Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
115,174 | 9,782,457,194 | IssuesEvent | 2019-06-07 23:47:58 | jruby/jruby | https://api.github.com/repos/jruby/jruby | opened | Inadequate testing of JMX features | beginner help wanted java integration tests | We don't have any tests that confirm the JMX endpoints we expose are working. As an example, the remote backtrace generation broke in JRuby 9.2.7.0 when we fixed how exception backtraces are created. I have fixed that in d2875a427a, but without tests obviously this and the rest of our mbeans are at risk of regressing a... | 1.0 | Inadequate testing of JMX features - We don't have any tests that confirm the JMX endpoints we expose are working. As an example, the remote backtrace generation broke in JRuby 9.2.7.0 when we fixed how exception backtraces are created. I have fixed that in d2875a427a, but without tests obviously this and the rest of o... | non_priority | inadequate testing of jmx features we don t have any tests that confirm the jmx endpoints we expose are working as an example the remote backtrace generation broke in jruby when we fixed how exception backtraces are created i have fixed that in but without tests obviously this and the rest of our mbeans... | 0 |
377,730 | 26,267,792,027 | IssuesEvent | 2023-01-06 14:12:55 | ynikitenko/yarsync | https://api.github.com/repos/ynikitenko/yarsync | closed | improve github-pages | documentation help wanted | - center the top button "View On GitHub" vertically,
- create navigation between pages?
- use hacker theme instead of midnight? Decide on its readability first. At the moment [fonts are unreadable](https://github.com/pages-themes/hacker/issues/112). Green sections look awesome, but maybe white is less distracting and... | 1.0 | improve github-pages - - center the top button "View On GitHub" vertically,
- create navigation between pages?
- use hacker theme instead of midnight? Decide on its readability first. At the moment [fonts are unreadable](https://github.com/pages-themes/hacker/issues/112). Green sections look awesome, but maybe white ... | non_priority | improve github pages center the top button view on github vertically create navigation between pages use hacker theme instead of midnight decide on its readability first at the moment green sections look awesome but maybe white is less distracting and better for reading a manual can t link to d... | 0 |
150,719 | 23,702,275,602 | IssuesEvent | 2022-08-29 20:13:56 | practice-uffs/programa | https://api.github.com/repos/practice-uffs/programa | opened | Postar novo membro nas redes sociais | ajuda:con-design ajuda:ger-aux | Criar imagem base como a feita para os demais bolsistas.
Revisar texto de apresentação [(linha 59)](https://docs.google.com/spreadsheets/d/15kGGrER8UTGQhPIvGm2jHhs3pEO6f7gqISZgRyqpMKE/edit#gid=745178717) | 1.0 | Postar novo membro nas redes sociais - Criar imagem base como a feita para os demais bolsistas.
Revisar texto de apresentação [(linha 59)](https://docs.google.com/spreadsheets/d/15kGGrER8UTGQhPIvGm2jHhs3pEO6f7gqISZgRyqpMKE/edit#gid=745178717) | non_priority | postar novo membro nas redes sociais criar imagem base como a feita para os demais bolsistas revisar texto de apresentação | 0 |
317,619 | 23,680,847,472 | IssuesEvent | 2022-08-28 19:28:27 | orbita-center/react-dadata-box | https://api.github.com/repos/orbita-center/react-dadata-box | closed | SpecificQueryModeResponse generic into docs | documentation | SpecificQueryModeResponse generic into docs for **customActions** & **type** sync | 1.0 | SpecificQueryModeResponse generic into docs - SpecificQueryModeResponse generic into docs for **customActions** & **type** sync | non_priority | specificquerymoderesponse generic into docs specificquerymoderesponse generic into docs for customactions type sync | 0 |
26,004 | 19,560,311,598 | IssuesEvent | 2022-01-03 15:23:02 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | CentralInfraSyncFacade::syncAll should run in its own DB transaction | infrastructure change s2s | ### Feature Description
The `syncAll` function of `CentralInfraSyncFacade` which pulls all infra data types we currently have.
### Problem Description
The function is currently not executed in a dedicated transactio. This means that if `loadAndStoreContinents` and `loadAndStoreSubcontinents` succeed, but `loadAndS... | 1.0 | CentralInfraSyncFacade::syncAll should run in its own DB transaction - ### Feature Description
The `syncAll` function of `CentralInfraSyncFacade` which pulls all infra data types we currently have.
### Problem Description
The function is currently not executed in a dedicated transactio. This means that if `loadAnd... | non_priority | centralinfrasyncfacade syncall should run in its own db transaction feature description the syncall function of centralinfrasyncfacade which pulls all infra data types we currently have problem description the function is currently not executed in a dedicated transactio this means that if loadand... | 0 |
61,628 | 14,632,130,183 | IssuesEvent | 2020-12-23 21:33:50 | Cacti/cacti | https://api.github.com/repos/Cacti/cacti | closed | In a recent audit of core Cacti code, there were a few stored XSS issues that can be exposed. | SECURITY resolved | # Describe the bug
There are a few places in the current code where an attacker, once having gained access to the Cacti database through a SQL injection, could modify data in tables to possibly expose an stored XSS bug in Cacti.
## Expected behavior
Cacti should never allow things like this to happen.
| True | In a recent audit of core Cacti code, there were a few stored XSS issues that can be exposed. - # Describe the bug
There are a few places in the current code where an attacker, once having gained access to the Cacti database through a SQL injection, could modify data in tables to possibly expose an stored XSS bug in... | non_priority | in a recent audit of core cacti code there were a few stored xss issues that can be exposed describe the bug there are a few places in the current code where an attacker once having gained access to the cacti database through a sql injection could modify data in tables to possibly expose an stored xss bug in... | 0 |
38,454 | 15,701,836,875 | IssuesEvent | 2021-03-26 11:46:37 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Need to know the ETA of one bug | command terminated with exit status=52 | DNS record propagated | Pri2 container-service/svc cxp product-bug triaged | When stopping and then starting the AKS cluster, we encounter the issue as below.
++++++++++++++
Agents are unable to resolve Kubernetes API server name. It's likely custom DNS server is not correctly configured, please see https://aka.ms/aks/private-cluster#hub-and-spoke-with-custom-dns for more information. Detail... | 1.0 | Need to know the ETA of one bug | command terminated with exit status=52 | DNS record propagated - When stopping and then starting the AKS cluster, we encounter the issue as below.
++++++++++++++
Agents are unable to resolve Kubernetes API server name. It's likely custom DNS server is not correctly configured, plea... | non_priority | need to know the eta of one bug command terminated with exit status dns record propagated when stopping and then starting the aks cluster we encounter the issue as below agents are unable to resolve kubernetes api server name it s likely custom dns server is not correctly configured pleas... | 0 |
79,470 | 9,906,349,018 | IssuesEvent | 2019-06-27 13:41:30 | unitsofmeasurement/indriya | https://api.github.com/repos/unitsofmeasurement/indriya | closed | Move AbstractConverter to function | design task | I know this is a slightly bigger step, but as a new redefined `MultiplyConverter` interface also got defined (in place of the earlier class) in the function package, and `AbstractUnitFormat` etc. are in the format package, it is consequent here. | 1.0 | Move AbstractConverter to function - I know this is a slightly bigger step, but as a new redefined `MultiplyConverter` interface also got defined (in place of the earlier class) in the function package, and `AbstractUnitFormat` etc. are in the format package, it is consequent here. | non_priority | move abstractconverter to function i know this is a slightly bigger step but as a new redefined multiplyconverter interface also got defined in place of the earlier class in the function package and abstractunitformat etc are in the format package it is consequent here | 0 |
1,064 | 3,023,679,036 | IssuesEvent | 2015-08-01 19:15:28 | Py64/Wolves | https://api.github.com/repos/Py64/Wolves | opened | Improve registration process | doing major security-high | - Sending activation mails
- If user exists, cancel
- Check is email fine | True | Improve registration process - - Sending activation mails
- If user exists, cancel
- Check is email fine | non_priority | improve registration process sending activation mails if user exists cancel check is email fine | 0 |
38,713 | 6,690,058,897 | IssuesEvent | 2017-10-09 07:23:29 | Sylius/Sylius | https://api.github.com/repos/Sylius/Sylius | closed | Custom shipping calculators - Outdated documentation | Documentation | In custom shipping calculators (http://docs.sylius.org/en/latest/bundles/SyliusShippingBundle/custom_calculators.html#configurable-calculators), code samples are outdated :
- `DHLCalculator` class should implements `Sylius\Component\Shipping\Calculator\CalculatorInterface` instead of extending old `Sylius\Bundle\Shi... | 1.0 | Custom shipping calculators - Outdated documentation - In custom shipping calculators (http://docs.sylius.org/en/latest/bundles/SyliusShippingBundle/custom_calculators.html#configurable-calculators), code samples are outdated :
- `DHLCalculator` class should implements `Sylius\Component\Shipping\Calculator\Calculato... | non_priority | custom shipping calculators outdated documentation in custom shipping calculators code samples are outdated dhlcalculator class should implements sylius component shipping calculator calculatorinterface instead of extending old sylius bundle shippingbundle calculator calculator class dhlcalcul... | 0 |
97,021 | 8,640,320,522 | IssuesEvent | 2018-11-24 04:03:54 | Fourdee/DietPi | https://api.github.com/repos/Fourdee/DietPi | closed | DietPi-Software | Pi-hole: Add support for blocking page | Feature Request :factory: Testing/testers required :arrow_down_small: | - At webserver conf level?
- Also outstanding issue with service not starting during boot, workaround has been applied to v6.13. | 2.0 | DietPi-Software | Pi-hole: Add support for blocking page - - At webserver conf level?
- Also outstanding issue with service not starting during boot, workaround has been applied to v6.13. | non_priority | dietpi software pi hole add support for blocking page at webserver conf level also outstanding issue with service not starting during boot workaround has been applied to | 0 |
30,524 | 24,894,587,879 | IssuesEvent | 2022-10-28 14:45:24 | DMPRoadmap/roadmap | https://api.github.com/repos/DMPRoadmap/roadmap | opened | Upgrade Rails to 7.x | infrastructure effort-large need-to-slice | We will eventually need to upgrade to 7.x.
Was pointed to this helpful guide (wish I had known about it earlier) https://www.fastruby.io/blog/rails/upgrades/upgrade-rails-6-1-to-7-0.html | 1.0 | Upgrade Rails to 7.x - We will eventually need to upgrade to 7.x.
Was pointed to this helpful guide (wish I had known about it earlier) https://www.fastruby.io/blog/rails/upgrades/upgrade-rails-6-1-to-7-0.html | non_priority | upgrade rails to x we will eventually need to upgrade to x was pointed to this helpful guide wish i had known about it earlier | 0 |
40,419 | 5,290,607,925 | IssuesEvent | 2017-02-08 20:19:54 | ansible/ansible | https://api.github.com/repos/ansible/ansible | closed | Wrong Shippable test on type(x).__name__ print | affects_2.3 bug_report test | <!---
Verify first that your issue/request is not already reported on GitHub.
Also test if the latest release, and master branch are affected too.
-->
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
<!--- Name of the module/plugin/task/feature -->
shippable
##### ANSIBLE VERSION
<!--- Paste verbatim... | 1.0 | Wrong Shippable test on type(x).__name__ print - <!---
Verify first that your issue/request is not already reported on GitHub.
Also test if the latest release, and master branch are affected too.
