Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
391,495 | 26,895,440,357 | IssuesEvent | 2023-02-06 12:04:47 | ethereum/solidity | https://api.github.com/repos/ethereum/solidity | closed | Add more details around what it means to use Ether units | documentation :book: waiting for more input closed-due-inactivity stale | ## Abstract
Right now, it is rather unclear based on reading the docs here: https://github.com/ethereum/solidity/blob/v0.8.2/docs/units-and-global-variables.rst what we can actually use ether units for.
## Motivation
Adding in more examples of how it can be used. I was specifically interested in how to solve ... | 1.0 | Add more details around what it means to use Ether units - ## Abstract
Right now, it is rather unclear based on reading the docs here: https://github.com/ethereum/solidity/blob/v0.8.2/docs/units-and-global-variables.rst what we can actually use ether units for.
## Motivation
Adding in more examples of how it ... | non_priority | add more details around what it means to use ether units abstract right now it is rather unclear based on reading the docs here what we can actually use ether units for motivation adding in more examples of how it can be used i was specifically interested in how to solve the division floating po... | 0 |
94,942 | 8,527,055,217 | IssuesEvent | 2018-11-02 18:13:06 | ValveSoftware/steamvr_unity_plugin | https://api.github.com/repos/ValveSoftware/steamvr_unity_plugin | closed | Mismatch between TrackedDeviceClass and TrackedDeviceProperty | Need Retest | Hi !
From time to time, while developing an app on Unity, I'm suddenly facing a mismatch between the TrackedDevice Class and the TrackDevice Property of some controllers. It appears to come randomly, usually after a turn off/on of one controller. Only the Property seems to be “stuck” in a previous state, the Class a... | 1.0 | Mismatch between TrackedDeviceClass and TrackedDeviceProperty - Hi !
From time to time, while developing an app on Unity, I'm suddenly facing a mismatch between the TrackedDevice Class and the TrackDevice Property of some controllers. It appears to come randomly, usually after a turn off/on of one controller. Only t... | non_priority | mismatch between trackeddeviceclass and trackeddeviceproperty hi from time to time while developing an app on unity i m suddenly facing a mismatch between the trackeddevice class and the trackdevice property of some controllers it appears to come randomly usually after a turn off on of one controller only t... | 0 |
92,847 | 15,872,893,729 | IssuesEvent | 2021-04-09 01:01:27 | KaterinaOrg/keycloak | https://api.github.com/repos/KaterinaOrg/keycloak | opened | CVE-2019-12402 (High) detected in commons-compress-1.18.jar | security vulnerability | ## CVE-2019-12402 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.18.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with
compre... | True | CVE-2019-12402 (High) detected in commons-compress-1.18.jar - ## CVE-2019-12402 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.18.jar</b></p></summary>
<p>Apache Co... | non_priority | cve high detected in commons compress jar cve high severity vulnerability vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress... | 0 |
307,220 | 23,189,820,560 | IssuesEvent | 2022-08-01 11:39:14 | QUT-Motorsport/QUTMS_Driverless | https://api.github.com/repos/QUT-Motorsport/QUTMS_Driverless | closed | 9 Sept: AV Wiring Diagram | Documentation Rules Compliance Electrical | Autonomous Vehicle Wiring Diagram
- [ ] Establish what's required
- [ ] Design diagram
- [ ] Submit | 1.0 | 9 Sept: AV Wiring Diagram - Autonomous Vehicle Wiring Diagram
- [ ] Establish what's required
- [ ] Design diagram
- [ ] Submit | non_priority | sept av wiring diagram autonomous vehicle wiring diagram establish what s required design diagram submit | 0 |
47,615 | 6,062,021,755 | IssuesEvent | 2017-06-14 08:23:42 | pythonapis/MLNGAHTE5T5NGNHWMPPDWFPE | https://api.github.com/repos/pythonapis/MLNGAHTE5T5NGNHWMPPDWFPE | reopened | dVpycdl8G4qrDKZZF/283HIUuAae7yh0UXZb+Dqan+MEjRWt6HTt43Q1SfQgPcLtg9b4833uLIkxgglppF82QkSgJyY6TDRGgaubNE5vQ4P8ZTjP2I08Cet2Qokff1CCnccVT+Or/yJ5PlziXdBHZkVhaes8Gv8CKNfQqzt0WVw= | design | jqaTtk6s2GG5crF4ZrvwdaA/3R0i58hHcX7+LQhhvqMu+Bp3+s0dkRouhlaoNprOYvraFRkl+QiziaD4iOiI9ZGhOVeujtklE1ut/EdoBbuYjVU0mumqHwCx3/aTxfMr/1sl9xwQvdqTh9ZQstpg9EkLllQSChFVBg73f/shhBHGCzl+fcJecvzK8XQzGyOm6reKfmaL32e4J4ItRomSQE+ABKR+isG3PJVy6PH8GYg+hV4Ohi/Q00FJaFzOvt74cjy/b7N2CUEeNaaZTDN0r8mXpiX2W5ikxGARc3p/I7s8CXQyj0vQmKA58qkUou2h... | 1.0 | dVpycdl8G4qrDKZZF/283HIUuAae7yh0UXZb+Dqan+MEjRWt6HTt43Q1SfQgPcLtg9b4833uLIkxgglppF82QkSgJyY6TDRGgaubNE5vQ4P8ZTjP2I08Cet2Qokff1CCnccVT+Or/yJ5PlziXdBHZkVhaes8Gv8CKNfQqzt0WVw= - jqaTtk6s2GG5crF4ZrvwdaA/3R0i58hHcX7+LQhhvqMu+Bp3+s0dkRouhlaoNprOYvraFRkl+QiziaD4iOiI9ZGhOVeujtklE1ut/EdoBbuYjVU0mumqHwCx3/aTxfMr/1sl9xwQvdqTh9ZQs... | non_priority | dqan or lqhhvqmu atxfmr shhbhgczl abkr ezvyadjoqek t xsvbe | 0 |
14,023 | 16,823,885,292 | IssuesEvent | 2021-06-17 15:58:52 | prisma/prisma | https://api.github.com/repos/prisma/prisma | closed | PANIC in query-engine/connectors/mongodb-query-connector/src/root_queries/read.rs:101:74called `Option::unwrap()` on a `None` value | bug/1-repro-available kind/bug process/candidate team/developer-productivity topic: mongodb | I am using mongoDB early-access and have noticed that the prisma client is not working. I was able to replicate the issue in a little demo app. Please find the autogenerated report and my code snippets below.
@matthewmueller, you asked me to create a feature request for one-directional relationships and to report a... | 1.0 | PANIC in query-engine/connectors/mongodb-query-connector/src/root_queries/read.rs:101:74called `Option::unwrap()` on a `None` value - I am using mongoDB early-access and have noticed that the prisma client is not working. I was able to replicate the issue in a little demo app. Please find the autogenerated report and m... | non_priority | panic in query engine connectors mongodb query connector src root queries read rs option unwrap on a none value i am using mongodb early access and have noticed that the prisma client is not working i was able to replicate the issue in a little demo app please find the autogenerated report and my code sn... | 0 |
332,469 | 29,478,081,480 | IssuesEvent | 2023-06-02 01:17:36 | DK96-OS/MathTools | https://api.github.com/repos/DK96-OS/MathTools | closed | Flaky Generator and Statistics Tests | testing | How to isolate these tests that occasionally fail due to statistical fluctuations, and use retry mechanics. | 1.0 | Flaky Generator and Statistics Tests - How to isolate these tests that occasionally fail due to statistical fluctuations, and use retry mechanics. | non_priority | flaky generator and statistics tests how to isolate these tests that occasionally fail due to statistical fluctuations and use retry mechanics | 0 |
54,142 | 11,198,099,323 | IssuesEvent | 2020-01-03 15:06:37 | tobiasanker/SakuraTree | https://api.github.com/repos/tobiasanker/SakuraTree | opened | Rework apt-blossoms | code cleanup / QA | ## Cleanup-request
### Description
The apt-blossoms have two big problems:
- They are specific for debian-based systems
- They are complex structures, which could be replaced by a set of multiple other existing blossoms and if-conditions.
That why the should be moved to a more generic structure. Beside thi... | 1.0 | Rework apt-blossoms - ## Cleanup-request
### Description
The apt-blossoms have two big problems:
- They are specific for debian-based systems
- They are complex structures, which could be replaced by a set of multiple other existing blossoms and if-conditions.
That why the should be moved to a more generic... | non_priority | rework apt blossoms cleanup request description the apt blossoms have two big problems they are specific for debian based systems they are complex structures which could be replaced by a set of multiple other existing blossoms and if conditions that why the should be moved to a more generic... | 0 |
95,970 | 8,582,092,820 | IssuesEvent | 2018-11-13 16:10:46 | spring-cloud/spring-cloud-dataflow-acceptance-tests | https://api.github.com/repos/spring-cloud/spring-cloud-dataflow-acceptance-tests | closed | Test the stream/task samples listed in the SCDF docs | in progress test-coverage | - [ ] Test all the samples
- [ ] Fix where possible right away
- [ ] Correct course when there is something that is not supported anymore
- [ ] Remove stale samples
- [ ] Automate all-the-things | 1.0 | Test the stream/task samples listed in the SCDF docs - - [ ] Test all the samples
- [ ] Fix where possible right away
- [ ] Correct course when there is something that is not supported anymore
- [ ] Remove stale samples
- [ ] Automate all-the-things | non_priority | test the stream task samples listed in the scdf docs test all the samples fix where possible right away correct course when there is something that is not supported anymore remove stale samples automate all the things | 0 |
8,873 | 8,444,531,677 | IssuesEvent | 2018-10-18 18:43:01 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Suggest moving paragraph down one paragraph | app-service/svc assigned-to-author doc-enhancement triaged | The id tokens, access tokens, and refresh tokens cached for the authenticated session, and they're accessible only by the associated user.
should be one paragraph down from where it is.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 13176d... | 1.0 | Suggest moving paragraph down one paragraph - The id tokens, access tokens, and refresh tokens cached for the authenticated session, and they're accessible only by the associated user.
should be one paragraph down from where it is.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.micros... | non_priority | suggest moving paragraph down one paragraph the id tokens access tokens and refresh tokens cached for the authenticated session and they re accessible only by the associated user should be one paragraph down from where it is document details ⚠ do not edit this section it is required for docs micros... | 0 |
32,547 | 7,545,551,070 | IssuesEvent | 2018-04-17 22:04:33 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | program | code-of-conduct container-registry cxp triaged |
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 11bbaa44-52ed-33fd-d710-af73d3665ec9
* Version Independent ID: b11deb17-311c-3aa3-78a7-1f8cdc7e9e5e
* Content: [Azure Container Registry authentication with s... | 1.0 | program -
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 11bbaa44-52ed-33fd-d710-af73d3665ec9
* Version Independent ID: b11deb17-311c-3aa3-78a7-1f8cdc7e9e5e
* Content: [Azure Container Registry authenticat... | non_priority | program document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container registry github login mmacy microsoft alias mar... | 0 |
163,043 | 20,257,653,558 | IssuesEvent | 2022-02-15 01:58:13 | kapseliboi/crowi | https://api.github.com/repos/kapseliboi/crowi | opened | CVE-2021-37712 (High) detected in tar-4.4.8.tgz, tar-6.0.2.tgz | security vulnerability | ## CVE-2021-37712 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tar-4.4.8.tgz</b>, <b>tar-6.0.2.tgz</b></p></summary>
<p>
<details><summary><b>tar-4.4.8.tgz</b></p></summary>
<p>t... | True | CVE-2021-37712 (High) detected in tar-4.4.8.tgz, tar-6.0.2.tgz - ## CVE-2021-37712 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>tar-4.4.8.tgz</b>, <b>tar-6.0.2.tgz</b></p></summary... | non_priority | cve high detected in tar tgz tar tgz cve high severity vulnerability vulnerable libraries tar tgz tar tgz tar tgz tar for node library home page a href dependency hierarchy cli tgz root library chokidar tgz ... | 0 |
285,866 | 21,556,947,536 | IssuesEvent | 2022-04-30 15:32:11 | BoettcherDasOriginal/LeoConsole | https://api.github.com/repos/BoettcherDasOriginal/LeoConsole | opened | [Documetation] Wiki rework & README rework | documentation verified | # Description
The README and wiki need to be made more informative and user-friendly
# To Do:
- [ ] rework README
- [ ] rework Wiki | 1.0 | [Documetation] Wiki rework & README rework - # Description
The README and wiki need to be made more informative and user-friendly
# To Do:
- [ ] rework README
- [ ] rework Wiki | non_priority | wiki rework readme rework description the readme and wiki need to be made more informative and user friendly to do rework readme rework wiki | 0 |
196,987 | 22,572,063,616 | IssuesEvent | 2022-06-28 01:51:19 | ignatandrei/SimpleBookRental | https://api.github.com/repos/ignatandrei/SimpleBookRental | opened | CVE-2021-42740 (High) detected in shell-quote-1.7.2.tgz | security vulnerability | ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p></summary>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://r... | True | CVE-2021-42740 (High) detected in shell-quote-1.7.2.tgz - ## CVE-2021-42740 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>shell-quote-1.7.2.tgz</b></p></summary>
<p>quote and parse s... | non_priority | cve high detected in shell quote tgz cve high severity vulnerability vulnerable library shell quote tgz quote and parse shell commands library home page a href path to dependency file src webdashboard book dashboard package json path to vulnerable library src webda... | 0 |
2,142 | 4,272,560,830 | IssuesEvent | 2016-07-13 14:50:46 | IBM-Bluemix/logistics-wizard | https://api.github.com/repos/IBM-Bluemix/logistics-wizard | opened | Use transaction in ERP simulator to avoid corruption of data in concurrent API calls | erp-service story | Aim of this story is to review the ERP simulator and use Loopback transactions whenever needed.
