Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
325,520 | 27,883,540,355 | IssuesEvent | 2023-03-21 21:25:33 | primitivefinance/arbiter | https://api.github.com/repos/primitivefinance/arbiter | closed | Let agents get events from contract interactions | Agents Testing & Error Handling | We want agents to be able to pick up on events that contracts emit, e.g., a change in price on a DEX.
- [ ] Create a test that displays this functionality. | 1.0 | Let agents get events from contract interactions - We want agents to be able to pick up on events that contracts emit, e.g., a change in price on a DEX.
- [ ] Create a test that displays this functionality. | test | let agents get events from contract interactions we want agents to be able to pick up on events that contracts emit e g a change in price on a dex create a test that displays this functionality | 1 |
153,723 | 12,158,629,139 | IssuesEvent | 2020-04-26 05:07:19 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: Jest Integration Tests.src/core/server/legacy/integration_tests - logging service compatibility logging config respects legacy logging settings "silent": true | failed-test | A test failed on a tracked branch
```
Error: Http server is not setup up yet
at HttpServer.start (/var/lib/jenkins/workspace/elastic+kibana+master/kibana/src/core/server/http/http_server.ts:145:13)
at HttpService.start (/var/lib/jenkins/workspace/elastic+kibana+master/kibana/src/core/server/http/http_service.ts:134:29)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+master/4693/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Integration Tests.src/core/server/legacy/integration_tests","test.name":"logging service compatibility logging config respects legacy logging settings \"silent\": true","test.failCount":19}} --> | 1.0 | Failing test: Jest Integration Tests.src/core/server/legacy/integration_tests - logging service compatibility logging config respects legacy logging settings "silent": true - A test failed on a tracked branch
```
Error: Http server is not setup up yet
at HttpServer.start (/var/lib/jenkins/workspace/elastic+kibana+master/kibana/src/core/server/http/http_server.ts:145:13)
at HttpService.start (/var/lib/jenkins/workspace/elastic+kibana+master/kibana/src/core/server/http/http_service.ts:134:29)
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+master/4693/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Jest Integration Tests.src/core/server/legacy/integration_tests","test.name":"logging service compatibility logging config respects legacy logging settings \"silent\": true","test.failCount":19}} --> | test | failing test jest integration tests src core server legacy integration tests logging service compatibility logging config respects legacy logging settings silent true a test failed on a tracked branch error http server is not setup up yet at httpserver start var lib jenkins workspace elastic kibana master kibana src core server http http server ts at httpservice start var lib jenkins workspace elastic kibana master kibana src core server http http service ts first failure | 1 |
814 | 10,632,192,697 | IssuesEvent | 2019-10-15 09:51:47 | Cha-OS/colabo | https://api.github.com/repos/Cha-OS/colabo | opened | resources-to-be-loaded for "User Actions Statuses" | moderation reliability visual_improvement | to provide "loading 1/5 ..." text
and to hide refreshing/loading info only when all resources are loaded
to provide the method for informing when all resources are loaded | True | resources-to-be-loaded for "User Actions Statuses" - to provide "loading 1/5 ..." text
and to hide refreshing/loading info only when all resources are loaded
to provide the method for informing when all resources are loaded | non_test | resources to be loaded for user actions statuses to provide loading text and to hide refreshing loading info only when all resources are loaded to provide the method for informing when all resources are loaded | 0 |
25,996 | 4,188,116,399 | IssuesEvent | 2016-06-23 19:39:33 | Microsoft/RTVS | https://api.github.com/repos/Microsoft/RTVS | reopened | Host related tests fail in batch with timeout | type:bug type:test issue | That is caused by C0000135 exit in the host (c0000135 is "Unable To Locate Component" )

| 1.0 | Host related tests fail in batch with timeout - That is caused by C0000135 exit in the host (c0000135 is "Unable To Locate Component" )

| test | host related tests fail in batch with timeout that is caused by exit in the host is unable to locate component | 1 |
6,243 | 6,266,264,709 | IssuesEvent | 2017-07-17 00:35:29 | OctopusDeploy/Issues | https://api.github.com/repos/OctopusDeploy/Issues | closed | Let's Encrypt integration does not support specific IP bindings | area/infrastructure bug | Source: http://help.octopusdeploy.com/discussions/problems/55745
Currently the Let's Encrypt integration is configured to bind certificates on 0.0.0.0, which is for any IP bound to the server. This can be a problem when trying to run additional Octopus Server instances (or IIS) on the same server.
