Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
15,302
| 19,340,533,201
|
IssuesEvent
|
2021-12-15 03:34:41
|
alexrp/system-terminal
|
https://api.github.com/repos/alexrp/system-terminal
|
opened
|
Expand `TerminalProcess` API surface to mirror `Process`
|
type: feature state: approved area: processes
|
Inspecting memory usage, threads, modules, etc is useful for diagnostic purposes.
|
1.0
|
Expand `TerminalProcess` API surface to mirror `Process` - Inspecting memory usage, threads, modules, etc is useful for diagnostic purposes.
|
process
|
expand terminalprocess api surface to mirror process inspecting memory usage threads modules etc is useful for diagnostic purposes
| 1
|
14,885
| 2,831,390,176
|
IssuesEvent
|
2015-05-24 15:55:02
|
nobodyguy/dslrdashboard
|
https://api.github.com/repos/nobodyguy/dslrdashboard
|
closed
|
nikon d700 not recognising
|
auto-migrated Priority-Medium Type-Defect
|
```
What steps will reproduce the problem?
1.
2.
3.
What is the expected output? What do you see instead?
What version of the product are you using? On what operating system?
Please provide any additional information below.
```
Original issue reported on code.google.com by `aryamanb...@gmail.com` on 25 May 2013 at 8:52
|
1.0
|
nikon d700 not recognising - ```
What steps will reproduce the problem?
1.
2.
3.
What is the expected output? What do you see instead?
What version of the product are you using? On what operating system?
Please provide any additional information below.
```
Original issue reported on code.google.com by `aryamanb...@gmail.com` on 25 May 2013 at 8:52
|
non_process
|
nikon not recognising what steps will reproduce the problem what is the expected output what do you see instead what version of the product are you using on what operating system please provide any additional information below original issue reported on code google com by aryamanb gmail com on may at
| 0
|
9,938
| 12,973,385,646
|
IssuesEvent
|
2020-07-21 13:58:35
|
pb866/TrackMatcher.jl
|
https://api.github.com/repos/pb866/TrackMatcher.jl
|
opened
|
Save non-essential CPro data
|
data processing enhancement
|
In addition to the data needed to calculate the intersections and monitor the features at the intersection, save the following cloud profile data in the vicinity of intersections to struct `CPro`:
- [ ] `Particulate_Depolarization_Ratio_Profile_532`
- [ ] `Day_Night_Flag`
- [ ] `Tropopause_Height`
- [ ] `Temperature`
- [ ] `Pressure`
- [ ] `Relative_Humidity`
- [ ] `Ice_Water_Content_Profile`
- [ ] `CAD_Score`
|
1.0
|
Save non-essential CPro data - In addition to the data needed to calculate the intersections and monitor the features at the intersection, save the following cloud profile data in the vicinity of intersections to struct `CPro`:
- [ ] `Particulate_Depolarization_Ratio_Profile_532`
- [ ] `Day_Night_Flag`
- [ ] `Tropopause_Height`
- [ ] `Temperature`
- [ ] `Pressure`
- [ ] `Relative_Humidity`
- [ ] `Ice_Water_Content_Profile`
- [ ] `CAD_Score`
|
process
|
save non essential cpro data in addition to the data needed to calculate the intersections and monitor the features at the intersection save the following cloud profile data in the vicinity of intersections to struct cpro particulate depolarization ratio profile day night flag tropopause height temperature pressure relative humidity ice water content profile cad score
| 1
|
632,461
| 20,197,950,037
|
IssuesEvent
|
2022-02-11 12:28:33
|
Tribler/py-ipv8
|
https://api.github.com/repos/Tribler/py-ipv8
|
closed
|
`create_test_coverage_report.py` incompatible with `coverage>=6.0`
|
priority: high
|
Since `coverage` version `5.0` the `Analysis` class `__init__` signature has changed:
```python
def __init__(self, data, file_reporter): # <= 4.5.4
def __init__(self, data, file_reporter, file_mapper): # < 6.0
def __init__(self, data, precision, file_reporter, file_mapper): # >= 6.0
```
This causes two of our three front-page builders to fail:

**Traceback and/or steps to reproduce**
```python
$ python3 create_test_coverage_report.py
Traceback (most recent call last):
File "create_test_coverage_report.py", line 78, in <module>
analysis = Analysis(cov.get_data(), file_reporter, abs_file)
TypeError: __init__() missing 1 required positional argument: 'file_mapper'
```
_Admin notice: this issue has been assigned high priority as it directly affects our ability to guarantee quality control. However, this does not cause crashes for users._
|
1.0
|
`create_test_coverage_report.py` incompatible with `coverage>=6.0` - Since `coverage` version `5.0` the `Analysis` class `__init__` signature has changed:
```python
def __init__(self, data, file_reporter): # <= 4.5.4
def __init__(self, data, file_reporter, file_mapper): # < 6.0
def __init__(self, data, precision, file_reporter, file_mapper): # >= 6.0
```
This causes two of our three front-page builders to fail:

**Traceback and/or steps to reproduce**
```python
$ python3 create_test_coverage_report.py
Traceback (most recent call last):
File "create_test_coverage_report.py", line 78, in <module>
analysis = Analysis(cov.get_data(), file_reporter, abs_file)
TypeError: __init__() missing 1 required positional argument: 'file_mapper'
```
_Admin notice: this issue has been assigned high priority as it directly affects our ability to guarantee quality control. However, this does not cause crashes for users._
|
non_process
|
create test coverage report py incompatible with coverage since coverage version the analysis class init signature has changed python def init self data file reporter def init self data file reporter file mapper def init self data precision file reporter file mapper this causes two of our three front page builders to fail traceback and or steps to reproduce python create test coverage report py traceback most recent call last file create test coverage report py line in analysis analysis cov get data file reporter abs file typeerror init missing required positional argument file mapper admin notice this issue has been assigned high priority as it directly affects our ability to guarantee quality control however this does not cause crashes for users
| 0
|
649,486
| 21,313,586,896
|
IssuesEvent
|
2022-04-16 00:14:52
|
apache/incubator-kyuubi
|
https://api.github.com/repos/apache/incubator-kyuubi
|
closed
|
[Bug] Travis CI Test Failed - hive process builder *** FAILED ***
|
kind:bug priority:major
|
### Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://www.apache.org/foundation/policies/conduct)
### Search before asking
- [X] I have searched in the [issues](https://github.com/apache/incubator-kyuubi/issues?q=is%3Aissue) and found no similar issues.
### Describe the bug
Travis CI test failed, seems travis config does not have java envrionment
```
- hive process builder *** FAILED ***
org.apache.kyuubi.KyuubiSQLException: JAVA_HOME is not set! For more information on installing and configuring JAVA_HOME, please visit https://kyuubi.apache.org/docs/latest/deployment/settings.html#environments
at org.apache.kyuubi.KyuubiSQLException$.apply(KyuubiSQLException.scala:69)
at org.apache.kyuubi.engine.ProcBuilder.validateEnv(ProcBuilder.scala:326)
at org.apache.kyuubi.engine.ProcBuilder.validateEnv$(ProcBuilder.scala:325)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.validateEnv(HiveProcessBuilder.scala:33)
at org.apache.kyuubi.engine.ProcBuilder.executable(ProcBuilder.scala:52)
at org.apache.kyuubi.engine.ProcBuilder.executable$(ProcBuilder.scala:49)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.executable(HiveProcessBuilder.scala:33)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.commands(HiveProcessBuilder.scala:47)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.toString(HiveProcessBuilder.scala:89)
at org.apache.kyuubi.engine.hive.HiveProcessBuilderSuite.$anonfun$new$1(HiveProcessBuilderSuite.scala:29)
```
### Affects Version(s)
master
### Kyuubi Server Log Output
_No response_
### Kyuubi Engine Log Output
_No response_
### Kyuubi Server Configurations
_No response_
### Kyuubi Engine Configurations
_No response_
### Additional context
_No response_
### Are you willing to submit PR?
- [ ] Yes I am willing to submit a PR!
|
1.0
|
[Bug] Travis CI Test Failed - hive process builder *** FAILED *** - ### Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://www.apache.org/foundation/policies/conduct)
### Search before asking
- [X] I have searched in the [issues](https://github.com/apache/incubator-kyuubi/issues?q=is%3Aissue) and found no similar issues.
### Describe the bug
Travis CI test failed, seems travis config does not have java envrionment
```
- hive process builder *** FAILED ***
org.apache.kyuubi.KyuubiSQLException: JAVA_HOME is not set! For more information on installing and configuring JAVA_HOME, please visit https://kyuubi.apache.org/docs/latest/deployment/settings.html#environments
at org.apache.kyuubi.KyuubiSQLException$.apply(KyuubiSQLException.scala:69)
at org.apache.kyuubi.engine.ProcBuilder.validateEnv(ProcBuilder.scala:326)
at org.apache.kyuubi.engine.ProcBuilder.validateEnv$(ProcBuilder.scala:325)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.validateEnv(HiveProcessBuilder.scala:33)
at org.apache.kyuubi.engine.ProcBuilder.executable(ProcBuilder.scala:52)
at org.apache.kyuubi.engine.ProcBuilder.executable$(ProcBuilder.scala:49)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.executable(HiveProcessBuilder.scala:33)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.commands(HiveProcessBuilder.scala:47)
at org.apache.kyuubi.engine.hive.HiveProcessBuilder.toString(HiveProcessBuilder.scala:89)
at org.apache.kyuubi.engine.hive.HiveProcessBuilderSuite.$anonfun$new$1(HiveProcessBuilderSuite.scala:29)
```
### Affects Version(s)
master
### Kyuubi Server Log Output
_No response_
### Kyuubi Engine Log Output
_No response_
### Kyuubi Server Configurations
_No response_
### Kyuubi Engine Configurations
_No response_
### Additional context
_No response_
### Are you willing to submit PR?
- [ ] Yes I am willing to submit a PR!
|
non_process
|
travis ci test failed hive process builder failed code of conduct i agree to follow this project s search before asking i have searched in the and found no similar issues describe the bug travis ci test failed seems travis config does not have java envrionment hive process builder failed org apache kyuubi kyuubisqlexception java home is not set for more information on installing and configuring java home please visit at org apache kyuubi kyuubisqlexception apply kyuubisqlexception scala at org apache kyuubi engine procbuilder validateenv procbuilder scala at org apache kyuubi engine procbuilder validateenv procbuilder scala at org apache kyuubi engine hive hiveprocessbuilder validateenv hiveprocessbuilder scala at org apache kyuubi engine procbuilder executable procbuilder scala at org apache kyuubi engine procbuilder executable procbuilder scala at org apache kyuubi engine hive hiveprocessbuilder executable hiveprocessbuilder scala at org apache kyuubi engine hive hiveprocessbuilder commands hiveprocessbuilder scala at org apache kyuubi engine hive hiveprocessbuilder tostring hiveprocessbuilder scala at org apache kyuubi engine hive hiveprocessbuildersuite anonfun new hiveprocessbuildersuite scala affects version s master kyuubi server log output no response kyuubi engine log output no response kyuubi server configurations no response kyuubi engine configurations no response additional context no response are you willing to submit pr yes i am willing to submit a pr
| 0
|
15,588
| 19,714,046,085
|
IssuesEvent
|
2022-01-13 09:15:00
|
ESMValGroup/ESMValCore
|
https://api.github.com/repos/ESMValGroup/ESMValCore
|
opened
|
Adapt `annual_statistics` to DCPP data
|
enhancement preprocessor
|
**Is your feature request related to a problem? Please describe.**
As mentioned in https://github.com/ESMValGroup/ESMValCore/issues/1120#issuecomment-843030860, a year in DCPP datasets spans 12 months but not necessarily starting in January. For this reason, aggregating these datasets by `year` number in `annual_statistics` is not very convenient, as a dataset with 12 months of data spanning from Nov 1960 to Oct 1961 would result in a cube with two time steps. It would be convenient to be able to compute annual statistics defining the year span as 12 months from the origin. In that way, the resulting cube for this example would have one timestep, as expected.
As for the implementation, maybe `annual_statistics` could have a `from_origin=False/True` parameter, with default value set to `False`:
```python
def annual_statistics(operator, from_origin=False):
if from_origin:
#Aggregate considering a year is 12 months of data
return cube
# continue with annual_statistics aggregating by year number
```
But suggestions are very much welcome.
**Would you be able to help out?**
Yes
|
1.0
|
Adapt `annual_statistics` to DCPP data - **Is your feature request related to a problem? Please describe.**
As mentioned in https://github.com/ESMValGroup/ESMValCore/issues/1120#issuecomment-843030860, a year in DCPP datasets spans 12 months but not necessarily starting in January. For this reason, aggregating these datasets by `year` number in `annual_statistics` is not very convenient, as a dataset with 12 months of data spanning from Nov 1960 to Oct 1961 would result in a cube with two time steps. It would be convenient to be able to compute annual statistics defining the year span as 12 months from the origin. In that way, the resulting cube for this example would have one timestep, as expected.
As for the implementation, maybe `annual_statistics` could have a `from_origin=False/True` parameter, with default value set to `False`:
```python
def annual_statistics(operator, from_origin=False):
if from_origin:
#Aggregate considering a year is 12 months of data
return cube
# continue with annual_statistics aggregating by year number
```
But suggestions are very much welcome.
**Would you be able to help out?**
Yes
|
process
|
adapt annual statistics to dcpp data is your feature request related to a problem please describe as mentioned in a year in dcpp datasets spans months but not necessarily starting in january for this reason aggregating these datasets by year number in annual statistics is not very convenient as a dataset with months of data spanning from nov to oct would result in a cube with two time steps it would be convenient to be able to compute annual statistics defining the year span as months from the origin in that way the resulting cube for this example would have one timestep as expected as for the implementation maybe annual statistics could have a from origin false true parameter with default value set to false python def annual statistics operator from origin false if from origin aggregate considering a year is months of data return cube continue with annual statistics aggregating by year number but suggestions are very much welcome would you be able to help out yes
| 1
|
4,313
| 7,203,329,729
|
IssuesEvent
|
2018-02-06 08:49:18
|
qgis/QGIS-Documentation
|
https://api.github.com/repos/qgis/QGIS-Documentation
|
closed
|
[FEATURE] Port Extract by Expression to new API, allow saving
non matching features to separate output
|
Automatic new feature Processing
|
Original commit: https://github.com/qgis/QGIS/commit/d8260b8c4788f2a03b9c306db4f7046a27fdd851 by nyalldawson
Unfortunately this naughty coder did not write a description... :-(
|
1.0
|
[FEATURE] Port Extract by Expression to new API, allow saving
non matching features to separate output - Original commit: https://github.com/qgis/QGIS/commit/d8260b8c4788f2a03b9c306db4f7046a27fdd851 by nyalldawson
Unfortunately this naughty coder did not write a description... :-(
|
process
|
port extract by expression to new api allow saving non matching features to separate output original commit by nyalldawson unfortunately this naughty coder did not write a description
| 1
|
9,534
| 12,503,613,724
|
IssuesEvent
|
2020-06-02 07:34:59
|
googleapis/gapic-generator-typescript
|
https://api.github.com/repos/googleapis/gapic-generator-typescript
|
closed
|
switch to es2018 in tsconfig.json once none are supporting Node 8
|
type: process
|
We should switch to es2018 as our default target for tsconfig.json, once this list of libraries has been ported:
https://github.com/googleapis/google-cloud-node/issues/2972
|
1.0
|
switch to es2018 in tsconfig.json once none are supporting Node 8 - We should switch to es2018 as our default target for tsconfig.json, once this list of libraries has been ported:
https://github.com/googleapis/google-cloud-node/issues/2972
|
process
|
switch to in tsconfig json once none are supporting node we should switch to as our default target for tsconfig json once this list of libraries has been ported
| 1
|
267,334
| 23,292,153,983
|
IssuesEvent
|
2022-08-06 02:24:20
|
danbudris/vulnerabilityProcessor
|
https://api.github.com/repos/danbudris/vulnerabilityProcessor
|
opened
|
HIGH vulnerability CVE-2021-30139 - apk-tools affecting 1 resources
|
hey there test severity/HIGH
|
Issue auto cut by Vulnerability Processor
Processor Version: `v0.0.0-dev`
Message Source: `EventBridge`
Finding Source: `inspectorV2`
HIGH vulnerability CVE-2021-30139 detected in 1 resources
- arn:aws:ecr:us-west-2:338155784195:repository/test-inspector/sha256:4266485e304a825d82c375d3584121b53c802e3540d6b520b212a9f0784d56f5
Affected Packages:
- apk-tools
Associated Pull Requests:
- https://github.com/danbudris/vulnerabilityProcessor/pull/1301
|
1.0
|
HIGH vulnerability CVE-2021-30139 - apk-tools affecting 1 resources - Issue auto cut by Vulnerability Processor
Processor Version: `v0.0.0-dev`
Message Source: `EventBridge`
Finding Source: `inspectorV2`
HIGH vulnerability CVE-2021-30139 detected in 1 resources
- arn:aws:ecr:us-west-2:338155784195:repository/test-inspector/sha256:4266485e304a825d82c375d3584121b53c802e3540d6b520b212a9f0784d56f5
Affected Packages:
- apk-tools
Associated Pull Requests:
- https://github.com/danbudris/vulnerabilityProcessor/pull/1301
|
non_process
|
high vulnerability cve apk tools affecting resources issue auto cut by vulnerability processor processor version dev message source eventbridge finding source high vulnerability cve detected in resources arn aws ecr us west repository test inspector affected packages apk tools associated pull requests
| 0
|
252,171
| 21,560,396,435
|
IssuesEvent
|
2022-05-01 04:11:42
|
Uuvana-Studios/longvinter-windows-client
|
https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client
|
closed
|
I installed the turret, but it disappeared... Spin it
|
Bug Not Tested
|
**Describe the bug**
A clear and concise description of what the bug is.
[

](url)
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See an error
**Expected behavior**
A clear and concise description of what you expected to happen.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version [e.g. 1.0]
- Steam Version [e.g. 1.0]
**Additional context**
Add any other context about the problem here.
|
1.0
|
I installed the turret, but it disappeared... Spin it - **Describe the bug**
A clear and concise description of what the bug is.
[

](url)
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See an error
**Expected behavior**
A clear and concise description of what you expected to happen.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version [e.g. 1.0]
- Steam Version [e.g. 1.0]
**Additional context**
Add any other context about the problem here.
|
non_process
|
i installed the turret but it disappeared spin it describe the bug a clear and concise description of what the bug is url to reproduce steps to reproduce the behavior go to click on scroll down to see an error expected behavior a clear and concise description of what you expected to happen screenshots if applicable add screenshots to help explain your problem desktop please complete the following information os game version steam version additional context add any other context about the problem here
| 0
|
16,115
| 20,377,106,796
|
IssuesEvent
|
2022-02-21 16:41:36
|
MicrosoftDocs/azure-devops-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-devops-docs
|
reopened
|
Output of `convertToJson` funtion is not using valid JSON syntax
|
devops/prod product-feedback cba Pri2 devops-cicd-process/tech
|
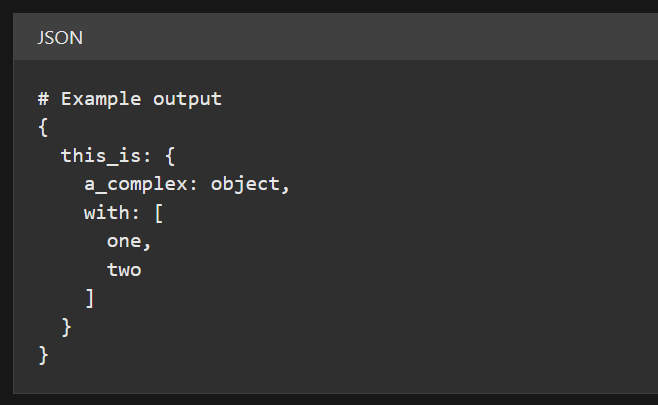
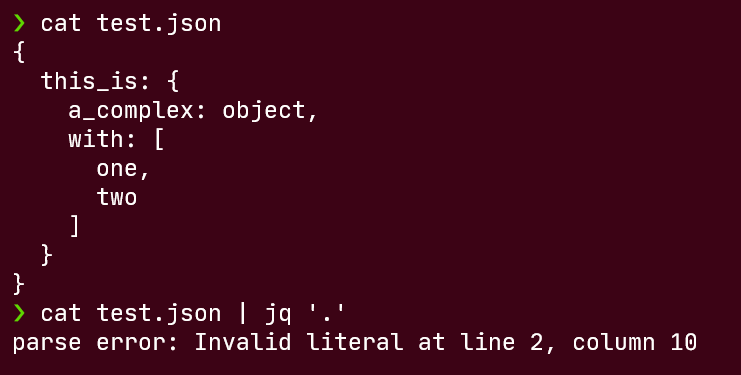
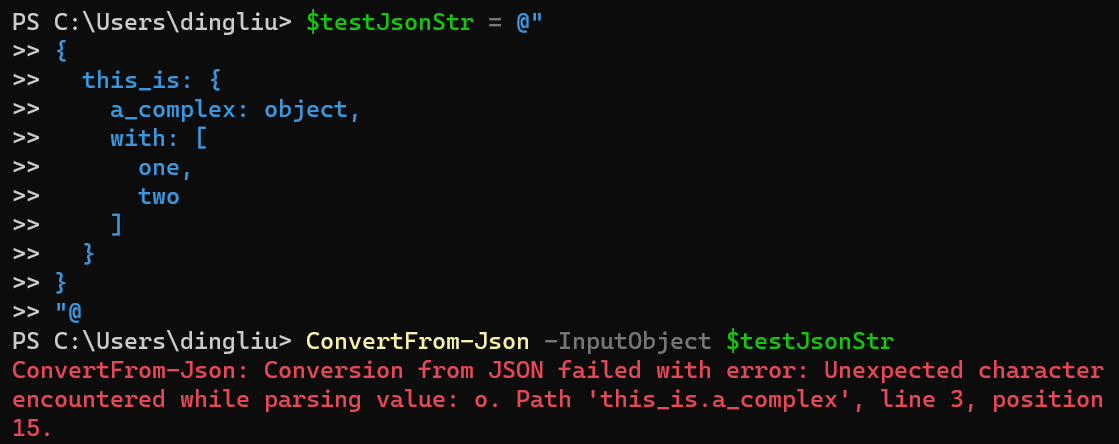
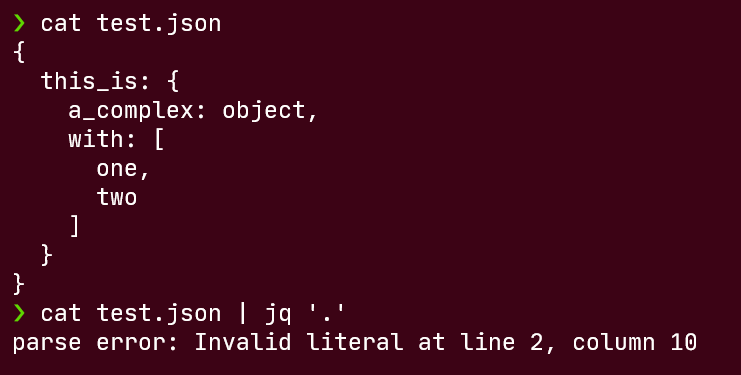
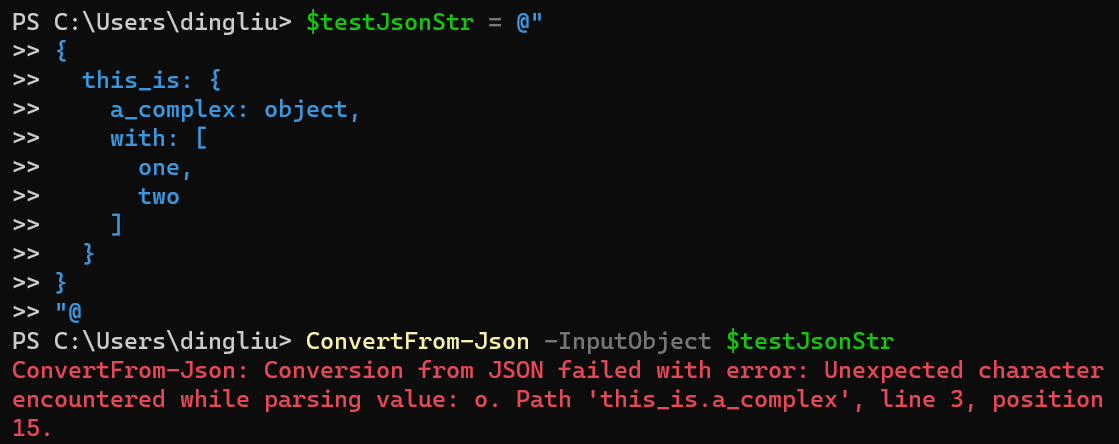
In Azure DevOps pipeline, expression function [`convertToJson`](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/expressions?view=azure-devops#converttojson) is documented as:
> Take a complex object and outputs it as JSON.
However, the output of this function is not using valid JSON syntax, because:
- The property names (or keys) are not double quoted
- The string values are not double quoted
To demonstrate this issue, trying to parse the example output either using [`jq`](https://stedolan.github.io/jq/) under bash or [`ConvertFrom-Json`](https://docs.microsoft.com/en-us/powershell/module/microsoft.powershell.utility/convertfrom-json?view=powershell-7.2) under PowerShell will both fail:
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 77c58a78-a567-e99a-9eb7-62dddd1b90b6
* Version Independent ID: 680a79bc-11de-39fc-43e3-e07dc762db18
* Content: [Expressions - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/expressions?view=azure-devops#converttojson)
* Content Source: [docs/pipelines/process/expressions.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/main/docs/pipelines/process/expressions.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam**
|
1.0
|
Output of `convertToJson` funtion is not using valid JSON syntax - In Azure DevOps pipeline, expression function [`convertToJson`](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/expressions?view=azure-devops#converttojson) is documented as:
> Take a complex object and outputs it as JSON.
However, the output of this function is not using valid JSON syntax, because:
- The property names (or keys) are not double quoted
- The string values are not double quoted
To demonstrate this issue, trying to parse the example output either using [`jq`](https://stedolan.github.io/jq/) under bash or [`ConvertFrom-Json`](https://docs.microsoft.com/en-us/powershell/module/microsoft.powershell.utility/convertfrom-json?view=powershell-7.2) under PowerShell will both fail:
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 77c58a78-a567-e99a-9eb7-62dddd1b90b6
* Version Independent ID: 680a79bc-11de-39fc-43e3-e07dc762db18
* Content: [Expressions - Azure Pipelines](https://docs.microsoft.com/en-us/azure/devops/pipelines/process/expressions?view=azure-devops#converttojson)
* Content Source: [docs/pipelines/process/expressions.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/main/docs/pipelines/process/expressions.md)
* Product: **devops**
* Technology: **devops-cicd-process**
* GitHub Login: @juliakm
* Microsoft Alias: **jukullam**
|
process
|
output of converttojson funtion is not using valid json syntax in azure devops pipeline expression function is documented as take a complex object and outputs it as json however the output of this function is not using valid json syntax because the property names or keys are not double quoted the string values are not double quoted to demonstrate this issue trying to parse the example output either using under bash or under powershell will both fail document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops cicd process github login juliakm microsoft alias jukullam
| 1
|
2,288
| 5,111,775,176
|
IssuesEvent
|
2017-01-06 08:16:42
|
rogerthat-platform/rogerthat-android-client
|
https://api.github.com/repos/rogerthat-platform/rogerthat-android-client
|
closed
|
Scrolling through news items with images is not very responsive
|
process_duplicate type_feature
|
Scrolling through the newsfeed with is not very responsive, probably due to the images being resized/rounded (on UI thread perhaps?)
|
1.0
|
Scrolling through news items with images is not very responsive - Scrolling through the newsfeed with is not very responsive, probably due to the images being resized/rounded (on UI thread perhaps?)
|
process
|
scrolling through news items with images is not very responsive scrolling through the newsfeed with is not very responsive probably due to the images being resized rounded on ui thread perhaps
| 1
|
4,790
| 7,674,617,938
|
IssuesEvent
|
2018-05-15 05:13:34
|
qgis/QGIS-Documentation
|
https://api.github.com/repos/qgis/QGIS-Documentation
|
closed
|
Move Processing config description out of Toolbox chapter?
|
Processing User Manual question
|
## Description
Processing configurations (settings --> Options --> Processing) is currently described at https://docs.qgis.org/testing/en/docs/user_manual/processing/toolbox.html#configuring-the-processing-framework inside the algorithm toolbox page. This does not look correct to me as configs are for all the Processing infrastructure and their current placement hides them and can be misleading.
I propose to move it out either:
* as a new page, between the Intro and the toolbox pages (https://docs.qgis.org/testing/en/docs/user_manual/processing/index.html). _The vector chapter should be removed if no objections at #2455._
* as a part of the [introduction](https://docs.qgis.org/testing/en/docs/user_manual/processing/intro.html) page, which will get a more config friendly title.
Opinions?
|
1.0
|
Move Processing config description out of Toolbox chapter? - ## Description
Processing configurations (settings --> Options --> Processing) is currently described at https://docs.qgis.org/testing/en/docs/user_manual/processing/toolbox.html#configuring-the-processing-framework inside the algorithm toolbox page. This does not look correct to me as configs are for all the Processing infrastructure and their current placement hides them and can be misleading.
I propose to move it out either:
* as a new page, between the Intro and the toolbox pages (https://docs.qgis.org/testing/en/docs/user_manual/processing/index.html). _The vector chapter should be removed if no objections at #2455._
* as a part of the [introduction](https://docs.qgis.org/testing/en/docs/user_manual/processing/intro.html) page, which will get a more config friendly title.
Opinions?
|
process
|
move processing config description out of toolbox chapter description processing configurations settings options processing is currently described at inside the algorithm toolbox page this does not look correct to me as configs are for all the processing infrastructure and their current placement hides them and can be misleading i propose to move it out either as a new page between the intro and the toolbox pages the vector chapter should be removed if no objections at as a part of the page which will get a more config friendly title opinions
| 1
|
258,135
| 27,563,858,618
|
IssuesEvent
|
2023-03-08 01:11:31
|
billmcchesney1/t-vault
|
https://api.github.com/repos/billmcchesney1/t-vault
|
opened
|
CVE-2021-23343 (High) detected in path-parse-1.0.6.tgz
|
security vulnerability
|
## CVE-2021-23343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>Path to dependency file: /tvaultui/package.json</p>
<p>Path to vulnerable library: /tvaultui/node_modules/path-parse/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- liftoff-2.5.0.tgz
- resolve-1.19.0.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution (path-parse): 1.0.7</p>
<p>Direct dependency fix Resolution (gulp): 4.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
|
True
|
CVE-2021-23343 (High) detected in path-parse-1.0.6.tgz - ## CVE-2021-23343 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>path-parse-1.0.6.tgz</b></p></summary>
<p>Node.js path.parse() ponyfill</p>
<p>Library home page: <a href="https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz">https://registry.npmjs.org/path-parse/-/path-parse-1.0.6.tgz</a></p>
<p>Path to dependency file: /tvaultui/package.json</p>
<p>Path to vulnerable library: /tvaultui/node_modules/path-parse/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- liftoff-2.5.0.tgz
- resolve-1.19.0.tgz
- :x: **path-parse-1.0.6.tgz** (Vulnerable Library)
<p>Found in base branch: <b>dev</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
All versions of package path-parse are vulnerable to Regular Expression Denial of Service (ReDoS) via splitDeviceRe, splitTailRe, and splitPathRe regular expressions. ReDoS exhibits polynomial worst-case time complexity.
<p>Publish Date: 2021-05-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-23343>CVE-2021-23343</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2021-05-04</p>
<p>Fix Resolution (path-parse): 1.0.7</p>
<p>Direct dependency fix Resolution (gulp): 4.0.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
|
non_process
|
cve high detected in path parse tgz cve high severity vulnerability vulnerable library path parse tgz node js path parse ponyfill library home page a href path to dependency file tvaultui package json path to vulnerable library tvaultui node modules path parse package json dependency hierarchy gulp tgz root library liftoff tgz resolve tgz x path parse tgz vulnerable library found in base branch dev vulnerability details all versions of package path parse are vulnerable to regular expression denial of service redos via splitdevicere splittailre and splitpathre regular expressions redos exhibits polynomial worst case time complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution path parse direct dependency fix resolution gulp rescue worker helmet automatic remediation is available for this issue
| 0
|
289,341
| 24,980,996,170
|
IssuesEvent
|
2022-11-02 11:41:16
|
benoitkugler/maths-online
|
https://api.github.com/repos/benoitkugler/maths-online
|
closed
|
[prof/editor] Possibilité de dupliquer une question d'un exercice
|
enhancement Accepté A tester
|
Possibilité de dupliquer un exercice complet (ex : utile pour les cas du signe de Delta, 3 exercices de fait sur le même modèle)
_Originally posted by @Guigui7707 in https://github.com/benoitkugler/maths-online/issues/92#issuecomment-1197936134_
|
1.0
|
[prof/editor] Possibilité de dupliquer une question d'un exercice - Possibilité de dupliquer un exercice complet (ex : utile pour les cas du signe de Delta, 3 exercices de fait sur le même modèle)
_Originally posted by @Guigui7707 in https://github.com/benoitkugler/maths-online/issues/92#issuecomment-1197936134_
|
non_process
|
possibilité de dupliquer une question d un exercice possibilité de dupliquer un exercice complet ex utile pour les cas du signe de delta exercices de fait sur le même modèle originally posted by in
| 0
|
22,860
| 3,974,167,749
|
IssuesEvent
|
2016-05-04 21:10:21
|
extnet/Ext.NET
|
https://api.github.com/repos/extnet/Ext.NET
|
closed
|
Store's AutoLoad="false" is ignored if RemoteFilter="true"
|
3.x extjs-test-pending review review-after-extjs-upgrade sencha
|
http://forums.ext.net/showthread.php?59870
**Test Case**
```
<%@ Page Language="C#" %>
<!DOCTYPE html>
<html>
<head runat="server">
<title>Ext.NET v4 Example</title>
</head>
<body>
<form runat="server">
<ext:ResourceManager runat="server" />
<ext:GridPanel ID="GridPanel1" runat="server">
<Store>
<ext:Store runat="server" AutoLoad="false" RemoteFilter="true">
<Model>
<ext:Model runat="server">
<Fields>
<ext:ModelField Name="test1" />
<ext:ModelField Name="test2" />
</Fields>
</ext:Model>
</Model>
<Proxy>
<ext:AjaxProxy Url="SomeFakeUrl" />
</Proxy>
</ext:Store>
</Store>
<ColumnModel runat="server">
<Columns>
<ext:Column runat="server" Text="Test 1" DataIndex="test1">
<Filter>
<ext:StringFilter />
</Filter>
</ext:Column>
<ext:Column runat="server" Text="Test 2" DataIndex="test2" />
</Columns>
</ColumnModel>
<Plugins>
<ext:GridFilters runat="server" />
</Plugins>
</ext:GridPanel>
</form>
</body>
</html>
```
Fixed in the revision 6511 (trunk).
Review after next ExtJS upgrade - 5.1.2 or later.
**UPDATE**: still reproducible with ExtJS 6.0.1.
|
1.0
|
Store's AutoLoad="false" is ignored if RemoteFilter="true" - http://forums.ext.net/showthread.php?59870
**Test Case**
```
<%@ Page Language="C#" %>
<!DOCTYPE html>
<html>
<head runat="server">
<title>Ext.NET v4 Example</title>
</head>
<body>
<form runat="server">
<ext:ResourceManager runat="server" />
<ext:GridPanel ID="GridPanel1" runat="server">
<Store>
<ext:Store runat="server" AutoLoad="false" RemoteFilter="true">
<Model>
<ext:Model runat="server">
<Fields>
<ext:ModelField Name="test1" />
<ext:ModelField Name="test2" />
</Fields>
</ext:Model>
</Model>
<Proxy>
<ext:AjaxProxy Url="SomeFakeUrl" />
</Proxy>
</ext:Store>
</Store>
<ColumnModel runat="server">
<Columns>
<ext:Column runat="server" Text="Test 1" DataIndex="test1">
<Filter>
<ext:StringFilter />
</Filter>
</ext:Column>
<ext:Column runat="server" Text="Test 2" DataIndex="test2" />
</Columns>
</ColumnModel>
<Plugins>
<ext:GridFilters runat="server" />
</Plugins>
</ext:GridPanel>
</form>
</body>
</html>
```
Fixed in the revision 6511 (trunk).
Review after next ExtJS upgrade - 5.1.2 or later.