Typically in demo.js, shipment.js, some remote methods alter multiple tables and objects at the same time. These methods should be protected against concurrent API calls that could potentially corrupt the data - as exampl... | 1.0 | Use transaction in ERP simulator to avoid corruption of data in concurrent API calls - Aim of this story is to review the ERP simulator and use Loopback transactions whenever needed.
Typically in demo.js, shipment.js, some remote methods alter multiple tables and objects at the same time. These methods should be pro... | non_priority | use transaction in erp simulator to avoid corruption of data in concurrent api calls aim of this story is to review the erp simulator and use loopback transactions whenever needed typically in demo js shipment js some remote methods alter multiple tables and objects at the same time these methods should be pro... | 0 |
236,454 | 18,097,964,142 | IssuesEvent | 2021-09-22 11:13:12 | alphagov/govuk-frontend | https://api.github.com/repos/alphagov/govuk-frontend | opened | Add info about automated tools to accessibility criteria document | documentation accessibility | ## What
Based on user feedback, add info about automated tools to [accessibility criteria doc](https://github.com/alphagov/govuk-frontend/blob/main/docs/contributing/test-components-using-accessibility-acceptance-criteria.md).
## Why
After we got 2i approval to publish our accessibility criteria, we realised i... | 1.0 | Add info about automated tools to accessibility criteria document - ## What
Based on user feedback, add info about automated tools to [accessibility criteria doc](https://github.com/alphagov/govuk-frontend/blob/main/docs/contributing/test-components-using-accessibility-acceptance-criteria.md).
## Why
After we ... | non_priority | add info about automated tools to accessibility criteria document what based on user feedback add info about automated tools to why after we got approval to publish our accessibility criteria we realised it lacked content about automated tools that help detect accessibility issues point... | 0 |
122,728 | 17,762,198,145 | IssuesEvent | 2021-08-29 22:32:38 | ghc-dev/Jeffrey-Robinson-III | https://api.github.com/repos/ghc-dev/Jeffrey-Robinson-III | opened | CVE-2019-5413 (High) detected in morgan-1.6.1.tgz | security vulnerability | ## CVE-2019-5413 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>morgan-1.6.1.tgz</b></p></summary>
<p>HTTP request logger middleware for node.js</p>
<p>Library home page: <a href="htt... | True | CVE-2019-5413 (High) detected in morgan-1.6.1.tgz - ## CVE-2019-5413 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>morgan-1.6.1.tgz</b></p></summary>
<p>HTTP request logger middlewar... | non_priority | cve high detected in morgan tgz cve high severity vulnerability vulnerable library morgan tgz http request logger middleware for node js library home page a href path to dependency file jeffrey robinson iii package json path to vulnerable library node modules morgan... | 0 |
113,937 | 24,515,603,367 | IssuesEvent | 2022-10-11 04:32:40 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | Detect URLs in string literals and make them clickable | team/code-intelligence | This would be a small but nice QoL improvement. Often one has URLs in string literals, GitHub and many editors detect these and make them clickable. I suspect it shouldn't be terribly hard to do given that it doesn't need to be reliably, and can probably be accomplished by using a non-backtracking regex to start out... | 1.0 | Detect URLs in string literals and make them clickable - This would be a small but nice QoL improvement. Often one has URLs in string literals, GitHub and many editors detect these and make them clickable. I suspect it shouldn't be terribly hard to do given that it doesn't need to be reliably, and can probably be accom... | non_priority | detect urls in string literals and make them clickable this would be a small but nice qol improvement often one has urls in string literals github and many editors detect these and make them clickable i suspect it shouldn t be terribly hard to do given that it doesn t need to be reliably and can probably be accom... | 0 |
7,760 | 8,050,637,409 | IssuesEvent | 2018-08-01 14:00:34 | google/recaptcha | https://api.github.com/repos/google/recaptcha | closed | Broken, doesn't work as a CAPTCHA service and should be removed from internet | service discussion | For the past year reCAPTCHA has been broken. 9 out of 10 correct CAPTCHA submissions are returned as "Please try again".
Many people have made videos about this but people just roll over and take it.
@rowan-m You really need to fix this. | 1.0 | Broken, doesn't work as a CAPTCHA service and should be removed from internet - For the past year reCAPTCHA has been broken. 9 out of 10 correct CAPTCHA submissions are returned as "Please try again".
Many people have made videos about this but people just roll over and take it.
@rowan-m You really need to fix th... | non_priority | broken doesn t work as a captcha service and should be removed from internet for the past year recaptcha has been broken out of correct captcha submissions are returned as please try again many people have made videos about this but people just roll over and take it rowan m you really need to fix thi... | 0 |
194,701 | 15,438,004,431 | IssuesEvent | 2021-03-07 18:46:51 | JosueNicholson/ufc-gc-equipe1-2020.2.io | https://api.github.com/repos/JosueNicholson/ufc-gc-equipe1-2020.2.io | opened | Criar README.md com os passos básicos para rodar o projeto. | documentation | Descrever no README.md como abrir o projeto, além de conter uma breve descrição das tecnologias usadas no projeto. | 1.0 | Criar README.md com os passos básicos para rodar o projeto. - Descrever no README.md como abrir o projeto, além de conter uma breve descrição das tecnologias usadas no projeto. | non_priority | criar readme md com os passos básicos para rodar o projeto descrever no readme md como abrir o projeto além de conter uma breve descrição das tecnologias usadas no projeto | 0 |
144,311 | 22,326,147,152 | IssuesEvent | 2022-06-14 10:48:04 | Khanhtran47/react-movie | https://api.github.com/repos/Khanhtran47/react-movie | opened | Filter component | feature design | sadge nextui chưa có component select :( chắc xài tạm hàng của mui hoặc đợi khi mô có select của next thì lm ✌️ | 1.0 | Filter component - sadge nextui chưa có component select :( chắc xài tạm hàng của mui hoặc đợi khi mô có select của next thì lm ✌️ | non_priority | filter component sadge nextui chưa có component select chắc xài tạm hàng của mui hoặc đợi khi mô có select của next thì lm ✌️ | 0 |
27,649 | 11,524,338,179 | IssuesEvent | 2020-02-15 00:10:37 | ambergkim/todo-api | https://api.github.com/repos/ambergkim/todo-api | opened | 1324:handlebars:Arbitrary Code Execution | high security | No CVE
CWE CWE-79
No References
Versions of `handlebars` prior to 4.5.3 are vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system. It is due to an incomplete fix for a [previous iss... | True | 1324:handlebars:Arbitrary Code Execution - No CVE
CWE CWE-79
No References
Versions of `handlebars` prior to 4.5.3 are vulnerable to Arbitrary Code Execution. The package's lookup helper fails to properly validate templates, allowing attackers to submit templates that execute arbitrary JavaScript in the system. It is d... | non_priority | handlebars arbitrary code execution no cve cwe cwe no references versions of handlebars prior to are vulnerable to arbitrary code execution the package s lookup helper fails to properly validate templates allowing attackers to submit templates that execute arbitrary javascript in the system it is due t... | 0 |
274,271 | 29,953,112,949 | IssuesEvent | 2023-06-23 04:20:24 | kxxt/aspeak | https://api.github.com/repos/kxxt/aspeak | closed | reqwest-0.11.18.crate: 1 vulnerabilities (highest severity is: 5.5) - autoclosed | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>reqwest-0.11.18.crate</b></p></summary>
<p></p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.co... | True | reqwest-0.11.18.crate: 1 vulnerabilities (highest severity is: 5.5) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>reqwest-0.11.18.crate</b></p></summary>
<p></p>
<p>
</details>
## Vulnerabilities... | non_priority | reqwest crate vulnerabilities highest severity is autoclosed vulnerable library reqwest crate vulnerabilities cve severity cvss dependency type fixed in reqwest version remediation available ... | 0 |
17,546 | 6,472,961,304 | IssuesEvent | 2017-08-17 14:59:10 | moby/moby | https://api.github.com/repos/moby/moby | closed | Docker Build returns Error code 100 | area/builder | <!--
If you are reporting a new issue, make sure that we do not have any duplicates
already open. You can ensure this by searching the issue list for this
repository. If there is a duplicate, please close your issue and add a comment
to the existing issue instead.
If you suspect your issue is a bug, please edit ... | 1.0 | Docker Build returns Error code 100 - <!--
If you are reporting a new issue, make sure that we do not have any duplicates
already open. You can ensure this by searching the issue list for this
repository. If there is a duplicate, please close your issue and add a comment
to the existing issue instead.
If you sus... | non_priority | docker build returns error code if you are reporting a new issue make sure that we do not have any duplicates already open you can ensure this by searching the issue list for this repository if there is a duplicate please close your issue and add a comment to the existing issue instead if you suspe... | 0 |
310,919 | 23,361,554,614 | IssuesEvent | 2022-08-10 12:11:08 | guardicore/monkey | https://api.github.com/repos/guardicore/monkey | closed | Host documentation on Linode | Documentation Impact: Low Complexity: Low | ## Description
The Hugo documentation needs to be hosted on Linode instead of Guardicore's server.
## Tasks
- [x] Work with IT to get Linode an infection monkey account and accounts/roles for everyone on the team to access the infection monkey Linode resources. (0d) @ilija-lazoroski
- [x] Configure an Object St... | 1.0 | Host documentation on Linode - ## Description
The Hugo documentation needs to be hosted on Linode instead of Guardicore's server.
## Tasks
- [x] Work with IT to get Linode an infection monkey account and accounts/roles for everyone on the team to access the infection monkey Linode resources. (0d) @ilija-lazoroski ... | non_priority | host documentation on linode description the hugo documentation needs to be hosted on linode instead of guardicore s server tasks work with it to get linode an infection monkey account and accounts roles for everyone on the team to access the infection monkey linode resources ilija lazoroski ... | 0 |
246,174 | 26,600,341,735 | IssuesEvent | 2023-01-23 15:21:08 | lukebrogan-mend/django.nV | https://api.github.com/repos/lukebrogan-mend/django.nV | closed | CVE-2016-2512 (Low) detected in Django-1.8.3-py2.py3-none-any.whl - autoclosed | security vulnerability | ## CVE-2016-2512 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.3-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid developme... | True | CVE-2016-2512 (Low) detected in Django-1.8.3-py2.py3-none-any.whl - autoclosed - ## CVE-2016-2512 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.3-py2.py3-none-any.whl</b></p... | non_priority | cve low detected in django none any whl autoclosed cve low severity vulnerability vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to dependency... | 0 |
317,272 | 27,223,898,964 | IssuesEvent | 2023-02-21 08:17:24 | PalisadoesFoundation/talawa | https://api.github.com/repos/PalisadoesFoundation/talawa | closed | Tests for chat_message_bubble.dart | good first issue test points 01 | - Please coordinate **issue assignment** and **PR reviews** with the contributors listed in this issue https://github.com/PalisadoesFoundation/talawa/issues/359
The Talawa code base needs to be 100% reliable. This means we need to have 100% test code coverage.
