Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 7
112
| repo_url
stringlengths 36
141
| action
stringclasses 3
values | title
stringlengths 1
744
| labels
stringlengths 4
574
| body
stringlengths 9
211k
| index
stringclasses 10
values | text_combine
stringlengths 96
211k
| label
stringclasses 2
values | text
stringlengths 96
188k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
20,438
| 27,099,615,300
|
IssuesEvent
|
2023-02-15 07:28:56
|
bazelbuild/bazel
|
https://api.github.com/repos/bazelbuild/bazel
|
closed
|
Force loading the Protobuf rules from the rules_proto repo
|
P3 type: process team-Rules-Server stale
|
This big breaking change will force users of the Protobuf rules to use the Starlark rules from the [@rules_proto](https://github.com/bazelbuild/rules_proto) repository. The rules there are currently only wrappers around native rules, but they will be rewritten in the future.
Design doc: https://docs.google.com/document/d/1Wai_okIK_NnhNJZai5nkTUvZVHdV5pp1YwNLFtWwpC4/edit?ts=5d2c8077
|
1.0
|
Force loading the Protobuf rules from the rules_proto repo - This big breaking change will force users of the Protobuf rules to use the Starlark rules from the [@rules_proto](https://github.com/bazelbuild/rules_proto) repository. The rules there are currently only wrappers around native rules, but they will be rewritten in the future.
Design doc: https://docs.google.com/document/d/1Wai_okIK_NnhNJZai5nkTUvZVHdV5pp1YwNLFtWwpC4/edit?ts=5d2c8077
|
process
|
force loading the protobuf rules from the rules proto repo this big breaking change will force users of the protobuf rules to use the starlark rules from the repository the rules there are currently only wrappers around native rules but they will be rewritten in the future design doc
| 1
|
333,120
| 29,509,062,817
|
IssuesEvent
|
2023-06-03 17:36:43
|
opensearch-project/sql
|
https://api.github.com/repos/opensearch-project/sql
|
opened
|
[AUTOCUT] Integration Test failed for sql: 2.8.0 deb distribution
|
untriaged autocut v2.8.0 integ-test-failure
|
The integration test failed at distribution level for component sql<br>Version: 2.8.0<br>Distribution: deb<br>Architecture: arm64<br>Platform: linux<br><br>Please check the logs: https://build.ci.opensearch.org/job/integ-test/5089/display/redirect<br><br> * Steps to reproduce: See https://github.com/opensearch-project/opensearch-build/tree/main/src/test_workflow#integration-tests<br>* Access components yml file:<br> - [With security](https://ci.opensearch.org/ci/dbc/integ-test/2.8.0/7935/linux/arm64/deb/test-results/5089/integ-test/sql/with-security/sql.yml) (if applicable)<br> - [Without security](https://ci.opensearch.org/ci/dbc/integ-test/2.8.0/7935/linux/arm64/deb/test-results/5089/integ-test/sql/without-security/sql.yml) (if applicable)<br><br> _Note: All in one test report manifest with all the details coming soon. See https://github.com/opensearch-project/opensearch-build/issues/1274_
|
1.0
|
[AUTOCUT] Integration Test failed for sql: 2.8.0 deb distribution - The integration test failed at distribution level for component sql<br>Version: 2.8.0<br>Distribution: deb<br>Architecture: arm64<br>Platform: linux<br><br>Please check the logs: https://build.ci.opensearch.org/job/integ-test/5089/display/redirect<br><br> * Steps to reproduce: See https://github.com/opensearch-project/opensearch-build/tree/main/src/test_workflow#integration-tests<br>* Access components yml file:<br> - [With security](https://ci.opensearch.org/ci/dbc/integ-test/2.8.0/7935/linux/arm64/deb/test-results/5089/integ-test/sql/with-security/sql.yml) (if applicable)<br> - [Without security](https://ci.opensearch.org/ci/dbc/integ-test/2.8.0/7935/linux/arm64/deb/test-results/5089/integ-test/sql/without-security/sql.yml) (if applicable)<br><br> _Note: All in one test report manifest with all the details coming soon. See https://github.com/opensearch-project/opensearch-build/issues/1274_
|
non_process
|
integration test failed for sql deb distribution the integration test failed at distribution level for component sql version distribution deb architecture platform linux please check the logs steps to reproduce see access components yml file if applicable if applicable note all in one test report manifest with all the details coming soon see
| 0
|
139,935
| 18,869,694,002
|
IssuesEvent
|
2021-11-13 01:08:55
|
samq-ghdemo/ori-kit
|
https://api.github.com/repos/samq-ghdemo/ori-kit
|
closed
|
WS-2021-0039 (Low) detected in core-9.0.0.tgz - autoclosed
|
security vulnerability
|
## WS-2021-0039 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>core-9.0.0.tgz</b></p></summary>
<p>Angular - the core framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/@angular/core/-/core-9.0.0.tgz">https://registry.npmjs.org/@angular/core/-/core-9.0.0.tgz</a></p>
<p>Path to dependency file: ori-kit/frontend/package.json</p>
<p>Path to vulnerable library: ori-kit/frontend/node_modules/codelyzer/node_modules/@angular/core/package.json</p>
<p>
Dependency Hierarchy:
- codelyzer-6.0.2.tgz (Root Library)
- :x: **core-9.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/ori-kit/commit/ba236fd18ec3e6450d68d675bce1609d2e5d3230">ba236fd18ec3e6450d68d675bce1609d2e5d3230</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-Site Scripting (XSS) vulnerability was found in @angular/core before 11.1.1. HTML doesn't specify any way to escape comment end text inside the comment.
<p>Publish Date: 2021-01-26
<p>URL: <a href=https://github.com/angular/angular/commit/97ec6e48493bf9418971436d885470a66e71f045>WS-2021-0039</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/angular/angular/releases/tag/11.1.1">https://github.com/angular/angular/releases/tag/11.1.1</a></p>
<p>Release Date: 2021-01-26</p>
<p>Fix Resolution: @angular/core - 11.1.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"@angular/core","packageVersion":"9.0.0","packageFilePaths":["/frontend/package.json"],"isTransitiveDependency":true,"dependencyTree":"codelyzer:6.0.2;@angular/core:9.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"@angular/core - 11.1.1"}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2021-0039","vulnerabilityDetails":"Cross-Site Scripting (XSS) vulnerability was found in @angular/core before 11.1.1. HTML doesn\u0027t specify any way to escape comment end text inside the comment.","vulnerabilityUrl":"https://github.com/angular/angular/commit/97ec6e48493bf9418971436d885470a66e71f045","cvss3Severity":"low","cvss3Score":"3.9","cvss3Metrics":{"A":"Low","AC":"High","PR":"High","S":"Unchanged","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> -->
|
True
|
WS-2021-0039 (Low) detected in core-9.0.0.tgz - autoclosed - ## WS-2021-0039 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>core-9.0.0.tgz</b></p></summary>
<p>Angular - the core framework</p>
<p>Library home page: <a href="https://registry.npmjs.org/@angular/core/-/core-9.0.0.tgz">https://registry.npmjs.org/@angular/core/-/core-9.0.0.tgz</a></p>
<p>Path to dependency file: ori-kit/frontend/package.json</p>
<p>Path to vulnerable library: ori-kit/frontend/node_modules/codelyzer/node_modules/@angular/core/package.json</p>
<p>
Dependency Hierarchy:
- codelyzer-6.0.2.tgz (Root Library)
- :x: **core-9.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/ori-kit/commit/ba236fd18ec3e6450d68d675bce1609d2e5d3230">ba236fd18ec3e6450d68d675bce1609d2e5d3230</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Cross-Site Scripting (XSS) vulnerability was found in @angular/core before 11.1.1. HTML doesn't specify any way to escape comment end text inside the comment.
<p>Publish Date: 2021-01-26
<p>URL: <a href=https://github.com/angular/angular/commit/97ec6e48493bf9418971436d885470a66e71f045>WS-2021-0039</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/angular/angular/releases/tag/11.1.1">https://github.com/angular/angular/releases/tag/11.1.1</a></p>
<p>Release Date: 2021-01-26</p>
<p>Fix Resolution: @angular/core - 11.1.1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"@angular/core","packageVersion":"9.0.0","packageFilePaths":["/frontend/package.json"],"isTransitiveDependency":true,"dependencyTree":"codelyzer:6.0.2;@angular/core:9.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"@angular/core - 11.1.1"}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2021-0039","vulnerabilityDetails":"Cross-Site Scripting (XSS) vulnerability was found in @angular/core before 11.1.1. HTML doesn\u0027t specify any way to escape comment end text inside the comment.","vulnerabilityUrl":"https://github.com/angular/angular/commit/97ec6e48493bf9418971436d885470a66e71f045","cvss3Severity":"low","cvss3Score":"3.9","cvss3Metrics":{"A":"Low","AC":"High","PR":"High","S":"Unchanged","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> -->
|
non_process
|
ws low detected in core tgz autoclosed ws low severity vulnerability vulnerable library core tgz angular the core framework library home page a href path to dependency file ori kit frontend package json path to vulnerable library ori kit frontend node modules codelyzer node modules angular core package json dependency hierarchy codelyzer tgz root library x core tgz vulnerable library found in head commit a href found in base branch main vulnerability details cross site scripting xss vulnerability was found in angular core before html doesn t specify any way to escape comment end text inside the comment publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction required scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution angular core isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree codelyzer angular core isminimumfixversionavailable true minimumfixversion angular core basebranches vulnerabilityidentifier ws vulnerabilitydetails cross site scripting xss vulnerability was found in angular core before html doesn specify any way to escape comment end text inside the comment vulnerabilityurl
| 0
|
93,384
| 26,935,461,649
|
IssuesEvent
|
2023-02-07 20:14:55
|
openhwgroup/cva6
|
https://api.github.com/repos/openhwgroup/cva6
|
closed
|
[BUG] Verilator 4.014 error | followed as per travis-ci
|
Component:Tool-and-build
|
### Is there an existing CVA6 bug for this?
- [X] I have searched the existing bug issues
### Bug Description
I have been trying to compile the simulation files of CVA6 using the ```make verilate``` command.
I have set everything using the scripts found in travis-ci-emul.sh
But execution of make command throws error as:
```
%Error: /home2/jayaraj/Desktop/cva-6-issue/cva6/corev_apu/src/tech_cells_generic/src/rtl/tc_sram.sv:93: Unsupported or unknown PLI call: $urandom
%Error: /home2/jayaraj/Desktop/cva-6-issue/cva6/corev_apu/src/tech_cells_generic/src/rtl/tc_clk.sv:87: syntax error, unexpected TIME NUMBER, expecting TYPE-IDENTIFIER
%Error: /home2/jayaraj/Desktop/cva-6-issue/cva6/corev_apu/src/tech_cells_generic/src/rtl/tc_clk.sv:90: syntax error, unexpected output, expecting IDENTIFIER or do or final
```
I think it is a verilator version issue. But I have used the same version mentioned in the script.
Operating System: Ubuntu 20.04.4 LTS
Kernel: Linux 5.11.0-27-generic
Architecture: x86-64
|
1.0
|
[BUG] Verilator 4.014 error | followed as per travis-ci - ### Is there an existing CVA6 bug for this?
- [X] I have searched the existing bug issues
### Bug Description
I have been trying to compile the simulation files of CVA6 using the ```make verilate``` command.
I have set everything using the scripts found in travis-ci-emul.sh
But execution of make command throws error as:
```
%Error: /home2/jayaraj/Desktop/cva-6-issue/cva6/corev_apu/src/tech_cells_generic/src/rtl/tc_sram.sv:93: Unsupported or unknown PLI call: $urandom
%Error: /home2/jayaraj/Desktop/cva-6-issue/cva6/corev_apu/src/tech_cells_generic/src/rtl/tc_clk.sv:87: syntax error, unexpected TIME NUMBER, expecting TYPE-IDENTIFIER
%Error: /home2/jayaraj/Desktop/cva-6-issue/cva6/corev_apu/src/tech_cells_generic/src/rtl/tc_clk.sv:90: syntax error, unexpected output, expecting IDENTIFIER or do or final
```
I think it is a verilator version issue. But I have used the same version mentioned in the script.
Operating System: Ubuntu 20.04.4 LTS
Kernel: Linux 5.11.0-27-generic
Architecture: x86-64
|
non_process
|
verilator error followed as per travis ci is there an existing bug for this i have searched the existing bug issues bug description i have been trying to compile the simulation files of using the make verilate command i have set everything using the scripts found in travis ci emul sh but execution of make command throws error as error jayaraj desktop cva issue corev apu src tech cells generic src rtl tc sram sv unsupported or unknown pli call urandom error jayaraj desktop cva issue corev apu src tech cells generic src rtl tc clk sv syntax error unexpected time number expecting type identifier error jayaraj desktop cva issue corev apu src tech cells generic src rtl tc clk sv syntax error unexpected output expecting identifier or do or final i think it is a verilator version issue but i have used the same version mentioned in the script operating system ubuntu lts kernel linux generic architecture
| 0
|
877
| 3,342,907,509
|
IssuesEvent
|
2015-11-15 01:42:25
|
technofreaky/woocomerce-quick-donation
|
https://api.github.com/repos/technofreaky/woocomerce-quick-donation
|
closed
|
User can not change donate amount after donate button is clicked
|
Enhancement Processing
|
Hi,
Here is my site http://taafng.org/.
Steps
1. enter an amount and click donation
2. plugin takes you to the checkout page
3. Lets say internet connection breaks or you can just click any other link
4. if you go back to the home page, change the amount and Click on the donation button, it now calls the checkout page but the amount showing is still the previous amount entered
Regards
Tomi
|
1.0
|
User can not change donate amount after donate button is clicked - Hi,
Here is my site http://taafng.org/.
Steps
1. enter an amount and click donation
2. plugin takes you to the checkout page
3. Lets say internet connection breaks or you can just click any other link
4. if you go back to the home page, change the amount and Click on the donation button, it now calls the checkout page but the amount showing is still the previous amount entered
Regards
Tomi
|
process
|
user can not change donate amount after donate button is clicked hi here is my site steps enter an amount and click donation plugin takes you to the checkout page lets say internet connection breaks or you can just click any other link if you go back to the home page change the amount and click on the donation button it now calls the checkout page but the amount showing is still the previous amount entered regards tomi
| 1
|
2,780
| 5,713,504,674
|
IssuesEvent
|
2017-04-19 07:57:46
|
g8os/grid
|
https://api.github.com/repos/g8os/grid
|
closed
|
Deployement of the Grid controller
|
process_wontfix state_inprogress type_feature
|
## Goal: Automate the installation of the grid controller
### Definitions:
- grid controller: composed of multiple component:
- AYS server
- AYS Repo of the grid API
- Grid API
- dnsmasq server
- http server
The controller will also run G8OS.
### Deployment scenario:
1. boot controller on G8OS from usb.
2. deploy a container with the [grid flist](https://hub.gig.tech/maxux/grid.flist)
2.1 The deployment is driven from another AYS server that can connect to the controller.
2.2 We send a blueprint with the information required to the controller and it get installed and configured
3. Once controller has AYS running. Continue installation by sending blueprint to the controller.
3.1 start a container that runs the dnsmasq server with tftp for ipxe boot and http server to server the kernel
3.2 configure iPXE to boot node with `append zerotier=netid`
3.3 create bootstrap.g8os service
3.4 boot the node and watch them beeing discover
|
1.0
|
Deployement of the Grid controller - ## Goal: Automate the installation of the grid controller
### Definitions:
- grid controller: composed of multiple component:
- AYS server
- AYS Repo of the grid API
- Grid API
- dnsmasq server
- http server
The controller will also run G8OS.
### Deployment scenario:
1. boot controller on G8OS from usb.
2. deploy a container with the [grid flist](https://hub.gig.tech/maxux/grid.flist)
2.1 The deployment is driven from another AYS server that can connect to the controller.
2.2 We send a blueprint with the information required to the controller and it get installed and configured
3. Once controller has AYS running. Continue installation by sending blueprint to the controller.
3.1 start a container that runs the dnsmasq server with tftp for ipxe boot and http server to server the kernel
3.2 configure iPXE to boot node with `append zerotier=netid`
3.3 create bootstrap.g8os service
3.4 boot the node and watch them beeing discover
|
process
|
deployement of the grid controller goal automate the installation of the grid controller definitions grid controller composed of multiple component ays server ays repo of the grid api grid api dnsmasq server http server the controller will also run deployment scenario boot controller on from usb deploy a container with the the deployment is driven from another ays server that can connect to the controller we send a blueprint with the information required to the controller and it get installed and configured once controller has ays running continue installation by sending blueprint to the controller start a container that runs the dnsmasq server with tftp for ipxe boot and http server to server the kernel configure ipxe to boot node with append zerotier netid create bootstrap service boot the node and watch them beeing discover
| 1
|
1,414
| 3,979,539,425
|
IssuesEvent
|
2016-05-06 00:19:09
|
mozilla/schedule-app-core
|
https://api.github.com/repos/mozilla/schedule-app-core
|
closed
|
Use "start time" to sort timeblocks
|
data processor script spreadsheet
|
Currently value of the `order` key in [`timeblock` object](https://github.com/mozilla/schedule-app-core/blob/gh-pages/docs/JSON_FORMAT.md#timeblocks-required) is manually entered on the Spreadsheet (e.g., there's a column called "order"). `timeblock` object has a `start time` key that we can use to sort a list of `timeblocks`. Our [Python script](https://github.com/mozilla/schedule-app-data-processor) should use make use of `start time` to automatically generate the `order` key instead.
One fewer column in the Spreadsheet to manage. YAY!
**Spreadsheet**
- [x] remove "order" column from `* Timeblock Values` sheet
**Python script**
- [x] generate `order` based on `start time` (https://github.com/mozilla/schedule-app-data-processor/issues/20)
|
1.0
|
Use "start time" to sort timeblocks - Currently value of the `order` key in [`timeblock` object](https://github.com/mozilla/schedule-app-core/blob/gh-pages/docs/JSON_FORMAT.md#timeblocks-required) is manually entered on the Spreadsheet (e.g., there's a column called "order"). `timeblock` object has a `start time` key that we can use to sort a list of `timeblocks`. Our [Python script](https://github.com/mozilla/schedule-app-data-processor) should use make use of `start time` to automatically generate the `order` key instead.
One fewer column in the Spreadsheet to manage. YAY!
**Spreadsheet**
- [x] remove "order" column from `* Timeblock Values` sheet
**Python script**
- [x] generate `order` based on `start time` (https://github.com/mozilla/schedule-app-data-processor/issues/20)
|
process
|
use start time to sort timeblocks currently value of the order key in is manually entered on the spreadsheet e g there s a column called order timeblock object has a start time key that we can use to sort a list of timeblocks our should use make use of start time to automatically generate the order key instead one fewer column in the spreadsheet to manage yay spreadsheet remove order column from timeblock values sheet python script generate order based on start time
| 1
|
4,676
| 7,517,294,569
|
IssuesEvent
|
2018-04-12 02:44:43
|
UnbFeelings/unb-feelings-GQA
|
https://api.github.com/repos/UnbFeelings/unb-feelings-GQA
|
closed
|
Estimar quantidade de auditorias
|
document help wanted process wiki
|
Nesta atividade, é considerada a lista dos objetos a serem auditados, para definir quantas auditorias serão necessárias para atender tal demanda. Contribuindo na criação do documento de descrição das auditorias planejadas.
|
1.0
|
Estimar quantidade de auditorias - Nesta atividade, é considerada a lista dos objetos a serem auditados, para definir quantas auditorias serão necessárias para atender tal demanda. Contribuindo na criação do documento de descrição das auditorias planejadas.
|
process
|
estimar quantidade de auditorias nesta atividade é considerada a lista dos objetos a serem auditados para definir quantas auditorias serão necessárias para atender tal demanda contribuindo na criação do documento de descrição das auditorias planejadas
| 1
|
12,231
| 14,743,624,715
|
IssuesEvent
|
2021-01-07 14:11:13
|
kdjstudios/SABillingGitlab
|
https://api.github.com/repos/kdjstudios/SABillingGitlab
|
closed
|
Triad - Missing Baserates | parent: 1601
|
anc-process anp-1 ant-bug ant-child/secondary has attachment
|
In GitLab by @kdjstudios on Sep 5, 2019, 13:04
**Submitted by:** "Amecia Snelling" <amecia.snelling@answernet.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/2019-09-05-73891
**Server:** Internal
**Client/Site:** Triad
**Account:** Multiple
**Issue:**
I am trying to process my billing but when finished I looked at the AR report and noticed that I had a lot of baserates missing. I looked at the Revenue Analysis and noticed that a lot of the baserates were not captured. Can someone check to see if some billing codes have been deleted? I will also need to know what can be done to fix this. Please see the spreadsheet that I have attached. All of the highlighted accounts are missing baserates. Please let me know if you have any questions.
[revenue_analysis_worksheet_09_03_2019_Master.csv](/uploads/33397d3672bdcecbdc07ed3a1439ce6a/revenue_analysis_worksheet_09_03_2019_Master.csv)
|
1.0
|
Triad - Missing Baserates | parent: 1601 - In GitLab by @kdjstudios on Sep 5, 2019, 13:04
**Submitted by:** "Amecia Snelling" <amecia.snelling@answernet.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/2019-09-05-73891
**Server:** Internal
**Client/Site:** Triad
**Account:** Multiple
**Issue:**
I am trying to process my billing but when finished I looked at the AR report and noticed that I had a lot of baserates missing. I looked at the Revenue Analysis and noticed that a lot of the baserates were not captured. Can someone check to see if some billing codes have been deleted? I will also need to know what can be done to fix this. Please see the spreadsheet that I have attached. All of the highlighted accounts are missing baserates. Please let me know if you have any questions.
[revenue_analysis_worksheet_09_03_2019_Master.csv](/uploads/33397d3672bdcecbdc07ed3a1439ce6a/revenue_analysis_worksheet_09_03_2019_Master.csv)
|
process
|
triad missing baserates parent in gitlab by kdjstudios on sep submitted by amecia snelling helpdesk server internal client site triad account multiple issue i am trying to process my billing but when finished i looked at the ar report and noticed that i had a lot of baserates missing i looked at the revenue analysis and noticed that a lot of the baserates were not captured can someone check to see if some billing codes have been deleted i will also need to know what can be done to fix this please see the spreadsheet that i have attached all of the highlighted accounts are missing baserates please let me know if you have any questions uploads revenue analysis worksheet master csv
| 1
|
4,203
| 7,164,522,815
|
IssuesEvent
|
2018-01-29 11:31:34
|
LOVDnl/LOVD3
|
https://api.github.com/repos/LOVDnl/LOVD3
|
opened
|
Make protein change field non-mandatory for non-coding transcripts
|
cat: interface cat: submission process feature request
|
Transcripts that are non-coding can be identified by their NCBI ID. `NR` and `XR` prefixes indicate a non-coding transcript. For these transcripts, the "Protein change" field should be optional and not mandatory.
|
1.0
|
Make protein change field non-mandatory for non-coding transcripts - Transcripts that are non-coding can be identified by their NCBI ID. `NR` and `XR` prefixes indicate a non-coding transcript. For these transcripts, the "Protein change" field should be optional and not mandatory.
|
process
|
make protein change field non mandatory for non coding transcripts transcripts that are non coding can be identified by their ncbi id nr and xr prefixes indicate a non coding transcript for these transcripts the protein change field should be optional and not mandatory
| 1
|
145,955
| 11,716,148,820
|
IssuesEvent
|
2020-03-09 15:12:54
|
ICIJ/datashare
|
https://api.github.com/repos/ICIJ/datashare
|
closed
|
Contextualize filters do not work anymore
|
bug front need testing
|
To reproduce :
- In "File Types", filter on PDFs (by example)
- Click on "Contextualize filters" to enable it
=> Look at the filters, it is not contextualized !
|
1.0
|
Contextualize filters do not work anymore - To reproduce :
- In "File Types", filter on PDFs (by example)
- Click on "Contextualize filters" to enable it
=> Look at the filters, it is not contextualized !
|
non_process
|
contextualize filters do not work anymore to reproduce in file types filter on pdfs by example click on contextualize filters to enable it look at the filters it is not contextualized
| 0
|
294,493
| 25,376,642,166
|
IssuesEvent
|
2022-11-21 14:34:37
|
NVIDIA/spark-rapids
|
https://api.github.com/repos/NVIDIA/spark-rapids
|
closed
|
[BUG] CPU mismatch GPU result in test_hash_groupby_collect_with_single_distinct intermittently
|
bug duplicate test
|
**Describe the bug**
test_hash_groupby_collect_with_single_distinct[[('a', RepeatSeq(Long)), ('b', RepeatSeq(Boolean)), ('c', LongRange(not_null))]][IGNORE_ORDER({'local': True})] - AssertionError: GPU and CPU boolean values are different at [18, 'sort_array(collect_list(b), true)', 3]
[2022-11-18T03:41:02.798Z] CPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[**False, False, False, True**, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
[2022-11-18T03:41:02.799Z] GPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[**False, False, False, False**, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
```
[2022-11-18T03:41:02.797Z] _ test_hash_groupby_collect_with_single_distinct[[('a', RepeatSeq(Long)), ('b', RepeatSeq(Boolean)), ('c', LongRange(not_null))]] _
[2022-11-18T03:41:02.797Z] [gw3] linux -- Python 3.8.15 /usr/bin/python
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] data_gen = [('a', RepeatSeq(Long)), ('b', RepeatSeq(Boolean)), ('c', LongRange(not_null))]
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] @ignore_order(local=True)
[2022-11-18T03:41:02.797Z] @pytest.mark.parametrize('data_gen', _full_gen_data_for_collect_op, ids=idfn)
[2022-11-18T03:41:02.797Z] def test_hash_groupby_collect_with_single_distinct(data_gen):
[2022-11-18T03:41:02.797Z] # test collect_ops with other distinct aggregations
[2022-11-18T03:41:02.797Z] > assert_gpu_and_cpu_are_equal_collect(
[2022-11-18T03:41:02.797Z] lambda spark: gen_df(spark, data_gen, length=100)
[2022-11-18T03:41:02.797Z] .groupby('a')
[2022-11-18T03:41:02.797Z] .agg(f.sort_array(f.collect_list('b')),
[2022-11-18T03:41:02.797Z] f.sort_array(f.collect_set('b')),
[2022-11-18T03:41:02.797Z] f.countDistinct('c'),
[2022-11-18T03:41:02.797Z] f.count('c')))
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] ../../src/main/python/hash_aggregate_test.py:736:
[2022-11-18T03:41:02.797Z] _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:548: in assert_gpu_and_cpu_are_equal_collect
[2022-11-18T03:41:02.797Z] _assert_gpu_and_cpu_are_equal(func, 'COLLECT', conf=conf, is_cpu_first=is_cpu_first)
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:479: in _assert_gpu_and_cpu_are_equal
[2022-11-18T03:41:02.797Z] assert_equal(from_cpu, from_gpu)
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:106: in assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu, gpu, float_check=get_float_check(), path=[])
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:42: in _assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:35: in _assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[field], gpu[field], float_check, path + [field])
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:42: in _assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.797Z] _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] cpu = True, gpu = False
