Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
80,714 | 10,198,265,678 | IssuesEvent | 2019-08-13 04:25:37 | Qiskit/qiskit | https://api.github.com/repos/Qiskit/qiskit | closed | do we need https://qiskit.org/documentation/advanced_use_of_ibm_q_devices.html | documentation | my feeling is we dont need. this page. If we do keep it we should make it much simpler it does not need to mimic the notebook | 1.0 | do we need https://qiskit.org/documentation/advanced_use_of_ibm_q_devices.html - my feeling is we dont need. this page. If we do keep it we should make it much simpler it does not need to mimic the notebook | non_priority | do we need my feeling is we dont need this page if we do keep it we should make it much simpler it does not need to mimic the notebook | 0 |
237,778 | 7,764,124,331 | IssuesEvent | 2018-06-01 19:04:46 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | drivers: can: stm32_can: bitrate ignored | bug priority: medium | The CAN peripheral prescaler is not calculated based on the bitrate passed in or overridden if not passed in, but always on cfg->bus_speed
Also the can.h interface doesn't really specify that bitrate can be zero and will then be overridden with a value from dts or kconfig, not sure if that matters
https://github.... | 1.0 | drivers: can: stm32_can: bitrate ignored - The CAN peripheral prescaler is not calculated based on the bitrate passed in or overridden if not passed in, but always on cfg->bus_speed
Also the can.h interface doesn't really specify that bitrate can be zero and will then be overridden with a value from dts or kconfig, ... | priority | drivers can can bitrate ignored the can peripheral prescaler is not calculated based on the bitrate passed in or overridden if not passed in but always on cfg bus speed also the can h interface doesn t really specify that bitrate can be zero and will then be overridden with a value from dts or kconfig not ... | 1 |
214,117 | 16,547,528,079 | IssuesEvent | 2021-05-28 03:06:12 | seyaFly/btp_sapUI5 | https://api.github.com/repos/seyaFly/btp_sapUI5 | closed | How to add logs in SAP UI5 | documentation | 1. add library
sap/base/log
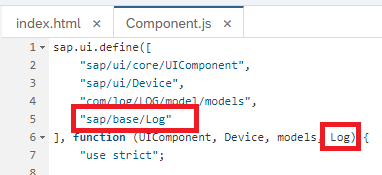
2. add log configration when initialize the page
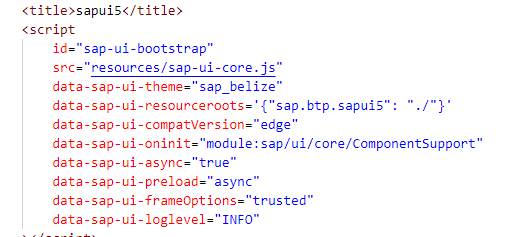
dat... | 1.0 | How to add logs in SAP UI5 - 1. add library
sap/base/log
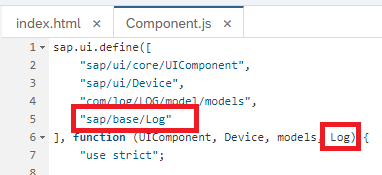
2. add log configration when initialize the page
 | oncall: distributed module: flaky-tests | ## 🐛 Bug
Example failures:
https://app.circleci.com/pipelines/github/pytorch/pytorch/337673/workflows/db188d30-2c92-4faf-ac2a-e90b70d1e8c2/jobs/14187632
https://app.circleci.com/pipelines/github/pytorch/pytorch/337701/workflows/6e6161a7-7346-403a-a458-97f5e7970279/jobs/14188746
https://app.circleci.com/pipelines... | 1.0 | DISABLED test_ddp_logging_data_cpu (__main__.TestDistBackendWithFork) - ## 🐛 Bug
Example failures:
https://app.circleci.com/pipelines/github/pytorch/pytorch/337673/workflows/db188d30-2c92-4faf-ac2a-e90b70d1e8c2/jobs/14187632
https://app.circleci.com/pipelines/github/pytorch/pytorch/337701/workflows/6e6161a7-7346-... | non_priority | disabled test ddp logging data cpu main testdistbackendwithfork 🐛 bug example failures cc pietern mrshenli zhaojuanmao satgera rohan varma gqchen aazzolini osalpekar jiayisuse agolynski scipioneer h huang mrzzd cbalioglu | 0 |
198,349 | 15,707,458,744 | IssuesEvent | 2021-03-26 18:55:00 | Qiskit/qiskit | https://api.github.com/repos/Qiskit/qiskit | closed | Unable to load images on "more circuit identities" page | documentation | ### Found broken image links
**Name of the page:**
more circuit identities
**Link of the page:**
https://qiskit.org/textbook/ch-gates/more-circuit-identities.html
**Current links that need to be changed:**
A doubly controlled version of a gate V:
https://s3.us-south.cloud-object-storage.appdomain.cloud/str... | 1.0 | Unable to load images on "more circuit identities" page - ### Found broken image links
**Name of the page:**
more circuit identities
**Link of the page:**
https://qiskit.org/textbook/ch-gates/more-circuit-identities.html
**Current links that need to be changed:**
A doubly controlled version of a gate V:
ht... | non_priority | unable to load images on more circuit identities page found broken image links name of the page more circuit identities link of the page current links that need to be changed a doubly controlled version of a gate v a toffoli | 0 |
11,757 | 9,477,895,779 | IssuesEvent | 2019-04-19 20:22:43 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | ACM certificate: wrong validation email for sub-domain | question service/acm | I have a sub-domain need to request to validate through email, however, terraform set output email domain as same as sub-domain. I tried with ACM web and there were no problems
Am I wrong or this is a bug?
```hcl
resource "aws_acm_certificate" "cert" {
domain_name = "sub.domain.com"
validation_method = ... | 1.0 | ACM certificate: wrong validation email for sub-domain - I have a sub-domain need to request to validate through email, however, terraform set output email domain as same as sub-domain. I tried with ACM web and there were no problems
Am I wrong or this is a bug?
```hcl
resource "aws_acm_certificate" "cert" {
doma... | non_priority | acm certificate wrong validation email for sub domain i have a sub domain need to request to validate through email however terraform set output email domain as same as sub domain i tried with acm web and there were no problems am i wrong or this is a bug hcl resource aws acm certificate cert doma... | 0 |
57,429 | 24,120,824,330 | IssuesEvent | 2022-09-20 18:32:30 | googleapis/nodejs-game-servers | https://api.github.com/repos/googleapis/nodejs-game-servers | closed | Game Servers Get Cluster Test: "after all" hook for "should get a Game Server cluster in a realm" failed | type: bug priority: p1 api: gameservices flakybot: issue | Note: #287 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 8f345d7c91748fbea14862ebb250e0c84e3f8dda
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/e41b1041-12c6-4e99-b799-d6c1f19aa7ec), [Sponge](http://sponge2/e41b1041-12c6-4e99-b... | 1.0 | Game Servers Get Cluster Test: "after all" hook for "should get a Game Server cluster in a realm" failed - Note: #287 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: 8f345d7c91748fbea14862ebb250e0c84e3f8dda
buildURL: [Build Status](https://source.cloud.google.... | non_priority | game servers get cluster test after all hook for should get a game server cluster in a realm failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output unauthenticated request had invalid authent... | 0 |
213,376 | 16,521,536,909 | IssuesEvent | 2021-05-26 15:01:38 | iter8-tools/iter8 | https://api.github.com/repos/iter8-tools/iter8 | closed | [Release checklist] Remaining items for Iter8 v0.3.0 release | Epic documentation enhancement testing | ### weight fix
- [x] Merge etc3 weight fix changes into etc3 repo
- [x] Update etc3 image in iter8-install repo
- [x] Create tagged release v0.3.0-pre.1 in iter8-install repo
- [x] Remove install folder from iter8 repo
- [ ] Merge new samples and documentation based on v0.3.0-pre.1 in iter8 repo
- [ ] Update d... | 1.0 | [Release checklist] Remaining items for Iter8 v0.3.0 release - ### weight fix
- [x] Merge etc3 weight fix changes into etc3 repo
- [x] Update etc3 image in iter8-install repo
- [x] Create tagged release v0.3.0-pre.1 in iter8-install repo
- [x] Remove install folder from iter8 repo
- [ ] Merge new samples and docu... | non_priority | remaining items for release weight fix merge weight fix changes into repo update image in install repo create tagged release pre in install repo remove install folder from repo merge new samples and documentation based on pre in repo update ... | 0 |
280,988 | 8,689,139,712 | IssuesEvent | 2018-12-03 17:51:34 | bounswe/bounswe2018group10 | https://api.github.com/repos/bounswe/bounswe2018group10 | closed | Fix profile page according to the changes in backend | enhancement frontend priority: low | Profile API is changed with #135. Frontend should be updated accordingly.
### I'm submitting a ...
<!--Check the most relevant one with an x-->
- [x] bug report
- [ ] feature request
- [ ] support request | 1.0 | Fix profile page according to the changes in backend - Profile API is changed with #135. Frontend should be updated accordingly.
### I'm submitting a ...
<!--Check the most relevant one with an x-->
- [x] bug report
- [ ] feature request
- [ ] support request | priority | fix profile page according to the changes in backend profile api is changed with frontend should be updated accordingly i m submitting a bug report feature request support request | 1 |
443,480 | 12,794,771,162 | IssuesEvent | 2020-07-02 07:34:42 | telerik/kendo-ui-core | https://api.github.com/repos/telerik/kendo-ui-core | closed | On Android the DateRangePicker change event close Calendar after selecting a Start Date | Bug C: DateRangePicker Kendo1 Next LIB Priority 1 SEV: Medium | ### Bug report
When the **change** event is used in kendoDateRangePicker the Calendar gets closed after selecting a Start Date.
### Reproduction of the problem
https://dojo.telerik.com/equPapaJ
https://dojo.telerik.com/@bratanov/OHikoHaC
### Current behavior
The calendar in kendoDateRangePicker close afte... | 1.0 | On Android the DateRangePicker change event close Calendar after selecting a Start Date - ### Bug report
When the **change** event is used in kendoDateRangePicker the Calendar gets closed after selecting a Start Date.
### Reproduction of the problem
https://dojo.telerik.com/equPapaJ
https://dojo.telerik.com/@... | priority | on android the daterangepicker change event close calendar after selecting a start date bug report when the change event is used in kendodaterangepicker the calendar gets closed after selecting a start date reproduction of the problem current behavior the calendar in kendodaterangep... | 1 |
586,812 | 17,597,981,612 | IssuesEvent | 2021-08-17 08:15:28 | FAForever/fa | https://api.github.com/repos/FAForever/fa | closed | Dummy weapons on shields and AA causing problems for AI | area: sim priority: high | AI moves around units in formation, before the shields and AA sticked in the formation, protecting what they should have, when other units stopped to shoot, the shields stopped with them and then continues to move together.
Now they stop long before that exposing all units they should be protecting.
I guess with ... | 1.0 | Dummy weapons on shields and AA causing problems for AI - AI moves around units in formation, before the shields and AA sticked in the formation, protecting what they should have, when other units stopped to shoot, the shields stopped with them and then continues to move together.
Now they stop long before that expo... | priority | dummy weapons on shields and aa causing problems for ai ai moves around units in formation before the shields and aa sticked in the formation protecting what they should have when other units stopped to shoot the shields stopped with them and then continues to move together now they stop long before that expo... | 1 |
152,962 | 19,702,052,016 | IssuesEvent | 2022-01-12 17:34:39 | harrinry/serverless-s3-local | https://api.github.com/repos/harrinry/serverless-s3-local | opened | CVE-2020-28500 (Medium) detected in lodash-4.17.15.tgz | security vulnerability | ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registr... | True | CVE-2020-28500 (Medium) detected in lodash-4.17.15.tgz - ## CVE-2020-28500 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-4.17.15.tgz</b></p></summary>
<p>Lodash modular util... | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file package json path to vulnerable library node modules lodash package json dependency hier... | 0 |
675,489 | 23,096,421,391 | IssuesEvent | 2022-07-26 20:02:46 | boy0001/FastAsyncWorldedit | https://api.github.com/repos/boy0001/FastAsyncWorldedit | closed | Malformed json in //paste | [-] Low Priority [!] WorldEdit bug | **Debug paste link**:
After using the command, nothing shows on the console... :X
**Description of the problem:**
After use the //paste command, the error shows up in the console, but the task runs.