Tests need to be written for file `lib/views/after_au... | 1.0 | Tests for chat_message_bubble.dart - - Please coordinate **issue assignment** and **PR reviews** with the contributors listed in this issue https://github.com/PalisadoesFoundation/talawa/issues/359
The Talawa code base needs to be 100% reliable. This means we need to have 100% test code coverage.
Tests need to be... | non_priority | tests for chat message bubble dart please coordinate issue assignment and pr reviews with the contributors listed in this issue the talawa code base needs to be reliable this means we need to have test code coverage tests need to be written for file lib views after auth screens chat widgets... | 0 |
19,877 | 3,786,296,742 | IssuesEvent | 2016-03-21 01:04:14 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Random mapping of ports is broken on upgrade | kind/bug status/resolved status/to-test | Rancher Version: Rancher 0.59.1
Docker Version: Docker 1.10.2
OS: Ubuntu 14.04.4 LTS
Steps to Reproduce:
1. Create a Rancher catalog entry that deploys a stack containing a service that gets assigned a random high value port. For example, you could have a snippet of docker-compose.yml that looks like this. N... | 1.0 | Random mapping of ports is broken on upgrade - Rancher Version: Rancher 0.59.1
Docker Version: Docker 1.10.2
OS: Ubuntu 14.04.4 LTS
Steps to Reproduce:
1. Create a Rancher catalog entry that deploys a stack containing a service that gets assigned a random high value port. For example, you could have a snippe... | non_priority | random mapping of ports is broken on upgrade rancher version rancher docker version docker os ubuntu lts steps to reproduce create a rancher catalog entry that deploys a stack containing a service that gets assigned a random high value port for example you could have a snippet of... | 0 |
230,623 | 18,680,154,845 | IssuesEvent | 2021-11-01 03:50:14 | sak007/MyDollarBot | https://api.github.com/repos/sak007/MyDollarBot | closed | Build Failed - Please fix styling and linting issues | bug test | Please fix the issues with the latest commit - build is failing, so need to fix this.
Problematic Commit 668268cd8c5bf686fc83b66d5012ee57d482714f | 1.0 | Build Failed - Please fix styling and linting issues - Please fix the issues with the latest commit - build is failing, so need to fix this.
Problematic Commit 668268cd8c5bf686fc83b66d5012ee57d482714f | non_priority | build failed please fix styling and linting issues please fix the issues with the latest commit build is failing so need to fix this problematic commit | 0 |
452,955 | 32,075,456,254 | IssuesEvent | 2023-09-25 10:41:25 | geosolutions-it/MapStore2 | https://api.github.com/repos/geosolutions-it/MapStore2 | closed | User Guide - Change video for Images management in Identify template | Documentation User Guide BackportNeeded C265-ATOLCD-2023-DEV_MS_CNR | ## Description
<!-- A few sentences describing the documentation request -->
<!-- screenshot, video, or link to mockup/prototype are welcome -->
Change video on [Identify template](https://docs.mapstore.geosolutionsgroup.com/en/latest/user-guide/layer-settings/#templates) section
*Documentation section involved*
... | 1.0 | User Guide - Change video for Images management in Identify template - ## Description
<!-- A few sentences describing the documentation request -->
<!-- screenshot, video, or link to mockup/prototype are welcome -->
Change video on [Identify template](https://docs.mapstore.geosolutionsgroup.com/en/latest/user-guide/... | non_priority | user guide change video for images management in identify template description change video on section documentation section involved user guide developer guide other useful information related to | 0 |
399,594 | 27,246,933,624 | IssuesEvent | 2023-02-22 03:20:25 | go-go-golems/glazed | https://api.github.com/repos/go-go-golems/glazed | opened | Add helpsystem support for layers | documentation enhancement | Now that we have clean layers, we can actually start adding doc pages that are directly linked to individual layers. | 1.0 | Add helpsystem support for layers - Now that we have clean layers, we can actually start adding doc pages that are directly linked to individual layers. | non_priority | add helpsystem support for layers now that we have clean layers we can actually start adding doc pages that are directly linked to individual layers | 0 |
46,762 | 24,709,812,241 | IssuesEvent | 2022-10-19 22:57:07 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | closed | intel qat compression hardware acceleration support ? | feature performance | While be possible to add support Intel QAT compression acceleration ?
Because they are integrate in new intel scalable cpu !
seem to 30% boost on hadoop :
https://www.intel.com/content/www/us/en/architecture-and-technology/faster-hadoop-run-times-quickassist-technology.html | True | intel qat compression hardware acceleration support ? - While be possible to add support Intel QAT compression acceleration ?
Because they are integrate in new intel scalable cpu !
seem to 30% boost on hadoop :
https://www.intel.com/content/www/us/en/architecture-and-technology/faster-hadoop-run-times-quickassist... | non_priority | intel qat compression hardware acceleration support while be possible to add support intel qat compression acceleration because they are integrate in new intel scalable cpu seem to boost on hadoop | 0 |
92,679 | 15,863,513,337 | IssuesEvent | 2021-04-08 12:52:28 | mickelsonmichael/JustPickSomething | https://api.github.com/repos/mickelsonmichael/JustPickSomething | opened | CVE-2020-7788 (High) detected in ini-1.3.5.tgz | security vulnerability | ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.5.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.... | True | CVE-2020-7788 (High) detected in ini-1.3.5.tgz - ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.5.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>... | non_priority | cve high detected in ini tgz cve high severity vulnerability vulnerable library ini tgz an ini encoder decoder for node library home page a href path to dependency file justpicksomething web package json path to vulnerable library justpicksomething web node modules i... | 0 |
374,192 | 26,104,874,210 | IssuesEvent | 2022-12-27 11:57:19 | Anglepi/My-Many-Reads | https://api.github.com/repos/Anglepi/My-Many-Reads | closed | User recommendations story had some missing actions | documentation | Seems like on the last pull request (#63) I forgot to commit the last review action.
I also noticed that the tasks to such story were not added to the docs. | 1.0 | User recommendations story had some missing actions - Seems like on the last pull request (#63) I forgot to commit the last review action.
I also noticed that the tasks to such story were not added to the docs. | non_priority | user recommendations story had some missing actions seems like on the last pull request i forgot to commit the last review action i also noticed that the tasks to such story were not added to the docs | 0 |
131,620 | 12,487,900,845 | IssuesEvent | 2020-05-31 11:38:02 | haskell-unordered-containers/unordered-containers | https://api.github.com/repos/haskell-unordered-containers/unordered-containers | closed | Maintain CHANGELOG | documentation | Please journal changes in a CHANGELOG.
Makes it much easier to decide whether new versions of unordered-containers are likely to work out-of-the-box, and upper bounds on version constraints can be safely relaxed.
| 1.0 | Maintain CHANGELOG - Please journal changes in a CHANGELOG.
Makes it much easier to decide whether new versions of unordered-containers are likely to work out-of-the-box, and upper bounds on version constraints can be safely relaxed.
| non_priority | maintain changelog please journal changes in a changelog makes it much easier to decide whether new versions of unordered containers are likely to work out of the box and upper bounds on version constraints can be safely relaxed | 0 |
35,185 | 7,919,491,122 | IssuesEvent | 2018-07-04 17:08:04 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] Atum pagination override | No Code Attached Yet | As you can see in this code it will generate TWO class attributes. you can only have ONE
https://github.com/joomla/joomla-cms/blob/4b01c64aad89d687ecb22c8a2d01fc8c86f2814d/administrator/templates/atum/html/pagination.php#L191-L199 | 1.0 | [4.0] Atum pagination override - As you can see in this code it will generate TWO class attributes. you can only have ONE
https://github.com/joomla/joomla-cms/blob/4b01c64aad89d687ecb22c8a2d01fc8c86f2814d/administrator/templates/atum/html/pagination.php#L191-L199 | non_priority | atum pagination override as you can see in this code it will generate two class attributes you can only have one | 0 |
13,594 | 8,290,501,108 | IssuesEvent | 2018-09-19 17:33:43 | jruby/jruby | https://api.github.com/repos/jruby/jruby | closed | Performance regression with `Time.parse` from 1.7 to 9k | JRuby 9000 performance regression | <!--
This is a simple template for filing JRuby isuses.
Please help us help you by providing the information below.
Text inside XML comment tags will not be shown in your report.
-->
### Environment
<!--
Provide at least:
* JRuby version (`jruby -v`) and command line (flags, JRUBY_OPTS, etc)
* Operating system and p... | True | Performance regression with `Time.parse` from 1.7 to 9k - <!--
This is a simple template for filing JRuby isuses.
Please help us help you by providing the information below.
Text inside XML comment tags will not be shown in your report.
-->
### Environment
<!--
Provide at least:
* JRuby version (`jruby -v`) and comm... | non_priority | performance regression with time parse from to this is a simple template for filing jruby isuses please help us help you by providing the information below text inside xml comment tags will not be shown in your report environment provide at least jruby version jruby v and comma... | 0 |
340,380 | 30,512,710,403 | IssuesEvent | 2023-07-18 22:30:02 | cassiosantana/book_publisher | https://api.github.com/repos/cassiosantana/book_publisher | opened | Fix factories that were changed after previously created tests | bug test | These changes caused errors in several tests that depended on the previous state of a certain factory | 1.0 | Fix factories that were changed after previously created tests - These changes caused errors in several tests that depended on the previous state of a certain factory | non_priority | fix factories that were changed after previously created tests these changes caused errors in several tests that depended on the previous state of a certain factory | 0 |
347,968 | 31,390,285,500 | IssuesEvent | 2023-08-26 08:45:25 | Azure/ResourceModules | https://api.github.com/repos/Azure/ResourceModules | closed | Convert example module to check overall impact | [cat] testing | convert storage account folder and references
open draft PR | 1.0 | Convert example module to check overall impact - convert storage account folder and references
open draft PR | non_priority | convert example module to check overall impact convert storage account folder and references open draft pr | 0 |
318,775 | 27,321,044,731 | IssuesEvent | 2023-02-24 19:52:26 | peviitor-ro/ui-js | https://api.github.com/repos/peviitor-ro/ui-js | closed | Rocket image size | bug TestQuality Medium | ## Precondition
URL: https://beta.peviitor.ro
Device: Iphone 12 Pro
Browser: Chrome
## Steps to Reproduce:
### Step 1 <span style="color:#58b880"> **[Pass]** </span>
Open URL in browser
#### Expected Result
The webpage is loaded without any errors
### Step 2 <span style="color:#ff5538"> **[Fail]** </span>
Check if t... | 1.0 | Rocket image size - ## Precondition
URL: https://beta.peviitor.ro
Device: Iphone 12 Pro
Browser: Chrome
## Steps to Reproduce:
### Step 1 <span style="color:#58b880"> **[Pass]** </span>
Open URL in browser
#### Expected Result
The webpage is loaded without any errors
### Step 2 <span style="color:#ff5538"> **[Fail]*... | non_priority | rocket image size precondition url device iphone pro browser chrome steps to reproduce step open url in browser expected result the webpage is loaded without any errors step check if the rocket icon is displayed as per design on figma expected result rocke... | 0 |
138,148 | 12,808,034,350 | IssuesEvent | 2020-07-03 12:47:53 | reapit/foundations | https://api.github.com/repos/reapit/foundations | closed | Improve webhooks documentation to clarify relationship between webhooks and platform API schemas | documentation platform-team | The documentation for our webhooks system includes details on the expected payload we will send, including an example.
We should make it clearer that the `new`, `old` and `diff` attributes will contain content that relates to the same schema as we expose in the APIs we document in our interactive API explorer. | 1.0 | Improve webhooks documentation to clarify relationship between webhooks and platform API schemas - The documentation for our webhooks system includes details on the expected payload we will send, including an example.
We should make it clearer that the `new`, `old` and `diff` attributes will contain content that re... | non_priority | improve webhooks documentation to clarify relationship between webhooks and platform api schemas the documentation for our webhooks system includes details on the expected payload we will send including an example we should make it clearer that the new old and diff attributes will contain content that re... | 0 |
333,789 | 24,391,444,430 | IssuesEvent | 2022-10-04 15:31:09 | microsoft/AzureTRE | https://api.github.com/repos/microsoft/AzureTRE | opened | Documentation: Shared service docs don't include makefile deployment step | bug documentation | **Describe the bug**
Currently the docs at https://github.com/microsoft/AzureTRE/blob/main/docs/tre-admins/setup-instructions/configuring-shared-services.md mention configuring shared services, but they don't include the deployment step (which was removed from the `make all` path).
