Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
757,605 | 26,520,661,815 | IssuesEvent | 2023-01-19 02:06:12 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [YSQL] Consistency issue: the row both exists and doesn't exist at the same time | kind/bug duplicate area/ysql priority/medium | Jira Link: [DB-4760](https://yugabyte.atlassian.net/browse/DB-4760)
I have a weird issue where a row both exists and doesn't exist at the same time, it has a unique index on it, but it can be added 2 times.
```sql
yugabyte=# select * from kv;
k | v
-------+---
count | 0
(1 row)
yugabyte=# select * from kv where k = 'count';
k | v
---+---
(0 rows) <--- what? where is it?
yugabyte=# select count(*) from kv;
count
-------
1
(1 row)
```
So, if you call `select * from kv where k = 'count'`, then the row does not exist, but if you call `select * from kv`, then it exists.
At the same time, despite the fact that I have a unique index on `k`, I can add it again, but only once:
```sql
yugabyte=# insert into kv (k,v) values ('count', 0);
INSERT 0 1
yugabyte=# insert into kv (k,v) values ('count', 0);
ERROR: duplicate key value violates unique constraint "kv_k_idx"
yugabyte=# select k, count(v) from kv group by 1;
k | count
-------+-------
count | 2
(1 row)
```
The bug is a bit hard to reproduce, as it can't be reproduced using `psql`, but rather you need to do a Python call using `orator` library:
```python
from orator import DatabaseManager
if __name__ == '__main__':
config = {
'pgsql': {
'driver': 'pgsql',
'host': '10.1.0.2',
'database': 'yugabyte',
'user': 'yugabyte',
'port': 5433,
'password': 'yugabyte'
}
}
db = DatabaseManager(config)
db.update('''
drop table if exists kv;
create table kv (k text, v int);
insert into kv (k, v) values ('count', 42);
create unique index on kv (k);
''')
print('the table contains:', db.select('select * from kv'))
print(db.select("select v from kv where k = 'count'"), '<-- this should be [42]')
print(db.select("select version()")[0][0])
print('can we add another one?')
db.update('''insert into kv (k, v) values ('count', 42);''')
print('the table now contains:', db.select('select * from kv'), 'despite the unique index')
```
Output:
```console
the table contains: [['count', 42]]
[] <-- this should be [42]
PostgreSQL 11.2-YB-2.9.0.0-b0 on x86_64-pc-linux-gnu, compiled by gcc (Homebrew gcc 5.5.0_4) 5.5.0, 64-bit
can we add another one?
the table now contains: [['count', 42], ['count', 42]] despite the unique index
```
Just to note, if you connect to Postgres with the same code, it doesn't have this issue.
I guess the problem is with this call:
```python
db.update('''
drop table if exists kv;
create table kv (k text, v int);
insert into kv (k, v) values ('cnt', 42);
create unique index on kv (k);
''')
```
...but then, again, Postgresql doesn't have any problems with it.
If I change the order to this, it works correctly:
```python
db.update('''
drop table if exists kv;
create table kv (k text, v int);
create unique index on kv (k);
insert into kv (k, v) values ('cnt', 42);
''')
```
| 1.0 | [YSQL] Consistency issue: the row both exists and doesn't exist at the same time - Jira Link: [DB-4760](https://yugabyte.atlassian.net/browse/DB-4760)
I have a weird issue where a row both exists and doesn't exist at the same time, it has a unique index on it, but it can be added 2 times.
```sql
yugabyte=# select * from kv;
k | v
-------+---
count | 0
(1 row)
yugabyte=# select * from kv where k = 'count';
k | v
---+---
(0 rows) <--- what? where is it?
yugabyte=# select count(*) from kv;
count
-------
1
(1 row)
```
So, if you call `select * from kv where k = 'count'`, then the row does not exist, but if you call `select * from kv`, then it exists.
At the same time, despite the fact that I have a unique index on `k`, I can add it again, but only once:
```sql
yugabyte=# insert into kv (k,v) values ('count', 0);
INSERT 0 1
yugabyte=# insert into kv (k,v) values ('count', 0);
ERROR: duplicate key value violates unique constraint "kv_k_idx"
yugabyte=# select k, count(v) from kv group by 1;
k | count
-------+-------
count | 2
(1 row)
```
The bug is a bit hard to reproduce, as it can't be reproduced using `psql`, but rather you need to do a Python call using `orator` library:
```python
from orator import DatabaseManager
if __name__ == '__main__':
config = {
'pgsql': {
'driver': 'pgsql',
'host': '10.1.0.2',
'database': 'yugabyte',
'user': 'yugabyte',
'port': 5433,
'password': 'yugabyte'
}
}
db = DatabaseManager(config)
db.update('''
drop table if exists kv;
create table kv (k text, v int);
insert into kv (k, v) values ('count', 42);
create unique index on kv (k);
''')
print('the table contains:', db.select('select * from kv'))
print(db.select("select v from kv where k = 'count'"), '<-- this should be [42]')
print(db.select("select version()")[0][0])
print('can we add another one?')
db.update('''insert into kv (k, v) values ('count', 42);''')
print('the table now contains:', db.select('select * from kv'), 'despite the unique index')
```
Output:
```console
the table contains: [['count', 42]]
[] <-- this should be [42]
PostgreSQL 11.2-YB-2.9.0.0-b0 on x86_64-pc-linux-gnu, compiled by gcc (Homebrew gcc 5.5.0_4) 5.5.0, 64-bit
can we add another one?
the table now contains: [['count', 42], ['count', 42]] despite the unique index
```
Just to note, if you connect to Postgres with the same code, it doesn't have this issue.
I guess the problem is with this call:
```python
db.update('''
drop table if exists kv;
create table kv (k text, v int);
insert into kv (k, v) values ('cnt', 42);
create unique index on kv (k);
''')
```
...but then, again, Postgresql doesn't have any problems with it.
If I change the order to this, it works correctly:
```python
db.update('''
drop table if exists kv;
create table kv (k text, v int);
create unique index on kv (k);
insert into kv (k, v) values ('cnt', 42);
''')
```
| non_test | consistency issue the row both exists and doesn t exist at the same time jira link i have a weird issue where a row both exists and doesn t exist at the same time it has a unique index on it but it can be added times sql yugabyte select from kv k v count row yugabyte select from kv where k count k v rows what where is it yugabyte select count from kv count row so if you call select from kv where k count then the row does not exist but if you call select from kv then it exists at the same time despite the fact that i have a unique index on k i can add it again but only once sql yugabyte insert into kv k v values count insert yugabyte insert into kv k v values count error duplicate key value violates unique constraint kv k idx yugabyte select k count v from kv group by k count count row the bug is a bit hard to reproduce as it can t be reproduced using psql but rather you need to do a python call using orator library python from orator import databasemanager if name main config pgsql driver pgsql host database yugabyte user yugabyte port password yugabyte db databasemanager config db update drop table if exists kv create table kv k text v int insert into kv k v values count create unique index on kv k print the table contains db select select from kv print db select select v from kv where k count this should be print db select select version print can we add another one db update insert into kv k v values count print the table now contains db select select from kv despite the unique index output console the table contains this should be postgresql yb on pc linux gnu compiled by gcc homebrew gcc bit can we add another one the table now contains despite the unique index just to note if you connect to postgres with the same code it doesn t have this issue i guess the problem is with this call python db update drop table if exists kv create table kv k text v int insert into kv k v values cnt create unique index on kv k but then again postgresql doesn t have any problems with it if i change the order to this it works correctly python db update drop table if exists kv create table kv k text v int create unique index on kv k insert into kv k v values cnt | 0 |
170,530 | 13,192,049,149 | IssuesEvent | 2020-08-13 13:11:17 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: import/tpch/nodes=8 failed | C-test-failure O-roachtest O-robot branch-release-20.1 release-blocker | [(roachtest).import/tpch/nodes=8 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2172557&tab=buildLog) on [release-20.1@607d3fb91a15fbd4613f22396d5828c4d27d390b](https://github.com/cockroachdb/cockroach/commits/607d3fb91a15fbd4613f22396d5828c4d27d390b):
```
| | main.newCluster
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:138
| | main.glob..func23
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1427
| | main.wrap.func1
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:266
| | github.com/spf13/cobra.(*Command).execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:830
| | github.com/spf13/cobra.(*Command).ExecuteC
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:914
| | github.com/spf13/cobra.(*Command).Execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:864
| | main.main
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1808
| | runtime.main
| | /usr/local/go/src/runtime/proc.go:203
| | runtime.goexit
| | /usr/local/go/src/runtime/asm_amd64.s:1357
| Wraps: (5) 2 safe details enclosed
| Wraps: (6) unknown cluster: teamcity-2172557-1597213822-37-n8cpu4
| Error types: (1) errors.Unclassified (2) *hintdetail.withHint (3) *hintdetail.withHint (4) *withstack.withStack (5) *safedetails.withSafeDetails (6) *errors.errorString
Wraps: (5) exit status 1
Error types: (1) *withstack.withStack (2) *safedetails.withSafeDetails (3) *errutil.withMessage (4) *main.withCommandDetails (5) *exec.ExitError
cluster.go:2597,import.go:167,test_runner.go:754: monitor failure: monitor task failed: t.Fatal() was called
(1) attached stack trace
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2585
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2593
| main.registerImportTPCH.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/import.go:167
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:754
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2641
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2555
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5228
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) t.Fatal() was called
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *errors.errorString
```
<details><summary>More</summary><p>
Artifacts: [/import/tpch/nodes=8](https://teamcity.cockroachdb.com/viewLog.html?buildId=2172557&tab=artifacts#/import/tpch/nodes=8)
Related:
- #52126 roachtest: import/tpch/nodes=8 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202007292238_v20.1.4](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202007292238_v20.1.4) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #51131 roachtest: import/tpch/nodes=8 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202007071743_v20.2.0-alpha.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202007071743_v20.2.0-alpha.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #50988 roachtest: import/tpch/nodes=8 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Aimport%2Ftpch%2Fnodes%3D8.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: import/tpch/nodes=8 failed - [(roachtest).import/tpch/nodes=8 failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2172557&tab=buildLog) on [release-20.1@607d3fb91a15fbd4613f22396d5828c4d27d390b](https://github.com/cockroachdb/cockroach/commits/607d3fb91a15fbd4613f22396d5828c4d27d390b):
```
| | main.newCluster
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:138
| | main.glob..func23
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1427
| | main.wrap.func1
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:266
| | github.com/spf13/cobra.(*Command).execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:830
| | github.com/spf13/cobra.(*Command).ExecuteC
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:914
| | github.com/spf13/cobra.(*Command).Execute
| | /home/agent/work/.go/pkg/mod/github.com/spf13/cobra@v0.0.5/command.go:864
| | main.main
| | /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1808
| | runtime.main
| | /usr/local/go/src/runtime/proc.go:203
| | runtime.goexit
| | /usr/local/go/src/runtime/asm_amd64.s:1357
| Wraps: (5) 2 safe details enclosed
| Wraps: (6) unknown cluster: teamcity-2172557-1597213822-37-n8cpu4
| Error types: (1) errors.Unclassified (2) *hintdetail.withHint (3) *hintdetail.withHint (4) *withstack.withStack (5) *safedetails.withSafeDetails (6) *errors.errorString
Wraps: (5) exit status 1
Error types: (1) *withstack.withStack (2) *safedetails.withSafeDetails (3) *errutil.withMessage (4) *main.withCommandDetails (5) *exec.ExitError
cluster.go:2597,import.go:167,test_runner.go:754: monitor failure: monitor task failed: t.Fatal() was called
(1) attached stack trace
| main.(*monitor).WaitE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2585
| main.(*monitor).Wait
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2593
| main.registerImportTPCH.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/import.go:167
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:754
Wraps: (2) monitor failure
Wraps: (3) attached stack trace
| main.(*monitor).wait.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2641
Wraps: (4) monitor task failed
Wraps: (5) attached stack trace
| main.init
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2555
| runtime.doInit
| /usr/local/go/src/runtime/proc.go:5228
| runtime.main
| /usr/local/go/src/runtime/proc.go:190
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1357
Wraps: (6) t.Fatal() was called
Error types: (1) *withstack.withStack (2) *errutil.withMessage (3) *withstack.withStack (4) *errutil.withMessage (5) *withstack.withStack (6) *errors.errorString
```
<details><summary>More</summary><p>
Artifacts: [/import/tpch/nodes=8](https://teamcity.cockroachdb.com/viewLog.html?buildId=2172557&tab=artifacts#/import/tpch/nodes=8)
Related:
- #52126 roachtest: import/tpch/nodes=8 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202007292238_v20.1.4](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202007292238_v20.1.4) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #51131 roachtest: import/tpch/nodes=8 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202007071743_v20.2.0-alpha.2](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202007071743_v20.2.0-alpha.2) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #50988 roachtest: import/tpch/nodes=8 failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-master](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-master) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Aimport%2Ftpch%2Fnodes%3D8.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| test | roachtest import tpch nodes failed on main newcluster home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go main glob home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go main wrap home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go github com cobra command execute home agent work go pkg mod github com cobra command go github com cobra command executec home agent work go pkg mod github com cobra command go github com cobra command execute home agent work go pkg mod github com cobra command go main main home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps safe details enclosed wraps unknown cluster teamcity error types errors unclassified hintdetail withhint hintdetail withhint withstack withstack safedetails withsafedetails errors errorstring wraps exit status error types withstack withstack safedetails withsafedetails errutil withmessage main withcommanddetails exec exiterror cluster go import go test runner go monitor failure monitor task failed t fatal was called attached stack trace main monitor waite home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main registerimporttpch home agent work go src github com cockroachdb cockroach pkg cmd roachtest import go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go wraps monitor failure wraps attached stack trace main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go wraps monitor task failed wraps attached stack trace main init home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go runtime doinit usr local go src runtime proc go runtime main usr local go src runtime proc go runtime goexit usr local go src runtime asm s wraps t fatal was called error types withstack withstack errutil withmessage withstack withstack errutil withmessage withstack withstack errors errorstring more artifacts related roachtest import tpch nodes failed roachtest import tpch nodes failed roachtest import tpch nodes failed powered by | 1 |
134,240 | 10,887,510,643 | IssuesEvent | 2019-11-18 14:40:50 | golang/go | https://api.github.com/repos/golang/go | closed | cmd/dist: (*tester).testDirTest fails when GOROOT is read-only | NeedsFix Testing | (Part of #28387, the continuing saga.)
From https://build.golang.org/log/768b654369166c3cf187e4625bd3ca01cd430449:
```
##### ../test/bench/go1
#####
go build command-line-arguments: copying /tmp/workdir-host-linux-mipsle-mengzhuo/tmp/go-build116186474/b001/exe/a.out: open runtest.exe: permission denied
XXXBANNERXXX:../test
2019/11/15 23:53:53 Failed: exit status 1
```
That suggests a failure in the sharded `../test` phase, and is locally reproducible with
```
GO_BUILDER_NAME=linux-amd64-bcmills go tool dist test test:0_10
```
CC @mengzhuo | 1.0 | cmd/dist: (*tester).testDirTest fails when GOROOT is read-only - (Part of #28387, the continuing saga.)
From https://build.golang.org/log/768b654369166c3cf187e4625bd3ca01cd430449:
```
##### ../test/bench/go1
#####
go build command-line-arguments: copying /tmp/workdir-host-linux-mipsle-mengzhuo/tmp/go-build116186474/b001/exe/a.out: open runtest.exe: permission denied
XXXBANNERXXX:../test
2019/11/15 23:53:53 Failed: exit status 1
```
That suggests a failure in the sharded `../test` phase, and is locally reproducible with
```
GO_BUILDER_NAME=linux-amd64-bcmills go tool dist test test:0_10
```
CC @mengzhuo | test | cmd dist tester testdirtest fails when goroot is read only part of the continuing saga from test bench go build command line arguments copying tmp workdir host linux mipsle mengzhuo tmp go exe a out open runtest exe permission denied xxxbannerxxx test failed exit status that suggests a failure in the sharded test phase and is locally reproducible with go builder name linux bcmills go tool dist test test cc mengzhuo | 1 |
164,773 | 12,812,914,327 | IssuesEvent | 2020-07-04 09:36:56 | aliasrobotics/RVD | https://api.github.com/repos/aliasrobotics/RVD | closed | RVD#2786: CWE-120 (buffer), Does not check for buffer overflows (CWE-120)... @ nder/gyro_calibration.cpp:516 | CWE-120 bug components software flawfinder flawfinder_level_4 mitigated robot component: PX4 static analysis testing triage version: v1.9.0 | ```yaml
id: 2786
title: 'RVD#2786: CWE-120 (buffer), Does not check for buffer overflows (CWE-120)...
@ nder/gyro_calibration.cpp:516'
type: bug
description: Does not check for buffer overflows (CWE-120). Use sprintf_s, snprintf,
or vsnprintf. . Happening @ ...nder/gyro_calibration.cpp:516
cwe:
- CWE-120
cve: None
keywords:
- flawfinder
- flawfinder_level_4
- static analysis
- testing
- triage
- CWE-120
- bug
- 'version: v1.9.0'
- 'robot component: PX4'
- components software
system: ./Firmware/src/modules/commander/gyro_calibration.cpp:516:11
vendor: null
severity:
rvss-score: 0
rvss-vector: ''
severity-description: ''
cvss-score: 0
cvss-vector: ''
links:
- https://github.com/aliasrobotics/RVD/issues/2786
flaw:
phase: testing
specificity: subject-specific
architectural-location: application-specific
application: N/A
subsystem: N/A
package: N/A
languages: None
date-detected: 2020-06-29 (15:20)
detected-by: Alias Robotics
detected-by-method: testing static
date-reported: 2020-06-29 (15:20)
reported-by: Alias Robotics
reported-by-relationship: automatic
issue: https://github.com/aliasrobotics/RVD/issues/2786
reproducibility: always
trace: (context) \t\t\t\t(void)sprintf(str, %s%u, GYRO_BASE_DEVICE_PATH, uorb_index);
reproduction: See artifacts below (if available)
reproduction-image: gitlab.com/aliasrobotics/offensive/alurity/pipelines/active/pipeline_px4/-/jobs/615913193/artifacts/download
exploitation:
description: ''
exploitation-image: ''
exploitation-vector: ''
exploitation-recipe: ''
mitigation:
description: Use sprintf_s, snprintf, or vsnprintf
pull-request: ''
date-mitigation: ''
``` | 1.0 | RVD#2786: CWE-120 (buffer), Does not check for buffer overflows (CWE-120)... @ nder/gyro_calibration.cpp:516 - ```yaml
id: 2786
title: 'RVD#2786: CWE-120 (buffer), Does not check for buffer overflows (CWE-120)...
@ nder/gyro_calibration.cpp:516'
type: bug
description: Does not check for buffer overflows (CWE-120). Use sprintf_s, snprintf,
or vsnprintf. . Happening @ ...nder/gyro_calibration.cpp:516
cwe:
- CWE-120
cve: None
keywords:
- flawfinder
- flawfinder_level_4
- static analysis
- testing
- triage
- CWE-120
- bug
- 'version: v1.9.0'
- 'robot component: PX4'
- components software
system: ./Firmware/src/modules/commander/gyro_calibration.cpp:516:11
vendor: null
severity:
rvss-score: 0
rvss-vector: ''
severity-description: ''
cvss-score: 0
cvss-vector: ''
links:
- https://github.com/aliasrobotics/RVD/issues/2786
flaw:
phase: testing
specificity: subject-specific
architectural-location: application-specific
application: N/A
subsystem: N/A
package: N/A
languages: None
date-detected: 2020-06-29 (15:20)
detected-by: Alias Robotics
detected-by-method: testing static
date-reported: 2020-06-29 (15:20)
reported-by: Alias Robotics
reported-by-relationship: automatic
issue: https://github.com/aliasrobotics/RVD/issues/2786
reproducibility: always
trace: (context) \t\t\t\t(void)sprintf(str, %s%u, GYRO_BASE_DEVICE_PATH, uorb_index);
reproduction: See artifacts below (if available)
reproduction-image: gitlab.com/aliasrobotics/offensive/alurity/pipelines/active/pipeline_px4/-/jobs/615913193/artifacts/download
exploitation:
description: ''
exploitation-image: ''
exploitation-vector: ''
exploitation-recipe: ''
mitigation:
description: Use sprintf_s, snprintf, or vsnprintf
pull-request: ''
date-mitigation: ''
``` | test | rvd cwe buffer does not check for buffer overflows cwe nder gyro calibration cpp yaml id title rvd cwe buffer does not check for buffer overflows cwe nder gyro calibration cpp type bug description does not check for buffer overflows cwe use sprintf s snprintf or vsnprintf happening nder gyro calibration cpp cwe cwe cve none keywords flawfinder flawfinder level static analysis testing triage cwe bug version robot component components software system firmware src modules commander gyro calibration cpp vendor null severity rvss score rvss vector severity description cvss score cvss vector links flaw phase testing specificity subject specific architectural location application specific application n a subsystem n a package n a languages none date detected detected by alias robotics detected by method testing static date reported reported by alias robotics reported by relationship automatic issue reproducibility always trace context t t t t void sprintf str s u gyro base device path uorb index reproduction see artifacts below if available reproduction image gitlab com aliasrobotics offensive alurity pipelines active pipeline jobs artifacts download exploitation description exploitation image exploitation vector exploitation recipe mitigation description use sprintf s snprintf or vsnprintf pull request date mitigation | 1 |
174,743 | 27,719,754,093 | IssuesEvent | 2023-03-14 19:36:57 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | UX Design: Understanding of user expectations for setting preferences | design research ux my-health my-health-CTO-HEALTH-TEAM my-health-INTEGRATION | ## Overview
Before we can make recommendations and design an experience for MHV preferences on VA.gov, we must first understand the current preferences on MHV, as well as how they overlap with preferences on VA.gov.
## Acceptance Criteria / Deliverables
- [ ] Identify any questions about user expectations for setting preferences
- [ ] Make UX recommendations prior to low-fi designs being created | 1.0 | UX Design: Understanding of user expectations for setting preferences - ## Overview
Before we can make recommendations and design an experience for MHV preferences on VA.gov, we must first understand the current preferences on MHV, as well as how they overlap with preferences on VA.gov.
## Acceptance Criteria / Deliverables
- [ ] Identify any questions about user expectations for setting preferences
- [ ] Make UX recommendations prior to low-fi designs being created | non_test | ux design understanding of user expectations for setting preferences overview before we can make recommendations and design an experience for mhv preferences on va gov we must first understand the current preferences on mhv as well as how they overlap with preferences on va gov acceptance criteria deliverables identify any questions about user expectations for setting preferences make ux recommendations prior to low fi designs being created | 0 |
96,581 | 8,617,661,420 | IssuesEvent | 2018-11-20 06:42:32 | humera987/FXLabs-Test-Automation | https://api.github.com/repos/humera987/FXLabs-Test-Automation | closed | projecttesting20 : ApiV1SkillsGetQueryParamPageInvalidDatatype | projecttesting20 | Project : projecttesting20
Job : uat 1
Env : uat
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=ZWU2MmUwOTgtNjUxOS00NjI5LWE0YmQtNmQ4MWQ4YmQ3N2M0; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 20 Nov 2018 06:20:02 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/skills?page=4BQjRn
Request :
Response :
{
"timestamp" : "2018-11-20T06:20:02.432+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/skills"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot --- | 1.0 | projecttesting20 : ApiV1SkillsGetQueryParamPageInvalidDatatype - Project : projecttesting20
Job : uat 1
Env : uat
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=ZWU2MmUwOTgtNjUxOS00NjI5LWE0YmQtNmQ4MWQ4YmQ3N2M0; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 20 Nov 2018 06:20:02 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/skills?page=4BQjRn
Request :
Response :
{
"timestamp" : "2018-11-20T06:20:02.432+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/skills"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot --- | test | project job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api skills logs assertion resolved to result assertion resolved to result fx bot | 1 |
279,023 | 30,702,436,223 | IssuesEvent | 2023-07-27 01:30:04 | artsking/packages_apps_settings_10.0.0_r33 | https://api.github.com/repos/artsking/packages_apps_settings_10.0.0_r33 | reopened | CVE-2020-0024 (High) detected in multiple libraries | Mend: dependency security vulnerability | ## CVE-2020-0024 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>Settingsandroid-10.0.0_r33</b>, <b>Settingsandroid-10.0.0_r33</b>, <b>Settingsandroid-10.0.0_r33</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In onCreate of SettingsBaseActivity.java, there is a possible unauthorized setting modification due to a permissions bypass. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-8.0Android ID: A-137015265
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0024>CVE-2020-0024</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-05-05</p>
<p>Fix Resolution: android-10.0.0_r34,android-8.1.0_r73</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-0024 (High) detected in multiple libraries - ## CVE-2020-0024 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>Settingsandroid-10.0.0_r33</b>, <b>Settingsandroid-10.0.0_r33</b>, <b>Settingsandroid-10.0.0_r33</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In onCreate of SettingsBaseActivity.java, there is a possible unauthorized setting modification due to a permissions bypass. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-8.0Android ID: A-137015265
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-0024>CVE-2020-0024</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2020-05-05</p>
<p>Fix Resolution: android-10.0.0_r34,android-8.1.0_r73</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries settingsandroid settingsandroid settingsandroid vulnerability details in oncreate of settingsbaseactivity java there is a possible unauthorized setting modification due to a permissions bypass this could lead to local escalation of privilege with no additional execution privileges needed user interaction is needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution android android step up your open source security game with mend | 0 |
97,058 | 12,199,252,240 | IssuesEvent | 2020-04-30 01:04:57 | Cryptodog/cryptodog | https://api.github.com/repos/Cryptodog/cryptodog | closed | Excessive lag when switching from private messages to main chat | design-flaw help wanted | Title. Web client hitches when clicking from private messages to main chat. Even on fresh connects its barely noticeable, but as chat history length increases, so does the length of the hitch. it is one way though, as moving from main to PM is smooth. | 1.0 | Excessive lag when switching from private messages to main chat - Title. Web client hitches when clicking from private messages to main chat. Even on fresh connects its barely noticeable, but as chat history length increases, so does the length of the hitch. it is one way though, as moving from main to PM is smooth. | non_test | excessive lag when switching from private messages to main chat title web client hitches when clicking from private messages to main chat even on fresh connects its barely noticeable but as chat history length increases so does the length of the hitch it is one way though as moving from main to pm is smooth | 0 |
226,139 | 17,953,330,252 | IssuesEvent | 2021-09-13 02:27:21 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | closed | Gorm-test unstable cause by env | type/bug component/test severity/major | ## Bug Report
Please answer these questions before submitting your issue. Thanks!
```
[2021-08-05T03:02:46.101Z] gormtest start
[2021-08-05T03:02:46.101Z] + cd gorm
[2021-08-05T03:02:46.101Z] + rm -rf ./gormtest_tidb-server
[2021-08-05T03:02:46.101Z] + rm -rf './tidb*.log'
[2021-08-05T03:02:46.101Z] + rm -rf ./data
[2021-08-05T03:02:46.102Z] ++ pwd
[2021-08-05T03:02:46.102Z] + echo /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/gorm
[2021-08-05T03:02:46.102Z] /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/gorm
[2021-08-05T03:02:46.102Z] + [[ -z /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/bin/tidb-server ]]
[2021-08-05T03:02:46.102Z] + [[ ! -e /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/bin/tidb-server ]]
[2021-08-05T03:02:46.102Z] + [[ -z '' ]]
[2021-08-05T03:02:46.102Z] + TIDB_CONFIG=../config.toml
[2021-08-05T03:02:46.102Z] + echo 'go path is /go'
[2021-08-05T03:02:46.102Z] go path is /go
[2021-08-05T03:02:46.102Z] + GO111MODULE=on
[2021-08-05T03:02:46.102Z] + go build
[2021-08-05T03:02:46.359Z] + '[' tikv = tikv ']'
[2021-08-05T03:02:46.359Z] + SERVER_PID=368
[2021-08-05T03:02:46.359Z] + sleep 3
[2021-08-05T03:02:46.359Z] + /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/bin/tidb-server -config ../config.toml -lease 0 -store tikv -path 127.0.0.1:2379
[2021-08-05T03:02:49.643Z] + GO111MODULE=on
[2021-08-05T03:02:49.643Z] + go test -count 1 -log-level=error
[2021-08-05T03:02:50.582Z] testing tidb...
[2021-08-05T03:02:50.582Z] panic: No error should happen when connecting to test database, but got err=dial tcp 127.0.0.1:4000: connect: connection refused
[2021-08-05T03:02:50.582Z]
[2021-08-05T03:02:50.582Z] goroutine 1 [running]:
[2021-08-05T03:02:50.582Z] github.com/pingcap/tidb-test/gorm_test/gorm_test.init.0()
[2021-08-05T03:02:50.582Z] /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/gorm/main_test.go:37 +0x26c
[2021-08-05T03:02:50.582Z] exit status 2
[2021-08-05T03:02:50.582Z] FAIL github.com/pingcap/tidb-test/gorm_test/gorm 0.017s
[2021-08-05T03:02:50.582Z] + EXIT_CODE=1
[2021-08-05T03:02:50.582Z] + kill -9 368
[2021-08-05T03:02:50.582Z] + echo gormtest end
[2021-08-05T03:02:50.582Z] gormtest end
```
### 1. Minimal reproduce step (Required)
in ci: https://ci.pingcap.net/blue/organizations/jenkins/tidb_ghpr_integration_common_test/detail/tidb_ghpr_integration_common_test/6005/pipeline/
### 2. What did you expect to see? (Required)
### 3. What did you see instead (Required)
### 4. What is your TiDB version? (Required)
<!-- Paste the output of SELECT tidb_version() -->
| 1.0 | Gorm-test unstable cause by env - ## Bug Report
Please answer these questions before submitting your issue. Thanks!
```
[2021-08-05T03:02:46.101Z] gormtest start
[2021-08-05T03:02:46.101Z] + cd gorm
[2021-08-05T03:02:46.101Z] + rm -rf ./gormtest_tidb-server
[2021-08-05T03:02:46.101Z] + rm -rf './tidb*.log'
[2021-08-05T03:02:46.101Z] + rm -rf ./data
[2021-08-05T03:02:46.102Z] ++ pwd
[2021-08-05T03:02:46.102Z] + echo /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/gorm
[2021-08-05T03:02:46.102Z] /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/gorm
[2021-08-05T03:02:46.102Z] + [[ -z /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/bin/tidb-server ]]
[2021-08-05T03:02:46.102Z] + [[ ! -e /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/bin/tidb-server ]]
[2021-08-05T03:02:46.102Z] + [[ -z '' ]]
[2021-08-05T03:02:46.102Z] + TIDB_CONFIG=../config.toml
[2021-08-05T03:02:46.102Z] + echo 'go path is /go'
[2021-08-05T03:02:46.102Z] go path is /go
[2021-08-05T03:02:46.102Z] + GO111MODULE=on
[2021-08-05T03:02:46.102Z] + go build
[2021-08-05T03:02:46.359Z] + '[' tikv = tikv ']'
[2021-08-05T03:02:46.359Z] + SERVER_PID=368
[2021-08-05T03:02:46.359Z] + sleep 3
[2021-08-05T03:02:46.359Z] + /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/bin/tidb-server -config ../config.toml -lease 0 -store tikv -path 127.0.0.1:2379
[2021-08-05T03:02:49.643Z] + GO111MODULE=on
[2021-08-05T03:02:49.643Z] + go test -count 1 -log-level=error
[2021-08-05T03:02:50.582Z] testing tidb...
[2021-08-05T03:02:50.582Z] panic: No error should happen when connecting to test database, but got err=dial tcp 127.0.0.1:4000: connect: connection refused
[2021-08-05T03:02:50.582Z]
[2021-08-05T03:02:50.582Z] goroutine 1 [running]:
[2021-08-05T03:02:50.582Z] github.com/pingcap/tidb-test/gorm_test/gorm_test.init.0()
[2021-08-05T03:02:50.582Z] /home/jenkins/agent/workspace/tidb_ghpr_integration_common_test/go/src/github.com/pingcap/tidb-test/gorm_test/gorm/main_test.go:37 +0x26c
[2021-08-05T03:02:50.582Z] exit status 2
[2021-08-05T03:02:50.582Z] FAIL github.com/pingcap/tidb-test/gorm_test/gorm 0.017s
[2021-08-05T03:02:50.582Z] + EXIT_CODE=1
[2021-08-05T03:02:50.582Z] + kill -9 368
[2021-08-05T03:02:50.582Z] + echo gormtest end
[2021-08-05T03:02:50.582Z] gormtest end
```
### 1. Minimal reproduce step (Required)
in ci: https://ci.pingcap.net/blue/organizations/jenkins/tidb_ghpr_integration_common_test/detail/tidb_ghpr_integration_common_test/6005/pipeline/
### 2. What did you expect to see? (Required)
### 3. What did you see instead (Required)
### 4. What is your TiDB version? (Required)
<!-- Paste the output of SELECT tidb_version() -->
| test | gorm test unstable cause by env bug report please answer these questions before submitting your issue thanks gormtest start cd gorm rm rf gormtest tidb server rm rf tidb log rm rf data pwd echo home jenkins agent workspace tidb ghpr integration common test go src github com pingcap tidb test gorm test gorm home jenkins agent workspace tidb ghpr integration common test go src github com pingcap tidb test gorm test gorm tidb config config toml echo go path is go go path is go on go build server pid sleep home jenkins agent workspace tidb ghpr integration common test go src github com pingcap tidb test gorm test bin tidb server config config toml lease store tikv path on go test count log level error testing tidb panic no error should happen when connecting to test database but got err dial tcp connect connection refused goroutine github com pingcap tidb test gorm test gorm test init home jenkins agent workspace tidb ghpr integration common test go src github com pingcap tidb test gorm test gorm main test go exit status fail github com pingcap tidb test gorm test gorm exit code kill echo gormtest end gormtest end minimal reproduce step required in ci what did you expect to see required what did you see instead required what is your tidb version required | 1 |
71,434 | 13,652,831,840 | IssuesEvent | 2020-09-27 09:35:32 | GTNewHorizons/GT-New-Horizons-Modpack | https://api.github.com/repos/GTNewHorizons/GT-New-Horizons-Modpack | closed | Galena + ic2 crop? | Type Need Code changes Type: recipe change | Galena right now only uses Argentia as the ic2 crop to 4x the output. That doesn't sound right, especially since it does not product any molten silver.
Recommend changing recipe to add 144 mB molten silver output to galena + 9 argentia + 1000mB water.
| 1.0 | Galena + ic2 crop? - Galena right now only uses Argentia as the ic2 crop to 4x the output. That doesn't sound right, especially since it does not product any molten silver.
Recommend changing recipe to add 144 mB molten silver output to galena + 9 argentia + 1000mB water.
| non_test | galena crop galena right now only uses argentia as the crop to the output that doesn t sound right especially since it does not product any molten silver recommend changing recipe to add mb molten silver output to galena argentia water | 0 |
247,444 | 7,918,717,552 | IssuesEvent | 2018-07-04 14:11:27 | badhoc/MA2-Theme-Again | https://api.github.com/repos/badhoc/MA2-Theme-Again | opened | Style returned search results | Low Priority | Reduce the size and increase the number of returned results on the search page. | 1.0 | Style returned search results - Reduce the size and increase the number of returned results on the search page. | non_test | style returned search results reduce the size and increase the number of returned results on the search page | 0 |
6,010 | 2,801,155,823 | IssuesEvent | 2015-05-13 14:24:32 | GoogleCloudPlatform/kubernetes | https://api.github.com/repos/GoogleCloudPlatform/kubernetes | closed | "Events should be sent by kubelets and the scheduler about pods scheduling and running" flaky on GKE 0.17.0 | area/test priority/P1 team/testing | Still early in diagnosis, but soon after cutting 0.17.0, our early internal testing show this test as flaking. It's pretty bizarre, though, given the test isn't flaking on GCE, or even the continuous integration runs on GKE. | 2.0 | "Events should be sent by kubelets and the scheduler about pods scheduling and running" flaky on GKE 0.17.0 - Still early in diagnosis, but soon after cutting 0.17.0, our early internal testing show this test as flaking. It's pretty bizarre, though, given the test isn't flaking on GCE, or even the continuous integration runs on GKE. | test | events should be sent by kubelets and the scheduler about pods scheduling and running flaky on gke still early in diagnosis but soon after cutting our early internal testing show this test as flaking it s pretty bizarre though given the test isn t flaking on gce or even the continuous integration runs on gke | 1 |
430,192 | 30,120,538,487 | IssuesEvent | 2023-06-30 14:49:52 | jrsteensen/OpenHornet | https://api.github.com/repos/jrsteensen/OpenHornet | closed | [Bug]: Cover Glass SVG file missing from Manufacturing FIles for Standby Instrument Module | Type: Bug/Obsolesce Type: Documentation Deposition: Abandoned Category: MCAD Priority: Normal | ### Discord Username
smgvbest (aka Sandra)
### Bug Summary
The Cover Glass used in 3 of the instruments in the Standby Instrument Module is missing. This part would be ACRL_.062_OHC0007-11 - 2IN GAUGE COVER GLASS_-_V1.SVG
### Expected Results
File should be created so part can be made by users
### Actual Results
generated part for self use and filled bug report
### Screenshots/Images/Files
_No response_
### Applicable Part Numbers
OHC0007-11 - 2IN GAUGE COVER GLASS
### Release Version
1.0.0-beta.1
### Category
Mechanical (Structure/Panels/Mechanisms)
### Applicable End Item(s)
Lower Instrument Panel (LIP)
### Built to print?
- [X] I built (or attempted to build) the part to the OpenHornet print without any deviations.
- [ ] I am not building this part to the OH print. (List deviations in detail in the Miscellaneous Info text area below.)
### Miscellaneous Info
_No response_ | 1.0 | [Bug]: Cover Glass SVG file missing from Manufacturing FIles for Standby Instrument Module - ### Discord Username
smgvbest (aka Sandra)
### Bug Summary
The Cover Glass used in 3 of the instruments in the Standby Instrument Module is missing. This part would be ACRL_.062_OHC0007-11 - 2IN GAUGE COVER GLASS_-_V1.SVG
### Expected Results
File should be created so part can be made by users
### Actual Results
generated part for self use and filled bug report
### Screenshots/Images/Files
_No response_
### Applicable Part Numbers
OHC0007-11 - 2IN GAUGE COVER GLASS
### Release Version
1.0.0-beta.1
### Category
Mechanical (Structure/Panels/Mechanisms)
### Applicable End Item(s)
Lower Instrument Panel (LIP)
### Built to print?
- [X] I built (or attempted to build) the part to the OpenHornet print without any deviations.
- [ ] I am not building this part to the OH print. (List deviations in detail in the Miscellaneous Info text area below.)