Error:
```
[17:58:50] [Server thread/INFO] [nucleus]: PotterCraft_ ran the command: //paste
[17:58:50] [ForkJ... | 1.0 | Malformed json in //paste - **Debug paste link**:
After using the command, nothing shows on the console... :X
**Description of the problem:**
After use the //paste command, the error shows up in the console, but the task runs.
Error:
```
[17:58:50] [Server thread/INFO] [nucleus]: PotterCraft_ ran the command... | priority | malformed json in paste debug paste link after using the command nothing shows on the console x description of the problem after use the paste command the error shows up in the console but the task runs error pottercraft ran the command paste com google gson... | 1 |
786,052 | 27,632,800,313 | IssuesEvent | 2023-03-10 12:14:03 | SkriptLang/Skript | https://api.github.com/repos/SkriptLang/Skript | closed | Impossible to shoot a projectile that is in a variable | bug priority: low PR available | ### Skript/Server Version
```markdown
2.6.4
1.19.3
```
### Bug Description
We can't shoot a projectile that is in a variable
### Expected Behavior
Normally, the projectile should have been shooted, but nothing happens.
### Steps to Reproduce
Basic Example:
```
on load:
set {customsnowb... | 1.0 | Impossible to shoot a projectile that is in a variable - ### Skript/Server Version
```markdown
2.6.4
1.19.3
```
### Bug Description
We can't shoot a projectile that is in a variable
### Expected Behavior
Normally, the projectile should have been shooted, but nothing happens.
### Steps to Reproduc... | priority | impossible to shoot a projectile that is in a variable skript server version markdown bug description we can t shoot a projectile that is in a variable expected behavior normally the projectile should have been shooted but nothing happens steps to reproduce... | 1 |
45,183 | 18,452,413,553 | IssuesEvent | 2021-10-15 12:32:15 | GovernIB/registre | https://api.github.com/repos/GovernIB/registre | opened | Paginació parametrizable entre REGWEB-CARPETA dels assentaments d'un ciutadà | Tipus:Nova_Funcionalitat Prioritat:Normal Lloc:EJB Lloc:WebServices Estimació: 3D | Es tracta d'homogenitzar la presentació d'informació de les diferents integracions de CARPETA (de moment SISTRA, REGWEB3 i NOTIB). Bàsicament les APIs haurien de permetre:
- Poder establir un filtre a la consulta (com a mínim textual sobre l'extracte)
- Retornar el nombre total de resultats de la consulta
- Permetre... | 1.0 | Paginació parametrizable entre REGWEB-CARPETA dels assentaments d'un ciutadà - Es tracta d'homogenitzar la presentació d'informació de les diferents integracions de CARPETA (de moment SISTRA, REGWEB3 i NOTIB). Bàsicament les APIs haurien de permetre:
- Poder establir un filtre a la consulta (com a mínim textual sobre... | non_priority | paginació parametrizable entre regweb carpeta dels assentaments d un ciutadà es tracta d homogenitzar la presentació d informació de les diferents integracions de carpeta de moment sistra i notib bàsicament les apis haurien de permetre poder establir un filtre a la consulta com a mínim textual sobre l ext... | 0 |
521,520 | 15,110,386,939 | IssuesEvent | 2021-02-08 19:09:05 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Missing translations for educational modals | OS/Android QA/Yes l10n priority/P2 release-notes/exclude release/blocking | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROV... | 1.0 | Missing translations for educational modals - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ... | priority | missing translations for educational modals have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will ... | 1 |
476,712 | 13,748,935,626 | IssuesEvent | 2020-10-06 09:45:24 | strapi/strapi | https://api.github.com/repos/strapi/strapi | closed | Custom authentication provider (e.g. AWS Cognito User Pools) not working because subdomain parameter not set in grant object configuration | Hacktoberfest priority: low source: plugin:users-permissions type: enhancement | **Describe the bug**
When trying to create a new custom authentication provider for strapi, I am calling the strapi server base url /connect/new_provider_name then I am getting a dns error from the browser. When looking at the network log I can see a 302 response with a redirection to https://[subdomain]/oauth2/author... | 1.0 | Custom authentication provider (e.g. AWS Cognito User Pools) not working because subdomain parameter not set in grant object configuration - **Describe the bug**
When trying to create a new custom authentication provider for strapi, I am calling the strapi server base url /connect/new_provider_name then I am getting a... | priority | custom authentication provider e g aws cognito user pools not working because subdomain parameter not set in grant object configuration describe the bug when trying to create a new custom authentication provider for strapi i am calling the strapi server base url connect new provider name then i am getting a... | 1 |
75,549 | 14,484,441,269 | IssuesEvent | 2020-12-10 16:20:45 | CosmWasm/cosmwasm | https://api.github.com/repos/CosmWasm/cosmwasm | closed | Limit size of linear memory in VM | Upgrade to Wasmer Reborn (Productionize Code) vm | The heap data of a smart contract execution is stored in a Wasm linear memory. Only zero or one linear memories can exist in the current Wasm standard. The maximum size of a linear memory is 4GB because it is addressed by uint32 offsets in 1 byte steps.
Right now, we ensure the upper memory limit is unset by the con... | 1.0 | Limit size of linear memory in VM - The heap data of a smart contract execution is stored in a Wasm linear memory. Only zero or one linear memories can exist in the current Wasm standard. The maximum size of a linear memory is 4GB because it is addressed by uint32 offsets in 1 byte steps.
Right now, we ensure the up... | non_priority | limit size of linear memory in vm the heap data of a smart contract execution is stored in a wasm linear memory only zero or one linear memories can exist in the current wasm standard the maximum size of a linear memory is because it is addressed by offsets in byte steps right now we ensure the upper mem... | 0 |
205,460 | 23,338,123,071 | IssuesEvent | 2022-08-09 11:51:29 | rsoreq/zaproxy | https://api.github.com/repos/rsoreq/zaproxy | closed | CVE-2021-21351 (High) detected in xstream-1.4.11.1.jar - autoclosed | security vulnerability | ## CVE-2021-21351 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.11.1.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p... | True | CVE-2021-21351 (High) detected in xstream-1.4.11.1.jar - autoclosed - ## CVE-2021-21351 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.11.1.jar</b></p></summary>
<p>XStrea... | non_priority | cve high detected in xstream jar autoclosed cve high severity vulnerability vulnerable library xstream jar xstream is a serialization library from java objects to xml and back library home page a href path to dependency file buildsrc build gradle kts path to v... | 0 |
227,795 | 7,542,856,819 | IssuesEvent | 2018-04-17 14:06:50 | azavea/azavea-branding-guide | https://api.github.com/repos/azavea/azavea-branding-guide | closed | Fix page navigation | Nice-to-have bug in progress priority backlog | The page navigation at the bottom of the guide does not work consistently. It should go to the next and previous pages. When there is no next/prev page, then the button should not be visible. | 1.0 | Fix page navigation - The page navigation at the bottom of the guide does not work consistently. It should go to the next and previous pages. When there is no next/prev page, then the button should not be visible. | priority | fix page navigation the page navigation at the bottom of the guide does not work consistently it should go to the next and previous pages when there is no next prev page then the button should not be visible | 1 |
326,139 | 9,948,125,206 | IssuesEvent | 2019-07-04 08:11:18 | WoWManiaUK/Blackwing-Lair | https://api.github.com/repos/WoWManiaUK/Blackwing-Lair | closed | [NPC] Spirit Healer Missing - Stagecoach Crash Site - Gilneas | Fixed Confirmed Fixed in Dev Low Priority Starting Zone | The grave yard at stagecoach crash site has no spirit to ress you. unable to find zone id

| 1.0 | [NPC] Spirit Healer Missing - Stagecoach Crash Site - Gilneas - The grave yard at stagecoach crash site has no spirit to ress you. unable to find zone id

| priority | spirit healer missing stagecoach crash site gilneas the grave yard at stagecoach crash site has no spirit to ress you unable to find zone id | 1 |
349,875 | 10,475,012,483 | IssuesEvent | 2019-09-23 15:30:26 | etternagame/etterna | https://api.github.com/repos/etternagame/etterna | opened | Fix/Reduce Textureman Leaks | Priority: Low Type: Maintenance | Jousway: replace the pointers with shared_ptr ;)
(investigate what is going on) | 1.0 | Fix/Reduce Textureman Leaks - Jousway: replace the pointers with shared_ptr ;)
(investigate what is going on) | priority | fix reduce textureman leaks jousway replace the pointers with shared ptr investigate what is going on | 1 |
42,831 | 22,959,904,130 | IssuesEvent | 2022-07-19 14:35:44 | scala/bug | https://api.github.com/repos/scala/bug | closed | For ArrayBuffer#min and max, Scala 2.13 is slower than 2.12 | help wanted has PR performance library:collections | ## Reproduction steps
Scala version: 2.13.8
The test program is as follows
```scala
private def min(numIters: Int, bufferSize: Int, loops: Int): Unit = {
val benchmark = new Benchmark("Array Buffer", loops, output = output)
val buffer = new mutable.ArrayBuffer[Int]()
(0 until bufferSize).fore... | True | For ArrayBuffer#min and max, Scala 2.13 is slower than 2.12 - ## Reproduction steps
Scala version: 2.13.8
The test program is as follows
```scala
private def min(numIters: Int, bufferSize: Int, loops: Int): Unit = {
val benchmark = new Benchmark("Array Buffer", loops, output = output)
val buffer =... | non_priority | for arraybuffer min and max scala is slower than reproduction steps scala version the test program is as follows scala private def min numiters int buffersize int loops int unit val benchmark new benchmark array buffer loops output output val buffer ne... | 0 |
229,875 | 17,581,036,988 | IssuesEvent | 2021-08-16 07:28:19 | astrolabsoftware/fink-broker | https://api.github.com/repos/astrolabsoftware/fink-broker | opened | Add a message to warn about schema creation upon release | documentation schema | **Describe the issue**
When fink-broker is updated, a new schema should be released in fink-client. In order to avoid (which I do often...), a message should appear in the PR template message, to warn the user. | 1.0 | Add a message to warn about schema creation upon release - **Describe the issue**
When fink-broker is updated, a new schema should be released in fink-client. In order to avoid (which I do often...), a message should appear in the PR template message, to warn the user. | non_priority | add a message to warn about schema creation upon release describe the issue when fink broker is updated a new schema should be released in fink client in order to avoid which i do often a message should appear in the pr template message to warn the user | 0 |
63,934 | 7,753,189,034 | IssuesEvent | 2018-05-30 23:13:13 | cityofaustin/techstack | https://api.github.com/repos/cityofaustin/techstack | closed | Mock up Images on Service Pages | Feature: Image Gallery Feature: Service Size: M Team: Design/Research | We don't have an image gallery as part of any service pages, yet. The Pick up free paint service is a challenge for residents in testing because they want to visualize the colors and also because, when translated–the colors are less clear across languages.
We haven't groomed out what an image module might look like ... | 1.0 | Mock up Images on Service Pages - We don't have an image gallery as part of any service pages, yet. The Pick up free paint service is a challenge for residents in testing because they want to visualize the colors and also because, when translated–the colors are less clear across languages.
