Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3
values | title stringlengths 1 1k | labels stringlengths 4 1.38k | body stringlengths 1 262k | index stringclasses 16
values | text_combine stringlengths 96 262k | label stringclasses 2
values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
646,709 | 21,057,394,501 | IssuesEvent | 2022-04-01 05:46:35 | turbot/steampipe-plugin-oci | https://api.github.com/repos/turbot/steampipe-plugin-oci | closed | Add table oci_resourcemanager_stack | enhancement new table priority:medium | **References**
Add any related links that will help us understand the resource, including vendor documentation, related GitHub issues, and Go SDK documentation.
Reference
https://registry.terraform.io/providers/oracle/oci/latest/docs/data-sources/resourcemanager_stacks | 1.0 | Add table oci_resourcemanager_stack - **References**
Add any related links that will help us understand the resource, including vendor documentation, related GitHub issues, and Go SDK documentation.
Reference
https://registry.terraform.io/providers/oracle/oci/latest/docs/data-sources/resourcemanager_stacks | priority | add table oci resourcemanager stack references add any related links that will help us understand the resource including vendor documentation related github issues and go sdk documentation reference | 1 |
759,545 | 26,600,631,652 | IssuesEvent | 2023-01-23 15:31:53 | kir-dev/konzisite-api | https://api.github.com/repos/kir-dev/konzisite-api | closed | Only return consultations where the user is member of the targetGroups | high priority | In `GET /consultations/`
- If the user isn't signed in, only return the consultations where there's no target groups
- Otherwise also return the consultations where the user is member of at least one of the target groups
In `GET /consultations/:id`
- return with 403 if the user is not in any of the target groups | 1.0 | Only return consultations where the user is member of the targetGroups - In `GET /consultations/`
- If the user isn't signed in, only return the consultations where there's no target groups
- Otherwise also return the consultations where the user is member of at least one of the target groups
In `GET /consultatio... | priority | only return consultations where the user is member of the targetgroups in get consultations if the user isn t signed in only return the consultations where there s no target groups otherwise also return the consultations where the user is member of at least one of the target groups in get consultatio... | 1 |
59,326 | 3,105,473,842 | IssuesEvent | 2015-08-31 21:06:11 | UniVR/GolfVR | https://api.github.com/repos/UniVR/GolfVR | opened | Explain rules introduction | priority:low type:idea | Explain the rules before the game begin
_Watch the ball to shoot (the time the ball is watched will define the power)
_... (to be defined) | 1.0 | Explain rules introduction - Explain the rules before the game begin
_Watch the ball to shoot (the time the ball is watched will define the power)
_... (to be defined) | priority | explain rules introduction explain the rules before the game begin watch the ball to shoot the time the ball is watched will define the power to be defined | 1 |
72,321 | 9,567,087,357 | IssuesEvent | 2019-05-06 01:39:48 | CompileIO/compile.io | https://api.github.com/repos/CompileIO/compile.io | closed | Project Documentation Review | documentation | # Description of Issue
As a stakeholder, I'd like to have a well documented project so that if this project went open-source, developers would have little to no trouble with the on-boarding process.
# Acceptance Criteria
- [x] Review Code and address areas lacking/needing Documentation
- [ ] Address additional D... | 1.0 | Project Documentation Review - # Description of Issue
As a stakeholder, I'd like to have a well documented project so that if this project went open-source, developers would have little to no trouble with the on-boarding process.
# Acceptance Criteria
- [x] Review Code and address areas lacking/needing Documentat... | non_priority | project documentation review description of issue as a stakeholder i d like to have a well documented project so that if this project went open source developers would have little to no trouble with the on boarding process acceptance criteria review code and address areas lacking needing documentatio... | 0 |
178,958 | 14,686,013,198 | IssuesEvent | 2021-01-01 12:40:21 | corona-warn-app/cwa-website | https://api.github.com/repos/corona-warn-app/cwa-website | closed | ENA.ExposureNotificationError-Fehler2 | documentation | <!--
Thanks for reporting an issue on the website 🙌 ❤️
Before opening a new issue, please make sure that we do not have any duplicates already open. You can ensure this by searching the issue list for this repository. If there is a duplicate, please close your issue and add a comment to the existing issue instead.... | 1.0 | ENA.ExposureNotificationError-Fehler2 - <!--
Thanks for reporting an issue on the website 🙌 ❤️
Before opening a new issue, please make sure that we do not have any duplicates already open. You can ensure this by searching the issue list for this repository. If there is a duplicate, please close your issue and add ... | non_priority | ena exposurenotificationerror thanks for reporting an issue on the website 🙌 ❤️ before opening a new issue please make sure that we do not have any duplicates already open you can ensure this by searching the issue list for this repository if there is a duplicate please close your issue and add a comm... | 0 |
822,342 | 30,866,484,082 | IssuesEvent | 2023-08-03 08:25:03 | telerik/kendo-react | https://api.github.com/repos/telerik/kendo-react | opened | [Editor] BackColor and ForeColor are not applied on table cells content if multiple cells are selected | bug pkg:editor Priority 1 SEV: High | If multiple cells/rows are selected in a table, applying changes to the BackColor and ForeColor fails in some scenarios.
To observe the issue, open the following example:
- https://stackblitz.com/edit/react-icvjor?file=app%2Fmain.jsx
Cases that fail:
- select with the mouse from row1cell1 to row2cell2 and cha... | 1.0 | [Editor] BackColor and ForeColor are not applied on table cells content if multiple cells are selected - If multiple cells/rows are selected in a table, applying changes to the BackColor and ForeColor fails in some scenarios.
To observe the issue, open the following example:
- https://stackblitz.com/edit/react-ic... | priority | backcolor and forecolor are not applied on table cells content if multiple cells are selected if multiple cells rows are selected in a table applying changes to the backcolor and forecolor fails in some scenarios to observe the issue open the following example cases that fail select with the mo... | 1 |
27,684 | 13,349,348,104 | IssuesEvent | 2020-08-30 00:11:18 | aws/aws-sdk-go | https://api.github.com/repos/aws/aws-sdk-go | closed | Presign performance. Can it it be improved? | performance | We are seeing heavy degrading of our services that generate payload with a significant number of presigned urls in. The effect is dramatic, on Heroku standard 1x machine the performence is a factor 20 lower and a profile pprof shows ~75% of cpu time goes into prsign related work (1/3 of which is some sort of rest xml p... | True | Presign performance. Can it it be improved? - We are seeing heavy degrading of our services that generate payload with a significant number of presigned urls in. The effect is dramatic, on Heroku standard 1x machine the performence is a factor 20 lower and a profile pprof shows ~75% of cpu time goes into prsign related... | non_priority | presign performance can it it be improved we are seeing heavy degrading of our services that generate payload with a significant number of presigned urls in the effect is dramatic on heroku standard machine the performence is a factor lower and a profile pprof shows of cpu time goes into prsign related wo... | 0 |
201,682 | 15,217,765,806 | IssuesEvent | 2021-02-17 16:59:32 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | closed | Brave nightly build `Bravearm 1.22.30.apk` is crashing | OS/Android QA/Test-Plan-Specified QA/Yes crash regression | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROV... | 1.0 | Brave nightly build `Bravearm 1.22.30.apk` is crashing - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSE... | non_priority | brave nightly build bravearm apk is crashing have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed ... | 0 |
11,559 | 2,610,141,745 | IssuesEvent | 2015-02-26 18:44:40 | chrsmith/hedgewars | https://api.github.com/repos/chrsmith/hedgewars | closed | Add [save as defaults] button to teams' key settings | auto-migrated Priority-Medium Type-Enhancement | ```
Currently players can't use their preferred key settings as spectators or in
quick single-player matches.
This is especially a problem with special default keys (like the current chat
history key) on different keyboard layouts.
Making it possible to save the key settings of a preferred team would solve
that pr... | 1.0 | Add [save as defaults] button to teams' key settings - ```
Currently players can't use their preferred key settings as spectators or in
quick single-player matches.
This is especially a problem with special default keys (like the current chat
history key) on different keyboard layouts.
Making it possible to save th... | priority | add button to teams key settings currently players can t use their preferred key settings as spectators or in quick single player matches this is especially a problem with special default keys like the current chat history key on different keyboard layouts making it possible to save the key settings of... | 1 |
781,178 | 27,425,875,439 | IssuesEvent | 2023-03-01 20:14:57 | DSpace/dspace-angular | https://api.github.com/repos/DSpace/dspace-angular | closed | [Deque Analysis] MyDSpace page's "serious" accessibility issues | bug accessibility component: MyDSpace medium priority Estimate TBD | > Serious: This issue results in serious barriers for people with disabilities, and will partially prevent them from accessing fundamental features or content. People relying on assistive technologies will experience significant frustration as a result. Issues falling under this category are major problems, and remedia... | 1.0 | [Deque Analysis] MyDSpace page's "serious" accessibility issues - > Serious: This issue results in serious barriers for people with disabilities, and will partially prevent them from accessing fundamental features or content. People relying on assistive technologies will experience significant frustration as a result. ... | priority | mydspace page s serious accessibility issues serious this issue results in serious barriers for people with disabilities and will partially prevent them from accessing fundamental features or content people relying on assistive technologies will experience significant frustration as a result issues falling ... | 1 |
185,671 | 6,726,550,547 | IssuesEvent | 2017-10-17 10:16:07 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | Estimate cardinality more precisely. | bug optimizer priority/P1 statistic | Once we analyze a table, its cardinality for each histogram will not update any more. So we should estimate it as ndv * (new count / old count) | 1.0 | Estimate cardinality more precisely. - Once we analyze a table, its cardinality for each histogram will not update any more. So we should estimate it as ndv * (new count / old count) | priority | estimate cardinality more precisely once we analyze a table its cardinality for each histogram will not update any more so we should estimate it as ndv new count old count | 1 |
146,233 | 19,393,981,389 | IssuesEvent | 2021-12-18 01:47:32 | peterwkc85/Spock_Testing_Framework | https://api.github.com/repos/peterwkc85/Spock_Testing_Framework | opened | CVE-2021-42550 (Medium) detected in logback-classic-0.9.26.jar | security vulnerability | ## CVE-2021-42550 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logback-classic-0.9.26.jar</b></p></summary>
<p>Logback: the reliable, generic, fast and flexible logging library fo... | True | CVE-2021-42550 (Medium) detected in logback-classic-0.9.26.jar - ## CVE-2021-42550 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>logback-classic-0.9.26.jar</b></p></summary>
<p>Log... | non_priority | cve medium detected in logback classic jar cve medium severity vulnerability vulnerable library logback classic jar logback the reliable generic fast and flexible logging library for java library home page a href path to dependency file spock testing framework java ... | 0 |
11,705 | 5,076,084,966 | IssuesEvent | 2016-12-27 23:37:11 | portainer/portainer | https://api.github.com/repos/portainer/portainer | opened | Setup a cache busting mechanism | area/build-system kind/enhancement | When upgrading Portainer, the JS/CSS files can be cached by the browser and this can lead to bugs/strange behaviours.
This can be achieved by using a combination of grunt plugins:
* https://github.com/sebdeckers/grunt-rev
* https://github.com/yeoman/grunt-usemin
This should help versioning the assets before r... | 1.0 | Setup a cache busting mechanism - When upgrading Portainer, the JS/CSS files can be cached by the browser and this can lead to bugs/strange behaviours.
