Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1
value | created_at stringlengths 19 19 | repo stringlengths 7 112 | repo_url stringlengths 36 141 | action stringclasses 3
values | title stringlengths 1 744 | labels stringlengths 4 574 | body stringlengths 9 211k | index stringclasses 10
values | text_combine stringlengths 96 211k | label stringclasses 2
values | text stringlengths 96 188k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
73,301 | 24,554,429,969 | IssuesEvent | 2022-10-12 14:51:16 | SeleniumHQ/selenium | https://api.github.com/repos/SeleniumHQ/selenium | opened | [🐛 Bug]: Unable to find an exact match for CDP version 106, so returning the closest version found: a no-op implementation | I-defect needs-triaging | ### What happened?
I am trying to save a screenshot from my RemoteWebDriver session (GRID 4 distributed mode) and it looks like there is an issue with the websocket connection or the cdp version is not compatiable with selenium-java version: 4.5.0
### How can we reproduce the issue?
```shell
Java code:
driver =... | 1.0 | [🐛 Bug]: Unable to find an exact match for CDP version 106, so returning the closest version found: a no-op implementation - ### What happened?
I am trying to save a screenshot from my RemoteWebDriver session (GRID 4 distributed mode) and it looks like there is an issue with the websocket connection or the cdp versio... | non_process | unable to find an exact match for cdp version so returning the closest version found a no op implementation what happened i am trying to save a screenshot from my remotewebdriver session grid distributed mode and it looks like there is an issue with the websocket connection or the cdp version is not ... | 0 |
77,993 | 15,569,908,899 | IssuesEvent | 2021-03-17 01:16:27 | Killy85/python-bot | https://api.github.com/repos/Killy85/python-bot | opened | CVE-2020-11538 (High) detected in Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl, Pillow-6.0.0-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2020-11538 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl</b>, <b>Pillow-6.0.0-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summar... | True | CVE-2020-11538 (High) detected in Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl, Pillow-6.0.0-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2020-11538 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable L... | non_process | cve high detected in pillow whl pillow whl cve high severity vulnerability vulnerable libraries pillow whl pillow whl pillow whl python imaging library fork library home page a href path t... | 0 |
289,894 | 32,003,900,981 | IssuesEvent | 2023-09-21 13:49:23 | hughcdemocorp-mend/WebGoat | https://api.github.com/repos/hughcdemocorp-mend/WebGoat | opened | xstream-1.4.5.jar: 35 vulnerabilities (highest severity is: 9.9) reachable | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objects to XML and back.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to v... | True | xstream-1.4.5.jar: 35 vulnerabilities (highest severity is: 9.9) reachable - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>xstream-1.4.5.jar</b></p></summary>
<p>XStream is a serialization library from Java objec... | non_process | xstream jar vulnerabilities highest severity is reachable vulnerable library xstream jar xstream is a serialization library from java objects to xml and back path to dependency file pom xml path to vulnerable library home wss scanner repository com thoughtworks xstream xs... | 0 |
9,652 | 12,624,898,409 | IssuesEvent | 2020-06-14 08:58:49 | frictionlessdata/forum | https://api.github.com/repos/frictionlessdata/forum | closed | Organizing this forum (and triaging issues) | Idea: Improvement Size: ★ Topic: Process | Having some structure to this forum would help us manage stuff as it comes in.
## Job Stories
When someone asks a question I want to make sure it gets answered so that they are helped
When new ideas/suggestions come in I want to triage them by topic and priority so that I can find them again, others can find t... | 1.0 | Organizing this forum (and triaging issues) - Having some structure to this forum would help us manage stuff as it comes in.
## Job Stories
When someone asks a question I want to make sure it gets answered so that they are helped
When new ideas/suggestions come in I want to triage them by topic and priority so... | process | organizing this forum and triaging issues having some structure to this forum would help us manage stuff as it comes in job stories when someone asks a question i want to make sure it gets answered so that they are helped when new ideas suggestions come in i want to triage them by topic and priority so... | 1 |
61,543 | 15,024,823,166 | IssuesEvent | 2021-02-01 20:11:31 | sandboxie-plus/Sandboxie | https://api.github.com/repos/sandboxie-plus/Sandboxie | closed | Sandboxie Plus: restore maximized state from systray | fixed in next build | First, maximize window and close.
systray icon -> contenxt menu -> show/hide = open maximized window, as expected
double left mouse click on systray icon = restore latest manual changed size and position before maximized state. | 1.0 | Sandboxie Plus: restore maximized state from systray - First, maximize window and close.
systray icon -> contenxt menu -> show/hide = open maximized window, as expected
double left mouse click on systray icon = restore latest manual changed size and position before maximized state. | non_process | sandboxie plus restore maximized state from systray first maximize window and close systray icon contenxt menu show hide open maximized window as expected double left mouse click on systray icon restore latest manual changed size and position before maximized state | 0 |
102,066 | 8,816,990,113 | IssuesEvent | 2018-12-30 17:49:59 | zeromq/libzmq | https://api.github.com/repos/zeromq/libzmq | closed | make check error: tests/test_shutdown_stress | Area (Testing) Platform (osx) stale | 
I try to compile libzmq on my mac: Yosemite 10.10.3
After successfully running ./autogen.sh and ./configure , I got the above error while doing make check ,is it curcial for compling libzmq ? I supposed not ,... | 1.0 | make check error: tests/test_shutdown_stress - 
I try to compile libzmq on my mac: Yosemite 10.10.3
After successfully running ./autogen.sh and ./configure , I got the above error while doing make check ,is it... | non_process | make check error tests test shutdown stress i try to compile libzmq on my mac yosemite after successfully running autogen sh and configure i got the above error while doing make check is it curcial for compling libzmq i supposed not but how does it happen and how to fix i know it it tes... | 0 |
18,972 | 24,947,632,089 | IssuesEvent | 2022-11-01 02:34:46 | solop-develop/frontend-core | https://api.github.com/repos/solop-develop/frontend-core | closed | [Bug Report] Procesos asociados a la pestaña duplicados | bug (PRC) Processes (RPT) Reports (WIN) Windows | <!--
Note: In order to better solve your problem, please refer to the template to provide complete information, accurately describe the problem, and the incomplete information issue will be closed.
-->
## Bug report
#### Steps to reproduce
1. Iniciar sesión con el rol `System`.
2. Abrir la ventana `Window... | 1.0 | [Bug Report] Procesos asociados a la pestaña duplicados - <!--
Note: In order to better solve your problem, please refer to the template to provide complete information, accurately describe the problem, and the incomplete information issue will be closed.
-->
## Bug report
#### Steps to reproduce
1. Inicia... | process | procesos asociados a la pestaña duplicados note in order to better solve your problem please refer to the template to provide complete information accurately describe the problem and the incomplete information issue will be closed bug report steps to reproduce iniciar sesión co... | 1 |
6,401 | 9,485,783,572 | IssuesEvent | 2019-04-22 11:40:40 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [ActionSheet] Mark ActionSheet theming extension ready | [ActionSheet] type:Process | This was filed as an internal issue. If you are a Googler, please visit [b/130716161](http://b/130716161) for more details.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/130716161](http://b/130716161) | 1.0 | [ActionSheet] Mark ActionSheet theming extension ready - This was filed as an internal issue. If you are a Googler, please visit [b/130716161](http://b/130716161) for more details.
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/130716161](http://b/130716161) | process | mark actionsheet theming extension ready this was filed as an internal issue if you are a googler please visit for more details internal data associated internal bug | 1 |
181,546 | 14,049,596,932 | IssuesEvent | 2020-11-02 10:29:59 | microsoft/CCF | https://api.github.com/repos/microsoft/CCF | closed | Run forum sample tests in CI | TODO js testing | `samples/apps/forum`, essentially `npm install && npm test`. Some changes may have to be done to `samples/apps/forum/test/util.ts` to allow testing different configurations (enclave type etc). | 1.0 | Run forum sample tests in CI - `samples/apps/forum`, essentially `npm install && npm test`. Some changes may have to be done to `samples/apps/forum/test/util.ts` to allow testing different configurations (enclave type etc). | non_process | run forum sample tests in ci samples apps forum essentially npm install npm test some changes may have to be done to samples apps forum test util ts to allow testing different configurations enclave type etc | 0 |
7,031 | 10,192,211,429 | IssuesEvent | 2019-08-12 10:28:23 | bisq-network/bisq | https://api.github.com/repos/bisq-network/bisq | closed | Cannot distinguish between instant offers and regular offers in portfolio view | in:gui in:trade-process was:dropped | It doesn't seem like someone with multiple offers open can tell which are instant and which aren't.
If I'm stepping away from my desk and need to disable a live offer, I need to check offer details until I find the ones that are instant.
