github.com/elastic/kibana/issues/51456
- [x] Overview
- [x] Integrations
- [x] Policies
- [x] Agents
- [x] Data steams
- [x] Settings | 3.0 | Fleet Accessibility Tests - This is part of https://github.com/elastic/kibana/issues/51456
- [x] Overview
- [x] Integrations
- [x] Policies
- [x] Agents
- [x] Data steams
- [x] Settings | non_priority | fleet accessibility tests this is part of overview integrations policies agents data steams settings | 0 |
282,362 | 30,889,298,406 | IssuesEvent | 2023-08-04 02:31:22 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2016-3134 (High) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2016-3134 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The netfilter subsystem in the Linux kernel through 4.5.2 does not validate certain offset fields, which allows local users to gain privileges or cause a denial of service (heap memory corruption) via an IPT_SO_SET_REPLACE setsockopt call.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3134>CVE-2016-3134</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3134">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3134</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: v4.6-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-3134 (High) detected in multiple libraries - ## CVE-2016-3134 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b>, <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The netfilter subsystem in the Linux kernel through 4.5.2 does not validate certain offset fields, which allows local users to gain privileges or cause a denial of service (heap memory corruption) via an IPT_SO_SET_REPLACE setsockopt call.
<p>Publish Date: 2016-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3134>CVE-2016-3134</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3134">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-3134</a></p>
<p>Release Date: 2016-04-27</p>
<p>Fix Resolution: v4.6-rc2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries linux stable linux stable linux stable vulnerability details the netfilter subsystem in the linux kernel through does not validate certain offset fields which allows local users to gain privileges or cause a denial of service heap memory corruption via an ipt so set replace setsockopt call publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
52,709 | 27,738,496,058 | IssuesEvent | 2023-03-15 12:54:17 | camunda/zeebe | https://api.github.com/repos/camunda/zeebe | opened | Unnecessary merging of variables during process instance creation | kind/toil area/performance component/engine | <!--
In case you have questions about our software we encourage everyone to participate in our community via the
- Camunda Platform community forum https://forum.camunda.io/ or
- Slack https://camunda-cloud.slack.com/ (For invite: https://camunda-slack-invite.herokuapp.com/)
There you can exchange ideas with other Zeebe and Camunda Platform 8 users, as well as the product developers, and use the search to find answer to similar questions.
This issue template is used by the Zeebe engineers to create general tasks.
-->
**Description**
Related to https://github.com/camunda/zeebe/issues/12035
_Related to https://github.com/camunda/zeebe/issues/12033_
_Came up in https://github.com/camunda/zeebe/issues/11813_
> _Setting variables during process instance creation_
>
> When a new process instance is created any given variables are set in the process instance scope. Therefore, it calls `#mergeLocalDocument()`:
>
> https://github.com/camunda/zeebe/blob/ae6dbfc5439c889ad8b8fd24d7431b46110c7900/engine/src/main/java/io/camunda/zeebe/engine/processing/variable/VariableBehavior.java#L60-L80
>
> This iterates over the variables to set and check if a variable with the given name already exists in the scope:
>
> https://github.com/camunda/zeebe/blob/ae6dbfc5439c889ad8b8fd24d7431b46110c7900/engine/src/main/java/io/camunda/zeebe/engine/processing/variable/VariableBehavior.java#L186-L187
>
> This results in unnecessary `get`s in RocksDB, because at that point could have known that it creates a new instance and set initially the variables. Instead, Zeebe could just set the variable without checking for any potential existing variables, see https://github.com/camunda/zeebe/commit/12b46995e58aeec99a6ce215961ab4487130e078
>
| True | Unnecessary merging of variables during process instance creation - <!--
In case you have questions about our software we encourage everyone to participate in our community via the
- Camunda Platform community forum https://forum.camunda.io/ or
- Slack https://camunda-cloud.slack.com/ (For invite: https://camunda-slack-invite.herokuapp.com/)
There you can exchange ideas with other Zeebe and Camunda Platform 8 users, as well as the product developers, and use the search to find answer to similar questions.
This issue template is used by the Zeebe engineers to create general tasks.
-->
**Description**
Related to https://github.com/camunda/zeebe/issues/12035
_Related to https://github.com/camunda/zeebe/issues/12033_
_Came up in https://github.com/camunda/zeebe/issues/11813_
> _Setting variables during process instance creation_
>
> When a new process instance is created any given variables are set in the process instance scope. Therefore, it calls `#mergeLocalDocument()`:
>
> https://github.com/camunda/zeebe/blob/ae6dbfc5439c889ad8b8fd24d7431b46110c7900/engine/src/main/java/io/camunda/zeebe/engine/processing/variable/VariableBehavior.java#L60-L80
>
> This iterates over the variables to set and check if a variable with the given name already exists in the scope:
>
> https://github.com/camunda/zeebe/blob/ae6dbfc5439c889ad8b8fd24d7431b46110c7900/engine/src/main/java/io/camunda/zeebe/engine/processing/variable/VariableBehavior.java#L186-L187
>
> This results in unnecessary `get`s in RocksDB, because at that point could have known that it creates a new instance and set initially the variables. Instead, Zeebe could just set the variable without checking for any potential existing variables, see https://github.com/camunda/zeebe/commit/12b46995e58aeec99a6ce215961ab4487130e078
>
| non_priority | unnecessary merging of variables during process instance creation in case you have questions about our software we encourage everyone to participate in our community via the camunda platform community forum or slack for invite there you can exchange ideas with other zeebe and camunda platform users as well as the product developers and use the search to find answer to similar questions this issue template is used by the zeebe engineers to create general tasks description related to related to came up in setting variables during process instance creation when a new process instance is created any given variables are set in the process instance scope therefore it calls mergelocaldocument this iterates over the variables to set and check if a variable with the given name already exists in the scope this results in unnecessary get s in rocksdb because at that point could have known that it creates a new instance and set initially the variables instead zeebe could just set the variable without checking for any potential existing variables see | 0 |
181,340 | 14,016,344,163 | IssuesEvent | 2020-10-29 14:25:06 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: redirects from a multiple IPs with a null for the query - ml conditional links redirects from a multiple IPs with a null for the query | Team: SecuritySolution Team:SIEM blocker failed-test skipped-test v7.10.0 | A test failed on a tracked branch
```
AssertionError: Timed out retrying: expected 'http://localhost:6111/app/security/network/flows?query=(language:kuery,query:%27((source.ip:%20%22127.0.0.1%22%20or%20destination.ip:%20%22127.0.0.1%22)%20or%20(source.ip:%20%22127.0.0.2%22%20or%20destination.ip:%20%22127.0.0.2%22))%27)&timerange=(global:(linkTo:!(timeline),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)),timeline:(linkTo:!(global),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)))&sourcerer=(default:!(%27auditbeat-*%27))' to include 'app/security/network/flows?query=(language:kuery,query:%27((source.ip:%20%22127.0.0.1%22%20or%20destination.ip:%20%22127.0.0.1%22)%20or%20(source.ip:%20%22127.0.0.2%22%20or%20destination.ip:%20%22127.0.0.2%22))%27)&sourcerer=(default:!(%27auditbeat-*%27))&timerange=(global:(linkTo:!(timeline),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)),timeline:(linkTo:!(global),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27))'
at Context.eval (http://localhost:6111/__cypress/tests?p=cypress/integration/ml_conditional_links.spec.ts:615:18)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/8325/)
<!-- kibanaCiData = {"failed-test":{"test.class":"redirects from a multiple IPs with a null for the query","test.name":"ml conditional links redirects from a multiple IPs with a null for the query","test.failCount":3}} --> | 2.0 | Failing test: redirects from a multiple IPs with a null for the query - ml conditional links redirects from a multiple IPs with a null for the query - A test failed on a tracked branch
```
AssertionError: Timed out retrying: expected 'http://localhost:6111/app/security/network/flows?query=(language:kuery,query:%27((source.ip:%20%22127.0.0.1%22%20or%20destination.ip:%20%22127.0.0.1%22)%20or%20(source.ip:%20%22127.0.0.2%22%20or%20destination.ip:%20%22127.0.0.2%22))%27)&timerange=(global:(linkTo:!(timeline),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)),timeline:(linkTo:!(global),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)))&sourcerer=(default:!(%27auditbeat-*%27))' to include 'app/security/network/flows?query=(language:kuery,query:%27((source.ip:%20%22127.0.0.1%22%20or%20destination.ip:%20%22127.0.0.1%22)%20or%20(source.ip:%20%22127.0.0.2%22%20or%20destination.ip:%20%22127.0.0.2%22))%27)&sourcerer=(default:!(%27auditbeat-*%27))&timerange=(global:(linkTo:!(timeline),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27)),timeline:(linkTo:!(global),timerange:(from:%272019-08-28T11:00:00.000Z%27,kind:absolute,to:%272019-08-28T13:59:59.999Z%27))'
at Context.eval (http://localhost:6111/__cypress/tests?p=cypress/integration/ml_conditional_links.spec.ts:615:18)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/8325/)
<!-- kibanaCiData = {"failed-test":{"test.class":"redirects from a multiple IPs with a null for the query","test.name":"ml conditional links redirects from a multiple IPs with a null for the query","test.failCount":3}} --> | non_priority | failing test redirects from a multiple ips with a null for the query ml conditional links redirects from a multiple ips with a null for the query a test failed on a tracked branch assertionerror timed out retrying expected to include app security network flows query language kuery query source ip ip source ip ip sourcerer default timerange global linkto timeline timerange from kind absolute to timeline linkto global timerange from kind absolute to at context eval first failure | 0 |
179,725 | 13,896,515,194 | IssuesEvent | 2020-10-19 17:18:39 | imixs/imixs-archive | https://api.github.com/repos/imixs/imixs-archive | closed | introduce environment variable WORKFLOW_SYNC_INITIALDELAY | enhancement testing | introduce environment variable WORKFLOW_SYNC_INITIALDELAY to deleay the first timer expiration
WORKFLOW_SYNC_INITIALDELAY = 30000 | 1.0 | introduce environment variable WORKFLOW_SYNC_INITIALDELAY - introduce environment variable WORKFLOW_SYNC_INITIALDELAY to deleay the first timer expiration
WORKFLOW_SYNC_INITIALDELAY = 30000 | non_priority | introduce environment variable workflow sync initialdelay introduce environment variable workflow sync initialdelay to deleay the first timer expiration workflow sync initialdelay | 0 |
5,980 | 4,106,500,287 | IssuesEvent | 2016-06-06 09:03:15 | MISP/MISP | https://api.github.com/repos/MISP/MISP | closed | Financial indicators: improvement to display lookup of bank identification number | enhancement functionality usability | A public repository of Issuer Identification Numbers (IIN) also called the "Bank Identification Numbers" (BIN) for the debit/credit cards is available:
- https://github.com/binlist/binlist-data
For the IBAN prefixes or BIC/SWIFT numbers, it seems there is no public and open database. If someone has a pointer, let us know. | True | Financial indicators: improvement to display lookup of bank identification number - A public repository of Issuer Identification Numbers (IIN) also called the "Bank Identification Numbers" (BIN) for the debit/credit cards is available:
- https://github.com/binlist/binlist-data
For the IBAN prefixes or BIC/SWIFT numbers, it seems there is no public and open database. If someone has a pointer, let us know. | non_priority | financial indicators improvement to display lookup of bank identification number a public repository of issuer identification numbers iin also called the bank identification numbers bin for the debit credit cards is available for the iban prefixes or bic swift numbers it seems there is no public and open database if someone has a pointer let us know | 0 |
58,451 | 16,541,787,209 | IssuesEvent | 2021-05-27 17:46:57 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | FreeBSD: xattr property is silently unsupported | Type: Defect | <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Platform | FreeBSD
Architecture | *
ZFS Version | *
SPL Version | *
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
The xattr property is ignored on FreeBSD, it always behaves as xattr=on. This used to be documented in FreeBSD, but it is not documented in zfsprops(8) for OpenZFS. We need to implement xattr=sa and I see no reason why xattr=off shouldn't be allowed to work either.
### Describe how to reproduce the problem
Try to read SA xattrs written from Linux. You can't, and not just because of the namespace issue. | 1.0 | FreeBSD: xattr property is silently unsupported - <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Platform | FreeBSD
Architecture | *
ZFS Version | *
SPL Version | *
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
The xattr property is ignored on FreeBSD, it always behaves as xattr=on. This used to be documented in FreeBSD, but it is not documented in zfsprops(8) for OpenZFS. We need to implement xattr=sa and I see no reason why xattr=off shouldn't be allowed to work either.
### Describe how to reproduce the problem
Try to read SA xattrs written from Linux. You can't, and not just because of the namespace issue. | non_priority | freebsd xattr property is silently unsupported thank you for reporting an issue important please check our issue tracker before opening a new issue additional valuable information can be found in the openzfs documentation and mailing list archives please fill in as much of the template as possible system information type version name platform freebsd architecture zfs version spl version commands to find zfs spl versions modinfo zfs grep iw version modinfo spl grep iw version describe the problem you re observing the xattr property is ignored on freebsd it always behaves as xattr on this used to be documented in freebsd but it is not documented in zfsprops for openzfs we need to implement xattr sa and i see no reason why xattr off shouldn t be allowed to work either describe how to reproduce the problem try to read sa xattrs written from linux you can t and not just because of the namespace issue | 0 |
192,799 | 15,358,855,711 | IssuesEvent | 2021-03-01 15:14:12 | operator-framework/operator-sdk | https://api.github.com/repos/operator-framework/operator-sdk | opened | Query regrading transition of existing workloads on k8s to Operator | kind/documentation | Is there a procedure/option to transition the existing workloads on k8s cluster, deployed using helm charts, to an Helm based operator.
The objective asking this question is to convert the existing deployments into an operator, and manage the life cycle/upgrades of the application and the operator using OLM.
No references found on the Operator-SDK Documentation on given scenario, and no on-line help on the similar scenarios.
### What is the URL of the document?
Operator-SDK documentation.
### Which section(s) is the issue in?
No relevant information in the Operator-SDK documentation
### What needs fixing?
Proving the reference on the brown field upgrade scenarios will be helpful
#### Additional context
| 1.0 | Query regrading transition of existing workloads on k8s to Operator - Is there a procedure/option to transition the existing workloads on k8s cluster, deployed using helm charts, to an Helm based operator.
The objective asking this question is to convert the existing deployments into an operator, and manage the life cycle/upgrades of the application and the operator using OLM.
No references found on the Operator-SDK Documentation on given scenario, and no on-line help on the similar scenarios.
### What is the URL of the document?
Operator-SDK documentation.
### Which section(s) is the issue in?
No relevant information in the Operator-SDK documentation
### What needs fixing?
Proving the reference on the brown field upgrade scenarios will be helpful
#### Additional context
| non_priority | query regrading transition of existing workloads on to operator is there a procedure option to transition the existing workloads on cluster deployed using helm charts to an helm based operator the objective asking this question is to convert the existing deployments into an operator and manage the life cycle upgrades of the application and the operator using olm no references found on the operator sdk documentation on given scenario and no on line help on the similar scenarios what is the url of the document operator sdk documentation which section s is the issue in no relevant information in the operator sdk documentation what needs fixing proving the reference on the brown field upgrade scenarios will be helpful additional context | 0 |
18,934 | 6,658,435,086 | IssuesEvent | 2017-09-30 19:13:58 | openMVG/openMVG | https://api.github.com/repos/openMVG/openMVG | closed | Update third_party | build enhancement | - [x] ceres-solver (1.13.0)
- [x] pushed,
- [x] CI validated
- [x] Eigen (3.3.4)
- [x] pushed,
- [x] CI validated
- [x] stlplus (3.03.14)
- [x] pushed,
- [x] CI validated
- [x] easyexif (Add support for FocalPlaneXResolution, FocalPlaneYResolution and FocalPlaneResolutionUnit, FocalLengthIn35mm)
- [x] pushed,
- [x] CI validated
--
- [x] merge to master | 1.0 | Update third_party - - [x] ceres-solver (1.13.0)
- [x] pushed,
- [x] CI validated
- [x] Eigen (3.3.4)
- [x] pushed,
- [x] CI validated
- [x] stlplus (3.03.14)
- [x] pushed,
- [x] CI validated
- [x] easyexif (Add support for FocalPlaneXResolution, FocalPlaneYResolution and FocalPlaneResolutionUnit, FocalLengthIn35mm)
- [x] pushed,
- [x] CI validated
--
- [x] merge to master | non_priority | update third party ceres solver pushed ci validated eigen pushed ci validated stlplus pushed ci validated easyexif add support for focalplanexresolution focalplaneyresolution and focalplaneresolutionunit pushed ci validated merge to master | 0 |
111,709 | 17,033,393,733 | IssuesEvent | 2021-07-05 01:09:21 | osgirl/Dunnhumby | https://api.github.com/repos/osgirl/Dunnhumby | opened | CVE-2019-8331 (Medium) detected in bootstrap-4.1.3.js, bootstrap-4.1.3.min.js | security vulnerability | ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-4.1.3.js</b>, <b>bootstrap-4.1.3.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-4.1.3.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.js</a></p>
<p>Path to vulnerable library: Dunnhumby/Armin.Dunnhumby/wwwroot/lib/bootstrap/dist/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-4.1.3.js** (Vulnerable Library)
</details>
<details><summary><b>bootstrap-4.1.3.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: Dunnhumby/Armin.Dunnhumby/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-4.1.3.min.js** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-8331 (Medium) detected in bootstrap-4.1.3.js, bootstrap-4.1.3.min.js - ## CVE-2019-8331 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-4.1.3.js</b>, <b>bootstrap-4.1.3.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-4.1.3.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.js</a></p>
<p>Path to vulnerable library: Dunnhumby/Armin.Dunnhumby/wwwroot/lib/bootstrap/dist/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-4.1.3.js** (Vulnerable Library)
</details>
<details><summary><b>bootstrap-4.1.3.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/4.1.3/js/bootstrap.min.js</a></p>
<p>Path to vulnerable library: Dunnhumby/Armin.Dunnhumby/wwwroot/lib/bootstrap/dist/js/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-4.1.3.min.js** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in bootstrap js bootstrap min js cve medium severity vulnerability vulnerable libraries bootstrap js bootstrap min js bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library dunnhumby armin dunnhumby wwwroot lib bootstrap dist js bootstrap js dependency hierarchy x bootstrap js vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library dunnhumby armin dunnhumby wwwroot lib bootstrap dist js bootstrap min js dependency hierarchy x bootstrap min js vulnerable library vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap bootstrap sass step up your open source security game with whitesource | 0 |
15,021 | 11,302,173,378 | IssuesEvent | 2020-01-17 17:03:41 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | opened | Official build doesn't produce RPM/Deb artifacts | area-Infrastructure-installer | I noticed while looking through a dev build (https://github.com/dotnet/runtime/pull/1859) for RPM/Debs that the official build isn't producing any at all. I think I missed updating this line during my refactor. Now that we no longer pass in `name` as a parameter it'll always disable the next lines:
https://github.com/dotnet/runtime/blob/704aa77547b5001fa551fd5baa8af656fe50de9e/eng/pipelines/installer/jobs/base-job.yml#L424-L425
I think it just needs to be tweaked to `platform`. Giving it a try. | 1.0 | Official build doesn't produce RPM/Deb artifacts - I noticed while looking through a dev build (https://github.com/dotnet/runtime/pull/1859) for RPM/Debs that the official build isn't producing any at all. I think I missed updating this line during my refactor. Now that we no longer pass in `name` as a parameter it'll always disable the next lines:
https://github.com/dotnet/runtime/blob/704aa77547b5001fa551fd5baa8af656fe50de9e/eng/pipelines/installer/jobs/base-job.yml#L424-L425
I think it just needs to be tweaked to `platform`. Giving it a try. | non_priority | official build doesn t produce rpm deb artifacts i noticed while looking through a dev build for rpm debs that the official build isn t producing any at all i think i missed updating this line during my refactor now that we no longer pass in name as a parameter it ll always disable the next lines i think it just needs to be tweaked to platform giving it a try | 0 |
53,830 | 13,262,361,382 | IssuesEvent | 2020-08-20 21:40:08 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | closed | [dataclasses] I3SuperDST decoding is borked (Trac #2153) | Migrated from Trac combo core defect | On macOS Sierra 10.12.6
```text
$ ./bin/dataclasses-test I3SuperDSTTest.cxx/Deserialize_32bit -s
I3SuperDSTTest.cxx...
