Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 844 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 12
values | text_combine stringlengths 96 261k | label stringclasses 2
values | text stringlengths 96 248k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
205,223 | 15,964,725,111 | IssuesEvent | 2021-04-16 06:43:36 | nicoleang09/pe | https://api.github.com/repos/nicoleang09/pe | opened | Ordering of deliveries not stated in sections where delivery status is set | severity.Low type.DocumentationBug | As a user who jumped straight into the features section, I was very confused when I marked orders 1, 2 and 3 as delivered and they disappeared from view. This behaviour is not stated in the `delivered` feature section and can potentially be confusing for users.
 | buildsystem compiler:msvc platform:windows | I'm (sort-of) interested in getting this working under VS2013, so I'd have a native-built neovim instead of relying on MinGW or similar (although this may be a valid goal as well)
I'd like to collate issues here that are stopping compilation of neovim on Windows on VS2013, in lieu of GitHub having proper blocker/iss... | 1.0 | [RFC] / Master issue: Compiling under Windows (VS2013) - I'm (sort-of) interested in getting this working under VS2013, so I'd have a native-built neovim instead of relying on MinGW or similar (although this may be a valid goal as well)
I'd like to collate issues here that are stopping compilation of neovim on Windo... | non_priority | master issue compiling under windows i m sort of interested in getting this working under so i d have a native built neovim instead of relying on mingw or similar although this may be a valid goal as well i d like to collate issues here that are stopping compilation of neovim on windows on in li... | 0 |
69,540 | 8,419,284,293 | IssuesEvent | 2018-10-15 06:06:04 | monteirocamis/trocatexproject | https://api.github.com/repos/monteirocamis/trocatexproject | opened | Logo TrocaTex | UX/UI designer frontend help wanted photoshop | We need a logo for our project that shows change, movement , eco and modern stuff .
Insert your idea on _Imgs_ folder | 1.0 | Logo TrocaTex - We need a logo for our project that shows change, movement , eco and modern stuff .
Insert your idea on _Imgs_ folder | non_priority | logo trocatex we need a logo for our project that shows change movement eco and modern stuff insert your idea on imgs folder | 0 |
2,865 | 10,271,528,735 | IssuesEvent | 2019-08-23 16:19:34 | arcticicestudio/arctic | https://api.github.com/repos/arcticicestudio/arctic | opened | GitHub code owners | context-workflow scope-maintainability scope-quality scope-stability type-task | <p align="center"><img src="https://user-images.githubusercontent.com/7836623/63598769-85c23200-c5c0-11e9-967e-c8b3e5b43458.png" width="18%" /></p>
The project should adapt to GitHub's [code owners][intro] feature. This will allow to define matching pattern for project paths to automatically add all required reviewe... | True | GitHub code owners - <p align="center"><img src="https://user-images.githubusercontent.com/7836623/63598769-85c23200-c5c0-11e9-967e-c8b3e5b43458.png" width="18%" /></p>
The project should adapt to GitHub's [code owners][intro] feature. This will allow to define matching pattern for project paths to automatically add... | non_priority | github code owners the project should adapt to github s feature this will allow to define matching pattern for project paths to automatically add all required reviewers of the core team and contributors to new prs see for more details sidebar for code owner pr r... | 0 |
410,310 | 27,779,249,657 | IssuesEvent | 2023-03-16 19:36:57 | mindsdb/mindsdb | https://api.github.com/repos/mindsdb/mindsdb | closed | [Docs] Update a link to the Apache Hive integration | help wanted good first issue documentation first-timers-only | ## Instructions :page_facing_up:
Here are the step-by-step instructions:
1. Go to the file `/mindsdb/README.md`.
2. Find the section titled `## Database Integrations`. This section contains a table with integrations and their logos.
3. Find the below HTML tag:
`<a href="https://docs.mindsdb.com/"><img sr... | 1.0 | [Docs] Update a link to the Apache Hive integration - ## Instructions :page_facing_up:
Here are the step-by-step instructions:
1. Go to the file `/mindsdb/README.md`.
2. Find the section titled `## Database Integrations`. This section contains a table with integrations and their logos.
3. Find the below HTM... | non_priority | update a link to the apache hive integration instructions page facing up here are the step by step instructions go to the file mindsdb readme md find the section titled database integrations this section contains a table with integrations and their logos find the below html tag... | 0 |
176,352 | 21,408,678,992 | IssuesEvent | 2022-04-22 01:40:32 | liaozan/houses_single | https://api.github.com/repos/liaozan/houses_single | closed | CVE-2016-10735 (Medium) detected in bootstrap-3.1.1.js, bootstrap-3.1.1.min.js | security vulnerability | ## CVE-2016-10735 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-3.1.1.js</b>, <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>
<details><summary><b>bootstrap-3.1.1.js</b... | True | CVE-2016-10735 (Medium) detected in bootstrap-3.1.1.js, bootstrap-3.1.1.min.js - ## CVE-2016-10735 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>bootstrap-3.1.1.js</b>, <b>bootstr... | non_priority | cve medium detected in bootstrap js bootstrap min js cve medium severity vulnerability vulnerable libraries bootstrap js bootstrap min js bootstrap js the most popular front end framework for developing responsive mobile first projects on the web ... | 0 |
24,935 | 4,118,267,941 | IssuesEvent | 2016-06-08 10:45:23 | mathjax/MathJax | https://api.github.com/repos/mathjax/MathJax | closed | [Math Processing Error] when replacing msub by msup in an expression with nested mmultiscripts | Accepted Merged Test Needed | Hi, here a surprising result I just encountered today :
The only difference between (A) and (C) is I replaced msub by msup, the difference between (B) and (C) seems to be the mrow.
**(A) This works:**
```
<math>
<mmultiscripts>
<mmultiscripts>
<mi>A</mi>
<mi>B</mi>
<mprescripts />
<none />
... | 1.0 | [Math Processing Error] when replacing msub by msup in an expression with nested mmultiscripts - Hi, here a surprising result I just encountered today :
The only difference between (A) and (C) is I replaced msub by msup, the difference between (B) and (C) seems to be the mrow.
**(A) This works:**
```
<math>
<mm... | non_priority | when replacing msub by msup in an expression with nested mmultiscripts hi here a surprising result i just encountered today the only difference between a and c is i replaced msub by msup the difference between b and c seems to be the mrow a this works a b ... | 0 |
98,393 | 8,675,533,318 | IssuesEvent | 2018-11-30 11:10:27 | NativeScript/nativescript-cli | https://api.github.com/repos/NativeScript/nativescript-cli | closed | Don't prepare the project on preview command | ready for test | **Is your feature request related to a problem? Please describe.**
The project is prepared on preview command but actually no prepare is needed. This way the liveSync to preview app will be faster.
| 1.0 | Don't prepare the project on preview command - **Is your feature request related to a problem? Please describe.**
The project is prepared on preview command but actually no prepare is needed. This way the liveSync to preview app will be faster.
| non_priority | don t prepare the project on preview command is your feature request related to a problem please describe the project is prepared on preview command but actually no prepare is needed this way the livesync to preview app will be faster | 0 |
9,635 | 24,939,272,677 | IssuesEvent | 2022-10-31 17:30:47 | Azure/azure-sdk | https://api.github.com/repos/Azure/azure-sdk | closed | Board Review: Event Grid new system events | architecture board-review | ## Contacts and Timeline
* Responsible service team: DataBox, APIM
* Main contacts: @JoshLove-msft
* Expected code complete date: 11/4
* Expected release date: 11/7
## About the Service
* Link to the service REST APIs:
https://github.com/Azure/azure-rest-api-specs/pull/21157
https://github.com/Azure/az... | 1.0 | Board Review: Event Grid new system events - ## Contacts and Timeline
* Responsible service team: DataBox, APIM
* Main contacts: @JoshLove-msft
* Expected code complete date: 11/4
* Expected release date: 11/7
## About the Service
* Link to the service REST APIs:
https://github.com/Azure/azure-rest-api-... | non_priority | board review event grid new system events contacts and timeline responsible service team databox apim main contacts joshlove msft expected code complete date expected release date about the service link to the service rest apis artifacts required per languag... | 0 |
359,873 | 25,259,614,612 | IssuesEvent | 2022-11-15 21:24:59 | bUnit-dev/bUnit | https://api.github.com/repos/bUnit-dev/bUnit | closed | Investigate QuickGrid in .NET7 | documentation | With the ASP.NET Core 7 Preview 6 announcements they also introduced QuickGrid as an external package. Even though this is not a first class citizen directly inside aspnet chances are lots of people will use it as a lightweight alternative to full blown grids.
Currently it is flagged experimental. We should have an e... | 1.0 | Investigate QuickGrid in .NET7 - With the ASP.NET Core 7 Preview 6 announcements they also introduced QuickGrid as an external package. Even though this is not a first class citizen directly inside aspnet chances are lots of people will use it as a lightweight alternative to full blown grids.
Currently it is flagged ... | non_priority | investigate quickgrid in with the asp net core preview announcements they also introduced quickgrid as an external package even though this is not a first class citizen directly inside aspnet chances are lots of people will use it as a lightweight alternative to full blown grids currently it is flagged exp... | 0 |
166,513 | 12,960,091,102 | IssuesEvent | 2020-07-20 13:54:43 | FreeRDP/FreeRDP | https://api.github.com/repos/FreeRDP/FreeRDP | closed | Backport Use CMake to detect availability of getlogin_r | backport-to-stable fixed-waiting-test | Releated pull request for master:
#6317 | 1.0 | Backport Use CMake to detect availability of getlogin_r - Releated pull request for master:
#6317 | non_priority | backport use cmake to detect availability of getlogin r releated pull request for master | 0 |
122,630 | 12,156,714,029 | IssuesEvent | 2020-04-25 18:31:54 | webpack/webpack | https://api.github.com/repos/webpack/webpack | closed | Create Outreach Communities | documentation inactive | Successfully we were able to help start and perpetuate a community for China for webpack. It's been extremely successful and we continue to see their traffic as 2nd to USA in docs, and repo page visitors.
However [it came to our attention on twitter](https://twitter.com/truth2_truth/status/848567713798791169) that ... | 1.0 | Create Outreach Communities - Successfully we were able to help start and perpetuate a community for China for webpack. It's been extremely successful and we continue to see their traffic as 2nd to USA in docs, and repo page visitors.
However [it came to our attention on twitter](https://twitter.com/truth2_truth/st... | non_priority | create outreach communities successfully we were able to help start and perpetuate a community for china for webpack it s been extremely successful and we continue to see their traffic as to usa in docs and repo page visitors however that we could maybe be doing more i m all for equality as access to op... | 0 |
78,128 | 10,040,842,708 | IssuesEvent | 2019-07-18 20:59:43 | Jerald/yolol-is-cylons | https://api.github.com/repos/Jerald/yolol-is-cylons | opened | Write getting started guide for YOLOL | documentation | - Should provide a "hello world"-like introduction to the language
- Should build a program by introducing and explaining new features
- Doesn't need to include every feature in YOLOL
- Should include: local vars, data fields, if statements, gotos, basic operators
- Should be written for a non-technical audience
-... | 1.0 | Write getting started guide for YOLOL - - Should provide a "hello world"-like introduction to the language
- Should build a program by introducing and explaining new features
- Doesn't need to include every feature in YOLOL
- Should include: local vars, data fields, if statements, gotos, basic operators
- Should be... | non_priority | write getting started guide for yolol should provide a hello world like introduction to the language should build a program by introducing and explaining new features doesn t need to include every feature in yolol should include local vars data fields if statements gotos basic operators should be... | 0 |
49,617 | 13,454,886,939 | IssuesEvent | 2020-09-09 04:54:19 | Techini/vulnado | https://api.github.com/repos/Techini/vulnado | opened | CVE-2019-14893 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-14893 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14893 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-14893 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm vulnado pom xml p... | 0 |
233,773 | 19,058,939,278 | IssuesEvent | 2021-11-26 03:13:51 | askoufis/vocab-vscode-extension | https://api.github.com/repos/askoufis/vocab-vscode-extension | closed | No unit tests | testing | There are a few simple functions that could do with some unit tests, just for sanity's sake. | 1.0 | No unit tests - There are a few simple functions that could do with some unit tests, just for sanity's sake. | non_priority | no unit tests there are a few simple functions that could do with some unit tests just for sanity s sake | 0 |
96,583 | 8,617,669,320 | IssuesEvent | 2018-11-20 06:44:49 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | projecttesting20 : ApiV1IssueTrackersSkillTypeTypeGetQueryParamPagesizeNegativeNumber | projecttesting20 | Project : projecttesting20
Job : uat 1
Env : uat
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set... | 1.0 | projecttesting20 : ApiV1IssueTrackersSkillTypeTypeGetQueryParamPagesizeNegativeNumber - Project : projecttesting20
Job : uat 1
Env : uat
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, ... | non_priority | project job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request respon... | 0 |
52,871 | 6,284,460,694 | IssuesEvent | 2017-07-19 07:50:23 | manchesergit/material-ui | https://api.github.com/repos/manchesergit/material-ui | opened | Test Avatar ID generation | unit testing | Tests need to be added to prove that Avatar
[ ] produces a unique ID for itself if none is given
[ ] uses the ID given in the properties | 1.0 | Test Avatar ID generation - Tests need to be added to prove that Avatar
[ ] produces a unique ID for itself if none is given
[ ] uses the ID given in the properties | non_priority | test avatar id generation tests need to be added to prove that avatar produces a unique id for itself if none is given uses the id given in the properties | 0 |
64,034 | 8,706,838,979 | IssuesEvent | 2018-12-06 04:58:55 | BrowseHandsfree/handsfreeJS | https://api.github.com/repos/BrowseHandsfree/handsfreeJS | closed | Settings API | ✨ enhancement 📖 Documentation 🔌 Plugin | Let's add in a settings API, which will allow people to run Handsfree.js on low-powered devices (or take advantage of beefier ones). This will also enable multi-tracking support and more
**Settings Route**
- [x] Create a `/settings` route. This route will be reused at browsehandsfree.com
- [x] Add FPS checker for ... | 1.0 | Settings API - Let's add in a settings API, which will allow people to run Handsfree.js on low-powered devices (or take advantage of beefier ones). This will also enable multi-tracking support and more
**Settings Route**
- [x] Create a `/settings` route. This route will be reused at browsehandsfree.com
- [x] Add F... | non_priority | settings api let s add in a settings api which will allow people to run handsfree js on low powered devices or take advantage of beefier ones this will also enable multi tracking support and more settings route create a settings route this route will be reused at browsehandsfree com add fps c... | 0 |
22,145 | 11,494,905,042 | IssuesEvent | 2020-02-12 03:04:07 | melanchall/drywetmidi | https://api.github.com/repos/melanchall/drywetmidi | closed | Parsing performance | performance | I seem to be getting slow results when parsing.