-->
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
<!--- Name of the module/plugin/task/feature -->
shippab... | non_priority | wrong shippable test on type x name print verify first that your issue request is not already reported on github also test if the latest release and master branch are affected too issue type bug report component name shippable ansible version devel ... | 0 |
33,129 | 12,190,112,921 | IssuesEvent | 2020-04-29 08:45:03 | lgmorand/aks-checklist | https://api.github.com/repos/lgmorand/aks-checklist | closed | CVE-2018-20822 (Medium) detected in node-sass-v4.13.1, node-sass-4.13.1.tgz | security vulnerability | ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.1.tgz</b></p></summary>
<p>
<details><summary><b>node-sass-4.13.1.tgz</b></p></summary>
<p>Wrapper... | True | CVE-2018-20822 (Medium) detected in node-sass-v4.13.1, node-sass-4.13.1.tgz - ## CVE-2018-20822 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.13.1.tgz</b></p></summary... | non_priority | cve medium detected in node sass node sass tgz cve medium severity vulnerability vulnerable libraries node sass tgz node sass tgz wrapper around libsass library home page a href path to dependency file tmp ws scm aks checklist package json path ... | 0 |
149,446 | 23,477,142,204 | IssuesEvent | 2022-08-17 07:18:18 | jupyterlab/jupyterlab | https://api.github.com/repos/jupyterlab/jupyterlab | closed | Future of ui-components package: drop Blueprint; should we use Material-UI? | status:Needs Discussion tag:Design System CSS | Refs:
#6828
#6890
There's currently an ongoing discussion about the future of the `ui-components` package in Jupyterlab core:
- There's no particular reason to keep the Blueprint dependency around. We should refactor out the sparse use of it in `ui-components` and drop the dep
- This should be easy, and it... | 1.0 | Future of ui-components package: drop Blueprint; should we use Material-UI? - Refs:
#6828
#6890
There's currently an ongoing discussion about the future of the `ui-components` package in Jupyterlab core:
- There's no particular reason to keep the Blueprint dependency around. We should refactor out the sparse us... | non_priority | future of ui components package drop blueprint should we use material ui refs there s currently an ongoing discussion about the future of the ui components package in jupyterlab core there s no particular reason to keep the blueprint dependency around we should refactor out the sparse use of i... | 0 |
317,448 | 27,238,103,567 | IssuesEvent | 2023-02-21 17:52:37 | Azure/azure-sdk-tools | https://api.github.com/repos/Azure/azure-sdk-tools | closed | [test-proxy] Consider using microsoft/reverse-proxy | Test-Proxy | https://github.com/microsoft/reverse-proxy is "a toolkit for developing high-performance HTTP reverse proxy applications".
It might be worth investigating this project, to see if it could makes sense to implement test-proxy on top of reverse-proxy. | 1.0 | [test-proxy] Consider using microsoft/reverse-proxy - https://github.com/microsoft/reverse-proxy is "a toolkit for developing high-performance HTTP reverse proxy applications".
It might be worth investigating this project, to see if it could makes sense to implement test-proxy on top of reverse-proxy. | non_priority | consider using microsoft reverse proxy is a toolkit for developing high performance http reverse proxy applications it might be worth investigating this project to see if it could makes sense to implement test proxy on top of reverse proxy | 0 |
54,981 | 6,886,021,385 | IssuesEvent | 2017-11-21 17:57:02 | cs340tabyu/cs340Fall2017 | https://api.github.com/repos/cs340tabyu/cs340Fall2017 | opened | Large click space for certain routes | P4: Aesthetic or Design Flaw The Fun Team | Not a huge problem, but I noticed if you click on the edges of the map it acts are though you're trying to claim one of the nearby routes. Maybe you designed it that way, but it felt a little weird | 1.0 | Large click space for certain routes - Not a huge problem, but I noticed if you click on the edges of the map it acts are though you're trying to claim one of the nearby routes. Maybe you designed it that way, but it felt a little weird | non_priority | large click space for certain routes not a huge problem but i noticed if you click on the edges of the map it acts are though you re trying to claim one of the nearby routes maybe you designed it that way but it felt a little weird | 0 |
196,808 | 15,610,590,071 | IssuesEvent | 2021-03-19 13:22:42 | thelastinuit/toad | https://api.github.com/repos/thelastinuit/toad | closed | Update Readme | documentation | ## Expected Behavior
It should be helpful to developers who want to use it or modify it.
## Current Behavior
README says nothing of value about this demo project.
## Possible Solution
Update Readme with:
- Steps on how to install it
- Steps on how to run it | 1.0 | Update Readme - ## Expected Behavior
It should be helpful to developers who want to use it or modify it.
## Current Behavior
README says nothing of value about this demo project.
## Possible Solution
Update Readme with:
- Steps on how to install it
- Steps on how to run it | non_priority | update readme expected behavior it should be helpful to developers who want to use it or modify it current behavior readme says nothing of value about this demo project possible solution update readme with steps on how to install it steps on how to run it | 0 |
329,950 | 24,239,553,708 | IssuesEvent | 2022-09-27 04:51:10 | easystats/easystats | https://api.github.com/repos/easystats/easystats | opened | Include reference to publication in `DESCRIPTION` | Core Packages :package: Documentation :books: | Of course, only if there is a publication corresponding to the package you are maintaining:
[Like so](https://cran.r-project.org/web/packages/brms/index.html):
<img width="679" alt="Screenshot 2022-09-27 at 06 48 15" src="https://user-images.githubusercontent.com/11330453/192434636-d97ae01c-f848-4f19-a1b8-3cb74e5... | 1.0 | Include reference to publication in `DESCRIPTION` - Of course, only if there is a publication corresponding to the package you are maintaining:
[Like so](https://cran.r-project.org/web/packages/brms/index.html):
<img width="679" alt="Screenshot 2022-09-27 at 06 48 15" src="https://user-images.githubusercontent.co... | non_priority | include reference to publication in description of course only if there is a publication corresponding to the package you are maintaining img width alt screenshot at src progress tracker insight bayestestr effectsize parameters performance corr... | 0 |
223,158 | 17,105,412,474 | IssuesEvent | 2021-07-09 16:55:27 | thcheetah777/alien | https://api.github.com/repos/thcheetah777/alien | closed | Organize main files into folders | documentation help wanted no coding simple | ## Steps:
- [x] Organize world.js by scenes
- [ ] Organize script.js by main scene class and config in another file | 1.0 | Organize main files into folders - ## Steps:
- [x] Organize world.js by scenes
- [ ] Organize script.js by main scene class and config in another file | non_priority | organize main files into folders steps organize world js by scenes organize script js by main scene class and config in another file | 0 |
323,589 | 23,955,827,313 | IssuesEvent | 2022-09-12 14:53:19 | tardis-sn/tardis | https://api.github.com/repos/tardis-sn/tardis | opened | Produce more in-depth documentation of the gamma-ray transport | documentation nebular | Gamma-ray transport needs more documentation to describe how it works and why it works as it does, ideally with paper references.
| 1.0 | Produce more in-depth documentation of the gamma-ray transport - Gamma-ray transport needs more documentation to describe how it works and why it works as it does, ideally with paper references.
| non_priority | produce more in depth documentation of the gamma ray transport gamma ray transport needs more documentation to describe how it works and why it works as it does ideally with paper references | 0 |
81,016 | 7,763,367,051 | IssuesEvent | 2018-06-01 16:18:42 | TheDMSGroup/mautic-extended-field | https://api.github.com/repos/TheDMSGroup/mautic-extended-field | closed | Installation prefix not implemented | bug needs testing | Hi guys,
There is an option to create table prefix during Mautic installation . It seems your plugin does not support this and sql queries do not work properly (tables are missing) . I'm putting the error message we got:
[2018-05-17 17:10:23] mautic.CRITICAL: Uncaught PHP Exception Doctrine\DBAL\Exception\Table... | 1.0 | Installation prefix not implemented - Hi guys,
There is an option to create table prefix during Mautic installation . It seems your plugin does not support this and sql queries do not work properly (tables are missing) . I'm putting the error message we got:
[2018-05-17 17:10:23] mautic.CRITICAL: Uncaught PHP ... | non_priority | installation prefix not implemented hi guys there is an option to create table prefix during mautic installation it seems your plugin does not support this and sql queries do not work properly tables are missing i m putting the error message we got mautic critical uncaught php exception doctrine d... | 0 |
44,640 | 23,719,805,948 | IssuesEvent | 2022-08-30 14:31:45 | simdjson/simdjson | https://api.github.com/repos/simdjson/simdjson | opened | Optimize to_bitmask() for ARM | performance | The current to_bitmask() implementation in ARM is expensive.
In simdutf, we reengineered the code to use a faster function...
https://github.com/simdutf/simdutf/blob/c0cb6dddb12256a261bb249255660b79c1fe67a2/src/simdutf/arm64/simd.h#L210-L212
Reference:
https://community.arm.com/arm-community-blogs/b/infrastruc... | True | Optimize to_bitmask() for ARM - The current to_bitmask() implementation in ARM is expensive.
In simdutf, we reengineered the code to use a faster function...
https://github.com/simdutf/simdutf/blob/c0cb6dddb12256a261bb249255660b79c1fe67a2/src/simdutf/arm64/simd.h#L210-L212
Reference:
https://community.arm.com... | non_priority | optimize to bitmask for arm the current to bitmask implementation in arm is expensive in simdutf we reengineered the code to use a faster function reference we should investigate this optimization credit to nathan kurz for the pointer | 0 |
162,321 | 12,643,453,279 | IssuesEvent | 2020-06-16 09:50:01 | jpmorganchase/nbcelltests | https://api.github.com/repos/jpmorganchase/nbcelltests | opened | Certain cell failures are not detected | bug cell tests | Inherited from nbval. E.g. test for bad magics is currently marked "known fail":
https://github.com/jpmorganchase/nbcelltests/blob/f6d206118ee336efd74049ff8c72fd827be1c739/nbcelltests/tests/test_test.py#L475-L481
(note: typo in above method name - "does _not_")
There might be other cases too, haven't investiga... | 1.0 | Certain cell failures are not detected - Inherited from nbval. E.g. test for bad magics is currently marked "known fail":
https://github.com/jpmorganchase/nbcelltests/blob/f6d206118ee336efd74049ff8c72fd827be1c739/nbcelltests/tests/test_test.py#L475-L481
(note: typo in above method name - "does _not_")
There mi... | non_priority | certain cell failures are not detected inherited from nbval e g test for bad magics is currently marked known fail note typo in above method name does not there might be other cases too haven t investigated | 0 |
90,297 | 18,106,355,277 | IssuesEvent | 2021-09-22 19:33:47 | UBC-Thunderbots/Software | https://api.github.com/repos/UBC-Thunderbots/Software | closed | DynamicParameters: Separate const parameters from dynamic parameters | Difficulty - 7 Code Quality | ### Description of the task
Currently we have `c_params` which get generated from `constant` parameters in a config definition yaml file, and we have `cpp_params` that are generated from both `const` and `non-const` parameters in the yaml file.
Marking a dynamic parameter as `const` is something that we realized wi... | 1.0 | DynamicParameters: Separate const parameters from dynamic parameters - ### Description of the task
Currently we have `c_params` which get generated from `constant` parameters in a config definition yaml file, and we have `cpp_params` that are generated from both `const` and `non-const` parameters in the yaml file.
... | non_priority | dynamicparameters separate const parameters from dynamic parameters description of the task currently we have c params which get generated from constant parameters in a config definition yaml file and we have cpp params that are generated from both const and non const parameters in the yaml file ... | 0 |
63,032 | 12,278,520,118 | IssuesEvent | 2020-05-08 10:08:16 | fac19/snake | https://api.github.com/repos/fac19/snake | opened | Good place for an explanatory comment? | code review documentation | The onKeyDown function is really interesting - I notice you plan to mention it in the presentation, which I'm looking forward to because tbh I don't get it. It might also be good to include an explanatory comment for yourself six months down the line. | 1.0 | Good place for an explanatory comment? - The onKeyDown function is really interesting - I notice you plan to mention it in the presentation, which I'm looking forward to because tbh I don't get it. It might also be good to include an explanatory comment for yourself six months down the line. | non_priority | good place for an explanatory comment the onkeydown function is really interesting i notice you plan to mention it in the presentation which i m looking forward to because tbh i don t get it it might also be good to include an explanatory comment for yourself six months down the line | 0 |
209,305 | 16,190,527,729 | IssuesEvent | 2021-05-04 07:49:06 | pmndrs/react-spring.io | https://api.github.com/repos/pmndrs/react-spring.io | closed | Add some guides | documentation enhancement help wanted | Everyone is encouraged to help out with these tasks:
- [ ] Add a "guide directory" page
- [ ] Write a short guide for getting started with each target platform (eg: web, zdog, three)
- [ ] Convert solved questions from https://github.com/react-spring/react-spring/issues into guided implementations
- [ ] Write a s... | 1.0 | Add some guides - Everyone is encouraged to help out with these tasks:
- [ ] Add a "guide directory" page
- [ ] Write a short guide for getting started with each target platform (eg: web, zdog, three)
- [ ] Convert solved questions from https://github.com/react-spring/react-spring/issues into guided implementation... | non_priority | add some guides everyone is encouraged to help out with these tasks add a guide directory page write a short guide for getting started with each target platform eg web zdog three convert solved questions from into guided implementations write a short guide about how you fixed a broken ... | 0 |
100,193 | 12,508,382,180 | IssuesEvent | 2020-06-02 15:28:33 | revelry-foundation/nightingale | https://api.github.com/repos/revelry-foundation/nightingale | opened | Landing Page - Hero Image - Stock Purchase | @done approve @done write @skipped estimate design | ## Background
We're using an image from Getty for the hero of the landing page, that seems to meet with everyone's approval. (see attachment below) We need to purchase this prior to launch. Pricing is below. Recommended resolution is the MEDIUM size.