This can be achieved by using a combination of grunt plugins:
* https://github.com/sebdeckers/grunt-rev
* https://github.com/yeoman/grunt-usemin
This should h... | non_priority | setup a cache busting mechanism when upgrading portainer the js css files can be cached by the browser and this can lead to bugs strange behaviours this can be achieved by using a combination of grunt plugins this should help versioning the assets before release which gives us the ability to let ... | 0 |
91,230 | 11,488,211,698 | IssuesEvent | 2020-02-11 13:31:03 | toggl/mobileapp | https://api.github.com/repos/toggl/mobileapp | closed | Use HH:mm format for 24-hour format | carry-over-to-native foundation needs-design | Higher echelons of power have decided that
`HH:mm` format
should be used on all clients for 24-hour mode (instead of previous `H:mm`).
| 1.0 | Use HH:mm format for 24-hour format - Higher echelons of power have decided that
`HH:mm` format
should be used on all clients for 24-hour mode (instead of previous `H:mm`).
| non_priority | use hh mm format for hour format higher echelons of power have decided that hh mm format should be used on all clients for hour mode instead of previous h mm | 0 |
383,460 | 11,356,338,345 | IssuesEvent | 2020-01-24 22:25:49 | DlfinBroom/UnleashedRage | https://api.github.com/repos/DlfinBroom/UnleashedRage | closed | GetLatestIssue() method in ComicPageDB does not work | Bug Database High Priority | GetLatestIssue() will always return a null value
The database part of the code will always throw an exception and catch the exception, returning a null value | 1.0 | GetLatestIssue() method in ComicPageDB does not work - GetLatestIssue() will always return a null value
The database part of the code will always throw an exception and catch the exception, returning a null value | priority | getlatestissue method in comicpagedb does not work getlatestissue will always return a null value the database part of the code will always throw an exception and catch the exception returning a null value | 1 |
270,148 | 23,494,002,569 | IssuesEvent | 2022-08-17 22:00:02 | rectorphp/rector | https://api.github.com/repos/rectorphp/rector | closed | NodeFactory->createArray doesn't support boolean Node elements | feature failing test case needed | # Bug Report
<!-- First, thank you for reporting a bug. That takes time and we appreciate that! -->
| Subject | Details |
| :------------- | :---------------------------------------------------------------|
| Rector version | 0.13.2 |
... | 1.0 | NodeFactory->createArray doesn't support boolean Node elements - # Bug Report
<!-- First, thank you for reporting a bug. That takes time and we appreciate that! -->
| Subject | Details |
| :------------- | :-------------------------------------------... | non_priority | nodefactory createarray doesn t support boolean node elements bug report subject details rector version minimal php ... | 0 |
618,271 | 19,431,293,523 | IssuesEvent | 2021-12-21 12:18:09 | openforis/arena | https://api.github.com/repos/openforis/arena | closed | Collect Import Report: Show full Xpath expression | Priority_2 | A long equation without spaces is now shown only partially:
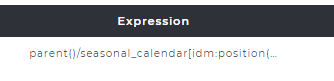
| 1.0 | Collect Import Report: Show full Xpath expression - A long equation without spaces is now shown only partially:
| priority | collect import report show full xpath expression a long equation without spaces is now shown only partially | 1 |
166,242 | 12,917,736,011 | IssuesEvent | 2020-07-16 00:39:20 | KCarlile/flashchord | https://api.github.com/repos/KCarlile/flashchord | closed | Add @Flash_Chord Twitter link | easy enhancement passed testing ready for testing | ## Background
In order for people to follow updates for Flash Chord, we have a Twitter account for announcing new features and other information: https://twitter.com/flash_chord
## Acceptance Criteria
- The Twitter icon followed by the `@Flash_Chord` handle text are linked to https://twitter.com/flash_chord in the... | 2.0 | Add @Flash_Chord Twitter link - ## Background
In order for people to follow updates for Flash Chord, we have a Twitter account for announcing new features and other information: https://twitter.com/flash_chord
## Acceptance Criteria
- The Twitter icon followed by the `@Flash_Chord` handle text are linked to https:... | non_priority | add flash chord twitter link background in order for people to follow updates for flash chord we have a twitter account for announcing new features and other information acceptance criteria the twitter icon followed by the flash chord handle text are linked to in the footer copyright section ... | 0 |
823,247 | 30,961,804,284 | IssuesEvent | 2023-08-08 05:03:13 | rpm-software-management/dnf5 | https://api.github.com/repos/rpm-software-management/dnf5 | closed | Handle duplicate REPOIDs somehow | Priority: HIGH | DNF4 warns like this:
> Repository REPOID is listed more than once in the configuration
And uses just one of them? Or merges the config?
With DNF5 it seems the `REPOID` is loaded twice as `libdnf::Repo`, per:
```
$ dnf5 repo list
REPOID Some repo name
REPOID Some repo name - the duplicate
``` | 1.0 | Handle duplicate REPOIDs somehow - DNF4 warns like this:
> Repository REPOID is listed more than once in the configuration
And uses just one of them? Or merges the config?
With DNF5 it seems the `REPOID` is loaded twice as `libdnf::Repo`, per:
```
$ dnf5 repo list
REPOID Some repo name
REPOID Some r... | priority | handle duplicate repoids somehow warns like this repository repoid is listed more than once in the configuration and uses just one of them or merges the config with it seems the repoid is loaded twice as libdnf repo per repo list repoid some repo name repoid some repo name ... | 1 |
74,241 | 15,325,439,518 | IssuesEvent | 2021-02-26 01:19:01 | idonthaveafifaaddiction/MapLoom | https://api.github.com/repos/idonthaveafifaaddiction/MapLoom | opened | WS-2017-0116 (Medium) detected in angular-v1.2.21 | security vulnerability | ## WS-2017-0116 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-v1.2.21</b></p></summary>
<p>null</p>
<p>Path to dependency file: MapLoom/bower.json</p>
<p>Path to vulnerable... | True | WS-2017-0116 (Medium) detected in angular-v1.2.21 - ## WS-2017-0116 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-v1.2.21</b></p></summary>
<p>null</p>
<p>Path to dependenc... | non_priority | ws medium detected in angular ws medium severity vulnerability vulnerable library angular null path to dependency file maploom bower json path to vulnerable library maploom vendor angular bower json maploom vendor angular bower json dependency hierarchy x an... | 0 |
445,707 | 12,835,347,805 | IssuesEvent | 2020-07-07 12:44:05 | radical-cybertools/radical.pilot | https://api.github.com/repos/radical-cybertools/radical.pilot | closed | Long queue times result in non-starting pilots on BW | comp:agent layer:utils priority:v2 topic:communication type:bug type:performance | In short a job just simply didn't start (no errors in the logs) on BW with `gsissh` from local cluster.
The DEBUG log (not captured) shows a heartbeat from SAGA (I think) about the job queue status (PENDING), that (the heartbeat) at some point just stops. That is the last line in the log, no errors.
Wonder if th... | 1.0 | Long queue times result in non-starting pilots on BW - In short a job just simply didn't start (no errors in the logs) on BW with `gsissh` from local cluster.
The DEBUG log (not captured) shows a heartbeat from SAGA (I think) about the job queue status (PENDING), that (the heartbeat) at some point just stops. That ... | priority | long queue times result in non starting pilots on bw in short a job just simply didn t start no errors in the logs on bw with gsissh from local cluster the debug log not captured shows a heartbeat from saga i think about the job queue status pending that the heartbeat at some point just stops that ... | 1 |
288,131 | 8,826,361,208 | IssuesEvent | 2019-01-03 01:33:12 | Lustrel/money-management | https://api.github.com/repos/Lustrel/money-management | closed | Move Select2 files to "assets" folder | high-priority | It seems that Heroku doesn't recognize the `bundles` folder. This way, we need to move all Select2 related files to the `assets` folder, since it seems that Heroku can load files from there. | 1.0 | Move Select2 files to "assets" folder - It seems that Heroku doesn't recognize the `bundles` folder. This way, we need to move all Select2 related files to the `assets` folder, since it seems that Heroku can load files from there. | priority | move files to assets folder it seems that heroku doesn t recognize the bundles folder this way we need to move all related files to the assets folder since it seems that heroku can load files from there | 1 |
600,902 | 18,361,495,299 | IssuesEvent | 2021-10-09 09:31:49 | AY2122S1-CS2103T-T17-3/tp | https://api.github.com/repos/AY2122S1-CS2103T-T17-3/tp | closed | Add command doesn't work | bug priority.HIGH severity.High | Todo:
- update UG (UG still says `create` to create a person)
- fix the add command
When I typed in `add n/John Doe` I got the following error.
```
Invalid command format!
add: Adds a person to the address book. Parameters: n/NAME p/PHONE e/EMAIL a/ADDRESS [t/TAG]...
Example: add n/John Doe p/98765432 e/john... | 1.0 | Add command doesn't work - Todo:
- update UG (UG still says `create` to create a person)
- fix the add command
When I typed in `add n/John Doe` I got the following error.
```
Invalid command format!
add: Adds a person to the address book. Parameters: n/NAME p/PHONE e/EMAIL a/ADDRESS [t/TAG]...
Example: add ... | priority | add command doesn t work todo update ug ug still says create to create a person fix the add command when i typed in add n john doe i got the following error invalid command format add adds a person to the address book parameters n name p phone e email a address example add n john... | 1 |
56,970 | 15,531,838,061 | IssuesEvent | 2021-03-14 01:56:35 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | SlideMenu - scrollbar appears, no height adjustment | Stale defect | SlideMenu shows vertical scrollbar if count of menuitems in next slides (submenus) is greater than the count of menuitems in prev. (initial) slide. I think a dynamic (at runtime) adjustment of SlideMenu's height is missing.
| 1.0 | SlideMenu - scrollbar appears, no height adjustment - SlideMenu shows vertical scrollbar if count of menuitems in next slides (submenus) is greater than the count of menuitems in prev. (initial) slide. I think a dynamic (at runtime) adjustment of SlideMenu's height is missing.
| non_priority | slidemenu scrollbar appears no height adjustment slidemenu shows vertical scrollbar if count of menuitems in next slides submenus is greater than the count of menuitems in prev initial slide i think a dynamic at runtime adjustment of slidemenu s height is missing | 0 |
225,614 | 17,272,032,286 | IssuesEvent | 2021-07-22 21:16:44 | endojs/endo | https://api.github.com/repos/endojs/endo | closed | add readme/mission-statement to SES repo | documentation | We need more justification/motivation
Add code snippets similar to the DWeb Summit talk | 1.0 | add readme/mission-statement to SES repo - We need more justification/motivation
Add code snippets similar to the DWeb Summit talk | non_priority | add readme mission statement to ses repo we need more justification motivation add code snippets similar to the dweb summit talk | 0 |
264,778 | 28,212,805,029 | IssuesEvent | 2023-04-05 06:32:36 | hshivhare67/platform_frameworks_av_AOSP10_r33_CVE-2023-20933 | https://api.github.com/repos/hshivhare67/platform_frameworks_av_AOSP10_r33_CVE-2023-20933 | closed | CVE-2020-0179 (High) detected in avandroid-10.0.0_r33 - autoclosed | Mend: dependency security vulnerability | ## CVE-2020-0179 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-10.0.0_r33</b></p></summary>
<p>
<p>Library home page: <a href=https://android.googlesource.com/platform/fram... | True | CVE-2020-0179 (High) detected in avandroid-10.0.0_r33 - autoclosed - ## CVE-2020-0179 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>avandroid-10.0.0_r33</b></p></summary>
<p>
<p>Libr... | non_priority | cve high detected in avandroid autoclosed cve high severity vulnerability vulnerable library avandroid library home page a href found in head commit a href found in base branch main vulnerable source files media mtp mtpserver cp... | 0 |
603,623 | 18,669,936,099 | IssuesEvent | 2021-10-30 14:12:11 | AY2122S1-CS2103T-T09-4/tp | https://api.github.com/repos/AY2122S1-CS2103T-T09-4/tp | closed | [PE-D] UG updating to match your app (2) | priority.High severity.High | 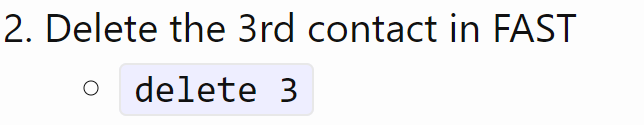
Again, you may want to change this to `del 3`
<!--session: 1635494405543-941eecba-97e4-468b-b880-fe6464b30d81-->
<!--Version: Web v3.4.1-->
-------------
Labels: `severity.VeryLow` `type.DocumentationBug`... | 1.0 | [PE-D] UG updating to match your app (2) - 
Again, you may want to change this to `del 3`
<!--session: 1635494405543-941eecba-97e4-468b-b880-fe6464b30d81-->
<!--Version: Web v3.4.1-->
-------------
Labels:... | priority | ug updating to match your app again you may want to change this to del labels severity verylow type documentationbug original pulpy y ped | 1 |
684,402 | 23,416,878,126 | IssuesEvent | 2022-08-13 04:34:31 | HaDuve/TravelCostNative | https://api.github.com/repos/HaDuve/TravelCostNative | closed | Add Trip Input Form | enhancement High Priority Frontend | - [x] new modal for the input fields
- [x] trip name
- [x] total budget
- [ ] invite other travellers
| 1.0 | Add Trip Input Form - - [x] new modal for the input fields
- [x] trip name
- [x] total budget
- [ ] invite other travellers
| priority | add trip input form new modal for the input fields trip name total budget invite other travellers | 1 |
425,341 | 12,339,051,995 | IssuesEvent | 2020-05-14 17:27:37 | mozilla/addons-server | https://api.github.com/repos/mozilla/addons-server | closed | prevent the `include_in_legacy` Block property from being set | priority: p4 state: pull request ready | The Block property `include_in_legacy` can be set/unset currently which doesn't make any sense when legacy blocklist submission is disabled (the default). Otherwise the Block doesn't actually get uploaded to the legacy blocklist. It should be read-only unless `blocklist_legacy_submit` is also enabled. | 1.0 | prevent the `include_in_legacy` Block property from being set - The Block property `include_in_legacy` can be set/unset currently which doesn't make any sense when legacy blocklist submission is disabled (the default). Otherwise the Block doesn't actually get uploaded to the legacy blocklist. It should be read-only... | priority | prevent the include in legacy block property from being set the block property include in legacy can be set unset currently which doesn t make any sense when legacy blocklist submission is disabled the default otherwise the block doesn t actually get uploaded to the legacy blocklist it should be read only... | 1 |
544,250 | 15,891,583,183 | IssuesEvent | 2021-04-10 19:50:59 | zeoflow/memo | https://api.github.com/repos/zeoflow/memo | closed | `@CompoundMethod` annotation | @feature @priority-medium | **Is your feature request related to a problem? Please describe.**
The `@CompoundMethod` annotation should be used for retrieving values based on different fields
