Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
38,396 | 8,796,418,467 | IssuesEvent | 2018-12-23 06:33:47 | prettydiff/prettydiff | https://api.github.com/repos/prettydiff/prettydiff | closed | Comments breaking vertical alignment of variable chains | 3.0.0 Beautification Defect | ```javascript
/*global global, prettydiff*/
(function beautify_style_init() {
"use strict";
const style = function beautify_style(options) {
const data = options.parsed, lf = (options.crlf === true)
? "\r\n"
: "\n", len = (options.end > 0)
? options.end + 1
... | 1.0 | Comments breaking vertical alignment of variable chains - ```javascript
/*global global, prettydiff*/
(function beautify_style_init() {
"use strict";
const style = function beautify_style(options) {
const data = options.parsed, lf = (options.crlf === true)
? "\r\n"
: "\n",... | non_priority | comments breaking vertical alignment of variable chains javascript global global prettydiff function beautify style init use strict const style function beautify style options const data options parsed lf options crlf true r n n ... | 0 |
167,391 | 13,024,022,985 | IssuesEvent | 2020-07-27 11:04:15 | sebastianbergmann/phpunit | https://api.github.com/repos/sebastianbergmann/phpunit | closed | Schema version is not migrated | feature/test-runner type/bug | With fec8d7d8e988c8be93e3301f127d4eb0e6d5d3cb in place, we finally get useful failure messages:
```
PHPUnit 9.3-gfec8d7d8e by Sebastian Bergmann and contributors.
Runtime: PHP 7.4.8
Configuration: /usr/local/src/phpunit/phpunit.xml
F 1 /... | 1.0 | Schema version is not migrated - With fec8d7d8e988c8be93e3301f127d4eb0e6d5d3cb in place, we finally get useful failure messages:
```
PHPUnit 9.3-gfec8d7d8e by Sebastian Bergmann and contributors.
Runtime: PHP 7.4.8
Configuration: /usr/local/src/phpunit/phpunit.xml
F ... | non_priority | schema version is not migrated with in place we finally get useful failure messages phpunit by sebastian bergmann and contributors runtime php configuration usr local src phpunit phpunit xml f time... | 0 |
176,409 | 6,559,225,413 | IssuesEvent | 2017-09-07 02:22:55 | NuGet/Home | https://api.github.com/repos/NuGet/Home | closed | Project.json restore should warn when top level packages violate constraints | Area: Restore Area:Error Handling Priority:0 Type:Bug | The below project.json should generate a warning for the constraint violation between Microsoft.ApplicationInsights >= 2.0.0 and == 1.2.3 required by the WindowsApp package.
Ideally there should also be a way to suppress these warnings.
``` json
{
"dependencies": {
"Microsoft.ApplicationInsights": "2.0.0",
... | 1.0 | Project.json restore should warn when top level packages violate constraints - The below project.json should generate a warning for the constraint violation between Microsoft.ApplicationInsights >= 2.0.0 and == 1.2.3 required by the WindowsApp package.
Ideally there should also be a way to suppress these warnings.
``... | priority | project json restore should warn when top level packages violate constraints the below project json should generate a warning for the constraint violation between microsoft applicationinsights and required by the windowsapp package ideally there should also be a way to suppress these warnings ... | 1 |
196,323 | 6,926,823,400 | IssuesEvent | 2017-11-30 20:32:44 | vmware/vic-ui | https://api.github.com/repos/vmware/vic-ui | closed | Create VCH wizard says "VM endpoint" instead of "Endpoint VM" | area/ui priority/low team/lifecycle | In the Compute page of the VCH deployment wizard, the text "VM endpoint settings" should be "VCH endpoint VM settings:
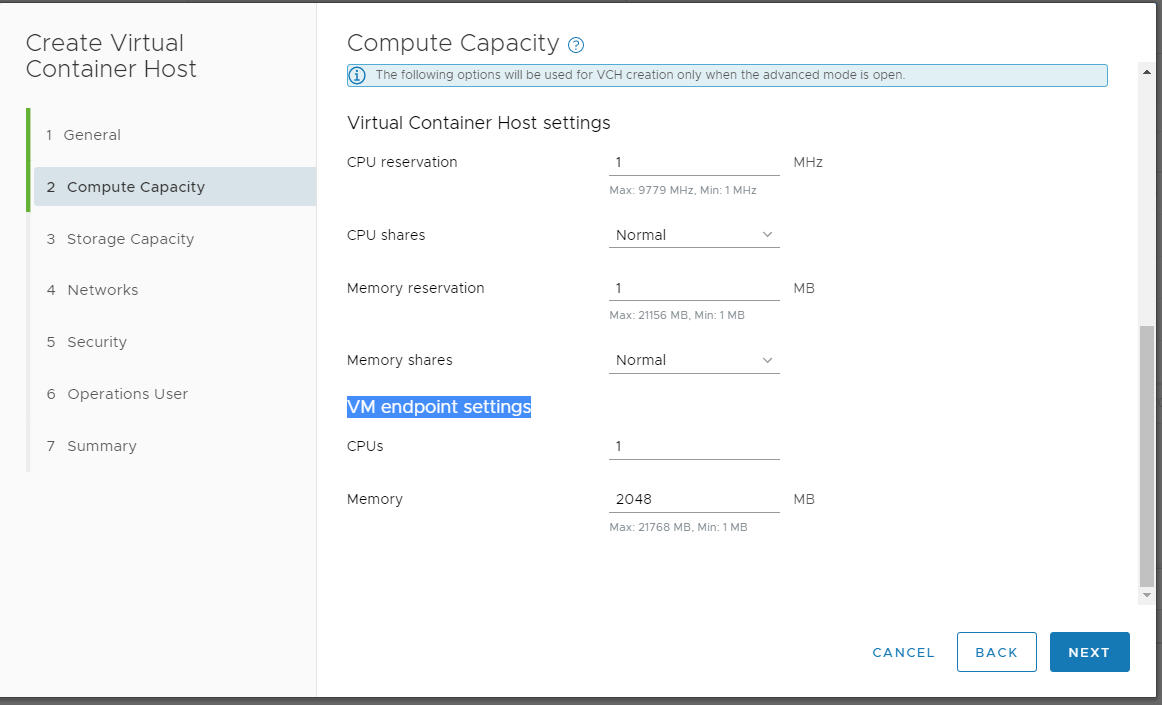
| 1.0 | Create VCH wizard says "VM endpoint" instead of "Endpoint VM" - In the Compute page of the VCH deployment wizard, the text "VM endpoint settings" should be "VCH endpoint VM settings:
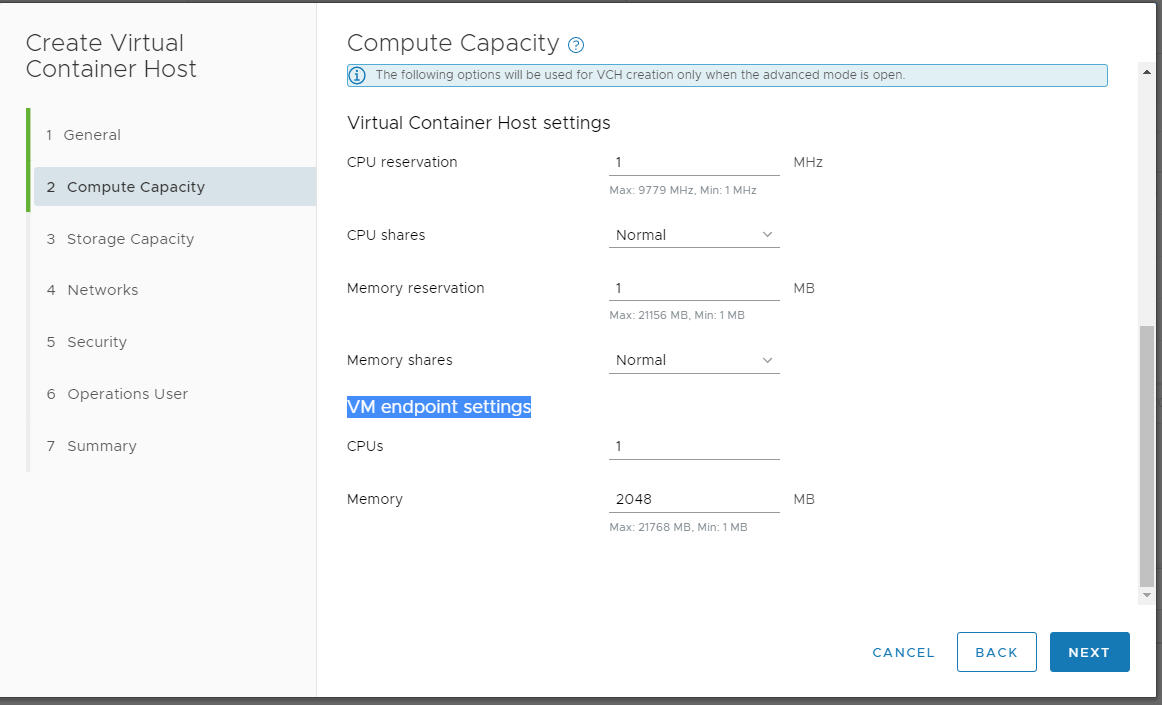
| priority | create vch wizard says vm endpoint instead of endpoint vm in the compute page of the vch deployment wizard the text vm endpoint settings should be vch endpoint vm settings | 1 |
73,353 | 15,253,651,294 | IssuesEvent | 2021-02-20 08:39:54 | gsylvie/madness | https://api.github.com/repos/gsylvie/madness | closed | CVE-2016-10006 Medium Severity Vulnerability detected by WhiteSource - autoclosed | security vulnerability | ## CVE-2016-10006 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>antisamy-1.4.3.jar</b></p></summary>
<p>The OWASP AntiSamy project is a collection of APIs for safely allow... | True | CVE-2016-10006 Medium Severity Vulnerability detected by WhiteSource - autoclosed - ## CVE-2016-10006 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>antisamy-1.4.3.jar</b></... | non_priority | cve medium severity vulnerability detected by whitesource autoclosed cve medium severity vulnerability vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnera... | 0 |
826,666 | 31,708,161,371 | IssuesEvent | 2023-09-09 01:04:40 | HughCraig/GHAP | https://api.github.com/repos/HughCraig/GHAP | opened | Dev access to test-ghap | priority 1 deployment Scope 1 Urgent Easy PriorityBP 1 Tranche Review | Set up access to the test-ghap.tlcmap.org server for:
Kaine Usher: kaine.usher1@gmail.com
Ivy Zheng: zhengzhixin2016@gmail.com
They will need:
SSH
SFTP
sudo
Please ensure access is established by October 1. Please contact them directly to coordinate this, with exchanging security keys etc, as Bill will be ... | 2.0 | Dev access to test-ghap - Set up access to the test-ghap.tlcmap.org server for:
Kaine Usher: kaine.usher1@gmail.com
Ivy Zheng: zhengzhixin2016@gmail.com
They will need:
SSH
SFTP
sudo
Please ensure access is established by October 1. Please contact them directly to coordinate this, with exchanging security ... | priority | dev access to test ghap set up access to the test ghap tlcmap org server for kaine usher kaine gmail com ivy zheng gmail com they will need ssh sftp sudo please ensure access is established by october please contact them directly to coordinate this with exchanging security keys etc as bill w... | 1 |
27,389 | 12,552,322,291 | IssuesEvent | 2020-06-06 17:42:50 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | "no_device" in "ephemeral_block_device" doesn't work as expected. | bug service/ec2 stale | ### Terraform Version
0.10.6
### Affected Resource(s)
aws_instance, aws_launch_configuration
### Terraform Configuration Files
```hcl
# Salt-master instance
resource "aws_instance" "salt-master" {
ami = "${data.aws_ami.ubuntu1404.id}"
instance_type = "${var.infra["salt_instan... | 1.0 | "no_device" in "ephemeral_block_device" doesn't work as expected. - ### Terraform Version
0.10.6
### Affected Resource(s)
aws_instance, aws_launch_configuration
### Terraform Configuration Files
```hcl
# Salt-master instance
resource "aws_instance" "salt-master" {
ami = "${data.aws_ami.u... | non_priority | no device in ephemeral block device doesn t work as expected terraform version affected resource s aws instance aws launch configuration terraform configuration files hcl salt master instance resource aws instance salt master ami data aws ami ... | 0 |
124,234 | 4,894,096,922 | IssuesEvent | 2016-11-19 03:48:45 | caver456/issue_test | https://api.github.com/repos/caver456/issue_test | opened | install | enhancement help wanted Priority:High | make a clean installer. Investigate from scratch. pyqtdeploy? py2exe? jython / jar? https://wiki.python.org/moin/Freeze (linux only) | 1.0 | install - make a clean installer. Investigate from scratch. pyqtdeploy? py2exe? jython / jar? https://wiki.python.org/moin/Freeze (linux only) | priority | install make a clean installer investigate from scratch pyqtdeploy jython jar linux only | 1 |
49,559 | 13,454,367,923 | IssuesEvent | 2020-09-09 03:30:53 | ErezDasa/RB2 | https://api.github.com/repos/ErezDasa/RB2 | opened | CVE-2019-14379 (High) detected in jackson-databind-2.9.9.jar | security vulnerability | ## CVE-2019-14379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14379 (High) detected in jackson-databind-2.9.9.jar - ## CVE-2019-14379 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.9.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm infra github pom ... | 0 |
521,110 | 15,102,739,821 | IssuesEvent | 2021-02-08 09:24:28 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | secure.totalav.com - site is not usable | browser-fenix engine-gecko ml-needsdiagnosis-false priority-normal | <!-- @browser: Firefox Mobile 86.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:86.0) Gecko/86.0 Firefox/86.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/66782 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://secure.totala... | 1.0 | secure.totalav.com - site is not usable - <!-- @browser: Firefox Mobile 86.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 9; Mobile; rv:86.0) Gecko/86.0 Firefox/86.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/66782 -->
<!-- @extra_labels: browser... | priority | secure totalav com site is not usable url browser version firefox mobile operating system android tested another browser yes chrome problem type site is not usable description page not loading correctly steps to reproduce rerouted too much page not loading ... | 1 |
73,683 | 19,760,954,775 | IssuesEvent | 2022-01-16 12:06:13 | Stupid4You/Digit | https://api.github.com/repos/Stupid4You/Digit | opened | Change from the beginning and not when we edit the file. | Easier Build | We now just change the 0000 in the checker then we have lesser code.