Midi file with 14,000 events:
`GetTempoMap() = 140-270ms `
`GetNotes() = 200-300ms`
`GetTimedEvents() + TimeAs() = 180-322ms`
```
foreach (TimedEvent e in midi.GetTimedEvents())
{ ... | True | Parsing performance - I seem to be getting slow results when parsing.
Midi file with 14,000 events:
`GetTempoMap() = 140-270ms `
`GetNotes() = 200-300ms`
`GetTimedEvents() + TimeAs() = 180-322ms`
```
foreach (TimedEvent e in midi.GetTimedEvents())
... | non_priority | parsing performance i seem to be getting slow results when parsing midi file with events gettempomap getnotes gettimedevents timeas foreach timedevent e in midi gettimedevents ... | 0 |
32,281 | 12,102,277,258 | IssuesEvent | 2020-04-20 16:26:23 | Hyraze/infinite | https://api.github.com/repos/Hyraze/infinite | opened | WS-2019-0063 (High) detected in js-yaml-3.7.0.tgz, js-yaml-3.12.1.tgz | security vulnerability | ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>js-yaml-3.7.0.tgz</b>, <b>js-yaml-3.12.1.tgz</b></p></summary>
<p>
<details><summary><b>js-yaml-3.7.0.tgz</b></p></sum... | True | WS-2019-0063 (High) detected in js-yaml-3.7.0.tgz, js-yaml-3.12.1.tgz - ## WS-2019-0063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>js-yaml-3.7.0.tgz</b>, <b>js-yaml-3.12.1.tgz</b... | non_priority | ws high detected in js yaml tgz js yaml tgz ws high severity vulnerability vulnerable libraries js yaml tgz js yaml tgz js yaml tgz yaml parser and serializer library home page a href path to dependency file tmp ws scm infinite packag... | 0 |
310,914 | 26,753,718,910 | IssuesEvent | 2023-01-30 21:53:00 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: Plugin Functional Tests.test/plugin_functional/test_suites/saved_objects_management/visible_in_management·ts - Saved Objects Management types with `visibleInManagement` "before all" hook in "types with `visibleInManagement` " | failed-test | A test failed on a tracked branch
```
Error: Forcing mocha to abort
at Object.next (node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/run_tests.js:42:25)
at SafeSubscriber.__tryOrUnsub (node_modules/rxjs/src/internal/Subscriber.ts:265:10)
at SafeSubscriber.next (node_modules/rxjs/src/inte... | 1.0 | Failing test: Plugin Functional Tests.test/plugin_functional/test_suites/saved_objects_management/visible_in_management·ts - Saved Objects Management types with `visibleInManagement` "before all" hook in "types with `visibleInManagement` " - A test failed on a tracked branch
```
Error: Forcing mocha to abort
at O... | non_priority | failing test plugin functional tests test plugin functional test suites saved objects management visible in management·ts saved objects management types with visibleinmanagement before all hook in types with visibleinmanagement a test failed on a tracked branch error forcing mocha to abort at o... | 0 |
41,102 | 6,891,241,217 | IssuesEvent | 2017-11-22 16:26:09 | rkt/rkt | https://api.github.com/repos/rkt/rkt | closed | run/volume: please document recursive=<bool> flag | area/usability component/stage0 kind/documentation low hanging fruit | We run `rkt` on a host with a lot of automount points (1000 or so). When using stage1-coreos, we could simply mount the parent directory into a pod, and have the automounter on the host resolve requests from the pod. This was great.
Having switched to stage1-fly (because of #3639), we see that submounts of parent ... | 1.0 | run/volume: please document recursive=<bool> flag - We run `rkt` on a host with a lot of automount points (1000 or so). When using stage1-coreos, we could simply mount the parent directory into a pod, and have the automounter on the host resolve requests from the pod. This was great.
Having switched to stage1-fly ... | non_priority | run volume please document recursive flag we run rkt on a host with a lot of automount points or so when using coreos we could simply mount the parent directory into a pod and have the automounter on the host resolve requests from the pod this was great having switched to fly because of w... | 0 |
75,107 | 9,201,885,633 | IssuesEvent | 2019-03-07 20:51:19 | open-apparel-registry/open-apparel-registry | https://api.github.com/repos/open-apparel-registry/open-apparel-registry | closed | Design review of the facility matching page | design tested/verified | ## Overview
Logged in users can upload a CSV facility list at /contribute and that data is programmatically matched to a master list of facilities. Errors and uncertainties in that matching process are shown in a table view. Review the table view interface and make suggestions to improve the organization and usabili... | 1.0 | Design review of the facility matching page - ## Overview
Logged in users can upload a CSV facility list at /contribute and that data is programmatically matched to a master list of facilities. Errors and uncertainties in that matching process are shown in a table view. Review the table view interface and make sugge... | non_priority | design review of the facility matching page overview logged in users can upload a csv facility list at contribute and that data is programmatically matched to a master list of facilities errors and uncertainties in that matching process are shown in a table view review the table view interface and make sugge... | 0 |
16,982 | 9,958,511,900 | IssuesEvent | 2019-07-05 21:30:37 | n-psk/reactIOTEAU | https://api.github.com/repos/n-psk/reactIOTEAU | opened | WS-2019-0040 (Medium) detected in highcharts-5.0.15.tgz | security vulnerability | ## WS-2019-0040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>highcharts-5.0.15.tgz</b></p></summary>
<p>JavaScript charting framework</p>
<p>Library home page: <a href="https://re... | True | WS-2019-0040 (Medium) detected in highcharts-5.0.15.tgz - ## WS-2019-0040 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>highcharts-5.0.15.tgz</b></p></summary>
<p>JavaScript charti... | non_priority | ws medium detected in highcharts tgz ws medium severity vulnerability vulnerable library highcharts tgz javascript charting framework library home page a href path to dependency file reactioteau iot package json path to vulnerable library reactioteau iot no... | 0 |
19,917 | 10,430,974,064 | IssuesEvent | 2019-09-17 08:06:06 | hapijs/iron | https://api.github.com/repos/hapijs/iron | closed | Exposing PBKDF2 hashing algorithm for key generation, or just upgrading it | enhancement security | I was glancing through Iron and I noticed that there was a slight mismatch between the minimum password length and the key derivation method, namely the SHA-1 hashing algorithm used inside PBKDF2.
This post explains it pretty concisely I think (https://www.chosenplaintext.ca/2015/10/08/pbkdf2-design-flaw.html).
T... | True | Exposing PBKDF2 hashing algorithm for key generation, or just upgrading it - I was glancing through Iron and I noticed that there was a slight mismatch between the minimum password length and the key derivation method, namely the SHA-1 hashing algorithm used inside PBKDF2.
This post explains it pretty concisely I th... | non_priority | exposing hashing algorithm for key generation or just upgrading it i was glancing through iron and i noticed that there was a slight mismatch between the minimum password length and the key derivation method namely the sha hashing algorithm used inside this post explains it pretty concisely i think ... | 0 |
108,852 | 23,671,728,150 | IssuesEvent | 2022-08-27 13:10:31 | kiwiproject/kiwi-test | https://api.github.com/repos/kiwiproject/kiwi-test | closed | Can we remove the dependency on commons-io from H2FileBasedDatabaseExtension? | investigation code cleanup | It is only required because the `H2FileBasedDatabaseExtension` uses `FileUtils.deleteDirectory` to recursively delete the H2 database directly. If we can find a JDK (or even Guava) alternative, then we can remove the `commons-io` dependency entirely since this is the only place `kiwi-test` uses anything from it. | 1.0 | Can we remove the dependency on commons-io from H2FileBasedDatabaseExtension? - It is only required because the `H2FileBasedDatabaseExtension` uses `FileUtils.deleteDirectory` to recursively delete the H2 database directly. If we can find a JDK (or even Guava) alternative, then we can remove the `commons-io` dependency... | non_priority | can we remove the dependency on commons io from it is only required because the uses fileutils deletedirectory to recursively delete the database directly if we can find a jdk or even guava alternative then we can remove the commons io dependency entirely since this is the only place kiwi test uses... | 0 |
7,928 | 8,124,120,793 | IssuesEvent | 2018-08-16 16:29:24 | Microsoft/visualfsharp | https://api.github.com/repos/Microsoft/visualfsharp | closed | Rename Feature Corrupts Unsaved Files in VS2017 15.7.1 | Area-IDE Language Service Urgency-Soon | When you rename a symbol that exists in another file that is open with pending changes, the rename operation is computed using the character positions of the _unsaved_ file. This means if you've added _any_ lines or changed target symbol positions in the target files, the replace operation will overwrite any text that ... | 1.0 | Rename Feature Corrupts Unsaved Files in VS2017 15.7.1 - When you rename a symbol that exists in another file that is open with pending changes, the rename operation is computed using the character positions of the _unsaved_ file. This means if you've added _any_ lines or changed target symbol positions in the target ... | non_priority | rename feature corrupts unsaved files in when you rename a symbol that exists in another file that is open with pending changes the rename operation is computed using the character positions of the unsaved file this means if you ve added any lines or changed target symbol positions in the target files ... | 0 |
152,821 | 19,697,598,591 | IssuesEvent | 2022-01-12 13:45:14 | RG4421/mmRTLS | https://api.github.com/repos/RG4421/mmRTLS | closed | CVE-2021-35065 (Medium) detected in glob-parent-2.0.0.tgz, glob-parent-5.1.2.tgz - autoclosed | security vulnerability | ## CVE-2021-35065 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-2.0.0.tgz</b>, <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-2.0.0.t... | True | CVE-2021-35065 (Medium) detected in glob-parent-2.0.0.tgz, glob-parent-5.1.2.tgz - autoclosed - ## CVE-2021-35065 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-2.0.0.t... | non_priority | cve medium detected in glob parent tgz glob parent tgz autoclosed cve medium severity vulnerability vulnerable libraries glob parent tgz glob parent tgz glob parent tgz strips glob magic from a string to provide the parent path library home pag... | 0 |
287,641 | 21,663,998,077 | IssuesEvent | 2022-05-07 00:02:58 | miversen33/netman.nvim | https://api.github.com/repos/miversen33/netman.nvim | closed | Netman Options (`netman.options`) Needs documentation | documentation Core | Title is self explanatory. Netman Options are used everywhere and have effectively no documentation.
We should absolutely have a vim doc for this, and probably also worth throwing something in the `wiki` for it. | 1.0 | Netman Options (`netman.options`) Needs documentation - Title is self explanatory. Netman Options are used everywhere and have effectively no documentation.
