Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
230,681 | 7,612,911,303 | IssuesEvent | 2018-05-01 19:15:38 | taneresme/swe.573.project | https://api.github.com/repos/taneresme/swe.573.project | closed | [It-11] Fix null balance issue | phase.implementation priority.high tier.api type.bug | **Environment:** SIT
**Application:** swe.573.project
**Module:** BalanceService
**Affected User:** taneresme
**Affected Customer:**
**Sample Information:**
SEVERE: Unexpected error occurred in scheduled task.
java.lang.NullPointerException
at com.wolower.ui.service.BalanceService.updateBalance(BalanceService.java:30)
at com.wolower.ui.service.payment.MasterpassPaymentScheduler.payment(MasterpassPaymentScheduler.java:75)
at sun.reflect.GeneratedMethodAccessor107.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:483)
at org.springframework.scheduling.support.ScheduledMethodRunnable.run(ScheduledMethodRunnable.java:65)
at org.springframework.scheduling.support.DelegatingErrorHandlingRunnable.run(DelegatingErrorHandlingRunnable.java:54)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.runAndReset(FutureTask.java:308)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.access$301(ScheduledThreadPoolExecutor.java:180)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.run(ScheduledThreadPoolExecutor.java:294)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1142)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at java.lang.Thread.run(Thread.java:745)
**Scenario it occurred:**
When saving new balance... | 1.0 | [It-11] Fix null balance issue - **Environment:** SIT
**Application:** swe.573.project
**Module:** BalanceService
**Affected User:** taneresme
**Affected Customer:**
**Sample Information:**
SEVERE: Unexpected error occurred in scheduled task.
java.lang.NullPointerException
at com.wolower.ui.service.BalanceService.updateBalance(BalanceService.java:30)
at com.wolower.ui.service.payment.MasterpassPaymentScheduler.payment(MasterpassPaymentScheduler.java:75)
at sun.reflect.GeneratedMethodAccessor107.invoke(Unknown Source)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:483)
at org.springframework.scheduling.support.ScheduledMethodRunnable.run(ScheduledMethodRunnable.java:65)
at org.springframework.scheduling.support.DelegatingErrorHandlingRunnable.run(DelegatingErrorHandlingRunnable.java:54)
at java.util.concurrent.Executors$RunnableAdapter.call(Executors.java:511)
at java.util.concurrent.FutureTask.runAndReset(FutureTask.java:308)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.access$301(ScheduledThreadPoolExecutor.java:180)
at java.util.concurrent.ScheduledThreadPoolExecutor$ScheduledFutureTask.run(ScheduledThreadPoolExecutor.java:294)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1142)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:617)
at java.lang.Thread.run(Thread.java:745)
**Scenario it occurred:**
When saving new balance... | non_test | fix null balance issue environment sit application swe project module balanceservice affected user taneresme affected customer sample information severe unexpected error occurred in scheduled task java lang nullpointerexception at com wolower ui service balanceservice updatebalance balanceservice java at com wolower ui service payment masterpasspaymentscheduler payment masterpasspaymentscheduler java at sun reflect invoke unknown source at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org springframework scheduling support scheduledmethodrunnable run scheduledmethodrunnable java at org springframework scheduling support delegatingerrorhandlingrunnable run delegatingerrorhandlingrunnable java at java util concurrent executors runnableadapter call executors java at java util concurrent futuretask runandreset futuretask java at java util concurrent scheduledthreadpoolexecutor scheduledfuturetask access scheduledthreadpoolexecutor java at java util concurrent scheduledthreadpoolexecutor scheduledfuturetask run scheduledthreadpoolexecutor java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java scenario it occurred when saving new balance | 0 |
244,388 | 7,874,770,819 | IssuesEvent | 2018-06-25 18:09:51 | facebook/prepack | https://api.github.com/repos/facebook/prepack | closed | FatalError recovery fallback missing for AbstractValue.throwIfNotConcrete case | bug optimized functions priority: high react compiler | Given this case:
```js
function fn(props, splitPoint) {
var text = props.text || "";
text = text.replace(/\s*$/, "");
if (splitPoint !== null) {
while (text[splitPoint - 1] === "\n") {
splitPoint--;
}
}
return splitPoint;
}
global.__optimize && __optimize(fn);
```
We get a `FatalError` that we don't recover from in pure scope. This is not optimal and we need to handle this case above in some form without bailing out of the entire function. | 1.0 | FatalError recovery fallback missing for AbstractValue.throwIfNotConcrete case - Given this case:
```js
function fn(props, splitPoint) {
var text = props.text || "";
text = text.replace(/\s*$/, "");
if (splitPoint !== null) {
while (text[splitPoint - 1] === "\n") {
splitPoint--;
}
}
return splitPoint;
}
global.__optimize && __optimize(fn);
```
We get a `FatalError` that we don't recover from in pure scope. This is not optimal and we need to handle this case above in some form without bailing out of the entire function. | non_test | fatalerror recovery fallback missing for abstractvalue throwifnotconcrete case given this case js function fn props splitpoint var text props text text text replace s if splitpoint null while text n splitpoint return splitpoint global optimize optimize fn we get a fatalerror that we don t recover from in pure scope this is not optimal and we need to handle this case above in some form without bailing out of the entire function | 0 |
211,703 | 16,343,041,854 | IssuesEvent | 2021-05-13 01:46:02 | mmcloughlin/addchain | https://api.github.com/repos/mmcloughlin/addchain | opened | alg/ensemble,internal/results: dedupe expensive tests | cleanup low testing | Both `alg/ensemble` and `internal/results` run expensive tests to confirm that algorithm results have not changed on targets of interest, but with slightly different goals:
* `alg/ensemble`: Ensure chain lengths for _every_ algorithm results are preserved, to verify no unexpected changes.
* `internal/results`: Ensure that our list of best-known chains is up-to-date, so our documentation is right. This checks the exact programs generated, not just their length.
These tests run every algorithm against every target in the results list, so they're expensive at the moment. The logic could be merged into one test.
Probably low priority because these should get a lot faster (after #60) and they're only run in long or stress test mode right now. | 1.0 | alg/ensemble,internal/results: dedupe expensive tests - Both `alg/ensemble` and `internal/results` run expensive tests to confirm that algorithm results have not changed on targets of interest, but with slightly different goals:
* `alg/ensemble`: Ensure chain lengths for _every_ algorithm results are preserved, to verify no unexpected changes.
* `internal/results`: Ensure that our list of best-known chains is up-to-date, so our documentation is right. This checks the exact programs generated, not just their length.
These tests run every algorithm against every target in the results list, so they're expensive at the moment. The logic could be merged into one test.
Probably low priority because these should get a lot faster (after #60) and they're only run in long or stress test mode right now. | test | alg ensemble internal results dedupe expensive tests both alg ensemble and internal results run expensive tests to confirm that algorithm results have not changed on targets of interest but with slightly different goals alg ensemble ensure chain lengths for every algorithm results are preserved to verify no unexpected changes internal results ensure that our list of best known chains is up to date so our documentation is right this checks the exact programs generated not just their length these tests run every algorithm against every target in the results list so they re expensive at the moment the logic could be merged into one test probably low priority because these should get a lot faster after and they re only run in long or stress test mode right now | 1 |
20,323 | 3,338,315,247 | IssuesEvent | 2015-11-13 06:21:34 | nucloudglobal/lms-ext | https://api.github.com/repos/nucloudglobal/lms-ext | opened | [DEFECT]student profile pic is blank (not empty) at the beginning, then will appear later | Proc.UAT S.02 S.08 S.22 S.27 Type.Defect | Step:
1. LMS
2.Check the course which has integrated user
3. people
4. view student profile
Expected result
user profile pic shall be integrated into LMS right after the user is integrated
Manage user account -> View student LMS profile
SS

| 1.0 | [DEFECT]student profile pic is blank (not empty) at the beginning, then will appear later - Step:
1. LMS
2.Check the course which has integrated user
3. people
4. view student profile
Expected result
user profile pic shall be integrated into LMS right after the user is integrated
Manage user account -> View student LMS profile
SS

| non_test | student profile pic is blank not empty at the beginning then will appear later step lms check the course which has integrated user people view student profile expected result user profile pic shall be integrated into lms right after the user is integrated manage user account view student lms profile ss | 0 |
323,418 | 27,723,285,385 | IssuesEvent | 2023-03-14 22:47:22 | gorakhargosh/watchdog | https://api.github.com/repos/gorakhargosh/watchdog | opened | tests: Improve `test_auto_restart_on_file_change_debounce()` stability | tests | `tests/test_0_watchmedo.py::test_auto_restart_on_file_change_debounce` fails frequently on all OSes.
Let's investigate, and see if we can make it more stable.
cc @altendky | 1.0 | tests: Improve `test_auto_restart_on_file_change_debounce()` stability - `tests/test_0_watchmedo.py::test_auto_restart_on_file_change_debounce` fails frequently on all OSes.
Let's investigate, and see if we can make it more stable.
cc @altendky | test | tests improve test auto restart on file change debounce stability tests test watchmedo py test auto restart on file change debounce fails frequently on all oses let s investigate and see if we can make it more stable cc altendky | 1 |
59,705 | 14,444,069,403 | IssuesEvent | 2020-12-07 20:38:44 | bunkerity/bunkerized-nginx | https://api.github.com/repos/bunkerity/bunkerized-nginx | closed | Vulnerabilities scan with Trivy | security | 0/ I ran a scan over this particular version: bunkerity/bunkerized-nginx:1.1.2 and got this:
> bunkerity/bunkerized-nginx:1.1.2 (alpine 3.11.6)
================================================
Total: 1 (UNKNOWN: 0, LOW: 0, MEDIUM: 1, HIGH: 0, CRITICAL: 0)
+----------+------------------+----------+-------------------+---------------+--------------------------------+
| LIBRARY | VULNERABILITY ID | SEVERITY | INSTALLED VERSION | FIXED VERSION | TITLE |
+----------+------------------+----------+-------------------+---------------+--------------------------------+
| freetype | CVE-2020-15999 | MEDIUM | 2.10.1-r0 | 2.10.1-r1 | freetype: Heap-based buffer overflow due to integer
truncation in Load_SBit_Png
+----------+------------------+----------+-------------------+---------------+--------------------------------+
Idk if its exploitable in any ways.
[Trivi](https://github.com/aquasecurity/trivy) Can be used with github actions and/or TravisCI, maybe it's a nice idea to integrate it or an other scanner like this to the workflow | True | Vulnerabilities scan with Trivy - 0/ I ran a scan over this particular version: bunkerity/bunkerized-nginx:1.1.2 and got this:
> bunkerity/bunkerized-nginx:1.1.2 (alpine 3.11.6)
================================================
Total: 1 (UNKNOWN: 0, LOW: 0, MEDIUM: 1, HIGH: 0, CRITICAL: 0)
+----------+------------------+----------+-------------------+---------------+--------------------------------+
| LIBRARY | VULNERABILITY ID | SEVERITY | INSTALLED VERSION | FIXED VERSION | TITLE |
+----------+------------------+----------+-------------------+---------------+--------------------------------+
| freetype | CVE-2020-15999 | MEDIUM | 2.10.1-r0 | 2.10.1-r1 | freetype: Heap-based buffer overflow due to integer
truncation in Load_SBit_Png
+----------+------------------+----------+-------------------+---------------+--------------------------------+
Idk if its exploitable in any ways.
[Trivi](https://github.com/aquasecurity/trivy) Can be used with github actions and/or TravisCI, maybe it's a nice idea to integrate it or an other scanner like this to the workflow | non_test | vulnerabilities scan with trivy i ran a scan over this particular version bunkerity bunkerized nginx and got this bunkerity bunkerized nginx alpine total unknown low medium high critical library vulnerability id severity installed version fixed version title freetype cve medium freetype heap based buffer overflow due to integer truncation in load sbit png idk if its exploitable in any ways can be used with github actions and or travisci maybe it s a nice idea to integrate it or an other scanner like this to the workflow | 0 |
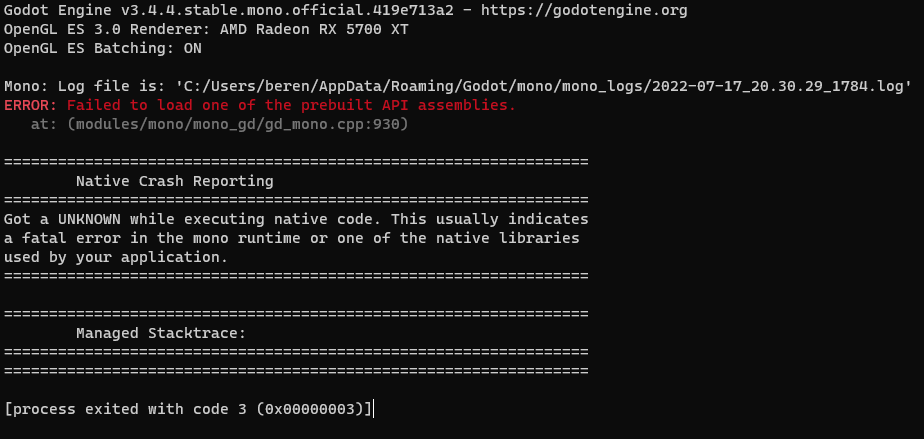
288,516 | 24,910,503,169 | IssuesEvent | 2022-10-29 20:02:43 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Godot Crashes On Start | bug platform:windows topic:editor needs testing topic:dotnet crash | ### Godot version
3.4.4-stable mono
### System information
Win 11, Ryzen 5 3600, 32GB RAM, Radeon 5700XT
### Issue description
Godot fails to launch
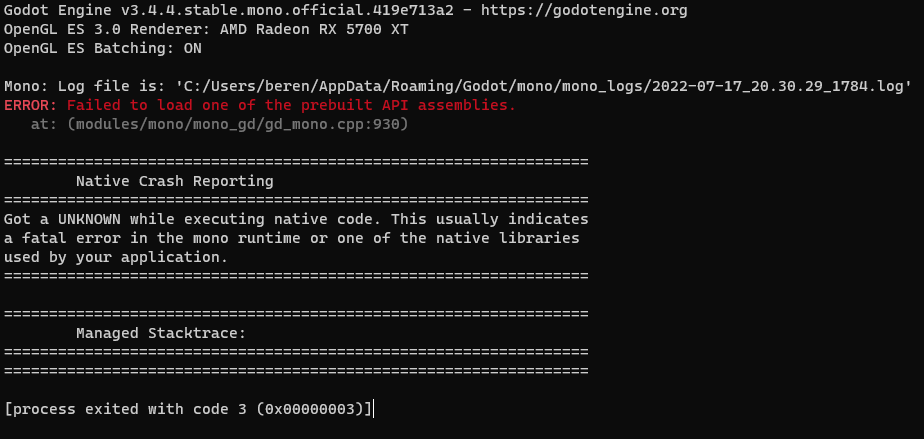
From the log:
`Config attempting to parse: 'D:/Gaming/Godot/GodotSharp/Mono/etc\mono\config'. (in domain Mono, info)
Image addref mscorlib[0000000019a87510] (asmctx DEFAULT) -> D:/Gaming/Godot/GodotSharp/Mono/lib/mono/4.5/mscorlib.dll[0000000019bb33c0]: 2 (in domain Mono, info)
Prepared to set up assembly 'mscorlib' (D:/Gaming/Godot/GodotSharp/Mono/lib/mono/4.5/mscorlib.dll) (in domain Mono, info)
AOT: image 'D:/Gaming/Godot/GodotSharp/Mono/lib/mono/4.5/mscorlib.dll.dll' not found: The system cannot find the file specified.
(in domain Mono, info)
AOT: image 'D:/Gaming/Godot/GodotSharp/Mono/lib/mono/aot-cache/amd64/mscorlib.dll.dll' not found: The system cannot find the path specified.
(in domain Mono, info)
Assembly mscorlib[0000000019a87510] added to domain GodotEngine.RootDomain, ref_count=1 (in domain Mono, info)
Assembly mscorlib[0000000019a87510] added to domain GodotEngine.Domain.Scripts, ref_count=2 (in domain Mono, info)
`
[2022-07-17_12.14.10_24232.log](https://github.com/godotengine/godot/files/9128073/2022-07-17_12.14.10_24232.log)
Its looking for mscorlib.dll.dll and not finding it. I checked the folder its looking in and mscorlib.dll exists but not the double extension file.
Also, the folder D:/Gaming/Godot/GodotSharp/Mono/lib/mono contains the directories 4.5 and v4.0, but not aot-cache
### Steps to reproduce
Download the 3.4.4 x64 mono verson of [godot ](https://downloads.tuxfamily.org/godotengine/3.4.4/mono/Godot_v3.4.4-stable_mono_win64.zip)from the website, extract and run the Godot_v3.4.4-stable_mono_win64.exe file
### Minimal reproduction project
_No response_ | 1.0 | Godot Crashes On Start - ### Godot version
3.4.4-stable mono
### System information
Win 11, Ryzen 5 3600, 32GB RAM, Radeon 5700XT
### Issue description
Godot fails to launch
From the log:
`Config attempting to parse: 'D:/Gaming/Godot/GodotSharp/Mono/etc\mono\config'. (in domain Mono, info)
Image addref mscorlib[0000000019a87510] (asmctx DEFAULT) -> D:/Gaming/Godot/GodotSharp/Mono/lib/mono/4.5/mscorlib.dll[0000000019bb33c0]: 2 (in domain Mono, info)
Prepared to set up assembly 'mscorlib' (D:/Gaming/Godot/GodotSharp/Mono/lib/mono/4.5/mscorlib.dll) (in domain Mono, info)
AOT: image 'D:/Gaming/Godot/GodotSharp/Mono/lib/mono/4.5/mscorlib.dll.dll' not found: The system cannot find the file specified.
(in domain Mono, info)
AOT: image 'D:/Gaming/Godot/GodotSharp/Mono/lib/mono/aot-cache/amd64/mscorlib.dll.dll' not found: The system cannot find the path specified.
(in domain Mono, info)
Assembly mscorlib[0000000019a87510] added to domain GodotEngine.RootDomain, ref_count=1 (in domain Mono, info)
Assembly mscorlib[0000000019a87510] added to domain GodotEngine.Domain.Scripts, ref_count=2 (in domain Mono, info)
`
[2022-07-17_12.14.10_24232.log](https://github.com/godotengine/godot/files/9128073/2022-07-17_12.14.10_24232.log)
Its looking for mscorlib.dll.dll and not finding it. I checked the folder its looking in and mscorlib.dll exists but not the double extension file.
Also, the folder D:/Gaming/Godot/GodotSharp/Mono/lib/mono contains the directories 4.5 and v4.0, but not aot-cache
### Steps to reproduce
Download the 3.4.4 x64 mono verson of [godot ](https://downloads.tuxfamily.org/godotengine/3.4.4/mono/Godot_v3.4.4-stable_mono_win64.zip)from the website, extract and run the Godot_v3.4.4-stable_mono_win64.exe file
### Minimal reproduction project
_No response_ | test | godot crashes on start godot version stable mono system information win ryzen ram radeon issue description godot fails to launch from the log config attempting to parse d gaming godot godotsharp mono etc mono config in domain mono info image addref mscorlib asmctx default d gaming godot godotsharp mono lib mono mscorlib dll in domain mono info prepared to set up assembly mscorlib d gaming godot godotsharp mono lib mono mscorlib dll in domain mono info aot image d gaming godot godotsharp mono lib mono mscorlib dll dll not found the system cannot find the file specified in domain mono info aot image d gaming godot godotsharp mono lib mono aot cache mscorlib dll dll not found the system cannot find the path specified in domain mono info assembly mscorlib added to domain godotengine rootdomain ref count in domain mono info assembly mscorlib added to domain godotengine domain scripts ref count in domain mono info its looking for mscorlib dll dll and not finding it i checked the folder its looking in and mscorlib dll exists but not the double extension file also the folder d gaming godot godotsharp mono lib mono contains the directories and but not aot cache steps to reproduce download the mono verson of the website extract and run the godot stable mono exe file minimal reproduction project no response | 1 |
185,258 | 14,346,574,183 | IssuesEvent | 2020-11-29 01:24:53 | sugarlabs/musicblocks | https://api.github.com/repos/sugarlabs/musicblocks | closed | Repetition of block names when searching a block name using search tool | Issue-Bug WF5-Needs testing | For example, type "if" in the search bar and it'll pop up two results for the same if-then block.
Same happens for a lot of other blocks. | 1.0 | Repetition of block names when searching a block name using search tool - For example, type "if" in the search bar and it'll pop up two results for the same if-then block.
Same happens for a lot of other blocks. | test | repetition of block names when searching a block name using search tool for example type if in the search bar and it ll pop up two results for the same if then block same happens for a lot of other blocks | 1 |
91,188 | 15,856,376,626 | IssuesEvent | 2021-04-08 02:11:57 | jinuem/vue-pdfjs-demo | https://api.github.com/repos/jinuem/vue-pdfjs-demo | opened | WS-2019-0181 (Medium) detected in lodash.defaultsdeep-4.6.0.tgz | security vulnerability | ## WS-2019-0181 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash.defaultsdeep-4.6.0.tgz</b></p></summary>
<p>The lodash method `_.defaultsDeep` exported as a module.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash.defaultsdeep/-/lodash.defaultsdeep-4.6.0.tgz">https://registry.npmjs.org/lodash.defaultsdeep/-/lodash.defaultsdeep-4.6.0.tgz</a></p>
<p>Path to dependency file: /vue-pdfjs-demo/package.json</p>
<p>Path to vulnerable library: vue-pdfjs-demo/node_modules/lodash.defaultsdeep/package.json</p>
<p>
Dependency Hierarchy:
- cli-service-3.7.0.tgz (Root Library)
- :x: **lodash.defaultsdeep-4.6.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash.defaultsdeep before 4.6.1 is vulnerable to Prototype Pollution. The function defaultsDeep() may allow a malicious user to modify the prototype of Object via __proto__ causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2019-08-14
<p>URL: <a href=https://github.com/lodash/lodash/compare/4.6.0...4.6.1>WS-2019-0181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1070">https://www.npmjs.com/advisories/1070</a></p>
<p>Release Date: 2019-08-14</p>
<p>Fix Resolution: 4.6.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2019-0181 (Medium) detected in lodash.defaultsdeep-4.6.0.tgz - ## WS-2019-0181 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash.defaultsdeep-4.6.0.tgz</b></p></summary>
<p>The lodash method `_.defaultsDeep` exported as a module.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash.defaultsdeep/-/lodash.defaultsdeep-4.6.0.tgz">https://registry.npmjs.org/lodash.defaultsdeep/-/lodash.defaultsdeep-4.6.0.tgz</a></p>
<p>Path to dependency file: /vue-pdfjs-demo/package.json</p>
<p>Path to vulnerable library: vue-pdfjs-demo/node_modules/lodash.defaultsdeep/package.json</p>
<p>
Dependency Hierarchy:
- cli-service-3.7.0.tgz (Root Library)
- :x: **lodash.defaultsdeep-4.6.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash.defaultsdeep before 4.6.1 is vulnerable to Prototype Pollution. The function defaultsDeep() may allow a malicious user to modify the prototype of Object via __proto__ causing the addition or modification of an existing property that will exist on all objects.
<p>Publish Date: 2019-08-14
<p>URL: <a href=https://github.com/lodash/lodash/compare/4.6.0...4.6.1>WS-2019-0181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.0</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1070">https://www.npmjs.com/advisories/1070</a></p>
<p>Release Date: 2019-08-14</p>
<p>Fix Resolution: 4.6.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | ws medium detected in lodash defaultsdeep tgz ws medium severity vulnerability vulnerable library lodash defaultsdeep tgz the lodash method defaultsdeep exported as a module library home page a href path to dependency file vue pdfjs demo package json path to vulnerable library vue pdfjs demo node modules lodash defaultsdeep package json dependency hierarchy cli service tgz root library x lodash defaultsdeep tgz vulnerable library vulnerability details lodash defaultsdeep before is vulnerable to prototype pollution the function defaultsdeep may allow a malicious user to modify the prototype of object via proto causing the addition or modification of an existing property that will exist on all objects publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
151,039 | 12,003,502,760 | IssuesEvent | 2020-04-09 09:43:53 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/transform/creation_saved_search·ts - transform creation_saved_search batch transform with terms groups and avg agg with saved search filter selects the source data | :ml failed-test | A test failed on a tracked branch
```
Error: expected testSubject(transformPageCreateTransform) to exist
at TestSubjects.existOrFail (/dev/shm/workspace/kibana/test/functional/services/test_subjects.ts:60:15)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/1766/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/transform/creation_saved_search·ts","test.name":"transform creation_saved_search batch transform with terms groups and avg agg with saved search filter selects the source data","test.failCount":5}} --> | 1.0 | Failing test: Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/transform/creation_saved_search·ts - transform creation_saved_search batch transform with terms groups and avg agg with saved search filter selects the source data - A test failed on a tracked branch
```
Error: expected testSubject(transformPageCreateTransform) to exist
at TestSubjects.existOrFail (/dev/shm/workspace/kibana/test/functional/services/test_subjects.ts:60:15)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.x/1766/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Chrome X-Pack UI Functional Tests.x-pack/test/functional/apps/transform/creation_saved_search·ts","test.name":"transform creation_saved_search batch transform with terms groups and avg agg with saved search filter selects the source data","test.failCount":5}} --> | test | failing test chrome x pack ui functional tests x pack test functional apps transform creation saved search·ts transform creation saved search batch transform with terms groups and avg agg with saved search filter selects the source data a test failed on a tracked branch error expected testsubject transformpagecreatetransform to exist at testsubjects existorfail dev shm workspace kibana test functional services test subjects ts first failure | 1 |
57,051 | 6,536,445,905 | IssuesEvent | 2017-08-31 18:10:58 | LDMW/cms | https://api.github.com/repos/LDMW/cms | closed | Make beta banner permanently white | please-test T25m | Now that the transparent nav bar is underneath it, it looks a bit strange and would be better being permanently white, not transparent on first load as it currently is.
| 1.0 | Make beta banner permanently white - Now that the transparent nav bar is underneath it, it looks a bit strange and would be better being permanently white, not transparent on first load as it currently is.
| test | make beta banner permanently white now that the transparent nav bar is underneath it it looks a bit strange and would be better being permanently white not transparent on first load as it currently is | 1 |
81,307 | 7,778,354,757 | IssuesEvent | 2018-06-05 13:59:05 | IDgis/geoportaal-test | https://api.github.com/repos/IDgis/geoportaal-test | closed | Download link aanwezig op home pagina maar geeft fout | bug gebruikerstest impact middel vraag | Wat kan hier aan de hand zijn? Er is wel een download link aanwezig, maar geen link naar de viewer.
En als ik de download probeer dan krijg ik een foutmelding als ik probeer de download uit te voeren. Bij de details in de metadata staat ook geen link naar een downloadlink.
Dan moet die toch ook niet op de homepagina staan?
De foutmelding is:
500 Interne server fout
Er ging iets mis bij het verwerken van het verzoek.
Foutcode: @772c945ao
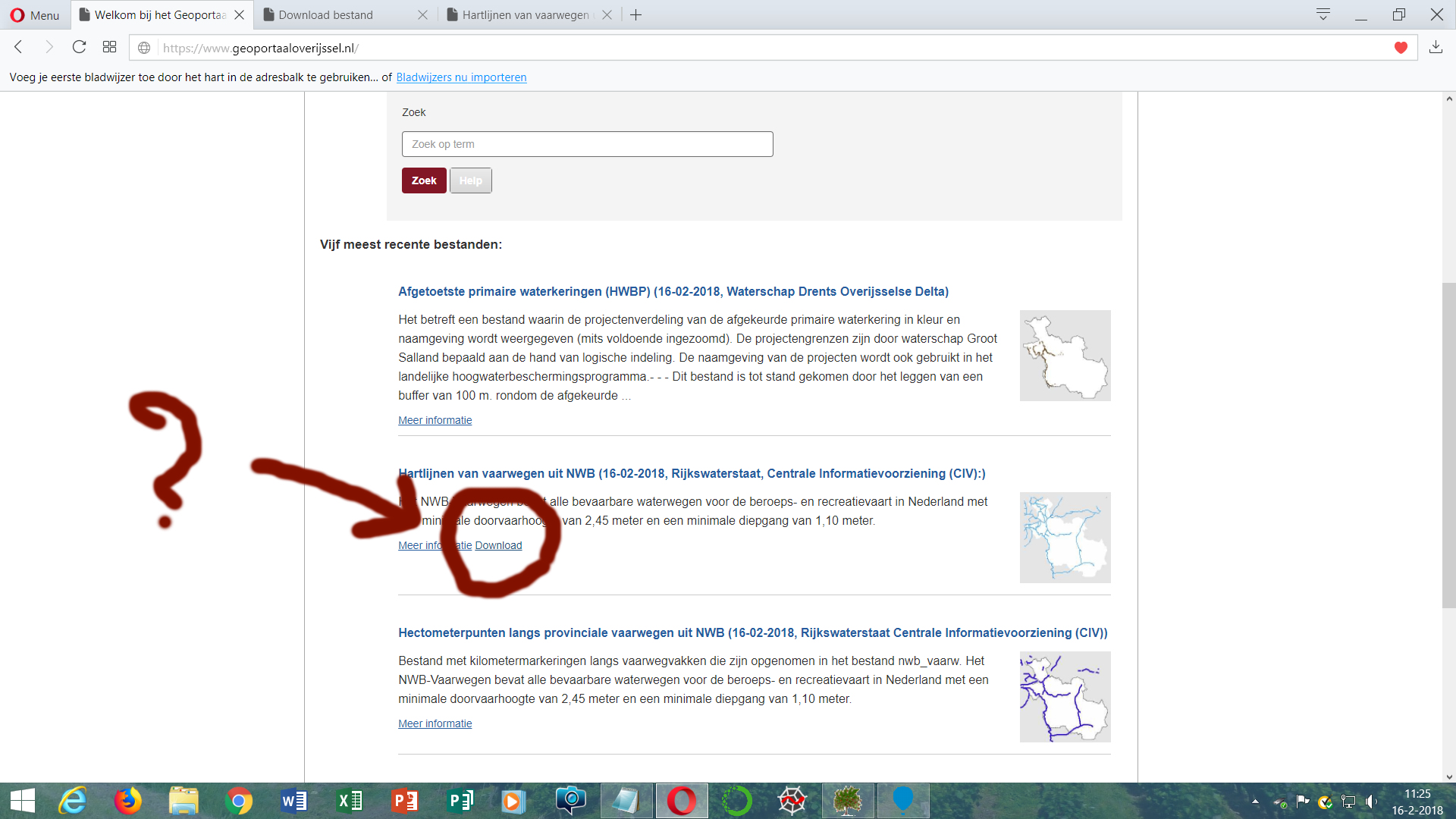
| 1.0 | Download link aanwezig op home pagina maar geeft fout - Wat kan hier aan de hand zijn? Er is wel een download link aanwezig, maar geen link naar de viewer.
En als ik de download probeer dan krijg ik een foutmelding als ik probeer de download uit te voeren. Bij de details in de metadata staat ook geen link naar een downloadlink.
Dan moet die toch ook niet op de homepagina staan?
De foutmelding is:
500 Interne server fout
Er ging iets mis bij het verwerken van het verzoek.
Foutcode: @772c945ao
| test | download link aanwezig op home pagina maar geeft fout wat kan hier aan de hand zijn er is wel een download link aanwezig maar geen link naar de viewer en als ik de download probeer dan krijg ik een foutmelding als ik probeer de download uit te voeren bij de details in de metadata staat ook geen link naar een downloadlink dan moet die toch ook niet op de homepagina staan de foutmelding is interne server fout er ging iets mis bij het verwerken van het verzoek foutcode | 1 |
218,936 | 7,332,814,264 | IssuesEvent | 2018-03-05 17:23:06 | NCEAS/metacat | https://api.github.com/repos/NCEAS/metacat | closed | Log-in form on SanPark skin doesn't work | Component: Bugzilla-Id Priority: Normal Status: Resolved Tracker: Bug | ---
Author Name: **Jing Tao** (Jing Tao)
Original Redmine Issue: 6427, https://projects.ecoinformatics.org/ecoinfo/issues/6427
Original Date: 2014-02-26
Original Assignee: Jing Tao
---
If you click the login button on the Sanpark skin even though input a valid user/password, the login doesn't go through. The browser's url text box will show a metacat login servlet url even with the password!
| 1.0 | Log-in form on SanPark skin doesn't work - ---
Author Name: **Jing Tao** (Jing Tao)
Original Redmine Issue: 6427, https://projects.ecoinformatics.org/ecoinfo/issues/6427
Original Date: 2014-02-26
Original Assignee: Jing Tao
---
If you click the login button on the Sanpark skin even though input a valid user/password, the login doesn't go through. The browser's url text box will show a metacat login servlet url even with the password!
| non_test | log in form on sanpark skin doesn t work author name jing tao jing tao original redmine issue original date original assignee jing tao if you click the login button on the sanpark skin even though input a valid user password the login doesn t go through the browser s url text box will show a metacat login servlet url even with the password | 0 |
32,412 | 4,770,263,022 | IssuesEvent | 2016-10-26 14:51:10 | Semantic-Org/Semantic-UI | https://api.github.com/repos/Semantic-Org/Semantic-UI | reopened | Placeholder in IE11 looks Bolder | Evaluating Bug / Change Needs Test Case | While using placeholder with Semantic UI for input tags in IE11, it looks bolder(like something have already made as an input). Please suggest if there is an default option/settings to avoid it. Thanks in advance... | 1.0 | Placeholder in IE11 looks Bolder - While using placeholder with Semantic UI for input tags in IE11, it looks bolder(like something have already made as an input). Please suggest if there is an default option/settings to avoid it. Thanks in advance... | test | placeholder in looks bolder while using placeholder with semantic ui for input tags in it looks bolder like something have already made as an input please suggest if there is an default option settings to avoid it thanks in advance | 1 |
13,893 | 8,713,959,466 | IssuesEvent | 2018-12-07 05:35:32 | OctopusDeploy/Issues | https://api.github.com/repos/OctopusDeploy/Issues | closed | Clicking on a step in the task summary doesn't navigate to the task log properly | area/usability kind/bug | # Prerequisites
- [x] I have verified the problem exists in the latest version
- [x] I have searched [open](https://github.com/OctopusDeploy/Issues/issues) and [closed](https://github.com/OctopusDeploy/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already reported
- [x] I have written a descriptive issue title
- [x] I have linked the original source of this report
- [x] I have tagged the issue appropriately (area/*, kind/bug, tag/regression?)
# The bug
When clicking on a step or target in the task summary, it takes you to the task log. Only problem is that sometimes the log element you wanted to view is under the stick header, and sometimes its nowhere to be seen.
