Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
31,649 | 2,735,073,186 | IssuesEvent | 2015-04-18 02:07:25 | GoogleCloudPlatform/kubernetes | https://api.github.com/repos/GoogleCloudPlatform/kubernetes | closed | the container data lost when restart k8s cluster env | priority/support | hi,
I meet some questions when use kubernetes cluster, please kindly help me if you know the reason.
1.The pod container's data lost when restart k8s cluster, I find replicatorController will create a new pod other than restart the pod container when start the cluster. I set the "restartPolicy" for replicatorControll... | 1.0 | the container data lost when restart k8s cluster env - hi,
I meet some questions when use kubernetes cluster, please kindly help me if you know the reason.
1.The pod container's data lost when restart k8s cluster, I find replicatorController will create a new pod other than restart the pod container when start the cl... | priority | the container data lost when restart cluster env hi i meet some questions when use kubernetes cluster please kindly help me if you know the reason the pod container s data lost when restart cluster i find replicatorcontroller will create a new pod other than restart the pod container when start the cluste... | 1 |
486,334 | 14,007,624,179 | IssuesEvent | 2020-10-28 21:55:11 | salesagility/SuiteCRM | https://api.github.com/repos/salesagility/SuiteCRM | closed | Cannot fully remove Module Loader package when custom fields are defined. | Area: Module Priority:Important Status:Fix Proposed Type:Bug | A change introduced in e808d92a5de24f3f51f8272c0504959039fd9677 [changed](https://github.com/salesagility/SuiteCRM/commit/e808d92a5de24f3f51f8272c0504959039fd9677#diff-b0a5d2e2814371306c2fac0d6282c675L1303) the way `uninstall_custom_fields()` invokes the `DynamicField` class was used. This change attempts to replace di... | 1.0 | Cannot fully remove Module Loader package when custom fields are defined. - A change introduced in e808d92a5de24f3f51f8272c0504959039fd9677 [changed](https://github.com/salesagility/SuiteCRM/commit/e808d92a5de24f3f51f8272c0504959039fd9677#diff-b0a5d2e2814371306c2fac0d6282c675L1303) the way `uninstall_custom_fields()` i... | priority | cannot fully remove module loader package when custom fields are defined a change introduced in the way uninstall custom fields invokes the dynamicfield class was used this change attempts to replace direct invocation of bean defined classes to use the cache enabled optimized beanfactory newbean ... | 1 |
539,490 | 15,789,676,642 | IssuesEvent | 2021-04-01 23:21:41 | dtcenter/METviewer | https://api.github.com/repos/dtcenter/METviewer | closed | Using Github actions to build documentation | priority: low type: new feature | *Replace italics below with details for this issue.*
## Describe the New Feature ##
*Provide a description of the new feature request here.*
### Acceptance Testing ###
*List input data types and sources.*
*Describe tests required for new functionality.*
### Time Estimate ###
*Estimate the amount of work re... | 1.0 | Using Github actions to build documentation - *Replace italics below with details for this issue.*
## Describe the New Feature ##
*Provide a description of the new feature request here.*
### Acceptance Testing ###
*List input data types and sources.*
*Describe tests required for new functionality.*
### Time... | priority | using github actions to build documentation replace italics below with details for this issue describe the new feature provide a description of the new feature request here acceptance testing list input data types and sources describe tests required for new functionality time... | 1 |
34,229 | 4,535,927,580 | IssuesEvent | 2016-09-08 18:49:45 | Tiendil/the-tale | https://api.github.com/repos/Tiendil/the-tale | closed | Мастера: добалансировать максимальное влияние на экономику | comp_game_logic cont_game_designe est_medium type_improvement | - учесть, что стабильность может снять только часть других параметров
- слишком сильно изменяется свобода и транспорт | 1.0 | Мастера: добалансировать максимальное влияние на экономику - - учесть, что стабильность может снять только часть других параметров
- слишком сильно изменяется свобода и транспорт | non_priority | мастера добалансировать максимальное влияние на экономику учесть что стабильность может снять только часть других параметров слишком сильно изменяется свобода и транспорт | 0 |
91,411 | 18,466,444,484 | IssuesEvent | 2021-10-17 00:39:46 | google/iree | https://api.github.com/repos/google/iree | opened | FlattenMemRefSubspanPass failing with rank-0 memrefs. | codegen | FoldSubspanOffsetIntoLoadStore currently expects that all loaded values are rank >1 - I'm hitting a case where this crashes with a null deref: https://github.com/google/iree/blob/e34c95d5db7a1fcb32a45fb72b31da2a9613166e/iree/compiler/Codegen/Common/FlattenMemRefSubspanPass.cpp#L514 because op.indices() is empty (on the... | 1.0 | FlattenMemRefSubspanPass failing with rank-0 memrefs. - FoldSubspanOffsetIntoLoadStore currently expects that all loaded values are rank >1 - I'm hitting a case where this crashes with a null deref: https://github.com/google/iree/blob/e34c95d5db7a1fcb32a45fb72b31da2a9613166e/iree/compiler/Codegen/Common/FlattenMemRefSu... | non_priority | flattenmemrefsubspanpass failing with rank memrefs foldsubspanoffsetintoloadstore currently expects that all loaded values are rank i m hitting a case where this crashes with a null deref because op indices is empty on the first memref store mlir module func main dispatch ... | 0 |
91,453 | 15,856,411,233 | IssuesEvent | 2021-04-08 02:16:47 | Sophobis76/angloAmerican | https://api.github.com/repos/Sophobis76/angloAmerican | opened | CVE-2020-8124 (Medium) detected in url-parse-1.4.4.tgz | security vulnerability | ## CVE-2020-8124 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.4.tgz</b></p></summary>
<p>Small footprint URL parser that works seamlessly across Node.js and browser ... | True | CVE-2020-8124 (Medium) detected in url-parse-1.4.4.tgz - ## CVE-2020-8124 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>url-parse-1.4.4.tgz</b></p></summary>
<p>Small footprint URL... | non_priority | cve medium detected in url parse tgz cve medium severity vulnerability vulnerable library url parse tgz small footprint url parser that works seamlessly across node js and browser environments library home page a href path to dependency file angloamerican package json ... | 0 |
58,005 | 14,263,204,880 | IssuesEvent | 2020-11-20 14:07:26 | slic3r/Slic3r | https://api.github.com/repos/slic3r/Slic3r | closed | Restart required when "Send to printer" fails due to slicing | Can't Reproduce - Development Build Host/Controller | ### Version
Version 1.3.0-dev
Slic3r-master.2017.08.14.1313.a54ca92.64bit
### Operating system type + version
Windows 10 64-bit
### Behavior
* "Send to printer" and "Export G-Code" buttons do not re-activate if slicing fails when "Send to printer" is clicked. To reproduce, load a model that fails to slice. F... | 1.0 | Restart required when "Send to printer" fails due to slicing - ### Version
Version 1.3.0-dev
Slic3r-master.2017.08.14.1313.a54ca92.64bit
### Operating system type + version
Windows 10 64-bit
### Behavior
* "Send to printer" and "Export G-Code" buttons do not re-activate if slicing fails when "Send to printer"... | non_priority | restart required when send to printer fails due to slicing version version dev master operating system type version windows bit behavior send to printer and export g code buttons do not re activate if slicing fails when send to printer is clicked to reproduc... | 0 |
320,425 | 9,780,821,667 | IssuesEvent | 2019-06-07 18:00:28 | thonny/thonny | https://api.github.com/repos/thonny/thonny | closed | Pasting doesn't replace active selection in XFCE | bug low priority | **[Original report](https://bitbucket.org/bitbucket-issue-migration\thonny-issues.zip/issue/395) by me.**
----------------------------------------
| 1.0 | Pasting doesn't replace active selection in XFCE - **[Original report](https://bitbucket.org/bitbucket-issue-migration\thonny-issues.zip/issue/395) by me.**
----------------------------------------
| priority | pasting doesn t replace active selection in xfce by me | 1 |
191,155 | 14,593,420,458 | IssuesEvent | 2020-12-19 22:43:31 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | alexcrownus/fabcar: vendor/github.com/google/certificate-transparency-go/fixchain/fixer_test.go; 27 LoC | fresh small test vendored |
Found a possible issue in [alexcrownus/fabcar](https://www.github.com/alexcrownus/fabcar) at [vendor/github.com/google/certificate-transparency-go/fixchain/fixer_test.go](https://github.com/alexcrownus/fabcar/blob/8d90c87788a72b2a497f2df6f651543827aaf69b/vendor/github.com/google/certificate-transparency-go/fixchain/fi... | 1.0 | alexcrownus/fabcar: vendor/github.com/google/certificate-transparency-go/fixchain/fixer_test.go; 27 LoC -
Found a possible issue in [alexcrownus/fabcar](https://www.github.com/alexcrownus/fabcar) at [vendor/github.com/google/certificate-transparency-go/fixchain/fixer_test.go](https://github.com/alexcrownus/fabcar/blob... | non_priority | alexcrownus fabcar vendor github com google certificate transparency go fixchain fixer test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideratio... | 0 |
6,509 | 3,399,136,031 | IssuesEvent | 2015-12-02 09:23:38 | hjwylde/omnifmt | https://api.github.com/repos/hjwylde/omnifmt | closed | Make the path outputs relative to the root directory | existing: enhancement kind: code | The root directory is the one that contains the '.omnifmt.yaml' file. | 1.0 | Make the path outputs relative to the root directory - The root directory is the one that contains the '.omnifmt.yaml' file. | non_priority | make the path outputs relative to the root directory the root directory is the one that contains the omnifmt yaml file | 0 |
81,445 | 23,464,554,435 | IssuesEvent | 2022-08-16 15:37:17 | mercedes-benz/sechub | https://api.github.com/repos/mercedes-benz/sechub | closed | Improve documentation branch - divide images + version locations | documentation enhancement build | ## Situation
Currently we got only one `latest` for all at https://daimler.github.io/sechub/
## Wanted
As a developer I want to update server documentation for a dedicated server without influencing PDS or SecHub client - e.g. when code base for those releases differ.