### Miscellaneous Info
_No response_ | non_test | cover glass svg file missing from manufacturing files for standby instrument module discord username smgvbest aka sandra bug summary the cover glass used in of the instruments in the standby instrument module is missing this part would be acrl gauge cover glass svg expected results file should be created so part can be made by users actual results generated part for self use and filled bug report screenshots images files no response applicable part numbers gauge cover glass release version beta category mechanical structure panels mechanisms applicable end item s lower instrument panel lip built to print i built or attempted to build the part to the openhornet print without any deviations i am not building this part to the oh print list deviations in detail in the miscellaneous info text area below miscellaneous info no response | 0 |
350,983 | 31,932,569,519 | IssuesEvent | 2023-09-19 08:25:35 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix linalg.test_eigh_tridiagonal | Sub Task Ivy API Experimental Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5638037172"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5574366763"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5574366763"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5678336380"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5736967150"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix linalg.test_eigh_tridiagonal - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5638037172"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5574366763"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5574366763"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5678336380"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5736967150"><img src=https://img.shields.io/badge/-failure-red></a>
| test | fix linalg test eigh tridiagonal jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 1 |
81,703 | 23,533,902,808 | IssuesEvent | 2022-08-19 18:16:23 | MetaMask/metamask-extension | https://api.github.com/repos/MetaMask/metamask-extension | closed | Add environment variable validation to the build script | type-enhancement area-buildSystem | Currently the build script doesn't validate that expected environment variables are set for production builds. This is because the build script doesn't know the difference between a real production build and a production-like build. We have one build target (`yarn build prod` a.k.a. `yarn dist`) that we use for local testing and for the real prod build, and environment variables are the only difference between the two. There's no way for the script to know whether a missing environment variable is intentional or not.
We should split this single build target into two: one target for production-like builds, and one for a real production build. The real production build target can include comprehensive validation that ensures all expected environment variables are set. | 1.0 | Add environment variable validation to the build script - Currently the build script doesn't validate that expected environment variables are set for production builds. This is because the build script doesn't know the difference between a real production build and a production-like build. We have one build target (`yarn build prod` a.k.a. `yarn dist`) that we use for local testing and for the real prod build, and environment variables are the only difference between the two. There's no way for the script to know whether a missing environment variable is intentional or not.
We should split this single build target into two: one target for production-like builds, and one for a real production build. The real production build target can include comprehensive validation that ensures all expected environment variables are set. | non_test | add environment variable validation to the build script currently the build script doesn t validate that expected environment variables are set for production builds this is because the build script doesn t know the difference between a real production build and a production like build we have one build target yarn build prod a k a yarn dist that we use for local testing and for the real prod build and environment variables are the only difference between the two there s no way for the script to know whether a missing environment variable is intentional or not we should split this single build target into two one target for production like builds and one for a real production build the real production build target can include comprehensive validation that ensures all expected environment variables are set | 0 |
753,760 | 26,360,642,490 | IssuesEvent | 2023-01-11 13:08:55 | OpenNebula/one | https://api.github.com/repos/OpenNebula/one | closed | Update VM templates after renaming the components referenced | Type: Backlog Category: Core & System Type: Feature Sponsored Category: API Priority: Low | **Description**
After issuing a rename API Call, like `one.image.rename`, the object new name doesn't appear updated on the VM Templates that reference it.
**Use case**
The calls could issue the name update for consistency purposes. Even though the operation remains fully functional due to the object ID being used for it.
**Additional Context**
This behavior can be implemented with API Hooks triggering on the rename calls.
<!--////////////////////////////////////////////-->
<!-- THIS SECTION IS FOR THE DEVELOPMENT TEAM -->
<!-- BOTH FOR BUGS AND ENHANCEMENT REQUESTS -->
<!-- PROGRESS WILL BE REFLECTED HERE -->
<!--////////////////////////////////////////////-->
## Progress Status
- [ ] Code committed
- [ ] Testing - QA
- [ ] Documentation (Release notes - resolved issues, compatibility, known issues)
| 1.0 | Update VM templates after renaming the components referenced - **Description**
After issuing a rename API Call, like `one.image.rename`, the object new name doesn't appear updated on the VM Templates that reference it.
**Use case**
The calls could issue the name update for consistency purposes. Even though the operation remains fully functional due to the object ID being used for it.
**Additional Context**
This behavior can be implemented with API Hooks triggering on the rename calls.
<!--////////////////////////////////////////////-->
<!-- THIS SECTION IS FOR THE DEVELOPMENT TEAM -->
<!-- BOTH FOR BUGS AND ENHANCEMENT REQUESTS -->
<!-- PROGRESS WILL BE REFLECTED HERE -->
<!--////////////////////////////////////////////-->
## Progress Status
- [ ] Code committed
- [ ] Testing - QA
- [ ] Documentation (Release notes - resolved issues, compatibility, known issues)
| non_test | update vm templates after renaming the components referenced description after issuing a rename api call like one image rename the object new name doesn t appear updated on the vm templates that reference it use case the calls could issue the name update for consistency purposes even though the operation remains fully functional due to the object id being used for it additional context this behavior can be implemented with api hooks triggering on the rename calls progress status code committed testing qa documentation release notes resolved issues compatibility known issues | 0 |
311,399 | 26,789,380,276 | IssuesEvent | 2023-02-01 07:05:40 | ushmz/subsuke | https://api.github.com/repos/ushmz/subsuke | closed | 正しくアイテムが登録されることを確認するテスト | test | ### Discussed in https://github.com/ushmz/subsuke/discussions/36
<div type='discussions-op-text'>
<sup>Originally posted by **chikowaka** October 22, 2022</sup>
誰が :
何をしたい:
テスト要件
前提条件 :
手順 :
入力値 :
期待する値:</div> | 1.0 | 正しくアイテムが登録されることを確認するテスト - ### Discussed in https://github.com/ushmz/subsuke/discussions/36
<div type='discussions-op-text'>
<sup>Originally posted by **chikowaka** October 22, 2022</sup>
誰が :
何をしたい:
テスト要件
前提条件 :
手順 :
入力値 :
期待する値:</div> | test | 正しくアイテムが登録されることを確認するテスト discussed in originally posted by chikowaka october 誰が : 何をしたい: テスト要件 前提条件 : 手順 : 入力値 : 期待する値: | 1 |
766,479 | 26,885,349,836 | IssuesEvent | 2023-02-06 02:20:54 | Waygone/JuiceJam | https://api.github.com/repos/Waygone/JuiceJam | closed | Collision box of a specific wall is too big. | bug priority: low environment | The player character collides with thin air when running into a specific wall.
Environment:
Unity preview on Windows 10. Latest commit: https://github.com/Waygone/JuiceJam/commit/8f45bf86e6e3051588960d2df6c90508e0ca2e3c
Reproducibility rate:
100%
Steps to reproduce:
1. Start the game and jump over the pit to the right
2. Climb the brown wall and keep going right until you hit another wall.
Expected result:
Player character collides with the wall normally.
Actual result:
Player character collides with thin air.
Video of issue:
https://user-images.githubusercontent.com/122162160/216400450-06ac2f03-3032-4ba5-8a78-4a607c343dfc.mp4
Screenshot:
| 1.0 | Collision box of a specific wall is too big. - The player character collides with thin air when running into a specific wall.
Environment:
Unity preview on Windows 10. Latest commit: https://github.com/Waygone/JuiceJam/commit/8f45bf86e6e3051588960d2df6c90508e0ca2e3c
Reproducibility rate:
100%
Steps to reproduce:
1. Start the game and jump over the pit to the right
2. Climb the brown wall and keep going right until you hit another wall.
Expected result:
Player character collides with the wall normally.
Actual result:
Player character collides with thin air.
Video of issue:
https://user-images.githubusercontent.com/122162160/216400450-06ac2f03-3032-4ba5-8a78-4a607c343dfc.mp4
Screenshot:
| non_test | collision box of a specific wall is too big the player character collides with thin air when running into a specific wall environment unity preview on windows latest commit reproducibility rate steps to reproduce start the game and jump over the pit to the right climb the brown wall and keep going right until you hit another wall expected result player character collides with the wall normally actual result player character collides with thin air video of issue screenshot | 0 |
443,226 | 12,768,374,926 | IssuesEvent | 2020-06-30 00:14:27 | usdigitalresponse/neighbor-express | https://api.github.com/repos/usdigitalresponse/neighbor-express | closed | Email | Priority |
We created mailmerge in airtable for Paterson and are almost done with Walnut Creek.
We want to get this documented (geoff prob already has that) and also passed off to someone else on the team to help with.
Ideally I’d also like us to have some kind of simple way for this to be implemented, and guidelines to accounts for what types of emails to promise.
We are in discussion with Sendgrid/twilio to figure out how to get some funds for this – another to do for product is to figure out sponsorship/funds for sendgrid
| 1.0 | Email -
We created mailmerge in airtable for Paterson and are almost done with Walnut Creek.
We want to get this documented (geoff prob already has that) and also passed off to someone else on the team to help with.
Ideally I’d also like us to have some kind of simple way for this to be implemented, and guidelines to accounts for what types of emails to promise.
We are in discussion with Sendgrid/twilio to figure out how to get some funds for this – another to do for product is to figure out sponsorship/funds for sendgrid
| non_test | email we created mailmerge in airtable for paterson and are almost done with walnut creek we want to get this documented geoff prob already has that and also passed off to someone else on the team to help with ideally i’d also like us to have some kind of simple way for this to be implemented and guidelines to accounts for what types of emails to promise we are in discussion with sendgrid twilio to figure out how to get some funds for this – another to do for product is to figure out sponsorship funds for sendgrid | 0 |
329,159 | 28,179,418,177 | IssuesEvent | 2023-04-04 00:24:52 | NASA-AMMOS/aerie | https://api.github.com/repos/NASA-AMMOS/aerie | opened | Finish MerlinBindingsTests | test | Currently, `MerlinBindingsTests` does not test any of the MerlinBindings, only `shouldEnableCors`. Completion of this ticket would involve either expanding this class or creating end-to-end tests to actually test MerlinBindings. | 1.0 | Finish MerlinBindingsTests - Currently, `MerlinBindingsTests` does not test any of the MerlinBindings, only `shouldEnableCors`. Completion of this ticket would involve either expanding this class or creating end-to-end tests to actually test MerlinBindings. | test | finish merlinbindingstests currently merlinbindingstests does not test any of the merlinbindings only shouldenablecors completion of this ticket would involve either expanding this class or creating end to end tests to actually test merlinbindings | 1 |
339,438 | 30,447,628,775 | IssuesEvent | 2023-07-15 22:11:34 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix extrema_finding.test_numpy_minimum | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix extrema_finding.test_numpy_minimum - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5564287164/jobs/10163795306"><img src=https://img.shields.io/badge/-success-success></a>
| test | fix extrema finding test numpy minimum jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 1 |
97,764 | 4,006,016,385 | IssuesEvent | 2016-05-12 13:42:22 | fgpv-vpgf/fgpv-vpgf | https://api.github.com/repos/fgpv-vpgf/fgpv-vpgf | opened | Initial layer order does not reflect layer order in the map stack | priority: high problem: bug | Layers are added to the legend in the order they appear in the config (thanks to legend placeholders); however, this doesn't exactly reflect the order of the map stack (there are two of them - one for feature layers: `graphicsLayerIds`; and one for everything else: layerIds; thanks James for elucidating this point).
This makes it difficult to tell if the layer reordering is working correctly and it might appear entirely broken to the user. See #272. | 1.0 | Initial layer order does not reflect layer order in the map stack - Layers are added to the legend in the order they appear in the config (thanks to legend placeholders); however, this doesn't exactly reflect the order of the map stack (there are two of them - one for feature layers: `graphicsLayerIds`; and one for everything else: layerIds; thanks James for elucidating this point).
This makes it difficult to tell if the layer reordering is working correctly and it might appear entirely broken to the user. See #272. | non_test | initial layer order does not reflect layer order in the map stack layers are added to the legend in the order they appear in the config thanks to legend placeholders however this doesn t exactly reflect the order of the map stack there are two of them one for feature layers graphicslayerids and one for everything else layerids thanks james for elucidating this point this makes it difficult to tell if the layer reordering is working correctly and it might appear entirely broken to the user see | 0 |
8,006 | 2,951,620,514 | IssuesEvent | 2015-07-07 00:59:48 | BI/octo-wookie | https://api.github.com/repos/BI/octo-wookie | closed | On phone, the About link gets cut off | show-stopper task test-me | Samsung S5:
On Home page; cannot see that "about" is a link because the underline is cut off.

| 1.0 | On phone, the About link gets cut off - Samsung S5:
On Home page; cannot see that "about" is a link because the underline is cut off.

| test | on phone the about link gets cut off samsung on home page cannot see that about is a link because the underline is cut off | 1 |
8,242 | 3,147,255,849 | IssuesEvent | 2015-09-15 06:49:55 | jMonkeyEngine-Contributions/Lemur | https://api.github.com/repos/jMonkeyEngine-Contributions/Lemur | opened | Docs:TextEntryComponent | documentation | Need to add content to the TextEntryComponent section of the GUI Components page. | 1.0 | Docs:TextEntryComponent - Need to add content to the TextEntryComponent section of the GUI Components page. | non_test | docs textentrycomponent need to add content to the textentrycomponent section of the gui components page | 0 |
330,974 | 24,285,253,561 | IssuesEvent | 2022-09-28 21:22:13 | flyteorg/flyte | https://api.github.com/repos/flyteorg/flyte | closed | [Deployment] Flyte on k3s. | documentation untriaged | ### Description
Provide the deployment guidance of flyte on k3s, as detailed as possible, thank you.
### Are you sure this issue hasn't been raised already?
- [X] Yes
### Have you read the Code of Conduct?
- [X] Yes | 1.0 | [Deployment] Flyte on k3s. - ### Description
Provide the deployment guidance of flyte on k3s, as detailed as possible, thank you.
### Are you sure this issue hasn't been raised already?
- [X] Yes
### Have you read the Code of Conduct?
- [X] Yes | non_test | flyte on description provide the deployment guidance of flyte on as detailed as possible thank you are you sure this issue hasn t been raised already yes have you read the code of conduct yes | 0 |
351,619 | 25,034,037,461 | IssuesEvent | 2022-11-04 14:38:40 | bounswe/bounswe2022group6 | https://api.github.com/repos/bounswe/bounswe2022group6 | opened | Specifying the requirements addressed in Milestone 1 | Type: Documentation Priority: High State: In Progress | We divided work into smaller pieces to complete the Milestone 1 Group report.
I will check the requirements addressed in this Milestone and add them to our group report.
To go with double check, @artun-akdogan will review after I finish. | 1.0 | Specifying the requirements addressed in Milestone 1 - We divided work into smaller pieces to complete the Milestone 1 Group report.
I will check the requirements addressed in this Milestone and add them to our group report.
To go with double check, @artun-akdogan will review after I finish. | non_test | specifying the requirements addressed in milestone we divided work into smaller pieces to complete the milestone group report i will check the requirements addressed in this milestone and add them to our group report to go with double check artun akdogan will review after i finish | 0 |
336,655 | 30,212,799,150 | IssuesEvent | 2023-07-05 13:49:07 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | [Failing Test] verify-master | sig/cli kind/failing-test needs-triage | ### Which jobs are failing?
master-informing:
- verify-master
### Which tests are failing?
`verify.yamlfmt`

### Since when has it been failing?
07-03 18:11 IST
### Testgrid link
https://testgrid.k8s.io/sig-release-master-blocking#verify-master
### Reason for failure (if possible)
```
Unexpected dirty working directory:
...
!!! [0704 11:10:07] 1: hack/make-rules/../../hack/verify-yamlfmt.sh:30 kube::util::ensure_clean_working_dir(...)
+++ exit code: 1
+++ error: 1
[0;31mFAILED verify-yamlfmt.sh 0s
```
### Anything else we need to know?
_No response_
### Relevant SIG(s)
/sig | 1.0 | [Failing Test] verify-master - ### Which jobs are failing?
master-informing:
- verify-master
### Which tests are failing?
`verify.yamlfmt`

### Since when has it been failing?
07-03 18:11 IST
### Testgrid link
https://testgrid.k8s.io/sig-release-master-blocking#verify-master
### Reason for failure (if possible)
```
Unexpected dirty working directory:
...
!!! [0704 11:10:07] 1: hack/make-rules/../../hack/verify-yamlfmt.sh:30 kube::util::ensure_clean_working_dir(...)
+++ exit code: 1
+++ error: 1
[0;31mFAILED verify-yamlfmt.sh 0s
```
### Anything else we need to know?
_No response_
### Relevant SIG(s)
/sig | test | verify master which jobs are failing master informing verify master which tests are failing verify yamlfmt since when has it been failing ist testgrid link reason for failure if possible unexpected dirty working directory hack make rules hack verify yamlfmt sh kube util ensure clean working dir exit code error verify yamlfmt sh anything else we need to know no response relevant sig s sig | 1 |
23,319 | 6,418,552,514 | IssuesEvent | 2017-08-08 19:11:57 | dotnet/coreclr | https://api.github.com/repos/dotnet/coreclr | opened | Revisit the strategy for fail fasts from compInlineResult->NoteFatal. | area-CodeGen Discussion | We do not have handlers for compDonotInline after some functions, that do "NoteFatal". For example after lvaGrabTemp. It creates problem, if we do NoteFatal for the second time, it blows the assert that compilation should be already interrupted.
There are two obvious solutions:
1) delete the assert and allow to continue execution with several "NoteFatal" before a handler;
2) do fail-fast check after the each function, that can do "NoteFatal".
The first will waste time for the work, that will be thrown out.
The second will need new intrusive checks in many places.
Attach #13271 . | 1.0 | Revisit the strategy for fail fasts from compInlineResult->NoteFatal. - We do not have handlers for compDonotInline after some functions, that do "NoteFatal". For example after lvaGrabTemp. It creates problem, if we do NoteFatal for the second time, it blows the assert that compilation should be already interrupted.
There are two obvious solutions:
1) delete the assert and allow to continue execution with several "NoteFatal" before a handler;
2) do fail-fast check after the each function, that can do "NoteFatal".
The first will waste time for the work, that will be thrown out.
The second will need new intrusive checks in many places.
Attach #13271 . | non_test | revisit the strategy for fail fasts from compinlineresult notefatal we do not have handlers for compdonotinline after some functions that do notefatal for example after lvagrabtemp it creates problem if we do notefatal for the second time it blows the assert that compilation should be already interrupted there are two obvious solutions delete the assert and allow to continue execution with several notefatal before a handler do fail fast check after the each function that can do notefatal the first will waste time for the work that will be thrown out the second will need new intrusive checks in many places attach | 0 |
201,346 | 15,190,708,156 | IssuesEvent | 2021-02-15 18:27:09 | gregorio-project/gregorio-test | https://api.github.com/repos/gregorio-project/gregorio-test | opened | Backward mode for gregorio-test.sh | enhancement test harness | There should be a `backward` mode for gregorio-test.sh which will convert given TEST into a backwards compatibility test (copying the files into `backwards/` and adding the `_B` as appropriate).
Further, review-results.sh should have an option where a failed test can be converted to a backwards compatibility test (with the current expectation) and the result (which failed against the old expectation) made into the future expectation for that test. | 1.0 | Backward mode for gregorio-test.sh - There should be a `backward` mode for gregorio-test.sh which will convert given TEST into a backwards compatibility test (copying the files into `backwards/` and adding the `_B` as appropriate).
Further, review-results.sh should have an option where a failed test can be converted to a backwards compatibility test (with the current expectation) and the result (which failed against the old expectation) made into the future expectation for that test. | test | backward mode for gregorio test sh there should be a backward mode for gregorio test sh which will convert given test into a backwards compatibility test copying the files into backwards and adding the b as appropriate further review results sh should have an option where a failed test can be converted to a backwards compatibility test with the current expectation and the result which failed against the old expectation made into the future expectation for that test | 1 |
5,252 | 8,041,332,841 | IssuesEvent | 2018-07-31 02:18:09 | rubberduck-vba/Rubberduck | https://api.github.com/repos/rubberduck-vba/Rubberduck | closed | Changing loaded projects during a unit test corrupts the RubberduckParserState cache. | bug critical feature-unit-testing parse-tree-processing | [See the discussion here](http://chat.stackexchange.com/transcript/message/35491743#35491743).
The project event handlers in the parser state reject events when the VBE isn't in design mode, and the state doesn't get refreshed after the test run completes. This creates "issues" if the code being tested does something dodgy like this:
```
'@TestMethod
Public Sub TestMethod1() 'TODO Rename test
On Error GoTo TestFail
Application.Workbooks("Book1.xlsx").Close
Assert.Inconclusive
TestExit:
Exit Sub
TestFail:
Assert.Fail "Test raised an error: #" & Err.Number & " - " & Err.Description
End Sub
```
Opening and renaming a project create similar issues. The tests complete just fine, but starting with the next parser refresh, the wheels come off. The first time this happened I had a hard Excel crash, other times I was getting miscellaneous errors on parsing sometimes, crashes at others.
My guess is that this is an issue with the API too - any code that calls `.Parse` and then modifies the project landscape in the same procedure is likely going to be problematic. | 1.0 | Changing loaded projects during a unit test corrupts the RubberduckParserState cache. - [See the discussion here](http://chat.stackexchange.com/transcript/message/35491743#35491743).
The project event handlers in the parser state reject events when the VBE isn't in design mode, and the state doesn't get refreshed after the test run completes. This creates "issues" if the code being tested does something dodgy like this:
```
'@TestMethod
Public Sub TestMethod1() 'TODO Rename test
On Error GoTo TestFail
Application.Workbooks("Book1.xlsx").Close
Assert.Inconclusive
TestExit:
Exit Sub
TestFail:
Assert.Fail "Test raised an error: #" & Err.Number & " - " & Err.Description
End Sub
```
Opening and renaming a project create similar issues. The tests complete just fine, but starting with the next parser refresh, the wheels come off. The first time this happened I had a hard Excel crash, other times I was getting miscellaneous errors on parsing sometimes, crashes at others.
My guess is that this is an issue with the API too - any code that calls `.Parse` and then modifies the project landscape in the same procedure is likely going to be problematic. | non_test | changing loaded projects during a unit test corrupts the rubberduckparserstate cache the project event handlers in the parser state reject events when the vbe isn t in design mode and the state doesn t get refreshed after the test run completes this creates issues if the code being tested does something dodgy like this testmethod public sub todo rename test on error goto testfail application workbooks xlsx close assert inconclusive testexit exit sub testfail assert fail test raised an error err number err description end sub opening and renaming a project create similar issues the tests complete just fine but starting with the next parser refresh the wheels come off the first time this happened i had a hard excel crash other times i was getting miscellaneous errors on parsing sometimes crashes at others my guess is that this is an issue with the api too any code that calls parse and then modifies the project landscape in the same procedure is likely going to be problematic | 0 |
41,339 | 6,900,746,948 | IssuesEvent | 2017-11-24 21:18:25 | awslabs/dynamodb-data-mapper-js | https://api.github.com/repos/awslabs/dynamodb-data-mapper-js | closed | Query/Scan limit is ignored | Documentation feature request | I can specify the limit parameter to query() and scan(), but because the result iterator keeps reading on using lastEvaluatedKey, all result rows are always returned and limit only becomes a batch size parameter.
Perhaps the iterator should manually check that if limit is reached, it stops yielding results?
| 1.0 | Query/Scan limit is ignored - I can specify the limit parameter to query() and scan(), but because the result iterator keeps reading on using lastEvaluatedKey, all result rows are always returned and limit only becomes a batch size parameter.
Perhaps the iterator should manually check that if limit is reached, it stops yielding results?
| non_test | query scan limit is ignored i can specify the limit parameter to query and scan but because the result iterator keeps reading on using lastevaluatedkey all result rows are always returned and limit only becomes a batch size parameter perhaps the iterator should manually check that if limit is reached it stops yielding results | 0 |
95,848 | 27,637,529,005 | IssuesEvent | 2023-03-10 15:30:18 | phil294/AHK_X11 | https://api.github.com/repos/phil294/AHK_X11 | closed | compile error on debian bullseye | bug build | sudo apt-get install libxinerama-dev libxkbcommon-dev libxtst-dev libgtk-3-dev libxi-dev libx11-dev libgirepository1.0-dev libatspi2.0-dev libssl-dev
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
libatspi2.0-dev is already the newest version (2.38.0-4).
libgirepository1.0-dev is already the newest version (1.66.1-1+b1).
libgtk-3-dev is already the newest version (3.24.24-4+deb11u2).
libx11-dev is already the newest version (2:1.7.2-1).
libxi-dev is already the newest version (2:1.7.10-1).
libxinerama-dev is already the newest version (2:1.1.4-2).
libxkbcommon-dev is already the newest version (1.0.3-2).
libxtst-dev is already the newest version (2:1.2.3-1).
libssl-dev is already the newest version (1.1.1n-0+deb11u3).
0 upgraded, 0 newly installed, 0 to remove and 4 not upgraded.
LANG=C curl -fsSL https://crystal-lang.org/install.sh | LANG=C sudo bash
...
Fetched 17.5 kB in 1s (17.0 kB/s)
Reading package lists... Done
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
gpg is already the newest version (2.2.27-2+deb11u2).
wget is already the newest version (1.21-1+deb11u1).
0 upgraded, 0 newly installed, 0 to remove and 4 not upgraded.
deb http://download.opensuse.org/repositories/devel:languages:crystal/Debian_Unstable/ /
...
Get:10 http://download.opensuse.org/repositories/devel:languages:crystal/Debian_Unstable InRelease [1557 B]
Get:20 http://download.opensuse.org/repositories/devel:languages:crystal/Debian_Unstable Packages [4798 B]
Fetched 23.8 kB in 2s (11.2 kB/s)
Reading package lists... Done
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
crystal is already the newest version (1.7.0-1+2.9).
shards install
Resolving dependencies
Fetching https://github.com/spider-gazelle/tasker.git
Fetching https://github.com/tamasszekeres/x11-cr.git
Fetching https://github.com/phil294/xtst-cr.git
Fetching https://github.com/phil294/x_do.cr.git
Fetching https://github.com/jhass/crystal-gobject.git
Fetching https://github.com/jhass/crystal-malloc_pthread_shim.git
Fetching https://github.com/kostya/cron_parser.git
Fetching https://github.com/crystal-community/future.cr.git
Shard "x11" version (1.0.0) doesn't match tag version (1.1.1)
Shard "x11" version (1.0.0) doesn't match tag version (1.1.1)
Installing cron_parser (0.4.0)
Installing future (1.0.0)
Installing tasker (2.0.7)
Installing x11 (1.1.1)
Installing xtst (1.0.0 at 202d2ae)
Installing x_do (0.8.3 at 94f755a)
Installing gobject (0.10.0)
Installing malloc_pthread_shim (0.1.0)
Postinstall of malloc_pthread_shim: make
./setup_dependencies.sh
building Gtk 3.0 namespace...
building xlib 2.0 namespace...
building GObject 2.0 namespace...
building GLib 2.0 namespace...
building Gio 2.0 namespace...
building GModule 2.0 namespace...
building Atk 1.0 namespace...
building freetype2 namespace...
building HarfBuzz 0.0 namespace...
building GdkPixbuf 2.0 namespace...
building cairo 1.0 namespace...
building Pango 1.0 namespace...
building Gdk 3.0 namespace...
building DBus 1.0 namespace...
building Atspi 2.0 namespace...
building GdkX11 3.0 namespace...
fix some dependency code...
shards build -Dpreview_mt
Dependencies are satisfied
Building: ahk_x11
Error target ahk_x11 failed to compile:
Showing last frame. Use --error-trace for full trace.
In src/cmd/x11/window/win-util.cr:18:54
18 | win = XDo::Window.new(thread.runner.display.x_do.xdo_p, wid)
^----
Error: private method 'xdo_p' called for XDo
Also tried this but same compile error
shards build -Dpreview_mt --link-flags="-no-pie -L$PWD/static -Wl,-Bstatic -lxdo -lxkbcommon -lXinerama -lXext -lXtst -lXi -levent_pthreads -levent -lpcre -Wl,-Bdynamic"
Dependencies are satisfied
Building: ahk_x11
Error target ahk_x11 failed to compile:
Showing last frame. Use --error-trace for full trace.
In src/cmd/x11/window/win-util.cr:18:54
18 | win = XDo::Window.new(thread.runner.display.x_do.xdo_p, wid)
^----
Error: private method 'xdo_p' called for XDo
With error trace i get even mor output....
shards build -Dpreview_mt --error-trace
Dependencies are satisfied
Building: ahk_x11
Error target ahk_x11 failed to compile:
In src/ahk_x11.cr:88:9
88 | runner.run
^--
Error: instantiating 'Run::Runner#run()'
In src/run/runner.cr:88:30
88 | spawn same_thread: true { clock }
^----
Error: instantiating 'clock()'
In src/run/runner.cr:119:4
119 | loop do
^---
Error: instantiating 'loop()'
In src/run/runner.cr:119:4
119 | loop do
^---
Error: instantiating 'loop()'
In src/run/runner.cr:133:30
133 | when exit_code = thread.next.receive?
^---
Error: instantiating 'Run::Thread#next()'
In src/run/thread.cr:95:14
95 | result = do_next
^------
Error: instantiating 'do_next()'
In src/run/thread.cr:132:18
132 | result = cmd.run(self, parsed_args)
^--
Error: instantiating 'Cmd::Base+#run(Run::Thread, Array(String))'
In src/cmd/x11/window/win-set.cr:10:8
10 | Util.match(thread, args[2..], empty_is_last_found: true, a_is_active: true) do |win|
^----
Error: instantiating 'Cmd::X11::Window::Util.class#match(Run::Thread, Array(String))'
In src/cmd/x11/window/win-util.cr:18:54
18 | win = XDo::Window.new(thread.runner.display.x_do.xdo_p, wid)
^----
Error: private method 'xdo_p' called for XDo
Any suggestions?
| 1.0 | compile error on debian bullseye - sudo apt-get install libxinerama-dev libxkbcommon-dev libxtst-dev libgtk-3-dev libxi-dev libx11-dev libgirepository1.0-dev libatspi2.0-dev libssl-dev
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
libatspi2.0-dev is already the newest version (2.38.0-4).
libgirepository1.0-dev is already the newest version (1.66.1-1+b1).
libgtk-3-dev is already the newest version (3.24.24-4+deb11u2).
libx11-dev is already the newest version (2:1.7.2-1).
libxi-dev is already the newest version (2:1.7.10-1).
libxinerama-dev is already the newest version (2:1.1.4-2).
libxkbcommon-dev is already the newest version (1.0.3-2).
libxtst-dev is already the newest version (2:1.2.3-1).
libssl-dev is already the newest version (1.1.1n-0+deb11u3).
0 upgraded, 0 newly installed, 0 to remove and 4 not upgraded.
LANG=C curl -fsSL https://crystal-lang.org/install.sh | LANG=C sudo bash
...
Fetched 17.5 kB in 1s (17.0 kB/s)
Reading package lists... Done
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
gpg is already the newest version (2.2.27-2+deb11u2).
wget is already the newest version (1.21-1+deb11u1).
0 upgraded, 0 newly installed, 0 to remove and 4 not upgraded.
deb http://download.opensuse.org/repositories/devel:languages:crystal/Debian_Unstable/ /
...
Get:10 http://download.opensuse.org/repositories/devel:languages:crystal/Debian_Unstable InRelease [1557 B]
Get:20 http://download.opensuse.org/repositories/devel:languages:crystal/Debian_Unstable Packages [4798 B]
Fetched 23.8 kB in 2s (11.2 kB/s)
Reading package lists... Done
Reading package lists... Done
Building dependency tree... Done
Reading state information... Done
crystal is already the newest version (1.7.0-1+2.9).
shards install
Resolving dependencies
Fetching https://github.com/spider-gazelle/tasker.git
Fetching https://github.com/tamasszekeres/x11-cr.git
Fetching https://github.com/phil294/xtst-cr.git
Fetching https://github.com/phil294/x_do.cr.git
Fetching https://github.com/jhass/crystal-gobject.git
Fetching https://github.com/jhass/crystal-malloc_pthread_shim.git
Fetching https://github.com/kostya/cron_parser.git
Fetching https://github.com/crystal-community/future.cr.git
Shard "x11" version (1.0.0) doesn't match tag version (1.1.1)
Shard "x11" version (1.0.0) doesn't match tag version (1.1.1)
Installing cron_parser (0.4.0)
Installing future (1.0.0)
Installing tasker (2.0.7)
Installing x11 (1.1.1)
Installing xtst (1.0.0 at 202d2ae)
Installing x_do (0.8.3 at 94f755a)
Installing gobject (0.10.0)
Installing malloc_pthread_shim (0.1.0)
Postinstall of malloc_pthread_shim: make
./setup_dependencies.sh
building Gtk 3.0 namespace...
building xlib 2.0 namespace...
building GObject 2.0 namespace...
building GLib 2.0 namespace...
building Gio 2.0 namespace...
building GModule 2.0 namespace...
building Atk 1.0 namespace...
building freetype2 namespace...
building HarfBuzz 0.0 namespace...
building GdkPixbuf 2.0 namespace...
building cairo 1.0 namespace...
building Pango 1.0 namespace...
building Gdk 3.0 namespace...
building DBus 1.0 namespace...
building Atspi 2.0 namespace...
building GdkX11 3.0 namespace...
fix some dependency code...
shards build -Dpreview_mt
Dependencies are satisfied
Building: ahk_x11
Error target ahk_x11 failed to compile:
Showing last frame. Use --error-trace for full trace.
In src/cmd/x11/window/win-util.cr:18:54
18 | win = XDo::Window.new(thread.runner.display.x_do.xdo_p, wid)
^----
Error: private method 'xdo_p' called for XDo
Also tried this but same compile error
shards build -Dpreview_mt --link-flags="-no-pie -L$PWD/static -Wl,-Bstatic -lxdo -lxkbcommon -lXinerama -lXext -lXtst -lXi -levent_pthreads -levent -lpcre -Wl,-Bdynamic"
Dependencies are satisfied
Building: ahk_x11
Error target ahk_x11 failed to compile:
Showing last frame. Use --error-trace for full trace.
In src/cmd/x11/window/win-util.cr:18:54
18 | win = XDo::Window.new(thread.runner.display.x_do.xdo_p, wid)
^----
Error: private method 'xdo_p' called for XDo
With error trace i get even mor output....
shards build -Dpreview_mt --error-trace
Dependencies are satisfied
Building: ahk_x11
Error target ahk_x11 failed to compile:
In src/ahk_x11.cr:88:9
88 | runner.run
^--
Error: instantiating 'Run::Runner#run()'
In src/run/runner.cr:88:30
88 | spawn same_thread: true { clock }
^----
Error: instantiating 'clock()'
In src/run/runner.cr:119:4
119 | loop do
^---
Error: instantiating 'loop()'
In src/run/runner.cr:119:4
119 | loop do
^---
Error: instantiating 'loop()'
In src/run/runner.cr:133:30
133 | when exit_code = thread.next.receive?
^---
Error: instantiating 'Run::Thread#next()'
In src/run/thread.cr:95:14
95 | result = do_next
^------
Error: instantiating 'do_next()'
In src/run/thread.cr:132:18
132 | result = cmd.run(self, parsed_args)
^--
Error: instantiating 'Cmd::Base+#run(Run::Thread, Array(String))'
In src/cmd/x11/window/win-set.cr:10:8
10 | Util.match(thread, args[2..], empty_is_last_found: true, a_is_active: true) do |win|
^----
Error: instantiating 'Cmd::X11::Window::Util.class#match(Run::Thread, Array(String))'
In src/cmd/x11/window/win-util.cr:18:54
18 | win = XDo::Window.new(thread.runner.display.x_do.xdo_p, wid)
^----
Error: private method 'xdo_p' called for XDo
Any suggestions?
| non_test | compile error on debian bullseye sudo apt get install libxinerama dev libxkbcommon dev libxtst dev libgtk dev libxi dev dev dev dev libssl dev reading package lists done building dependency tree done reading state information done dev is already the newest version dev is already the newest version libgtk dev is already the newest version dev is already the newest version libxi dev is already the newest version libxinerama dev is already the newest version libxkbcommon dev is already the newest version libxtst dev is already the newest version libssl dev is already the newest version upgraded newly installed to remove and not upgraded lang c curl fssl lang c sudo bash fetched kb in kb s reading package lists done reading package lists done building dependency tree done reading state information done gpg is already the newest version wget is already the newest version upgraded newly installed to remove and not upgraded deb get inrelease get packages fetched kb in kb s reading package lists done reading package lists done building dependency tree done reading state information done crystal is already the newest version shards install resolving dependencies fetching fetching fetching fetching fetching fetching fetching fetching shard version doesn t match tag version shard version doesn t match tag version installing cron parser installing future installing tasker installing installing xtst at installing x do at installing gobject installing malloc pthread shim postinstall of malloc pthread shim make setup dependencies sh building gtk namespace building xlib namespace building gobject namespace building glib namespace building gio namespace building gmodule namespace building atk namespace building namespace building harfbuzz namespace building gdkpixbuf namespace building cairo namespace building pango namespace building gdk namespace building dbus namespace building atspi namespace building namespace fix some dependency code shards build dpreview mt dependencies are satisfied building ahk error target ahk failed to compile showing last frame use error trace for full trace in src cmd window win util cr win xdo window new thread runner display x do xdo p wid error private method xdo p called for xdo also tried this but same compile error shards build dpreview mt link flags no pie l pwd static wl bstatic lxdo lxkbcommon lxinerama lxext lxtst lxi levent pthreads levent lpcre wl bdynamic dependencies are satisfied building ahk error target ahk failed to compile showing last frame use error trace for full trace in src cmd window win util cr win xdo window new thread runner display x do xdo p wid error private method xdo p called for xdo with error trace i get even mor output shards build dpreview mt error trace dependencies are satisfied building ahk error target ahk failed to compile in src ahk cr runner run error instantiating run runner run in src run runner cr spawn same thread true clock error instantiating clock in src run runner cr loop do error instantiating loop in src run runner cr loop do error instantiating loop in src run runner cr when exit code thread next receive error instantiating run thread next in src run thread cr result do next error instantiating do next in src run thread cr result cmd run self parsed args error instantiating cmd base run run thread array string in src cmd window win set cr util match thread args empty is last found true a is active true do win error instantiating cmd window util class match run thread array string in src cmd window win util cr win xdo window new thread runner display x do xdo p wid error private method xdo p called for xdo any suggestions | 0 |
67,503 | 16,989,999,650 | IssuesEvent | 2021-06-30 19:05:45 | hashicorp/packer | https://api.github.com/repos/hashicorp/packer | closed | azure: Communication configuration | breaking-change bug builder/azure docs post-1.0 remote-plugin/azure track-internal | Related to #4172
- [ ] Don't set a default `ssh_username` [in a builder](https://github.com/hashicorp/packer/blob/676c3a21bf1858d5786ea3c74efbd1e7a2a24ad4/builder/azure/arm/config.go#L688).