**UPDATE**: still reproducible with ExtJS 6.0.1.
|
non_process
|
store s autoload false is ignored if remotefilter true test case ext net example fixed in the revision trunk review after next extjs upgrade or later update still reproducible with extjs
| 0
|
8,810
| 11,908,307,676
|
IssuesEvent
|
2020-03-31 00:34:36
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
Add ”Select by rectangle” in modeler
|
Feature Request Processing
|
Author Name: **Magnus Nilsson** (Magnus Nilsson)
Original Redmine Issue: [5453](https://issues.qgis.org/issues/5453)
Redmine category:processing/modeller
Assignee: Victor Olaya
---
Add possibility to select multiple objects with ”Select by rectangle” in modeler.
---
Related issue(s): #24173 (duplicates)
Redmine related issue(s): [16263](https://issues.qgis.org/issues/16263)
---
|
1.0
|
Add ”Select by rectangle” in modeler - Author Name: **Magnus Nilsson** (Magnus Nilsson)
Original Redmine Issue: [5453](https://issues.qgis.org/issues/5453)
Redmine category:processing/modeller
Assignee: Victor Olaya
---
Add possibility to select multiple objects with ”Select by rectangle” in modeler.
---
Related issue(s): #24173 (duplicates)
Redmine related issue(s): [16263](https://issues.qgis.org/issues/16263)
---
|
process
|
add ”select by rectangle” in modeler author name magnus nilsson magnus nilsson original redmine issue redmine category processing modeller assignee victor olaya add possibility to select multiple objects with ”select by rectangle” in modeler related issue s duplicates redmine related issue s
| 1
|
15,579
| 19,703,728,504
|
IssuesEvent
|
2022-01-12 19:23:15
|
googleapis/nodejs-grafeas
|
https://api.github.com/repos/googleapis/nodejs-grafeas
|
opened
|
Your .repo-metadata.json file has a problem 🤒
|
type: process repo-metadata: lint
|
You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'grafeas' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
1.0
|
Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'grafeas' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
process
|
your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 api shortname grafeas invalid in repo metadata json ☝️ once you correct these problems you can close this issue reach out to go github automation if you have any questions
| 1
|
130,303
| 12,426,226,883
|
IssuesEvent
|
2020-05-24 20:07:03
|
music-encoding/guidelines
|
https://api.github.com/repos/music-encoding/guidelines
|
closed
|
Revise 06: Repertoire: Neume Notation
|
documentation
|
This issue can be used to discuss chapter 6 of the guidelines.
|
1.0
|
Revise 06: Repertoire: Neume Notation - This issue can be used to discuss chapter 6 of the guidelines.
|
non_process
|
revise repertoire neume notation this issue can be used to discuss chapter of the guidelines
| 0
|
19,908
| 26,362,329,056
|
IssuesEvent
|
2023-01-11 14:15:56
|
geneontology/go-ontology
|
https://api.github.com/repos/geneontology/go-ontology
|
closed
|
multi-symbiont biological processes
|
waiting for feedback multi-species process
|
An email discussion about phage processes stimulated me to make this issue, but I also wonder if it applies to non-viral situations.
Looking at the ontology, we have terms like
GO:0039634 killing by virus of host cell during superinfection exclusion,
where virus A modifies the host physiology in response to superinfection by virus B. But what if virus A does exclusion by other mechanisms, such as degrading the DNA of virus B? Is this still a modification of host physiology because the virus A gene product required host translation? What if virus A brought the gene product with it (I don't know an example of this, but I would not be surprised)?
Some cases:
1) The paradigm lambda immunity system. Lambda prophages make a repressor that is a negative regulator of transcription initiation. It is annotated to those processes:
http://www.ebi.ac.uk/QuickGO/GProtein?ac=P03034
But there are no annotations that capture the role in preventing productive superinfections.
2) P22 antirepressor. P22 ant negatively regulates its own repressor, but also negatively regulates the repressors of other phages. The IEAs for this don't capture that (and are wrong, IMO).
http://www.ebi.ac.uk/QuickGO/GProtein?ac=P03037
3) Capsid size determination by phage P4
http://www.uniprot.org/uniprot/P05461
The P4 sid protein is required to make P4-sized capsids using proteins from helper phage P2. There are no GO annotations associated with this protein.
These may all work as children of modification of host by symbiont. But the second symbiont seems to be lost in the ontology structure.
|
1.0
|
multi-symbiont biological processes - An email discussion about phage processes stimulated me to make this issue, but I also wonder if it applies to non-viral situations.
Looking at the ontology, we have terms like
GO:0039634 killing by virus of host cell during superinfection exclusion,
where virus A modifies the host physiology in response to superinfection by virus B. But what if virus A does exclusion by other mechanisms, such as degrading the DNA of virus B? Is this still a modification of host physiology because the virus A gene product required host translation? What if virus A brought the gene product with it (I don't know an example of this, but I would not be surprised)?
Some cases:
1) The paradigm lambda immunity system. Lambda prophages make a repressor that is a negative regulator of transcription initiation. It is annotated to those processes:
http://www.ebi.ac.uk/QuickGO/GProtein?ac=P03034
But there are no annotations that capture the role in preventing productive superinfections.
2) P22 antirepressor. P22 ant negatively regulates its own repressor, but also negatively regulates the repressors of other phages. The IEAs for this don't capture that (and are wrong, IMO).
http://www.ebi.ac.uk/QuickGO/GProtein?ac=P03037
3) Capsid size determination by phage P4
http://www.uniprot.org/uniprot/P05461
The P4 sid protein is required to make P4-sized capsids using proteins from helper phage P2. There are no GO annotations associated with this protein.
These may all work as children of modification of host by symbiont. But the second symbiont seems to be lost in the ontology structure.
|
process
|
multi symbiont biological processes an email discussion about phage processes stimulated me to make this issue but i also wonder if it applies to non viral situations looking at the ontology we have terms like go killing by virus of host cell during superinfection exclusion where virus a modifies the host physiology in response to superinfection by virus b but what if virus a does exclusion by other mechanisms such as degrading the dna of virus b is this still a modification of host physiology because the virus a gene product required host translation what if virus a brought the gene product with it i don t know an example of this but i would not be surprised some cases the paradigm lambda immunity system lambda prophages make a repressor that is a negative regulator of transcription initiation it is annotated to those processes but there are no annotations that capture the role in preventing productive superinfections antirepressor ant negatively regulates its own repressor but also negatively regulates the repressors of other phages the ieas for this don t capture that and are wrong imo capsid size determination by phage the sid protein is required to make sized capsids using proteins from helper phage there are no go annotations associated with this protein these may all work as children of modification of host by symbiont but the second symbiont seems to be lost in the ontology structure
| 1
|
140,670
| 12,945,144,040
|
IssuesEvent
|
2020-07-18 14:04:50
|
vmck/acs-interface
|
https://api.github.com/repos/vmck/acs-interface
|
closed
|
Information dashboard
|
documentation enhancement
|
VMCK runs on a nomad cluster that contains the service `grafana`. We should leverage that, and create a dashboard with at least the following information:
* Number of submissions that are pending
* Number of submissions that are running
* Average time it takes for a submission to finish
|
1.0
|
Information dashboard - VMCK runs on a nomad cluster that contains the service `grafana`. We should leverage that, and create a dashboard with at least the following information:
* Number of submissions that are pending
* Number of submissions that are running
* Average time it takes for a submission to finish
|
non_process
|
information dashboard vmck runs on a nomad cluster that contains the service grafana we should leverage that and create a dashboard with at least the following information number of submissions that are pending number of submissions that are running average time it takes for a submission to finish
| 0
|
218,008
| 16,904,013,243
|
IssuesEvent
|
2021-06-24 03:45:59
|
golang/go
|
https://api.github.com/repos/golang/go
|
closed
|
net: TestDialParallel spuriously fails due to hard-coded timeout in dialClosedPort
|
NeedsInvestigation Testing
|
We know from past experience that hard-coded timeouts lead to flaky tests. The `dialClosedPort` helper function has one such hard-coded timeout:
https://github.com/golang/go/blob/82517acae866d60a9754d44d004bfa159e656c07/src/net/dial_test.go#L159-L168
The test provides no rationale for why we expect 1500ms to be a firm upper bound on Windows. For that matter, it provides no rationale as to why we expect 95 or 150ms to be firm upper bounds on other platforms.
And, indeed, it isn't a firm upper bound on those other platforms either:
https://github.com/golang/go/blob/82517acae866d60a9754d44d004bfa159e656c07/src/net/dial_test.go#L177-L179
----
So it comes as no surprise that the test consistently fails on my new Surface Book 3:
```
PS C:\Users\bryan\src\go\src> ..\bin\go version
go version devel go1.17-0ebd5a8de0 Tue Jun 22 16:59:10 2021 +0000 windows/amd64
PS C:\Users\bryan\src\go\src> ..\bin\go env
set GO111MODULE=
set GOARCH=amd64
set GOBIN=
set GOCACHE=C:\Users\bryan\AppData\Local\go-build
set GOENV=C:\Users\bryan\AppData\Roaming\go\env
set GOEXE=.exe
set GOFLAGS=
set GOHOSTARCH=amd64
set GOHOSTOS=windows
set GOINSECURE=
set GOMODCACHE=C:\Users\bryan\go\pkg\mod
set GONOPROXY=
set GONOSUMDB=
set GOOS=windows
set GOPATH=C:\Users\bryan\go
set GOPRIVATE=
set GOPROXY=https://proxy.golang.org,direct
set GOROOT=C:\Users\bryan\src\go
set GOSUMDB=sum.golang.org
set GOTMPDIR=
set GOTOOLDIR=C:\Users\bryan\src\go\pkg\tool\windows_amd64
set GOVCS=
set GOVERSION=devel go1.17-0ebd5a8de0 Tue Jun 22 16:59:10 2021 +0000
set GCCGO=gccgo
set AR=ar
set CC=gcc
set CXX=g++
set CGO_ENABLED=1
set GOMOD=C:\Users\bryan\src\go\src\go.mod
set CGO_CFLAGS=-g -O2
set CGO_CPPFLAGS=
set CGO_CXXFLAGS=-g -O2
set CGO_FFLAGS=-g -O2
set CGO_LDFLAGS=-g -O2
set PKG_CONFIG=pkg-config
set GOGCCFLAGS=-m64 -mthreads -fmessage-length=0 -fdebug-prefix-map=C:\Users\bryan\AppData\Local\Temp\go-build2503220696=/tmp/go-build -gno-record-gcc-switches
PS C:\Users\bryan\src\go\src> ..\bin\go test net
--- FAIL: TestDialParallel (12.92s)
dial_test.go:188: dialClosedPort: measured delay 2.0038828s
dial_test.go:203: got 2.0038828s; want <= 1.5s
FAIL
FAIL net 45.755s
FAIL
PS C:\Users\bryan\src\go\src>
```
Probably the tests should be reworked not to rely on hard-coded timeouts at all.
|
1.0
|
net: TestDialParallel spuriously fails due to hard-coded timeout in dialClosedPort - We know from past experience that hard-coded timeouts lead to flaky tests. The `dialClosedPort` helper function has one such hard-coded timeout:
https://github.com/golang/go/blob/82517acae866d60a9754d44d004bfa159e656c07/src/net/dial_test.go#L159-L168
The test provides no rationale for why we expect 1500ms to be a firm upper bound on Windows. For that matter, it provides no rationale as to why we expect 95 or 150ms to be firm upper bounds on other platforms.
And, indeed, it isn't a firm upper bound on those other platforms either:
https://github.com/golang/go/blob/82517acae866d60a9754d44d004bfa159e656c07/src/net/dial_test.go#L177-L179
----
So it comes as no surprise that the test consistently fails on my new Surface Book 3:
```
PS C:\Users\bryan\src\go\src> ..\bin\go version
go version devel go1.17-0ebd5a8de0 Tue Jun 22 16:59:10 2021 +0000 windows/amd64
PS C:\Users\bryan\src\go\src> ..\bin\go env
set GO111MODULE=
set GOARCH=amd64
set GOBIN=
set GOCACHE=C:\Users\bryan\AppData\Local\go-build
set GOENV=C:\Users\bryan\AppData\Roaming\go\env
set GOEXE=.exe
set GOFLAGS=
set GOHOSTARCH=amd64
set GOHOSTOS=windows
set GOINSECURE=
set GOMODCACHE=C:\Users\bryan\go\pkg\mod
set GONOPROXY=
set GONOSUMDB=
set GOOS=windows
set GOPATH=C:\Users\bryan\go
set GOPRIVATE=
set GOPROXY=https://proxy.golang.org,direct
set GOROOT=C:\Users\bryan\src\go
set GOSUMDB=sum.golang.org
set GOTMPDIR=
set GOTOOLDIR=C:\Users\bryan\src\go\pkg\tool\windows_amd64
set GOVCS=
set GOVERSION=devel go1.17-0ebd5a8de0 Tue Jun 22 16:59:10 2021 +0000
set GCCGO=gccgo
set AR=ar
set CC=gcc
set CXX=g++
set CGO_ENABLED=1
set GOMOD=C:\Users\bryan\src\go\src\go.mod
set CGO_CFLAGS=-g -O2
set CGO_CPPFLAGS=
set CGO_CXXFLAGS=-g -O2
set CGO_FFLAGS=-g -O2
set CGO_LDFLAGS=-g -O2
set PKG_CONFIG=pkg-config
set GOGCCFLAGS=-m64 -mthreads -fmessage-length=0 -fdebug-prefix-map=C:\Users\bryan\AppData\Local\Temp\go-build2503220696=/tmp/go-build -gno-record-gcc-switches
PS C:\Users\bryan\src\go\src> ..\bin\go test net
--- FAIL: TestDialParallel (12.92s)
dial_test.go:188: dialClosedPort: measured delay 2.0038828s
dial_test.go:203: got 2.0038828s; want <= 1.5s
FAIL
FAIL net 45.755s
FAIL
PS C:\Users\bryan\src\go\src>
```
Probably the tests should be reworked not to rely on hard-coded timeouts at all.
|
non_process
|
net testdialparallel spuriously fails due to hard coded timeout in dialclosedport we know from past experience that hard coded timeouts lead to flaky tests the dialclosedport helper function has one such hard coded timeout the test provides no rationale for why we expect to be a firm upper bound on windows for that matter it provides no rationale as to why we expect or to be firm upper bounds on other platforms and indeed it isn t a firm upper bound on those other platforms either so it comes as no surprise that the test consistently fails on my new surface book ps c users bryan src go src bin go version go version devel tue jun windows ps c users bryan src go src bin go env set set goarch set gobin set gocache c users bryan appdata local go build set goenv c users bryan appdata roaming go env set goexe exe set goflags set gohostarch set gohostos windows set goinsecure set gomodcache c users bryan go pkg mod set gonoproxy set gonosumdb set goos windows set gopath c users bryan go set goprivate set goproxy set goroot c users bryan src go set gosumdb sum golang org set gotmpdir set gotooldir c users bryan src go pkg tool windows set govcs set goversion devel tue jun set gccgo gccgo set ar ar set cc gcc set cxx g set cgo enabled set gomod c users bryan src go src go mod set cgo cflags g set cgo cppflags set cgo cxxflags g set cgo fflags g set cgo ldflags g set pkg config pkg config set gogccflags mthreads fmessage length fdebug prefix map c users bryan appdata local temp go tmp go build gno record gcc switches ps c users bryan src go src bin go test net fail testdialparallel dial test go dialclosedport measured delay dial test go got want fail fail net fail ps c users bryan src go src probably the tests should be reworked not to rely on hard coded timeouts at all
| 0
|
471,925
| 13,613,190,491
|
IssuesEvent
|
2020-09-23 11:29:41
|
knative/eventing
|
https://api.github.com/repos/knative/eventing
|
closed
|
pingsource-controller cannot update pingsources/status
|
area/sources kind/bug kind/good-first-issue priority/important-soon
|
**Describe the bug**
seeing this in the log:
```
Warning UpdateFailed 44s (x5 over 44s) pingsource-controller Failed to update status for "pinger": pingsources.sources.knative.dev "pinger" is forbidden: User "system:serviceaccount:knative-eventing:pingsource-mt-adapter" cannot update resource "pingsources/status" in API group "sources.knative.dev" in the namespace "test"
```
**Expected behavior**
no error
**To Reproduce**
Steps to reproduce the behavior.
**Knative release version**
**Additional context**
Add any other context about the problem here such as proposed priority
|
1.0
|
pingsource-controller cannot update pingsources/status - **Describe the bug**
seeing this in the log:
```
Warning UpdateFailed 44s (x5 over 44s) pingsource-controller Failed to update status for "pinger": pingsources.sources.knative.dev "pinger" is forbidden: User "system:serviceaccount:knative-eventing:pingsource-mt-adapter" cannot update resource "pingsources/status" in API group "sources.knative.dev" in the namespace "test"
```
**Expected behavior**
no error
**To Reproduce**
Steps to reproduce the behavior.
**Knative release version**
**Additional context**
Add any other context about the problem here such as proposed priority
|
non_process
|
pingsource controller cannot update pingsources status describe the bug seeing this in the log warning updatefailed over pingsource controller failed to update status for pinger pingsources sources knative dev pinger is forbidden user system serviceaccount knative eventing pingsource mt adapter cannot update resource pingsources status in api group sources knative dev in the namespace test expected behavior no error to reproduce steps to reproduce the behavior knative release version additional context add any other context about the problem here such as proposed priority
| 0
|
17,772
| 23,699,802,430
|
IssuesEvent
|
2022-08-29 17:52:07
|
dtcenter/MET
|
https://api.github.com/repos/dtcenter/MET
|
opened
|
Add support for new interpolation methods for Point2Grid
|
type: enhancement priority: medium alert: NEED ACCOUNT KEY alert: NEED PROJECT ASSIGNMENT requestor: METplus Team MET: PreProcessing Tools (Point)
|
## Describe the Enhancement ##
This issue arose via dtcenter/METplus#1768. None of the existing interpolation methods (min/max/median/uw_mean) are appropriate for categorical data such as precipitation type. Recommend enhancing Point2Grid to keep track of the distance between each observation location and the nearest grid point. But consider only doing so for `-method nearest` and `-method dw_mean` to avoid increasing the runtimes in general. Use the distance information to add support for these two interpolation methods.
Also, review other interpolation methods supported by other MET tools to see if any other can be easily added.
### Time Estimate ###
2 days.
### Sub-Issues ###
Consider breaking the enhancement down into sub-issues.
None needed.
### Relevant Deadlines ###
*List relevant project deadlines here or state NONE.*
### Funding Source ###
*Define the source of funding and account keys here or state NONE.*
## Define the Metadata ##
### Assignee ###
- [ ] Select **engineer(s)** or **no engineer** required
- [ ] Select **scientist(s)** or **no scientist** required
### Labels ###
- [x] Select **component(s)**
- [x] Select **priority**
- [x] Select **requestor(s)**
### Projects and Milestone ###
- [x] Select **Repository** and/or **Organization** level **Project(s)** or add **alert: NEED PROJECT ASSIGNMENT** label
- [x] Select **Milestone** as the next official version or **Future Versions**
## Define Related Issue(s) ##
Consider the impact to the other METplus components.
- [x] [METplus](https://github.com/dtcenter/METplus/issues/new/choose), [MET](https://github.com/dtcenter/MET/issues/new/choose), [METdataio](https://github.com/dtcenter/METdataio/issues/new/choose), [METviewer](https://github.com/dtcenter/METviewer/issues/new/choose), [METexpress](https://github.com/dtcenter/METexpress/issues/new/choose), [METcalcpy](https://github.com/dtcenter/METcalcpy/issues/new/choose), [METplotpy](https://github.com/dtcenter/METplotpy/issues/new/choose)
- [ ] May need a METplus issue to make this more configurable... or maybe not?
## Enhancement Checklist ##
See the [METplus Workflow](https://metplus.readthedocs.io/en/latest/Contributors_Guide/github_workflow.html) for details.
- [ ] Complete the issue definition above, including the **Time Estimate** and **Funding Source**.
- [ ] Fork this repository or create a branch of **develop**.
Branch name: `feature_<Issue Number>_<Description>`
- [ ] Complete the development and test your changes.
- [ ] Add/update log messages for easier debugging.
- [ ] Add/update unit tests.
- [ ] Add/update documentation.
- [ ] Push local changes to GitHub.
- [ ] Submit a pull request to merge into **develop**.
Pull request: `feature <Issue Number> <Description>`
- [ ] Define the pull request metadata, as permissions allow.
Select: **Reviewer(s)** and **Linked issues**
Select: **Repository** level development cycle **Project** for the next official release
Select: **Milestone** as the next official version
- [ ] Iterate until the reviewer(s) accept and merge your changes.
- [ ] Delete your fork or branch.
- [ ] Close this issue.
|
1.0
|
Add support for new interpolation methods for Point2Grid - ## Describe the Enhancement ##
This issue arose via dtcenter/METplus#1768. None of the existing interpolation methods (min/max/median/uw_mean) are appropriate for categorical data such as precipitation type. Recommend enhancing Point2Grid to keep track of the distance between each observation location and the nearest grid point. But consider only doing so for `-method nearest` and `-method dw_mean` to avoid increasing the runtimes in general. Use the distance information to add support for these two interpolation methods.
Also, review other interpolation methods supported by other MET tools to see if any other can be easily added.
### Time Estimate ###
2 days.
### Sub-Issues ###
Consider breaking the enhancement down into sub-issues.
None needed.
### Relevant Deadlines ###
*List relevant project deadlines here or state NONE.*
### Funding Source ###
*Define the source of funding and account keys here or state NONE.*
## Define the Metadata ##
### Assignee ###
- [ ] Select **engineer(s)** or **no engineer** required
- [ ] Select **scientist(s)** or **no scientist** required
### Labels ###
- [x] Select **component(s)**
- [x] Select **priority**
- [x] Select **requestor(s)**
### Projects and Milestone ###
- [x] Select **Repository** and/or **Organization** level **Project(s)** or add **alert: NEED PROJECT ASSIGNMENT** label
- [x] Select **Milestone** as the next official version or **Future Versions**
## Define Related Issue(s) ##
Consider the impact to the other METplus components.
- [x] [METplus](https://github.com/dtcenter/METplus/issues/new/choose), [MET](https://github.com/dtcenter/MET/issues/new/choose), [METdataio](https://github.com/dtcenter/METdataio/issues/new/choose), [METviewer](https://github.com/dtcenter/METviewer/issues/new/choose), [METexpress](https://github.com/dtcenter/METexpress/issues/new/choose), [METcalcpy](https://github.com/dtcenter/METcalcpy/issues/new/choose), [METplotpy](https://github.com/dtcenter/METplotpy/issues/new/choose)
- [ ] May need a METplus issue to make this more configurable... or maybe not?
## Enhancement Checklist ##
See the [METplus Workflow](https://metplus.readthedocs.io/en/latest/Contributors_Guide/github_workflow.html) for details.
- [ ] Complete the issue definition above, including the **Time Estimate** and **Funding Source**.
- [ ] Fork this repository or create a branch of **develop**.
Branch name: `feature_<Issue Number>_<Description>`
- [ ] Complete the development and test your changes.
- [ ] Add/update log messages for easier debugging.
- [ ] Add/update unit tests.
- [ ] Add/update documentation.
- [ ] Push local changes to GitHub.
- [ ] Submit a pull request to merge into **develop**.
Pull request: `feature <Issue Number> <Description>`
- [ ] Define the pull request metadata, as permissions allow.
Select: **Reviewer(s)** and **Linked issues**
Select: **Repository** level development cycle **Project** for the next official release
Select: **Milestone** as the next official version
- [ ] Iterate until the reviewer(s) accept and merge your changes.
- [ ] Delete your fork or branch.
- [ ] Close this issue.
|
process
|
add support for new interpolation methods for describe the enhancement this issue arose via dtcenter metplus none of the existing interpolation methods min max median uw mean are appropriate for categorical data such as precipitation type recommend enhancing to keep track of the distance between each observation location and the nearest grid point but consider only doing so for method nearest and method dw mean to avoid increasing the runtimes in general use the distance information to add support for these two interpolation methods also review other interpolation methods supported by other met tools to see if any other can be easily added time estimate days sub issues consider breaking the enhancement down into sub issues none needed relevant deadlines list relevant project deadlines here or state none funding source define the source of funding and account keys here or state none define the metadata assignee select engineer s or no engineer required select scientist s or no scientist required labels select component s select priority select requestor s projects and milestone select repository and or organization level project s or add alert need project assignment label select milestone as the next official version or future versions define related issue s consider the impact to the other metplus components may need a metplus issue to make this more configurable or maybe not enhancement checklist see the for details complete the issue definition above including the time estimate and funding source fork this repository or create a branch of develop branch name feature complete the development and test your changes add update log messages for easier debugging add update unit tests add update documentation push local changes to github submit a pull request to merge into develop pull request feature define the pull request metadata as permissions allow select reviewer s and linked issues select repository level development cycle project for the next official release select milestone as the next official version iterate until the reviewer s accept and merge your changes delete your fork or branch close this issue
| 1
|
49,863
| 6,274,904,108
|
IssuesEvent
|
2017-07-18 04:26:10
|
phetsims/ohms-law
|
https://api.github.com/repos/phetsims/ohms-law
|
closed
|
Screen layout is scaled way too high
|
design:general priority:3-medium
|
Somewhere down the road (between the release of 1.2.0 and 1.3.0), the layout of many things on the screen changed.
1.2.0 (the good one)
<img width="1920" alt="screen shot 2017-07-12 at 11 37 06 am" src="https://user-images.githubusercontent.com/5863899/28131234-831035b4-66f6-11e7-927d-c1d670da0b96.png">
Every version 1.3.0+
<img width="1920" alt="screen shot 2017-07-12 at 11 37 19 am" src="https://user-images.githubusercontent.com/5863899/28131237-86f54d04-66f6-11e7-8041-da1406d07063.png">
Generally, it looks like the entire screen was "zoomed in" causing everything to be larger and:
- The equation and circuit (all parts of it) are shifted down to the left
- The panel and the buttons below are shifted right and up
@zepumph, myself and @ariel-phet recommend changing the screen layout back to its original size (like that of 1.2.0).
For phetsims/QA/issues/18.
|
1.0
|
Screen layout is scaled way too high - Somewhere down the road (between the release of 1.2.0 and 1.3.0), the layout of many things on the screen changed.
1.2.0 (the good one)
<img width="1920" alt="screen shot 2017-07-12 at 11 37 06 am" src="https://user-images.githubusercontent.com/5863899/28131234-831035b4-66f6-11e7-927d-c1d670da0b96.png">
Every version 1.3.0+
<img width="1920" alt="screen shot 2017-07-12 at 11 37 19 am" src="https://user-images.githubusercontent.com/5863899/28131237-86f54d04-66f6-11e7-8041-da1406d07063.png">
Generally, it looks like the entire screen was "zoomed in" causing everything to be larger and:
- The equation and circuit (all parts of it) are shifted down to the left
- The panel and the buttons below are shifted right and up
@zepumph, myself and @ariel-phet recommend changing the screen layout back to its original size (like that of 1.2.0).
For phetsims/QA/issues/18.
|
non_process
|
screen layout is scaled way too high somewhere down the road between the release of and the layout of many things on the screen changed the good one img width alt screen shot at am src every version img width alt screen shot at am src generally it looks like the entire screen was zoomed in causing everything to be larger and the equation and circuit all parts of it are shifted down to the left the panel and the buttons below are shifted right and up zepumph myself and ariel phet recommend changing the screen layout back to its original size like that of for phetsims qa issues
| 0
|
14,514
| 17,611,587,631
|
IssuesEvent
|
2021-08-18 02:34:07
|
googleapis/python-spanner
|
https://api.github.com/repos/googleapis/python-spanner
|
closed
|
tests.system.test_session_api: many tests failed
|
api: spanner type: process priority: p1 flakybot: issue flakybot: flaky
|
Many tests failed at the same time in this package.
* I will close this issue when there are no more failures in this package _and_
there is at least one pass.
* No new issues will be filed for this package until this issue is closed.
* If there are already issues for individual test cases, I will close them when
the corresponding test passes. You can close them earlier, if you prefer, and
I won't reopen them while this issue is still open.
Here are the tests that failed:
* test_session_crud
* test_batch_insert_then_read
* test_batch_insert_then_read_string_array_of_string
* test_batch_insert_then_read_all_datatypes
* test_batch_insert_or_update_then_query
* test_batch_insert_w_commit_timestamp
* test_transaction_read_and_insert_then_rollback
* test_transaction_read_and_insert_then_exception
* test_transaction_read_and_insert_or_update_then_commit
* test_transaction_execute_sql_w_dml_read_rollback
* test_transaction_execute_update_read_commit
* test_transaction_execute_update_then_insert_commit (#485)
* test_transaction_batch_update_success
* test_transaction_batch_update_and_execute_dml
* test_transaction_batch_update_w_syntax_error
* test_transaction_batch_update_wo_statements
* test_execute_partitioned_dml
* test_transaction_read_w_concurrent_updates
* test_transaction_query_w_concurrent_updates
* test_transaction_read_w_abort
* test_read_with_single_keys_index
* test_empty_read_with_single_keys_index
* test_read_with_multiple_keys_index
* test_snapshot_read_w_various_staleness
* test_multiuse_snapshot_read_isolation_strong
* test_multiuse_snapshot_read_isolation_read_timestamp
* test_multiuse_snapshot_read_isolation_exact_staleness
* test_read_w_index
* test_read_w_single_key
* test_empty_read
* test_read_w_multiple_keys
* test_read_w_limit
* test_read_w_ranges
* test_read_partial_range_until_end
* test_read_partial_range_from_beginning
* test_read_with_range_keys_index_single_key
* test_read_with_range_keys_index_closed_closed
* test_read_with_range_keys_index_closed_open
* test_read_with_range_keys_index_open_closed
* test_read_with_range_keys_index_open_open
* test_read_with_range_keys_index_limit_closed_closed
* test_read_with_range_keys_index_limit_closed_open
* test_read_with_range_keys_index_limit_open_closed
* test_read_with_range_keys_index_limit_open_open
* test_read_with_range_keys_and_index_closed_closed
* test_read_with_range_keys_and_index_closed_open
* test_read_with_range_keys_and_index_open_closed
* test_read_with_range_keys_and_index_open_open
* test_partition_read_w_index
* test_execute_sql_w_manual_consume
* test_multiuse_snapshot_execute_sql_isolation_strong
* test_execute_sql_returning_array_of_struct
* test_execute_sql_returning_empty_array_of_struct
* test_invalid_type
* test_execute_sql_select_1
* test_execute_sql_w_string_bindings
* test_execute_sql_w_bool_bindings
* test_execute_sql_w_int64_bindings
* test_execute_sql_w_float64_bindings
* test_execute_sql_w_float_bindings_transfinite
* test_execute_sql_w_bytes_bindings
* test_execute_sql_w_timestamp_bindings
* test_execute_sql_w_date_bindings
* test_execute_sql_w_numeric_bindings
* test_execute_sql_w_query_param_struct
* test_execute_sql_returning_transfinite_floats
* test_partition_query
-----
commit: 492ad09d6394c5f6d743dcd1dc8fccc1a5ebfdae
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/e8d034d6-c790-4330-b6ff-4aa511b1f809), [Sponge](http://sponge2/e8d034d6-c790-4330-b6ff-4aa511b1f809)
status: failed
|
1.0
|
tests.system.test_session_api: many tests failed - Many tests failed at the same time in this package.
* I will close this issue when there are no more failures in this package _and_
there is at least one pass.
* No new issues will be filed for this package until this issue is closed.
* If there are already issues for individual test cases, I will close them when
the corresponding test passes. You can close them earlier, if you prefer, and
I won't reopen them while this issue is still open.
Here are the tests that failed:
* test_session_crud
* test_batch_insert_then_read
* test_batch_insert_then_read_string_array_of_string
* test_batch_insert_then_read_all_datatypes
* test_batch_insert_or_update_then_query
* test_batch_insert_w_commit_timestamp
* test_transaction_read_and_insert_then_rollback
* test_transaction_read_and_insert_then_exception
* test_transaction_read_and_insert_or_update_then_commit
* test_transaction_execute_sql_w_dml_read_rollback
* test_transaction_execute_update_read_commit
* test_transaction_execute_update_then_insert_commit (#485)
* test_transaction_batch_update_success
* test_transaction_batch_update_and_execute_dml
* test_transaction_batch_update_w_syntax_error
* test_transaction_batch_update_wo_statements
* test_execute_partitioned_dml
* test_transaction_read_w_concurrent_updates
* test_transaction_query_w_concurrent_updates
* test_transaction_read_w_abort
* test_read_with_single_keys_index
* test_empty_read_with_single_keys_index
* test_read_with_multiple_keys_index
* test_snapshot_read_w_various_staleness
* test_multiuse_snapshot_read_isolation_strong
* test_multiuse_snapshot_read_isolation_read_timestamp
* test_multiuse_snapshot_read_isolation_exact_staleness
* test_read_w_index
* test_read_w_single_key
* test_empty_read
* test_read_w_multiple_keys
* test_read_w_limit
* test_read_w_ranges
* test_read_partial_range_until_end
* test_read_partial_range_from_beginning
* test_read_with_range_keys_index_single_key
* test_read_with_range_keys_index_closed_closed
* test_read_with_range_keys_index_closed_open
* test_read_with_range_keys_index_open_closed
* test_read_with_range_keys_index_open_open
* test_read_with_range_keys_index_limit_closed_closed
* test_read_with_range_keys_index_limit_closed_open
* test_read_with_range_keys_index_limit_open_closed
* test_read_with_range_keys_index_limit_open_open
* test_read_with_range_keys_and_index_closed_closed
* test_read_with_range_keys_and_index_closed_open
* test_read_with_range_keys_and_index_open_closed
* test_read_with_range_keys_and_index_open_open
* test_partition_read_w_index
* test_execute_sql_w_manual_consume
* test_multiuse_snapshot_execute_sql_isolation_strong
* test_execute_sql_returning_array_of_struct
* test_execute_sql_returning_empty_array_of_struct
* test_invalid_type
* test_execute_sql_select_1
* test_execute_sql_w_string_bindings
* test_execute_sql_w_bool_bindings
* test_execute_sql_w_int64_bindings
* test_execute_sql_w_float64_bindings
* test_execute_sql_w_float_bindings_transfinite
* test_execute_sql_w_bytes_bindings
* test_execute_sql_w_timestamp_bindings
* test_execute_sql_w_date_bindings
* test_execute_sql_w_numeric_bindings
* test_execute_sql_w_query_param_struct
* test_execute_sql_returning_transfinite_floats
* test_partition_query
-----
commit: 492ad09d6394c5f6d743dcd1dc8fccc1a5ebfdae
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/e8d034d6-c790-4330-b6ff-4aa511b1f809), [Sponge](http://sponge2/e8d034d6-c790-4330-b6ff-4aa511b1f809)
status: failed
|
process
|
tests system test session api many tests failed many tests failed at the same time in this package i will close this issue when there are no more failures in this package and there is at least one pass no new issues will be filed for this package until this issue is closed if there are already issues for individual test cases i will close them when the corresponding test passes you can close them earlier if you prefer and i won t reopen them while this issue is still open here are the tests that failed test session crud test batch insert then read test batch insert then read string array of string test batch insert then read all datatypes test batch insert or update then query test batch insert w commit timestamp test transaction read and insert then rollback test transaction read and insert then exception test transaction read and insert or update then commit test transaction execute sql w dml read rollback test transaction execute update read commit test transaction execute update then insert commit test transaction batch update success test transaction batch update and execute dml test transaction batch update w syntax error test transaction batch update wo statements test execute partitioned dml test transaction read w concurrent updates test transaction query w concurrent updates test transaction read w abort test read with single keys index test empty read with single keys index test read with multiple keys index test snapshot read w various staleness test multiuse snapshot read isolation strong test multiuse snapshot read isolation read timestamp test multiuse snapshot read isolation exact staleness test read w index test read w single key test empty read test read w multiple keys test read w limit test read w ranges test read partial range until end test read partial range from beginning test read with range keys index single key test read with range keys index closed closed test read with range keys index closed open test read with range keys index open closed test read with range keys index open open test read with range keys index limit closed closed test read with range keys index limit closed open test read with range keys index limit open closed test read with range keys index limit open open test read with range keys and index closed closed test read with range keys and index closed open test read with range keys and index open closed test read with range keys and index open open test partition read w index test execute sql w manual consume test multiuse snapshot execute sql isolation strong test execute sql returning array of struct test execute sql returning empty array of struct test invalid type test execute sql select test execute sql w string bindings test execute sql w bool bindings test execute sql w bindings test execute sql w bindings test execute sql w float bindings transfinite test execute sql w bytes bindings test execute sql w timestamp bindings test execute sql w date bindings test execute sql w numeric bindings test execute sql w query param struct test execute sql returning transfinite floats test partition query commit buildurl status failed
| 1
|
3,155
| 6,205,830,417
|
IssuesEvent
|
2017-07-06 17:01:05
|
linked-art/linked.art
|
https://api.github.com/repos/linked-art/linked.art
|
closed
|
Make slack /mark response a link to the issue
|
enhancement process website
|
If we can figure out how to get the response to render markdown or html, rather than just raw text.
|
1.0
|
Make slack /mark response a link to the issue -
If we can figure out how to get the response to render markdown or html, rather than just raw text.
|
process
|
make slack mark response a link to the issue if we can figure out how to get the response to render markdown or html rather than just raw text
| 1
|
11,124
| 13,957,686,825
|
IssuesEvent
|
2020-10-24 08:09:04
|
alexanderkotsev/geoportal
|
https://api.github.com/repos/alexanderkotsev/geoportal
|
opened
|
Download services with username/password protection
|
DK - Denmark Geoportal Harvesting process
|
Dear help-team
It is clear that when so many has raised issues here in the helpdesk regarding the same topic it calls for action. The new logic implemented in the harvesting procedure to the Geoportal goes beyond the Directive.
