Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
452,084 | 32,049,445,667 | IssuesEvent | 2023-09-23 11:29:58 | hxijxe/ict-inf2001-p3-6 | https://api.github.com/repos/hxijxe/ict-inf2001-p3-6 | closed | #Task 1.3.2: Detailed Use Case Description (UC-5 to UC-7) | documentation | Task title ID: https://github.com/hxijxe/ict-inf2001-p3-6/issues/12
What is the task about? Please describe in detail.
The task involves creating detailed use case descriptions for Use Cases 5, 6 and 7, which are "Manage Shift", "Manage Shift Location" and "Manage Shift Preference" respectively.
What are the goals of... | 1.0 | #Task 1.3.2: Detailed Use Case Description (UC-5 to UC-7) - Task title ID: https://github.com/hxijxe/ict-inf2001-p3-6/issues/12
What is the task about? Please describe in detail.
The task involves creating detailed use case descriptions for Use Cases 5, 6 and 7, which are "Manage Shift", "Manage Shift Location" and "M... | non_priority | task detailed use case description uc to uc task title id what is the task about please describe in detail the task involves creating detailed use case descriptions for use cases and which are manage shift manage shift location and manage shift preference respectively what are the... | 0 |
486,810 | 14,014,986,467 | IssuesEvent | 2020-10-29 12:43:51 | geosolutions-it/austrocontrol-C125 | https://api.github.com/repos/geosolutions-it/austrocontrol-C125 | closed | Responsive Design - Info Box - Update of the WYSIWYG | Accepted Priority: Medium Project: C125 | Update of the WYSIWYG used by the current Details tool to allow aligning and resizing images.
Use the new WYSIWYG editor implemented for Stories (draftJS editor). This means not only adapting the new Text editor to the existing Details tool, but also readapting it in order to include and manage additional utilities ... | 1.0 | Responsive Design - Info Box - Update of the WYSIWYG - Update of the WYSIWYG used by the current Details tool to allow aligning and resizing images.
Use the new WYSIWYG editor implemented for Stories (draftJS editor). This means not only adapting the new Text editor to the existing Details tool, but also readapting ... | priority | responsive design info box update of the wysiwyg update of the wysiwyg used by the current details tool to allow aligning and resizing images use the new wysiwyg editor implemented for stories draftjs editor this means not only adapting the new text editor to the existing details tool but also readapting ... | 1 |
477,822 | 13,768,920,478 | IssuesEvent | 2020-10-07 17:48:49 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | opened | [Coverity CID :214875] Dereference after null check in subsys/emul/spi/emul_bmi160.c | Coverity bug priority: low |
Static code scan issues found in file:
https://github.com/zephyrproject-rtos/zephyr/tree/master/subsys/emul/spi/emul_bmi160.c
Category: Null pointer dereferences
Function: `bmi160_emul_io`
Component: Other
CID: [214875](https://scan9.coverity.com/reports.htm#v29726/p12996/mergedDefectId=214875)
Please fix or provid... | 1.0 | [Coverity CID :214875] Dereference after null check in subsys/emul/spi/emul_bmi160.c -
Static code scan issues found in file:
https://github.com/zephyrproject-rtos/zephyr/tree/master/subsys/emul/spi/emul_bmi160.c
Category: Null pointer dereferences
Function: `bmi160_emul_io`
Component: Other
CID: [214875](https://sc... | priority | dereference after null check in subsys emul spi emul c static code scan issues found in file category null pointer dereferences function emul io component other cid please fix or provide comments in coverity using the link note this issue was created automatically priority was set based ... | 1 |
28,361 | 5,242,753,496 | IssuesEvent | 2017-01-31 18:53:55 | bridgedotnet/Bridge | https://api.github.com/repos/bridgedotnet/Bridge | closed | Can't resolve generic alias in method<TA> from within Action<TB<TC>> | defect in progress | ### Steps To Reproduce
http://deck.net/7c9c1ee892b60cdcd72febeeb3b3c078
```c#
public struct V2<TA, TB>
{
public TA a;
public TB b;
}
public interface IThing<TC,TD>
{
void MyMethod();
}
public class BugTest<TX>
{
IThing<V2<TX,double>,V2<double,double>> _MyThing;
public void ... | 1.0 | Can't resolve generic alias in method<TA> from within Action<TB<TC>> - ### Steps To Reproduce
http://deck.net/7c9c1ee892b60cdcd72febeeb3b3c078
```c#
public struct V2<TA, TB>
{
public TA a;
public TB b;
}
public interface IThing<TC,TD>
{
void MyMethod();
}
public class BugTest<TX>
{
... | non_priority | can t resolve generic alias in method from within action steps to reproduce c public struct public ta a public tb b public interface ithing void mymethod public class bugtest ithing mything public void dostuff action... | 0 |
41,625 | 21,796,761,320 | IssuesEvent | 2022-05-15 18:54:05 | antlr/antlr4 | https://api.github.com/repos/antlr/antlr4 | opened | ANTLR tool takes 6s to process 1772 line parser grammar | atn-analysis grammars comp:performance | [issue was identified in plugin](https://github.com/antlr/intellij-plugin-v4/issues/553) by @KitsuneAlex
This [FerrousParser.g4](https://git.karmakrafts.dev/kk/ferrous-project/vanadium/-/blob/master/src/main/antlr/FerrousParser.g4) takes 6s to process with antlr tool. It seems to be stuck in SLL(1) static analysis.... | True | ANTLR tool takes 6s to process 1772 line parser grammar - [issue was identified in plugin](https://github.com/antlr/intellij-plugin-v4/issues/553) by @KitsuneAlex
This [FerrousParser.g4](https://git.karmakrafts.dev/kk/ferrous-project/vanadium/-/blob/master/src/main/antlr/FerrousParser.g4) takes 6s to process with an... | non_priority | antlr tool takes to process line parser grammar by kitsunealex this takes to process with antlr tool it seems to be stuck in sll static analysis could be murmur hash sharwell this likely affects your optimized fork as well simple test rig java import org antlr runtime antlrfil... | 0 |
131,160 | 18,214,761,869 | IssuesEvent | 2021-09-30 01:53:04 | tt9133github/Python | https://api.github.com/repos/tt9133github/Python | opened | CVE-2021-29063 (High) detected in mpmath-1.1.0.tar.gz | security vulnerability | ## CVE-2021-29063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mpmath-1.1.0.tar.gz</b></p></summary>
<p>Python library for arbitrary-precision floating-point arithmetic</p>
<p>Libra... | True | CVE-2021-29063 (High) detected in mpmath-1.1.0.tar.gz - ## CVE-2021-29063 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mpmath-1.1.0.tar.gz</b></p></summary>
<p>Python library for ar... | non_priority | cve high detected in mpmath tar gz cve high severity vulnerability vulnerable library mpmath tar gz python library for arbitrary precision floating point arithmetic library home page a href path to dependency file python optimization requirements txt path to vulnerabl... | 0 |
7,573 | 2,911,335,793 | IssuesEvent | 2015-06-22 08:52:45 | red/red | https://api.github.com/repos/red/red | closed | length? on tuple! | Red status.built status.tested type.review | red>> length? 1.2.3
*** Script error: length? does not allow tuple for its series argument
*** Where: length?
| 1.0 | length? on tuple! - red>> length? 1.2.3
*** Script error: length? does not allow tuple for its series argument
*** Where: length?
| non_priority | length on tuple red length script error length does not allow tuple for its series argument where length | 0 |
333,116 | 24,364,643,951 | IssuesEvent | 2022-10-03 14:19:24 | r-lib/pak | https://api.github.com/repos/r-lib/pak | closed | `?ignore`d packages is not ignored | documentation | Related to #421, I'm trying to ignore the package `lixoftConnectors` when installing dependencies.
When I used `lixoftConnectors?ignore` in the `extra-packages` list, I got the following error indicating that it was not ignored:
https://github.com/nlmixr2/babelmixr2/actions/runs/3169455077/jobs/5161378366#step:5:... | 1.0 | `?ignore`d packages is not ignored - Related to #421, I'm trying to ignore the package `lixoftConnectors` when installing dependencies.
When I used `lixoftConnectors?ignore` in the `extra-packages` list, I got the following error indicating that it was not ignored:
https://github.com/nlmixr2/babelmixr2/actions/ru... | non_priority | ignore d packages is not ignored related to i m trying to ignore the package lixoftconnectors when installing dependencies when i used lixoftconnectors ignore in the extra packages list i got the following error indicating that it was not ignored the instructions i used were i was t... | 0 |
61,174 | 14,942,775,629 | IssuesEvent | 2021-01-25 21:50:58 | quicklisp/quicklisp-projects | https://api.github.com/repos/quicklisp/quicklisp-projects | closed | Please add inheriting-readers | canbuild | inheriting-readers provides a simple yet powerful value inheritance scheme.
Project's home: https://www.hexstreamsoft.com/libraries/inheriting-readers/
GitHub: https://github.com/Hexstream/inheriting-readers
Quicklisp should pull from the tarball: https://tarballs.hexstreamsoft.com/libraries/latest/inheriting-... | 1.0 | Please add inheriting-readers - inheriting-readers provides a simple yet powerful value inheritance scheme.
Project's home: https://www.hexstreamsoft.com/libraries/inheriting-readers/
GitHub: https://github.com/Hexstream/inheriting-readers
Quicklisp should pull from the tarball: https://tarballs.hexstreamsoft.... | non_priority | please add inheriting readers inheriting readers provides a simple yet powerful value inheritance scheme project s home github quicklisp should pull from the tarball | 0 |
115,740 | 14,882,456,588 | IssuesEvent | 2021-01-20 11:55:55 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [APM] Discovery - need to re-evaluate implementation of filters and kuery bar across APM UI | Team:apm [zube]: Backlog discuss needs design | **Describe the feature:**
APM already offers various filters on different pages, like environments, hosts, K8s pods, containers, etc.
In 7.8 we started adding cloud metadata to be collected by APM agents.
... | 1.0 | [APM] Discovery - need to re-evaluate implementation of filters and kuery bar across APM UI - **Describe the feature:**
APM already offers various filters on different pages, like environments, hosts, K8s pods, containers, etc.
In 7.8 we started adding cloud metadata to be collected by APM agents.