## Solution
We must differ between
- Se... | 1.0 | Improve documentation branch - divide images + version locations - ## Situation
Currently we got only one `latest` for all at https://daimler.github.io/sechub/
## Wanted
As a developer I want to update server documentation for a dedicated server without influencing PDS or SecHub client - e.g. when code base for th... | non_priority | improve documentation branch divide images version locations situation currently we got only one latest for all at wanted as a developer i want to update server documentation for a dedicated server without influencing pds or sechub client e g when code base for those releases differ solut... | 0 |
698,246 | 23,971,246,391 | IssuesEvent | 2022-09-13 07:57:12 | nelsonic/nelsonic.github.io | https://api.github.com/repos/nelsonic/nelsonic.github.io | opened | Bike Baby Seat | enhancement help wanted question external-dependency technical T25m priority-2 | @SimonLab is this the seat you guys have?
Thule Yepp Mini: https://www.thule.com/en-us/child-bike-seats/front-mounted-child-bike-seats/thule-yepp-mini-_-12020101
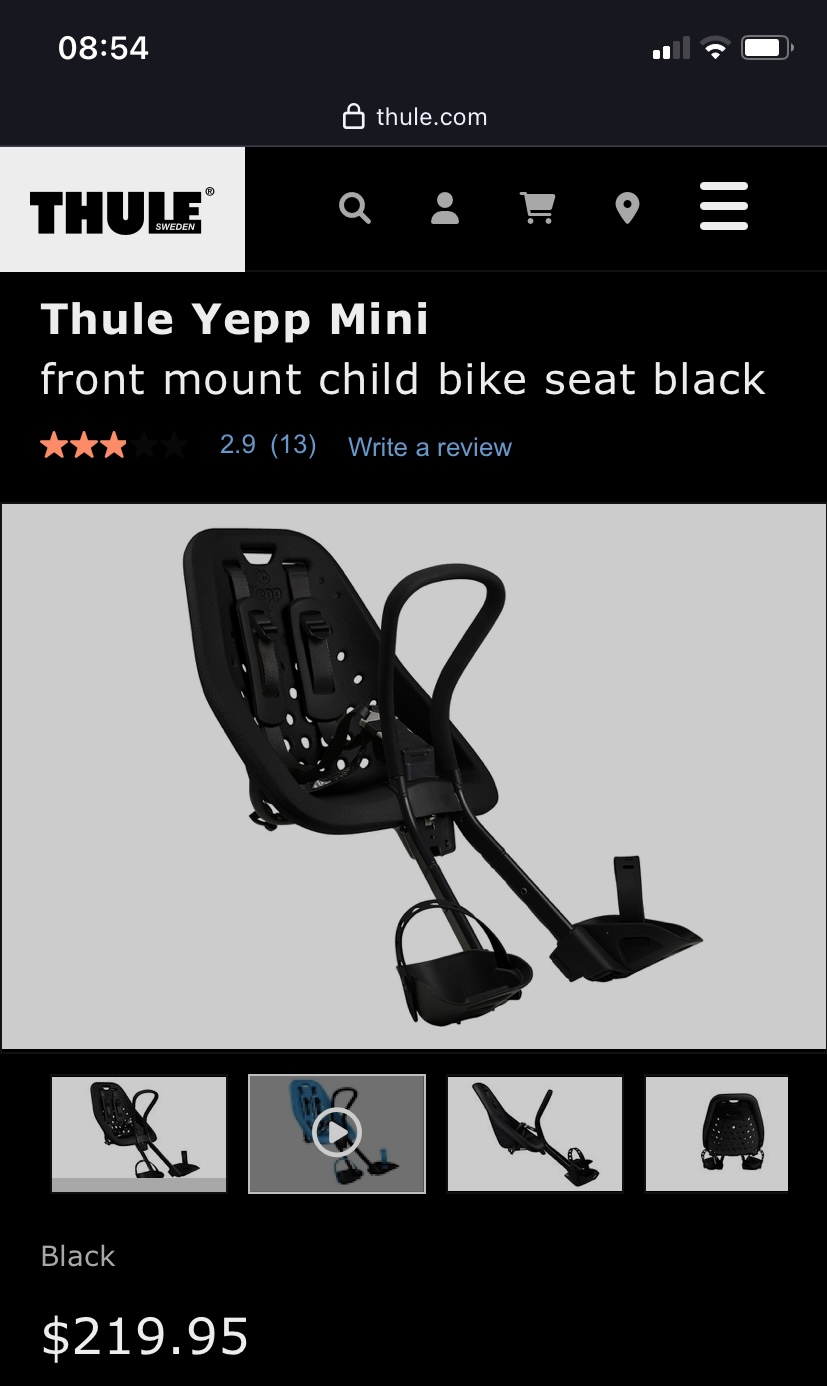
http... | 1.0 | Bike Baby Seat - @SimonLab is this the seat you guys have?