<img width="350" alt="Screen Shot 2020-06-02 at 10 27 44" src="ht... | 1.0 | Landing Page - Hero Image - Stock Purchase - ## Background
We're using an image from Getty for the hero of the landing page, that seems to meet with everyone's approval. (see attachment below) We need to purchase this prior to launch. Pricing is below. Recommended resolution is the MEDIUM size.
<img width="350" alt... | non_priority | landing page hero image stock purchase background we re using an image from getty for the hero of the landing page that seems to meet with everyone s approval see attachment below we need to purchase this prior to launch pricing is below recommended resolution is the medium size img width alt ... | 0 |
81,776 | 10,179,859,877 | IssuesEvent | 2019-08-09 08:52:11 | LiskHQ/lisk-hub | https://api.github.com/repos/LiskHQ/lisk-hub | closed | Align app loader animation to design | Unplanned severity: medium stretch goals type: design | ## Current behaviour
App loading screen (the one before splash screen) was not updated to the latest design

## Expected behaviour
App loading screen should be updated to the la... | 1.0 | Align app loader animation to design - ## Current behaviour
App loading screen (the one before splash screen) was not updated to the latest design

## Expected behaviour
App loa... | non_priority | align app loader animation to design current behaviour app loading screen the one before splash screen was not updated to the latest design expected behaviour app loading screen should be updated to the latest design provided by design team the animation should be something like | 0 |
249,321 | 26,911,338,134 | IssuesEvent | 2023-02-07 00:12:20 | Enterprise-CMCS/macpro-appian-connector | https://api.github.com/repos/Enterprise-CMCS/macpro-appian-connector | closed | SecurityHub Finding - SNS.1 SNS topics should be encrypted at-rest using AWS KMS | security-hub us-east-1 MEDIUM master | **************************************************************
__This issue was generated from Security Hub data and is managed through automation.__
Please do not edit the title or body of this issue, or remove the security-hub tag. All other edits/comments are welcome.
Finding Title: SNS.1 SNS topics should be encry... | True | SecurityHub Finding - SNS.1 SNS topics should be encrypted at-rest using AWS KMS - **************************************************************
__This issue was generated from Security Hub data and is managed through automation.__
Please do not edit the title or body of this issue, or remove the security-hub tag. Al... | non_priority | securityhub finding sns sns topics should be encrypted at rest using aws kms this issue was generated from security hub data and is managed through automation please do not edit the title or body of this issue or remove the security hub tag al... | 0 |
111,436 | 14,079,628,442 | IssuesEvent | 2020-11-04 15:06:50 | laurent22/joplin | https://api.github.com/repos/laurent22/joplin | closed | Markdown export, exports also name of Note - Makes it non MD compliant | as designed | ## Environment
Joplin version:
Joplin for Desktop
Copyright © 2016-2020 Laurent Cozic
Joplin 1.2.6 (prod, win32)
Client ID: 92e2017594e141ffb762ac52e679bb96
Sync Version: 2
Profile Version: 34
Keychain Supported: Yes
Revision: f5f117cb (master)
Platform: Windows 10 - 10.0.18363.0
OS specifics:
... | 1.0 | Markdown export, exports also name of Note - Makes it non MD compliant - ## Environment
Joplin version:
Joplin for Desktop
Copyright © 2016-2020 Laurent Cozic
Joplin 1.2.6 (prod, win32)
Client ID: 92e2017594e141ffb762ac52e679bb96
Sync Version: 2
Profile Version: 34
Keychain Supported: Yes
Revision: f5... | non_priority | markdown export exports also name of note makes it non md compliant environment joplin version joplin for desktop copyright © laurent cozic joplin prod client id sync version profile version keychain supported yes revision master platform windows ... | 0 |
357,999 | 25,176,598,749 | IssuesEvent | 2022-11-11 09:49:03 | jeyvia/pe | https://api.github.com/repos/jeyvia/pe | opened | DG Design & Implementation missing documentations | severity.High type.DocumentationBug | Design & Implementation only includes:
1. Save/Withdraw/Deposite feature
2. Add/Remove personal currency feature
It is missing:
1. Account feature
2. List feature
3. Transfer feature
4. Info about currencies feature
5. Currency conversion feature
6. balance feature
7. help feature
and many more features that lack bot... | 1.0 | DG Design & Implementation missing documentations - Design & Implementation only includes:
1. Save/Withdraw/Deposite feature
2. Add/Remove personal currency feature
It is missing:
1. Account feature
2. List feature
3. Transfer feature
4. Info about currencies feature
5. Currency conversion feature
6. balance feature
7... | non_priority | dg design implementation missing documentations design implementation only includes save withdraw deposite feature add remove personal currency feature it is missing account feature list feature transfer feature info about currencies feature currency conversion feature balance feature ... | 0 |
184,260 | 21,784,841,544 | IssuesEvent | 2022-05-14 01:30:56 | Thezone1975/tabliss | https://api.github.com/repos/Thezone1975/tabliss | closed | WS-2020-0218 (High) detected in merge-1.2.0.tgz - autoclosed | security vulnerability | ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.0.tgz</b></p></summary>
<p>Merge multiple objects into one, optionally creating a new cloned object. Similar t... | True | WS-2020-0218 (High) detected in merge-1.2.0.tgz - autoclosed - ## WS-2020-0218 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>merge-1.2.0.tgz</b></p></summary>
<p>Merge multiple objec... | non_priority | ws high detected in merge tgz autoclosed ws high severity vulnerability vulnerable library merge tgz merge multiple objects into one optionally creating a new cloned object similar to the jquery extend but more flexible works in node js and the browser library home page ... | 0 |
256,849 | 19,473,291,678 | IssuesEvent | 2021-12-24 07:09:55 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | opened | Missing Document Viewer widget documentation | Documentation | @Pranay105 added the documentation for the document viewer widget here. https://www.notion.so/appsmith/Document-Viewer-1a36c9ff38b3440eb3d47ac41341bd90
Please review this and let me know | 1.0 | Missing Document Viewer widget documentation - @Pranay105 added the documentation for the document viewer widget here. https://www.notion.so/appsmith/Document-Viewer-1a36c9ff38b3440eb3d47ac41341bd90
Please review this and let me know | non_priority | missing document viewer widget documentation added the documentation for the document viewer widget here please review this and let me know | 0 |
104,756 | 9,008,205,469 | IssuesEvent | 2019-02-05 02:36:03 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: synctest failed | C-test-failure O-robot | SHA: https://github.com/cockroachdb/cockroach/commits/407932a95f3ad53d61481e5a7493fc4ed468faa9
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace... | 1.0 | roachtest: synctest failed - SHA: https://github.com/cockroachdb/cockroach/commits/407932a95f3ad53d61481e5a7493fc4ed468faa9
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using... | non_priority | roachtest synctest failed sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which controls concurren... | 0 |
55,219 | 13,994,746,644 | IssuesEvent | 2020-10-28 01:30:43 | GooseWSS/apollo | https://api.github.com/repos/GooseWSS/apollo | opened | CVE-2019-6286 (Medium) detected in node-sass-4.14.1.tgz, node-sassv4.13.1 | security vulnerability | ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b>, <b>node-sassv4.13.1</b></p></summary>
<p>
<details><summary><b>node-sass-4.14.1.tgz</b></... | True | CVE-2019-6286 (Medium) detected in node-sass-4.14.1.tgz, node-sassv4.13.1 - ## CVE-2019-6286 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>node-sass-4.14.1.tgz</b>, <b>node-sassv4... | non_priority | cve medium detected in node sass tgz node cve medium severity vulnerability vulnerable libraries node sass tgz node node sass tgz wrapper around libsass library home page a href path to dependency file apollo modules dreamview frontend pac... | 0 |
367,812 | 25,763,443,472 | IssuesEvent | 2022-12-08 22:49:50 | mlte-team/mlte | https://api.github.com/repos/mlte-team/mlte | opened | Develop a Roadmap for Integrations | documentation question | We want to expand MLTE to integrate with various third-party libraries for ML. We should develop a roadmap for integration that prioritizes specific functionality in specific libraries. | 1.0 | Develop a Roadmap for Integrations - We want to expand MLTE to integrate with various third-party libraries for ML. We should develop a roadmap for integration that prioritizes specific functionality in specific libraries. | non_priority | develop a roadmap for integrations we want to expand mlte to integrate with various third party libraries for ml we should develop a roadmap for integration that prioritizes specific functionality in specific libraries | 0 |
42,612 | 11,171,239,272 | IssuesEvent | 2019-12-28 18:01:38 | markstory/asset_compress | https://api.github.com/repos/markstory/asset_compress | closed | build command throws error with CakePHP 4.0.0 | defect | see https://travis-ci.org/foodcoopshop/foodcoopshop/jobs/629496999
`$ bin/cake asset_compress build`
Exception: Too few arguments to function Cake\Console\Shell::out(), 0 passed in /home/travis/build/foodcoopshop/foodcoopshop/vendor/markstory/asset_compress/src/Shell/AssetCompressShell.php on line 51 and at least... | 1.0 | build command throws error with CakePHP 4.0.0 - see https://travis-ci.org/foodcoopshop/foodcoopshop/jobs/629496999
`$ bin/cake asset_compress build`
Exception: Too few arguments to function Cake\Console\Shell::out(), 0 passed in /home/travis/build/foodcoopshop/foodcoopshop/vendor/markstory/asset_compress/src/Shel... | non_priority | build command throws error with cakephp see bin cake asset compress build exception too few arguments to function cake console shell out passed in home travis build foodcoopshop foodcoopshop vendor markstory asset compress src shell assetcompressshell php on line and at least expected i... | 0 |
192,680 | 14,625,874,810 | IssuesEvent | 2020-12-23 09:20:54 | eclipse/che | https://api.github.com/repos/eclipse/che | closed | Git SSH flow E2E UI tests failed on 'Generate a SSH key' step | area/qe e2e-test/failure kind/bug severity/P1 | ### Describe the bug
Git SSH flow E2E UI tests failed on 'Generate a SSH key' step because workspace wasn't ready at the time:
https://codeready-workspaces-jenkins.rhev-ci-vms.eng.rdu2.redhat.com/job/basic-MultiUser-Che-check-e2e-tests-against-k8s/2343/
```
▼ TopMenu.selectOption "View"
▼ TopMe... | 1.0 | Git SSH flow E2E UI tests failed on 'Generate a SSH key' step - ### Describe the bug
Git SSH flow E2E UI tests failed on 'Generate a SSH key' step because workspace wasn't ready at the time:
https://codeready-workspaces-jenkins.rhev-ci-vms.eng.rdu2.redhat.com/job/basic-MultiUser-Che-check-e2e-tests-against-k8s/2343/
... | non_priority | git ssh flow ui tests failed on generate a ssh key step describe the bug git ssh flow ui tests failed on generate a ssh key step because workspace wasn t ready at the time ▼ topmenu selectoption view ▼ topmenu clickontopmenubutton view ▼ ide closeallnotificat... | 0 |
166,022 | 20,711,379,498 | IssuesEvent | 2022-03-12 01:14:25 | snowflakedb/snowflake-jdbc | https://api.github.com/repos/snowflakedb/snowflake-jdbc | closed | SNOW-558862: CVE-2019-10202 (High) detected in jackson-databind-2.9.8.jar - autoclosed | security vulnerability | ## CVE-2019-10202 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | SNOW-558862: CVE-2019-10202 (High) detected in jackson-databind-2.9.8.jar - autoclosed - ## CVE-2019-10202 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b>... | non_priority | snow cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws ua... | 0 |
61,893 | 12,196,459,197 | IssuesEvent | 2020-04-29 19:07:07 | kwk/test-llvm-bz-import-5 | https://api.github.com/repos/kwk/test-llvm-bz-import-5 | closed | Assertion `FieldNo < FieldCount && "Invalid Field No"' | BZ-BUG-STATUS: RESOLVED BZ-RESOLUTION: FIXED clang/LLVM Codegen dummy import from bugzilla | This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=10912. | 1.0 | Assertion `FieldNo < FieldCount && "Invalid Field No"' - This issue was imported from Bugzilla https://bugs.llvm.org/show_bug.cgi?id=10912. | non_priority | assertion fieldno fieldcount invalid field no this issue was imported from bugzilla | 0 |
79,154 | 28,019,051,856 | IssuesEvent | 2023-03-28 02:48:38 | salsadigitalauorg/civictheme_source | https://api.github.com/repos/salsadigitalauorg/civictheme_source | opened | [DEFECT] Test Jira GH integration | Type: Defect | ### Summary
Summary
### Steps to reproduce
Steps
### Observed outcome
Observed
### Expected outcome
Expected | 1.0 | [DEFECT] Test Jira GH integration - ### Summary
Summary
### Steps to reproduce
Steps
### Observed outcome
Observed
### Expected outcome
Expected | non_priority | test jira gh integration summary summary steps to reproduce steps observed outcome observed expected outcome expected | 0 |
15,587 | 5,147,069,109 | IssuesEvent | 2017-01-13 04:57:19 | rubberduck-vba/Rubberduck | https://api.github.com/repos/rubberduck-vba/Rubberduck | closed | Code inspection allows refresh of project with missing references | bug code-explorer code-inspections | I managed to get a project with a missing reference (VBE warned on open). The status bar stuck on "Resolving references", which (I guess) was to be expected. However, the refresh button on the Code Inspection window was still active. So... being the button pusher that I am, I clicked on it and ended up with a perpet... | 2.0 | Code inspection allows refresh of project with missing references - I managed to get a project with a missing reference (VBE warned on open). The status bar stuck on "Resolving references", which (I guess) was to be expected. However, the refresh button on the Code Inspection window was still active. So... being the... | non_priority | code inspection allows refresh of project with missing references i managed to get a project with a missing reference vbe warned on open the status bar stuck on resolving references which i guess was to be expected however the refresh button on the code inspection window was still active so being the... | 0 |
357,549 | 25,176,403,391 | IssuesEvent | 2022-11-11 09:38:58 | jwdavis0200/pe | https://api.github.com/repos/jwdavis0200/pe | opened | Commons class is used by multiple classes but yet is not so in the architecture diagram. | type.DocumentationBug severity.VeryLow | 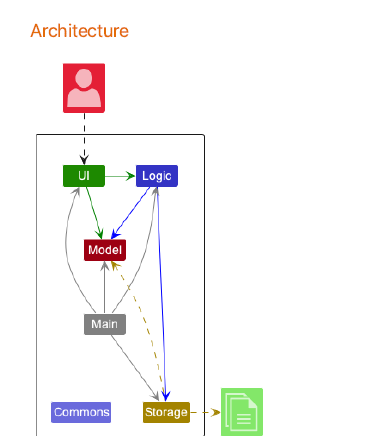
The commons components is shown to be isolated here, which may confuse developers and give them the impression that it is either a deprecated component or an isolated component in the architecture.