We should include the deployment ... | 1.0 | Documentation: Shared service docs don't include makefile deployment step - **Describe the bug**
Currently the docs at https://github.com/microsoft/AzureTRE/blob/main/docs/tre-admins/setup-instructions/configuring-shared-services.md mention configuring shared services, but they don't include the deployment step (which... | non_priority | documentation shared service docs don t include makefile deployment step describe the bug currently the docs at mention configuring shared services but they don t include the deployment step which was removed from the make all path we should include the deployment steps as part of the set up guide fo... | 0 |
55,032 | 23,387,108,101 | IssuesEvent | 2022-08-11 14:35:53 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | Add ability to create a new locations note | Type: Feature Impact: 2-Major Service: Dev Need: 1-Must Have Workgroup: VZ Product: Vision Zero Crash Data System | Copied from #9497
A user with editor access should be able to create a new note
- [ ] Conditionally display form field for "Date" and "Note" text if user is an editor. Hide when user only has read-only access
- [ ] When the user clicks "Add" button, send a graphQL mutation to insert a new record into the `notes` tabl... | 1.0 | Add ability to create a new locations note - Copied from #9497
A user with editor access should be able to create a new note
- [ ] Conditionally display form field for "Date" and "Note" text if user is an editor. Hide when user only has read-only access
- [ ] When the user clicks "Add" button, send a graphQL mutation... | non_priority | add ability to create a new locations note copied from a user with editor access should be able to create a new note conditionally display form field for date and note text if user is an editor hide when user only has read only access when the user clicks add button send a graphql mutation to ins... | 0 |
167,947 | 26,570,896,254 | IssuesEvent | 2023-01-21 05:37:37 | BlossomLabs/OsmoticFund | https://api.github.com/repos/BlossomLabs/OsmoticFund | opened | Contracts: add a project list contract | 👩🎨 design | Create a middle contract between the `ProjectRegistry` and the `OsmoticPool` so we can have a filter of the project registry and avoid the need of registering project in the pool. | 1.0 | Contracts: add a project list contract - Create a middle contract between the `ProjectRegistry` and the `OsmoticPool` so we can have a filter of the project registry and avoid the need of registering project in the pool. | non_priority | contracts add a project list contract create a middle contract between the projectregistry and the osmoticpool so we can have a filter of the project registry and avoid the need of registering project in the pool | 0 |
248,089 | 20,994,121,275 | IssuesEvent | 2022-03-29 12:05:29 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | opened | ../src/Interpreters/ExternalLoader.cpp:1159:33: runtime error: member call on address 0x7fdb3c210500 which does not point to an object of type 'DB::IExternalLoadable' 0x7fdb3c210500: note: object is of type 'DB::CatBoostModel' | testing | test_catboost_model_first_evaluate ubsan
```
../src/Interpreters/ExternalLoader.cpp:1159:33: runtime error: member call on address 0x7fdb3c210500 which does not point to an object of type 'DB::IExternalLoadable'
0x7fdb3c210500: note: object is of type 'DB::CatBoostModel'
00 00 00 00 88 29 52 0a 00 00 00 00 00 ... | 1.0 | ../src/Interpreters/ExternalLoader.cpp:1159:33: runtime error: member call on address 0x7fdb3c210500 which does not point to an object of type 'DB::IExternalLoadable' 0x7fdb3c210500: note: object is of type 'DB::CatBoostModel' - test_catboost_model_first_evaluate ubsan
```
../src/Interpreters/ExternalLoader.cpp:115... | non_priority | src interpreters externalloader cpp runtime error member call on address which does not point to an object of type db iexternalloadable note object is of type db catboostmodel test catboost model first evaluate ubsan src interpreters externalloader cpp runtime error member call o... | 0 |
271,462 | 20,674,902,459 | IssuesEvent | 2022-03-10 08:15:58 | renatogallo27/gruppo-coniche-G-C-P-C-F-M-T-D | https://api.github.com/repos/renatogallo27/gruppo-coniche-G-C-P-C-F-M-T-D | opened | diagramma di flusso | documentation | prima di procedere ad una seconda verifica del diagramma di flusso va ricostruito in modo corretto.
- i blocchi devono essere descritti da una singola parola, che sarà il nome della funzione da creare per quel blocco. raggruppate, se possibile più blocchi in funzioni singole. ad esempio il primo potrebbe essere disegn... | 1.0 | diagramma di flusso - prima di procedere ad una seconda verifica del diagramma di flusso va ricostruito in modo corretto.
- i blocchi devono essere descritti da una singola parola, che sarà il nome della funzione da creare per quel blocco. raggruppate, se possibile più blocchi in funzioni singole. ad esempio il primo ... | non_priority | diagramma di flusso prima di procedere ad una seconda verifica del diagramma di flusso va ricostruito in modo corretto i blocchi devono essere descritti da una singola parola che sarà il nome della funzione da creare per quel blocco raggruppate se possibile più blocchi in funzioni singole ad esempio il primo ... | 0 |
113,755 | 11,813,446,636 | IssuesEvent | 2020-03-19 22:26:05 | react-hook-form/react-hook-form | https://api.github.com/repos/react-hook-form/react-hook-form | closed | Using Controller with React DatePicker | improve documentation question | I am trying to get some sanitised error reporting on the DatePicker custom input
**Codesandbox link (Required)**
Please check this out
https://codesandbox.io/s/react-hook-form-and-react-date-picker-wrapped-at-controller-cyc48
- When first loaded the errors are {} and display the error style
- If I hit submit... | 1.0 | Using Controller with React DatePicker - I am trying to get some sanitised error reporting on the DatePicker custom input
**Codesandbox link (Required)**
Please check this out
https://codesandbox.io/s/react-hook-form-and-react-date-picker-wrapped-at-controller-cyc48
- When first loaded the errors are {} and d... | non_priority | using controller with react datepicker i am trying to get some sanitised error reporting on the datepicker custom input codesandbox link required please check this out when first loaded the errors are and display the error style if i hit submit immediately datepicker takes over and does some... | 0 |
33,149 | 6,159,996,460 | IssuesEvent | 2017-06-29 02:53:55 | IQSS/dataverse | https://api.github.com/repos/IQSS/dataverse | reopened | Dev Guide should give more guidance on type safety, code quality, code style, etc. | Component: Developer Guide Help Wanted: Documentation Mentor: pdurbin Type: Suggestion | We should mention the following
4 spaces
javadoc
dev-list
options -> editor -> code completion -> auto popup
create a settings bundle to import?
We should add sample code, like the code from Netbeans tabs and spaces thing.
We could separate into code style and code quality. | 1.0 | Dev Guide should give more guidance on type safety, code quality, code style, etc. - We should mention the following
4 spaces
javadoc
dev-list
options -> editor -> code completion -> auto popup
create a settings bundle to import?
We should add sample code, like the code from Netbeans tabs and spaces thing.
We co... | non_priority | dev guide should give more guidance on type safety code quality code style etc we should mention the following spaces javadoc dev list options editor code completion auto popup create a settings bundle to import we should add sample code like the code from netbeans tabs and spaces thing we co... | 0 |
342,776 | 30,637,782,703 | IssuesEvent | 2023-07-24 19:11:43 | galaxyproject/galaxy | https://api.github.com/repos/galaxyproject/galaxy | closed | release notes bullhorn is blinking on every visit | kind/bug area/UI-UX release-testing-23.1 | Every page reload resets the blinking so our use of localstorage for state persistence seems to not work correctly.
xref https://github.com/galaxyproject/galaxy/pull/16049 | 1.0 | release notes bullhorn is blinking on every visit - Every page reload resets the blinking so our use of localstorage for state persistence seems to not work correctly.
xref https://github.com/galaxyproject/galaxy/pull/16049 | non_priority | release notes bullhorn is blinking on every visit every page reload resets the blinking so our use of localstorage for state persistence seems to not work correctly xref | 0 |
180,396 | 21,625,725,094 | IssuesEvent | 2022-05-05 01:40:45 | Sh2dowFi3nd/Test_2 | https://api.github.com/repos/Sh2dowFi3nd/Test_2 | closed | CVE-2017-9787 (High) detected in struts2-core-2.3.31.jar - autoclosed | security vulnerability | ## CVE-2017-9787 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>struts2-core-2.3.31.jar</b></p></summary>
<p>Apache Struts 2</p>
<p>Library home page: <a href="http://struts.apache.or... | True | CVE-2017-9787 (High) detected in struts2-core-2.3.31.jar - autoclosed - ## CVE-2017-9787 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>struts2-core-2.3.31.jar</b></p></summary>
<p>Ap... | non_priority | cve high detected in core jar autoclosed cve high severity vulnerability vulnerable library core jar apache struts library home page a href dependency hierarchy x core jar vulnerable library found in head commit a href vuln... | 0 |
145,019 | 19,319,014,521 | IssuesEvent | 2021-12-14 01:50:03 | peterwkc85/selenium-jupiter | https://api.github.com/repos/peterwkc85/selenium-jupiter | opened | CVE-2019-12402 (High) detected in commons-compress-1.18.jar | security vulnerability | ## CVE-2019-12402 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.18.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with
compre... | True | CVE-2019-12402 (High) detected in commons-compress-1.18.jar - ## CVE-2019-12402 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.18.jar</b></p></summary>
<p>Apache Co... | non_priority | cve high detected in commons compress jar cve high severity vulnerability vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress... | 0 |
288,237 | 31,861,205,405 | IssuesEvent | 2023-09-15 11:03:10 | nidhi7598/linux-v4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564 | opened | CVE-2019-15222 (Medium) detected in linuxlinux-4.19.294 | Mend: dependency security vulnerability | ## CVE-2019-15222 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge... | True | CVE-2019-15222 (Medium) detected in linuxlinux-4.19.294 - ## CVE-2019-15222 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Ker... | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files sound usb help... | 0 |
319,314 | 27,364,852,550 | IssuesEvent | 2023-02-27 18:20:13 | metalbear-co/mirrord | https://api.github.com/repos/metalbear-co/mirrord | closed | Remove the word "test" from all tests. | enhancement easy tests | All of our tests are called `test_...`. Seems redundant.
Since tests are marked with `#[rstest]`, we don't need to mark them with the word "test" at the beginning of their name.
I suggest we just call them as what they are testing, so if a test is testing that a feature like http mirroring works, then we just call ... | 1.0 | Remove the word "test" from all tests. - All of our tests are called `test_...`. Seems redundant.
Since tests are marked with `#[rstest]`, we don't need to mark them with the word "test" at the beginning of their name.