[2022-11-18T03:41:02.797Z] float_check = <function get_float_check.<locals>.<lambda> at 0x7fcbd6f26ee0>
[2022-11-18T03:41:02.797Z] path = [18, 'sort_array(collect_list(b), true)', 3]
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] def _assert_equal(cpu, gpu, float_check, path):
[2022-11-18T03:41:02.797Z] t = type(cpu)
[2022-11-18T03:41:02.797Z] if (t is Row):
[2022-11-18T03:41:02.797Z] assert len(cpu) == len(gpu), "CPU and GPU row have different lengths at {} CPU: {} GPU: {}".format(path, len(cpu), len(gpu))
[2022-11-18T03:41:02.797Z] if hasattr(cpu, "__fields__") and hasattr(gpu, "__fields__"):
[2022-11-18T03:41:02.797Z] assert cpu.__fields__ == gpu.__fields__, "CPU and GPU row have different fields at {} CPU: {} GPU: {}".format(path, cpu.__fields__, gpu.__fields__)
[2022-11-18T03:41:02.797Z] for field in cpu.__fields__:
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[field], gpu[field], float_check, path + [field])
[2022-11-18T03:41:02.797Z] else:
[2022-11-18T03:41:02.797Z] for index in range(len(cpu)):
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.797Z] elif (t is list):
[2022-11-18T03:41:02.797Z] assert len(cpu) == len(gpu), "CPU and GPU list have different lengths at {} CPU: {} GPU: {}".format(path, len(cpu), len(gpu))
[2022-11-18T03:41:02.798Z] for index in range(len(cpu)):
[2022-11-18T03:41:02.798Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.798Z] elif (t is tuple):
[2022-11-18T03:41:02.798Z] assert len(cpu) == len(gpu), "CPU and GPU list have different lengths at {} CPU: {} GPU: {}".format(path, len(cpu), len(gpu))
[2022-11-18T03:41:02.798Z] for index in range(len(cpu)):
[2022-11-18T03:41:02.798Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.798Z] elif (t is pytypes.GeneratorType):
[2022-11-18T03:41:02.798Z] index = 0
[2022-11-18T03:41:02.798Z] # generator has no zip :( so we have to do this the hard way
[2022-11-18T03:41:02.798Z] done = False
[2022-11-18T03:41:02.798Z] while not done:
[2022-11-18T03:41:02.798Z] sub_cpu = None
[2022-11-18T03:41:02.798Z] sub_gpu = None
[2022-11-18T03:41:02.798Z] try:
[2022-11-18T03:41:02.798Z] sub_cpu = next(cpu)
[2022-11-18T03:41:02.798Z] except StopIteration:
[2022-11-18T03:41:02.798Z] done = True
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] try:
[2022-11-18T03:41:02.798Z] sub_gpu = next(gpu)
[2022-11-18T03:41:02.798Z] except StopIteration:
[2022-11-18T03:41:02.798Z] done = True
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] if done:
[2022-11-18T03:41:02.798Z] assert sub_cpu == sub_gpu and sub_cpu == None, "CPU and GPU generators have different lengths at {}".format(path)
[2022-11-18T03:41:02.798Z] else:
[2022-11-18T03:41:02.798Z] _assert_equal(sub_cpu, sub_gpu, float_check, path + [index])
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] index = index + 1
[2022-11-18T03:41:02.798Z] elif (t is dict):
[2022-11-18T03:41:02.798Z] # The order of key/values is not guaranteed in python dicts, nor are they guaranteed by Spark
[2022-11-18T03:41:02.798Z] # so sort the items to do our best with ignoring the order of dicts
[2022-11-18T03:41:02.798Z] cpu_items = list(cpu.items()).sort(key=_RowCmp)
[2022-11-18T03:41:02.798Z] gpu_items = list(gpu.items()).sort(key=_RowCmp)
[2022-11-18T03:41:02.798Z] _assert_equal(cpu_items, gpu_items, float_check, path + ["map"])
[2022-11-18T03:41:02.798Z] elif (t is int):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU int values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif (t is float):
[2022-11-18T03:41:02.798Z] if (math.isnan(cpu)):
[2022-11-18T03:41:02.798Z] assert math.isnan(gpu), "GPU and CPU float values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] else:
[2022-11-18T03:41:02.798Z] assert float_check(cpu, gpu), "GPU and CPU float values are different {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, str):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU string values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, datetime):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU timestamp values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, date):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU date values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, bool):
[2022-11-18T03:41:02.798Z] > assert cpu == gpu, "GPU and CPU boolean values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] E AssertionError: GPU and CPU boolean values are different at [18, 'sort_array(collect_list(b), true)', 3]
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] ../../src/main/python/asserts.py:90: AssertionError
[2022-11-18T03:41:02.798Z] ----------------------------- Captured stdout call -----------------------------
[2022-11-18T03:41:02.798Z] ### CPU RUN ###
[2022-11-18T03:41:02.798Z] ### GPU RUN ###
[2022-11-18T03:41:02.798Z] ### COLLECT: GPU TOOK 0.2924313545227051 CPU TOOK 0.29257845878601074 ###
[2022-11-18T03:41:02.798Z] CPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[False, False, False, True, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
[2022-11-18T03:41:02.799Z] GPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[False, False, False, False, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
```
**Steps/Code to reproduce bug**
Not always reproducible, just saw one fail right now
|
1.0
|
[BUG] CPU mismatch GPU result in test_hash_groupby_collect_with_single_distinct intermittently - **Describe the bug**
test_hash_groupby_collect_with_single_distinct[[('a', RepeatSeq(Long)), ('b', RepeatSeq(Boolean)), ('c', LongRange(not_null))]][IGNORE_ORDER({'local': True})] - AssertionError: GPU and CPU boolean values are different at [18, 'sort_array(collect_list(b), true)', 3]
[2022-11-18T03:41:02.798Z] CPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[**False, False, False, True**, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
[2022-11-18T03:41:02.799Z] GPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[**False, False, False, False**, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
```
[2022-11-18T03:41:02.797Z] _ test_hash_groupby_collect_with_single_distinct[[('a', RepeatSeq(Long)), ('b', RepeatSeq(Boolean)), ('c', LongRange(not_null))]] _
[2022-11-18T03:41:02.797Z] [gw3] linux -- Python 3.8.15 /usr/bin/python
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] data_gen = [('a', RepeatSeq(Long)), ('b', RepeatSeq(Boolean)), ('c', LongRange(not_null))]
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] @ignore_order(local=True)
[2022-11-18T03:41:02.797Z] @pytest.mark.parametrize('data_gen', _full_gen_data_for_collect_op, ids=idfn)
[2022-11-18T03:41:02.797Z] def test_hash_groupby_collect_with_single_distinct(data_gen):
[2022-11-18T03:41:02.797Z] # test collect_ops with other distinct aggregations
[2022-11-18T03:41:02.797Z] > assert_gpu_and_cpu_are_equal_collect(
[2022-11-18T03:41:02.797Z] lambda spark: gen_df(spark, data_gen, length=100)
[2022-11-18T03:41:02.797Z] .groupby('a')
[2022-11-18T03:41:02.797Z] .agg(f.sort_array(f.collect_list('b')),
[2022-11-18T03:41:02.797Z] f.sort_array(f.collect_set('b')),
[2022-11-18T03:41:02.797Z] f.countDistinct('c'),
[2022-11-18T03:41:02.797Z] f.count('c')))
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] ../../src/main/python/hash_aggregate_test.py:736:
[2022-11-18T03:41:02.797Z] _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:548: in assert_gpu_and_cpu_are_equal_collect
[2022-11-18T03:41:02.797Z] _assert_gpu_and_cpu_are_equal(func, 'COLLECT', conf=conf, is_cpu_first=is_cpu_first)
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:479: in _assert_gpu_and_cpu_are_equal
[2022-11-18T03:41:02.797Z] assert_equal(from_cpu, from_gpu)
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:106: in assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu, gpu, float_check=get_float_check(), path=[])
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:42: in _assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:35: in _assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[field], gpu[field], float_check, path + [field])
[2022-11-18T03:41:02.797Z] ../../src/main/python/asserts.py:42: in _assert_equal
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.797Z] _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] cpu = True, gpu = False
[2022-11-18T03:41:02.797Z] float_check = <function get_float_check.<locals>.<lambda> at 0x7fcbd6f26ee0>
[2022-11-18T03:41:02.797Z] path = [18, 'sort_array(collect_list(b), true)', 3]
[2022-11-18T03:41:02.797Z]
[2022-11-18T03:41:02.797Z] def _assert_equal(cpu, gpu, float_check, path):
[2022-11-18T03:41:02.797Z] t = type(cpu)
[2022-11-18T03:41:02.797Z] if (t is Row):
[2022-11-18T03:41:02.797Z] assert len(cpu) == len(gpu), "CPU and GPU row have different lengths at {} CPU: {} GPU: {}".format(path, len(cpu), len(gpu))
[2022-11-18T03:41:02.797Z] if hasattr(cpu, "__fields__") and hasattr(gpu, "__fields__"):
[2022-11-18T03:41:02.797Z] assert cpu.__fields__ == gpu.__fields__, "CPU and GPU row have different fields at {} CPU: {} GPU: {}".format(path, cpu.__fields__, gpu.__fields__)
[2022-11-18T03:41:02.797Z] for field in cpu.__fields__:
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[field], gpu[field], float_check, path + [field])
[2022-11-18T03:41:02.797Z] else:
[2022-11-18T03:41:02.797Z] for index in range(len(cpu)):
[2022-11-18T03:41:02.797Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.797Z] elif (t is list):
[2022-11-18T03:41:02.797Z] assert len(cpu) == len(gpu), "CPU and GPU list have different lengths at {} CPU: {} GPU: {}".format(path, len(cpu), len(gpu))
[2022-11-18T03:41:02.798Z] for index in range(len(cpu)):
[2022-11-18T03:41:02.798Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.798Z] elif (t is tuple):
[2022-11-18T03:41:02.798Z] assert len(cpu) == len(gpu), "CPU and GPU list have different lengths at {} CPU: {} GPU: {}".format(path, len(cpu), len(gpu))
[2022-11-18T03:41:02.798Z] for index in range(len(cpu)):
[2022-11-18T03:41:02.798Z] _assert_equal(cpu[index], gpu[index], float_check, path + [index])
[2022-11-18T03:41:02.798Z] elif (t is pytypes.GeneratorType):
[2022-11-18T03:41:02.798Z] index = 0
[2022-11-18T03:41:02.798Z] # generator has no zip :( so we have to do this the hard way
[2022-11-18T03:41:02.798Z] done = False
[2022-11-18T03:41:02.798Z] while not done:
[2022-11-18T03:41:02.798Z] sub_cpu = None
[2022-11-18T03:41:02.798Z] sub_gpu = None
[2022-11-18T03:41:02.798Z] try:
[2022-11-18T03:41:02.798Z] sub_cpu = next(cpu)
[2022-11-18T03:41:02.798Z] except StopIteration:
[2022-11-18T03:41:02.798Z] done = True
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] try:
[2022-11-18T03:41:02.798Z] sub_gpu = next(gpu)
[2022-11-18T03:41:02.798Z] except StopIteration:
[2022-11-18T03:41:02.798Z] done = True
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] if done:
[2022-11-18T03:41:02.798Z] assert sub_cpu == sub_gpu and sub_cpu == None, "CPU and GPU generators have different lengths at {}".format(path)
[2022-11-18T03:41:02.798Z] else:
[2022-11-18T03:41:02.798Z] _assert_equal(sub_cpu, sub_gpu, float_check, path + [index])
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] index = index + 1
[2022-11-18T03:41:02.798Z] elif (t is dict):
[2022-11-18T03:41:02.798Z] # The order of key/values is not guaranteed in python dicts, nor are they guaranteed by Spark
[2022-11-18T03:41:02.798Z] # so sort the items to do our best with ignoring the order of dicts
[2022-11-18T03:41:02.798Z] cpu_items = list(cpu.items()).sort(key=_RowCmp)
[2022-11-18T03:41:02.798Z] gpu_items = list(gpu.items()).sort(key=_RowCmp)
[2022-11-18T03:41:02.798Z] _assert_equal(cpu_items, gpu_items, float_check, path + ["map"])
[2022-11-18T03:41:02.798Z] elif (t is int):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU int values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif (t is float):
[2022-11-18T03:41:02.798Z] if (math.isnan(cpu)):
[2022-11-18T03:41:02.798Z] assert math.isnan(gpu), "GPU and CPU float values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] else:
[2022-11-18T03:41:02.798Z] assert float_check(cpu, gpu), "GPU and CPU float values are different {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, str):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU string values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, datetime):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU timestamp values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, date):
[2022-11-18T03:41:02.798Z] assert cpu == gpu, "GPU and CPU date values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] elif isinstance(cpu, bool):
[2022-11-18T03:41:02.798Z] > assert cpu == gpu, "GPU and CPU boolean values are different at {}".format(path)
[2022-11-18T03:41:02.798Z] E AssertionError: GPU and CPU boolean values are different at [18, 'sort_array(collect_list(b), true)', 3]
[2022-11-18T03:41:02.798Z]
[2022-11-18T03:41:02.798Z] ../../src/main/python/asserts.py:90: AssertionError
[2022-11-18T03:41:02.798Z] ----------------------------- Captured stdout call -----------------------------
[2022-11-18T03:41:02.798Z] ### CPU RUN ###
[2022-11-18T03:41:02.798Z] ### GPU RUN ###
[2022-11-18T03:41:02.798Z] ### COLLECT: GPU TOOK 0.2924313545227051 CPU TOOK 0.29257845878601074 ###
[2022-11-18T03:41:02.798Z] CPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[False, False, False, True, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
[2022-11-18T03:41:02.799Z] GPU OUTPUT: [Row(a=-7540734677356764604, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-5831592707909023540, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-5133656973475552689, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-4426181692283497353, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-3917032101531217289, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-3502159106106506455, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=-2697073954890740236, sort_array(collect_list(b), true)=[False, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-2123199122092230623, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=-1, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=207981845540287738, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=393905103838704542, sort_array(collect_list(b), true)=[False, False, False, False, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=875130347651831881, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=4751953708995107450, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=6084712057446794809, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7198729688045931692, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7528354001793048440, sort_array(collect_list(b), true)=[False, False, False, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=7618709293599214015, sort_array(collect_list(b), true)=[True, True, True, True, True], sort_array(collect_set(b), true)=[True], count(c)=5, count(c)=5), Row(a=7984374766242566542, sort_array(collect_list(b), true)=[False, False, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=5, count(c)=5), Row(a=9223372036854775807, sort_array(collect_list(b), true)=[False, False, False, False, True, True, True, True, True, True], sort_array(collect_set(b), true)=[False, True], count(c)=10, count(c)=10)]
```
**Steps/Code to reproduce bug**
Not always reproducible, just saw one fail right now
|
non_process
|
cpu mismatch gpu result in test hash groupby collect with single distinct intermittently describe the bug test hash groupby collect with single distinct assertionerror gpu and cpu boolean values are different at cpu output sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c gpu output sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c test hash groupby collect with single distinct linux python usr bin python data gen ignore order local true pytest mark parametrize data gen full gen data for collect op ids idfn def test hash groupby collect with single distinct data gen test collect ops with other distinct aggregations assert gpu and cpu are equal collect lambda spark gen df spark data gen length groupby a agg f sort array f collect list b f sort array f collect set b f countdistinct c f count c src main python hash aggregate test py src main python asserts py in assert gpu and cpu are equal collect assert gpu and cpu are equal func collect conf conf is cpu first is cpu first src main python asserts py in assert gpu and cpu are equal assert equal from cpu from gpu src main python asserts py in assert equal assert equal cpu gpu float check get float check path src main python asserts py in assert equal assert equal cpu gpu float check path src main python asserts py in assert equal assert equal cpu gpu float check path src main python asserts py in assert equal assert equal cpu gpu float check path cpu true gpu false float check at path def assert equal cpu gpu float check path t type cpu if t is row assert len cpu len gpu cpu and gpu row have different lengths at cpu gpu format path len cpu len gpu if hasattr cpu fields and hasattr gpu fields assert cpu fields gpu fields cpu and gpu row have different fields at cpu gpu format path cpu fields gpu fields for field in cpu fields assert equal cpu gpu float check path else for index in range len cpu assert equal cpu gpu float check path elif t is list assert len cpu len gpu cpu and gpu list have different lengths at cpu gpu format path len cpu len gpu for index in range len cpu assert equal cpu gpu float check path elif t is tuple assert len cpu len gpu cpu and gpu list have different lengths at cpu gpu format path len cpu len gpu for index in range len cpu assert equal cpu gpu float check path elif t is pytypes generatortype index generator has no zip so we have to do this the hard way done false while not done sub cpu none sub gpu none try sub cpu next cpu except stopiteration done true try sub gpu next gpu except stopiteration done true if done assert sub cpu sub gpu and sub cpu none cpu and gpu generators have different lengths at format path else assert equal sub cpu sub gpu float check path index index elif t is dict the order of key values is not guaranteed in python dicts nor are they guaranteed by spark so sort the items to do our best with ignoring the order of dicts cpu items list cpu items sort key rowcmp gpu items list gpu items sort key rowcmp assert equal cpu items gpu items float check path elif t is int assert cpu gpu gpu and cpu int values are different at format path elif t is float if math isnan cpu assert math isnan gpu gpu and cpu float values are different at format path else assert float check cpu gpu gpu and cpu float values are different format path elif isinstance cpu str assert cpu gpu gpu and cpu string values are different at format path elif isinstance cpu datetime assert cpu gpu gpu and cpu timestamp values are different at format path elif isinstance cpu date assert cpu gpu gpu and cpu date values are different at format path elif isinstance cpu bool assert cpu gpu gpu and cpu boolean values are different at format path e assertionerror gpu and cpu boolean values are different at src main python asserts py assertionerror captured stdout call cpu run gpu run collect gpu took cpu took cpu output sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c gpu output sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c row a sort array collect list b true sort array collect set b true count c count c steps code to reproduce bug not always reproducible just saw one fail right now
| 0
|
15,253
| 19,190,521,314
|
IssuesEvent
|
2021-12-05 22:38:57
|
km4ack/pi-build
|
https://api.github.com/repos/km4ack/pi-build
|
closed
|
hamlib (rigctl) won't install on Bullseye SOLVED
|
bug in process
|
libusb-1.0 not available in bullseye. Need to compile from source with:
```
sudo apt install -y libusb-dev libudev-dev
cd ~/Downloads
wget https://github.com/libusb/libusb/releases/download/v1.0.23/libusb-1.0.23.tar.bz2
tar -xvf libusb-1.0.23.tar.bz2
cd libusb-1.0.23/
./configure
make
sudo make install
sudo ldconfig
```
now run hamlib install as before with BAP
|
1.0
|
hamlib (rigctl) won't install on Bullseye SOLVED - libusb-1.0 not available in bullseye. Need to compile from source with:
```
sudo apt install -y libusb-dev libudev-dev
cd ~/Downloads
wget https://github.com/libusb/libusb/releases/download/v1.0.23/libusb-1.0.23.tar.bz2
tar -xvf libusb-1.0.23.tar.bz2
cd libusb-1.0.23/
./configure
make
sudo make install
sudo ldconfig
```
now run hamlib install as before with BAP
|
process
|
hamlib rigctl won t install on bullseye solved libusb not available in bullseye need to compile from source with sudo apt install y libusb dev libudev dev cd downloads wget tar xvf libusb tar cd libusb configure make sudo make install sudo ldconfig now run hamlib install as before with bap
| 1
|
109,284
| 13,758,112,051
|
IssuesEvent
|
2020-10-06 23:08:59
|
dotnet/roslyn
|
https://api.github.com/repos/dotnet/roslyn
|
closed
|
Provide a way to visually inspect the inheritance hierarchy
|
Area-IDE Feature Request InternalAsk Need Design Review
|
View type/member hierarchy - display a hierarchy with links to base and derived types/members.
Go To Implementation provides a list of derived types/members, but without (a) base types/members or (b) showing the inheritance relationship between different items
|
1.0
|
Provide a way to visually inspect the inheritance hierarchy - View type/member hierarchy - display a hierarchy with links to base and derived types/members.
Go To Implementation provides a list of derived types/members, but without (a) base types/members or (b) showing the inheritance relationship between different items
|
non_process
|
provide a way to visually inspect the inheritance hierarchy view type member hierarchy display a hierarchy with links to base and derived types members go to implementation provides a list of derived types members but without a base types members or b showing the inheritance relationship between different items
| 0
|
342,724
| 10,320,898,221
|
IssuesEvent
|
2019-08-30 22:14:23
|
HackGT/bolt
|
https://api.github.com/repos/HackGT/bolt
|
opened
|
Track request change history
|
component / requests priority / medium type / feature
|
Create a new database table for tracking changes to requests - user, item, quantity, or status (old and new) - and the time it occurred. This will provide better visibility into requests and give us the data to have analytics like average time to approve/fulfill requests, which items are most in demand, etc.
|
1.0
|
Track request change history - Create a new database table for tracking changes to requests - user, item, quantity, or status (old and new) - and the time it occurred. This will provide better visibility into requests and give us the data to have analytics like average time to approve/fulfill requests, which items are most in demand, etc.
|
non_process
|
track request change history create a new database table for tracking changes to requests user item quantity or status old and new and the time it occurred this will provide better visibility into requests and give us the data to have analytics like average time to approve fulfill requests which items are most in demand etc
| 0
|
750
| 3,223,389,891
|
IssuesEvent
|
2015-10-09 09:37:54
|
MTG/freesound
|
https://api.github.com/repos/MTG/freesound
|
opened
|
Refactor sound processing state handling
|
Improvement _Processing
|
The current way in which we handle processing state and processing of sounds does not allow for optimised workflows when we want to reprocess sounds. To improve this, the processing_state field in the sound model should only be used to say that a sound has either failed processing or being successfully processed (similarity to the moderation state). Another property 'processing_ongoing_state' should be used to set the state of the actual processing activity (either queued, processing or finished).
This will allow to better handle reprocessing of sounds and optimise other related stuff such as removing sounds from solr and similarity when they fail processing and updating packs, num_sounds on user profiles and other related stuff when sounds change their processing_state.
|
1.0
|
Refactor sound processing state handling - The current way in which we handle processing state and processing of sounds does not allow for optimised workflows when we want to reprocess sounds. To improve this, the processing_state field in the sound model should only be used to say that a sound has either failed processing or being successfully processed (similarity to the moderation state). Another property 'processing_ongoing_state' should be used to set the state of the actual processing activity (either queued, processing or finished).
This will allow to better handle reprocessing of sounds and optimise other related stuff such as removing sounds from solr and similarity when they fail processing and updating packs, num_sounds on user profiles and other related stuff when sounds change their processing_state.
|
process
|
refactor sound processing state handling the current way in which we handle processing state and processing of sounds does not allow for optimised workflows when we want to reprocess sounds to improve this the processing state field in the sound model should only be used to say that a sound has either failed processing or being successfully processed similarity to the moderation state another property processing ongoing state should be used to set the state of the actual processing activity either queued processing or finished this will allow to better handle reprocessing of sounds and optimise other related stuff such as removing sounds from solr and similarity when they fail processing and updating packs num sounds on user profiles and other related stuff when sounds change their processing state
| 1
|
506,236
| 14,660,527,857
|
IssuesEvent
|
2020-12-29 00:03:31
|
bounswe/bounswe2020group8
|
https://api.github.com/repos/bounswe/bounswe2020group8
|
closed
|
Implement Main Product listing for admins
|
Priority: Medium enhancement web
|
**Describe the feature**
The admins should be able to list and delete main products.
**Describe solutions you've considered**
The same pattern of normal products will follow here.
|
1.0
|
Implement Main Product listing for admins - **Describe the feature**
The admins should be able to list and delete main products.
**Describe solutions you've considered**
The same pattern of normal products will follow here.
|
non_process
|
implement main product listing for admins describe the feature the admins should be able to list and delete main products describe solutions you ve considered the same pattern of normal products will follow here
| 0
|
2,564
| 5,316,087,379
|
IssuesEvent
|
2017-02-13 18:59:25
|
jlm2017/jlm-video-subtitles
|
https://api.github.com/repos/jlm2017/jlm-video-subtitles
|
closed
|
[subtitles] [fr] «Nous sommes tes fils, Révolution !» - Mélenchon citant Hugo en meeting
|
Language: French Process: [6] Approved
|
# Video title
«Nous sommes tes fils, Révolution !» - Mélenchon citant Hugo en meeting
# URL
https://www.youtube.com/watch?v=B8xROYog8KE
# Youtube subtitles language
French
# Duration
2:28
# Subtitles URL
https://www.youtube.com/timedtext_editor?tab=captions&v=B8xROYog8KE&action_mde_edit_form=1&ui=hd&ref=player&bl=vmp&lang=fr
|
1.0
|
[subtitles] [fr] «Nous sommes tes fils, Révolution !» - Mélenchon citant Hugo en meeting - # Video title
«Nous sommes tes fils, Révolution !» - Mélenchon citant Hugo en meeting
# URL
https://www.youtube.com/watch?v=B8xROYog8KE
# Youtube subtitles language
French
# Duration
2:28
# Subtitles URL
https://www.youtube.com/timedtext_editor?tab=captions&v=B8xROYog8KE&action_mde_edit_form=1&ui=hd&ref=player&bl=vmp&lang=fr
|
process
|
«nous sommes tes fils révolution » mélenchon citant hugo en meeting video title «nous sommes tes fils révolution » mélenchon citant hugo en meeting url youtube subtitles language french duration subtitles url
| 1
|
2,024
| 4,846,818,235
|
IssuesEvent
|
2016-11-10 13:07:57
|
Alfresco/alfresco-ng2-components
|
https://api.github.com/repos/Alfresco/alfresco-ng2-components
|
opened
|
When starting a process should user need to provide a name?
|
comp: activiti-processList
|
Comparing starting a process within Activiti to that in the adf components there are some differences, which may be intentional?
1. Unsure what the dropdown 'type' refers to, should this be 'process'?
2. A process can only be started if a name is added ('start' option is greyed out), should renaming a process be avaliable to the user and if so should it be optional?
3. If the name is optional should, when the process is started, include the process name or the name given when starting the task?
**Components**

