Unnamed: 0 int64 1 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3 values | title stringlengths 3 438 | labels stringlengths 4 308 | body stringlengths 7 254k | index stringclasses 7 values | text_combine stringlengths 96 254k | label stringclasses 2 values | text stringlengths 96 246k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
360,798 | 25,311,127,226 | IssuesEvent | 2022-11-17 17:31:36 | komutilo/dmark | https://api.github.com/repos/komutilo/dmark | opened | Provide documentation | documentation | # Dmark docs by topic:
- [ ] Overview
- [ ] Why Dmark?
- [ ] local state management
- [ ] handling multiple config files
- [ ] DRY and multi-stage management
- [ ] managing no HCP projects
- [ ] Terragrunt (compare solutions)
- [ ] Dmark CLI
- [ ] Dmark and Terraform commands
- [ ] Dmark CLI parameters
- [ ] config
- [ ] stage
- [ ] stack
- [ ] label
- [ ] fmt
- [ ] upgrade
- [ ] migrate-state
- [ ] auto-approve
- [ ] no-init
- [ ] delete-lock
- [ ] Stack
- [ ] What is a stack?
- [ ] Stage
- [ ] What is a stage?
- [ ] The `__all__` stage
- [ ] Ignoring stages
- [ ] Stageless project
- [ ] Local state management
- [ ] Local property
- [ ] boolean
- [ ] with path
- [ ] Multiple stages for the same local stack
- [ ] Remote state management
- [ ] How to setup a remote stack
- [ ] general
- [ ] AWS S3
- [ ] Order
- [ ] Managing deploy order
- [ ] Labels
- [ ] Labeling the stacks
- [ ] Errors handling
- [ ] Deploy error handling by Dmark
- [ ] Dmark source code
- [ ] Dmark license
- [ ] Dmark maintainers
- [ ] Dmark brand
- [ ] Node.js, npm and pnpm motivations
- [ ] How to setup development environment
- [ ] How to contribute
- [ ] issues
- [ ] lint
- [ ] unit tests and coverage
- [ ] integration tests
- [ ] PR | 1.0 | Provide documentation - # Dmark docs by topic:
- [ ] Overview
- [ ] Why Dmark?
- [ ] local state management
- [ ] handling multiple config files
- [ ] DRY and multi-stage management
- [ ] managing no HCP projects
- [ ] Terragrunt (compare solutions)
- [ ] Dmark CLI
- [ ] Dmark and Terraform commands
- [ ] Dmark CLI parameters
- [ ] config
- [ ] stage
- [ ] stack
- [ ] label
- [ ] fmt
- [ ] upgrade
- [ ] migrate-state
- [ ] auto-approve
- [ ] no-init
- [ ] delete-lock
- [ ] Stack
- [ ] What is a stack?
- [ ] Stage
- [ ] What is a stage?
- [ ] The `__all__` stage
- [ ] Ignoring stages
- [ ] Stageless project
- [ ] Local state management
- [ ] Local property
- [ ] boolean
- [ ] with path
- [ ] Multiple stages for the same local stack
- [ ] Remote state management
- [ ] How to setup a remote stack
- [ ] general
- [ ] AWS S3
- [ ] Order
- [ ] Managing deploy order
- [ ] Labels
- [ ] Labeling the stacks
- [ ] Errors handling
- [ ] Deploy error handling by Dmark
- [ ] Dmark source code
- [ ] Dmark license
- [ ] Dmark maintainers
- [ ] Dmark brand
- [ ] Node.js, npm and pnpm motivations
- [ ] How to setup development environment
- [ ] How to contribute
- [ ] issues
- [ ] lint
- [ ] unit tests and coverage
- [ ] integration tests
- [ ] PR | non_main | provide documentation dmark docs by topic overview why dmark local state management handling multiple config files dry and multi stage management managing no hcp projects terragrunt compare solutions dmark cli dmark and terraform commands dmark cli parameters config stage stack label fmt upgrade migrate state auto approve no init delete lock stack what is a stack stage what is a stage the all stage ignoring stages stageless project local state management local property boolean with path multiple stages for the same local stack remote state management how to setup a remote stack general aws order managing deploy order labels labeling the stacks errors handling deploy error handling by dmark dmark source code dmark license dmark maintainers dmark brand node js npm and pnpm motivations how to setup development environment how to contribute issues lint unit tests and coverage integration tests pr | 0 |
590,749 | 17,786,780,948 | IssuesEvent | 2021-08-31 12:04:29 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | [Coverity CID: 237072] Uninitialized pointer read in subsys/bluetooth/controller/ll_sw/ull_adv_aux.c | bug priority: medium Coverity has-pr |
Static code scan issues found in file:
https://github.com/zephyrproject-rtos/zephyr/tree/8c68a7a587b884fb12ee6a31658281b2f9929485/subsys/bluetooth/controller/ll_sw/ull_adv_aux.c#L321
Category: Memory - illegal accesses
Function: `ll_adv_aux_sr_data_set`
Component: Bluetooth
CID: [237072](https://scan9.coverity.com/reports.htm#v29726/p12996/mergedDefectId=237072)
Details:
https://github.com/zephyrproject-rtos/zephyr/blob/8c68a7a587b884fb12ee6a31658281b2f9929485/subsys/bluetooth/controller/ll_sw/ull_adv_aux.c#L323
```
315
316 /* Finish PDU */
317 sr_pdu->len = sr_dptr - &sr_pdu->payload[0];
318
319 sr_data_set_did_update:
320 /* Trigger DID update */
>>> CID 237072: Memory - illegal accesses (UNINIT)
>>> Using uninitialized value "sr_adi" when calling "ull_adv_aux_hdr_set_clear".
321 err = ull_adv_aux_hdr_set_clear(adv, 0, 0, NULL, sr_adi, &pri_idx);
322 if (err) {
323 return err;
324 }
325
326 /* NOTE: No update to primary channel PDU time reservation */
```
For more information about the violation, check the [Coverity Reference](https://scan9.coverity.com/doc/en/cov_checker_ref.html#static_checker_UNINIT). ([CWE-457](http://cwe.mitre.org/data/definitions/457.html))
Please fix or provide comments in coverity using the link:
https://scan9.coverity.com/reports.htm#v29271/p12996
Note: This issue was created automatically. Priority was set based on classification
of the file affected and the impact field in coverity. Assignees were set using the CODEOWNERS file.
| 1.0 | [Coverity CID: 237072] Uninitialized pointer read in subsys/bluetooth/controller/ll_sw/ull_adv_aux.c -
Static code scan issues found in file:
https://github.com/zephyrproject-rtos/zephyr/tree/8c68a7a587b884fb12ee6a31658281b2f9929485/subsys/bluetooth/controller/ll_sw/ull_adv_aux.c#L321
Category: Memory - illegal accesses
Function: `ll_adv_aux_sr_data_set`
Component: Bluetooth
CID: [237072](https://scan9.coverity.com/reports.htm#v29726/p12996/mergedDefectId=237072)
Details:
https://github.com/zephyrproject-rtos/zephyr/blob/8c68a7a587b884fb12ee6a31658281b2f9929485/subsys/bluetooth/controller/ll_sw/ull_adv_aux.c#L323
```
315
316 /* Finish PDU */
317 sr_pdu->len = sr_dptr - &sr_pdu->payload[0];
318
319 sr_data_set_did_update:
320 /* Trigger DID update */
>>> CID 237072: Memory - illegal accesses (UNINIT)
>>> Using uninitialized value "sr_adi" when calling "ull_adv_aux_hdr_set_clear".
321 err = ull_adv_aux_hdr_set_clear(adv, 0, 0, NULL, sr_adi, &pri_idx);
322 if (err) {
323 return err;
324 }
325
326 /* NOTE: No update to primary channel PDU time reservation */
```
For more information about the violation, check the [Coverity Reference](https://scan9.coverity.com/doc/en/cov_checker_ref.html#static_checker_UNINIT). ([CWE-457](http://cwe.mitre.org/data/definitions/457.html))
Please fix or provide comments in coverity using the link:
https://scan9.coverity.com/reports.htm#v29271/p12996
Note: This issue was created automatically. Priority was set based on classification
of the file affected and the impact field in coverity. Assignees were set using the CODEOWNERS file.
| non_main | uninitialized pointer read in subsys bluetooth controller ll sw ull adv aux c static code scan issues found in file category memory illegal accesses function ll adv aux sr data set component bluetooth cid details finish pdu sr pdu len sr dptr sr pdu payload sr data set did update trigger did update cid memory illegal accesses uninit using uninitialized value sr adi when calling ull adv aux hdr set clear err ull adv aux hdr set clear adv null sr adi pri idx if err return err note no update to primary channel pdu time reservation for more information about the violation check the please fix or provide comments in coverity using the link note this issue was created automatically priority was set based on classification of the file affected and the impact field in coverity assignees were set using the codeowners file | 0 |
2,161 | 7,524,233,597 | IssuesEvent | 2018-04-13 06:05:54 | RalfKoban/MiKo-Analyzers | https://api.github.com/repos/RalfKoban/MiKo-Analyzers | closed | Public/internal/interface methods should not have IList, IDictionary, ICollection as parameters | Area: analyzer Area: maintainability duplicate feature next | Methods should not have IList, IDictionary, ICollection as parameters.
Instead they should have the read-only or immutable variants to avoid modifications. | True | Public/internal/interface methods should not have IList, IDictionary, ICollection as parameters - Methods should not have IList, IDictionary, ICollection as parameters.
Instead they should have the read-only or immutable variants to avoid modifications. | main | public internal interface methods should not have ilist idictionary icollection as parameters methods should not have ilist idictionary icollection as parameters instead they should have the read only or immutable variants to avoid modifications | 1 |
40,878 | 5,280,882,856 | IssuesEvent | 2017-02-07 15:16:34 | DroidKaigi/conference-app-2017 | https://api.github.com/repos/DroidKaigi/conference-app-2017 | closed | Add notification icon | design welcome contribute | ## Overview (Required)
- We need to prepare notification icon.
- On DroidKaigi2016 app, @yulily100 did it. Great.
## Links
- https://github.com/konifar/droidkaigi2016/pull/250 | 1.0 | Add notification icon - ## Overview (Required)
- We need to prepare notification icon.
- On DroidKaigi2016 app, @yulily100 did it. Great.
## Links
- https://github.com/konifar/droidkaigi2016/pull/250 | non_main | add notification icon overview required we need to prepare notification icon on app did it great links | 0 |
417 | 3,488,258,685 | IssuesEvent | 2016-01-02 19:51:41 | espeak-ng/espeak-ng | https://api.github.com/repos/espeak-ng/espeak-ng | closed | Rework the C API and provide espeak compatibility. | maintainability resolved/fixed | The `speak_lib.h` API should be redesigned to better fit the usage, provide more detailed status codes, etc. and be placed in `espeak_ng.h`. This will allow the eSpeak NG API to be used independently of the eSpeak API, and make it possible to evolve the API to meet the needs of eSpeak NG to provide new features.
For eSpeak compatibility, the `speak_lib.h` methods should be implemented in `speak_lib.c` -- these should forward to the `espeak_ng.h` APIs, map the status codes, etc.. | True | Rework the C API and provide espeak compatibility. - The `speak_lib.h` API should be redesigned to better fit the usage, provide more detailed status codes, etc. and be placed in `espeak_ng.h`. This will allow the eSpeak NG API to be used independently of the eSpeak API, and make it possible to evolve the API to meet the needs of eSpeak NG to provide new features.
For eSpeak compatibility, the `speak_lib.h` methods should be implemented in `speak_lib.c` -- these should forward to the `espeak_ng.h` APIs, map the status codes, etc.. | main | rework the c api and provide espeak compatibility the speak lib h api should be redesigned to better fit the usage provide more detailed status codes etc and be placed in espeak ng h this will allow the espeak ng api to be used independently of the espeak api and make it possible to evolve the api to meet the needs of espeak ng to provide new features for espeak compatibility the speak lib h methods should be implemented in speak lib c these should forward to the espeak ng h apis map the status codes etc | 1 |
4,115 | 19,533,226,038 | IssuesEvent | 2021-12-30 21:45:58 | backdrop-ops/contrib | https://api.github.com/repos/backdrop-ops/contrib | closed | Contrib Group Application: | Maintainer application | Hello and welcome to the contrib application process! We're happy to have you :)
**Please indicate how you intend to help the Backdrop community by joining this group**
* Option #1: I would like to contribute a project
* Option #2: I would like to maintain a project, but have nothing to contribute at this time
* Option #3: I would like to update documentation and/or triage issue queues
<!-- example: Option 1 -->Option 1 and/or Option 3
## Based on your selection above, please provide the following information:
**(option #1) The name of your module, theme, or layout**
<!-- example: Forum Access -->s3fs
## (option #1) Please note these 3 requirements for new contrib projects:
- [x] Include a README.md file containing license and maintainer information.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/README.md
- [x] Include a LICENSE.txt file.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/LICENSE.txt.
- [x] If porting a Drupal 7 project, Maintain the Git history from Drupal.
**(option #1 -- optional) Post a link here to an issue in the drupal.org queue notifying the Drupal 7 maintainers that you are working on a Backdrop port of their project**
[https://www.drupal.org/project/s3fs/issues/3238353](https://www.drupal.org/project/s3fs/issues/3238353)
**Post a link to your new Backdrop project under your own GitHub account (option #1)**
[https://github.com/keiserjb/s3fs](https://github.com/keiserjb/s3fs)
**If you have chosen option #2 or #1 above, do you agree to the [Backdrop Contributed Project Agreement](https://github.com/backdrop-ops/contrib#backdrop-contributed-project-agreement)**
YES
| True | Contrib Group Application: - Hello and welcome to the contrib application process! We're happy to have you :)
**Please indicate how you intend to help the Backdrop community by joining this group**
* Option #1: I would like to contribute a project
* Option #2: I would like to maintain a project, but have nothing to contribute at this time
* Option #3: I would like to update documentation and/or triage issue queues
<!-- example: Option 1 -->Option 1 and/or Option 3
## Based on your selection above, please provide the following information:
**(option #1) The name of your module, theme, or layout**
<!-- example: Forum Access -->s3fs
## (option #1) Please note these 3 requirements for new contrib projects:
- [x] Include a README.md file containing license and maintainer information.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/README.md
- [x] Include a LICENSE.txt file.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/LICENSE.txt.
- [x] If porting a Drupal 7 project, Maintain the Git history from Drupal.
**(option #1 -- optional) Post a link here to an issue in the drupal.org queue notifying the Drupal 7 maintainers that you are working on a Backdrop port of their project**
[https://www.drupal.org/project/s3fs/issues/3238353](https://www.drupal.org/project/s3fs/issues/3238353)
**Post a link to your new Backdrop project under your own GitHub account (option #1)**
[https://github.com/keiserjb/s3fs](https://github.com/keiserjb/s3fs)
**If you have chosen option #2 or #1 above, do you agree to the [Backdrop Contributed Project Agreement](https://github.com/backdrop-ops/contrib#backdrop-contributed-project-agreement)**
YES
| main | contrib group application hello and welcome to the contrib application process we re happy to have you please indicate how you intend to help the backdrop community by joining this group option i would like to contribute a project option i would like to maintain a project but have nothing to contribute at this time option i would like to update documentation and or triage issue queues option and or option based on your selection above please provide the following information option the name of your module theme or layout option please note these requirements for new contrib projects include a readme md file containing license and maintainer information you can use this example include a license txt file you can use this example if porting a drupal project maintain the git history from drupal option optional post a link here to an issue in the drupal org queue notifying the drupal maintainers that you are working on a backdrop port of their project post a link to your new backdrop project under your own github account option if you have chosen option or above do you agree to the yes | 1 |
3,422 | 13,182,101,140 | IssuesEvent | 2020-08-12 15:16:04 | duo-labs/cloudmapper | https://api.github.com/repos/duo-labs/cloudmapper | closed | Filter only recources in one or several CloudFormation stacks (--stack-names option) | enhancement map unmaintained_functionality | This is an awesome project. Bravo.
We have AWS accounts with many projects and huge number of resources in each of them. Current filters do not allow to ignore 99% resources and we have crowd of resources mixed from different projects. Web server getting overloaded very slow. It takes couple of minutes to generate web page in browser and result is not informative.
Is it possible do add filter like "--stack-names" that will filter resources only from one/two/three... CloudFormation stacks. Stacks usually have 5-25 resources and visualisation will be much better.
In this case we can start many web servers on different ports and see each project on personal port.
Thank you for you fantastic work. | True | Filter only recources in one or several CloudFormation stacks (--stack-names option) - This is an awesome project. Bravo.
We have AWS accounts with many projects and huge number of resources in each of them. Current filters do not allow to ignore 99% resources and we have crowd of resources mixed from different projects. Web server getting overloaded very slow. It takes couple of minutes to generate web page in browser and result is not informative.
Is it possible do add filter like "--stack-names" that will filter resources only from one/two/three... CloudFormation stacks. Stacks usually have 5-25 resources and visualisation will be much better.
In this case we can start many web servers on different ports and see each project on personal port.
Thank you for you fantastic work. | main | filter only recources in one or several cloudformation stacks stack names option this is an awesome project bravo we have aws accounts with many projects and huge number of resources in each of them current filters do not allow to ignore resources and we have crowd of resources mixed from different projects web server getting overloaded very slow it takes couple of minutes to generate web page in browser and result is not informative is it possible do add filter like stack names that will filter resources only from one two three cloudformation stacks stacks usually have resources and visualisation will be much better in this case we can start many web servers on different ports and see each project on personal port thank you for you fantastic work | 1 |
4,017 | 18,752,070,326 | IssuesEvent | 2021-11-05 04:17:28 | beefproject/beef | https://api.github.com/repos/beefproject/beef | opened | Gem 'nokogiri' listed in Gemfile but is never required | Maintainability | Investigate whether nokogiri is required in Gemfile. | True | Gem 'nokogiri' listed in Gemfile but is never required - Investigate whether nokogiri is required in Gemfile. | main | gem nokogiri listed in gemfile but is never required investigate whether nokogiri is required in gemfile | 1 |
4,978 | 25,549,910,973 | IssuesEvent | 2022-11-29 22:27:05 | carbon-design-system/carbon | https://api.github.com/repos/carbon-design-system/carbon | closed | Text Input - Invalid state | type: question ❓ status: waiting for maintainer response 💬 | Hi there!
I'm a UXE on C&CS and currently working on building [common components/patterns for the C&CS library](https://github.com/carbon-design-system/ibm-cloud-cognitive).
I've been working a lot on the [Create patterns](https://www.carbondesignsystem.com/community/patterns/create-flows/) for modals and side panels and notice that with proper form validation, the `TextInput` components will push down /expand the height of the modal/panel.
This behavior isn't obvious if you have an `optionalText` prop because it replaces this text with the invalid text, however, if you do not utilize this prop, you can see the height change.
My question is -- is there anyway to update the `TextInput` component so that it accounts for the additional space needed for the invalid text? This way it doesn't add additional height to whatever container the component is being used in? | True | Text Input - Invalid state - Hi there!
I'm a UXE on C&CS and currently working on building [common components/patterns for the C&CS library](https://github.com/carbon-design-system/ibm-cloud-cognitive).
I've been working a lot on the [Create patterns](https://www.carbondesignsystem.com/community/patterns/create-flows/) for modals and side panels and notice that with proper form validation, the `TextInput` components will push down /expand the height of the modal/panel.
This behavior isn't obvious if you have an `optionalText` prop because it replaces this text with the invalid text, however, if you do not utilize this prop, you can see the height change.
My question is -- is there anyway to update the `TextInput` component so that it accounts for the additional space needed for the invalid text? This way it doesn't add additional height to whatever container the component is being used in? | main | text input invalid state hi there i m a uxe on c cs and currently working on building i ve been working a lot on the for modals and side panels and notice that with proper form validation the textinput components will push down expand the height of the modal panel this behavior isn t obvious if you have an optionaltext prop because it replaces this text with the invalid text however if you do not utilize this prop you can see the height change my question is is there anyway to update the textinput component so that it accounts for the additional space needed for the invalid text this way it doesn t add additional height to whatever container the component is being used in | 1 |
5,722 | 30,257,556,246 | IssuesEvent | 2023-07-07 05:00:10 | garret1317/yt-dlp-rajiko | https://api.github.com/repos/garret1317/yt-dlp-rajiko | opened | unified time handling might be a good idea | maintainance | some of it's a bit fragmented and hacky at the moment, might be a good idea to make a big unified one that uses datetime
todo:specific examples | True | unified time handling might be a good idea - some of it's a bit fragmented and hacky at the moment, might be a good idea to make a big unified one that uses datetime
todo:specific examples | main | unified time handling might be a good idea some of it s a bit fragmented and hacky at the moment might be a good idea to make a big unified one that uses datetime todo specific examples | 1 |
325,182 | 27,853,596,434 | IssuesEvent | 2023-03-20 20:44:29 | nitnelave/lldap | https://api.github.com/repos/nitnelave/lldap | closed | Upgrade to a recent version of Yew | enhancement help wanted dependencies rust frontend tests | The front-end was written with yew 0.18, and from 0.19 they have made significant breaking changes. As a result, updating is hard.
However, it is required to address #247 (and maybe #392), as well as keep up with the best practices. It would also help clean up the code. Potentially as well add testing.
Another option, though much heavier, would be to rewrite the entire frontend since it's not too complicated. This could be done either in another, more stable Rust framework, or in another language (typescript?). Rust is preferred for the compatibility with the authentication protocol OPAQUE. | 1.0 | Upgrade to a recent version of Yew - The front-end was written with yew 0.18, and from 0.19 they have made significant breaking changes. As a result, updating is hard.
However, it is required to address #247 (and maybe #392), as well as keep up with the best practices. It would also help clean up the code. Potentially as well add testing.
Another option, though much heavier, would be to rewrite the entire frontend since it's not too complicated. This could be done either in another, more stable Rust framework, or in another language (typescript?). Rust is preferred for the compatibility with the authentication protocol OPAQUE. | non_main | upgrade to a recent version of yew the front end was written with yew and from they have made significant breaking changes as a result updating is hard however it is required to address and maybe as well as keep up with the best practices it would also help clean up the code potentially as well add testing another option though much heavier would be to rewrite the entire frontend since it s not too complicated this could be done either in another more stable rust framework or in another language typescript rust is preferred for the compatibility with the authentication protocol opaque | 0 |
90,960 | 15,856,350,753 | IssuesEvent | 2021-04-08 02:08:06 | rvvergara/battleship | https://api.github.com/repos/rvvergara/battleship | opened | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz | security vulnerability | ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: battleship/package.json</p>
<p>Path to vulnerable library: battleship/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- webpack-4.29.6.tgz (Root Library)
- node-libs-browser-2.2.0.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0427 (Medium) detected in elliptic-6.4.1.tgz - ## WS-2019-0427 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elliptic-6.4.1.tgz</b></p></summary>
<p>EC cryptography</p>
<p>Library home page: <a href="https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz">https://registry.npmjs.org/elliptic/-/elliptic-6.4.1.tgz</a></p>
<p>Path to dependency file: battleship/package.json</p>
<p>Path to vulnerable library: battleship/node_modules/elliptic/package.json</p>
<p>
Dependency Hierarchy:
- webpack-4.29.6.tgz (Root Library)
- node-libs-browser-2.2.0.tgz
- crypto-browserify-3.12.0.tgz
- browserify-sign-4.0.4.tgz
- :x: **elliptic-6.4.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The function getNAF() in elliptic library has information leakage. This issue is mitigated in version 6.5.2
<p>Publish Date: 2019-11-22
<p>URL: <a href=https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a>WS-2019-0427</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a">https://github.com/indutny/elliptic/commit/ec735edde187a43693197f6fa3667ceade751a3a</a></p>
<p>Release Date: 2020-05-24</p>
<p>Fix Resolution: v6.5.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | ws medium detected in elliptic tgz ws medium severity vulnerability vulnerable library elliptic tgz ec cryptography library home page a href path to dependency file battleship package json path to vulnerable library battleship node modules elliptic package json dependency hierarchy webpack tgz root library node libs browser tgz crypto browserify tgz browserify sign tgz x elliptic tgz vulnerable library vulnerability details the function getnaf in elliptic library has information leakage this issue is mitigated in version publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
5,861 | 31,714,444,400 | IssuesEvent | 2023-09-09 17:31:22 | aws/aws-sam-cli | https://api.github.com/repos/aws/aws-sam-cli | closed | Support publishing of SAM-CLI to Windows Package Manager | type/feature platform/windows area/installation maintainer/need-followup | <!-- Make sure we don't have an existing Issue that reports the bug you are seeing (both open and closed). -->
### Describe your idea/feature/enhancement
Windows now has an official package manager aka WinGet. There's a [winget-pkgs](https://github.com/microsoft/winget-pkgs) repository maintained by the community and there, the SAM-CLI package is currently updated by the automation or moderators. Most of the times when automation is having issues or is under maintenance mode, it is left outdated unless someone manually looks at and updates the package manifests.
### Proposal
Add details of how to add this to the product.
Using a GitHub workflow which can auto-generate manifests and submit them at winget-pkgs repository through a PR. The PR will be approved by moderators and merged.
Things to consider:
1. Will this require any updates to the [SAM Spec](https://github.com/awslabs/serverless-application-model): No
### Additional Details
There's already a pull request which adds an action that is triggered when a GitHub release (not a draft/pre-release) is published, and it automatically generates manifests for the new version and submits them at winget-pkgs repository using a personal access token (PAT). It can be re-opened and merged ;)
- https://github.com/aws/aws-sam-cli/pull/3858
cc @jfuss | True | Support publishing of SAM-CLI to Windows Package Manager - <!-- Make sure we don't have an existing Issue that reports the bug you are seeing (both open and closed). -->
### Describe your idea/feature/enhancement
Windows now has an official package manager aka WinGet. There's a [winget-pkgs](https://github.com/microsoft/winget-pkgs) repository maintained by the community and there, the SAM-CLI package is currently updated by the automation or moderators. Most of the times when automation is having issues or is under maintenance mode, it is left outdated unless someone manually looks at and updates the package manifests.
### Proposal
Add details of how to add this to the product.
Using a GitHub workflow which can auto-generate manifests and submit them at winget-pkgs repository through a PR. The PR will be approved by moderators and merged.
Things to consider:
1. Will this require any updates to the [SAM Spec](https://github.com/awslabs/serverless-application-model): No
### Additional Details
There's already a pull request which adds an action that is triggered when a GitHub release (not a draft/pre-release) is published, and it automatically generates manifests for the new version and submits them at winget-pkgs repository using a personal access token (PAT). It can be re-opened and merged ;)
- https://github.com/aws/aws-sam-cli/pull/3858
cc @jfuss | main | support publishing of sam cli to windows package manager describe your idea feature enhancement windows now has an official package manager aka winget there s a repository maintained by the community and there the sam cli package is currently updated by the automation or moderators most of the times when automation is having issues or is under maintenance mode it is left outdated unless someone manually looks at and updates the package manifests proposal add details of how to add this to the product using a github workflow which can auto generate manifests and submit them at winget pkgs repository through a pr the pr will be approved by moderators and merged things to consider will this require any updates to the no additional details there s already a pull request which adds an action that is triggered when a github release not a draft pre release is published and it automatically generates manifests for the new version and submits them at winget pkgs repository using a personal access token pat it can be re opened and merged cc jfuss | 1 |
5,881 | 32,007,379,014 | IssuesEvent | 2023-09-21 15:37:02 | centerofci/mathesar-website | https://api.github.com/repos/centerofci/mathesar-website | closed | Add Survey Banner to Website | restricted: maintainers status: draft type: enhancement work: frontend work: product | To gather feedback and understand our users' needs, we're introducing a user survey. The goal is to embed a survey banner on the Mathesar website to facilitate feedback collection, allowing us to improve our product based on user insights.
- The banner should be fixed at the top of the website.
- It should be visible on all pages of the website
- Provide users an option to close the banner. Once closed, the banner should not reappear for that user during the same browsing session.
- The banner should contain a direct link to the provided "Quick User Check-in" survey form.
#### Suggested Banner Content:
> **Help Shape Mathesar's Future!**
> Your insights are invaluable to us. Please spare less than 2 minutes for our survey and let us know how we can enhance Mathesar for you. [Take the Survey](https://docs.google.com/forms/d/1A2yS2C2Sw7-usDJ6wrNUIn177AxJavETrZJU9kdp25I/edit) | [X] (to close the banner)
---
**To Do**:
- [ ] Design the banner
- [ ] Embed the banner at the top of the website. | True | Add Survey Banner to Website - To gather feedback and understand our users' needs, we're introducing a user survey. The goal is to embed a survey banner on the Mathesar website to facilitate feedback collection, allowing us to improve our product based on user insights.
- The banner should be fixed at the top of the website.
- It should be visible on all pages of the website
- Provide users an option to close the banner. Once closed, the banner should not reappear for that user during the same browsing session.
- The banner should contain a direct link to the provided "Quick User Check-in" survey form.
#### Suggested Banner Content:
> **Help Shape Mathesar's Future!**
> Your insights are invaluable to us. Please spare less than 2 minutes for our survey and let us know how we can enhance Mathesar for you. [Take the Survey](https://docs.google.com/forms/d/1A2yS2C2Sw7-usDJ6wrNUIn177AxJavETrZJU9kdp25I/edit) | [X] (to close the banner)
---
**To Do**:
- [ ] Design the banner
- [ ] Embed the banner at the top of the website. | main | add survey banner to website to gather feedback and understand our users needs we re introducing a user survey the goal is to embed a survey banner on the mathesar website to facilitate feedback collection allowing us to improve our product based on user insights the banner should be fixed at the top of the website it should be visible on all pages of the website provide users an option to close the banner once closed the banner should not reappear for that user during the same browsing session the banner should contain a direct link to the provided quick user check in survey form suggested banner content help shape mathesar s future your insights are invaluable to us please spare less than minutes for our survey and let us know how we can enhance mathesar for you to close the banner to do design the banner embed the banner at the top of the website | 1 |
3,476 | 13,385,780,971 | IssuesEvent | 2020-09-02 13:54:47 | DynamoRIO/dynamorio | https://api.github.com/repos/DynamoRIO/dynamorio | closed | remove guard page counts from heap and cache runtime option values | Maintainability Type-Feature | For heap and cache unit sizes specified in runtime options, we take guard pages
out of the requested size: so asking for 64K gives only 56K of usable space for
4K pages. The original logic was tuned for Windows without -vm_reserve where
the OS allocation granularity matters and we don't want to waste space.
On UNIX, however, with the new 4K (or page size) vmm blocks, and with
-vm_reserve covering most allocations at least for smaller applications, the OS
granularity is less important: xref #2597.
Having the guards included makes it difficult to tune the default sizes based on
actual usage (and even more so when guard pages are sometimes turned off). This
isssue covers making the heap and cache sizes like the cache sizes where the
guard pages are added on top of the requested size. (In #2592 I removed the
debug-build STACK_GUARD_PAGE which was removing a page from the given stack size
to make a guard page: now it matches release where what you ask for is the
usable size you get, for stacks.)
| True | remove guard page counts from heap and cache runtime option values - For heap and cache unit sizes specified in runtime options, we take guard pages
out of the requested size: so asking for 64K gives only 56K of usable space for
4K pages. The original logic was tuned for Windows without -vm_reserve where
the OS allocation granularity matters and we don't want to waste space.
On UNIX, however, with the new 4K (or page size) vmm blocks, and with
-vm_reserve covering most allocations at least for smaller applications, the OS
granularity is less important: xref #2597.
Having the guards included makes it difficult to tune the default sizes based on
actual usage (and even more so when guard pages are sometimes turned off). This
isssue covers making the heap and cache sizes like the cache sizes where the
guard pages are added on top of the requested size. (In #2592 I removed the
debug-build STACK_GUARD_PAGE which was removing a page from the given stack size
to make a guard page: now it matches release where what you ask for is the
usable size you get, for stacks.)
| main | remove guard page counts from heap and cache runtime option values for heap and cache unit sizes specified in runtime options we take guard pages out of the requested size so asking for gives only of usable space for pages the original logic was tuned for windows without vm reserve where the os allocation granularity matters and we don t want to waste space on unix however with the new or page size vmm blocks and with vm reserve covering most allocations at least for smaller applications the os granularity is less important xref having the guards included makes it difficult to tune the default sizes based on actual usage and even more so when guard pages are sometimes turned off this isssue covers making the heap and cache sizes like the cache sizes where the guard pages are added on top of the requested size in i removed the debug build stack guard page which was removing a page from the given stack size to make a guard page now it matches release where what you ask for is the usable size you get for stacks | 1 |
89,813 | 25,899,190,952 | IssuesEvent | 2022-12-15 02:59:23 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | SyndicationFeed_Write_RSS_Atom test failing with "IOException : The file '/tmp/' already exists." | arch-wasm area-System.ServiceModel.Syndication blocking-clean-ci Known Build Error | ## Build Information
Build: https://dev.azure.com/dnceng-public/cbb18261-c48f-4abb-8651-8cdcb5474649/_build/results?buildId=84790
Build error leg or test failing: System.ServiceModel.Syndication.Tests.BasicScenarioTests.SyndicationFeed_Write_RSS_Atom
Pull request: https://github.com/dotnet/runtime/pull/78424
Stack trace:
```
at Interop.ThrowExceptionForIoErrno(ErrorInfo errorInfo, String path, Boolean isDirError)
at Interop.CheckIo(Int64 result, String path, Boolean isDirError)
at Interop.CheckIo(IntPtr result, String path, Boolean isDirError)
at System.IO.Path.GetTempFileName()
at System.ServiceModel.Syndication.Tests.BasicScenarioTests.SyndicationFeed_Write_RSS_Atom()
at System.Reflection.MethodInvoker.InterpretedInvoke(Object obj, Span`1 args, BindingFlags invokeAttr)
```
## Error Message
Fill the error message using [known issues guidance](https://github.com/dotnet/arcade/blob/main/Documentation/Projects/Build%20Analysis/KnownIssues.md#how-to-fill-out-a-known-issue-error-message-section).
```json
{
"ErrorMessage": "System.IO.IOException : The file '/tmp/' already exists.",
"BuildRetry": false
}
```
<!--Known issue error report start -->
### Report
|Build|Definition|Test|Pull Request|
|---|---|---|---|
|[112560](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112560)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112560&view=ms.vss-test-web.build-test-results-tab&runId=2391060&resultId=180350)|dotnet/runtime#79669|
|[112553](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112553)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112553&view=ms.vss-test-web.build-test-results-tab&runId=2390960&resultId=180350)|dotnet/runtime#79672|
|[112315](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112315)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112315&view=ms.vss-test-web.build-test-results-tab&runId=2387184&resultId=180350)|dotnet/runtime#79659|
|[111843](https://dev.azure.com/dnceng-public/public/_build/results?buildId=111843)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=111843&view=ms.vss-test-web.build-test-results-tab&runId=2376302&resultId=180373)|dotnet/runtime#79334|
|[108189](https://dev.azure.com/dnceng-public/public/_build/results?buildId=108189)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=108189&view=ms.vss-test-web.build-test-results-tab&runId=2305990&resultId=180328)|dotnet/runtime#79472|
|[106860](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106860)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106860&view=ms.vss-test-web.build-test-results-tab&runId=2283296&resultId=180305)|dotnet/runtime#79427|
|[106356](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106356)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106356&view=ms.vss-test-web.build-test-results-tab&runId=2274394&resultId=180304)|dotnet/runtime#79385|
|[105443](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105443)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105443&view=ms.vss-test-web.build-test-results-tab&runId=2255908&resultId=180294)|dotnet/runtime#79339|
|[105198](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105198)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105198&view=ms.vss-test-web.build-test-results-tab&runId=2253062&resultId=180306)|dotnet/runtime#75012|
|[102113](https://dev.azure.com/dnceng-public/public/_build/results?buildId=102113)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=102113&view=ms.vss-test-web.build-test-results-tab&runId=2214458&resultId=180286)|dotnet/runtime#79215|
|[101941](https://dev.azure.com/dnceng-public/public/_build/results?buildId=101941)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=101941&view=ms.vss-test-web.build-test-results-tab&runId=2185800&resultId=180274)|dotnet/runtime#76500|
|[98594](https://dev.azure.com/dnceng-public/public/_build/results?buildId=98594)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=98594&view=ms.vss-test-web.build-test-results-tab&runId=2103720&resultId=180265)|dotnet/runtime#79048|
|[96704](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96704)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96704&view=ms.vss-test-web.build-test-results-tab&runId=2052810&resultId=180250)||
|[96495](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96495)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96495&view=ms.vss-test-web.build-test-results-tab&runId=2046234&resultId=180250)|dotnet/runtime#78888|
|[94682](https://dev.azure.com/dnceng-public/public/_build/results?buildId=94682)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=94682&view=ms.vss-test-web.build-test-results-tab&runId=1997434&resultId=180249)|dotnet/runtime#78888|
|[93017](https://dev.azure.com/dnceng-public/public/_build/results?buildId=93017)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=93017&view=ms.vss-test-web.build-test-results-tab&runId=1958718&resultId=180245)|dotnet/runtime#78817|
|[92390](https://dev.azure.com/dnceng-public/public/_build/results?buildId=92390)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=92390&view=ms.vss-test-web.build-test-results-tab&runId=1945750&resultId=180247)|dotnet/runtime#76436|
|[91316](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91316)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91316&view=ms.vss-test-web.build-test-results-tab&runId=1923836&resultId=180242)|dotnet/runtime#78725|
|[91016](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91016)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91016&view=ms.vss-test-web.build-test-results-tab&runId=1917904&resultId=180242)|dotnet/runtime#78591|
|[90961](https://dev.azure.com/dnceng-public/public/_build/results?buildId=90961)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=90961&view=ms.vss-test-web.build-test-results-tab&runId=1916606&resultId=180242)|dotnet/runtime#78562|
|[89671](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89671)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89671&view=ms.vss-test-web.build-test-results-tab&runId=1892272&resultId=180243)|dotnet/runtime#76462|
|[89555](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89555)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89555&view=ms.vss-test-web.build-test-results-tab&runId=1889094&resultId=180241)|dotnet/runtime#78637|
|[88571](https://dev.azure.com/dnceng-public/public/_build/results?buildId=88571)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=88571&view=ms.vss-test-web.build-test-results-tab&runId=1865004&resultId=179626)|dotnet/runtime#78557|
|[86376](https://dev.azure.com/dnceng-public/public/_build/results?buildId=86376)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=86376&view=ms.vss-test-web.build-test-results-tab&runId=1810340&resultId=179563)|dotnet/runtime#78446|
|[85957](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85957)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85957&view=ms.vss-test-web.build-test-results-tab&runId=1798330&resultId=179563)|dotnet/runtime#70944|
|[85690](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85690)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85690&view=ms.vss-test-web.build-test-results-tab&runId=1793338&resultId=179826)|dotnet/runtime#76642|
|[85275](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85275)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85275&view=ms.vss-test-web.build-test-results-tab&runId=1784674&resultId=179538)||
|[84790](https://dev.azure.com/dnceng-public/public/_build/results?buildId=84790)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=84790&view=ms.vss-test-web.build-test-results-tab&runId=1773054&resultId=179538)|dotnet/runtime#78424|
#### Summary
|24-Hour Hit Count|7-Day Hit Count|1-Month Count|
|---|---|---|
|4|8|28|
<!--Known issue error report end --> | 1.0 | SyndicationFeed_Write_RSS_Atom test failing with "IOException : The file '/tmp/' already exists." - ## Build Information
Build: https://dev.azure.com/dnceng-public/cbb18261-c48f-4abb-8651-8cdcb5474649/_build/results?buildId=84790
Build error leg or test failing: System.ServiceModel.Syndication.Tests.BasicScenarioTests.SyndicationFeed_Write_RSS_Atom
Pull request: https://github.com/dotnet/runtime/pull/78424
Stack trace:
```
at Interop.ThrowExceptionForIoErrno(ErrorInfo errorInfo, String path, Boolean isDirError)
at Interop.CheckIo(Int64 result, String path, Boolean isDirError)
at Interop.CheckIo(IntPtr result, String path, Boolean isDirError)
at System.IO.Path.GetTempFileName()
at System.ServiceModel.Syndication.Tests.BasicScenarioTests.SyndicationFeed_Write_RSS_Atom()
at System.Reflection.MethodInvoker.InterpretedInvoke(Object obj, Span`1 args, BindingFlags invokeAttr)
```
## Error Message
Fill the error message using [known issues guidance](https://github.com/dotnet/arcade/blob/main/Documentation/Projects/Build%20Analysis/KnownIssues.md#how-to-fill-out-a-known-issue-error-message-section).