We haven't groomed out wha... | non_priority | mock up images on service pages we don t have an image gallery as part of any service pages yet the pick up free paint service is a challenge for residents in testing because they want to visualize the colors and also because when translated–the colors are less clear across languages we haven t groomed out wha... | 0 |
94,134 | 10,797,958,728 | IssuesEvent | 2019-11-06 09:04:54 | piku/piku | https://api.github.com/repos/piku/piku | closed | Document Procfile | documentation | The Procfile documentation is spread out in various places. Would be good to bring it together into a single place like the ENV file. | 1.0 | Document Procfile - The Procfile documentation is spread out in various places. Would be good to bring it together into a single place like the ENV file. | non_priority | document procfile the procfile documentation is spread out in various places would be good to bring it together into a single place like the env file | 0 |
319,930 | 9,762,215,067 | IssuesEvent | 2019-06-05 10:43:51 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | www.bbc.com - design is broken | browser-fenix engine-gecko priority-critical | <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://www.bbc.com/reel/video/p07c6sb6/the-downsides-of-positive-thinking
**Browser / Version**: Firefox Mobile 68.... | 1.0 | www.bbc.com - design is broken - <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0.1; Mobile; rv:68.0) Gecko/68.0 Firefox/68.0 -->
<!-- @reported_with: -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://www.bbc.com/reel/video/p07c6sb6/the-downsides-of-positive-thinking
**Browse... | priority | design is broken url browser version firefox mobile operating system android tested another browser unknown problem type design is broken description full screen video doesnt work properly steps to reproduce clicked full screen entered in full sccreen m... | 1 |
239,622 | 19,904,679,460 | IssuesEvent | 2022-01-25 11:31:16 | status-im/status-react | https://api.github.com/repos/status-im/status-react | opened | Parallel e2e based on amount of sessions for each test | tests | # Bug Report
## Problem
Currently several e2e each test run failed with ERROR: concurrency limit, because runner doesn't know how many tests it should run based on the amount of sessions (can be 1,2,3).
In fact we have 16 parallel sessions and we shouldn't increase this limit.
#### Expected behavior
No more... | 1.0 | Parallel e2e based on amount of sessions for each test - # Bug Report
## Problem
Currently several e2e each test run failed with ERROR: concurrency limit, because runner doesn't know how many tests it should run based on the amount of sessions (can be 1,2,3).
In fact we have 16 parallel sessions and we shouldn... | non_priority | parallel based on amount of sessions for each test bug report problem currently several each test run failed with error concurrency limit because runner doesn t know how many tests it should run based on the amount of sessions can be in fact we have parallel sessions and we shouldn t in... | 0 |
464,769 | 13,339,548,283 | IssuesEvent | 2020-08-28 13:04:36 | presscustomizr/customizr | https://api.github.com/repos/presscustomizr/customizr | opened | [search icon] when displayed on the left in the main header, search field is partially hidden when revealed | [Priority:urgent] bug | https://secure.helpscout.net/conversation/1248600655/222664?folderId=607547 | 1.0 | [search icon] when displayed on the left in the main header, search field is partially hidden when revealed - https://secure.helpscout.net/conversation/1248600655/222664?folderId=607547 | priority | when displayed on the left in the main header search field is partially hidden when revealed | 1 |
213,444 | 7,253,883,705 | IssuesEvent | 2018-02-16 08:37:41 | quantopian/pyfolio | https://api.github.com/repos/quantopian/pyfolio | closed | Update package on quantopian channel for anaconda | help wanted high priority | The package is still on version 0.5.1, which forces the use of pip in anaconda.
Please consider updating as for zipline, thank you.
AN | 1.0 | Update package on quantopian channel for anaconda - The package is still on version 0.5.1, which forces the use of pip in anaconda.
Please consider updating as for zipline, thank you.
AN | priority | update package on quantopian channel for anaconda the package is still on version which forces the use of pip in anaconda please consider updating as for zipline thank you an | 1 |
120,276 | 4,787,579,227 | IssuesEvent | 2016-10-30 03:05:55 | JKGDevs/JediKnightGalaxies | https://api.github.com/repos/JKGDevs/JediKnightGalaxies | closed | Server browser shows non-JKG servers with JKG-only filter on | bug priority:medium | Happening as of latest commit. Tried reverting 1e0fff7 but found the issue persists even after cycling game modes. This occurs in the FFA game mode only, as far as I can tell. Switching to Faction Battle shows the JKG dev server.
| 1.0 | Server browser shows non-JKG servers with JKG-only filter on - Happening as of latest commit. Tried reverting 1e0fff7 but found the issue persists even after cycling game modes. This occurs in the FFA game mode only, as far as I can tell. Switching to Faction Battle shows the JKG dev server.
| priority | server browser shows non jkg servers with jkg only filter on happening as of latest commit tried reverting but found the issue persists even after cycling game modes this occurs in the ffa game mode only as far as i can tell switching to faction battle shows the jkg dev server | 1 |
498,825 | 14,434,312,526 | IssuesEvent | 2020-12-07 06:50:22 | ityonemo/zigler | https://api.github.com/repos/ityonemo/zigler | closed | address phantom segfaults in yielding mode | bug help wanted high priority | - [x] the segfaults that prevent cleaning up the yielding mode resources (there is a 1K resource leak each time you call a yielding nif)
- [x] segfault that can sometimes happen long after your yield completes. | 1.0 | address phantom segfaults in yielding mode - - [x] the segfaults that prevent cleaning up the yielding mode resources (there is a 1K resource leak each time you call a yielding nif)
- [x] segfault that can sometimes happen long after your yield completes. | priority | address phantom segfaults in yielding mode the segfaults that prevent cleaning up the yielding mode resources there is a resource leak each time you call a yielding nif segfault that can sometimes happen long after your yield completes | 1 |
675,382 | 23,092,747,904 | IssuesEvent | 2022-07-26 16:30:59 | googleapis/doc-pipeline | https://api.github.com/repos/googleapis/doc-pipeline | closed | generate: docfx-python-redis-1.0.1.tar.gz failed | type: bug priority: p1 flakybot: issue | This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
commit: 48f1842f3b0d9af10dc09c10d8864233056129c1
b... | 1.0 | generate: docfx-python-redis-1.0.1.tar.gz failed - This test failed!
To configure my behavior, see [the Flaky Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/main/packages/flakybot).
If I'm commenting on this issue too often, add the `flakybot: quiet` label and
I will stop commenting.
---
... | priority | generate docfx python redis tar gz failed this test failed to configure my behavior see if i m commenting on this issue too often add the flakybot quiet label and i will stop commenting commit buildurl status failed | 1 |
9,878 | 11,889,535,309 | IssuesEvent | 2020-03-28 14:20:17 | dreamer/dosbox-staging | https://api.github.com/repos/dreamer/dosbox-staging | closed | Albion crash | game compatibility | * Description
Game will crash right after the intro/before showing the main menu.
* To Reproduce
Launch Albion (ALBILOW.BAT). I'm using a cue/cd version which is mounted prior launching the game. Watch or pass the intro... game will crash exactly at that point.
NOTE: with the current Dosbox SVN (default in Retrop... | True | Albion crash - * Description
Game will crash right after the intro/before showing the main menu.
* To Reproduce
Launch Albion (ALBILOW.BAT). I'm using a cue/cd version which is mounted prior launching the game. Watch or pass the intro... game will crash exactly at that point.
NOTE: with the current Dosbox SVN (de... | non_priority | albion crash description game will crash right after the intro before showing the main menu to reproduce launch albion albilow bat i m using a cue cd version which is mounted prior launching the game watch or pass the intro game will crash exactly at that point note with the current dosbox svn de... | 0 |
19,624 | 2,622,156,513 | IssuesEvent | 2015-03-04 00:08:19 | byzhang/terrastore | https://api.github.com/repos/byzhang/terrastore | closed | Algebraic sum update function | auto-migrated Milestone-0.6.0 Priority-Medium Project-Terrastore Type-Feature | ```
Update Function for modifying integer values by addition or subtraction
```
Original issue reported on code.google.com by `johansso...@gmail.com` on 18 Jul 2010 at 6:06
* Blocking: #18 | 1.0 | Algebraic sum update function - ```
Update Function for modifying integer values by addition or subtraction
```
Original issue reported on code.google.com by `johansso...@gmail.com` on 18 Jul 2010 at 6:06
* Blocking: #18 | priority | algebraic sum update function update function for modifying integer values by addition or subtraction original issue reported on code google com by johansso gmail com on jul at blocking | 1 |
311,133 | 23,372,415,931 | IssuesEvent | 2022-08-10 21:15:52 | SatelCreative/spylib | https://api.github.com/repos/SatelCreative/spylib | closed | The Document Version seems off | Type: Documentation | The document versioning has been deployed: https://satelcreative.github.io/spylib
**1.** It has the option to switch between versions 0.7.0 and 0.6.0 at the moment. Should we see more versions?
**2.** Some content don't match with the version's actual content.
For example, [0.6.0](https://github.com/SatelCreat... | 1.0 | The Document Version seems off - The document versioning has been deployed: https://satelcreative.github.io/spylib
**1.** It has the option to switch between versions 0.7.0 and 0.6.0 at the moment. Should we see more versions?
**2.** Some content don't match with the version's actual content.
For example, [0.6... | non_priority | the document version seems off the document versioning has been deployed it has the option to switch between versions and at the moment should we see more versions some content don t match with the version s actual content for example doesn t have multipass but it shows i... | 0 |
132,432 | 28,142,031,805 | IssuesEvent | 2023-04-02 03:01:31 | dtcxzyw/llvm-ci | https://api.github.com/repos/dtcxzyw/llvm-ci | closed | Regressions Report [rv64gc-O3-thinlto] March 27th 2023, 7:10:45 pm | regression codegen | ## Metadata
+ Workflow URL: https://github.com/dtcxzyw/llvm-ci/actions/runs/4535454894
## Change Logs
from 1d1b3c49531bb80bcd28870d4eafb71d97049e02 to fd059ea7ec044198fd75bb2b3aa30734bcace33e
[fd059ea7ec044198fd75bb2b3aa30734bcace33e](https://github.com/llvm/llvm-project/commit/fd059ea7ec044198fd75bb2b3aa30734bcace33e... | 1.0 | Regressions Report [rv64gc-O3-thinlto] March 27th 2023, 7:10:45 pm - ## Metadata
+ Workflow URL: https://github.com/dtcxzyw/llvm-ci/actions/runs/4535454894
## Change Logs
from 1d1b3c49531bb80bcd28870d4eafb71d97049e02 to fd059ea7ec044198fd75bb2b3aa30734bcace33e
[fd059ea7ec044198fd75bb2b3aa30734bcace33e](https://github.... | non_priority | regressions report march pm metadata workflow url change logs from to simplify enabling the gpu build for libc avoid legacy target and move gt amp to conventional location recommit quot relax opcode restriction for insn quot add missing cast functions to ... | 0 |
120,077 | 12,058,635,018 | IssuesEvent | 2020-04-15 17:48:44 | cjpleasant88/Grab-Go | https://api.github.com/repos/cjpleasant88/Grab-Go | opened | Create Sprint 1 for Project | documentation enhancement good first issue | [ ] Create new project called Sprint 1
[ ] Use a kanban template to categorize issues (Todo, WIP, Done) | 1.0 | Create Sprint 1 for Project - [ ] Create new project called Sprint 1
[ ] Use a kanban template to categorize issues (Todo, WIP, Done) | non_priority | create sprint for project create new project called sprint use a kanban template to categorize issues todo wip done | 0 |
559,548 | 16,565,549,750 | IssuesEvent | 2021-05-29 10:25:26 | sopra-fs21-group-26/client | https://api.github.com/repos/sopra-fs21-group-26/client | closed | Rework CSS (px to % transformation) | medium priority task | <h2>Sub-Tasks:</h2>
- [x] Rework Home Component
- [x] Rework Login Component
- [x] Rework Register Component
- [x] Rework Menu Component
- [x] Rework Profile Component
- [x] Rework Leaderboard
<h2>Estimate: 2h</h2> | 1.0 | Rework CSS (px to % transformation) - <h2>Sub-Tasks:</h2>
- [x] Rework Home Component
- [x] Rework Login Component
- [x] Rework Register Component
- [x] Rework Menu Component
- [x] Rework Profile Component
- [x] Rework Leaderboard
<h2>Estimate: 2h</h2> | priority | rework css px to transformation sub tasks rework home component rework login component rework register component rework menu component rework profile component rework leaderboard estimate | 1 |
381,947 | 11,298,555,295 | IssuesEvent | 2020-01-17 09:16:44 | ntop/ntopng | https://api.github.com/repos/ntop/ntopng | closed | Implementation of flow score | priority ticket user scripts | Each flow has a numerical (>= 0) value named score that summarizes all the issues related to the flow. In essence every flow has already a bitmap of issues, such as high retransmission rate, or communication with blacklisted hosts. The score is a way to move from this high-level and non-numerical, to a numerical value ... | 1.0 | Implementation of flow score - Each flow has a numerical (>= 0) value named score that summarizes all the issues related to the flow. In essence every flow has already a bitmap of issues, such as high retransmission rate, or communication with blacklisted hosts. The score is a way to move from this high-level and non-n... | priority | implementation of flow score each flow has a numerical value named score that summarizes all the issues related to the flow in essence every flow has already a bitmap of issues such as high retransmission rate or communication with blacklisted hosts the score is a way to move from this high level and non n... | 1 |
91,794 | 26,488,245,943 | IssuesEvent | 2023-01-17 20:00:57 | expo/expo | https://api.github.com/repos/expo/expo | closed | [expo-updates] Updates API does not expose "channel" property at runtime when switching between branch updates via Expo Dev Client | needs review Development Builds | ### Summary
This issue is a continuation of #20431 and is related to PR #16865.