- [ ] [The default to both](https://github.com/hashicorp/packer/blob/676c3a21bf1858d5786ea3c74efbd1e7a2a24ad4/builder/azure/arm/config.go#L580) `ssh`and `winrm` communicator is really weird and undocumented. I think it should be removed, even if it breaks BC, or at least clearly documented. Currently some valid configurations will be ignored or not work as expected. | 1.0 | azure: Communication configuration - Related to #4172
- [ ] Don't set a default `ssh_username` [in a builder](https://github.com/hashicorp/packer/blob/676c3a21bf1858d5786ea3c74efbd1e7a2a24ad4/builder/azure/arm/config.go#L688).
- [ ] [The default to both](https://github.com/hashicorp/packer/blob/676c3a21bf1858d5786ea3c74efbd1e7a2a24ad4/builder/azure/arm/config.go#L580) `ssh`and `winrm` communicator is really weird and undocumented. I think it should be removed, even if it breaks BC, or at least clearly documented. Currently some valid configurations will be ignored or not work as expected. | non_test | azure communication configuration related to don t set a default ssh username ssh and winrm communicator is really weird and undocumented i think it should be removed even if it breaks bc or at least clearly documented currently some valid configurations will be ignored or not work as expected | 0 |
20,885 | 27,708,211,644 | IssuesEvent | 2023-03-14 12:40:53 | toggl/track-windows-feedback | https://api.github.com/repos/toggl/track-windows-feedback | closed | Shortcuts (@ and #) don't work in manual mode | bug processed | **Describe the bug**
If Toggl app is used in manual mode, the shortcuts for project and hashtags don't work.
**Steps to reproduce**
1. Swith the app to Manual Mode
2. Press the "Enter Time Manually" button
3. Press @ or # in the description pop-up and then first letters of project or tag
4. Nothing happens
**Expected behavior**
App should propose the project after pressing @ and the tag after pressing # basic on the letters you are typing.
**Environment (please complete the following information):**
- Version 8.0.9 | 1.0 | Shortcuts (@ and #) don't work in manual mode - **Describe the bug**
If Toggl app is used in manual mode, the shortcuts for project and hashtags don't work.
**Steps to reproduce**
1. Swith the app to Manual Mode
2. Press the "Enter Time Manually" button
3. Press @ or # in the description pop-up and then first letters of project or tag
4. Nothing happens
**Expected behavior**
App should propose the project after pressing @ and the tag after pressing # basic on the letters you are typing.
**Environment (please complete the following information):**
- Version 8.0.9 | non_test | shortcuts and don t work in manual mode describe the bug if toggl app is used in manual mode the shortcuts for project and hashtags don t work steps to reproduce swith the app to manual mode press the enter time manually button press or in the description pop up and then first letters of project or tag nothing happens expected behavior app should propose the project after pressing and the tag after pressing basic on the letters you are typing environment please complete the following information version | 0 |
26,757 | 4,241,393,772 | IssuesEvent | 2016-07-06 16:10:45 | mattimaier/bnote | https://api.github.com/repos/mattimaier/bnote | closed | Überarbeitung Startseite | enhancement to test User Request | * Bessere Anzeige der einzelnen Items, z.B. Kommentare schneller Anzeigen, keine 3 verschiedenen Aktionen auf Titel/Diskussion/Abstimmung
* Konfigurierbar optional anzeigen: Reservierungen und nächste Tour-Riding-Termine | 1.0 | Überarbeitung Startseite - * Bessere Anzeige der einzelnen Items, z.B. Kommentare schneller Anzeigen, keine 3 verschiedenen Aktionen auf Titel/Diskussion/Abstimmung
* Konfigurierbar optional anzeigen: Reservierungen und nächste Tour-Riding-Termine | test | überarbeitung startseite bessere anzeige der einzelnen items z b kommentare schneller anzeigen keine verschiedenen aktionen auf titel diskussion abstimmung konfigurierbar optional anzeigen reservierungen und nächste tour riding termine | 1 |
4,719 | 24,342,579,446 | IssuesEvent | 2022-10-01 22:24:27 | beekama/NutritionApp | https://api.github.com/repos/beekama/NutritionApp | closed | Document ExtendedBarChart Magic Numbers | maintainability | ExtendeBarChart has some unclear variable names in Line 65-68, where magic numbers 1 & 3 are used without explanation, make 1 and 3 variables with a name indicating their function.
While you're on that fix the Array definition warning. | True | Document ExtendedBarChart Magic Numbers - ExtendeBarChart has some unclear variable names in Line 65-68, where magic numbers 1 & 3 are used without explanation, make 1 and 3 variables with a name indicating their function.
While you're on that fix the Array definition warning. | non_test | document extendedbarchart magic numbers extendebarchart has some unclear variable names in line where magic numbers are used without explanation make and variables with a name indicating their function while you re on that fix the array definition warning | 0 |
179,106 | 6,621,600,649 | IssuesEvent | 2017-09-21 19:49:45 | Polymer/polymer-cli | https://api.github.com/repos/Polymer/polymer-cli | closed | Bundled build fails silently when html imports are not found | Priority: High Status: Available Type: Bug | This seems to be a known issue in the community, but when a html import doesn't resolve, bundled builds fail silently.
I only figured this out due to a helpful comment on https://github.com/Polymer/polymer-cli/issues/821
Failing silently is a pretty ridiculous. | 1.0 | Bundled build fails silently when html imports are not found - This seems to be a known issue in the community, but when a html import doesn't resolve, bundled builds fail silently.
I only figured this out due to a helpful comment on https://github.com/Polymer/polymer-cli/issues/821
Failing silently is a pretty ridiculous. | non_test | bundled build fails silently when html imports are not found this seems to be a known issue in the community but when a html import doesn t resolve bundled builds fail silently i only figured this out due to a helpful comment on failing silently is a pretty ridiculous | 0 |
39,853 | 2,860,578,605 | IssuesEvent | 2015-06-03 16:28:31 | KaeYuri/hub_intra_proto | https://api.github.com/repos/KaeYuri/hub_intra_proto | opened | [Droits] Liste de roles : admin/staff/pedago (/rien) | new feature priority:medium | Pedago : Possibilité de valider les projets
Staff : Tous les droits pour créer et modifier des projets
Admin : god mod | 1.0 | [Droits] Liste de roles : admin/staff/pedago (/rien) - Pedago : Possibilité de valider les projets
Staff : Tous les droits pour créer et modifier des projets
Admin : god mod | non_test | liste de roles admin staff pedago rien pedago possibilité de valider les projets staff tous les droits pour créer et modifier des projets admin god mod | 0 |
101,184 | 8,780,513,762 | IssuesEvent | 2018-12-19 17:31:55 | sot/proseco | https://api.github.com/repos/sot/proseco | closed | Document updates to guide star summary file | Matlab testing | Is there a spec for updates to the guide star summary output in the MATLAB proseco release? | 1.0 | Document updates to guide star summary file - Is there a spec for updates to the guide star summary output in the MATLAB proseco release? | test | document updates to guide star summary file is there a spec for updates to the guide star summary output in the matlab proseco release | 1 |
334,891 | 29,995,891,745 | IssuesEvent | 2023-06-26 05:27:22 | 3DAsset-eCommerce/3D-BE | https://api.github.com/repos/3DAsset-eCommerce/3D-BE | closed | [feat] 위시리스트 담기 | Available Medium Test | ## Description
>> 위시리스트에 에셋을 담는 기능
## Tasks
- [x] 사용자의 id와 조회를 요청한 id가 같은지 확인
- [x] 에셋 id로 에셋 조회
- [x] 유저와 에셋을 담아 wishListRepository에 save
- [x] Controller Test
- [x] Service Test
| 1.0 | [feat] 위시리스트 담기 - ## Description
>> 위시리스트에 에셋을 담는 기능
## Tasks
- [x] 사용자의 id와 조회를 요청한 id가 같은지 확인
- [x] 에셋 id로 에셋 조회
- [x] 유저와 에셋을 담아 wishListRepository에 save
- [x] Controller Test
- [x] Service Test
| test | 위시리스트 담기 description 위시리스트에 에셋을 담는 기능 tasks 사용자의 id와 조회를 요청한 id가 같은지 확인 에셋 id로 에셋 조회 유저와 에셋을 담아 wishlistrepository에 save controller test service test | 1 |
97,585 | 8,663,044,549 | IssuesEvent | 2018-11-28 16:23:42 | gitcoinco/web | https://api.github.com/repos/gitcoinco/web | opened | Fix failing tests | Tests backend bug will tip for turnaround | The CI/CD pipeline is currently kaput due to failing test cases in `master`.
## Fix relevant tests
- `TestAssembleLeaderboards.test_command_handle`
- `TestExpirationTip.test_handle`
## Failure Output
### TestAssembleLeaderboards.test_command_handle
```shell
_________________ TestAssembleLeaderboards.test_command_handle _________________
self = <test_assemble_leaderboards.TestAssembleLeaderboards testMethod=test_command_handle>
def test_command_handle(self):
"""Test command assemble leaderboards."""
Command().handle()
> assert LeaderboardRank.objects.all().count() == 255
E AssertionError: assert 225 == 255
E + where 225 = <bound method QuerySetMixin.count of <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <Lea...rdRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']>>()
E + where <bound method QuerySetMixin.count of <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <Lea...rdRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']>> = <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <LeaderboardRank: all_fulfilled, gitcoinc...ardRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']>.count
E + where <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <LeaderboardRank: all_fulfilled, gitcoinc...ardRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']> = <bound method BaseManager.all of <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80>>()
E + where <bound method BaseManager.all of <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80>> = <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80>.all
E + where <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80> = LeaderboardRank.objects
app/marketing/tests/management/commands/test_assemble_leaderboards.py:284: AssertionError
```
### TestExpirationTip.test_handle
```shell
________________________ TestExpirationTip.test_handle _________________________
self = <test_expiration_tip.TestExpirationTip testMethod=test_handle>
mock_func = <MagicMock name='tip_email' id='140510852069976'>
@patch('marketing.management.commands.expiration_tip.tip_email')
def test_handle(self, mock_func):
"""Test command expiration tip."""
tip = Tip.objects.create(
emails=['john@bar.com'],
tokenName='USDT',
amount=7,
username='john',
expires_date=timezone.now() + timedelta(days=1, hours=1),
tokenAddress='0x0000000000000000000000000000000000000000',
network='mainnet',
)
Command().handle()
> assert mock_func.call_count == 1
E AssertionError: assert 0 == 1
E + where 0 = <MagicMock name='tip_email' id='140510852069976'>.call_count
app/marketing/tests/management/commands/test_expiration_tip.py:47: AssertionError
----------------------------- Captured stdout call -----------------------------
day 1 got 0 tips
day 2 got 0 tips
``` | 1.0 | Fix failing tests - The CI/CD pipeline is currently kaput due to failing test cases in `master`.
## Fix relevant tests
- `TestAssembleLeaderboards.test_command_handle`
- `TestExpirationTip.test_handle`
## Failure Output
### TestAssembleLeaderboards.test_command_handle
```shell
_________________ TestAssembleLeaderboards.test_command_handle _________________
self = <test_assemble_leaderboards.TestAssembleLeaderboards testMethod=test_command_handle>
def test_command_handle(self):
"""Test command assemble leaderboards."""
Command().handle()
> assert LeaderboardRank.objects.all().count() == 255
E AssertionError: assert 225 == 255
E + where 225 = <bound method QuerySetMixin.count of <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <Lea...rdRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']>>()
E + where <bound method QuerySetMixin.count of <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <Lea...rdRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']>> = <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <LeaderboardRank: all_fulfilled, gitcoinc...ardRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']>.count
E + where <LeaderboardRankQuerySet [<LeaderboardRank: all_fulfilled, flintstone: 3.0>, <LeaderboardRank: all_fulfilled, gitcoinc...ardRank: all_all, USDT: 3.0>, <LeaderboardRank: all_all, Cuyahoga Falls: 3.0>, '...(remaining elements truncated)...']> = <bound method BaseManager.all of <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80>>()
E + where <bound method BaseManager.all of <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80>> = <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80>.all
E + where <django.db.models.manager.ManagerFromLeaderboardRankQuerySet object at 0x7fcb4803be80> = LeaderboardRank.objects
app/marketing/tests/management/commands/test_assemble_leaderboards.py:284: AssertionError
```
### TestExpirationTip.test_handle
```shell
________________________ TestExpirationTip.test_handle _________________________
self = <test_expiration_tip.TestExpirationTip testMethod=test_handle>
mock_func = <MagicMock name='tip_email' id='140510852069976'>
@patch('marketing.management.commands.expiration_tip.tip_email')
def test_handle(self, mock_func):
"""Test command expiration tip."""
tip = Tip.objects.create(
emails=['john@bar.com'],
tokenName='USDT',
amount=7,
username='john',
expires_date=timezone.now() + timedelta(days=1, hours=1),
tokenAddress='0x0000000000000000000000000000000000000000',
network='mainnet',
)
Command().handle()
> assert mock_func.call_count == 1
E AssertionError: assert 0 == 1
E + where 0 = <MagicMock name='tip_email' id='140510852069976'>.call_count
app/marketing/tests/management/commands/test_expiration_tip.py:47: AssertionError
----------------------------- Captured stdout call -----------------------------
day 1 got 0 tips
day 2 got 0 tips
``` | test | fix failing tests the ci cd pipeline is currently kaput due to failing test cases in master fix relevant tests testassembleleaderboards test command handle testexpirationtip test handle failure output testassembleleaderboards test command handle shell testassembleleaderboards test command handle self def test command handle self test command assemble leaderboards command handle assert leaderboardrank objects all count e assertionerror assert e where e where count e where e where all e where leaderboardrank objects app marketing tests management commands test assemble leaderboards py assertionerror testexpirationtip test handle shell testexpirationtip test handle self mock func patch marketing management commands expiration tip tip email def test handle self mock func test command expiration tip tip tip objects create emails tokenname usdt amount username john expires date timezone now timedelta days hours tokenaddress network mainnet command handle assert mock func call count e assertionerror assert e where call count app marketing tests management commands test expiration tip py assertionerror captured stdout call day got tips day got tips | 1 |
1,315 | 5,533,035,373 | IssuesEvent | 2017-03-21 12:18:37 | luyadev/luya | https://api.github.com/repos/luyadev/luya | closed | Crawler ActiveDataProvider | architecture:break_api | Search Crawler should return an ActiveDataProvider instead of ActiveRecord Iterator. | 1.0 | Crawler ActiveDataProvider - Search Crawler should return an ActiveDataProvider instead of ActiveRecord Iterator. | non_test | crawler activedataprovider search crawler should return an activedataprovider instead of activerecord iterator | 0 |
235,367 | 19,341,443,728 | IssuesEvent | 2021-12-15 05:22:09 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | Calling test/quantization/test_quantized_op.py directly doesn't do anything | oncall: quantization module: tests triaged | Invoking test files directly should result in unittest runner being invoked
cc @mruberry @VitalyFedyunin @walterddr @jerryzh168 @jianyuh @dzhulgakov @raghuramank100 @jamesr66a @vkuzo | 1.0 | Calling test/quantization/test_quantized_op.py directly doesn't do anything - Invoking test files directly should result in unittest runner being invoked
cc @mruberry @VitalyFedyunin @walterddr @jerryzh168 @jianyuh @dzhulgakov @raghuramank100 @jamesr66a @vkuzo | test | calling test quantization test quantized op py directly doesn t do anything invoking test files directly should result in unittest runner being invoked cc mruberry vitalyfedyunin walterddr jianyuh dzhulgakov vkuzo | 1 |
202,661 | 15,294,504,546 | IssuesEvent | 2021-02-24 02:38:08 | IntellectualSites/FastAsyncWorldEdit | https://api.github.com/repos/IntellectualSites/FastAsyncWorldEdit | opened | Block Rollback Broken | Requires Testing | <!-- ⚠️⚠️ Do Not Delete This! You must follow this template. ⚠️⚠️ -->
<!--- Incomplete reports will be marked as invalid, and closed, with few exceptions.-->
<!--- If you are using 1.14 or 1.15 consider updating to 1.16.5 before raising an issue -->
<!--- The priority lays on 1.16 right now, so issues reported for or 1.15 will be fixed for the 1.16 versions -->
**[REQUIRED] FastAsyncWorldEdit Configuration Files**
<!--- Issue /fawe debugpaste in game or in your console and copy the supplied URL here -->
<!--- If you are unwilling to supply the information we need, we reserve the right to not assist you. Redact IP addresses if you need to. -->
**/fawe debugpaste**: https://athion.net/ISPaster/paste/view/008e841f796d45c79001de214ac45e5c
**Required Information**
- FAWE Version Number (`/version FastAsyncWorldEdit`): 1.16-610;bc686a6
- Spigot/Paper Version Number (`/version`): [02:37:02 INFO]: This server is running Tuinity version git-Tuinity-"1d169e7" (MC: 1.16.5) (Implementing API version 1.16.5-R0.1-SNAPSHOT)
- Minecraft Version: [e.g. 1.16.5] 1.16.5
**Describe the bug**
Block data does not restore
**To Reproduce**
Steps to reproduce the behavior:
1. Do a //sphere on an area
2. //undo it
3. Blocks lose their block entity data, even if they are in the history NBT files.
**Plugins being used on the server**
<!--- Optional but recommended - issue "/plugins" in-game or in console and copy/paste the list -->
**Checklist**:
<!--- Make sure you've completed the following steps (put an "X" between of brackets): -->
- [x] I included all information required in the sections above
- [x] I made sure there are no duplicates of this report [(Use Search)](https://github.com/IntellectualSites/FastAsyncWorldEdit/issues?q=is%3Aissue)
- [x] I made sure I am using an up-to-date version of [FastAsyncWorldEdit for 1.16.5](https://ci.athion.net/job/FastAsyncWorldEdit-1.16/)
- [x] I made sure the bug/error is not caused by any other plugin
| 1.0 | Block Rollback Broken - <!-- ⚠️⚠️ Do Not Delete This! You must follow this template. ⚠️⚠️ -->
<!--- Incomplete reports will be marked as invalid, and closed, with few exceptions.-->
<!--- If you are using 1.14 or 1.15 consider updating to 1.16.5 before raising an issue -->
<!--- The priority lays on 1.16 right now, so issues reported for or 1.15 will be fixed for the 1.16 versions -->
**[REQUIRED] FastAsyncWorldEdit Configuration Files**
<!--- Issue /fawe debugpaste in game or in your console and copy the supplied URL here -->
<!--- If you are unwilling to supply the information we need, we reserve the right to not assist you. Redact IP addresses if you need to. -->
**/fawe debugpaste**: https://athion.net/ISPaster/paste/view/008e841f796d45c79001de214ac45e5c
**Required Information**
- FAWE Version Number (`/version FastAsyncWorldEdit`): 1.16-610;bc686a6
- Spigot/Paper Version Number (`/version`): [02:37:02 INFO]: This server is running Tuinity version git-Tuinity-"1d169e7" (MC: 1.16.5) (Implementing API version 1.16.5-R0.1-SNAPSHOT)
- Minecraft Version: [e.g. 1.16.5] 1.16.5
**Describe the bug**
Block data does not restore
**To Reproduce**
Steps to reproduce the behavior:
1. Do a //sphere on an area
2. //undo it
3. Blocks lose their block entity data, even if they are in the history NBT files.
**Plugins being used on the server**
<!--- Optional but recommended - issue "/plugins" in-game or in console and copy/paste the list -->
**Checklist**:
<!--- Make sure you've completed the following steps (put an "X" between of brackets): -->
- [x] I included all information required in the sections above
- [x] I made sure there are no duplicates of this report [(Use Search)](https://github.com/IntellectualSites/FastAsyncWorldEdit/issues?q=is%3Aissue)
- [x] I made sure I am using an up-to-date version of [FastAsyncWorldEdit for 1.16.5](https://ci.athion.net/job/FastAsyncWorldEdit-1.16/)
- [x] I made sure the bug/error is not caused by any other plugin
| test | block rollback broken fastasyncworldedit configuration files fawe debugpaste required information fawe version number version fastasyncworldedit spigot paper version number version this server is running tuinity version git tuinity mc implementing api version snapshot minecraft version describe the bug block data does not restore to reproduce steps to reproduce the behavior do a sphere on an area undo it blocks lose their block entity data even if they are in the history nbt files plugins being used on the server checklist i included all information required in the sections above i made sure there are no duplicates of this report i made sure i am using an up to date version of i made sure the bug error is not caused by any other plugin | 1 |
414,024 | 27,976,213,167 | IssuesEvent | 2023-03-25 16:09:44 | Skeptick/libres | https://api.github.com/repos/Skeptick/libres | closed | Add Chapter about LibresSettings (changing Locale dynamic) in README | documentation enhancement | Now we must research the source code, to know how to change Language dynamics. Please, add a section in README (or attach link, where to search). | 1.0 | Add Chapter about LibresSettings (changing Locale dynamic) in README - Now we must research the source code, to know how to change Language dynamics. Please, add a section in README (or attach link, where to search). | non_test | add chapter about libressettings changing locale dynamic in readme now we must research the source code to know how to change language dynamics please add a section in readme or attach link where to search | 0 |
68,181 | 7,088,761,112 | IssuesEvent | 2018-01-11 22:47:46 | rancher/rancher | https://api.github.com/repos/rancher/rancher | closed | Search on Node list page does not include Name and includes ID | area/host area/ui kind/bug status/resolved status/to-test version/2.0 | **Rancher versions:** 2.0 master 12/28
**Steps to Reproduce:**
1. Add nodes
2. Edit the nodes and put a name in them
3. Search on the name
4. Now search on the ID (which isn't showing in the UI) of one of the nodes
**Results:** The search is not looking for Name and if you search on ID of a node it shows up.
| 1.0 | Search on Node list page does not include Name and includes ID - **Rancher versions:** 2.0 master 12/28
**Steps to Reproduce:**
1. Add nodes
2. Edit the nodes and put a name in them
3. Search on the name
4. Now search on the ID (which isn't showing in the UI) of one of the nodes
**Results:** The search is not looking for Name and if you search on ID of a node it shows up.
| test | search on node list page does not include name and includes id rancher versions master steps to reproduce add nodes edit the nodes and put a name in them search on the name now search on the id which isn t showing in the ui of one of the nodes results the search is not looking for name and if you search on id of a node it shows up | 1 |
114,639 | 9,745,574,247 | IssuesEvent | 2019-06-03 09:57:00 | hazelcast/hazelcast-jet | https://api.github.com/repos/hazelcast/hazelcast-jet | closed | `GroupAggregateBuilder` is missing code coverage | pipeline-api test-coverage | `BatchStageWithKey.aggregateBuilder(@Nonnull AggregateOperation1<? super T, ?, ? extends R0> aggrOp0)` is not tested | 1.0 | `GroupAggregateBuilder` is missing code coverage - `BatchStageWithKey.aggregateBuilder(@Nonnull AggregateOperation1<? super T, ?, ? extends R0> aggrOp0)` is not tested | test | groupaggregatebuilder is missing code coverage batchstagewithkey aggregatebuilder nonnull is not tested | 1 |
88,890 | 8,180,063,728 | IssuesEvent | 2018-08-28 18:17:34 | metafizzy/infinite-scroll | https://api.github.com/repos/metafizzy/infinite-scroll | closed | IE: WrongDocumentError | test case required | Hi there,
I cannot provide a CodePen example as this error for some reason doesn't appear in that demo but it occurs in my application though. I am just going to explain what happens in detail, present my solution and let you decide for yourself what to do with that particular information.
This problem does only occur in Internet Explorer (not Edge), I am "using" version 11.48.17134.0.
Just like in your [CodePen example](https://codepen.io/desandro/pen/WOjqNM) I initialize InfiniteScroll and when the first page gets loaded the plugin trys to append the new items to the existing DOM. Therefore it appends all items to a [`fragment`](https://developer.mozilla.org/de/docs/Web/API/DocumentFragment). This is where I get the [`WrongDocumentError`](https://developer.mozilla.org/de/docs/Web/API/DOMError) error in my application using IE 11. I included to [un-minified version](https://unpkg.com/infinite-scroll@3/dist/infinite-scroll.pkgd.js) of the plugin and the error is located in the following function:
```javascript {.line-numbers}
function getItemsFragment( items ) {
// add items to fragment
var fragment = document.createDocumentFragment();
for ( var i=0; items && i < items.length; i++ ) {
fragment.appendChild( items[i] );
}
return fragment;
}
```
It happens when the first item is supposed to get appended to the `fragment`. I don't know why that happens in my application but won't happen in the demo. I could solve the problem though by altering the code as follows (found final hint [here](https://stackoverflow.com/questions/1759137/domelement-cloning-and-appending-wrong-document-error)):
```javascript {.line-numbers}
function getItemsFragment( items ) {
// add items to fragment
var fragment = document.createDocumentFragment();
for ( var i=0; items && i < items.length; i++ ) {
var newNode = document.importNode(items[i], true);
fragment.appendChild( newNode );
}
return fragment;
}
```
Did anyone ever encounter that problem as well? | 1.0 | IE: WrongDocumentError - Hi there,
I cannot provide a CodePen example as this error for some reason doesn't appear in that demo but it occurs in my application though. I am just going to explain what happens in detail, present my solution and let you decide for yourself what to do with that particular information.
This problem does only occur in Internet Explorer (not Edge), I am "using" version 11.48.17134.0.
Just like in your [CodePen example](https://codepen.io/desandro/pen/WOjqNM) I initialize InfiniteScroll and when the first page gets loaded the plugin trys to append the new items to the existing DOM. Therefore it appends all items to a [`fragment`](https://developer.mozilla.org/de/docs/Web/API/DocumentFragment). This is where I get the [`WrongDocumentError`](https://developer.mozilla.org/de/docs/Web/API/DOMError) error in my application using IE 11. I included to [un-minified version](https://unpkg.com/infinite-scroll@3/dist/infinite-scroll.pkgd.js) of the plugin and the error is located in the following function:
```javascript {.line-numbers}
function getItemsFragment( items ) {
// add items to fragment
var fragment = document.createDocumentFragment();
for ( var i=0; items && i < items.length; i++ ) {
fragment.appendChild( items[i] );
}
return fragment;
}
```
It happens when the first item is supposed to get appended to the `fragment`. I don't know why that happens in my application but won't happen in the demo. I could solve the problem though by altering the code as follows (found final hint [here](https://stackoverflow.com/questions/1759137/domelement-cloning-and-appending-wrong-document-error)):
```javascript {.line-numbers}
function getItemsFragment( items ) {
// add items to fragment
var fragment = document.createDocumentFragment();
for ( var i=0; items && i < items.length; i++ ) {
var newNode = document.importNode(items[i], true);
fragment.appendChild( newNode );
}
return fragment;
}
```
Did anyone ever encounter that problem as well? | test | ie wrongdocumenterror hi there i cannot provide a codepen example as this error for some reason doesn t appear in that demo but it occurs in my application though i am just going to explain what happens in detail present my solution and let you decide for yourself what to do with that particular information this problem does only occur in internet explorer not edge i am using version just like in your i initialize infinitescroll and when the first page gets loaded the plugin trys to append the new items to the existing dom therefore it appends all items to a this is where i get the error in my application using ie i included to of the plugin and the error is located in the following function javascript line numbers function getitemsfragment items add items to fragment var fragment document createdocumentfragment for var i items i items length i fragment appendchild items return fragment it happens when the first item is supposed to get appended to the fragment i don t know why that happens in my application but won t happen in the demo i could solve the problem though by altering the code as follows found final hint javascript line numbers function getitemsfragment items add items to fragment var fragment document createdocumentfragment for var i items i items length i var newnode document importnode items true fragment appendchild newnode return fragment did anyone ever encounter that problem as well | 1 |
133,700 | 5,206,997,687 | IssuesEvent | 2017-01-24 22:10:43 | The-Compiler/qutebrowser | https://api.github.com/repos/The-Compiler/qutebrowser | closed | Segfaults when opening second instance | bug priority: 0 - high | This is rather hard to reproduce and probably even harder to fix... :unamused:
It seems sometimes the second instance (IPC client) segfaults on quit - which isn't immediately apparent, but spams the user's journal with coredumps, which isn't nice...
Seems to mostly happen on Archlinux.
| 1.0 | Segfaults when opening second instance - This is rather hard to reproduce and probably even harder to fix... :unamused:
It seems sometimes the second instance (IPC client) segfaults on quit - which isn't immediately apparent, but spams the user's journal with coredumps, which isn't nice...
Seems to mostly happen on Archlinux.
| non_test | segfaults when opening second instance this is rather hard to reproduce and probably even harder to fix unamused it seems sometimes the second instance ipc client segfaults on quit which isn t immediately apparent but spams the user s journal with coredumps which isn t nice seems to mostly happen on archlinux | 0 |
255,462 | 19,303,737,973 | IssuesEvent | 2021-12-13 09:19:13 | Azure/data-landing-zone | https://api.github.com/repos/Azure/data-landing-zone | closed | Name Change | documentation backlog | Please change all instances of "Enterprise-scale analytics and ai" to "Data Management and Analytics Scenario" to align to marketing ask. This should happen for one-clicks and all documentation. | 1.0 | Name Change - Please change all instances of "Enterprise-scale analytics and ai" to "Data Management and Analytics Scenario" to align to marketing ask. This should happen for one-clicks and all documentation. | non_test | name change please change all instances of enterprise scale analytics and ai to data management and analytics scenario to align to marketing ask this should happen for one clicks and all documentation | 0 |
484,632 | 13,943,070,723 | IssuesEvent | 2020-10-22 22:14:23 | octobercms/october | https://api.github.com/repos/octobercms/october | closed | Don't redownload existing plugins when attaching a project ID to an instance of October | Priority: Medium Status: Accepted Type: Enhancement | Current behaviour:
- When you attach a project ID to an October instance that already has plugins in it, and those plugins are also available on the marketplace, the updating system will automatically attach all of those plugins to the marketplace project and then redownload them, overwriting the files that already exist in the instance.
This is a massive pain for two reasons:
1. You could be using your own marketplace plugin in an instance and making changes to it that you plan on committing to the main plugin repo once the project is finished, but when you go to attach your project ID, suddenly all of your changes are overwritten by the marketplace version.
2. You load plugins that are available through the marketplace and composer through composer instead of the marketplace, and then when you attach the project to get your marketplace-only plugins the composer versions are overwritten with the marketplace versions, which is an undesirable outcome.
Solutions:
- Do not overwrite existing files when attaching an October instance to a project ID
- Ask for user confirmation before adding plugins detected in the current instance to the marketplace project ID | 1.0 | Don't redownload existing plugins when attaching a project ID to an instance of October - Current behaviour:
- When you attach a project ID to an October instance that already has plugins in it, and those plugins are also available on the marketplace, the updating system will automatically attach all of those plugins to the marketplace project and then redownload them, overwriting the files that already exist in the instance.
This is a massive pain for two reasons:
1. You could be using your own marketplace plugin in an instance and making changes to it that you plan on committing to the main plugin repo once the project is finished, but when you go to attach your project ID, suddenly all of your changes are overwritten by the marketplace version.
2. You load plugins that are available through the marketplace and composer through composer instead of the marketplace, and then when you attach the project to get your marketplace-only plugins the composer versions are overwritten with the marketplace versions, which is an undesirable outcome.
Solutions:
- Do not overwrite existing files when attaching an October instance to a project ID
- Ask for user confirmation before adding plugins detected in the current instance to the marketplace project ID | non_test | don t redownload existing plugins when attaching a project id to an instance of october current behaviour when you attach a project id to an october instance that already has plugins in it and those plugins are also available on the marketplace the updating system will automatically attach all of those plugins to the marketplace project and then redownload them overwriting the files that already exist in the instance this is a massive pain for two reasons you could be using your own marketplace plugin in an instance and making changes to it that you plan on committing to the main plugin repo once the project is finished but when you go to attach your project id suddenly all of your changes are overwritten by the marketplace version you load plugins that are available through the marketplace and composer through composer instead of the marketplace and then when you attach the project to get your marketplace only plugins the composer versions are overwritten with the marketplace versions which is an undesirable outcome solutions do not overwrite existing files when attaching an october instance to a project id ask for user confirmation before adding plugins detected in the current instance to the marketplace project id | 0 |
37,104 | 15,170,552,224 | IssuesEvent | 2021-02-12 23:35:29 | BCDevOps/OpenShift4-RollOut | https://api.github.com/repos/BCDevOps/OpenShift4-RollOut | closed | Installation of Aporeto on CLAB | Blocked env/lab site/calgary team/DXC team/bcgov-platform-services tech/networking | **Describe the issue**
Aporeto is required to be installed on CLAB with all enforcement policies verified.
**Which Sprint Goal is this issue related to?**
**Additional context**
**Definition of done Checklist (where applicable)**
- [x] Aporeto installed
- [x] Aporeto Operator installed
- [x] All tests passed (specify what kind of testing is done) *Detail to be added for tests/validation required*
| 1.0 | Installation of Aporeto on CLAB - **Describe the issue**
Aporeto is required to be installed on CLAB with all enforcement policies verified.
**Which Sprint Goal is this issue related to?**
**Additional context**
**Definition of done Checklist (where applicable)**
- [x] Aporeto installed
- [x] Aporeto Operator installed
- [x] All tests passed (specify what kind of testing is done) *Detail to be added for tests/validation required*
| non_test | installation of aporeto on clab describe the issue aporeto is required to be installed on clab with all enforcement policies verified which sprint goal is this issue related to additional context definition of done checklist where applicable aporeto installed aporeto operator installed all tests passed specify what kind of testing is done detail to be added for tests validation required | 0 |
70,415 | 13,463,804,473 | IssuesEvent | 2020-09-09 18:11:41 | dotnet/interactive | https://api.github.com/repos/dotnet/interactive | opened | Changing cell type doesn't work | Area-VS Code Extension Impact-High bug | If you create a cell in one language, then use the language switcher to choose a different language, the submission is still treated as the original language.

| 1.0 | Changing cell type doesn't work - If you create a cell in one language, then use the language switcher to choose a different language, the submission is still treated as the original language.

| non_test | changing cell type doesn t work if you create a cell in one language then use the language switcher to choose a different language the submission is still treated as the original language | 0 |
268,918 | 23,404,236,340 | IssuesEvent | 2022-08-12 11:08:15 | harvester/harvester | https://api.github.com/repos/harvester/harvester | closed | [BUG]Polish harvester machine config | bug area/ui severity/2 reproduce/always not-require/test-plan | **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
https://github.com/harvester/dashboard/pull/391#pullrequestreview-1055169778
1. Namespace options of pod affinity should be in harvester cluster.
<img width="1673" alt="image" src="https://user-images.githubusercontent.com/24985926/181735326-c1562fc6-dd90-44ba-bae3-09fc572a9bb9.png">
2. If is a imported cluster, the namespaces field should be selectable.
4. The namespace is not updated when editing.
**To Reproduce**
Steps to reproduce the behavior:
#### Aspect of namespace options(_Both of RKE1 and RKE2_)
1. Go to create Harvester cluster
3. Add pod affinity
4. Options for namespaces are affiliated in management cluster
#### Aspect of the namespace field(_Both of RKE1 and RKE2_)
1. Go to create Harvester cluster
2. The Namespace filed of pod affinity is only inputable if the cluster is imported and the user logged in only has local owner role.
#### Aspect of namespace field updating
1. Go to create Harvester cluster
2. Add pod affinity with namespaces
3. Edit the cluster config is just created
5. Modify the namespaces of pod affinity
6. The namespaces of pod affinity cannot update.
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
#### Aspect of namespace options
The options for namespaces should belong to harvester cluster.
#### Aspect of the namespace field
The namespace field should be selectable if the cluster is imported.
#### Aspect of namespace field updating
The namespace filed can update as expected.
**Support bundle**
<!--
You can generate a support bundle in the bottom of Harvester UI (https://docs.harvesterhci.io/v1.0/troubleshooting/harvester/#generate-a-support-bundle). It includes logs and configurations that help diagnose the issue.
Tokens, passwords, and secrets are automatically removed from support bundles. If you feel it's not appropriate to share the bundle files publicly, please consider:
- Wait for a developer to reach you and provide the bundle file by any secure methods.
- Join our Slack community (https://rancher-users.slack.com/archives/C01GKHKAG0K) to provide the bundle.
- Send the bundle to harvester-support-bundle@suse.com with the correct issue ID. -->
**Environment**
- Harvester ISO version:
- Underlying Infrastructure (e.g. Baremetal with Dell PowerEdge R630):
**Additional context**
Add any other context about the problem here.
| 1.0 | [BUG]Polish harvester machine config - **Describe the bug**
<!-- A clear and concise description of what the bug is. -->
https://github.com/harvester/dashboard/pull/391#pullrequestreview-1055169778
1. Namespace options of pod affinity should be in harvester cluster.
<img width="1673" alt="image" src="https://user-images.githubusercontent.com/24985926/181735326-c1562fc6-dd90-44ba-bae3-09fc572a9bb9.png">
2. If is a imported cluster, the namespaces field should be selectable.
4. The namespace is not updated when editing.
**To Reproduce**
Steps to reproduce the behavior:
#### Aspect of namespace options(_Both of RKE1 and RKE2_)
1. Go to create Harvester cluster
3. Add pod affinity
4. Options for namespaces are affiliated in management cluster
#### Aspect of the namespace field(_Both of RKE1 and RKE2_)
1. Go to create Harvester cluster
2. The Namespace filed of pod affinity is only inputable if the cluster is imported and the user logged in only has local owner role.
#### Aspect of namespace field updating
1. Go to create Harvester cluster
2. Add pod affinity with namespaces
3. Edit the cluster config is just created
5. Modify the namespaces of pod affinity
6. The namespaces of pod affinity cannot update.
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
#### Aspect of namespace options
The options for namespaces should belong to harvester cluster.
#### Aspect of the namespace field
The namespace field should be selectable if the cluster is imported.
#### Aspect of namespace field updating
The namespace filed can update as expected.
**Support bundle**
<!--
You can generate a support bundle in the bottom of Harvester UI (https://docs.harvesterhci.io/v1.0/troubleshooting/harvester/#generate-a-support-bundle). It includes logs and configurations that help diagnose the issue.
Tokens, passwords, and secrets are automatically removed from support bundles. If you feel it's not appropriate to share the bundle files publicly, please consider:
- Wait for a developer to reach you and provide the bundle file by any secure methods.
- Join our Slack community (https://rancher-users.slack.com/archives/C01GKHKAG0K) to provide the bundle.