Thule Yepp Mini: https://www.thule.com/en-us/child-bike-seats/front-mounted-child-bike-seats/thule-yepp-mini-_-12020101
 detected in hibernate-validator-5.3.4.Final.jar - autoclosed | security vulnerability | ## CVE-2020-10693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hibernate-validator-5.3.4.Final.jar</b></p></summary>
<p>Hibernate's Bean Validation (JSR-303) reference implementat... | True | CVE-2020-10693 (Medium) detected in hibernate-validator-5.3.4.Final.jar - autoclosed - ## CVE-2020-10693 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>hibernate-validator-5.3.4.Fina... | non_priority | cve medium detected in hibernate validator final jar autoclosed cve medium severity vulnerability vulnerable library hibernate validator final jar hibernate s bean validation jsr reference implementation library home page a href path to dependency file resiliency... | 0 |
511,994 | 14,886,702,875 | IssuesEvent | 2021-01-20 17:17:33 | dermestid/bold-phylodiv-scripts | https://api.github.com/repos/dermestid/bold-phylodiv-scripts | opened | use pre-generated sample PD for heroku deployment | enhancement lower priority ui | Since getting executables to work on heroku is a pain, skip that step for now and include "demo" data in the app. | 1.0 | use pre-generated sample PD for heroku deployment - Since getting executables to work on heroku is a pain, skip that step for now and include "demo" data in the app. | priority | use pre generated sample pd for heroku deployment since getting executables to work on heroku is a pain skip that step for now and include demo data in the app | 1 |
124,600 | 12,235,238,605 | IssuesEvent | 2020-05-04 14:36:29 | vmware-samples/vcenter-event-broker-appliance | https://api.github.com/repos/vmware-samples/vcenter-event-broker-appliance | closed | Document VEBA deployment to existing K8s Cluster | documentation | We've had a number of requests from both customers/field on being able to deploy VEBA to an existing K8s Cluster and since VEBA itself is a K8s app, this is something that just needs to be done. | 1.0 | Document VEBA deployment to existing K8s Cluster - We've had a number of requests from both customers/field on being able to deploy VEBA to an existing K8s Cluster and since VEBA itself is a K8s app, this is something that just needs to be done. | non_priority | document veba deployment to existing cluster we ve had a number of requests from both customers field on being able to deploy veba to an existing cluster and since veba itself is a app this is something that just needs to be done | 0 |
68,319 | 28,353,801,766 | IssuesEvent | 2023-04-12 05:30:32 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | closed | [QUERY] Distributed tracing Activity scope for batched Service Bus Functions | Service Bus Client customer-reported question issue-addressed | ### Library name and version
Azure.Messaging.ServiceBus 7.13.1
Microsoft.Azure.WebJobs.Extensions.ServiceBus 5.9.0
### Query/Question
There currently exists discrepancies when processing Service Bus messages in either a batched versus singular fashion regarding Activity scoping and how the Functions consider ... | 1.0 | [QUERY] Distributed tracing Activity scope for batched Service Bus Functions - ### Library name and version
Azure.Messaging.ServiceBus 7.13.1
Microsoft.Azure.WebJobs.Extensions.ServiceBus 5.9.0
### Query/Question
There currently exists discrepancies when processing Service Bus messages in either a batched ver... | non_priority | distributed tracing activity scope for batched service bus functions library name and version azure messaging servicebus microsoft azure webjobs extensions servicebus query question there currently exists discrepancies when processing service bus messages in either a batched versus sin... | 0 |
112,384 | 14,243,852,699 | IssuesEvent | 2020-11-19 05:35:06 | ppy/osu-web | https://api.github.com/repos/ppy/osu-web | closed | Forum reply box on mobile catch-all issue | area:forum platform:mobile type:design type:ux | This is a catch-all summary issue for all the issues with the forum reply box (originally https://github.com/ppy/osu-web/issues/2138#issuecomment-460536581):
Replying while on a mobile device seems pretty broken in general with different combinations of:
- not being able to unpin the reply box because the button do... | 1.0 | Forum reply box on mobile catch-all issue - This is a catch-all summary issue for all the issues with the forum reply box (originally https://github.com/ppy/osu-web/issues/2138#issuecomment-460536581):
Replying while on a mobile device seems pretty broken in general with different combinations of:
- not being able ... | non_priority | forum reply box on mobile catch all issue this is a catch all summary issue for all the issues with the forum reply box originally replying while on a mobile device seems pretty broken in general with different combinations of not being able to unpin the reply box because the button doesn t fit on the scree... | 0 |
224,434 | 17,187,674,888 | IssuesEvent | 2021-07-16 06:10:05 | captaincobbs/ESG-Mod | https://api.github.com/repos/captaincobbs/ESG-Mod | opened | Fix vanilla bug with minor civ ship spawns | bug in testing needs documentation | For certain types and stress levels of minors, the "endless" fleets were weaker than the middle-difficulty fleets; these have been reorganized into the proper order | 1.0 | Fix vanilla bug with minor civ ship spawns - For certain types and stress levels of minors, the "endless" fleets were weaker than the middle-difficulty fleets; these have been reorganized into the proper order | non_priority | fix vanilla bug with minor civ ship spawns for certain types and stress levels of minors the endless fleets were weaker than the middle difficulty fleets these have been reorganized into the proper order | 0 |
400,286 | 11,771,859,598 | IssuesEvent | 2020-03-16 01:46:45 | AY1920S2-CS2103-W14-3/main | https://api.github.com/repos/AY1920S2-CS2103-W14-3/main | closed | As a busy university student I want to be reminded of my friend's birthdays as and when they are approaching | priority.High type.Story | so that I do not need to memorise all my friend's birthdays but will still be able to celebrate it for them. | 1.0 | As a busy university student I want to be reminded of my friend's birthdays as and when they are approaching - so that I do not need to memorise all my friend's birthdays but will still be able to celebrate it for them. | priority | as a busy university student i want to be reminded of my friend s birthdays as and when they are approaching so that i do not need to memorise all my friend s birthdays but will still be able to celebrate it for them | 1 |
437,083 | 12,560,080,620 | IssuesEvent | 2020-06-07 20:58:31 | Tyresius92/le-chat | https://api.github.com/repos/Tyresius92/le-chat | closed | Set up Continuous Integration | Priority: High Status: Ready for Review Type: Enhancement/Feature Type: Maintenance | I've used both CircleCI and TravisCI. I have a slight preference for CircleCI.
I'm going to hold off on setting up the integration for a couple more days, to give folks time to object to using CircleCI if they don't want to use that thing. | 1.0 | Set up Continuous Integration - I've used both CircleCI and TravisCI. I have a slight preference for CircleCI.
I'm going to hold off on setting up the integration for a couple more days, to give folks time to object to using CircleCI if they don't want to use that thing. | priority | set up continuous integration i ve used both circleci and travisci i have a slight preference for circleci i m going to hold off on setting up the integration for a couple more days to give folks time to object to using circleci if they don t want to use that thing | 1 |
491,631 | 14,167,766,050 | IssuesEvent | 2020-11-12 10:44:56 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.bing.com - see bug description | browser-fenix engine-gecko priority-critical | <!-- @browser: Firefox Mobile 83.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:83.0) Gecko/83.0 Firefox/83.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/61577 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://www.bing.com/... | 1.0 | www.bing.com - see bug description - <!-- @browser: Firefox Mobile 83.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:83.0) Gecko/83.0 Firefox/83.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/61577 -->
<!-- @extra_labels: browser-feni... | priority | see bug description url browser version firefox mobile operating system android tested another browser yes opera problem type something else description stutter on scrolling images that open on clicking image in bing steps to reproduce choppy scrolling on ... | 1 |
522,075 | 15,148,372,668 | IssuesEvent | 2021-02-11 10:31:03 | duncanpeacock/fragalysis-backend | https://api.github.com/repos/duncanpeacock/fragalysis-backend | closed | WP1 Hypothesis Capture – Action Capture - Phase 1 delivery | High Priority enhancement | #### Description
Once POC is finalised, revise design / database schema / api calls as necessary to agree first stable production version and revise future roadmap. Implement this version of code / database migrations.
#### Deliverable
Phase 1 Code and database delivery
Parent: (https://github.com/xchem/fr... | 1.0 | WP1 Hypothesis Capture – Action Capture - Phase 1 delivery - #### Description
Once POC is finalised, revise design / database schema / api calls as necessary to agree first stable production version and revise future roadmap. Implement this version of code / database migrations.
#### Deliverable
Phase 1 Code ... | priority | hypothesis capture – action capture phase delivery description once poc is finalised revise design database schema api calls as necessary to agree first stable production version and revise future roadmap implement this version of code database migrations deliverable phase code an... | 1 |
222,142 | 7,428,561,119 | IssuesEvent | 2018-03-24 03:03:14 | TrustWallet/trust-wallet-ios | https://api.github.com/repos/TrustWallet/trust-wallet-ios | closed | DApp bookmarks crashes on master | bug critical priority dapp | The app crashes when trying to open bookmarks. @VKoskiv can you take a look?
<sub>Sent with <a href="http://githawk.com">GitHawk</a></sub> | 1.0 | DApp bookmarks crashes on master - The app crashes when trying to open bookmarks. @VKoskiv can you take a look?