Deserialize_32bit...........................................INFO (I3Module): Opened file /cvmfs/icecube.opensciencegrid.org/data//i3-test-data//superdst/test_data_1115_ia32.i3.gz (I3Reader.cxx:180 in void I3Reader::OpenNextFile())
4294967295
FATAL (I3SuperDST): Assertion failed: dt <= 31 (I3SuperDST.cxx:452 in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))
ERROR (I3Module): pruefer: Exception thrown (I3Module.cxx:123 in void I3Module::Do(void (I3Module::*)()))
UNCAUGHT:Assertion failed: dt <= 31 (in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))
Test Results:
===================================================================
Pass: 0
Fail: 1
***** THESE TESTS FAIL *****
I3SuperDSTTest.cxx/Deserialize_32bit
Returning 1
```
```text
$ clang --version
Apple LLVM version 9.0.0 (clang-900.0.39.2)
Target: x86_64-apple-darwin16.7.0
Thread model: posix
InstalledDir: /Library/Developer/CommandLineTools/usr/bin
$ xcode-select --version
xcode-select version 2347.
```
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2153">https://code.icecube.wisc.edu/projects/icecube/ticket/2153</a>, reported by kjmeagherand owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-03-27T16:25:07",
"_ts": "1553703907985721",
"description": "On macOS Sierra 10.12.6 \n{{{\n$ ./bin/dataclasses-test I3SuperDSTTest.cxx/Deserialize_32bit -s\nI3SuperDSTTest.cxx...\n Deserialize_32bit...........................................INFO (I3Module): Opened file /cvmfs/icecube.opensciencegrid.org/data//i3-test-data//superdst/test_data_1115_ia32.i3.gz (I3Reader.cxx:180 in void I3Reader::OpenNextFile())\n4294967295\nFATAL (I3SuperDST): Assertion failed: dt <= 31 (I3SuperDST.cxx:452 in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))\nERROR (I3Module): pruefer: Exception thrown (I3Module.cxx:123 in void I3Module::Do(void (I3Module::*)()))\n UNCAUGHT:Assertion failed: dt <= 31 (in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))\n\nTest Results:\n===================================================================\nPass: 0\nFail: 1\n ***** THESE TESTS FAIL *****\n I3SuperDSTTest.cxx/Deserialize_32bit\n\nReturning 1\n\n}}}\n\n\n{{{\n$ clang --version\nApple LLVM version 9.0.0 (clang-900.0.39.2)\nTarget: x86_64-apple-darwin16.7.0\nThread model: posix\nInstalledDir: /Library/Developer/CommandLineTools/usr/bin\n\n$ xcode-select --version\nxcode-select version 2347.\n\n}}}\n\n",
"reporter": "kjmeagher",
"cc": "",
"resolution": "duplicate",
"time": "2018-05-16T16:12:31",
"component": "combo core",
"summary": "[dataclasses] I3SuperDST decoding is borked",
"priority": "normal",
"keywords": "",
"milestone": "Vernal Equinox 2019",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| 1.0 | [dataclasses] I3SuperDST decoding is borked (Trac #2153) - On macOS Sierra 10.12.6
```text
$ ./bin/dataclasses-test I3SuperDSTTest.cxx/Deserialize_32bit -s
I3SuperDSTTest.cxx...
Deserialize_32bit...........................................INFO (I3Module): Opened file /cvmfs/icecube.opensciencegrid.org/data//i3-test-data//superdst/test_data_1115_ia32.i3.gz (I3Reader.cxx:180 in void I3Reader::OpenNextFile())
4294967295
FATAL (I3SuperDST): Assertion failed: dt <= 31 (I3SuperDST.cxx:452 in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))
ERROR (I3Module): pruefer: Exception thrown (I3Module.cxx:123 in void I3Module::Do(void (I3Module::*)()))
UNCAUGHT:Assertion failed: dt <= 31 (in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))
Test Results:
===================================================================
Pass: 0
Fail: 1
***** THESE TESTS FAIL *****
I3SuperDSTTest.cxx/Deserialize_32bit
Returning 1
```
```text
$ clang --version
Apple LLVM version 9.0.0 (clang-900.0.39.2)
Target: x86_64-apple-darwin16.7.0
Thread model: posix
InstalledDir: /Library/Developer/CommandLineTools/usr/bin
$ xcode-select --version
xcode-select version 2347.
```
<details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/2153">https://code.icecube.wisc.edu/projects/icecube/ticket/2153</a>, reported by kjmeagherand owned by jvansanten</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-03-27T16:25:07",
"_ts": "1553703907985721",
"description": "On macOS Sierra 10.12.6 \n{{{\n$ ./bin/dataclasses-test I3SuperDSTTest.cxx/Deserialize_32bit -s\nI3SuperDSTTest.cxx...\n Deserialize_32bit...........................................INFO (I3Module): Opened file /cvmfs/icecube.opensciencegrid.org/data//i3-test-data//superdst/test_data_1115_ia32.i3.gz (I3Reader.cxx:180 in void I3Reader::OpenNextFile())\n4294967295\nFATAL (I3SuperDST): Assertion failed: dt <= 31 (I3SuperDST.cxx:452 in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))\nERROR (I3Module): pruefer: Exception thrown (I3Module.cxx:123 in void I3Module::Do(void (I3Module::*)()))\n UNCAUGHT:Assertion failed: dt <= 31 (in static double I3SuperDST::DecodeWidth(uint32_t, unsigned int))\n\nTest Results:\n===================================================================\nPass: 0\nFail: 1\n ***** THESE TESTS FAIL *****\n I3SuperDSTTest.cxx/Deserialize_32bit\n\nReturning 1\n\n}}}\n\n\n{{{\n$ clang --version\nApple LLVM version 9.0.0 (clang-900.0.39.2)\nTarget: x86_64-apple-darwin16.7.0\nThread model: posix\nInstalledDir: /Library/Developer/CommandLineTools/usr/bin\n\n$ xcode-select --version\nxcode-select version 2347.\n\n}}}\n\n",
"reporter": "kjmeagher",
"cc": "",
"resolution": "duplicate",
"time": "2018-05-16T16:12:31",
"component": "combo core",
"summary": "[dataclasses] I3SuperDST decoding is borked",
"priority": "normal",
"keywords": "",
"milestone": "Vernal Equinox 2019",
"owner": "jvansanten",
"type": "defect"
}
```
</p>
</details>
| non_priority | decoding is borked trac on macos sierra text bin dataclasses test cxx deserialize s cxx deserialize info opened file cvmfs icecube opensciencegrid org data test data superdst test data gz cxx in void opennextfile fatal assertion failed dt cxx in static double decodewidth t unsigned int error pruefer exception thrown cxx in void do void uncaught assertion failed dt in static double decodewidth t unsigned int test results pass fail these tests fail cxx deserialize returning text clang version apple llvm version clang target apple thread model posix installeddir library developer commandlinetools usr bin xcode select version xcode select version migrated from json status closed changetime ts description on macos sierra n n bin dataclasses test cxx deserialize s cxx n deserialize info opened file cvmfs icecube opensciencegrid org data test data superdst test data gz cxx in void opennextfile nfatal assertion failed dt cxx in static double decodewidth t unsigned int nerror pruefer exception thrown cxx in void do void n uncaught assertion failed dt in static double decodewidth t unsigned int n ntest results n npass nfail n these tests fail n cxx deserialize n nreturning n n n n n n clang version napple llvm version clang ntarget apple nthread model posix ninstalleddir library developer commandlinetools usr bin n n xcode select version nxcode select version n n n n reporter kjmeagher cc resolution duplicate time component combo core summary decoding is borked priority normal keywords milestone vernal equinox owner jvansanten type defect | 0 |
267,800 | 28,509,228,915 | IssuesEvent | 2023-04-19 01:46:38 | dpteam/RK3188_TABLET | https://api.github.com/repos/dpteam/RK3188_TABLET | closed | CVE-2014-5207 (High) detected in linuxv3.0.70 - autoclosed | Mend: dependency security vulnerability | ## CVE-2014-5207 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0.70</b></p></summary>
<p>
<p>Development tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git>https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/linux/mount.h</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
fs/namespace.c in the Linux kernel through 3.16.1 does not properly restrict clearing MNT_NODEV, MNT_NOSUID, and MNT_NOEXEC and changing MNT_ATIME_MASK during a remount of a bind mount, which allows local users to gain privileges, interfere with backups and auditing on systems that had atime enabled, or cause a denial of service (excessive filesystem updating) on systems that had atime disabled via a "mount -o remount" command within a user namespace.
<p>Publish Date: 2014-08-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-5207>CVE-2014-5207</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5207">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5207</a></p>
<p>Release Date: 2014-08-18</p>
<p>Fix Resolution: v3.17-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2014-5207 (High) detected in linuxv3.0.70 - autoclosed - ## CVE-2014-5207 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxv3.0.70</b></p></summary>
<p>
<p>Development tree</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git>https://git.kernel.org/pub/scm/linux/kernel/git/keithp/linux.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/dpteam/RK3188_TABLET/commit/0c501f5a0fd72c7b2ac82904235363bd44fd8f9e">0c501f5a0fd72c7b2ac82904235363bd44fd8f9e</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/include/linux/mount.h</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
fs/namespace.c in the Linux kernel through 3.16.1 does not properly restrict clearing MNT_NODEV, MNT_NOSUID, and MNT_NOEXEC and changing MNT_ATIME_MASK during a remount of a bind mount, which allows local users to gain privileges, interfere with backups and auditing on systems that had atime enabled, or cause a denial of service (excessive filesystem updating) on systems that had atime disabled via a "mount -o remount" command within a user namespace.
<p>Publish Date: 2014-08-18
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-5207>CVE-2014-5207</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5207">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-5207</a></p>
<p>Release Date: 2014-08-18</p>
<p>Fix Resolution: v3.17-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in autoclosed cve high severity vulnerability vulnerable library development tree library home page a href found in head commit a href found in base branch master vulnerable source files include linux mount h vulnerability details fs namespace c in the linux kernel through does not properly restrict clearing mnt nodev mnt nosuid and mnt noexec and changing mnt atime mask during a remount of a bind mount which allows local users to gain privileges interfere with backups and auditing on systems that had atime enabled or cause a denial of service excessive filesystem updating on systems that had atime disabled via a mount o remount command within a user namespace publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
291,294 | 25,135,330,699 | IssuesEvent | 2022-11-09 18:06:45 | lowRISC/opentitan | https://api.github.com/repos/lowRISC/opentitan | closed | [test-triage] chip_sw_uart_tx_rx_alt_clk_freq | Component:TestTriage | ### Hierarchy of regression failure
Chip Level
### Failure Description
Test chip_sw_uart_tx_rx_alt_clk_freq_low_speed has 5 failures.
0.chip_sw_uart_tx_rx_alt_clk_freq_low_speed.4270074077
Line 622, in log /container/opentitan-public/scratch/os_regression/chip_earlgrey_asic-sim-vcs/0.chip_sw_uart_tx_rx_alt_clk_freq_low_speed/latest/run.log
Offending '$stable(gen_check_clock.main_clk_cycles)'
UVM_ERROR @ 2375.787441 us: (pwrmgr_ast_sva_if.sv:64) [ASSERT FAILED] MainClkStopped_A
UVM_INFO @ 2375.787441 us: (uvm_report_catcher.svh:705) [UVM/REPORT/CATCHER]
--- UVM Report catcher Summary ---
1.chip_sw_uart_tx_rx_alt_clk_freq_low_speed.1596940983
Line 624, in log /container/opentitan-public/scratch/os_regression/chip_earlgrey_asic-sim-vcs/1.chip_sw_uart_tx_rx_alt_clk_freq_low_speed/latest/run.log
Offending '$stable(gen_check_clock.main_clk_cycles)'
UVM_ERROR @ 2464.845136 us: (pwrmgr_ast_sva_if.sv:64) [ASSERT FAILED] MainClkStopped_A
UVM_INFO @ 2464.845136 us: (uvm_report_catcher.svh:705) [UVM/REPORT/CATCHER]
--- UVM Report catcher Summary ---
### Steps to Reproduce
- GitHub Revision: [3e32a31a2](https://github.com/lowrisc/opentitan/tree/3e32a31a2ba47298a1041913daa27e827b5068b0)
- dvsim invocation command to reproduce the failure, inclusive of build and run seeds:
./util/dvsim/dvsim.py hw/top_earlgrey/dv/chip_sim_cfg.hjson -i chip_sw_uart_tx_rx_alt_clk_freq --build-seed 2797157030 --fixed-seed 4270074077 --waves fsdb
### Tests with similar or related failures
Note that there are multiple tests with the same failing assertion signature:
- [ ] chip_sw_uart_tx_rx_alt_clk_freq_low_speed
- [ ] chip_sw_clkmgr_external_clk_src_for_sw_fast
- [ ] chip_sw_clkmgr_external_clk_src_for_sw_slow
This failure is very likely due to the reset reorganization in https://github.com/lowRISC/opentitan/pull/15602.
CC @tjaychen @jeoongp @matutem
| 1.0 | [test-triage] chip_sw_uart_tx_rx_alt_clk_freq - ### Hierarchy of regression failure
Chip Level
### Failure Description
Test chip_sw_uart_tx_rx_alt_clk_freq_low_speed has 5 failures.
0.chip_sw_uart_tx_rx_alt_clk_freq_low_speed.4270074077
Line 622, in log /container/opentitan-public/scratch/os_regression/chip_earlgrey_asic-sim-vcs/0.chip_sw_uart_tx_rx_alt_clk_freq_low_speed/latest/run.log
Offending '$stable(gen_check_clock.main_clk_cycles)'
UVM_ERROR @ 2375.787441 us: (pwrmgr_ast_sva_if.sv:64) [ASSERT FAILED] MainClkStopped_A
UVM_INFO @ 2375.787441 us: (uvm_report_catcher.svh:705) [UVM/REPORT/CATCHER]
--- UVM Report catcher Summary ---
1.chip_sw_uart_tx_rx_alt_clk_freq_low_speed.1596940983
Line 624, in log /container/opentitan-public/scratch/os_regression/chip_earlgrey_asic-sim-vcs/1.chip_sw_uart_tx_rx_alt_clk_freq_low_speed/latest/run.log
Offending '$stable(gen_check_clock.main_clk_cycles)'
UVM_ERROR @ 2464.845136 us: (pwrmgr_ast_sva_if.sv:64) [ASSERT FAILED] MainClkStopped_A
UVM_INFO @ 2464.845136 us: (uvm_report_catcher.svh:705) [UVM/REPORT/CATCHER]
--- UVM Report catcher Summary ---
### Steps to Reproduce
- GitHub Revision: [3e32a31a2](https://github.com/lowrisc/opentitan/tree/3e32a31a2ba47298a1041913daa27e827b5068b0)
- dvsim invocation command to reproduce the failure, inclusive of build and run seeds:
./util/dvsim/dvsim.py hw/top_earlgrey/dv/chip_sim_cfg.hjson -i chip_sw_uart_tx_rx_alt_clk_freq --build-seed 2797157030 --fixed-seed 4270074077 --waves fsdb
### Tests with similar or related failures
Note that there are multiple tests with the same failing assertion signature:
- [ ] chip_sw_uart_tx_rx_alt_clk_freq_low_speed
- [ ] chip_sw_clkmgr_external_clk_src_for_sw_fast
- [ ] chip_sw_clkmgr_external_clk_src_for_sw_slow
This failure is very likely due to the reset reorganization in https://github.com/lowRISC/opentitan/pull/15602.
CC @tjaychen @jeoongp @matutem
| non_priority | chip sw uart tx rx alt clk freq hierarchy of regression failure chip level failure description test chip sw uart tx rx alt clk freq low speed has failures chip sw uart tx rx alt clk freq low speed line in log container opentitan public scratch os regression chip earlgrey asic sim vcs chip sw uart tx rx alt clk freq low speed latest run log offending stable gen check clock main clk cycles uvm error us pwrmgr ast sva if sv mainclkstopped a uvm info us uvm report catcher svh uvm report catcher summary chip sw uart tx rx alt clk freq low speed line in log container opentitan public scratch os regression chip earlgrey asic sim vcs chip sw uart tx rx alt clk freq low speed latest run log offending stable gen check clock main clk cycles uvm error us pwrmgr ast sva if sv mainclkstopped a uvm info us uvm report catcher svh uvm report catcher summary steps to reproduce github revision dvsim invocation command to reproduce the failure inclusive of build and run seeds util dvsim dvsim py hw top earlgrey dv chip sim cfg hjson i chip sw uart tx rx alt clk freq build seed fixed seed waves fsdb tests with similar or related failures note that there are multiple tests with the same failing assertion signature chip sw uart tx rx alt clk freq low speed chip sw clkmgr external clk src for sw fast chip sw clkmgr external clk src for sw slow this failure is very likely due to the reset reorganization in cc tjaychen jeoongp matutem | 0 |
17,745 | 10,763,670,052 | IssuesEvent | 2019-11-01 05:10:51 | aws-amplify/amplify-js | https://api.github.com/repos/aws-amplify/amplify-js | closed | updateUserAttributes options | Auth Cognito Service Team needs-discussion pending-close-response-required | When I want to update the user attributes I use `updateUserAttributes` from the Amplify library.
If I am updating the `email` I will receive a confirmation code.
Is it possible or is there an option object to decide whether receive this confirmation code?
With the current implementation looks like I cannot pass any option.
If not could it be possible to have this feature?
Thanks | 1.0 | updateUserAttributes options - When I want to update the user attributes I use `updateUserAttributes` from the Amplify library.
If I am updating the `email` I will receive a confirmation code.
Is it possible or is there an option object to decide whether receive this confirmation code?
With the current implementation looks like I cannot pass any option.
If not could it be possible to have this feature?
Thanks | non_priority | updateuserattributes options when i want to update the user attributes i use updateuserattributes from the amplify library if i am updating the email i will receive a confirmation code is it possible or is there an option object to decide whether receive this confirmation code with the current implementation looks like i cannot pass any option if not could it be possible to have this feature thanks | 0 |
61,962 | 8,564,069,753 | IssuesEvent | 2018-11-09 15:46:18 | mothur/mothur | https://api.github.com/repos/mothur/mothur | closed | What to include in a bug report? | Bugs Documentation New mothur user Support | Have you checked out the frequently asked questions? https://mothur.org/wiki/Frequently_asked_questions
To help us resolve issues quickly, please include the following:
- A detailed description of the error. The more specific you can be the easier it is for us to solve the problem. There is no detail too small or insignificant.
