Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
413,445 | 27,952,389,724 | IssuesEvent | 2023-03-24 09:51:10 | ESMValGroup/ESMValCore | https://api.github.com/repos/ESMValGroup/ESMValCore | opened | ESMValCore 'stable' build still points to v2.7.1 | documentation | The build for the 'stable' version of the ESMValCore documentation [failed](https://readthedocs.org/projects/esmvalcore/builds/19880948/), so the 'stable' label still points to the previous release.
It looks like this happened because it tried to resolve links to the 'stable' ESMValTool documentation (which still points to ESMValTool v2.7), which are not available yet because they were introduced after that release.
```
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:142: WARNING: undefined label: 'esmvaltool:backward-compatibility-policy'
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:586: WARNING: undefined label: 'esmvaltool:backward-compatibility-policy'
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:758: WARNING: undefined label: 'esmvaltool:release_steps'
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:805: WARNING: undefined label: 'esmvaltool:backward-compatibility-policy'
``` | 1.0 | ESMValCore 'stable' build still points to v2.7.1 - The build for the 'stable' version of the ESMValCore documentation [failed](https://readthedocs.org/projects/esmvalcore/builds/19880948/), so the 'stable' label still points to the previous release.
It looks like this happened because it tried to resolve links to the 'stable' ESMValTool documentation (which still points to ESMValTool v2.7), which are not available yet because they were introduced after that release.
```
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:142: WARNING: undefined label: 'esmvaltool:backward-compatibility-policy'
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:586: WARNING: undefined label: 'esmvaltool:backward-compatibility-policy'
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:758: WARNING: undefined label: 'esmvaltool:release_steps'
/home/docs/checkouts/readthedocs.org/user_builds/esmvalcore/checkouts/stable/doc/contributing.rst:805: WARNING: undefined label: 'esmvaltool:backward-compatibility-policy'
``` | non_priority | esmvalcore stable build still points to the build for the stable version of the esmvalcore documentation so the stable label still points to the previous release it looks like this happened because it tried to resolve links to the stable esmvaltool documentation which still points to esmvaltool which are not available yet because they were introduced after that release home docs checkouts readthedocs org user builds esmvalcore checkouts stable doc contributing rst warning undefined label esmvaltool backward compatibility policy home docs checkouts readthedocs org user builds esmvalcore checkouts stable doc contributing rst warning undefined label esmvaltool backward compatibility policy home docs checkouts readthedocs org user builds esmvalcore checkouts stable doc contributing rst warning undefined label esmvaltool release steps home docs checkouts readthedocs org user builds esmvalcore checkouts stable doc contributing rst warning undefined label esmvaltool backward compatibility policy | 0 |
279,828 | 8,674,065,802 | IssuesEvent | 2018-11-30 05:52:09 | leo-project/leofs | https://api.github.com/repos/leo-project/leofs | opened | [docs] Add a FAQ - How to count the number of files in a specific bucket | Document Priority-MIDDLE v1.4 | As I answered in https://github.com/leo-project/leofs/issues/1142#issuecomment-442707443, using the file generated by leofs-adm diagnose-start would be most efficient to count the number of files in a specific bucket. Other ways like using "s3cmd ls" or something similar with aws-sdk would be very inefficient and take much longer time so we have to recommend the way using leofs-adm diagnose-start in our official docs. | 1.0 | [docs] Add a FAQ - How to count the number of files in a specific bucket - As I answered in https://github.com/leo-project/leofs/issues/1142#issuecomment-442707443, using the file generated by leofs-adm diagnose-start would be most efficient to count the number of files in a specific bucket. Other ways like using "s3cmd ls" or something similar with aws-sdk would be very inefficient and take much longer time so we have to recommend the way using leofs-adm diagnose-start in our official docs. | priority | add a faq how to count the number of files in a specific bucket as i answered in using the file generated by leofs adm diagnose start would be most efficient to count the number of files in a specific bucket other ways like using ls or something similar with aws sdk would be very inefficient and take much longer time so we have to recommend the way using leofs adm diagnose start in our official docs | 1 |
49,761 | 6,039,394,265 | IssuesEvent | 2017-06-10 02:36:28 | ClassicWoW/Nefarian_1.12.1_Bugtracker | https://api.github.com/repos/ClassicWoW/Nefarian_1.12.1_Bugtracker | closed | [Naxxramas]Steinhautgargoyle | Auf Testserver Dev Behoben Script Kreaturen | Welches Verhalten wird beobachtet?
Die Giftsalve kommt zu häufig, sie kommt circa alle [4 Sekunden](https://youtu.be/Olzvyf7ccso?t=1h15m).
Wie sollte es sich verhalten?
Die Salve sollte deutlich seltener kommen, nur circa alle 8-10 Sekunden.
Schritte zur Reproduzierung
Gargoyle pullen und die Frequenz der Salve überprüfen
Zusätzliche Informationen (Screenshots, Videos, Klasse, Rasse, Level, etc.)
[Hier](https://youtu.be/FH7ytRnmgDc?t=4m) sieht man, dass die Gargoyles die Salve nicht alle 4 Sekunden, sondern mit einer niedrigeren Frequenz benutzen.
[Steinhautgargoyle auf Wowwiki](http://wowwiki.wikia.com/wiki/Stoneskin_Gargoyle?oldid=338320)
Alle Kreaturen, Items, Objekte, Quests, Zauber etc. müssen aus unserer Datenbank verlinkt sein.
https://datenbank.classic-wow.org/?npc=16168#abilities
https://datenbank.classic-wow.org/?spell=29325 | 1.0 | [Naxxramas]Steinhautgargoyle - Welches Verhalten wird beobachtet?
Die Giftsalve kommt zu häufig, sie kommt circa alle [4 Sekunden](https://youtu.be/Olzvyf7ccso?t=1h15m).
Wie sollte es sich verhalten?
Die Salve sollte deutlich seltener kommen, nur circa alle 8-10 Sekunden.
Schritte zur Reproduzierung
Gargoyle pullen und die Frequenz der Salve überprüfen
Zusätzliche Informationen (Screenshots, Videos, Klasse, Rasse, Level, etc.)
[Hier](https://youtu.be/FH7ytRnmgDc?t=4m) sieht man, dass die Gargoyles die Salve nicht alle 4 Sekunden, sondern mit einer niedrigeren Frequenz benutzen.
[Steinhautgargoyle auf Wowwiki](http://wowwiki.wikia.com/wiki/Stoneskin_Gargoyle?oldid=338320)
Alle Kreaturen, Items, Objekte, Quests, Zauber etc. müssen aus unserer Datenbank verlinkt sein.
https://datenbank.classic-wow.org/?npc=16168#abilities
https://datenbank.classic-wow.org/?spell=29325 | non_priority | steinhautgargoyle welches verhalten wird beobachtet die giftsalve kommt zu häufig sie kommt circa alle wie sollte es sich verhalten die salve sollte deutlich seltener kommen nur circa alle sekunden schritte zur reproduzierung gargoyle pullen und die frequenz der salve überprüfen zusätzliche informationen screenshots videos klasse rasse level etc sieht man dass die gargoyles die salve nicht alle sekunden sondern mit einer niedrigeren frequenz benutzen alle kreaturen items objekte quests zauber etc müssen aus unserer datenbank verlinkt sein | 0 |
115,000 | 4,650,619,582 | IssuesEvent | 2016-10-03 05:59:36 | TauCetiStation/TauCetiClassic | https://api.github.com/repos/TauCetiStation/TauCetiClassic | closed | Баг отображения Т-образной трубы. | bug priority: low | <!--
1. ОТВЕТЫ ОСТАВЛЯТЬ ПОД СООТВЕТСТВУЮЩИЕ ЗАГОЛОВКИ
(они в самом низу, после всех правил)
2. В ОДНОМ РЕПОРТЕ ДОЛЖНО БЫТЬ ОПИСАНИЕ ТОЛЬКО ОДНОЙ ПРОБЛЕМЫ
3. КОРРЕКТНОЕ НАЗВАНИЕ РЕПОРТА НЕ МЕНЕЕ ВАЖНО ЧЕМ ОПИСАНИЕ
-. Ниже описание каждого пункта.
1. Весь данный текст что уже написан до вас -
НЕ УДАЛЯТЬ И НЕ РЕДАКТИРОВАТЬ.
Если нечего написать в тот или иной пункт -
просто оставить пустым.
2. Не надо описывать пачку багов в одном репорте,
(!даже если там все описать можно парой слов!)
шанс что их исправят за раз, крайне мал.
А вот использовать на гите удобную функцию -
автозакрытия репорта при мерже пулл реквеста -
исправляющего данный репорт, будет невозможно.
3. Корректное и в меру подробное название репорта -
тоже очень важно! Чтобы даже не заходя в сам репорт -
было понятно что за проблема.
Плохой пример: "Ковер." - что мы должны понять из такого названия?
Хороший пример: "Некорректное отображение спрайтов ковра." -
а вот так уже будет понятно о чем репорт.
Это надо как минимум для того, чтобы вам же самим -
было видно, что репорта_нейм еще нет или наоборот,
уже есть, и это можно было понять не углубляясь в -
чтение каждого репорта внутри. Когда название не имеет конкретики, из -
которого нельзя понять о чем репорт, это также затрудняет функцию поиска.
-->
#### Подробное описание проблемы
Тобразная трубы отображена не верно.

Также если еще чтото прикрутить к Т-трубе ее отобразит как полная. | 1.0 | Баг отображения Т-образной трубы. - <!--
1. ОТВЕТЫ ОСТАВЛЯТЬ ПОД СООТВЕТСТВУЮЩИЕ ЗАГОЛОВКИ
(они в самом низу, после всех правил)
2. В ОДНОМ РЕПОРТЕ ДОЛЖНО БЫТЬ ОПИСАНИЕ ТОЛЬКО ОДНОЙ ПРОБЛЕМЫ
3. КОРРЕКТНОЕ НАЗВАНИЕ РЕПОРТА НЕ МЕНЕЕ ВАЖНО ЧЕМ ОПИСАНИЕ
-. Ниже описание каждого пункта.
1. Весь данный текст что уже написан до вас -
НЕ УДАЛЯТЬ И НЕ РЕДАКТИРОВАТЬ.
Если нечего написать в тот или иной пункт -
просто оставить пустым.
2. Не надо описывать пачку багов в одном репорте,
(!даже если там все описать можно парой слов!)
шанс что их исправят за раз, крайне мал.
А вот использовать на гите удобную функцию -
автозакрытия репорта при мерже пулл реквеста -
исправляющего данный репорт, будет невозможно.
3. Корректное и в меру подробное название репорта -
тоже очень важно! Чтобы даже не заходя в сам репорт -
было понятно что за проблема.
Плохой пример: "Ковер." - что мы должны понять из такого названия?
Хороший пример: "Некорректное отображение спрайтов ковра." -
а вот так уже будет понятно о чем репорт.
Это надо как минимум для того, чтобы вам же самим -
было видно, что репорта_нейм еще нет или наоборот,
уже есть, и это можно было понять не углубляясь в -
чтение каждого репорта внутри. Когда название не имеет конкретики, из -
которого нельзя понять о чем репорт, это также затрудняет функцию поиска.
-->
#### Подробное описание проблемы
Тобразная трубы отображена не верно.

Также если еще чтото прикрутить к Т-трубе ее отобразит как полная. | priority | баг отображения т образной трубы ответы оставлять под соответствующие заголовки они в самом низу после всех правил в одном репорте должно быть описание только одной проблемы корректное название репорта не менее важно чем описание ниже описание каждого пункта весь данный текст что уже написан до вас не удалять и не редактировать если нечего написать в тот или иной пункт просто оставить пустым не надо описывать пачку багов в одном репорте даже если там все описать можно парой слов шанс что их исправят за раз крайне мал а вот использовать на гите удобную функцию автозакрытия репорта при мерже пулл реквеста исправляющего данный репорт будет невозможно корректное и в меру подробное название репорта тоже очень важно чтобы даже не заходя в сам репорт было понятно что за проблема плохой пример ковер что мы должны понять из такого названия хороший пример некорректное отображение спрайтов ковра а вот так уже будет понятно о чем репорт это надо как минимум для того чтобы вам же самим было видно что репорта нейм еще нет или наоборот уже есть и это можно было понять не углубляясь в чтение каждого репорта внутри когда название не имеет конкретики из которого нельзя понять о чем репорт это также затрудняет функцию поиска подробное описание проблемы тобразная трубы отображена не верно также если еще чтото прикрутить к т трубе ее отобразит как полная | 1 |
82,288 | 10,277,096,432 | IssuesEvent | 2019-08-25 00:25:37 | acaloiaro/prwatch | https://api.github.com/repos/acaloiaro/prwatch | closed | Improve README.md | documentation | - Document that only Jira projects are supported (for now)
- Document how Pull Requests require a project key, e.g. `MYPROJ-1234` anywhere in the description as a URL or plain text | 1.0 | Improve README.md - - Document that only Jira projects are supported (for now)
- Document how Pull Requests require a project key, e.g. `MYPROJ-1234` anywhere in the description as a URL or plain text | non_priority | improve readme md document that only jira projects are supported for now document how pull requests require a project key e g myproj anywhere in the description as a url or plain text | 0 |
218,316 | 7,331,065,934 | IssuesEvent | 2018-03-05 12:11:27 | NCEAS/metacat | https://api.github.com/repos/NCEAS/metacat | closed | ESA path in data package acceptance email is incorrect | Category: metacat Component: Bugzilla-Id Priority: Normal Status: Resolved Tracker: Bug | ---
Author Name: **Callie Bowdish** (Callie Bowdish)
Original Redmine Issue: 3362, https://projects.ecoinformatics.org/ecoinfo/issues/3362
Original Date: 2008-06-03
Original Assignee: Jing Tao
---
ESA email from moderator when the data package is accepted does not have the correct path to the data package.
-------------
Example
Dear Callie Bowdish,
We are happy to inform you that the metadata entry for your article submission,
Cedar creek, has been accepted. This part of the submission process is now
complete. Your metadata entry can be cited in the future as <LSID>, and will be
viewable online at /metacat/metacat?action=read&cfg=esa&docid=esa.5 after publication. Thank you for your cooperation.
The Ecological Society of America
| 1.0 | ESA path in data package acceptance email is incorrect - ---
Author Name: **Callie Bowdish** (Callie Bowdish)
Original Redmine Issue: 3362, https://projects.ecoinformatics.org/ecoinfo/issues/3362
Original Date: 2008-06-03
Original Assignee: Jing Tao
---
ESA email from moderator when the data package is accepted does not have the correct path to the data package.
-------------
Example
Dear Callie Bowdish,
We are happy to inform you that the metadata entry for your article submission,
Cedar creek, has been accepted. This part of the submission process is now
complete. Your metadata entry can be cited in the future as <LSID>, and will be
viewable online at /metacat/metacat?action=read&cfg=esa&docid=esa.5 after publication. Thank you for your cooperation.
The Ecological Society of America
| priority | esa path in data package acceptance email is incorrect author name callie bowdish callie bowdish original redmine issue original date original assignee jing tao esa email from moderator when the data package is accepted does not have the correct path to the data package example dear callie bowdish we are happy to inform you that the metadata entry for your article submission cedar creek has been accepted this part of the submission process is now complete your metadata entry can be cited in the future as and will be viewable online at metacat metacat action read cfg esa docid esa after publication thank you for your cooperation the ecological society of america | 1 |
51,445 | 13,635,124,799 | IssuesEvent | 2020-09-25 01:58:10 | nasifimtiazohi/openmrs-module-referencedemodata-1.4.5 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-referencedemodata-1.4.5 | opened | CVE-2019-2692 (Medium) detected in mysql-connector-java-5.1.28.jar | security vulnerability | ## CVE-2019-2692 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.28.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: openmrs-module-referencedemodata-1.4.5/api-1.10/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/mysql/mysql-connector-java/5.1.28/mysql-connector-java-5.1.28.jar</p>
<p>
Dependency Hierarchy:
- openmrs-test-1.10.2.pom (Root Library)
- databene-benerator-0.5.9.jar
- :x: **mysql-connector-java-5.1.28.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-referencedemodata-1.4.5/commit/bde9ded52a5d0cbe44d5b0945266860e2a9a582a">bde9ded52a5d0cbe44d5b0945266860e2a9a582a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692>CVE-2019-2692</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jcq3-cprp-m333">https://github.com/advisories/GHSA-jcq3-cprp-m333</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: mysql:mysql-connector-java:8.0.16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-2692 (Medium) detected in mysql-connector-java-5.1.28.jar - ## CVE-2019-2692 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.28.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http://dev.mysql.com/doc/connector-j/en/">http://dev.mysql.com/doc/connector-j/en/</a></p>
<p>Path to dependency file: openmrs-module-referencedemodata-1.4.5/api-1.10/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/mysql/mysql-connector-java/5.1.28/mysql-connector-java-5.1.28.jar</p>
<p>
Dependency Hierarchy:
- openmrs-test-1.10.2.pom (Root Library)
- databene-benerator-0.5.9.jar
- :x: **mysql-connector-java-5.1.28.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-referencedemodata-1.4.5/commit/bde9ded52a5d0cbe44d5b0945266860e2a9a582a">bde9ded52a5d0cbe44d5b0945266860e2a9a582a</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Vulnerability in the MySQL Connectors component of Oracle MySQL (subcomponent: Connector/J). Supported versions that are affected are 8.0.15 and prior. Difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where MySQL Connectors executes to compromise MySQL Connectors. Successful attacks require human interaction from a person other than the attacker. Successful attacks of this vulnerability can result in takeover of MySQL Connectors. CVSS 3.0 Base Score 6.3 (Confidentiality, Integrity and Availability impacts). CVSS Vector: (CVSS:3.0/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H).
<p>Publish Date: 2019-04-23
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2692>CVE-2019-2692</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jcq3-cprp-m333">https://github.com/advisories/GHSA-jcq3-cprp-m333</a></p>
<p>Release Date: 2019-04-23</p>
<p>Fix Resolution: mysql:mysql-connector-java:8.0.16</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in mysql connector java jar cve medium severity vulnerability vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file openmrs module referencedemodata api pom xml path to vulnerable library home wss scanner repository mysql mysql connector java mysql connector java jar dependency hierarchy openmrs test pom root library databene benerator jar x mysql connector java jar vulnerable library found in head commit a href found in base branch master vulnerability details vulnerability in the mysql connectors component of oracle mysql subcomponent connector j supported versions that are affected are and prior difficult to exploit vulnerability allows high privileged attacker with logon to the infrastructure where mysql connectors executes to compromise mysql connectors successful attacks require human interaction from a person other than the attacker successful attacks of this vulnerability can result in takeover of mysql connectors cvss base score confidentiality integrity and availability impacts cvss vector cvss av l ac h pr h ui r s u c h i h a h publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required high user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution mysql mysql connector java step up your open source security game with whitesource | 0 |
283,552 | 8,719,850,506 | IssuesEvent | 2018-12-08 05:18:21 | aowen87/BAR | https://api.github.com/repos/aowen87/BAR | closed | We need host profiles for the new LLNL machines aztec, edge and inca | asc enhancement priority reviewed | We need to create new host profiles for the LLNL machines aztec, edge and inca. The aztec one will probably be equivalent to yana and the inca one will be equivalent to hopi. The edge one will probably be like atlas.
-----------------------REDMINE MIGRATION-----------------------
This ticket was migrated from Redmine. As such, not all
information was able to be captured in the transition. Below is
a complete record of the original redmine ticket.
Ticket number: 431
Status: Resolved
Project: VisIt
Tracker: Feature
Priority: High
Subject: We need host profiles for the new LLNL machines aztec, edge and inca
Assigned to: Eric Brugger
Category:
Target version: 2.1.1
Author: Eric Brugger
Start: 10/15/2010
Due date:
% Done: 100
Estimated time: 1.0
Created: 10/15/2010 11:49 am
Updated: 10/29/2010 01:51 pm
Likelihood:
Severity:
Found in version:
Impact: 3 - Medium
Expected Use: 3 - Occasional
OS: All
Support Group: DOE/ASC
Description:
We need to create new host profiles for the LLNL machines aztec, edge and inca. The aztec one will probably be equivalent to yana and the inca one will be equivalent to hopi. The edge one will probably be like atlas.
Comments:
I also think our hera profile lists 8 procs as the default, however the nodes have 16 procs, so we should consider updating this as well.
| 1.0 | We need host profiles for the new LLNL machines aztec, edge and inca - We need to create new host profiles for the LLNL machines aztec, edge and inca. The aztec one will probably be equivalent to yana and the inca one will be equivalent to hopi. The edge one will probably be like atlas.
-----------------------REDMINE MIGRATION-----------------------
This ticket was migrated from Redmine. As such, not all
information was able to be captured in the transition. Below is
a complete record of the original redmine ticket.
Ticket number: 431
Status: Resolved
Project: VisIt
Tracker: Feature
Priority: High
Subject: We need host profiles for the new LLNL machines aztec, edge and inca
Assigned to: Eric Brugger
Category:
Target version: 2.1.1
Author: Eric Brugger
Start: 10/15/2010
Due date:
% Done: 100
Estimated time: 1.0
Created: 10/15/2010 11:49 am
Updated: 10/29/2010 01:51 pm
Likelihood:
Severity:
Found in version:
Impact: 3 - Medium
Expected Use: 3 - Occasional
OS: All
Support Group: DOE/ASC
Description:
We need to create new host profiles for the LLNL machines aztec, edge and inca. The aztec one will probably be equivalent to yana and the inca one will be equivalent to hopi. The edge one will probably be like atlas.
Comments:
I also think our hera profile lists 8 procs as the default, however the nodes have 16 procs, so we should consider updating this as well.
| priority | we need host profiles for the new llnl machines aztec edge and inca we need to create new host profiles for the llnl machines aztec edge and inca the aztec one will probably be equivalent to yana and the inca one will be equivalent to hopi the edge one will probably be like atlas redmine migration this ticket was migrated from redmine as such not all information was able to be captured in the transition below is a complete record of the original redmine ticket ticket number status resolved project visit tracker feature priority high subject we need host profiles for the new llnl machines aztec edge and inca assigned to eric brugger category target version author eric brugger start due date done estimated time created am updated pm likelihood severity found in version impact medium expected use occasional os all support group doe asc description we need to create new host profiles for the llnl machines aztec edge and inca the aztec one will probably be equivalent to yana and the inca one will be equivalent to hopi the edge one will probably be like atlas comments i also think our hera profile lists procs as the default however the nodes have procs so we should consider updating this as well | 1 |
222,197 | 17,398,707,789 | IssuesEvent | 2021-08-02 16:28:42 | nasa/cFE | https://api.github.com/repos/nasa/cFE | closed | Add (unsigned int) cast to MIR prints in time_UT.c | bug unit-test | **Is your feature request related to a problem? Please describe.**
MIR prints in time_UT.c break the RTEMS build because %u expects (unsigned int), but uint32 in RTEMS is an unsigned long.
**Describe the solution you'd like**
Add (unsigned int) cast to MIR prints in time_UT.c
**Requester Info**
Jose F. Martinez Pedraza / NASA GSFC | 1.0 | Add (unsigned int) cast to MIR prints in time_UT.c - **Is your feature request related to a problem? Please describe.**
MIR prints in time_UT.c break the RTEMS build because %u expects (unsigned int), but uint32 in RTEMS is an unsigned long.
**Describe the solution you'd like**
Add (unsigned int) cast to MIR prints in time_UT.c
**Requester Info**
Jose F. Martinez Pedraza / NASA GSFC | non_priority | add unsigned int cast to mir prints in time ut c is your feature request related to a problem please describe mir prints in time ut c break the rtems build because u expects unsigned int but in rtems is an unsigned long describe the solution you d like add unsigned int cast to mir prints in time ut c requester info jose f martinez pedraza nasa gsfc | 0 |
395,122 | 27,055,748,625 | IssuesEvent | 2023-02-13 16:03:50 | oemof/oemof-solph | https://api.github.com/repos/oemof/oemof-solph | opened | Add an example for the OffsetTransformer with two series of coefficients | documentation | Just to show, how that can be used/implemented. | 1.0 | Add an example for the OffsetTransformer with two series of coefficients - Just to show, how that can be used/implemented. | non_priority | add an example for the offsettransformer with two series of coefficients just to show how that can be used implemented | 0 |
363,958 | 25,475,839,127 | IssuesEvent | 2022-11-25 14:22:19 | swaros/contxt | https://api.github.com/repos/swaros/contxt | closed | update readme | documentation | todos
- finalize structure documentation
- add macros documentation
- add documentation about templating
- update main docu dependind windows builds
- link the docus (toc) | 1.0 | update readme - todos
- finalize structure documentation
- add macros documentation
- add documentation about templating
- update main docu dependind windows builds
- link the docus (toc) | non_priority | update readme todos finalize structure documentation add macros documentation add documentation about templating update main docu dependind windows builds link the docus toc | 0 |
185,198 | 15,013,893,636 | IssuesEvent | 2021-02-01 05:31:20 | arturo-lang/arturo | https://api.github.com/repos/arturo-lang/arturo | closed | How to compile without GTK? | documentation installer | The documentation says that GTK is required only for “complete” builds, but it doesn't specify how non make a non-“complete” build. Any help? | 1.0 | How to compile without GTK? - The documentation says that GTK is required only for “complete” builds, but it doesn't specify how non make a non-“complete” build. Any help? | non_priority | how to compile without gtk the documentation says that gtk is required only for “complete” builds but it doesn t specify how non make a non “complete” build any help | 0 |
127,444 | 12,323,075,810 | IssuesEvent | 2020-05-13 11:30:40 | Students-of-the-city-of-Kostroma/trpo_automation | https://api.github.com/repos/Students-of-the-city-of-Kostroma/trpo_automation | closed | Разработать сценарии тестирования лабораторной работы в виде гугл таблицы. | documentation | По итогу предоставить отчет о выполнении тестов, готовые сценарии, | 1.0 | Разработать сценарии тестирования лабораторной работы в виде гугл таблицы. - По итогу предоставить отчет о выполнении тестов, готовые сценарии, | non_priority | разработать сценарии тестирования лабораторной работы в виде гугл таблицы по итогу предоставить отчет о выполнении тестов готовые сценарии | 0 |
737,719 | 25,528,316,091 | IssuesEvent | 2022-11-29 05:39:27 | Hexlet/hexlet-cv | https://api.github.com/repos/Hexlet/hexlet-cv | closed | Add notice in tg and slack | help wanted good first issue hacktoberfest-accepted Priority: High | Make it so that the career track employee in the admin, when he repeatedly posted the same job, it will be added automatically to Slack and Telegram | 1.0 | Add notice in tg and slack - Make it so that the career track employee in the admin, when he repeatedly posted the same job, it will be added automatically to Slack and Telegram | priority | add notice in tg and slack make it so that the career track employee in the admin when he repeatedly posted the same job it will be added automatically to slack and telegram | 1 |
51,461 | 27,086,809,415 | IssuesEvent | 2023-02-14 17:35:25 | gchq/stroom | https://api.github.com/repos/gchq/stroom | opened | Consider changing `meta_val` table to be single row with multiple columns | enhancement f:performance | Currently meta is 1:* with meta_val, with ~10 meta_val records per meta. The meta_val KV pairs are pretty much a static set of keys so we could have a meta_attributes table that has one column per attr key. This would reduce the number of rows being inserted and would reduce the number of joins needed when querying meta with attr val conditions.
Tests would be needed to see how this impacts insert and query performance. | True | Consider changing `meta_val` table to be single row with multiple columns - Currently meta is 1:* with meta_val, with ~10 meta_val records per meta. The meta_val KV pairs are pretty much a static set of keys so we could have a meta_attributes table that has one column per attr key. This would reduce the number of rows being inserted and would reduce the number of joins needed when querying meta with attr val conditions.
Tests would be needed to see how this impacts insert and query performance. | non_priority | consider changing meta val table to be single row with multiple columns currently meta is with meta val with meta val records per meta the meta val kv pairs are pretty much a static set of keys so we could have a meta attributes table that has one column per attr key this would reduce the number of rows being inserted and would reduce the number of joins needed when querying meta with attr val conditions tests would be needed to see how this impacts insert and query performance | 0 |
113,606 | 4,565,614,442 | IssuesEvent | 2016-09-15 01:28:03 | rm-code/On-The-Roadside | https://api.github.com/repos/rm-code/On-The-Roadside | opened | Allow "opening" of backpacks in the inventory | Priority: Low Status: Accepted Type: Enhancement | One of the most annoying parts of the inventory is that the player has to equip backpacks if he wants to look into them. It would be nicer if you could click on a backpack and it would open a new list (replacing the "current" item list).
By implementing this we could also get rid of the backpack list completely.
| 1.0 | Allow "opening" of backpacks in the inventory - One of the most annoying parts of the inventory is that the player has to equip backpacks if he wants to look into them. It would be nicer if you could click on a backpack and it would open a new list (replacing the "current" item list).
By implementing this we could also get rid of the backpack list completely.
| priority | allow opening of backpacks in the inventory one of the most annoying parts of the inventory is that the player has to equip backpacks if he wants to look into them it would be nicer if you could click on a backpack and it would open a new list replacing the current item list by implementing this we could also get rid of the backpack list completely | 1 |
442,113 | 30,818,046,320 | IssuesEvent | 2023-08-01 14:36:08 | siemens/ix | https://api.github.com/repos/siemens/ix | closed | Improve migration guide | type: bug component: documentation triage | ### What happened?
Include breaking changes on comonent level to migration guide (link changelog) | 1.0 | Improve migration guide - ### What happened?
Include breaking changes on comonent level to migration guide (link changelog) | non_priority | improve migration guide what happened include breaking changes on comonent level to migration guide link changelog | 0 |
768,984 | 26,989,853,013 | IssuesEvent | 2023-02-09 18:57:23 | chaotic-aur/packages | https://api.github.com/repos/chaotic-aur/packages | closed | [Request] monkeysphere | request:new-pkg interfere required priority:low | ### Link to the package base(s) in the AUR
https://aur.archlinux.org/packages/monkeysphere
### Utility this package has for you
Leverage the OpenPGP web of trust for OpenSSH and Web authentication
Lol, I just used to to convert my GPG key to an OenSSH one.
### Do you consider the package(s) to be useful for every Chaotic-AUR user?
No, but for a few.
### Do you consider the package to be useful for feature testing/preview?
- [ ] Yes
### Have you tested if the package builds in a clean chroot?
- [ ] Yes
### Does the package's license allow redistributing it?
YES!
### Have you searched the issues to ensure this request is unique?
- [X] YES!
### Have you read the README to ensure this package is not banned?
- [X] YES!
### More information
Actually, build failed. | 1.0 | [Request] monkeysphere - ### Link to the package base(s) in the AUR
https://aur.archlinux.org/packages/monkeysphere
### Utility this package has for you
Leverage the OpenPGP web of trust for OpenSSH and Web authentication
Lol, I just used to to convert my GPG key to an OenSSH one.
### Do you consider the package(s) to be useful for every Chaotic-AUR user?
No, but for a few.
### Do you consider the package to be useful for feature testing/preview?
- [ ] Yes
### Have you tested if the package builds in a clean chroot?
- [ ] Yes
### Does the package's license allow redistributing it?
YES!
### Have you searched the issues to ensure this request is unique?
- [X] YES!
### Have you read the README to ensure this package is not banned?
- [X] YES!
### More information
Actually, build failed. | priority | monkeysphere link to the package base s in the aur utility this package has for you leverage the openpgp web of trust for openssh and web authentication lol i just used to to convert my gpg key to an oenssh one do you consider the package s to be useful for every chaotic aur user no but for a few do you consider the package to be useful for feature testing preview yes have you tested if the package builds in a clean chroot yes does the package s license allow redistributing it yes have you searched the issues to ensure this request is unique yes have you read the readme to ensure this package is not banned yes more information actually build failed | 1 |
299,839 | 9,205,902,306 | IssuesEvent | 2019-03-08 12:03:02 | qissue-bot/QGIS | https://api.github.com/repos/qissue-bot/QGIS | closed | detect invalid split if splitting line ends in polygon | Category: Digitising Component: Affected QGIS version Component: Crashes QGIS or corrupts data Component: Easy fix? Component: Operating System Component: Pull Request or Patch supplied Component: Regression? Component: Resolution Priority: Low Project: QGIS Application Status: Closed Tracker: Bug report | ---
Author Name: **Marco Hugentobler** (Marco Hugentobler)
Original Redmine Issue: 1201, https://issues.qgis.org/issues/1201
Original Assignee: Marco Hugentobler
---
If a splitting line starts outside a polygon and ends inside it, the user should receive an error message. Instead, a vertex is added where the split line crosses the polygon border.
| 1.0 | detect invalid split if splitting line ends in polygon - ---
Author Name: **Marco Hugentobler** (Marco Hugentobler)
Original Redmine Issue: 1201, https://issues.qgis.org/issues/1201
Original Assignee: Marco Hugentobler
---
If a splitting line starts outside a polygon and ends inside it, the user should receive an error message. Instead, a vertex is added where the split line crosses the polygon border.
| priority | detect invalid split if splitting line ends in polygon author name marco hugentobler marco hugentobler original redmine issue original assignee marco hugentobler if a splitting line starts outside a polygon and ends inside it the user should receive an error message instead a vertex is added where the split line crosses the polygon border | 1 |
371,424 | 25,951,529,743 | IssuesEvent | 2022-12-17 17:14:34 | ashn-dot-dev/sunder | https://api.github.com/repos/ashn-dot-dev/sunder | closed | Add compiler reference | documentation wontfix | Add high level documentation for the architecture of the compiler. This documentation should provide a high-level overview of the compiler, the phases of compilation, and the data structures used throughout the compiler's C source.
It may be worth waiting until the compiler is stabilized before beginning this document as the language and compiler are still undergoing rapid changes. | 1.0 | Add compiler reference - Add high level documentation for the architecture of the compiler. This documentation should provide a high-level overview of the compiler, the phases of compilation, and the data structures used throughout the compiler's C source.