if len(str(num)) == 2:
num0 = "00"
if len(str(num)) == 3:
num0 = "0"
if len(str(num)) == 4:
num0 = ""
if num >= 9999:
done = 1 | 1.0 | Change from the beginning and not when we edit the file. - We now just change the 0000 in the checker then we have lesser code.
if len(str(num)) == 2:
num0 = "00"
if len(str(num)) == 3:
num0 = "0"
if len(str(num)) == 4:
num0 = ""
if num >= 9999:
done = 1 | non_priority | change from the beginning and not when we edit the file we now just change the in the checker then we have lesser code if len str num if len str num if len str num if num done | 0 |
16,292 | 6,153,468,346 | IssuesEvent | 2017-06-28 10:02:01 | scikit-learn/scikit-learn | https://api.github.com/repos/scikit-learn/scikit-learn | closed | travis flake8 checks all files, not only python files? | Build / CI | I'm a bit surprised that this hasn't bitten us and I feel like I'm missing something obvious (because why doesn't this always fail for rst files?)
Anyhow changing the mailmap or the travis config seems to make it fail, at least for me locally and in the 0.18.X branch:
https://travis-ci.org/scikit-learn/scikit-learn/j... | 1.0 | travis flake8 checks all files, not only python files? - I'm a bit surprised that this hasn't bitten us and I feel like I'm missing something obvious (because why doesn't this always fail for rst files?)
Anyhow changing the mailmap or the travis config seems to make it fail, at least for me locally and in the 0.18.X b... | non_priority | travis checks all files not only python files i m a bit surprised that this hasn t bitten us and i feel like i m missing something obvious because why doesn t this always fail for rst files anyhow changing the mailmap or the travis config seems to make it fail at least for me locally and in the x branch ... | 0 |
676,134 | 23,117,208,871 | IssuesEvent | 2022-07-27 17:51:42 | maurosoria/dirsearch | https://api.github.com/repos/maurosoria/dirsearch | closed | [Feature Request] Report files and directories found in crawled file | enhancement Priority: Medium | First of all, thank you for this wonderful tool which is the first that I use on CTF.
I would like to know if it possible to add the ability to dirsearch to parse crawled file to extract and report present path and use it for recursive searching.
To avoid massive report, Dirsearch should only report files of the targ... | 1.0 | [Feature Request] Report files and directories found in crawled file - First of all, thank you for this wonderful tool which is the first that I use on CTF.
I would like to know if it possible to add the ability to dirsearch to parse crawled file to extract and report present path and use it for recursive searching.
... | priority | report files and directories found in crawled file first of all thank you for this wonderful tool which is the first that i use on ctf i would like to know if it possible to add the ability to dirsearch to parse crawled file to extract and report present path and use it for recursive searching to avoid massive... | 1 |
354,331 | 10,565,650,843 | IssuesEvent | 2019-10-05 13:10:35 | kubeflow/kubeflow | https://api.github.com/repos/kubeflow/kubeflow | closed | Define Kubeflow cluster role and combine roles (was default roles should include virtualservices) | area/auth area/kfctl kind/feature priority/p0 | /kind feature
It looks like permission to create virtual services aren't attached by default to the roles created in namespaces. See below
**Why you need this feature:**
[Is your feature request related to a problem? Please describe in details]
editors should probably have the ability to edit virtual services... | 1.0 | Define Kubeflow cluster role and combine roles (was default roles should include virtualservices) - /kind feature
It looks like permission to create virtual services aren't attached by default to the roles created in namespaces. See below
**Why you need this feature:**
[Is your feature request related to a prob... | priority | define kubeflow cluster role and combine roles was default roles should include virtualservices kind feature it looks like permission to create virtual services aren t attached by default to the roles created in namespaces see below why you need this feature editors should probably have the abil... | 1 |
80,510 | 23,227,946,321 | IssuesEvent | 2022-08-03 03:35:06 | PowerShell/PowerShell | https://api.github.com/repos/PowerShell/PowerShell | closed | Add test for verifying the default language mode | BVT/DRT Area-Maintainers-Build Up-for-Grabs In-PR | ## Steps to reproduce
Potentially a test issue.
.\runlite -suite Scripting.CoreLanguage.CoreLanguageTest -pri -test DefaultExecutionContextSessionStateLanguageModeInRemoteSession
## Expected behavior
The language mode is FullLanguage.
## Actual behavior
LanguageMode is 3.
Exception calling "Invoke" with "0" argu... | 1.0 | Add test for verifying the default language mode - ## Steps to reproduce
Potentially a test issue.
.\runlite -suite Scripting.CoreLanguage.CoreLanguageTest -pri -test DefaultExecutionContextSessionStateLanguageModeInRemoteSession
## Expected behavior
The language mode is FullLanguage.
## Actual behavior
LanguageMo... | non_priority | add test for verifying the default language mode steps to reproduce potentially a test issue runlite suite scripting corelanguage corelanguagetest pri test defaultexecutioncontextsessionstatelanguagemodeinremotesession expected behavior the language mode is fulllanguage actual behavior languagemo... | 0 |
9,280 | 2,615,142,944 | IssuesEvent | 2015-03-01 06:18:09 | chrsmith/html5rocks | https://api.github.com/repos/chrsmith/html5rocks | closed | Over quota | auto-migrated Priority-Medium Type-Defect | ```
Please describe the issue:
Hi. The website is giving 503 over quota errors, from app engine (i guess).
It's your own dogfood, so why this could happen ?
Please provide any additional information below.
```
Original issue reported on code.google.com by `alfue...@gmail.com` on 22 Jun 2010 at 7:56 | 1.0 | Over quota - ```
Please describe the issue:
Hi. The website is giving 503 over quota errors, from app engine (i guess).
It's your own dogfood, so why this could happen ?
Please provide any additional information below.
```
Original issue reported on code.google.com by `alfue...@gmail.com` on 22 Jun 2010 at 7:56 | non_priority | over quota please describe the issue hi the website is giving over quota errors from app engine i guess it s your own dogfood so why this could happen please provide any additional information below original issue reported on code google com by alfue gmail com on jun at | 0 |
107,569 | 23,441,062,874 | IssuesEvent | 2022-08-15 14:55:20 | arduino/arduino-ide | https://api.github.com/repos/arduino/arduino-ide | closed | Close compilation/upload error notifications on subsequent actions | type: enhancement topic: code | ### Describe the request
Automatically close compilation and upload error notifications when a subsequent compilation or upload is triggered.
🙂 The user will only be presented with relevant notifications.
### Describe the current behavior
The Arduino IDE opens a notification when compilation or upload of a... | 1.0 | Close compilation/upload error notifications on subsequent actions - ### Describe the request
Automatically close compilation and upload error notifications when a subsequent compilation or upload is triggered.
🙂 The user will only be presented with relevant notifications.
### Describe the current behavior
... | non_priority | close compilation upload error notifications on subsequent actions describe the request automatically close compilation and upload error notifications when a subsequent compilation or upload is triggered 🙂 the user will only be presented with relevant notifications describe the current behavior ... | 0 |
256,184 | 22,041,792,847 | IssuesEvent | 2022-05-29 13:17:29 | oreillyross/brainy-notes | https://api.github.com/repos/oreillyross/brainy-notes | closed | #1 Add test for Add note form | testing | describe("<AddNote/>", () => {
it("renders the form", () => {
})
})
create a utils folder with a data-tests file which is exported functions that create objects of data for testing.
import {render, screen} from "@testing-library/react" Think of the screen object as the browser window.
import {MockedPr... | 1.0 | #1 Add test for Add note form - describe("<AddNote/>", () => {
it("renders the form", () => {
})
})
create a utils folder with a data-tests file which is exported functions that create objects of data for testing.