###### We also happily accept [pull requests](https://github.com/zeoflow/memo/pulls).
| 1.0 | `@CompoundMethod` annotation - **Is your feature request related to a problem? Please describe.**
The `@CompoundMethod` annotation should be used for retrieving values based on different fields
###### We also happily accept [pull requests](https://github.com/zeoflow/memo/pulls).
| priority | compoundmethod annotation is your feature request related to a problem please describe the compoundmethod annotation should be used for retrieving values based on different fields we also happily accept | 1 |
593,527 | 18,010,506,320 | IssuesEvent | 2021-09-16 08:03:18 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | When the type is inferred via `var` and the inferred type is from an un-imported module shell emit `Unknown Type 'XXX`` error | Type/Bug Priority/Blocker Team/CompilerFETools Points/2 Area/Shell | **Description:**
```shell
=$ var t = int.typeIds() took 0 ms
=$ t took 530 ms
| error: unknown type 'TypeI... | 1.0 | When the type is inferred via `var` and the inferred type is from an un-imported module shell emit `Unknown Type 'XXX`` error - **Description:**
```shell
=$ var t = int.typeIds() took 0 ms
=$ t ... | priority | when the type is inferred via var and the inferred type is from an un imported module shell emit unknown type xxx error description shell var t int typeids took ms t ... | 1 |
68,858 | 8,357,316,509 | IssuesEvent | 2018-10-02 21:10:24 | ManageIQ/manageiq-v2v | https://api.github.com/repos/ManageIQ/manageiq-v2v | opened | Show the Mapping type in the Infrastructure Mappings list view | enhancement needs-design v1.1 | We should show the mapping type in the list view now that we have multiple types (RHV and OpenStack). Question is where to put it? | 1.0 | Show the Mapping type in the Infrastructure Mappings list view - We should show the mapping type in the list view now that we have multiple types (RHV and OpenStack). Question is where to put it? | non_priority | show the mapping type in the infrastructure mappings list view we should show the mapping type in the list view now that we have multiple types rhv and openstack question is where to put it | 0 |
51,158 | 6,496,708,279 | IssuesEvent | 2017-08-22 11:11:53 | tarantool/doc | https://api.github.com/repos/tarantool/doc | closed | Inconsistent version switcher at doc main | design LT | after PR merge https://github.com/tarantool/doc/pull/216: at the doc main page, a horizontal version switcher at the top is present in 1.7/1.8 and missing in 1.6 (it duplicates the "Manual for other versions" list from the left menu, so the horizontal switcher should be removed from the doc **main page** in all version... | 1.0 | Inconsistent version switcher at doc main - after PR merge https://github.com/tarantool/doc/pull/216: at the doc main page, a horizontal version switcher at the top is present in 1.7/1.8 and missing in 1.6 (it duplicates the "Manual for other versions" list from the left menu, so the horizontal switcher should be remov... | non_priority | inconsistent version switcher at doc main after pr merge at the doc main page a horizontal version switcher at the top is present in and missing in it duplicates the manual for other versions list from the left menu so the horizontal switcher should be removed from the doc main page in all vers... | 0 |
70,738 | 15,105,644,432 | IssuesEvent | 2021-02-08 13:19:45 | rammatzkvosky/epsagon-java | https://api.github.com/repos/rammatzkvosky/epsagon-java | opened | CVE-2020-36182 (High) detected in jackson-databind-2.9.10.5.jar | security vulnerability | ## CVE-2020-36182 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core strea... | True | CVE-2020-36182 (High) detected in jackson-databind-2.9.10.5.jar - ## CVE-2020-36182 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.5.jar</b></p></summary>
<p>G... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file epsagon java epsagon pom xm... | 0 |
5,636 | 2,957,571,778 | IssuesEvent | 2015-07-08 16:59:57 | GoogleCloudPlatform/kubernetes | https://api.github.com/repos/GoogleCloudPlatform/kubernetes | closed | `kubectl describe` docs: explain what happens if the object doesn't exist | component/CLI kind/documentation priority/P2 team/friction team/UX | In kube-apiserver.INFO, I see a failed API call being attempted roughly every second:
```
kube-apiserver.INFO:I0624 15:26:22.970228 3508 handlers.go:135] GET /api/v1/namespaces/ns-mything/pods/mything: (1.662407ms) 404 [[kubectl/v0.19.3 (linux/amd64) kubernetes/3103c8c] 10.0.0.2:45055]
kube-apiserver.INFO:I0624... | 1.0 | `kubectl describe` docs: explain what happens if the object doesn't exist - In kube-apiserver.INFO, I see a failed API call being attempted roughly every second:
```
kube-apiserver.INFO:I0624 15:26:22.970228 3508 handlers.go:135] GET /api/v1/namespaces/ns-mything/pods/mything: (1.662407ms) 404 [[kubectl/v0.19.3 ... | non_priority | kubectl describe docs explain what happens if the object doesn t exist in kube apiserver info i see a failed api call being attempted roughly every second kube apiserver info handlers go get api namespaces ns mything pods mything kube apiserver info ... | 0 |
143,474 | 5,517,705,042 | IssuesEvent | 2017-03-18 01:04:03 | prologinsandbox/site-issues | https://api.github.com/repos/prologinsandbox/site-issues | closed | Nombre de problèmes résolus incorrect | priority:minor state:resolved type:bug | > ###### Originally posted 2015-10-31 11:55 by *some anonymous* on Bitbucket
Au questionnaire de sélection 2016, j'ai résolu entièrement 4 problèmes, et j'ai fait plusieurs tentatives ratées sur le dernier. Pourtant, sur la page d'accueil, il est affiché "5/5 problèmes résolus". | 1.0 | Nombre de problèmes résolus incorrect - > ###### Originally posted 2015-10-31 11:55 by *some anonymous* on Bitbucket
Au questionnaire de sélection 2016, j'ai résolu entièrement 4 problèmes, et j'ai fait plusieurs tentatives ratées sur le dernier. Pourtant, sur la page d'accueil, il est affiché "5/5 problèmes résolus". | priority | nombre de problèmes résolus incorrect originally posted by some anonymous on bitbucket au questionnaire de sélection j ai résolu entièrement problèmes et j ai fait plusieurs tentatives ratées sur le dernier pourtant sur la page d accueil il est affiché problèmes résolus | 1 |
487,326 | 14,040,502,624 | IssuesEvent | 2020-11-01 03:00:53 | codidact/qpixel | https://api.github.com/repos/codidact/qpixel | opened | Tools button isn't clickable for some users (Chrome) | area: frontend complexity: unassessed priority: medium type: bug | https://meta.codidact.com/questions/278096
The reporting user has enough reputation to use one of the tools (Change Category), but clicking on the button doesn't do anything. The question reports:
Chrome for Windows (Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/85.0.418... | 1.0 | Tools button isn't clickable for some users (Chrome) - https://meta.codidact.com/questions/278096
The reporting user has enough reputation to use one of the tools (Change Category), but clicking on the button doesn't do anything. The question reports:
Chrome for Windows (Mozilla/5.0 (Windows NT 10.0; Win64; x64)... | priority | tools button isn t clickable for some users chrome the reporting user has enough reputation to use one of the tools change category but clicking on the button doesn t do anything the question reports chrome for windows mozilla windows nt applewebkit khtml like gecko chrome ... | 1 |
105,069 | 16,624,021,386 | IssuesEvent | 2021-06-03 07:17:53 | Thanraj/OpenSSL_1.0.1_stable | https://api.github.com/repos/Thanraj/OpenSSL_1.0.1_stable | opened | CVE-2008-5077 (Medium) detected in opensslOpenSSL_1_0_1u | security vulnerability | ## CVE-2008-5077 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1u</b></p></summary>
<p>
<p>Android (AOSP) build for libcrypto and libssl on branch VidityOpenSSL<... | True | CVE-2008-5077 (Medium) detected in opensslOpenSSL_1_0_1u - ## CVE-2008-5077 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>opensslOpenSSL_1_0_1u</b></p></summary>
<p>
<p>Android (AO... | non_priority | cve medium detected in opensslopenssl cve medium severity vulnerability vulnerable library opensslopenssl android aosp build for libcrypto and libssl on branch vidityopenssl library home page a href found in head commit a href found in base branch master ... | 0 |
765,095 | 26,833,056,972 | IssuesEvent | 2023-02-02 17:18:50 | vortexntnu/pca9685-interface | https://api.github.com/repos/vortexntnu/pca9685-interface | closed | Limit ESC Driver code to run thrusters at 70% | enhancement High Priority | Max thrust must be set to 70%. More than that and we risk draining to much current from the batteries X-X
- Set Max backwards thrust PWM: 1220
- Set Max forward thrust PWM: 1780
Set max thrust on ESC Hardware with the specific software it uses
- Set Max backwards thrust PWM: 1220
- Set Max forward thrust PWM: 1780 | 1.0 | Limit ESC Driver code to run thrusters at 70% - Max thrust must be set to 70%. More than that and we risk draining to much current from the batteries X-X
- Set Max backwards thrust PWM: 1220
- Set Max forward thrust PWM: 1780
Set max thrust on ESC Hardware with the specific software it uses
- Set Max backwards thrust ... | priority | limit esc driver code to run thrusters at max thrust must be set to more than that and we risk draining to much current from the batteries x x set max backwards thrust pwm set max forward thrust pwm set max thrust on esc hardware with the specific software it uses set max backwards thrust pwm ... | 1 |
233,092 | 7,693,577,662 | IssuesEvent | 2018-05-18 04:38:28 | ElektraInitiative/libelektra | https://api.github.com/repos/ElektraInitiative/libelektra | opened | doc: changes to icheck script | low priority | Forgot to add section to doc/news/_preparation_next_release.md mentioning that the icheck script now no longer leaves the base directory. | 1.0 | doc: changes to icheck script - Forgot to add section to doc/news/_preparation_next_release.md mentioning that the icheck script now no longer leaves the base directory. | priority | doc changes to icheck script forgot to add section to doc news preparation next release md mentioning that the icheck script now no longer leaves the base directory | 1 |
162,765 | 6,167,977,210 | IssuesEvent | 2017-06-30 00:53:57 | afranka70/AbOutIssues | https://api.github.com/repos/afranka70/AbOutIssues | closed | Add "Administrator" designation to Users | AbOutPE Administrator New Feature Priority2 Users | # AbOut Version
DevPEv0.2
# Description
The current User list does not show the user role:

In DevPEv0.3 with the AbOutPE1 database, a few users can take the role of administrator. The only other rol... | 1.0 | Add "Administrator" designation to Users - # AbOut Version
DevPEv0.2
# Description
The current User list does not show the user role:

In DevPEv0.3 with the AbOutPE1 database, a few users can take the... | priority | add administrator designation to users about version description the current user list does not show the user role in with the database a few users can take the role of administrator the only other role is instructor since the instructors may need to contact an administrator this ... | 1 |
18,800 | 13,237,323,439 | IssuesEvent | 2020-08-18 21:26:27 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Strings are not automatically converted to StringNames | bug topic:gdscript usability | <!-- Please search existing issues for potential duplicates before filing yours:
https://github.com/godotengine/godot/issues?q=is%3Aissue
-->
**Godot version:**
<!-- Specify commit hash if using non-official build. -->
08d3d06
**Issue description:**
<!-- What happened, and what was expected. -->
This does... | True | Strings are not automatically converted to StringNames - <!-- Please search existing issues for potential duplicates before filing yours:
https://github.com/godotengine/godot/issues?q=is%3Aissue
-->
**Godot version:**
<!-- Specify commit hash if using non-official build. -->
08d3d06
**Issue description:**
... | non_priority | strings are not automatically converted to stringnames please search existing issues for potential duplicates before filing yours godot version issue description this doesn t work connect body entered callable self entered you need to use stringname expli... | 0 |
403,022 | 27,398,204,158 | IssuesEvent | 2023-02-28 21:34:51 | o3de/o3de.org | https://api.github.com/repos/o3de/o3de.org | closed | Multiplayer Template | feature/networking kind/documentation priority/major sig/network triage/accepted | ## Describe the issue briefly
The Multiplayer Template should be mentioned somewhere in documentation for users trying to set up multiplayer