It may be worth waiting until the compiler is stabilized before beginning this document as the language and compiler are still undergoing rapid changes. | non_priority | add compiler reference add high level documentation for the architecture of the compiler this documentation should provide a high level overview of the compiler the phases of compilation and the data structures used throughout the compiler s c source it may be worth waiting until the compiler is stabilized before beginning this document as the language and compiler are still undergoing rapid changes | 0 |
183,169 | 21,714,465,472 | IssuesEvent | 2022-05-10 16:29:56 | svg-GHC-2/test_django.nv | https://api.github.com/repos/svg-GHC-2/test_django.nv | opened | bootstrap-3.2.0.js: 6 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.2.0.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-8331](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.0, 4.0.0-beta.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0, 4.0.0-beta.2</p>
</p>
<p></p>
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-8331","vulnerabilityDetails":"In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14040","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20677","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20676","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0, 4.0.0-beta.2","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | True | bootstrap-3.2.0.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.2.0.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-8331](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | bootstrap-3.2.0.js | Direct | bootstrap - 3.4.0, 4.0.0-beta.2 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/28236">https://github.com/twbs/bootstrap/pull/28236</a></p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/pull/26630">https://github.com/twbs/bootstrap/pull/26630</a></p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.2.0.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.2.0/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /taskManager/static/taskManager/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.2.0.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/svg-GHC-2/test_django.nv/commit/021af4213e779168babc65f6444b6f78dda744c3">021af4213e779168babc65f6444b6f78dda744c3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10735</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0, 4.0.0-beta.2</p>
</p>
<p></p>
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-8331","vulnerabilityDetails":"In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-8331","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14040","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14040","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20677","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20677","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20676","vulnerabilityDetails":"In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20676","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-14042","vulnerabilityDetails":"In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-14042","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.2.0","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.2.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bootstrap - 3.4.0, 4.0.0-beta.2","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}]</REMEDIATE> --> | non_priority | bootstrap js vulnerabilities highest severity is vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium bootstrap js direct bootstrap bootstrap sass medium bootstrap js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap js direct bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter medium bootstrap js direct bootstrap medium bootstrap js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap js direct bootstrap beta details cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap bootstrap sass cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library taskmanager static taskmanager js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch main vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap beta istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap bootstrap sass isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before and x before xss is possible in the tooltip or popover data template attribute vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion org webjars npm bootstrap org webjars bootstrap isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the collapse data parent attribute vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the affix configuration target property vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the tooltip data viewport attribute vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion org webjars npm bootstrap org webjars bootstrap isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap before xss is possible in the data container property of tooltip vulnerabilityurl istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion bootstrap beta isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve vulnerabilityurl | 0 |
121,212 | 4,806,464,733 | IssuesEvent | 2016-11-02 18:37:22 | BlythMeister/Gallifrey | https://api.github.com/repos/BlythMeister/Gallifrey | closed | Export Time to Harvest | Enhancement Low Priority | Using a config switch export time to harvests rather than jira.
When config on, allow user to enter their harvest login details.
When using harvest, the following needs to happen:
1) background export check run against harvest not jira
2) exported time check prior to exports check harvest and not jira
3) the time export goes to harvest rather than add work log to jira
4) remaining time adjustment still happen in jira
| 1.0 | Export Time to Harvest - Using a config switch export time to harvests rather than jira.
When config on, allow user to enter their harvest login details.
When using harvest, the following needs to happen:
1) background export check run against harvest not jira
2) exported time check prior to exports check harvest and not jira
3) the time export goes to harvest rather than add work log to jira
4) remaining time adjustment still happen in jira
| priority | export time to harvest using a config switch export time to harvests rather than jira when config on allow user to enter their harvest login details when using harvest the following needs to happen background export check run against harvest not jira exported time check prior to exports check harvest and not jira the time export goes to harvest rather than add work log to jira remaining time adjustment still happen in jira | 1 |
204,812 | 23,283,659,012 | IssuesEvent | 2022-08-05 14:25:18 | hirosystems/explorer | https://api.github.com/repos/hirosystems/explorer | closed | Word wrap for code lines (to increase visibility of hidden codes of any malicious exploit) | Enhancement 💡 P4 Enhancement 🕯 Security | **Is your feature request related to a problem? Please describe.**
Time taken to search for hidden codes & exploits, e.g. during Arkadiko hack the exploit codes were hidden outside of the immediate visible view, even if you scroll down vertically, hidden exploit code could not be found. Eventually the hidden exploit was found by scrolling horizontally to the far far right hand side.
Exploit contract: https://explorer.stacks.co/txid/0x4d78fe328be831db1b68e50c4eab7fc57c328af5f441d40238436893d1b8ee28?chain=mainnet
<img src="https://user-images.githubusercontent.com/92864860/167154633-499bb732-a1e1-4faf-a634-19b3fab708a8.png" width="350px" />
**Describe the solution you'd like**
* Word wrap (such as on the Windows Notepad) the lines that out of the immediate screen real estate, so ALL codes are visible immediate as you look at any page loaded.
e.g. like below example solution. In the Arkadiko exploit the codes were hidden far right side out of the screen, you had to scroll horizontally a lot to find the hidden exploit codes
<img src="https://user-images.githubusercontent.com/92864860/167013127-f6bf6460-a1bf-44be-acca-6b6783609457.png" width="650px" />
<img src="https://user-images.githubusercontent.com/92864860/167013253-7a322544-22aa-4e6c-8c08-f4e121acef16.png" width="200px" />
<img src="https://user-images.githubusercontent.com/92864860/167013184-d6cfb461-5023-4466-9047-18c37bd5116d.png" width="650px" />
**Describe alternatives you've considered**
* A scroll bar at the top (Tho there is a scroll bar, but can be easily be missed as it's at the very bottom of the page.)
* A scroll bar appear when you hover the code lines.
**Benefits**
* No codes can escape the view of the current window. Can identify the exploits or bugs much quicker, in order to deploy a counter-exploit much quicker, potentially save a lot of money from the hack.
cc: @wileyj @philipdesmedt | True | Word wrap for code lines (to increase visibility of hidden codes of any malicious exploit) - **Is your feature request related to a problem? Please describe.**
Time taken to search for hidden codes & exploits, e.g. during Arkadiko hack the exploit codes were hidden outside of the immediate visible view, even if you scroll down vertically, hidden exploit code could not be found. Eventually the hidden exploit was found by scrolling horizontally to the far far right hand side.
Exploit contract: https://explorer.stacks.co/txid/0x4d78fe328be831db1b68e50c4eab7fc57c328af5f441d40238436893d1b8ee28?chain=mainnet
<img src="https://user-images.githubusercontent.com/92864860/167154633-499bb732-a1e1-4faf-a634-19b3fab708a8.png" width="350px" />
**Describe the solution you'd like**
* Word wrap (such as on the Windows Notepad) the lines that out of the immediate screen real estate, so ALL codes are visible immediate as you look at any page loaded.
e.g. like below example solution. In the Arkadiko exploit the codes were hidden far right side out of the screen, you had to scroll horizontally a lot to find the hidden exploit codes
<img src="https://user-images.githubusercontent.com/92864860/167013127-f6bf6460-a1bf-44be-acca-6b6783609457.png" width="650px" />
<img src="https://user-images.githubusercontent.com/92864860/167013253-7a322544-22aa-4e6c-8c08-f4e121acef16.png" width="200px" />
<img src="https://user-images.githubusercontent.com/92864860/167013184-d6cfb461-5023-4466-9047-18c37bd5116d.png" width="650px" />
**Describe alternatives you've considered**
* A scroll bar at the top (Tho there is a scroll bar, but can be easily be missed as it's at the very bottom of the page.)
* A scroll bar appear when you hover the code lines.
**Benefits**
* No codes can escape the view of the current window. Can identify the exploits or bugs much quicker, in order to deploy a counter-exploit much quicker, potentially save a lot of money from the hack.
cc: @wileyj @philipdesmedt | non_priority | word wrap for code lines to increase visibility of hidden codes of any malicious exploit is your feature request related to a problem please describe time taken to search for hidden codes exploits e g during arkadiko hack the exploit codes were hidden outside of the immediate visible view even if you scroll down vertically hidden exploit code could not be found eventually the hidden exploit was found by scrolling horizontally to the far far right hand side exploit contract describe the solution you d like word wrap such as on the windows notepad the lines that out of the immediate screen real estate so all codes are visible immediate as you look at any page loaded e g like below example solution in the arkadiko exploit the codes were hidden far right side out of the screen you had to scroll horizontally a lot to find the hidden exploit codes describe alternatives you ve considered a scroll bar at the top tho there is a scroll bar but can be easily be missed as it s at the very bottom of the page a scroll bar appear when you hover the code lines benefits no codes can escape the view of the current window can identify the exploits or bugs much quicker in order to deploy a counter exploit much quicker potentially save a lot of money from the hack cc wileyj philipdesmedt | 0 |
136,351 | 18,734,096,901 | IssuesEvent | 2021-11-04 03:39:33 | Dima2022/kaltura-sample-code | https://api.github.com/repos/Dima2022/kaltura-sample-code | opened | CVE-2018-12022 (High) detected in jackson-databind-2.8.9.jar | security vulnerability | ## CVE-2018-12022 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: kaltura-sample-code/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.9/jackson-databind-2.8.9.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.6.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/kaltura-sample-code/commit/e022312630d07a000d07ace8bd86a7f0590a0f65">e022312630d07a000d07ace8bd86a7f0590a0f65</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022>CVE-2018-12022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022</a></p>
<p>Release Date: 2019-03-21</p>
<p>Fix Resolution: 2.7.9.4, 2.8.11.2, 2.9.6</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.9","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.6.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.8.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.7.9.4, 2.8.11.2, 2.9.6"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-12022","vulnerabilityDetails":"An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-12022 (High) detected in jackson-databind-2.8.9.jar - ## CVE-2018-12022 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: kaltura-sample-code/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.9/jackson-databind-2.8.9.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.5.6.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Dima2022/kaltura-sample-code/commit/e022312630d07a000d07ace8bd86a7f0590a0f65">e022312630d07a000d07ace8bd86a7f0590a0f65</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.
<p>Publish Date: 2019-03-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022>CVE-2018-12022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022</a></p>
<p>Release Date: 2019-03-21</p>
<p>Fix Resolution: 2.7.9.4, 2.8.11.2, 2.9.6</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.9","packageFilePaths":["/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.5.6.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.8.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.7.9.4, 2.8.11.2, 2.9.6"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-12022","vulnerabilityDetails":"An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12022","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file kaltura sample code pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details an issue was discovered in fasterxml jackson databind prior to and when default typing is enabled either globally or for a specific property the service has the jodd db jar for database access for the jodd framework in the classpath and an attacker can provide an ldap service to access it is possible to make the service execute a malicious payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails an issue was discovered in fasterxml jackson databind prior to and when default typing is enabled either globally or for a specific property the service has the jodd db jar for database access for the jodd framework in the classpath and an attacker can provide an ldap service to access it is possible to make the service execute a malicious payload vulnerabilityurl | 0 |
272,923 | 29,795,133,492 | IssuesEvent | 2023-06-16 01:13:45 | billmcchesney1/pacbot | https://api.github.com/repos/billmcchesney1/pacbot | closed | CVE-2019-7614 (Medium) detected in elasticsearch-5.6.2.jar, elasticsearch-5.6.8.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2019-7614 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>elasticsearch-5.6.2.jar</b>, <b>elasticsearch-5.6.8.jar</b></p></summary>
<p>
<details><summary><b>elasticsearch-5.6.2.jar</b></p></summary>
<p>Elasticsearch subproject :core</p>
<p>Library home page: <a href="https://github.com/elastic/elasticsearch">https://github.com/elastic/elasticsearch</a></p>
<p>Path to dependency file: /api/pacman-api-compliance/pom.xml</p>
<p>Path to vulnerable library: /canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **elasticsearch-5.6.2.jar** (Vulnerable Library)
</details>
<details><summary><b>elasticsearch-5.6.8.jar</b></p></summary>
<p>Elasticsearch subproject :core</p>
<p>Library home page: <a href="https://github.com/elastic/elasticsearch">https://github.com/elastic/elasticsearch</a></p>
<p>Path to dependency file: /jobs/pacman-rule-engine-2.0/pom.xml</p>
<p>Path to vulnerable library: /canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.8/elasticsearch-5.6.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **elasticsearch-5.6.8.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/pacbot/commit/acf9a0620c1a37cee4f2896d71e1c3731c5c7b06">acf9a0620c1a37cee4f2896d71e1c3731c5c7b06</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A race condition flaw was found in the response headers Elasticsearch versions before 7.2.1 and 6.8.2 returns to a request. On a system with multiple users submitting requests, it could be possible for an attacker to gain access to response header containing sensitive data from another user.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-7614>CVE-2019-7614</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-7614">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-7614</a></p>
<p>Release Date: 2019-07-30</p>
<p>Fix Resolution: 6.8.2</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| True | CVE-2019-7614 (Medium) detected in elasticsearch-5.6.2.jar, elasticsearch-5.6.8.jar - autoclosed - ## CVE-2019-7614 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>elasticsearch-5.6.2.jar</b>, <b>elasticsearch-5.6.8.jar</b></p></summary>
<p>
<details><summary><b>elasticsearch-5.6.2.jar</b></p></summary>
<p>Elasticsearch subproject :core</p>
<p>Library home page: <a href="https://github.com/elastic/elasticsearch">https://github.com/elastic/elasticsearch</a></p>
<p>Path to dependency file: /api/pacman-api-compliance/pom.xml</p>
<p>Path to vulnerable library: /canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar,/canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.2/elasticsearch-5.6.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **elasticsearch-5.6.2.jar** (Vulnerable Library)
</details>
<details><summary><b>elasticsearch-5.6.8.jar</b></p></summary>
<p>Elasticsearch subproject :core</p>
<p>Library home page: <a href="https://github.com/elastic/elasticsearch">https://github.com/elastic/elasticsearch</a></p>
<p>Path to dependency file: /jobs/pacman-rule-engine-2.0/pom.xml</p>
<p>Path to vulnerable library: /canner/.m2/repository/org/elasticsearch/elasticsearch/5.6.8/elasticsearch-5.6.8.jar</p>
<p>
Dependency Hierarchy:
- :x: **elasticsearch-5.6.8.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/pacbot/commit/acf9a0620c1a37cee4f2896d71e1c3731c5c7b06">acf9a0620c1a37cee4f2896d71e1c3731c5c7b06</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
A race condition flaw was found in the response headers Elasticsearch versions before 7.2.1 and 6.8.2 returns to a request. On a system with multiple users submitting requests, it could be possible for an attacker to gain access to response header containing sensitive data from another user.
<p>Publish Date: 2019-07-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-7614>CVE-2019-7614</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-7614">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-7614</a></p>
<p>Release Date: 2019-07-30</p>
<p>Fix Resolution: 6.8.2</p>
</p>
</details>
<p></p>
***
<!-- REMEDIATE-OPEN-PR-START -->
- [ ] Check this box to open an automated fix PR
<!-- REMEDIATE-OPEN-PR-END -->
| non_priority | cve medium detected in elasticsearch jar elasticsearch jar autoclosed cve medium severity vulnerability vulnerable libraries elasticsearch jar elasticsearch jar elasticsearch jar elasticsearch subproject core library home page a href path to dependency file api pacman api compliance pom xml path to vulnerable library canner repository org elasticsearch elasticsearch elasticsearch jar canner repository org elasticsearch elasticsearch elasticsearch jar canner repository org elasticsearch elasticsearch elasticsearch jar canner repository org elasticsearch elasticsearch elasticsearch jar canner repository org elasticsearch elasticsearch elasticsearch jar canner repository org elasticsearch elasticsearch elasticsearch jar dependency hierarchy x elasticsearch jar vulnerable library elasticsearch jar elasticsearch subproject core library home page a href path to dependency file jobs pacman rule engine pom xml path to vulnerable library canner repository org elasticsearch elasticsearch elasticsearch jar dependency hierarchy x elasticsearch jar vulnerable library found in head commit a href found in base branch master vulnerability details a race condition flaw was found in the response headers elasticsearch versions before and returns to a request on a system with multiple users submitting requests it could be possible for an attacker to gain access to response header containing sensitive data from another user publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution check this box to open an automated fix pr | 0 |
709,257 | 24,371,902,334 | IssuesEvent | 2022-10-03 20:05:40 | red-hat-storage/ocs-ci | https://api.github.com/repos/red-hat-storage/ocs-ci | closed | Handling existing cluster outside qe | High Priority lifecycle/stale | We have seen couple of issues that needs to be addressed when existing cluster is used from outside qe
1) Download of oc binary in bin/folder if not already present
2) Dont bailout on report version checks in operators and catalog namespace
ex:
"""
-OPERATOR_CATALOG_SOURCE_NAME = "ocs-catalogsource"
+OPERATOR_CATALOG_SOURCE_NAME = "redhat-operators"
$ oc -n openshift-marketplace --kubeconfig /Users/kylebader/src/infra-nodes/kb/auth/kubeconfig get CatalogSource ocs-catalogsource -n openshift-marketplace -o yaml
Error from server (NotFound): catalogsources.operators.coreos.com "ocs-catalogsource" not found
"""
3) cluster-name should not be mandatory
4) mcg tests loads s3 config in pytest customization - add exception checks
| 1.0 | Handling existing cluster outside qe - We have seen couple of issues that needs to be addressed when existing cluster is used from outside qe
1) Download of oc binary in bin/folder if not already present
2) Dont bailout on report version checks in operators and catalog namespace
ex:
"""
-OPERATOR_CATALOG_SOURCE_NAME = "ocs-catalogsource"
+OPERATOR_CATALOG_SOURCE_NAME = "redhat-operators"
$ oc -n openshift-marketplace --kubeconfig /Users/kylebader/src/infra-nodes/kb/auth/kubeconfig get CatalogSource ocs-catalogsource -n openshift-marketplace -o yaml
Error from server (NotFound): catalogsources.operators.coreos.com "ocs-catalogsource" not found
"""
3) cluster-name should not be mandatory
4) mcg tests loads s3 config in pytest customization - add exception checks
| priority | handling existing cluster outside qe we have seen couple of issues that needs to be addressed when existing cluster is used from outside qe download of oc binary in bin folder if not already present dont bailout on report version checks in operators and catalog namespace ex operator catalog source name ocs catalogsource operator catalog source name redhat operators oc n openshift marketplace kubeconfig users kylebader src infra nodes kb auth kubeconfig get catalogsource ocs catalogsource n openshift marketplace o yaml error from server notfound catalogsources operators coreos com ocs catalogsource not found cluster name should not be mandatory mcg tests loads config in pytest customization add exception checks | 1 |
16,876 | 10,575,968,907 | IssuesEvent | 2019-10-07 16:49:09 | cityofaustin/atd-vz-data | https://api.github.com/repos/cityofaustin/atd-vz-data | opened | VZD/E: Need ability to modify fatality flag | MVP Project: Vision Zero Crash Data System Service: Dev Workgroup: VZ | - [ ] Add Two new columns to Crash DB Table:
- `apd_confirmed_fatality`
- `apd_confirmed_death_count`
- [ ] Add these fields as editable records on the Crash details page. | 1.0 | VZD/E: Need ability to modify fatality flag - - [ ] Add Two new columns to Crash DB Table:
- `apd_confirmed_fatality`
- `apd_confirmed_death_count`
- [ ] Add these fields as editable records on the Crash details page. | non_priority | vzd e need ability to modify fatality flag add two new columns to crash db table apd confirmed fatality apd confirmed death count add these fields as editable records on the crash details page | 0 |
277,258 | 30,610,816,814 | IssuesEvent | 2023-07-23 15:31:32 | tyhal/tyhal.com | https://api.github.com/repos/tyhal/tyhal.com | closed | CVE-2021-24033 (Medium) detected in react-dev-utils-11.0.0.tgz | security vulnerability | ## CVE-2021-24033 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>react-dev-utils-11.0.0.tgz</b></p></summary>
<p>webpack utilities used by Create React App</p>
<p>Library home page: <a href="https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-11.0.0.tgz">https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-11.0.0.tgz</a></p>
<p>Path to dependency file: tyhal.com/package.json</p>
<p>Path to vulnerable library: tyhal.com/node_modules/react-dev-utils/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- :x: **react-dev-utils-11.0.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
react-dev-utils prior to v11.0.4 exposes a function, getProcessForPort, where an input argument is concatenated into a command string to be executed. This function is typically used from react-scripts (in Create React App projects), where the usage is safe. Only when this function is manually invoked with user-provided values (ie: by custom code) is there the potential for command injection. If you're consuming it from react-scripts then this issue does not affect you.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24033>CVE-2021-24033</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.facebook.com/security/advisories/cve-2021-24033">https://www.facebook.com/security/advisories/cve-2021-24033</a></p>
<p>Release Date: 2021-03-09</p>
<p>Fix Resolution: react-dev-utils-11.0.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-24033 (Medium) detected in react-dev-utils-11.0.0.tgz - ## CVE-2021-24033 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>react-dev-utils-11.0.0.tgz</b></p></summary>
<p>webpack utilities used by Create React App</p>
<p>Library home page: <a href="https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-11.0.0.tgz">https://registry.npmjs.org/react-dev-utils/-/react-dev-utils-11.0.0.tgz</a></p>
<p>Path to dependency file: tyhal.com/package.json</p>
<p>Path to vulnerable library: tyhal.com/node_modules/react-dev-utils/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- :x: **react-dev-utils-11.0.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
react-dev-utils prior to v11.0.4 exposes a function, getProcessForPort, where an input argument is concatenated into a command string to be executed. This function is typically used from react-scripts (in Create React App projects), where the usage is safe. Only when this function is manually invoked with user-provided values (ie: by custom code) is there the potential for command injection. If you're consuming it from react-scripts then this issue does not affect you.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-24033>CVE-2021-24033</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.facebook.com/security/advisories/cve-2021-24033">https://www.facebook.com/security/advisories/cve-2021-24033</a></p>
<p>Release Date: 2021-03-09</p>
<p>Fix Resolution: react-dev-utils-11.0.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in react dev utils tgz cve medium severity vulnerability vulnerable library react dev utils tgz webpack utilities used by create react app library home page a href path to dependency file tyhal com package json path to vulnerable library tyhal com node modules react dev utils package json dependency hierarchy react scripts tgz root library x react dev utils tgz vulnerable library found in base branch master vulnerability details react dev utils prior to exposes a function getprocessforport where an input argument is concatenated into a command string to be executed this function is typically used from react scripts in create react app projects where the usage is safe only when this function is manually invoked with user provided values ie by custom code is there the potential for command injection if you re consuming it from react scripts then this issue does not affect you publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution react dev utils step up your open source security game with whitesource | 0 |
321,200 | 9,794,968,580 | IssuesEvent | 2019-06-11 01:30:52 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | iontelevision.com - The TV schedule is not properly rendered | browser-firefox engine-gecko priority-normal severity-minor | <!-- @browser: Firefox Nightly 68.0a1 (2019-06-07) -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 Safari/537.36 -->
<!-- @reported_with: -->
**URL**: https://iontelevision.com/schedule
**Browser / Version**: Firefox Nightly 68.0a1 (2019-06-07)
**Operating System**: Huawei P10 (Android 8.0) - 1080 x 1920 pixels (~432 ppi pixel density)
**Tested Another Browser**: Yes
**Problem type**: Design is broken
**Description**: The TV schedule is not properly rendered
**Steps to Reproduce**:
1. Navigate to https://iontelevision.com/schedule
2. Observe the displayed TV schedule.
**Expected Behavior:**
The TV schedule must be properly rendered.
**Actual Behavior:**
The schedule is not properly rendered. The layout is messed up and some dates and the weekdays from the top of the schedule are missing. The schedule is correctly displayed after a light scroll down the page.
**Notes:**
1. The issue is not reproducible on Chrome Mobile 74.0.3729.157
2. Screenshots attached.
**Watchers:**
@softvision-oana-arbuzov
@softvision-sergiulogigan
@cipriansv
sv;
[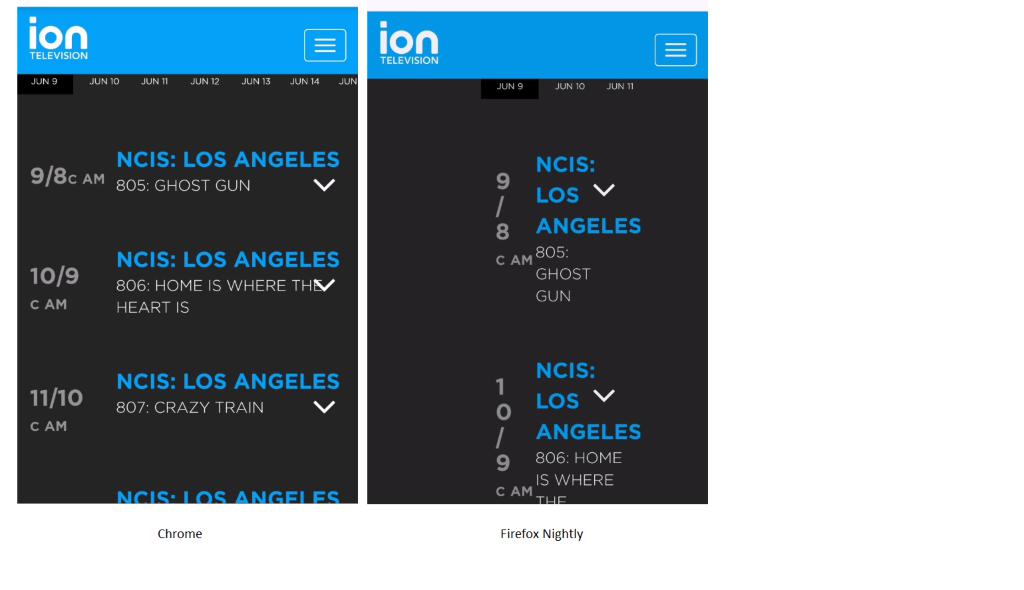](https://webcompat.com/uploads/2019/6/5cee1810-3642-4c9b-af6d-45f78a2b13d6.jpg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | 1.0 | iontelevision.com - The TV schedule is not properly rendered - <!-- @browser: Firefox Nightly 68.0a1 (2019-06-07) -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/74.0.3729.169 Safari/537.36 -->
<!-- @reported_with: -->
**URL**: https://iontelevision.com/schedule
**Browser / Version**: Firefox Nightly 68.0a1 (2019-06-07)
**Operating System**: Huawei P10 (Android 8.0) - 1080 x 1920 pixels (~432 ppi pixel density)
**Tested Another Browser**: Yes
**Problem type**: Design is broken
**Description**: The TV schedule is not properly rendered
**Steps to Reproduce**:
1. Navigate to https://iontelevision.com/schedule
2. Observe the displayed TV schedule.
**Expected Behavior:**
The TV schedule must be properly rendered.
**Actual Behavior:**
The schedule is not properly rendered. The layout is messed up and some dates and the weekdays from the top of the schedule are missing. The schedule is correctly displayed after a light scroll down the page.
**Notes:**
1. The issue is not reproducible on Chrome Mobile 74.0.3729.157
2. Screenshots attached.
**Watchers:**
@softvision-oana-arbuzov
@softvision-sergiulogigan
@cipriansv
sv;
[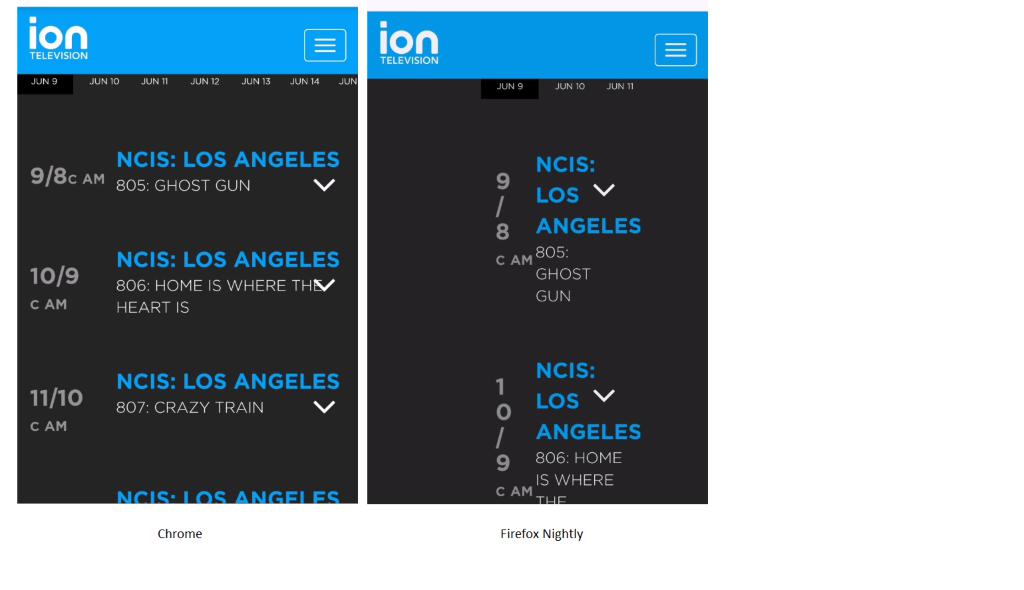](https://webcompat.com/uploads/2019/6/5cee1810-3642-4c9b-af6d-45f78a2b13d6.jpg)
<details>
<summary>Browser Configuration</summary>
<ul>
<li>None</li>
</ul>
</details>
_From [webcompat.com](https://webcompat.com/) with ❤️_ | priority | iontelevision com the tv schedule is not properly rendered url browser version firefox nightly operating system huawei android x pixels ppi pixel density tested another browser yes problem type design is broken description the tv schedule is not properly rendered steps to reproduce navigate to observe the displayed tv schedule expected behavior the tv schedule must be properly rendered actual behavior the schedule is not properly rendered the layout is messed up and some dates and the weekdays from the top of the schedule are missing the schedule is correctly displayed after a light scroll down the page notes the issue is not reproducible on chrome mobile screenshots attached watchers softvision oana arbuzov softvision sergiulogigan cipriansv sv browser configuration none from with ❤️ | 1 |
34,075 | 6,288,618,324 | IssuesEvent | 2017-07-19 17:23:16 | hammerandchisel/discord-api-docs | https://api.github.com/repos/hammerandchisel/discord-api-docs | closed | Session Start Rate Limit | documentation needed | We're deploying a change soon that will hopefully automatically reset your bot's token if you're starting way too many sessions within a 24 hour period. Right now - that limit is 1,000 sessions (meaning successfully calling `IDENTIFY` via the websocket -`RESUME`s do not count).
The reasoning behind this is that due to bad restart scripts/code, bots tend to get into "restart loops" - indefinitely until the bot operator notices. The idea here is to make it so that if your bot gets stuck into a restart loop, you'll have to manually intervene by updating it's token.
When you reach the limit, you'll receive a notification e-mail saying your bot token has been reset. When this happens all active sessions for that bot will be terminated.
This limit is for the given bot application, and is global across all shards. If you are running a large bot across many shards, having a test bot that you test stuff on is recommended rather than testing on your large bot and restarting it.
## TODO:
- [x] Deploy This
- [x] Add to Docs | 1.0 | Session Start Rate Limit - We're deploying a change soon that will hopefully automatically reset your bot's token if you're starting way too many sessions within a 24 hour period. Right now - that limit is 1,000 sessions (meaning successfully calling `IDENTIFY` via the websocket -`RESUME`s do not count).
The reasoning behind this is that due to bad restart scripts/code, bots tend to get into "restart loops" - indefinitely until the bot operator notices. The idea here is to make it so that if your bot gets stuck into a restart loop, you'll have to manually intervene by updating it's token.
When you reach the limit, you'll receive a notification e-mail saying your bot token has been reset. When this happens all active sessions for that bot will be terminated.
This limit is for the given bot application, and is global across all shards. If you are running a large bot across many shards, having a test bot that you test stuff on is recommended rather than testing on your large bot and restarting it.
## TODO:
- [x] Deploy This
- [x] Add to Docs | non_priority | session start rate limit we re deploying a change soon that will hopefully automatically reset your bot s token if you re starting way too many sessions within a hour period right now that limit is sessions meaning successfully calling identify via the websocket resume s do not count the reasoning behind this is that due to bad restart scripts code bots tend to get into restart loops indefinitely until the bot operator notices the idea here is to make it so that if your bot gets stuck into a restart loop you ll have to manually intervene by updating it s token when you reach the limit you ll receive a notification e mail saying your bot token has been reset when this happens all active sessions for that bot will be terminated this limit is for the given bot application and is global across all shards if you are running a large bot across many shards having a test bot that you test stuff on is recommended rather than testing on your large bot and restarting it todo deploy this add to docs | 0 |
455,540 | 13,128,710,087 | IssuesEvent | 2020-08-06 12:46:32 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | opened | Use `hashed_guid`/`hashed_addon_id` for the download stats | component: statistics priority: p3 | BQ will expose a `hashed_addon_id` column instead of the currently exposed `addon_id`. We introduced a `hashed_guid` field on the `AddonGUID` model in #15189. This issue is about using hashes to query the download stats (in `stats/utils.py`) as well as updating the CRON job for the weekly downloads. | 1.0 | Use `hashed_guid`/`hashed_addon_id` for the download stats - BQ will expose a `hashed_addon_id` column instead of the currently exposed `addon_id`. We introduced a `hashed_guid` field on the `AddonGUID` model in #15189. This issue is about using hashes to query the download stats (in `stats/utils.py`) as well as updating the CRON job for the weekly downloads. | priority | use hashed guid hashed addon id for the download stats bq will expose a hashed addon id column instead of the currently exposed addon id we introduced a hashed guid field on the addonguid model in this issue is about using hashes to query the download stats in stats utils py as well as updating the cron job for the weekly downloads | 1 |
224,050 | 17,657,824,213 | IssuesEvent | 2021-08-21 00:05:30 | nasa/cFE | https://api.github.com/repos/nasa/cFE | closed | No Success Test for CFE_ES_RestartApp | good first issue unit-test | **Is your feature request related to a problem? Please describe.**
From #548. No Success Test for CFE_ES_RestartApp.
**Describe the solution you'd like**
Add a success test for CFE_ES_RestartApp in cFE/modules/es/ut-coverage/es_UT.c.