- Send the bundle to harvester-support-bundle@suse.com with the correct issue ID. -->
**Environment**
- Harvester ISO version:
- Underlying Infrastructure (e.g. Baremetal with Dell PowerEdge R630):
**Additional context**
Add any other context about the problem here.
| test | polish harvester machine config describe the bug namespace options of pod affinity should be in harvester cluster img width alt image src if is a imported cluster the namespaces field should be selectable the namespace is not updated when editing to reproduce steps to reproduce the behavior aspect of namespace options both of and go to create harvester cluster add pod affinity options for namespaces are affiliated in management cluster aspect of the namespace field both of and go to create harvester cluster the namespace filed of pod affinity is only inputable if the cluster is imported and the user logged in only has local owner role aspect of namespace field updating go to create harvester cluster add pod affinity with namespaces edit the cluster config is just created modify the namespaces of pod affinity the namespaces of pod affinity cannot update expected behavior aspect of namespace options the options for namespaces should belong to harvester cluster aspect of the namespace field the namespace field should be selectable if the cluster is imported aspect of namespace field updating the namespace filed can update as expected support bundle you can generate a support bundle in the bottom of harvester ui it includes logs and configurations that help diagnose the issue tokens passwords and secrets are automatically removed from support bundles if you feel it s not appropriate to share the bundle files publicly please consider wait for a developer to reach you and provide the bundle file by any secure methods join our slack community to provide the bundle send the bundle to harvester support bundle suse com with the correct issue id environment harvester iso version underlying infrastructure e g baremetal with dell poweredge additional context add any other context about the problem here | 1 |
175,386 | 21,301,003,094 | IssuesEvent | 2022-04-15 03:05:25 | Thezone1975/send | https://api.github.com/repos/Thezone1975/send | opened | CVE-2022-1243 (Medium) detected in urijs-1.19.1.tgz | security vulnerability | ## CVE-2022-1243 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>urijs-1.19.1.tgz</b></p></summary>
<p>URI.js is a Javascript library for working with URLs.</p>
<p>Library home page: <a href="https://registry.npmjs.org/urijs/-/urijs-1.19.1.tgz">https://registry.npmjs.org/urijs/-/urijs-1.19.1.tgz</a></p>
<p>Path to dependency file: /send/package.json</p>
<p>Path to vulnerable library: /node_modules/urijs/package.json</p>
<p>
Dependency Hierarchy:
- selenium-standalone-6.16.0.tgz (Root Library)
- :x: **urijs-1.19.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
CRHTLF can lead to invalid protocol extraction potentially leading to XSS in GitHub repository medialize/uri.js prior to 1.19.11.
<p>Publish Date: 2022-04-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1243>CVE-2022-1243</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/8c5afc47-1553-4eba-a98e-024e4cc3dfb7/">https://huntr.dev/bounties/8c5afc47-1553-4eba-a98e-024e4cc3dfb7/</a></p>
<p>Release Date: 2022-04-05</p>
<p>Fix Resolution (urijs): 1.19.11</p>
<p>Direct dependency fix Resolution (selenium-standalone): 6.17.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-1243 (Medium) detected in urijs-1.19.1.tgz - ## CVE-2022-1243 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>urijs-1.19.1.tgz</b></p></summary>
<p>URI.js is a Javascript library for working with URLs.</p>
<p>Library home page: <a href="https://registry.npmjs.org/urijs/-/urijs-1.19.1.tgz">https://registry.npmjs.org/urijs/-/urijs-1.19.1.tgz</a></p>
<p>Path to dependency file: /send/package.json</p>
<p>Path to vulnerable library: /node_modules/urijs/package.json</p>
<p>
Dependency Hierarchy:
- selenium-standalone-6.16.0.tgz (Root Library)
- :x: **urijs-1.19.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
CRHTLF can lead to invalid protocol extraction potentially leading to XSS in GitHub repository medialize/uri.js prior to 1.19.11.
<p>Publish Date: 2022-04-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1243>CVE-2022-1243</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/8c5afc47-1553-4eba-a98e-024e4cc3dfb7/">https://huntr.dev/bounties/8c5afc47-1553-4eba-a98e-024e4cc3dfb7/</a></p>
<p>Release Date: 2022-04-05</p>
<p>Fix Resolution (urijs): 1.19.11</p>
<p>Direct dependency fix Resolution (selenium-standalone): 6.17.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in urijs tgz cve medium severity vulnerability vulnerable library urijs tgz uri js is a javascript library for working with urls library home page a href path to dependency file send package json path to vulnerable library node modules urijs package json dependency hierarchy selenium standalone tgz root library x urijs tgz vulnerable library vulnerability details crhtlf can lead to invalid protocol extraction potentially leading to xss in github repository medialize uri js prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution urijs direct dependency fix resolution selenium standalone step up your open source security game with whitesource | 0 |
273,153 | 23,732,893,587 | IssuesEvent | 2022-08-31 04:37:17 | stores-cedcommerce/Lameka-Home-Page-Design | https://api.github.com/repos/stores-cedcommerce/Lameka-Home-Page-Design | closed | The chatbot is missing in the lameka. | Desktop Ready to test fixed homepage | **Actual result:**
The chatbot is missing in the lameka.
**Expectedresult:**
These are free app, we can use, it will be much better. | 1.0 | The chatbot is missing in the lameka. - **Actual result:**
The chatbot is missing in the lameka.
**Expectedresult:**
These are free app, we can use, it will be much better. | test | the chatbot is missing in the lameka actual result the chatbot is missing in the lameka expectedresult these are free app we can use it will be much better | 1 |
90,137 | 15,856,079,977 | IssuesEvent | 2021-04-08 01:28:19 | rgordon95/ecommerce-react-redux-saga-demo | https://api.github.com/repos/rgordon95/ecommerce-react-redux-saga-demo | opened | CVE-2019-19919 (High) detected in handlebars-4.0.10.tgz | security vulnerability | ## CVE-2019-19919 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.10.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.10.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.10.tgz</a></p>
<p>Path to dependency file: /ecommerce-react-redux-saga-demo/redux-saga-cart/package.json</p>
<p>Path to vulnerable library: ecommerce-react-redux-saga-demo/redux-saga-cart/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-20.0.4.tgz (Root Library)
- jest-cli-20.0.4.tgz
- istanbul-api-1.1.10.tgz
- istanbul-reports-1.1.1.tgz
- :x: **handlebars-4.0.10.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object's __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19919>CVE-2019-19919</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1164">https://www.npmjs.com/advisories/1164</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: 4.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19919 (High) detected in handlebars-4.0.10.tgz - ## CVE-2019-19919 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.0.10.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.0.10.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.0.10.tgz</a></p>
<p>Path to dependency file: /ecommerce-react-redux-saga-demo/redux-saga-cart/package.json</p>
<p>Path to vulnerable library: ecommerce-react-redux-saga-demo/redux-saga-cart/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- jest-20.0.4.tgz (Root Library)
- jest-cli-20.0.4.tgz
- istanbul-api-1.1.10.tgz
- istanbul-reports-1.1.1.tgz
- :x: **handlebars-4.0.10.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object's __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19919>CVE-2019-19919</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1164">https://www.npmjs.com/advisories/1164</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: 4.3.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in handlebars tgz cve high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file ecommerce react redux saga demo redux saga cart package json path to vulnerable library ecommerce react redux saga demo redux saga cart node modules handlebars package json dependency hierarchy jest tgz root library jest cli tgz istanbul api tgz istanbul reports tgz x handlebars tgz vulnerable library vulnerability details versions of handlebars prior to are vulnerable to prototype pollution leading to remote code execution templates may alter an object s proto and definegetter properties which may allow an attacker to execute arbitrary code through crafted payloads publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
653,851 | 21,628,552,771 | IssuesEvent | 2022-05-05 07:09:56 | ppy/osu-framework | https://api.github.com/repos/ppy/osu-framework | opened | `ScrollContainer.ScrollIntoView` does not handle non-loaded drawable targets | area:UI type:reliability priority:1 | Raised in https://github.com/ppy/osu/pull/18090#issuecomment-1117218050 with brief explanation and discussion in https://github.com/ppy/osu/pull/18090#issuecomment-1118136311.
In summary, `ScrollContainer` cannot compute the bounds of a non-loaded target, as it doesn't have a parent yet to inherit from its `DrawInfo` (even then, it needs to be laid out in the flow properly before it can be scrolled to).
This could be solved by scheduling the operation to happen after the drawable is loaded as in https://github.com/ppy/osu/pull/18090#issuecomment-1118186680, but a better approach may be to store the next target to a field until the operation can be achieved, as mentioned in https://github.com/ppy/osu/pull/18090#issuecomment-1118193621. | 1.0 | `ScrollContainer.ScrollIntoView` does not handle non-loaded drawable targets - Raised in https://github.com/ppy/osu/pull/18090#issuecomment-1117218050 with brief explanation and discussion in https://github.com/ppy/osu/pull/18090#issuecomment-1118136311.
In summary, `ScrollContainer` cannot compute the bounds of a non-loaded target, as it doesn't have a parent yet to inherit from its `DrawInfo` (even then, it needs to be laid out in the flow properly before it can be scrolled to).
This could be solved by scheduling the operation to happen after the drawable is loaded as in https://github.com/ppy/osu/pull/18090#issuecomment-1118186680, but a better approach may be to store the next target to a field until the operation can be achieved, as mentioned in https://github.com/ppy/osu/pull/18090#issuecomment-1118193621. | non_test | scrollcontainer scrollintoview does not handle non loaded drawable targets raised in with brief explanation and discussion in in summary scrollcontainer cannot compute the bounds of a non loaded target as it doesn t have a parent yet to inherit from its drawinfo even then it needs to be laid out in the flow properly before it can be scrolled to this could be solved by scheduling the operation to happen after the drawable is loaded as in but a better approach may be to store the next target to a field until the operation can be achieved as mentioned in | 0 |
17,986 | 10,864,964,093 | IssuesEvent | 2019-11-14 17:57:19 | cityofaustin/atd-vz-data | https://api.github.com/repos/cityofaustin/atd-vz-data | closed | VZE: Bug: Location page breaks when there is no Comprehensive cost data | Impact: 2-Major Project: Vision Zero Crash Data System Service: Dev Type: Bug Report Workgroup: VZ | I think I unintentionally found a bug in VZE, it is present in all environments (production, staging, local):
https://visionzero.austin.gov/editor/#/locations/5553142
https://visionzero-staging.austinmobility.io/editor/#/locations/5553142
https://localhost:3000/#/locations/5553142 (edited)
 | 1.0 | VZE: Bug: Location page breaks when there is no Comprehensive cost data - I think I unintentionally found a bug in VZE, it is present in all environments (production, staging, local):
https://visionzero.austin.gov/editor/#/locations/5553142
https://visionzero-staging.austinmobility.io/editor/#/locations/5553142
https://localhost:3000/#/locations/5553142 (edited)
 | non_test | vze bug location page breaks when there is no comprehensive cost data i think i unintentionally found a bug in vze it is present in all environments production staging local edited | 0 |
319,525 | 23,776,755,639 | IssuesEvent | 2022-09-01 21:52:19 | pyvista/pyvista | https://api.github.com/repos/pyvista/pyvista | opened | Some docs pages seem misaligned | bug documentation | In the devdocs I came across the docs of [`PolyData.is_manifold`](https://dev.pyvista.org/api/core/_autosummary/pyvista.PolyData.is_manifold.html?highlight=is_manifold#pyvista.PolyData.is_manifold). The page looks like this right now:
Note the huge gap above the API doc section. I thought this was related to this being a property, but e.g. [`PolyData.is_all_triangles`](https://dev.pyvista.org/api/core/_autosummary/pyvista.PolyData.is_all_triangles.html) doesn't have the same bug.
And I assume this is related to the super fancy new docs layout, presumably due to the recently bumped `pydata-sphinx-theme`:
| 1.0 | Some docs pages seem misaligned - In the devdocs I came across the docs of [`PolyData.is_manifold`](https://dev.pyvista.org/api/core/_autosummary/pyvista.PolyData.is_manifold.html?highlight=is_manifold#pyvista.PolyData.is_manifold). The page looks like this right now:
Note the huge gap above the API doc section. I thought this was related to this being a property, but e.g. [`PolyData.is_all_triangles`](https://dev.pyvista.org/api/core/_autosummary/pyvista.PolyData.is_all_triangles.html) doesn't have the same bug.
And I assume this is related to the super fancy new docs layout, presumably due to the recently bumped `pydata-sphinx-theme`:
| non_test | some docs pages seem misaligned in the devdocs i came across the docs of the page looks like this right now note the huge gap above the api doc section i thought this was related to this being a property but e g doesn t have the same bug and i assume this is related to the super fancy new docs layout presumably due to the recently bumped pydata sphinx theme | 0 |
220,773 | 7,370,703,008 | IssuesEvent | 2018-03-13 09:23:45 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | scatter_add_ doesn't support scalar source | bug medium priority | I was looking to use `scatter_add_` to do `bincount`.
```python
import torch
a = torch.LongTensor([2, 0, 3, 3])
r = torch.LongTensor(5)
# works
r.zero_().scatter_(0, a, 1)
# 1
# 0
# 1
# 1
# 0
# [torch.LongTensor of size 5]
# scalar source doesn't work
r.zero_().scatter_add_(0, a, 1)
#Traceback (most recent call last):
# File "<stdin>", line 1, in <module>
#TypeError: scatter_add_ received an invalid combination of arguments - got (int, torch.LongTensor, int), #but expected (int dim, torch.LongTensor index, torch.LongTensor src)
# no broadcasting? but no checking for memory bounds either?
r.zero_().scatter_add_(0, a, torch.LongTensor([1]))
#1.4033e+14
# 0.0000e+00
# 1.0000e+00
# 5.4931e+18
# 0.0000e+00
# [torch.LongTensor of size 5]
# works ok
r.zero_().scatter_add_(0, a, torch.LongTensor([1]).expand_as(a))
# 1
# 0
# 1
# 2
# 0
# [torch.LongTensor of size 5]
```
at `0.4.0a0+1fdb392`
| 1.0 | scatter_add_ doesn't support scalar source - I was looking to use `scatter_add_` to do `bincount`.
```python
import torch
a = torch.LongTensor([2, 0, 3, 3])
r = torch.LongTensor(5)
# works
r.zero_().scatter_(0, a, 1)
# 1
# 0
# 1
# 1
# 0
# [torch.LongTensor of size 5]
# scalar source doesn't work
r.zero_().scatter_add_(0, a, 1)
#Traceback (most recent call last):
# File "<stdin>", line 1, in <module>
#TypeError: scatter_add_ received an invalid combination of arguments - got (int, torch.LongTensor, int), #but expected (int dim, torch.LongTensor index, torch.LongTensor src)
# no broadcasting? but no checking for memory bounds either?
r.zero_().scatter_add_(0, a, torch.LongTensor([1]))
#1.4033e+14
# 0.0000e+00
# 1.0000e+00
# 5.4931e+18
# 0.0000e+00
# [torch.LongTensor of size 5]
# works ok
r.zero_().scatter_add_(0, a, torch.LongTensor([1]).expand_as(a))
# 1
# 0
# 1
# 2
# 0
# [torch.LongTensor of size 5]
```
at `0.4.0a0+1fdb392`
| non_test | scatter add doesn t support scalar source i was looking to use scatter add to do bincount python import torch a torch longtensor r torch longtensor works r zero scatter a scalar source doesn t work r zero scatter add a traceback most recent call last file line in typeerror scatter add received an invalid combination of arguments got int torch longtensor int but expected int dim torch longtensor index torch longtensor src no broadcasting but no checking for memory bounds either r zero scatter add a torch longtensor works ok r zero scatter add a torch longtensor expand as a at | 0 |
172,350 | 13,302,971,490 | IssuesEvent | 2020-08-25 14:55:17 | ubtue/DatenProbleme | https://api.github.com/repos/ubtue/DatenProbleme | reopened | ISSN 1612-9768 | International journal of practical theology | Translator mangelhaft | Fehlerquelle: Translator New Translator Zotero_SEMI-AUTO ready for testing | **URL**
https://www.degruyter.com/view/journals/ijpt/24/1/ijpt.24.issue-1.xml
https://www.degruyter.com/view/journals/ijpt/24/1/article-p5.xml?tab_body=pdf-78589
**Ausführliche Problembeschreibung**
Im Multi-DL wird kein Translator angeboten und im Single nur "Embedded Metadata" oder "DOI". Bei letzteren beiden fehlen die Keywords und es wird nur ein Abstract von zweien übertragen.
**Offenbare Lösungen**
Translator anpassen
| 1.0 | ISSN 1612-9768 | International journal of practical theology | Translator mangelhaft - **URL**
https://www.degruyter.com/view/journals/ijpt/24/1/ijpt.24.issue-1.xml
https://www.degruyter.com/view/journals/ijpt/24/1/article-p5.xml?tab_body=pdf-78589
**Ausführliche Problembeschreibung**
Im Multi-DL wird kein Translator angeboten und im Single nur "Embedded Metadata" oder "DOI". Bei letzteren beiden fehlen die Keywords und es wird nur ein Abstract von zweien übertragen.
**Offenbare Lösungen**
Translator anpassen
| test | issn international journal of practical theology translator mangelhaft url ausführliche problembeschreibung im multi dl wird kein translator angeboten und im single nur embedded metadata oder doi bei letzteren beiden fehlen die keywords und es wird nur ein abstract von zweien übertragen offenbare lösungen translator anpassen | 1 |
79,078 | 7,695,224,922 | IssuesEvent | 2018-05-18 11:30:34 | tomato42/tlsfuzzer | https://api.github.com/repos/tomato42/tlsfuzzer | closed | TLS 1.3 zero-length alert records | good first issue help wanted new test script | # New test script idea
## What TLS message this idea relates to?
Alert
## What is the behaviour the test script should test?
send an encrypted record layer (using early data, handshake or application keys) with an empty payload but Alert ContentType, verify that it is rejected with `unexpected_message` alert
## Are there scripts that test related functionality?
not for tls1.3
## Additional information
verify that the padding requirements for records are checked by server
| 1.0 | TLS 1.3 zero-length alert records - # New test script idea
## What TLS message this idea relates to?
Alert
## What is the behaviour the test script should test?
send an encrypted record layer (using early data, handshake or application keys) with an empty payload but Alert ContentType, verify that it is rejected with `unexpected_message` alert
## Are there scripts that test related functionality?
not for tls1.3
## Additional information
verify that the padding requirements for records are checked by server
| test | tls zero length alert records new test script idea what tls message this idea relates to alert what is the behaviour the test script should test send an encrypted record layer using early data handshake or application keys with an empty payload but alert contenttype verify that it is rejected with unexpected message alert are there scripts that test related functionality not for additional information verify that the padding requirements for records are checked by server | 1 |
323,027 | 27,661,981,346 | IssuesEvent | 2023-03-12 16:23:37 | opentibiabr/canary | https://api.github.com/repos/opentibiabr/canary | closed | Bug: Getting RAW XP (file) instead of Staged EXP / Config Rates | Type: Bug Priority: High Status: Pending Test | ### Priority
High
### Area
- [X] Datapack
- [ ] Source
- [ ] Map
- [ ] Other
### What happened?
Hello everyone.
Im using the latest version of Canary. I was testing my leveling progress in the game and I noticed monsters are not giving the exp * stage OR exp * rates.
Example in Tibia Rl
Troll gives 20 points of experience, it should give 30 points of experience with green stamina.
After killing Troll, it just gives me the 100% XP (20 points) and throws this error in console
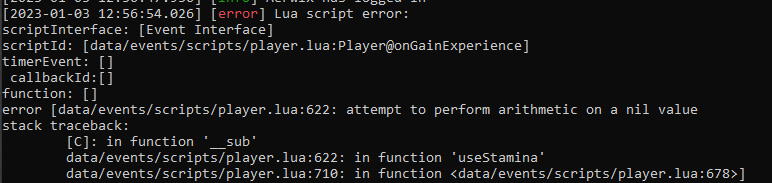
I already checked with other old forks and I found we had some changes:
Result: https://www.diffchecker.com/nI1QetUk/
_Important Note: The left side is the Original Source and the right side it's the Checked Source._
[Original Source](https://github.com/opentibiabr/canary/blob/main/data/events/scripts/player.lua)
[Checked Source](https://github.com/marcosvf132/canary/blob/multiprotocol/data/events/scripts/player.lua)
This bug was tested in Ubuntu 22.04 and Windows 10
### What OS are you seeing the problem on?
Linux, Windows
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | 1.0 | Bug: Getting RAW XP (file) instead of Staged EXP / Config Rates - ### Priority
High
### Area
- [X] Datapack
- [ ] Source
- [ ] Map
- [ ] Other
### What happened?
Hello everyone.
Im using the latest version of Canary. I was testing my leveling progress in the game and I noticed monsters are not giving the exp * stage OR exp * rates.
Example in Tibia Rl
Troll gives 20 points of experience, it should give 30 points of experience with green stamina.
After killing Troll, it just gives me the 100% XP (20 points) and throws this error in console
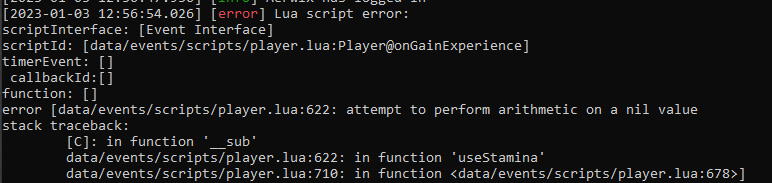
I already checked with other old forks and I found we had some changes:
Result: https://www.diffchecker.com/nI1QetUk/
_Important Note: The left side is the Original Source and the right side it's the Checked Source._
[Original Source](https://github.com/opentibiabr/canary/blob/main/data/events/scripts/player.lua)
[Checked Source](https://github.com/marcosvf132/canary/blob/multiprotocol/data/events/scripts/player.lua)
This bug was tested in Ubuntu 22.04 and Windows 10
### What OS are you seeing the problem on?
Linux, Windows
### Code of Conduct
- [X] I agree to follow this project's Code of Conduct | test | bug getting raw xp file instead of staged exp config rates priority high area datapack source map other what happened hello everyone im using the latest version of canary i was testing my leveling progress in the game and i noticed monsters are not giving the exp stage or exp rates example in tibia rl troll gives points of experience it should give points of experience with green stamina after killing troll it just gives me the xp points and throws this error in console i already checked with other old forks and i found we had some changes result important note the left side is the original source and the right side it s the checked source this bug was tested in ubuntu and windows what os are you seeing the problem on linux windows code of conduct i agree to follow this project s code of conduct | 1 |
295,368 | 9,085,421,552 | IssuesEvent | 2019-02-18 08:14:58 | canonical-websites/snapcraft.io | https://api.github.com/repos/canonical-websites/snapcraft.io | closed | Change no snap icon placeholder image | Priority: High | When a snap does not have an icon, snapcraft.io uses the Snapcraft logo in a circle as a substitute. Current examples include [Wavebox](https://snapcraft.io/wavebox) and [qcomicbook](https://snapcraft.io/qcomicbook).
This is not a good idea, for three reasons:
- It gives the Snapcraft logo an association of “something is missing”.
- It gives the Snapcraft logo an association with a snap that might be terrible.
- It means snapcraft.io snap pages have three Snapcraft icons in succession: browser tab, header logo, snap icon. (And all three of them have different color schemes!)
What should happen: Snaps without icons should have a generic icon that does not include the Snapcraft logo.
(The gnome-software equivalent is [LP#1775798](https://launchpad.net/bugs/1775798).) | 1.0 | Change no snap icon placeholder image - When a snap does not have an icon, snapcraft.io uses the Snapcraft logo in a circle as a substitute. Current examples include [Wavebox](https://snapcraft.io/wavebox) and [qcomicbook](https://snapcraft.io/qcomicbook).
This is not a good idea, for three reasons:
- It gives the Snapcraft logo an association of “something is missing”.
- It gives the Snapcraft logo an association with a snap that might be terrible.
- It means snapcraft.io snap pages have three Snapcraft icons in succession: browser tab, header logo, snap icon. (And all three of them have different color schemes!)
What should happen: Snaps without icons should have a generic icon that does not include the Snapcraft logo.
(The gnome-software equivalent is [LP#1775798](https://launchpad.net/bugs/1775798).) | non_test | change no snap icon placeholder image when a snap does not have an icon snapcraft io uses the snapcraft logo in a circle as a substitute current examples include and this is not a good idea for three reasons it gives the snapcraft logo an association of “something is missing” it gives the snapcraft logo an association with a snap that might be terrible it means snapcraft io snap pages have three snapcraft icons in succession browser tab header logo snap icon and all three of them have different color schemes what should happen snaps without icons should have a generic icon that does not include the snapcraft logo the gnome software equivalent is | 0 |
159,969 | 12,498,547,522 | IssuesEvent | 2020-06-01 18:29:21 | openenclave/openenclave | https://api.github.com/repos/openenclave/openenclave | closed | oe_verify_report (enclave) takes seconds to execute | SGX attestation investigation triaged | In CCF, we've recently observed that a call to `oe_verify_report()` in the enclave can take a significant amount of time to execute (about 2 seconds). We rely on this function to verify the quote of new nodes joining a CCF network.
This is an issue (https://github.com/microsoft/CCF/issues/480) for us as the CCF's enclave code is single-threaded for now and such calls block execution of other commands. Since CCF uses consensus algorithms that are sensitive to time (Raft election timeout in particular), this creates unwanted behaviours in many of our tests and real scenarios as Raft elections get triggered when `oe_verify_report()` takes too long to execute.
This is something that we observed very rarely a while back (probably on OE v0.5.0 or v0.6.0) but it seems to have got worse/more frequent with v0.7.0 RCs.
Looking at the logs briefly (`OE_LOG_LEVEL=verbose`), it seems that most of the time is spent during the `curl`s in the DCAP client code and the many `clock_gettime` (that I believe are used by mbedtls for the certificates/CRL verification?):
```
2019-10-28T10:38:40.500037Z [(E)WARN] tid(0x7f78e51ff700) | libloggingenc.so.signed:syscall num=228 not handled [../syscall/syscall.c:_syscall:815]
```
**Related issues:**
DCAP client caching of collaterals: microsoft/Azure-DCAP-Client#88
Code optimization for new collaterals: #2792
| 1.0 | oe_verify_report (enclave) takes seconds to execute - In CCF, we've recently observed that a call to `oe_verify_report()` in the enclave can take a significant amount of time to execute (about 2 seconds). We rely on this function to verify the quote of new nodes joining a CCF network.
This is an issue (https://github.com/microsoft/CCF/issues/480) for us as the CCF's enclave code is single-threaded for now and such calls block execution of other commands. Since CCF uses consensus algorithms that are sensitive to time (Raft election timeout in particular), this creates unwanted behaviours in many of our tests and real scenarios as Raft elections get triggered when `oe_verify_report()` takes too long to execute.
This is something that we observed very rarely a while back (probably on OE v0.5.0 or v0.6.0) but it seems to have got worse/more frequent with v0.7.0 RCs.
Looking at the logs briefly (`OE_LOG_LEVEL=verbose`), it seems that most of the time is spent during the `curl`s in the DCAP client code and the many `clock_gettime` (that I believe are used by mbedtls for the certificates/CRL verification?):
```
2019-10-28T10:38:40.500037Z [(E)WARN] tid(0x7f78e51ff700) | libloggingenc.so.signed:syscall num=228 not handled [../syscall/syscall.c:_syscall:815]
```
**Related issues:**
DCAP client caching of collaterals: microsoft/Azure-DCAP-Client#88
Code optimization for new collaterals: #2792
| test | oe verify report enclave takes seconds to execute in ccf we ve recently observed that a call to oe verify report in the enclave can take a significant amount of time to execute about seconds we rely on this function to verify the quote of new nodes joining a ccf network this is an issue for us as the ccf s enclave code is single threaded for now and such calls block execution of other commands since ccf uses consensus algorithms that are sensitive to time raft election timeout in particular this creates unwanted behaviours in many of our tests and real scenarios as raft elections get triggered when oe verify report takes too long to execute this is something that we observed very rarely a while back probably on oe or but it seems to have got worse more frequent with rcs looking at the logs briefly oe log level verbose it seems that most of the time is spent during the curl s in the dcap client code and the many clock gettime that i believe are used by mbedtls for the certificates crl verification tid libloggingenc so signed syscall num not handled related issues dcap client caching of collaterals microsoft azure dcap client code optimization for new collaterals | 1 |
154,511 | 24,306,861,187 | IssuesEvent | 2022-09-29 18:14:06 | CMSgov/eAPD | https://api.github.com/repos/CMSgov/eAPD | closed | [Design Issue] Create a page in MMIS Figma file to show each validation component in the system | Design medium | Create a page in MMIS Figma file to show each validation component in the system
On this page we should document each type of input field in the eAPD system, and show an example of the validation pattern for that input field. We should generally have examples of all fields somewhere in the HITECH Figma file that can be copy/pasted into the MMIS file, and it will be useful to have a page in the MMIS file that documents these components in one place.
### This task is done when…
- [x] Make a list of all input components
- [x] In Figma, show validation content and visual pattern for each input component
- [x] Note in the file what the page is for, and how we use the design system for these components (or how we deviate)
- [x] Note in the file which validations we do inline and which we do in the admin check.
- [ ] Include a link to the admin check pages in Mural? (Maybe)
- [x] Add a link to the validation Mural in #2054 where the validation content and considerations are kept (this Mural is 90+% accurate still, but what is in each validation ticket and coded into the eAPD system should be considered the source of truth at this point)
- [ ] Add an "important design links" section somewhere in the wiki and link to this new page
| 1.0 | [Design Issue] Create a page in MMIS Figma file to show each validation component in the system - Create a page in MMIS Figma file to show each validation component in the system
On this page we should document each type of input field in the eAPD system, and show an example of the validation pattern for that input field. We should generally have examples of all fields somewhere in the HITECH Figma file that can be copy/pasted into the MMIS file, and it will be useful to have a page in the MMIS file that documents these components in one place.
### This task is done when…
- [x] Make a list of all input components
- [x] In Figma, show validation content and visual pattern for each input component
- [x] Note in the file what the page is for, and how we use the design system for these components (or how we deviate)
- [x] Note in the file which validations we do inline and which we do in the admin check.
- [ ] Include a link to the admin check pages in Mural? (Maybe)
- [x] Add a link to the validation Mural in #2054 where the validation content and considerations are kept (this Mural is 90+% accurate still, but what is in each validation ticket and coded into the eAPD system should be considered the source of truth at this point)
- [ ] Add an "important design links" section somewhere in the wiki and link to this new page
| non_test | create a page in mmis figma file to show each validation component in the system create a page in mmis figma file to show each validation component in the system on this page we should document each type of input field in the eapd system and show an example of the validation pattern for that input field we should generally have examples of all fields somewhere in the hitech figma file that can be copy pasted into the mmis file and it will be useful to have a page in the mmis file that documents these components in one place this task is done when… make a list of all input components in figma show validation content and visual pattern for each input component note in the file what the page is for and how we use the design system for these components or how we deviate note in the file which validations we do inline and which we do in the admin check include a link to the admin check pages in mural maybe add a link to the validation mural in where the validation content and considerations are kept this mural is accurate still but what is in each validation ticket and coded into the eapd system should be considered the source of truth at this point add an important design links section somewhere in the wiki and link to this new page | 0 |
191,367 | 6,828,417,512 | IssuesEvent | 2017-11-08 20:20:34 | zephyrproject-rtos/zephyr | https://api.github.com/repos/zephyrproject-rtos/zephyr | closed | [Coverity CID:178786] Memory - corruptions in /samples/net/http_server/src/main.c | area: Samples bug priority: medium | Static code scan issues seen in File: /samples/net/http_server/src/main.c
Category: Memory - corruptions
Function: main
Component: Samples
CID: 178786
Please fix or provide comments to square it off in coverity in the link: https://scan9.coverity.com/reports.htm#v32951/p12996 | 1.0 | [Coverity CID:178786] Memory - corruptions in /samples/net/http_server/src/main.c - Static code scan issues seen in File: /samples/net/http_server/src/main.c
Category: Memory - corruptions
Function: main
Component: Samples
CID: 178786
Please fix or provide comments to square it off in coverity in the link: https://scan9.coverity.com/reports.htm#v32951/p12996 | non_test | memory corruptions in samples net http server src main c static code scan issues seen in file samples net http server src main c category memory corruptions function main component samples cid please fix or provide comments to square it off in coverity in the link | 0 |
326,070 | 27,975,356,183 | IssuesEvent | 2023-03-25 14:13:33 | dudykr/stc | https://api.github.com/repos/dudykr/stc | opened | Fix unit test: `tests/pass-only/conformance/classes/members/privateNames/privateNameComputedPropertyName3/.1.ts` | tsc-unit-test |
---
Related test: https://github.com/dudykr/stc/blob/main/crates/stc_ts_file_analyzer/tests/pass-only/conformance/classes/members/privateNames/privateNameComputedPropertyName3/.1.ts
---
This issue is created by sync script.
| 1.0 | Fix unit test: `tests/pass-only/conformance/classes/members/privateNames/privateNameComputedPropertyName3/.1.ts` -
---
Related test: https://github.com/dudykr/stc/blob/main/crates/stc_ts_file_analyzer/tests/pass-only/conformance/classes/members/privateNames/privateNameComputedPropertyName3/.1.ts
---
This issue is created by sync script.
| test | fix unit test tests pass only conformance classes members privatenames ts related test this issue is created by sync script | 1 |
288,868 | 21,724,712,696 | IssuesEvent | 2022-05-11 06:22:34 | VIGNESH-824/Group03_FREERTOS_STM32 | https://api.github.com/repos/VIGNESH-824/Group03_FREERTOS_STM32 | opened | Documentation | documentation | This issue has been created to keep a track of the documentation of the particular repository. | 1.0 | Documentation - This issue has been created to keep a track of the documentation of the particular repository. | non_test | documentation this issue has been created to keep a track of the documentation of the particular repository | 0 |
16,156 | 30,206,477,675 | IssuesEvent | 2023-07-05 09:46:20 | scholokov/qax-portal-2 | https://api.github.com/repos/scholokov/qax-portal-2 | closed | Requirements - The button "Записатися" should be different from the button "Продовжити" in color | Bug High prio S3 Requirements | **Steps to reproduce:**
1. Open [requirements](https://github.com/scholokov/qax-portal-2/wiki/1.7.-Materials)
2. Pay attention to the course card requirements
**Actual result:** Requirements for the button color "Записатися" and "Продовжити" is miss
**Expected result:** Requirements include: The button "Записатися" should be different from the button "Продовжити" in color
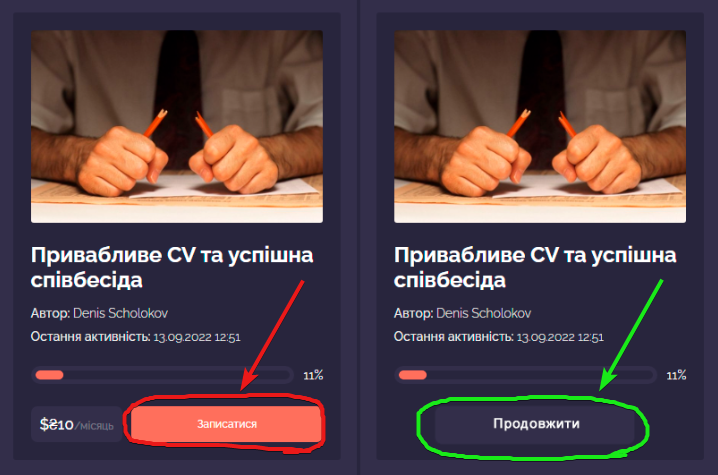
| 1.0 | Requirements - The button "Записатися" should be different from the button "Продовжити" in color - **Steps to reproduce:**
1. Open [requirements](https://github.com/scholokov/qax-portal-2/wiki/1.7.-Materials)
2. Pay attention to the course card requirements
**Actual result:** Requirements for the button color "Записатися" and "Продовжити" is miss
**Expected result:** Requirements include: The button "Записатися" should be different from the button "Продовжити" in color
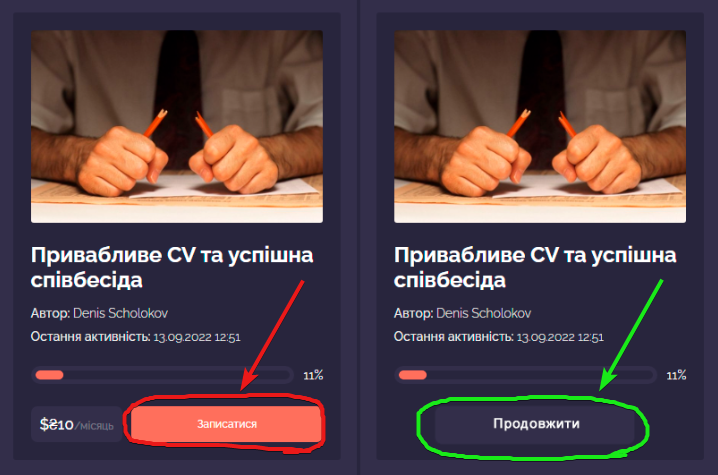
| non_test | requirements the button записатися should be different from the button продовжити in color steps to reproduce open pay attention to the course card requirements actual result requirements for the button color записатися and продовжити is miss expected result requirements include the button записатися should be different from the button продовжити in color | 0 |
549,698 | 16,098,282,198 | IssuesEvent | 2021-04-27 05:27:54 | bancorprotocol/webapp | https://api.github.com/repos/bancorprotocol/webapp | closed | withdraw protected position error | bug high-priority | **Describe the bug**
trying to remove protected position.
remove BNT (50%) from my enjbnt pool position.
reproduce:
1. find a BNT protected position
2. try to withdraw it
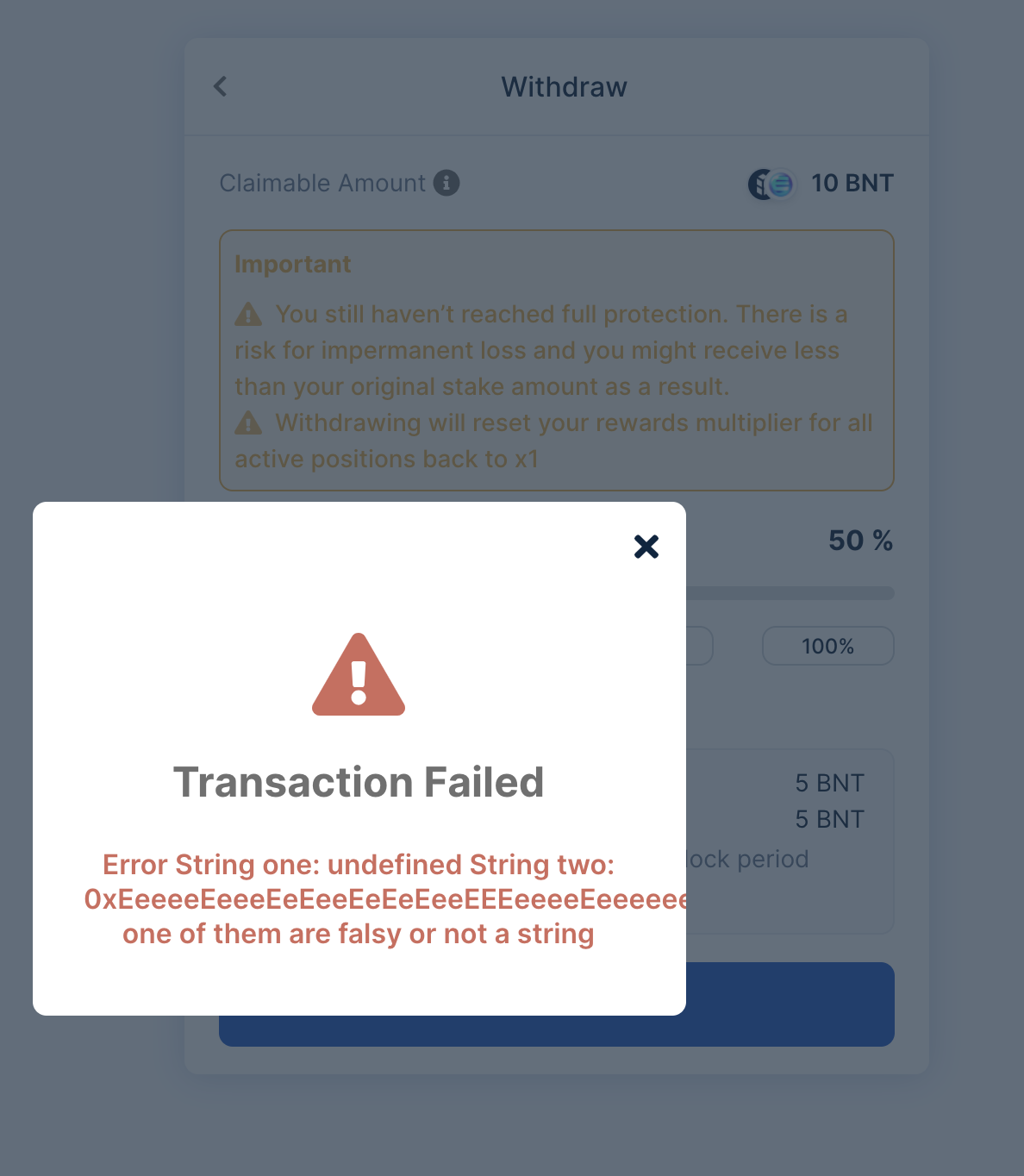
| 1.0 | withdraw protected position error - **Describe the bug**
trying to remove protected position.