## What I expected to happen
It should scroll to the the expected element and make it visible
## Steps to reproduce
1. Go to the task summary of a task with many steps `Synchronize external security groups` is often a good one.
2. Click on the first item in the log
-> you are switched to the task log, but the expected element is under the sticky header
## Affected versions
**Octopus Server:** 4.x until fixed
## Workarounds
Scroll up to find the element if its hidden
## Links
source: internally raised | True | Clicking on a step in the task summary doesn't navigate to the task log properly - # Prerequisites
- [x] I have verified the problem exists in the latest version
- [x] I have searched [open](https://github.com/OctopusDeploy/Issues/issues) and [closed](https://github.com/OctopusDeploy/Issues/issues?utf8=%E2%9C%93&q=is%3Aissue+is%3Aclosed) issues to make sure it isn't already reported
- [x] I have written a descriptive issue title
- [x] I have linked the original source of this report
- [x] I have tagged the issue appropriately (area/*, kind/bug, tag/regression?)
# The bug
When clicking on a step or target in the task summary, it takes you to the task log. Only problem is that sometimes the log element you wanted to view is under the stick header, and sometimes its nowhere to be seen.
## What I expected to happen
It should scroll to the the expected element and make it visible
## Steps to reproduce
1. Go to the task summary of a task with many steps `Synchronize external security groups` is often a good one.
2. Click on the first item in the log
-> you are switched to the task log, but the expected element is under the sticky header
## Affected versions
**Octopus Server:** 4.x until fixed
## Workarounds
Scroll up to find the element if its hidden
## Links
source: internally raised | non_test | clicking on a step in the task summary doesn t navigate to the task log properly prerequisites i have verified the problem exists in the latest version i have searched and issues to make sure it isn t already reported i have written a descriptive issue title i have linked the original source of this report i have tagged the issue appropriately area kind bug tag regression the bug when clicking on a step or target in the task summary it takes you to the task log only problem is that sometimes the log element you wanted to view is under the stick header and sometimes its nowhere to be seen what i expected to happen it should scroll to the the expected element and make it visible steps to reproduce go to the task summary of a task with many steps synchronize external security groups is often a good one click on the first item in the log you are switched to the task log but the expected element is under the sticky header affected versions octopus server x until fixed workarounds scroll up to find the element if its hidden links source internally raised | 0 |
7,056 | 6,732,757,900 | IssuesEvent | 2017-10-18 12:45:06 | kubernetes-incubator/kubespray | https://api.github.com/repos/kubernetes-incubator/kubespray | closed | Elevate individual tasks to super user only as needed | security | I was going to give kargo a try for rolling a kubernetes cluster but it got stuck at:
```
TASK [adduser : User | Create User Group] **************************************
fatal: [k8s-etcd-3]: FAILED! => {"changed": false, "failed": true, "msg": "groupadd: Permission denied.\ngroupadd: cannot lock /etc/group; try again later.\n", "name": "kube-cert"}
fatal: [k8s-etcd-2]: FAILED! => {"changed": false, "failed": true, "msg": "groupadd: Permission denied.\ngroupadd: cannot lock /etc/group; try again later.\n", "name": "kube-cert"}
fatal: [k8s-etcd-1]: FAILED! => {"changed": false, "failed": true, "msg": "groupadd: Permission denied.\ngroupadd: cannot lock /etc/group; try again later.\n", "name": "kube-cert"}
```
I checked in the ansible files and it seemed that the task had no `become: true` annotation which seemed odd given it requires super user permissions. I asked about this and was told that people using kargo normally add the become on the command line. But that would mean running all tasks as a super user. This seems wrong and instead only tasks requiring super user privileges should become a super user.
| True | Elevate individual tasks to super user only as needed - I was going to give kargo a try for rolling a kubernetes cluster but it got stuck at:
```
TASK [adduser : User | Create User Group] **************************************
fatal: [k8s-etcd-3]: FAILED! => {"changed": false, "failed": true, "msg": "groupadd: Permission denied.\ngroupadd: cannot lock /etc/group; try again later.\n", "name": "kube-cert"}
fatal: [k8s-etcd-2]: FAILED! => {"changed": false, "failed": true, "msg": "groupadd: Permission denied.\ngroupadd: cannot lock /etc/group; try again later.\n", "name": "kube-cert"}
fatal: [k8s-etcd-1]: FAILED! => {"changed": false, "failed": true, "msg": "groupadd: Permission denied.\ngroupadd: cannot lock /etc/group; try again later.\n", "name": "kube-cert"}
```
I checked in the ansible files and it seemed that the task had no `become: true` annotation which seemed odd given it requires super user permissions. I asked about this and was told that people using kargo normally add the become on the command line. But that would mean running all tasks as a super user. This seems wrong and instead only tasks requiring super user privileges should become a super user.
| non_test | elevate individual tasks to super user only as needed i was going to give kargo a try for rolling a kubernetes cluster but it got stuck at task fatal failed changed false failed true msg groupadd permission denied ngroupadd cannot lock etc group try again later n name kube cert fatal failed changed false failed true msg groupadd permission denied ngroupadd cannot lock etc group try again later n name kube cert fatal failed changed false failed true msg groupadd permission denied ngroupadd cannot lock etc group try again later n name kube cert i checked in the ansible files and it seemed that the task had no become true annotation which seemed odd given it requires super user permissions i asked about this and was told that people using kargo normally add the become on the command line but that would mean running all tasks as a super user this seems wrong and instead only tasks requiring super user privileges should become a super user | 0 |
81,686 | 15,630,110,597 | IssuesEvent | 2021-03-22 01:23:24 | johnnymythology/material-blog-jp | https://api.github.com/repos/johnnymythology/material-blog-jp | closed | CVE-2018-19826 (Medium) detected in node-sass-v4.11.0 - autoclosed | security vulnerability | ## CVE-2018-19826 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/johnnymythology/material-blog-jp/commit/b32aa2b2c0c66e5829b13877b5425dd83501c412">b32aa2b2c0c66e5829b13877b5425dd83501c412</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (4)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /material-blog-jp/_layouts/material_lite/_site/node_modules/node-sass/src/binding.cpp
- /material-blog-jp/_layouts/material_lite/node_modules/node-sass/src/libsass/src/inspect.cpp
- /material-blog-jp/_layouts/material_lite/_site/node_modules/node-sass/src/libsass/src/operators.cpp
- /material-blog-jp/_layouts/material_lite/_site/node_modules/node-sass/src/libsass/src/parser.cpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** In inspect.cpp in LibSass 3.5.5, a high memory footprint caused by an endless loop (containing a Sass::Inspect::operator()(Sass::String_Quoted*) stack frame) may cause a Denial of Service via crafted sass input files with stray '&' or '/' characters. NOTE: Upstream comments indicate this issue is closed as "won't fix" and "works as intended" by design.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19826>CVE-2018-19826</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19826 (Medium) detected in node-sass-v4.11.0 - autoclosed - ## CVE-2018-19826 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/johnnymythology/material-blog-jp/commit/b32aa2b2c0c66e5829b13877b5425dd83501c412">b32aa2b2c0c66e5829b13877b5425dd83501c412</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Library Source Files (4)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /material-blog-jp/_layouts/material_lite/_site/node_modules/node-sass/src/binding.cpp
- /material-blog-jp/_layouts/material_lite/node_modules/node-sass/src/libsass/src/inspect.cpp
- /material-blog-jp/_layouts/material_lite/_site/node_modules/node-sass/src/libsass/src/operators.cpp
- /material-blog-jp/_layouts/material_lite/_site/node_modules/node-sass/src/libsass/src/parser.cpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
** DISPUTED ** In inspect.cpp in LibSass 3.5.5, a high memory footprint caused by an endless loop (containing a Sass::Inspect::operator()(Sass::String_Quoted*) stack frame) may cause a Denial of Service via crafted sass input files with stray '&' or '/' characters. NOTE: Upstream comments indicate this issue is closed as "won't fix" and "works as intended" by design.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19826>CVE-2018-19826</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in node sass autoclosed cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href found in head commit a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries material blog jp layouts material lite site node modules node sass src binding cpp material blog jp layouts material lite node modules node sass src libsass src inspect cpp material blog jp layouts material lite site node modules node sass src libsass src operators cpp material blog jp layouts material lite site node modules node sass src libsass src parser cpp vulnerability details disputed in inspect cpp in libsass a high memory footprint caused by an endless loop containing a sass inspect operator sass string quoted stack frame may cause a denial of service via crafted sass input files with stray or characters note upstream comments indicate this issue is closed as won t fix and works as intended by design publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href step up your open source security game with whitesource | 0 |
23,308 | 21,649,457,076 | IssuesEvent | 2022-05-06 07:48:01 | microsoft/win32metadata | https://api.github.com/repos/microsoft/win32metadata | closed | WaitForMultipleObjects returns a u32, but we can't match over WAIT_TIMEOUT and WAIT_FAILED | usability | ### Which crate is this about?
windows
### Crate version
0.36.1
### Summary
I want to do this:
```rust
let result = unsafe {
th::WaitForMultipleObjects(
&self.events,
false,
wp::INFINITE,
)
};
match result {
th::WAIT_ABANDONED_0 => /* wait abandoned */,
t::WAIT_TIMEOUT => /* do something on timeout */,
f::WAIT_FAILED => /* do something on error, like Error::from_win32() */,
other => {
let base = th::WAIT_OBJECT_0;
if other < base {
panic!("other out of bounds; other = {}", other);
}
let index = (other - base) as usize;
/* do something with index */
}
}
```
But `WAIT_TIMEOUT` and `WAIT_FAILED` can no longer immediately be used in a match statement like the above, since they are now wrapped in a `WIN32_ERROR`, instead we have to make your own wrapper for `WAIT_ABANDONED_0`:
```rust
const WAIT_ABANDONED_0 : f::WIN32_ERROR = f::WIN32_ERROR(th::WAIT_ABANDONED_0);
match f::WIN32_ERROR(result) {
WAIT_ABANDONED_0 => /* wait abandoned */,
t::WAIT_TIMEOUT => /* do something on timeout */,
f::WAIT_FAILED => /* do something on error, like Error::from_win32() */,
f::WIN32_ERROR(other) => {
let base = th::WAIT_OBJECT_0;
if other < base {
panic!("other out of bounds; other = {}", other);
}
let index = (other - base) as usize;
/* do something with index */
}
}
```
### Toolchain version/configuration
_No response_
### Reproducible example
_No response_
### Crate manifest
_No response_
### Expected behavior
_No response_
### Actual behavior
_No response_
### Additional comments
_No response_ | True | WaitForMultipleObjects returns a u32, but we can't match over WAIT_TIMEOUT and WAIT_FAILED - ### Which crate is this about?
windows
### Crate version
0.36.1
### Summary
I want to do this:
```rust
let result = unsafe {
th::WaitForMultipleObjects(
&self.events,
false,
wp::INFINITE,
)
};
match result {
th::WAIT_ABANDONED_0 => /* wait abandoned */,
t::WAIT_TIMEOUT => /* do something on timeout */,
f::WAIT_FAILED => /* do something on error, like Error::from_win32() */,
other => {
let base = th::WAIT_OBJECT_0;
if other < base {
panic!("other out of bounds; other = {}", other);
}
let index = (other - base) as usize;
/* do something with index */
}
}
```
But `WAIT_TIMEOUT` and `WAIT_FAILED` can no longer immediately be used in a match statement like the above, since they are now wrapped in a `WIN32_ERROR`, instead we have to make your own wrapper for `WAIT_ABANDONED_0`:
```rust
const WAIT_ABANDONED_0 : f::WIN32_ERROR = f::WIN32_ERROR(th::WAIT_ABANDONED_0);
match f::WIN32_ERROR(result) {
WAIT_ABANDONED_0 => /* wait abandoned */,
t::WAIT_TIMEOUT => /* do something on timeout */,
f::WAIT_FAILED => /* do something on error, like Error::from_win32() */,
f::WIN32_ERROR(other) => {
let base = th::WAIT_OBJECT_0;
if other < base {
panic!("other out of bounds; other = {}", other);
}
let index = (other - base) as usize;
/* do something with index */
}
}
```
### Toolchain version/configuration
_No response_
### Reproducible example
_No response_
### Crate manifest
_No response_
### Expected behavior
_No response_
### Actual behavior
_No response_
### Additional comments
_No response_ | non_test | waitformultipleobjects returns a but we can t match over wait timeout and wait failed which crate is this about windows crate version summary i want to do this rust let result unsafe th waitformultipleobjects self events false wp infinite match result th wait abandoned wait abandoned t wait timeout do something on timeout f wait failed do something on error like error from other let base th wait object if other base panic other out of bounds other other let index other base as usize do something with index but wait timeout and wait failed can no longer immediately be used in a match statement like the above since they are now wrapped in a error instead we have to make your own wrapper for wait abandoned rust const wait abandoned f error f error th wait abandoned match f error result wait abandoned wait abandoned t wait timeout do something on timeout f wait failed do something on error like error from f error other let base th wait object if other base panic other out of bounds other other let index other base as usize do something with index toolchain version configuration no response reproducible example no response crate manifest no response expected behavior no response actual behavior no response additional comments no response | 0 |
18,203 | 4,238,668,923 | IssuesEvent | 2016-07-06 05:37:47 | sakshamsaxena/sails-hook-jbvcs | https://api.github.com/repos/sakshamsaxena/sails-hook-jbvcs | opened | Update wiki and Readme | Documentation Need Research | Need to write about promises now. And also about the usage in sails project (test that too) | 1.0 | Update wiki and Readme - Need to write about promises now. And also about the usage in sails project (test that too) | non_test | update wiki and readme need to write about promises now and also about the usage in sails project test that too | 0 |
90,658 | 8,251,771,923 | IssuesEvent | 2018-09-12 08:51:41 | mesg-foundation/core | https://api.github.com/repos/mesg-foundation/core | closed | [list] add equivalent tests for the tests deleted by cmd refactor | unit testing | [tests were exists in the older version of dev](https://github.com/mesg-foundation/core/blob/33fb3a31bb84eeee8ade9b1b04f193cddfb56bd7/cmd/service/list_test.go)
```go
func TestServiceStatusString(t *testing.T) {
s := service.Service{Name: "TestServiceStatusString"}
status := serviceStatus{
service: &s,
status: service.RUNNING,
}
require.Contains(t, status.String(), "[Running]")
require.Contains(t, status.String(), s.ID)
require.Contains(t, status.String(), s.Name)
}
func TestSort(t *testing.T) {
status := []serviceStatus{
{status: service.PARTIAL, service: &service.Service{Name: "Partial"}},
{status: service.RUNNING, service: &service.Service{Name: "Running"}},
{status: service.STOPPED, service: &service.Service{Name: "Stopped"}},
}
sort.Sort(byStatus(status))
require.Equal(t, status[0].status, service.RUNNING)
require.Equal(t, status[1].status, service.PARTIAL)
require.Equal(t, status[2].status, service.STOPPED)
}
func TestServicesWithStatus(t *testing.T) {
services := append([]*service.Service{}, &service.Service{Name: "TestServicesWithStatus"})
status, err := servicesWithStatus(services)
require.Nil(t, err)
require.Equal(t, status[0].status, service.STOPPED)
}
``` | 1.0 | [list] add equivalent tests for the tests deleted by cmd refactor - [tests were exists in the older version of dev](https://github.com/mesg-foundation/core/blob/33fb3a31bb84eeee8ade9b1b04f193cddfb56bd7/cmd/service/list_test.go)
```go
func TestServiceStatusString(t *testing.T) {
s := service.Service{Name: "TestServiceStatusString"}
status := serviceStatus{
service: &s,
status: service.RUNNING,
}
require.Contains(t, status.String(), "[Running]")
require.Contains(t, status.String(), s.ID)
require.Contains(t, status.String(), s.Name)
}
func TestSort(t *testing.T) {
status := []serviceStatus{
{status: service.PARTIAL, service: &service.Service{Name: "Partial"}},
{status: service.RUNNING, service: &service.Service{Name: "Running"}},
{status: service.STOPPED, service: &service.Service{Name: "Stopped"}},
}
sort.Sort(byStatus(status))
require.Equal(t, status[0].status, service.RUNNING)
require.Equal(t, status[1].status, service.PARTIAL)
require.Equal(t, status[2].status, service.STOPPED)
}
func TestServicesWithStatus(t *testing.T) {
services := append([]*service.Service{}, &service.Service{Name: "TestServicesWithStatus"})
status, err := servicesWithStatus(services)
require.Nil(t, err)
require.Equal(t, status[0].status, service.STOPPED)
}
``` | test | add equivalent tests for the tests deleted by cmd refactor go func testservicestatusstring t testing t s service service name testservicestatusstring status servicestatus service s status service running require contains t status string require contains t status string s id require contains t status string s name func testsort t testing t status servicestatus status service partial service service service name partial status service running service service service name running status service stopped service service service name stopped sort sort bystatus status require equal t status status service running require equal t status status service partial require equal t status status service stopped func testserviceswithstatus t testing t services append service service service service name testserviceswithstatus status err serviceswithstatus services require nil t err require equal t status status service stopped | 1 |
103,445 | 8,909,401,546 | IssuesEvent | 2019-01-18 06:05:35 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: upgrade/oldVersion=v2.1.3/nodes=5 failed | C-test-failure O-robot | SHA: https://github.com/cockroachdb/cockroach/commits/89ce71e9b733df3855b370aa20bb809db3d4362c
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
stdbuf -oL -eL \
make stressrace TESTS=upgrade/oldVersion=v2.1.3/nodes=5 PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1098977&tab=buildLog
```
The test failed on provisional_201901161553_v2.1.4:
test.go:718,upgrade.go:240,upgrade.go:263: cluster setting version is not upgraded, still 2.1
``` | 1.0 | roachtest: upgrade/oldVersion=v2.1.3/nodes=5 failed - SHA: https://github.com/cockroachdb/cockroach/commits/89ce71e9b733df3855b370aa20bb809db3d4362c
Parameters:
To repro, try:
```
# Don't forget to check out a clean suitable branch and experiment with the
# stress invocation until the desired results present themselves. For example,
# using stress instead of stressrace and passing the '-p' stressflag which
# controls concurrency.
./scripts/gceworker.sh start && ./scripts/gceworker.sh mosh
cd ~/go/src/github.com/cockroachdb/cockroach && \
stdbuf -oL -eL \
make stressrace TESTS=upgrade/oldVersion=v2.1.3/nodes=5 PKG=roachtest TESTTIMEOUT=5m STRESSFLAGS='-maxtime 20m -timeout 10m' 2>&1 | tee /tmp/stress.log
```
Failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=1098977&tab=buildLog
```
The test failed on provisional_201901161553_v2.1.4:
test.go:718,upgrade.go:240,upgrade.go:263: cluster setting version is not upgraded, still 2.1
``` | test | roachtest upgrade oldversion nodes failed sha parameters to repro try don t forget to check out a clean suitable branch and experiment with the stress invocation until the desired results present themselves for example using stress instead of stressrace and passing the p stressflag which controls concurrency scripts gceworker sh start scripts gceworker sh mosh cd go src github com cockroachdb cockroach stdbuf ol el make stressrace tests upgrade oldversion nodes pkg roachtest testtimeout stressflags maxtime timeout tee tmp stress log failed test the test failed on provisional test go upgrade go upgrade go cluster setting version is not upgraded still | 1 |
462,533 | 13,248,758,353 | IssuesEvent | 2020-08-19 19:33:11 | googleapis/nodejs-common | https://api.github.com/repos/googleapis/nodejs-common | closed | Allow non-JSON error response to be parsed and request retried | priority: p2 type: bug | It has become known that the service API can return non-JSON response body for some retryable errors like 503 - Service Unavailable.
Here is a stack trace of customer reported failures:
```
err: {
message: "Cannot parse response as JSON: Service Unavailable"
response: {…}
stack: "Error: Cannot parse response as JSON: Service Unavailable
at Util.parseHttpRespBody (/usr/src/app/node_modules/@google-cloud/common/build/src/util.js:189:42)
at Util.handleResp (/usr/src/app/node_modules/@google-cloud/common/build/src/util.js:135:117)
at /usr/src/app/node_modules/@google-cloud/common/build/src/util.js:434:22
at onResponse (/usr/src/app/node_modules/retry-request/index.js:206:7)
at /usr/src/app/node_modules/teeny-request/build/src/index.js:170:17
at runMicrotasks (<anonymous>)
at processTicksAndRejections (internal/process/task_queues.js:97:5)"
type: "ApiError"
}
```
We should update `parseHttpRespBody` to allow non-JSON responses:
https://github.com/googleapis/nodejs-common/blob/master/src/util.ts#L413-L434 | 1.0 | Allow non-JSON error response to be parsed and request retried - It has become known that the service API can return non-JSON response body for some retryable errors like 503 - Service Unavailable.
Here is a stack trace of customer reported failures:
```
err: {
message: "Cannot parse response as JSON: Service Unavailable"
response: {…}
stack: "Error: Cannot parse response as JSON: Service Unavailable
at Util.parseHttpRespBody (/usr/src/app/node_modules/@google-cloud/common/build/src/util.js:189:42)
at Util.handleResp (/usr/src/app/node_modules/@google-cloud/common/build/src/util.js:135:117)
at /usr/src/app/node_modules/@google-cloud/common/build/src/util.js:434:22
at onResponse (/usr/src/app/node_modules/retry-request/index.js:206:7)
at /usr/src/app/node_modules/teeny-request/build/src/index.js:170:17
at runMicrotasks (<anonymous>)
at processTicksAndRejections (internal/process/task_queues.js:97:5)"
type: "ApiError"
}
```
We should update `parseHttpRespBody` to allow non-JSON responses:
https://github.com/googleapis/nodejs-common/blob/master/src/util.ts#L413-L434 | non_test | allow non json error response to be parsed and request retried it has become known that the service api can return non json response body for some retryable errors like service unavailable here is a stack trace of customer reported failures err message cannot parse response as json service unavailable response … stack error cannot parse response as json service unavailable at util parsehttprespbody usr src app node modules google cloud common build src util js at util handleresp usr src app node modules google cloud common build src util js at usr src app node modules google cloud common build src util js at onresponse usr src app node modules retry request index js at usr src app node modules teeny request build src index js at runmicrotasks at processticksandrejections internal process task queues js type apierror we should update parsehttprespbody to allow non json responses | 0 |
457,688 | 13,160,197,113 | IssuesEvent | 2020-08-10 17:09:02 | wso2/product-apim | https://api.github.com/repos/wso2/product-apim | closed | Errors thrown when deploying API when we have special characters in the admin password even with CDATA | Priority/Normal Type/Bug | ### Description:
Unable to deploy sample API when having special characters in super admin password. As per the document [1], We can not include @ or % without URL encoding. So, assumption is all others should be possible.
### Steps to reproduce:
Use following super admin password :
```
[super_admin]
username = "foo_admin"
password = "<![CDATA[~^&*#`43d:3;]]>"
```
Login and try to deploy the sample API
[1]: https://apim.docs.wso2.com/en/next/install-and-setup/setup/security/logins-and-passwords/maintaining-logins-and-passwords/#change-the-super-admin-credentials
### Affected Product Version:
APIM 3.2.0 - RC2
[TenantDeployAPIError.txt](https://github.com/wso2/product-apim/files/5048086/TenantDeployAPIError.txt)
| 1.0 | Errors thrown when deploying API when we have special characters in the admin password even with CDATA - ### Description:
Unable to deploy sample API when having special characters in super admin password. As per the document [1], We can not include @ or % without URL encoding. So, assumption is all others should be possible.
### Steps to reproduce:
Use following super admin password :
```
[super_admin]
username = "foo_admin"
password = "<![CDATA[~^&*#`43d:3;]]>"
```
Login and try to deploy the sample API
[1]: https://apim.docs.wso2.com/en/next/install-and-setup/setup/security/logins-and-passwords/maintaining-logins-and-passwords/#change-the-super-admin-credentials
### Affected Product Version:
APIM 3.2.0 - RC2
[TenantDeployAPIError.txt](https://github.com/wso2/product-apim/files/5048086/TenantDeployAPIError.txt)
| non_test | errors thrown when deploying api when we have special characters in the admin password even with cdata description unable to deploy sample api when having special characters in super admin password as per the document we can not include or without url encoding so assumption is all others should be possible steps to reproduce use following super admin password username foo admin password login and try to deploy the sample api affected product version apim | 0 |
232,882 | 18,921,265,779 | IssuesEvent | 2021-11-17 02:09:30 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: kv/multi-store-with-overload failed [perm denied #72635] | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.kv/multi-store-with-overload [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3705715&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3705715&tab=artifacts#/kv/multi-store-with-overload) on master @ [2de17e7fbe66e14039fc7969a76139625761438f](https://github.com/cockroachdb/cockroach/commits/2de17e7fbe66e14039fc7969a76139625761438f):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/kv/multi-store-with-overload/run_1
cluster.go:1856,kv.go:847,kv.go:914,test_runner.go:777: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --store-count=2 teamcity-3705715-1636529870-49-n2cpu8:1 returned: exit status 7
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --store-count=2 teamcity-3705715-1636529870-49-n2cpu8:1 returned
| stderr:
|
| stdout:
| <... some data truncated by circular buffer; go to artifacts for details ...>
| nc9(0x1a19940, 0xc0004a2780, 0x1, 0x2, 0xc0006bfa10, 0xc0006bfa38)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:457 +0xdf
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !main.wrap.func1(0x1a19940, 0xc0004a2780, 0x1, 0x2)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:123 +0x6b
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !github.com/spf13/cobra.(*Command).execute(0x1a19940, 0xc0004a2760, 0x2, 0x2, 0x1a19940, 0xc0004a2760)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:856 +0x2c2
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !github.com/spf13/cobra.(*Command).ExecuteC(0x1a196c0, 0x0, 0x0, 0xc00044a8c0)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:960 +0x375
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !github.com/spf13/cobra.(*Command).Execute(...)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:897
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !main.main()
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1170 +0x26a5
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !****************************************************************************
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !This node experienced a fatal error (printed above), and as a result the
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !process is terminating.
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !Fatal errors can occur due to faulty hardware (disks, memory, clocks) or a
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !problem in CockroachDB. With your help, the support team at Cockroach Labs
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !will try to determine the root cause, recommend next steps, and we can
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !improve CockroachDB based on your report.
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !Please submit a crash report by following the instructions here:
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! https://github.com/cockroachdb/cockroach/issues/new/choose
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !If you would rather not post publicly, please contact us directly at:
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! support@cockroachlabs.com
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !The Cockroach Labs team appreciates your feedback.
Wraps: (2) exit status 7
Error types: (1) *cluster.WithCommandDetails (2) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
|
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*kv/multi-store-with-overload.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: kv/multi-store-with-overload failed [perm denied #72635] - roachtest.kv/multi-store-with-overload [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3705715&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3705715&tab=artifacts#/kv/multi-store-with-overload) on master @ [2de17e7fbe66e14039fc7969a76139625761438f](https://github.com/cockroachdb/cockroach/commits/2de17e7fbe66e14039fc7969a76139625761438f):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/kv/multi-store-with-overload/run_1
cluster.go:1856,kv.go:847,kv.go:914,test_runner.go:777: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --store-count=2 teamcity-3705715-1636529870-49-n2cpu8:1 returned: exit status 7
(1) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod start --store-count=2 teamcity-3705715-1636529870-49-n2cpu8:1 returned
| stderr:
|
| stdout:
| <... some data truncated by circular buffer; go to artifacts for details ...>
| nc9(0x1a19940, 0xc0004a2780, 0x1, 0x2, 0xc0006bfa10, 0xc0006bfa38)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:457 +0xdf
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !main.wrap.func1(0x1a19940, 0xc0004a2780, 0x1, 0x2)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:123 +0x6b
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !github.com/spf13/cobra.(*Command).execute(0x1a19940, 0xc0004a2760, 0x2, 0x2, 0x1a19940, 0xc0004a2760)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:856 +0x2c2
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !github.com/spf13/cobra.(*Command).ExecuteC(0x1a196c0, 0x0, 0x0, 0xc00044a8c0)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:960 +0x375
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !github.com/spf13/cobra.(*Command).Execute(...)
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/vendor/github.com/spf13/cobra/command.go:897
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !main.main()
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachprod/main.go:1170 +0x26a5
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !****************************************************************************
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !This node experienced a fatal error (printed above), and as a result the
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !process is terminating.
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !Fatal errors can occur due to faulty hardware (disks, memory, clocks) or a
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !problem in CockroachDB. With your help, the support team at Cockroach Labs
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !will try to determine the root cause, recommend next steps, and we can
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !improve CockroachDB based on your report.
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !Please submit a crash report by following the instructions here:
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! https://github.com/cockroachdb/cockroach/issues/new/choose
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !If you would rather not post publicly, please contact us directly at:
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 ! support@cockroachlabs.com
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !
| F211110 10:46:33.101406 1 roachprod/install/cluster_synced.go:1777 [-] 2 !The Cockroach Labs team appreciates your feedback.
Wraps: (2) exit status 7
Error types: (1) *cluster.WithCommandDetails (2) *exec.ExitError
```
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
|
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*kv/multi-store-with-overload.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | roachtest kv multi store with overload failed roachtest kv multi store with overload with on master the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts kv multi store with overload run cluster go kv go kv go test runner go home agent work go src github com cockroachdb cockroach bin roachprod start store count teamcity returned exit status home agent work go src github com cockroachdb cockroach bin roachprod start store count teamcity returned stderr stdout roachprod install cluster synced go home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go roachprod install cluster synced go main wrap roachprod install cluster synced go home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go roachprod install cluster synced go github com cobra command execute roachprod install cluster synced go home agent work go src github com cockroachdb cockroach vendor github com cobra command go roachprod install cluster synced go github com cobra command executec roachprod install cluster synced go home agent work go src github com cockroachdb cockroach vendor github com cobra command go roachprod install cluster synced go github com cobra command execute roachprod install cluster synced go home agent work go src github com cockroachdb cockroach vendor github com cobra command go roachprod install cluster synced go main main roachprod install cluster synced go home agent work go src github com cockroachdb cockroach pkg cmd roachprod main go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go this node experienced a fatal error printed above and as a result the roachprod install cluster synced go process is terminating roachprod install cluster synced go roachprod install cluster synced go fatal errors can occur due to faulty hardware disks memory clocks or a roachprod install cluster synced go problem in cockroachdb with your help the support team at cockroach labs roachprod install cluster synced go will try to determine the root cause recommend next steps and we can roachprod install cluster synced go improve cockroachdb based on your report roachprod install cluster synced go roachprod install cluster synced go please submit a crash report by following the instructions here roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go roachprod install cluster synced go if you would rather not post publicly please contact us directly at roachprod install cluster synced go roachprod install cluster synced go support cockroachlabs com roachprod install cluster synced go roachprod install cluster synced go the cockroach labs team appreciates your feedback wraps exit status error types cluster withcommanddetails exec exiterror help see see cc cockroachdb kv triage | 1 |
102,528 | 8,847,132,804 | IssuesEvent | 2019-01-08 00:10:47 | heshamkelbashandy/ess-dive-catalog | https://api.github.com/repos/heshamkelbashandy/ess-dive-catalog | closed | Inconsistent Selenium Tests | testing | In GitLab by @vchendrix on Mar 1, 2018, 09:21
Selenium tests fail inconsistently. | 1.0 | Inconsistent Selenium Tests - In GitLab by @vchendrix on Mar 1, 2018, 09:21
Selenium tests fail inconsistently. | test | inconsistent selenium tests in gitlab by vchendrix on mar selenium tests fail inconsistently | 1 |
182,694 | 6,672,699,839 | IssuesEvent | 2017-10-04 12:44:41 | ox-it/ords-ui | https://api.github.com/repos/ox-it/ords-ui | opened | Delete table button required in database explorer | Database Explorer enhancement Medium priority | This is just for convenience, currently to remove a table from a database you need to upon up the schema designer and delete it there. | 1.0 | Delete table button required in database explorer - This is just for convenience, currently to remove a table from a database you need to upon up the schema designer and delete it there. | non_test | delete table button required in database explorer this is just for convenience currently to remove a table from a database you need to upon up the schema designer and delete it there | 0 |
132,213 | 10,737,097,354 | IssuesEvent | 2019-10-29 12:23:44 | Venom0us/Emberpoint | https://api.github.com/repos/Venom0us/Emberpoint | closed | Add entity test coverage | TestCoverage | Right now we cannot test the entity class because it needs a running game instance.
To mock this we should make a seperate entity that only derives from the IEntity interface. | 1.0 | Add entity test coverage - Right now we cannot test the entity class because it needs a running game instance.