## Which page(s) / section(s) are affected?
Please add a link for how to use the Multiplayer Template here so new users dont fall into a rabbit hole of having to edit cmake f... | 1.0 | Multiplayer Template - ## Describe the issue briefly
The Multiplayer Template should be mentioned somewhere in documentation for users trying to set up multiplayer
## Which page(s) / section(s) are affected?
Please add a link for how to use the Multiplayer Template here so new users dont fall into a rabbit hole of... | non_priority | multiplayer template describe the issue briefly the multiplayer template should be mentioned somewhere in documentation for users trying to set up multiplayer which page s section s are affected please add a link for how to use the multiplayer template here so new users dont fall into a rabbit hole of... | 0 |
71,141 | 15,183,284,824 | IssuesEvent | 2021-02-15 07:53:32 | devikab2b/mavenwitthwhitesource | https://api.github.com/repos/devikab2b/mavenwitthwhitesource | opened | CVE-2020-8908 (Low) detected in guava-11.0.2.jar | security vulnerability | ## CVE-2020-8908 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guava-11.0.2.jar</b></p></summary>
<p>Guava is a suite of core and expanded libraries that include
utility classes, ... | True | CVE-2020-8908 (Low) detected in guava-11.0.2.jar - ## CVE-2020-8908 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guava-11.0.2.jar</b></p></summary>
<p>Guava is a suite of core and ex... | non_priority | cve low detected in guava jar cve low severity vulnerability vulnerable library guava jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more this project is a complete packaging of all ... | 0 |
34,665 | 12,294,678,297 | IssuesEvent | 2020-05-11 01:06:14 | LevyForchh/ant-design-pro | https://api.github.com/repos/LevyForchh/ant-design-pro | opened | WS-2020-0068 (High) detected in yargs-parser-16.1.0.tgz, yargs-parser-10.1.0.tgz | security vulnerability | ## WS-2020-0068 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-16.1.0.tgz</b>, <b>yargs-parser-10.1.0.tgz</b></p></summary>
<p>
<details><summary><b>yargs-parser-16.1.0... | True | WS-2020-0068 (High) detected in yargs-parser-16.1.0.tgz, yargs-parser-10.1.0.tgz - ## WS-2020-0068 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>yargs-parser-16.1.0.tgz</b>, <b>yarg... | non_priority | ws high detected in yargs parser tgz yargs parser tgz ws high severity vulnerability vulnerable libraries yargs parser tgz yargs parser tgz yargs parser tgz the mighty option parser used by yargs library home page a href path to dependency ... | 0 |
132,578 | 5,188,817,102 | IssuesEvent | 2017-01-20 21:09:37 | DSheirer/sdrtrunk | https://api.github.com/repos/DSheirer/sdrtrunk | opened | Add capability to blacklist Tuners by serial number | enhancement Priority-Medium | Add capability for user to select a tuner and designate it as 'blacklisted', meaning that the tuner should not be used by the application.
Since this can only be done if/when the application is aware of the tuner, add the capability to the 'Tuners' pane and indicate to the user that they must restart the application... | 1.0 | Add capability to blacklist Tuners by serial number - Add capability for user to select a tuner and designate it as 'blacklisted', meaning that the tuner should not be used by the application.
Since this can only be done if/when the application is aware of the tuner, add the capability to the 'Tuners' pane and indic... | priority | add capability to blacklist tuners by serial number add capability for user to select a tuner and designate it as blacklisted meaning that the tuner should not be used by the application since this can only be done if when the application is aware of the tuner add the capability to the tuners pane and indic... | 1 |
744,867 | 25,958,769,527 | IssuesEvent | 2022-12-18 15:51:19 | CosmosOS/Cosmos | https://api.github.com/repos/CosmosOS/Cosmos | closed | Deleting file and directory not working | Bug Up for Grabs Complexity: Medium Priority: Low Area: File System | #### Area of Cosmos - What area of Cosmos are we dealing with?
File system
#### Expected Behaviour - What do you think that should happen?
I should be able to delete files and directories when I want.
#### Actual Behaviour - What unexpectedly happens?
I can only delete files and directories after I created the... | 1.0 | Deleting file and directory not working - #### Area of Cosmos - What area of Cosmos are we dealing with?
File system
#### Expected Behaviour - What do you think that should happen?
I should be able to delete files and directories when I want.
#### Actual Behaviour - What unexpectedly happens?
I can only delete... | priority | deleting file and directory not working area of cosmos what area of cosmos are we dealing with file system expected behaviour what do you think that should happen i should be able to delete files and directories when i want actual behaviour what unexpectedly happens i can only delete... | 1 |
20,901 | 10,559,069,657 | IssuesEvent | 2019-10-04 10:36:13 | ChetanSankhala/LoadGenerator | https://api.github.com/repos/ChetanSankhala/LoadGenerator | opened | CVE-2019-14439 (High) detected in jackson-databind-2.9.8.jar | security vulnerability | ## CVE-2019-14439 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streamin... | True | CVE-2019-14439 (High) detected in jackson-databind-2.9.8.jar - ## CVE-2019-14439 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library root gradle caches modules... | 0 |
500,233 | 14,493,909,364 | IssuesEvent | 2020-12-11 09:09:11 | renovatebot/renovate | https://api.github.com/repos/renovatebot/renovate | closed | Support limiting concurrent requests per host | priority-3-normal type:feature | **What would you like Renovate to be able to do?**
Provide a configurable way and sensible defaults for concurrent limits per host.
**Describe the solution you'd like**
Implement it in the util/http logic. Mostly it should just work, but users can tweak it using hostRules.
**Describe alternatives you've co... | 1.0 | Support limiting concurrent requests per host - **What would you like Renovate to be able to do?**
Provide a configurable way and sensible defaults for concurrent limits per host.
**Describe the solution you'd like**
Implement it in the util/http logic. Mostly it should just work, but users can tweak it using ... | priority | support limiting concurrent requests per host what would you like renovate to be able to do provide a configurable way and sensible defaults for concurrent limits per host describe the solution you d like implement it in the util http logic mostly it should just work but users can tweak it using ... | 1 |
830,644 | 32,019,769,063 | IssuesEvent | 2023-09-22 02:47:08 | UNopenGIS/7 | https://api.github.com/repos/UNopenGIS/7 | closed | Project Airbase: プロジェクトアイディア | help wanted priority/SHOULD | #214 直前の今考えるべきことではないかも知れませんが、 #221 での議論を踏まえ、 #205 Kalaja Architecture を踏まえて、Raspberry Pi 群をリモートに配置する形で研修環境を提供するというアイディアについて少し練ってみました。後で考えるためにおいておきます。
## 情報: Kalaja アーキテクチャ

## 基本的アイディア
- Raspberry Pi をリモート化した場合、問題となるのはアカウン... | 1.0 | Project Airbase: プロジェクトアイディア - #214 直前の今考えるべきことではないかも知れませんが、 #221 での議論を踏まえ、 #205 Kalaja Architecture を踏まえて、Raspberry Pi 群をリモートに配置する形で研修環境を提供するというアイディアについて少し練ってみました。後で考えるためにおいておきます。
## 情報: Kalaja アーキテクチャ

## 基本的アイディア
- Rasp... | priority | project airbase プロジェクトアイディア 直前の今考えるべきことではないかも知れませんが、 での議論を踏まえ、 kalaja architecture を踏まえて、raspberry pi 群をリモートに配置する形で研修環境を提供するというアイディアについて少し練ってみました。後で考えるためにおいておきます。 情報 kalaja アーキテクチャ 基本的アイディア raspberry pi をリモート化した場合、問題となるのはアカウントの配布方法であろう。 とりあえず、 sshキーベースのログイン を求めるのが枯れていて順当であろう。 ... | 1 |
144,473 | 5,540,865,262 | IssuesEvent | 2017-03-22 11:14:26 | bedita/bedita | https://api.github.com/repos/bedita/bedita | closed | Patching an entity with `date_ranges` adds new ranges instead of replacing | Priority - High Topic - API Type - Bug | When issuing a `PATCH` request on a BEdita object that already had one or more `date_ranges`, the ranges passed in the request are added to the list of object's ranges, instead of replacing existent ones. | 1.0 | Patching an entity with `date_ranges` adds new ranges instead of replacing - When issuing a `PATCH` request on a BEdita object that already had one or more `date_ranges`, the ranges passed in the request are added to the list of object's ranges, instead of replacing existent ones. | priority | patching an entity with date ranges adds new ranges instead of replacing when issuing a patch request on a bedita object that already had one or more date ranges the ranges passed in the request are added to the list of object s ranges instead of replacing existent ones | 1 |
626,133 | 19,785,976,500 | IssuesEvent | 2022-01-18 06:47:32 | Valdes-Tresanco-MS/gmx_MMPBSA | https://api.github.com/repos/Valdes-Tresanco-MS/gmx_MMPBSA | closed | Improve gmx_MMPBSA_test | low priority improvement | - [ ] Add a flag to overwrite or not the folder where the repository with the examples was cloned.
It would be something like `gmx_MMPBSA_test` [`-nr` / `-noreuse`] (Default = True)
`-nr` will store a 'store_false' action
- [ ] Add a flag to delete the test folder once finished
- [x] Add the use of MPI fo... | 1.0 | Improve gmx_MMPBSA_test - - [ ] Add a flag to overwrite or not the folder where the repository with the examples was cloned.