 Gecko/20100101 Firefox/64.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://durington.info/XZEYY?tag_id=715349&sub_id1=59&sub_id2=BF78A1D5-713D-4674-8E18-492B43CFC078&cookie_id=9cedd5fa-dc74-4e95-8463-547442c3e... | 1.0 | durington.info - see bug description - <!-- @browser: Firefox 64.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:64.0) Gecko/20100101 Firefox/64.0 -->
<!-- @reported_with: desktop-reporter -->
**URL**: https://durington.info/XZEYY?tag_id=715349&sub_id1=59&sub_id2=BF78A1D5-713D-4674-8E18-492B43CFC078&cook... | priority | durington info see bug description url browser version firefox operating system windows tested another browser yes problem type something else description it opens always in background use cmd prompt automatic opening of site hangs pc irritable steps to repro... | 1 |
12,942 | 3,103,153,537 | IssuesEvent | 2015-08-31 07:49:14 | osakagamba/7GIQSKRNE5P3AVTZCEFXE3ON | https://api.github.com/repos/osakagamba/7GIQSKRNE5P3AVTZCEFXE3ON | closed | bIHT0vqN8SdqTWLmpVrcP2ptQn9f/r5zfwHcPK5Bi5Jbc6tjAKhtPfVNhyuvf0VVpn3CHe+TRHT9hicK8WovClCK2CorvLKpiXQShxYDhPk+tgNtYW3RtigSXrjmqVs/12SMzG2Dt/ioHl/ZqsiAWkY39nLpWvhd7SzTbK+oMBY= | design | fSS166lCfoE0L/zWHg5ySeyyN7zoU8dIgazEwBHybrI77oJrNZpSxN1DbyM+ZGGKUURPhxnRWARiyiOJorKJAWdQFC3ksbfOgHl6wteiUO0SCGQaNeUA9B5p9gbAYJAHcB35cTVPy6NONuxGywlJVe7KJ1dUhHzMk4cHqkBS6MDb51l8HTHEvpWXtOOwPKPbr0iJSXQO0Ht+TC+b0JUvJdSxry4SiKMjyJiyBzj+z77trt2teMTI6yzQMkj22IR4r0iJSXQO0Ht+TC+b0JUvJVxgQZqyN9vzuf9yHSffgAe5ccrSKRaievUIyJKo/LKD... | 1.0 | bIHT0vqN8SdqTWLmpVrcP2ptQn9f/r5zfwHcPK5Bi5Jbc6tjAKhtPfVNhyuvf0VVpn3CHe+TRHT9hicK8WovClCK2CorvLKpiXQShxYDhPk+tgNtYW3RtigSXrjmqVs/12SMzG2Dt/ioHl/ZqsiAWkY39nLpWvhd7SzTbK+oMBY= - fSS166lCfoE0L/zWHg5ySeyyN7zoU8dIgazEwBHybrI77oJrNZpSxN1DbyM+ZGGKUURPhxnRWARiyiOJorKJAWdQFC3ksbfOgHl6wteiUO0SCGQaNeUA9B5p9gbAYJAHcB35cTVPy6NONuxGy... | non_priority | iohl omby tc tc tc tc nlysiz xyqxlbkoomybwrufhj ownicmrbvluobig uxs | 0 |
66,017 | 12,702,963,867 | IssuesEvent | 2020-06-22 21:14:09 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Document the use of import-boss | area/code-organization kind/bug kind/documentation priority/important-longterm sig/testing | [import-boss](https://github.com/kubernetes/kubernetes/blob/master/staging/src/k8s.io/code-generator/cmd/import-boss/main.go) is used in our CI tests ([./hack/verify-import-boss.sh](https://github.com/kubernetes/kubernetes/blob/master/hack/verify-import-boss.sh)) to verify import restrictions in various places througho... | 1.0 | Document the use of import-boss - [import-boss](https://github.com/kubernetes/kubernetes/blob/master/staging/src/k8s.io/code-generator/cmd/import-boss/main.go) is used in our CI tests ([./hack/verify-import-boss.sh](https://github.com/kubernetes/kubernetes/blob/master/hack/verify-import-boss.sh)) to verify import restr... | non_priority | document the use of import boss is used in our ci tests to verify import restrictions in various places throughout k k currently the only existing documentation is within the script itself and this xref import boss ignores import in a test go file xref failed to implement verify import res... | 0 |
153,926 | 5,906,082,427 | IssuesEvent | 2017-05-19 14:23:53 | swimlane/ngx-charts | https://api.github.com/repos/swimlane/ngx-charts | closed | turn off transition (live data) | Backlog Effort: High Enhancement Priority: Med | **I'm submitting a ...** (check one with "x")
```
[ ] bug report => search github for a similar issue or PR before submitting
[x] feature request
[ ] support request => Please do not submit support request here
```
**Current behavior**
plunkr: [https://plnkr.co/edit/Nij7gO4jgqdN2mNPIFJp](https://plnkr.co/edit... | 1.0 | turn off transition (live data) - **I'm submitting a ...** (check one with "x")
```
[ ] bug report => search github for a similar issue or PR before submitting
[x] feature request
[ ] support request => Please do not submit support request here
```
**Current behavior**
plunkr: [https://plnkr.co/edit/Nij7gO4jg... | priority | turn off transition live data i m submitting a check one with x bug report search github for a similar issue or pr before submitting feature request support request please do not submit support request here current behavior plunkr expected behavior shift th... | 1 |
646,070 | 21,036,357,246 | IssuesEvent | 2022-03-31 08:13:57 | AY2122S2-CS2103-F11-2/tp | https://api.github.com/repos/AY2122S2-CS2103-F11-2/tp | opened | Update `Help` window | type.Bug priority.Medium Functionality | Currently the help window does not contain all available commands in this version.
Let's update it to contain all commands. | 1.0 | Update `Help` window - Currently the help window does not contain all available commands in this version.
Let's update it to contain all commands. | priority | update help window currently the help window does not contain all available commands in this version let s update it to contain all commands | 1 |
309,691 | 26,672,684,081 | IssuesEvent | 2023-01-26 11:44:00 | MarinoFajardo/ControlaTuGasto | https://api.github.com/repos/MarinoFajardo/ControlaTuGasto | closed | [M2] Es necesario comprobar que el comportamiento de la clase parada es el esperado. | invalid test | En #25 de describen una serie de comportamientos que debe cumplir la clase parada para que su funcionamiento sea el esperado:
- Para comprobar el comportamiento correcto de esta clase, es necesario que si dos paradas tienen el mismo id sean la misma parada, es decir, no puede haber dos paradas que tengan el mismo id y... | 1.0 | [M2] Es necesario comprobar que el comportamiento de la clase parada es el esperado. - En #25 de describen una serie de comportamientos que debe cumplir la clase parada para que su funcionamiento sea el esperado:
- Para comprobar el comportamiento correcto de esta clase, es necesario que si dos paradas tienen el mismo... | non_priority | es necesario comprobar que el comportamiento de la clase parada es el esperado en de describen una serie de comportamientos que debe cumplir la clase parada para que su funcionamiento sea el esperado para comprobar el comportamiento correcto de esta clase es necesario que si dos paradas tienen el mismo id ... | 0 |
424,872 | 29,181,547,129 | IssuesEvent | 2023-05-19 12:20:15 | awslabs/aws-lambda-powertools-typescript | https://api.github.com/repos/awslabs/aws-lambda-powertools-typescript | closed | Docs: fix inappropriate hilighted lines | area/documentation status/discussing | ### What were you searching in the docs?
Some highlighted lines in the sample code are inappropriate. Some are pointing to the wrong place, others to a line that does not exist.
The most obvious example is the "Example CloudWatch Logs excerpt" in Metric's "Adding metadata". It should be specified by highlighting ... | 1.0 | Docs: fix inappropriate hilighted lines - ### What were you searching in the docs?
Some highlighted lines in the sample code are inappropriate. Some are pointing to the wrong place, others to a line that does not exist.
The most obvious example is the "Example CloudWatch Logs excerpt" in Metric's "Adding metadata... | non_priority | docs fix inappropriate hilighted lines what were you searching in the docs some highlighted lines in the sample code are inappropriate some are pointing to the wrong place others to a line that does not exist the most obvious example is the example cloudwatch logs excerpt in metric s adding metadata... | 0 |
642,332 | 20,885,321,461 | IssuesEvent | 2022-03-23 04:00:12 | CobeyH/SENG-480A | https://api.github.com/repos/CobeyH/SENG-480A | closed | Icon sizes are too big on Safari | bug A Priority 1 | **Describe the bug**
When creating a group on Safari, the icon profile pictures aren't the correct size.
**To Reproduce**
Steps to reproduce the behavior:
1. Open the app on Safari
2. Create a new group
3. View the "Icon Profile Pictures"
**Expected behavior**
The icons will look the same on Safari and Chro... | 1.0 | Icon sizes are too big on Safari - **Describe the bug**
When creating a group on Safari, the icon profile pictures aren't the correct size.
**To Reproduce**
Steps to reproduce the behavior:
1. Open the app on Safari
2. Create a new group
3. View the "Icon Profile Pictures"
**Expected behavior**
The icons wi... | priority | icon sizes are too big on safari describe the bug when creating a group on safari the icon profile pictures aren t the correct size to reproduce steps to reproduce the behavior open the app on safari create a new group view the icon profile pictures expected behavior the icons wi... | 1 |
314,376 | 9,596,062,469 | IssuesEvent | 2019-05-09 17:37:42 | aiidateam/aiida-quantumespresso | https://api.github.com/repos/aiidateam/aiida-quantumespresso | closed | Bundle all CLI launchers in single click console script | priority/nice to have topic/cli type/accepted feature | Adding a single console script for each calculation and workflow launcher that we would like to make available is not tenable. | 1.0 | Bundle all CLI launchers in single click console script - Adding a single console script for each calculation and workflow launcher that we would like to make available is not tenable. | priority | bundle all cli launchers in single click console script adding a single console script for each calculation and workflow launcher that we would like to make available is not tenable | 1 |
318,085 | 27,284,453,320 | IssuesEvent | 2023-02-23 12:30:51 | cosmos/interchain-security | https://api.github.com/repos/cosmos/interchain-security | closed | Code review: Using ibc-go (cosmos/interchain-security) | testing | - [x] ibc-go team needs to review the code from an IBC perspective | 1.0 | Code review: Using ibc-go (cosmos/interchain-security) - - [x] ibc-go team needs to review the code from an IBC perspective | non_priority | code review using ibc go cosmos interchain security ibc go team needs to review the code from an ibc perspective | 0 |
40,477 | 12,797,753,299 | IssuesEvent | 2020-07-02 12:52:18 | RG4421/react-credit-card-input | https://api.github.com/repos/RG4421/react-credit-card-input | opened | CVE-2020-7660 (High) detected in serialize-javascript-1.9.1.tgz | security vulnerability | ## CVE-2020-7660 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>Serialize JavaScript to a superset of JSON that includes regular ex... | True | CVE-2020-7660 (High) detected in serialize-javascript-1.9.1.tgz - ## CVE-2020-7660 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>serialize-javascript-1.9.1.tgz</b></p></summary>
<p>S... | non_priority | cve high detected in serialize javascript tgz cve high severity vulnerability vulnerable library serialize javascript tgz serialize javascript to a superset of json that includes regular expressions and functions library home page a href path to dependency file tmp ws... | 0 |
43,027 | 12,965,164,764 | IssuesEvent | 2020-07-20 21:48:48 | jtimberlake/griffin | https://api.github.com/repos/jtimberlake/griffin | opened | WS-2019-0333 (Medium) detected in handlebars-1.3.0.tgz | security vulnerability | ## WS-2019-0333 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-1.3.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates ... | True | WS-2019-0333 (Medium) detected in handlebars-1.3.0.tgz - ## WS-2019-0333 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-1.3.0.tgz</b></p></summary>
<p>Handlebars provides... | non_priority | ws medium detected in handlebars tgz ws medium severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file tmp ws s... | 0 |
813,352 | 30,454,740,079 | IssuesEvent | 2023-07-16 18:45:45 | priyankarpal/ProjectsHut | https://api.github.com/repos/priyankarpal/ProjectsHut | closed | feat:Adding hover effect on the links | 🛠 goal: fix ⭐ goal: addition 🟩 priority: low 🏁 status: ready for dev | ### What feature?
addition of the hover effect on the links will look great!!