As far as I understand when reading all the frustrated questions and answers from JRC, the Geoportal now looks for download services that actually works and return data. That sounds fair – also from a user perspective.
I can see that five of the Danish download services (pre-defined WFS with stored queries) has been rejected – the response time is too high. Fair enough. That is understandable.
What I cannot understand is that my Agency´s download services (pre-defined Atom feed) has been rejected with the reason (see issue #3677) that they are protected behind username/password. I question if this within the legal frame of the Directive and, please point out for me where JRC has the legality to require that INSPIRE download services shall be open and free! I cannot find that legal requirement and I therefor asked my agency´s internal legal service to assist me. That seems by the way irrelevant when reading Angelo´s answer to Ine in issue #3679:
It is highly frustrating to face this kind of interruption without any kind of warning! It is not the right way to postpone an explanation until the MIG-T meeting in mid-October. It has to handled immediately and MIG-T is indeed not the right forum – when the new logic has such high impact on the national implementation (requirement of open services) it has to go through MIG (P).
Br
Lars
|
1.0
|
Download services with username/password protection - Dear help-team
It is clear that when so many has raised issues here in the helpdesk regarding the same topic it calls for action. The new logic implemented in the harvesting procedure to the Geoportal goes beyond the Directive.
As far as I understand when reading all the frustrated questions and answers from JRC, the Geoportal now looks for download services that actually works and return data. That sounds fair – also from a user perspective.
I can see that five of the Danish download services (pre-defined WFS with stored queries) has been rejected – the response time is too high. Fair enough. That is understandable.
What I cannot understand is that my Agency´s download services (pre-defined Atom feed) has been rejected with the reason (see issue #3677) that they are protected behind username/password. I question if this within the legal frame of the Directive and, please point out for me where JRC has the legality to require that INSPIRE download services shall be open and free! I cannot find that legal requirement and I therefor asked my agency´s internal legal service to assist me. That seems by the way irrelevant when reading Angelo´s answer to Ine in issue #3679:
It is highly frustrating to face this kind of interruption without any kind of warning! It is not the right way to postpone an explanation until the MIG-T meeting in mid-October. It has to handled immediately and MIG-T is indeed not the right forum – when the new logic has such high impact on the national implementation (requirement of open services) it has to go through MIG (P).
Br
Lars
|
process
|
download services with username password protection dear help team it is clear that when so many has raised issues here in the helpdesk regarding the same topic it calls for action the new logic implemented in the harvesting procedure to the geoportal goes beyond the directive as far as i understand when reading all the frustrated questions and answers from jrc the geoportal now looks for download services that actually works and return data that sounds fair ndash also from a user perspective i can see that five of the danish download services pre defined wfs with stored queries has been rejected ndash the response time is too high fair enough that is understandable what i cannot understand is that my agency acute s download services pre defined atom feed has been rejected with the reason see issue that they are protected behind username password i question if this within the legal frame of the directive and please point out for me where jrc has the legality to require that inspire download services shall be open and free i cannot find that legal requirement and i therefor asked my agency acute s internal legal service to assist me that seems by the way irrelevant when reading angelo acute s answer to ine in issue it is highly frustrating to face this kind of interruption without any kind of warning it is not the right way to postpone an explanation until the mig t meeting in mid october it has to handled immediately and mig t is indeed not the right forum ndash when the new logic has such high impact on the national implementation requirement of open services it has to go through mig p br lars
| 1
|
12,739
| 3,642,420,944
|
IssuesEvent
|
2016-02-14 09:58:30
|
lorenzofox3/Smart-Table
|
https://api.github.com/repos/lorenzofox3/Smart-Table
|
closed
|
Share our plugins
|
documentation
|
Hi
Could we somehow share our extensions for your plugin?
I think it would be great, then some people don't have to rewrite stuff already implemented.
|
1.0
|
Share our plugins - Hi
Could we somehow share our extensions for your plugin?
I think it would be great, then some people don't have to rewrite stuff already implemented.
|
non_process
|
share our plugins hi could we somehow share our extensions for your plugin i think it would be great then some people don t have to rewrite stuff already implemented
| 0
|
326,942
| 28,033,071,129
|
IssuesEvent
|
2023-03-28 13:33:44
|
adoptium/infrastructure
|
https://api.github.com/repos/adoptium/infrastructure
|
closed
|
test-marist-ubuntu2204-s390x-1 has run out of storage space
|
arch:s390x (zLinux) provider:marist testFail
|
- test suite/name (e.g, BUILD_LIST, TARGET, CUSTOM_TARGET)?
extended.openjdk
- a link into recent `Test_` job on https://ci.adoptium.net which showed the failure
https://ci.adoptium.net/job/Test_openjdk17_hs_extended.openjdk_s390x_linux_testList_2/81/console
- Is there an existing issue elsewhere covering this?
Not that I can find.
- Which machine(s) does it work on?
All other machines, it appears.
- Which machine(s) does it fail on?
test-marist-ubuntu2204-s390x-1
Any other details:
```
java.nio.file.FileSystemException: /home/jenkins/workspace/Test_openjdk17_hs_extended.openjdk_s390x_linux_testList_2: No space left on device
```
|
1.0
|
test-marist-ubuntu2204-s390x-1 has run out of storage space - - test suite/name (e.g, BUILD_LIST, TARGET, CUSTOM_TARGET)?
extended.openjdk
- a link into recent `Test_` job on https://ci.adoptium.net which showed the failure
https://ci.adoptium.net/job/Test_openjdk17_hs_extended.openjdk_s390x_linux_testList_2/81/console
- Is there an existing issue elsewhere covering this?
Not that I can find.
- Which machine(s) does it work on?
All other machines, it appears.
- Which machine(s) does it fail on?
test-marist-ubuntu2204-s390x-1
Any other details:
```
java.nio.file.FileSystemException: /home/jenkins/workspace/Test_openjdk17_hs_extended.openjdk_s390x_linux_testList_2: No space left on device
```
|
non_process
|
test marist has run out of storage space test suite name e g build list target custom target extended openjdk a link into recent test job on which showed the failure is there an existing issue elsewhere covering this not that i can find which machine s does it work on all other machines it appears which machine s does it fail on test marist any other details java nio file filesystemexception home jenkins workspace test hs extended openjdk linux testlist no space left on device
| 0
|
15,750
| 19,911,654,480
|
IssuesEvent
|
2022-01-25 17:45:58
|
input-output-hk/high-assurance-legacy
|
https://api.github.com/repos/input-output-hk/high-assurance-legacy
|
closed
|
Move the proofs of bisimilarity core laws into separate theories
|
language: isabelle topic: process calculus type: improvement
|
Currently the proofs of the bisimilarity core laws of the basic and the proper transition system are part of the theories `Basic_Transition_System` and `Proper_Transition_System` respectively. Our plan is to move them into new, dedicated theories `Basic_Bisimilarity_Core_Laws` and `Proper_Bisimilarity_Core_Laws`.
|
1.0
|
Move the proofs of bisimilarity core laws into separate theories - Currently the proofs of the bisimilarity core laws of the basic and the proper transition system are part of the theories `Basic_Transition_System` and `Proper_Transition_System` respectively. Our plan is to move them into new, dedicated theories `Basic_Bisimilarity_Core_Laws` and `Proper_Bisimilarity_Core_Laws`.
|
process
|
move the proofs of bisimilarity core laws into separate theories currently the proofs of the bisimilarity core laws of the basic and the proper transition system are part of the theories basic transition system and proper transition system respectively our plan is to move them into new dedicated theories basic bisimilarity core laws and proper bisimilarity core laws
| 1
|
22,735
| 32,055,310,859
|
IssuesEvent
|
2023-09-24 02:17:09
|
levaintech/contented
|
https://api.github.com/repos/levaintech/contented
|
closed
|
`contented-extra`
|
kind/feature needs/triage area/contented-processor
|
<!-- Please only use this template for submitting enhancement/feature requests -->
#### What would you like to be added:
- [ ] Parse `js/ts` documentations into Markdown into HTML
- [x] Parse `jest` documentations/comments into Markdown into HTML (Better DX, instead of parsing markdown into jest)
- [ ] Parse `GRPC` documentations/comments into Markdown into HTM
#### Why is this needed:
Contextual documentations.
/triage accepted
/area contented-processor
|
1.0
|
`contented-extra` - <!-- Please only use this template for submitting enhancement/feature requests -->
#### What would you like to be added:
- [ ] Parse `js/ts` documentations into Markdown into HTML
- [x] Parse `jest` documentations/comments into Markdown into HTML (Better DX, instead of parsing markdown into jest)
- [ ] Parse `GRPC` documentations/comments into Markdown into HTM
#### Why is this needed:
Contextual documentations.
/triage accepted
/area contented-processor
|
process
|
contented extra what would you like to be added parse js ts documentations into markdown into html parse jest documentations comments into markdown into html better dx instead of parsing markdown into jest parse grpc documentations comments into markdown into htm why is this needed contextual documentations triage accepted area contented processor
| 1
|
85,383
| 16,657,728,533
|
IssuesEvent
|
2021-06-05 20:51:05
|
JAMart01/robot-gladiators
|
https://api.github.com/repos/JAMart01/robot-gladiators
|
closed
|
Initial game functionality - MVP
|
initial-code
|
_Must Have_
- Build a game where a player's robot can fight another robot until one of them loses.
- If the enemy-robot loses first, the player's robot will move on to fight another enemy-robot.
_Features_
- The player's robot's name can be dynamically created by the player through the browser.
- The player is given the option to skip the fight by paying a penalty fee, or continue with the fight.
|
1.0
|
Initial game functionality - MVP - _Must Have_
- Build a game where a player's robot can fight another robot until one of them loses.
- If the enemy-robot loses first, the player's robot will move on to fight another enemy-robot.
_Features_
- The player's robot's name can be dynamically created by the player through the browser.
- The player is given the option to skip the fight by paying a penalty fee, or continue with the fight.
|
non_process
|
initial game functionality mvp must have build a game where a player s robot can fight another robot until one of them loses if the enemy robot loses first the player s robot will move on to fight another enemy robot features the player s robot s name can be dynamically created by the player through the browser the player is given the option to skip the fight by paying a penalty fee or continue with the fight
| 0
|
7,329
| 10,468,939,388
|
IssuesEvent
|
2019-09-22 17:11:21
|
produvia/ai-platform
|
https://api.github.com/repos/produvia/ai-platform
|
closed
|
Text Generation
|
natural-language-processing task
|
# Goal(s)
- Generate text which appears indistinguishable to human-written text
# Input(s)
- Parameters
# Output(s)
- Sentence
# Objective Function(s)
- TBD
|
1.0
|
Text Generation - # Goal(s)
- Generate text which appears indistinguishable to human-written text
# Input(s)
- Parameters
# Output(s)
- Sentence
# Objective Function(s)
- TBD
|
process
|
text generation goal s generate text which appears indistinguishable to human written text input s parameters output s sentence objective function s tbd
| 1
|
257,680
| 27,563,807,705
|
IssuesEvent
|
2023-03-08 01:07:56
|
samqws-marketing/coursera_naptime
|
https://api.github.com/repos/samqws-marketing/coursera_naptime
|
opened
|
guice-multibindings-4.1.0.jar: 2 vulnerabilities (highest severity is: 5.9)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guice-multibindings-4.1.0.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.google.guava/guava/bundles/guava-19.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/coursera_naptime/commit/19874cd7130f9fd589f25c8113d6a8cb697bb729">19874cd7130f9fd589f25c8113d6a8cb697bb729</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (guice-multibindings version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2018-10237](https://www.mend.io/vulnerability-database/CVE-2018-10237) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | guava-19.0.jar | Transitive | 4.2.1 | ❌ |
| [CVE-2020-8908](https://www.mend.io/vulnerability-database/CVE-2020-8908) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | guava-19.0.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-10237</summary>
### Vulnerable Library - <b>guava-19.0.jar</b></p>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.google.guava/guava/bundles/guava-19.0.jar</p>
<p>
Dependency Hierarchy:
- guice-multibindings-4.1.0.jar (Root Library)
- guice-4.1.0.jar
- :x: **guava-19.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/coursera_naptime/commit/19874cd7130f9fd589f25c8113d6a8cb697bb729">19874cd7130f9fd589f25c8113d6a8cb697bb729</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Unbounded memory allocation in Google Guava 11.0 through 24.x before 24.1.1 allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker-provided data, because the AtomicDoubleArray class (when serialized with Java serialization) and the CompoundOrdering class (when serialized with GWT serialization) perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable.
<p>Publish Date: 2018-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-10237>CVE-2018-10237</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-10237">https://nvd.nist.gov/vuln/detail/CVE-2018-10237</a></p>
<p>Release Date: 2018-04-26</p>
<p>Fix Resolution (com.google.guava:guava): 24.1.1-android</p>
<p>Direct dependency fix Resolution (com.google.inject.extensions:guice-multibindings): 4.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-8908</summary>
### Vulnerable Library - <b>guava-19.0.jar</b></p>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.google.guava/guava/bundles/guava-19.0.jar</p>
<p>
Dependency Hierarchy:
- guice-multibindings-4.1.0.jar (Root Library)
- guice-4.1.0.jar
- :x: **guava-19.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/coursera_naptime/commit/19874cd7130f9fd589f25c8113d6a8cb697bb729">19874cd7130f9fd589f25c8113d6a8cb697bb729</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (readable by an attacker with access to the system). The method in question has been marked @Deprecated in versions 30.0 and later and should not be used. For Android developers, we recommend choosing a temporary directory API provided by Android, such as context.getCacheDir(). For other Java developers, we recommend migrating to the Java 7 API java.nio.file.Files.createTempDirectory() which explicitly configures permissions of 700, or configuring the Java runtime's java.io.tmpdir system property to point to a location whose permissions are appropriately configured.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8908>CVE-2020-8908</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: v30.0</p>
</p>
<p></p>
</details>
|
True
|
guice-multibindings-4.1.0.jar: 2 vulnerabilities (highest severity is: 5.9) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>guice-multibindings-4.1.0.jar</b></p></summary>
<p></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.google.guava/guava/bundles/guava-19.0.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/coursera_naptime/commit/19874cd7130f9fd589f25c8113d6a8cb697bb729">19874cd7130f9fd589f25c8113d6a8cb697bb729</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (guice-multibindings version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2018-10237](https://www.mend.io/vulnerability-database/CVE-2018-10237) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | guava-19.0.jar | Transitive | 4.2.1 | ❌ |
| [CVE-2020-8908](https://www.mend.io/vulnerability-database/CVE-2020-8908) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 3.3 | guava-19.0.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-10237</summary>
### Vulnerable Library - <b>guava-19.0.jar</b></p>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.google.guava/guava/bundles/guava-19.0.jar</p>
<p>
Dependency Hierarchy:
- guice-multibindings-4.1.0.jar (Root Library)
- guice-4.1.0.jar
- :x: **guava-19.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/coursera_naptime/commit/19874cd7130f9fd589f25c8113d6a8cb697bb729">19874cd7130f9fd589f25c8113d6a8cb697bb729</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Unbounded memory allocation in Google Guava 11.0 through 24.x before 24.1.1 allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker-provided data, because the AtomicDoubleArray class (when serialized with Java serialization) and the CompoundOrdering class (when serialized with GWT serialization) perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable.
<p>Publish Date: 2018-04-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-10237>CVE-2018-10237</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2018-10237">https://nvd.nist.gov/vuln/detail/CVE-2018-10237</a></p>
<p>Release Date: 2018-04-26</p>
<p>Fix Resolution (com.google.guava:guava): 24.1.1-android</p>
<p>Direct dependency fix Resolution (com.google.inject.extensions:guice-multibindings): 4.2.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> CVE-2020-8908</summary>
### Vulnerable Library - <b>guava-19.0.jar</b></p>
<p>Guava is a suite of core and expanded libraries that include
utility classes, google's collections, io classes, and much
much more.
Guava has only one code dependency - javax.annotation,
per the JSR-305 spec.</p>
<p>Library home page: <a href="https://github.com/google/guava">https://github.com/google/guava</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.ivy2/cache/com.google.guava/guava/bundles/guava-19.0.jar</p>
<p>
Dependency Hierarchy:
- guice-multibindings-4.1.0.jar (Root Library)
- guice-4.1.0.jar
- :x: **guava-19.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samqws-marketing/coursera_naptime/commit/19874cd7130f9fd589f25c8113d6a8cb697bb729">19874cd7130f9fd589f25c8113d6a8cb697bb729</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A temp directory creation vulnerability exists in all versions of Guava, allowing an attacker with access to the machine to potentially access data in a temporary directory created by the Guava API com.google.common.io.Files.createTempDir(). By default, on unix-like systems, the created directory is world-readable (readable by an attacker with access to the system). The method in question has been marked @Deprecated in versions 30.0 and later and should not be used. For Android developers, we recommend choosing a temporary directory API provided by Android, such as context.getCacheDir(). For other Java developers, we recommend migrating to the Java 7 API java.nio.file.Files.createTempDirectory() which explicitly configures permissions of 700, or configuring the Java runtime's java.io.tmpdir system property to point to a location whose permissions are appropriately configured.
<p>Publish Date: 2020-12-10
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-8908>CVE-2020-8908</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>3.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8908</a></p>
<p>Release Date: 2020-12-10</p>
<p>Fix Resolution: v30.0</p>
</p>
<p></p>
</details>
|
non_process
|
guice multibindings jar vulnerabilities highest severity is vulnerable library guice multibindings jar path to vulnerable library home wss scanner cache com google guava guava bundles guava jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in guice multibindings version remediation available medium guava jar transitive low guava jar transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library guava jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more guava has only one code dependency javax annotation per the jsr spec library home page a href path to vulnerable library home wss scanner cache com google guava guava bundles guava jar dependency hierarchy guice multibindings jar root library guice jar x guava jar vulnerable library found in head commit a href found in base branch master vulnerability details unbounded memory allocation in google guava through x before allows remote attackers to conduct denial of service attacks against servers that depend on this library and deserialize attacker provided data because the atomicdoublearray class when serialized with java serialization and the compoundordering class when serialized with gwt serialization perform eager allocation without appropriate checks on what a client has sent and whether the data size is reasonable publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com google guava guava android direct dependency fix resolution com google inject extensions guice multibindings cve vulnerable library guava jar guava is a suite of core and expanded libraries that include utility classes google s collections io classes and much much more guava has only one code dependency javax annotation per the jsr spec library home page a href path to vulnerable library home wss scanner cache com google guava guava bundles guava jar dependency hierarchy guice multibindings jar root library guice jar x guava jar vulnerable library found in head commit a href found in base branch master vulnerability details a temp directory creation vulnerability exists in all versions of guava allowing an attacker with access to the machine to potentially access data in a temporary directory created by the guava api com google common io files createtempdir by default on unix like systems the created directory is world readable readable by an attacker with access to the system the method in question has been marked deprecated in versions and later and should not be used for android developers we recommend choosing a temporary directory api provided by android such as context getcachedir for other java developers we recommend migrating to the java api java nio file files createtempdirectory which explicitly configures permissions of or configuring the java runtime s java io tmpdir system property to point to a location whose permissions are appropriately configured publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution
| 0
|
8,055
| 11,221,614,364
|
IssuesEvent
|
2020-01-07 18:15:09
|
prisma/prisma2
|
https://api.github.com/repos/prisma/prisma2
|
closed
|
ENV Variables with SQLite
|
bug/2-confirmed kind/bug process/candidate topic: env
|
I was trying out how the .env settings worked with schema.prisma.
Setting the url of a sqlite database dynamically using an env variable does not work.
```
datasource sqlite {
provider = "sqlite"
url = env("SQLITE_FILE")
enabled = true
}
```
That schema throws an error
```
Error:
Invalid `photon.()` invocation in /Users/jlarmst/Downloads/boombox/prisma/seed.js:5:36
undefined target="exit" timestamp="2019-12-14T22:53:34.018Z" fields={"message":"1"}
at PhotonFetcher.<anonymous> (/Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/index.js:65:27)
at Generator.throw (<anonymous>)
at rejected (/Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/index.js:6:65)
(node:2244) UnhandledPromiseRejectionWarning: Error: undefined target="exit" timestamp="2019-12-14T22:53:34.018Z" fields={"message":"1"}
at NodeEngine.engineReady (/Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/runtime/index.js:3533:23)
at async /Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/runtime/index.js:3456:21
(node:2244) UnhandledPromiseRejectionWarning: Unhandled promise rejection. This error originated either by throwing inside of an async function without a catch block, or by rejecting a promise which was not handled with .catch(). (rejection id: 1)
(node:2244) [DEP0018] DeprecationWarning: Unhandled promise rejections are deprecated. In the future, promise rejections that are not handled will terminate the Node.js process with a non-zero exit code.
```
However, defining two sqlite datasources with the enabled property set in the .env does work.
```
datasource sqlite {
provider = "sqlite"
url = "file:dev2.db"
enabled = env("SQLITE_ENABLED")
}
```
Note that the env has to be a boolean, or it crashes. The [documentation](https://github.com/prisma/prisma2/blob/master/docs/prisma-schema-file.md#using-environment-variables) shows setting the enabled env to the same url variable.
```
Error
Error: Schema parsing
error: Expected a boolean value, but failed while parsing "file:./dev2.db": fail
ed to parse bool.
--> schema.prisma:8
|
7 | url = "file:dev.db"
8 | enabled = env("SQLITE_URL")
9 | }
|
at Object.<anonymous> (/Users/jlarmst/env/lib/node_modules/prisma2/build/ind
ex.js:74991:23)
at Generator.throw (<anonymous>)
at rejected (/Users/jlarmst/env/lib/node_modules/prisma2/build/index.js:7488
6:65)
at processTicksAndRejections (internal/process/task_queues.js:97:5)
```
|
1.0
|
ENV Variables with SQLite - I was trying out how the .env settings worked with schema.prisma.
Setting the url of a sqlite database dynamically using an env variable does not work.
```
datasource sqlite {
provider = "sqlite"
url = env("SQLITE_FILE")
enabled = true
}
```
That schema throws an error
```
Error:
Invalid `photon.()` invocation in /Users/jlarmst/Downloads/boombox/prisma/seed.js:5:36
undefined target="exit" timestamp="2019-12-14T22:53:34.018Z" fields={"message":"1"}
at PhotonFetcher.<anonymous> (/Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/index.js:65:27)
at Generator.throw (<anonymous>)
at rejected (/Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/index.js:6:65)
(node:2244) UnhandledPromiseRejectionWarning: Error: undefined target="exit" timestamp="2019-12-14T22:53:34.018Z" fields={"message":"1"}
at NodeEngine.engineReady (/Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/runtime/index.js:3533:23)
at async /Users/jlarmst/Downloads/boombox/node_modules/@prisma/photon/runtime/index.js:3456:21
(node:2244) UnhandledPromiseRejectionWarning: Unhandled promise rejection. This error originated either by throwing inside of an async function without a catch block, or by rejecting a promise which was not handled with .catch(). (rejection id: 1)
(node:2244) [DEP0018] DeprecationWarning: Unhandled promise rejections are deprecated. In the future, promise rejections that are not handled will terminate the Node.js process with a non-zero exit code.
```
However, defining two sqlite datasources with the enabled property set in the .env does work.
```
datasource sqlite {
provider = "sqlite"
url = "file:dev2.db"
enabled = env("SQLITE_ENABLED")
}
```
Note that the env has to be a boolean, or it crashes. The [documentation](https://github.com/prisma/prisma2/blob/master/docs/prisma-schema-file.md#using-environment-variables) shows setting the enabled env to the same url variable.
```
Error
Error: Schema parsing
error: Expected a boolean value, but failed while parsing "file:./dev2.db": fail
ed to parse bool.
--> schema.prisma:8
|
7 | url = "file:dev.db"
8 | enabled = env("SQLITE_URL")
9 | }
|
at Object.<anonymous> (/Users/jlarmst/env/lib/node_modules/prisma2/build/ind
ex.js:74991:23)
at Generator.throw (<anonymous>)
at rejected (/Users/jlarmst/env/lib/node_modules/prisma2/build/index.js:7488
6:65)
at processTicksAndRejections (internal/process/task_queues.js:97:5)
```
|
process
|
env variables with sqlite i was trying out how the env settings worked with schema prisma setting the url of a sqlite database dynamically using an env variable does not work datasource sqlite provider sqlite url env sqlite file enabled true that schema throws an error error invalid photon invocation in users jlarmst downloads boombox prisma seed js undefined target exit timestamp fields message at photonfetcher users jlarmst downloads boombox node modules prisma photon index js at generator throw at rejected users jlarmst downloads boombox node modules prisma photon index js node unhandledpromiserejectionwarning error undefined target exit timestamp fields message at nodeengine engineready users jlarmst downloads boombox node modules prisma photon runtime index js at async users jlarmst downloads boombox node modules prisma photon runtime index js node unhandledpromiserejectionwarning unhandled promise rejection this error originated either by throwing inside of an async function without a catch block or by rejecting a promise which was not handled with catch rejection id node deprecationwarning unhandled promise rejections are deprecated in the future promise rejections that are not handled will terminate the node js process with a non zero exit code however defining two sqlite datasources with the enabled property set in the env does work datasource sqlite provider sqlite url file db enabled env sqlite enabled note that the env has to be a boolean or it crashes the shows setting the enabled env to the same url variable error error schema parsing error expected a boolean value but failed while parsing file db fail ed to parse bool schema prisma url file dev db enabled env sqlite url at object users jlarmst env lib node modules build ind ex js at generator throw at rejected users jlarmst env lib node modules build index js at processticksandrejections internal process task queues js
| 1
|
11,769
| 13,883,292,797
|
IssuesEvent
|
2020-10-18 11:17:56
|
ORelio/Minecraft-Console-Client
|
https://api.github.com/repos/ORelio/Minecraft-Console-Client
|
closed
|
Can't join 1.15.2 forge server
|
a:enhancement in:connect-to-server in:protocol-compatibility resolved
|
Whenever i want to join 1.15.2 Forge server i am getting "This server has mods that require Forge to be installed on the client. Contact your server admin for more details.
Failed to login to this server."
|
True
|
Can't join 1.15.2 forge server - Whenever i want to join 1.15.2 Forge server i am getting "This server has mods that require Forge to be installed on the client. Contact your server admin for more details.
Failed to login to this server."
|
non_process
|
can t join forge server whenever i want to join forge server i am getting this server has mods that require forge to be installed on the client contact your server admin for more details failed to login to this server
| 0
|
349,007
| 31,766,532,732
|
IssuesEvent
|
2023-09-12 09:06:56
|
gchq/sleeper
|
https://api.github.com/repos/gchq/sleeper
|
opened
|
Improve logging in NightlyTestOutput.uploadToS3
|
system-test-module
|
### Background
We had a nightly test execution where the results were not uploaded to S3, and the logs didn't say anything about what happened.
### Description
We'd like to log the progress of the nightly test uploads to S3.
|
1.0
|
Improve logging in NightlyTestOutput.uploadToS3 - ### Background
We had a nightly test execution where the results were not uploaded to S3, and the logs didn't say anything about what happened.
### Description
We'd like to log the progress of the nightly test uploads to S3.
|
non_process
|
improve logging in nightlytestoutput background we had a nightly test execution where the results were not uploaded to and the logs didn t say anything about what happened description we d like to log the progress of the nightly test uploads to
| 0
|
13,809
| 16,569,075,171
|
IssuesEvent
|
2021-05-30 02:47:31
|
laugharn/link
|
https://api.github.com/repos/laugharn/link
|
closed
|
User names
|
kind/feature process/selected size/md team/back team/devops team/front
|
- [x] Users should have the ability to optionally set a name after they have logged in
- [x] We should handle the display logic if a user does or does not have a name
- [x] We should handle the filter logic if a user does or does not have a name
- [x] We should create a list of reserved user names that are forbidden
- [ ] We should consider making a user on a pass optional and refactoring start to require a name for user creation
- [x] We should do design and code tweaks as necessary
|
1.0
|
User names - - [x] Users should have the ability to optionally set a name after they have logged in
- [x] We should handle the display logic if a user does or does not have a name
- [x] We should handle the filter logic if a user does or does not have a name
- [x] We should create a list of reserved user names that are forbidden
- [ ] We should consider making a user on a pass optional and refactoring start to require a name for user creation
- [x] We should do design and code tweaks as necessary
|
process
|
user names users should have the ability to optionally set a name after they have logged in we should handle the display logic if a user does or does not have a name we should handle the filter logic if a user does or does not have a name we should create a list of reserved user names that are forbidden we should consider making a user on a pass optional and refactoring start to require a name for user creation we should do design and code tweaks as necessary
| 1
|
11,690
| 14,543,331,560
|
IssuesEvent
|
2020-12-15 16:45:05
|
dotnet/runtime
|
https://api.github.com/repos/dotnet/runtime
|
closed
|
System.Diagnostics.Process.WorkingSet64 is static value in .Net Core 3.1
|
area-System.Diagnostics.Process
|
---
**Issue moved from microsoft/dotnet#1277**
- Please respond to @ChristianKern97.
---
_From @ChristianKern97 on Tuesday, December 8, 2020 12:36:59 PM_
I'm using the WorkingSet64 endpoint to measure the RAM usage of multiple processes with my application, this worked fine, but for some reason it stopped working as it should and it only returns a static value, which is different for different processes but it is not updating.
I only get this issue on Windows 10 with the newest updates. On my Windows Server 2019 everything works just fine. I tried using a PerformanceCounter instead but it had the same behaviour.
Another thing i tried is using .NET 5.0 but the same behaviour there.
My best guess is it has something to do with a recent Windows 10 update, but i have no clue.
|
1.0
|
System.Diagnostics.Process.WorkingSet64 is static value in .Net Core 3.1 - ---
**Issue moved from microsoft/dotnet#1277**
- Please respond to @ChristianKern97.
---
_From @ChristianKern97 on Tuesday, December 8, 2020 12:36:59 PM_
I'm using the WorkingSet64 endpoint to measure the RAM usage of multiple processes with my application, this worked fine, but for some reason it stopped working as it should and it only returns a static value, which is different for different processes but it is not updating.
I only get this issue on Windows 10 with the newest updates. On my Windows Server 2019 everything works just fine. I tried using a PerformanceCounter instead but it had the same behaviour.
Another thing i tried is using .NET 5.0 but the same behaviour there.
My best guess is it has something to do with a recent Windows 10 update, but i have no clue.
|
process
|
system diagnostics process is static value in net core issue moved from microsoft dotnet please respond to from on tuesday december pm i m using the endpoint to measure the ram usage of multiple processes with my application this worked fine but for some reason it stopped working as it should and it only returns a static value which is different for different processes but it is not updating i only get this issue on windows with the newest updates on my windows server everything works just fine i tried using a performancecounter instead but it had the same behaviour another thing i tried is using net but the same behaviour there my best guess is it has something to do with a recent windows update but i have no clue
| 1
|
29,693
| 5,661,484,873
|
IssuesEvent
|
2017-04-10 17:28:47
|
graphite-project/graphite-web
|
https://api.github.com/repos/graphite-project/graphite-web
|
closed
|
Fix changelog before 1.0.0 release
|
documentation
|
https://github.com/graphite-project/graphite-web/blob/20d443b7158b3e601b0f77279247804ca7b4fc3a/docs/releases/0_10_0.rst should be renamed to 1_0_0.rst and we need to update info there too
|
1.0
|
Fix changelog before 1.0.0 release - https://github.com/graphite-project/graphite-web/blob/20d443b7158b3e601b0f77279247804ca7b4fc3a/docs/releases/0_10_0.rst should be renamed to 1_0_0.rst and we need to update info there too
|
non_process
|
fix changelog before release should be renamed to rst and we need to update info there too
| 0
|
196,213
| 15,585,919,265
|
IssuesEvent
|
2021-03-18 00:45:27
|
microsoft/MixedRealityToolkit-Unity
|
https://api.github.com/repos/microsoft/MixedRealityToolkit-Unity
|
closed
|
"SerializedObjectNotCreatableException: Object at index 0 is null exceptions" when configuring scene for Hololens 1
|
Bug Documentation XR SDK
|
## Describe the bug
Configuring the MixedReality Toolkit with cloned default Hololens 1 profile produces 48 exceptions on start each are:
"SerializedObjectNotCreatableException: Object at index 0 is null exceptions"
from various parts of MRTK.
After build the scene is not working as intended: the whole scene is fixed in front of the user and follows the user when turning around.
## To reproduce
1. Create new unity projcet
2. Add MRT through UPM
3. Add new Scene
4. Add mrtk to scene
5. On the MixedRealityToolkit asset select the DefaultMixedRealityToolkitConfigurationProfile
The same bug is present when using the Hololens1 profile, cloning it, and fixing the broken default profiles with no luck. The same is also true for hololens 2
## Expected behavior
Default Hololens 1 profile should work out of the box for hololens 1
## Screenshots

## Your setup (please complete the following information)
- Unity Version 2020.1.6
- MRTK Version 2.5.0
## Target platform (please complete the following information)
- HoloLens 1
- HoloLens 2
## Additional context
[profiles.zip](https://github.com/microsoft/MixedRealityToolkit-Unity/files/5317966/profiles.zip) The configuration I tried to use.
Using 2.4.0 the default Hololens 1/2 settings worked as expected
|
1.0
|
"SerializedObjectNotCreatableException: Object at index 0 is null exceptions" when configuring scene for Hololens 1 - ## Describe the bug
Configuring the MixedReality Toolkit with cloned default Hololens 1 profile produces 48 exceptions on start each are:
"SerializedObjectNotCreatableException: Object at index 0 is null exceptions"
from various parts of MRTK.
After build the scene is not working as intended: the whole scene is fixed in front of the user and follows the user when turning around.
## To reproduce
1. Create new unity projcet
2. Add MRT through UPM
3. Add new Scene
4. Add mrtk to scene
5. On the MixedRealityToolkit asset select the DefaultMixedRealityToolkitConfigurationProfile
The same bug is present when using the Hololens1 profile, cloning it, and fixing the broken default profiles with no luck. The same is also true for hololens 2
## Expected behavior
Default Hololens 1 profile should work out of the box for hololens 1
## Screenshots

## Your setup (please complete the following information)
- Unity Version 2020.1.6
- MRTK Version 2.5.0
## Target platform (please complete the following information)
- HoloLens 1
- HoloLens 2
## Additional context
[profiles.zip](https://github.com/microsoft/MixedRealityToolkit-Unity/files/5317966/profiles.zip) The configuration I tried to use.