 detected in linuxlinux-4.19.88, linuxlinux-4.19.88 - autoclosed | security vulnerability | ## CVE-2021-26931 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.19.88</b>, <b>linuxlinux-4.19.88</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><im... | True | CVE-2021-26931 (Medium) detected in linuxlinux-4.19.88, linuxlinux-4.19.88 - autoclosed - ## CVE-2021-26931 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.19.88</b>, <... | non_process | cve medium detected in linuxlinux linuxlinux autoclosed cve medium severity vulnerability vulnerable libraries linuxlinux linuxlinux vulnerability details an issue was discovered in the linux kernel through as used in xen bloc... | 0 |
253,283 | 8,053,703,799 | IssuesEvent | 2018-08-02 00:37:18 | MSFREACH/msf-reach | https://api.github.com/repos/MSFREACH/msf-reach | closed | error once we click on email address on test environment | High Priority bug | 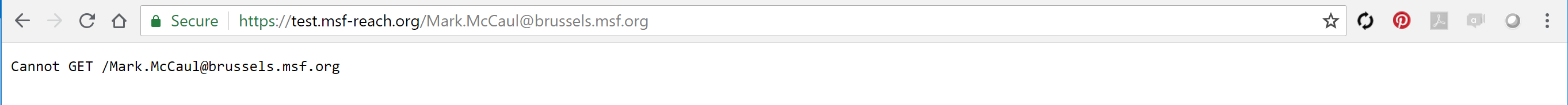
This is the case for all email address link
Pretty urgent as we have demo for South Africa tomorrow morning (CET). will do it in test environment. | 1.0 | error once we click on email address on test environment - 
This is the case for all email address link
Pretty urgent as we have demo for South Africa tomorrow morning (CET). will do it in test environment. | non_process | error once we click on email address on test environment this is the case for all email address link pretty urgent as we have demo for south africa tomorrow morning cet will do it in test environment | 0 |
19,570 | 25,887,966,136 | IssuesEvent | 2022-12-14 15:48:53 | daoanhhuy26012001/training-responsive-example | https://api.github.com/repos/daoanhhuy26012001/training-responsive-example | closed | Setup project | in-process | - [x] update package.json
- [x] create .gitignore
- [x] create reset.css
- [x] create variables.css
- [x] add fonts word
- [x] add images
- [x] create index.css
- [x] create index.html | 1.0 | Setup project - - [x] update package.json
- [x] create .gitignore
- [x] create reset.css
- [x] create variables.css
- [x] add fonts word
- [x] add images
- [x] create index.css
- [x] create index.html | process | setup project update package json create gitignore create reset css create variables css add fonts word add images create index css create index html | 1 |
18,456 | 24,548,794,412 | IssuesEvent | 2022-10-12 10:53:56 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | [PM] When clicked on Cancel button in My account screen, Admins are navigated to Studies screen | Bug P1 Participant manager Process: Fixed Process: Tested dev | **AR:** When clicked on 'Cancel' button in My account screen, Admins are navigated to 'Studies' screen
**ER:** When clicked on 'Cancel' button in My account screen, Admins should be navigated to 'Sites' screen | 2.0 | [PM] When clicked on Cancel button in My account screen, Admins are navigated to Studies screen - **AR:** When clicked on 'Cancel' button in My account screen, Admins are navigated to 'Studies' screen
**ER:** When clicked on 'Cancel' button in My account screen, Admins should be navigated to 'Sites' screen | process | when clicked on cancel button in my account screen admins are navigated to studies screen ar when clicked on cancel button in my account screen admins are navigated to studies screen er when clicked on cancel button in my account screen admins should be navigated to sites screen | 1 |
14,748 | 18,019,200,576 | IssuesEvent | 2021-09-16 17:09:35 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | Merge GO:1902187 negative regulation of viral release from host cell and GO:0044790 negative regulation by host of viral release from host cell | multi-species process | * Merge GO:1902187 negative regulation of viral release from host cell and
GO:0044790 negative regulation by host of viral release from host cell
*Merge and change label to 'suppression of viral release by host'
*change subclass to 'defense response to virus' (instead of GO:1902186 regulation of viral release from ... | 1.0 | Merge GO:1902187 negative regulation of viral release from host cell and GO:0044790 negative regulation by host of viral release from host cell - * Merge GO:1902187 negative regulation of viral release from host cell and
GO:0044790 negative regulation by host of viral release from host cell
*Merge and change label t... | process | merge go negative regulation of viral release from host cell and go negative regulation by host of viral release from host cell merge go negative regulation of viral release from host cell and go negative regulation by host of viral release from host cell merge and change label to suppression of viral ... | 1 |
63,010 | 15,396,424,616 | IssuesEvent | 2021-03-03 20:37:27 | spack/spack | https://api.github.com/repos/spack/spack | closed | Installation issue: <callpath, mpileaks> | build-error | ### Steps to reproduce the issue
Minimal test case: following the Spack packaging tutorial with Docker (https://spack-tutorial.readthedocs.io/en/latest/tutorial_packaging.html, I used the Docker image for OSX: https://hub.docker.com/editions/community/docker-ce-desktop-mac/), the mpileaks packaging example won't work ... | 1.0 | Installation issue: <callpath, mpileaks> - ### Steps to reproduce the issue
Minimal test case: following the Spack packaging tutorial with Docker (https://spack-tutorial.readthedocs.io/en/latest/tutorial_packaging.html, I used the Docker image for OSX: https://hub.docker.com/editions/community/docker-ce-desktop-mac/),... | non_process | installation issue steps to reproduce the issue minimal test case following the spack packaging tutorial with docker i used the docker image for osx the mpileaks packaging example won t work after adding depends on callpath console spack install mpileaks error not supported ... | 0 |
14,384 | 17,402,348,882 | IssuesEvent | 2021-08-02 21:44:58 | googleapis/python-firestore | https://api.github.com/repos/googleapis/python-firestore | opened | Split out system tests into separate Kokoro job | type: process | Working to reduce CI latency.Here are timings on my local machine (note the pre-run with `--install-only` to avoid measuring virtualenv creation time):
```bash
$ for job in $(nox --list | grep "^\*" | cut -d " " -f 2); do
echo $job;
nox -e $job --install-only;
time nox -re $job;
done
lint
... | 1.0 | Split out system tests into separate Kokoro job - Working to reduce CI latency.Here are timings on my local machine (note the pre-run with `--install-only` to avoid measuring virtualenv creation time):
```bash
$ for job in $(nox --list | grep "^\*" | cut -d " " -f 2); do
echo $job;
nox -e $job --insta... | process | split out system tests into separate kokoro job working to reduce ci latency here are timings on my local machine note the pre run with install only to avoid measuring virtualenv creation time bash for job in nox list grep cut d f do echo job nox e job insta... | 1 |
38,951 | 8,559,455,272 | IssuesEvent | 2018-11-08 21:19:43 | inspec/inspec | https://api.github.com/repos/inspec/inspec | opened | True Source Code Parsing | CLI: check Component: Code Generation Type: Feature Request Type: RFC | ### 🎛 Description
🙋 feature request
When InSpec examines a profile, it evaluates the profile code directly. This makes some operations, such as code generation, `check`, and profile inheritance, difficult and hard to debug.
An alternate approach might be to parse the source code of the profile, then manipul... | 1.0 | True Source Code Parsing - ### 🎛 Description
🙋 feature request
When InSpec examines a profile, it evaluates the profile code directly. This makes some operations, such as code generation, `check`, and profile inheritance, difficult and hard to debug.
An alternate approach might be to parse the source code o... | non_process | true source code parsing 🎛 description 🙋 feature request when inspec examines a profile it evaluates the profile code directly this makes some operations such as code generation check and profile inheritance difficult and hard to debug an alternate approach might be to parse the source code o... | 0 |
368,900 | 25,813,465,204 | IssuesEvent | 2022-12-12 01:50:36 | MAKAIABootcamp/demo-day-projects-ruta-mental | https://api.github.com/repos/MAKAIABootcamp/demo-day-projects-ruta-mental | closed | Creación Readme | documentation | Crear el readme del proyecto
- [x] Hacer descripción técnica de la app y algunos de sus funciones
- [x] Describir el uso de firebase
- [x] Describir los pre-requisitos
- [x] Instrucciones para correr el proyecto local | 1.0 | Creación Readme - Crear el readme del proyecto
- [x] Hacer descripción técnica de la app y algunos de sus funciones
- [x] Describir el uso de firebase
- [x] Describir los pre-requisitos
- [x] Instrucciones para correr el proyecto local | non_process | creación readme crear el readme del proyecto hacer descripción técnica de la app y algunos de sus funciones describir el uso de firebase describir los pre requisitos instrucciones para correr el proyecto local | 0 |
82,705 | 16,016,991,458 | IssuesEvent | 2021-04-20 17:15:17 | mozilla/fxa | https://api.github.com/repos/mozilla/fxa | closed | sasslint errors should cause Circle to fail | code_quality | Follow on from #1285 and #1328, @vladikoff noticed several sasslint errors. @mirefly fixed those in #1328. It brings up, sasslint errors should cause Circle to fail like any other lint error.
┆Issue is synchronized with this [Jira Task](https://jira.mozilla.com/browse/FXA-112)
┆Issue Number: FXA-112
| 1.0 | sasslint errors should cause Circle to fail - Follow on from #1285 and #1328, @vladikoff noticed several sasslint errors. @mirefly fixed those in #1328. It brings up, sasslint errors should cause Circle to fail like any other lint error.
┆Issue is synchronized with this [Jira Task](https://jira.mozilla.com/browse/FXA-... | non_process | sasslint errors should cause circle to fail follow on from and vladikoff noticed several sasslint errors mirefly fixed those in it brings up sasslint errors should cause circle to fail like any other lint error ┆issue is synchronized with this ┆issue number fxa | 0 |
20,530 | 6,896,572,172 | IssuesEvent | 2017-11-23 18:41:23 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | opened | Fold runtime/compiler/trj9 directory | comp:build comp:jit | Now that `tr.source` has been renamed to `compiler` as part of https://github.com/eclipse/openj9/pull/589 I wanted to start a discussion on possibly folding the `trj9` directory as well. To me it currently serves no purpose as it's parent `compiler` directory is completely empty.
@0xdaryl notes down some thoughts in... | 1.0 | Fold runtime/compiler/trj9 directory - Now that `tr.source` has been renamed to `compiler` as part of https://github.com/eclipse/openj9/pull/589 I wanted to start a discussion on possibly folding the `trj9` directory as well. To me it currently serves no purpose as it's parent `compiler` directory is completely empty.
... | non_process | fold runtime compiler directory now that tr source has been renamed to compiler as part of i wanted to start a discussion on possibly folding the directory as well to me it currently serves no purpose as it s parent compiler directory is completely empty notes down some thoughts in which may p... | 0 |
8,935 | 12,052,802,465 | IssuesEvent | 2020-04-15 08:17:56 | MHRA/products | https://api.github.com/repos/MHRA/products | opened | Job set to error status even though it was being retried | BUG :bug: EPIC - Auto Batch Process :oncoming_automobile: | **Describe the bug**
A delete job failed because it was unable to reach the search service, the job status was changed to `Error(: error sending request for url (https://mhraproductsnonprod.search.windows.net/indexes/products-index/docs?api-version=2019-05-06&highlight=content&queryType=full&%40count=true&%40top=10&%4... | 1.0 | Job set to error status even though it was being retried - **Describe the bug**
A delete job failed because it was unable to reach the search service, the job status was changed to `Error(: error sending request for url (https://mhraproductsnonprod.search.windows.net/indexes/products-index/docs?api-version=2019-05-06... | process | job set to error status even though it was being retried describe the bug a delete job failed because it was unable to reach the search service the job status was changed to error error sending request for url error trying to connect unexpected eof it was then retried and was successful the consu... | 1 |
120,431 | 4,789,114,939 | IssuesEvent | 2016-10-30 22:14:52 | vidalborromeo/eecshelp-beta | https://api.github.com/repos/vidalborromeo/eecshelp-beta | opened | The "favicon.ico" File Is Not Loading | Bug Priority: Low | v2.0.60
Chrome/Firefox
Instead of the M logo, it just shows the default GWT logo. | 1.0 | The "favicon.ico" File Is Not Loading - v2.0.60
Chrome/Firefox
Instead of the M logo, it just shows the default GWT logo. | non_process | the favicon ico file is not loading chrome firefox instead of the m logo it just shows the default gwt logo | 0 |
19,417 | 25,565,288,566 | IssuesEvent | 2022-11-30 13:53:47 | open-telemetry/opentelemetry-collector-contrib | https://api.github.com/repos/open-telemetry/opentelemetry-collector-contrib | closed | The type of kafka_producer_connection_count keeps changing between counter and gauge | bug exporter/prometheus needs triage processor/servicegraph | ### Component(s)
cmd/otelcontribcol, exporter/prometheus, processor/servicegraph
### What happened?
The type of kafka_producer_connection_count keeps changing between counter and gauge
```
# HELP kafka_producer_connection_count The current number of active connections.
# TYPE kafka_producer_connection_count cou... | 1.0 | The type of kafka_producer_connection_count keeps changing between counter and gauge - ### Component(s)
cmd/otelcontribcol, exporter/prometheus, processor/servicegraph
### What happened?
The type of kafka_producer_connection_count keeps changing between counter and gauge
```
# HELP kafka_producer_connection_coun... | process | the type of kafka producer connection count keeps changing between counter and gauge component s cmd otelcontribcol exporter prometheus processor servicegraph what happened the type of kafka producer connection count keeps changing between counter and gauge help kafka producer connection coun... | 1 |
431,142 | 12,475,656,737 | IssuesEvent | 2020-05-29 12:03:05 | zairza-cetb/bench-routes | https://api.github.com/repos/zairza-cetb/bench-routes | opened | Extend system-metrics with additional details | feature priority:high | Currently, system-metrics monitor the following:
1. CPU usage (percent)
2. Memory usage (percent)
3. Memory cache
4. Disk I/O
There are tons of other details that are required:
1. Network speed
2. CPU clock rate
3. Total number of threads (OS and kernel)
4. Per-core performance
Feel free to comment for ot... | 1.0 | Extend system-metrics with additional details - Currently, system-metrics monitor the following:
1. CPU usage (percent)
2. Memory usage (percent)
3. Memory cache
4. Disk I/O
There are tons of other details that are required:
1. Network speed
2. CPU clock rate
3. Total number of threads (OS and kernel)
4. Per... | non_process | extend system metrics with additional details currently system metrics monitor the following cpu usage percent memory usage percent memory cache disk i o there are tons of other details that are required network speed cpu clock rate total number of threads os and kernel per... | 0 |
16,530 | 21,558,535,595 | IssuesEvent | 2022-04-30 20:53:15 | gfx-rs/naga | https://api.github.com/repos/gfx-rs/naga | closed | Secure out-of-bounds accesses | kind: feature area: processing | For WebGPU, we need to guarantee that all out-of-bound accesses are not really happening. We can employ one of the following strategies:
1. Read zeroes, write nothing (follows D3D)
2. Clamp reads and writes (one of the possible behaviors of Vulkan)
3. Detect this and early return (signalling a failure of any s... | 1.0 | Secure out-of-bounds accesses - For WebGPU, we need to guarantee that all out-of-bound accesses are not really happening. We can employ one of the following strategies:
1. Read zeroes, write nothing (follows D3D)
2. Clamp reads and writes (one of the possible behaviors of Vulkan)
3. Detect this and early retur... | process | secure out of bounds accesses for webgpu we need to guarantee that all out of bound accesses are not really happening we can employ one of the following strategies read zeroes write nothing follows clamp reads and writes one of the possible behaviors of vulkan detect this and early return ... | 1 |
69,331 | 7,131,506,665 | IssuesEvent | 2018-01-22 11:14:48 | dwyl/product-owner-guide | https://api.github.com/repos/dwyl/product-owner-guide | closed | How do I know what's happening on a project? | T1h enhancement please-test | As a product owner
I would like to be able to take a look at the project's backlog and know where things are at
So that I don't have to rely on emails or telephone exchanges with the team. | 1.0 | How do I know what's happening on a project? - As a product owner
I would like to be able to take a look at the project's backlog and know where things are at
So that I don't have to rely on emails or telephone exchanges with the team. | non_process | how do i know what s happening on a project as a product owner i would like to be able to take a look at the project s backlog and know where things are at so that i don t have to rely on emails or telephone exchanges with the team | 0 |
430,818 | 12,466,506,875 | IssuesEvent | 2020-05-28 15:34:44 | kiudee/cs-ranking | https://api.github.com/repos/kiudee/cs-ranking | opened | Check if dataset generator exists and otherwise raise an exception | Priority: Medium | Currently, if the dataset generator receives an invalid dataset, it silently picks a default generator.