remove BNT (50%) from my enjbnt pool position.
reproduce:
1. find a BNT protected position
2. try to withdraw it
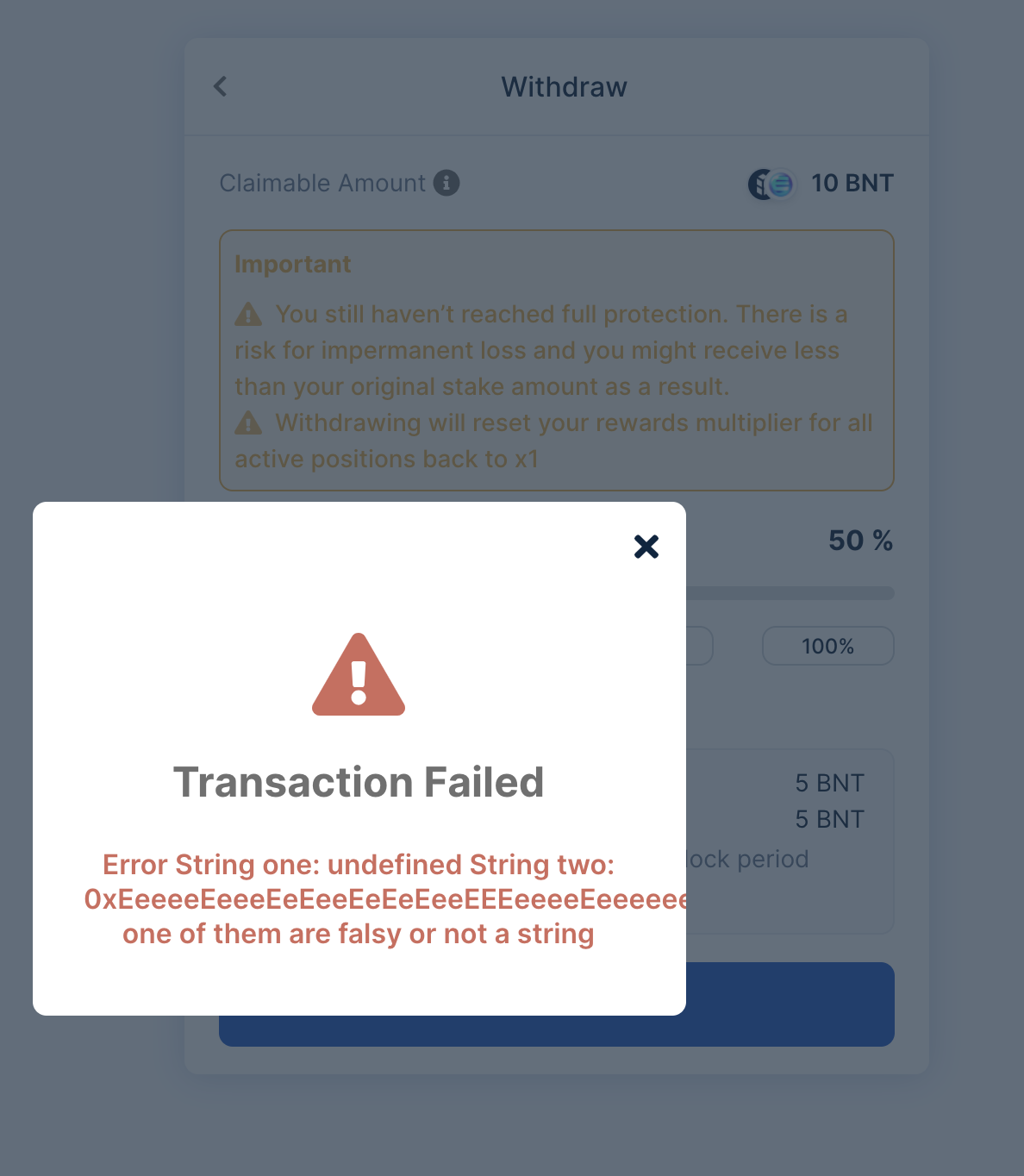
| non_test | withdraw protected position error describe the bug trying to remove protected position remove bnt from my enjbnt pool position reproduce find a bnt protected position try to withdraw it | 0 |
601,685 | 18,426,678,167 | IssuesEvent | 2021-10-13 23:24:50 | dotnet/wcf | https://api.github.com/repos/dotnet/wcf | closed | Channel Factory caching | feature request priority 2 | I'm trying to figure out what the best approach is for caching with the new wcf library now that ClientBase no longer caches.
I have a middleware asp.net core web service which in turn needs to call out to a 3rd party soap service using wcf. The 3rd party service is at a single fixed url https endpoint.
My understanding is that everything in the wcf layer is threadsafe - is this correct? If so am I better off caching the generated clientBase derived object, a channel factory, or a channel proxy?
Calls to the 3rd party service will be sporadic so will I be facing any timeout issues with any of the 3 options? Is it recommended to cache local to where I need to make the calls, or use DI on the channel factor or proxy?
Due to the size of the 3rd party wsdl generating a new clientBase each call is not an option. The creating time is on the order of 500ms.
| 1.0 | Channel Factory caching - I'm trying to figure out what the best approach is for caching with the new wcf library now that ClientBase no longer caches.
I have a middleware asp.net core web service which in turn needs to call out to a 3rd party soap service using wcf. The 3rd party service is at a single fixed url https endpoint.
My understanding is that everything in the wcf layer is threadsafe - is this correct? If so am I better off caching the generated clientBase derived object, a channel factory, or a channel proxy?
Calls to the 3rd party service will be sporadic so will I be facing any timeout issues with any of the 3 options? Is it recommended to cache local to where I need to make the calls, or use DI on the channel factor or proxy?
Due to the size of the 3rd party wsdl generating a new clientBase each call is not an option. The creating time is on the order of 500ms.
| non_test | channel factory caching i m trying to figure out what the best approach is for caching with the new wcf library now that clientbase no longer caches i have a middleware asp net core web service which in turn needs to call out to a party soap service using wcf the party service is at a single fixed url https endpoint my understanding is that everything in the wcf layer is threadsafe is this correct if so am i better off caching the generated clientbase derived object a channel factory or a channel proxy calls to the party service will be sporadic so will i be facing any timeout issues with any of the options is it recommended to cache local to where i need to make the calls or use di on the channel factor or proxy due to the size of the party wsdl generating a new clientbase each call is not an option the creating time is on the order of | 0 |
106,628 | 13,328,084,399 | IssuesEvent | 2020-08-27 14:03:06 | carbon-design-system/digital-design-ideation | https://api.github.com/repos/carbon-design-system/digital-design-ideation | closed | Validate patterns future state work with adopters | Design Research | ### Background
DDS team and leads have agreed to move all current layout patterns into components. In the future, we will label/categorize anything that is coded as a component, while design intents and best practices will be known as patterns. Before we make this change we need to validate the proposal one last time with adopters.
**Previous feedback from adopters and DDS documented here:**
https://github.com/carbon-design-system/digital-design-ideation/issues/74
### Tasks
- [x] Lara to share proposal and prototypes to Support and Cloud
- [x] Lara to document and share back their feedback
| 1.0 | Validate patterns future state work with adopters - ### Background
DDS team and leads have agreed to move all current layout patterns into components. In the future, we will label/categorize anything that is coded as a component, while design intents and best practices will be known as patterns. Before we make this change we need to validate the proposal one last time with adopters.
**Previous feedback from adopters and DDS documented here:**
https://github.com/carbon-design-system/digital-design-ideation/issues/74
### Tasks
- [x] Lara to share proposal and prototypes to Support and Cloud
- [x] Lara to document and share back their feedback
| non_test | validate patterns future state work with adopters background dds team and leads have agreed to move all current layout patterns into components in the future we will label categorize anything that is coded as a component while design intents and best practices will be known as patterns before we make this change we need to validate the proposal one last time with adopters previous feedback from adopters and dds documented here tasks lara to share proposal and prototypes to support and cloud lara to document and share back their feedback | 0 |
170,828 | 6,472,382,969 | IssuesEvent | 2017-08-17 13:53:17 | patternfly/angular-patternfly | https://api.github.com/repos/patternfly/angular-patternfly | opened | Do not set id="title" in empty state component | bug Priority 2 | We shouldn't use id="title" in the empty state message. That's a really generic ID, and IDs need to be unique on the page. | 1.0 | Do not set id="title" in empty state component - We shouldn't use id="title" in the empty state message. That's a really generic ID, and IDs need to be unique on the page. | non_test | do not set id title in empty state component we shouldn t use id title in the empty state message that s a really generic id and ids need to be unique on the page | 0 |
222,748 | 17,090,459,608 | IssuesEvent | 2021-07-08 16:43:53 | loopfabrik/xsdVucemMaritmoValidaCarga | https://api.github.com/repos/loopfabrik/xsdVucemMaritmoValidaCarga | closed | Update the readme file | documentation | update the file with all the information about the use and about the fields
- [ ] How to use
- [ ] Required fields
- [ ] Optional fields
- [ ] Important Observations | 1.0 | Update the readme file - update the file with all the information about the use and about the fields
- [ ] How to use
- [ ] Required fields
- [ ] Optional fields
- [ ] Important Observations | non_test | update the readme file update the file with all the information about the use and about the fields how to use required fields optional fields important observations | 0 |
691,063 | 23,681,616,407 | IssuesEvent | 2022-08-28 21:54:23 | ooni/probe | https://api.github.com/repos/ooni/probe | closed | oohelperd: add support for prometheus metrics | priority/medium | We discussed which metrics today with @FedericoCeratto and @hellais and we mentioned:
- [ ] time it takes to serve a request
- [ ] number of errors
- [ ] number of running workers
- [x] additionally, it should not listen on *:8080 (not strictly prometheus but completementary) [https://github.com/ooni/probe-cli/pull/887]
- [x] additionally, we should also have logs (not strictly prometheus but completementary) [https://github.com/ooni/probe-cli/pull/896] | 1.0 | oohelperd: add support for prometheus metrics - We discussed which metrics today with @FedericoCeratto and @hellais and we mentioned:
- [ ] time it takes to serve a request
- [ ] number of errors
- [ ] number of running workers
- [x] additionally, it should not listen on *:8080 (not strictly prometheus but completementary) [https://github.com/ooni/probe-cli/pull/887]
- [x] additionally, we should also have logs (not strictly prometheus but completementary) [https://github.com/ooni/probe-cli/pull/896] | non_test | oohelperd add support for prometheus metrics we discussed which metrics today with federicoceratto and hellais and we mentioned time it takes to serve a request number of errors number of running workers additionally it should not listen on not strictly prometheus but completementary additionally we should also have logs not strictly prometheus but completementary | 0 |
198,792 | 14,997,497,909 | IssuesEvent | 2021-01-29 16:59:17 | tendermint/tendermint | https://api.github.com/repos/tendermint/tendermint | closed | libs/sync: undefined deadlock.Once | T:dependencies T:test | `sync.Closer` relies on `deadlock.Once`, but `deadlock.Once` is not available in go-deadlock 0.2 (the latest release), so running `go test -tags deadlock` errors with `undefined: deadlock.Once`.
In any case, `deadlock.Once` is just an alias for `sync.Once` so there is no point in using it; I suggest we move `sync.Closer` to a separate file and use `sync.Once`. | 1.0 | libs/sync: undefined deadlock.Once - `sync.Closer` relies on `deadlock.Once`, but `deadlock.Once` is not available in go-deadlock 0.2 (the latest release), so running `go test -tags deadlock` errors with `undefined: deadlock.Once`.
In any case, `deadlock.Once` is just an alias for `sync.Once` so there is no point in using it; I suggest we move `sync.Closer` to a separate file and use `sync.Once`. | test | libs sync undefined deadlock once sync closer relies on deadlock once but deadlock once is not available in go deadlock the latest release so running go test tags deadlock errors with undefined deadlock once in any case deadlock once is just an alias for sync once so there is no point in using it i suggest we move sync closer to a separate file and use sync once | 1 |
239,952 | 26,246,262,089 | IssuesEvent | 2023-01-05 15:29:12 | AS-Mend/VulnerableJava | https://api.github.com/repos/AS-Mend/VulnerableJava | opened | esapi-2.1.0.1.jar: 22 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p></summary>
<p>The Enterprise Security API (ESAPI) project is an OWASP project
to create simple strong security controls for every web platform.
Security controls are not simple to build. You can read about the
hundreds of pitfalls for unwary developers on the OWASP web site. By
providing developers with a set of strong controls, we aim to
eliminate some of the complexity of creating secure web applications.
This can result in significant cost savings across the SDLC.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/esapi/esapi/2.1.0.1/esapi-2.1.0.1.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (esapi version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-23457](https://www.mend.io/vulnerability-database/CVE-2022-23457) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | esapi-2.1.0.1.jar | Direct | 2.3.0.0 | ✅ |
| [CVE-2016-1000031](https://www.mend.io/vulnerability-database/CVE-2016-1000031) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2016-2510](https://www.mend.io/vulnerability-database/CVE-2016-2510) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | bsh-core-2.0b4.jar | Transitive | N/A* | ❌ |
| [CVE-2016-3092](https://www.mend.io/vulnerability-database/CVE-2016-3092) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2022-34169](https://www.mend.io/vulnerability-database/CVE-2022-34169) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xalan-2.7.0.jar | Transitive | N/A* | ❌ |
| [CVE-2022-24839](https://www.mend.io/vulnerability-database/CVE-2022-24839) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Transitive | N/A* | ❌ |
| [CVE-2012-0881](https://www.mend.io/vulnerability-database/CVE-2012-0881) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [WS-2014-0034](https://commons.apache.org/proper/commons-fileupload/changes-report.html) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.4.0.0 | ✅ |
| [CVE-2014-0107](https://www.mend.io/vulnerability-database/CVE-2014-0107) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | xalan-2.7.0.jar | Transitive | 2.5.0.0 | ✅ |
| [CVE-2019-10086](https://www.mend.io/vulnerability-database/CVE-2019-10086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | N/A* | ❌ |
| [CVE-2014-0114](https://www.mend.io/vulnerability-database/CVE-2014-0114) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | N/A* | ❌ |
| [CVE-2022-23437](https://www.mend.io/vulnerability-database/CVE-2022-23437) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [CVE-2016-10006](https://www.mend.io/vulnerability-database/CVE-2016-10006) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2022-29577](https://www.mend.io/vulnerability-database/CVE-2022-29577) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.3.0.0 | ✅ |
| [CVE-2022-28367](https://www.mend.io/vulnerability-database/CVE-2022-28367) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.3.0.0 | ✅ |
| [CVE-2021-35043](https://www.mend.io/vulnerability-database/CVE-2021-35043) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.3.0.0 | ✅ |
| [CVE-2022-24891](https://www.mend.io/vulnerability-database/CVE-2022-24891) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | esapi-2.1.0.1.jar | Direct | 2.3.0.0 | ✅ |
| [CVE-2017-14735](https://www.mend.io/vulnerability-database/CVE-2017-14735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2013-4002](https://www.mend.io/vulnerability-database/CVE-2013-4002) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [CVE-2009-2625](https://www.mend.io/vulnerability-database/CVE-2009-2625) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [CVE-2012-5783](https://www.mend.io/vulnerability-database/CVE-2012-5783) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-httpclient-3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2021-29425](https://www.mend.io/vulnerability-database/CVE-2021-29425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-io-2.2.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-23457</summary>
### Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p>
<p>The Enterprise Security API (ESAPI) project is an OWASP project
to create simple strong security controls for every web platform.
Security controls are not simple to build. You can read about the
hundreds of pitfalls for unwary developers on the OWASP web site. By
providing developers with a set of strong controls, we aim to
eliminate some of the complexity of creating secure web applications.
This can result in significant cost savings across the SDLC.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/esapi/esapi/2.1.0.1/esapi-2.1.0.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **esapi-2.1.0.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ESAPI (The OWASP Enterprise Security API) is a free, open source, web application security control library. Prior to version 2.3.0.0, the default implementation of `Validator.getValidDirectoryPath(String, String, File, boolean)` may incorrectly treat the tested input string as a child of the specified parent directory. This potentially could allow control-flow bypass checks to be defeated if an attack can specify the entire string representing the 'input' path. This vulnerability is patched in release 2.3.0.0 of ESAPI. As a workaround, it is possible to write one's own implementation of the Validator interface. However, maintainers do not recommend this.
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23457>CVE-2022-23457</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/ESAPI/esapi-java-legacy/security/advisories/GHSA-8m5h-hrqm-pxm2">https://github.com/ESAPI/esapi-java-legacy/security/advisories/GHSA-8m5h-hrqm-pxm2</a></p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1000031</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons FileUpload before 1.3.3 DiskFileItem File Manipulation Remote Code Execution
<p>Publish Date: 2016-10-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1000031>CVE-2016-1000031</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031</a></p>
<p>Release Date: 2016-10-25</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.3</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2510</summary>
### Vulnerable Library - <b>bsh-core-2.0b4.jar</b></p>
<p>BeanShell core</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/beanshell/bsh-core/2.0b4/bsh-core-2.0b4.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **bsh-core-2.0b4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
BeanShell (bsh) before 2.0b6, when included on the classpath by an application that uses Java serialization or XStream, allows remote attackers to execute arbitrary code via crafted serialized data, related to XThis.Handler.
<p>Publish Date: 2016-04-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2510>CVE-2016-2510</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2510">https://nvd.nist.gov/vuln/detail/CVE-2016-2510</a></p>
<p>Release Date: 2016-04-07</p>
<p>Fix Resolution: 2.0b6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-3092</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MultipartStream class in Apache Commons Fileupload before 1.3.2, as used in Apache Tomcat 7.x before 7.0.70, 8.x before 8.0.36, 8.5.x before 8.5.3, and 9.x before 9.0.0.M7 and other products, allows remote attackers to cause a denial of service (CPU consumption) via a long boundary string.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3092>CVE-2016-3092</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.2</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-34169</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Apache Xalan Java XSLT library is vulnerable to an integer truncation issue when processing malicious XSLT stylesheets. This can be used to corrupt Java class files generated by the internal XSLTC compiler and execute arbitrary Java bytecode. The Apache Xalan Java project is dormant and in the process of being retired. No future releases of Apache Xalan Java to address this issue are expected. Note: Java runtimes (such as OpenJDK) include repackaged copies of Xalan.
<p>Publish Date: 2022-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-34169>CVE-2022-34169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24839</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- antisamy-1.5.3.jar
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
org.cyberneko.html is an html parser written in Java. The fork of `org.cyberneko.html` used by Nokogiri (Rubygem) raises a `java.lang.OutOfMemoryError` exception when parsing ill-formed HTML markup. Users are advised to upgrade to `>= 1.9.22.noko2`. Note: The upstream library `org.cyberneko.html` is no longer maintained. Nokogiri uses its own fork of this library located at https://github.com/sparklemotion/nekohtml and this CVE applies only to that fork. Other forks of nekohtml may have a similar vulnerability.
<p>Publish Date: 2022-04-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24839>CVE-2022-24839</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv">https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv</a></p>
<p>Release Date: 2022-04-11</p>
<p>Fix Resolution: net.sourceforge.nekohtml:nekohtml:1.9.22.noko2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-0881</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Xerces2 Java Parser before 2.12.0 allows remote attackers to cause a denial of service (CPU consumption) via a crafted message to an XML service, which triggers hash table collisions.
<p>Publish Date: 2017-10-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2012-0881>CVE-2012-0881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881</a></p>
<p>Release Date: 2017-10-30</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2014-0034</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The class FileUploadBase in Apache Commons Fileupload before 1.4 has potential resource leak - InputStream not closed on exception.
<p>Publish Date: 2014-02-17
<p>URL: <a href=https://commons.apache.org/proper/commons-fileupload/changes-report.html>WS-2014-0034</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2014-02-17</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.4</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0107</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The TransformerFactory in Apache Xalan-Java before 2.7.2 does not properly restrict access to certain properties when FEATURE_SECURE_PROCESSING is enabled, which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted (1) xalan:content-header, (2) xalan:entities, (3) xslt:content-header, or (4) xslt:entities property, or a Java property that is bound to the XSLT 1.0 system-property function.
<p>Publish Date: 2014-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0107>CVE-2014-0107</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107</a></p>
<p>Release Date: 2014-04-15</p>
<p>Fix Resolution (xalan:xalan): 2.7.2</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.5.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10086</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons Beanutils 1.9.2, a special BeanIntrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all Java objects. We, however were not using this by default characteristic of the PropertyUtilsBean.
<p>Publish Date: 2019-08-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10086>CVE-2019-10086</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-20</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0114</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23437</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There's a vulnerability within the Apache Xerces Java (XercesJ) XML parser when handling specially crafted XML document payloads. This causes, the XercesJ XML parser to wait in an infinite loop, which may sometimes consume system resources for prolonged duration. This vulnerability is present within XercesJ version 2.12.1 and the previous versions.
<p>Publish Date: 2022-01-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23437>CVE-2022-23437</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h65f-jvqw-m9fj">https://github.com/advisories/GHSA-h65f-jvqw-m9fj</a></p>
<p>Release Date: 2022-01-24</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10006</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In OWASP AntiSamy before 1.5.5, by submitting a specially crafted input (a tag that supports style with active content), you could bypass the library protections and supply executable code. The impact is XSS.
<p>Publish Date: 2016-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10006>CVE-2016-10006</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006</a></p>
<p>Release Date: 2016-12-24</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.5</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-29577</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.6.7 allows XSS via HTML tag smuggling on STYLE content with crafted input. The output serializer does not properly encode the supposed Cascading Style Sheets (CSS) content. NOTE: this issue exists because of an incomplete fix for CVE-2022-28367.
<p>Publish Date: 2022-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29577>CVE-2022-29577</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29577">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29577</a></p>
<p>Release Date: 2022-04-21</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.6.7</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-28367</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.6.6 allows XSS via HTML tag smuggling on STYLE content with crafted input. The output serializer does not properly encode the supposed Cascading Style Sheets (CSS) content.
<p>Publish Date: 2022-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-28367>CVE-2022-28367</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28367">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28367</a></p>
<p>Release Date: 2022-04-21</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.6.6</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-35043</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.6.4 allows XSS via HTML attributes when using the HTML output serializer (XHTML is not affected). This was demonstrated by a javascript: URL with : as the replacement for the : character.
<p>Publish Date: 2021-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35043>CVE-2021-35043</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-35043">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-35043</a></p>
<p>Release Date: 2021-07-19</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.6.4</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24891</summary>
### Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p>
<p>The Enterprise Security API (ESAPI) project is an OWASP project
to create simple strong security controls for every web platform.
Security controls are not simple to build. You can read about the
hundreds of pitfalls for unwary developers on the OWASP web site. By
providing developers with a set of strong controls, we aim to
eliminate some of the complexity of creating secure web applications.
This can result in significant cost savings across the SDLC.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/esapi/esapi/2.1.0.1/esapi-2.1.0.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **esapi-2.1.0.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ESAPI (The OWASP Enterprise Security API) is a free, open source, web application security control library. Prior to version 2.3.0.0, there is a potential for a cross-site scripting vulnerability in ESAPI caused by a incorrect regular expression for "onsiteURL" in the **antisamy-esapi.xml** configuration file that can cause "javascript:" URLs to fail to be correctly sanitized. This issue is patched in ESAPI 2.3.0.0. As a workaround, manually edit the **antisamy-esapi.xml** configuration files to change the "onsiteURL" regular expression. More information about remediation of the vulnerability, including the workaround, is available in the maintainers' release notes and security bulletin.
<p>Publish Date: 2022-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24891>CVE-2022-24891</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-q77q-vx4q-xx6q">https://github.com/advisories/GHSA-q77q-vx4q-xx6q</a></p>
<p>Release Date: 2022-04-27</p>
<p>Fix Resolution: 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-14735</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.5.7 allows XSS via HTML5 entities, as demonstrated by use of : to construct a javascript: URL.
<p>Publish Date: 2017-09-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-14735>CVE-2017-14735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735</a></p>
<p>Release Date: 2017-09-25</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.7</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-4002</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLscanner.java in Apache Xerces2 Java Parser before 2.12.0, as used in the Java Runtime Environment (JRE) in IBM Java 5.0 before 5.0 SR16-FP3, 6 before 6 SR14, 6.0.1 before 6.0.1 SR6, and 7 before 7 SR5 as well as Oracle Java SE 7u40 and earlier, Java SE 6u60 and earlier, Java SE 5.0u51 and earlier, JRockit R28.2.8 and earlier, JRockit R27.7.6 and earlier, Java SE Embedded 7u40 and earlier, and possibly other products allows remote attackers to cause a denial of service via vectors related to XML attribute names.
<p>Publish Date: 2013-07-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-4002>CVE-2013-4002</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002</a></p>
<p>Release Date: 2013-07-23</p>
<p>Fix Resolution: xerces:xercesImpl:Xerces-J_2_12_0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2009-2625</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.
<p>Publish Date: 2009-08-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2009-2625>CVE-2009-2625</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-2625">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-2625</a></p>
<p>Release Date: 2009-08-06</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-5783</summary>
### Vulnerable Library - <b>commons-httpclient-3.1.jar</b></p>
<p>The HttpClient component supports the client-side of RFC 1945 (HTTP/1.0) and RFC 2616 (HTTP/1.1) , several related specifications (RFC 2109 (Cookies) , RFC 2617 (HTTP Authentication) , etc.), and provides a framework by which new request types (methods) or HTTP extensions can be created easily.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-httpclient/commons-httpclient/3.1/commons-httpclient-3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- antisamy-1.5.3.jar
- :x: **commons-httpclient-3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons HttpClient 3.x, as used in Amazon Flexible Payments Service (FPS) merchant Java SDK and other products, does not verify that the server hostname matches a domain name in the subject's Common Name (CN) or subjectAltName field of the X.509 certificate, which allows man-in-the-middle attackers to spoof SSL servers via an arbitrary valid certificate.
<p>Publish Date: 2012-11-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2012-5783>CVE-2012-5783</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-5783">https://nvd.nist.gov/vuln/detail/CVE-2012-5783</a></p>
<p>Release Date: 2012-11-04</p>
<p>Fix Resolution (commons-httpclient:commons-httpclient): 20020423</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-29425</summary>
### Vulnerable Library - <b>commons-io-2.2.jar</b></p>
<p>The Commons IO library contains utility classes, stream implementations, file filters,
file comparators, endian transformation classes, and much more.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-io/commons-io/2.2/commons-io-2.2.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- commons-fileupload-1.3.1.jar
- :x: **commons-io-2.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons IO before 2.7, When invoking the method FileNameUtils.normalize with an improper input string, like "//../foo", or "\\..\foo", the result would be the same value, thus possibly providing access to files in the parent directory, but not further above (thus "limited" path traversal), if the calling code would use the result to construct a path value.
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-29425>CVE-2021-29425</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425</a></p>
<p>Release Date: 2021-04-13</p>
<p>Fix Resolution: commons-io:commons-io:2.7</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | esapi-2.1.0.1.jar: 22 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p></summary>
<p>The Enterprise Security API (ESAPI) project is an OWASP project
to create simple strong security controls for every web platform.
Security controls are not simple to build. You can read about the
hundreds of pitfalls for unwary developers on the OWASP web site. By
providing developers with a set of strong controls, we aim to
eliminate some of the complexity of creating secure web applications.
This can result in significant cost savings across the SDLC.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/esapi/esapi/2.1.0.1/esapi-2.1.0.1.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (esapi version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-23457](https://www.mend.io/vulnerability-database/CVE-2022-23457) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | esapi-2.1.0.1.jar | Direct | 2.3.0.0 | ✅ |
| [CVE-2016-1000031](https://www.mend.io/vulnerability-database/CVE-2016-1000031) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2016-2510](https://www.mend.io/vulnerability-database/CVE-2016-2510) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | bsh-core-2.0b4.jar | Transitive | N/A* | ❌ |
| [CVE-2016-3092](https://www.mend.io/vulnerability-database/CVE-2016-3092) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2022-34169](https://www.mend.io/vulnerability-database/CVE-2022-34169) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xalan-2.7.0.jar | Transitive | N/A* | ❌ |
| [CVE-2022-24839](https://www.mend.io/vulnerability-database/CVE-2022-24839) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | nekohtml-1.9.16.jar | Transitive | N/A* | ❌ |
| [CVE-2012-0881](https://www.mend.io/vulnerability-database/CVE-2012-0881) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [WS-2014-0034](https://commons.apache.org/proper/commons-fileupload/changes-report.html) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | commons-fileupload-1.3.1.jar | Transitive | 2.4.0.0 | ✅ |
| [CVE-2014-0107](https://www.mend.io/vulnerability-database/CVE-2014-0107) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | xalan-2.7.0.jar | Transitive | 2.5.0.0 | ✅ |
| [CVE-2019-10086](https://www.mend.io/vulnerability-database/CVE-2019-10086) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | N/A* | ❌ |
| [CVE-2014-0114](https://www.mend.io/vulnerability-database/CVE-2014-0114) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | commons-beanutils-core-1.8.3.jar | Transitive | N/A* | ❌ |
| [CVE-2022-23437](https://www.mend.io/vulnerability-database/CVE-2022-23437) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [CVE-2016-10006](https://www.mend.io/vulnerability-database/CVE-2016-10006) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2022-29577](https://www.mend.io/vulnerability-database/CVE-2022-29577) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.3.0.0 | ✅ |
| [CVE-2022-28367](https://www.mend.io/vulnerability-database/CVE-2022-28367) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.3.0.0 | ✅ |
| [CVE-2021-35043](https://www.mend.io/vulnerability-database/CVE-2021-35043) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.3.0.0 | ✅ |
| [CVE-2022-24891](https://www.mend.io/vulnerability-database/CVE-2022-24891) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | esapi-2.1.0.1.jar | Direct | 2.3.0.0 | ✅ |
| [CVE-2017-14735](https://www.mend.io/vulnerability-database/CVE-2017-14735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | antisamy-1.5.3.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2013-4002](https://www.mend.io/vulnerability-database/CVE-2013-4002) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.9 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [CVE-2009-2625](https://www.mend.io/vulnerability-database/CVE-2009-2625) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | xercesImpl-2.8.0.jar | Transitive | N/A* | ❌ |
| [CVE-2012-5783](https://www.mend.io/vulnerability-database/CVE-2012-5783) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-httpclient-3.1.jar | Transitive | 2.2.0.0 | ✅ |
| [CVE-2021-29425](https://www.mend.io/vulnerability-database/CVE-2021-29425) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | commons-io-2.2.jar | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-23457</summary>
### Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p>
<p>The Enterprise Security API (ESAPI) project is an OWASP project
to create simple strong security controls for every web platform.
Security controls are not simple to build. You can read about the
hundreds of pitfalls for unwary developers on the OWASP web site. By
providing developers with a set of strong controls, we aim to
eliminate some of the complexity of creating secure web applications.
This can result in significant cost savings across the SDLC.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/esapi/esapi/2.1.0.1/esapi-2.1.0.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **esapi-2.1.0.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ESAPI (The OWASP Enterprise Security API) is a free, open source, web application security control library. Prior to version 2.3.0.0, the default implementation of `Validator.getValidDirectoryPath(String, String, File, boolean)` may incorrectly treat the tested input string as a child of the specified parent directory. This potentially could allow control-flow bypass checks to be defeated if an attack can specify the entire string representing the 'input' path. This vulnerability is patched in release 2.3.0.0 of ESAPI. As a workaround, it is possible to write one's own implementation of the Validator interface. However, maintainers do not recommend this.
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23457>CVE-2022-23457</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/ESAPI/esapi-java-legacy/security/advisories/GHSA-8m5h-hrqm-pxm2">https://github.com/ESAPI/esapi-java-legacy/security/advisories/GHSA-8m5h-hrqm-pxm2</a></p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-1000031</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons FileUpload before 1.3.3 DiskFileItem File Manipulation Remote Code Execution
<p>Publish Date: 2016-10-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-1000031>CVE-2016-1000031</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-1000031</a></p>
<p>Release Date: 2016-10-25</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.3</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-2510</summary>
### Vulnerable Library - <b>bsh-core-2.0b4.jar</b></p>
<p>BeanShell core</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/beanshell/bsh-core/2.0b4/bsh-core-2.0b4.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **bsh-core-2.0b4.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
BeanShell (bsh) before 2.0b6, when included on the classpath by an application that uses Java serialization or XStream, allows remote attackers to execute arbitrary code via crafted serialized data, related to XThis.Handler.
<p>Publish Date: 2016-04-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-2510>CVE-2016-2510</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2016-2510">https://nvd.nist.gov/vuln/detail/CVE-2016-2510</a></p>
<p>Release Date: 2016-04-07</p>
<p>Fix Resolution: 2.0b6</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2016-3092</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The MultipartStream class in Apache Commons Fileupload before 1.3.2, as used in Apache Tomcat 7.x before 7.0.70, 8.x before 8.0.36, 8.5.x before 8.5.3, and 9.x before 9.0.0.M7 and other products, allows remote attackers to cause a denial of service (CPU consumption) via a long boundary string.
<p>Publish Date: 2016-07-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-3092>CVE-2016-3092</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-3092</a></p>
<p>Release Date: 2016-07-04</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.3.2</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-34169</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The Apache Xalan Java XSLT library is vulnerable to an integer truncation issue when processing malicious XSLT stylesheets. This can be used to corrupt Java class files generated by the internal XSLTC compiler and execute arbitrary Java bytecode. The Apache Xalan Java project is dormant and in the process of being retired. No future releases of Apache Xalan Java to address this issue are expected. Note: Java runtimes (such as OpenJDK) include repackaged copies of Xalan.
<p>Publish Date: 2022-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-34169>CVE-2022-34169</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24839</summary>
### Vulnerable Library - <b>nekohtml-1.9.16.jar</b></p>
<p>An HTML parser and tag balancer.</p>
<p>Library home page: <a href="http://nekohtml.sourceforge.net/">http://nekohtml.sourceforge.net/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/net/sourceforge/nekohtml/nekohtml/1.9.16/nekohtml-1.9.16.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- antisamy-1.5.3.jar
- :x: **nekohtml-1.9.16.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
org.cyberneko.html is an html parser written in Java. The fork of `org.cyberneko.html` used by Nokogiri (Rubygem) raises a `java.lang.OutOfMemoryError` exception when parsing ill-formed HTML markup. Users are advised to upgrade to `>= 1.9.22.noko2`. Note: The upstream library `org.cyberneko.html` is no longer maintained. Nokogiri uses its own fork of this library located at https://github.com/sparklemotion/nekohtml and this CVE applies only to that fork. Other forks of nekohtml may have a similar vulnerability.
<p>Publish Date: 2022-04-11
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24839>CVE-2022-24839</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv">https://github.com/sparklemotion/nekohtml/security/advisories/GHSA-9849-p7jc-9rmv</a></p>
<p>Release Date: 2022-04-11</p>
<p>Fix Resolution: net.sourceforge.nekohtml:nekohtml:1.9.22.noko2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2012-0881</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Xerces2 Java Parser before 2.12.0 allows remote attackers to cause a denial of service (CPU consumption) via a crafted message to an XML service, which triggers hash table collisions.
<p>Publish Date: 2017-10-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2012-0881>CVE-2012-0881</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0881</a></p>
<p>Release Date: 2017-10-30</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2014-0034</summary>
### Vulnerable Library - <b>commons-fileupload-1.3.1.jar</b></p>
<p>The Apache Commons FileUpload component provides a simple yet flexible means of adding support for multipart
file upload functionality to servlets and web applications.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-fileupload/commons-fileupload/1.3.1/commons-fileupload-1.3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-fileupload-1.3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The class FileUploadBase in Apache Commons Fileupload before 1.4 has potential resource leak - InputStream not closed on exception.
<p>Publish Date: 2014-02-17
<p>URL: <a href=https://commons.apache.org/proper/commons-fileupload/changes-report.html>WS-2014-0034</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2014-02-17</p>
<p>Fix Resolution (commons-fileupload:commons-fileupload): 1.4</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.4.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0107</summary>
### Vulnerable Library - <b>xalan-2.7.0.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xalan/xalan/2.7.0/xalan-2.7.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xalan-2.7.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The TransformerFactory in Apache Xalan-Java before 2.7.2 does not properly restrict access to certain properties when FEATURE_SECURE_PROCESSING is enabled, which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted (1) xalan:content-header, (2) xalan:entities, (3) xslt:content-header, or (4) xslt:entities property, or a Java property that is bound to the XSLT 1.0 system-property function.
<p>Publish Date: 2014-04-15
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0107>CVE-2014-0107</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0107</a></p>
<p>Release Date: 2014-04-15</p>
<p>Fix Resolution (xalan:xalan): 2.7.2</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.5.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-10086</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons Beanutils 1.9.2, a special BeanIntrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all Java objects. We, however were not using this by default characteristic of the PropertyUtilsBean.