### Add screenshots

### Record
- [X] I agree to follow this project's Code of Conduct
- [ ] I'm ... | 1.0 | feat:Adding hover effect on the links - ### What feature?
addition of the hover effect on the links will look great!!
### Add screenshots

### Record
- [X] I agree to follow t... | priority | feat adding hover effect on the links what feature addition of the hover effect on the links will look great add screenshots record i agree to follow this project s code of conduct i m a gssoc contributor i want to work on this issue | 1 |
548,215 | 16,060,333,621 | IssuesEvent | 2021-04-23 11:37:16 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.samplicio.us - see bug description | browser-fenix engine-gecko ml-needsdiagnosis-false priority-normal | <!-- @browser: Firefox Mobile 88.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.1.0; Mobile; rv:88.0) Gecko/88.0 Firefox/88.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/71450 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://www.sampl... | 1.0 | www.samplicio.us - see bug description - <!-- @browser: Firefox Mobile 88.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.1.0; Mobile; rv:88.0) Gecko/88.0 Firefox/88.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/71450 -->
<!-- @extra_labels: brow... | priority | see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description lost connection steps to reproduce every survey failed loading can not connected survey site ... | 1 |
171,911 | 21,007,659,465 | IssuesEvent | 2022-03-30 01:16:53 | Satheesh575555/kernel-mm-huge_memory | https://api.github.com/repos/Satheesh575555/kernel-mm-huge_memory | opened | CVE-2021-29154 (High) detected in linuxlinux-4.19.236 | security vulnerability | ## CVE-2021-29154 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.236</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.k... | True | CVE-2021-29154 (High) detected in linuxlinux-4.19.236 - ## CVE-2021-29154 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.236</b></p></summary>
<p>
<p>The Linux Kernel<... | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in base branch master vulnerable source files vulnerability details bpf jit ... | 0 |
554,631 | 16,435,033,187 | IssuesEvent | 2021-05-20 08:17:49 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | 9.3 1966 - Rent currency does not default to what treasury has set | Category: Gameplay Priority: Low Squad: Wild Turkey Type: Bug | As per subject, rent's currency does not default to the currency that the treasury has set.
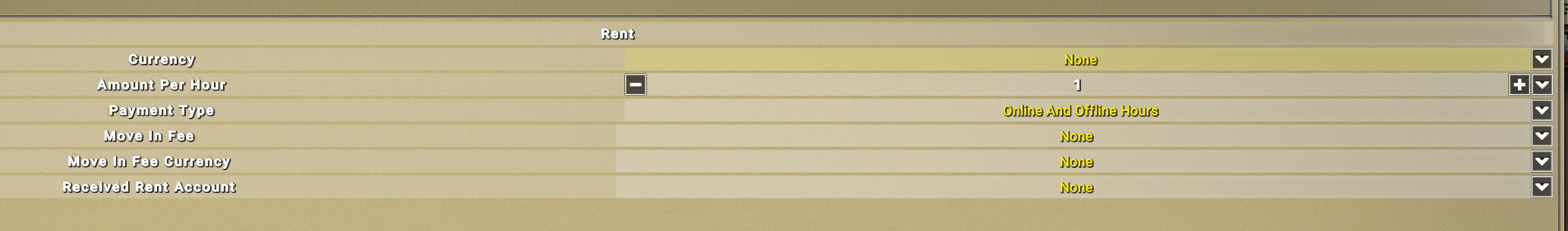

 when it is a residential occupancy type.
Terry manually added these fees to the application in PROD.
 when it is a residential occupancy type.
Terry manually added these ... | priority | building permits capacity spring view estates subdivision fees capacity residential single family dwelling ap the spring view estates subdivision code needs to automatically add the residential sewer fee when it is a residential occupancy type terry manually added these fees to the applic... | 1 |
673,443 | 22,969,835,113 | IssuesEvent | 2022-07-20 01:16:33 | stackcollision/Nebulous-BugReporting | https://api.github.com/repos/stackcollision/Nebulous-BugReporting | closed | Sprint stage on hybrid missiles (Cyclone, Atlatl) with max speed settings have sprint stages seperate with insufficient range. | bug branch-modmis incorrect behavior priority high | **Describe the bug**
Sprint stage on hybrid missiles (Cyclone, Atlatl) with max speed settings have sprint stages seperate with insufficient range.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to Missile Designer
2. Create new hybrid missile (Cyclone, Atlatl) and set sprint stage to maximum speed.
3.... | 1.0 | Sprint stage on hybrid missiles (Cyclone, Atlatl) with max speed settings have sprint stages seperate with insufficient range. - **Describe the bug**
Sprint stage on hybrid missiles (Cyclone, Atlatl) with max speed settings have sprint stages seperate with insufficient range.
**To Reproduce**
Steps to reproduce th... | priority | sprint stage on hybrid missiles cyclone atlatl with max speed settings have sprint stages seperate with insufficient range describe the bug sprint stage on hybrid missiles cyclone atlatl with max speed settings have sprint stages seperate with insufficient range to reproduce steps to reproduce th... | 1 |
359,951 | 10,682,735,166 | IssuesEvent | 2019-10-22 06:31:05 | bounswe/bounswe2019group8 | https://api.github.com/repos/bounswe/bounswe2019group8 | closed | Add data picker and check valid cases for sign up. | Effort: High Mobile Platform: Mobile Priority: High Status: Done Status: In Progress Type: Feature | **Actions:**
1. Add data picker in sign up.
2. Check valid for iban and id numbers.
3. Check user exists.
**Notes:**
- [x] Add data picker in sign up.
- [x] Check valid for iban and id numbers.
- [x] Check user exists.
**Deadline:** 22.10.2019 - 11.00 | 1.0 | Add data picker and check valid cases for sign up. - **Actions:**
1. Add data picker in sign up.
2. Check valid for iban and id numbers.
3. Check user exists.
**Notes:**
- [x] Add data picker in sign up.
- [x] Check valid for iban and id numbers.
- [x] Check user exists.
**Deadline:** 22.10.2019 - 11.00 | priority | add data picker and check valid cases for sign up actions add data picker in sign up check valid for iban and id numbers check user exists notes add data picker in sign up check valid for iban and id numbers check user exists deadline | 1 |
23,435 | 6,419,940,820 | IssuesEvent | 2017-08-08 22:30:30 | xhqiao89/HydroDesktop_test | https://api.github.com/repos/xhqiao89/HydroDesktop_test | closed | Add a series to a theme (from another theme) | CodePlex | <b>dtarb[CodePlex]</b> <br />I would like to be able to:
Add a series to a theme (from another theme)
this feature can be added as a new context menu item in the series selector menu.
| 1.0 | Add a series to a theme (from another theme) - <b>dtarb[CodePlex]</b> <br />I would like to be able to:
Add a series to a theme (from another theme)
this feature can be added as a new context menu item in the series selector menu.
| non_priority | add a series to a theme from another theme dtarb i would like to be able to add a series to a theme from another theme this feature can be added as a new context menu item in the series selector menu | 0 |
5,482 | 2,576,697,805 | IssuesEvent | 2015-02-12 12:12:52 | olga-jane/prizm | https://api.github.com/repos/olga-jane/prizm | closed | Add file button should be at the left, Close at the right at ExternalFile dialog | Attachments bug bug - UI Coding MEDIUM priority | Add file button should be at the left, Close at the right at ExternalFile dialog.
Now both buttons are at the right. | 1.0 | Add file button should be at the left, Close at the right at ExternalFile dialog - Add file button should be at the left, Close at the right at ExternalFile dialog.
Now both buttons are at the right. | priority | add file button should be at the left close at the right at externalfile dialog add file button should be at the left close at the right at externalfile dialog now both buttons are at the right | 1 |
35,748 | 7,800,527,202 | IssuesEvent | 2018-06-09 10:32:10 | StrikeNP/trac_test | https://api.github.com/repos/StrikeNP/trac_test | closed | Divide integer, public declarations in stats_variables.F90 into smaller blocks in order to avoid ANSI warning (Trac #545) | Migrated from Trac clubb_src defect raut@uwm.edu |
'''Introduction'''
We try to keep CLUBB compatible with ANSI standards in order to enhance portability. ANSI requires that no more than 39 continuation characters (i.e. &) be used for one line. However, when we add new variables to declaration lists, we sometimes exceed 39 continuation characters, thereby triggerin... | 1.0 | Divide integer, public declarations in stats_variables.F90 into smaller blocks in order to avoid ANSI warning (Trac #545) -
'''Introduction'''
We try to keep CLUBB compatible with ANSI standards in order to enhance portability. ANSI requires that no more than 39 continuation characters (i.e. &) be used for one line.... | non_priority | divide integer public declarations in stats variables into smaller blocks in order to avoid ansi warning trac introduction we try to keep clubb compatible with ansi standards in order to enhance portability ansi requires that no more than continuation characters i e be used for one line how... | 0 |
57,142 | 3,081,243,195 | IssuesEvent | 2015-08-22 14:33:35 | bitfighter/bitfighter | https://api.github.com/repos/bitfighter/bitfighter | closed | Seekers seek teammates in single-team rabbit | 019a bug imported Priority-Medium | _From [buckyballreaction](https://code.google.com/u/buckyballreaction/) on January 07, 2014 11:59:38_
Seekers seek teammates in single-team rabbit
_Original issue: http://code.google.com/p/bitfighter/issues/detail?id=365_ | 1.0 | Seekers seek teammates in single-team rabbit - _From [buckyballreaction](https://code.google.com/u/buckyballreaction/) on January 07, 2014 11:59:38_
Seekers seek teammates in single-team rabbit
_Original issue: http://code.google.com/p/bitfighter/issues/detail?id=365_ | priority | seekers seek teammates in single team rabbit from on january seekers seek teammates in single team rabbit original issue | 1 |
5,633 | 2,577,816,936 | IssuesEvent | 2015-02-12 19:18:42 | phetsims/tasks | https://api.github.com/repos/phetsims/tasks | closed | Update budgets through Jan | Accounting Top Priority | @arnabp Please prioritize updating these budgets through Jan 2015:
Moore NSF DRK12 NSF DRK12 Matching NSF TUES CHEM
Also, your laptop is in F1011 - should hopefully get labeled today. | 1.0 | Update budgets through Jan - @arnabp Please prioritize updating these budgets through Jan 2015:
Moore NSF DRK12 NSF DRK12 Matching NSF TUES CHEM
Also, your laptop is in F1011 - should hopefully get labeled today. | priority | update budgets through jan arnabp please prioritize updating these budgets through jan moore nsf nsf matching nsf tues chem also your laptop is in should hopefully get labeled today | 1 |
82,579 | 15,648,357,771 | IssuesEvent | 2021-03-23 05:33:29 | YJSoft/namuhub | https://api.github.com/repos/YJSoft/namuhub | closed | CVE-2019-16789 (High) detected in waitress-0.8.9.tar.gz - autoclosed | security vulnerability | ## CVE-2019-16789 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>waitress-0.8.9.tar.gz</b></p></summary>
<p>Waitress WSGI server</p>
<p>Library home page: <a href="https://files.pytho... | True | CVE-2019-16789 (High) detected in waitress-0.8.9.tar.gz - autoclosed - ## CVE-2019-16789 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>waitress-0.8.9.tar.gz</b></p></summary>
<p>Wait... | non_priority | cve high detected in waitress tar gz autoclosed cve high severity vulnerability vulnerable library waitress tar gz waitress wsgi server library home page a href path to dependency file namuhub requirements txt path to vulnerable library namuhub requirements txt ... | 0 |
633,805 | 20,266,249,369 | IssuesEvent | 2022-02-15 12:21:41 | HabitRPG/habitica-ios | https://api.github.com/repos/HabitRPG/habitica-ios | closed | Japanese not showing correctly for login incentive rewards | Type: Bug Help wanted Priority: minor | natalie checked the string, and that seems fine. there just seems to be an issue with displaying the characters?