https://github.com/kiudee/cs-ranking/blob/5bdc0e414dde196761b7c827369b605a024bae42/csrank/dataset_reader/objectranking/object_ranking_data_generator.py#L35-L36
This is unexpected behavior and should be changed. If ... | 1.0 | Check if dataset generator exists and otherwise raise an exception - Currently, if the dataset generator receives an invalid dataset, it silently picks a default generator.
https://github.com/kiudee/cs-ranking/blob/5bdc0e414dde196761b7c827369b605a024bae42/csrank/dataset_reader/objectranking/object_ranking_data_generat... | non_process | check if dataset generator exists and otherwise raise an exception currently if the dataset generator receives an invalid dataset it silently picks a default generator this is unexpected behavior and should be changed if the dataset generator is unknown an exception should be raised | 0 |
21,238 | 3,875,699,887 | IssuesEvent | 2016-04-12 02:52:37 | ComputationalRadiationPhysics/libSplash | https://api.github.com/repos/ComputationalRadiationPhysics/libSplash | closed | readMeta: ColType is "Random" (First) | affects latest release bug | As commented [here](https://github.com/ComputationalRadiationPhysics/libSplash/pull/203/files#r59259938) the `readMeta` function is acidently returning the `CollectionType` of the *first* found entry in a `id` (time step) instead of the matched entry by name. | 1.0 | readMeta: ColType is "Random" (First) - As commented [here](https://github.com/ComputationalRadiationPhysics/libSplash/pull/203/files#r59259938) the `readMeta` function is acidently returning the `CollectionType` of the *first* found entry in a `id` (time step) instead of the matched entry by name. | non_process | readmeta coltype is random first as commented the readmeta function is acidently returning the collectiontype of the first found entry in a id time step instead of the matched entry by name | 0 |
18,816 | 24,717,914,304 | IssuesEvent | 2022-10-20 08:29:09 | NEARWEEK/CORE | https://api.github.com/repos/NEARWEEK/CORE | closed | Facilitate weekly synch & monthly evaluation calls | Process | ## 🎉 Subtasks
- [x] 1 hour (when not needed reduced to 30 min) weekly start of week call
- [x] Daily check in call of 20 min
- [x] Monthly process evaluation call
## 🤼♂️ Reviewer
@P3ter-NEARWEEK & rest of NEARWEEK team
| 1.0 | Facilitate weekly synch & monthly evaluation calls - ## 🎉 Subtasks
- [x] 1 hour (when not needed reduced to 30 min) weekly start of week call
- [x] Daily check in call of 20 min
- [x] Monthly process evaluation call
## 🤼♂️ Reviewer
@P3ter-NEARWEEK & rest of NEARWEEK team
| process | facilitate weekly synch monthly evaluation calls 🎉 subtasks hour when not needed reduced to min weekly start of week call daily check in call of min monthly process evaluation call 🤼♂️ reviewer nearweek rest of nearweek team | 1 |
280,765 | 21,315,158,444 | IssuesEvent | 2022-04-16 06:24:03 | brandonrhan/pe | https://api.github.com/repos/brandonrhan/pe | opened | The error message of add command is different from UG | severity.Low type.DocumentationBug | The parameter is p/PHONE_NUMBER in UG but it is p/PHONE in error message
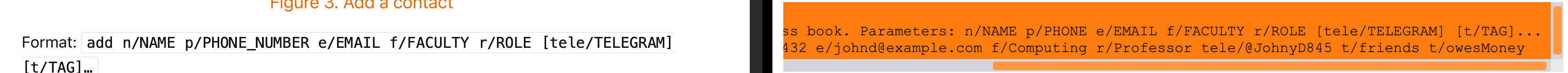
<!--session: 1650088334924-14f9646a-82c3-4f8e-a7ee-2eb0f6619db9-->
<!--Version: Desktop v3.4.2--... | 1.0 | The error message of add command is different from UG - The parameter is p/PHONE_NUMBER in UG but it is p/PHONE in error message
<!--session: 1650088334924-14f9646a-82c3... | non_process | the error message of add command is different from ug the parameter is p phone number in ug but it is p phone in error message | 0 |
137,171 | 20,085,573,314 | IssuesEvent | 2022-02-05 00:18:29 | Azure/WALinuxAgent | https://api.github.com/repos/Azure/WALinuxAgent | closed | [BUG] System crash may cause waagent exception | by design | **Describe the bug: A clear and concise description of what the bug is.**
After system crash and reboot, sometimes there are exceptions in waagent.log:
```
2022-01-06T14:07:06.202463Z ERROR TelemetryEventsCollector ExtHandler Event: name=WALinuxAgent, op=CollectEventErrors, message=DroppedEventsCount: 6
Reasons (fi... | 1.0 | [BUG] System crash may cause waagent exception - **Describe the bug: A clear and concise description of what the bug is.**
After system crash and reboot, sometimes there are exceptions in waagent.log:
```
2022-01-06T14:07:06.202463Z ERROR TelemetryEventsCollector ExtHandler Event: name=WALinuxAgent, op=CollectEventE... | non_process | system crash may cause waagent exception describe the bug a clear and concise description of what the bug is after system crash and reboot sometimes there are exceptions in waagent log error telemetryeventscollector exthandler event name walinuxagent op collecteventerrors message dropp... | 0 |
70,745 | 15,105,715,970 | IssuesEvent | 2021-02-08 13:25:26 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | closed | [Bug]Screenshot feature in private browsing mode | Feature:Privacy&Security Feature:PrivateBrowsing eng:qa:needed 🐞 bug | ## Steps to reproduce
EDIT: Uploaded video to be more clear.
1. Take a screenshot.
2. Minimize the application.
3. Go back to Fenix.
4. Take a screenshot.
### Expected behavior
You will be able to take a screenshot.
### Actual behavior
Fenix will say "This app doesn't allow taking screenshots".
... | True | [Bug]Screenshot feature in private browsing mode - ## Steps to reproduce
EDIT: Uploaded video to be more clear.
1. Take a screenshot.
2. Minimize the application.
3. Go back to Fenix.
4. Take a screenshot.
### Expected behavior
You will be able to take a screenshot.
### Actual behavior
Fenix will s... | non_process | screenshot feature in private browsing mode steps to reproduce edit uploaded video to be more clear take a screenshot minimize the application go back to fenix take a screenshot expected behavior you will be able to take a screenshot actual behavior fenix will say ... | 0 |
7,713 | 10,819,971,158 | IssuesEvent | 2019-11-08 15:27:25 | deeplearningunb/pneumonia-diagnose | https://api.github.com/repos/deeplearningunb/pneumonia-diagnose | opened | Adicionar funcoes de data augmentation | preprocessing | Adicionar funcoes relevantes para o tipo de dado trabalhado
- Zoom
- Random rotation
- Flip
etc | 1.0 | Adicionar funcoes de data augmentation - Adicionar funcoes relevantes para o tipo de dado trabalhado
- Zoom
- Random rotation
- Flip
etc | process | adicionar funcoes de data augmentation adicionar funcoes relevantes para o tipo de dado trabalhado zoom random rotation flip etc | 1 |
13,632 | 16,240,796,010 | IssuesEvent | 2021-05-07 09:17:51 | hermeznetwork/hermez-node | https://api.github.com/repos/hermeznetwork/hermez-node | closed | Save sender IP address at TX table | txprocessor | ## Rationale
Today sender's IP address is stored at tx-pool table but it is not stored in tx table after the transaction has been forged. We need to save sender's IP address also in tx table. | 1.0 | Save sender IP address at TX table - ## Rationale
Today sender's IP address is stored at tx-pool table but it is not stored in tx table after the transaction has been forged. We need to save sender's IP address also in tx table. | process | save sender ip address at tx table rationale today sender s ip address is stored at tx pool table but it is not stored in tx table after the transaction has been forged we need to save sender s ip address also in tx table | 1 |
2,096 | 4,931,466,634 | IssuesEvent | 2016-11-28 10:17:16 | tomlutzenberger/frontal-coding-guideline | https://api.github.com/repos/tomlutzenberger/frontal-coding-guideline | opened | Browser-Sync | process suggestion | **BrowserSync (https://www.browsersync.io)**
Im Gegensatz zu `grunt-watch`, werden hier die Aktionen in allen Browsern (Scroll, Click etc.) syncronisiert und ermöglichen so paralleles Testing (gedacht für manuelle Tests) | 1.0 | Browser-Sync - **BrowserSync (https://www.browsersync.io)**
Im Gegensatz zu `grunt-watch`, werden hier die Aktionen in allen Browsern (Scroll, Click etc.) syncronisiert und ermöglichen so paralleles Testing (gedacht für manuelle Tests) | process | browser sync browsersync im gegensatz zu grunt watch werden hier die aktionen in allen browsern scroll click etc syncronisiert und ermöglichen so paralleles testing gedacht für manuelle tests | 1 |
51,958 | 12,829,931,710 | IssuesEvent | 2020-07-07 00:32:06 | googleapis/nodejs-dlp | https://api.github.com/repos/googleapis/nodejs-dlp | closed | redact: should redact multiple sensitive data types from an image failed | api: dlp buildcop: issue priority: p1 type: bug | This test failed!
To configure my behavior, see [the Build Cop Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop).
If I'm commenting on this issue too often, add the `buildcop: quiet` label and
I will stop commenting.
---
commit: 10a87626c46bdc5753d366fe02d189461485... | 1.0 | redact: should redact multiple sensitive data types from an image failed - This test failed!
To configure my behavior, see [the Build Cop Bot documentation](https://github.com/googleapis/repo-automation-bots/tree/master/packages/buildcop).
If I'm commenting on this issue too often, add the `buildcop: quiet` label and... | non_process | redact should redact multiple sensitive data types from an image failed this test failed to configure my behavior see if i m commenting on this issue too often add the buildcop quiet label and i will stop commenting commit buildurl status failed test output expected to be belo... | 0 |
18,144 | 24,186,783,995 | IssuesEvent | 2022-09-23 13:56:42 | cloudfoundry/korifi | https://api.github.com/repos/cloudfoundry/korifi | closed | [Feature]: Developer can push apps using the top-level `health-check-http-endpoint` field in the manifest | Top-level process config | ### Background
**As a** developer
**I want** top-level process configuration in manifests to be supported
**So that** I can use shortcut `cf push` flags like `-c`, `-i`, `-m` etc.
### Acceptance Criteria
* **GIVEN** I have the following node app:
```js
var http = require('http');
http.createServer(f... | 1.0 | [Feature]: Developer can push apps using the top-level `health-check-http-endpoint` field in the manifest - ### Background
**As a** developer
**I want** top-level process configuration in manifests to be supported
**So that** I can use shortcut `cf push` flags like `-c`, `-i`, `-m` etc.
### Acceptance Criteria
... | process | developer can push apps using the top level health check http endpoint field in the manifest background as a developer i want top level process configuration in manifests to be supported so that i can use shortcut cf push flags like c i m etc acceptance criteria g... | 1 |
19,044 | 25,045,768,657 | IssuesEvent | 2022-11-05 08:04:11 | googleapis/google-cloud-python | https://api.github.com/repos/googleapis/google-cloud-python | opened | Your .repo-metadata.json file has a problem 🤒 | type: process repo-metadata: lint | You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'apiName' invalid in containers/python-bootstrap-container/.repo-metadata.json
☝️ Once you address these problems, you can close this issue.