Using 2.4.0 the default Hololens 1/2 settings worked as expected
|
non_process
|
serializedobjectnotcreatableexception object at index is null exceptions when configuring scene for hololens describe the bug configuring the mixedreality toolkit with cloned default hololens profile produces exceptions on start each are serializedobjectnotcreatableexception object at index is null exceptions from various parts of mrtk after build the scene is not working as intended the whole scene is fixed in front of the user and follows the user when turning around to reproduce create new unity projcet add mrt through upm add new scene add mrtk to scene on the mixedrealitytoolkit asset select the defaultmixedrealitytoolkitconfigurationprofile the same bug is present when using the profile cloning it and fixing the broken default profiles with no luck the same is also true for hololens expected behavior default hololens profile should work out of the box for hololens screenshots your setup please complete the following information unity version mrtk version target platform please complete the following information hololens hololens additional context the configuration i tried to use using the default hololens settings worked as expected
| 0
|
15,741
| 3,481,443,719
|
IssuesEvent
|
2015-12-29 16:11:15
|
slivne/try_git
|
https://api.github.com/repos/slivne/try_git
|
opened
|
repair : test_multiple_repair_test
|
dtest repair
|
Check that repair is accompilshed when multiple repairs are initiated in parallel 1. Create a cluster of 3 nodes with rf=3 2. Insert data 3. Stop node 2 4. Insert data 5. Stop node 3 6. Insert data 7. Start node 2, Start node 3 8. Start repair on node 2, node 3 9. Stop node 1,node 3 - does node 2 hold all the data 10. Stop node 1,node 2 - does node 3 hold all the data
|
1.0
|
repair : test_multiple_repair_test - Check that repair is accompilshed when multiple repairs are initiated in parallel 1. Create a cluster of 3 nodes with rf=3 2. Insert data 3. Stop node 2 4. Insert data 5. Stop node 3 6. Insert data 7. Start node 2, Start node 3 8. Start repair on node 2, node 3 9. Stop node 1,node 3 - does node 2 hold all the data 10. Stop node 1,node 2 - does node 3 hold all the data
|
non_process
|
repair test multiple repair test check that repair is accompilshed when multiple repairs are initiated in parallel create a cluster of nodes with rf insert data stop node insert data stop node insert data start node start node start repair on node node stop node node does node hold all the data stop node node does node hold all the data
| 0
|
4,469
| 4,366,743,585
|
IssuesEvent
|
2016-08-03 15:10:11
|
driftyco/ionic
|
https://api.github.com/repos/driftyco/ionic
|
closed
|
Too many layers can cause memory usage issues
|
performance v2
|
#### Short description of the problem:

In the above screenshot you can see each separate layer that gets created by the browser indicated by the orange boxes. Any component that is surrounded by an orange box is being rendered on its own layer. As you can see with even a pretty basic layout it is being rendered by chrome as 8 separate layers, which can potentially cause memory usage issues, especially in apps that have a good amount of pages. In fact, when testing the app in the screenshot in Firefox, Firefox throws a warning in its dev tools about this page having too many layers and potentially causing memory issues on mobile devices. Potential solutions to this issue include making sure were not being too zealous with our use `will-change` and being careful about using fixed position elements.
read more about layers [here](http://www.html5rocks.com/en/tutorials/speed/layers/).
**Which Ionic Version?** 2.x
|
True
|
Too many layers can cause memory usage issues - #### Short description of the problem:

In the above screenshot you can see each separate layer that gets created by the browser indicated by the orange boxes. Any component that is surrounded by an orange box is being rendered on its own layer. As you can see with even a pretty basic layout it is being rendered by chrome as 8 separate layers, which can potentially cause memory usage issues, especially in apps that have a good amount of pages. In fact, when testing the app in the screenshot in Firefox, Firefox throws a warning in its dev tools about this page having too many layers and potentially causing memory issues on mobile devices. Potential solutions to this issue include making sure were not being too zealous with our use `will-change` and being careful about using fixed position elements.
read more about layers [here](http://www.html5rocks.com/en/tutorials/speed/layers/).
**Which Ionic Version?** 2.x
|
non_process
|
too many layers can cause memory usage issues short description of the problem in the above screenshot you can see each separate layer that gets created by the browser indicated by the orange boxes any component that is surrounded by an orange box is being rendered on its own layer as you can see with even a pretty basic layout it is being rendered by chrome as separate layers which can potentially cause memory usage issues especially in apps that have a good amount of pages in fact when testing the app in the screenshot in firefox firefox throws a warning in its dev tools about this page having too many layers and potentially causing memory issues on mobile devices potential solutions to this issue include making sure were not being too zealous with our use will change and being careful about using fixed position elements read more about layers which ionic version x
| 0
|
82,850
| 23,898,403,049
|
IssuesEvent
|
2022-09-08 16:30:23
|
scipy/scipy
|
https://api.github.com/repos/scipy/scipy
|
opened
|
ENH: Compile pocketfft with newer vector instructions?
|
enhancement Build issues scipy.fft
|
### Is your feature request related to a problem? Please describe.
`pocketfft` supports vectorization of batched transforms, but currently our releases only compile with some variant of SSE instruction sets. A simple `%timeit` benchmark of `scipy.fft` shows noticeable speedups, particularly in the jump from SSE to AVX registers (2 x float64 to 4 x float64).
| Function | Shape | SSE4.2 (us) | AVX (us) | AVX2 (us) |
|----------|-------------|-------------|----------|-----------|
| fft | (1000, 120) | 361 | 286 | 289 |
| | (400, 200) | 228 | 202 | 203 |
| rfft | (1000, 120) | 180 | 157 | 155 |
| | (400, 200) | 120 | 99 | 101 |
### Describe the solution you'd like.
AVX is suffieciently old that we may just be able to ship binaries with AVX by default. Quoting [the wikipedia page](https://en.wikipedia.org/wiki/Advanced_Vector_Extensions)
>[AVX was] first supported by Intel with the Sandy Bridge processor shipping in Q1 2011 and later by AMD with the Bulldozer processor shipping in Q3 2011.
So any x86 computer without AVX support should be at least a decade old by this point.
cc @rgommers
### Describe alternatives you've considered.
An alternative solution may be to compile pocketfft twice with and without AVX, then import only the version supported by the CPU using runtime cpu feature detection.
### Additional context (e.g. screenshots, GIFs)
_No response_
|
1.0
|
ENH: Compile pocketfft with newer vector instructions? - ### Is your feature request related to a problem? Please describe.
`pocketfft` supports vectorization of batched transforms, but currently our releases only compile with some variant of SSE instruction sets. A simple `%timeit` benchmark of `scipy.fft` shows noticeable speedups, particularly in the jump from SSE to AVX registers (2 x float64 to 4 x float64).
| Function | Shape | SSE4.2 (us) | AVX (us) | AVX2 (us) |
|----------|-------------|-------------|----------|-----------|
| fft | (1000, 120) | 361 | 286 | 289 |
| | (400, 200) | 228 | 202 | 203 |
| rfft | (1000, 120) | 180 | 157 | 155 |
| | (400, 200) | 120 | 99 | 101 |
### Describe the solution you'd like.
AVX is suffieciently old that we may just be able to ship binaries with AVX by default. Quoting [the wikipedia page](https://en.wikipedia.org/wiki/Advanced_Vector_Extensions)
>[AVX was] first supported by Intel with the Sandy Bridge processor shipping in Q1 2011 and later by AMD with the Bulldozer processor shipping in Q3 2011.
So any x86 computer without AVX support should be at least a decade old by this point.
cc @rgommers
### Describe alternatives you've considered.
An alternative solution may be to compile pocketfft twice with and without AVX, then import only the version supported by the CPU using runtime cpu feature detection.
### Additional context (e.g. screenshots, GIFs)
_No response_
|
non_process
|
enh compile pocketfft with newer vector instructions is your feature request related to a problem please describe pocketfft supports vectorization of batched transforms but currently our releases only compile with some variant of sse instruction sets a simple timeit benchmark of scipy fft shows noticeable speedups particularly in the jump from sse to avx registers x to x function shape us avx us us fft rfft describe the solution you d like avx is suffieciently old that we may just be able to ship binaries with avx by default quoting first supported by intel with the sandy bridge processor shipping in and later by amd with the bulldozer processor shipping in so any computer without avx support should be at least a decade old by this point cc rgommers describe alternatives you ve considered an alternative solution may be to compile pocketfft twice with and without avx then import only the version supported by the cpu using runtime cpu feature detection additional context e g screenshots gifs no response
| 0
|
709,597
| 24,384,255,451
|
IssuesEvent
|
2022-10-04 10:22:17
|
trustwallet/wallet-core
|
https://api.github.com/repos/trustwallet/wallet-core
|
opened
|
Support custom EVM chain without code change, but runtime data
|
enhancement priority:low size:medium improvements
|
**Is your feature request related to a problem? Please describe.**
Support for a new EVM-clone chain has been simplified (see #2214), but still requires code change and new release in wallet-core. It would be nice if new custom chain can be added to a wallet dynamically at runtime, but still some support from wallet core.
**Describe the solution you'd like**
Two possible solutions in the wallet app:
1. A custom EVM-clone chain can be added by the user, and then app uses Ethereum coin for address derivation, and Ethereum coin and custom chainId for signing. No involvement from wallet core.
2. A custom EVM-clone chain can be added by the user. App 'registers' the new chain properties with wallet code. Wallet core extends its relevant coin-specific methods to also support the dynamically registered chains (additionally to the ones statically defined in `registry.json`).
**Limitation**
Since dynamically registered types are not known at build time, generated sources will not contain these coins.
**Describe alternatives you've considered**
See above number 1).
**Checklist**
<!--- Group checklist per issue needed, one specific feature of your goal -->
<!--- Each big task can have subtask, doesn't hesitate to split into small pull request to simplify the review process -->
- [ ] task number 1
- [ ] subtask number 1
- [ ] subtask number 2
- [ ] task number 2
- [ ] task number 3
**Resources**
<!--- Link resources this way: [My Resource Title](link) -->
|
1.0
|
Support custom EVM chain without code change, but runtime data - **Is your feature request related to a problem? Please describe.**
Support for a new EVM-clone chain has been simplified (see #2214), but still requires code change and new release in wallet-core. It would be nice if new custom chain can be added to a wallet dynamically at runtime, but still some support from wallet core.
**Describe the solution you'd like**
Two possible solutions in the wallet app:
1. A custom EVM-clone chain can be added by the user, and then app uses Ethereum coin for address derivation, and Ethereum coin and custom chainId for signing. No involvement from wallet core.
2. A custom EVM-clone chain can be added by the user. App 'registers' the new chain properties with wallet code. Wallet core extends its relevant coin-specific methods to also support the dynamically registered chains (additionally to the ones statically defined in `registry.json`).
**Limitation**
Since dynamically registered types are not known at build time, generated sources will not contain these coins.
**Describe alternatives you've considered**
See above number 1).
**Checklist**
<!--- Group checklist per issue needed, one specific feature of your goal -->
<!--- Each big task can have subtask, doesn't hesitate to split into small pull request to simplify the review process -->
- [ ] task number 1
- [ ] subtask number 1
- [ ] subtask number 2
- [ ] task number 2
- [ ] task number 3
**Resources**
<!--- Link resources this way: [My Resource Title](link) -->
|
non_process
|
support custom evm chain without code change but runtime data is your feature request related to a problem please describe support for a new evm clone chain has been simplified see but still requires code change and new release in wallet core it would be nice if new custom chain can be added to a wallet dynamically at runtime but still some support from wallet core describe the solution you d like two possible solutions in the wallet app a custom evm clone chain can be added by the user and then app uses ethereum coin for address derivation and ethereum coin and custom chainid for signing no involvement from wallet core a custom evm clone chain can be added by the user app registers the new chain properties with wallet code wallet core extends its relevant coin specific methods to also support the dynamically registered chains additionally to the ones statically defined in registry json limitation since dynamically registered types are not known at build time generated sources will not contain these coins describe alternatives you ve considered see above number checklist task number subtask number subtask number task number task number resources
| 0
|
65,447
| 14,727,802,723
|
IssuesEvent
|
2021-01-06 09:04:45
|
rdharmedran/codeguru
|
https://api.github.com/repos/rdharmedran/codeguru
|
opened
|
CVE-2020-24750 (High) detected in jackson-databind-2.9.5.jar
|
security vulnerability
|
## CVE-2020-24750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: codeguru/example/example/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- google-cloud-dataflow-java-sdk-all-2.5.0.jar (Root Library)
- beam-sdks-java-core-2.5.0.jar
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rdharmedran/codeguru/commit/03eef59d90cd24cc5959d727fe7321d9ac8aa466">03eef59d90cd24cc5959d727fe7321d9ac8aa466</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.6 mishandles the interaction between serialization gadgets and typing, related to com.pastdev.httpcomponents.configuration.JndiConfiguration.
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750>CVE-2020-24750</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616</a></p>
<p>Release Date: 2020-08-28</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2020-24750 (High) detected in jackson-databind-2.9.5.jar - ## CVE-2020-24750 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: codeguru/example/example/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- google-cloud-dataflow-java-sdk-all-2.5.0.jar (Root Library)
- beam-sdks-java-core-2.5.0.jar
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/rdharmedran/codeguru/commit/03eef59d90cd24cc5959d727fe7321d9ac8aa466">03eef59d90cd24cc5959d727fe7321d9ac8aa466</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.6 mishandles the interaction between serialization gadgets and typing, related to com.pastdev.httpcomponents.configuration.JndiConfiguration.
<p>Publish Date: 2020-09-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-24750>CVE-2020-24750</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-24616</a></p>
<p>Release Date: 2020-08-28</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file codeguru example example pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy google cloud dataflow java sdk all jar root library beam sdks java core jar x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to com pastdev httpcomponents configuration jndiconfiguration publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource
| 0
|
372,246
| 11,011,522,292
|
IssuesEvent
|
2019-12-04 16:27:00
|
salesagility/SuiteCRM
|
https://api.github.com/repos/salesagility/SuiteCRM
|
opened
|
Small part of Error bar appears within a few menus
|
Bug Low Priority Styling
|
<!--- Provide a general summary of the issue in the **Title** above -->
<!--- Before you open an issue, please check if a similar issue already exists or has been closed before. --->
<!--- If you have discovered a security risk please report it by emailing security@suitecrm.com. This will be delivered to the product team who handle security issues. Please don't disclose security bugs publicly until they have been handled by the security team. --->
#### Issue
<!--- Provide a more detailed introduction to the issue itself, and why you consider it to be a bug -->
<!--- Ensure that all code ``` is surrounded ``` by triple back quotes. This can also be done over multiple lines -->
Small styling issue found within a few single page menus.
I've found this in System Settings, Local and a few other Single Page menus
#### Context
<!--- How has this bug affected you? What were you trying to accomplish? -->
<!--- If you feel this should be a low/medium/high priority then please state so -->
Looks incorrect
#### Your Environment
<!--- Include as many relevant details about the environment you experienced the bug in -->
* SuiteCRM Version used: Hotfix-7.10.x
|
1.0
|
Small part of Error bar appears within a few menus - <!--- Provide a general summary of the issue in the **Title** above -->
<!--- Before you open an issue, please check if a similar issue already exists or has been closed before. --->
<!--- If you have discovered a security risk please report it by emailing security@suitecrm.com. This will be delivered to the product team who handle security issues. Please don't disclose security bugs publicly until they have been handled by the security team. --->
#### Issue
<!--- Provide a more detailed introduction to the issue itself, and why you consider it to be a bug -->
<!--- Ensure that all code ``` is surrounded ``` by triple back quotes. This can also be done over multiple lines -->
Small styling issue found within a few single page menus.
I've found this in System Settings, Local and a few other Single Page menus
#### Context
<!--- How has this bug affected you? What were you trying to accomplish? -->
<!--- If you feel this should be a low/medium/high priority then please state so -->
Looks incorrect
#### Your Environment
<!--- Include as many relevant details about the environment you experienced the bug in -->
* SuiteCRM Version used: Hotfix-7.10.x
|
non_process
|
small part of error bar appears within a few menus issue small styling issue found within a few single page menus i ve found this in system settings local and a few other single page menus context looks incorrect your environment suitecrm version used hotfix x
| 0
|
14,005
| 16,813,575,720
|
IssuesEvent
|
2021-06-17 03:11:46
|
atsign-foundation/atsign.dev
|
https://api.github.com/repos/atsign-foundation/atsign.dev
|
closed
|
Open Source Policies & Processes
|
5 SP PR11 PR12 PR12.5 PR13 Policy Process atsign.dev 2.0
|
Denise Lead
- [x] Resolve review comments @cpswan
- [x] Write section based on Flutter model @atsigndenise
- [x] Review/edit section
- [x] Determine Schedule for Completion @atsigndenise
|
1.0
|
Open Source Policies & Processes - Denise Lead
- [x] Resolve review comments @cpswan
- [x] Write section based on Flutter model @atsigndenise
- [x] Review/edit section
- [x] Determine Schedule for Completion @atsigndenise
|
process
|
open source policies processes denise lead resolve review comments cpswan write section based on flutter model atsigndenise review edit section determine schedule for completion atsigndenise
| 1
|
21,747
| 30,261,147,126
|
IssuesEvent
|
2023-07-07 08:19:14
|
symfony/symfony
|
https://api.github.com/repos/symfony/symfony
|
closed
|
[Process] STDIN/STDOUT/STDERR with PhpProcess
|
Bug Process Status: Needs Review
|
### Symfony version(s) affected
6.3.x-dev
### Description
`PhpProcess` is using STDIN to feed the script, which makes STDIN/STDOUT/STDERR are not availble (see php/php-src#11104)
Note: it's tested with `6.3.x-dev` but it should be reproducible with old versions like `5.4.x` as well
### How to reproduce
```php
<?php
include './vendor/autoload.php';
use Symfony\Component\Process\PhpProcess;
$process = new PhpProcess(<<<PHP
<?php
var_dump(php_sapi_name());
var_dump(STDOUT);
PHP
);
```
### Possible Solution
Create a temporary script before running, just following what are done for phpdbg (https://github.com/symfony/process/blob/6.2/PhpProcess.php#L43-L47),
### Additional Context
_No response_
|
1.0
|
[Process] STDIN/STDOUT/STDERR with PhpProcess - ### Symfony version(s) affected
6.3.x-dev
### Description
`PhpProcess` is using STDIN to feed the script, which makes STDIN/STDOUT/STDERR are not availble (see php/php-src#11104)
Note: it's tested with `6.3.x-dev` but it should be reproducible with old versions like `5.4.x` as well
### How to reproduce
```php
<?php
include './vendor/autoload.php';
use Symfony\Component\Process\PhpProcess;
$process = new PhpProcess(<<<PHP
<?php
var_dump(php_sapi_name());
var_dump(STDOUT);
PHP
);
```
### Possible Solution
Create a temporary script before running, just following what are done for phpdbg (https://github.com/symfony/process/blob/6.2/PhpProcess.php#L43-L47),
### Additional Context
_No response_
|
process
|
stdin stdout stderr with phpprocess symfony version s affected x dev description phpprocess is using stdin to feed the script which makes stdin stdout stderr are not availble see php php src note it s tested with x dev but it should be reproducible with old versions like x as well how to reproduce php php include vendor autoload php use symfony component process phpprocess process new phpprocess php php var dump php sapi name var dump stdout php possible solution create a temporary script before running just following what are done for phpdbg additional context no response
| 1
|
14,682
| 17,798,245,819
|
IssuesEvent
|
2021-09-01 02:39:12
|
qgis/QGIS
|
https://api.github.com/repos/qgis/QGIS
|
closed
|
python error
|
Feedback stale Processing Bug
|
2021-07-20T10:51:56 WARNING Traceback (most recent call last):
File "C:\PROGRA~1/QGIS32~1.0/apps/qgis/./python/plugins\processing\algs\grass7\Grass7AlgorithmProvider.py", line 124, in loadAlgorithms
version = Grass7Utils.installedVersion(True)
File "C:\PROGRA~1/QGIS32~1.0/apps/qgis/./python/plugins\processing\algs\grass7\Grass7Utils.py", line 116, in installedVersion
with subprocess.Popen(
File "C:\PROGRA~1\QGIS32~1.0\apps\Python39\lib\subprocess.py", line 951, in __init__
self._execute_child(args, executable, preexec_fn, close_fds,
File "C:\PROGRA~1\QGIS32~1.0\apps\Python39\lib\subprocess.py", line 1420, in _execute_child
hp, ht, pid, tid = _winapi.CreateProcess(executable, args,
OSError: [WinError 87] El parámetro no es correcto
|
1.0
|
python error - 2021-07-20T10:51:56 WARNING Traceback (most recent call last):
File "C:\PROGRA~1/QGIS32~1.0/apps/qgis/./python/plugins\processing\algs\grass7\Grass7AlgorithmProvider.py", line 124, in loadAlgorithms
version = Grass7Utils.installedVersion(True)
File "C:\PROGRA~1/QGIS32~1.0/apps/qgis/./python/plugins\processing\algs\grass7\Grass7Utils.py", line 116, in installedVersion
with subprocess.Popen(
File "C:\PROGRA~1\QGIS32~1.0\apps\Python39\lib\subprocess.py", line 951, in __init__
self._execute_child(args, executable, preexec_fn, close_fds,
File "C:\PROGRA~1\QGIS32~1.0\apps\Python39\lib\subprocess.py", line 1420, in _execute_child
hp, ht, pid, tid = _winapi.CreateProcess(executable, args,
OSError: [WinError 87] El parámetro no es correcto
|
process
|
python error warning traceback most recent call last file c progra apps qgis python plugins processing algs py line in loadalgorithms version installedversion true file c progra apps qgis python plugins processing algs py line in installedversion with subprocess popen file c progra apps lib subprocess py line in init self execute child args executable preexec fn close fds file c progra apps lib subprocess py line in execute child hp ht pid tid winapi createprocess executable args oserror el parámetro no es correcto
| 1
|
443,545
| 30,923,281,235
|
IssuesEvent
|
2023-08-06 06:56:39
|
apache/airflow
|
https://api.github.com/repos/apache/airflow
|
opened
|
Add an example for custom executor
|
kind:bug kind:documentation needs-triage
|
### What do you see as an issue?
Hi, Community,
I've been trying to add my custom executor recently, searching in the network, and only found there is no 'How-To-Guides' for this feature.
https://airflow.apache.org/docs/apache-airflow/stable/core-concepts/executor/index.html#executor-types

I guess it should be similar to https://airflow.apache.org/docs/apache-airflow/stable/howto/custom-operator.html
But I would like here to add an page link to howto, and add a related page here.
What's your suggestion?
### Solving the problem
_No response_
### Anything else
_No response_
### Are you willing to submit PR?
- [X] Yes I am willing to submit a PR!
### Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://github.com/apache/airflow/blob/main/CODE_OF_CONDUCT.md)
|
1.0
|
Add an example for custom executor - ### What do you see as an issue?
Hi, Community,
I've been trying to add my custom executor recently, searching in the network, and only found there is no 'How-To-Guides' for this feature.
https://airflow.apache.org/docs/apache-airflow/stable/core-concepts/executor/index.html#executor-types

I guess it should be similar to https://airflow.apache.org/docs/apache-airflow/stable/howto/custom-operator.html
But I would like here to add an page link to howto, and add a related page here.
What's your suggestion?
### Solving the problem
_No response_
### Anything else
_No response_
### Are you willing to submit PR?
- [X] Yes I am willing to submit a PR!
### Code of Conduct
- [X] I agree to follow this project's [Code of Conduct](https://github.com/apache/airflow/blob/main/CODE_OF_CONDUCT.md)
|
non_process
|
add an example for custom executor what do you see as an issue hi community i ve been trying to add my custom executor recently searching in the network and only found there is no how to guides for this feature i guess it should be similar to but i would like here to add an page link to howto and add a related page here what s your suggestion solving the problem no response anything else no response are you willing to submit pr yes i am willing to submit a pr code of conduct i agree to follow this project s
| 0
|
21,830
| 30,318,346,561
|
IssuesEvent
|
2023-07-10 17:13:01
|
geneontology/go-ontology
|
https://api.github.com/repos/geneontology/go-ontology
|
closed
|
Disruption of host signaling pathways
|
multi-species process
|
Hi @genegodbold
We have terms for these for viruses:
- PATHGO:0000302 | disrupts JAK-STAT signaling in another organism [Gene--I provide eukaryotic and bacterial examples below]
- PATHGO:0000304 | disrupts PKR activity in another organism [Gene--all the examples I have are viral]
- PATHGO:0000306 | disrupts RIG-I signaling in another organism [Gene--I have one bacterial example below]
- PATHGO:0000306 | disrupts RIG-I signaling in another organism
- PATHGO:0000314 | modulates TRAF signaling in another organism [Gene--I provide eukaryotic and bacterial examples below]
- PATHGO:0000329 | modulates ISGylation in another organism (Gene--I only have viral which I have mentioned below)
- PATHGO:0000382 | suppresses interferon signaling in another organism (Gene--I've got one eukaryotic and one (maybe) bacterial, see below
-- | --
If you have examples of these outside viruses, I can create more general terms.
Thanks, Pascale
|
1.0
|
Disruption of host signaling pathways - Hi @genegodbold
We have terms for these for viruses:
- PATHGO:0000302 | disrupts JAK-STAT signaling in another organism [Gene--I provide eukaryotic and bacterial examples below]
- PATHGO:0000304 | disrupts PKR activity in another organism [Gene--all the examples I have are viral]
- PATHGO:0000306 | disrupts RIG-I signaling in another organism [Gene--I have one bacterial example below]
- PATHGO:0000306 | disrupts RIG-I signaling in another organism
- PATHGO:0000314 | modulates TRAF signaling in another organism [Gene--I provide eukaryotic and bacterial examples below]
- PATHGO:0000329 | modulates ISGylation in another organism (Gene--I only have viral which I have mentioned below)
- PATHGO:0000382 | suppresses interferon signaling in another organism (Gene--I've got one eukaryotic and one (maybe) bacterial, see below
-- | --
If you have examples of these outside viruses, I can create more general terms.
Thanks, Pascale
|
process
|
disruption of host signaling pathways hi genegodbold we have terms for these for viruses pathgo disrupts jak stat signaling in another organism pathgo disrupts pkr activity in another organism pathgo disrupts rig i signaling in another organism pathgo disrupts rig i signaling in another organism pathgo modulates traf signaling in another organism pathgo modulates isgylation in another organism gene i only have viral which i have mentioned below pathgo suppresses interferon signaling in another organism gene i ve got one eukaryotic and one maybe bacterial see below if you have examples of these outside viruses i can create more general terms thanks pascale
| 1
|
308,193
| 9,435,989,769
|
IssuesEvent
|
2019-04-13 02:00:50
|
avored/laravel-ecommerce
|
https://api.github.com/repos/avored/laravel-ecommerce
|
closed
|
select2 - bad work
|
High Priority backend bug
|
Hi.
Please review the select2 in product/basic. This selection not work properly
**In addition, you have consider to publish the admin UI?**
|
1.0
|
select2 - bad work - Hi.
Please review the select2 in product/basic. This selection not work properly
**In addition, you have consider to publish the admin UI?**
|
non_process
|
bad work hi please review the in product basic this selection not work properly in addition you have consider to publish the admin ui
| 0
|
139,267
| 20,820,718,681
|
IssuesEvent
|
2022-03-18 15:06:48
|
microsoft/pyright
|
https://api.github.com/repos/microsoft/pyright
|
closed
|
Cannot use both TypeGuard and bool in return type for same `@overload`
|
as designed
|
**Describe the bug**
It appears that you cannot have a pair of `@overload` cases where one returns a `TypeGuard[T]` and the other returns a `bool`.
**To Reproduce**
* With the following two files, with Python 3.8 installed:
```
# pyproject.toml
[tool.pyright]
include = ["."]
pythonPlatform = "All"
# trycast_mini.py
from typing import get_args, get_origin, Literal, overload, Type, TypeVar, Union
from typing_extensions import TypeGuard
_T = TypeVar("_T")
@overload
def isassignable(value: object, tp: Type[_T]) -> TypeGuard[_T]: ...
@overload
def isassignable(value: object, tp: object) -> bool: ...
def isassignable(value, tp):
if get_origin(tp) is Union:
if get_args(tp) == (int, str):
return isinstance(value, int) or isinstance(value, str)
raise NotImplementedError()
return isinstance(value, tp)
```
* ...run the following commands:
* `pip3 install pyright==1.1.230`
* `pyright`
**Expected behavior**
There should be no typechecking errors.
**Actual behavior**
Pyright gives the following error:
```
/Users/me/tmp/trycast_mini.py
/Users/me/tmp/trycast_mini.py:19:5 - error: Overloaded function implementation is not consistent with signature of overload 1
Function return type "TypeGuard[_T@isassignable]" is incompatible with type "bool"
"TypeGuard[_T@isassignable]" is incompatible with "bool" (reportGeneralTypeIssues)
1 errors, 0 warnings, 0 informations
```
Mypy gives no error on the same code.
**Additional context**
I am trying to get [isassignable()](https://github.com/davidfstr/trycast#isassignable) from the example above to typecheck in _both_ Pyright and Mypy. Mypy differs from Pyright in that it does **not** consider a _non-class_ type form such as `Union[int, str]` to be compatible with `Type[T]`; it only considers it to be compatible with `object`. Therefore I have to use an `@overload` that has both a `(Type[T]) -> TypeGuard[T]` case and an `(object) -> bool` case in order to have a function that accepts all type forms that works in both typecheckers. Unfortunately Pyright doesn't appear to like both `TypeGuard[T]` and `bool` appearing in the return type for different cases of the same `@overload`.
|
1.0
|
Cannot use both TypeGuard and bool in return type for same `@overload` - **Describe the bug**
It appears that you cannot have a pair of `@overload` cases where one returns a `TypeGuard[T]` and the other returns a `bool`.
**To Reproduce**
* With the following two files, with Python 3.8 installed:
```
# pyproject.toml
[tool.pyright]
include = ["."]
pythonPlatform = "All"
# trycast_mini.py
from typing import get_args, get_origin, Literal, overload, Type, TypeVar, Union
from typing_extensions import TypeGuard
_T = TypeVar("_T")
@overload
def isassignable(value: object, tp: Type[_T]) -> TypeGuard[_T]: ...
@overload
def isassignable(value: object, tp: object) -> bool: ...
def isassignable(value, tp):
if get_origin(tp) is Union:
if get_args(tp) == (int, str):
return isinstance(value, int) or isinstance(value, str)
raise NotImplementedError()
return isinstance(value, tp)
```
* ...run the following commands:
* `pip3 install pyright==1.1.230`
* `pyright`
**Expected behavior**
There should be no typechecking errors.
**Actual behavior**
Pyright gives the following error:
```
/Users/me/tmp/trycast_mini.py
/Users/me/tmp/trycast_mini.py:19:5 - error: Overloaded function implementation is not consistent with signature of overload 1
Function return type "TypeGuard[_T@isassignable]" is incompatible with type "bool"
"TypeGuard[_T@isassignable]" is incompatible with "bool" (reportGeneralTypeIssues)
1 errors, 0 warnings, 0 informations
```
Mypy gives no error on the same code.
**Additional context**
I am trying to get [isassignable()](https://github.com/davidfstr/trycast#isassignable) from the example above to typecheck in _both_ Pyright and Mypy. Mypy differs from Pyright in that it does **not** consider a _non-class_ type form such as `Union[int, str]` to be compatible with `Type[T]`; it only considers it to be compatible with `object`. Therefore I have to use an `@overload` that has both a `(Type[T]) -> TypeGuard[T]` case and an `(object) -> bool` case in order to have a function that accepts all type forms that works in both typecheckers. Unfortunately Pyright doesn't appear to like both `TypeGuard[T]` and `bool` appearing in the return type for different cases of the same `@overload`.
|
non_process
|
cannot use both typeguard and bool in return type for same overload describe the bug it appears that you cannot have a pair of overload cases where one returns a typeguard and the other returns a bool to reproduce with the following two files with python installed pyproject toml include pythonplatform all trycast mini py from typing import get args get origin literal overload type typevar union from typing extensions import typeguard t typevar t overload def isassignable value object tp type typeguard overload def isassignable value object tp object bool def isassignable value tp if get origin tp is union if get args tp int str return isinstance value int or isinstance value str raise notimplementederror return isinstance value tp run the following commands install pyright pyright expected behavior there should be no typechecking errors actual behavior pyright gives the following error users me tmp trycast mini py users me tmp trycast mini py error overloaded function implementation is not consistent with signature of overload function return type typeguard is incompatible with type bool typeguard is incompatible with bool reportgeneraltypeissues errors warnings informations mypy gives no error on the same code additional context i am trying to get from the example above to typecheck in both pyright and mypy mypy differs from pyright in that it does not consider a non class type form such as union to be compatible with type it only considers it to be compatible with object therefore i have to use an overload that has both a type typeguard case and an object bool case in order to have a function that accepts all type forms that works in both typecheckers unfortunately pyright doesn t appear to like both typeguard and bool appearing in the return type for different cases of the same overload
| 0
|
9,334
| 3,036,685,847
|
IssuesEvent
|
2015-08-06 13:27:12
|
NAVADMC/ADSM
|
https://api.github.com/repos/NAVADMC/ADSM
|
closed
|
Parameters for Lognormal clinical periods weren't copied correctly into ADSM
|
bug High Priority Test Needed User Feedback 3.3.0 Beta
|
Input
Use the input file provided from Michelle Meyer to reproduce. Attached in comments.
Problem
The parameters for Lognormal clinical periods weren't copied correctly into ADSM. They were [1. NAADSM Mean = 37.263001, Std Dev 1.057998; ADSM Mean = 3.617598, Std. Dev 0.028387; 2. NAADSM Mean = 36.307009, Std Dev = 1.051018; ADSM Mean = 3.591592 Std Dev. = 0.028942, 3. NAADSM Mean = 36.415994, Std Dev = 1.051986; ADSM Mean = 3.594591 Std Dev. = 0.028882]
|
1.0
|
Parameters for Lognormal clinical periods weren't copied correctly into ADSM - Input
Use the input file provided from Michelle Meyer to reproduce. Attached in comments.
Problem
The parameters for Lognormal clinical periods weren't copied correctly into ADSM. They were [1. NAADSM Mean = 37.263001, Std Dev 1.057998; ADSM Mean = 3.617598, Std. Dev 0.028387; 2. NAADSM Mean = 36.307009, Std Dev = 1.051018; ADSM Mean = 3.591592 Std Dev. = 0.028942, 3. NAADSM Mean = 36.415994, Std Dev = 1.051986; ADSM Mean = 3.594591 Std Dev. = 0.028882]
|
non_process
|
parameters for lognormal clinical periods weren t copied correctly into adsm input use the input file provided from michelle meyer to reproduce attached in comments problem the parameters for lognormal clinical periods weren t copied correctly into adsm they were
| 0
|
11,288
| 14,086,635,603
|
IssuesEvent
|
2020-11-05 04:17:34
|
ubclaunchpad/when3meet
|
https://api.github.com/repos/ubclaunchpad/when3meet
|
closed
|
Add github issue and pull request templates
|
Process
|
Add templates for github issues and pull requests for consistency.
|
1.0
|
Add github issue and pull request templates - Add templates for github issues and pull requests for consistency.
|
process
|
add github issue and pull request templates add templates for github issues and pull requests for consistency
| 1
|
5,506
| 8,376,357,968
|
IssuesEvent
|
2018-10-05 19:32:39
|
hackcambridge/hack-cambridge-website
|
https://api.github.com/repos/hackcambridge/hack-cambridge-website
|
closed
|
Add YAML file validation to build process
|
Epic: Dev process
|
Test resources files to make sure the YAML is valid — if it isn't, this could cause a runtime error when rendering pages.
|
1.0
|
Add YAML file validation to build process - Test resources files to make sure the YAML is valid — if it isn't, this could cause a runtime error when rendering pages.
|
process
|
add yaml file validation to build process test resources files to make sure the yaml is valid — if it isn t this could cause a runtime error when rendering pages
| 1
|
14,159
| 17,082,761,183
|
IssuesEvent
|
2021-07-08 07:59:12
|
darktable-org/darktable
|
https://api.github.com/repos/darktable-org/darktable
|
closed
|
eigf posterization
|
bug: pending reproduce: random scope: image processing understood: incomplete
|
eigf produces posterization effects, while averaged eigf does not (with all other settings the same). Changing filter diffusion, edges refinement has no effect.


**Expected behavior**
No posterization
**Platform**
* darktable version : current master
* OS : Linux - kernel 5.0.37
* Linux - Distro Ubuntu 18.04
* Memory 8G
* OpenCL installed : no
* OpenCL activated : no
* Desktop : KDE
* gcc : 11
|
1.0
|
eigf posterization - eigf produces posterization effects, while averaged eigf does not (with all other settings the same). Changing filter diffusion, edges refinement has no effect.


**Expected behavior**
No posterization
**Platform**
* darktable version : current master
* OS : Linux - kernel 5.0.37
* Linux - Distro Ubuntu 18.04
* Memory 8G
* OpenCL installed : no
* OpenCL activated : no
* Desktop : KDE
* gcc : 11
|
process
|
eigf posterization eigf produces posterization effects while averaged eigf does not with all other settings the same changing filter diffusion edges refinement has no effect expected behavior no posterization platform darktable version current master os linux kernel linux distro ubuntu memory opencl installed no opencl activated no desktop kde gcc
| 1
|
5,864
| 8,683,599,994
|
IssuesEvent
|
2018-12-02 19:33:22
|
bitshares/bitshares-community-ui
|
https://api.github.com/repos/bitshares/bitshares-community-ui
|
closed
|
Decouple Validated and Regular Inputs
|
process refactoring ui
|
Sometimes validation is not needed (e.g. seach input), we need to split current Input component (validated) into regular one + validation layer component over it.
|
1.0
|
Decouple Validated and Regular Inputs - Sometimes validation is not needed (e.g. seach input), we need to split current Input component (validated) into regular one + validation layer component over it.
|
process
|
decouple validated and regular inputs sometimes validation is not needed e g seach input we need to split current input component validated into regular one validation layer component over it
| 1
|
316,964
| 27,200,381,993
|
IssuesEvent
|
2023-02-20 09:18:11
|
godotengine/godot
|
https://api.github.com/repos/godotengine/godot
|
closed
|
About support for Apple pencil(Version 3.5) When apple pencil is clicked on the scrollcontainer, it will become a slide
|
platform:ios topic:porting needs testing topic:input
|
### Godot version
3.5
### System information
macos 13.0.1 (22A400)
### Issue description
Godot exports the project to the iPad.