To mock this we should make a seperate entity that only derives from the IEntity interface. | test | add entity test coverage right now we cannot test the entity class because it needs a running game instance to mock this we should make a seperate entity that only derives from the ientity interface | 1 |
311,262 | 26,779,269,495 | IssuesEvent | 2023-01-31 19:42:04 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Kibana CCS Tests.test/functional/apps/dashboard/group3/dashboard_time_picker·ts - dashboard app - group 3 dashboard time picker Saved search updated when time picker changes | Team:Presentation failed-test | A test failed on a tracked branch
```
Error: retry.try timeout: Error: Local nav not visible yet
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-4472929ebc8f0b52/elastic/kibana-on-merge/kibana/test/functional/page_objects/common_page.ts:410:15
at runAttempt (test/common/services/retry/retry_for_success.ts:29:15)
at retryForSuccess (test/common/services/retry/retry_for_success.ts:68:21)
at RetryService.try (test/common/services/retry/retry.ts:31:12)
at CommonPageObject.waitForTopNavToBeVisible (test/functional/page_objects/common_page.ts:407:5)
at HeaderPageObject.clickDiscover (test/functional/page_objects/header_page.ts:24:5)
at DashboardVisualizationsService.createSavedSearch (test/functional/services/dashboard/visualizations.ts:46:5)
at DashboardVisualizationsService.createAndAddSavedSearch (test/functional/services/dashboard/visualizations.ts:76:5)
at Context.<anonymous> (test/functional/apps/dashboard/group3/dashboard_time_picker.ts:57:7)
at Object.apply (node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/wrap_function.js:87:16)
at onFailure (test/common/services/retry/retry_for_success.ts:17:9)
at retryForSuccess (test/common/services/retry/retry_for_success.ts:59:13)
at RetryService.try (test/common/services/retry/retry.ts:31:12)
at CommonPageObject.waitForTopNavToBeVisible (test/functional/page_objects/common_page.ts:407:5)
at HeaderPageObject.clickDiscover (test/functional/page_objects/header_page.ts:24:5)
at DashboardVisualizationsService.createSavedSearch (test/functional/services/dashboard/visualizations.ts:46:5)
at DashboardVisualizationsService.createAndAddSavedSearch (test/functional/services/dashboard/visualizations.ts:76:5)
at Context.<anonymous> (test/functional/apps/dashboard/group3/dashboard_time_picker.ts:57:7)
at Object.apply (node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/wrap_function.js:87:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/19009#0182432e-acfc-46cc-aa57-e5e939667045)
<!-- kibanaCiData = {"failed-test":{"test.class":"Kibana CCS Tests.test/functional/apps/dashboard/group3/dashboard_time_picker·ts","test.name":"dashboard app - group 3 dashboard time picker Saved search updated when time picker changes","test.failCount":4}} --> | 1.0 | Failing test: Kibana CCS Tests.test/functional/apps/dashboard/group3/dashboard_time_picker·ts - dashboard app - group 3 dashboard time picker Saved search updated when time picker changes - A test failed on a tracked branch
```
Error: retry.try timeout: Error: Local nav not visible yet
at /var/lib/buildkite-agent/builds/kb-n2-4-spot-4472929ebc8f0b52/elastic/kibana-on-merge/kibana/test/functional/page_objects/common_page.ts:410:15
at runAttempt (test/common/services/retry/retry_for_success.ts:29:15)
at retryForSuccess (test/common/services/retry/retry_for_success.ts:68:21)
at RetryService.try (test/common/services/retry/retry.ts:31:12)
at CommonPageObject.waitForTopNavToBeVisible (test/functional/page_objects/common_page.ts:407:5)
at HeaderPageObject.clickDiscover (test/functional/page_objects/header_page.ts:24:5)
at DashboardVisualizationsService.createSavedSearch (test/functional/services/dashboard/visualizations.ts:46:5)
at DashboardVisualizationsService.createAndAddSavedSearch (test/functional/services/dashboard/visualizations.ts:76:5)
at Context.<anonymous> (test/functional/apps/dashboard/group3/dashboard_time_picker.ts:57:7)
at Object.apply (node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/wrap_function.js:87:16)
at onFailure (test/common/services/retry/retry_for_success.ts:17:9)
at retryForSuccess (test/common/services/retry/retry_for_success.ts:59:13)
at RetryService.try (test/common/services/retry/retry.ts:31:12)
at CommonPageObject.waitForTopNavToBeVisible (test/functional/page_objects/common_page.ts:407:5)
at HeaderPageObject.clickDiscover (test/functional/page_objects/header_page.ts:24:5)
at DashboardVisualizationsService.createSavedSearch (test/functional/services/dashboard/visualizations.ts:46:5)
at DashboardVisualizationsService.createAndAddSavedSearch (test/functional/services/dashboard/visualizations.ts:76:5)
at Context.<anonymous> (test/functional/apps/dashboard/group3/dashboard_time_picker.ts:57:7)
at Object.apply (node_modules/@kbn/test/target_node/functional_test_runner/lib/mocha/wrap_function.js:87:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/19009#0182432e-acfc-46cc-aa57-e5e939667045)
<!-- kibanaCiData = {"failed-test":{"test.class":"Kibana CCS Tests.test/functional/apps/dashboard/group3/dashboard_time_picker·ts","test.name":"dashboard app - group 3 dashboard time picker Saved search updated when time picker changes","test.failCount":4}} --> | test | failing test kibana ccs tests test functional apps dashboard dashboard time picker·ts dashboard app group dashboard time picker saved search updated when time picker changes a test failed on a tracked branch error retry try timeout error local nav not visible yet at var lib buildkite agent builds kb spot elastic kibana on merge kibana test functional page objects common page ts at runattempt test common services retry retry for success ts at retryforsuccess test common services retry retry for success ts at retryservice try test common services retry retry ts at commonpageobject waitfortopnavtobevisible test functional page objects common page ts at headerpageobject clickdiscover test functional page objects header page ts at dashboardvisualizationsservice createsavedsearch test functional services dashboard visualizations ts at dashboardvisualizationsservice createandaddsavedsearch test functional services dashboard visualizations ts at context test functional apps dashboard dashboard time picker ts at object apply node modules kbn test target node functional test runner lib mocha wrap function js at onfailure test common services retry retry for success ts at retryforsuccess test common services retry retry for success ts at retryservice try test common services retry retry ts at commonpageobject waitfortopnavtobevisible test functional page objects common page ts at headerpageobject clickdiscover test functional page objects header page ts at dashboardvisualizationsservice createsavedsearch test functional services dashboard visualizations ts at dashboardvisualizationsservice createandaddsavedsearch test functional services dashboard visualizations ts at context test functional apps dashboard dashboard time picker ts at object apply node modules kbn test target node functional test runner lib mocha wrap function js first failure | 1 |
259,860 | 27,740,545,401 | IssuesEvent | 2023-03-15 14:04:42 | srivatsamarichi/spring-petclinic | https://api.github.com/repos/srivatsamarichi/spring-petclinic | opened | CVE-2021-43980 (Low) detected in tomcat-embed-core-9.0.60.jar | Mend: dependency security vulnerability | ## CVE-2021-43980 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.60.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.60/tomcat-embed-core-9.0.60.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.6.6.jar (Root Library)
- spring-boot-starter-tomcat-2.6.6.jar
- :x: **tomcat-embed-core-9.0.60.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/srivatsamarichi/spring-petclinic/commit/c7cc758357875e62601940d33eaf04316ec686ca">c7cc758357875e62601940d33eaf04316ec686ca</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The simplified implementation of blocking reads and writes introduced in Tomcat 10 and back-ported to Tomcat 9.0.47 onwards exposed a long standing (but extremely hard to trigger) concurrency bug in Apache Tomcat 10.1.0 to 10.1.0-M12, 10.0.0-M1 to 10.0.18, 9.0.0-M1 to 9.0.60 and 8.5.0 to 8.5.77 that could cause client connections to share an Http11Processor instance resulting in responses, or part responses, to be received by the wrong client.
<p>Publish Date: 2022-09-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43980>CVE-2021-43980</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3">https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3</a></p>
<p>Release Date: 2022-09-28</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.62</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.6.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-43980 (Low) detected in tomcat-embed-core-9.0.60.jar - ## CVE-2021-43980 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.60.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.60/tomcat-embed-core-9.0.60.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.6.6.jar (Root Library)
- spring-boot-starter-tomcat-2.6.6.jar
- :x: **tomcat-embed-core-9.0.60.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/srivatsamarichi/spring-petclinic/commit/c7cc758357875e62601940d33eaf04316ec686ca">c7cc758357875e62601940d33eaf04316ec686ca</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The simplified implementation of blocking reads and writes introduced in Tomcat 10 and back-ported to Tomcat 9.0.47 onwards exposed a long standing (but extremely hard to trigger) concurrency bug in Apache Tomcat 10.1.0 to 10.1.0-M12, 10.0.0-M1 to 10.0.18, 9.0.0-M1 to 9.0.60 and 8.5.0 to 8.5.77 that could cause client connections to share an Http11Processor instance resulting in responses, or part responses, to be received by the wrong client.
<p>Publish Date: 2022-09-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43980>CVE-2021-43980</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3">https://lists.apache.org/thread/3jjqbsp6j88b198x5rmg99b1qr8ht3g3</a></p>
<p>Release Date: 2022-09-28</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.62</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-web): 2.6.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve low detected in tomcat embed core jar cve low severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter web jar root library spring boot starter tomcat jar x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details the simplified implementation of blocking reads and writes introduced in tomcat and back ported to tomcat onwards exposed a long standing but extremely hard to trigger concurrency bug in apache tomcat to to to and to that could cause client connections to share an instance resulting in responses or part responses to be received by the wrong client publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core direct dependency fix resolution org springframework boot spring boot starter web step up your open source security game with mend | 0 |
247,568 | 18,857,931,953 | IssuesEvent | 2021-11-12 09:11:41 | JWweiyin/pe | https://api.github.com/repos/JWweiyin/pe | opened | Details of opposite bus stop should be explained | severity.Low type.DocumentationBug | 
The user guide does not specify which bus stops are opposite each other. Hence a user may not understand why the program asks them to board the bus from PGP instead of PGPR. Could be improved by giving an index of which bus stops are opposite each other in the user guide.
<!--session: 1636704336392-d259903b-55df-4789-a33c-31deddc0be86-->
<!--Version: Web v3.4.1--> | 1.0 | Details of opposite bus stop should be explained - 
The user guide does not specify which bus stops are opposite each other. Hence a user may not understand why the program asks them to board the bus from PGP instead of PGPR. Could be improved by giving an index of which bus stops are opposite each other in the user guide.
<!--session: 1636704336392-d259903b-55df-4789-a33c-31deddc0be86-->
<!--Version: Web v3.4.1--> | non_test | details of opposite bus stop should be explained the user guide does not specify which bus stops are opposite each other hence a user may not understand why the program asks them to board the bus from pgp instead of pgpr could be improved by giving an index of which bus stops are opposite each other in the user guide | 0 |
594,604 | 18,049,209,787 | IssuesEvent | 2021-09-19 12:51:18 | AY2122S1-CS2103T-W17-1/tp | https://api.github.com/repos/AY2122S1-CS2103T-W17-1/tp | opened | Delete an entry | priority.Medium :2nd_place_medal: | As a user, I want to deletes the specified entry from the list of applications so that I can eliminate the ones that I don't want.
| 1.0 | Delete an entry - As a user, I want to deletes the specified entry from the list of applications so that I can eliminate the ones that I don't want.
| non_test | delete an entry as a user i want to deletes the specified entry from the list of applications so that i can eliminate the ones that i don t want | 0 |
51,975 | 13,710,432,325 | IssuesEvent | 2020-10-02 01:03:58 | jgeraigery/TwxAzureDataLakeConnector | https://api.github.com/repos/jgeraigery/TwxAzureDataLakeConnector | opened | CVE-2019-20922 (High) detected in handlebars-4.1.0.tgz | security vulnerability | ## CVE-2019-20922 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz</a></p>
<p>Path to dependency file: TwxAzureDataLakeConnector/dist/ptc-adls-connector-1-0-0/ptc-adls-connector/package.json</p>
<p>Path to vulnerable library: TwxAzureDataLakeConnector/src/node_modules/nyc/node_modules/handlebars/package.json,TwxAzureDataLakeConnector/src/node_modules/nyc/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- nyc-13.3.0.tgz (Root Library)
- istanbul-reports-2.1.1.tgz
- :x: **handlebars-4.1.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20922>CVE-2019-20922</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20922">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20922</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: 4.4.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.1.0","isTransitiveDependency":true,"dependencyTree":"nyc:13.3.0;istanbul-reports:2.1.1;handlebars:4.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.5"}],"vulnerabilityIdentifier":"CVE-2019-20922","vulnerabilityDetails":"Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20922","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-20922 (High) detected in handlebars-4.1.0.tgz - ## CVE-2019-20922 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>handlebars-4.1.0.tgz</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz">https://registry.npmjs.org/handlebars/-/handlebars-4.1.0.tgz</a></p>
<p>Path to dependency file: TwxAzureDataLakeConnector/dist/ptc-adls-connector-1-0-0/ptc-adls-connector/package.json</p>
<p>Path to vulnerable library: TwxAzureDataLakeConnector/src/node_modules/nyc/node_modules/handlebars/package.json,TwxAzureDataLakeConnector/src/node_modules/nyc/node_modules/handlebars/package.json</p>
<p>
Dependency Hierarchy:
- nyc-13.3.0.tgz (Root Library)
- istanbul-reports-2.1.1.tgz
- :x: **handlebars-4.1.0.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.
<p>Publish Date: 2020-09-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20922>CVE-2019-20922</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20922">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20922</a></p>
<p>Release Date: 2020-09-30</p>
<p>Fix Resolution: 4.4.5</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"handlebars","packageVersion":"4.1.0","isTransitiveDependency":true,"dependencyTree":"nyc:13.3.0;istanbul-reports:2.1.1;handlebars:4.1.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.4.5"}],"vulnerabilityIdentifier":"CVE-2019-20922","vulnerabilityDetails":"Handlebars before 4.4.5 allows Regular Expression Denial of Service (ReDoS) because of eager matching. The parser may be forced into an endless loop while processing crafted templates. This may allow attackers to exhaust system resources.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-20922","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in handlebars tgz cve high severity vulnerability vulnerable library handlebars tgz handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href path to dependency file twxazuredatalakeconnector dist ptc adls connector ptc adls connector package json path to vulnerable library twxazuredatalakeconnector src node modules nyc node modules handlebars package json twxazuredatalakeconnector src node modules nyc node modules handlebars package json dependency hierarchy nyc tgz root library istanbul reports tgz x handlebars tgz vulnerable library vulnerability details handlebars before allows regular expression denial of service redos because of eager matching the parser may be forced into an endless loop while processing crafted templates this may allow attackers to exhaust system resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails handlebars before allows regular expression denial of service redos because of eager matching the parser may be forced into an endless loop while processing crafted templates this may allow attackers to exhaust system resources vulnerabilityurl | 0 |
80,259 | 9,990,506,436 | IssuesEvent | 2019-07-11 08:58:56 | greatnewcls/KNLWKKGOTE62XGFSVAZIMVUH | https://api.github.com/repos/greatnewcls/KNLWKKGOTE62XGFSVAZIMVUH | reopened | wxRGk8w2NUJ6A/wAaVI7jBjzqVG0JzJ5Eq7RYjPp39a7NAIEAkafPzyf46IMY396bKd+WUg6hiUPR+pNQj60a3WbRUOovvI8vM7E6HQEhud47mg3Bu/niwywLukQLDUplVTKmjv6lBfyI1ppbZemzT1wMN4/EYIrEGRkaMiddX8= | design | l9Mm+JgGDlj8RHbiXvFnWj4leFEcOKVrFVyV/Ub10Wwq1im6NDnNYiVwNrE2LqZ+vIWsnLi7Fsi96YnatVrqr7V6qQ6ym72JD4DlCxpqZtb+L6pxAk/k9FjUyAiXNRD8yrd0NAMpQWk5ghRdxyUvMHeT0OTYLXj2ymzc5iHJB/jxmo5XsbJlfEEiDhYhallTbJeUXEU3CIaO85J03eNH5/dnF7bU4R2LUVCDHJ1pYR87YcjAuk85vHCM76IPxq5P/aZTMsAPmq3Rleyp00/deRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgpl7pp8Zun4M6jgfWPa0zuUTy3gDxeWF1bhmlnrnmuWeolgKm0qBxWRPkpCSaq+AHGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqDFrH6ScxWZXriBJ67DPJiX/orktH4RbcO/brMWI+OCTnPb26n1xYv50tZPb7LTmnUYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoJYgOuIFDv8fyTPGnvbVVzHbYPeGEvCwaqw0ZApihjdoCHfG6dtEpyBfzI0xkdjdNRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgJoE3RWNRlbm/640mTuOUy9tg94YS8LBqrDRkCmKGN2hm7Qg4kKAiLp8EyYtgyXg5GA2oSgi0f+BhLeEJ4EQNdHbGoHFBL02iTIEUE9857vLpKlabfxgR1uEpqvC0aZHNYtKy3TQlYMaqvvnJAzNAqeXXho3P7FJDZ3Enj2a8Zf0YDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoFO0lAvTeUMKoQ2/qUt0JNEFmAj4/j1MuyTjjhEZk0knQiNG2MZn4EpUMmpiizNRrRgNqEoItH/gYS3hCeBEDXR2xqBxQS9NokyBFBPfOe7yfJ0FtYMHiQPwRB9ueCzokgktU3QF1+Uakti9wt9Hzxaff6zM3p71wK/hqUIM3p8bGA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqBieW1PxynvxYcRYG+SRWHz22D3hhLwsGqsNGQKYoY3aFDTk/+WyXwZFOk/Y8FkKd4YDahKCLR/4GEt4QngRA10ilqziqoKg3B8TZ8GxKCjbGXZWQs+/6W2v4u8FhtHldvjn0hkpII4+d6/odSNSM3OO/3mHE7lakTKwU7IMVs3nRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKghZ2Pek1beqMHQoyG28D1+uOfSGSkgjj53r+h1I1Izc4HTk25qOEIuDNu8dkGb/7kGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqBlJfnzrHSS2qP9d3PLcARvyq76CPmvHcI/E/DCrncbgt5ZvHh0bwg4NtmtjVSTFoIYDahKCLR/4GEt4QngRA10NAieHhs1ojDdxuH1V5s70s0WO7j7H50+1q6t1twfnKztEXJZ0xFKNaj5Um3VqFE9smVhLg8MuWSIZMDQft1lJBgNqEoItH/gYS3hCeBEDXS9FxK7pWAwej5gik14we2H+C3IFExLUmhS+GkZuNICqeOfSGSkgjj53r+h1I1Izc4YfEYdut7DOEAVhgxO5S+rGA2oSgi0f+BhLeEJ4EQNdNlAvONhK5R3Kg9unT0IFqOUygwBNLyiD1SmngCfsPjj459IZKSCOPnev6HUjUjNzqPnZndQa1luz3Dayw9bfCUYDahKCLR/4GEt4QngRA10OGl6PxYsrYF6LyRaOxZTPQU00bTdQTib3KQ17I1X/iXjn0hkpII4+d6/odSNSM3O6ok7Vj3F2SczUP44ZfHJIRgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKg6hjhl7SZxJpXyQ5lDojjKeOfSGSkgjj53r+h1I1Izc4Ug78R/vVEV7g1Sy08SJ04GA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqDRkte7/ErqnWSGa7lOLNFk459IZKSCOPnev6HUjUjNzobnnMTrC4w5FbKU4feYjsEYDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoEM8h0dwYBup7TRV93sZ9oyEwcvxYrTVp1+bodPw/65G3NW8kvCevjbfL7omQJBz6xgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKgBomqPwr/zJu752c2TSdWmITyzNr/dqFvGDoA9BuLLSYV/puo48iGbLSOkxNXUJ1bGA2oSgi0f+BhLeEJ4EQNdJ7SgUi15MaObEfM5i2mNMtizGek2P+HNAkDkX9SIGox22D3hhLwsGqsNGQKYoY3aN2MCqsNsM11sWumZuKvHo8YDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoG3zhVP+bCJAJkA5iJU8JJbjn0hkpII4+d6/odSNSM3Oia9Ia5WeEsqpI4T6eBmX2RgNqEoItH/gYS3hCeBEDXQyobTHTCTiPygvxdg3AUlbVXLPZGxtqnTUFH+lj4RJ5+OfSGSkgjj53r+h1I1Izc73OKiyT/hea5NhnSy2QcqgGA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqCvYfiNpza8j26TTXx8//RZ7RFyWdMRSjWo+VJt1ahRPbkYcK0B8xS1ZVjlXa9ISD4YDahKCLR/4GEt4QngRA10VY6RmUEe29o/PCjSWySsEtfjO0HiioRbLBK/+sIYvsUPTzNAa4n0WnZWTit0RZses6fdL7qMvjUquQ6XPfaVThgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgJ6qbsRwzRGBrWk+6kDnu+P6K5LR+EW3Dv26zFiPjgk5pTtoReSs38bDC7IE6GCBtGA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqCk1XSyok6ZUHJNZsMEd8mj22D3hhLwsGqsNGQKYoY3aFepSC8gnCoowXW13UwtCecYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoABPImmlr53JeqhHJgEaBOVCfEln3FwAyLbQtmoH1sn3LQZbjW9Y8fjU+v88MdzPrhgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKgKqVorBsTmJdHJW3yvNM0sv6K5LR+EW3Dv26zFiPjgk4DJjuLIlBo3KO6KLJzzc4SGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqB6YoNia0eZg7PgPZltXmrNoMoe/W/mDsC3NB710hcEKe/Ngu/hucifYOSDlYTmFtMYDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoH50jr5zPuH8bdLscrlgDyaPjTWKLyIhQnioDQA9gC6g316wnod+rXt8JtXq1CV+iRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgEdJGPF9S2oR0tw0VT/jCseS7TELEe8fPd4x/uI7Lgwlz0rRvQzh0EDnFhrQ2ofVAGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqDfckpxvlAwfIgrX9w8su9rJ6GJfFmP2TIg73P2ihIFyZokrFd133efHdRe0N2S9sUYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoMmIK4j6SngDy3Xfc/ovhN0noYl8WY/ZMiDvc/aKEgXJQJnyibDRpGU4t0F7WZfwfRgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKg5/6CXX1fX6oWEzUYAw40Au0RclnTEUo1qPlSbdWoUT2aNn5Jg37DtXA3cChZl4F6GA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqCUCQlTkZYqGhcVRIEw8o6X459IZKSCOPnev6HUjUjNzlnMig7z8V57GDiU3RzI88EYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoOVIJvYA+OH39aH4BjwiIqjjn0hkpII4+d6/odSNSM3O+33mszChCULW1X/nDhpL6hgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKg34X/f6JyQeWbDfHQ7Vn/MeOfSGSkgjj53r+h1I1Izc7vhDa2Uoij0OoINuPv5Kd6GA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqD2sVpfZlaMqUVU3NTc8rlM459IZKSCOPnev6HUjUjNziUXVFZIkrEKqyO0hNv3QNMYDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoIr3VjSTiBwUfcWt8QpyXIy3Occk9dgKHeHHTdFVWg48pprhl870syq0jdCOtnQvAhgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgHhEyw/D0ZbjF9MASL7YVD2BDCEYCwJfNCr9ugsU7O8RmECPmoj5H5yGfsgNXuv7nFak1lr9xOTJH5uHUstk90KflvVRAmE9ZSJgW96je1x97G2dI7qCxO6lsB6BRNMjiuOza241Ty22z282q5a6ERdECBsfxAVHWewpEOpoymH1homiifAwCdCwOPEr6Oh26oGr7d2mp+XJY/KX707V5F04PjPKUPyyRN6ES1jijqfFKjdaPWEd4lf3/AvBUuaKb50z3+mHmRXZI4xj5METW9y2Y606KOcGAlmp6SY/lpu1kBksTW82iHmH61+OD79vshBfOqYslOwkm9FxNgWcYuz+88yHmfHmJAFcL4nc/m8WT5r0z3vDc/uotsW47qZqDvNB4+gIStsr0U7Y5QNk1Xg0BF8y4ayW9b92x1/9SEXIKXz0v8PNJt3cEzsdFAZb9Xf2DdIRqJAA4Q6S/EFCx0Kri15Xk3PejRz2Ga2IjUkVm2E6k2Iy0coybT0zFcOntP3pc9TqrIPuVHSWfIR2U4UTS5xopAcKUl0tmDsh/3S5lbq2tQVb3W3Ae4fdETAOB/GW7XthDqPKJzp7QI/RyyoR2FTqPGU/rRNa2STIYOsztn2no2ShQYTSS59bwCp2V/083OPnYkf7sBzF7+9YxZNrMJIL06svJx8ZQ290pfTk= | 1.0 | wxRGk8w2NUJ6A/wAaVI7jBjzqVG0JzJ5Eq7RYjPp39a7NAIEAkafPzyf46IMY396bKd+WUg6hiUPR+pNQj60a3WbRUOovvI8vM7E6HQEhud47mg3Bu/niwywLukQLDUplVTKmjv6lBfyI1ppbZemzT1wMN4/EYIrEGRkaMiddX8= - l9Mm+JgGDlj8RHbiXvFnWj4leFEcOKVrFVyV/Ub10Wwq1im6NDnNYiVwNrE2LqZ+vIWsnLi7Fsi96YnatVrqr7V6qQ6ym72JD4DlCxpqZtb+L6pxAk/k9FjUyAiXNRD8yrd0NAMpQWk5ghRdxyUvMHeT0OTYLXj2ymzc5iHJB/jxmo5XsbJlfEEiDhYhallTbJeUXEU3CIaO85J03eNH5/dnF7bU4R2LUVCDHJ1pYR87YcjAuk85vHCM76IPxq5P/aZTMsAPmq3Rleyp00/deRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgpl7pp8Zun4M6jgfWPa0zuUTy3gDxeWF1bhmlnrnmuWeolgKm0qBxWRPkpCSaq+AHGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqDFrH6ScxWZXriBJ67DPJiX/orktH4RbcO/brMWI+OCTnPb26n1xYv50tZPb7LTmnUYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoJYgOuIFDv8fyTPGnvbVVzHbYPeGEvCwaqw0ZApihjdoCHfG6dtEpyBfzI0xkdjdNRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgJoE3RWNRlbm/640mTuOUy9tg94YS8LBqrDRkCmKGN2hm7Qg4kKAiLp8EyYtgyXg5GA2oSgi0f+BhLeEJ4EQNdHbGoHFBL02iTIEUE9857vLpKlabfxgR1uEpqvC0aZHNYtKy3TQlYMaqvvnJAzNAqeXXho3P7FJDZ3Enj2a8Zf0YDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoFO0lAvTeUMKoQ2/qUt0JNEFmAj4/j1MuyTjjhEZk0knQiNG2MZn4EpUMmpiizNRrRgNqEoItH/gYS3hCeBEDXR2xqBxQS9NokyBFBPfOe7yfJ0FtYMHiQPwRB9ueCzokgktU3QF1+Uakti9wt9Hzxaff6zM3p71wK/hqUIM3p8bGA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqBieW1PxynvxYcRYG+SRWHz22D3hhLwsGqsNGQKYoY3aFDTk/+WyXwZFOk/Y8FkKd4YDahKCLR/4GEt4QngRA10ilqziqoKg3B8TZ8GxKCjbGXZWQs+/6W2v4u8FhtHldvjn0hkpII4+d6/odSNSM3OO/3mHE7lakTKwU7IMVs3nRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKghZ2Pek1beqMHQoyG28D1+uOfSGSkgjj53r+h1I1Izc4HTk25qOEIuDNu8dkGb/7kGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqBlJfnzrHSS2qP9d3PLcARvyq76CPmvHcI/E/DCrncbgt5ZvHh0bwg4NtmtjVSTFoIYDahKCLR/4GEt4QngRA10NAieHhs1ojDdxuH1V5s70s0WO7j7H50+1q6t1twfnKztEXJZ0xFKNaj5Um3VqFE9smVhLg8MuWSIZMDQft1lJBgNqEoItH/gYS3hCeBEDXS9FxK7pWAwej5gik14we2H+C3IFExLUmhS+GkZuNICqeOfSGSkgjj53r+h1I1Izc4YfEYdut7DOEAVhgxO5S+rGA2oSgi0f+BhLeEJ4EQNdNlAvONhK5R3Kg9unT0IFqOUygwBNLyiD1SmngCfsPjj459IZKSCOPnev6HUjUjNzqPnZndQa1luz3Dayw9bfCUYDahKCLR/4GEt4QngRA10OGl6PxYsrYF6LyRaOxZTPQU00bTdQTib3KQ17I1X/iXjn0hkpII4+d6/odSNSM3O6ok7Vj3F2SczUP44ZfHJIRgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKg6hjhl7SZxJpXyQ5lDojjKeOfSGSkgjj53r+h1I1Izc4Ug78R/vVEV7g1Sy08SJ04GA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqDRkte7/ErqnWSGa7lOLNFk459IZKSCOPnev6HUjUjNzobnnMTrC4w5FbKU4feYjsEYDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoEM8h0dwYBup7TRV93sZ9oyEwcvxYrTVp1+bodPw/65G3NW8kvCevjbfL7omQJBz6xgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKgBomqPwr/zJu752c2TSdWmITyzNr/dqFvGDoA9BuLLSYV/puo48iGbLSOkxNXUJ1bGA2oSgi0f+BhLeEJ4EQNdJ7SgUi15MaObEfM5i2mNMtizGek2P+HNAkDkX9SIGox22D3hhLwsGqsNGQKYoY3aN2MCqsNsM11sWumZuKvHo8YDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoG3zhVP+bCJAJkA5iJU8JJbjn0hkpII4+d6/odSNSM3Oia9Ia5WeEsqpI4T6eBmX2RgNqEoItH/gYS3hCeBEDXQyobTHTCTiPygvxdg3AUlbVXLPZGxtqnTUFH+lj4RJ5+OfSGSkgjj53r+h1I1Izc73OKiyT/hea5NhnSy2QcqgGA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqCvYfiNpza8j26TTXx8//RZ7RFyWdMRSjWo+VJt1ahRPbkYcK0B8xS1ZVjlXa9ISD4YDahKCLR/4GEt4QngRA10VY6RmUEe29o/PCjSWySsEtfjO0HiioRbLBK/+sIYvsUPTzNAa4n0WnZWTit0RZses6fdL7qMvjUquQ6XPfaVThgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgJ6qbsRwzRGBrWk+6kDnu+P6K5LR+EW3Dv26zFiPjgk5pTtoReSs38bDC7IE6GCBtGA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqCk1XSyok6ZUHJNZsMEd8mj22D3hhLwsGqsNGQKYoY3aFepSC8gnCoowXW13UwtCecYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoABPImmlr53JeqhHJgEaBOVCfEln3FwAyLbQtmoH1sn3LQZbjW9Y8fjU+v88MdzPrhgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKgKqVorBsTmJdHJW3yvNM0sv6K5LR+EW3Dv26zFiPjgk4DJjuLIlBo3KO6KLJzzc4SGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqB6YoNia0eZg7PgPZltXmrNoMoe/W/mDsC3NB710hcEKe/Ngu/hucifYOSDlYTmFtMYDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoH50jr5zPuH8bdLscrlgDyaPjTWKLyIhQnioDQA9gC6g316wnod+rXt8JtXq1CV+iRgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgEdJGPF9S2oR0tw0VT/jCseS7TELEe8fPd4x/uI7Lgwlz0rRvQzh0EDnFhrQ2ofVAGA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqDfckpxvlAwfIgrX9w8su9rJ6GJfFmP2TIg73P2ihIFyZokrFd133efHdRe0N2S9sUYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoMmIK4j6SngDy3Xfc/ovhN0noYl8WY/ZMiDvc/aKEgXJQJnyibDRpGU4t0F7WZfwfRgNqEoItH/gYS3hCeBEDXTAaZCwFYuwqK6ayIgiTZKg5/6CXX1fX6oWEzUYAw40Au0RclnTEUo1qPlSbdWoUT2aNn5Jg37DtXA3cChZl4F6GA2oSgi0f+BhLeEJ4EQNdNc7AkzjcOU4LFjvJHO6EqCUCQlTkZYqGhcVRIEw8o6X459IZKSCOPnev6HUjUjNzlnMig7z8V57GDiU3RzI88EYDahKCLR/4GEt4QngRA101zsCTONw5TgsWO8kc7oSoOVIJvYA+OH39aH4BjwiIqjjn0hkpII4+d6/odSNSM3O+33mszChCULW1X/nDhpL6hgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKg34X/f6JyQeWbDfHQ7Vn/MeOfSGSkgjj53r+h1I1Izc7vhDa2Uoij0OoINuPv5Kd6GA2oSgi0f+BhLeEJ4EQNdMBpkLAVi7CorprIiCJNkqD2sVpfZlaMqUVU3NTc8rlM459IZKSCOPnev6HUjUjNziUXVFZIkrEKqyO0hNv3QNMYDahKCLR/4GEt4QngRA10wGmQsBWLsKiumsiIIk2SoIr3VjSTiBwUfcWt8QpyXIy3Occk9dgKHeHHTdFVWg48pprhl870syq0jdCOtnQvAhgNqEoItH/gYS3hCeBEDXTXOwJM43DlOCxY7yRzuhKgHhEyw/D0ZbjF9MASL7YVD2BDCEYCwJfNCr9ugsU7O8RmECPmoj5H5yGfsgNXuv7nFak1lr9xOTJH5uHUstk90KflvVRAmE9ZSJgW96je1x97G2dI7qCxO6lsB6BRNMjiuOza241Ty22z282q5a6ERdECBsfxAVHWewpEOpoymH1homiifAwCdCwOPEr6Oh26oGr7d2mp+XJY/KX707V5F04PjPKUPyyRN6ES1jijqfFKjdaPWEd4lf3/AvBUuaKb50z3+mHmRXZI4xj5METW9y2Y606KOcGAlmp6SY/lpu1kBksTW82iHmH61+OD79vshBfOqYslOwkm9FxNgWcYuz+88yHmfHmJAFcL4nc/m8WT5r0z3vDc/uotsW47qZqDvNB4+gIStsr0U7Y5QNk1Xg0BF8y4ayW9b92x1/9SEXIKXz0v8PNJt3cEzsdFAZb9Xf2DdIRqJAA4Q6S/EFCx0Kri15Xk3PejRz2Ga2IjUkVm2E6k2Iy0coybT0zFcOntP3pc9TqrIPuVHSWfIR2U4UTS5xopAcKUl0tmDsh/3S5lbq2tQVb3W3Ae4fdETAOB/GW7XthDqPKJzp7QI/RyyoR2FTqPGU/rRNa2STIYOsztn2no2ShQYTSS59bwCp2V/083OPnYkf7sBzF7+9YxZNrMJIL06svJx8ZQ290pfTk= | non_test | dergnqeoith brmwi wyxwzfok e bodpw w ngu hucifyosdlytmftmydahkclr irgnqeoith zmidvc xjy | 0 |
53,685 | 6,341,258,021 | IssuesEvent | 2017-07-27 13:08:20 | dzhw/zofar | https://api.github.com/repos/dzhw/zofar | closed | test infrastructure | category: zofar et: 16 prio: 1 status: testing type: backlog.task | To Do:
dev:
- [x] create maven plugin
- [x] maven configuration
- [x] adapt http client
- [x] jenkins configuration
- [x] debugging
Used Time including extensions of existing Methods: 24 | 1.0 | test infrastructure - To Do:
dev:
- [x] create maven plugin
- [x] maven configuration
- [x] adapt http client
- [x] jenkins configuration
- [x] debugging
Used Time including extensions of existing Methods: 24 | test | test infrastructure to do dev create maven plugin maven configuration adapt http client jenkins configuration debugging used time including extensions of existing methods | 1 |
55,041 | 13,505,180,005 | IssuesEvent | 2020-09-13 21:32:35 | mp3splt/mp3splt | https://api.github.com/repos/mp3splt/mp3splt | closed | mp3splt 2.5.1: configure does not check version of libmp3splt | bugs build_system sourceforge | Imported from SourceForge on 2020-09-13 16:32:34
Created by **[hartwork](https://sourceforge.net/u/hartwork/)** on 2013-01-27 21:22:49
Original: https://sourceforge.net/p/mp3splt/bugs/145
---
configure.ac reads:
> MP3SPLT_CHECK(,[ AC_MSG_ERROR(libmp3splt version 0.8.1 needed :
It only checks for the presence of libmp3splt but not for its version. So with libmp3splt 0.7.* installed, we get compile errors that configure could have predicted. Have you considered using pkg-config and its autoconf macros?
| 1.0 | mp3splt 2.5.1: configure does not check version of libmp3splt - Imported from SourceForge on 2020-09-13 16:32:34
Created by **[hartwork](https://sourceforge.net/u/hartwork/)** on 2013-01-27 21:22:49
Original: https://sourceforge.net/p/mp3splt/bugs/145
---
configure.ac reads:
> MP3SPLT_CHECK(,[ AC_MSG_ERROR(libmp3splt version 0.8.1 needed :
It only checks for the presence of libmp3splt but not for its version. So with libmp3splt 0.7.* installed, we get compile errors that configure could have predicted. Have you considered using pkg-config and its autoconf macros?
| non_test | configure does not check version of imported from sourceforge on created by on original configure ac reads check ac msg error version needed it only checks for the presence of but not for its version so with installed we get compile errors that configure could have predicted have you considered using pkg config and its autoconf macros | 0 |
144,563 | 11,624,193,288 | IssuesEvent | 2020-02-27 10:19:34 | DND-PickMe/pickme-back | https://api.github.com/repos/DND-PickMe/pickme-back | closed | Add GET Account | Add Test | - `index.adoc`
- 자신의 프로필을 가져오는 리소스 추가
- 모든 구직자를 가져오는 리소스 추가
- 구직자의 정보를 가져오는 리소스 추가
- `AccountController.class`
- 자신의 프로필 가져오는 api 수정
- 모든 구직자를 가져오는 api 추가
- 기존에 구직자와 기업 담당자 모두 불러오는 로직을 구직자만 불러오도록 수정
- 구직자의 정보를 가져오는 api 추가
- `LoginController.class`
- 모든 유저를 가져오는 링크 정보 추가 | 1.0 | Add GET Account - - `index.adoc`
- 자신의 프로필을 가져오는 리소스 추가
- 모든 구직자를 가져오는 리소스 추가
- 구직자의 정보를 가져오는 리소스 추가
- `AccountController.class`
- 자신의 프로필 가져오는 api 수정
- 모든 구직자를 가져오는 api 추가
- 기존에 구직자와 기업 담당자 모두 불러오는 로직을 구직자만 불러오도록 수정
- 구직자의 정보를 가져오는 api 추가
- `LoginController.class`
- 모든 유저를 가져오는 링크 정보 추가 | test | add get account index adoc 자신의 프로필을 가져오는 리소스 추가 모든 구직자를 가져오는 리소스 추가 구직자의 정보를 가져오는 리소스 추가 accountcontroller class 자신의 프로필 가져오는 api 수정 모든 구직자를 가져오는 api 추가 기존에 구직자와 기업 담당자 모두 불러오는 로직을 구직자만 불러오도록 수정 구직자의 정보를 가져오는 api 추가 logincontroller class 모든 유저를 가져오는 링크 정보 추가 | 1 |
327,245 | 24,124,696,292 | IssuesEvent | 2022-09-20 22:26:34 | cloudflare/cloudflare-docs | https://api.github.com/repos/cloudflare/cloudflare-docs | opened | [R2] Workers Runtime APIs layout & formatting | documentation content:edit | ### Which Cloudflare product does this pertain to?