We should absolutely have a vim doc for this, and probably also worth throwing something in the `wiki` for it. | non_priority | netman options netman options needs documentation title is self explanatory netman options are used everywhere and have effectively no documentation we should absolutely have a vim doc for this and probably also worth throwing something in the wiki for it | 0 |
95,532 | 16,096,805,712 | IssuesEvent | 2021-04-27 01:51:40 | emilwareus/spring-boot | https://api.github.com/repos/emilwareus/spring-boot | opened | CVE-2021-28168 (Medium) detected in jersey-common-2.28.jar | security vulnerability | ## CVE-2021-28168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jersey-common-2.28.jar</b></p></summary>
<p>Jersey core common packages</p>
<p>Library home page: <a href="https://p... | True | CVE-2021-28168 (Medium) detected in jersey-common-2.28.jar - ## CVE-2021-28168 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jersey-common-2.28.jar</b></p></summary>
<p>Jersey core... | non_priority | cve medium detected in jersey common jar cve medium severity vulnerability vulnerable library jersey common jar jersey core common packages library home page a href path to dependency file spring boot spring boot project spring boot autoconfigure pom xml path to vulnerab... | 0 |
281,703 | 24,413,370,035 | IssuesEvent | 2022-10-05 14:07:07 | apache/beam | https://api.github.com/repos/apache/beam | closed | Dataflow streaming tests failing new AfterSynchronizedProcessingTime test | runners dataflow P1 bug test-failures flake | The new test `org.apache.beam.sdk.transforms.GroupByKeyTest$BasicTests.testAfterProcessingTimeContinuationTriggerUsingState` is failing on Dataflow streaming. Most likely the delays are not large enough for Dataflow's bundle latency, so the triggering does not occur early.
https://ci-beam.apache.org/job/beam_PostCom... | 1.0 | Dataflow streaming tests failing new AfterSynchronizedProcessingTime test - The new test `org.apache.beam.sdk.transforms.GroupByKeyTest$BasicTests.testAfterProcessingTimeContinuationTriggerUsingState` is failing on Dataflow streaming. Most likely the delays are not large enough for Dataflow's bundle latency, so the tri... | non_priority | dataflow streaming tests failing new aftersynchronizedprocessingtime test the new test org apache beam sdk transforms groupbykeytest basictests testafterprocessingtimecontinuationtriggerusingstate is failing on dataflow streaming most likely the delays are not large enough for dataflow s bundle latency so the tri... | 0 |
39,259 | 5,064,659,089 | IssuesEvent | 2016-12-23 08:00:18 | tor4kichi/Hohoema | https://api.github.com/repos/tor4kichi/Hohoema | opened | メニューを含めたベースレイアウトを修正 | ui_design | 以下の画面タイプごとにレイアウトが適用されるように変更します。
* 中~大画面向け
* モバイル向け
* XInput向け
PCで操作中の場合にXInputレイアウトを使用しないオプションを利用可能にします。 | 1.0 | メニューを含めたベースレイアウトを修正 - 以下の画面タイプごとにレイアウトが適用されるように変更します。
* 中~大画面向け
* モバイル向け
* XInput向け
PCで操作中の場合にXInputレイアウトを使用しないオプションを利用可能にします。 | non_priority | メニューを含めたベースレイアウトを修正 以下の画面タイプごとにレイアウトが適用されるように変更します。 中~大画面向け モバイル向け xinput向け pcで操作中の場合にxinputレイアウトを使用しないオプションを利用可能にします。 | 0 |
31,814 | 6,001,046,088 | IssuesEvent | 2017-06-05 07:52:04 | brave/browser-laptop | https://api.github.com/repos/brave/browser-laptop | closed | Snap Package for Brave | documentation ✍ installation OS/linux-distros QA/no-qa-needed release-notes/exclude suggestion | - Did you search for similar issues before submitting this one?
**Yes**
- Describe the issue you encountered:
**Installing on Ubuntu, derivatives, and Linux in general could be much easier.**
- Platform (Win7, 8, 10? macOS? Linux distro?):
**Ubuntu and Elementary (Linux)**
### What are Snaps?
Snap packagin... | 1.0 | Snap Package for Brave - - Did you search for similar issues before submitting this one?
**Yes**
- Describe the issue you encountered:
**Installing on Ubuntu, derivatives, and Linux in general could be much easier.**
- Platform (Win7, 8, 10? macOS? Linux distro?):
**Ubuntu and Elementary (Linux)**
### What ... | non_priority | snap package for brave did you search for similar issues before submitting this one yes describe the issue you encountered installing on ubuntu derivatives and linux in general could be much easier platform macos linux distro ubuntu and elementary linux what are ... | 0 |
4,881 | 3,897,418,196 | IssuesEvent | 2016-04-16 12:01:58 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 15632010: Cycling between spaces for an application by clicking the dock icon does not update keyboard focus | classification:ui/usability reproducible:always status:open | #### Description
Summary:
On 10.9 (I don't have a 10.8 machine handy to test against), clicking the dock icon for an application with windows on multiple spaces does not update keyboard focus cycling between spaces.
Steps to Reproduce:
1. Open two TextEdit windows. (I've also reproduced this with Preview, Safari,... | True | 15632010: Cycling between spaces for an application by clicking the dock icon does not update keyboard focus - #### Description
Summary:
On 10.9 (I don't have a 10.8 machine handy to test against), clicking the dock icon for an application with windows on multiple spaces does not update keyboard focus cycling between... | non_priority | cycling between spaces for an application by clicking the dock icon does not update keyboard focus description summary on i don t have a machine handy to test against clicking the dock icon for an application with windows on multiple spaces does not update keyboard focus cycling between spaces ... | 0 |
128,108 | 17,410,631,314 | IssuesEvent | 2021-08-03 11:52:42 | Joystream/atlas | https://api.github.com/repos/Joystream/atlas | closed | Atlas Player: Design Ideas Backlog | design enhancement idea player ⚙ component:player | # Document Purpose
This document aims to gather all ideas for improvements and new functionalities around Atlas' video player. Design-wise, ideally, all the things below are tackled during one go.
Implementation-wise, the below items can be taken apart from the list and implemented at different points in time, as ... | 1.0 | Atlas Player: Design Ideas Backlog - # Document Purpose
This document aims to gather all ideas for improvements and new functionalities around Atlas' video player. Design-wise, ideally, all the things below are tackled during one go.
Implementation-wise, the below items can be taken apart from the list and impleme... | non_priority | atlas player design ideas backlog document purpose this document aims to gather all ideas for improvements and new functionalities around atlas video player design wise ideally all the things below are tackled during one go implementation wise the below items can be taken apart from the list and impleme... | 0 |
138,802 | 18,795,945,487 | IssuesEvent | 2021-11-08 22:20:41 | Dima2022/blueflood | https://api.github.com/repos/Dima2022/blueflood | opened | CVE-2020-36184 (High) detected in jackson-databind-2.3.1.jar, jackson-databind-2.9.2.jar | security vulnerability | ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.3.1.jar</b>, <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>
<details><summary><b>jackson-dat... | True | CVE-2020-36184 (High) detected in jackson-databind-2.3.1.jar, jackson-databind-2.9.2.jar - ## CVE-2020-36184 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.3.1.jar... | non_priority | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streami... | 0 |
7,171 | 16,902,649,427 | IssuesEvent | 2021-06-24 00:25:32 | privacy-tech-lab/optmeowt-browser-extension | https://api.github.com/repos/privacy-tech-lab/optmeowt-browser-extension | closed | New dev environment using Webpack to build Firefox & Chrome versions | architecture core functionality | This is the last big sensitive refactoring issue. Ideally, we will have one repo for both the Chrome and Firefox versions we will be developing. However, since the Firefox version will be diverging from Chrome in the near future, as well as for the sake of codebase simplicity, we need to find a way to abstract away the... | 1.0 | New dev environment using Webpack to build Firefox & Chrome versions - This is the last big sensitive refactoring issue. Ideally, we will have one repo for both the Chrome and Firefox versions we will be developing. However, since the Firefox version will be diverging from Chrome in the near future, as well as for the ... | non_priority | new dev environment using webpack to build firefox chrome versions this is the last big sensitive refactoring issue ideally we will have one repo for both the chrome and firefox versions we will be developing however since the firefox version will be diverging from chrome in the near future as well as for the ... | 0 |
22,094 | 18,668,954,968 | IssuesEvent | 2021-10-30 10:28:46 | AntennaPod/AntennaPod | https://api.github.com/repos/AntennaPod/AntennaPod | closed | 'Keep sorted' and 'Lock queue' interfere: hide latter when former is active | Type: Enhancement Area: Usability | # Checklist
<!-- Place an x in the boxes to tick them: [x] -->
- [x ] I have used the search function to see if someone else has already submitted the same feature request.
- [x ] I will only create one feature request per issue.
- [x ] I will describe the problem with as much detail as possible.
# System info
**App... | True | 'Keep sorted' and 'Lock queue' interfere: hide latter when former is active - # Checklist
<!-- Place an x in the boxes to tick them: [x] -->
- [x ] I have used the search function to see if someone else has already submitted the same feature request.
- [x ] I will only create one feature request per issue.
- [x ] I wi... | non_priority | keep sorted and lock queue interfere hide latter when former is active checklist i have used the search function to see if someone else has already submitted the same feature request i will only create one feature request per issue i will describe the problem with as much detail as possible ... | 0 |
63,155 | 17,396,327,442 | IssuesEvent | 2021-08-02 13:53:54 | vector-im/element-web | https://api.github.com/repos/vector-im/element-web | closed | silently stops receiving new messages | P-low P3 S-Critical T-Defect | Riot seems to sometimes spontaneously stop receiving new messages. :(
Sending messages works, but they don't seem to come back down the sync.
I've sent a couple of rageshakes.
FF57.0b14 on Debian, using /develop | 1.0 | silently stops receiving new messages - Riot seems to sometimes spontaneously stop receiving new messages. :(
Sending messages works, but they don't seem to come back down the sync.
I've sent a couple of rageshakes.
FF57.0b14 on Debian, using /develop | non_priority | silently stops receiving new messages riot seems to sometimes spontaneously stop receiving new messages sending messages works but they don t seem to come back down the sync i ve sent a couple of rageshakes on debian using develop | 0 |
176,118 | 21,366,963,767 | IssuesEvent | 2022-04-20 03:28:58 | jitrapon/glom-android | https://api.github.com/repos/jitrapon/glom-android | opened | CVE-2021-35515 (High) detected in commons-compress-1.12.jar | security vulnerability | ## CVE-2021-35515 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.12.jar</b></p></summary>
<p>Apache Commons Compress software defines an API for working with
compre... | True | CVE-2021-35515 (High) detected in commons-compress-1.12.jar - ## CVE-2021-35515 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-compress-1.12.jar</b></p></summary>
<p>Apache Co... | non_priority | cve high detected in commons compress jar cve high severity vulnerability vulnerable library commons compress jar apache commons compress software defines an api for working with compression and archive formats these include gzip lzma xz snappy traditional unix compress... | 0 |
86,931 | 17,106,078,444 | IssuesEvent | 2021-07-09 17:58:09 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Potential performance regression in the `*IterateForEach*Span*` benchmarks | amd-perf arch-arm64 area-CodeGen-coreclr tenet-performance untriaged | While doing the .NET 5 vs .NET 6 preview 7 manual perf run I've found something that seems to be ARM64, ARM and AMD (x64) specific regression.
Repro:
```cmd
py .\scripts\benchmarks_ci.py -f net5.0 net6.0 --filter "System.Collections.IterateForEach<int32>.ReadOnlySpan" --bdn-arguments "--disasm true --memoryRando... | 1.0 | Potential performance regression in the `*IterateForEach*Span*` benchmarks - While doing the .NET 5 vs .NET 6 preview 7 manual perf run I've found something that seems to be ARM64, ARM and AMD (x64) specific regression.
Repro:
```cmd
py .\scripts\benchmarks_ci.py -f net5.0 net6.0 --filter "System.Collections.Ite... | non_priority | potential performance regression in the iterateforeach span benchmarks while doing the net vs net preview manual perf run i ve found something that seems to be arm and amd specific regression repro cmd py scripts benchmarks ci py f filter system collections iterateforeach ... | 0 |
161,774 | 25,399,225,989 | IssuesEvent | 2022-11-22 10:49:18 | team113/messenger | https://api.github.com/repos/team113/messenger | opened | Pagination | enhancement k::design k::refactor | ## Background
У любого списка должна быть пагинация.
## Problem to solve
На данный момент список контактов, чатов и сообщений прогружает N элементов без возможности что-то догружать. Нужна пагинация.
## Possible solutions
Исследовать каким образом можно удобно и универсально реализовать механ... | 1.0 | Pagination - ## Background
У любого списка должна быть пагинация.
## Problem to solve
На данный момент список контактов, чатов и сообщений прогружает N элементов без возможности что-то догружать. Нужна пагинация.
## Possible solutions
Исследовать каким образом можно удобно и универсально реал... | non_priority | pagination background у любого списка должна быть пагинация problem to solve на данный момент список контактов чатов и сообщений прогружает n элементов без возможности что то догружать нужна пагинация possible solutions исследовать каким образом можно удобно и универсально реал... | 0 |
85,545 | 15,755,010,487 | IssuesEvent | 2021-03-31 01:01:25 | yaeljacobs67/fs-agent | https://api.github.com/repos/yaeljacobs67/fs-agent | opened | CVE-2021-23358 (High) detected in underscore-1.9.1.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.9.1.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page... | True | CVE-2021-23358 (High) detected in underscore-1.9.1.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.9.1.tgz</b></p></summary>
<p>JavaScript's functi... | non_priority | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file fs agent test input ksa ksa web root ksa web src main webapp rs bo... | 0 |
1,720 | 3,353,328,447 | IssuesEvent | 2015-11-18 04:53:13 | elmsln/elmsln | https://api.github.com/repos/elmsln/elmsln | closed | rm-site.sh changes | drush related enhancement infrastructure | - [x] backup site db w/ drush before killing
- [x] back up config before killing
- [ ] try to auto target and remove the lines from the sites.php file
- [ ] remove all the confirmation and make it initial confirms, this was built by a sys admin so it asks too many questions that would need to be understood to keep a... | 1.0 | rm-site.sh changes - - [x] backup site db w/ drush before killing
- [x] back up config before killing
- [ ] try to auto target and remove the lines from the sites.php file
- [ ] remove all the confirmation and make it initial confirms, this was built by a sys admin so it asks too many questions that would need to be... | non_priority | rm site sh changes backup site db w drush before killing back up config before killing try to auto target and remove the lines from the sites php file remove all the confirmation and make it initial confirms this was built by a sys admin so it asks too many questions that would need to be underst... | 0 |
109,456 | 16,845,821,053 | IssuesEvent | 2021-06-19 13:09:01 | mukul-seagate11/cortx-s3server | https://api.github.com/repos/mukul-seagate11/cortx-s3server | closed | CVE-2018-19362 (High) detected in jackson-databind-2.6.6.jar | security vulnerability | ## CVE-2018-19362 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2018-19362 (High) detected in jackson-databind-2.6.6.jar - ## CVE-2018-19362 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.6.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file cortx auth utils jclient pom ... | 0 |
143,987 | 11,590,404,994 | IssuesEvent | 2020-02-24 06:36:49 | escobard/create-app | https://api.github.com/repos/escobard/create-app | closed | UI - Note tests | Refactor UI Unit Tests enhancement | Part of the #39