<p>Publish Date: 2019-08-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-10086>CVE-2019-10086</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-08-20</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2014-0114</summary>
### Vulnerable Library - <b>commons-beanutils-core-1.8.3.jar</b></p>
<p></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils-core/1.8.3/commons-beanutils-core-1.8.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **commons-beanutils-core-1.8.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
<p>Publish Date: 2014-04-30
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2014-0114>CVE-2014-0114</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114</a></p>
<p>Release Date: 2014-04-30</p>
<p>Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-23437</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
There's a vulnerability within the Apache Xerces Java (XercesJ) XML parser when handling specially crafted XML document payloads. This causes, the XercesJ XML parser to wait in an infinite loop, which may sometimes consume system resources for prolonged duration. This vulnerability is present within XercesJ version 2.12.1 and the previous versions.
<p>Publish Date: 2022-01-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-23437>CVE-2022-23437</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-h65f-jvqw-m9fj">https://github.com/advisories/GHSA-h65f-jvqw-m9fj</a></p>
<p>Release Date: 2022-01-24</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.2</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2016-10006</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In OWASP AntiSamy before 1.5.5, by submitting a specially crafted input (a tag that supports style with active content), you could bypass the library protections and supply executable code. The impact is XSS.
<p>Publish Date: 2016-12-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10006>CVE-2016-10006</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-10006</a></p>
<p>Release Date: 2016-12-24</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.5</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-29577</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.6.7 allows XSS via HTML tag smuggling on STYLE content with crafted input. The output serializer does not properly encode the supposed Cascading Style Sheets (CSS) content. NOTE: this issue exists because of an incomplete fix for CVE-2022-28367.
<p>Publish Date: 2022-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29577>CVE-2022-29577</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29577">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29577</a></p>
<p>Release Date: 2022-04-21</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.6.7</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-28367</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.6.6 allows XSS via HTML tag smuggling on STYLE content with crafted input. The output serializer does not properly encode the supposed Cascading Style Sheets (CSS) content.
<p>Publish Date: 2022-04-21
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-28367>CVE-2022-28367</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28367">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-28367</a></p>
<p>Release Date: 2022-04-21</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.6.6</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-35043</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.6.4 allows XSS via HTML attributes when using the HTML output serializer (XHTML is not affected). This was demonstrated by a javascript: URL with : as the replacement for the : character.
<p>Publish Date: 2021-07-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-35043>CVE-2021-35043</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-35043">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-35043</a></p>
<p>Release Date: 2021-07-19</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.6.4</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24891</summary>
### Vulnerable Library - <b>esapi-2.1.0.1.jar</b></p>
<p>The Enterprise Security API (ESAPI) project is an OWASP project
to create simple strong security controls for every web platform.
Security controls are not simple to build. You can read about the
hundreds of pitfalls for unwary developers on the OWASP web site. By
providing developers with a set of strong controls, we aim to
eliminate some of the complexity of creating secure web applications.
This can result in significant cost savings across the SDLC.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/esapi/esapi/2.1.0.1/esapi-2.1.0.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **esapi-2.1.0.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
ESAPI (The OWASP Enterprise Security API) is a free, open source, web application security control library. Prior to version 2.3.0.0, there is a potential for a cross-site scripting vulnerability in ESAPI caused by a incorrect regular expression for "onsiteURL" in the **antisamy-esapi.xml** configuration file that can cause "javascript:" URLs to fail to be correctly sanitized. This issue is patched in ESAPI 2.3.0.0. As a workaround, manually edit the **antisamy-esapi.xml** configuration files to change the "onsiteURL" regular expression. More information about remediation of the vulnerability, including the workaround, is available in the maintainers' release notes and security bulletin.
<p>Publish Date: 2022-04-27
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24891>CVE-2022-24891</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-q77q-vx4q-xx6q">https://github.com/advisories/GHSA-q77q-vx4q-xx6q</a></p>
<p>Release Date: 2022-04-27</p>
<p>Fix Resolution: 2.3.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2017-14735</summary>
### Vulnerable Library - <b>antisamy-1.5.3.jar</b></p>
<p>The OWASP AntiSamy project is a collection of APIs for safely allowing users to supply their own HTML
and CSS without exposing the site to XSS vulnerabilities.</p>
<p>Library home page: <a href="http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project">http://www.owasp.org/index.php/Category:OWASP_AntiSamy_Project</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/owasp/antisamy/antisamy/1.5.3/antisamy-1.5.3.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- :x: **antisamy-1.5.3.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
OWASP AntiSamy before 1.5.7 allows XSS via HTML5 entities, as demonstrated by use of : to construct a javascript: URL.
<p>Publish Date: 2017-09-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-14735>CVE-2017-14735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-14735</a></p>
<p>Release Date: 2017-09-25</p>
<p>Fix Resolution (org.owasp.antisamy:antisamy): 1.5.7</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2013-4002</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLscanner.java in Apache Xerces2 Java Parser before 2.12.0, as used in the Java Runtime Environment (JRE) in IBM Java 5.0 before 5.0 SR16-FP3, 6 before 6 SR14, 6.0.1 before 6.0.1 SR6, and 7 before 7 SR5 as well as Oracle Java SE 7u40 and earlier, Java SE 6u60 and earlier, Java SE 5.0u51 and earlier, JRockit R28.2.8 and earlier, JRockit R27.7.6 and earlier, Java SE Embedded 7u40 and earlier, and possibly other products allows remote attackers to cause a denial of service via vectors related to XML attribute names.
<p>Publish Date: 2013-07-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2013-4002>CVE-2013-4002</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.9</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2013-4002</a></p>
<p>Release Date: 2013-07-23</p>
<p>Fix Resolution: xerces:xercesImpl:Xerces-J_2_12_0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2009-2625</summary>
### Vulnerable Library - <b>xercesImpl-2.8.0.jar</b></p>
<p>Xerces2 is the next generation of high performance, fully compliant XML parsers in the
Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI),
a complete framework for building parser components and configurations that is extremely
modular and easy to program.</p>
<p>Library home page: <a href="http://xerces.apache.org/xerces2-j">http://xerces.apache.org/xerces2-j</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.8.0/xercesImpl-2.8.0.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- xom-1.2.5.jar
- :x: **xercesImpl-2.8.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
XMLScanner.java in Apache Xerces2 Java, as used in Sun Java Runtime Environment (JRE) in JDK and JRE 6 before Update 15 and JDK and JRE 5.0 before Update 20, and in other products, allows remote attackers to cause a denial of service (infinite loop and application hang) via malformed XML input, as demonstrated by the Codenomicon XML fuzzing framework.
<p>Publish Date: 2009-08-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2009-2625>CVE-2009-2625</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-2625">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2009-2625</a></p>
<p>Release Date: 2009-08-06</p>
<p>Fix Resolution: xerces:xercesImpl:2.12.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2012-5783</summary>
### Vulnerable Library - <b>commons-httpclient-3.1.jar</b></p>
<p>The HttpClient component supports the client-side of RFC 1945 (HTTP/1.0) and RFC 2616 (HTTP/1.1) , several related specifications (RFC 2109 (Cookies) , RFC 2617 (HTTP Authentication) , etc.), and provides a framework by which new request types (methods) or HTTP extensions can be created easily.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-httpclient/commons-httpclient/3.1/commons-httpclient-3.1.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- antisamy-1.5.3.jar
- :x: **commons-httpclient-3.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Apache Commons HttpClient 3.x, as used in Amazon Flexible Payments Service (FPS) merchant Java SDK and other products, does not verify that the server hostname matches a domain name in the subject's Common Name (CN) or subjectAltName field of the X.509 certificate, which allows man-in-the-middle attackers to spoof SSL servers via an arbitrary valid certificate.
<p>Publish Date: 2012-11-04
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2012-5783>CVE-2012-5783</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2012-5783">https://nvd.nist.gov/vuln/detail/CVE-2012-5783</a></p>
<p>Release Date: 2012-11-04</p>
<p>Fix Resolution (commons-httpclient:commons-httpclient): 20020423</p>
<p>Direct dependency fix Resolution (org.owasp.esapi:esapi): 2.2.0.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2021-29425</summary>
### Vulnerable Library - <b>commons-io-2.2.jar</b></p>
<p>The Commons IO library contains utility classes, stream implementations, file filters,
file comparators, endian transformation classes, and much more.</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-io/commons-io/2.2/commons-io-2.2.jar</p>
<p>
Dependency Hierarchy:
- esapi-2.1.0.1.jar (Root Library)
- commons-fileupload-1.3.1.jar
- :x: **commons-io-2.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AS-Mend/VulnerableJava/commit/52fe477d91388eb7305bb5d6d3664a8ae0847f42">52fe477d91388eb7305bb5d6d3664a8ae0847f42</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache Commons IO before 2.7, When invoking the method FileNameUtils.normalize with an improper input string, like "//../foo", or "\\..\foo", the result would be the same value, thus possibly providing access to files in the parent directory, but not further above (thus "limited" path traversal), if the calling code would use the result to construct a path value.
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-29425>CVE-2021-29425</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>4.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-29425</a></p>
<p>Release Date: 2021-04-13</p>
<p>Fix Resolution: commons-io:commons-io:2.7</p>
</p>
<p></p>
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_test | esapi jar vulnerabilities highest severity is vulnerable library esapi jar the enterprise security api esapi project is an owasp project to create simple strong security controls for every web platform security controls are not simple to build you can read about the hundreds of pitfalls for unwary developers on the owasp web site by providing developers with a set of strong controls we aim to eliminate some of the complexity of creating secure web applications this can result in significant cost savings across the sdlc path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp esapi esapi esapi jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in esapi version remediation available high esapi jar direct high commons fileupload jar transitive high bsh core jar transitive n a high commons fileupload jar transitive high xalan jar transitive n a high nekohtml jar transitive n a high xercesimpl jar transitive n a high commons fileupload jar transitive high xalan jar transitive high commons beanutils core jar transitive n a high commons beanutils core jar transitive n a medium xercesimpl jar transitive n a medium antisamy jar transitive medium antisamy jar transitive medium antisamy jar transitive medium antisamy jar transitive medium esapi jar direct medium antisamy jar transitive medium xercesimpl jar transitive n a medium xercesimpl jar transitive n a medium commons httpclient jar transitive medium commons io jar transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library esapi jar the enterprise security api esapi project is an owasp project to create simple strong security controls for every web platform security controls are not simple to build you can read about the hundreds of pitfalls for unwary developers on the owasp web site by providing developers with a set of strong controls we aim to eliminate some of the complexity of creating secure web applications this can result in significant cost savings across the sdlc path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp esapi esapi esapi jar dependency hierarchy x esapi jar vulnerable library found in head commit a href found in base branch master vulnerability details esapi the owasp enterprise security api is a free open source web application security control library prior to version the default implementation of validator getvaliddirectorypath string string file boolean may incorrectly treat the tested input string as a child of the specified parent directory this potentially could allow control flow bypass checks to be defeated if an attack can specify the entire string representing the input path this vulnerability is patched in release of esapi as a workaround it is possible to write one s own implementation of the validator interface however maintainers do not recommend this publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications path to dependency file pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy esapi jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons fileupload before diskfileitem file manipulation remote code execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons fileupload commons fileupload direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library bsh core jar beanshell core path to dependency file pom xml path to vulnerable library home wss scanner repository org beanshell bsh core bsh core jar dependency hierarchy esapi jar root library x bsh core jar vulnerable library found in head commit a href found in base branch master vulnerability details beanshell bsh before when included on the classpath by an application that uses java serialization or xstream allows remote attackers to execute arbitrary code via crafted serialized data related to xthis handler publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution cve vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications path to dependency file pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy esapi jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch master vulnerability details the multipartstream class in apache commons fileupload before as used in apache tomcat x before x before x before and x before and other products allows remote attackers to cause a denial of service cpu consumption via a long boundary string publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons fileupload commons fileupload direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library xalan jar path to dependency file pom xml path to vulnerable library home wss scanner repository xalan xalan xalan jar dependency hierarchy esapi jar root library xom jar x xalan jar vulnerable library found in head commit a href found in base branch master vulnerability details the apache xalan java xslt library is vulnerable to an integer truncation issue when processing malicious xslt stylesheets this can be used to corrupt java class files generated by the internal xsltc compiler and execute arbitrary java bytecode the apache xalan java project is dormant and in the process of being retired no future releases of apache xalan java to address this issue are expected note java runtimes such as openjdk include repackaged copies of xalan publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href cve vulnerable library nekohtml jar an html parser and tag balancer library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository net sourceforge nekohtml nekohtml nekohtml jar dependency hierarchy esapi jar root library antisamy jar x nekohtml jar vulnerable library found in head commit a href found in base branch master vulnerability details org cyberneko html is an html parser written in java the fork of org cyberneko html used by nokogiri rubygem raises a java lang outofmemoryerror exception when parsing ill formed html markup users are advised to upgrade to note the upstream library org cyberneko html is no longer maintained nokogiri uses its own fork of this library located at and this cve applies only to that fork other forks of nekohtml may have a similar vulnerability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution net sourceforge nekohtml nekohtml cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details apache java parser before allows remote attackers to cause a denial of service cpu consumption via a crafted message to an xml service which triggers hash table collisions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl ws vulnerable library commons fileupload jar the apache commons fileupload component provides a simple yet flexible means of adding support for multipart file upload functionality to servlets and web applications path to dependency file pom xml path to vulnerable library home wss scanner repository commons fileupload commons fileupload commons fileupload jar dependency hierarchy esapi jar root library x commons fileupload jar vulnerable library found in head commit a href found in base branch master vulnerability details the class fileuploadbase in apache commons fileupload before has potential resource leak inputstream not closed on exception publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution commons fileupload commons fileupload direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library xalan jar path to dependency file pom xml path to vulnerable library home wss scanner repository xalan xalan xalan jar dependency hierarchy esapi jar root library xom jar x xalan jar vulnerable library found in head commit a href found in base branch master vulnerability details the transformerfactory in apache xalan java before does not properly restrict access to certain properties when feature secure processing is enabled which allows remote attackers to bypass expected restrictions and load arbitrary classes or access external resources via a crafted xalan content header xalan entities xslt content header or xslt entities property or a java property that is bound to the xslt system property function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xalan xalan direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library commons beanutils core jar path to dependency file pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils core commons beanutils core jar dependency hierarchy esapi jar root library x commons beanutils core jar vulnerable library found in head commit a href found in base branch master vulnerability details in apache commons beanutils a special beanintrospector class was added which allows suppressing the ability for an attacker to access the classloader via the class property available on all java objects we however were not using this by default characteristic of the propertyutilsbean publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version release date fix resolution commons beanutils commons beanutils cve vulnerable library commons beanutils core jar path to dependency file pom xml path to vulnerable library home wss scanner repository commons beanutils commons beanutils core commons beanutils core jar dependency hierarchy esapi jar root library x commons beanutils core jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons beanutils as distributed in lib commons beanutils jar in apache struts x through and in other products requiring commons beanutils through does not suppress the class property which allows remote attackers to manipulate the classloader and execute arbitrary code via the class parameter as demonstrated by the passing of this parameter to the getclass method of the actionform object in struts publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons beanutils commons beanutils org apache struts core cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details there s a vulnerability within the apache xerces java xercesj xml parser when handling specially crafted xml document payloads this causes the xercesj xml parser to wait in an infinite loop which may sometimes consume system resources for prolonged duration this vulnerability is present within xercesj version and the previous versions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details in owasp antisamy before by submitting a specially crafted input a tag that supports style with active content you could bypass the library protections and supply executable code the impact is xss publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details owasp antisamy before allows xss via html tag smuggling on style content with crafted input the output serializer does not properly encode the supposed cascading style sheets css content note this issue exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details owasp antisamy before allows xss via html tag smuggling on style content with crafted input the output serializer does not properly encode the supposed cascading style sheets css content publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details owasp antisamy before allows xss via html attributes when using the html output serializer xhtml is not affected this was demonstrated by a javascript url with as the replacement for the character publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library esapi jar the enterprise security api esapi project is an owasp project to create simple strong security controls for every web platform security controls are not simple to build you can read about the hundreds of pitfalls for unwary developers on the owasp web site by providing developers with a set of strong controls we aim to eliminate some of the complexity of creating secure web applications this can result in significant cost savings across the sdlc path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp esapi esapi esapi jar dependency hierarchy x esapi jar vulnerable library found in head commit a href found in base branch master vulnerability details esapi the owasp enterprise security api is a free open source web application security control library prior to version there is a potential for a cross site scripting vulnerability in esapi caused by a incorrect regular expression for onsiteurl in the antisamy esapi xml configuration file that can cause javascript urls to fail to be correctly sanitized this issue is patched in esapi as a workaround manually edit the antisamy esapi xml configuration files to change the onsiteurl regular expression more information about remediation of the vulnerability including the workaround is available in the maintainers release notes and security bulletin publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue cve vulnerable library antisamy jar the owasp antisamy project is a collection of apis for safely allowing users to supply their own html and css without exposing the site to xss vulnerabilities library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org owasp antisamy antisamy antisamy jar dependency hierarchy esapi jar root library x antisamy jar vulnerable library found in head commit a href found in base branch master vulnerability details owasp antisamy before allows xss via entities as demonstrated by use of colon to construct a javascript url publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org owasp antisamy antisamy direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details xmlscanner java in apache java parser before as used in the java runtime environment jre in ibm java before before before and before as well as oracle java se and earlier java se and earlier java se and earlier jrockit and earlier jrockit and earlier java se embedded and earlier and possibly other products allows remote attackers to cause a denial of service via vectors related to xml attribute names publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl xerces j cve vulnerable library xercesimpl jar is the next generation of high performance fully compliant xml parsers in the apache xerces family this new version of xerces introduces the xerces native interface xni a complete framework for building parser components and configurations that is extremely modular and easy to program library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository xerces xercesimpl xercesimpl jar dependency hierarchy esapi jar root library xom jar x xercesimpl jar vulnerable library found in head commit a href found in base branch master vulnerability details xmlscanner java in apache java as used in sun java runtime environment jre in jdk and jre before update and jdk and jre before update and in other products allows remote attackers to cause a denial of service infinite loop and application hang via malformed xml input as demonstrated by the codenomicon xml fuzzing framework publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution xerces xercesimpl cve vulnerable library commons httpclient jar the httpclient component supports the client side of rfc http and rfc http several related specifications rfc cookies rfc http authentication etc and provides a framework by which new request types methods or http extensions can be created easily path to dependency file pom xml path to vulnerable library home wss scanner repository commons httpclient commons httpclient commons httpclient jar dependency hierarchy esapi jar root library antisamy jar x commons httpclient jar vulnerable library found in head commit a href found in base branch master vulnerability details apache commons httpclient x as used in amazon flexible payments service fps merchant java sdk and other products does not verify that the server hostname matches a domain name in the subject s common name cn or subjectaltname field of the x certificate which allows man in the middle attackers to spoof ssl servers via an arbitrary valid certificate publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons httpclient commons httpclient direct dependency fix resolution org owasp esapi esapi rescue worker helmet automatic remediation is available for this issue cve vulnerable library commons io jar the commons io library contains utility classes stream implementations file filters file comparators endian transformation classes and much more path to dependency file pom xml path to vulnerable library home wss scanner repository commons io commons io commons io jar dependency hierarchy esapi jar root library commons fileupload jar x commons io jar vulnerable library found in head commit a href found in base branch master vulnerability details in apache commons io before when invoking the method filenameutils normalize with an improper input string like foo or foo the result would be the same value thus possibly providing access to files in the parent directory but not further above thus limited path traversal if the calling code would use the result to construct a path value publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution commons io commons io rescue worker helmet automatic remediation is available for this issue | 0 |
100,775 | 8,754,444,535 | IssuesEvent | 2018-12-14 11:41:57 | Kademi/kademi-dev | https://api.github.com/repos/Kademi/kademi-dev | closed | Orders EDM component, new layout option | Ready to Test - Dev enhancement | Please create a new EDM component in KCom2 similar to purchasedProductsComponent with a layout like this:
This will show the product image on the left, with textual information on the right
- always show the product title and quantity, as shown
- option for whether to show the product brief
- option to show the line item cost (tax inclusive)
| 1.0 | Orders EDM component, new layout option - Please create a new EDM component in KCom2 similar to purchasedProductsComponent with a layout like this:
This will show the product image on the left, with textual information on the right
- always show the product title and quantity, as shown
- option for whether to show the product brief
- option to show the line item cost (tax inclusive)
| test | orders edm component new layout option please create a new edm component in similar to purchasedproductscomponent with a layout like this this will show the product image on the left with textual information on the right always show the product title and quantity as shown option for whether to show the product brief option to show the line item cost tax inclusive | 1 |
791,522 | 27,866,504,650 | IssuesEvent | 2023-03-21 10:36:55 | JanssenProject/jans | https://api.github.com/repos/JanssenProject/jans | opened | fix(jans-auth-server): CRITICAL - logger does not log all lines for some reason. | kind-bug comp-jans-auth-server priority-1 | **Describe the bug**
Issue was spotted during debugging of https://github.com/JanssenProject/jans/issues/4237
In linear execution path when we have
```
logger1.debug("1");
logger2.debug("2");
```
In log file we get `2` but not `1` which is not possible from execution path point of view. There is bug in loggers.
This bug is critical because when we troubleshoot issues we rely on logs. "Bad" logs leads to mis-understanding.
| 1.0 | fix(jans-auth-server): CRITICAL - logger does not log all lines for some reason. - **Describe the bug**
Issue was spotted during debugging of https://github.com/JanssenProject/jans/issues/4237
In linear execution path when we have
```
logger1.debug("1");
logger2.debug("2");
```
In log file we get `2` but not `1` which is not possible from execution path point of view. There is bug in loggers.
This bug is critical because when we troubleshoot issues we rely on logs. "Bad" logs leads to mis-understanding.
| non_test | fix jans auth server critical logger does not log all lines for some reason describe the bug issue was spotted during debugging of in linear execution path when we have debug debug in log file we get but not which is not possible from execution path point of view there is bug in loggers this bug is critical because when we troubleshoot issues we rely on logs bad logs leads to mis understanding | 0 |
46,277 | 24,456,529,249 | IssuesEvent | 2022-10-07 07:18:55 | getsentry/develop | https://api.github.com/repos/getsentry/develop | closed | Document Contexts.trace | enhancement performance | https://develop.sentry.dev/sdk/event-payloads/contexts/
Apparently, it's the same as a [Span](https://develop.sentry.dev/sdk/event-payloads/span/), that's what I learn here https://develop.sentry.dev/sdk/event-payloads/transaction/#contextstrace
if so, it'd be nice to add an Entry to the [Contexts](https://develop.sentry.dev/sdk/event-payloads/contexts/) page and link to the Spans one
@brustolin | True | Document Contexts.trace - https://develop.sentry.dev/sdk/event-payloads/contexts/
Apparently, it's the same as a [Span](https://develop.sentry.dev/sdk/event-payloads/span/), that's what I learn here https://develop.sentry.dev/sdk/event-payloads/transaction/#contextstrace
if so, it'd be nice to add an Entry to the [Contexts](https://develop.sentry.dev/sdk/event-payloads/contexts/) page and link to the Spans one
@brustolin | non_test | document contexts trace apparently it s the same as a that s what i learn here if so it d be nice to add an entry to the page and link to the spans one brustolin | 0 |
108,645 | 9,313,239,905 | IssuesEvent | 2019-03-26 05:02:44 | SatelliteQE/robottelo | https://api.github.com/repos/SatelliteQE/robottelo | closed | AssertionError: 4 != 0 tests/upgrades/test_errata.py:303: AssertionError | 6.5 Upgrade Scenario test-failure | Error Message
AssertionError: 4 != 0
Stacktrace
self = <tests.upgrades.test_errata.Scenario_errata_count testMethod=test_post_scenario_errata_count_installtion>
@post_upgrade
def test_post_scenario_errata_count_installtion(self):
"""Post-upgrade scenario that installs the package on pre-upgrade
client remotely and then verifies if the package installed.
:id: 88fd28e6-b4df-46c0-91d6-784859fd1c21
:steps:
1. Recovered pre_upgrade data for post_upgrade verification
2. Verifying errata count has not changed on satellite
3. Update Katello-agent and Restart goferd
4. Verifying the errata_ids
5. Verifying installation errata passes successfully
6. Verifying that package installation passed successfully by remote docker exec
:expectedresults:
1. errata count, erratum list should same after satellite upgrade
2. Installation of errata should be pass successfully
"""
entity_data = get_entity_data(self.__class__.__name__)
client = entity_data.get('rhel_client')
client_container_id = list(client.values())[0]
custom_repo_id = entity_data.get('custom_repo_id')
product_id = entity_data.get('product_id')
conten_view_id = entity_data.get('conten_view_id')
product = entities.Product(id=product_id).read()
content_view = entities.ContentView(id=conten_view_id).read()
custom_yum_repo = entities.Repository(id=custom_repo_id).read()
activation_key = entity_data.get('activation_key')
host = entities.Host().search(query={
'search': 'activation_key={0}'.format(activation_key)})[0]
applicable_errata_count = host.content_facet_attributes[
'errata_counts']['total']
tools_repo, rhel_repo = self._create_custom_rhel_tools_repos(product)
product.sync()
for repo in (tools_repo, rhel_repo):
content_view.repository.append(repo)
content_view = content_view.update(['repository'])
content_view.publish()
content_view = content_view.read()
self._install_or_update_package(client_container_id,
"katello-agent",
update=True)
self._run_goferd(client_container_id)
self.assertGreater(applicable_errata_count, 1)
erratum_list = entities.Errata(repository=custom_yum_repo).search(query={
'order': 'updated ASC',
'per_page': 1000,
})
errata_ids = [errata.errata_id for errata in erratum_list]
self.assertEqual(sorted(errata_ids), sorted(FAKE_9_YUM_ERRATUM))
for errata in FAKE_9_YUM_ERRATUM:
host.errata_apply(data={'errata_ids': [errata]})
applicable_errata_count -= 1
self.assertEqual(
host.content_facet_attributes['errata_counts']['total'],
> 0
)
E AssertionError: 4 != 0
tests/upgrades/test_errata.py:303: AssertionError | 1.0 | AssertionError: 4 != 0 tests/upgrades/test_errata.py:303: AssertionError - Error Message
AssertionError: 4 != 0
Stacktrace
self = <tests.upgrades.test_errata.Scenario_errata_count testMethod=test_post_scenario_errata_count_installtion>
@post_upgrade
def test_post_scenario_errata_count_installtion(self):
"""Post-upgrade scenario that installs the package on pre-upgrade
client remotely and then verifies if the package installed.
:id: 88fd28e6-b4df-46c0-91d6-784859fd1c21
:steps:
1. Recovered pre_upgrade data for post_upgrade verification
2. Verifying errata count has not changed on satellite
3. Update Katello-agent and Restart goferd
4. Verifying the errata_ids
5. Verifying installation errata passes successfully
6. Verifying that package installation passed successfully by remote docker exec
:expectedresults:
1. errata count, erratum list should same after satellite upgrade
2. Installation of errata should be pass successfully
"""
entity_data = get_entity_data(self.__class__.__name__)
client = entity_data.get('rhel_client')
client_container_id = list(client.values())[0]
custom_repo_id = entity_data.get('custom_repo_id')
product_id = entity_data.get('product_id')
conten_view_id = entity_data.get('conten_view_id')
product = entities.Product(id=product_id).read()
content_view = entities.ContentView(id=conten_view_id).read()
custom_yum_repo = entities.Repository(id=custom_repo_id).read()
activation_key = entity_data.get('activation_key')
host = entities.Host().search(query={
'search': 'activation_key={0}'.format(activation_key)})[0]
applicable_errata_count = host.content_facet_attributes[
'errata_counts']['total']
tools_repo, rhel_repo = self._create_custom_rhel_tools_repos(product)
product.sync()
for repo in (tools_repo, rhel_repo):
content_view.repository.append(repo)
content_view = content_view.update(['repository'])
content_view.publish()
content_view = content_view.read()
self._install_or_update_package(client_container_id,
"katello-agent",
update=True)
self._run_goferd(client_container_id)
self.assertGreater(applicable_errata_count, 1)
erratum_list = entities.Errata(repository=custom_yum_repo).search(query={
'order': 'updated ASC',
'per_page': 1000,
})
errata_ids = [errata.errata_id for errata in erratum_list]
self.assertEqual(sorted(errata_ids), sorted(FAKE_9_YUM_ERRATUM))
for errata in FAKE_9_YUM_ERRATUM:
host.errata_apply(data={'errata_ids': [errata]})
applicable_errata_count -= 1
self.assertEqual(
host.content_facet_attributes['errata_counts']['total'],
> 0
)
E AssertionError: 4 != 0
tests/upgrades/test_errata.py:303: AssertionError | test | assertionerror tests upgrades test errata py assertionerror error message assertionerror stacktrace self post upgrade def test post scenario errata count installtion self post upgrade scenario that installs the package on pre upgrade client remotely and then verifies if the package installed id steps recovered pre upgrade data for post upgrade verification verifying errata count has not changed on satellite update katello agent and restart goferd verifying the errata ids verifying installation errata passes successfully verifying that package installation passed successfully by remote docker exec expectedresults errata count erratum list should same after satellite upgrade installation of errata should be pass successfully entity data get entity data self class name client entity data get rhel client client container id list client values custom repo id entity data get custom repo id product id entity data get product id conten view id entity data get conten view id product entities product id product id read content view entities contentview id conten view id read custom yum repo entities repository id custom repo id read activation key entity data get activation key host entities host search query search activation key format activation key applicable errata count host content facet attributes errata counts tools repo rhel repo self create custom rhel tools repos product product sync for repo in tools repo rhel repo content view repository append repo content view content view update content view publish content view content view read self install or update package client container id katello agent update true self run goferd client container id self assertgreater applicable errata count erratum list entities errata repository custom yum repo search query order updated asc per page errata ids self assertequal sorted errata ids sorted fake yum erratum for errata in fake yum erratum host errata apply data errata ids applicable errata count self assertequal host content facet attributes e assertionerror tests upgrades test errata py assertionerror | 1 |
198,111 | 22,617,897,303 | IssuesEvent | 2022-06-30 01:20:40 | faizulho/sgmelayu-sanity-gatsby-blog | https://api.github.com/repos/faizulho/sgmelayu-sanity-gatsby-blog | opened | CVE-2022-2216 (High) detected in parse-url-5.0.2.tgz, parse-url-5.0.1.tgz | security vulnerability | ## CVE-2022-2216 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>parse-url-5.0.2.tgz</b>, <b>parse-url-5.0.1.tgz</b></p></summary>
<p>
<details><summary><b>parse-url-5.0.2.tgz</b></p></summary>
<p>An advanced url parser supporting git urls too.</p>
<p>Library home page: <a href="https://registry.npmjs.org/parse-url/-/parse-url-5.0.2.tgz">https://registry.npmjs.org/parse-url/-/parse-url-5.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/parse-url/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- github-client-3.22.0.tgz
- git-url-parse-11.1.3.tgz
- git-up-4.0.2.tgz
- :x: **parse-url-5.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>parse-url-5.0.1.tgz</b></p></summary>
<p>An advanced url parser supporting git urls too.</p>
<p>Library home page: <a href="https://registry.npmjs.org/parse-url/-/parse-url-5.0.1.tgz">https://registry.npmjs.org/parse-url/-/parse-url-5.0.1.tgz</a></p>
<p>Path to dependency file: /web/package.json</p>
<p>Path to vulnerable library: /web/node_modules/parse-url/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-2.23.9.tgz (Root Library)
- gatsby-telemetry-1.3.13.tgz
- git-up-4.0.1.tgz
- :x: **parse-url-5.0.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/faizulho/sgmelayu-sanity-gatsby-blog/commit/59a4b939cc45411ed504a2bb8ccd758b8585d577">59a4b939cc45411ed504a2bb8ccd758b8585d577</a></p>
<p>Found in base branch: <b>production</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Server-Side Request Forgery (SSRF) in GitHub repository ionicabizau/parse-url prior to 7.0.0.
<p>Publish Date: 2022-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-2216>CVE-2022-2216</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/505a3d39-2723-4a06-b1f7-9b2d133c92e1/">https://huntr.dev/bounties/505a3d39-2723-4a06-b1f7-9b2d133c92e1/</a></p>
<p>Release Date: 2022-06-27</p>
<p>Fix Resolution: parse-url - 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-2216 (High) detected in parse-url-5.0.2.tgz, parse-url-5.0.1.tgz - ## CVE-2022-2216 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>parse-url-5.0.2.tgz</b>, <b>parse-url-5.0.1.tgz</b></p></summary>
<p>
<details><summary><b>parse-url-5.0.2.tgz</b></p></summary>
<p>An advanced url parser supporting git urls too.</p>
<p>Library home page: <a href="https://registry.npmjs.org/parse-url/-/parse-url-5.0.2.tgz">https://registry.npmjs.org/parse-url/-/parse-url-5.0.2.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/parse-url/package.json</p>
<p>
Dependency Hierarchy:
- lerna-3.22.1.tgz (Root Library)
- version-3.22.1.tgz
- github-client-3.22.0.tgz
- git-url-parse-11.1.3.tgz
- git-up-4.0.2.tgz
- :x: **parse-url-5.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>parse-url-5.0.1.tgz</b></p></summary>
<p>An advanced url parser supporting git urls too.</p>
<p>Library home page: <a href="https://registry.npmjs.org/parse-url/-/parse-url-5.0.1.tgz">https://registry.npmjs.org/parse-url/-/parse-url-5.0.1.tgz</a></p>
<p>Path to dependency file: /web/package.json</p>
<p>Path to vulnerable library: /web/node_modules/parse-url/package.json</p>
<p>
Dependency Hierarchy:
- gatsby-2.23.9.tgz (Root Library)
- gatsby-telemetry-1.3.13.tgz
- git-up-4.0.1.tgz
- :x: **parse-url-5.0.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/faizulho/sgmelayu-sanity-gatsby-blog/commit/59a4b939cc45411ed504a2bb8ccd758b8585d577">59a4b939cc45411ed504a2bb8ccd758b8585d577</a></p>
<p>Found in base branch: <b>production</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Server-Side Request Forgery (SSRF) in GitHub repository ionicabizau/parse-url prior to 7.0.0.
<p>Publish Date: 2022-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-2216>CVE-2022-2216</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/505a3d39-2723-4a06-b1f7-9b2d133c92e1/">https://huntr.dev/bounties/505a3d39-2723-4a06-b1f7-9b2d133c92e1/</a></p>
<p>Release Date: 2022-06-27</p>
<p>Fix Resolution: parse-url - 6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in parse url tgz parse url tgz cve high severity vulnerability vulnerable libraries parse url tgz parse url tgz parse url tgz an advanced url parser supporting git urls too library home page a href path to dependency file package json path to vulnerable library node modules parse url package json dependency hierarchy lerna tgz root library version tgz github client tgz git url parse tgz git up tgz x parse url tgz vulnerable library parse url tgz an advanced url parser supporting git urls too library home page a href path to dependency file web package json path to vulnerable library web node modules parse url package json dependency hierarchy gatsby tgz root library gatsby telemetry tgz git up tgz x parse url tgz vulnerable library found in head commit a href found in base branch production vulnerability details server side request forgery ssrf in github repository ionicabizau parse url prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution parse url step up your open source security game with mend | 0 |
102,438 | 16,566,596,654 | IssuesEvent | 2021-05-29 14:43:53 | Xcov19/mycovidconnect | https://api.github.com/repos/Xcov19/mycovidconnect | closed | CVE-2021-23386 (High) detected in dns-packet-1.3.1.tgz - autoclosed | security vulnerability | ## CVE-2021-23386 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dns-packet-1.3.1.tgz</b></p></summary>
<p>An abstract-encoding compliant module for encoding / decoding DNS packets</p>
<p>Library home page: <a href="https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz">https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz</a></p>
<p>Path to dependency file: mycovidconnect/package.json</p>
<p>Path to vulnerable library: mycovidconnect/node_modules/dns-packet/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- bonjour-3.5.0.tgz
- multicast-dns-6.2.3.tgz
- :x: **dns-packet-1.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Xcov19/mycovidconnect/commit/d88880e86833de5f6befa1e02233ccd1d1ffe86f">d88880e86833de5f6befa1e02233ccd1d1ffe86f</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package dns-packet before 5.2.2. It creates buffers with allocUnsafe and does not always fill them before forming network packets. This can expose internal application memory over unencrypted network when querying crafted invalid domain names.
<p>Publish Date: 2021-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23386>CVE-2021-23386</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386</a></p>
<p>Release Date: 2021-05-20</p>
<p>Fix Resolution: dns-packet - 5.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23386 (High) detected in dns-packet-1.3.1.tgz - autoclosed - ## CVE-2021-23386 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>dns-packet-1.3.1.tgz</b></p></summary>
<p>An abstract-encoding compliant module for encoding / decoding DNS packets</p>
<p>Library home page: <a href="https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz">https://registry.npmjs.org/dns-packet/-/dns-packet-1.3.1.tgz</a></p>
<p>Path to dependency file: mycovidconnect/package.json</p>
<p>Path to vulnerable library: mycovidconnect/node_modules/dns-packet/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-3.4.4.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- bonjour-3.5.0.tgz
- multicast-dns-6.2.3.tgz
- :x: **dns-packet-1.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Xcov19/mycovidconnect/commit/d88880e86833de5f6befa1e02233ccd1d1ffe86f">d88880e86833de5f6befa1e02233ccd1d1ffe86f</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package dns-packet before 5.2.2. It creates buffers with allocUnsafe and does not always fill them before forming network packets. This can expose internal application memory over unencrypted network when querying crafted invalid domain names.
<p>Publish Date: 2021-05-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23386>CVE-2021-23386</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23386</a></p>
<p>Release Date: 2021-05-20</p>
<p>Fix Resolution: dns-packet - 5.2.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in dns packet tgz autoclosed cve high severity vulnerability vulnerable library dns packet tgz an abstract encoding compliant module for encoding decoding dns packets library home page a href path to dependency file mycovidconnect package json path to vulnerable library mycovidconnect node modules dns packet package json dependency hierarchy react scripts tgz root library webpack dev server tgz bonjour tgz multicast dns tgz x dns packet tgz vulnerable library found in head commit a href found in base branch develop vulnerability details this affects the package dns packet before it creates buffers with allocunsafe and does not always fill them before forming network packets this can expose internal application memory over unencrypted network when querying crafted invalid domain names publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required low user interaction none scope changed impact metrics confidentiality impact high integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution dns packet step up your open source security game with whitesource | 0 |
8,229 | 2,967,792,176 | IssuesEvent | 2015-07-13 04:31:00 | sass/libsass | https://api.github.com/repos/sass/libsass | reopened | CSS comments inside selectors yields invalid top-level expression | Bug - Confirmed Dev - PR Ready test written | The following SCSS (taken from normalize.css) causes an "invalid top-level expression" error.
Removing the `/* 1 */` comment makes it work.
```css
button,
html input[type="button"], /* 1 */
input[type="reset"],
input[type="submit"] {
-webkit-appearance: button; /* 2 */
cursor: pointer; /* 3 */
}
```
I can write a sass-spec PR a bit later. | 1.0 | CSS comments inside selectors yields invalid top-level expression - The following SCSS (taken from normalize.css) causes an "invalid top-level expression" error.