Howev... | 1.0 | Commons class is used by multiple classes but yet is not so in the architecture diagram. - 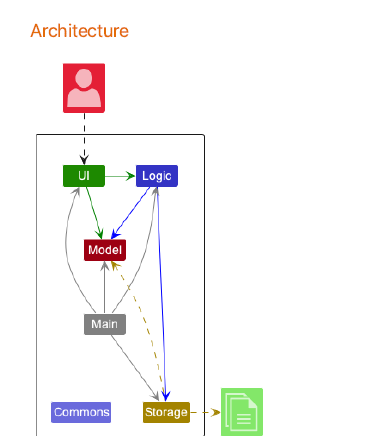
The commons components is shown to be isolated here, which may confuse developers and give them the impression th... | non_priority | commons class is used by multiple classes but yet is not so in the architecture diagram the commons components is shown to be isolated here which may confuse developers and give them the impression that it is either a deprecated component or an isolated component in the architecture however later in the dg... | 0 |
96,965 | 8,638,743,436 | IssuesEvent | 2018-11-23 15:47:09 | EyeSeeTea/dhis2-newsletter | https://api.github.com/repos/EyeSeeTea/dhis2-newsletter | closed | Add unsubscribe link to newsletters | testing | Add Unsubscribe link to emails:
- [x] @mention Notifications
- [x] Newsletters | 1.0 | Add unsubscribe link to newsletters - Add Unsubscribe link to emails:
- [x] @mention Notifications
- [x] Newsletters | non_priority | add unsubscribe link to newsletters add unsubscribe link to emails mention notifications newsletters | 0 |
69,736 | 9,330,441,009 | IssuesEvent | 2019-03-28 06:56:13 | GluuFederation/oxTrust | https://api.github.com/repos/GluuFederation/oxTrust | closed | Add form for passport configuration management | Needs Documentation Needs screenshot new development | Related #1531
The `conf` section of `gluuPassportConfiguration` json looks like:
```
{
"serverURI": "...",
"serverWebPort": 8090,
"postProfileEndpoint": "...",
"spTLSCert": "...",
"spTLSKey": "...",
"logging": {
"level": "...",
"consoleLogOnly" : true/false,
"activeMQConf": {
"enabled": t... | 1.0 | Add form for passport configuration management - Related #1531
The `conf` section of `gluuPassportConfiguration` json looks like:
```
{
"serverURI": "...",
"serverWebPort": 8090,
"postProfileEndpoint": "...",
"spTLSCert": "...",
"spTLSKey": "...",
"logging": {
"level": "...",
"consoleLogOnly" : ... | non_priority | add form for passport configuration management related the conf section of gluupassportconfiguration json looks like serveruri serverwebport postprofileendpoint sptlscert sptlskey logging level consolelogonly true f... | 0 |
21,009 | 11,046,548,123 | IssuesEvent | 2019-12-09 17:03:57 | statsmodels/statsmodels | https://api.github.com/repos/statsmodels/statsmodels | opened | REF/Review computational shortcuts for OLS outlier influence regression diagnostics | Performance comp-graphics comp-regression comp-stats comp-tools | outlier influence and similar regression diagnostics might still have some inefficient computations.
(I improved those as I semi-randomly found computational shortcuts)
article that summarizes several computational shortcuts
Velleman, Paul F., and Roy E. Welsch. 1981. “Efficient Computing of Regression Diagnosti... | True | REF/Review computational shortcuts for OLS outlier influence regression diagnostics - outlier influence and similar regression diagnostics might still have some inefficient computations.
(I improved those as I semi-randomly found computational shortcuts)
article that summarizes several computational shortcuts
Ve... | non_priority | ref review computational shortcuts for ols outlier influence regression diagnostics outlier influence and similar regression diagnostics might still have some inefficient computations i improved those as i semi randomly found computational shortcuts article that summarizes several computational shortcuts ve... | 0 |
211,332 | 16,196,711,065 | IssuesEvent | 2021-05-04 15:22:38 | hashgraph/hedera-services | https://api.github.com/repos/hashgraph/hedera-services | closed | Reconnect test scenarios for Files | Test Development enhancement | **Summary**
Add reconnect test scenario in which the following file operations are done during and after reconnect
1. Files are created
2. Files are Updated
3. Files are Appended
Validate if the reconnect is successful with the file operations. | 1.0 | Reconnect test scenarios for Files - **Summary**
Add reconnect test scenario in which the following file operations are done during and after reconnect
1. Files are created
2. Files are Updated
3. Files are Appended
Validate if the reconnect is successful with the file operations. | non_priority | reconnect test scenarios for files summary add reconnect test scenario in which the following file operations are done during and after reconnect files are created files are updated files are appended validate if the reconnect is successful with the file operations | 0 |
206,747 | 23,396,871,822 | IssuesEvent | 2022-08-12 01:18:41 | Baneeishaque/comingsoon_03-colorlib | https://api.github.com/repos/Baneeishaque/comingsoon_03-colorlib | opened | CVE-2022-24785 (High) detected in moment-2.20.1.min.js | security vulnerability | ## CVE-2022-24785 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-2.20.1.min.js</b></p></summary>
<p>Parse, validate, manipulate, and display dates</p>
<p>Library home page: <a ... | True | CVE-2022-24785 (High) detected in moment-2.20.1.min.js - ## CVE-2022-24785 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>moment-2.20.1.min.js</b></p></summary>
<p>Parse, validate, ma... | non_priority | cve high detected in moment min js cve high severity vulnerability vulnerable library moment min js parse validate manipulate and display dates library home page a href path to dependency file index html path to vulnerable library vendor countdowntime moment min... | 0 |
4,267 | 3,342,867,400 | IssuesEvent | 2015-11-15 00:46:52 | SecUpwN/Android-IMSI-Catcher-Detector | https://api.github.com/repos/SecUpwN/Android-IMSI-Catcher-Detector | reopened | Build: Automatic version and app name update with Gradle | BUILD ENHANCEMENT | Implement automatic build and version updates when using Travis-CI and Gradle, to build our App.
The `build.gradle` script to do this, is described [HERE](http://bryankrosenbaum.com/2013/11/27/getting-to-know-gradle-auto-increment-version-and-signing-releases/), and lastest version can be found [HERE](https://github.... | 1.0 | Build: Automatic version and app name update with Gradle - Implement automatic build and version updates when using Travis-CI and Gradle, to build our App.
The `build.gradle` script to do this, is described [HERE](http://bryankrosenbaum.com/2013/11/27/getting-to-know-gradle-auto-increment-version-and-signing-release... | non_priority | build automatic version and app name update with gradle implement automatic build and version updates when using travis ci and gradle to build our app the build gradle script to do this is described and lastest version can be found this would obviously require a few modifications in the regex as ou... | 0 |
86,816 | 15,755,875,730 | IssuesEvent | 2021-03-31 02:32:25 | turkdevops/node | https://api.github.com/repos/turkdevops/node | opened | WS-2017-0266 (Low) detected in http-signature-0.10.0.tgz | security vulnerability | ## WS-2017-0266 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-signature-0.10.0.tgz</b></p></summary>
<p>Reference implementation of Joyent's HTTP Signature Scheme</p>
<p>Library ... | True | WS-2017-0266 (Low) detected in http-signature-0.10.0.tgz - ## WS-2017-0266 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>http-signature-0.10.0.tgz</b></p></summary>
<p>Reference imple... | non_priority | ws low detected in http signature tgz ws low severity vulnerability vulnerable library http signature tgz reference implementation of joyent s http signature scheme library home page a href path to dependency file node deps npm package json path to vulnerable library ... | 0 |
27,350 | 6,841,269,583 | IssuesEvent | 2017-11-11 11:22:06 | justDoji/TrackMeUp | https://api.github.com/repos/justDoji/TrackMeUp | opened | QualityAssurance: increase test coverage of Java component | code-quality | Increase the test coverage indicated by the Sonar Cloud analysis.
Target coverage is 70%, only non-trivial functions should be tested.
(no private constructor or getter tests). | 1.0 | QualityAssurance: increase test coverage of Java component - Increase the test coverage indicated by the Sonar Cloud analysis.
Target coverage is 70%, only non-trivial functions should be tested.