> iOS Version: 15.1
Device: iPhone 8
App Version: 3.4.4 (649)
User ID: e0b0a48b-c8a... | 1.0 | Japanese not showing correctly for login incentive rewards - natalie checked the string, and that seems fine. there just seems to be an issue with displaying the characters?
> iOS Version: 15.1
Devi... | priority | japanese not showing correctly for login incentive rewards natalie checked the string and that seems fine there just seems to be an issue with displaying the characters ios version device iphone app version user id level class warrior is in inn false uses c... | 1 |
392,549 | 26,946,996,586 | IssuesEvent | 2023-02-08 08:55:00 | trixi-framework/Trixi.jl | https://api.github.com/repos/trixi-framework/Trixi.jl | opened | Update instructions to build docs locally | documentation | Developing Trixi on a fork may include adding types / function with corresponding docstrings. Previewing the documentation from a fork online is not available for security reasons. To preview the docs with your local documentation changes and updates one needs to use the following commands (taken directly from #668)
`... | 1.0 | Update instructions to build docs locally - Developing Trixi on a fork may include adding types / function with corresponding docstrings. Previewing the documentation from a fork online is not available for security reasons. To preview the docs with your local documentation changes and updates one needs to use the foll... | non_priority | update instructions to build docs locally developing trixi on a fork may include adding types function with corresponding docstrings previewing the documentation from a fork online is not available for security reasons to preview the docs with your local documentation changes and updates one needs to use the foll... | 0 |
49,736 | 26,280,927,535 | IssuesEvent | 2023-01-07 09:35:19 | python/cpython | https://api.github.com/repos/python/cpython | opened | Make `copy.deepcopy` faster for `slice` objects | type-feature performance | ## `slice`
Right now `slice` objects are deepcopied using `__reduce__` defined as:
https://github.com/python/cpython/blob/26ff43625ed7bf09542ad8f149cb6af710b41e15/Objects/sliceobject.c#L559-L563
It is one of last branches of `deepcopy` logic:
https://github.com/python/cpython/blob/26ff43625ed7bf09542ad8f149cb6a... | True | Make `copy.deepcopy` faster for `slice` objects - ## `slice`
Right now `slice` objects are deepcopied using `__reduce__` defined as:
https://github.com/python/cpython/blob/26ff43625ed7bf09542ad8f149cb6af710b41e15/Objects/sliceobject.c#L559-L563
It is one of last branches of `deepcopy` logic:
https://github.com/... | non_priority | make copy deepcopy faster for slice objects slice right now slice objects are deepcopied using reduce defined as it is one of last branches of deepcopy logic but since slice is an immutable type we can optimize its deepcopy as python d deepcopy atomic befo... | 0 |
708,992 | 24,364,446,397 | IssuesEvent | 2022-10-03 14:11:34 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.google.com - site is not usable | priority-critical browser-focus-geckoview engine-gecko | <!-- @browser: Firefox Mobile 105.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 12; Mobile; rv:105.0) Gecko/105.0 Firefox/105.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/111744 -->
<!-- @extra_labels: browser-focus-geckoview -->
**URL**: https... | 1.0 | www.google.com - site is not usable - <!-- @browser: Firefox Mobile 105.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 12; Mobile; rv:105.0) Gecko/105.0 Firefox/105.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/111744 -->
<!-- @extra_labels: brows... | priority | site is not usable url browser version firefox mobile operating system android tested another browser no problem type site is not usable description page not loading correctly steps to reproduce screen goes black and only refreshes black also tried on and... | 1 |
58,303 | 14,359,635,449 | IssuesEvent | 2020-11-30 15:51:55 | acxz/pkgbuilds | https://api.github.com/repos/acxz/pkgbuilds | closed | [openvsp] Missing unzip | build error | ```
==> Entering fakeroot environment...
==> Starting package()...
/startdir/PKGBUILD: line 74: unzip: command not found
==> ERROR: A failure occurred in package().
Aborting...
``` | 1.0 | [openvsp] Missing unzip - ```
==> Entering fakeroot environment...
==> Starting package()...
/startdir/PKGBUILD: line 74: unzip: command not found
==> ERROR: A failure occurred in package().
Aborting...
``` | non_priority | missing unzip entering fakeroot environment starting package startdir pkgbuild line unzip command not found error a failure occurred in package aborting | 0 |
102,867 | 4,161,915,420 | IssuesEvent | 2016-06-17 18:20:32 | ReactiveX/rxjs | https://api.github.com/repos/ReactiveX/rxjs | closed | A method Rx.Observable.when | priority: low status: PRs welcome | Hi all! Exists in plan implementing methods like `Rx.Observable.when` and `Rx.Observable.update`? | 1.0 | A method Rx.Observable.when - Hi all! Exists in plan implementing methods like `Rx.Observable.when` and `Rx.Observable.update`? | priority | a method rx observable when hi all exists in plan implementing methods like rx observable when and rx observable update | 1 |
275,677 | 8,578,773,271 | IssuesEvent | 2018-11-13 06:46:33 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.instagram.com - see bug description | browser-firefox-mobile priority-critical | <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.1.0; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.instagram.com/
**Browser / Version**: Firefox Mobile 65.0
**Operating System**: Android 8.1.0
**Tested Another Browser**: Yes
... | 1.0 | www.instagram.com - see bug description - <!-- @browser: Firefox Mobile 65.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 8.1.0; Mobile; rv:65.0) Gecko/65.0 Firefox/65.0 -->
<!-- @reported_with: mobile-reporter -->
**URL**: https://www.instagram.com/
**Browser / Version**: Firefox Mobile 65.0
**Operating System**: Andro... | priority | see bug description url browser version firefox mobile operating system android tested another browser yes problem type something else description scrolling does not work as it should steps to reproduce while scrolling the page although it is loaded the... | 1 |
802,126 | 28,718,311,306 | IssuesEvent | 2023-04-28 00:04:28 | LiskHQ/lisk-desktop | https://api.github.com/repos/LiskHQ/lisk-desktop | opened | Inaccessible hardware wallet accounts stored in account list | type: bug priority: medium domain: hardware-wallet | ### Expected behavior
Previous selected and unintialized hardware wallet accounts should be removed from the account list after hardware wallet is disconnected
### Actual behavior
Both previously selected and uninitialized hardware wallet accounts remain in account list after hardware wallet is disconnected
![lis... | 1.0 | Inaccessible hardware wallet accounts stored in account list - ### Expected behavior
Previous selected and unintialized hardware wallet accounts should be removed from the account list after hardware wallet is disconnected
### Actual behavior
Both previously selected and uninitialized hardware wallet accounts rema... | priority | inaccessible hardware wallet accounts stored in account list expected behavior previous selected and unintialized hardware wallet accounts should be removed from the account list after hardware wallet is disconnected actual behavior both previously selected and uninitialized hardware wallet accounts rema... | 1 |
104,619 | 16,619,403,257 | IssuesEvent | 2021-06-02 21:30:33 | MythicDrops/MythicDrops | https://api.github.com/repos/MythicDrops/MythicDrops | closed | CVE-2021-27290 (High) detected in ssri-6.0.1.tgz - autoclosed | security vulnerability | ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ssri-6.0.1.tgz</b></p></summary>
<p>Standard Subresource Integrity library -- parses, serializes, generates, and veri... | True | CVE-2021-27290 (High) detected in ssri-6.0.1.tgz - autoclosed - ## CVE-2021-27290 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ssri-6.0.1.tgz</b></p></summary>
<p>Standard Subresour... | non_priority | cve high detected in ssri tgz autoclosed cve high severity vulnerability vulnerable library ssri tgz standard subresource integrity library parses serializes generates and verifies integrity metadata according to the sri spec library home page a href path to de... | 0 |
72,288 | 9,562,589,768 | IssuesEvent | 2019-05-04 10:32:41 | openscript/beefindr | https://api.github.com/repos/openscript/beefindr | closed | Risikoanalyse | documentation | # Ziel
Schutzbedarf und Risikoanalyse erstellen (die Excel Vorlagen verwenden)
# Auftrag
- [x] Schutzbedarf und Risikoanalyse erstellen (die Excel Vorlagen verwenden)
https://www.isb.admin.ch/isb/de/home/ikt-vorgaben/prozesse-methoden/p041-schutzbedarfsanalyse_schuban.html
https://www.isb.admin.ch/isb/de/home... | 1.0 | Risikoanalyse - # Ziel
Schutzbedarf und Risikoanalyse erstellen (die Excel Vorlagen verwenden)
# Auftrag
- [x] Schutzbedarf und Risikoanalyse erstellen (die Excel Vorlagen verwenden)
https://www.isb.admin.ch/isb/de/home/ikt-vorgaben/prozesse-methoden/p041-schutzbedarfsanalyse_schuban.html
https://www.isb.admi... | non_priority | risikoanalyse ziel schutzbedarf und risikoanalyse erstellen die excel vorlagen verwenden auftrag schutzbedarf und risikoanalyse erstellen die excel vorlagen verwenden auswahl der geeigneten schutzmassnahmen konfigurieren der massnahmen für den service und das gui umsetzen und teste... | 0 |
176,925 | 21,464,438,422 | IssuesEvent | 2022-04-26 01:09:20 | alexcorvi/apexo | https://api.github.com/repos/alexcorvi/apexo | closed | CVE-2020-7789 (Medium) detected in node-notifier-5.4.3.tgz - autoclosed | security vulnerability | ## CVE-2020-7789 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-notifier-5.4.3.tgz</b></p></summary>
<p>A Node.js module for sending notifications on native Mac, Windows (post ... | True | CVE-2020-7789 (Medium) detected in node-notifier-5.4.3.tgz - autoclosed - ## CVE-2020-7789 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-notifier-5.4.3.tgz</b></p></summary>
<... | non_priority | cve medium detected in node notifier tgz autoclosed cve medium severity vulnerability vulnerable library node notifier tgz a node js module for sending notifications on native mac windows post and pre and linux or growl as fallback library home page a href path ... | 0 |
374,175 | 26,103,747,599 | IssuesEvent | 2022-12-27 10:29:36 | WorldHealthOrganization/open-source-communication-channel | https://api.github.com/repos/WorldHealthOrganization/open-source-communication-channel | closed | Update projects on README | documentation | Update README file to include Step-by-step and Em Care to list of projects and project points of contact. | 1.0 | Update projects on README - Update README file to include Step-by-step and Em Care to list of projects and project points of contact. | non_priority | update projects on readme update readme file to include step by step and em care to list of projects and project points of contact | 0 |
425 | 2,496,666,619 | IssuesEvent | 2015-01-06 21:18:39 | cytoscape/cytoscape.js | https://api.github.com/repos/cytoscape/cytoscape.js | opened | Private renderer.renderTo() motionblur conflict | 1-high-priority bug renderer | Seems to be timeout related, as the forced context case should not affect the main rendering logic. | 1.0 | Private renderer.renderTo() motionblur conflict - Seems to be timeout related, as the forced context case should not affect the main rendering logic. | priority | private renderer renderto motionblur conflict seems to be timeout related as the forced context case should not affect the main rendering logic | 1 |
242,163 | 20,201,516,548 | IssuesEvent | 2022-02-11 15:41:40 | ubtue/DatenProbleme | https://api.github.com/repos/ubtue/DatenProbleme | reopened | ISSN 2513-1389 | Zeitschrift für christlich-jüdische Begegnung im Kontext | Seitenangabe | ready for testing Zotero_SEMI-AUTO | **URL**
https://zfbeg.org/ojs/index.php/cjbk/issue/view/28
**Import-Translator**
ubtue_Open Journal Systems Standard.js
(Einzel- und Mehrfach-Import)
**Problembeschreibung**
Bei der Seitenangabe wird der Ausdruck "S." mit importiert sowie am Ende ein Punkt-Zeichen, was dann zum gleichen Export führt. ... | 1.0 | ISSN 2513-1389 | Zeitschrift für christlich-jüdische Begegnung im Kontext | Seitenangabe - **URL**
https://zfbeg.org/ojs/index.php/cjbk/issue/view/28
**Import-Translator**
ubtue_Open Journal Systems Standard.js
(Einzel- und Mehrfach-Import)
**Problembeschreibung**
Bei der Seitenangabe wird der Ausdruc... | non_priority | issn zeitschrift für christlich jüdische begegnung im kontext seitenangabe url import translator ubtue open journal systems standard js einzel und mehrfach import problembeschreibung bei der seitenangabe wird der ausdruck s mit importiert sowie am ende ein punkt zeichen ... | 0 |
339,905 | 10,264,130,306 | IssuesEvent | 2019-08-22 15:41:33 | medic/medic-conf | https://api.github.com/repos/medic/medic-conf | closed | Declarative Configuration - Ability to control which contact is associated with emitted task | Priority: 1 - High enhancement | Tasks which are emitted by app_settings configuration contain a contact attribute which controls which contact is associated with the task. In the declarative configuration system, the contact associated with the task is the owner of the report that generated the task. [Here](https://github.com/medic/medic-conf/blob/ma... | 1.0 | Declarative Configuration - Ability to control which contact is associated with emitted task - Tasks which are emitted by app_settings configuration contain a contact attribute which controls which contact is associated with the task. In the declarative configuration system, the contact associated with the task is the ... | priority | declarative configuration ability to control which contact is associated with emitted task tasks which are emitted by app settings configuration contain a contact attribute which controls which contact is associated with the task in the declarative configuration system the contact associated with the task is the ... | 1 |
92,591 | 10,758,944,835 | IssuesEvent | 2019-10-31 15:47:43 | microsoft/PowerToys | https://api.github.com/repos/microsoft/PowerToys | closed | PowerRename - capturing and using regex parts | PowerRename documentation | I wanted to check if capturing and using regex parts is possible - I'm used to this from Visual Studio and Notepad++. Found it by accident, it should be documented.