<sub>Sent with <a href="http://githawk.com">GitHawk</a></sub> | priority | dapp bookmarks crashes on master the app crashes when trying to open bookmarks vkoskiv can you take a look sent with a href | 1 |
172,967 | 13,368,910,440 | IssuesEvent | 2020-09-01 08:03:27 | tgstation/tgstation | https://api.github.com/repos/tgstation/tgstation | closed | Using the swap equipment hotkey lets you carry things in suit storage you shouldn't be able to | Bug Tested/Reproduced | ## Round ID:
reproduced on a local on the latest master, but did it in 143425
## Reproduction:
Using the swap equipment hotkey on a suit (harduits, eva suits, labcoats, aprons, etc) doesn't drop the item from suit storage, allowing you to carry things in suit storage you shouldn't be able to
here's a labcoat ... | 1.0 | Using the swap equipment hotkey lets you carry things in suit storage you shouldn't be able to - ## Round ID:
reproduced on a local on the latest master, but did it in 143425
## Reproduction:
Using the swap equipment hotkey on a suit (harduits, eva suits, labcoats, aprons, etc) doesn't drop the item from suit s... | non_priority | using the swap equipment hotkey lets you carry things in suit storage you shouldn t be able to round id reproduced on a local on the latest master but did it in reproduction using the swap equipment hotkey on a suit harduits eva suits labcoats aprons etc doesn t drop the item from suit storag... | 0 |
59,191 | 11,948,446,708 | IssuesEvent | 2020-04-03 11:53:04 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [4.0] restful curl result {"errors":[{"title":"Forbidden"}]} | No Code Attached Yet | ### Steps to reproduce the issue
install joomla 4
enable plugin API Authentication - Basic Auth
and try to get something with curl (https://docs.joomla.org/J4.x:Joomla_Core_APIs)
open msdos
curl -X GET https://{dnsname}/j4/api/index.php/v1/banners --user user_name:password
### Expected result
json with the ... | 1.0 | [4.0] restful curl result {"errors":[{"title":"Forbidden"}]} - ### Steps to reproduce the issue
install joomla 4
enable plugin API Authentication - Basic Auth
and try to get something with curl (https://docs.joomla.org/J4.x:Joomla_Core_APIs)
open msdos
curl -X GET https://{dnsname}/j4/api/index.php/v1/banners -... | non_priority | restful curl result errors steps to reproduce the issue install joomla enable plugin api authentication basic auth and try to get something with curl open msdos curl x get user user name password expected result json with the list of elements banners articles act... | 0 |
257,938 | 27,563,834,811 | IssuesEvent | 2023-03-08 01:09:53 | LynRodWS/alcor | https://api.github.com/repos/LynRodWS/alcor | opened | CVE-2022-3509 (High) detected in protobuf-java-3.8.0.jar | security vulnerability | ## CVE-2022-3509 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>protobuf-java-3.8.0.jar</b></p></summary>
<p>Core Protocol Buffers library. Protocol Buffers are a way of encoding stru... | True | CVE-2022-3509 (High) detected in protobuf-java-3.8.0.jar - ## CVE-2022-3509 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>protobuf-java-3.8.0.jar</b></p></summary>
<p>Core Protocol B... | non_priority | cve high detected in protobuf java jar cve high severity vulnerability vulnerable library protobuf java jar core protocol buffers library protocol buffers are a way of encoding structured data in an efficient yet extensible format library home page a href path to d... | 0 |
373,595 | 11,045,923,931 | IssuesEvent | 2019-12-09 15:57:16 | edvinnn/Green-Power | https://api.github.com/repos/edvinnn/Green-Power | closed | Keep the current prosumer consumption somewhat more constant | Priority medium good first issue | I think that the consumption fluctuates a bit to much right now :) | 1.0 | Keep the current prosumer consumption somewhat more constant - I think that the consumption fluctuates a bit to much right now :) | priority | keep the current prosumer consumption somewhat more constant i think that the consumption fluctuates a bit to much right now | 1 |
380,791 | 11,271,019,951 | IssuesEvent | 2020-01-14 12:09:26 | googleapis/nodejs-containeranalysis | https://api.github.com/repos/googleapis/nodejs-containeranalysis | opened | Synthesis failed for nodejs-containeranalysis | autosynth failure priority: p1 type: bug | Hello! Autosynth couldn't regenerate nodejs-containeranalysis. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth'
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib/python3.6/runpy.py", line 193, in _run_module_a... | 1.0 | Synthesis failed for nodejs-containeranalysis - Hello! Autosynth couldn't regenerate nodejs-containeranalysis. :broken_heart:
Here's the output from running `synth.py`:
```
Cloning into 'working_repo'...
Switched to branch 'autosynth'
Traceback (most recent call last):
File "/home/kbuilder/.pyenv/versions/3.6.1/lib... | priority | synthesis failed for nodejs containeranalysis hello autosynth couldn t regenerate nodejs containeranalysis broken heart here s the output from running synth py cloning into working repo switched to branch autosynth traceback most recent call last file home kbuilder pyenv versions lib... | 1 |
107,532 | 4,310,159,351 | IssuesEvent | 2016-07-21 18:18:09 | dhowe/AdNauseam | https://api.github.com/repos/dhowe/AdNauseam | closed | Bug in CSS on homepage (gh-pages) | Bug PRIORITY: High | see commit cf90c3e0ff8cc368c96
also, see #291
<img width="632" alt="screen shot 2016-07-19 at 12 37 47 pm" src="https://cloud.githubusercontent.com/assets/737638/16959124/765ad5a4-4db1-11e6-8241-2f21c3609c66.png">
| 1.0 | Bug in CSS on homepage (gh-pages) - see commit cf90c3e0ff8cc368c96
also, see #291
<img width="632" alt="screen shot 2016-07-19 at 12 37 47 pm" src="https://cloud.githubusercontent.com/assets/737638/16959124/765ad5a4-4db1-11e6-8241-2f21c3609c66.png">
| priority | bug in css on homepage gh pages see commit also see img width alt screen shot at pm src | 1 |
45,852 | 9,819,400,210 | IssuesEvent | 2019-06-13 21:54:02 | certbot/certbot | https://api.github.com/repos/certbot/certbot | closed | Dedupe the Apache and Nginx plugins | area: code health area: refactoring needs-update | The Nginx plugin was modeled very closely after the Apache plugin. Recently our linter started complaining about duplicated code and we fixed it with a hack (see #3881). We should actually fix this.
How best to do this depends a lot on what's actually duplicated and I haven't looked into it closely. One potential op... | 1.0 | Dedupe the Apache and Nginx plugins - The Nginx plugin was modeled very closely after the Apache plugin. Recently our linter started complaining about duplicated code and we fixed it with a hack (see #3881). We should actually fix this.
How best to do this depends a lot on what's actually duplicated and I haven't lo... | non_priority | dedupe the apache and nginx plugins the nginx plugin was modeled very closely after the apache plugin recently our linter started complaining about duplicated code and we fixed it with a hack see we should actually fix this how best to do this depends a lot on what s actually duplicated and i haven t looke... | 0 |
44,397 | 2,904,557,884 | IssuesEvent | 2015-06-18 18:47:58 | openshift/origin | https://api.github.com/repos/openshift/origin | closed | "osc get all" doesn't prefix elements | area/usability component/cli priority/P3 | ```
[joe@ose3-master beta4]$ osc get all
NAME TYPE SOURCE
NAME TYPE STATUS POD
NAME DOCKER REPO TAGS UPDATED
NAME TRIGGERS LATEST VERSION
CONTROLLER CONTAINER(S) IMAGE(S) SELECTOR REPLICAS
NAME HOST/PORT PATH ... | 1.0 | "osc get all" doesn't prefix elements - ```
[joe@ose3-master beta4]$ osc get all
NAME TYPE SOURCE
NAME TYPE STATUS POD
NAME DOCKER REPO TAGS UPDATED
NAME TRIGGERS LATEST VERSION
CONTROLLER CONTAINER(S) IMAGE(S) SELECTOR REPLICAS
NAME HOST/PORT ... | priority | osc get all doesn t prefix elements osc get all name type source name type status pod name docker repo tags updated name triggers latest version controller container s image s selector replicas name host port ... | 1 |
776,660 | 27,264,532,694 | IssuesEvent | 2023-02-22 17:02:08 | ascheid/itsg33-pbmm-issue-gen | https://api.github.com/repos/ascheid/itsg33-pbmm-issue-gen | opened | CM-5(6): Access Restrictions For Change | Limit Library Privileges | Priority: P2 Suggested Assignment: IT Security Function ITSG-33 Class: Operational Control: CM-5 | # Control Definition
ACCESS RESTRICTIONS FOR CHANGE | LIMIT LIBRARY PRIVILEGES
The organization limits privileges to change software resident within software libraries.