**Activiti**

|
1.0
|
When starting a process should user need to provide a name? - Comparing starting a process within Activiti to that in the adf components there are some differences, which may be intentional?
1. Unsure what the dropdown 'type' refers to, should this be 'process'?
2. A process can only be started if a name is added ('start' option is greyed out), should renaming a process be avaliable to the user and if so should it be optional?
3. If the name is optional should, when the process is started, include the process name or the name given when starting the task?
**Components**

**Activiti**

|
process
|
when starting a process should user need to provide a name comparing starting a process within activiti to that in the adf components there are some differences which may be intentional unsure what the dropdown type refers to should this be process a process can only be started if a name is added start option is greyed out should renaming a process be avaliable to the user and if so should it be optional if the name is optional should when the process is started include the process name or the name given when starting the task components activiti
| 1
|
280,524
| 8,683,389,347
|
IssuesEvent
|
2018-12-02 17:42:59
|
sem5640-2018/gatekeeper
|
https://api.github.com/repos/sem5640-2018/gatekeeper
|
closed
|
Batch user data API
|
enhancement high priority
|
Some services need to make multiple calls to the API to get user data for indexes. Having a single API call would lower the amount of calls. Plz do.
|
1.0
|
Batch user data API - Some services need to make multiple calls to the API to get user data for indexes. Having a single API call would lower the amount of calls. Plz do.
|
non_process
|
batch user data api some services need to make multiple calls to the api to get user data for indexes having a single api call would lower the amount of calls plz do
| 0
|
9,772
| 12,760,870,849
|
IssuesEvent
|
2020-06-29 08:48:33
|
ClickHouse/ClickHouse
|
https://api.github.com/repos/ClickHouse/ClickHouse
|
opened
|
UNION ALL issue with processors
|
bug comp-processors
|
```
set experimental_use_processors=0;
SELECT count()
FROM
(
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
UNION ALL
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
)
┌───count()─┐
│ 200000000 │
└───────────┘
1 rows in set. Elapsed: 0.213 sec. Processed 263.52 million rows, 2.11 GB (1.24 billion rows/s., 9.89 GB/s.)
```
```
set experimental_use_processors=0;
SELECT count()
FROM
(
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
UNION ALL
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
)
↓ Progress: 29.44 billion rows, 235.48 GB (2.58 billion rows/s., 20.62 GB/s.) Cancelling query.
↙ Progress: 29.68 billion rows, 237.41 GB (2.58 billion rows/s., 20.61 GB/s.) Ok.
Query was cancelled.
0 rows in set. Elapsed: 11.521 sec. Processed 29.68 billion rows, 237.41 GB (2.58 billion rows/s., 20.61 GB/s.)
-- never finishes.
```
|
1.0
|
UNION ALL issue with processors - ```
set experimental_use_processors=0;
SELECT count()
FROM
(
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
UNION ALL
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
)
┌───count()─┐
│ 200000000 │
└───────────┘
1 rows in set. Elapsed: 0.213 sec. Processed 263.52 million rows, 2.11 GB (1.24 billion rows/s., 9.89 GB/s.)
```
```
set experimental_use_processors=0;
SELECT count()
FROM
(
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
UNION ALL
SELECT number
FROM system.numbers_mt
WHERE number <= 100000000
LIMIT 100000000
)
↓ Progress: 29.44 billion rows, 235.48 GB (2.58 billion rows/s., 20.62 GB/s.) Cancelling query.
↙ Progress: 29.68 billion rows, 237.41 GB (2.58 billion rows/s., 20.61 GB/s.) Ok.
Query was cancelled.
0 rows in set. Elapsed: 11.521 sec. Processed 29.68 billion rows, 237.41 GB (2.58 billion rows/s., 20.61 GB/s.)
-- never finishes.
```
|
process
|
union all issue with processors set experimental use processors select count from select number from system numbers mt where number limit union all select number from system numbers mt where number limit ┌───count ─┐ │ │ └───────────┘ rows in set elapsed sec processed million rows gb billion rows s gb s set experimental use processors select count from select number from system numbers mt where number limit union all select number from system numbers mt where number limit ↓ progress billion rows gb billion rows s gb s cancelling query ↙ progress billion rows gb billion rows s gb s ok query was cancelled rows in set elapsed sec processed billion rows gb billion rows s gb s never finishes
| 1
|
22,672
| 31,896,194,403
|
IssuesEvent
|
2023-09-18 02:05:03
|
rust-lang/cargo
|
https://api.github.com/repos/rust-lang/cargo
|
closed
|
Tracking Issue for credential-process RFC 2730
|
T-cargo C-tracking-issue final-comment-period disposition-merge Z-credential-process A-registry-authentication S-waiting-on-feedback
|
**Summary**
RFC: https://github.com/rust-lang/rfcs/pull/2730
Implementation: #8934
Documentation: https://doc.rust-lang.org/nightly/cargo/reference/unstable.html#credential-process
Issues: https://github.com/rust-lang/cargo/labels/Z-credential-process
This feature provides a configuration option to specify a process to fetch a token to authenticate with a registry.
**Unresolved issues**
* [X] Is this approach useful enough? Things like macos keychain don't protect against being executed to extract tokens (and I don't see a way to require a password, or force the process to be untrusted). The lack of signatures also cause issues (each update of the toolchain will cause it to become untrusted again).
* Making the built-in providers like `cargo:macos-keychain` part of the cargo binary improves security here, since only the Cargo binary is accessing the Keychain. If we get Cargo signed by Apple, then it would be further improved.
* [X] Should the `login` API be changed? Providers that need to be interactive need to be able to read from stdin.
* This is worked around by having the credential-provider re-open `stdin` from `/dev/tty` or `$CONIN`
* [X] Should the storage key off the registry name? [RFC 3139](https://github.com/rust-lang/rfcs/pull/3139) discusses problems with this. RESOLVED: credential helpers are now keying off the index url via #10592.
* [x] Should it be possible to pass additional arguments on the command line for `cargo login` that would be sent to the provider? E.g. `cargo login -- --extra-arg-for-provider`
* Implemented in #12499
* [X] Figure out the name for `cargo:basic`: `cargo:token-from-stdout`
* [X] Remove cargo-1password as a built-in (add the `fn main` so it can be published separately).
* [x] Create a new `-Z` flag for `cargo:paseto`.
* [x] Publish `cargo-credential-1password` to crates.io
* [x] Figure out MSRV support. rust-lang/cargo#12381 is proposing to set MSRV for all packages in the repo. I think it will be important that the credential provider libraries have a relatively relaxed requirement (like stable-2 or something). I think this will be important to figure out before stabilization. This may be complicated with CI costs, so I'm wondering if `cargo-credential` could grow a few independent tests on its own so we could test just the library with an older rust? https://github.com/rust-lang/cargo/pull/12623
* [x] Testing of forwards-compatibility support. It is important that when a user installs a new credential provider that it does not necessarily cause older `cargo`s to fail. There is a version field when we need to do breaking changes, but we need tests that are actually verifying that is working. https://github.com/rust-lang/cargo/pull/12622
* [x] A test with some manually generated JSON with an invalid version file fed into a credential provider should provide the correct error message.
* [x] A test with some manually generated JSON with the current V1 format that is fed into a credential provider, and validate that it behaves correctly. This will make sure that if any changes to the credential provider are made that are not compatible with the old format that the test will fail.
* [x] Resolve rust-lang/cargo#12642
* [ ] Stabilization PR - #12649
* [ ] Publish `cargo-credential` `v0.4` to [crates.io](https://crates.io/crates/cargo-credential)
* [ ] Publish `cargo-credential-1password` `v0.4` to [crates.io](https://crates.io/crates/cargo-credential-1password)
**About tracking issues**
Tracking issues are used to record the overall progress of implementation.
They are also used as hubs connecting to other relevant issues, e.g., bugs or open design questions.
A tracking issue is however *not* meant for large scale discussion, questions, or bug reports about a feature.
Instead, open a dedicated issue for the specific matter and add the relevant feature gate label.
|
1.0
|
Tracking Issue for credential-process RFC 2730 - **Summary**
RFC: https://github.com/rust-lang/rfcs/pull/2730
Implementation: #8934
Documentation: https://doc.rust-lang.org/nightly/cargo/reference/unstable.html#credential-process
Issues: https://github.com/rust-lang/cargo/labels/Z-credential-process
This feature provides a configuration option to specify a process to fetch a token to authenticate with a registry.
**Unresolved issues**
* [X] Is this approach useful enough? Things like macos keychain don't protect against being executed to extract tokens (and I don't see a way to require a password, or force the process to be untrusted). The lack of signatures also cause issues (each update of the toolchain will cause it to become untrusted again).
* Making the built-in providers like `cargo:macos-keychain` part of the cargo binary improves security here, since only the Cargo binary is accessing the Keychain. If we get Cargo signed by Apple, then it would be further improved.
* [X] Should the `login` API be changed? Providers that need to be interactive need to be able to read from stdin.
* This is worked around by having the credential-provider re-open `stdin` from `/dev/tty` or `$CONIN`
* [X] Should the storage key off the registry name? [RFC 3139](https://github.com/rust-lang/rfcs/pull/3139) discusses problems with this. RESOLVED: credential helpers are now keying off the index url via #10592.
* [x] Should it be possible to pass additional arguments on the command line for `cargo login` that would be sent to the provider? E.g. `cargo login -- --extra-arg-for-provider`
* Implemented in #12499
* [X] Figure out the name for `cargo:basic`: `cargo:token-from-stdout`
* [X] Remove cargo-1password as a built-in (add the `fn main` so it can be published separately).
* [x] Create a new `-Z` flag for `cargo:paseto`.
* [x] Publish `cargo-credential-1password` to crates.io
* [x] Figure out MSRV support. rust-lang/cargo#12381 is proposing to set MSRV for all packages in the repo. I think it will be important that the credential provider libraries have a relatively relaxed requirement (like stable-2 or something). I think this will be important to figure out before stabilization. This may be complicated with CI costs, so I'm wondering if `cargo-credential` could grow a few independent tests on its own so we could test just the library with an older rust? https://github.com/rust-lang/cargo/pull/12623
* [x] Testing of forwards-compatibility support. It is important that when a user installs a new credential provider that it does not necessarily cause older `cargo`s to fail. There is a version field when we need to do breaking changes, but we need tests that are actually verifying that is working. https://github.com/rust-lang/cargo/pull/12622
* [x] A test with some manually generated JSON with an invalid version file fed into a credential provider should provide the correct error message.
* [x] A test with some manually generated JSON with the current V1 format that is fed into a credential provider, and validate that it behaves correctly. This will make sure that if any changes to the credential provider are made that are not compatible with the old format that the test will fail.
* [x] Resolve rust-lang/cargo#12642
* [ ] Stabilization PR - #12649
* [ ] Publish `cargo-credential` `v0.4` to [crates.io](https://crates.io/crates/cargo-credential)
* [ ] Publish `cargo-credential-1password` `v0.4` to [crates.io](https://crates.io/crates/cargo-credential-1password)
**About tracking issues**
Tracking issues are used to record the overall progress of implementation.
They are also used as hubs connecting to other relevant issues, e.g., bugs or open design questions.
A tracking issue is however *not* meant for large scale discussion, questions, or bug reports about a feature.
Instead, open a dedicated issue for the specific matter and add the relevant feature gate label.
|
process
|
tracking issue for credential process rfc summary rfc implementation documentation issues this feature provides a configuration option to specify a process to fetch a token to authenticate with a registry unresolved issues is this approach useful enough things like macos keychain don t protect against being executed to extract tokens and i don t see a way to require a password or force the process to be untrusted the lack of signatures also cause issues each update of the toolchain will cause it to become untrusted again making the built in providers like cargo macos keychain part of the cargo binary improves security here since only the cargo binary is accessing the keychain if we get cargo signed by apple then it would be further improved should the login api be changed providers that need to be interactive need to be able to read from stdin this is worked around by having the credential provider re open stdin from dev tty or conin should the storage key off the registry name discusses problems with this resolved credential helpers are now keying off the index url via should it be possible to pass additional arguments on the command line for cargo login that would be sent to the provider e g cargo login extra arg for provider implemented in figure out the name for cargo basic cargo token from stdout remove cargo as a built in add the fn main so it can be published separately create a new z flag for cargo paseto publish cargo credential to crates io figure out msrv support rust lang cargo is proposing to set msrv for all packages in the repo i think it will be important that the credential provider libraries have a relatively relaxed requirement like stable or something i think this will be important to figure out before stabilization this may be complicated with ci costs so i m wondering if cargo credential could grow a few independent tests on its own so we could test just the library with an older rust testing of forwards compatibility support it is important that when a user installs a new credential provider that it does not necessarily cause older cargo s to fail there is a version field when we need to do breaking changes but we need tests that are actually verifying that is working a test with some manually generated json with an invalid version file fed into a credential provider should provide the correct error message a test with some manually generated json with the current format that is fed into a credential provider and validate that it behaves correctly this will make sure that if any changes to the credential provider are made that are not compatible with the old format that the test will fail resolve rust lang cargo stabilization pr publish cargo credential to publish cargo credential to about tracking issues tracking issues are used to record the overall progress of implementation they are also used as hubs connecting to other relevant issues e g bugs or open design questions a tracking issue is however not meant for large scale discussion questions or bug reports about a feature instead open a dedicated issue for the specific matter and add the relevant feature gate label
| 1
|
12,217
| 14,743,029,777
|
IssuesEvent
|
2021-01-07 13:17:33
|
kdjstudios/SABillingGitlab
|
https://api.github.com/repos/kdjstudios/SABillingGitlab
|
closed
|
recurring charges not on invoice
|
anc-process anp-important ant-bug ant-support
|
In GitLab by @kdjstudios on Jul 1, 2019, 14:58
**Submitted by:** Gaylan Garrett <Gaylan.Garrett@Nexa.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/8690702
**Server:** External
**Client/Site:** Keener
**Account:** Multiple
**Issue:**
I have four accounts that the recurring did not show up on the 6/23/2019 invoice even though it is an active transaction in the account.
4342360555, 4343940337, 4343337359 and 6106282263. Can you let me know what happened ?
|
1.0
|
recurring charges not on invoice - In GitLab by @kdjstudios on Jul 1, 2019, 14:58
**Submitted by:** Gaylan Garrett <Gaylan.Garrett@Nexa.com>
**Helpdesk:** http://www.servicedesk.answernet.com/profiles/ticket/8690702
**Server:** External
**Client/Site:** Keener
**Account:** Multiple
**Issue:**
I have four accounts that the recurring did not show up on the 6/23/2019 invoice even though it is an active transaction in the account.
4342360555, 4343940337, 4343337359 and 6106282263. Can you let me know what happened ?
|
process
|
recurring charges not on invoice in gitlab by kdjstudios on jul submitted by gaylan garrett helpdesk server external client site keener account multiple issue i have four accounts that the recurring did not show up on the invoice even though it is an active transaction in the account and can you let me know what happened
| 1
|
22,573
| 31,799,305,925
|
IssuesEvent
|
2023-09-13 10:01:49
|
open-telemetry/opentelemetry-collector-contrib
|
https://api.github.com/repos/open-telemetry/opentelemetry-collector-contrib
|
closed
|
[processor/resourcedetection] system detector sets `host.id` to an empty value on containerized setups
|
bug Stale priority:p2 processor/resourcedetection
|
### Component(s)
processor/resourcedetection
### What happened?
## Description
The `host.id` resource attribute is set by the `system` detector to an empty string value when running on containerized setups.
## Steps to Reproduce
Run the Collector contrib Docker image with the configuration provided below. This is also reproducible with custom builds if one has some base images (e.g. `alpine:3.16`).
## Expected Result
The detector works in accordance to [the specification](https://github.com/open-telemetry/semantic-conventions/blob/c6efa4b2b44f9950b332a46311834e23b85bf979/docs/resource/host.md) which states that (emphasis mine):
> Unique host ID. For Cloud, this must be the instance_id assigned by the cloud provider. For **non-containerized systems,** this should be the machine-id. See the table below for the sources to use to determine the machine-id based on operating system.
AIUI, an empty string is not valid since it's not unique, and on containerized environments, this should not be the machine-id since a container is not 'really' a host.
My expectation would be either that on containerized environments the `host.id` resource attribute is not set or that it is set to a value that persists across restarts.
## Actual Result
On v0.80.0, an empty string is set on `host.id`, which is not a "unique host ID". On v0.72.0 up to v0.79.0, a random UUID that varies on each container restart is set on `host.id`.
### Collector version
v0.80.0
### Environment information
## Environment
Running the docker image `otel/opentelemetry-collector-contrib:0.80.0` with the configuration provided below reproduces this.
### OpenTelemetry Collector configuration
```yaml
receivers:
# Put a dummy receiver just to generate some metrics
hostmetrics:
collection_interval: 10s
scrapers:
load:
processors:
resourcedetection:
detectors: [system]
exporters:
logging:
verbosity: detailed
service:
pipelines:
metrics:
receivers: [hostmetrics]
processors: [resourcedetection]
exporters: [logging]
```
### Log output
```shell
2023-07-12T10:15:03.905Z info service/telemetry.go:81 Setting up own telemetry...
2023-07-12T10:15:03.907Z info service/telemetry.go:104 Serving Prometheus metrics {"address": ":8888", "level": "Basic"}
2023-07-12T10:15:03.907Z info exporter@v0.80.0/exporter.go:275 Development component. May change in the future. {"kind": "exporter", "data_type": "metrics", "name": "logging"}
2023-07-12T10:15:03.910Z info service/service.go:131 Starting otelcol-contrib... {"Version": "0.80.0", "NumCPU": 20}
2023-07-12T10:15:03.910Z info extensions/extensions.go:30 Starting extensions...
2023-07-12T10:15:03.910Z info internal/resourcedetection.go:125 began detecting resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics"}
2023-07-12T10:15:03.912Z info internal/resourcedetection.go:139 detected resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics", "resource": {"host.id":"","host.name":"d5ad29786527","os.type":"linux"}}
```
### Additional context
Prior to v0.80.0 (in particular, in between v0.72.0 that included #18618 and before #18740) this would generate a random UUID on each container restart. An example run of the same configuration on v0.79.0:
```
2023-07-07T11:04:20.764Z info service/telemetry.go:104 Setting up own telemetry...
2023-07-07T11:04:20.764Z info service/telemetry.go:127 Serving Prometheus metrics {"address": ":8888", "level": "Basic"}
2023-07-07T11:04:20.764Z info exporter@v0.79.0/exporter.go:275 Development component. May change in the future. {"kind": "exporter", "data_type": "metrics", "name": "logging"}
2023-07-07T11:04:20.766Z info service/service.go:131 Starting otelcol-contrib... {"Version": "0.79.0", "NumCPU": 20}
2023-07-07T11:04:20.766Z info extensions/extensions.go:30 Starting extensions...
2023-07-07T11:04:20.766Z info internal/resourcedetection.go:125 began detecting resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics"}
2023-07-07T11:04:20.766Z info internal/resourcedetection.go:139 detected resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics", "resource": {"host.id":"d8aeac44-921a-449b-a1d9-aa1621c50d3d","host.name":"43a4683d77f0","os.type":"linux"}}
```
This was reported on https://github.com/open-telemetry/opentelemetry-collector-contrib/pull/18618#issuecomment-1539413938 and happens because [this code path](https://github.com/panta/machineid/blob/c77705a58e0650035e15e10df9d594c9d169dedf/id_linux.go#L48-L53) is taken on the dependency used by #18618 to run this.
|
1.0
|
[processor/resourcedetection] system detector sets `host.id` to an empty value on containerized setups - ### Component(s)
processor/resourcedetection
### What happened?
## Description
The `host.id` resource attribute is set by the `system` detector to an empty string value when running on containerized setups.
## Steps to Reproduce
Run the Collector contrib Docker image with the configuration provided below. This is also reproducible with custom builds if one has some base images (e.g. `alpine:3.16`).
## Expected Result
The detector works in accordance to [the specification](https://github.com/open-telemetry/semantic-conventions/blob/c6efa4b2b44f9950b332a46311834e23b85bf979/docs/resource/host.md) which states that (emphasis mine):
> Unique host ID. For Cloud, this must be the instance_id assigned by the cloud provider. For **non-containerized systems,** this should be the machine-id. See the table below for the sources to use to determine the machine-id based on operating system.
AIUI, an empty string is not valid since it's not unique, and on containerized environments, this should not be the machine-id since a container is not 'really' a host.
My expectation would be either that on containerized environments the `host.id` resource attribute is not set or that it is set to a value that persists across restarts.
## Actual Result
On v0.80.0, an empty string is set on `host.id`, which is not a "unique host ID". On v0.72.0 up to v0.79.0, a random UUID that varies on each container restart is set on `host.id`.
### Collector version
v0.80.0
### Environment information
## Environment
Running the docker image `otel/opentelemetry-collector-contrib:0.80.0` with the configuration provided below reproduces this.
### OpenTelemetry Collector configuration
```yaml
receivers:
# Put a dummy receiver just to generate some metrics
hostmetrics:
collection_interval: 10s
scrapers:
load:
processors:
resourcedetection:
detectors: [system]
exporters:
logging:
verbosity: detailed
service:
pipelines:
metrics:
receivers: [hostmetrics]
processors: [resourcedetection]
exporters: [logging]
```
### Log output
```shell
2023-07-12T10:15:03.905Z info service/telemetry.go:81 Setting up own telemetry...
2023-07-12T10:15:03.907Z info service/telemetry.go:104 Serving Prometheus metrics {"address": ":8888", "level": "Basic"}
2023-07-12T10:15:03.907Z info exporter@v0.80.0/exporter.go:275 Development component. May change in the future. {"kind": "exporter", "data_type": "metrics", "name": "logging"}
2023-07-12T10:15:03.910Z info service/service.go:131 Starting otelcol-contrib... {"Version": "0.80.0", "NumCPU": 20}
2023-07-12T10:15:03.910Z info extensions/extensions.go:30 Starting extensions...
2023-07-12T10:15:03.910Z info internal/resourcedetection.go:125 began detecting resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics"}
2023-07-12T10:15:03.912Z info internal/resourcedetection.go:139 detected resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics", "resource": {"host.id":"","host.name":"d5ad29786527","os.type":"linux"}}
```
### Additional context
Prior to v0.80.0 (in particular, in between v0.72.0 that included #18618 and before #18740) this would generate a random UUID on each container restart. An example run of the same configuration on v0.79.0:
```
2023-07-07T11:04:20.764Z info service/telemetry.go:104 Setting up own telemetry...
2023-07-07T11:04:20.764Z info service/telemetry.go:127 Serving Prometheus metrics {"address": ":8888", "level": "Basic"}
2023-07-07T11:04:20.764Z info exporter@v0.79.0/exporter.go:275 Development component. May change in the future. {"kind": "exporter", "data_type": "metrics", "name": "logging"}
2023-07-07T11:04:20.766Z info service/service.go:131 Starting otelcol-contrib... {"Version": "0.79.0", "NumCPU": 20}
2023-07-07T11:04:20.766Z info extensions/extensions.go:30 Starting extensions...
2023-07-07T11:04:20.766Z info internal/resourcedetection.go:125 began detecting resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics"}
2023-07-07T11:04:20.766Z info internal/resourcedetection.go:139 detected resource information {"kind": "processor", "name": "resourcedetection", "pipeline": "metrics", "resource": {"host.id":"d8aeac44-921a-449b-a1d9-aa1621c50d3d","host.name":"43a4683d77f0","os.type":"linux"}}
```
This was reported on https://github.com/open-telemetry/opentelemetry-collector-contrib/pull/18618#issuecomment-1539413938 and happens because [this code path](https://github.com/panta/machineid/blob/c77705a58e0650035e15e10df9d594c9d169dedf/id_linux.go#L48-L53) is taken on the dependency used by #18618 to run this.
|
process
|
system detector sets host id to an empty value on containerized setups component s processor resourcedetection what happened description the host id resource attribute is set by the system detector to an empty string value when running on containerized setups steps to reproduce run the collector contrib docker image with the configuration provided below this is also reproducible with custom builds if one has some base images e g alpine expected result the detector works in accordance to which states that emphasis mine unique host id for cloud this must be the instance id assigned by the cloud provider for non containerized systems this should be the machine id see the table below for the sources to use to determine the machine id based on operating system aiui an empty string is not valid since it s not unique and on containerized environments this should not be the machine id since a container is not really a host my expectation would be either that on containerized environments the host id resource attribute is not set or that it is set to a value that persists across restarts actual result on an empty string is set on host id which is not a unique host id on up to a random uuid that varies on each container restart is set on host id collector version environment information environment running the docker image otel opentelemetry collector contrib with the configuration provided below reproduces this opentelemetry collector configuration yaml receivers put a dummy receiver just to generate some metrics hostmetrics collection interval scrapers load processors resourcedetection detectors exporters logging verbosity detailed service pipelines metrics receivers processors exporters log output shell info service telemetry go setting up own telemetry info service telemetry go serving prometheus metrics address level basic info exporter exporter go development component may change in the future kind exporter data type metrics name logging info service service go starting otelcol contrib version numcpu info extensions extensions go starting extensions info internal resourcedetection go began detecting resource information kind processor name resourcedetection pipeline metrics info internal resourcedetection go detected resource information kind processor name resourcedetection pipeline metrics resource host id host name os type linux additional context prior to in particular in between that included and before this would generate a random uuid on each container restart an example run of the same configuration on info service telemetry go setting up own telemetry info service telemetry go serving prometheus metrics address level basic info exporter exporter go development component may change in the future kind exporter data type metrics name logging info service service go starting otelcol contrib version numcpu info extensions extensions go starting extensions info internal resourcedetection go began detecting resource information kind processor name resourcedetection pipeline metrics info internal resourcedetection go detected resource information kind processor name resourcedetection pipeline metrics resource host id host name os type linux this was reported on and happens because is taken on the dependency used by to run this
| 1
|
22,328
| 30,913,675,441
|
IssuesEvent
|
2023-08-05 02:34:44
|
h4sh5/pypi-auto-scanner
|
https://api.github.com/repos/h4sh5/pypi-auto-scanner
|
opened
|
pih 1.48036 has 2 GuardDog issues
|
guarddog typosquatting silent-process-execution
|
https://pypi.org/project/pih
https://inspector.pypi.io/project/pih
```{
"dependency": "pih",
"version": "1.48036",
"result": {
"issues": 2,
"errors": {},
"results": {
"typosquatting": "This package closely ressembles the following package names, and might be a typosquatting attempt: pid, pip",
"silent-process-execution": [
{
"location": "pih-1.48036/pih/tools.py:781",
"code": " result = subprocess.run(command, stdin=subprocess.DEVNULL, stdout=subprocess.DEVNULL, stderr=subprocess.DEVNULL)",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
}
]
},
"path": "/tmp/tmp1cvfe72r/pih"
}
}```
|
1.0
|
pih 1.48036 has 2 GuardDog issues - https://pypi.org/project/pih
https://inspector.pypi.io/project/pih
```{
"dependency": "pih",
"version": "1.48036",
"result": {
"issues": 2,
"errors": {},
"results": {
"typosquatting": "This package closely ressembles the following package names, and might be a typosquatting attempt: pid, pip",
"silent-process-execution": [
{
"location": "pih-1.48036/pih/tools.py:781",
"code": " result = subprocess.run(command, stdin=subprocess.DEVNULL, stdout=subprocess.DEVNULL, stderr=subprocess.DEVNULL)",
"message": "This package is silently executing an external binary, redirecting stdout, stderr and stdin to /dev/null"
}
]
},
"path": "/tmp/tmp1cvfe72r/pih"
}
}```
|
process
|
pih has guarddog issues dependency pih version result issues errors results typosquatting this package closely ressembles the following package names and might be a typosquatting attempt pid pip silent process execution location pih pih tools py code result subprocess run command stdin subprocess devnull stdout subprocess devnull stderr subprocess devnull message this package is silently executing an external binary redirecting stdout stderr and stdin to dev null path tmp pih
| 1
|
21,234
| 28,350,152,080
|
IssuesEvent
|
2023-04-12 01:34:58
|
bazelbuild/bazel
|
https://api.github.com/repos/bazelbuild/bazel
|
closed
|
--show_task_finish no longer has an implementation
|
P2 type: process team-OSS stale
|
### Description of the problem / feature request:
I tried using the `--show_task_finish` option with `bazel build --curses=no`, and discovered that it had no effect on the output.
I looked in the bazel code, and noticed that while it was recognized as an option, the option no longer had an implementation.
The last use of `showTaskFinish` was removed in 3e9eec42f9523bd835d3185f98e5cacc431bb4bd.
### Feature requests: what underlying problem are you trying to solve with this feature?
It would be helpful to either implement the option (preferred), or to remove it altogether.
### Bugs: what's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
Try using `--show_task_finish`
### What operating system are you running Bazel on?
Ubuntu 18.04
### What's the output of `bazel info release`?
release 3.1.0
|
1.0
|
--show_task_finish no longer has an implementation - ### Description of the problem / feature request:
I tried using the `--show_task_finish` option with `bazel build --curses=no`, and discovered that it had no effect on the output.
I looked in the bazel code, and noticed that while it was recognized as an option, the option no longer had an implementation.
The last use of `showTaskFinish` was removed in 3e9eec42f9523bd835d3185f98e5cacc431bb4bd.
### Feature requests: what underlying problem are you trying to solve with this feature?
It would be helpful to either implement the option (preferred), or to remove it altogether.
### Bugs: what's the simplest, easiest way to reproduce this bug? Please provide a minimal example if possible.
Try using `--show_task_finish`
### What operating system are you running Bazel on?
Ubuntu 18.04
### What's the output of `bazel info release`?
release 3.1.0
|
process
|
show task finish no longer has an implementation description of the problem feature request i tried using the show task finish option with bazel build curses no and discovered that it had no effect on the output i looked in the bazel code and noticed that while it was recognized as an option the option no longer had an implementation the last use of showtaskfinish was removed in feature requests what underlying problem are you trying to solve with this feature it would be helpful to either implement the option preferred or to remove it altogether bugs what s the simplest easiest way to reproduce this bug please provide a minimal example if possible try using show task finish what operating system are you running bazel on ubuntu what s the output of bazel info release release
| 1
|
70,109
| 18,018,259,207
|
IssuesEvent
|
2021-09-16 16:05:21
|
golang/go
|
https://api.github.com/repos/golang/go
|
opened
|
x/build: ios-arm64-corellium builders have long wait times
|
Builders NeedsFix
|
Users have reported long wait times with ios-arm64-corellium builds:
```
• ios-arm64-corellium | running 1h38m44s
```
```
ios-arm64-corellium rev cfa233d7 (sub-repo mobile rev 855b5ad0) (trybot set for Ib1a2f53); waiting_for_machine; (nil *buildlet.Client), 1h45m36s ago
2021-09-16T14:15:15Z checking_for_snapshot
2021-09-16T14:15:15Z finish_checking_for_snapshot after 35ms
2021-09-16T14:15:15Z get_buildlet
+6335.7s (now)
```
`host-ios-arm64-corellium-ios: 2/2 (1 missing)`
Perhaps the builders need to be rebooted.
@eliasnaur @golang/release
|
1.0
|
x/build: ios-arm64-corellium builders have long wait times - Users have reported long wait times with ios-arm64-corellium builds:
```
• ios-arm64-corellium | running 1h38m44s
```
```
ios-arm64-corellium rev cfa233d7 (sub-repo mobile rev 855b5ad0) (trybot set for Ib1a2f53); waiting_for_machine; (nil *buildlet.Client), 1h45m36s ago
2021-09-16T14:15:15Z checking_for_snapshot
2021-09-16T14:15:15Z finish_checking_for_snapshot after 35ms
2021-09-16T14:15:15Z get_buildlet
+6335.7s (now)
```
`host-ios-arm64-corellium-ios: 2/2 (1 missing)`
Perhaps the builders need to be rebooted.
@eliasnaur @golang/release
|
non_process
|
x build ios corellium builders have long wait times users have reported long wait times with ios corellium builds • ios corellium running ios corellium rev sub repo mobile rev trybot set for waiting for machine nil buildlet client ago checking for snapshot finish checking for snapshot after get buildlet now host ios corellium ios missing perhaps the builders need to be rebooted eliasnaur golang release
| 0
|
197,042
| 14,901,662,478
|
IssuesEvent
|
2021-01-21 16:42:45
|
idaholab/moose
|
https://api.github.com/repos/idaholab/moose
|
closed
|
Add option to show the longest running jobs in TestHarness
|
C: TestHarness P: normal T: task
|
## Reason
To keep test timing to a minimum, it would be useful to print out the longest running jobs at the end of execution in the test harness.
## Design
Add a `--longest-jobs` options to TestHarness that will print the longest running jobs at the end.
## Impact
Better management of test timing.
|
1.0
|
Add option to show the longest running jobs in TestHarness - ## Reason
To keep test timing to a minimum, it would be useful to print out the longest running jobs at the end of execution in the test harness.
## Design
Add a `--longest-jobs` options to TestHarness that will print the longest running jobs at the end.
## Impact
Better management of test timing.
|
non_process
|
add option to show the longest running jobs in testharness reason to keep test timing to a minimum it would be useful to print out the longest running jobs at the end of execution in the test harness design add a longest jobs options to testharness that will print the longest running jobs at the end impact better management of test timing
| 0
|
222,584
| 24,709,177,726
|
IssuesEvent
|
2022-10-19 22:08:18
|
lukebrogan-mend/Umbraco-CMS
|
https://api.github.com/repos/lukebrogan-mend/Umbraco-CMS
|
closed
|
CVE-2020-28481 (Medium) detected in socket.io-2.1.1.tgz - autoclosed
|
security vulnerability
|
## CVE-2020-28481 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>socket.io-2.1.1.tgz</b></p></summary>
<p>node.js realtime framework server</p>
<p>Library home page: <a href="https://registry.npmjs.org/socket.io/-/socket.io-2.1.1.tgz">https://registry.npmjs.org/socket.io/-/socket.io-2.1.1.tgz</a></p>
<p>Path to dependency file: /src/Umbraco.Web.UI.Client/package.json</p>
<p>Path to vulnerable library: /src/Umbraco.Web.UI.Client/node_modules/socket.io/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.4.1.tgz (Root Library)
- :x: **socket.io-2.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/Umbraco-CMS/commit/24bd18757bbbe3324d85424fdabf1d6bdaf1695e">24bd18757bbbe3324d85424fdabf1d6bdaf1695e</a></p>
<p>Found in base branch: <b>v8/contrib</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package socket.io before 2.4.0 are vulnerable to Insecure Defaults due to CORS Misconfiguration. All domains are whitelisted by default.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28481>CVE-2020-28481</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28481">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28481</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution (socket.io): 2.4.0</p>
<p>Direct dependency fix Resolution (karma): 5.0.8</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
|
True
|
CVE-2020-28481 (Medium) detected in socket.io-2.1.1.tgz - autoclosed - ## CVE-2020-28481 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>socket.io-2.1.1.tgz</b></p></summary>
<p>node.js realtime framework server</p>
<p>Library home page: <a href="https://registry.npmjs.org/socket.io/-/socket.io-2.1.1.tgz">https://registry.npmjs.org/socket.io/-/socket.io-2.1.1.tgz</a></p>
<p>Path to dependency file: /src/Umbraco.Web.UI.Client/package.json</p>
<p>Path to vulnerable library: /src/Umbraco.Web.UI.Client/node_modules/socket.io/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.4.1.tgz (Root Library)
- :x: **socket.io-2.1.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/lukebroganws/Umbraco-CMS/commit/24bd18757bbbe3324d85424fdabf1d6bdaf1695e">24bd18757bbbe3324d85424fdabf1d6bdaf1695e</a></p>
<p>Found in base branch: <b>v8/contrib</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The package socket.io before 2.4.0 are vulnerable to Insecure Defaults due to CORS Misconfiguration. All domains are whitelisted by default.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28481>CVE-2020-28481</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28481">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28481</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution (socket.io): 2.4.0</p>
<p>Direct dependency fix Resolution (karma): 5.0.8</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
|
non_process
|
cve medium detected in socket io tgz autoclosed cve medium severity vulnerability vulnerable library socket io tgz node js realtime framework server library home page a href path to dependency file src umbraco web ui client package json path to vulnerable library src umbraco web ui client node modules socket io package json dependency hierarchy karma tgz root library x socket io tgz vulnerable library found in head commit a href found in base branch contrib vulnerability details the package socket io before are vulnerable to insecure defaults due to cors misconfiguration all domains are whitelisted by default publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution socket io direct dependency fix resolution karma rescue worker helmet automatic remediation is available for this issue
| 0
|
4,291
| 7,191,972,477
|
IssuesEvent
|
2018-02-02 23:27:37
|
amaster507/ifbmt
|
https://api.github.com/repos/amaster507/ifbmt
|
closed
|
Call Log with Reminders
|
enhancement idea process
|
@jrwilliams27
A feature that would be very useful would be a way to record a call/contact log for calls/emails/contact to a church - apart from the notes or integrated into the notes. The date/time could be automatically recorded (or changed), a note made, and a scheduled time to contact the church again could be made. A reminder option could give options to notify at a certain date/time, and then when that time is due, the reminder notifies you of the contact(s) needed to be made, filter out the contact(s), that list would be generated, and then one can work through the contact(s).
|
1.0
|
Call Log with Reminders - @jrwilliams27
A feature that would be very useful would be a way to record a call/contact log for calls/emails/contact to a church - apart from the notes or integrated into the notes. The date/time could be automatically recorded (or changed), a note made, and a scheduled time to contact the church again could be made. A reminder option could give options to notify at a certain date/time, and then when that time is due, the reminder notifies you of the contact(s) needed to be made, filter out the contact(s), that list would be generated, and then one can work through the contact(s).
|
process
|
call log with reminders a feature that would be very useful would be a way to record a call contact log for calls emails contact to a church apart from the notes or integrated into the notes the date time could be automatically recorded or changed a note made and a scheduled time to contact the church again could be made a reminder option could give options to notify at a certain date time and then when that time is due the reminder notifies you of the contact s needed to be made filter out the contact s that list would be generated and then one can work through the contact s
| 1
|
15,759
| 27,848,810,888
|
IssuesEvent
|
2023-03-20 17:11:39
|
dgidb/dgidb-v5
|
https://api.github.com/repos/dgidb/dgidb-v5
|
closed
|
Interaction Record Page
|
requirement frontend priority:high
|
We have individual record pages for genes and drugs. We need to implement this for interactions.
Prod example: https://www.dgidb.org/interactions/b8e5098d-4915-4c3f-974a-8a0cf9b97bd6#_summary
|
1.0
|
Interaction Record Page - We have individual record pages for genes and drugs. We need to implement this for interactions.
Prod example: https://www.dgidb.org/interactions/b8e5098d-4915-4c3f-974a-8a0cf9b97bd6#_summary
|
non_process
|
interaction record page we have individual record pages for genes and drugs we need to implement this for interactions prod example