import {render, screen} from "@testing-library/react" Think of the screen object as the bro... | non_priority | add test for add note form describe it renders the form create a utils folder with a data tests file which is exported functions that create objects of data for testing import render screen from testing library react think of the screen object as the browser wind... | 0 |
5,783 | 2,971,819,058 | IssuesEvent | 2015-07-14 09:41:35 | RIOT-OS/RIOT | https://api.github.com/repos/RIOT-OS/RIOT | opened | doc: wrong hierarchy level for some modules | bug documentation | For some weird reasons some modules (e.g. 6LoWPAN or IEEE802.15.4e) show up at the wrong hierarchy level at http://doc.riot-os.org/modules.html. Building the documentation locally seems to generate the expected hierarchy. The documentation on the web page is generated by doxygen version 1.8.8 - locally I have 1.8.9.1. ... | 1.0 | doc: wrong hierarchy level for some modules - For some weird reasons some modules (e.g. 6LoWPAN or IEEE802.15.4e) show up at the wrong hierarchy level at http://doc.riot-os.org/modules.html. Building the documentation locally seems to generate the expected hierarchy. The documentation on the web page is generated by do... | non_priority | doc wrong hierarchy level for some modules for some weird reasons some modules e g or show up at the wrong hierarchy level at building the documentation locally seems to generate the expected hierarchy the documentation on the web page is generated by doxygen version locally i have can... | 0 |
138,427 | 18,793,921,172 | IssuesEvent | 2021-11-08 19:52:48 | Dima2022/hygieia-codequality-sonar-collector | https://api.github.com/repos/Dima2022/hygieia-codequality-sonar-collector | opened | CVE-2016-1000343 (High) detected in bcprov-jdk15on-1.55.jar | security vulnerability | ## CVE-2016-1000343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.55.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptograp... | True | CVE-2016-1000343 (High) detected in bcprov-jdk15on-1.55.jar - ## CVE-2016-1000343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.55.jar</b></p></summary>
<p>The Bounc... | non_priority | cve high detected in bcprov jar cve high severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk... | 0 |
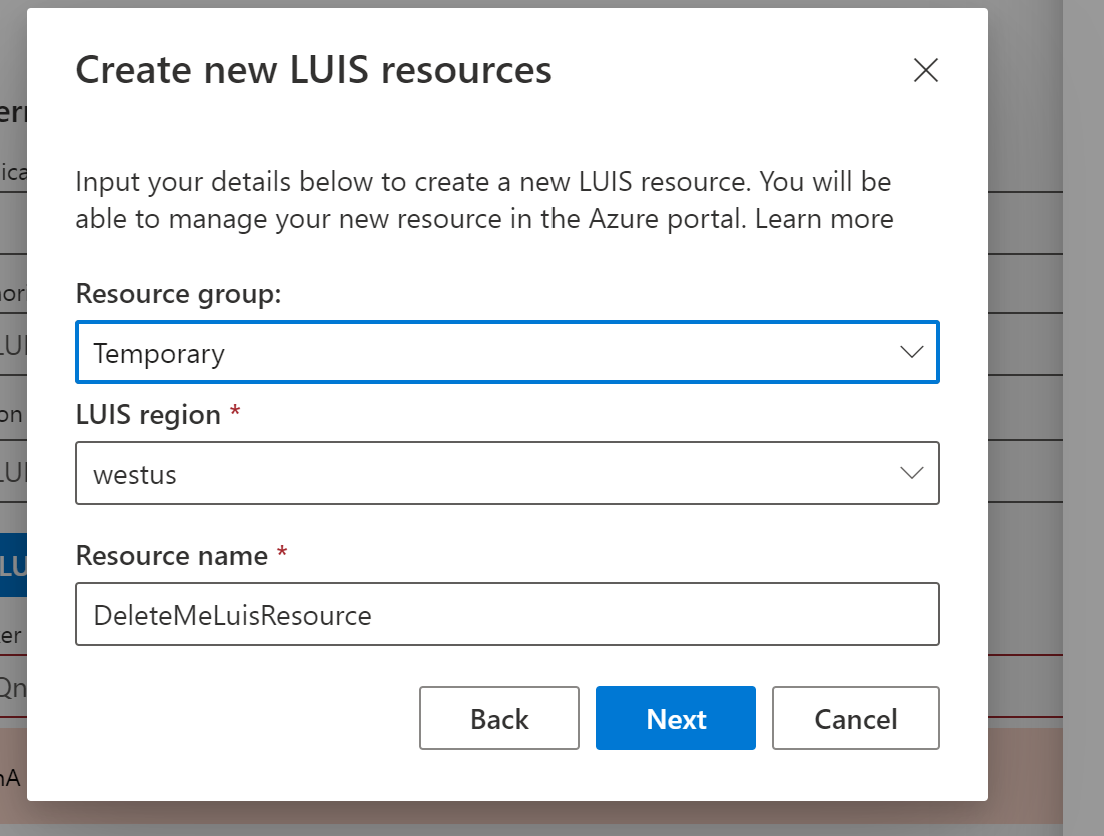
121,613 | 16,005,060,087 | IssuesEvent | 2021-04-20 01:09:19 | microsoft/BotFramework-Composer | https://api.github.com/repos/microsoft/BotFramework-Composer | opened | UX on "Create new LUIS resources" screen | Needs-triage R13 Bugbash Type: Bug UX Design | ## Describe the bug
Several UX issues on this screen:
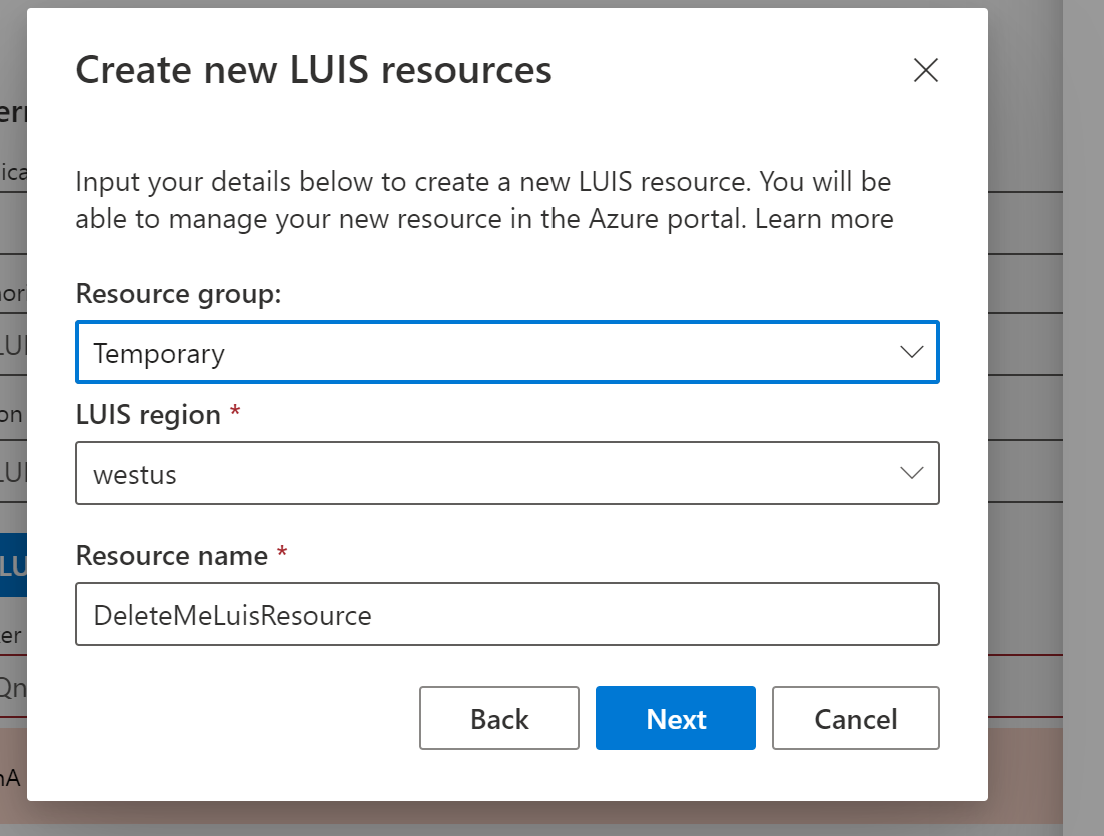
The issues are:
1. The "*" on the LUIS region and "resource name" text is a mystery. What does the "*" mean?
2. The dialog is "LUIS resources" (p... | 1.0 | UX on "Create new LUIS resources" screen - ## Describe the bug
Several UX issues on this screen:
The issues are:
1. The "*" on the LUIS region and "resource name" text is a mystery. What does the "*" m... | non_priority | ux on create new luis resources screen describe the bug several ux issues on this screen the issues are the on the luis region and resource name text is a mystery what does the mean the dialog is luis resources plural but the text is resource name singular the previou... | 0 |
304,535 | 26,286,667,520 | IssuesEvent | 2023-01-07 22:49:34 | ker0olos/fable | https://api.github.com/repos/ker0olos/fable | closed | Add more unit tests | tests needed | Some parts of the code are still untested.
- [x] searching for media
- [x] searching for characters
- [x] searching for theme songs
- [x] searching for the next episode | 1.0 | Add more unit tests - Some parts of the code are still untested.
- [x] searching for media
- [x] searching for characters
- [x] searching for theme songs
- [x] searching for the next episode | non_priority | add more unit tests some parts of the code are still untested searching for media searching for characters searching for theme songs searching for the next episode | 0 |
608,961 | 18,851,790,726 | IssuesEvent | 2021-11-11 21:58:54 | fao89/pulp-operator | https://api.github.com/repos/fao89/pulp-operator | opened | Document using https://pypi.org/project/pulpcore-releases/ for the installer | Status: NEW Priority: Normal Tracker: Task Category: Installer - Moved to GitHub issues Sprint: 122 | Author: bmbouter (bmbouter)
Redmine Issue: 6904, https://pulp.plan.io/issues/6904
---
The Pulp Dependency Checker is a great tool to show compatibility between a pulpcore version and various concerns.
We should do three things:
1) Move the pdc tool to the pulp org.
2) Add a very obvious link to the pulp_ins... | 1.0 | Document using https://pypi.org/project/pulpcore-releases/ for the installer - Author: bmbouter (bmbouter)
Redmine Issue: 6904, https://pulp.plan.io/issues/6904
---
The Pulp Dependency Checker is a great tool to show compatibility between a pulpcore version and various concerns.
We should do three things:
1) M... | priority | document using for the installer author bmbouter bmbouter redmine issue the pulp dependency checker is a great tool to show compatibility between a pulpcore version and various concerns we should do three things move the pdc tool to the pulp org add a very obvious link to the pulp ... | 1 |
252,084 | 21,555,772,316 | IssuesEvent | 2022-04-30 11:45:15 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Godot 3.5 BETA 2 is not working with GLES2 project | bug topic:rendering needs testing regression | ### Godot version
Godot_v3.5-beta2_x11.64
### System information
Linux, GLES2
### Issue description
Godot 3.5 BETA 2 is crashing with a project with GLES2
### Steps to reproduce
Just open a GLES2 project working with Godot 3.5 BETA 1, with this new BETA 2 I got these errors
ERROR: Condition "array.size() != a... | 1.0 | Godot 3.5 BETA 2 is not working with GLES2 project - ### Godot version
Godot_v3.5-beta2_x11.64
### System information
Linux, GLES2
### Issue description
Godot 3.5 BETA 2 is crashing with a project with GLES2
### Steps to reproduce
Just open a GLES2 project working with Godot 3.5 BETA 1, with this new BETA 2 I go... | non_priority | godot beta is not working with project godot version godot system information linux issue description godot beta is crashing with a project with steps to reproduce just open a project working with godot beta with this new beta i got these errors error ... | 0 |
137,492 | 30,701,135,893 | IssuesEvent | 2023-07-26 23:35:49 | SAST-UP-DEV/SAST-Test-Repo-d65e35ec-761d-4cbe-9254-a4f76b577a86 | https://api.github.com/repos/SAST-UP-DEV/SAST-Test-Repo-d65e35ec-761d-4cbe-9254-a4f76b577a86 | opened | Code Security Report: 24 high severity findings, 38 total findings | Mend: code security findings | # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-26 11:32pm
**Total Findings:** 38 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 422
**Detected Programming Languages:** 2 (Java*, JavaScript / Node.js)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigg... | 1.0 | Code Security Report: 24 high severity findings, 38 total findings - # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-07-26 11:32pm
**Total Findings:** 38 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 422
**Detected Programming Languages:** 2 (Java*, JavaScript / Node.js)
<... | non_priority | code security report high severity findings total findings code security report scan metadata latest scan total findings new findings resolved findings tested project files detected programming languages java javascript node js check thi... | 0 |
723,780 | 24,907,880,191 | IssuesEvent | 2022-10-29 13:45:58 | bounswe/bounswe2022group7 | https://api.github.com/repos/bounswe/bounswe2022group7 | closed | Implement Single Art Item Endpoint | Status: Pending Review Priority: High Difficulty: Medium Type: Implementation Target: Backend | We need to implement an endpoint that returns a single art item to the art item detail page. The art item should be requested given the id of the art item which is an art item's primary key.
**Deadline:** 28/10/2022 23.59
**Reviewer:** @demet47 | 1.0 | Implement Single Art Item Endpoint - We need to implement an endpoint that returns a single art item to the art item detail page. The art item should be requested given the id of the art item which is an art item's primary key.
**Deadline:** 28/10/2022 23.59
**Reviewer:** @demet47 | priority | implement single art item endpoint we need to implement an endpoint that returns a single art item to the art item detail page the art item should be requested given the id of the art item which is an art item s primary key deadline reviewer | 1 |
89,549 | 25,832,267,447 | IssuesEvent | 2022-12-12 16:54:13 | aws-amplify/amplify-flutter | https://api.github.com/repos/aws-amplify/amplify-flutter | closed | Following aws flutter tutorial results in xcode build error | iOS pending-close-response-required GraphQL API Build pending-triage | ### Description
I am experimenting with the aws amplify todo flutter tutorial - all works great (I can get the todo list working, etc) until I reach this page related to auth:
https://docs.amplify.aws/start/getting-started/add-api/q/integration/flutter/#add-api-and-auth-plugins
The xcode build fails and I've iso... | 1.0 | Following aws flutter tutorial results in xcode build error - ### Description
I am experimenting with the aws amplify todo flutter tutorial - all works great (I can get the todo list working, etc) until I reach this page related to auth:
https://docs.amplify.aws/start/getting-started/add-api/q/integration/flutter/#... | non_priority | following aws flutter tutorial results in xcode build error description i am experimenting with the aws amplify todo flutter tutorial all works great i can get the todo list working etc until i reach this page related to auth the xcode build fails and i ve isolated it to adding this library to the ... | 0 |
396,031 | 11,700,391,601 | IssuesEvent | 2020-03-06 17:23:50 | department-of-veterans-affairs/caseflow | https://api.github.com/repos/department-of-veterans-affairs/caseflow | closed | Investigate cache job runtime increase, part 2! | Priority: Low Team: Echo 🐬 Type: Investigation Type: Tech-Improvement | Runtimes for [the `UpdateCachedAppealsAttributesJob`](https://github.com/department-of-veterans-affairs/caseflow/blob/master/app/jobs/update_cached_appeals_attributes_job.rb) increased from significantly after [recent changes](https://github.com/department-of-veterans-affairs/caseflow/pull/13285). Short runtimes allow ... | 1.0 | Investigate cache job runtime increase, part 2! - Runtimes for [the `UpdateCachedAppealsAttributesJob`](https://github.com/department-of-veterans-affairs/caseflow/blob/master/app/jobs/update_cached_appeals_attributes_job.rb) increased from significantly after [recent changes](https://github.com/department-of-veterans-a... | priority | investigate cache job runtime increase part runtimes for increased from significantly after short runtimes allow us to run the job more frequently and keep the cache more up to date this ticket exists to determine why runtimes increased and address it if possible acceptance criter... | 1 |
282,533 | 30,889,358,512 | IssuesEvent | 2023-08-04 02:36:23 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | reopened | CVE-2015-8962 (High) detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2015-8962 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page... | True | CVE-2015-8962 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2015-8962 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwri... | non_priority | cve high detected in linux stable cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files drivers scsi sg ... | 0 |
506,998 | 14,677,859,716 | IssuesEvent | 2020-12-31 01:02:05 | ampproject/amphtml | https://api.github.com/repos/ampproject/amphtml | closed | amp-analytics: documentExit only works within same domain | Component: amp-analytics P1: High Priority Stale Type: Bug WG: analytics | ## What's the issue?