### Need help?
* [Schema definition](https://github.com/googleapis/repo-automation-b... | 1.0 | Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* api_shortname 'apiName' invalid in containers/python-bootstrap-container/.repo-metadata.json
☝️ Once you address these problems, you can close this issue.
### Need help?
* [Schema definition... | process | your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 api shortname apiname invalid in containers python bootstrap container repo metadata json ☝️ once you address these problems you can close this issue need help lists valid op... | 1 |
359,432 | 10,676,044,634 | IssuesEvent | 2019-10-21 13:01:33 | rubyforgood/babywearing | https://api.github.com/repos/rubyforgood/babywearing | closed | Item images in browsable inventory should be the same size | Hacktoberfest Priority: High beginner friendly | See #59
All images (placeholder and uploaded) should be the same size.
- Each `item` (ie `/carriers/5/edit) has a photo upload option that is used for that specific item. | 1.0 | Item images in browsable inventory should be the same size - See #59
All images (placeholder and uploaded) should be the same size.
- Each `item` (ie `/carriers/5/edit) has a photo upload option that is used for that specific item. | non_process | item images in browsable inventory should be the same size see all images placeholder and uploaded should be the same size each item ie carriers edit has a photo upload option that is used for that specific item | 0 |
21,608 | 30,014,299,021 | IssuesEvent | 2023-06-26 17:27:09 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | System.Diagnostics.Process with CreateNoWindow does not redirect stdout/stderr to parent process | area-System.Diagnostics.Process needs-author-action | ### Description
When using `System.Diagnostics.Process` with `CreateNoWindow = true` the output does not get redirected to the parent process. It will end up in no output.
The [docs](https://docs.microsoft.com/en-us/dotnet/api/system.diagnostics.processstartinfo.createnowindow?view=net-6.0) don't say anything abo... | 1.0 | System.Diagnostics.Process with CreateNoWindow does not redirect stdout/stderr to parent process - ### Description
When using `System.Diagnostics.Process` with `CreateNoWindow = true` the output does not get redirected to the parent process. It will end up in no output.
The [docs](https://docs.microsoft.com/en-us... | process | system diagnostics process with createnowindow does not redirect stdout stderr to parent process description when using system diagnostics process with createnowindow true the output does not get redirected to the parent process it will end up in no output the don t say anything about this behav... | 1 |
21,116 | 28,079,791,165 | IssuesEvent | 2023-03-30 04:58:09 | AssetRipper/AssetRipper | https://api.github.com/repos/AssetRipper/AssetRipper | closed | [Bug]: Fonts material problems | bug help wanted good first issue export processing | ### Describe the issue
### Are you on the latest version of AssetRipper?
Yes, I'm on the latest release of AssetRipper.
### Which release are you using?
Linux x64
### Which game did this occur on?
My own test project here (ignore the name, it doesn't have to do with shaders):
[ShadersExportTest.zip](... | 1.0 | [Bug]: Fonts material problems - ### Describe the issue
### Are you on the latest version of AssetRipper?
Yes, I'm on the latest release of AssetRipper.
### Which release are you using?
Linux x64
### Which game did this occur on?
My own test project here (ignore the name, it doesn't have to do with shad... | process | fonts material problems describe the issue are you on the latest version of assetripper yes i m on the latest release of assetripper which release are you using linux which game did this occur on my own test project here ignore the name it doesn t have to do with shaders ... | 1 |
9,747 | 12,734,482,024 | IssuesEvent | 2020-06-25 13:58:20 | nodejs/node | https://api.github.com/repos/nodejs/node | opened | implement process.exitWithException() | feature request process | In the stalled PR https://github.com/nodejs/node/pull/25715, @Fishrock123 was working to introduce a new API... from the original description:
> Adds a public way to access node::FatalException from javascript, as process.exitWithException().
>
> If an error stack is available on the value, this method of exiting ... | 1.0 | implement process.exitWithException() - In the stalled PR https://github.com/nodejs/node/pull/25715, @Fishrock123 was working to introduce a new API... from the original description:
> Adds a public way to access node::FatalException from javascript, as process.exitWithException().
>
> If an error stack is availab... | process | implement process exitwithexception in the stalled pr was working to introduce a new api from the original description adds a public way to access node fatalexception from javascript as process exitwithexception if an error stack is available on the value this method of exiting does not ad... | 1 |
387,977 | 11,472,768,530 | IssuesEvent | 2020-02-09 19:12:43 | Code-and-Response/Prometeo | https://api.github.com/repos/Code-and-Response/Prometeo | closed | Logistics/operations: Prepare scope for February field test | high-priority logistics-operations | There is a prescribed or preventative burn that will occur in mid-February. Several fires are intentionally lit at several locations throughout Catalonia in order to remove combustible material ahead of real wildfires.
This will involve both the local GRAF team as well as the 70 plus firefighters around the area. At... | 1.0 | Logistics/operations: Prepare scope for February field test - There is a prescribed or preventative burn that will occur in mid-February. Several fires are intentionally lit at several locations throughout Catalonia in order to remove combustible material ahead of real wildfires.
This will involve both the local GRA... | non_process | logistics operations prepare scope for february field test there is a prescribed or preventative burn that will occur in mid february several fires are intentionally lit at several locations throughout catalonia in order to remove combustible material ahead of real wildfires this will involve both the local gra... | 0 |
119,059 | 4,760,279,794 | IssuesEvent | 2016-10-25 02:20:36 | PowerlineApp/powerline-mobile | https://api.github.com/repos/PowerlineApp/powerline-mobile | opened | New Event - Pre-fill RSVP Options | bug P4 - Really Low Priority | It would be great if the first two RSVP answer options were pre-filled with:
"Yes, I can make it"
"No, I can't make it"
But still editable by the user. | 1.0 | New Event - Pre-fill RSVP Options - It would be great if the first two RSVP answer options were pre-filled with:
"Yes, I can make it"
"No, I can't make it"
But still editable by the user. | non_process | new event pre fill rsvp options it would be great if the first two rsvp answer options were pre filled with yes i can make it no i can t make it but still editable by the user | 0 |
96,548 | 8,617,574,510 | IssuesEvent | 2018-11-20 06:17:43 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | opened | projecttesting20 : ApiV1DashboardCountRunsBetweenGetPathParamFromdateMysqlSqlInjectionTimebound | projecttesting20 | Project : projecttesting20
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-C... | 1.0 | projecttesting20 : ApiV1DashboardCountRunsBetweenGetPathParamFromdateMysqlSqlInjectionTimebound - Project : projecttesting20
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no... | non_process | project job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response... | 0 |
31,698 | 4,714,507,299 | IssuesEvent | 2016-10-15 01:09:24 | institutotim/timtec | https://api.github.com/repos/institutotim/timtec | reopened | [importante] Melhorar o cadastro de usuário | waiting test | 1. [x] No form de cadastro inicial, verificar se o campo "nome de usuário" corresponde a "login". Se sim e não for obrigatório, retirar;
2. [x] Ainda no form de cadastro inicial, acrescentar os campos "primeiro nome", "sobrenome", "estado" e "cidade" e deixar como campos obrigatórios;
3. [x] No form de cadastro inter... | 1.0 | [importante] Melhorar o cadastro de usuário - 1. [x] No form de cadastro inicial, verificar se o campo "nome de usuário" corresponde a "login". Se sim e não for obrigatório, retirar;
2. [x] Ainda no form de cadastro inicial, acrescentar os campos "primeiro nome", "sobrenome", "estado" e "cidade" e deixar como campos o... | non_process | melhorar o cadastro de usuário no form de cadastro inicial verificar se o campo nome de usuário corresponde a login se sim e não for obrigatório retirar ainda no form de cadastro inicial acrescentar os campos primeiro nome sobrenome estado e cidade e deixar como campos obrigatórios ... | 0 |
21,961 | 30,456,171,093 | IssuesEvent | 2023-07-16 22:52:32 | h4sh5/pypi-auto-scanner | https://api.github.com/repos/h4sh5/pypi-auto-scanner | opened | roblox-pyc 1.16.25 has 2 GuardDog issues | guarddog silent-process-execution | https://pypi.org/project/roblox-pyc
https://inspector.pypi.io/project/roblox-pyc
```{
"dependency": "roblox-pyc",
"version": "1.16.25",
"result": {
"issues": 2,
"errors": {},
"results": {
"silent-process-execution": [
{
"location": "roblox-pyc-1.16.25/src/robloxpy.py:86",
... | 1.0 | roblox-pyc 1.16.25 has 2 GuardDog issues - https://pypi.org/project/roblox-pyc
https://inspector.pypi.io/project/roblox-pyc
```{
"dependency": "roblox-pyc",
"version": "1.16.25",
"result": {
"issues": 2,
"errors": {},
"results": {
"silent-process-execution": [
{
"location": "ro... | process | roblox pyc has guarddog issues dependency roblox pyc version result issues errors results silent process execution location roblox pyc src robloxpy py code subprocess call ... | 1 |
45,403 | 12,793,792,240 | IssuesEvent | 2020-07-02 05:10:51 | fieldenms/tg | https://api.github.com/repos/fieldenms/tg | closed | Missing adjustment for JS API method for editor value promotion | Actions Defect Entity master Property editor Pull request Regression Selection criteria | ### Description
Method `setEditorValue4PropertyFromConcreteValue` has not been adjusted during #1044 issue implementation. This has been slipped through a crack when multitude of API changes were provisioned and corresponding platform / application code adjusted. Web tests are required to employ early check of its fun... | 1.0 | Missing adjustment for JS API method for editor value promotion - ### Description
Method `setEditorValue4PropertyFromConcreteValue` has not been adjusted during #1044 issue implementation. This has been slipped through a crack when multitude of API changes were provisioned and corresponding platform / application code... | non_process | missing adjustment for js api method for editor value promotion description method has not been adjusted during issue implementation this has been slipped through a crack when multitude of api changes were provisioned and corresponding platform application code adjusted web tests are required to emplo... | 0 |
227,172 | 17,376,126,933 | IssuesEvent | 2021-07-30 21:36:21 | Carmoruda/JetBrains-Academy-Projects | https://api.github.com/repos/Carmoruda/JetBrains-Academy-Projects | closed | README | documentation | - [x] Change the type of headline from the difficulty of the projects in the README document (Python Developer).
- [x] Append the link to the document with the stage 1 code (Coffee Machine) | 1.0 | README - - [x] Change the type of headline from the difficulty of the projects in the README document (Python Developer).
- [x] Append the link to the document with the stage 1 code (Coffee Machine) | non_process | readme change the type of headline from the difficulty of the projects in the readme document python developer append the link to the document with the stage code coffee machine | 0 |
217,473 | 16,718,088,968 | IssuesEvent | 2021-06-10 01:31:42 | streamnative/pulsar | https://api.github.com/repos/streamnative/pulsar | closed | ISSUE-10237: [Doc + Website] generate 2.8.0-SNAPSHOT for various API docs | component/documentation component/website | Original Issue: apache/pulsar#10237
---
[All API docs](https://pulsar.apache.org/api/) should be automatically generated after each release.
However, the following API docs do not have 2.8.0-SNAPSHOT currently.
- [Java admin API](https://github.com/apache/pulsar/tree/asf-site/content/api/admin)
- [pulsar-bro... | 1.0 | ISSUE-10237: [Doc + Website] generate 2.8.0-SNAPSHOT for various API docs - Original Issue: apache/pulsar#10237
---
[All API docs](https://pulsar.apache.org/api/) should be automatically generated after each release.
However, the following API docs do not have 2.8.0-SNAPSHOT currently.