```json
{
"ErrorMessage": "System.IO.IOException : The file '/tmp/' already exists.",
"BuildRetry": false
}
```
<!--Known issue error report start -->
### Report
|Build|Definition|Test|Pull Request|
|---|---|---|---|
|[112560](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112560)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112560&view=ms.vss-test-web.build-test-results-tab&runId=2391060&resultId=180350)|dotnet/runtime#79669|
|[112553](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112553)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112553&view=ms.vss-test-web.build-test-results-tab&runId=2390960&resultId=180350)|dotnet/runtime#79672|
|[112315](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112315)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=112315&view=ms.vss-test-web.build-test-results-tab&runId=2387184&resultId=180350)|dotnet/runtime#79659|
|[111843](https://dev.azure.com/dnceng-public/public/_build/results?buildId=111843)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=111843&view=ms.vss-test-web.build-test-results-tab&runId=2376302&resultId=180373)|dotnet/runtime#79334|
|[108189](https://dev.azure.com/dnceng-public/public/_build/results?buildId=108189)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=108189&view=ms.vss-test-web.build-test-results-tab&runId=2305990&resultId=180328)|dotnet/runtime#79472|
|[106860](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106860)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106860&view=ms.vss-test-web.build-test-results-tab&runId=2283296&resultId=180305)|dotnet/runtime#79427|
|[106356](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106356)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=106356&view=ms.vss-test-web.build-test-results-tab&runId=2274394&resultId=180304)|dotnet/runtime#79385|
|[105443](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105443)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105443&view=ms.vss-test-web.build-test-results-tab&runId=2255908&resultId=180294)|dotnet/runtime#79339|
|[105198](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105198)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=105198&view=ms.vss-test-web.build-test-results-tab&runId=2253062&resultId=180306)|dotnet/runtime#75012|
|[102113](https://dev.azure.com/dnceng-public/public/_build/results?buildId=102113)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=102113&view=ms.vss-test-web.build-test-results-tab&runId=2214458&resultId=180286)|dotnet/runtime#79215|
|[101941](https://dev.azure.com/dnceng-public/public/_build/results?buildId=101941)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=101941&view=ms.vss-test-web.build-test-results-tab&runId=2185800&resultId=180274)|dotnet/runtime#76500|
|[98594](https://dev.azure.com/dnceng-public/public/_build/results?buildId=98594)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=98594&view=ms.vss-test-web.build-test-results-tab&runId=2103720&resultId=180265)|dotnet/runtime#79048|
|[96704](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96704)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96704&view=ms.vss-test-web.build-test-results-tab&runId=2052810&resultId=180250)||
|[96495](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96495)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=96495&view=ms.vss-test-web.build-test-results-tab&runId=2046234&resultId=180250)|dotnet/runtime#78888|
|[94682](https://dev.azure.com/dnceng-public/public/_build/results?buildId=94682)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=94682&view=ms.vss-test-web.build-test-results-tab&runId=1997434&resultId=180249)|dotnet/runtime#78888|
|[93017](https://dev.azure.com/dnceng-public/public/_build/results?buildId=93017)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=93017&view=ms.vss-test-web.build-test-results-tab&runId=1958718&resultId=180245)|dotnet/runtime#78817|
|[92390](https://dev.azure.com/dnceng-public/public/_build/results?buildId=92390)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=92390&view=ms.vss-test-web.build-test-results-tab&runId=1945750&resultId=180247)|dotnet/runtime#76436|
|[91316](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91316)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91316&view=ms.vss-test-web.build-test-results-tab&runId=1923836&resultId=180242)|dotnet/runtime#78725|
|[91016](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91016)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=91016&view=ms.vss-test-web.build-test-results-tab&runId=1917904&resultId=180242)|dotnet/runtime#78591|
|[90961](https://dev.azure.com/dnceng-public/public/_build/results?buildId=90961)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=90961&view=ms.vss-test-web.build-test-results-tab&runId=1916606&resultId=180242)|dotnet/runtime#78562|
|[89671](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89671)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89671&view=ms.vss-test-web.build-test-results-tab&runId=1892272&resultId=180243)|dotnet/runtime#76462|
|[89555](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89555)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=89555&view=ms.vss-test-web.build-test-results-tab&runId=1889094&resultId=180241)|dotnet/runtime#78637|
|[88571](https://dev.azure.com/dnceng-public/public/_build/results?buildId=88571)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=88571&view=ms.vss-test-web.build-test-results-tab&runId=1865004&resultId=179626)|dotnet/runtime#78557|
|[86376](https://dev.azure.com/dnceng-public/public/_build/results?buildId=86376)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=86376&view=ms.vss-test-web.build-test-results-tab&runId=1810340&resultId=179563)|dotnet/runtime#78446|
|[85957](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85957)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85957&view=ms.vss-test-web.build-test-results-tab&runId=1798330&resultId=179563)|dotnet/runtime#70944|
|[85690](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85690)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85690&view=ms.vss-test-web.build-test-results-tab&runId=1793338&resultId=179826)|dotnet/runtime#76642|
|[85275](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85275)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=85275&view=ms.vss-test-web.build-test-results-tab&runId=1784674&resultId=179538)||
|[84790](https://dev.azure.com/dnceng-public/public/_build/results?buildId=84790)|dotnet/runtime|[WasmTestOnBrowser-System.ServiceModel.Syndication.Tests.WorkItemExecution](https://dev.azure.com/dnceng-public/public/_build/results?buildId=84790&view=ms.vss-test-web.build-test-results-tab&runId=1773054&resultId=179538)|dotnet/runtime#78424|
#### Summary
|24-Hour Hit Count|7-Day Hit Count|1-Month Count|
|---|---|---|
|4|8|28|
<!--Known issue error report end --> | non_main | syndicationfeed write rss atom test failing with ioexception the file tmp already exists build information build build error leg or test failing system servicemodel syndication tests basicscenariotests syndicationfeed write rss atom pull request stack trace at interop throwexceptionforioerrno errorinfo errorinfo string path boolean isdirerror at interop checkio result string path boolean isdirerror at interop checkio intptr result string path boolean isdirerror at system io path gettempfilename at system servicemodel syndication tests basicscenariotests syndicationfeed write rss atom at system reflection methodinvoker interpretedinvoke object obj span args bindingflags invokeattr error message fill the error message using json errormessage system io ioexception the file tmp already exists buildretry false report build definition test pull request summary hour hit count day hit count month count | 0 |
8,072 | 3,669,892,874 | IssuesEvent | 2016-02-21 14:39:33 | numbbo/coco | https://api.github.com/repos/numbbo/coco | opened | formating of RLD figure algorithm name annotation | Code-Postprocessing Priority-High | <img width="1310" alt="screen shot 2016-02-21 at 15 22 50" src="https://cloud.githubusercontent.com/assets/7316439/13203150/b02f834a-d8b0-11e5-8924-5b235b57b2d8.png">
The problem: about 1/2 of the visible area is empty useless space. A solution is to cut the annotated name to the minimum needed to differentiate between all shown algorithms plus, say, 2 letters. Or to cut the figures when displayed in the html. | 1.0 | formating of RLD figure algorithm name annotation - <img width="1310" alt="screen shot 2016-02-21 at 15 22 50" src="https://cloud.githubusercontent.com/assets/7316439/13203150/b02f834a-d8b0-11e5-8924-5b235b57b2d8.png">
The problem: about 1/2 of the visible area is empty useless space. A solution is to cut the annotated name to the minimum needed to differentiate between all shown algorithms plus, say, 2 letters. Or to cut the figures when displayed in the html. | non_main | formating of rld figure algorithm name annotation img width alt screen shot at src the problem about of the visible area is empty useless space a solution is to cut the annotated name to the minimum needed to differentiate between all shown algorithms plus say letters or to cut the figures when displayed in the html | 0 |
3,389 | 13,160,109,415 | IssuesEvent | 2020-08-10 16:59:44 | ipfs-shipyard/ipfs-webui | https://api.github.com/repos/ipfs-shipyard/ipfs-webui | opened | Document (via comments) logic of make function in bundles/files/utils | P1 dif/expert effort/hours kind/maintenance need/maintainer-input need/triage | At the moment purpose and logic of following code is unclear:
https://github.com/ipfs-shipyard/ipfs-webui/blob/master/src/bundles/files/utils.js#L11-L79
Specifically there are some unclear assumptions about arguments of functions that are been decorated
https://github.com/ipfs-shipyard/ipfs-webui/blob/master/src/bundles/files/utils.js#L11-L79
| True | Document (via comments) logic of make function in bundles/files/utils - At the moment purpose and logic of following code is unclear:
https://github.com/ipfs-shipyard/ipfs-webui/blob/master/src/bundles/files/utils.js#L11-L79
Specifically there are some unclear assumptions about arguments of functions that are been decorated
https://github.com/ipfs-shipyard/ipfs-webui/blob/master/src/bundles/files/utils.js#L11-L79
| main | document via comments logic of make function in bundles files utils at the moment purpose and logic of following code is unclear specifically there are some unclear assumptions about arguments of functions that are been decorated | 1 |
4,010 | 18,720,185,134 | IssuesEvent | 2021-11-03 10:52:12 | precice/precice | https://api.github.com/repos/precice/precice | opened | CMake cleanup after baseline update | maintainability compatibility | **Please describe the problem you are trying to solve.**
We drop support for Ubuntu 18.04 LTS with the release of Ubuntu 22.04 LTS.
This lifts our baseline to Ubuntu 20.04 LTS, which ships with CMake 3.16.
This allows us to clean-up and modernize our CMake code:
* We can remove the deprecated `FindPythonInterp` and `FindPythonLibs` #1123
* `FindLibXml2` defines the target `LibXml2::LibXml2`
* We can use pkg-config to directly generate [an imported target](https://cmake.org/cmake/help/v3.16/module/FindPkgConfig.html?highlight=pkg_config#command:pkg_check_modules), simplifying our custom `FindPETSc` | True | CMake cleanup after baseline update - **Please describe the problem you are trying to solve.**
We drop support for Ubuntu 18.04 LTS with the release of Ubuntu 22.04 LTS.
This lifts our baseline to Ubuntu 20.04 LTS, which ships with CMake 3.16.
This allows us to clean-up and modernize our CMake code:
* We can remove the deprecated `FindPythonInterp` and `FindPythonLibs` #1123
* `FindLibXml2` defines the target `LibXml2::LibXml2`
* We can use pkg-config to directly generate [an imported target](https://cmake.org/cmake/help/v3.16/module/FindPkgConfig.html?highlight=pkg_config#command:pkg_check_modules), simplifying our custom `FindPETSc` | main | cmake cleanup after baseline update please describe the problem you are trying to solve we drop support for ubuntu lts with the release of ubuntu lts this lifts our baseline to ubuntu lts which ships with cmake this allows us to clean up and modernize our cmake code we can remove the deprecated findpythoninterp and findpythonlibs defines the target we can use pkg config to directly generate simplifying our custom findpetsc | 1 |
3,492 | 13,633,500,838 | IssuesEvent | 2020-09-24 21:33:22 | chocolatey-community/chocolatey-package-requests | https://api.github.com/repos/chocolatey-community/chocolatey-package-requests | closed | RFM - gMKVExtractGUI | Status: Available For Maintainer(s) | ## Current Maintainer
- [x] I am the maintainer of the package and wish to pass it to someone else;
## I DON'T Want To Become The Maintainer
- [x] I have followed the Package Triage Process and I do NOT want to become maintainer of the package;
- [x] There is no existing open maintainer request for this package;
## Checklist
- [x] Issue title starts with 'RFM - '
## Existing Package Details
Package URL: https://chocolatey.org/packages/gmkvextractgui
Package source URL: https://github.com/abejenaru/chocolatey-packages/tree/master/automatic/gmkvextractgui
| True | RFM - gMKVExtractGUI - ## Current Maintainer
- [x] I am the maintainer of the package and wish to pass it to someone else;
## I DON'T Want To Become The Maintainer
- [x] I have followed the Package Triage Process and I do NOT want to become maintainer of the package;
- [x] There is no existing open maintainer request for this package;
## Checklist
- [x] Issue title starts with 'RFM - '
## Existing Package Details
Package URL: https://chocolatey.org/packages/gmkvextractgui
Package source URL: https://github.com/abejenaru/chocolatey-packages/tree/master/automatic/gmkvextractgui
| main | rfm gmkvextractgui current maintainer i am the maintainer of the package and wish to pass it to someone else i don t want to become the maintainer i have followed the package triage process and i do not want to become maintainer of the package there is no existing open maintainer request for this package checklist issue title starts with rfm existing package details package url package source url | 1 |
1,269 | 5,375,433,003 | IssuesEvent | 2017-02-23 04:46:23 | wojno/movie_manager | https://api.github.com/repos/wojno/movie_manager | opened | As an authenticated user, I want to edit a movie in my collection | Maintain Collection | As an `authenticated user`, I want to edit a movie in my `collection` so that when I change my mind about a `rating` or make a mistake in the `format selected` it can be `adjusted` | True | As an authenticated user, I want to edit a movie in my collection - As an `authenticated user`, I want to edit a movie in my `collection` so that when I change my mind about a `rating` or make a mistake in the `format selected` it can be `adjusted` | main | as an authenticated user i want to edit a movie in my collection as an authenticated user i want to edit a movie in my collection so that when i change my mind about a rating or make a mistake in the format selected it can be adjusted | 1 |
65,713 | 14,750,018,252 | IssuesEvent | 2021-01-08 00:59:27 | kadirselcuk/apps | https://api.github.com/repos/kadirselcuk/apps | closed | CVE-2019-1010266 (Medium) detected in lodash-4.17.4.tgz, lodash-3.10.1.tgz - autoclosed | security vulnerability | ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.4.tgz</b>, <b>lodash-3.10.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.4.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz</a></p>
<p>Path to dependency file: apps/package.json</p>
<p>Path to vulnerable library: apps/node_modules/cheerio/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- cheerio-1.0.0-rc.2.tgz (Root Library)
- :x: **lodash-4.17.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: apps/package.json</p>
<p>Path to vulnerable library: apps/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- get-image-colors-1.8.1.tgz (Root Library)
- get-svg-colors-1.3.0.tgz
- cheerio-0.19.0.tgz
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kadirselcuk/apps/commit/43b8e010a5d3fccab3804151574bd1dfe80aadab">43b8e010a5d3fccab3804151574bd1dfe80aadab</a></p>
<p>Found in base branch: <b>add-graphql-playground</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-1010266 (Medium) detected in lodash-4.17.4.tgz, lodash-3.10.1.tgz - autoclosed - ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.17.4.tgz</b>, <b>lodash-3.10.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.17.4.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.4.tgz</a></p>
<p>Path to dependency file: apps/package.json</p>
<p>Path to vulnerable library: apps/node_modules/cheerio/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- cheerio-1.0.0-rc.2.tgz (Root Library)
- :x: **lodash-4.17.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: apps/package.json</p>
<p>Path to vulnerable library: apps/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- get-image-colors-1.8.1.tgz (Root Library)
- get-svg-colors-1.3.0.tgz
- cheerio-0.19.0.tgz
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/kadirselcuk/apps/commit/43b8e010a5d3fccab3804151574bd1dfe80aadab">43b8e010a5d3fccab3804151574bd1dfe80aadab</a></p>
<p>Found in base branch: <b>add-graphql-playground</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve medium detected in lodash tgz lodash tgz autoclosed cve medium severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file apps package json path to vulnerable library apps node modules cheerio node modules lodash package json dependency hierarchy cheerio rc tgz root library x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file apps package json path to vulnerable library apps node modules lodash package json dependency hierarchy get image colors tgz root library get svg colors tgz cheerio tgz x lodash tgz vulnerable library found in head commit a href found in base branch add graphql playground vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
44,907 | 7,134,591,289 | IssuesEvent | 2018-01-22 21:24:40 | plangrid/ReactiveLists | https://api.github.com/repos/plangrid/ReactiveLists | closed | [Docs] Cleanup file header comments, use plist template | documentation | Use template: https://oleb.net/blog/2017/07/xcode-9-text-macros/
```swift
//
// PlanGrid
// https://www.plangrid.com
// https://medium.com/plangrid-technology
//
// Documentation
// https://plangrid.github.io/ReactiveLists
//
// GitHub
// https://github.com/plangrid/ReactiveLists
//
// License
// Copyright © 2018-present PlanGrid, Inc.
// Released under an MIT license: https://opensource.org/licenses/MIT
//
``` | 1.0 | [Docs] Cleanup file header comments, use plist template - Use template: https://oleb.net/blog/2017/07/xcode-9-text-macros/
```swift
//
// PlanGrid
// https://www.plangrid.com
// https://medium.com/plangrid-technology
//
// Documentation
// https://plangrid.github.io/ReactiveLists
//
// GitHub
// https://github.com/plangrid/ReactiveLists
//
// License
// Copyright © 2018-present PlanGrid, Inc.
// Released under an MIT license: https://opensource.org/licenses/MIT
//
``` | non_main | cleanup file header comments use plist template use template swift plangrid documentation github license copyright © present plangrid inc released under an mit license | 0 |
1,158 | 5,050,694,579 | IssuesEvent | 2016-12-20 19:32:22 | betaflight/betaflight | https://api.github.com/repos/betaflight/betaflight | closed | XRacerSPI with BF3.0.1 & BF3.1 Alpha: PPM_RX broken | Feedback Required For Target Maintainer | On XRacer 3.1 (SPI) target with BF 3.0.1 and PPM receiver all set to default parameters:
- when Multishot protocol is selected in synched mode, the PPM receiver signal traces in BF Configurator show regular spikes of about 300µs amplitude. Jitter of the PPM traces is otherwise normal (~1µs)

- when Multishot protocol is selected in unsynched 32k, all PPM receiver signal traces show abnormal jitter of about 10µs amplitude, but no spikes anymore

The CPU load is also behaving reverse when changing from synched to unsyched as changing to unsynched increases CPU load by about 2% when it normally should reduce the load.
The above issue does not exist on BF 3.0.0.
| True | XRacerSPI with BF3.0.1 & BF3.1 Alpha: PPM_RX broken - On XRacer 3.1 (SPI) target with BF 3.0.1 and PPM receiver all set to default parameters:
- when Multishot protocol is selected in synched mode, the PPM receiver signal traces in BF Configurator show regular spikes of about 300µs amplitude. Jitter of the PPM traces is otherwise normal (~1µs)

- when Multishot protocol is selected in unsynched 32k, all PPM receiver signal traces show abnormal jitter of about 10µs amplitude, but no spikes anymore

The CPU load is also behaving reverse when changing from synched to unsyched as changing to unsynched increases CPU load by about 2% when it normally should reduce the load.
The above issue does not exist on BF 3.0.0.
| main | xracerspi with alpha ppm rx broken on xracer spi target with bf and ppm receiver all set to default parameters when multishot protocol is selected in synched mode the ppm receiver signal traces in bf configurator show regular spikes of about amplitude jitter of the ppm traces is otherwise normal when multishot protocol is selected in unsynched all ppm receiver signal traces show abnormal jitter of about amplitude but no spikes anymore the cpu load is also behaving reverse when changing from synched to unsyched as changing to unsynched increases cpu load by about when it normally should reduce the load the above issue does not exist on bf | 1 |
3,394 | 13,161,856,088 | IssuesEvent | 2020-08-10 20:22:59 | RapidField/solid-instruments | https://api.github.com/repos/RapidField/solid-instruments | closed | Release v1.0.26-preview1 | Category-ProductionRelease Source-Maintainer Stage-3-InProgress Subcategory-Delivery Verdict-Pending Version-1.0.26 WindowForDelivery-2020-Q3 | # Maintenance Request
This issue represents a request for documentation, testing, refactoring or other non-functional changes.
## Overview
Issue a production release for `v1.0.26-preview`.
## Statement of work
The following list describes the work to be done.
- [x] Update documentation and release notes to reflect changes.
- [x] Update `appveyor.yml` with new version number.
- [x] Submit a pull request against `master`.
- [ ] Close and cleanup branches.
## Revision control plan
**Solid Instruments** uses the [**RapidField Revision Control Workflow**](https://github.com/RapidField/solid-instruments/blob/master/CONTRIBUTING.md#revision-control-strategy). Individual contributors should follow the branching plan below when working on this issue.
- `master` is the pull request target for
- `release/v1.0.26-preview1`, which is the pull request target for
- `develop` | True | Release v1.0.26-preview1 - # Maintenance Request
This issue represents a request for documentation, testing, refactoring or other non-functional changes.
## Overview
Issue a production release for `v1.0.26-preview`.
## Statement of work
The following list describes the work to be done.
- [x] Update documentation and release notes to reflect changes.
- [x] Update `appveyor.yml` with new version number.
- [x] Submit a pull request against `master`.
- [ ] Close and cleanup branches.
## Revision control plan
**Solid Instruments** uses the [**RapidField Revision Control Workflow**](https://github.com/RapidField/solid-instruments/blob/master/CONTRIBUTING.md#revision-control-strategy). Individual contributors should follow the branching plan below when working on this issue.
- `master` is the pull request target for
- `release/v1.0.26-preview1`, which is the pull request target for
- `develop` | main | release maintenance request this issue represents a request for documentation testing refactoring or other non functional changes overview issue a production release for preview statement of work the following list describes the work to be done update documentation and release notes to reflect changes update appveyor yml with new version number submit a pull request against master close and cleanup branches revision control plan solid instruments uses the individual contributors should follow the branching plan below when working on this issue master is the pull request target for release which is the pull request target for develop | 1 |
75,199 | 20,719,841,420 | IssuesEvent | 2022-03-13 07:50:37 | JetBrains/compose-jb | https://api.github.com/repos/JetBrains/compose-jb | closed | Text Edit: can not place a cursor inside a ligature | bug desktop wait for build | Reproduce: in `TextField`
1) Type `ff`
2) Try to move cursor one character left
3) Cursor moves to the beginning of the line (`|ff`) instead of `f|f` | 1.0 | Text Edit: can not place a cursor inside a ligature - Reproduce: in `TextField`
1) Type `ff`
2) Try to move cursor one character left
3) Cursor moves to the beginning of the line (`|ff`) instead of `f|f` | non_main | text edit can not place a cursor inside a ligature reproduce in textfield type ff try to move cursor one character left cursor moves to the beginning of the line ff instead of f f | 0 |
3,482 | 13,465,450,723 | IssuesEvent | 2020-09-09 20:53:56 | backdrop-ops/contrib | https://api.github.com/repos/backdrop-ops/contrib | opened | Application to join: testing | Maintainer application | Hello and welcome to the contrib application process! We're happy to have you :)
## Please note these 3 requirements for new contrib projects:
- [ ] Include a README.md file containing license and maintainer information.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/README.md
- [ ] Include a LICENSE.txt file.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/LICENSE.txt.
- [ ] If porting a Drupal 7 project, Maintain the Git history from Drupal.
## Please provide the following information:
**The name of your module, theme, or layout**
<!-- example: Forum Access -->
**(Optional) Post a link here to an issue in the drupal.org queue notifying the Drupal 7 maintainers that you are working on a Backdrop port of their project**
#example: https://www.drupal.org/project/forum_access/issues/3070491
**Post a link to your new Backdrop project under your own GitHub account (option #1)**
<!-- example: https://github.com/jenlampton/forum_access -->
**OR (option #2) If you have already contributed code to Backdrop core or contrib projects, please provide 1-3 links to pull requests or commits**
**OR (option #3) If you do not intend to contribute code, but would like to update documentation, manage issue queues, etc, please tag an existing contrib group member so they can post their recommendation**
<!-- example: @jenlampton -->
**If you have chosen option #2 or #1 above, do you agree to the [Backdrop Contributed Project Agreement](https://github.com/backdrop-ops/contrib#backdrop-contributed-project-agreement)**
YES/no
**If you have chosen option #3 above, do you agree to undergo this same maintainer application process again, should you decide to contribute code in the future?**
YES/no
<!-- Once we have a chance to review your project, we will check for the 3 requirements at the top of this issue. If those requirements are met, you will be invited to the @backdrop-contrib group. At that point you will be able to transfer the project. -->
<!-- Please note that we may also include additional feedback in the code review, but anything else is only intended to be helpful, and is NOT a requirement for joining the contrib group. -->
| True | Application to join: testing - Hello and welcome to the contrib application process! We're happy to have you :)
## Please note these 3 requirements for new contrib projects:
- [ ] Include a README.md file containing license and maintainer information.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/README.md
- [ ] Include a LICENSE.txt file.
You can use this example: https://raw.githubusercontent.com/backdrop-ops/contrib/master/examples/LICENSE.txt.
- [ ] If porting a Drupal 7 project, Maintain the Git history from Drupal.
## Please provide the following information:
**The name of your module, theme, or layout**
<!-- example: Forum Access -->
**(Optional) Post a link here to an issue in the drupal.org queue notifying the Drupal 7 maintainers that you are working on a Backdrop port of their project**
#example: https://www.drupal.org/project/forum_access/issues/3070491
**Post a link to your new Backdrop project under your own GitHub account (option #1)**
<!-- example: https://github.com/jenlampton/forum_access -->
**OR (option #2) If you have already contributed code to Backdrop core or contrib projects, please provide 1-3 links to pull requests or commits**
**OR (option #3) If you do not intend to contribute code, but would like to update documentation, manage issue queues, etc, please tag an existing contrib group member so they can post their recommendation**
<!-- example: @jenlampton -->
**If you have chosen option #2 or #1 above, do you agree to the [Backdrop Contributed Project Agreement](https://github.com/backdrop-ops/contrib#backdrop-contributed-project-agreement)**
YES/no
**If you have chosen option #3 above, do you agree to undergo this same maintainer application process again, should you decide to contribute code in the future?**
YES/no
<!-- Once we have a chance to review your project, we will check for the 3 requirements at the top of this issue. If those requirements are met, you will be invited to the @backdrop-contrib group. At that point you will be able to transfer the project. -->
<!-- Please note that we may also include additional feedback in the code review, but anything else is only intended to be helpful, and is NOT a requirement for joining the contrib group. -->
| main | application to join testing hello and welcome to the contrib application process we re happy to have you please note these requirements for new contrib projects include a readme md file containing license and maintainer information you can use this example include a license txt file you can use this example if porting a drupal project maintain the git history from drupal please provide the following information the name of your module theme or layout optional post a link here to an issue in the drupal org queue notifying the drupal maintainers that you are working on a backdrop port of their project example post a link to your new backdrop project under your own github account option or option if you have already contributed code to backdrop core or contrib projects please provide links to pull requests or commits or option if you do not intend to contribute code but would like to update documentation manage issue queues etc please tag an existing contrib group member so they can post their recommendation if you have chosen option or above do you agree to the yes no if you have chosen option above do you agree to undergo this same maintainer application process again should you decide to contribute code in the future yes no | 1 |
153,682 | 19,708,555,618 | IssuesEvent | 2022-01-13 01:40:36 | artsking/linux-4.19.72_CVE-2020-14386 | https://api.github.com/repos/artsking/linux-4.19.72_CVE-2020-14386 | opened | CVE-2019-2181 (High) detected in linux-yoctov5.4.51 | security vulnerability | ## CVE-2019-2181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/android/binder.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In binder_transaction of binder.c in the Android kernel, there is a possible out of bounds write due to an integer overflow. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is needed for exploitation.
<p>Publish Date: 2019-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2181>CVE-2019-2181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2181">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2181</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.2-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-2181 (High) detected in linux-yoctov5.4.51 - ## CVE-2019-2181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/android/binder.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In binder_transaction of binder.c in the Android kernel, there is a possible out of bounds write due to an integer overflow. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is needed for exploitation.
<p>Publish Date: 2019-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2181>CVE-2019-2181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2181">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-2181</a></p>
<p>Release Date: 2020-08-24</p>
<p>Fix Resolution: v5.2-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve high detected in linux cve high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in base branch master vulnerable source files drivers android binder c vulnerability details in binder transaction of binder c in the android kernel there is a possible out of bounds write due to an integer overflow this could lead to local escalation of privilege with no additional execution privileges needed user interaction is needed for exploitation publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
2,782 | 9,978,595,139 | IssuesEvent | 2019-07-09 20:18:25 | dgets/lasttime | https://api.github.com/repos/dgets/lasttime | opened | Search code for places to verify valid records | enhancement help wanted maintainability | Go through all of the different apps and search for places where administration records are looked up. Most of these will require verification that the record is valid (ie not to be completely ignored by 95% of the code). It'll be a good time to update the pydoc and clean up the code a bit, as well. | True | Search code for places to verify valid records - Go through all of the different apps and search for places where administration records are looked up. Most of these will require verification that the record is valid (ie not to be completely ignored by 95% of the code). It'll be a good time to update the pydoc and clean up the code a bit, as well. | main | search code for places to verify valid records go through all of the different apps and search for places where administration records are looked up most of these will require verification that the record is valid ie not to be completely ignored by of the code it ll be a good time to update the pydoc and clean up the code a bit as well | 1 |
937 | 4,650,400,508 | IssuesEvent | 2016-10-03 03:58:26 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Timezone fails on CentOS 6 | affects_2.2 bug_report waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
timezone
##### ANSIBLE VERSION
```
ansible 2.2.0 (devel cf4d436e07) last updated 2016/09/23 13:30:05 (GMT +100)
lib/ansible/modules/core: (detached HEAD 0f505378c3) last updated 2016/09/23 13:30:20 (GMT +100)
lib/ansible/modules/extras: (detached HEAD 1ade801f65) last updated 2016/09/23 13:30:21 (GMT +100)
config file =
configured module search path = Default w/o overrides
```
##### CONFIGURATION
```
[defaults]
ansible_managed = Ansible managed: Modified by {uid} on {host}
inventory=hosts
```
##### OS / ENVIRONMENT
Control machine: Windows 10 Pro - Bash on Windows
Host machine: CentOS 6
##### SUMMARY
Setting timezone on CentOS 6 machine breaks. OK on CentOS 7.
##### STEPS TO REPRODUCE
```
---
- name: set timezone
timezone: name=Europe/London
```
##### EXPECTED RESULTS
Timezone to be set
##### ACTUAL RESULTS
```
fatal: [vagrant]: FAILED! => {"changed": false, "failed": true, "module_stderr": "", "module_stdout": "Traceback (most recent call last):\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 462, in <module>\r\n main()\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 445, in main\r\n tz.change()\r\n
File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 191, in change\r\n self.set(key, value['planned'])\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 417, in set\r\n self.set_timezone(value)\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 405, in set_timezone\r\n value=self.tzline_format.format % value)\r\nTypeError: unsupported operand type(s) for %: 'builtin_function_or_method' and 'str'\r\n", "msg": "MODULE FAILURE"}
``` | True | Timezone fails on CentOS 6 - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
timezone
##### ANSIBLE VERSION
```
ansible 2.2.0 (devel cf4d436e07) last updated 2016/09/23 13:30:05 (GMT +100)
lib/ansible/modules/core: (detached HEAD 0f505378c3) last updated 2016/09/23 13:30:20 (GMT +100)
lib/ansible/modules/extras: (detached HEAD 1ade801f65) last updated 2016/09/23 13:30:21 (GMT +100)
config file =
configured module search path = Default w/o overrides
```
##### CONFIGURATION
```
[defaults]
ansible_managed = Ansible managed: Modified by {uid} on {host}
inventory=hosts
```
##### OS / ENVIRONMENT
Control machine: Windows 10 Pro - Bash on Windows
Host machine: CentOS 6
##### SUMMARY
Setting timezone on CentOS 6 machine breaks. OK on CentOS 7.
##### STEPS TO REPRODUCE
```
---
- name: set timezone
timezone: name=Europe/London
```
##### EXPECTED RESULTS
Timezone to be set
##### ACTUAL RESULTS
```
fatal: [vagrant]: FAILED! => {"changed": false, "failed": true, "module_stderr": "", "module_stdout": "Traceback (most recent call last):\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 462, in <module>\r\n main()\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 445, in main\r\n tz.change()\r\n
File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 191, in change\r\n self.set(key, value['planned'])\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 417, in set\r\n self.set_timezone(value)\r\n File \"/tmp/ansible_NcYCV8/ansible_module_timezone.py\", line 405, in set_timezone\r\n value=self.tzline_format.format % value)\r\nTypeError: unsupported operand type(s) for %: 'builtin_function_or_method' and 'str'\r\n", "msg": "MODULE FAILURE"}
``` | main | timezone fails on centos issue type bug report component name timezone ansible version ansible devel last updated gmt lib ansible modules core detached head last updated gmt lib ansible modules extras detached head last updated gmt config file configured module search path default w o overrides configuration ansible managed ansible managed modified by uid on host inventory hosts os environment control machine windows pro bash on windows host machine centos summary setting timezone on centos machine breaks ok on centos steps to reproduce name set timezone timezone name europe london expected results timezone to be set actual results fatal failed changed false failed true module stderr module stdout traceback most recent call last r n file tmp ansible ansible module timezone py line in r n main r n file tmp ansible ansible module timezone py line in main r n tz change r n file tmp ansible ansible module timezone py line in change r n self set key value r n file tmp ansible ansible module timezone py line in set r n self set timezone value r n file tmp ansible ansible module timezone py line in set timezone r n value self tzline format format value r ntypeerror unsupported operand type s for builtin function or method and str r n msg module failure | 1 |
4,325 | 21,777,049,113 | IssuesEvent | 2022-05-13 14:44:43 | tethysplatform/tethys | https://api.github.com/repos/tethysplatform/tethys | opened | Publish tethys_dataset_services on conda-forge | maintain dependencies | - [ ] Add recipes for dependencies that need to be added to conda forge | True | Publish tethys_dataset_services on conda-forge - - [ ] Add recipes for dependencies that need to be added to conda forge | main | publish tethys dataset services on conda forge add recipes for dependencies that need to be added to conda forge | 1 |
127,659 | 18,018,485,353 | IssuesEvent | 2021-09-16 16:19:56 | harrinry/spark-on-k8s-operator | https://api.github.com/repos/harrinry/spark-on-k8s-operator | opened | CVE-2019-11254 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2019-11254 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>github.com/dnaeon/go-vcr-v1.0.1</b>, <b>github.com/kubernetes-sigs/kustomize-v2.0.3</b>, <b>github.com/kubernetes/kubernetes-v1.16.6</b></p></summary>
<p>
<details><summary><b>github.com/dnaeon/go-vcr-v1.0.1</b></p></summary>
<p>Record and replay your HTTP interactions for fast, deterministic and accurate tests</p>
<p>
Dependency Hierarchy:
- github.com/google/go-cloud-v0.1.1 (Root Library)
- :x: **github.com/dnaeon/go-vcr-v1.0.1** (Vulnerable Library)
</details>
<details><summary><b>github.com/kubernetes-sigs/kustomize-v2.0.3</b></p></summary>
<p>Customization of kubernetes YAML configurations</p>
<p>
Dependency Hierarchy:
- github.com/kubernetes/kubectl-v0.16.6 (Root Library)
- github.com/kubernetes/cli-runtime-v0.16.6
- :x: **github.com/kubernetes-sigs/kustomize-v2.0.3** (Vulnerable Library)
</details>
<details><summary><b>github.com/kubernetes/kubernetes-v1.16.6</b></p></summary>
<p>Production-Grade Container Scheduling and Management</p>
<p>
Dependency Hierarchy:
- :x: **github.com/kubernetes/kubernetes-v1.16.6** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/harrinry/spark-on-k8s-operator/commit/23cd89752b5978470bb8f7c88cae5ab268573cea">23cd89752b5978470bb8f7c88cae5ab268573cea</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Kubernetes API Server component in versions 1.1-1.14, and versions prior to 1.15.10, 1.16.7 and 1.17.3 allows an authorized user who sends malicious YAML payloads to cause the kube-apiserver to consume excessive CPU cycles while parsing YAML.
<p>Publish Date: 2020-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11254>CVE-2019-11254</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/go-yaml/yaml/tree/v2.2.8">https://github.com/go-yaml/yaml/tree/v2.2.8</a></p>
<p>Release Date: 2020-04-01</p>
<p>Fix Resolution: v2.2.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/dnaeon/go-vcr","packageVersion":"v1.0.1","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/google/go-cloud:v0.1.1;github.com/dnaeon/go-vcr:v1.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.2.8"},{"packageType":"GO","packageName":"github.com/kubernetes-sigs/kustomize","packageVersion":"v2.0.3","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/kubernetes/kubectl:v0.16.6;github.com/kubernetes/cli-runtime:v0.16.6;github.com/kubernetes-sigs/kustomize:v2.0.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.2.8"},{"packageType":"GO","packageName":"github.com/kubernetes/kubernetes","packageVersion":"v1.16.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/kubernetes/kubernetes:v1.16.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.2.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11254","vulnerabilityDetails":"The Kubernetes API Server component in versions 1.1-1.14, and versions prior to 1.15.10, 1.16.7 and 1.17.3 allows an authorized user who sends malicious YAML payloads to cause the kube-apiserver to consume excessive CPU cycles while parsing YAML.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11254","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-11254 (Medium) detected in multiple libraries - ## CVE-2019-11254 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>github.com/dnaeon/go-vcr-v1.0.1</b>, <b>github.com/kubernetes-sigs/kustomize-v2.0.3</b>, <b>github.com/kubernetes/kubernetes-v1.16.6</b></p></summary>
<p>
<details><summary><b>github.com/dnaeon/go-vcr-v1.0.1</b></p></summary>
<p>Record and replay your HTTP interactions for fast, deterministic and accurate tests</p>
<p>
Dependency Hierarchy:
- github.com/google/go-cloud-v0.1.1 (Root Library)
- :x: **github.com/dnaeon/go-vcr-v1.0.1** (Vulnerable Library)
</details>
<details><summary><b>github.com/kubernetes-sigs/kustomize-v2.0.3</b></p></summary>
<p>Customization of kubernetes YAML configurations</p>
<p>
Dependency Hierarchy:
- github.com/kubernetes/kubectl-v0.16.6 (Root Library)
- github.com/kubernetes/cli-runtime-v0.16.6
- :x: **github.com/kubernetes-sigs/kustomize-v2.0.3** (Vulnerable Library)
</details>
<details><summary><b>github.com/kubernetes/kubernetes-v1.16.6</b></p></summary>
<p>Production-Grade Container Scheduling and Management</p>
<p>
Dependency Hierarchy:
- :x: **github.com/kubernetes/kubernetes-v1.16.6** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/harrinry/spark-on-k8s-operator/commit/23cd89752b5978470bb8f7c88cae5ab268573cea">23cd89752b5978470bb8f7c88cae5ab268573cea</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Kubernetes API Server component in versions 1.1-1.14, and versions prior to 1.15.10, 1.16.7 and 1.17.3 allows an authorized user who sends malicious YAML payloads to cause the kube-apiserver to consume excessive CPU cycles while parsing YAML.