Supplemental Guidance: Software libraries include privileged programs. Related control: AC-2.
# Class
Operational
# Suggested Assignment
IT Security... | 1.0 | CM-5(6): Access Restrictions For Change | Limit Library Privileges - # Control Definition
ACCESS RESTRICTIONS FOR CHANGE | LIMIT LIBRARY PRIVILEGES
The organization limits privileges to change software resident within software libraries.
Supplemental Guidance: Software libraries include privileged programs. Related co... | priority | cm access restrictions for change limit library privileges control definition access restrictions for change limit library privileges the organization limits privileges to change software resident within software libraries supplemental guidance software libraries include privileged programs related co... | 1 |
736,166 | 25,460,782,057 | IssuesEvent | 2022-11-24 18:42:00 | TalaoDAO/AltMe | https://api.github.com/repos/TalaoDAO/AltMe | closed | Change text screen IA | Priority NO GO | replace "ID document check" by "Real-time photo + ID document check"
position the IA on top of the list
add check box by default select teh IA
add button "Start"
| 1.0 | Change text screen IA - replace "ID document check" by "Real-time photo + ID document check"
position the IA on top of the list
add check box by default select teh IA
add button "Start"
| priority | change text screen ia replace id document check by real time photo id document check position the ia on top of the list add check box by default select teh ia add button start | 1 |
249,623 | 21,180,615,705 | IssuesEvent | 2022-04-08 07:33:04 | milvus-io/milvus | https://api.github.com/repos/milvus-io/milvus | opened | [Bug]: [benchmark][standalone] RpcError: _MultiThreadedRendezvous: StatusCode.DEADLINE_EXCEEDED, Deadline Exceeded | kind/bug needs-triage test/benchmark | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Environment
```markdown
- Milvus version: master-20220406-1e6f6bd0
- Deployment mode(standalone or cluster): standalone
- SDK version(e.g. pymilvus v2.0.0rc2): 2.1.0.dev18
- OS(Ubuntu or CentOS):
- CPU/Memory:
- GPU:
- Ot... | 1.0 | [Bug]: [benchmark][standalone] RpcError: _MultiThreadedRendezvous: StatusCode.DEADLINE_EXCEEDED, Deadline Exceeded - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Environment
```markdown
- Milvus version: master-20220406-1e6f6bd0
- Deployment mode(standalone or cluster): sta... | non_priority | rpcerror multithreadedrendezvous statuscode deadline exceeded deadline exceeded is there an existing issue for this i have searched the existing issues environment markdown milvus version master deployment mode standalone or cluster standalone sdk version e g pymilvus ... | 0 |
85,488 | 7,973,864,182 | IssuesEvent | 2018-07-17 01:48:33 | owncloud/core | https://api.github.com/repos/owncloud/core | opened | Federation acceptance tests should test incoming and outgoing separately | app:federation dev:acceptance-tests | Federation acceptance tests should test permutations like:
- [ ] Incoming only - incoming stuff is accepted, outgoing is not allowed
- [ ] Outgoing only - outgoing stuff is accepted, incoming is not allowed
- [ ] Incoming and outgoing - it all works
- [ ] Neither - no federation shares are allowed
| 1.0 | Federation acceptance tests should test incoming and outgoing separately - Federation acceptance tests should test permutations like:
- [ ] Incoming only - incoming stuff is accepted, outgoing is not allowed
- [ ] Outgoing only - outgoing stuff is accepted, incoming is not allowed
- [ ] Incoming and outgoing - it ... | non_priority | federation acceptance tests should test incoming and outgoing separately federation acceptance tests should test permutations like incoming only incoming stuff is accepted outgoing is not allowed outgoing only outgoing stuff is accepted incoming is not allowed incoming and outgoing it all wo... | 0 |
157,474 | 19,957,388,872 | IssuesEvent | 2022-01-28 01:58:59 | faizulho/sanity-gatsby-blog | https://api.github.com/repos/faizulho/sanity-gatsby-blog | opened | CVE-2022-0355 (High) detected in simple-get-4.0.0.tgz | security vulnerability | ## CVE-2022-0355 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>simple-get-4.0.0.tgz</b></p></summary>
<p>Simplest way to make http get requests. Supports HTTPS, redirects, gzip/defla... | True | CVE-2022-0355 (High) detected in simple-get-4.0.0.tgz - ## CVE-2022-0355 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>simple-get-4.0.0.tgz</b></p></summary>
<p>Simplest way to make ... | non_priority | cve high detected in simple get tgz cve high severity vulnerability vulnerable library simple get tgz simplest way to make http get requests supports https redirects gzip deflate streams in library home page a href path to dependency file studio package json pat... | 0 |
55,843 | 23,616,516,443 | IssuesEvent | 2022-08-24 16:19:33 | BCDevOps/developer-experience | https://api.github.com/repos/BCDevOps/developer-experience | closed | Enable Argo CD for JAG_RBAC | automation ops and shared services app-development | **Describe the issue**
Devise a plan for the management of OCP RBAC in Argo CD for the entire justice ministry using the Warden Operator and the "GitOpsAlliance" resource.
**Additional context**
Because the project sets to be included have multiple ministry IDs, a new label will have to be added to each project set's ... | 1.0 | Enable Argo CD for JAG_RBAC - **Describe the issue**
Devise a plan for the management of OCP RBAC in Argo CD for the entire justice ministry using the Warden Operator and the "GitOpsAlliance" resource.
**Additional context**
Because the project sets to be included have multiple ministry IDs, a new label will have to b... | non_priority | enable argo cd for jag rbac describe the issue devise a plan for the management of ocp rbac in argo cd for the entire justice ministry using the warden operator and the gitopsalliance resource additional context because the project sets to be included have multiple ministry ids a new label will have to b... | 0 |
49,577 | 3,003,705,151 | IssuesEvent | 2015-07-25 05:47:17 | jayway/powermock | https://api.github.com/repos/jayway/powermock | opened | PowerMock+TestNG+DataProvider RuntimeException | bug imported Priority-Medium | _From [Ignas.Tr...@gmail.com](https://code.google.com/u/112024306843858881334/) on October 01, 2013 15:01:03_
What steps will reproduce the problem? ======================================
@Test
@PrepareForTest
public class StaticTest extends PowerMockTestCase {
@DataProvider
public final Object[][] ge... | 1.0 | PowerMock+TestNG+DataProvider RuntimeException - _From [Ignas.Tr...@gmail.com](https://code.google.com/u/112024306843858881334/) on October 01, 2013 15:01:03_
What steps will reproduce the problem? ======================================
@Test
@PrepareForTest
public class StaticTest extends PowerMockTestCase {
... | priority | powermock testng dataprovider runtimeexception from on october what steps will reproduce the problem test preparefortest public class statictest extends powermocktestcase dataprovider public final object getweekday return n... | 1 |
135,781 | 19,663,509,095 | IssuesEvent | 2022-01-10 19:37:50 | elementary/switchboard-plug-power | https://api.github.com/repos/elementary/switchboard-plug-power | opened | Expose automatic lower power mode setting | Needs Design | ### Problem
GNOME Settings Daemon includes a setting for automatic low power mode, but we don't expose it in the UI.