- The log file - The log file includes important information for us about your hardware, version of mothur and release date. It also shows us the workflow and helps us spot simple errors. The log file helps us diagnose most issues quickly without the need for additional data.
Additional information you are welcome to provide:
- The input files use with the command causing the issue. If they are too large to attach often a small sample of the file is enough. To select the first 500 lines from a file you can use the head system command. ex. head -n 500 yourInputFile > newFileNameForSampling
| 1.0 | What to include in a bug report? - Have you checked out the frequently asked questions? https://mothur.org/wiki/Frequently_asked_questions
To help us resolve issues quickly, please include the following:
- A detailed description of the error. The more specific you can be the easier it is for us to solve the problem. There is no detail too small or insignificant.
- The log file - The log file includes important information for us about your hardware, version of mothur and release date. It also shows us the workflow and helps us spot simple errors. The log file helps us diagnose most issues quickly without the need for additional data.
Additional information you are welcome to provide:
- The input files use with the command causing the issue. If they are too large to attach often a small sample of the file is enough. To select the first 500 lines from a file you can use the head system command. ex. head -n 500 yourInputFile > newFileNameForSampling
| non_priority | what to include in a bug report have you checked out the frequently asked questions to help us resolve issues quickly please include the following a detailed description of the error the more specific you can be the easier it is for us to solve the problem there is no detail too small or insignificant the log file the log file includes important information for us about your hardware version of mothur and release date it also shows us the workflow and helps us spot simple errors the log file helps us diagnose most issues quickly without the need for additional data additional information you are welcome to provide the input files use with the command causing the issue if they are too large to attach often a small sample of the file is enough to select the first lines from a file you can use the head system command ex head n yourinputfile newfilenameforsampling | 0 |
331,845 | 29,117,815,563 | IssuesEvent | 2023-05-17 03:39:58 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | DISABLED test_build_tuple_unpack (__main__.StaticDefaultDynamicShapesMiscTests) | triaged module: flaky-tests skipped module: dynamo | Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_build_tuple_unpack&suite=StaticDefaultDynamicShapesMiscTests) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/undefined).
Over the past 3 hours, it has been determined flaky in 3 workflow(s) with 3 failures and 3 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT ASSUME THINGS ARE OKAY IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_build_tuple_unpack`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
Test file path: `dynamo/test_dynamic_shapes.py` or `dynamo/test_dynamic_shapes.py`
cc @voznesenskym @penguinwu @anijain2305 @EikanWang @jgong5 @Guobing-Chen @XiaobingSuper @zhuhaozhe @blzheng @Xia-Weiwen @wenzhe-nrv @jiayisunx @desertfire | 1.0 | DISABLED test_build_tuple_unpack (__main__.StaticDefaultDynamicShapesMiscTests) - Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_build_tuple_unpack&suite=StaticDefaultDynamicShapesMiscTests) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/undefined).
Over the past 3 hours, it has been determined flaky in 3 workflow(s) with 3 failures and 3 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT ASSUME THINGS ARE OKAY IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_build_tuple_unpack`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
Test file path: `dynamo/test_dynamic_shapes.py` or `dynamo/test_dynamic_shapes.py`
cc @voznesenskym @penguinwu @anijain2305 @EikanWang @jgong5 @Guobing-Chen @XiaobingSuper @zhuhaozhe @blzheng @Xia-Weiwen @wenzhe-nrv @jiayisunx @desertfire | non_priority | disabled test build tuple unpack main staticdefaultdynamicshapesmisctests platforms linux this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with failures and successes debugging instructions after clicking on the recent samples link do not assume things are okay if the ci is green we now shield flaky tests from developers so ci will thus be green but it will be harder to parse the logs to find relevant log snippets click on the workflow logs linked above click on the test step of the job so that it is expanded otherwise the grepping will not work grep for test build tuple unpack there should be several instances run as flaky tests are rerun in ci from which you can study the logs test file path dynamo test dynamic shapes py or dynamo test dynamic shapes py cc voznesenskym penguinwu eikanwang guobing chen xiaobingsuper zhuhaozhe blzheng xia weiwen wenzhe nrv jiayisunx desertfire | 0 |
436,053 | 30,535,412,620 | IssuesEvent | 2023-07-19 16:58:39 | BishopFox/sliver | https://api.github.com/repos/BishopFox/sliver | closed | The COFF Loader fails to load BOF in obj format. | documentation | Problem:
The COFF Loader fails to load BOF in obj format.
Test environment:
MacOS
Test process:
Using the loader.exe compiled from [https://github.com/trustedsec/COFFLoader ↗](https://github.com/trustedsec/COFFLoader) to load BOF in obj format was successful. However, loading failed in Sliver.
<img width="562" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/203b6a5e-f6e6-4aca-bbb9-e25999bd7f4a">
Sliver loade err
MAC
<img width="1174" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/f1c28c39-9960-490b-a190-0a2b546789cf">
<img width="602" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/6b5ad1c1-14de-4377-b36d-170996c4eab9">
Windows
<img width="1131" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/2d666498-2a9e-4a0d-a6ea-3e479143d50e">
| 1.0 | The COFF Loader fails to load BOF in obj format. - Problem:
The COFF Loader fails to load BOF in obj format.
Test environment:
MacOS
Test process:
Using the loader.exe compiled from [https://github.com/trustedsec/COFFLoader ↗](https://github.com/trustedsec/COFFLoader) to load BOF in obj format was successful. However, loading failed in Sliver.
<img width="562" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/203b6a5e-f6e6-4aca-bbb9-e25999bd7f4a">
Sliver loade err
MAC
<img width="1174" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/f1c28c39-9960-490b-a190-0a2b546789cf">
<img width="602" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/6b5ad1c1-14de-4377-b36d-170996c4eab9">
Windows
<img width="1131" alt="image" src="https://github.com/BishopFox/sliver/assets/82130343/2d666498-2a9e-4a0d-a6ea-3e479143d50e">
| non_priority | the coff loader fails to load bof in obj format problem the coff loader fails to load bof in obj format test environment macos test process using the loader exe compiled from to load bof in obj format was successful however loading failed in sliver img width alt image src sliver loade err mac img width alt image src img width alt image src windows img width alt image src | 0 |
42,136 | 10,821,290,741 | IssuesEvent | 2019-11-08 18:19:12 | supertuxkart/stk-code | https://api.github.com/repos/supertuxkart/stk-code | closed | Invisible wall in Fort Magma | C: 3D Modelling P4: minor T: defect | There is an invisible wall in Fort Magma track, exactly at the point shown in the video below.
https://drive.google.com/open?id=1Sp6DKCghWPm8ly1zA6tmrSgZJrTTS5et
| 1.0 | Invisible wall in Fort Magma - There is an invisible wall in Fort Magma track, exactly at the point shown in the video below.
https://drive.google.com/open?id=1Sp6DKCghWPm8ly1zA6tmrSgZJrTTS5et
| non_priority | invisible wall in fort magma there is an invisible wall in fort magma track exactly at the point shown in the video below | 0 |
166,016 | 12,888,427,388 | IssuesEvent | 2020-07-13 13:00:57 | ComputationalRadiationPhysics/picongpu | https://api.github.com/repos/ComputationalRadiationPhysics/picongpu | closed | PML with uneven domains is not output and check pointed correctly | affects latest release bug component: plugin | The logic of writing and reading of PML fields relies on the domains being of equal size. It equally concerns output and checkpointing.
Here is the code that assumed it: [1](https://github.com/ComputationalRadiationPhysics/picongpu/blob/fe322db49e69b09258691c4aa781769470fe693d/include/picongpu/plugins/hdf5/writer/Field.hpp#L119-L142), [2](https://github.com/ComputationalRadiationPhysics/picongpu/blob/fe322db49e69b09258691c4aa781769470fe693d/include/picongpu/plugins/hdf5/restart/RestartFieldLoader.hpp#L93-L115), and similar for the other two output plugins. The error is that while the allocated-for PML thickness is indeed the same (even for internal domains), that does not imply the buffer size is the same, as the latter also depends on the local domain size.
This concerns input/output only, not the correctness of the computational part. Note that the PML fields are actually not needed in the normal simulation output and their output is not enabled by default. However, for checkpointing they are required and enabled.
The incorrect behavior discovered by @Anton-Le | 1.0 | PML with uneven domains is not output and check pointed correctly - The logic of writing and reading of PML fields relies on the domains being of equal size. It equally concerns output and checkpointing.
Here is the code that assumed it: [1](https://github.com/ComputationalRadiationPhysics/picongpu/blob/fe322db49e69b09258691c4aa781769470fe693d/include/picongpu/plugins/hdf5/writer/Field.hpp#L119-L142), [2](https://github.com/ComputationalRadiationPhysics/picongpu/blob/fe322db49e69b09258691c4aa781769470fe693d/include/picongpu/plugins/hdf5/restart/RestartFieldLoader.hpp#L93-L115), and similar for the other two output plugins. The error is that while the allocated-for PML thickness is indeed the same (even for internal domains), that does not imply the buffer size is the same, as the latter also depends on the local domain size.
This concerns input/output only, not the correctness of the computational part. Note that the PML fields are actually not needed in the normal simulation output and their output is not enabled by default. However, for checkpointing they are required and enabled.
The incorrect behavior discovered by @Anton-Le | non_priority | pml with uneven domains is not output and check pointed correctly the logic of writing and reading of pml fields relies on the domains being of equal size it equally concerns output and checkpointing here is the code that assumed it and similar for the other two output plugins the error is that while the allocated for pml thickness is indeed the same even for internal domains that does not imply the buffer size is the same as the latter also depends on the local domain size this concerns input output only not the correctness of the computational part note that the pml fields are actually not needed in the normal simulation output and their output is not enabled by default however for checkpointing they are required and enabled the incorrect behavior discovered by anton le | 0 |
81,189 | 15,604,304,006 | IssuesEvent | 2021-03-19 03:37:47 | tuanducdesign/service_tuanducdesign | https://api.github.com/repos/tuanducdesign/service_tuanducdesign | closed | CVE-2020-28498 (Medium) detected in elliptic-6.5.3.tgz - autoclosed | security vulnerability | ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.3.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz</a></p>
<p>Path to dependency file: service_tuanducdesign/package.json</p>
<p>Path to vulnerable library: service_tuanducdesign/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- next-9.5.4.tgz (Root Library)
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.1.tgz
- :x: **elliptic-6.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanducdesign/service_tuanducdesign/commit/f72a34fbb239009a68359e76c1ef54e5a315abc7">f72a34fbb239009a68359e76c1ef54e5a315abc7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution: v6.5.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28498 (Medium) detected in elliptic-6.5.3.tgz - autoclosed - ## CVE-2020-28498 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.5.3.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.5.3.tgz</a></p>
<p>Path to dependency file: service_tuanducdesign/package.json</p>
<p>Path to vulnerable library: service_tuanducdesign/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- next-9.5.4.tgz (Root Library)
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.2.1.tgz
- :x: **elliptic-6.5.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tuanducdesign/service_tuanducdesign/commit/f72a34fbb239009a68359e76c1ef54e5a315abc7">f72a34fbb239009a68359e76c1ef54e5a315abc7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package elliptic before 6.5.4 are vulnerable to Cryptographic Issues via the secp256k1 implementation in elliptic/ec/key.js. There is no check to confirm that the public key point passed into the derive function actually exists on the secp256k1 curve. This results in the potential for the private key used in this implementation to be revealed after a number of ECDH operations are performed.
<p>Publish Date: 2021-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28498>CVE-2020-28498</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28498</a></p>
<p>Release Date: 2021-02-02</p>
<p>Fix Resolution: v6.5.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in elliptic tgz autoclosed cve medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file service tuanducdesign package json path to vulnerable library service tuanducdesign node modules elliptic package json dependency hierarchy next tgz root library crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package elliptic before are vulnerable to cryptographic issues via the implementation in elliptic ec key js there is no check to confirm that the public key point passed into the derive function actually exists on the curve this results in the potential for the private key used in this implementation to be revealed after a number of ecdh operations are performed publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
182,247 | 21,664,493,548 | IssuesEvent | 2022-05-07 01:32:20 | Watemlifts/wagtail | https://api.github.com/repos/Watemlifts/wagtail | closed | WS-2019-0100 (Medium) detected in fstream-1.0.11.tgz - autoclosed | security vulnerability | ## WS-2019-0100 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fstream-1.0.11.tgz</b></p></summary>
<p>Advanced file system stream things</p>
<p>Library home page: <a href="https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz">https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz</a></p>
<p>Path to dependency file: /wagtail/package.json</p>
<p>Path to vulnerable library: /tmp/git/wagtail/node_modules/fstream/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-4.0.1.tgz (Root Library)
- node-sass-4.9.2.tgz
- node-gyp-3.7.0.tgz
- :x: **fstream-1.0.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Watemlifts/wagtail/commits/2050ccf64e9d82c3b9a62456d104fe095a2a3d71">2050ccf64e9d82c3b9a62456d104fe095a2a3d71</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of fstream prior to 1.0.12 are vulnerable to Arbitrary File Overwrite.
<p>Publish Date: 2019-05-23
<p>URL: <a href=https://github.com/npm/fstream/commit/6a77d2fa6e1462693cf8e46f930da96ec1b0bb22>WS-2019-0100</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/886">https://www.npmjs.com/advisories/886</a></p>
<p>Release Date: 2019-05-23</p>
<p>Fix Resolution: 1.0.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0100 (Medium) detected in fstream-1.0.11.tgz - autoclosed - ## WS-2019-0100 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fstream-1.0.11.tgz</b></p></summary>
<p>Advanced file system stream things</p>
<p>Library home page: <a href="https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz">https://registry.npmjs.org/fstream/-/fstream-1.0.11.tgz</a></p>
<p>Path to dependency file: /wagtail/package.json</p>
<p>Path to vulnerable library: /tmp/git/wagtail/node_modules/fstream/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-4.0.1.tgz (Root Library)
- node-sass-4.9.2.tgz
- node-gyp-3.7.0.tgz
- :x: **fstream-1.0.11.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/Watemlifts/wagtail/commits/2050ccf64e9d82c3b9a62456d104fe095a2a3d71">2050ccf64e9d82c3b9a62456d104fe095a2a3d71</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of fstream prior to 1.0.12 are vulnerable to Arbitrary File Overwrite.
<p>Publish Date: 2019-05-23
<p>URL: <a href=https://github.com/npm/fstream/commit/6a77d2fa6e1462693cf8e46f930da96ec1b0bb22>WS-2019-0100</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/886">https://www.npmjs.com/advisories/886</a></p>
<p>Release Date: 2019-05-23</p>
<p>Fix Resolution: 1.0.12</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in fstream tgz autoclosed ws medium severity vulnerability vulnerable library fstream tgz advanced file system stream things library home page a href path to dependency file wagtail package json path to vulnerable library tmp git wagtail node modules fstream package json dependency hierarchy gulp sass tgz root library node sass tgz node gyp tgz x fstream tgz vulnerable library found in head commit a href vulnerability details versions of fstream prior to are vulnerable to arbitrary file overwrite publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
12,936 | 15,301,995,031 | IssuesEvent | 2021-02-24 14:16:01 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | opened | Release 4.1 - March 2021 | P1 release team-XProduct type: process | # Status of Bazel 4.1
This release will use Bazel 4.0.0 as its baseline and we will apply selected cherry-picks and backports on top of it. Please request cherry-picks that you'd like to get into Bazel 4.1.0 here via a comment.
- Expected release date: March 2021
- [List of release blockers](https://github.com/bazelbuild/bazel/labels/Release%20blocker)
To report a release-blocking bug, please file a bug using the `Release blocker` label, and cc me.
Task list:
- [ ] Pick release baseline: https://github.com/bazelbuild/bazel/commit/6b33bdb1e22514304c0e35ce8e067f2175685245
- [ ] Create release candidate: https://releases.bazel.build/4.1.0/rc1/
- [ ] Check downstream projects:
- [ ] [Create draft release announcement](https://docs.google.com/document/d/1wDvulLlj4NAlPZamdlEVFORks3YXJonCjyuQMUQEmB0/edit)
- [ ] Send for review the release announcement PR:
- [ ] Push the release, notify package maintainers:
- [ ] Update the documentation
- [ ] Push the blog post
- [ ] Update the [release page](https://github.com/bazelbuild/bazel/releases/)
| 1.0 | Release 4.1 - March 2021 - # Status of Bazel 4.1
This release will use Bazel 4.0.0 as its baseline and we will apply selected cherry-picks and backports on top of it. Please request cherry-picks that you'd like to get into Bazel 4.1.0 here via a comment.
- Expected release date: March 2021
- [List of release blockers](https://github.com/bazelbuild/bazel/labels/Release%20blocker)
To report a release-blocking bug, please file a bug using the `Release blocker` label, and cc me.
Task list:
- [ ] Pick release baseline: https://github.com/bazelbuild/bazel/commit/6b33bdb1e22514304c0e35ce8e067f2175685245
- [ ] Create release candidate: https://releases.bazel.build/4.1.0/rc1/
- [ ] Check downstream projects:
- [ ] [Create draft release announcement](https://docs.google.com/document/d/1wDvulLlj4NAlPZamdlEVFORks3YXJonCjyuQMUQEmB0/edit)
- [ ] Send for review the release announcement PR:
- [ ] Push the release, notify package maintainers:
- [ ] Update the documentation
- [ ] Push the blog post
- [ ] Update the [release page](https://github.com/bazelbuild/bazel/releases/)
| non_priority | release march status of bazel this release will use bazel as its baseline and we will apply selected cherry picks and backports on top of it please request cherry picks that you d like to get into bazel here via a comment expected release date march to report a release blocking bug please file a bug using the release blocker label and cc me task list pick release baseline create release candidate check downstream projects send for review the release announcement pr push the release notify package maintainers update the documentation push the blog post update the | 0 |
38,599 | 8,924,971,976 | IssuesEvent | 2019-01-21 20:44:11 | idaholab/moose | https://api.github.com/repos/idaholab/moose | opened | Python utils check file size can fail (race condition) | C: MOOSE Scripts C: TestHarness P: normal T: defect | ## Rationale
<!--What is the reason for this enhancement or what error are you reporting?-->
The python/mooseutils/tests.check_file_size test can fail due to a race condition. The problem is that this test runs concurrently with several other tests on the system and it does an os.walk() looking for files sizes to sum up. It's possible for the file list to change (e.g. files can be removed) while this test is running causing the `os.stat()` command to fail. This test should be cleaned up to work in either a clean directory where other test outputs are not being written, or the test should be serialized and isolated.
## Description
<!--Provide details of the enhancement or instructions for reproducing the error.-->
Race condition in python testing (mooseutils.check_file_size). This failure is difficult to replicate, but it should be fairly easy to clean up. See description above.
## Impact
<!--How will the changes impact the code, developers, and users? Discuss changes to the
internal interfaces and public API.-->
minor: Does not affect MOOSE, but can impede testing. | 1.0 | Python utils check file size can fail (race condition) - ## Rationale
<!--What is the reason for this enhancement or what error are you reporting?-->
The python/mooseutils/tests.check_file_size test can fail due to a race condition. The problem is that this test runs concurrently with several other tests on the system and it does an os.walk() looking for files sizes to sum up. It's possible for the file list to change (e.g. files can be removed) while this test is running causing the `os.stat()` command to fail. This test should be cleaned up to work in either a clean directory where other test outputs are not being written, or the test should be serialized and isolated.