1. Note CSS cleanup.
1. No Note logic & generic error logic setup.
1. No note and generic error catalog.
1. Note PropTypes.
1. Note unit tests. | 1.0 | UI - Note tests - Part of the #39
1. Note CSS cleanup.
1. No Note logic & generic error logic setup.
1. No note and generic error catalog.
1. Note PropTypes.
1. Note unit tests. | non_priority | ui note tests part of the note css cleanup no note logic generic error logic setup no note and generic error catalog note proptypes note unit tests | 0 |
148,990 | 23,410,973,219 | IssuesEvent | 2022-08-12 17:28:54 | piro17-Archive/FilmArchive | https://api.github.com/repos/piro17-Archive/FilmArchive | closed | [design] main 페이지 | 도윤 예진 design | ### 목적
> main 페이지 디자인하기
### 작업 상세 내용
- [x] 4페이지 swiper 적용
- [x] swiper autoplay 적용
- [x] 1, 2, 3등 프레임, 포즈/컨셉 순위
- [x] 네 컷 아카이브 설명
- [x] My 네 컷 앨범 자세히
- [x] My 네 컷 앨범 캘린더
- [x] 인생네컷 공유 프레임 자세히
- [x] 포즈 및 컨셉 추천 자세히
- [x] 한정판 프레임 자세히
### 유의사항
1,2,3등 기능이 완성되면 css 적용할 것
| 1.0 | [design] main 페이지 - ### 목적
> main 페이지 디자인하기
### 작업 상세 내용
- [x] 4페이지 swiper 적용
- [x] swiper autoplay 적용
- [x] 1, 2, 3등 프레임, 포즈/컨셉 순위
- [x] 네 컷 아카이브 설명
- [x] My 네 컷 앨범 자세히
- [x] My 네 컷 앨범 캘린더
- [x] 인생네컷 공유 프레임 자세히
- [x] 포즈 및 컨셉 추천 자세히
- [x] 한정판 프레임 자세히
### 유의사항
1,2,3등 기능이 완성되면 css 적용할 것
| non_priority | main 페이지 목적 main 페이지 디자인하기 작업 상세 내용 swiper 적용 swiper autoplay 적용 프레임 포즈 컨셉 순위 네 컷 아카이브 설명 my 네 컷 앨범 자세히 my 네 컷 앨범 캘린더 인생네컷 공유 프레임 자세히 포즈 및 컨셉 추천 자세히 한정판 프레임 자세히 유의사항 기능이 완성되면 css 적용할 것 | 0 |
49,345 | 13,186,625,418 | IssuesEvent | 2020-08-13 00:47:21 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | [clast] TODOs (Trac #1207) | Incomplete Migration Migrated from Trac combo reconstruction defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1207">https://code.icecube.wisc.edu/ticket/1207</a>, reported by david.schultz and owned by markw04</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:14:55",
"description": "Looks like there is... | 1.0 | [clast] TODOs (Trac #1207) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1207">https://code.icecube.wisc.edu/ticket/1207</a>, reported by david.schultz and owned by markw04</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:14:55",
"descr... | non_priority | todos trac migrated from json status closed changetime description looks like there is more to be said let s fill that in or make some tickets n n npublic clast h todo there is probably more to be said here as david b would put it npublic cl... | 0 |
290,632 | 25,081,591,425 | IssuesEvent | 2022-11-07 19:49:39 | hashicorp/terraform-provider-google | https://api.github.com/repos/hashicorp/terraform-provider-google | closed | Failing test(s): TestAccComputeDisk_imageDiffSuppressPublicVendorsFamilyNames | size/xs test failure crosslinked | <!--- This is a template for reporting test failures on nightly builds. It should only be used by core contributors who have access to our CI/CD results. --->
<!-- i.e. "Consistently since X date" or "X% failure in MONTH" -->
Failure rate: 100% since 2022-10-23
<!-- List all impacted tests for searchability. The... | 1.0 | Failing test(s): TestAccComputeDisk_imageDiffSuppressPublicVendorsFamilyNames - <!--- This is a template for reporting test failures on nightly builds. It should only be used by core contributors who have access to our CI/CD results. --->
<!-- i.e. "Consistently since X date" or "X% failure in MONTH" -->
Failure ra... | non_priority | failing test s testacccomputedisk imagediffsuppresspublicvendorsfamilynames failure rate since impacted tests testacccomputedisk imagediffsuppresspublicvendorsfamilynames nightly builds message resource compute disk test go should suppress diff for image ... | 0 |
59,956 | 14,514,644,909 | IssuesEvent | 2020-12-13 09:13:59 | TalErez86/Test-Repository123 | https://api.github.com/repos/TalErez86/Test-Repository123 | opened | CVE-2020-17521 (Medium) detected in groovy-3.0.0.jar | security vulnerability | ## CVE-2020-17521 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>groovy-3.0.0.jar</b></p></summary>
<p>Groovy: A powerful, dynamic language for the JVM</p>
<p>Library home page: <a ... | True | CVE-2020-17521 (Medium) detected in groovy-3.0.0.jar - ## CVE-2020-17521 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>groovy-3.0.0.jar</b></p></summary>
<p>Groovy: A powerful, dyn... | non_priority | cve medium detected in groovy jar cve medium severity vulnerability vulnerable library groovy jar groovy a powerful dynamic language for the jvm library home page a href path to dependency file test multi module maven project master register service pom xml path t... | 0 |
7,290 | 5,962,202,896 | IssuesEvent | 2017-05-29 21:00:16 | JuliaLang/julia | https://api.github.com/repos/JuliaLang/julia | closed | spzeros and speye are really slow | performance sparse | I searched and couldn't find any open issue on this, which surprised me.
Not too sure what the problem is with the code in Base, but if I write my own `spzeros`, it is much faster (the same thing happens with `speye`):
```julia
julia> using BenchmarkTools
julia> @benchmark spzeros(5,5)
BenchmarkTools.Trial:
... | True | spzeros and speye are really slow - I searched and couldn't find any open issue on this, which surprised me.
Not too sure what the problem is with the code in Base, but if I write my own `spzeros`, it is much faster (the same thing happens with `speye`):
```julia
julia> using BenchmarkTools
julia> @benchmark ... | non_priority | spzeros and speye are really slow i searched and couldn t find any open issue on this which surprised me not too sure what the problem is with the code in base but if i write my own spzeros it is much faster the same thing happens with speye julia julia using benchmarktools julia benchmark ... | 0 |
35,918 | 7,834,258,272 | IssuesEvent | 2018-06-16 11:16:50 | StrikeNP/trac_test | https://api.github.com/repos/StrikeNP/trac_test | closed | Determine SILHS sampling level based on within-cloud rcm (Trac #758) | Migrated from Trac clubb_src defect raut@uwm.edu | **Introduction**
In https://github.com/larson-group/clubb/issues/752, we saw that calculating `k_lh_start` as `rcm / cloud_frac` improved results.
**Technical spec**
In this ticket, let's test and commit that change.
**Test**
Post plots.
Output should bin-diff identical for non-SILHS cases.
Attachments:
[r7424_... | 1.0 | Determine SILHS sampling level based on within-cloud rcm (Trac #758) - **Introduction**
In https://github.com/larson-group/clubb/issues/752, we saw that calculating `k_lh_start` as `rcm / cloud_frac` improved results.
**Technical spec**
In this ticket, let's test and commit that change.
**Test**
Post plots.
Outpu... | non_priority | determine silhs sampling level based on within cloud rcm trac introduction in we saw that calculating k lh start as rcm cloud frac improved results technical spec in this ticket let s test and commit that change test post plots output should bin diff identical for non silhs cases ... | 0 |
169,992 | 14,238,122,244 | IssuesEvent | 2020-11-18 18:09:51 | agustinanisaf/SquareCheck-android | https://api.github.com/repos/agustinanisaf/SquareCheck-android | closed | Create Github Issue Template | documentation | What to do
---
- [x] Create **New Feature** Issue Template
- [x] Create **Bug Report** Issue Template
References
---
- [Github Docs](https://docs.github.com/en/free-pro-team@latest/github/building-a-strong-community/configuring-issue-templates-for-your-repository) | 1.0 | Create Github Issue Template - What to do
---
- [x] Create **New Feature** Issue Template
- [x] Create **Bug Report** Issue Template
References
---
- [Github Docs](https://docs.github.com/en/free-pro-team@latest/github/building-a-strong-community/configuring-issue-templates-for-your-repository) | non_priority | create github issue template what to do create new feature issue template create bug report issue template references | 0 |
44,170 | 5,764,992,640 | IssuesEvent | 2017-04-27 00:23:59 | quicwg/base-drafts | https://api.github.com/repos/quicwg/base-drafts | closed | Get rid of the concurrent stream limit by advertising a maximum stream ID | design transport | We've already had a lot of discussions about the concurrent streams limit, which all brought us back to the problem that at every given moment both peers have to agree about the number of open streams, which seems to require a non-trivial amount of bookkeeping (of ACKs received for all STREAM frames sent on a given str... | 1.0 | Get rid of the concurrent stream limit by advertising a maximum stream ID - We've already had a lot of discussions about the concurrent streams limit, which all brought us back to the problem that at every given moment both peers have to agree about the number of open streams, which seems to require a non-trivial amoun... | non_priority | get rid of the concurrent stream limit by advertising a maximum stream id we ve already had a lot of discussions about the concurrent streams limit which all brought us back to the problem that at every given moment both peers have to agree about the number of open streams which seems to require a non trivial amoun... | 0 |
256,329 | 27,561,650,831 | IssuesEvent | 2023-03-07 22:37:53 | samqws-marketing/nutanix_Nutanix-Calm-Jenkins-Plugin | https://api.github.com/repos/samqws-marketing/nutanix_Nutanix-Calm-Jenkins-Plugin | closed | CVE-2021-4104 (High) detected in log4j-1.2.17.jar - autoclosed | security vulnerability | ## CVE-2021-4104 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerab... | True | CVE-2021-4104 (High) detected in log4j-1.2.17.jar - autoclosed - ## CVE-2021-4104 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2... | non_priority | cve high detected in jar autoclosed cve high severity vulnerability vulnerable library jar apache path to dependency file pom xml path to vulnerable library home wss scanner repository jar dependency hierarchy jsse jar roo... | 0 |
111,710 | 9,539,544,545 | IssuesEvent | 2019-04-30 17:13:26 | kcigeospatial/Fred_Co_Land-Management | https://api.github.com/repos/kcigeospatial/Fred_Co_Land-Management | closed | Planning-APFO-stuck in under review | Ready For Retest | stuck in under review. There is no review to review.
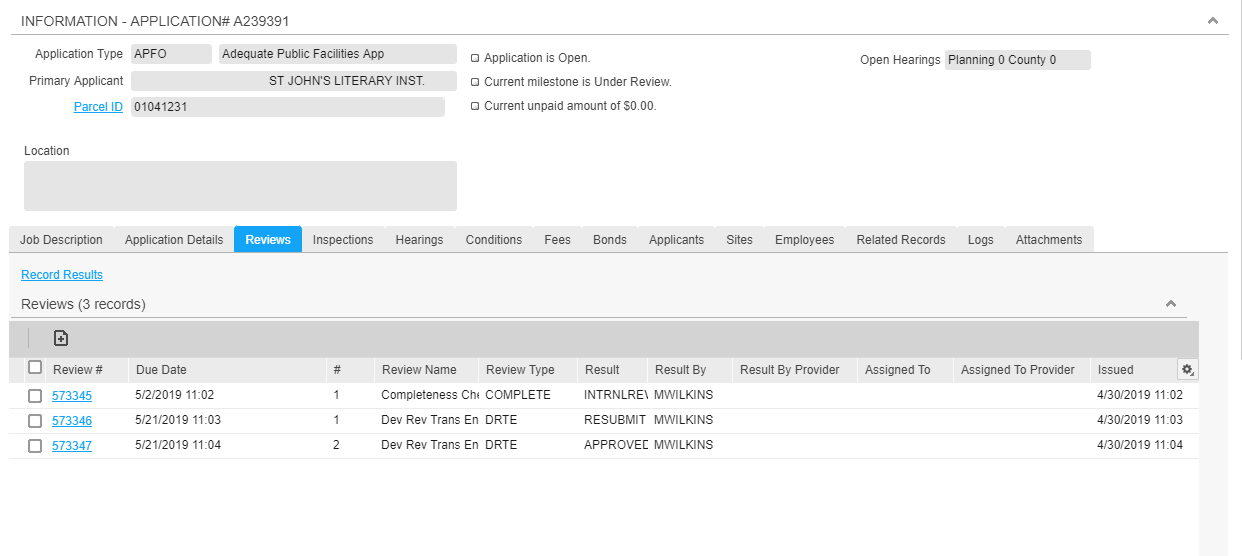
MW | 1.0 | Planning-APFO-stuck in under review - stuck in under review. There is no review to review.