Removing the `/* 1 */` comment makes it work.
```css
button,
html input[type="button"], /* 1 */
input[type="reset"],
input[type="submit"] {
-webkit-appearance: button; /* 2 */
cursor: pointer; /* 3 */
}
```
I can write a sass-spec PR a bit later. | test | css comments inside selectors yields invalid top level expression the following scss taken from normalize css causes an invalid top level expression error removing the comment makes it work css button html input input input webkit appearance button cursor pointer i can write a sass spec pr a bit later | 1 |
27,477 | 5,030,442,118 | IssuesEvent | 2016-12-16 00:49:18 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | i18n - Specified key was too long | Defect | This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.3.10.
* Platform and Target: Linux with MySQL version: 5.1.45p1-log - PHP Version 5.5.17 -
### What you did
I run i18n.sql
```sql
CREATE TABLE i18n (
id int NOT NULL auto_increment,
locale varchar(6) NOT NULL,
model varchar(255) NOT NULL,
foreign_key int(10) NOT NULL,
field varchar(255) NOT NULL,
content text,
PRIMARY KEY (id),
UNIQUE INDEX I18N_LOCALE_FIELD(locale, model, foreign_key, field),
INDEX I18N_FIELD(model, foreign_key, field)
)
```
### What happened
I got this error
```Error in query (1071): Specified key was too long; max key length is 1000 bytes```
### What you expected to happen
I expect that the i18n table should be created.
| 1.0 | i18n - Specified key was too long - This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.3.10.
* Platform and Target: Linux with MySQL version: 5.1.45p1-log - PHP Version 5.5.17 -
### What you did
I run i18n.sql
```sql
CREATE TABLE i18n (
id int NOT NULL auto_increment,
locale varchar(6) NOT NULL,
model varchar(255) NOT NULL,
foreign_key int(10) NOT NULL,
field varchar(255) NOT NULL,
content text,
PRIMARY KEY (id),
UNIQUE INDEX I18N_LOCALE_FIELD(locale, model, foreign_key, field),
INDEX I18N_FIELD(model, foreign_key, field)
)
```
### What happened
I got this error
```Error in query (1071): Specified key was too long; max key length is 1000 bytes```
### What you expected to happen
I expect that the i18n table should be created.
| non_test | specified key was too long this is a multiple allowed bug enhancement feature discussion rfc cakephp version platform and target linux with mysql version log php version what you did i run sql sql create table id int not null auto increment locale varchar not null model varchar not null foreign key int not null field varchar not null content text primary key id unique index locale field locale model foreign key field index field model foreign key field what happened i got this error error in query specified key was too long max key length is bytes what you expected to happen i expect that the table should be created | 0 |
238,354 | 19,714,860,625 | IssuesEvent | 2022-01-13 09:59:45 | pingcap/tiflow | https://api.github.com/repos/pingcap/tiflow | opened | Flaky test:redo/writer | component/test | ### Which jobs are flaking?
https://ci2.pingcap.net/blue/organizations/jenkins/cdc_ghpr_leak_test/detail/cdc_ghpr_leak_test/18115/pipeline
### Which test(s) are flaking?
redo/writer
### Jenkins logs or GitHub Actions link
```log
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:51.480 +08:00] [WARN] [file.go:448] ["delete redo log in s3 fail"] [error="[CDC:ErrS3StorageAPI]s3 storage api: ignore err; ignore err"] [errorVerbose="[CDC:ErrS3StorageAPI]s3 storage api: ignore err; ignore err\ngithub.com/pingcap/errors.AddStack\n\t/go/pkg/mod/github.com/pingcap/errors@v0.11.5-0.20211224045212-9687c2b0f87c/errors.go:174\ngithub.com/pingcap/errors.(*Error).GenWithStackByArgs\n\t/go/pkg/mod/github.com/pingcap/errors@v0.11.5-0.20211224045212-9687c2b0f87c/normalize.go:164\ngithub.com/pingcap/tiflow/pkg/errors.WrapError\n\t/home/jenkins/agent/workspace/cdc_ghpr_leak_test/go/src/github.com/pingcap/tiflow/pkg/errors/helper.go:30\ngithub.com/pingcap/tiflow/cdc/redo/writer.(*Writer).GC.func1\n\t/home/jenkins/agent/workspace/cdc_ghpr_leak_test/go/src/github.com/pingcap/tiflow/cdc/redo/writer/file.go:447\nruntime.goexit\n\t/usr/local/go/src/runtime/asm_amd64.s:1371"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:51.581 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open /tmp/redo-GC072093596not-exist: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.620 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.620 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.621 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.621 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] --- FAIL: TestWriterRedoGC (0.01s)
[2022-01-13T09:27:26.994Z] writer_test.go:760:
[2022-01-13T09:27:26.994Z] Error Trace: writer_test.go:760
[2022-01-13T09:27:26.994Z] Error: Should have called with given arguments
[2022-01-13T09:27:26.994Z] Test: TestWriterRedoGC
[2022-01-13T09:27:26.994Z] Messages: Expected "GC" to have been called with:
[2022-01-13T09:27:26.994Z] [mock.Anything]
[2022-01-13T09:27:26.994Z] but actual calls were:
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] FAIL
[2022-01-13T09:27:26.994Z] FAIL github.com/pingcap/tiflow/cdc/redo/writer 3.554s
```
### Anything else we need to know
- Does this test exist for other branches as well?
- Has there been a high frequency of failure lately? | 1.0 | Flaky test:redo/writer - ### Which jobs are flaking?
https://ci2.pingcap.net/blue/organizations/jenkins/cdc_ghpr_leak_test/detail/cdc_ghpr_leak_test/18115/pipeline
### Which test(s) are flaking?
redo/writer
### Jenkins logs or GitHub Actions link
```log
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:51.480 +08:00] [WARN] [file.go:448] ["delete redo log in s3 fail"] [error="[CDC:ErrS3StorageAPI]s3 storage api: ignore err; ignore err"] [errorVerbose="[CDC:ErrS3StorageAPI]s3 storage api: ignore err; ignore err\ngithub.com/pingcap/errors.AddStack\n\t/go/pkg/mod/github.com/pingcap/errors@v0.11.5-0.20211224045212-9687c2b0f87c/errors.go:174\ngithub.com/pingcap/errors.(*Error).GenWithStackByArgs\n\t/go/pkg/mod/github.com/pingcap/errors@v0.11.5-0.20211224045212-9687c2b0f87c/normalize.go:164\ngithub.com/pingcap/tiflow/pkg/errors.WrapError\n\t/home/jenkins/agent/workspace/cdc_ghpr_leak_test/go/src/github.com/pingcap/tiflow/pkg/errors/helper.go:30\ngithub.com/pingcap/tiflow/cdc/redo/writer.(*Writer).GC.func1\n\t/home/jenkins/agent/workspace/cdc_ghpr_leak_test/go/src/github.com/pingcap/tiflow/cdc/redo/writer/file.go:447\nruntime.goexit\n\t/usr/local/go/src/runtime/asm_amd64.s:1371"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:51.581 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open /tmp/redo-GC072093596not-exist: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.620 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.620 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.621 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] [2022/01/13 17:25:53.621 +08:00] [WARN] [file.go:475] ["check removed log dir fail"] [error="open dirt: no such file or directory"]
[2022-01-13T09:27:26.994Z] --- FAIL: TestWriterRedoGC (0.01s)
[2022-01-13T09:27:26.994Z] writer_test.go:760:
[2022-01-13T09:27:26.994Z] Error Trace: writer_test.go:760
[2022-01-13T09:27:26.994Z] Error: Should have called with given arguments
[2022-01-13T09:27:26.994Z] Test: TestWriterRedoGC
[2022-01-13T09:27:26.994Z] Messages: Expected "GC" to have been called with:
[2022-01-13T09:27:26.994Z] [mock.Anything]
[2022-01-13T09:27:26.994Z] but actual calls were:
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] []
[2022-01-13T09:27:26.994Z] FAIL
[2022-01-13T09:27:26.994Z] FAIL github.com/pingcap/tiflow/cdc/redo/writer 3.554s
```
### Anything else we need to know
- Does this test exist for other branches as well?
- Has there been a high frequency of failure lately? | test | flaky test:redo writer which jobs are flaking which test s are flaking redo writer jenkins logs or github actions link log storage api ignore err ignore err storage api ignore err ignore err ngithub com pingcap errors addstack n t go pkg mod github com pingcap errors errors go ngithub com pingcap errors error genwithstackbyargs n t go pkg mod github com pingcap errors normalize go ngithub com pingcap tiflow pkg errors wraperror n t home jenkins agent workspace cdc ghpr leak test go src github com pingcap tiflow pkg errors helper go ngithub com pingcap tiflow cdc redo writer writer gc n t home jenkins agent workspace cdc ghpr leak test go src github com pingcap tiflow cdc redo writer file go nruntime goexit n t usr local go src runtime asm s fail testwriterredogc writer test go error trace writer test go error should have called with given arguments test testwriterredogc messages expected gc to have been called with but actual calls were fail fail github com pingcap tiflow cdc redo writer anything else we need to know does this test exist for other branches as well has there been a high frequency of failure lately | 1 |
408,647 | 27,700,940,683 | IssuesEvent | 2023-03-14 07:57:45 | spring-projects/spring-data-redis | https://api.github.com/repos/spring-projects/spring-data-redis | closed | Documentation inaccuracy for Redis Pub/Sub section | type: documentation | Hi
Here's the code from the reference documentation to attach custom message handler:
```
@Bean
RedisMessageListenerContainer redisMessageListenerContainer(RedisConnectionFactory connectionFactory, DefaultMessageDelegate listener) {
RedisMessageListenerContainer container = new RedisMessageListenerContainer();
container.setConnectionFactory(connectionFactory);
container.addMessageListener(new MessageListenerAdapter(listener, "handleMessage"), ChannelTopic.of("chatroom"));
return container;
}
```
However it would fail with the error message:
```
java.lang.NullPointerException: Cannot invoke "org.springframework.data.redis.listener.adapter.MessageListenerAdapter$MethodInvoker.getMethodName()" because "this.invoker" is null
at org.springframework.data.redis.listener.adapter.MessageListenerAdapter.onMessage(MessageListenerAdapter.java:307)
at org.springframework.data.redis.listener.RedisMessageListenerContainer.processMessage(RedisMessageListenerContainer.java:845)
at org.springframework.data.redis.listener.RedisMessageListenerContainer.lambda$dispatchMessage$7(RedisMessageListenerContainer.java:993)
at java.base/java.lang.Thread.run(Thread.java:1589)
```
The issue that this code doesn't invoke afterPropertiesSet as clearly mentioned in JavaDocs of MessageListenerAdapter:
`Make sure to call {@link #afterPropertiesSet()} after setting all the parameters on the adapter.`
| 1.0 | Documentation inaccuracy for Redis Pub/Sub section - Hi
Here's the code from the reference documentation to attach custom message handler:
```
@Bean
RedisMessageListenerContainer redisMessageListenerContainer(RedisConnectionFactory connectionFactory, DefaultMessageDelegate listener) {
RedisMessageListenerContainer container = new RedisMessageListenerContainer();
container.setConnectionFactory(connectionFactory);
container.addMessageListener(new MessageListenerAdapter(listener, "handleMessage"), ChannelTopic.of("chatroom"));
return container;
}
```
However it would fail with the error message:
```
java.lang.NullPointerException: Cannot invoke "org.springframework.data.redis.listener.adapter.MessageListenerAdapter$MethodInvoker.getMethodName()" because "this.invoker" is null
at org.springframework.data.redis.listener.adapter.MessageListenerAdapter.onMessage(MessageListenerAdapter.java:307)
at org.springframework.data.redis.listener.RedisMessageListenerContainer.processMessage(RedisMessageListenerContainer.java:845)
at org.springframework.data.redis.listener.RedisMessageListenerContainer.lambda$dispatchMessage$7(RedisMessageListenerContainer.java:993)
at java.base/java.lang.Thread.run(Thread.java:1589)
```
The issue that this code doesn't invoke afterPropertiesSet as clearly mentioned in JavaDocs of MessageListenerAdapter:
`Make sure to call {@link #afterPropertiesSet()} after setting all the parameters on the adapter.`
| non_test | documentation inaccuracy for redis pub sub section hi here s the code from the reference documentation to attach custom message handler bean redismessagelistenercontainer redismessagelistenercontainer redisconnectionfactory connectionfactory defaultmessagedelegate listener redismessagelistenercontainer container new redismessagelistenercontainer container setconnectionfactory connectionfactory container addmessagelistener new messagelisteneradapter listener handlemessage channeltopic of chatroom return container however it would fail with the error message java lang nullpointerexception cannot invoke org springframework data redis listener adapter messagelisteneradapter methodinvoker getmethodname because this invoker is null at org springframework data redis listener adapter messagelisteneradapter onmessage messagelisteneradapter java at org springframework data redis listener redismessagelistenercontainer processmessage redismessagelistenercontainer java at org springframework data redis listener redismessagelistenercontainer lambda dispatchmessage redismessagelistenercontainer java at java base java lang thread run thread java the issue that this code doesn t invoke afterpropertiesset as clearly mentioned in javadocs of messagelisteneradapter make sure to call link afterpropertiesset after setting all the parameters on the adapter | 0 |
121,428 | 10,168,247,460 | IssuesEvent | 2019-08-07 20:19:16 | CityOfBoston/boston.gov-d8 | https://api.github.com/repos/CityOfBoston/boston.gov-d8 | opened | Articles: Address thumbnail image formatting issues | max-testing | Under the right column where the phone number, email, and address is listed, the address thumbnail image does not snap to the top like the D7 site.
D7: https://www.boston.gov/departments/environment/air-pollution-control-commission/downtown-parking-freeze
D8: http://bostond8dev.prod.acquia-sites.com/downtown-parking-freeze
Tested on Chrome 76 on OS X Mojave | 1.0 | Articles: Address thumbnail image formatting issues - Under the right column where the phone number, email, and address is listed, the address thumbnail image does not snap to the top like the D7 site.
D7: https://www.boston.gov/departments/environment/air-pollution-control-commission/downtown-parking-freeze
D8: http://bostond8dev.prod.acquia-sites.com/downtown-parking-freeze
Tested on Chrome 76 on OS X Mojave | test | articles address thumbnail image formatting issues under the right column where the phone number email and address is listed the address thumbnail image does not snap to the top like the site tested on chrome on os x mojave | 1 |
97,946 | 29,116,611,287 | IssuesEvent | 2023-05-17 01:56:16 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Protocol Buffer error - critical I cannot import tensorflow | stat:awaiting response type:bug type:build/install stale TF 2.11 | <details><summary>Click to expand!</summary>
### Issue Type
Bug
### Have you reproduced the bug with TF nightly?
No
### Source
binary
### Tensorflow Version
2.11
### Custom Code
No
### OS Platform and Distribution
_No response_
### Mobile device
_No response_
### Python version
3.10.6
### Bazel version
_No response_
### GCC/Compiler version
_No response_
### CUDA/cuDNN version
_No response_
### GPU model and memory
_No response_
### Current Behaviour?
Bug occurred today when reloading a jupyter notebook.
I previously tried to install cuML
https://docs.rapids.ai/install#pip-install
but the trace error seems unrelated to it, but mention `Protocol Buffers`:
### Standalone code to reproduce the issue
```shell
The error occurs when :
`import tensorflow`
and consequently any other import of libraries based on tf, such as:
`import umap`
will fail.
I cannot use TF anymore.
```
### Relevant log output
```shell
---------------------------------------------------------------------------
TypeError Traceback (most recent call last)
Cell In[33], line 1
----> 1 import tensorflow as tf
2 #import umap
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/__init__.py:37
34 import sys as _sys
35 import typing as _typing
---> 37 from tensorflow.python.tools import module_util as _module_util
38 from tensorflow.python.util.lazy_loader import LazyLoader as _LazyLoader
40 # Make sure code inside the TensorFlow codebase can use tf2.enabled() at import.
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/python/__init__.py:37
29 # We aim to keep this file minimal and ideally remove completely.
30 # If you are adding a new file with @tf_export decorators,
31 # import it in modules_with_exports.py instead.
32
33 # go/tf-wildcard-import
34 # pylint: disable=wildcard-import,g-bad-import-order,g-import-not-at-top
36 from tensorflow.python import pywrap_tensorflow as _pywrap_tensorflow
---> 37 from tensorflow.python.eager import context
39 # pylint: enable=wildcard-import
40
41 # Bring in subpackages.
42 from tensorflow.python import data
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/python/eager/context.py:28
25 from absl import logging
26 import numpy as np
---> 28 from tensorflow.core.framework import function_pb2
29 from tensorflow.core.protobuf import config_pb2
30 from tensorflow.core.protobuf import coordination_config_pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/function_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import attr_value_pb2 as tensorflow_dot_core_dot_framework_dot_attr__value__pb2
17 from tensorflow.core.framework import node_def_pb2 as tensorflow_dot_core_dot_framework_dot_node__def__pb2
18 from tensorflow.core.framework import op_def_pb2 as tensorflow_dot_core_dot_framework_dot_op__def__pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/attr_value_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import tensor_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__pb2
17 from tensorflow.core.framework import tensor_shape_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2
18 from tensorflow.core.framework import types_pb2 as tensorflow_dot_core_dot_framework_dot_types__pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/tensor_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import resource_handle_pb2 as tensorflow_dot_core_dot_framework_dot_resource__handle__pb2
17 from tensorflow.core.framework import tensor_shape_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2
18 from tensorflow.core.framework import types_pb2 as tensorflow_dot_core_dot_framework_dot_types__pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/resource_handle_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import tensor_shape_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2
17 from tensorflow.core.framework import types_pb2 as tensorflow_dot_core_dot_framework_dot_types__pb2
20 DESCRIPTOR = _descriptor.FileDescriptor(
21 name='tensorflow/core/framework/resource_handle.proto',
22 package='tensorflow',
(...)
26 ,
27 dependencies=[tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2.DESCRIPTOR,tensorflow_dot_core_dot_framework_dot_types__pb2.DESCRIPTOR,])
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/tensor_shape_pb2.py:36
13 _sym_db = _symbol_database.Default()
18 DESCRIPTOR = _descriptor.FileDescriptor(
19 name='tensorflow/core/framework/tensor_shape.proto',
20 package='tensorflow',
(...)
23 serialized_pb=_b('\n,tensorflow/core/framework/tensor_shape.proto\x12\ntensorflow\"z\n\x10TensorShapeProto\x12-\n\x03\x64im\x18\x02 \x03(\x0b\x32 .tensorflow.TensorShapeProto.Dim\x12\x14\n\x0cunknown_rank\x18\x03 \x01(\x08\x1a!\n\x03\x44im\x12\x0c\n\x04size\x18\x01 \x01(\x03\x12\x0c\n\x04name\x18\x02 \x01(\tB\x87\x01\n\x18org.tensorflow.frameworkB\x11TensorShapeProtosP\x01ZSgithub.com/tensorflow/tensorflow/tensorflow/go/core/framework/tensor_shape_go_proto\xf8\x01\x01\x62\x06proto3')
24 )
29 _TENSORSHAPEPROTO_DIM = _descriptor.Descriptor(
30 name='Dim',
31 full_name='tensorflow.TensorShapeProto.Dim',
32 filename=None,
33 file=DESCRIPTOR,
34 containing_type=None,
35 fields=[
---> 36 _descriptor.FieldDescriptor(
37 name='size', full_name='tensorflow.TensorShapeProto.Dim.size', index=0,
38 number=1, type=3, cpp_type=2, label=1,
39 has_default_value=False, default_value=0,
40 message_type=None, enum_type=None, containing_type=None,
41 is_extension=False, extension_scope=None,
42 serialized_options=None, file=DESCRIPTOR),
43 _descriptor.FieldDescriptor(
44 name='name', full_name='tensorflow.TensorShapeProto.Dim.name', index=1,
45 number=2, type=9, cpp_type=9, label=1,
46 has_default_value=False, default_value=_b("").decode('utf-8'),
47 message_type=None, enum_type=None, containing_type=None,
48 is_extension=False, extension_scope=None,
49 serialized_options=None, file=DESCRIPTOR),
50 ],
51 extensions=[
52 ],
53 nested_types=[],
54 enum_types=[
55 ],
56 serialized_options=None,
57 is_extendable=False,
58 syntax='proto3',
59 extension_ranges=[],
60 oneofs=[
61 ],
62 serialized_start=149,
63 serialized_end=182,
64 )
66 _TENSORSHAPEPROTO = _descriptor.Descriptor(
67 name='TensorShapeProto',
68 full_name='tensorflow.TensorShapeProto',
(...)
100 serialized_end=182,
101 )
103 _TENSORSHAPEPROTO_DIM.containing_type = _TENSORSHAPEPROTO
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/google/protobuf/descriptor.py:560, in FieldDescriptor.__new__(cls, name, full_name, index, number, type, cpp_type, label, default_value, message_type, enum_type, containing_type, is_extension, extension_scope, options, serialized_options, has_default_value, containing_oneof, json_name, file, create_key)
554 def __new__(cls, name, full_name, index, number, type, cpp_type, label,
555 default_value, message_type, enum_type, containing_type,
556 is_extension, extension_scope, options=None,
557 serialized_options=None,
558 has_default_value=True, containing_oneof=None, json_name=None,
559 file=None, create_key=None): # pylint: disable=redefined-builtin
--> 560 _message.Message._CheckCalledFromGeneratedFile()
561 if is_extension:
562 return _message.default_pool.FindExtensionByName(full_name)
TypeError: Descriptors cannot not be created directly.
If this call came from a _pb2.py file, your generated code is out of date and must be regenerated with protoc >= 3.19.0.
If you cannot immediately regenerate your protos, some other possible workarounds are:
1. Downgrade the protobuf package to 3.20.x or lower.
2. Set PROTOCOL_BUFFERS_PYTHON_IMPLEMENTATION=python (but this will use pure-Python parsing and will be much slower).
More information: https://developers.google.com/protocol-buffers/docs/news/2022-05-06#python-updates
```
</details> | 1.0 | Protocol Buffer error - critical I cannot import tensorflow - <details><summary>Click to expand!</summary>
### Issue Type
Bug
### Have you reproduced the bug with TF nightly?
No
### Source
binary
### Tensorflow Version
2.11
### Custom Code
No
### OS Platform and Distribution
_No response_
### Mobile device
_No response_
### Python version
3.10.6
### Bazel version
_No response_
### GCC/Compiler version
_No response_
### CUDA/cuDNN version
_No response_
### GPU model and memory
_No response_
### Current Behaviour?
Bug occurred today when reloading a jupyter notebook.
I previously tried to install cuML
https://docs.rapids.ai/install#pip-install
but the trace error seems unrelated to it, but mention `Protocol Buffers`:
### Standalone code to reproduce the issue
```shell
The error occurs when :
`import tensorflow`
and consequently any other import of libraries based on tf, such as:
`import umap`
will fail.
I cannot use TF anymore.
```
### Relevant log output
```shell
---------------------------------------------------------------------------
TypeError Traceback (most recent call last)
Cell In[33], line 1
----> 1 import tensorflow as tf
2 #import umap
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/__init__.py:37
34 import sys as _sys
35 import typing as _typing
---> 37 from tensorflow.python.tools import module_util as _module_util
38 from tensorflow.python.util.lazy_loader import LazyLoader as _LazyLoader
40 # Make sure code inside the TensorFlow codebase can use tf2.enabled() at import.
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/python/__init__.py:37
29 # We aim to keep this file minimal and ideally remove completely.
30 # If you are adding a new file with @tf_export decorators,
31 # import it in modules_with_exports.py instead.
32
33 # go/tf-wildcard-import
34 # pylint: disable=wildcard-import,g-bad-import-order,g-import-not-at-top
36 from tensorflow.python import pywrap_tensorflow as _pywrap_tensorflow
---> 37 from tensorflow.python.eager import context
39 # pylint: enable=wildcard-import
40
41 # Bring in subpackages.
42 from tensorflow.python import data
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/python/eager/context.py:28
25 from absl import logging
26 import numpy as np
---> 28 from tensorflow.core.framework import function_pb2
29 from tensorflow.core.protobuf import config_pb2
30 from tensorflow.core.protobuf import coordination_config_pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/function_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import attr_value_pb2 as tensorflow_dot_core_dot_framework_dot_attr__value__pb2
17 from tensorflow.core.framework import node_def_pb2 as tensorflow_dot_core_dot_framework_dot_node__def__pb2
18 from tensorflow.core.framework import op_def_pb2 as tensorflow_dot_core_dot_framework_dot_op__def__pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/attr_value_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import tensor_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__pb2
17 from tensorflow.core.framework import tensor_shape_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2
18 from tensorflow.core.framework import types_pb2 as tensorflow_dot_core_dot_framework_dot_types__pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/tensor_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import resource_handle_pb2 as tensorflow_dot_core_dot_framework_dot_resource__handle__pb2
17 from tensorflow.core.framework import tensor_shape_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2
18 from tensorflow.core.framework import types_pb2 as tensorflow_dot_core_dot_framework_dot_types__pb2
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/resource_handle_pb2.py:16
11 # @@protoc_insertion_point(imports)
13 _sym_db = _symbol_database.Default()
---> 16 from tensorflow.core.framework import tensor_shape_pb2 as tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2
17 from tensorflow.core.framework import types_pb2 as tensorflow_dot_core_dot_framework_dot_types__pb2
20 DESCRIPTOR = _descriptor.FileDescriptor(
21 name='tensorflow/core/framework/resource_handle.proto',
22 package='tensorflow',
(...)
26 ,
27 dependencies=[tensorflow_dot_core_dot_framework_dot_tensor__shape__pb2.DESCRIPTOR,tensorflow_dot_core_dot_framework_dot_types__pb2.DESCRIPTOR,])
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/tensorflow/core/framework/tensor_shape_pb2.py:36
13 _sym_db = _symbol_database.Default()
18 DESCRIPTOR = _descriptor.FileDescriptor(
19 name='tensorflow/core/framework/tensor_shape.proto',
20 package='tensorflow',
(...)
23 serialized_pb=_b('\n,tensorflow/core/framework/tensor_shape.proto\x12\ntensorflow\"z\n\x10TensorShapeProto\x12-\n\x03\x64im\x18\x02 \x03(\x0b\x32 .tensorflow.TensorShapeProto.Dim\x12\x14\n\x0cunknown_rank\x18\x03 \x01(\x08\x1a!\n\x03\x44im\x12\x0c\n\x04size\x18\x01 \x01(\x03\x12\x0c\n\x04name\x18\x02 \x01(\tB\x87\x01\n\x18org.tensorflow.frameworkB\x11TensorShapeProtosP\x01ZSgithub.com/tensorflow/tensorflow/tensorflow/go/core/framework/tensor_shape_go_proto\xf8\x01\x01\x62\x06proto3')
24 )
29 _TENSORSHAPEPROTO_DIM = _descriptor.Descriptor(
30 name='Dim',
31 full_name='tensorflow.TensorShapeProto.Dim',
32 filename=None,
33 file=DESCRIPTOR,
34 containing_type=None,
35 fields=[
---> 36 _descriptor.FieldDescriptor(
37 name='size', full_name='tensorflow.TensorShapeProto.Dim.size', index=0,
38 number=1, type=3, cpp_type=2, label=1,
39 has_default_value=False, default_value=0,
40 message_type=None, enum_type=None, containing_type=None,
41 is_extension=False, extension_scope=None,
42 serialized_options=None, file=DESCRIPTOR),
43 _descriptor.FieldDescriptor(
44 name='name', full_name='tensorflow.TensorShapeProto.Dim.name', index=1,
45 number=2, type=9, cpp_type=9, label=1,
46 has_default_value=False, default_value=_b("").decode('utf-8'),
47 message_type=None, enum_type=None, containing_type=None,
48 is_extension=False, extension_scope=None,
49 serialized_options=None, file=DESCRIPTOR),
50 ],
51 extensions=[
52 ],
53 nested_types=[],
54 enum_types=[
55 ],
56 serialized_options=None,
57 is_extendable=False,
58 syntax='proto3',
59 extension_ranges=[],
60 oneofs=[
61 ],
62 serialized_start=149,
63 serialized_end=182,
64 )
66 _TENSORSHAPEPROTO = _descriptor.Descriptor(
67 name='TensorShapeProto',
68 full_name='tensorflow.TensorShapeProto',
(...)
100 serialized_end=182,
101 )
103 _TENSORSHAPEPROTO_DIM.containing_type = _TENSORSHAPEPROTO
File /data0/home/h21/luas6629/venv/lib/python3.10/site-packages/google/protobuf/descriptor.py:560, in FieldDescriptor.__new__(cls, name, full_name, index, number, type, cpp_type, label, default_value, message_type, enum_type, containing_type, is_extension, extension_scope, options, serialized_options, has_default_value, containing_oneof, json_name, file, create_key)
554 def __new__(cls, name, full_name, index, number, type, cpp_type, label,
555 default_value, message_type, enum_type, containing_type,
556 is_extension, extension_scope, options=None,
557 serialized_options=None,
558 has_default_value=True, containing_oneof=None, json_name=None,
559 file=None, create_key=None): # pylint: disable=redefined-builtin
--> 560 _message.Message._CheckCalledFromGeneratedFile()
561 if is_extension:
562 return _message.default_pool.FindExtensionByName(full_name)
TypeError: Descriptors cannot not be created directly.
If this call came from a _pb2.py file, your generated code is out of date and must be regenerated with protoc >= 3.19.0.
If you cannot immediately regenerate your protos, some other possible workarounds are:
1. Downgrade the protobuf package to 3.20.x or lower.
2. Set PROTOCOL_BUFFERS_PYTHON_IMPLEMENTATION=python (but this will use pure-Python parsing and will be much slower).
More information: https://developers.google.com/protocol-buffers/docs/news/2022-05-06#python-updates
```
</details> | non_test | protocol buffer error critical i cannot import tensorflow click to expand issue type bug have you reproduced the bug with tf nightly no source binary tensorflow version custom code no os platform and distribution no response mobile device no response python version bazel version no response gcc compiler version no response cuda cudnn version no response gpu model and memory no response current behaviour bug occurred today when reloading a jupyter notebook i previously tried to install cuml but the trace error seems unrelated to it but mention protocol buffers standalone code to reproduce the issue shell the error occurs when import tensorflow and consequently any other import of libraries based on tf such as import umap will fail i cannot use tf anymore relevant log output shell typeerror traceback most recent call last cell in line import tensorflow as tf import umap file home venv lib site packages tensorflow init py import sys as sys import typing as typing from tensorflow python tools import module util as module util from tensorflow python util lazy loader import lazyloader as lazyloader make sure code inside the tensorflow codebase can use enabled at import file home venv lib site packages tensorflow python init py we aim to keep this file minimal and ideally remove completely if you are adding a new file with tf export decorators import it in modules with exports py instead go tf wildcard import pylint disable wildcard import g bad import order g import not at top from tensorflow python import pywrap tensorflow as pywrap tensorflow from tensorflow python eager import context pylint enable wildcard import bring in subpackages from tensorflow python import data file home venv lib site packages tensorflow python eager context py from absl import logging import numpy as np from tensorflow core framework import function from tensorflow core protobuf import config from tensorflow core protobuf import coordination config file home venv lib site packages tensorflow core framework function py protoc insertion point imports sym db symbol database default from tensorflow core framework import attr value as tensorflow dot core dot framework dot attr value from tensorflow core framework import node def as tensorflow dot core dot framework dot node def from tensorflow core framework import op def as tensorflow dot core dot framework dot op def file home venv lib site packages tensorflow core framework attr value py protoc insertion point imports sym db symbol database default from tensorflow core framework import tensor as tensorflow dot core dot framework dot tensor from tensorflow core framework import tensor shape as tensorflow dot core dot framework dot tensor shape from tensorflow core framework import types as tensorflow dot core dot framework dot types file home venv lib site packages tensorflow core framework tensor py protoc insertion point imports sym db symbol database default from tensorflow core framework import resource handle as tensorflow dot core dot framework dot resource handle from tensorflow core framework import tensor shape as tensorflow dot core dot framework dot tensor shape from tensorflow core framework import types as tensorflow dot core dot framework dot types file home venv lib site packages tensorflow core framework resource handle py protoc insertion point imports sym db symbol database default from tensorflow core framework import tensor shape as tensorflow dot core dot framework dot tensor shape from tensorflow core framework import types as tensorflow dot core dot framework dot types descriptor descriptor filedescriptor name tensorflow core framework resource handle proto package tensorflow dependencies file home venv lib site packages tensorflow core framework tensor shape py sym db symbol database default descriptor descriptor filedescriptor name tensorflow core framework tensor shape proto package tensorflow serialized pb b n tensorflow core framework tensor shape proto ntensorflow z n n tensorflow tensorshapeproto dim n rank n n n tb n tensorflow frameworkb com tensorflow tensorflow tensorflow go core framework tensor shape go proto tensorshapeproto dim descriptor descriptor name dim full name tensorflow tensorshapeproto dim filename none file descriptor containing type none fields descriptor fielddescriptor name size full name tensorflow tensorshapeproto dim size index number type cpp type label has default value false default value message type none enum type none containing type none is extension false extension scope none serialized options none file descriptor descriptor fielddescriptor name name full name tensorflow tensorshapeproto dim name index number type cpp type label has default value false default value b decode utf message type none enum type none containing type none is extension false extension scope none serialized options none file descriptor extensions nested types enum types serialized options none is extendable false syntax extension ranges oneofs serialized start serialized end tensorshapeproto descriptor descriptor name tensorshapeproto full name tensorflow tensorshapeproto serialized end tensorshapeproto dim containing type tensorshapeproto file home venv lib site packages google protobuf descriptor py in fielddescriptor new cls name full name index number type cpp type label default value message type enum type containing type is extension extension scope options serialized options has default value containing oneof json name file create key def new cls name full name index number type cpp type label default value message type enum type containing type is extension extension scope options none serialized options none has default value true containing oneof none json name none file none create key none pylint disable redefined builtin message message checkcalledfromgeneratedfile if is extension return message default pool findextensionbyname full name typeerror descriptors cannot not be created directly if this call came from a py file your generated code is out of date and must be regenerated with protoc if you cannot immediately regenerate your protos some other possible workarounds are downgrade the protobuf package to x or lower set protocol buffers python implementation python but this will use pure python parsing and will be much slower more information | 0 |
179,845 | 13,907,224,135 | IssuesEvent | 2020-10-20 12:20:32 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Jest Integration Tests.src/cli/serve/integration_tests - Server logging configuration legacy logging should recreate file handle on SIGHUP | failed-test | A test failed on a tracked branch
```
Error: Failed: "watchFileUntil timed out for \"/setting up root/\""
at Env.it (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmineAsyncInstall.js:89:24)
at it (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/jasmineLight.js:100:21)
at Suite.describe (/dev/shm/workspace/parallel/3/kibana/src/cli/serve/integration_tests/reload_logging_config.test.ts:157:5)
at addSpecsToSuite (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:444:51)
at Env.describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:414:11)
at describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/jasmineLight.js:88:18)
at Suite.<anonymous> (/dev/shm/workspace/parallel/3/kibana/src/cli/serve/integration_tests/reload_logging_config.test.ts:110:3)
at addSpecsToSuite (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:444:51)
at Env.describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:414:11)
at describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/jasmineLight.js:88:18)
at Object.<anonymous> (/dev/shm/workspace/parallel/3/kibana/src/cli/serve/integration_tests/reload_logging_config.test.ts:86:1)
at Runtime._execModule (/dev/shm/workspace/kibana/node_modules/jest-runtime/build/index.js:1205:24)
at Runtime._loadModule (/dev/shm/workspace/kibana/node_modules/jest-runtime/build/index.js:805:12)
at Runtime.requireModule (/dev/shm/workspace/kibana/node_modules/jest-runtime/build/index.js:662:10)
at jasmine2 (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/index.js:228:13)
at runTestInternal (/dev/shm/workspace/kibana/node_modules/jest-runner/build/runTest.js:385:22)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/8017/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Integration Tests.src/cli/serve/integration_tests","test.name":"Server logging configuration legacy logging should recreate file handle on SIGHUP","test.failCount":2}} --> | 1.0 | Failing test: Jest Integration Tests.src/cli/serve/integration_tests - Server logging configuration legacy logging should recreate file handle on SIGHUP - A test failed on a tracked branch
```
Error: Failed: "watchFileUntil timed out for \"/setting up root/\""
at Env.it (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmineAsyncInstall.js:89:24)
at it (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/jasmineLight.js:100:21)
at Suite.describe (/dev/shm/workspace/parallel/3/kibana/src/cli/serve/integration_tests/reload_logging_config.test.ts:157:5)
at addSpecsToSuite (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:444:51)
at Env.describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:414:11)
at describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/jasmineLight.js:88:18)
at Suite.<anonymous> (/dev/shm/workspace/parallel/3/kibana/src/cli/serve/integration_tests/reload_logging_config.test.ts:110:3)
at addSpecsToSuite (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:444:51)
at Env.describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/Env.js:414:11)
at describe (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/jasmine/jasmineLight.js:88:18)
at Object.<anonymous> (/dev/shm/workspace/parallel/3/kibana/src/cli/serve/integration_tests/reload_logging_config.test.ts:86:1)
at Runtime._execModule (/dev/shm/workspace/kibana/node_modules/jest-runtime/build/index.js:1205:24)
at Runtime._loadModule (/dev/shm/workspace/kibana/node_modules/jest-runtime/build/index.js:805:12)
at Runtime.requireModule (/dev/shm/workspace/kibana/node_modules/jest-runtime/build/index.js:662:10)
at jasmine2 (/dev/shm/workspace/kibana/node_modules/jest-jasmine2/build/index.js:228:13)
at runTestInternal (/dev/shm/workspace/kibana/node_modules/jest-runner/build/runTest.js:385:22)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/8017/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Integration Tests.src/cli/serve/integration_tests","test.name":"Server logging configuration legacy logging should recreate file handle on SIGHUP","test.failCount":2}} --> | test | failing test jest integration tests src cli serve integration tests server logging configuration legacy logging should recreate file handle on sighup a test failed on a tracked branch error failed watchfileuntil timed out for setting up root at env it dev shm workspace kibana node modules jest build jasmineasyncinstall js at it dev shm workspace kibana node modules jest build jasmine jasminelight js at suite describe dev shm workspace parallel kibana src cli serve integration tests reload logging config test ts at addspecstosuite dev shm workspace kibana node modules jest build jasmine env js at env describe dev shm workspace kibana node modules jest build jasmine env js at describe dev shm workspace kibana node modules jest build jasmine jasminelight js at suite dev shm workspace parallel kibana src cli serve integration tests reload logging config test ts at addspecstosuite dev shm workspace kibana node modules jest build jasmine env js at env describe dev shm workspace kibana node modules jest build jasmine env js at describe dev shm workspace kibana node modules jest build jasmine jasminelight js at object dev shm workspace parallel kibana src cli serve integration tests reload logging config test ts at runtime execmodule dev shm workspace kibana node modules jest runtime build index js at runtime loadmodule dev shm workspace kibana node modules jest runtime build index js at runtime requiremodule dev shm workspace kibana node modules jest runtime build index js at dev shm workspace kibana node modules jest build index js at runtestinternal dev shm workspace kibana node modules jest runner build runtest js first failure | 1 |
203,835 | 15,391,251,697 | IssuesEvent | 2021-03-03 14:22:02 | WoWManiaUK/Redemption | https://api.github.com/repos/WoWManiaUK/Redemption | closed | [Item] Hook of the Master Angler has on-equip cooldown | Fixed on PTR - Tester Confirmed | **Links:**
https://wow-mania.com/armory/?item=19979
**What is Happening:**
Hook of the Master Angler has on-equip cooldown
**What Should happen:**
Hook of the Master Angler should not have on-equip cooldown https://youtu.be/S-PysysL6QQ?t=33
| 1.0 | [Item] Hook of the Master Angler has on-equip cooldown - **Links:**
https://wow-mania.com/armory/?item=19979
**What is Happening:**
Hook of the Master Angler has on-equip cooldown
**What Should happen:**
Hook of the Master Angler should not have on-equip cooldown https://youtu.be/S-PysysL6QQ?t=33
| test | hook of the master angler has on equip cooldown links what is happening hook of the master angler has on equip cooldown what should happen hook of the master angler should not have on equip cooldown | 1 |
44,476 | 5,830,615,119 | IssuesEvent | 2017-05-08 17:17:28 | nextcloud/server | https://api.github.com/repos/nextcloud/server | opened | Contacts drop down too short if only one result shown | bug design papercut | * open the contacts drop down
* search for a term where only one contact is returned
* open the three dots menu
* expected: menu is shown properly
* actual: menu is cut and you need to scroll
<img width="390" alt="bildschirmfoto 2017-05-08 um 12 15 06" src="https://cloud.githubusercontent.com/assets/245432/25815979/3df7e42c-33e8-11e7-9b93-34a1863f6d30.png">
cc @georgehrke @ChristophWurst | 1.0 | Contacts drop down too short if only one result shown - * open the contacts drop down
* search for a term where only one contact is returned
* open the three dots menu
* expected: menu is shown properly
* actual: menu is cut and you need to scroll
<img width="390" alt="bildschirmfoto 2017-05-08 um 12 15 06" src="https://cloud.githubusercontent.com/assets/245432/25815979/3df7e42c-33e8-11e7-9b93-34a1863f6d30.png">
cc @georgehrke @ChristophWurst | non_test | contacts drop down too short if only one result shown open the contacts drop down search for a term where only one contact is returned open the three dots menu expected menu is shown properly actual menu is cut and you need to scroll img width alt bildschirmfoto um src cc georgehrke christophwurst | 0 |
285,855 | 24,702,833,948 | IssuesEvent | 2022-10-19 16:32:05 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | opened | FTS: Jakarta 10 Authorization 2.1 | Feature Test Summary | ## Test Strategy
**Describe the test strategy & approach for this feature, and describe how the approach verifies the functions delivered by this feature.**
---> https://ibm.ent.box.com/notes/1044265481814
_For any feature, be aware that only FAT tests (not unit or BVT) are executed in our cross platform testing. To ensure cross platform testing ensure you have sufficient FAT coverage to verify the feature._
_If delivering tests outside of the standard Liberty FAT framework, do the tests push the results into cognitive testing database (if not, consult with the CSI Team who can provide advice and verify if results are being received)?_
### List of FAT projects affected
* com.ibm.ws.ejbcontainer.security.jacc_fat.2.1
### Test strategy
* What functionality is new or modified by this feature? https://ibm.ent.box.com/notes/1044265481814
* What are the positive and negative tests for that functionality? (Tell me the specific scenarios you tested. What kind of tests do you have for when everything ends up working (positive tests)? What about tests that verify we fail gracefully when things go wrong (negative tests)? See the [Positive and negative tests](https://github.ibm.com/websphere/WS-CD-Open/wiki/Feature-Review-(Feature-Test-Summary-Process)#positive-and-negative-tests) section of the Feature Test Summary Process wiki for more detail.)