**Requester Info**
Ariel Adams, ASRC Federal
| 1.0 | No Success Test for CFE_ES_RestartApp - **Is your feature request related to a problem? Please describe.**
From #548. No Success Test for CFE_ES_RestartApp.
**Describe the solution you'd like**
Add a success test for CFE_ES_RestartApp in cFE/modules/es/ut-coverage/es_UT.c.
**Requester Info**
Ariel Adams, ASRC Federal
| non_priority | no success test for cfe es restartapp is your feature request related to a problem please describe from no success test for cfe es restartapp describe the solution you d like add a success test for cfe es restartapp in cfe modules es ut coverage es ut c requester info ariel adams asrc federal | 0 |
74,816 | 9,807,919,560 | IssuesEvent | 2019-06-12 14:38:41 | gitcoinco/web | https://api.github.com/repos/gitcoinco/web | closed | Cannot create bounties without Github API Key | bug documentation | **Describe the bug**
If you do not enter a github account as noted in the local.env...
```
# These settings will enable github API notification
# and gitcoinbot sync's. They are not necessary unless you are planning on
# using the Github API
```
...you cannot create/fund bounties on your local instance
**To Reproduce**
Use docker, do not enter Github API, try to create a new bounty
**Expected behavior**
Allow bounty creation
**Screenshots**
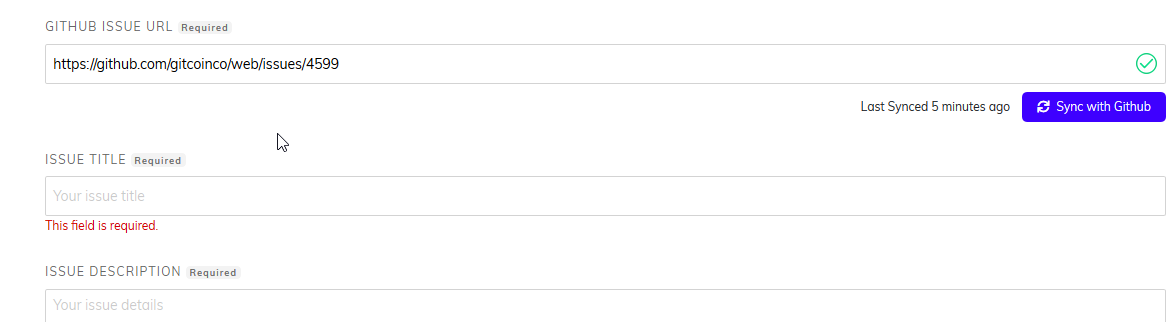
```
web_1 | 10.0.2.2 - - [10/Jun/2019 14:07:48] "GET /static/v2/images/close-red.png HTTP/1.1" 200 -
web_1 | WARNING 2019-06-10 14:07:50,459 helpers 17 140381402012392 401 {'message': 'Bad credentials', 'documentation_url': 'https://developer.github.com/v3'}
web_1 | 10.0.2.2 - - [10/Jun/2019 14:07:50] "GET /sync/get_issue_details?url=https%3A%2F%2Fgithub.com%2Fgitcoinco%2Fweb%2Fissues%2F4599&token= HTTP/1.1" 200 -
web_1 | WARNING 2019-06-10 14:07:53,889 helpers 17 140381402012392 401 {'message': 'Bad credentials', 'documentation_url': 'https://developer.github.com/v3'}
web_1 | 10.0.2.2 - - [10/Jun/2019 14:07:53] "GET /sync/get_issue_details?url=https%3A%2F%2Fgithub.com%2Fgitcoinco%2Fweb%2Fissues%2F4599&token= HTTP/1.1" 200 -
``` | 1.0 | Cannot create bounties without Github API Key - **Describe the bug**
If you do not enter a github account as noted in the local.env...
```
# These settings will enable github API notification
# and gitcoinbot sync's. They are not necessary unless you are planning on
# using the Github API
```
...you cannot create/fund bounties on your local instance
**To Reproduce**
Use docker, do not enter Github API, try to create a new bounty
**Expected behavior**
Allow bounty creation
**Screenshots**
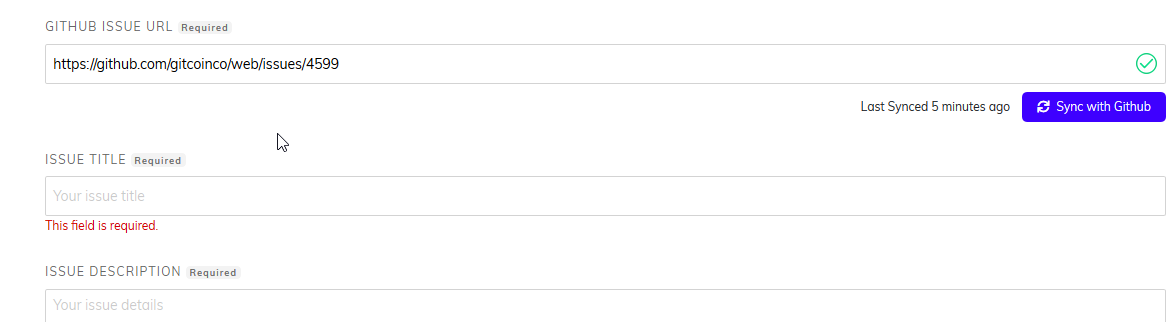
```
web_1 | 10.0.2.2 - - [10/Jun/2019 14:07:48] "GET /static/v2/images/close-red.png HTTP/1.1" 200 -
web_1 | WARNING 2019-06-10 14:07:50,459 helpers 17 140381402012392 401 {'message': 'Bad credentials', 'documentation_url': 'https://developer.github.com/v3'}
web_1 | 10.0.2.2 - - [10/Jun/2019 14:07:50] "GET /sync/get_issue_details?url=https%3A%2F%2Fgithub.com%2Fgitcoinco%2Fweb%2Fissues%2F4599&token= HTTP/1.1" 200 -
web_1 | WARNING 2019-06-10 14:07:53,889 helpers 17 140381402012392 401 {'message': 'Bad credentials', 'documentation_url': 'https://developer.github.com/v3'}
web_1 | 10.0.2.2 - - [10/Jun/2019 14:07:53] "GET /sync/get_issue_details?url=https%3A%2F%2Fgithub.com%2Fgitcoinco%2Fweb%2Fissues%2F4599&token= HTTP/1.1" 200 -
``` | non_priority | cannot create bounties without github api key describe the bug if you do not enter a github account as noted in the local env these settings will enable github api notification and gitcoinbot sync s they are not necessary unless you are planning on using the github api you cannot create fund bounties on your local instance to reproduce use docker do not enter github api try to create a new bounty expected behavior allow bounty creation screenshots web get static images close red png http web warning helpers message bad credentials documentation url web get sync get issue details url https com token http web warning helpers message bad credentials documentation url web get sync get issue details url https com token http | 0 |
186,785 | 6,742,692,801 | IssuesEvent | 2017-10-20 08:52:46 | YetiForceCompany/YetiForceCRM | https://api.github.com/repos/YetiForceCompany/YetiForceCRM | closed | Global search issue | Category::Bug Subcategory::HighPriority | <!--- Before you create a new issue, please check out our [manual] (https://yetiforce.com/en/github/issues/126-issues.html) --->
#### Issue
<!--- Provide a more detailed introduction to the issue itself, and why you consider it to be a bug. Descriptions can be provided in English or Polish (remember to add [PL] for Polish in the title). -->
Global search for all records is not working.
#### Actual Behavior
<!--- Describe the result -->
#### Expected Behavior
<!--- Describe what you would want the result to be -->
#### How to trigger the error
<!--- If possible, please make a video using [ScreenToGif] (https://screentogif.codeplex.com/) or any other program used for recording actions from your desktop. -->
1.
2.
3.
#### Your Environment
<!---Describe the environment -->
* YetiForce Version used:
* Browser name and version:
* Environment name and version:
* Operating System and version:
<!--- Please check on your issue from time to time, in case we have questions or need some extra information. --->
| 1.0 | Global search issue - <!--- Before you create a new issue, please check out our [manual] (https://yetiforce.com/en/github/issues/126-issues.html) --->
#### Issue
<!--- Provide a more detailed introduction to the issue itself, and why you consider it to be a bug. Descriptions can be provided in English or Polish (remember to add [PL] for Polish in the title). -->
Global search for all records is not working.
#### Actual Behavior
<!--- Describe the result -->
#### Expected Behavior
<!--- Describe what you would want the result to be -->
#### How to trigger the error
<!--- If possible, please make a video using [ScreenToGif] (https://screentogif.codeplex.com/) or any other program used for recording actions from your desktop. -->
1.
2.
3.
#### Your Environment
<!---Describe the environment -->
* YetiForce Version used:
* Browser name and version:
* Environment name and version:
* Operating System and version:
<!--- Please check on your issue from time to time, in case we have questions or need some extra information. --->
| priority | global search issue issue global search for all records is not working actual behavior expected behavior how to trigger the error your environment yetiforce version used browser name and version environment name and version operating system and version | 1 |
46,256 | 2,951,885,478 | IssuesEvent | 2015-07-07 03:54:58 | rossPatton/stylint | https://api.github.com/repos/rossPatton/stylint | closed | Version 0.9.3 reports selector depth greater than <limit> in-error | bug low priority | ```css
//
// Fonts for Bootstrap
//
// Import the fonts - using styles produced from fontsquirrel.com
@font-face
font-family: 'Corpid Heavy'
src: url($icon-font-path + 'corpidc1s-heavy-webfont.eot')
src: url($icon-font-path + 'corpidc1s-heavy-webfont.eot?#iefix') format('embedded-opentype'),
url($icon-font-path + 'corpidc1s-heavy-webfont.woff2') format('woff2'),
url($icon-font-path + 'corpidc1s-heavy-webfont.woff') format('woff'),
url($icon-font-path + 'corpidc1s-heavy-webfont.ttf') format('truetype'),
url($icon-font-path + 'corpidc1s-heavy-webfont.svg#CorpidC1sHeavyRegular') format('svg')
font-style: normal
font-weight: 500
...
```
Console log:
```console
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 10: url($icon-font-path + 'corpidc1s-heavy-webfont.woff2') format('woff2'),
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 11: url($icon-font-path + 'corpidc1s-heavy-webfont.woff') format('woff'),
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 12: url($icon-font-path + 'corpidc1s-heavy-webfont.ttf') format('truetype'),
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 13: url($icon-font-path + 'corpidc1s-heavy-webfont.svg#CorpidC1sHeavyRegular') format('svg')
```
Config:
```json
{
"alphabetical": false,
"borderNone": true,
"brackets": false,
"colons": false,
"colors": false,
"commaSpace": true,
"commentSpace": false,
"cssLiteral": false,
"depthLimit": 3,
"duplicates": false,
"efficient": true,
"enforceBlockStyle": false,
"enforceVarStyle": true,
"extendPref": "@extend",
"globalDupe": true,
"indentSpaces": 2,
"leadingZero": false,
"maxWarnings": 50,
"maxWarningsKill": false,
"mixed": true,
"namingConvention": "BEM",
"parenSpace": false,
"placeholders": false,
"semicolons": false,
"universal": true,
"valid": true,
"whitespace": true,
"zeroUnits": true,
"zIndexDuplicates": false,
"zIndexNormalize": false
}
```
Stylint Version 0.9.4
Also, the line break in the warning message makes it harder to understand the error.
Sorry for the trouble, Ross. I'll revert to 0.9.2 again. | 1.0 | Version 0.9.3 reports selector depth greater than <limit> in-error - ```css
//
// Fonts for Bootstrap
//
// Import the fonts - using styles produced from fontsquirrel.com
@font-face
font-family: 'Corpid Heavy'
src: url($icon-font-path + 'corpidc1s-heavy-webfont.eot')
src: url($icon-font-path + 'corpidc1s-heavy-webfont.eot?#iefix') format('embedded-opentype'),
url($icon-font-path + 'corpidc1s-heavy-webfont.woff2') format('woff2'),
url($icon-font-path + 'corpidc1s-heavy-webfont.woff') format('woff'),
url($icon-font-path + 'corpidc1s-heavy-webfont.ttf') format('truetype'),
url($icon-font-path + 'corpidc1s-heavy-webfont.svg#CorpidC1sHeavyRegular') format('svg')
font-style: normal
font-weight: 500
...
```
Console log:
```console
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 10: url($icon-font-path + 'corpidc1s-heavy-webfont.woff2') format('woff2'),
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 11: url($icon-font-path + 'corpidc1s-heavy-webfont.woff') format('woff'),
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 12: url($icon-font-path + 'corpidc1s-heavy-webfont.ttf') format('truetype'),
Warning: selector depth greater than
Warning: 3:
File: src/modules/core/styles/component/fonts.styl
Line: 13: url($icon-font-path + 'corpidc1s-heavy-webfont.svg#CorpidC1sHeavyRegular') format('svg')
```
Config:
```json
{
"alphabetical": false,
"borderNone": true,
"brackets": false,
"colons": false,
"colors": false,
"commaSpace": true,
"commentSpace": false,
"cssLiteral": false,
"depthLimit": 3,
"duplicates": false,
"efficient": true,
"enforceBlockStyle": false,
"enforceVarStyle": true,
"extendPref": "@extend",
"globalDupe": true,
"indentSpaces": 2,
"leadingZero": false,
"maxWarnings": 50,
"maxWarningsKill": false,
"mixed": true,
"namingConvention": "BEM",
"parenSpace": false,
"placeholders": false,
"semicolons": false,
"universal": true,
"valid": true,
"whitespace": true,
"zeroUnits": true,
"zIndexDuplicates": false,
"zIndexNormalize": false
}
```
Stylint Version 0.9.4
Also, the line break in the warning message makes it harder to understand the error.
Sorry for the trouble, Ross. I'll revert to 0.9.2 again. | priority | version reports selector depth greater than in error css fonts for bootstrap import the fonts using styles produced from fontsquirrel com font face font family corpid heavy src url icon font path heavy webfont eot src url icon font path heavy webfont eot iefix format embedded opentype url icon font path heavy webfont format url icon font path heavy webfont woff format woff url icon font path heavy webfont ttf format truetype url icon font path heavy webfont svg format svg font style normal font weight console log console warning selector depth greater than warning file src modules core styles component fonts styl line url icon font path heavy webfont format warning selector depth greater than warning file src modules core styles component fonts styl line url icon font path heavy webfont woff format woff warning selector depth greater than warning file src modules core styles component fonts styl line url icon font path heavy webfont ttf format truetype warning selector depth greater than warning file src modules core styles component fonts styl line url icon font path heavy webfont svg format svg config json alphabetical false bordernone true brackets false colons false colors false commaspace true commentspace false cssliteral false depthlimit duplicates false efficient true enforceblockstyle false enforcevarstyle true extendpref extend globaldupe true indentspaces leadingzero false maxwarnings maxwarningskill false mixed true namingconvention bem parenspace false placeholders false semicolons false universal true valid true whitespace true zerounits true zindexduplicates false zindexnormalize false stylint version also the line break in the warning message makes it harder to understand the error sorry for the trouble ross i ll revert to again | 1 |
100,050 | 11,171,782,182 | IssuesEvent | 2019-12-28 22:56:37 | nori-io/nori | https://api.github.com/repos/nori-io/nori | opened | Nori Documentation: Intro / Get started | Documentation task | Create documentation: Intro / Get started:
#### Intro / Get started
There are two main ways to get started with Nori
- [ ] Tutorial: Step-by-step instructions on how to install Nori, use and develop plugins.
- [ ] Quick start: One page summary of how to install Nori and use plugins. | 1.0 | Nori Documentation: Intro / Get started - Create documentation: Intro / Get started:
#### Intro / Get started
There are two main ways to get started with Nori
- [ ] Tutorial: Step-by-step instructions on how to install Nori, use and develop plugins.
- [ ] Quick start: One page summary of how to install Nori and use plugins. | non_priority | nori documentation intro get started create documentation intro get started intro get started there are two main ways to get started with nori tutorial step by step instructions on how to install nori use and develop plugins quick start one page summary of how to install nori and use plugins | 0 |
18,874 | 6,652,451,084 | IssuesEvent | 2017-09-29 01:32:58 | HypothesisWorks/hypothesis-python | https://api.github.com/repos/HypothesisWorks/hypothesis-python | opened | Failing build on master due to pulled Numpy release | CI-and-build | https://travis-ci.org/HypothesisWorks/hypothesis-python/builds/281109967
https://www.reddit.com/r/Python/comments/731x9g/numpy_1132_released_with_security_fix/
https://pypi.python.org/pypi/numpy/1.13.2
- [ ] Wait for the Numpy team to release a fixed version
- [ ] Merge the Pyup pull when it comes (or push a manual fix)
- [ ] Build should pass and automatically deploy from master
Hopefully this won't push our removal of 3.3 back to after the EOL date! | 1.0 | Failing build on master due to pulled Numpy release - https://travis-ci.org/HypothesisWorks/hypothesis-python/builds/281109967
https://www.reddit.com/r/Python/comments/731x9g/numpy_1132_released_with_security_fix/
https://pypi.python.org/pypi/numpy/1.13.2
- [ ] Wait for the Numpy team to release a fixed version
- [ ] Merge the Pyup pull when it comes (or push a manual fix)
- [ ] Build should pass and automatically deploy from master
Hopefully this won't push our removal of 3.3 back to after the EOL date! | non_priority | failing build on master due to pulled numpy release wait for the numpy team to release a fixed version merge the pyup pull when it comes or push a manual fix build should pass and automatically deploy from master hopefully this won t push our removal of back to after the eol date | 0 |
178,428 | 6,608,692,183 | IssuesEvent | 2017-09-19 12:03:00 | chez-nestor/backoffice | https://api.github.com/repos/chez-nestor/backoffice | closed | Create an API endpoint on our API to list available rooms by city | [priority] P1 [type] enhancement | - [x] Modify the "extractWordpress" script to also return the url of the room
- [x] Write a script that, for each room in the db:
1. finds the url of the room page from the data extracted previously
1. tries to fetch the html of the room page on chez-nestor.com, (otherwise, throws an error so that we can fix it manually)
1. parse the html using headless-chrome to list the photos of the room
1. generates a json listing all photos of all rooms
- [x] Create a `Photo` smart-collection (see `Invoice` example)
- [x] Add a `Photos` smart-association to Room that returns the list of photos from the pre-built JSON
And we need to remember to run that script every time a room is added to the WordPress | 1.0 | Create an API endpoint on our API to list available rooms by city - - [x] Modify the "extractWordpress" script to also return the url of the room
- [x] Write a script that, for each room in the db:
1. finds the url of the room page from the data extracted previously
1. tries to fetch the html of the room page on chez-nestor.com, (otherwise, throws an error so that we can fix it manually)
1. parse the html using headless-chrome to list the photos of the room
1. generates a json listing all photos of all rooms
- [x] Create a `Photo` smart-collection (see `Invoice` example)
- [x] Add a `Photos` smart-association to Room that returns the list of photos from the pre-built JSON
And we need to remember to run that script every time a room is added to the WordPress | priority | create an api endpoint on our api to list available rooms by city modify the extractwordpress script to also return the url of the room write a script that for each room in the db finds the url of the room page from the data extracted previously tries to fetch the html of the room page on chez nestor com otherwise throws an error so that we can fix it manually parse the html using headless chrome to list the photos of the room generates a json listing all photos of all rooms create a photo smart collection see invoice example add a photos smart association to room that returns the list of photos from the pre built json and we need to remember to run that script every time a room is added to the wordpress | 1 |
235,826 | 19,430,362,520 | IssuesEvent | 2021-12-21 11:12:13 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: jepsen/multi-register/start-stop-2 failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.jepsen/multi-register/start-stop-2 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=artifacts#/jepsen/multi-register/start-stop-2) on master @ [3f95a4bd83cce2952a12497de82692866b4da659](https://github.com/cockroachdb/cockroach/commits/3f95a4bd83cce2952a12497de82692866b4da659):
```
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2050
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:172
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func3
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:210
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1581
Wraps: (2) output in run_134034.325146640_n6_bash
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3948712-1639818405-77-n6cpu4:6 -- bash -e -c "\
| cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| ~/lein run test \
| --tarball file://${PWD}/cockroach.tgz \
| --username ${USER} \
| --ssh-private-key ~/.ssh/id_rsa \
| --os ubuntu \
| --time-limit 300 \
| --concurrency 30 \
| --recovery-time 25 \
| --test-count 1 \
| -n 10.142.1.99 -n 10.142.1.90 -n 10.142.1.63 -n 10.142.1.92 -n 10.142.1.105 \
| --test multi-register --nemesis start-stop-2 \
| > invoke.log 2>&1 \
| " returned
| stderr:
| Error: SSH_PROBLEM: exit status 255
| (1) SSH_PROBLEM
| Wraps: (2) Node 6. Command with error:
| | ``````
| | bash -e -c "\
| | cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| | ~/lein run test \
| | --tarball file://${PWD}/cockroach.tgz \
| | --username ${USER} \
| | --ssh-private-key ~/.ssh/id_rsa \
| | --os ubuntu \
| | --time-limit 300 \
| | --concurrency 30 \
| | --recovery-time 25 \
| | --test-count 1 \
| | -n 10.142.1.99 -n 10.142.1.90 -n 10.142.1.63 -n 10.142.1.92 -n 10.142.1.105 \
| | --test multi-register --nemesis start-stop-2 \
| | > invoke.log 2>&1 \
| | "
| | ``````
| Wraps: (3) exit status 255
| Error types: (1) errors.SSH (2) *hintdetail.withDetail (3) *exec.ExitError
|
| stdout:
Wraps: (4) exit status 10
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/multi-register/start-stop-2.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: jepsen/multi-register/start-stop-2 failed - roachtest.jepsen/multi-register/start-stop-2 [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3948712&tab=artifacts#/jepsen/multi-register/start-stop-2) on master @ [3f95a4bd83cce2952a12497de82692866b4da659](https://github.com/cockroachdb/cockroach/commits/3f95a4bd83cce2952a12497de82692866b4da659):
```
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2050
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:172
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen.func3
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:210
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1581
Wraps: (2) output in run_134034.325146640_n6_bash
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3948712-1639818405-77-n6cpu4:6 -- bash -e -c "\
| cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| ~/lein run test \
| --tarball file://${PWD}/cockroach.tgz \
| --username ${USER} \
| --ssh-private-key ~/.ssh/id_rsa \
| --os ubuntu \
| --time-limit 300 \
| --concurrency 30 \
| --recovery-time 25 \
| --test-count 1 \
| -n 10.142.1.99 -n 10.142.1.90 -n 10.142.1.63 -n 10.142.1.92 -n 10.142.1.105 \
| --test multi-register --nemesis start-stop-2 \
| > invoke.log 2>&1 \
| " returned
| stderr:
| Error: SSH_PROBLEM: exit status 255
| (1) SSH_PROBLEM
| Wraps: (2) Node 6. Command with error:
| | ``````
| | bash -e -c "\
| | cd /mnt/data1/jepsen/cockroachdb && set -eo pipefail && \
| | ~/lein run test \
| | --tarball file://${PWD}/cockroach.tgz \
| | --username ${USER} \
| | --ssh-private-key ~/.ssh/id_rsa \
| | --os ubuntu \
| | --time-limit 300 \
| | --concurrency 30 \
| | --recovery-time 25 \
| | --test-count 1 \
| | -n 10.142.1.99 -n 10.142.1.90 -n 10.142.1.63 -n 10.142.1.92 -n 10.142.1.105 \
| | --test multi-register --nemesis start-stop-2 \
| | > invoke.log 2>&1 \
| | "
| | ``````
| Wraps: (3) exit status 255
| Error types: (1) errors.SSH (2) *hintdetail.withDetail (3) *exec.ExitError
|
| stdout:
Wraps: (4) exit status 10
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/multi-register/start-stop-2.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| non_priority | roachtest jepsen multi register start stop failed roachtest jepsen multi register start stop with on master home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go github com cockroachdb cockroach pkg cmd roachtest tests runjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go github com cockroachdb cockroach pkg cmd roachtest tests runjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go runtime goexit usr local go src runtime asm s wraps output in run bash wraps home agent work go src github com cockroachdb cockroach bin roachprod run teamcity bash e c cd mnt jepsen cockroachdb set eo pipefail lein run test tarball file pwd cockroach tgz username user ssh private key ssh id rsa os ubuntu time limit concurrency recovery time test count n n n n n test multi register nemesis start stop invoke log returned stderr error ssh problem exit status ssh problem wraps node command with error bash e c cd mnt jepsen cockroachdb set eo pipefail lein run test tarball file pwd cockroach tgz username user ssh private key ssh id rsa os ubuntu time limit concurrency recovery time test count n n n n n test multi register nemesis start stop invoke log wraps exit status error types errors ssh hintdetail withdetail exec exiterror stdout wraps exit status error types withstack withstack errutil withprefix cluster withcommanddetails exec exiterror help see see cc cockroachdb kv triage | 0 |
105,863 | 16,661,239,939 | IssuesEvent | 2021-06-06 11:08:20 | AlexRogalskiy/weather-time | https://api.github.com/repos/AlexRogalskiy/weather-time | opened | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz | security vulnerability | ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: weather-time/package.json</p>
<p>Path to vulnerable library: weather-time/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsonlint-1.6.3.tgz (Root Library)
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/weather-time/commit/1553379ffedec7816ab860950e51a5683cc1da71">1553379ffedec7816ab860950e51a5683cc1da71</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23358 (High) detected in underscore-1.6.0.tgz - ## CVE-2021-23358 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>underscore-1.6.0.tgz</b></p></summary>
<p>JavaScript's functional programming helper library.</p>
<p>Library home page: <a href="https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz">https://registry.npmjs.org/underscore/-/underscore-1.6.0.tgz</a></p>
<p>Path to dependency file: weather-time/package.json</p>
<p>Path to vulnerable library: weather-time/node_modules/underscore/package.json</p>
<p>
Dependency Hierarchy:
- jsonlint-1.6.3.tgz (Root Library)
- nomnom-1.8.1.tgz
- :x: **underscore-1.6.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/weather-time/commit/1553379ffedec7816ab860950e51a5683cc1da71">1553379ffedec7816ab860950e51a5683cc1da71</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package underscore from 1.13.0-0 and before 1.13.0-2, from 1.3.2 and before 1.12.1 are vulnerable to Arbitrary Code Injection via the template function, particularly when a variable property is passed as an argument as it is not sanitized.
<p>Publish Date: 2021-03-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23358>CVE-2021-23358</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23358</a></p>
<p>Release Date: 2021-03-29</p>
<p>Fix Resolution: underscore - 1.12.1,1.13.0-2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in underscore tgz cve high severity vulnerability vulnerable library underscore tgz javascript s functional programming helper library library home page a href path to dependency file weather time package json path to vulnerable library weather time node modules underscore package json dependency hierarchy jsonlint tgz root library nomnom tgz x underscore tgz vulnerable library found in head commit a href found in base branch master vulnerability details the package underscore from and before from and before are vulnerable to arbitrary code injection via the template function particularly when a variable property is passed as an argument as it is not sanitized publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution underscore step up your open source security game with whitesource | 0 |
616,719 | 19,318,880,080 | IssuesEvent | 2021-12-14 01:34:58 | ethereum/ethereum-org-website | https://api.github.com/repos/ethereum/ethereum-org-website | closed | Add section on crypto mining pool scams | feature :sparkles: help wanted content :fountain_pen: high priority good first issue | **Is your feature request related to a problem? Please describe.**
Crypto mining pool scams seem to be the newest popular attack vector for scamming people out of their crypto. We should add this to our security page (and try to optimise for ranking for the term @samajammin ?)
**Describe the solution you'd like**
Add a section on crypto mining pool scams here on our [security and scam prevention page](https://ethereum.org/en/security/)
**Additional context**
https://www.indiatimes.com/technology/news/crypto-mining-pool-scam-on-twitter-555251.html
https://www.reddit.com/r/CoinBase/comments/r0qe0e/scam_or_possible_incredible_payout/
https://www.reddit.com/r/CryptoCurrency/comments/r2atqi/im_the_guy_from_a_few_days_ago_that_got_scammed/
**Want to contribute?**
We love contributions from the Ethereum community! Please comment on an issue if you're interested in helping out with a PR.
| 1.0 | Add section on crypto mining pool scams - **Is your feature request related to a problem? Please describe.**
Crypto mining pool scams seem to be the newest popular attack vector for scamming people out of their crypto. We should add this to our security page (and try to optimise for ranking for the term @samajammin ?)
**Describe the solution you'd like**
Add a section on crypto mining pool scams here on our [security and scam prevention page](https://ethereum.org/en/security/)
**Additional context**
https://www.indiatimes.com/technology/news/crypto-mining-pool-scam-on-twitter-555251.html
https://www.reddit.com/r/CoinBase/comments/r0qe0e/scam_or_possible_incredible_payout/
https://www.reddit.com/r/CryptoCurrency/comments/r2atqi/im_the_guy_from_a_few_days_ago_that_got_scammed/
**Want to contribute?**
We love contributions from the Ethereum community! Please comment on an issue if you're interested in helping out with a PR.
| priority | add section on crypto mining pool scams is your feature request related to a problem please describe crypto mining pool scams seem to be the newest popular attack vector for scamming people out of their crypto we should add this to our security page and try to optimise for ranking for the term samajammin describe the solution you d like add a section on crypto mining pool scams here on our additional context want to contribute we love contributions from the ethereum community please comment on an issue if you re interested in helping out with a pr | 1 |
129,265 | 12,403,273,987 | IssuesEvent | 2020-05-21 13:38:08 | NovelCOVID/API | https://api.github.com/repos/NovelCOVID/API | closed | Add CONTRIBUTION guideline | documentation enhancement | Add CONTRIBUTION guideline for improved collaboration in the open source project. It enables a self-onboarding concept for developers. | 1.0 | Add CONTRIBUTION guideline - Add CONTRIBUTION guideline for improved collaboration in the open source project. It enables a self-onboarding concept for developers. | non_priority | add contribution guideline add contribution guideline for improved collaboration in the open source project it enables a self onboarding concept for developers | 0 |
117,125 | 11,945,722,625 | IssuesEvent | 2020-04-03 06:34:42 | alushingg/ped | https://api.github.com/repos/alushingg/ped | opened | Admin commands details are not in the UG | severity.Low type.DocumentationBug | In the UG there is only `admin`.
However, there seems to be many different types of admin commands which you can consider adding into the UG.
| 1.0 | Admin commands details are not in the UG - In the UG there is only `admin`.
However, there seems to be many different types of admin commands which you can consider adding into the UG.
| non_priority | admin commands details are not in the ug in the ug there is only admin however there seems to be many different types of admin commands which you can consider adding into the ug | 0 |
194,146 | 6,891,929,776 | IssuesEvent | 2017-11-22 18:53:22 | GoogleChrome/lighthouse | https://api.github.com/repos/GoogleChrome/lighthouse | opened | TypeError: Cannot read property '_timing' of undefined | bug needs-priority Sentry | ```
TypeError: Cannot read property '_timing' of undefined
File "/usr/lib/node_modules/lighthouse/lighthouse-core/audits/time-to-first-byte.js", line 29, col 26, in Function.caclulateTTFB
const timing = record._timing;
File "/usr/lib/node_modules/lighthouse/lighthouse-core/audits/time-to-first-byte.js", line 47, col 33, in artifacts.requestNetworkRecords.then
const ttfb = TTFBMetric.caclulateTTFB(finalUrlRequest);
File "internal/process/next_tick.js", line 135, col 7, in process._tickDomainCallback
```
https://sentry.io/google-lighthouse/lighthouse/issues/407357986/ | 1.0 | TypeError: Cannot read property '_timing' of undefined - ```
TypeError: Cannot read property '_timing' of undefined
File "/usr/lib/node_modules/lighthouse/lighthouse-core/audits/time-to-first-byte.js", line 29, col 26, in Function.caclulateTTFB
const timing = record._timing;
File "/usr/lib/node_modules/lighthouse/lighthouse-core/audits/time-to-first-byte.js", line 47, col 33, in artifacts.requestNetworkRecords.then
const ttfb = TTFBMetric.caclulateTTFB(finalUrlRequest);
File "internal/process/next_tick.js", line 135, col 7, in process._tickDomainCallback
```
https://sentry.io/google-lighthouse/lighthouse/issues/407357986/ | priority | typeerror cannot read property timing of undefined typeerror cannot read property timing of undefined file usr lib node modules lighthouse lighthouse core audits time to first byte js line col in function caclulatettfb const timing record timing file usr lib node modules lighthouse lighthouse core audits time to first byte js line col in artifacts requestnetworkrecords then const ttfb ttfbmetric caclulatettfb finalurlrequest file internal process next tick js line col in process tickdomaincallback | 1 |
699,880 | 24,035,967,680 | IssuesEvent | 2022-09-15 19:12:19 | ME-ICA/tedana | https://api.github.com/repos/ME-ICA/tedana | opened | Improve summaries and visualizations of results with modularized decision tree | enhancement help wanted good first issue reports priority: medium impact: medium |
Write code to automatically create a flow chart or other summary/visualization for a decision tree. This can also be used to make a run-specific visualization that shows how components were reclassified at each node of the decision tree.
### Summary
The decision tree modularization (#756) is getting close to done. The "Decision Tree" is the series of steps through which each ICA component is classified as accepted or rejected. A nice feature of this work is a lot of useful information about what happened during processing is logged in structured formats. This information can be visualized and summarized in ways that will help users better understand what is happening and better understand their own data. This can be done by someone who enjoys writing code for interactive visualizations and flow charts even if they don't know much about the internal workings of tedana.
### Additional Detail
#### Flow chart for decision tree
- #355 has an extended discussion on different ways to visualize the decision tree in flow charts. All of these were semi-manually visualized.
- [./tedana/resources/decision_trees](https://github.com/jbteves/tedana/tree/JT_DTM/tedana/resources/decision_trees) contains JSON files for each decision tree that is distributed with tedana. There are a series of elements that detail each step in the process and these can be used to generate a flow chart
- After tedana is run on a dataset, a file called `desc-ICA_decision_tree.json` is saved with the rest of the program's outputts. That file contains the same decision tree that was ran along with an `output` key for each step in the process. Information on what how many component classifications changed and what they changed to is stored there. Other values, such as calculations for various thresholds are also stored. It should be possible to generate a flow charts that highlights exactly which steps affected component classifications.