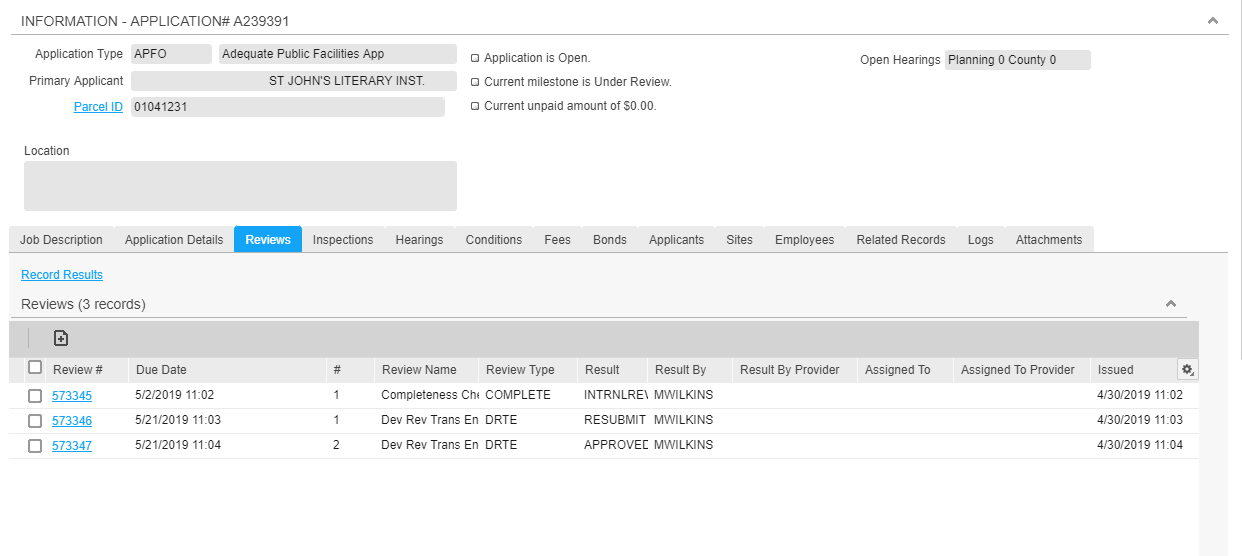
MW | non_priority | planning apfo stuck in under review stuck in under review there is no review to review mw | 0 |
179,240 | 30,204,769,581 | IssuesEvent | 2023-07-05 08:41:41 | Tonomy-Foundation/Tonomy-ID-Management | https://api.github.com/repos/Tonomy-Foundation/Tonomy-ID-Management | opened | Design what happens if user uses bad password | design |
Acceptance criteria
- [ ] design view for if the user password has been used before
Inspiration
- https://haveibeenpwned.com/Passwords | 1.0 | Design what happens if user uses bad password -
Acceptance criteria
- [ ] design view for if the user password has been used before
Inspiration
- https://haveibeenpwned.com/Passwords | non_priority | design what happens if user uses bad password acceptance criteria design view for if the user password has been used before inspiration | 0 |
46,098 | 13,150,337,597 | IssuesEvent | 2020-08-09 10:57:28 | shaundmorris/ddf | https://api.github.com/repos/shaundmorris/ddf | closed | CVE-2018-11695 High Severity Vulnerability detected by WhiteSource | security vulnerability wontfix | ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.9.4</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a h... | True | CVE-2018-11695 High Severity Vulnerability detected by WhiteSource - ## CVE-2018-11695 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.9.4</b></p></summary>
<p>
<p... | non_priority | cve high severity vulnerability detected by whitesource cve high severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matc... | 0 |
38,449 | 6,671,655,675 | IssuesEvent | 2017-10-04 08:21:22 | encode/django-rest-framework | https://api.github.com/repos/encode/django-rest-framework | closed | Documenting your API: add highlighted chunk of code in docstrings | Enhancement Interactive API Documentation | Thinking that also highlighted code-blocks were enabled in the dynamic documentation I started to investigate why code-block (also without highlight) not works and at the end I found that there is a strip that remove any kind of indentation, that is bad for code-blocks.
```
--- schemas_orig.py 2017-08-30 14:45:38.061... | 1.0 | Documenting your API: add highlighted chunk of code in docstrings - Thinking that also highlighted code-blocks were enabled in the dynamic documentation I started to investigate why code-block (also without highlight) not works and at the end I found that there is a strip that remove any kind of indentation, that is b... | non_priority | documenting your api add highlighted chunk of code in docstrings thinking that also highlighted code blocks were enabled in the dynamic documentation i started to investigate why code block also without highlight not works and at the end i found that there is a strip that remove any kind of indentation that is b... | 0 |
262,596 | 27,972,681,020 | IssuesEvent | 2023-03-25 07:29:32 | elastic/integrations | https://api.github.com/repos/elastic/integrations | closed | [Check Point] Improved Documentation | Team:Security-External Integrations Integration:Checkpoint | Our [Check Point integration](https://docs.elastic.co/integrations/checkpoint) does not follow our [documentation guidelines](https://github.com/elastic/integrations/blob/main/docs/documentation_guidelines.md) and needs to be updated to ensure users can successfully configure the integration. Our documentation can be b... | True | [Check Point] Improved Documentation - Our [Check Point integration](https://docs.elastic.co/integrations/checkpoint) does not follow our [documentation guidelines](https://github.com/elastic/integrations/blob/main/docs/documentation_guidelines.md) and needs to be updated to ensure users can successfully configure the ... | non_priority | improved documentation our does not follow our and needs to be updated to ensure users can successfully configure the integration our documentation can be based on the steps to configure checkpoint s current os no need to focus on steps for eol os such as and i ll can get a marketing blurb from... | 0 |
27,503 | 21,795,357,227 | IssuesEvent | 2022-05-15 14:48:55 | dotnet/sdk | https://api.github.com/repos/dotnet/sdk | closed | Single EXE build takes minutes to launch, self contained build launches in seconds | Area-Infrastructure untriaged | ### Describe the bug
Links two different builds of the same program:
- Self contained, ready to run, win-x86 - [selfcontained.zip](https://drive.google.com/file/d/1ePBlypgj5QspcndbHw412vRMgWtbPDwo/view?usp=sharing)
- Single EXE, ready to run, win-86 - [singleexe.zip](https://drive.google.com/file/d/1VGUauy-8Q4G4_... | 1.0 | Single EXE build takes minutes to launch, self contained build launches in seconds - ### Describe the bug
Links two different builds of the same program:
- Self contained, ready to run, win-x86 - [selfcontained.zip](https://drive.google.com/file/d/1ePBlypgj5QspcndbHw412vRMgWtbPDwo/view?usp=sharing)
- Single EXE, r... | non_priority | single exe build takes minutes to launch self contained build launches in seconds describe the bug links two different builds of the same program self contained ready to run win single exe ready to run win both programs run however the single exe version takes over two minutes ... | 0 |
177,534 | 21,478,663,310 | IssuesEvent | 2022-04-26 15:38:14 | tamirverthim/fitbit-api-example-java | https://api.github.com/repos/tamirverthim/fitbit-api-example-java | closed | CVE-2017-12597 High Severity Vulnerability detected by WhiteSource - autoclosed | security vulnerability | ## CVE-2017-12597 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-webmvc-4.3.2.RELEASE.jar</b></p></summary>
<p>Spring Web MVC</p>
<p>path: /root/.m2/repository/org/spr... | True | CVE-2017-12597 High Severity Vulnerability detected by WhiteSource - autoclosed - ## CVE-2017-12597 - High Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-webmvc-4.3.2.RELEASE.... | non_priority | cve high severity vulnerability detected by whitesource autoclosed cve high severity vulnerability vulnerable library spring webmvc release jar spring web mvc path root repository org springframework spring webmvc release spring webmvc release jar library home ... | 0 |
331,772 | 24,325,429,356 | IssuesEvent | 2022-09-30 14:23:43 | connor-makowski/type_enforced | https://api.github.com/repos/connor-makowski/type_enforced | closed | Fix broken docstrings related to functools.partial | bug documentation | When using docstrings in classes and calling type_enforced, the headers for help strings get broken by functools.partial | 1.0 | Fix broken docstrings related to functools.partial - When using docstrings in classes and calling type_enforced, the headers for help strings get broken by functools.partial | non_priority | fix broken docstrings related to functools partial when using docstrings in classes and calling type enforced the headers for help strings get broken by functools partial | 0 |
82,170 | 32,038,554,837 | IssuesEvent | 2023-09-22 17:17:17 | SasView/sasview | https://api.github.com/repos/SasView/sasview | closed | better custom model error diagnostics (Trac #570) | Defect Major | When defining a custom model but having a bad parameter table, the custom model compile menu item claimed that the model loaded without difficulty. Similarly when there were errors in the C code for the model.
The compile button needs to run the model with some nominal value (e.g., Iq([0.1, 0.2, 0.3]) and Iqxy([0.1, ... | 1.0 | better custom model error diagnostics (Trac #570) - When defining a custom model but having a bad parameter table, the custom model compile menu item claimed that the model loaded without difficulty. Similarly when there were errors in the C code for the model.
The compile button needs to run the model with some nomi... | non_priority | better custom model error diagnostics trac when defining a custom model but having a bad parameter table the custom model compile menu item claimed that the model loaded without difficulty similarly when there were errors in the c code for the model the compile button needs to run the model with some nomina... | 0 |
349,101 | 31,774,669,744 | IssuesEvent | 2023-09-12 13:47:50 | red-hat-storage/ocs-ci | https://api.github.com/repos/red-hat-storage/ocs-ci | opened | Test Mon Failures with In-Transit Encryption Tests Failing on Teardown | TestCase failing Squad/Green | Description:
During the execution of the "test_mon_failures_with_intransit_encryption" a test failure occurred during the teardown phase. The failure message indicates the following:
Test Name: test_mon_failures_with_intransit_encryption
Failure Message: "Failed on teardown with 'ocs_ci.ocs.exceptions.CephHealthE... | 1.0 | Test Mon Failures with In-Transit Encryption Tests Failing on Teardown - Description:
During the execution of the "test_mon_failures_with_intransit_encryption" a test failure occurred during the teardown phase. The failure message indicates the following:
Test Name: test_mon_failures_with_intransit_encryption
Fai... | non_priority | test mon failures with in transit encryption tests failing on teardown description during the execution of the test mon failures with intransit encryption a test failure occurred during the teardown phase the failure message indicates the following test name test mon failures with intransit encryption fai... | 0 |
115,996 | 11,893,353,635 | IssuesEvent | 2020-03-29 11:09:41 | mtyn/polar | https://api.github.com/repos/mtyn/polar | closed | Vim screenshot shows in progress theme | documentation | The screenshot for vim shows colours that shouldn't be used in this theme. This has since been fixed, but the screenshot wasn't updated.
Fix the screenshot. | 1.0 | Vim screenshot shows in progress theme - The screenshot for vim shows colours that shouldn't be used in this theme. This has since been fixed, but the screenshot wasn't updated.
Fix the screenshot. | non_priority | vim screenshot shows in progress theme the screenshot for vim shows colours that shouldn t be used in this theme this has since been fixed but the screenshot wasn t updated fix the screenshot | 0 |
86,913 | 8,053,393,745 | IssuesEvent | 2018-08-01 22:48:07 | Microsoft/AzureStorageExplorer | https://api.github.com/repos/Microsoft/AzureStorageExplorer | closed | There is no prompt message after inputting Unicode characters for blob's properties | :white_check_mark: merged testing | **Storage Explorer Version**: 1.4.0
**Platform/OS Version**: Windows/Linux Ubuntu 16.04/Mac
**Architecture**: ia32/x64
**Build Number**:20180801.3
**Commit**: 7cdb5326
**Regression From**: Not a regression
#### Steps to Reproduce: ####
1. Expand one account -> Open a blob container which contains one blob at l... | 1.0 | There is no prompt message after inputting Unicode characters for blob's properties - **Storage Explorer Version**: 1.4.0
**Platform/OS Version**: Windows/Linux Ubuntu 16.04/Mac
**Architecture**: ia32/x64
**Build Number**:20180801.3
**Commit**: 7cdb5326
**Regression From**: Not a regression
#### Steps to Reprod... | non_priority | there is no prompt message after inputting unicode characters for blob s properties storage explorer version platform os version windows linux ubuntu mac architecture build number commit regression from not a regression steps to reproduce expand ... | 0 |
29,816 | 13,173,420,308 | IssuesEvent | 2020-08-11 20:17:08 | dockstore/dockstore | https://api.github.com/repos/dockstore/dockstore | closed | Galaxy subclass should be GALAXY in .dockstore.yml | bug review web-service | **Describe the bug**
To specify a Galaxy workflow in .dockstore.yml, you currently specify subclass `GXFORMAT2`. This is imprecise, because Dockstore is able to handle both the old and new formats of Galaxy workflows.
**Describe the solution you'd like**
Allow the subclass to be `GALAXY` in Dockstore workflows.
For b... | 1.0 | Galaxy subclass should be GALAXY in .dockstore.yml - **Describe the bug**
To specify a Galaxy workflow in .dockstore.yml, you currently specify subclass `GXFORMAT2`. This is imprecise, because Dockstore is able to handle both the old and new formats of Galaxy workflows.