R2
### Existing documentation URL(s)
- https://developers.cloudflare.com/r2/data-access/workers-api/workers-api-reference/
### Section that requires update
Layout and formatting.
### What needs to change?
The current layout, whilst satisfactory for a type reference, will struggle to scale as the APIs gain more options and require more explanations/walkthroughs on how to properly utilise them.
As an example, the addition of the new checksums supported in `R2PutOptions` means that either:
1) Every checksum is listed on it's own, with an aside that only one can be used at a time.
2) The type for the 'checksum' in `R2PutOptions` becomes `md5 | sha1 | sha256 | sha384 | sha512`
Either way, it becomes very verbose and will easily confuse people.
### How should it change?
Taking inspiration from well-regarded documentation layouts such as `docs.rs` (i.e https://doc.rust-lang.org/stable/std/collections/struct.HashMap.html), we should come up with a consistent structure on documenting Worker's Runtime APIs that we can then extend to refactoring the pages for KV, Durable Objects and the like.
We want a good middle-ground between providing a reference, and providing a how-to, without going too in-depth that the material would be better split off into it's own how-to page.
As an example of one potential layout that was discussed by myself and @Frederik-Baetens:
<img width="643" alt="image" src="https://user-images.githubusercontent.com/94662631/191375548-9e5244fe-85be-4ca1-929a-4af793699941.png">
Using the [<details>](https://developer.mozilla.org/en-US/docs/Web/HTML/Element/details) element, this allows us to:
1) Provide a lot of value without cluttering the rest of the page, as it's expandable.
2) Preserve the 'searchability' of the content, as CTRL+F on the majority of browsers will 'look inside' a `<details>` element.
3) Additionally include small examples, not in-depth or niche enough for their own page, under additional `<details>` elements.
<img width="654" alt="image" src="https://user-images.githubusercontent.com/94662631/191375800-c884bf3c-dade-43a3-8aed-f3e48f1d6b21.png">
### Additional information
Original discussion: https://github.com/cloudflare/cloudflare-docs/pull/5897 | 1.0 | [R2] Workers Runtime APIs layout & formatting - ### Which Cloudflare product does this pertain to?
R2
### Existing documentation URL(s)
- https://developers.cloudflare.com/r2/data-access/workers-api/workers-api-reference/
### Section that requires update
Layout and formatting.
### What needs to change?
The current layout, whilst satisfactory for a type reference, will struggle to scale as the APIs gain more options and require more explanations/walkthroughs on how to properly utilise them.
As an example, the addition of the new checksums supported in `R2PutOptions` means that either:
1) Every checksum is listed on it's own, with an aside that only one can be used at a time.
2) The type for the 'checksum' in `R2PutOptions` becomes `md5 | sha1 | sha256 | sha384 | sha512`
Either way, it becomes very verbose and will easily confuse people.
### How should it change?
Taking inspiration from well-regarded documentation layouts such as `docs.rs` (i.e https://doc.rust-lang.org/stable/std/collections/struct.HashMap.html), we should come up with a consistent structure on documenting Worker's Runtime APIs that we can then extend to refactoring the pages for KV, Durable Objects and the like.
We want a good middle-ground between providing a reference, and providing a how-to, without going too in-depth that the material would be better split off into it's own how-to page.
As an example of one potential layout that was discussed by myself and @Frederik-Baetens:
<img width="643" alt="image" src="https://user-images.githubusercontent.com/94662631/191375548-9e5244fe-85be-4ca1-929a-4af793699941.png">
Using the [<details>](https://developer.mozilla.org/en-US/docs/Web/HTML/Element/details) element, this allows us to:
1) Provide a lot of value without cluttering the rest of the page, as it's expandable.
2) Preserve the 'searchability' of the content, as CTRL+F on the majority of browsers will 'look inside' a `<details>` element.
3) Additionally include small examples, not in-depth or niche enough for their own page, under additional `<details>` elements.
<img width="654" alt="image" src="https://user-images.githubusercontent.com/94662631/191375800-c884bf3c-dade-43a3-8aed-f3e48f1d6b21.png">
### Additional information
Original discussion: https://github.com/cloudflare/cloudflare-docs/pull/5897 | non_test | workers runtime apis layout formatting which cloudflare product does this pertain to existing documentation url s section that requires update layout and formatting what needs to change the current layout whilst satisfactory for a type reference will struggle to scale as the apis gain more options and require more explanations walkthroughs on how to properly utilise them as an example the addition of the new checksums supported in means that either every checksum is listed on it s own with an aside that only one can be used at a time the type for the checksum in becomes either way it becomes very verbose and will easily confuse people how should it change taking inspiration from well regarded documentation layouts such as docs rs i e we should come up with a consistent structure on documenting worker s runtime apis that we can then extend to refactoring the pages for kv durable objects and the like we want a good middle ground between providing a reference and providing a how to without going too in depth that the material would be better split off into it s own how to page as an example of one potential layout that was discussed by myself and frederik baetens img width alt image src using the element this allows us to provide a lot of value without cluttering the rest of the page as it s expandable preserve the searchability of the content as ctrl f on the majority of browsers will look inside a element additionally include small examples not in depth or niche enough for their own page under additional elements img width alt image src additional information original discussion | 0 |
261,743 | 22,772,236,219 | IssuesEvent | 2022-07-08 11:08:25 | systemd/systemd | https://api.github.com/repos/systemd/systemd | opened | TEST-35-LOGIN appears to be flaky when systemd is built with coverage | tests | I haven't seen this fail, yet, on a non-coverage build.
As described in https://github.com/systemd/systemd/pull/23930#issuecomment-1178781984, the expected D-Bus message in `test_lock_idle_action()` might never appear, causing the test to fail. This is reliably reproducible with
```
# meson build -Dinstall-tests=true -Db_coverage=true
# ninja -C build
# make -C test/TEST-35-LOGIN clean setup run QEMU_SMP=1
```
```
Jul 08 04:45:10 H systemd-logind[595]: Got message type=signal sender=:1.1 destination=n/a path=/org/freedesktop/systemd1 interface=org.freedesktop.systemd1.Manager member=Reloading cookie=3258 reply_cookie=0 signature=b error-name=n/a error-message=n/a
Jul 08 04:45:10 H systemd-logind[595]: System manager has been reloaded, rechecking sessions...
Jul 08 04:45:10 H systemd-logind[595]: System idle. Will be locked now.
Jul 08 04:45:10 H systemd-logind[595]: Locking sessions...
...
Jul 08 04:45:12 H testsuite-35.sh[260]: + assert_eq tty2 tty2
Jul 08 04:45:12 H testsuite-35.sh[676]: + set +ex
Jul 08 04:45:12 H testsuite-35.sh[260]: + timeout 35 bash -c 'while [[ "$(journalctl -b -u systemd-logind.service --since=02:45:10 | grep -c '\''Sent message type=signal .* member=Lock'\'')" -lt 1 ]]; do sleep 1; done'
Jul 08 04:45:37 H systemd-logind[595]: System idle.
Jul 08 04:45:37 H systemd[1]: systemd-journald.service: Got notification message from PID 225 (WATCHDOG=1)
Jul 08 04:45:47 H systemd[1]: Received SIGCHLD from PID 814 (sleep).
Jul 08 04:45:47 H systemd[1]: Child 814 (sleep) died (code=killed, status=15/TERM)
Jul 08 04:45:47 H testsuite-35.sh[260]: + cleanup_test_user
```
Full log: https://jenkins-systemd.apps.ocp.ci.centos.org/job/upstream-cron-build/665/artifact//systemd-centos-ci/artifacts_all/artifacts_mq_ifqlt/vagrant-logs.rfi/vagrant-arch-coverage-testsuite.cKl/TEST-35-LOGIN/system.journal
As I mentioned in #23930, this doesn't seem like a timing issue, since the behavior remains same with large timeout values as well (10 minutes). | 1.0 | TEST-35-LOGIN appears to be flaky when systemd is built with coverage - I haven't seen this fail, yet, on a non-coverage build.
As described in https://github.com/systemd/systemd/pull/23930#issuecomment-1178781984, the expected D-Bus message in `test_lock_idle_action()` might never appear, causing the test to fail. This is reliably reproducible with
```
# meson build -Dinstall-tests=true -Db_coverage=true
# ninja -C build
# make -C test/TEST-35-LOGIN clean setup run QEMU_SMP=1
```
```
Jul 08 04:45:10 H systemd-logind[595]: Got message type=signal sender=:1.1 destination=n/a path=/org/freedesktop/systemd1 interface=org.freedesktop.systemd1.Manager member=Reloading cookie=3258 reply_cookie=0 signature=b error-name=n/a error-message=n/a
Jul 08 04:45:10 H systemd-logind[595]: System manager has been reloaded, rechecking sessions...
Jul 08 04:45:10 H systemd-logind[595]: System idle. Will be locked now.
Jul 08 04:45:10 H systemd-logind[595]: Locking sessions...
...
Jul 08 04:45:12 H testsuite-35.sh[260]: + assert_eq tty2 tty2
Jul 08 04:45:12 H testsuite-35.sh[676]: + set +ex
Jul 08 04:45:12 H testsuite-35.sh[260]: + timeout 35 bash -c 'while [[ "$(journalctl -b -u systemd-logind.service --since=02:45:10 | grep -c '\''Sent message type=signal .* member=Lock'\'')" -lt 1 ]]; do sleep 1; done'
Jul 08 04:45:37 H systemd-logind[595]: System idle.
Jul 08 04:45:37 H systemd[1]: systemd-journald.service: Got notification message from PID 225 (WATCHDOG=1)
Jul 08 04:45:47 H systemd[1]: Received SIGCHLD from PID 814 (sleep).
Jul 08 04:45:47 H systemd[1]: Child 814 (sleep) died (code=killed, status=15/TERM)
Jul 08 04:45:47 H testsuite-35.sh[260]: + cleanup_test_user
```
Full log: https://jenkins-systemd.apps.ocp.ci.centos.org/job/upstream-cron-build/665/artifact//systemd-centos-ci/artifacts_all/artifacts_mq_ifqlt/vagrant-logs.rfi/vagrant-arch-coverage-testsuite.cKl/TEST-35-LOGIN/system.journal
As I mentioned in #23930, this doesn't seem like a timing issue, since the behavior remains same with large timeout values as well (10 minutes). | test | test login appears to be flaky when systemd is built with coverage i haven t seen this fail yet on a non coverage build as described in the expected d bus message in test lock idle action might never appear causing the test to fail this is reliably reproducible with meson build dinstall tests true db coverage true ninja c build make c test test login clean setup run qemu smp jul h systemd logind got message type signal sender destination n a path org freedesktop interface org freedesktop manager member reloading cookie reply cookie signature b error name n a error message n a jul h systemd logind system manager has been reloaded rechecking sessions jul h systemd logind system idle will be locked now jul h systemd logind locking sessions jul h testsuite sh assert eq jul h testsuite sh set ex jul h testsuite sh timeout bash c while do sleep done jul h systemd logind system idle jul h systemd systemd journald service got notification message from pid watchdog jul h systemd received sigchld from pid sleep jul h systemd child sleep died code killed status term jul h testsuite sh cleanup test user full log as i mentioned in this doesn t seem like a timing issue since the behavior remains same with large timeout values as well minutes | 1 |
77,442 | 9,995,206,662 | IssuesEvent | 2019-07-11 19:39:14 | udistrital/movimientos_mid | https://api.github.com/repos/udistrital/movimientos_mid | closed | Creación repositorio middleware movimientos y documentación | documentation | Se solicita crear el middleware para movimientos :
- [x] Generar API MID con beego
- [x] Crear y documentar el readme.md | 1.0 | Creación repositorio middleware movimientos y documentación - Se solicita crear el middleware para movimientos :
- [x] Generar API MID con beego
- [x] Crear y documentar el readme.md | non_test | creación repositorio middleware movimientos y documentación se solicita crear el middleware para movimientos generar api mid con beego crear y documentar el readme md | 0 |
187,389 | 22,045,692,831 | IssuesEvent | 2022-05-30 01:15:28 | Nivaskumark/kernel_v4.1.15 | https://api.github.com/repos/Nivaskumark/kernel_v4.1.15 | closed | CVE-2019-19815 (Medium) detected in multiple libraries - autoclosed | security vulnerability | ## CVE-2019-19815 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel 5.0.21, mounting a crafted f2fs filesystem image can cause a NULL pointer dereference in f2fs_recover_fsync_data in fs/f2fs/recovery.c. This is related to F2FS_P_SB in fs/f2fs/f2fs.h.
<p>Publish Date: 2019-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19815>CVE-2019-19815</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19816">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19816</a></p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: v5.3-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19815 (Medium) detected in multiple libraries - autoclosed - ## CVE-2019-19815 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In the Linux kernel 5.0.21, mounting a crafted f2fs filesystem image can cause a NULL pointer dereference in f2fs_recover_fsync_data in fs/f2fs/recovery.c. This is related to F2FS_P_SB in fs/f2fs/f2fs.h.
<p>Publish Date: 2019-12-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19815>CVE-2019-19815</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19816">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19816</a></p>
<p>Release Date: 2020-01-03</p>
<p>Fix Resolution: v5.3-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in multiple libraries autoclosed cve medium severity vulnerability vulnerable libraries linuxlinux linuxlinux linuxlinux vulnerability details in the linux kernel mounting a crafted filesystem image can cause a null pointer dereference in recover fsync data in fs recovery c this is related to p sb in fs h publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
54,100 | 13,251,714,297 | IssuesEvent | 2020-08-20 03:01:13 | pyne/pyne | https://api.github.com/repos/pyne/pyne | closed | Add build option for AHOT | build feature | The AHOT module in PyNE adds dependencies (FORTRAN/BLAS/LAPACK) that can be non-trivial on many environments. It would be useful to have a build option that turns off building this module, possibly by default. | 1.0 | Add build option for AHOT - The AHOT module in PyNE adds dependencies (FORTRAN/BLAS/LAPACK) that can be non-trivial on many environments. It would be useful to have a build option that turns off building this module, possibly by default. | non_test | add build option for ahot the ahot module in pyne adds dependencies fortran blas lapack that can be non trivial on many environments it would be useful to have a build option that turns off building this module possibly by default | 0 |
409,764 | 27,752,040,525 | IssuesEvent | 2023-03-15 21:38:15 | paritytech/ink-docs | https://api.github.com/repos/paritytech/ink-docs | closed | [Metadata] Document our Metadata Format | documentation | Currently this is the only information in the docs wrt our metadata format: https://paritytech.github.io/ink-docs/getting-started/building-your-contract/.
We should have a dedicated section which explains the format and its intention in more depth. Ideally we would have a typical `foo.contract` and just explain every key-value pair. | 1.0 | [Metadata] Document our Metadata Format - Currently this is the only information in the docs wrt our metadata format: https://paritytech.github.io/ink-docs/getting-started/building-your-contract/.
We should have a dedicated section which explains the format and its intention in more depth. Ideally we would have a typical `foo.contract` and just explain every key-value pair. | non_test | document our metadata format currently this is the only information in the docs wrt our metadata format we should have a dedicated section which explains the format and its intention in more depth ideally we would have a typical foo contract and just explain every key value pair | 0 |
299,560 | 25,910,923,029 | IssuesEvent | 2022-12-15 13:56:01 | rootzoll/raspiblitz | https://api.github.com/repos/rootzoll/raspiblitz | closed | BTC Pay Server more robust install script | final testing | If on first try the install of BTCPay fails - further install attemts just might do an hard exit:
https://github.com/rootzoll/raspiblitz/blob/v1.7/home.admin/config.scripts/bonus.btcpayserver.sh#L259
Check how to improve this. Maybe clean up (check user & delete first) on second install? | 1.0 | BTC Pay Server more robust install script - If on first try the install of BTCPay fails - further install attemts just might do an hard exit:
https://github.com/rootzoll/raspiblitz/blob/v1.7/home.admin/config.scripts/bonus.btcpayserver.sh#L259
Check how to improve this. Maybe clean up (check user & delete first) on second install? | test | btc pay server more robust install script if on first try the install of btcpay fails further install attemts just might do an hard exit check how to improve this maybe clean up check user delete first on second install | 1 |
197,534 | 22,595,766,697 | IssuesEvent | 2022-06-29 02:42:03 | interserver/mailbaby-api-samples | https://api.github.com/repos/interserver/mailbaby-api-samples | closed | CVE-2021-33037 (Medium) detected in tomcat-embed-core-9.0.37.jar - autoclosed | security vulnerability | ## CVE-2021-33037 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.37.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /swagger-client/spring/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.37/tomcat-embed-core-9.0.37.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-tomcat-2.1.16.RELEASE.jar (Root Library)
- :x: **tomcat-embed-core-9.0.37.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/interserver/mailbaby-api-samples/commit/0879348474e22463e77dc76ba5e5f7e6300a2b6c">0879348474e22463e77dc76ba5e5f7e6300a2b6c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Tomcat 10.0.0-M1 to 10.0.6, 9.0.0.M1 to 9.0.46 and 8.5.0 to 8.5.66 did not correctly parse the HTTP transfer-encoding request header in some circumstances leading to the possibility to request smuggling when used with a reverse proxy. Specifically: - Tomcat incorrectly ignored the transfer encoding header if the client declared it would only accept an HTTP/1.0 response; - Tomcat honoured the identify encoding; and - Tomcat did not ensure that, if present, the chunked encoding was the final encoding.
<p>Publish Date: 2021-07-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33037>CVE-2021-33037</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rd84fae1f474597bdf358f5bdc0a5c453c507bd527b83e8be6b5ea3f4%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rd84fae1f474597bdf358f5bdc0a5c453c507bd527b83e8be6b5ea3f4%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-07-12</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.48</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-tomcat): 2.2.0.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33037 (Medium) detected in tomcat-embed-core-9.0.37.jar - autoclosed - ## CVE-2021-33037 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.37.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: /swagger-client/spring/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.37/tomcat-embed-core-9.0.37.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-tomcat-2.1.16.RELEASE.jar (Root Library)
- :x: **tomcat-embed-core-9.0.37.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/interserver/mailbaby-api-samples/commit/0879348474e22463e77dc76ba5e5f7e6300a2b6c">0879348474e22463e77dc76ba5e5f7e6300a2b6c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Tomcat 10.0.0-M1 to 10.0.6, 9.0.0.M1 to 9.0.46 and 8.5.0 to 8.5.66 did not correctly parse the HTTP transfer-encoding request header in some circumstances leading to the possibility to request smuggling when used with a reverse proxy. Specifically: - Tomcat incorrectly ignored the transfer encoding header if the client declared it would only accept an HTTP/1.0 response; - Tomcat honoured the identify encoding; and - Tomcat did not ensure that, if present, the chunked encoding was the final encoding.
<p>Publish Date: 2021-07-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-33037>CVE-2021-33037</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rd84fae1f474597bdf358f5bdc0a5c453c507bd527b83e8be6b5ea3f4%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rd84fae1f474597bdf358f5bdc0a5c453c507bd527b83e8be6b5ea3f4%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-07-12</p>
<p>Fix Resolution (org.apache.tomcat.embed:tomcat-embed-core): 9.0.48</p>
<p>Direct dependency fix Resolution (org.springframework.boot:spring-boot-starter-tomcat): 2.2.0.RELEASE</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in tomcat embed core jar autoclosed cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file swagger client spring pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter tomcat release jar root library x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details apache tomcat to to and to did not correctly parse the http transfer encoding request header in some circumstances leading to the possibility to request smuggling when used with a reverse proxy specifically tomcat incorrectly ignored the transfer encoding header if the client declared it would only accept an http response tomcat honoured the identify encoding and tomcat did not ensure that if present the chunked encoding was the final encoding publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat embed tomcat embed core direct dependency fix resolution org springframework boot spring boot starter tomcat release step up your open source security game with mend | 0 |
434,658 | 12,521,513,140 | IssuesEvent | 2020-06-03 17:31:02 | dmwm/WMCore | https://api.github.com/repos/dmwm/WMCore | closed | MSOutput: Wrong number of requests by status retrieved from Reqmgr2 in log message | Medium Priority ReqMgr2MS | **Impact of the bug**
Reqmgr2ms
**Describe the bug**
There is a wrong number of requests by status in the following log message [1] in MSOutput micro service. It always shows the full length of the `requestRecords` dictionary but not the length of the result from the current status.
[1]
https://github.com/dmwm/WMCore/blob/d1db5986c6b09f09f96ef38cf4f9d549373edd98/src/python/WMCore/MicroService/Unified/MSOutput.py#L185
**How to reproduce it**
An inspection of the logs from the current implementation is enough.
**Expected behavior**
The log message should reflect the numbers from the current query regarding every status separately.
**Additional context and error message**
N/A
| 1.0 | MSOutput: Wrong number of requests by status retrieved from Reqmgr2 in log message - **Impact of the bug**
Reqmgr2ms
**Describe the bug**
There is a wrong number of requests by status in the following log message [1] in MSOutput micro service. It always shows the full length of the `requestRecords` dictionary but not the length of the result from the current status.
[1]
https://github.com/dmwm/WMCore/blob/d1db5986c6b09f09f96ef38cf4f9d549373edd98/src/python/WMCore/MicroService/Unified/MSOutput.py#L185
**How to reproduce it**
An inspection of the logs from the current implementation is enough.
**Expected behavior**
The log message should reflect the numbers from the current query regarding every status separately.
**Additional context and error message**
N/A
| non_test | msoutput wrong number of requests by status retrieved from in log message impact of the bug describe the bug there is a wrong number of requests by status in the following log message in msoutput micro service it always shows the full length of the requestrecords dictionary but not the length of the result from the current status how to reproduce it an inspection of the logs from the current implementation is enough expected behavior the log message should reflect the numbers from the current query regarding every status separately additional context and error message n a | 0 |
155,789 | 12,270,321,321 | IssuesEvent | 2020-05-07 15:19:53 | servo/servo | https://api.github.com/repos/servo/servo | closed | Hover color transition only affects direct text children | A-layout/text C-has-manual-testcase | ```html
<style>
div { transition: color 0.1s; color: black }
div:hover { color: red; }
</style>
<div><span>hi</span> there</div>
```
Due to #17667, this testcase is completely broken unless non-incremental layout (`-i`) is enabled. Even with non-incremental layout, however, the text in the span does not change color when the mouse is over any part of the containing div. | 1.0 | Hover color transition only affects direct text children - ```html
<style>
div { transition: color 0.1s; color: black }
div:hover { color: red; }
</style>
<div><span>hi</span> there</div>
```
Due to #17667, this testcase is completely broken unless non-incremental layout (`-i`) is enabled. Even with non-incremental layout, however, the text in the span does not change color when the mouse is over any part of the containing div. | test | hover color transition only affects direct text children html div transition color color black div hover color red hi there due to this testcase is completely broken unless non incremental layout i is enabled even with non incremental layout however the text in the span does not change color when the mouse is over any part of the containing div | 1 |
334,389 | 29,833,884,047 | IssuesEvent | 2023-06-18 15:49:13 | litestar-org/litestar | https://api.github.com/repos/litestar-org/litestar | opened | Refactor: Reorganise test suite | help wanted refactor tests-issue | Our test suite has grown with the project, but as a result has become a bit disorganised in quite a few places. It should be efactored in a way that structures it in a more consistent and logical way. | 1.0 | Refactor: Reorganise test suite - Our test suite has grown with the project, but as a result has become a bit disorganised in quite a few places. It should be efactored in a way that structures it in a more consistent and logical way. | test | refactor reorganise test suite our test suite has grown with the project but as a result has become a bit disorganised in quite a few places it should be efactored in a way that structures it in a more consistent and logical way | 1 |
18,960 | 3,735,575,509 | IssuesEvent | 2016-03-08 12:47:50 | phracek/rebase-helper | https://api.github.com/repos/phracek/rebase-helper | closed | tox usage for rebase-helper test | enhancement unit tests | On the base of discussion with @thozza we could switch our tests to tox.
Is there any volunteer who can handle it? | 1.0 | tox usage for rebase-helper test - On the base of discussion with @thozza we could switch our tests to tox.
Is there any volunteer who can handle it? | test | tox usage for rebase helper test on the base of discussion with thozza we could switch our tests to tox is there any volunteer who can handle it | 1 |
621,697 | 19,594,957,507 | IssuesEvent | 2022-01-05 16:47:17 | craftercms/craftercms | https://api.github.com/repos/craftercms/craftercms | closed | [studio-ui] There are errors when viewing an edited ftl file via left-click on the Site Explorer | bug priority: high | ### Bug Report
#### Crafter CMS Version
Studio Version Number:
4.0.0-SNAPSHOT-9e4304
#### Date of Build
Build Date:
1/4/2022, 7:35 AM
#### Describe the bug
When you edit an ftl file and try to view the file by left-clicking on it from the `Site Explorer`, it tries to preview the file showing lots of errors instead of opening a dialog displaying the file.
<img width="1308" alt="Screen Shot 2022-01-04 at 7 52 47 AM" src="https://user-images.githubusercontent.com/25483966/148062274-b11e7f2c-46da-437c-a53f-e0c010766efe.png">
Steps to reproduce the behavior:
1. Create a site using the Website Editorial bp
2. Navigate to `templates/web/pages and left click on one of the items there, say the `category-landing.ftl`
3. Notice that this opens a dialog displaying the contents of the ftl file
<img width="1311" alt="Screen Shot 2022-01-04 at 7 52 30 AM" src="https://user-images.githubusercontent.com/25483966/148062866-9b54b17d-53a0-4dd2-840e-db56ad465a11.png">
4. Edit one of the ftl files, say `article.ftl`
5. From the `Site Explorer`, left click on `article.ftl`. Notice the errors on the screen and in the catalina log. It looks like it tries to preview the file showing lots of errors instead of opening a dialog displaying the file.
<img width="1310" alt="Screen Shot 2022-01-04 at 8 16 48 AM" src="https://user-images.githubusercontent.com/25483966/148064779-eb11a046-7811-4206-b389-c374d1177777.png">
#### Logs
https://gist.github.com/alhambrav/937675230001f3dfdd0aabe75f98eafd
#### Screenshots
{{If applicable, add screenshots to help explain your problem.}}
| 1.0 | [studio-ui] There are errors when viewing an edited ftl file via left-click on the Site Explorer - ### Bug Report
#### Crafter CMS Version
Studio Version Number:
4.0.0-SNAPSHOT-9e4304
#### Date of Build
Build Date:
1/4/2022, 7:35 AM
#### Describe the bug
When you edit an ftl file and try to view the file by left-clicking on it from the `Site Explorer`, it tries to preview the file showing lots of errors instead of opening a dialog displaying the file.
<img width="1308" alt="Screen Shot 2022-01-04 at 7 52 47 AM" src="https://user-images.githubusercontent.com/25483966/148062274-b11e7f2c-46da-437c-a53f-e0c010766efe.png">
Steps to reproduce the behavior:
1. Create a site using the Website Editorial bp
2. Navigate to `templates/web/pages and left click on one of the items there, say the `category-landing.ftl`
3. Notice that this opens a dialog displaying the contents of the ftl file
<img width="1311" alt="Screen Shot 2022-01-04 at 7 52 30 AM" src="https://user-images.githubusercontent.com/25483966/148062866-9b54b17d-53a0-4dd2-840e-db56ad465a11.png">
4. Edit one of the ftl files, say `article.ftl`
5. From the `Site Explorer`, left click on `article.ftl`. Notice the errors on the screen and in the catalina log. It looks like it tries to preview the file showing lots of errors instead of opening a dialog displaying the file.
<img width="1310" alt="Screen Shot 2022-01-04 at 8 16 48 AM" src="https://user-images.githubusercontent.com/25483966/148064779-eb11a046-7811-4206-b389-c374d1177777.png">
#### Logs
https://gist.github.com/alhambrav/937675230001f3dfdd0aabe75f98eafd
#### Screenshots
{{If applicable, add screenshots to help explain your problem.}}
| non_test | there are errors when viewing an edited ftl file via left click on the site explorer bug report crafter cms version studio version number snapshot date of build build date am describe the bug when you edit an ftl file and try to view the file by left clicking on it from the site explorer it tries to preview the file showing lots of errors instead of opening a dialog displaying the file img width alt screen shot at am src steps to reproduce the behavior create a site using the website editorial bp navigate to templates web pages and left click on one of the items there say the category landing ftl notice that this opens a dialog displaying the contents of the ftl file img width alt screen shot at am src edit one of the ftl files say article ftl from the site explorer left click on article ftl notice the errors on the screen and in the catalina log it looks like it tries to preview the file showing lots of errors instead of opening a dialog displaying the file img width alt screen shot at am src logs screenshots if applicable add screenshots to help explain your problem | 0 |
256,981 | 8,131,009,490 | IssuesEvent | 2018-08-17 20:44:16 | ItzSomebody/Radon | https://api.github.com/repos/ItzSomebody/Radon | closed | Renamer Issue affects all other Exempts | Radon Bug Top Priority | **Which version of Radon are you using? (Do not say "latest", if you do, your issue will be immediately closed)** Happens on all versions currently.
**What kind of Jar file did you obfuscate? (Android/Standalone/Plugin)** Doesn't matter.
**What transformers did you use which caused an error?**
* Renamer
* Put random transformer here
**Is Radon the issue or the jar Radon obfuscated the issue? (if the obfuscated jar is the issue, make sure to provide the jar)** Radon
**What is the error produced? (Copy-and-paste error into [PasteBin](http://pastebin.com) or [HasteBin](http://hastebin.com) and link it here)** N/A
**Any other information? (i.e. You combined Radon with other obfuscators)** When the Renamer transformer is used, it also removes the information used in exempting classes/methods/fields for other classes.
| 1.0 | Renamer Issue affects all other Exempts - **Which version of Radon are you using? (Do not say "latest", if you do, your issue will be immediately closed)** Happens on all versions currently.
**What kind of Jar file did you obfuscate? (Android/Standalone/Plugin)** Doesn't matter.
**What transformers did you use which caused an error?**
* Renamer
* Put random transformer here
**Is Radon the issue or the jar Radon obfuscated the issue? (if the obfuscated jar is the issue, make sure to provide the jar)** Radon
**What is the error produced? (Copy-and-paste error into [PasteBin](http://pastebin.com) or [HasteBin](http://hastebin.com) and link it here)** N/A
**Any other information? (i.e. You combined Radon with other obfuscators)** When the Renamer transformer is used, it also removes the information used in exempting classes/methods/fields for other classes.
| non_test | renamer issue affects all other exempts which version of radon are you using do not say latest if you do your issue will be immediately closed happens on all versions currently what kind of jar file did you obfuscate android standalone plugin doesn t matter what transformers did you use which caused an error renamer put random transformer here is radon the issue or the jar radon obfuscated the issue if the obfuscated jar is the issue make sure to provide the jar radon what is the error produced copy and paste error into or and link it here n a any other information i e you combined radon with other obfuscators when the renamer transformer is used it also removes the information used in exempting classes methods fields for other classes | 0 |
80,639 | 15,527,738,131 | IssuesEvent | 2021-03-13 07:35:11 | samsunghappytree123/makead | https://api.github.com/repos/samsunghappytree123/makead | closed | [오픈소스 사용] Kimbab Promotional 사용 공지 | Use of source code (소스코드 사용) | ## 디스코드 정보를 기재해주세요.
+ 디스코드 닉네임#태그 (Discord#0000) : !안꿀꿀!
#3704
+ 디스코드 ID (123456789) : 552103947662524416
## 오픈소스를 사용하며 라이센스를 지킬 수 있으신가요?
네
<1-- ``네`` 또는 ``아니오``로 입력해주세요. -->
| 1.0 | [오픈소스 사용] Kimbab Promotional 사용 공지 - ## 디스코드 정보를 기재해주세요.
+ 디스코드 닉네임#태그 (Discord#0000) : !안꿀꿀!