## Description
<!--Provide details of the enhancement or instructions for reproducing the error.-->
Race condition in python testing (mooseutils.check_file_size). This failure is difficult to replicate, but it should be fairly easy to clean up. See description above.
## Impact
<!--How will the changes impact the code, developers, and users? Discuss changes to the
internal interfaces and public API.-->
minor: Does not affect MOOSE, but can impede testing. | non_priority | python utils check file size can fail race condition rationale the python mooseutils tests check file size test can fail due to a race condition the problem is that this test runs concurrently with several other tests on the system and it does an os walk looking for files sizes to sum up it s possible for the file list to change e g files can be removed while this test is running causing the os stat command to fail this test should be cleaned up to work in either a clean directory where other test outputs are not being written or the test should be serialized and isolated description race condition in python testing mooseutils check file size this failure is difficult to replicate but it should be fairly easy to clean up see description above impact how will the changes impact the code developers and users discuss changes to the internal interfaces and public api minor does not affect moose but can impede testing | 0 |
77,523 | 7,575,437,449 | IssuesEvent | 2018-04-24 01:41:47 | intesar/Fx-Test-Data | https://api.github.com/repos/intesar/Fx-Test-Data | reopened | Test-bvpoGI : enterprise_user_signup_valid | Test-bvpoGI | Project : Test-bvpoGI
Job : Stg
Env : Stg
Region : FxLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 24 Apr 2018 00:53:37 GMT]}
Endpoint : http://stg1.fxlabs.io/api/v1/users/enterprise-sign-up
Request :
{
"name" : "fn1 ln",
"email" : "5bARjrl7mu2P@fxlabs.io",
"password" : "12345678",
"company" : "MNsqW7Xdv"
}
Response :
{
"requestId" : "None",
"requestTime" : "2018-04-24T00:53:37.879+0000",
"errors" : false,
"messages" : [ {
"type" : "INFO",
"key" : "",
"value" : "Sign-up successful!"
} ],
"data" : true,
"totalPages" : 1,
"totalElements" : 1
}
Logs :
Assertion [@Response.errors == false] passed, expected [false] and found [false]Assertion [@StatusCode == 200] passed, expected [200] and found [200]
| 1.0 | Test-bvpoGI : enterprise_user_signup_valid - Project : Test-bvpoGI
Job : Stg
Env : Stg
Region : FxLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 24 Apr 2018 00:53:37 GMT]}
Endpoint : http://stg1.fxlabs.io/api/v1/users/enterprise-sign-up
Request :
{
"name" : "fn1 ln",
"email" : "5bARjrl7mu2P@fxlabs.io",
"password" : "12345678",
"company" : "MNsqW7Xdv"
}
Response :
{
"requestId" : "None",
"requestTime" : "2018-04-24T00:53:37.879+0000",
"errors" : false,
"messages" : [ {
"type" : "INFO",
"key" : "",
"value" : "Sign-up successful!"
} ],
"data" : true,
"totalPages" : 1,
"totalElements" : 1
}
Logs :
Assertion [@Response.errors == false] passed, expected [false] and found [false]Assertion [@StatusCode == 200] passed, expected [200] and found [200]
| non_priority | test bvpogi enterprise user signup valid project test bvpogi job stg env stg region fxlabs us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options content type transfer encoding date endpoint request name ln email fxlabs io password company response requestid none requesttime errors false messages type info key value sign up successful data true totalpages totalelements logs assertion passed expected and found assertion passed expected and found | 0 |
118,323 | 15,278,217,804 | IssuesEvent | 2021-02-23 00:58:20 | dotnet/msbuild | https://api.github.com/repos/dotnet/msbuild | opened | Implement IBuildEngine Extension Point | Needs Design untriaged | Issue tracking discussion that started here: https://github.com/dotnet/msbuild/pull/6174#issuecomment-782423719
### Issue Description
Adding new information the task can access from the build engine is cumbersome. Current process:
1. Create IBuildEngineX
2. Add one property
3. Modify TaskHost and OOPTaskHost to implement the interface.
### Potential Path Forward
1. Create an IBuildEngineX that contains a `Dictionary<string, object>` where object is serializable.
2. Mihai suggested an IBE with an abstract class called `EngineServices`.
| 1.0 | Implement IBuildEngine Extension Point - Issue tracking discussion that started here: https://github.com/dotnet/msbuild/pull/6174#issuecomment-782423719
### Issue Description
Adding new information the task can access from the build engine is cumbersome. Current process:
1. Create IBuildEngineX
2. Add one property
3. Modify TaskHost and OOPTaskHost to implement the interface.
### Potential Path Forward
1. Create an IBuildEngineX that contains a `Dictionary<string, object>` where object is serializable.
2. Mihai suggested an IBE with an abstract class called `EngineServices`.
| non_priority | implement ibuildengine extension point issue tracking discussion that started here issue description adding new information the task can access from the build engine is cumbersome current process create ibuildenginex add one property modify taskhost and ooptaskhost to implement the interface potential path forward create an ibuildenginex that contains a dictionary where object is serializable mihai suggested an ibe with an abstract class called engineservices | 0 |
2,724 | 9,612,818,489 | IssuesEvent | 2019-05-13 09:47:37 | precice/precice | https://api.github.com/repos/precice/precice | opened | Refactor static ids | maintainability | preCICE currently has to manage a set of `static` IDs due to some prior design decisions regarding simpler object creation. The additional bookkeeping, however, is error-prone and already lead to issues #378.
Affected classes are:
1) Participant via `_participantsSize`
2) Mesh via `_managePropertyID`
3) Data via `_dataCount`
These static IDs should be refactored out of the affected classes into the objects responsible for the generation of IDed objects. The object lifetime of the generators should then correctly handle the bookkeeping.
These generators are most likely going to be configuration objects. | True | Refactor static ids - preCICE currently has to manage a set of `static` IDs due to some prior design decisions regarding simpler object creation. The additional bookkeeping, however, is error-prone and already lead to issues #378.
Affected classes are:
1) Participant via `_participantsSize`
2) Mesh via `_managePropertyID`
3) Data via `_dataCount`
These static IDs should be refactored out of the affected classes into the objects responsible for the generation of IDed objects. The object lifetime of the generators should then correctly handle the bookkeeping.
These generators are most likely going to be configuration objects. | non_priority | refactor static ids precice currently has to manage a set of static ids due to some prior design decisions regarding simpler object creation the additional bookkeeping however is error prone and already lead to issues affected classes are participant via participantssize mesh via managepropertyid data via datacount these static ids should be refactored out of the affected classes into the objects responsible for the generation of ided objects the object lifetime of the generators should then correctly handle the bookkeeping these generators are most likely going to be configuration objects | 0 |
87,600 | 17,334,352,222 | IssuesEvent | 2021-07-28 08:22:53 | tokio-rs/tokio | https://api.github.com/repos/tokio-rs/tokio | closed | [tokio-util] Build FramedRead and FramedWrite using buffers in FramedParts | A-tokio-util M-codec | I've got an instance of `Framed<TcpStream, Codec>` that I want to split into `FramedRead<tcp::OwnedReadHalf, Codec>` and `FramedWrite<tcp::OwnedWriteHalf, Codec>`.
While I can get the codec and stream split into halves to feed into `FramedRead::new(...)` and `FramedWrite::new(...)`, I don't see any way to re-assign the existing read and write buffers that are exposed in `FramedParts<TcpStream, Codec>`, which means that I potentially drop partial frames for both reading and writing.
`Framed::into_parts()` provides me with the data I need to feed into the individual halves, but I can't figure out how to re-add the buffers.
Is there a practice for how to do this? Anything I missed? | 1.0 | [tokio-util] Build FramedRead and FramedWrite using buffers in FramedParts - I've got an instance of `Framed<TcpStream, Codec>` that I want to split into `FramedRead<tcp::OwnedReadHalf, Codec>` and `FramedWrite<tcp::OwnedWriteHalf, Codec>`.
While I can get the codec and stream split into halves to feed into `FramedRead::new(...)` and `FramedWrite::new(...)`, I don't see any way to re-assign the existing read and write buffers that are exposed in `FramedParts<TcpStream, Codec>`, which means that I potentially drop partial frames for both reading and writing.
`Framed::into_parts()` provides me with the data I need to feed into the individual halves, but I can't figure out how to re-add the buffers.
Is there a practice for how to do this? Anything I missed? | non_priority | build framedread and framedwrite using buffers in framedparts i ve got an instance of framed that i want to split into framedread and framedwrite while i can get the codec and stream split into halves to feed into framedread new and framedwrite new i don t see any way to re assign the existing read and write buffers that are exposed in framedparts which means that i potentially drop partial frames for both reading and writing framed into parts provides me with the data i need to feed into the individual halves but i can t figure out how to re add the buffers is there a practice for how to do this anything i missed | 0 |
140,857 | 11,364,114,980 | IssuesEvent | 2020-01-27 07:15:34 | terraform-providers/terraform-provider-google | https://api.github.com/repos/terraform-providers/terraform-provider-google | opened | Fix `_updateBigquerySink` tests | test failure | `TestAccLoggingBillingAccountSink_updateBigquerySink`
`TestAccLoggingFolderSink_updateBigquerySink`
`TestAccLoggingOrganizationSink_updateBigquerySink` | 1.0 | Fix `_updateBigquerySink` tests - `TestAccLoggingBillingAccountSink_updateBigquerySink`
`TestAccLoggingFolderSink_updateBigquerySink`
`TestAccLoggingOrganizationSink_updateBigquerySink` | non_priority | fix updatebigquerysink tests testaccloggingbillingaccountsink updatebigquerysink testaccloggingfoldersink updatebigquerysink testaccloggingorganizationsink updatebigquerysink | 0 |
17,634 | 6,488,129,444 | IssuesEvent | 2017-08-20 14:34:17 | HypothesisWorks/hypothesis-python | https://api.github.com/repos/HypothesisWorks/hypothesis-python | closed | Travis CI should build new changelog before checking documentation | CI-and-build | It's currently something of a hole in our build process - we're not actually building the up to date changelog as part of the documentation build because it doesn't get updated until we do the deploy. | 1.0 | Travis CI should build new changelog before checking documentation - It's currently something of a hole in our build process - we're not actually building the up to date changelog as part of the documentation build because it doesn't get updated until we do the deploy. | non_priority | travis ci should build new changelog before checking documentation it s currently something of a hole in our build process we re not actually building the up to date changelog as part of the documentation build because it doesn t get updated until we do the deploy | 0 |
15,013 | 3,916,818,888 | IssuesEvent | 2016-04-21 04:30:55 | systemd/systemd | https://api.github.com/repos/systemd/systemd | closed | freedesktop wiki: outdated and broken links to gummiboot on pages referenced from man | documentation sd-boot | ### Submission type
[x] Bug report
### systemd version the issue has been seen with
> 229
### Used distribution
> Arch Linux
### In case of bug report: Expected behaviour you didn't see
> All links from the documentation should be valid, including nested links.
### In case of bug report: Unexpected behaviour you saw
> Broken links in the documentation.
### In case of bug report: Steps to reproduce the problem
>
1. `man 1 bootctl`
2. Follow these links:
>
> >NOTES
> 1. Boot loader specification
http://www.freedesktop.org/wiki/Specifications/BootLoaderSpec
> 2. Systemd boot loader interface
http://www.freedesktop.org/wiki/Software/systemd/BootLoaderInterface
3. Scroll to the bottom of those pages.
4. Click on
>
> > http://www.freedesktop.org/wiki/Software/gummiboot/
>
> and
>
> > This interface is currently implemented by [http://freedesktop.org/wiki/Software/gummiboot](Gummiboot).
5. You will see 404 pages. That shouldn't happen when browsing the documentation. | 1.0 | freedesktop wiki: outdated and broken links to gummiboot on pages referenced from man - ### Submission type
[x] Bug report
### systemd version the issue has been seen with
> 229
### Used distribution
> Arch Linux
### In case of bug report: Expected behaviour you didn't see
> All links from the documentation should be valid, including nested links.
### In case of bug report: Unexpected behaviour you saw
> Broken links in the documentation.
### In case of bug report: Steps to reproduce the problem
>
1. `man 1 bootctl`
2. Follow these links:
>
> >NOTES
> 1. Boot loader specification
http://www.freedesktop.org/wiki/Specifications/BootLoaderSpec
> 2. Systemd boot loader interface
http://www.freedesktop.org/wiki/Software/systemd/BootLoaderInterface
3. Scroll to the bottom of those pages.
4. Click on
>
> > http://www.freedesktop.org/wiki/Software/gummiboot/
>
> and
>
> > This interface is currently implemented by [http://freedesktop.org/wiki/Software/gummiboot](Gummiboot).
5. You will see 404 pages. That shouldn't happen when browsing the documentation. | non_priority | freedesktop wiki outdated and broken links to gummiboot on pages referenced from man submission type bug report systemd version the issue has been seen with used distribution arch linux in case of bug report expected behaviour you didn t see all links from the documentation should be valid including nested links in case of bug report unexpected behaviour you saw broken links in the documentation in case of bug report steps to reproduce the problem man bootctl follow these links notes boot loader specification systemd boot loader interface scroll to the bottom of those pages click on and this interface is currently implemented by gummiboot you will see pages that shouldn t happen when browsing the documentation | 0 |
308,359 | 26,602,215,656 | IssuesEvent | 2023-01-23 16:31:57 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix hyperbolic_functions.test_numpy_arccosh | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/3958342682/jobs/6779812379" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/3958342682/jobs/6779834630" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/3958585409/jobs/6780365361" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/3947997454/jobs/6757477264" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
<details>
<summary>Not found</summary>
Not found
</details>
| 1.0 | Fix hyperbolic_functions.test_numpy_arccosh - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/3958342682/jobs/6779812379" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/3958342682/jobs/6779834630" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/3958585409/jobs/6780365361" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/3947997454/jobs/6757477264" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
<details>
<summary>Not found</summary>
Not found
</details>
| non_priority | fix hyperbolic functions test numpy arccosh tensorflow img src torch img src numpy img src jax img src not found not found | 0 |
244,005 | 26,343,944,347 | IssuesEvent | 2023-01-10 20:10:53 | Virinas-code/white-rabbit | https://api.github.com/repos/Virinas-code/white-rabbit | closed | rich-12.6.0-py3-none-any.whl: 1 vulnerabilities (highest severity is: 7.5) - autoclosed | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rich-12.6.0-py3-none-any.whl</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Virinas-code/white-rabbit/commit/2e072e76ed480142a45f2d35a97118a016a2abde">2e072e76ed480142a45f2d35a97118a016a2abde</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (rich version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-42969](https://www.mend.io/vulnerability-database/CVE-2022-42969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | py-1.11.0-py2.py3-none-any.whl | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-42969</summary>
### Vulnerable Library - <b>py-1.11.0-py2.py3-none-any.whl</b></p>
<p>library with cross-python path, ini-parsing, io, code, log facilities</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/f6/f0/10642828a8dfb741e5f3fbaac830550a518a775c7fff6f04a007259b0548/py-1.11.0-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/f6/f0/10642828a8dfb741e5f3fbaac830550a518a775c7fff6f04a007259b0548/py-1.11.0-py2.py3-none-any.whl</a></p>
<p>
Dependency Hierarchy:
- rich-12.6.0-py3-none-any.whl (Root Library)
- ipywidgets-7.7.2-py2.py3-none-any.whl
- ipykernel-6.17.1-py3-none-any.whl
- jupyter_client-7.4.7-py3-none-any.whl
- pyzmq-24.0.1.tar.gz
- :x: **py-1.11.0-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Virinas-code/white-rabbit/commit/2e072e76ed480142a45f2d35a97118a016a2abde">2e072e76ed480142a45f2d35a97118a016a2abde</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The py library through 1.11.0 for Python allows remote attackers to conduct a ReDoS (Regular expression Denial of Service) attack via a Subversion repository with crafted info data, because the InfoSvnCommand argument is mishandled.
<p>Publish Date: 2022-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42969>CVE-2022-42969</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | rich-12.6.0-py3-none-any.whl: 1 vulnerabilities (highest severity is: 7.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rich-12.6.0-py3-none-any.whl</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Virinas-code/white-rabbit/commit/2e072e76ed480142a45f2d35a97118a016a2abde">2e072e76ed480142a45f2d35a97118a016a2abde</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (rich version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-42969](https://www.mend.io/vulnerability-database/CVE-2022-42969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | py-1.11.0-py2.py3-none-any.whl | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-42969</summary>
### Vulnerable Library - <b>py-1.11.0-py2.py3-none-any.whl</b></p>
<p>library with cross-python path, ini-parsing, io, code, log facilities</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/f6/f0/10642828a8dfb741e5f3fbaac830550a518a775c7fff6f04a007259b0548/py-1.11.0-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/f6/f0/10642828a8dfb741e5f3fbaac830550a518a775c7fff6f04a007259b0548/py-1.11.0-py2.py3-none-any.whl</a></p>
<p>
Dependency Hierarchy:
- rich-12.6.0-py3-none-any.whl (Root Library)
- ipywidgets-7.7.2-py2.py3-none-any.whl
- ipykernel-6.17.1-py3-none-any.whl
- jupyter_client-7.4.7-py3-none-any.whl
- pyzmq-24.0.1.tar.gz
- :x: **py-1.11.0-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Virinas-code/white-rabbit/commit/2e072e76ed480142a45f2d35a97118a016a2abde">2e072e76ed480142a45f2d35a97118a016a2abde</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The py library through 1.11.0 for Python allows remote attackers to conduct a ReDoS (Regular expression Denial of Service) attack via a Subversion repository with crafted info data, because the InfoSvnCommand argument is mishandled.
<p>Publish Date: 2022-10-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-42969>CVE-2022-42969</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | rich none any whl vulnerabilities highest severity is autoclosed vulnerable library rich none any whl found in head commit a href vulnerabilities cve severity cvss dependency type fixed in rich version remediation available high py none any whl transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library py none any whl library with cross python path ini parsing io code log facilities library home page a href dependency hierarchy rich none any whl root library ipywidgets none any whl ipykernel none any whl jupyter client none any whl pyzmq tar gz x py none any whl vulnerable library found in head commit a href found in base branch master vulnerability details the py library through for python allows remote attackers to conduct a redos regular expression denial of service attack via a subversion repository with crafted info data because the infosvncommand argument is mishandled publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with mend | 0 |
307,521 | 23,202,639,648 | IssuesEvent | 2022-08-01 23:45:51 | stephen-kern/robot-gladiators | https://api.github.com/repos/stephen-kern/robot-gladiators | closed | Restructure data with JS objects | documentation | - Create and use JavaScript objects to organize data related to the player and data related to the enemies.
- Create object methods to perform player actions. | 1.0 | Restructure data with JS objects - - Create and use JavaScript objects to organize data related to the player and data related to the enemies.