### Proposal
Include a switch for `org.gnome.settings-daemon.plugins.power power-saver-profile-on-low-battery`
### Prior Art (Optional)
_No response_ | 1.0 | Expose automatic lower power mode setting - ### Problem
GNOME Settings Daemon includes a setting for automatic low power mode, but we don't expose it in the UI.
### Proposal
Include a switch for `org.gnome.settings-daemon.plugins.power power-saver-profile-on-low-battery`
### Prior Art (Optional)
_No response_ | non_priority | expose automatic lower power mode setting problem gnome settings daemon includes a setting for automatic low power mode but we don t expose it in the ui proposal include a switch for org gnome settings daemon plugins power power saver profile on low battery prior art optional no response | 0 |
43,968 | 17,775,659,723 | IssuesEvent | 2021-08-30 18:52:18 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | opened | In markings_specialty_point feature layer, in Subtype Name for "D_ATD_SPEC_PNT_OTHER_SUB" add " 2 Gr... | Workgroup: SMB Service: Geo | <!-- Email -->
<!-- susanne.gov@austintexas.gov -->
> What application are you using?
ArcGIS
> Describe the problem.
In markings_specialty_point feature layer, in Subtype Name for "D_ATD_SPEC_PNT_OTHER_SUB" add " 2 Green Pads with chevron"
> How soon do you need this?
Soon — This week
> Is there anything else w... | 1.0 | In markings_specialty_point feature layer, in Subtype Name for "D_ATD_SPEC_PNT_OTHER_SUB" add " 2 Gr... - <!-- Email -->
<!-- susanne.gov@austintexas.gov -->
> What application are you using?
ArcGIS
> Describe the problem.
In markings_specialty_point feature layer, in Subtype Name for "D_ATD_SPEC_PNT_OTHER_SUB" add... | non_priority | in markings specialty point feature layer in subtype name for d atd spec pnt other sub add gr what application are you using arcgis describe the problem in markings specialty point feature layer in subtype name for d atd spec pnt other sub add green pads with chevron how soon do you... | 0 |
268,802 | 28,835,534,761 | IssuesEvent | 2023-05-04 01:02:36 | vital-dev-org/Spring-Boot-Sample-Project | https://api.github.com/repos/vital-dev-org/Spring-Boot-Sample-Project | opened | spring-boot-starter-data-rest-2.1.3.RELEASE.jar: 19 vulnerabilities (highest severity is: 9.8) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-data-rest-2.1.3.RELEASE.jar</b></p></summary>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m... | True | spring-boot-starter-data-rest-2.1.3.RELEASE.jar: 19 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-boot-starter-data-rest-2.1.3.RELEASE.jar</b></p></summary>
<p>... | non_priority | spring boot starter data rest release jar vulnerabilities highest severity is vulnerable library spring boot starter data rest release jar path to dependency file pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core ... | 0 |
225,956 | 17,293,787,981 | IssuesEvent | 2021-07-25 10:03:03 | RandomCoderOrg/ubuntu-on-android | https://api.github.com/repos/RandomCoderOrg/ubuntu-on-android | opened | Discribution url is not defined for gpu architecture armv8l | documentation question | Hello please help me !!
When I type this command :
# download installer
curl -L -o install.sh https://git.io/hippo-installer
# run the installer
bash install.sh
# Install ubuntu with this command
hippo --install
/ / /
I get error :
 LFX Security Training (16 - 20 hours / person)
- [x] (5) Issue acknowledgement (specific timeframe: 2 - 12 months)
- [ ] (2) Address Sonar hotspots (only for protected branches) | 1.0 | Zowe CLI - Known Passing CII Badge Requirements - - [x] (5) LFX Security Training (16 - 20 hours / person)
- [x] (5) Issue acknowledgement (specific timeframe: 2 - 12 months)
- [ ] (2) Address Sonar hotspots (only for protected branches) | priority | zowe cli known passing cii badge requirements lfx security training hours person issue acknowledgement specific timeframe months address sonar hotspots only for protected branches | 1 |
199,414 | 22,693,327,601 | IssuesEvent | 2022-07-05 01:13:39 | ondrejrozsypal/test | https://api.github.com/repos/ondrejrozsypal/test | closed | CVE-2020-13596 (Medium) detected in Django-1.8.15-py2.py3-none-any.whl - autoclosed | security vulnerability | ## CVE-2020-13596 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.15-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Python Web framework that encourages rapid deve... | True | CVE-2020-13596 (Medium) detected in Django-1.8.15-py2.py3-none-any.whl - autoclosed - ## CVE-2020-13596 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Django-1.8.15-py2.py3-none-any.... | non_priority | cve medium detected in django none any whl autoclosed cve medium severity vulnerability vulnerable library django none any whl a high level python web framework that encourages rapid development and clean pragmatic design library home page a href path to depe... | 0 |
600,135 | 18,290,151,972 | IssuesEvent | 2021-10-05 14:29:06 | CDH-Studio/I-Talent | https://api.github.com/repos/CDH-Studio/I-Talent | closed | The Email and Job Title not read to screen reader | :lady_beetle: bug :warning: high priority :wheelchair: accessibility | **Describe the bug**
The job title and email should be read even though they are disabled in the contact form
| 1.0 | The Email and Job Title not read to screen reader - **Describe the bug**
The job title and email should be read even though they are disabled in the contact form
| priority | the email and job title not read to screen reader describe the bug the job title and email should be read even though they are disabled in the contact form | 1 |
272,405 | 23,671,191,776 | IssuesEvent | 2022-08-27 11:31:46 | marco-at-bit/test-quality-sdk | https://api.github.com/repos/marco-at-bit/test-quality-sdk | closed | Req with highest prio | bug TestQuality Highest |
## Steps to Reproduce:
### Step 1 <span style="color:#ff9000"> **[Pending]** </span>
Step nr one
### Step 2 <span style="color:#ff9000"> **[Pending]** </span>
Second step
| 1.0 | Req with highest prio -
## Steps to Reproduce:
### Step 1 <span style="color:#ff9000"> **[Pending]** </span>
Step nr one
### Step 2 <span style="color:#ff9000"> **[Pending]** </span>
Second step
| non_priority | req with highest prio steps to reproduce step step nr one step second step | 0 |
191,317 | 15,284,819,322 | IssuesEvent | 2021-02-23 12:45:39 | allenai/ir_datasets | https://api.github.com/repos/allenai/ir_datasets | opened | arriving at documentation page from search engine is disorienting | documentation | The flow from the main result index page seems fine, but when you reach a documentation page from a search engine, it's rather disorienting. Some description at the top would probably help. | 1.0 | arriving at documentation page from search engine is disorienting - The flow from the main result index page seems fine, but when you reach a documentation page from a search engine, it's rather disorienting. Some description at the top would probably help. | non_priority | arriving at documentation page from search engine is disorienting the flow from the main result index page seems fine but when you reach a documentation page from a search engine it s rather disorienting some description at the top would probably help | 0 |
258,728 | 27,579,395,182 | IssuesEvent | 2023-03-08 15:13:44 | Dima2021/railsgoat | https://api.github.com/repos/Dima2021/railsgoat | opened | better_errors-2.5.1.gem: 7 vulnerabilities (highest severity is: 10.0) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>better_errors-2.5.1.gem</b></p></summary>
<p>Provides a better error page for Rails and other Rack apps. Includes source code inspection, a live REPL and local/instan... | True | better_errors-2.5.1.gem: 7 vulnerabilities (highest severity is: 10.0) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>better_errors-2.5.1.gem</b></p></summary>
<p>Provides a better error page for Rails and other... | non_priority | better errors gem vulnerabilities highest severity is vulnerable library better errors gem provides a better error page for rails and other rack apps includes source code inspection a live repl and local instance variable inspection for all stack frames library home page a hre... | 0 |
728,466 | 25,080,330,277 | IssuesEvent | 2022-11-07 18:43:46 | serokell/tezos-packaging | https://api.github.com/repos/serokell/tezos-packaging | closed | [BUG] services using non-default node data directory enter infinite crash/restart loop after upgrade | in progress high priority | # Description
<!--
A clear and concise description of what the bug is.