Provide the ability to specify IP address when configuring Let's Encrypt.
| 1.0 | Let's Encrypt integration does not support specific IP bindings - Source: http://help.octopusdeploy.com/discussions/problems/55745
Currently the Let's Encrypt integration is configured to bind certificates on 0.0.0.0, which is for any IP bound to the server. This can be a problem when trying to run additional Octopus Server instances (or IIS) on the same server.
Provide the ability to specify IP address when configuring Let's Encrypt.
| non_test | let s encrypt integration does not support specific ip bindings source currently the let s encrypt integration is configured to bind certificates on which is for any ip bound to the server this can be a problem when trying to run additional octopus server instances or iis on the same server provide the ability to specify ip address when configuring let s encrypt | 0 |
280,062 | 24,278,002,890 | IssuesEvent | 2022-09-28 15:07:58 | PublicDataWorks/complaint-manager | https://api.github.com/repos/PublicDataWorks/complaint-manager | closed | Running lighthouse against CI | improve testing 🧪 | **Describe the bug**
Lighthouse is running against demo (urls are found in `lighthouserc.json`). We want to run it against CI. The issue we face is we get stuck on the login page when using CI urls. We want to bypass this.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'lighthousesrc.json'
2. Replace the demo URLS to point against CI.
3. Push the code.
4. Go to the lighthouse job in pipeline
5. Expand the "lhci autorun" tab
6. View the accessibility error and find the corresponding link to each warning
7. You'll see a small screenshot of login page instead of the actual page desired for accessibility checks.
**Expected behavior**
1. To be able to mimic the behavior when lighthouse is ran against demo. (Having no issues with authentication)
**Additional context**
https://github.com/GoogleChrome/lighthouse-ci/blob/main/docs/configuration.md
We can try using puppeteerScript. Description and steps are in the link above.
| 1.0 | Running lighthouse against CI - **Describe the bug**
Lighthouse is running against demo (urls are found in `lighthouserc.json`). We want to run it against CI. The issue we face is we get stuck on the login page when using CI urls. We want to bypass this.
**To Reproduce**
Steps to reproduce the behavior:
1. Go to 'lighthousesrc.json'
2. Replace the demo URLS to point against CI.
3. Push the code.
4. Go to the lighthouse job in pipeline
5. Expand the "lhci autorun" tab
6. View the accessibility error and find the corresponding link to each warning
7. You'll see a small screenshot of login page instead of the actual page desired for accessibility checks.
**Expected behavior**
1. To be able to mimic the behavior when lighthouse is ran against demo. (Having no issues with authentication)
**Additional context**
https://github.com/GoogleChrome/lighthouse-ci/blob/main/docs/configuration.md
We can try using puppeteerScript. Description and steps are in the link above.
| test | running lighthouse against ci describe the bug lighthouse is running against demo urls are found in lighthouserc json we want to run it against ci the issue we face is we get stuck on the login page when using ci urls we want to bypass this to reproduce steps to reproduce the behavior go to lighthousesrc json replace the demo urls to point against ci push the code go to the lighthouse job in pipeline expand the lhci autorun tab view the accessibility error and find the corresponding link to each warning you ll see a small screenshot of login page instead of the actual page desired for accessibility checks expected behavior to be able to mimic the behavior when lighthouse is ran against demo having no issues with authentication additional context we can try using puppeteerscript description and steps are in the link above | 1 |
224,519 | 17,753,739,988 | IssuesEvent | 2021-08-28 10:19:47 | sot/proseco | https://api.github.com/repos/sot/proseco | closed | API: provide obsid to proseco | enhancement Matlab testing | In the context of catalog checking (thumbs up) there can be different rules for ORs and ERs. An obsid is the normal way of differentiating.
Strictly speaking this might be needed only for aca_review, but putting it upstream in the proseco ACA table object would be nice. | 1.0 | API: provide obsid to proseco - In the context of catalog checking (thumbs up) there can be different rules for ORs and ERs. An obsid is the normal way of differentiating.