- Another potentially useful output is `desc-ICA_status_table.tsv` which has a row for each component and a column for each step (node) in the decision process. Each components classification after each node is stored there.
#### Interactive report visualizations
- When tedana is run, the output includes an interactive visualization of the results in `tedana_report.html` This currently includes the components with there kappa values, rho values, variance explained, final classifications, spatial maps, and time series. This information is displayed across several subplots.
- Currently accepted components are green and rejected components are red.
- We will now be saving classification tags for each component and each component could have more than one tag. It would be useful to be able to highlight subsets of components using these classification tags.
- Additional information, such as a mini summary of when components changed their classifications and thresholding metrics that were calculated across components could also be visualized or summarized in this report.
### Next Steps
- If you are interested in working on this, and haven't previously contributed to tedana, let @handwerkerd know so that he can provide additional guidance
- A bit more information on how things are named and stored is in [./tedana/docs/building_decision_trees.rst](https://github.com/jbteves/tedana/blob/JT_DTM/docs/building%20decision%20trees.rst) | 1.0 | Improve summaries and visualizations of results with modularized decision tree -
Write code to automatically create a flow chart or other summary/visualization for a decision tree. This can also be used to make a run-specific visualization that shows how components were reclassified at each node of the decision tree.
### Summary
The decision tree modularization (#756) is getting close to done. The "Decision Tree" is the series of steps through which each ICA component is classified as accepted or rejected. A nice feature of this work is a lot of useful information about what happened during processing is logged in structured formats. This information can be visualized and summarized in ways that will help users better understand what is happening and better understand their own data. This can be done by someone who enjoys writing code for interactive visualizations and flow charts even if they don't know much about the internal workings of tedana.
### Additional Detail
#### Flow chart for decision tree
- #355 has an extended discussion on different ways to visualize the decision tree in flow charts. All of these were semi-manually visualized.
- [./tedana/resources/decision_trees](https://github.com/jbteves/tedana/tree/JT_DTM/tedana/resources/decision_trees) contains JSON files for each decision tree that is distributed with tedana. There are a series of elements that detail each step in the process and these can be used to generate a flow chart
- After tedana is run on a dataset, a file called `desc-ICA_decision_tree.json` is saved with the rest of the program's outputts. That file contains the same decision tree that was ran along with an `output` key for each step in the process. Information on what how many component classifications changed and what they changed to is stored there. Other values, such as calculations for various thresholds are also stored. It should be possible to generate a flow charts that highlights exactly which steps affected component classifications.
- Another potentially useful output is `desc-ICA_status_table.tsv` which has a row for each component and a column for each step (node) in the decision process. Each components classification after each node is stored there.
#### Interactive report visualizations
- When tedana is run, the output includes an interactive visualization of the results in `tedana_report.html` This currently includes the components with there kappa values, rho values, variance explained, final classifications, spatial maps, and time series. This information is displayed across several subplots.
- Currently accepted components are green and rejected components are red.
- We will now be saving classification tags for each component and each component could have more than one tag. It would be useful to be able to highlight subsets of components using these classification tags.
- Additional information, such as a mini summary of when components changed their classifications and thresholding metrics that were calculated across components could also be visualized or summarized in this report.
### Next Steps
- If you are interested in working on this, and haven't previously contributed to tedana, let @handwerkerd know so that he can provide additional guidance
- A bit more information on how things are named and stored is in [./tedana/docs/building_decision_trees.rst](https://github.com/jbteves/tedana/blob/JT_DTM/docs/building%20decision%20trees.rst) | priority | improve summaries and visualizations of results with modularized decision tree write code to automatically create a flow chart or other summary visualization for a decision tree this can also be used to make a run specific visualization that shows how components were reclassified at each node of the decision tree summary the decision tree modularization is getting close to done the decision tree is the series of steps through which each ica component is classified as accepted or rejected a nice feature of this work is a lot of useful information about what happened during processing is logged in structured formats this information can be visualized and summarized in ways that will help users better understand what is happening and better understand their own data this can be done by someone who enjoys writing code for interactive visualizations and flow charts even if they don t know much about the internal workings of tedana additional detail flow chart for decision tree has an extended discussion on different ways to visualize the decision tree in flow charts all of these were semi manually visualized contains json files for each decision tree that is distributed with tedana there are a series of elements that detail each step in the process and these can be used to generate a flow chart after tedana is run on a dataset a file called desc ica decision tree json is saved with the rest of the program s outputts that file contains the same decision tree that was ran along with an output key for each step in the process information on what how many component classifications changed and what they changed to is stored there other values such as calculations for various thresholds are also stored it should be possible to generate a flow charts that highlights exactly which steps affected component classifications another potentially useful output is desc ica status table tsv which has a row for each component and a column for each step node in the decision process each components classification after each node is stored there interactive report visualizations when tedana is run the output includes an interactive visualization of the results in tedana report html this currently includes the components with there kappa values rho values variance explained final classifications spatial maps and time series this information is displayed across several subplots currently accepted components are green and rejected components are red we will now be saving classification tags for each component and each component could have more than one tag it would be useful to be able to highlight subsets of components using these classification tags additional information such as a mini summary of when components changed their classifications and thresholding metrics that were calculated across components could also be visualized or summarized in this report next steps if you are interested in working on this and haven t previously contributed to tedana let handwerkerd know so that he can provide additional guidance a bit more information on how things are named and stored is in | 1 |
145,530 | 19,339,485,137 | IssuesEvent | 2021-12-15 01:36:53 | billmcchesney1/t-vault | https://api.github.com/repos/billmcchesney1/t-vault | opened | WS-2018-0650 (High) detected in useragent-2.3.0.tgz | security vulnerability | ## WS-2018-0650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>useragent-2.3.0.tgz</b></p></summary>
<p>Fastest, most accurate & effecient user agent string parser, uses Browserscope's research for parsing</p>
<p>Library home page: <a href="https://registry.npmjs.org/useragent/-/useragent-2.3.0.tgz">https://registry.npmjs.org/useragent/-/useragent-2.3.0.tgz</a></p>
<p>Path to dependency file: t-vault/tvaultui/package.json</p>
<p>Path to vulnerable library: t-vault/tvaultui/node_modules/useragent/package.json</p>
<p>
Dependency Hierarchy:
- karma-0.13.22.tgz (Root Library)
- :x: **useragent-2.3.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Regular Expression Denial of Service (ReDoS) vulnerability was found in useragent through 2.3.0.
<p>Publish Date: 2018-02-27
<p>URL: <a href=https://hackerone.com/reports/320159>WS-2018-0650</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"useragent","packageVersion":"2.3.0","packageFilePaths":["/tvaultui/package.json"],"isTransitiveDependency":true,"dependencyTree":"karma:0.13.22;useragent:2.3.0","isMinimumFixVersionAvailable":false,"isBinary":false}],"baseBranches":["dev"],"vulnerabilityIdentifier":"WS-2018-0650","vulnerabilityDetails":"Regular Expression Denial of Service (ReDoS) vulnerability was found in useragent through 2.3.0.","vulnerabilityUrl":"https://hackerone.com/reports/320159","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | WS-2018-0650 (High) detected in useragent-2.3.0.tgz - ## WS-2018-0650 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>useragent-2.3.0.tgz</b></p></summary>
<p>Fastest, most accurate & effecient user agent string parser, uses Browserscope's research for parsing</p>
<p>Library home page: <a href="https://registry.npmjs.org/useragent/-/useragent-2.3.0.tgz">https://registry.npmjs.org/useragent/-/useragent-2.3.0.tgz</a></p>
<p>Path to dependency file: t-vault/tvaultui/package.json</p>
<p>Path to vulnerable library: t-vault/tvaultui/node_modules/useragent/package.json</p>
<p>
Dependency Hierarchy:
- karma-0.13.22.tgz (Root Library)
- :x: **useragent-2.3.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Regular Expression Denial of Service (ReDoS) vulnerability was found in useragent through 2.3.0.
<p>Publish Date: 2018-02-27
<p>URL: <a href=https://hackerone.com/reports/320159>WS-2018-0650</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"useragent","packageVersion":"2.3.0","packageFilePaths":["/tvaultui/package.json"],"isTransitiveDependency":true,"dependencyTree":"karma:0.13.22;useragent:2.3.0","isMinimumFixVersionAvailable":false,"isBinary":false}],"baseBranches":["dev"],"vulnerabilityIdentifier":"WS-2018-0650","vulnerabilityDetails":"Regular Expression Denial of Service (ReDoS) vulnerability was found in useragent through 2.3.0.","vulnerabilityUrl":"https://hackerone.com/reports/320159","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | ws high detected in useragent tgz ws high severity vulnerability vulnerable library useragent tgz fastest most accurate effecient user agent string parser uses browserscope s research for parsing library home page a href path to dependency file t vault tvaultui package json path to vulnerable library t vault tvaultui node modules useragent package json dependency hierarchy karma tgz root library x useragent tgz vulnerable library found in base branch dev vulnerability details regular expression denial of service redos vulnerability was found in useragent through publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree karma useragent isminimumfixversionavailable false isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails regular expression denial of service redos vulnerability was found in useragent through vulnerabilityurl | 0 |
43,374 | 11,210,043,365 | IssuesEvent | 2020-01-06 12:08:25 | angular/angular-cli | https://api.github.com/repos/angular/angular-cli | closed | ({}).toString.call(null) returns [object Window] for ES6 only builds | comp: devkit/build-angular freq1: low severity3: broken type: bug/fix | # 🐞 Bug report
### Command (mark with an `x`)
- [ ] new
- [x] build
- [ ] serve
- [ ] test
- [ ] e2e
- [ ] generate
- [ ] add
- [ ] update
- [ ] lint
- [ ] xi18n
- [ ] run
- [ ] config
- [ ] help
- [ ] version
- [ ] doc
### Is this a regression?
Unsure.
### Description
On a project with a `browserslist` that only ends up targeting ES6 browsers, the result of `({}).toString.call(null)` is `"[object Window]"`, not `"[object Null]"` as expected.
I came across this bug as our project only targets ES6 and we recently upgraded to Bootstrap 4.4 which uses this method for checking the type of parameters. In https://github.com/twbs/bootstrap/pull/29251 an new option was added which has a default value of `null`, which returns a type of `window` in their type checker which causes an error with this CLI configuration.
## 🔬 Minimal Reproduction
- `ng new toStringRepo`
- `ng serve`
- Open console of served app
- Execute `({}).toString.call(null)` and observe that it returns `"[object Null]"`
- Stop serving
- Change content of `browserslist` to `last 2 Chrome versions`
- `ng serve`
- Open console of served app
- Execute `({}).toString.call(null)` and observe that it returns `"[object Window]"`
## 🔥 Exception or Error
None
## 🌍 Your Environment
<pre><code>$ ng version
_ _ ____ _ ___
/ \ _ __ __ _ _ _| | __ _ _ __ / ___| | |_ _|
/ △ \ | '_ \ / _` | | | | |/ _` | '__| | | | | | |
/ ___ \| | | | (_| | |_| | | (_| | | | |___| |___ | |
/_/ \_\_| |_|\__, |\__,_|_|\__,_|_| \____|_____|___|
|___/
Angular CLI: 8.3.21
Node: 10.15.3
OS: win32 x64
Angular: 8.2.14
... animations, common, compiler, compiler-cli, core, forms
... language-service, platform-browser, platform-browser-dynamic
... router
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.803.21
@angular-devkit/build-angular 0.803.21
@angular-devkit/build-optimizer 0.803.21
@angular-devkit/build-webpack 0.803.21
@angular-devkit/core 8.3.21
@angular-devkit/schematics 8.3.21
@angular/cli 8.3.21
@ngtools/webpack 8.3.21
@schematics/angular 8.3.21
@schematics/update 0.803.21
rxjs 6.4.0
typescript 3.5.3
webpack 4.39.2
</code></pre>
**Anything else relevant?**
Upgrading the test project to Angular 9 with `ng update @angular/core @angular/cli --next` resolves the issue.
| 1.0 | ({}).toString.call(null) returns [object Window] for ES6 only builds - # 🐞 Bug report
### Command (mark with an `x`)
- [ ] new
- [x] build
- [ ] serve
- [ ] test
- [ ] e2e
- [ ] generate
- [ ] add
- [ ] update
- [ ] lint
- [ ] xi18n
- [ ] run
- [ ] config
- [ ] help
- [ ] version
- [ ] doc
### Is this a regression?
Unsure.
### Description
On a project with a `browserslist` that only ends up targeting ES6 browsers, the result of `({}).toString.call(null)` is `"[object Window]"`, not `"[object Null]"` as expected.
I came across this bug as our project only targets ES6 and we recently upgraded to Bootstrap 4.4 which uses this method for checking the type of parameters. In https://github.com/twbs/bootstrap/pull/29251 an new option was added which has a default value of `null`, which returns a type of `window` in their type checker which causes an error with this CLI configuration.
## 🔬 Minimal Reproduction
- `ng new toStringRepo`
- `ng serve`
- Open console of served app
- Execute `({}).toString.call(null)` and observe that it returns `"[object Null]"`
- Stop serving
- Change content of `browserslist` to `last 2 Chrome versions`
- `ng serve`
- Open console of served app
- Execute `({}).toString.call(null)` and observe that it returns `"[object Window]"`
## 🔥 Exception or Error
None
## 🌍 Your Environment
<pre><code>$ ng version
_ _ ____ _ ___
/ \ _ __ __ _ _ _| | __ _ _ __ / ___| | |_ _|
/ △ \ | '_ \ / _` | | | | |/ _` | '__| | | | | | |
/ ___ \| | | | (_| | |_| | | (_| | | | |___| |___ | |
/_/ \_\_| |_|\__, |\__,_|_|\__,_|_| \____|_____|___|
|___/
Angular CLI: 8.3.21
Node: 10.15.3
OS: win32 x64
Angular: 8.2.14
... animations, common, compiler, compiler-cli, core, forms
... language-service, platform-browser, platform-browser-dynamic
... router
Package Version
-----------------------------------------------------------
@angular-devkit/architect 0.803.21
@angular-devkit/build-angular 0.803.21
@angular-devkit/build-optimizer 0.803.21
@angular-devkit/build-webpack 0.803.21
@angular-devkit/core 8.3.21
@angular-devkit/schematics 8.3.21
@angular/cli 8.3.21
@ngtools/webpack 8.3.21
@schematics/angular 8.3.21
@schematics/update 0.803.21
rxjs 6.4.0
typescript 3.5.3
webpack 4.39.2
</code></pre>
**Anything else relevant?**
Upgrading the test project to Angular 9 with `ng update @angular/core @angular/cli --next` resolves the issue.
| non_priority | tostring call null returns for only builds 🐞 bug report command mark with an x new build serve test generate add update lint run config help version doc is this a regression unsure description on a project with a browserslist that only ends up targeting browsers the result of tostring call null is not as expected i came across this bug as our project only targets and we recently upgraded to bootstrap which uses this method for checking the type of parameters in an new option was added which has a default value of null which returns a type of window in their type checker which causes an error with this cli configuration 🔬 minimal reproduction ng new tostringrepo ng serve open console of served app execute tostring call null and observe that it returns stop serving change content of browserslist to last chrome versions ng serve open console of served app execute tostring call null and observe that it returns 🔥 exception or error none 🌍 your environment ng version △ angular cli node os angular animations common compiler compiler cli core forms language service platform browser platform browser dynamic router package version angular devkit architect angular devkit build angular angular devkit build optimizer angular devkit build webpack angular devkit core angular devkit schematics angular cli ngtools webpack schematics angular schematics update rxjs typescript webpack anything else relevant upgrading the test project to angular with ng update angular core angular cli next resolves the issue | 0 |
215,017 | 16,587,595,317 | IssuesEvent | 2021-06-01 00:30:55 | fleetdm/fleet | https://api.github.com/repos/fleetdm/fleet | opened | Document tier requirements in API docs | documentation idea | ### Goal
It should be clear to a Fleet user which license tier is required to use a given API.
Let's document this in the API documentation.
| 1.0 | Document tier requirements in API docs - ### Goal
It should be clear to a Fleet user which license tier is required to use a given API.
Let's document this in the API documentation.
| non_priority | document tier requirements in api docs goal it should be clear to a fleet user which license tier is required to use a given api let s document this in the api documentation | 0 |
55,175 | 6,444,677,444 | IssuesEvent | 2017-08-12 15:31:46 | disco-lang/disco | https://api.github.com/repos/disco-lang/disco | closed | Allow QuickCheck properties in test suite | U-Testing | The title of the issue says it all. We need an easy way to incorporate randomized, property-based testing into the test suite. | 1.0 | Allow QuickCheck properties in test suite - The title of the issue says it all. We need an easy way to incorporate randomized, property-based testing into the test suite. | non_priority | allow quickcheck properties in test suite the title of the issue says it all we need an easy way to incorporate randomized property based testing into the test suite | 0 |
806,387 | 29,819,933,806 | IssuesEvent | 2023-06-17 00:30:25 | googleapis/google-cloud-go | https://api.github.com/repos/googleapis/google-cloud-go | closed | spanner: many tests failed | type: bug priority: p1 api: spanner flakybot: issue | Many tests failed at the same time in this package.
* I will close this issue when there are no more failures in this package _and_
there is at least one pass.
* No new issues will be filed for this package until this issue is closed.
* If there are already issues for individual test cases, I will close them when
the corresponding test passes. You can close them earlier, if you prefer, and
I won't reopen them while this issue is still open.
Here are the tests that failed:
* TestPartitionRoundTrip
* TestClient_Single
* TestClient_Single_Unavailable
* TestClient_Single_InvalidArgument
* TestClient_Single_SessionNotFound
* TestClient_Single_Read_SessionNotFound
* TestClient_Single_ReadRow_SessionNotFound
* TestClient_Single_RetryableErrorOnPartialResultSet
* TestClient_Single_NonRetryableErrorOnPartialResultSet
* TestClient_Single_NonRetryableInternalErrors
* TestClient_Single_DeadlineExceeded_WithErrors
* TestClient_ReturnDatabaseName
* TestClient_ReadWriteTransactionCommitAborted
* TestClient_ReadWriteTransaction_SessionNotFoundOnCommit
* TestClient_ReadWriteTransaction_SessionNotFoundOnBeginTransaction
* TestClient_ReadWriteTransaction_SessionNotFoundOnExecuteUpdate
* TestClient_ReadWriteTransaction_FirstStatementAsQueryReturnsUnavailableRetryReturnsAborted
* TestClient_ReadWriteTransaction_BatchDmlWithErrorOnFirstStatement
* TestClient_ReadWriteTransaction_BatchDmlWithErrorOnSecondStatement
* TestClient_ReadWriteTransaction_MultipleReadsWithoutNext
* TestClient_ReadWriteTransaction_WithCancelledContext
* TestClient_ApplyAtLeastOnce
* TestClient_ApplyAtLeastOnceReuseSession
* TestClient_ApplyAtLeastOnceInvalidArgument
* TestClient_ApplyAtLeastOnce_NonRetryableInternalErrors
* TestClient_Apply_ApplyOptions
* TestReadWriteTransaction_ErrUnexpectedEOF
* TestReadWriteTransaction_WrapError
* TestReadWriteTransaction_WrapSessionNotFoundError
* TestClient_WriteStructWithPointers
* TestClient_WriteStructWithCustomTypes
* TestReadWriteTransaction_ContextTimeoutDuringCommit
* TestFailedCommit_NoRollback
* TestFailedUpdate_ShouldRollback
* TestClient_NumChannels
* TestClient_WithGRPCConnectionPool
* TestClient_WithGRPCConnectionPoolAndNumChannels
* TestClient_WithGRPCConnectionPoolAndNumChannels_Misconfigured
* TestClient_WithCustomBatchTimeout
* TestClient_WithoutCustomBatchTimeout
* TestClient_CallOptions
* TestClient_QueryWithCallOptions
* TestClient_Single_Read_WithNumericKey
* TestIntegration_DbRemovalRecovery (#7677)
* TestIntegration_QueryWithRoles
-----
commit: b429aa13975e41e45f9978e5de3f9f6054941e35
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/c69e871d-e4b1-441b-b32a-2c980b9676ac), [Sponge](http://sponge2/c69e871d-e4b1-441b-b32a-2c980b9676ac)
status: failed | 1.0 | spanner: many tests failed - Many tests failed at the same time in this package.
* I will close this issue when there are no more failures in this package _and_
there is at least one pass.
* No new issues will be filed for this package until this issue is closed.
* If there are already issues for individual test cases, I will close them when
the corresponding test passes. You can close them earlier, if you prefer, and
I won't reopen them while this issue is still open.
Here are the tests that failed:
* TestPartitionRoundTrip
* TestClient_Single
* TestClient_Single_Unavailable
* TestClient_Single_InvalidArgument
* TestClient_Single_SessionNotFound
* TestClient_Single_Read_SessionNotFound
* TestClient_Single_ReadRow_SessionNotFound
* TestClient_Single_RetryableErrorOnPartialResultSet
* TestClient_Single_NonRetryableErrorOnPartialResultSet
* TestClient_Single_NonRetryableInternalErrors
* TestClient_Single_DeadlineExceeded_WithErrors
* TestClient_ReturnDatabaseName
* TestClient_ReadWriteTransactionCommitAborted
* TestClient_ReadWriteTransaction_SessionNotFoundOnCommit
* TestClient_ReadWriteTransaction_SessionNotFoundOnBeginTransaction
* TestClient_ReadWriteTransaction_SessionNotFoundOnExecuteUpdate
* TestClient_ReadWriteTransaction_FirstStatementAsQueryReturnsUnavailableRetryReturnsAborted
* TestClient_ReadWriteTransaction_BatchDmlWithErrorOnFirstStatement
* TestClient_ReadWriteTransaction_BatchDmlWithErrorOnSecondStatement
* TestClient_ReadWriteTransaction_MultipleReadsWithoutNext
* TestClient_ReadWriteTransaction_WithCancelledContext
* TestClient_ApplyAtLeastOnce
* TestClient_ApplyAtLeastOnceReuseSession
* TestClient_ApplyAtLeastOnceInvalidArgument
* TestClient_ApplyAtLeastOnce_NonRetryableInternalErrors
* TestClient_Apply_ApplyOptions
* TestReadWriteTransaction_ErrUnexpectedEOF
* TestReadWriteTransaction_WrapError
* TestReadWriteTransaction_WrapSessionNotFoundError
* TestClient_WriteStructWithPointers
* TestClient_WriteStructWithCustomTypes
* TestReadWriteTransaction_ContextTimeoutDuringCommit
* TestFailedCommit_NoRollback
* TestFailedUpdate_ShouldRollback
* TestClient_NumChannels
* TestClient_WithGRPCConnectionPool
* TestClient_WithGRPCConnectionPoolAndNumChannels
* TestClient_WithGRPCConnectionPoolAndNumChannels_Misconfigured
* TestClient_WithCustomBatchTimeout
* TestClient_WithoutCustomBatchTimeout
* TestClient_CallOptions
* TestClient_QueryWithCallOptions
* TestClient_Single_Read_WithNumericKey
* TestIntegration_DbRemovalRecovery (#7677)
* TestIntegration_QueryWithRoles
-----
commit: b429aa13975e41e45f9978e5de3f9f6054941e35
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/c69e871d-e4b1-441b-b32a-2c980b9676ac), [Sponge](http://sponge2/c69e871d-e4b1-441b-b32a-2c980b9676ac)
status: failed | priority | spanner many tests failed many tests failed at the same time in this package i will close this issue when there are no more failures in this package and there is at least one pass no new issues will be filed for this package until this issue is closed if there are already issues for individual test cases i will close them when the corresponding test passes you can close them earlier if you prefer and i won t reopen them while this issue is still open here are the tests that failed testpartitionroundtrip testclient single testclient single unavailable testclient single invalidargument testclient single sessionnotfound testclient single read sessionnotfound testclient single readrow sessionnotfound testclient single retryableerroronpartialresultset testclient single nonretryableerroronpartialresultset testclient single nonretryableinternalerrors testclient single deadlineexceeded witherrors testclient returndatabasename testclient readwritetransactioncommitaborted testclient readwritetransaction sessionnotfoundoncommit testclient readwritetransaction sessionnotfoundonbegintransaction testclient readwritetransaction sessionnotfoundonexecuteupdate testclient readwritetransaction firststatementasqueryreturnsunavailableretryreturnsaborted testclient readwritetransaction batchdmlwitherroronfirststatement testclient readwritetransaction batchdmlwitherroronsecondstatement testclient readwritetransaction multiplereadswithoutnext testclient readwritetransaction withcancelledcontext testclient applyatleastonce testclient applyatleastoncereusesession testclient applyatleastonceinvalidargument testclient applyatleastonce nonretryableinternalerrors testclient apply applyoptions testreadwritetransaction errunexpectedeof testreadwritetransaction wraperror testreadwritetransaction wrapsessionnotfounderror testclient writestructwithpointers testclient writestructwithcustomtypes testreadwritetransaction contexttimeoutduringcommit testfailedcommit norollback testfailedupdate shouldrollback testclient numchannels testclient withgrpcconnectionpool testclient withgrpcconnectionpoolandnumchannels testclient withgrpcconnectionpoolandnumchannels misconfigured testclient withcustombatchtimeout testclient withoutcustombatchtimeout testclient calloptions testclient querywithcalloptions testclient single read withnumerickey testintegration dbremovalrecovery testintegration querywithroles commit buildurl status failed | 1 |
155,050 | 13,609,332,590 | IssuesEvent | 2020-09-23 04:57:49 | backdrop/backdrop-issues | https://api.github.com/repos/backdrop/backdrop-issues | opened | hook_taxonomy_term_page_alter() isn't documented | good first issue type - documentation | [Line 69](https://github.com/backdrop/backdrop/blob/1.x/core/modules/taxonomy/taxonomy.pages.inc#L69) of taxonomy.pages.inc has this:
> `backdrop_alter('taxonomy_term_page', $build);`
This means that you can implement `hook_taxonomy_term_page_alter()`, however that hook isn't documented.It should be detailed in [taxonomy.api.php](https://github.com/backdrop/backdrop/blob/1.x/core/modules/taxonomy/taxonomy.api.php). | 1.0 | hook_taxonomy_term_page_alter() isn't documented - [Line 69](https://github.com/backdrop/backdrop/blob/1.x/core/modules/taxonomy/taxonomy.pages.inc#L69) of taxonomy.pages.inc has this:
> `backdrop_alter('taxonomy_term_page', $build);`
This means that you can implement `hook_taxonomy_term_page_alter()`, however that hook isn't documented.It should be detailed in [taxonomy.api.php](https://github.com/backdrop/backdrop/blob/1.x/core/modules/taxonomy/taxonomy.api.php). | non_priority | hook taxonomy term page alter isn t documented of taxonomy pages inc has this backdrop alter taxonomy term page build this means that you can implement hook taxonomy term page alter however that hook isn t documented it should be detailed in | 0 |
759,207 | 26,584,379,628 | IssuesEvent | 2023-01-22 21:02:30 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [YSQL] Delete query takes more time for foreign key referenced table | kind/bug area/ysql priority/medium status/awaiting-triage | Jira Link: [DB-5064](https://yugabyte.atlassian.net/browse/DB-5064)
### Description
DB Version: `2.17.1.0-b432`
**Steps**:
1. Create universe with Turn ON the GFlag enable_replicate_transaction_status_table on master and disable automatic tablet splitting
2. Create database and 2 tables and 3 indexes
```
CREATE EXTENSION IF NOT EXISTS "uuid-ossp";
CREATE TYPE complex AS (re float8, im float8);
CREATE TABLE table1 (id text, uuid_col uuid DEFAULT uuid_generate_v4 (), name text, f_name text, c complex, info json, contact JSONB, arr smallint[], cash money, i inet, m macaddr, i2 serial, i3 bigserial, val smallint, age int, collated_data text collate "POSIX",date DATE,n NUMERIC (3, 2),r real, c1 CHAR(1), created_at timestamptz, uuid0 uuid DEFAULT uuid_nil(), uuid1 uuid DEFAULT uuid_generate_v1(), p1 POINT,t1 TIME,ts1 TIMESTAMP,i4 INTERVAL,p2 path, p3 polygon,b box, c2 circle, l line, l1 lseg, a2 text[][], primary key (id ASC));
CREATE TABLE table2 (id text, uuid_col uuid DEFAULT uuid_generate_v4 (), name text primary key, f_name text, c complex, info json, contact JSONB, arr smallint[], cash money, i inet, m macaddr, i2 serial, i3 bigserial, val smallint, age int, collated_data text collate "POSIX",date DATE,n NUMERIC (3, 2),r real, c1 CHAR(1), created_at timestamptz, uuid0 uuid DEFAULT uuid_nil(), uuid1 uuid DEFAULT uuid_generate_v1(), p1 POINT,t1 TIME,ts1 TIMESTAMP,i4 INTERVAL,p2 path, p3 polygon,b box, c2 circle, l line, l1 lseg, a2 text[][], CONSTRAINT fk_table1 FOREIGN KEY(id) REFERENCES table1(id)) SPLIT INTO 8 TABLETS;
create index idx_1 on table1(age) where age>10 and age< 50;
create index idx_2 on table2(f_name);
create index idx_3 on table1(created_at) include(uuid1);
```
3. Run transactional workload(load 100K+ rows in each table)
4. Stop workload, wait for some time
5. Run bootstrap_cdc_producer command # not necessary step, mentioned as I used
6. Run delete queries
`delete from table1 where age>15 and age<20;` - Fails with `ERROR: update or delete on table "table1" violates foreign key constraint "fk_table1" on table "table2”. ` —— expected
`delete from table2 where age>15 and age<20;` - Works(takes < 5 seconds)
`delete from table1 where age>15 and age<20; ` - takes more than 10 min to complete for 7K rows
[DB-5064]: https://yugabyte.atlassian.net/browse/DB-5064?atlOrigin=eyJpIjoiNWRkNTljNzYxNjVmNDY3MDlhMDU5Y2ZhYzA5YTRkZjUiLCJwIjoiZ2l0aHViLWNvbS1KU1cifQ | 1.0 | [YSQL] Delete query takes more time for foreign key referenced table - Jira Link: [DB-5064](https://yugabyte.atlassian.net/browse/DB-5064)
### Description
DB Version: `2.17.1.0-b432`
**Steps**:
1. Create universe with Turn ON the GFlag enable_replicate_transaction_status_table on master and disable automatic tablet splitting
2. Create database and 2 tables and 3 indexes
```
CREATE EXTENSION IF NOT EXISTS "uuid-ossp";
CREATE TYPE complex AS (re float8, im float8);
CREATE TABLE table1 (id text, uuid_col uuid DEFAULT uuid_generate_v4 (), name text, f_name text, c complex, info json, contact JSONB, arr smallint[], cash money, i inet, m macaddr, i2 serial, i3 bigserial, val smallint, age int, collated_data text collate "POSIX",date DATE,n NUMERIC (3, 2),r real, c1 CHAR(1), created_at timestamptz, uuid0 uuid DEFAULT uuid_nil(), uuid1 uuid DEFAULT uuid_generate_v1(), p1 POINT,t1 TIME,ts1 TIMESTAMP,i4 INTERVAL,p2 path, p3 polygon,b box, c2 circle, l line, l1 lseg, a2 text[][], primary key (id ASC));
CREATE TABLE table2 (id text, uuid_col uuid DEFAULT uuid_generate_v4 (), name text primary key, f_name text, c complex, info json, contact JSONB, arr smallint[], cash money, i inet, m macaddr, i2 serial, i3 bigserial, val smallint, age int, collated_data text collate "POSIX",date DATE,n NUMERIC (3, 2),r real, c1 CHAR(1), created_at timestamptz, uuid0 uuid DEFAULT uuid_nil(), uuid1 uuid DEFAULT uuid_generate_v1(), p1 POINT,t1 TIME,ts1 TIMESTAMP,i4 INTERVAL,p2 path, p3 polygon,b box, c2 circle, l line, l1 lseg, a2 text[][], CONSTRAINT fk_table1 FOREIGN KEY(id) REFERENCES table1(id)) SPLIT INTO 8 TABLETS;
create index idx_1 on table1(age) where age>10 and age< 50;
create index idx_2 on table2(f_name);
create index idx_3 on table1(created_at) include(uuid1);
```
3. Run transactional workload(load 100K+ rows in each table)
4. Stop workload, wait for some time
5. Run bootstrap_cdc_producer command # not necessary step, mentioned as I used
6. Run delete queries
`delete from table1 where age>15 and age<20;` - Fails with `ERROR: update or delete on table "table1" violates foreign key constraint "fk_table1" on table "table2”. ` —— expected
`delete from table2 where age>15 and age<20;` - Works(takes < 5 seconds)
`delete from table1 where age>15 and age<20; ` - takes more than 10 min to complete for 7K rows
[DB-5064]: https://yugabyte.atlassian.net/browse/DB-5064?atlOrigin=eyJpIjoiNWRkNTljNzYxNjVmNDY3MDlhMDU5Y2ZhYzA5YTRkZjUiLCJwIjoiZ2l0aHViLWNvbS1KU1cifQ | priority | delete query takes more time for foreign key referenced table jira link description db version steps create universe with turn on the gflag enable replicate transaction status table on master and disable automatic tablet splitting create database and tables and indexes create extension if not exists uuid ossp create type complex as re im create table id text uuid col uuid default uuid generate name text f name text c complex info json contact jsonb arr smallint cash money i inet m macaddr serial bigserial val smallint age int collated data text collate posix date date n numeric r real char created at timestamptz uuid default uuid nil uuid default uuid generate point time timestamp interval path polygon b box circle l line lseg text primary key id asc create table id text uuid col uuid default uuid generate name text primary key f name text c complex info json contact jsonb arr smallint cash money i inet m macaddr serial bigserial val smallint age int collated data text collate posix date date n numeric r real char created at timestamptz uuid default uuid nil uuid default uuid generate point time timestamp interval path polygon b box circle l line lseg text constraint fk foreign key id references id split into tablets create index idx on age where age and age create index idx on f name create index idx on created at include run transactional workload load rows in each table stop workload wait for some time run bootstrap cdc producer command not necessary step mentioned as i used run delete queries delete from where age and age fails with error update or delete on table violates foreign key constraint fk on table ” —— expected delete from where age and age works takes seconds delete from where age and age takes more than min to complete for rows | 1 |
167,323 | 6,336,622,570 | IssuesEvent | 2017-07-26 21:31:13 | Esri/solutions-geoprocessing-toolbox | https://api.github.com/repos/Esri/solutions-geoprocessing-toolbox | closed | Position Analysis Template RangeRings.py with german localization. "is not working with with floating-point numbers" | 4 - Done B - Known Issue F - Data Management priority-moderate | Position Analysis Template
Reported on 11/16/2015:
[ArcGIS.com ](http://www.arcgis.com/home/item.html?id=f10d78ae29cd471ebe2e96bad9b67277)
The Range Rings model is not working with floating-point numbers when using a german localization. Within the RangeRings.py you should use:
`ringInterval = arcpy.GetParameter(2) instead of: ringInterval = float(arcpy.GetParameterAsText(2))`
otherwise there will be an error when the script is trying to parse e.g. ‘5,6’
No further information.