When you click on the list of iPad applications with an Apple pencil,
the list will have a little sliding effect.
scroll_deadzone has been set to 10.
### Steps to reproduce
When you click on the list of iPad applications with an Apple pencil
### Minimal reproduction project
N/A
|
1.0
|
About support for Apple pencil(Version 3.5) When apple pencil is clicked on the scrollcontainer, it will become a slide - ### Godot version
3.5
### System information
macos 13.0.1 (22A400)
### Issue description
Godot exports the project to the iPad.
When you click on the list of iPad applications with an Apple pencil,
the list will have a little sliding effect.
scroll_deadzone has been set to 10.
### Steps to reproduce
When you click on the list of iPad applications with an Apple pencil
### Minimal reproduction project
N/A
|
non_process
|
about support for apple pencil version when apple pencil is clicked on the scrollcontainer it will become a slide godot version system information macos issue description godot exports the project to the ipad when you click on the list of ipad applications with an apple pencil the list will have a little sliding effect scroll deadzone has been set to steps to reproduce when you click on the list of ipad applications with an apple pencil minimal reproduction project n a
| 0
|
129,739
| 18,109,731,080
|
IssuesEvent
|
2021-09-23 01:00:58
|
maorkuriel/ksa
|
https://api.github.com/repos/maorkuriel/ksa
|
opened
|
CVE-2015-3192 (Medium) detected in spring-web-3.1.1.RELEASE.jar
|
security vulnerability
|
## CVE-2015-3192 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-3.1.1.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: ksa/ksa-web-root/ksa-system-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,er/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-3.1.1.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Spring Framework before 3.2.14 and 4.x before 4.1.7 do not properly process inline DTD declarations when DTD is not entirely disabled, which allows remote attackers to cause a denial of service (memory consumption and out-of-memory errors) via a crafted XML file.
<p>Publish Date: 2016-07-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3192>CVE-2015-3192</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-3192">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-3192</a></p>
<p>Release Date: 2016-07-12</p>
<p>Fix Resolution: org.springframework:spring-web:3.2.14.RELEASE,4.1.7.RELEASE,org.springframework:spring-oxm:3.2.14.RELEASE,4.1.7.RELEASE</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"3.1.1.RELEASE","packageFilePaths":["/ksa-web-root/ksa-system-web/pom.xml","/ksa-web-root/ksa-statistics-web/pom.xml","/ksa-web-core/pom.xml","/ksa-web-root/ksa-web/pom.xml","/ksa-web-root/ksa-logistics-web/pom.xml","/ksa-web-root/ksa-bd-web/pom.xml","/ksa-web-root/ksa-security-web/pom.xml","/ksa-web-root/ksa-finance-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:3.1.1.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:3.2.14.RELEASE,4.1.7.RELEASE,org.springframework:spring-oxm:3.2.14.RELEASE,4.1.7.RELEASE"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-3192","vulnerabilityDetails":"Pivotal Spring Framework before 3.2.14 and 4.x before 4.1.7 do not properly process inline DTD declarations when DTD is not entirely disabled, which allows remote attackers to cause a denial of service (memory consumption and out-of-memory errors) via a crafted XML file.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3192","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2015-3192 (Medium) detected in spring-web-3.1.1.RELEASE.jar - ## CVE-2015-3192 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-web-3.1.1.RELEASE.jar</b></p></summary>
<p>Spring Framework Parent</p>
<p>Path to dependency file: ksa/ksa-web-root/ksa-system-web/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,er/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-web/3.1.1.RELEASE/spring-web-3.1.1.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- :x: **spring-web-3.1.1.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Pivotal Spring Framework before 3.2.14 and 4.x before 4.1.7 do not properly process inline DTD declarations when DTD is not entirely disabled, which allows remote attackers to cause a denial of service (memory consumption and out-of-memory errors) via a crafted XML file.
<p>Publish Date: 2016-07-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3192>CVE-2015-3192</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-3192">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2015-3192</a></p>
<p>Release Date: 2016-07-12</p>
<p>Fix Resolution: org.springframework:spring-web:3.2.14.RELEASE,4.1.7.RELEASE,org.springframework:spring-oxm:3.2.14.RELEASE,4.1.7.RELEASE</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-web","packageVersion":"3.1.1.RELEASE","packageFilePaths":["/ksa-web-root/ksa-system-web/pom.xml","/ksa-web-root/ksa-statistics-web/pom.xml","/ksa-web-core/pom.xml","/ksa-web-root/ksa-web/pom.xml","/ksa-web-root/ksa-logistics-web/pom.xml","/ksa-web-root/ksa-bd-web/pom.xml","/ksa-web-root/ksa-security-web/pom.xml","/ksa-web-root/ksa-finance-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"org.springframework:spring-web:3.1.1.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-web:3.2.14.RELEASE,4.1.7.RELEASE,org.springframework:spring-oxm:3.2.14.RELEASE,4.1.7.RELEASE"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2015-3192","vulnerabilityDetails":"Pivotal Spring Framework before 3.2.14 and 4.x before 4.1.7 do not properly process inline DTD declarations when DTD is not entirely disabled, which allows remote attackers to cause a denial of service (memory consumption and out-of-memory errors) via a crafted XML file.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2015-3192","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
cve medium detected in spring web release jar cve medium severity vulnerability vulnerable library spring web release jar spring framework parent path to dependency file ksa ksa web root ksa system web pom xml path to vulnerable library home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar er repository org springframework spring web release spring web release jar ksa web root ksa web target root web inf lib spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar home wss scanner repository org springframework spring web release spring web release jar dependency hierarchy x spring web release jar vulnerable library found in base branch master vulnerability details pivotal spring framework before and x before do not properly process inline dtd declarations when dtd is not entirely disabled which allows remote attackers to cause a denial of service memory consumption and out of memory errors via a crafted xml file publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring web release release org springframework spring oxm release release rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree org springframework spring web release isminimumfixversionavailable true minimumfixversion org springframework spring web release release org springframework spring oxm release release basebranches vulnerabilityidentifier cve vulnerabilitydetails pivotal spring framework before and x before do not properly process inline dtd declarations when dtd is not entirely disabled which allows remote attackers to cause a denial of service memory consumption and out of memory errors via a crafted xml file vulnerabilityurl
| 0
|
16,997
| 22,358,832,409
|
IssuesEvent
|
2022-06-15 18:16:50
|
bazelbuild/bazel
|
https://api.github.com/repos/bazelbuild/bazel
|
opened
|
Release 5.3 - August 2022
|
P1 type: process release team-OSS
|
# Status of Bazel X.Y
<!-- The first item is only needed for major releases (X.0.0) -->
- Target baseline: [date]
- Expected release date: 08/08/2022
- [List of release blockers](link-to-milestone)
To report a release-blocking bug, please add a comment with the text `@bazel-io flag` to the issue. A release manager will triage it and add it to the milestone.
To cherry-pick a mainline commit into X.Y, simply send a PR against the `release-X.Y.0` branch.
Task list:
<!-- The first three items are only needed for major releases (X.0.0) -->
- [ ] Pick release baseline:
- [ ] Create release candidate:
- [ ] Check downstream projects:
- [ ] [Create draft release announcement](https://docs.google.com/document/d/1wDvulLlj4NAlPZamdlEVFORks3YXJonCjyuQMUQEmB0/edit)
- [ ] Send for review the release announcement PR:
- [ ] Push the release, notify package maintainers:
- [ ] Update the documentation
- [ ] Push the blog post
- [ ] Update the [release page](https://github.com/bazelbuild/bazel/releases/)
|
1.0
|
Release 5.3 - August 2022 - # Status of Bazel X.Y
<!-- The first item is only needed for major releases (X.0.0) -->
- Target baseline: [date]
- Expected release date: 08/08/2022
- [List of release blockers](link-to-milestone)
To report a release-blocking bug, please add a comment with the text `@bazel-io flag` to the issue. A release manager will triage it and add it to the milestone.
To cherry-pick a mainline commit into X.Y, simply send a PR against the `release-X.Y.0` branch.
Task list:
<!-- The first three items are only needed for major releases (X.0.0) -->
- [ ] Pick release baseline:
- [ ] Create release candidate:
- [ ] Check downstream projects:
- [ ] [Create draft release announcement](https://docs.google.com/document/d/1wDvulLlj4NAlPZamdlEVFORks3YXJonCjyuQMUQEmB0/edit)
- [ ] Send for review the release announcement PR:
- [ ] Push the release, notify package maintainers:
- [ ] Update the documentation
- [ ] Push the blog post
- [ ] Update the [release page](https://github.com/bazelbuild/bazel/releases/)
|
process
|
release august status of bazel x y target baseline expected release date link to milestone to report a release blocking bug please add a comment with the text bazel io flag to the issue a release manager will triage it and add it to the milestone to cherry pick a mainline commit into x y simply send a pr against the release x y branch task list pick release baseline create release candidate check downstream projects send for review the release announcement pr push the release notify package maintainers update the documentation push the blog post update the
| 1
|
64,421
| 26,723,870,072
|
IssuesEvent
|
2023-01-29 13:23:44
|
microsoftgraph/microsoft-graph-explorer-v4
|
https://api.github.com/repos/microsoftgraph/microsoft-graph-explorer-v4
|
closed
|
Blue Consent button not visible
|
API: Graph Needs: Attention 👋 Needs: Author Feedback Area: Permissions Service issue
|
**Describe the bug**
Trying to test the `https://graph.microsoft.com/v1.0/users/<id>/mailFolders/inbox/messageRules` API but the consent button is not showing.
Calling `https://graph.microsoft.com/v1.0/me/mailFolders/inbox/messageRules` but not for others. I receive 403 error.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to Graph Explorer and sign in
2. Try to execute `https://graph.microsoft.com/v1.0/me/mailFolders/inbox/messageRules`
3. Now try to call into another user's mailbox `https://graph.microsoft.com/v1.0/users/<id>/mailFolders/inbox/messageRules`
4. See error
5. See `Unconsent` text/button.
**Expected behavior**
If consent is missing the blue consent button should be visible on the `Modify permissions` tab.
**Screenshots**
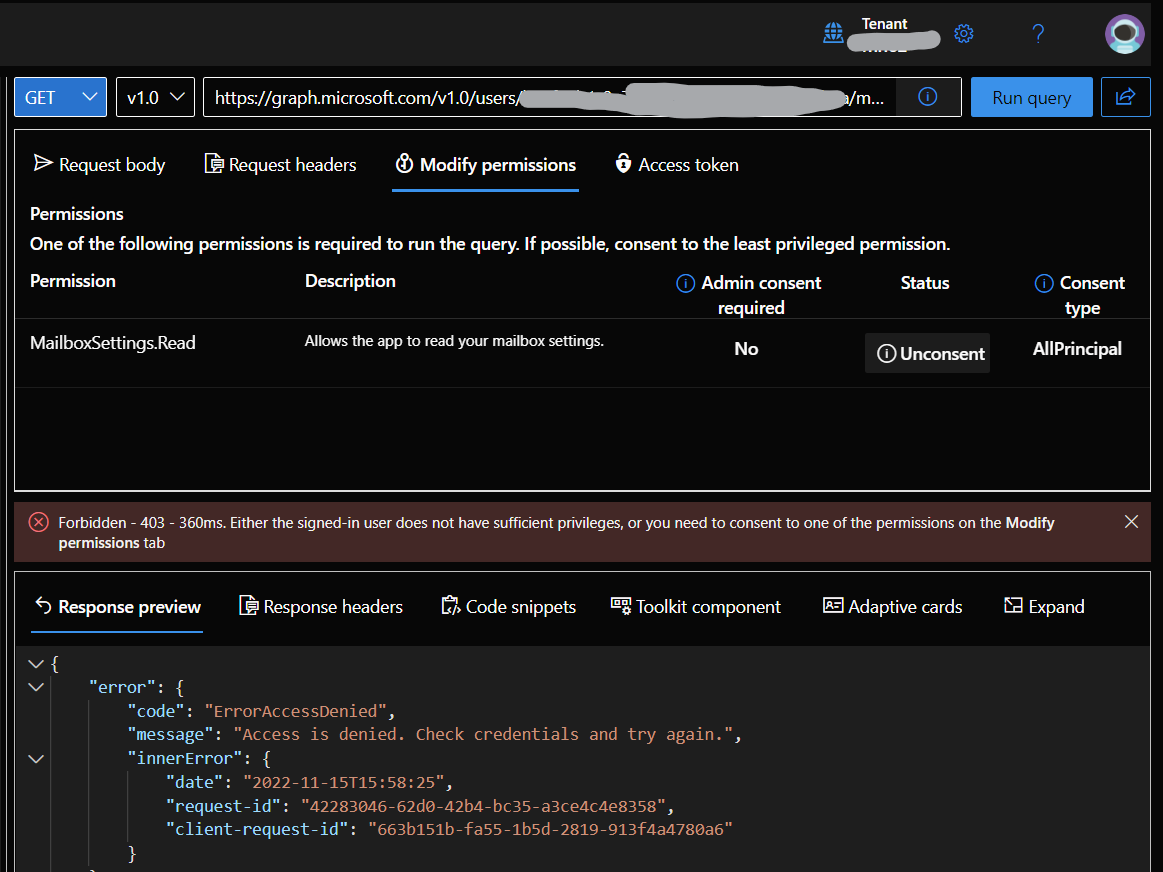
**Desktop (please complete the following information):**
- OS: Windows 11
- Browser Microsoft Edge
- Version 108.0.1462.15
**Additional context**
Add any other context about the problem here.
|
1.0
|
Blue Consent button not visible - **Describe the bug**
Trying to test the `https://graph.microsoft.com/v1.0/users/<id>/mailFolders/inbox/messageRules` API but the consent button is not showing.
Calling `https://graph.microsoft.com/v1.0/me/mailFolders/inbox/messageRules` but not for others. I receive 403 error.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to Graph Explorer and sign in
2. Try to execute `https://graph.microsoft.com/v1.0/me/mailFolders/inbox/messageRules`
3. Now try to call into another user's mailbox `https://graph.microsoft.com/v1.0/users/<id>/mailFolders/inbox/messageRules`
4. See error
5. See `Unconsent` text/button.
**Expected behavior**
If consent is missing the blue consent button should be visible on the `Modify permissions` tab.
**Screenshots**
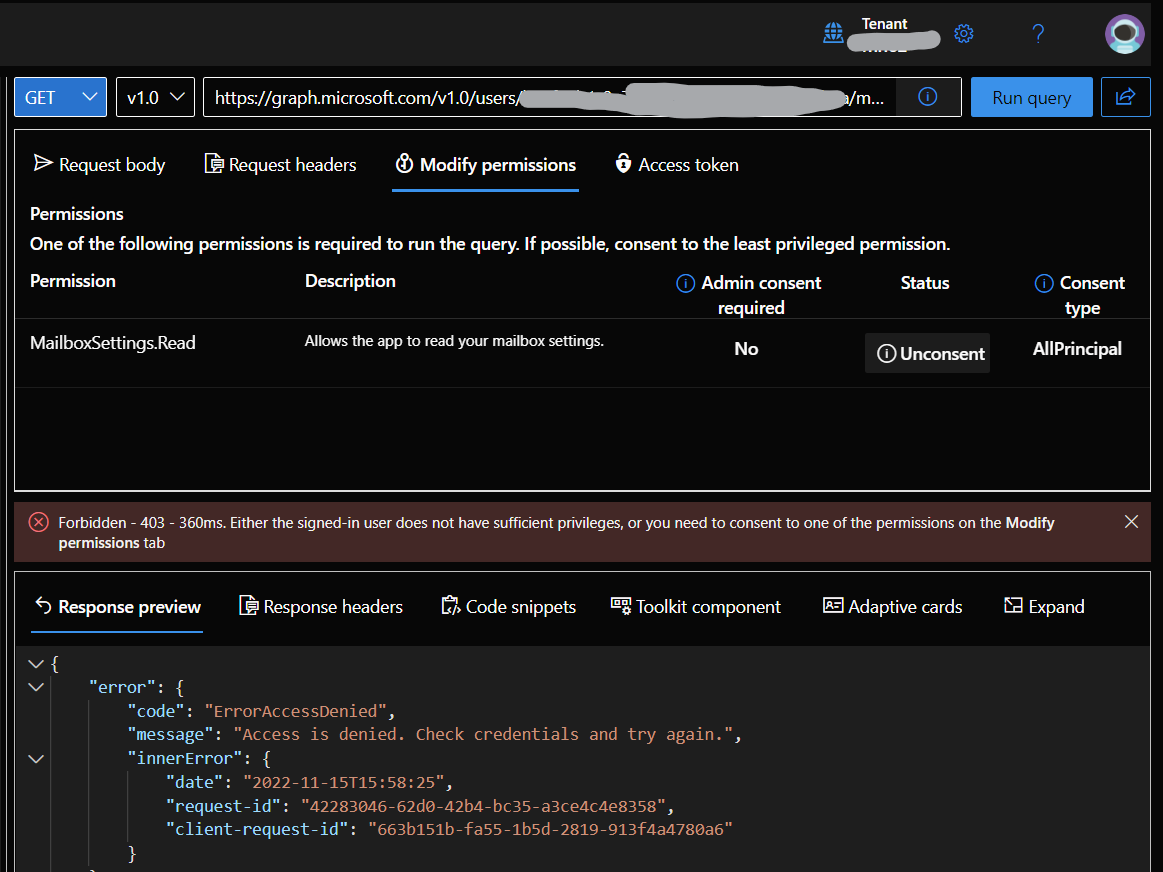
**Desktop (please complete the following information):**
- OS: Windows 11
- Browser Microsoft Edge
- Version 108.0.1462.15
**Additional context**
Add any other context about the problem here.
|
non_process
|
blue consent button not visible describe the bug trying to test the api but the consent button is not showing calling but not for others i receive error to reproduce steps to reproduce the behavior go to graph explorer and sign in try to execute now try to call into another user s mailbox see error see unconsent text button expected behavior if consent is missing the blue consent button should be visible on the modify permissions tab screenshots desktop please complete the following information os windows browser microsoft edge version additional context add any other context about the problem here
| 0
|
11,286
| 14,079,838,824
|
IssuesEvent
|
2020-11-04 15:22:34
|
TIBCOSoftware/genxdm
|
https://api.github.com/repos/TIBCOSoftware/genxdm
|
closed
|
Add element name (typically from ElementDefinition, not from XML instance) to SimpleTypeException constructor override
|
Component-API Component-Processors enhancement
|
We've had pushback on exceptions thrown (usually during validation) for simple types, because they do not provide sufficient context to find the problem (if the string representing the invalid value is sufficiently unique, that can be used, but that's often not the case). Per Aditya Wagle (as demonstrated in pull request 171), we can do this within the validator, in many cases.
So let's do it. Add an override to the SimpleTypeException constructor, change the construction of the message, and where possible (where we have an ElementDefinition, an element's QName, or even just an element's localName), invoke the new constructor.
|
1.0
|
Add element name (typically from ElementDefinition, not from XML instance) to SimpleTypeException constructor override - We've had pushback on exceptions thrown (usually during validation) for simple types, because they do not provide sufficient context to find the problem (if the string representing the invalid value is sufficiently unique, that can be used, but that's often not the case). Per Aditya Wagle (as demonstrated in pull request 171), we can do this within the validator, in many cases.
So let's do it. Add an override to the SimpleTypeException constructor, change the construction of the message, and where possible (where we have an ElementDefinition, an element's QName, or even just an element's localName), invoke the new constructor.
|
process
|
add element name typically from elementdefinition not from xml instance to simpletypeexception constructor override we ve had pushback on exceptions thrown usually during validation for simple types because they do not provide sufficient context to find the problem if the string representing the invalid value is sufficiently unique that can be used but that s often not the case per aditya wagle as demonstrated in pull request we can do this within the validator in many cases so let s do it add an override to the simpletypeexception constructor change the construction of the message and where possible where we have an elementdefinition an element s qname or even just an element s localname invoke the new constructor
| 1
|
325,388
| 27,873,646,897
|
IssuesEvent
|
2023-03-21 14:52:04
|
sebastianbergmann/phpunit
|
https://api.github.com/repos/sebastianbergmann/phpunit
|
closed
|
Tests from test class with same non-fully qualified class name as another test class are sometimes not discovered
|
type/bug feature/test-runner version/10
|
| Q | A
| --------------------| ---------------
| PHPUnit version | 10.0.16
| PHP version | 8.2.3
| Installation Method | Composer
#### Summary
Not sure to understand what happen, but since I updated one of my project to PHPUnit 10, I got some conflicts with test classes having same names but in different namespaces (I'm using some obscur static mecanisms).
Let say class `\MyTests\A\MyClassTest` and `\MyTests\B\MyClassTest` having common `\MyTests\C\MyTestCasse` parent for example.
I tried to investigate a little bit, and found [this line](https://github.com/sebastianbergmann/phpunit/blob/36fba38dc8cced013c122bcd90636d76367e578d/src/Runner/TestSuiteLoader.php#L80) is overriding `$suiteClassName` using first loaded class having same name, whatever namespace is. Is it expected ?
Thanks!
|
1.0
|
Tests from test class with same non-fully qualified class name as another test class are sometimes not discovered - | Q | A
| --------------------| ---------------
| PHPUnit version | 10.0.16
| PHP version | 8.2.3
| Installation Method | Composer
#### Summary
Not sure to understand what happen, but since I updated one of my project to PHPUnit 10, I got some conflicts with test classes having same names but in different namespaces (I'm using some obscur static mecanisms).
Let say class `\MyTests\A\MyClassTest` and `\MyTests\B\MyClassTest` having common `\MyTests\C\MyTestCasse` parent for example.
I tried to investigate a little bit, and found [this line](https://github.com/sebastianbergmann/phpunit/blob/36fba38dc8cced013c122bcd90636d76367e578d/src/Runner/TestSuiteLoader.php#L80) is overriding `$suiteClassName` using first loaded class having same name, whatever namespace is. Is it expected ?
Thanks!
|
non_process
|
tests from test class with same non fully qualified class name as another test class are sometimes not discovered q a phpunit version php version installation method composer summary not sure to understand what happen but since i updated one of my project to phpunit i got some conflicts with test classes having same names but in different namespaces i m using some obscur static mecanisms let say class mytests a myclasstest and mytests b myclasstest having common mytests c mytestcasse parent for example i tried to investigate a little bit and found is overriding suiteclassname using first loaded class having same name whatever namespace is is it expected thanks
| 0
|
18,607
| 24,578,669,266
|
IssuesEvent
|
2022-10-13 14:08:23
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
[Android] Share icon is disabled in the mobile app > If PDF resources title is configured with slash special character in the study builder
|
Bug P1 Android Process: Fixed Process: Tested QA Process: Tested dev
|
**Steps:**
1. Configure PDF resources with slash special character as title in SB. ( Eg:PDF/ )
2. Now in mobile app, Navigate to resources screen
3. Open that particular PDF resource
4. Click on Share icon and Verify
**AR:** Share icon is disabled in the mobile app , If PDF resources title is configured with slash special character in the study builder
**ER:** Share icon should not be disabled in the mobile app , If PDF resources title is configured with slash special character in the study builder
|
3.0
|
[Android] Share icon is disabled in the mobile app > If PDF resources title is configured with slash special character in the study builder - **Steps:**
1. Configure PDF resources with slash special character as title in SB. ( Eg:PDF/ )
2. Now in mobile app, Navigate to resources screen
3. Open that particular PDF resource
4. Click on Share icon and Verify
**AR:** Share icon is disabled in the mobile app , If PDF resources title is configured with slash special character in the study builder
**ER:** Share icon should not be disabled in the mobile app , If PDF resources title is configured with slash special character in the study builder
|
process
|
share icon is disabled in the mobile app if pdf resources title is configured with slash special character in the study builder steps configure pdf resources with slash special character as title in sb eg pdf now in mobile app navigate to resources screen open that particular pdf resource click on share icon and verify ar share icon is disabled in the mobile app if pdf resources title is configured with slash special character in the study builder er share icon should not be disabled in the mobile app if pdf resources title is configured with slash special character in the study builder
| 1
|
38,319
| 10,169,980,536
|
IssuesEvent
|
2019-08-08 03:05:07
|
JuliaLang/julia
|
https://api.github.com/repos/JuliaLang/julia
|
closed
|
Problem with win64 source build with clang
|
build windows
|
Hello,
I've followed the instruction for custom build of julia + modification of Make.user from CXX.jl install instruction. I've ended up with following `make` error that I cannot solve by myself:
```
phlavenk@BROPHYSWS3 MSYS /e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia
$ make
/usr/bin/tar: test/Driver/Inputs/basic_cross_linux_tree/usr/bin/x86_64-unknown-linux-gnu-ld: Cannot create symlink to ‘x86_64-unknown-linux-gnu-ld.gold’: No such file or directory
/usr/bin/tar: test/Driver/Inputs/basic_cross_linux_tree/usr/bin/i386-unknown-linux-gnu-ld: Cannot create symlink to ‘i386-unknown-linux-gnu-ld.gold’: No such file or directory
/usr/bin/tar: test/Driver/Inputs/multilib_64bit_linux_tree/usr/bin/as: Cannot create symlink to ‘x86_64-unknown-linux-gnu-as’: No such file or directory
/usr/bin/tar: test/Driver/Inputs/multilib_32bit_linux_tree/usr/bin/as: Cannot create symlink to ‘i386-unknown-linux-gnu-as’: No such file or directory
/usr/bin/tar: Exiting with failure status due to previous errors
make[1]: *** [/e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia/deps/llvm.mk:332: /e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia/deps/srccache/llvm-3.7.1.extracted] Error 2
make: *** [Makefile:81: julia-deps] Error 2
```
I've looked for the referenced file and have found it in
```
phlavenk@BROPHYSWS3 MSYS /e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia/deps/srccache/llvm-3.7.1/tools/clang/test/Driver/Inputs/basic_cross_linux_tree/usr/bin
$ ls -L -l -H
total 6
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 i386-unknown-linux-gnu-as
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 i386-unknown-linux-gnu-ld.bfd
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 i386-unknown-linux-gnu-ld.gold
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 x86_64-unknown-linux-gnu-as
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 x86_64-unknown-linux-gnu-ld.bfd
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 x86_64-unknown-linux-gnu-ld.gold
```
Running on Windows server 2012r2, x86-64, 2x Intel XeonE5-4669 v3, with sources from the `git checkout release-0.5` branch. I'm not familiar with the `make` machinery, so I don't know where to look for build logs.
Unfortunately I cannot rely on the binary distribution of Julia 0.5 because of the lack of binaries required to run CXX.jl. So I have to build from sources.
Does anyone have any idea what's wrong with the LLVM/Clang build process on my machine?
|
1.0
|
Problem with win64 source build with clang - Hello,
I've followed the instruction for custom build of julia + modification of Make.user from CXX.jl install instruction. I've ended up with following `make` error that I cannot solve by myself:
```
phlavenk@BROPHYSWS3 MSYS /e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia
$ make
/usr/bin/tar: test/Driver/Inputs/basic_cross_linux_tree/usr/bin/x86_64-unknown-linux-gnu-ld: Cannot create symlink to ‘x86_64-unknown-linux-gnu-ld.gold’: No such file or directory
/usr/bin/tar: test/Driver/Inputs/basic_cross_linux_tree/usr/bin/i386-unknown-linux-gnu-ld: Cannot create symlink to ‘i386-unknown-linux-gnu-ld.gold’: No such file or directory
/usr/bin/tar: test/Driver/Inputs/multilib_64bit_linux_tree/usr/bin/as: Cannot create symlink to ‘x86_64-unknown-linux-gnu-as’: No such file or directory
/usr/bin/tar: test/Driver/Inputs/multilib_32bit_linux_tree/usr/bin/as: Cannot create symlink to ‘i386-unknown-linux-gnu-as’: No such file or directory
/usr/bin/tar: Exiting with failure status due to previous errors
make[1]: *** [/e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia/deps/llvm.mk:332: /e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia/deps/srccache/llvm-3.7.1.extracted] Error 2
make: *** [Makefile:81: julia-deps] Error 2
```
I've looked for the referenced file and have found it in
```
phlavenk@BROPHYSWS3 MSYS /e/Users/phlavenk/Documents/programs/Julia_0.5_src/julia/deps/srccache/llvm-3.7.1/tools/clang/test/Driver/Inputs/basic_cross_linux_tree/usr/bin
$ ls -L -l -H
total 6
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 i386-unknown-linux-gnu-as
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 i386-unknown-linux-gnu-ld.bfd
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 i386-unknown-linux-gnu-ld.gold
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 x86_64-unknown-linux-gnu-as
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 x86_64-unknown-linux-gnu-ld.bfd
-rwxr-xr-x 1 phlavenk None 12 Jun 21 2013 x86_64-unknown-linux-gnu-ld.gold
```
Running on Windows server 2012r2, x86-64, 2x Intel XeonE5-4669 v3, with sources from the `git checkout release-0.5` branch. I'm not familiar with the `make` machinery, so I don't know where to look for build logs.
Unfortunately I cannot rely on the binary distribution of Julia 0.5 because of the lack of binaries required to run CXX.jl. So I have to build from sources.
Does anyone have any idea what's wrong with the LLVM/Clang build process on my machine?
|
non_process
|
problem with source build with clang hello i ve followed the instruction for custom build of julia modification of make user from cxx jl install instruction i ve ended up with following make error that i cannot solve by myself phlavenk msys e users phlavenk documents programs julia src julia make usr bin tar test driver inputs basic cross linux tree usr bin unknown linux gnu ld cannot create symlink to ‘ unknown linux gnu ld gold’ no such file or directory usr bin tar test driver inputs basic cross linux tree usr bin unknown linux gnu ld cannot create symlink to ‘ unknown linux gnu ld gold’ no such file or directory usr bin tar test driver inputs multilib linux tree usr bin as cannot create symlink to ‘ unknown linux gnu as’ no such file or directory usr bin tar test driver inputs multilib linux tree usr bin as cannot create symlink to ‘ unknown linux gnu as’ no such file or directory usr bin tar exiting with failure status due to previous errors make error make error i ve looked for the referenced file and have found it in phlavenk msys e users phlavenk documents programs julia src julia deps srccache llvm tools clang test driver inputs basic cross linux tree usr bin ls l l h total rwxr xr x phlavenk none jun unknown linux gnu as rwxr xr x phlavenk none jun unknown linux gnu ld bfd rwxr xr x phlavenk none jun unknown linux gnu ld gold rwxr xr x phlavenk none jun unknown linux gnu as rwxr xr x phlavenk none jun unknown linux gnu ld bfd rwxr xr x phlavenk none jun unknown linux gnu ld gold running on windows server intel with sources from the git checkout release branch i m not familiar with the make machinery so i don t know where to look for build logs unfortunately i cannot rely on the binary distribution of julia because of the lack of binaries required to run cxx jl so i have to build from sources does anyone have any idea what s wrong with the llvm clang build process on my machine
| 0
|
2,603
| 5,356,458,194
|
IssuesEvent
|
2017-02-20 15:42:35
|
openvstorage/gobjfs
|
https://api.github.com/repos/openvstorage/gobjfs
|
closed
|
Fix error propagation
|
process_wontfix type_bug
|
Related to #6:
We observe error code `5` (or `-5`, indicating `EIO`) being reported to the client while the actual cause is the absence of the fragment / file. The latter does not necessarily indicate an error from the client's POV as the requested fragment / file could have been moved away by a maintenance process.
This causes excessive logging.
|
1.0
|
Fix error propagation - Related to #6:
We observe error code `5` (or `-5`, indicating `EIO`) being reported to the client while the actual cause is the absence of the fragment / file. The latter does not necessarily indicate an error from the client's POV as the requested fragment / file could have been moved away by a maintenance process.
This causes excessive logging.
|
process
|
fix error propagation related to we observe error code or indicating eio being reported to the client while the actual cause is the absence of the fragment file the latter does not necessarily indicate an error from the client s pov as the requested fragment file could have been moved away by a maintenance process this causes excessive logging
| 1
|
10,284
| 14,920,737,547
|
IssuesEvent
|
2021-01-23 06:27:40
|
ayoung19/wi21-cse110-lab3
|
https://api.github.com/repos/ayoung19/wi21-cse110-lab3
|
closed
|
Grid
|
requirement
|
Requirement Details:
- Must have more than two children within the element that is using grid. Must use minimum three of the flexbox related attributes.
|
1.0
|
Grid - Requirement Details:
- Must have more than two children within the element that is using grid. Must use minimum three of the flexbox related attributes.
|
non_process
|
grid requirement details must have more than two children within the element that is using grid must use minimum three of the flexbox related attributes
| 0
|
11,849
| 14,662,619,693
|
IssuesEvent
|
2020-12-29 07:42:56
|
GoogleCloudPlatform/fda-mystudies
|
https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies
|
closed
|
Add URLS_ERROR to Hydra terraform config
|
Deployment Feature request Hydra P1 Process: Fixed Process: Tested dev
|
@zohrehj We've fixed the issue and added `GenericErrorController `class to redirect to error page instead of displaying Hydra's fallback error page. @harisboston will raise the PR today with tests.
Please add below env in deployment script.
`-e URLS_ERROR="http://<AUTH_SERVER_URL>/error" `
_Originally posted by @dhanyak-btc in https://github.com/GoogleCloudPlatform/fda-mystudies/issues/2269#issuecomment-742367185_
|
2.0
|
Add URLS_ERROR to Hydra terraform config - @zohrehj We've fixed the issue and added `GenericErrorController `class to redirect to error page instead of displaying Hydra's fallback error page. @harisboston will raise the PR today with tests.
Please add below env in deployment script.
`-e URLS_ERROR="http://<AUTH_SERVER_URL>/error" `
_Originally posted by @dhanyak-btc in https://github.com/GoogleCloudPlatform/fda-mystudies/issues/2269#issuecomment-742367185_
|
process
|
add urls error to hydra terraform config zohrehj we ve fixed the issue and added genericerrorcontroller class to redirect to error page instead of displaying hydra s fallback error page harisboston will raise the pr today with tests please add below env in deployment script e urls error originally posted by dhanyak btc in
| 1
|
21,762
| 30,278,566,679
|
IssuesEvent
|
2023-07-07 22:34:53
|
RConsortium/submissions-pilot3-adam
|
https://api.github.com/repos/RConsortium/submissions-pilot3-adam
|
closed
|
Call to R Consortium Review Pilot 3 Proposal
|
submission process
|
Hello R Consortium.
Here is the link to the current draft of the [Pilot 3 Proposal](https://github.com/RConsortium/submissions-pilot3-adam/blob/main/vignettes/fda/R_Submission_Pilot_3_ADaM_FDA_Execution_Proposal_02Dec2022.pdf).
Please review at your earliest convenience before 13JAN2023. Per your review, feel free to leave comments, feedback or any questions you may have in this issue. Many thanks for taking the time to review.
Best,
@thomas-neitmann & @laxamanaj
|
1.0
|
Call to R Consortium Review Pilot 3 Proposal - Hello R Consortium.
Here is the link to the current draft of the [Pilot 3 Proposal](https://github.com/RConsortium/submissions-pilot3-adam/blob/main/vignettes/fda/R_Submission_Pilot_3_ADaM_FDA_Execution_Proposal_02Dec2022.pdf).
Please review at your earliest convenience before 13JAN2023. Per your review, feel free to leave comments, feedback or any questions you may have in this issue. Many thanks for taking the time to review.
Best,
@thomas-neitmann & @laxamanaj
|
process
|
call to r consortium review pilot proposal hello r consortium here is the link to the current draft of the please review at your earliest convenience before per your review feel free to leave comments feedback or any questions you may have in this issue many thanks for taking the time to review best thomas neitmann laxamanaj
| 1
|
57,191
| 7,043,826,607
|
IssuesEvent
|
2017-12-31 13:32:53
|
NITDgpOS/AirHockey
|
https://api.github.com/repos/NITDgpOS/AirHockey
|
closed
|
Using time limit for each round
|
assigned design enhancement medium
|
if there will be three rounds ,use constant time limit for each round, because :--
1> global best points will remain open ended,hence can be updated with the score
2> I gotta think of more reasons
I can work on this even @Aniq55
|
1.0
|
Using time limit for each round - if there will be three rounds ,use constant time limit for each round, because :--
1> global best points will remain open ended,hence can be updated with the score
2> I gotta think of more reasons
I can work on this even @Aniq55
|
non_process
|
using time limit for each round if there will be three rounds use constant time limit for each round because global best points will remain open ended hence can be updated with the score i gotta think of more reasons i can work on this even
| 0
|
8,551
| 8,356,241,683
|
IssuesEvent
|
2018-10-02 17:54:59
|
Azure/azure-sdk-for-python
|
https://api.github.com/repos/Azure/azure-sdk-for-python
|
closed
|
azure.mgmt.scheduler.operations.JobsOperations.create_update() Malformed Job Object
|
ARM Bug Scheduler Service Attention
|
Hello,
I am trying to create a new Job in the Azure Scheduler using the Python SDK. However, the respond from the API is not providing enough details of the error and I have tried to find my own problem re-checking the API's doc multiple times but I haven't been able to found the error.