When using `amp-analytics` page visibility trigger with the `visibilitySpec` configured to use `documentExit`, the event will only fire when navigating between documents on the same domain but if you navigate to a different domain, the event won’t fire.
```
...
"on": "visible",
"reques... | 1.0 | amp-analytics: documentExit only works within same domain - ## What's the issue?
When using `amp-analytics` page visibility trigger with the `visibilitySpec` configured to use `documentExit`, the event will only fire when navigating between documents on the same domain but if you navigate to a different domain, the ... | priority | amp analytics documentexit only works within same domain what s the issue when using amp analytics page visibility trigger with the visibilityspec configured to use documentexit the event will only fire when navigating between documents on the same domain but if you navigate to a different domain the ... | 1 |
283,731 | 30,913,533,419 | IssuesEvent | 2023-08-05 02:09:36 | hshivhare67/kernel_v4.19.72 | https://api.github.com/repos/hshivhare67/kernel_v4.19.72 | reopened | CVE-2018-20669 (High) detected in linuxlinux-4.19.282 | Mend: dependency security vulnerability | ## CVE-2018-20669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.k... | True | CVE-2018-20669 (High) detected in linuxlinux-4.19.282 - ## CVE-2018-20669 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel<... | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files vuln... | 0 |
160,166 | 20,099,652,527 | IssuesEvent | 2022-02-07 01:19:30 | venkateshreddypala/post-it-a4 | https://api.github.com/repos/venkateshreddypala/post-it-a4 | opened | CVE-2022-0437 (Medium) detected in karma-1.7.0.tgz | security vulnerability | ## CVE-2022-0437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>karma-1.7.0.tgz</b></p></summary>
<p>Spectacular Test Runner for JavaScript.</p>
<p>Library home page: <a href="https... | True | CVE-2022-0437 (Medium) detected in karma-1.7.0.tgz - ## CVE-2022-0437 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>karma-1.7.0.tgz</b></p></summary>
<p>Spectacular Test Runner for... | non_priority | cve medium detected in karma tgz cve medium severity vulnerability vulnerable library karma tgz spectacular test runner for javascript library home page a href path to dependency file post it package json path to vulnerable library post it node modules karma p... | 0 |
188,827 | 6,782,321,265 | IssuesEvent | 2017-10-30 07:27:59 | Cloud-CV/EvalAI | https://api.github.com/repos/Cloud-CV/EvalAI | opened | Add feature to invite users to host team using URL | backend dependent hard-to-fix new-feature priority-high | Very similar to #1346.
## Deliverables
Add a feature to invite new team member to a participant team using a Unique URL. Also, don't forget to write unit tests. :)
## Steps
1. **user1** enters the email of his teammate (let's say **user2**)
2. Send an email to **user2** (if he/she is registered on EvalAI... | 1.0 | Add feature to invite users to host team using URL - Very similar to #1346.
## Deliverables
Add a feature to invite new team member to a participant team using a Unique URL. Also, don't forget to write unit tests. :)
## Steps
1. **user1** enters the email of his teammate (let's say **user2**)
2. Send an ... | priority | add feature to invite users to host team using url very similar to deliverables add a feature to invite new team member to a participant team using a unique url also don t forget to write unit tests steps enters the email of his teammate let s say send an email to ... | 1 |
307,019 | 9,414,124,187 | IssuesEvent | 2019-04-10 09:25:46 | StrangeLoopGames/EcoIssues | https://api.github.com/repos/StrangeLoopGames/EcoIssues | closed | Shaper and Electric planer have "out of collision" parts. | Medium Priority Push Candidate | Found some notes about bugs, want to place it before stop volontier work.
| 1.0 | Shaper and Electric planer have "out of collision" parts. - Found some notes about bugs, want to place it before stop volontier work.
. I had no .ts files open at the time. Let me know if you need any more information.
After restarting Atom, it didn't show any updates for Atom TypeScript. It was indeed installed, but only partially? It didn'... | 1.0 | Atom TypeScript Update Failure - Just got this, this morning while trying to update Atom TypeScript to new version. I'm on Windows 7 (64-bit). I had no .ts files open at the time. Let me know if you need any more information.
After restarting Atom, it didn't show any updates for Atom TypeScript. It was indeed instal... | priority | atom typescript update failure just got this this morning while trying to update atom typescript to new version i m on windows bit i had no ts files open at the time let me know if you need any more information after restarting atom it didn t show any updates for atom typescript it was indeed install... | 1 |
25,316 | 4,153,344,731 | IssuesEvent | 2016-06-16 07:16:30 | IDgis/geoportaal-test | https://api.github.com/repos/IDgis/geoportaal-test | closed | Mutatiedatum niet gebruikt bij volgorde lijst geoportaal | bug gebruikerstest | Als ik de mutatiedatum aanpas, bij geodatasets of bij statische kaarten, dan kan eventueel de volgorde in de lijst van gevonden bestanden veranderen. Dat gaat echter niet goed: ik heb de mutatiedatum van statische kaarten aangepast (op vandaag gezet) en in de lijst blijkt dat er enkele niet op volgorde staan: het blijk... | 1.0 | Mutatiedatum niet gebruikt bij volgorde lijst geoportaal - Als ik de mutatiedatum aanpas, bij geodatasets of bij statische kaarten, dan kan eventueel de volgorde in de lijst van gevonden bestanden veranderen. Dat gaat echter niet goed: ik heb de mutatiedatum van statische kaarten aangepast (op vandaag gezet) en in de l... | non_priority | mutatiedatum niet gebruikt bij volgorde lijst geoportaal als ik de mutatiedatum aanpas bij geodatasets of bij statische kaarten dan kan eventueel de volgorde in de lijst van gevonden bestanden veranderen dat gaat echter niet goed ik heb de mutatiedatum van statische kaarten aangepast op vandaag gezet en in de l... | 0 |
318,919 | 9,716,977,308 | IssuesEvent | 2019-05-29 08:11:37 | huridocs/uwazi | https://api.github.com/repos/huridocs/uwazi | opened | Semantic search BETA | Priority: High Status: Sprint | - [ ] Remove launching the search from the selection of documents. Launch always on the filtered documents/whole library.
- [ ] When we have pagination it will only run the search on the documents displayed. It should run the search in all the documents affected by the filtering.
- [ ] Remove the search box from the ... | 1.0 | Semantic search BETA - - [ ] Remove launching the search from the selection of documents. Launch always on the filtered documents/whole library.
- [ ] When we have pagination it will only run the search on the documents displayed. It should run the search in all the documents affected by the filtering.
- [ ] Remove t... | priority | semantic search beta remove launching the search from the selection of documents launch always on the filtered documents whole library when we have pagination it will only run the search on the documents displayed it should run the search in all the documents affected by the filtering remove the sea... | 1 |
566,187 | 16,814,555,611 | IssuesEvent | 2021-06-17 05:16:47 | neo-one-suite/neo-one | https://api.github.com/repos/neo-one-suite/neo-one | opened | Investigate/fix new max key size for map stack items | area/compiler good first issue kind/bug kind/cleanup priority/important-soon | Map stack items now have a max key size. We need to make sure that anywhere that we set key-value pairs in map stack items the key has to be sliced if it's too large. And then all key lookups need to slice the key the same way before doing the lookup. This is handled by the `SliceKeyHelper` and may have even been done ... | 1.0 | Investigate/fix new max key size for map stack items - Map stack items now have a max key size. We need to make sure that anywhere that we set key-value pairs in map stack items the key has to be sliced if it's too large. And then all key lookups need to slice the key the same way before doing the lookup. This is handl... | priority | investigate fix new max key size for map stack items map stack items now have a max key size we need to make sure that anywhere that we set key value pairs in map stack items the key has to be sliced if it s too large and then all key lookups need to slice the key the same way before doing the lookup this is handl... | 1 |
199,635 | 6,992,760,132 | IssuesEvent | 2017-12-15 08:35:26 | xwikisas/application-onlyoffice-connector | https://api.github.com/repos/xwikisas/application-onlyoffice-connector | closed | Update XWikiOnlyOfficeCode.ConfigurationClass to use the #getMissingLicenseMessage macro | Priority: Minor Type: Improvement | We should use the #getMissingLicenseMessage macro instead of the current implementation: https://github.com/xwikisas/application-onlyoffice-connector/blob/fa245efa8c5f00b80a0284480f7879df8716ea3e/application-onlyoffice-connector-ui/src/main/resources/XWikiOnlyOfficeCode/ConfigurationClass.xml#L84
The macro also make... | 1.0 | Update XWikiOnlyOfficeCode.ConfigurationClass to use the #getMissingLicenseMessage macro - We should use the #getMissingLicenseMessage macro instead of the current implementation: https://github.com/xwikisas/application-onlyoffice-connector/blob/fa245efa8c5f00b80a0284480f7879df8716ea3e/application-onlyoffice-connector-... | priority | update xwikionlyofficecode configurationclass to use the getmissinglicensemessage macro we should use the getmissinglicensemessage macro instead of the current implementation the macro also makes sure the link always points to the main wiki example usage of the macro here | 1 |
712,032 | 24,482,597,367 | IssuesEvent | 2022-10-09 02:30:26 | chaotic-aur/packages | https://api.github.com/repos/chaotic-aur/packages | closed | [Request] openssl3-git | request:new-pkg priority:low | ### Link to the package(s) in the AUR
https://aur.archlinux.org/packages/openssl3-git
### Utility this package has for you
provides library file for ruffle, a flash emulator
### Do you consider the package(s) to be useful for every Chaotic-AUR user?
No, but for a few.
### Do you consider the package to be useful ... | 1.0 | [Request] openssl3-git - ### Link to the package(s) in the AUR
https://aur.archlinux.org/packages/openssl3-git
### Utility this package has for you
provides library file for ruffle, a flash emulator
### Do you consider the package(s) to be useful for every Chaotic-AUR user?
No, but for a few.
### Do you consider ... | priority | git link to the package s in the aur utility this package has for you provides library file for ruffle a flash emulator do you consider the package s to be useful for every chaotic aur user no but for a few do you consider the package to be useful for feature testing preview ye... | 1 |
18,735 | 4,308,853,241 | IssuesEvent | 2016-07-21 14:20:45 | Bouke/django-two-factor-auth | https://api.github.com/repos/Bouke/django-two-factor-auth | closed | Django 1.7 still listed as supported, while it isn't | documentation | In the docs and the readme Django 1.7 is still listed as being supported, while it isn't. The docs and readme should be updated to reflect this. | 1.0 | Django 1.7 still listed as supported, while it isn't - In the docs and the readme Django 1.7 is still listed as being supported, while it isn't. The docs and readme should be updated to reflect this. | non_priority | django still listed as supported while it isn t in the docs and the readme django is still listed as being supported while it isn t the docs and readme should be updated to reflect this | 0 |
24,490 | 6,546,812,915 | IssuesEvent | 2017-09-04 12:05:31 | yiisoft/yii2 | https://api.github.com/repos/yiisoft/yii2 | closed | Codeception Yii2 module should use `andWhere`. | Codeception | ### What steps will reproduce the problem?
Create an AR query that explicitly disables `where`.
Motivation: my AR query filters deleted records and I do not want parts of my code to intentionally or unintentionally retrieve those records.
### What is the expected result?
When I use `$this->tester->seeRecord(User:... | 1.0 | Codeception Yii2 module should use `andWhere`. - ### What steps will reproduce the problem?
Create an AR query that explicitly disables `where`.