┆Issue is synchronized with this [Asana task](https://app.asana.com/0/129342386639048/129373015346259)
| 1.0 | Position Analysis Template RangeRings.py with german localization. "is not working with with floating-point numbers" - Position Analysis Template
Reported on 11/16/2015:
[ArcGIS.com ](http://www.arcgis.com/home/item.html?id=f10d78ae29cd471ebe2e96bad9b67277)
The Range Rings model is not working with floating-point numbers when using a german localization. Within the RangeRings.py you should use:
`ringInterval = arcpy.GetParameter(2) instead of: ringInterval = float(arcpy.GetParameterAsText(2))`
otherwise there will be an error when the script is trying to parse e.g. ‘5,6’
No further information.
┆Issue is synchronized with this [Asana task](https://app.asana.com/0/129342386639048/129373015346259)
| priority | position analysis template rangerings py with german localization is not working with with floating point numbers position analysis template reported on the range rings model is not working with floating point numbers when using a german localization within the rangerings py you should use ringinterval arcpy getparameter instead of ringinterval float arcpy getparameterastext otherwise there will be an error when the script is trying to parse e g ‘ ’ no further information ┆issue is synchronized with this | 1 |
294,931 | 9,050,707,512 | IssuesEvent | 2019-02-12 09:25:41 | prometheus/tsdb | https://api.github.com/repos/prometheus/tsdb | closed | Compaction blocks Prometheus shutdown | bug help wanted priority: medium | When Prometheus starts a SIGTERM shutdown any in-flight compaction operations will block the shutdown. | 1.0 | Compaction blocks Prometheus shutdown - When Prometheus starts a SIGTERM shutdown any in-flight compaction operations will block the shutdown. | priority | compaction blocks prometheus shutdown when prometheus starts a sigterm shutdown any in flight compaction operations will block the shutdown | 1 |
26,366 | 2,684,340,517 | IssuesEvent | 2015-03-28 21:54:01 | ConEmu/old-issues | https://api.github.com/repos/ConEmu/old-issues | closed | ConEmu Crashes at boot (assertion lbFound at ConEmu.cpp:13657) | 11–20 stars bug imported Priority-Medium | _From [simen.kj...@gmail.com](https://code.google.com/u/116127060082078003686/) on April 22, 2013 02:19:52_
OS version: Win7 SP1 x64 ConEmu version: 130421
I just updated ConEmu to v. 130421, and it gives a dialog box at startup, with this message: ConEmu 130421 [64]
Assertion
lbFound
at ConEmu .cpp:13657
Press \<Retry> to copy text information to clipboard and report a bug (open project web page)
If I press \<retry>, I get another message, this time from powershell:
powershell (admin)r
CreateDumpForReport called, create dump file failed
C:\Users\%username%\Desktop\ConEmuTap\Trap-130421-2744.dmp
Press \<Yes> to copy this text to clipboard
and open project web page
LastError 0x00000020
The process cannot access the file because it is being used by another process.
After which ConEmu crashes.
Now, if I don't press \<retry>, it continues working with no hiccups yet.
_Original issue: http://code.google.com/p/conemu-maximus5/issues/detail?id=1035_ | 1.0 | ConEmu Crashes at boot (assertion lbFound at ConEmu.cpp:13657) - _From [simen.kj...@gmail.com](https://code.google.com/u/116127060082078003686/) on April 22, 2013 02:19:52_
OS version: Win7 SP1 x64 ConEmu version: 130421
I just updated ConEmu to v. 130421, and it gives a dialog box at startup, with this message: ConEmu 130421 [64]
Assertion
lbFound
at ConEmu .cpp:13657
Press \<Retry> to copy text information to clipboard and report a bug (open project web page)
If I press \<retry>, I get another message, this time from powershell:
powershell (admin)r
CreateDumpForReport called, create dump file failed
C:\Users\%username%\Desktop\ConEmuTap\Trap-130421-2744.dmp
Press \<Yes> to copy this text to clipboard
and open project web page
LastError 0x00000020
The process cannot access the file because it is being used by another process.
After which ConEmu crashes.
Now, if I don't press \<retry>, it continues working with no hiccups yet.
_Original issue: http://code.google.com/p/conemu-maximus5/issues/detail?id=1035_ | priority | conemu crashes at boot assertion lbfound at conemu cpp from on april os version conemu version i just updated conemu to v and it gives a dialog box at startup with this message conemu assertion lbfound at conemu cpp press to copy text information to clipboard and report a bug open project web page if i press i get another message this time from powershell powershell admin r createdumpforreport called create dump file failed c users username desktop conemutap trap dmp press to copy this text to clipboard and open project web page lasterror the process cannot access the file because it is being used by another process after which conemu crashes now if i don t press it continues working with no hiccups yet original issue | 1 |
20,818 | 3,420,915,975 | IssuesEvent | 2015-12-08 16:38:30 | dkfans/keeperfx | https://api.github.com/repos/dkfans/keeperfx | closed | Creatures do not come from the Portal anymore after dropping some into it [original levels 2,3,4] | Branch-Stable Component-Logic Priority-Critical Status-Fixed Type-Defect | Game version: 0.4.6
This similar issue happened to me in original levels 2, 3 and 4. However, I failed to replicate the issue in a new game.
What did I do?
In level 2, after I had built my Training Room, I dropped my Flies into the Portal. Then creatures do not come from the Portal anymore.
Save file: 
(Please change the filename, including the extension, to fx1g0000.sav after downloading.)
Similarly, in level 3, after I had built my Library, I dropped my Flies into the Portal. Then creatures do not come from the Portal anymore.
Save file: 
(Please change the filename, including the extension, to fx1g0001.sav after downloading.)
In level 4, I dropped my Flies into the portal. After that if I build a Workshop (at least 3x3), then creatures do not come from the Portal anymore. The following save file was created just before building a Workshop.
Save file: 
(Please change the filename, including the extension, to fx1g0002.sav after downloading.) | 1.0 | Creatures do not come from the Portal anymore after dropping some into it [original levels 2,3,4] - Game version: 0.4.6
This similar issue happened to me in original levels 2, 3 and 4. However, I failed to replicate the issue in a new game.
What did I do?
In level 2, after I had built my Training Room, I dropped my Flies into the Portal. Then creatures do not come from the Portal anymore.
Save file: 
(Please change the filename, including the extension, to fx1g0000.sav after downloading.)
Similarly, in level 3, after I had built my Library, I dropped my Flies into the Portal. Then creatures do not come from the Portal anymore.
Save file: 
(Please change the filename, including the extension, to fx1g0001.sav after downloading.)
In level 4, I dropped my Flies into the portal. After that if I build a Workshop (at least 3x3), then creatures do not come from the Portal anymore. The following save file was created just before building a Workshop.
Save file: 
(Please change the filename, including the extension, to fx1g0002.sav after downloading.) | non_priority | creatures do not come from the portal anymore after dropping some into it game version this similar issue happened to me in original levels and however i failed to replicate the issue in a new game what did i do in level after i had built my training room i dropped my flies into the portal then creatures do not come from the portal anymore save file please change the filename including the extension to sav after downloading similarly in level after i had built my library i dropped my flies into the portal then creatures do not come from the portal anymore save file please change the filename including the extension to sav after downloading in level i dropped my flies into the portal after that if i build a workshop at least then creatures do not come from the portal anymore the following save file was created just before building a workshop save file please change the filename including the extension to sav after downloading | 0 |
1,040 | 4,845,426,833 | IssuesEvent | 2016-11-10 08:10:37 | ansible/ansible-modules-extras | https://api.github.com/repos/ansible/ansible-modules-extras | closed | Haproxy module fails - itertools.imap object has no attribute __getitem__ | affects_2.2 bug_report networking waiting_on_maintainer | ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
haproxy module
##### ANSIBLE VERSION
```
ansible 2.2.0.0
```
##### CONFIGURATION
##### OS / ENVIRONMENT
Ubuntu 14.04.1 LTS
##### SUMMARY
Can't change backend status using haproxy module with ansible 2.2.0.0. It fails with unexpected error.
##### STEPS TO REPRODUCE
playbook :
```yaml
- name: "disable backend server"
haproxy: "state=disabled host={{ haproxy_server_name }} socket={{ hostvars[item]['haproxy_socket_path'] }} backend={{ haproxy_backend_name }} wait=yes"
delegate_to: "{{ item }}"
with_items: "{{ groups['proxy'] }}"
become_user: root
```
inventory:
```yaml
haproxy-01
haproxy-02
[proxy]
haproxy-01
haproxy-02
```
group_vars:
```yaml
haproxy_socket_path: /run/haproxy.sock
```
host_vars:
``` yaml
haproxy_server_name: app01
```
vars:
``` yaml
haproxy_backend_name: myapp
```
##### EXPECTED RESULTS
```
TASK [disable backend server] ***************************
changed: [appserver01 -> 172.X.X.X] => (item=haproxy-01)
```
##### ACTUAL RESULTS
```
An exception occurred during task execution. To see the full traceback, use -vvv. The error was: TypeError: 'itertools.imap' object has no attribute '__getitem__'
failed: [appserver01 -> 172.X.X.X] (item=haproxy-01) => {"failed": true, "item": "haproxy-01", "module_stderr": "Traceback (most recent call last):\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 350, in <module>\n main()\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 345, in main\n ansible_haproxy.act()\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 306, in act\n self.disabled(self.host, self.backend, self.shutdown_sessions)\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 291, in disabled\n self.execute_for_backends(cmd, backend, host, 'MAINT')\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 237, in execute_for_backends\n self.wait_until_status(backend, svname, wait_for_status)\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 262, in wait_until_status\n if state[0]['status'] == status:\nTypeError: 'itertools.imap' object has no attribute '__getitem__'\n", "module_stdout": "", "msg": "MODULE FAILURE"}
An exception occurred during task execution. To see the full traceback, use -vvv. The error was: TypeError: 'itertools.imap' object has no attribute '__getitem__'
failed: [appserver01 -> 172.X.X.Y] (item=haproxy-02) => {"failed": true, "item": "haproxy-02", "module_stderr": "Traceback (most recent call last):\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 350, in <module>\n main()\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 345, in main\n ansible_haproxy.act()\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 306, in act\n self.disabled(self.host, self.backend, self.shutdown_sessions)\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 291, in disabled\n self.execute_for_backends(cmd, backend, host, 'MAINT')\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 237, in execute_for_backends\n self.wait_until_status(backend, svname, wait_for_status)\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 262, in wait_until_status\n if state[0]['status'] == status:\nTypeError: 'itertools.imap' object has no attribute '__getitem__'\n", "module_stdout": "", "msg": "MODULE FAILURE"}
```
This relates to https://github.com/ansible/ansible-modules-extras/issues/3364. | True | Haproxy module fails - itertools.imap object has no attribute __getitem__ - ##### ISSUE TYPE
- Bug Report
##### COMPONENT NAME
haproxy module
##### ANSIBLE VERSION
```
ansible 2.2.0.0
```
##### CONFIGURATION
##### OS / ENVIRONMENT
Ubuntu 14.04.1 LTS
##### SUMMARY
Can't change backend status using haproxy module with ansible 2.2.0.0. It fails with unexpected error.
##### STEPS TO REPRODUCE
playbook :
```yaml
- name: "disable backend server"
haproxy: "state=disabled host={{ haproxy_server_name }} socket={{ hostvars[item]['haproxy_socket_path'] }} backend={{ haproxy_backend_name }} wait=yes"
delegate_to: "{{ item }}"
with_items: "{{ groups['proxy'] }}"
become_user: root
```
inventory:
```yaml
haproxy-01
haproxy-02
[proxy]
haproxy-01
haproxy-02
```
group_vars:
```yaml
haproxy_socket_path: /run/haproxy.sock
```
host_vars:
``` yaml
haproxy_server_name: app01
```
vars:
``` yaml
haproxy_backend_name: myapp
```
##### EXPECTED RESULTS
```
TASK [disable backend server] ***************************
changed: [appserver01 -> 172.X.X.X] => (item=haproxy-01)
```
##### ACTUAL RESULTS
```
An exception occurred during task execution. To see the full traceback, use -vvv. The error was: TypeError: 'itertools.imap' object has no attribute '__getitem__'
failed: [appserver01 -> 172.X.X.X] (item=haproxy-01) => {"failed": true, "item": "haproxy-01", "module_stderr": "Traceback (most recent call last):\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 350, in <module>\n main()\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 345, in main\n ansible_haproxy.act()\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 306, in act\n self.disabled(self.host, self.backend, self.shutdown_sessions)\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 291, in disabled\n self.execute_for_backends(cmd, backend, host, 'MAINT')\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 237, in execute_for_backends\n self.wait_until_status(backend, svname, wait_for_status)\n File \"/tmp/ansible_eJMmvQ/ansible_module_haproxy.py\", line 262, in wait_until_status\n if state[0]['status'] == status:\nTypeError: 'itertools.imap' object has no attribute '__getitem__'\n", "module_stdout": "", "msg": "MODULE FAILURE"}
An exception occurred during task execution. To see the full traceback, use -vvv. The error was: TypeError: 'itertools.imap' object has no attribute '__getitem__'
failed: [appserver01 -> 172.X.X.Y] (item=haproxy-02) => {"failed": true, "item": "haproxy-02", "module_stderr": "Traceback (most recent call last):\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 350, in <module>\n main()\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 345, in main\n ansible_haproxy.act()\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 306, in act\n self.disabled(self.host, self.backend, self.shutdown_sessions)\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 291, in disabled\n self.execute_for_backends(cmd, backend, host, 'MAINT')\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 237, in execute_for_backends\n self.wait_until_status(backend, svname, wait_for_status)\n File \"/tmp/ansible_X3ixtX/ansible_module_haproxy.py\", line 262, in wait_until_status\n if state[0]['status'] == status:\nTypeError: 'itertools.imap' object has no attribute '__getitem__'\n", "module_stdout": "", "msg": "MODULE FAILURE"}
```
This relates to https://github.com/ansible/ansible-modules-extras/issues/3364. | non_priority | haproxy module fails itertools imap object has no attribute getitem issue type bug report component name haproxy module ansible version ansible configuration os environment ubuntu lts summary can t change backend status using haproxy module with ansible it fails with unexpected error steps to reproduce playbook yaml name disable backend server haproxy state disabled host haproxy server name socket hostvars backend haproxy backend name wait yes delegate to item with items groups become user root inventory yaml haproxy haproxy haproxy haproxy group vars yaml haproxy socket path run haproxy sock host vars yaml haproxy server name vars yaml haproxy backend name myapp expected results task changed item haproxy actual results an exception occurred during task execution to see the full traceback use vvv the error was typeerror itertools imap object has no attribute getitem failed item haproxy failed true item haproxy module stderr traceback most recent call last n file tmp ansible ejmmvq ansible module haproxy py line in n main n file tmp ansible ejmmvq ansible module haproxy py line in main n ansible haproxy act n file tmp ansible ejmmvq ansible module haproxy py line in act n self disabled self host self backend self shutdown sessions n file tmp ansible ejmmvq ansible module haproxy py line in disabled n self execute for backends cmd backend host maint n file tmp ansible ejmmvq ansible module haproxy py line in execute for backends n self wait until status backend svname wait for status n file tmp ansible ejmmvq ansible module haproxy py line in wait until status n if state status ntypeerror itertools imap object has no attribute getitem n module stdout msg module failure an exception occurred during task execution to see the full traceback use vvv the error was typeerror itertools imap object has no attribute getitem failed item haproxy failed true item haproxy module stderr traceback most recent call last n file tmp ansible ansible module haproxy py line in n main n file tmp ansible ansible module haproxy py line in main n ansible haproxy act n file tmp ansible ansible module haproxy py line in act n self disabled self host self backend self shutdown sessions n file tmp ansible ansible module haproxy py line in disabled n self execute for backends cmd backend host maint n file tmp ansible ansible module haproxy py line in execute for backends n self wait until status backend svname wait for status n file tmp ansible ansible module haproxy py line in wait until status n if state status ntypeerror itertools imap object has no attribute getitem n module stdout msg module failure this relates to | 0 |
828,858 | 31,845,417,649 | IssuesEvent | 2023-09-14 19:31:50 | GoogleCloudPlatform/alloydb-auth-proxy | https://api.github.com/repos/GoogleCloudPlatform/alloydb-auth-proxy | opened | tests: TestPostgresAuthWithCredentialsJSON failed | type: bug priority: p2 flakybot: issue | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: a176cce63958e448ddac90c92a56f96424f04b3f
buildURL: https://github.com/GoogleCloudPlatform/alloydb-auth-proxy/actions/runs/6189779161
status: failed
<details><summary>Test output</summary><br><pre> connection_test.go:87: unable to verify proxy was serving: 2023/09/14 19:31:06 The proxy has encountered a terminal error: unable to start: [alloydb-connector-testing.us-central1.cluster.instance] Unable to mount socket: listen tcp 127.0.0.1:5432: bind: address already in use
</pre></details> | 1.0 | tests: TestPostgresAuthWithCredentialsJSON failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: a176cce63958e448ddac90c92a56f96424f04b3f
buildURL: https://github.com/GoogleCloudPlatform/alloydb-auth-proxy/actions/runs/6189779161
status: failed
<details><summary>Test output</summary><br><pre> connection_test.go:87: unable to verify proxy was serving: 2023/09/14 19:31:06 The proxy has encountered a terminal error: unable to start: [alloydb-connector-testing.us-central1.cluster.instance] Unable to mount socket: listen tcp 127.0.0.1:5432: bind: address already in use
</pre></details> | priority | tests testpostgresauthwithcredentialsjson failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed test output connection test go unable to verify proxy was serving the proxy has encountered a terminal error unable to start unable to mount socket listen tcp bind address already in use | 1 |
375,886 | 11,135,670,467 | IssuesEvent | 2019-12-20 14:53:51 | overture-stack/billing | https://api.github.com/repos/overture-stack/billing | closed | Fix Remaining Vulnerabilities in 'billing-invoice', 'invoice-api' | Priority: High bug | Fix remaining Github security vulnerabilities in these services:
* billing-invoice
* invoice-api
This could not be done until Python was upgraded and @yuanhengzhao had fixed the missing billing tests | 1.0 | Fix Remaining Vulnerabilities in 'billing-invoice', 'invoice-api' - Fix remaining Github security vulnerabilities in these services:
* billing-invoice
* invoice-api
This could not be done until Python was upgraded and @yuanhengzhao had fixed the missing billing tests | priority | fix remaining vulnerabilities in billing invoice invoice api fix remaining github security vulnerabilities in these services billing invoice invoice api this could not be done until python was upgraded and yuanhengzhao had fixed the missing billing tests | 1 |
384,976 | 26,610,387,023 | IssuesEvent | 2023-01-23 23:23:45 | marloss/konohASCII | https://api.github.com/repos/marloss/konohASCII | closed | Preset system / Programozható rendszer | documentation | When launching the game, it creates a text file, where it saves the presets (like button mappings). If the player changes mappings, or game settings, after applying, the game overwrites said text file.
Amikor a játék elindul, létrehoz egy txt fájlt, ahova lementi a beállításokat (mint a gomb kiosztást). Ha a játékos beállít a játékban egy új beállítást, miután alkalmazta, a játék fellülírja az említett fájlt. | 1.0 | Preset system / Programozható rendszer - When launching the game, it creates a text file, where it saves the presets (like button mappings). If the player changes mappings, or game settings, after applying, the game overwrites said text file.
Amikor a játék elindul, létrehoz egy txt fájlt, ahova lementi a beállításokat (mint a gomb kiosztást). Ha a játékos beállít a játékban egy új beállítást, miután alkalmazta, a játék fellülírja az említett fájlt. | non_priority | preset system programozható rendszer when launching the game it creates a text file where it saves the presets like button mappings if the player changes mappings or game settings after applying the game overwrites said text file amikor a játék elindul létrehoz egy txt fájlt ahova lementi a beállításokat mint a gomb kiosztást ha a játékos beállít a játékban egy új beállítást miután alkalmazta a játék fellülírja az említett fájlt | 0 |
65,188 | 7,860,818,709 | IssuesEvent | 2018-06-21 21:18:51 | publiclab/plots2 | https://api.github.com/repos/publiclab/plots2 | opened | Don't allow newcomers to make/edit wiki pages until they've 1 question/post/note/activity approved | Ruby break-me-up design help-wanted | This still needs some more specific design thoughts -- something like:
* a lock icon where the wiki edit tab is, for newcomers, and
* have it popup a tooltip saying `Please post a question or other content before editing the wiki. Click to learn why.` or something.
* a rerouting of /wiki/new or the new wiki form to the dashboard with a similar friendly message alert for newcomers.
This is a temporary solution while we make a plan for a more robust wiki moderation system.
Any help on this appreciated! | 1.0 | Don't allow newcomers to make/edit wiki pages until they've 1 question/post/note/activity approved - This still needs some more specific design thoughts -- something like:
* a lock icon where the wiki edit tab is, for newcomers, and
* have it popup a tooltip saying `Please post a question or other content before editing the wiki. Click to learn why.` or something.
* a rerouting of /wiki/new or the new wiki form to the dashboard with a similar friendly message alert for newcomers.
This is a temporary solution while we make a plan for a more robust wiki moderation system.
Any help on this appreciated! | non_priority | don t allow newcomers to make edit wiki pages until they ve question post note activity approved this still needs some more specific design thoughts something like a lock icon where the wiki edit tab is for newcomers and have it popup a tooltip saying please post a question or other content before editing the wiki click to learn why or something a rerouting of wiki new or the new wiki form to the dashboard with a similar friendly message alert for newcomers this is a temporary solution while we make a plan for a more robust wiki moderation system any help on this appreciated | 0 |
46,648 | 19,350,659,246 | IssuesEvent | 2021-12-15 15:20:19 | geometry-labs/icon-status-page | https://api.github.com/repos/geometry-labs/icon-status-page | opened | 🛑 EU Mainnet Contracts Service is down | status eu-mainnet-contracts-service | In [`f12ff57`](https://github.com/geometry-labs/icon-status-page/commit/f12ff57f3c6fcc863e4b8ecb774b1a8e48e5efba
), EU Mainnet Contracts Service (https://euw1.tracker.icon.geometry.io/api/v1/contracts) was **down**:
- HTTP code: 503
- Response time: 73 ms
| 1.0 | 🛑 EU Mainnet Contracts Service is down - In [`f12ff57`](https://github.com/geometry-labs/icon-status-page/commit/f12ff57f3c6fcc863e4b8ecb774b1a8e48e5efba
), EU Mainnet Contracts Service (https://euw1.tracker.icon.geometry.io/api/v1/contracts) was **down**:
- HTTP code: 503
- Response time: 73 ms
| non_priority | 🛑 eu mainnet contracts service is down in eu mainnet contracts service was down http code response time ms | 0 |
828,442 | 31,829,314,577 | IssuesEvent | 2023-09-14 09:33:02 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | reopened | arc64 local variable corruption in z_init_static_threads | bug priority: low area: ARC area: picolibc | **Describe the bug**
When running the sample.portability.cmsis_rtos_v2.timer_synchronization test on arc64 under qemu using picolibc, `z_init_static_threads` goes into an infinite loop in the second instance of `_FOREACH_STATIC_THREAD` where it's calling `schedule_new_thread`.
Debugging this, I discover that the register holding the termination value has been trashed and holds a completely bogus value (0x4275de2 instead of 0x80407594). Perturbing the code above the loop in essentially any way at all (I added `__asm__("")` just after `k_sched_lock()`) makes this issue go away. The difference in the assembly code is trivial -- it moves the load of `__static_thread_data_list_start` after the call to `k_sched_lock`
Please also mention any information which could help others to understand
the problem you're facing:
- What target platform are you using?
- qemu_arc_hs5x
- SDK version zephyr-sdk-0.16.2-rc1-5-g8d9b4fe
- picolibc instead of minimal C library.
- What have you tried to diagnose or workaround this issue?
Modifying the code in even trivial ways appears to work around this issue. I applied this diff:
```
diff --git a/kernel/thread.c b/kernel/thread.c
index fb578eb48d..5721023929 100644
--- a/kernel/thread.c
+++ b/kernel/thread.c
@@ -783,6 +783,7 @@ void z_init_static_threads(void)
* delay of K_FOREVER.
*/
k_sched_lock();
+ __asm__("");
_FOREACH_STATIC_THREAD(thread_data) {
if (thread_data->init_delay != K_TICKS_FOREVER) {
schedule_new_thread(thread_data->init_thread,
```
This generated the following change in the generated code:
```
--- broken.S 2023-07-05 23:27:30.536430480 -0700
+++ working.S 2023-07-05 23:27:18.483894200 -0700
@@ -1073,8 +1073,8 @@
add2 r14,r14,11
.L106:
blo_s .L107
- mov_s r14,@__static_thread_data_list_start
bl @k_sched_lock
+ mov_s r14,@__static_thread_data_list_start
.L108:
mov_s r0,@__static_thread_data_list_end
cmp_s r14,r0
```
setting a break point on the `cmp_s` instruction here also makes things work. That makes me suspect that qemu might be at fault somehow?
- Is this a regression? If yes, have you been able to "git bisect" it to a
specific commit?
- I haven't tried bisecting.
**To Reproduce**
Steps to reproduce the behavior:
1. ./scripts/twister -O arc64-bug -xCONFIG_PICOLIBC=y -p qemu_arc_hs5x --test samples/subsys/portability/cmsis_rtos_v2/timer_synchronization/sample.portability.cmsis_rtos_v2.timer_synchronization
**Expected behavior**
Test completes successfully
**Impact**
This will delay the switch to using picolibc as the default C library.
**Environment (please complete the following information):**
- OS: Debian unstable
- Toolchain: SDK version 0.16.2-rc1-5-g8d9b4fe
- Commit SHA or Version used: 8560fb319249e3fad3122f8541df4c4beef6e5e2 (main as of this writing) | 1.0 | arc64 local variable corruption in z_init_static_threads - **Describe the bug**
When running the sample.portability.cmsis_rtos_v2.timer_synchronization test on arc64 under qemu using picolibc, `z_init_static_threads` goes into an infinite loop in the second instance of `_FOREACH_STATIC_THREAD` where it's calling `schedule_new_thread`.
Debugging this, I discover that the register holding the termination value has been trashed and holds a completely bogus value (0x4275de2 instead of 0x80407594). Perturbing the code above the loop in essentially any way at all (I added `__asm__("")` just after `k_sched_lock()`) makes this issue go away. The difference in the assembly code is trivial -- it moves the load of `__static_thread_data_list_start` after the call to `k_sched_lock`
Please also mention any information which could help others to understand
the problem you're facing:
- What target platform are you using?
- qemu_arc_hs5x
- SDK version zephyr-sdk-0.16.2-rc1-5-g8d9b4fe
- picolibc instead of minimal C library.
- What have you tried to diagnose or workaround this issue?
Modifying the code in even trivial ways appears to work around this issue. I applied this diff:
```
diff --git a/kernel/thread.c b/kernel/thread.c
index fb578eb48d..5721023929 100644
--- a/kernel/thread.c
+++ b/kernel/thread.c
@@ -783,6 +783,7 @@ void z_init_static_threads(void)
* delay of K_FOREVER.
*/
k_sched_lock();
+ __asm__("");
_FOREACH_STATIC_THREAD(thread_data) {
if (thread_data->init_delay != K_TICKS_FOREVER) {
schedule_new_thread(thread_data->init_thread,
```
This generated the following change in the generated code:
```
--- broken.S 2023-07-05 23:27:30.536430480 -0700
+++ working.S 2023-07-05 23:27:18.483894200 -0700
@@ -1073,8 +1073,8 @@
add2 r14,r14,11
.L106:
blo_s .L107
- mov_s r14,@__static_thread_data_list_start
bl @k_sched_lock
+ mov_s r14,@__static_thread_data_list_start
.L108:
mov_s r0,@__static_thread_data_list_end
cmp_s r14,r0
```
setting a break point on the `cmp_s` instruction here also makes things work. That makes me suspect that qemu might be at fault somehow?
- Is this a regression? If yes, have you been able to "git bisect" it to a
specific commit?
- I haven't tried bisecting.
**To Reproduce**
Steps to reproduce the behavior:
1. ./scripts/twister -O arc64-bug -xCONFIG_PICOLIBC=y -p qemu_arc_hs5x --test samples/subsys/portability/cmsis_rtos_v2/timer_synchronization/sample.portability.cmsis_rtos_v2.timer_synchronization
**Expected behavior**
Test completes successfully
**Impact**
This will delay the switch to using picolibc as the default C library.
**Environment (please complete the following information):**
- OS: Debian unstable
- Toolchain: SDK version 0.16.2-rc1-5-g8d9b4fe
- Commit SHA or Version used: 8560fb319249e3fad3122f8541df4c4beef6e5e2 (main as of this writing) | priority | local variable corruption in z init static threads describe the bug when running the sample portability cmsis rtos timer synchronization test on under qemu using picolibc z init static threads goes into an infinite loop in the second instance of foreach static thread where it s calling schedule new thread debugging this i discover that the register holding the termination value has been trashed and holds a completely bogus value instead of perturbing the code above the loop in essentially any way at all i added asm just after k sched lock makes this issue go away the difference in the assembly code is trivial it moves the load of static thread data list start after the call to k sched lock please also mention any information which could help others to understand the problem you re facing what target platform are you using qemu arc sdk version zephyr sdk picolibc instead of minimal c library what have you tried to diagnose or workaround this issue modifying the code in even trivial ways appears to work around this issue i applied this diff diff git a kernel thread c b kernel thread c index a kernel thread c b kernel thread c void z init static threads void delay of k forever k sched lock asm foreach static thread thread data if thread data init delay k ticks forever schedule new thread thread data init thread this generated the following change in the generated code broken s working s blo s mov s static thread data list start bl k sched lock mov s static thread data list start mov s static thread data list end cmp s setting a break point on the cmp s instruction here also makes things work that makes me suspect that qemu might be at fault somehow is this a regression if yes have you been able to git bisect it to a specific commit i haven t tried bisecting to reproduce steps to reproduce the behavior scripts twister o bug xconfig picolibc y p qemu arc test samples subsys portability cmsis rtos timer synchronization sample portability cmsis rtos timer synchronization expected behavior test completes successfully impact this will delay the switch to using picolibc as the default c library environment please complete the following information os debian unstable toolchain sdk version commit sha or version used main as of this writing | 1 |
79,611 | 3,537,667,790 | IssuesEvent | 2016-01-18 03:40:18 | flike/kingshard | https://api.github.com/repos/flike/kingshard | closed | SQL执行结果错误,ks有数据返回,mysql没有 | bug fixed low priority | 仅用一个节点做测试:
错误描述,where a.id=b.id应该等效内连接,ks有结果返回,mysql没有
/*左表(分区)全部数据*/
[root@127.0.0.1]-[test]>select * from test_shard_hash a where 1 = 1;
+----+------+------+-------+-----+------+
| id | str | f | e | u | i |
+----+------+------+-------+-----+------+
| 1 | abc1 | 3.14 | test1 | 255 | -127 |
| 2 | abc2 | 3.14 | test2 | 255 | -127 |
| 3 | abc3 | 3.14 | test3 | 255 | -127 |
| 4 | abc4 | 3.14 | test4 | 255 | -127 |
| 5 | abc5 | 3.14 | test5 | 255 | -127 |
+----+------+------+-------+-----+------+
5 rows in set (0.01 sec)
/*右表全部数据*/
[root@127.0.0.1]-[test]>select * from test_bug;
Empty set (0.01 sec)
/*ks执行*/
[root@127.0.0.1]-[test]>select * from test_shard_hash a,test_bug b where a.id = b.id;
+----+------+------+-------+-----+------+
| id | str | f | e | u | i |
+----+------+------+-------+-----+------+
| 1 | abc1 | 3.14 | test1 | 255 | -127 |
| 2 | abc2 | 3.14 | test2 | 255 | -127 |
| 3 | abc3 | 3.14 | test3 | 255 | -127 |
| 4 | abc4 | 3.14 | test4 | 255 | -127 |
| 5 | abc5 | 3.14 | test5 | 255 | -127 |
+----+------+------+-------+-----+------+
5 rows in set (0.01 sec)
/*mysql执行*/
[root@127.0.0.1]-[test]>select * from test_shard_hash_0000 a,test_bug b where a.id = b.id;
Empty set (0.01 sec) | 1.0 | SQL执行结果错误,ks有数据返回,mysql没有 - 仅用一个节点做测试:
错误描述,where a.id=b.id应该等效内连接,ks有结果返回,mysql没有
/*左表(分区)全部数据*/
[root@127.0.0.1]-[test]>select * from test_shard_hash a where 1 = 1;
+----+------+------+-------+-----+------+
| id | str | f | e | u | i |
+----+------+------+-------+-----+------+
| 1 | abc1 | 3.14 | test1 | 255 | -127 |
| 2 | abc2 | 3.14 | test2 | 255 | -127 |
| 3 | abc3 | 3.14 | test3 | 255 | -127 |
| 4 | abc4 | 3.14 | test4 | 255 | -127 |
| 5 | abc5 | 3.14 | test5 | 255 | -127 |
+----+------+------+-------+-----+------+
5 rows in set (0.01 sec)
/*右表全部数据*/
[root@127.0.0.1]-[test]>select * from test_bug;
Empty set (0.01 sec)
/*ks执行*/
[root@127.0.0.1]-[test]>select * from test_shard_hash a,test_bug b where a.id = b.id;
+----+------+------+-------+-----+------+
| id | str | f | e | u | i |
+----+------+------+-------+-----+------+
| 1 | abc1 | 3.14 | test1 | 255 | -127 |
| 2 | abc2 | 3.14 | test2 | 255 | -127 |
| 3 | abc3 | 3.14 | test3 | 255 | -127 |
| 4 | abc4 | 3.14 | test4 | 255 | -127 |
| 5 | abc5 | 3.14 | test5 | 255 | -127 |
+----+------+------+-------+-----+------+
5 rows in set (0.01 sec)
/*mysql执行*/
[root@127.0.0.1]-[test]>select * from test_shard_hash_0000 a,test_bug b where a.id = b.id;
Empty set (0.01 sec) | priority | sql执行结果错误,ks有数据返回,mysql没有 仅用一个节点做测试: 错误描述,where a id b id应该等效内连接,ks有结果返回,mysql没有 左表(分区)全部数据 select from test shard hash a where id str f e u i rows in set sec 右表全部数据 select from test bug empty set sec ks执行 select from test shard hash a test bug b where a id b id id str f e u i rows in set sec mysql执行 select from test shard hash a test bug b where a id b id empty set sec | 1 |
61,263 | 12,157,225,342 | IssuesEvent | 2020-04-25 20:54:54 | Sonia-corporation/il-est-midi-discord | https://api.github.com/repos/Sonia-corporation/il-est-midi-discord | closed | Fix "method_lines" issue in src/features/github/functions/get-humanized-release-notes.ts | code-climate | Function `getHumanizedReleaseNotes` has 30 lines of code (exceeds 25 allowed). Consider refactoring.
https://codeclimate.com/github/Sonia-corporation/il-est-midi-discord/src/features/github/functions/get-humanized-release-notes.ts#issue_5e81d19376162700010000b8 | 1.0 | Fix "method_lines" issue in src/features/github/functions/get-humanized-release-notes.ts - Function `getHumanizedReleaseNotes` has 30 lines of code (exceeds 25 allowed). Consider refactoring.
https://codeclimate.com/github/Sonia-corporation/il-est-midi-discord/src/features/github/functions/get-humanized-release-notes.ts#issue_5e81d19376162700010000b8 | non_priority | fix method lines issue in src features github functions get humanized release notes ts function gethumanizedreleasenotes has lines of code exceeds allowed consider refactoring | 0 |
330,926 | 28,496,125,890 | IssuesEvent | 2023-04-18 14:21:22 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | opened | Build failed: EditorMemento - use with editor input Assertion failed: (timeout != -1) | unit-test-failure | Build: https://dev.azure.com/monacotools/a6d41577-0fa3-498e-af22-257312ff0545/_build/results?buildId=211221
Changes: https://github.com/Microsoft/vscode/compare/7559567...498b681

| 1.0 | Build failed: EditorMemento - use with editor input Assertion failed: (timeout != -1) - Build: https://dev.azure.com/monacotools/a6d41577-0fa3-498e-af22-257312ff0545/_build/results?buildId=211221
Changes: https://github.com/Microsoft/vscode/compare/7559567...498b681

| non_priority | build failed editormemento use with editor input assertion failed timeout build changes | 0 |
356,905 | 10,599,053,185 | IssuesEvent | 2019-10-10 06:59:19 | constellation-app/constellation | https://api.github.com/repos/constellation-app/constellation | opened | Support for a generic JDBC connector | enhancement priority request | <!--
### Requirements
* Filling out the template is required. Any pull request that does not include
enough information to be reviewed in a timely manner may be closed at the
maintainers' discretion.