(no private constructor or getter tests). | non_priority | qualityassurance increase test coverage of java component increase the test coverage indicated by the sonar cloud analysis target coverage is only non trivial functions should be tested no private constructor or getter tests | 0 |
132,485 | 12,509,501,577 | IssuesEvent | 2020-06-02 17:08:48 | nipype/pydra | https://api.github.com/repos/nipype/pydra | opened | Expand docstrings in specs.py and core.py to numpy docstring style | documentation | Docstrings are not complete, so it's not clear how the classes are related to each other and what some of the functions and class methods do etc. | 1.0 | Expand docstrings in specs.py and core.py to numpy docstring style - Docstrings are not complete, so it's not clear how the classes are related to each other and what some of the functions and class methods do etc. | non_priority | expand docstrings in specs py and core py to numpy docstring style docstrings are not complete so it s not clear how the classes are related to each other and what some of the functions and class methods do etc | 0 |
109,714 | 9,411,676,933 | IssuesEvent | 2019-04-10 00:31:07 | filecoin-project/go-filecoin | https://api.github.com/repos/filecoin-project/go-filecoin | opened | Resolve long low-CPU delays during tests | A-tests C-dev-productivity | ### Description
When running tests, I observe periods of intense CPU work and periods where my CPU is near idle (maybe 1 core working). This suggests that the total duration required to run tests is longer than necessary, not constrained by resources. My guess is that there are some lengthy tests that are not but shou... | 1.0 | Resolve long low-CPU delays during tests - ### Description
When running tests, I observe periods of intense CPU work and periods where my CPU is near idle (maybe 1 core working). This suggests that the total duration required to run tests is longer than necessary, not constrained by resources. My guess is that there a... | non_priority | resolve long low cpu delays during tests description when running tests i observe periods of intense cpu work and periods where my cpu is near idle maybe core working this suggests that the total duration required to run tests is longer than necessary not constrained by resources my guess is that there a... | 0 |
160,881 | 20,120,316,292 | IssuesEvent | 2022-02-08 01:07:02 | AkshayMukkavilli/Tensorflow | https://api.github.com/repos/AkshayMukkavilli/Tensorflow | opened | CVE-2022-23573 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2022-23573 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning... | True | CVE-2022-23573 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2022-23573 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-m... | non_priority | cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file tensorflow src requirements ... | 0 |
3,304 | 12,749,105,772 | IssuesEvent | 2020-06-26 21:46:43 | tgstation/tgstation-server | https://api.github.com/repos/tgstation/tgstation-server | closed | Create a checklist for the release process | CI Maintainability Issue Work In Progress | Things to include
- Release note touchup on PRs
- Major/Minor/Patch selection
- API/Client/Server versioning
- Proper use of TGSDeploy and NugetDeploy
- Announcement channels | True | Create a checklist for the release process - Things to include
- Release note touchup on PRs
- Major/Minor/Patch selection
- API/Client/Server versioning
- Proper use of TGSDeploy and NugetDeploy
- Announcement channels | non_priority | create a checklist for the release process things to include release note touchup on prs major minor patch selection api client server versioning proper use of tgsdeploy and nugetdeploy announcement channels | 0 |
245,549 | 18,787,332,601 | IssuesEvent | 2021-11-08 13:32:05 | philippabele/irrigation-springler | https://api.github.com/repos/philippabele/irrigation-springler | closed | Update readme / literature review | documentation | - Inform the reader about, what work has been done before. What ideas and models have already been developed.
- List the relevant literature, blogs, educational platforms and sites to highlight sources for background information of this project.
| 1.0 | Update readme / literature review - - Inform the reader about, what work has been done before. What ideas and models have already been developed.
- List the relevant literature, blogs, educational platforms and sites to highlight sources for background information of this project.
| non_priority | update readme literature review inform the reader about what work has been done before what ideas and models have already been developed list the relevant literature blogs educational platforms and sites to highlight sources for background information of this project | 0 |
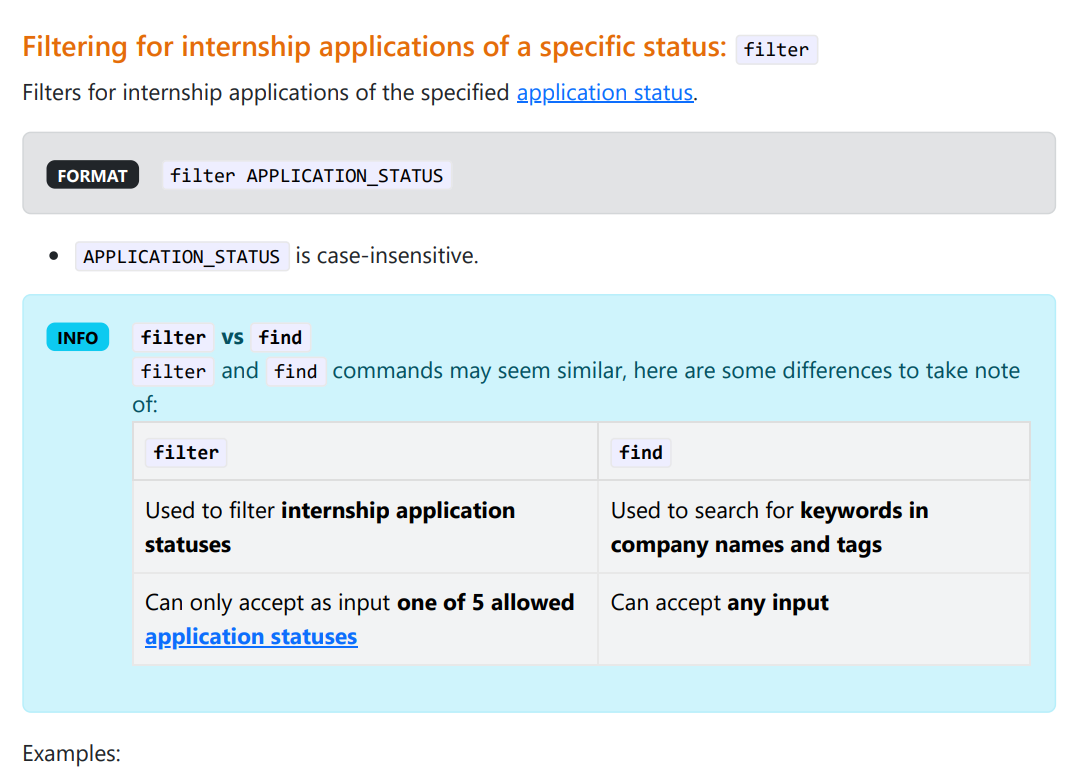
356,181 | 25,176,131,301 | IssuesEvent | 2022-11-11 09:25:16 | autumn-sonata/pe | https://api.github.com/repos/autumn-sonata/pe | opened | [User guide] Some commands lacking any visuals to aid the user in following along with the examples | severity.VeryLow type.DocumentationBug |
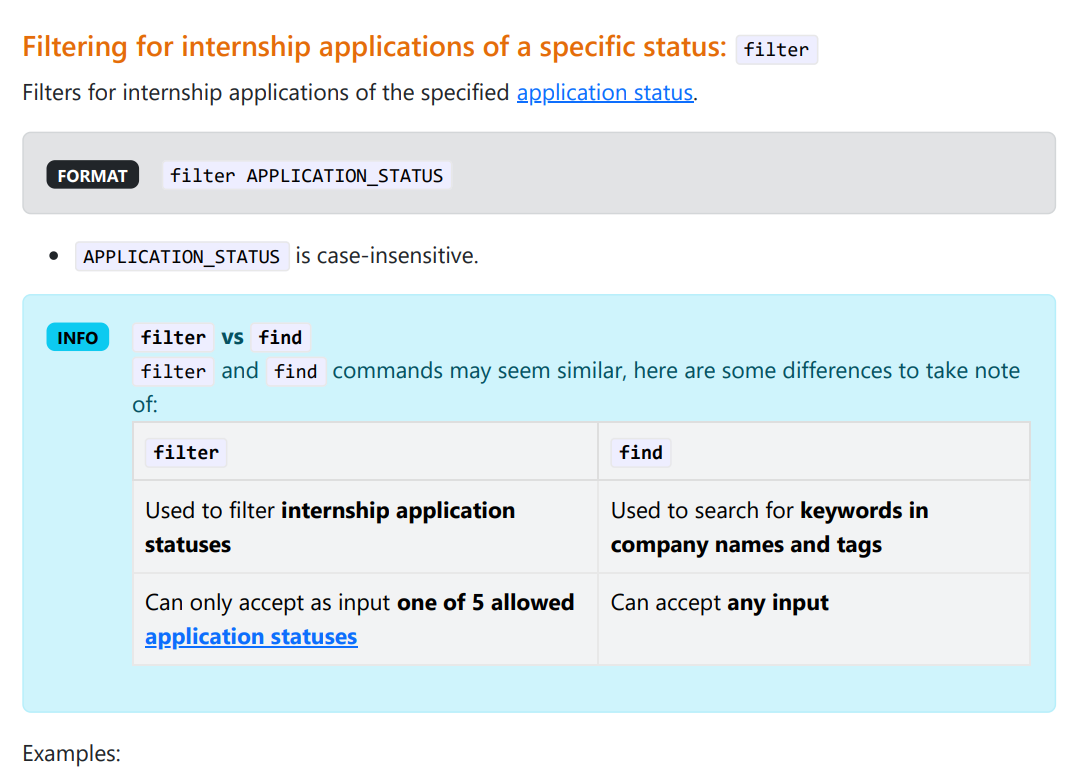
In this case, to better distinguish between the `find` and `filter` command, there should be an example with visuals.
<!--session: 1668154499182-004918ce-c7c4-4d19-a42b-a278b5192249-->
<!--Version: W... | 1.0 | [User guide] Some commands lacking any visuals to aid the user in following along with the examples -
In this case, to better distinguish between the `find` and `filter` command, there should be an exa... | non_priority | some commands lacking any visuals to aid the user in following along with the examples in this case to better distinguish between the find and filter command there should be an example with visuals | 0 |
291,207 | 21,917,624,928 | IssuesEvent | 2022-05-22 04:01:19 | cynkra/dm | https://api.github.com/repos/cynkra/dm | closed | Remove all calls of soft deprecated functionalities | documentation | an example:
https://github.com/cynkra/dm/blob/0cd852445b5e41fcc93fc2f428bf02c22d2cc165/vignettes/tech-dm-join.Rmd#L98-L100
results the following:
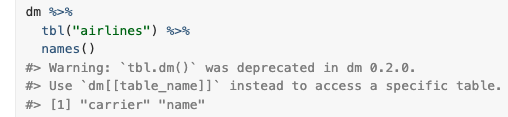
Looking into the code - there are more soft-deprecated... | 1.0 | Remove all calls of soft deprecated functionalities - an example:
https://github.com/cynkra/dm/blob/0cd852445b5e41fcc93fc2f428bf02c22d2cc165/vignettes/tech-dm-join.Rmd#L98-L100
results the following:
... | non_priority | remove all calls of soft deprecated functionalities an example results the following looking into the code there are more soft deprecated functions would be worth to clean this up | 0 |
178,936 | 13,804,666,674 | IssuesEvent | 2020-10-11 10:06:42 | add-ons/plugin.video.vtm.go | https://api.github.com/repos/add-ons/plugin.video.vtm.go | closed | Run some CI tests every few hours to check authentication flow | testing | Given the recent breakages in the login flow, it would make sense to run some CI tests related to authentication every few hours. Maybe like every 6 hours, that's 4 times a day.
@dagwieers can you help with that? I think you've set that up for VRT NU. Do we get an e-mail when something breaks? | 1.0 | Run some CI tests every few hours to check authentication flow - Given the recent breakages in the login flow, it would make sense to run some CI tests related to authentication every few hours. Maybe like every 6 hours, that's 4 times a day.