| 0
|
22,315
| 30,870,180,952
|
IssuesEvent
|
2023-08-03 10:45:40
|
benthosdev/benthos
|
https://api.github.com/repos/benthosdev/benthos
|
closed
|
Bloblang interpolation in http jwt claims
|
enhancement question processors
|
Hi, I was trying to use http processor with jwt enabled and I need to set the "iat" claim with current timestamp using this code:
```
jwt:
enabled: true
private_key_file: private.pem
signing_method: RS256
claims:
iss: iotbuilder
sub: benthos
iat: ${! timestamp_unix() * 1000 }
```
but on the server the decoded JWT is:
```
{
iat: '${! timestamp_unix() * 1000 }',
iss: 'iotbuilder',
sub: 'benthos'
}
```
The iat claim is not interpolated.
|
1.0
|
Bloblang interpolation in http jwt claims - Hi, I was trying to use http processor with jwt enabled and I need to set the "iat" claim with current timestamp using this code:
```
jwt:
enabled: true
private_key_file: private.pem
signing_method: RS256
claims:
iss: iotbuilder
sub: benthos
iat: ${! timestamp_unix() * 1000 }
```
but on the server the decoded JWT is:
```
{
iat: '${! timestamp_unix() * 1000 }',
iss: 'iotbuilder',
sub: 'benthos'
}
```
The iat claim is not interpolated.
|
process
|
bloblang interpolation in http jwt claims hi i was trying to use http processor with jwt enabled and i need to set the iat claim with current timestamp using this code jwt enabled true private key file private pem signing method claims iss iotbuilder sub benthos iat timestamp unix but on the server the decoded jwt is iat timestamp unix iss iotbuilder sub benthos the iat claim is not interpolated
| 1
|
31,663
| 6,583,086,205
|
IssuesEvent
|
2017-09-13 03:07:00
|
hazelcast/hazelcast
|
https://api.github.com/repos/hazelcast/hazelcast
|
closed
|
[client] networkconfig address validation missing
|
Team: Client Type: Defect
|
The following program runs fine even though no valid address has been added.
```
public class Main {
public static void main(String[] args){
HazelcastInstance server = Hazelcast.newHazelcastInstance();
ClientConfig clientConfig = new ClientConfig();
clientConfig.getNetworkConfig().addAddress("");
HazelcastInstance client = HazelcastClient.newHazelcastClient(clientConfig);
System.out.println(client.getAtomicLong("foo").incrementAndGet());
}
}
```
So we violate fail-fast.
We should check if the passed address is a valid ip address or hostname.
|
1.0
|
[client] networkconfig address validation missing - The following program runs fine even though no valid address has been added.
```
public class Main {
public static void main(String[] args){
HazelcastInstance server = Hazelcast.newHazelcastInstance();
ClientConfig clientConfig = new ClientConfig();
clientConfig.getNetworkConfig().addAddress("");
HazelcastInstance client = HazelcastClient.newHazelcastClient(clientConfig);
System.out.println(client.getAtomicLong("foo").incrementAndGet());
}
}
```
So we violate fail-fast.
We should check if the passed address is a valid ip address or hostname.
|
non_process
|
networkconfig address validation missing the following program runs fine even though no valid address has been added public class main public static void main string args hazelcastinstance server hazelcast newhazelcastinstance clientconfig clientconfig new clientconfig clientconfig getnetworkconfig addaddress hazelcastinstance client hazelcastclient newhazelcastclient clientconfig system out println client getatomiclong foo incrementandget so we violate fail fast we should check if the passed address is a valid ip address or hostname
| 0
|
230,822
| 17,647,444,025
|
IssuesEvent
|
2021-08-20 08:24:47
|
sertit/eoreader
|
https://api.github.com/repos/sertit/eoreader
|
closed
|
DOC: Updates
|
documentation
|
It could be cool to create one page for every supported sensor.
This could be useful to:
- Show what product type is not used for a specific sensor
- Warn the user about some specificity
- ...
[EDIT]: Not really useful until a user needs it
|
1.0
|
DOC: Updates - It could be cool to create one page for every supported sensor.
This could be useful to:
- Show what product type is not used for a specific sensor
- Warn the user about some specificity
- ...
[EDIT]: Not really useful until a user needs it
|
non_process
|
doc updates it could be cool to create one page for every supported sensor this could be useful to show what product type is not used for a specific sensor warn the user about some specificity not really useful until a user needs it
| 0
|
245,666
| 7,889,254,256
|
IssuesEvent
|
2018-06-28 02:55:33
|
ThePoptartCrpr/DawnOfMan
|
https://api.github.com/repos/ThePoptartCrpr/DawnOfMan
|
closed
|
Inventory icon overlap with Nutrition
|
category: compatibility priority: high type: bug
|
# Description
<!-- Please describe your issue in detail below. -->
Nutrition's icon in the inventory overlaps the sort icon added by Quark, as seen below. This can be fixed by modifying the position of Nutrition's icon in the inventory via configs.
# Evidence
<!-- Please attach any useful evidence below, i.e. logs or screenshots -->

|
1.0
|
Inventory icon overlap with Nutrition - # Description
<!-- Please describe your issue in detail below. -->
Nutrition's icon in the inventory overlaps the sort icon added by Quark, as seen below. This can be fixed by modifying the position of Nutrition's icon in the inventory via configs.
# Evidence
<!-- Please attach any useful evidence below, i.e. logs or screenshots -->

|
non_process
|
inventory icon overlap with nutrition description nutrition s icon in the inventory overlaps the sort icon added by quark as seen below this can be fixed by modifying the position of nutrition s icon in the inventory via configs evidence
| 0
|
12,928
| 15,296,184,558
|
IssuesEvent
|
2021-02-24 06:23:45
|
scikit-learn/scikit-learn
|
https://api.github.com/repos/scikit-learn/scikit-learn
|
closed
|
Let NaNs pass through in OrdinalEncoder
|
Hard New Feature module:preprocessing
|
We should allow NaNs to pass-through in `OrdinalEncoder`. One reason is for supporting categorical features with NaNs in the `HistGradientBoosting ` estimators:
For the native categorical support, we require categories to be encoded as done by `OrdinalEncoder`. Yet, `OrdinalEncoder` is unable to be fitted with NaNs. So we can't use the native categorical support of the Hist-GBDT if the categorical features have NaNs... Which is ironic because we do support NaNs as a native category in the Hist-GBDT code.
In terms of API, we'd need a new `handle_missing={'error', 'passthrough'}` parameter which would default to 'error'.
CC @ogrisel @lorentzenchr @thomasjpfan
(Note: This is a subset of the feature request from https://github.com/scikit-learn/scikit-learn/issues/17123)
(Marking as "Hard" because anything encoding-related is usually a headache ;) )
|
1.0
|
Let NaNs pass through in OrdinalEncoder - We should allow NaNs to pass-through in `OrdinalEncoder`. One reason is for supporting categorical features with NaNs in the `HistGradientBoosting ` estimators:
For the native categorical support, we require categories to be encoded as done by `OrdinalEncoder`. Yet, `OrdinalEncoder` is unable to be fitted with NaNs. So we can't use the native categorical support of the Hist-GBDT if the categorical features have NaNs... Which is ironic because we do support NaNs as a native category in the Hist-GBDT code.
In terms of API, we'd need a new `handle_missing={'error', 'passthrough'}` parameter which would default to 'error'.
CC @ogrisel @lorentzenchr @thomasjpfan
(Note: This is a subset of the feature request from https://github.com/scikit-learn/scikit-learn/issues/17123)
(Marking as "Hard" because anything encoding-related is usually a headache ;) )
|
process
|
let nans pass through in ordinalencoder we should allow nans to pass through in ordinalencoder one reason is for supporting categorical features with nans in the histgradientboosting estimators for the native categorical support we require categories to be encoded as done by ordinalencoder yet ordinalencoder is unable to be fitted with nans so we can t use the native categorical support of the hist gbdt if the categorical features have nans which is ironic because we do support nans as a native category in the hist gbdt code in terms of api we d need a new handle missing error passthrough parameter which would default to error cc ogrisel lorentzenchr thomasjpfan note this is a subset of the feature request from marking as hard because anything encoding related is usually a headache
| 1
|
3,684
| 6,714,762,424
|
IssuesEvent
|
2017-10-13 18:14:42
|
syndesisio/syndesis
|
https://api.github.com/repos/syndesisio/syndesis
|
opened
|
Feature toggle
|
process/retro
|
Discussion: Should we use feature toggles?
Actually, I think that's a very good thing as it allows to avoid branching (which I really would love to avoid as long as possible). This means we add new features guarded by toggles which can be enabled / disabled via configuration. That way we can deliver path release directly from `master`.
My only concern here is, how to tackle heavy refactorings like changing our domain model or fundamental API changes (until we get to a proper versioned API ?)
|
1.0
|
Feature toggle - Discussion: Should we use feature toggles?
Actually, I think that's a very good thing as it allows to avoid branching (which I really would love to avoid as long as possible). This means we add new features guarded by toggles which can be enabled / disabled via configuration. That way we can deliver path release directly from `master`.
My only concern here is, how to tackle heavy refactorings like changing our domain model or fundamental API changes (until we get to a proper versioned API ?)
|
process
|
feature toggle discussion should we use feature toggles actually i think that s a very good thing as it allows to avoid branching which i really would love to avoid as long as possible this means we add new features guarded by toggles which can be enabled disabled via configuration that way we can deliver path release directly from master my only concern here is how to tackle heavy refactorings like changing our domain model or fundamental api changes until we get to a proper versioned api
| 1
|
17,912
| 23,899,873,068
|
IssuesEvent
|
2022-09-08 17:45:09
|
hashgraph/hedera-json-rpc-relay
|
https://api.github.com/repos/hashgraph/hedera-json-rpc-relay
|
closed
|
Bump local node for services 0.30.0-alpha.0 and mirror 0.64.0-beta1
|
enhancement P2 process
|
### Problem
The services 0.30.0-alpha.0 and mirror 0.64.0-beta1 versions are available
### Solution
Update the index.spec.ts with
```
process.env['NETWORK_NODE_IMAGE_TAG'] = '0.30.0-alpha.0';
process.env['HAVEGED_IMAGE_TAG'] = '0.30.0-alpha.0';
process.env['MIRROR_IMAGE_TAG'] = '0.64.0-beta1';
```
### Alternatives
_No response_
|
1.0
|
Bump local node for services 0.30.0-alpha.0 and mirror 0.64.0-beta1 - ### Problem
The services 0.30.0-alpha.0 and mirror 0.64.0-beta1 versions are available
### Solution
Update the index.spec.ts with
```
process.env['NETWORK_NODE_IMAGE_TAG'] = '0.30.0-alpha.0';
process.env['HAVEGED_IMAGE_TAG'] = '0.30.0-alpha.0';
process.env['MIRROR_IMAGE_TAG'] = '0.64.0-beta1';
```
### Alternatives
_No response_
|
process
|
bump local node for services alpha and mirror problem the services alpha and mirror versions are available solution update the index spec ts with process env alpha process env alpha process env alternatives no response
| 1
|
290,726
| 25,090,428,863
|
IssuesEvent
|
2022-11-08 05:31:34
|
crispindeity/issue-tracker
|
https://api.github.com/repos/crispindeity/issue-tracker
|
closed
|
Add Label Integration Test
|
📬 API BE ✅ Test
|
# Description
- Label Integration Test 코드 작성
- [x] Long save()
- [x] ResponseLablesDto findAll()
- [x] void delete()
- [x] Long update()
|
1.0
|
Add Label Integration Test - # Description
- Label Integration Test 코드 작성
- [x] Long save()
- [x] ResponseLablesDto findAll()
- [x] void delete()
- [x] Long update()
|
non_process
|
add label integration test description label integration test 코드 작성 long save responselablesdto findall void delete long update
| 0
|
21,781
| 30,294,584,378
|
IssuesEvent
|
2023-07-09 17:45:27
|
The-Data-Alchemists-Manipal/MindWave
|
https://api.github.com/repos/The-Data-Alchemists-Manipal/MindWave
|
closed
|
Counting People in a frame using OpenCV
|
image-processing
|
### Is your feature request related to a problem? Please describe.
There are various occasions in which we need to study an image or video. In doing so, first thing we capture is people. What if we can count them automatically coming in and out of a video. It doesn't matter if they are completely in the frame, but any part of there body tells they are present in the frame.
### Describe the solution you'd like
To do so, i would use OpenCV to count the number of people in a frame, using face, body, legs analysis.
### Describe alternatives you've considered
_No response_
### Additional context
Under GSSOC'23 please assign me this task.
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
|
1.0
|
Counting People in a frame using OpenCV - ### Is your feature request related to a problem? Please describe.
There are various occasions in which we need to study an image or video. In doing so, first thing we capture is people. What if we can count them automatically coming in and out of a video. It doesn't matter if they are completely in the frame, but any part of there body tells they are present in the frame.
### Describe the solution you'd like
To do so, i would use OpenCV to count the number of people in a frame, using face, body, legs analysis.
### Describe alternatives you've considered
_No response_
### Additional context
Under GSSOC'23 please assign me this task.
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct
|
process
|
counting people in a frame using opencv is your feature request related to a problem please describe there are various occasions in which we need to study an image or video in doing so first thing we capture is people what if we can count them automatically coming in and out of a video it doesn t matter if they are completely in the frame but any part of there body tells they are present in the frame describe the solution you d like to do so i would use opencv to count the number of people in a frame using face body legs analysis describe alternatives you ve considered no response additional context under gssoc please assign me this task code of conduct i agree to follow this project s code of conduct
| 1
|
276,688
| 30,519,959,142
|
IssuesEvent
|
2023-07-19 07:22:16
|
elastic/integrations
|
https://api.github.com/repos/elastic/integrations
|
closed
|
[O365] Migrate to CEL input
|
Team:Security-External Integrations Integration:o365 8.8 candidate 8.9 candidate
|
Our O365 integration relies on the[ O365 Management API input](https://www.elastic.co/guide/en/beats/filebeat/current/filebeat-input-o365audit.html), which is still under a Beta flag. O365 is the only integration leveraging this input and we should look at migrating to the httpjson or cel input as a more suitable alternative. This would avoid us having to maintain and support the o365 input for one integration, and bring the integration inline with our other API based integration.
**Questions**
1. Are there other integrations using the O365 Management API input?
2. Does moving to httpjson allos us to address https://github.com/elastic/integrations/issues/1868
|
True
|
[O365] Migrate to CEL input - Our O365 integration relies on the[ O365 Management API input](https://www.elastic.co/guide/en/beats/filebeat/current/filebeat-input-o365audit.html), which is still under a Beta flag. O365 is the only integration leveraging this input and we should look at migrating to the httpjson or cel input as a more suitable alternative. This would avoid us having to maintain and support the o365 input for one integration, and bring the integration inline with our other API based integration.
**Questions**
1. Are there other integrations using the O365 Management API input?
2. Does moving to httpjson allos us to address https://github.com/elastic/integrations/issues/1868
|
non_process
|
migrate to cel input our integration relies on the which is still under a beta flag is the only integration leveraging this input and we should look at migrating to the httpjson or cel input as a more suitable alternative this would avoid us having to maintain and support the input for one integration and bring the integration inline with our other api based integration questions are there other integrations using the management api input does moving to httpjson allos us to address
| 0
|
213,682
| 24,016,302,174
|
IssuesEvent
|
2022-09-15 01:16:22
|
Baneeishaque/locations
|
https://api.github.com/repos/Baneeishaque/locations
|
opened
|
WS-2020-0042 (High) detected in acorn-5.7.4.tgz
|
security vulnerability
|
## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>acorn-5.7.4.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- jest-expo-27.0.1.tgz (Root Library)
- jest-22.4.4.tgz
- jest-cli-22.4.4.tgz
- jest-environment-jsdom-22.4.3.tgz
- jsdom-11.12.0.tgz
- :x: **acorn-5.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/locations/commit/b8d5a4143a4e0caa970dcb555e1daf11e1ebbc43">b8d5a4143a4e0caa970dcb555e1daf11e1ebbc43</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-01</p>
<p>Fix Resolution (acorn): 6.4.1</p>
<p>Direct dependency fix Resolution (jest-expo): 38.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2020-0042 (High) detected in acorn-5.7.4.tgz - ## WS-2020-0042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>acorn-5.7.4.tgz</b></p></summary>
<p>ECMAScript parser</p>
<p>Library home page: <a href="https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz">https://registry.npmjs.org/acorn/-/acorn-5.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/acorn/package.json</p>
<p>
Dependency Hierarchy:
- jest-expo-27.0.1.tgz (Root Library)
- jest-22.4.4.tgz
- jest-cli-22.4.4.tgz
- jest-environment-jsdom-22.4.3.tgz
- jsdom-11.12.0.tgz
- :x: **acorn-5.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Baneeishaque/locations/commit/b8d5a4143a4e0caa970dcb555e1daf11e1ebbc43">b8d5a4143a4e0caa970dcb555e1daf11e1ebbc43</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
acorn is vulnerable to REGEX DoS. A regex of the form /[x-\ud800]/u causes the parser to enter an infinite loop. attackers may leverage the vulnerability leading to a Denial of Service since the string is not valid UTF16 and it results in it being sanitized before reaching the parser.
<p>Publish Date: 2020-03-01
<p>URL: <a href=https://github.com/acornjs/acorn/commit/b5c17877ac0511e31579ea31e7650ba1a5871e51>WS-2020-0042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1488">https://www.npmjs.com/advisories/1488</a></p>
<p>Release Date: 2020-03-01</p>
<p>Fix Resolution (acorn): 6.4.1</p>
<p>Direct dependency fix Resolution (jest-expo): 38.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
ws high detected in acorn tgz ws high severity vulnerability vulnerable library acorn tgz ecmascript parser library home page a href path to dependency file package json path to vulnerable library node modules acorn package json dependency hierarchy jest expo tgz root library jest tgz jest cli tgz jest environment jsdom tgz jsdom tgz x acorn tgz vulnerable library found in head commit a href vulnerability details acorn is vulnerable to regex dos a regex of the form u causes the parser to enter an infinite loop attackers may leverage the vulnerability leading to a denial of service since the string is not valid and it results in it being sanitized before reaching the parser publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution acorn direct dependency fix resolution jest expo step up your open source security game with mend
| 0
|
1,135
| 3,619,369,370
|
IssuesEvent
|
2016-02-08 15:47:53
|
NuCivic/dkan
|
https://api.github.com/repos/NuCivic/dkan
|
closed
|
Invalid argument supplied for foreach() entity_rdf.module:49
|
bug Component: Viz Entity Processed/JIRA
|
Getting that notice from Viz Entity module operations.
|
1.0
|
Invalid argument supplied for foreach() entity_rdf.module:49 - Getting that notice from Viz Entity module operations.
|
process
|
invalid argument supplied for foreach entity rdf module getting that notice from viz entity module operations
| 1
|
259,684
| 8,198,925,032
|
IssuesEvent
|
2018-08-31 18:10:21
|
johannbrehmer/madminer
|
https://api.github.com/repos/johannbrehmer/madminer
|
closed
|
Load MadMiner settings to GoldMine
|
enhancement high priority
|
Add a function that loads the parameter, benchmark, and morphing setup from an HDF5 file to the GoldMine class.
|
1.0
|
Load MadMiner settings to GoldMine - Add a function that loads the parameter, benchmark, and morphing setup from an HDF5 file to the GoldMine class.
|
non_process
|
load madminer settings to goldmine add a function that loads the parameter benchmark and morphing setup from an file to the goldmine class
| 0
|
5,715
| 8,567,917,329
|
IssuesEvent
|
2018-11-10 16:33:55
|
Great-Hill-Corporation/quickBlocks
|
https://api.github.com/repos/Great-Hill-Corporation/quickBlocks
|
closed
|
Extend getTokenInfo to accept other queries
|
libs-tokenlib status-inprocess type-enhancement
|
Currently, getTokenInfo call in the file getTokenBal.cpp only accepts a value of "balance". It would be easy to extend that to accept many other queries on standard tokens.
|
1.0
|
Extend getTokenInfo to accept other queries - Currently, getTokenInfo call in the file getTokenBal.cpp only accepts a value of "balance". It would be easy to extend that to accept many other queries on standard tokens.
|
process
|
extend gettokeninfo to accept other queries currently gettokeninfo call in the file gettokenbal cpp only accepts a value of balance it would be easy to extend that to accept many other queries on standard tokens
| 1
|
3,552
| 6,587,491,179
|
IssuesEvent
|
2017-09-13 21:17:36
|
cliffparnitzky/ApparelManager
|
https://api.github.com/repos/cliffparnitzky/ApparelManager
|
closed
|
Add notification tokens for BE user and order creator
|
Comp - notification Improvement ⚙ - Processed
|
Add notification tokens for
- [ ] BE user
- [ ] order creator
|
1.0
|
Add notification tokens for BE user and order creator - Add notification tokens for
- [ ] BE user
- [ ] order creator
|
process
|
add notification tokens for be user and order creator add notification tokens for be user order creator
| 1
|
226,471
| 18,020,514,707
|
IssuesEvent
|
2021-09-16 18:47:28
|
arfc/moltres
|
https://api.github.com/repos/arfc/moltres
|
closed
|
Fix ManuHX Jacobian term, allow heat transfer coeff to vary with time, & make a test for ManuHX
|
Comp:Core Difficulty:2-Challenging Priority:1-Critical Status:4-In Progress Type:Bug Type:Feature Type:Test
|
This issue can be closed when the following three objectives involving `ManuHX` are met:
1. Fix the Jacobian term. It is currently missing a `_phi[_j][_qp]` term.
2. Allow the heat transfer coeff `htc` to vary with time by making it `controllable` under MOOSE's `Control` system. This allows us to model a loss of heat sink accident when using `ManuHX` as a heat exchanger
3. Make a test for `ManuHX`. It is currently not covered under any existing tests.
4. (optional) Come up with a more intuitive/mnemonic name for `ManuHX` e.g. `VolumetricHeatSink` or `ConvectiveHeatSink`.
|
1.0
|
Fix ManuHX Jacobian term, allow heat transfer coeff to vary with time, & make a test for ManuHX - This issue can be closed when the following three objectives involving `ManuHX` are met:
1. Fix the Jacobian term. It is currently missing a `_phi[_j][_qp]` term.
2. Allow the heat transfer coeff `htc` to vary with time by making it `controllable` under MOOSE's `Control` system. This allows us to model a loss of heat sink accident when using `ManuHX` as a heat exchanger
3. Make a test for `ManuHX`. It is currently not covered under any existing tests.
4. (optional) Come up with a more intuitive/mnemonic name for `ManuHX` e.g. `VolumetricHeatSink` or `ConvectiveHeatSink`.
|
non_process
|
fix manuhx jacobian term allow heat transfer coeff to vary with time make a test for manuhx this issue can be closed when the following three objectives involving manuhx are met fix the jacobian term it is currently missing a phi term allow the heat transfer coeff htc to vary with time by making it controllable under moose s control system this allows us to model a loss of heat sink accident when using manuhx as a heat exchanger make a test for manuhx it is currently not covered under any existing tests optional come up with a more intuitive mnemonic name for manuhx e g volumetricheatsink or convectiveheatsink
| 0
|
1,636
| 4,258,072,805
|
IssuesEvent
|
2016-07-11 03:54:44
|
triplea-game/triplea
|
https://api.github.com/repos/triplea-game/triplea
|
opened
|
1.9.0.0 release!
|
High Priority Process
|
Let's begin the release process! Is everything in that we would want for the 1.9.0.0 release?
I started this source forge thread to let folks know about the prerelease: http://tripleadev.1671093.n2.nabble.com/TripleA-1-9-0-0-Prerelease-td7592899.html
For now, I would like to nominate version 1.9.0.0.2461 for the 1.9.0.0 release. My thoughts are we will test that specific version and see if we find any issues that we would want to fix. If so, we'll roll forward to the next latest version and repeat until we are happy. Ideally this will not involve any delays or pauses in normal development. After a week of testing or so, we will then call the release official and begin to migrate folks over.
As is, we need to determine how to migrate Derby DB data as well to a new lobby instance, I'm not sure right now how to do that.
Otherwise let's use this thread to discuss the next release, process and progress.
|
1.0
|
1.9.0.0 release! - Let's begin the release process! Is everything in that we would want for the 1.9.0.0 release?
I started this source forge thread to let folks know about the prerelease: http://tripleadev.1671093.n2.nabble.com/TripleA-1-9-0-0-Prerelease-td7592899.html
For now, I would like to nominate version 1.9.0.0.2461 for the 1.9.0.0 release. My thoughts are we will test that specific version and see if we find any issues that we would want to fix. If so, we'll roll forward to the next latest version and repeat until we are happy. Ideally this will not involve any delays or pauses in normal development. After a week of testing or so, we will then call the release official and begin to migrate folks over.
As is, we need to determine how to migrate Derby DB data as well to a new lobby instance, I'm not sure right now how to do that.
Otherwise let's use this thread to discuss the next release, process and progress.
|
process
|
release let s begin the release process is everything in that we would want for the release i started this source forge thread to let folks know about the prerelease for now i would like to nominate version for the release my thoughts are we will test that specific version and see if we find any issues that we would want to fix if so we ll roll forward to the next latest version and repeat until we are happy ideally this will not involve any delays or pauses in normal development after a week of testing or so we will then call the release official and begin to migrate folks over as is we need to determine how to migrate derby db data as well to a new lobby instance i m not sure right now how to do that otherwise let s use this thread to discuss the next release process and progress
| 1
|
8,552
| 2,611,517,501
|
IssuesEvent
|
2015-02-27 05:52:12
|
chrsmith/hedgewars
|
https://api.github.com/repos/chrsmith/hedgewars
|
closed
|
Fort mode does not work
|
auto-migrated Priority-Medium Type-Defect
|
```
When starting a fort game, it does not load and returns to game options
menu(team select, map and mode select etc.)
```
Original issue reported on code.google.com by `pako.a...@gmail.com` on 12 Apr 2013 at 5:28
|
1.0
|
Fort mode does not work - ```
When starting a fort game, it does not load and returns to game options
menu(team select, map and mode select etc.)
```
Original issue reported on code.google.com by `pako.a...@gmail.com` on 12 Apr 2013 at 5:28
|
non_process
|
fort mode does not work when starting a fort game it does not load and returns to game options menu team select map and mode select etc original issue reported on code google com by pako a gmail com on apr at
| 0
|
15,508
| 19,703,265,794
|
IssuesEvent
|
2022-01-12 18:52:15
|
googleapis/java-channel
|
https://api.github.com/repos/googleapis/java-channel
|
opened
|
Your .repo-metadata.json file has a problem 🤒
|
type: process repo-metadata: lint
|
You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'channel' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
1.0
|
Your .repo-metadata.json file has a problem 🤒 - You have a problem with your .repo-metadata.json file:
Result of scan 📈:
* release_level must be equal to one of the allowed values in .repo-metadata.json
* api_shortname 'channel' invalid in .repo-metadata.json
☝️ Once you correct these problems, you can close this issue.
Reach out to **go/github-automation** if you have any questions.
|
process
|
your repo metadata json file has a problem 🤒 you have a problem with your repo metadata json file result of scan 📈 release level must be equal to one of the allowed values in repo metadata json api shortname channel invalid in repo metadata json ☝️ once you correct these problems you can close this issue reach out to go github automation if you have any questions
| 1
|
19,549
| 25,867,519,081
|
IssuesEvent
|
2022-12-13 22:21:16
|
NationalSecurityAgency/ghidra
|
https://api.github.com/repos/NationalSecurityAgency/ghidra
|
closed
|
X86 disassembler fails to recognize FWAIT and FDISI
|
Feature: Processor/x86 Status: Internal
|
**Describe the bug**
In some situations the ghidra disassembler fails to recognize certain floating point instructions.
**To Reproduce**
Steps to reproduce the behavior:
1. If you disassemble the following binary blob (from the OpenWatcom C library - function __FPE2Handler) [50 53 51 52 56 57 55 1e 06 83 ec 1c 89 e5 d9 75 00 9b 9b db e2 9b db e1 fb e8 92 4b fb] you will get this:
00109ac8 50 PUSH EAX
00109ac9 53 PUSH EBX
00109aca 51 PUSH ECX
00109acb 52 PUSH EDX
00109acc 56 PUSH ESI
00109acd 57 PUSH EDI
00109ace 55 PUSH EBP
00109acf 1e PUSH DS
00109ad0 06 PUSH ES
00109ad1 83 ec 1c SUB ESP,0x1c
00109ad4 89 e5 MOV EBP,ESP
00109ad6 d9 75 00 FNSTENV [EBP]=>local_40
00109ad9 9b WAIT
00109ada 9b db e2 FCLEX
00109add 9b WAIT
00109ade db ?? DBh
00109adf e1 ?? E1h
00109ae0 fb STI
with an error bookmark at 00109ade saying "Error [Bad Instruction]: Unable to resolve constructor at 00109ade (flow from 00109add)"
**Expected behavior**
00109ad9 through 00109adf are not disassembled correctly here. If you look at the original assembly listing for the function in the OpenWatcom sources (https://github.com/open-watcom/open-watcom-v2/blob/6b9cb4438959d845a2b4dd4bf19f7908ecd608e9/bld/clib/math/a/fpeinth.asm) you'll see that they should be disassembled as:
FWAIT
FDISI
**Screenshots**
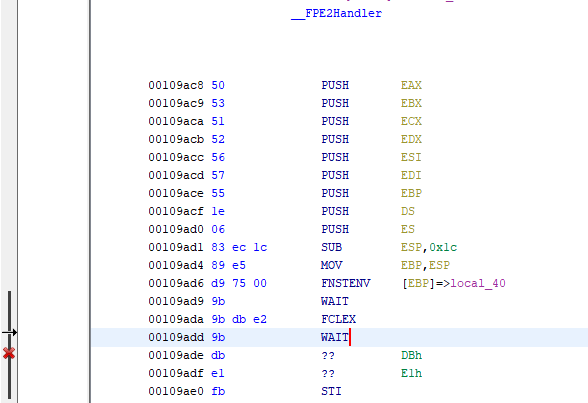
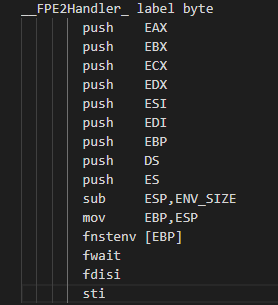
**Attachments**
**Environment (please complete the following information):**
- OS: Windows 10 Pro 20H2
- Java Version: 12.0.1
- Ghidra Version: 10.1
- Ghidra Origin: GitHub releases
**Additional context**
|
1.0
|
X86 disassembler fails to recognize FWAIT and FDISI - **Describe the bug**
In some situations the ghidra disassembler fails to recognize certain floating point instructions.
**To Reproduce**
Steps to reproduce the behavior:
1. If you disassemble the following binary blob (from the OpenWatcom C library - function __FPE2Handler) [50 53 51 52 56 57 55 1e 06 83 ec 1c 89 e5 d9 75 00 9b 9b db e2 9b db e1 fb e8 92 4b fb] you will get this:
00109ac8 50 PUSH EAX
00109ac9 53 PUSH EBX
00109aca 51 PUSH ECX
00109acb 52 PUSH EDX
00109acc 56 PUSH ESI
00109acd 57 PUSH EDI
00109ace 55 PUSH EBP
00109acf 1e PUSH DS
00109ad0 06 PUSH ES
00109ad1 83 ec 1c SUB ESP,0x1c
00109ad4 89 e5 MOV EBP,ESP
00109ad6 d9 75 00 FNSTENV [EBP]=>local_40
00109ad9 9b WAIT
00109ada 9b db e2 FCLEX
00109add 9b WAIT
00109ade db ?? DBh
00109adf e1 ?? E1h
00109ae0 fb STI
with an error bookmark at 00109ade saying "Error [Bad Instruction]: Unable to resolve constructor at 00109ade (flow from 00109add)"
**Expected behavior**
00109ad9 through 00109adf are not disassembled correctly here. If you look at the original assembly listing for the function in the OpenWatcom sources (https://github.com/open-watcom/open-watcom-v2/blob/6b9cb4438959d845a2b4dd4bf19f7908ecd608e9/bld/clib/math/a/fpeinth.asm) you'll see that they should be disassembled as:
FWAIT
FDISI
**Screenshots**
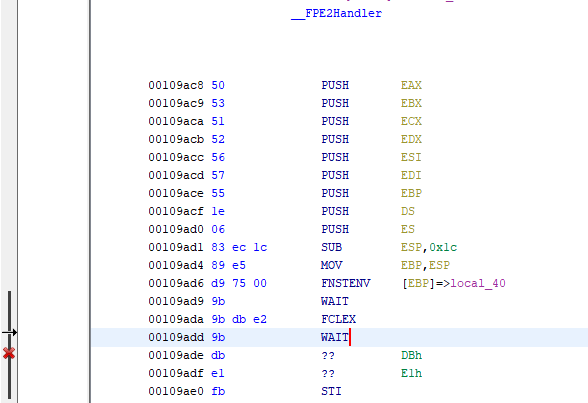
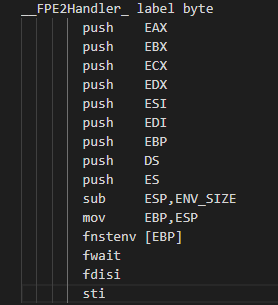
**Attachments**
**Environment (please complete the following information):**
- OS: Windows 10 Pro 20H2
- Java Version: 12.0.1
- Ghidra Version: 10.1
- Ghidra Origin: GitHub releases
**Additional context**
|
process
|
disassembler fails to recognize fwait and fdisi describe the bug in some situations the ghidra disassembler fails to recognize certain floating point instructions to reproduce steps to reproduce the behavior if you disassemble the following binary blob from the openwatcom c library function you will get this push eax push ebx push ecx push edx push esi push edi push ebp push ds push es ec sub esp mov ebp esp fnstenv local wait db fclex wait db dbh fb sti with an error bookmark at saying error unable to resolve constructor at flow from expected behavior through are not disassembled correctly here if you look at the original assembly listing for the function in the openwatcom sources you ll see that they should be disassembled as fwait fdisi screenshots attachments environment please complete the following information os windows pro java version ghidra version ghidra origin github releases additional context
| 1
|
324,007
| 27,769,205,724
|
IssuesEvent
|
2023-03-16 13:29:21
|
matrix-org/synapse
|
https://api.github.com/repos/matrix-org/synapse
|
closed
|
Complement `TestPartialStateJoin/Outgoing_device_list_updates/Device_list_updates_reach_newly_joined_servers_in_partial_state_rooms` is flakey
|
A-Federated-Join A-Device-List-Tracking S-Major T-Task Z-Flake Z-Dev-Wishlist O-Frequent A-Testing
|
https://github.com/matrix-org/synapse/actions/runs/3172224388/jobs/5166469780#step:4:2964
```
client.go:604: [CSAPI] GET hs1/_matrix/client/v3/sync => 200 OK (125.434036ms)
federation_room_join_partial_state_test.go:1674: @t24alice:hs1's partial state join to !0:host.docker.internal:38237 completed.
client.go:604: [CSAPI] PUT hs1/_matrix/client/v3/devices/PBJFBBTZIN => 200 OK (18.65378ms)
federation_room_join_partial_state_test.go:1677: @t24alice:hs1 sent device list update.
federation_room_join_partial_state_test.go:1534: Complement server received m.device_list_update: {"device_display_name":"A new device name 3","device_id":"PBJFBBTZIN","org.matrix.opentracing_context":"{}","prev_id":[35],"stream_id":38,"user_id":"@t24alice:hs1"}
federation_room_join_partial_state_test.go:1534: Complement server received m.device_list_update: {"device_display_name":"A new device name 3","device_id":"PBJFBBTZIN","org.matrix.opentracing_context":"{}","prev_id":[36],"stream_id":40,"user_id":"@t24alice:hs1"}
federation_room_join_partial_state_test.go:1680: @charlie, @derek and @elsie received device list update.
federation_room_join_partial_state_test.go:1534: Complement server received m.device_list_update: {"device_display_name":"A new device name 3","device_id":"PBJFBBTZIN","org.matrix.opentracing_context":"{}","prev_id":[38],"stream_id":39,"user_id":"@t24alice:hs1"}
panic: test timed out after 1h0m0s
goroutine 3428 [running]:
testing.(*M).startAlarm.func1()
/opt/hostedtoolcache/go/1.17.13/x64/src/testing/testing.go:1788 +0x8e
created by time.goFunc
/opt/hostedtoolcache/go/1.17.13/x64/src/time/sleep.go:180 +0x31
```
Synapse sent an extra device update, which the test wasn't interested in. I think putting the device update in a channel blocked, and then the test timed out after an hour.
|
1.0
|
Complement `TestPartialStateJoin/Outgoing_device_list_updates/Device_list_updates_reach_newly_joined_servers_in_partial_state_rooms` is flakey - https://github.com/matrix-org/synapse/actions/runs/3172224388/jobs/5166469780#step:4:2964
```
client.go:604: [CSAPI] GET hs1/_matrix/client/v3/sync => 200 OK (125.434036ms)
federation_room_join_partial_state_test.go:1674: @t24alice:hs1's partial state join to !0:host.docker.internal:38237 completed.
client.go:604: [CSAPI] PUT hs1/_matrix/client/v3/devices/PBJFBBTZIN => 200 OK (18.65378ms)
federation_room_join_partial_state_test.go:1677: @t24alice:hs1 sent device list update.
federation_room_join_partial_state_test.go:1534: Complement server received m.device_list_update: {"device_display_name":"A new device name 3","device_id":"PBJFBBTZIN","org.matrix.opentracing_context":"{}","prev_id":[35],"stream_id":38,"user_id":"@t24alice:hs1"}
federation_room_join_partial_state_test.go:1534: Complement server received m.device_list_update: {"device_display_name":"A new device name 3","device_id":"PBJFBBTZIN","org.matrix.opentracing_context":"{}","prev_id":[36],"stream_id":40,"user_id":"@t24alice:hs1"}
federation_room_join_partial_state_test.go:1680: @charlie, @derek and @elsie received device list update.
federation_room_join_partial_state_test.go:1534: Complement server received m.device_list_update: {"device_display_name":"A new device name 3","device_id":"PBJFBBTZIN","org.matrix.opentracing_context":"{}","prev_id":[38],"stream_id":39,"user_id":"@t24alice:hs1"}
panic: test timed out after 1h0m0s
goroutine 3428 [running]:
testing.(*M).startAlarm.func1()
/opt/hostedtoolcache/go/1.17.13/x64/src/testing/testing.go:1788 +0x8e
created by time.goFunc
/opt/hostedtoolcache/go/1.17.13/x64/src/time/sleep.go:180 +0x31
```
Synapse sent an extra device update, which the test wasn't interested in. I think putting the device update in a channel blocked, and then the test timed out after an hour.
|
non_process
|
complement testpartialstatejoin outgoing device list updates device list updates reach newly joined servers in partial state rooms is flakey client go get matrix client sync ok federation room join partial state test go s partial state join to host docker internal completed client go put matrix client devices pbjfbbtzin ok federation room join partial state test go sent device list update federation room join partial state test go complement server received m device list update device display name a new device name device id pbjfbbtzin org matrix opentracing context prev id stream id user id federation room join partial state test go complement server received m device list update device display name a new device name device id pbjfbbtzin org matrix opentracing context prev id stream id user id federation room join partial state test go charlie derek and elsie received device list update federation room join partial state test go complement server received m device list update device display name a new device name device id pbjfbbtzin org matrix opentracing context prev id stream id user id panic test timed out after goroutine testing m startalarm opt hostedtoolcache go src testing testing go created by time gofunc opt hostedtoolcache go src time sleep go synapse sent an extra device update which the test wasn t interested in i think putting the device update in a channel blocked and then the test timed out after an hour
| 0
|
231,782
| 7,643,286,581
|
IssuesEvent
|
2018-05-08 12:12:35
|
robotology/wb-toolbox
|
https://api.github.com/repos/robotology/wb-toolbox
|
closed
|
Implement the new parameter parsing method for Simulink
|
complexity:medium component:library-mex priority:normal status:in-progress type:task
|
Implement in `SimulinkBlockInformation` the new logic for parsing parameters from the masks. Many of the methods currently declared in `BlockInformation` will be ported in the `SimulinkBlockInformation` implementation.
|
1.0
|
Implement the new parameter parsing method for Simulink - Implement in `SimulinkBlockInformation` the new logic for parsing parameters from the masks. Many of the methods currently declared in `BlockInformation` will be ported in the `SimulinkBlockInformation` implementation.
|
non_process
|
implement the new parameter parsing method for simulink implement in simulinkblockinformation the new logic for parsing parameters from the masks many of the methods currently declared in blockinformation will be ported in the simulinkblockinformation implementation
| 0
|
17,121
| 22,638,792,586
|
IssuesEvent
|
2022-06-30 22:12:08
|
open-telemetry/opentelemetry-collector-contrib
|
https://api.github.com/repos/open-telemetry/opentelemetry-collector-contrib
|
closed
|
[processor/transform] Refactor newPathGetSetters to share similar cases
|
help wanted good first issue priority:p3 comp: transformprocessor
|
**Is your feature request related to a problem? Please describe.**
Right now in the transform processor each signal's newPathGetSetter function has the same logic for `resource` and `instrumentation_scope`, resulting in duplicate code and unit tests.
**Describe the solution you'd like**
The access logic for `resource` and `instrumentation_scope` should be moved to the `common` package and then reused in each signal. Unit tests should be moved as well.
|
1.0
|
[processor/transform] Refactor newPathGetSetters to share similar cases - **Is your feature request related to a problem? Please describe.**
Right now in the transform processor each signal's newPathGetSetter function has the same logic for `resource` and `instrumentation_scope`, resulting in duplicate code and unit tests.
**Describe the solution you'd like**
The access logic for `resource` and `instrumentation_scope` should be moved to the `common` package and then reused in each signal. Unit tests should be moved as well.
|
process
|
refactor newpathgetsetters to share similar cases is your feature request related to a problem please describe right now in the transform processor each signal s newpathgetsetter function has the same logic for resource and instrumentation scope resulting in duplicate code and unit tests describe the solution you d like the access logic for resource and instrumentation scope should be moved to the common package and then reused in each signal unit tests should be moved as well
| 1
|
3,693
| 6,718,474,277
|
IssuesEvent
|
2017-10-15 13:20:52
|
PaddlePaddle/models
|
https://api.github.com/repos/PaddlePaddle/models
|
closed
|
add text classification demo for nested sequence data
|
model in process
|
text classification with nested sequence data in paddle.v2
|
1.0
|
add text classification demo for nested sequence data - text classification with nested sequence data in paddle.v2
|
process
|
add text classification demo for nested sequence data text classification with nested sequence data in paddle
| 1
|
16,807
| 22,053,710,781
|
IssuesEvent
|
2022-05-30 10:56:49
|
0xffset/rOSt
|
https://api.github.com/repos/0xffset/rOSt
|
closed
|
Implement syscall return for kernel-mode processes
|
syscalls processes
|
Currently the syscall is returning using the `sysretq` instruction, which is fine and all, but if we want to support kernel processes (for drivers etc.) we need to use `iretq` instead, because `sysretq` changes the privilege mode to Ring3.
|
1.0
|
Implement syscall return for kernel-mode processes - Currently the syscall is returning using the `sysretq` instruction, which is fine and all, but if we want to support kernel processes (for drivers etc.) we need to use `iretq` instead, because `sysretq` changes the privilege mode to Ring3.
|
process
|
implement syscall return for kernel mode processes currently the syscall is returning using the sysretq instruction which is fine and all but if we want to support kernel processes for drivers etc we need to use iretq instead because sysretq changes the privilege mode to
| 1
|
17,774
| 5,513,112,795
|
IssuesEvent
|
2017-03-17 11:29:18
|
akvo/akvo-flow
|
https://api.github.com/repos/akvo/akvo-flow
|
closed
|
Remove duplicated elements across dashboard
|
Legacy clean-up & Code Refactoring Ready for release
|
Currently there are a few elements across the dashboard that do not have any purpose, provide no new information to the user or guidance, and are duplicated. With this issue, we will identify these elements and remove them all at once. Simplify. Declutter. Simplify.