Capturing a part can be done like "(...)", using the captured values in the replace can be done with "$1"..."$n".
This is very useful and should be a... | 1.0 | PowerRename - capturing and using regex parts - I wanted to check if capturing and using regex parts is possible - I'm used to this from Visual Studio and Notepad++. Found it by accident, it should be documented.
Capturing a part can be done like "(...)", using the captured values in the replace can be done with "$1... | non_priority | powerrename capturing and using regex parts i wanted to check if capturing and using regex parts is possible i m used to this from visual studio and notepad found it by accident it should be documented capturing a part can be done like using the captured values in the replace can be done with ... | 0 |
27,272 | 4,049,144,372 | IssuesEvent | 2016-05-23 13:13:30 | duckduckgo/community-platform | https://api.github.com/repos/duckduckgo/community-platform | closed | An idea to make it quicker to delete spam | Design Forum | The spam has been heavy lately. That and the fact that my laptop has a small screen has forced to scoll up and down tons of times to be able click the "Leave invisible" button, whenever there was a difference in the length of the content of the spam-post (and thus the height of `div` containing it).
I quickly checke... | 1.0 | An idea to make it quicker to delete spam - The spam has been heavy lately. That and the fact that my laptop has a small screen has forced to scoll up and down tons of times to be able click the "Leave invisible" button, whenever there was a difference in the length of the content of the spam-post (and thus the height ... | non_priority | an idea to make it quicker to delete spam the spam has been heavy lately that and the fact that my laptop has a small screen has forced to scoll up and down tons of times to be able click the leave invisible button whenever there was a difference in the length of the content of the spam post and thus the height ... | 0 |
809,251 | 30,182,186,142 | IssuesEvent | 2023-07-04 09:36:35 | pendulum-chain/spacewalk | https://api.github.com/repos/pendulum-chain/spacewalk | closed | Support 'confirm' SCP messages in the stellar-relay when proving transaction validity | priority:high | # Problem
With the current implementation, the `stellar-relay` pallet only considers `ScpStatementExternalize` consensus messages to prove the validity of a Stellar transaction. However, we identified that Stellar archive entries usually only contain just **one** externalized message but many other 'ScpStatementConfim... | 1.0 | Support 'confirm' SCP messages in the stellar-relay when proving transaction validity - # Problem
With the current implementation, the `stellar-relay` pallet only considers `ScpStatementExternalize` consensus messages to prove the validity of a Stellar transaction. However, we identified that Stellar archive entries u... | priority | support confirm scp messages in the stellar relay when proving transaction validity problem with the current implementation the stellar relay pallet only considers scpstatementexternalize consensus messages to prove the validity of a stellar transaction however we identified that stellar archive entries u... | 1 |
615,974 | 19,287,131,076 | IssuesEvent | 2021-12-11 05:48:53 | Vyxal/Vyxal | https://api.github.com/repos/Vyxal/Vyxal | closed | Mold modifies inputs | bug difficulty: average priority:high | When one of the arguments passed to Mold is input, whether taken implicitly or explicitly, it permanently modifies that input to be whatever the output of the Mold command was.
Examples:
[1 Input](https://vyxal.pythonanywhere.com/#WyIiLCIiLCI/LD8sIMK2LCDin6hcXGF8XFxifFxcY+KfqT8g4oCiID8sPywiLCIiLCJbMSwyLDMsNCw1LDY... | 1.0 | Mold modifies inputs - When one of the arguments passed to Mold is input, whether taken implicitly or explicitly, it permanently modifies that input to be whatever the output of the Mold command was.
Examples:
[1 Input](https://vyxal.pythonanywhere.com/#WyIiLCIiLCI/LD8sIMK2LCDin6hcXGF8XFxifFxcY+KfqT8g4oCiID8sPywi... | priority | mold modifies inputs when one of the arguments passed to mold is input whether taken implicitly or explicitly it permanently modifies that input to be whatever the output of the mold command was examples | 1 |
582,547 | 17,363,986,114 | IssuesEvent | 2021-07-30 03:06:18 | ReliaQualAssociates/ramstk | https://api.github.com/repos/ReliaQualAssociates/ramstk | closed | Remove do_get_tree() from Hardware Datamanager | priority: normal status: inprogress type: refactor | **Describe the chore that needs to be addressed.**
1. The do_get_tree() method should be deleted.
2. The pub.subscribe should be deleted.
3. _tag attributes needs to be singular.
4. Fix tests that expect _tag to be plural.
5. Fix export and test_export
- [ ] This issue is an epic issue which subsumes the follow... | 1.0 | Remove do_get_tree() from Hardware Datamanager - **Describe the chore that needs to be addressed.**
1. The do_get_tree() method should be deleted.
2. The pub.subscribe should be deleted.
3. _tag attributes needs to be singular.
4. Fix tests that expect _tag to be plural.
5. Fix export and test_export
- [ ] This... | priority | remove do get tree from hardware datamanager describe the chore that needs to be addressed the do get tree method should be deleted the pub subscribe should be deleted tag attributes needs to be singular fix tests that expect tag to be plural fix export and test export this i... | 1 |
636,906 | 20,612,641,003 | IssuesEvent | 2022-03-07 10:08:50 | Soulcialize/souldragonknight | https://api.github.com/repos/Soulcialize/souldragonknight | opened | Add stamina and mana system | type.Enhancement priority.Medium | The knight will have stamina while the dragon has mana. These two resources are depleted when attacking and will recharge over time.
This would discourage players from spamming their attacks which would make the enemies too easy to defeat. Players will have to cooperate more closely so that they do not waste stamina/m... | 1.0 | Add stamina and mana system - The knight will have stamina while the dragon has mana. These two resources are depleted when attacking and will recharge over time.
This would discourage players from spamming their attacks which would make the enemies too easy to defeat. Players will have to cooperate more closely so th... | priority | add stamina and mana system the knight will have stamina while the dragon has mana these two resources are depleted when attacking and will recharge over time this would discourage players from spamming their attacks which would make the enemies too easy to defeat players will have to cooperate more closely so th... | 1 |
705,014 | 24,218,361,781 | IssuesEvent | 2022-09-26 08:47:21 | AY2223S1-CS2103T-T12-2/tp | https://api.github.com/repos/AY2223S1-CS2103T-T12-2/tp | closed | Update site-wide settings | type.Task priority.High | ## Tasks
- Follow guide for [Using Jekyll for project documentation @SE-EDU/guides](https://se-education.org/guides/tutorials/jekyll.html)
- The text `AB-3` in `docs\_sass\minima\_base.scss` needs updating (it comes into play when you convert documentation to PDF formats)
[Link](https://nus-cs2103-ay2223s1.git... | 1.0 | Update site-wide settings - ## Tasks
- Follow guide for [Using Jekyll for project documentation @SE-EDU/guides](https://se-education.org/guides/tutorials/jekyll.html)
- The text `AB-3` in `docs\_sass\minima\_base.scss` needs updating (it comes into play when you convert documentation to PDF formats)
[Link](htt... | priority | update site wide settings tasks follow guide for the text ab in docs sass minima base scss needs updating it comes into play when you convert documentation to pdf formats to details | 1 |
121,511 | 15,954,004,112 | IssuesEvent | 2021-04-15 13:06:48 | department-of-veterans-affairs/vets-design-system-documentation | https://api.github.com/repos/department-of-veterans-affairs/vets-design-system-documentation | closed | Rename action link class to match documented naming convention | vsp-design-system-team | # Bug Report
- [x] I’ve searched for any related issues and avoided creating a duplicate issue.