<p>Publish Date: 2020-04-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11254>CVE-2019-11254</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/go-yaml/yaml/tree/v2.2.8">https://github.com/go-yaml/yaml/tree/v2.2.8</a></p>
<p>Release Date: 2020-04-01</p>
<p>Fix Resolution: v2.2.8</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"GO","packageName":"github.com/dnaeon/go-vcr","packageVersion":"v1.0.1","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/google/go-cloud:v0.1.1;github.com/dnaeon/go-vcr:v1.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.2.8"},{"packageType":"GO","packageName":"github.com/kubernetes-sigs/kustomize","packageVersion":"v2.0.3","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"github.com/kubernetes/kubectl:v0.16.6;github.com/kubernetes/cli-runtime:v0.16.6;github.com/kubernetes-sigs/kustomize:v2.0.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.2.8"},{"packageType":"GO","packageName":"github.com/kubernetes/kubernetes","packageVersion":"v1.16.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"github.com/kubernetes/kubernetes:v1.16.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v2.2.8"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-11254","vulnerabilityDetails":"The Kubernetes API Server component in versions 1.1-1.14, and versions prior to 1.15.10, 1.16.7 and 1.17.3 allows an authorized user who sends malicious YAML payloads to cause the kube-apiserver to consume excessive CPU cycles while parsing YAML.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-11254","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_main | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries github com dnaeon go vcr github com kubernetes sigs kustomize github com kubernetes kubernetes github com dnaeon go vcr record and replay your http interactions for fast deterministic and accurate tests dependency hierarchy github com google go cloud root library x github com dnaeon go vcr vulnerable library github com kubernetes sigs kustomize customization of kubernetes yaml configurations dependency hierarchy github com kubernetes kubectl root library github com kubernetes cli runtime x github com kubernetes sigs kustomize vulnerable library github com kubernetes kubernetes production grade container scheduling and management dependency hierarchy x github com kubernetes kubernetes vulnerable library found in head commit a href found in base branch master vulnerability details the kubernetes api server component in versions and versions prior to and allows an authorized user who sends malicious yaml payloads to cause the kube apiserver to consume excessive cpu cycles while parsing yaml publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree github com google go cloud github com dnaeon go vcr isminimumfixversionavailable true minimumfixversion packagetype go packagename github com kubernetes sigs kustomize packageversion packagefilepaths istransitivedependency true dependencytree github com kubernetes kubectl github com kubernetes cli runtime github com kubernetes sigs kustomize isminimumfixversionavailable true minimumfixversion packagetype go packagename github com kubernetes kubernetes packageversion packagefilepaths istransitivedependency false dependencytree github com kubernetes kubernetes isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails the kubernetes api server component in versions and versions prior to and allows an authorized user who sends malicious yaml payloads to cause the kube apiserver to consume excessive cpu cycles while parsing yaml vulnerabilityurl | 0 |
99,985 | 11,170,088,289 | IssuesEvent | 2019-12-28 11:02:42 | zopefoundation/ZODB | https://api.github.com/repos/zopefoundation/ZODB | opened | Better documentation of _v_* | documentation | In https://github.com/zopefoundation/ZODB/blob/master/doc/guide/writing-persistent-objects.rst#special-attributes The `_v_` attribute is documented.
I was never sure how it works exactly. Now I had the need to look deeper into it. I always thought (for >15years), in a ZEO setup _v_ is local to the connection and does not get propagated to other clients, which is *wrong*. No idea where I got that from... but in fact the `_v_` is propagated to the other connections/clients after commit. It is just not stored in the Data.fs as far as I understand.
So, lucky me, this made it simple for my case.
But the documentation is bit thin here. Maybe this needs to go in the ZEO documentation, because its ZEO special? How does RelStorage and other backends do here? | 1.0 | Better documentation of _v_* - In https://github.com/zopefoundation/ZODB/blob/master/doc/guide/writing-persistent-objects.rst#special-attributes The `_v_` attribute is documented.
I was never sure how it works exactly. Now I had the need to look deeper into it. I always thought (for >15years), in a ZEO setup _v_ is local to the connection and does not get propagated to other clients, which is *wrong*. No idea where I got that from... but in fact the `_v_` is propagated to the other connections/clients after commit. It is just not stored in the Data.fs as far as I understand.
So, lucky me, this made it simple for my case.
But the documentation is bit thin here. Maybe this needs to go in the ZEO documentation, because its ZEO special? How does RelStorage and other backends do here? | non_main | better documentation of v in the v attribute is documented i was never sure how it works exactly now i had the need to look deeper into it i always thought for in a zeo setup v is local to the connection and does not get propagated to other clients which is wrong no idea where i got that from but in fact the v is propagated to the other connections clients after commit it is just not stored in the data fs as far as i understand so lucky me this made it simple for my case but the documentation is bit thin here maybe this needs to go in the zeo documentation because its zeo special how does relstorage and other backends do here | 0 |
20,530 | 6,896,572,172 | IssuesEvent | 2017-11-23 18:41:23 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | opened | Fold runtime/compiler/trj9 directory | comp:build comp:jit | Now that `tr.source` has been renamed to `compiler` as part of https://github.com/eclipse/openj9/pull/589 I wanted to start a discussion on possibly folding the `trj9` directory as well. To me it currently serves no purpose as it's parent `compiler` directory is completely empty.
@0xdaryl notes down some thoughts in https://github.com/eclipse/openj9/issues/550#issuecomment-344695397 which may possibly cause problems. I think the only way to find out would be to implement the change and see what fails.
Before we go down this road, do people even support this idea? Do we have internal or external dependencies on this? As I understand the compiler makefile currently resides in the `trj9` directory. Moving it one level up is sure to break _something_? What is this _something_? Any ideas, comments, or concerns are welcome. | 1.0 | Fold runtime/compiler/trj9 directory - Now that `tr.source` has been renamed to `compiler` as part of https://github.com/eclipse/openj9/pull/589 I wanted to start a discussion on possibly folding the `trj9` directory as well. To me it currently serves no purpose as it's parent `compiler` directory is completely empty.
@0xdaryl notes down some thoughts in https://github.com/eclipse/openj9/issues/550#issuecomment-344695397 which may possibly cause problems. I think the only way to find out would be to implement the change and see what fails.
Before we go down this road, do people even support this idea? Do we have internal or external dependencies on this? As I understand the compiler makefile currently resides in the `trj9` directory. Moving it one level up is sure to break _something_? What is this _something_? Any ideas, comments, or concerns are welcome. | non_main | fold runtime compiler directory now that tr source has been renamed to compiler as part of i wanted to start a discussion on possibly folding the directory as well to me it currently serves no purpose as it s parent compiler directory is completely empty notes down some thoughts in which may possibly cause problems i think the only way to find out would be to implement the change and see what fails before we go down this road do people even support this idea do we have internal or external dependencies on this as i understand the compiler makefile currently resides in the directory moving it one level up is sure to break something what is this something any ideas comments or concerns are welcome | 0 |
5,776 | 30,597,936,909 | IssuesEvent | 2023-07-22 02:25:32 | googleforgames/agones | https://api.github.com/repos/googleforgames/agones | closed | Should we rebase images from alpine to gcr.io/distroless/static ? | kind/feature help wanted good first issue area/operations awaiting-maintainer | Kubernetes has moved to using gcr.io/distroless/static for most base images (see https://github.com/kubernetes/enhancements/blob/master/keps/sig-release/20190316-rebase-images-to-distroless.md#implementation-history). We should investigate whether it makes sense to move from alpine to gcr.io/distroless/static for Agones.
| True | Should we rebase images from alpine to gcr.io/distroless/static ? - Kubernetes has moved to using gcr.io/distroless/static for most base images (see https://github.com/kubernetes/enhancements/blob/master/keps/sig-release/20190316-rebase-images-to-distroless.md#implementation-history). We should investigate whether it makes sense to move from alpine to gcr.io/distroless/static for Agones.
| main | should we rebase images from alpine to gcr io distroless static kubernetes has moved to using gcr io distroless static for most base images see we should investigate whether it makes sense to move from alpine to gcr io distroless static for agones | 1 |
1,726 | 6,574,652,744 | IssuesEvent | 2017-09-11 13:39:18 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | VLAN idempotency breaks with special case in eos_config | affects_2.3 bug_report networking waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
eos_config
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.3.0
config file = /home/vagrant/iostest/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
<!---
-->
Using default config
##### OS / ENVIRONMENT
<!---
-->
Ubuntu managing Arista
##### SUMMARY
<!---
-->
In this special case when multiple VLANS are created without a name (or the same name) associated to them, the "show run" of an Arista config puts them in one line such as "vlan 10-11". This breaks the idempotency since it will attempt to add the VLAN again. It will attempt to add VLAN 10 or 11 again, for example. It appears as though during the running config check, the module is parsing for an individual VLAN line with that particualr VLAN.
##### STEPS TO REPRODUCE
<!---
-->
1) Create a task that adds a NEW vlan to an arista switch. Do not add a name to this vlan at this time.
2) Run the task again but change make vlan 11 instead of vlan 10
3) Run the exact task in step 1...adding vlan 10 to the switch again
<!--- Paste example playbooks or commands between quotes below -->
```
#eos.yaml
- name: role add vlan using eos_config module
connection: local
eos_config:
lines:
- vlan 10
provider: "{{ cli }}"
register: vlan_created_out
#arista-vlan.yaml
---
- name: playbook - vlan add using eos_config
hosts: eos
gather_facts: no
connection: local
vars_files:
- creds.yaml
roles:
- { role: vlan_add }
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
Step 1) Expected output, changed=1 and new vlan 10 created
Step 2) Expected output, changed=1 and new vlan 11 created
Step 3) Expected output, changed=0 and vlan 10 not attempted to be created
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with extra verbosity (-vvvv) -->
Step 1) Expected output, changed=1 and new vlan 10 created
Step 2) Expected output, changed=1 and new vlan 11 created
Step 3) Expected output, changed=1 and vlan 10 attempted to be created again...you can see when logging AAA commands that the vlan is attempting to be created every time.
<!--- Paste verbatim command output between quotes below -->
```
```
| True | VLAN idempotency breaks with special case in eos_config - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
eos_config
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.3.0
config file = /home/vagrant/iostest/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
<!---
-->
Using default config
##### OS / ENVIRONMENT
<!---
-->
Ubuntu managing Arista
##### SUMMARY
<!---
-->
In this special case when multiple VLANS are created without a name (or the same name) associated to them, the "show run" of an Arista config puts them in one line such as "vlan 10-11". This breaks the idempotency since it will attempt to add the VLAN again. It will attempt to add VLAN 10 or 11 again, for example. It appears as though during the running config check, the module is parsing for an individual VLAN line with that particualr VLAN.
##### STEPS TO REPRODUCE
<!---
-->
1) Create a task that adds a NEW vlan to an arista switch. Do not add a name to this vlan at this time.
2) Run the task again but change make vlan 11 instead of vlan 10
3) Run the exact task in step 1...adding vlan 10 to the switch again
<!--- Paste example playbooks or commands between quotes below -->
```
#eos.yaml
- name: role add vlan using eos_config module
connection: local
eos_config:
lines:
- vlan 10
provider: "{{ cli }}"
register: vlan_created_out
#arista-vlan.yaml
---
- name: playbook - vlan add using eos_config
hosts: eos
gather_facts: no
connection: local
vars_files:
- creds.yaml
roles:
- { role: vlan_add }
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
Step 1) Expected output, changed=1 and new vlan 10 created
Step 2) Expected output, changed=1 and new vlan 11 created
Step 3) Expected output, changed=0 and vlan 10 not attempted to be created
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with extra verbosity (-vvvv) -->
Step 1) Expected output, changed=1 and new vlan 10 created
Step 2) Expected output, changed=1 and new vlan 11 created
Step 3) Expected output, changed=1 and vlan 10 attempted to be created again...you can see when logging AAA commands that the vlan is attempting to be created every time.
<!--- Paste verbatim command output between quotes below -->
```
```
| main | vlan idempotency breaks with special case in eos config issue type bug report component name eos config ansible version ansible config file home vagrant iostest ansible cfg configured module search path default w o overrides configuration using default config os environment ubuntu managing arista summary in this special case when multiple vlans are created without a name or the same name associated to them the show run of an arista config puts them in one line such as vlan this breaks the idempotency since it will attempt to add the vlan again it will attempt to add vlan or again for example it appears as though during the running config check the module is parsing for an individual vlan line with that particualr vlan steps to reproduce create a task that adds a new vlan to an arista switch do not add a name to this vlan at this time run the task again but change make vlan instead of vlan run the exact task in step adding vlan to the switch again eos yaml name role add vlan using eos config module connection local eos config lines vlan provider cli register vlan created out arista vlan yaml name playbook vlan add using eos config hosts eos gather facts no connection local vars files creds yaml roles role vlan add expected results step expected output changed and new vlan created step expected output changed and new vlan created step expected output changed and vlan not attempted to be created actual results step expected output changed and new vlan created step expected output changed and new vlan created step expected output changed and vlan attempted to be created again you can see when logging aaa commands that the vlan is attempting to be created every time | 1 |
172,057 | 14,349,840,939 | IssuesEvent | 2020-11-29 18:17:34 | MarkusReynolds1989/OpenProgramming | https://api.github.com/repos/MarkusReynolds1989/OpenProgramming | opened | Show how to run unit tests TS | documentation good first issue help wanted | Show the students how to run unit tests with TypeScript/NPM.
We can either do this through a "Step 0" type of thing or refer a video. Prefer to have documentation over a video for reference. | 1.0 | Show how to run unit tests TS - Show the students how to run unit tests with TypeScript/NPM.
We can either do this through a "Step 0" type of thing or refer a video. Prefer to have documentation over a video for reference. | non_main | show how to run unit tests ts show the students how to run unit tests with typescript npm we can either do this through a step type of thing or refer a video prefer to have documentation over a video for reference | 0 |
2,949 | 10,594,986,715 | IssuesEvent | 2019-10-09 17:59:13 | 18F/cg-product | https://api.github.com/repos/18F/cg-product | reopened | Merge isolation segment work | contractor-3-maintainability operations | In order to ensure our development environment is fully driven by code rather than hand-propped changes, we want to capture work in that environment that's not in the `isolation-segments` branch, then merge the branch so it's maintained.
## Acceptance criteria
- [ ] `deploy-cf-deployment` is green in `dev`
- [ ] isolation segment configuration is consistent across `dev`, `staging`, and `prod`
- [ ] Resolve smoke test failures
- [ ] Create documentation for support requests
## Next steps
- [ ] Update & resolve conflicts on PR: https://github.com/18F/cg-provision/pull/468
- [ ] Update & resolve conflicts on PR: https://github.com/18F/cg-deploy-cf/pull/366
- [ ] Check into status and details on isolation segment configuration per environment | True | Merge isolation segment work - In order to ensure our development environment is fully driven by code rather than hand-propped changes, we want to capture work in that environment that's not in the `isolation-segments` branch, then merge the branch so it's maintained.
## Acceptance criteria
- [ ] `deploy-cf-deployment` is green in `dev`
- [ ] isolation segment configuration is consistent across `dev`, `staging`, and `prod`
- [ ] Resolve smoke test failures
- [ ] Create documentation for support requests
## Next steps
- [ ] Update & resolve conflicts on PR: https://github.com/18F/cg-provision/pull/468
- [ ] Update & resolve conflicts on PR: https://github.com/18F/cg-deploy-cf/pull/366
- [ ] Check into status and details on isolation segment configuration per environment | main | merge isolation segment work in order to ensure our development environment is fully driven by code rather than hand propped changes we want to capture work in that environment that s not in the isolation segments branch then merge the branch so it s maintained acceptance criteria deploy cf deployment is green in dev isolation segment configuration is consistent across dev staging and prod resolve smoke test failures create documentation for support requests next steps update resolve conflicts on pr update resolve conflicts on pr check into status and details on isolation segment configuration per environment | 1 |
262,171 | 22,821,147,912 | IssuesEvent | 2022-07-12 02:30:54 | devstream-io/devstream | https://api.github.com/repos/devstream-io/devstream | closed | :four_leaf_clover: `Proposal`: Make unit test not rely on network | test | ## What Would You Like to Add? Why Is This Needed?
The test logic in `internal/pkg/pluginmanager/downloader_test.go` will try to download file from website, this will make test slow and prone to failture. we can mock this download logic to make test smooth.
## Design
make download logic a field of `DownloadClient`,when we init class pass this func as field, like below
<img width="1197" alt="image" src="https://user-images.githubusercontent.com/13215800/177903187-486ec74a-fe59-4aa5-8d5c-fd251546fc64.png">
| 1.0 | :four_leaf_clover: `Proposal`: Make unit test not rely on network - ## What Would You Like to Add? Why Is This Needed?
The test logic in `internal/pkg/pluginmanager/downloader_test.go` will try to download file from website, this will make test slow and prone to failture. we can mock this download logic to make test smooth.
## Design
make download logic a field of `DownloadClient`,when we init class pass this func as field, like below
<img width="1197" alt="image" src="https://user-images.githubusercontent.com/13215800/177903187-486ec74a-fe59-4aa5-8d5c-fd251546fc64.png">
| non_main | four leaf clover proposal make unit test not rely on network what would you like to add why is this needed the test logic in internal pkg pluginmanager downloader test go will try to download file from website this will make test slow and prone to failture we can mock this download logic to make test smooth design make download logic a field of downloadclient ,when we init class pass this func as field like below img width alt image src | 0 |
1,484 | 6,416,007,991 | IssuesEvent | 2017-08-08 14:00:28 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | Deregistering an instance from an ELB causes health check to fail. | affects_2.2 aws bug_report cloud waiting_on_maintainer | ##### ISSUE TYPE
Bug Report
##### COMPONENT NAME
ec2_elb_lb module
##### ANSIBLE VERSION
N/A
##### SUMMARY
When I deregister an instance from an ELB it causes the health check to fail and sets off alerts. Why wouldn't is just remove the instance from the pool immediately? What is actually doing behind the scenes?
| True | Deregistering an instance from an ELB causes health check to fail. - ##### ISSUE TYPE
Bug Report
##### COMPONENT NAME
ec2_elb_lb module
##### ANSIBLE VERSION
N/A
##### SUMMARY
When I deregister an instance from an ELB it causes the health check to fail and sets off alerts. Why wouldn't is just remove the instance from the pool immediately? What is actually doing behind the scenes?
| main | deregistering an instance from an elb causes health check to fail issue type bug report component name elb lb module ansible version n a summary when i deregister an instance from an elb it causes the health check to fail and sets off alerts why wouldn t is just remove the instance from the pool immediately what is actually doing behind the scenes | 1 |
1,154 | 5,037,475,876 | IssuesEvent | 2016-12-17 17:51:57 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | package module: Add update_cache option | affects_2.1 feature_idea waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Feature Idea
##### COMPONENT NAME
pacakge
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.1.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### OS / ENVIRONMENT
Fedora
##### SUMMARY
The package module should have the ability to update the package system cache
| True | package module: Add update_cache option - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Feature Idea
##### COMPONENT NAME
pacakge
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.1.0
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### OS / ENVIRONMENT
Fedora
##### SUMMARY
The package module should have the ability to update the package system cache
| main | package module add update cache option issue type feature idea component name pacakge ansible version ansible config file etc ansible ansible cfg configured module search path default w o overrides os environment fedora summary the package module should have the ability to update the package system cache | 1 |
3,664 | 3,213,149,930 | IssuesEvent | 2015-10-06 18:35:22 | Secretchronicles/TSC | https://api.github.com/repos/Secretchronicles/TSC | closed | Force UTF-8 encoding in gem files | Build system | When trying to build 2.0.0 on Mageia's buildsystem, I ran into this issue:
```
[ 12%] Generating credits.cpp
rake aborted!
ArgumentError: invalid byte sequence in US-ASCII
/home/iurt/rpmbuild/BUILD/TSC-2.0.0/tsc/Rakefile:23:in `match'
/home/iurt/rpmbuild/BUILD/TSC-2.0.0/tsc/Rakefile:23:in `match'
/home/iurt/rpmbuild/BUILD/TSC-2.0.0/tsc/Rakefile:23:in `<top (required)>'
(See full trace by running task with --trace)
CMakeFiles/tsc.dir/build.make:61: recipe for target 'credits.cpp' failed
```
Full build log: http://pkgsubmit.mageia.org/uploads/failure/cauldron/core/release/20150927093845.akien.valstar.31482/log/tsc-2.0.0-1.mga6/build.0.20150927093906.log
According to this stackoverflow topic [1], it could be fixed either on my side by forcing en_US.UTF-8 on Mageia's buildsystem (I guess right now it might be simply "C"), or on your side by forcing UTF-8 encoding in the gem files. I guess the second solution is probably cleaner since you do want to enforce UTF-8 anyway.
[1] http://stackoverflow.com/questions/17031651/invalid-byte-sequence-in-us-ascii-argument-error-when-i-run-rake-dbseed-in-ra | 1.0 | Force UTF-8 encoding in gem files - When trying to build 2.0.0 on Mageia's buildsystem, I ran into this issue:
```
[ 12%] Generating credits.cpp
rake aborted!
ArgumentError: invalid byte sequence in US-ASCII
/home/iurt/rpmbuild/BUILD/TSC-2.0.0/tsc/Rakefile:23:in `match'
/home/iurt/rpmbuild/BUILD/TSC-2.0.0/tsc/Rakefile:23:in `match'
/home/iurt/rpmbuild/BUILD/TSC-2.0.0/tsc/Rakefile:23:in `<top (required)>'
(See full trace by running task with --trace)
CMakeFiles/tsc.dir/build.make:61: recipe for target 'credits.cpp' failed
```
Full build log: http://pkgsubmit.mageia.org/uploads/failure/cauldron/core/release/20150927093845.akien.valstar.31482/log/tsc-2.0.0-1.mga6/build.0.20150927093906.log
According to this stackoverflow topic [1], it could be fixed either on my side by forcing en_US.UTF-8 on Mageia's buildsystem (I guess right now it might be simply "C"), or on your side by forcing UTF-8 encoding in the gem files. I guess the second solution is probably cleaner since you do want to enforce UTF-8 anyway.
[1] http://stackoverflow.com/questions/17031651/invalid-byte-sequence-in-us-ascii-argument-error-when-i-run-rake-dbseed-in-ra | non_main | force utf encoding in gem files when trying to build on mageia s buildsystem i ran into this issue generating credits cpp rake aborted argumenterror invalid byte sequence in us ascii home iurt rpmbuild build tsc tsc rakefile in match home iurt rpmbuild build tsc tsc rakefile in match home iurt rpmbuild build tsc tsc rakefile in see full trace by running task with trace cmakefiles tsc dir build make recipe for target credits cpp failed full build log according to this stackoverflow topic it could be fixed either on my side by forcing en us utf on mageia s buildsystem i guess right now it might be simply c or on your side by forcing utf encoding in the gem files i guess the second solution is probably cleaner since you do want to enforce utf anyway | 0 |
5,120 | 26,088,119,264 | IssuesEvent | 2022-12-26 07:09:56 | OctoFarm/OctoFarm | https://api.github.com/repos/OctoFarm/OctoFarm | opened | [NOTICE] Dropping the monolithic docker image | notice seeking-maintainer | ### OctoFarm Version
1.8.0
### OctoPrint Version(s)
any
### pm2 or docker?
pm2
### Operating System
docker
### Description of the problem
This is a notice that the docker monolithic variant that includes monolithic docker container is going to stop receiving updates.
I'm no longer able to maintain the image myself, and I'm under the opinion those should be run as separate containers.
If anyone would like to maintain this image themselves then please let me know.
### Steps taken to reproduce
docker... | True | [NOTICE] Dropping the monolithic docker image - ### OctoFarm Version
1.8.0
### OctoPrint Version(s)
any
### pm2 or docker?
pm2
### Operating System
docker
### Description of the problem
This is a notice that the docker monolithic variant that includes monolithic docker container is going to stop receiving updates.
I'm no longer able to maintain the image myself, and I'm under the opinion those should be run as separate containers.
If anyone would like to maintain this image themselves then please let me know.
### Steps taken to reproduce
docker... | main | dropping the monolithic docker image octofarm version octoprint version s any or docker operating system docker description of the problem this is a notice that the docker monolithic variant that includes monolithic docker container is going to stop receiving updates i m no longer able to maintain the image myself and i m under the opinion those should be run as separate containers if anyone would like to maintain this image themselves then please let me know steps taken to reproduce docker | 1 |
5,828 | 30,849,982,196 | IssuesEvent | 2023-08-02 16:01:56 | obi1kenobi/trustfall | https://api.github.com/repos/obi1kenobi/trustfall | opened | Consider switching fuzzer backends to LibAFL | C-maintainability | LibFuzzer is in [maintenance mode](https://llvm.org/docs/LibFuzzer.html#status):
> The original authors of libFuzzer have stopped active work on it and switched to working on another fuzzing engine, [Centipede](https://github.com/google/centipede).
We should consider switching to LibAFL or another implementation, since it seems that we can get both fuzzing performance and maintainability improvements.
More info:
https://hachyderm.io/@addison@infosec.exchange/110820552409622753
https://github.com/rust-fuzz/cargo-fuzz/issues/330 | True | Consider switching fuzzer backends to LibAFL - LibFuzzer is in [maintenance mode](https://llvm.org/docs/LibFuzzer.html#status):
> The original authors of libFuzzer have stopped active work on it and switched to working on another fuzzing engine, [Centipede](https://github.com/google/centipede).
We should consider switching to LibAFL or another implementation, since it seems that we can get both fuzzing performance and maintainability improvements.
More info:
https://hachyderm.io/@addison@infosec.exchange/110820552409622753
https://github.com/rust-fuzz/cargo-fuzz/issues/330 | main | consider switching fuzzer backends to libafl libfuzzer is in the original authors of libfuzzer have stopped active work on it and switched to working on another fuzzing engine we should consider switching to libafl or another implementation since it seems that we can get both fuzzing performance and maintainability improvements more info | 1 |
5,243 | 26,564,217,774 | IssuesEvent | 2023-01-20 18:31:38 | snorklerjoe/CubeServer | https://api.github.com/repos/snorklerjoe/CubeServer | opened | Add default rules config to config.py | enhancement On Hold trivial maintainability | Current default game params are hard-coded (changable via admin panel, but should be in a config file) | True | Add default rules config to config.py - Current default game params are hard-coded (changable via admin panel, but should be in a config file) | main | add default rules config to config py current default game params are hard coded changable via admin panel but should be in a config file | 1 |
715 | 4,308,400,170 | IssuesEvent | 2016-07-21 12:53:40 | topogram/topogram | https://api.github.com/repos/topogram/topogram | opened | ./build.sh script should be called from within the Docker file | bug maintaining | Right now you have to build the node app from Meteor before building the Docker image, which causes the Docker image compilation to fail. One single Dockerfile should be the only thing you need to create a Docker image. | True | ./build.sh script should be called from within the Docker file - Right now you have to build the node app from Meteor before building the Docker image, which causes the Docker image compilation to fail. One single Dockerfile should be the only thing you need to create a Docker image. | main | build sh script should be called from within the docker file right now you have to build the node app from meteor before building the docker image which causes the docker image compilation to fail one single dockerfile should be the only thing you need to create a docker image | 1 |
1,993 | 6,695,213,962 | IssuesEvent | 2017-10-10 07:14:22 | cannawen/metric_units_reddit_bot | https://api.github.com/repos/cannawen/metric_units_reddit_bot | closed | Discussion - Discussions | discussion maintainer approved | GitHub issues does not seem like a great platform for discussions. The conversation is linearly organized and chronologically ordered.
Should only the top post be made on GitHub, and then locked while linking to a discussion thread on /r/metric_units subreddit? Reddit seems like a much more natural place for discussions, where each point can be a separate comment and there can be comment replies. Sorting by upvotes would also be nice
Pros:
- better discussion format
- Redditors without GitHub accounts can contribute
Cons:
- you need to create a Reddit account to contribute
- information scattered across platforms (you need to check Reddit and GitHub to keep current)
Once a "decision" has been reached on reddit, the decision can be copied back to Github and the Reddit post can be locked.
Re-visiting a discussion on the topic must be done through a new issue/thread
Any feedback from the community?
Give a thumbs up if you like the Reddit idea, thumbs down if you don't. | True | Discussion - Discussions - GitHub issues does not seem like a great platform for discussions. The conversation is linearly organized and chronologically ordered.
Should only the top post be made on GitHub, and then locked while linking to a discussion thread on /r/metric_units subreddit? Reddit seems like a much more natural place for discussions, where each point can be a separate comment and there can be comment replies. Sorting by upvotes would also be nice
Pros:
- better discussion format
- Redditors without GitHub accounts can contribute
Cons:
- you need to create a Reddit account to contribute
- information scattered across platforms (you need to check Reddit and GitHub to keep current)
Once a "decision" has been reached on reddit, the decision can be copied back to Github and the Reddit post can be locked.
Re-visiting a discussion on the topic must be done through a new issue/thread
Any feedback from the community?
Give a thumbs up if you like the Reddit idea, thumbs down if you don't. | main | discussion discussions github issues does not seem like a great platform for discussions the conversation is linearly organized and chronologically ordered should only the top post be made on github and then locked while linking to a discussion thread on r metric units subreddit reddit seems like a much more natural place for discussions where each point can be a separate comment and there can be comment replies sorting by upvotes would also be nice pros better discussion format redditors without github accounts can contribute cons you need to create a reddit account to contribute information scattered across platforms you need to check reddit and github to keep current once a decision has been reached on reddit the decision can be copied back to github and the reddit post can be locked re visiting a discussion on the topic must be done through a new issue thread any feedback from the community give a thumbs up if you like the reddit idea thumbs down if you don t | 1 |
194,845 | 14,690,017,894 | IssuesEvent | 2021-01-02 13:09:16 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | pbolla0818/oci_terraform: oci/cloud_guard_responder_recipe_test.go; 16 LoC | fresh small test |
Found a possible issue in [pbolla0818/oci_terraform](https://www.github.com/pbolla0818/oci_terraform) at [oci/cloud_guard_responder_recipe_test.go](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/cloud_guard_responder_recipe_test.go#L342-L357)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to responderRecipeId is reassigned at line 346
[Click here to see the code in its original context.](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/cloud_guard_responder_recipe_test.go#L342-L357)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, responderRecipeId := range responderRecipeIds {
if ok := SweeperDefaultResourceId[responderRecipeId]; !ok {
deleteResponderRecipeRequest := oci_cloud_guard.DeleteResponderRecipeRequest{}
deleteResponderRecipeRequest.ResponderRecipeId = &responderRecipeId
deleteResponderRecipeRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "cloud_guard")
_, error := cloudGuardClient.DeleteResponderRecipe(context.Background(), deleteResponderRecipeRequest)
if error != nil {
fmt.Printf("Error deleting ResponderRecipe %s %s, It is possible that the resource is already deleted. Please verify manually \n", responderRecipeId, error)
continue
}
waitTillCondition(testAccProvider, &responderRecipeId, responderRecipeSweepWaitCondition, time.Duration(3*time.Minute),
responderRecipeSweepResponseFetchOperation, "cloud_guard", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c233d54c5fe32f12c234d6dceefba0a9b4ab3022
| 1.0 | pbolla0818/oci_terraform: oci/cloud_guard_responder_recipe_test.go; 16 LoC -
Found a possible issue in [pbolla0818/oci_terraform](https://www.github.com/pbolla0818/oci_terraform) at [oci/cloud_guard_responder_recipe_test.go](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/cloud_guard_responder_recipe_test.go#L342-L357)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to responderRecipeId is reassigned at line 346
[Click here to see the code in its original context.](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/cloud_guard_responder_recipe_test.go#L342-L357)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, responderRecipeId := range responderRecipeIds {
if ok := SweeperDefaultResourceId[responderRecipeId]; !ok {
deleteResponderRecipeRequest := oci_cloud_guard.DeleteResponderRecipeRequest{}
deleteResponderRecipeRequest.ResponderRecipeId = &responderRecipeId
deleteResponderRecipeRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "cloud_guard")
_, error := cloudGuardClient.DeleteResponderRecipe(context.Background(), deleteResponderRecipeRequest)
if error != nil {
fmt.Printf("Error deleting ResponderRecipe %s %s, It is possible that the resource is already deleted. Please verify manually \n", responderRecipeId, error)
continue
}
waitTillCondition(testAccProvider, &responderRecipeId, responderRecipeSweepWaitCondition, time.Duration(3*time.Minute),
responderRecipeSweepResponseFetchOperation, "cloud_guard", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c233d54c5fe32f12c234d6dceefba0a9b4ab3022
| non_main | oci terraform oci cloud guard responder recipe test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to responderrecipeid is reassigned at line click here to show the line s of go which triggered the analyzer go for responderrecipeid range responderrecipeids if ok sweeperdefaultresourceid ok deleteresponderreciperequest oci cloud guard deleteresponderreciperequest deleteresponderreciperequest responderrecipeid responderrecipeid deleteresponderreciperequest requestmetadata retrypolicy getretrypolicy true cloud guard error cloudguardclient deleteresponderrecipe context background deleteresponderreciperequest if error nil fmt printf error deleting responderrecipe s s it is possible that the resource is already deleted please verify manually n responderrecipeid error continue waittillcondition testaccprovider responderrecipeid responderrecipesweepwaitcondition time duration time minute responderrecipesweepresponsefetchoperation cloud guard true leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
3,925 | 17,663,820,314 | IssuesEvent | 2021-08-22 03:28:33 | restqa/restqa | https://api.github.com/repos/restqa/restqa | opened | [DASHBOARD] UTM on sponsors link | enhancement good first issue help wanted pair with maintainer | Hello 👋,
### 👀 Background
Sponsors have their logo displayed on the dashboard, however there is no way for the sponsor to know that someone access to their website from the RestQA dashboard
### ✌️ What is the actual behavior?
On the RestQA Dashboard main page when the user is clicking on the logo he is redirected to the sponsor website.
### 🕵️♀️ How to reproduce the current behavior?
* Install RestQA `npm i -g @restqa/restqa`
* Initiate a RestQA project `restqa init`
* Run the dashboard `restqa dashboard`
* Access to the dashboard from your browser
* Click on one for the sponsor logo.
### 🤞 What is the expected behavior?
When we click on the sponsor logo we should be redirected to the sponsor website, the sponsor should be able to know the source of the traffic
### 😎 Proposed solution.
- [ ] Add utm information on the sponsor url: `https://example.com?utm_source=dashboard&utm_medium=referral&utm_campaign=restqa`
Cheers.
| True | [DASHBOARD] UTM on sponsors link - Hello 👋,
### 👀 Background
Sponsors have their logo displayed on the dashboard, however there is no way for the sponsor to know that someone access to their website from the RestQA dashboard
### ✌️ What is the actual behavior?
On the RestQA Dashboard main page when the user is clicking on the logo he is redirected to the sponsor website.
### 🕵️♀️ How to reproduce the current behavior?
* Install RestQA `npm i -g @restqa/restqa`
* Initiate a RestQA project `restqa init`
* Run the dashboard `restqa dashboard`
* Access to the dashboard from your browser
* Click on one for the sponsor logo.
### 🤞 What is the expected behavior?
When we click on the sponsor logo we should be redirected to the sponsor website, the sponsor should be able to know the source of the traffic
### 😎 Proposed solution.
- [ ] Add utm information on the sponsor url: `https://example.com?utm_source=dashboard&utm_medium=referral&utm_campaign=restqa`
Cheers.
| main | utm on sponsors link hello 👋 👀 background sponsors have their logo displayed on the dashboard however there is no way for the sponsor to know that someone access to their website from the restqa dashboard ✌️ what is the actual behavior on the restqa dashboard main page when the user is clicking on the logo he is redirected to the sponsor website 🕵️♀️ how to reproduce the current behavior install restqa npm i g restqa restqa initiate a restqa project restqa init run the dashboard restqa dashboard access to the dashboard from your browser click on one for the sponsor logo 🤞 what is the expected behavior when we click on the sponsor logo we should be redirected to the sponsor website the sponsor should be able to know the source of the traffic 😎 proposed solution add utm information on the sponsor url cheers | 1 |
3,343 | 12,964,756,269 | IssuesEvent | 2020-07-20 21:03:05 | cncf/sig-contributor-strategy | https://api.github.com/repos/cncf/sig-contributor-strategy | closed | Maintainers Circle Proposal | new-wg wg/maintainer | Leadership circles help in large environments where many people operate independently. In this specific case, maintainers at 40+ CNCF projects. //add more summary here
**Goals:**
- Training
- Collaboration points on strategic issues; tackling size:L OSS issues
- Camaraderie / bringing people together
- Listening (to build better programs, relationships, and sustainability efforts)
- Share Best Practices
- Highlight successes
**NonGoals:**
- Sell to you - zero tolerance
**Next Steps**
- [x] Recruit (paris, stephen, COULD BE YOU - comment here!)
- [x] Define maintainer here (zach) / update README with this information
- "A maintainer is anyone recognized as a maintainer of a project by that project's standards."
- We will include 2-3 examples of project maintainer definitions on the readme, too.
- someone who commits, has an overview of their project area or whole project, usually the final responsibility
- [x] Update goals above and create a robust README (paris)
- [x] send welcome email to dev lists.
- [x] set up inputs and outputs: slack channel and ways to get a hold of each other - submitted CNCF servicedesk ticket for #maintainers-circle
- [x] Bring in Liz, gb reps (michelle, matt), and others to see how we can all work together on similar goals under the same umbrella. they have n cadence meetings with similar maintainer crowd for governing board representation - see if they can come to thursdays meeting - continue this on a separate issue
***What does done look like for this issue?***
When we have a "come hang out with us" email ready to ship and approved by the group
**Open Ended Questions**
- //add more here | True | Maintainers Circle Proposal - Leadership circles help in large environments where many people operate independently. In this specific case, maintainers at 40+ CNCF projects. //add more summary here
**Goals:**
- Training
- Collaboration points on strategic issues; tackling size:L OSS issues
- Camaraderie / bringing people together
- Listening (to build better programs, relationships, and sustainability efforts)
- Share Best Practices
- Highlight successes
**NonGoals:**
- Sell to you - zero tolerance
**Next Steps**
- [x] Recruit (paris, stephen, COULD BE YOU - comment here!)
- [x] Define maintainer here (zach) / update README with this information
- "A maintainer is anyone recognized as a maintainer of a project by that project's standards."
- We will include 2-3 examples of project maintainer definitions on the readme, too.
- someone who commits, has an overview of their project area or whole project, usually the final responsibility
- [x] Update goals above and create a robust README (paris)
- [x] send welcome email to dev lists.
- [x] set up inputs and outputs: slack channel and ways to get a hold of each other - submitted CNCF servicedesk ticket for #maintainers-circle
- [x] Bring in Liz, gb reps (michelle, matt), and others to see how we can all work together on similar goals under the same umbrella. they have n cadence meetings with similar maintainer crowd for governing board representation - see if they can come to thursdays meeting - continue this on a separate issue
***What does done look like for this issue?***
When we have a "come hang out with us" email ready to ship and approved by the group
**Open Ended Questions**
- //add more here | main | maintainers circle proposal leadership circles help in large environments where many people operate independently in this specific case maintainers at cncf projects add more summary here goals training collaboration points on strategic issues tackling size l oss issues camaraderie bringing people together listening to build better programs relationships and sustainability efforts share best practices highlight successes nongoals sell to you zero tolerance next steps recruit paris stephen could be you comment here define maintainer here zach update readme with this information a maintainer is anyone recognized as a maintainer of a project by that project s standards we will include examples of project maintainer definitions on the readme too someone who commits has an overview of their project area or whole project usually the final responsibility update goals above and create a robust readme paris send welcome email to dev lists set up inputs and outputs slack channel and ways to get a hold of each other submitted cncf servicedesk ticket for maintainers circle bring in liz gb reps michelle matt and others to see how we can all work together on similar goals under the same umbrella they have n cadence meetings with similar maintainer crowd for governing board representation see if they can come to thursdays meeting continue this on a separate issue what does done look like for this issue when we have a come hang out with us email ready to ship and approved by the group open ended questions add more here | 1 |
1,103 | 4,972,751,846 | IssuesEvent | 2016-12-05 22:29:47 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | openvswitch_port cannot set port property on the 'openvswitch' port | affects_2.0 bug_report networking waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
network/openvswitch_port.py
##### ANSIBLE VERSION
```
$ ansible --version
ansible 2.0.0.2
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
N/A
##### OS / ENVIRONMENT
Managing Open vSwitch running on Ubuntu 14.04/16.04.