-->
# To Reproduce
Steps to reproduce the behavior:
- set up baking with tezos-setup-wizard on using octez 13 packages
- apt update, apt upgrade
- observe baker and node services now constantly restart with "Pack_error: "Migration_need... | 1.0 | [BUG] services using non-default node data directory enter infinite crash/restart loop after upgrade - # Description
<!--
A clear and concise description of what the bug is.
-->
# To Reproduce
Steps to reproduce the behavior:
- set up baking with tezos-setup-wizard on using octez 13 packages
- apt update, ... | priority | services using non default node data directory enter infinite crash restart loop after upgrade description a clear and concise description of what the bug is to reproduce steps to reproduce the behavior set up baking with tezos setup wizard on using octez packages apt update apt u... | 1 |
134,250 | 10,887,809,717 | IssuesEvent | 2019-11-18 15:11:35 | golang/go | https://api.github.com/repos/golang/go | closed | cmd/fix: incorrect loop variable aliasing in TestRewrite | NeedsFix Testing | ### What version of Go are you using (`go version`)?
<pre>
$ go version
go version devel +c20b71eb37 Sat Nov 16 02:06:39 2019 +0000 linux/amd6
</pre>
### Does this issue reproduce with the latest release?
Yes.
### What operating system and processor architecture are you using (`go env`)?
<details><sum... | 1.0 | cmd/fix: incorrect loop variable aliasing in TestRewrite - ### What version of Go are you using (`go version`)?
<pre>
$ go version
go version devel +c20b71eb37 Sat Nov 16 02:06:39 2019 +0000 linux/amd6
</pre>
### Does this issue reproduce with the latest release?
Yes.
### What operating system and proces... | non_priority | cmd fix incorrect loop variable aliasing in testrewrite what version of go are you using go version go version go version devel sat nov linux does this issue reproduce with the latest release yes what operating system and processor architecture are you using ... | 0 |
99,348 | 20,958,419,038 | IssuesEvent | 2022-03-27 12:41:13 | Onelinerhub/onelinerhub | https://api.github.com/repos/Onelinerhub/onelinerhub | opened | Short solution needed: "How to load data frame from CSV" (python-pandas) | help wanted good first issue code python-pandas | Please help us write most modern and shortest code solution for this issue:
**How to load data frame from CSV** (technology: [python-pandas](https://onelinerhub.com/python-pandas))
### Fast way
Just write the code solution in the comments.
### Prefered way
1. Create pull request with a new code file inside [inbox fol... | 1.0 | Short solution needed: "How to load data frame from CSV" (python-pandas) - Please help us write most modern and shortest code solution for this issue:
**How to load data frame from CSV** (technology: [python-pandas](https://onelinerhub.com/python-pandas))
### Fast way
Just write the code solution in the comments.
###... | non_priority | short solution needed how to load data frame from csv python pandas please help us write most modern and shortest code solution for this issue how to load data frame from csv technology fast way just write the code solution in the comments prefered way create pull request with a new code... | 0 |
256,519 | 27,561,683,769 | IssuesEvent | 2023-03-07 22:39:54 | samqws-marketing/amzn-ion-hive-serde | https://api.github.com/repos/samqws-marketing/amzn-ion-hive-serde | closed | CVE-2020-36183 (High) detected in jackson-databind-2.6.5.jar - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-36183 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2020-36183 (High) detected in jackson-databind-2.6.5.jar - autoclosed - ## CVE-2020-36183 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.5.jar</b></p></summary... | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file integration test ... | 0 |
681,156 | 23,299,058,299 | IssuesEvent | 2022-08-07 03:01:33 | wso2/product-is | https://api.github.com/repos/wso2/product-is | closed | UI loading continuously when view the assigned users in 'Roles' section in the sub-organization | Priority/Highest Severity/Critical bug Affected-6.0.0 QA-Reported Organization Management | **Describe the issue:**
If the sub-organization doesn't have users initially and then if we view 'Users' in the 'Roles' section, it doesn't show the expected result. Please refer to this screencast.
https://user-images.githubusercontent.com/13362482/182848081-90b5aa68-b40c-450b-b428-dd58f5d91399.mov
It shows the... | 1.0 | UI loading continuously when view the assigned users in 'Roles' section in the sub-organization - **Describe the issue:**
If the sub-organization doesn't have users initially and then if we view 'Users' in the 'Roles' section, it doesn't show the expected result. Please refer to this screencast.
https://user-images... | priority | ui loading continuously when view the assigned users in roles section in the sub organization describe the issue if the sub organization doesn t have users initially and then if we view users in the roles section it doesn t show the expected result please refer to this screencast it shows the e... | 1 |
279,014 | 21,105,196,020 | IssuesEvent | 2022-04-04 18:02:38 | spacetimedotnet/spacetime | https://api.github.com/repos/spacetimedotnet/spacetime | opened | Create MSIX installer for alpha builds | documentation enhancement help wanted | Create an MSIX installer for Alpha builds - using a self signed certificate.
- [ ] MSIX Installer
- [ ] Certificate generated
- [ ] Documentation added | 1.0 | Create MSIX installer for alpha builds - Create an MSIX installer for Alpha builds - using a self signed certificate.
- [ ] MSIX Installer
- [ ] Certificate generated
- [ ] Documentation added | non_priority | create msix installer for alpha builds create an msix installer for alpha builds using a self signed certificate msix installer certificate generated documentation added | 0 |
817,191 | 30,630,150,575 | IssuesEvent | 2023-07-24 14:04:43 | wp-media/wp-rocket | https://api.github.com/repos/wp-media/wp-rocket | closed | Cache clearing not working on a per-post basis in conjunction with WPML (non-encoded URL / special chars?) | type: bug 3rd party compatibility module: cache priority: medium severity: major | **Before submitting an issue please check that you’ve completed the following steps:**
- [x] Made sure you’re on the latest version
- [x] Used the search feature to ensure that the bug hasn’t been reported before
**Describe the bug**
We're using WP Rocket in conjunction with WPML and I have noticed a faulty behav... | 1.0 | Cache clearing not working on a per-post basis in conjunction with WPML (non-encoded URL / special chars?) - **Before submitting an issue please check that you’ve completed the following steps:**
- [x] Made sure you’re on the latest version
- [x] Used the search feature to ensure that the bug hasn’t been reported bef... | priority | cache clearing not working on a per post basis in conjunction with wpml non encoded url special chars before submitting an issue please check that you’ve completed the following steps made sure you’re on the latest version used the search feature to ensure that the bug hasn’t been reported before ... | 1 |
357,309 | 10,604,970,852 | IssuesEvent | 2019-10-10 19:22:56 | SkriptLang/Skript | https://api.github.com/repos/SkriptLang/Skript | closed | Can't set player list name of a variable containing a player | bug priority: medium | ### Description
Skript doesn't allow you to set the player list name of a variable that contains a player.
(the player list name of {variable} can't be set to anything)
### Steps to Reproduce
1. Set a variable to any player object
2. Try to set the tablist name of that variable
### Expected Behavior
The tabl... | 1.0 | Can't set player list name of a variable containing a player - ### Description
Skript doesn't allow you to set the player list name of a variable that contains a player.