- [Java admin API](htt... | non_process | issue generate snapshot for various api docs original issue apache pulsar should be automatically generated after each release however the following api docs do not have snapshot currently besides the always fails in recent days tuteng thinks... | 0 |
715,828 | 24,611,452,260 | IssuesEvent | 2022-10-14 22:05:10 | phylum-dev/cli | https://api.github.com/repos/phylum-dev/cli | closed | Command line argument `--no-check-certificate` is saved to config | bug high priority | # Overview
Setting `--no-check-certificate` on the command line gets saved to the config so that all future runs no longer check certificates. And since we do not have a `--check-certificate` option (see #483), the only way to get phylum to start checking certificates again is to manually modify the config file. This ... | 1.0 | Command line argument `--no-check-certificate` is saved to config - # Overview
Setting `--no-check-certificate` on the command line gets saved to the config so that all future runs no longer check certificates. And since we do not have a `--check-certificate` option (see #483), the only way to get phylum to start chec... | non_process | command line argument no check certificate is saved to config overview setting no check certificate on the command line gets saved to the config so that all future runs no longer check certificates and since we do not have a check certificate option see the only way to get phylum to start checki... | 0 |
808 | 3,286,527,006 | IssuesEvent | 2015-10-29 03:25:59 | t3kt/vjzual2 | https://api.github.com/repos/t3kt/vjzual2 | closed | create sub-modules within the feedback module | enhancement video processing | it's basically just a shell that wraps a chain of effects | 1.0 | create sub-modules within the feedback module - it's basically just a shell that wraps a chain of effects | process | create sub modules within the feedback module it s basically just a shell that wraps a chain of effects | 1 |
276,276 | 20,976,956,388 | IssuesEvent | 2022-03-28 16:01:47 | devonfw-forge/devon4flutter | https://api.github.com/repos/devonfw-forge/devon4flutter | closed | Introduction to Flutter | documentation Campus_21_4_flutter | **Description**
Give a small introduction to Flutter.
**Acceptance Criteria**
- What you can do with Flutter
- What operating systems Flutter Applications run on
- How to get started in the installation
- What are the key points that one needs to know before developing
**Developer Hints**
- [Flutter](https://flutt... | 1.0 | Introduction to Flutter - **Description**
Give a small introduction to Flutter.
**Acceptance Criteria**
- What you can do with Flutter
- What operating systems Flutter Applications run on
- How to get started in the installation
- What are the key points that one needs to know before developing
**Developer Hints**
... | non_process | introduction to flutter description give a small introduction to flutter acceptance criteria what you can do with flutter what operating systems flutter applications run on how to get started in the installation what are the key points that one needs to know before developing developer hints ... | 0 |
182,140 | 6,667,471,594 | IssuesEvent | 2017-10-03 12:43:55 | zero-os/0-Disk | https://api.github.com/repos/zero-os/0-Disk | closed | add `zeroctl describe snapshot` command | priority_minor state_inprogress type_feature | The `zeroctl describe snapshot` command will be used to print out (to the STDOUT) all the information that can be given for a given snapshot, and will thus be heavily related to the import/export vdisk commands.
The output would look something like this:
```javascript
{
snapshotID: "mybackup", // required... | 1.0 | add `zeroctl describe snapshot` command - The `zeroctl describe snapshot` command will be used to print out (to the STDOUT) all the information that can be given for a given snapshot, and will thus be heavily related to the import/export vdisk commands.
The output would look something like this:
```javascript
{
... | non_process | add zeroctl describe snapshot command the zeroctl describe snapshot command will be used to print out to the stdout all the information that can be given for a given snapshot and will thus be heavily related to the import export vdisk commands the output would look something like this javascript ... | 0 |
14,986 | 18,524,085,890 | IssuesEvent | 2021-10-20 18:13:54 | googleapis/python-bigtable | https://api.github.com/repos/googleapis/python-bigtable | closed | 'tableadmin_test.test_run_table_operations' sample fails with 503 UNAVAILABLE | api: bigtable type: process samples | From these failed Kokoro builds:
- https://source.cloud.google.com/results/invocations/5981cd7b-ad3b-47e6-81f4-4170b8e6a265/targets/github%2Fpython-bigtable%2Fsamples%2Ftableadmin/tests
- https://source.cloud.google.com/results/invocations/a5e95556-50cf-456e-952c-2ce0d1857586/targets/github%2Fpython-bigtable%2Fsample... | 1.0 | 'tableadmin_test.test_run_table_operations' sample fails with 503 UNAVAILABLE - From these failed Kokoro builds:
- https://source.cloud.google.com/results/invocations/5981cd7b-ad3b-47e6-81f4-4170b8e6a265/targets/github%2Fpython-bigtable%2Fsamples%2Ftableadmin/tests
- https://source.cloud.google.com/results/invocation... | process | tableadmin test test run table operations sample fails with unavailable from these failed kokoro builds python failed google api core exceptions serviceunavailable the service is currently unavailable args name projects python docs samples tests instances bigtable test tables tableadm... | 1 |
21,423 | 29,359,592,568 | IssuesEvent | 2023-05-28 00:37:01 | devssa/onde-codar-em-salvador | https://api.github.com/repos/devssa/onde-codar-em-salvador | closed | [Hibrido / Belo Horizonte/MG] Backend Developer C# na Coodesh | SALVADOR BACK-END BANCO DE DADOS CSS3 MVC PLENO SQL GIT BOOTSTRAP WEB API ENTITY FRAMEWORK REQUISITOS ASP.NET PROCESSOS BACKEND GITHUB UMA C QUALIDADE METODOLOGIAS ÁGEIS MANUTENÇÃO ALOCADO Stale | ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/desenvolvedor-c-104634397?utm_source=... | 1.0 | [Hibrido / Belo Horizonte/MG] Backend Developer C# na Coodesh - ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com]... | process | backend developer c na coodesh descrição da vaga esta é uma vaga de um parceiro da plataforma coodesh ao candidatar se você terá acesso as informações completas sobre a empresa e benefícios fique atento ao redirecionamento que vai te levar para uma url com o pop up personalizado de candidatura 👋... | 1 |
20,654 | 27,329,653,531 | IssuesEvent | 2023-02-25 13:07:44 | cse442-at-ub/project_s23-cinco | https://api.github.com/repos/cse442-at-ub/project_s23-cinco | closed | Create a guide showing how to download PHP as well as methods to connect to UB servers | Processing Task Sprint 1 | Test
1. Go to
https://docs.google.com/document/d/1s0OLPXXsEa-N_cE0BFlYoYBbPwZfH25x2ZHevvdn5jg/edit
2. Confirm that you can view the document
3. Look through the information and verify you are able to follow the instructions and download PHP as well as access UB servers | 1.0 | Create a guide showing how to download PHP as well as methods to connect to UB servers - Test
1. Go to
https://docs.google.com/document/d/1s0OLPXXsEa-N_cE0BFlYoYBbPwZfH25x2ZHevvdn5jg/edit
2. Confirm that you can view the document
3. Look through the information and verify you are able to follow the instructions and d... | process | create a guide showing how to download php as well as methods to connect to ub servers test go to confirm that you can view the document look through the information and verify you are able to follow the instructions and download php as well as access ub servers | 1 |
55,447 | 11,431,441,403 | IssuesEvent | 2020-02-04 12:09:28 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | [0.9.702] Campaign Shop Filter does not work correctly | Bug Code | - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
When typing items into the filter, it does not refresh the list of items to match the filter. Once you actually purchase something random, or another player with manage campaign does, the list then refreshes wit... | 1.0 | [0.9.702] Campaign Shop Filter does not work correctly - - [x] I have searched the issue tracker to check if the issue has already been reported.
**Description**
When typing items into the filter, it does not refresh the list of items to match the filter. Once you actually purchase something random, or another play... | non_process | campaign shop filter does not work correctly i have searched the issue tracker to check if the issue has already been reported description when typing items into the filter it does not refresh the list of items to match the filter once you actually purchase something random or another player with ma... | 0 |
4,141 | 7,097,115,387 | IssuesEvent | 2018-01-14 15:52:54 | bojanrajkovic/Volley | https://api.github.com/repos/bojanrajkovic/Volley | opened | Generate manifest file for homepage to pull artifacts from | Release Process | The manifest should include the artifact URL, a hash, and either a link to a detached signature or an indication that the artifact is "signed" internally (for RPM/DEB artifacts). | 1.0 | Generate manifest file for homepage to pull artifacts from - The manifest should include the artifact URL, a hash, and either a link to a detached signature or an indication that the artifact is "signed" internally (for RPM/DEB artifacts). | process | generate manifest file for homepage to pull artifacts from the manifest should include the artifact url a hash and either a link to a detached signature or an indication that the artifact is signed internally for rpm deb artifacts | 1 |
76,652 | 9,959,803,284 | IssuesEvent | 2019-07-06 10:32:06 | SpankChain/community | https://api.github.com/repos/SpankChain/community | opened | OBS Documentation | documentation enhancement good first issue help wanted | You can now use OBS on SPANK.live, but the documentation for it is swirling about the ether.
There should be something on Discord, but we need much more content.
This is a good issue for the community-created content. | 1.0 | OBS Documentation - You can now use OBS on SPANK.live, but the documentation for it is swirling about the ether.
There should be something on Discord, but we need much more content.
This is a good issue for the community-created content. | non_process | obs documentation you can now use obs on spank live but the documentation for it is swirling about the ether there should be something on discord but we need much more content this is a good issue for the community created content | 0 |
103,345 | 4,167,512,078 | IssuesEvent | 2016-06-20 09:48:15 | prometheus/alertmanager | https://api.github.com/repos/prometheus/alertmanager | closed | AM version 0.1.1 just dies without any reason | kind/bug priority/P0 | Guys, this is becoming a major issue.
Even under a very small load the service just stops ...
The only thing visible in the log is the below lines repeating themselves
{"level":"error","msg":"Error on notify: context deadline exceeded","source":"notify.go:152","time":"2016-04-27T10:37:09-04:00"}
{"level":"erro... | 1.0 | AM version 0.1.1 just dies without any reason - Guys, this is becoming a major issue.
Even under a very small load the service just stops ...
The only thing visible in the log is the below lines repeating themselves
{"level":"error","msg":"Error on notify: context deadline exceeded","source":"notify.go:152","ti... | non_process | am version just dies without any reason guys this is becoming a major issue even under a very small load the service just stops the only thing visible in the log is the below lines repeating themselves level error msg error on notify context deadline exceeded source notify go time... | 0 |
17,702 | 23,580,113,157 | IssuesEvent | 2022-08-23 06:52:50 | streamnative/flink | https://api.github.com/repos/streamnative/flink | closed | [BUG] Pulsar Source StartCursor uses exclusive messageId by default, should change the implementation. | compute/data-processing type/bug | By default when pulsar consumer seek to messageId x, it will consume next messageId from x. Currently the pulsar source implementation assumes it will consume messageId x.
Expected behaviours: imagine there are 10 messages before subscription that is not acknowledged
when user use startCursor#earliest() : consu... | 1.0 | [BUG] Pulsar Source StartCursor uses exclusive messageId by default, should change the implementation. - By default when pulsar consumer seek to messageId x, it will consume next messageId from x. Currently the pulsar source implementation assumes it will consume messageId x.
Expected behaviours: imagine there are ... | process | pulsar source startcursor uses exclusive messageid by default should change the implementation by default when pulsar consumer seek to messageid x it will consume next messageid from x currently the pulsar source implementation assumes it will consume messageid x expected behaviours imagine there are me... | 1 |
47,434 | 5,892,492,337 | IssuesEvent | 2017-05-17 19:36:18 | elastic/logstash | https://api.github.com/repos/elastic/logstash | closed | Gradle/Java Tests are not Run as Part of the Unit-Tests? | tests-infra v5.5.0 v6.0.0 | Currently the rake task for the unit tests `test:core` does not execute the Java/Gradle unit-tests.
Also, the Gradle build is not documented in the Readme at all.
Shouldn't we run the Gradle UTs as part of `test:core` automatically (or if there is reasons not to do that at least document them in the Readme)? | 1.0 | Gradle/Java Tests are not Run as Part of the Unit-Tests? - Currently the rake task for the unit tests `test:core` does not execute the Java/Gradle unit-tests.
Also, the Gradle build is not documented in the Readme at all.