### Here is the stack trace of the respond from the API
```
Traceback (most recent call last):
File "<console>", line 1, in <module>
File "/home/student/DataLions/Server/DataLionsAPI/rest/AzureScheduler.py", line 56, in create
self._setJobDefinition(event))
File "/home/student/DataLions/Server/DataLionsAPI/env/lib/python3.5/site-packages/azure/mgmt/scheduler/operations/jobs_operations.py", line 164, in create_or_update
raise exp
msrestazure.azure_exceptions.CloudError: Azure Error: BadRequest
Message: Malformed Job Object
```
I have replaced subscriptionId and the uri with a mock one for security purposes.
### Here is the code I am using to send the request.
#### Important! event['endDate'] = "2018-01-19"
```python
from msrest.serialization import Serializer, Deserializer
from msrest.configuration import Configuration
from msrest.service_client import ServiceClient
from azure.mgmt.scheduler import SchedulerManagementClient
from azure.mgmt.scheduler.operations import JobsOperations
from azure.mgmt.scheduler.models import JobDefinition, JobProperties, JobAction
from azure.mgmt.scheduler.models import HttpRequest, HttpAuthentication, JobState
from azure.mgmt.scheduler.models import JobRecurrence, RetryPolicy, StorageQueueMessage
from azure.mgmt.scheduler.models import JobActionType
from datetime import datetime, timedelta
import importlib, inspect
# Wrapper for the Azure Microsoft API
class AzureScheduler:
# The constructor setups the essential configuration to use the Scheduler
# from Microsoft Azure
def __init__(self, credentials, subscriptionId="mocksubscriptionId",
resourceGroupName="syncResource", jobCollectionName="apisync"):
self.subscriptionId = subscriptionId
self.resourceGroupName = resourceGroupName
self.jobCollectionName = jobCollectionName
self.schedulerClient = SchedulerManagementClient(credentials, subscriptionId)
self.serviceClient = ServiceClient(credentials,Configuration("https://management.azure.com/"))
classes = self.__setClasses()
self.jobsOperations = JobsOperations(self.serviceClient, self.schedulerClient.config,
Serializer(classes=classes), Deserializer(classes=classes))
# Setup a Dictionary with all the classes from the Scheduler Model.
# Required to Serialize and Deserialize objects/JSONs
def __setClasses(self):
classes = {}
model = "azure.mgmt.scheduler.models"
mod = importlib.import_module(model)
for mod_name, mod_obj in inspect.getmembers(mod, predicate=inspect.isclass):
classes[mod_name] = mod_obj
return classes
# List all the Jobs inside the Job Collection (jobCollectionName)
def list(self):
return self.jobsOperations.list(self.resourceGroupName,self.jobCollectionName)
# first jobName datalionScheduler
# Gets the description of the job requested
def get(self, jobName):
return self.jobsOperations.get(self.resourceGroupName,self.jobCollectionName,jobName)
# Creates a job in the Job Collection
def create(self, jobName, event):
return self.jobsOperations.create_or_update(self.resourceGroupName,
self.jobCollectionName, jobName,
self._setJobDefinition(event))
# Deletes the job (jobName)
def delete(self, jobName):
return self.jobsOperations.delete(self.resourceGroupName,self.jobCollectionName,jobName)
def _setJobDefinition(self, event):
return JobDefinition(properties=self._setJobProperties(event))
def _setJobProperties(self, event):
return JobProperties(
start_time=datetime.strptime(event['endDate']+ " 9:50pm -0500", '%Y-%m-%d %I:%M%p %z'),
action=self._setJobAction(),
state=JobState("Enabled"),
recurrence=self._setJobRecurrence(event))
def _setJobAction(self):
return JobAction(type=JobActionType('Http'),request=self._setHttpRequest(), retry_policy=self._setRetryPolicy(), queue_message=self._setStorageQueueMessage())
def _setHttpRequest(self):
return HttpRequest(uri="http://test.ngrok.io/rest/player/?format=json", method='GET', authentication=HttpAuthentication('NotSpecified'), body="", headers={})
def _setStorageQueueMessage(self):
return StorageQueueMessage(storage_account="datalions", queue_name="Training Session", sas_token=None, message="Sync after Training")
def _setRetryPolicy(self):
return RetryPolicy(retry_type='Fixed', retry_interval=timedelta(minutes=3), retry_count=3)
def _setJobRecurrence(self, event):
return JobRecurrence(
frequency='Hour',
interval=1,end_time=datetime.strptime(event['endDate']+ " 11:50pm -0500",
'%Y-%m-%d %I:%M%p %z'))
```
|
1.0
|
azure.mgmt.scheduler.operations.JobsOperations.create_update() Malformed Job Object - Hello,
I am trying to create a new Job in the Azure Scheduler using the Python SDK. However, the respond from the API is not providing enough details of the error and I have tried to find my own problem re-checking the API's doc multiple times but I haven't been able to found the error.
### Here is the stack trace of the respond from the API
```
Traceback (most recent call last):
File "<console>", line 1, in <module>
File "/home/student/DataLions/Server/DataLionsAPI/rest/AzureScheduler.py", line 56, in create
self._setJobDefinition(event))
File "/home/student/DataLions/Server/DataLionsAPI/env/lib/python3.5/site-packages/azure/mgmt/scheduler/operations/jobs_operations.py", line 164, in create_or_update
raise exp
msrestazure.azure_exceptions.CloudError: Azure Error: BadRequest
Message: Malformed Job Object
```
I have replaced subscriptionId and the uri with a mock one for security purposes.
### Here is the code I am using to send the request.
#### Important! event['endDate'] = "2018-01-19"
```python
from msrest.serialization import Serializer, Deserializer
from msrest.configuration import Configuration
from msrest.service_client import ServiceClient
from azure.mgmt.scheduler import SchedulerManagementClient
from azure.mgmt.scheduler.operations import JobsOperations
from azure.mgmt.scheduler.models import JobDefinition, JobProperties, JobAction
from azure.mgmt.scheduler.models import HttpRequest, HttpAuthentication, JobState
from azure.mgmt.scheduler.models import JobRecurrence, RetryPolicy, StorageQueueMessage
from azure.mgmt.scheduler.models import JobActionType
from datetime import datetime, timedelta
import importlib, inspect
# Wrapper for the Azure Microsoft API
class AzureScheduler:
# The constructor setups the essential configuration to use the Scheduler
# from Microsoft Azure
def __init__(self, credentials, subscriptionId="mocksubscriptionId",
resourceGroupName="syncResource", jobCollectionName="apisync"):
self.subscriptionId = subscriptionId
self.resourceGroupName = resourceGroupName
self.jobCollectionName = jobCollectionName
self.schedulerClient = SchedulerManagementClient(credentials, subscriptionId)
self.serviceClient = ServiceClient(credentials,Configuration("https://management.azure.com/"))
classes = self.__setClasses()
self.jobsOperations = JobsOperations(self.serviceClient, self.schedulerClient.config,
Serializer(classes=classes), Deserializer(classes=classes))
# Setup a Dictionary with all the classes from the Scheduler Model.
# Required to Serialize and Deserialize objects/JSONs
def __setClasses(self):
classes = {}
model = "azure.mgmt.scheduler.models"
mod = importlib.import_module(model)
for mod_name, mod_obj in inspect.getmembers(mod, predicate=inspect.isclass):
classes[mod_name] = mod_obj
return classes
# List all the Jobs inside the Job Collection (jobCollectionName)
def list(self):
return self.jobsOperations.list(self.resourceGroupName,self.jobCollectionName)
# first jobName datalionScheduler
# Gets the description of the job requested
def get(self, jobName):
return self.jobsOperations.get(self.resourceGroupName,self.jobCollectionName,jobName)
# Creates a job in the Job Collection
def create(self, jobName, event):
return self.jobsOperations.create_or_update(self.resourceGroupName,
self.jobCollectionName, jobName,
self._setJobDefinition(event))
# Deletes the job (jobName)
def delete(self, jobName):
return self.jobsOperations.delete(self.resourceGroupName,self.jobCollectionName,jobName)
def _setJobDefinition(self, event):
return JobDefinition(properties=self._setJobProperties(event))
def _setJobProperties(self, event):
return JobProperties(
start_time=datetime.strptime(event['endDate']+ " 9:50pm -0500", '%Y-%m-%d %I:%M%p %z'),
action=self._setJobAction(),
state=JobState("Enabled"),
recurrence=self._setJobRecurrence(event))
def _setJobAction(self):
return JobAction(type=JobActionType('Http'),request=self._setHttpRequest(), retry_policy=self._setRetryPolicy(), queue_message=self._setStorageQueueMessage())
def _setHttpRequest(self):
return HttpRequest(uri="http://test.ngrok.io/rest/player/?format=json", method='GET', authentication=HttpAuthentication('NotSpecified'), body="", headers={})
def _setStorageQueueMessage(self):
return StorageQueueMessage(storage_account="datalions", queue_name="Training Session", sas_token=None, message="Sync after Training")
def _setRetryPolicy(self):
return RetryPolicy(retry_type='Fixed', retry_interval=timedelta(minutes=3), retry_count=3)
def _setJobRecurrence(self, event):
return JobRecurrence(
frequency='Hour',
interval=1,end_time=datetime.strptime(event['endDate']+ " 11:50pm -0500",
'%Y-%m-%d %I:%M%p %z'))
```
|
non_process
|
azure mgmt scheduler operations jobsoperations create update malformed job object hello i am trying to create a new job in the azure scheduler using the python sdk however the respond from the api is not providing enough details of the error and i have tried to find my own problem re checking the api s doc multiple times but i haven t been able to found the error here is the stack trace of the respond from the api traceback most recent call last file line in file home student datalions server datalionsapi rest azurescheduler py line in create self setjobdefinition event file home student datalions server datalionsapi env lib site packages azure mgmt scheduler operations jobs operations py line in create or update raise exp msrestazure azure exceptions clouderror azure error badrequest message malformed job object i have replaced subscriptionid and the uri with a mock one for security purposes here is the code i am using to send the request important event python from msrest serialization import serializer deserializer from msrest configuration import configuration from msrest service client import serviceclient from azure mgmt scheduler import schedulermanagementclient from azure mgmt scheduler operations import jobsoperations from azure mgmt scheduler models import jobdefinition jobproperties jobaction from azure mgmt scheduler models import httprequest httpauthentication jobstate from azure mgmt scheduler models import jobrecurrence retrypolicy storagequeuemessage from azure mgmt scheduler models import jobactiontype from datetime import datetime timedelta import importlib inspect wrapper for the azure microsoft api class azurescheduler the constructor setups the essential configuration to use the scheduler from microsoft azure def init self credentials subscriptionid mocksubscriptionid resourcegroupname syncresource jobcollectionname apisync self subscriptionid subscriptionid self resourcegroupname resourcegroupname self jobcollectionname jobcollectionname self schedulerclient schedulermanagementclient credentials subscriptionid self serviceclient serviceclient credentials configuration classes self setclasses self jobsoperations jobsoperations self serviceclient self schedulerclient config serializer classes classes deserializer classes classes setup a dictionary with all the classes from the scheduler model required to serialize and deserialize objects jsons def setclasses self classes model azure mgmt scheduler models mod importlib import module model for mod name mod obj in inspect getmembers mod predicate inspect isclass classes mod obj return classes list all the jobs inside the job collection jobcollectionname def list self return self jobsoperations list self resourcegroupname self jobcollectionname first jobname datalionscheduler gets the description of the job requested def get self jobname return self jobsoperations get self resourcegroupname self jobcollectionname jobname creates a job in the job collection def create self jobname event return self jobsoperations create or update self resourcegroupname self jobcollectionname jobname self setjobdefinition event deletes the job jobname def delete self jobname return self jobsoperations delete self resourcegroupname self jobcollectionname jobname def setjobdefinition self event return jobdefinition properties self setjobproperties event def setjobproperties self event return jobproperties start time datetime strptime event y m d i m p z action self setjobaction state jobstate enabled recurrence self setjobrecurrence event def setjobaction self return jobaction type jobactiontype http request self sethttprequest retry policy self setretrypolicy queue message self setstoragequeuemessage def sethttprequest self return httprequest uri method get authentication httpauthentication notspecified body headers def setstoragequeuemessage self return storagequeuemessage storage account datalions queue name training session sas token none message sync after training def setretrypolicy self return retrypolicy retry type fixed retry interval timedelta minutes retry count def setjobrecurrence self event return jobrecurrence frequency hour interval end time datetime strptime event y m d i m p z
| 0
|
15,037
| 18,758,145,548
|
IssuesEvent
|
2021-11-05 13:31:33
|
opensafely-core/job-server
|
https://api.github.com/repos/opensafely-core/job-server
|
opened
|
Allow Simple Text Formatting in Applications
|
application-process
|
While moving existing appliations into job-server (#1140) I've found many of the purpose and project descriptions include some level of formatting, which can nearly all be handled with plain text. However the confirmation page for a User and the ApplicationDetail page in the Staff Area collapse newlines and contiguous whitespace (because HTML).
We can avoid the newlines being collapsed by applying the filter [`linebreaksbr`](https://docs.djangoproject.com/en/3.2/ref/templates/builtins/#linebreaksbr).
The contiguous spaces can be dealt with by applying `white-space: pre-wrap` to the surround element (a style attribute is fine for this case).
|
1.0
|
Allow Simple Text Formatting in Applications - While moving existing appliations into job-server (#1140) I've found many of the purpose and project descriptions include some level of formatting, which can nearly all be handled with plain text. However the confirmation page for a User and the ApplicationDetail page in the Staff Area collapse newlines and contiguous whitespace (because HTML).
We can avoid the newlines being collapsed by applying the filter [`linebreaksbr`](https://docs.djangoproject.com/en/3.2/ref/templates/builtins/#linebreaksbr).
The contiguous spaces can be dealt with by applying `white-space: pre-wrap` to the surround element (a style attribute is fine for this case).
|
process
|
allow simple text formatting in applications while moving existing appliations into job server i ve found many of the purpose and project descriptions include some level of formatting which can nearly all be handled with plain text however the confirmation page for a user and the applicationdetail page in the staff area collapse newlines and contiguous whitespace because html we can avoid the newlines being collapsed by applying the filter the contiguous spaces can be dealt with by applying white space pre wrap to the surround element a style attribute is fine for this case
| 1
|
259,850
| 8,200,659,836
|
IssuesEvent
|
2018-09-01 07:28:23
|
BultApp/Client
|
https://api.github.com/repos/BultApp/Client
|
closed
|
Automatically open default browser on run.
|
Priority: Low Type: Enhancement
|
Right now users have to manually type in the web address after they open the application.
|
1.0
|
Automatically open default browser on run. - Right now users have to manually type in the web address after they open the application.
|
non_process
|
automatically open default browser on run right now users have to manually type in the web address after they open the application
| 0
|
1,458
| 4,033,470,696
|
IssuesEvent
|
2016-05-19 01:26:47
|
mitchellh/packer
|
https://api.github.com/repos/mitchellh/packer
|
closed
|
[post-processor: vsphere]: Truncating ".period" when uploading ovf to vCenter
|
bug post-processor/vsphere regression
|
Getting truncation errors with the latest packer (released) build 8.6 when calling ovftools,
this didn't happen on the previous release of packer
`
Error: Failed to create directory: "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources\3\
`
The Resource pool line seems to be truncating "3.Bronze" to "3"
will attempt to use hex code "%2E" instead to see if that works
`
2016/02/14 22:28:24 ui: vmware-iso (vsphere): Uploading output\Redhat-7.2-x86_64_Template_20160214.2207\Redhat-7.2-x86_64_Template_20160214.2207.vmx to vSphere
2016/02/14 22:28:24 packer.exe: 2016/02/14 22:28:24 Starting ovftool with parameters: --noSSLVerify=true --acceptAllEulas --name="Redhat-7.2-x86_64_Template_20160214.2207" --datastore="Site_1" --diskMode="thin" --network="<#network removed#>" --vmFolder="Templates" output\Redhat-7.2-x86_64_Template_20160214.2207\Redhat-7.2-x86_64_Template_20160214.2207.vmx "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources/3.Bronze"
`
* Post-processor failed: Failed: exit status 1
Stdout: Opening VMX source: output\Redhat-7.2-x86_64_Template_20160214.2207\Redhat-7.2-x86_64_Template_20160214.2207.vmx
Opening OVF target: "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources/3.Bronze"
Error: Failed to create directory: "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources\3\
Completed with errors
|
1.0
|
[post-processor: vsphere]: Truncating ".period" when uploading ovf to vCenter - Getting truncation errors with the latest packer (released) build 8.6 when calling ovftools,
this didn't happen on the previous release of packer
`
Error: Failed to create directory: "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources\3\
`
The Resource pool line seems to be truncating "3.Bronze" to "3"
will attempt to use hex code "%2E" instead to see if that works
`
2016/02/14 22:28:24 ui: vmware-iso (vsphere): Uploading output\Redhat-7.2-x86_64_Template_20160214.2207\Redhat-7.2-x86_64_Template_20160214.2207.vmx to vSphere
2016/02/14 22:28:24 packer.exe: 2016/02/14 22:28:24 Starting ovftool with parameters: --noSSLVerify=true --acceptAllEulas --name="Redhat-7.2-x86_64_Template_20160214.2207" --datastore="Site_1" --diskMode="thin" --network="<#network removed#>" --vmFolder="Templates" output\Redhat-7.2-x86_64_Template_20160214.2207\Redhat-7.2-x86_64_Template_20160214.2207.vmx "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources/3.Bronze"
`
* Post-processor failed: Failed: exit status 1
Stdout: Opening VMX source: output\Redhat-7.2-x86_64_Template_20160214.2207\Redhat-7.2-x86_64_Template_20160214.2207.vmx
Opening OVF target: "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources/3.Bronze"
Error: Failed to create directory: "vi://Administrator%40vsphere.local:<#removed#>@<#vcenter removed #>/DC1/host/Cluster1/Resources\3\
Completed with errors
|
process
|
truncating period when uploading ovf to vcenter getting truncation errors with the latest packer released build when calling ovftools this didn t happen on the previous release of packer error failed to create directory vi administrator local host resources the resource pool line seems to be truncating bronze to will attempt to use hex code instead to see if that works ui vmware iso vsphere uploading output redhat template redhat template vmx to vsphere packer exe starting ovftool with parameters nosslverify true acceptalleulas name redhat template datastore site diskmode thin network vmfolder templates output redhat template redhat template vmx vi administrator local host resources bronze post processor failed failed exit status stdout opening vmx source output redhat template redhat template vmx opening ovf target vi administrator local host resources bronze error failed to create directory vi administrator local host resources completed with errors
| 1
|
8,696
| 11,838,786,984
|
IssuesEvent
|
2020-03-23 16:09:43
|
ESMValGroup/ESMValCore
|
https://api.github.com/repos/ESMValGroup/ESMValCore
|
closed
|
Zonal preprocessor return type float64
|
bug preprocessor
|
**Describe the bug**
The zonal preprocessor returns a cube of type `float64`, instead of `float32` as for other preprocessors.
This is an issue for the NCL diagnostics, which are designed to work with variable of `float32` type (as per CMOR standard).
Hopefully it is easy to fix this.
|
1.0
|
Zonal preprocessor return type float64 - **Describe the bug**
The zonal preprocessor returns a cube of type `float64`, instead of `float32` as for other preprocessors.
This is an issue for the NCL diagnostics, which are designed to work with variable of `float32` type (as per CMOR standard).
Hopefully it is easy to fix this.
|
process
|
zonal preprocessor return type describe the bug the zonal preprocessor returns a cube of type instead of as for other preprocessors this is an issue for the ncl diagnostics which are designed to work with variable of type as per cmor standard hopefully it is easy to fix this
| 1
|
86,356
| 16,979,029,863
|
IssuesEvent
|
2021-06-30 06:10:33
|
joomla/joomla-cms
|
https://api.github.com/repos/joomla/joomla-cms
|
closed
|
TinyMCE Broken features
|
J4 Issue No Code Attached Yet Release Blocker
|
Issues in Joomla 4.0 rc3-dev!
### Steps to reproduce the issue
Just did a clone from Git an noticed that some functionality from TinyMCE are broken.
1. The icon configurator is empty:

When TinyMCE is saved in this state I get an error when I use the article editor: Notice: Trying to get property '2' of non-object in W:\wamp64\www\testeditor\plugins\editors\tinymce\tinymce.php on line 200

2. Content Template Directory/functionality is not working
There is new a functionality added to the TinyMCE called Content Templates. With this functionality you can select predefined content templates from Cassiopeia html/tinymce folder. As the folder selector is there in the TinyMCE, it only shows - Default -. Also the functionality is not working as TinyMCE only shows the predefined templates from the old location.

3. Custom CSS Classes not working
Selecting a custom CSS file is not working in TinyMCE. It will only load the editor.css

### Expected result
### Actual result
### System information (as much as possible)
### Additional comments
|
1.0
|
TinyMCE Broken features - Issues in Joomla 4.0 rc3-dev!
### Steps to reproduce the issue
Just did a clone from Git an noticed that some functionality from TinyMCE are broken.
1. The icon configurator is empty:

When TinyMCE is saved in this state I get an error when I use the article editor: Notice: Trying to get property '2' of non-object in W:\wamp64\www\testeditor\plugins\editors\tinymce\tinymce.php on line 200

2. Content Template Directory/functionality is not working
There is new a functionality added to the TinyMCE called Content Templates. With this functionality you can select predefined content templates from Cassiopeia html/tinymce folder. As the folder selector is there in the TinyMCE, it only shows - Default -. Also the functionality is not working as TinyMCE only shows the predefined templates from the old location.

3. Custom CSS Classes not working
Selecting a custom CSS file is not working in TinyMCE. It will only load the editor.css

### Expected result
### Actual result
### System information (as much as possible)
### Additional comments
|
non_process
|
tinymce broken features issues in joomla dev steps to reproduce the issue just did a clone from git an noticed that some functionality from tinymce are broken the icon configurator is empty when tinymce is saved in this state i get an error when i use the article editor notice trying to get property of non object in w www testeditor plugins editors tinymce tinymce php on line content template directory functionality is not working there is new a functionality added to the tinymce called content templates with this functionality you can select predefined content templates from cassiopeia html tinymce folder as the folder selector is there in the tinymce it only shows default also the functionality is not working as tinymce only shows the predefined templates from the old location custom css classes not working selecting a custom css file is not working in tinymce it will only load the editor css expected result actual result system information as much as possible additional comments
| 0
|
18,852
| 4,317,428,660
|
IssuesEvent
|
2016-07-23 09:21:27
|
HackIllinois/api-2017
|
https://api.github.com/repos/HackIllinois/api-2017
|
reopened
|
Applicant Listings
|
application database documentation feature
|
In general, reviewers will want to be able to access the applicants in a listing format. This will give them a limited amount of information for each applicant about which they can query, sort, and select. These resources should be reasonably compatible with some client-side table format. We will not design these resources off of a specific format, but it is a good thing to keep in mind the context of use.
It goes without saying that these resources should also be restricted to the proper roled users. We will need to discuss exactly which roles are allowed.
|
1.0
|
Applicant Listings - In general, reviewers will want to be able to access the applicants in a listing format. This will give them a limited amount of information for each applicant about which they can query, sort, and select. These resources should be reasonably compatible with some client-side table format. We will not design these resources off of a specific format, but it is a good thing to keep in mind the context of use.
It goes without saying that these resources should also be restricted to the proper roled users. We will need to discuss exactly which roles are allowed.
|
non_process
|
applicant listings in general reviewers will want to be able to access the applicants in a listing format this will give them a limited amount of information for each applicant about which they can query sort and select these resources should be reasonably compatible with some client side table format we will not design these resources off of a specific format but it is a good thing to keep in mind the context of use it goes without saying that these resources should also be restricted to the proper roled users we will need to discuss exactly which roles are allowed
| 0
|
5,281
| 8,069,689,213
|
IssuesEvent
|
2018-08-06 07:06:03
|
proophsoftware/es-emergency-call
|
https://api.github.com/repos/proophsoftware/es-emergency-call
|
closed
|
Process manager and projections problem
|
Distributed DDD event-sourcing process manager
|
Looks like I have a problem with one of the more complicated parts of our system. Since it seems like something that could happen in other systems as well I'll try to ask here to hopefully reach some proper solution.
### The relevant part of the domain
The company (which owns the application) has some clients. Every month the system generates some fees which the clients are supposed to pay. Later on the client payments are imported into the system.
About once a month an admin clicks a button to process all the fees and payments and pair them (to see which fee is covered by which payment). It is not enough to just calculate account ballance, we really need the pairing to know when the client payed which fee. (Of course some payment may cover multiple fees or one fee can be covered by multiple payments. That's not really important for this issue.)
In some cases the fees can be negative which means the company is supposed to send some money back to the client.
Some of the payments can be outgoing payments which means the company sent some money back to the client.
### The pairing process
Now when the admin clicks the button, here is a pseudo-code of what should happen:
```
var clients = findAllClients()
foreach (clients as client) {
payments = findPaymentsSentByTheCompanyToTheClient(client)
fees = findClientsNegativeFees(client)
allocate(payments, fees)
convertRemainingNegativeFeesToVirtualIncomingPayments(fees)
convertRemainingOutgoingPaymentsToVirtualFees(payments)
payments = findPaymentsSentByTheClient(client)
fees = findClientsNormalFees(client)
allocate(payments, fees)
}
```
Explanation of `convertRemainingNegativeFeesToVirtualIncomingPayments(payments)`:
There is an unpaired negative fee which means the company should have sent some money to the client but didn't do so. In this case we convert the negative fee to a virtual incoming payment and use it to cover the normal fees of the client.
Explanation of `convertRemainingOutgoingPaymentsToVirtualFees(payments)`:
There is an unpaired outgoing payment which means the company sent some money to the client by accident (or sent more than it should have). In this case we convert the payment to a new fee, essentially asking the client to send the money back.
### The implementation
When the admin clicks the button, it triggers some command (`AllocatePaymentsToFeesCommand`). There is no aggregate for this so the command handler just creates an event (`PaymentAllocationsRequested`) and runs it into EventBus. The event is then consumed by a process manager.
This process manager basically has the pseudocode from above. The `convertRemainingNegativeFeesToVirtualIncomingPayments`, `convertRemainingOutgoingPaymentsToVirtualFees` and `allocate` parts are all generating some new commands which are then dispatched to the command bus.
Does this make sense so far? If you'd recommend any changes based on what I wrote above, please tell me.
### The problem
The issue we're facing is that the new virtual payments and fees from the convert* parts should also be processed by the last part of the process manager. This of course won't be the case now because the find* functions are searching the projections which were not yet updated to contain these new virtual payments and fees - the commands to create them were dispatched just above and didn't have time to go through the entire command->handler->aggregate->event->projection process.
Can you give me some ideas how to solve cases like these when the process manager cannot continue because projections are not up to date? I think I missed some important lesson on how to implement a process manager...
|
1.0
|
Process manager and projections problem - Looks like I have a problem with one of the more complicated parts of our system. Since it seems like something that could happen in other systems as well I'll try to ask here to hopefully reach some proper solution.
### The relevant part of the domain
The company (which owns the application) has some clients. Every month the system generates some fees which the clients are supposed to pay. Later on the client payments are imported into the system.
About once a month an admin clicks a button to process all the fees and payments and pair them (to see which fee is covered by which payment). It is not enough to just calculate account ballance, we really need the pairing to know when the client payed which fee. (Of course some payment may cover multiple fees or one fee can be covered by multiple payments. That's not really important for this issue.)
In some cases the fees can be negative which means the company is supposed to send some money back to the client.
Some of the payments can be outgoing payments which means the company sent some money back to the client.
### The pairing process
Now when the admin clicks the button, here is a pseudo-code of what should happen:
```
var clients = findAllClients()
foreach (clients as client) {
payments = findPaymentsSentByTheCompanyToTheClient(client)
fees = findClientsNegativeFees(client)
allocate(payments, fees)
convertRemainingNegativeFeesToVirtualIncomingPayments(fees)
convertRemainingOutgoingPaymentsToVirtualFees(payments)
payments = findPaymentsSentByTheClient(client)
fees = findClientsNormalFees(client)
allocate(payments, fees)
}
```
Explanation of `convertRemainingNegativeFeesToVirtualIncomingPayments(payments)`:
There is an unpaired negative fee which means the company should have sent some money to the client but didn't do so. In this case we convert the negative fee to a virtual incoming payment and use it to cover the normal fees of the client.
Explanation of `convertRemainingOutgoingPaymentsToVirtualFees(payments)`:
There is an unpaired outgoing payment which means the company sent some money to the client by accident (or sent more than it should have). In this case we convert the payment to a new fee, essentially asking the client to send the money back.
### The implementation
When the admin clicks the button, it triggers some command (`AllocatePaymentsToFeesCommand`). There is no aggregate for this so the command handler just creates an event (`PaymentAllocationsRequested`) and runs it into EventBus. The event is then consumed by a process manager.
This process manager basically has the pseudocode from above. The `convertRemainingNegativeFeesToVirtualIncomingPayments`, `convertRemainingOutgoingPaymentsToVirtualFees` and `allocate` parts are all generating some new commands which are then dispatched to the command bus.
Does this make sense so far? If you'd recommend any changes based on what I wrote above, please tell me.
### The problem
The issue we're facing is that the new virtual payments and fees from the convert* parts should also be processed by the last part of the process manager. This of course won't be the case now because the find* functions are searching the projections which were not yet updated to contain these new virtual payments and fees - the commands to create them were dispatched just above and didn't have time to go through the entire command->handler->aggregate->event->projection process.
Can you give me some ideas how to solve cases like these when the process manager cannot continue because projections are not up to date? I think I missed some important lesson on how to implement a process manager...
|
process
|
process manager and projections problem looks like i have a problem with one of the more complicated parts of our system since it seems like something that could happen in other systems as well i ll try to ask here to hopefully reach some proper solution the relevant part of the domain the company which owns the application has some clients every month the system generates some fees which the clients are supposed to pay later on the client payments are imported into the system about once a month an admin clicks a button to process all the fees and payments and pair them to see which fee is covered by which payment it is not enough to just calculate account ballance we really need the pairing to know when the client payed which fee of course some payment may cover multiple fees or one fee can be covered by multiple payments that s not really important for this issue in some cases the fees can be negative which means the company is supposed to send some money back to the client some of the payments can be outgoing payments which means the company sent some money back to the client the pairing process now when the admin clicks the button here is a pseudo code of what should happen var clients findallclients foreach clients as client payments findpaymentssentbythecompanytotheclient client fees findclientsnegativefees client allocate payments fees convertremainingnegativefeestovirtualincomingpayments fees convertremainingoutgoingpaymentstovirtualfees payments payments findpaymentssentbytheclient client fees findclientsnormalfees client allocate payments fees explanation of convertremainingnegativefeestovirtualincomingpayments payments there is an unpaired negative fee which means the company should have sent some money to the client but didn t do so in this case we convert the negative fee to a virtual incoming payment and use it to cover the normal fees of the client explanation of convertremainingoutgoingpaymentstovirtualfees payments there is an unpaired outgoing payment which means the company sent some money to the client by accident or sent more than it should have in this case we convert the payment to a new fee essentially asking the client to send the money back the implementation when the admin clicks the button it triggers some command allocatepaymentstofeescommand there is no aggregate for this so the command handler just creates an event paymentallocationsrequested and runs it into eventbus the event is then consumed by a process manager this process manager basically has the pseudocode from above the convertremainingnegativefeestovirtualincomingpayments convertremainingoutgoingpaymentstovirtualfees and allocate parts are all generating some new commands which are then dispatched to the command bus does this make sense so far if you d recommend any changes based on what i wrote above please tell me the problem the issue we re facing is that the new virtual payments and fees from the convert parts should also be processed by the last part of the process manager this of course won t be the case now because the find functions are searching the projections which were not yet updated to contain these new virtual payments and fees the commands to create them were dispatched just above and didn t have time to go through the entire command handler aggregate event projection process can you give me some ideas how to solve cases like these when the process manager cannot continue because projections are not up to date i think i missed some important lesson on how to implement a process manager
| 1
|
17,764
| 23,697,155,502
|
IssuesEvent
|
2022-08-29 15:32:43
|
GSA/EDX
|
https://api.github.com/repos/GSA/EDX
|
opened
|
Improve measurement criteria - DLP Management Checklist
|
process policy Fall 2022
|
## Summary
Select five (5) policy items from the DLP Management Checklist and work with SMEs to identify clear measurement criteria. Goal is to help GSA web managers understand what "done" looks like, when trying to comply with vaguely-worded web policy.
## Additional context and links
[DLP-MANAGEMENT Checklist for GSA Websites](https://docs.google.com/spreadsheets/d/1o_NMWBbbOpeKvAmLOLTGHbk3ldOeyO3g1SKb-EP5ZWs/edit#gid=1232597517)
## Checklist
- [ ] Identify 5 policy items
- [ ] review [2021 Capacity Assessment](https://docs.google.com/spreadsheets/d/18dbV0CV1b-vi_aSvBYJZfCAr3MfMyTXWiQYtdb4c0yA/edit#gid=2135783770) (maturity self-eval used by HISPs) to see if it could be helpful
- [ ] Identify SMEs
- [ ] Interview SMEs to determine how best to measure things
- [ ] Align criteria w/GSA performance goals
- [ ] Update checklist
|
1.0
|
Improve measurement criteria - DLP Management Checklist - ## Summary
Select five (5) policy items from the DLP Management Checklist and work with SMEs to identify clear measurement criteria. Goal is to help GSA web managers understand what "done" looks like, when trying to comply with vaguely-worded web policy.
## Additional context and links
[DLP-MANAGEMENT Checklist for GSA Websites](https://docs.google.com/spreadsheets/d/1o_NMWBbbOpeKvAmLOLTGHbk3ldOeyO3g1SKb-EP5ZWs/edit#gid=1232597517)
## Checklist
- [ ] Identify 5 policy items
- [ ] review [2021 Capacity Assessment](https://docs.google.com/spreadsheets/d/18dbV0CV1b-vi_aSvBYJZfCAr3MfMyTXWiQYtdb4c0yA/edit#gid=2135783770) (maturity self-eval used by HISPs) to see if it could be helpful
- [ ] Identify SMEs
- [ ] Interview SMEs to determine how best to measure things
- [ ] Align criteria w/GSA performance goals
- [ ] Update checklist
|
process
|
improve measurement criteria dlp management checklist summary select five policy items from the dlp management checklist and work with smes to identify clear measurement criteria goal is to help gsa web managers understand what done looks like when trying to comply with vaguely worded web policy additional context and links checklist identify policy items review maturity self eval used by hisps to see if it could be helpful identify smes interview smes to determine how best to measure things align criteria w gsa performance goals update checklist
| 1
|
8,099
| 11,275,766,367
|
IssuesEvent
|
2020-01-14 21:31:06
|
MicrosoftDocs/azure-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-docs
|
closed
|
Au Central Missing from region list
|
Pri1 assigned-to-author automation/svc doc-enhancement process-automation/subsvc triaged
|
Azure automation is now available in Australia Central region - could you please update the table above to reflect the dns endpoints there?
ac-agentservice-prod-1.azure-automation.net
ac-jobruntimedata-prod-1a.azure-automation.net
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 3092ee3a-3c57-cc53-186b-b454e7d9d190
* Version Independent ID: 6f6b5a07-397a-98a2-6091-941244a77837
* Content: [Azure Automation Hybrid Runbook Worker](https://docs.microsoft.com/en-us/azure/automation/automation-hybrid-runbook-worker#network-planning)
* Content Source: [articles/automation/automation-hybrid-runbook-worker.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/automation-hybrid-runbook-worker.md)
* Service: **automation**
* Sub-service: **process-automation**
* GitHub Login: @MGoedtel
* Microsoft Alias: **magoedte**
|
1.0
|
Au Central Missing from region list - Azure automation is now available in Australia Central region - could you please update the table above to reflect the dns endpoints there?
ac-agentservice-prod-1.azure-automation.net
ac-jobruntimedata-prod-1a.azure-automation.net
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 3092ee3a-3c57-cc53-186b-b454e7d9d190
* Version Independent ID: 6f6b5a07-397a-98a2-6091-941244a77837
* Content: [Azure Automation Hybrid Runbook Worker](https://docs.microsoft.com/en-us/azure/automation/automation-hybrid-runbook-worker#network-planning)
* Content Source: [articles/automation/automation-hybrid-runbook-worker.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/automation-hybrid-runbook-worker.md)
* Service: **automation**
* Sub-service: **process-automation**
* GitHub Login: @MGoedtel
* Microsoft Alias: **magoedte**
|
process
|
au central missing from region list azure automation is now available in australia central region could you please update the table above to reflect the dns endpoints there ac agentservice prod azure automation net ac jobruntimedata prod azure automation net document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service automation sub service process automation github login mgoedtel microsoft alias magoedte
| 1
|
412,383
| 27,856,289,688
|
IssuesEvent
|
2023-03-20 23:21:23
|
amphp/http-server
|
https://api.github.com/repos/amphp/http-server
|
closed
|
Example in README.md is outdated
|
documentation
|
I'm trying to run a simple test with this libray, but I'm unable to find up to date documentation, even the example in the README.md file is outdated and don't work with all the changes to use Revolt. The link to the "Official Documentation" (http://amphp.org/http-server/) is also broken.