#3704
+ 디스코드 ID (123456789) : 552103947662524416
## 오픈소스를 사용하며 라이센스를 지킬 수 있으신가요?
네
<1-- ``네`` 또는 ``아니오``로 입력해주세요. -->
| non_test | kimbab promotional 사용 공지 디스코드 정보를 기재해주세요 디스코드 닉네임 태그 discord 안꿀꿀 디스코드 id 오픈소스를 사용하며 라이센스를 지킬 수 있으신가요 네 | 0 |
3,323 | 2,846,479,383 | IssuesEvent | 2015-05-29 11:48:02 | ExCiteS/geokey | https://api.github.com/repos/ExCiteS/geokey | opened | Leaflet cannot load on SSL | code enhancement | Failed to load resource: net::ERR_INSECURE_RESPONSE
https://cdn.leafletjs.com/leaflet-0.7.3/leaflet.js
There have been issues with Leaflet's CDN recently, maybe a local fallback would be in consideration? | 1.0 | Leaflet cannot load on SSL - Failed to load resource: net::ERR_INSECURE_RESPONSE
https://cdn.leafletjs.com/leaflet-0.7.3/leaflet.js
There have been issues with Leaflet's CDN recently, maybe a local fallback would be in consideration? | non_test | leaflet cannot load on ssl failed to load resource net err insecure response there have been issues with leaflet s cdn recently maybe a local fallback would be in consideration | 0 |
161,820 | 25,408,242,849 | IssuesEvent | 2022-11-22 16:48:07 | sboxgame/issues | https://api.github.com/repos/sboxgame/issues | closed | Custom Asset Types aren't converted to the Asset itself. When using [ResourceType] | review api design | **What it is**
Custom Asset Types set in Hammer have to be on String Properties rather than on the Asset type itself.
This causes an unnecessary step that should be avoided.
this is the current way you need to set an Asset if exposed to Hammer:
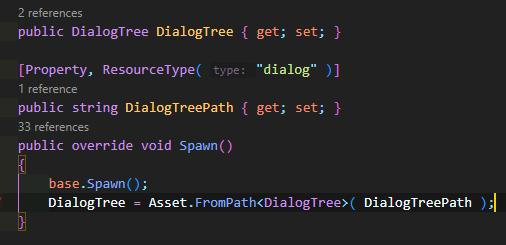
Having to manually get the Asset instead of it Auto Assigning to the correct AssetType. Seems like a Redundant step.
**What it should be**
The ResourceType Attribute should directly return the Correct Asset type so this Extra step isn't needed.
instead of how its shown in the picture above it should be as simple as:
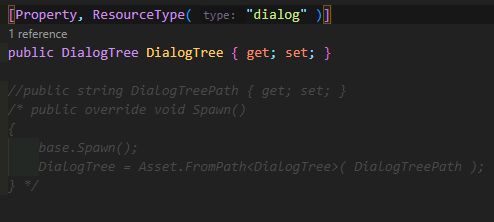
Perhaps even without the Library Type name, since it could just derive the Type from the Property Type.
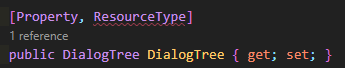
| 1.0 | Custom Asset Types aren't converted to the Asset itself. When using [ResourceType] - **What it is**
Custom Asset Types set in Hammer have to be on String Properties rather than on the Asset type itself.
This causes an unnecessary step that should be avoided.
this is the current way you need to set an Asset if exposed to Hammer:
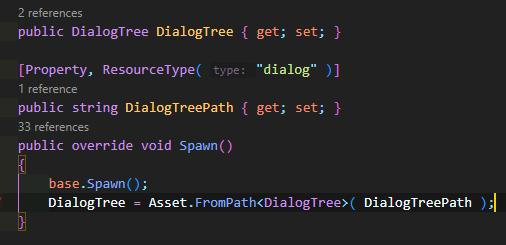
Having to manually get the Asset instead of it Auto Assigning to the correct AssetType. Seems like a Redundant step.
**What it should be**
The ResourceType Attribute should directly return the Correct Asset type so this Extra step isn't needed.
instead of how its shown in the picture above it should be as simple as:
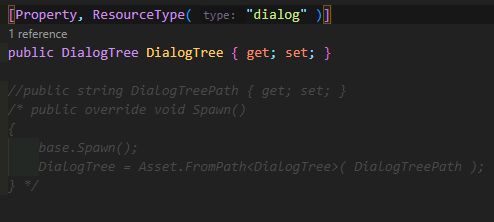
Perhaps even without the Library Type name, since it could just derive the Type from the Property Type.
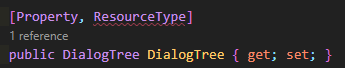
| non_test | custom asset types aren t converted to the asset itself when using what it is custom asset types set in hammer have to be on string properties rather than on the asset type itself this causes an unnecessary step that should be avoided this is the current way you need to set an asset if exposed to hammer having to manually get the asset instead of it auto assigning to the correct assettype seems like a redundant step what it should be the resourcetype attribute should directly return the correct asset type so this extra step isn t needed instead of how its shown in the picture above it should be as simple as perhaps even without the library type name since it could just derive the type from the property type | 0 |
194,859 | 14,690,017,909 | IssuesEvent | 2021-01-02 13:09:16 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | pbolla0818/oci_terraform: oci/apigateway_api_test.go; 16 LoC | fresh small test |
Found a possible issue in [pbolla0818/oci_terraform](https://www.github.com/pbolla0818/oci_terraform) at [oci/apigateway_api_test.go](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/apigateway_api_test.go#L277-L292)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to apiId is reassigned at line 281
[Click here to see the code in its original context.](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/apigateway_api_test.go#L277-L292)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, apiId := range apiIds {
if ok := SweeperDefaultResourceId[apiId]; !ok {
deleteApiRequest := oci_apigateway.DeleteApiRequest{}
deleteApiRequest.ApiId = &apiId
deleteApiRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "apigateway")
_, error := apiGatewayClient.DeleteApi(context.Background(), deleteApiRequest)
if error != nil {
fmt.Printf("Error deleting Api %s %s, It is possible that the resource is already deleted. Please verify manually \n", apiId, error)
continue
}
waitTillCondition(testAccProvider, &apiId, apiSweepWaitCondition, time.Duration(3*time.Minute),
apiSweepResponseFetchOperation, "apigateway", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c233d54c5fe32f12c234d6dceefba0a9b4ab3022
| 1.0 | pbolla0818/oci_terraform: oci/apigateway_api_test.go; 16 LoC -
Found a possible issue in [pbolla0818/oci_terraform](https://www.github.com/pbolla0818/oci_terraform) at [oci/apigateway_api_test.go](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/apigateway_api_test.go#L277-L292)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to apiId is reassigned at line 281
[Click here to see the code in its original context.](https://github.com/pbolla0818/oci_terraform/blob/c233d54c5fe32f12c234d6dceefba0a9b4ab3022/oci/apigateway_api_test.go#L277-L292)
<details>
<summary>Click here to show the 16 line(s) of Go which triggered the analyzer.</summary>
```go
for _, apiId := range apiIds {
if ok := SweeperDefaultResourceId[apiId]; !ok {
deleteApiRequest := oci_apigateway.DeleteApiRequest{}
deleteApiRequest.ApiId = &apiId
deleteApiRequest.RequestMetadata.RetryPolicy = getRetryPolicy(true, "apigateway")
_, error := apiGatewayClient.DeleteApi(context.Background(), deleteApiRequest)
if error != nil {
fmt.Printf("Error deleting Api %s %s, It is possible that the resource is already deleted. Please verify manually \n", apiId, error)
continue
}
waitTillCondition(testAccProvider, &apiId, apiSweepWaitCondition, time.Duration(3*time.Minute),
apiSweepResponseFetchOperation, "apigateway", true)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: c233d54c5fe32f12c234d6dceefba0a9b4ab3022
| test | oci terraform oci apigateway api test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to apiid is reassigned at line click here to show the line s of go which triggered the analyzer go for apiid range apiids if ok sweeperdefaultresourceid ok deleteapirequest oci apigateway deleteapirequest deleteapirequest apiid apiid deleteapirequest requestmetadata retrypolicy getretrypolicy true apigateway error apigatewayclient deleteapi context background deleteapirequest if error nil fmt printf error deleting api s s it is possible that the resource is already deleted please verify manually n apiid error continue waittillcondition testaccprovider apiid apisweepwaitcondition time duration time minute apisweepresponsefetchoperation apigateway true leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
264,924 | 23,145,072,591 | IssuesEvent | 2022-07-28 23:13:24 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Seridores - Registro por lotação - Augusto de Lima | generalization test development template-Síntese tecnologia informatica tag-Servidores subtag-Registro por lotação | DoD: Realizar o teste de Generalização do validador da tag Seridores - Registro por lotação para o Município de Augusto de Lima. | 1.0 | Teste de generalizacao para a tag Seridores - Registro por lotação - Augusto de Lima - DoD: Realizar o teste de Generalização do validador da tag Seridores - Registro por lotação para o Município de Augusto de Lima. | test | teste de generalizacao para a tag seridores registro por lotação augusto de lima dod realizar o teste de generalização do validador da tag seridores registro por lotação para o município de augusto de lima | 1 |
203,980 | 15,396,258,456 | IssuesEvent | 2021-03-03 20:23:03 | openservicemesh/osm | https://api.github.com/repos/openservicemesh/osm | opened | test: pkg/cli EnvSettings.Namespace() | tests | In `pkg/cli` `EnvSettings.Namespace()` does not have good unit test coverage.
It would be great to write a small test for this function.
We should mock `s.config.ToRawKubeConfigLoader()...` and return an error to test this
The `default` string should also be a constant.
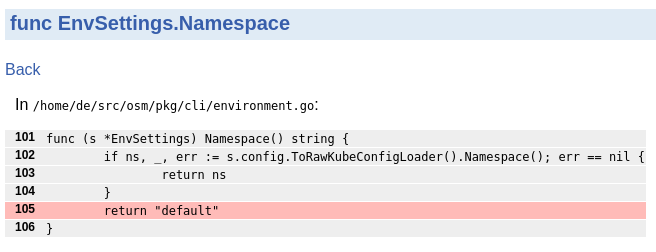
| 1.0 | test: pkg/cli EnvSettings.Namespace() - In `pkg/cli` `EnvSettings.Namespace()` does not have good unit test coverage.
It would be great to write a small test for this function.
We should mock `s.config.ToRawKubeConfigLoader()...` and return an error to test this
The `default` string should also be a constant.
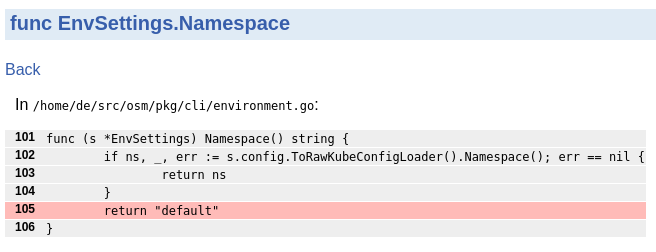
| test | test pkg cli envsettings namespace in pkg cli envsettings namespace does not have good unit test coverage it would be great to write a small test for this function we should mock s config torawkubeconfigloader and return an error to test this the default string should also be a constant | 1 |
48,712 | 5,967,903,598 | IssuesEvent | 2017-05-30 16:56:27 | Fielo-Plugins/fielocms-fieloplt | https://api.github.com/repos/Fielo-Plugins/fielocms-fieloplt | opened | Preview de Site y Acceso - Cancela con Authorization Required cuando no hay Home | bug High To Test | Cuando no hay navigations (y por ende no hay Home en el layout) al presionar el boton Preview o acceder a la URL, cancela, cuando deberia mostrar un mensaje especificando que falta setear una Home. | 1.0 | Preview de Site y Acceso - Cancela con Authorization Required cuando no hay Home - Cuando no hay navigations (y por ende no hay Home en el layout) al presionar el boton Preview o acceder a la URL, cancela, cuando deberia mostrar un mensaje especificando que falta setear una Home. | test | preview de site y acceso cancela con authorization required cuando no hay home cuando no hay navigations y por ende no hay home en el layout al presionar el boton preview o acceder a la url cancela cuando deberia mostrar un mensaje especificando que falta setear una home | 1 |
222,773 | 24,711,319,597 | IssuesEvent | 2022-10-20 01:13:07 | ignatandrei/InfoValutar | https://api.github.com/repos/ignatandrei/InfoValutar | opened | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz | security vulnerability | ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>Path to dependency file: /InfovalutarWebAng/package.json</p>
<p>Path to vulnerable library: /InfovalutarWebAng/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.1.0.tgz (Root Library)
- chokidar-2.1.8.tgz
- fsevents-1.2.11.tgz
- node-pre-gyp-0.14.0.tgz
- rimraf-2.7.1.tgz
- glob-7.1.6.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ignatandrei/InfoValutar/commit/bf5331c9561161f0425df3896315b57768d59fbf">bf5331c9561161f0425df3896315b57768d59fbf</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-3517 (High) detected in minimatch-3.0.4.tgz - ## CVE-2022-3517 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>minimatch-3.0.4.tgz</b></p></summary>
<p>a glob matcher in javascript</p>
<p>Library home page: <a href="https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz">https://registry.npmjs.org/minimatch/-/minimatch-3.0.4.tgz</a></p>
<p>Path to dependency file: /InfovalutarWebAng/package.json</p>
<p>Path to vulnerable library: /InfovalutarWebAng/node_modules/minimatch/package.json</p>
<p>
Dependency Hierarchy:
- karma-4.1.0.tgz (Root Library)
- chokidar-2.1.8.tgz
- fsevents-1.2.11.tgz
- node-pre-gyp-0.14.0.tgz
- rimraf-2.7.1.tgz
- glob-7.1.6.tgz
- :x: **minimatch-3.0.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ignatandrei/InfoValutar/commit/bf5331c9561161f0425df3896315b57768d59fbf">bf5331c9561161f0425df3896315b57768d59fbf</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A vulnerability was found in the minimatch package. This flaw allows a Regular Expression Denial of Service (ReDoS) when calling the braceExpand function with specific arguments, resulting in a Denial of Service.
<p>Publish Date: 2022-10-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-3517>CVE-2022-3517</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-17</p>
<p>Fix Resolution: minimatch - 3.0.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in minimatch tgz cve high severity vulnerability vulnerable library minimatch tgz a glob matcher in javascript library home page a href path to dependency file infovalutarwebang package json path to vulnerable library infovalutarwebang node modules minimatch package json dependency hierarchy karma tgz root library chokidar tgz fsevents tgz node pre gyp tgz rimraf tgz glob tgz x minimatch tgz vulnerable library found in head commit a href vulnerability details a vulnerability was found in the minimatch package this flaw allows a regular expression denial of service redos when calling the braceexpand function with specific arguments resulting in a denial of service publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution minimatch step up your open source security game with mend | 0 |
409,476 | 11,963,252,749 | IssuesEvent | 2020-04-05 15:16:12 | inexorgame/vulkan-renderer | https://api.github.com/repos/inexorgame/vulkan-renderer | closed | Fix shader compilation batch script on Windows. | difficulty: easy platform: Microsoft Windows priority: high problem: shaders | If we want to compile shaders using `glslangValidator.exe`, we must make sure vertex shaders end with `.vert` and fragment shaders end with `.frag`. The current batch script is broken. | 1.0 | Fix shader compilation batch script on Windows. - If we want to compile shaders using `glslangValidator.exe`, we must make sure vertex shaders end with `.vert` and fragment shaders end with `.frag`. The current batch script is broken. | non_test | fix shader compilation batch script on windows if we want to compile shaders using glslangvalidator exe we must make sure vertex shaders end with vert and fragment shaders end with frag the current batch script is broken | 0 |
349,097 | 31,774,471,799 | IssuesEvent | 2023-09-12 13:41:45 | NFDI4Chem/nmrxiv | https://api.github.com/repos/NFDI4Chem/nmrxiv | closed | Bioschema controllers and API | testing | - [x] Add condition check in API to just fetch public models.
- [x] add "[distribution](http://schema.org/distribution)" when available | 1.0 | Bioschema controllers and API - - [x] Add condition check in API to just fetch public models.
- [x] add "[distribution](http://schema.org/distribution)" when available | test | bioschema controllers and api add condition check in api to just fetch public models add when available | 1 |
344,922 | 30,772,505,924 | IssuesEvent | 2023-07-31 01:53:28 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | closed | The red border and error message that caused by invalid filter key/value do not disappear after selecting 'Prefix' option | :heavy_check_mark: merged 🧪 testing :gear: blobs :beetle: regression | **Storage Explorer Version**: 1.31.0-dev
**Build Number**: 20230728.3
**Branch**: main
**Platform/OS**: Windows 10/Linux Ubuntu 20.04/MacOS Ventura 13.4.1 (Apple M1 Pro)
**Architecture**: x64/x64/arm64
**How Found**: Ad-hoc testing
**Regression From**: Previous release (1.30.1)
## Steps to Reproduce ##
1. Expand one storage account -> Blob Containers.
2. Create a blob container -> Right click the blob container -> Click 'Open in React'.
3. Open the view options panel -> Select 'Tag Query' option.
4. Type ',' as the tag key -> A red border shows for the tag key box and an error message appears.
5. Select 'Prefix' option.
6. Check whether the red border and the error message disappear.
## Expected Experience ##
The red border and the error message disappear.

## Actual Experience ##
The red border and the error message do not disappear.
 | 1.0 | The red border and error message that caused by invalid filter key/value do not disappear after selecting 'Prefix' option - **Storage Explorer Version**: 1.31.0-dev
**Build Number**: 20230728.3
**Branch**: main
**Platform/OS**: Windows 10/Linux Ubuntu 20.04/MacOS Ventura 13.4.1 (Apple M1 Pro)
**Architecture**: x64/x64/arm64
**How Found**: Ad-hoc testing
**Regression From**: Previous release (1.30.1)
## Steps to Reproduce ##
1. Expand one storage account -> Blob Containers.
2. Create a blob container -> Right click the blob container -> Click 'Open in React'.
3. Open the view options panel -> Select 'Tag Query' option.
4. Type ',' as the tag key -> A red border shows for the tag key box and an error message appears.
5. Select 'Prefix' option.
6. Check whether the red border and the error message disappear.
## Expected Experience ##
The red border and the error message disappear.

## Actual Experience ##
The red border and the error message do not disappear.
 | test | the red border and error message that caused by invalid filter key value do not disappear after selecting prefix option storage explorer version dev build number branch main platform os windows linux ubuntu macos ventura apple pro architecture how found ad hoc testing regression from previous release steps to reproduce expand one storage account blob containers create a blob container right click the blob container click open in react open the view options panel select tag query option type as the tag key a red border shows for the tag key box and an error message appears select prefix option check whether the red border and the error message disappear expected experience the red border and the error message disappear actual experience the red border and the error message do not disappear | 1 |
132,805 | 10,764,713,744 | IssuesEvent | 2019-11-01 09:06:06 | loadimpact/k6 | https://api.github.com/repos/loadimpact/k6 | closed | stats/cloud: TestCloudCollector is flaky | high prio tests | Running the test:
```
$ cd stats/cloud
$ go test -count=100 -race
```
Sample error output:
```
--- FAIL: TestCloudCollector (0.07s)
Error Trace: collector_test.go:58
server.go:2007
server.go:2387
server.go:2802
server.go:1890
asm_amd64.s:1357
Error: "[{Points http_req_li_all %!s(*cloud.SampleDataMap=&{{143841000 63707865704 0x22e8cc0} 0 0xc000225ca0 map[http_req_blocked:100.20751 http_req_connecting:200.41502 http_req_duration:1503.112655 http_req_receiving:601.245062 http_req_sending:400.830041 http_req_tls_handshaking:300.622531 http_req_waiting:501.037552 http_reqs:1]})} {Points http_req_li_all %!s(*cloud.SampleDataMap=&{{143841000 63707865704 0x22e8cc0} 0 0xc000225e00 map[http_req_blocked:239.951032 http_req_connecting:479.902064 http_req_duration:3599.265483 http_req_receiving:1439.706193 http_req_sending:959.804129 http_req_tls_handshaking:719.853096 http_req_waiting:1199.755161 http_reqs:1]})} {AggregatedPoints http_req_li_all %!s(*cloud.SampleDataAggregatedHTTPReqs=&{{145000000 63707865704 0x22e8cc0} aggregated_trend 24 0xc000225fc0 {{0 0 0 1510.304694 1574.301317 1545.3932262083333} {0 0 0 100.686979 104.953421 103.02621479166667} {0 0 0 201.373959 209.906842 206.05242991666668} {0 0 0 302.060939 314.860263 309.07864512500004} {0 0 0 402.747918 419.813684 412.1048602083333} {0 0 0 503.434898 524.767106 515.131075375} {0 0 0 604.121878 629.720527 618.157290625}}})}]" should have 2 item(s), but has 3
Test: TestCloudCollector
``` | 1.0 | stats/cloud: TestCloudCollector is flaky - Running the test:
```
$ cd stats/cloud
$ go test -count=100 -race
```
Sample error output:
```
--- FAIL: TestCloudCollector (0.07s)
Error Trace: collector_test.go:58
server.go:2007
server.go:2387
server.go:2802
server.go:1890
asm_amd64.s:1357
Error: "[{Points http_req_li_all %!s(*cloud.SampleDataMap=&{{143841000 63707865704 0x22e8cc0} 0 0xc000225ca0 map[http_req_blocked:100.20751 http_req_connecting:200.41502 http_req_duration:1503.112655 http_req_receiving:601.245062 http_req_sending:400.830041 http_req_tls_handshaking:300.622531 http_req_waiting:501.037552 http_reqs:1]})} {Points http_req_li_all %!s(*cloud.SampleDataMap=&{{143841000 63707865704 0x22e8cc0} 0 0xc000225e00 map[http_req_blocked:239.951032 http_req_connecting:479.902064 http_req_duration:3599.265483 http_req_receiving:1439.706193 http_req_sending:959.804129 http_req_tls_handshaking:719.853096 http_req_waiting:1199.755161 http_reqs:1]})} {AggregatedPoints http_req_li_all %!s(*cloud.SampleDataAggregatedHTTPReqs=&{{145000000 63707865704 0x22e8cc0} aggregated_trend 24 0xc000225fc0 {{0 0 0 1510.304694 1574.301317 1545.3932262083333} {0 0 0 100.686979 104.953421 103.02621479166667} {0 0 0 201.373959 209.906842 206.05242991666668} {0 0 0 302.060939 314.860263 309.07864512500004} {0 0 0 402.747918 419.813684 412.1048602083333} {0 0 0 503.434898 524.767106 515.131075375} {0 0 0 604.121878 629.720527 618.157290625}}})}]" should have 2 item(s), but has 3
Test: TestCloudCollector
``` | test | stats cloud testcloudcollector is flaky running the test cd stats cloud go test count race sample error output fail testcloudcollector error trace collector test go server go server go server go server go asm s error points http req li all s cloud sampledatamap map aggregatedpoints http req li all s cloud sampledataaggregatedhttpreqs aggregated trend should have item s but has test testcloudcollector | 1 |
125,445 | 10,343,057,726 | IssuesEvent | 2019-09-04 08:06:40 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | VisibilityNotifier is Broken | bug needs testing topic:core | ```
print("Is starfighter's notifier null? ", (starfighterNotifier==null))
func _process(deltaTime):
if (Input.is_action_pressed("Right")):
rotate_y(-deltaTime)
if (Input.is_action_pressed("Left")):
rotate_y(deltaTime)
if (Input.is_action_just_pressed("ui_accept")):
look_at(bigShip.transform.origin, Vector3(0, 1, 0))
if (starfighterNotifier.is_on_screen()):
selectedShip = starfighter
```
**Godot version:**
3.1.1 Stable
**OS/device including version:**
Windows 10, GPU NVidia Optimus
**Issue description:**
The above printout tells me the visibility notifier variable is NOT null. But in _process, I repeatedly get the message, "Attempt to call function 'is_on_screen' in base 'null instance' on a null instance." | 1.0 | VisibilityNotifier is Broken - ```
print("Is starfighter's notifier null? ", (starfighterNotifier==null))
func _process(deltaTime):
if (Input.is_action_pressed("Right")):
rotate_y(-deltaTime)
if (Input.is_action_pressed("Left")):
rotate_y(deltaTime)
if (Input.is_action_just_pressed("ui_accept")):
look_at(bigShip.transform.origin, Vector3(0, 1, 0))
if (starfighterNotifier.is_on_screen()):
selectedShip = starfighter
```
**Godot version:**
3.1.1 Stable
**OS/device including version:**
Windows 10, GPU NVidia Optimus
**Issue description:**
The above printout tells me the visibility notifier variable is NOT null. But in _process, I repeatedly get the message, "Attempt to call function 'is_on_screen' in base 'null instance' on a null instance." | test | visibilitynotifier is broken print is starfighter s notifier null starfighternotifier null func process deltatime if input is action pressed right rotate y deltatime if input is action pressed left rotate y deltatime if input is action just pressed ui accept look at bigship transform origin if starfighternotifier is on screen selectedship starfighter godot version stable os device including version windows gpu nvidia optimus issue description the above printout tells me the visibility notifier variable is not null but in process i repeatedly get the message attempt to call function is on screen in base null instance on a null instance | 1 |
302,046 | 26,119,595,771 | IssuesEvent | 2022-12-28 10:55:18 | kubernetes-sigs/cluster-api | https://api.github.com/repos/kubernetes-sigs/cluster-api | closed | CI failure: capi-e2e-release-1-1-1-23-1-24 is failing consistently | kind/bug kind/failing-test triage/accepted | release-1.1 branch https://testgrid.k8s.io/sig-cluster-lifecycle-cluster-api-1.1#capi-e2e-release-1-1-1-23-1-24 job is failing consistently since December 9th.
Logs from the corresponding prow job:
```
capi-e2e: When upgrading a workload cluster using ClusterClass and testing K8S conformance [Conformance] [K8s-Upgrade] Should create and upgrade a workload cluster and run kubetest expand_less | 20m54s
-- | --
{ Failure /home/prow/go/src/sigs.k8s.io/cluster-api/test/e2e/cluster_upgrade.go:115 Failed to run Kubernetes conformance Unexpected error: <*errors.withStack \| 0xc001dd0a80>: { error: <*errors.withMessage \| 0xc0010a6240>{ cause: <*errors.errorString \| 0xc00086ce40>{ s: "error container run failed with exit code 1", }, msg: "Unable to run conformance tests", }, stack: [0x1ad532a, 0x1b1a468, 0x73c37a, 0x73bd45, 0x73b43b, 0x7411c9, 0x740ba7, 0x7621c5, 0x761ee5, 0x761725, 0x7639d2, 0x76fb65, 0x76f97e, 0x1b34e11, 0x515662, 0x46b321], } Unable to run conformance tests: error container run failed with exit code 1 occurred /home/prow/go/src/sigs.k8s.io/cluster-api/test/e2e/cluster_upgrade.go:232}
```
`
Dec 15 12:41:10.938: INFO: At 2022-12-15 12:31:23 +0000 UTC - event for coredns-74f7f66b6f-s6m5s: {kubelet k8s-upgrade-and-conformance-0v458z-md-0-lcjxn-69fd749f7f-5dlnz} Failed: Failed to pull image "k8s.gcr.io/coredns:v1.8.6": rpc error: code = NotFound desc = failed to pull and unpack image "k8s.gcr.io/coredns:v1.8.6": failed to resolve reference "k8s.gcr.io/coredns:v1.8.6": k8s.gcr.io/coredns:v1.8.6: not found
`
**Anything else you would like to add:**
[Miscellaneous information that will assist in solving the issue.]
/kind bug
[One or more /area label. See https://github.com/kubernetes-sigs/cluster-api/labels?q=area for the list of labels]
**To sum up:**
This is fixed in https://github.com/kubernetes-sigs/cluster-api/pull/7787 but I will keep this open for few days to see the CI signal and close it after. In CAPI release-1.1 branch e2e tests the registry was pinned to ` k8s.gcr.io` as default and removing the registry pinning and leaving it empty solved the CI failure reported in this issue.
Also, please check the comments/suggestions from @sbueringer [here](https://github.com/kubernetes-sigs/cluster-api/issues/7768#issuecomment-1358082144) and [here](https://github.com/kubernetes-sigs/cluster-api/issues/7768#issuecomment-1359379155) to further understand the root cause of the issue and the possible ways to fix it forward in case you are seeing it. | 1.0 | CI failure: capi-e2e-release-1-1-1-23-1-24 is failing consistently - release-1.1 branch https://testgrid.k8s.io/sig-cluster-lifecycle-cluster-api-1.1#capi-e2e-release-1-1-1-23-1-24 job is failing consistently since December 9th.
Logs from the corresponding prow job:
```
capi-e2e: When upgrading a workload cluster using ClusterClass and testing K8S conformance [Conformance] [K8s-Upgrade] Should create and upgrade a workload cluster and run kubetest expand_less | 20m54s
-- | --
{ Failure /home/prow/go/src/sigs.k8s.io/cluster-api/test/e2e/cluster_upgrade.go:115 Failed to run Kubernetes conformance Unexpected error: <*errors.withStack \| 0xc001dd0a80>: { error: <*errors.withMessage \| 0xc0010a6240>{ cause: <*errors.errorString \| 0xc00086ce40>{ s: "error container run failed with exit code 1", }, msg: "Unable to run conformance tests", }, stack: [0x1ad532a, 0x1b1a468, 0x73c37a, 0x73bd45, 0x73b43b, 0x7411c9, 0x740ba7, 0x7621c5, 0x761ee5, 0x761725, 0x7639d2, 0x76fb65, 0x76f97e, 0x1b34e11, 0x515662, 0x46b321], } Unable to run conformance tests: error container run failed with exit code 1 occurred /home/prow/go/src/sigs.k8s.io/cluster-api/test/e2e/cluster_upgrade.go:232}
```
`
Dec 15 12:41:10.938: INFO: At 2022-12-15 12:31:23 +0000 UTC - event for coredns-74f7f66b6f-s6m5s: {kubelet k8s-upgrade-and-conformance-0v458z-md-0-lcjxn-69fd749f7f-5dlnz} Failed: Failed to pull image "k8s.gcr.io/coredns:v1.8.6": rpc error: code = NotFound desc = failed to pull and unpack image "k8s.gcr.io/coredns:v1.8.6": failed to resolve reference "k8s.gcr.io/coredns:v1.8.6": k8s.gcr.io/coredns:v1.8.6: not found
`
**Anything else you would like to add:**
[Miscellaneous information that will assist in solving the issue.]
/kind bug
[One or more /area label. See https://github.com/kubernetes-sigs/cluster-api/labels?q=area for the list of labels]
**To sum up:**
This is fixed in https://github.com/kubernetes-sigs/cluster-api/pull/7787 but I will keep this open for few days to see the CI signal and close it after. In CAPI release-1.1 branch e2e tests the registry was pinned to ` k8s.gcr.io` as default and removing the registry pinning and leaving it empty solved the CI failure reported in this issue.
Also, please check the comments/suggestions from @sbueringer [here](https://github.com/kubernetes-sigs/cluster-api/issues/7768#issuecomment-1358082144) and [here](https://github.com/kubernetes-sigs/cluster-api/issues/7768#issuecomment-1359379155) to further understand the root cause of the issue and the possible ways to fix it forward in case you are seeing it. | test | ci failure capi release is failing consistently release branch job is failing consistently since december logs from the corresponding prow job capi when upgrading a workload cluster using clusterclass and testing conformance should create and upgrade a workload cluster and run kubetest expand less failure home prow go src sigs io cluster api test cluster upgrade go failed to run kubernetes conformance unexpected error error cause s error container run failed with exit code msg unable to run conformance tests stack unable to run conformance tests error container run failed with exit code occurred home prow go src sigs io cluster api test cluster upgrade go dec info at utc event for coredns kubelet upgrade and conformance md lcjxn failed failed to pull image gcr io coredns rpc error code notfound desc failed to pull and unpack image gcr io coredns failed to resolve reference gcr io coredns gcr io coredns not found anything else you would like to add kind bug to sum up this is fixed in but i will keep this open for few days to see the ci signal and close it after in capi release branch tests the registry was pinned to gcr io as default and removing the registry pinning and leaving it empty solved the ci failure reported in this issue also please check the comments suggestions from sbueringer and to further understand the root cause of the issue and the possible ways to fix it forward in case you are seeing it | 1 |
294,784 | 25,404,356,238 | IssuesEvent | 2022-11-22 14:20:16 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | opened | Test failure: KeyringServiceUnitTest.DevWalletPassword | QA/No release-notes/exclude ci-concern bot/type/test bot/channel/nightly bot/platform/android bot/arch/x86-mono bot/branch/v1.47 | Greetings human!
Bad news. `KeyringServiceUnitTest.DevWalletPassword` [failed on android x86-mono nightly v1.47.94](https://ci.brave.com/job/brave-browser-build-android-variant/7400/testReport/junit/(root)/KeyringServiceUnitTest/test___test_unit___DevWalletPassword).
<details>
<summary>Stack trace</summary>
```
[ RUN ] KeyringServiceUnitTest.DevWalletPassword
../../brave/browser/brave_wallet/keyring_service_unittest.cc:4439: Failure
Value of: service.IsLocked()
Actual: true
Expected: false
Stack trace:
[ FAILED ] KeyringServiceUnitTest.DevWalletPassword (882 ms)
[----------] 1 test from KeyringServiceUnitTest (903 ms total)
[----------] Global test environment tear-down
[==========] 1 test from 1 test suite ran. (903 ms total)
[ PASSED ] 0 tests.
[ FAILED ] 1 test, listed below:
[ FAILED ] KeyringServiceUnitTest.DevWalletPassword
Stack Trace:
RELADDR FUNCTION FILE:LINE
031d3792 brave_wallet::KeyringServiceUnitTest_DevWalletPassword_Test::TestBody() ../../brave/browser/brave_wallet/keyring_service_unittest.cc:4439:5
0584cf87 bool testing::internal::HandleExceptionsInMethodIfSupported<testing::internal::UnitTestImpl, bool>(testing::internal::UnitTestImpl*, bool (testing::internal::UnitTestImpl::*)(), char const*) ../../third_party/googletest/src/googletest/src/gtest.cc:0:0
failed
```
</details>
| 1.0 | Test failure: KeyringServiceUnitTest.DevWalletPassword - Greetings human!
Bad news. `KeyringServiceUnitTest.DevWalletPassword` [failed on android x86-mono nightly v1.47.94](https://ci.brave.com/job/brave-browser-build-android-variant/7400/testReport/junit/(root)/KeyringServiceUnitTest/test___test_unit___DevWalletPassword).