I suggest we just call them as what they are testing, so if a test is testing that a feature like... | non_priority | remove the word test from all tests all of our tests are called test seems redundant since tests are marked with we don t need to mark them with the word test at the beginning of their name i suggest we just call them as what they are testing so if a test is testing that a feature like http m... | 0 |
19,095 | 6,670,661,006 | IssuesEvent | 2017-10-04 01:14:32 | Amber-MD/cmake-buildscripts | https://api.github.com/repos/Amber-MD/cmake-buildscripts | closed | need to handle dependencies between tools with FORCE_DISABLE_TOOLS | potential build error | Also, I need to rename that variable to `DISABLE_TOOLS` once it is less of a hack | 1.0 | need to handle dependencies between tools with FORCE_DISABLE_TOOLS - Also, I need to rename that variable to `DISABLE_TOOLS` once it is less of a hack | non_priority | need to handle dependencies between tools with force disable tools also i need to rename that variable to disable tools once it is less of a hack | 0 |
15,990 | 10,422,162,438 | IssuesEvent | 2019-09-16 08:22:06 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | Get-AzureRmHDInsightOperationsManagementSuite throwing an error | Bug HDInsight Service Attention | ### Cmdlet(s)
Get-AzureRmHDInsightOperationsManagementSuite
### PowerShell Version
5.1.16299.64
### Module Version
5.1.1
### OS Version
10.0.16299.64
### Description
The cmdlet Get-AzureRmHDInsightOperationsManagementSuite or Get-AzureRmHDInsightOMS throws an error saying "Get-AzureRmHDInsightOMS : Can... | 1.0 | Get-AzureRmHDInsightOperationsManagementSuite throwing an error - ### Cmdlet(s)
Get-AzureRmHDInsightOperationsManagementSuite
### PowerShell Version
5.1.16299.64
### Module Version
5.1.1
### OS Version
10.0.16299.64
### Description
The cmdlet Get-AzureRmHDInsightOperationsManagementSuite or Get-AzureRm... | non_priority | get azurermhdinsightoperationsmanagementsuite throwing an error cmdlet s get azurermhdinsightoperationsmanagementsuite powershell version module version os version description the cmdlet get azurermhdinsightoperationsmanagementsuite or get azurermhdinsightom... | 0 |
67,226 | 12,890,056,617 | IssuesEvent | 2020-07-13 15:24:51 | spotify/backstage | https://api.github.com/repos/spotify/backstage | opened | TechDocs: Reading Documentation | docs-like-code documentation | <!--- Provide a general summary of the feature request in the Title above -->
Create a guide that walks through what reading documentation in TechDocs looks like. Screenshots, some basic explanation of the tech, etc. The consumers of this should be mostly non-technical (i.e. engineering managers, leads, etc) who are... | 1.0 | TechDocs: Reading Documentation - <!--- Provide a general summary of the feature request in the Title above -->
Create a guide that walks through what reading documentation in TechDocs looks like. Screenshots, some basic explanation of the tech, etc. The consumers of this should be mostly non-technical (i.e. enginee... | non_priority | techdocs reading documentation create a guide that walks through what reading documentation in techdocs looks like screenshots some basic explanation of the tech etc the consumers of this should be mostly non technical i e engineering managers leads etc who are considering deploying techdocs in their o... | 0 |
21,486 | 7,030,577,260 | IssuesEvent | 2017-12-26 11:03:28 | chros73/build-mc | https://api.github.com/repos/chros73/build-mc | closed | Add initial content | build enhancement git | Add initial content and:
- update Readme
- add `.gitignore`
- add changelog | 1.0 | Add initial content - Add initial content and:
- update Readme
- add `.gitignore`
- add changelog | non_priority | add initial content add initial content and update readme add gitignore add changelog | 0 |
24,772 | 3,910,936,751 | IssuesEvent | 2016-04-20 01:56:29 | hotosm/hotosm-website | https://api.github.com/repos/hotosm/hotosm-website | closed | website analysis (summary) | design/theming enhancement | I made a very simple visual sitemap to get a better understanding of the structure. I also considered page content like text, links, pictures.
In general I have to say that the problem is not so much content and structure, but usability and visual conception. The mission and projects of HOT are widely covered, all ... | 1.0 | website analysis (summary) - I made a very simple visual sitemap to get a better understanding of the structure. I also considered page content like text, links, pictures.
In general I have to say that the problem is not so much content and structure, but usability and visual conception. The mission and projects of... | non_priority | website analysis summary i made a very simple visual sitemap to get a better understanding of the structure i also considered page content like text links pictures in general i have to say that the problem is not so much content and structure but usability and visual conception the mission and projects of... | 0 |
3,778 | 5,969,058,607 | IssuesEvent | 2017-05-30 19:27:25 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | security & networking field are not being saved | area/container area/service area/ui kind/bug status/resolved status/to-test | **Rancher versions:** 5/24
**Steps to Reproduce:**
1. Create a container where every field in Security/Host config section is changed or has new value
2. View details of container
**Results:** Pull Image, Physical Memory and Swap Memory are not saving
| 1.0 | security & networking field are not being saved - **Rancher versions:** 5/24
**Steps to Reproduce:**
1. Create a container where every field in Security/Host config section is changed or has new value
2. View details of container
**Results:** Pull Image, Physical Memory and Swap Memory are not saving
| non_priority | security networking field are not being saved rancher versions steps to reproduce create a container where every field in security host config section is changed or has new value view details of container results pull image physical memory and swap memory are not saving | 0 |
52,442 | 12,965,574,456 | IssuesEvent | 2020-07-20 22:40:13 | walkingeyerobot/r38 | https://api.github.com/repos/walkingeyerobot/r38 | closed | deckbuilder should use image_uris instead of /proxy | deckbuilder | I deleted /proxy because the uris in the image_uris array are correctly cached. | 1.0 | deckbuilder should use image_uris instead of /proxy - I deleted /proxy because the uris in the image_uris array are correctly cached. | non_priority | deckbuilder should use image uris instead of proxy i deleted proxy because the uris in the image uris array are correctly cached | 0 |
132,971 | 28,455,164,953 | IssuesEvent | 2023-04-17 06:22:04 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Bug]: For nested list, the onItemClick action is throwing Syntax error | Bug App Viewers Pod Needs Triaging Release Blocker FE Coders Pod List Widget V2 Action Selector | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Description
https://www.loom.com/share/f28977e6ea044fee9c0e90cecc77ddc2
### Steps To Reproduce
1. DnD a list and drop another child List
2. Configure the onItemClick of the child list
3. Click on child item
### Publ... | 1.0 | [Bug]: For nested list, the onItemClick action is throwing Syntax error - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Description
https://www.loom.com/share/f28977e6ea044fee9c0e90cecc77ddc2
### Steps To Reproduce
1. DnD a list and drop another child List
2. Con... | non_priority | for nested list the onitemclick action is throwing syntax error is there an existing issue for this i have searched the existing issues description steps to reproduce dnd a list and drop another child list configure the onitemclick of the child list click on child item... | 0 |
200,800 | 15,801,812,155 | IssuesEvent | 2021-04-03 06:40:53 | Winniehyx/ped | https://api.github.com/repos/Winniehyx/ped | opened | User guide seems to be a little messy, why is there example commands? | severity.VeryLow type.DocumentationBug | No details provided.
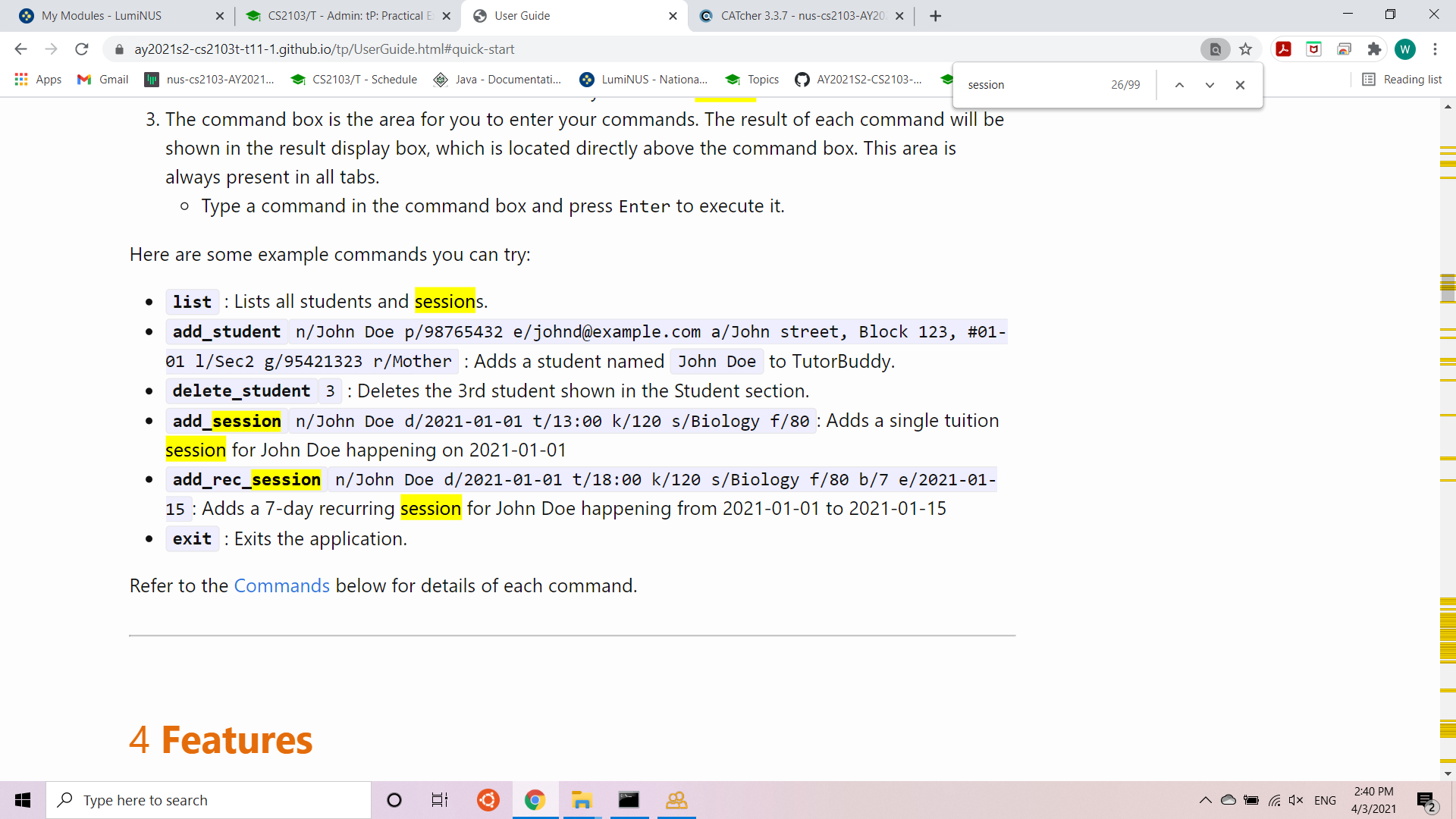
<!--session: 1617429874885-4d901b2f-3afa-46d5-a5f4-bd27c581edab--> | 1.0 | User guide seems to be a little messy, why is there example commands? - No details provided.