Motivation: my AR query filters deleted records and I do not want parts of my code to intentionally or unintentionally retrieve those records.
### What is the expected re... | non_priority | codeception module should use andwhere what steps will reproduce the problem create an ar query that explicitly disables where motivation my ar query filters deleted records and i do not want parts of my code to intentionally or unintentionally retrieve those records what is the expected resul... | 0 |
626,392 | 19,822,369,301 | IssuesEvent | 2022-01-20 00:00:32 | unitaryfund/mitiq | https://api.github.com/repos/unitaryfund/mitiq | closed | Bayes factory fails on Windows build due to pymc3 install / dependencies | priority/p1 zne zne/inference stale | Full message:
```
================================== FAILURES ===================================
_____________________________ test_exp_bayes_extr _____________________________
[gw1] win32 -- Python 3.8.8 c:\hostedtoolcache\windows\python\3.8.8\x64\python.exe
def test_exp_bayes_extr():
"""Test of t... | 1.0 | Bayes factory fails on Windows build due to pymc3 install / dependencies - Full message:
```
================================== FAILURES ===================================
_____________________________ test_exp_bayes_extr _____________________________
[gw1] win32 -- Python 3.8.8 c:\hostedtoolcache\windows\python\... | priority | bayes factory fails on windows build due to install dependencies full message failures test exp bayes extr python c hostedtoolcache windows python pyth... | 1 |
553,519 | 16,373,267,335 | IssuesEvent | 2021-05-15 15:30:29 | csingh27sewts/Masterarbeit | https://api.github.com/repos/csingh27sewts/Masterarbeit | opened | Run original cartpole_problem by Phil, check results and compare the experiment with your experiment. | Implementation Medium priority | To check why it is not learning with cloth envionment. | 1.0 | Run original cartpole_problem by Phil, check results and compare the experiment with your experiment. - To check why it is not learning with cloth envionment. | priority | run original cartpole problem by phil check results and compare the experiment with your experiment to check why it is not learning with cloth envionment | 1 |
472,923 | 13,633,251,591 | IssuesEvent | 2020-09-24 21:04:27 | metabase/metabase | https://api.github.com/repos/metabase/metabase | closed | Greyed out filtered by and grouped by when creating new custom questions | Database/Postgres Priority:P2 Querying/GUI Type:Bug |
Hello
When trying to create custom questions I have Greyed out filtered by and grouped by
Environment
metabase 0.28.5, JRE 8 Update 16, Windows 2012 R2, Chrome 65.0.3325.181, internal DB H2, Datasource is GreenPlum 4.3.9
The issue
When trying to create custom questions I have Greyed out filtered by and g... | 1.0 | Greyed out filtered by and grouped by when creating new custom questions -
Hello
When trying to create custom questions I have Greyed out filtered by and grouped by
Environment
metabase 0.28.5, JRE 8 Update 16, Windows 2012 R2, Chrome 65.0.3325.181, internal DB H2, Datasource is GreenPlum 4.3.9
The issue
... | priority | greyed out filtered by and grouped by when creating new custom questions hello when trying to create custom questions i have greyed out filtered by and grouped by environment metabase jre update windows chrome internal db datasource is greenplum the issue when trying ... | 1 |
81,835 | 15,807,313,283 | IssuesEvent | 2021-04-04 09:50:39 | dEAduction/dEAduction | https://api.github.com/repos/dEAduction/dEAduction | opened | Weird context | approved::new area::code priority::high type::bug | <!-- Any text between such tags will not appear on the issue. -->
### Bug description
<!-- Clear, precise, concise description of your bug. Include:
- [ ] expected behavior / what you wanted to do;
- [ ] what happened instead / what was the bug;
- [ ] error message (if any);
- [ ] if you are a developper, commi... | 1.0 | Weird context - <!-- Any text between such tags will not appear on the issue. -->
### Bug description
<!-- Clear, precise, concise description of your bug. Include:
- [ ] expected behavior / what you wanted to do;
- [ ] what happened instead / what was the bug;
- [ ] error message (if any);
- [ ] if you are a d... | non_priority | weird context bug description clear precise concise description of your bug include expected behavior what you wanted to do what happened instead what was the bug error message if any if you are a developper commit id and which branch you were on provide any useful i... | 0 |
684,061 | 23,405,436,532 | IssuesEvent | 2022-08-12 12:22:27 | FirebirdSQL/firebird | https://api.github.com/repos/FirebirdSQL/firebird | closed | key size exceeds implementation restriction [CORE3499] | priority: major type: bug resolution: incomplete affect-version: 2.5.0 | Submitted by: Dieter Blume (blume-edv)
When using Firebird 2\.5, the following error occurs:
Unsuccessful metadata update
key size exceeds implementation restriction for index "RDB$PRIMARY23"
Statement:
CREATE TABLE OBD \(OBJEKT VARCHAR\(20\) NOT NULL,
DATEI VARCHAR\(180\) NOT NULL,
USRIN... | 1.0 | key size exceeds implementation restriction [CORE3499] - Submitted by: Dieter Blume (blume-edv)
When using Firebird 2\.5, the following error occurs:
Unsuccessful metadata update
key size exceeds implementation restriction for index "RDB$PRIMARY23"
Statement:
CREATE TABLE OBD \(OBJEKT VARCHAR\(20\) NOT NULL,
... | priority | key size exceeds implementation restriction submitted by dieter blume blume edv when using firebird the following error occurs unsuccessful metadata update key size exceeds implementation restriction for index rdb statement create table obd objekt varchar not null datei v... | 1 |
125,788 | 26,727,845,356 | IssuesEvent | 2023-01-29 22:56:37 | Plant-Coach/plant_coach_be | https://api.github.com/repos/Plant-Coach/plant_coach_be | closed | Refactor: Create Garden Plant process | enhancement code refactor | - [x] Use callbacks instead of the manual create method currently used.
- [x] Debug this issue with the `seeds.rb` file. | 1.0 | Refactor: Create Garden Plant process - - [x] Use callbacks instead of the manual create method currently used.
- [x] Debug this issue with the `seeds.rb` file. | non_priority | refactor create garden plant process use callbacks instead of the manual create method currently used debug this issue with the seeds rb file | 0 |
308,193 | 9,435,989,769 | IssuesEvent | 2019-04-13 02:00:50 | avored/laravel-ecommerce | https://api.github.com/repos/avored/laravel-ecommerce | closed | select2 - bad work | High Priority backend bug | Hi.
Please review the select2 in product/basic. This selection not work properly
**In addition, you have consider to publish the admin UI?**
| 1.0 | select2 - bad work - Hi.
Please review the select2 in product/basic. This selection not work properly
**In addition, you have consider to publish the admin UI?**
| priority | bad work hi please review the in product basic this selection not work properly in addition you have consider to publish the admin ui | 1 |
152,069 | 5,832,362,753 | IssuesEvent | 2017-05-08 21:37:27 | HabitRPG/habitica | https://api.github.com/repos/HabitRPG/habitica | closed | add one-time "donate" option that doesn't grant in-game purchase | priority: medium status: issue: suggestion-discussion | Just as important as a code issue: if I donate to developers, I can just buy all of the things I would have otherwise earned on the site. Because of this, I don't think I'd ever want to donate- it would make rewards feel meaningless. I know it feels like a good idea but don't you think there are ways to get people to d... | 1.0 | add one-time "donate" option that doesn't grant in-game purchase - Just as important as a code issue: if I donate to developers, I can just buy all of the things I would have otherwise earned on the site. Because of this, I don't think I'd ever want to donate- it would make rewards feel meaningless. I know it feels lik... | priority | add one time donate option that doesn t grant in game purchase just as important as a code issue if i donate to developers i can just buy all of the things i would have otherwise earned on the site because of this i don t think i d ever want to donate it would make rewards feel meaningless i know it feels lik... | 1 |
395,317 | 11,683,656,781 | IssuesEvent | 2020-03-05 04:09:59 | StudioTBA/CoronaIO | https://api.github.com/repos/StudioTBA/CoronaIO | opened | Shooting for police officers | Character development Priority: High | **Is your feature request related to a problem? Please describe.**
Police officers should be able to shoot at the horde to defeat it.
**Describe the solution you would like**
Use raycasts and detect collisions. Next issue after this will involve lowering the horde's health. | 1.0 | Shooting for police officers - **Is your feature request related to a problem? Please describe.**
Police officers should be able to shoot at the horde to defeat it.
**Describe the solution you would like**
Use raycasts and detect collisions. Next issue after this will involve lowering the horde's health. | priority | shooting for police officers is your feature request related to a problem please describe police officers should be able to shoot at the horde to defeat it describe the solution you would like use raycasts and detect collisions next issue after this will involve lowering the horde s health | 1 |
288,714 | 8,850,684,910 | IssuesEvent | 2019-01-08 13:56:53 | cosmos/voyager | https://api.github.com/repos/cosmos/voyager | opened | Balance header availability not updated after submitting proposal | governance-1 :ballot_box: high priority | Description:
<!-- Steps to reproduce, logs, and screenshots are helpful for us to resolve the bug -->
Still shows original value. Maybe we should refactor how we're updating the header (or update it after querying the account) because this has been a recurring issue. | 1.0 | Balance header availability not updated after submitting proposal - Description:
<!-- Steps to reproduce, logs, and screenshots are helpful for us to resolve the bug -->
Still shows original value. Maybe we should refactor how we're updating the header (or update it after querying the account) because this has be... | priority | balance header availability not updated after submitting proposal description still shows original value maybe we should refactor how we re updating the header or update it after querying the account because this has been a recurring issue | 1 |
93,128 | 11,741,343,460 | IssuesEvent | 2020-03-11 21:31:37 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Allow totally enabling autoplay | design feature/settings priority/P3 | Right now, autoplay can be blocked or allowed one-at-a-time. We should add a state for always allowed — beyond just adding a wildcard entry to the list. | 1.0 | Allow totally enabling autoplay - Right now, autoplay can be blocked or allowed one-at-a-time. We should add a state for always allowed — beyond just adding a wildcard entry to the list. | non_priority | allow totally enabling autoplay right now autoplay can be blocked or allowed one at a time we should add a state for always allowed — beyond just adding a wildcard entry to the list | 0 |
169,869 | 6,419,326,803 | IssuesEvent | 2017-08-08 20:57:55 | FrogTheFrog/steam-rom-manager | https://api.github.com/repos/FrogTheFrog/steam-rom-manager | closed | Reduce amount of color variables | priority | Up until now, user could change UI color, however this complicates things on my end by having to define A LOT of color variables. Also, I doubt that color picker is used actively. For this and previous reasons UI color panel will be left available only to developers and all color variables will be generalized. This mea... | 1.0 | Reduce amount of color variables - Up until now, user could change UI color, however this complicates things on my end by having to define A LOT of color variables. Also, I doubt that color picker is used actively. For this and previous reasons UI color panel will be left available only to developers and all color vari... | priority | reduce amount of color variables up until now user could change ui color however this complicates things on my end by having to define a lot of color variables also i doubt that color picker is used actively for this and previous reasons ui color panel will be left available only to developers and all color vari... | 1 |
47,930 | 13,262,294,105 | IssuesEvent | 2020-08-20 21:29:11 | akivamprager/sefaria-interactive-simple | https://api.github.com/repos/akivamprager/sefaria-interactive-simple | opened | CVE-2012-6708 (Medium) detected in jquery-1.7.2.min.js | security vulnerability | ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="htt... | True | CVE-2012-6708 (Medium) detected in jquery-1.7.2.min.js - ## CVE-2012-6708 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library ... | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file tmp ws scm sefaria interactive simple public fonts hadasimclm regular demo htm... | 0 |
25,542 | 4,381,556,367 | IssuesEvent | 2016-08-06 09:27:55 | scipy/scipy | https://api.github.com/repos/scipy/scipy | closed | expm_multiply, complex matrices not working using start,stop,ect... | defect scipy.sparse.linalg |
Hi,
There is a bug with expm_multiply. If I just use a complex matrix and vector the function returns the correct vector but when I use the linear grid feature it seems to be casting the vector to a float while iterating through the grid points:
site-packages/scipy/sparse/linalg/_expm_multiply.py:568: Complex... | 1.0 | expm_multiply, complex matrices not working using start,stop,ect... -
Hi,
There is a bug with expm_multiply. If I just use a complex matrix and vector the function returns the correct vector but when I use the linear grid feature it seems to be casting the vector to a float while iterating through the grid point... | non_priority | expm multiply complex matrices not working using start stop ect hi there is a bug with expm multiply if i just use a complex matrix and vector the function returns the correct vector but when i use the linear grid feature it seems to be casting the vector to a float while iterating through the grid point... | 0 |
606,502 | 18,763,635,585 | IssuesEvent | 2021-11-05 19:47:31 | vmware-tanzu/carvel-ytt | https://api.github.com/repos/vmware-tanzu/carvel-ytt | closed | Test failure with go1.17 | bug carvel accepted priority/important-soon | **What steps did you take:**
[A clear and concise description steps and yaml files that can be used to reproduce the problem.]