I would appreciate if someone could guide me where to find documentation or examples using Revolt and Amphp to set up an http server.
|
1.0
|
Example in README.md is outdated - I'm trying to run a simple test with this libray, but I'm unable to find up to date documentation, even the example in the README.md file is outdated and don't work with all the changes to use Revolt. The link to the "Official Documentation" (http://amphp.org/http-server/) is also broken.
I would appreciate if someone could guide me where to find documentation or examples using Revolt and Amphp to set up an http server.
|
non_process
|
example in readme md is outdated i m trying to run a simple test with this libray but i m unable to find up to date documentation even the example in the readme md file is outdated and don t work with all the changes to use revolt the link to the official documentation is also broken i would appreciate if someone could guide me where to find documentation or examples using revolt and amphp to set up an http server
| 0
|
902
| 3,367,587,754
|
IssuesEvent
|
2015-11-22 09:40:26
|
213cy/github_test2
|
https://api.github.com/repos/213cy/github_test2
|
opened
|
魔兽地形文件(war3map.w3e war3map.doo)制作
|
Image Processing
|
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%% 更改地形放置文件war3map.w3e 需要图片矩阵D
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
cd('C:\Documents and Settings\morlet\桌面')
%
fileID = fopen('war3map.w3e','r');%
w3e=fread(fileID,'*uint8');
fclose(fileID);
ind=(73+1:7:length(w3e));
w3e(ind)=D(:);
%
fileID = fopen('aaa\war3map.w3e','w');%
fwrite(fileID, w3e)
fclose(fileID)
%%
%hist(double(w3e(ind)))
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%% 更改树木放置文件war3map.doo 需要图片矩阵C
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
cd('C:\Documents and Settings\morlet\桌面')
%
fileID = fopen('war3map.doo','r');%
% ftell(fileID)
% fseek(fileID, 24, -1)
% A = fread(fileID,2,'*single')
% fread(fileID,2,'*float')
% fread(fileID,2,'*float32')
doo=fread(fileID,'*uint8');
fclose(fileID);
%%
[row,col] = find(C==3);
x=num2hex(single((col-65)*128));
y=num2hex(single((65-row)*128));
M=size(x,1)-1;
%xy=zeros(M,8);
doo(25:42:25+42*M)=hex2dec(x(:,7:8));
doo(26:42:26+42*M)=hex2dec(x(:,5:6));
doo(27:42:27+42*M)=hex2dec(x(:,3:4));
doo(28:42:28+42*M)=hex2dec(x(:,1:2));
doo(29:42:29+42*M)=hex2dec(y(:,7:8));
doo(30:42:30+42*M)=hex2dec(y(:,5:6));
doo(31:42:31+42*M)=hex2dec(y(:,3:4));
doo(32:42:32+42*M)=hex2dec(y(:,1:2));
%%
fileID = fopen('aaa\war3map.doo','w');%
fwrite(fileID, doo)
fclose(fileID)
%%
%char(doo(17:20))
% doo(25:42:25+42*M)
% doo(25:28)
% doo(29:32)
|
1.0
|
魔兽地形文件(war3map.w3e war3map.doo)制作 - %%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%% 更改地形放置文件war3map.w3e 需要图片矩阵D
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
cd('C:\Documents and Settings\morlet\桌面')
%
fileID = fopen('war3map.w3e','r');%
w3e=fread(fileID,'*uint8');
fclose(fileID);
ind=(73+1:7:length(w3e));
w3e(ind)=D(:);
%
fileID = fopen('aaa\war3map.w3e','w');%
fwrite(fileID, w3e)
fclose(fileID)
%%
%hist(double(w3e(ind)))
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
%% 更改树木放置文件war3map.doo 需要图片矩阵C
%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%
cd('C:\Documents and Settings\morlet\桌面')
%
fileID = fopen('war3map.doo','r');%
% ftell(fileID)
% fseek(fileID, 24, -1)
% A = fread(fileID,2,'*single')
% fread(fileID,2,'*float')
% fread(fileID,2,'*float32')
doo=fread(fileID,'*uint8');
fclose(fileID);
%%
[row,col] = find(C==3);
x=num2hex(single((col-65)*128));
y=num2hex(single((65-row)*128));
M=size(x,1)-1;
%xy=zeros(M,8);
doo(25:42:25+42*M)=hex2dec(x(:,7:8));
doo(26:42:26+42*M)=hex2dec(x(:,5:6));
doo(27:42:27+42*M)=hex2dec(x(:,3:4));
doo(28:42:28+42*M)=hex2dec(x(:,1:2));
doo(29:42:29+42*M)=hex2dec(y(:,7:8));
doo(30:42:30+42*M)=hex2dec(y(:,5:6));
doo(31:42:31+42*M)=hex2dec(y(:,3:4));
doo(32:42:32+42*M)=hex2dec(y(:,1:2));
%%
fileID = fopen('aaa\war3map.doo','w');%
fwrite(fileID, doo)
fclose(fileID)
%%
%char(doo(17:20))
% doo(25:42:25+42*M)
% doo(25:28)
% doo(29:32)
|
process
|
魔兽地形文件 doo 制作 需要图片矩阵d cd c documents and settings morlet 桌面 fileid fopen r fread fileid fclose fileid ind length ind d fileid fopen aaa w fwrite fileid fclose fileid hist double ind doo 需要图片矩阵c cd c documents and settings morlet 桌面 fileid fopen doo r ftell fileid fseek fileid a fread fileid single fread fileid float fread fileid doo fread fileid fclose fileid find c x single col y single row m size x xy zeros m doo m x doo m x doo m x doo m x doo m y doo m y doo m y doo m y fileid fopen aaa doo w fwrite fileid doo fclose fileid char doo doo m doo doo
| 1
|
133,176
| 18,281,020,275
|
IssuesEvent
|
2021-10-05 03:21:47
|
sun-yryr/github-actions-playground
|
https://api.github.com/repos/sun-yryr/github-actions-playground
|
opened
|
Security Alert
|
security
|
<table>
<colgroup>
<col style="width: 20%" />
<col style="width: 13%" />
<col style="width: 8%" />
<col style="width: 14%" />
<col style="width: 11%" />
<col style="width: 30%" />
</colgroup>
<tbody>
<tr class="odd">
<td> LIBRARY</td>
<td>VULNERABILITY ID</td>
<td>SEVERITY</td>
<td>INSTALLED VERSION</td>
<td>FIXED VERSION</td>
<td> TITLE</td>
</tr>
<tr class="even">
<td>binutils</td>
<td>CVE-2018-12934</td>
<td>HIGH</td>
<td>2.35.2-2</td>
<td></td>
<td>binutils: Uncontrolled Resource Consumption in remember_Ktype in cplus-dem.c –>avd.aquasec.com/nvd/cve-2018-12934</td>
</tr>
</tbody>
</table>
<ul>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ + +—————+—————————————–+ | binutils-common | CVE-2018-12934 | | | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ + +—————+—————————————–+ | binutils-x86-64-linux-gnu | CVE-2018-12934 | | | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | curl | CVE-2021-22945 | | 7.74.0-1.3 | | curl: use-after-free and | | | | | | | double-free in MQTT sending | | | | | | | –>avd.aquasec.com/nvd/cve-2021-22945 | +—————————+——————+ +——————-+—————+—————————————–+ | libbinutils | CVE-2018-12934 | | 2.35.2-2 | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
<table>
<colgroup>
<col style="width: 20%" />
<col style="width: 13%" />
<col style="width: 8%" />
<col style="width: 14%" />
<col style="width: 11%" />
<col style="width: 30%" />
</colgroup>
<tbody>
<tr class="odd">
<td>libc-bin</td>
<td>CVE-2019-1010022</td>
<td>CRITICAL</td>
<td>2.31-13</td>
<td></td>
<td>glibc: stack guard protection bypass –>avd.aquasec.com/nvd/cve-2019-1010022</td>
</tr>
</tbody>
</table></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+———-+ +—————+—————————————–+ | libc-dev-bin | CVE-2019-1010022 | CRITICAL | | | glibc: stack guard protection bypass | | | | | | | –>avd.aquasec.com/nvd/cve-2019-1010022 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+———-+ +—————+—————————————–+ | libc6 | CVE-2019-1010022 | CRITICAL | | | glibc: stack guard protection bypass | | | | | | | –>avd.aquasec.com/nvd/cve-2019-1010022 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+———-+ +—————+—————————————–+ | libc6-dev | CVE-2019-1010022 | CRITICAL | | | glibc: stack guard protection bypass | | | | | | | –>avd.aquasec.com/nvd/cve-2019-1010022 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | libctf-nobfd0 | CVE-2018-12934 | | 2.35.2-2 | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ + +—————+—————————————–+ | libctf0 | CVE-2018-12934 | | | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | libcurl4 | CVE-2021-22945 | | 7.74.0-1.3 | | curl: use-after-free and | | | | | | | double-free in MQTT sending | | | | | | | –>avd.aquasec.com/nvd/cve-2021-22945 | +—————————+——————+ +——————-+—————+—————————————–+ | libgcrypt20 | CVE-2018-6829 | | 1.8.7-6 | | libgcrypt: ElGamal implementation | | | | | | | doesn’t have semantic security due | | | | | | | to incorrectly encoded plaintexts… | | | | | | | –>avd.aquasec.com/nvd/cve-2018-6829 | +—————————+——————+ +——————-+—————+—————————————–+ | libgssapi-krb5-2 | CVE-2018-5709 | | 1.18.3-6 | | krb5: integer overflow | | | | | | | in dbentry->n_key_data | | | | | | | in kadmin/dbutil/dump.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-5709 | +—————————+ + + +—————+ + | libk5crypto3 | | | | | | | | | | | | | | | | | | | | | | | | | | | +—————————+ + + +—————+ + | libkrb5-3 | | | | | | | | | | | | | | | | | | | | | | | | | | | +—————————+ + + +—————+ + | libkrb5support0 | | | | | | | | | | | | | | | | | | | | | | | | | | | +—————————+——————+ +——————-+—————+—————————————–+ | libldap-2.4-2 | CVE-2017-17740 | | 2.4.57+dfsg-3 | | openldap: | | | | | | | contrib/slapd-modules/nops/nops.c | | | | | | | attempts to free stack buffer | | | | | | | allowing remote attackers to cause… | | | | | | | –>avd.aquasec.com/nvd/cve-2017-17740 | +—————————+——————+ +——————-+—————+—————————————–+ | libpcre3 | CVE-2017-11164 | | 2:8.39-13 | | pcre: OP_KETRMAX feature in the | | | | | | | match function in pcre_exec.c | | | | | | | –>avd.aquasec.com/nvd/cve-2017-11164 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2017-7245 | | | | pcre: stack-based buffer overflow |<br />
| | | | | write in pcre32_copy_substring |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2017-7245 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2017-7246 | | | | pcre: stack-based buffer overflow |<br />
| | | | | write in pcre32_copy_substring |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2017-7246 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-20838 | | | | pcre: buffer over-read in |<br />
| | | | | JIT when UTF is disabled |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-20838 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | libperl5.32 | CVE-2011-4116 | | 5.32.1-4+deb11u1 | | perl: File::Temp insecure | | | | | | | temporary file handling | | | | | | | –>avd.aquasec.com/nvd/cve-2011-4116 | +—————————+——————+ +——————-+—————+—————————————–+ | libsqlite3-0 | CVE-2021-36690 | | 3.34.1-3 | | ** DISPUTED ** A segmentation | | | | | | | fault can occur in the | | | | | | | sqlite3.exe command-line… | | | | | | | –>avd.aquasec.com/nvd/cve-2021-36690 | +—————————+——————+ +——————-+—————+—————————————–+ | libtinfo6 | CVE-2021-39537 | | 6.2+20201114-2 | | ncurses: heap-based buffer overflow | | | | | | | in _nc_captoinfo() in captoinfo.c | | | | | | | –>avd.aquasec.com/nvd/cve-2021-39537 | +—————————+——————+ +——————-+—————+—————————————–+ | linux-libc-dev | CVE-2008-4609 | | 5.10.46-5 | | kernel: TCP protocol | | | | | | | vulnerabilities from Outpost24 | | | | | | | –>avd.aquasec.com/nvd/cve-2008-4609 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2013-7445 | | | | kernel: memory exhaustion via |<br />
| | | | | crafted Graphics Execution |<br />
| | | | | Manager (GEM) objects |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2013-7445 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-12456 | | | | kernel: double fetch in the |<br />
| | | | | MPT3COMMAND case in _ctl_ioctl_main |<br />
| | | | | in drivers/scsi/mpt3sas/mpt3sas_ctl.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-12456 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19070 | | | | kernel: A memory leak in the |<br />
| | | | | spi_gpio_probe() function in |<br />
| | | | | drivers/spi/spi-gpio.c allows for… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19070 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19378 | | | | kernel: out-of-bounds write in |<br />
| | | | | index_rbio_pages in fs/btrfs/raid56.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19378 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19449 | | | | kernel: mounting a crafted |<br />
| | | | | f2fs filesystem image can lead |<br />
| | | | | to slab-out-of-bounds read… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19449 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19814 | | | | kernel: out-of-bounds write |<br />
| | | | | in __remove_dirty_segment |<br />
| | | | | in fs/f2fs/segment.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19814 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-11725 | | | | kernel: improper handling of |<br />
| | | | | private_size*count multiplication |<br />
| | | | | due to count=info->owner typo |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-11725 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-12362 | | | | kernel: Integer overflow in |<br />
| | | | | Intel(R) Graphics Drivers |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-12362 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26556 | | | | kernel: malleable commitment |<br />
| | | | | Bluetooth Mesh Provisioning |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26556 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26557 | | | | kernel: predictable |<br />
| | | | | Authvalue in Bluetooth Mesh |<br />
| | | | | Provisioning Leads to MITM |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26557 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26559 | | | | kernel: Authvalue leak in |<br />
| | | | | Bluetooth Mesh Provisioning |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26559 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26560 | | | | kernel: impersonation attack |<br />
| | | | | in Bluetooth Mesh Provisioning |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26560 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-26934 | | | | An issue was discovered in the Linux |<br />
| | | | | kernel 4.18 through 5.10.16, as… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-26934 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-32078 | | | | kernel: out-of-bounds read in |<br />
| | | | | arch/arm/mach-footbridge/personal-pci.c |<br />
| | | | | due to improper input validation |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-32078 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-35039 | | | | kernel: allows loading |<br />
| | | | | unsigned kernel modules |<br />
| | | | | via init_module syscall |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-35039 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3752 | | | | kernel: possible use-after-free |<br />
| | | | | in bluetooth module |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3752 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-38300 | | | | kernel: crafting anomalous |<br />
| | | | | machine code may lead to |<br />
| | | | | arbitrary Kernel code execution… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-38300 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | login | CVE-2019-19882 | | 1:4.8.1-1 | | shadow-utils: local users can | | | | | | | obtain root access because setuid | | | | | | | programs are misconfigured… | | | | | | | –>avd.aquasec.com/nvd/cve-2019-19882 | +—————————+——————+ +——————-+—————+—————————————–+ | m4 | CVE-2008-1687 | | 1.4.18-5 | | m4: unquoted output of | | | | | | | maketemp and mkstemp | | | | | | | –>avd.aquasec.com/nvd/cve-2008-1687 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2008-1688 | | | | m4: code execution via -F argument |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2008-1688 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | ncurses-base | CVE-2021-39537 | | 6.2+20201114-2 | | ncurses: heap-based buffer overflow | | | | | | | in _nc_captoinfo() in captoinfo.c | | | | | | | –>avd.aquasec.com/nvd/cve-2021-39537 | +—————————+ + + +—————+ + | ncurses-bin | | | | | | | | | | | | | | | | | | | | +—————————+——————+ +——————-+—————+—————————————–+ | passwd | CVE-2019-19882 | | 1:4.8.1-1 | | shadow-utils: local users can | | | | | | | obtain root access because setuid | | | | | | | programs are misconfigured… | | | | | | | –>avd.aquasec.com/nvd/cve-2019-19882 | +—————————+——————+ +——————-+—————+—————————————–+ | patch | CVE-2018-6951 | | 2.7.6-7 | | patch: NULL pointer dereference | | | | | | | in pch.c:intuit_diff_type() | | | | | | | causes a crash | | | | | | | –>avd.aquasec.com/nvd/cve-2018-6951 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-6952 | | | | patch: Double free of memory in |<br />
| | | | | pch.c:another_hunk() causes a crash |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-6952 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | perl | CVE-2011-4116 | | 5.32.1-4+deb11u1 | | perl: File::Temp insecure | | | | | | | temporary file handling | | | | | | | –>avd.aquasec.com/nvd/cve-2011-4116 | +—————————+ + + +—————+ + | perl-base | | | | | | | | | | | | | | | | | | | | +—————————+ + + +—————+ + | perl-modules-5.32 | | | | | | | | | | | | | | | | | | | | +—————————+——————+ +——————-+—————+—————————————–+ | tar | CVE-2005-2541 | | 1.34+dfsg-1 | | tar: does not properly warn the user | | | | | | | when extracting setuid or setgid… | | | | | | | –>avd.aquasec.com/nvd/cve-2005-2541 | +—————————+——————+———-+——————-+—————+—————————————–+</li>
</ul>
|
True
|
Security Alert - <table>
<colgroup>
<col style="width: 20%" />
<col style="width: 13%" />
<col style="width: 8%" />
<col style="width: 14%" />
<col style="width: 11%" />
<col style="width: 30%" />
</colgroup>
<tbody>
<tr class="odd">
<td> LIBRARY</td>
<td>VULNERABILITY ID</td>
<td>SEVERITY</td>
<td>INSTALLED VERSION</td>
<td>FIXED VERSION</td>
<td> TITLE</td>
</tr>
<tr class="even">
<td>binutils</td>
<td>CVE-2018-12934</td>
<td>HIGH</td>
<td>2.35.2-2</td>
<td></td>
<td>binutils: Uncontrolled Resource Consumption in remember_Ktype in cplus-dem.c –>avd.aquasec.com/nvd/cve-2018-12934</td>
</tr>
</tbody>
</table>
<ul>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ + +—————+—————————————–+ | binutils-common | CVE-2018-12934 | | | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ + +—————+—————————————–+ | binutils-x86-64-linux-gnu | CVE-2018-12934 | | | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | curl | CVE-2021-22945 | | 7.74.0-1.3 | | curl: use-after-free and | | | | | | | double-free in MQTT sending | | | | | | | –>avd.aquasec.com/nvd/cve-2021-22945 | +—————————+——————+ +——————-+—————+—————————————–+ | libbinutils | CVE-2018-12934 | | 2.35.2-2 | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
<table>
<colgroup>
<col style="width: 20%" />
<col style="width: 13%" />
<col style="width: 8%" />
<col style="width: 14%" />
<col style="width: 11%" />
<col style="width: 30%" />
</colgroup>
<tbody>
<tr class="odd">
<td>libc-bin</td>
<td>CVE-2019-1010022</td>
<td>CRITICAL</td>
<td>2.31-13</td>
<td></td>
<td>glibc: stack guard protection bypass –>avd.aquasec.com/nvd/cve-2019-1010022</td>
</tr>
</tbody>
</table></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+———-+ +—————+—————————————–+ | libc-dev-bin | CVE-2019-1010022 | CRITICAL | | | glibc: stack guard protection bypass | | | | | | | –>avd.aquasec.com/nvd/cve-2019-1010022 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+———-+ +—————+—————————————–+ | libc6 | CVE-2019-1010022 | CRITICAL | | | glibc: stack guard protection bypass | | | | | | | –>avd.aquasec.com/nvd/cve-2019-1010022 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+———-+ +—————+—————————————–+ | libc6-dev | CVE-2019-1010022 | CRITICAL | | | glibc: stack guard protection bypass | | | | | | | –>avd.aquasec.com/nvd/cve-2019-1010022 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-33574 | | | | glibc: mq_notify does |<br />
| | | | | not handle separately |<br />
| | | | | allocated thread attributes |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-33574 |</div></li>
<li> +------------------+----------+ +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-20796 | HIGH | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-20796 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-1010023 | | | | glibc: running ldd on malicious ELF |<br />
| | | | | leads to code execution because of… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-1010023 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-9192 | | | | glibc: uncontrolled recursion in |<br />
| | | | | function check_dst_limits_calc_pos_1 |<br />
| | | | | in posix/regexec.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-9192 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | libctf-nobfd0 | CVE-2018-12934 | | 2.35.2-2 | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ + +—————+—————————————–+ | libctf0 | CVE-2018-12934 | | | | binutils: Uncontrolled | | | | | | | Resource Consumption in | | | | | | | remember_Ktype in cplus-dem.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-12934 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-18483 | | | | binutils: Integer overflow |<br />
| | | | | in cplus-dem.c:get_count() |<br />
| | | | | allows for denial of service |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-18483 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3530 | | | | binutils: stack memory exhaustion in |<br />
| | | | | demangle_path() in rust-demangle.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3530 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3549 | | | | binutils: heap-based |<br />
| | | | | buffer overflow in |<br />
| | | | | avr_elf32_load_records_from_section() |<br />
| | | | | via large section parameter |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3549 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | libcurl4 | CVE-2021-22945 | | 7.74.0-1.3 | | curl: use-after-free and | | | | | | | double-free in MQTT sending | | | | | | | –>avd.aquasec.com/nvd/cve-2021-22945 | +—————————+——————+ +——————-+—————+—————————————–+ | libgcrypt20 | CVE-2018-6829 | | 1.8.7-6 | | libgcrypt: ElGamal implementation | | | | | | | doesn’t have semantic security due | | | | | | | to incorrectly encoded plaintexts… | | | | | | | –>avd.aquasec.com/nvd/cve-2018-6829 | +—————————+——————+ +——————-+—————+—————————————–+ | libgssapi-krb5-2 | CVE-2018-5709 | | 1.18.3-6 | | krb5: integer overflow | | | | | | | in dbentry->n_key_data | | | | | | | in kadmin/dbutil/dump.c | | | | | | | –>avd.aquasec.com/nvd/cve-2018-5709 | +—————————+ + + +—————+ + | libk5crypto3 | | | | | | | | | | | | | | | | | | | | | | | | | | | +—————————+ + + +—————+ + | libkrb5-3 | | | | | | | | | | | | | | | | | | | | | | | | | | | +—————————+ + + +—————+ + | libkrb5support0 | | | | | | | | | | | | | | | | | | | | | | | | | | | +—————————+——————+ +——————-+—————+—————————————–+ | libldap-2.4-2 | CVE-2017-17740 | | 2.4.57+dfsg-3 | | openldap: | | | | | | | contrib/slapd-modules/nops/nops.c | | | | | | | attempts to free stack buffer | | | | | | | allowing remote attackers to cause… | | | | | | | –>avd.aquasec.com/nvd/cve-2017-17740 | +—————————+——————+ +——————-+—————+—————————————–+ | libpcre3 | CVE-2017-11164 | | 2:8.39-13 | | pcre: OP_KETRMAX feature in the | | | | | | | match function in pcre_exec.c | | | | | | | –>avd.aquasec.com/nvd/cve-2017-11164 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2017-7245 | | | | pcre: stack-based buffer overflow |<br />
| | | | | write in pcre32_copy_substring |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2017-7245 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2017-7246 | | | | pcre: stack-based buffer overflow |<br />
| | | | | write in pcre32_copy_substring |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2017-7246 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-20838 | | | | pcre: buffer over-read in |<br />
| | | | | JIT when UTF is disabled |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-20838 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | libperl5.32 | CVE-2011-4116 | | 5.32.1-4+deb11u1 | | perl: File::Temp insecure | | | | | | | temporary file handling | | | | | | | –>avd.aquasec.com/nvd/cve-2011-4116 | +—————————+——————+ +——————-+—————+—————————————–+ | libsqlite3-0 | CVE-2021-36690 | | 3.34.1-3 | | ** DISPUTED ** A segmentation | | | | | | | fault can occur in the | | | | | | | sqlite3.exe command-line… | | | | | | | –>avd.aquasec.com/nvd/cve-2021-36690 | +—————————+——————+ +——————-+—————+—————————————–+ | libtinfo6 | CVE-2021-39537 | | 6.2+20201114-2 | | ncurses: heap-based buffer overflow | | | | | | | in _nc_captoinfo() in captoinfo.c | | | | | | | –>avd.aquasec.com/nvd/cve-2021-39537 | +—————————+——————+ +——————-+—————+—————————————–+ | linux-libc-dev | CVE-2008-4609 | | 5.10.46-5 | | kernel: TCP protocol | | | | | | | vulnerabilities from Outpost24 | | | | | | | –>avd.aquasec.com/nvd/cve-2008-4609 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2013-7445 | | | | kernel: memory exhaustion via |<br />
| | | | | crafted Graphics Execution |<br />
| | | | | Manager (GEM) objects |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2013-7445 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-12456 | | | | kernel: double fetch in the |<br />
| | | | | MPT3COMMAND case in _ctl_ioctl_main |<br />
| | | | | in drivers/scsi/mpt3sas/mpt3sas_ctl.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-12456 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19070 | | | | kernel: A memory leak in the |<br />
| | | | | spi_gpio_probe() function in |<br />
| | | | | drivers/spi/spi-gpio.c allows for… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19070 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19378 | | | | kernel: out-of-bounds write in |<br />
| | | | | index_rbio_pages in fs/btrfs/raid56.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19378 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19449 | | | | kernel: mounting a crafted |<br />
| | | | | f2fs filesystem image can lead |<br />
| | | | | to slab-out-of-bounds read… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19449 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2019-19814 | | | | kernel: out-of-bounds write |<br />
| | | | | in __remove_dirty_segment |<br />
| | | | | in fs/f2fs/segment.c |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2019-19814 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-11725 | | | | kernel: improper handling of |<br />
| | | | | private_size*count multiplication |<br />
| | | | | due to count=info->owner typo |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-11725 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-12362 | | | | kernel: Integer overflow in |<br />
| | | | | Intel(R) Graphics Drivers |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-12362 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26556 | | | | kernel: malleable commitment |<br />
| | | | | Bluetooth Mesh Provisioning |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26556 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26557 | | | | kernel: predictable |<br />
| | | | | Authvalue in Bluetooth Mesh |<br />
| | | | | Provisioning Leads to MITM |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26557 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26559 | | | | kernel: Authvalue leak in |<br />
| | | | | Bluetooth Mesh Provisioning |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26559 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2020-26560 | | | | kernel: impersonation attack |<br />
| | | | | in Bluetooth Mesh Provisioning |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2020-26560 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-26934 | | | | An issue was discovered in the Linux |<br />
| | | | | kernel 4.18 through 5.10.16, as… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-26934 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-32078 | | | | kernel: out-of-bounds read in |<br />
| | | | | arch/arm/mach-footbridge/personal-pci.c |<br />
| | | | | due to improper input validation |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-32078 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-35039 | | | | kernel: allows loading |<br />
| | | | | unsigned kernel modules |<br />
| | | | | via init_module syscall |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-35039 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-3752 | | | | kernel: possible use-after-free |<br />
| | | | | in bluetooth module |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-3752 |</div></li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2021-38300 | | | | kernel: crafting anomalous |<br />
| | | | | machine code may lead to |<br />
| | | | | arbitrary Kernel code execution… |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2021-38300 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | login | CVE-2019-19882 | | 1:4.8.1-1 | | shadow-utils: local users can | | | | | | | obtain root access because setuid | | | | | | | programs are misconfigured… | | | | | | | –>avd.aquasec.com/nvd/cve-2019-19882 | +—————————+——————+ +——————-+—————+—————————————–+ | m4 | CVE-2008-1687 | | 1.4.18-5 | | m4: unquoted output of | | | | | | | maketemp and mkstemp | | | | | | | –>avd.aquasec.com/nvd/cve-2008-1687 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2008-1688 | | | | m4: code execution via -F argument |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2008-1688 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | ncurses-base | CVE-2021-39537 | | 6.2+20201114-2 | | ncurses: heap-based buffer overflow | | | | | | | in _nc_captoinfo() in captoinfo.c | | | | | | | –>avd.aquasec.com/nvd/cve-2021-39537 | +—————————+ + + +—————+ + | ncurses-bin | | | | | | | | | | | | | | | | | | | | +—————————+——————+ +——————-+—————+—————————————–+ | passwd | CVE-2019-19882 | | 1:4.8.1-1 | | shadow-utils: local users can | | | | | | | obtain root access because setuid | | | | | | | programs are misconfigured… | | | | | | | –>avd.aquasec.com/nvd/cve-2019-19882 | +—————————+——————+ +——————-+—————+—————————————–+ | patch | CVE-2018-6951 | | 2.7.6-7 | | patch: NULL pointer dereference | | | | | | | in pch.c:intuit_diff_type() | | | | | | | causes a crash | | | | | | | –>avd.aquasec.com/nvd/cve-2018-6951 |</li>
<li> +------------------+ + +---------------+-----------------------------------------+
<div class="line-block"> | CVE-2018-6952 | | | | patch: Double free of memory in |<br />
| | | | | pch.c:another_hunk() causes a crash |<br />
| | | | | –>avd.aquasec.com/nvd/cve-2018-6952 |</div>
+—————————+——————+ +——————-+—————+—————————————–+ | perl | CVE-2011-4116 | | 5.32.1-4+deb11u1 | | perl: File::Temp insecure | | | | | | | temporary file handling | | | | | | | –>avd.aquasec.com/nvd/cve-2011-4116 | +—————————+ + + +—————+ + | perl-base | | | | | | | | | | | | | | | | | | | | +—————————+ + + +—————+ + | perl-modules-5.32 | | | | | | | | | | | | | | | | | | | | +—————————+——————+ +——————-+—————+—————————————–+ | tar | CVE-2005-2541 | | 1.34+dfsg-1 | | tar: does not properly warn the user | | | | | | | when extracting setuid or setgid… | | | | | | | –>avd.aquasec.com/nvd/cve-2005-2541 | +—————————+——————+———-+——————-+—————+—————————————–+</li>
</ul>
|
non_process
|
security alert library vulnerability id severity installed version fixed version title binutils cve high binutils uncontrolled resource consumption in remember ktype in cplus dem c – gt avd aquasec com nvd cve cve binutils integer overflow in cplus dem c get count allows for denial of service – gt avd aquasec com nvd cve cve binutils stack memory exhaustion in demangle path in rust demangle c – gt avd aquasec com nvd cve cve binutils heap based buffer overflow in avr load records from section via large section parameter – gt avd aquasec com nvd cve ————————— —————— ————— —————————————– binutils common cve binutils uncontrolled resource consumption in remember ktype in cplus dem c – gt avd aquasec com nvd cve cve binutils integer overflow in cplus dem c get count allows for denial of service – gt avd aquasec com nvd cve cve binutils stack memory exhaustion in demangle path in rust demangle c – gt avd aquasec com nvd cve cve binutils heap based buffer overflow in avr load records from section via large section parameter – gt avd aquasec com nvd cve ————————— —————— ————— —————————————– binutils linux gnu cve binutils uncontrolled resource consumption in remember ktype in cplus dem c – gt avd aquasec com nvd cve cve binutils integer overflow in cplus dem c get count allows for denial of service – gt avd aquasec com nvd cve cve binutils stack memory exhaustion in demangle path in rust demangle c – gt avd aquasec com nvd cve cve binutils heap based buffer overflow in avr load records from section via large section parameter – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– curl cve curl use after free and double free in mqtt sending – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– libbinutils cve binutils uncontrolled resource consumption in remember ktype in cplus dem c – gt avd aquasec com nvd cve cve binutils integer overflow in cplus dem c get count allows for denial of service – gt avd aquasec com nvd cve cve binutils stack memory exhaustion in demangle path in rust demangle c – gt avd aquasec com nvd cve cve binutils heap based buffer overflow in avr load records from section via large section parameter – gt avd aquasec com nvd cve libc bin cve critical glibc stack guard protection bypass – gt avd aquasec com nvd cve cve glibc mq notify does not handle separately allocated thread attributes – gt avd aquasec com nvd cve cve high glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve cve glibc running ldd on malicious elf leads to code execution because of… – gt avd aquasec com nvd cve cve glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve ————————— —————— ——— ————— —————————————– libc dev bin cve critical glibc stack guard protection bypass – gt avd aquasec com nvd cve cve glibc mq notify does not handle separately allocated thread attributes – gt avd aquasec com nvd cve cve high glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve cve glibc running ldd on malicious elf leads to code execution because of… – gt avd aquasec com nvd cve cve glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve ————————— —————— ——— ————— —————————————– cve critical glibc stack guard protection bypass – gt avd aquasec com nvd cve cve glibc mq notify does not handle separately allocated thread attributes – gt avd aquasec com nvd cve cve high glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve cve glibc running ldd on malicious elf leads to code execution because of… – gt avd aquasec com nvd cve cve glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve ————————— —————— ——— ————— —————————————– dev cve critical glibc stack guard protection bypass – gt avd aquasec com nvd cve cve glibc mq notify does not handle separately allocated thread attributes – gt avd aquasec com nvd cve cve high glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve cve glibc running ldd on malicious elf leads to code execution because of… – gt avd aquasec com nvd cve cve glibc uncontrolled recursion in function check dst limits calc pos in posix regexec c – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– libctf cve binutils uncontrolled resource consumption in remember ktype in cplus dem c – gt avd aquasec com nvd cve cve binutils integer overflow in cplus dem c get count allows for denial of service – gt avd aquasec com nvd cve cve binutils stack memory exhaustion in demangle path in rust demangle c – gt avd aquasec com nvd cve cve binutils heap based buffer overflow in avr load records from section via large section parameter – gt avd aquasec com nvd cve ————————— —————— ————— —————————————– cve binutils uncontrolled resource consumption in remember ktype in cplus dem c – gt avd aquasec com nvd cve cve binutils integer overflow in cplus dem c get count allows for denial of service – gt avd aquasec com nvd cve cve binutils stack memory exhaustion in demangle path in rust demangle c – gt avd aquasec com nvd cve cve binutils heap based buffer overflow in avr load records from section via large section parameter – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve curl use after free and double free in mqtt sending – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve libgcrypt elgamal implementation doesn’t have semantic security due to incorrectly encoded plaintexts… – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– libgssapi cve integer overflow in dbentry gt n key data in kadmin dbutil dump c – gt avd aquasec com nvd cve ————————— ————— ————————— ————— ————————— ————— ————————— —————— —————— ————— —————————————– libldap cve dfsg openldap contrib slapd modules nops nops c attempts to free stack buffer allowing remote attackers to cause… – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve pcre op ketrmax feature in the match function in pcre exec c – gt avd aquasec com nvd cve cve pcre stack based buffer overflow write in copy substring – gt avd aquasec com nvd cve cve pcre stack based buffer overflow write in copy substring – gt avd aquasec com nvd cve cve pcre buffer over read in jit when utf is disabled – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve perl file temp insecure temporary file handling – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve disputed a segmentation fault can occur in the exe command line… – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve ncurses heap based buffer overflow in nc captoinfo in captoinfo c – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– linux libc dev cve kernel tcp protocol vulnerabilities from – gt avd aquasec com nvd cve cve kernel memory exhaustion via crafted graphics execution manager gem objects – gt avd aquasec com nvd cve cve kernel double fetch in the case in ctl ioctl main in drivers scsi ctl c – gt avd aquasec com nvd cve cve kernel a memory leak in the spi gpio probe function in drivers spi spi gpio c allows for… – gt avd aquasec com nvd cve cve kernel out of bounds write in index rbio pages in fs btrfs c – gt avd aquasec com nvd cve cve kernel mounting a crafted filesystem image can lead to slab out of bounds read… – gt avd aquasec com nvd cve cve kernel out of bounds write in remove dirty segment in fs segment c – gt avd aquasec com nvd cve cve kernel improper handling of private size count multiplication due to count info gt owner typo – gt avd aquasec com nvd cve cve kernel integer overflow in intel r graphics drivers – gt avd aquasec com nvd cve cve kernel malleable commitment bluetooth mesh provisioning – gt avd aquasec com nvd cve cve kernel predictable authvalue in bluetooth mesh provisioning leads to mitm – gt avd aquasec com nvd cve cve kernel authvalue leak in bluetooth mesh provisioning – gt avd aquasec com nvd cve cve kernel impersonation attack in bluetooth mesh provisioning – gt avd aquasec com nvd cve cve an issue was discovered in the linux kernel through as… – gt avd aquasec com nvd cve cve kernel out of bounds read in arch arm mach footbridge personal pci c due to improper input validation – gt avd aquasec com nvd cve cve kernel allows loading unsigned kernel modules via init module syscall – gt avd aquasec com nvd cve cve kernel possible use after free in bluetooth module – gt avd aquasec com nvd cve cve kernel crafting anomalous machine code may lead to arbitrary kernel code execution… – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– login cve shadow utils local users can obtain root access because setuid programs are misconfigured… – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– cve unquoted output of maketemp and mkstemp – gt avd aquasec com nvd cve cve code execution via f argument – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– ncurses base cve ncurses heap based buffer overflow in nc captoinfo in captoinfo c – gt avd aquasec com nvd cve ————————— ————— ncurses bin ————————— —————— —————— ————— —————————————– passwd cve shadow utils local users can obtain root access because setuid programs are misconfigured… – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– patch cve patch null pointer dereference in pch c intuit diff type causes a crash – gt avd aquasec com nvd cve cve patch double free of memory in pch c another hunk causes a crash – gt avd aquasec com nvd cve ————————— —————— —————— ————— —————————————– perl cve perl file temp insecure temporary file handling – gt avd aquasec com nvd cve ————————— ————— perl base ————————— ————— perl modules ————————— —————— —————— ————— —————————————– tar cve dfsg tar does not properly warn the user when extracting setuid or setgid… – gt avd aquasec com nvd cve ————————— —————— ——— —————— ————— —————————————–
| 0
|
735,124
| 25,380,170,660
|
IssuesEvent
|
2022-11-21 16:55:25
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
www.nonolive.com - Page jumps to bottom when the chat loads
|
browser-firefox priority-normal os-win engine-gecko
|
<!-- @browser: Firefox 92.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:92.0) Gecko/20100101 Firefox/92.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/80319 -->
**URL**: https://www.nonolive.com/sbtcclear
**Browser / Version**: Firefox 92.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: This page automatically scrolls to the bottom when chat frame scrolls (with content). This happens when chat frame runs too fast.