---->
/**
* Verify the following:
* <OL>
* <LI> Add excluded permissions to the Policy
* <LI> Extract those exclded permissions by invoking the new method getExcludedPermissions
* </OL>
* <P> Expected Results:
* <OL>
* <LI> The input and output excluded permissions should be the same
* <LI>
* </OL>
*/
@Mode(TestMode.LITE)
@Test
public void testGetExcludedPermissionsMethod() throws Exception {
Positive test: Adds excluded permissions, and then calls new method getExcludedPermissions() to verify that we get all of the added excluded permissions back adn that the number of excluded permissions is the same. Test succeeds if true.
Negative test: If we do not get the same number of excluded permissions, or the names of the permissions do not precisely match, we through an exception and fail the test.
/**
* Verify the following:
* <OL>
* <LI> Add unchecked permissions to the Policy
* <LI> Extract those unchecked permissions by invoking the new method getUncheckedPermissions
* </OL>
* <P> Expected Results:
* <OL>
* <LI> The input and output unchecked permissions should be the same
* <LI>
* </OL>
*/
@Mode(TestMode.LITE)
@Test
public void testGetUncheckedPermissionsMethod() throws Exception {
Positive test: Adds unchecked permissions, and then calls new method getUncheckedPermissions() to verify that we get all of the added unchecked permissions back and that the number of unchecked permissions is the same. Test succeeds if true.
Negative test: If we do not get the same number of unchecked permissions, or the names of the permissions do not precisely match, we through an exception and fail the test.
/**
* Verify the following:
* <OL>
* <LI> Add permissions to several roles permissions to the Policy
* <LI> Extract those permissions by invoking the new method getPerRolePermissions
* </OL>
* <P> Expected Results:
* <OL>
* <LI> The input and output unchecked permissions per roleshould be the same
* <LI>
* </OL>
*/
@Mode(TestMode.LITE)
@Test
public void testGetPerRoleMethod() throws Exception {
Positive test: Adds different permissions to several roles, and then calls new method getPerRoleMethod() to verify that we get all of the added permissions back per role that we added per role, and that the number of permissions is the same per role method. Test succeeds if true.
Negative test: If we do not get the same number of permissions per role , or the names of the permissions do not precisely match, we through an exception and fail the test.
public void testGetPolicyConfigWithNoContextId() throws Exception {
Postive test: Create a new PolicyConfiguration with a set contextID and set the PolicyContext with that ID. Add permissions. Retrieve the contextID using the getPolicyConfiguration() and if the ID is not null and the permissions retrieved match in name and number, succeed.
Negative test: If the ID is null or if the permissions retrieved do not match in name and number, fail
public void testGetPolicyConfigWithContextId() throws Exception {
Postive test: Create a new PolicyConfiguration with a set contextID and set the PolicyContext with that ID. Add permissions. Retrieve the contextID using the getPolicyConfiguration(contextID) and if the ID from getPolicyConfiguration.getContextID() is identical to the set contextID and the permissions retrieved match in name and number, succeed.
Negative test: If the ID does not match or if the permissions retrieved do not match in name and number, fail
---->
* What manual tests are there (if any)? (Note: Automated testing is expected for all features with manual testing considered an exception to the rule.). All tests are automated; no manual testing
## Confidence Level
**Collectively as a team you need to assess your confidence in the testing delivered based on the values below. This should be done as a team and not an individual to ensure more eyes are on it and that pressures to deliver quickly are absorbed by the team as a whole.**
Please indicate your confidence in the testing (up to and including FAT) delivered with this feature by selecting one of these values:
0 - No automated testing delivered
1 - We have minimal automated coverage of the feature including golden paths. There is a relatively high risk that defects or issues could be found in this feature.
2 - We have delivered a reasonable automated coverage of the golden paths of this feature but are aware of gaps and extra testing that could be done here. Error/outlying scenarios are not really covered. There are likely risks that issues may exist in the golden paths
3 - We have delivered all automated testing we believe is needed for the golden paths of this feature and minimal coverage of the error/outlying scenarios. There is a risk when the feature is used outside the golden paths however we are confident on the golden path. Note: This may still be a valid end state for a feature... things like Beta features may well suffice at this level.
4 - We have delivered all automated testing we believe is needed for the golden paths of this feature and have good coverage of the error/outlying scenarios. While more testing of the error/outlying scenarios could be added we believe there is minimal risk here and the cost of providing these is considered higher than the benefit they would provide.
5 - We have delivered all automated testing we believe is needed for this feature. The testing covers all golden path cases as well as all the error/outlying scenarios that make sense. We are not aware of any gaps in the testing at this time. No manual testing is required to verify this feature.
5
Based on your answer above, for any answer other than a 4 or 5 please provide details of what drove your answer. Please be aware, it may be perfectly reasonable in some scenarios to deliver with any value above. We may accept no automated testing is needed for some features, we may be happy with low levels of testing on samples for instance so please don't feel the need to drive to a 5. We need your honest assessment as a team and the reasoning for why you believe shipping at that level is valid. What are the gaps, what is the risk etc. Please also provide links to the follow on work that is needed to close the gaps (should you deem it needed)
| 1.0 | FTS: Jakarta 10 Authorization 2.1 - ## Test Strategy
**Describe the test strategy & approach for this feature, and describe how the approach verifies the functions delivered by this feature.**
---> https://ibm.ent.box.com/notes/1044265481814
_For any feature, be aware that only FAT tests (not unit or BVT) are executed in our cross platform testing. To ensure cross platform testing ensure you have sufficient FAT coverage to verify the feature._
_If delivering tests outside of the standard Liberty FAT framework, do the tests push the results into cognitive testing database (if not, consult with the CSI Team who can provide advice and verify if results are being received)?_
### List of FAT projects affected
* com.ibm.ws.ejbcontainer.security.jacc_fat.2.1
### Test strategy
* What functionality is new or modified by this feature? https://ibm.ent.box.com/notes/1044265481814
* What are the positive and negative tests for that functionality? (Tell me the specific scenarios you tested. What kind of tests do you have for when everything ends up working (positive tests)? What about tests that verify we fail gracefully when things go wrong (negative tests)? See the [Positive and negative tests](https://github.ibm.com/websphere/WS-CD-Open/wiki/Feature-Review-(Feature-Test-Summary-Process)#positive-and-negative-tests) section of the Feature Test Summary Process wiki for more detail.)
---->
/**
* Verify the following:
* <OL>
* <LI> Add excluded permissions to the Policy
* <LI> Extract those exclded permissions by invoking the new method getExcludedPermissions
* </OL>
* <P> Expected Results:
* <OL>
* <LI> The input and output excluded permissions should be the same
* <LI>
* </OL>
*/
@Mode(TestMode.LITE)
@Test
public void testGetExcludedPermissionsMethod() throws Exception {
Positive test: Adds excluded permissions, and then calls new method getExcludedPermissions() to verify that we get all of the added excluded permissions back adn that the number of excluded permissions is the same. Test succeeds if true.
Negative test: If we do not get the same number of excluded permissions, or the names of the permissions do not precisely match, we through an exception and fail the test.
/**
* Verify the following:
* <OL>
* <LI> Add unchecked permissions to the Policy
* <LI> Extract those unchecked permissions by invoking the new method getUncheckedPermissions
* </OL>
* <P> Expected Results:
* <OL>
* <LI> The input and output unchecked permissions should be the same
* <LI>
* </OL>
*/
@Mode(TestMode.LITE)
@Test
public void testGetUncheckedPermissionsMethod() throws Exception {
Positive test: Adds unchecked permissions, and then calls new method getUncheckedPermissions() to verify that we get all of the added unchecked permissions back and that the number of unchecked permissions is the same. Test succeeds if true.
Negative test: If we do not get the same number of unchecked permissions, or the names of the permissions do not precisely match, we through an exception and fail the test.
/**
* Verify the following:
* <OL>
* <LI> Add permissions to several roles permissions to the Policy
* <LI> Extract those permissions by invoking the new method getPerRolePermissions
* </OL>
* <P> Expected Results:
* <OL>
* <LI> The input and output unchecked permissions per roleshould be the same
* <LI>
* </OL>
*/
@Mode(TestMode.LITE)
@Test
public void testGetPerRoleMethod() throws Exception {
Positive test: Adds different permissions to several roles, and then calls new method getPerRoleMethod() to verify that we get all of the added permissions back per role that we added per role, and that the number of permissions is the same per role method. Test succeeds if true.
Negative test: If we do not get the same number of permissions per role , or the names of the permissions do not precisely match, we through an exception and fail the test.
public void testGetPolicyConfigWithNoContextId() throws Exception {
Postive test: Create a new PolicyConfiguration with a set contextID and set the PolicyContext with that ID. Add permissions. Retrieve the contextID using the getPolicyConfiguration() and if the ID is not null and the permissions retrieved match in name and number, succeed.
Negative test: If the ID is null or if the permissions retrieved do not match in name and number, fail
public void testGetPolicyConfigWithContextId() throws Exception {
Postive test: Create a new PolicyConfiguration with a set contextID and set the PolicyContext with that ID. Add permissions. Retrieve the contextID using the getPolicyConfiguration(contextID) and if the ID from getPolicyConfiguration.getContextID() is identical to the set contextID and the permissions retrieved match in name and number, succeed.
Negative test: If the ID does not match or if the permissions retrieved do not match in name and number, fail
---->
* What manual tests are there (if any)? (Note: Automated testing is expected for all features with manual testing considered an exception to the rule.). All tests are automated; no manual testing
## Confidence Level
**Collectively as a team you need to assess your confidence in the testing delivered based on the values below. This should be done as a team and not an individual to ensure more eyes are on it and that pressures to deliver quickly are absorbed by the team as a whole.**
Please indicate your confidence in the testing (up to and including FAT) delivered with this feature by selecting one of these values:
0 - No automated testing delivered
1 - We have minimal automated coverage of the feature including golden paths. There is a relatively high risk that defects or issues could be found in this feature.
2 - We have delivered a reasonable automated coverage of the golden paths of this feature but are aware of gaps and extra testing that could be done here. Error/outlying scenarios are not really covered. There are likely risks that issues may exist in the golden paths
3 - We have delivered all automated testing we believe is needed for the golden paths of this feature and minimal coverage of the error/outlying scenarios. There is a risk when the feature is used outside the golden paths however we are confident on the golden path. Note: This may still be a valid end state for a feature... things like Beta features may well suffice at this level.
4 - We have delivered all automated testing we believe is needed for the golden paths of this feature and have good coverage of the error/outlying scenarios. While more testing of the error/outlying scenarios could be added we believe there is minimal risk here and the cost of providing these is considered higher than the benefit they would provide.
5 - We have delivered all automated testing we believe is needed for this feature. The testing covers all golden path cases as well as all the error/outlying scenarios that make sense. We are not aware of any gaps in the testing at this time. No manual testing is required to verify this feature.
5
Based on your answer above, for any answer other than a 4 or 5 please provide details of what drove your answer. Please be aware, it may be perfectly reasonable in some scenarios to deliver with any value above. We may accept no automated testing is needed for some features, we may be happy with low levels of testing on samples for instance so please don't feel the need to drive to a 5. We need your honest assessment as a team and the reasoning for why you believe shipping at that level is valid. What are the gaps, what is the risk etc. Please also provide links to the follow on work that is needed to close the gaps (should you deem it needed)
| test | fts jakarta authorization test strategy describe the test strategy approach for this feature and describe how the approach verifies the functions delivered by this feature for any feature be aware that only fat tests not unit or bvt are executed in our cross platform testing to ensure cross platform testing ensure you have sufficient fat coverage to verify the feature if delivering tests outside of the standard liberty fat framework do the tests push the results into cognitive testing database if not consult with the csi team who can provide advice and verify if results are being received list of fat projects affected com ibm ws ejbcontainer security jacc fat test strategy what functionality is new or modified by this feature what are the positive and negative tests for that functionality tell me the specific scenarios you tested what kind of tests do you have for when everything ends up working positive tests what about tests that verify we fail gracefully when things go wrong negative tests see the section of the feature test summary process wiki for more detail verify the following add excluded permissions to the policy extract those exclded permissions by invoking the new method getexcludedpermissions expected results the input and output excluded permissions should be the same mode testmode lite test public void testgetexcludedpermissionsmethod throws exception positive test adds excluded permissions and then calls new method getexcludedpermissions to verify that we get all of the added excluded permissions back adn that the number of excluded permissions is the same test succeeds if true negative test if we do not get the same number of excluded permissions or the names of the permissions do not precisely match we through an exception and fail the test verify the following add unchecked permissions to the policy extract those unchecked permissions by invoking the new method getuncheckedpermissions expected results the input and output unchecked permissions should be the same mode testmode lite test public void testgetuncheckedpermissionsmethod throws exception positive test adds unchecked permissions and then calls new method getuncheckedpermissions to verify that we get all of the added unchecked permissions back and that the number of unchecked permissions is the same test succeeds if true negative test if we do not get the same number of unchecked permissions or the names of the permissions do not precisely match we through an exception and fail the test verify the following add permissions to several roles permissions to the policy extract those permissions by invoking the new method getperrolepermissions expected results the input and output unchecked permissions per roleshould be the same mode testmode lite test public void testgetperrolemethod throws exception positive test adds different permissions to several roles and then calls new method getperrolemethod to verify that we get all of the added permissions back per role that we added per role and that the number of permissions is the same per role method test succeeds if true negative test if we do not get the same number of permissions per role or the names of the permissions do not precisely match we through an exception and fail the test public void testgetpolicyconfigwithnocontextid throws exception postive test create a new policyconfiguration with a set contextid and set the policycontext with that id add permissions retrieve the contextid using the getpolicyconfiguration and if the id is not null and the permissions retrieved match in name and number succeed negative test if the id is null or if the permissions retrieved do not match in name and number fail public void testgetpolicyconfigwithcontextid throws exception postive test create a new policyconfiguration with a set contextid and set the policycontext with that id add permissions retrieve the contextid using the getpolicyconfiguration contextid and if the id from getpolicyconfiguration getcontextid is identical to the set contextid and the permissions retrieved match in name and number succeed negative test if the id does not match or if the permissions retrieved do not match in name and number fail what manual tests are there if any note automated testing is expected for all features with manual testing considered an exception to the rule all tests are automated no manual testing confidence level collectively as a team you need to assess your confidence in the testing delivered based on the values below this should be done as a team and not an individual to ensure more eyes are on it and that pressures to deliver quickly are absorbed by the team as a whole please indicate your confidence in the testing up to and including fat delivered with this feature by selecting one of these values no automated testing delivered we have minimal automated coverage of the feature including golden paths there is a relatively high risk that defects or issues could be found in this feature we have delivered a reasonable automated coverage of the golden paths of this feature but are aware of gaps and extra testing that could be done here error outlying scenarios are not really covered there are likely risks that issues may exist in the golden paths we have delivered all automated testing we believe is needed for the golden paths of this feature and minimal coverage of the error outlying scenarios there is a risk when the feature is used outside the golden paths however we are confident on the golden path note this may still be a valid end state for a feature things like beta features may well suffice at this level we have delivered all automated testing we believe is needed for the golden paths of this feature and have good coverage of the error outlying scenarios while more testing of the error outlying scenarios could be added we believe there is minimal risk here and the cost of providing these is considered higher than the benefit they would provide we have delivered all automated testing we believe is needed for this feature the testing covers all golden path cases as well as all the error outlying scenarios that make sense we are not aware of any gaps in the testing at this time no manual testing is required to verify this feature based on your answer above for any answer other than a or please provide details of what drove your answer please be aware it may be perfectly reasonable in some scenarios to deliver with any value above we may accept no automated testing is needed for some features we may be happy with low levels of testing on samples for instance so please don t feel the need to drive to a we need your honest assessment as a team and the reasoning for why you believe shipping at that level is valid what are the gaps what is the risk etc please also provide links to the follow on work that is needed to close the gaps should you deem it needed | 1 |
190,113 | 6,808,867,669 | IssuesEvent | 2017-11-04 09:46:33 | minishift/minishift | https://api.github.com/repos/minishift/minishift | closed | Use named pipes on windows to communicate with Hyper-V image | kind/feature os/windows priority/major status/needs-investigation status/stale | My corporate VPN takes over all routes (including reserved ips: 10.x, 192.168.x, ...) This means that if i try to access the openshift image using tcp the traffic gets rerouted over the VPN at which point the 10.x addresses no longer map to my VM switch and the communication fails. Docker for Windows works because it uses npipe blackmagic for the docker commands (_and probably exposing ports from containers cause that works too..._). I understand if this is not high priority, but it would be nice if minishift implemented the same approach.
_(I mentioned this in [this comment](https://github.com/minishift/minishift/issues/1256#issuecomment-323127164) and on the [mailing list](https://lists.minishift.io/archives/list/minishift@lists.minishift.io/thread/JHQ3PMP5ZR5ZGECEBYWKN7PY4N4BYUOP/?sort=date), but figured it would be worth opening its own issue for tracking purposes)_ | 1.0 | Use named pipes on windows to communicate with Hyper-V image - My corporate VPN takes over all routes (including reserved ips: 10.x, 192.168.x, ...) This means that if i try to access the openshift image using tcp the traffic gets rerouted over the VPN at which point the 10.x addresses no longer map to my VM switch and the communication fails. Docker for Windows works because it uses npipe blackmagic for the docker commands (_and probably exposing ports from containers cause that works too..._). I understand if this is not high priority, but it would be nice if minishift implemented the same approach.
_(I mentioned this in [this comment](https://github.com/minishift/minishift/issues/1256#issuecomment-323127164) and on the [mailing list](https://lists.minishift.io/archives/list/minishift@lists.minishift.io/thread/JHQ3PMP5ZR5ZGECEBYWKN7PY4N4BYUOP/?sort=date), but figured it would be worth opening its own issue for tracking purposes)_ | non_test | use named pipes on windows to communicate with hyper v image my corporate vpn takes over all routes including reserved ips x x this means that if i try to access the openshift image using tcp the traffic gets rerouted over the vpn at which point the x addresses no longer map to my vm switch and the communication fails docker for windows works because it uses npipe blackmagic for the docker commands and probably exposing ports from containers cause that works too i understand if this is not high priority but it would be nice if minishift implemented the same approach i mentioned this in and on the but figured it would be worth opening its own issue for tracking purposes | 0 |
4,123 | 4,822,386,617 | IssuesEvent | 2016-11-05 20:38:06 | devtools-html/debugger.html | https://api.github.com/repos/devtools-html/debugger.html | closed | Testing - fix unit test warnings | infrastructure | We should clean up the unit test output, which can be confusing.
> When doing the unit tests, there were some warnings. Is it something on my end?

| 1.0 | Testing - fix unit test warnings - We should clean up the unit test output, which can be confusing.
> When doing the unit tests, there were some warnings. Is it something on my end?

| non_test | testing fix unit test warnings we should clean up the unit test output which can be confusing when doing the unit tests there were some warnings is it something on my end | 0 |
3,108 | 13,099,330,636 | IssuesEvent | 2020-08-03 21:22:02 | jcallaghan/home-assistant-config | https://api.github.com/repos/jcallaghan/home-assistant-config | reopened | Bath water level sensor | area : bathroom connection: zigbee integration: alert integration: automation | *** draft
Consider how TTS and my notification engine #83 can make use of the alert integration. | 1.0 | Bath water level sensor - *** draft
Consider how TTS and my notification engine #83 can make use of the alert integration. | non_test | bath water level sensor draft consider how tts and my notification engine can make use of the alert integration | 0 |
57,249 | 6,541,534,322 | IssuesEvent | 2017-09-01 20:27:33 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | some EditAndContinue integration tests are flakey | Area-Interactive Disabled Test Flaky Test | **Version Used**:
**Steps to Reproduce**:
https://ci.dot.net/job/dotnet_roslyn/job/master/job/windows_release_vs-integration_prtest/4014/
https://ci.dot.net/job/dotnet_roslyn/job/master/job/windows_debug_vs-integration_prtest/4036/
https://ci.dot.net/job/dotnet_roslyn/job/master/job/windows_release_vs-integration_prtest/3990/
1. Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.AddTryCatchAroundActiveStatement
> Stacktrace
>
> MESSAGE:
> System.Runtime.InteropServices.COMException : Operation not supported. Unknown error: 0x8971003c.
> +++++++++++++++++++
> STACK TRACE:
> Server stack trace: at EnvDTE.Debugger.StepOver(Boolean WaitForBreakOrEnd) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.StepOver(Boolean waitForBreakOrEnd) at System.Runtime.Remoting.Messaging.StackBuilderSink._PrivateProcessMessage(IntPtr md, Object[] args, Object server, Object[]& outArgs) at System.Runtime.Remoting.Messaging.StackBuilderSink.SyncProcessMessage(IMessage msg) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.StepOver(Boolean waitForBreakOrEnd) at Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.AddTryCatchAroundActiveStatement() in q:\roslyn\src\VisualStudio\IntegrationTest\IntegrationTests\VisualBasic\BasicEditAndContinue.cs:line 81
>
>
2. Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.WatchWindowUpdatesCorrectlyDuringEnC
> MESSAGE:
> System.Runtime.InteropServices.COMException : Operation not supported. Unknown error: 0x8971003b.
> +++++++++++++++++++
> STACK TRACE:
> Server stack trace: at EnvDTE.Debugger.Go(Boolean WaitForBreakOrEnd) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.Go(Boolean waitForBreakMode) at System.Runtime.Remoting.Messaging.StackBuilderSink._PrivateProcessMessage(IntPtr md, Object[] args, Object server, Object[]& outArgs) at System.Runtime.Remoting.Messaging.StackBuilderSink.SyncProcessMessage(IMessage msg) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.Go(Boolean waitForBreakMode) at Microsoft.VisualStudio.IntegrationTest.Utilities.OutOfProcess.Debugger_OutOfProc.Go(Boolean waitForBreakMode) at Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.WatchWindowUpdatesCorrectlyDuringEnC() in q:\roslyn\src\VisualStudio\IntegrationTest\IntegrationTests\VisualBasic\BasicEditAndContinue.cs:line 321
3. Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpSendToInteractive.ResetInteractiveFromProjectAndVerify
> MESSAGE:
> System.Exception : Predicate never assigned a value after 10000 milliseconds and no exceptions were thrown. REPL text: > #reset\r\nResetting execution engine.\r\nLoading context from 'CSharpInteractive.rsp'.\r\n> using System;\r\n> #reset\r\nResetting execution engine.\r\nLoading context from 'CSharpInteractive.rsp'.\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Core.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Xml.Linq.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Data.DataSetExtensions.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\Microsoft.CSharp.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Data.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Net.Http.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Xml.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Windows.Forms.dll\"\r\n> #r \"TestProj.exe\"\r\n> using TestProj;\r\n> x\r\n(1,1): error CS0103: The name 'x' does not exist in the current context\r\n> (new TestProj.C()).M()\r\n(1,15): error CS0234: The type or namespace name 'C' does not exist in the namespace 'TestProj' (are you missing an assembly reference?)\r\n> .
> +++++++++++++++++++
> STACK TRACE:
> Server stack trace: at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.InteractiveWindow_InProc.WaitForPredicate(Func`1 predicate) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.InteractiveWindow_InProc.WaitForLastReplOutput(String outputText) at System.Runtime.Remoting.Messaging.StackBuilderSink._PrivateProcessMessage(IntPtr md, Object[] args, Object server, Object[]& outArgs) at System.Runtime.Remoting.Messaging.StackBuilderSink.SyncProcessMessage(IMessage msg) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.InteractiveWindow_InProc.WaitForLastReplOutput(String outputText) at Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpSendToInteractive.ResetInteractiveFromProjectAndVerify() in q:\roslyn\src\VisualStudio\IntegrationTest\IntegrationTests\CSharp\CSharpSendToInteractive.cs:line 237 | 2.0 | some EditAndContinue integration tests are flakey - **Version Used**:
**Steps to Reproduce**:
https://ci.dot.net/job/dotnet_roslyn/job/master/job/windows_release_vs-integration_prtest/4014/
https://ci.dot.net/job/dotnet_roslyn/job/master/job/windows_debug_vs-integration_prtest/4036/
https://ci.dot.net/job/dotnet_roslyn/job/master/job/windows_release_vs-integration_prtest/3990/
1. Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.AddTryCatchAroundActiveStatement
> Stacktrace
>
> MESSAGE:
> System.Runtime.InteropServices.COMException : Operation not supported. Unknown error: 0x8971003c.
> +++++++++++++++++++
> STACK TRACE:
> Server stack trace: at EnvDTE.Debugger.StepOver(Boolean WaitForBreakOrEnd) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.StepOver(Boolean waitForBreakOrEnd) at System.Runtime.Remoting.Messaging.StackBuilderSink._PrivateProcessMessage(IntPtr md, Object[] args, Object server, Object[]& outArgs) at System.Runtime.Remoting.Messaging.StackBuilderSink.SyncProcessMessage(IMessage msg) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.StepOver(Boolean waitForBreakOrEnd) at Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.AddTryCatchAroundActiveStatement() in q:\roslyn\src\VisualStudio\IntegrationTest\IntegrationTests\VisualBasic\BasicEditAndContinue.cs:line 81
>
>
2. Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.WatchWindowUpdatesCorrectlyDuringEnC
> MESSAGE:
> System.Runtime.InteropServices.COMException : Operation not supported. Unknown error: 0x8971003b.
> +++++++++++++++++++
> STACK TRACE:
> Server stack trace: at EnvDTE.Debugger.Go(Boolean WaitForBreakOrEnd) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.Go(Boolean waitForBreakMode) at System.Runtime.Remoting.Messaging.StackBuilderSink._PrivateProcessMessage(IntPtr md, Object[] args, Object server, Object[]& outArgs) at System.Runtime.Remoting.Messaging.StackBuilderSink.SyncProcessMessage(IMessage msg) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.Debugger_InProc.Go(Boolean waitForBreakMode) at Microsoft.VisualStudio.IntegrationTest.Utilities.OutOfProcess.Debugger_OutOfProc.Go(Boolean waitForBreakMode) at Roslyn.VisualStudio.IntegrationTests.VisualBasic.BasicEditAndContinue.WatchWindowUpdatesCorrectlyDuringEnC() in q:\roslyn\src\VisualStudio\IntegrationTest\IntegrationTests\VisualBasic\BasicEditAndContinue.cs:line 321
3. Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpSendToInteractive.ResetInteractiveFromProjectAndVerify
> MESSAGE:
> System.Exception : Predicate never assigned a value after 10000 milliseconds and no exceptions were thrown. REPL text: > #reset\r\nResetting execution engine.\r\nLoading context from 'CSharpInteractive.rsp'.\r\n> using System;\r\n> #reset\r\nResetting execution engine.\r\nLoading context from 'CSharpInteractive.rsp'.\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Core.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Xml.Linq.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Data.DataSetExtensions.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\Microsoft.CSharp.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Data.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Net.Http.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Xml.dll\"\r\n> #r \"C:\\Program Files (x86)\\Reference Assemblies\\Microsoft\\Framework\\.NETFramework\\v4.5\\System.Windows.Forms.dll\"\r\n> #r \"TestProj.exe\"\r\n> using TestProj;\r\n> x\r\n(1,1): error CS0103: The name 'x' does not exist in the current context\r\n> (new TestProj.C()).M()\r\n(1,15): error CS0234: The type or namespace name 'C' does not exist in the namespace 'TestProj' (are you missing an assembly reference?)\r\n> .
> +++++++++++++++++++
> STACK TRACE:
> Server stack trace: at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.InteractiveWindow_InProc.WaitForPredicate(Func`1 predicate) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.InteractiveWindow_InProc.WaitForLastReplOutput(String outputText) at System.Runtime.Remoting.Messaging.StackBuilderSink._PrivateProcessMessage(IntPtr md, Object[] args, Object server, Object[]& outArgs) at System.Runtime.Remoting.Messaging.StackBuilderSink.SyncProcessMessage(IMessage msg) Exception rethrown at [0]: at System.Runtime.Remoting.Proxies.RealProxy.HandleReturnMessage(IMessage reqMsg, IMessage retMsg) at System.Runtime.Remoting.Proxies.RealProxy.PrivateInvoke(MessageData& msgData, Int32 type) at Microsoft.VisualStudio.IntegrationTest.Utilities.InProcess.InteractiveWindow_InProc.WaitForLastReplOutput(String outputText) at Roslyn.VisualStudio.IntegrationTests.CSharp.CSharpSendToInteractive.ResetInteractiveFromProjectAndVerify() in q:\roslyn\src\VisualStudio\IntegrationTest\IntegrationTests\CSharp\CSharpSendToInteractive.cs:line 237 | test | some editandcontinue integration tests are flakey version used steps to reproduce roslyn visualstudio integrationtests visualbasic basiceditandcontinue addtrycatcharoundactivestatement stacktrace message system runtime interopservices comexception operation not supported unknown error stack trace server stack trace at envdte debugger stepover boolean waitforbreakorend at microsoft visualstudio integrationtest utilities inprocess debugger inproc stepover boolean waitforbreakorend at system runtime remoting messaging stackbuildersink privateprocessmessage intptr md object args object server object outargs at system runtime remoting messaging stackbuildersink syncprocessmessage imessage msg exception rethrown at at system runtime remoting proxies realproxy handlereturnmessage imessage reqmsg imessage retmsg at system runtime remoting proxies realproxy privateinvoke messagedata msgdata type at microsoft visualstudio integrationtest utilities inprocess debugger inproc stepover boolean waitforbreakorend at roslyn visualstudio integrationtests visualbasic basiceditandcontinue addtrycatcharoundactivestatement in q roslyn src visualstudio integrationtest integrationtests visualbasic basiceditandcontinue cs line roslyn visualstudio integrationtests visualbasic basiceditandcontinue watchwindowupdatescorrectlyduringenc message system runtime interopservices comexception operation not supported unknown error stack trace server stack trace at envdte debugger go boolean waitforbreakorend at microsoft visualstudio integrationtest utilities inprocess debugger inproc go boolean waitforbreakmode at system runtime remoting messaging stackbuildersink privateprocessmessage intptr md object args object server object outargs at system runtime remoting messaging stackbuildersink syncprocessmessage imessage msg exception rethrown at at system runtime remoting proxies realproxy handlereturnmessage imessage reqmsg imessage retmsg at system runtime remoting proxies realproxy privateinvoke messagedata msgdata type at microsoft visualstudio integrationtest utilities inprocess debugger inproc go boolean waitforbreakmode at microsoft visualstudio integrationtest utilities outofprocess debugger outofproc go boolean waitforbreakmode at roslyn visualstudio integrationtests visualbasic basiceditandcontinue watchwindowupdatescorrectlyduringenc in q roslyn src visualstudio integrationtest integrationtests visualbasic basiceditandcontinue cs line roslyn visualstudio integrationtests csharp csharpsendtointeractive resetinteractivefromprojectandverify message system exception predicate never assigned a value after milliseconds and no exceptions were thrown repl text reset r nresetting execution engine r nloading context from csharpinteractive rsp r n using system r n reset r nresetting execution engine r nloading context from csharpinteractive rsp r n r c program files reference assemblies microsoft framework netframework system dll r n r c program files reference assemblies microsoft framework netframework system core dll r n r c program files reference assemblies microsoft framework netframework system xml linq dll r n r c program files reference assemblies microsoft framework netframework system data datasetextensions dll r n r c program files reference assemblies microsoft framework netframework microsoft csharp dll r n r c program files reference assemblies microsoft framework netframework system data dll r n r c program files reference assemblies microsoft framework netframework system net http dll r n r c program files reference assemblies microsoft framework netframework system xml dll r n r c program files reference assemblies microsoft framework netframework system windows forms dll r n r testproj exe r n using testproj r n x r n error the name x does not exist in the current context r n new testproj c m r n error the type or namespace name c does not exist in the namespace testproj are you missing an assembly reference r n stack trace server stack trace at microsoft visualstudio integrationtest utilities inprocess interactivewindow inproc waitforpredicate func predicate at microsoft visualstudio integrationtest utilities inprocess interactivewindow inproc waitforlastreploutput string outputtext at system runtime remoting messaging stackbuildersink privateprocessmessage intptr md object args object server object outargs at system runtime remoting messaging stackbuildersink syncprocessmessage imessage msg exception rethrown at at system runtime remoting proxies realproxy handlereturnmessage imessage reqmsg imessage retmsg at system runtime remoting proxies realproxy privateinvoke messagedata msgdata type at microsoft visualstudio integrationtest utilities inprocess interactivewindow inproc waitforlastreploutput string outputtext at roslyn visualstudio integrationtests csharp csharpsendtointeractive resetinteractivefromprojectandverify in q roslyn src visualstudio integrationtest integrationtests csharp csharpsendtointeractive cs line | 1 |
85,096 | 7,961,228,467 | IssuesEvent | 2018-07-13 10:00:27 | Microsoft/AzureStorageExplorer | https://api.github.com/repos/Microsoft/AzureStorageExplorer | opened | List the value of 'Table Endpoint' to the 'Primary Connection String' for Cosmos DB accounts with Table API | testing | **Storage Explorer Version**: 1.3.0
**Platform/OS Version**: Windows 10/MacOS High Sierra/ Linux Ubuntu 16.04
**Architecture**: ia32/x64
**Build Number**: 20180711.4
**Commit**: 47039639
**Regression From**: Not a regression
#### Steps to Reproduce: ####
1. Open Storage Explorer and navigate to one Cosmos DB account with Table API.
2. Go to 'Properties' window and check the value of 'Table Endpoint' and 'Primary Connection String'.
#### Expected Experience: ####
It displays well in 'Table Endpoint' and it is included in 'Primary Connection String'.
#### Actual Experience: ####
Display '(Not Applicable)' for 'Table Endpoint' and it is included in 'Primary Connection String'. | 1.0 | List the value of 'Table Endpoint' to the 'Primary Connection String' for Cosmos DB accounts with Table API - **Storage Explorer Version**: 1.3.0
**Platform/OS Version**: Windows 10/MacOS High Sierra/ Linux Ubuntu 16.04
**Architecture**: ia32/x64
**Build Number**: 20180711.4
**Commit**: 47039639
**Regression From**: Not a regression
#### Steps to Reproduce: ####
1. Open Storage Explorer and navigate to one Cosmos DB account with Table API.
2. Go to 'Properties' window and check the value of 'Table Endpoint' and 'Primary Connection String'.
#### Expected Experience: ####
It displays well in 'Table Endpoint' and it is included in 'Primary Connection String'.
#### Actual Experience: ####
Display '(Not Applicable)' for 'Table Endpoint' and it is included in 'Primary Connection String'. | test | list the value of table endpoint to the primary connection string for cosmos db accounts with table api storage explorer version platform os version windows macos high sierra linux ubuntu architecture build number commit regression from not a regression steps to reproduce open storage explorer and navigate to one cosmos db account with table api go to properties window and check the value of table endpoint and primary connection string expected experience it displays well in table endpoint and it is included in primary connection string actual experience display not applicable for table endpoint and it is included in primary connection string | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.