It would be something like `gmx_MMPBSA_test` [`-nr` / `-noreuse`] (Default = True)
`-nr` will store a 'store_false' action
- [ ] Add a flag to delete the test folder once finished
-... | priority | improve gmx mmpbsa test add a flag to overwrite or not the folder where the repository with the examples was cloned it would be something like gmx mmpbsa test default true nr will store a store false action add a flag to delete the test folder once finished add the use of mpi f... | 1 |
55,361 | 14,403,623,168 | IssuesEvent | 2020-12-03 16:16:46 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | closed | Wrong SQL generated when DomainDataType is loaded before base SQLDataType for SQLDialect.DEFAULT | C: Functionality E: All Editions P: Medium T: Defect | I'm not sure how easy it is to reproduce this, but a recent change in the integration tests lead to the situation where a PostgreSQL domain type that is based on JSONB from #10309 for this table:
```sql
create domain u_10309 as jsonb;
create table t_10309 (
id int,
c1 jsonb,
c2 u_10309,
c3 jsonb[],
... | 1.0 | Wrong SQL generated when DomainDataType is loaded before base SQLDataType for SQLDialect.DEFAULT - I'm not sure how easy it is to reproduce this, but a recent change in the integration tests lead to the situation where a PostgreSQL domain type that is based on JSONB from #10309 for this table:
```sql
create domain ... | non_priority | wrong sql generated when domaindatatype is loaded before base sqldatatype for sqldialect default i m not sure how easy it is to reproduce this but a recent change in the integration tests lead to the situation where a postgresql domain type that is based on jsonb from for this table sql create domain u ... | 0 |
98,243 | 4,019,086,349 | IssuesEvent | 2016-05-16 13:43:30 | BugBusterSWE/MaaS | https://api.github.com/repos/BugBusterSWE/MaaS | closed | DatabaseModel.ts | backend priority:medium Programmer | Activity #2
Scrivere il modulo DatabaseModel.ts.
Vedere la documentazione nella ST per i dettagli
Link task: [https://bugbusters.teamwork.com/tasks/6538118](https://bugbusters.teamwork.com/tasks/6538118) | 1.0 | DatabaseModel.ts - Activity #2
Scrivere il modulo DatabaseModel.ts.
Vedere la documentazione nella ST per i dettagli
Link task: [https://bugbusters.teamwork.com/tasks/6538118](https://bugbusters.teamwork.com/tasks/6538118) | priority | databasemodel ts activity scrivere il modulo databasemodel ts vedere la documentazione nella st per i dettagli link task | 1 |
387,374 | 11,460,299,217 | IssuesEvent | 2020-02-07 09:27:36 | nhsconnect/gpconnect-demonstrator | https://api.github.com/repos/nhsconnect/gpconnect-demonstrator | closed | Add representative clinical data to the demonstrator | 1.2.3 Low Priority Structured | Placeholder note for now, while clinical data is produced by Pete and colleagues. | 1.0 | Add representative clinical data to the demonstrator - Placeholder note for now, while clinical data is produced by Pete and colleagues. | priority | add representative clinical data to the demonstrator placeholder note for now while clinical data is produced by pete and colleagues | 1 |
60,236 | 14,531,609,926 | IssuesEvent | 2020-12-14 21:03:42 | hydrogen-dev/SDK | https://api.github.com/repos/hydrogen-dev/SDK | opened | CVE-2020-13956 (Medium) detected in httpclient-4.5.2.jar | security vulnerability | ## CVE-2020-13956 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>httpclient-4.5.2.jar</b></p></summary>
<p>Apache HttpComponents Client</p>
<p>Path to dependency file: SDK/hydro/rai... | True | CVE-2020-13956 (Medium) detected in httpclient-4.5.2.jar - ## CVE-2020-13956 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>httpclient-4.5.2.jar</b></p></summary>
<p>Apache HttpComp... | non_priority | cve medium detected in httpclient jar cve medium severity vulnerability vulnerable library httpclient jar apache httpcomponents client path to dependency file sdk hydro raindrop java pom xml path to vulnerable library home wss scanner repository org apache httpcomponen... | 0 |
123,333 | 17,772,209,481 | IssuesEvent | 2021-08-30 14:51:25 | kapseliboi/bitmidi.com | https://api.github.com/repos/kapseliboi/bitmidi.com | opened | CVE-2021-23382 (Medium) detected in postcss-7.0.35.tgz, postcss-7.0.32.tgz | security vulnerability | ## CVE-2021-23382 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.35.tgz</b>, <b>postcss-7.0.32.tgz</b></p></summary>
<p>
<details><summary><b>postcss-7.0.35.tgz</b></p... | True | CVE-2021-23382 (Medium) detected in postcss-7.0.35.tgz, postcss-7.0.32.tgz - ## CVE-2021-23382 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>postcss-7.0.35.tgz</b>, <b>postcss-7.0... | non_priority | cve medium detected in postcss tgz postcss tgz cve medium severity vulnerability vulnerable libraries postcss tgz postcss tgz postcss tgz tool for transforming styles with js plugins library home page a href path to dependency file bitmidi... | 0 |
72,978 | 9,634,505,772 | IssuesEvent | 2019-05-15 21:26:11 | confluentinc/schema-registry | https://api.github.com/repos/confluentinc/schema-registry | closed | Update Documentation for MAGIC_BYTE=1 | documentation | Regarding: https://github.com/confluentinc/schema-registry/commit/28d5c02df4c355281ddbafb7684a18f5cc14b49f, MAGIC_BYTE was updated to include `1` as well as `0`. cc @mageshn
[In documentation](https://github.com/confluentinc/schema-registry/blob/master/docs/serializer-formatter.rst#wire-format), this is no longer a... | 1.0 | Update Documentation for MAGIC_BYTE=1 - Regarding: https://github.com/confluentinc/schema-registry/commit/28d5c02df4c355281ddbafb7684a18f5cc14b49f, MAGIC_BYTE was updated to include `1` as well as `0`. cc @mageshn
[In documentation](https://github.com/confluentinc/schema-registry/blob/master/docs/serializer-formatt... | non_priority | update documentation for magic byte regarding magic byte was updated to include as well as cc mageshn this is no longer accurate confluent serialization format version number currently always should it be documented when or is used | 0 |
466,269 | 13,399,112,834 | IssuesEvent | 2020-09-03 14:04:08 | googleapis/python-securitycenter | https://api.github.com/repos/googleapis/python-securitycenter | closed | Synthesis failed for python-securitycenter | api: securitycenter autosynth failure priority: p1 type: bug | Hello! Autosynth couldn't regenerate python-securitycenter. :broken_heart:
Here's the output from running `synth.py`:
```
ages/30/9e/f663a2aa66a09d838042ae1a2c5659828bb9b41ea3a6efa20a20fd92b121/Jinja2-2.11.2-py2.py3-none-any.whl
Saved ./Jinja2-2.11.2-py2.py3-none-any.whl
Collecting MarkupSafe==1.1.1 (from -r /home/... | 1.0 | Synthesis failed for python-securitycenter - Hello! Autosynth couldn't regenerate python-securitycenter. :broken_heart:
Here's the output from running `synth.py`:
```
ages/30/9e/f663a2aa66a09d838042ae1a2c5659828bb9b41ea3a6efa20a20fd92b121/Jinja2-2.11.2-py2.py3-none-any.whl
Saved ./Jinja2-2.11.2-py2.py3-none-any.whl... | priority | synthesis failed for python securitycenter hello autosynth couldn t regenerate python securitycenter broken heart here s the output from running synth py ages none any whl saved none any whl collecting markupsafe from r home kbuilder cache bazel bazel kbuilde... | 1 |
341,408 | 10,295,395,113 | IssuesEvent | 2019-08-27 22:06:19 | metabase/metabase | https://api.github.com/repos/metabase/metabase | opened | Unbinned geo mapping broken | Priority:P2 Type:Bug Visualization/ | Sample dataset; Orders grouped by Users/long, Users/lat, both unbinned:
Problem 1:
The default map is grid which errors out on un-binned coordinates
Problem 2:
If I manually choose pin map, nothing gets mapped, while pin map works for binned coordinates. | 1.0 | Unbinned geo mapping broken - Sample dataset; Orders grouped by Users/long, Users/lat, both unbinned:
Problem 1:
The default map is grid which errors out on un-binned coordinates
Problem 2:
If I manually choose pin map, nothing gets mapped, while pin map works for binned coordinates. | priority | unbinned geo mapping broken sample dataset orders grouped by users long users lat both unbinned problem the default map is grid which errors out on un binned coordinates problem if i manually choose pin map nothing gets mapped while pin map works for binned coordinates | 1 |
745,785 | 26,000,667,625 | IssuesEvent | 2022-12-20 15:05:28 | o3de/o3de | https://api.github.com/repos/o3de/o3de | closed | [Terrain] Painting on a tiny texture doesn't allow for per-pixel painting. | kind/bug sig/content triage/accepted priority/minor feature/terrain | **Describe the bug**
When a tiny texture is mapped to a large world space, and the paintbrush is the size of a pixel, painting doesn't let you paint anything.
**Steps to reproduce**
Steps to reproduce the behavior:
1. Create a new level.
2. Add a Terrain World and a Terrain World Renderer component.
3. Create a... | 1.0 | [Terrain] Painting on a tiny texture doesn't allow for per-pixel painting. - **Describe the bug**
When a tiny texture is mapped to a large world space, and the paintbrush is the size of a pixel, painting doesn't let you paint anything.
**Steps to reproduce**
Steps to reproduce the behavior:
1. Create a new level.... | priority | painting on a tiny texture doesn t allow for per pixel painting describe the bug when a tiny texture is mapped to a large world space and the paintbrush is the size of a pixel painting doesn t let you paint anything steps to reproduce steps to reproduce the behavior create a new level add... | 1 |
63,244 | 3,194,335,609 | IssuesEvent | 2015-09-30 11:32:24 | fusioninventory/fusioninventory-for-glpi | https://api.github.com/repos/fusioninventory/fusioninventory-for-glpi | closed | SNMP: Allow deletion of OIDs | Category: SNMP Component: For junior contributor Component: Found in version Priority: Normal Status: Closed Tracker: Bug | ---
Author Name: **Mat Simon** (@matsimon)
Original Redmine Issue: 1846, http://forge.fusioninventory.org/issues/1846
Original Date: 2012-10-08
Original Assignee: David Durieux
---
If one needs to add an additional OID for let's say firnware information, one sometimes needs to try and error. Please add removal opti... | 1.0 | SNMP: Allow deletion of OIDs - ---
Author Name: **Mat Simon** (@matsimon)
Original Redmine Issue: 1846, http://forge.fusioninventory.org/issues/1846
Original Date: 2012-10-08
Original Assignee: David Durieux
---
If one needs to add an additional OID for let's say firnware information, one sometimes needs to try and... | priority | snmp allow deletion of oids author name mat simon matsimon original redmine issue original date original assignee david durieux if one needs to add an additional oid for let s say firnware information one sometimes needs to try and error please add removal option example may have... | 1 |
351,419 | 10,518,291,263 | IssuesEvent | 2019-09-29 09:44:38 | pixelfed/pixelfed | https://api.github.com/repos/pixelfed/pixelfed | closed | [Masterpost] Missing functionality and related issues from the beta launch | 🚨 Priority: Critical | Figured it'd be good to maintain a list of things that are currently missing and would be expected to be implemented.
## Timeline/posts
Posts
- [x] ~Posting UI should be separated from timeline (#89, #86 #168, fixed #349 )~
- [x] ~Post without a caption (#110)~
- [x] ~Show caption limit before posting (#121, fix... | 1.0 | [Masterpost] Missing functionality and related issues from the beta launch - Figured it'd be good to maintain a list of things that are currently missing and would be expected to be implemented.