**Describe the solution you'd like**
Allow the s... | non_priority | galaxy subclass should be galaxy in dockstore yml describe the bug to specify a galaxy workflow in dockstore yml you currently specify subclass this is imprecise because dockstore is able to handle both the old and new formats of galaxy workflows describe the solution you d like allow the subclass ... | 0 |
8,048 | 7,196,736,612 | IssuesEvent | 2018-02-05 05:18:05 | kolide/fleet | https://api.github.com/repos/kolide/fleet | closed | Add windows network information to cards | Feature: Infrastructure Good First Issue Help Wanted | Originally, we left off network information (IP address, MAC, etc) from host cards because the information wasn't available in osquery (https://github.com/facebook/osquery/issues/2907) but that is no longer the case. Let's add Windows detail queries to populate this information for Windows hosts. | 1.0 | Add windows network information to cards - Originally, we left off network information (IP address, MAC, etc) from host cards because the information wasn't available in osquery (https://github.com/facebook/osquery/issues/2907) but that is no longer the case. Let's add Windows detail queries to populate this informatio... | non_priority | add windows network information to cards originally we left off network information ip address mac etc from host cards because the information wasn t available in osquery but that is no longer the case let s add windows detail queries to populate this information for windows hosts | 0 |
7,804 | 7,042,661,818 | IssuesEvent | 2017-12-30 16:21:32 | SimonKinds/4temps-tournament | https://api.github.com/repos/SimonKinds/4temps-tournament | closed | Create authorization middleware for express routes that checks if user is logged in | enhancement security | An example of how this can clean up code and make the code easier to read exists in `src/routes/tournament/index.js`
Currently these routes have a block of code like this
```js
if (req.session.user == null) {
res.sendStatus(401);
return;
}
```
This code duplication is not only bad because of the duplication... | True | Create authorization middleware for express routes that checks if user is logged in - An example of how this can clean up code and make the code easier to read exists in `src/routes/tournament/index.js`
Currently these routes have a block of code like this
```js
if (req.session.user == null) {
res.sendStatus(401)... | non_priority | create authorization middleware for express routes that checks if user is logged in an example of how this can clean up code and make the code easier to read exists in src routes tournament index js currently these routes have a block of code like this js if req session user null res sendstatus ... | 0 |
25,180 | 6,628,593,661 | IssuesEvent | 2017-09-23 19:59:32 | connected-web/gamebot | https://api.github.com/repos/connected-web/gamebot | closed | Add a command to view team mates | codenames suggestion | It would be nice if there was a command to remind who your team mates are - maybe something like 'who are my team?". Maybe the teams could be listed when calling 'game state' as well? | 1.0 | Add a command to view team mates - It would be nice if there was a command to remind who your team mates are - maybe something like 'who are my team?". Maybe the teams could be listed when calling 'game state' as well? | non_priority | add a command to view team mates it would be nice if there was a command to remind who your team mates are maybe something like who are my team maybe the teams could be listed when calling game state as well | 0 |
55,311 | 30,685,799,736 | IssuesEvent | 2023-07-26 12:17:08 | ArturGin/request_enforcer | https://api.github.com/repos/ArturGin/request_enforcer | opened | After adding gem, it takes a while to start the application | enhancement performance | It seems like Sniffer takes a while to load in | True | After adding gem, it takes a while to start the application - It seems like Sniffer takes a while to load in | non_priority | after adding gem it takes a while to start the application it seems like sniffer takes a while to load in | 0 |
67,051 | 8,071,061,593 | IssuesEvent | 2018-08-06 11:57:17 | PLUS-POSTECH/Owl | https://api.github.com/repos/PLUS-POSTECH/Owl | closed | Make owl-daemon DB aware of exploit test and dummy exploits | design new feature | 사용 케이스 중에 익스플로잇이 제대로 작동하는지 실험해보는 부분이 있는데, 이를 고려해서 DB 내역을 수정할 필요가 있습니다.
- [x] Fix migration schema
- [x] Update schema.rs
- [x] Update models.rs | 1.0 | Make owl-daemon DB aware of exploit test and dummy exploits - 사용 케이스 중에 익스플로잇이 제대로 작동하는지 실험해보는 부분이 있는데, 이를 고려해서 DB 내역을 수정할 필요가 있습니다.
- [x] Fix migration schema
- [x] Update schema.rs
- [x] Update models.rs | non_priority | make owl daemon db aware of exploit test and dummy exploits 사용 케이스 중에 익스플로잇이 제대로 작동하는지 실험해보는 부분이 있는데 이를 고려해서 db 내역을 수정할 필요가 있습니다 fix migration schema update schema rs update models rs | 0 |
12,210 | 9,597,377,952 | IssuesEvent | 2019-05-09 21:07:40 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | closed | [Service Bus Client] Rename test environment variable | Client Service Bus | For consistency, @jsquire and I agreed to use the environment variable `SERVICE_BUS_CONNECTION_STRING` for all Service Bus tests in all languages. In this repo, the variable should be renamed from `AZ_SERVICE_BUS_CONNECTION` to `SERVICE_BUS_CONNECTION_STRING`.
Related: https://github.com/Azure/azure-sdk-for-js/issu... | 1.0 | [Service Bus Client] Rename test environment variable - For consistency, @jsquire and I agreed to use the environment variable `SERVICE_BUS_CONNECTION_STRING` for all Service Bus tests in all languages. In this repo, the variable should be renamed from `AZ_SERVICE_BUS_CONNECTION` to `SERVICE_BUS_CONNECTION_STRING`.
... | non_priority | rename test environment variable for consistency jsquire and i agreed to use the environment variable service bus connection string for all service bus tests in all languages in this repo the variable should be renamed from az service bus connection to service bus connection string related | 0 |
104,508 | 11,412,577,257 | IssuesEvent | 2020-02-01 14:09:39 | oscrud/oscrud | https://api.github.com/repos/oscrud/oscrud | closed | Transport | documentation | # Feature
* Event-Driven
* Lookup-able routing
* Path-based routing
# Integration
* Go-HTTP
* SocketIO
* Echo
# Example
* Integration API
* Example of Integration
* Example of Registering Transport | 1.0 | Transport - # Feature
* Event-Driven
* Lookup-able routing
* Path-based routing
# Integration
* Go-HTTP
* SocketIO
* Echo
# Example
* Integration API
* Example of Integration
* Example of Registering Transport | non_priority | transport feature event driven lookup able routing path based routing integration go http socketio echo example integration api example of integration example of registering transport | 0 |
37,467 | 15,301,411,428 | IssuesEvent | 2021-02-24 13:35:14 | wellcomecollection/platform | https://api.github.com/repos/wellcomecollection/platform | closed | Storage service shouldn't return a 500 error if you ask for a malformed external identifier | 🐛 Bug 📦 Storage service | If you request external identifier `a.b` from the bags API, you get a 500 error. That's because it gets an IllegalArgumentException, thrown when you try to construct the ExternalIdentifier. | 1.0 | Storage service shouldn't return a 500 error if you ask for a malformed external identifier - If you request external identifier `a.b` from the bags API, you get a 500 error. That's because it gets an IllegalArgumentException, thrown when you try to construct the ExternalIdentifier. | non_priority | storage service shouldn t return a error if you ask for a malformed external identifier if you request external identifier a b from the bags api you get a error that s because it gets an illegalargumentexception thrown when you try to construct the externalidentifier | 0 |
4,692 | 3,427,996,174 | IssuesEvent | 2015-12-10 06:31:45 | angular/angular | https://api.github.com/repos/angular/angular | closed | flaky perf test on Firefox | comp: build/dev-productivity type: bug | This is currently the most common flake that I know of, can we disable the test on FF or do something else to prevent it from failing the builds several times a day?
```
Failures:
1) firefox extension should measure performance
Message:
Expected false to be truthy.
Stack:
Error: Failed expectation
... | 1.0 | flaky perf test on Firefox - This is currently the most common flake that I know of, can we disable the test on FF or do something else to prevent it from failing the builds several times a day?
```
Failures:
1) firefox extension should measure performance
Message:
Expected false to be truthy.
Stack:
... | non_priority | flaky perf test on firefox this is currently the most common flake that i know of can we disable the test on ff or do something else to prevent it from failing the builds several times a day failures firefox extension should measure performance message expected false to be truthy stack ... | 0 |
27,820 | 6,905,184,710 | IssuesEvent | 2017-11-27 05:25:21 | cs340tabyu/cs340Fall2017 | https://api.github.com/repos/cs340tabyu/cs340Fall2017 | closed | Mismatch in player stats (train cars) | P3: Affects Gameplay Section 2 The Jedi Coders | 
Differing number displayed of Red Player TrainCars between two clients. Unsure of wha... | 1.0 | Mismatch in player stats (train cars) - 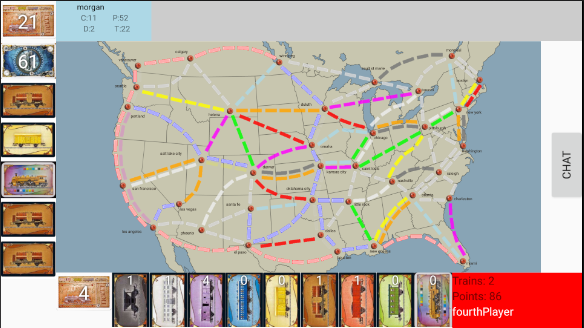
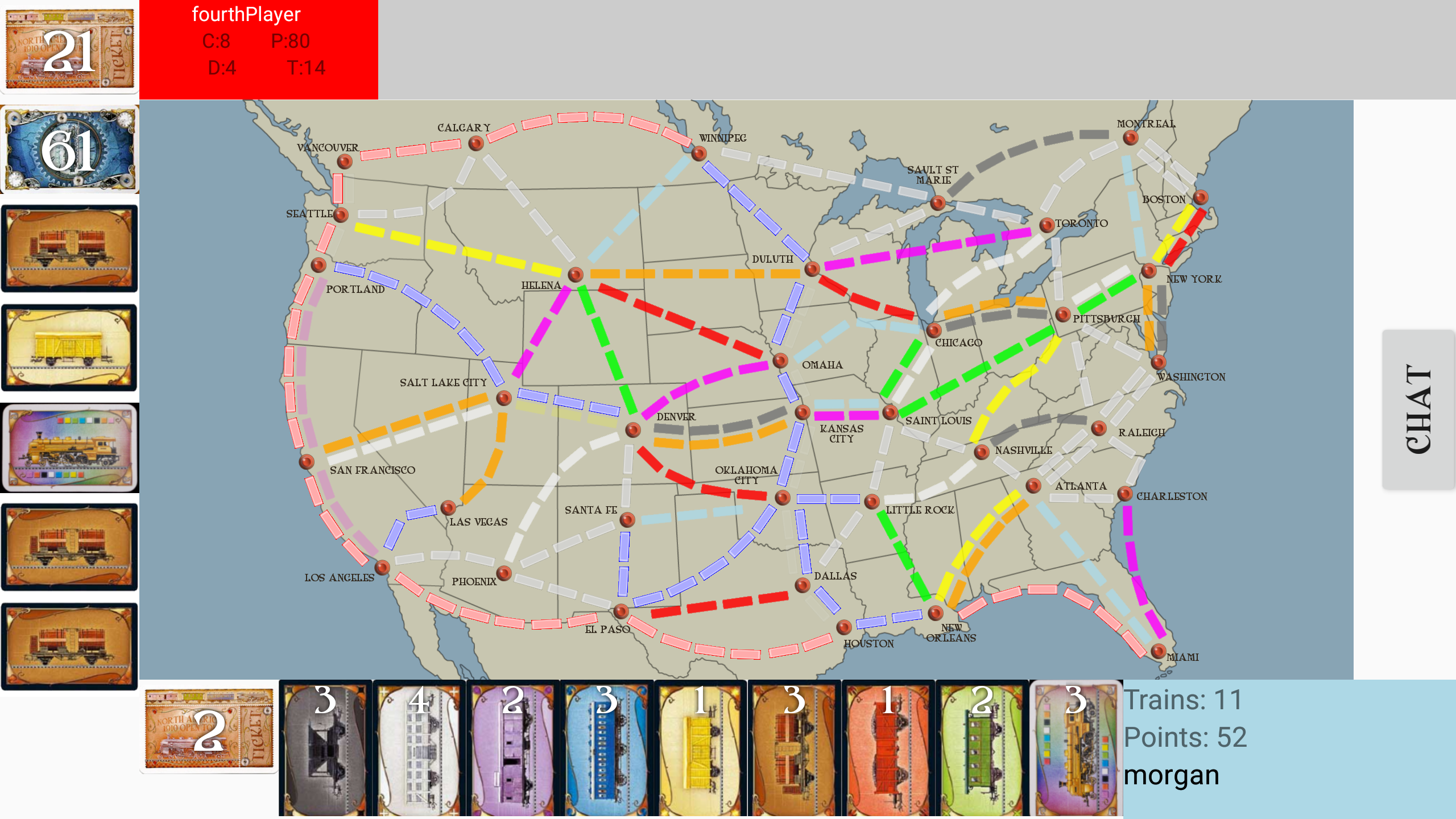
Differing number displayed of Red Player Trai... | non_priority | mismatch in player stats train cars differing number displayed of red player traincars between two clients unsure of what the server has possibly related to claimed route errors subtracting trains even when route not claimed | 0 |
28,456 | 11,634,679,319 | IssuesEvent | 2020-02-28 10:51:01 | solid/user-stories | https://api.github.com/repos/solid/user-stories | reopened | As a pod provider I'd like to see aggregated histories of access attempts to pods I host so that I can manage hotspots, charge per usage, prevent DoS attacks, etc. | Auditing Security | This may raise issues of privacy (e.g. for individual pod owners), but I think this needs to be balanced with the legitimate needs of the pod provider to effectively manage the infrastructure they provide for pod hosting (hence I mention in the title the possibly of the provider only having 'aggregated histories' of ac... | True | As a pod provider I'd like to see aggregated histories of access attempts to pods I host so that I can manage hotspots, charge per usage, prevent DoS attacks, etc. - This may raise issues of privacy (e.g. for individual pod owners), but I think this needs to be balanced with the legitimate needs of the pod provider to ... | non_priority | as a pod provider i d like to see aggregated histories of access attempts to pods i host so that i can manage hotspots charge per usage prevent dos attacks etc this may raise issues of privacy e g for individual pod owners but i think this needs to be balanced with the legitimate needs of the pod provider to ... | 0 |
107,798 | 16,762,314,727 | IssuesEvent | 2021-06-14 01:36:28 | benlazarine/status-site | https://api.github.com/repos/benlazarine/status-site | opened | WS-2017-3772 (High) detected in underscore.string-3.2.3.tgz | security vulnerability | ## WS-2017-3772 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore.string-3.2.3.tgz</b></p></summary>
<p>String manipulation extensions for Underscore.js javascript library.</p... | True | WS-2017-3772 (High) detected in underscore.string-3.2.3.tgz - ## WS-2017-3772 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore.string-3.2.3.tgz</b></p></summary>
<p>String ma... | non_priority | ws high detected in underscore string tgz ws high severity vulnerability vulnerable library underscore string tgz string manipulation extensions for underscore js javascript library library home page a href path to dependency file status site package json path to vul... | 0 |
117,027 | 15,039,041,262 | IssuesEvent | 2021-02-02 18:09:21 | pekrau/notebooks | https://api.github.com/repos/pekrau/notebooks | closed | Should expansion of note tree display be remembered? | design question | Write into index.json file: "expanded" = [...] | 1.0 | Should expansion of note tree display be remembered? - Write into index.json file: "expanded" = [...] | non_priority | should expansion of note tree display be remembered write into index json file expanded | 0 |
39,488 | 10,345,858,644 | IssuesEvent | 2019-09-04 14:15:16 | haskell/haskell-ide-engine | https://api.github.com/repos/haskell/haskell-ide-engine | closed | Cannot do cabal 3.0 build for 8.6.5 | build good first issue os: linux os: windows | Trying to install `cabal-hie-8.6.5` gives me the following error instead:
```
Warning: Failed to build documentation for haddock-api-2.22.0 (which is
required by test:wrapper-test from haskell-ide-engine-0.9.0.0, test:unit-test
from haskell-ide-engine-0.9.0.0 and others).