When switching between different branches via the Expo Dev Client GUI, the Updates API does not expose the new value of its `channel` property, as it is set at build time in native code. Again (as said in #20431), this is a big issue ... | 1.0 | [expo-updates] Updates API does not expose "channel" property at runtime when switching between branch updates via Expo Dev Client - ### Summary
This issue is a continuation of #20431 and is related to PR #16865.
When switching between different branches via the Expo Dev Client GUI, the Updates API does not expos... | non_priority | updates api does not expose channel property at runtime when switching between branch updates via expo dev client summary this issue is a continuation of and is related to pr when switching between different branches via the expo dev client gui the updates api does not expose the new value of it... | 0 |
343,681 | 10,334,894,451 | IssuesEvent | 2019-09-03 09:21:38 | trustwallet/web-core | https://api.github.com/repos/trustwallet/web-core | closed | Add support for TrustAPI RPC | Priority: High Type: Enhancement | Add support for TrustAPI prices endpoint. Example:
Endpoint: `POST api.trustwallet.com/prices`
Body:
```
{
currency: 'USD',
tokens: [
contract: 'address'
]
}
``` | 1.0 | Add support for TrustAPI RPC - Add support for TrustAPI prices endpoint. Example:
Endpoint: `POST api.trustwallet.com/prices`
Body:
```
{
currency: 'USD',
tokens: [
contract: 'address'
]
}
``` | priority | add support for trustapi rpc add support for trustapi prices endpoint example endpoint post api trustwallet com prices body currency usd tokens contract address | 1 |
693,136 | 23,764,643,281 | IssuesEvent | 2022-09-01 11:49:13 | running-elephant/datart | https://api.github.com/repos/running-elephant/datart | closed | [bug] 创建图表<类型为表格> 列拖动到字段区后 字符串类型列 无法改变顺序 数值列可以 | status: validating type: bug priority: p3 difficulty: medium | **Datart Version**
rc1 /demo环境
**Describe the bug**
A clear and concise description of what the bug is.
**To Reproduce**
Steps to reproduce the behavior:
1. 创建图表<类型为表格>
2. 列拖动到字段区
3. 上下拖动字符串类型列改变显示顺序 发现无法改变列的位置顺序 但是数值列可以
**Expected behavior**
A clear and concise description of what you expected to happ... | 1.0 | [bug] 创建图表<类型为表格> 列拖动到字段区后 字符串类型列 无法改变顺序 数值列可以 - **Datart Version**
rc1 /demo环境
**Describe the bug**
A clear and concise description of what the bug is.
**To Reproduce**
Steps to reproduce the behavior:
1. 创建图表<类型为表格>
2. 列拖动到字段区
3. 上下拖动字符串类型列改变显示顺序 发现无法改变列的位置顺序 但是数值列可以
**Expected behavior**
A clear and... | priority | 创建图表 列拖动到字段区后 字符串类型列 无法改变顺序 数值列可以 datart version demo环境 describe the bug a clear and concise description of what the bug is to reproduce steps to reproduce the behavior 创建图表 列拖动到字段区 上下拖动字符串类型列改变显示顺序 发现无法改变列的位置顺序 但是数值列可以 expected behavior a clear and concise descripti... | 1 |
3,762 | 6,734,899,697 | IssuesEvent | 2017-10-18 19:43:39 | cypress-io/cypress | https://api.github.com/repos/cypress-io/cypress | closed | Jazz up the Readme | process: contributing | The `README.md` for this repo is kind of sad. 😢 I would like to see the readme more focused on explaining what cypress is, why you would use cypress, **simple install instructions**, etc - for our users and have contributing the secondary focus.
**Ideas to jazz up**
- Add header from old readme branch.
- Embed... | 1.0 | Jazz up the Readme - The `README.md` for this repo is kind of sad. 😢 I would like to see the readme more focused on explaining what cypress is, why you would use cypress, **simple install instructions**, etc - for our users and have contributing the secondary focus.
**Ideas to jazz up**
- Add header from old rea... | non_priority | jazz up the readme the readme md for this repo is kind of sad 😢 i would like to see the readme more focused on explaining what cypress is why you would use cypress simple install instructions etc for our users and have contributing the secondary focus ideas to jazz up add header from old rea... | 0 |
54,828 | 11,309,718,462 | IssuesEvent | 2020-01-19 15:01:28 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | [com_fields] Problem with Attributes TITLE and ALT in Media Field | J3 Issue No Code Attached Yet | ### Steps to reproduce the issue
Creating a new custom media field does not require ALT and TITLE attributes
### Expected result
Side frontend should display the ALT and TITLE attributes for SEO purposes
### Actual result
Side frontend media does not have any ALT and TITLE attributes but only some manage... | 1.0 | [com_fields] Problem with Attributes TITLE and ALT in Media Field - ### Steps to reproduce the issue
Creating a new custom media field does not require ALT and TITLE attributes
### Expected result
Side frontend should display the ALT and TITLE attributes for SEO purposes
### Actual result
Side frontend m... | non_priority | problem with attributes title and alt in media field steps to reproduce the issue creating a new custom media field does not require alt and title attributes expected result side frontend should display the alt and title attributes for seo purposes actual result side frontend media does n... | 0 |
88,988 | 3,788,324,500 | IssuesEvent | 2016-03-21 14:24:34 | BradWBeer/clinch | https://api.github.com/repos/BradWBeer/clinch | closed | Add 3b's ClassImp (assimp wrapper) extension | enhancement Low Priority | I'm not certain how this will work with shaders, but at least it can import data. | 1.0 | Add 3b's ClassImp (assimp wrapper) extension - I'm not certain how this will work with shaders, but at least it can import data. | priority | add s classimp assimp wrapper extension i m not certain how this will work with shaders but at least it can import data | 1 |
254,964 | 21,891,772,561 | IssuesEvent | 2022-05-20 03:00:59 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Despesas com diárias - Despesas com diárias - Siplanweb - Lima Duarte | generalization test development template-Siplanweb tag-Despesas com diárias subtag-Despesas com diárias | DoD: Realizar o teste de Generalização do validador da tag Despesas com diárias - Despesas com diárias - Siplanweb para o Município de Lima Duarte. | 1.0 | Teste de generalizacao para a tag Despesas com diárias - Despesas com diárias - Siplanweb - Lima Duarte - DoD: Realizar o teste de Generalização do validador da tag Despesas com diárias - Despesas com diárias - Siplanweb para o Município de Lima Duarte. | non_priority | teste de generalizacao para a tag despesas com diárias despesas com diárias siplanweb lima duarte dod realizar o teste de generalização do validador da tag despesas com diárias despesas com diárias siplanweb para o município de lima duarte | 0 |
764,723 | 26,813,884,274 | IssuesEvent | 2023-02-02 01:42:52 | apcountryman/picolibrary | https://api.github.com/repos/apcountryman/picolibrary | closed | Improve structure of event driver state machine facilities documentation | priority-normal status-awaiting_review type-refactoring | Improve structure of event driver state machine facilities documentation by splitting, joining, and reordering paragraphs. | 1.0 | Improve structure of event driver state machine facilities documentation - Improve structure of event driver state machine facilities documentation by splitting, joining, and reordering paragraphs. | priority | improve structure of event driver state machine facilities documentation improve structure of event driver state machine facilities documentation by splitting joining and reordering paragraphs | 1 |
175,708 | 6,553,196,364 | IssuesEvent | 2017-09-05 21:25:58 | ProjectSidewalk/SidewalkWebpage | https://api.github.com/repos/ProjectSidewalk/SidewalkWebpage | closed | When a user finishes the last street in a region, ask if they want a new region | feature-request in progress Priority: Low ui-update | If a user is auditing and they finish a street that brings the neighborhood completion (across ALL users) to 100%, then we should have a pop-up asking if they want to move on to a new neighborhood. Overlapping data is nice and all, but right now we are having a hard time hitting 100% coverage of DC, so we should be doi... | 1.0 | When a user finishes the last street in a region, ask if they want a new region - If a user is auditing and they finish a street that brings the neighborhood completion (across ALL users) to 100%, then we should have a pop-up asking if they want to move on to a new neighborhood. Overlapping data is nice and all, but ri... | priority | when a user finishes the last street in a region ask if they want a new region if a user is auditing and they finish a street that brings the neighborhood completion across all users to then we should have a pop up asking if they want to move on to a new neighborhood overlapping data is nice and all but righ... | 1 |
412,559 | 12,044,092,660 | IssuesEvent | 2020-04-14 13:31:09 | HGustavs/LenaSYS | https://api.github.com/repos/HGustavs/LenaSYS | closed | Line thickness slider gets hidden in the Firefox browser when draged | Diagram Group-4-2020 a18petha bug lowPriority | 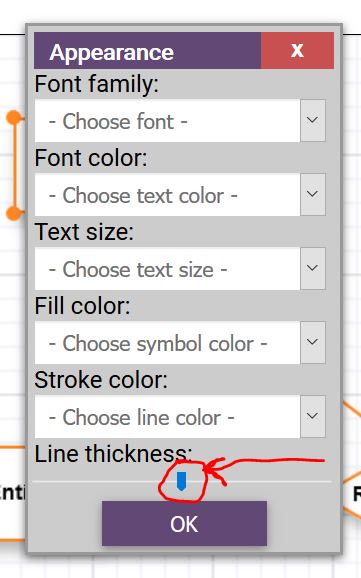
When using the Firefox browser, the slider gets hidden while being clicked and dragged. It would be nice if this could be fixed. | 1.0 | Line thickness slider gets hidden in the Firefox browser when draged - 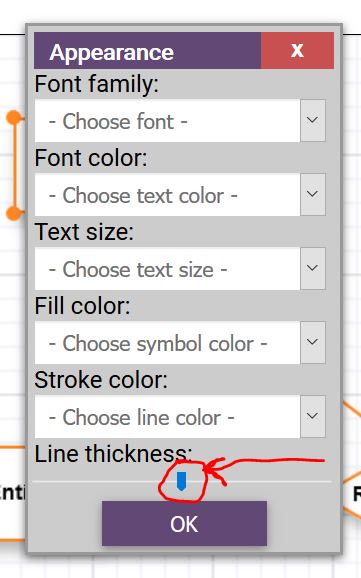
When using the Firefox browser, the slider gets hidden while being clicked and dragged. It would be nice if this could be f... | priority | line thickness slider gets hidden in the firefox browser when draged when using the firefox browser the slider gets hidden while being clicked and dragged it would be nice if this could be fixed | 1 |
61,873 | 17,023,796,973 | IssuesEvent | 2021-07-03 03:54:32 | tomhughes/trac-tickets | https://api.github.com/repos/tomhughes/trac-tickets | closed | Nominatium for Riga street finds Tukums street. | Component: nominatim Priority: minor Resolution: fixed Type: defect | **[Submitted to the original trac issue database at 3.22pm, Wednesday, 9th May 2012]**
, graudu, Riga, LV
should find this street -
http://www.openstreetmap.org/?lat=56.91112&lon=24.08622&zoom=17&layers=M
instead it shows:
, graudu, Jelgava, LV | 1.0 | Nominatium for Riga street finds Tukums street. - **[Submitted to the original trac issue database at 3.22pm, Wednesday, 9th May 2012]**
, graudu, Riga, LV
should find this street -
http://www.openstreetmap.org/?lat=56.91112&lon=24.08622&zoom=17&layers=M
instead it shows:
, graudu, Jelgava, LV | non_priority | nominatium for riga street finds tukums street graudu riga lv should find this street instead it shows graudu jelgava lv | 0 |
806,207 | 29,806,001,651 | IssuesEvent | 2023-06-16 11:43:54 | opencrvs/opencrvs-core | https://api.github.com/repos/opencrvs/opencrvs-core | closed | Bride & Groom signature not appearing when printing certificate | 👹 Bug ❗️ Priority: High | After moving the signatures to minio, they are not appearing in the certificates | 1.0 | Bride & Groom signature not appearing when printing certificate - After moving the signatures to minio, they are not appearing in the certificates | priority | bride groom signature not appearing when printing certificate after moving the signatures to minio they are not appearing in the certificates | 1 |
61,206 | 25,407,315,205 | IssuesEvent | 2022-11-22 16:10:41 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | [AirWatch] Remove any Juan V off of iOS AirWatch profiles for Parking Services group, wipe device. | Workgroup: PE Type: IT Support Service: Apps Type: Tablet Support | <!-- Email -->
<!-- jacob.coronado@austintexas.gov -->
> What application are you using?