*(example of a duplicated submenu and page title)
|
1.0
|
Remove duplicated elements across dashboard - Currently there are a few elements across the dashboard that do not have any purpose, provide no new information to the user or guidance, and are duplicated. With this issue, we will identify these elements and remove them all at once. Simplify. Declutter. Simplify.

*(example of a duplicated submenu and page title)
|
non_process
|
remove duplicated elements across dashboard currently there are a few elements across the dashboard that do not have any purpose provide no new information to the user or guidance and are duplicated with this issue we will identify these elements and remove them all at once simplify declutter simplify example of a duplicated submenu and page title
| 0
|
7,046
| 10,207,861,060
|
IssuesEvent
|
2019-08-14 08:45:39
|
endlessm/azafea
|
https://api.github.com/repos/endlessm/azafea
|
closed
|
Activation records don't have their vendors normalized
|
bug endless event processors
|
It seems I only did it for ping records (where this is essential, to deduplicate the ping configurations), but not for activation records.
|
1.0
|
Activation records don't have their vendors normalized - It seems I only did it for ping records (where this is essential, to deduplicate the ping configurations), but not for activation records.
|
process
|
activation records don t have their vendors normalized it seems i only did it for ping records where this is essential to deduplicate the ping configurations but not for activation records
| 1
|
43,661
| 7,057,766,697
|
IssuesEvent
|
2018-01-04 17:38:19
|
aeternity/elixir-wallet
|
https://api.github.com/repos/aeternity/elixir-wallet
|
closed
|
Add packages that the user needs to install in README
|
documentation
|
Add the packages/libraries that the user must install prior to running the elixir-wallet project. This is related to issue #65
|
1.0
|
Add packages that the user needs to install in README - Add the packages/libraries that the user must install prior to running the elixir-wallet project. This is related to issue #65
|
non_process
|
add packages that the user needs to install in readme add the packages libraries that the user must install prior to running the elixir wallet project this is related to issue
| 0
|
62,019
| 6,773,501,248
|
IssuesEvent
|
2017-10-27 06:21:37
|
kubernetes/test-infra
|
https://api.github.com/repos/kubernetes/test-infra
|
closed
|
Should check GOPATH in kubetest/util.go
|
area/kubetest
|
If there is no `GOPATH` env configed, `k8s` func will return `src/k8s.io/...`,
so `Build` func will construct cmd such as:
```shell
$ make -C src/k8s.io/kubernetes quick-release
```
and `kubetest` will throw error `make[1]: *** src/k8s.io/kubernetes: No such file or directory. Stop.`
|
1.0
|
Should check GOPATH in kubetest/util.go - If there is no `GOPATH` env configed, `k8s` func will return `src/k8s.io/...`,
so `Build` func will construct cmd such as:
```shell
$ make -C src/k8s.io/kubernetes quick-release
```
and `kubetest` will throw error `make[1]: *** src/k8s.io/kubernetes: No such file or directory. Stop.`
|
non_process
|
should check gopath in kubetest util go if there is no gopath env configed func will return src io so build func will construct cmd such as shell make c src io kubernetes quick release and kubetest will throw error make src io kubernetes no such file or directory stop
| 0
|
10,066
| 13,044,161,802
|
IssuesEvent
|
2020-07-29 03:47:26
|
tikv/tikv
|
https://api.github.com/repos/tikv/tikv
|
closed
|
UCP: Migrate scalar function `StrToDateDatetime` from TiDB
|
challenge-program-2 component/coprocessor difficulty/easy sig/coprocessor
|
## Description
Port the scalar function `StrToDateDatetime` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @andylokandy
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
|
2.0
|
UCP: Migrate scalar function `StrToDateDatetime` from TiDB -
## Description
Port the scalar function `StrToDateDatetime` from TiDB to coprocessor.
## Score
* 50
## Mentor(s)
* @andylokandy
## Recommended Skills
* Rust programming
## Learning Materials
Already implemented expressions ported from TiDB
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/rpn_expr)
- https://github.com/tikv/tikv/tree/master/components/tidb_query/src/expr)
|
process
|
ucp migrate scalar function strtodatedatetime from tidb description port the scalar function strtodatedatetime from tidb to coprocessor score mentor s andylokandy recommended skills rust programming learning materials already implemented expressions ported from tidb
| 1
|
13,279
| 15,759,848,671
|
IssuesEvent
|
2021-03-31 08:22:08
|
prisma/prisma
|
https://api.github.com/repos/prisma/prisma
|
opened
|
(migrate/MySQL) Print visible warnings when a user-edited migration contains explicit database names
|
process/candidate team/migrations
|
Explicit database names will not work nicely with the shadow database — the inferred schemas will be wrong and drift will always be detected. See https://github.com/prisma/prisma/issues/5987 for an example. We can detect prefixed identifiers in migration scripts, so we should warn about them.
|
1.0
|
(migrate/MySQL) Print visible warnings when a user-edited migration contains explicit database names - Explicit database names will not work nicely with the shadow database — the inferred schemas will be wrong and drift will always be detected. See https://github.com/prisma/prisma/issues/5987 for an example. We can detect prefixed identifiers in migration scripts, so we should warn about them.
|
process
|
migrate mysql print visible warnings when a user edited migration contains explicit database names explicit database names will not work nicely with the shadow database — the inferred schemas will be wrong and drift will always be detected see for an example we can detect prefixed identifiers in migration scripts so we should warn about them
| 1
|
179,767
| 30,296,465,963
|
IssuesEvent
|
2023-07-09 22:42:11
|
Esri/calcite-design-system
|
https://api.github.com/repos/Esri/calcite-design-system
|
reopened
|
Audit components `open`/`closed` props for consistency
|
enhancement p - low Calcite (design) needs milestone design-complete
|
### Description
Perform an audit across components with the `open`/`expanded`/`active` prop for consistency.
The audit results can lead us to add deprecations and/or update values across components.
cc @geospatialem @ashetland @macandcheese @jcfranco
<img width="1427" alt="image" src="https://github.com/Esri/calcite-components/assets/29716057/5d221faa-3994-4c9c-826e-bc3d0d6c0deb">
### Acceptance Criteria
`open` (Reveals a floating element)
Applies to: Combobox, Input Date Picker, Input Time Picker, Modal, Dropdown, Popover, & Tooltip
`expanded` (Reveals extended content)
Applies to: Accordion, Block, Tree Item, List Item, & Action Bar
Deprecated `closed` prop on **Block** and **List Item** and added `expanded` prop
### Which Component
Applies across multiple components using a `open`/`expanded`/`active` prop:
Block, Combobox, Input Date Picker, Input Time Picker, List Item, Modal, Dropdown, Popover, Tooltip, Accordion, Tree Item, & Action Bar
### Esri team
Calcite (design)
|
2.0
|
Audit components `open`/`closed` props for consistency - ### Description
Perform an audit across components with the `open`/`expanded`/`active` prop for consistency.
The audit results can lead us to add deprecations and/or update values across components.
cc @geospatialem @ashetland @macandcheese @jcfranco
<img width="1427" alt="image" src="https://github.com/Esri/calcite-components/assets/29716057/5d221faa-3994-4c9c-826e-bc3d0d6c0deb">
### Acceptance Criteria
`open` (Reveals a floating element)
Applies to: Combobox, Input Date Picker, Input Time Picker, Modal, Dropdown, Popover, & Tooltip
`expanded` (Reveals extended content)
Applies to: Accordion, Block, Tree Item, List Item, & Action Bar
Deprecated `closed` prop on **Block** and **List Item** and added `expanded` prop
### Which Component
Applies across multiple components using a `open`/`expanded`/`active` prop:
Block, Combobox, Input Date Picker, Input Time Picker, List Item, Modal, Dropdown, Popover, Tooltip, Accordion, Tree Item, & Action Bar
### Esri team
Calcite (design)
|
non_process
|
audit components open closed props for consistency description perform an audit across components with the open expanded active prop for consistency the audit results can lead us to add deprecations and or update values across components cc geospatialem ashetland macandcheese jcfranco img width alt image src acceptance criteria open reveals a floating element applies to combobox input date picker input time picker modal dropdown popover tooltip expanded reveals extended content applies to accordion block tree item list item action bar deprecated closed prop on block and list item and added expanded prop which component applies across multiple components using a open expanded active prop block combobox input date picker input time picker list item modal dropdown popover tooltip accordion tree item action bar esri team calcite design
| 0
|
1,960
| 4,777,570,933
|
IssuesEvent
|
2016-10-27 16:39:34
|
paulkornikov/Pragonas
|
https://api.github.com/repos/paulkornikov/Pragonas
|
closed
|
Provision existe mais le processus provision recrée la provision
|
a-bug financement - provisions processus workload III
|
pour le compte ibis, duplication des provisions existantes depuis la date de création de la famille.
|
1.0
|
Provision existe mais le processus provision recrée la provision - pour le compte ibis, duplication des provisions existantes depuis la date de création de la famille.
|
process
|
provision existe mais le processus provision recrée la provision pour le compte ibis duplication des provisions existantes depuis la date de création de la famille
| 1
|
35,502
| 2,789,932,261
|
IssuesEvent
|
2015-05-08 22:30:47
|
google/google-visualization-api-issues
|
https://api.github.com/repos/google/google-visualization-api-issues
|
opened
|
Feature Request: Add option to have vertical grid lines
|
Priority-Low Type-Enhancement
|
Original [issue 556](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=556) created by orwant on 2011-03-20T19:12:41.000Z:
<b>What would you like to see us add to this API?</b>
Add option to have vertical grid lines.
<b>What component is this issue related to (PieChart, LineChart, DataTable,</b>
<b>Query, etc)?</b>
LineChart.
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
|
1.0
|
Feature Request: Add option to have vertical grid lines - Original [issue 556](https://code.google.com/p/google-visualization-api-issues/issues/detail?id=556) created by orwant on 2011-03-20T19:12:41.000Z:
<b>What would you like to see us add to this API?</b>
Add option to have vertical grid lines.
<b>What component is this issue related to (PieChart, LineChart, DataTable,</b>
<b>Query, etc)?</b>
LineChart.
<b>*********************************************************</b>
<b>For developers viewing this issue: please click the 'star' icon to be</b>
<b>notified of future changes, and to let us know how many of you are</b>
<b>interested in seeing it resolved.</b>
<b>*********************************************************</b>
|
non_process
|
feature request add option to have vertical grid lines original created by orwant on what would you like to see us add to this api add option to have vertical grid lines what component is this issue related to piechart linechart datatable query etc linechart for developers viewing this issue please click the star icon to be notified of future changes and to let us know how many of you are interested in seeing it resolved
| 0
|
17,318
| 23,138,300,003
|
IssuesEvent
|
2022-07-28 15:59:30
|
metabase/metabase
|
https://api.github.com/repos/metabase/metabase
|
closed
|
MySQL JSON fields' filters don't work for heterogeneous type fields
|
Type:Bug Database/MySQL Querying/Processor .Correctness .Regression/master
|
MySQL JSON fields, but not Postgres JSON fields, will coerce to the [JSON type automagically when given comparisons](https://dev.mysql.com/doc/refman/8.0/en/json.html#json-comparison) like we do in the filters, which is highly unintuitive in our specific situation. We want to coerce to the ordinary types upon querying and have the hierarchical field type behavior like we do in the Postgres JSON fields.
Consider this under #22174, given the epic isn't closed out yet.
**To Reproduce**
1. Insert a JSON column into a setup MySQL database table with heterogeneous members, like something with two rows `{"blah": 123"}` and `{"blah": "some stuff"}` on column `some_json`.
2. Go to the table and filter on the values of `some_json -> blah`
3. You will always get null results, if the JSON column is heterogeneous in type
**Expected behavior**
Filtering happens, we get the rows corresponding to that value or what-have-you
**Screenshot**
from Nick:
https://files.slack.com/files-pri/T078VCLCR-F03QN355UEM/chrome_lpjzn5qnuk.gif
**Information about your Metabase Installation:**
`{
"browser-info": {
"language": "en-US",
"platform": "MacIntel",
"userAgent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36",
"vendor": "Google Inc."
},
"system-info": {
"file.encoding": "UTF-8",
"java.runtime.name": "OpenJDK Runtime Environment",
"java.runtime.version": "16.0.1+9",
"java.vendor": "AdoptOpenJDK",
"java.vendor.url": "https://adoptopenjdk.net/",
"java.version": "16.0.1",
"java.vm.name": "OpenJDK 64-Bit Server VM",
"java.vm.version": "16.0.1+9",
"os.name": "Mac OS X",
"os.version": "11.2",
"user.language": "en",
"user.timezone": "UTC"
},
"metabase-info": {
"databases": [
"h2",
"mysql"
],
"hosting-env": "unknown",
"application-database": "mysql",
"application-database-details": {
"database": {
"name": "MySQL",
"version": "8.0.29"
},
"jdbc-driver": {
"name": "MariaDB Connector/J",
"version": "2.7.5"
}
},
"run-mode": "dev",
"version": {
"date": "2022-01-19",
"src_hash": "71e53e611d2b59048e8c28fc64b297b472c8920a",
"tag": "v0.42.1-SNAPSHOT",
"branch": "cleanup-sv-2",
"hash": "1e8dc79"
},
"settings": {
"report-timezone": null
}
}
}`
**Severity**
We haven't released MySQL yet, but I am going to put a ticket in here so I can refer in PR
**Additional context**
Internal slack https://metaboat.slack.com/archives/C03E8MQJZBM/p1658327516672559
|
1.0
|
MySQL JSON fields' filters don't work for heterogeneous type fields - MySQL JSON fields, but not Postgres JSON fields, will coerce to the [JSON type automagically when given comparisons](https://dev.mysql.com/doc/refman/8.0/en/json.html#json-comparison) like we do in the filters, which is highly unintuitive in our specific situation. We want to coerce to the ordinary types upon querying and have the hierarchical field type behavior like we do in the Postgres JSON fields.
Consider this under #22174, given the epic isn't closed out yet.
**To Reproduce**
1. Insert a JSON column into a setup MySQL database table with heterogeneous members, like something with two rows `{"blah": 123"}` and `{"blah": "some stuff"}` on column `some_json`.
2. Go to the table and filter on the values of `some_json -> blah`
3. You will always get null results, if the JSON column is heterogeneous in type
**Expected behavior**
Filtering happens, we get the rows corresponding to that value or what-have-you
**Screenshot**
from Nick:
https://files.slack.com/files-pri/T078VCLCR-F03QN355UEM/chrome_lpjzn5qnuk.gif
**Information about your Metabase Installation:**
`{
"browser-info": {
"language": "en-US",
"platform": "MacIntel",
"userAgent": "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36",
"vendor": "Google Inc."
},
"system-info": {
"file.encoding": "UTF-8",
"java.runtime.name": "OpenJDK Runtime Environment",
"java.runtime.version": "16.0.1+9",
"java.vendor": "AdoptOpenJDK",
"java.vendor.url": "https://adoptopenjdk.net/",
"java.version": "16.0.1",
"java.vm.name": "OpenJDK 64-Bit Server VM",
"java.vm.version": "16.0.1+9",
"os.name": "Mac OS X",
"os.version": "11.2",
"user.language": "en",
"user.timezone": "UTC"
},
"metabase-info": {
"databases": [
"h2",
"mysql"
],
"hosting-env": "unknown",
"application-database": "mysql",
"application-database-details": {
"database": {
"name": "MySQL",
"version": "8.0.29"
},
"jdbc-driver": {
"name": "MariaDB Connector/J",
"version": "2.7.5"
}
},
"run-mode": "dev",
"version": {
"date": "2022-01-19",
"src_hash": "71e53e611d2b59048e8c28fc64b297b472c8920a",
"tag": "v0.42.1-SNAPSHOT",
"branch": "cleanup-sv-2",
"hash": "1e8dc79"
},
"settings": {
"report-timezone": null
}
}
}`
**Severity**
We haven't released MySQL yet, but I am going to put a ticket in here so I can refer in PR
**Additional context**
Internal slack https://metaboat.slack.com/archives/C03E8MQJZBM/p1658327516672559
|
process
|
mysql json fields filters don t work for heterogeneous type fields mysql json fields but not postgres json fields will coerce to the like we do in the filters which is highly unintuitive in our specific situation we want to coerce to the ordinary types upon querying and have the hierarchical field type behavior like we do in the postgres json fields consider this under given the epic isn t closed out yet to reproduce insert a json column into a setup mysql database table with heterogeneous members like something with two rows blah and blah some stuff on column some json go to the table and filter on the values of some json blah you will always get null results if the json column is heterogeneous in type expected behavior filtering happens we get the rows corresponding to that value or what have you screenshot from nick information about your metabase installation browser info language en us platform macintel useragent mozilla macintosh intel mac os x applewebkit khtml like gecko chrome safari vendor google inc system info file encoding utf java runtime name openjdk runtime environment java runtime version java vendor adoptopenjdk java vendor url java version java vm name openjdk bit server vm java vm version os name mac os x os version user language en user timezone utc metabase info databases mysql hosting env unknown application database mysql application database details database name mysql version jdbc driver name mariadb connector j version run mode dev version date src hash tag snapshot branch cleanup sv hash settings report timezone null severity we haven t released mysql yet but i am going to put a ticket in here so i can refer in pr additional context internal slack
| 1
|
21,224
| 28,310,618,662
|
IssuesEvent
|
2023-04-10 15:05:02
|
cse442-at-ub/project_s23-iweatherify
|
https://api.github.com/repos/cse442-at-ub/project_s23-iweatherify
|
closed
|
Connect Unit Settings to the Logged-in Homepage reflecting different weather data based on unit preferences selected
|
Processing Task Sprint 3
|
**Tests**
Test Setup: Visit https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/homepage as a logged-in user with a new valid registered account
*Test 1*
1) Check to confirm your newly registered account has the defaults unit of Fahrenheit, mph for wind speed, and Hg for pressure

2) As a logged-in user visit the Unit Settings page
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/unitsSettings

3) Change the default Temperature from °F to °C
4) Change The Wind option from mph to km/h
5) Change for Pressure Hg to mb
6) Click on Save

7) Visit the logged-in homepage
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/homepage
8) Confirm that the units have changed to C for temperature, km/h for Wind Speed and mb for Pressure

*Test 2*
1) After completing test 1 go back to the unit settings page
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/unitsSettings
2) Check that the Temperature has °C, Wind on km/h, and pressure on MB

3) Change the default Temperature from °C to °F
4) Change The Wind option from km/h to mph
5) Change for Pressure mb to to Hg
6) Click on Save

7) Visit the logged-in homepage
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/homepage
8) Confirm that the units have changed to F for temperature, mph for Wind Speed and Hg for Pressure

|
1.0
|
Connect Unit Settings to the Logged-in Homepage reflecting different weather data based on unit preferences selected - **Tests**
Test Setup: Visit https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/homepage as a logged-in user with a new valid registered account
*Test 1*
1) Check to confirm your newly registered account has the defaults unit of Fahrenheit, mph for wind speed, and Hg for pressure

2) As a logged-in user visit the Unit Settings page
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/unitsSettings

3) Change the default Temperature from °F to °C
4) Change The Wind option from mph to km/h
5) Change for Pressure Hg to mb
6) Click on Save

7) Visit the logged-in homepage
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/homepage
8) Confirm that the units have changed to C for temperature, km/h for Wind Speed and mb for Pressure

*Test 2*
1) After completing test 1 go back to the unit settings page
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/unitsSettings
2) Check that the Temperature has °C, Wind on km/h, and pressure on MB

3) Change the default Temperature from °C to °F
4) Change The Wind option from km/h to mph
5) Change for Pressure mb to to Hg
6) Click on Save

7) Visit the logged-in homepage
https://www-student.cse.buffalo.edu/CSE442-542/2023-Spring/cse-442a/#/homepage
8) Confirm that the units have changed to F for temperature, mph for Wind Speed and Hg for Pressure

|
process
|
connect unit settings to the logged in homepage reflecting different weather data based on unit preferences selected tests test setup visit as a logged in user with a new valid registered account test check to confirm your newly registered account has the defaults unit of fahrenheit mph for wind speed and hg for pressure as a logged in user visit the unit settings page change the default temperature from °f to °c change the wind option from mph to km h change for pressure hg to mb click on save visit the logged in homepage confirm that the units have changed to c for temperature km h for wind speed and mb for pressure test after completing test go back to the unit settings page check that the temperature has °c wind on km h and pressure on mb change the default temperature from °c to °f change the wind option from km h to mph change for pressure mb to to hg click on save visit the logged in homepage confirm that the units have changed to f for temperature mph for wind speed and hg for pressure
| 1
|
670,167
| 22,678,387,432
|
IssuesEvent
|
2022-07-04 07:39:38
|
nakhll-company/nakhll_frontend
|
https://api.github.com/repos/nakhll-company/nakhll_frontend
|
opened
|
لطفا ابتدا وارد سایت شوید
|
bug Priority 1
|
اگر وارد سایت نشده باشیم در صفحه لندینگ ارور "لطفا ابتدا وارد شوید" نمایش داده می شود ولی اگر در سایت باشیم و Session اکسپایر شود، این ارور در همه صفحات نمایش داده می شود و با کلیک روی پروفایل برای ورود دوباره، ارور 500 می دهد. باید حتما یک بار سایت را رفرش کرد تا بتوانیم دوباره وارد بشویم.
|
1.0
|
لطفا ابتدا وارد سایت شوید - اگر وارد سایت نشده باشیم در صفحه لندینگ ارور "لطفا ابتدا وارد شوید" نمایش داده می شود ولی اگر در سایت باشیم و Session اکسپایر شود، این ارور در همه صفحات نمایش داده می شود و با کلیک روی پروفایل برای ورود دوباره، ارور 500 می دهد. باید حتما یک بار سایت را رفرش کرد تا بتوانیم دوباره وارد بشویم.
|
non_process
|
لطفا ابتدا وارد سایت شوید اگر وارد سایت نشده باشیم در صفحه لندینگ ارور لطفا ابتدا وارد شوید نمایش داده می شود ولی اگر در سایت باشیم و session اکسپایر شود، این ارور در همه صفحات نمایش داده می شود و با کلیک روی پروفایل برای ورود دوباره، ارور می دهد باید حتما یک بار سایت را رفرش کرد تا بتوانیم دوباره وارد بشویم
| 0
|
42,804
| 5,538,157,784
|
IssuesEvent
|
2017-03-22 00:28:31
|
archesproject/arches
|
https://api.github.com/repos/archesproject/arches
|
closed
|
Remove or Implement Tile Name in Card Configuration
|
bug Card Designer
|
### User Story
Currently a user is able to enter a "Tile Name" in a Card's settings, when multiple values are enabled for that card.

This feature is not actually implemented in the rest of the app.
### Definition of Done
Before full documentation of the Card Designer can be finished, the Tile Name entry should either be removed (from the screenshot above as well as the card preview), or it should be fully implemented.
|
1.0
|
Remove or Implement Tile Name in Card Configuration - ### User Story
Currently a user is able to enter a "Tile Name" in a Card's settings, when multiple values are enabled for that card.

This feature is not actually implemented in the rest of the app.
### Definition of Done
Before full documentation of the Card Designer can be finished, the Tile Name entry should either be removed (from the screenshot above as well as the card preview), or it should be fully implemented.
|
non_process
|
remove or implement tile name in card configuration user story currently a user is able to enter a tile name in a card s settings when multiple values are enabled for that card this feature is not actually implemented in the rest of the app definition of done before full documentation of the card designer can be finished the tile name entry should either be removed from the screenshot above as well as the card preview or it should be fully implemented
| 0
|
457,453
| 13,156,810,674
|
IssuesEvent
|
2020-08-10 11:32:52
|
webcompat/web-bugs
|
https://api.github.com/repos/webcompat/web-bugs
|
closed
|
www.instagram.com - see bug description
|
browser-firefox-mobile engine-gecko ml-needsdiagnosis-false priority-critical
|
<!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0; Mobile; rv:68.0) Gecko/20100101 Firefox/68.0 -->
<!-- @reported_with: mobile-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/56375 -->
**URL**: https://www.instagram.com/
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android 6.0
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: can't login
**Steps to Reproduce**:
Login says it cant connect to instagram i should get online
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2020/8/8ed13eec-b136-49df-8a4a-ffede8b2c0e5.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20200501050101</li><li>channel: alpha</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2020/8/28f22538-6474-4562-8309-afdb0f86604a)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
1.0
|
www.instagram.com - see bug description - <!-- @browser: Firefox Mobile 68.0 -->
<!-- @ua_header: Mozilla/5.0 (Android 6.0; Mobile; rv:68.0) Gecko/20100101 Firefox/68.0 -->
<!-- @reported_with: mobile-reporter -->
<!-- @public_url: https://github.com/webcompat/web-bugs/issues/56375 -->
**URL**: https://www.instagram.com/
**Browser / Version**: Firefox Mobile 68.0
**Operating System**: Android 6.0
**Tested Another Browser**: Yes Chrome
**Problem type**: Something else
**Description**: can't login
**Steps to Reproduce**:
Login says it cant connect to instagram i should get online
<details>
<summary>View the screenshot</summary>
<img alt="Screenshot" src="https://webcompat.com/uploads/2020/8/8ed13eec-b136-49df-8a4a-ffede8b2c0e5.jpeg">
</details>
<details>
<summary>Browser Configuration</summary>
<ul>
<li>gfx.webrender.all: false</li><li>gfx.webrender.blob-images: true</li><li>gfx.webrender.enabled: false</li><li>image.mem.shared: true</li><li>buildID: 20200501050101</li><li>channel: alpha</li><li>hasTouchScreen: true</li><li>mixed active content blocked: false</li><li>mixed passive content blocked: false</li><li>tracking content blocked: false</li>
</ul>
</details>
[View console log messages](https://webcompat.com/console_logs/2020/8/28f22538-6474-4562-8309-afdb0f86604a)
_From [webcompat.com](https://webcompat.com/) with ❤️_
|
non_process
|
see bug description url browser version firefox mobile operating system android tested another browser yes chrome problem type something else description can t login steps to reproduce login says it cant connect to instagram i should get online view the screenshot img alt screenshot src browser configuration gfx webrender all false gfx webrender blob images true gfx webrender enabled false image mem shared true buildid channel alpha hastouchscreen true mixed active content blocked false mixed passive content blocked false tracking content blocked false from with ❤️
| 0
|
159,693
| 20,085,893,620
|
IssuesEvent
|
2022-02-05 01:08:09
|
AkshayMukkavilli/Analyzing-the-Significance-of-Structure-in-Amazon-Review-Data-Using-Machine-Learning-Approaches
|
https://api.github.com/repos/AkshayMukkavilli/Analyzing-the-Significance-of-Structure-in-Amazon-Review-Data-Using-Machine-Learning-Approaches
|
opened
|
CVE-2022-21727 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl
|
security vulnerability
|
## CVE-2022-21727 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /FinalProject/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_8b9e071c-3b11-4aa9-ba60-cdeb60d053b7/20190525011350_65403/20190525011256_depth_0/9/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Tensorflow is an Open Source Machine Learning Framework. The implementation of shape inference for `Dequantize` is vulnerable to an integer overflow weakness. The `axis` argument can be `-1` (the default value for the optional argument) or any other positive value at most the number of dimensions of the input. Unfortunately, the upper bound is not checked, and, since the code computes `axis + 1`, an attacker can trigger an integer overflow. The fix will be included in TensorFlow 2.8.0. We will also cherrypick this commit on TensorFlow 2.7.1, TensorFlow 2.6.3, and TensorFlow 2.5.3, as these are also affected and still in supported range.
<p>Publish Date: 2022-02-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21727>CVE-2022-21727</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-c6fh-56w7-fvjw">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-c6fh-56w7-fvjw</a></p>
<p>Release Date: 2022-02-03</p>
<p>Fix Resolution: tensorflow - 2.5.3,2.6.3,2.7.1;tensorflow-cpu - 2.5.3,2.6.3,2.7.1;tensorflow-gpu - 2.5.3,2.6.3,2.7.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-21727 (High) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2022-21727 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to dependency file: /FinalProject/requirements.txt</p>
<p>Path to vulnerable library: /teSource-ArchiveExtractor_8b9e071c-3b11-4aa9-ba60-cdeb60d053b7/20190525011350_65403/20190525011256_depth_0/9/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64/tensorflow-1.13.1.data/purelib/tensorflow</p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Tensorflow is an Open Source Machine Learning Framework. The implementation of shape inference for `Dequantize` is vulnerable to an integer overflow weakness. The `axis` argument can be `-1` (the default value for the optional argument) or any other positive value at most the number of dimensions of the input. Unfortunately, the upper bound is not checked, and, since the code computes `axis + 1`, an attacker can trigger an integer overflow. The fix will be included in TensorFlow 2.8.0. We will also cherrypick this commit on TensorFlow 2.7.1, TensorFlow 2.6.3, and TensorFlow 2.5.3, as these are also affected and still in supported range.
<p>Publish Date: 2022-02-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-21727>CVE-2022-21727</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-c6fh-56w7-fvjw">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-c6fh-56w7-fvjw</a></p>
<p>Release Date: 2022-02-03</p>
<p>Fix Resolution: tensorflow - 2.5.3,2.6.3,2.7.1;tensorflow-cpu - 2.5.3,2.6.3,2.7.1;tensorflow-gpu - 2.5.3,2.6.3,2.7.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_process
|
cve high detected in tensorflow whl cve high severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href path to dependency file finalproject requirements txt path to vulnerable library tesource archiveextractor depth tensorflow tensorflow data purelib tensorflow dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an open source machine learning framework the implementation of shape inference for dequantize is vulnerable to an integer overflow weakness the axis argument can be the default value for the optional argument or any other positive value at most the number of dimensions of the input unfortunately the upper bound is not checked and since the code computes axis an attacker can trigger an integer overflow the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with whitesource
| 0
|
286,779
| 24,784,584,754
|
IssuesEvent
|
2022-10-24 08:44:51
|
zephyrproject-rtos/zephyr
|
https://api.github.com/repos/zephyrproject-rtos/zephyr
|
closed
|
Test uart async failed on Nucleo F429ZI
|
bug priority: low area: UART area: DMA platform: STM32 area: Tests
|
**Describe the bug**
The test `tests/drivers/uart/uart_async_api/drivers.uart.async_api` fails on Nucleo F429ZI with the following error
`Assertion failed at WEST_TOPDIR/zephyr/tests/drivers/uart/uart_async_api/src/test_uart_async.c:526: uart_async_write_abort_test_write_abort: (sent not equal to received)
Sent is not equal to received.`
|
1.0
|
Test uart async failed on Nucleo F429ZI - **Describe the bug**
The test `tests/drivers/uart/uart_async_api/drivers.uart.async_api` fails on Nucleo F429ZI with the following error
`Assertion failed at WEST_TOPDIR/zephyr/tests/drivers/uart/uart_async_api/src/test_uart_async.c:526: uart_async_write_abort_test_write_abort: (sent not equal to received)
Sent is not equal to received.`
|
non_process
|
test uart async failed on nucleo describe the bug the test tests drivers uart uart async api drivers uart async api fails on nucleo with the following error assertion failed at west topdir zephyr tests drivers uart uart async api src test uart async c uart async write abort test write abort sent not equal to received sent is not equal to received
| 0
|
680,190
| 23,261,735,048
|
IssuesEvent
|
2022-08-04 14:01:21
|
Earthcomputer/multiconnect
|
https://api.github.com/repos/Earthcomputer/multiconnect
|
closed
|
[1.19] -> [1.18.2] Biome types not translated (correctly)
|
bug priority: low
|
Biome types are not correctly translated in the newest [1.6-beta.16](https://github.com/Earthcomputer/multiconnect/commit/837b2821d4bcf6cd6fbd4926a650ed69bd788a74)
1.19 protocol (correct biome):

forced 1.18 protocol (wrong biome):