@dagwieers can you help with that? I think you've set that up for VRT NU. ... | non_priority | run some ci tests every few hours to check authentication flow given the recent breakages in the login flow it would make sense to run some ci tests related to authentication every few hours maybe like every hours that s times a day dagwieers can you help with that i think you ve set that up for vrt nu ... | 0 |
1,637 | 2,613,015,160 | IssuesEvent | 2015-02-27 18:08:07 | scento/lingua | https://api.github.com/repos/scento/lingua | opened | CLDR Language | documentation feature implementation testcase | **Implementation:**
The class `\Lingua\Setup\Processor\CldrLanguage` should process the data generated by `Lingua\Setup\Downloader\Iana`, `Lingua\Setup\Downloader\Icu` and `Lingua\Setup\Downloader\Sil` to generate the following files:
* `iso639-1.json`
* `iso639-1_to_iso639-3.json`
* `iso639-1_to_bcp47.json`
* `is... | 1.0 | CLDR Language - **Implementation:**
The class `\Lingua\Setup\Processor\CldrLanguage` should process the data generated by `Lingua\Setup\Downloader\Iana`, `Lingua\Setup\Downloader\Icu` and `Lingua\Setup\Downloader\Sil` to generate the following files:
* `iso639-1.json`
* `iso639-1_to_iso639-3.json`
* `iso639-1_to_bc... | non_priority | cldr language implementation the class lingua setup processor cldrlanguage should process the data generated by lingua setup downloader iana lingua setup downloader icu and lingua setup downloader sil to generate the following files json to json to json json ... | 0 |
303,945 | 26,240,851,904 | IssuesEvent | 2023-01-05 11:21:25 | woocommerce/woocommerce-blocks | https://api.github.com/repos/woocommerce/woocommerce-blocks | closed | Product Query: [Tests] Add E2E tests for Popular Filters | category: tests 🔹 block-type: product-query | The test should cover:
- Newest
- Best Selling
- Top rated
We should test against a reference to avoid false positive tests. A possible reference is the WooCommerce products shortcode. | 1.0 | Product Query: [Tests] Add E2E tests for Popular Filters - The test should cover:
- Newest
- Best Selling
- Top rated
We should test against a reference to avoid false positive tests. A possible reference is the WooCommerce products shortcode. | non_priority | product query add tests for popular filters the test should cover newest best selling top rated we should test against a reference to avoid false positive tests a possible reference is the woocommerce products shortcode | 0 |
284,166 | 30,913,598,962 | IssuesEvent | 2023-08-05 02:21:24 | Satheesh575555/linux-4.1.15_CVE-2022-45934 | https://api.github.com/repos/Satheesh575555/linux-4.1.15_CVE-2022-45934 | reopened | CVE-2022-24958 (High) detected in linuxlinux-4.6 | Mend: dependency security vulnerability | ## CVE-2022-24958 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel... | True | CVE-2022-24958 (High) detected in linuxlinux-4.6 - ## CVE-2022-24958 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.6</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Lib... | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files vulnerab... | 0 |
115,765 | 24,808,303,072 | IssuesEvent | 2022-10-25 07:22:45 | sast-automation-dev/railsgoat-45 | https://api.github.com/repos/sast-automation-dev/railsgoat-45 | opened | Code Security Report: 20 high severity findings, 30 total findings | code security findings | # Code Security Report
**Latest Scan:** 2022-10-25 07:20am
**Total Findings:** 30
**Tested Project Files:** 134
**Detected Programming Languages:** 2
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
## Language: JavaScript / Node.js
| Severity | CWE | Vuln... | 1.0 | Code Security Report: 20 high severity findings, 30 total findings - # Code Security Report
**Latest Scan:** 2022-10-25 07:20am
**Total Findings:** 30
**Tested Project Files:** 134
**Detected Programming Languages:** 2
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCA... | non_priority | code security report high severity findings total findings code security report latest scan total findings tested project files detected programming languages check this box to manually trigger a scan language javascript node js severity cwe vulnerabi... | 0 |
7,823 | 10,996,990,856 | IssuesEvent | 2019-12-03 08:10:22 | Altinn/altinn-studio | https://api.github.com/repos/Altinn/altinn-studio | closed | isArchived is not set to True when an instance is sent in | area/message-box area/process kind/bug solution/sbl team/nusse | ## Describe the bug
isArchived is not set to True when an instance is sent in by an user from SBL
## To Reproduce
Steps to reproduce the behavior:
1. Login to AT21 and start a instance of a deployed app
2. Fill in data and send inn the instance
3. The receipt page is presented to the user
4. Navigate back to i... | 1.0 | isArchived is not set to True when an instance is sent in - ## Describe the bug
isArchived is not set to True when an instance is sent in by an user from SBL
## To Reproduce
Steps to reproduce the behavior:
1. Login to AT21 and start a instance of a deployed app
2. Fill in data and send inn the instance
3. The ... | non_priority | isarchived is not set to true when an instance is sent in describe the bug isarchived is not set to true when an instance is sent in by an user from sbl to reproduce steps to reproduce the behavior login to and start a instance of a deployed app fill in data and send inn the instance the rec... | 0 |
44,903 | 9,658,568,826 | IssuesEvent | 2019-05-20 11:21:12 | OpenXRay/xray-16 | https://api.github.com/repos/OpenXRay/xray-16 | closed | Split xrCore/ModuleLookup.cpp to Windows and Linux versions | Code Quality Core Developer Experience Infrastructure | Split the file to something like `ModuleLookupWindows.cpp` and `ModuleLookupLinux.cpp` | 1.0 | Split xrCore/ModuleLookup.cpp to Windows and Linux versions - Split the file to something like `ModuleLookupWindows.cpp` and `ModuleLookupLinux.cpp` | non_priority | split xrcore modulelookup cpp to windows and linux versions split the file to something like modulelookupwindows cpp and modulelookuplinux cpp | 0 |
15,574 | 8,961,578,414 | IssuesEvent | 2019-01-28 10:02:18 | bazelbuild/bazel | https://api.github.com/repos/bazelbuild/bazel | closed | [aquery] Add a label to TreeArtifact in text output | P2 team-Performance | ### Description of the problem / feature request:
It is useful for the users to know if an output artifact of an action is a TreeArtifact. We already have this information in the proto output. It should be added to the text output as well. | True | [aquery] Add a label to TreeArtifact in text output - ### Description of the problem / feature request:
It is useful for the users to know if an output artifact of an action is a TreeArtifact. We already have this information in the proto output. It should be added to the text output as well. | non_priority | add a label to treeartifact in text output description of the problem feature request it is useful for the users to know if an output artifact of an action is a treeartifact we already have this information in the proto output it should be added to the text output as well | 0 |
167,377 | 14,111,412,303 | IssuesEvent | 2020-11-07 00:09:47 | JulianaMurillo1509/git_web_practice_branch | https://api.github.com/repos/JulianaMurillo1509/git_web_practice_branch | closed | Un commit que no sigue la convención de código o arreglo a realizar | documentation | La convención de código a seguir: `<Identificador comentario>: <Comentario>`
Igualmente, solo hay 1 arreglo a realizar. Al realizar cada paso y completarlo se creará un issue con las instrucciones a realizar para continuar.
Para realizar la corrección del mensaje de commit usar `git commit --amend` y `git commit push... | 1.0 | Un commit que no sigue la convención de código o arreglo a realizar - La convención de código a seguir: `<Identificador comentario>: <Comentario>`
Igualmente, solo hay 1 arreglo a realizar. Al realizar cada paso y completarlo se creará un issue con las instrucciones a realizar para continuar.
Para realizar la correcc... | non_priority | un commit que no sigue la convención de código o arreglo a realizar la convención de código a seguir igualmente solo hay arreglo a realizar al realizar cada paso y completarlo se creará un issue con las instrucciones a realizar para continuar para realizar la corrección del mensaje de commit usar git ... | 0 |
133,540 | 12,543,844,814 | IssuesEvent | 2020-06-05 16:13:34 | SE2-Busfahrer-SS20/SE2-Busfahrer-SS20 | https://api.github.com/repos/SE2-Busfahrer-SS20/SE2-Busfahrer-SS20 | closed | [E07 Story 04] - Schummelfunktion Refactoring/Testen/Dokumentation | Effort: 5 Test documentation | Schummelfunktion Refactoring/Testen/Dokumentation | 1.0 | [E07 Story 04] - Schummelfunktion Refactoring/Testen/Dokumentation - Schummelfunktion Refactoring/Testen/Dokumentation | non_priority | schummelfunktion refactoring testen dokumentation schummelfunktion refactoring testen dokumentation | 0 |
22,135 | 6,229,488,462 | IssuesEvent | 2017-07-11 04:10:12 | XceedBoucherS/TestImport5 | https://api.github.com/repos/XceedBoucherS/TestImport5 | closed | Do not handle PreviewMouseDown on PropertyItem | CodePlex | <b>emartin[CodePlex]</b> <br />Need expressed from patch 13449 (
http://wpftoolkit.codeplex.com/SourceControl/list/patches )
This handling is actually done to affect the quotIsSelectedquot property. Handling this event may interfere with the underlying editor that need to handle the MouseDown event too.
| 1.0 | Do not handle PreviewMouseDown on PropertyItem - <b>emartin[CodePlex]</b> <br />Need expressed from patch 13449 (
http://wpftoolkit.codeplex.com/SourceControl/list/patches )
This handling is actually done to affect the quotIsSelectedquot property. Handling this event may interfere with the underlying editor that n... | non_priority | do not handle previewmousedown on propertyitem emartin need expressed from patch this handling is actually done to affect the quotisselectedquot property handling this event may interfere with the underlying editor that need to handle the mousedown event too | 0 |
136,792 | 11,083,736,704 | IssuesEvent | 2019-12-13 15:05:08 | ipfs/go-ipfs | https://api.github.com/repos/ipfs/go-ipfs | opened | go-ipfs-api test timeout | test failure | The go-ipfs-api tests are timing out randomly when run against go-ipfs master (using CircleCI, at least).
Example failure (no output): https://circleci.com/gh/ipfs/go-ipfs/22908 | 1.0 | go-ipfs-api test timeout - The go-ipfs-api tests are timing out randomly when run against go-ipfs master (using CircleCI, at least).
Example failure (no output): https://circleci.com/gh/ipfs/go-ipfs/22908 | non_priority | go ipfs api test timeout the go ipfs api tests are timing out randomly when run against go ipfs master using circleci at least example failure no output | 0 |
174,248 | 21,259,432,979 | IssuesEvent | 2022-04-13 01:21:44 | GuyBarGil/WebGoat | https://api.github.com/repos/GuyBarGil/WebGoat | opened | WS-2019-0490 (High) detected in jcommander-1.72.jar | security vulnerability | ## WS-2019-0490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jcommander-1.72.jar</b></p></summary>
<p>Command line parsing</p>
<p>Library home page: <a href="http://jcommander.org">... | True | WS-2019-0490 (High) detected in jcommander-1.72.jar - ## WS-2019-0490 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jcommander-1.72.jar</b></p></summary>
<p>Command line parsing</p>
... | non_priority | ws high detected in jcommander jar ws high severity vulnerability vulnerable library jcommander jar command line parsing library home page a href path to dependency file webgoat integration tests pom xml path to vulnerable library home wss scanner repository com beu... | 0 |
278,530 | 30,702,347,396 | IssuesEvent | 2023-07-27 01:22:27 | hshivhare67/kernel_v4.1.15_CVE-2019-10220 | https://api.github.com/repos/hshivhare67/kernel_v4.1.15_CVE-2019-10220 | closed | CVE-2016-7117 (Critical) detected in linuxlinux-4.4.302 - autoclosed | Mend: dependency security vulnerability | ## CVE-2016-7117 - Critical Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge... | True | CVE-2016-7117 (Critical) detected in linuxlinux-4.4.302 - autoclosed - ## CVE-2016-7117 - Critical Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.4.302</b></p></summary>
<p>
<p>... | non_priority | cve critical detected in linuxlinux autoclosed cve critical severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files vulnerability det... | 0 |
126,132 | 16,980,083,288 | IssuesEvent | 2021-06-30 07:43:07 | nextcloud/spreed | https://api.github.com/repos/nextcloud/spreed | closed | Add icons for Mark as read and unread | 3. to review design | **Is your feature request related to a problem? Please describe.**
There are no icons for both the "Mark as read" and "Mark as unread" context menu options which looks odd next to the other options which do have icons.
**Describe the solution you'd like**
Icons should be added for the "Mark as read" and "Mark as u... | 1.0 | Add icons for Mark as read and unread - **Is your feature request related to a problem? Please describe.**
There are no icons for both the "Mark as read" and "Mark as unread" context menu options which looks odd next to the other options which do have icons.