##### SUMMARY
For each Open vSwitch instance (such as those created by using the network/openvswitch_bridge module), an implicit 'openvswitch' port that has the same name with the bridge itself is created. For example,
```
# ovs-vsctl add-br br0
# ovs-vsctl list port br0
_uuid : d32b978e-e828-4c5d-a368-877b2bc676a1
bond_active_slave : []
bond_downdelay : 0
bond_fake_iface : false
bond_mode : []
bond_updelay : 0
external_ids : {}
fake_bridge : false
interfaces : [0a67c10e-e341-484a-9af2-3feb2f7539d5]
lacp : []
mac : []
name : "br0"
other_config : {}
qos : []
rstp_statistics : {}
rstp_status : {}
statistics : {}
status : {}
tag : []
trunks : []
vlan_mode : []
# ovs-vsctl list interface br0
_uuid : 0a67c10e-e341-484a-9af2-3feb2f7539d5
admin_state : down
bfd : {}
bfd_status : {}
cfm_fault : []
cfm_fault_status : []
cfm_flap_count : []
cfm_health : []
cfm_mpid : []
cfm_remote_mpids : []
cfm_remote_opstate : []
duplex : []
error : []
external_ids : {}
ifindex : 1220
ingress_policing_burst: 0
ingress_policing_rate: 0
lacp_current : []
link_resets : 0
link_speed : []
link_state : down
lldp : {}
mac : []
mac_in_use : "1a:16:94:02:c9:42"
mtu : 1500
name : "br0"
ofport : 65534
ofport_request : []
options : {}
other_config : {}
statistics : {collisions=0, rx_bytes=0, rx_crc_err=0, rx_dropped=0, rx_errors=0, rx_frame_err=0, rx_over_err=0, rx_packets=0, tx_bytes=0, tx_dropped=0, tx_errors=0, tx_packets=0}
status : {driver_name=openvswitch}
type : internal
```
However, the 'list-ports' commands do not return this port. For example,
```
# ovs-vsctl list-ports br0
<returns nothing>
```
Therefore, if one uses the openvswitch_port module to set properties on this port, the module would try to create this port first and result in failure (because the port already exists.)
This can be easily fixed by taking into account that a port that has the same name with the bridge itself always exists. This is a one-line change in OVSPort.exists(), such as:
```
--- openvswitch_port.py.orig 2016-11-09 13:46:57.957148377 -0800
+++ openvswitch_port.py 2016-11-09 13:47:27.641029747 -0800
@@ -136,7 +136,7 @@
if rtc != 0:
self.module.fail_json(msg=err)
- return any(port.rstrip() == self.port for port in out.split('\n'))
+ return any(port.rstrip() == self.port for port in out.split('\n')) or (self.port == self.bridge)
def set(self, set_opt):
""" Set attributes on a port. """
```
##### STEPS TO REPRODUCE
```
$ ansible all -m openvswitch_bridge -a 'bridge=br0'
$ ansible all -m openvswitch_port -a 'bridge=br0 port=br0 set="Port br0 tag=0"'
```
##### EXPECTED RESULTS
```
# ansible all -m openvswitch_bridge -a 'bridge=br0'
localhost | SUCCESS => {
"changed": true
}
root@xenial:~# ansible -vvvv all -m openvswitch_port -a 'bridge=br0 port=br0 set="Port br0 tag=0"'
localhost | SUCCESS => {
"changed": true,
"invocation": {
"module_args": {
"bridge": "br0",
"external_ids": {},
"port": "br0",
"set": "Port br0 tag=0",
"state": "present",
"timeout": 5
},
"module_name": "openvswitch_port"
}
}
```
##### ACTUAL RESULTS
```
$ ansible all -m openvswitch_bridge -a 'bridge=br0'
localhost | SUCCESS => {
"changed": true
}
$ ansible all -m openvswitch_port -a 'bridge=br0 port=br0 set="Port br0 tag=0"'
localhost | FAILED! => {
"changed": false,
"cmd": "ovs-vsctl -t 5 add-port br0 br0 -- set Port br0 tag=0",
"failed": true,
"msg": "ovs-vsctl: cannot create a port named br0 because a bridge named br0 already exists",
"rc": 1,
"stderr": "ovs-vsctl: cannot create a port named br0 because a bridge named br0 already exists\n",
"stdout": "",
"stdout_lines": []
}
```
The 'add-port br0 br0' part shouldn't be part of the command to be run. | True | openvswitch_port cannot set port property on the 'openvswitch' port - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
network/openvswitch_port.py
##### ANSIBLE VERSION
```
$ ansible --version
ansible 2.0.0.2
config file = /etc/ansible/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
N/A
##### OS / ENVIRONMENT
Managing Open vSwitch running on Ubuntu 14.04/16.04.
##### SUMMARY
For each Open vSwitch instance (such as those created by using the network/openvswitch_bridge module), an implicit 'openvswitch' port that has the same name with the bridge itself is created. For example,
```
# ovs-vsctl add-br br0
# ovs-vsctl list port br0
_uuid : d32b978e-e828-4c5d-a368-877b2bc676a1
bond_active_slave : []
bond_downdelay : 0
bond_fake_iface : false
bond_mode : []
bond_updelay : 0
external_ids : {}
fake_bridge : false
interfaces : [0a67c10e-e341-484a-9af2-3feb2f7539d5]
lacp : []
mac : []
name : "br0"
other_config : {}
qos : []
rstp_statistics : {}
rstp_status : {}
statistics : {}
status : {}
tag : []
trunks : []
vlan_mode : []
# ovs-vsctl list interface br0
_uuid : 0a67c10e-e341-484a-9af2-3feb2f7539d5
admin_state : down
bfd : {}
bfd_status : {}
cfm_fault : []
cfm_fault_status : []
cfm_flap_count : []
cfm_health : []
cfm_mpid : []
cfm_remote_mpids : []
cfm_remote_opstate : []
duplex : []
error : []
external_ids : {}
ifindex : 1220
ingress_policing_burst: 0
ingress_policing_rate: 0
lacp_current : []
link_resets : 0
link_speed : []
link_state : down
lldp : {}
mac : []
mac_in_use : "1a:16:94:02:c9:42"
mtu : 1500
name : "br0"
ofport : 65534
ofport_request : []
options : {}
other_config : {}
statistics : {collisions=0, rx_bytes=0, rx_crc_err=0, rx_dropped=0, rx_errors=0, rx_frame_err=0, rx_over_err=0, rx_packets=0, tx_bytes=0, tx_dropped=0, tx_errors=0, tx_packets=0}
status : {driver_name=openvswitch}
type : internal
```
However, the 'list-ports' commands do not return this port. For example,
```
# ovs-vsctl list-ports br0
<returns nothing>
```
Therefore, if one uses the openvswitch_port module to set properties on this port, the module would try to create this port first and result in failure (because the port already exists.)
This can be easily fixed by taking into account that a port that has the same name with the bridge itself always exists. This is a one-line change in OVSPort.exists(), such as:
```
--- openvswitch_port.py.orig 2016-11-09 13:46:57.957148377 -0800
+++ openvswitch_port.py 2016-11-09 13:47:27.641029747 -0800
@@ -136,7 +136,7 @@
if rtc != 0:
self.module.fail_json(msg=err)
- return any(port.rstrip() == self.port for port in out.split('\n'))
+ return any(port.rstrip() == self.port for port in out.split('\n')) or (self.port == self.bridge)
def set(self, set_opt):
""" Set attributes on a port. """
```
##### STEPS TO REPRODUCE
```
$ ansible all -m openvswitch_bridge -a 'bridge=br0'
$ ansible all -m openvswitch_port -a 'bridge=br0 port=br0 set="Port br0 tag=0"'
```
##### EXPECTED RESULTS
```
# ansible all -m openvswitch_bridge -a 'bridge=br0'
localhost | SUCCESS => {
"changed": true
}
root@xenial:~# ansible -vvvv all -m openvswitch_port -a 'bridge=br0 port=br0 set="Port br0 tag=0"'
localhost | SUCCESS => {
"changed": true,
"invocation": {
"module_args": {
"bridge": "br0",
"external_ids": {},
"port": "br0",
"set": "Port br0 tag=0",
"state": "present",
"timeout": 5
},
"module_name": "openvswitch_port"
}
}
```
##### ACTUAL RESULTS
```
$ ansible all -m openvswitch_bridge -a 'bridge=br0'
localhost | SUCCESS => {
"changed": true
}
$ ansible all -m openvswitch_port -a 'bridge=br0 port=br0 set="Port br0 tag=0"'
localhost | FAILED! => {
"changed": false,
"cmd": "ovs-vsctl -t 5 add-port br0 br0 -- set Port br0 tag=0",
"failed": true,
"msg": "ovs-vsctl: cannot create a port named br0 because a bridge named br0 already exists",
"rc": 1,
"stderr": "ovs-vsctl: cannot create a port named br0 because a bridge named br0 already exists\n",
"stdout": "",
"stdout_lines": []
}
```
The 'add-port br0 br0' part shouldn't be part of the command to be run. | main | openvswitch port cannot set port property on the openvswitch port issue type bug report component name network openvswitch port py ansible version ansible version ansible config file etc ansible ansible cfg configured module search path default w o overrides configuration n a os environment managing open vswitch running on ubuntu summary for each open vswitch instance such as those created by using the network openvswitch bridge module an implicit openvswitch port that has the same name with the bridge itself is created for example ovs vsctl add br ovs vsctl list port uuid bond active slave bond downdelay bond fake iface false bond mode bond updelay external ids fake bridge false interfaces lacp mac name other config qos rstp statistics rstp status statistics status tag trunks vlan mode ovs vsctl list interface uuid admin state down bfd bfd status cfm fault cfm fault status cfm flap count cfm health cfm mpid cfm remote mpids cfm remote opstate duplex error external ids ifindex ingress policing burst ingress policing rate lacp current link resets link speed link state down lldp mac mac in use mtu name ofport ofport request options other config statistics collisions rx bytes rx crc err rx dropped rx errors rx frame err rx over err rx packets tx bytes tx dropped tx errors tx packets status driver name openvswitch type internal however the list ports commands do not return this port for example ovs vsctl list ports therefore if one uses the openvswitch port module to set properties on this port the module would try to create this port first and result in failure because the port already exists this can be easily fixed by taking into account that a port that has the same name with the bridge itself always exists this is a one line change in ovsport exists such as openvswitch port py orig openvswitch port py if rtc self module fail json msg err return any port rstrip self port for port in out split n return any port rstrip self port for port in out split n or self port self bridge def set self set opt set attributes on a port steps to reproduce ansible all m openvswitch bridge a bridge ansible all m openvswitch port a bridge port set port tag expected results ansible all m openvswitch bridge a bridge localhost success changed true root xenial ansible vvvv all m openvswitch port a bridge port set port tag localhost success changed true invocation module args bridge external ids port set port tag state present timeout module name openvswitch port actual results ansible all m openvswitch bridge a bridge localhost success changed true ansible all m openvswitch port a bridge port set port tag localhost failed changed false cmd ovs vsctl t add port set port tag failed true msg ovs vsctl cannot create a port named because a bridge named already exists rc stderr ovs vsctl cannot create a port named because a bridge named already exists n stdout stdout lines the add port part shouldn t be part of the command to be run | 1 |
753,357 | 26,344,781,523 | IssuesEvent | 2023-01-10 20:57:20 | GoogleCloudPlatform/python-docs-samples | https://api.github.com/repos/GoogleCloudPlatform/python-docs-samples | closed | jobs.v3.api_client.auto_complete_sample_test: test_auto_complete_sample failed | priority: p1 type: bug api: jobs samples flakybot: issue | Note: #6852 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 66e069f916ffc0c3f19899f5083d32ebc514a8f3
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/fea8fe56-8bef-4375-a365-e791f47ba958), [Sponge](http://sponge2/fea8fe56-8bef-4375-a365-e791f47ba958)
status: failed
<details><summary>Test output</summary><br><pre>Traceback (most recent call last):
File "/workspace/jobs/v3/api_client/auto_complete_sample_test.py", line 25, in company_name
company_name, job_name = auto_complete_sample.set_up()
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/workspace/jobs/v3/api_client/auto_complete_sample.py", line 57, in set_up
company_created = base_company_sample.create_company(
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/workspace/jobs/v3/api_client/base_company_sample.py", line 62, in create_company
raise e
File "/workspace/jobs/v3/api_client/base_company_sample.py", line 57, in create_company
parent=parent, body=request).execute()
^^^^^^^^^
File "/workspace/jobs/v3/api_client/.nox/py-3-11/lib/python3.11/site-packages/googleapiclient/_helpers.py", line 131, in positional_wrapper
return wrapped(*args, **kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^
File "/workspace/jobs/v3/api_client/.nox/py-3-11/lib/python3.11/site-packages/googleapiclient/http.py", line 937, in execute
raise HttpError(resp, content, uri=self.uri)
googleapiclient.errors.HttpError: <HttpError 400 when requesting https://jobs.googleapis.com/v3/projects/python-docs-samples-tests-311/companies?alt=json returned "Service must be permitted to access job and behavioral data to improve common machine learning models, so only data deletion calls are accessible if these terms have not been opted in to. See https://console.cloud.google.com/talent-solution/data-permission-onboard for more information.. Request ID for tracking: 134357cf-b62f-41f4-a942-2cdc2f5ec0d6:APAb7ITnaUb6sP2FwjDw/xhEDCVlw7+TwA==". Details: "Service must be permitted to access job and behavioral data to improve common machine learning models, so only data deletion calls are accessible if these terms have not been opted in to. See https://console.cloud.google.com/talent-solution/data-permission-onboard for more information.. Request ID for tracking: 134357cf-b62f-41f4-a942-2cdc2f5ec0d6:APAb7ITnaUb6sP2FwjDw/xhEDCVlw7+TwA=="></pre></details> | 1.0 | jobs.v3.api_client.auto_complete_sample_test: test_auto_complete_sample failed - Note: #6852 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 66e069f916ffc0c3f19899f5083d32ebc514a8f3
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/fea8fe56-8bef-4375-a365-e791f47ba958), [Sponge](http://sponge2/fea8fe56-8bef-4375-a365-e791f47ba958)
status: failed
<details><summary>Test output</summary><br><pre>Traceback (most recent call last):
File "/workspace/jobs/v3/api_client/auto_complete_sample_test.py", line 25, in company_name
company_name, job_name = auto_complete_sample.set_up()
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/workspace/jobs/v3/api_client/auto_complete_sample.py", line 57, in set_up
company_created = base_company_sample.create_company(
^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^^
File "/workspace/jobs/v3/api_client/base_company_sample.py", line 62, in create_company
raise e
File "/workspace/jobs/v3/api_client/base_company_sample.py", line 57, in create_company
parent=parent, body=request).execute()
^^^^^^^^^
File "/workspace/jobs/v3/api_client/.nox/py-3-11/lib/python3.11/site-packages/googleapiclient/_helpers.py", line 131, in positional_wrapper
return wrapped(*args, **kwargs)
^^^^^^^^^^^^^^^^^^^^^^^^
File "/workspace/jobs/v3/api_client/.nox/py-3-11/lib/python3.11/site-packages/googleapiclient/http.py", line 937, in execute
raise HttpError(resp, content, uri=self.uri)
googleapiclient.errors.HttpError: <HttpError 400 when requesting https://jobs.googleapis.com/v3/projects/python-docs-samples-tests-311/companies?alt=json returned "Service must be permitted to access job and behavioral data to improve common machine learning models, so only data deletion calls are accessible if these terms have not been opted in to. See https://console.cloud.google.com/talent-solution/data-permission-onboard for more information.. Request ID for tracking: 134357cf-b62f-41f4-a942-2cdc2f5ec0d6:APAb7ITnaUb6sP2FwjDw/xhEDCVlw7+TwA==". Details: "Service must be permitted to access job and behavioral data to improve common machine learning models, so only data deletion calls are accessible if these terms have not been opted in to. See https://console.cloud.google.com/talent-solution/data-permission-onboard for more information.. Request ID for tracking: 134357cf-b62f-41f4-a942-2cdc2f5ec0d6:APAb7ITnaUb6sP2FwjDw/xhEDCVlw7+TwA=="></pre></details> | non_main | jobs api client auto complete sample test test auto complete sample failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output traceback most recent call last file workspace jobs api client auto complete sample test py line in company name company name job name auto complete sample set up file workspace jobs api client auto complete sample py line in set up company created base company sample create company file workspace jobs api client base company sample py line in create company raise e file workspace jobs api client base company sample py line in create company parent parent body request execute file workspace jobs api client nox py lib site packages googleapiclient helpers py line in positional wrapper return wrapped args kwargs file workspace jobs api client nox py lib site packages googleapiclient http py line in execute raise httperror resp content uri self uri googleapiclient errors httperror | 0 |
954 | 4,699,525,802 | IssuesEvent | 2016-10-12 15:54:08 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | ec2_asg sets desired_capacity=0 when min_size=0 - terminates existing instances | affects_2.1 aws bug_report cloud waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ec2_asg
##### ANSIBLE VERSION
```
ansible 2.1.2.0
```
##### CONFIGURATION
<!---
Mention any settings you have changed/added/removed in ansible.cfg
(or using the ANSIBLE_* environment variables).
-->
##### OS / ENVIRONMENT
AmazonLinux
4.4.19-29.55.amzn1.x86_64
amzn-ami-hvm-2016.03.0.x86_64-gp2 (ami-31328842)
##### SUMMARY
Setting min_size to zero also sets desired_capacity to zero
##### STEPS TO REPRODUCE
Playbook creates ASG with the following values:
```
ec2_asg:
...
min_size: 0
max_size: 3
desired_capacity: 1
...
```
##### EXPECTED RESULTS
ASG has min_size=0 but desired_capacity remains as set and no instances are terminated unnecessarily.
##### ACTUAL RESULTS
ASG has min_size=0 and desired_capacity=0, existing instances are terminated
| True | ec2_asg sets desired_capacity=0 when min_size=0 - terminates existing instances - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ec2_asg
##### ANSIBLE VERSION
```
ansible 2.1.2.0
```
##### CONFIGURATION
<!---
Mention any settings you have changed/added/removed in ansible.cfg
(or using the ANSIBLE_* environment variables).
-->
##### OS / ENVIRONMENT
AmazonLinux
4.4.19-29.55.amzn1.x86_64
amzn-ami-hvm-2016.03.0.x86_64-gp2 (ami-31328842)
##### SUMMARY
Setting min_size to zero also sets desired_capacity to zero
##### STEPS TO REPRODUCE
Playbook creates ASG with the following values:
```
ec2_asg:
...
min_size: 0
max_size: 3
desired_capacity: 1
...
```
##### EXPECTED RESULTS
ASG has min_size=0 but desired_capacity remains as set and no instances are terminated unnecessarily.
##### ACTUAL RESULTS
ASG has min_size=0 and desired_capacity=0, existing instances are terminated
| main | asg sets desired capacity when min size terminates existing instances issue type bug report component name asg ansible version ansible configuration mention any settings you have changed added removed in ansible cfg or using the ansible environment variables os environment amazonlinux amzn ami hvm ami summary setting min size to zero also sets desired capacity to zero steps to reproduce playbook creates asg with the following values asg min size max size desired capacity expected results asg has min size but desired capacity remains as set and no instances are terminated unnecessarily actual results asg has min size and desired capacity existing instances are terminated | 1 |
98,840 | 30,193,928,752 | IssuesEvent | 2023-07-04 18:18:47 | easybuilders/easybuild | https://api.github.com/repos/easybuilders/easybuild | closed | Toolchain Support Policy - EasyBuild 5 | EasyBuild-5.0 feedback | Work has started on [EasyBuild 5](https://docs.easybuild.io/easybuild-v5/overview-of-changes) and we, the EasyBuild maintainers, are requesting community feedback on some potential changes. If you will be impacted by this proposed change then please leave feedback below.
## Proposed Change
For the central EasyBuild repositories, we will support a set of toolchain generations. In year *X* (example using 2023):
* Accept PRs only for toolchains *X-2*
* `2023a/b`, `2022a/b`, `2021a/b`
* Deprecate toolchains *X-3*
* `2020a/b`
* Close PRs and issues for these toolchains
* Archive easyconfigs using toolchain version *X-4*
* `2019a/b` (and older)
## Background
The central easyconfigs repository is intended to provide references easyconfigs. For the reference easyconfigs we aim to have only one version of a software being used as a dependency in each toolchain generation. (There are exceptions, but we aim to keep these limited.)
Sites and users can then supplement these easyconfigs via there own collection of easyconfigs. This additional collection is added via the [robot search path](https://docs.easybuild.io/using-easybuild/#robot_search_path).
## Benefits
* Toolchain generations are year based and this aligns the support with that, rather than EasyBuild versions.
* Focus community effort of the more recent toolchain generations.
* Reduce maintainer workload, and testing time, related to processing easyconfigs from older toolchain generations.
## Drawbacks
* There are currently only 4 supported toolchain generations.
## Alternatives
### Alternative 1
As above, but with each step being 1 year older. So, review (*X-3*); deprecate and close (*X-4*); and archive (*X-5*)
### Alternative 2
Base it on the last *6* common toolchains, instead of years. So, review (last *6*); deprecate and close (*7*); and archive (*8*).
| 1.0 | Toolchain Support Policy - EasyBuild 5 - Work has started on [EasyBuild 5](https://docs.easybuild.io/easybuild-v5/overview-of-changes) and we, the EasyBuild maintainers, are requesting community feedback on some potential changes. If you will be impacted by this proposed change then please leave feedback below.
## Proposed Change
For the central EasyBuild repositories, we will support a set of toolchain generations. In year *X* (example using 2023):
* Accept PRs only for toolchains *X-2*
* `2023a/b`, `2022a/b`, `2021a/b`
* Deprecate toolchains *X-3*
* `2020a/b`
* Close PRs and issues for these toolchains
* Archive easyconfigs using toolchain version *X-4*
* `2019a/b` (and older)
## Background
The central easyconfigs repository is intended to provide references easyconfigs. For the reference easyconfigs we aim to have only one version of a software being used as a dependency in each toolchain generation. (There are exceptions, but we aim to keep these limited.)
Sites and users can then supplement these easyconfigs via there own collection of easyconfigs. This additional collection is added via the [robot search path](https://docs.easybuild.io/using-easybuild/#robot_search_path).
## Benefits
* Toolchain generations are year based and this aligns the support with that, rather than EasyBuild versions.
* Focus community effort of the more recent toolchain generations.
* Reduce maintainer workload, and testing time, related to processing easyconfigs from older toolchain generations.
## Drawbacks
* There are currently only 4 supported toolchain generations.
## Alternatives
### Alternative 1
As above, but with each step being 1 year older. So, review (*X-3*); deprecate and close (*X-4*); and archive (*X-5*)
### Alternative 2
Base it on the last *6* common toolchains, instead of years. So, review (last *6*); deprecate and close (*7*); and archive (*8*).
| non_main | toolchain support policy easybuild work has started on and we the easybuild maintainers are requesting community feedback on some potential changes if you will be impacted by this proposed change then please leave feedback below proposed change for the central easybuild repositories we will support a set of toolchain generations in year x example using accept prs only for toolchains x b b b deprecate toolchains x b close prs and issues for these toolchains archive easyconfigs using toolchain version x b and older background the central easyconfigs repository is intended to provide references easyconfigs for the reference easyconfigs we aim to have only one version of a software being used as a dependency in each toolchain generation there are exceptions but we aim to keep these limited sites and users can then supplement these easyconfigs via there own collection of easyconfigs this additional collection is added via the benefits toolchain generations are year based and this aligns the support with that rather than easybuild versions focus community effort of the more recent toolchain generations reduce maintainer workload and testing time related to processing easyconfigs from older toolchain generations drawbacks there are currently only supported toolchain generations alternatives alternative as above but with each step being year older so review x deprecate and close x and archive x alternative base it on the last common toolchains instead of years so review last deprecate and close and archive | 0 |
5,607 | 28,067,162,659 | IssuesEvent | 2023-03-29 16:13:54 | beyarkay/eskom-calendar | https://api.github.com/repos/beyarkay/eskom-calendar | closed | Add regression tests on build artifacts | enhancement waiting-on-maintainer | Loadshedding scheduled for 14:00 to 16:30 today 25 September for Stage 3 but your calendar doesnt show it. | True | Add regression tests on build artifacts - Loadshedding scheduled for 14:00 to 16:30 today 25 September for Stage 3 but your calendar doesnt show it. | main | add regression tests on build artifacts loadshedding scheduled for to today september for stage but your calendar doesnt show it | 1 |
532,231 | 15,531,751,841 | IssuesEvent | 2021-03-14 01:25:01 | Tautulli/Tautulli-Remote | https://api.github.com/repos/Tautulli/Tautulli-Remote | closed | Use Tautulli Time Format in Tautulli Remote | enhancement priority:normal | **Describe the solution you'd like**
Use the Time Format that is set in Tautulli.
Address concerns like #103
| 1.0 | Use Tautulli Time Format in Tautulli Remote - **Describe the solution you'd like**
Use the Time Format that is set in Tautulli.
Address concerns like #103
| non_main | use tautulli time format in tautulli remote describe the solution you d like use the time format that is set in tautulli address concerns like | 0 |
5,578 | 27,948,981,974 | IssuesEvent | 2023-03-24 07:03:55 | centerofci/mathesar | https://api.github.com/repos/centerofci/mathesar | closed | Release 0.1.1 | restricted: maintainers status: started work: release | # 2023-03-17
```[tasklist]
- [x] Cut 0.1.1 release branch, freeze code
- [x] Update version number in all places in the new branch
- [x] Make an image from the branch with tag `0.1.1`, push to Dockerhub
- [x] Test installation with the new image
- [x] Test upgrade
```
# 2023-03-20
```[tasklist]
- [x] Smoke test Mathesar
- [x] Follow up on https://github.com/centerofci/mathesar/issues/2714. Moved to 0.1.2.
```
# 2032-03-21
```[tasklist]
- [x] Fix https://github.com/centerofci/mathesar/issues/2715
- [x] Fix https://github.com/centerofci/mathesar/issues/2717
- [x] Fix https://github.com/centerofci/mathesar/issues/2718
- [x] Write up release notes, get review from team
```
# 2023-03-22
```[tasklist]
- [x] Follow up on https://github.com/centerofci/mathesar/pull/2729
- [x] Make new image for `0.1.1`, push to Dockerhub
- [x] Test installation with the new image
- [x] Test upgrade
```
# 2023-03-23
```[tasklist]
- [x] Smoke test Mathesar, during IST hours
- [x] Deploy to library.mathesar.org and test backend changes mentioned by Brent
- [x] Merge 0.1.1 to master
- [x] Create new GH tag 0.1.1 and create new release with that tag, add release notes
- [x] Tag the image for 0.1.1 as latest on Dockerhub
- [x] Merge master into develop
```
Tracked separately via mail
- ~~[ ] Deploy to demo and other private servers~~
- ~~[ ] Send email to mathesar-developers announcing release~~ | True | Release 0.1.1 - # 2023-03-17
```[tasklist]
- [x] Cut 0.1.1 release branch, freeze code
- [x] Update version number in all places in the new branch
- [x] Make an image from the branch with tag `0.1.1`, push to Dockerhub
- [x] Test installation with the new image
- [x] Test upgrade
```
# 2023-03-20
```[tasklist]
- [x] Smoke test Mathesar
- [x] Follow up on https://github.com/centerofci/mathesar/issues/2714. Moved to 0.1.2.
```
# 2032-03-21
```[tasklist]
- [x] Fix https://github.com/centerofci/mathesar/issues/2715
- [x] Fix https://github.com/centerofci/mathesar/issues/2717
- [x] Fix https://github.com/centerofci/mathesar/issues/2718
- [x] Write up release notes, get review from team
```
# 2023-03-22
```[tasklist]
- [x] Follow up on https://github.com/centerofci/mathesar/pull/2729
- [x] Make new image for `0.1.1`, push to Dockerhub
- [x] Test installation with the new image
- [x] Test upgrade
```
# 2023-03-23
```[tasklist]
- [x] Smoke test Mathesar, during IST hours
- [x] Deploy to library.mathesar.org and test backend changes mentioned by Brent
- [x] Merge 0.1.1 to master
- [x] Create new GH tag 0.1.1 and create new release with that tag, add release notes
- [x] Tag the image for 0.1.1 as latest on Dockerhub
- [x] Merge master into develop
```
Tracked separately via mail
- ~~[ ] Deploy to demo and other private servers~~
- ~~[ ] Send email to mathesar-developers announcing release~~ | main | release cut release branch freeze code update version number in all places in the new branch make an image from the branch with tag push to dockerhub test installation with the new image test upgrade smoke test mathesar follow up on moved to fix fix fix write up release notes get review from team follow up on make new image for push to dockerhub test installation with the new image test upgrade smoke test mathesar during ist hours deploy to library mathesar org and test backend changes mentioned by brent merge to master create new gh tag and create new release with that tag add release notes tag the image for as latest on dockerhub merge master into develop tracked separately via mail deploy to demo and other private servers send email to mathesar developers announcing release | 1 |
196,789 | 15,610,053,292 | IssuesEvent | 2021-03-19 12:43:18 | FirebaseExtended/flutterfire | https://api.github.com/repos/FirebaseExtended/flutterfire | closed | [firebase_admob] What does analyticsEnabled param do? | type: documentation | I can't find documentation about initialize method "analyticsEnabled" param. What does this param do? Is it for printing analytics info to console? | 1.0 | [firebase_admob] What does analyticsEnabled param do? - I can't find documentation about initialize method "analyticsEnabled" param. What does this param do? Is it for printing analytics info to console? | non_main | what does analyticsenabled param do i can t find documentation about initialize method analyticsenabled param what does this param do is it for printing analytics info to console | 0 |
1,513 | 6,543,951,398 | IssuesEvent | 2017-09-03 09:02:53 | cucumber/aruba | https://api.github.com/repos/cucumber/aruba | closed | Improve branch-model | needs-feedback/by-maintainer | ## Summary
Improve branch-model to make contributing easier.
<!--- Provide a general summary of the issue in the Title above -->
## Expected Behavior
Taken from [here](https://gitter.im/cucumber/aruba?at=56fd558f76b6f9de194cefef).
it's mostly bugfixes and new features (like Docker), so there shouldn't be any conflicts. If that's an issue, it's best to switch master to 1.x, branch off 0.14 for backporting, and just focus on releasing 1.x ASAP. It's no problem to then work on 2.x a month from now - no one will complain because of "too many major releases". Aruba is complex, so learning is expected. And if learning is reflected in "multiple major releases", that's just an indication of how much learning (or rework) was needed, nothing else. I'm guessing it's actually more useful to just skip to 2.x (master - without releasing), branch off 1.x as unreleased as "work in progress" (too keep the branches). E.g. I'm (as a contributor) only interested in master and not backward compatibility or deprecations - so it makes no sense to add an artificial "burden" on master. You can always work on a "transition release" - but only if there's a genuine need in the community. Master branch should be optimized for quickly accepting PRs. (If PRs don't have priority over other work, contributing feels very discouraging - as if there's a ton of "bureaucracy"). It doesn't make sense to expect contributors to make backports of their own fixes (that they don't need themselves).
<!--- If you're describing a bug, tell us what should happen -->
<!--- If you're suggesting a change/improvement, tell us how it should work -->
## Current Behavior
It takes a long time to release a major release.
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggesting a change/improvement, explain the difference from current behavior -->
## Possible Solution
Release faster.
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change -->
| True | Improve branch-model - ## Summary
Improve branch-model to make contributing easier.
<!--- Provide a general summary of the issue in the Title above -->
## Expected Behavior
Taken from [here](https://gitter.im/cucumber/aruba?at=56fd558f76b6f9de194cefef).
it's mostly bugfixes and new features (like Docker), so there shouldn't be any conflicts. If that's an issue, it's best to switch master to 1.x, branch off 0.14 for backporting, and just focus on releasing 1.x ASAP. It's no problem to then work on 2.x a month from now - no one will complain because of "too many major releases". Aruba is complex, so learning is expected. And if learning is reflected in "multiple major releases", that's just an indication of how much learning (or rework) was needed, nothing else. I'm guessing it's actually more useful to just skip to 2.x (master - without releasing), branch off 1.x as unreleased as "work in progress" (too keep the branches). E.g. I'm (as a contributor) only interested in master and not backward compatibility or deprecations - so it makes no sense to add an artificial "burden" on master. You can always work on a "transition release" - but only if there's a genuine need in the community. Master branch should be optimized for quickly accepting PRs. (If PRs don't have priority over other work, contributing feels very discouraging - as if there's a ton of "bureaucracy"). It doesn't make sense to expect contributors to make backports of their own fixes (that they don't need themselves).
<!--- If you're describing a bug, tell us what should happen -->
<!--- If you're suggesting a change/improvement, tell us how it should work -->
## Current Behavior
It takes a long time to release a major release.
<!--- If describing a bug, tell us what happens instead of the expected behavior -->
<!--- If suggesting a change/improvement, explain the difference from current behavior -->
## Possible Solution
Release faster.
<!--- Not obligatory, but suggest a fix/reason for the bug, -->
<!--- or ideas how to implement the addition or change -->
| main | improve branch model summary improve branch model to make contributing easier expected behavior taken from it s mostly bugfixes and new features like docker so there shouldn t be any conflicts if that s an issue it s best to switch master to x branch off for backporting and just focus on releasing x asap it s no problem to then work on x a month from now no one will complain because of too many major releases aruba is complex so learning is expected and if learning is reflected in multiple major releases that s just an indication of how much learning or rework was needed nothing else i m guessing it s actually more useful to just skip to x master without releasing branch off x as unreleased as work in progress too keep the branches e g i m as a contributor only interested in master and not backward compatibility or deprecations so it makes no sense to add an artificial burden on master you can always work on a transition release but only if there s a genuine need in the community master branch should be optimized for quickly accepting prs if prs don t have priority over other work contributing feels very discouraging as if there s a ton of bureaucracy it doesn t make sense to expect contributors to make backports of their own fixes that they don t need themselves current behavior it takes a long time to release a major release possible solution release faster | 1 |
4,495 | 23,416,157,942 | IssuesEvent | 2022-08-13 02:00:55 | aws/aws-sam-cli | https://api.github.com/repos/aws/aws-sam-cli | closed | Process Amazon S3 Events Example not show Trigger in Lambda function | type/question maintainer/need-followup | <!-- Make sure we don't have an existing Issue that reports the bug you are seeing (both open and closed). -->
### Describe your idea/feature/enhancement
I tried [Process Amazon S3 Events](https://docs.aws.amazon.com/serverless-application-model/latest/developerguide/serverless-example-s3.html), after I run `sam deploy --template-file packaged.yaml --stack-name aws-sam-ocr --capabilities CAPABILITY_IAM`, I can upload a picture and found a record in dynamoDB.
You can there S3 event like this
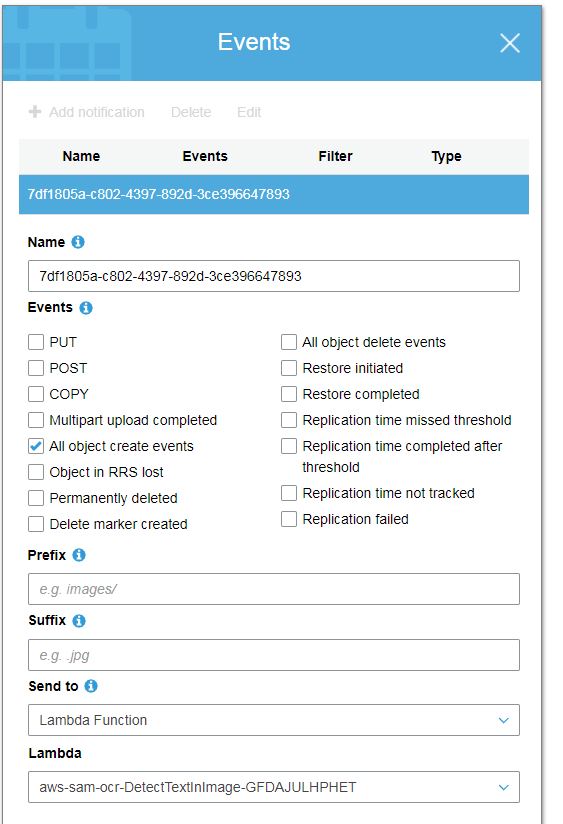
### Proposal
But when open Lambda function in Designer, I found there is no trigger from S3
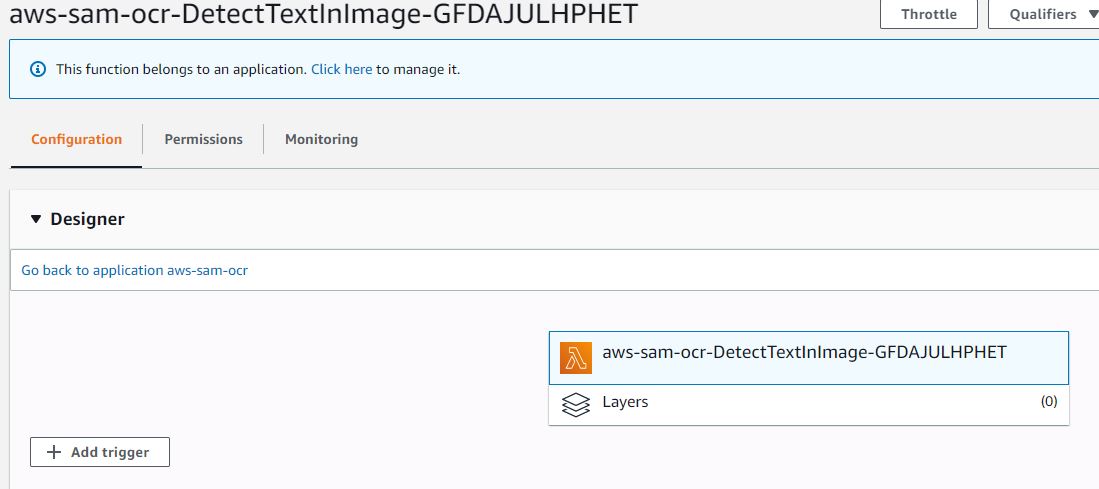
I want to know how can I let Lambda function to show S3 trigger in Designer?
### Additional Details
| True | Process Amazon S3 Events Example not show Trigger in Lambda function - <!-- Make sure we don't have an existing Issue that reports the bug you are seeing (both open and closed). -->
### Describe your idea/feature/enhancement
I tried [Process Amazon S3 Events](https://docs.aws.amazon.com/serverless-application-model/latest/developerguide/serverless-example-s3.html), after I run `sam deploy --template-file packaged.yaml --stack-name aws-sam-ocr --capabilities CAPABILITY_IAM`, I can upload a picture and found a record in dynamoDB.