Shouldn't we run the Gradle UTs as part of `test:core` automatically (or if there is reasons n... | non_process | gradle java tests are not run as part of the unit tests currently the rake task for the unit tests test core does not execute the java gradle unit tests also the gradle build is not documented in the readme at all shouldn t we run the gradle uts as part of test core automatically or if there is reasons n... | 0 |
15,518 | 11,571,503,214 | IssuesEvent | 2020-02-20 21:42:28 | enarx/enarx | https://api.github.com/repos/enarx/enarx | closed | Don't run tests in a container if not necessary | infrastructure | Our current CI setup runs all our tests inside a container, even when such tests don't require it. We should run those tests outside the container to speed things up. | 1.0 | Don't run tests in a container if not necessary - Our current CI setup runs all our tests inside a container, even when such tests don't require it. We should run those tests outside the container to speed things up. | non_process | don t run tests in a container if not necessary our current ci setup runs all our tests inside a container even when such tests don t require it we should run those tests outside the container to speed things up | 0 |
70,827 | 8,582,641,528 | IssuesEvent | 2018-11-13 17:29:00 | code-dot-org/dance-party | https://api.github.com/repos/code-dot-org/dance-party | closed | I can't customize the certificate on /congrats page | by design | I'm not seeing an option to customize / add my name on staging-studio.code/congrats

| 1.0 | I can't customize the certificate on /congrats page - I'm not seeing an option to customize / add my name on staging-studio.code/congrats

| non_process | i can t customize the certificate on congrats page i m not seeing an option to customize add my name on staging studio code congrats | 0 |
105,224 | 22,961,929,722 | IssuesEvent | 2022-07-19 16:03:21 | trezor/trezor-suite | https://api.github.com/repos/trezor/trezor-suite | closed | Fix handling asynchronicity of init process to prevent race conditions | code tor Team Connect | @szymonlesisz have noticed that the init process is no longer synchronous which may (and probably is) causing race conditions on application start.
Main purpose of suiteMiddleware was to control the initialization process correct order until all essential data/prerequisites are initialized:
1. SUITE.INIT (should be f... | 1.0 | Fix handling asynchronicity of init process to prevent race conditions - @szymonlesisz have noticed that the init process is no longer synchronous which may (and probably is) causing race conditions on application start.
Main purpose of suiteMiddleware was to control the initialization process correct order until all ... | non_process | fix handling asynchronicity of init process to prevent race conditions szymonlesisz have noticed that the init process is no longer synchronous which may and probably is causing race conditions on application start main purpose of suitemiddleware was to control the initialization process correct order until all ... | 0 |
179,290 | 14,700,832,874 | IssuesEvent | 2021-01-04 10:50:30 | GitTools/GitVersion | https://api.github.com/repos/GitTools/GitVersion | opened | [Docs] Documentation references Deprecated version of GitVersionTask | documentation | Page at https://gitversion.net/docs/build-server-support/build-server/azure-devops references installing the GitVersionTask task here : [https://www.nuget.org/packages/GitVersionTask/ ](https://www.nuget.org/packages/GitVersionTask/ )
as well as a deprecated GitVersion Extension here:
[https://marketplace.visualstudi... | 1.0 | [Docs] Documentation references Deprecated version of GitVersionTask - Page at https://gitversion.net/docs/build-server-support/build-server/azure-devops references installing the GitVersionTask task here : [https://www.nuget.org/packages/GitVersionTask/ ](https://www.nuget.org/packages/GitVersionTask/ )
as well as a... | non_process | documentation references deprecated version of gitversiontask page at references installing the gitversiontask task here as well as a deprecated gitversion extension here the new versions of the tools don t seem to work the same when following the existing documentation | 0 |
17,873 | 23,817,262,113 | IssuesEvent | 2022-09-05 08:01:07 | Tencent/tdesign-miniprogram | https://api.github.com/repos/Tencent/tdesign-miniprogram | closed | [tabs] 希望事件能够获取label的名称 | enhancement good first issue in process | ### 这个功能解决了什么问题
现在只是单一的获取选项卡的值,label名称是获取不到的,如果在不用循环出tab panel时候,pannel中的内容是不一样的,所以需要获取更多值会更好一些
### 你建议的方案是什么
增加官方提供的属性的值,或则还能拓展data-x得值 | 1.0 | [tabs] 希望事件能够获取label的名称 - ### 这个功能解决了什么问题
现在只是单一的获取选项卡的值,label名称是获取不到的,如果在不用循环出tab panel时候,pannel中的内容是不一样的,所以需要获取更多值会更好一些
### 你建议的方案是什么
增加官方提供的属性的值,或则还能拓展data-x得值 | process | 希望事件能够获取label的名称 这个功能解决了什么问题 现在只是单一的获取选项卡的值,label名称是获取不到的,如果在不用循环出tab panel时候,pannel中的内容是不一样的,所以需要获取更多值会更好一些 你建议的方案是什么 增加官方提供的属性的值,或则还能拓展data x得值 | 1 |
7,654 | 10,739,753,181 | IssuesEvent | 2019-10-29 16:54:36 | openopps/openopps-platform | https://api.github.com/repos/openopps/openopps-platform | closed | Student apply process: Work experience should display newest to oldest | Apply Process Approved Requirements Ready State Dept. | Who: applicants
What: reviewing their work experience should display newest to oldest
Why: to be in line with the resume and USAJOBS
Acceptance Criteria:
Student application - work experience page: When a student applies, the work experience on the experience page should display newest to oldest like USAJOBS
| 1.0 | Student apply process: Work experience should display newest to oldest - Who: applicants
What: reviewing their work experience should display newest to oldest
Why: to be in line with the resume and USAJOBS
Acceptance Criteria:
Student application - work experience page: When a student applies, the work experience... | process | student apply process work experience should display newest to oldest who applicants what reviewing their work experience should display newest to oldest why to be in line with the resume and usajobs acceptance criteria student application work experience page when a student applies the work experience... | 1 |
8,353 | 11,502,845,822 | IssuesEvent | 2020-02-12 19:53:40 | googleapis/python-storage | https://api.github.com/repos/googleapis/python-storage | opened | Add support for shared conformance tests | api: storage testing type: process | We need to add a test suite which exercises the cross-language tests in https://github.com/googleapis/conformance-tests/blob/master/storage/v1/proto/google/cloud/conformance/storage/v1/tests.proto, and fix anything where we don't pass.
/cc @frankyn | 1.0 | Add support for shared conformance tests - We need to add a test suite which exercises the cross-language tests in https://github.com/googleapis/conformance-tests/blob/master/storage/v1/proto/google/cloud/conformance/storage/v1/tests.proto, and fix anything where we don't pass.
/cc @frankyn | process | add support for shared conformance tests we need to add a test suite which exercises the cross language tests in and fix anything where we don t pass cc frankyn | 1 |
292,712 | 25,231,479,607 | IssuesEvent | 2022-11-14 20:13:31 | enioka-Haute-Couture/pyoupyou | https://api.github.com/repos/enioka-Haute-Couture/pyoupyou | closed | Create view test case | test | Ensure we test:
- home
- process creation
- process details
- interview minute (ro and w)
| 1.0 | Create view test case - Ensure we test:
- home
- process creation
- process details
- interview minute (ro and w)
| non_process | create view test case ensure we test home process creation process details interview minute ro and w | 0 |
22,521 | 31,567,883,266 | IssuesEvent | 2023-09-04 01:26:04 | tdwg/hc | https://api.github.com/repos/tdwg/hc | opened | New Term - targetHabitatScope | Term - add normative Process - under public review Class - Event | ## New term
* Submitter: Humboldt Extension Task Group
* Efficacy Justification (why is this term necessary?): Part of a package of terms in support of biological inventory data.
* Demand Justification (name at least two organizations that independently need this term): The Humboldt Extension Task Group proposing ... | 1.0 | New Term - targetHabitatScope - ## New term
* Submitter: Humboldt Extension Task Group
* Efficacy Justification (why is this term necessary?): Part of a package of terms in support of biological inventory data.
* Demand Justification (name at least two organizations that independently need this term): The Humboldt... | process | new term targethabitatscope new term submitter humboldt extension task group efficacy justification why is this term necessary part of a package of terms in support of biological inventory data demand justification name at least two organizations that independently need this term the humboldt... | 1 |
8,120 | 11,303,180,180 | IssuesEvent | 2020-01-17 19:28:15 | bcgov/entity | https://api.github.com/repos/bcgov/entity | closed | Web update comms process | OCM_Int Processes | - [x] create process with Cameron & Genvieve
- [x] Simona to document process
- [ ] Genvieve review
- [ ] Cameron review
- [x] Katherine review | 1.0 | Web update comms process - - [x] create process with Cameron & Genvieve
- [x] Simona to document process
- [ ] Genvieve review
- [ ] Cameron review
- [x] Katherine review | process | web update comms process create process with cameron genvieve simona to document process genvieve review cameron review katherine review | 1 |
270,627 | 29,043,977,422 | IssuesEvent | 2023-05-13 10:06:25 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] 1 Million WordPress Sites Impacted by Exploited Plugin Vulnerability | SecurityWeek Stale |
Exploitation of a critical vulnerability in the Essential Addons for Elementor WordPress plugin started immediately after a patch was released.
The post [1 Million WordPress Sites Impacted by Exploited Plugin Vulnerability](https://www.securityweek.com/1-million-wordpress-sites-impacted-by-exploited-plugin-vulnerabi... | True | [SecurityWeek] 1 Million WordPress Sites Impacted by Exploited Plugin Vulnerability -
Exploitation of a critical vulnerability in the Essential Addons for Elementor WordPress plugin started immediately after a patch was released.
The post [1 Million WordPress Sites Impacted by Exploited Plugin Vulnerability](https:/... | non_process | million wordpress sites impacted by exploited plugin vulnerability exploitation of a critical vulnerability in the essential addons for elementor wordpress plugin started immediately after a patch was released the post appeared first on | 0 |
429,273 | 12,422,762,327 | IssuesEvent | 2020-05-24 00:27:09 | eclipse-ee4j/glassfish | https://api.github.com/repos/eclipse-ee4j/glassfish | closed | WSIT pipes may be cached | Component: jbi ERR: Assignee Priority: Minor Stale Type: Bug as91-na | HTTP BC uses the asynchronous transport so HTTP SOAP processing is asynchronous
by default. When WSIT policies are present, we expect to see synchronous
behavior.
However, once a WSIT feature is used in any JBI project (with SOAP request
processed by HTTP BC), all subsequent SOAP processing will fall back to sync
mode,... | 1.0 | WSIT pipes may be cached - HTTP BC uses the asynchronous transport so HTTP SOAP processing is asynchronous
by default. When WSIT policies are present, we expect to see synchronous
behavior.
However, once a WSIT feature is used in any JBI project (with SOAP request
processed by HTTP BC), all subsequent SOAP processing w... | non_process | wsit pipes may be cached http bc uses the asynchronous transport so http soap processing is asynchronous by default when wsit policies are present we expect to see synchronous behavior however once a wsit feature is used in any jbi project with soap request processed by http bc all subsequent soap processing w... | 0 |
22,118 | 30,650,379,637 | IssuesEvent | 2023-07-25 08:30:34 | 0xPolygonMiden/miden-vm | https://api.github.com/repos/0xPolygonMiden/miden-vm | opened | Consider adding instructions to read memory of the parent context | enhancement instruction set processor | One of the consequences of #948, is that we would get access to the parent context ID via `prnt_ctx` column. This means, we would be able to execute operations which read values from (and even write values to) parent memory.
While writing values into parent context may lead to potential security issues, reading valu... | 1.0 | Consider adding instructions to read memory of the parent context - One of the consequences of #948, is that we would get access to the parent context ID via `prnt_ctx` column. This means, we would be able to execute operations which read values from (and even write values to) parent memory.
While writing values int... | process | consider adding instructions to read memory of the parent context one of the consequences of is that we would get access to the parent context id via prnt ctx column this means we would be able to execute operations which read values from and even write values to parent memory while writing values into ... | 1 |
18,863 | 24,787,139,190 | IssuesEvent | 2022-10-24 10:45:24 | goblint/analyzer | https://api.github.com/repos/goblint/analyzer | closed | Polish `__goblint_check` | cleanup testing preprocessing | In #278 all the `assert`s in tests were changed to `__goblint_check`, which is declared by a `goblint.h` header that we forcefully include into every analyzed file via `-include`. This makes the programs normally uncompilable and most of them still include `assert.h`, which now is excessive.