## Timeline/posts
Posts
- [x] ~Posting UI should be separated from timeline (#89, #86 #168, fixed #349 )~
- [x] ~Post w... | priority | missing functionality and related issues from the beta launch figured it d be good to maintain a list of things that are currently missing and would be expected to be implemented timeline posts posts posting ui should be separated from timeline fixed post without a caption ... | 1 |
264,547 | 8,316,517,518 | IssuesEvent | 2018-09-25 09:16:24 | telerik/kendo-ui-core | https://api.github.com/repos/telerik/kendo-ui-core | closed | Command with template throws an error when command.visible handler is added | Bug C: Grid Kendo1 Priority 1 SEV: Low | ### Reproduction of the problem
1. Run [this dojo](https://dojo.telerik.com/OHeXajOF)
1. Error occurs and the content of the grid does not render
### Environment
* **Kendo UI version:** 2018.3.911
| 1.0 | Command with template throws an error when command.visible handler is added - ### Reproduction of the problem
1. Run [this dojo](https://dojo.telerik.com/OHeXajOF)
1. Error occurs and the content of the grid does not render
### Environment
* **Kendo UI version:** 2018.3.911
| priority | command with template throws an error when command visible handler is added reproduction of the problem run error occurs and the content of the grid does not render environment kendo ui version | 1 |
152,821 | 19,697,598,591 | IssuesEvent | 2022-01-12 13:45:14 | RG4421/mmRTLS | https://api.github.com/repos/RG4421/mmRTLS | closed | CVE-2021-35065 (Medium) detected in glob-parent-2.0.0.tgz, glob-parent-5.1.2.tgz - autoclosed | security vulnerability | ## CVE-2021-35065 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-2.0.0.tgz</b>, <b>glob-parent-5.1.2.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-2.0.0.t... | True | CVE-2021-35065 (Medium) detected in glob-parent-2.0.0.tgz, glob-parent-5.1.2.tgz - autoclosed - ## CVE-2021-35065 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-2.0.0.t... | non_priority | cve medium detected in glob parent tgz glob parent tgz autoclosed cve medium severity vulnerability vulnerable libraries glob parent tgz glob parent tgz glob parent tgz strips glob magic from a string to provide the parent path library home pag... | 0 |
195,012 | 6,901,654,760 | IssuesEvent | 2017-11-25 10:39:10 | gabrielkrell/strain-rig | https://api.github.com/repos/gabrielkrell/strain-rig | closed | Use interrupts to move motor | Priority: High Status: Completed Type: Enhancement | For best results, the motor should get a tick about every 110µs. Printing everything to serial takes way longer than that, so we should use interrupts to make sure it always happens. | 1.0 | Use interrupts to move motor - For best results, the motor should get a tick about every 110µs. Printing everything to serial takes way longer than that, so we should use interrupts to make sure it always happens. | priority | use interrupts to move motor for best results the motor should get a tick about every printing everything to serial takes way longer than that so we should use interrupts to make sure it always happens | 1 |
387,575 | 26,727,321,463 | IssuesEvent | 2023-01-29 21:35:28 | aws/aws-cdk | https://api.github.com/repos/aws/aws-cdk | opened | aws_cdk.RemovalPolicy: Default is stated incorrectly as Destroy | needs-triage documentation | ### Describe the issue
**Destroy** is indicated as the default which is incorrect for AWS CDK as can be seen in:
- CDK Developer Guide
RemovalPolicy.RETAIN Keep the contents of the resource when destroying the stack (default). The resource is orphaned from the stack and must be deleted manually. If you attempt t... | 1.0 | aws_cdk.RemovalPolicy: Default is stated incorrectly as Destroy - ### Describe the issue
**Destroy** is indicated as the default which is incorrect for AWS CDK as can be seen in:
- CDK Developer Guide
RemovalPolicy.RETAIN Keep the contents of the resource when destroying the stack (default). The resource is orph... | non_priority | aws cdk removalpolicy default is stated incorrectly as destroy describe the issue destroy is indicated as the default which is incorrect for aws cdk as can be seen in cdk developer guide removalpolicy retain keep the contents of the resource when destroying the stack default the resource is orph... | 0 |
474,084 | 13,652,456,629 | IssuesEvent | 2020-09-27 07:37:51 | AY2021S1-CS2103T-T10-4/tp | https://api.github.com/repos/AY2021S1-CS2103T-T10-4/tp | closed | Delete classes | priority.High type.Story | As a tutor, I want to delete classes so that I can remove classes that I have stopped teaching. | 1.0 | Delete classes - As a tutor, I want to delete classes so that I can remove classes that I have stopped teaching. | priority | delete classes as a tutor i want to delete classes so that i can remove classes that i have stopped teaching | 1 |
319,178 | 9,739,657,954 | IssuesEvent | 2019-06-01 13:30:51 | Abnaxos/compose | https://api.github.com/repos/Abnaxos/compose | closed | Method not accessible: wrong error message | component: model priority: major type: bug | The error message for inaccessible methods is wrong: "Method not accessible to <inaccessible method>". The correct message should be something like "Method <inaccessible method> not accessible to <class>". | 1.0 | Method not accessible: wrong error message - The error message for inaccessible methods is wrong: "Method not accessible to <inaccessible method>". The correct message should be something like "Method <inaccessible method> not accessible to <class>". | priority | method not accessible wrong error message the error message for inaccessible methods is wrong method not accessible to the correct message should be something like method not accessible to | 1 |
55,272 | 3,072,617,101 | IssuesEvent | 2015-08-19 17:49:36 | RobotiumTech/robotium | https://api.github.com/repos/RobotiumTech/robotium | closed | Strange behaviours on big projects | bug imported Priority-Medium | _From [alex.gi...@gmail.com](https://code.google.com/u/106277910938818275510/) on April 18, 2012 03:18:02_
What steps will reproduce the problem? 1.Create test steps with one intent flagged ACTIVITY_CLEAR_TOP or other flags that Robotium conception does not take into account.
2.Call solo.finishOpenedActivities() What... | 1.0 | Strange behaviours on big projects - _From [alex.gi...@gmail.com](https://code.google.com/u/106277910938818275510/) on April 18, 2012 03:18:02_
What steps will reproduce the problem? 1.Create test steps with one intent flagged ACTIVITY_CLEAR_TOP or other flags that Robotium conception does not take into account.
2.Ca... | priority | strange behaviours on big projects from on april what steps will reproduce the problem create test steps with one intent flagged activity clear top or other flags that robotium conception does not take into account call solo finishopenedactivities what is the expected output what do you se... | 1 |
4,858 | 6,882,412,990 | IssuesEvent | 2017-11-21 03:48:20 | ZcashFoundation/GrantProposals-2017Q4 | https://api.github.com/repos/ZcashFoundation/GrantProposals-2017Q4 | reopened | ZEC <-> XLM Service | financial-interoperability online-service | # ZEC <-> XLM Service
## Motivation and overview
The overarching motivation is widespread adoption of cryptocurrencies and privacy-focused cryptocurrencies, to protect our civil liberties.
Stellar's built-in exchange and Anchor functionality has made it an ideal choice for remittance and money transfer in gene... | 1.0 | ZEC <-> XLM Service - # ZEC <-> XLM Service
## Motivation and overview
The overarching motivation is widespread adoption of cryptocurrencies and privacy-focused cryptocurrencies, to protect our civil liberties.
Stellar's built-in exchange and Anchor functionality has made it an ideal choice for remittance and ... | non_priority | zec xlm service zec xlm service motivation and overview the overarching motivation is widespread adoption of cryptocurrencies and privacy focused cryptocurrencies to protect our civil liberties stellar s built in exchange and anchor functionality has made it an ideal choice for remittance and mone... | 0 |
5,641 | 5,842,253,260 | IssuesEvent | 2017-05-10 05:06:25 | hzi-braunschweig/SORMAS-Open | https://api.github.com/repos/hzi-braunschweig/SORMAS-Open | closed | App Error Report Form [1] | Infrastructure sormas-app | - [x] user should be able to send manual error or problem information to the system
- [x] use a simple text field
- [x] should be possible from any view/activity | 1.0 | App Error Report Form [1] - - [x] user should be able to send manual error or problem information to the system
- [x] use a simple text field
- [x] should be possible from any view/activity | non_priority | app error report form user should be able to send manual error or problem information to the system use a simple text field should be possible from any view activity | 0 |
621,911 | 19,599,346,374 | IssuesEvent | 2022-01-05 22:18:01 | softmatterlab/Braph-2.0-Matlab | https://api.github.com/repos/softmatterlab/Braph-2.0-Matlab | opened | Minimize and Close Plot | low priority GUI | Write functions to minimize and close figures as in cb_bring_to_front():
- [ ] base functions cb_minimize() and cb_close() in Plot
- [ ] follow-up functions where needed (e.g., GUI, PlotElement, PPBrainAtlas_Surf, PPGroup_SUBDIct, ...)
- [ ] change callbacks for closing windows to these functions. | 1.0 | Minimize and Close Plot - Write functions to minimize and close figures as in cb_bring_to_front():
- [ ] base functions cb_minimize() and cb_close() in Plot
- [ ] follow-up functions where needed (e.g., GUI, PlotElement, PPBrainAtlas_Surf, PPGroup_SUBDIct, ...)
- [ ] change callbacks for closing windows to these fun... | priority | minimize and close plot write functions to minimize and close figures as in cb bring to front base functions cb minimize and cb close in plot follow up functions where needed e g gui plotelement ppbrainatlas surf ppgroup subdict change callbacks for closing windows to these functions... | 1 |
57,024 | 3,081,231,394 | IssuesEvent | 2015-08-22 14:19:05 | bitfighter/bitfighter | https://api.github.com/repos/bitfighter/bitfighter | closed | Add self-healing turrets/ffps to help | 019 bug imported Priority-Medium | _From [watusim...@bitfighter.org](https://code.google.com/u/105427273526970468779/) on October 19, 2013 18:13:35_
Add self-healing turret and ffp to help. Probably alternate between regular and self-healing rather than use new slots. Text should alternate as well to explain the different images. Graphics should alt... | 1.0 | Add self-healing turrets/ffps to help - _From [watusim...@bitfighter.org](https://code.google.com/u/105427273526970468779/) on October 19, 2013 18:13:35_
Add self-healing turret and ffp to help. Probably alternate between regular and self-healing rather than use new slots. Text should alternate as well to explain th... | priority | add self healing turrets ffps to help from on october add self healing turret and ffp to help probably alternate between regular and self healing rather than use new slots text should alternate as well to explain the different images graphics should alternate on their own rhythm and not be syn... | 1 |
100,310 | 30,670,502,847 | IssuesEvent | 2023-07-25 21:59:06 | actonlang/acton | https://api.github.com/repos/actonlang/acton | closed | Fix makefile deps on lib_deps/libActonDeps.. | bug build system | lib_deps/libActonDeps actually requires deps/*.o but doesn't declare a dependency on it | 1.0 | Fix makefile deps on lib_deps/libActonDeps.. - lib_deps/libActonDeps actually requires deps/*.o but doesn't declare a dependency on it | non_priority | fix makefile deps on lib deps libactondeps lib deps libactondeps actually requires deps o but doesn t declare a dependency on it | 0 |
12,536 | 14,857,702,816 | IssuesEvent | 2021-01-18 15:46:37 | Cyberark-workato-dev/conjur-authn-k8s-client | https://api.github.com/repos/Cyberark-workato-dev/conjur-authn-k8s-client | opened | new bug from JIRA 00 | Bugtype/Compatibility ONYX-6432 Severity/Low | ##description
Steps to reproduce:
Current Results:
Expected Results:
Error Messages:
Logs:
Other Symptoms:
Tenant ID / Pod Number:
##Found in version
11.4
##Workaround Complexity
There's an easy workaround
##Workaround Description
asd
##Link to JIRA bug
https://ca-il-jira-test.il.cyber-ark.com/bro... | True | new bug from JIRA 00 - ##description
Steps to reproduce:
Current Results:
Expected Results:
Error Messages:
Logs:
Other Symptoms:
Tenant ID / Pod Number:
##Found in version
11.4
##Workaround Complexity
There's an easy workaround
##Workaround Description
asd
##Link to JIRA bug
https://ca-il-jira-te... | non_priority | new bug from jira description steps to reproduce current results expected results error messages logs other symptoms tenant id pod number found in version workaround complexity there s an easy workaround workaround description asd link to jira bug | 0 |
396,180 | 11,704,955,991 | IssuesEvent | 2020-03-07 12:58:49 | eJourn-al/eJournal | https://api.github.com/repos/eJourn-al/eJournal | closed | Files can sometimes get stored with the wrong filename | Priority: Critical Status: Available Type: Bug Workload: Medium | **Describe the bug**
Files get stored with the wrong filename. When using sites like webp.net to resize the image, the filename sometimes does not get changed propperly. This causes our system to store them wrongly.