<details>
<summary>Stack trace</summary>
```
[ RUN ] KeyringServiceUnitTest.DevWalletPassword
../../brave/browser/brave_wallet/keyring_service_unittest.cc:4439: Failure
Value of: service.IsLocked()
Actual: true
Expected: false
Stack trace:
[ FAILED ] KeyringServiceUnitTest.DevWalletPassword (882 ms)
[----------] 1 test from KeyringServiceUnitTest (903 ms total)
[----------] Global test environment tear-down
[==========] 1 test from 1 test suite ran. (903 ms total)
[ PASSED ] 0 tests.
[ FAILED ] 1 test, listed below:
[ FAILED ] KeyringServiceUnitTest.DevWalletPassword
Stack Trace:
RELADDR FUNCTION FILE:LINE
031d3792 brave_wallet::KeyringServiceUnitTest_DevWalletPassword_Test::TestBody() ../../brave/browser/brave_wallet/keyring_service_unittest.cc:4439:5
0584cf87 bool testing::internal::HandleExceptionsInMethodIfSupported<testing::internal::UnitTestImpl, bool>(testing::internal::UnitTestImpl*, bool (testing::internal::UnitTestImpl::*)(), char const*) ../../third_party/googletest/src/googletest/src/gtest.cc:0:0
failed
```
</details>
| test | test failure keyringserviceunittest devwalletpassword greetings human bad news keyringserviceunittest devwalletpassword stack trace keyringserviceunittest devwalletpassword brave browser brave wallet keyring service unittest cc failure value of service islocked actual true expected false stack trace keyringserviceunittest devwalletpassword ms test from keyringserviceunittest ms total global test environment tear down test from test suite ran ms total tests test listed below keyringserviceunittest devwalletpassword stack trace reladdr function file line brave wallet keyringserviceunittest devwalletpassword test testbody brave browser brave wallet keyring service unittest cc bool testing internal handleexceptionsinmethodifsupported testing internal unittestimpl bool testing internal unittestimpl char const third party googletest src googletest src gtest cc failed | 1 |
16,956 | 3,586,836,658 | IssuesEvent | 2016-01-30 00:21:31 | pink-mist/sbotools | https://api.github.com/repos/pink-mist/sbotools | opened | sboinstall -v errors | bug minor testing | ```sboinstall -v: Undefined subroutine &main::show_version called at /usr/sbin/sboinstall line 67.```
Seems I forgot to import show_version when I did the EXPORT_OK overhaul. This is also true for the other utilities.
Need to add tests for this as well. | 1.0 | sboinstall -v errors - ```sboinstall -v: Undefined subroutine &main::show_version called at /usr/sbin/sboinstall line 67.```
Seems I forgot to import show_version when I did the EXPORT_OK overhaul. This is also true for the other utilities.
Need to add tests for this as well. | test | sboinstall v errors sboinstall v undefined subroutine main show version called at usr sbin sboinstall line seems i forgot to import show version when i did the export ok overhaul this is also true for the other utilities need to add tests for this as well | 1 |
785,207 | 27,604,362,763 | IssuesEvent | 2023-03-09 12:02:28 | pendulum-chain/spacewalk | https://api.github.com/repos/pendulum-chain/spacewalk | opened | Add extrinsics to change the values of the minimum transfer amounts | priority:high | The `issue`, `redeem` and `replace` pallet currently each have a storage item that defines the minimum transfer amount. However, there is no extrinsic to change them after genesis. We should add such extrinsic to each pallet that let's us set this value.
- [ ] Add a new extrinsic to set the minimum transfer amount storage item which is only callable from a root account
- [ ] Add benchmarks and weights for them | 1.0 | Add extrinsics to change the values of the minimum transfer amounts - The `issue`, `redeem` and `replace` pallet currently each have a storage item that defines the minimum transfer amount. However, there is no extrinsic to change them after genesis. We should add such extrinsic to each pallet that let's us set this value.
- [ ] Add a new extrinsic to set the minimum transfer amount storage item which is only callable from a root account
- [ ] Add benchmarks and weights for them | non_test | add extrinsics to change the values of the minimum transfer amounts the issue redeem and replace pallet currently each have a storage item that defines the minimum transfer amount however there is no extrinsic to change them after genesis we should add such extrinsic to each pallet that let s us set this value add a new extrinsic to set the minimum transfer amount storage item which is only callable from a root account add benchmarks and weights for them | 0 |
119,278 | 10,037,272,170 | IssuesEvent | 2019-07-18 12:48:37 | mantidproject/mantid | https://api.github.com/repos/mantidproject/mantid | closed | Unscripted Testing Sample Transmission calculator | Quality: Manual Tests | 1. Read http://www.mantidproject.org/Unscripted_Manual_Testing
1. Comment against this ticket the OS environment you are testing against.
1. Don't spend more than a few hours on the testing as fatigue will kick in.
1. If you find errors in the possibly scant documentation, then correct them.
1. Close the this issue once you are done.
If you find bugs:
* Search to see if an issue already exists
* create an issue if it is new
* Urgent bugs or crashes should by against the current release, and assigned to a developer, then go and talk to the developer if possible.
* Less urgent bugs should be against a subsequent release, and assigned if the correct developer is known.
### Specific Notes:
Make sure that inputs and outputs work sensibly, stress test with some bad inputs (e.g. letters in a numeric input)
See http://docs.mantidproject.org/v3.7.2/interfaces/SampleTransmissionCalculator.html | 1.0 | Unscripted Testing Sample Transmission calculator - 1. Read http://www.mantidproject.org/Unscripted_Manual_Testing
1. Comment against this ticket the OS environment you are testing against.
1. Don't spend more than a few hours on the testing as fatigue will kick in.
1. If you find errors in the possibly scant documentation, then correct them.
1. Close the this issue once you are done.
If you find bugs:
* Search to see if an issue already exists
* create an issue if it is new
* Urgent bugs or crashes should by against the current release, and assigned to a developer, then go and talk to the developer if possible.
* Less urgent bugs should be against a subsequent release, and assigned if the correct developer is known.
### Specific Notes:
Make sure that inputs and outputs work sensibly, stress test with some bad inputs (e.g. letters in a numeric input)
See http://docs.mantidproject.org/v3.7.2/interfaces/SampleTransmissionCalculator.html | test | unscripted testing sample transmission calculator read comment against this ticket the os environment you are testing against don t spend more than a few hours on the testing as fatigue will kick in if you find errors in the possibly scant documentation then correct them close the this issue once you are done if you find bugs search to see if an issue already exists create an issue if it is new urgent bugs or crashes should by against the current release and assigned to a developer then go and talk to the developer if possible less urgent bugs should be against a subsequent release and assigned if the correct developer is known specific notes make sure that inputs and outputs work sensibly stress test with some bad inputs e g letters in a numeric input see | 1 |
798,859 | 28,300,417,905 | IssuesEvent | 2023-04-10 05:17:02 | googleapis/google-cloud-ruby | https://api.github.com/repos/googleapis/google-cloud-ruby | closed | [Nightly CI Failures] Failures detected for google-cloud-gaming-v1 | type: bug priority: p1 nightly failure | At 2023-04-09 09:00:40 UTC, detected failures in google-cloud-gaming-v1 for: yard
report_key_1222c06ae04d9e452af8501ae502831f | 1.0 | [Nightly CI Failures] Failures detected for google-cloud-gaming-v1 - At 2023-04-09 09:00:40 UTC, detected failures in google-cloud-gaming-v1 for: yard
report_key_1222c06ae04d9e452af8501ae502831f | non_test | failures detected for google cloud gaming at utc detected failures in google cloud gaming for yard report key | 0 |
364,018 | 25,478,148,417 | IssuesEvent | 2022-11-25 16:36:09 | PESTILLILAB/bids-connectivity | https://api.github.com/repos/PESTILLILAB/bids-connectivity | closed | Change the BIDS Connectivity Workshop Picture to BIDS Connectivity Project | documentation enhancement | I would like to update the image we have now "BIDS Connectivity Workshop" To represent the new goal of the website -> "BIDS Connectivity Project"
Can you please take a look?
@PeerHerholz | 1.0 | Change the BIDS Connectivity Workshop Picture to BIDS Connectivity Project - I would like to update the image we have now "BIDS Connectivity Workshop" To represent the new goal of the website -> "BIDS Connectivity Project"
Can you please take a look?
@PeerHerholz | non_test | change the bids connectivity workshop picture to bids connectivity project i would like to update the image we have now bids connectivity workshop to represent the new goal of the website bids connectivity project can you please take a look peerherholz | 0 |
70,251 | 8,515,246,610 | IssuesEvent | 2018-10-31 20:58:50 | guylepage3/lepage.cc | https://api.github.com/repos/guylepage3/lepage.cc | opened | Define vertical spacing and rhythm | coding design ui | **Description**
Define vertical spacing and rhythm
**Reference**
See [#58 Define typography](https://github.com/guylepage3/lepage.cc/issues/58) | 1.0 | Define vertical spacing and rhythm - **Description**
Define vertical spacing and rhythm
**Reference**
See [#58 Define typography](https://github.com/guylepage3/lepage.cc/issues/58) | non_test | define vertical spacing and rhythm description define vertical spacing and rhythm reference see | 0 |
80,627 | 7,752,337,193 | IssuesEvent | 2018-05-30 19:57:50 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | opened | String and associated tests should be run with -XX:+CompactStrings | comp:test | In #1913 @fjeremic suggests: 'we should run the entire JCL_TEST_Java-Lang with compact strings enabled explicitly and disabled explicitly. Or at the very least run all the String, StringBuffer, StringBuilder, Integer, Long, and StringCoding tests in both variations.'
Although I think running the entire JCL_TEST_Java-Lang again would add too much overhead to the sanity testing. | 1.0 | String and associated tests should be run with -XX:+CompactStrings - In #1913 @fjeremic suggests: 'we should run the entire JCL_TEST_Java-Lang with compact strings enabled explicitly and disabled explicitly. Or at the very least run all the String, StringBuffer, StringBuilder, Integer, Long, and StringCoding tests in both variations.'
Although I think running the entire JCL_TEST_Java-Lang again would add too much overhead to the sanity testing. | test | string and associated tests should be run with xx compactstrings in fjeremic suggests we should run the entire jcl test java lang with compact strings enabled explicitly and disabled explicitly or at the very least run all the string stringbuffer stringbuilder integer long and stringcoding tests in both variations although i think running the entire jcl test java lang again would add too much overhead to the sanity testing | 1 |
188,659 | 15,167,127,352 | IssuesEvent | 2021-02-12 17:19:36 | cpauvert/in-phi-luence | https://api.github.com/repos/cpauvert/in-phi-luence | closed | Fix creation date of data sources | bug documentation | Perhaps with a additional tabs after the details of the influences that indicate the source of the data, how and how recent it is.
| 1.0 | Fix creation date of data sources - Perhaps with a additional tabs after the details of the influences that indicate the source of the data, how and how recent it is.
| non_test | fix creation date of data sources perhaps with a additional tabs after the details of the influences that indicate the source of the data how and how recent it is | 0 |
70,969 | 30,765,712,229 | IssuesEvent | 2023-07-30 09:16:28 | femiwiki/femiwiki | https://api.github.com/repos/femiwiki/femiwiki | closed | NET::ERR_CERT_DATE_INVALID | service disruption | 디스코드에서 보고됨
`nomad alloc logs -tail -n 100 -job -stderr http | grep acme`:
```json
{
"level": "error",
"ts": 1690684058.6517003,
"logger": "tls.renew",
"msg": "could not get certificate from issuer",
"identifier": "*.femiwiki.com",
"issuer": "acme-v02.api.letsencrypt.org-directory",
"error": "[*.femiwiki.com] solving challenges: presenting for challenge: adding temporary record for zone femiwiki.com.: Error unquoting TXT/SPF record: invalid syntax (order=https://acme-staging-v02.api.letsencrypt.org/acme/order/19158926/10020220564) (ca=https://acme-staging-v02.api.letsencrypt.org/directory)"
}
```
https://caddy.community/t/error-unquoting-txt-spf-record/17572/2 | 1.0 | NET::ERR_CERT_DATE_INVALID - 디스코드에서 보고됨
`nomad alloc logs -tail -n 100 -job -stderr http | grep acme`:
```json
{
"level": "error",
"ts": 1690684058.6517003,
"logger": "tls.renew",
"msg": "could not get certificate from issuer",
"identifier": "*.femiwiki.com",
"issuer": "acme-v02.api.letsencrypt.org-directory",
"error": "[*.femiwiki.com] solving challenges: presenting for challenge: adding temporary record for zone femiwiki.com.: Error unquoting TXT/SPF record: invalid syntax (order=https://acme-staging-v02.api.letsencrypt.org/acme/order/19158926/10020220564) (ca=https://acme-staging-v02.api.letsencrypt.org/directory)"
}
```
https://caddy.community/t/error-unquoting-txt-spf-record/17572/2 | non_test | net err cert date invalid 디스코드에서 보고됨 nomad alloc logs tail n job stderr http grep acme json level error ts logger tls renew msg could not get certificate from issuer identifier femiwiki com issuer acme api letsencrypt org directory error solving challenges presenting for challenge adding temporary record for zone femiwiki com error unquoting txt spf record invalid syntax order ca | 0 |
293,501 | 25,298,551,033 | IssuesEvent | 2022-11-17 08:58:59 | jdi-testing/jdi-light | https://api.github.com/repos/jdi-testing/jdi-light | closed | Update test-site: element Icon | TestSite Vuetify | Need to add testable features:
- [x] accessibility (aria-hidden)
- [x] theme (dark)
- [x] enabled/disabled | 1.0 | Update test-site: element Icon - Need to add testable features:
- [x] accessibility (aria-hidden)
- [x] theme (dark)
- [x] enabled/disabled | test | update test site element icon need to add testable features accessibility aria hidden theme dark enabled disabled | 1 |
39,125 | 2,851,199,887 | IssuesEvent | 2015-06-01 03:44:32 | syl20bnr/spacemacs | https://api.github.com/repos/syl20bnr/spacemacs | closed | ```SPC-/``` executes Tcl parser tools | bug :-( Fixed in current `release-x.x` Fixed in `develop` High Priority Hotfix Required | Tcl installs parser tools to ```/usr/bin/pt```. Since spacemacs now checks for the executable ```pt``` to exist and prefers it to the other search options, ```SPC-/``` is broken for any Linux distribution that installs Tcl, or any user that must install it due to other packages that require it, such as the "expect" command. | 1.0 | ```SPC-/``` executes Tcl parser tools - Tcl installs parser tools to ```/usr/bin/pt```. Since spacemacs now checks for the executable ```pt``` to exist and prefers it to the other search options, ```SPC-/``` is broken for any Linux distribution that installs Tcl, or any user that must install it due to other packages that require it, such as the "expect" command. | non_test | spc executes tcl parser tools tcl installs parser tools to usr bin pt since spacemacs now checks for the executable pt to exist and prefers it to the other search options spc is broken for any linux distribution that installs tcl or any user that must install it due to other packages that require it such as the expect command | 0 |
81,550 | 15,630,078,244 | IssuesEvent | 2021-03-22 01:17:23 | ignatandrei/stankins | https://api.github.com/repos/ignatandrei/stankins | opened | CVE-2021-23337 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.0.2.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash-2.4.2.tgz</b>, <b>lodash-4.6.1.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/jsdoctypeparser/node_modules/lodash/package.json,stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/xmlbuilder/node_modules/lodash/package.json,stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/grunt-contrib-csslint/node_modules/lodash/package.json,stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/jscs/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jscs-3.0.1.tgz (Root Library)
- jscs-3.0.7.tgz
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/fg-lodash/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-saucelabs-9.0.1.tgz (Root Library)
- requestretry-1.9.1.tgz
- fg-lodash-0.0.2.tgz
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.6.1.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.6.1.tgz">https://registry.npmjs.org/lodash/-/lodash-4.6.1.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/grunt-jscs/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jscs-3.0.1.tgz (Root Library)
- :x: **lodash-4.6.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: stankins/stankinsv2/solution/StankinsV2/StankinsAliveAngular/package.json</p>
<p>Path to vulnerable library: stankins/stankinsv2/solution/StankinsV2/StankinsAliveAngular/node_modules/lodash/package.json,stankins/stankinsv2/solution/StankinsV2/StankinsElectron/node_modules/lodash/package.json,stankins/stankinsv2/solution/StankinsV2/StankinsDataWebAngular/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- karma-3.0.0.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-23337 (High) detected in multiple libraries - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-1.0.2.tgz</b>, <b>lodash-3.10.1.tgz</b>, <b>lodash-2.4.2.tgz</b>, <b>lodash-4.6.1.tgz</b>, <b>lodash-4.17.11.tgz</b></p></summary>
<p>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- gulp-3.9.1.tgz (Root Library)
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/jsdoctypeparser/node_modules/lodash/package.json,stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/xmlbuilder/node_modules/lodash/package.json,stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/grunt-contrib-csslint/node_modules/lodash/package.json,stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/jscs/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jscs-3.0.1.tgz (Root Library)
- jscs-3.0.7.tgz
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/fg-lodash/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-saucelabs-9.0.1.tgz (Root Library)
- requestretry-1.9.1.tgz
- fg-lodash-0.0.2.tgz
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.6.1.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.6.1.tgz">https://registry.npmjs.org/lodash/-/lodash-4.6.1.tgz</a></p>
<p>Path to dependency file: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/package.json</p>
<p>Path to vulnerable library: stankins/stankinsV1/HtmlGenerator/wwwroot/lib/bootstrap/node_modules/grunt-jscs/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-jscs-3.0.1.tgz (Root Library)
- :x: **lodash-4.6.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: stankins/stankinsv2/solution/StankinsV2/StankinsAliveAngular/package.json</p>
<p>Path to vulnerable library: stankins/stankinsv2/solution/StankinsV2/StankinsAliveAngular/node_modules/lodash/package.json,stankins/stankinsv2/solution/StankinsV2/StankinsElectron/node_modules/lodash/package.json,stankins/stankinsv2/solution/StankinsV2/StankinsDataWebAngular/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- karma-3.0.0.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file stankins htmlgenerator package json path to vulnerable library stankins htmlgenerator node modules lodash package json dependency hierarchy gulp tgz root library vinyl fs tgz glob watcher tgz gaze tgz globule tgz x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file stankins htmlgenerator wwwroot lib bootstrap package json path to vulnerable library stankins htmlgenerator wwwroot lib bootstrap node modules jsdoctypeparser node modules lodash package json stankins htmlgenerator wwwroot lib bootstrap node modules xmlbuilder node modules lodash package json stankins htmlgenerator wwwroot lib bootstrap node modules grunt contrib csslint node modules lodash package json stankins htmlgenerator wwwroot lib bootstrap node modules jscs node modules lodash package json dependency hierarchy grunt jscs tgz root library jscs tgz x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file stankins htmlgenerator wwwroot lib bootstrap package json path to vulnerable library stankins htmlgenerator wwwroot lib bootstrap node modules fg lodash node modules lodash package json dependency hierarchy grunt saucelabs tgz root library requestretry tgz fg lodash tgz x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file stankins htmlgenerator wwwroot lib bootstrap package json path to vulnerable library stankins htmlgenerator wwwroot lib bootstrap node modules grunt jscs node modules lodash package json dependency hierarchy grunt jscs tgz root library x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file stankins solution stankinsaliveangular package json path to vulnerable library stankins solution stankinsaliveangular node modules lodash package json stankins solution stankinselectron node modules lodash package json stankins solution stankinsdatawebangular node modules lodash package json dependency hierarchy karma tgz root library x lodash tgz vulnerable library found in base branch master vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash step up your open source security game with whitesource | 0 |
349,382 | 31,797,153,889 | IssuesEvent | 2023-09-13 08:45:43 | kyverno/kyverno | https://api.github.com/repos/kyverno/kyverno | closed | [Bug] [CLI] Testing a generate rule for a custom resource fails | bug type:cli end user created cli:test | ### Kyverno CLI Version
1.10.1
### Description
Kyverno test for a generate clone policy cannot find resource when cloning a custom resource
### Steps to reproduce
1. Write policy to clone a custom resource
2. Write test to test the policy
3. run `kyverno test .`
4. Receive errors the resource cannot be found
kyverno-test.yaml
```yaml
name: generate-tests
policies:
- clonePullSecretToNs.yaml
resources:
- namespace.yaml
results:
- policy: sync-pull-image-secrets
rule: sync-image-pull-secret
kind: Namespace
resource: test-ns
generatedResource: generatedExternalSecret.yaml
cloneSourceResource: cloneExternalSecret.yaml
result: pass
```
namespace.yaml
```yaml
apiVersion: v1
kind: Namespace
metadata:
name: test-ns
```
generatedExternalSecret.yaml
```yaml
apiVersion: external-secrets.io/v1beta1
kind: ExternalSecret
metadata:
name: devops-docker-pull-image-secret
namespace: test-ns
spec:
data:
- remoteRef:
conversionStrategy: Default
decodingStrategy: None
key: secrets/devops-docker-pull-image-secret
property: dockerconfigjson
secretKey: .dockerconfigjson
refreshInterval: 10s
secretStoreRef:
kind: ClusterSecretStore
name: vault-backend
target:
creationPolicy: Owner
deletionPolicy: Retain
name: devops-docker-pull-image-secret
```
cloneExternalSecret.yaml
```yaml
apiVersion: external-secrets.io/v1beta1
kind: ExternalSecret
metadata:
name: devops-docker-pull-image-secret
namespace: default
spec:
data:
- remoteRef:
conversionStrategy: Default
decodingStrategy: None
key: secrets/devops-docker-pull-image-secret
property: dockerconfigjson
secretKey: .dockerconfigjson
refreshInterval: 10s
secretStoreRef:
kind: ClusterSecretStore
name: vault-backend
target:
creationPolicy: Owner
deletionPolicy: Retain
name: devops-docker-pull-image-secret
```
clonePullSecretToNs.yaml
```yaml
apiVersion: kyverno.io/v1
kind: ClusterPolicy
metadata:
name: sync-pull-image-secrets
annotations:
policies.kyverno.io/title: Sync pull image secrets
policies.kyverno.io/category: Secrets
policies.kyverno.io/severity: low
policies.kyverno.io/subject: secret
policies.kyverno.io/minversion: 1.6.0
policies.kyverno.io/description: >-
Copies the pullSecret ESO resources into all namespaces
this will mean we're never missing the secret when we need it.
spec:
rules:
- name: sync-image-pull-secret
match:
any:
- resources:
kinds:
- Namespace
generate:
apiVersion: external-secrets.io/v1beta1
kind: ExternalSecret
name: devops-docker-pull-image-secret
namespace: "{{request.object.metadata.name}}"
synchronize: true
clone:
namespace: default
name: devops-docker-pull-image-secret
```
### Expected behavior
Test should work for custom resource and pass
### Screenshots
_No response_
### Kyverno logs
```shell
I0719 13:56:47.924491 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.authentication.v1.TokenRequest" "reason"="gvk not found by the given definition name io.k8s.api.authentication.v1.TokenRequest, [v1/TokenRequest]"
I0719 13:56:47.924590 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.autoscaling.v1.Scale" "reason"="gvk not found by the given definition name io.k8s.api.autoscaling.v1.Scale, [v1/Scale apps/v1/Scale apps/v1/Scale apps/v1/Scale]"
I0719 13:56:47.924664 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.batch.v1.CronJob" "reason"="gvk not found by the given definition name io.k8s.api.batch.v1.CronJob, [batch/v1beta1/CronJob]"
I0719 13:56:47.924827 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.discovery.v1.EndpointSlice" "reason"="gvk not found by the given definition name io.k8s.api.discovery.v1.EndpointSlice, [discovery.k8s.io/v1beta1/EndpointSlice]"
I0719 13:56:47.924900 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.node.v1alpha1.RuntimeClass" "reason"="gvk not found by the given definition name io.k8s.api.node.v1alpha1.RuntimeClass, [node.k8s.io/v1/RuntimeClass node.k8s.io/v1beta1/RuntimeClass]"
I0719 13:56:47.924918 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.policy.v1.PodDisruptionBudget" "reason"="gvk not found by the given definition name io.k8s.api.policy.v1.PodDisruptionBudget, [policy/v1beta1/PodDisruptionBudget]"
I0719 13:56:47.924929 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.policy.v1beta1.Eviction" "reason"="gvk not found by the given definition name io.k8s.api.policy.v1beta1.Eviction, [v1/Eviction]"
I0719 13:56:47.924961 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.ClusterRole" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.ClusterRole, [rbac.authorization.k8s.io/v1/ClusterRole rbac.authorization.k8s.io/v1beta1/ClusterRole]"
I0719 13:56:47.924971 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.ClusterRoleBinding" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.ClusterRoleBinding, [rbac.authorization.k8s.io/v1/ClusterRoleBinding rbac.authorization.k8s.io/v1beta1/ClusterRoleBinding]"
I0719 13:56:47.924982 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.Role" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.Role, [rbac.authorization.k8s.io/v1/Role rbac.authorization.k8s.io/v1beta1/Role]"
I0719 13:56:47.924991 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.RoleBinding" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.RoleBinding, [rbac.authorization.k8s.io/v1/RoleBinding rbac.authorization.k8s.io/v1beta1/RoleBinding]"
I0719 13:56:47.925049 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.scheduling.v1alpha1.PriorityClass" "reason"="gvk not found by the given definition name io.k8s.api.scheduling.v1alpha1.PriorityClass, [scheduling.k8s.io/v1/PriorityClass scheduling.k8s.io/v1beta1/PriorityClass]"
I0719 13:56:47.925075 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.storage.v1.TokenRequest" "reason"="gvk not found by the given definition name io.k8s.api.storage.v1.TokenRequest, [v1/TokenRequest]"
I0719 13:56:47.925092 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.storage.v1alpha1.VolumeAttachment" "reason"="gvk not found by the given definition name io.k8s.api.storage.v1alpha1.VolumeAttachment, [storage.k8s.io/v1/VolumeAttachment storage.k8s.io/v1beta1/VolumeAttachment]"
I0719 13:56:47.925114 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.storage.v1beta1.TokenRequest" "reason"="gvk not found by the given definition name io.k8s.api.storage.v1beta1.TokenRequest, [v1/TokenRequest]"
Executing generate-tests...I0719 13:56:47.944203 97043 common.go:344] "msg"="Defaulting request.operation to CREATE"
I0719 13:56:47.944235 97043 common.go:108] "msg"="reading policies" "path"="../../policies/generate/clonePullSecretToNs.yaml"
I0719 13:56:47.947392 97043 common.go:200] "msg"="read policies" "errors"=0 "policies"=1
I0719 13:56:47.948308 97043 common.go:938] "msg"="mutated Policy:" "{\"kind\":\"ClusterPolicy\",\"apiVersion\":\"kyverno.io/v1\",\"metadata\":{\"name\":\"sync-pull-image-secrets\",\"creationTimestamp\":null,\"annotations\":{\"policies.kyverno.io/category\":\"Secrets\",\"policies.kyverno.io/description\":\"Copies the pullSecret ESO resources into all namespaces this will mean we're never missing the secret when we need it. \",\"policies.kyverno.io/minversion\":\"1.6.0\",\"policies.kyverno.io/severity\":\"low\",\"policies.kyverno.io/subject\":\"secret\",\"policies.kyverno.io/title\":\"Sync pull image secrets\"}},\"spec\":{\"rules\":[{\"name\":\"sync-image-pull-secret\",\"match\":{\"any\":[{\"resources\":{\"kinds\":[\"Namespace\"]}}],\"resources\":{}},\"exclude\":{\"resources\":{}},\"mutate\":{},\"validate\":{},\"generate\":{\"apiVersion\":\"external-secrets.io/v1beta1\",\"kind\":\"ExternalSecret\",\"namespace\":\"{{request.object.metadata.name}}\",\"name\":\"devops-docker-pull-image-secret\",\"synchronize\":true,\"clone\":{\"namespace\":\"default\",\"name\":\"devops-docker-pull-image-secret\"},\"cloneList\":{}}}]},\"status\":{\"ready\":false,\"autogen\":{},\"rulecount\":{\"validate\":0,\"generate\":0,\"mutate\":0,\"verifyimages\":0}}}"="(MISSING)"
applying 1 policy to 1 resource...
I0719 13:56:47.952246 97043 vars.go:398] "msg"="variable substituted" "path"="/generate/namespace" "value"=null "variable"="{{request.object.metadata.name}}"
I0719 13:56:47.952892 97043 validate.go:174] "msg"="name & namespace uses variables, so cannot be resolved. Skipping Auth Checks."
I0719 13:56:47.953056 97043 common.go:424] "msg"="applying policy on resource" "policy"="sync-pull-image-secrets" "resource"="default/Namespace/test-ns"
I0719 13:56:47.953880 97043 mutation.go:39] EngineMutate "msg"="start mutate policy processing" "kind"="Namespace" "name"="test-ns" "namespace"="default" "policy"="sync-pull-image-secrets" "startTime"="2023-07-19T13:56:47.953536+01:00"
I0719 13:56:47.953942 97043 mutation.go:379] EngineMutate "msg"="finished processing policy" "kind"="Namespace" "mutationRulesApplied"=0 "name"="test-ns" "namespace"="default" "policy"="sync-pull-image-secrets" "processingTime"="364.358µs"
I0719 13:56:47.954489 97043 imageVerify.go:83] EngineVerifyImages "msg"="processed image verification rules" "applied"=0 "kind"="Namespace" "name"="test-ns" "namespace"="default" "policy"="sync-pull-image-secrets" "successful"=true "time"="235.696µs"
I0719 13:56:47.957541 97043 vars.go:398] "msg"="variable substituted" "path"="/generate/namespace" "value"="test-ns" "variable"="{{request.object.metadata.name}}"
E0719 13:56:47.958072 97043 generate.go:460] "msg"="failed to generate resource" "error"="source resource external-secrets.io/v1beta1 ExternalSecret/default/devops-docker-pull-image-secret not found. \"devops-docker-pull-image-secret\" not found" "genAPIVersion"="external-secrets.io/v1beta1" "genKind"="ExternalSecret" "genName"="devops-docker-pull-image-secret" "genNamespace"="test-ns" "mode"="SKIP"
E0719 13:56:47.958097 97043 generate.go:364] "msg"="failed to apply generate rule" "error"="source resource external-secrets.io/v1beta1 ExternalSecret/default/devops-docker-pull-image-secret not found. \"devops-docker-pull-image-secret\" not found" "policy"="sync-pull-image-secrets" "resource"="test-ns" "rule"="sync-image-pull-secret" "suggestion"="users need to grant Kyverno's service account additional privileges"
E0719 13:56:47.958112 97043 common.go:539] "msg"="failed to apply generate policy" "error"="source resource external-secrets.io/v1beta1 ExternalSecret/default/devops-docker-pull-image-secret not found. \"devops-docker-pull-image-secret\" not found"
I0719 13:56:47.958754 97043 validate.go:43] "msg"="Pattern and resource have different structures." "current"="<nil>" "expected"="map[string]interface {}" "path"="/spec/"
I0719 13:56:47.959105 97043 test_command.go:702] "msg"="generatedResource mismatch" "error"="pattern and resource have different structures. Path: /spec/. Expected map[string]interface {}, found <nil>"
I0719 13:56:47.959155 97043 test_command.go:1092] "msg"="result mismatch" "expected"="pass" "key"="sync-pull-image-secrets-sync-image-pull-secret-Namespace-test-ns" "received"="fail"
```
### Slack discussion
https://kubernetes.slack.com/archives/CLGR9BJU9/p1689770650790889
### Troubleshooting
- [X] I have read and followed the [troubleshooting guide](https://kyverno.io/docs/troubleshooting/).