## Description
The documentation on design.va.gov describes naming conventions for `formation` component classes:
 detected in multiple libraries | security vulnerability | ## CVE-2022-24999 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-6.5.2.tgz</b>, <b>qs-6.7.0.tgz</b>, <b>qs-6.4.0.tgz</b></p></summary>
<p>
<details><summary><b>qs-6.5.2.tgz</b>... | True | CVE-2022-24999 (Medium) detected in multiple libraries - ## CVE-2022-24999 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>qs-6.5.2.tgz</b>, <b>qs-6.7.0.tgz</b>, <b>qs-6.4.0.tgz</b>... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries qs tgz qs tgz qs tgz qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency f... | 0 |
178,314 | 29,668,094,332 | IssuesEvent | 2023-06-11 03:30:55 | calcom/cal.com | https://api.github.com/repos/calcom/cal.com | closed | [CAL-1734] Clarify what Sender ID means in Workflows | 🎨 needs design 🧹 Improvements ⚡ Quick Wins :scroll: Needs Documentation Update Low priority | There's a portion that says "Sender ID" when setting up a workflow when the action is "Send SMS" it may exist for other actions too.
No idea what this Sender ID means or how it is presented for the user. This should be explained with some explainer text below the field.
 on which you encountered this issue.
... | 1.0 | Unable to restore stack! Double continuation! - <!-- NOTE: Anything within these brackets will be hidden on the preview of the Issue. -->
* **rAthena Hash**: 79766cd99eebbc507c82f1900df60e909e46a23e
<!-- Please specify the rAthena [GitHub hash](https://help.github.com/articles/autolinked-references-and-urls/#comm... | priority | unable to restore stack double continuation rathena hash please specify the rathena on which you encountered this issue how to get your github hash cd your rathena directory git rev parse short head copy the resulting hash client date se... | 1 |
17,090 | 3,354,268,211 | IssuesEvent | 2015-11-18 11:13:15 | vigour-io/hub | https://api.github.com/repos/vigour-io/hub | closed | [Current Implementation] Region example | new:design | to get an idea what we are using this for , this an example of a region of the mtv app
[] | 1.0 | [Current Implementation] Region example - to get an idea what we are using this for , this an example of a region of the mtv app
[] | non_priority | region example to get an idea what we are using this for this an example of a region of the mtv app | 0 |
51,873 | 3,015,025,053 | IssuesEvent | 2015-07-29 17:33:20 | brharp/hjckrrh | https://api.github.com/repos/brharp/hjckrrh | closed | G13 General Taxonomy results | feature: general (G) priority: high | Please remove the Read More buttons as Titles will link to the content | 1.0 | G13 General Taxonomy results - Please remove the Read More buttons as Titles will link to the content | priority | general taxonomy results please remove the read more buttons as titles will link to the content | 1 |
763,638 | 26,766,353,290 | IssuesEvent | 2023-01-31 10:55:26 | minio/mc | https://api.github.com/repos/minio/mc | closed | Display arn:bucketname under mc replicate ls | community priority: medium | ## Expected behavior
The current display under mc replicate ls displays entire arn value under Destbucket column
## Actual behavior
The Destbucket column should display arn:buckname instead of entire arn value.
## Steps to reproduce the behavior
Set up replication rule for a bucket on an instance.
Run comman mc... | 1.0 | Display arn:bucketname under mc replicate ls - ## Expected behavior
The current display under mc replicate ls displays entire arn value under Destbucket column
## Actual behavior
The Destbucket column should display arn:buckname instead of entire arn value.
## Steps to reproduce the behavior
Set up replication r... | priority | display arn bucketname under mc replicate ls expected behavior the current display under mc replicate ls displays entire arn value under destbucket column actual behavior the destbucket column should display arn buckname instead of entire arn value steps to reproduce the behavior set up replication r... | 1 |
563,163 | 16,676,991,828 | IssuesEvent | 2021-06-07 17:28:28 | googleapis/java-aiplatform | https://api.github.com/repos/googleapis/java-aiplatform | closed | aiplatform.CreateTrainingPipelineImageObjectDetectionSampleTest: testCreateTrainingPipelineImageObjectDetectionSample failed | api: aiplatform flakybot: flaky flakybot: issue priority: p1 type: bug | Note: #216 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: dafca5d9fc1c0d77fc0c3f26c08c6827e53492a3
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/d828fa34-eac2-4ee9-98e4-0f94a6d7d73f), [Sponge](http://sponge2/d828fa34-eac2-4ee9-9... | 1.0 | aiplatform.CreateTrainingPipelineImageObjectDetectionSampleTest: testCreateTrainingPipelineImageObjectDetectionSample failed - Note: #216 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: dafca5d9fc1c0d77fc0c3f26c08c6827e53492a3
buildURL: [Build Status](https://... | priority | aiplatform createtrainingpipelineimageobjectdetectionsampletest testcreatetrainingpipelineimageobjectdetectionsample failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output com google api gax rpc fai... | 1 |
73,562 | 7,344,302,423 | IssuesEvent | 2018-03-07 14:18:21 | italia/spid | https://api.github.com/repos/italia/spid | closed | Richiesta di validazione e deploy metadati - Comune di Cilavegna | metadata nuovo md test supporto amministrativo verifica implementazione | Buongiorno,
si richiede la verifica e il deploy dei metadati per conto del Comune di Cilavegna:
```
https://www.suaplomellina.info/simplesaml/module.php/saml/sp/metadata.php/suaplomellina
```
Si tratta di uno Sportello conforme a quelli già precedentemente validati da GLOBO.
Grazie | 1.0 | Richiesta di validazione e deploy metadati - Comune di Cilavegna - Buongiorno,
si richiede la verifica e il deploy dei metadati per conto del Comune di Cilavegna:
```
https://www.suaplomellina.info/simplesaml/module.php/saml/sp/metadata.php/suaplomellina
```
Si tratta di uno Sportello conforme a quelli già prece... | non_priority | richiesta di validazione e deploy metadati comune di cilavegna buongiorno si richiede la verifica e il deploy dei metadati per conto del comune di cilavegna si tratta di uno sportello conforme a quelli già precedentemente validati da globo grazie | 0 |
798,900 | 28,300,437,617 | IssuesEvent | 2023-04-10 05:18:21 | googleapis/google-cloud-ruby | https://api.github.com/repos/googleapis/google-cloud-ruby | closed | [Nightly CI Failures] Failures detected for google-cloud-bigquery-analytics_hub-v1 | type: bug priority: p1 nightly failure | At 2023-04-09 08:59:15 UTC, detected failures in google-cloud-bigquery-analytics_hub-v1 for: yard
report_key_e2e3dbfae4be82dcbd05632e6618c5d7 | 1.0 | [Nightly CI Failures] Failures detected for google-cloud-bigquery-analytics_hub-v1 - At 2023-04-09 08:59:15 UTC, detected failures in google-cloud-bigquery-analytics_hub-v1 for: yard
report_key_e2e3dbfae4be82dcbd05632e6618c5d7 | priority | failures detected for google cloud bigquery analytics hub at utc detected failures in google cloud bigquery analytics hub for yard report key | 1 |
240,898 | 20,100,616,357 | IssuesEvent | 2022-02-07 03:19:44 | SpenceKonde/ATTinyCore | https://api.github.com/repos/SpenceKonde/ATTinyCore | closed | tinyNeoPixel can be made to not need the menu, I think... | enhancement work complete but untested | The reason we need the menu is that we have to use OUT rather than ST in the event of a zero bit. But we *can* do that with the 2 cycle ST instruction.... it just doesn't leave us with enough spare time to meet the exact timing constraints on the final bit of each byte.
More recent investigations, however, have show... | 1.0 | tinyNeoPixel can be made to not need the menu, I think... - The reason we need the menu is that we have to use OUT rather than ST in the event of a zero bit. But we *can* do that with the 2 cycle ST instruction.... it just doesn't leave us with enough spare time to meet the exact timing constraints on the final bit of... | non_priority | tinyneopixel can be made to not need the menu i think the reason we need the menu is that we have to use out rather than st in the event of a zero bit but we can do that with the cycle st instruction it just doesn t leave us with enough spare time to meet the exact timing constraints on the final bit of... | 0 |
796,452 | 28,112,881,588 | IssuesEvent | 2023-03-31 08:35:21 | YangCatalog/backend | https://api.github.com/repos/YangCatalog/backend | closed | Remove unnecessary git clones | Priority: Low maintenance | `pull_local.py`, `openconfigPullLocal.py`, `ietf_push.py` and `iana_push.py` for various reasons all trigger clones of repositories already downloaded in `/var/yang/nonietf`.
Usually the reason is needing an up to date copy of the repository, or needing to add files to the repository without impacting other scripts.
... | 1.0 | Remove unnecessary git clones - `pull_local.py`, `openconfigPullLocal.py`, `ietf_push.py` and `iana_push.py` for various reasons all trigger clones of repositories already downloaded in `/var/yang/nonietf`.
Usually the reason is needing an up to date copy of the repository, or needing to add files to the repository wi... | priority | remove unnecessary git clones pull local py openconfigpulllocal py ietf push py and iana push py for various reasons all trigger clones of repositories already downloaded in var yang nonietf usually the reason is needing an up to date copy of the repository or needing to add files to the repository wi... | 1 |
25,481 | 7,718,007,930 | IssuesEvent | 2018-05-23 15:07:47 | grafana/grafana | https://api.github.com/repos/grafana/grafana | closed | Publish archives and packages for all platforms to s3 and grafana.com | type: build & packaging | The new crossplatform build supplies archives and packages for linux, windows, darwin, armv7 and arm64. Currently only amd64/linux is published to grafana.com through the normal build pipeline.
- [x] update build pipeline to publish the artifacts
- [ ] update grafana.com to support showing the new artifacts
Rela... | 1.0 | Publish archives and packages for all platforms to s3 and grafana.com - The new crossplatform build supplies archives and packages for linux, windows, darwin, armv7 and arm64. Currently only amd64/linux is published to grafana.com through the normal build pipeline.
- [x] update build pipeline to publish the artifact... | non_priority | publish archives and packages for all platforms to and grafana com the new crossplatform build supplies archives and packages for linux windows darwin and currently only linux is published to grafana com through the normal build pipeline update build pipeline to publish the artifacts update g... | 0 |
649,943 | 21,330,710,108 | IssuesEvent | 2022-04-18 07:58:13 | ZapSquared/Quaver | https://api.github.com/repos/ZapSquared/Quaver | closed | Queue command crashes Quaver | type:bug released on @next affects:functionality priority:p0 | **Describe the bug**
What isn't working as intended, and what does it affect?
**Affected versions**
What versions are affected by this bug? (e.g. >=3.0.1, 2.5.1-2.6.3, >=1.2.0)
3.4.0-next.34
**Steps to reproduce**
Steps to reproduce the behavior. (e.g. click on a button, enter a value, etc. and see error)
1.... | 1.0 | Queue command crashes Quaver - **Describe the bug**
What isn't working as intended, and what does it affect?