* Have you read Constellation's Code of Conduct? By filing an issue, you are
expected to comply with it, including treating everyone with respect:
https://github.com/constellation-app/constellation/blob/master/CODE_OF_CONDUCT.md
-->
### Prerequisites
* [X] Put an X between the brackets on this line if you have done all of the following:
* Running the latest version of Constellation
* Attached the ***Support Package*** via `Help` > `Support Package`
* Checked the FAQs: https://github.com/constellation-app/constellation/wiki/FAQ
* Checked that your issue isn't already filed: https://github.com/constellation-app/constellation/issues
* Checked that there is not already a module that provides the described functionality: https://github.com/constellation-app/constellation/wiki/Catalogue-of-Repositories
### Description
The ability to connect Constellation to a database using JDBC is required for end users to be able to import data into Constellation without needing to be a developer and writing their own connector.
The JDBC Import GUI should allow a user to connect to a database by providing the host, port, database, username and password.
You should be able type your SQL query and then map the results to node or transaction attributes.
Consider using the Import From Delimited to achieve this.
Suggestions welcomed. | 1.0 | Support for a generic JDBC connector - <!--
### Requirements
* Filling out the template is required. Any pull request that does not include
enough information to be reviewed in a timely manner may be closed at the
maintainers' discretion.
* Have you read Constellation's Code of Conduct? By filing an issue, you are
expected to comply with it, including treating everyone with respect:
https://github.com/constellation-app/constellation/blob/master/CODE_OF_CONDUCT.md
-->
### Prerequisites
* [X] Put an X between the brackets on this line if you have done all of the following:
* Running the latest version of Constellation
* Attached the ***Support Package*** via `Help` > `Support Package`
* Checked the FAQs: https://github.com/constellation-app/constellation/wiki/FAQ
* Checked that your issue isn't already filed: https://github.com/constellation-app/constellation/issues
* Checked that there is not already a module that provides the described functionality: https://github.com/constellation-app/constellation/wiki/Catalogue-of-Repositories
### Description
The ability to connect Constellation to a database using JDBC is required for end users to be able to import data into Constellation without needing to be a developer and writing their own connector.
The JDBC Import GUI should allow a user to connect to a database by providing the host, port, database, username and password.
You should be able type your SQL query and then map the results to node or transaction attributes.
Consider using the Import From Delimited to achieve this.
Suggestions welcomed. | priority | support for a generic jdbc connector requirements filling out the template is required any pull request that does not include enough information to be reviewed in a timely manner may be closed at the maintainers discretion have you read constellation s code of conduct by filing an issue you are expected to comply with it including treating everyone with respect prerequisites put an x between the brackets on this line if you have done all of the following running the latest version of constellation attached the support package via help support package checked the faqs checked that your issue isn t already filed checked that there is not already a module that provides the described functionality description the ability to connect constellation to a database using jdbc is required for end users to be able to import data into constellation without needing to be a developer and writing their own connector the jdbc import gui should allow a user to connect to a database by providing the host port database username and password you should be able type your sql query and then map the results to node or transaction attributes consider using the import from delimited to achieve this suggestions welcomed | 1 |
78,466 | 22,284,212,203 | IssuesEvent | 2022-06-11 11:03:27 | cgeo/cgeo | https://api.github.com/repos/cgeo/cgeo | opened | Runtime JAR files in the classpath should have the same version | CI server / Build tools | ### Describe your problem!
since PR #12883 with integration of loupe(`implementation 'io.github.igreenwood.loupe:loupe:1.2.2'`)
we see this warning in the gradle output:
~~~
11:47:38 > Task :main:lintBasicDebug
11:47:38 w: Runtime JAR files in the classpath should have the same version. These files were found in the classpath:
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-common/1.5.31/43331609c7de811fed085e0dfd150874b157c32/kotlin-stdlib-common-1.5.31.jar (version 1.5)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-jdk8/1.4.21/3ad7f99fb330947a12451ea16767d192d763600a/kotlin-stdlib-jdk8-1.4.21.jar (version 1.4)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-jdk7/1.5.31/77e0f2568912e45d26c31fd417a332458508acdf/kotlin-stdlib-jdk7-1.5.31.jar (version 1.5)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib/1.5.31/6628d61d0f5603568e72d2d5915d2c034b4f1c55/kotlin-stdlib-1.5.31.jar (version 1.5)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-jdk7/1.4.21/26b6082f9296911bdcb8e72a7cc68692c7025a03/kotlin-stdlib-jdk7-1.4.21.jar (version 1.4)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib/1.4.21/4a668382d7c38688d3490afde93b6a113ed46698/kotlin-stdlib-1.4.21.jar (version 1.4)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-common/1.4.21/7f48a062aa4b53215998780f7c245a4276828e1d/kotlin-stdlib-common-1.4.21.jar (version 1.4)
11:47:38 w: Some runtime JAR files in the classpath have an incompatible version. Consider removing them from the classpath
~~~
### How to reproduce?
see the Jenkins console output
### Actual result after these steps?
_No response_
### Expected result after these steps?
_No response_
### Reproducible
Yes
### c:geo Version
today nightly, PR, Release 220606
### System information
```text
https://ci.cgeo.org/job/cgeo%20nightly/2691/console
https://ci.cgeo.org/job/cgeo%20release/115/console
```
### Additional Information
_No response_ | 1.0 | Runtime JAR files in the classpath should have the same version - ### Describe your problem!
since PR #12883 with integration of loupe(`implementation 'io.github.igreenwood.loupe:loupe:1.2.2'`)
we see this warning in the gradle output:
~~~
11:47:38 > Task :main:lintBasicDebug
11:47:38 w: Runtime JAR files in the classpath should have the same version. These files were found in the classpath:
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-common/1.5.31/43331609c7de811fed085e0dfd150874b157c32/kotlin-stdlib-common-1.5.31.jar (version 1.5)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-jdk8/1.4.21/3ad7f99fb330947a12451ea16767d192d763600a/kotlin-stdlib-jdk8-1.4.21.jar (version 1.4)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-jdk7/1.5.31/77e0f2568912e45d26c31fd417a332458508acdf/kotlin-stdlib-jdk7-1.5.31.jar (version 1.5)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib/1.5.31/6628d61d0f5603568e72d2d5915d2c034b4f1c55/kotlin-stdlib-1.5.31.jar (version 1.5)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-jdk7/1.4.21/26b6082f9296911bdcb8e72a7cc68692c7025a03/kotlin-stdlib-jdk7-1.4.21.jar (version 1.4)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib/1.4.21/4a668382d7c38688d3490afde93b6a113ed46698/kotlin-stdlib-1.4.21.jar (version 1.4)
11:47:38 /home/jenkins/.gradle/caches/modules-2/files-2.1/org.jetbrains.kotlin/kotlin-stdlib-common/1.4.21/7f48a062aa4b53215998780f7c245a4276828e1d/kotlin-stdlib-common-1.4.21.jar (version 1.4)
11:47:38 w: Some runtime JAR files in the classpath have an incompatible version. Consider removing them from the classpath
~~~
### How to reproduce?
see the Jenkins console output
### Actual result after these steps?
_No response_
### Expected result after these steps?
_No response_
### Reproducible
Yes
### c:geo Version
today nightly, PR, Release 220606
### System information
```text
https://ci.cgeo.org/job/cgeo%20nightly/2691/console
https://ci.cgeo.org/job/cgeo%20release/115/console
```
### Additional Information
_No response_ | non_priority | runtime jar files in the classpath should have the same version describe your problem since pr with integration of loupe implementation io github igreenwood loupe loupe we see this warning in the gradle output task main lintbasicdebug w runtime jar files in the classpath should have the same version these files were found in the classpath home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib common kotlin stdlib common jar version home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib kotlin stdlib jar version home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib kotlin stdlib jar version home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib kotlin stdlib jar version home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib kotlin stdlib jar version home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib kotlin stdlib jar version home jenkins gradle caches modules files org jetbrains kotlin kotlin stdlib common kotlin stdlib common jar version w some runtime jar files in the classpath have an incompatible version consider removing them from the classpath how to reproduce see the jenkins console output actual result after these steps no response expected result after these steps no response reproducible yes c geo version today nightly pr release system information text additional information no response | 0 |
139,820 | 18,855,911,598 | IssuesEvent | 2021-11-12 06:14:45 | kubesphere/kubesphere | https://api.github.com/repos/kubesphere/kubesphere | closed | Secure third-party services | area/security kind/need-to-verify kind/feature-request | **What's it about?**
Some services like Kiali or Jaeger didn't provide a built-in authentication mechanism or security setup up with default settings. All the tenancies could access those services directly within the cluster, so there a potential risk of information exposure.
We need to find a proper way to protect each of the third-party services. And use secure connections between ks-apiserver and third-party services.
**What's the reason why we need it?**
Security is one of the most important features of KubeSphere.
Some other discussions in the [forum](https://kubesphere.com.cn/forum/d/4970-kubersphere-310-kiali)
**Area Suggestion**
/area security
/kind feature-request
/cc @wansir @zryfish
| True | Secure third-party services - **What's it about?**
Some services like Kiali or Jaeger didn't provide a built-in authentication mechanism or security setup up with default settings. All the tenancies could access those services directly within the cluster, so there a potential risk of information exposure.
We need to find a proper way to protect each of the third-party services. And use secure connections between ks-apiserver and third-party services.
**What's the reason why we need it?**
Security is one of the most important features of KubeSphere.
Some other discussions in the [forum](https://kubesphere.com.cn/forum/d/4970-kubersphere-310-kiali)
**Area Suggestion**
/area security
/kind feature-request
/cc @wansir @zryfish
| non_priority | secure third party services what s it about some services like kiali or jaeger didn t provide a built in authentication mechanism or security setup up with default settings all the tenancies could access those services directly within the cluster so there a potential risk of information exposure we need to find a proper way to protect each of the third party services and use secure connections between ks apiserver and third party services what s the reason why we need it security is one of the most important features of kubesphere some other discussions in the area suggestion area security kind feature request cc wansir zryfish | 0 |
365,349 | 10,780,943,654 | IssuesEvent | 2019-11-04 14:01:11 | vigetlabs/npm | https://api.github.com/repos/vigetlabs/npm | closed | [QA] Quote block polish | High Priority Needs QA Fixes | * [x] **Carousel functionality doesn’t appear to be working**—if multiple testimonials are added, nothing happens when I click the arrows (image and text doesn’t change).
* [x] If there’s **only one testimonial in the testimonial block** (carousel w/ image on homepage), the arrows should be hidden.
* [x] **Image should take up the full height of the block** (teal background). ([screenshot with comp on left, staging on right](https://www.dropbox.com/s/u012285ylik35f7/Screenshot%202019-10-18%2008.30.25.png?dl=0))
| 1.0 | [QA] Quote block polish - * [x] **Carousel functionality doesn’t appear to be working**—if multiple testimonials are added, nothing happens when I click the arrows (image and text doesn’t change).
* [x] If there’s **only one testimonial in the testimonial block** (carousel w/ image on homepage), the arrows should be hidden.
* [x] **Image should take up the full height of the block** (teal background). ([screenshot with comp on left, staging on right](https://www.dropbox.com/s/u012285ylik35f7/Screenshot%202019-10-18%2008.30.25.png?dl=0))
| priority | quote block polish carousel functionality doesn’t appear to be working —if multiple testimonials are added nothing happens when i click the arrows image and text doesn’t change if there’s only one testimonial in the testimonial block carousel w image on homepage the arrows should be hidden image should take up the full height of the block teal background | 1 |
443,289 | 12,780,803,798 | IssuesEvent | 2020-07-01 01:55:48 | wearable-learning-cloud-platform/wlcp-issues | https://api.github.com/repos/wearable-learning-cloud-platform/wlcp-issues | closed | Game Editor: On State Cancel State Name Persists | bug game editor low priority | Steps for Replication:
1. Make a state
2. Type something into the state description (first field)
3. Hit cancel on the state
The state name is changed on the diagram despite cancelling. | 1.0 | Game Editor: On State Cancel State Name Persists - Steps for Replication:
1. Make a state
2. Type something into the state description (first field)
3. Hit cancel on the state
The state name is changed on the diagram despite cancelling. | priority | game editor on state cancel state name persists steps for replication make a state type something into the state description first field hit cancel on the state the state name is changed on the diagram despite cancelling | 1 |
96,085 | 19,897,257,456 | IssuesEvent | 2022-01-25 01:26:16 | WISE-Community/WISE-Client | https://api.github.com/repos/WISE-Community/WISE-Client | closed | Remove componentController | Code Quality | ### Description
ComponentController is no longer used. It was part of AngularJS app and has been replaced by ComponentStudent in Angular. Remove and test that everything works as before.
| 1.0 | Remove componentController - ### Description
ComponentController is no longer used. It was part of AngularJS app and has been replaced by ComponentStudent in Angular. Remove and test that everything works as before.
| non_priority | remove componentcontroller description componentcontroller is no longer used it was part of angularjs app and has been replaced by componentstudent in angular remove and test that everything works as before | 0 |
476,316 | 13,736,754,690 | IssuesEvent | 2020-10-05 12:14:57 | DimiMikadze/create-social-network | https://api.github.com/repos/DimiMikadze/create-social-network | opened | Detect no authorized request | priority: critical source: api source: frontend | Detect if a User isn't authorized to make a request and automatically sign out from the application. | 1.0 | Detect no authorized request - Detect if a User isn't authorized to make a request and automatically sign out from the application. | priority | detect no authorized request detect if a user isn t authorized to make a request and automatically sign out from the application | 1 |
3,413 | 4,402,570,078 | IssuesEvent | 2016-08-11 01:57:11 | zcash/zcash | https://api.github.com/repos/zcash/zcash | closed | Address Sanitizer Finding alloc-dealloc-mismatch | bug PoW and mining SECURITY | 0x602004828bd0 is located 0 bytes inside of 16-byte region [0x602004828bd0,0x602004828be0)
allocated by thread T0 here:
#0 0x560f9b129090 in operator new[](unsigned long) (/home/rcs/Test/zcash/zcash/src/test/test_bitcoin+0x14e090)
#1 0x560f9b4dec0d in TruncatedStepRow<20ul>::GetTruncatedIndices(unsigned long, unsigned long) const crypto/equihash.cpp:203
#2 0x560f9b4dec0d in Equihash<96u, 5u>::OptimisedSolve(crypto_generichash_blake2b_state const&, std::function<bool (std::vector<unsigned int, std::allocator<unsigned int> >)>, std::function<bool (EhSolverCancelCheck)>) crypto/equihash.cpp:428
#3 0x560f9b1e10f3 in EhOptimisedSolve(unsigned int, unsigned int, crypto_generichash_blake2b_state const&, std::function<bool (std::vector<unsigned int, std::allocator<unsigned int> >)>, std::function<bool (EhSolverCancelCheck)>) crypto/equihash.h:224
#4 0x560f9b1e10f3 in EhOptimisedSolveUncancellable(unsigned int, unsigned int, crypto_generichash_blake2b_state const&, std::function<bool (std::vector<unsigned int, std::allocator<unsigned int> >)>) crypto/equihash.h:236
#5 0x560f9b1e10f3 in equihash_tests::TestEquihashSolvers(unsigned int, unsigned int, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > const&, arith_uint256 const&, std::set<std::vector<unsigned int, std::allocator<unsigned int> >, std::less<std::vector<unsigned int, std::allocator<unsigned int> > >, std::allocator<std::vector<unsigned int, std::allocator<unsigned int> > > > const&) test/equihash_tests.cpp:72
#6 0x560f9b1e1acc in equihash_tests::solver_testvectors::test_method() test/equihash_tests.cpp:98
#7 0xb (<unknown module>)
#8 0xac0b210072656460 (<unknown module>)
SUMMARY: AddressSanitizer: alloc-dealloc-mismatch (/home/rcs/Test/zcash/zcash/src/test/test_bitcoin+0x14e570) in operator delete(void*)
| True | Address Sanitizer Finding alloc-dealloc-mismatch - 0x602004828bd0 is located 0 bytes inside of 16-byte region [0x602004828bd0,0x602004828be0)
allocated by thread T0 here:
#0 0x560f9b129090 in operator new[](unsigned long) (/home/rcs/Test/zcash/zcash/src/test/test_bitcoin+0x14e090)
#1 0x560f9b4dec0d in TruncatedStepRow<20ul>::GetTruncatedIndices(unsigned long, unsigned long) const crypto/equihash.cpp:203
#2 0x560f9b4dec0d in Equihash<96u, 5u>::OptimisedSolve(crypto_generichash_blake2b_state const&, std::function<bool (std::vector<unsigned int, std::allocator<unsigned int> >)>, std::function<bool (EhSolverCancelCheck)>) crypto/equihash.cpp:428
#3 0x560f9b1e10f3 in EhOptimisedSolve(unsigned int, unsigned int, crypto_generichash_blake2b_state const&, std::function<bool (std::vector<unsigned int, std::allocator<unsigned int> >)>, std::function<bool (EhSolverCancelCheck)>) crypto/equihash.h:224
#4 0x560f9b1e10f3 in EhOptimisedSolveUncancellable(unsigned int, unsigned int, crypto_generichash_blake2b_state const&, std::function<bool (std::vector<unsigned int, std::allocator<unsigned int> >)>) crypto/equihash.h:236
#5 0x560f9b1e10f3 in equihash_tests::TestEquihashSolvers(unsigned int, unsigned int, std::__cxx11::basic_string<char, std::char_traits<char>, std::allocator<char> > const&, arith_uint256 const&, std::set<std::vector<unsigned int, std::allocator<unsigned int> >, std::less<std::vector<unsigned int, std::allocator<unsigned int> > >, std::allocator<std::vector<unsigned int, std::allocator<unsigned int> > > > const&) test/equihash_tests.cpp:72
#6 0x560f9b1e1acc in equihash_tests::solver_testvectors::test_method() test/equihash_tests.cpp:98
#7 0xb (<unknown module>)
#8 0xac0b210072656460 (<unknown module>)
SUMMARY: AddressSanitizer: alloc-dealloc-mismatch (/home/rcs/Test/zcash/zcash/src/test/test_bitcoin+0x14e570) in operator delete(void*)
| non_priority | address sanitizer finding alloc dealloc mismatch is located bytes inside of byte region allocated by thread here in operator new unsigned long home rcs test zcash zcash src test test bitcoin in truncatedsteprow gettruncatedindices unsigned long unsigned long const crypto equihash cpp in equihash optimisedsolve crypto generichash state const std function std function crypto equihash cpp in ehoptimisedsolve unsigned int unsigned int crypto generichash state const std function std function crypto equihash h in ehoptimisedsolveuncancellable unsigned int unsigned int crypto generichash state const std function crypto equihash h in equihash tests testequihashsolvers unsigned int unsigned int std basic string std allocator const arith const std set std less std allocator const test equihash tests cpp in equihash tests solver testvectors test method test equihash tests cpp summary addresssanitizer alloc dealloc mismatch home rcs test zcash zcash src test test bitcoin in operator delete void | 0 |
103,117 | 4,164,703,282 | IssuesEvent | 2016-06-19 00:29:14 | notsecure/uTox | https://api.github.com/repos/notsecure/uTox | closed | Timed history clear | enhancement low_priority | Clear messages after X time would be very useful for those that do not use remember history but keep uTox running in places where closing is not needed but auto clear would be good. | 1.0 | Timed history clear - Clear messages after X time would be very useful for those that do not use remember history but keep uTox running in places where closing is not needed but auto clear would be good. | priority | timed history clear clear messages after x time would be very useful for those that do not use remember history but keep utox running in places where closing is not needed but auto clear would be good | 1 |
168,688 | 14,170,189,061 | IssuesEvent | 2020-11-12 14:14:04 | NRL-Plasma-Physics-Division/turbopy | https://api.github.com/repos/NRL-Plasma-Physics-Division/turbopy | opened | Add "Attribution" section to the readme | documentation | There should be more details in the readme file on how to appropriately cite turboPy. | 1.0 | Add "Attribution" section to the readme - There should be more details in the readme file on how to appropriately cite turboPy. | non_priority | add attribution section to the readme there should be more details in the readme file on how to appropriately cite turbopy | 0 |
79,690 | 10,137,199,752 | IssuesEvent | 2019-08-02 14:45:04 | pesser/edflow | https://api.github.com/repos/pesser/edflow | opened | document features | documentation | some features were added and we should find a place to document them:
- expansion with retrieve
- path based command line updates of config
- path based variable substitution in config
other existing functionality also needs some promotion:
- pprint and pp2mkdtable are useful but forgotten
- retrieve, set_value, walk, contains_key offer nice functionality for path based dictionary manipulations | 1.0 | document features - some features were added and we should find a place to document them:
- expansion with retrieve
- path based command line updates of config
- path based variable substitution in config
other existing functionality also needs some promotion:
- pprint and pp2mkdtable are useful but forgotten
- retrieve, set_value, walk, contains_key offer nice functionality for path based dictionary manipulations | non_priority | document features some features were added and we should find a place to document them expansion with retrieve path based command line updates of config path based variable substitution in config other existing functionality also needs some promotion pprint and are useful but forgotten retrieve set value walk contains key offer nice functionality for path based dictionary manipulations | 0 |
231,874 | 25,552,078,106 | IssuesEvent | 2022-11-30 01:11:48 | massimobonanni/AzureFunctionsSamples | https://api.github.com/repos/massimobonanni/AzureFunctionsSamples | closed | CVE-2017-0249 (High) detected in system.net.http.4.3.0.nupkg - autoclosed | security vulnerability | ## CVE-2017-0249 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>system.net.http.4.3.0.nupkg</b></p></summary>
<p>Provides a programming interface for modern HTTP applications, including HTTP client components that...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.net.http.4.3.0.nupkg">https://api.nuget.org/packages/system.net.http.4.3.0.nupkg</a></p>
<p>Path to dependency file: /AppConfigSyncFunction/AppConfigSyncFunction.Tests/AppConfigSyncFunction.Tests.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.net.http/4.3.0/system.net.http.4.3.0.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.net.sdk.functions.3.0.10.nupkg (Root Library)
- microsoft.azure.webjobs.extensions.http.3.0.0.nupkg
- microsoft.aspnet.webapi.client.5.2.4.nupkg
- newtonsoft.json.bson.1.0.1.nupkg
- netstandard.library.1.6.1.nupkg
- :x: **system.net.http.4.3.0.nupkg** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An elevation of privilege vulnerability exists when the ASP.NET Core fails to properly sanitize web requests.
<p>Publish Date: 2017-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-0249>CVE-2017-0249</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-05-12</p>
<p>Fix Resolution: System.Text.Encodings.Web - 4.0.1,4.3.1;System.Net.Http - 4.1.2,4.3.2;System.Net.Http.WinHttpHandler - 4.0.2,4.3.1;System.Net.Security - 4.0.1,4.3.1;System.Net.WebSockets.Client - 4.0.1,4.3.1;Microsoft.AspNetCore.Mvc - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Core - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Abstractions - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ApiExplorer - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Cors - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.DataAnnotations - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Json - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Xml - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Localization - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor.Host - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.TagHelpers - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ViewFeatures - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.WebApiCompatShim - 1.0.4,1.1.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-0249 (High) detected in system.net.http.4.3.0.nupkg - autoclosed - ## CVE-2017-0249 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>system.net.http.4.3.0.nupkg</b></p></summary>
<p>Provides a programming interface for modern HTTP applications, including HTTP client components that...</p>
<p>Library home page: <a href="https://api.nuget.org/packages/system.net.http.4.3.0.nupkg">https://api.nuget.org/packages/system.net.http.4.3.0.nupkg</a></p>
<p>Path to dependency file: /AppConfigSyncFunction/AppConfigSyncFunction.Tests/AppConfigSyncFunction.Tests.csproj</p>
<p>Path to vulnerable library: /home/wss-scanner/.nuget/packages/system.net.http/4.3.0/system.net.http.4.3.0.nupkg</p>
<p>
Dependency Hierarchy:
- microsoft.net.sdk.functions.3.0.10.nupkg (Root Library)
- microsoft.azure.webjobs.extensions.http.3.0.0.nupkg
- microsoft.aspnet.webapi.client.5.2.4.nupkg
- newtonsoft.json.bson.1.0.1.nupkg
- netstandard.library.1.6.1.nupkg
- :x: **system.net.http.4.3.0.nupkg** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An elevation of privilege vulnerability exists when the ASP.NET Core fails to properly sanitize web requests.
<p>Publish Date: 2017-05-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-0249>CVE-2017-0249</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-05-12</p>
<p>Fix Resolution: System.Text.Encodings.Web - 4.0.1,4.3.1;System.Net.Http - 4.1.2,4.3.2;System.Net.Http.WinHttpHandler - 4.0.2,4.3.1;System.Net.Security - 4.0.1,4.3.1;System.Net.WebSockets.Client - 4.0.1,4.3.1;Microsoft.AspNetCore.Mvc - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Core - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Abstractions - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ApiExplorer - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Cors - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.DataAnnotations - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Json - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Formatters.Xml - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Localization - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor.Host - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.Razor - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.TagHelpers - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.ViewFeatures - 1.0.4,1.1.3;Microsoft.AspNetCore.Mvc.WebApiCompatShim - 1.0.4,1.1.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in system net http nupkg autoclosed cve high severity vulnerability vulnerable library system net http nupkg provides a programming interface for modern http applications including http client components that library home page a href path to dependency file appconfigsyncfunction appconfigsyncfunction tests appconfigsyncfunction tests csproj path to vulnerable library home wss scanner nuget packages system net http system net http nupkg dependency hierarchy microsoft net sdk functions nupkg root library microsoft azure webjobs extensions http nupkg microsoft aspnet webapi client nupkg newtonsoft json bson nupkg netstandard library nupkg x system net http nupkg vulnerable library found in base branch master vulnerability details an elevation of privilege vulnerability exists when the asp net core fails to properly sanitize web requests publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution system text encodings web system net http system net http winhttphandler system net security system net websockets client microsoft aspnetcore mvc microsoft aspnetcore mvc core microsoft aspnetcore mvc abstractions microsoft aspnetcore mvc apiexplorer microsoft aspnetcore mvc cors microsoft aspnetcore mvc dataannotations microsoft aspnetcore mvc formatters json microsoft aspnetcore mvc formatters xml microsoft aspnetcore mvc localization microsoft aspnetcore mvc razor host microsoft aspnetcore mvc razor microsoft aspnetcore mvc taghelpers microsoft aspnetcore mvc viewfeatures microsoft aspnetcore mvc webapicompatshim step up your open source security game with mend | 0 |
679,844 | 23,247,448,529 | IssuesEvent | 2022-08-03 21:50:35 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | [Android] Verified Twitch account doesn't show verified in BR panel | feature/rewards priority/P3 QA/Yes OS/Android | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description <!--Provide a brief description of the issue-->
Verified Twitch account doesn't show verified in BR panel
## Steps to Reproduce <!--Please add a series of steps to reproduce the issue-->
1. Open verified twitch account on staging
2. Check the BR panel, shows non-verified
3. Open a-c list, shows as verified
## Actual result: <!--Please add screenshots if needed-->


## Expected result:
Should show verified in all places
## Issue reproduces how often: <!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
## Issue happens on: <!-- Mention yes or no -->
- Current Playstore version?
- Beta build?
## Device Details:
- Install Type(ARM, x86):ARM
- Device(Phone, Tablet, Phablet): Phone
- Android Version: 9.0
## Brave version:
1.0.85
### Website problems only:
- Does the issue resolve itself when disabling Brave Shields?
- Is the issue reproducible on the latest version of Chrome?
### Additional Information
<!--Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue-->
| 1.0 | [Android] Verified Twitch account doesn't show verified in BR panel - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description <!--Provide a brief description of the issue-->
Verified Twitch account doesn't show verified in BR panel
## Steps to Reproduce <!--Please add a series of steps to reproduce the issue-->
1. Open verified twitch account on staging
2. Check the BR panel, shows non-verified
3. Open a-c list, shows as verified
## Actual result: <!--Please add screenshots if needed-->


## Expected result:
Should show verified in all places
## Issue reproduces how often: <!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
## Issue happens on: <!-- Mention yes or no -->
- Current Playstore version?
- Beta build?
## Device Details:
- Install Type(ARM, x86):ARM
- Device(Phone, Tablet, Phablet): Phone
- Android Version: 9.0
## Brave version:
1.0.85
### Website problems only:
- Does the issue resolve itself when disabling Brave Shields?
- Is the issue reproducible on the latest version of Chrome?
### Additional Information
<!--Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue-->
| priority | verified twitch account doesn t show verified in br panel have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will only be reopened after sufficient info is provided description verified twitch account doesn t show verified in br panel steps to reproduce open verified twitch account on staging check the br panel shows non verified open a c list shows as verified actual result expected result should show verified in all places issue reproduces how often issue happens on current playstore version beta build device details install type arm arm device phone tablet phablet phone android version brave version website problems only does the issue resolve itself when disabling brave shields is the issue reproducible on the latest version of chrome additional information | 1 |
793,990 | 28,019,044,663 | IssuesEvent | 2023-03-28 02:48:02 | insightsengineering/tern | https://api.github.com/repos/insightsengineering/tern | closed | Wrapper for split_cols_by overall level | research priority | In future `rtables` releases the argument `add_overall_col` may be deprecated.
Propose a design for a layout function in `tern` that can be a wrapper for `split_cols_by(split_fun = add_overall_level(xx))`
Provenance:
```
Creator: anajens
``` | 1.0 | Wrapper for split_cols_by overall level - In future `rtables` releases the argument `add_overall_col` may be deprecated.
Propose a design for a layout function in `tern` that can be a wrapper for `split_cols_by(split_fun = add_overall_level(xx))`
Provenance:
```
Creator: anajens
``` | priority | wrapper for split cols by overall level in future rtables releases the argument add overall col may be deprecated propose a design for a layout function in tern that can be a wrapper for split cols by split fun add overall level xx provenance creator anajens | 1 |
141,104 | 5,429,199,045 | IssuesEvent | 2017-03-03 17:47:37 | NoffearrDeathProjecT/DeathCore | https://api.github.com/repos/NoffearrDeathProjecT/DeathCore | closed | Build failed | Branch-7.x.x InvalidReport Platform-Win Priority:Low | hi see this post !!!!