- Create object methods to perform player actions. | non_priority | restructure data with js objects create and use javascript objects to organize data related to the player and data related to the enemies create object methods to perform player actions | 0 |
45,965 | 13,146,458,421 | IssuesEvent | 2020-08-08 09:59:47 | shaundmorris/ddf | https://api.github.com/repos/shaundmorris/ddf | closed | CVE-2018-11695 High Severity Vulnerability detected by WhiteSource | security vulnerability wontfix | ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (121)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/bind.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/base.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cencode.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.cpp
- /ddf/ui/node_modules/node-sass/src/callback_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass2scss.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/paths.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/json.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/string.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debugger.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/factory.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/operation.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/value.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.hpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /ddf/ui/node_modules/node-sass/src/binding.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/functions.h
- /ddf/ui/node_modules/node-sass/src/custom_function_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/values.cpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/b64/encode.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/number.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/c99func.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/backtrace.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/values.h
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/null.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/context.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debug.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.2. A NULL pointer dereference was found in the function Sass::Expand::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11695>CVE-2018-11695</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-11695 High Severity Vulnerability detected by WhiteSource - ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (121)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/output.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/bind.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/base.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cencode.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.cpp
- /ddf/ui/node_modules/node-sass/src/callback_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass2scss.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/paths.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/source_map.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/json.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/listize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/eval.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/string.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/environment.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/emitter.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/extend.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/lexer.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debugger.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/factory.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/operation.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/constants.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/boolean.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/value.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/functions.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/position.hpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/cssize.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /ddf/ui/node_modules/node-sass/src/binding.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/list.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/functions.h
- /ddf/ui/node_modules/node-sass/src/custom_function_bridge.cpp
- /ddf/ui/node_modules/node-sass/src/custom_importer_bridge.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/ast.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/values.cpp
- /ddf/ui/node_modules/node-sass/src/sass_context_wrapper.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/b64/encode.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/number.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/c99func.c
- /ddf/ui/node_modules/node-sass/src/libsass/src/node.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/backtrace.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/values.h
- /ddf/ui/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /ddf/ui/node_modules/node-sass/src/sass_types/null.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/expand.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/context.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/include/sass/context.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/inspect.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_c.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/util.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/file.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/map.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/units.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/plugins.hpp
- /ddf/ui/node_modules/node-sass/src/sass_types/color.h
- /ddf/ui/node_modules/node-sass/src/libsass/src/to_value.cpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/debug.hpp
- /ddf/ui/node_modules/node-sass/src/libsass/src/parser.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in LibSass through 3.5.2. A NULL pointer dereference was found in the function Sass::Expand::operator which could be leveraged by an attacker to cause a denial of service (application crash) or possibly have unspecified other impact.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-11695>CVE-2018-11695</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries ddf ui node modules node sass src libsass src error handling cpp ddf ui node modules node sass src libsass src output cpp ddf ui node modules node sass src libsass src output hpp ddf ui node modules node sass src libsass src sass values hpp ddf ui node modules node sass src libsass src check nesting cpp ddf ui node modules node sass src libsass src check nesting hpp ddf ui node modules node sass src libsass src bind cpp ddf ui node modules node sass src libsass test test node cpp ddf ui node modules node sass src libsass src constants cpp ddf ui node modules node sass src libsass src plugins cpp ddf ui node modules node sass src libsass src eval hpp ddf ui node modules node sass src libsass include sass base h ddf ui node modules node sass src libsass src prelexer hpp ddf ui node modules node sass src libsass src subset map hpp ddf ui node modules node sass src libsass src extend cpp ddf ui node modules node sass src custom importer bridge cpp ddf ui node modules node sass src libsass contrib plugin cpp ddf ui node modules node sass src libsass src lexer hpp ddf ui node modules node sass src libsass src sass util cpp ddf ui node modules node sass src libsass test test superselector cpp ddf ui node modules node sass src libsass src cencode c ddf ui node modules node sass src libsass src ast fwd decl hpp ddf ui node modules node sass src libsass src string hpp ddf ui node modules node sass src libsass src file cpp ddf ui node modules node sass src callback bridge h ddf ui node modules node sass src libsass src subset map cpp ddf ui node modules node sass src libsass include h ddf ui node modules node sass src libsass src sass functions hpp ddf ui node modules node sass src libsass src emitter cpp ddf ui node modules node sass src libsass src environment cpp ddf ui node modules node sass src libsass src ast def macros hpp ddf ui node modules node sass src libsass src paths hpp ddf ui node modules node sass src libsass src expand cpp ddf ui node modules node sass src libsass src listize cpp ddf ui node modules node sass src libsass test test unification cpp ddf ui node modules node sass src libsass src source map cpp ddf ui node modules node sass src libsass src inspect cpp ddf ui node modules node sass src libsass src source map hpp ddf ui node modules node sass src sass types list h ddf ui node modules node sass src libsass src json cpp ddf ui node modules node sass src libsass src sass functions cpp ddf ui node modules node sass src libsass src sass util hpp ddf ui node modules node sass src libsass src position cpp ddf ui node modules node sass src libsass src listize hpp ddf ui node modules node sass src libsass src error handling hpp ddf ui node modules node sass src libsass src eval cpp ddf ui node modules node sass src sass types string cpp ddf ui node modules node sass src libsass src environment hpp ddf ui node modules node sass src sass types boolean h ddf ui node modules node sass src libsass src emitter hpp ddf ui node modules node sass src libsass src extend hpp ddf ui node modules node sass src libsass src lexer cpp ddf ui node modules node sass src libsass src functions cpp ddf ui node modules node sass src libsass src debugger hpp ddf ui node modules node sass src libsass src prelexer cpp ddf ui node modules node sass src sass types factory cpp ddf ui node modules node sass src sass types color cpp ddf ui node modules node sass src libsass src operation hpp ddf ui node modules node sass src libsass src ast cpp ddf ui node modules node sass src libsass src sass hpp ddf ui node modules node sass src libsass src constants hpp ddf ui node modules node sass src sass types boolean cpp ddf ui node modules node sass src libsass src context hpp ddf ui node modules node sass src sass types value h ddf ui node modules node sass src libsass src units cpp ddf ui node modules node sass src libsass src cssize hpp ddf ui node modules node sass src libsass src parser cpp ddf ui node modules node sass src libsass src functions hpp ddf ui node modules node sass src libsass src position hpp ddf ui node modules node sass src sass context wrapper cpp ddf ui node modules node sass src libsass src sass context hpp ddf ui node modules node sass src libsass src node cpp ddf ui node modules node sass src libsass src ast fwd decl cpp ddf ui node modules node sass src libsass src cssize cpp ddf ui node modules node sass src libsass src remove placeholders cpp ddf ui node modules node sass src binding cpp ddf ui node modules node sass src sass types list cpp ddf ui node modules node sass src libsass include sass functions h ddf ui node modules node sass src custom function bridge cpp ddf ui node modules node sass src custom importer bridge h ddf ui node modules node sass src libsass src color maps cpp ddf ui node modules node sass src libsass src string cpp ddf ui node modules node sass src sass types sass value wrapper h ddf ui node modules node sass src libsass src ast hpp ddf ui node modules node sass src libsass src values cpp ddf ui node modules node sass src sass context wrapper h ddf ui node modules node sass src libsass src encode h ddf ui node modules node sass src libsass src sass cpp ddf ui node modules node sass src libsass src cpp ddf ui node modules node sass src sass types number cpp ddf ui node modules node sass src libsass src c ddf ui node modules node sass src libsass src node hpp ddf ui node modules node sass src libsass src remove placeholders hpp ddf ui node modules node sass src libsass src util cpp ddf ui node modules node sass src libsass src memory sharedptr hpp ddf ui node modules node sass src libsass src backtrace hpp ddf ui node modules node sass src libsass include sass values h ddf ui node modules node sass src libsass test test subset map cpp ddf ui node modules node sass src libsass src cpp ddf ui node modules node sass src libsass src sass context cpp ddf ui node modules node sass src libsass src memory sharedptr cpp ddf ui node modules node sass src sass types null cpp ddf ui node modules node sass src libsass src expand hpp ddf ui node modules node sass src libsass src to value hpp ddf ui node modules node sass src libsass src context cpp ddf ui node modules node sass src libsass include sass context h ddf ui node modules node sass src libsass src to c cpp ddf ui node modules node sass src libsass src sass values cpp ddf ui node modules node sass src libsass src color maps hpp ddf ui node modules node sass src libsass src inspect hpp ddf ui node modules node sass src libsass script test leaks pl ddf ui node modules node sass src libsass src to c hpp ddf ui node modules node sass src libsass src util hpp ddf ui node modules node sass src libsass src file hpp ddf ui node modules node sass src sass types map cpp ddf ui node modules node sass src libsass src units hpp ddf ui node modules node sass src libsass src plugins hpp ddf ui node modules node sass src sass types color h ddf ui node modules node sass src libsass src to value cpp ddf ui node modules node sass src libsass src debug hpp ddf ui node modules node sass src libsass src parser hpp vulnerability details an issue was discovered in libsass through a null pointer dereference was found in the function sass expand operator which could be leveraged by an attacker to cause a denial of service application crash or possibly have unspecified other impact publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
144,037 | 19,268,480,818 | IssuesEvent | 2021-12-10 00:51:07 | leanswift/bob-frontend | https://api.github.com/repos/leanswift/bob-frontend | opened | CVE-2020-13822 (High) detected in elliptic-6.4.0.tgz | security vulnerability | ## CVE-2020-13822 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.0.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.0.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.0.tgz</a></p>
<p>Path to dependency file: bob-frontend/package.json</p>
<p>Path to vulnerable library: bob-frontend/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- karma-2.0.0.tgz (Root Library)
- browserify-14.5.0.tgz
- crypto-browserify-3.12.0.tgz
- create-ecdh-4.0.0.tgz
- :x: **elliptic-6.4.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/leanswift/bob-frontend/commit/e09ef1e3a45be925a41a2e1aa6a0bcbc6b3c41ea">e09ef1e3a45be925a41a2e1aa6a0bcbc6b3c41ea</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Elliptic package 6.5.2 for Node.js allows ECDSA signature malleability via variations in encoding, leading '\0' bytes, or integer overflows. This could conceivably have a security-relevant impact if an application relied on a single canonical signature.
<p>Publish Date: 2020-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13822>CVE-2020-13822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/tree/v6.5.3">https://github.com/indutny/elliptic/tree/v6.5.3</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: v6.5.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"karma:2.0.0;browserify:14.5.0;crypto-browserify:3.12.0;create-ecdh:4.0.0;elliptic:6.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.3","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-13822","vulnerabilityDetails":"The Elliptic package 6.5.2 for Node.js allows ECDSA signature malleability via variations in encoding, leading \u0027\\0\u0027 bytes, or integer overflows. This could conceivably have a security-relevant impact if an application relied on a single canonical signature.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13822","cvss3Severity":"high","cvss3Score":"7.7","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-13822 (High) detected in elliptic-6.4.0.tgz - ## CVE-2020-13822 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.0.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.0.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.0.tgz</a></p>
<p>Path to dependency file: bob-frontend/package.json</p>
<p>Path to vulnerable library: bob-frontend/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- karma-2.0.0.tgz (Root Library)
- browserify-14.5.0.tgz
- crypto-browserify-3.12.0.tgz
- create-ecdh-4.0.0.tgz
- :x: **elliptic-6.4.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/leanswift/bob-frontend/commit/e09ef1e3a45be925a41a2e1aa6a0bcbc6b3c41ea">e09ef1e3a45be925a41a2e1aa6a0bcbc6b3c41ea</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Elliptic package 6.5.2 for Node.js allows ECDSA signature malleability via variations in encoding, leading '\0' bytes, or integer overflows. This could conceivably have a security-relevant impact if an application relied on a single canonical signature.
<p>Publish Date: 2020-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13822>CVE-2020-13822</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/tree/v6.5.3">https://github.com/indutny/elliptic/tree/v6.5.3</a></p>
<p>Release Date: 2020-07-02</p>
<p>Fix Resolution: v6.5.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"elliptic","packageVersion":"6.4.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"karma:2.0.0;browserify:14.5.0;crypto-browserify:3.12.0;create-ecdh:4.0.0;elliptic:6.4.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v6.5.3","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-13822","vulnerabilityDetails":"The Elliptic package 6.5.2 for Node.js allows ECDSA signature malleability via variations in encoding, leading \u0027\\0\u0027 bytes, or integer overflows. This could conceivably have a security-relevant impact if an application relied on a single canonical signature.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13822","cvss3Severity":"high","cvss3Score":"7.7","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in elliptic tgz cve high severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file bob frontend package json path to vulnerable library bob frontend node modules elliptic package json dependency hierarchy karma tgz root library browserify tgz crypto browserify tgz create ecdh tgz x elliptic tgz vulnerable library found in head commit a href found in base branch master vulnerability details the elliptic package for node js allows ecdsa signature malleability via variations in encoding leading bytes or integer overflows this could conceivably have a security relevant impact if an application relied on a single canonical signature publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree karma browserify crypto browserify create ecdh elliptic isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the elliptic package for node js allows ecdsa signature malleability via variations in encoding leading bytes or integer overflows this could conceivably have a security relevant impact if an application relied on a single canonical signature vulnerabilityurl | 0 |
354,152 | 25,152,719,616 | IssuesEvent | 2022-11-10 11:13:12 | mishagrol/pyRothC | https://api.github.com/repos/mishagrol/pyRothC | opened | RothC documentation | documentation | Task: Read and analyse RothC manual
https://www.rothamsted.ac.uk/sites/default/files/RothC_guide_DOS.pdf
Q: Functions of temp and moisture, how to?
| 1.0 | RothC documentation - Task: Read and analyse RothC manual
https://www.rothamsted.ac.uk/sites/default/files/RothC_guide_DOS.pdf
Q: Functions of temp and moisture, how to?
| non_priority | rothc documentation task read and analyse rothc manual q functions of temp and moisture how to | 0 |
161,114 | 25,288,066,978 | IssuesEvent | 2022-11-16 21:08:10 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | closed | USWDS v3 - Radio button - Accessibility review | accessibility vsp-design-system-team va-radio | ## Issue Description
We need to conduct a review of the accessibility guidance on USWDS for the Radio buttons component (https://designsystem.digital.gov/components/radio-buttons/) and compare it to the a11y guidance in the VA DS. (https://design.va.gov/components/form/radio-button)
## Tasks
- [x] Full review of accessibility guidance for the component on both USWDS and VA DS.
- [x] Identify and document the differences between the two
- [x] Make a recommendation on which guidance to use and include brief explanation on why (feedback can be in this ticket)
- [x] Review final recommendation with the team (can be done during standup)
- [x] Add a11y guidance updates to the documentation ticket [Conversion to USWDS v3 - Radio Button - Documentation](https://github.com/department-of-veterans-affairs/vets-design-system-documentation/issues/1269) (if needed)
## Acceptance Criteria
- [ ] Differences of the a11y guidance for the component has been documented (can be in this ticket)
- [ ] Recommendation has been shared with the team
- [ ] Documentation ticket has been updated with the revised text for a11y guidance (if needed)
| 1.0 | USWDS v3 - Radio button - Accessibility review - ## Issue Description
We need to conduct a review of the accessibility guidance on USWDS for the Radio buttons component (https://designsystem.digital.gov/components/radio-buttons/) and compare it to the a11y guidance in the VA DS. (https://design.va.gov/components/form/radio-button)
## Tasks
- [x] Full review of accessibility guidance for the component on both USWDS and VA DS.
- [x] Identify and document the differences between the two
- [x] Make a recommendation on which guidance to use and include brief explanation on why (feedback can be in this ticket)
- [x] Review final recommendation with the team (can be done during standup)
- [x] Add a11y guidance updates to the documentation ticket [Conversion to USWDS v3 - Radio Button - Documentation](https://github.com/department-of-veterans-affairs/vets-design-system-documentation/issues/1269) (if needed)
## Acceptance Criteria
- [ ] Differences of the a11y guidance for the component has been documented (can be in this ticket)
- [ ] Recommendation has been shared with the team
- [ ] Documentation ticket has been updated with the revised text for a11y guidance (if needed)
| non_priority | uswds radio button accessibility review issue description we need to conduct a review of the accessibility guidance on uswds for the radio buttons component and compare it to the guidance in the va ds tasks full review of accessibility guidance for the component on both uswds and va ds identify and document the differences between the two make a recommendation on which guidance to use and include brief explanation on why feedback can be in this ticket review final recommendation with the team can be done during standup add guidance updates to the documentation ticket if needed acceptance criteria differences of the guidance for the component has been documented can be in this ticket recommendation has been shared with the team documentation ticket has been updated with the revised text for guidance if needed | 0 |
161,014 | 20,120,383,749 | IssuesEvent | 2022-02-08 01:13:40 | SelvaMiru/WebGoat | https://api.github.com/repos/SelvaMiru/WebGoat | opened | CVE-2022-21724 (High) detected in postgresql-42.2.23.jar | security vulnerability | ## CVE-2022-21724 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postgresql-42.2.23.jar</b></p></summary>
<p>PostgreSQL JDBC Driver Postgresql</p>
<p>Library home page: <a href="https://jdbc.postgresql.org">https://jdbc.postgresql.org</a></p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /m2/repository/org/postgresql/postgresql/42.2.23/postgresql-42.2.23.jar,/m2/repository/org/postgresql/postgresql/42.2.23/postgresql-42.2.23.jar,/home/wss-scanner/.m2/repository/org/postgresql/postgresql/42.2.23/postgresql-42.2.23.jar</p>
<p>
Dependency Hierarchy:
- :x: **postgresql-42.2.23.jar** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
pgjdbc is the offical PostgreSQL JDBC Driver. A security hole was found in the jdbc driver for postgresql database while doing security research. The system using the postgresql library will be attacked when attacker control the jdbc url or properties. pgjdbc instantiates plugin instances based on class names provided via `authenticationPluginClassName`, `sslhostnameverifier`, `socketFactory`, `sslfactory`, `sslpasswordcallback` connection properties. However, the driver did not verify if the class implements the expected interface before instantiating the class. This can lead to code execution loaded via arbitrary classes. Users using plugins are advised to upgrade. There are no known workarounds for this issue.
<p>Publish Date: 2022-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21724>CVE-2022-21724</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-v7wg-cpwc-24m4">https://github.com/advisories/GHSA-v7wg-cpwc-24m4</a></p>
<p>Release Date: 2022-02-02</p>
<p>Fix Resolution: org.postgresql:postgresql:42.2.25,42.3.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-21724 (High) detected in postgresql-42.2.23.jar - ## CVE-2022-21724 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>postgresql-42.2.23.jar</b></p></summary>
<p>PostgreSQL JDBC Driver Postgresql</p>
<p>Library home page: <a href="https://jdbc.postgresql.org">https://jdbc.postgresql.org</a></p>
<p>Path to dependency file: /webwolf/pom.xml</p>
<p>Path to vulnerable library: /m2/repository/org/postgresql/postgresql/42.2.23/postgresql-42.2.23.jar,/m2/repository/org/postgresql/postgresql/42.2.23/postgresql-42.2.23.jar,/home/wss-scanner/.m2/repository/org/postgresql/postgresql/42.2.23/postgresql-42.2.23.jar</p>
<p>
Dependency Hierarchy:
- :x: **postgresql-42.2.23.jar** (Vulnerable Library)
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
pgjdbc is the offical PostgreSQL JDBC Driver. A security hole was found in the jdbc driver for postgresql database while doing security research. The system using the postgresql library will be attacked when attacker control the jdbc url or properties. pgjdbc instantiates plugin instances based on class names provided via `authenticationPluginClassName`, `sslhostnameverifier`, `socketFactory`, `sslfactory`, `sslpasswordcallback` connection properties. However, the driver did not verify if the class implements the expected interface before instantiating the class. This can lead to code execution loaded via arbitrary classes. Users using plugins are advised to upgrade. There are no known workarounds for this issue.