- [X] I have searched other issues in this repository and mine is not recorded. | 1.0 | [Bug] [CLI] Testing a generate rule for a custom resource fails - ### Kyverno CLI Version
1.10.1
### Description
Kyverno test for a generate clone policy cannot find resource when cloning a custom resource
### Steps to reproduce
1. Write policy to clone a custom resource
2. Write test to test the policy
3. run `kyverno test .`
4. Receive errors the resource cannot be found
kyverno-test.yaml
```yaml
name: generate-tests
policies:
- clonePullSecretToNs.yaml
resources:
- namespace.yaml
results:
- policy: sync-pull-image-secrets
rule: sync-image-pull-secret
kind: Namespace
resource: test-ns
generatedResource: generatedExternalSecret.yaml
cloneSourceResource: cloneExternalSecret.yaml
result: pass
```
namespace.yaml
```yaml
apiVersion: v1
kind: Namespace
metadata:
name: test-ns
```
generatedExternalSecret.yaml
```yaml
apiVersion: external-secrets.io/v1beta1
kind: ExternalSecret
metadata:
name: devops-docker-pull-image-secret
namespace: test-ns
spec:
data:
- remoteRef:
conversionStrategy: Default
decodingStrategy: None
key: secrets/devops-docker-pull-image-secret
property: dockerconfigjson
secretKey: .dockerconfigjson
refreshInterval: 10s
secretStoreRef:
kind: ClusterSecretStore
name: vault-backend
target:
creationPolicy: Owner
deletionPolicy: Retain
name: devops-docker-pull-image-secret
```
cloneExternalSecret.yaml
```yaml
apiVersion: external-secrets.io/v1beta1
kind: ExternalSecret
metadata:
name: devops-docker-pull-image-secret
namespace: default
spec:
data:
- remoteRef:
conversionStrategy: Default
decodingStrategy: None
key: secrets/devops-docker-pull-image-secret
property: dockerconfigjson
secretKey: .dockerconfigjson
refreshInterval: 10s
secretStoreRef:
kind: ClusterSecretStore
name: vault-backend
target:
creationPolicy: Owner
deletionPolicy: Retain
name: devops-docker-pull-image-secret
```
clonePullSecretToNs.yaml
```yaml
apiVersion: kyverno.io/v1
kind: ClusterPolicy
metadata:
name: sync-pull-image-secrets
annotations:
policies.kyverno.io/title: Sync pull image secrets
policies.kyverno.io/category: Secrets
policies.kyverno.io/severity: low
policies.kyverno.io/subject: secret
policies.kyverno.io/minversion: 1.6.0
policies.kyverno.io/description: >-
Copies the pullSecret ESO resources into all namespaces
this will mean we're never missing the secret when we need it.
spec:
rules:
- name: sync-image-pull-secret
match:
any:
- resources:
kinds:
- Namespace
generate:
apiVersion: external-secrets.io/v1beta1
kind: ExternalSecret
name: devops-docker-pull-image-secret
namespace: "{{request.object.metadata.name}}"
synchronize: true
clone:
namespace: default
name: devops-docker-pull-image-secret
```
### Expected behavior
Test should work for custom resource and pass
### Screenshots
_No response_
### Kyverno logs
```shell
I0719 13:56:47.924491 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.authentication.v1.TokenRequest" "reason"="gvk not found by the given definition name io.k8s.api.authentication.v1.TokenRequest, [v1/TokenRequest]"
I0719 13:56:47.924590 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.autoscaling.v1.Scale" "reason"="gvk not found by the given definition name io.k8s.api.autoscaling.v1.Scale, [v1/Scale apps/v1/Scale apps/v1/Scale apps/v1/Scale]"
I0719 13:56:47.924664 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.batch.v1.CronJob" "reason"="gvk not found by the given definition name io.k8s.api.batch.v1.CronJob, [batch/v1beta1/CronJob]"
I0719 13:56:47.924827 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.discovery.v1.EndpointSlice" "reason"="gvk not found by the given definition name io.k8s.api.discovery.v1.EndpointSlice, [discovery.k8s.io/v1beta1/EndpointSlice]"
I0719 13:56:47.924900 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.node.v1alpha1.RuntimeClass" "reason"="gvk not found by the given definition name io.k8s.api.node.v1alpha1.RuntimeClass, [node.k8s.io/v1/RuntimeClass node.k8s.io/v1beta1/RuntimeClass]"
I0719 13:56:47.924918 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.policy.v1.PodDisruptionBudget" "reason"="gvk not found by the given definition name io.k8s.api.policy.v1.PodDisruptionBudget, [policy/v1beta1/PodDisruptionBudget]"
I0719 13:56:47.924929 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.policy.v1beta1.Eviction" "reason"="gvk not found by the given definition name io.k8s.api.policy.v1beta1.Eviction, [v1/Eviction]"
I0719 13:56:47.924961 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.ClusterRole" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.ClusterRole, [rbac.authorization.k8s.io/v1/ClusterRole rbac.authorization.k8s.io/v1beta1/ClusterRole]"
I0719 13:56:47.924971 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.ClusterRoleBinding" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.ClusterRoleBinding, [rbac.authorization.k8s.io/v1/ClusterRoleBinding rbac.authorization.k8s.io/v1beta1/ClusterRoleBinding]"
I0719 13:56:47.924982 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.Role" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.Role, [rbac.authorization.k8s.io/v1/Role rbac.authorization.k8s.io/v1beta1/Role]"
I0719 13:56:47.924991 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.rbac.v1alpha1.RoleBinding" "reason"="gvk not found by the given definition name io.k8s.api.rbac.v1alpha1.RoleBinding, [rbac.authorization.k8s.io/v1/RoleBinding rbac.authorization.k8s.io/v1beta1/RoleBinding]"
I0719 13:56:47.925049 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.scheduling.v1alpha1.PriorityClass" "reason"="gvk not found by the given definition name io.k8s.api.scheduling.v1alpha1.PriorityClass, [scheduling.k8s.io/v1/PriorityClass scheduling.k8s.io/v1beta1/PriorityClass]"
I0719 13:56:47.925075 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.storage.v1.TokenRequest" "reason"="gvk not found by the given definition name io.k8s.api.storage.v1.TokenRequest, [v1/TokenRequest]"
I0719 13:56:47.925092 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.storage.v1alpha1.VolumeAttachment" "reason"="gvk not found by the given definition name io.k8s.api.storage.v1alpha1.VolumeAttachment, [storage.k8s.io/v1/VolumeAttachment storage.k8s.io/v1beta1/VolumeAttachment]"
I0719 13:56:47.925114 97043 manager.go:179] "msg"="unable to cache OpenAPISchema" "definitionName"="io.k8s.api.storage.v1beta1.TokenRequest" "reason"="gvk not found by the given definition name io.k8s.api.storage.v1beta1.TokenRequest, [v1/TokenRequest]"
Executing generate-tests...I0719 13:56:47.944203 97043 common.go:344] "msg"="Defaulting request.operation to CREATE"
I0719 13:56:47.944235 97043 common.go:108] "msg"="reading policies" "path"="../../policies/generate/clonePullSecretToNs.yaml"
I0719 13:56:47.947392 97043 common.go:200] "msg"="read policies" "errors"=0 "policies"=1
I0719 13:56:47.948308 97043 common.go:938] "msg"="mutated Policy:" "{\"kind\":\"ClusterPolicy\",\"apiVersion\":\"kyverno.io/v1\",\"metadata\":{\"name\":\"sync-pull-image-secrets\",\"creationTimestamp\":null,\"annotations\":{\"policies.kyverno.io/category\":\"Secrets\",\"policies.kyverno.io/description\":\"Copies the pullSecret ESO resources into all namespaces this will mean we're never missing the secret when we need it. \",\"policies.kyverno.io/minversion\":\"1.6.0\",\"policies.kyverno.io/severity\":\"low\",\"policies.kyverno.io/subject\":\"secret\",\"policies.kyverno.io/title\":\"Sync pull image secrets\"}},\"spec\":{\"rules\":[{\"name\":\"sync-image-pull-secret\",\"match\":{\"any\":[{\"resources\":{\"kinds\":[\"Namespace\"]}}],\"resources\":{}},\"exclude\":{\"resources\":{}},\"mutate\":{},\"validate\":{},\"generate\":{\"apiVersion\":\"external-secrets.io/v1beta1\",\"kind\":\"ExternalSecret\",\"namespace\":\"{{request.object.metadata.name}}\",\"name\":\"devops-docker-pull-image-secret\",\"synchronize\":true,\"clone\":{\"namespace\":\"default\",\"name\":\"devops-docker-pull-image-secret\"},\"cloneList\":{}}}]},\"status\":{\"ready\":false,\"autogen\":{},\"rulecount\":{\"validate\":0,\"generate\":0,\"mutate\":0,\"verifyimages\":0}}}"="(MISSING)"
applying 1 policy to 1 resource...
I0719 13:56:47.952246 97043 vars.go:398] "msg"="variable substituted" "path"="/generate/namespace" "value"=null "variable"="{{request.object.metadata.name}}"
I0719 13:56:47.952892 97043 validate.go:174] "msg"="name & namespace uses variables, so cannot be resolved. Skipping Auth Checks."
I0719 13:56:47.953056 97043 common.go:424] "msg"="applying policy on resource" "policy"="sync-pull-image-secrets" "resource"="default/Namespace/test-ns"
I0719 13:56:47.953880 97043 mutation.go:39] EngineMutate "msg"="start mutate policy processing" "kind"="Namespace" "name"="test-ns" "namespace"="default" "policy"="sync-pull-image-secrets" "startTime"="2023-07-19T13:56:47.953536+01:00"
I0719 13:56:47.953942 97043 mutation.go:379] EngineMutate "msg"="finished processing policy" "kind"="Namespace" "mutationRulesApplied"=0 "name"="test-ns" "namespace"="default" "policy"="sync-pull-image-secrets" "processingTime"="364.358µs"
I0719 13:56:47.954489 97043 imageVerify.go:83] EngineVerifyImages "msg"="processed image verification rules" "applied"=0 "kind"="Namespace" "name"="test-ns" "namespace"="default" "policy"="sync-pull-image-secrets" "successful"=true "time"="235.696µs"
I0719 13:56:47.957541 97043 vars.go:398] "msg"="variable substituted" "path"="/generate/namespace" "value"="test-ns" "variable"="{{request.object.metadata.name}}"
E0719 13:56:47.958072 97043 generate.go:460] "msg"="failed to generate resource" "error"="source resource external-secrets.io/v1beta1 ExternalSecret/default/devops-docker-pull-image-secret not found. \"devops-docker-pull-image-secret\" not found" "genAPIVersion"="external-secrets.io/v1beta1" "genKind"="ExternalSecret" "genName"="devops-docker-pull-image-secret" "genNamespace"="test-ns" "mode"="SKIP"
E0719 13:56:47.958097 97043 generate.go:364] "msg"="failed to apply generate rule" "error"="source resource external-secrets.io/v1beta1 ExternalSecret/default/devops-docker-pull-image-secret not found. \"devops-docker-pull-image-secret\" not found" "policy"="sync-pull-image-secrets" "resource"="test-ns" "rule"="sync-image-pull-secret" "suggestion"="users need to grant Kyverno's service account additional privileges"
E0719 13:56:47.958112 97043 common.go:539] "msg"="failed to apply generate policy" "error"="source resource external-secrets.io/v1beta1 ExternalSecret/default/devops-docker-pull-image-secret not found. \"devops-docker-pull-image-secret\" not found"
I0719 13:56:47.958754 97043 validate.go:43] "msg"="Pattern and resource have different structures." "current"="<nil>" "expected"="map[string]interface {}" "path"="/spec/"
I0719 13:56:47.959105 97043 test_command.go:702] "msg"="generatedResource mismatch" "error"="pattern and resource have different structures. Path: /spec/. Expected map[string]interface {}, found <nil>"
I0719 13:56:47.959155 97043 test_command.go:1092] "msg"="result mismatch" "expected"="pass" "key"="sync-pull-image-secrets-sync-image-pull-secret-Namespace-test-ns" "received"="fail"
```
### Slack discussion
https://kubernetes.slack.com/archives/CLGR9BJU9/p1689770650790889
### Troubleshooting
- [X] I have read and followed the [troubleshooting guide](https://kyverno.io/docs/troubleshooting/).
- [X] I have searched other issues in this repository and mine is not recorded. | test | testing a generate rule for a custom resource fails kyverno cli version description kyverno test for a generate clone policy cannot find resource when cloning a custom resource steps to reproduce write policy to clone a custom resource write test to test the policy run kyverno test receive errors the resource cannot be found kyverno test yaml yaml name generate tests policies clonepullsecrettons yaml resources namespace yaml results policy sync pull image secrets rule sync image pull secret kind namespace resource test ns generatedresource generatedexternalsecret yaml clonesourceresource cloneexternalsecret yaml result pass namespace yaml yaml apiversion kind namespace metadata name test ns generatedexternalsecret yaml yaml apiversion external secrets io kind externalsecret metadata name devops docker pull image secret namespace test ns spec data remoteref conversionstrategy default decodingstrategy none key secrets devops docker pull image secret property dockerconfigjson secretkey dockerconfigjson refreshinterval secretstoreref kind clustersecretstore name vault backend target creationpolicy owner deletionpolicy retain name devops docker pull image secret cloneexternalsecret yaml yaml apiversion external secrets io kind externalsecret metadata name devops docker pull image secret namespace default spec data remoteref conversionstrategy default decodingstrategy none key secrets devops docker pull image secret property dockerconfigjson secretkey dockerconfigjson refreshinterval secretstoreref kind clustersecretstore name vault backend target creationpolicy owner deletionpolicy retain name devops docker pull image secret clonepullsecrettons yaml yaml apiversion kyverno io kind clusterpolicy metadata name sync pull image secrets annotations policies kyverno io title sync pull image secrets policies kyverno io category secrets policies kyverno io severity low policies kyverno io subject secret policies kyverno io minversion policies kyverno io description copies the pullsecret eso resources into all namespaces this will mean we re never missing the secret when we need it spec rules name sync image pull secret match any resources kinds namespace generate apiversion external secrets io kind externalsecret name devops docker pull image secret namespace request object metadata name synchronize true clone namespace default name devops docker pull image secret expected behavior test should work for custom resource and pass screenshots no response kyverno logs shell manager go msg unable to cache openapischema definitionname io api authentication tokenrequest reason gvk not found by the given definition name io api authentication tokenrequest manager go msg unable to cache openapischema definitionname io api autoscaling scale reason gvk not found by the given definition name io api autoscaling scale manager go msg unable to cache openapischema definitionname io api batch cronjob reason gvk not found by the given definition name io api batch cronjob manager go msg unable to cache openapischema definitionname io api discovery endpointslice reason gvk not found by the given definition name io api discovery endpointslice manager go msg unable to cache openapischema definitionname io api node runtimeclass reason gvk not found by the given definition name io api node runtimeclass manager go msg unable to cache openapischema definitionname io api policy poddisruptionbudget reason gvk not found by the given definition name io api policy poddisruptionbudget manager go msg unable to cache openapischema definitionname io api policy eviction reason gvk not found by the given definition name io api policy eviction manager go msg unable to cache openapischema definitionname io api rbac clusterrole reason gvk not found by the given definition name io api rbac clusterrole manager go msg unable to cache openapischema definitionname io api rbac clusterrolebinding reason gvk not found by the given definition name io api rbac clusterrolebinding manager go msg unable to cache openapischema definitionname io api rbac role reason gvk not found by the given definition name io api rbac role manager go msg unable to cache openapischema definitionname io api rbac rolebinding reason gvk not found by the given definition name io api rbac rolebinding manager go msg unable to cache openapischema definitionname io api scheduling priorityclass reason gvk not found by the given definition name io api scheduling priorityclass manager go msg unable to cache openapischema definitionname io api storage tokenrequest reason gvk not found by the given definition name io api storage tokenrequest manager go msg unable to cache openapischema definitionname io api storage volumeattachment reason gvk not found by the given definition name io api storage volumeattachment manager go msg unable to cache openapischema definitionname io api storage tokenrequest reason gvk not found by the given definition name io api storage tokenrequest executing generate tests common go msg defaulting request operation to create common go msg reading policies path policies generate clonepullsecrettons yaml common go msg read policies errors policies common go msg mutated policy kind clusterpolicy apiversion kyverno io metadata name sync pull image secrets creationtimestamp null annotations policies kyverno io category secrets policies kyverno io description copies the pullsecret eso resources into all namespaces this will mean we re never missing the secret when we need it policies kyverno io minversion policies kyverno io severity low policies kyverno io subject secret policies kyverno io title sync pull image secrets spec rules resources exclude resources mutate validate generate apiversion external secrets io kind externalsecret namespace request object metadata name name devops docker pull image secret synchronize true clone namespace default name devops docker pull image secret clonelist status ready false autogen rulecount validate generate mutate verifyimages missing applying policy to resource vars go msg variable substituted path generate namespace value null variable request object metadata name validate go msg name namespace uses variables so cannot be resolved skipping auth checks common go msg applying policy on resource policy sync pull image secrets resource default namespace test ns mutation go enginemutate msg start mutate policy processing kind namespace name test ns namespace default policy sync pull image secrets starttime mutation go enginemutate msg finished processing policy kind namespace mutationrulesapplied name test ns namespace default policy sync pull image secrets processingtime imageverify go engineverifyimages msg processed image verification rules applied kind namespace name test ns namespace default policy sync pull image secrets successful true time vars go msg variable substituted path generate namespace value test ns variable request object metadata name generate go msg failed to generate resource error source resource external secrets io externalsecret default devops docker pull image secret not found devops docker pull image secret not found genapiversion external secrets io genkind externalsecret genname devops docker pull image secret gennamespace test ns mode skip generate go msg failed to apply generate rule error source resource external secrets io externalsecret default devops docker pull image secret not found devops docker pull image secret not found policy sync pull image secrets resource test ns rule sync image pull secret suggestion users need to grant kyverno s service account additional privileges common go msg failed to apply generate policy error source resource external secrets io externalsecret default devops docker pull image secret not found devops docker pull image secret not found validate go msg pattern and resource have different structures current expected map interface path spec test command go msg generatedresource mismatch error pattern and resource have different structures path spec expected map interface found test command go msg result mismatch expected pass key sync pull image secrets sync image pull secret namespace test ns received fail slack discussion troubleshooting i have read and followed the i have searched other issues in this repository and mine is not recorded | 1 |
52,299 | 10,820,208,321 | IssuesEvent | 2019-11-08 15:55:45 | ExtendedXmlSerializer/ExtendedXmlSerializer | https://api.github.com/repos/ExtendedXmlSerializer/ExtendedXmlSerializer | closed | Enable Monitoring (Callbacks) of Serialization Pipeline | enhancement sample code | A callback on deserialization for particular object would be very useful (e.g. events hooking). Could be easily achieved by either object implementing specific interface or by decorating method by attribute (e.g. OnDeserializedAttribute like in DataContractSerializer implementation) | 1.0 | Enable Monitoring (Callbacks) of Serialization Pipeline - A callback on deserialization for particular object would be very useful (e.g. events hooking). Could be easily achieved by either object implementing specific interface or by decorating method by attribute (e.g. OnDeserializedAttribute like in DataContractSerializer implementation) | non_test | enable monitoring callbacks of serialization pipeline a callback on deserialization for particular object would be very useful e g events hooking could be easily achieved by either object implementing specific interface or by decorating method by attribute e g ondeserializedattribute like in datacontractserializer implementation | 0 |
107,638 | 23,456,041,182 | IssuesEvent | 2022-08-16 08:57:33 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | closed | Rename "Code graph" section to "Code graph data" | team/code-intelligence team/language-platform-and-navigation | Rename the following mentions of "Code graph" to "Code graph data"
Code graph data button
Code graph data page
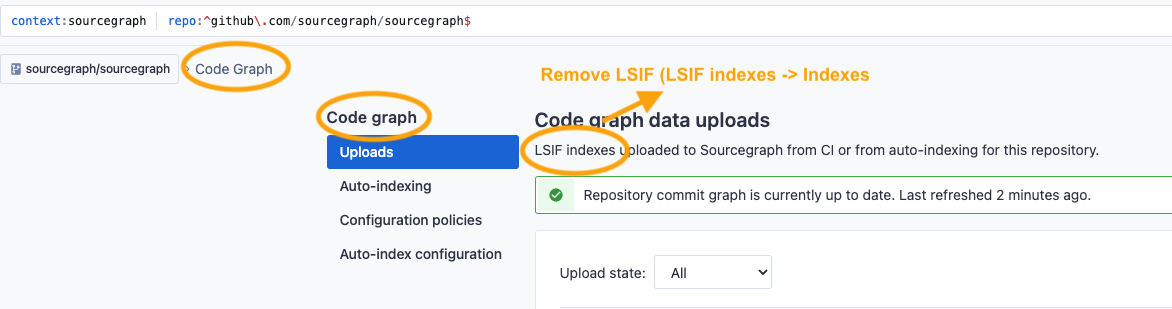
| 1.0 | Rename "Code graph" section to "Code graph data" - Rename the following mentions of "Code graph" to "Code graph data"
Code graph data button
Code graph data page
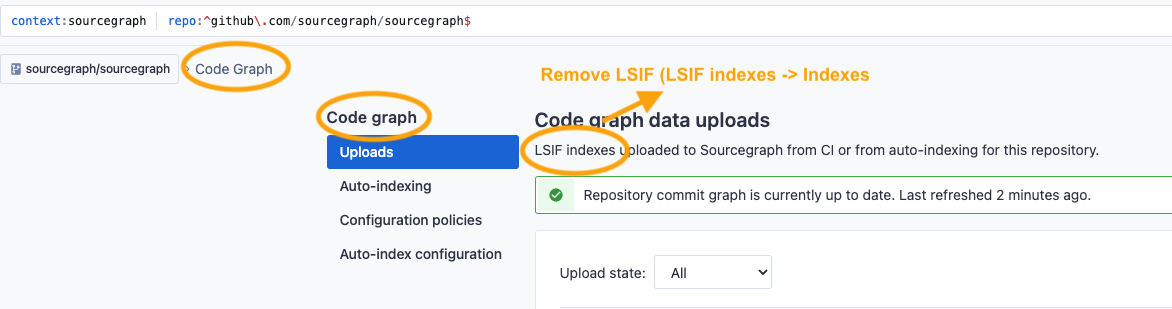
| non_test | rename code graph section to code graph data rename the following mentions of code graph to code graph data code graph data button code graph data page | 0 |
243,087 | 20,361,644,502 | IssuesEvent | 2022-02-20 19:21:48 | mennaelkashef/eShop | https://api.github.com/repos/mennaelkashef/eShop | opened | No description entered by the user. | Hello! RULE-GOT-APPLIED DOES-NOT-CONTAIN-STRING Rule-works-on-convert-to-bug test instabug | # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2022-02-20 19:17:22 UTC
Email | kgomaa@instabug.com
Categories | Report a bug
Tags | test, Hello!, RULE-GOT-APPLIED, DOES-NOT-CONTAIN-STRING, Rule-works-on-convert-to-bug, instabug
App Version | 1.1 (1)
Session Duration | 572
Device | Google Android SDK built for arm64, OS Level 29
Display | 1080x2220 (xhdpi)
Location | Cairo, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?utm_source=github&utm_medium=integrations) :point_left:
___
# :iphone: View Hierarchy
This bug was reported from **com.example.app.main.MainFragment**
Find its interactive view hierarchy with all its subviews here: :point_right: **[Check View Hierarchy](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-hierarchy-view=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
Used Memory | 52.5% - 1.02/1.95 GB
Used Storage | 39.7% - 2.31/5.81 GB
Connectivity | WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
key_name -794257878: key value bla bla bla la
key_name -920041066: key value bla bla bla la
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
19:12:11 Tap in "include" of type "androidx.appcompat.widget.Toolbar" in "com.example.app.main.MainActivity"
19:13:47 Tap in "Sdk version: 10..." of type "androidx.appcompat.widget.AppCompatTextView" in "com.example.app.main.MainActivity"
19:13:47 com.example.app.main.MainActivity was paused.
19:13:47 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
19:13:49 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
19:13:50 Tap in "include" of type "androidx.appcompat.widget.Toolbar" in "com.example.app.main.MainActivity"
19:17:20 Tap in "Sdk version: 10..." of type "androidx.appcompat.widget.AppCompatTextView" in "com.example.app.main.MainActivity"
19:17:20 com.example.app.main.MainActivity was paused.
19:17:20 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
19:17:21 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
19:17:22 D/IB-ActivityViewInspectorTask( 4579): bug ! null,converting>json started
19:17:22 D/IB-ActivityViewInspectorTask( 4579): bug ! null,converting>json ended
19:17:22 D/IB-ActivityViewInspectorTask( 4579): bug ! null,set inspection state
19:17:22 D/IB-BaseReportingPresenter( 4579): receive a view hierarchy inspection action, action value: COMPLETED
19:17:22 D/IB-BaseReportingPresenter( 4579): receive a view hierarchy inspection action, action value: COMPLETED
19:17:23 D/LeakCanary( 4579): Setting up flushing for Thread[PixelCopy,5,main]
19:17:23 D/EGL_emulation( 4579): eglMakeCurrent: 0x718d9de4c0: ver 3 0 (tinfo 0x718d9a6340)
19:17:23 D/IB-BaseReportingPresenter( 4579): checkUserEmailValid :non-empty-email
19:17:23 D/IB-ActionsOrchestrator( 4579): runAction
19:17:23 D/IB-AttachmentsUtility( 4579): encryptAttachments
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/17893016/3f86c74e410f3a26685e37d8b9cc08fc_original/25102163/bug_1645384640899_.jpg?Expires=4801058506&Signature=hsfGmsBoKEJbh7RA3OC2OVYtbuYuGXR9nvcj-H-tnny~yqpDJ60kGDNnx0WtIt9DvbNN3uoNoPeLMgDuDuQ0RdrWrufGMn3-PXUpp4ib6CHCMviopNLIO97VwjCng-1jMTZG-8SJQslcmIVREKm111cZ8dgtBrVmzvujIq3~LoBKEnFJqFzWtMYWKfcxko6WkWtOL4F9lvmR9aW1bhJY50MeFww3bjDI0p6qIf3lFox22QXm-eAmBp~0GuudhrogNCOrUOye40pTnO-H2HhkvF-f6Tv5enU8RQ2N8cqlV0owGEiu7Y5SJCgc0VQww4bq1Y4w9lX0yPcYuSauUrv9Cw__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using HttpUrlConnection or Okhttp requests, [**check the details mentioned here**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations#section-network-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations). | 1.0 | No description entered by the user. - # :clipboard: Bug Details
>No description entered by the user.
key | value
--|--
Reported At | 2022-02-20 19:17:22 UTC
Email | kgomaa@instabug.com
Categories | Report a bug
Tags | test, Hello!, RULE-GOT-APPLIED, DOES-NOT-CONTAIN-STRING, Rule-works-on-convert-to-bug, instabug
App Version | 1.1 (1)
Session Duration | 572
Device | Google Android SDK built for arm64, OS Level 29
Display | 1080x2220 (xhdpi)
Location | Cairo, Egypt (en)
## :point_right: [View Full Bug Report on Instabug](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?utm_source=github&utm_medium=integrations) :point_left:
___
# :iphone: View Hierarchy
This bug was reported from **com.example.app.main.MainFragment**
Find its interactive view hierarchy with all its subviews here: :point_right: **[Check View Hierarchy](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-hierarchy-view=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :chart_with_downwards_trend: Session Profiler
Here is what the app was doing right before the bug was reported:
Key | Value
--|--
Used Memory | 52.5% - 1.02/1.95 GB
Used Storage | 39.7% - 2.31/5.81 GB
Connectivity | WiFi
Battery | 100% - unplugged
Orientation | portrait
Find all the changes that happened in the parameters mentioned above during the last 60 seconds before the bug was reported here: :point_right: **[View Full Session Profiler](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-session-profiler=true&utm_source=github&utm_medium=integrations)** :point_left:
___
# :bust_in_silhouette: User Info
### User Attributes
```
key_name -794257878: key value bla bla bla la
key_name -920041066: key value bla bla bla la
```
___
# :mag_right: Logs
### User Steps
Here are the last 10 steps done by the user right before the bug was reported:
```
19:12:11 Tap in "include" of type "androidx.appcompat.widget.Toolbar" in "com.example.app.main.MainActivity"
19:13:47 Tap in "Sdk version: 10..." of type "androidx.appcompat.widget.AppCompatTextView" in "com.example.app.main.MainActivity"
19:13:47 com.example.app.main.MainActivity was paused.
19:13:47 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
19:13:49 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
19:13:50 Tap in "include" of type "androidx.appcompat.widget.Toolbar" in "com.example.app.main.MainActivity"
19:17:20 Tap in "Sdk version: 10..." of type "androidx.appcompat.widget.AppCompatTextView" in "com.example.app.main.MainActivity"
19:17:20 com.example.app.main.MainActivity was paused.
19:17:20 In activity com.example.app.main.MainActivity: fragment com.example.app.main.MainFragment was paused.
19:17:21 Tap in "androidx.constraintlayout.widget.ConstraintLayout" in "com.example.app.main.MainActivity"
```
Find all the user steps done by the user throughout the session here: :point_right: **[View All User Steps](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-logs=user_steps&utm_source=github&utm_medium=integrations)** :point_left:
### Console Log
Here are the last 10 console logs logged right before the bug was reported:
```
19:17:22 D/IB-ActivityViewInspectorTask( 4579): bug ! null,converting>json started
19:17:22 D/IB-ActivityViewInspectorTask( 4579): bug ! null,converting>json ended
19:17:22 D/IB-ActivityViewInspectorTask( 4579): bug ! null,set inspection state
19:17:22 D/IB-BaseReportingPresenter( 4579): receive a view hierarchy inspection action, action value: COMPLETED
19:17:22 D/IB-BaseReportingPresenter( 4579): receive a view hierarchy inspection action, action value: COMPLETED
19:17:23 D/LeakCanary( 4579): Setting up flushing for Thread[PixelCopy,5,main]
19:17:23 D/EGL_emulation( 4579): eglMakeCurrent: 0x718d9de4c0: ver 3 0 (tinfo 0x718d9a6340)
19:17:23 D/IB-BaseReportingPresenter( 4579): checkUserEmailValid :non-empty-email
19:17:23 D/IB-ActionsOrchestrator( 4579): runAction
19:17:23 D/IB-AttachmentsUtility( 4579): encryptAttachments
```
Find all the logged console logs throughout the session here: :point_right: **[View All Console Log](https://dashboard.instabug.com/applications/android-sample/beta/bugs/8504?show-logs=console_log&utm_source=github&utm_medium=integrations)** :point_left:
___
# :camera: Images
[](https://d38gnqwzxziyyy.cloudfront.net/attachments/bugs/17893016/3f86c74e410f3a26685e37d8b9cc08fc_original/25102163/bug_1645384640899_.jpg?Expires=4801058506&Signature=hsfGmsBoKEJbh7RA3OC2OVYtbuYuGXR9nvcj-H-tnny~yqpDJ60kGDNnx0WtIt9DvbNN3uoNoPeLMgDuDuQ0RdrWrufGMn3-PXUpp4ib6CHCMviopNLIO97VwjCng-1jMTZG-8SJQslcmIVREKm111cZ8dgtBrVmzvujIq3~LoBKEnFJqFzWtMYWKfcxko6WkWtOL4F9lvmR9aW1bhJY50MeFww3bjDI0p6qIf3lFox22QXm-eAmBp~0GuudhrogNCOrUOye40pTnO-H2HhkvF-f6Tv5enU8RQ2N8cqlV0owGEiu7Y5SJCgc0VQww4bq1Y4w9lX0yPcYuSauUrv9Cw__&Key-Pair-Id=APKAIXAG65U6UUX7JAQQ)
___
# :warning: Looking for More Details?
1. **Network Log**: we are unable to capture your network requests automatically. If you are using HttpUrlConnection or Okhttp requests, [**check the details mentioned here**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations#section-network-logs).
2. **User Events**: start capturing custom User Events to send them along with each report. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations).
3. **Instabug Log**: start adding Instabug logs to see them right inside each report you receive. [**Find all the details in the docs**](https://docs.instabug.com/docs/android-logging?utm_source=github&utm_medium=integrations). | test | no description entered by the user clipboard bug details no description entered by the user key value reported at utc email kgomaa instabug com categories report a bug tags test hello rule got applied does not contain string rule works on convert to bug instabug app version session duration device google android sdk built for os level display xhdpi location cairo egypt en point right point left iphone view hierarchy this bug was reported from com example app main mainfragment find its interactive view hierarchy with all its subviews here point right point left chart with downwards trend session profiler here is what the app was doing right before the bug was reported key value used memory gb used storage gb connectivity wifi battery unplugged orientation portrait find all the changes that happened in the parameters mentioned above during the last seconds before the bug was reported here point right point left bust in silhouette user info user attributes key name key value bla bla bla la key name key value bla bla bla la mag right logs user steps here are the last steps done by the user right before the bug was reported tap in include of type androidx appcompat widget toolbar in com example app main mainactivity tap in sdk version of type androidx appcompat widget appcompattextview in com example app main mainactivity com example app main mainactivity was paused in activity com example app main mainactivity fragment com example app main mainfragment was paused tap in androidx constraintlayout widget constraintlayout in com example app main mainactivity tap in include of type androidx appcompat widget toolbar in com example app main mainactivity tap in sdk version of type androidx appcompat widget appcompattextview in com example app main mainactivity com example app main mainactivity was paused in activity com example app main mainactivity fragment com example app main mainfragment was paused tap in androidx constraintlayout widget constraintlayout in com example app main mainactivity find all the user steps done by the user throughout the session here point right point left console log here are the last console logs logged right before the bug was reported d ib activityviewinspectortask bug null converting json started d ib activityviewinspectortask bug null converting json ended d ib activityviewinspectortask bug null set inspection state d ib basereportingpresenter receive a view hierarchy inspection action action value completed d ib basereportingpresenter receive a view hierarchy inspection action action value completed d leakcanary setting up flushing for thread d egl emulation eglmakecurrent ver tinfo d ib basereportingpresenter checkuseremailvalid non empty email d ib actionsorchestrator runaction d ib attachmentsutility encryptattachments find all the logged console logs throughout the session here point right point left camera images warning looking for more details network log we are unable to capture your network requests automatically if you are using httpurlconnection or okhttp requests user events start capturing custom user events to send them along with each report instabug log start adding instabug logs to see them right inside each report you receive | 1 |
67,161 | 7,037,038,214 | IssuesEvent | 2017-12-28 12:29:20 | vgstation-coders/vgstation13 | https://api.github.com/repos/vgstation-coders/vgstation13 | closed | (WEB REPORT BY: edwarus REMOTE: 198.245.63.50:7777) jukebox unmovable | Needs Moar Testing | > Revision (Should be above if you're viewing this from ingame!)
>
> General description of the issue
> Cant unwrench the jukebox
>
> What you expected to happen
> the jukebox to move
>
> What actually happened
> nothing
>
> Steps to reproduce if possible
> I turned the jukebox to syndie mode then back so i could mess with settings not sure why its unwrenchable i might just be overlooking something but i dont think so
| 1.0 | (WEB REPORT BY: edwarus REMOTE: 198.245.63.50:7777) jukebox unmovable - > Revision (Should be above if you're viewing this from ingame!)
>
> General description of the issue
> Cant unwrench the jukebox
>
> What you expected to happen
> the jukebox to move
>
> What actually happened
> nothing
>
> Steps to reproduce if possible
> I turned the jukebox to syndie mode then back so i could mess with settings not sure why its unwrenchable i might just be overlooking something but i dont think so
| test | web report by edwarus remote jukebox unmovable revision should be above if you re viewing this from ingame general description of the issue cant unwrench the jukebox what you expected to happen the jukebox to move what actually happened nothing steps to reproduce if possible i turned the jukebox to syndie mode then back so i could mess with settings not sure why its unwrenchable i might just be overlooking something but i dont think so | 1 |
9,741 | 3,315,960,947 | IssuesEvent | 2015-11-06 14:55:41 | flynn/flynn | https://api.github.com/repos/flynn/flynn | opened | docs: Document how to use Flynn behind an AWS ELB | documentation enhancement | Using an AWS ELB (or equivalent) gives users more control over routing / health checks than relying on DNS for load balancing.
We should document the process, and advise users if their cluster is only accessible via the ELB using security groups they will need to direct controller / dashboard / git requests via the ELB too. | 1.0 | docs: Document how to use Flynn behind an AWS ELB - Using an AWS ELB (or equivalent) gives users more control over routing / health checks than relying on DNS for load balancing.
We should document the process, and advise users if their cluster is only accessible via the ELB using security groups they will need to direct controller / dashboard / git requests via the ELB too. | non_test | docs document how to use flynn behind an aws elb using an aws elb or equivalent gives users more control over routing health checks than relying on dns for load balancing we should document the process and advise users if their cluster is only accessible via the elb using security groups they will need to direct controller dashboard git requests via the elb too | 0 |
179,943 | 21,606,789,231 | IssuesEvent | 2022-05-04 04:54:11 | jamandujanoa/WASA | https://api.github.com/repos/jamandujanoa/WASA | opened | Use service endpoints and private links where appropriate | WARP-Import WAF-Assessment Security Networking & Connectivity Connectivity | <a href="https://docs.microsoft.com/azure/architecture/framework/security/design-network-endpoints#public-endpoints">Use service endpoints and private links where appropriate</a>
<p><b>Why Consider This?</b></p>
Service Endpoints and Private Link can be leveraged to restrict access to PaaS endpoints only from authorized virtual networks, effectively mitigating data intrusion risks and associated impact to application availability. Service Endpoints provide service level access to a PaaS service, while Private Link provides direct access to a specific PaaS resource to mitigate data exfiltration risks (e.g. malicious admin scenarios).