You can there S3 event like this
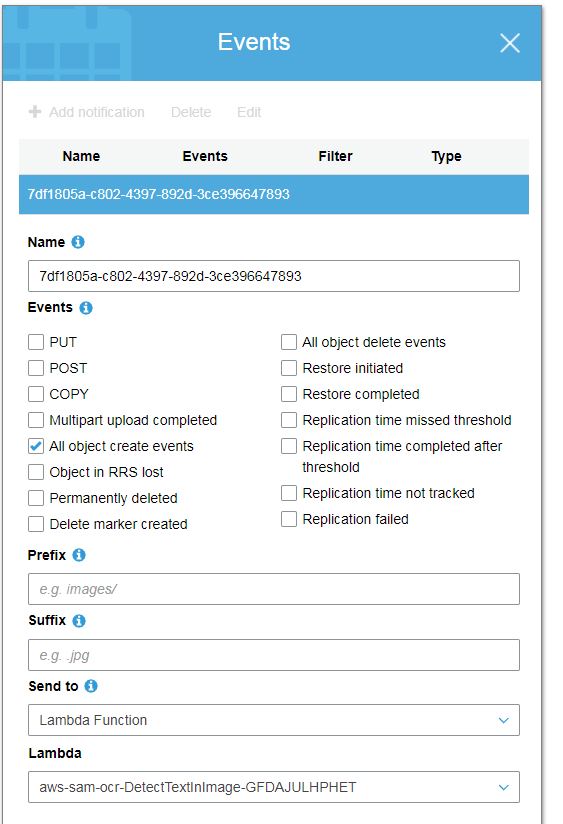
### Proposal
But when open Lambda function in Designer, I found there is no trigger from S3
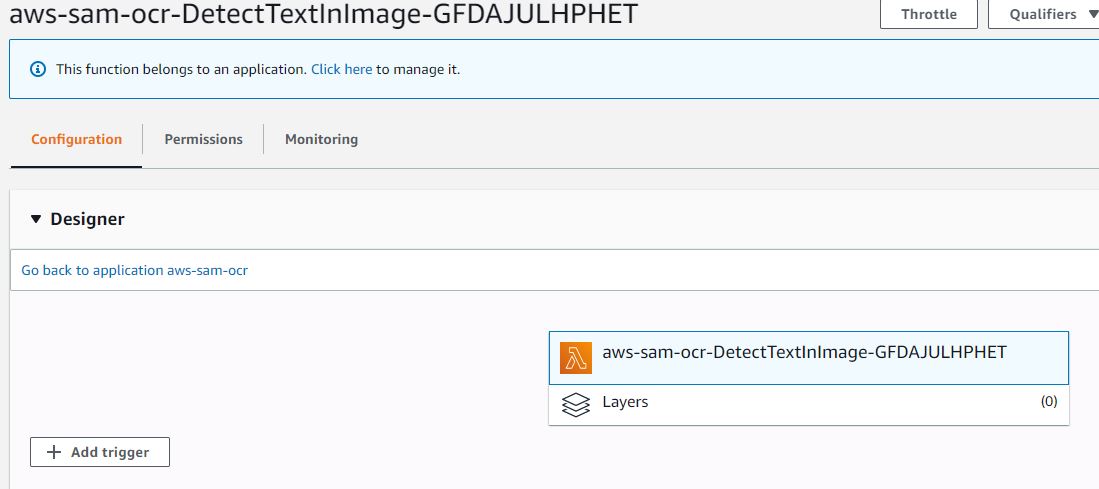
I want to know how can I let Lambda function to show S3 trigger in Designer?
### Additional Details
| main | process amazon events example not show trigger in lambda function describe your idea feature enhancement i tried after i run sam deploy template file packaged yaml stack name aws sam ocr capabilities capability iam i can upload a picture and found a record in dynamodb you can there event like this proposal but when open lambda function in designer i found there is no trigger from i want to know how can i let lambda function to show trigger in designer additional details | 1 |
788 | 4,389,635,622 | IssuesEvent | 2016-08-08 22:54:24 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | BUG: Amazon ec2 instance is always created, unless instance_id is set | aws bug_report cloud waiting_on_maintainer | ##### Issue Type:
- Bug Report
##### Component Name:
ec2 module
##### Ansible Version:
```
ansible 2.0.1.0
```
##### Ansible Configuration:
##### Environment:
Ubuntu 15.10 Wily Werewolf
##### Summary:
Using the AWS ec2 config "state: present", will always create a new instance, unless "instance_id" is set. Instances should ONLY be created when an instance cannot be found with identical settings.
##### Steps To Reproduce:
```
- name: Ensure EC2 Instance exists
ec2:
key_name: KeyPair
region: "{{aws_region}}"
image: "{{ami_id}}"
group_id: "{{security_group_id}}"
instance_type: "{{instance_type}}"
instance_tags: '{"Name":"InstanceName","DeploymentType":"Production","ServerType":"Infrastructure"}'
monitoring: yes
vpc_subnet_id: "{{ vpc_subnet_id }}"
wait: yes
state: present
```
##### Expected Results:
When I run this script twice, no new EC2 instance should be created.
##### Actual Results:
A new EC2 instance is created. | True | BUG: Amazon ec2 instance is always created, unless instance_id is set - ##### Issue Type:
- Bug Report
##### Component Name:
ec2 module
##### Ansible Version:
```
ansible 2.0.1.0
```
##### Ansible Configuration:
##### Environment:
Ubuntu 15.10 Wily Werewolf
##### Summary:
Using the AWS ec2 config "state: present", will always create a new instance, unless "instance_id" is set. Instances should ONLY be created when an instance cannot be found with identical settings.
##### Steps To Reproduce:
```
- name: Ensure EC2 Instance exists
ec2:
key_name: KeyPair
region: "{{aws_region}}"
image: "{{ami_id}}"
group_id: "{{security_group_id}}"
instance_type: "{{instance_type}}"
instance_tags: '{"Name":"InstanceName","DeploymentType":"Production","ServerType":"Infrastructure"}'
monitoring: yes
vpc_subnet_id: "{{ vpc_subnet_id }}"
wait: yes
state: present
```
##### Expected Results:
When I run this script twice, no new EC2 instance should be created.
##### Actual Results:
A new EC2 instance is created. | main | bug amazon instance is always created unless instance id is set issue type bug report component name module ansible version ansible ansible configuration environment ubuntu wily werewolf summary using the aws config state present will always create a new instance unless instance id is set instances should only be created when an instance cannot be found with identical settings steps to reproduce name ensure instance exists key name keypair region aws region image ami id group id security group id instance type instance type instance tags name instancename deploymenttype production servertype infrastructure monitoring yes vpc subnet id vpc subnet id wait yes state present expected results when i run this script twice no new instance should be created actual results a new instance is created | 1 |
57,889 | 14,239,349,916 | IssuesEvent | 2020-11-18 20:00:05 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | Can't run tests in Eclipse | :Delivery/Build >bug Team:Delivery needs:triage | In #64841 started validating the codebases existed in our security policy. This broke running tests in Eclipse because we include a special policy for IntelliJ if we're not running in gradle. Eclipse doesn't run in gradle and doesn't have the IntelliJ policy. | 1.0 | Can't run tests in Eclipse - In #64841 started validating the codebases existed in our security policy. This broke running tests in Eclipse because we include a special policy for IntelliJ if we're not running in gradle. Eclipse doesn't run in gradle and doesn't have the IntelliJ policy. | non_main | can t run tests in eclipse in started validating the codebases existed in our security policy this broke running tests in eclipse because we include a special policy for intellij if we re not running in gradle eclipse doesn t run in gradle and doesn t have the intellij policy | 0 |
152,483 | 23,981,310,901 | IssuesEvent | 2022-09-13 15:15:16 | EscolaDeSaudePublica/DesignLab | https://api.github.com/repos/EscolaDeSaudePublica/DesignLab | opened | Revisão e finalização de configurações de Analytics | Site Felicilab | Site Sem Projeto Definido Prioridade Design: Alta | ## **Objetivo**
**Como** designer
**Quero** revisar e configurar o analytics
**Para** refinar a implementação final do site do Felicilab
## **Contexto**
- O site do Felicilab está em seu processo final de desenvolvimento. Até o fim do defeso eleitoral, o seu novo design precisa estar no ar. Neste processo, após todas as revisões tenham sido concluídas no ambiente de homologação, e implementado no domínio sus.ce.gov.br/felicilab, o site precisará ser novamente revisto e ter o Analytics configurado.
## **Escopo**
| 1.0 | Revisão e finalização de configurações de Analytics | Site Felicilab - ## **Objetivo**
**Como** designer
**Quero** revisar e configurar o analytics
**Para** refinar a implementação final do site do Felicilab
## **Contexto**
- O site do Felicilab está em seu processo final de desenvolvimento. Até o fim do defeso eleitoral, o seu novo design precisa estar no ar. Neste processo, após todas as revisões tenham sido concluídas no ambiente de homologação, e implementado no domínio sus.ce.gov.br/felicilab, o site precisará ser novamente revisto e ter o Analytics configurado.
## **Escopo**
| non_main | revisão e finalização de configurações de analytics site felicilab objetivo como designer quero revisar e configurar o analytics para refinar a implementação final do site do felicilab contexto o site do felicilab está em seu processo final de desenvolvimento até o fim do defeso eleitoral o seu novo design precisa estar no ar neste processo após todas as revisões tenham sido concluídas no ambiente de homologação e implementado no domínio sus ce gov br felicilab o site precisará ser novamente revisto e ter o analytics configurado escopo | 0 |
5,144 | 26,224,782,524 | IssuesEvent | 2023-01-04 17:38:23 | backdrop-contrib/rules | https://api.github.com/repos/backdrop-contrib/rules | closed | rules_i18n.test.info specifies wrong test file | pr - maintainer review requested | The file `rules_i18n.tests.info` specifies the test file `rules_scheduler.test`.
This is incorrect; it should be `rules_i18n.test`.
This failed silently in the past, until https://github.com/backdrop/backdrop-issues/issues/5491 got merged, which now flags wrong file paths.
Unfortunately, with the correct file path, the tests run, but fail. Probably because https://github.com/backdrop-contrib/rules/issues/167 is still open. | True | rules_i18n.test.info specifies wrong test file - The file `rules_i18n.tests.info` specifies the test file `rules_scheduler.test`.
This is incorrect; it should be `rules_i18n.test`.
This failed silently in the past, until https://github.com/backdrop/backdrop-issues/issues/5491 got merged, which now flags wrong file paths.
Unfortunately, with the correct file path, the tests run, but fail. Probably because https://github.com/backdrop-contrib/rules/issues/167 is still open. | main | rules test info specifies wrong test file the file rules tests info specifies the test file rules scheduler test this is incorrect it should be rules test this failed silently in the past until got merged which now flags wrong file paths unfortunately with the correct file path the tests run but fail probably because is still open | 1 |
258,049 | 27,563,849,282 | IssuesEvent | 2023-03-08 01:10:52 | LynRodWS/alcor | https://api.github.com/repos/LynRodWS/alcor | opened | CVE-2019-12384 (Medium) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2019-12384 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /services/api_gateway/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-netflix-hystrix-2.1.2.RELEASE.jar (Root Library)
- hystrix-serialization-1.5.18.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.9.1 might allow attackers to have a variety of impacts by leveraging failure to block the logback-core class from polymorphic deserialization. Depending on the classpath content, remote code execution may be possible.
<p>Publish Date: 2019-06-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-12384>CVE-2019-12384</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12384">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12384</a></p>
<p>Release Date: 2019-06-24</p>
<p>Fix Resolution (com.fasterxml.jackson.core:jackson-databind): 2.9.9.1</p>
<p>Direct dependency fix Resolution (org.springframework.cloud:spring-cloud-starter-netflix-hystrix): 2.1.3.RELEASE</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2019-12384 (Medium) detected in jackson-databind-2.9.9.jar - ## CVE-2019-12384 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /services/api_gateway/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- spring-cloud-starter-netflix-hystrix-2.1.2.RELEASE.jar (Root Library)
- hystrix-serialization-1.5.18.jar
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.9.1 might allow attackers to have a variety of impacts by leveraging failure to block the logback-core class from polymorphic deserialization. Depending on the classpath content, remote code execution may be possible.
<p>Publish Date: 2019-06-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-12384>CVE-2019-12384</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12384">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12384</a></p>
<p>Release Date: 2019-06-24</p>
<p>Fix Resolution (com.fasterxml.jackson.core:jackson-databind): 2.9.9.1</p>
<p>Direct dependency fix Resolution (org.springframework.cloud:spring-cloud-starter-netflix-hystrix): 2.1.3.RELEASE</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_main | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file services api gateway pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring cloud starter netflix hystrix release jar root library hystrix serialization jar x jackson databind jar vulnerable library found in base branch master vulnerability details fasterxml jackson databind x before might allow attackers to have a variety of impacts by leveraging failure to block the logback core class from polymorphic deserialization depending on the classpath content remote code execution may be possible publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind direct dependency fix resolution org springframework cloud spring cloud starter netflix hystrix release check this box to open an automated fix pr | 0 |
73,633 | 8,908,325,984 | IssuesEvent | 2019-01-18 00:18:57 | influxdata/influxdb | https://api.github.com/repos/influxdata/influxdb | closed | Update Collectors Page | ui/needs-design | - Rename the menu item to Telegraf
- Page title should be "Telegraf Configurations"
- Add subtext to the page explaining what Telegraf is and where to get it. link to telegraf docs | 1.0 | Update Collectors Page - - Rename the menu item to Telegraf
- Page title should be "Telegraf Configurations"
- Add subtext to the page explaining what Telegraf is and where to get it. link to telegraf docs | non_main | update collectors page rename the menu item to telegraf page title should be telegraf configurations add subtext to the page explaining what telegraf is and where to get it link to telegraf docs | 0 |
15,484 | 5,968,636,955 | IssuesEvent | 2017-05-30 18:31:47 | jupyterlab/jupyterlab | https://api.github.com/repos/jupyterlab/jupyterlab | closed | Reduce memory usage in the build | tag:Build System type:Bug | As reported by @Analect on gitter: https://gist.github.com/Analect/2863bc621471e58d2079d0688a67ea71.
The key is the "process out of memory" error.
Options from looking at open WebPack issues relating to memory:
- Stop using the `ExtractTextPlugin` - we had already planned to do this to enable theming.
- Use `cheap-source-map`
- Set the memory limit for node `node --max_old_space_size=4096`
https://github.com/webpack/webpack/issues/1914
https://github.com/webpack/webpack/issues/2157
| 1.0 | Reduce memory usage in the build - As reported by @Analect on gitter: https://gist.github.com/Analect/2863bc621471e58d2079d0688a67ea71.
The key is the "process out of memory" error.
Options from looking at open WebPack issues relating to memory:
- Stop using the `ExtractTextPlugin` - we had already planned to do this to enable theming.
- Use `cheap-source-map`
- Set the memory limit for node `node --max_old_space_size=4096`
https://github.com/webpack/webpack/issues/1914
https://github.com/webpack/webpack/issues/2157
| non_main | reduce memory usage in the build as reported by analect on gitter the key is the process out of memory error options from looking at open webpack issues relating to memory stop using the extracttextplugin we had already planned to do this to enable theming use cheap source map set the memory limit for node node max old space size | 0 |
5,080 | 25,985,186,880 | IssuesEvent | 2022-12-19 23:04:50 | aws/aws-sam-cli-pipeline-init-templates | https://api.github.com/repos/aws/aws-sam-cli-pipeline-init-templates | closed | NameError: name 'ssm' is not defined | maintainer/need-response | The Inline Code for the Serverless Function ``` MonorepoTriggerFunction ``` defined in the AWS-CodePipeline/sam-monorepo-pipeline-template/{{cookiecutter.outputDir}}/codepipeline.yaml has missing boto3 client for Amazon Simple Systems Manager (SSM).
The lambda threw an error when it was invoked on updates pushed to the branch in the Codecommit Repository.
Error -
```
[ERROR] NameError: name 'ssm' is not defined
Traceback (most recent call last):
File "/opt/python/aws_lambda_powertools/logging/logger.py", line 354, in decorate
return lambda_handler(event, context, *args, **kwargs)
File "/var/task/index.py", line 22, in lambda_handler
update_last_commit(repository, commit_id, branch_name)
File "/var/task/index.py", line 47, in update_last_commit
ssm.put_parameter(Name=param_name_last_commit(repository, branch_name),
```
It can be assigned to me so I can create a PR for the fix. Thanks! | True | NameError: name 'ssm' is not defined - The Inline Code for the Serverless Function ``` MonorepoTriggerFunction ``` defined in the AWS-CodePipeline/sam-monorepo-pipeline-template/{{cookiecutter.outputDir}}/codepipeline.yaml has missing boto3 client for Amazon Simple Systems Manager (SSM).
The lambda threw an error when it was invoked on updates pushed to the branch in the Codecommit Repository.
Error -
```
[ERROR] NameError: name 'ssm' is not defined
Traceback (most recent call last):
File "/opt/python/aws_lambda_powertools/logging/logger.py", line 354, in decorate
return lambda_handler(event, context, *args, **kwargs)
File "/var/task/index.py", line 22, in lambda_handler
update_last_commit(repository, commit_id, branch_name)
File "/var/task/index.py", line 47, in update_last_commit
ssm.put_parameter(Name=param_name_last_commit(repository, branch_name),
```
It can be assigned to me so I can create a PR for the fix. Thanks! | main | nameerror name ssm is not defined the inline code for the serverless function monorepotriggerfunction defined in the aws codepipeline sam monorepo pipeline template cookiecutter outputdir codepipeline yaml has missing client for amazon simple systems manager ssm the lambda threw an error when it was invoked on updates pushed to the branch in the codecommit repository error nameerror name ssm is not defined traceback most recent call last file opt python aws lambda powertools logging logger py line in decorate return lambda handler event context args kwargs file var task index py line in lambda handler update last commit repository commit id branch name file var task index py line in update last commit ssm put parameter name param name last commit repository branch name it can be assigned to me so i can create a pr for the fix thanks | 1 |
4,874 | 25,020,479,264 | IssuesEvent | 2022-11-03 23:44:12 | aws/serverless-application-model | https://api.github.com/repos/aws/serverless-application-model | closed | Impossible to create AWS::Serverless::Api Auth property conditionally | type/bug area/resource/api area/intrinsics maintainer/need-followup | ### Description:
Impossible to assign `!Ref AWS::NoValue` to `AWS::Serverless::Api` `Auth` property.
### Steps to reproduce:
```yaml
ResourceName:
Type: AWS::Serverless::Api
Properties:
StageName: Prod
Auth: !Ref AWS::NoValue
```
or
```yaml
ResourceName:
Type: AWS::Serverless::Api
Properties:
StageName: Prod
Auth: !If [someCondition, !Ref AWS::NoValue, !Ref AWS::NoValue]
```
### Observed result:
AWS SAM fails to create changeset with `Invalid value for 'Auth' property` error.
### Expected result:
`!Ref AWS::NoValu` should remove `Auth` property altogether (at least if used with `!If`) according to:
https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/pseudo-parameter-reference.html
This is required to create `Auth` property conditionally, e.g. in non-Prod env only.
### Additional environment details (Ex: Windows, Mac, Amazon Linux etc)
1. MacOS
2. SAM CLI version 1.15.0
3. AWS region eu-west-1
| True | Impossible to create AWS::Serverless::Api Auth property conditionally - ### Description:
Impossible to assign `!Ref AWS::NoValue` to `AWS::Serverless::Api` `Auth` property.
### Steps to reproduce:
```yaml
ResourceName:
Type: AWS::Serverless::Api
Properties:
StageName: Prod
Auth: !Ref AWS::NoValue
```
or
```yaml
ResourceName:
Type: AWS::Serverless::Api
Properties:
StageName: Prod
Auth: !If [someCondition, !Ref AWS::NoValue, !Ref AWS::NoValue]
```
### Observed result:
AWS SAM fails to create changeset with `Invalid value for 'Auth' property` error.
### Expected result:
`!Ref AWS::NoValu` should remove `Auth` property altogether (at least if used with `!If`) according to:
https://docs.aws.amazon.com/AWSCloudFormation/latest/UserGuide/pseudo-parameter-reference.html
This is required to create `Auth` property conditionally, e.g. in non-Prod env only.
### Additional environment details (Ex: Windows, Mac, Amazon Linux etc)
1. MacOS
2. SAM CLI version 1.15.0
3. AWS region eu-west-1
| main | impossible to create aws serverless api auth property conditionally description impossible to assign ref aws novalue to aws serverless api auth property steps to reproduce yaml resourcename type aws serverless api properties stagename prod auth ref aws novalue or yaml resourcename type aws serverless api properties stagename prod auth if observed result aws sam fails to create changeset with invalid value for auth property error expected result ref aws novalu should remove auth property altogether at least if used with if according to this is required to create auth property conditionally e g in non prod env only additional environment details ex windows mac amazon linux etc macos sam cli version aws region eu west | 1 |
181,897 | 14,078,664,662 | IssuesEvent | 2020-11-04 13:53:08 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Test hang in derivatives of ConnectedStreamConformanceTests.ReadWrite_Success_Large | area-System.IO blocking-clean-ci test-run-core untriaged | Multiple variants of `ReadWrite_Success_Large` seem to hang for:
- System.IO.Pipes:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-48cab5614cff412b89/System.IO.Pipes.Tests/console.12bb341d.log?sv=2019-07-07&se=2020-11-24T10%3A28%3A57Z&sr=c&sp=rl&sig=G%2Fo9RFSCGrqX1QrTQjJ5w64H8JalPjohEl4SFcsUfbk%3D
- System.Net.Security:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-48cab5614cff412b89/System.Net.Security.Tests/console.f64a4d19.log?sv=2019-07-07&se=2020-11-24T10%3A28%3A57Z&sr=c&sp=rl&sig=G%2Fo9RFSCGrqX1QrTQjJ5w64H8JalPjohEl4SFcsUfbk%3D
- `NetworkStream`:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-705cd6d200ad41959c/System.Net.Sockets.Tests/console.e0769fa2.log?sv=2019-07-07&se=2020-11-23T18%3A40%3A33Z&sr=c&sp=rl&sig=SsVgIB%2BAl%2FU7inuCHZ2Vg%2BdFUiIuc3CCshSHcPBmfOw%3D
- System.IO.Compression:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-03a19939df064ce390/System.IO.Compression.Brotli.Tests/console.7851c28b.log?sv=2019-07-07&se=2020-11-24T10%3A29%3A00Z&sr=c&sp=rl&sig=L4fSJGOfBHi7WXpVeQfiOlf5k49k4JDOkUwaEfnS3DI%3D
Hits in #44202:
- https://dev.azure.com/dnceng/public/_build/results?buildId=874418&view=ms.vss-test-web.build-test-results-tab
- https://dev.azure.com/dnceng/public/_build/results?buildId=875289&view=ms.vss-test-web.build-test-results-tab
/cc @stephentoub (might be related to #44069?) | 1.0 | Test hang in derivatives of ConnectedStreamConformanceTests.ReadWrite_Success_Large - Multiple variants of `ReadWrite_Success_Large` seem to hang for:
- System.IO.Pipes:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-48cab5614cff412b89/System.IO.Pipes.Tests/console.12bb341d.log?sv=2019-07-07&se=2020-11-24T10%3A28%3A57Z&sr=c&sp=rl&sig=G%2Fo9RFSCGrqX1QrTQjJ5w64H8JalPjohEl4SFcsUfbk%3D
- System.Net.Security:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-48cab5614cff412b89/System.Net.Security.Tests/console.f64a4d19.log?sv=2019-07-07&se=2020-11-24T10%3A28%3A57Z&sr=c&sp=rl&sig=G%2Fo9RFSCGrqX1QrTQjJ5w64H8JalPjohEl4SFcsUfbk%3D
- `NetworkStream`:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-705cd6d200ad41959c/System.Net.Sockets.Tests/console.e0769fa2.log?sv=2019-07-07&se=2020-11-23T18%3A40%3A33Z&sr=c&sp=rl&sig=SsVgIB%2BAl%2FU7inuCHZ2Vg%2BdFUiIuc3CCshSHcPBmfOw%3D
- System.IO.Compression:
https://helixre8s23ayyeko0k025g8.blob.core.windows.net/dotnet-runtime-refs-pull-44202-merge-03a19939df064ce390/System.IO.Compression.Brotli.Tests/console.7851c28b.log?sv=2019-07-07&se=2020-11-24T10%3A29%3A00Z&sr=c&sp=rl&sig=L4fSJGOfBHi7WXpVeQfiOlf5k49k4JDOkUwaEfnS3DI%3D
Hits in #44202:
- https://dev.azure.com/dnceng/public/_build/results?buildId=874418&view=ms.vss-test-web.build-test-results-tab
- https://dev.azure.com/dnceng/public/_build/results?buildId=875289&view=ms.vss-test-web.build-test-results-tab
/cc @stephentoub (might be related to #44069?) | non_main | test hang in derivatives of connectedstreamconformancetests readwrite success large multiple variants of readwrite success large seem to hang for system io pipes system net security networkstream system io compression hits in cc stephentoub might be related to | 0 |
2,102 | 7,110,441,988 | IssuesEvent | 2018-01-17 10:38:20 | ocaml/opam-repository | https://api.github.com/repos/ocaml/opam-repository | closed | camlp4 fails to install with +32bit compilers (mac os) | bug needs maintainer action | Tried with both `4.02.3+32bit` and `4.03.0+32bit`.
```
=-=- Installing packages =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= 🐫
Building camlp4.4.03+1:
./configure --bindir=/Users/lostman/.opam/4.03.0+32bit/bin --libdir=/Users/lostman/.opam/4.03.0+32bit/lib/ocaml --pkgdir=/Users/lostman/.opam/4.03.0+32bit/lib
make all
make install install-META
[ERROR] The compilation of camlp4.4.03+1 failed.
Removing camlp4.4.03+1.
rm -rf /Users/lostman/.opam/4.03.0+32bit/lib/camlp4
rm -f /Users/lostman/.opam/4.03.0+32bit/bin/camlp4 /Users/lostman/.opam/4.03.0+32bit/bin/camlp4boot /Users/lostman/.opam/4.03.0+32bit/bin/mkcamlp4 /Users/lostman/.opam/4.03.0+32bit/bin/camlp4r /Users/lostman/.opam/4.03.0+32bit/bin/camlp4rf /Users/lostman/.opam/4.03.0+32bit/bin/camlp4orf /Users/lostman/.opam/4.03.0+32bit/bin/camlp4o /Users/lostman/.opam/4.03.0+32bit/bin/camlp4of /Users/lostman/.opam/4.03.0+32bit/bin/camlp4oof /Users/lostman/.opam/4.03.0+32bit/bin/camlp4prof /Users/lostman/.opam/4.03.0+32bit/bin/camlp4rf.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4orf.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4o.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4oof.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4r.opt
#=== ERROR while installing camlp4.4.03+1 =====================================#
# opam-version 1.2.0
# os darwin
# command make all
# path /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1
# compiler 4.03.0+32bit
# exit-code 2
# env-file /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1/camlp4-5250-6d07ae.env
# stdout-file /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1/camlp4-5250-6d07ae.out
# stderr-file /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1/camlp4-5250-6d07ae.err
### stdout ###
# ...[truncated]
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlc.opt -c -g -w Z -I camlp4/import -I camlp4/config -I camlp4 -o camlp4/config/Camlp4_import.cmo camlp4/config/Camlp4_import.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w Z -I camlp4/import -I camlp4/config -I camlp4 -o camlp4/config/Camlp4_import.cmx camlp4/config/Camlp4_import.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w Z -I camlp4/import -I camlp4/config -I camlp4 -o camlp4/config/Camlp4_config.cmx camlp4/config/Camlp4_config.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w a -I camlp4/import -I camlp4/config -I camlp4/boot -o camlp4/boot/Camlp4.cmx camlp4/boot/Camlp4.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w a -I camlp4/import -I camlp4/config -I camlp4/boot -o camlp4/boot/camlp4boot.cmx camlp4/boot/camlp4boot.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt dynlink.cmxa -g camlp4/config/Camlp4_import.cmx camlp4/config/Camlp4_config.cmx camlp4/boot/Camlp4.cmx camlp4/boot/camlp4boot.cmx -o camlp4/boot/camlp4boot.native
# + /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt dynlink.cmxa -g camlp4/config/Camlp4_import.cmx camlp4/config/Camlp4_config.cmx camlp4/boot/Camlp4.cmx camlp4/boot/camlp4boot.cmx -o camlp4/boot/camlp4boot.native
# File "_none_", line 1:
# Error: Cannot find file dynlink.cmxa
# Command exited with code 2.
### stderr ###
# + echo camlp4/Camlp4.cmo camlp4/Camlp4Top.cmo camlp4/camlp4prof.byte camlp4/mkcamlp4.byte camlp4/camlp4.byte camlp4/camlp4fulllib.cma camlp4/camlp4boot.byte camlp4/camlp4boot.cma camlp4/camlp4r.byte camlp4/camlp4r.cma camlp4/camlp4rf.byte camlp4/camlp4rf.cma camlp4/camlp4o.byte camlp4/camlp4o.cma camlp4/camlp4of.byte camlp4/camlp4of.cma camlp4/camlp4oof.byte camlp4/camlp4oof.cma camlp4/camlp4orf.b...[truncated]
# make: *** [byte] Error 10
```
| True | camlp4 fails to install with +32bit compilers (mac os) - Tried with both `4.02.3+32bit` and `4.03.0+32bit`.
```
=-=- Installing packages =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= 🐫
Building camlp4.4.03+1:
./configure --bindir=/Users/lostman/.opam/4.03.0+32bit/bin --libdir=/Users/lostman/.opam/4.03.0+32bit/lib/ocaml --pkgdir=/Users/lostman/.opam/4.03.0+32bit/lib
make all
make install install-META
[ERROR] The compilation of camlp4.4.03+1 failed.
Removing camlp4.4.03+1.
rm -rf /Users/lostman/.opam/4.03.0+32bit/lib/camlp4
rm -f /Users/lostman/.opam/4.03.0+32bit/bin/camlp4 /Users/lostman/.opam/4.03.0+32bit/bin/camlp4boot /Users/lostman/.opam/4.03.0+32bit/bin/mkcamlp4 /Users/lostman/.opam/4.03.0+32bit/bin/camlp4r /Users/lostman/.opam/4.03.0+32bit/bin/camlp4rf /Users/lostman/.opam/4.03.0+32bit/bin/camlp4orf /Users/lostman/.opam/4.03.0+32bit/bin/camlp4o /Users/lostman/.opam/4.03.0+32bit/bin/camlp4of /Users/lostman/.opam/4.03.0+32bit/bin/camlp4oof /Users/lostman/.opam/4.03.0+32bit/bin/camlp4prof /Users/lostman/.opam/4.03.0+32bit/bin/camlp4rf.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4orf.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4o.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4oof.opt /Users/lostman/.opam/4.03.0+32bit/bin/camlp4r.opt
#=== ERROR while installing camlp4.4.03+1 =====================================#
# opam-version 1.2.0
# os darwin
# command make all
# path /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1
# compiler 4.03.0+32bit
# exit-code 2
# env-file /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1/camlp4-5250-6d07ae.env
# stdout-file /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1/camlp4-5250-6d07ae.out
# stderr-file /Users/lostman/.opam/4.03.0+32bit/build/camlp4.4.03+1/camlp4-5250-6d07ae.err
### stdout ###
# ...[truncated]
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlc.opt -c -g -w Z -I camlp4/import -I camlp4/config -I camlp4 -o camlp4/config/Camlp4_import.cmo camlp4/config/Camlp4_import.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w Z -I camlp4/import -I camlp4/config -I camlp4 -o camlp4/config/Camlp4_import.cmx camlp4/config/Camlp4_import.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w Z -I camlp4/import -I camlp4/config -I camlp4 -o camlp4/config/Camlp4_config.cmx camlp4/config/Camlp4_config.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w a -I camlp4/import -I camlp4/config -I camlp4/boot -o camlp4/boot/Camlp4.cmx camlp4/boot/Camlp4.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt -c -g -w a -I camlp4/import -I camlp4/config -I camlp4/boot -o camlp4/boot/camlp4boot.cmx camlp4/boot/camlp4boot.ml
# /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt dynlink.cmxa -g camlp4/config/Camlp4_import.cmx camlp4/config/Camlp4_config.cmx camlp4/boot/Camlp4.cmx camlp4/boot/camlp4boot.cmx -o camlp4/boot/camlp4boot.native
# + /Users/lostman/.opam/4.03.0+32bit/bin/ocamlopt.opt dynlink.cmxa -g camlp4/config/Camlp4_import.cmx camlp4/config/Camlp4_config.cmx camlp4/boot/Camlp4.cmx camlp4/boot/camlp4boot.cmx -o camlp4/boot/camlp4boot.native
# File "_none_", line 1:
# Error: Cannot find file dynlink.cmxa
# Command exited with code 2.
### stderr ###
# + echo camlp4/Camlp4.cmo camlp4/Camlp4Top.cmo camlp4/camlp4prof.byte camlp4/mkcamlp4.byte camlp4/camlp4.byte camlp4/camlp4fulllib.cma camlp4/camlp4boot.byte camlp4/camlp4boot.cma camlp4/camlp4r.byte camlp4/camlp4r.cma camlp4/camlp4rf.byte camlp4/camlp4rf.cma camlp4/camlp4o.byte camlp4/camlp4o.cma camlp4/camlp4of.byte camlp4/camlp4of.cma camlp4/camlp4oof.byte camlp4/camlp4oof.cma camlp4/camlp4orf.b...[truncated]
# make: *** [byte] Error 10
```
| main | fails to install with compilers mac os tried with both and installing packages 🐫 building configure bindir users lostman opam bin libdir users lostman opam lib ocaml pkgdir users lostman opam lib make all make install install meta the compilation of failed removing rm rf users lostman opam lib rm f users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin users lostman opam bin opt users lostman opam bin opt users lostman opam bin opt users lostman opam bin opt users lostman opam bin opt error while installing opam version os darwin command make all path users lostman opam build compiler exit code env file users lostman opam build env stdout file users lostman opam build out stderr file users lostman opam build err stdout users lostman opam bin ocamlc opt c g w z i import i config i o config import cmo config import ml users lostman opam bin ocamlopt opt c g w z i import i config i o config import cmx config import ml users lostman opam bin ocamlopt opt c g w z i import i config i o config config cmx config config ml users lostman opam bin ocamlopt opt c g w a i import i config i boot o boot cmx boot ml users lostman opam bin ocamlopt opt c g w a i import i config i boot o boot cmx boot ml users lostman opam bin ocamlopt opt dynlink cmxa g config import cmx config config cmx boot cmx boot cmx o boot native users lostman opam bin ocamlopt opt dynlink cmxa g config import cmx config config cmx boot cmx boot cmx o boot native file none line error cannot find file dynlink cmxa command exited with code stderr echo cmo cmo byte byte byte cma byte cma byte cma byte cma byte cma byte cma byte cma b make error | 1 |
1,879 | 6,577,510,302 | IssuesEvent | 2017-09-12 01:25:05 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | ec2 module does not warn about invalid dictionary entries for volumes | affects_2.0 aws bug_report cloud waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ec2 module
##### ANSIBLE VERSION
```
2.0.1.0
```
##### CONFIGURATION
NA
##### OS / ENVIRONMENT
Ubuntu / Ubuntu
##### SUMMARY
When passing invalid or unused values to the ec2 module's volumes node, they are just ignored and no warning is produced.
##### STEPS TO REPRODUCE
Run the example task. The volumes[0][tags] attribute is not used (that feature doesn't seem to exist) but no warning is emitted.
```
- name: Create ec2 instance
local_action:
module: ec2
profile: example_profile
key_name: "{{ ec2_keypair }}"
image: "{{ ec2_ami }}"
instance_type: "{{ ec2_instance_type }}"
group: "{{ search_security_group_name }}"
region: "{{ aws_region }}"
volumes:
- device_name: /dev/sda1
delete_on_termination: true
volume_size: 60
device_type: gp2
tags:
tagName: tagValue
wait: yes
```
##### EXPECTED RESULTS
An error or warning, e.g. "ec2 volumes do not support "tags""
##### ACTUAL RESULTS
tags is simply ignored
| True | ec2 module does not warn about invalid dictionary entries for volumes - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
ec2 module
##### ANSIBLE VERSION
```
2.0.1.0
```
##### CONFIGURATION
NA
##### OS / ENVIRONMENT
Ubuntu / Ubuntu
##### SUMMARY
When passing invalid or unused values to the ec2 module's volumes node, they are just ignored and no warning is produced.
##### STEPS TO REPRODUCE
Run the example task. The volumes[0][tags] attribute is not used (that feature doesn't seem to exist) but no warning is emitted.
```
- name: Create ec2 instance
local_action:
module: ec2
profile: example_profile
key_name: "{{ ec2_keypair }}"
image: "{{ ec2_ami }}"
instance_type: "{{ ec2_instance_type }}"
group: "{{ search_security_group_name }}"
region: "{{ aws_region }}"
volumes:
- device_name: /dev/sda1
delete_on_termination: true
volume_size: 60
device_type: gp2
tags:
tagName: tagValue
wait: yes
```
##### EXPECTED RESULTS
An error or warning, e.g. "ec2 volumes do not support "tags""
##### ACTUAL RESULTS
tags is simply ignored
| main | module does not warn about invalid dictionary entries for volumes issue type bug report component name module ansible version configuration na os environment ubuntu ubuntu summary when passing invalid or unused values to the module s volumes node they are just ignored and no warning is produced steps to reproduce run the example task the volumes attribute is not used that feature doesn t seem to exist but no warning is emitted name create instance local action module profile example profile key name keypair image ami instance type instance type group search security group name region aws region volumes device name dev delete on termination true volume size device type tags tagname tagvalue wait yes expected results an error or warning e g volumes do not support tags actual results tags is simply ignored | 1 |
207,588 | 23,459,555,450 | IssuesEvent | 2022-08-16 11:59:37 | Gal-Doron/Baragon-test-10 | https://api.github.com/repos/Gal-Doron/Baragon-test-10 | opened | jackson-databind-2.9.9.jar: 50 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-14540](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2019-17531](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-16335](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-17267](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-16942](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2020-8840](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.3 | ✅ |
| [CVE-2019-16943](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-14893](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-14892](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2020-9546](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-14379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-9547](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-9548](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-20330](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2020-10968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10969](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11111](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11113](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11112](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10672](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10673](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11619](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-35728](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36189](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36188](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-11620](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10650](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10650) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-36181](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36180](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36183](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35490](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35490) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36182](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35491](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36187](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36186](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2021-20190](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2020-36179](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-24616](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14060](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14061](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14062](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-24750](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14195](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-25649](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2019-14439](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-36518](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.12.6.1 | ✅ |
| [CVE-2019-12814](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
| [CVE-2019-12384](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
## Details
> Partial details (19 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: 2.9.10.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-09-04</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20330</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10968</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968>CVE-2020-10968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10968">https://nvd.nist.gov/vuln/detail/CVE-2020-10968</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10969</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane.
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969>CVE-2020-10969</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11111</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.activemq.* (aka activemq-jms, activemq-core, activemq-pool, and activemq-pool-jms).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111>CVE-2020-11111</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11113</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.openjpa.ee.WASRegistryManagedRuntime (aka openjpa).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113>CVE-2020-11113</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11112</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | jackson-databind-2.9.9.jar: 50 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-14540](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2019-17531](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-16335](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-17267](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-16942](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2020-8840](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.3 | ✅ |
| [CVE-2019-16943](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.1 | ✅ |
| [CVE-2019-14893](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2019-14892](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10 | ✅ |
| [CVE-2020-9546](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-14379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-9547](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-9548](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2019-20330](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.2 | ✅ |
| [CVE-2020-10968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10969](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11111](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11113](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11112](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10672](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10672) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10673](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10673) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-11619](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11619) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-35728](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35728) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36189](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36189) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36188](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36188) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-11620](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11620) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-10650](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10650) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.4 | ✅ |
| [CVE-2020-36181](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36181) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36180](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36183](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36183) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35490](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35490) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36182](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36182) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36185) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-35491](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35491) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-36184](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36184) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36187](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36187) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-36186](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36186) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2021-20190](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2020-36179](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36179) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.8 | ✅ |
| [CVE-2020-24616](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24616) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14060](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14061](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14061) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14062](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14062) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-24750](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-14195](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | jackson-databind-2.9.9.jar | Direct | 2.9.10.5 | ✅ |
| [CVE-2020-25649](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25649) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.10.7 | ✅ |
| [CVE-2019-14439](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.9.9.2 | ✅ |
| [CVE-2020-36518](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36518) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | jackson-databind-2.9.9.jar | Direct | 2.12.6.1 | ✅ |
| [CVE-2019-12814](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12814) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
| [CVE-2019-12384](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12384) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | jackson-databind-2.9.9.jar | Direct | 2.9.9.1 | ✅ |
## Details
> Partial details (19 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the Mend Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14540</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14540>CVE-2019-14540</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540</a></p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17531</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17531>CVE-2019-17531</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531</a></p>
<p>Release Date: 2019-10-12</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16335</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
<p>Publish Date: 2019-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16335>CVE-2019-16335</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-09-15</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-17267</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
<p>Publish Date: 2019-10-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-17267>CVE-2019-17267</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-10-07</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16942</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16942>CVE-2019-16942</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-8840</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
<p>Publish Date: 2020-02-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8840>CVE-2020-8840</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-02-10</p>
<p>Fix Resolution: 2.9.10.3</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16943</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the p6spy (3.8.6) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of com.p6spy.engine.spy.P6DataSource mishandling.