Other / Not sure
> Describe the problem.
Juan V was a temp tech in our group. His assignment completed and we need to remove any access he had.
<!-- juan.valdez@austintexas.gov -->
Please let me know if anything ... | 1.0 | [AirWatch] Remove any Juan V off of iOS AirWatch profiles for Parking Services group, wipe device. - <!-- Email -->
<!-- jacob.coronado@austintexas.gov -->
> What application are you using?
Other / Not sure
> Describe the problem.
Juan V was a temp tech in our group. His assignment completed and we need to... | non_priority | remove any juan v off of ios airwatch profiles for parking services group wipe device what application are you using other not sure describe the problem juan v was a temp tech in our group his assignment completed and we need to remove any access he had please let me know if any... | 0 |
124,774 | 26,534,341,017 | IssuesEvent | 2023-01-19 14:40:57 | carbon-design-system/carbon | https://api.github.com/repos/carbon-design-system/carbon | closed | Code snippet showing background color changing on hover on disabled state | type: bug 🐛 component: code-snippet | ### Package
@carbon/react
### Browser
_No response_
### Package version
Latest
### React version
_No response_
### Description
Code snippet, all variants (inline, single line, multi line), are showing background color changing on hover on disabled state. The playground is also showing a weird demo where the sa... | 1.0 | Code snippet showing background color changing on hover on disabled state - ### Package
@carbon/react
### Browser
_No response_
### Package version
Latest
### React version
_No response_
### Description
Code snippet, all variants (inline, single line, multi line), are showing background color changing on hover... | non_priority | code snippet showing background color changing on hover on disabled state package carbon react browser no response package version latest react version no response description code snippet all variants inline single line multi line are showing background color changing on hover... | 0 |
369,824 | 10,918,600,285 | IssuesEvent | 2019-11-21 17:12:13 | RhoInc/Webcharts | https://api.github.com/repos/RhoInc/Webcharts | opened | Avoid jittery pagination caused by the table resizing its container. | low priority table | implement styling that maintains a constant div height | 1.0 | Avoid jittery pagination caused by the table resizing its container. - implement styling that maintains a constant div height | priority | avoid jittery pagination caused by the table resizing its container implement styling that maintains a constant div height | 1 |
27,198 | 21,409,564,144 | IssuesEvent | 2022-04-22 03:20:09 | phpmyadmin/phpmyadmin | https://api.github.com/repos/phpmyadmin/phpmyadmin | opened | Probot Stale bot should be replaced with the Close Stale Issues action | help wanted infrastructure newbie good first issue | Looks like [Probot Stale](https://github.com/probot/stale) bot is not working properly lately, so it should be replaced with the [Close Stale Issues](https://github.com/marketplace/actions/close-stale-issues) GitHub Action.
The Probot Stale configuration file is located at `.github/stale.yml`.
| 1.0 | Probot Stale bot should be replaced with the Close Stale Issues action - Looks like [Probot Stale](https://github.com/probot/stale) bot is not working properly lately, so it should be replaced with the [Close Stale Issues](https://github.com/marketplace/actions/close-stale-issues) GitHub Action.
The Probot Stale con... | non_priority | probot stale bot should be replaced with the close stale issues action looks like bot is not working properly lately so it should be replaced with the github action the probot stale configuration file is located at github stale yml | 0 |
192,452 | 6,850,049,745 | IssuesEvent | 2017-11-14 00:59:36 | flosse/kartevonmorgen | https://api.github.com/repos/flosse/kartevonmorgen | closed | Description length | 12 low-priority | I think we should extend the short description to 500 characters.
And the Title could have 50 characters.
What do you think? Of cours, in the search result it shows not everything, but on the entrypage it should show all characters. | 1.0 | Description length - I think we should extend the short description to 500 characters.
And the Title could have 50 characters.
What do you think? Of cours, in the search result it shows not everything, but on the entrypage it should show all characters. | priority | description length i think we should extend the short description to characters and the title could have characters what do you think of cours in the search result it shows not everything but on the entrypage it should show all characters | 1 |
19,590 | 10,370,904,001 | IssuesEvent | 2019-09-08 16:13:54 | ZyC0R3/gulp-watch | https://api.github.com/repos/ZyC0R3/gulp-watch | closed | WS-2018-0347 (Medium) detected in eslint-1.10.3.tgz | bug security vulnerability | ## WS-2018-0347 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eslint-1.10.3.tgz</b></p></summary>
<p>An AST-based pattern checker for JavaScript.</p>
<p>Library home page: <a href=... | True | WS-2018-0347 (Medium) detected in eslint-1.10.3.tgz - ## WS-2018-0347 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>eslint-1.10.3.tgz</b></p></summary>
<p>An AST-based pattern chec... | non_priority | ws medium detected in eslint tgz ws medium severity vulnerability vulnerable library eslint tgz an ast based pattern checker for javascript library home page a href path to dependency file gulp watch package json path to vulnerable library tmp git gulp watch node ... | 0 |
9,943 | 7,042,621,510 | IssuesEvent | 2017-12-30 15:45:56 | dannypsnl/redux | https://api.github.com/repos/dannypsnl/redux | closed | [Drop feature]DispatchC | performance TODO wontfix | As title, the reason is two API cause confusion.
And concurrency code can enjoy the improvement from Go or computer or System.
So I decide to drop the sequential version. | True | [Drop feature]DispatchC - As title, the reason is two API cause confusion.
And concurrency code can enjoy the improvement from Go or computer or System.
So I decide to drop the sequential version. | non_priority | dispatchc as title the reason is two api cause confusion and concurrency code can enjoy the improvement from go or computer or system so i decide to drop the sequential version | 0 |
244,299 | 7,873,240,894 | IssuesEvent | 2018-06-25 13:46:53 | Repair-DeskPOS/RepairDesk-Bugs | https://api.github.com/repos/Repair-DeskPOS/RepairDesk-Bugs | closed | Customer Group Discounts Incorrect on Invoice | Discount Medium Priority Resolved bug | I have a friends and family discount group that provides a 25% discount on all accessories. The discount applies properly to the ticket, but when it creates an invoice the discount calculates wrong.
Look at open ticket #0-110 in my RepairDesk right now and you will see a tempered glass screen protector for $34.99 t... | 1.0 | Customer Group Discounts Incorrect on Invoice - I have a friends and family discount group that provides a 25% discount on all accessories. The discount applies properly to the ticket, but when it creates an invoice the discount calculates wrong.
Look at open ticket #0-110 in my RepairDesk right now and you will se... | priority | customer group discounts incorrect on invoice i have a friends and family discount group that provides a discount on all accessories the discount applies properly to the ticket but when it creates an invoice the discount calculates wrong look at open ticket in my repairdesk right now and you will see a... | 1 |
104,294 | 8,969,923,089 | IssuesEvent | 2019-01-29 12:13:30 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | opened | [CI] HotThreadsIT.testHotThreadsDontFail failure on master | :Core/Infra/Core >test-failure | Logs: https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+master+multijob-unix-compatibility/os=centos/211/console
REPRODUCE WITH:
```
/gradlew :server:integTest \
-Dtests.seed=233C30BFCE2B7117 \
-Dtests.class=org.elasticsearch.action.admin.HotThreadsIT \
-Dtests.method="testHotThreadsDontFail" ... | 1.0 | [CI] HotThreadsIT.testHotThreadsDontFail failure on master - Logs: https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+master+multijob-unix-compatibility/os=centos/211/console
REPRODUCE WITH:
```
/gradlew :server:integTest \
-Dtests.seed=233C30BFCE2B7117 \
-Dtests.class=org.elasticsearch.action.adm... | non_priority | hotthreadsit testhotthreadsdontfail failure on master logs reproduce with gradlew server integtest dtests seed dtests class org elasticsearch action admin hotthreadsit dtests method testhotthreadsdontfail dtests security manager true dtests locale es mx dtests ... | 0 |
77,241 | 9,985,477,727 | IssuesEvent | 2019-07-10 16:39:14 | HaxeFoundation/haxe | https://api.github.com/repos/HaxeFoundation/haxe | closed | Date.getTime documentation should be improved | Hacktoberfest documentation help wanted standard library | The [Date.getTime()](https://github.com/HaxeFoundation/haxe/blob/development/std/Date.hx#L53-L56) [documentation](http://api.haxe.org/Date.html#getTime) states:
> Returns the timestamp of the date. It might only have a per-second precision depending on the platforms.
The word _might_ is not ideal in technical documen... | 1.0 | Date.getTime documentation should be improved - The [Date.getTime()](https://github.com/HaxeFoundation/haxe/blob/development/std/Date.hx#L53-L56) [documentation](http://api.haxe.org/Date.html#getTime) states:
> Returns the timestamp of the date. It might only have a per-second precision depending on the platforms.
Th... | non_priority | date gettime documentation should be improved the states returns the timestamp of the date it might only have a per second precision depending on the platforms the word might is not ideal in technical documents and could turn off potential haxe users perusing the docs and handling time is a pretty ... | 0 |
608,740 | 18,847,870,227 | IssuesEvent | 2021-11-11 16:53:23 | wellcomecollection/wellcomecollection.org | https://api.github.com/repos/wellcomecollection/wellcomecollection.org | closed | Change email flow mixed up with membership flow | type: bug epic: requesting priority: medium needs: ux needs: dev | ### Problem
When a user changes their email address from the account page, this puts them into the same email verification flow that happens during new account creation.