<p>Publish Date: 2022-02-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21724>CVE-2022-21724</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-v7wg-cpwc-24m4">https://github.com/advisories/GHSA-v7wg-cpwc-24m4</a></p>
<p>Release Date: 2022-02-02</p>
<p>Fix Resolution: org.postgresql:postgresql:42.2.25,42.3.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in postgresql jar cve high severity vulnerability vulnerable library postgresql jar postgresql jdbc driver postgresql library home page a href path to dependency file webwolf pom xml path to vulnerable library repository org postgresql postgresql postgresql jar repository org postgresql postgresql postgresql jar home wss scanner repository org postgresql postgresql postgresql jar dependency hierarchy x postgresql jar vulnerable library found in base branch develop vulnerability details pgjdbc is the offical postgresql jdbc driver a security hole was found in the jdbc driver for postgresql database while doing security research the system using the postgresql library will be attacked when attacker control the jdbc url or properties pgjdbc instantiates plugin instances based on class names provided via authenticationpluginclassname sslhostnameverifier socketfactory sslfactory sslpasswordcallback connection properties however the driver did not verify if the class implements the expected interface before instantiating the class this can lead to code execution loaded via arbitrary classes users using plugins are advised to upgrade there are no known workarounds for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org postgresql postgresql step up your open source security game with whitesource | 0 |
272,074 | 29,794,978,981 | IssuesEvent | 2023-06-16 01:01:32 | billmcchesney1/singleton | https://api.github.com/repos/billmcchesney1/singleton | closed | CVE-2021-36374 (Medium) detected in ant-1.10.9.jar, ant-1.9.4.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-36374 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ant-1.10.9.jar</b>, <b>ant-1.9.4.jar</b></p></summary>
<p>
<details><summary><b>ant-1.10.9.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://ant.apache.org/">https://ant.apache.org/</a></p>
<p>Path to dependency file: /g11n-ws/modules/md-data-initdb/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/org.apache.ant/ant/1.10.9/a8a0c9bc4473acdac25832d0a9da2ca9fd9cd35f/ant-1.10.9.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.ant/ant/1.10.9/a8a0c9bc4473acdac25832d0a9da2ca9fd9cd35f/ant-1.10.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **ant-1.10.9.jar** (Vulnerable Library)
</details>
<details><summary><b>ant-1.9.4.jar</b></p></summary>
<p>master POM</p>
<p>Path to dependency file: /g11n-ws/modules/md-data-initdb/build.gradle</p>
<p>Path to vulnerable library: /tmp/ws-ua_20210106195852_ULCRPO/downloadResource_IBRKBS/20210106200323/ant-1.9.4.jar</p>
<p>
Dependency Hierarchy:
- cglib-3.2.0.jar (Root Library)
- :x: **ant-1.9.4.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/singleton/commit/2bb883ae0b199f3e432621e91d0f801cfc406a89">2bb883ae0b199f3e432621e91d0f801cfc406a89</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
When reading a specially crafted ZIP archive, or a derived formats, an Apache Ant build can be made to allocate large amounts of memory that leads to an out of memory error, even for small inputs. This can be used to disrupt builds using Apache Ant. Commonly used derived formats from ZIP archives are for instance JAR files and many office files. Apache Ant prior to 1.9.16 and 1.10.11 were affected.
<p>Publish Date: 2021-07-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-36374>CVE-2021-36374</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://ant.apache.org/security.html">https://ant.apache.org/security.html</a></p>
<p>Release Date: 2021-07-14</p>
<p>Fix Resolution: 1.10.11</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2021-36374 (Medium) detected in ant-1.10.9.jar, ant-1.9.4.jar - autoclosed - ## CVE-2021-36374 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>ant-1.10.9.jar</b>, <b>ant-1.9.4.jar</b></p></summary>
<p>
<details><summary><b>ant-1.10.9.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="https://ant.apache.org/">https://ant.apache.org/</a></p>
<p>Path to dependency file: /g11n-ws/modules/md-data-initdb/build.gradle</p>
<p>Path to vulnerable library: /canner/.gradle/caches/modules-2/files-2.1/org.apache.ant/ant/1.10.9/a8a0c9bc4473acdac25832d0a9da2ca9fd9cd35f/ant-1.10.9.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.ant/ant/1.10.9/a8a0c9bc4473acdac25832d0a9da2ca9fd9cd35f/ant-1.10.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **ant-1.10.9.jar** (Vulnerable Library)
</details>
<details><summary><b>ant-1.9.4.jar</b></p></summary>
<p>master POM</p>
<p>Path to dependency file: /g11n-ws/modules/md-data-initdb/build.gradle</p>
<p>Path to vulnerable library: /tmp/ws-ua_20210106195852_ULCRPO/downloadResource_IBRKBS/20210106200323/ant-1.9.4.jar</p>
<p>
Dependency Hierarchy:
- cglib-3.2.0.jar (Root Library)
- :x: **ant-1.9.4.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/singleton/commit/2bb883ae0b199f3e432621e91d0f801cfc406a89">2bb883ae0b199f3e432621e91d0f801cfc406a89</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
When reading a specially crafted ZIP archive, or a derived formats, an Apache Ant build can be made to allocate large amounts of memory that leads to an out of memory error, even for small inputs. This can be used to disrupt builds using Apache Ant. Commonly used derived formats from ZIP archives are for instance JAR files and many office files. Apache Ant prior to 1.9.16 and 1.10.11 were affected.
<p>Publish Date: 2021-07-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-36374>CVE-2021-36374</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://ant.apache.org/security.html">https://ant.apache.org/security.html</a></p>
<p>Release Date: 2021-07-14</p>
<p>Fix Resolution: 1.10.11</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in ant jar ant jar autoclosed cve medium severity vulnerability vulnerable libraries ant jar ant jar ant jar library home page a href path to dependency file ws modules md data initdb build gradle path to vulnerable library canner gradle caches modules files org apache ant ant ant jar home wss scanner gradle caches modules files org apache ant ant ant jar dependency hierarchy x ant jar vulnerable library ant jar master pom path to dependency file ws modules md data initdb build gradle path to vulnerable library tmp ws ua ulcrpo downloadresource ibrkbs ant jar dependency hierarchy cglib jar root library x ant jar vulnerable library found in head commit a href found in base branch master vulnerability details when reading a specially crafted zip archive or a derived formats an apache ant build can be made to allocate large amounts of memory that leads to an out of memory error even for small inputs this can be used to disrupt builds using apache ant commonly used derived formats from zip archives are for instance jar files and many office files apache ant prior to and were affected publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
103,250 | 8,886,652,733 | IssuesEvent | 2019-01-15 01:35:48 | rancher/longhorn | https://api.github.com/repos/rancher/longhorn | closed | Longhorn CSI test cases freeze on K8s 1.11 clusters | area/driver area/kubernetes area/test bug | Kubernetes version: v1.11.2 (installed with Rancher)
Longhorn version: v0.3.1-rc1
Longhorn-test versions afflicted: v0.3.0, v0.3.1-rc1
Deploy the Longhorn test pod with following arguments:
```
args: ["-m", "csi"]
````
When `test_csi_io` runs, it will hang indefinitely after `csi-io-test` Pod is created and running. Manually testing CSI plugin on K8s 1.11 succeeds. This automated test succeeds on previous versions of Kubernetes such as 1.10 | 1.0 | Longhorn CSI test cases freeze on K8s 1.11 clusters - Kubernetes version: v1.11.2 (installed with Rancher)
Longhorn version: v0.3.1-rc1
Longhorn-test versions afflicted: v0.3.0, v0.3.1-rc1
Deploy the Longhorn test pod with following arguments:
```
args: ["-m", "csi"]
````
When `test_csi_io` runs, it will hang indefinitely after `csi-io-test` Pod is created and running. Manually testing CSI plugin on K8s 1.11 succeeds. This automated test succeeds on previous versions of Kubernetes such as 1.10 | non_priority | longhorn csi test cases freeze on clusters kubernetes version installed with rancher longhorn version longhorn test versions afflicted deploy the longhorn test pod with following arguments args when test csi io runs it will hang indefinitely after csi io test pod is created and running manually testing csi plugin on succeeds this automated test succeeds on previous versions of kubernetes such as | 0 |
98,122 | 8,674,826,660 | IssuesEvent | 2018-11-30 09:04:02 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] org.elasticsearch.xpack.ccr.action.ShardChangesTests testMissingOperations fails reproducably with seed | :Distributed/CCR >test-failure | Build URL:
https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.x+matrix-java-periodic/ES_BUILD_JAVA=java11,ES_RUNTIME_JAVA=java11,nodes=virtual&&linux/44/console
Reproduce command (fails reproducably on 6.x but not on master) :
```
./gradlew :x-pack:plugin:ccr:test \
-Dtests.seed=FAF7E61619663B98 \
-Dtests.class=org.elasticsearch.xpack.ccr.action.ShardChangesTests \
-Dtests.method="testMissingOperations" \
-Dtests.security.manager=true \
-Dtests.locale=en-VG \
-Dtests.timezone=Europe/Istanbul \
-Dcompiler.java=11 \
-Druntime.java=11
```
It looks like this test is expecting operations to no longer be available and CCR to throw an exception but it doesn't get the exception thrown in this case
Stack trace:
```
FAILURE 4.09s | ShardChangesTests.testMissingOperations <<< FAILURES!
> Throwable #1: junit.framework.AssertionFailedError: Expected exception ElasticsearchException but no exception was thrown
> at __randomizedtesting.SeedInfo.seed([FAF7E61619663B98:3B044284D8D8EB2]:0)
> at org.apache.lucene.util.LuceneTestCase.expectThrows(LuceneTestCase.java:2697)
> at org.apache.lucene.util.LuceneTestCase.expectThrows(LuceneTestCase.java:2682)
> at org.elasticsearch.xpack.ccr.action.ShardChangesTests.testMissingOperations(ShardChangesTests.java:114)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
> at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
> at java.base/java.lang.reflect.Method.invoke(Method.java:566)
> at java.base/java.lang.Thread.run(Thread.java:834)
``` | 1.0 | [CI] org.elasticsearch.xpack.ccr.action.ShardChangesTests testMissingOperations fails reproducably with seed - Build URL:
https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+6.x+matrix-java-periodic/ES_BUILD_JAVA=java11,ES_RUNTIME_JAVA=java11,nodes=virtual&&linux/44/console
Reproduce command (fails reproducably on 6.x but not on master) :
```
./gradlew :x-pack:plugin:ccr:test \
-Dtests.seed=FAF7E61619663B98 \
-Dtests.class=org.elasticsearch.xpack.ccr.action.ShardChangesTests \
-Dtests.method="testMissingOperations" \
-Dtests.security.manager=true \
-Dtests.locale=en-VG \
-Dtests.timezone=Europe/Istanbul \
-Dcompiler.java=11 \
-Druntime.java=11
```
It looks like this test is expecting operations to no longer be available and CCR to throw an exception but it doesn't get the exception thrown in this case
Stack trace:
```
FAILURE 4.09s | ShardChangesTests.testMissingOperations <<< FAILURES!
> Throwable #1: junit.framework.AssertionFailedError: Expected exception ElasticsearchException but no exception was thrown
> at __randomizedtesting.SeedInfo.seed([FAF7E61619663B98:3B044284D8D8EB2]:0)
> at org.apache.lucene.util.LuceneTestCase.expectThrows(LuceneTestCase.java:2697)
> at org.apache.lucene.util.LuceneTestCase.expectThrows(LuceneTestCase.java:2682)
> at org.elasticsearch.xpack.ccr.action.ShardChangesTests.testMissingOperations(ShardChangesTests.java:114)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
> at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
> at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
> at java.base/java.lang.reflect.Method.invoke(Method.java:566)
> at java.base/java.lang.Thread.run(Thread.java:834)
``` | non_priority | org elasticsearch xpack ccr action shardchangestests testmissingoperations fails reproducably with seed build url reproduce command fails reproducably on x but not on master gradlew x pack plugin ccr test dtests seed dtests class org elasticsearch xpack ccr action shardchangestests dtests method testmissingoperations dtests security manager true dtests locale en vg dtests timezone europe istanbul dcompiler java druntime java it looks like this test is expecting operations to no longer be available and ccr to throw an exception but it doesn t get the exception thrown in this case stack trace failure shardchangestests testmissingoperations failures throwable junit framework assertionfailederror expected exception elasticsearchexception but no exception was thrown at randomizedtesting seedinfo seed at org apache lucene util lucenetestcase expectthrows lucenetestcase java at org apache lucene util lucenetestcase expectthrows lucenetestcase java at org elasticsearch xpack ccr action shardchangestests testmissingoperations shardchangestests java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at java base java lang thread run thread java | 0 |
141,397 | 12,967,195,542 | IssuesEvent | 2020-07-21 02:31:07 | mondobrain/lupa | https://api.github.com/repos/mondobrain/lupa | closed | Update documentation for @lupa/mock | c³ ⋅ PR welcome good first issue t² 📚 documentation | ### Lupa Version
`0.2.0`
### Affected Packages
<!-- if all packages are affected just use `@ALL`. If unsure which package is having the issue list all the ones you are using. -->
- `@lupa/mock`: `0.2.0`
README.md examples are not functional. The `<MockDataset>` is missing the `data` prop
| 1.0 | Update documentation for @lupa/mock - ### Lupa Version
`0.2.0`
### Affected Packages
<!-- if all packages are affected just use `@ALL`. If unsure which package is having the issue list all the ones you are using. -->
- `@lupa/mock`: `0.2.0`
README.md examples are not functional. The `<MockDataset>` is missing the `data` prop
| non_priority | update documentation for lupa mock lupa version affected packages lupa mock readme md examples are not functional the is missing the data prop | 0 |
54,741 | 7,921,655,860 | IssuesEvent | 2018-07-05 08:18:03 | bincrafters/community | https://api.github.com/repos/bincrafters/community | closed | conan-wt documentation refers to a package that doesn't exist | bug documentation feedback | ### Description of Problem
The instructions for [conan-wt](https://github.com/bincrafters/conan-wt) point to a "testing" package, which does not exist.
From https://github.com/bincrafters/conan-wt/blob/testing/4.0.3/README.md
and
https://github.com/bincrafters/conan-wt/blob/stable/4.0.3/README.md
(the branches are currently even):
> ### Basic setup
>
> $ conan install wt/4.0.3@bincrafters/testing
>
> ### Project setup
>
> If you handle multiple dependencies in your project is better to add a *conanfile.txt*
>
> [requires]
> wt/4.0.3@bincrafters/testing
>
> [generators]
> cmake
s/testing/stable in those commands fixes the problem of the package not being found in testing.
### Package Details
* Package Name/Version: **wt/4.0.3**
* Operating System: **MacOS 10.13.5**
* Compiler+version: **clang-9.1**
| 1.0 | conan-wt documentation refers to a package that doesn't exist - ### Description of Problem
The instructions for [conan-wt](https://github.com/bincrafters/conan-wt) point to a "testing" package, which does not exist.
From https://github.com/bincrafters/conan-wt/blob/testing/4.0.3/README.md
and
https://github.com/bincrafters/conan-wt/blob/stable/4.0.3/README.md
(the branches are currently even):
> ### Basic setup
>
> $ conan install wt/4.0.3@bincrafters/testing
>
> ### Project setup
>
> If you handle multiple dependencies in your project is better to add a *conanfile.txt*
>
> [requires]
> wt/4.0.3@bincrafters/testing
>
> [generators]
> cmake
s/testing/stable in those commands fixes the problem of the package not being found in testing.
### Package Details
* Package Name/Version: **wt/4.0.3**
* Operating System: **MacOS 10.13.5**
* Compiler+version: **clang-9.1**
| non_priority | conan wt documentation refers to a package that doesn t exist description of problem the instructions for point to a testing package which does not exist from and the branches are currently even basic setup conan install wt bincrafters testing project setup if you handle multiple dependencies in your project is better to add a conanfile txt wt bincrafters testing cmake s testing stable in those commands fixes the problem of the package not being found in testing package details package name version wt operating system macos compiler version clang | 0 |
260,741 | 22,644,848,742 | IssuesEvent | 2022-07-01 07:41:48 | devtdq1701/upptime-nextify | https://api.github.com/repos/devtdq1701/upptime-nextify | closed | 🛑 Test Telegram is down | status test-telegram | In [`30ec8e3`](https://github.com/devtdq1701/upptime-nextify/commit/30ec8e37dad0d233a9d6c88249d1b72f5459abe3
), Test Telegram (https://test.com) was **down**:
- HTTP code: 0
- Response time: 0 ms
| 1.0 | 🛑 Test Telegram is down - In [`30ec8e3`](https://github.com/devtdq1701/upptime-nextify/commit/30ec8e37dad0d233a9d6c88249d1b72f5459abe3
), Test Telegram (https://test.com) was **down**:
- HTTP code: 0
- Response time: 0 ms
| non_priority | 🛑 test telegram is down in test telegram was down http code response time ms | 0 |
229,519 | 18,361,152,261 | IssuesEvent | 2021-10-09 08:16:19 | BiGilSoft/WindowTop | https://api.github.com/repos/BiGilSoft/WindowTop | closed | Loss of mouse control during initial setup/entry of key | compatibility-issue fixed testing... | During the initial setup the mouse would only respond in a very odd way, as if another was controlling it. I could move it in the general direction of where I wanted to click, but there was absolutely no accuracy. If I released the mouse, it would wander all over, then suddenly zip to the left side of the screen. This continued until after I entered the key, but only happened when the settings window was on top. After entering the key and closing the settings window, this has not recurred. I have not yet been able to reproduce this.
EDIT: OK, I've been able to reproduce this issue. It seems to happen when making/changing/saving a setting on a Windows Explorer window. It somewhat acts like massive, massive lag, but I had Task Manager open (no problems adjusting settings on that, even with Windows Explorer window open) but saw no increase in mem usage, ethernet usage, cpu usage (AMD Threadripper 2970wx) or gpu usage (AMD Radeon Vega 64). I'll add more info if I encounter it. | 1.0 | Loss of mouse control during initial setup/entry of key - During the initial setup the mouse would only respond in a very odd way, as if another was controlling it. I could move it in the general direction of where I wanted to click, but there was absolutely no accuracy. If I released the mouse, it would wander all over, then suddenly zip to the left side of the screen. This continued until after I entered the key, but only happened when the settings window was on top. After entering the key and closing the settings window, this has not recurred. I have not yet been able to reproduce this.