This situation should be... | 1.0 | Polish `__goblint_check` - In #278 all the `assert`s in tests were changed to `__goblint_check`, which is declared by a `goblint.h` header that we forcefully include into every analyzed file via `-include`. This makes the programs normally uncompilable and most of them still include `assert.h`, which now is excessive.
... | process | polish goblint check in all the assert s in tests were changed to goblint check which is declared by a goblint h header that we forcefully include into every analyzed file via include this makes the programs normally uncompilable and most of them still include assert h which now is excessive ... | 1 |
703,419 | 24,158,312,550 | IssuesEvent | 2022-09-22 09:30:40 | younginnovations/iatipublisher | https://api.github.com/repos/younginnovations/iatipublisher | closed | Bug : Arrangement of label fields | type: bug type: UI/UX priority: high Frontend | - [x] **Issue 1: Iati- Identifier**
Actual Result
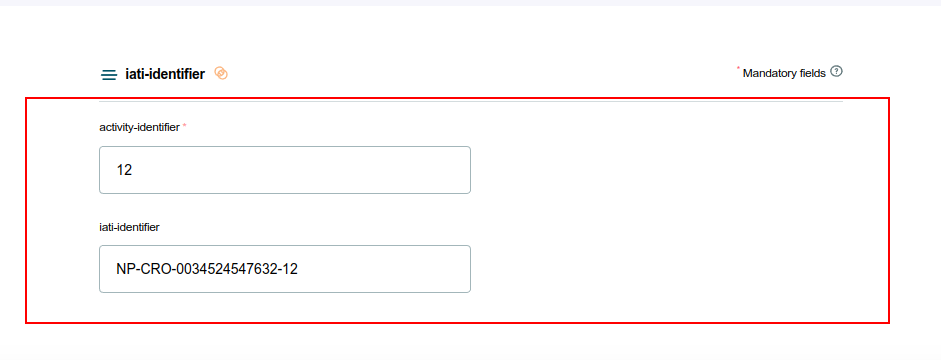
Expected Result
- Should be aligned in the same line
- [x] **Issue 2: Transactions**
Actual Result
![Screenshot from... | 1.0 | Bug : Arrangement of label fields - - [x] **Issue 1: Iati- Identifier**
Actual Result
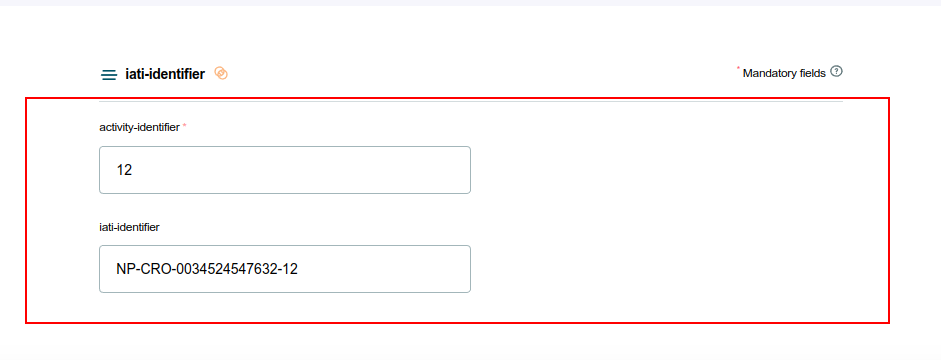
Expected Result
- Should be aligned in the same line
- [x] **Issue 2: Transactions... | non_process | bug arrangement of label fields issue iati identifier actual result expected result should be aligned in the same line issue transactions actual result expected result issue result actual result expected result should be aligned in... | 0 |
39,100 | 10,297,869,051 | IssuesEvent | 2019-08-28 08:54:26 | angular/angular-cli | https://api.github.com/repos/angular/angular-cli | opened | Subresource Integrity for lazy modules is broken when DL is enabled | comp: devkit/build-angular freq3: high severity5: regression type: bug/fix | <!--🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅
Oh hi there! 😄
To expedite issue processing please search open and closed issues before submitting a new one.
Existing issues often contain information about workarounds, resolution, or progress updates.
🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅... | 1.0 | Subresource Integrity for lazy modules is broken when DL is enabled - <!--🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅
Oh hi there! 😄
To expedite issue processing please search open and closed issues before submitting a new one.
Existing issues often contain information about workarounds, reso... | non_process | subresource integrity for lazy modules is broken when dl is enabled 🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅🔅 oh hi there 😄 to expedite issue processing please search open and closed issues before submitting a new one existing issues often contain information about workarounds reso... | 0 |
772,647 | 27,130,809,096 | IssuesEvent | 2023-02-16 09:39:10 | GoogleCloudPlatform/java-docs-samples | https://api.github.com/repos/GoogleCloudPlatform/java-docs-samples | opened | CommuteSearchJobsTest: testCommuteSearchJobs failed | type: bug priority: p1 flakybot: issue | Note: #6610 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: f3ac816370643d418b10e0fe93859e6a984bb44d
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/eb0701d2-5dc6-4a0a-b634-515b3facb6e3), [Sponge](http://sponge2/eb0701d2-5dc6-4a0a-... | 1.0 | CommuteSearchJobsTest: testCommuteSearchJobs failed - Note: #6610 was also for this test, but it was closed more than 10 days ago. So, I didn't mark it flaky.
----
commit: f3ac816370643d418b10e0fe93859e6a984bb44d
buildURL: [Build Status](https://source.cloud.google.com/results/invocations/eb0701d2-5dc6-4a0a-b634-515b... | non_process | commutesearchjobstest testcommutesearchjobs failed note was also for this test but it was closed more than days ago so i didn t mark it flaky commit buildurl status failed test output com google api gax rpc internalexception io grpc statusruntimeexception internal encountered une... | 0 |
25,484 | 3,933,127,800 | IssuesEvent | 2016-04-25 18:04:05 | mozilla/science.mozilla.org | https://api.github.com/repos/mozilla/science.mozilla.org | closed | Comps for Blog | design Epic | - [x] Individual page
- [x] List view of all blogs
Use Onesie! This should be generic enough to apply to other blogs.
**Individual Post**
Each post, no matter what site it lives on, will have...
* Title
* Date and time published & updated
* Author (and link to posts by that author)
* Full text
* List of ... | 1.0 | Comps for Blog - - [x] Individual page
- [x] List view of all blogs
Use Onesie! This should be generic enough to apply to other blogs.
**Individual Post**
Each post, no matter what site it lives on, will have...
* Title
* Date and time published & updated
* Author (and link to posts by that author)
* Full... | non_process | comps for blog individual page list view of all blogs use onesie this should be generic enough to apply to other blogs individual post each post no matter what site it lives on will have title date and time published updated author and link to posts by that author full tex... | 0 |
162,299 | 20,178,667,886 | IssuesEvent | 2022-02-10 16:27:06 | vital-ws/empty | https://api.github.com/repos/vital-ws/empty | opened | CVE-2022-22816 (High) detected in Pillow-8.3.2-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl | security vulnerability | ## CVE-2022-22816 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-8.3.2-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fo... | True | CVE-2022-22816 (High) detected in Pillow-8.3.2-cp37-cp37m-manylinux_2_17_x86_64.manylinux2014_x86_64.whl - ## CVE-2022-22816 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-8.3.2... | non_process | cve high detected in pillow manylinux whl cve high severity vulnerability vulnerable library pillow manylinux whl python imaging library fork library home page a href path to dependency file requirements txt path to vulnerable li... | 0 |
75,677 | 9,308,559,213 | IssuesEvent | 2019-03-25 14:47:37 | iov-one/weave | https://api.github.com/repos/iov-one/weave | closed | Move `Memo` and `ChainID` to top level Tx codec | design | **Is your feature request related to a problem? Please describe.**
* `Memo` - is a free text field that can be used to submit extra information by the sender
* `ChainID` - is the name of the blockchain and used to prevent replay attacks
We should be on the safe side with replay attacks on all our messages. We should... | 1.0 | Move `Memo` and `ChainID` to top level Tx codec - **Is your feature request related to a problem? Please describe.**
* `Memo` - is a free text field that can be used to submit extra information by the sender
* `ChainID` - is the name of the blockchain and used to prevent replay attacks
We should be on the safe side ... | non_process | move memo and chainid to top level tx codec is your feature request related to a problem please describe memo is a free text field that can be used to submit extra information by the sender chainid is the name of the blockchain and used to prevent replay attacks we should be on the safe side ... | 0 |
41,644 | 10,552,668,312 | IssuesEvent | 2019-10-03 15:35:29 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | Codegen throw NoClassDefFoundError on org/reactivestreams/Publisher | T: Defect | ### Expected behavior and actual behavior:
Expected behaviour would be the same as in the tutorial for jooq, as seen here:
https://www.jooq.org/doc/3.12/manual/getting-started/tutorials/jooq-in-7-steps/jooq-in-7-steps-step3/
ONLY difference is that I am using `mysql-connector-java-8.0.17.jar` instead of the bin.... | 1.0 | Codegen throw NoClassDefFoundError on org/reactivestreams/Publisher - ### Expected behavior and actual behavior:
Expected behaviour would be the same as in the tutorial for jooq, as seen here:
https://www.jooq.org/doc/3.12/manual/getting-started/tutorials/jooq-in-7-steps/jooq-in-7-steps-step3/
ONLY difference is... | non_process | codegen throw noclassdeffounderror on org reactivestreams publisher expected behavior and actual behavior expected behaviour would be the same as in the tutorial for jooq as seen here only difference is that i am using mysql connector java jar instead of the bin i have no idea where to get th... | 0 |
18,345 | 24,467,582,590 | IssuesEvent | 2022-10-07 16:23:21 | bondaleksey/credit-card-fraud-detection | https://api.github.com/repos/bondaleksey/credit-card-fraud-detection | opened | data preprocessing | work plan data preprocessing | - data cleaning, transformation, feature engineering,
- save results to HDFS,
- automate regular data preprocessing with AirFlow. | 1.0 | data preprocessing - - data cleaning, transformation, feature engineering,
- save results to HDFS,
- automate regular data preprocessing with AirFlow. | process | data preprocessing data cleaning transformation feature engineering save results to hdfs automate regular data preprocessing with airflow | 1 |
13,605 | 16,191,040,327 | IssuesEvent | 2021-05-04 08:31:43 | e4exp/paper_manager_abstract | https://api.github.com/repos/e4exp/paper_manager_abstract | opened | Entailment as Few-Shot Learner | 2021 Few Shot Learning Language Model Natural Language Processing |
事前に学習された大規模な言語モデル(LM)は,少数の学習者として優れた能力を発揮します.
しかし、その成功は、モデルのパラメータのスケーリングに大きく依存しているため、学習やサービスの提供が困難になっています。
この論文では、EFLと呼ばれる新しいアプローチを提案します。
このアプローチは、小さなLMをより優れた少数決学習者に変えることができます。
このアプローチの鍵となるアイデアは、潜在的なNLPタスクを関連性のあるタスクに再定式化し、わずか8つの例でモデルを微調整することである。
さらに、我々の提案する手法が以下のことを可能にすることを実証する。
さらに、我々の提案する手法は、
(i)教師なしの対照学習に基... | 1.0 | Entailment as Few-Shot Learner -
事前に学習された大規模な言語モデル(LM)は,少数の学習者として優れた能力を発揮します.