Tested on server `gommehd.net` (lobby).
|
1.0
|
[1.19] -> [1.18.2] Biome types not translated (correctly) - Biome types are not correctly translated in the newest [1.6-beta.16](https://github.com/Earthcomputer/multiconnect/commit/837b2821d4bcf6cd6fbd4926a650ed69bd788a74)
1.19 protocol (correct biome):

forced 1.18 protocol (wrong biome):

Tested on server `gommehd.net` (lobby).
|
non_process
|
biome types not translated correctly biome types are not correctly translated in the newest protocol correct biome forced protocol wrong biome tested on server gommehd net lobby
| 0
|
155,702
| 5,959,334,470
|
IssuesEvent
|
2017-05-29 10:42:05
|
siteorigin/siteorigin-panels
|
https://api.github.com/repos/siteorigin/siteorigin-panels
|
closed
|
Compatibility with new WordPress 4.8 widgets
|
priority-1
|
WordPress 4.8 (beta) introduces a few widgets with more dynamic forms. These forms all come up blank in Page Builder.
We need to try trigger actions and enqueue scripts to get these new widgets working.
The widgets are
* Video
* Audio
* Image
* Text (which replaces the old text widget with a rich text TinyMCE widget).
We need to make sure that we introduce compatibility in a backwards compatible way for the text widget.
|
1.0
|
Compatibility with new WordPress 4.8 widgets - WordPress 4.8 (beta) introduces a few widgets with more dynamic forms. These forms all come up blank in Page Builder.
We need to try trigger actions and enqueue scripts to get these new widgets working.
The widgets are
* Video
* Audio
* Image
* Text (which replaces the old text widget with a rich text TinyMCE widget).
We need to make sure that we introduce compatibility in a backwards compatible way for the text widget.
|
non_process
|
compatibility with new wordpress widgets wordpress beta introduces a few widgets with more dynamic forms these forms all come up blank in page builder we need to try trigger actions and enqueue scripts to get these new widgets working the widgets are video audio image text which replaces the old text widget with a rich text tinymce widget we need to make sure that we introduce compatibility in a backwards compatible way for the text widget
| 0
|
810,262
| 30,233,673,365
|
IssuesEvent
|
2023-07-06 08:45:55
|
AdguardTeam/AdguardBrowserExtension
|
https://api.github.com/repos/AdguardTeam/AdguardBrowserExtension
|
closed
|
add screen warning to Adguard extension for Firefox Mobile (Android)
|
Feature Request Priority: P4
|
### Issue Details
When i visit malicious website Adguard extension doesn't trigger warning message.The link is in the list of Online malicious URLs
### Proposed solution
_No response_
### Alternative solution
The screen warning message should be appear for Adguard Firefox mobile. User can decide to continue or go back from the site
|
1.0
|
add screen warning to Adguard extension for Firefox Mobile (Android) - ### Issue Details
When i visit malicious website Adguard extension doesn't trigger warning message.The link is in the list of Online malicious URLs
### Proposed solution
_No response_
### Alternative solution
The screen warning message should be appear for Adguard Firefox mobile. User can decide to continue or go back from the site
|
non_process
|
add screen warning to adguard extension for firefox mobile android issue details when i visit malicious website adguard extension doesn t trigger warning message the link is in the list of online malicious urls proposed solution no response alternative solution the screen warning message should be appear for adguard firefox mobile user can decide to continue or go back from the site
| 0
|
18,325
| 24,444,030,971
|
IssuesEvent
|
2022-10-06 16:26:02
|
MPMG-DCC-UFMG/C01
|
https://api.github.com/repos/MPMG-DCC-UFMG/C01
|
closed
|
Passo Opções
|
[1] Bug [2] Alta Prioridade [0] Desenvolvimento [3] Processamento Dinâmico
|
## Comportamento Esperado
Espera-se que a configuração do passo Opções não apresente problemas na branch `dev`, assim como na branch `master`.
## Comportamento Atual
Durante a execução de coletores utilizando o passo Opções, temos exceções semelhantes a essa (log bruto):
> `"message": "2022-08-25 06:42:33 [scrapy.core.scraper] ERROR: Spider error processing <GET http://api.conectbr.com.br/Licitacao/Busca/?token=XEOk3i50lCa5IcpiNG7vXQ==> (referer: https://use.fontawesome.com/a61dc1ee64.css)\nTraceback (most recent call last):\n File \"/usr/local/lib/python3.8/dist-packages/twisted/internet/defer.py\", line 824, in adapt\n extracted = result.result()\n File \"/usr/local/lib/python3.8/dist-packages/scrapy/utils/py36.py\", line 8, in collect_asyncgen\n async for x in result:\n File \"/usr/src/app/crawling/spiders/static_page.py\", line 372, in parse\n responses = await self.dynamic_processing(response)\n File \"/usr/src/app/crawling/spiders/static_page.py\", line 328, in dynamic_processing\n page_dict = await steps.execute_steps(pagina=page)\n File \"<string>\", line 11, in execute_steps\n File \"/usr/local/lib/python3.8/dist-packages/step_crawler/functions_file.py\", line 140, in opcoes\n options.append(value.toString().split(\":\")[-1])\nAttributeError: 'NoneType' object has no attribute 'toString'"`
Na interface:
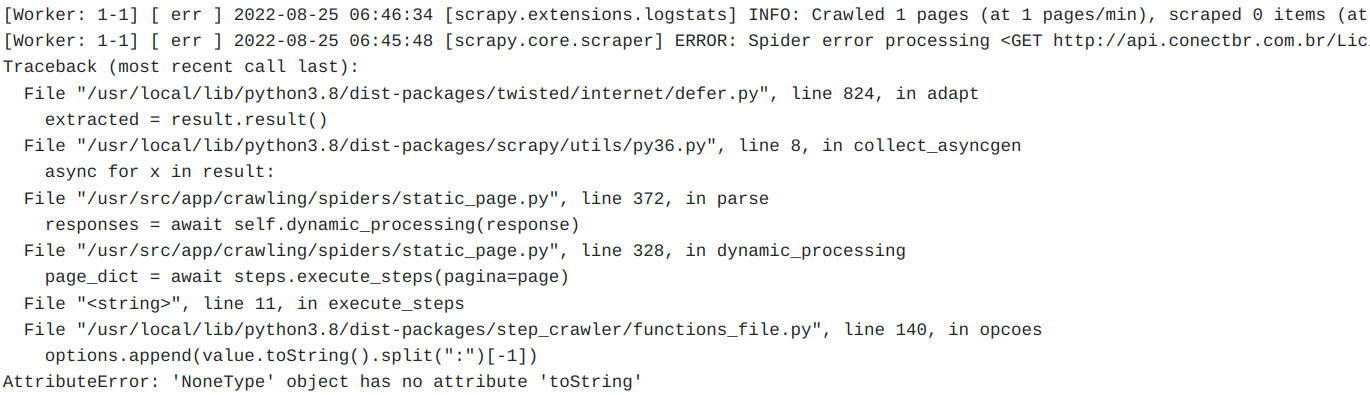
## Passos para reproduzir o erro
Executar um coletor usando o passo de Opções (exemplo abaixo) e verificar problemas em seu funcionamento.
## Especificações da Coleta
```
{
"source_name": "Licita\u00e7\u00f5es Itabirito",
"base_url": "http:\/\/api.conectbr.com.br\/Licitacao\/Busca\/?token=XEOk3i50lCa5IcpiNG7vXQ==",
"obey_robots": false,
"crawler_description": "Teste passo op\u00e7\u00f5es.",
"crawler_type_desc": "Outro",
"crawler_issue": 5850,
"data_path": "5850IT",
"sc_scheduler_persist": true,
"sc_scheduler_queue_refresh": 10,
"sc_queue_hits": 10,
"sc_queue_window": 60,
"sc_queue_moderated": true,
"sc_dupefilter_timeout": 600,
"sc_global_page_per_domain_limit": null,
"sc_global_page_per_domain_limit_timeout": 600,
"sc_domain_max_page_timeout": 600,
"sc_scheduler_ip_refresh": 60,
"sc_scheduler_backlog_blacklist": true,
"sc_scheduler_type_enabled": true,
"sc_scheduler_ip_enabled": true,
"sc_scheduler_item_retries": 3,
"sc_scheduler_queue_timeout": 3600,
"sc_httperror_allow_all": true,
"sc_retry_times": 3,
"sc_download_timeout": 10,
"antiblock_download_delay": 2,
"antiblock_autothrottle_enabled": false,
"antiblock_autothrottle_start_delay": 2,
"antiblock_autothrottle_max_delay": 10,
"antiblock_ip_rotation_enabled": false,
"antiblock_ip_rotation_type": "tor",
"antiblock_max_reqs_per_ip": 10,
"antiblock_max_reuse_rounds": 10,
"antiblock_proxy_list": "",
"antiblock_user_agent_rotation_enabled": false,
"antiblock_reqs_per_user_agent": 100,
"antiblock_user_agents_list": "",
"antiblock_insert_cookies_enabled": false,
"antiblock_cookies_list": "",
"captcha": "none",
"has_webdriver": false,
"webdriver_path": "",
"img_xpath": "",
"sound_xpath": "",
"dynamic_processing": true,
"browser_type": "chromium",
"skip_iter_errors": false,
"browser_resolution_width": 1280,
"browser_resolution_height": 720,
"explore_links": true,
"link_extractor_max_depth": 1,
"link_extractor_allow_url": "^(http:\\\/\\\/api.conectbr.com.br\\\/Licitacao\\\/AbreArquivo\\\/.*)",
"link_extractor_allow_domains": "",
"link_extractor_tags": "",
"link_extractor_attrs": "",
"link_extractor_check_type": false,
"link_extractor_process_value": "",
"download_files": true,
"download_files_allow_url": "^(http:\\\/\\\/api.conectbr.com.br\\\/Licitacao\\\/AbreArquivo\\\/.*)",
"download_files_allow_extensions": "pdf,doc",
"download_files_allow_domains": "",
"download_files_tags": "",
"download_files_attrs": "",
"download_files_process_value": "",
"download_files_check_large_content": true,
"download_imgs": false,
"steps": "{\"step\":\"root\",\"depth\":0,\"children\":[{\"step\":\"espere\",\"depth\":1,\"arguments\":{\"segundos\":\"5\"}},{\"step\":\"para_cada\",\"depth\":1,\"iterator\":\"ano\",\"children\":[{\"step\":\"selecione\",\"depth\":2,\"arguments\":{\"xpath\":\"'\/\/*[@id=\\\"NUM_ANO_REFERENCIA\\\"]'\",\"opcao\":\"ano\"}},{\"step\":\"espere\",\"depth\":2,\"arguments\":{\"segundos\":\"5\"}},{\"step\":\"clique\",\"depth\":2,\"arguments\":{\"elemento\":\"'\/\/*[@id=\\\"formDados\\\"]\/fieldset\/div\/div[7]\/input'\"}},{\"step\":\"espere\",\"depth\":2,\"arguments\":{\"segundos\":\"5\"}},{\"step\":\"screenshot\",\"depth\":2,\"arguments\":{}}],\"iterable\":{\"call\":{\"step\":\"opcoes\",\"arguments\":{\"xpath\":\"'\/html\/body\/div[1]\/div\/form\/fieldset\/div\/div[1]\/select'\",
"encoding_detection_method": 1,
"expected_runtime_category": "medium",
"templated_url_parameter_handlers": [],
"templated_url_response_handlers": [],
"instance_id": "166198811654876",
"crawler_id": 2
}
```
## Sistema (caso necessário)
- MP ou local: local.
- Branch específica: `dev`.
- Sistema diferente: não.
## Screenshots (caso necessário)
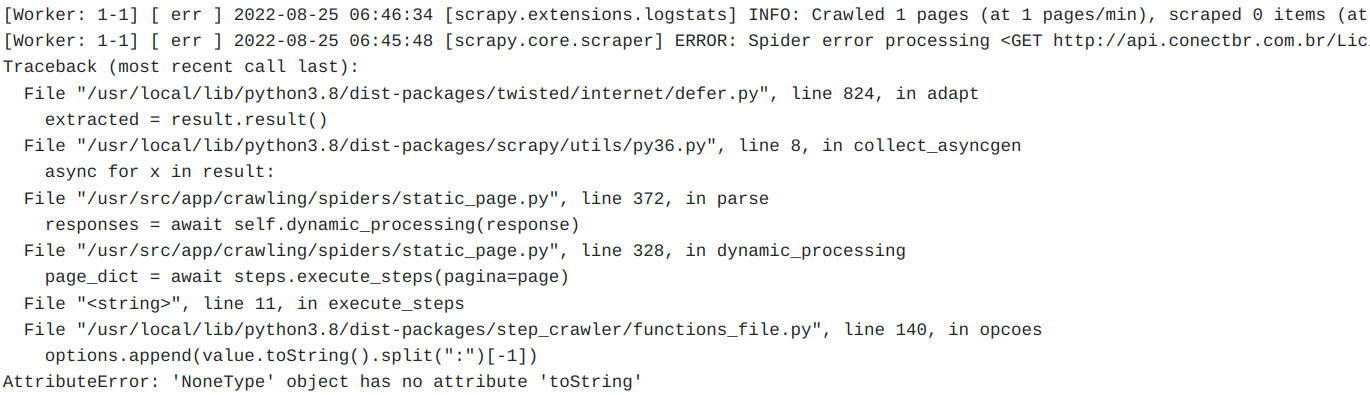
EDIT: troquei a coleta de exemplo para uma equivalente, porém mais sucinta, para que a testagem da funcionalidade seja mais objetiva.
|
1.0
|
Passo Opções - ## Comportamento Esperado
Espera-se que a configuração do passo Opções não apresente problemas na branch `dev`, assim como na branch `master`.
## Comportamento Atual
Durante a execução de coletores utilizando o passo Opções, temos exceções semelhantes a essa (log bruto):
> `"message": "2022-08-25 06:42:33 [scrapy.core.scraper] ERROR: Spider error processing <GET http://api.conectbr.com.br/Licitacao/Busca/?token=XEOk3i50lCa5IcpiNG7vXQ==> (referer: https://use.fontawesome.com/a61dc1ee64.css)\nTraceback (most recent call last):\n File \"/usr/local/lib/python3.8/dist-packages/twisted/internet/defer.py\", line 824, in adapt\n extracted = result.result()\n File \"/usr/local/lib/python3.8/dist-packages/scrapy/utils/py36.py\", line 8, in collect_asyncgen\n async for x in result:\n File \"/usr/src/app/crawling/spiders/static_page.py\", line 372, in parse\n responses = await self.dynamic_processing(response)\n File \"/usr/src/app/crawling/spiders/static_page.py\", line 328, in dynamic_processing\n page_dict = await steps.execute_steps(pagina=page)\n File \"<string>\", line 11, in execute_steps\n File \"/usr/local/lib/python3.8/dist-packages/step_crawler/functions_file.py\", line 140, in opcoes\n options.append(value.toString().split(\":\")[-1])\nAttributeError: 'NoneType' object has no attribute 'toString'"`
Na interface:
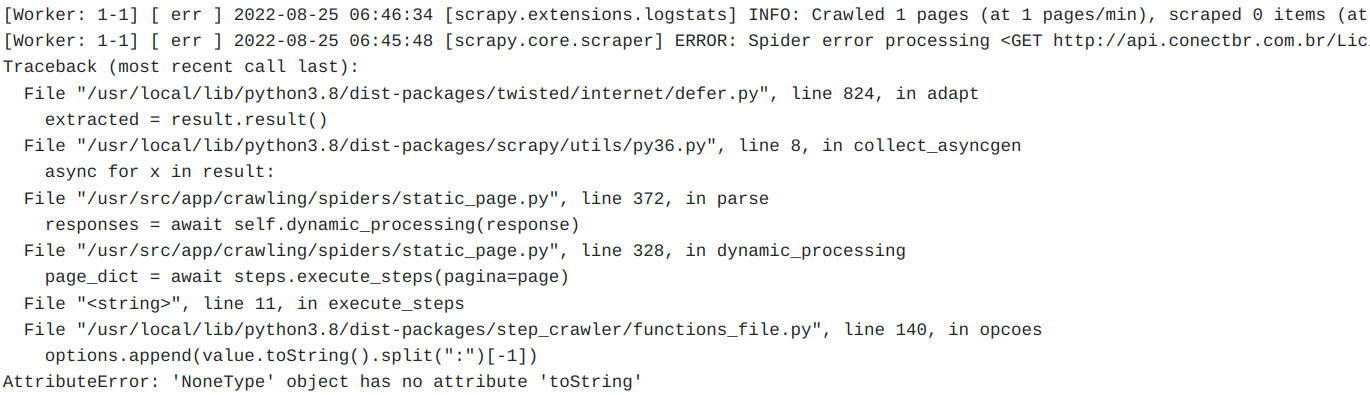
## Passos para reproduzir o erro
Executar um coletor usando o passo de Opções (exemplo abaixo) e verificar problemas em seu funcionamento.
## Especificações da Coleta
```
{
"source_name": "Licita\u00e7\u00f5es Itabirito",
"base_url": "http:\/\/api.conectbr.com.br\/Licitacao\/Busca\/?token=XEOk3i50lCa5IcpiNG7vXQ==",
"obey_robots": false,
"crawler_description": "Teste passo op\u00e7\u00f5es.",
"crawler_type_desc": "Outro",
"crawler_issue": 5850,
"data_path": "5850IT",
"sc_scheduler_persist": true,
"sc_scheduler_queue_refresh": 10,
"sc_queue_hits": 10,
"sc_queue_window": 60,
"sc_queue_moderated": true,
"sc_dupefilter_timeout": 600,
"sc_global_page_per_domain_limit": null,
"sc_global_page_per_domain_limit_timeout": 600,
"sc_domain_max_page_timeout": 600,
"sc_scheduler_ip_refresh": 60,
"sc_scheduler_backlog_blacklist": true,
"sc_scheduler_type_enabled": true,
"sc_scheduler_ip_enabled": true,
"sc_scheduler_item_retries": 3,
"sc_scheduler_queue_timeout": 3600,
"sc_httperror_allow_all": true,
"sc_retry_times": 3,
"sc_download_timeout": 10,
"antiblock_download_delay": 2,
"antiblock_autothrottle_enabled": false,
"antiblock_autothrottle_start_delay": 2,
"antiblock_autothrottle_max_delay": 10,
"antiblock_ip_rotation_enabled": false,
"antiblock_ip_rotation_type": "tor",
"antiblock_max_reqs_per_ip": 10,
"antiblock_max_reuse_rounds": 10,
"antiblock_proxy_list": "",
"antiblock_user_agent_rotation_enabled": false,
"antiblock_reqs_per_user_agent": 100,
"antiblock_user_agents_list": "",
"antiblock_insert_cookies_enabled": false,
"antiblock_cookies_list": "",
"captcha": "none",
"has_webdriver": false,
"webdriver_path": "",
"img_xpath": "",
"sound_xpath": "",
"dynamic_processing": true,
"browser_type": "chromium",
"skip_iter_errors": false,
"browser_resolution_width": 1280,
"browser_resolution_height": 720,
"explore_links": true,
"link_extractor_max_depth": 1,
"link_extractor_allow_url": "^(http:\\\/\\\/api.conectbr.com.br\\\/Licitacao\\\/AbreArquivo\\\/.*)",
"link_extractor_allow_domains": "",
"link_extractor_tags": "",
"link_extractor_attrs": "",
"link_extractor_check_type": false,
"link_extractor_process_value": "",
"download_files": true,
"download_files_allow_url": "^(http:\\\/\\\/api.conectbr.com.br\\\/Licitacao\\\/AbreArquivo\\\/.*)",
"download_files_allow_extensions": "pdf,doc",
"download_files_allow_domains": "",
"download_files_tags": "",
"download_files_attrs": "",
"download_files_process_value": "",
"download_files_check_large_content": true,
"download_imgs": false,
"steps": "{\"step\":\"root\",\"depth\":0,\"children\":[{\"step\":\"espere\",\"depth\":1,\"arguments\":{\"segundos\":\"5\"}},{\"step\":\"para_cada\",\"depth\":1,\"iterator\":\"ano\",\"children\":[{\"step\":\"selecione\",\"depth\":2,\"arguments\":{\"xpath\":\"'\/\/*[@id=\\\"NUM_ANO_REFERENCIA\\\"]'\",\"opcao\":\"ano\"}},{\"step\":\"espere\",\"depth\":2,\"arguments\":{\"segundos\":\"5\"}},{\"step\":\"clique\",\"depth\":2,\"arguments\":{\"elemento\":\"'\/\/*[@id=\\\"formDados\\\"]\/fieldset\/div\/div[7]\/input'\"}},{\"step\":\"espere\",\"depth\":2,\"arguments\":{\"segundos\":\"5\"}},{\"step\":\"screenshot\",\"depth\":2,\"arguments\":{}}],\"iterable\":{\"call\":{\"step\":\"opcoes\",\"arguments\":{\"xpath\":\"'\/html\/body\/div[1]\/div\/form\/fieldset\/div\/div[1]\/select'\",
"encoding_detection_method": 1,
"expected_runtime_category": "medium",
"templated_url_parameter_handlers": [],
"templated_url_response_handlers": [],
"instance_id": "166198811654876",
"crawler_id": 2
}
```
## Sistema (caso necessário)
- MP ou local: local.
- Branch específica: `dev`.
- Sistema diferente: não.
## Screenshots (caso necessário)
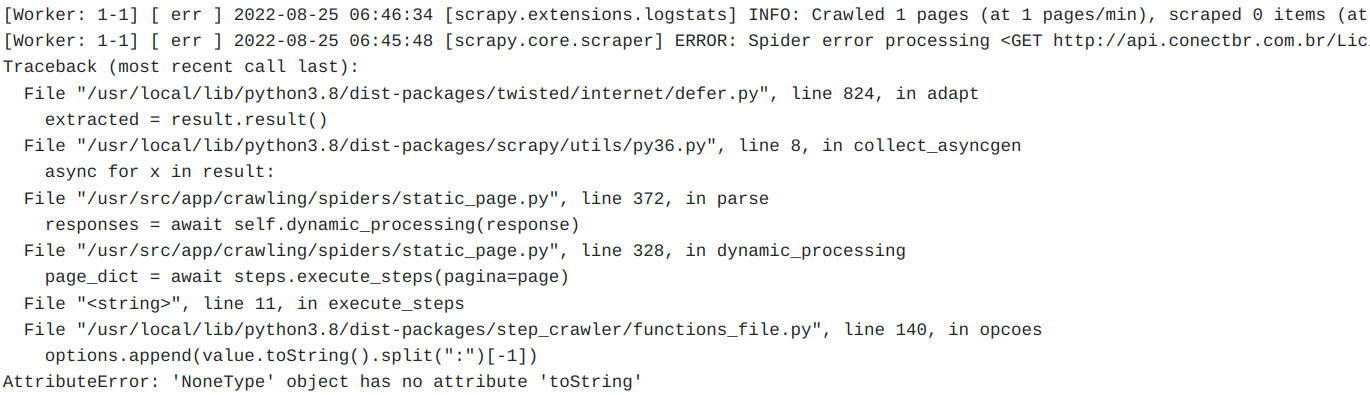
EDIT: troquei a coleta de exemplo para uma equivalente, porém mais sucinta, para que a testagem da funcionalidade seja mais objetiva.
|
process
|
passo opções comportamento esperado espera se que a configuração do passo opções não apresente problemas na branch dev assim como na branch master comportamento atual durante a execução de coletores utilizando o passo opções temos exceções semelhantes a essa log bruto message error spider error processing line in execute steps n file usr local lib dist packages step crawler functions file py line in opcoes n options append value tostring split nattributeerror nonetype object has no attribute tostring na interface passos para reproduzir o erro executar um coletor usando o passo de opções exemplo abaixo e verificar problemas em seu funcionamento especificações da coleta source name licita itabirito base url http api conectbr com br licitacao busca token obey robots false crawler description teste passo op crawler type desc outro crawler issue data path sc scheduler persist true sc scheduler queue refresh sc queue hits sc queue window sc queue moderated true sc dupefilter timeout sc global page per domain limit null sc global page per domain limit timeout sc domain max page timeout sc scheduler ip refresh sc scheduler backlog blacklist true sc scheduler type enabled true sc scheduler ip enabled true sc scheduler item retries sc scheduler queue timeout sc httperror allow all true sc retry times sc download timeout antiblock download delay antiblock autothrottle enabled false antiblock autothrottle start delay antiblock autothrottle max delay antiblock ip rotation enabled false antiblock ip rotation type tor antiblock max reqs per ip antiblock max reuse rounds antiblock proxy list antiblock user agent rotation enabled false antiblock reqs per user agent antiblock user agents list antiblock insert cookies enabled false antiblock cookies list captcha none has webdriver false webdriver path img xpath sound xpath dynamic processing true browser type chromium skip iter errors false browser resolution width browser resolution height explore links true link extractor max depth link extractor allow url http api conectbr com br licitacao abrearquivo link extractor allow domains link extractor tags link extractor attrs link extractor check type false link extractor process value download files true download files allow url http api conectbr com br licitacao abrearquivo download files allow extensions pdf doc download files allow domains download files tags download files attrs download files process value download files check large content true download imgs false steps step root depth children opcao ano step espere depth arguments segundos step clique depth arguments elemento fieldset div div input step espere depth arguments segundos step screenshot depth arguments iterable call step opcoes arguments xpath html body div div form fieldset div div select encoding detection method expected runtime category medium templated url parameter handlers templated url response handlers instance id crawler id sistema caso necessário mp ou local local branch específica dev sistema diferente não screenshots caso necessário edit troquei a coleta de exemplo para uma equivalente porém mais sucinta para que a testagem da funcionalidade seja mais objetiva
| 1
|
17,311
| 9,695,271,516
|
IssuesEvent
|
2019-05-24 21:46:44
|
PowerShell/PowerShellEditorServices
|
https://api.github.com/repos/PowerShell/PowerShellEditorServices
|
closed
|
Consider moving to netstandard2.0
|
Area-General Issue-Enhancement Issue-Performance Waiting-v2
|
It seems this isn't necessary just yet for PowerShell 6.0.0-beta1, the netstandard1.6 binaries load just fine there. We should evaluate what we'd gain by moving to netstandard2.0 in terms of APIs, though.
This work was started here but not merged yet: https://github.com/PowerShell/PowerShellEditorServices/pull/448
|
True
|
Consider moving to netstandard2.0 - It seems this isn't necessary just yet for PowerShell 6.0.0-beta1, the netstandard1.6 binaries load just fine there. We should evaluate what we'd gain by moving to netstandard2.0 in terms of APIs, though.
This work was started here but not merged yet: https://github.com/PowerShell/PowerShellEditorServices/pull/448
|
non_process
|
consider moving to it seems this isn t necessary just yet for powershell the binaries load just fine there we should evaluate what we d gain by moving to in terms of apis though this work was started here but not merged yet
| 0
|
450,939
| 32,000,184,529
|
IssuesEvent
|
2023-09-21 11:47:38
|
Bisaloo/cran-task-view-analysis
|
https://api.github.com/repos/Bisaloo/cran-task-view-analysis
|
opened
|
Discussion
|
documentation help wanted question
|
from https://github.com/WHO-Collaboratory/collaboratory-epipipeline-community/discussions/6
# Comments from reviewers
## General comments
The team has done a lot of great work flagging issues and making pull requests for existing packages to improve the overall health of the epi pipeline ecosystem.
The finalised report is likely most useful for the package developer community. It is not clear how unaware developers would be of the fact that their packages fail the presented checks.
For package users, this likely would not influence decision making on which packages to use - this is primarily determined by functionality.
We were confused about the deprecated deps check - would this cause the package to become archived in CRAN?
## Future directions
Integration of checks into the existing task view or into a platform that lists functionality and categorises packages by into subtopics would be helpful
It would be helpful to understand what proportion of epi packages are not captured through the epidemiology CRAN tag (github or improperly tagged CRAN packages)
|
1.0
|
Discussion - from https://github.com/WHO-Collaboratory/collaboratory-epipipeline-community/discussions/6
# Comments from reviewers
## General comments
The team has done a lot of great work flagging issues and making pull requests for existing packages to improve the overall health of the epi pipeline ecosystem.
The finalised report is likely most useful for the package developer community. It is not clear how unaware developers would be of the fact that their packages fail the presented checks.
For package users, this likely would not influence decision making on which packages to use - this is primarily determined by functionality.
We were confused about the deprecated deps check - would this cause the package to become archived in CRAN?
## Future directions
Integration of checks into the existing task view or into a platform that lists functionality and categorises packages by into subtopics would be helpful
It would be helpful to understand what proportion of epi packages are not captured through the epidemiology CRAN tag (github or improperly tagged CRAN packages)
|
non_process
|
discussion from comments from reviewers general comments the team has done a lot of great work flagging issues and making pull requests for existing packages to improve the overall health of the epi pipeline ecosystem the finalised report is likely most useful for the package developer community it is not clear how unaware developers would be of the fact that their packages fail the presented checks for package users this likely would not influence decision making on which packages to use this is primarily determined by functionality we were confused about the deprecated deps check would this cause the package to become archived in cran future directions integration of checks into the existing task view or into a platform that lists functionality and categorises packages by into subtopics would be helpful it would be helpful to understand what proportion of epi packages are not captured through the epidemiology cran tag github or improperly tagged cran packages
| 0
|
11,893
| 14,688,939,277
|
IssuesEvent
|
2021-01-02 06:20:49
|
wangbjun/blog
|
https://api.github.com/repos/wangbjun/blog
|
opened
|
PHP多进程编程应用 | JWang的博客
|
/2017/coding/php/php-multi-process.html Gitalk
|
https://wangbjun.site/2017/coding/php/php-multi-process.html
在日常开发中,我们经常会遇到需要使用脚本处理一些数据,在数据量比较大的情况下,我们可以采用并行的方式处理,比如说: 1.启动多个实例这种方式简单实用,推荐,比如说使用下面的shell脚本我们就可以轻松的启动多个进程去处理 12345678#!/bin/bash for((i=1;i<=8;i++))do /usr/bi
|
1.0
|
PHP多进程编程应用 | JWang的博客 - https://wangbjun.site/2017/coding/php/php-multi-process.html
在日常开发中,我们经常会遇到需要使用脚本处理一些数据,在数据量比较大的情况下,我们可以采用并行的方式处理,比如说: 1.启动多个实例这种方式简单实用,推荐,比如说使用下面的shell脚本我们就可以轻松的启动多个进程去处理 12345678#!/bin/bash for((i=1;i<=8;i++))do /usr/bi
|
process
|
php多进程编程应用 jwang的博客 在日常开发中,我们经常会遇到需要使用脚本处理一些数据,在数据量比较大的情况下,我们可以采用并行的方式处理,比如说: 启动多个实例这种方式简单实用,推荐,比如说使用下面的shell脚本我们就可以轻松的启动多个进程去处理 bin bash for i i i do usr bi
| 1
|
21,418
| 29,359,591,047
|
IssuesEvent
|
2023-05-28 00:36:45
|
devssa/onde-codar-em-salvador
|
https://api.github.com/repos/devssa/onde-codar-em-salvador
|
closed
|
[Brasília] Fullstack Developer (Bolsa CNPq) na Coodesh
|
SALVADOR INFRAESTRUTURA JAVA MYSQL JAVASCRIPT FULL-STACK HTML POSTGRESQL REQUISITOS PROCESSOS GITHUB UMA DOCUMENTAÇÃO SUBVERSION TREINAMENTO HARDWARE ALOCADO Stale
|
## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/bolsa-cnpq-145745456?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open) com o pop-up personalizado de candidatura. 👋
<p>A <strong>Alelo Recursos Genéticos</strong> está em busca de <strong><ins>Fullstack Developer (Bolsa CNPq)</ins></strong> para compor seu time!<br></p>
<p>A Plataforma Alelo Recursos Genéticos é uma plataforma de serviços de tecnologia da informação (TI), de base Web, dedicada às atividades de pesquisa em conservação e enriquecimento de recursos genéticos (RG) desenvolvida pela Empresa Brasileira de Pesquisa Agropecuária (Embrapa). A Plataforma Alelo é formada pela infraestrutura de informática (hardware), bases de dados e sistemas de tecnologia da informação (softwares), processos e serviços dedicados à gestão, treinamento e apoio à documentação de dados e informações (peopleware) das atividades desenvolvidas em núcleos de criação (animal), coleções biológicas (microrganismos), coleções e bancos de germoplasma (vegetal) com foco no tema RG.</p>
## Alelo Recursos Genéticos:
<p>A Plataforma Alelo Recursos Genéticos é uma plataforma de serviços de tecnologia da informação (TI), de base Web, dedicada às atividades de pesquisa em conservação e enriquecimento de recursos genéticos (RG) desenvolvida pela Empresa Brasileira de Pesquisa Agropecuária (Embrapa). A Plataforma Alelo é formada pela infraestrutura de informática (hardware), bases de dados e sistemas de tecnologia da informação (softwares), processos e serviços dedicados à gestão, treinamento e apoio à documentação de dados e informações (peopleware) das atividades desenvolvidas em núcleos de criação (animal), coleções biológicas (microrganismos), coleções e bancos de germoplasma (vegetal) com foco no tema RG.</p>
</p>
## Habilidades:
- Java
- Javascript
- PostgreSQL
- MySQL
- HTML 5
- CSS 3
## Local:
Brasília
## Requisitos:
- Experiência em projetos de P&D;
- Currículo Lattes preenchido com a experiência;
- Conhecimentos em Java;
- Conhecimentos em Subversion;
- Conhecimentos em JavaScript;
- Conhecimentos em PostgresSQL e MySQL;
- Conhecimentos em HTML/CSS.
## Como se candidatar:
Candidatar-se exclusivamente através da plataforma Coodesh no link a seguir: [Fullstack Developer (Bolsa CNPq) na Alelo Recursos Genéticos](https://coodesh.com/vagas/bolsa-cnpq-145745456?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open)
Após candidatar-se via plataforma Coodesh e validar o seu login, você poderá acompanhar e receber todas as interações do processo por lá. Utilize a opção **Pedir Feedback** entre uma etapa e outra na vaga que se candidatou. Isso fará com que a pessoa **Recruiter** responsável pelo processo na empresa receba a notificação.
## Labels
#### Alocação
Alocado
#### Categoria
Full-Stack
|
1.0
|
[Brasília] Fullstack Developer (Bolsa CNPq) na Coodesh - ## Descrição da vaga:
Esta é uma vaga de um parceiro da plataforma Coodesh, ao candidatar-se você terá acesso as informações completas sobre a empresa e benefícios.
Fique atento ao redirecionamento que vai te levar para uma url [https://coodesh.com](https://coodesh.com/vagas/bolsa-cnpq-145745456?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open) com o pop-up personalizado de candidatura. 👋
<p>A <strong>Alelo Recursos Genéticos</strong> está em busca de <strong><ins>Fullstack Developer (Bolsa CNPq)</ins></strong> para compor seu time!<br></p>
<p>A Plataforma Alelo Recursos Genéticos é uma plataforma de serviços de tecnologia da informação (TI), de base Web, dedicada às atividades de pesquisa em conservação e enriquecimento de recursos genéticos (RG) desenvolvida pela Empresa Brasileira de Pesquisa Agropecuária (Embrapa). A Plataforma Alelo é formada pela infraestrutura de informática (hardware), bases de dados e sistemas de tecnologia da informação (softwares), processos e serviços dedicados à gestão, treinamento e apoio à documentação de dados e informações (peopleware) das atividades desenvolvidas em núcleos de criação (animal), coleções biológicas (microrganismos), coleções e bancos de germoplasma (vegetal) com foco no tema RG.</p>
## Alelo Recursos Genéticos:
<p>A Plataforma Alelo Recursos Genéticos é uma plataforma de serviços de tecnologia da informação (TI), de base Web, dedicada às atividades de pesquisa em conservação e enriquecimento de recursos genéticos (RG) desenvolvida pela Empresa Brasileira de Pesquisa Agropecuária (Embrapa). A Plataforma Alelo é formada pela infraestrutura de informática (hardware), bases de dados e sistemas de tecnologia da informação (softwares), processos e serviços dedicados à gestão, treinamento e apoio à documentação de dados e informações (peopleware) das atividades desenvolvidas em núcleos de criação (animal), coleções biológicas (microrganismos), coleções e bancos de germoplasma (vegetal) com foco no tema RG.</p>
</p>
## Habilidades:
- Java
- Javascript
- PostgreSQL
- MySQL
- HTML 5
- CSS 3
## Local:
Brasília
## Requisitos:
- Experiência em projetos de P&D;
- Currículo Lattes preenchido com a experiência;
- Conhecimentos em Java;
- Conhecimentos em Subversion;
- Conhecimentos em JavaScript;
- Conhecimentos em PostgresSQL e MySQL;
- Conhecimentos em HTML/CSS.
## Como se candidatar:
Candidatar-se exclusivamente através da plataforma Coodesh no link a seguir: [Fullstack Developer (Bolsa CNPq) na Alelo Recursos Genéticos](https://coodesh.com/vagas/bolsa-cnpq-145745456?utm_source=github&utm_medium=devssa-onde-codar-em-salvador&modal=open)
Após candidatar-se via plataforma Coodesh e validar o seu login, você poderá acompanhar e receber todas as interações do processo por lá. Utilize a opção **Pedir Feedback** entre uma etapa e outra na vaga que se candidatou. Isso fará com que a pessoa **Recruiter** responsável pelo processo na empresa receba a notificação.
## Labels
#### Alocação
Alocado
#### Categoria
Full-Stack
|
process
|
fullstack developer bolsa cnpq na coodesh descrição da vaga esta é uma vaga de um parceiro da plataforma coodesh ao candidatar se você terá acesso as informações completas sobre a empresa e benefícios fique atento ao redirecionamento que vai te levar para uma url com o pop up personalizado de candidatura 👋 a alelo recursos genéticos está em busca de fullstack developer bolsa cnpq para compor seu time a plataforma alelo recursos genéticos é uma plataforma de serviços de tecnologia da informação ti de base web dedicada às atividades de pesquisa em conservação e enriquecimento de recursos genéticos rg desenvolvida pela empresa brasileira de pesquisa agropecuária embrapa a plataforma alelo é formada pela infraestrutura de informática hardware bases de dados e sistemas de tecnologia da informação softwares processos e serviços dedicados à gestão treinamento e apoio à documentação de dados e informações peopleware das atividades desenvolvidas em núcleos de criação animal coleções biológicas microrganismos coleções e bancos de germoplasma vegetal com foco no tema rg alelo recursos genéticos a plataforma alelo recursos genéticos é uma plataforma de serviços de tecnologia da informação ti de base web dedicada às atividades de pesquisa em conservação e enriquecimento de recursos genéticos rg desenvolvida pela empresa brasileira de pesquisa agropecuária embrapa a plataforma alelo é formada pela infraestrutura de informática hardware bases de dados e sistemas de tecnologia da informação softwares processos e serviços dedicados à gestão treinamento e apoio à documentação de dados e informações peopleware das atividades desenvolvidas em núcleos de criação animal coleções biológicas microrganismos coleções e bancos de germoplasma vegetal com foco no tema rg habilidades java javascript postgresql mysql html css local brasília requisitos experiência em projetos de p d currículo lattes preenchido com a experiência conhecimentos em java conhecimentos em subversion conhecimentos em javascript conhecimentos em postgressql e mysql conhecimentos em html css como se candidatar candidatar se exclusivamente através da plataforma coodesh no link a seguir após candidatar se via plataforma coodesh e validar o seu login você poderá acompanhar e receber todas as interações do processo por lá utilize a opção pedir feedback entre uma etapa e outra na vaga que se candidatou isso fará com que a pessoa recruiter responsável pelo processo na empresa receba a notificação labels alocação alocado categoria full stack
| 1
|
15,278
| 19,269,459,057
|
IssuesEvent
|
2021-12-10 02:12:20
|
googleapis/repo-automation-bots
|
https://api.github.com/repos/googleapis/repo-automation-bots
|
closed
|
Add container test for bazel-bot Docker image
|
type: process
|
We should have an easy way to ensure the bazel-bot image contains what we want.
See https://github.com/googleapis/repo-automation-bots/blob/main/packages/release-trigger/cloudbuild-test.yaml as an example
|
1.0
|
Add container test for bazel-bot Docker image - We should have an easy way to ensure the bazel-bot image contains what we want.
See https://github.com/googleapis/repo-automation-bots/blob/main/packages/release-trigger/cloudbuild-test.yaml as an example
|
process
|
add container test for bazel bot docker image we should have an easy way to ensure the bazel bot image contains what we want see as an example
| 1
|
6,754
| 9,881,537,875
|
IssuesEvent
|
2019-06-24 14:53:22
|
usgpo/bill-status
|
https://api.github.com/repos/usgpo/bill-status
|
closed
|
To Include Bill Version in Bill Status Document
|
reprocessing files working on it
|
Legislation may be changed or amended as it makes its way through the legislative process. You will sometimes see different bill text versions in the Text tab of a bill record. A list of the different versions are in the [link](https://www.gpo.gov/help/about_congressional_bills.htm).