Build is faild
because : https://github.com/NoffearrDeathProjecT/DeathCore/commit/f2e528cf75ff8c9ed7882f35655ffc2a6889a83a
When compile this source has given errors:
Severity Code Description Project File Line Suppression State
Error C2039 'SpellEffectExtraData': is not a member of 'Movement' game D:\src\server\game\Entities\Unit\Unit.h 1686 | 1.0 | Build failed - hi see this post !!!!
Build is faild
because : https://github.com/NoffearrDeathProjecT/DeathCore/commit/f2e528cf75ff8c9ed7882f35655ffc2a6889a83a
When compile this source has given errors:
Severity Code Description Project File Line Suppression State
Error C2039 'SpellEffectExtraData': is not a member of 'Movement' game D:\src\server\game\Entities\Unit\Unit.h 1686 | priority | build failed hi see this post build is faild because when compile this source has given errors severity code description project file line suppression state error spelleffectextradata is not a member of movement game d src server game entities unit unit h | 1 |
366,370 | 25,580,501,010 | IssuesEvent | 2022-12-01 03:39:22 | tubearchivist/tubearchivist | https://api.github.com/repos/tubearchivist/tubearchivist | closed | [Installation]: Installation instructions need updating for v0.2.4 | documentation | ### Installation instructions
- [X] I have read and understand the [installation instructions](https://github.com/tubearchivist/tubearchivist#installing-and-updating).
- [X] My issue is not described in the [potential pitfalls](https://github.com/tubearchivist/tubearchivist#potential-pitfalls) section.
### Operating System
Synology
### Your installation or setup question
Instructions require update for v0.2.4.
### Relevant log output
```shell
Not required. This is for tracking required changes for documentation.
```
| 1.0 | [Installation]: Installation instructions need updating for v0.2.4 - ### Installation instructions
- [X] I have read and understand the [installation instructions](https://github.com/tubearchivist/tubearchivist#installing-and-updating).
- [X] My issue is not described in the [potential pitfalls](https://github.com/tubearchivist/tubearchivist#potential-pitfalls) section.
### Operating System
Synology
### Your installation or setup question
Instructions require update for v0.2.4.
### Relevant log output
```shell
Not required. This is for tracking required changes for documentation.
```
| non_priority | installation instructions need updating for installation instructions i have read and understand the my issue is not described in the section operating system synology your installation or setup question instructions require update for relevant log output shell not required this is for tracking required changes for documentation | 0 |
76,069 | 26,225,177,076 | IssuesEvent | 2023-01-04 17:59:58 | department-of-veterans-affairs/va.gov-cms | https://api.github.com/repos/department-of-veterans-affairs/va.gov-cms | closed | Homepage modal: Using a screen reader when closing modal announces header before skip link | Defect VA.gov frontend VA.gov homepage ⭐️ Public Websites | ## Describe the defect
Using a screen reader, when the homepage modal is closed, regardless of how it's closed (X, button, ESC key), before the skip link is announced, the first header in the footer (Veterans programs and services) is announced.
## To Reproduce
Steps to reproduce the behavior:
1. Turn on your screen reader (i.e. NVDA)
2. Go to (when this is deployed I can add the staging homepage)
3. Close the modal by using the ESC key, the X in the corner or the "Not today..." button
4. Note that the screen reader announces "Veterans programs and services" then announces "Skip to content"
5. However, visually the Skip link is shown as focused immediately
## AC / Expected behavior
- [ ] When the modal is closed (using the X, the button or the ESC), the SR should announce the same element as what is visually focused - in this case the Skip to content link
- [ ] When resolved / verified in prod, also close https://github.com/department-of-veterans-affairs/va.gov-team/issues/51155
## Additional Context
@jtmst mentioned he thought he knew what was going on here and what would need to be looked at to resolve it:
> there was an issue with set-focus not working properly when closing the modal, a solution ive used for similar bugs is adding a 50ms delay before changing focus. I didnt anticipate it affecting screen readers this way.
### CMS Team
Please check the team(s) that will do this work.
- [ ] `Program`
- [ ] `Platform CMS Team`
- [ ] `Sitewide Crew`
- [ ] `⭐️ Sitewide CMS`
- [x] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
| 1.0 | Homepage modal: Using a screen reader when closing modal announces header before skip link - ## Describe the defect
Using a screen reader, when the homepage modal is closed, regardless of how it's closed (X, button, ESC key), before the skip link is announced, the first header in the footer (Veterans programs and services) is announced.
## To Reproduce
Steps to reproduce the behavior:
1. Turn on your screen reader (i.e. NVDA)
2. Go to (when this is deployed I can add the staging homepage)
3. Close the modal by using the ESC key, the X in the corner or the "Not today..." button
4. Note that the screen reader announces "Veterans programs and services" then announces "Skip to content"
5. However, visually the Skip link is shown as focused immediately
## AC / Expected behavior
- [ ] When the modal is closed (using the X, the button or the ESC), the SR should announce the same element as what is visually focused - in this case the Skip to content link
- [ ] When resolved / verified in prod, also close https://github.com/department-of-veterans-affairs/va.gov-team/issues/51155
## Additional Context
@jtmst mentioned he thought he knew what was going on here and what would need to be looked at to resolve it:
> there was an issue with set-focus not working properly when closing the modal, a solution ive used for similar bugs is adding a 50ms delay before changing focus. I didnt anticipate it affecting screen readers this way.
### CMS Team
Please check the team(s) that will do this work.
- [ ] `Program`
- [ ] `Platform CMS Team`
- [ ] `Sitewide Crew`
- [ ] `⭐️ Sitewide CMS`
- [x] `⭐️ Public Websites`
- [ ] `⭐️ Facilities`
- [ ] `⭐️ User support`
| non_priority | homepage modal using a screen reader when closing modal announces header before skip link describe the defect using a screen reader when the homepage modal is closed regardless of how it s closed x button esc key before the skip link is announced the first header in the footer veterans programs and services is announced to reproduce steps to reproduce the behavior turn on your screen reader i e nvda go to when this is deployed i can add the staging homepage close the modal by using the esc key the x in the corner or the not today button note that the screen reader announces veterans programs and services then announces skip to content however visually the skip link is shown as focused immediately ac expected behavior when the modal is closed using the x the button or the esc the sr should announce the same element as what is visually focused in this case the skip to content link when resolved verified in prod also close additional context jtmst mentioned he thought he knew what was going on here and what would need to be looked at to resolve it there was an issue with set focus not working properly when closing the modal a solution ive used for similar bugs is adding a delay before changing focus i didnt anticipate it affecting screen readers this way cms team please check the team s that will do this work program platform cms team sitewide crew ⭐️ sitewide cms ⭐️ public websites ⭐️ facilities ⭐️ user support | 0 |
478,849 | 13,786,454,434 | IssuesEvent | 2020-10-09 01:53:52 | kubeapps/kubeapps | https://api.github.com/repos/kubeapps/kubeapps | closed | Ability to view the history of events on a release | component/dashboard component/helm help wanted kind/feature priority/low wontfix | It would be nice to be able to view the list of events that happened to a release .
The description of the bug is awfully short but I am not sure what else I can add. | 1.0 | Ability to view the history of events on a release - It would be nice to be able to view the list of events that happened to a release .
The description of the bug is awfully short but I am not sure what else I can add. | priority | ability to view the history of events on a release it would be nice to be able to view the list of events that happened to a release the description of the bug is awfully short but i am not sure what else i can add | 1 |
351,057 | 25,011,925,033 | IssuesEvent | 2022-11-03 15:49:19 | Noovolari/leapp | https://api.github.com/repos/Noovolari/leapp | closed | How to use AWS AssumeRole with MFA | bug documentation | Sorry, this is not really a bug nor a feature request.
My colleague is experimenting with `aws-vault` so we can enforce MFA for our cluster. He has a aws config file like this:
```
[profile xx-xx-prod]
role_arn=arn:aws:iam::xx:role/xxAdminAccessForLogin
source_profile=xx-login
mfa_serial=arn:aws:iam::xx:mfa/XXXXXXXXXXX
region=eu-west-1
[profile xx-xx-staging]
role_arn=arn:aws:iam::xx:role/xxAdminAccessForLogin
source_profile=xx-login
mfa_serial=arn:aws:iam::xx:mfa/XXXXXXXXXXXXXXXXXX
region=eu-central-1
[profile xx-login]
#yes, nothing here
```
He can then use this to do `terraform` commands and for example start Lens through:
`aws-vault exec xx-xx-staging -- kontena-lens --context=arn:aws:eks:eu-central-1:xx:cluster/xx-xx-staging`
However I don't really like this as this prevents the option from having multiple clusters open in one Lens window. You would need to restart it every time.
So: then I found Leapp. If I understand it correctly this should solve the problem described above. However I don't really understand how to set it up.
First I add a session for the 'login' account:
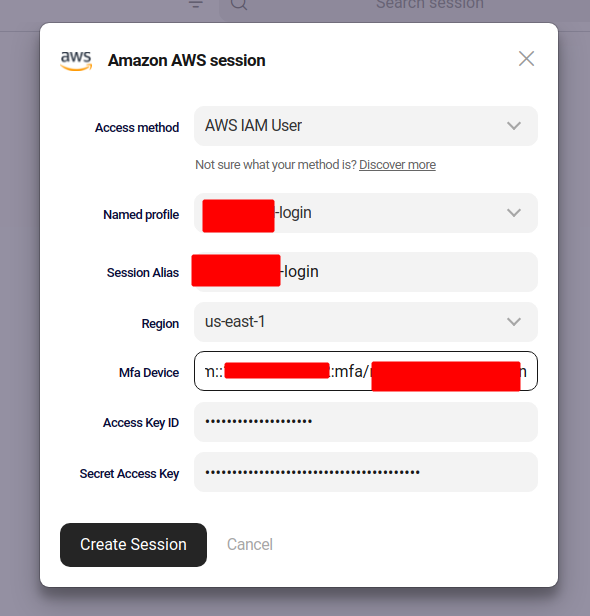
When I start that session I get asked for a MFA serial and then it succeeds.
Then I want to add the account I use to "AssumeRole":
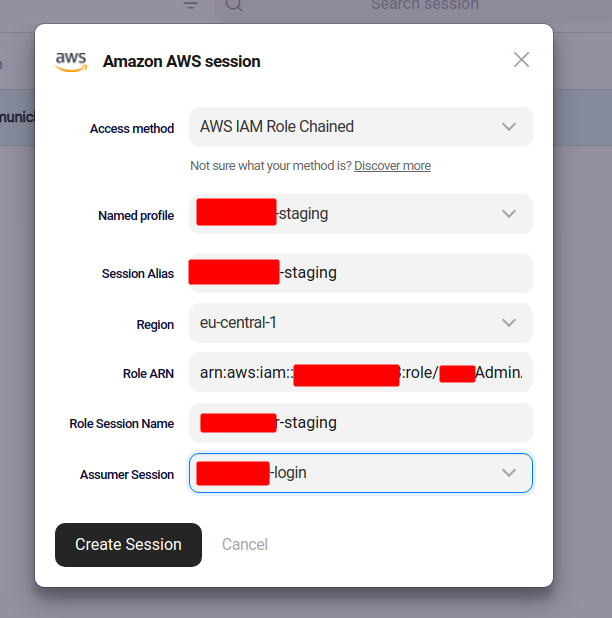
I can also create/start this session with no problem. I do see credentials in `~/.aws/credentials`.
However when I want to run a `terraform apply` for example I get this error:
```
╷
│ Error: Kubernetes cluster unreachable: invalid configuration: no configuration has been provided, try setting KUBERNETES_MASTER environment variable
│
│
╵
╷
│ Error: error configuring Terraform AWS Provider: no valid credential sources for Terraform AWS Provider found.
│
│ Please see https://registry.terraform.io/providers/hashicorp/aws
│ for more information about providing credentials.
│
│ Error: NoCredentialProviders: no valid providers in chain
│ caused by: EnvAccessKeyNotFound: failed to find credentials in the environment.
│ SharedCredsLoad: failed to load profile, .
│ EC2RoleRequestError: no EC2 instance role found
│ caused by: RequestError: send request failed
│ caused by: Get "http://169.254.169.254/latest/meta-data/iam/security-credentials/": context deadline exceeded (Client.Timeout exceeded while awaiting headers)
│
│
│ with module.shared.provider["registry.terraform.io/hashicorp/aws"],
│ on ../shared/main.tf line 41, in provider "aws":
│ 41: provider "aws" {
│
```
I cannot post the entire terraform files but I think this is the relevant part:
```
terraform {
backend "s3" {
bucket = "xx-terraform-state-xx-staging"
key = "network/terraform.tfstate"
region = "eu-central-1"
profile="xx-xx-staging"
}
required_providers {
aws = {
source = "hashicorp/aws"
version = "3.72.0"
}
}
}
provider "aws" {
region = "eu-central-1"
profile="xx-xx-staging"
}
```
If I remove the profile from the terraform files and run init I get:
```
│ Error: error configuring S3 Backend: no valid credential sources for S3 Backend found.
│
│ Please see https://www.terraform.io/docs/language/settings/backends/s3.html
│ for more information about providing credentials.
│
│ Error: NoCredentialProviders: no valid providers in chain. Deprecated.
│ For verbose messaging see aws.Config.CredentialsChainVerboseErrors
```
So I am hoping that there are some people here that have some experience and can give some pointers. Can we even use Leapp to solve the problem as described? I'm I using the wrong config? I don't really understand how it should work.
edit:
incuded the wrong error | 1.0 | How to use AWS AssumeRole with MFA - Sorry, this is not really a bug nor a feature request.
My colleague is experimenting with `aws-vault` so we can enforce MFA for our cluster. He has a aws config file like this:
```
[profile xx-xx-prod]
role_arn=arn:aws:iam::xx:role/xxAdminAccessForLogin
source_profile=xx-login
mfa_serial=arn:aws:iam::xx:mfa/XXXXXXXXXXX
region=eu-west-1
[profile xx-xx-staging]
role_arn=arn:aws:iam::xx:role/xxAdminAccessForLogin
source_profile=xx-login
mfa_serial=arn:aws:iam::xx:mfa/XXXXXXXXXXXXXXXXXX
region=eu-central-1
[profile xx-login]
#yes, nothing here
```
He can then use this to do `terraform` commands and for example start Lens through:
`aws-vault exec xx-xx-staging -- kontena-lens --context=arn:aws:eks:eu-central-1:xx:cluster/xx-xx-staging`
However I don't really like this as this prevents the option from having multiple clusters open in one Lens window. You would need to restart it every time.
So: then I found Leapp. If I understand it correctly this should solve the problem described above. However I don't really understand how to set it up.
First I add a session for the 'login' account:
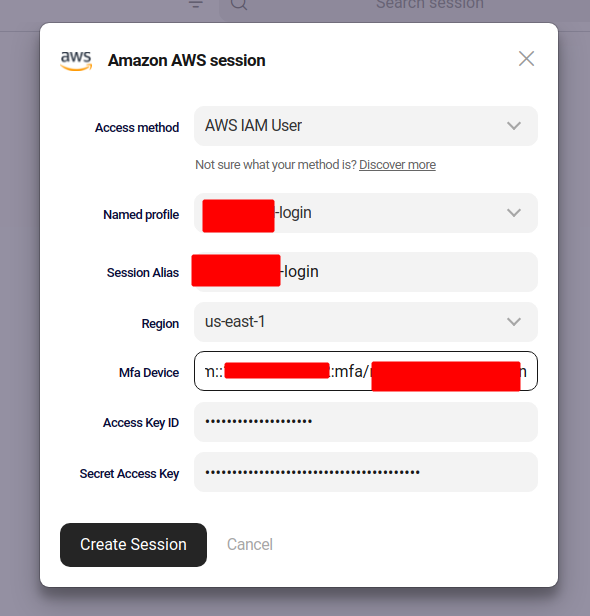
When I start that session I get asked for a MFA serial and then it succeeds.
Then I want to add the account I use to "AssumeRole":
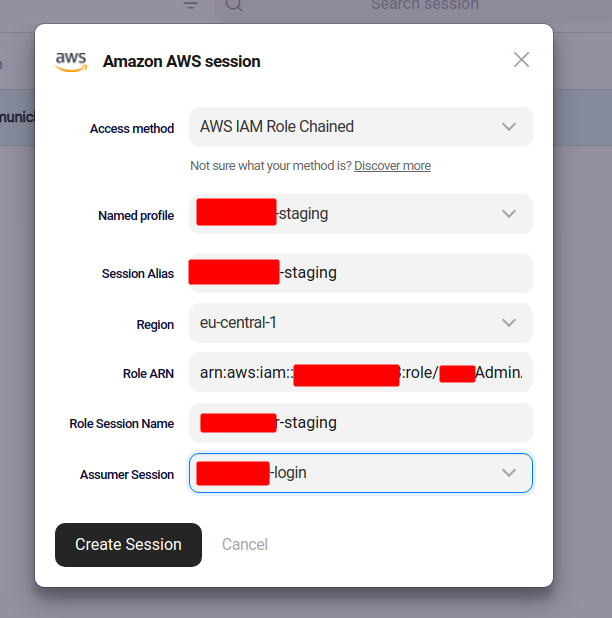
I can also create/start this session with no problem. I do see credentials in `~/.aws/credentials`.
However when I want to run a `terraform apply` for example I get this error:
```
╷
│ Error: Kubernetes cluster unreachable: invalid configuration: no configuration has been provided, try setting KUBERNETES_MASTER environment variable
│
│
╵
╷
│ Error: error configuring Terraform AWS Provider: no valid credential sources for Terraform AWS Provider found.
│
│ Please see https://registry.terraform.io/providers/hashicorp/aws
│ for more information about providing credentials.
│
│ Error: NoCredentialProviders: no valid providers in chain
│ caused by: EnvAccessKeyNotFound: failed to find credentials in the environment.
│ SharedCredsLoad: failed to load profile, .
│ EC2RoleRequestError: no EC2 instance role found
│ caused by: RequestError: send request failed
│ caused by: Get "http://169.254.169.254/latest/meta-data/iam/security-credentials/": context deadline exceeded (Client.Timeout exceeded while awaiting headers)
│
│
│ with module.shared.provider["registry.terraform.io/hashicorp/aws"],
│ on ../shared/main.tf line 41, in provider "aws":
│ 41: provider "aws" {
│
```
I cannot post the entire terraform files but I think this is the relevant part:
```
terraform {
backend "s3" {
bucket = "xx-terraform-state-xx-staging"
key = "network/terraform.tfstate"
region = "eu-central-1"
profile="xx-xx-staging"
}
required_providers {
aws = {
source = "hashicorp/aws"
version = "3.72.0"
}
}
}
provider "aws" {
region = "eu-central-1"
profile="xx-xx-staging"
}
```
If I remove the profile from the terraform files and run init I get:
```
│ Error: error configuring S3 Backend: no valid credential sources for S3 Backend found.
│
│ Please see https://www.terraform.io/docs/language/settings/backends/s3.html
│ for more information about providing credentials.
│
│ Error: NoCredentialProviders: no valid providers in chain. Deprecated.
│ For verbose messaging see aws.Config.CredentialsChainVerboseErrors
```
So I am hoping that there are some people here that have some experience and can give some pointers. Can we even use Leapp to solve the problem as described? I'm I using the wrong config? I don't really understand how it should work.
edit:
incuded the wrong error | non_priority | how to use aws assumerole with mfa sorry this is not really a bug nor a feature request my colleague is experimenting with aws vault so we can enforce mfa for our cluster he has a aws config file like this role arn arn aws iam xx role xxadminaccessforlogin source profile xx login mfa serial arn aws iam xx mfa xxxxxxxxxxx region eu west role arn arn aws iam xx role xxadminaccessforlogin source profile xx login mfa serial arn aws iam xx mfa xxxxxxxxxxxxxxxxxx region eu central yes nothing here he can then use this to do terraform commands and for example start lens through aws vault exec xx xx staging kontena lens context arn aws eks eu central xx cluster xx xx staging however i don t really like this as this prevents the option from having multiple clusters open in one lens window you would need to restart it every time so then i found leapp if i understand it correctly this should solve the problem described above however i don t really understand how to set it up first i add a session for the login account when i start that session i get asked for a mfa serial and then it succeeds then i want to add the account i use to assumerole i can also create start this session with no problem i do see credentials in aws credentials however when i want to run a terraform apply for example i get this error ╷ │ error kubernetes cluster unreachable invalid configuration no configuration has been provided try setting kubernetes master environment variable │ │ ╵ ╷ │ error error configuring terraform aws provider no valid credential sources for terraform aws provider found │ │ please see │ for more information about providing credentials │ │ error nocredentialproviders no valid providers in chain │ caused by envaccesskeynotfound failed to find credentials in the environment │ sharedcredsload failed to load profile │ no instance role found │ caused by requesterror send request failed │ caused by get context deadline exceeded client timeout exceeded while awaiting headers │ │ │ with module shared provider │ on shared main tf line in provider aws │ provider aws │ i cannot post the entire terraform files but i think this is the relevant part terraform backend bucket xx terraform state xx staging key network terraform tfstate region eu central profile xx xx staging required providers aws source hashicorp aws version provider aws region eu central profile xx xx staging if i remove the profile from the terraform files and run init i get │ error error configuring backend no valid credential sources for backend found │ │ please see │ for more information about providing credentials │ │ error nocredentialproviders no valid providers in chain deprecated │ for verbose messaging see aws config credentialschainverboseerrors so i am hoping that there are some people here that have some experience and can give some pointers can we even use leapp to solve the problem as described i m i using the wrong config i don t really understand how it should work edit incuded the wrong error | 0 |
35,826 | 2,793,203,747 | IssuesEvent | 2015-05-11 09:22:10 | synergy/synergy | https://api.github.com/repos/synergy/synergy | opened | High logging rate causes Windows service to crash | bug priority-urgent | After seeing #4650, it looks like the high rate of logging (which is stored in a buffer) causes the Windows service to crash (probably because it runs out of memory).
The IPC logging buffer should store only 1000 lines.... any more than that is probably useless anyway. | 1.0 | High logging rate causes Windows service to crash - After seeing #4650, it looks like the high rate of logging (which is stored in a buffer) causes the Windows service to crash (probably because it runs out of memory).
The IPC logging buffer should store only 1000 lines.... any more than that is probably useless anyway. | priority | high logging rate causes windows service to crash after seeing it looks like the high rate of logging which is stored in a buffer causes the windows service to crash probably because it runs out of memory the ipc logging buffer should store only lines any more than that is probably useless anyway | 1 |
639,727 | 20,763,331,884 | IssuesEvent | 2022-03-15 18:10:05 | npm/cli | https://api.github.com/repos/npm/cli | closed | [BUG] npm install attempts to fetch already bundled indirect dependency from registry | Release 7.x Bug Priority 1 | It appears that `npm install` sometimes attempts to fetch indirect dependencies from the registry even though they have already been bundled with the package being installed. This causes issues if these dependencies are only available in an internal registry during install/pack-time but not available on the registry where the package is published to and eventually installed from. My understanding is that dependencies listed in `bundledDependencies` also include indirect dependencies.
I can only reproduce this on Windows with npm 7. The package installs just fine with npm 6 on Windows and with npm 7 on macOS.
I've created a minimal repro from my original package and used a `file:` dependency to avoid the need for a custom registry. The error looks a little different than with my original package since it fails with an error saying that it cannot find the package on the registry but I think it's the same cause. This is what my repro package looks like:
`package.json`:
```
{
"name": "foo",
"version": "1.0.0",
"dependencies": {
"bar": "file:bar-1.0.0.tgz",
"tmp": "0.0.33"
},
"bundledDependencies": [
"bar",
"tmp"
]
}
```
where `bar-1.0.0.tgz` contains a single file `bar/package.json`:
```
{
"name": "bar",
"version": "1.0.0",
"dependencies": {
"tmp-promise": "2.0.2"
}
}
```
Here's a zip file with the above files: [foo.zip](https://github.com/npm/cli/files/6025260/foo.zip)
There are a couple of issues already that appear similar but I'm not entirely sure they're the same:
- https://github.com/npm/cli/issues/1817 (the issue I'm seeing only reproduced on npm 7)
- https://github.com/npm/cli/issues/2143
### Current Behavior:
Install fails on npm@7.5.6 as it attempts to fetch already bundled indirect dependency `rimraf` from the dummy registry `https://0.0.0.0` even though it should already be bundled with the package:
```
PS C:\Users\salva\Desktop\repro\foo> node --version
v15.9.0
PS C:\Users\salva\Desktop\repro\foo> npm --version
7.5.6
PS C:\Users\salva\Desktop\repro\foo> npm list -g
C:\Users\salva\AppData\Roaming\npm
`-- npm@7.5.6
PS C:\Users\salva\Desktop\repro\foo> npm install
added 17 packages, and audited 18 packages in 1s
1 package is looking for funding
run `npm fund` for details
found 0 vulnerabilities
PS C:\Users\salva\Desktop\repro\foo> npm pack
npm notice
npm notice package: foo@1.0.0
npm notice === Tarball Contents ===
npm notice 228B bar-1.0.0.tgz
npm notice 173B package.json
npm notice === Bundled Dependencies ===
npm notice balanced-match
npm notice brace-expansion
npm notice concat-map
npm notice fs.realpath
npm notice glob
npm notice inflight
npm notice inherits
npm notice minimatch
npm notice once
npm notice os-tmpdir
npm notice path-is-absolute
npm notice rimraf
npm notice tmp-promise
npm notice tmp
npm notice wrappy
npm notice bar
npm notice === Tarball Details ===
npm notice name: foo
npm notice version: 1.0.0
npm notice filename: foo-1.0.0.tgz
npm notice package size: 62.2 kB
npm notice unpacked size: 238.5 kB
npm notice shasum: f5b9dea47ae5d48a40f7079d99728e905a48e808
npm notice integrity: sha512-P9Yat2HlAmr2b[...]1/ACmYuDlxUZw==
npm notice bundled deps: 16
npm notice bundled files: 0
npm notice own files: 81
npm notice total files: 81
npm notice
foo-1.0.0.tgz
PS C:\Users\salva\Desktop\repro\foo> npm install -g --registry https://0.0.0.0 foo-1.0.0.tgz
npm ERR! code ECONNREFUSED
npm ERR! syscall connect
npm ERR! errno ECONNREFUSED
npm ERR! FetchError: request to https://0.0.0.0/rimraf failed, reason: connect ECONNREFUSED 0.0.0.0:443
npm ERR! at ClientRequest.<anonymous> (C:\Users\salva\AppData\Roaming\npm\node_modules\npm\node_modules\minipass-fetch\lib\index.js:97:14)
npm ERR! at ClientRequest.emit (node:events:378:20)
npm ERR! at TLSSocket.socketErrorListener (node:_http_client:462:9)
npm ERR! at TLSSocket.emit (node:events:390:22)
npm ERR! at emitErrorNT (node:internal/streams/destroy:188:8)
npm ERR! at emitErrorCloseNT (node:internal/streams/destroy:153:3)
npm ERR! at processTicksAndRejections (node:internal/process/task_queues:81:21)
npm ERR! FetchError: request to https://0.0.0.0/rimraf failed, reason: connect ECONNREFUSED 0.0.0.0:443
npm ERR! at ClientRequest.<anonymous> (C:\Users\salva\AppData\Roaming\npm\node_modules\npm\node_modules\minipass-fetch\lib\index.js:97:14)
npm ERR! at ClientRequest.emit (node:events:378:20)
npm ERR! at TLSSocket.socketErrorListener (node:_http_client:462:9)
npm ERR! at TLSSocket.emit (node:events:390:22)
npm ERR! at emitErrorNT (node:internal/streams/destroy:188:8)
npm ERR! at emitErrorCloseNT (node:internal/streams/destroy:153:3)
npm ERR! at processTicksAndRejections (node:internal/process/task_queues:81:21) {
npm ERR! code: 'ECONNREFUSED',
npm ERR! errno: 'ECONNREFUSED',
npm ERR! syscall: 'connect',
npm ERR! address: '0.0.0.0',
npm ERR! port: 443,
npm ERR! type: 'system'
npm ERR! }
npm ERR!
npm ERR! If you are behind a proxy, please make sure that the
npm ERR! 'proxy' config is set properly. See: 'npm help config'
npm ERR! A complete log of this run can be found in:
npm ERR! C:\Users\salva\AppData\Local\npm-cache\_logs\2021-02-22T21_35_06_434Z-debug.log
```
[2021-02-22T21_35_06_434Z-debug.log](https://github.com/npm/cli/files/6025301/2021-02-22T21_35_06_434Z-debug.log)
### Expected Behavior:
Install succeeds on npm@6.14.11:
```
PS C:\Users\salva\Desktop\repro\foo> node --version
v15.9.0
PS C:\Users\salva\Desktop\repro\foo> npm --version
6.14.11
PS C:\Users\salva\Desktop\repro\foo> npm list -g --depth=0
C:\Users\salva\AppData\Roaming\npm
`-- npm@6.14.11
PS C:\Users\salva\Desktop\repro\foo> npm install
npm notice created a lockfile as package-lock.json. You should commit this file.
npm WARN foo@1.0.0 No description
npm WARN foo@1.0.0 No repository field.
npm WARN foo@1.0.0 No license field.
added 17 packages from 6 contributors and audited 17 packages in 1.766s
1 package is looking for funding
run `npm fund` for details
found 0 vulnerabilities
PS C:\Users\salva\Desktop\repro\foo> npm pack
npm notice
npm notice package: foo@1.0.0
npm notice === Tarball Contents ===
npm notice 173B package.json
npm notice 228B bar-1.0.0.tgz
npm notice === Bundled Dependencies ===
npm notice tmp
npm notice bar
npm notice === Tarball Details ===
npm notice name: foo
npm notice version: 1.0.0
npm notice filename: foo-1.0.0.tgz
npm notice package size: 65.3 kB
npm notice unpacked size: 254.1 kB
npm notice shasum: 238cc607fa070001da971e27992fb1da963f1f63
npm notice integrity: sha512-YYaLB9+Lv5qmo[...]NvWxcaPI3fHPQ==
npm notice bundled deps: 2
npm notice bundled files: 79
npm notice own files: 2
npm notice total files: 81
npm notice
foo-1.0.0.tgz
PS C:\Users\salva\Desktop\repro\foo> npm install -g --registry https://0.0.0.0 foo-1.0.0.tgz
+ foo@1.0.0
added 18 packages from 6 contributors in 0.524s
```
### Steps To Reproduce:
1. Download [foo.zip](https://github.com/npm/cli/files/6025260/foo.zip)
2. Extract foo.zip
3. `cd foo`
4. `npm install`
5. `npm pack`
6. `npm install -g --registry https://0.0.0.0 foo-1.0.0.tgz`
7. Observe error (after timeout) when npm attempts to fetch indirect dependency `rimraf` from the dummy registry `https://0.0.0.0`
### Environment:
- OS: Windows 10.0.19042 Build 19042
- Node: 15.9.0
- npm: 7.5.6 | 1.0 | [BUG] npm install attempts to fetch already bundled indirect dependency from registry - It appears that `npm install` sometimes attempts to fetch indirect dependencies from the registry even though they have already been bundled with the package being installed. This causes issues if these dependencies are only available in an internal registry during install/pack-time but not available on the registry where the package is published to and eventually installed from. My understanding is that dependencies listed in `bundledDependencies` also include indirect dependencies.
I can only reproduce this on Windows with npm 7. The package installs just fine with npm 6 on Windows and with npm 7 on macOS.