**Affected versions**
What versions are affected by this bug? (e.g. >=3.0.1, 2.5.1-2.6.3, >=1.2.0)
3.4.0-next.34
**Steps to reproduce**
Steps to reproduce the behavior. (e.g. click on a button, enter a... | priority | queue command crashes quaver describe the bug what isn t working as intended and what does it affect affected versions what versions are affected by this bug e g next steps to reproduce steps to reproduce the behavior e g click on a button enter a ... | 1 |
225,080 | 17,225,366,391 | IssuesEvent | 2021-07-20 00:17:47 | FourierFlows/FourierFlows.jl | https://api.github.com/repos/FourierFlows/FourierFlows.jl | reopened | JOSS todo list | GPU MPI documentation enhancement | This is a proposed list for things we should implement before we announce the code in an open source journal, e.g., JOSS
- [x] GPU
- [x] Full GPU functionality on all modules
- [ ] 3D grid + 3DNavierStokes Module
- [x] Full Docs
- [x] Examples (w/ Literate.jl) that include animations where appropriate
- [ ] Cho... | 1.0 | JOSS todo list - This is a proposed list for things we should implement before we announce the code in an open source journal, e.g., JOSS
- [x] GPU
- [x] Full GPU functionality on all modules
- [ ] 3D grid + 3DNavierStokes Module
- [x] Full Docs
- [x] Examples (w/ Literate.jl) that include animations where appro... | non_priority | joss todo list this is a proposed list for things we should implement before we announce the code in an open source journal e g joss gpu full gpu functionality on all modules grid module full docs examples w literate jl that include animations where appropriate choose pro... | 0 |
150,947 | 23,739,079,150 | IssuesEvent | 2022-08-31 10:44:32 | stores-cedcommerce/Lucy-Store-Design | https://api.github.com/repos/stores-cedcommerce/Lucy-Store-Design | opened | The handle needed to be update on the collection page. | Header section Desktop Design / UI / UX | **Actual result:**
The handle needed to be update on the collection page.
https://bellabrina-boutique.myshopify.com/collections/pants-1
https://bellabrina-boutique.myshopify.com/collections/shoes-1
https://bellabrina-boutique.myshopify.com/collections/accessories-1
**Expected result:**
The handle needed to be u... | 1.0 | The handle needed to be update on the collection page. - **Actual result:**
The handle needed to be update on the collection page.
https://bellabrina-boutique.myshopify.com/collections/pants-1
https://bellabrina-boutique.myshopify.com/collections/shoes-1
https://bellabrina-boutique.myshopify.com/collections/accesso... | non_priority | the handle needed to be update on the collection page actual result the handle needed to be update on the collection page expected result the handle needed to be updated | 0 |
178,108 | 6,599,128,081 | IssuesEvent | 2017-09-16 15:45:50 | zerobias/telegram-mtproto | https://api.github.com/repos/zerobias/telegram-mtproto | opened | Support media DC (or possibly CDNs?) | Priority: High Type: Bug | Can't load avatars from different DC even when `FILE_MIGRATE_x` works because we have different DCs for media content (I think `media_only` thing matters) and for messages. But I'm not sure about this. | 1.0 | Support media DC (or possibly CDNs?) - Can't load avatars from different DC even when `FILE_MIGRATE_x` works because we have different DCs for media content (I think `media_only` thing matters) and for messages. But I'm not sure about this. | priority | support media dc or possibly cdns can t load avatars from different dc even when file migrate x works because we have different dcs for media content i think media only thing matters and for messages but i m not sure about this | 1 |
750,908 | 26,224,426,017 | IssuesEvent | 2023-01-04 17:20:28 | restarone/violet_rails | https://api.github.com/repos/restarone/violet_rails | closed | run error actions (if any) when recaptcha fails | enhancement high priority API - data pipeline v3 | **Is your feature request related to a problem? Please describe.**
Currently we don't fire error actions when recaptcha fails
**Describe the solution you'd like**
fire error actions when recaptcha fails
<img width="1728" alt="Screen Shot 2022-07-30 at 1 21 42 PM" src="https://user-images.githubusercontent.c... | 1.0 | run error actions (if any) when recaptcha fails - **Is your feature request related to a problem? Please describe.**
Currently we don't fire error actions when recaptcha fails
**Describe the solution you'd like**
fire error actions when recaptcha fails
<img width="1728" alt="Screen Shot 2022-07-30 at 1 21 4... | priority | run error actions if any when recaptcha fails is your feature request related to a problem please describe currently we don t fire error actions when recaptcha fails describe the solution you d like fire error actions when recaptcha fails img width alt screen shot at pm src ... | 1 |
99,579 | 4,057,023,161 | IssuesEvent | 2016-05-24 20:39:46 | opencaching/okapi | https://api.github.com/repos/opencaching/okapi | closed | User can log cache even if is already banned | bug Priority-Critical | Hi!
There was an issue in oc.pl repo:
https://github.com/opencaching/opencaching-pl/issues/646
How I understand architecture of OKAPI, this have to be solved here. | 1.0 | User can log cache even if is already banned - Hi!
There was an issue in oc.pl repo:
https://github.com/opencaching/opencaching-pl/issues/646
How I understand architecture of OKAPI, this have to be solved here. | priority | user can log cache even if is already banned hi there was an issue in oc pl repo how i understand architecture of okapi this have to be solved here | 1 |
88,701 | 10,577,875,000 | IssuesEvent | 2019-10-07 21:06:38 | mRemoteNG/mRemoteNG | https://api.github.com/repos/mRemoteNG/mRemoteNG | closed | Code style: Place attributes on a separate line | Documentation | In the recent code cleanup, attributes were placed in-line with the code that they decorate. I propose we place attributes on a separate line before the target code that they decorate.
## Current style
```csharp
[Browsable(false)] public RootPuttySessionsNodeInfo RootRootPuttySessionsInfo { get; set; }
```
## ... | 1.0 | Code style: Place attributes on a separate line - In the recent code cleanup, attributes were placed in-line with the code that they decorate. I propose we place attributes on a separate line before the target code that they decorate.
## Current style
```csharp
[Browsable(false)] public RootPuttySessionsNodeInfo R... | non_priority | code style place attributes on a separate line in the recent code cleanup attributes were placed in line with the code that they decorate i propose we place attributes on a separate line before the target code that they decorate current style csharp public rootputtysessionsnodeinfo rootrootputtysessi... | 0 |
152,374 | 5,846,019,271 | IssuesEvent | 2017-05-10 15:21:06 | vmware/vic | https://api.github.com/repos/vmware/vic | closed | HTML5 Plugin displays wrong port number when using --no-tls | area/ui kind/bug kind/customer-found priority/high | When creating a VCH with the --no-tls option, HTML5 plugin displays wrong port number (2376 instead of 2375). I attached a screenshot.
May 5 2017 13:06:57.777Z INFO ### Installing VCH ####
May 5 2017 13:06:57.778Z INFO vSphere password for administrator@corp.local:
May 5 2017 13:07:01.063Z WARN Using adminis... | 1.0 | HTML5 Plugin displays wrong port number when using --no-tls - When creating a VCH with the --no-tls option, HTML5 plugin displays wrong port number (2376 instead of 2375). I attached a screenshot.
May 5 2017 13:06:57.777Z INFO ### Installing VCH ####
May 5 2017 13:06:57.778Z INFO vSphere password for administra... | priority | plugin displays wrong port number when using no tls when creating a vch with the no tls option plugin displays wrong port number instead of i attached a screenshot may info installing vch may info vsphere password for administrator corp local may ... | 1 |
375,720 | 26,174,578,777 | IssuesEvent | 2023-01-02 07:59:40 | deepchecks/deepchecks | https://api.github.com/repos/deepchecks/deepchecks | closed | [BUG] Fix Typo in docs/source/getting-started/installation.rst | documentation bug | **Describe the bug**
In [docs/source/getting-started/installation.rst](https://github.com/deepchecks/deepchecks/blob/cdfcfc5fbc23d7daf99a74505c0cfd17fc320a17/docs/source/getting-started/installation.rst) fix typo located at line 73
Before
```
Istallation of deepchecks for CV should be stated explicitly and it inc... | 1.0 | [BUG] Fix Typo in docs/source/getting-started/installation.rst - **Describe the bug**
In [docs/source/getting-started/installation.rst](https://github.com/deepchecks/deepchecks/blob/cdfcfc5fbc23d7daf99a74505c0cfd17fc320a17/docs/source/getting-started/installation.rst) fix typo located at line 73
Before
```
Istall... | non_priority | fix typo in docs source getting started installation rst describe the bug in fix typo located at line before istallation of deepchecks for cv should be stated explicitly and it includes after installation of deepchecks for cv should be stated explicitly and it includes | 0 |
650,397 | 21,390,327,701 | IssuesEvent | 2022-04-21 06:17:59 | TerriaJS/terriajs | https://api.github.com/repos/TerriaJS/terriajs | opened | Shared link should always work | T-Bug High priority | When creating a catalog item's shared link before adding the item to the map, the shared link is not usable. Besides, if using the shared link, `Explore map data` will become unclickable. | 1.0 | Shared link should always work - When creating a catalog item's shared link before adding the item to the map, the shared link is not usable. Besides, if using the shared link, `Explore map data` will become unclickable. | priority | shared link should always work when creating a catalog item s shared link before adding the item to the map the shared link is not usable besides if using the shared link explore map data will become unclickable | 1 |
6,955 | 2,610,319,325 | IssuesEvent | 2015-02-26 19:43:02 | chrsmith/republic-at-war | https://api.github.com/repos/chrsmith/republic-at-war | closed | Text | auto-migrated Priority-Medium Type-Defect | ```
AA9 transport [missing] description
```
-----
Original issue reported on code.google.com by `z3r0...@gmail.com` on 7 May 2011 at 11:37 | 1.0 | Text - ```
AA9 transport [missing] description
```
-----
Original issue reported on code.google.com by `z3r0...@gmail.com` on 7 May 2011 at 11:37 | non_priority | text transport description original issue reported on code google com by gmail com on may at | 0 |
29,400 | 4,500,789,768 | IssuesEvent | 2016-09-01 06:51:53 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | teamcity: failed tests on develop: test/TestRaftRemoveRace | Robot test-failure | The following tests appear to have failed:
[#17097](https://teamcity.cockroachdb.com/viewLog.html?buildId=17097):
```
--- FAIL: test/TestRaftRemoveRace (0.013s)
client_test.go:884: change replicas of range 1 aborted due to failed preemptive snapshot: range=1: remote couldn't accept snapshot with error: permanently r... | 1.0 | teamcity: failed tests on develop: test/TestRaftRemoveRace - The following tests appear to have failed:
[#17097](https://teamcity.cockroachdb.com/viewLog.html?buildId=17097):
```
--- FAIL: test/TestRaftRemoveRace (0.013s)
client_test.go:884: change replicas of range 1 aborted due to failed preemptive snapshot: range... | non_priority | teamcity failed tests on develop test testraftremoverace the following tests appear to have failed fail test testraftremoverace client test go change replicas of range aborted due to failed preemptive snapshot range remote couldn t accept snapshot with error permanently rejected sna... | 0 |
800,332 | 28,361,348,999 | IssuesEvent | 2023-04-12 10:58:39 | netdata/netdata | https://api.github.com/repos/netdata/netdata | closed | Install script should support OpenWRT | area/packaging feature request priority/medium | Netdata should install and run on OpenWRT with the install script.
It is important for us that cloud works also (meaning cloud dependencies and cloud build should also work)
However, right now there are some basic problems - i.e. old version of tar being used by the install script.
See
https://forum.openwrt.... | 1.0 | Install script should support OpenWRT - Netdata should install and run on OpenWRT with the install script.