Versions are needed for accessing bills the following xml pages:
[Bill Summary (In URL)](https://www.gpo.gov/fdsys/pkg/BILLS-115hconres1eh/html/BILLS-115hconres1eh.htm)
[CONGRESSIONAL BILLS - BULK DATA](https://www.gpo.gov/fdsys/bulkdata/BILLS/115/1/hr)
|
1.0
|
To Include Bill Version in Bill Status Document - Legislation may be changed or amended as it makes its way through the legislative process. You will sometimes see different bill text versions in the Text tab of a bill record. A list of the different versions are in the [link](https://www.gpo.gov/help/about_congressional_bills.htm).
Versions are needed for accessing bills the following xml pages:
[Bill Summary (In URL)](https://www.gpo.gov/fdsys/pkg/BILLS-115hconres1eh/html/BILLS-115hconres1eh.htm)
[CONGRESSIONAL BILLS - BULK DATA](https://www.gpo.gov/fdsys/bulkdata/BILLS/115/1/hr)
|
process
|
to include bill version in bill status document legislation may be changed or amended as it makes its way through the legislative process you will sometimes see different bill text versions in the text tab of a bill record a list of the different versions are in the versions are needed for accessing bills the following xml pages
| 1
|
12,321
| 14,879,490,839
|
IssuesEvent
|
2021-01-20 07:46:39
|
lutraconsulting/qgis-crayfish-plugin
|
https://api.github.com/repos/lutraconsulting/qgis-crayfish-plugin
|
closed
|
Issues with polygon contours
|
critical bug processing
|
Polygons generated from contour processing algorithm are not very usable. They contain lots of very tight angles, sliver polygons, self-intersecting, duplicate nodes, polygons with less than 3 nodes and small areas:
|
1.0
|
Issues with polygon contours - Polygons generated from contour processing algorithm are not very usable. They contain lots of very tight angles, sliver polygons, self-intersecting, duplicate nodes, polygons with less than 3 nodes and small areas:
|
process
|
issues with polygon contours polygons generated from contour processing algorithm are not very usable they contain lots of very tight angles sliver polygons self intersecting duplicate nodes polygons with less than nodes and small areas
| 1
|
203,981
| 15,396,353,620
|
IssuesEvent
|
2021-03-03 20:31:07
|
mozilla/foundation.mozilla.org
|
https://api.github.com/repos/mozilla/foundation.mozilla.org
|
closed
|
Add a new CI task that actually tests pages
|
engineering testing
|
We currently have a Cypress CI task set up that exists purely to take snapshots for Percy to then look at. However, we should create a separate Cypress CI task to actually test our end points: do the pages exist? Do all their CSS and JS requirements load? etc.
Not having this caught us out because a build rewrite changed the build for "mozfest.compiled.js" to "index.compiled.js" and this caused the mozfest site to be unable to load its JS bundle, which on prod (with DEBUG=False) means users were getting a server error 500.
- [ ] start with copying all Percy tests, but removing the snapshot instructions and instead checking whether the pages even load
|
1.0
|
Add a new CI task that actually tests pages - We currently have a Cypress CI task set up that exists purely to take snapshots for Percy to then look at. However, we should create a separate Cypress CI task to actually test our end points: do the pages exist? Do all their CSS and JS requirements load? etc.
Not having this caught us out because a build rewrite changed the build for "mozfest.compiled.js" to "index.compiled.js" and this caused the mozfest site to be unable to load its JS bundle, which on prod (with DEBUG=False) means users were getting a server error 500.
- [ ] start with copying all Percy tests, but removing the snapshot instructions and instead checking whether the pages even load
|
non_process
|
add a new ci task that actually tests pages we currently have a cypress ci task set up that exists purely to take snapshots for percy to then look at however we should create a separate cypress ci task to actually test our end points do the pages exist do all their css and js requirements load etc not having this caught us out because a build rewrite changed the build for mozfest compiled js to index compiled js and this caused the mozfest site to be unable to load its js bundle which on prod with debug false means users were getting a server error start with copying all percy tests but removing the snapshot instructions and instead checking whether the pages even load
| 0
|
2,752
| 3,146,325,638
|
IssuesEvent
|
2015-09-14 22:21:46
|
cortoproject/corto
|
https://api.github.com/repos/cortoproject/corto
|
closed
|
Introduce hidden and alias members
|
Corto:TypeSystem Corto:Usability enhancement Style
|
In certain cases, a class will want to control the order in which members appear, to increase usability when providing an initializer. This can introduce problems, when the class inherits from another class, and the base class exposes members that should appear after the members of the subclass.
A workaround has been to make the baseclass visibility PRIVATE, add a member to the subclass (usually with the same name) and copy the value of that member manually to the base class (usually in the constructor). An example:
```c++
class Foo ::
b: int32
class Bar: Foo, private ::
a: int32
b: int32
int32 construct():
super.a = this.a
Bar o: 10, 20 // a = 10, b = 20
```
That is not a very nice solution since it introduces a redundant member with the same value, which needs to be kept in sync manually. The following proposal introduces two extra features to the type system that address this problem in a cleaner way.
The first new feature is `alias`. An alias is a member that occupies the same memory space as another member. An alias may not be declared in a context where the member it points to is also visible, and may also not point to a member it doesn't have access to (private). The above example with an alias:
```c++
class Foo ::
b: int32
class Bar: Foo, local ::
a: int32
alias b: Foo::b
Bar o: 10, 20 // a = 10, b = 20
```
Notice the usage of `local` here: a local member won't show up in an initializer, but doesn't protect the member from outside access.
This approach has another drawback however, and that is that `Foo` in this context now needs to be local. Local has semantics associated with whether data is relevant outside the context of the application (does it need to be persistently stored) and this wouldn't be a very orthogonal solution.
Hence the introduction of hidden:
```c++
class Foo ::
b: int32
class Bar: Foo, hidden ::
a: int32
alias b: Foo::b
Bar o: 10, 20 // a = 10, b = 20
```
Hidden simply hides the members of a and doesn't affect the way in which members can be accessed or should be serialized. Therefore, the combination of `hidden` and `alias` can be a powerful tool in controlling the order of members in initializers, and thus increase the usability of types.
An alias shall always mirror the attributes of the original member (modifiers, state and weak) in order to not break the model. When the inheritance modifier(s) of the base class are more restrictive than the modifiers of the aliassed member itself, the most restrictive applies. In practice, that will mean that alias members are only useful for hidden members, or hidden base classes. For example:
```c++
class Foo ::
b: int32 // global, public
class Bar: Foo, private ::
a: int32
alias b: Foo::b // NOT OK: can't access Foo::b
```
```c++
class Foo ::
b: int32 // global, public
class Bar: Foo, local ::
a: int32
alias b: Foo::b // NOT OK: useless, since a local members don't show up in initializers
```
```c++
class Foo ::
b: int32 // global, public
class Bar: Foo, hidden ::
a: int32
alias b: Foo::b // OK: member is hidden by inheritance modifier
```
```c++
class Foo ::
b: int32, hidden
class Bar: Foo ::
a: int32
alias b: Foo::b // OK: member is hidden itself
```
|
True
|
Introduce hidden and alias members - In certain cases, a class will want to control the order in which members appear, to increase usability when providing an initializer. This can introduce problems, when the class inherits from another class, and the base class exposes members that should appear after the members of the subclass.
A workaround has been to make the baseclass visibility PRIVATE, add a member to the subclass (usually with the same name) and copy the value of that member manually to the base class (usually in the constructor). An example:
```c++
class Foo ::
b: int32
class Bar: Foo, private ::
a: int32
b: int32
int32 construct():
super.a = this.a
Bar o: 10, 20 // a = 10, b = 20
```
That is not a very nice solution since it introduces a redundant member with the same value, which needs to be kept in sync manually. The following proposal introduces two extra features to the type system that address this problem in a cleaner way.
The first new feature is `alias`. An alias is a member that occupies the same memory space as another member. An alias may not be declared in a context where the member it points to is also visible, and may also not point to a member it doesn't have access to (private). The above example with an alias:
```c++
class Foo ::
b: int32
class Bar: Foo, local ::
a: int32
alias b: Foo::b
Bar o: 10, 20 // a = 10, b = 20
```
Notice the usage of `local` here: a local member won't show up in an initializer, but doesn't protect the member from outside access.
This approach has another drawback however, and that is that `Foo` in this context now needs to be local. Local has semantics associated with whether data is relevant outside the context of the application (does it need to be persistently stored) and this wouldn't be a very orthogonal solution.
Hence the introduction of hidden:
```c++
class Foo ::
b: int32
class Bar: Foo, hidden ::
a: int32
alias b: Foo::b
Bar o: 10, 20 // a = 10, b = 20
```
Hidden simply hides the members of a and doesn't affect the way in which members can be accessed or should be serialized. Therefore, the combination of `hidden` and `alias` can be a powerful tool in controlling the order of members in initializers, and thus increase the usability of types.
An alias shall always mirror the attributes of the original member (modifiers, state and weak) in order to not break the model. When the inheritance modifier(s) of the base class are more restrictive than the modifiers of the aliassed member itself, the most restrictive applies. In practice, that will mean that alias members are only useful for hidden members, or hidden base classes. For example:
```c++
class Foo ::
b: int32 // global, public
class Bar: Foo, private ::
a: int32
alias b: Foo::b // NOT OK: can't access Foo::b
```
```c++
class Foo ::
b: int32 // global, public
class Bar: Foo, local ::
a: int32
alias b: Foo::b // NOT OK: useless, since a local members don't show up in initializers
```
```c++
class Foo ::
b: int32 // global, public
class Bar: Foo, hidden ::
a: int32
alias b: Foo::b // OK: member is hidden by inheritance modifier
```
```c++
class Foo ::
b: int32, hidden
class Bar: Foo ::
a: int32
alias b: Foo::b // OK: member is hidden itself
```
|
non_process
|
introduce hidden and alias members in certain cases a class will want to control the order in which members appear to increase usability when providing an initializer this can introduce problems when the class inherits from another class and the base class exposes members that should appear after the members of the subclass a workaround has been to make the baseclass visibility private add a member to the subclass usually with the same name and copy the value of that member manually to the base class usually in the constructor an example c class foo b class bar foo private a b construct super a this a bar o a b that is not a very nice solution since it introduces a redundant member with the same value which needs to be kept in sync manually the following proposal introduces two extra features to the type system that address this problem in a cleaner way the first new feature is alias an alias is a member that occupies the same memory space as another member an alias may not be declared in a context where the member it points to is also visible and may also not point to a member it doesn t have access to private the above example with an alias c class foo b class bar foo local a alias b foo b bar o a b notice the usage of local here a local member won t show up in an initializer but doesn t protect the member from outside access this approach has another drawback however and that is that foo in this context now needs to be local local has semantics associated with whether data is relevant outside the context of the application does it need to be persistently stored and this wouldn t be a very orthogonal solution hence the introduction of hidden c class foo b class bar foo hidden a alias b foo b bar o a b hidden simply hides the members of a and doesn t affect the way in which members can be accessed or should be serialized therefore the combination of hidden and alias can be a powerful tool in controlling the order of members in initializers and thus increase the usability of types an alias shall always mirror the attributes of the original member modifiers state and weak in order to not break the model when the inheritance modifier s of the base class are more restrictive than the modifiers of the aliassed member itself the most restrictive applies in practice that will mean that alias members are only useful for hidden members or hidden base classes for example c class foo b global public class bar foo private a alias b foo b not ok can t access foo b c class foo b global public class bar foo local a alias b foo b not ok useless since a local members don t show up in initializers c class foo b global public class bar foo hidden a alias b foo b ok member is hidden by inheritance modifier c class foo b hidden class bar foo a alias b foo b ok member is hidden itself
| 0
|
9,165
| 12,219,631,321
|
IssuesEvent
|
2020-05-01 22:17:15
|
jyn514/rcc
|
https://api.github.com/repos/jyn514/rcc
|
opened
|
\n is a valid preprocessing token
|
bug preprocessor
|
### Expected behavior
<!-- A description of what you expected to happen.
You could also paste the output of another compiler,
I like `clang -x c - -Wall -Wextra -pedantic` -->
`\n` should be a valid preprocessor token so that it can be used in token pasting.
Found in `/usr/include/sys/sysmacros.h`. glibc is cursed.
### Code
<!-- The code that was not interpreted correctly goes here.
This should also include the error message you got. -->
```c
#define __SYSMACROS_DM(symbol) __SYSMACROS_DM1 (a b \n c)
#define __SYSMACROS_DM1(...) __glibc_macro_warning (#__VA_ARGS__)
__SYSMACROS_DM(a)
<stdin>:1:53 error: invalid token: unknown token: '\'
#define __SYSMACROS_DM(symbol) __SYSMACROS_DM1 (a b \n c)
^
```
Output from `clang -E`:
```c
__glibc_macro_warning ("a b \n c")
```
<!-- If you know where to find it, include the relevant part of the C standard
There's a copy at http://port70.net/~nsz/c/c11/n1570.html -->
http://port70.net/~nsz/c/c11/n1570.html#6.4p3:
> The categories of preprocessing tokens are: header names, identifiers, preprocessing numbers, character constants, string literals, punctuators, and single non-white-space characters that do not lexically match the other preprocessing token categories.
"If it's not whitespace, it's valid!" :facepalm:
|
1.0
|
\n is a valid preprocessing token - ### Expected behavior
<!-- A description of what you expected to happen.
You could also paste the output of another compiler,
I like `clang -x c - -Wall -Wextra -pedantic` -->
`\n` should be a valid preprocessor token so that it can be used in token pasting.
Found in `/usr/include/sys/sysmacros.h`. glibc is cursed.
### Code
<!-- The code that was not interpreted correctly goes here.
This should also include the error message you got. -->
```c
#define __SYSMACROS_DM(symbol) __SYSMACROS_DM1 (a b \n c)
#define __SYSMACROS_DM1(...) __glibc_macro_warning (#__VA_ARGS__)
__SYSMACROS_DM(a)
<stdin>:1:53 error: invalid token: unknown token: '\'
#define __SYSMACROS_DM(symbol) __SYSMACROS_DM1 (a b \n c)
^
```
Output from `clang -E`:
```c
__glibc_macro_warning ("a b \n c")
```
<!-- If you know where to find it, include the relevant part of the C standard
There's a copy at http://port70.net/~nsz/c/c11/n1570.html -->
http://port70.net/~nsz/c/c11/n1570.html#6.4p3:
> The categories of preprocessing tokens are: header names, identifiers, preprocessing numbers, character constants, string literals, punctuators, and single non-white-space characters that do not lexically match the other preprocessing token categories.
"If it's not whitespace, it's valid!" :facepalm:
|
process
|
n is a valid preprocessing token expected behavior a description of what you expected to happen you could also paste the output of another compiler i like clang x c wall wextra pedantic n should be a valid preprocessor token so that it can be used in token pasting found in usr include sys sysmacros h glibc is cursed code the code that was not interpreted correctly goes here this should also include the error message you got c define sysmacros dm symbol sysmacros a b n c define sysmacros glibc macro warning va args sysmacros dm a error invalid token unknown token define sysmacros dm symbol sysmacros a b n c output from clang e c glibc macro warning a b n c if you know where to find it include the relevant part of the c standard there s a copy at the categories of preprocessing tokens are header names identifiers preprocessing numbers character constants string literals punctuators and single non white space characters that do not lexically match the other preprocessing token categories if it s not whitespace it s valid facepalm
| 1
|
10,747
| 13,541,450,986
|
IssuesEvent
|
2020-09-16 15:54:02
|
department-of-veterans-affairs/notification-api
|
https://api.github.com/repos/department-of-veterans-affairs/notification-api
|
closed
|
Procure SSL certificates
|
Process Task Release
|
**Notes:**
- Need to setup the domain
- We need the commercial certs
- We need the VA certs
|
1.0
|
Procure SSL certificates - **Notes:**
- Need to setup the domain
- We need the commercial certs
- We need the VA certs
|
process
|
procure ssl certificates notes need to setup the domain we need the commercial certs we need the va certs
| 1
|
15,327
| 19,433,139,472
|
IssuesEvent
|
2021-12-21 14:16:00
|
threefoldtech/tfchain
|
https://api.github.com/repos/threefoldtech/tfchain
|
closed
|
npos: Test and document hard fork scenario in case grandpa is stalled
|
process_wontfix
|
Given the testing in #122
> If more than 1/3 of the nodes die, GRANDPA finalization dies. At this point, new validators will be elected (as described above). However, the GRANDPA validator set only updates if the block in which the update is triggered is finalized. Since GRANDPA is currently dead in this scenario, the block will never finalize, and GRANDPA will stall forever.
To recover from this scenario, a hard fork scenario is a solution.
|
1.0
|
npos: Test and document hard fork scenario in case grandpa is stalled - Given the testing in #122
> If more than 1/3 of the nodes die, GRANDPA finalization dies. At this point, new validators will be elected (as described above). However, the GRANDPA validator set only updates if the block in which the update is triggered is finalized. Since GRANDPA is currently dead in this scenario, the block will never finalize, and GRANDPA will stall forever.
To recover from this scenario, a hard fork scenario is a solution.
|
process
|
npos test and document hard fork scenario in case grandpa is stalled given the testing in if more than of the nodes die grandpa finalization dies at this point new validators will be elected as described above however the grandpa validator set only updates if the block in which the update is triggered is finalized since grandpa is currently dead in this scenario the block will never finalize and grandpa will stall forever to recover from this scenario a hard fork scenario is a solution
| 1
|
285,796
| 21,554,979,460
|
IssuesEvent
|
2022-04-30 08:50:38
|
twistedsistem/OCTGN-Marvel-Champions
|
https://api.github.com/repos/twistedsistem/OCTGN-Marvel-Champions
|
closed
|
Keyboard Shortcuts
|
documentation enhancement
|
Definitely one of the most useful things that can be added, in my opinion.
Also, I just want to say that you've nailed the double-click actions. Definitely very intuitive for each card type. You've also nailed the add/remove for threat/damage!
Based on 12-15 playthroughs, I've found these to be the most important actions to have a shortcut. As always, these are merely suggestions, and if nothing else possibly just a place to have discussion.
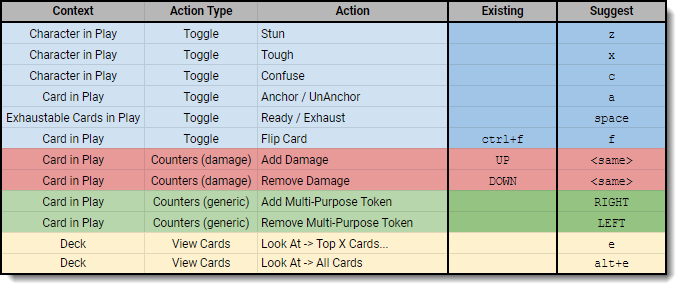
|
1.0
|
Keyboard Shortcuts - Definitely one of the most useful things that can be added, in my opinion.
Also, I just want to say that you've nailed the double-click actions. Definitely very intuitive for each card type. You've also nailed the add/remove for threat/damage!
Based on 12-15 playthroughs, I've found these to be the most important actions to have a shortcut. As always, these are merely suggestions, and if nothing else possibly just a place to have discussion.
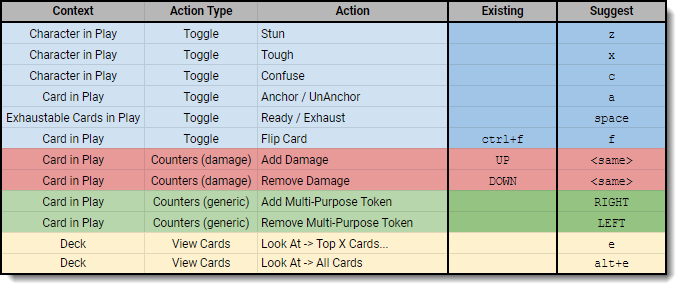
|
non_process
|
keyboard shortcuts definitely one of the most useful things that can be added in my opinion also i just want to say that you ve nailed the double click actions definitely very intuitive for each card type you ve also nailed the add remove for threat damage based on playthroughs i ve found these to be the most important actions to have a shortcut as always these are merely suggestions and if nothing else possibly just a place to have discussion
| 0
|
27,231
| 4,939,525,681
|
IssuesEvent
|
2016-11-29 14:37:49
|
jfabry/LiveRobotProgramming
|
https://api.github.com/repos/jfabry/LiveRobotProgramming
|
closed
|
Import of a program that does not parse crashes the interpreter
|
Component-Parser Priority-High Type-Defect
|
We should check in LRPProgram>>exportedMachines and loadImports if the current ast is not a failure
|
1.0
|
Import of a program that does not parse crashes the interpreter - We should check in LRPProgram>>exportedMachines and loadImports if the current ast is not a failure
|
non_process
|
import of a program that does not parse crashes the interpreter we should check in lrpprogram exportedmachines and loadimports if the current ast is not a failure
| 0
|
19,304
| 10,367,593,689
|
IssuesEvent
|
2019-09-07 09:41:17
|
emscripten-core/emscripten
|
https://api.github.com/repos/emscripten-core/emscripten
|
closed
|
Unnecessary label variables
|
fastcomp performance wontfix
|
I looked for small testcases where OdinMonkey has more phis (even after EliminatePhis and other optimizations) than emscripten's LLVM IR. One of the interesting cases I found was emscripten/tests/emscripten_get_now.cpp (compiled with emcc -O2).
One thing that's happening is that the Relooper is using a label variable to share control paths that aren't shared in the LLVM IR. To an optimizer that doesn't understand label variables, this makes it look like more blocks are reachable from more places, which means that some blocks no longer dominate some blocks they used to, which means that the optimizer inserts more phis.
The generated JS code looks roughly like this:
```
o = 0;
while (1) {
...
if (...) {
o = 6;
break;
}
if (...) {
o = 10;
break;
}
if (...) {
break;
}
}
if (o == 6) {
...
} else if (o == 10) {
...
} else {
...
}
```
In cases like this, it would be preferable to avoid the label variable by moving the ending code into the if statements inside the loop. I manually edited the JS file to try this, and it eliminated several of the interesting phis in the resulting MIR.
This would intermix loop and non-loop blocks even more, but that's something we should fix in the JIT itself anyway [0].
[0] https://bugzilla.mozilla.org/show_bug.cgi?id=844779
|
True
|
Unnecessary label variables - I looked for small testcases where OdinMonkey has more phis (even after EliminatePhis and other optimizations) than emscripten's LLVM IR. One of the interesting cases I found was emscripten/tests/emscripten_get_now.cpp (compiled with emcc -O2).
One thing that's happening is that the Relooper is using a label variable to share control paths that aren't shared in the LLVM IR. To an optimizer that doesn't understand label variables, this makes it look like more blocks are reachable from more places, which means that some blocks no longer dominate some blocks they used to, which means that the optimizer inserts more phis.
The generated JS code looks roughly like this:
```
o = 0;
while (1) {
...
if (...) {
o = 6;
break;
}
if (...) {
o = 10;
break;
}
if (...) {
break;
}
}
if (o == 6) {
...
} else if (o == 10) {
...
} else {
...
}
```
In cases like this, it would be preferable to avoid the label variable by moving the ending code into the if statements inside the loop. I manually edited the JS file to try this, and it eliminated several of the interesting phis in the resulting MIR.
This would intermix loop and non-loop blocks even more, but that's something we should fix in the JIT itself anyway [0].
[0] https://bugzilla.mozilla.org/show_bug.cgi?id=844779
|
non_process
|
unnecessary label variables i looked for small testcases where odinmonkey has more phis even after eliminatephis and other optimizations than emscripten s llvm ir one of the interesting cases i found was emscripten tests emscripten get now cpp compiled with emcc one thing that s happening is that the relooper is using a label variable to share control paths that aren t shared in the llvm ir to an optimizer that doesn t understand label variables this makes it look like more blocks are reachable from more places which means that some blocks no longer dominate some blocks they used to which means that the optimizer inserts more phis the generated js code looks roughly like this o while if o break if o break if break if o else if o else in cases like this it would be preferable to avoid the label variable by moving the ending code into the if statements inside the loop i manually edited the js file to try this and it eliminated several of the interesting phis in the resulting mir this would intermix loop and non loop blocks even more but that s something we should fix in the jit itself anyway
| 0
|
19,525
| 25,835,760,502
|
IssuesEvent
|
2022-12-12 19:30:09
|
AcademySoftwareFoundation/OpenCue
|
https://api.github.com/repos/AcademySoftwareFoundation/OpenCue
|
closed
|
Upgrade log4j
|
process
|
**Describe the process**
Upgrade to a version of log4j which is not affected by the Log4Shell vulnerability.
|
1.0
|
Upgrade log4j - **Describe the process**
Upgrade to a version of log4j which is not affected by the Log4Shell vulnerability.
|
process
|
upgrade describe the process upgrade to a version of which is not affected by the vulnerability
| 1
|
5,022
| 7,845,729,742
|
IssuesEvent
|
2018-06-19 13:44:51
|
openvstorage/framework
|
https://api.github.com/repos/openvstorage/framework
|
closed
|
Saving a vdisk builds a huge sequence
|
process_wontfix type_bug
|
### Problem description
When saving a vdisk, a huge sequence is generated. (56MB!)
```
ArakoonException: Unknown error code 0x26, server said: update Sequence([Assert ;"ovs_index_vdisk|volume_id|faf9b4e98b061d61f43807bc846f426971f4cc84";0; Set ;"ovs_index_vdisk|volume_id|faf9b4e98b061d61f43807bc846f426971f4cc84";55;"..."; Set ;"ovs_reverseindex_vpool_b0e66d3d-bd12-45e0-ba6a-224a510d485b|vdisks|e23014b6-da6d-4992-b818-5999c214ee5f";1;"..."; Replace ;"ovs_listcache_vdisk|ovs_list_a42d01310e7f8d8f1a0523a68714c362c12753fefc1de5dee9a9e22393bc52f5|__all";0; Replace ;"ovs_listcache_vdisk|ovs_list_a42d01310e7f8d8f1a0523a68714c362c12753fefc1de5dee9a9e22393bc52f5|parentsnapshot";0; Replace ;"ovs_listcache_vdisk|ovs_list_d
*SNIP*
;"ovs_listcache_vdisk|ovs_list_e80bbf9602e3746a33d8b5ba378b0be2fa4f0fae6745b3f271c788b087afba3d|__all";0; Replace ;"ovs_listcache_vdisk|ovs_list_e80bbf9602e3746a33d8b5ba378b0be2fa4f0fae6745b3f271c788b087afba3d|parentsnapshot";0; Replace ;"ovs_listcache_vdisk|ovs_list_cde7e94cdb25a1a20fd708d33b2d8ebb96a99f69fd527dfb5cadf0f75844e0cd|__all";0; ... (475334 more) ]) has size 53484496 > 33554432
```
```
/opt/OpenvStorage/ovs/dal/dataobject.pyc in save(self, recursive, skip, _hook)
693 self._mutex_version.acquire(30)
694 self._persistent.set(self._key, self._data, transaction=transaction)
--> 695 self._persistent.apply_transaction(transaction)
696 self._volatile.delete(self._key)
697 successful = True
/usr/lib/python2.7/dist-packages/ovs_extensions/storage/persistent/pyrakoonstore.pyc in apply_transaction(self, transaction)
140 """
141 try:
--> 142 return self._client.apply_transaction(transaction)
143 except ArakoonAssertionFailed as assertion:
144 raise AssertException(assertion)
/usr/lib/python2.7/dist-packages/ovs_extensions/db/arakoon/pyrakoon/client.pyc in apply_transaction(self, transaction)
198 Applies a transaction
199 """
--> 200 return PyrakoonClient._try(self._identifier, self._client.sequence, self._sequences[transaction], max_duration=1)
201
202 @staticmethod
/usr/lib/python2.7/dist-packages/ovs_extensions/db/arakoon/pyrakoon/client.pyc in _try(identifier, method, *args, **kwargs)
212 start = time.time()
213 try:
--> 214 return_value = method(*args, **kwargs)
215 except (ArakoonSockNotReadable, ArakoonSockReadNoBytes, ArakoonSockSendError):
216 logger.debug('Error during arakoon call {0}, retry'.format(method.__name__))
<update_argspec> in sequence(self, seq, sync)
/usr/lib/python2.7/dist-packages/ovs_extensions/db/arakoon/pyrakoon/pyrakoon/compat.pyc in wrapped(*args, **kwargs)
165 raise
166
--> 167 raise new_exception
168
169 return wrapped
```
This error was given back by Arakoon because the sequence was too big. This should be looked into
Statistics of the environment:
- 76MB ovs-db size
- +-500 vdisks
|
1.0
|
Saving a vdisk builds a huge sequence - ### Problem description
When saving a vdisk, a huge sequence is generated. (56MB!)
```
ArakoonException: Unknown error code 0x26, server said: update Sequence([Assert ;"ovs_index_vdisk|volume_id|faf9b4e98b061d61f43807bc846f426971f4cc84";0; Set ;"ovs_index_vdisk|volume_id|faf9b4e98b061d61f43807bc846f426971f4cc84";55;"..."; Set ;"ovs_reverseindex_vpool_b0e66d3d-bd12-45e0-ba6a-224a510d485b|vdisks|e23014b6-da6d-4992-b818-5999c214ee5f";1;"..."; Replace ;"ovs_listcache_vdisk|ovs_list_a42d01310e7f8d8f1a0523a68714c362c12753fefc1de5dee9a9e22393bc52f5|__all";0; Replace ;"ovs_listcache_vdisk|ovs_list_a42d01310e7f8d8f1a0523a68714c362c12753fefc1de5dee9a9e22393bc52f5|parentsnapshot";0; Replace ;"ovs_listcache_vdisk|ovs_list_d
*SNIP*
;"ovs_listcache_vdisk|ovs_list_e80bbf9602e3746a33d8b5ba378b0be2fa4f0fae6745b3f271c788b087afba3d|__all";0; Replace ;"ovs_listcache_vdisk|ovs_list_e80bbf9602e3746a33d8b5ba378b0be2fa4f0fae6745b3f271c788b087afba3d|parentsnapshot";0; Replace ;"ovs_listcache_vdisk|ovs_list_cde7e94cdb25a1a20fd708d33b2d8ebb96a99f69fd527dfb5cadf0f75844e0cd|__all";0; ... (475334 more) ]) has size 53484496 > 33554432
```
```
/opt/OpenvStorage/ovs/dal/dataobject.pyc in save(self, recursive, skip, _hook)
693 self._mutex_version.acquire(30)
694 self._persistent.set(self._key, self._data, transaction=transaction)
--> 695 self._persistent.apply_transaction(transaction)
696 self._volatile.delete(self._key)
697 successful = True
/usr/lib/python2.7/dist-packages/ovs_extensions/storage/persistent/pyrakoonstore.pyc in apply_transaction(self, transaction)
140 """
141 try:
--> 142 return self._client.apply_transaction(transaction)
143 except ArakoonAssertionFailed as assertion:
144 raise AssertException(assertion)
/usr/lib/python2.7/dist-packages/ovs_extensions/db/arakoon/pyrakoon/client.pyc in apply_transaction(self, transaction)
198 Applies a transaction
199 """
--> 200 return PyrakoonClient._try(self._identifier, self._client.sequence, self._sequences[transaction], max_duration=1)
201
202 @staticmethod
/usr/lib/python2.7/dist-packages/ovs_extensions/db/arakoon/pyrakoon/client.pyc in _try(identifier, method, *args, **kwargs)
212 start = time.time()
213 try:
--> 214 return_value = method(*args, **kwargs)
215 except (ArakoonSockNotReadable, ArakoonSockReadNoBytes, ArakoonSockSendError):
216 logger.debug('Error during arakoon call {0}, retry'.format(method.__name__))
<update_argspec> in sequence(self, seq, sync)
/usr/lib/python2.7/dist-packages/ovs_extensions/db/arakoon/pyrakoon/pyrakoon/compat.pyc in wrapped(*args, **kwargs)
165 raise
166
--> 167 raise new_exception
168
169 return wrapped
```
This error was given back by Arakoon because the sequence was too big. This should be looked into
Statistics of the environment:
- 76MB ovs-db size
- +-500 vdisks
|
process
|