<p><b>Context</b></p>
<p><b>Suggested Actions</b></p>
<p><span>Configure service endpoints and private links where appropriate.</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/virtual-network/virtual-network-service-endpoints-overview" target="_blank"><span>https://docs.microsoft.com/en-us/azure/virtual-network/virtual-network-service-endpoints-overview</span></a><span /></p><p><a href="https://docs.microsoft.com/en-us/azure/private-link/private-endpoint-overview" target="_blank"><span>https://docs.microsoft.com/en-us/azure/private-link/private-endpoint-overview</span></a><span /></p> | True | Use service endpoints and private links where appropriate - <a href="https://docs.microsoft.com/azure/architecture/framework/security/design-network-endpoints#public-endpoints">Use service endpoints and private links where appropriate</a>
<p><b>Why Consider This?</b></p>
Service Endpoints and Private Link can be leveraged to restrict access to PaaS endpoints only from authorized virtual networks, effectively mitigating data intrusion risks and associated impact to application availability. Service Endpoints provide service level access to a PaaS service, while Private Link provides direct access to a specific PaaS resource to mitigate data exfiltration risks (e.g. malicious admin scenarios).
<p><b>Context</b></p>
<p><b>Suggested Actions</b></p>
<p><span>Configure service endpoints and private links where appropriate.</span></p>
<p><b>Learn More</b></p>
<p><a href="https://docs.microsoft.com/en-us/azure/virtual-network/virtual-network-service-endpoints-overview" target="_blank"><span>https://docs.microsoft.com/en-us/azure/virtual-network/virtual-network-service-endpoints-overview</span></a><span /></p><p><a href="https://docs.microsoft.com/en-us/azure/private-link/private-endpoint-overview" target="_blank"><span>https://docs.microsoft.com/en-us/azure/private-link/private-endpoint-overview</span></a><span /></p> | non_test | use service endpoints and private links where appropriate why consider this service endpoints and private link can be leveraged to restrict access to paas endpoints only from authorized virtual networks effectively mitigating data intrusion risks and associated impact to application availability service endpoints provide service level access to a paas service while private link provides direct access to a specific paas resource to mitigate data exfiltration risks e g malicious admin scenarios context suggested actions configure service endpoints and private links where appropriate learn more | 0 |
20,427 | 6,040,170,423 | IssuesEvent | 2017-06-10 11:37:52 | tzulberti/archery-training | https://api.github.com/repos/tzulberti/archery-training | closed | Remove all fragments newInstance | Code enhacement | When creating a new fragment and using the parameters, I am using the `newInstance` method. This should be removed and use the common way to pass values.
Check: https://stackoverflow.com/questions/16036572/how-to-pass-values-between-fragments | 1.0 | Remove all fragments newInstance - When creating a new fragment and using the parameters, I am using the `newInstance` method. This should be removed and use the common way to pass values.
Check: https://stackoverflow.com/questions/16036572/how-to-pass-values-between-fragments | non_test | remove all fragments newinstance when creating a new fragment and using the parameters i am using the newinstance method this should be removed and use the common way to pass values check | 0 |
233,254 | 18,957,516,524 | IssuesEvent | 2021-11-18 22:16:59 | NumerischeSimulation/NumSim | https://api.github.com/repos/NumerischeSimulation/NumSim | closed | Interpolation at the domain boundaries | needs testing | Does not work for only vertical/horizontal interpolation at the boundaries. | 1.0 | Interpolation at the domain boundaries - Does not work for only vertical/horizontal interpolation at the boundaries. | test | interpolation at the domain boundaries does not work for only vertical horizontal interpolation at the boundaries | 1 |
243,196 | 20,369,238,071 | IssuesEvent | 2022-02-21 09:36:44 | microsoft/AzureStorageExplorer | https://api.github.com/repos/microsoft/AzureStorageExplorer | opened | No response when clicking 'Open/Cancel' in the prompt native dialog if uploading files/folders on Storage Explorer which is installed by snap | 🧪 testing :computer: linux | **Storage Explorer Version:** 1.23.0-dev
**Build Number:** 20220219.5
**Branch:** rel/1.23.0
**Platform/OS:** Linux Ubuntu 20.04
**Architecture:** x64
**How Found:** From running test cases
**Regression From:** Not a regression
## Steps to Reproduce ##
1. Install Storage Explorer by snap -> Launch Storage Explorer.
2. Expand one storage account -> Blob Containers.
3. Create a blob container -> Click 'Upload -> Upload Files...'.
4. Click 'No files selected' box -> Select one file.
5. Click 'Open/Cancel' -> Check whether the prompt native dialog is closed.
## Expected Experience ##
The prompt native dialog is closed.
## Actual Experience ##
No response when clicking 'Open'/'Cancel' in the prompt native dialog.
## Additional Context ##
1. This issue also reproduces when removing storage azure account/downloading files.
2. In the previous release (1.22.1), this issue only reproduces for one time.
3. This issue doesn't reproduce when the Storage Explorer is installed by tar.gz.
4. This issue doesn't reproduce after reloading Storage Explorer.
5. This issue cannot be reproduced consistently.
| 1.0 | No response when clicking 'Open/Cancel' in the prompt native dialog if uploading files/folders on Storage Explorer which is installed by snap - **Storage Explorer Version:** 1.23.0-dev
**Build Number:** 20220219.5
**Branch:** rel/1.23.0
**Platform/OS:** Linux Ubuntu 20.04
**Architecture:** x64
**How Found:** From running test cases
**Regression From:** Not a regression
## Steps to Reproduce ##
1. Install Storage Explorer by snap -> Launch Storage Explorer.
2. Expand one storage account -> Blob Containers.
3. Create a blob container -> Click 'Upload -> Upload Files...'.
4. Click 'No files selected' box -> Select one file.
5. Click 'Open/Cancel' -> Check whether the prompt native dialog is closed.
## Expected Experience ##
The prompt native dialog is closed.
## Actual Experience ##
No response when clicking 'Open'/'Cancel' in the prompt native dialog.
## Additional Context ##
1. This issue also reproduces when removing storage azure account/downloading files.
2. In the previous release (1.22.1), this issue only reproduces for one time.
3. This issue doesn't reproduce when the Storage Explorer is installed by tar.gz.
4. This issue doesn't reproduce after reloading Storage Explorer.
5. This issue cannot be reproduced consistently.
| test | no response when clicking open cancel in the prompt native dialog if uploading files folders on storage explorer which is installed by snap storage explorer version dev build number branch rel platform os linux ubuntu architecture how found from running test cases regression from not a regression steps to reproduce install storage explorer by snap launch storage explorer expand one storage account blob containers create a blob container click upload upload files click no files selected box select one file click open cancel check whether the prompt native dialog is closed expected experience the prompt native dialog is closed actual experience no response when clicking open cancel in the prompt native dialog additional context this issue also reproduces when removing storage azure account downloading files in the previous release this issue only reproduces for one time this issue doesn t reproduce when the storage explorer is installed by tar gz this issue doesn t reproduce after reloading storage explorer this issue cannot be reproduced consistently | 1 |
283,868 | 30,913,562,908 | IssuesEvent | 2023-08-05 02:15:10 | hshivhare67/kernel_v4.19.72 | https://api.github.com/repos/hshivhare67/kernel_v4.19.72 | reopened | CVE-2020-11494 (Medium) detected in linuxlinux-4.19.282 | Mend: dependency security vulnerability | ## CVE-2020-11494 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/hshivhare67/kernel_v4.19.72/commit/139c4e073703974ca0b05255c4cff6dcd52a8e31">139c4e073703974ca0b05255c4cff6dcd52a8e31</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/can/slcan.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/can/slcan.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in slc_bump in drivers/net/can/slcan.c in the Linux kernel 3.16 through 5.6.2. It allows attackers to read uninitialized can_frame data, potentially containing sensitive information from kernel stack memory, if the configuration lacks CONFIG_INIT_STACK_ALL, aka CID-b9258a2cece4.
<p>Publish Date: 2020-04-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11494>CVE-2020-11494</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-11494">https://nvd.nist.gov/vuln/detail/CVE-2020-11494</a></p>
<p>Release Date: 2020-04-02</p>
<p>Fix Resolution: linux- v5.7-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11494 (Medium) detected in linuxlinux-4.19.282 - ## CVE-2020-11494 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.282</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/hshivhare67/kernel_v4.19.72/commit/139c4e073703974ca0b05255c4cff6dcd52a8e31">139c4e073703974ca0b05255c4cff6dcd52a8e31</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/can/slcan.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/net/can/slcan.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in slc_bump in drivers/net/can/slcan.c in the Linux kernel 3.16 through 5.6.2. It allows attackers to read uninitialized can_frame data, potentially containing sensitive information from kernel stack memory, if the configuration lacks CONFIG_INIT_STACK_ALL, aka CID-b9258a2cece4.
<p>Publish Date: 2020-04-02
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2020-11494>CVE-2020-11494</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.4</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-11494">https://nvd.nist.gov/vuln/detail/CVE-2020-11494</a></p>
<p>Release Date: 2020-04-02</p>
<p>Fix Resolution: linux- v5.7-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers net can slcan c drivers net can slcan c vulnerability details an issue was discovered in slc bump in drivers net can slcan c in the linux kernel through it allows attackers to read uninitialized can frame data potentially containing sensitive information from kernel stack memory if the configuration lacks config init stack all aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux step up your open source security game with mend | 0 |
288,326 | 24,898,720,194 | IssuesEvent | 2022-10-28 18:27:03 | happinessk/AWS-Custom-CRM | https://api.github.com/repos/happinessk/AWS-Custom-CRM | closed | Test Case 1 - Happiness | bug Test | Follow the this test case and comment the outcome below:
- [x] 1. Create an emails.csv file (can contain up to three email addresses: your email, the professor's email, and/or my email )
- [x] 2. Visit the WordPress website
- [x] 3. upload the file in the File Uploads page.
- [x] 4. If file uploaded after 5pm CDT, then the email will go out at 6pm CDT the following day (and every day after that at 6pm CDT until the file is replaced with another emails.csv). | 1.0 | Test Case 1 - Happiness - Follow the this test case and comment the outcome below:
- [x] 1. Create an emails.csv file (can contain up to three email addresses: your email, the professor's email, and/or my email )
- [x] 2. Visit the WordPress website
- [x] 3. upload the file in the File Uploads page.
- [x] 4. If file uploaded after 5pm CDT, then the email will go out at 6pm CDT the following day (and every day after that at 6pm CDT until the file is replaced with another emails.csv). | test | test case happiness follow the this test case and comment the outcome below create an emails csv file can contain up to three email addresses your email the professor s email and or my email visit the wordpress website upload the file in the file uploads page if file uploaded after cdt then the email will go out at cdt the following day and every day after that at cdt until the file is replaced with another emails csv | 1 |
250,612 | 27,107,656,410 | IssuesEvent | 2023-02-15 13:17:05 | Seagate/cortx-re | https://api.github.com/repos/Seagate/cortx-re | opened | CVE-2023-25577 (High) detected in Werkzeug-2.2.2-py3-none-any.whl | security vulnerability | ## CVE-2023-25577 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-2.2.2-py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/c8/27/be6ddbcf60115305205de79c29004a0c6bc53cec814f733467b1bb89386d/Werkzeug-2.2.2-py3-none-any.whl">https://files.pythonhosted.org/packages/c8/27/be6ddbcf60115305205de79c29004a0c6bc53cec814f733467b1bb89386d/Werkzeug-2.2.2-py3-none-any.whl</a></p>
<p>
Dependency Hierarchy:
- :x: **Werkzeug-2.2.2-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Werkzeug is a comprehensive WSGI web application library. Prior to version 2.2.3, Werkzeug's multipart form data parser will parse an unlimited number of parts, including file parts. Parts can be a small amount of bytes, but each requires CPU time to parse and may use more memory as Python data. If a request can be made to an endpoint that accesses `request.data`, `request.form`, `request.files`, or `request.get_data(parse_form_data=False)`, it can cause unexpectedly high resource usage. This allows an attacker to cause a denial of service by sending crafted multipart data to an endpoint that will parse it. The amount of CPU time required can block worker processes from handling legitimate requests. The amount of RAM required can trigger an out of memory kill of the process. Unlimited file parts can use up memory and file handles. If many concurrent requests are sent continuously, this can exhaust or kill all available workers. Version 2.2.3 contains a patch for this issue.
<p>Publish Date: 2023-02-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-25577>CVE-2023-25577</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-25577">https://www.cve.org/CVERecord?id=CVE-2023-25577</a></p>
<p>Release Date: 2023-02-14</p>
<p>Fix Resolution: Werkzeug - 2.2.3</p>
</p>
</details>
<p></p>
| True | CVE-2023-25577 (High) detected in Werkzeug-2.2.2-py3-none-any.whl - ## CVE-2023-25577 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Werkzeug-2.2.2-py3-none-any.whl</b></p></summary>
<p>The comprehensive WSGI web application library.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/c8/27/be6ddbcf60115305205de79c29004a0c6bc53cec814f733467b1bb89386d/Werkzeug-2.2.2-py3-none-any.whl">https://files.pythonhosted.org/packages/c8/27/be6ddbcf60115305205de79c29004a0c6bc53cec814f733467b1bb89386d/Werkzeug-2.2.2-py3-none-any.whl</a></p>
<p>
Dependency Hierarchy:
- :x: **Werkzeug-2.2.2-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Werkzeug is a comprehensive WSGI web application library. Prior to version 2.2.3, Werkzeug's multipart form data parser will parse an unlimited number of parts, including file parts. Parts can be a small amount of bytes, but each requires CPU time to parse and may use more memory as Python data. If a request can be made to an endpoint that accesses `request.data`, `request.form`, `request.files`, or `request.get_data(parse_form_data=False)`, it can cause unexpectedly high resource usage. This allows an attacker to cause a denial of service by sending crafted multipart data to an endpoint that will parse it. The amount of CPU time required can block worker processes from handling legitimate requests. The amount of RAM required can trigger an out of memory kill of the process. Unlimited file parts can use up memory and file handles. If many concurrent requests are sent continuously, this can exhaust or kill all available workers. Version 2.2.3 contains a patch for this issue.
<p>Publish Date: 2023-02-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-25577>CVE-2023-25577</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-25577">https://www.cve.org/CVERecord?id=CVE-2023-25577</a></p>
<p>Release Date: 2023-02-14</p>
<p>Fix Resolution: Werkzeug - 2.2.3</p>
</p>
</details>
<p></p>
| non_test | cve high detected in werkzeug none any whl cve high severity vulnerability vulnerable library werkzeug none any whl the comprehensive wsgi web application library library home page a href dependency hierarchy x werkzeug none any whl vulnerable library found in base branch main vulnerability details werkzeug is a comprehensive wsgi web application library prior to version werkzeug s multipart form data parser will parse an unlimited number of parts including file parts parts can be a small amount of bytes but each requires cpu time to parse and may use more memory as python data if a request can be made to an endpoint that accesses request data request form request files or request get data parse form data false it can cause unexpectedly high resource usage this allows an attacker to cause a denial of service by sending crafted multipart data to an endpoint that will parse it the amount of cpu time required can block worker processes from handling legitimate requests the amount of ram required can trigger an out of memory kill of the process unlimited file parts can use up memory and file handles if many concurrent requests are sent continuously this can exhaust or kill all available workers version contains a patch for this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution werkzeug | 0 |
297,179 | 25,705,866,796 | IssuesEvent | 2022-12-07 00:36:07 | devssa/onde-codar-em-salvador | https://api.github.com/repos/devssa/onde-codar-em-salvador | closed | Analista de Automação Junior na [Ericsson Inovação S.A] | SALVADOR SQL TESTE AUTOMATIZADO RUBY LINUX SELENIUM CUCUMBER TESTE MANUAL TESTE FUNCIONAL JMETER LÓGICA DE PROGRAMAÇÃO QUALITY CENTER Stale | <!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA SALVADOR E CIDADES VIZINHAS!
Use: "Desenvolvedor Front-end" ao invés de
"Front-End Developer" \o/
Exemplo: `[JAVASCRIPT] [MYSQL] [NODE.JS] Desenvolvedor Front-End na [NOME DA EMPRESA]`
==================================================
-->
## Analista de Automação Junior
- Execução dos testes manuais e automatizados, além de gerar massa de dados para a execução dos testes;
- Execução dos testes funcionais e defeitos de produção;
- Envio diário de reports sobre a evolução dos testes;
- Garantir atualização dos status da demanda na ferramenta de gestão de testes;
- Tratativas de defeitos (análise, coleta de evidência, tramitação para desenvolvimento, fechamento seguindo os padrões);
- Executar workshops dos projetos para o cliente;
- Atendimento ao cliente e acompanhamento de homologações;
- Monitorar correções e liberações de pacotes de homologação e produção;
- Acompanhar backlog dos defeitos da homologação e produção;
**FORMAÇÃO**
> Completa em Engenharia da Computação, Análise de Sistemas, Ciência da Computação e áreas afins;
**Horário de trabalho:** 9hs às 18hs.
## Local
Tecnocentro - Salvador/Baêa
## Benefícios
- Vale- Refeição e/ ou Alimentação;
- Além dos benefícios de alimentação e refeição, cedemos espaço para almoço com copa;
- Vale- transporte;
- Assistência médica;
- Assistência odontológica;
- Bonificação de férias;
- Seguro de vida;
- Participação nos lucros e resultados;
- Frutas, biscoitos e café completo;
- Home Office;
- Jornada flexível.
## Requisitos
**Obrigatórios:**
- Forte lógica de programação
- Experiência e atuação com metodologias de testes;
- Conhecimentos em SQL e LINUX
- Conhecimentos em ferramentas de automação de testes(Quality Center/Jmeter/Cucumber/Selenium, Ruby);
## Ericsson Inovação S.A
A Ericsson Inovação S.A é uma combinação singular de skills e competências na entrega de serviços profissionais na área de Suporte aos negócios e a Operação, atuamos com uma das maiores operações de telecomunicações do mundo, além de ser certificada pelo Great Place to Work, como uma das melhores empresas para se trabalhar no segmento de tecnologia da informação.
## Como se candidatar
https://jobs.kenoby.com/eisa/job/analista-de-automacao-junior/5d546b61c0c6f943d2175c68
| 3.0 | Analista de Automação Junior na [Ericsson Inovação S.A] - <!--
==================================================
POR FAVOR, SÓ POSTE SE A VAGA FOR PARA SALVADOR E CIDADES VIZINHAS!
Use: "Desenvolvedor Front-end" ao invés de
"Front-End Developer" \o/
Exemplo: `[JAVASCRIPT] [MYSQL] [NODE.JS] Desenvolvedor Front-End na [NOME DA EMPRESA]`
==================================================
-->
## Analista de Automação Junior
- Execução dos testes manuais e automatizados, além de gerar massa de dados para a execução dos testes;
- Execução dos testes funcionais e defeitos de produção;
- Envio diário de reports sobre a evolução dos testes;
- Garantir atualização dos status da demanda na ferramenta de gestão de testes;
- Tratativas de defeitos (análise, coleta de evidência, tramitação para desenvolvimento, fechamento seguindo os padrões);
- Executar workshops dos projetos para o cliente;
- Atendimento ao cliente e acompanhamento de homologações;
- Monitorar correções e liberações de pacotes de homologação e produção;
- Acompanhar backlog dos defeitos da homologação e produção;
**FORMAÇÃO**
> Completa em Engenharia da Computação, Análise de Sistemas, Ciência da Computação e áreas afins;
**Horário de trabalho:** 9hs às 18hs.
## Local
Tecnocentro - Salvador/Baêa
## Benefícios
- Vale- Refeição e/ ou Alimentação;
- Além dos benefícios de alimentação e refeição, cedemos espaço para almoço com copa;
- Vale- transporte;
- Assistência médica;
- Assistência odontológica;
- Bonificação de férias;
- Seguro de vida;
- Participação nos lucros e resultados;
- Frutas, biscoitos e café completo;
- Home Office;
- Jornada flexível.
## Requisitos
**Obrigatórios:**
- Forte lógica de programação
- Experiência e atuação com metodologias de testes;
- Conhecimentos em SQL e LINUX
- Conhecimentos em ferramentas de automação de testes(Quality Center/Jmeter/Cucumber/Selenium, Ruby);
## Ericsson Inovação S.A
A Ericsson Inovação S.A é uma combinação singular de skills e competências na entrega de serviços profissionais na área de Suporte aos negócios e a Operação, atuamos com uma das maiores operações de telecomunicações do mundo, além de ser certificada pelo Great Place to Work, como uma das melhores empresas para se trabalhar no segmento de tecnologia da informação.
## Como se candidatar
https://jobs.kenoby.com/eisa/job/analista-de-automacao-junior/5d546b61c0c6f943d2175c68
| test | analista de automação junior na por favor só poste se a vaga for para salvador e cidades vizinhas use desenvolvedor front end ao invés de front end developer o exemplo desenvolvedor front end na analista de automação junior execução dos testes manuais e automatizados além de gerar massa de dados para a execução dos testes execução dos testes funcionais e defeitos de produção envio diário de reports sobre a evolução dos testes garantir atualização dos status da demanda na ferramenta de gestão de testes tratativas de defeitos análise coleta de evidência tramitação para desenvolvimento fechamento seguindo os padrões executar workshops dos projetos para o cliente atendimento ao cliente e acompanhamento de homologações monitorar correções e liberações de pacotes de homologação e produção acompanhar backlog dos defeitos da homologação e produção formação completa em engenharia da computação análise de sistemas ciência da computação e áreas afins horário de trabalho às local tecnocentro salvador baêa benefícios vale refeição e ou alimentação além dos benefícios de alimentação e refeição cedemos espaço para almoço com copa vale transporte assistência médica assistência odontológica bonificação de férias seguro de vida participação nos lucros e resultados frutas biscoitos e café completo home office jornada flexível requisitos obrigatórios forte lógica de programação experiência e atuação com metodologias de testes conhecimentos em sql e linux conhecimentos em ferramentas de automação de testes quality center jmeter cucumber selenium ruby ericsson inovação s a a ericsson inovação s a é uma combinação singular de skills e competências na entrega de serviços profissionais na área de suporte aos negócios e a operação atuamos com uma das maiores operações de telecomunicações do mundo além de ser certificada pelo great place to work como uma das melhores empresas para se trabalhar no segmento de tecnologia da informação como se candidatar | 1 |
14,256 | 2,796,736,793 | IssuesEvent | 2015-05-12 09:30:04 | marcopar/ethernetip4j | https://api.github.com/repos/marcopar/ethernetip4j | closed | several bug fixes and enhancements | auto-migrated Priority-Medium Type-Defect | ```
Hi,
please find the attached small patch that addresses the follow issues:
- Fix for fragmented read.
Current version threats the response always as an array. That is not the case
when you are reading the maximum object numbers that fit a single fragment + 1.
In that case the "+1" is returned as a simple object. So check like the one
done for normal read should be done.
- In CipCommandSpecificDataRequest.fillBuffer the parameters
routePathLinkedAddress and routePathPort are swapped.
The patch also adds support for reading the STRING datatype using the
SimpleLogixCommunicator class
```
Original issue reported on code.google.com by `marco...@gmail.com` on 18 Mar 2014 at 4:10
Attachments:
* [eip4j.patch](https://storage.googleapis.com/google-code-attachments/ethernetip4j/issue-2/comment-0/eip4j.patch)
| 1.0 | several bug fixes and enhancements - ```
Hi,
please find the attached small patch that addresses the follow issues:
- Fix for fragmented read.
Current version threats the response always as an array. That is not the case
when you are reading the maximum object numbers that fit a single fragment + 1.
In that case the "+1" is returned as a simple object. So check like the one
done for normal read should be done.
- In CipCommandSpecificDataRequest.fillBuffer the parameters
routePathLinkedAddress and routePathPort are swapped.
The patch also adds support for reading the STRING datatype using the
SimpleLogixCommunicator class
```
Original issue reported on code.google.com by `marco...@gmail.com` on 18 Mar 2014 at 4:10
Attachments:
* [eip4j.patch](https://storage.googleapis.com/google-code-attachments/ethernetip4j/issue-2/comment-0/eip4j.patch)
| non_test | several bug fixes and enhancements hi please find the attached small patch that addresses the follow issues fix for fragmented read current version threats the response always as an array that is not the case when you are reading the maximum object numbers that fit a single fragment in that case the is returned as a simple object so check like the one done for normal read should be done in cipcommandspecificdatarequest fillbuffer the parameters routepathlinkedaddress and routepathport are swapped the patch also adds support for reading the string datatype using the simplelogixcommunicator class original issue reported on code google com by marco gmail com on mar at attachments | 0 |
384,987 | 26,610,851,172 | IssuesEvent | 2023-01-24 00:01:08 | foundryvtt/foundryvtt | https://api.github.com/repos/foundryvtt/foundryvtt | opened | Improve clarity of documentation for combatTurn and combatRound hooks | documentation api | from: `@Kamátikos#9012`
https://foundryvtt.com/api/modules/hookEvents.html#combatTurn
> A hook event that fires when the turn of the Combat encounter changes.
When combat is started or when the round is changed, and the value of the combat's turn number is modified, this hook does not fire.
https://foundryvtt.com/api/modules/hookEvents.html#combatRound
> A hook event that fires when the round of the Combat encounter changes.
When combat is started, the value of the combat's round number is modified, but this hook does not fire.
As a suggestion, add a note which mentions that these hooks fire before the update occurs. | 1.0 | Improve clarity of documentation for combatTurn and combatRound hooks - from: `@Kamátikos#9012`
https://foundryvtt.com/api/modules/hookEvents.html#combatTurn
> A hook event that fires when the turn of the Combat encounter changes.
When combat is started or when the round is changed, and the value of the combat's turn number is modified, this hook does not fire.
https://foundryvtt.com/api/modules/hookEvents.html#combatRound
> A hook event that fires when the round of the Combat encounter changes.
When combat is started, the value of the combat's round number is modified, but this hook does not fire.
As a suggestion, add a note which mentions that these hooks fire before the update occurs. | non_test | improve clarity of documentation for combatturn and combatround hooks from kamátikos a hook event that fires when the turn of the combat encounter changes when combat is started or when the round is changed and the value of the combat s turn number is modified this hook does not fire a hook event that fires when the round of the combat encounter changes when combat is started the value of the combat s round number is modified but this hook does not fire as a suggestion add a note which mentions that these hooks fire before the update occurs | 0 |
282,737 | 24,494,039,778 | IssuesEvent | 2022-10-10 06:55:30 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | opened | DISABLED test_cuda_simple (__main__.TestMultiprocessing) | module: flaky-tests skipped module: unknown | Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_cuda_simple&suite=TestMultiprocessing) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/8793519436).
Over the past 3 hours, it has been determined flaky in 1 workflow(s) with 1 failures and 1 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT BE ALARMED IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_cuda_simple`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
| 1.0 | DISABLED test_cuda_simple (__main__.TestMultiprocessing) - Platforms: linux
This test was disabled because it is failing in CI. See [recent examples](https://hud.pytorch.org/flakytest?name=test_cuda_simple&suite=TestMultiprocessing) and the most recent trunk [workflow logs](https://github.com/pytorch/pytorch/runs/8793519436).
Over the past 3 hours, it has been determined flaky in 1 workflow(s) with 1 failures and 1 successes.
**Debugging instructions (after clicking on the recent samples link):**
DO NOT BE ALARMED IF THE CI IS GREEN. We now shield flaky tests from developers so CI will thus be green but it will be harder to parse the logs.
To find relevant log snippets:
1. Click on the workflow logs linked above
2. Click on the Test step of the job so that it is expanded. Otherwise, the grepping will not work.
3. Grep for `test_cuda_simple`
4. There should be several instances run (as flaky tests are rerun in CI) from which you can study the logs.
| test | disabled test cuda simple main testmultiprocessing platforms linux this test was disabled because it is failing in ci see and the most recent trunk over the past hours it has been determined flaky in workflow s with failures and successes debugging instructions after clicking on the recent samples link do not be alarmed if the ci is green we now shield flaky tests from developers so ci will thus be green but it will be harder to parse the logs to find relevant log snippets click on the workflow logs linked above click on the test step of the job so that it is expanded otherwise the grepping will not work grep for test cuda simple there should be several instances run as flaky tests are rerun in ci from which you can study the logs | 1 |
41,428 | 2,869,005,122 | IssuesEvent | 2015-06-05 22:31:24 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | closed | tag name selectors inside of a scoped style tag are exposed. | Area-Pkg Pkg-Csslib Priority-Unassigned Triaged Type-Enhancement | For example:
<br> div {<br> background-color: black;<br> }<br>
foo
the div selector is not localized to the component. Only work around is:
<br> .myDiv {<br> background-color: black;<br> }<br>
foo
Need to look at not mangling the selector (id and class name) but synthesizing a class so all selectors are contained inside a synthesized class selector. | 1.0 | tag name selectors inside of a scoped style tag are exposed. - For example:
<br> div {<br> background-color: black;<br> }<br>
foo
the div selector is not localized to the component. Only work around is:
<br> .myDiv {<br> background-color: black;<br> }<br>
foo
Need to look at not mangling the selector (id and class name) but synthesizing a class so all selectors are contained inside a synthesized class selector. | non_test | tag name selectors inside of a scoped style tag are exposed for example lt br gt div lt br gt background color black lt br gt lt br gt foo the div selector is not localized to the component only work around is lt br gt mydiv lt br gt background color black lt br gt lt br gt foo need to look at not mangling the selector id and class name but synthesizing a class so all selectors are contained inside a synthesized class selector | 0 |
198,381 | 14,976,924,970 | IssuesEvent | 2021-01-28 08:48:00 | ubtue/DatenProbleme | https://api.github.com/repos/ubtue/DatenProbleme | closed | ISSN 1945-1369 | Journal of drug issues | Orcid 3-fach | Einspielung_Zotero_AUTO Fehlerquelle: Translator Zotero_AUTO_RSS ready for testing | Wie bereits in #1326 thematisiert.
Dieses Phänomen gibt es auch hier, ebenfalls Sage:
https://journals.sagepub.com/doi/full/10.1177/0022042620971857
| 1.0 | ISSN 1945-1369 | Journal of drug issues | Orcid 3-fach - Wie bereits in #1326 thematisiert.
Dieses Phänomen gibt es auch hier, ebenfalls Sage:
https://journals.sagepub.com/doi/full/10.1177/0022042620971857
| test | issn journal of drug issues orcid fach wie bereits in thematisiert dieses phänomen gibt es auch hier ebenfalls sage | 1 |
766,886 | 26,903,050,264 | IssuesEvent | 2023-02-06 16:56:22 | restarone/violet_rails | https://api.github.com/repos/restarone/violet_rails | opened | fix list view in API Resources #Index | enhancement high priority | **Is your feature request related to a problem? Please describe.**
<img width="1728" alt="Screen Shot 2023-02-06 at 11 53 52 AM" src="https://user-images.githubusercontent.com/35935196/217034697-39e2bf16-2011-4d69-ba9f-8c70072e59d2.png">
Currently list views in API Resources #index are non-responsive. They show the entire JSON object so in cases where we have massive objects like Nikean's story platform-- the list view becomes unmanageable
**Describe the solution you'd like**
design and implement a better list view for managing API Resources. Move API Resources #index further up the page so the user can access it easier. Make filtering/sorting work over AJAX
| 1.0 | fix list view in API Resources #Index - **Is your feature request related to a problem? Please describe.**
<img width="1728" alt="Screen Shot 2023-02-06 at 11 53 52 AM" src="https://user-images.githubusercontent.com/35935196/217034697-39e2bf16-2011-4d69-ba9f-8c70072e59d2.png">
Currently list views in API Resources #index are non-responsive. They show the entire JSON object so in cases where we have massive objects like Nikean's story platform-- the list view becomes unmanageable
**Describe the solution you'd like**
design and implement a better list view for managing API Resources. Move API Resources #index further up the page so the user can access it easier. Make filtering/sorting work over AJAX
| non_test | fix list view in api resources index is your feature request related to a problem please describe img width alt screen shot at am src currently list views in api resources index are non responsive they show the entire json object so in cases where we have massive objects like nikean s story platform the list view becomes unmanageable describe the solution you d like design and implement a better list view for managing api resources move api resources index further up the page so the user can access it easier make filtering sorting work over ajax | 0 |
206,344 | 15,726,490,254 | IssuesEvent | 2021-03-29 11:23:19 | dascritch/cpu-audio | https://api.github.com/repos/dascritch/cpu-audio | closed | Example of React integration | doc write enhancement good first issue help wanted tests | May be React developers may be interested in this component. We need to show an example and document caveats. | 1.0 | Example of React integration - May be React developers may be interested in this component. We need to show an example and document caveats. | test | example of react integration may be react developers may be interested in this component we need to show an example and document caveats | 1 |
359,827 | 25,257,323,078 | IssuesEvent | 2022-11-15 19:16:52 | usc-isi-i2/kgtk | https://api.github.com/repos/usc-isi-i2/kgtk | opened | Readthedocs for `kgtk cat` Has Formatting Trouble | bug documentation | Invalid formatting according to readthedocs. | 1.0 | Readthedocs for `kgtk cat` Has Formatting Trouble - Invalid formatting according to readthedocs. | non_test | readthedocs for kgtk cat has formatting trouble invalid formatting according to readthedocs | 0 |
188,204 | 14,441,287,647 | IssuesEvent | 2020-12-07 16:36:07 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | bspanda98/nuclear: swarm/pss/forwarding_test.go; 3 LoC | fresh test tiny |
Found a possible issue in [bspanda98/nuclear](https://www.github.com/bspanda98/nuclear) at [swarm/pss/forwarding_test.go](https://github.com/bspanda98/nuclear/blob/43cc610d20fc2f852858571d8aac68455079132d/swarm/pss/forwarding_test.go#L251-L253)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to c at line 252 may start a goroutine
[Click here to see the code in its original context.](https://github.com/bspanda98/nuclear/blob/43cc610d20fc2f852858571d8aac68455079132d/swarm/pss/forwarding_test.go#L251-L253)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, c := range testCases {
testForwardMsg(t, ps, &c)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 43cc610d20fc2f852858571d8aac68455079132d
| 1.0 | bspanda98/nuclear: swarm/pss/forwarding_test.go; 3 LoC -
Found a possible issue in [bspanda98/nuclear](https://www.github.com/bspanda98/nuclear) at [swarm/pss/forwarding_test.go](https://github.com/bspanda98/nuclear/blob/43cc610d20fc2f852858571d8aac68455079132d/swarm/pss/forwarding_test.go#L251-L253)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to c at line 252 may start a goroutine
[Click here to see the code in its original context.](https://github.com/bspanda98/nuclear/blob/43cc610d20fc2f852858571d8aac68455079132d/swarm/pss/forwarding_test.go#L251-L253)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, c := range testCases {
testForwardMsg(t, ps, &c)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 43cc610d20fc2f852858571d8aac68455079132d
| test | nuclear swarm pss forwarding test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to c at line may start a goroutine click here to show the line s of go which triggered the analyzer go for c range testcases testforwardmsg t ps c leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.