Try to run testsuite with `go test -v $(go list ./...|grep -v yaml.v2)`
**What happened:**
[A small description of the result or the yaml that was generated]
```
checking filetests/ytt-... | 1.0 | Test failure with go1.17 - **What steps did you take:**
[A clear and concise description steps and yaml files that can be used to reproduce the problem.]
Try to run testsuite with `go test -v $(go list ./...|grep -v yaml.v2)`
**What happened:**
[A small description of the result or the yaml that was generated]
`... | priority | test failure with what steps did you take try to run testsuite with go test v go list grep v yaml what happened checking filetests ytt replace map item yml template test go checking filetests ytt library url url yml eval error ... | 1 |
553,904 | 16,384,932,860 | IssuesEvent | 2021-05-17 09:12:21 | gardener/landscaper | https://api.github.com/repos/gardener/landscaper | closed | Conditional SubInstallations | area/usability effort/1w kind/enhancement kind/epic priority/3 | **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also state the commands multiple times... | 1.0 | Conditional SubInstallations - **How to categorize this issue?**
<!--
Please select area, kind, and priority for this issue. This helps the community categorizing it.
Replace below TODOs or exchange the existing identifiers with those that fit best in your opinion.
If multiple identifiers make sense you can also st... | priority | conditional subinstallations how to categorize this issue please select area kind and priority for this issue this helps the community categorizing it replace below todos or exchange the existing identifiers with those that fit best in your opinion if multiple identifiers make sense you can also st... | 1 |
27,433 | 13,249,118,618 | IssuesEvent | 2020-08-19 20:12:56 | flutter/flutter | https://api.github.com/repos/flutter/flutter | closed | Metal backend does not properly release image memory | P1 customer: fun (g3) dependency: skia engine perf: memory platform-ios severe: performance severe: regression | Tested on engine revision flutter/engine@d3b81f19fc98076283892c1152d30e2567b6406e
run the attached program below at framework revision 45e097da16
Press the `LOAD IMAGE` button, note memory usage increase. Press the `CLEAR IMAGE` button. Press the `CHECK ALLOC PROFILE (Try GC)`. Note that memory does not decrease.... | True | Metal backend does not properly release image memory - Tested on engine revision flutter/engine@d3b81f19fc98076283892c1152d30e2567b6406e
run the attached program below at framework revision 45e097da16
Press the `LOAD IMAGE` button, note memory usage increase. Press the `CLEAR IMAGE` button. Press the `CHECK ALLOC... | non_priority | metal backend does not properly release image memory tested on engine revision flutter engine run the attached program below at framework revision press the load image button note memory usage increase press the clear image button press the check alloc profile try gc note that memory does not de... | 0 |
710,832 | 24,437,302,534 | IssuesEvent | 2022-10-06 12:25:22 | leaningtech/webvm | https://api.github.com/repos/leaningtech/webvm | closed | Unexpected file `/nbody.js` | Type: maintenance Priority: medium | Looks like there's a nearly identical copy of `~/examples/nodejs/nbody.js` in the root directory | 1.0 | Unexpected file `/nbody.js` - Looks like there's a nearly identical copy of `~/examples/nodejs/nbody.js` in the root directory | priority | unexpected file nbody js looks like there s a nearly identical copy of examples nodejs nbody js in the root directory | 1 |
87,593 | 15,786,538,547 | IssuesEvent | 2021-04-01 17:53:51 | joshnewton31080/experian-java | https://api.github.com/repos/joshnewton31080/experian-java | opened | CVE-2018-11307 (High) detected in jackson-databind-2.9.2.jar | security vulnerability | ## CVE-2018-11307 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2018-11307 (High) detected in jackson-databind-2.9.2.jar - ## CVE-2018-11307 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.2.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file experian java mavenworkspace bi... | 0 |
120,239 | 15,713,331,269 | IssuesEvent | 2021-03-27 15:44:20 | mateugazi/SelfImprovement | https://api.github.com/repos/mateugazi/SelfImprovement | opened | Implementing DTOs, Mappers & the Repository Pattern using the Sequelize ORM with Examples - DDD w/ TypeScript | DomainDrivenDesign Typescript | https://khalilstemmler.com/articles/typescript-domain-driven-design/repository-dto-mapper/ | 1.0 | Implementing DTOs, Mappers & the Repository Pattern using the Sequelize ORM with Examples - DDD w/ TypeScript - https://khalilstemmler.com/articles/typescript-domain-driven-design/repository-dto-mapper/ | non_priority | implementing dtos mappers the repository pattern using the sequelize orm with examples ddd w typescript | 0 |
97,455 | 16,236,321,957 | IssuesEvent | 2021-05-07 01:28:49 | joaonetoo/saaddeploy | https://api.github.com/repos/joaonetoo/saaddeploy | opened | CVE-2019-16892 (Medium) detected in rubyzip-1.0.0.gem | security vulnerability | ## CVE-2019-16892 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rubyzip-1.0.0.gem</b></p></summary>
<p></p>
<p>Library home page: <a href="https://rubygems.org/gems/rubyzip-1.0.0.g... | True | CVE-2019-16892 (Medium) detected in rubyzip-1.0.0.gem - ## CVE-2019-16892 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>rubyzip-1.0.0.gem</b></p></summary>
<p></p>
<p>Library home ... | non_priority | cve medium detected in rubyzip gem cve medium severity vulnerability vulnerable library rubyzip gem library home page a href dependency hierarchy axlsx rails gem root library axlsx gem x rubyzip gem vulnerable library ... | 0 |
66,548 | 7,006,294,181 | IssuesEvent | 2017-12-19 07:49:13 | foodtiny/native | https://api.github.com/repos/foodtiny/native | closed | Add test cases for native | feature test | Add test cases, reformat code for :
- [x] Java.Util.HashMap
- [x] java.util.ArrayList.hpp
- [x] java.util.Vector
- [x] java.lang.Bytes
- [x] java.lang.ClassCastException
- [x] java.lang.ArithmeticException
- [x] java.lang.Throwable | 1.0 | Add test cases for native - Add test cases, reformat code for :
- [x] Java.Util.HashMap
- [x] java.util.ArrayList.hpp
- [x] java.util.Vector
- [x] java.lang.Bytes
- [x] java.lang.ClassCastException
- [x] java.lang.ArithmeticException
- [x] java.lang.Throwable | non_priority | add test cases for native add test cases reformat code for java util hashmap java util arraylist hpp java util vector java lang bytes java lang classcastexception java lang arithmeticexception java lang throwable | 0 |
21,795 | 3,560,494,144 | IssuesEvent | 2016-01-23 03:41:27 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Inline refactor isn't always correct and the output can be cleaned up | analyzer-refactoring area-analyzer priority-high Type-Defect | When it works it's awesome, but I've noticed that the inline refactor for a method doesn't always work. In `pkg/compiler/lib/src/cps_ir/cps_ir_builder.dart` in the SDK, search for method buildInvokeStatic, choose Refactor -> Inline... -> Inline all references and remove the method.
There is one call site that looke... | 1.0 | Inline refactor isn't always correct and the output can be cleaned up - When it works it's awesome, but I've noticed that the inline refactor for a method doesn't always work. In `pkg/compiler/lib/src/cps_ir/cps_ir_builder.dart` in the SDK, search for method buildInvokeStatic, choose Refactor -> Inline... -> Inline al... | non_priority | inline refactor isn t always correct and the output can be cleaned up when it works it s awesome but i ve noticed that the inline refactor for a method doesn t always work in pkg compiler lib src cps ir cps ir builder dart in the sdk search for method buildinvokestatic choose refactor inline inline al... | 0 |
92,778 | 8,378,119,931 | IssuesEvent | 2018-10-06 10:32:49 | CS2103-AY1819S1-T16-2/main | https://api.github.com/repos/CS2103-AY1819S1-T16-2/main | opened | Automated Tests for the Assignment class | tests | Currently there are no tests for the Assignment class.
Suggested tests:
- Ensure proper creation / initialization of Assignment
- Ensure Assignments are saved properly in the XML files
- Ensure Assignments can only have students who are present in the TutorialGroup.
- Ensure duplicate Assignments in a Tutorial... | 1.0 | Automated Tests for the Assignment class - Currently there are no tests for the Assignment class.
Suggested tests:
- Ensure proper creation / initialization of Assignment
- Ensure Assignments are saved properly in the XML files
- Ensure Assignments can only have students who are present in the TutorialGroup.
-... | non_priority | automated tests for the assignment class currently there are no tests for the assignment class suggested tests ensure proper creation initialization of assignment ensure assignments are saved properly in the xml files ensure assignments can only have students who are present in the tutorialgroup ... | 0 |
207,415 | 15,815,366,808 | IssuesEvent | 2021-04-05 11:10:01 | NillerMedDild/Enigmatica6 | https://api.github.com/repos/NillerMedDild/Enigmatica6 | opened | RS Large Patterns | Status: Ready For Testing Suggestion | **CurseForge Link**
https://www.curseforge.com/minecraft/mc-mods/rslargepatterns
**Mod description**
Write a short description of the mod here.
**Why would you like the mod added?**
**Screenshots if applicable.**
| 1.0 | RS Large Patterns - **CurseForge Link**
https://www.curseforge.com/minecraft/mc-mods/rslargepatterns
**Mod description**
Write a short description of the mod here.
**Why would you like the mod added?**
**Screenshots if applicable.**
| non_priority | rs large patterns curseforge link mod description write a short description of the mod here why would you like the mod added screenshots if applicable | 0 |
233,182 | 18,952,609,864 | IssuesEvent | 2021-11-18 16:35:42 | w3c/epub-tests | https://api.github.com/repos/w3c/epub-tests | opened | Tests on the rendition properties | tests claimed | I will create tests for the [Rendition flow properties](https://www.w3.org/TR/epub-rs-33/#flow) (see also [in the content document](https://www.w3.org/TR/epub-33/#flow)).
---
Note, for the record, that these tests are not really my own. I looked at the old [IDPF test suite for 3.0](https://github.com/IDPF/epub-te... | 1.0 | Tests on the rendition properties - I will create tests for the [Rendition flow properties](https://www.w3.org/TR/epub-rs-33/#flow) (see also [in the content document](https://www.w3.org/TR/epub-33/#flow)).