**Steps to Reproduce**:
Just open Firefox (you can create new profile with no add-on and test it) and enter any live room in Nonolive (like Truc Tiep Game or SBTC Clear,....) and this page will be automatically scroll to bottom if chat frame scrolls too fast. Chromium browsers do not affect this issue.
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2021/7/7e8bb500-35b5-479e-baea-0a89b6a1e328.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20210715215249</li><li>channel: nightly</li><li>hasTouchScreen: false</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2021/7/afa6c933-7d9a-43fb-a4ee-c7dd47f8ab60)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
www.nonolive.com - Page jumps to bottom when the chat loads - <!-- @browser: Firefox 92.0 -->
<!-- @ua_header: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:92.0) Gecko/20100101 Firefox/92.0 -->
<!-- @reported_with: desktop-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/80319 -->
**URL**: https://www.nonolive.com/sbtcclear
**Browser / Version**: Firefox 92.0
**Operating System**: Windows 10
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: This page automatically scrolls to the bottom when chat frame scrolls (with content). This happens when chat frame runs too fast.
**Steps to Reproduce**:
Just open Firefox (you can create new profile with no add-on and test it) and enter any live room in Nonolive (like Truc Tiep Game or SBTC Clear,....) and this page will be automatically scroll to bottom if chat frame scrolls too fast. Chromium browsers do not affect this issue.
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2021/7/7e8bb500-35b5-479e-baea-0a89b6a1e328.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20210715215249</li><li>channel: nightly</li><li>hasTouchScreen: false</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2021/7/afa6c933-7d9a-43fb-a4ee-c7dd47f8ab60)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_process
|
page jumps to bottom when the chat loads url browser version firefox operating system windows tested another browser yes chrome problem type something else description this page automatically scrolls to the bottom when chat frame scrolls with content this happens when chat frame runs too fast steps to reproduce just open firefox you can create new profile with no add on and test it and enter any live room in nonolive like truc tiep game or sbtc clear and this page will be automatically scroll to bottom if chat frame scrolls too fast chromium browsers do not affect this issue view the screenshot img alt screenshot src browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel nightly hastouchscreen false mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️
| 0
|
793,496
| 27,999,277,186
|
IssuesEvent
|
2023-03-27 10:34:46
|
abelt120/github-issues-template
|
https://api.github.com/repos/abelt120/github-issues-template
|
opened
|
Page with errors
|
bug Severity 3 Priority 3
|
**Describe the bug**
several error was found on several pages
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'https://datayze.com/site-validator'
2. Paste in URL to index page
3. View erros
**Expected behavior**
Page should be error free
**Additional context**
Click here to view page errors:
https://datayze.com/site-validator?domain=https%3A%2F%2Fabelt120.github.io%2Fgithub-issues-template%2Ftours%2Ftour_detail_bigsur.html¶meters=&exclude=
|
1.0
|
Page with errors - **Describe the bug**
several error was found on several pages
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'https://datayze.com/site-validator'
2. Paste in URL to index page
3. View erros
**Expected behavior**
Page should be error free
**Additional context**
Click here to view page errors:
https://datayze.com/site-validator?domain=https%3A%2F%2Fabelt120.github.io%2Fgithub-issues-template%2Ftours%2Ftour_detail_bigsur.html¶meters=&exclude=
|
non_process
|
page with errors describe the bug several error was found on several pages to reproduce steps to reproduce the behavior go to paste in url to index page view erros expected behavior page should be error free additional context click here to view page errors
| 0
|
180,024
| 14,736,960,082
|
IssuesEvent
|
2021-01-07 00:28:11
|
OpenMined/sycret
|
https://api.github.com/repos/OpenMined/sycret
|
opened
|
Publish and document the Rust crate
|
Type: Documentation :books:
|
After https://github.com/OpenMined/sycret/issues/2 and https://github.com/OpenMined/sycret/issues/4, create a workflow that publishes the Rust crate to https://crates.io with some documentation.
|
1.0
|
Publish and document the Rust crate - After https://github.com/OpenMined/sycret/issues/2 and https://github.com/OpenMined/sycret/issues/4, create a workflow that publishes the Rust crate to https://crates.io with some documentation.
|
non_process
|
publish and document the rust crate after and create a workflow that publishes the rust crate to with some documentation
| 0
|
59,929
| 12,033,537,412
|
IssuesEvent
|
2020-04-13 14:26:09
|
ST-Apps/CS-ParallelRoadTool
|
https://api.github.com/repos/ST-Apps/CS-ParallelRoadTool
|
closed
|
Upgrade functionality
|
code dev enhancement
|
It would be awesome if we could upgrade a segment, and PRT would also add new segments to existing roads.
road "upgrade to" road
......................................road
......................................road
|
1.0
|
Upgrade functionality - It would be awesome if we could upgrade a segment, and PRT would also add new segments to existing roads.
road "upgrade to" road
......................................road
......................................road
|
non_process
|
upgrade functionality it would be awesome if we could upgrade a segment and prt would also add new segments to existing roads road upgrade to road road road
| 0
|
374,826
| 26,134,788,791
|
IssuesEvent
|
2022-12-29 10:38:18
|
Denisshingala/autism
|
https://api.github.com/repos/Denisshingala/autism
|
closed
|
Improve README.md
|
documentation enhancement
|
Update README.md file to reflect what the project is all about
Tasks:
- [ ] Setup
- [ ] Introduction
|
1.0
|
Improve README.md - Update README.md file to reflect what the project is all about
Tasks:
- [ ] Setup
- [ ] Introduction
|
non_process
|
improve readme md update readme md file to reflect what the project is all about tasks setup introduction
| 0
|
12,900
| 2,725,611,125
|
IssuesEvent
|
2015-04-15 02:07:55
|
cakephp/cakephp
|
https://api.github.com/repos/cakephp/cakephp
|
closed
|
3.0 - patchEntity ignores accessibleFields setting
|
Defect On hold ORM
|
Hello,
I just noticed unexpected behavior (using dev-master). Assuming Posts belongsTo Category - I am trying to patchEntity of (actual entity class debug data stripped for brevity)
```
$post = [
'title' => 'foo title',
'category' => [
'id' => 1,
'title' => 'cat 1 title'
]
]
```
with
```
$post = [
'title' => 'foo title edited',
'category' => [
'id' => 2
]
]
```
there are two different results depending on where accessibility of category id is declared:
in Category entity
```
$post = [
'title' => 'foo title edited',
'category' => [
'id' => 2,
'title' => 'cat title 1' // this is wierd, actually title of cat 1
]
]
```
or by `['associated' => ['Category' => ['accessibleFields => ['id' => true]]]` passed to patchEntity
```
$post = [
'title' => 'foo title edited',
'category' => [ // not changed at all
'id' => 1,
'title' => 'cat title 1'
]
]
```
|
1.0
|
3.0 - patchEntity ignores accessibleFields setting - Hello,
I just noticed unexpected behavior (using dev-master). Assuming Posts belongsTo Category - I am trying to patchEntity of (actual entity class debug data stripped for brevity)
```
$post = [
'title' => 'foo title',
'category' => [
'id' => 1,
'title' => 'cat 1 title'
]
]
```
with
```
$post = [
'title' => 'foo title edited',
'category' => [
'id' => 2
]
]
```
there are two different results depending on where accessibility of category id is declared:
in Category entity
```
$post = [
'title' => 'foo title edited',
'category' => [
'id' => 2,
'title' => 'cat title 1' // this is wierd, actually title of cat 1
]
]
```
or by `['associated' => ['Category' => ['accessibleFields => ['id' => true]]]` passed to patchEntity
```
$post = [
'title' => 'foo title edited',
'category' => [ // not changed at all
'id' => 1,
'title' => 'cat title 1'
]
]
```
|
non_process
|
patchentity ignores accessiblefields setting hello i just noticed unexpected behavior using dev master assuming posts belongsto category i am trying to patchentity of actual entity class debug data stripped for brevity post title foo title category id title cat title with post title foo title edited category id there are two different results depending on where accessibility of category id is declared in category entity post title foo title edited category id title cat title this is wierd actually title of cat or by passed to patchentity post title foo title edited category not changed at all id title cat title
| 0
|
53,610
| 22,959,685,513
|
IssuesEvent
|
2022-07-19 14:26:53
|
GC-HBOC/HerediVar
|
https://api.github.com/repos/GC-HBOC/HerediVar
|
closed
|
Parse PHANTM
|
annotation service
|
Insert PHenotypic ANnotation of TP53 Mutations (PHANTM: http://mutantp53.broadinstitute.org/heatMap/login) **combined phenotype scores** to HerediVar
PHANTM paper: https://www.nature.com/articles/s41588-018-0204-y
|
1.0
|
Parse PHANTM - Insert PHenotypic ANnotation of TP53 Mutations (PHANTM: http://mutantp53.broadinstitute.org/heatMap/login) **combined phenotype scores** to HerediVar
PHANTM paper: https://www.nature.com/articles/s41588-018-0204-y
|
non_process
|
parse phantm insert phenotypic annotation of mutations phantm combined phenotype scores to heredivar phantm paper
| 0
|
629,036
| 20,021,630,264
|
IssuesEvent
|
2022-02-01 16:54:39
|
woocommerce/woocommerce-gutenberg-products-block
|
https://api.github.com/repos/woocommerce/woocommerce-gutenberg-products-block
|
closed
|
Investigate usage of @wordpress/icons in place of our current @woocommerce/icons aliased package.
|
type: enhancement category: components type: cooldown priority: low
|
We implemented our own icons aliased package because at the time `@wordpress/icons` was not available. I think we should consider:
- Can we use `@wordpress/icons` directly and just enhance with our own icons? What impact does this make to bundle size?
- Should we submit our icons upstream in a pr on the `@wordpress/icons` package as additional icons for that package?
- Are there icons we can use from the `@wordpress/icons` package instead of custom ones we're using to make things more consistent with the WordPress ui/ux?
cc @senadir and @LevinMedia - I don't think we need to do this immediately, but it'd be a good cooldown task to audit. Also David, it's good to be aware that the icons in this package are available for future designs (if you weren't already aware).
|
1.0
|
Investigate usage of @wordpress/icons in place of our current @woocommerce/icons aliased package. - We implemented our own icons aliased package because at the time `@wordpress/icons` was not available. I think we should consider:
- Can we use `@wordpress/icons` directly and just enhance with our own icons? What impact does this make to bundle size?
- Should we submit our icons upstream in a pr on the `@wordpress/icons` package as additional icons for that package?
- Are there icons we can use from the `@wordpress/icons` package instead of custom ones we're using to make things more consistent with the WordPress ui/ux?
cc @senadir and @LevinMedia - I don't think we need to do this immediately, but it'd be a good cooldown task to audit. Also David, it's good to be aware that the icons in this package are available for future designs (if you weren't already aware).
|
non_process
|
investigate usage of wordpress icons in place of our current woocommerce icons aliased package we implemented our own icons aliased package because at the time wordpress icons was not available i think we should consider can we use wordpress icons directly and just enhance with our own icons what impact does this make to bundle size should we submit our icons upstream in a pr on the wordpress icons package as additional icons for that package are there icons we can use from the wordpress icons package instead of custom ones we re using to make things more consistent with the wordpress ui ux cc senadir and levinmedia i don t think we need to do this immediately but it d be a good cooldown task to audit also david it s good to be aware that the icons in this package are available for future designs if you weren t already aware
| 0
|
7,494
| 10,582,073,082
|
IssuesEvent
|
2019-10-08 10:37:12
|
leecade/react-native-swiper
|
https://api.github.com/repos/leecade/react-native-swiper
|
closed
|
v1.6.0-rc.1: slider doesn't work
|
Resolution: No Template 🚧processing
|
I have migrated to the v1.6.0-rc.1 and the result is **dreadful**:
- slider autoply doesn't work, it shows only the last image
- drag to scroll doesn't work
(tested on both Android and iOS)
|
1.0
|
v1.6.0-rc.1: slider doesn't work - I have migrated to the v1.6.0-rc.1 and the result is **dreadful**:
- slider autoply doesn't work, it shows only the last image
- drag to scroll doesn't work
(tested on both Android and iOS)
|
process
|
rc slider doesn t work i have migrated to the rc and the result is dreadful slider autoply doesn t work it shows only the last image drag to scroll doesn t work tested on both android and ios
| 1
|
17,368
| 23,191,264,584
|
IssuesEvent
|
2022-08-01 12:52:17
|
dotnet/runtime
|
https://api.github.com/repos/dotnet/runtime
|
closed
|
linux ThreadWaitReason Unknown
|
area-System.Diagnostics.Process
|
### Description
Get the wating reasons of all threads in the current process , but all waiting reasons are unknown
### Reproduction Steps
## code
```
public ValueTask<dynamic> GetThreadConsumeAsync()
{
Process proc = Process.GetCurrentProcess();
var enumerator = proc.Threads.GetEnumerator();
var result = new List<dynamic>();
while (enumerator.MoveNext())
{
try
{
var thread = enumerator.Current as ProcessThread;
var threadInfo = new
{
thread.Id,
thread.PriorityBoostEnabled,
thread.StartTime,
thread.TotalProcessorTime,
thread.UserProcessorTime,
PriorityLevel = thread.PriorityLevel.ToString(),
ThreadState = thread.ThreadState.ToString(),
WaitReason = thread.ThreadState switch
{
ThreadState.Wait => thread.WaitReason.ToString(),
_ => null
},
};
result.Add(threadInfo);
}
catch
{
}
}
System.Threading.ThreadPool.GetMaxThreads(out int maxWorkerThreads, out int maxCompletionPortThreads);
System.Threading.ThreadPool.GetAvailableThreads(out int availableWorkerThreads, out int availableCompletionPortThreads);
return new ValueTask<dynamic>(new
{
maxWorkerThreads,
maxCompletionPortThreads,
availableWorkerThreads,
availableCompletionPortThreads,
threads = result
});
}
```
## vscode task
```
{
"label": "publish",
"command": "dotnet",
"type": "process",
"args": [
"publish",
"xxxx.csproj",
"/p:GenerateFullPaths=true",
"/p:PublishDir=${workspaceFolder}/.output",
"/p:Configuration=Release",
"/p:RuntimeIdentifier=linux-x64",
"/consoleloggerparameters:NoSummary"
],
"problemMatcher": "$msCompile"
},
```
### Expected behavior
actual wait reason
### Actual behavior
all waiting reasons are unknown
### Regression?
_No response_
### Known Workarounds
_No response_
### Configuration
|dev os|run os|net version|
|--|--|--|
|win 11|centos 7 x64|net6|
### Other information
output json
```json
{
"maxWorkerThreads": 32767,
"maxCompletionPortThreads": 1000,
"availableWorkerThreads": 32761,
"availableCompletionPortThreads": 1000,
"threads": [
{
"id": 198,
"priorityBoostEnabled": false,
"startTime": "2022-07-29T16:21:12.57+08:00",
"totalProcessorTime": "00:00:01.3000000",
"userProcessorTime": "00:00:00.8900000",
"priorityLevel": "Normal",
"threadState": "Wait",
"waitReason": "Unknown"
}
... other threads
]
}
```
|
1.0
|
linux ThreadWaitReason Unknown - ### Description
Get the wating reasons of all threads in the current process , but all waiting reasons are unknown
### Reproduction Steps
## code
```
public ValueTask<dynamic> GetThreadConsumeAsync()
{
Process proc = Process.GetCurrentProcess();
var enumerator = proc.Threads.GetEnumerator();
var result = new List<dynamic>();
while (enumerator.MoveNext())
{
try
{
var thread = enumerator.Current as ProcessThread;
var threadInfo = new
{
thread.Id,
thread.PriorityBoostEnabled,
thread.StartTime,
thread.TotalProcessorTime,
thread.UserProcessorTime,
PriorityLevel = thread.PriorityLevel.ToString(),
ThreadState = thread.ThreadState.ToString(),
WaitReason = thread.ThreadState switch
{
ThreadState.Wait => thread.WaitReason.ToString(),
_ => null
},
};
result.Add(threadInfo);
}
catch
{
}
}
System.Threading.ThreadPool.GetMaxThreads(out int maxWorkerThreads, out int maxCompletionPortThreads);
System.Threading.ThreadPool.GetAvailableThreads(out int availableWorkerThreads, out int availableCompletionPortThreads);
return new ValueTask<dynamic>(new
{
maxWorkerThreads,
maxCompletionPortThreads,
availableWorkerThreads,
availableCompletionPortThreads,
threads = result
});
}
```
## vscode task
```
{
"label": "publish",
"command": "dotnet",
"type": "process",
"args": [
"publish",
"xxxx.csproj",
"/p:GenerateFullPaths=true",
"/p:PublishDir=${workspaceFolder}/.output",
"/p:Configuration=Release",
"/p:RuntimeIdentifier=linux-x64",
"/consoleloggerparameters:NoSummary"
],
"problemMatcher": "$msCompile"
},
```
### Expected behavior
actual wait reason
### Actual behavior
all waiting reasons are unknown
### Regression?
_No response_
### Known Workarounds
_No response_
### Configuration
|dev os|run os|net version|
|--|--|--|
|win 11|centos 7 x64|net6|
### Other information
output json
```json
{
"maxWorkerThreads": 32767,
"maxCompletionPortThreads": 1000,
"availableWorkerThreads": 32761,
"availableCompletionPortThreads": 1000,
"threads": [
{
"id": 198,
"priorityBoostEnabled": false,
"startTime": "2022-07-29T16:21:12.57+08:00",
"totalProcessorTime": "00:00:01.3000000",
"userProcessorTime": "00:00:00.8900000",
"priorityLevel": "Normal",
"threadState": "Wait",
"waitReason": "Unknown"
}
... other threads
]
}
```
|
process
|
linux threadwaitreason unknown description get the wating reasons of all threads in the current process but all waiting reasons are unknown reproduction steps code public valuetask getthreadconsumeasync process proc process getcurrentprocess var enumerator proc threads getenumerator var result new list while enumerator movenext try var thread enumerator current as processthread var threadinfo new thread id thread priorityboostenabled thread starttime thread totalprocessortime thread userprocessortime prioritylevel thread prioritylevel tostring threadstate thread threadstate tostring waitreason thread threadstate switch threadstate wait thread waitreason tostring null result add threadinfo catch system threading threadpool getmaxthreads out int maxworkerthreads out int maxcompletionportthreads system threading threadpool getavailablethreads out int availableworkerthreads out int availablecompletionportthreads return new valuetask new maxworkerthreads maxcompletionportthreads availableworkerthreads availablecompletionportthreads threads result vscode task label publish command dotnet type process args publish xxxx csproj p generatefullpaths true p publishdir workspacefolder output p configuration release p runtimeidentifier linux consoleloggerparameters nosummary problemmatcher mscompile expected behavior actual wait reason actual behavior all waiting reasons are unknown regression no response known workarounds no response configuration dev os run os net version win centos other information output json json maxworkerthreads maxcompletionportthreads availableworkerthreads availablecompletionportthreads threads id priorityboostenabled false starttime totalprocessortime userprocessortime prioritylevel normal threadstate wait waitreason unknown other threads
| 1
|
86,680
| 10,514,093,491
|
IssuesEvent
|
2019-09-27 22:48:17
|
MASTERPC-CIA/fedeloja
|
https://api.github.com/repos/MASTERPC-CIA/fedeloja
|
closed
|
Reportes de Resultados Grafico Por Deportista
|
documentation
|
Como: Director Tecncio
Quiero: Reporte de resultados grafico para Panatalla Gigante
Para : publicar los resultados de una rutina de una deposrtitas indicando datos como:
1.0 Nombre deposrtista
2.0 nombre club o ciudad
3.0 resultado dificultas D1+D2
4.0 resultado Global de Rutina
este reporte se podrá visualizar al cerra competencia el Director Técnico por deportista y servirá para visualizar en una pantalla Grande .
|
1.0
|
Reportes de Resultados Grafico Por Deportista - Como: Director Tecncio
Quiero: Reporte de resultados grafico para Panatalla Gigante
Para : publicar los resultados de una rutina de una deposrtitas indicando datos como:
1.0 Nombre deposrtista
2.0 nombre club o ciudad
3.0 resultado dificultas D1+D2
4.0 resultado Global de Rutina
este reporte se podrá visualizar al cerra competencia el Director Técnico por deportista y servirá para visualizar en una pantalla Grande .
|
non_process
|
reportes de resultados grafico por deportista como director tecncio quiero reporte de resultados grafico para panatalla gigante para publicar los resultados de una rutina de una deposrtitas indicando datos como nombre deposrtista nombre club o ciudad resultado dificultas resultado global de rutina este reporte se podrá visualizar al cerra competencia el director técnico por deportista y servirá para visualizar en una pantalla grande
| 0
|
793,582
| 28,002,170,440
|
IssuesEvent
|
2023-03-27 13:26:25
|
bigomics/omicsplayground
|
https://api.github.com/repos/bigomics/omicsplayground
|
closed
|
png/pdf download broken
|
bug high priority
|
png/pdf download is not working anymore. This might have to do with the cards implementation in plotmodule?
|
1.0
|
png/pdf download broken - png/pdf download is not working anymore. This might have to do with the cards implementation in plotmodule?
|
non_process
|
png pdf download broken png pdf download is not working anymore this might have to do with the cards implementation in plotmodule
| 0
|
1,437
| 4,005,025,295
|
IssuesEvent
|
2016-05-12 09:45:59
|
DevExpress/testcafe-hammerhead
|
https://api.github.com/repos/DevExpress/testcafe-hammerhead
|
closed
|
Named function incorrectly processes
|
!IMPORTANT! AREA: client AREA: server COMPLEXITY: easy SYSTEM: resource processing TYPE: bug
|
```javascript
function localStorage(){}
```
-->
```javascript
function __get$Storage(localStorage)(){}
```
|
1.0
|
Named function incorrectly processes - ```javascript
function localStorage(){}
```
-->
```javascript
function __get$Storage(localStorage)(){}
```
|
process
|
named function incorrectly processes javascript function localstorage javascript function get storage localstorage
| 1
|
144,785
| 5,545,832,385
|
IssuesEvent
|
2017-03-22 22:40:45
|
zulip/zulip-android
|
https://api.github.com/repos/zulip/zulip-android
|
opened
|
Crash in CustomHtmlToSpannedConverter
|
bug help wanted high-priority
|
Fatal Exception: java.lang.NullPointerException: Attempt to invoke virtual method 'int java.lang.String.length()' on a null object reference
at java.io.StringReader.<init>(StringReader.java:47)
at com.zulip.android.util.CustomHtmlToSpannedConverter.convert(CustomHtmlToSpannedConverter.java:485)
at com.zulip.android.models.Message.formatContent(Message.java:367)
at com.zulip.android.models.Message.getFormattedContent(Message.java:553)
at com.zulip.android.activities.RecyclerMessageAdapter.onBindViewHolder(RecyclerMessageAdapter.java:377)
at android.support.v7.widget.RecyclerView$Adapter.onBindViewHolder(RecyclerView.java:5768)
at android.support.v7.widget.RecyclerView$Adapter.bindViewHolder(RecyclerView.java:5801)
at android.support.v7.widget.RecyclerView$Recycler.getViewForPosition(RecyclerView.java:5037)
at android.support.v7.widget.RecyclerView$Recycler.getViewForPosition(RecyclerView.java:4913)
at android.support.v7.widget.LinearLayoutManager$LayoutState.next(LinearLayoutManager.java:2029)
at android.support.v7.widget.LinearLayoutManager.layoutChunk(LinearLayoutManager.java:1414)
at android.support.v7.widget.LinearLayoutManager.fill(LinearLayoutManager.java:1377)
at android.support.v7.widget.LinearLayoutManager.onLayoutChildren(LinearLayoutManager.java:563)
at android.support.v7.widget.RecyclerView.dispatchLayoutStep2(RecyclerView.java:3260)
at android.support.v7.widget.RecyclerView.dispatchLayout(RecyclerView.java:3069)
at android.support.v7.widget.RecyclerView.onLayout(RecyclerView.java:3518)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.LinearLayout.setChildFrame(LinearLayout.java:1742)
at android.widget.LinearLayout.layoutVertical(LinearLayout.java:1585)
at android.widget.LinearLayout.onLayout(LinearLayout.java:1494)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.support.design.widget.CoordinatorLayout.layoutChild(CoordinatorLayout.java:1100)
at android.support.design.widget.CoordinatorLayout.onLayoutChild(CoordinatorLayout.java:804)
at android.support.design.widget.CoordinatorLayout.onLayout(CoordinatorLayout.java:818)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.support.v4.widget.DrawerLayout.onLayout(DrawerLayout.java:1191)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.LinearLayout.setChildFrame(LinearLayout.java:1742)
at android.widget.LinearLayout.layoutVertical(LinearLayout.java:1585)
at android.widget.LinearLayout.onLayout(LinearLayout.java:1494)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.LinearLayout.setChildFrame(LinearLayout.java:1742)
at android.widget.LinearLayout.layoutVertical(LinearLayout.java:1585)
at android.widget.LinearLayout.onLayout(LinearLayout.java:1494)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at com.android.internal.policy.PhoneWindow$DecorView.onLayout(PhoneWindow.java:3178)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.view.ViewRootImpl.performLayout(ViewRootImpl.java:2716)
at android.view.ViewRootImpl.performTraversals(ViewRootImpl.java:2417)
at android.view.ViewRootImpl.doTraversal(ViewRootImpl.java:1487)
at android.view.ViewRootImpl$TraversalRunnable.run(ViewRootImpl.java:7450)
at android.view.Choreographer$CallbackRecord.run(Choreographer.java:920)
at android.view.Choreographer.doCallbacks(Choreographer.java:695)
at android.view.Choreographer.doFrame(Choreographer.java:631)
at android.view.Choreographer$FrameDisplayEventReceiver.run(Choreographer.java:906)
at android.os.Handler.handleCallback(Handler.java:739)
at android.os.Handler.dispatchMessage(Handler.java:95)
at android.os.Looper.loop(Looper.java:158)
at android.app.ActivityThread.main(ActivityThread.java:7237)
at java.lang.reflect.Method.invoke(Method.java)
at com.android.internal.os.ZygoteInit$MethodAndArgsCaller.run(ZygoteInit.java:1230)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:1120)
|
1.0
|
Crash in CustomHtmlToSpannedConverter - Fatal Exception: java.lang.NullPointerException: Attempt to invoke virtual method 'int java.lang.String.length()' on a null object reference
at java.io.StringReader.<init>(StringReader.java:47)
at com.zulip.android.util.CustomHtmlToSpannedConverter.convert(CustomHtmlToSpannedConverter.java:485)
at com.zulip.android.models.Message.formatContent(Message.java:367)
at com.zulip.android.models.Message.getFormattedContent(Message.java:553)
at com.zulip.android.activities.RecyclerMessageAdapter.onBindViewHolder(RecyclerMessageAdapter.java:377)
at android.support.v7.widget.RecyclerView$Adapter.onBindViewHolder(RecyclerView.java:5768)
at android.support.v7.widget.RecyclerView$Adapter.bindViewHolder(RecyclerView.java:5801)
at android.support.v7.widget.RecyclerView$Recycler.getViewForPosition(RecyclerView.java:5037)
at android.support.v7.widget.RecyclerView$Recycler.getViewForPosition(RecyclerView.java:4913)
at android.support.v7.widget.LinearLayoutManager$LayoutState.next(LinearLayoutManager.java:2029)
at android.support.v7.widget.LinearLayoutManager.layoutChunk(LinearLayoutManager.java:1414)
at android.support.v7.widget.LinearLayoutManager.fill(LinearLayoutManager.java:1377)
at android.support.v7.widget.LinearLayoutManager.onLayoutChildren(LinearLayoutManager.java:563)
at android.support.v7.widget.RecyclerView.dispatchLayoutStep2(RecyclerView.java:3260)
at android.support.v7.widget.RecyclerView.dispatchLayout(RecyclerView.java:3069)
at android.support.v7.widget.RecyclerView.onLayout(RecyclerView.java:3518)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.LinearLayout.setChildFrame(LinearLayout.java:1742)
at android.widget.LinearLayout.layoutVertical(LinearLayout.java:1585)
at android.widget.LinearLayout.onLayout(LinearLayout.java:1494)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.support.design.widget.CoordinatorLayout.layoutChild(CoordinatorLayout.java:1100)
at android.support.design.widget.CoordinatorLayout.onLayoutChild(CoordinatorLayout.java:804)
at android.support.design.widget.CoordinatorLayout.onLayout(CoordinatorLayout.java:818)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.support.v4.widget.DrawerLayout.onLayout(DrawerLayout.java:1191)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.LinearLayout.setChildFrame(LinearLayout.java:1742)
at android.widget.LinearLayout.layoutVertical(LinearLayout.java:1585)
at android.widget.LinearLayout.onLayout(LinearLayout.java:1494)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.LinearLayout.setChildFrame(LinearLayout.java:1742)
at android.widget.LinearLayout.layoutVertical(LinearLayout.java:1585)
at android.widget.LinearLayout.onLayout(LinearLayout.java:1494)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.widget.FrameLayout.layoutChildren(FrameLayout.java:344)
at android.widget.FrameLayout.onLayout(FrameLayout.java:281)
at com.android.internal.policy.PhoneWindow$DecorView.onLayout(PhoneWindow.java:3178)
at android.view.View.layout(View.java:17945)
at android.view.ViewGroup.layout(ViewGroup.java:5812)
at android.view.ViewRootImpl.performLayout(ViewRootImpl.java:2716)
at android.view.ViewRootImpl.performTraversals(ViewRootImpl.java:2417)
at android.view.ViewRootImpl.doTraversal(ViewRootImpl.java:1487)
at android.view.ViewRootImpl$TraversalRunnable.run(ViewRootImpl.java:7450)
at android.view.Choreographer$CallbackRecord.run(Choreographer.java:920)
at android.view.Choreographer.doCallbacks(Choreographer.java:695)
at android.view.Choreographer.doFrame(Choreographer.java:631)
at android.view.Choreographer$FrameDisplayEventReceiver.run(Choreographer.java:906)
at android.os.Handler.handleCallback(Handler.java:739)
at android.os.Handler.dispatchMessage(Handler.java:95)
at android.os.Looper.loop(Looper.java:158)
at android.app.ActivityThread.main(ActivityThread.java:7237)
at java.lang.reflect.Method.invoke(Method.java)
at com.android.internal.os.ZygoteInit$MethodAndArgsCaller.run(ZygoteInit.java:1230)
at com.android.internal.os.ZygoteInit.main(ZygoteInit.java:1120)
|
non_process
|
crash in customhtmltospannedconverter fatal exception java lang nullpointerexception attempt to invoke virtual method int java lang string length on a null object reference at java io stringreader stringreader java at com zulip android util customhtmltospannedconverter convert customhtmltospannedconverter java at com zulip android models message formatcontent message java at com zulip android models message getformattedcontent message java at com zulip android activities recyclermessageadapter onbindviewholder recyclermessageadapter java at android support widget recyclerview adapter onbindviewholder recyclerview java at android support widget recyclerview adapter bindviewholder recyclerview java at android support widget recyclerview recycler getviewforposition recyclerview java at android support widget recyclerview recycler getviewforposition recyclerview java at android support widget linearlayoutmanager layoutstate next linearlayoutmanager java at android support widget linearlayoutmanager layoutchunk linearlayoutmanager java at android support widget linearlayoutmanager fill linearlayoutmanager java at android support widget linearlayoutmanager onlayoutchildren linearlayoutmanager java at android support widget recyclerview recyclerview java at android support widget recyclerview dispatchlayout recyclerview java at android support widget recyclerview onlayout recyclerview java at android view view layout view java at android view viewgroup layout viewgroup java at android widget linearlayout setchildframe linearlayout java at android widget linearlayout layoutvertical linearlayout java at android widget linearlayout onlayout linearlayout java at android view view layout view java at android view viewgroup layout viewgroup java at android widget framelayout layoutchildren framelayout java at android widget framelayout onlayout framelayout java at android view view layout view java at android view viewgroup layout viewgroup java at android support design widget coordinatorlayout layoutchild coordinatorlayout java at android support design widget coordinatorlayout onlayoutchild coordinatorlayout java at android support design widget coordinatorlayout onlayout coordinatorlayout java at android view view layout view java at android view viewgroup layout viewgroup java at android support widget drawerlayout onlayout drawerlayout java at android view view layout view java at android view viewgroup layout viewgroup java at android widget framelayout layoutchildren framelayout java at android widget framelayout onlayout framelayout java at android view view layout view java at android view viewgroup layout viewgroup java at android widget linearlayout setchildframe linearlayout java at android widget linearlayout layoutvertical linearlayout java at android widget linearlayout onlayout linearlayout java at android view view layout view java at android view viewgroup layout viewgroup java at android widget framelayout layoutchildren framelayout java at android widget framelayout onlayout framelayout java at android view view layout view java at android view viewgroup layout viewgroup java at android widget linearlayout setchildframe linearlayout java at android widget linearlayout layoutvertical linearlayout java at android widget linearlayout onlayout linearlayout java at android view view layout view java at android view viewgroup layout viewgroup java at android widget framelayout layoutchildren framelayout java at android widget framelayout onlayout framelayout java at com android internal policy phonewindow decorview onlayout phonewindow java at android view view layout view java at android view viewgroup layout viewgroup java at android view viewrootimpl performlayout viewrootimpl java at android view viewrootimpl performtraversals viewrootimpl java at android view viewrootimpl dotraversal viewrootimpl java at android view viewrootimpl traversalrunnable run viewrootimpl java at android view choreographer callbackrecord run choreographer java at android view choreographer docallbacks choreographer java at android view choreographer doframe choreographer java at android view choreographer framedisplayeventreceiver run choreographer java at android os handler handlecallback handler java at android os handler dispatchmessage handler java at android os looper loop looper java at android app activitythread main activitythread java at java lang reflect method invoke method java at com android internal os zygoteinit methodandargscaller run zygoteinit java at com android internal os zygoteinit main zygoteinit java
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.