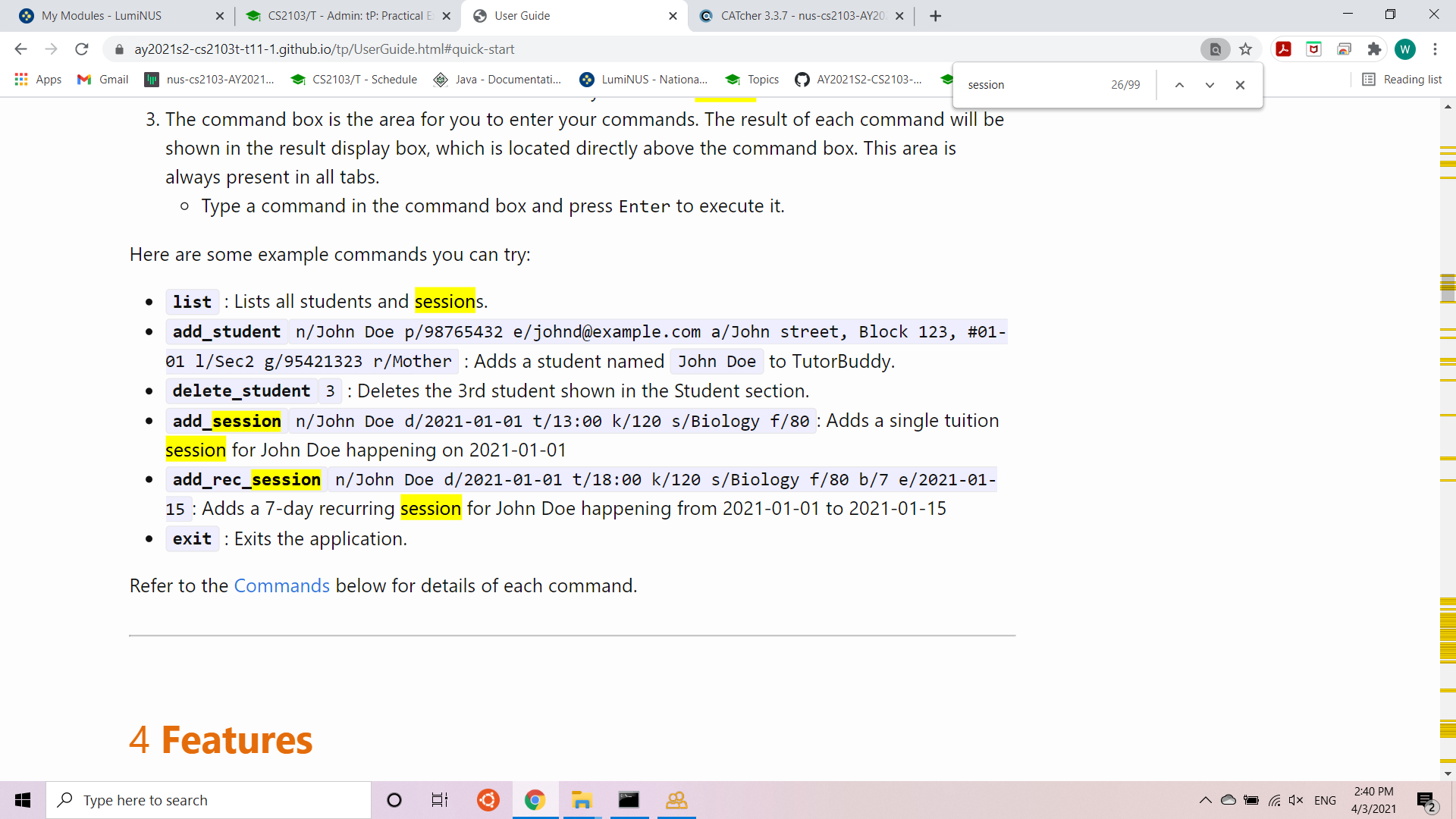
<!--session: 1617429874885-4d901b2f-3afa-46d5-a5f4-bd27c581edab--> | non_priority | user guide seems to be a little messy why is there example commands no details provided | 0 |
41,479 | 10,723,121,533 | IssuesEvent | 2019-10-27 16:36:30 | letscontrolit/ESPEasy | https://api.github.com/repos/letscontrolit/ESPEasy | closed | since 20181004 NeoPixel SK6812/WS2812B pixel errors (2.4.1 vs 2.4.2) | Category: Build Category: Plugin Category: Stabiliy | ### If you self compile, please state this and PLEASE try to ONLY REPORT ISSUES WITH OFFICIAL BUILDS! ###
<!--- If you self compile, please state this and PLEASE try to ONLY REPORT ISSUES WITH OFFICIAL BUILDS! --->
<!--- NOTE: This is not a support forum! For questions and support go here: --->
<!--- https://www.le... | 1.0 | since 20181004 NeoPixel SK6812/WS2812B pixel errors (2.4.1 vs 2.4.2) - ### If you self compile, please state this and PLEASE try to ONLY REPORT ISSUES WITH OFFICIAL BUILDS! ###
<!--- If you self compile, please state this and PLEASE try to ONLY REPORT ISSUES WITH OFFICIAL BUILDS! --->
<!--- NOTE: This is not a suppo... | non_priority | since neopixel pixel errors vs if you self compile please state this and please try to only report issues with official builds summarize of the problem feature request i use a precompiled version espeasy mega test vcc since this version there are probl... | 0 |
48,001 | 7,370,510,079 | IssuesEvent | 2018-03-13 08:44:15 | ABI-Team-30/Fresnel-Forms | https://api.github.com/repos/ABI-Team-30/Fresnel-Forms | opened | hideProperties works if in code through other means than FF GUI | check documentation | See if hideProperties works even if in code through other means than the Fresnel Forms tab GUI. Examples of such means include text editing the saved file and then reloading in Protégé. It is less likely but still work checking if one can use the individual tab in Protégé to add the hideProperty triples to a lens. If i... | 1.0 | hideProperties works if in code through other means than FF GUI - See if hideProperties works even if in code through other means than the Fresnel Forms tab GUI. Examples of such means include text editing the saved file and then reloading in Protégé. It is less likely but still work checking if one can use the individ... | non_priority | hideproperties works if in code through other means than ff gui see if hideproperties works even if in code through other means than the fresnel forms tab gui examples of such means include text editing the saved file and then reloading in protégé it is less likely but still work checking if one can use the individ... | 0 |
350,903 | 25,005,596,506 | IssuesEvent | 2022-11-03 11:34:35 | spring-projects/spring-graphql | https://api.github.com/repos/spring-projects/spring-graphql | closed | Provide guidance on how to set up multiple GraphQL endpoints | type: documentation status: superseded | I want two separate endpoints, each with their own schemas to not expose our internal schemas to clients through GraphiQL. Both will need have different security configurations as well. (Just reiterating that this is something we need to do)
I found this stack overflow asking for something similar, but was hoping to... | 1.0 | Provide guidance on how to set up multiple GraphQL endpoints - I want two separate endpoints, each with their own schemas to not expose our internal schemas to clients through GraphiQL. Both will need have different security configurations as well. (Just reiterating that this is something we need to do)
I found this... | non_priority | provide guidance on how to set up multiple graphql endpoints i want two separate endpoints each with their own schemas to not expose our internal schemas to clients through graphiql both will need have different security configurations as well just reiterating that this is something we need to do i found this... | 0 |
58,883 | 14,499,537,614 | IssuesEvent | 2020-12-11 16:50:36 | aiorazabala/qmethod | https://api.github.com/repos/aiorazabala/qmethod | closed | spurious travis CI build fail | build | I'm trying to set up Travis continuous integration for our development (as per #88).
Unfortunately, part of my `array.viz.R` calls the package `stringr`, which causes Travis to fail (apparently intermittently).
Also reported in:
- https://github.com/Rexamine/stringi/issues/155
- https://github.com/hadley/stringr/issu... | 1.0 | spurious travis CI build fail - I'm trying to set up Travis continuous integration for our development (as per #88).
Unfortunately, part of my `array.viz.R` calls the package `stringr`, which causes Travis to fail (apparently intermittently).
Also reported in:
- https://github.com/Rexamine/stringi/issues/155
- https:... | non_priority | spurious travis ci build fail i m trying to set up travis continuous integration for our development as per unfortunately part of my array viz r calls the package stringr which causes travis to fail apparently intermittently also reported in this seems to be an artefact of travis not of my... | 0 |
261,172 | 27,794,017,381 | IssuesEvent | 2023-03-17 11:04:35 | PowerDNS-Admin/PowerDNS-Admin | https://api.github.com/repos/PowerDNS-Admin/PowerDNS-Admin | closed | Feature: configurable OTP label | feature / request mod / accepted bug / security-vulnerability | Hi,
Right now the OTP label is hardcoded to be `PowerDNS-Admin`
https://github.com/PowerDNS-Admin/PowerDNS-Admin/blob/204c996c81f2f2ef14f6d98e5ea907e69a7ede92/powerdnsadmin/models/user.py#L92
It would be great for it to either be configurable or to match the `site_name`, as some authenticator apps tend to overwr... | True | Feature: configurable OTP label - Hi,
Right now the OTP label is hardcoded to be `PowerDNS-Admin`
https://github.com/PowerDNS-Admin/PowerDNS-Admin/blob/204c996c81f2f2ef14f6d98e5ea907e69a7ede92/powerdnsadmin/models/user.py#L92
It would be great for it to either be configurable or to match the `site_name`, as some... | non_priority | feature configurable otp label hi right now the otp label is hardcoded to be powerdns admin it would be great for it to either be configurable or to match the site name as some authenticator apps tend to overwrite the key if the label is the same proposed change diff original py ... | 0 |
110,505 | 9,458,615,643 | IssuesEvent | 2019-04-17 06:04:12 | appium/appium | https://api.github.com/repos/appium/appium | closed | Xcode 10.1 has a maximum SDK version of 12.1. It does not support iOS version 12.1.2 | Bug XCUITest | ## The problem
Xcode 10.1 has a maximum SDK version of 12.1. It does not support iOS version 12.1.2
## Environment
* Appium 1.12.1
* macOS Mojave version 10.14.4 (18E226)
* iPhone 7 Plus with iOS 12.1.2
* Real device
## Details
Error message comes from appium-xcuitest-driver.
https://github.com/appiu... | 1.0 | Xcode 10.1 has a maximum SDK version of 12.1. It does not support iOS version 12.1.2 - ## The problem
Xcode 10.1 has a maximum SDK version of 12.1. It does not support iOS version 12.1.2
## Environment
* Appium 1.12.1
* macOS Mojave version 10.14.4 (18E226)
* iPhone 7 Plus with iOS 12.1.2
* Real device
#... | non_priority | xcode has a maximum sdk version of it does not support ios version the problem xcode has a maximum sdk version of it does not support ios version environment appium macos mojave version iphone plus with ios real device details er... | 0 |
181,468 | 21,658,684,038 | IssuesEvent | 2022-05-06 16:39:17 | doc-ai/snipe-it | https://api.github.com/repos/doc-ai/snipe-it | closed | WS-2020-0003 (High) detected in phpunit/phpunit-5.7.27 - autoclosed | security vulnerability | ## WS-2020-0003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>phpunit/phpunit-5.7.27</b></p></summary>
<p>The PHP Unit Testing framework.</p>
<p>
Dependency Hierarchy:
- phpunit/p... | True | WS-2020-0003 (High) detected in phpunit/phpunit-5.7.27 - autoclosed - ## WS-2020-0003 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>phpunit/phpunit-5.7.27</b></p></summary>
<p>The PH... | non_priority | ws high detected in phpunit phpunit autoclosed ws high severity vulnerability vulnerable library phpunit phpunit the php unit testing framework dependency hierarchy phpunit php token stream root library x phpunit phpunit vulnerable library ... | 0 |
41,022 | 10,266,659,120 | IssuesEvent | 2019-08-22 22:08:23 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | opened | [SCREENREADER]: GIBCT® VETTEC - We should set focus on the H1 when users click Search Schools and school detail links | 508-defect-2 508/Accessibility BAH | ## Description
<!-- This is a detailed description of the issue. It should include a restatement of the title, and provide more background information. -->
We are not managing focus when users click on the `Search Schools` button or click on a school detail link like "GALVANIZE INC". This focus management is important... | 1.0 | [SCREENREADER]: GIBCT® VETTEC - We should set focus on the H1 when users click Search Schools and school detail links - ## Description
<!-- This is a detailed description of the issue. It should include a restatement of the title, and provide more background information. -->
We are not managing focus when users click ... | non_priority | gibct® vettec we should set focus on the when users click search schools and school detail links description we are not managing focus when users click on the search schools button or click on a school detail link like galvanize inc this focus management is important for screen reader users to under... | 0 |
27,046 | 13,168,509,451 | IssuesEvent | 2020-08-11 12:15:37 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | FNX-5136 ⁃ [Bug] Experiment loading happens on the main thread and blocks startup | eng:performance 🐞 bug | ## Steps to reproduce
Start the application.
### Expected behavior
Experiments should be loaded (more quickly than they are)
### Actual behavior
Experiments are loaded, but only after having blocked progress on the main thread.
### Device information
* Android device: Any
* Fenix version: Nightly
| True | FNX-5136 ⁃ [Bug] Experiment loading happens on the main thread and blocks startup - ## Steps to reproduce
Start the application.
### Expected behavior
Experiments should be loaded (more quickly than they are)
### Actual behavior
Experiments are loaded, but only after having blocked progress on the main thread.
### D... | non_priority | fnx ⁃ experiment loading happens on the main thread and blocks startup steps to reproduce start the application expected behavior experiments should be loaded more quickly than they are actual behavior experiments are loaded but only after having blocked progress on the main thread device i... | 0 |
85,917 | 8,007,283,475 | IssuesEvent | 2018-07-24 01:30:08 | ryuichl/v3-report | https://api.github.com/repos/ryuichl/v3-report | closed | 【問題】無法建立序號 | bug wating-for-test | 加入序號機元件後 點選建立序號機 卻出現這個畫面
<img width="325" alt="2018-07-23 3 20 53" src="https://user-images.githubusercontent.com/34560641/43062669-307170de-8e8c-11e8-863b-a78703cd8077.png">
點選啟用序號機後 會顯示 「無權限」
<img width="325" alt="2018-07-23 3 22 29" src="https://user-images.githubusercontent.com/34560641/43062706-46b65a80-8e8c-11... | 1.0 | 【問題】無法建立序號 - 加入序號機元件後 點選建立序號機 卻出現這個畫面
<img width="325" alt="2018-07-23 3 20 53" src="https://user-images.githubusercontent.com/34560641/43062669-307170de-8e8c-11e8-863b-a78703cd8077.png">
點選啟用序號機後 會顯示 「無權限」
<img width="325" alt="2018-07-23 3 22 29" src="https://user-images.githubusercontent.com/34560641/43062706-46b... | non_priority | 【問題】無法建立序號 加入序號機元件後 點選建立序號機 卻出現這個畫面 img width alt src 點選啟用序號機後 會顯示 「無權限」 img width alt src 求解求解 | 0 |
262,272 | 22,828,098,413 | IssuesEvent | 2022-07-12 10:23:20 | foundry-rs/foundry | https://api.github.com/repos/foundry-rs/foundry | closed | Allow forking from different RPCs/block numbers when testing | A-evm T-feature Cmd-forge-test C-forge Cmd-forge-debug | ### Component
Forge
### Describe the feature you would like
Currently if you want to test against mainnet state, you can pass in an RPC url and block number to fork from. However it isn't possible to run tests on multiple networks or fork from different block numbers.