<p>Publish Date: 2019-10-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16943>CVE-2019-16943</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16943</a></p>
<p>Release Date: 2019-10-01</p>
<p>Fix Resolution: 2.9.10.1</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14893</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in FasterXML jackson-databind in all versions before 2.9.10 and 2.10.0, where it would permit polymorphic deserialization of malicious objects using the xalan JNDI gadget when used in conjunction with polymorphic type handling methods such as `enableDefaultTyping()` or when @JsonTypeInfo is using `Id.CLASS` or `Id.MINIMAL_CLASS` or in any other way which ObjectMapper.readValue might instantiate objects from unsafe sources. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14893>CVE-2019-14893</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14893</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14892</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A flaw was discovered in jackson-databind in versions before 2.9.10, 2.8.11.5 and 2.6.7.3, where it would permit polymorphic deserialization of a malicious object using commons-configuration 1 and 2 JNDI classes. An attacker could use this flaw to execute arbitrary code.
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14892>CVE-2019-14892</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-09-04</p>
<p>Fix Resolution: 2.9.10</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9546</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.hadoop.shaded.com.zaxxer.hikari.HikariConfig (aka shaded hikari-config).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9546>CVE-2020-9546</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9546</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-14379</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
SubTypeValidator.java in FasterXML jackson-databind before 2.9.9.2 mishandles default typing when ehcache is used (because of net.sf.ehcache.transaction.manager.DefaultTransactionManagerLookup), leading to remote code execution.
<p>Publish Date: 2019-07-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14379>CVE-2019-14379</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14379</a></p>
<p>Release Date: 2019-07-29</p>
<p>Fix Resolution: 2.9.9.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9547</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig (aka ibatis-sqlmap).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9547>CVE-2020-9547</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9547</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-9548</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to br.com.anteros.dbcp.AnterosDBCPConfig (aka anteros-core).
<p>Publish Date: 2020-03-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-9548>CVE-2020-9548</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-9548</a></p>
<p>Release Date: 2020-03-02</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-20330</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.2 lacks certain net.sf.ehcache blocking.
<p>Publish Date: 2020-01-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20330>CVE-2019-20330</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: 2.9.10.2</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10968</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.aoju.bus.proxy.provider.remoting.RmiProvider (aka bus-proxy).
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10968>CVE-2020-10968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-10968">https://nvd.nist.gov/vuln/detail/CVE-2020-10968</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-10969</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to javax.swing.JEditorPane.
<p>Publish Date: 2020-03-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-10969>CVE-2020-10969</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-10969</a></p>
<p>Release Date: 2020-03-26</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11111</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.activemq.* (aka activemq-jms, activemq-core, activemq-pool, and activemq-pool-jms).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11111>CVE-2020-11111</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11113</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.openjpa.ee.WASRegistryManagedRuntime (aka openjpa).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11113>CVE-2020-11113</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11113</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-11112</summary>
### Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /BaragonClient/pom.xml</p>
<p>Path to vulnerable library: /itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar,/itory/com/fasterxml/jackson/core/jackson-databind/2.9.9/jackson-databind-2.9.9.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Gal-Doron/Baragon-test-10/commit/ad783b5f93a5095e0f7b4e1975fad0a54bdc7287">ad783b5f93a5095e0f7b4e1975fad0a54bdc7287</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.proxy.provider.remoting.RmiProvider (aka apache/commons-proxy).
<p>Publish Date: 2020-03-31
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11112>CVE-2020-11112</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11112</a></p>
<p>Release Date: 2020-03-31</p>
<p>Fix Resolution: 2.9.10.4</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_main | jackson databind jar vulnerabilities highest severity is vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct high jackson databind jar direct medium jackson databind jar direct medium jackson databind jar direct details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the mend application cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikariconfig publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the apache extra version x jar in the classpath and an attacker can provide a jndi service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to com zaxxer hikari hikaridatasource this is a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind before it is related to net sf ehcache hibernate ehcachejtatransactionmanagerlookup publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the commons dbcp jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of org apache commons dbcp datasources sharedpooldatasource and org apache commons dbcp datasources peruserpooldatasource mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind through lacks certain xbean reflect jndi blocking as demonstrated by org apache xbean propertyeditor jndiconverter publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind through when default typing is enabled either globally or for a specific property for an externally exposed json endpoint and the service has the jar in the classpath and an attacker can find an rmi service endpoint to access it is possible to make the service execute a malicious payload this issue exists because of com engine spy mishandling publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was discovered in fasterxml jackson databind in all versions before and where it would permit polymorphic deserialization of malicious objects using the xalan jndi gadget when used in conjunction with polymorphic type handling methods such as enabledefaulttyping or when jsontypeinfo is using id class or id minimal class or in any other way which objectmapper readvalue might instantiate objects from unsafe sources an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details a flaw was discovered in jackson databind in versions before and where it would permit polymorphic deserialization of a malicious object using commons configuration and jndi classes an attacker could use this flaw to execute arbitrary code publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache hadoop shaded com zaxxer hikari hikariconfig aka shaded hikari config publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details subtypevalidator java in fasterxml jackson databind before mishandles default typing when ehcache is used because of net sf ehcache transaction manager defaulttransactionmanagerlookup leading to remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com ibatis sqlmap engine transaction jta jtatransactionconfig aka ibatis sqlmap publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to br com anteros dbcp anterosdbcpconfig aka anteros core publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before lacks certain net sf ehcache blocking publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org aoju bus proxy provider remoting rmiprovider aka bus proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to javax swing jeditorpane publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache activemq aka activemq jms activemq core activemq pool and activemq pool jms publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache openjpa ee wasregistrymanagedruntime aka openjpa publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file baragonclient pom xml path to vulnerable library itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar itory com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons proxy provider remoting rmiprovider aka apache commons proxy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
385,800 | 11,425,873,108 | IssuesEvent | 2020-02-03 20:43:51 | kubeflow/pipelines | https://api.github.com/repos/kubeflow/pipelines | closed | Add ability to rename resources | area/api kind/feature priority/p2 | It would be nice to be able to rename pipelines, experiments, and run names. | 1.0 | Add ability to rename resources - It would be nice to be able to rename pipelines, experiments, and run names. | non_main | add ability to rename resources it would be nice to be able to rename pipelines experiments and run names | 0 |
3,807 | 16,489,310,883 | IssuesEvent | 2021-05-24 23:47:17 | ipfs/aegir | https://api.github.com/repos/ipfs/aegir | opened | Standardize automatic NPM publishing | P1 effort/weeks kind/maintenance need/analysis need/maintainer-input | This is a placeholder issue for figuring out interplanetary conventions for automatic publishing to NPM.
## Current state
- We have competing conventions and publishing flows across JS libs (IPFS/libp2p/ipld/multiformates):
- JS IPFS libs usually require maintainer to do manual publishing via `aegir release`
- Various IPLD repos use [mikeal/merge-release](https://github.com/mikeal/merge-release) + Github Action to publish to NPM on every merge to the main branch (major, minor or patch sem. version is picked based on commit messages)
## Unifying publishing across JS repos
Details TBD, but during triage discussion we hinted at upstreaming some convention, perhaps to aegir/CI template, just like we did for tests and other checks in https://github.com/ipfs/aegir/blob/master/md/github-actions.md
### Prior Art
- [mikeal/merge-release](https://github.com/mikeal/merge-release) avoid commits on purpose
- merge-release had some problems recently dealing with >1 commits in a merge and figuring out the right semver bump (a major ended up as a patch and required a scramble to fix – annoying, but fixable)
- [release-please](https://github.com/googleapis/release-please) makes a PR so the maintainer is the one making the commits.
- This hybrid approach gives maintainer a bit of control (to batch changes together or to release every commit), and makes it possible to eyeball what the next release will be, before it's released.
- Seems to be blocked on support for npm workspaces/monorepos like js-ipfs one
- Release-please also has an extra tool that allows 2FA to be on and avoid automation tokens. But you need to configure it and deploy it to Google engine thing and that will do the 2FA for you.
- @hugomrdias did a PoC in [hugomrdias/playwright-test ](https://github.com/hugomrdias/playwright-test) where a PR is created from any outstanding changes and publish to NPM occurs when the aggregator PR is merged. | True | Standardize automatic NPM publishing - This is a placeholder issue for figuring out interplanetary conventions for automatic publishing to NPM.
## Current state
- We have competing conventions and publishing flows across JS libs (IPFS/libp2p/ipld/multiformates):
- JS IPFS libs usually require maintainer to do manual publishing via `aegir release`
- Various IPLD repos use [mikeal/merge-release](https://github.com/mikeal/merge-release) + Github Action to publish to NPM on every merge to the main branch (major, minor or patch sem. version is picked based on commit messages)
## Unifying publishing across JS repos
Details TBD, but during triage discussion we hinted at upstreaming some convention, perhaps to aegir/CI template, just like we did for tests and other checks in https://github.com/ipfs/aegir/blob/master/md/github-actions.md
### Prior Art
- [mikeal/merge-release](https://github.com/mikeal/merge-release) avoid commits on purpose
- merge-release had some problems recently dealing with >1 commits in a merge and figuring out the right semver bump (a major ended up as a patch and required a scramble to fix – annoying, but fixable)
- [release-please](https://github.com/googleapis/release-please) makes a PR so the maintainer is the one making the commits.
- This hybrid approach gives maintainer a bit of control (to batch changes together or to release every commit), and makes it possible to eyeball what the next release will be, before it's released.
- Seems to be blocked on support for npm workspaces/monorepos like js-ipfs one
- Release-please also has an extra tool that allows 2FA to be on and avoid automation tokens. But you need to configure it and deploy it to Google engine thing and that will do the 2FA for you.
- @hugomrdias did a PoC in [hugomrdias/playwright-test ](https://github.com/hugomrdias/playwright-test) where a PR is created from any outstanding changes and publish to NPM occurs when the aggregator PR is merged. | main | standardize automatic npm publishing this is a placeholder issue for figuring out interplanetary conventions for automatic publishing to npm current state we have competing conventions and publishing flows across js libs ipfs ipld multiformates js ipfs libs usually require maintainer to do manual publishing via aegir release various ipld repos use github action to publish to npm on every merge to the main branch major minor or patch sem version is picked based on commit messages unifying publishing across js repos details tbd but during triage discussion we hinted at upstreaming some convention perhaps to aegir ci template just like we did for tests and other checks in prior art avoid commits on purpose merge release had some problems recently dealing with commits in a merge and figuring out the right semver bump a major ended up as a patch and required a scramble to fix – annoying but fixable makes a pr so the maintainer is the one making the commits this hybrid approach gives maintainer a bit of control to batch changes together or to release every commit and makes it possible to eyeball what the next release will be before it s released seems to be blocked on support for npm workspaces monorepos like js ipfs one release please also has an extra tool that allows to be on and avoid automation tokens but you need to configure it and deploy it to google engine thing and that will do the for you hugomrdias did a poc in where a pr is created from any outstanding changes and publish to npm occurs when the aggregator pr is merged | 1 |
1,989 | 6,694,278,686 | IssuesEvent | 2017-10-10 00:50:22 | duckduckgo/zeroclickinfo-spice | https://api.github.com/repos/duckduckgo/zeroclickinfo-spice | closed | Videos: Youtube channel page link not working with newer channel link formats | Maintainer Input Requested | after searching for an video the link to the uploaders youtube channel does not work with newer /channel/XXXXX channels it goes to the /user/XXXXX page which often does not exist
how to reproduce the problem:
search something (example search: "duckduckgo")
click the "video's" tab
select a result (for example the first one)
click on the channel name (in the example its "Tekzilla")
you will be redirected to youtube.com/user/Tekzilla and it will give an error the real page for the uploader is using the new youtube channel page link format: https://www.youtube.com/channel/UCMkhrrPkmx7xxlolSP9qEsA
---
IA Page: http://duck.co/ia/view/videos
[Maintainer](http://docs.duckduckhack.com/maintaining/guidelines.html): @bsstoner
| True | Videos: Youtube channel page link not working with newer channel link formats - after searching for an video the link to the uploaders youtube channel does not work with newer /channel/XXXXX channels it goes to the /user/XXXXX page which often does not exist
how to reproduce the problem:
search something (example search: "duckduckgo")
click the "video's" tab
select a result (for example the first one)
click on the channel name (in the example its "Tekzilla")
you will be redirected to youtube.com/user/Tekzilla and it will give an error the real page for the uploader is using the new youtube channel page link format: https://www.youtube.com/channel/UCMkhrrPkmx7xxlolSP9qEsA
---
IA Page: http://duck.co/ia/view/videos
[Maintainer](http://docs.duckduckhack.com/maintaining/guidelines.html): @bsstoner
| main | videos youtube channel page link not working with newer channel link formats after searching for an video the link to the uploaders youtube channel does not work with newer channel xxxxx channels it goes to the user xxxxx page which often does not exist how to reproduce the problem search something example search duckduckgo click the video s tab select a result for example the first one click on the channel name in the example its tekzilla you will be redirected to youtube com user tekzilla and it will give an error the real page for the uploader is using the new youtube channel page link format ia page bsstoner | 1 |
9,576 | 8,672,849,895 | IssuesEvent | 2018-11-29 23:37:38 | Azure/azure-cli | https://api.github.com/repos/Azure/azure-cli | closed | [KeyVault] KeyVault Mgmt 2016-10-01 | Feature KeyVault Service Attention | Update KeyVault mgmt SDK and support for the following:
- [x] Deleted vault operations (show, list, purge)
- [x] Add support for 'soft delete', 'create mode' and 'storage permissions
- [ ] Add support for Managed Storage Account Keys
See:
https://github.com/Azure/azure-sdk-for-python/pull/1186
https://github.com/Azure/azure-sdk-for-python/pull/1182 | 1.0 | [KeyVault] KeyVault Mgmt 2016-10-01 - Update KeyVault mgmt SDK and support for the following:
- [x] Deleted vault operations (show, list, purge)
- [x] Add support for 'soft delete', 'create mode' and 'storage permissions
- [ ] Add support for Managed Storage Account Keys
See:
https://github.com/Azure/azure-sdk-for-python/pull/1186
https://github.com/Azure/azure-sdk-for-python/pull/1182 | non_main | keyvault mgmt update keyvault mgmt sdk and support for the following deleted vault operations show list purge add support for soft delete create mode and storage permissions add support for managed storage account keys see | 0 |
167,821 | 14,118,141,084 | IssuesEvent | 2020-11-08 12:22:41 | Guillergood/DailyReport-2.0 | https://api.github.com/repos/Guillergood/DailyReport-2.0 | closed | Prepara documentación para hito 2 | documentation | Configuración correcta del gestor de tareas y justificación de la misma.
Elección y justificación de la biblioteca de aserciones usada.
Eección y justificación del marco de pruebas usado. | 1.0 | Prepara documentación para hito 2 - Configuración correcta del gestor de tareas y justificación de la misma.
Elección y justificación de la biblioteca de aserciones usada.
Eección y justificación del marco de pruebas usado. | non_main | prepara documentación para hito configuración correcta del gestor de tareas y justificación de la misma elección y justificación de la biblioteca de aserciones usada eección y justificación del marco de pruebas usado | 0 |
1,788 | 6,575,880,684 | IssuesEvent | 2017-09-11 17:41:25 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | module apt: No package matching 'libXrender1' is available | affects_2.1 bug_report waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
apt
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.0.0
config file = /home/mgrimm/workspace/automated-deployment/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
<!---
Mention any settings you have changed/added/removed in ansible.cfg
(or using the ANSIBLE_* environment variables).
-->
no changes
##### OS / ENVIRONMENT
<!---
Mention the OS you are running Ansible from, and the OS you are
managing, or say “N/A” for anything that is not platform-specific.
-->
running from Ubuntu 16.04 LTS
running on Debian 7 Wheezy
##### SUMMARY
<!--- Explain the problem briefly -->
When running module apt with name=libXrender1, I get the following error message:
```
No package matching 'libXrender1' is available
```
I can install the lib manually with `sudo apt-get install libXrender1`. The error persists also when the library is already installed.
##### STEPS TO REPRODUCE
<!---
For bugs, show exactly how to reproduce the problem.
For new features, show how the feature would be used.
-->
Just run the playbook.
<!--- Paste example playbooks or commands between quotes below -->
playbook `configure-tp-server.yml`:
```
- name: Configure prduction TP server
hosts: all
become: True
roles:
- tpserver-setup
```
`tpserver-setup/tasks/main.yml`:
```
- apt: name=libXrender1
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
libXrender1 should get installed without errors.
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with extra verbosity (-vvvv) -->
<!--- Paste verbatim command output between quotes below -->
```
$ ansible-playbook configure-tp-server.yml -i production --limit "tp-10015" -vvvv
Using /home/mgrimm/workspace/automated-deployment/ansible.cfg as config file
Loaded callback default of type stdout, v2.0
PLAYBOOK: configure-tp-server.yml **********************************************
1 plays in configure-tp-server.yml
PLAY [Configure prduction TP server] *******************************************
TASK [setup] *******************************************************************
<ip> ESTABLISH SSH CONNECTION FOR USER: <user>
<ip> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r <ip> '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042 `" && echo ansible-tmp-1474924752.61-24700385564042="` echo $HOME/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042 `" ) && sleep 0'"'"''
<ip> PUT /tmp/tmpEaNTPo TO /home/<user>/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042/setup
<ip> SSH: EXEC sftp -b - -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r '[<ip>]'
<<ip>> ESTABLISH SSH CONNECTION FOR USER: <user>
<<ip>> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r -tt <ip> '/bin/sh -c '"'"'sudo -H -S -p "[sudo via ansible, key=gtgdkwqkitajhqfqjqgmesejbryahsec] password: " -u root /bin/sh -c '"'"'"'"'"'"'"'"'echo BECOME-SUCCESS-gtgdkwqkitajhqfqjqgmesejbryahsec; LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 /usr/bin/python /home/<user>/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042/setup; rm -rf "/home/<user>/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042/" > /dev/null 2>&1'"'"'"'"'"'"'"'"' && sleep 0'"'"''
ok: [tp-10015]
TASK [tpserver-setup : apt] ****************************************************
task path: /home/mgrimm/workspace/automated-deployment/roles/tpserver-setup/tasks/main.yml:1
<ip> ESTABLISH SSH CONNECTION FOR USER: <user>
<ip> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r <ip> '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228 `" && echo ansible-tmp-1474924754.53-63418801820228="` echo $HOME/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228 `" ) && sleep 0'"'"''
<<ip>> PUT /tmp/tmp23cv6m TO /home/<user>/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228/apt
<<ip>> SSH: EXEC sftp -b - -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r '[<ip>]'
<<ip>> ESTABLISH SSH CONNECTION FOR USER: <user>
<<ip>> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r -tt <ip> '/bin/sh -c '"'"'sudo -H -S -p "[sudo via ansible, key=myzoijofvcxkaoxxufjaxrpvbmciltvn] password: " -u root /bin/sh -c '"'"'"'"'"'"'"'"'echo BECOME-SUCCESS-myzoijofvcxkaoxxufjaxrpvbmciltvn; LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 /usr/bin/python /home/<user>/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228/apt; rm -rf "/home/<user>/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228/" > /dev/null 2>&1'"'"'"'"'"'"'"'"' && sleep 0'"'"''
fatal: [tp-10015]: FAILED! => {"changed": false, "failed": true, "invocation": {"module_args": {"allow_unauthenticated": false, "autoremove": false, "cache_valid_time": null, "deb": null, "default_release": null, "dpkg_options": "force-confdef,force-confold", "force": false, "install_recommends": null, "name": "libXrender1", "only_upgrade": false, "package": ["libXrender1"], "purge": false, "state": "present", "update_cache": false, "upgrade": null}, "module_name": "apt"}, "msg": "No package matching 'libXrender1' is available"}
NO MORE HOSTS LEFT *************************************************************
PLAY RECAP *********************************************************************
tp-10015 : ok=1 changed=0 unreachable=0 failed=1
```
I have replaced the address and username of the target host by `<ip>` and `<user>` for security reasons.
| True | module apt: No package matching 'libXrender1' is available - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
<!--- Name of the plugin/module/task -->
apt
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
ansible 2.1.0.0
config file = /home/mgrimm/workspace/automated-deployment/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
<!---
Mention any settings you have changed/added/removed in ansible.cfg
(or using the ANSIBLE_* environment variables).
-->
no changes
##### OS / ENVIRONMENT
<!---
Mention the OS you are running Ansible from, and the OS you are
managing, or say “N/A” for anything that is not platform-specific.
-->
running from Ubuntu 16.04 LTS
running on Debian 7 Wheezy
##### SUMMARY
<!--- Explain the problem briefly -->
When running module apt with name=libXrender1, I get the following error message:
```
No package matching 'libXrender1' is available
```
I can install the lib manually with `sudo apt-get install libXrender1`. The error persists also when the library is already installed.
##### STEPS TO REPRODUCE
<!---
For bugs, show exactly how to reproduce the problem.
For new features, show how the feature would be used.
-->
Just run the playbook.
<!--- Paste example playbooks or commands between quotes below -->
playbook `configure-tp-server.yml`:
```
- name: Configure prduction TP server
hosts: all
become: True
roles:
- tpserver-setup
```
`tpserver-setup/tasks/main.yml`:
```
- apt: name=libXrender1
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
libXrender1 should get installed without errors.
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with extra verbosity (-vvvv) -->
<!--- Paste verbatim command output between quotes below -->
```
$ ansible-playbook configure-tp-server.yml -i production --limit "tp-10015" -vvvv
Using /home/mgrimm/workspace/automated-deployment/ansible.cfg as config file
Loaded callback default of type stdout, v2.0
PLAYBOOK: configure-tp-server.yml **********************************************
1 plays in configure-tp-server.yml
PLAY [Configure prduction TP server] *******************************************
TASK [setup] *******************************************************************
<ip> ESTABLISH SSH CONNECTION FOR USER: <user>
<ip> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r <ip> '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042 `" && echo ansible-tmp-1474924752.61-24700385564042="` echo $HOME/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042 `" ) && sleep 0'"'"''
<ip> PUT /tmp/tmpEaNTPo TO /home/<user>/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042/setup
<ip> SSH: EXEC sftp -b - -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r '[<ip>]'
<<ip>> ESTABLISH SSH CONNECTION FOR USER: <user>
<<ip>> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r -tt <ip> '/bin/sh -c '"'"'sudo -H -S -p "[sudo via ansible, key=gtgdkwqkitajhqfqjqgmesejbryahsec] password: " -u root /bin/sh -c '"'"'"'"'"'"'"'"'echo BECOME-SUCCESS-gtgdkwqkitajhqfqjqgmesejbryahsec; LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 /usr/bin/python /home/<user>/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042/setup; rm -rf "/home/<user>/.ansible/tmp/ansible-tmp-1474924752.61-24700385564042/" > /dev/null 2>&1'"'"'"'"'"'"'"'"' && sleep 0'"'"''
ok: [tp-10015]
TASK [tpserver-setup : apt] ****************************************************
task path: /home/mgrimm/workspace/automated-deployment/roles/tpserver-setup/tasks/main.yml:1
<ip> ESTABLISH SSH CONNECTION FOR USER: <user>
<ip> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r <ip> '/bin/sh -c '"'"'( umask 77 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228 `" && echo ansible-tmp-1474924754.53-63418801820228="` echo $HOME/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228 `" ) && sleep 0'"'"''
<<ip>> PUT /tmp/tmp23cv6m TO /home/<user>/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228/apt
<<ip>> SSH: EXEC sftp -b - -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r '[<ip>]'
<<ip>> ESTABLISH SSH CONNECTION FOR USER: <user>
<<ip>> SSH: EXEC ssh -C -vvv -o ControlMaster=auto -o ControlPersist=60s -o StrictHostKeyChecking=no -o Port=22 -o 'IdentityFile="/home/mgrimm/.ssh/id_rsa"' -o KbdInteractiveAuthentication=no -o PreferredAuthentications=gssapi-with-mic,gssapi-keyex,hostbased,publickey -o PasswordAuthentication=no -o User=<user> -o ConnectTimeout=10 -o ControlPath=/home/mgrimm/.ansible/cp/ansible-ssh-%h-%p-%r -tt <ip> '/bin/sh -c '"'"'sudo -H -S -p "[sudo via ansible, key=myzoijofvcxkaoxxufjaxrpvbmciltvn] password: " -u root /bin/sh -c '"'"'"'"'"'"'"'"'echo BECOME-SUCCESS-myzoijofvcxkaoxxufjaxrpvbmciltvn; LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 /usr/bin/python /home/<user>/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228/apt; rm -rf "/home/<user>/.ansible/tmp/ansible-tmp-1474924754.53-63418801820228/" > /dev/null 2>&1'"'"'"'"'"'"'"'"' && sleep 0'"'"''
fatal: [tp-10015]: FAILED! => {"changed": false, "failed": true, "invocation": {"module_args": {"allow_unauthenticated": false, "autoremove": false, "cache_valid_time": null, "deb": null, "default_release": null, "dpkg_options": "force-confdef,force-confold", "force": false, "install_recommends": null, "name": "libXrender1", "only_upgrade": false, "package": ["libXrender1"], "purge": false, "state": "present", "update_cache": false, "upgrade": null}, "module_name": "apt"}, "msg": "No package matching 'libXrender1' is available"}
NO MORE HOSTS LEFT *************************************************************
PLAY RECAP *********************************************************************
tp-10015 : ok=1 changed=0 unreachable=0 failed=1
```
I have replaced the address and username of the target host by `<ip>` and `<user>` for security reasons.
| main | module apt no package matching is available issue type bug report component name apt ansible version ansible config file home mgrimm workspace automated deployment ansible cfg configured module search path default w o overrides configuration mention any settings you have changed added removed in ansible cfg or using the ansible environment variables no changes os environment mention the os you are running ansible from and the os you are managing or say “n a” for anything that is not platform specific running from ubuntu lts running on debian wheezy summary when running module apt with name i get the following error message no package matching is available i can install the lib manually with sudo apt get install the error persists also when the library is already installed steps to reproduce for bugs show exactly how to reproduce the problem for new features show how the feature would be used just run the playbook playbook configure tp server yml name configure prduction tp server hosts all become true roles tpserver setup tpserver setup tasks main yml apt name expected results should get installed without errors actual results ansible playbook configure tp server yml i production limit tp vvvv using home mgrimm workspace automated deployment ansible cfg as config file loaded callback default of type stdout playbook configure tp server yml plays in configure tp server yml play task establish ssh connection for user ssh exec ssh c vvv o controlmaster auto o controlpersist o stricthostkeychecking no o port o identityfile home mgrimm ssh id rsa o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user o connecttimeout o controlpath home mgrimm ansible cp ansible ssh h p r bin sh c umask mkdir p echo home ansible tmp ansible tmp echo ansible tmp echo home ansible tmp ansible tmp sleep put tmp tmpeantpo to home ansible tmp ansible tmp setup ssh exec sftp b c vvv o controlmaster auto o controlpersist o stricthostkeychecking no o port o identityfile home mgrimm ssh id rsa o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user o connecttimeout o controlpath home mgrimm ansible cp ansible ssh h p r establish ssh connection for user ssh exec ssh c vvv o controlmaster auto o controlpersist o stricthostkeychecking no o port o identityfile home mgrimm ssh id rsa o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user o connecttimeout o controlpath home mgrimm ansible cp ansible ssh h p r tt bin sh c sudo h s p password u root bin sh c echo become success gtgdkwqkitajhqfqjqgmesejbryahsec lang en us utf lc all en us utf lc messages en us utf usr bin python home ansible tmp ansible tmp setup rm rf home ansible tmp ansible tmp dev null sleep ok task task path home mgrimm workspace automated deployment roles tpserver setup tasks main yml establish ssh connection for user ssh exec ssh c vvv o controlmaster auto o controlpersist o stricthostkeychecking no o port o identityfile home mgrimm ssh id rsa o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user o connecttimeout o controlpath home mgrimm ansible cp ansible ssh h p r bin sh c umask mkdir p echo home ansible tmp ansible tmp echo ansible tmp echo home ansible tmp ansible tmp sleep put tmp to home ansible tmp ansible tmp apt ssh exec sftp b c vvv o controlmaster auto o controlpersist o stricthostkeychecking no o port o identityfile home mgrimm ssh id rsa o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user o connecttimeout o controlpath home mgrimm ansible cp ansible ssh h p r establish ssh connection for user ssh exec ssh c vvv o controlmaster auto o controlpersist o stricthostkeychecking no o port o identityfile home mgrimm ssh id rsa o kbdinteractiveauthentication no o preferredauthentications gssapi with mic gssapi keyex hostbased publickey o passwordauthentication no o user o connecttimeout o controlpath home mgrimm ansible cp ansible ssh h p r tt bin sh c sudo h s p password u root bin sh c echo become success myzoijofvcxkaoxxufjaxrpvbmciltvn lang en us utf lc all en us utf lc messages en us utf usr bin python home ansible tmp ansible tmp apt rm rf home ansible tmp ansible tmp dev null sleep fatal failed changed false failed true invocation module args allow unauthenticated false autoremove false cache valid time null deb null default release null dpkg options force confdef force confold force false install recommends null name only upgrade false package purge false state present update cache false upgrade null module name apt msg no package matching is available no more hosts left play recap tp ok changed unreachable failed i have replaced the address and username of the target host by and for security reasons | 1 |
1,264 | 5,357,530,396 | IssuesEvent | 2017-02-20 18:49:23 | DynamoRIO/dynamorio | https://api.github.com/repos/DynamoRIO/dynamorio | opened | gdb fails to see app threads in some cases | Bug-AppFail Maintainability OpSys-Linux | Xref #2199
I have run large proprietary apps where gdb shows only 2 threads while DR (in its data structs or logfiles for debug build) and `/proc/self/task` show hundreds of threads.
I checked typical reasons for gdb failing to see threads: a stripped libpthread.so.0, and a non-matching libthread_db.so.1. Those are not the problem: the same app, natively, has all of its hundreds of threads show up under gdb. The problem only happens under DR.
It's something to do with TLS and the pthread data structures. It may be -mangle_app_seg, where the app's TLS is stolen to better support private libraries. DR restores the app's TLS on explicit app actions that view the underlying state, but gdb using ptrace is going to see the non-app state.
As for how to fix it, perhaps we could make a convenience function we could call from gdb to restore the app TLS state, and again to reverse? Although I have had trouble executing functions in gdb on some of these large apps (gdb bugs or shortcomings of some kind I believe). | True | gdb fails to see app threads in some cases - Xref #2199
I have run large proprietary apps where gdb shows only 2 threads while DR (in its data structs or logfiles for debug build) and `/proc/self/task` show hundreds of threads.
I checked typical reasons for gdb failing to see threads: a stripped libpthread.so.0, and a non-matching libthread_db.so.1. Those are not the problem: the same app, natively, has all of its hundreds of threads show up under gdb. The problem only happens under DR.
It's something to do with TLS and the pthread data structures. It may be -mangle_app_seg, where the app's TLS is stolen to better support private libraries. DR restores the app's TLS on explicit app actions that view the underlying state, but gdb using ptrace is going to see the non-app state.
As for how to fix it, perhaps we could make a convenience function we could call from gdb to restore the app TLS state, and again to reverse? Although I have had trouble executing functions in gdb on some of these large apps (gdb bugs or shortcomings of some kind I believe). | main | gdb fails to see app threads in some cases xref i have run large proprietary apps where gdb shows only threads while dr in its data structs or logfiles for debug build and proc self task show hundreds of threads i checked typical reasons for gdb failing to see threads a stripped libpthread so and a non matching libthread db so those are not the problem the same app natively has all of its hundreds of threads show up under gdb the problem only happens under dr it s something to do with tls and the pthread data structures it may be mangle app seg where the app s tls is stolen to better support private libraries dr restores the app s tls on explicit app actions that view the underlying state but gdb using ptrace is going to see the non app state as for how to fix it perhaps we could make a convenience function we could call from gdb to restore the app tls state and again to reverse although i have had trouble executing functions in gdb on some of these large apps gdb bugs or shortcomings of some kind i believe | 1 |
1,613 | 6,572,632,362 | IssuesEvent | 2017-09-11 03:55:26 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | profitbricks_volume delete needs to know which volume to delete | affects_2.2 bug_report cloud waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
cloud/profitbricks/profitbricks_volume.py
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
devel 2.2
```
##### SUMMARY
Ran pyflakes on the profitbricks_volume module and found that the delete_volume() function does not define the volume variable which it uses. This would appear to make the module fail to delete a volume with a traceback in some cases.
The code in question is here: https://github.com/ansible/ansible-modules-extras/blob/devel/cloud/profitbricks/profitbricks_volume.py#L319
volume is not defined earlier in that function.
| True | profitbricks_volume delete needs to know which volume to delete - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
cloud/profitbricks/profitbricks_volume.py
##### ANSIBLE VERSION
<!--- Paste verbatim output from “ansible --version” between quotes below -->
```
devel 2.2
```
##### SUMMARY
Ran pyflakes on the profitbricks_volume module and found that the delete_volume() function does not define the volume variable which it uses. This would appear to make the module fail to delete a volume with a traceback in some cases.
The code in question is here: https://github.com/ansible/ansible-modules-extras/blob/devel/cloud/profitbricks/profitbricks_volume.py#L319
volume is not defined earlier in that function.
| main | profitbricks volume delete needs to know which volume to delete issue type bug report component name cloud profitbricks profitbricks volume py ansible version devel summary ran pyflakes on the profitbricks volume module and found that the delete volume function does not define the volume variable which it uses this would appear to make the module fail to delete a volume with a traceback in some cases the code in question is here volume is not defined earlier in that function | 1 |
3,458 | 13,232,453,942 | IssuesEvent | 2020-08-18 13:23:27 | ipfs/go-ipfs | https://api.github.com/repos/ipfs/go-ipfs | closed | Implement GitFlow | need/maintainers-input topic/meta | We're switching to a fixed release model where we'll have to branch off a new release every 6 weeks, releasing three weeks after branching. That means:
* Each release has 6 weeks of features, 3 weeks of baking.
* This means that every release will get:
* 3 weeks of "shared" time with the previous release.
* 3 weeks of focus time.
Given that we can't afford to lose that shared time, we need to find a way to keep merging when the next release is baking. Git-flow was designed for exactly this kind of scheduled release cycle.
First of all, any objections from the team? Specifically, the model I'm talking about is https://nvie.com/posts/a-successful-git-branching-model/.
Second, we have two options:
* A: True git-flow. That is, the model described in the link above.
* B: Use "master" as gitflow's develop (as we do now) and a "release" branch as gitflow's master (which is almost what we do now).
That is:
* A: patches go to develop, "master" is the stable release branch.
* B: patches go to master, "release" is the stable release branch.
I'm leaning towards B given that:
1. For 99% of users, this work flow will look like the standard GitHub PR model.
2. We're already half-way there (we already have a release branch).
The main thing we need to implement full git-flow is to start doing the back merges (e.g., https://github.com/ipfs/go-ipfs/pull/7243), so we can easily deploy hot patches at any time.
Thoughts?
_Originally posted by @Stebalien in https://github.com/ipfs/go-ipfs/issues/2753#issuecomment-620866691_
Note: B was proposed in https://github.com/ipfs/go-ipfs/issues/2753 but I'm forking this into a new issue because that issue doesn't _quite_ describe git-flow and I don't wan to introduce too much confusion. | True | Implement GitFlow - We're switching to a fixed release model where we'll have to branch off a new release every 6 weeks, releasing three weeks after branching. That means:
* Each release has 6 weeks of features, 3 weeks of baking.
* This means that every release will get:
* 3 weeks of "shared" time with the previous release.
* 3 weeks of focus time.
Given that we can't afford to lose that shared time, we need to find a way to keep merging when the next release is baking. Git-flow was designed for exactly this kind of scheduled release cycle.
First of all, any objections from the team? Specifically, the model I'm talking about is https://nvie.com/posts/a-successful-git-branching-model/.
Second, we have two options:
* A: True git-flow. That is, the model described in the link above.
* B: Use "master" as gitflow's develop (as we do now) and a "release" branch as gitflow's master (which is almost what we do now).
That is:
* A: patches go to develop, "master" is the stable release branch.
* B: patches go to master, "release" is the stable release branch.
I'm leaning towards B given that:
1. For 99% of users, this work flow will look like the standard GitHub PR model.
2. We're already half-way there (we already have a release branch).
The main thing we need to implement full git-flow is to start doing the back merges (e.g., https://github.com/ipfs/go-ipfs/pull/7243), so we can easily deploy hot patches at any time.
Thoughts?
_Originally posted by @Stebalien in https://github.com/ipfs/go-ipfs/issues/2753#issuecomment-620866691_
Note: B was proposed in https://github.com/ipfs/go-ipfs/issues/2753 but I'm forking this into a new issue because that issue doesn't _quite_ describe git-flow and I don't wan to introduce too much confusion. | main | implement gitflow we re switching to a fixed release model where we ll have to branch off a new release every weeks releasing three weeks after branching that means each release has weeks of features weeks of baking this means that every release will get weeks of shared time with the previous release weeks of focus time given that we can t afford to lose that shared time we need to find a way to keep merging when the next release is baking git flow was designed for exactly this kind of scheduled release cycle first of all any objections from the team specifically the model i m talking about is second we have two options a true git flow that is the model described in the link above b use master as gitflow s develop as we do now and a release branch as gitflow s master which is almost what we do now that is a patches go to develop master is the stable release branch b patches go to master release is the stable release branch i m leaning towards b given that for of users this work flow will look like the standard github pr model we re already half way there we already have a release branch the main thing we need to implement full git flow is to start doing the back merges e g so we can easily deploy hot patches at any time thoughts originally posted by stebalien in note b was proposed in but i m forking this into a new issue because that issue doesn t quite describe git flow and i don t wan to introduce too much confusion | 1 |
731,873 | 25,234,799,701 | IssuesEvent | 2022-11-14 23:22:13 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Adjust scroll position when removing tabs and activating tabs | OS/Linux OS/Windows priority/P3 QA/No release-notes/exclude | > When closing the active tab (through any method: Ctrl+W, X button, context menu), the vertical tab list scrolling will be reset to the top. You need enough tabs open to spill off the bottom of the screen for it to become a problem, but it's quite inconvenient when attempting to close multiple tabs in a row out of a large set. | 1.0 | Adjust scroll position when removing tabs and activating tabs - > When closing the active tab (through any method: Ctrl+W, X button, context menu), the vertical tab list scrolling will be reset to the top. You need enough tabs open to spill off the bottom of the screen for it to become a problem, but it's quite inconvenient when attempting to close multiple tabs in a row out of a large set. | non_main | adjust scroll position when removing tabs and activating tabs when closing the active tab through any method ctrl w x button context menu the vertical tab list scrolling will be reset to the top you need enough tabs open to spill off the bottom of the screen for it to become a problem but it s quite inconvenient when attempting to close multiple tabs in a row out of a large set | 0 |
842 | 4,489,167,060 | IssuesEvent | 2016-08-30 09:59:26 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | User module - existing user groups removed, even with append set as yes (OS X) | bug_report waiting_on_maintainer | ##### Issue Type:
Bug Report
##### Ansible Version:
```
ansible 1.9.3
configured module search path = None
```
##### Ansible Configuration:
```
cat: /etc/ansible/ansible.cfg: No such file or directory
cat: ~/.ansible.cfg: No such file or directory
```
##### Environment:
OS X 10.11 Beta (15A243d)
##### Summary:
I attempted to add a new group **groupexample** to the user that was running the playbook, and added `append: yes` per the [docs](http://docs.ansible.com/ansible/user_module.html), as I wanted to ensure that the existing groups were left intact.