**Describe the solution you'd like**
Icons should be add... | non_priority | add icons for mark as read and unread is your feature request related to a problem please describe there are no icons for both the mark as read and mark as unread context menu options which looks odd next to the other options which do have icons describe the solution you d like icons should be add... | 0 |
185,137 | 21,785,083,775 | IssuesEvent | 2022-05-14 02:25:35 | turkdevops/angular | https://api.github.com/repos/turkdevops/angular | opened | CVE-2022-1650 (High) detected in eventsource-1.0.7.tgz | security vulnerability | ## CVE-2022-1650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eventsource-1.0.7.tgz</b></p></summary>
<p>W3C compliant EventSource client for Node.js and browser (polyfill)</p>
<p>L... | True | CVE-2022-1650 (High) detected in eventsource-1.0.7.tgz - ## CVE-2022-1650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eventsource-1.0.7.tgz</b></p></summary>
<p>W3C compliant Event... | non_priority | cve high detected in eventsource tgz cve high severity vulnerability vulnerable library eventsource tgz compliant eventsource client for node js and browser polyfill library home page a href path to dependency file integration cli hello world lazy rollup package js... | 0 |
152,494 | 19,685,361,295 | IssuesEvent | 2022-01-11 21:26:57 | eclipse/rdf4j | https://api.github.com/repos/eclipse/rdf4j | closed | Upgrade to Spring 5.3.14 | 🐞 bug security dependencies | ### Current Behavior
Current 5.3 version may have a log injection vulnerability
### Expected Behavior
Upgrade to latest patch version to fix the issue
### Steps To Reproduce
_No response_
### Version
3.7.4
### Are you interested in contributing a solution yourself?
Yes
### Anything else?
https://spring.io/bl... | True | Upgrade to Spring 5.3.14 - ### Current Behavior
Current 5.3 version may have a log injection vulnerability
### Expected Behavior
Upgrade to latest patch version to fix the issue
### Steps To Reproduce
_No response_
### Version
3.7.4
### Are you interested in contributing a solution yourself?
Yes
### Anything ... | non_priority | upgrade to spring current behavior current version may have a log injection vulnerability expected behavior upgrade to latest patch version to fix the issue steps to reproduce no response version are you interested in contributing a solution yourself yes anything e... | 0 |
45,557 | 7,190,224,600 | IssuesEvent | 2018-02-02 16:32:40 | CCI-MOC/hil | https://api.github.com/repos/CCI-MOC/hil | closed | More consistent terminology | cleanup documentation naming | There are a number of concepts in the HaaS that we have redundant names for throughout the code, which makes variable names less consistent and thus less predictable. Here are some examples:
- [ ] name/label
...okay just the one example for now. We can edit this if/when we find more, I feel like they're there.
| 1.0 | More consistent terminology - There are a number of concepts in the HaaS that we have redundant names for throughout the code, which makes variable names less consistent and thus less predictable. Here are some examples:
- [ ] name/label
...okay just the one example for now. We can edit this if/when we find more, I fe... | non_priority | more consistent terminology there are a number of concepts in the haas that we have redundant names for throughout the code which makes variable names less consistent and thus less predictable here are some examples name label okay just the one example for now we can edit this if when we find more i feel... | 0 |
201,813 | 15,814,086,953 | IssuesEvent | 2021-04-05 08:51:47 | asiisii/Fitness-Tracker | https://api.github.com/repos/asiisii/Fitness-Tracker | closed | Charts are not updating | bug documentation | When the date or week or the user name is changed, charts need to remove the orignal data, and update it with new data. | 1.0 | Charts are not updating - When the date or week or the user name is changed, charts need to remove the orignal data, and update it with new data. | non_priority | charts are not updating when the date or week or the user name is changed charts need to remove the orignal data and update it with new data | 0 |
132,367 | 18,716,895,383 | IssuesEvent | 2021-11-03 06:48:21 | woocommerce/woocommerce-gutenberg-products-block | https://api.github.com/repos/woocommerce/woocommerce-gutenberg-products-block | closed | Decide on and design template block placeholders for the editor | needs design category: fse 🔹 block-type: templates | ## Context
For the [WooCommerce Store Editing Templates v1](https://github.com/woocommerce/woocommerce-gutenberg-products-block/issues/4926), we're converting a set of WooCommerce PHP templates to a block each. Initially, the goal is not to create fully-featured blocks but instead create one basic block per PHP temp... | 1.0 | Decide on and design template block placeholders for the editor - ## Context
For the [WooCommerce Store Editing Templates v1](https://github.com/woocommerce/woocommerce-gutenberg-products-block/issues/4926), we're converting a set of WooCommerce PHP templates to a block each. Initially, the goal is not to create ful... | non_priority | decide on and design template block placeholders for the editor context for the we re converting a set of woocommerce php templates to a block each initially the goal is not to create fully featured blocks but instead create one basic block per php template that renders a placeholder in the editor and the... | 0 |
121,973 | 12,138,355,449 | IssuesEvent | 2020-04-23 17:06:43 | CTeX-org/ctex-kit | https://api.github.com/repos/CTeX-org/ctex-kit | closed | ctex: \CTEXifname 的名称和用法问题 | ctex documentation | 目前 `ctex` 文档中对 `\CTEXifname` 的说明如下:
> `\CTEXifname` 用于根据当前章节的名字的有无设置不同的格式。……例如,设置章的标题有名字时左对齐,无名字时居中对齐,并且在标题后画一条横线。
但在代码部分的注释却是「用于判断当前标题是否有编号」,且从后续代码来看确实是用来判断是否有编号而非名字的。
所以,是否应当重新命名这一命令,或是仅仅修改文档?以及这一名称的由来有什么解释吗?
有关信息:`\CTEXifname` 是在 fbfc484f81c1a9568c02642c541d249562b74e26 引入的,之后基本没有做过修改。 | 1.0 | ctex: \CTEXifname 的名称和用法问题 - 目前 `ctex` 文档中对 `\CTEXifname` 的说明如下:
> `\CTEXifname` 用于根据当前章节的名字的有无设置不同的格式。……例如,设置章的标题有名字时左对齐,无名字时居中对齐,并且在标题后画一条横线。
但在代码部分的注释却是「用于判断当前标题是否有编号」,且从后续代码来看确实是用来判断是否有编号而非名字的。
所以,是否应当重新命名这一命令,或是仅仅修改文档?以及这一名称的由来有什么解释吗?
有关信息:`\CTEXifname` 是在 fbfc484f81c1a9568c02642c541d249562b74e26 引入的,之... | non_priority | ctex ctexifname 的名称和用法问题 目前 ctex 文档中对 ctexifname 的说明如下: ctexifname 用于根据当前章节的名字的有无设置不同的格式。……例如,设置章的标题有名字时左对齐,无名字时居中对齐,并且在标题后画一条横线。 但在代码部分的注释却是「用于判断当前标题是否有编号」,且从后续代码来看确实是用来判断是否有编号而非名字的。 所以,是否应当重新命名这一命令,或是仅仅修改文档?以及这一名称的由来有什么解释吗? 有关信息: ctexifname 是在 引入的,之后基本没有做过修改。 | 0 |
112,679 | 14,273,563,399 | IssuesEvent | 2020-11-21 22:20:28 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Implement material icon toggles | P4 f: material design framework severe: new feature | Icon and IconButton doesn't use colors from the current theme, it should probably read them from the primaryIconTheme property of the ThemeData. Also, by default the theme uses black and white colors while the material design spec says they should be gray.
| 1.0 | Implement material icon toggles - Icon and IconButton doesn't use colors from the current theme, it should probably read them from the primaryIconTheme property of the ThemeData. Also, by default the theme uses black and white colors while the material design spec says they should be gray.
| non_priority | implement material icon toggles icon and iconbutton doesn t use colors from the current theme it should probably read them from the primaryicontheme property of the themedata also by default the theme uses black and white colors while the material design spec says they should be gray | 0 |
64,371 | 6,901,100,074 | IssuesEvent | 2017-11-25 01:40:53 | alleyinteractive/wordpress-fieldmanager | https://api.github.com/repos/alleyinteractive/wordpress-fieldmanager | closed | Increase selector specificity for initializing display-if fields | needs-tests scope:display-if scope:field | As @danielbachhuber [noted](https://github.com/alleyinteractive/wordpress-fieldmanager/pull/399#discussion_r46553341), targeting any element with the `display-if` class has a high potential for false positives. We could reduce that potential by using a selector with some more FM-specific information.
| 1.0 | Increase selector specificity for initializing display-if fields - As @danielbachhuber [noted](https://github.com/alleyinteractive/wordpress-fieldmanager/pull/399#discussion_r46553341), targeting any element with the `display-if` class has a high potential for false positives. We could reduce that potential by using a ... | non_priority | increase selector specificity for initializing display if fields as danielbachhuber targeting any element with the display if class has a high potential for false positives we could reduce that potential by using a selector with some more fm specific information | 0 |
5,053 | 2,902,499,769 | IssuesEvent | 2015-06-18 07:27:15 | excilys/androidannotations | https://api.github.com/repos/excilys/androidannotations | closed | REST POST | Documentation | There are no more arguments and file uploading example?
I pass parameters through the following form, not accepted by the server.
@Post("/user/register")
@Accept(MediaType.APPLICATION_JSON)
ResponseEntity<User> register(MultiValueMap multiValueMap);
There is, if the multi-parameter and multi-file upload t... | 1.0 | REST POST - There are no more arguments and file uploading example?
I pass parameters through the following form, not accepted by the server.
@Post("/user/register")
@Accept(MediaType.APPLICATION_JSON)
ResponseEntity<User> register(MultiValueMap multiValueMap);
There is, if the multi-parameter and multi-... | non_priority | rest post there are no more arguments and file uploading example i pass parameters through the following form not accepted by the server post user register accept mediatype application json responseentity register multivaluemap multivaluemap there is if the multi parameter and multi file ... | 0 |
47,885 | 13,259,114,867 | IssuesEvent | 2020-08-20 16:16:11 | tech256/jobs | https://api.github.com/repos/tech256/jobs | closed | Cyber Analyst (#1405711) | Active Clearance Required Cyber Security Hiring stale | PeopleTec is currently seeking a Cyber Analyst to support our Huntsville, AL location.
PeopleTec is currently searching for a Cyber Analyst to support an Aviation customer in our Huntsville, AL location. The ideal candidate will be responsible for development of the Assess and Authorize package for various Avia... | True | Cyber Analyst (#1405711) - PeopleTec is currently seeking a Cyber Analyst to support our Huntsville, AL location.
PeopleTec is currently searching for a Cyber Analyst to support an Aviation customer in our Huntsville, AL location. The ideal candidate will be responsible for development of the Assess and Authori... | non_priority | cyber analyst peopletec is currently seeking a cyber analyst to support our huntsville al location peopletec is currently searching for a cyber analyst to support an aviation customer in our huntsville al location the ideal candidate will be responsible for development of the assess and authorize pac... | 0 |
20,701 | 27,385,849,614 | IssuesEvent | 2023-02-28 13:16:10 | microsoftgraph/msgraph-metadata | https://api.github.com/repos/microsoftgraph/msgraph-metadata | closed | beta generation failing because of delta function | Generator: Metadata Preprocessor metadata-issue blocking | [beta weekly generation is currently failing](https://microsoftgraph.visualstudio.com/Graph%20Developer%20Experiences/_build/results?buildId=106293&view=logs&j=4c81e8e4-6eb9-5def-7261-b44ad0fc1b7d&t=163839c6-f69e-5b5d-39e2-5b38e97d3fe3) because [a delta function on directory objects was added](https://dev.azure.com/msa... | 1.0 | beta generation failing because of delta function - [beta weekly generation is currently failing](https://microsoftgraph.visualstudio.com/Graph%20Developer%20Experiences/_build/results?buildId=106293&view=logs&j=4c81e8e4-6eb9-5def-7261-b44ad0fc1b7d&t=163839c6-f69e-5b5d-39e2-5b38e97d3fe3) because [a delta function on di... | non_priority | beta generation failing because of delta function because which conflicts with the derived types delta functions i believe we should introduce an xsl fix that removes the functions on the derived types only for beta only for kiota based sdk for the time being until the service fixes their definition to ... | 0 |
38,209 | 5,168,753,999 | IssuesEvent | 2017-01-17 22:28:02 | mozilla/activity-stream | https://api.github.com/repos/mozilla/activity-stream | closed | Add tests to make sure we add listeners for each event from content | Chore P3 Tests | Right now we don't actually have tests to make sure we've added listeners for every event content will send.