* They are redirected to a page that talks about verifying their account.
* The link in the verification email takes them to a confirmation tha... | 1.0 | Change email flow mixed up with membership flow - ### Problem
When a user changes their email address from the account page, this puts them into the same email verification flow that happens during new account creation.
* They are redirected to a page that talks about verifying their account.
* The link in the v... | priority | change email flow mixed up with membership flow problem when a user changes their email address from the account page this puts them into the same email verification flow that happens during new account creation they are redirected to a page that talks about verifying their account the link in the v... | 1 |
110,100 | 16,976,946,140 | IssuesEvent | 2021-06-30 01:21:17 | LevyForch/SilverKing | https://api.github.com/repos/LevyForch/SilverKing | opened | CVE-2020-11619 (High) detected in jackson-databind-2.6.7.1.jar | security vulnerability | ## CVE-2020-11619 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core stream... | True | CVE-2020-11619 (High) detected in jackson-databind-2.6.7.1.jar - ## CVE-2020-11619 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.1.jar</b></p></summary>
<p>Gen... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library silverking lib aws java ... | 0 |
169,385 | 14,219,467,969 | IssuesEvent | 2020-11-17 13:19:49 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | [Discovery] - Topline summary for wizard migration research | documentation research ux vsa-public-websites | Create topline summary [based on this template](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/teams/vsa/design/topline-summary-template.md) after conclusion of final session and share with team.
**AC**
- [x] Summary created and posted in GH
- [x] Schedule meeting to review w/ team
-... | 1.0 | [Discovery] - Topline summary for wizard migration research - Create topline summary [based on this template](https://github.com/department-of-veterans-affairs/va.gov-team/blob/master/teams/vsa/design/topline-summary-template.md) after conclusion of final session and share with team.
**AC**
- [x] Summary created... | non_priority | topline summary for wizard migration research create topline summary after conclusion of final session and share with team ac summary created and posted in gh schedule meeting to review w team feedback from team gathered and captured for incorporation into final analysis | 0 |
819,735 | 30,749,802,092 | IssuesEvent | 2023-07-28 18:07:39 | streamlit/streamlit | https://api.github.com/repos/streamlit/streamlit | closed | replace deprecated imghdr library | type:bug area:dependencies status:confirmed priority:P1 | ### Checklist
- [X] I have searched the [existing issues](https://github.com/streamlit/streamlit/issues) for similar issues.
- [X] I added a very descriptive title to this issue.
- [X] I have provided sufficient information below to help reproduce this issue.
### Summary
The `imghdr` module is deprecated in ... | 1.0 | replace deprecated imghdr library - ### Checklist
- [X] I have searched the [existing issues](https://github.com/streamlit/streamlit/issues) for similar issues.
- [X] I added a very descriptive title to this issue.
- [X] I have provided sufficient information below to help reproduce this issue.
### Summary
T... | priority | replace deprecated imghdr library checklist i have searched the for similar issues i added a very descriptive title to this issue i have provided sufficient information below to help reproduce this issue summary the imghdr module is deprecated in python by and is slated... | 1 |
734,070 | 25,337,385,749 | IssuesEvent | 2022-11-18 18:03:21 | nanoframework/Home | https://api.github.com/repos/nanoframework/Home | closed | Bug in json library unit test | Type: Bug trivial up-for-grabs good first issue Priority: Low Area: CL-nanoFramework.Json | ### Library/API/IoT binding
json library
### Visual Studio version
_No response_
### .NET nanoFramework extension version
_No response_
### Target name(s)
_No response_
### Firmware version
_No response_
### Device capabilities
_No response_
### Description
Sonarcloud is reporting... | 1.0 | Bug in json library unit test - ### Library/API/IoT binding
json library
### Visual Studio version
_No response_
### .NET nanoFramework extension version
_No response_
### Target name(s)
_No response_
### Firmware version
_No response_
### Device capabilities
_No response_
### Descri... | priority | bug in json library unit test library api iot binding json library visual studio version no response net nanoframework extension version no response target name s no response firmware version no response device capabilities no response descri... | 1 |
71,804 | 30,921,517,293 | IssuesEvent | 2023-08-06 00:46:53 | Zahlungsmittel/Zahlungsmittel | https://api.github.com/repos/Zahlungsmittel/Zahlungsmittel | opened | [CLOSED] refactor(backend): eslint security | refactor service: backend imported | <a href="https://github.com/ulfgebhardt"><img src="https://avatars.githubusercontent.com/u/1238238?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ulfgebhardt](https://github.com/ulfgebhardt)**
_Wednesday May 10, 2023 at 10:20 GMT_
_Originally opened as https://github.com/gradido/gradido/pul... | 1.0 | [CLOSED] refactor(backend): eslint security - <a href="https://github.com/ulfgebhardt"><img src="https://avatars.githubusercontent.com/u/1238238?v=4" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [ulfgebhardt](https://github.com/ulfgebhardt)**
_Wednesday May 10, 2023 at 10:20 GMT_
_Originally op... | non_priority | refactor backend eslint security issue by wednesday may at gmt originally opened as 🍰 pullrequest this pr introduces the eslint security plugin which does code analysis to warn about potential security issues while the pr fixes one security issue it it ignores... | 0 |
580,448 | 17,258,173,640 | IssuesEvent | 2021-07-22 01:00:42 | infinyon/fluvio | https://api.github.com/repos/infinyon/fluvio | closed | [Bug]: TLS error in `fluvio install` | CI bug priority/blocked | We noticed in the `CD_Dev` workflow that the `install.sh` script was failing when using `VERSION=latest`:
https://github.com/infinyon/fluvio/runs/3120104226?check_suite_focus=true
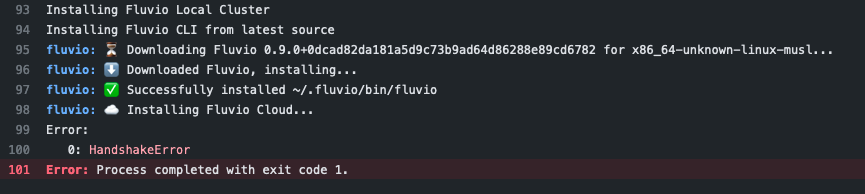
After some digging, ... | 1.0 | [Bug]: TLS error in `fluvio install` - We noticed in the `CD_Dev` workflow that the `install.sh` script was failing when using `VERSION=latest`:
https://github.com/infinyon/fluvio/runs/3120104226?check_suite_focus=true
 detected in multiple libraries - autoclosed | Mend: dependency security vulnerability | ## CVE-2021-22096 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-4.3.9.RELEASE.jar</b>, <b>spring-webmvc-4.3.9.RELEASE.jar</b>, <b>spring-core-5.2.6.RELEASE.jar</b>, <b>... | True | CVE-2021-22096 (Medium) detected in multiple libraries - autoclosed - ## CVE-2021-22096 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>spring-web-4.3.9.RELEASE.jar</b>, <b>spring-w... | non_priority | cve medium detected in multiple libraries autoclosed cve medium severity vulnerability vulnerable libraries spring web release jar spring webmvc release jar spring core release jar spring webmvc release jar spring web release jar spring web ... | 0 |
519,043 | 15,039,130,860 | IssuesEvent | 2021-02-02 18:16:07 | microsoft/PowerToys | https://api.github.com/repos/microsoft/PowerToys | closed | [ColorPicker - Editor] In edit color mode the centered color is clickable | Area-User Interface Issue-Bug Priority-3 Product-Color Picker Resolution-Fix-Committed | <!--
**Important: When reporting BSODs or security issues, DO NOT attach memory dumps, logs, or traces to Github issues**.
Instead, send dumps/traces to secure@microsoft.com, referencing this GitHub issue.
-->
## ℹ Computer information
- PowerToys version: 0.29.0
- PowerToy Utility: ColorPicker
- Running Pow... | 1.0 | [ColorPicker - Editor] In edit color mode the centered color is clickable - <!--
**Important: When reporting BSODs or security issues, DO NOT attach memory dumps, logs, or traces to Github issues**.
Instead, send dumps/traces to secure@microsoft.com, referencing this GitHub issue.
-->
## ℹ Computer information
... | priority | in edit color mode the centered color is clickable important when reporting bsods or security issues do not attach memory dumps logs or traces to github issues instead send dumps traces to secure microsoft com referencing this github issue ℹ computer information powertoys version ... | 1 |
192,181 | 6,847,449,113 | IssuesEvent | 2017-11-13 15:28:16 | huridocs/uwazi | https://api.github.com/repos/huridocs/uwazi | closed | Cannot see any uploaded files on ihrda.uwazi.io | Priority: Medium Type: Bug | Hey guys,
So, we at IHRDA cannot see any files on Uploads in IHRDA.uwazi.io
This is what we see. After uploading several docs. So, we are stuck. **Cannot #work.**
@kjantin @danicatalan @konzz
<img width="960" alt="ihrda1" src="https://user-images.githubusercontent.com/22650647/32490711-2deb7d10-c3c5-11e7-9584-386... | 1.0 | Cannot see any uploaded files on ihrda.uwazi.io - Hey guys,
So, we at IHRDA cannot see any files on Uploads in IHRDA.uwazi.io
This is what we see. After uploading several docs. So, we are stuck. **Cannot #work.**
@kjantin @danicatalan @konzz
<img width="960" alt="ihrda1" src="https://user-images.githubusercontent... | priority | cannot see any uploaded files on ihrda uwazi io hey guys so we at ihrda cannot see any files on uploads in ihrda uwazi io this is what we see after uploading several docs so we are stuck cannot work kjantin danicatalan konzz img width alt src | 1 |
105,917 | 4,249,486,756 | IssuesEvent | 2016-07-08 00:13:38 | rathena/rathena | https://api.github.com/repos/rathena/rathena | closed | GTB should bypass | bug:core bug:skill mode:renewal priority:low server:map | GTB should bypass these skills:
White Imprison
Masquarade skills
Genetic skills
Source: pRO and iRO according to other bug reports and forum entries
http://forums.irowiki.org/index.php?topic=106953.0
**Would be great if this could be tested and fixed accordingly.** | 1.0 | GTB should bypass - GTB should bypass these skills:
White Imprison
Masquarade skills
Genetic skills
Source: pRO and iRO according to other bug reports and forum entries
http://forums.irowiki.org/index.php?topic=106953.0
**Would be great if this could be tested and fixed accordingly.** | priority | gtb should bypass gtb should bypass these skills white imprison masquarade skills genetic skills source pro and iro according to other bug reports and forum entries would be great if this could be tested and fixed accordingly | 1 |
634,502 | 20,363,362,573 | IssuesEvent | 2022-02-21 00:32:16 | holy-tanuki/Ether-Bot | https://api.github.com/repos/holy-tanuki/Ether-Bot | closed | Fix/support (pycord.)wavelink | bug priority: hight | Currently, just wavelink, waiting for a v1.0.0 of pycord.wavelink | 1.0 | Fix/support (pycord.)wavelink - Currently, just wavelink, waiting for a v1.0.0 of pycord.wavelink | priority | fix support pycord wavelink currently just wavelink waiting for a of pycord wavelink | 1 |
386,939 | 26,708,055,571 | IssuesEvent | 2023-01-27 20:10:40 | longturn/freeciv21 | https://api.github.com/repos/longturn/freeciv21 | closed | Add "center unit" button to units control bar | documentation enhancement gui | The units control bar establishes a mouse-driven alternative to the keyboard-driven handling of units.
If the player choses to uncheck "auto center unit" in the interface options the unit controls bar is not sufficient for this because the unit has to be centered manually pressing "c".