It is important for us that cloud works also (meaning cloud dependencies and cloud build should also work)
However, right now there are some basic problems - i.e. old version of tar being used by the install... | priority | install script should support openwrt netdata should install and run on openwrt with the install script it is important for us that cloud works also meaning cloud dependencies and cloud build should also work however right now there are some basic problems i e old version of tar being used by the install... | 1 |
5,563 | 7,214,145,422 | IssuesEvent | 2018-02-08 00:39:30 | wesnoth/wesnoth | https://api.github.com/repos/wesnoth/wesnoth | closed | support anonymous issues | Services | it would be nice to be have some form to enable users to report bugs without creating a github account. since this is a public repo we could just have a dummy account that doesn't even need access to the wesnoth repo to let a script create issues with it. One of the problems with suhc a solution that is that i am unuse... | 1.0 | support anonymous issues - it would be nice to be have some form to enable users to report bugs without creating a github account. since this is a public repo we could just have a dummy account that doesn't even need access to the wesnoth repo to let a script create issues with it. One of the problems with suhc a solut... | non_priority | support anonymous issues it would be nice to be have some form to enable users to report bugs without creating a github account since this is a public repo we could just have a dummy account that doesn t even need access to the wesnoth repo to let a script create issues with it one of the problems with suhc a solut... | 0 |
87,510 | 25,136,211,577 | IssuesEvent | 2022-11-09 18:49:28 | libreswan/libreswan | https://api.github.com/repos/libreswan/libreswan | closed | delete include/unbound/unbound-event.h | build upstream FreeBSD blocked | | OS | Status |
|-|-|
| Linux | installed |
| NetBSD | installed |
| OpenBSD | 7.2 |
| FreeBSD | submitted https://bugs.freebsd.org/bugzilla/show_bug.cgi?id=263838 | | 1.0 | delete include/unbound/unbound-event.h - | OS | Status |
|-|-|
| Linux | installed |
| NetBSD | installed |
| OpenBSD | 7.2 |
| FreeBSD | submitted https://bugs.freebsd.org/bugzilla/show_bug.cgi?id=263838 | | non_priority | delete include unbound unbound event h os status linux installed netbsd installed openbsd freebsd submitted | 0 |
42,873 | 7,006,765,603 | IssuesEvent | 2017-12-19 09:45:51 | PaddlePaddle/Paddle | https://api.github.com/repos/PaddlePaddle/Paddle | closed | Navigation of Distributed Training is wrong | documentation | In the Chinese version, we can use the downward arrow:
But in the English version, this arrow is missing:

But in the English version, this arrow is missing:
 detected in opennms-opennms-source-22.0.1-1 | security vulnerability | ## CVE-2018-11698 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-22.0.1-1</b></p></summary>
<p>
<p>A Java based fault and performance management system</p>
<p>Li... | True | CVE-2018-11698 (High) detected in opennms-opennms-source-22.0.1-1 - ## CVE-2018-11698 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opennmsopennms-source-22.0.1-1</b></p></summary>
<p... | non_priority | cve high detected in opennms opennms source cve high severity vulnerability vulnerable library opennmsopennms source a java based fault and performance management system library home page a href found in head commit a href library source files ... | 0 |
8,812 | 2,886,714,497 | IssuesEvent | 2015-06-12 10:16:42 | quantmind/lux | https://api.github.com/repos/quantmind/lux | opened | template url for views with parameters | AngularJS bug extension requires design effort | The `lux` way for serving templates to angular [ui-roter](https://github.com/angular-ui/ui-router) pages for a give url ``/foo`` is:
```
GET /foo?template=ui
```
This is added by a router via the [angular_page](https://github.com/quantmind/lux/blob/dev/lux/core/wrappers.py#L169) method which is invoked by the [add_... | 1.0 | template url for views with parameters - The `lux` way for serving templates to angular [ui-roter](https://github.com/angular-ui/ui-router) pages for a give url ``/foo`` is:
```
GET /foo?template=ui
```
This is added by a router via the [angular_page](https://github.com/quantmind/lux/blob/dev/lux/core/wrappers.py#L... | non_priority | template url for views with parameters the lux way for serving templates to angular pages for a give url foo is get foo template ui this is added by a router via the method which is invoked by the function in the angular extension this method does not work well when the router is ... | 0 |
157,286 | 19,957,083,829 | IssuesEvent | 2022-01-28 01:22:39 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | opened | CVE-2015-8787 (High) detected in linuxlinux-4.1.17 | security vulnerability | ## CVE-2015-8787 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.17</b></p></summary>
<p>
<p>Apache Software Foundation (ASF)</p>
<p>Library home page: <a href=https://m... | True | CVE-2015-8787 (High) detected in linuxlinux-4.1.17 - ## CVE-2015-8787 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.1.17</b></p></summary>
<p>
<p>Apache Software Foundat... | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux apache software foundation asf library home page a href found in base branch master vulnerable source files net netfilter nf nat redirect c ... | 0 |
692,946 | 23,755,875,882 | IssuesEvent | 2022-09-01 03:00:29 | brainhackorg/brainhack_cloud | https://api.github.com/repos/brainhackorg/brainhack_cloud | closed | Layout of landing page: suboptimal responsiveness | website low_priority | For certain devices the layout will not be optimal.

| 1.0 | Layout of landing page: suboptimal responsiveness - For certain devices the layout will not be optimal.

| priority | layout of landing page suboptimal responsiveness for certain devices the layout will not be optimal | 1 |
728,527 | 25,082,980,156 | IssuesEvent | 2022-11-07 21:01:44 | rmlockwood/FLExTrans | https://api.github.com/repos/rmlockwood/FLExTrans | closed | [Live Rule Tester] Refresh rules on advanced transfer unchecks the other tabs that aren't in focus | bug medium priority | All rules in all tabs should remain in the checked state they were in. | 1.0 | [Live Rule Tester] Refresh rules on advanced transfer unchecks the other tabs that aren't in focus - All rules in all tabs should remain in the checked state they were in. | priority | refresh rules on advanced transfer unchecks the other tabs that aren t in focus all rules in all tabs should remain in the checked state they were in | 1 |
156,925 | 24,626,336,907 | IssuesEvent | 2022-10-16 15:13:46 | baloise-incubator/design-system | https://api.github.com/repos/baloise-incubator/design-system | closed | Exchange Fallback Avatars | 🆕 Enhancement 💁 Help Wanted 🎨 Design Support | We got the feedback that the avatars that were created by Meta do not match our use-case. Therefore we have to create new ones in order that IBM can replace them.
Following tasks should be completed:
- [x] Prepare briefing for Stadtluft (2:3)
- [x] Update Figma
- [x] Send new icons to Leo (upload to Frontify)
- [x... | 1.0 | Exchange Fallback Avatars - We got the feedback that the avatars that were created by Meta do not match our use-case. Therefore we have to create new ones in order that IBM can replace them.
Following tasks should be completed:
- [x] Prepare briefing for Stadtluft (2:3)
- [x] Update Figma
- [x] Send new icons to Le... | non_priority | exchange fallback avatars we got the feedback that the avatars that were created by meta do not match our use case therefore we have to create new ones in order that ibm can replace them following tasks should be completed prepare briefing for stadtluft update figma send new icons to leo upl... | 0 |
731,881 | 25,235,242,911 | IssuesEvent | 2022-11-14 23:58:54 | open-telemetry/opentelemetry-collector | https://api.github.com/repos/open-telemetry/opentelemetry-collector | closed | Make default config per type (metric, traces, etc.) | enhancement priority:p3 release:after-ga area:config |
**Is your feature request related to a problem? Please describe.**
Created from https://github.com/open-telemetry/opentelemetry-collector/pull/1966#discussion_r524005206
I want to create default config that is different for each entity (traces, metrics, logs). Currently the `Factory.createDefaultConfig` creat... | 1.0 | Make default config per type (metric, traces, etc.) -
**Is your feature request related to a problem? Please describe.**
Created from https://github.com/open-telemetry/opentelemetry-collector/pull/1966#discussion_r524005206
I want to create default config that is different for each entity (traces, metrics, lo... | priority | make default config per type metric traces etc is your feature request related to a problem please describe created from i want to create default config that is different for each entity traces metrics logs currently the factory createdefaultconfig creates a default config for all entiti... | 1 |
23,125 | 2,652,930,884 | IssuesEvent | 2015-03-16 20:08:10 | GoogleCloudPlatform/kubernetes | https://api.github.com/repos/GoogleCloudPlatform/kubernetes | closed | Write an e2e test that specifically tests kubectl functionality | area/reliability priority/P2 team/UX | As #3130 nears completion, we want to make sure that kubectl coverage isn't lost by moving to go tests. | 1.0 | Write an e2e test that specifically tests kubectl functionality - As #3130 nears completion, we want to make sure that kubectl coverage isn't lost by moving to go tests. | priority | write an test that specifically tests kubectl functionality as nears completion we want to make sure that kubectl coverage isn t lost by moving to go tests | 1 |
2,978 | 3,050,761,564 | IssuesEvent | 2015-08-12 01:30:35 | Carthage/Carthage | https://api.github.com/repos/Carthage/Carthage | closed | Carthage build fails with iOS 7.1 simulator installed | bug build help wanted | Steps to reproduce:
- Install the iOS 7.1 Simulator in Xcode 6.2
- Create a new Cocoa Touch Framework project in Xcode
- Run `carthage build --no-skip-current` in the directory that the Framework project was created in
You will receive the following build error:
```
CompileC ...
invalid architecture 'arm64... | 1.0 | Carthage build fails with iOS 7.1 simulator installed - Steps to reproduce:
- Install the iOS 7.1 Simulator in Xcode 6.2
- Create a new Cocoa Touch Framework project in Xcode
- Run `carthage build --no-skip-current` in the directory that the Framework project was created in
You will receive the following build ... | non_priority | carthage build fails with ios simulator installed steps to reproduce install the ios simulator in xcode create a new cocoa touch framework project in xcode run carthage build no skip current in the directory that the framework project was created in you will receive the following build ... | 0 |
342,074 | 30,607,469,966 | IssuesEvent | 2023-07-23 07:20:27 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix manipulations.test_jax_resize | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5491105443/jobs/10007308085"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5491105443/jobs/10007308085"><img src=https://img.shields.io/badge/-success-success></a>
... | 1.0 | Fix manipulations.test_jax_resize - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5491105443/jobs/10007308085"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5491105443/jobs/10007308085"><img src=https://img.shie... | non_priority | fix manipulations test jax resize jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 0 |
206,200 | 7,110,073,518 | IssuesEvent | 2018-01-17 09:22:40 | vanilla-framework/vanilla-framework | https://api.github.com/repos/vanilla-framework/vanilla-framework | closed | Go live: Update DNS to point docs.vanillaframework.io at the Kubernetes ingress | Priority: High Status: Blocked Type: Maintenance | I believe we control the DNS. When (and only when) we've confirmed that the Kubernetes environment is correctly able to serve docs.staging.vanillaframework.io and docs.vanillaframework.io, with correct HTTPS certificates, then we should switch over DNS to point to Kubernetes. | 1.0 | Go live: Update DNS to point docs.vanillaframework.io at the Kubernetes ingress - I believe we control the DNS. When (and only when) we've confirmed that the Kubernetes environment is correctly able to serve docs.staging.vanillaframework.io and docs.vanillaframework.io, with correct HTTPS certificates, then we should s... | priority | go live update dns to point docs vanillaframework io at the kubernetes ingress i believe we control the dns when and only when we ve confirmed that the kubernetes environment is correctly able to serve docs staging vanillaframework io and docs vanillaframework io with correct https certificates then we should s... | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.