We should make sure all actions defined in `common/action-manager`, such as `NOTIFY_USER_EVENT`, actually triggers a handler in the addon.
| 1.0 | Add tests to make sure we add listeners for each event from content - Right now we don't actually have tests to make sure we've added listeners for every event content will send.
We should make sure all actions defined in `common/action-manager`, such as `NOTIFY_USER_EVENT`, actually triggers a handler in the addon.
| non_priority | add tests to make sure we add listeners for each event from content right now we don t actually have tests to make sure we ve added listeners for every event content will send we should make sure all actions defined in common action manager such as notify user event actually triggers a handler in the addon | 0 |
262,984 | 19,850,257,377 | IssuesEvent | 2022-01-21 11:27:49 | RaphaelNeubert/I5_GPS_Tracks | https://api.github.com/repos/RaphaelNeubert/I5_GPS_Tracks | opened | UC Tracks auflisten (Optionale Fortsetzung) Loeschen | documentation | Track loeschen als optionale Fortsetzung von UC Tracks auflisten hinzufuegen | 1.0 | UC Tracks auflisten (Optionale Fortsetzung) Loeschen - Track loeschen als optionale Fortsetzung von UC Tracks auflisten hinzufuegen | non_priority | uc tracks auflisten optionale fortsetzung loeschen track loeschen als optionale fortsetzung von uc tracks auflisten hinzufuegen | 0 |
244,199 | 26,373,668,870 | IssuesEvent | 2023-01-11 23:16:44 | snowdensb/job-dsl-plugin | https://api.github.com/repos/snowdensb/job-dsl-plugin | opened | CVE-2021-37533 (Medium) detected in commons-net-3.6.jar | security vulnerability | ## CVE-2021-37533 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-net-3.6.jar</b></p></summary>
<p>Apache Commons Net library contains a collection of network utilities and p... | True | CVE-2021-37533 (Medium) detected in commons-net-3.6.jar - ## CVE-2021-37533 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-net-3.6.jar</b></p></summary>
<p>Apache Commons Ne... | non_priority | cve medium detected in commons net jar cve medium severity vulnerability vulnerable library commons net jar apache commons net library contains a collection of network utilities and protocol implementations supported protocols include echo finger ftp nntp ntp s smtp s t... | 0 |
1,219 | 5,290,444,148 | IssuesEvent | 2017-02-08 19:54:35 | reactphp/react | https://api.github.com/repos/reactphp/react | closed | Move Buffer to EventLoop component, add libevent implementation | architecture event-loop | The write buffer is currently in the Socket component. But it really is more general purpose. For libevent we can provide an implementation that uses [event_buffer_write](http://php.net/event_buffer_write), which may give us some speed improvements.
| 1.0 | Move Buffer to EventLoop component, add libevent implementation - The write buffer is currently in the Socket component. But it really is more general purpose. For libevent we can provide an implementation that uses [event_buffer_write](http://php.net/event_buffer_write), which may give us some speed improvements.
| non_priority | move buffer to eventloop component add libevent implementation the write buffer is currently in the socket component but it really is more general purpose for libevent we can provide an implementation that uses which may give us some speed improvements | 0 |
401,685 | 27,335,962,739 | IssuesEvent | 2023-02-26 07:46:28 | MLNLP-World/AI-Paper-Collector | https://api.github.com/repos/MLNLP-World/AI-Paper-Collector | closed | [Question]搜索的时候会出错怎么办 | documentation | **Question**
本地和colab上执行都会出错,请问下这怎么解决呢
**Screenshots**
Traceback (most recent call last):
File "main.py", line 60, in <module>
main()
File "main.py", line 43, in main
results = exec_search(indexes, candidates, query, mode, threshold, confs, limit)
File "/content/AI-Paper-Collector/searcher.py"... | 1.0 | [Question]搜索的时候会出错怎么办 - **Question**
本地和colab上执行都会出错,请问下这怎么解决呢
**Screenshots**
Traceback (most recent call last):
File "main.py", line 60, in <module>
main()
File "main.py", line 43, in main
results = exec_search(indexes, candidates, query, mode, threshold, confs, limit)
File "/content/AI-Pape... | non_priority | 搜索的时候会出错怎么办 question 本地和colab上执行都会出错,请问下这怎么解决呢 screenshots traceback most recent call last file main py line in main file main py line in main results exec search indexes candidates query mode threshold confs limit file content ai paper collector search... | 0 |
92,256 | 11,616,199,230 | IssuesEvent | 2020-02-26 15:21:22 | nextcloud/mail | https://api.github.com/repos/nextcloud/mail | closed | Dark theme in mail app | 1. to develop design help wanted papercut | *Note: I don't know if I should post here or on mail tracker. I can repost if needed.*
### Actual behaviour
With Dark theme enabled, I see the following inconsistencies:
* Folder icons are still black
 detected in xstream-1.4.5.jar | security vulnerability | ## CVE-2021-21342 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Pa... | True | CVE-2021-21342 (High) detected in xstream-1.4.5.jar - ## CVE-2021-21342 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serializatio... | non_priority | cve high detected in xstream jar cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back path to dependency file webgoat lessons vulnerable components pom xml path to vulnerable library reposi... | 0 |
342,973 | 24,762,961,532 | IssuesEvent | 2022-10-22 06:08:32 | ryan-way/newgameplus | https://api.github.com/repos/ryan-way/newgameplus | closed | Game Architecture Requirements | documentation | - Persistence
- Logging
- Monitoring (data gathering)
- Allow for long running jobs | 1.0 | Game Architecture Requirements - - Persistence
- Logging
- Monitoring (data gathering)
- Allow for long running jobs | non_priority | game architecture requirements persistence logging monitoring data gathering allow for long running jobs | 0 |
23,200 | 7,297,651,164 | IssuesEvent | 2018-02-26 14:51:14 | debrief/debrief | https://api.github.com/repos/debrief/debrief | opened | Improved Twitter posting | build help wanted | We send automated Tweets on new releases.
But, they're very boring Tweets:
We should follow an improved process. I think it's currently done by IFTTT. We should try to exte... | 1.0 | Improved Twitter posting - We send automated Tweets on new releases.
But, they're very boring Tweets:
We should follow an improved process. I think it's currently done by IF... | non_priority | improved twitter posting we send automated tweets on new releases but they re very boring tweets we should follow an improved process i think it s currently done by ifttt we should try to extend modify the function to include an image if there is on in the release notes include more descrip... | 0 |
161,222 | 12,534,179,299 | IssuesEvent | 2020-06-04 18:57:05 | astropy/astropy | https://api.github.com/repos/astropy/astropy | closed | tox -e codestyle fails on astropy/_erfa/core.py | Bug Docs testing | <!-- This comments are hidden when you submit the issue,
so you do not need to remove them! -->
<!-- Please be sure to check out our contributing guidelines,
https://github.com/astropy/astropy/blob/master/CONTRIBUTING.md .
Please be sure to check out our code of conduct,
https://github.com/astropy/astropy/blob/m... | 1.0 | tox -e codestyle fails on astropy/_erfa/core.py - <!-- This comments are hidden when you submit the issue,
so you do not need to remove them! -->
<!-- Please be sure to check out our contributing guidelines,
https://github.com/astropy/astropy/blob/master/CONTRIBUTING.md .
Please be sure to check out our code of c... | non_priority | tox e codestyle fails on astropy erfa core py this comments are hidden when you submit the issue so you do not need to remove them please be sure to check out our contributing guidelines please be sure to check out our code of conduct please have a search on our github r... | 0 |
156,089 | 19,809,459,601 | IssuesEvent | 2022-01-19 10:35:00 | benchmarkdebricked/angular | https://api.github.com/repos/benchmarkdebricked/angular | opened | CVE-2018-20834 (High) detected in tar-2.2.1.tgz | security vulnerability | ## CVE-2018-20834 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/ta... | True | CVE-2018-20834 (High) detected in tar-2.2.1.tgz - ## CVE-2018-20834 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-2.2.1.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home ... | non_priority | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href dependency hierarchy compiler cli tgz root library chokidar tgz fsevents tgz node pre gyp ... | 0 |
65,927 | 12,697,398,558 | IssuesEvent | 2020-06-22 11:45:37 | Abbassihraf/P-curiosity-LAB | https://api.github.com/repos/Abbassihraf/P-curiosity-LAB | opened | Learning center | Code | - All versions
- [ ] include nav
- [ ] latest projects webinars and posts
- [ ] new Blog posts
- [ ] popular blog posts
- [ ] events
- [ ] get started
- [ ] include footer | 1.0 | Learning center - - All versions
- [ ] include nav
- [ ] latest projects webinars and posts
- [ ] new Blog posts
- [ ] popular blog posts
- [ ] events
- [ ] get started
- [ ] include footer | non_priority | learning center all versions include nav latest projects webinars and posts new blog posts popular blog posts events get started include footer | 0 |
127,367 | 17,263,574,501 | IssuesEvent | 2021-07-22 10:58:27 | gitpod-io/gitpod | https://api.github.com/repos/gitpod-io/gitpod | closed | [Dashboard] Project Configuration | component: dashboard needs visual design 💄 roadmap item: teams & projects 🧑🚀 crew: teams and projects | Part of the [onboarding flow](https://www.notion.so/gitpod/Onboarding-Flow-bc21ce30f91c42b88bbce42ab58d17c2) (internal) after importing a git repository as a project is to guide users through the configuration steps in order to get them into a prebuilt ready-to-code dev environment.
This includes a) configuring `.gi... | 1.0 | [Dashboard] Project Configuration - Part of the [onboarding flow](https://www.notion.so/gitpod/Onboarding-Flow-bc21ce30f91c42b88bbce42ab58d17c2) (internal) after importing a git repository as a project is to guide users through the configuration steps in order to get them into a prebuilt ready-to-code dev environment.
... | non_priority | project configuration part of the internal after importing a git repository as a project is to guide users through the configuration steps in order to get them into a prebuilt ready to code dev environment this includes a configuring gitpod yml and gitpod dockerfile for the project b triggering a... | 0 |
490 | 7,022,469,429 | IssuesEvent | 2017-12-22 10:42:58 | zcash/zcash | https://api.github.com/repos/zcash/zcash | opened | Improve serialization of MerklePath | portability protocol fragility | `MerklePath` contains vectors of `bool`. Currently, these are [directly serialized](https://github.com/zcash/zcash/blob/master/src/zcash/IncrementalMerkleTree.hpp#L15), which causes the `bool`s to be converted to `char`s [](https://github.com/zcash/zcash/blob/master/src/serialize.h#L230). This is an ambiguous serializa... | True | Improve serialization of MerklePath - `MerklePath` contains vectors of `bool`. Currently, these are [directly serialized](https://github.com/zcash/zcash/blob/master/src/zcash/IncrementalMerkleTree.hpp#L15), which causes the `bool`s to be converted to `char`s [](https://github.com/zcash/zcash/blob/master/src/serialize.h... | non_priority | improve serialization of merklepath merklepath contains vectors of bool currently these are which causes the bool s to be converted to char s this is an ambiguous serialization but is also very inefficient a more efficient format would be to use bit arrays one question i haven t yet dete... | 0 |
199,415 | 22,693,327,655 | IssuesEvent | 2022-07-05 01:13:40 | Kijacode/dotfiles | https://api.github.com/repos/Kijacode/dotfiles | opened | CVE-2022-23302 (High) detected in org.apache.log4j_1.2.15.v201012070815.jar | security vulnerability | ## CVE-2022-23302 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>org.apache.log4j_1.2.15.v201012070815.jar</b></p></summary>
<p></p>
<p>Library home page: <a href="http://eclipse.mirr... | True | CVE-2022-23302 (High) detected in org.apache.log4j_1.2.15.v201012070815.jar - ## CVE-2022-23302 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>org.apache.log4j_1.2.15.v201012070815.jar... | non_priority | cve high detected in org apache jar cve high severity vulnerability vulnerable library org apache jar library home page a href path to vulnerable library vscode extensions redhat java server plugins org apache jar dependency hierarchy ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.