For example, you might want 1 test to run aga... | 1.0 | Allow forking from different RPCs/block numbers when testing - ### Component
Forge
### Describe the feature you would like
Currently if you want to test against mainnet state, you can pass in an RPC url and block number to fork from. However it isn't possible to run tests on multiple networks or fork from different ... | non_priority | allow forking from different rpcs block numbers when testing component forge describe the feature you would like currently if you want to test against mainnet state you can pass in an rpc url and block number to fork from however it isn t possible to run tests on multiple networks or fork from different ... | 0 |
451,338 | 32,024,210,063 | IssuesEvent | 2023-09-22 07:39:47 | JoberChipFrappuccino/joberchip-fe | https://api.github.com/repos/JoberChipFrappuccino/joberchip-fe | closed | 중간 점검 제출 전 사전 문서 작업 및 기능 정리 | documentation | # 기능
중간 점검 제출 전 사전 문서 작업 및 기능 정리를 진행합니다.
# 적용되는 페이지
# 추가 설명
# 예상 시작일
2023-09-22
# 예상 완료일
2023-09-22
| 1.0 | 중간 점검 제출 전 사전 문서 작업 및 기능 정리 - # 기능
중간 점검 제출 전 사전 문서 작업 및 기능 정리를 진행합니다.
# 적용되는 페이지
# 추가 설명
# 예상 시작일
2023-09-22
# 예상 완료일
2023-09-22
| non_priority | 중간 점검 제출 전 사전 문서 작업 및 기능 정리 기능 중간 점검 제출 전 사전 문서 작업 및 기능 정리를 진행합니다 적용되는 페이지 추가 설명 예상 시작일 예상 완료일 | 0 |
141,730 | 11,433,369,927 | IssuesEvent | 2020-02-04 15:35:28 | libuv/libuv | https://api.github.com/repos/libuv/libuv | reopened | ci,macos: flaky process_title_threadsafe test | macos test | It times out frequently again after 00c6b1649d13fdd94bedbfe7ad26c9269c80b32c was reverted in 97e86dde84198208984b4ed107adb76b8632409f:
```
not ok 195 - process_title_threadsafe
# timeout
# Output from process `process_title_threadsafe`: (no output)
```
<hr>
Observation by @cjihrig in https://github.com/libuv/l... | 1.0 | ci,macos: flaky process_title_threadsafe test - It times out frequently again after 00c6b1649d13fdd94bedbfe7ad26c9269c80b32c was reverted in 97e86dde84198208984b4ed107adb76b8632409f:
```
not ok 195 - process_title_threadsafe
# timeout
# Output from process `process_title_threadsafe`: (no output)
```
<hr>
Obser... | non_priority | ci macos flaky process title threadsafe test it times out frequently again after was reverted in not ok process title threadsafe timeout output from process process title threadsafe no output observation by cjihrig in moving the psetapplicationisdaemon noerr check... | 0 |
36,575 | 6,540,580,596 | IssuesEvent | 2017-09-01 15:59:03 | endless-sky/endless-sky | https://api.github.com/repos/endless-sky/endless-sky | closed | webhook for discord server | documentation | hey MZ, you probably know we have this discord server, and it would be neat if a update alert was automatically pushed to our announcement channel. more information is in the e-mail i sent you a while back, but since i figured that that one month vacation is just a vacation from heavy tasks, i decided to bring this up.... | 1.0 | webhook for discord server - hey MZ, you probably know we have this discord server, and it would be neat if a update alert was automatically pushed to our announcement channel. more information is in the e-mail i sent you a while back, but since i figured that that one month vacation is just a vacation from heavy tasks... | non_priority | webhook for discord server hey mz you probably know we have this discord server and it would be neat if a update alert was automatically pushed to our announcement channel more information is in the e mail i sent you a while back but since i figured that that one month vacation is just a vacation from heavy tasks... | 0 |
7,321 | 3,535,728,771 | IssuesEvent | 2016-01-16 18:56:13 | marthjod/jeux | https://api.github.com/repos/marthjod/jeux | opened | Remove `previousRoundId` from code and DB schema | code enhancement | Only roundId remains somewhat necessary (for sorting purposes). Since a round switch is no longer a round switch but carried out on a per-group basis, previous round info is no longer needed. | 1.0 | Remove `previousRoundId` from code and DB schema - Only roundId remains somewhat necessary (for sorting purposes). Since a round switch is no longer a round switch but carried out on a per-group basis, previous round info is no longer needed. | non_priority | remove previousroundid from code and db schema only roundid remains somewhat necessary for sorting purposes since a round switch is no longer a round switch but carried out on a per group basis previous round info is no longer needed | 0 |
203,185 | 15,873,733,027 | IssuesEvent | 2021-04-09 03:10:58 | AY2021S2-CS2103T-W15-3/tp | https://api.github.com/repos/AY2021S2-CS2103T-W15-3/tp | closed | [PE-D] Command format given in user guide for adding a dish does not match with the command format accepted by Jjimy. | type.Documentation | In the user guide the command format for adding a dish is given as `menu add n/[NAME] p/[PRICE]` as can be seen in the screenshot below.

However, when using this command format in the application I... | 1.0 | [PE-D] Command format given in user guide for adding a dish does not match with the command format accepted by Jjimy. - In the user guide the command format for adding a dish is given as `menu add n/[NAME] p/[PRICE]` as can be seen in the screenshot below.
 detected in handlebars-4.1.2.tgz - autoclosed | security vulnerability | ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates ef... | True | WS-2019-0333 (High) detected in handlebars-4.1.2.tgz - autoclosed - ## WS-2019-0333 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.2.tgz</b></p></summary>
<p>Handlebars... | non_priority | ws high detected in handlebars tgz autoclosed ws high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file ... | 0 |
213,393 | 16,521,858,201 | IssuesEvent | 2021-05-26 15:19:06 | mjd-programming/Tetris | https://api.github.com/repos/mjd-programming/Tetris | closed | Create logging functionality | big issue/addition documentation | create logging functionality for testing purposes; there are a couple of issues in the game (freezing/lines not being properly cleared) and the log files will be used to determine where the problems are coming from and an entry will be added to the log file whenever a line is cleared
logs are to include:
date/time
... | 1.0 | Create logging functionality - create logging functionality for testing purposes; there are a couple of issues in the game (freezing/lines not being properly cleared) and the log files will be used to determine where the problems are coming from and an entry will be added to the log file whenever a line is cleared
l... | non_priority | create logging functionality create logging functionality for testing purposes there are a couple of issues in the game freezing lines not being properly cleared and the log files will be used to determine where the problems are coming from and an entry will be added to the log file whenever a line is cleared l... | 0 |
155,701 | 13,631,858,465 | IssuesEvent | 2020-09-24 18:41:32 | PerfectStorms/java-interview-questions | https://api.github.com/repos/PerfectStorms/java-interview-questions | closed | Implement task with stream api | documentation | There is a task with the list of EPAM interviews, with the condition of the solution with streams. Please, implement a task and surrond it with java code style | 1.0 | Implement task with stream api - There is a task with the list of EPAM interviews, with the condition of the solution with streams. Please, implement a task and surrond it with java code style | non_priority | implement task with stream api there is a task with the list of epam interviews with the condition of the solution with streams please implement a task and surrond it with java code style | 0 |
73,388 | 8,870,584,937 | IssuesEvent | 2019-01-11 09:56:51 | cockpit-project/cockpit | https://api.github.com/repos/cockpit-project/cockpit | closed | docker: Display cpu quota and not just shares | needsdesign review-2019-01 | Seems when cpu quota is set shares stays at zero. We should display the quota as well.
https://bugzilla.redhat.com/show_bug.cgi?id=1523646 | 1.0 | docker: Display cpu quota and not just shares - Seems when cpu quota is set shares stays at zero. We should display the quota as well.
https://bugzilla.redhat.com/show_bug.cgi?id=1523646 | non_priority | docker display cpu quota and not just shares seems when cpu quota is set shares stays at zero we should display the quota as well | 0 |
226,823 | 17,363,201,970 | IssuesEvent | 2021-07-30 01:08:57 | mygoodsupporter/mygoodsupporter | https://api.github.com/repos/mygoodsupporter/mygoodsupporter | closed | [Kickstarter]API | Documentation Help wanted | # Kickstarter
## User
GET'/settings/account/
POST'/profile'
```
email
newPassword
confirmPassword
currentPassword
```
GET'/settings/profile'
POST'/profile'
```
name
avatar(profile_image)
biography
```
view Profile
```
https://www.kickstarter.com/profile/637606299/about
```
... | 1.0 | [Kickstarter]API - # Kickstarter
## User
GET'/settings/account/
POST'/profile'
```
email
newPassword
confirmPassword
currentPassword
```
GET'/settings/profile'
POST'/profile'
```
name
avatar(profile_image)
biography
```
view Profile
```
https://www.kickstarter.com/profile/637606... | non_priority | api kickstarter user get settings account post profile email newpassword confirmpassword currentpassword get settings profile post profile name avatar profile image biography view profile get profile credit cards payment met... | 0 |
110,403 | 16,979,887,447 | IssuesEvent | 2021-06-30 07:27:36 | SmartBear/ready-mqtt-plugin | https://api.github.com/repos/SmartBear/ready-mqtt-plugin | closed | CVE-2020-36184 (High) detected in jackson-databind-2.1.4.jar - autoclosed | security vulnerability | ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.1.4.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-36184 (High) detected in jackson-databind-2.1.4.jar - autoclosed - ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.1.4.jar</b></p></summary... | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api path to dependency file ready mqtt plugin pom xml path to vulnerable li... | 0 |
294,833 | 22,163,741,616 | IssuesEvent | 2022-06-04 22:37:30 | cloudflare/cloudflare-docs | https://api.github.com/repos/cloudflare/cloudflare-docs | opened | "R2 get started guide" has missing steps | documentation content:edit | ### Which Cloudflare product does this pertain to?
R2
### Existing documentation URL(s)
https://developers.cloudflare.com/r2/get-started/
### Section that requires update
5. Access your R2 bucket from your Worker
7. Deploy your bucket
### What needs to change?
when following document as written, multiple iss... | 1.0 | "R2 get started guide" has missing steps - ### Which Cloudflare product does this pertain to?
R2
### Existing documentation URL(s)
https://developers.cloudflare.com/r2/get-started/
### Section that requires update
5. Access your R2 bucket from your Worker
7. Deploy your bucket
### What needs to change?
when ... | non_priority | get started guide has missing steps which cloudflare product does this pertain to existing documentation url s section that requires update access your bucket from your worker deploy your bucket what needs to change when following document as written multiple issues are ... | 0 |
78,690 | 22,348,350,590 | IssuesEvent | 2022-06-15 09:46:09 | flutter/flutter | https://api.github.com/repos/flutter/flutter | reopened | `flutter build apk --analyze-size --target-platform android-arm` fails with `Exception: AOT snapshotter exited with code -2147483645` | severe: crash platform-android waiting for customer response tool dependency: dart t: gradle a: build | When I run `flutter build apk --analyze-size --target-platform android-arm` I get:
<pre>
<code>
Dart snapshot generator failed with exit code -2147483645
FAILURE: Build failed with an exception.