saving a vdisk builds a huge sequence problem description when saving a vdisk a huge sequence is generated arakoonexception unknown error code server said update sequence assert ovs index vdisk volume id set ovs index vdisk volume id set ovs reverseindex vpool vdisks replace ovs listcache vdisk ovs list all replace ovs listcache vdisk ovs list parentsnapshot replace ovs listcache vdisk ovs list d snip ovs listcache vdisk ovs list all replace ovs listcache vdisk ovs list parentsnapshot replace ovs listcache vdisk ovs list all more has size opt openvstorage ovs dal dataobject pyc in save self recursive skip hook self mutex version acquire self persistent set self key self data transaction transaction self persistent apply transaction transaction self volatile delete self key successful true usr lib dist packages ovs extensions storage persistent pyrakoonstore pyc in apply transaction self transaction try return self client apply transaction transaction except arakoonassertionfailed as assertion raise assertexception assertion usr lib dist packages ovs extensions db arakoon pyrakoon client pyc in apply transaction self transaction applies a transaction return pyrakoonclient try self identifier self client sequence self sequences max duration staticmethod usr lib dist packages ovs extensions db arakoon pyrakoon client pyc in try identifier method args kwargs start time time try return value method args kwargs except arakoonsocknotreadable arakoonsockreadnobytes arakoonsocksenderror logger debug error during arakoon call retry format method name in sequence self seq sync usr lib dist packages ovs extensions db arakoon pyrakoon pyrakoon compat pyc in wrapped args kwargs raise raise new exception return wrapped this error was given back by arakoon because the sequence was too big this should be looked into statistics of the environment ovs db size vdisks
| 1
|
290,245
| 32,045,667,578
|
IssuesEvent
|
2023-09-23 01:34:27
|
Chiencc/asuswrt-gt-ac5300
|
https://api.github.com/repos/Chiencc/asuswrt-gt-ac5300
|
reopened
|
jquery-ui-1.10.3.min.js: 5 vulnerabilities (highest severity is: 6.1)
|
Mend: dependency security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery-ui version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-41184](https://www.mend.io/vulnerability-database/CVE-2021-41184) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.0 | ❌ |
| [CVE-2021-41183](https://www.mend.io/vulnerability-database/CVE-2021-41183) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.0 | ❌ |
| [CVE-2021-41182](https://www.mend.io/vulnerability-database/CVE-2021-41182) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.0 | ❌ |
| [CVE-2022-31160](https://www.mend.io/vulnerability-database/CVE-2022-31160) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.2 | ❌ |
| [CVE-2016-7103](https://www.mend.io/vulnerability-database/CVE-2016-7103) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | katello - 4.7.2 | ❌ |
<p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-41184</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery-UI is the official jQuery user interface library. Prior to version 1.13.0, accepting the value of the `of` option of the `.position()` util from untrusted sources may execute untrusted code. The issue is fixed in jQuery UI 1.13.0. Any string value passed to the `of` option is now treated as a CSS selector. A workaround is to not accept the value of the `of` option from untrusted sources.
<p>Publish Date: 2021-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-41184>CVE-2021-41184</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41184">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41184</a></p>
<p>Release Date: 2021-10-26</p>
<p>Fix Resolution: jquery-ui - 1.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-41183</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery-UI is the official jQuery user interface library. Prior to version 1.13.0, accepting the value of various `*Text` options of the Datepicker widget from untrusted sources may execute untrusted code. The issue is fixed in jQuery UI 1.13.0. The values passed to various `*Text` options are now always treated as pure text, not HTML. A workaround is to not accept the value of the `*Text` options from untrusted sources.
<p>Publish Date: 2021-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-41183>CVE-2021-41183</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41183">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41183</a></p>
<p>Release Date: 2021-10-26</p>
<p>Fix Resolution: jquery-ui - 1.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-41182</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery-UI is the official jQuery user interface library. Prior to version 1.13.0, accepting the value of the `altField` option of the Datepicker widget from untrusted sources may execute untrusted code. The issue is fixed in jQuery UI 1.13.0. Any string value passed to the `altField` option is now treated as a CSS selector. A workaround is to not accept the value of the `altField` option from untrusted sources.
<p>Publish Date: 2021-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-41182>CVE-2021-41182</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41182">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41182</a></p>
<p>Release Date: 2021-10-26</p>
<p>Fix Resolution: jquery-ui - 1.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-31160</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery UI is a curated set of user interface interactions, effects, widgets, and themes built on top of jQuery. Versions prior to 1.13.2 are potentially vulnerable to cross-site scripting. Initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label. Calling `.checkboxradio( "refresh" )` on such a widget and the initial HTML contained encoded HTML entities will make them erroneously get decoded. This can lead to potentially executing JavaScript code. The bug has been patched in jQuery UI 1.13.2. To remediate the issue, someone who can change the initial HTML can wrap all the non-input contents of the `label` in a `span`.
<p>Publish Date: 2022-07-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31160>CVE-2022-31160</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160</a></p>
<p>Release Date: 2022-07-20</p>
<p>Fix Resolution: jquery-ui - 1.13.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-7103</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in jQuery UI before 1.12.0 might allow remote attackers to inject arbitrary web script or HTML via the closeText parameter of the dialog function.
<p>Publish Date: 2017-03-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-7103>CVE-2016-7103</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-03-15</p>
<p>Fix Resolution: katello - 4.7.2</p>
</p>
<p></p>
</details>
|
True
|
jquery-ui-1.10.3.min.js: 5 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p></summary>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (jquery-ui version) | Remediation Possible** |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2021-41184](https://www.mend.io/vulnerability-database/CVE-2021-41184) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.0 | ❌ |
| [CVE-2021-41183](https://www.mend.io/vulnerability-database/CVE-2021-41183) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.0 | ❌ |
| [CVE-2021-41182](https://www.mend.io/vulnerability-database/CVE-2021-41182) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.0 | ❌ |
| [CVE-2022-31160](https://www.mend.io/vulnerability-database/CVE-2022-31160) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | jquery-ui - 1.13.2 | ❌ |
| [CVE-2016-7103](https://www.mend.io/vulnerability-database/CVE-2016-7103) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | jquery-ui-1.10.3.min.js | Direct | katello - 4.7.2 | ❌ |
<p>**In some cases, Remediation PR cannot be created automatically for a vulnerability despite the availability of remediation</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-41184</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery-UI is the official jQuery user interface library. Prior to version 1.13.0, accepting the value of the `of` option of the `.position()` util from untrusted sources may execute untrusted code. The issue is fixed in jQuery UI 1.13.0. Any string value passed to the `of` option is now treated as a CSS selector. A workaround is to not accept the value of the `of` option from untrusted sources.
<p>Publish Date: 2021-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-41184>CVE-2021-41184</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41184">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41184</a></p>
<p>Release Date: 2021-10-26</p>
<p>Fix Resolution: jquery-ui - 1.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-41183</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery-UI is the official jQuery user interface library. Prior to version 1.13.0, accepting the value of various `*Text` options of the Datepicker widget from untrusted sources may execute untrusted code. The issue is fixed in jQuery UI 1.13.0. The values passed to various `*Text` options are now always treated as pure text, not HTML. A workaround is to not accept the value of the `*Text` options from untrusted sources.
<p>Publish Date: 2021-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-41183>CVE-2021-41183</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41183">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41183</a></p>
<p>Release Date: 2021-10-26</p>
<p>Fix Resolution: jquery-ui - 1.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2021-41182</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery-UI is the official jQuery user interface library. Prior to version 1.13.0, accepting the value of the `altField` option of the Datepicker widget from untrusted sources may execute untrusted code. The issue is fixed in jQuery UI 1.13.0. Any string value passed to the `altField` option is now treated as a CSS selector. A workaround is to not accept the value of the `altField` option from untrusted sources.
<p>Publish Date: 2021-10-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-41182>CVE-2021-41182</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41182">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-41182</a></p>
<p>Release Date: 2021-10-26</p>
<p>Fix Resolution: jquery-ui - 1.13.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2022-31160</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
jQuery UI is a curated set of user interface interactions, effects, widgets, and themes built on top of jQuery. Versions prior to 1.13.2 are potentially vulnerable to cross-site scripting. Initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label. Calling `.checkboxradio( "refresh" )` on such a widget and the initial HTML contained encoded HTML entities will make them erroneously get decoded. This can lead to potentially executing JavaScript code. The bug has been patched in jQuery UI 1.13.2. To remediate the issue, someone who can change the initial HTML can wrap all the non-input contents of the `label` in a `span`.
<p>Publish Date: 2022-07-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-31160>CVE-2022-31160</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-31160</a></p>
<p>Release Date: 2022-07-20</p>
<p>Fix Resolution: jquery-ui - 1.13.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-7103</summary>
### Vulnerable Library - <b>jquery-ui-1.10.3.min.js</b></p>
<p>A curated set of user interface interactions, effects, widgets, and themes built on top of the jQuery JavaScript Library.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js">https://cdnjs.cloudflare.com/ajax/libs/jqueryui/1.10.3/jquery-ui.min.js</a></p>
<p>Path to dependency file: /release/src/router/www/AdaptiveQoS_Bandwidth_Monitor.asp</p>
<p>Path to vulnerable library: /release/src/router/www/calendar/jquery-ui.js,/release/src/router/www/device-map/../calendar/jquery-ui.js,/release/src/router/www/calendar/jquery-ui.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-ui-1.10.3.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Chiencc/asuswrt-gt-ac5300/commit/0c45ce909374d16605095db4fce9a89b9b6bafd5">0c45ce909374d16605095db4fce9a89b9b6bafd5</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Cross-site scripting (XSS) vulnerability in jQuery UI before 1.12.0 might allow remote attackers to inject arbitrary web script or HTML via the closeText parameter of the dialog function.
<p>Publish Date: 2017-03-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-7103>CVE-2016-7103</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2017-03-15</p>
<p>Fix Resolution: katello - 4.7.2</p>
</p>
<p></p>
</details>
|
non_process
|
jquery ui min js vulnerabilities highest severity is vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file release src router www adaptiveqos bandwidth monitor asp path to vulnerable library release src router www calendar jquery ui js release src router www device map calendar jquery ui js release src router www calendar jquery ui js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in jquery ui version remediation possible medium jquery ui min js direct jquery ui medium jquery ui min js direct jquery ui medium jquery ui min js direct jquery ui medium jquery ui min js direct jquery ui medium jquery ui min js direct katello in some cases remediation pr cannot be created automatically for a vulnerability despite the availability of remediation details cve vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file release src router www adaptiveqos bandwidth monitor asp path to vulnerable library release src router www calendar jquery ui js release src router www device map calendar jquery ui js release src router www calendar jquery ui js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery ui is the official jquery user interface library prior to version accepting the value of the of option of the position util from untrusted sources may execute untrusted code the issue is fixed in jquery ui any string value passed to the of option is now treated as a css selector a workaround is to not accept the value of the of option from untrusted sources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery ui cve vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file release src router www adaptiveqos bandwidth monitor asp path to vulnerable library release src router www calendar jquery ui js release src router www device map calendar jquery ui js release src router www calendar jquery ui js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery ui is the official jquery user interface library prior to version accepting the value of various text options of the datepicker widget from untrusted sources may execute untrusted code the issue is fixed in jquery ui the values passed to various text options are now always treated as pure text not html a workaround is to not accept the value of the text options from untrusted sources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery ui cve vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file release src router www adaptiveqos bandwidth monitor asp path to vulnerable library release src router www calendar jquery ui js release src router www device map calendar jquery ui js release src router www calendar jquery ui js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery ui is the official jquery user interface library prior to version accepting the value of the altfield option of the datepicker widget from untrusted sources may execute untrusted code the issue is fixed in jquery ui any string value passed to the altfield option is now treated as a css selector a workaround is to not accept the value of the altfield option from untrusted sources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery ui cve vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file release src router www adaptiveqos bandwidth monitor asp path to vulnerable library release src router www calendar jquery ui js release src router www device map calendar jquery ui js release src router www calendar jquery ui js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch master vulnerability details jquery ui is a curated set of user interface interactions effects widgets and themes built on top of jquery versions prior to are potentially vulnerable to cross site scripting initializing a checkboxradio widget on an input enclosed within a label makes that parent label contents considered as the input label calling checkboxradio refresh on such a widget and the initial html contained encoded html entities will make them erroneously get decoded this can lead to potentially executing javascript code the bug has been patched in jquery ui to remediate the issue someone who can change the initial html can wrap all the non input contents of the label in a span publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery ui cve vulnerable library jquery ui min js a curated set of user interface interactions effects widgets and themes built on top of the jquery javascript library library home page a href path to dependency file release src router www adaptiveqos bandwidth monitor asp path to vulnerable library release src router www calendar jquery ui js release src router www device map calendar jquery ui js release src router www calendar jquery ui js dependency hierarchy x jquery ui min js vulnerable library found in head commit a href found in base branch master vulnerability details cross site scripting xss vulnerability in jquery ui before might allow remote attackers to inject arbitrary web script or html via the closetext parameter of the dialog function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution katello
| 0
|
21,222
| 28,307,230,279
|
IssuesEvent
|
2023-04-10 12:15:58
|
ASWE-PDA/Personal-Digital-Agent
|
https://api.github.com/repos/ASWE-PDA/Personal-Digital-Agent
|
reopened
|
Speech-to-text
|
enhancement adapter speech processing
|
As a user,
I want the agent to understand what I'm saying
so that the agent can work according to my statements.
Acceptance criteria:
- [x] API for speech-to-text has been selected
- [x] API can be called by an adapter module in the backend
|
1.0
|
Speech-to-text - As a user,
I want the agent to understand what I'm saying
so that the agent can work according to my statements.
Acceptance criteria:
- [x] API for speech-to-text has been selected
- [x] API can be called by an adapter module in the backend
|
process
|
speech to text as a user i want the agent to understand what i m saying so that the agent can work according to my statements acceptance criteria api for speech to text has been selected api can be called by an adapter module in the backend
| 1
|
246,954
| 20,946,810,105
|
IssuesEvent
|
2022-03-26 02:10:54
|
Uuvana-Studios/longvinter-windows-client
|
https://api.github.com/repos/Uuvana-Studios/longvinter-windows-client
|
closed
|
Duplicate item bug
|
bug High Priority Tested
|
**Describe the bug**
When placing an item down such as a lamp post or a turret if you left click mutliple times quickly it will duplicate the item.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
**Expected behavior**
A clear and concise description of what you expected to happen.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version [e.g. 1.0]
- Steam Version [e.g. 1.0]
**Additional context**
Add any other context about the problem here.
|
1.0
|
Duplicate item bug - **Describe the bug**
When placing an item down such as a lamp post or a turret if you left click mutliple times quickly it will duplicate the item.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
**Expected behavior**
A clear and concise description of what you expected to happen.
**Screenshots**
If applicable, add screenshots to help explain your problem.
**Desktop (please complete the following information):**
- OS: [e.g. Windows]
- Game Version [e.g. 1.0]
- Steam Version [e.g. 1.0]
**Additional context**
Add any other context about the problem here.
|
non_process
|
duplicate item bug describe the bug when placing an item down such as a lamp post or a turret if you left click mutliple times quickly it will duplicate the item to reproduce steps to reproduce the behavior go to click on scroll down to see error expected behavior a clear and concise description of what you expected to happen screenshots if applicable add screenshots to help explain your problem desktop please complete the following information os game version steam version additional context add any other context about the problem here
| 0
|
210
| 2,636,664,195
|
IssuesEvent
|
2015-03-10 06:42:47
|
fabric8io/fabric8
|
https://api.github.com/repos/fabric8io/fabric8
|
closed
|
[Process Controller] Create file system IO API for process controller
|
process manager
|
It will be nice to have the API (somewhere near the `ProcessController` level) so process controller could read and write files within its sandbox.
|
1.0
|
[Process Controller] Create file system IO API for process controller - It will be nice to have the API (somewhere near the `ProcessController` level) so process controller could read and write files within its sandbox.
|
process
|
create file system io api for process controller it will be nice to have the api somewhere near the processcontroller level so process controller could read and write files within its sandbox
| 1
|
21,181
| 28,149,441,071
|
IssuesEvent
|
2023-04-02 21:28:58
|
zotero/zotero
|
https://api.github.com/repos/zotero/zotero
|
opened
|
Prevent selection of child items in classic citation dialog
|
Papercuts Word Processor Integration
|
https://forums.zotero.org/discussion/104070/one-bibliography-position-deviates-cause-not-found and many others
Until we get rid of the classic citation dialog, we should prevent attachments and notes from being selected. Not sure if we can hide those easily in the tree — even if we only showed top-level items, there could be standalone attachments and notes — so maybe there just needs to be a check for item type with an error dialog that prevents accepting the dialog?
|
1.0
|
Prevent selection of child items in classic citation dialog - https://forums.zotero.org/discussion/104070/one-bibliography-position-deviates-cause-not-found and many others
Until we get rid of the classic citation dialog, we should prevent attachments and notes from being selected. Not sure if we can hide those easily in the tree — even if we only showed top-level items, there could be standalone attachments and notes — so maybe there just needs to be a check for item type with an error dialog that prevents accepting the dialog?
|
process
|
prevent selection of child items in classic citation dialog and many others until we get rid of the classic citation dialog we should prevent attachments and notes from being selected not sure if we can hide those easily in the tree — even if we only showed top level items there could be standalone attachments and notes — so maybe there just needs to be a check for item type with an error dialog that prevents accepting the dialog
| 1
|
3,825
| 6,802,323,753
|
IssuesEvent
|
2017-11-02 19:47:34
|
WikiWatershed/model-my-watershed
|
https://api.github.com/repos/WikiWatershed/model-my-watershed
|
closed
|
Geoprocessing API: Validate analyze AOI's size
|
Geoprocessing API tested/verified WPF
|
### AOI Area
Check that shapes submitted to the analyze endpoints have an area less than the [`MMW_MAX_AREA`](https://github.com/WikiWatershed/model-my-watershed/blob/develop/src/mmw/mmw/settings/base.py#L384).
### Payload size
This check should already be performed by nginx, and [limit the request body size to 5mb](https://github.com/WikiWatershed/model-my-watershed/blob/develop/deployment/ansible/roles/model-my-watershed.app/templates/nginx-app.conf.j2#L11)
|
1.0
|
Geoprocessing API: Validate analyze AOI's size - ### AOI Area
Check that shapes submitted to the analyze endpoints have an area less than the [`MMW_MAX_AREA`](https://github.com/WikiWatershed/model-my-watershed/blob/develop/src/mmw/mmw/settings/base.py#L384).
### Payload size
This check should already be performed by nginx, and [limit the request body size to 5mb](https://github.com/WikiWatershed/model-my-watershed/blob/develop/deployment/ansible/roles/model-my-watershed.app/templates/nginx-app.conf.j2#L11)
|
process
|
geoprocessing api validate analyze aoi s size aoi area check that shapes submitted to the analyze endpoints have an area less than the payload size this check should already be performed by nginx and
| 1
|
12,069
| 8,582,909,160
|
IssuesEvent
|
2018-11-13 18:14:15
|
PowerShell/Announcements
|
https://api.github.com/repos/PowerShell/Announcements
|
opened
|
Microsoft Security Advisory CVE-2018-8415: Microsoft PowerShell Tampering Vulnerability
|
PowerShell Security
|
# Microsoft Security Advisory CVE-2018-8415: Microsoft PowerShell Tampering Vulnerability
## Executive Summary
A tampering vulnerability exists in PowerShell that could allow an attacker to execute unlogged code.
To exploit this vulnerability, an attacker would need to log on to the affected system and run a specially crafted application.
The security update addresses the vulnerability by correcting log management of special characters.System administrators are advised to update PowerShell Core to version `6.0.5` or `6.1.1`.
## Discussion
Please use PowerShell/PowerShell#8254 for discussion of this advisory.
## Affected Software
The vulnerability affects PowerShell Core prior to the following versions:
| PowerShell Core Version | Fixed in |
|-------------------------|-------------------|
| 6.0 | 6.0.5 |
| 6.1 | 6.1.1 |
| 6.2 | https://github.com/PowerShell/PowerShell/pull/8253 |
## Advisory FAQ
### How do I know if I am affected?
If all of the following are true:
1. Run `pwsh -v`, then, check the version in the table in [Affected Software](#affected-software) to see if your version of PowerShell Core is affected.
1. If you are running a version of PowerShell Core where the executable is not `pwsh` or `pwsh.exe`, then you are affected. This only existed for preview version of `6.0`.
### How do I update to an unaffected version?
Follow the instructions at [Installing PowerShell Core](https://docs.microsoft.com/en-us/powershell/scripting/setup/installing-powershell?view=powershell-6) to install the latest version of PowerShell Core.
## Other Information
### Commit IDs
[f8f3774d](https://github.com/PowerShell/PowerShell/commit/f8f3774dfca94557ff05446c87192ea1edbb356d)
### Reporting Security Issues
If you have found a potential security issue in PowerShell Core,
please email details to secure@microsoft.com.
### Support
You can ask questions about this issue on GitHub in the PowerShell organization.
This is located at https://github.com/PowerShell/.
The Announcements repo (https://github.com/PowerShell/Announcements)
will contain this bulletin as an issue and will include a link to a discussion issue where you can ask questions.
### What if the update breaks my script or module?
You can uninstall the newer version of PowerShell Core and install the previous version of PowerShell Core.
This should be treated as a temporary measure.
Therefore, the script or module should be updated to work with the patched version of PowerShell Core.
### Acknowledgments
Microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure.
See [acknowledgments](https://portal.msrc.microsoft.com/en-us/security-guidance/acknowledgments) for more information.
### External Links
[CVE-2018-8415](https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8415)
### Revisions
V1.0 (November 13, 2018): Advisory published.
*Version 1.0*
*Last Updated 2018-11-13*
|
True
|
Microsoft Security Advisory CVE-2018-8415: Microsoft PowerShell Tampering Vulnerability - # Microsoft Security Advisory CVE-2018-8415: Microsoft PowerShell Tampering Vulnerability
## Executive Summary
A tampering vulnerability exists in PowerShell that could allow an attacker to execute unlogged code.
To exploit this vulnerability, an attacker would need to log on to the affected system and run a specially crafted application.
The security update addresses the vulnerability by correcting log management of special characters.System administrators are advised to update PowerShell Core to version `6.0.5` or `6.1.1`.
## Discussion
Please use PowerShell/PowerShell#8254 for discussion of this advisory.
## Affected Software
The vulnerability affects PowerShell Core prior to the following versions:
| PowerShell Core Version | Fixed in |
|-------------------------|-------------------|
| 6.0 | 6.0.5 |
| 6.1 | 6.1.1 |
| 6.2 | https://github.com/PowerShell/PowerShell/pull/8253 |
## Advisory FAQ
### How do I know if I am affected?
If all of the following are true:
1. Run `pwsh -v`, then, check the version in the table in [Affected Software](#affected-software) to see if your version of PowerShell Core is affected.
1. If you are running a version of PowerShell Core where the executable is not `pwsh` or `pwsh.exe`, then you are affected. This only existed for preview version of `6.0`.
### How do I update to an unaffected version?
Follow the instructions at [Installing PowerShell Core](https://docs.microsoft.com/en-us/powershell/scripting/setup/installing-powershell?view=powershell-6) to install the latest version of PowerShell Core.
## Other Information
### Commit IDs
[f8f3774d](https://github.com/PowerShell/PowerShell/commit/f8f3774dfca94557ff05446c87192ea1edbb356d)
### Reporting Security Issues
If you have found a potential security issue in PowerShell Core,
please email details to secure@microsoft.com.
### Support
You can ask questions about this issue on GitHub in the PowerShell organization.
This is located at https://github.com/PowerShell/.
The Announcements repo (https://github.com/PowerShell/Announcements)
will contain this bulletin as an issue and will include a link to a discussion issue where you can ask questions.
### What if the update breaks my script or module?
You can uninstall the newer version of PowerShell Core and install the previous version of PowerShell Core.
This should be treated as a temporary measure.
Therefore, the script or module should be updated to work with the patched version of PowerShell Core.
### Acknowledgments
Microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure.
See [acknowledgments](https://portal.msrc.microsoft.com/en-us/security-guidance/acknowledgments) for more information.
### External Links
[CVE-2018-8415](https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8415)
### Revisions
V1.0 (November 13, 2018): Advisory published.
*Version 1.0*
*Last Updated 2018-11-13*
|
non_process
|
microsoft security advisory cve microsoft powershell tampering vulnerability microsoft security advisory cve microsoft powershell tampering vulnerability executive summary a tampering vulnerability exists in powershell that could allow an attacker to execute unlogged code to exploit this vulnerability an attacker would need to log on to the affected system and run a specially crafted application the security update addresses the vulnerability by correcting log management of special characters system administrators are advised to update powershell core to version or discussion please use powershell powershell for discussion of this advisory affected software the vulnerability affects powershell core prior to the following versions powershell core version fixed in advisory faq how do i know if i am affected if all of the following are true run pwsh v then check the version in the table in affected software to see if your version of powershell core is affected if you are running a version of powershell core where the executable is not pwsh or pwsh exe then you are affected this only existed for preview version of how do i update to an unaffected version follow the instructions at to install the latest version of powershell core other information commit ids reporting security issues if you have found a potential security issue in powershell core please email details to secure microsoft com support you can ask questions about this issue on github in the powershell organization this is located at the announcements repo will contain this bulletin as an issue and will include a link to a discussion issue where you can ask questions what if the update breaks my script or module you can uninstall the newer version of powershell core and install the previous version of powershell core this should be treated as a temporary measure therefore the script or module should be updated to work with the patched version of powershell core acknowledgments microsoft recognizes the efforts of those in the security community who help us protect customers through coordinated vulnerability disclosure see for more information external links revisions november advisory published version last updated
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.