**To Reproduce**
Steps to reproduce the behavior:
1. Resize on image on webp.net
2. Upload it (wi... | 1.0 | Files can sometimes get stored with the wrong filename - **Describe the bug**
Files get stored with the wrong filename. When using sites like webp.net to resize the image, the filename sometimes does not get changed propperly. This causes our system to store them wrongly.
**To Reproduce**
Steps to reproduce the be... | priority | files can sometimes get stored with the wrong filename describe the bug files get stored with the wrong filename when using sites like webp net to resize the image the filename sometimes does not get changed propperly this causes our system to store them wrongly to reproduce steps to reproduce the be... | 1 |
604,359 | 18,682,582,400 | IssuesEvent | 2021-11-01 08:15:11 | webcompat/web-bugs | https://api.github.com/repos/webcompat/web-bugs | closed | support.mozilla.org - video or audio doesn't play | priority-important browser-fenix engine-gecko | <!-- @browser: Firefox Mobile 94.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:94.0) Gecko/94.0 Firefox/94.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/91967 -->
<!-- @extra_labels: browser-fenix -->
**URL**: https://support.mozi... | 1.0 | support.mozilla.org - video or audio doesn't play - <!-- @browser: Firefox Mobile 94.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 10; Mobile; rv:94.0) Gecko/94.0 Firefox/94.0 -->
<!-- @reported_with: android-components-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/91967 -->
<!-- @extra_labe... | priority | support mozilla org video or audio doesn t play url browser version firefox mobile operating system android tested another browser yes chrome problem type video or audio doesn t play description there is no audio steps to reproduce firefox beta chrome beta... | 1 |
40,803 | 10,580,528,452 | IssuesEvent | 2019-10-08 07:01:18 | yodaos-project/ShadowNode | https://api.github.com/repos/yodaos-project/ShadowNode | opened | Best practice of building on macOS | build doc | We should document the best practice of building on macOS with dbus installed with brew.
As pkg-config could find dbus related stuff: https://github.com/yodaos-project/ShadowNode/blob/master/cmake/iotjs.cmake#L405-L407
It might be much more convenient to `brew install pkg-config` then build. | 1.0 | Best practice of building on macOS - We should document the best practice of building on macOS with dbus installed with brew.
As pkg-config could find dbus related stuff: https://github.com/yodaos-project/ShadowNode/blob/master/cmake/iotjs.cmake#L405-L407
It might be much more convenient to `brew install pkg-conf... | non_priority | best practice of building on macos we should document the best practice of building on macos with dbus installed with brew as pkg config could find dbus related stuff it might be much more convenient to brew install pkg config then build | 0 |
160,544 | 20,109,715,937 | IssuesEvent | 2022-02-07 14:03:31 | jgeraigery/herman-1 | https://api.github.com/repos/jgeraigery/herman-1 | opened | CVE-2020-36181 (High) detected in jackson-databind-2.6.7.3.jar | security vulnerability | ## CVE-2020-36181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.3.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core stream... | True | CVE-2020-36181 (High) detected in jackson-databind-2.6.7.3.jar - ## CVE-2020-36181 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.6.7.3.jar</b></p></summary>
<p>Gen... | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file pom xml path to vulnerab... | 0 |
282,428 | 24,474,846,527 | IssuesEvent | 2022-10-08 03:19:46 | lowRISC/opentitan | https://api.github.com/repos/lowRISC/opentitan | closed | [test-triage] chip_rv_dm_ndm_reset_req | Component:TestTriage | ### Hierarchy of regression failure
Chip Level
### Failure Description
UVM_ERROR @ 4213.817590 us: (sw_logger_if.sv:521) [rv_dm_ndm_reset_req_prog_sim_dv(sw/device/tests/sim_dv/rv_dm_ndm_reset_req.c:214)] CHECK-fail: reg[1]: obs:0x0 exp:0x44
### Steps to Reproduce
GH revision: [9c0b24ddb](https://github.com/l... | 1.0 | [test-triage] chip_rv_dm_ndm_reset_req - ### Hierarchy of regression failure
Chip Level
### Failure Description
UVM_ERROR @ 4213.817590 us: (sw_logger_if.sv:521) [rv_dm_ndm_reset_req_prog_sim_dv(sw/device/tests/sim_dv/rv_dm_ndm_reset_req.c:214)] CHECK-fail: reg[1]: obs:0x0 exp:0x44
### Steps to Reproduce
GH... | non_priority | chip rv dm ndm reset req hierarchy of regression failure chip level failure description uvm error us sw logger if sv check fail reg obs exp steps to reproduce gh revision util dvsim dvsim py hw top earlgrey dv chip sim cfg hjson i chip rv dm ndm reset req build s... | 0 |
179,980 | 30,335,880,013 | IssuesEvent | 2023-07-11 09:32:13 | audacity/audacity | https://api.github.com/repos/audacity/audacity | closed | [Design] Add new track and new types of tracks | Design / UX Task medium feature | Visual hint in the main UI for adding a new audio (or other types) tracks, and ability to specify what kind of track if other
| 1.0 | [Design] Add new track and new types of tracks - Visual hint in the main UI for adding a new audio (or other types) tracks, and ability to specify what kind of track if other
| non_priority | add new track and new types of tracks visual hint in the main ui for adding a new audio or other types tracks and ability to specify what kind of track if other | 0 |
12,029 | 18,783,349,365 | IssuesEvent | 2021-11-08 09:32:45 | The-GNTL-Project/Exchange | https://api.github.com/repos/The-GNTL-Project/Exchange | closed | Fees being charged on orders rather than transactions | bug go live requirement testing | Fees should be charged on the value of completed transactions at time of execution, not on the order value at the time the order is placed. Charging a full fee on a partially fulfilled order disincentivizes placing any order that risks not being completely filled, and imo will be highly off-putting to big money and sma... | 1.0 | Fees being charged on orders rather than transactions - Fees should be charged on the value of completed transactions at time of execution, not on the order value at the time the order is placed. Charging a full fee on a partially fulfilled order disincentivizes placing any order that risks not being completely filled,... | non_priority | fees being charged on orders rather than transactions fees should be charged on the value of completed transactions at time of execution not on the order value at the time the order is placed charging a full fee on a partially fulfilled order disincentivizes placing any order that risks not being completely filled ... | 0 |
115,154 | 11,866,531,082 | IssuesEvent | 2020-03-26 04:01:44 | WilliamChan4/SENG2021_TheFastGroup | https://api.github.com/repos/WilliamChan4/SENG2021_TheFastGroup | opened | Rename pipelines Staging and Production and Add Badges to GitHub | documentation enhancement | The pipelines should be renamed to staging and production and the badges for both the pipelines and deployments put on the README.md page. | 1.0 | Rename pipelines Staging and Production and Add Badges to GitHub - The pipelines should be renamed to staging and production and the badges for both the pipelines and deployments put on the README.md page. | non_priority | rename pipelines staging and production and add badges to github the pipelines should be renamed to staging and production and the badges for both the pipelines and deployments put on the readme md page | 0 |
747,105 | 26,073,625,321 | IssuesEvent | 2022-12-24 06:19:33 | CreeperMagnet/the-creepers-code | https://api.github.com/repos/CreeperMagnet/the-creepers-code | closed | Teapots can be duplicated by riding a boat into them | priority: high | This can be fixed by... I don't know. There's too many of these stupid boat bugs. I'll probably have to change its kill method from a teleport now. | 1.0 | Teapots can be duplicated by riding a boat into them - This can be fixed by... I don't know. There's too many of these stupid boat bugs. I'll probably have to change its kill method from a teleport now. | priority | teapots can be duplicated by riding a boat into them this can be fixed by i don t know there s too many of these stupid boat bugs i ll probably have to change its kill method from a teleport now | 1 |
271,581 | 8,485,379,223 | IssuesEvent | 2018-10-26 07:36:01 | swe-ms-boun/2018fall-swe574-g1 | https://api.github.com/repos/swe-ms-boun/2018fall-swe574-g1 | opened | Annotations page | module.annotation priority.low tier.ui type.feature | * Development of annotations page. Associated requirements:
* The system should allow registered users to view their annotations.
* The system should allow the registered users to go to the memories by using their annotations.
* Registered users should be able to view their all tags they use when annotating th... | 1.0 | Annotations page - * Development of annotations page. Associated requirements:
* The system should allow registered users to view their annotations.
* The system should allow the registered users to go to the memories by using their annotations.
* Registered users should be able to view their all tags they use... | priority | annotations page development of annotations page associated requirements the system should allow registered users to view their annotations the system should allow the registered users to go to the memories by using their annotations registered users should be able to view their all tags they use... | 1 |
75,836 | 7,494,474,232 | IssuesEvent | 2018-04-07 10:09:13 | rakudo/rakudo | https://api.github.com/repos/rakudo/rakudo | closed | LTA Error when Proc::Async.bind-stdout/err get unopened IO::Handle | LTA testneeded | ```
with Proc::Async.new: :out, :err, $*EXECUTABLE, $program.absolute {
my $out-path := make-temp-file;
my $err-path := make-temp-file;
.bind-stdout: $out-path.IO.open: :w, :!out-buffer;
.bind-stderr: $err-path.IO.open: :w, :!out-buffer;
...
```
gives `"get native descrip... | 1.0 | LTA Error when Proc::Async.bind-stdout/err get unopened IO::Handle - ```
with Proc::Async.new: :out, :err, $*EXECUTABLE, $program.absolute {
my $out-path := make-temp-file;
my $err-path := make-temp-file;
.bind-stdout: $out-path.IO.open: :w, :!out-buffer;
.bind-stderr: $err-path... | non_priority | lta error when proc async bind stdout err get unopened io handle with proc async new out err executable program absolute my out path make temp file my err path make temp file bind stdout out path io open w out buffer bind stderr err path... | 0 |
352,003 | 10,526,318,830 | IssuesEvent | 2019-09-30 16:50:14 | ronaldoapf/PDS1 | https://api.github.com/repos/ronaldoapf/PDS1 | closed | User Story 2: Criar setores | Epic Priority "Must" User Story | ## Como adminstrador do aplicativo de setores desejo criar um mapa de setores para Monte Carmelo, com objetivo de agrupar as regiões da cidade.
> Com a criação do mapa de setores a prefeitura terá grandes benefícios no que diz respeito a organização administrativa da cidade. Vale ressaltar que o administrador tem o ... | 1.0 | User Story 2: Criar setores - ## Como adminstrador do aplicativo de setores desejo criar um mapa de setores para Monte Carmelo, com objetivo de agrupar as regiões da cidade.
> Com a criação do mapa de setores a prefeitura terá grandes benefícios no que diz respeito a organização administrativa da cidade. Vale ressa... | priority | user story criar setores como adminstrador do aplicativo de setores desejo criar um mapa de setores para monte carmelo com objetivo de agrupar as regiões da cidade com a criação do mapa de setores a prefeitura terá grandes benefícios no que diz respeito a organização administrativa da cidade vale ressa... | 1 |
688,392 | 23,580,337,676 | IssuesEvent | 2022-08-23 07:05:38 | pystardust/ani-cli | https://api.github.com/repos/pystardust/ani-cli | closed | Allow other programs using terminal to use ani-cli | type: feature request priority 4: wishlist | **Is your feature request related to a problem? Please describe.**
There is a problem with trackma when it hooks ani-cli for play. It seems to keep opening and closing the episodes as it goes down the line until there are none left. I left a issue with them at
https://github.com/z411/trackma/issues/637
**Descr... | 1.0 | Allow other programs using terminal to use ani-cli - **Is your feature request related to a problem? Please describe.**
There is a problem with trackma when it hooks ani-cli for play. It seems to keep opening and closing the episodes as it goes down the line until there are none left. I left a issue with them at
... | priority | allow other programs using terminal to use ani cli is your feature request related to a problem please describe there is a problem with trackma when it hooks ani cli for play it seems to keep opening and closing the episodes as it goes down the line until there are none left i left a issue with them at ... | 1 |
11,064 | 7,047,609,758 | IssuesEvent | 2018-01-02 14:20:26 | Yakindu/statecharts | https://api.github.com/repos/Yakindu/statecharts | closed | Split sc editor and interface editor in multipage editor | Comp-Graphical Editor is-Feature-Request is-Usability-Issue Status-Consolidate | Currently, the interface declaration is a textfield inside of the graphical editor. This solution has certain advantages and drawbacks.