---
Note, for the record, that these tests are not really my own. I looked at the old [IDPF test suite for ... | non_priority | tests on the rendition properties i will create tests for the see also note for the record that these tests are not really my own i looked at the old to see whether and how those tests can be repurposed by adapting them to and the tests on rendition seem to be the simplest to convert man... | 0 |
3,302 | 4,210,814,285 | IssuesEvent | 2016-06-29 11:23:24 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | Build of ARM version of dart executable fails on our ARM hardware - libc mismatch. | area-infrastructure os-linux P1 high Type: bug | Since updating our builder to trusty ubuntu, and installing the up-to-date arm cross-compiler, the arm dart executable requires glibc 2.16, which isn't present on our target. The error message is: /lib/arm-linux-gnueabihf/libc.so.6: version `GLIBC_2.16' not found (required by out/ReleaseXARM/dart)
We need to get th... | 1.0 | Build of ARM version of dart executable fails on our ARM hardware - libc mismatch. - Since updating our builder to trusty ubuntu, and installing the up-to-date arm cross-compiler, the arm dart executable requires glibc 2.16, which isn't present on our target. The error message is: /lib/arm-linux-gnueabihf/libc.so.6: v... | non_priority | build of arm version of dart executable fails on our arm hardware libc mismatch since updating our builder to trusty ubuntu and installing the up to date arm cross compiler the arm dart executable requires glibc which isn t present on our target the error message is lib arm linux gnueabihf libc so ve... | 0 |
7,019 | 24,125,758,739 | IssuesEvent | 2022-09-21 00:05:33 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | PhysX Collider Component returns a memory access violation when getting its Component Property Tree with types | kind/bug triage/accepted priority/critical kind/automation sig/simulation | **Describe the bug**
When attempting to get the **Component Property Tree** from a **PhysX Collider Component** a memory access violation is returned
**Steps to reproduce**
Steps to reproduce the behavior:
1. Create a Python Editor Test that makes a call to get the **Component Property Tree** from the **PhysX C... | 1.0 | PhysX Collider Component returns a memory access violation when getting its Component Property Tree with types - **Describe the bug**
When attempting to get the **Component Property Tree** from a **PhysX Collider Component** a memory access violation is returned
**Steps to reproduce**
Steps to reproduce the behavi... | non_priority | physx collider component returns a memory access violation when getting its component property tree with types describe the bug when attempting to get the component property tree from a physx collider component a memory access violation is returned steps to reproduce steps to reproduce the behavi... | 0 |
619,277 | 19,520,872,504 | IssuesEvent | 2021-12-29 18:11:37 | pystardust/ani-cli | https://api.github.com/repos/pystardust/ani-cli | closed | Request - Include list of anime that's popular, new, etc | type: feature request Priority 4: wishlist status: out of scope | Not an issue, but a request. Can you add an option to get a list of new and popular anime? That way we can check which one to look for to watch/download, for example, if new episodes are added. | 1.0 | Request - Include list of anime that's popular, new, etc - Not an issue, but a request. Can you add an option to get a list of new and popular anime? That way we can check which one to look for to watch/download, for example, if new episodes are added. | priority | request include list of anime that s popular new etc not an issue but a request can you add an option to get a list of new and popular anime that way we can check which one to look for to watch download for example if new episodes are added | 1 |
113,358 | 17,135,192,019 | IssuesEvent | 2021-07-13 00:25:25 | turkdevops/gitea | https://api.github.com/repos/turkdevops/gitea | opened | CVE-2020-11022 (Medium) detected in multiple libraries | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>golang.org/x/tools/go/analysis/passes/loopclosure-v0.1.0</b>, <b>golang.org/x/tools/go/analysis/passes/copylock-v0.... | True | CVE-2020-11022 (Medium) detected in multiple libraries - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>golang.org/x/tools/go/analysis/passes/loopclosure-v0.1.0</... | non_priority | cve medium detected in multiple libraries cve medium severity vulnerability vulnerable libraries golang org x tools go analysis passes loopclosure golang org x tools go analysis passes copylock golang org x tools go analysis golang org x tools go analysis passes bools ... | 0 |
25,645 | 5,188,992,270 | IssuesEvent | 2017-01-20 21:43:39 | Esri/military-symbol-editor-addin-wpf | https://api.github.com/repos/Esri/military-symbol-editor-addin-wpf | closed | Make Corrections to Install Military Symbol Editor topic from Pro Doc | 3 - Verify B - Affects Documentation B - Bug effort-small | 
We removed this install topic for the other parts of military tools, so I'm going to go ahead and remove this for consistency sake.
| 1.0 | Make Corrections to Install Military Symbol Editor topic from Pro Doc - 
We removed this install topic for the other parts of military tools, so I'm going to go ahead and remove this for consistency sake.
... | non_priority | make corrections to install military symbol editor topic from pro doc we removed this install topic for the other parts of military tools so i m going to go ahead and remove this for consistency sake | 0 |
668,586 | 22,590,755,039 | IssuesEvent | 2022-06-28 19:36:03 | googleapis/google-api-nodejs-client | https://api.github.com/repos/googleapis/google-api-nodejs-client | opened | @googleapis/runtimeconfig submodule is not available from npm | type: bug priority: p2 | I tried to install the `@googleapis/runtimeconfig` submodule as as instructed by the link below:
https://github.com/googleapis/google-api-nodejs-client/tree/main/src/apis/runtimeconfig
But the package is not present on NPM.
I check the `@google-cloud` nodejs client libraries as well but to no avail.
Please ... | 1.0 | @googleapis/runtimeconfig submodule is not available from npm - I tried to install the `@googleapis/runtimeconfig` submodule as as instructed by the link below:
https://github.com/googleapis/google-api-nodejs-client/tree/main/src/apis/runtimeconfig
But the package is not present on NPM.
I check the `@google-cl... | priority | googleapis runtimeconfig submodule is not available from npm i tried to install the googleapis runtimeconfig submodule as as instructed by the link below but the package is not present on npm i check the google cloud nodejs client libraries as well but to no avail please make it available on n... | 1 |
353,205 | 10,549,975,415 | IssuesEvent | 2019-10-03 09:57:04 | jenkins-x/jx | https://api.github.com/repos/jenkins-x/jx | opened | Upgrade process needs to make sure needs to make sure not to fail existing builds | area/upgrade kind/task priority/important-soon | The update process as defined now will update and restart essential Jenksins X components which will fail builds in progress.
Ideally, once upgrade starts no new builds are submitted and existing builds are allowed to complete, before the upgrade process continues.
After upgrade completion builds should resume.
| 1.0 | Upgrade process needs to make sure needs to make sure not to fail existing builds - The update process as defined now will update and restart essential Jenksins X components which will fail builds in progress.
Ideally, once upgrade starts no new builds are submitted and existing builds are allowed to complete, before ... | priority | upgrade process needs to make sure needs to make sure not to fail existing builds the update process as defined now will update and restart essential jenksins x components which will fail builds in progress ideally once upgrade starts no new builds are submitted and existing builds are allowed to complete before ... | 1 |
185,817 | 6,730,853,842 | IssuesEvent | 2017-10-18 03:48:51 | wireservice/csvkit | https://api.github.com/repos/wireservice/csvkit | closed | Install with Homebrew | feature Low Priority | [Homebrew](http://brew.sh)
Tried with `brew diy` but
```
Error: Couldn't determine build system
```
| 1.0 | Install with Homebrew - [Homebrew](http://brew.sh)
Tried with `brew diy` but
```
Error: Couldn't determine build system
```
| priority | install with homebrew tried with brew diy but error couldn t determine build system | 1 |
1,640 | 2,653,006,727 | IssuesEvent | 2015-03-16 20:34:44 | concrete5/concrete5-5.7.0 | https://api.github.com/repos/concrete5/concrete5-5.7.0 | closed | Block actions do not work in Stacks | code:core classes severity:high status:awaiting development type:bug | Block action URLs do not seem to work properly in a stack.
To reproduce:
1. Create a stack
2. Place a form in the stack
3. Show the stack on a page
4. Try to submit the form
Please note that this needs to work on both situations:
- When a stack is added manually to the page
- When a stack is displayed progr... | 1.0 | Block actions do not work in Stacks - Block action URLs do not seem to work properly in a stack.
To reproduce:
1. Create a stack
2. Place a form in the stack
3. Show the stack on a page
4. Try to submit the form
Please note that this needs to work on both situations:
- When a stack is added manually to the p... | non_priority | block actions do not work in stacks block action urls do not seem to work properly in a stack to reproduce create a stack place a form in the stack show the stack on a page try to submit the form please note that this needs to work on both situations when a stack is added manually to the p... | 0 |
18,084 | 12,751,396,854 | IssuesEvent | 2020-06-27 10:44:32 | merely-useful/merely-useful.github.io | https://api.github.com/repos/merely-useful/merely-useful.github.io | closed | Spacing items in table of contents in PDF version | bug good first issue infrastructure | We have a lot of chapters and sections. When there are two digits' worth of each (e.g., Section 14.11), the number in the table of contents in the PDF version bumps up against the section title. Fix the LaTeX preamble so that this doesn't happen.
, the number in the table of contents in the PDF version bumps up against the section title. Fix the LaTeX preamble so that this doesn't happen.
![Screen Shot 2019-0... | non_priority | spacing items in table of contents in pdf version we have a lot of chapters and sections when there are two digits worth of each e g section the number in the table of contents in the pdf version bumps up against the section title fix the latex preamble so that this doesn t happen | 0 |
559,928 | 16,581,083,796 | IssuesEvent | 2021-05-31 11:56:52 | grpc/grpc | https://api.github.com/repos/grpc/grpc | closed | Bidirectional streaming with python client and go server having issue | kind/bug lang/Python priority/P2 | ### What version of gRPC and what language are you using?
v1.31
### What operating system (Linux, Windows,...) and version?
Ubuntu 18.04 5.4.0-47-generic
### What runtime / compiler are you using (e.g. python version or version of gcc)
Python 3.7 and Go 1.15
### What did you do?
- I have created one simple... | 1.0 | Bidirectional streaming with python client and go server having issue - ### What version of gRPC and what language are you using?
v1.31
### What operating system (Linux, Windows,...) and version?
Ubuntu 18.04 5.4.0-47-generic
### What runtime / compiler are you using (e.g. python version or version of gcc)
Pyt... | priority | bidirectional streaming with python client and go server having issue what version of grpc and what language are you using what operating system linux windows and version ubuntu generic what runtime compiler are you using e g python version or version of gcc python ... | 1 |
582,662 | 17,367,218,384 | IssuesEvent | 2021-07-30 08:59:55 | gambitph/Stackable | https://api.github.com/repos/gambitph/Stackable | closed | divider reset options not working properly | [block] divider bug medium priority | - resetting divider width changes the value to 100% instead of the default 50%
- divider disappears in editor when resetting height (it appears in the front end and is resetted
properly)


.
However, the build now seems to stall https://travis-ci.org/KristofferC/ContMechTensors.jl/jobs/184179783#L200.
Any help d... | 1.0 | Travis build stalls on 0.5 when make.jl is run - Due to my package suddenly started failing on nightly I swapped to using 0.5 for the build (https://github.com/KristofferC/ContMechTensors.jl/commit/593ce54b36cf25e83ee8b32459b4dccb1d643797).
However, the build now seems to stall https://travis-ci.org/KristofferC/Cont... | priority | travis build stalls on when make jl is run due to my package suddenly started failing on nightly i swapped to using for the build however the build now seems to stall any help debugging this is appreciated | 1 |
70,771 | 9,440,803,487 | IssuesEvent | 2019-04-14 20:32:44 | fsharp/FAKE | https://api.github.com/repos/fsharp/FAKE | closed | Install Paket as dotnet tool | documentation enhancement help wanted | Since the new [alfa of Paket](https://github.com/fsprojects/Paket/pull/3183), we can install it as dotnet global tool.
I've made a little [sample script](https://github.com/nojaf/fable-docker/blob/remove-mono/sample/build.fsx) where I first install Paket and later use the existing module.
```fsharp
Target.create... | 1.0 | Install Paket as dotnet tool - Since the new [alfa of Paket](https://github.com/fsprojects/Paket/pull/3183), we can install it as dotnet global tool.
I've made a little [sample script](https://github.com/nojaf/fable-docker/blob/remove-mono/sample/build.fsx) where I first install Paket and later use the existing modu... | non_priority | install paket as dotnet tool since the new we can install it as dotnet global tool i ve made a little where i first install paket and later use the existing module fsharp target create installpaket fun if not file exists paketexe then dotnet exec id tool install tool p... | 0 |
128,428 | 18,048,395,511 | IssuesEvent | 2021-09-19 09:51:34 | phildav06/Groupomania | https://api.github.com/repos/phildav06/Groupomania | opened | CVE-2021-37713 (High) detected in tar-6.1.0.tgz | security vulnerability | ## CVE-2021-37713 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-6.1.0.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/ta... | True | CVE-2021-37713 (High) detected in tar-6.1.0.tgz - ## CVE-2021-37713 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tar-6.1.0.tgz</b></p></summary>
<p>tar for node</p>
<p>Library home ... | non_priority | cve high detected in tar tgz cve high severity vulnerability vulnerable library tar tgz tar for node library home page a href path to dependency file groupomania backend package json path to vulnerable library groupomania backend node modules tar package json dep... | 0 |
234,971 | 7,733,363,178 | IssuesEvent | 2018-05-26 10:44:14 | tuskyapp/Tusky | https://api.github.com/repos/tuskyapp/Tusky | closed | Remaining characters are calculated wrongly | bug priority: high | Links in Mastodon statuses are only counted as 23 characters, no matter how long they are. Tusky ignores this, which means you have less characters in Tusky than on Mastodon web. | 1.0 | Remaining characters are calculated wrongly - Links in Mastodon statuses are only counted as 23 characters, no matter how long they are. Tusky ignores this, which means you have less characters in Tusky than on Mastodon web. | priority | remaining characters are calculated wrongly links in mastodon statuses are only counted as characters no matter how long they are tusky ignores this which means you have less characters in tusky than on mastodon web | 1 |
670,084 | 22,669,291,346 | IssuesEvent | 2022-07-03 11:17:08 | FAIRplus/FAIR_wizard | https://api.github.com/repos/FAIRplus/FAIR_wizard | opened | assessment page - DSM content - landing on page Level -1 | priority:1 importance:3 | TBD
Level 0 is a baseline level and every project is at level 0 by default. This way, it doesn't make sense to start the assessment from Level 0.