EDIT: OK, I've been able to reproduce this issue. It seems to happen when making/changing/saving a setting on a Windows Explorer window. It somewhat acts like massive, massive lag, but I had Task Manager open (no problems adjusting settings on that, even with Windows Explorer window open) but saw no increase in mem usage, ethernet usage, cpu usage (AMD Threadripper 2970wx) or gpu usage (AMD Radeon Vega 64). I'll add more info if I encounter it. | non_priority | loss of mouse control during initial setup entry of key during the initial setup the mouse would only respond in a very odd way as if another was controlling it i could move it in the general direction of where i wanted to click but there was absolutely no accuracy if i released the mouse it would wander all over then suddenly zip to the left side of the screen this continued until after i entered the key but only happened when the settings window was on top after entering the key and closing the settings window this has not recurred i have not yet been able to reproduce this edit ok i ve been able to reproduce this issue it seems to happen when making changing saving a setting on a windows explorer window it somewhat acts like massive massive lag but i had task manager open no problems adjusting settings on that even with windows explorer window open but saw no increase in mem usage ethernet usage cpu usage amd threadripper or gpu usage amd radeon vega i ll add more info if i encounter it | 0 |
311,566 | 23,393,383,529 | IssuesEvent | 2022-08-11 20:13:23 | kunalkeshan/SRMIST-B.Tech-ECE-Notes-2022-24 | https://api.github.com/repos/kunalkeshan/SRMIST-B.Tech-ECE-Notes-2022-24 | opened | Semester 8 Information to be added | documentation enhancement help wanted good first issue notes | - [ ] Notes Upload in Drive.
- [ ] Notes Upload in GitHub.
- [ ] Update Readme with Subject code, name, credits, difficulty.
- [ ] Create DownGit download links for each subject.
- [ ] Add how to study for Each subject.
- [ ] Update Notes Information in Website Data JSON.
- [ ] Add Notification information in Website Data. | 1.0 | Semester 8 Information to be added - - [ ] Notes Upload in Drive.
- [ ] Notes Upload in GitHub.
- [ ] Update Readme with Subject code, name, credits, difficulty.
- [ ] Create DownGit download links for each subject.
- [ ] Add how to study for Each subject.
- [ ] Update Notes Information in Website Data JSON.
- [ ] Add Notification information in Website Data. | non_priority | semester information to be added notes upload in drive notes upload in github update readme with subject code name credits difficulty create downgit download links for each subject add how to study for each subject update notes information in website data json add notification information in website data | 0 |
287,694 | 24,853,004,049 | IssuesEvent | 2022-10-26 22:01:30 | phetsims/scenery-phet | https://api.github.com/repos/phetsims/scenery-phet | closed | CT: FlowConstraint assertion failures | type:automated-testing | CT is reporting 2 different failures in FlowConstraint.js:
```
scenery-phet : multitouch-fuzz : unbuilt
https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/scenery-phet/scenery-phet_en.html?continuousTest=%7B%22test%22%3A%5B%22scenery-phet%22%2C%22multitouch-fuzz%22%2C%22unbuilt%22%5D%2C%22snapshotName%22%3A%22snapshot-1643729262081%22%2C%22timestamp%22%3A1643731431926%7D&brand=phet&ea&fuzz&fuzzPointers=2&memoryLimit=1000&supportsPanAndZoom=false
Query: brand=phet&ea&fuzz&fuzzPointers=2&memoryLimit=1000&supportsPanAndZoom=false
Uncaught Error: Assertion failed: Will not be able to fit in this preferred size
Error: Assertion failed: Will not be able to fit in this preferred size
at window.assertions.assertFunction (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/assert/js/assert.js:25:13)
at FlowConstraint.layout (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/FlowConstraint.js:175:15)
at FlowConstraint.updateLayout (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/LayoutConstraint.js:92:14)
at FlowConstraint.updateLayoutAutomatically (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/LayoutConstraint.js:106:12)
at TinyProperty.emit (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyEmitter.js:69:9)
at TinyProperty.notifyListeners (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyProperty.js:122:10)
at TinyProperty.set (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyProperty.js:58:12)
at TinyProperty.set value [as value] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyProperty.js:67:10)
at FlowBox.set preferredWidth [as preferredWidth] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/WidthSizable.js:28:41)
at https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery-phet/js/demo/ComponentsScreenView.js:1013:30
id: Bayes Chrome
Snapshot from 2/1/2022, 8:27:42 AM
```
```
scenery-phet : fuzz : unbuilt
https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/scenery-phet/scenery-phet_en.html?continuousTest=%7B%22test%22%3A%5B%22scenery-phet%22%2C%22fuzz%22%2C%22unbuilt%22%5D%2C%22snapshotName%22%3A%22snapshot-1643711167223%22%2C%22timestamp%22%3A1643715325413%7D&brand=phet&ea&fuzz&memoryLimit=1000
Query: brand=phet&ea&fuzz&memoryLimit=1000
Uncaught Error: Assertion failed
Error: Assertion failed
at window.assertions.assertFunction (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/assert/js/assert.js:25:13)
at FlowConstraint.set orientation [as orientation] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/layout/FlowConfigurable.js:147:17)
at FlowBox.set orientation [as orientation] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/layout/FlowBox.js:155:34)
at https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/nodes/Node.js:6019:21
at arrayEach (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/sherpa/lib/lodash-4.17.4.js:537:11)
at Function.forEach (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/sherpa/lib/lodash-4.17.4.js:9359:14)
at FlowBox.mutate (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/nodes/Node.js:6006:7)
at new FlowBox (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/layout/FlowBox.js:44:10)
at Object.demoFlowBox [as createNode] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery-phet/js/demo/ComponentsScreenView.js:1220:23)
at https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/sun/js/demo/DemosScreenView.js:116:26
id: Bayes Chrome
Snapshot from 2/1/2022, 3:26:07 AM
``` | 1.0 | CT: FlowConstraint assertion failures - CT is reporting 2 different failures in FlowConstraint.js:
```
scenery-phet : multitouch-fuzz : unbuilt
https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/scenery-phet/scenery-phet_en.html?continuousTest=%7B%22test%22%3A%5B%22scenery-phet%22%2C%22multitouch-fuzz%22%2C%22unbuilt%22%5D%2C%22snapshotName%22%3A%22snapshot-1643729262081%22%2C%22timestamp%22%3A1643731431926%7D&brand=phet&ea&fuzz&fuzzPointers=2&memoryLimit=1000&supportsPanAndZoom=false
Query: brand=phet&ea&fuzz&fuzzPointers=2&memoryLimit=1000&supportsPanAndZoom=false
Uncaught Error: Assertion failed: Will not be able to fit in this preferred size
Error: Assertion failed: Will not be able to fit in this preferred size
at window.assertions.assertFunction (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/assert/js/assert.js:25:13)
at FlowConstraint.layout (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/FlowConstraint.js:175:15)
at FlowConstraint.updateLayout (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/LayoutConstraint.js:92:14)
at FlowConstraint.updateLayoutAutomatically (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/LayoutConstraint.js:106:12)
at TinyProperty.emit (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyEmitter.js:69:9)
at TinyProperty.notifyListeners (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyProperty.js:122:10)
at TinyProperty.set (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyProperty.js:58:12)
at TinyProperty.set value [as value] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/axon/js/TinyProperty.js:67:10)
at FlowBox.set preferredWidth [as preferredWidth] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery/js/layout/WidthSizable.js:28:41)
at https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643729262081/chipper/dist/js/scenery-phet/js/demo/ComponentsScreenView.js:1013:30
id: Bayes Chrome
Snapshot from 2/1/2022, 8:27:42 AM
```
```
scenery-phet : fuzz : unbuilt
https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/scenery-phet/scenery-phet_en.html?continuousTest=%7B%22test%22%3A%5B%22scenery-phet%22%2C%22fuzz%22%2C%22unbuilt%22%5D%2C%22snapshotName%22%3A%22snapshot-1643711167223%22%2C%22timestamp%22%3A1643715325413%7D&brand=phet&ea&fuzz&memoryLimit=1000
Query: brand=phet&ea&fuzz&memoryLimit=1000
Uncaught Error: Assertion failed
Error: Assertion failed
at window.assertions.assertFunction (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/assert/js/assert.js:25:13)
at FlowConstraint.set orientation [as orientation] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/layout/FlowConfigurable.js:147:17)
at FlowBox.set orientation [as orientation] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/layout/FlowBox.js:155:34)
at https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/nodes/Node.js:6019:21
at arrayEach (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/sherpa/lib/lodash-4.17.4.js:537:11)
at Function.forEach (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/sherpa/lib/lodash-4.17.4.js:9359:14)
at FlowBox.mutate (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/nodes/Node.js:6006:7)
at new FlowBox (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery/js/layout/FlowBox.js:44:10)
at Object.demoFlowBox [as createNode] (https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/scenery-phet/js/demo/ComponentsScreenView.js:1220:23)
at https://bayes.colorado.edu/continuous-testing/ct-snapshots/1643711167223/chipper/dist/js/sun/js/demo/DemosScreenView.js:116:26
id: Bayes Chrome
Snapshot from 2/1/2022, 3:26:07 AM
``` | non_priority | ct flowconstraint assertion failures ct is reporting different failures in flowconstraint js scenery phet multitouch fuzz unbuilt query brand phet ea fuzz fuzzpointers memorylimit supportspanandzoom false uncaught error assertion failed will not be able to fit in this preferred size error assertion failed will not be able to fit in this preferred size at window assertions assertfunction at flowconstraint layout at flowconstraint updatelayout at flowconstraint updatelayoutautomatically at tinyproperty emit at tinyproperty notifylisteners at tinyproperty set at tinyproperty set value at flowbox set preferredwidth at id bayes chrome snapshot from am scenery phet fuzz unbuilt query brand phet ea fuzz memorylimit uncaught error assertion failed error assertion failed at window assertions assertfunction at flowconstraint set orientation at flowbox set orientation at at arrayeach at function foreach at flowbox mutate at new flowbox at object demoflowbox at id bayes chrome snapshot from am | 0 |
22,554 | 7,189,532,463 | IssuesEvent | 2018-02-02 14:22:15 | Great-Hill-Corporation/quickBlocks | https://api.github.com/repos/Great-Hill-Corporation/quickBlocks | closed | Windows port | build-windows status-inprocess type-question | I am only putting this here as a reminder of later work. I made it status-delayed and Milestone 0.5.0.
Please make very short notes on your thoughts on how hard this will be. What would be involved? Is it mostly changes to CMake or will there be code changes?
Also--please note how, very briefly, how to set myself up with a build environment. (but don't actually set anything up).
Once you've added your thoughts, please re-assign this to me. | 1.0 | Windows port - I am only putting this here as a reminder of later work. I made it status-delayed and Milestone 0.5.0.
Please make very short notes on your thoughts on how hard this will be. What would be involved? Is it mostly changes to CMake or will there be code changes?
Also--please note how, very briefly, how to set myself up with a build environment. (but don't actually set anything up).
Once you've added your thoughts, please re-assign this to me. | non_priority | windows port i am only putting this here as a reminder of later work i made it status delayed and milestone please make very short notes on your thoughts on how hard this will be what would be involved is it mostly changes to cmake or will there be code changes also please note how very briefly how to set myself up with a build environment but don t actually set anything up once you ve added your thoughts please re assign this to me | 0 |
5,050 | 25,874,266,099 | IssuesEvent | 2022-12-14 06:26:11 | microsoft/DirectXTex | https://api.github.com/repos/microsoft/DirectXTex | closed | Add Spectre mitigation support to NuGet and vcpkg | maintainence | For **NuGet**, add an alternative library built with `/p:SpectreMitigation=Spectre` for Desktop (not supported by UWP).
For **vcpkg**, add a ``spectre`` feature that sets a CMake build option ``ENABLE_SPECTRE_MITIGATION=ON``.
| True | Add Spectre mitigation support to NuGet and vcpkg - For **NuGet**, add an alternative library built with `/p:SpectreMitigation=Spectre` for Desktop (not supported by UWP).
For **vcpkg**, add a ``spectre`` feature that sets a CMake build option ``ENABLE_SPECTRE_MITIGATION=ON``.
| non_priority | add spectre mitigation support to nuget and vcpkg for nuget add an alternative library built with p spectremitigation spectre for desktop not supported by uwp for vcpkg add a spectre feature that sets a cmake build option enable spectre mitigation on | 0 |
154,302 | 13,543,706,199 | IssuesEvent | 2020-09-16 19:24:13 | AzureAD/microsoft-authentication-library-for-js | https://api.github.com/repos/AzureAD/microsoft-authentication-library-for-js | opened | Angular MSAL.js 2.0 B2C sample needs to call a B2C-protected API instead of MS Graph API | documentation question | Please follow the issue template below. Failure to do so will result in a delay in answering your question.
## Library
- [ ] `msal@1.x.x` or `@azure/msal@1.x.x`
- [x] `@azure/msal-browser@2.x.x`
- [ ] `@azure/msal-angular@0.x.x`
- [ ] `@azure/msal-angular@1.x.x`
- [ ] `@azure/msal-angularjs@1.x.x`
## Documentation location
- [ ] docs.microsoft.com
- [ ] MSAL.js Github Wiki
- [ ] README file
- [x] Other (sample in b2c-e2e-sample2.0 branch)
- [ ] Documentation does not exist
## Description
I'm working through an Angular setup with MSAL.js 2.0 and B2C for a client, and found my way to the _angular10-browser-sample_ in [this PR](https://github.com/AzureAD/microsoft-authentication-library-for-js/pull/2148). First, thank you for all the great work on this! :) Second, can you provide some guidance on how to call a B2C-protected API from Angular in that sample? The sample currently has:
```
protectedResourceMap.set('https://graph.microsoft.com/v1.0/me', ['user.read'])
```
This doesn't work since B2C tokens can't be used to make MS Graph API calls. I tried setting up my own but the following doesn't seem to work correctly, and instead I get an infinite redirect loop with B2C and the app -- I'm guessing the app doesn't consider the signed-in user to have the required scopes? I did grant admin consent to the app and ensured that the redirect URLs are configured with SPA, and that the implicit grant is disabled.
```
protectedResourceMap.set('https://[myapi]/hello', ['https://[myb2ctenant].onmicrosoft.com/api/demo.read'])
```
@tnorling FYI. | 1.0 | Angular MSAL.js 2.0 B2C sample needs to call a B2C-protected API instead of MS Graph API - Please follow the issue template below. Failure to do so will result in a delay in answering your question.
## Library
- [ ] `msal@1.x.x` or `@azure/msal@1.x.x`
- [x] `@azure/msal-browser@2.x.x`
- [ ] `@azure/msal-angular@0.x.x`
- [ ] `@azure/msal-angular@1.x.x`
- [ ] `@azure/msal-angularjs@1.x.x`
## Documentation location
- [ ] docs.microsoft.com
- [ ] MSAL.js Github Wiki
- [ ] README file
- [x] Other (sample in b2c-e2e-sample2.0 branch)
- [ ] Documentation does not exist
## Description
I'm working through an Angular setup with MSAL.js 2.0 and B2C for a client, and found my way to the _angular10-browser-sample_ in [this PR](https://github.com/AzureAD/microsoft-authentication-library-for-js/pull/2148). First, thank you for all the great work on this! :) Second, can you provide some guidance on how to call a B2C-protected API from Angular in that sample? The sample currently has:
```
protectedResourceMap.set('https://graph.microsoft.com/v1.0/me', ['user.read'])
```
This doesn't work since B2C tokens can't be used to make MS Graph API calls. I tried setting up my own but the following doesn't seem to work correctly, and instead I get an infinite redirect loop with B2C and the app -- I'm guessing the app doesn't consider the signed-in user to have the required scopes? I did grant admin consent to the app and ensured that the redirect URLs are configured with SPA, and that the implicit grant is disabled.
```
protectedResourceMap.set('https://[myapi]/hello', ['https://[myb2ctenant].onmicrosoft.com/api/demo.read'])
```
@tnorling FYI. | non_priority | angular msal js sample needs to call a protected api instead of ms graph api please follow the issue template below failure to do so will result in a delay in answering your question library msal x x or azure msal x x azure msal browser x x azure msal angular x x azure msal angular x x azure msal angularjs x x documentation location docs microsoft com msal js github wiki readme file other sample in branch documentation does not exist description i m working through an angular setup with msal js and for a client and found my way to the browser sample in first thank you for all the great work on this second can you provide some guidance on how to call a protected api from angular in that sample the sample currently has protectedresourcemap set this doesn t work since tokens can t be used to make ms graph api calls i tried setting up my own but the following doesn t seem to work correctly and instead i get an infinite redirect loop with and the app i m guessing the app doesn t consider the signed in user to have the required scopes i did grant admin consent to the app and ensured that the redirect urls are configured with spa and that the implicit grant is disabled protectedresourcemap set https hello onmicrosoft com api demo read tnorling fyi | 0 |
51,931 | 10,739,658,336 | IssuesEvent | 2019-10-29 16:44:35 | MicrosoftDocs/PowerShell-Docs | https://api.github.com/repos/MicrosoftDocs/PowerShell-Docs | opened | Bring back doc for `Get-Counter` cmdlet for PS7 | Waiting-on-code-PR | <!--
Use this template to report issues with documentation. This can include typos, technical and factual
errors, grammar, spelling, formatting, presentation, etc.
Be sure to change the issue title. Titles should be brief and meaningful.
-->
# Documentation Issue
`Get-Counter` is coming back for PS7 (note that Import-Counter and Export-Counter are NOT): https://github.com/PowerShell/PowerShell/pull/10933
## Context of the issue
- URL to the article (Docs or GitHub URL):
- Issue affects the following content (check all that apply):
**Cmdlet reference & about_ topics**
- [ ] Version 7 content
- [ ] Version 6 content
- [ ] Version 5.1 content
**Conceptual articles**
- [ ] Fundamental conceptual articles
- [ ] Script sample articles
- [ ] DSC articles
- [ ] Gallery articles
- [ ] JEA articles
- [ ] WMF articles
- [ ] SDK articles
- Is the issue specific to a platform (Y/N - Win/macOS/Linux):
## Detailed description of the issue
<!--
Enter your problem description below. Use markdown code fences for example code and output.
-->
| 1.0 | Bring back doc for `Get-Counter` cmdlet for PS7 - <!--
Use this template to report issues with documentation. This can include typos, technical and factual
errors, grammar, spelling, formatting, presentation, etc.
Be sure to change the issue title. Titles should be brief and meaningful.
-->
# Documentation Issue
`Get-Counter` is coming back for PS7 (note that Import-Counter and Export-Counter are NOT): https://github.com/PowerShell/PowerShell/pull/10933
## Context of the issue
- URL to the article (Docs or GitHub URL):
- Issue affects the following content (check all that apply):
**Cmdlet reference & about_ topics**
- [ ] Version 7 content
- [ ] Version 6 content
- [ ] Version 5.1 content
**Conceptual articles**
- [ ] Fundamental conceptual articles
- [ ] Script sample articles
- [ ] DSC articles
- [ ] Gallery articles
- [ ] JEA articles
- [ ] WMF articles
- [ ] SDK articles
- Is the issue specific to a platform (Y/N - Win/macOS/Linux):
## Detailed description of the issue
<!--
Enter your problem description below. Use markdown code fences for example code and output.
-->
| non_priority | bring back doc for get counter cmdlet for use this template to report issues with documentation this can include typos technical and factual errors grammar spelling formatting presentation etc be sure to change the issue title titles should be brief and meaningful documentation issue get counter is coming back for note that import counter and export counter are not context of the issue url to the article docs or github url issue affects the following content check all that apply cmdlet reference about topics version content version content version content conceptual articles fundamental conceptual articles script sample articles dsc articles gallery articles jea articles wmf articles sdk articles is the issue specific to a platform y n win macos linux detailed description of the issue enter your problem description below use markdown code fences for example code and output | 0 |
29,635 | 4,178,112,967 | IssuesEvent | 2016-06-22 04:36:44 | stamen/bluegreenway | https://api.github.com/repos/stamen/bluegreenway | closed | Map Toggle/content collision | Design Polish p1 | Per the design, when the window is too small to accommodate the map toggle on the right side of the design, the toggles should be moved above the page content.