While centering the unit is no... | 1.0 | Add "center unit" button to units control bar - The units control bar establishes a mouse-driven alternative to the keyboard-driven handling of units.
If the player choses to uncheck "auto center unit" in the interface options the unit controls bar is not sufficient for this because the unit has to be centered manual... | non_priority | add center unit button to units control bar the units control bar establishes a mouse driven alternative to the keyboard driven handling of units if the player choses to uncheck auto center unit in the interface options the unit controls bar is not sufficient for this because the unit has to be centered manual... | 0 |
174,456 | 21,300,072,525 | IssuesEvent | 2022-04-15 01:03:48 | shaimael/easybuggy2 | https://api.github.com/repos/shaimael/easybuggy2 | closed | CVE-2020-2875 (Medium) detected in mysql-connector-java-5.1.25.jar - autoclosed | security vulnerability | ## CVE-2020-2875 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b></p></summary>
<p>MySQL JDBC Type 4 driver</p>
<p>Library home page: <a href="http... | True | CVE-2020-2875 (Medium) detected in mysql-connector-java-5.1.25.jar - autoclosed - ## CVE-2020-2875 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql-connector-java-5.1.25.jar</b><... | non_priority | cve medium detected in mysql connector java jar autoclosed cve medium severity vulnerability vulnerable library mysql connector java jar mysql jdbc type driver library home page a href path to dependency file pom xml path to vulnerable library repository mysql ... | 0 |
77,634 | 3,507,190,081 | IssuesEvent | 2016-01-08 11:47:55 | OregonCore/OregonCore | https://api.github.com/repos/OregonCore/OregonCore | closed | GM commands while drunk (BB #617) | migrated Priority: Low Type: Bug | This issue was migrated from bitbucket.
**Original Reporter:** LordUsagi
**Original Date:** 28.07.2014 20:52:26 GMT+0000
**Original Priority:** trivial
**Original Type:** bug
**Original State:** invalid
**Direct Link:** https://bitbucket.org/oregon/oregoncore/issues/617
<hr>
If you're drunk in game and you type in a gm... | 1.0 | GM commands while drunk (BB #617) - This issue was migrated from bitbucket.
**Original Reporter:** LordUsagi
**Original Date:** 28.07.2014 20:52:26 GMT+0000
**Original Priority:** trivial
**Original Type:** bug
**Original State:** invalid
**Direct Link:** https://bitbucket.org/oregon/oregoncore/issues/617
<hr>
If you'r... | priority | gm commands while drunk bb this issue was migrated from bitbucket original reporter lordusagi original date gmt original priority trivial original type bug original state invalid direct link if you re drunk in game and you type in a gm command sometimes you get ... | 1 |
3,931 | 2,711,618,242 | IssuesEvent | 2015-04-09 07:56:53 | romait2014/57KYXHZ5S3DYAOHNPXRMLQTB | https://api.github.com/repos/romait2014/57KYXHZ5S3DYAOHNPXRMLQTB | closed | Feozi6mWRQfV+CPKCdNtykK4Nl+xAjKHoMJvPn3i8EksYfROVz8j8Y5Yv/Bjjgh6WDKpiAR38QlGf8bgmoCz6jvLLeslL38Y1C7miBx3Pp8+v/Vt/qEpfs7aQo3Djnr6rz3e5ZtJfHv00pJkOe/p/Vhk3I5r8VTT+KlTfqIka3M= | design | +QY0xAGQnBoKU+n0Y833B2cs6lPYuAamMqbstiXduUN7l96ularkI/vTE8O3AF2IEyzFeHdG+jvSl7Ld4sEWMFgOnXxbbllq25b851bK7AKXii495JQFmhAZFpwp1BcSn6H/NYbM9yslz8BiqGf1uwgA6WI3JVpj43VASyfAwcbsjxhErwAiT2+ob8bs1o/N3UHdZJpzTNcSYlSag2imhJXgCEAPPt4npi8mxS3dcQMwmVe8ty3KGxxsXD4j3Sb2SaqCpykop/t0eVRdQl5jvXmsnBNqifAg227KVxP43eU+QxDBnqBRMySEz5t1p3+F... | 1.0 | Feozi6mWRQfV+CPKCdNtykK4Nl+xAjKHoMJvPn3i8EksYfROVz8j8Y5Yv/Bjjgh6WDKpiAR38QlGf8bgmoCz6jvLLeslL38Y1C7miBx3Pp8+v/Vt/qEpfs7aQo3Djnr6rz3e5ZtJfHv00pJkOe/p/Vhk3I5r8VTT+KlTfqIka3M= - +QY0xAGQnBoKU+n0Y833B2cs6lPYuAamMqbstiXduUN7l96ularkI/vTE8O3AF2IEyzFeHdG+jvSl7Ld4sEWMFgOnXxbbllq25b851bK7AKXii495JQFmhAZFpwp1BcSn6H/NYbM9yslz8Biq... | non_priority | v vt p nijkq nojab mva zlle ibcp c | 0 |
41,033 | 2,868,966,308 | IssuesEvent | 2015-06-05 22:15:24 | dart-lang/pub | https://api.github.com/repos/dart-lang/pub | closed | "pub serve" should provide the ability to look up mappings between source and output lines | enhancement Fixed Priority-Medium Pub-Serve | <a href="https://github.com/nex3"><img src="https://avatars.githubusercontent.com/u/188?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [nex3](https://github.com/nex3)**
_Originally opened as dart-lang/sdk#16061_
----
It should be possible (via the "pub serve" websocket API) to pro... | 1.0 | "pub serve" should provide the ability to look up mappings between source and output lines - <a href="https://github.com/nex3"><img src="https://avatars.githubusercontent.com/u/188?v=3" align="left" width="96" height="96"hspace="10"></img></a> **Issue by [nex3](https://github.com/nex3)**
_Originally opened as dart-lang... | priority | pub serve should provide the ability to look up mappings between source and output lines issue by originally opened as dart lang sdk it should be possible via the quot pub serve quot websocket api to provide the server with a source file and line number and get the corresponding output url ... | 1 |
579,454 | 17,191,831,385 | IssuesEvent | 2021-07-16 12:09:19 | NinjaEnterprise/NinjaConfiguration | https://api.github.com/repos/NinjaEnterprise/NinjaConfiguration | closed | [FEATURE] Creating a configuration service. | priority: low status: backlog type: enhancement | **Description of functionality**
You need to create a configuration service, which is needed in order to receive settings for all other services.
- [ ] Creation and configuration of a multi-module structure;
- [ ] Using a separate database to store the settings;
- [ ] Adding a REST module for editing settings;
- [... | 1.0 | [FEATURE] Creating a configuration service. - **Description of functionality**
You need to create a configuration service, which is needed in order to receive settings for all other services.
- [ ] Creation and configuration of a multi-module structure;
- [ ] Using a separate database to store the settings;
- [ ] A... | priority | creating a configuration service description of functionality you need to create a configuration service which is needed in order to receive settings for all other services creation and configuration of a multi module structure using a separate database to store the settings adding a rest m... | 1 |
386,143 | 11,432,706,210 | IssuesEvent | 2020-02-04 14:31:46 | ooni/ooni.org | https://api.github.com/repos/ooni/ooni.org | opened | Add drill down searching for count tables | discuss priority/medium ux | Use them in the search page in Explorer to provide drill-down searching (e.g. avoid returning many thousand msmts if the users cannot reasonably browse them).
This came from ooni/backend#234 | 1.0 | Add drill down searching for count tables - Use them in the search page in Explorer to provide drill-down searching (e.g. avoid returning many thousand msmts if the users cannot reasonably browse them).
This came from ooni/backend#234 | priority | add drill down searching for count tables use them in the search page in explorer to provide drill down searching e g avoid returning many thousand msmts if the users cannot reasonably browse them this came from ooni backend | 1 |
70,367 | 13,457,178,440 | IssuesEvent | 2020-09-09 08:51:33 | eclipse-theia/theia | https://api.github.com/repos/eclipse-theia/theia | closed | [Plugin-Api] Apply authentication API | help wanted plug-in system vscode | <!-- Please fill out the following content for a feature request. -->
Apply `authentication` VsCode Plugin API. Is needed for [vscode-github-pr-plugin](https://github.com/microsoft/vscode-pull-request-github) authentication.
<!-- Please provide a clear description of the feature and any relevant information. -->
###... | 1.0 | [Plugin-Api] Apply authentication API - <!-- Please fill out the following content for a feature request. -->
Apply `authentication` VsCode Plugin API. Is needed for [vscode-github-pr-plugin](https://github.com/microsoft/vscode-pull-request-github) authentication.
<!-- Please provide a clear description of the featur... | non_priority | apply authentication api apply authentication vscode plugin api is needed for authentication feature description vscode implementation | 0 |
32,783 | 12,149,767,965 | IssuesEvent | 2020-04-24 16:43:59 | vancopayments/rt-web-internal-docs | https://api.github.com/repos/vancopayments/rt-web-internal-docs | opened | WS-2018-0021 (Medium) detected in bootstrap-3.0.0.min.js | security vulnerability | ## WS-2018-0021 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.0.0.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile fir... | True | WS-2018-0021 (Medium) detected in bootstrap-3.0.0.min.js - ## WS-2018-0021 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.0.0.min.js</b></p></summary>
<p>The most popula... | non_priority | ws medium detected in bootstrap min js ws medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file tmp ws scm rt ... | 0 |
103,797 | 4,185,989,020 | IssuesEvent | 2016-06-23 13:10:18 | DistrictDataLabs/logbook | https://api.github.com/repos/DistrictDataLabs/logbook | opened | Person Search | priority: high type: feature | The primary use case that I've been using Logbook for is to look someone up for their contact information, and even to annotate details about them.
Right now however, there is no filter by name or search capabilities some ideas are:
- autocomplete filter/text box
- an actual text search on first, last name and emai... | 1.0 | Person Search - The primary use case that I've been using Logbook for is to look someone up for their contact information, and even to annotate details about them.
Right now however, there is no filter by name or search capabilities some ideas are:
- autocomplete filter/text box
- an actual text search on first, la... | priority | person search the primary use case that i ve been using logbook for is to look someone up for their contact information and even to annotate details about them right now however there is no filter by name or search capabilities some ideas are autocomplete filter text box an actual text search on first la... | 1 |
77,470 | 27,008,492,488 | IssuesEvent | 2023-02-10 13:39:29 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | opened | MatchMode: returns STARTS_WITH by default if blank | :lady_beetle: defect :bangbang: needs-triage | ### Describe the bug
Follwing up discussing in #9767
`MatchMode` returns `STARTS_WITH` if blank, and throw exception if unkown value
### Reproducer
_No response_
### Expected behavior
Be lenient with blank value, and prevent further error
### PrimeFaces edition
Community
### PrimeFaces version
13.0.0-SNAPS... | 1.0 | MatchMode: returns STARTS_WITH by default if blank - ### Describe the bug
Follwing up discussing in #9767
`MatchMode` returns `STARTS_WITH` if blank, and throw exception if unkown value
### Reproducer
_No response_
### Expected behavior
Be lenient with blank value, and prevent further error
### PrimeFaces edi... | non_priority | matchmode returns starts with by default if blank describe the bug follwing up discussing in matchmode returns starts with if blank and throw exception if unkown value reproducer no response expected behavior be lenient with blank value and prevent further error primefaces editio... | 0 |
41,038 | 10,605,143,184 | IssuesEvent | 2019-10-10 19:47:17 | lyft/amundsen | https://api.github.com/repos/lyft/amundsen | closed | Position databuilder more clearly as an ETL tool(box) in its own right | amundsendatabuilder keep fresh | Background originated in Q&A on this PR https://github.com/lyft/amundsendatabuilder/pull/31#issuecomment-488501046
- - - -
> Hence making databuilder not aware of the search service could help to grow the library into a more generic way.