しかし、その成功は、モデルのパラメータのスケーリングに大きく依存しているため、学習やサービスの提供が困難になっています。
この論文では、EFLと呼ばれる新しいアプローチを提案します。
このアプローチは、小さなLMをより優れた少数決学習者に変えることができます。
このアプローチの鍵となるアイデアは、潜在的なNLPタスクを関連性のあるタスクに再定式化し、わずか8つの例でモデルを微調整することである。
さらに、我々の提案する手法が以下のことを可能にすることを実証する。... | process | entailment as few shot learner 事前に学習された大規模な言語モデル(lm)は,少数の学習者として優れた能力を発揮します. しかし、その成功は、モデルのパラメータのスケーリングに大きく依存しているため、学習やサービスの提供が困難になっています。 この論文では、eflと呼ばれる新しいアプローチを提案します。 このアプローチは、小さなlmをより優れた少数決学習者に変えることができます。 このアプローチの鍵となるアイデアは、潜在的なnlpタスクを関連性のあるタスクに再定式化し、 。 さらに、我々の提案する手法が以下のことを可能にすることを実証する。 さらに、我々の提案する手法は、 i... | 1 |
199,950 | 15,084,025,110 | IssuesEvent | 2021-02-05 16:36:09 | phetsims/isotopes-and-atomic-mass | https://api.github.com/repos/phetsims/isotopes-and-atomic-mass | opened | CT cannot read property globalToLocalPoint of undefined | type:automated-testing | ```
isotopes-and-atomic-mass : multitouch-fuzz : unbuilt
https://bayes.colorado.edu/continuous-testing/ct-snapshots/1612485936684/isotopes-and-atomic-mass/isotopes-and-atomic-mass_en.html?continuousTest=%7B%22test%22%3A%5B%22isotopes-and-atomic-mass%22%2C%22multitouch-fuzz%22%2C%22unbuilt%22%5D%2C%22snapshotName%22%3... | 1.0 | CT cannot read property globalToLocalPoint of undefined - ```
isotopes-and-atomic-mass : multitouch-fuzz : unbuilt
https://bayes.colorado.edu/continuous-testing/ct-snapshots/1612485936684/isotopes-and-atomic-mass/isotopes-and-atomic-mass_en.html?continuousTest=%7B%22test%22%3A%5B%22isotopes-and-atomic-mass%22%2C%22mu... | non_process | ct cannot read property globaltolocalpoint of undefined isotopes and atomic mass multitouch fuzz unbuilt query brand phet ea fuzz fuzzpointers memorylimit uncaught typeerror cannot read property globaltolocalpoint of undefined typeerror cannot read property globaltolocalpoint of undefined a... | 0 |
352,120 | 25,048,033,099 | IssuesEvent | 2022-11-05 14:15:32 | vuetifyjs/vuetify | https://api.github.com/repos/vuetifyjs/vuetify | closed | [Documentation] `Invert Example Color` not working when Dark/System Followed Theme is Enabled | T: documentation | ### Environment
**Browsers:** Chrome 107.0.0.0
**OS:** Mac OS 10.15.7
### Steps to reproduce
Open any component page and Select either one of the following theme from Site settings
1. Dark
2. System
In case of any of above theme, the `Invert Example Color` button on the component preview will not work.
... | 1.0 | [Documentation] `Invert Example Color` not working when Dark/System Followed Theme is Enabled - ### Environment
**Browsers:** Chrome 107.0.0.0
**OS:** Mac OS 10.15.7
### Steps to reproduce
Open any component page and Select either one of the following theme from Site settings
1. Dark
2. System
In case of... | non_process | invert example color not working when dark system followed theme is enabled environment browsers chrome os mac os steps to reproduce open any component page and select either one of the following theme from site settings dark system in case of any of above them... | 0 |
8,258 | 11,424,941,665 | IssuesEvent | 2020-02-03 18:48:24 | kubeflow/manifests | https://api.github.com/repos/kubeflow/manifests | closed | Update Metadata Docker images for Kubeflow 1.0? | area/metadata kind/process priority/p0 | Do we need to update the docker images used by metadata for 1.0 or are the images in
https://github.com/kubeflow/manifests/blob/master/metadata/base/kustomization.yaml
Up to date.
Once kubeflow/testing#587 we should be able to just add the requisite specs to that file to auto-build and update the docker images u... | 1.0 | Update Metadata Docker images for Kubeflow 1.0? - Do we need to update the docker images used by metadata for 1.0 or are the images in
https://github.com/kubeflow/manifests/blob/master/metadata/base/kustomization.yaml
Up to date.
Once kubeflow/testing#587 we should be able to just add the requisite specs to that... | process | update metadata docker images for kubeflow do we need to update the docker images used by metadata for or are the images in up to date once kubeflow testing we should be able to just add the requisite specs to that file to auto build and update the docker images used by metadata assign zhen... | 1 |
5,353 | 8,180,316,187 | IssuesEvent | 2018-08-28 19:04:27 | yvesgoeleven/BasketLummen | https://api.github.com/repos/yvesgoeleven/BasketLummen | closed | Document Issue Tracking process | Size: M State: Backlog Type: Process Improvement | ## What is the problem?
Need to keep track of things to do, describe what problems are solved and how to approach them. Guidance is needed to learn how to maintain these issues over time.
## Discussion and conclusions
## Plan of attack
- [ ] Write document that describes the process | 1.0 | Document Issue Tracking process - ## What is the problem?
Need to keep track of things to do, describe what problems are solved and how to approach them. Guidance is needed to learn how to maintain these issues over time.
## Discussion and conclusions
## Plan of attack
- [ ] Write document that describes th... | process | document issue tracking process what is the problem need to keep track of things to do describe what problems are solved and how to approach them guidance is needed to learn how to maintain these issues over time discussion and conclusions plan of attack write document that describes the ... | 1 |
163,639 | 25,851,324,250 | IssuesEvent | 2022-12-13 10:35:11 | atteneder/glTFast | https://api.github.com/repos/atteneder/glTFast | opened | Inconsistent Image Resolution | bug export design-time | When exporting to glTF from the Editor, sometimes the original texture (resolution) is exported and sometimes the texture import settings' Max Size resolution is used.
A first look showed that whether the original texture file is used (or the texture is re-encoded with a different size and format) can depend on whet... | 1.0 | Inconsistent Image Resolution - When exporting to glTF from the Editor, sometimes the original texture (resolution) is exported and sometimes the texture import settings' Max Size resolution is used.
A first look showed that whether the original texture file is used (or the texture is re-encoded with a different siz... | non_process | inconsistent image resolution when exporting to gltf from the editor sometimes the original texture resolution is exported and sometimes the texture import settings max size resolution is used a first look showed that whether the original texture file is used or the texture is re encoded with a different siz... | 0 |
20,023 | 26,502,085,012 | IssuesEvent | 2023-01-18 11:03:02 | geneontology/go-ontology | https://api.github.com/repos/geneontology/go-ontology | closed | GO:0048478 replication fork protection | cell cycle and DNA processes obsoletion ready | GO:0048478 replication fork protection
This is currently a "regulation of process" term, based on parentage.
Really it's more like a collection of things including "replication restart" and "processing of collapsed replication forks"
Chatting with @pgaudet we thought this term, based on its position, and mean... | 1.0 | GO:0048478 replication fork protection - GO:0048478 replication fork protection
This is currently a "regulation of process" term, based on parentage.
Really it's more like a collection of things including "replication restart" and "processing of collapsed replication forks"
Chatting with @pgaudet we thought t... | process | go replication fork protection go replication fork protection this is currently a regulation of process term based on parentage really it s more like a collection of things including replication restart and processing of collapsed replication forks chatting with pgaudet we thought this term ba... | 1 |
28,391 | 13,653,505,386 | IssuesEvent | 2020-09-27 13:05:45 | comunica/comunica | https://api.github.com/repos/comunica/comunica | closed | TEMP: This is a test issue | performance 🐌 | #### Issue type:
- :bug: Bug <!--Don't change this issue type!-->
____
#### Description:
Test issue
____
#### Environment:
<!--Output of the `comunica-sparql -v` command.-->
<!--If running in a development environment, this must be the output of `node ./packages/actor-init-sparql/bin/query.js -v`-->
... | True | TEMP: This is a test issue - #### Issue type:
- :bug: Bug <!--Don't change this issue type!-->
____
#### Description:
Test issue
____
#### Environment:
<!--Output of the `comunica-sparql -v` command.-->
<!--If running in a development environment, this must be the output of `node ./packages/actor-init... | non_process | temp this is a test issue issue type bug bug description test issue environment crash log don t paste contents here directly but use something like | 0 |
359,516 | 25,242,144,516 | IssuesEvent | 2022-11-15 08:24:47 | confused-Techie/atom-backend | https://api.github.com/repos/confused-Techie/atom-backend | opened | Track Tests Against API Endpoints | documentation | This issue serves to track what endpoints have enough tests to consider complete written for them.
While more tests on a completed endpoint is never a bad thing, this can help use semi-determine the stability of the overall application, since these tests are full integration tests of the whole codebase.
* [ ] GET `... | 1.0 | Track Tests Against API Endpoints - This issue serves to track what endpoints have enough tests to consider complete written for them.
While more tests on a completed endpoint is never a bad thing, this can help use semi-determine the stability of the overall application, since these tests are full integration tests o... | non_process | track tests against api endpoints this issue serves to track what endpoints have enough tests to consider complete written for them while more tests on a completed endpoint is never a bad thing this can help use semi determine the stability of the overall application since these tests are full integration tests o... | 0 |
14,397 | 17,409,170,404 | IssuesEvent | 2021-08-03 10:01:33 | ESMValGroup/ESMValCore | https://api.github.com/repos/ESMValGroup/ESMValCore | closed | Remove os.walk from datafinder | preprocessor question | We are currently use to find data files python`os.walk` function. This means that we search recursively on all folders inside the path constructed from the drs.
I have experimented some problems because of it:
- Defined correctly the rootpath in JASMIN and forgetting to setup the drs led to search in all CMIP5/6 ... | 1.0 | Remove os.walk from datafinder - We are currently use to find data files python`os.walk` function. This means that we search recursively on all folders inside the path constructed from the drs.
I have experimented some problems because of it:
- Defined correctly the rootpath in JASMIN and forgetting to setup the ... | process | remove os walk from datafinder we are currently use to find data files python os walk function this means that we search recursively on all folders inside the path constructed from the drs i have experimented some problems because of it defined correctly the rootpath in jasmin and forgetting to setup the ... | 1 |
41,148 | 5,341,771,851 | IssuesEvent | 2017-02-17 04:40:51 | Gallopsled/pwntools | https://api.github.com/repos/Gallopsled/pwntools | closed | Members missing from __all__ are not documented or tested | bug testing | In any module which has an `__all__` attribute, any functions or classes not exported are ignored by Sphinx `autodoc`, and subsequently also by Sphinx `doctest`. | 1.0 | Members missing from __all__ are not documented or tested - In any module which has an `__all__` attribute, any functions or classes not exported are ignored by Sphinx `autodoc`, and subsequently also by Sphinx `doctest`. | non_process | members missing from all are not documented or tested in any module which has an all attribute any functions or classes not exported are ignored by sphinx autodoc and subsequently also by sphinx doctest | 0 |
9,429 | 12,419,041,896 | IssuesEvent | 2020-05-23 03:33:29 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Add information on whether the jobs are run in parallel or not | Pri1 automation/svc cxp process-automation/subsvc product-question triaged | Hi,
This page doesn't explain if a Hybrid worker can run multiple jobs at the same time or not. Could you please clarify if a single hybrid worker can run multiple jobs in parallel or not?
Thanks,
Pranav
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue link... | 1.0 | Add information on whether the jobs are run in parallel or not - Hi,
This page doesn't explain if a Hybrid worker can run multiple jobs at the same time or not. Could you please clarify if a single hybrid worker can run multiple jobs in parallel or not?
Thanks,
Pranav
---
#### Document Details
⚠ *Do not edit this s... | process | add information on whether the jobs are run in parallel or not hi this page doesn t explain if a hybrid worker can run multiple jobs at the same time or not could you please clarify if a single hybrid worker can run multiple jobs in parallel or not thanks pranav document details ⚠ do not edit this s... | 1 |
603,954 | 18,674,605,553 | IssuesEvent | 2021-10-31 10:42:16 | AY2122S1-CS2103T-W13-3/tp | https://api.github.com/repos/AY2122S1-CS2103T-W13-3/tp | closed | [PE-D] Bug in Add Command | bug priority.High Error messages | Incorrect Input Add Command
Steps:
* Start application
* Insert the following add command taken from the User Guide Provided:
Command: `add /g poker /s 100 /e 120 /date /dur /loc /tag`
Shows Command Success, however, I think an error should be thrown for empty input.
 detected in linux-stable-rtv4.1.33 - autoclosed | security vulnerability | ## CVE-2019-19060 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home pag... | True | CVE-2019-19060 (High) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2019-19060 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<... | non_process | cve high detected in linux stable autoclosed cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable... | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.