Pro:
- The interface declaration and the statechart can be seen simultaneously side by side. Elements in the statechart can easily be referenced in the interface declaration.
- The sta... | True | Split sc editor and interface editor in multipage editor - Currently, the interface declaration is a textfield inside of the graphical editor. This solution has certain advantages and drawbacks.
Pro:
- The interface declaration and the statechart can be seen simultaneously side by side. Elements in the statechart can e... | non_priority | split sc editor and interface editor in multipage editor currently the interface declaration is a textfield inside of the graphical editor this solution has certain advantages and drawbacks pro the interface declaration and the statechart can be seen simultaneously side by side elements in the statechart can e... | 0 |
327,293 | 28,052,010,886 | IssuesEvent | 2023-03-29 06:42:51 | ALTA-LapakUMKM-Group-2/LapakUMKM-APITesting | https://api.github.com/repos/ALTA-LapakUMKM-Group-2/LapakUMKM-APITesting | closed | [User-016] POST Update User With Complete Data In Json | Manual Api Testing | **Given** Post update data users
**When** User fills in the json data by complete data
**Then** Send post update data
**And** API Should be 200 OK
**And** Validate post update data resource json schema | 1.0 | [User-016] POST Update User With Complete Data In Json - **Given** Post update data users
**When** User fills in the json data by complete data
**Then** Send post update data
**And** API Should be 200 OK
**And** Validate post update data resource json schema | non_priority | post update user with complete data in json given post update data users when user fills in the json data by complete data then send post update data and api should be ok and validate post update data resource json schema | 0 |
17,206 | 9,654,438,719 | IssuesEvent | 2019-05-19 14:07:00 | Beep6581/RawTherapee | https://api.github.com/repos/Beep6581/RawTherapee | closed | Don't preprocess and demosaic again when using coarse rotation or flip | performance | Currently, when using coarse rotation or flip, the image gets raw preprocessed and demosaiced again, which imho is not necessary.
This simple patch fixes it:
```diff
diff --git a/rtengine/refreshmap.cc b/rtengine/refreshmap.cc
index 7a5214d75..d741b1744 100644
--- a/rtengine/refreshmap.cc
+++ b/rtengine/refre... | True | Don't preprocess and demosaic again when using coarse rotation or flip - Currently, when using coarse rotation or flip, the image gets raw preprocessed and demosaiced again, which imho is not necessary.
This simple patch fixes it:
```diff
diff --git a/rtengine/refreshmap.cc b/rtengine/refreshmap.cc
index 7a5214... | non_priority | don t preprocess and demosaic again when using coarse rotation or flip currently when using coarse rotation or flip the image gets raw preprocessed and demosaiced again which imho is not necessary this simple patch fixes it diff diff git a rtengine refreshmap cc b rtengine refreshmap cc index ... | 0 |
249,171 | 26,889,995,815 | IssuesEvent | 2023-02-06 08:08:47 | valtech-ch/microservice-kubernetes-cluster | https://api.github.com/repos/valtech-ch/microservice-kubernetes-cluster | closed | CVE-2022-25857 (High) detected in snakeyaml-1.30.jar - autoclosed | security vulnerability | ## CVE-2022-25857 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.30.jar</b></p></summary>
<p>YAML 1.1 parser and emitter for Java</p>
<p>Library home page: <a href="https:... | True | CVE-2022-25857 (High) detected in snakeyaml-1.30.jar - autoclosed - ## CVE-2022-25857 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>snakeyaml-1.30.jar</b></p></summary>
<p>YAML 1.1 p... | non_priority | cve high detected in snakeyaml jar autoclosed cve high severity vulnerability vulnerable library snakeyaml jar yaml parser and emitter for java library home page a href path to dependency file security build gradle path to vulnerable library home wss scanner gra... | 0 |
18,518 | 2,615,172,712 | IssuesEvent | 2015-03-01 06:54:46 | chrsmith/html5rocks | https://api.github.com/repos/chrsmith/html5rocks | opened | How to get started with WebSocket | auto-migrated Milestone-X New Priority-P2 Tutorial Type-Feature | ```
Write an tutorial article introducing how to get started with WebSocket.
This article will include:
- how to build server, what options you have
- how to send/receive text data using WebSocket
- how to send/receive binary data using WebSocket
```
Original issue reported on code.google.com by `agek...@google.com` o... | 1.0 | How to get started with WebSocket - ```
Write an tutorial article introducing how to get started with WebSocket.
This article will include:
- how to build server, what options you have
- how to send/receive text data using WebSocket
- how to send/receive binary data using WebSocket
```
Original issue reported on code.... | priority | how to get started with websocket write an tutorial article introducing how to get started with websocket this article will include how to build server what options you have how to send receive text data using websocket how to send receive binary data using websocket original issue reported on code ... | 1 |
133,929 | 29,670,450,083 | IssuesEvent | 2023-06-11 10:41:35 | dtcxzyw/llvm-ci | https://api.github.com/repos/dtcxzyw/llvm-ci | closed | Regressions Report [rv32gc-O3-thinlto] April 27th 2023, 2:15:47 pm | regression codegen reasonable | ## Metadata
+ Workflow URL: https://github.com/dtcxzyw/llvm-ci/actions/runs/4820681730
## Change Logs
from fe3ed6550ef277f5c47a9ccdbdd466fa225f4a99 to 51297a7a720c83f831b072df4666877673f87cfa
[51297a7a720c83f831b072df4666877673f87cfa](https://github.com/llvm/llvm-project/commit/51297a7a720c83f831b072df4666877673f87cfa... | 1.0 | Regressions Report [rv32gc-O3-thinlto] April 27th 2023, 2:15:47 pm - ## Metadata
+ Workflow URL: https://github.com/dtcxzyw/llvm-ci/actions/runs/4820681730
## Change Logs
from fe3ed6550ef277f5c47a9ccdbdd466fa225f4a99 to 51297a7a720c83f831b072df4666877673f87cfa
[51297a7a720c83f831b072df4666877673f87cfa](https://github.... | non_priority | regressions report april pm metadata workflow url change logs from to minor code cleanup precommit tests for vector shuffle change shufflevector undef mask to poison add frozen for the condition value of selectinst add tests from my fix for drop lc... | 0 |
20,029 | 27,945,268,113 | IssuesEvent | 2023-03-24 02:09:54 | TakosThings/Fluent-Discord | https://api.github.com/repos/TakosThings/Fluent-Discord | opened | Plugin name here | better discord plugin compatibility | ### Plugin Link
https://betterdiscord.app/plugin/QuickMention
### Notes
I think this is the same plugin from Vencord, that I'm using... not sure though
Vencord Plugin:
https://gist.github.com/Vendicated/8696cde7b92548064a3ae92ead84d033#QuickMention | True | Plugin name here - ### Plugin Link
https://betterdiscord.app/plugin/QuickMention
### Notes
I think this is the same plugin from Vencord, that I'm using... not sure though
Vencord Plugin:
https://gist.github.com/Vendicated/8696cde7b92548064a3ae92ead84d033#QuickMention | non_priority | plugin name here plugin link notes i think this is the same plugin from vencord that i m using not sure though vencord plugin | 0 |
331,642 | 10,075,805,505 | IssuesEvent | 2019-07-24 14:57:30 | clearlinux/distribution | https://api.github.com/repos/clearlinux/distribution | closed | Bundle "virt-manager" depends on bundle "virt-manager-gui" to work, possible to merge the 2 into one? | bug desktop medium priority | **Is your feature request related to a problem? Please describe.**
I'm not sure what is the reason for having both "virt-manager" and "virt-manager-gui".
"virt-manager" installs the GUI, but it fails (see screenshot) because it's missing Gtk-vnc. Once I install "virt-manager-gui" (which contains Gtk-vnc), the is... | 1.0 | Bundle "virt-manager" depends on bundle "virt-manager-gui" to work, possible to merge the 2 into one? - **Is your feature request related to a problem? Please describe.**
I'm not sure what is the reason for having both "virt-manager" and "virt-manager-gui".
"virt-manager" installs the GUI, but it fails (see scree... | priority | bundle virt manager depends on bundle virt manager gui to work possible to merge the into one is your feature request related to a problem please describe i m not sure what is the reason for having both virt manager and virt manager gui virt manager installs the gui but it fails see scree... | 1 |
682,118 | 23,333,297,486 | IssuesEvent | 2022-08-09 07:46:15 | grpc/grpc | https://api.github.com/repos/grpc/grpc | closed | cross compile for aarch64 use bazel meet error | kind/bug lang/c++ priority/P2 untriaged | Like the issues #30257. I had update boringssl with newest master_with_bazel branch but the problem is exist.
Some build errors as bellow.
.....
external/boringssl/src/crypto/hrss/asm/poly_rq_mul.S: Assembler messages:
external/boringssl/src/crypto/hrss/asm/poly_rq_mul.S:303: Error: unknown pseudo-op: `.att_syn... | 1.0 | cross compile for aarch64 use bazel meet error - Like the issues #30257. I had update boringssl with newest master_with_bazel branch but the problem is exist.
Some build errors as bellow.
.....
external/boringssl/src/crypto/hrss/asm/poly_rq_mul.S: Assembler messages:
external/boringssl/src/crypto/hrss/asm/poly_... | priority | cross compile for use bazel meet error like the issues i had update boringssl with newest master with bazel branch but the problem is exist some build errors as bellow external boringssl src crypto hrss asm poly rq mul s assembler messages external boringssl src crypto hrss asm poly rq mul s ... | 1 |
37,079 | 12,467,796,769 | IssuesEvent | 2020-05-28 17:42:03 | geofffranks/spruce | https://api.github.com/repos/geofffranks/spruce | closed | CVE-2020-11022 (Medium) detected in jquery-2.1.0.js | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.0.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https:... | True | CVE-2020-11022 (Medium) detected in jquery-2.1.0.js - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.0.js</b></p></summary>
<p>JavaScript library for DO... | non_priority | cve medium detected in jquery js cve medium severity vulnerability vulnerable library jquery js javascript library for dom operations library home page a href path to dependency file tmp ws scm spruce vendor github com smartystreets goconvey web client index html pat... | 0 |
109,828 | 11,659,450,743 | IssuesEvent | 2020-03-03 00:04:42 | gatsbyjs/gatsby | https://api.github.com/repos/gatsbyjs/gatsby | closed | gatsby tutorial sidebar animation bug | stale? type: documentation | **Summary**
I'm going through the [gatsby tutorial part one](https://www.gatsbyjs.org/tutorial/part-one/) and noticed that the sidebar animation shows the "linking between pages" highlighted when not in that section and that when in the "linking between pages" section the sidebar animation has "deploying a gatsby site... | 1.0 | gatsby tutorial sidebar animation bug - **Summary**
I'm going through the [gatsby tutorial part one](https://www.gatsbyjs.org/tutorial/part-one/) and noticed that the sidebar animation shows the "linking between pages" highlighted when not in that section and that when in the "linking between pages" section the sideba... | non_priority | gatsby tutorial sidebar animation bug summary i m going through the and noticed that the sidebar animation shows the linking between pages highlighted when not in that section and that when in the linking between pages section the sidebar animation has deploying a gatsby site selected i ve also tested... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.