Yes, that framing certainly puts a different perspective on databuilder. ... | 1.0 | Position databuilder more clearly as an ETL tool(box) in its own right - Background originated in Q&A on this PR https://github.com/lyft/amundsendatabuilder/pull/31#issuecomment-488501046
- - - -
> Hence making databuilder not aware of the search service could help to grow the library into a more generic way.
... | non_priority | position databuilder more clearly as an etl tool box in its own right background originated in q a on this pr hence making databuilder not aware of the search service could help to grow the library into a more generic way yes that framing certainly puts a different perspective on databuilder ... | 0 |
725,353 | 24,959,702,774 | IssuesEvent | 2022-11-01 14:37:45 | AY2223S1-CS2103T-W15-4/tp | https://api.github.com/repos/AY2223S1-CS2103T-W15-4/tp | closed | [PE-D][Tester E] Not sure what alias done | type.Bug priority.High severity.Medium | 
Think could be more specific when explaining what does alias mean and what the command does
<!--session: 1666944265112-3d5780d8-add8-45ea-831e-933088a9871a-->
<!--Version: Web v3.... | 1.0 | [PE-D][Tester E] Not sure what alias done - 
Think could be more specific when explaining what does alias mean and what the command does
<!--session: 1666944265112-3d5780d8-add8-45... | priority | not sure what alias done think could be more specific when explaining what does alias mean and what the command does labels severity verylow type documentationbug original limweijun ped | 1 |
286,471 | 31,652,401,402 | IssuesEvent | 2023-09-07 00:14:53 | samq-wsdemo/cassandra | https://api.github.com/repos/samq-wsdemo/cassandra | opened | CVE-2023-34455 (High) detected in snappy-java-1.1.1.7.jar | Mend: dependency security vulnerability | ## CVE-2023-34455 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snappy-java-1.1.1.7.jar</b></p></summary>
<p>snappy-java: A fast compression/decompression library</p>
<p>Path to vuln... | True | CVE-2023-34455 (High) detected in snappy-java-1.1.1.7.jar - ## CVE-2023-34455 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snappy-java-1.1.1.7.jar</b></p></summary>
<p>snappy-java: ... | non_priority | cve high detected in snappy java jar cve high severity vulnerability vulnerable library snappy java jar snappy java a fast compression decompression library path to vulnerable library lib snappy java jar dependency hierarchy x snappy java ja... | 0 |
375,992 | 11,136,839,753 | IssuesEvent | 2019-12-20 17:37:42 | SETI/pds-opus | https://api.github.com/repos/SETI/pds-opus | closed | Metadata Selector drag-and-drop broken when scrolling | A-Bug B-OPUS JS Effort 2 Medium Priority 4 Useful | B063: Add enough slugs to select metadata to require a scrollbar on the right side. Actually scroll down some. Then try to drag a metadata item. Instead of showing up under your mouse, it shows it being dragged further up on the screen by the amount the window has been scrolled. | 1.0 | Metadata Selector drag-and-drop broken when scrolling - B063: Add enough slugs to select metadata to require a scrollbar on the right side. Actually scroll down some. Then try to drag a metadata item. Instead of showing up under your mouse, it shows it being dragged further up on the screen by the amount the window has... | priority | metadata selector drag and drop broken when scrolling add enough slugs to select metadata to require a scrollbar on the right side actually scroll down some then try to drag a metadata item instead of showing up under your mouse it shows it being dragged further up on the screen by the amount the window has be... | 1 |
396,509 | 11,709,730,023 | IssuesEvent | 2020-03-08 20:30:01 | open-gunz/source | https://api.github.com/repos/open-gunz/source | opened | Interface UX suggestions | Moderate Priority | * [ ] "Play now" button's clickable area is much larger than the actual button (indicated by the green area when the button is clicked).
* [x] The lobby numbers for 1/2/3/4/5/6 should be moved slightly lower to be in the center.
* [x] The Join/Create/Play now buttons should be moved slightly higher to be in the c... | 1.0 | Interface UX suggestions - * [ ] "Play now" button's clickable area is much larger than the actual button (indicated by the green area when the button is clicked).
* [x] The lobby numbers for 1/2/3/4/5/6 should be moved slightly lower to be in the center.
* [x] The Join/Create/Play now buttons should be moved sli... | priority | interface ux suggestions play now button s clickable area is much larger than the actual button indicated by the green area when the button is clicked the lobby numbers for should be moved slightly lower to be in the center the join create play now buttons should be moved slightly ... | 1 |
203,366 | 7,060,378,186 | IssuesEvent | 2018-01-05 08:28:17 | wso2/product-is | https://api.github.com/repos/wso2/product-is | opened | BPS profile name front end validation missing which must only contain letters and numbers | Affected/5.4.0 Priority/High Type/Bug | When creating BPS profile, ** Profile Name** must only contain letters and numbers. But in fronted its not validated and only giving error as
> Error when adding the BPS profile.
Below error can be seen in the backend
```
[-1234] [] [2018-01-05 07:51:38,255] ERROR {org.wso2.carbon.identity.workflow.impl.Wo... | 1.0 | BPS profile name front end validation missing which must only contain letters and numbers - When creating BPS profile, ** Profile Name** must only contain letters and numbers. But in fronted its not validated and only giving error as
> Error when adding the BPS profile.
Below error can be seen in the backend... | priority | bps profile name front end validation missing which must only contain letters and numbers when creating bps profile profile name must only contain letters and numbers but in fronted its not validated and only giving error as error when adding the bps profile below error can be seen in the backend... | 1 |
198,523 | 6,973,918,974 | IssuesEvent | 2017-12-11 22:16:45 | opencurrents/opencurrents | https://api.github.com/repos/opencurrents/opencurrents | closed | openCurrents.com - Size: I think the site looks better when zoomed in at 125%, see the difference. Have had a few folks tell me the same. | mvp? priority low | 
| 1.0 | openCurrents.com - Size: I think the site looks better when zoomed in at 125%, see the difference. Have had a few folks tell me the same. - 

| 1.0 | Documentation for the last panel in the Grafana Dashboard - We need to add documentation for the below panels under the Grafana for the end user's visibility.
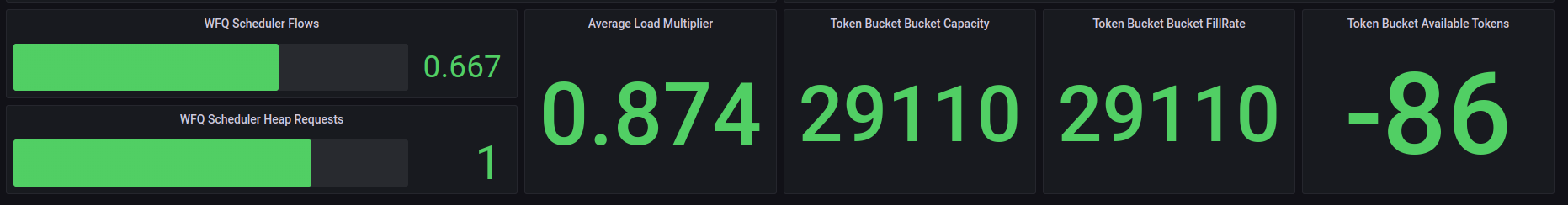
| non_priority | documentation for the last panel in the grafana dashboard we need to add documentation for the below panels under the grafana for the end user s visibility | 0 |
369,151 | 10,888,930,049 | IssuesEvent | 2019-11-18 17:09:45 | lowRISC/opentitan | https://api.github.com/repos/lowRISC/opentitan | opened | [site] Add favicon to docs.opentitan.org | Component:Tooling Priority:P3 Type:Enhancement | Nice looking favicon is only at the opentitan.org. It would be good if docs.opentitan.org also has same favicon :) | 1.0 | [site] Add favicon to docs.opentitan.org - Nice looking favicon is only at the opentitan.org. It would be good if docs.opentitan.org also has same favicon :) | priority | add favicon to docs opentitan org nice looking favicon is only at the opentitan org it would be good if docs opentitan org also has same favicon | 1 |
301,898 | 9,232,416,374 | IssuesEvent | 2019-03-13 07:01:50 | BentoBoxWorld/BentoBox | https://api.github.com/repos/BentoBoxWorld/BentoBox | closed | Players able to /is sethome on island that they are cooped/trusted on | Priority: High Type: Bug | ### Description
#### Describe the bug
- Players are able to /is sethome on island that they are cooped/ trusted on
- If they have no warp-sign or a player on their island to tp them back, they are unable to go to their island with /is, since it leads to the one they set it to. Of course, even if the `Island respawn:... | 1.0 | Players able to /is sethome on island that they are cooped/trusted on - ### Description
#### Describe the bug
- Players are able to /is sethome on island that they are cooped/ trusted on
- If they have no warp-sign or a player on their island to tp them back, they are unable to go to their island with /is, since it ... | priority | players able to is sethome on island that they are cooped trusted on description describe the bug players are able to is sethome on island that they are cooped trusted on if they have no warp sign or a player on their island to tp them back they are unable to go to their island with is since it ... | 1 |
343,103 | 30,652,309,867 | IssuesEvent | 2023-07-25 09:42:47 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix jax_numpy_statistical.test_jax_average | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5609939117"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5609939117"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://githu... | 1.0 | Fix jax_numpy_statistical.test_jax_average - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5609939117"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5609939117"><img src=https://img.shields.io/badge/-success-suc... | non_priority | fix jax numpy statistical test jax average numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
262,106 | 27,850,914,719 | IssuesEvent | 2023-03-20 18:37:26 | jgeraigery/HubSpot-Test-Repo-2 | https://api.github.com/repos/jgeraigery/HubSpot-Test-Repo-2 | opened | handlebars-1.3.1.jar: 1 vulnerabilities (highest severity is: 9.8) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-1.3.1.jar</b></p></summary>
<p>Logic-less and semantic templates with Java</p>
<p>Library home page: <a href="https://github.com/jknack/handlebars.java">ht... | True | handlebars-1.3.1.jar: 1 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-1.3.1.jar</b></p></summary>
<p>Logic-less and semantic templates with Java</p>
<p>Libr... | non_priority | handlebars jar vulnerabilities highest severity is vulnerable library handlebars jar logic less and semantic templates with java library home page a href path to dependency file singularityexecutorcleanup pom xml path to vulnerable library home wss scanner repository... | 0 |
86,548 | 15,755,678,485 | IssuesEvent | 2021-03-31 02:12:16 | Thezone1975/Wallie_Bot | https://api.github.com/repos/Thezone1975/Wallie_Bot | opened | WS-2018-0076 (Medium) detected in tunnel-agent-0.4.3.tgz | security vulnerability | ## WS-2018-0076 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tunnel-agent-0.4.3.tgz</b></p></summary>
<p>HTTP proxy tunneling agent. Formerly part of mikeal/request, now a standal... | True | WS-2018-0076 (Medium) detected in tunnel-agent-0.4.3.tgz - ## WS-2018-0076 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tunnel-agent-0.4.3.tgz</b></p></summary>
<p>HTTP proxy tunn... | non_priority | ws medium detected in tunnel agent tgz ws medium severity vulnerability vulnerable library tunnel agent tgz http proxy tunneling agent formerly part of mikeal request now a standalone module library home page a href path to dependency file watsonsocketbot package js... | 0 |
133,222 | 18,285,461,117 | IssuesEvent | 2021-10-05 09:46:11 | AlexRogalskiy/quotes | https://api.github.com/repos/AlexRogalskiy/quotes | opened | CVE-2018-3721 (Medium) detected in lodash-2.4.2.tgz | security vulnerability | ## CVE-2018-3721 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.... | True | CVE-2018-3721 (Medium) detected in lodash-2.4.2.tgz - ## CVE-2018-3721 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library deliver... | non_priority | cve medium detected in lodash tgz cve medium severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file quotes package json path to vulnerable li... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.