Current:
<img width="1145" alt="screen shot 2016-06-16 at 11 11 50 am" src="https://cloud.githubusercontent.com/assets/5263476/16127919/614b73b6-33b3-11e6-828d-8fde32b6b289.png">
Desired:

| 1.0 | Map Toggle/content collision - Per the design, when the window is too small to accommodate the map toggle on the right side of the design, the toggles should be moved above the page content.
Current:
<img width="1145" alt="screen shot 2016-06-16 at 11 11 50 am" src="https://cloud.githubusercontent.com/assets/5263476/16127919/614b73b6-33b3-11e6-828d-8fde32b6b289.png">
Desired:

| non_priority | map toggle content collision per the design when the window is too small to accommodate the map toggle on the right side of the design the toggles should be moved above the page content current img width alt screen shot at am src desired | 0 |
104,670 | 16,619,985,216 | IssuesEvent | 2021-06-02 22:33:26 | jtimberlake/tds-core | https://api.github.com/repos/jtimberlake/tds-core | opened | CVE-2021-28918 (High) detected in netmask-1.0.6.tgz | security vulnerability | ## CVE-2021-28918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netmask-1.0.6.tgz</b></p></summary>
<p>Parse and lookup IP network blocks</p>
<p>Library home page: <a href="https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz">https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz</a></p>
<p>Path to dependency file: tds-core/package.json</p>
<p>Path to vulnerable library: tds-core/node_modules/netmask/package.json</p>
<p>
Dependency Hierarchy:
- nightwatch-1.2.4.tgz (Root Library)
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- pac-resolver-3.0.0.tgz
- :x: **netmask-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/tds-core/commit/dea0d6818322df63aea1fb950dce6e8cb94c53ba">dea0d6818322df63aea1fb950dce6e8cb94c53ba</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.
<p>Publish Date: 2021-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918>CVE-2021-28918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pch5-whg9-qr2r">https://github.com/advisories/GHSA-pch5-whg9-qr2r</a></p>
<p>Release Date: 2021-03-19</p>
<p>Fix Resolution: netmask - 2.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"netmask","packageVersion":"1.0.6","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"nightwatch:1.2.4;proxy-agent:3.1.1;pac-proxy-agent:3.0.1;pac-resolver:3.0.0;netmask:1.0.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"netmask - 2.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-28918","vulnerabilityDetails":"Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-28918 (High) detected in netmask-1.0.6.tgz - ## CVE-2021-28918 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netmask-1.0.6.tgz</b></p></summary>
<p>Parse and lookup IP network blocks</p>
<p>Library home page: <a href="https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz">https://registry.npmjs.org/netmask/-/netmask-1.0.6.tgz</a></p>
<p>Path to dependency file: tds-core/package.json</p>
<p>Path to vulnerable library: tds-core/node_modules/netmask/package.json</p>
<p>
Dependency Hierarchy:
- nightwatch-1.2.4.tgz (Root Library)
- proxy-agent-3.1.1.tgz
- pac-proxy-agent-3.0.1.tgz
- pac-resolver-3.0.0.tgz
- :x: **netmask-1.0.6.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jtimberlake/tds-core/commit/dea0d6818322df63aea1fb950dce6e8cb94c53ba">dea0d6818322df63aea1fb950dce6e8cb94c53ba</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.
<p>Publish Date: 2021-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918>CVE-2021-28918</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-pch5-whg9-qr2r">https://github.com/advisories/GHSA-pch5-whg9-qr2r</a></p>
<p>Release Date: 2021-03-19</p>
<p>Fix Resolution: netmask - 2.0.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"netmask","packageVersion":"1.0.6","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"nightwatch:1.2.4;proxy-agent:3.1.1;pac-proxy-agent:3.0.1;pac-resolver:3.0.0;netmask:1.0.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"netmask - 2.0.1"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-28918","vulnerabilityDetails":"Improper input validation of octal strings in netmask npm package v1.0.6 and below allows unauthenticated remote attackers to perform indeterminate SSRF, RFI, and LFI attacks on many of the dependent packages. A remote unauthenticated attacker can bypass packages relying on netmask to filter IPs and reach critical VPN or LAN hosts.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-28918","cvss3Severity":"high","cvss3Score":"9.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in netmask tgz cve high severity vulnerability vulnerable library netmask tgz parse and lookup ip network blocks library home page a href path to dependency file tds core package json path to vulnerable library tds core node modules netmask package json dependency hierarchy nightwatch tgz root library proxy agent tgz pac proxy agent tgz pac resolver tgz x netmask tgz vulnerable library found in head commit a href found in base branch master vulnerability details improper input validation of octal strings in netmask npm package and below allows unauthenticated remote attackers to perform indeterminate ssrf rfi and lfi attacks on many of the dependent packages a remote unauthenticated attacker can bypass packages relying on netmask to filter ips and reach critical vpn or lan hosts publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution netmask isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree nightwatch proxy agent pac proxy agent pac resolver netmask isminimumfixversionavailable true minimumfixversion netmask basebranches vulnerabilityidentifier cve vulnerabilitydetails improper input validation of octal strings in netmask npm package and below allows unauthenticated remote attackers to perform indeterminate ssrf rfi and lfi attacks on many of the dependent packages a remote unauthenticated attacker can bypass packages relying on netmask to filter ips and reach critical vpn or lan hosts vulnerabilityurl | 0 |
9,160 | 12,218,280,725 | IssuesEvent | 2020-05-01 18:59:40 | hashgraph/hedera-mirror-node | https://api.github.com/repos/hashgraph/hedera-mirror-node | closed | Kubernetes: Helm chart CI | P3 enhancement process | **Problem**
Follow up to #653 to run those tests on every commit inside CI
**Solution**
Run a test job in CI that:
- Installs and starts k3d
- Installs helm
- Installs [helm test tools](https://github.com/helm/chart-testing)
- ct lint
- ct install
**Alternatives**
- Deploy to a static environment for branches
**Additional Context**
See [similar setup](https://github.com/grafana/loki/blob/8e5fa03de3b3cf7efa15e4959bd5b7decae2d944/.circleci/config.yml#L109) I wrote for Loki.
| 1.0 | Kubernetes: Helm chart CI - **Problem**
Follow up to #653 to run those tests on every commit inside CI
**Solution**
Run a test job in CI that:
- Installs and starts k3d
- Installs helm
- Installs [helm test tools](https://github.com/helm/chart-testing)
- ct lint
- ct install
**Alternatives**
- Deploy to a static environment for branches
**Additional Context**
See [similar setup](https://github.com/grafana/loki/blob/8e5fa03de3b3cf7efa15e4959bd5b7decae2d944/.circleci/config.yml#L109) I wrote for Loki.
| non_priority | kubernetes helm chart ci problem follow up to to run those tests on every commit inside ci solution run a test job in ci that installs and starts installs helm installs ct lint ct install alternatives deploy to a static environment for branches additional context see i wrote for loki | 0 |
6,539 | 7,674,004,044 | IssuesEvent | 2018-05-15 01:16:44 | dotnet/project-system | https://api.github.com/repos/dotnet/project-system | closed | CS8032: analyzer cannot be created after changing PackageReference | Area-New-Project-System Bug Feature-Language-Service | When changing the version of a package reference that includes an analyzer, the project system will generate a bunch of CS8032 warnings. The warning says that the analyzer from the old version of the PackageReference cannot be created, even though this has been uninstalled.
**Repro**
1. Create a new test project that references xunit 2.3.0-beta2: https://www.nuget.org/packages/xunit/2.3.0-beta2-build3683. This has xunit.analyzers 0.1.0
2. Open in VS
3. Keeping VS open, edit the csproj file and change xunit to 2.3.0-beta4: https://www.nuget.org/packages/xunit/2.3.0-beta4-build3742. This has xunit.analyzers 0.6.0
**Result**
The Error List window displays hundreds of CS8032 warnings, all with the same message. They don't go away, even if you unload/reload the project.
```
Warning CS8032: An instance of analyzer Xunit.Analyzers.MemberDataShouldReferenceValidMember cannot be created from C:\Users\namc\.nuget\packages\xunit.analyzers\0.6.1\analyzers\dotnet\cs\xunit.analyzers.dll: Could not load type 'Xunit.Analyzers.MemberDataShouldReferenceValidMember' from assembly 'xunit.analyzers, Version=0.1.0.0, Culture=neutral, PublicKeyToken=null'.. FS.Composite.Tests(net461) 1 Active
```
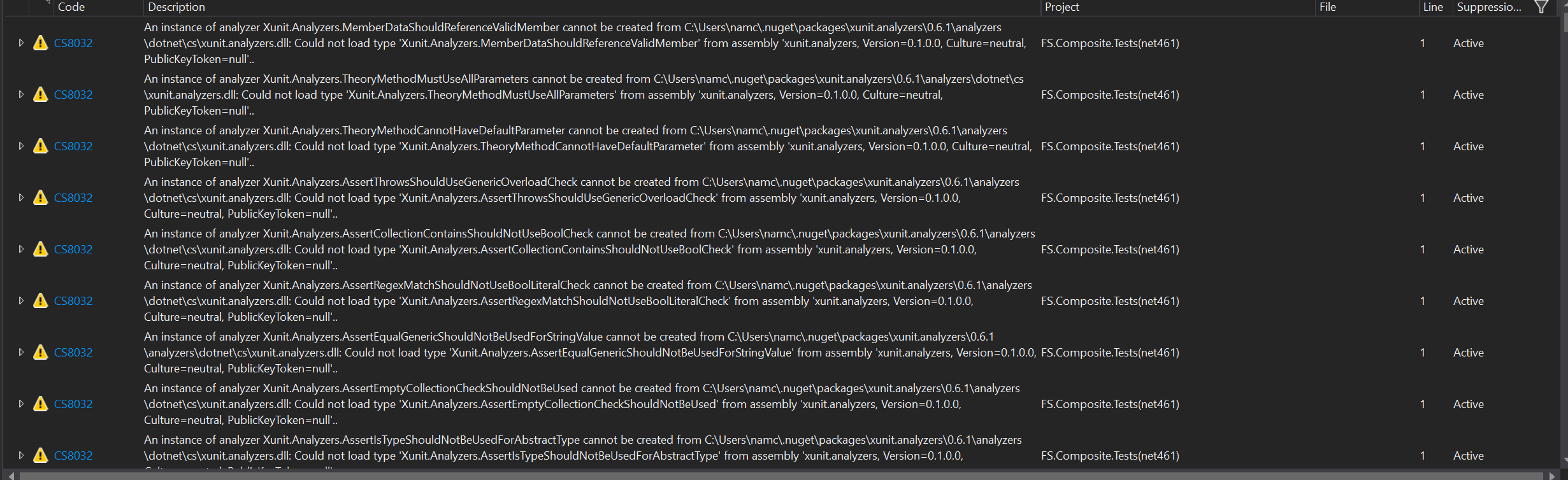
cref https://github.com/xunit/xunit/issues/1307
| 1.0 | CS8032: analyzer cannot be created after changing PackageReference - When changing the version of a package reference that includes an analyzer, the project system will generate a bunch of CS8032 warnings. The warning says that the analyzer from the old version of the PackageReference cannot be created, even though this has been uninstalled.
**Repro**
1. Create a new test project that references xunit 2.3.0-beta2: https://www.nuget.org/packages/xunit/2.3.0-beta2-build3683. This has xunit.analyzers 0.1.0
2. Open in VS
3. Keeping VS open, edit the csproj file and change xunit to 2.3.0-beta4: https://www.nuget.org/packages/xunit/2.3.0-beta4-build3742. This has xunit.analyzers 0.6.0
**Result**
The Error List window displays hundreds of CS8032 warnings, all with the same message. They don't go away, even if you unload/reload the project.
```
Warning CS8032: An instance of analyzer Xunit.Analyzers.MemberDataShouldReferenceValidMember cannot be created from C:\Users\namc\.nuget\packages\xunit.analyzers\0.6.1\analyzers\dotnet\cs\xunit.analyzers.dll: Could not load type 'Xunit.Analyzers.MemberDataShouldReferenceValidMember' from assembly 'xunit.analyzers, Version=0.1.0.0, Culture=neutral, PublicKeyToken=null'.. FS.Composite.Tests(net461) 1 Active
```
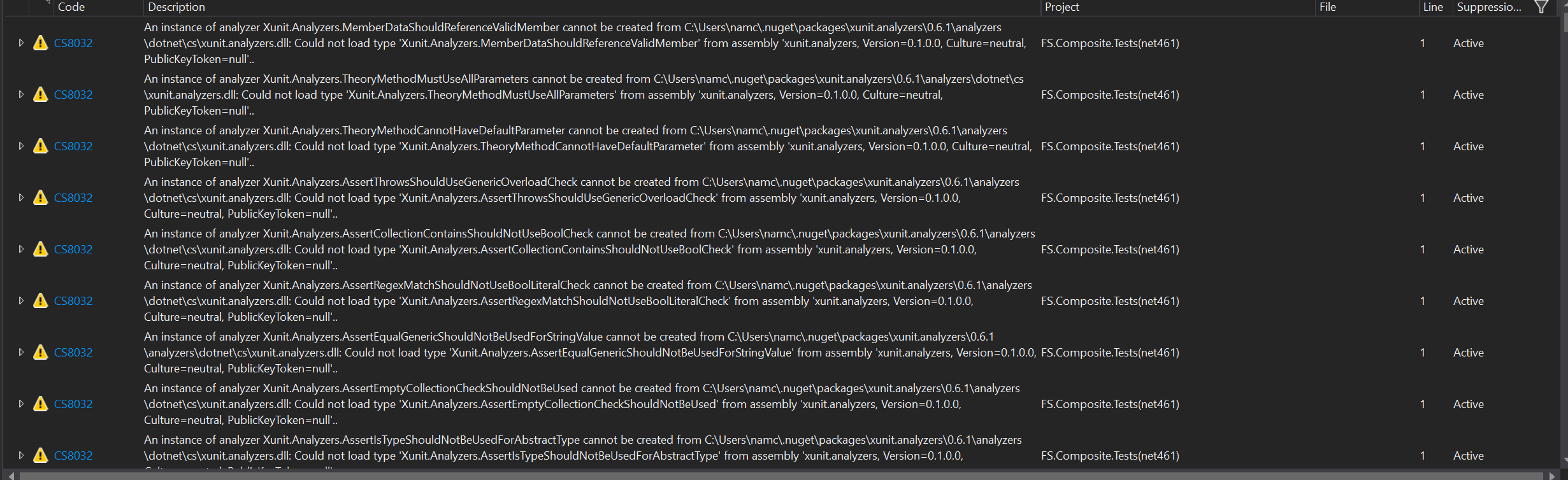
cref https://github.com/xunit/xunit/issues/1307
| non_priority | analyzer cannot be created after changing packagereference when changing the version of a package reference that includes an analyzer the project system will generate a bunch of warnings the warning says that the analyzer from the old version of the packagereference cannot be created even though this has been uninstalled repro create a new test project that references xunit this has xunit analyzers open in vs keeping vs open edit the csproj file and change xunit to this has xunit analyzers result the error list window displays hundreds of warnings all with the same message they don t go away even if you unload reload the project warning an instance of analyzer xunit analyzers memberdatashouldreferencevalidmember cannot be created from c users namc nuget packages xunit analyzers analyzers dotnet cs xunit analyzers dll could not load type xunit analyzers memberdatashouldreferencevalidmember from assembly xunit analyzers version culture neutral publickeytoken null fs composite tests active cref | 0 |
114,721 | 11,854,880,998 | IssuesEvent | 2020-03-25 02:20:12 | tanishizawa/alibaba_research_4 | https://api.github.com/repos/tanishizawa/alibaba_research_4 | opened | pullリクエスト作成時のカンバンへの連携 | bug documentation | ## 目的
pullリクエスト作成時に情報がカンバンへ連携されることを確認する #16
## TaskList
+ [作業ブランチからmasterブランチに対してpullリクエストを作成する ]
## Doneの定義
pullリクエストがカンバンに登録されること
## 参考
## 留意事項
+
## 検討事項
+ | 1.0 | pullリクエスト作成時のカンバンへの連携 - ## 目的
pullリクエスト作成時に情報がカンバンへ連携されることを確認する #16
## TaskList
+ [作業ブランチからmasterブランチに対してpullリクエストを作成する ]
## Doneの定義
pullリクエストがカンバンに登録されること
## 参考
## 留意事項
+
## 検討事項
+ | non_priority | pullリクエスト作成時のカンバンへの連携 目的 pullリクエスト作成時に情報がカンバンへ連携されることを確認する tasklist doneの定義 pullリクエストがカンバンに登録されること 参考 留意事項 検討事項 | 0 |
230,905 | 25,482,797,792 | IssuesEvent | 2022-11-26 01:33:38 | maddyCode23/linux-4.1.15 | https://api.github.com/repos/maddyCode23/linux-4.1.15 | reopened | CVE-2016-9794 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2016-9794 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/sound/core/pcm_lib.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Race condition in the snd_pcm_period_elapsed function in sound/core/pcm_lib.c in the ALSA subsystem in the Linux kernel before 4.7 allows local users to cause a denial of service (use-after-free) or possibly have unspecified other impact via a crafted SNDRV_PCM_TRIGGER_START command.
<p>Publish Date: 2016-12-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-9794>CVE-2016-9794</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9794">https://nvd.nist.gov/vuln/detail/CVE-2016-9794</a></p>
<p>Release Date: 2016-12-28</p>
<p>Fix Resolution: 4.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-9794 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2016-9794 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/maddyCode23/linux-4.1.15/commit/f1f3d2b150be669390b32dfea28e773471bdd6e7">f1f3d2b150be669390b32dfea28e773471bdd6e7</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/sound/core/pcm_lib.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Race condition in the snd_pcm_period_elapsed function in sound/core/pcm_lib.c in the ALSA subsystem in the Linux kernel before 4.7 allows local users to cause a denial of service (use-after-free) or possibly have unspecified other impact via a crafted SNDRV_PCM_TRIGGER_START command.
<p>Publish Date: 2016-12-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-9794>CVE-2016-9794</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-9794">https://nvd.nist.gov/vuln/detail/CVE-2016-9794</a></p>
<p>Release Date: 2016-12-28</p>
<p>Fix Resolution: 4.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files sound core pcm lib c vulnerability details race condition in the snd pcm period elapsed function in sound core pcm lib c in the alsa subsystem in the linux kernel before allows local users to cause a denial of service use after free or possibly have unspecified other impact via a crafted sndrv pcm trigger start command publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
42,519 | 6,987,506,886 | IssuesEvent | 2017-12-14 09:29:57 | SUSE/DeepSea | https://api.github.com/repos/SUSE/DeepSea | opened | Add zypper command to log output on failure | documentation enhancement | when `packagemanager.py` fails add the executed command to the deubg log output. | 1.0 | Add zypper command to log output on failure - when `packagemanager.py` fails add the executed command to the deubg log output. | non_priority | add zypper command to log output on failure when packagemanager py fails add the executed command to the deubg log output | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.