I've created a minimal repro from my original package and used a `file:` dependency to avoid the need for a custom registry. The error looks a little different than with my original package since it fails with an error saying that it cannot find the package on the registry but I think it's the same cause. This is what my repro package looks like:
`package.json`:
```
{
"name": "foo",
"version": "1.0.0",
"dependencies": {
"bar": "file:bar-1.0.0.tgz",
"tmp": "0.0.33"
},
"bundledDependencies": [
"bar",
"tmp"
]
}
```
where `bar-1.0.0.tgz` contains a single file `bar/package.json`:
```
{
"name": "bar",
"version": "1.0.0",
"dependencies": {
"tmp-promise": "2.0.2"
}
}
```
Here's a zip file with the above files: [foo.zip](https://github.com/npm/cli/files/6025260/foo.zip)
There are a couple of issues already that appear similar but I'm not entirely sure they're the same:
- https://github.com/npm/cli/issues/1817 (the issue I'm seeing only reproduced on npm 7)
- https://github.com/npm/cli/issues/2143
### Current Behavior:
Install fails on npm@7.5.6 as it attempts to fetch already bundled indirect dependency `rimraf` from the dummy registry `https://0.0.0.0` even though it should already be bundled with the package:
```
PS C:\Users\salva\Desktop\repro\foo> node --version
v15.9.0
PS C:\Users\salva\Desktop\repro\foo> npm --version
7.5.6
PS C:\Users\salva\Desktop\repro\foo> npm list -g
C:\Users\salva\AppData\Roaming\npm
`-- npm@7.5.6
PS C:\Users\salva\Desktop\repro\foo> npm install
added 17 packages, and audited 18 packages in 1s
1 package is looking for funding
run `npm fund` for details
found 0 vulnerabilities
PS C:\Users\salva\Desktop\repro\foo> npm pack
npm notice
npm notice package: foo@1.0.0
npm notice === Tarball Contents ===
npm notice 228B bar-1.0.0.tgz
npm notice 173B package.json
npm notice === Bundled Dependencies ===
npm notice balanced-match
npm notice brace-expansion
npm notice concat-map
npm notice fs.realpath
npm notice glob
npm notice inflight
npm notice inherits
npm notice minimatch
npm notice once
npm notice os-tmpdir
npm notice path-is-absolute
npm notice rimraf
npm notice tmp-promise
npm notice tmp
npm notice wrappy
npm notice bar
npm notice === Tarball Details ===
npm notice name: foo
npm notice version: 1.0.0
npm notice filename: foo-1.0.0.tgz
npm notice package size: 62.2 kB
npm notice unpacked size: 238.5 kB
npm notice shasum: f5b9dea47ae5d48a40f7079d99728e905a48e808
npm notice integrity: sha512-P9Yat2HlAmr2b[...]1/ACmYuDlxUZw==
npm notice bundled deps: 16
npm notice bundled files: 0
npm notice own files: 81
npm notice total files: 81
npm notice
foo-1.0.0.tgz
PS C:\Users\salva\Desktop\repro\foo> npm install -g --registry https://0.0.0.0 foo-1.0.0.tgz
npm ERR! code ECONNREFUSED
npm ERR! syscall connect
npm ERR! errno ECONNREFUSED
npm ERR! FetchError: request to https://0.0.0.0/rimraf failed, reason: connect ECONNREFUSED 0.0.0.0:443
npm ERR! at ClientRequest.<anonymous> (C:\Users\salva\AppData\Roaming\npm\node_modules\npm\node_modules\minipass-fetch\lib\index.js:97:14)
npm ERR! at ClientRequest.emit (node:events:378:20)
npm ERR! at TLSSocket.socketErrorListener (node:_http_client:462:9)
npm ERR! at TLSSocket.emit (node:events:390:22)
npm ERR! at emitErrorNT (node:internal/streams/destroy:188:8)
npm ERR! at emitErrorCloseNT (node:internal/streams/destroy:153:3)
npm ERR! at processTicksAndRejections (node:internal/process/task_queues:81:21)
npm ERR! FetchError: request to https://0.0.0.0/rimraf failed, reason: connect ECONNREFUSED 0.0.0.0:443
npm ERR! at ClientRequest.<anonymous> (C:\Users\salva\AppData\Roaming\npm\node_modules\npm\node_modules\minipass-fetch\lib\index.js:97:14)
npm ERR! at ClientRequest.emit (node:events:378:20)
npm ERR! at TLSSocket.socketErrorListener (node:_http_client:462:9)
npm ERR! at TLSSocket.emit (node:events:390:22)
npm ERR! at emitErrorNT (node:internal/streams/destroy:188:8)
npm ERR! at emitErrorCloseNT (node:internal/streams/destroy:153:3)
npm ERR! at processTicksAndRejections (node:internal/process/task_queues:81:21) {
npm ERR! code: 'ECONNREFUSED',
npm ERR! errno: 'ECONNREFUSED',
npm ERR! syscall: 'connect',
npm ERR! address: '0.0.0.0',
npm ERR! port: 443,
npm ERR! type: 'system'
npm ERR! }
npm ERR!
npm ERR! If you are behind a proxy, please make sure that the
npm ERR! 'proxy' config is set properly. See: 'npm help config'
npm ERR! A complete log of this run can be found in:
npm ERR! C:\Users\salva\AppData\Local\npm-cache\_logs\2021-02-22T21_35_06_434Z-debug.log
```
[2021-02-22T21_35_06_434Z-debug.log](https://github.com/npm/cli/files/6025301/2021-02-22T21_35_06_434Z-debug.log)
### Expected Behavior:
Install succeeds on npm@6.14.11:
```
PS C:\Users\salva\Desktop\repro\foo> node --version
v15.9.0
PS C:\Users\salva\Desktop\repro\foo> npm --version
6.14.11
PS C:\Users\salva\Desktop\repro\foo> npm list -g --depth=0
C:\Users\salva\AppData\Roaming\npm
`-- npm@6.14.11
PS C:\Users\salva\Desktop\repro\foo> npm install
npm notice created a lockfile as package-lock.json. You should commit this file.
npm WARN foo@1.0.0 No description
npm WARN foo@1.0.0 No repository field.
npm WARN foo@1.0.0 No license field.
added 17 packages from 6 contributors and audited 17 packages in 1.766s
1 package is looking for funding
run `npm fund` for details
found 0 vulnerabilities
PS C:\Users\salva\Desktop\repro\foo> npm pack
npm notice
npm notice package: foo@1.0.0
npm notice === Tarball Contents ===
npm notice 173B package.json
npm notice 228B bar-1.0.0.tgz
npm notice === Bundled Dependencies ===
npm notice tmp
npm notice bar
npm notice === Tarball Details ===
npm notice name: foo
npm notice version: 1.0.0
npm notice filename: foo-1.0.0.tgz
npm notice package size: 65.3 kB
npm notice unpacked size: 254.1 kB
npm notice shasum: 238cc607fa070001da971e27992fb1da963f1f63
npm notice integrity: sha512-YYaLB9+Lv5qmo[...]NvWxcaPI3fHPQ==
npm notice bundled deps: 2
npm notice bundled files: 79
npm notice own files: 2
npm notice total files: 81
npm notice
foo-1.0.0.tgz
PS C:\Users\salva\Desktop\repro\foo> npm install -g --registry https://0.0.0.0 foo-1.0.0.tgz
+ foo@1.0.0
added 18 packages from 6 contributors in 0.524s
```
### Steps To Reproduce:
1. Download [foo.zip](https://github.com/npm/cli/files/6025260/foo.zip)
2. Extract foo.zip
3. `cd foo`
4. `npm install`
5. `npm pack`
6. `npm install -g --registry https://0.0.0.0 foo-1.0.0.tgz`
7. Observe error (after timeout) when npm attempts to fetch indirect dependency `rimraf` from the dummy registry `https://0.0.0.0`
### Environment:
- OS: Windows 10.0.19042 Build 19042
- Node: 15.9.0
- npm: 7.5.6 | priority | npm install attempts to fetch already bundled indirect dependency from registry it appears that npm install sometimes attempts to fetch indirect dependencies from the registry even though they have already been bundled with the package being installed this causes issues if these dependencies are only available in an internal registry during install pack time but not available on the registry where the package is published to and eventually installed from my understanding is that dependencies listed in bundleddependencies also include indirect dependencies i can only reproduce this on windows with npm the package installs just fine with npm on windows and with npm on macos i ve created a minimal repro from my original package and used a file dependency to avoid the need for a custom registry the error looks a little different than with my original package since it fails with an error saying that it cannot find the package on the registry but i think it s the same cause this is what my repro package looks like package json name foo version dependencies bar file bar tgz tmp bundleddependencies bar tmp where bar tgz contains a single file bar package json name bar version dependencies tmp promise here s a zip file with the above files there are a couple of issues already that appear similar but i m not entirely sure they re the same the issue i m seeing only reproduced on npm current behavior install fails on npm as it attempts to fetch already bundled indirect dependency rimraf from the dummy registry even though it should already be bundled with the package ps c users salva desktop repro foo node version ps c users salva desktop repro foo npm version ps c users salva desktop repro foo npm list g c users salva appdata roaming npm npm ps c users salva desktop repro foo npm install added packages and audited packages in package is looking for funding run npm fund for details found vulnerabilities ps c users salva desktop repro foo npm pack npm notice npm notice package foo npm notice tarball contents npm notice bar tgz npm notice package json npm notice bundled dependencies npm notice balanced match npm notice brace expansion npm notice concat map npm notice fs realpath npm notice glob npm notice inflight npm notice inherits npm notice minimatch npm notice once npm notice os tmpdir npm notice path is absolute npm notice rimraf npm notice tmp promise npm notice tmp npm notice wrappy npm notice bar npm notice tarball details npm notice name foo npm notice version npm notice filename foo tgz npm notice package size kb npm notice unpacked size kb npm notice shasum npm notice integrity acmyudlxuzw npm notice bundled deps npm notice bundled files npm notice own files npm notice total files npm notice foo tgz ps c users salva desktop repro foo npm install g registry foo tgz npm err code econnrefused npm err syscall connect npm err errno econnrefused npm err fetcherror request to failed reason connect econnrefused npm err at clientrequest c users salva appdata roaming npm node modules npm node modules minipass fetch lib index js npm err at clientrequest emit node events npm err at tlssocket socketerrorlistener node http client npm err at tlssocket emit node events npm err at emiterrornt node internal streams destroy npm err at emiterrorclosent node internal streams destroy npm err at processticksandrejections node internal process task queues npm err fetcherror request to failed reason connect econnrefused npm err at clientrequest c users salva appdata roaming npm node modules npm node modules minipass fetch lib index js npm err at clientrequest emit node events npm err at tlssocket socketerrorlistener node http client npm err at tlssocket emit node events npm err at emiterrornt node internal streams destroy npm err at emiterrorclosent node internal streams destroy npm err at processticksandrejections node internal process task queues npm err code econnrefused npm err errno econnrefused npm err syscall connect npm err address npm err port npm err type system npm err npm err npm err if you are behind a proxy please make sure that the npm err proxy config is set properly see npm help config npm err a complete log of this run can be found in npm err c users salva appdata local npm cache logs debug log expected behavior install succeeds on npm ps c users salva desktop repro foo node version ps c users salva desktop repro foo npm version ps c users salva desktop repro foo npm list g depth c users salva appdata roaming npm npm ps c users salva desktop repro foo npm install npm notice created a lockfile as package lock json you should commit this file npm warn foo no description npm warn foo no repository field npm warn foo no license field added packages from contributors and audited packages in package is looking for funding run npm fund for details found vulnerabilities ps c users salva desktop repro foo npm pack npm notice npm notice package foo npm notice tarball contents npm notice package json npm notice bar tgz npm notice bundled dependencies npm notice tmp npm notice bar npm notice tarball details npm notice name foo npm notice version npm notice filename foo tgz npm notice package size kb npm notice unpacked size kb npm notice shasum npm notice integrity npm notice bundled deps npm notice bundled files npm notice own files npm notice total files npm notice foo tgz ps c users salva desktop repro foo npm install g registry foo tgz foo added packages from contributors in steps to reproduce download extract foo zip cd foo npm install npm pack npm install g registry foo tgz observe error after timeout when npm attempts to fetch indirect dependency rimraf from the dummy registry environment os windows build node npm | 1 |
343,594 | 30,675,140,353 | IssuesEvent | 2023-07-26 04:11:42 | snack-exercise/snack-exercise-server | https://api.github.com/repos/snack-exercise/snack-exercise-server | closed | [Test] Repository, Service 계층 단위 테스트 코드 작성 | ✅ Test 🔮 진서 🔮 | ## 💡 이슈 내용
- Member, JoinList, Exgroup, Mission Repository 계층 단위 테스트 작성
- Exgroup Service 계층 테스트 코드 작성
## Repository Test
- Service와의 결합을 끊고 Repository의 기능만 테스트하기 위해 @DataJpaTest 사용
### DataJpaTest
- JPA 관련된 설정만 로드한다. (WebMVC와 관련된 Bean이나 기능은 로드되지 않는다)
- JPA를 사용해서 CRUD 테스트 가능
- @Transactional을 기본적으로 내장하고 있으므로, 매 테스트 코드가 종료되면 자동으로 DB가 롤백된다.
- 기본적으로 내장 DB를 사용하는데, 설정을 통해 실제 DB로 테스트도 가능하다.
- @Entity가 선언된 클래스를 스캔하여 저장소를 구성한다.
## ServiceTest
- Controller와의 연결을 끊으려면 Web에 대한 의존성을 받으면 안된다. (@WebMvcTest, @SpringBootTest 사용 X)
- Repository와의 연결을 끊기 위해 (실제로 DB에 저장하지 않으면서 도메인의 비즈니스 로직은 수행) Repository Bean에 의존하면 안된다.
- 따라서 Repository 객체는 Mocking 사용
| 1.0 | [Test] Repository, Service 계층 단위 테스트 코드 작성 - ## 💡 이슈 내용
- Member, JoinList, Exgroup, Mission Repository 계층 단위 테스트 작성
- Exgroup Service 계층 테스트 코드 작성
## Repository Test
- Service와의 결합을 끊고 Repository의 기능만 테스트하기 위해 @DataJpaTest 사용
### DataJpaTest
- JPA 관련된 설정만 로드한다. (WebMVC와 관련된 Bean이나 기능은 로드되지 않는다)
- JPA를 사용해서 CRUD 테스트 가능
- @Transactional을 기본적으로 내장하고 있으므로, 매 테스트 코드가 종료되면 자동으로 DB가 롤백된다.
- 기본적으로 내장 DB를 사용하는데, 설정을 통해 실제 DB로 테스트도 가능하다.
- @Entity가 선언된 클래스를 스캔하여 저장소를 구성한다.
## ServiceTest
- Controller와의 연결을 끊으려면 Web에 대한 의존성을 받으면 안된다. (@WebMvcTest, @SpringBootTest 사용 X)
- Repository와의 연결을 끊기 위해 (실제로 DB에 저장하지 않으면서 도메인의 비즈니스 로직은 수행) Repository Bean에 의존하면 안된다.
- 따라서 Repository 객체는 Mocking 사용
| non_priority | repository service 계층 단위 테스트 코드 작성 💡 이슈 내용 member joinlist exgroup mission repository 계층 단위 테스트 작성 exgroup service 계층 테스트 코드 작성 repository test service와의 결합을 끊고 repository의 기능만 테스트하기 위해 datajpatest 사용 datajpatest jpa 관련된 설정만 로드한다 webmvc와 관련된 bean이나 기능은 로드되지 않는다 jpa를 사용해서 crud 테스트 가능 transactional을 기본적으로 내장하고 있으므로 매 테스트 코드가 종료되면 자동으로 db가 롤백된다 기본적으로 내장 db를 사용하는데 설정을 통해 실제 db로 테스트도 가능하다 entity가 선언된 클래스를 스캔하여 저장소를 구성한다 servicetest controller와의 연결을 끊으려면 web에 대한 의존성을 받으면 안된다 webmvctest springboottest 사용 x repository와의 연결을 끊기 위해 실제로 db에 저장하지 않으면서 도메인의 비즈니스 로직은 수행 repository bean에 의존하면 안된다 따라서 repository 객체는 mocking 사용 | 0 |
265,900 | 8,360,206,538 | IssuesEvent | 2018-10-03 10:44:59 | metasfresh/metasfresh-webui-frontend | https://api.github.com/repos/metasfresh/metasfresh-webui-frontend | opened | QR code support | priority:high | ### Is this a bug or feature request?
FR
### What is the current behavior?
QR code is not supported
#### Which are the steps to reproduce?
e.g.
* open Manufacturing Orders view: https://w101.metasfresh.com:8443/window/53009
* click on Issue/Receipt (barcode) action
* try to scan an QR code => it shall be recognized. NOTE: i don't care if that order# does exist.
### What is the expected or desired behavior?
The barcode reading functionality shall seamless support regular 1D barcodes (EAN etc) and QR codes too.
| 1.0 | QR code support - ### Is this a bug or feature request?
FR
### What is the current behavior?
QR code is not supported
#### Which are the steps to reproduce?
e.g.
* open Manufacturing Orders view: https://w101.metasfresh.com:8443/window/53009
* click on Issue/Receipt (barcode) action
* try to scan an QR code => it shall be recognized. NOTE: i don't care if that order# does exist.
### What is the expected or desired behavior?
The barcode reading functionality shall seamless support regular 1D barcodes (EAN etc) and QR codes too.
| priority | qr code support is this a bug or feature request fr what is the current behavior qr code is not supported which are the steps to reproduce e g open manufacturing orders view click on issue receipt barcode action try to scan an qr code it shall be recognized note i don t care if that order does exist what is the expected or desired behavior the barcode reading functionality shall seamless support regular barcodes ean etc and qr codes too | 1 |
145,946 | 5,584,346,002 | IssuesEvent | 2017-03-29 04:35:36 | dondi/GRNsight | https://api.github.com/repos/dondi/GRNsight | closed | Implement adaptive drafting board resizing algorithm | feature request functionality priority 0 review requested | If the user has selected an adaptive drafting board (Issue #396), an algorithm needs to detect when nodes hit the edge of the drafting board and expand it gradually. | 1.0 | Implement adaptive drafting board resizing algorithm - If the user has selected an adaptive drafting board (Issue #396), an algorithm needs to detect when nodes hit the edge of the drafting board and expand it gradually. | priority | implement adaptive drafting board resizing algorithm if the user has selected an adaptive drafting board issue an algorithm needs to detect when nodes hit the edge of the drafting board and expand it gradually | 1 |
41,229 | 2,868,987,376 | IssuesEvent | 2015-06-05 22:23:50 | dart-lang/pub | https://api.github.com/repos/dart-lang/pub | closed | Pub Serve not noticing file changes from editors in 'safe write' mode (e.g., IntelliJ) on OSX | bug Fixed Priority-High Pub-Serve | <a href="https://github.com/pq"><img src="https://avatars.githubusercontent.com/u/67586?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [pq](https://github.com/pq)**
_Originally opened as dart-lang/sdk#21402_
----
Pub serve does not appear to play nice with editors (specifically IntelliJ/IDEA) on OS X that use a 'safe write' mode (e.g., new file content is first saved to a temporary file, then the original file is deleted after which the temporary file is renamed to the original file name).
We were able to reproduce with InitelliJ on OSX using the Finance_Dart sample like so:
\* Open Finance_Dart/client/web/app.html in browser (Chrome or Dartium or ...). Wait for page load.
\* Modify Finance_Dart.client/web/app/view/item_list/day_purchases_list.html. For example, change
border-bottom: 1px dashed;
to:
border-bottom: 1px dashed red;
\* Refresh browser and you won't see dashed line color change. :( Only restarting pub serve will do it.
NOTE: this issue does NOT affect Dart Editor as it triggers explicit reloads itself on text editor pane content changes.
It would be super awesome if we could get this looked at for 1.8. :) | 1.0 | Pub Serve not noticing file changes from editors in 'safe write' mode (e.g., IntelliJ) on OSX - <a href="https://github.com/pq"><img src="https://avatars.githubusercontent.com/u/67586?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [pq](https://github.com/pq)**
_Originally opened as dart-lang/sdk#21402_
----
Pub serve does not appear to play nice with editors (specifically IntelliJ/IDEA) on OS X that use a 'safe write' mode (e.g., new file content is first saved to a temporary file, then the original file is deleted after which the temporary file is renamed to the original file name).
We were able to reproduce with InitelliJ on OSX using the Finance_Dart sample like so:
\* Open Finance_Dart/client/web/app.html in browser (Chrome or Dartium or ...). Wait for page load.
\* Modify Finance_Dart.client/web/app/view/item_list/day_purchases_list.html. For example, change
border-bottom: 1px dashed;
to:
border-bottom: 1px dashed red;
\* Refresh browser and you won't see dashed line color change. :( Only restarting pub serve will do it.
NOTE: this issue does NOT affect Dart Editor as it triggers explicit reloads itself on text editor pane content changes.
It would be super awesome if we could get this looked at for 1.8. :) | priority | pub serve not noticing file changes from editors in safe write mode e g intellij on osx issue by originally opened as dart lang sdk pub serve does not appear to play nice with editors specifically intellij idea on os x that use a safe write mode e g new file content is first saved to a temporary file then the original file is deleted after which the temporary file is renamed to the original file name we were able to reproduce with initellij on osx using the finance dart sample like so nbsp nbsp open finance dart client web app html in browser chrome or dartium or wait for page load nbsp nbsp modify finance dart client web app view item list day purchases list html for example change nbsp nbsp nbsp nbsp nbsp nbsp nbsp border bottom dashed nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp nbsp to nbsp nbsp nbsp nbsp nbsp nbsp nbsp border bottom dashed red nbsp nbsp refresh browser and you won t see dashed line color change only restarting pub serve will do it note this issue does not affect dart editor as it triggers explicit reloads itself on text editor pane content changes it would be super awesome if we could get this looked at for | 1 |
350,183 | 24,972,006,903 | IssuesEvent | 2022-11-02 02:39:31 | kevinren1108/Apollo-Capstone-Project | https://api.github.com/repos/kevinren1108/Apollo-Capstone-Project | opened | Project Scope | documentation | Stakeholders will need to know the scope of this project.
- [ ] Stakeholders need to know the general goals for the project.
- [ ] Stakeholders need to know the business opportunity for the project.
- [ ] Stakeholders need to know the project's objectives and some acceptance criteria. | 1.0 | Project Scope - Stakeholders will need to know the scope of this project.
- [ ] Stakeholders need to know the general goals for the project.
- [ ] Stakeholders need to know the business opportunity for the project.
- [ ] Stakeholders need to know the project's objectives and some acceptance criteria. | non_priority | project scope stakeholders will need to know the scope of this project stakeholders need to know the general goals for the project stakeholders need to know the business opportunity for the project stakeholders need to know the project s objectives and some acceptance criteria | 0 |
129,300 | 27,439,455,296 | IssuesEvent | 2023-03-02 09:58:50 | microsoft/AL | https://api.github.com/repos/microsoft/AL | closed | Warn on FlowFilter as Column in Query Object | static-code-analysis requires-triage | <!--
Read the contributing https://github.com/microsoft/AL/blob/master/CONTRIBUTING.md guide before proceeding
Please follow this template in order for our developers to investigate your issue efficiently.
Do not edit or remove the titles; e.g. "Describe the bug".
Use the latest version of the AL language extension from the [Visual Studio Code Marketplace](https://marketplace.visualstudio.com/items?itemName=ms-dynamics-smb.al) or shipped as part of the [AL Developer Preview builds](README.md#al-developer-preview-builds) for Dynamics 365 Business Central.
Disable all extensions except the AL Language extension.
-->
Please include the following with each issue:
**1. Describe the bug**
When you use a FlowFilter as Column in a Query the Query Object cannot be used.
**2. To Reproduce**
Add any FlowFilter field to a query object
``` AL
query 50000 MyQuery
{
QueryType = Normal;
elements
{
dataitem(Customer;Customer)
{
column(No_;"No.")
{
}
filter(Date_Filter;"Date Filter")
{
}
}
}
}
```
**3. Expected behavior**
The compiler should at least warn on a FlowFilter field in the query column. Better would be an error.
**4. Actual behavior**
No warning or error. A runtime Error occurs at executing the query.
**5. Versions:**
- AL Language: v10.2.719883
- Visual Studio Code: 1.74.2
- Business Central: AT Business Central 21.2 (Platform 21.0.49939.51260 + Application 21.2.49946.49990)
- List of Visual Studio Code extensions that you have installed:
| 1.0 | Warn on FlowFilter as Column in Query Object - <!--
Read the contributing https://github.com/microsoft/AL/blob/master/CONTRIBUTING.md guide before proceeding
Please follow this template in order for our developers to investigate your issue efficiently.
Do not edit or remove the titles; e.g. "Describe the bug".
Use the latest version of the AL language extension from the [Visual Studio Code Marketplace](https://marketplace.visualstudio.com/items?itemName=ms-dynamics-smb.al) or shipped as part of the [AL Developer Preview builds](README.md#al-developer-preview-builds) for Dynamics 365 Business Central.
Disable all extensions except the AL Language extension.
-->
Please include the following with each issue:
**1. Describe the bug**
When you use a FlowFilter as Column in a Query the Query Object cannot be used.
**2. To Reproduce**
Add any FlowFilter field to a query object
``` AL
query 50000 MyQuery
{
QueryType = Normal;
elements
{
dataitem(Customer;Customer)
{
column(No_;"No.")
{
}
filter(Date_Filter;"Date Filter")
{
}
}
}
}
```
**3. Expected behavior**
The compiler should at least warn on a FlowFilter field in the query column. Better would be an error.
**4. Actual behavior**
No warning or error. A runtime Error occurs at executing the query.
**5. Versions:**
- AL Language: v10.2.719883
- Visual Studio Code: 1.74.2
- Business Central: AT Business Central 21.2 (Platform 21.0.49939.51260 + Application 21.2.49946.49990)
- List of Visual Studio Code extensions that you have installed:
| non_priority | warn on flowfilter as column in query object read the contributing guide before proceeding please follow this template in order for our developers to investigate your issue efficiently do not edit or remove the titles e g describe the bug use the latest version of the al language extension from the or shipped as part of the readme md al developer preview builds for dynamics business central disable all extensions except the al language extension please include the following with each issue describe the bug when you use a flowfilter as column in a query the query object cannot be used to reproduce add any flowfilter field to a query object al query myquery querytype normal elements dataitem customer customer column no no filter date filter date filter expected behavior the compiler should at least warn on a flowfilter field in the query column better would be an error actual behavior no warning or error a runtime error occurs at executing the query versions al language visual studio code business central at business central platform application list of visual studio code extensions that you have installed | 0 |
292,978 | 22,040,916,956 | IssuesEvent | 2022-05-29 10:43:13 | luigiberrettini/NLog.Targets.Syslog | https://api.github.com/repos/luigiberrettini/NLog.Targets.Syslog | closed | Build badges in README are not relevant | documentation | **Describe the problem to solve**
Build badges in README still refer to AppVeyor and TravisCI.
**Describe the improvement proposed**
Remove out-of-date badges and add GitHub badge. | 1.0 | Build badges in README are not relevant - **Describe the problem to solve**
Build badges in README still refer to AppVeyor and TravisCI.
**Describe the improvement proposed**
Remove out-of-date badges and add GitHub badge. | non_priority | build badges in readme are not relevant describe the problem to solve build badges in readme still refer to appveyor and travisci describe the improvement proposed remove out of date badges and add github badge | 0 |
158,420 | 6,026,974,509 | IssuesEvent | 2017-06-08 12:45:40 | OperationCode/operationcode_frontend | https://api.github.com/repos/OperationCode/operationcode_frontend | closed | Add Hacker Rank Logo to Partners | Priority: Medium Status: In Progress | <!-- Please fill out one of the sections below based on the type of issue you're creating -->
# Feature
## Why is this feature being added?
<!-- What problem is it solving? What value does it add? -->
We're partnering with hacker rank and can now add their logo to our page
## What should your feature do?
Add the attached logo to our partners section

| 1.0 | Add Hacker Rank Logo to Partners - <!-- Please fill out one of the sections below based on the type of issue you're creating -->
# Feature
## Why is this feature being added?
<!-- What problem is it solving? What value does it add? -->
We're partnering with hacker rank and can now add their logo to our page
## What should your feature do?
Add the attached logo to our partners section

| priority | add hacker rank logo to partners feature why is this feature being added we re partnering with hacker rank and can now add their logo to our page what should your feature do add the attached logo to our partners section | 1 |
302,203 | 26,131,045,147 | IssuesEvent | 2022-12-29 05:00:03 | boostup-project/boostup-project | https://api.github.com/repos/boostup-project/boostup-project | opened | [BE] 리뷰 컨트롤러 테스트 - 1 | BE조경민 ✅ Test | ## 📝 Github Issue
리뷰 컨트롤러 테스트
## 💫 Branch
feat/이슈요약#[이슈번호]
> ex) feat/member#0
## ✔️ Check List
> 이슈 체크리스트
- [ ] BookmarkCreateTest
- [ ] BookmarkDeleteTest
- [ ] BookmarkGetTest
- [ ] MyPageBookmarkGetTest
| 1.0 | [BE] 리뷰 컨트롤러 테스트 - 1 - ## 📝 Github Issue
리뷰 컨트롤러 테스트
## 💫 Branch
feat/이슈요약#[이슈번호]
> ex) feat/member#0
## ✔️ Check List
> 이슈 체크리스트
- [ ] BookmarkCreateTest
- [ ] BookmarkDeleteTest
- [ ] BookmarkGetTest
- [ ] MyPageBookmarkGetTest
| non_priority | 리뷰 컨트롤러 테스트 📝 github issue 리뷰 컨트롤러 테스트 💫 branch feat 이슈요약 ex feat member ✔️ check list 이슈 체크리스트 bookmarkcreatetest bookmarkdeletetest bookmarkgettest mypagebookmarkgettest | 0 |
41,079 | 2,868,971,764 | IssuesEvent | 2015-06-05 22:17:36 | dart-lang/pub | https://api.github.com/repos/dart-lang/pub | closed | Pub serve exits if an error occurs in a transformer during startup | bug Fixed Priority-Medium Pub-Serve | <a href="https://github.com/munificent"><img src="https://avatars.githubusercontent.com/u/46275?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [munificent](https://github.com/munificent)**
_Originally opened as dart-lang/sdk#17415_
----
Once pub serve is up and running, we catch errors from transformers and keep going.
But, while pub serve is being started up, if a transformer emits an error, we exit. This is deliberate so that if an error occurs while loading the transformer itself, we don't continue to run pub serve with a broken or missing transformer.
The problem is that most errors coming from transformers while pub serve is starting up don't actually effect the transformers being loaded. For example, the "rewrite imports" transformer parses all .dart files and emits an error if the file has a syntax error. That means you can't run pub serve if any .dart file in your application -- even ones not imported by any transformers -- have syntax errors.
We should loosen this so that those errors are reported but don't take down the system. | 1.0 | Pub serve exits if an error occurs in a transformer during startup - <a href="https://github.com/munificent"><img src="https://avatars.githubusercontent.com/u/46275?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [munificent](https://github.com/munificent)**
_Originally opened as dart-lang/sdk#17415_
----
Once pub serve is up and running, we catch errors from transformers and keep going.
But, while pub serve is being started up, if a transformer emits an error, we exit. This is deliberate so that if an error occurs while loading the transformer itself, we don't continue to run pub serve with a broken or missing transformer.
The problem is that most errors coming from transformers while pub serve is starting up don't actually effect the transformers being loaded. For example, the "rewrite imports" transformer parses all .dart files and emits an error if the file has a syntax error. That means you can't run pub serve if any .dart file in your application -- even ones not imported by any transformers -- have syntax errors.
We should loosen this so that those errors are reported but don't take down the system. | priority | pub serve exits if an error occurs in a transformer during startup issue by originally opened as dart lang sdk once pub serve is up and running we catch errors from transformers and keep going but while pub serve is being started up if a transformer emits an error we exit this is deliberate so that if an error occurs while loading the transformer itself we don t continue to run pub serve with a broken or missing transformer the problem is that most errors coming from transformers while pub serve is starting up don t actually effect the transformers being loaded for example the quot rewrite imports quot transformer parses all dart files and emits an error if the file has a syntax error that means you can t run pub serve if any dart file in your application even ones not imported by any transformers have syntax errors we should loosen this so that those errors are reported but don t take down the system | 1 |
219,962 | 17,139,199,966 | IssuesEvent | 2021-07-13 07:42:28 | milvus-io/milvus | https://api.github.com/repos/milvus-io/milvus | opened | Support multi clients in test runners | sig/testing | **Please state your issue using the following template and, most importantly, in English.**
Support multi test clients in locust runner, used in load testing.
**What would you like to be added ?**
**Why is this needed ?**
| 1.0 | Support multi clients in test runners - **Please state your issue using the following template and, most importantly, in English.**
Support multi test clients in locust runner, used in load testing.
**What would you like to be added ?**
**Why is this needed ?**
| non_priority | support multi clients in test runners please state your issue using the following template and most importantly in english support multi test clients in locust runner used in load testing what would you like to be added why is this needed | 0 |
180,397 | 13,930,467,542 | IssuesEvent | 2020-10-22 02:31:53 | ota-rider/zohowebhooktest | https://api.github.com/repos/ota-rider/zohowebhooktest | closed | test | test 文賢 | テスト本文テスト本文テスト本文 テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文 | 1.0 | test - テスト本文テスト本文テスト本文 テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文 | non_priority | test テスト本文テスト本文テスト本文 テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文テスト本文 | 0 |
652,801 | 21,562,134,738 | IssuesEvent | 2022-05-01 10:19:03 | PyPSA/pypsa-eur | https://api.github.com/repos/PyPSA/pypsa-eur | closed | Provide `Dockerfile` and docker image for quick start | enhancement low priority | The idea is to provide a `Dockerfile` in the PyPSA-Eur repository for tutorials (and maybe continuous integration) that contains
- the `pypsa-eur` environment provided in `environment.yaml`
- an already extracted data bundle (e.g. minimal data bundle #40)
- an open-source solver or commercial solver (e.g. like Gurobi) without a license
One could then run everything from the docker image without having to install and copy the data bundles.
One can copy results for post-processing to the host with
```shell
docker cp CONTAINER-ID:/docker-container/source-path /host/target-path
```
One can get a list of `CONTAINER-ID`s with `docker ps`.
Copying also works vice-versa (e.g. copying a modified `config.yaml` or a Gurobi license file)
Open questions:
- [x] Can we use a minimal data-bundle docker image and open-source solvers for continuous integration (#40)? This way the image would have a twofold use to us: tutorials and CI. YES
- [x] It probably would not make much sense to provide a docker image with the full data bundle and only an open-source solver. Maybe a complete data-bundle and a Gurobi installation -- where the user has to copy the Gurobi license file if Gurobi is selected -- is a viable way?
- [x] Where to host the docker image? [Docker Hub](https://hub.docker.com/) or own public repository? | 1.0 | Provide `Dockerfile` and docker image for quick start - The idea is to provide a `Dockerfile` in the PyPSA-Eur repository for tutorials (and maybe continuous integration) that contains
- the `pypsa-eur` environment provided in `environment.yaml`
- an already extracted data bundle (e.g. minimal data bundle #40)
- an open-source solver or commercial solver (e.g. like Gurobi) without a license
One could then run everything from the docker image without having to install and copy the data bundles.
One can copy results for post-processing to the host with
```shell
docker cp CONTAINER-ID:/docker-container/source-path /host/target-path
```
One can get a list of `CONTAINER-ID`s with `docker ps`.
Copying also works vice-versa (e.g. copying a modified `config.yaml` or a Gurobi license file)
Open questions:
- [x] Can we use a minimal data-bundle docker image and open-source solvers for continuous integration (#40)? This way the image would have a twofold use to us: tutorials and CI. YES
- [x] It probably would not make much sense to provide a docker image with the full data bundle and only an open-source solver. Maybe a complete data-bundle and a Gurobi installation -- where the user has to copy the Gurobi license file if Gurobi is selected -- is a viable way?
- [x] Where to host the docker image? [Docker Hub](https://hub.docker.com/) or own public repository? | priority | provide dockerfile and docker image for quick start the idea is to provide a dockerfile in the pypsa eur repository for tutorials and maybe continuous integration that contains the pypsa eur environment provided in environment yaml an already extracted data bundle e g minimal data bundle an open source solver or commercial solver e g like gurobi without a license one could then run everything from the docker image without having to install and copy the data bundles one can copy results for post processing to the host with shell docker cp container id docker container source path host target path one can get a list of container id s with docker ps copying also works vice versa e g copying a modified config yaml or a gurobi license file open questions can we use a minimal data bundle docker image and open source solvers for continuous integration this way the image would have a twofold use to us tutorials and ci yes it probably would not make much sense to provide a docker image with the full data bundle and only an open source solver maybe a complete data bundle and a gurobi installation where the user has to copy the gurobi license file if gurobi is selected is a viable way where to host the docker image or own public repository | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.