The task completed successfully, and the new group **groupexample** was added the the user successfully, but the user was now missing other (very important!) system groups, such as **admin**.
##### Steps To Reproduce:
```
$ cat playbook.yml
---
- hosts: all
connection: local
tasks:
- name: ensure groupexample group exists
become: yes
group:
name: groupexample
state: present
- name: add groupexample group to current user
become: yes
user:
name: "{{ ansible_user_id }}"
groups: groupexample
append: yes
```
```
$ ansible-playbook --ask-become-pass playbook.yml -i inventory/hosts
SUDO password:
PLAY [all] ********************************************************************
GATHERING FACTS ***************************************************************
ok: [localhost]
TASK: [ensure groupexample group exists] **************************************
changed: [localhost]
TASK: [add groupexample group to current user] ********************************
changed: [localhost]
PLAY RECAP ********************************************************************
localhost : ok=3 changed=2 unreachable=0 failed=0
```
##### Expected Results:
```
$ groups
staff admin wheel everyone localaccounts groupexample
```
(OS X underscore and com groups removed for brevity)
##### Actual Results:
```
$ groups
groupexample everyone localaccounts
```
(OS X underscore and com groups removed for brevity)
##### Other notes
For any other poor souls that may also be running a single user machine who then loose the groups that allow them to administer the OS:
- Boot into single user mode (power off, hold command+s, power on)
- Run `visudo`
- Add your username to list of sudoers, for example
```
root ALL=(ALL) ALL
%admin ALL=(ALL) ALL
yourusernamehere ALL=(ALL) ALL
```
- Save, quit, `reboot`
- You can now boot into OS X normally, and re add your lost groups with:
```
sudo dseditgroup -o edit -a yourusernamehere -t user admin
sudo dseditgroup -o edit -a yourusernamehere -t user wheel
sudo dseditgroup -o edit -a yourusernamehere -t user staff
``` | True | User module - existing user groups removed, even with append set as yes (OS X) - ##### Issue Type:
Bug Report
##### Ansible Version:
```
ansible 1.9.3
configured module search path = None
```
##### Ansible Configuration:
```
cat: /etc/ansible/ansible.cfg: No such file or directory
cat: ~/.ansible.cfg: No such file or directory
```
##### Environment:
OS X 10.11 Beta (15A243d)
##### Summary:
I attempted to add a new group **groupexample** to the user that was running the playbook, and added `append: yes` per the [docs](http://docs.ansible.com/ansible/user_module.html), as I wanted to ensure that the existing groups were left intact.
The task completed successfully, and the new group **groupexample** was added the the user successfully, but the user was now missing other (very important!) system groups, such as **admin**.
##### Steps To Reproduce:
```
$ cat playbook.yml
---
- hosts: all
connection: local
tasks:
- name: ensure groupexample group exists
become: yes
group:
name: groupexample
state: present
- name: add groupexample group to current user
become: yes
user:
name: "{{ ansible_user_id }}"
groups: groupexample
append: yes
```
```
$ ansible-playbook --ask-become-pass playbook.yml -i inventory/hosts
SUDO password:
PLAY [all] ********************************************************************
GATHERING FACTS ***************************************************************
ok: [localhost]
TASK: [ensure groupexample group exists] **************************************
changed: [localhost]
TASK: [add groupexample group to current user] ********************************
changed: [localhost]
PLAY RECAP ********************************************************************
localhost : ok=3 changed=2 unreachable=0 failed=0
```
##### Expected Results:
```
$ groups
staff admin wheel everyone localaccounts groupexample
```
(OS X underscore and com groups removed for brevity)
##### Actual Results:
```
$ groups
groupexample everyone localaccounts
```
(OS X underscore and com groups removed for brevity)
##### Other notes
For any other poor souls that may also be running a single user machine who then loose the groups that allow them to administer the OS:
- Boot into single user mode (power off, hold command+s, power on)
- Run `visudo`
- Add your username to list of sudoers, for example
```
root ALL=(ALL) ALL
%admin ALL=(ALL) ALL
yourusernamehere ALL=(ALL) ALL
```
- Save, quit, `reboot`
- You can now boot into OS X normally, and re add your lost groups with:
```
sudo dseditgroup -o edit -a yourusernamehere -t user admin
sudo dseditgroup -o edit -a yourusernamehere -t user wheel
sudo dseditgroup -o edit -a yourusernamehere -t user staff
``` | main | user module existing user groups removed even with append set as yes os x issue type bug report ansible version ansible configured module search path none ansible configuration cat etc ansible ansible cfg no such file or directory cat ansible cfg no such file or directory environment os x beta summary i attempted to add a new group groupexample to the user that was running the playbook and added append yes per the as i wanted to ensure that the existing groups were left intact the task completed successfully and the new group groupexample was added the the user successfully but the user was now missing other very important system groups such as admin steps to reproduce cat playbook yml hosts all connection local tasks name ensure groupexample group exists become yes group name groupexample state present name add groupexample group to current user become yes user name ansible user id groups groupexample append yes ansible playbook ask become pass playbook yml i inventory hosts sudo password play gathering facts ok task changed task changed play recap localhost ok changed unreachable failed expected results groups staff admin wheel everyone localaccounts groupexample os x underscore and com groups removed for brevity actual results groups groupexample everyone localaccounts os x underscore and com groups removed for brevity other notes for any other poor souls that may also be running a single user machine who then loose the groups that allow them to administer the os boot into single user mode power off hold command s power on run visudo add your username to list of sudoers for example root all all all admin all all all yourusernamehere all all all save quit reboot you can now boot into os x normally and re add your lost groups with sudo dseditgroup o edit a yourusernamehere t user admin sudo dseditgroup o edit a yourusernamehere t user wheel sudo dseditgroup o edit a yourusernamehere t user staff | 1 |
21,093 | 4,676,201,535 | IssuesEvent | 2016-10-07 10:51:24 | andrekirst/school | https://api.github.com/repos/andrekirst/school | closed | Prüfung und Erstellung eines Release-Notes-Dokument | documentation | **Anforderung:** Es soll geprüft werden, ob es eine gute Möglichkeit gibt, Release-Notes zu beschreiben, nachdem man ein Feature bzw. ein Bugfix gelöst hat. Wenn es Sinn macht, soll dies umgesetzt werden. Dafür muss auch die Datei `documentation/project/issue-guide.md` für die Vorlagen angepasst werden.
**Dokumentationsanpassungen:**
* [x] Deployment-Handbuch (**!**)
* [x] Release-Notes (**!**) | 1.0 | Prüfung und Erstellung eines Release-Notes-Dokument - **Anforderung:** Es soll geprüft werden, ob es eine gute Möglichkeit gibt, Release-Notes zu beschreiben, nachdem man ein Feature bzw. ein Bugfix gelöst hat. Wenn es Sinn macht, soll dies umgesetzt werden. Dafür muss auch die Datei `documentation/project/issue-guide.md` für die Vorlagen angepasst werden.
**Dokumentationsanpassungen:**
* [x] Deployment-Handbuch (**!**)
* [x] Release-Notes (**!**) | non_main | prüfung und erstellung eines release notes dokument anforderung es soll geprüft werden ob es eine gute möglichkeit gibt release notes zu beschreiben nachdem man ein feature bzw ein bugfix gelöst hat wenn es sinn macht soll dies umgesetzt werden dafür muss auch die datei documentation project issue guide md für die vorlagen angepasst werden dokumentationsanpassungen deployment handbuch release notes | 0 |
59,826 | 14,479,222,206 | IssuesEvent | 2020-12-10 09:31:11 | ElliotChen/spring_boot_example | https://api.github.com/repos/ElliotChen/spring_boot_example | closed | CVE-2020-7019 (Medium) detected in elasticsearch-7.6.2.jar - autoclosed | security vulnerability | ## CVE-2020-7019 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elasticsearch-7.6.2.jar</b></p></summary>
<p>Elasticsearch subproject :server</p>
<p>Library home page: <a href="https://github.com/elastic/elasticsearch">https://github.com/elastic/elasticsearch</a></p>
<p>Path to dependency file: spring_boot_example/16log/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/elasticsearch/elasticsearch/7.6.2/elasticsearch-7.6.2.jar,/home/wss-scanner/.m2/repository/org/elasticsearch/elasticsearch/7.6.2/elasticsearch-7.6.2.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-data-elasticsearch-2.3.4.RELEASE.jar (Root Library)
- spring-data-elasticsearch-4.0.3.RELEASE.jar
- elasticsearch-rest-high-level-client-7.6.2.jar
- :x: **elasticsearch-7.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ElliotChen/spring_boot_example/commit/81388107fdba1e98fb2903d936713ef7c96bca44">81388107fdba1e98fb2903d936713ef7c96bca44</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Elasticsearch before 7.9.0 and 6.8.12 a field disclosure flaw was found when running a scrolling search with Field Level Security. If a user runs the same query another more privileged user recently ran, the scrolling search can leak fields that should be hidden. This could result in an attacker gaining additional permissions against a restricted index.
<p>Publish Date: 2020-08-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7019>CVE-2020-7019</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7019 (Medium) detected in elasticsearch-7.6.2.jar - autoclosed - ## CVE-2020-7019 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>elasticsearch-7.6.2.jar</b></p></summary>
<p>Elasticsearch subproject :server</p>
<p>Library home page: <a href="https://github.com/elastic/elasticsearch">https://github.com/elastic/elasticsearch</a></p>
<p>Path to dependency file: spring_boot_example/16log/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/elasticsearch/elasticsearch/7.6.2/elasticsearch-7.6.2.jar,/home/wss-scanner/.m2/repository/org/elasticsearch/elasticsearch/7.6.2/elasticsearch-7.6.2.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-data-elasticsearch-2.3.4.RELEASE.jar (Root Library)
- spring-data-elasticsearch-4.0.3.RELEASE.jar
- elasticsearch-rest-high-level-client-7.6.2.jar
- :x: **elasticsearch-7.6.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ElliotChen/spring_boot_example/commit/81388107fdba1e98fb2903d936713ef7c96bca44">81388107fdba1e98fb2903d936713ef7c96bca44</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Elasticsearch before 7.9.0 and 6.8.12 a field disclosure flaw was found when running a scrolling search with Field Level Security. If a user runs the same query another more privileged user recently ran, the scrolling search can leak fields that should be hidden. This could result in an attacker gaining additional permissions against a restricted index.
<p>Publish Date: 2020-08-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7019>CVE-2020-7019</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_main | cve medium detected in elasticsearch jar autoclosed cve medium severity vulnerability vulnerable library elasticsearch jar elasticsearch subproject server library home page a href path to dependency file spring boot example pom xml path to vulnerable library home wss scanner repository org elasticsearch elasticsearch elasticsearch jar home wss scanner repository org elasticsearch elasticsearch elasticsearch jar dependency hierarchy spring boot starter data elasticsearch release jar root library spring data elasticsearch release jar elasticsearch rest high level client jar x elasticsearch jar vulnerable library found in head commit a href found in base branch master vulnerability details in elasticsearch before and a field disclosure flaw was found when running a scrolling search with field level security if a user runs the same query another more privileged user recently ran the scrolling search can leak fields that should be hidden this could result in an attacker gaining additional permissions against a restricted index publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with whitesource | 0 |
24,331 | 12,066,011,262 | IssuesEvent | 2020-04-16 10:59:18 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | spike: experiment with performant git archive replacement | estimate/2d gitserver perf spike team/core-services | We currently use archives (tar and zip) generated by `git archive` all over our infrastructure. This task is about experimenting with a new format which would suit our needs more directly.
### Requirements
- Random access (like zip)
- Streamable (like tar)
- Includes git metadata (like OID of object)
- Include multiple commits of data (eg zoekt indexing multiple branches)
- Performant (shouldn't be slower than normal git archive)
- Filterable. We often exclude large files or binary data. It would be great to filter those out at the git layer, and save the network waste and unneccessary gitserver disk access.
### Nice to haves
- Mergeable / splittable. This property is useful for scaling out infrastructure since small repos can be merged to amortize costs, while large monorepos can be split.
- Modern compression. Save on network and disk with something like zstd.
- Plays nice with mmap. We rely on mmap in searcher.
### Spike (2d)
git-archive like binary which spits something out. Ideally something written in Go, but this may not be performant enough. Experimenting with some C code + libgit2 is not out of the question. If we want to make the spike longer we could even do Rust :P | 1.0 | spike: experiment with performant git archive replacement - We currently use archives (tar and zip) generated by `git archive` all over our infrastructure. This task is about experimenting with a new format which would suit our needs more directly.
### Requirements
- Random access (like zip)
- Streamable (like tar)
- Includes git metadata (like OID of object)
- Include multiple commits of data (eg zoekt indexing multiple branches)
- Performant (shouldn't be slower than normal git archive)
- Filterable. We often exclude large files or binary data. It would be great to filter those out at the git layer, and save the network waste and unneccessary gitserver disk access.
### Nice to haves
- Mergeable / splittable. This property is useful for scaling out infrastructure since small repos can be merged to amortize costs, while large monorepos can be split.
- Modern compression. Save on network and disk with something like zstd.
- Plays nice with mmap. We rely on mmap in searcher.
### Spike (2d)
git-archive like binary which spits something out. Ideally something written in Go, but this may not be performant enough. Experimenting with some C code + libgit2 is not out of the question. If we want to make the spike longer we could even do Rust :P | non_main | spike experiment with performant git archive replacement we currently use archives tar and zip generated by git archive all over our infrastructure this task is about experimenting with a new format which would suit our needs more directly requirements random access like zip streamable like tar includes git metadata like oid of object include multiple commits of data eg zoekt indexing multiple branches performant shouldn t be slower than normal git archive filterable we often exclude large files or binary data it would be great to filter those out at the git layer and save the network waste and unneccessary gitserver disk access nice to haves mergeable splittable this property is useful for scaling out infrastructure since small repos can be merged to amortize costs while large monorepos can be split modern compression save on network and disk with something like zstd plays nice with mmap we rely on mmap in searcher spike git archive like binary which spits something out ideally something written in go but this may not be performant enough experimenting with some c code is not out of the question if we want to make the spike longer we could even do rust p | 0 |
5,873 | 31,877,747,434 | IssuesEvent | 2023-09-16 02:31:39 | gemarkode/codebase | https://api.github.com/repos/gemarkode/codebase | closed | Perbaikan Project CodeBase 2023 | maintainers | Perbaikan Website
- [ ] Menambahkan Bahasa Indonesia, jadi nantinya ada 2 Bahasa yaitu Indonesia dan Ingris
- [ ] Mengganti tampilan website
Isi Konten CodeBase
- [ ] Menambahkan Studi kasus dan beberapa contoh penyelesaian masalah (Solusi) tentang masalah Coding
- [ ] Menambahkan Studi kasus dan beberapa contoh penyelesaian masalah (Solusi) tentang masalah SQL Query | True | Perbaikan Project CodeBase 2023 - Perbaikan Website
- [ ] Menambahkan Bahasa Indonesia, jadi nantinya ada 2 Bahasa yaitu Indonesia dan Ingris
- [ ] Mengganti tampilan website
Isi Konten CodeBase
- [ ] Menambahkan Studi kasus dan beberapa contoh penyelesaian masalah (Solusi) tentang masalah Coding
- [ ] Menambahkan Studi kasus dan beberapa contoh penyelesaian masalah (Solusi) tentang masalah SQL Query | main | perbaikan project codebase perbaikan website menambahkan bahasa indonesia jadi nantinya ada bahasa yaitu indonesia dan ingris mengganti tampilan website isi konten codebase menambahkan studi kasus dan beberapa contoh penyelesaian masalah solusi tentang masalah coding menambahkan studi kasus dan beberapa contoh penyelesaian masalah solusi tentang masalah sql query | 1 |
4,948 | 25,455,552,322 | IssuesEvent | 2022-11-24 13:55:26 | pace/bricks | https://api.github.com/repos/pace/bricks | closed | Follow-up from "Resolve "Add label for all http request related stats to filter"" | T::Maintainance | `pace_http_request_size_bytes` should be named `pace_http_response_size_bytes` | True | Follow-up from "Resolve "Add label for all http request related stats to filter"" - `pace_http_request_size_bytes` should be named `pace_http_response_size_bytes` | main | follow up from resolve add label for all http request related stats to filter pace http request size bytes should be named pace http response size bytes | 1 |
746 | 4,350,941,179 | IssuesEvent | 2016-07-31 15:30:54 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | digital_ocean backup_enabled: yes is enabling private_networking | bug_report cloud digital_ocean waiting_on_maintainer | <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
digital_ocean
##### ANSIBLE VERSION
```
$ ansible --version
ansible 2.0.2.0
config file = /Users/jln/git/jpw/black-ops/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
<!---
[defaults]
host_key_checking=False
-->
##### OS / ENVIRONMENT
<!---
Control Machine: OSX 10.10.5
Droplet: ubuntu-14-04-x64
-->
##### SUMMARY
Attempting to create a DO droplet with private_networking and back_up enabled. If I set only private_networking: yes, private networking is not enabled on the droplet. If I set only backups_enabled: yes, backups are not enabled, but private networking is. If I set both private_networking: yes and backups_enabled: yes, private networking is enabled but backups are not.
##### STEPS TO REPRODUCE
<!---
For bugs, show exactly how to reproduce the problem.
For new features, show how the feature would be used.
-->
```
- name: create database droplet
digital_ocean:
state: present
command: droplet
name: testWithNetworking
size_id: 2gb
region_id: nyc3
image_id: ubuntu-14-04-x64
unique_name: yes
private_networking: yes
register: droplet
- name: create database droplet
digital_ocean:
state: present
command: droplet
name: testWithBackups
size_id: 2gb
region_id: nyc3
image_id: ubuntu-14-04-x64
unique_name: yes
backups_enabled: yes
register: droplet
- name: create database droplet
digital_ocean:
state: present
command: droplet
name: testWithBoth
size_id: 2gb
region_id: nyc3
image_id: ubuntu-14-04-x64
unique_name: yes
private_networking: yes
backups_enabled: yes
register: droplet
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
I expected three droplets:
* One with Private Networking enabled, but not Backups.
* One with Backups enabled, but not Private Networking.
* One with Private Networking and Backups enabled.
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->



```
Using /Users/jln/git/jpw/black-ops/ansible.cfg as config file
Loaded callback default of type stdout, v2.0
PLAYBOOK: create_db_server.yml *************************************************
2 plays in create_db_server.yml
PLAY [local] *******************************************************************
TASK [setup] *******************************************************************
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmpureuWb TO /Users/jln/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626/setup
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626/setup; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626/" > /dev/null 2>&1'
ok: [localhost]
TASK [droplet : create database droplet] ***************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:10
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmp1K1RbK TO /Users/jln/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174/digital_ocean
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174/digital_ocean; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174/" > /dev/null 2>&1'
changed: [localhost] => {"changed": true, "droplet": {"backup_ids": [], "created_at": "2016-04-26T20:13:25Z", "disk": 40, "drives": [], "features": ["ipv6", "virtio"], "id": 14185559, "image": {"created_at": "2016-02-23T23:01:40Z", "distribution": "Ubuntu", "id": 15943679, "min_disk_size": 20, "name": "14.04.4 x64", "public": true, "regions": ["nyc1", "sfo1", "nyc2", "ams2", "sgp1", "lon1", "nyc3", "ams3", "fra1", "tor1", "sfo2"], "size_gigabytes": 1.58, "slug": "ubuntu-14-04-x64", "type": "snapshot"}, "ip_address": "104.236.71.85", "kernel": null, "locked": false, "memory": 2048, "name": "testWithNetworking", "networks": {"v4": [{"gateway": "104.236.64.1", "ip_address": "104.236.71.85", "netmask": "255.255.192.0", "type": "public"}], "v6": [{"gateway": "2604:A880:0800:0010:0000:0000:0000:0001", "ip_address": "2604:A880:0800:0010:0000:0000:0B1E:1001", "netmask": 64, "type": "public"}]}, "next_backup_window": null, "region": {"available": true, "features": ["private_networking", "backups", "ipv6", "metadata"], "name": "New York 3", "sizes": ["32gb", "16gb", "2gb", "1gb", "4gb", "8gb", "512mb", "64gb", "48gb"], "slug": "nyc3"}, "size": {"available": true, "disk": 40, "memory": 2048, "price_hourly": 0.02976, "price_monthly": 20.0, "regions": ["ams1", "ams2", "ams3", "fra1", "lon1", "nyc1", "nyc2", "nyc3", "sfo1", "sgp1", "tor1"], "slug": "2gb", "transfer": 3.0, "vcpus": 2}, "size_slug": "2gb", "snapshot_ids": [], "status": "active", "tags": [], "vcpus": 2}, "invocation": {"module_args": {"api_token": null, "backups_enabled": false, "command": "droplet", "id": null, "image_id": "ubuntu-14-04-x64", "name": "testWithNetworking", "private_networking": true, "region_id": "nyc3", "size_id": "2gb", "ssh_key_ids": null, "ssh_pub_key": null, "state": "present", "unique_name": true, "user_data": null, "virtio": true, "wait": true, "wait_timeout": 300}, "module_name": "digital_ocean"}}
TASK [droplet : create database droplet] ***************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:22
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmp62vX08 TO /Users/jln/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555/digital_ocean
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555/digital_ocean; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555/" > /dev/null 2>&1'
changed: [localhost] => {"changed": true, "droplet": {"backup_ids": [], "created_at": "2016-04-26T20:14:09Z", "disk": 40, "drives": [], "features": ["private_networking", "virtio"], "id": 14185593, "image": {"created_at": "2016-02-23T23:01:40Z", "distribution": "Ubuntu", "id": 15943679, "min_disk_size": 20, "name": "14.04.4 x64", "public": true, "regions": ["nyc1", "sfo1", "nyc2", "ams2", "sgp1", "lon1", "nyc3", "ams3", "fra1", "tor1", "sfo2"], "size_gigabytes": 1.58, "slug": "ubuntu-14-04-x64", "type": "snapshot"}, "ip_address": "10.132.15.191", "kernel": null, "locked": false, "memory": 2048, "name": "testWithBackups", "networks": {"v4": [{"gateway": "10.132.0.1", "ip_address": "10.132.15.191", "netmask": "255.255.0.0", "type": "private"}, {"gateway": "104.236.192.1", "ip_address": "104.236.236.56", "netmask": "255.255.192.0", "type": "public"}], "v6": []}, "next_backup_window": null, "region": {"available": true, "features": ["private_networking", "backups", "ipv6", "metadata"], "name": "New York 3", "sizes": ["32gb", "16gb", "2gb", "1gb", "4gb", "8gb", "512mb", "64gb", "48gb"], "slug": "nyc3"}, "size": {"available": true, "disk": 40, "memory": 2048, "price_hourly": 0.02976, "price_monthly": 20.0, "regions": ["ams1", "ams2", "ams3", "fra1", "lon1", "nyc1", "nyc2", "nyc3", "sfo1", "sgp1", "tor1"], "slug": "2gb", "transfer": 3.0, "vcpus": 2}, "size_slug": "2gb", "snapshot_ids": [], "status": "active", "tags": [], "vcpus": 2}, "invocation": {"module_args": {"api_token": null, "backups_enabled": true, "command": "droplet", "id": null, "image_id": "ubuntu-14-04-x64", "name": "testWithBackups", "private_networking": false, "region_id": "nyc3", "size_id": "2gb", "ssh_key_ids": null, "ssh_pub_key": null, "state": "present", "unique_name": true, "user_data": null, "virtio": true, "wait": true, "wait_timeout": 300}, "module_name": "digital_ocean"}}
TASK [droplet : create database droplet] ***************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:34
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmppdM6x9 TO /Users/jln/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663/digital_ocean
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663/digital_ocean; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663/" > /dev/null 2>&1'
changed: [localhost] => {"changed": true, "droplet": {"backup_ids": [], "created_at": "2016-04-26T20:14:52Z", "disk": 40, "drives": [], "features": ["private_networking", "ipv6", "virtio"], "id": 14185606, "image": {"created_at": "2016-02-23T23:01:40Z", "distribution": "Ubuntu", "id": 15943679, "min_disk_size": 20, "name": "14.04.4 x64", "public": true, "regions": ["nyc1", "sfo1", "nyc2", "ams2", "sgp1", "lon1", "nyc3", "ams3", "fra1", "tor1", "sfo2"], "size_gigabytes": 1.58, "slug": "ubuntu-14-04-x64", "type": "snapshot"}, "ip_address": "10.132.2.33", "kernel": null, "locked": false, "memory": 2048, "name": "testWithBoth", "networks": {"v4": [{"gateway": "10.132.0.1", "ip_address": "10.132.2.33", "netmask": "255.255.0.0", "type": "private"}, {"gateway": "104.131.0.1", "ip_address": "104.131.52.215", "netmask": "255.255.192.0", "type": "public"}], "v6": [{"gateway": "2604:A880:0800:0010:0000:0000:0000:0001", "ip_address": "2604:A880:0800:0010:0000:0000:0B1E:2001", "netmask": 64, "type": "public"}]}, "next_backup_window": null, "region": {"available": true, "features": ["private_networking", "backups", "ipv6", "metadata"], "name": "New York 3", "sizes": ["32gb", "16gb", "2gb", "1gb", "4gb", "8gb", "512mb", "64gb", "48gb"], "slug": "nyc3"}, "size": {"available": true, "disk": 40, "memory": 2048, "price_hourly": 0.02976, "price_monthly": 20.0, "regions": ["ams1", "ams2", "ams3", "fra1", "lon1", "nyc1", "nyc2", "nyc3", "sfo1", "sgp1", "tor1"], "slug": "2gb", "transfer": 3.0, "vcpus": 2}, "size_slug": "2gb", "snapshot_ids": [], "status": "active", "tags": [], "vcpus": 2}, "invocation": {"module_args": {"api_token": null, "backups_enabled": true, "command": "droplet", "id": null, "image_id": "ubuntu-14-04-x64", "name": "testWithBoth", "private_networking": true, "region_id": "nyc3", "size_id": "2gb", "ssh_key_ids": null, "ssh_pub_key": null, "state": "present", "unique_name": true, "user_data": null, "virtio": true, "wait": true, "wait_timeout": 300}, "module_name": "digital_ocean"}}
TASK [droplet : debug] *********************************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:61
ok: [localhost] => {
"msg": "testWithBoth(14185606) - 10.132.2.33"
}
PLAY [db] **********************************************************************
skipping: no hosts matched
PLAY RECAP *********************************************************************
localhost : ok=5 changed=3 unreachable=0 failed=0``` | True | digital_ocean backup_enabled: yes is enabling private_networking - <!--- Verify first that your issue/request is not already reported in GitHub -->
##### ISSUE TYPE
<!--- Pick one below and delete the rest: -->
- Bug Report
##### COMPONENT NAME
digital_ocean
##### ANSIBLE VERSION
```
$ ansible --version
ansible 2.0.2.0
config file = /Users/jln/git/jpw/black-ops/ansible.cfg
configured module search path = Default w/o overrides
```
##### CONFIGURATION
<!---
[defaults]
host_key_checking=False
-->
##### OS / ENVIRONMENT
<!---
Control Machine: OSX 10.10.5
Droplet: ubuntu-14-04-x64
-->
##### SUMMARY
Attempting to create a DO droplet with private_networking and back_up enabled. If I set only private_networking: yes, private networking is not enabled on the droplet. If I set only backups_enabled: yes, backups are not enabled, but private networking is. If I set both private_networking: yes and backups_enabled: yes, private networking is enabled but backups are not.
##### STEPS TO REPRODUCE
<!---
For bugs, show exactly how to reproduce the problem.
For new features, show how the feature would be used.
-->
```
- name: create database droplet
digital_ocean:
state: present
command: droplet
name: testWithNetworking
size_id: 2gb
region_id: nyc3
image_id: ubuntu-14-04-x64
unique_name: yes
private_networking: yes
register: droplet
- name: create database droplet
digital_ocean:
state: present
command: droplet
name: testWithBackups
size_id: 2gb
region_id: nyc3
image_id: ubuntu-14-04-x64
unique_name: yes
backups_enabled: yes
register: droplet
- name: create database droplet
digital_ocean:
state: present
command: droplet
name: testWithBoth
size_id: 2gb
region_id: nyc3
image_id: ubuntu-14-04-x64
unique_name: yes
private_networking: yes
backups_enabled: yes
register: droplet
```
<!--- You can also paste gist.github.com links for larger files -->
##### EXPECTED RESULTS
<!--- What did you expect to happen when running the steps above? -->
I expected three droplets:
* One with Private Networking enabled, but not Backups.
* One with Backups enabled, but not Private Networking.
* One with Private Networking and Backups enabled.
##### ACTUAL RESULTS
<!--- What actually happened? If possible run with high verbosity (-vvvv) -->



```
Using /Users/jln/git/jpw/black-ops/ansible.cfg as config file
Loaded callback default of type stdout, v2.0
PLAYBOOK: create_db_server.yml *************************************************
2 plays in create_db_server.yml
PLAY [local] *******************************************************************
TASK [setup] *******************************************************************
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmpureuWb TO /Users/jln/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626/setup
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626/setup; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701603.74-47521402779626/" > /dev/null 2>&1'
ok: [localhost]
TASK [droplet : create database droplet] ***************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:10
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmp1K1RbK TO /Users/jln/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174/digital_ocean
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174/digital_ocean; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701604.63-264720731229174/" > /dev/null 2>&1'
changed: [localhost] => {"changed": true, "droplet": {"backup_ids": [], "created_at": "2016-04-26T20:13:25Z", "disk": 40, "drives": [], "features": ["ipv6", "virtio"], "id": 14185559, "image": {"created_at": "2016-02-23T23:01:40Z", "distribution": "Ubuntu", "id": 15943679, "min_disk_size": 20, "name": "14.04.4 x64", "public": true, "regions": ["nyc1", "sfo1", "nyc2", "ams2", "sgp1", "lon1", "nyc3", "ams3", "fra1", "tor1", "sfo2"], "size_gigabytes": 1.58, "slug": "ubuntu-14-04-x64", "type": "snapshot"}, "ip_address": "104.236.71.85", "kernel": null, "locked": false, "memory": 2048, "name": "testWithNetworking", "networks": {"v4": [{"gateway": "104.236.64.1", "ip_address": "104.236.71.85", "netmask": "255.255.192.0", "type": "public"}], "v6": [{"gateway": "2604:A880:0800:0010:0000:0000:0000:0001", "ip_address": "2604:A880:0800:0010:0000:0000:0B1E:1001", "netmask": 64, "type": "public"}]}, "next_backup_window": null, "region": {"available": true, "features": ["private_networking", "backups", "ipv6", "metadata"], "name": "New York 3", "sizes": ["32gb", "16gb", "2gb", "1gb", "4gb", "8gb", "512mb", "64gb", "48gb"], "slug": "nyc3"}, "size": {"available": true, "disk": 40, "memory": 2048, "price_hourly": 0.02976, "price_monthly": 20.0, "regions": ["ams1", "ams2", "ams3", "fra1", "lon1", "nyc1", "nyc2", "nyc3", "sfo1", "sgp1", "tor1"], "slug": "2gb", "transfer": 3.0, "vcpus": 2}, "size_slug": "2gb", "snapshot_ids": [], "status": "active", "tags": [], "vcpus": 2}, "invocation": {"module_args": {"api_token": null, "backups_enabled": false, "command": "droplet", "id": null, "image_id": "ubuntu-14-04-x64", "name": "testWithNetworking", "private_networking": true, "region_id": "nyc3", "size_id": "2gb", "ssh_key_ids": null, "ssh_pub_key": null, "state": "present", "unique_name": true, "user_data": null, "virtio": true, "wait": true, "wait_timeout": 300}, "module_name": "digital_ocean"}}
TASK [droplet : create database droplet] ***************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:22
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmp62vX08 TO /Users/jln/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555/digital_ocean
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555/digital_ocean; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701648.46-30799619553555/" > /dev/null 2>&1'
changed: [localhost] => {"changed": true, "droplet": {"backup_ids": [], "created_at": "2016-04-26T20:14:09Z", "disk": 40, "drives": [], "features": ["private_networking", "virtio"], "id": 14185593, "image": {"created_at": "2016-02-23T23:01:40Z", "distribution": "Ubuntu", "id": 15943679, "min_disk_size": 20, "name": "14.04.4 x64", "public": true, "regions": ["nyc1", "sfo1", "nyc2", "ams2", "sgp1", "lon1", "nyc3", "ams3", "fra1", "tor1", "sfo2"], "size_gigabytes": 1.58, "slug": "ubuntu-14-04-x64", "type": "snapshot"}, "ip_address": "10.132.15.191", "kernel": null, "locked": false, "memory": 2048, "name": "testWithBackups", "networks": {"v4": [{"gateway": "10.132.0.1", "ip_address": "10.132.15.191", "netmask": "255.255.0.0", "type": "private"}, {"gateway": "104.236.192.1", "ip_address": "104.236.236.56", "netmask": "255.255.192.0", "type": "public"}], "v6": []}, "next_backup_window": null, "region": {"available": true, "features": ["private_networking", "backups", "ipv6", "metadata"], "name": "New York 3", "sizes": ["32gb", "16gb", "2gb", "1gb", "4gb", "8gb", "512mb", "64gb", "48gb"], "slug": "nyc3"}, "size": {"available": true, "disk": 40, "memory": 2048, "price_hourly": 0.02976, "price_monthly": 20.0, "regions": ["ams1", "ams2", "ams3", "fra1", "lon1", "nyc1", "nyc2", "nyc3", "sfo1", "sgp1", "tor1"], "slug": "2gb", "transfer": 3.0, "vcpus": 2}, "size_slug": "2gb", "snapshot_ids": [], "status": "active", "tags": [], "vcpus": 2}, "invocation": {"module_args": {"api_token": null, "backups_enabled": true, "command": "droplet", "id": null, "image_id": "ubuntu-14-04-x64", "name": "testWithBackups", "private_networking": false, "region_id": "nyc3", "size_id": "2gb", "ssh_key_ids": null, "ssh_pub_key": null, "state": "present", "unique_name": true, "user_data": null, "virtio": true, "wait": true, "wait_timeout": 300}, "module_name": "digital_ocean"}}
TASK [droplet : create database droplet] ***************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:34
ESTABLISH LOCAL CONNECTION FOR USER: jln
localhost EXEC /bin/sh -c '( umask 22 && mkdir -p "` echo $HOME/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663 `" && echo "` echo $HOME/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663 `" )'
localhost PUT /var/folders/6g/mhwwnt7j3259lddvql8jhkbw0000gn/T/tmppdM6x9 TO /Users/jln/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663/digital_ocean
localhost EXEC /bin/sh -c 'LANG=en_US.UTF-8 LC_ALL=en_US.UTF-8 LC_MESSAGES=en_US.UTF-8 python /Users/jln/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663/digital_ocean; rm -rf "/Users/jln/.ansible/tmp/ansible-tmp-1461701690.74-258804638768663/" > /dev/null 2>&1'
changed: [localhost] => {"changed": true, "droplet": {"backup_ids": [], "created_at": "2016-04-26T20:14:52Z", "disk": 40, "drives": [], "features": ["private_networking", "ipv6", "virtio"], "id": 14185606, "image": {"created_at": "2016-02-23T23:01:40Z", "distribution": "Ubuntu", "id": 15943679, "min_disk_size": 20, "name": "14.04.4 x64", "public": true, "regions": ["nyc1", "sfo1", "nyc2", "ams2", "sgp1", "lon1", "nyc3", "ams3", "fra1", "tor1", "sfo2"], "size_gigabytes": 1.58, "slug": "ubuntu-14-04-x64", "type": "snapshot"}, "ip_address": "10.132.2.33", "kernel": null, "locked": false, "memory": 2048, "name": "testWithBoth", "networks": {"v4": [{"gateway": "10.132.0.1", "ip_address": "10.132.2.33", "netmask": "255.255.0.0", "type": "private"}, {"gateway": "104.131.0.1", "ip_address": "104.131.52.215", "netmask": "255.255.192.0", "type": "public"}], "v6": [{"gateway": "2604:A880:0800:0010:0000:0000:0000:0001", "ip_address": "2604:A880:0800:0010:0000:0000:0B1E:2001", "netmask": 64, "type": "public"}]}, "next_backup_window": null, "region": {"available": true, "features": ["private_networking", "backups", "ipv6", "metadata"], "name": "New York 3", "sizes": ["32gb", "16gb", "2gb", "1gb", "4gb", "8gb", "512mb", "64gb", "48gb"], "slug": "nyc3"}, "size": {"available": true, "disk": 40, "memory": 2048, "price_hourly": 0.02976, "price_monthly": 20.0, "regions": ["ams1", "ams2", "ams3", "fra1", "lon1", "nyc1", "nyc2", "nyc3", "sfo1", "sgp1", "tor1"], "slug": "2gb", "transfer": 3.0, "vcpus": 2}, "size_slug": "2gb", "snapshot_ids": [], "status": "active", "tags": [], "vcpus": 2}, "invocation": {"module_args": {"api_token": null, "backups_enabled": true, "command": "droplet", "id": null, "image_id": "ubuntu-14-04-x64", "name": "testWithBoth", "private_networking": true, "region_id": "nyc3", "size_id": "2gb", "ssh_key_ids": null, "ssh_pub_key": null, "state": "present", "unique_name": true, "user_data": null, "virtio": true, "wait": true, "wait_timeout": 300}, "module_name": "digital_ocean"}}
TASK [droplet : debug] *********************************************************
task path: /Users/jln/git/jpw/black-ops/roles/droplet/tasks/main.yml:61
ok: [localhost] => {
"msg": "testWithBoth(14185606) - 10.132.2.33"
}
PLAY [db] **********************************************************************
skipping: no hosts matched
PLAY RECAP *********************************************************************
localhost : ok=5 changed=3 unreachable=0 failed=0``` | main | digital ocean backup enabled yes is enabling private networking issue type bug report component name digital ocean ansible version ansible version ansible config file users jln git jpw black ops ansible cfg configured module search path default w o overrides configuration host key checking false os environment control machine osx droplet ubuntu summary attempting to create a do droplet with private networking and back up enabled if i set only private networking yes private networking is not enabled on the droplet if i set only backups enabled yes backups are not enabled but private networking is if i set both private networking yes and backups enabled yes private networking is enabled but backups are not steps to reproduce for bugs show exactly how to reproduce the problem for new features show how the feature would be used name create database droplet digital ocean state present command droplet name testwithnetworking size id region id image id ubuntu unique name yes private networking yes register droplet name create database droplet digital ocean state present command droplet name testwithbackups size id region id image id ubuntu unique name yes backups enabled yes register droplet name create database droplet digital ocean state present command droplet name testwithboth size id region id image id ubuntu unique name yes private networking yes backups enabled yes register droplet expected results i expected three droplets one with private networking enabled but not backups one with backups enabled but not private networking one with private networking and backups enabled actual results using users jln git jpw black ops ansible cfg as config file loaded callback default of type stdout playbook create db server yml plays in create db server yml play task establish local connection for user jln localhost exec bin sh c umask mkdir p echo home ansible tmp ansible tmp echo echo home ansible tmp ansible tmp localhost put var folders t tmpureuwb to users jln ansible tmp ansible tmp setup localhost exec bin sh c lang en us utf lc all en us utf lc messages en us utf python users jln ansible tmp ansible tmp setup rm rf users jln ansible tmp ansible tmp dev null ok task task path users jln git jpw black ops roles droplet tasks main yml establish local connection for user jln localhost exec bin sh c umask mkdir p echo home ansible tmp ansible tmp echo echo home ansible tmp ansible tmp localhost put var folders t to users jln ansible tmp ansible tmp digital ocean localhost exec bin sh c lang en us utf lc all en us utf lc messages en us utf python users jln ansible tmp ansible tmp digital ocean rm rf users jln ansible tmp ansible tmp dev null changed changed true droplet backup ids created at disk drives features id image created at distribution ubuntu id min disk size name public true regions size gigabytes slug ubuntu type snapshot ip address kernel null locked false memory name testwithnetworking networks next backup window null region available true features name new york sizes slug size available true disk memory price hourly price monthly regions slug transfer vcpus size slug snapshot ids status active tags vcpus invocation module args api token null backups enabled false command droplet id null image id ubuntu name testwithnetworking private networking true region id size id ssh key ids null ssh pub key null state present unique name true user data null virtio true wait true wait timeout module name digital ocean task task path users jln git jpw black ops roles droplet tasks main yml establish local connection for user jln localhost exec bin sh c umask mkdir p echo home ansible tmp ansible tmp echo echo home ansible tmp ansible tmp localhost put var folders t to users jln ansible tmp ansible tmp digital ocean localhost exec bin sh c lang en us utf lc all en us utf lc messages en us utf python users jln ansible tmp ansible tmp digital ocean rm rf users jln ansible tmp ansible tmp dev null changed changed true droplet backup ids created at disk drives features id image created at distribution ubuntu id min disk size name public true regions size gigabytes slug ubuntu type snapshot ip address kernel null locked false memory name testwithbackups networks next backup window null region available true features name new york sizes slug size available true disk memory price hourly price monthly regions slug transfer vcpus size slug snapshot ids status active tags vcpus invocation module args api token null backups enabled true command droplet id null image id ubuntu name testwithbackups private networking false region id size id ssh key ids null ssh pub key null state present unique name true user data null virtio true wait true wait timeout module name digital ocean task task path users jln git jpw black ops roles droplet tasks main yml establish local connection for user jln localhost exec bin sh c umask mkdir p echo home ansible tmp ansible tmp echo echo home ansible tmp ansible tmp localhost put var folders t to users jln ansible tmp ansible tmp digital ocean localhost exec bin sh c lang en us utf lc all en us utf lc messages en us utf python users jln ansible tmp ansible tmp digital ocean rm rf users jln ansible tmp ansible tmp dev null changed changed true droplet backup ids created at disk drives features id image created at distribution ubuntu id min disk size name public true regions size gigabytes slug ubuntu type snapshot ip address kernel null locked false memory name testwithboth networks next backup window null region available true features name new york sizes slug size available true disk memory price hourly price monthly regions slug transfer vcpus size slug snapshot ids status active tags vcpus invocation module args api token null backups enabled true command droplet id null image id ubuntu name testwithboth private networking true region id size id ssh key ids null ssh pub key null state present unique name true user data null virtio true wait true wait timeout module name digital ocean task task path users jln git jpw black ops roles droplet tasks main yml ok msg testwithboth play skipping no hosts matched play recap localhost ok changed unreachable failed | 1 |
15,359 | 3,953,376,223 | IssuesEvent | 2016-04-29 13:16:03 | tomchristie/django-rest-framework | https://api.github.com/repos/tomchristie/django-rest-framework | closed | docs.authentication: schema migration required by `authtoken` explained only for South | Documentation | In `docs/api-guide/authentication.md`, section "API Reference" / "TokenAuthentication" / "Schema migrations", a migration requirement is mentioned if a custom user model is being used. However, it is explained how to do that only for South and not when using its official successor (Django migrations).