(the player list name of {variable} can't be set to anything)
### Steps to Reproduce
1. Set a variable to any player object
2. Try to set the t... | priority | can t set player list name of a variable containing a player description skript doesn t allow you to set the player list name of a variable that contains a player the player list name of variable can t be set to anything steps to reproduce set a variable to any player object try to set the t... | 1 |
228,497 | 18,238,586,841 | IssuesEvent | 2021-10-01 10:03:11 | Sifchain/sifnode | https://api.github.com/repos/Sifchain/sifnode | opened | Exploration of automated IBC status monitoring and debugging | ChainOps Testing Sifnode | Explore options for detailed automated status page for IBC channels and transactions to provide constant monitoring and sustainable and scalable debugging of what is happening with chains, channels, accounts and transfers. | 1.0 | Exploration of automated IBC status monitoring and debugging - Explore options for detailed automated status page for IBC channels and transactions to provide constant monitoring and sustainable and scalable debugging of what is happening with chains, channels, accounts and transfers. | non_priority | exploration of automated ibc status monitoring and debugging explore options for detailed automated status page for ibc channels and transactions to provide constant monitoring and sustainable and scalable debugging of what is happening with chains channels accounts and transfers | 0 |
438,958 | 12,664,193,444 | IssuesEvent | 2020-06-18 03:50:25 | AuDigitalHealth/ci-fhir-r4 | https://api.github.com/repos/AuDigitalHealth/ci-fhir-r4 | closed | Pathology Report with atomic content | feature/new-profile size/medium status/in-progress tag/priority | # Prerequisites
- [x] I have searched [open](https://github.com/ci-fhir-r4/Issues/issues) and [closed](https://github.com/ci-fhir-r4/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already requested or reported
- [x] I have written a descriptive issue title
# The feature
## Cha... | 1.0 | Pathology Report with atomic content - # Prerequisites
- [x] I have searched [open](https://github.com/ci-fhir-r4/Issues/issues) and [closed](https://github.com/ci-fhir-r4/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already requested or reported
- [x] I have written a descripti... | priority | pathology report with atomic content prerequisites i have searched and issues to make sure it isn t already requested or reported i have written a descriptive issue title the feature change description the purpose of this profile is to define an atomic representation of a pathology repor... | 1 |
68,777 | 8,345,767,834 | IssuesEvent | 2018-10-01 05:17:02 | caicloud/ciao | https://api.github.com/repos/caicloud/ciao | closed | [discussion] Use PVC or Configmap to avoid Docker building/pushing | kind/design | /kind discussion
I am not sure if it works. If we build and push a Docker image every time we run the code, overhead is definitely high. | 1.0 | [discussion] Use PVC or Configmap to avoid Docker building/pushing - /kind discussion
I am not sure if it works. If we build and push a Docker image every time we run the code, overhead is definitely high. | non_priority | use pvc or configmap to avoid docker building pushing kind discussion i am not sure if it works if we build and push a docker image every time we run the code overhead is definitely high | 0 |
584,356 | 17,422,089,812 | IssuesEvent | 2021-08-04 03:31:47 | brave/qa-resources | https://api.github.com/repos/brave/qa-resources | closed | 1.27.x - Release #2 | ARM OS/Android priority/P1 x86 | ### <img src="https://www.rebron.org/wordpress/wp-content/uploads/2019/06/Android.png"> `1.27.x - Release #2`
#### Release Date/Target:
#### Release Date/Target:
* Release Date: **`July 27, 2021`**
#### Summary:
Includes the following features/fixes:
* ability to change “Block trackers & ads” to eithe... | 1.0 | 1.27.x - Release #2 - ### <img src="https://www.rebron.org/wordpress/wp-content/uploads/2019/06/Android.png"> `1.27.x - Release #2`
#### Release Date/Target:
#### Release Date/Target:
* Release Date: **`July 27, 2021`**
#### Summary:
Includes the following features/fixes:
* ability to change “Block tr... | priority | x release img src x release release date target release date target release date july summary includes the following features fixes ability to change “block trackers ads” to either “standard” “aggressive” or “allow all” via the shield... | 1 |
49,478 | 13,453,470,105 | IssuesEvent | 2020-09-09 01:03:07 | nasifimtiazohi/openmrs-module-coreapps-1.28.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-coreapps-1.28.0 | opened | WS-2018-0590 (High) detected in diff-1.4.0.tgz | security vulnerability | ## WS-2018-0590 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>diff-1.4.0.tgz</b></p></summary>
<p>A javascript text diff implementation.</p>
<p>Library home page: <a href="https://re... | True | WS-2018-0590 (High) detected in diff-1.4.0.tgz - ## WS-2018-0590 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>diff-1.4.0.tgz</b></p></summary>
<p>A javascript text diff implementati... | non_priority | ws high detected in diff tgz ws high severity vulnerability vulnerable library diff tgz a javascript text diff implementation library home page a href path to dependency file tmp ws scm openmrs module coreapps package json path to vulnerable library tmp ws s... | 0 |
301,310 | 9,218,972,227 | IssuesEvent | 2019-03-11 14:31:57 | blackbaud/skyux-sdk-builder | https://api.github.com/repos/blackbaud/skyux-sdk-builder | closed | Command `skyux watch` disconnects if linting takes too long | Priority: Critical Type: Bug | During `skyux watch`, if the linting process takes longer than 20 (or so) seconds, I'll get the following messages:
```
Disconnected (0 times)Client disconnected from CONNECTED state (ping timeout) Chrome 72.0.3626 (Mac OS X 10.14.3) ERROR DisconnectedClient disconnected from CONNECTED state (ping timeout)
```
... | 1.0 | Command `skyux watch` disconnects if linting takes too long - During `skyux watch`, if the linting process takes longer than 20 (or so) seconds, I'll get the following messages:
```
Disconnected (0 times)Client disconnected from CONNECTED state (ping timeout) Chrome 72.0.3626 (Mac OS X 10.14.3) ERROR DisconnectedCl... | priority | command skyux watch disconnects if linting takes too long during skyux watch if the linting process takes longer than or so seconds i ll get the following messages disconnected times client disconnected from connected state ping timeout chrome mac os x error disconnectedclient di... | 1 |
177,348 | 21,473,445,309 | IssuesEvent | 2022-04-26 11:39:45 | nanopathi/framework_base_AOSP10_r33_CVE-2021-39704 | https://api.github.com/repos/nanopathi/framework_base_AOSP10_r33_CVE-2021-39704 | opened | CVE-2021-0315 (High) detected in baseandroid-10.0.0_r34 | security vulnerability | ## CVE-2021-0315 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r34</b></p></summary>
<p>
<p>Android framework classes and services</p>
<p>Library home page: <a hre... | True | CVE-2021-0315 (High) detected in baseandroid-10.0.0_r34 - ## CVE-2021-0315 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>baseandroid-10.0.0_r34</b></p></summary>
<p>
<p>Android frame... | non_priority | cve high detected in baseandroid cve high severity vulnerability vulnerable library baseandroid android framework classes and services library home page a href found in head commit a href found in base branch master vulnerable source files ... | 0 |
87,458 | 17,270,649,860 | IssuesEvent | 2021-07-22 19:20:34 | WarEmu/WarBugs | https://api.github.com/repos/WarEmu/WarBugs | closed | Death From Below quest: Brauk kill not counted | Dungeon: Sigmar's Crypt Dungeon: Warpblade Tunnels Fix Pending NPC Quests Scripting Sourcecode | Brauk boss (who is an ad to Skrot boss) gets despawned after the main boss is killed, and is not counted as kill in the Death From Below quest.
I don't have evidence from the site, but I can provide quest logs from two different chars that were doing full run of C&T, you can see that the Brauk kill is missed by 1 fo... | 1.0 | Death From Below quest: Brauk kill not counted - Brauk boss (who is an ad to Skrot boss) gets despawned after the main boss is killed, and is not counted as kill in the Death From Below quest.
I don't have evidence from the site, but I can provide quest logs from two different chars that were doing full run of C&T, ... | non_priority | death from below quest brauk kill not counted brauk boss who is an ad to skrot boss gets despawned after the main boss is killed and is not counted as kill in the death from below quest i don t have evidence from the site but i can provide quest logs from two different chars that were doing full run of c t ... | 0 |
555,647 | 16,460,022,337 | IssuesEvent | 2021-05-21 17:29:07 | ucfopen/Obojobo | https://api.github.com/repos/ucfopen/Obojobo | closed | Question Bank options not being updated | bug high priority | Tried this on dev/21 - Seems that changing the option on a Question Bank from "All questions" to "Pick 1" isn't saving correctly. | 1.0 | Question Bank options not being updated - Tried this on dev/21 - Seems that changing the option on a Question Bank from "All questions" to "Pick 1" isn't saving correctly. | priority | question bank options not being updated tried this on dev seems that changing the option on a question bank from all questions to pick isn t saving correctly | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.