* Where:
Script 'D:\flutter\packages\flutter_tools\gradle\flutter.gradle' line: 1102
* What went wrong:
Exe... | 1.0 | `flutter build apk --analyze-size --target-platform android-arm` fails with `Exception: AOT snapshotter exited with code -2147483645` - When I run `flutter build apk --analyze-size --target-platform android-arm` I get:
<pre>
<code>
Dart snapshot generator failed with exit code -2147483645
FAILURE: Build faile... | non_priority | flutter build apk analyze size target platform android arm fails with exception aot snapshotter exited with code when i run flutter build apk analyze size target platform android arm i get dart snapshot generator failed with exit code failure build failed with an exception w... | 0 |
77,360 | 15,528,259,373 | IssuesEvent | 2021-03-13 10:06:37 | jonathan-wiens/hwr-kurs19a-g2 | https://api.github.com/repos/jonathan-wiens/hwr-kurs19a-g2 | opened | CVE-2018-19827 (High) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz | security vulnerability | ## CVE-2018-19827 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0-1</b>, <b>node-sass-4.14.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.1... | True | CVE-2018-19827 (High) detected in opennmsopennms-source-26.0.0-1, node-sass-4.14.1.tgz - ## CVE-2018-19827 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>opennmsopennms-source-26.0.0... | non_priority | cve high detected in opennmsopennms source node sass tgz cve high severity vulnerability vulnerable libraries opennmsopennms source node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file hwr... | 0 |
68,152 | 28,152,980,635 | IssuesEvent | 2023-04-03 04:10:52 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Email points to Email page, but description points to SMS | triaged cxp product-question Pri1 azure-communication-services/svc |
Under common scenarios heading, check first table for errant description.
Page uses phone (mostly) but also telephone. Different meaning?
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: d5c2b60c-dd58-86ec-9186-2e18720f66c5
*... | 1.0 | Email points to Email page, but description points to SMS -
Under common scenarios heading, check first table for errant description.
Page uses phone (mostly) but also telephone. Different meaning?
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub iss... | non_priority | email points to email page but description points to sms under common scenarios heading check first table for errant description page uses phone mostly but also telephone different meaning document details ⚠ do not edit this section it is required for learn microsoft com ➟ github iss... | 0 |
298,298 | 25,811,901,908 | IssuesEvent | 2022-12-11 23:01:21 | Metalab/mos | https://api.github.com/repos/Metalab/mos | closed | iCal Export doesn't properly parse Wiki Page URLs | bug calendar needs tests | Enter a Wiki Page with Spaces in the title.
MediaWiki does replace them with underscores.
iCal Export cuts off at the first space instead of replacing them with underscores.
This results in URLs in the iCal exported events that point to a defunct or a totally different wiki page.
| 1.0 | iCal Export doesn't properly parse Wiki Page URLs - Enter a Wiki Page with Spaces in the title.
MediaWiki does replace them with underscores.
iCal Export cuts off at the first space instead of replacing them with underscores.
This results in URLs in the iCal exported events that point to a defunct or a totally differen... | non_priority | ical export doesn t properly parse wiki page urls enter a wiki page with spaces in the title mediawiki does replace them with underscores ical export cuts off at the first space instead of replacing them with underscores this results in urls in the ical exported events that point to a defunct or a totally differen... | 0 |
231,790 | 17,755,035,565 | IssuesEvent | 2021-08-28 15:34:52 | petrusjt/youtube-remote | https://api.github.com/repos/petrusjt/youtube-remote | opened | Remove part related to mouse controller from README.md | documentation | Mouse controller is not needed in the application since commit 58c1b6fb9788d5111bec5af606078ffd8ff28a99.
The related part of README.md was not removed since. | 1.0 | Remove part related to mouse controller from README.md - Mouse controller is not needed in the application since commit 58c1b6fb9788d5111bec5af606078ffd8ff28a99.
The related part of README.md was not removed since. | non_priority | remove part related to mouse controller from readme md mouse controller is not needed in the application since commit the related part of readme md was not removed since | 0 |
140,075 | 31,828,080,517 | IssuesEvent | 2023-09-14 08:50:09 | amplication/amplication | https://api.github.com/repos/amplication/amplication | closed | Server: Connected Repository Default README.md | type: feature request git code sync status: assigned | Creare default amplication README.md file for connected GitHub repositories.
When users create a new GitHub repository through Amplication, repositories should be created with Amplication default README.md file. | 1.0 | Server: Connected Repository Default README.md - Creare default amplication README.md file for connected GitHub repositories.
When users create a new GitHub repository through Amplication, repositories should be created with Amplication default README.md file. | non_priority | server connected repository default readme md creare default amplication readme md file for connected github repositories when users create a new github repository through amplication repositories should be created with amplication default readme md file | 0 |
29,609 | 14,214,259,360 | IssuesEvent | 2020-11-17 04:45:46 | golang/protobuf | https://api.github.com/repos/golang/protobuf | closed | proto.Unmarshal consumes a lot of cpu, any idea to fix this? | performance waiting-for-info | env:
protobuf: github.com/golang/protobuf v1.4.3
protoc: 3.5.1
golang: go1.13 linux/amd64
in my application, the whole process work like this:
* start a thrift server
* accept request, an get pb_bytes from cache
* unmarshal all the pb_bytes, and do my business logic
* return my response to the client
pb_by... | True | proto.Unmarshal consumes a lot of cpu, any idea to fix this? - env:
protobuf: github.com/golang/protobuf v1.4.3
protoc: 3.5.1
golang: go1.13 linux/amd64
in my application, the whole process work like this:
* start a thrift server
* accept request, an get pb_bytes from cache
* unmarshal all the pb_bytes, and do... | non_priority | proto unmarshal consumes a lot of cpu any idea to fix this env protobuf github com golang protobuf protoc golang linux in my application the whole process work like this start a thrift server accept request an get pb bytes from cache unmarshal all the pb bytes and do my busi... | 0 |
66,051 | 12,705,466,973 | IssuesEvent | 2020-06-23 04:44:10 | topcoder-platform/community-app | https://api.github.com/repos/topcoder-platform/community-app | closed | [$40]Submission: 404 error is displayed when clicking on submit button | Beta Env Challenge Details Screen P0 QA Pass Test Env tcx_Assigned tcx_FixAccepted v5-intgration-sub-code | Submission: 404 error is displayed when clicking on submit button
example:
https://beta-community-app.topcoder.com/challenges/3724cf55-e2ab-427e-a30f-863c750a277c/submit
(user must be registered)
https://test-community-app.topcoder-dev.com/challenges/68a1cb52-a313-4130-8900-87a21959fdae
(user:dan_developer/dantopc... | 1.0 | [$40]Submission: 404 error is displayed when clicking on submit button - Submission: 404 error is displayed when clicking on submit button
example:
https://beta-community-app.topcoder.com/challenges/3724cf55-e2ab-427e-a30f-863c750a277c/submit
(user must be registered)
https://test-community-app.topcoder-dev.com/cha... | non_priority | submission error is displayed when clicking on submit button submission error is displayed when clicking on submit button example user must be registered user dan developer img width alt screenshot at am src | 0 |
222,167 | 24,684,694,580 | IssuesEvent | 2022-10-19 01:55:32 | kapseliboi/Node-Data | https://api.github.com/repos/kapseliboi/Node-Data | opened | CVE-2022-3517 (High) detected in multiple libraries | security vulnerability | ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimatch-2.0.10.tgz</b>, <b>minimatch-3.0.4.tgz</b>, <b>minimatch-0.3.0.tgz</b>, <b>minimatch-0.2.14.tgz</b></p></sum... | True | CVE-2022-3517 (High) detected in multiple libraries - ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimatch-2.0.10.tgz</b>, <b>minimatch-3.0.4.tgz</b>, <b>minimat... | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries minimatch tgz minimatch tgz minimatch tgz minimatch tgz minimatch tgz a glob matcher in javascript library home page a href path to dependency... | 0 |
6,325 | 2,809,515,190 | IssuesEvent | 2015-05-16 02:56:07 | robotlolita/raven | https://api.github.com/repos/robotlolita/raven | closed | Support changing the font sizes and paragraph styles | 0 - Backlog C-design E-unknown K-enhancement P-low | Maybe this could be supported by themes. But iunno
<!---
@huboard:{"order":0.0003662109375,"milestone_order":71,"custom_state":""}
-->
| 1.0 | Support changing the font sizes and paragraph styles - Maybe this could be supported by themes. But iunno
<!---
@huboard:{"order":0.0003662109375,"milestone_order":71,"custom_state":""}
-->
| non_priority | support changing the font sizes and paragraph styles maybe this could be supported by themes but iunno huboard order milestone order custom state | 0 |
13,964 | 10,562,542,444 | IssuesEvent | 2019-10-04 18:35:47 | dotnet/corefx | https://api.github.com/repos/dotnet/corefx | closed | Installing System.Net.Http using Install-Package fails with "Dependency loop detected for package" | area-Infrastructure | I am installing packages to a folder using the following pwsh commands:
`Register-PackageSource -Location https://www.nuget.org/api/v2 -Name Nuget -ProviderName Nuget -Trusted -force`
`Install-Package -Name System.Net.Http -ProviderName Nuget -Destination $somedir`
It fails with:
```
Install-Package : Depen... | 1.0 | Installing System.Net.Http using Install-Package fails with "Dependency loop detected for package" - I am installing packages to a folder using the following pwsh commands:
`Register-PackageSource -Location https://www.nuget.org/api/v2 -Name Nuget -ProviderName Nuget -Trusted -force`
`Install-Package -Name System... | non_priority | installing system net http using install package fails with dependency loop detected for package i am installing packages to a folder using the following pwsh commands register packagesource location name nuget providername nuget trusted force install package name system net http providername nu... | 0 |
47,691 | 13,248,502,568 | IssuesEvent | 2020-08-19 19:05:17 | kenferrara/cbp-theme | https://api.github.com/repos/kenferrara/cbp-theme | opened | CVE-2016-7103 (Medium) detected in jquery-ui-1.10.3.js | security vulnerability | ## CVE-2016-7103 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-ui-1.10.3.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes b... | True | CVE-2016-7103 (Medium) detected in jquery-ui-1.10.3.js - ## CVE-2016-7103 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-ui-1.10.3.js</b></p></summary>
<p>A curated set of us... | non_priority | cve medium detected in jquery ui js cve medium severity vulnerability vulnerable library jquery ui js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency fil... | 0 |
186,024 | 21,910,353,715 | IssuesEvent | 2022-05-21 01:07:56 | tctc008/WebGoat-develop | https://api.github.com/repos/tctc008/WebGoat-develop | opened | CVE-2022-22976 (Medium) detected in spring-security-crypto-5.5.2.jar | security vulnerability | ## CVE-2022-22976 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-crypto-5.5.2.jar</b></p></summary>
<p>Spring Security</p>
<p>Library home page: <a href="https://spr... | True | CVE-2022-22976 (Medium) detected in spring-security-crypto-5.5.2.jar - ## CVE-2022-22976 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-security-crypto-5.5.2.jar</b></p></summ... | non_priority | cve medium detected in spring security crypto jar cve medium severity vulnerability vulnerable library spring security crypto jar spring security library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss ... | 0 |
104,490 | 8,973,386,410 | IssuesEvent | 2019-01-29 20:53:26 | tikv/tikv | https://api.github.com/repos/tikv/tikv | reopened | server::load_statistics::linux::tests::test_thread_load_statistic fails unexpectedly | C: Test/Bench T: Bug | As stated in title. I've seen this fail recently. No further info. | 1.0 | server::load_statistics::linux::tests::test_thread_load_statistic fails unexpectedly - As stated in title. I've seen this fail recently. No further info. | non_priority | server load statistics linux tests test thread load statistic fails unexpectedly as stated in title i ve seen this fail recently no further info | 0 |
248,924 | 26,866,144,102 | IssuesEvent | 2023-02-04 00:08:50 | elastic/beats | https://api.github.com/repos/elastic/beats | closed | Update auditbeat docs for systemd to add LimitNOFILE to systemd service | docs Auditbeat Stalled Team:Docs Team:Security-External Integrations | The current docs only talk about macOS when getting "too many open files":
https://www.elastic.co/guide/en/beats/auditbeat/master/ulimit.html
However this can also be an issue with systemd as it only applies the default 1024. In production this can be too low as well as seen here for example:
https://discuss.e... | True | Update auditbeat docs for systemd to add LimitNOFILE to systemd service - The current docs only talk about macOS when getting "too many open files":
https://www.elastic.co/guide/en/beats/auditbeat/master/ulimit.html
However this can also be an issue with systemd as it only applies the default 1024. In production ... | non_priority | update auditbeat docs for systemd to add limitnofile to systemd service the current docs only talk about macos when getting too many open files however this can also be an issue with systemd as it only applies the default in production this can be too low as well as seen here for example the do... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.