> You can do so by inserting a needed_by attribute in your user migration
> ...
> For more details, see the south documentation on dependencies.
It seems replacing `needed_by` with `run_before` is enough but I'm not sure.
## Checklist
- [x] I have verified that that issue exists against the `master` branch of Django REST framework.
- [x] I have searched for similar issues in both open and closed tickets and cannot find a duplicate.
- [x] This is not a usage question. (Those should be directed to the [discussion group](https://groups.google.com/forum/#!forum/django-rest-framework) instead.)
- [x] This cannot be dealt with as a third party library. (We prefer new functionality to be [in the form of third party libraries](http://www.django-rest-framework.org/topics/third-party-resources/#about-third-party-packages) where possible.)
- [x] I have reduced the issue to the simplest possible case.
- [ ] I have included a failing test as a pull request. (If you are unable to do so we can still accept the issue.)
## Steps to reproduce
N/A
## Expected behavior
N/A
## Actual behavior
N/A
| 1.0 | docs.authentication: schema migration required by `authtoken` explained only for South - In `docs/api-guide/authentication.md`, section "API Reference" / "TokenAuthentication" / "Schema migrations", a migration requirement is mentioned if a custom user model is being used. However, it is explained how to do that only for South and not when using its official successor (Django migrations).
> You can do so by inserting a needed_by attribute in your user migration
> ...
> For more details, see the south documentation on dependencies.
It seems replacing `needed_by` with `run_before` is enough but I'm not sure.
## Checklist
- [x] I have verified that that issue exists against the `master` branch of Django REST framework.
- [x] I have searched for similar issues in both open and closed tickets and cannot find a duplicate.
- [x] This is not a usage question. (Those should be directed to the [discussion group](https://groups.google.com/forum/#!forum/django-rest-framework) instead.)
- [x] This cannot be dealt with as a third party library. (We prefer new functionality to be [in the form of third party libraries](http://www.django-rest-framework.org/topics/third-party-resources/#about-third-party-packages) where possible.)
- [x] I have reduced the issue to the simplest possible case.
- [ ] I have included a failing test as a pull request. (If you are unable to do so we can still accept the issue.)
## Steps to reproduce
N/A
## Expected behavior
N/A
## Actual behavior
N/A
| non_main | docs authentication schema migration required by authtoken explained only for south in docs api guide authentication md section api reference tokenauthentication schema migrations a migration requirement is mentioned if a custom user model is being used however it is explained how to do that only for south and not when using its official successor django migrations you can do so by inserting a needed by attribute in your user migration for more details see the south documentation on dependencies it seems replacing needed by with run before is enough but i m not sure checklist i have verified that that issue exists against the master branch of django rest framework i have searched for similar issues in both open and closed tickets and cannot find a duplicate this is not a usage question those should be directed to the instead this cannot be dealt with as a third party library we prefer new functionality to be where possible i have reduced the issue to the simplest possible case i have included a failing test as a pull request if you are unable to do so we can still accept the issue steps to reproduce n a expected behavior n a actual behavior n a | 0 |
1,802 | 6,575,923,959 | IssuesEvent | 2017-09-11 17:51:11 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | supervisorctl should support restarting service only if config changed | affects_2.2 feature_idea waiting_on_maintainer | ##### ISSUE TYPE
- Feature Idea
##### COMPONENT NAME
supervisorctl
##### ANSIBLE VERSION
```
2.2
```
##### SUMMARY
`supervisorctl` module has no way to conditionally restart a service only if the config changed. This is currently possible with supervisor--call `supervisor reread` and if supervisor reports the config file changed, then we should call `supervisor restart`, otherwise do nothing.
I suggest a new `state` value, although I'm not sure what to call it... `restart_when_config_changed` seems overly verbose.
| True | supervisorctl should support restarting service only if config changed - ##### ISSUE TYPE
- Feature Idea
##### COMPONENT NAME
supervisorctl
##### ANSIBLE VERSION
```
2.2
```
##### SUMMARY
`supervisorctl` module has no way to conditionally restart a service only if the config changed. This is currently possible with supervisor--call `supervisor reread` and if supervisor reports the config file changed, then we should call `supervisor restart`, otherwise do nothing.
I suggest a new `state` value, although I'm not sure what to call it... `restart_when_config_changed` seems overly verbose.
| main | supervisorctl should support restarting service only if config changed issue type feature idea component name supervisorctl ansible version summary supervisorctl module has no way to conditionally restart a service only if the config changed this is currently possible with supervisor call supervisor reread and if supervisor reports the config file changed then we should call supervisor restart otherwise do nothing i suggest a new state value although i m not sure what to call it restart when config changed seems overly verbose | 1 |
1,690 | 6,574,179,228 | IssuesEvent | 2017-09-11 11:50:50 | ansible/ansible-modules-core | https://api.github.com/repos/ansible/ansible-modules-core | closed | negative lookahead assertion broken in Ansible 2 | affects_2.2 bug_report waiting_on_maintainer |
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
replace
##### ANSIBLE VERSION
ansible 2.2.0.0
config file = /home/pdxmft/ansible/config/ansible.cfg
configured module search path = ['/usr/share/ansible/']
```
```
##### CONFIGURATION
ANSIBLE_HOSTS=/home/pdxmft/ansible/config/hosts
ANSIBLE_CONFIG=/home/pdxmft/ansible/config/ansible.cfg
ansible.cfg is stock
##### OS / ENVIRONMENT
Server: RHEL 7.2
Client: RHEL 7.2
##### SUMMARY
```
Negative lookahead assertions in regular expressions do not appear to be working in Ansible 2, but work perfectly in Ansible 1.9
```
##### STEPS TO REPRODUCE
```
I wrote the below to ensure certain options are set in a server's /etc/fstab file for CIS compliance:
- name: Describe file system options
set_fact:
filesystems:
- fs: /tmp
options:
- nodev
- nosuid
- fs: /home
options:
- nodev
- fs: /dev/shm
options:
- nodev
- nosuid
- noexec
- name: CIS - Set options for file systems
replace: dest=/etc/fstab
regexp='(^[/\-\w]*\s+{{item.0.fs}}\s+\w+\s+(?!.*\b{{item.1}}\b))([\w,]+)(\s+[0-9]\s+[0-9])$'
replace='\1\2,{{item.1}}\3'
with_subelements:
- "{{filesystems}}"
- options
My fstab file starts out like this:
/dev/mapper/VolGroup00-root / xfs defaults 1 1
UUID=55b51f79-af10-4590-88df-8aefeeedb3fc /boot xfs defaults 0 0
/dev/mapper/VolGroup00-home /home xfs defaults 0 0
/dev/mapper/VolGroup00-tmp /tmp xfs defaults 0 0
/dev/mapper/VolGroup00-var /var xfs defaults 0 0
UUID=c56d0641-b1ef-4ef5-ba3c-1dfb983e28ce swap swap defaults 0 0
The expectation is that options listed under a given file system name will be added to the options for that file system. For example:
/dev/mapper/VolGroup00-home /home xfs defaults,nodev 0 0
/dev/mapper/VolGroup00-tmp /tmp xfs defaults,nodev,nosuid 0 0
This worked perfectly on Ansible version 1.9.4, but when I ported it to Ansible 2.1.2, it broke. When I run it on 2.1.2, Ansible no longer detects that the options have already been applied and applies them again. Each time the playbook is run against the servers, another set of options is added to the already existing set:
/dev/mapper/VolGroup00-home /home xfs defaults,nodev,nodev 0 0
/dev/mapper/VolGroup00-tmp /tmp xfs defaults,nodev,nosuid,nodev,nosuid 0 0
```
##### EXPECTED RESULTS
The options listed for each file system should be applied to the line for that file system just once, and should not be applied again if the options already exist in the line.
##### ACTUAL RESULTS
The options are applied each time the playbook is run regardless of if the options are already present for the line. This occurs with Ansible 2, but not with Ansible 1.9.4.
<!--- Paste verbatim command output between quotes below -->
```
TASK [CIS - Set options for file systems] **************************************
changed: [localhost] => (item=({u'fs': u'/tmp'}, u'nodev'))
changed: [localhost] => (item=({u'fs': u'/tmp'}, u'nosuid'))
changed: [localhost] => (item=({u'fs': u'/home'}, u'nodev'))
```
| True | negative lookahead assertion broken in Ansible 2 -
##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
replace
##### ANSIBLE VERSION
ansible 2.2.0.0
config file = /home/pdxmft/ansible/config/ansible.cfg
configured module search path = ['/usr/share/ansible/']
```
```
##### CONFIGURATION
ANSIBLE_HOSTS=/home/pdxmft/ansible/config/hosts
ANSIBLE_CONFIG=/home/pdxmft/ansible/config/ansible.cfg
ansible.cfg is stock
##### OS / ENVIRONMENT
Server: RHEL 7.2
Client: RHEL 7.2
##### SUMMARY
```
Negative lookahead assertions in regular expressions do not appear to be working in Ansible 2, but work perfectly in Ansible 1.9
```
##### STEPS TO REPRODUCE
```
I wrote the below to ensure certain options are set in a server's /etc/fstab file for CIS compliance:
- name: Describe file system options
set_fact:
filesystems:
- fs: /tmp
options:
- nodev
- nosuid
- fs: /home
options:
- nodev
- fs: /dev/shm
options:
- nodev
- nosuid
- noexec
- name: CIS - Set options for file systems
replace: dest=/etc/fstab
regexp='(^[/\-\w]*\s+{{item.0.fs}}\s+\w+\s+(?!.*\b{{item.1}}\b))([\w,]+)(\s+[0-9]\s+[0-9])$'
replace='\1\2,{{item.1}}\3'
with_subelements:
- "{{filesystems}}"
- options
My fstab file starts out like this:
/dev/mapper/VolGroup00-root / xfs defaults 1 1
UUID=55b51f79-af10-4590-88df-8aefeeedb3fc /boot xfs defaults 0 0
/dev/mapper/VolGroup00-home /home xfs defaults 0 0
/dev/mapper/VolGroup00-tmp /tmp xfs defaults 0 0
/dev/mapper/VolGroup00-var /var xfs defaults 0 0
UUID=c56d0641-b1ef-4ef5-ba3c-1dfb983e28ce swap swap defaults 0 0
The expectation is that options listed under a given file system name will be added to the options for that file system. For example:
/dev/mapper/VolGroup00-home /home xfs defaults,nodev 0 0
/dev/mapper/VolGroup00-tmp /tmp xfs defaults,nodev,nosuid 0 0
This worked perfectly on Ansible version 1.9.4, but when I ported it to Ansible 2.1.2, it broke. When I run it on 2.1.2, Ansible no longer detects that the options have already been applied and applies them again. Each time the playbook is run against the servers, another set of options is added to the already existing set:
/dev/mapper/VolGroup00-home /home xfs defaults,nodev,nodev 0 0
/dev/mapper/VolGroup00-tmp /tmp xfs defaults,nodev,nosuid,nodev,nosuid 0 0
```
##### EXPECTED RESULTS
The options listed for each file system should be applied to the line for that file system just once, and should not be applied again if the options already exist in the line.
##### ACTUAL RESULTS
The options are applied each time the playbook is run regardless of if the options are already present for the line. This occurs with Ansible 2, but not with Ansible 1.9.4.
<!--- Paste verbatim command output between quotes below -->
```
TASK [CIS - Set options for file systems] **************************************
changed: [localhost] => (item=({u'fs': u'/tmp'}, u'nodev'))
changed: [localhost] => (item=({u'fs': u'/tmp'}, u'nosuid'))
changed: [localhost] => (item=({u'fs': u'/home'}, u'nodev'))
```
| main | negative lookahead assertion broken in ansible issue type bug report component name replace ansible version ansible config file home pdxmft ansible config ansible cfg configured module search path configuration ansible hosts home pdxmft ansible config hosts ansible config home pdxmft ansible config ansible cfg ansible cfg is stock os environment server rhel client rhel summary negative lookahead assertions in regular expressions do not appear to be working in ansible but work perfectly in ansible steps to reproduce i wrote the below to ensure certain options are set in a server s etc fstab file for cis compliance name describe file system options set fact filesystems fs tmp options nodev nosuid fs home options nodev fs dev shm options nodev nosuid noexec name cis set options for file systems replace dest etc fstab regexp s item fs s w s b item b s s replace item with subelements filesystems options my fstab file starts out like this dev mapper root xfs defaults uuid boot xfs defaults dev mapper home home xfs defaults dev mapper tmp tmp xfs defaults dev mapper var var xfs defaults uuid swap swap defaults the expectation is that options listed under a given file system name will be added to the options for that file system for example dev mapper home home xfs defaults nodev dev mapper tmp tmp xfs defaults nodev nosuid this worked perfectly on ansible version but when i ported it to ansible it broke when i run it on ansible no longer detects that the options have already been applied and applies them again each time the playbook is run against the servers another set of options is added to the already existing set dev mapper home home xfs defaults nodev nodev dev mapper tmp tmp xfs defaults nodev nosuid nodev nosuid expected results the options listed for each file system should be applied to the line for that file system just once and should not be applied again if the options already exist in the line actual results the options are applied each time the playbook is run regardless of if the options are already present for the line this occurs with ansible but not with ansible task changed item u fs u tmp u nodev changed item u fs u tmp u nosuid changed item u fs u home u nodev | 1 |
3,085 | 11,714,864,253 | IssuesEvent | 2020-03-09 13:11:36 | custom-cards/flex-table-card | https://api.github.com/repos/custom-cards/flex-table-card | closed | Hacs install lists type as module, should be js | docs maintaining | When looking at this component in HACS it says to list the type as module when including it in the list of resources in the yaml. This doesn't work though, it only works when type is js. It says the correct type in the readme of this repo but the HACS guide needs to be updated to match | True | Hacs install lists type as module, should be js - When looking at this component in HACS it says to list the type as module when including it in the list of resources in the yaml. This doesn't work though, it only works when type is js. It says the correct type in the readme of this repo but the HACS guide needs to be updated to match | main | hacs install lists type as module should be js when looking at this component in hacs it says to list the type as module when including it in the list of resources in the yaml this doesn t work though it only works when type is js it says the correct type in the readme of this repo but the hacs guide needs to be updated to match | 1 |
3,713 | 15,254,759,962 | IssuesEvent | 2021-02-20 13:22:08 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | closed | Vulnerability roundup 93: keycloak-10.0.2: 1 advisory [7.5] | 1.severity: security 9.needs: maintainer feedback | [search](https://search.nix.gsc.io/?q=keycloak&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=keycloak+in%3Apath&type=Code)
* [ ] [CVE-2020-10758](https://nvd.nist.gov/vuln/detail/CVE-2020-10758) CVSSv3=7.5 (nixos-20.09)
Scanned versions: nixos-20.09: ad3a5d5092e.
Cc @ngerstle
| True | Vulnerability roundup 93: keycloak-10.0.2: 1 advisory [7.5] - [search](https://search.nix.gsc.io/?q=keycloak&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=keycloak+in%3Apath&type=Code)
* [ ] [CVE-2020-10758](https://nvd.nist.gov/vuln/detail/CVE-2020-10758) CVSSv3=7.5 (nixos-20.09)
Scanned versions: nixos-20.09: ad3a5d5092e.
Cc @ngerstle
| main | vulnerability roundup keycloak advisory nixos scanned versions nixos cc ngerstle | 1 |
5,019 | 25,776,063,601 | IssuesEvent | 2022-12-09 12:05:41 | maticnetwork/matic-docs | https://api.github.com/repos/maticnetwork/matic-docs | closed | trying deploy full node on google cloud but below errors | help wanted question T2: Maintain | Welcome to Cloud Shell! Type "help" to get started.
Your Cloud Platform project in this session is set to polygon-346517.
Use “gcloud config set project [PROJECT_ID]” to change to a different project.
ramesh_ram0341@cloudshell:~ (polygon-346517)$ export POLYGON_NETWORK=mainnet
export POLYGON_NODETYPE=fullnode
export POLYGON_BOOTSTRAP_MODE=snapshot
export POLYGON_RPC_PORT=8747
export GCP_NETWORK_TAG=polygon
export EXTRA_VAR="bor_branch=v0.2.14 heimdall_branch=v0.2.8 network_version=mainnet-v1 node_type=sentry/sentry heimdall_network=${POLYGON_NETWORK}"
gcloud compute firewall-rules create "polygon-p2p" --allow=tcp:26656,tcp:30303,udp:30303 --description="polygon p2p" --target-tags=${GCP_NETWORK_TAG}
gcloud compute firewall-rules create "polygon-rpc" --allow=tcp:${POLYGON_RPC_PORT} --description="polygon rpc" --target-tags=${GCP_NETWORK_TAG}
export INSTANCE_NAME=polygon-0
export INSTANCE_TYPE=e2-standard-8
export BOR_EXT_DISK_SIZE=1024
{POLYGON_NETWORK}' -m '${POLYGON_NODETYPE}' -s '${POLYGON_BOOTSTRAP_MODE}' -p '${POLYGON_RPC_PORT}' -e \"'${EXTRA_VAR}'\"; bash"'.sh | bash -s -- -n '$
Creating firewall...failed.
ERROR: (gcloud.compute.firewall-rules.create) Could not fetch resource:
- The resource 'projects/polygon-346517/global/firewalls/polygon-p2p' already exists
Creating firewall...failed.
ERROR: (gcloud.compute.firewall-rules.create) Could not fetch resource:
- The resource 'projects/polygon-346517/global/firewalls/polygon-rpc' already exists
ERROR: (gcloud.compute.instances.create) unrecognized arguments:
heimdall_branch=v0.2.8
network_version=mainnet-v1 (did you mean '--network-tier'?)
node_type=sentry/sentry
heimdall_network=mainnet\"; bash"
To search the help text of gcloud commands, run:
gcloud help -- SEARCH_TERMS | True | trying deploy full node on google cloud but below errors - Welcome to Cloud Shell! Type "help" to get started.
Your Cloud Platform project in this session is set to polygon-346517.
Use “gcloud config set project [PROJECT_ID]” to change to a different project.
ramesh_ram0341@cloudshell:~ (polygon-346517)$ export POLYGON_NETWORK=mainnet
export POLYGON_NODETYPE=fullnode
export POLYGON_BOOTSTRAP_MODE=snapshot
export POLYGON_RPC_PORT=8747
export GCP_NETWORK_TAG=polygon
export EXTRA_VAR="bor_branch=v0.2.14 heimdall_branch=v0.2.8 network_version=mainnet-v1 node_type=sentry/sentry heimdall_network=${POLYGON_NETWORK}"
gcloud compute firewall-rules create "polygon-p2p" --allow=tcp:26656,tcp:30303,udp:30303 --description="polygon p2p" --target-tags=${GCP_NETWORK_TAG}
gcloud compute firewall-rules create "polygon-rpc" --allow=tcp:${POLYGON_RPC_PORT} --description="polygon rpc" --target-tags=${GCP_NETWORK_TAG}
export INSTANCE_NAME=polygon-0
export INSTANCE_TYPE=e2-standard-8
export BOR_EXT_DISK_SIZE=1024
{POLYGON_NETWORK}' -m '${POLYGON_NODETYPE}' -s '${POLYGON_BOOTSTRAP_MODE}' -p '${POLYGON_RPC_PORT}' -e \"'${EXTRA_VAR}'\"; bash"'.sh | bash -s -- -n '$
Creating firewall...failed.
ERROR: (gcloud.compute.firewall-rules.create) Could not fetch resource:
- The resource 'projects/polygon-346517/global/firewalls/polygon-p2p' already exists
Creating firewall...failed.
ERROR: (gcloud.compute.firewall-rules.create) Could not fetch resource:
- The resource 'projects/polygon-346517/global/firewalls/polygon-rpc' already exists
ERROR: (gcloud.compute.instances.create) unrecognized arguments:
heimdall_branch=v0.2.8
network_version=mainnet-v1 (did you mean '--network-tier'?)
node_type=sentry/sentry
heimdall_network=mainnet\"; bash"
To search the help text of gcloud commands, run:
gcloud help -- SEARCH_TERMS | main | trying deploy full node on google cloud but below errors welcome to cloud shell type help to get started your cloud platform project in this session is set to polygon use “gcloud config set project ” to change to a different project ramesh cloudshell polygon export polygon network mainnet export polygon nodetype fullnode export polygon bootstrap mode snapshot export polygon rpc port export gcp network tag polygon export extra var bor branch heimdall branch network version mainnet node type sentry sentry heimdall network polygon network gcloud compute firewall rules create polygon allow tcp tcp udp description polygon target tags gcp network tag gcloud compute firewall rules create polygon rpc allow tcp polygon rpc port description polygon rpc target tags gcp network tag export instance name polygon export instance type standard export bor ext disk size polygon network m polygon nodetype s polygon bootstrap mode p polygon rpc port e extra var bash sh bash s n creating firewall failed error gcloud compute firewall rules create could not fetch resource the resource projects polygon global firewalls polygon already exists creating firewall failed error gcloud compute firewall rules create could not fetch resource the resource projects polygon global firewalls polygon rpc already exists error gcloud compute instances create unrecognized arguments heimdall branch network version mainnet did you mean network tier node type sentry sentry heimdall network mainnet bash to search the help text of gcloud commands run gcloud help search terms | 1 |
473,004 | 13,634,943,509 | IssuesEvent | 2020-09-25 01:24:08 | jeaninebeckle/knit-picker | https://api.github.com/repos/jeaninebeckle/knit-picker | closed | UPDATE project | lower priority | # User Story
As a
# AC
**WHEN**
**THEN**
**AND**
# Dev Notes
*
* | 1.0 | UPDATE project - # User Story
As a
# AC
**WHEN**
**THEN**
**AND**
# Dev Notes
*
* | non_main | update project user story as a ac when then and dev notes | 0 |
2,423 | 8,607,171,924 | IssuesEvent | 2018-11-17 19:34:28 | arcticicestudio/nord-docs | https://api.github.com/repos/arcticicestudio/nord-docs | closed | Husky | context-workflow scope-maintainability type-task | <p align="center"><img src="https://user-images.githubusercontent.com/7836623/48658801-30ad2a80-ea48-11e8-9323-16bb0b25002b.png" width="20%" /></p>
> Must be resolved **after** #17
Integrate [Husky][gh-husky], the tool that make Git hooks easy and can prevent bad Git commits, pushes and more :dog: _woof_!
### Configuration
The configuration file `.huskyrc.js` will be placed in the project root and includes the command to run for any [supported Git hook][gh-husky-docs-hooks]. It will at least contain configs for the following hooks:
- `pre-commit` - Run lint-staged (#17) before each commit (via `lint-staged` command) to ensure all staged files are compliant to all style guides.
## Tasks
- [x] Install [husky][npm-husky] package.
- [x] Implement `.huskyrc.js` configuration file.
[gh-husky]: https://github.com/typicode/husky
[gh-husky-docs-hooks]: https://github.com/typicode/husky/blob/master/DOCS.md#supported-hooks
[npm-husky]: https://www.npmjs.com/package/husky | True | Husky - <p align="center"><img src="https://user-images.githubusercontent.com/7836623/48658801-30ad2a80-ea48-11e8-9323-16bb0b25002b.png" width="20%" /></p>
> Must be resolved **after** #17
Integrate [Husky][gh-husky], the tool that make Git hooks easy and can prevent bad Git commits, pushes and more :dog: _woof_!
### Configuration
The configuration file `.huskyrc.js` will be placed in the project root and includes the command to run for any [supported Git hook][gh-husky-docs-hooks]. It will at least contain configs for the following hooks:
- `pre-commit` - Run lint-staged (#17) before each commit (via `lint-staged` command) to ensure all staged files are compliant to all style guides.
## Tasks
- [x] Install [husky][npm-husky] package.
- [x] Implement `.huskyrc.js` configuration file.
[gh-husky]: https://github.com/typicode/husky
[gh-husky-docs-hooks]: https://github.com/typicode/husky/blob/master/DOCS.md#supported-hooks
[npm-husky]: https://www.npmjs.com/package/husky | main | husky must be resolved after integrate the tool that make git hooks easy and can prevent bad git commits pushes and more dog woof configuration the configuration file huskyrc js will be placed in the project root and includes the command to run for any it will at least contain configs for the following hooks pre commit run lint staged before each commit via lint staged command to ensure all staged files are compliant to all style guides tasks install package implement huskyrc js configuration file | 1 |
4,902 | 25,185,584,333 | IssuesEvent | 2022-11-11 17:36:37 | mozilla/foundation.mozilla.org | https://api.github.com/repos/mozilla/foundation.mozilla.org | closed | Spike | Review Wagtail 3.0 upgrade | engineering Maintain | Goal of the spike: review upcoming Wagtail upgrade and highlight any potential risks/breakages/dependencies that we need to be aware of when making the upgrade
# Dev tasks
- [x] Check changelog of the planned Wagtail 3.0 release (especially the "upgrade considerations") and check impact against out code.
- [x] Check out third-party dependencies and which are likely to break due to the Wagtail 3.0 upgrade.
- [x] Create tickets for steps to prepare the codebase for the Wagtail 3.0 upgrade.
# Acceptance criteria
- [x] We have an idea of how likely the Wagtail 3.0 upgrade is going to break the functionality of the site.
- [x] We have a list of our dependencies that are likely to break due to the Wagtail 3.0 upgrade.
- [x] If there are steps we can/have to take to prepare for the Wagtail 3.0 upgrade, tickets for these steps have been created.
- [x] We have a ticket for the Wagtail 3.0 upgrade.
- [x] If we the Wagtail upgrade is blocked by other steps/tickets, the tickets have the respective dependencies in Zenhub.
| True | Spike | Review Wagtail 3.0 upgrade - Goal of the spike: review upcoming Wagtail upgrade and highlight any potential risks/breakages/dependencies that we need to be aware of when making the upgrade
# Dev tasks
- [x] Check changelog of the planned Wagtail 3.0 release (especially the "upgrade considerations") and check impact against out code.
- [x] Check out third-party dependencies and which are likely to break due to the Wagtail 3.0 upgrade.
- [x] Create tickets for steps to prepare the codebase for the Wagtail 3.0 upgrade.
# Acceptance criteria
- [x] We have an idea of how likely the Wagtail 3.0 upgrade is going to break the functionality of the site.
- [x] We have a list of our dependencies that are likely to break due to the Wagtail 3.0 upgrade.
- [x] If there are steps we can/have to take to prepare for the Wagtail 3.0 upgrade, tickets for these steps have been created.
- [x] We have a ticket for the Wagtail 3.0 upgrade.
- [x] If we the Wagtail upgrade is blocked by other steps/tickets, the tickets have the respective dependencies in Zenhub.
| main | spike review wagtail upgrade goal of the spike review upcoming wagtail upgrade and highlight any potential risks breakages dependencies that we need to be aware of when making the upgrade dev tasks check changelog of the planned wagtail release especially the upgrade considerations and check impact against out code check out third party dependencies and which are likely to break due to the wagtail upgrade create tickets for steps to prepare the codebase for the wagtail upgrade acceptance criteria we have an idea of how likely the wagtail upgrade is going to break the functionality of the site we have a list of our dependencies that are likely to break due to the wagtail upgrade if there are steps we can have to take to prepare for the wagtail upgrade tickets for these steps have been created we have a ticket for the wagtail upgrade if we the wagtail upgrade is blocked by other steps tickets the tickets have the respective dependencies in zenhub | 1 |
38,026 | 8,402,321,175 | IssuesEvent | 2018-10-11 06:06:16 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | reopened | RyuJIT: By-ref assignment with null leads to runtime crash | area-CodeGen | The following example crashes the runtime when compiled and run in either debug or release:
```csharp
class C0
{
}
struct S0
{
public C0 F0;
public ulong F4;
}
class C1
{
public S0 F3;
}
struct S1
{
public S0 F3;
}
public class Program
{
static S1 s_38;
static C1 s_43;
public static void Main()
{
s_38.F3 = s_43.F3;
}
}
```
In debug (and probably checked) builds, this assertion triggers:
```
Assert failure(PID 20848 [0x00005170], Thread: 17420 [0x440c]): Consistency check failed: AV in clr at this callstack:
------
CORECLR! JIT_ByRefWriteBarrier + 0x0 (0x00007ffc`5e207d70)
<no module>! <no symbol> + 0x0 (0x00007ffb`fef22611)
<no module>! <no symbol> + 0x0 (0x00007ffb`fee045e0)
<no module>! <no symbol> + 0x0 (0x000000fa`00000005)
<no module>! <no symbol> + 0x0 (0x000000fa`2077d580)
-----
.AV on tid=0x440c (17420), cxr=000000FA2077CE00, exr=000000FA2077D2F0
FAILED: false
CORECLR! CHECK::Trigger + 0x275 (0x00007ffc`5db0cea5)
CORECLR! CLRVectoredExceptionHandlerPhase3 + 0x332 (0x00007ffc`5dc1bd62)
CORECLR! CLRVectoredExceptionHandlerPhase2 + 0x8C (0x00007ffc`5dc1b70c)
CORECLR! CLRVectoredExceptionHandler + 0x275 (0x00007ffc`5dc1b665)
CORECLR! CLRVectoredExceptionHandlerShim + 0x18D (0x00007ffc`5dc1c04d)
NTDLL! RtlInitializeCriticalSection + 0x1D8 (0x00007ffc`c5bd5678)
NTDLL! RtlWalkFrameChain + 0x109A (0x00007ffc`c5b7692a)
NTDLL! KiUserExceptionDispatcher + 0x2E (0x00007ffc`c5c0dc1e)
CORECLR! JIT_ByRefWriteBarrier + 0x0 (0x00007ffc`5e207d70)
<no module>! <no symbol> + 0x0 (0x00007ffb`fef22611)
File: z:\programming\dotnet\coreclr\src\vm\excep.cpp Line: 7831
Image: Z:\Programming\dotnet\coreclr\bin\Product\Windows_NT.x64.Debug\CoreRun.exe
```
The code generated is:
```asm
; Assembly listing for method Program:Main()
; Emitting BLENDED_CODE for X64 CPU with AVX
; optimized code
; rsp based frame
; partially interruptible
; Final local variable assignments
;
; V00 OutArgs [V00 ] ( 1, 1 ) lclBlk (32) [rsp+0x00]
; V01 cse0 [V01,T00] ( 5, 5 ) long -> [rsp+0x20]
;
; Lcl frame size = 40
G_M5092_IG01:
57 push rdi
56 push rsi
4883EC28 sub rsp, 40
G_M5092_IG02:
48B9E045E3FEFB7F0000 mov rcx, 0x7FFBFEE345E0
BA05000000 mov edx, 5
E8461E455F call CORINFO_HELP_GETSHARED_NONGCSTATIC_BASE
48B87829001091010000 mov rax, 0x19110002978
488B00 mov rax, gword ptr [rax]
488D7008 lea rsi, bword ptr [rax+8]
48B87029001091010000 mov rax, 0x19110002970
488B00 mov rax, gword ptr [rax]
488D7808 lea rdi, bword ptr [rax+8]
E85F572B5F call CORINFO_HELP_ASSIGN_BYREF
48A5 movsq
G_M5092_IG03:
4883C428 add rsp, 40
5E pop rsi
5F pop rdi
C3 ret
; Total bytes of code 74, prolog size 6 for method Program:Main()
;
```
Question: How will this normally be handled by CoreCLR? Should the runtime turn the AV in `CORINFO_HELP_ASSIGN_BYREF` into a managed NRE, or is the caller supposed to null-check/deref the reference before calling `CORINFO_HELP_ASSIGN_BYREF`? | 1.0 | RyuJIT: By-ref assignment with null leads to runtime crash - The following example crashes the runtime when compiled and run in either debug or release:
```csharp
class C0
{
}
struct S0
{
public C0 F0;
public ulong F4;
}
class C1
{
public S0 F3;
}
struct S1
{
public S0 F3;
}
public class Program
{
static S1 s_38;
static C1 s_43;
public static void Main()
{
s_38.F3 = s_43.F3;
}
}
```
In debug (and probably checked) builds, this assertion triggers:
```
Assert failure(PID 20848 [0x00005170], Thread: 17420 [0x440c]): Consistency check failed: AV in clr at this callstack:
------
CORECLR! JIT_ByRefWriteBarrier + 0x0 (0x00007ffc`5e207d70)
<no module>! <no symbol> + 0x0 (0x00007ffb`fef22611)
<no module>! <no symbol> + 0x0 (0x00007ffb`fee045e0)
<no module>! <no symbol> + 0x0 (0x000000fa`00000005)
<no module>! <no symbol> + 0x0 (0x000000fa`2077d580)
-----
.AV on tid=0x440c (17420), cxr=000000FA2077CE00, exr=000000FA2077D2F0
FAILED: false
CORECLR! CHECK::Trigger + 0x275 (0x00007ffc`5db0cea5)
CORECLR! CLRVectoredExceptionHandlerPhase3 + 0x332 (0x00007ffc`5dc1bd62)
CORECLR! CLRVectoredExceptionHandlerPhase2 + 0x8C (0x00007ffc`5dc1b70c)
CORECLR! CLRVectoredExceptionHandler + 0x275 (0x00007ffc`5dc1b665)
CORECLR! CLRVectoredExceptionHandlerShim + 0x18D (0x00007ffc`5dc1c04d)
NTDLL! RtlInitializeCriticalSection + 0x1D8 (0x00007ffc`c5bd5678)
NTDLL! RtlWalkFrameChain + 0x109A (0x00007ffc`c5b7692a)
NTDLL! KiUserExceptionDispatcher + 0x2E (0x00007ffc`c5c0dc1e)
CORECLR! JIT_ByRefWriteBarrier + 0x0 (0x00007ffc`5e207d70)
<no module>! <no symbol> + 0x0 (0x00007ffb`fef22611)
File: z:\programming\dotnet\coreclr\src\vm\excep.cpp Line: 7831
Image: Z:\Programming\dotnet\coreclr\bin\Product\Windows_NT.x64.Debug\CoreRun.exe
```
The code generated is:
```asm
; Assembly listing for method Program:Main()
; Emitting BLENDED_CODE for X64 CPU with AVX
; optimized code
; rsp based frame
; partially interruptible
; Final local variable assignments
;
; V00 OutArgs [V00 ] ( 1, 1 ) lclBlk (32) [rsp+0x00]
; V01 cse0 [V01,T00] ( 5, 5 ) long -> [rsp+0x20]
;
; Lcl frame size = 40
G_M5092_IG01:
57 push rdi
56 push rsi
4883EC28 sub rsp, 40
G_M5092_IG02:
48B9E045E3FEFB7F0000 mov rcx, 0x7FFBFEE345E0
BA05000000 mov edx, 5
E8461E455F call CORINFO_HELP_GETSHARED_NONGCSTATIC_BASE
48B87829001091010000 mov rax, 0x19110002978
488B00 mov rax, gword ptr [rax]
488D7008 lea rsi, bword ptr [rax+8]
48B87029001091010000 mov rax, 0x19110002970
488B00 mov rax, gword ptr [rax]
488D7808 lea rdi, bword ptr [rax+8]
E85F572B5F call CORINFO_HELP_ASSIGN_BYREF
48A5 movsq
G_M5092_IG03:
4883C428 add rsp, 40
5E pop rsi
5F pop rdi
C3 ret
; Total bytes of code 74, prolog size 6 for method Program:Main()
;
```
Question: How will this normally be handled by CoreCLR? Should the runtime turn the AV in `CORINFO_HELP_ASSIGN_BYREF` into a managed NRE, or is the caller supposed to null-check/deref the reference before calling `CORINFO_HELP_ASSIGN_BYREF`? | non_main | ryujit by ref assignment with null leads to runtime crash the following example crashes the runtime when compiled and run in either debug or release csharp class struct public public ulong class public struct public public class program static s static s public static void main s s in debug and probably checked builds this assertion triggers assert failure pid thread consistency check failed av in clr at this callstack coreclr jit byrefwritebarrier av on tid cxr exr failed false coreclr check trigger coreclr coreclr coreclr clrvectoredexceptionhandler coreclr clrvectoredexceptionhandlershim ntdll rtlinitializecriticalsection ntdll rtlwalkframechain ntdll kiuserexceptiondispatcher coreclr jit byrefwritebarrier file z programming dotnet coreclr src vm excep cpp line image z programming dotnet coreclr bin product windows nt debug corerun exe the code generated is asm assembly listing for method program main emitting blended code for cpu with avx optimized code rsp based frame partially interruptible final local variable assignments outargs lclblk long lcl frame size g push rdi push rsi sub rsp g mov rcx mov edx call corinfo help getshared nongcstatic base mov rax mov rax gword ptr lea rsi bword ptr mov rax mov rax gword ptr lea rdi bword ptr call corinfo help assign byref movsq g add rsp pop rsi pop rdi ret total bytes of code prolog size for method program main question how will this normally be handled by coreclr should the runtime turn the av in corinfo help assign byref into a managed nre or is the caller supposed to null check deref the reference before calling corinfo help assign byref | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.