# stack (for cabal-hie-8.6.5)
# cabal (... | 1.0 | Cannot do cabal 3.0 build for 8.6.5 - Trying to install `cabal-hie-8.6.5` gives me the following error instead:
```
Warning: Failed to build documentation for haddock-api-2.22.0 (which is
required by test:wrapper-test from haskell-ide-engine-0.9.0.0, test:unit-test
from haskell-ide-engine-0.9.0.0 and others).
# ... | non_priority | cannot do cabal build for trying to install cabal hie gives me the following error instead warning failed to build documentation for haddock api which is required by test wrapper test from haskell ide engine test unit test from haskell ide engine and others s... | 0 |
92,314 | 18,820,429,126 | IssuesEvent | 2021-11-10 07:34:15 | redhat-developer/vscode-openshift-tools | https://api.github.com/repos/redhat-developer/vscode-openshift-tools | closed | Provide filters for started/not started clusters | resolution/wontfix kind/feature upstream/vscode-k8s-tools | in my case, I have a lot of clusters registered, only one is started and I need to scroll to find it
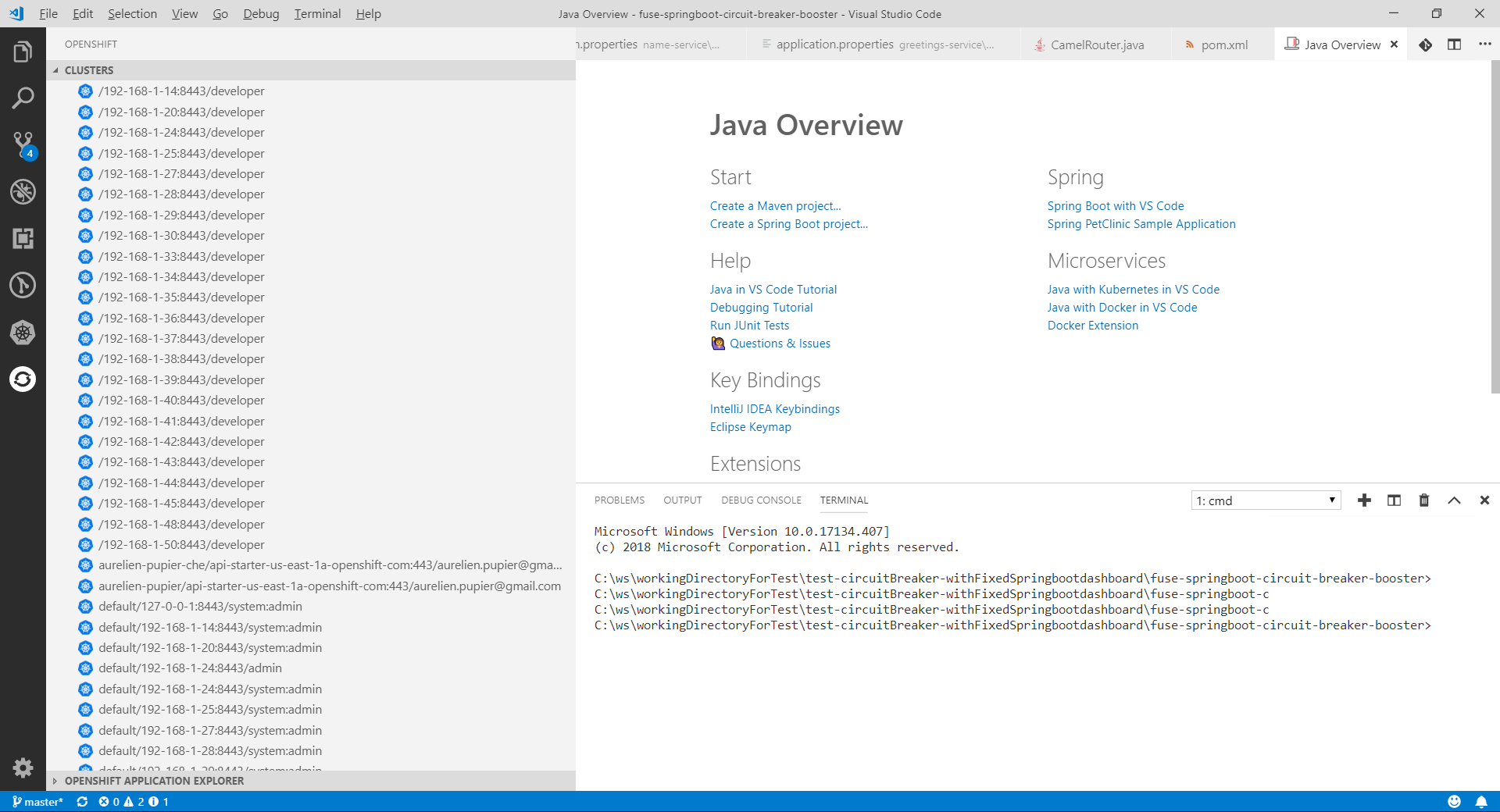
instead of filter it might also be 2 top-level tree nodes.
nota having a marker to mention if it start... | 1.0 | Provide filters for started/not started clusters - in my case, I have a lot of clusters registered, only one is started and I need to scroll to find it
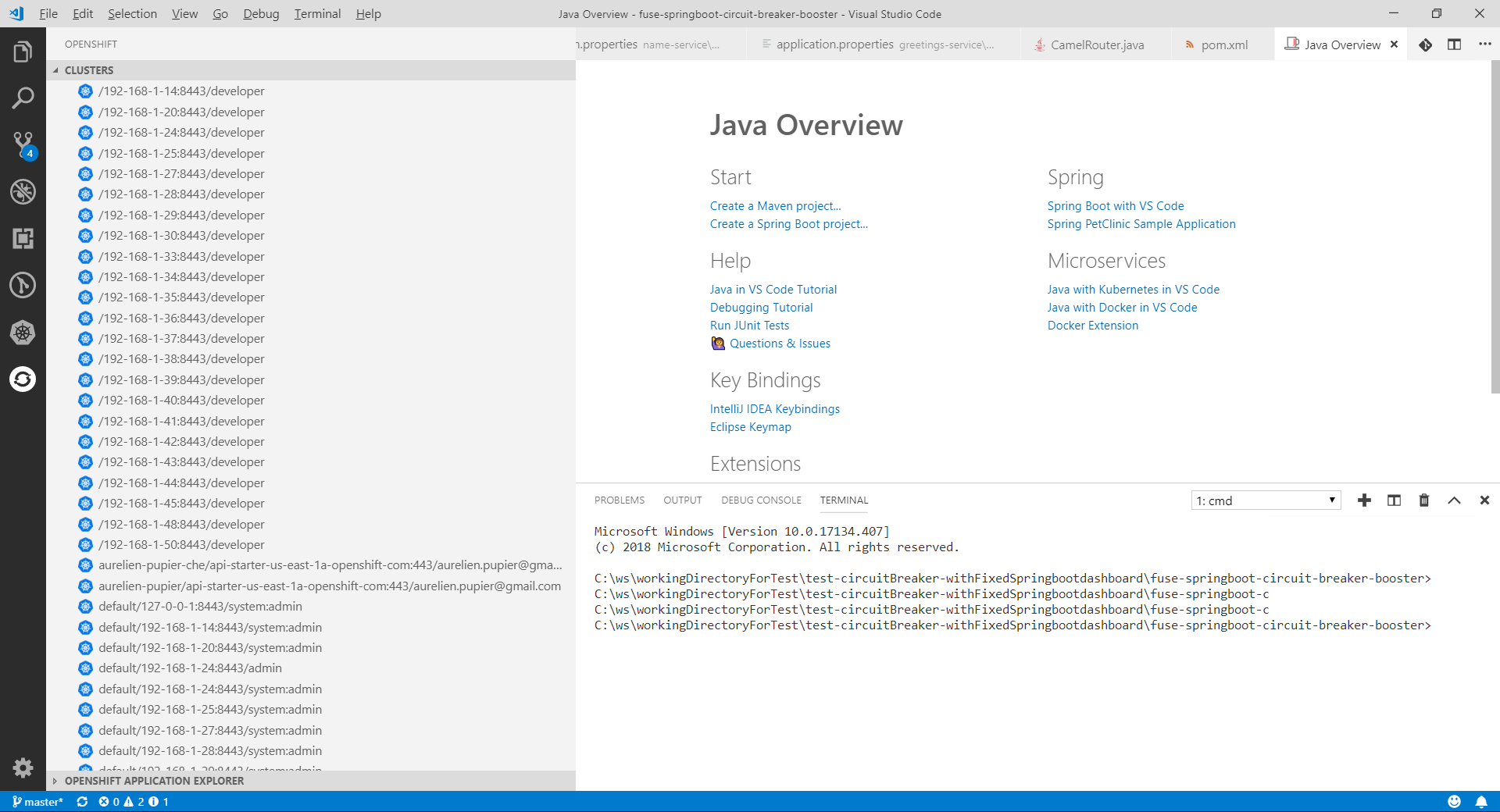
instead of filter it might also be 2 top-level tree ... | non_priority | provide filters for started not started clusters in my case i have a lot of clusters registered only one is started and i need to scroll to find it instead of filter it might also be top level tree nodes nota having a marker to mention if it started or not would be nice too in case of filter not use... | 0 |
9,237 | 3,869,861,936 | IssuesEvent | 2016-04-10 21:02:33 | wevote/WebApp | https://api.github.com/repos/wevote/WebApp | closed | Mobile display too wide, iPhone Safari | code review | - [x] Many pages are too wide (and offer left/right scrolling) in an iPhone 6 in Safari. (Note: I think our minimum phone width should be iPhone 5) These include Ballot, Candidate, More Opinions
- [x] "1 positive (up arrow)" and "0 negative (down arrow)" should fit on one line (See attached photos, for both ballot pag... | 1.0 | Mobile display too wide, iPhone Safari - - [x] Many pages are too wide (and offer left/right scrolling) in an iPhone 6 in Safari. (Note: I think our minimum phone width should be iPhone 5) These include Ballot, Candidate, More Opinions
- [x] "1 positive (up arrow)" and "0 negative (down arrow)" should fit on one line ... | non_priority | mobile display too wide iphone safari many pages are too wide and offer left right scrolling in an iphone in safari note i think our minimum phone width should be iphone these include ballot candidate more opinions positive up arrow and negative down arrow should fit on one line see... | 0 |
233,764 | 19,044,247,418 | IssuesEvent | 2021-11-25 04:37:47 | systemd/systemd | https://api.github.com/repos/systemd/systemd | closed | Spurious fails in TEST-46-HOMED | bug 🐛 tests homed ci-blocker 🚧 | **systemd version the issue has been seen with**
> latest master
<!-- **NOTE:** Do not submit bug reports about anything but the two most recently released *major* systemd versions upstream! -->
<!-- If there have been multiple stable releases for that major version, please consider updating to a recent... | 1.0 | Spurious fails in TEST-46-HOMED - **systemd version the issue has been seen with**
> latest master
<!-- **NOTE:** Do not submit bug reports about anything but the two most recently released *major* systemd versions upstream! -->
<!-- If there have been multiple stable releases for that major version, pl... | non_priority | spurious fails in test homed systemd version the issue has been seen with latest master used distribution arch linux in several latest centos ci results i noticed an intermittent fail in test homed testsuite sh diff i s disk size free floor ceiling ... | 0 |
65,548 | 12,619,533,483 | IssuesEvent | 2020-06-13 01:04:59 | asartalo/ctse | https://api.github.com/repos/asartalo/ctse | closed | Fix "method_lines" issue in lib/Session.js | code-quality | Function `_objectify` has 31 lines of code (exceeds 25 allowed). Consider refactoring.
https://codeclimate.com/github/asartalo/ctse/lib/Session.js#issue_5ee2aaef02a4580001000046 | 1.0 | Fix "method_lines" issue in lib/Session.js - Function `_objectify` has 31 lines of code (exceeds 25 allowed). Consider refactoring.
https://codeclimate.com/github/asartalo/ctse/lib/Session.js#issue_5ee2aaef02a4580001000046 | non_priority | fix method lines issue in lib session js function objectify has lines of code exceeds allowed consider refactoring | 0 |
76,804 | 9,965,830,825 | IssuesEvent | 2019-07-08 09:40:22 | tidyverse/dplyr | https://api.github.com/repos/tidyverse/dplyr | closed | Documentation of NA types (NA_real_, etc.) in recode function | documentation help wanted :heart: tidy-dev-day :nerd_face: | I was reading issue #3202, which relates to the need to use the correct type of NA on the RHS of the case_when function (i.e. NA_real_, NA_character_) etc. The author indicated that they have never heard of different types of NA and I hadn't either. They opened a PR to add an example to the documentation.