Howerver, the assessment team is designing a new tool for performing assessment. need to check with them
| 1.0 | assessment page - DSM content - landing on page Level -1 - TBD
Level 0 is a baseline level and every project is at level 0 by default. This way, it doesn't make sense to start the assessment from Level 0.
Howerver, the assessment team is designing a new tool for performing assessment. need to check with them
| priority | assessment page dsm content landing on page level tbd level is a baseline level and every project is at level by default this way it doesn t make sense to start the assessment from level howerver the assessment team is designing a new tool for performing assessment need to check with them | 1 |
433,362 | 30,323,998,193 | IssuesEvent | 2023-07-10 21:44:02 | ArcadeData/arcadedb-docs | https://api.github.com/repos/ArcadeData/arcadedb-docs | opened | Add example of usage for DbVisualizer tool | documentation | Now that we have the Compatible Tool section, it would be nice to add a quick guide on using DbVisualizer with ArcadeDB. | 1.0 | Add example of usage for DbVisualizer tool - Now that we have the Compatible Tool section, it would be nice to add a quick guide on using DbVisualizer with ArcadeDB. | non_priority | add example of usage for dbvisualizer tool now that we have the compatible tool section it would be nice to add a quick guide on using dbvisualizer with arcadedb | 0 |
87,635 | 10,551,496,729 | IssuesEvent | 2019-10-03 13:27:44 | sylabs/singularity | https://api.github.com/repos/sylabs/singularity | closed | test-plugin should probably do something when its called | Documentation PluginExample | ## Version of Singularity:
3.2.0rc2
The `test-plugin` in the `examples/plugins` directory should probably do something when it is executed. Even if that something is just to print a message. Right now it just prints a `usage` statement, so I can't tell if its working by looking at the output.
```
$ singularit... | 1.0 | test-plugin should probably do something when its called - ## Version of Singularity:
3.2.0rc2
The `test-plugin` in the `examples/plugins` directory should probably do something when it is executed. Even if that something is just to print a message. Right now it just prints a `usage` statement, so I can't tell if... | non_priority | test plugin should probably do something when its called version of singularity the test plugin in the examples plugins directory should probably do something when it is executed even if that something is just to print a message right now it just prints a usage statement so i can t tell if it... | 0 |
424,324 | 12,309,542,548 | IssuesEvent | 2020-05-12 09:07:42 | our-city-app/mobicage-backend | https://api.github.com/repos/our-city-app/mobicage-backend | closed | Sharing services/profile via Facebook | priority_minor type_feature | Need to set `og:image` tag for the pages that are shared on facebook because in the iOS SDK we cannot set the content.imageURL anymore. It has to be server side using `og:image`.
- `service.actionMenu.shareLinkUrl` (https://rogerth.at/M/-8LHYOB9.01?email&target=fbWall&from=phone) has to have `og:image` that points to... | 1.0 | Sharing services/profile via Facebook - Need to set `og:image` tag for the pages that are shared on facebook because in the iOS SDK we cannot set the content.imageURL anymore. It has to be server side using `og:image`.
- `service.actionMenu.shareLinkUrl` (https://rogerth.at/M/-8LHYOB9.01?email&target=fbWall&from=phon... | priority | sharing services profile via facebook need to set og image tag for the pages that are shared on facebook because in the ios sdk we cannot set the content imageurl anymore it has to be server side using og image service actionmenu sharelinkurl has to have og image that points to service actionmenu sh... | 1 |
543,998 | 15,888,488,379 | IssuesEvent | 2021-04-10 07:35:22 | bryntum/support | https://api.github.com/repos/bryntum/support | closed | Enable yarn support for installing packages | angular bug high-priority ionic react resolved vue | `@bryntum/gantt` package can be installed via npm, but yarn throws error.
```
node 14.2.0
yarn 1.17.3
npm 6.14.4
``` | 1.0 | Enable yarn support for installing packages - `@bryntum/gantt` package can be installed via npm, but yarn throws error.
```
node 14.2.0
yarn 1.17.3
npm 6.14.4
``` | priority | enable yarn support for installing packages bryntum gantt package can be installed via npm but yarn throws error node yarn npm | 1 |
221,469 | 7,388,804,182 | IssuesEvent | 2018-03-16 05:12:17 | opensmc/get-connected-smc | https://api.github.com/repos/opensmc/get-connected-smc | reopened | Users Without Kids Eligible for WIC and Free/Reduced Price School Lunches | High Priority bug help wanted | If a user responds that they do not have children, the results screen still shows that they may be eligible for WIC and free/reduced price school lunches.
Pregnant women with no other children are eligible for WIC, but users without children should not see free/reduced price school lunch.
Can we change the logic... | 1.0 | Users Without Kids Eligible for WIC and Free/Reduced Price School Lunches - If a user responds that they do not have children, the results screen still shows that they may be eligible for WIC and free/reduced price school lunches.
Pregnant women with no other children are eligible for WIC, but users without children... | priority | users without kids eligible for wic and free reduced price school lunches if a user responds that they do not have children the results screen still shows that they may be eligible for wic and free reduced price school lunches pregnant women with no other children are eligible for wic but users without children... | 1 |
6,123 | 3,333,457,496 | IssuesEvent | 2015-11-12 01:30:10 | bobombolo/realterrain | https://api.github.com/repos/bobombolo/realterrain | closed | config file | code refactor feature request | Suggestion to include a default settings file in the mod's main directory, this way, all default settings can be removed from the code, and the user can treat it as a 'master' or default setting file.
If no settings file is found in the worldpath in load_settings, copy the default one, then read it.
| 1.0 | config file - Suggestion to include a default settings file in the mod's main directory, this way, all default settings can be removed from the code, and the user can treat it as a 'master' or default setting file.
If no settings file is found in the worldpath in load_settings, copy the default one, then read it.
... | non_priority | config file suggestion to include a default settings file in the mod s main directory this way all default settings can be removed from the code and the user can treat it as a master or default setting file if no settings file is found in the worldpath in load settings copy the default one then read it ... | 0 |
638,078 | 20,712,387,198 | IssuesEvent | 2022-03-12 04:44:51 | blackmichael/f1-pickem | https://api.github.com/repos/blackmichael/f1-pickem | opened | Add temporary email->userID lookup in submit-picks lambda | high priority backend | ## Description
User auth is a lot of work. Gather emails, map them to static user IDs, reject unknown emails. | 1.0 | Add temporary email->userID lookup in submit-picks lambda - ## Description
User auth is a lot of work. Gather emails, map them to static user IDs, reject unknown emails. | priority | add temporary email userid lookup in submit picks lambda description user auth is a lot of work gather emails map them to static user ids reject unknown emails | 1 |
728,716 | 25,089,468,481 | IssuesEvent | 2022-11-08 04:17:20 | openmsupply/mobile | https://api.github.com/repos/openmsupply/mobile | closed | React-native failed to build | Priority: immediate Bug: development Status: In PR Solution: Agreed | ## Describe the bug
All of the sudden from today react-native failed to build our mobile app
```
yarn run v1.22.19
$ react-native run-android
info Running jetifier to migrate libraries to AndroidX. You can disable it using "--no-jetifier" flag.
Jetifier found 1423 file(s) to forward-jetify. Using 10 workers..... | 1.0 | React-native failed to build - ## Describe the bug
All of the sudden from today react-native failed to build our mobile app
```
yarn run v1.22.19
$ react-native run-android
info Running jetifier to migrate libraries to AndroidX. You can disable it using "--no-jetifier" flag.
Jetifier found 1423 file(s) to for... | priority | react native failed to build describe the bug all of the sudden from today react native failed to build our mobile app yarn run react native run android info running jetifier to migrate libraries to androidx you can disable it using no jetifier flag jetifier found file s to forward j... | 1 |
248,555 | 7,933,849,996 | IssuesEvent | 2018-07-08 12:14:16 | RocketMod/Rocket | https://api.github.com/repos/RocketMod/Rocket | closed | Plugins attempting to install with https instead of http | Priority: Normal bug confirmed | http://prntscr.com/jzaknp
Operating System and Version:
<!-- Please specify the versions you use, you can see them with /rocket -->
Unturned Version:
Rocketmod Version:
<!--
Please be as accurate as possible, and include as much information as possible.
Share related configuration or/and your ... | 1.0 | Plugins attempting to install with https instead of http - http://prntscr.com/jzaknp
Operating System and Version:
<!-- Please specify the versions you use, you can see them with /rocket -->
Unturned Version:
Rocketmod Version:
<!--
Please be as accurate as possible, and include as much information ... | priority | plugins attempting to install with https instead of http operating system and version unturned version rocketmod version please be as accurate as possible and include as much information as possible share related configuration or and your rocket log you can find it in rocket ... | 1 |
36,308 | 4,726,436,945 | IssuesEvent | 2016-10-18 10:12:09 | pixelhumain/communecter | https://api.github.com/repos/pixelhumain/communecter | closed | Agenda - Bug de l'affichage des étiquettes | bug design Production bug | Les étiquettes s'affichent en dessous de l'événement de l'agenda.
Ce comportement est visible lorsque des événements sont affichés une semaine sur l'autre. Dans ce cas l'étiquette de l'événement est caché par l'événement en dessous.
 | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql_connector_python-8.0.6-py2.py3-none-any.whl</b></p></summary>
<p>MySQL driver written in Python</p>
<p>Library home page: <a href="https://files.pythonhosted.or... | True | mysql_connector_python-8.0.6-py2.py3-none-any.whl: 1 vulnerabilities (highest severity is: 8.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mysql_connector_python-8.0.6-py2.py3-none-any.whl</b></p></summary>
... | non_priority | mysql connector python none any whl vulnerabilities highest severity is vulnerable library mysql connector python none any whl mysql driver written in python library home page a href path to dependency file requirements txt path to vulnerable library requirement... | 0 |
3,133 | 2,810,651,741 | IssuesEvent | 2015-05-17 02:51:37 | HeavensGate/Eternal | https://api.github.com/repos/HeavensGate/Eternal | opened | Chaplain | code complex/difficult discuss/uncertain Gate/writing longterm mapping spriting | We intend to be working on the Chaplain, once we have a little more ground on the forces he opposes. More on this later; pending discussions abound. | 1.0 | Chaplain - We intend to be working on the Chaplain, once we have a little more ground on the forces he opposes. More on this later; pending discussions abound. | non_priority | chaplain we intend to be working on the chaplain once we have a little more ground on the forces he opposes more on this later pending discussions abound | 0 |
47,365 | 24,970,910,744 | IssuesEvent | 2022-11-02 01:00:08 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Use Automatic Feature Suspension to protect against known issues | Feature Request Area-Performance | **Brief description:**
[Automatic Feature Suspension](https://docs.microsoft.com/en-us/visualstudio/code-quality/automatic-feature-suspension?view=vs-2019) guards against bad experiences with Roslyn. When a user has limited memory, it prioritizes their experience by disabling some advanced features.
This guard ca... | True | Use Automatic Feature Suspension to protect against known issues - **Brief description:**
[Automatic Feature Suspension](https://docs.microsoft.com/en-us/visualstudio/code-quality/automatic-feature-suspension?view=vs-2019) guards against bad experiences with Roslyn. When a user has limited memory, it prioritizes the... | non_priority | use automatic feature suspension to protect against known issues brief description guards against bad experiences with roslyn when a user has limited memory it prioritizes their experience by disabling some advanced features this guard can be expanded to cover other known scenarios issues relating ... | 0 |
151,174 | 12,016,494,922 | IssuesEvent | 2020-04-10 16:13:29 | mathjax/MathJax | https://api.github.com/repos/mathjax/MathJax | closed | processEscapes set to true doesn't work | Accepted Fixed Merged Test Needed v3 | using version 3.0.1, using "_processEscapes_" set to "_true_" stops MathJax from working, giving the error "**TypeError: Q.setAttribute is not a function**". The folloowing is the minimal example that I tested:
```
<!DOCTYPE html>
<head>
<meta charset="utf-8">
<meta http-equiv="x-ua-compatible" content="ie=edg... | 1.0 | processEscapes set to true doesn't work - using version 3.0.1, using "_processEscapes_" set to "_true_" stops MathJax from working, giving the error "**TypeError: Q.setAttribute is not a function**". The folloowing is the minimal example that I tested:
```
<!DOCTYPE html>
<head>
<meta charset="utf-8">
<meta ht... | non_priority | processescapes set to true doesn t work using version using processescapes set to true stops mathjax from working giving the error typeerror q setattribute is not a function the folloowing is the minimal example that i tested mathjax with tex input and svg outp... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.