I think I'... | 1.0 | Documentation of NA types (NA_real_, etc.) in recode function - I was reading issue #3202, which relates to the need to use the correct type of NA on the RHS of the case_when function (i.e. NA_real_, NA_character_) etc. The author indicated that they have never heard of different types of NA and I hadn't either. They o... | non_priority | documentation of na types na real etc in recode function i was reading issue which relates to the need to use the correct type of na on the rhs of the case when function i e na real na character etc the author indicated that they have never heard of different types of na and i hadn t either they open... | 0 |
26,748 | 4,241,331,102 | IssuesEvent | 2016-07-06 16:00:14 | Shopify/sarama | https://api.github.com/repos/Shopify/sarama | closed | Check the received message value in producer mocks | enhancement producer tests | Hi guys, not sure if this is a valid issue.
When developing a unit test for a program that uses the sync/asyc producer, I can only say that I expect to receive a message and that I want the mock response to be success/error.
For my test I need to check the value inside the message, so I propose to extend the `produce... | 1.0 | Check the received message value in producer mocks - Hi guys, not sure if this is a valid issue.
When developing a unit test for a program that uses the sync/asyc producer, I can only say that I expect to receive a message and that I want the mock response to be success/error.
For my test I need to check the value in... | non_priority | check the received message value in producer mocks hi guys not sure if this is a valid issue when developing a unit test for a program that uses the sync asyc producer i can only say that i expect to receive a message and that i want the mock response to be success error for my test i need to check the value in... | 0 |
166,538 | 26,371,046,675 | IssuesEvent | 2023-01-11 20:42:49 | elementor/elementor | https://api.github.com/repos/elementor/elementor | closed | ✔️ 🔗 🚀 Feature Request: A more flexible section with auto-width columns (Related to #2219) | request/enhancement type/responsive component/layout component/design solved_by_container 🚀 shipped solved_by_custom_units | <!-- Before opening a new issue, please search for duplicate issues to prevent opening a duplicate feature request. If there is already an open existing request, please leave a comment there. -->
## Prerequisites
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] I have searched for similar features requests in bot... | 1.0 | ✔️ 🔗 🚀 Feature Request: A more flexible section with auto-width columns (Related to #2219) - <!-- Before opening a new issue, please search for duplicate issues to prevent opening a duplicate feature request. If there is already an open existing request, please leave a comment there. -->
## Prerequisites
<!-- MAR... | non_priority | ✔️ 🔗 🚀 feature request a more flexible section with auto width columns related to prerequisites i have searched for similar features requests in both open and closed tickets and cannot find a duplicate the feature is still missing in the latest stable version of elementor elementor p... | 0 |
12,197 | 4,386,539,829 | IssuesEvent | 2016-08-08 13:11:35 | ColinGilbert/noobwerkz-engine | https://api.github.com/repos/ColinGilbert/noobwerkz-engine | closed | Banish -fpermissive | best practices bug code correctness perpetual security stability | Having this thing is useful in a pinch, but a horror in production code that allows certain awful things right through. | 1.0 | Banish -fpermissive - Having this thing is useful in a pinch, but a horror in production code that allows certain awful things right through. | non_priority | banish fpermissive having this thing is useful in a pinch but a horror in production code that allows certain awful things right through | 0 |
6,276 | 3,006,833,090 | IssuesEvent | 2015-07-27 13:09:48 | centresource/generator-playbook | https://api.github.com/repos/centresource/generator-playbook | closed | Add upgrade instructions? | documentation question | Should we consider adding some documentation on how to upgrade an existing project from v1 to v2?
Maybe the wiki is a good place for this. | 1.0 | Add upgrade instructions? - Should we consider adding some documentation on how to upgrade an existing project from v1 to v2?
Maybe the wiki is a good place for this. | non_priority | add upgrade instructions should we consider adding some documentation on how to upgrade an existing project from to maybe the wiki is a good place for this | 0 |
18,311 | 6,574,378,138 | IssuesEvent | 2017-09-11 12:40:08 | pioneerspacesim/pioneer | https://api.github.com/repos/pioneerspacesim/pioneer | closed | macOS build failure due to ARFLAGS | Build Platform Specific | ```
Making install in miniz
make[3]: Nothing to be done for `install-exec-am'.
make[3]: Nothing to be done for `install-data-am'.
Making install in jenkins
CC lookup3.o
AR libjenkins.a
/Applications/Xcode.app/Contents/Developer/Toolchains/XcodeDefault.xctoolchain/usr/bin/ar: illegal option -- j
... | 1.0 | macOS build failure due to ARFLAGS - ```
Making install in miniz
make[3]: Nothing to be done for `install-exec-am'.
make[3]: Nothing to be done for `install-data-am'.
Making install in jenkins
CC lookup3.o
AR libjenkins.a
/Applications/Xcode.app/Contents/Developer/Toolchains/XcodeDefault.xctoolch... | non_priority | macos build failure due to arflags making install in miniz make nothing to be done for install exec am make nothing to be done for install data am making install in jenkins cc o ar libjenkins a applications xcode app contents developer toolchains xcodedefault xctoolchain usr bi... | 0 |
105,381 | 9,081,711,324 | IssuesEvent | 2019-02-17 04:31:36 | phan/phan | https://api.github.com/repos/phan/phan | closed | "Serialization of 'Closure' is not allowed" exception running unit tests of Phan | tests | Noticed when fixing phpunit xml configurations.
Recording this because Phan frequently uses static closures for performance reasons and some fail to be added to the test cases' ` protected $backupStaticAttributesBlacklist`
This was due to the $closure_map (src/Phan/AST/ASTReverter.php on line 71)
Steps used to... | 1.0 | "Serialization of 'Closure' is not allowed" exception running unit tests of Phan - Noticed when fixing phpunit xml configurations.
Recording this because Phan frequently uses static closures for performance reasons and some fail to be added to the test cases' ` protected $backupStaticAttributesBlacklist`
This was... | non_priority | serialization of closure is not allowed exception running unit tests of phan noticed when fixing phpunit xml configurations recording this because phan frequently uses static closures for performance reasons and some fail to be added to the test cases protected backupstaticattributesblacklist this was... | 0 |
146,622 | 11,741,863,624 | IssuesEvent | 2020-03-11 22:52:36 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | [k3s-upgrade] Workload-apply-k3s-worker-plan stuck while upgrading cluster from v1.16.3 to v1.16.7. | [zube]: To Test area/import-k3s kind/bug-qa | <!--
Please search for existing issues first, then read https://rancher.com/docs/rancher/v2.x/en/contributing/#bugs-issues-or-questions to see what we expect in an issue
For security issues, please email security@rancher.com instead of posting a public issue in GitHub. You may (but are not required to) use the GPG ke... | 1.0 | [k3s-upgrade] Workload-apply-k3s-worker-plan stuck while upgrading cluster from v1.16.3 to v1.16.7. - <!--
Please search for existing issues first, then read https://rancher.com/docs/rancher/v2.x/en/contributing/#bugs-issues-or-questions to see what we expect in an issue
For security issues, please email security@ran... | non_priority | workload apply worker plan stuck while upgrading cluster from to please search for existing issues first then read to see what we expect in an issue for security issues please email security rancher com instead of posting a public issue in github you may but are not required to use the ... | 0 |
104,103 | 16,613,422,334 | IssuesEvent | 2021-06-02 14:07:25 | Thanraj/linux-4.1.15 | https://api.github.com/repos/Thanraj/linux-4.1.15 | opened | CVE-2017-18079 (High) detected in linux-stable-rtv4.1.33 | security vulnerability | ## CVE-2017-18079 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home pag... | True | CVE-2017-18079 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2017-18079 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartw... | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files... | 0 |
13,562 | 16,081,114,093 | IssuesEvent | 2021-04-26 04:50:12 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | opened | Disabling block widgets via theme supports wipes out content | Backwards Compatibility [Feature] Widgets Customizer [Feature] Widgets Screen [Package] Edit Widgets [Type] Bug | <!--
Please fill out ALL required sections. Bug reports with missing information will
be closed.
Before submitting a bug report:
- Check if the bug has already been fixed by updating WordPress and/or Gutenberg.
- Check if the bug is caused by a plugin by deactivating all plugins except Gutenberg.
- Check if t... | True | Disabling block widgets via theme supports wipes out content - <!--
Please fill out ALL required sections. Bug reports with missing information will
be closed.
Before submitting a bug report:
- Check if the bug has already been fixed by updating WordPress and/or Gutenberg.
- Check if the bug is caused by a plu... | non_priority | disabling block widgets via theme supports wipes out content please fill out all required sections bug reports with missing information will be closed before submitting a bug report check if the bug has already been fixed by updating wordpress and or gutenberg check if the bug is caused by a plu... | 0 |
49,521 | 26,189,353,423 | IssuesEvent | 2023-01-03 07:08:30 | thesofproject/sof | https://api.github.com/repos/thesofproject/sof | closed | [FEATURE] Setup performance build to evaluate each pipeline/task performance. | enhancement performance | We want to measure the SOF performance in 3 dimensions. This would benefit new platform/feature enabling, core assignment and other topics.
- [ ] **Memory**: break down the whole memory usage of SOF, include TEXT/DATA/BSS.
Plan:
1. a dedicated map file for all TEXT/DATA/BSS and its details for each link... | True | [FEATURE] Setup performance build to evaluate each pipeline/task performance. - We want to measure the SOF performance in 3 dimensions. This would benefit new platform/feature enabling, core assignment and other topics.
- [ ] **Memory**: break down the whole memory usage of SOF, include TEXT/DATA/BSS.
Plan:
... | non_priority | setup performance build to evaluate each pipeline task performance we want to measure the sof performance in dimensions this would benefit new platform feature enabling core assignment and other topics memory break down the whole memory usage of sof include text data bss plan a ... | 0 |
232,794 | 18,909,443,788 | IssuesEvent | 2021-11-16 12:39:48 | IgniteUI/igniteui-webcomponents | https://api.github.com/repos/IgniteUI/igniteui-webcomponents | closed | Button - Bootstrap Theme - When theme is applied, button does not look like a bootstrap button | bug status: awaiting-test | ## Description
When the bootstrap theme is applied, the button component does not look like a bootstrap button.
Here is what the bootstrap buttons look like depending on which button style (primary, secondary, success, etc) they use:
![image](https://user-images.githubusercontent.com/835562/140168620-b14d1196-... | 1.0 | Button - Bootstrap Theme - When theme is applied, button does not look like a bootstrap button - ## Description
When the bootstrap theme is applied, the button component does not look like a bootstrap button.
Here is what the bootstrap buttons look like depending on which button style (primary, secondary, success... | non_priority | button bootstrap theme when theme is applied button does not look like a bootstrap button description when the bootstrap theme is applied the button component does not look like a bootstrap button here is what the bootstrap buttons look like depending on which button style primary secondary success... | 0 |
23,469 | 21,950,970,845 | IssuesEvent | 2022-05-24 07:54:03 | maykinmedia/sdg-invoervoorziening | https://api.github.com/repos/maykinmedia/sdg-invoervoorziening | closed | Add update catalogus tests | enhancement inschatten epic:Usability | add the following tests:
- test_create_catalog_from_reference_if_enabled
- test_no_create_catalog_from_reference_if_disabled
- test_create_products_from_reference_product
- test_no_create_products_from_reference_without_active_version
- test_correct_products_if_no_initial_version
- test_correct_products_if_no_t... | True | Add update catalogus tests - add the following tests:
- test_create_catalog_from_reference_if_enabled
- test_no_create_catalog_from_reference_if_disabled
- test_create_products_from_reference_product
- test_no_create_products_from_reference_without_active_version
- test_correct_products_if_no_initial_version
- ... | non_priority | add update catalogus tests add the following tests test create catalog from reference if enabled test no create catalog from reference if disabled test create products from reference product test no create products from reference without active version test correct products if no initial version ... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.