Strictly speaking this might be needed only for aca_review, but putting it upstream in the proseco ACA table object would be nice. | test | api provide obsid to proseco in the context of catalog checking thumbs up there can be different rules for ors and ers an obsid is the normal way of differentiating strictly speaking this might be needed only for aca review but putting it upstream in the proseco aca table object would be nice | 1 |
137,536 | 11,140,404,598 | IssuesEvent | 2019-12-21 14:08:27 | dexpenses/dexpenses-extract | https://api.github.com/repos/dexpenses/dexpenses-extract | closed | Implement test receipt normal/hannover-dinea-cash | enhancement test-data | Receipt to implement:
 | 1.0 | Implement test receipt normal/hannover-dinea-cash - Receipt to implement:
 | test | implement test receipt normal hannover dinea cash receipt to implement normal hannover dinea cash | 1 |
66,617 | 27,528,009,882 | IssuesEvent | 2023-03-06 19:37:45 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Missing Migration steps from "old" aad-pod-identity | container-service/svc triaged assigned-to-author doc-enhancement Pri2 | since this is preview feature , most of the users of AAD-Pod-Identity come from https://azure.github.io/aad-pod-identity/docs/demo/standard_walkthrough/
thus migration steps from that "manual" mode to this new "managed" mode is much required.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: c3c187c0-27f1-11c9-41af-6c65ca36e77e
* Version Independent ID: 249a570b-90ba-4a11-4467-320f0369ec25
* Content: [Use Azure Active Directory pod-managed identities in Azure Kubernetes Service (Preview) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/use-azure-ad-pod-identity)
* Content Source: [articles/aks/use-azure-ad-pod-identity.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/use-azure-ad-pod-identity.md)
* Service: **container-service**
* GitHub Login: @zr-msft
* Microsoft Alias: **zarhoads** | 1.0 | Missing Migration steps from "old" aad-pod-identity - since this is preview feature , most of the users of AAD-Pod-Identity come from https://azure.github.io/aad-pod-identity/docs/demo/standard_walkthrough/
thus migration steps from that "manual" mode to this new "managed" mode is much required.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: c3c187c0-27f1-11c9-41af-6c65ca36e77e
* Version Independent ID: 249a570b-90ba-4a11-4467-320f0369ec25
* Content: [Use Azure Active Directory pod-managed identities in Azure Kubernetes Service (Preview) - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/use-azure-ad-pod-identity)
* Content Source: [articles/aks/use-azure-ad-pod-identity.md](https://github.com/MicrosoftDocs/azure-docs/blob/master/articles/aks/use-azure-ad-pod-identity.md)
* Service: **container-service**
* GitHub Login: @zr-msft
* Microsoft Alias: **zarhoads** | non_test | missing migration steps from old aad pod identity since this is preview feature most of the users of aad pod identity come from thus migration steps from that manual mode to this new managed mode is much required document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login zr msft microsoft alias zarhoads | 0 |
50,576 | 6,402,316,438 | IssuesEvent | 2017-08-06 08:08:04 | aeonlang/designs | https://api.github.com/repos/aeonlang/designs | opened | File Structures | Compiler Design | ## Intro
This document describes the initial document structures for projects and solutions.
## Pretext
The key words "MUST", "MUST NOT", "REQUIRED", "SHALL", "SHALL", "SHOULD", "SHOULD NOT", "RECOMMENDED", "MAY", and "OPTIONAL" in this document are to be interpreted as described in [RFC 2119](https://www.ietf.org/rfc/rfc2119.txt).
## aeon.json
`aeon.json` is the solution level file that has the following format:
{
"projectDirectories": ["src", "tests"],
"targetFrameworks": ["win_x64", "win_x86", "MSIL"],
"buildConfigurations": [ // anything set in here gets inherited by all projects in the src/tests directory
{
"name": "debug",
"compilationOptions": {
"applyOptimizations": false,
"compiledFiles": ["**/*.fli"], // default
"excludedFiles": ["**/*.dll"], // for example, default is empty
"copiedFiles": ["**/*.png"] // files to be copied to output directory, default is empty
}
}
]
}
## aeonproj.json
`aeonproj.json` is the project level file that has the following format:
{
"packageName": "fli.sample",
"version": "1.0.0", // semver
"authors": [{
"name": "Stuart Blackler", // required
"email": "not@areal.email", // optional
"website": "https://im5tu.io" // optional
}],
"licenseUrl": "https://im5tu.io", // required
"projectUrl": "https://im5tu.io", // required
}
## aeontool.json
`aeontool.json` is the tool definition file that has the following format:
{
toolName: "aeon-compile",
repository: "git@github.com:aeonlang/compiler.git"
configuration: [
{ key: "", value: "" }
]
}
Properties:
- `toolName`: The name of the executable (minus extensions) that is ran.
- `configuration`: Default key value pairs which are passed to the application when called from `aeon.exe` | 1.0 | File Structures - ## Intro
This document describes the initial document structures for projects and solutions.
## Pretext
The key words "MUST", "MUST NOT", "REQUIRED", "SHALL", "SHALL", "SHOULD", "SHOULD NOT", "RECOMMENDED", "MAY", and "OPTIONAL" in this document are to be interpreted as described in [RFC 2119](https://www.ietf.org/rfc/rfc2119.txt).
## aeon.json
`aeon.json` is the solution level file that has the following format:
{
"projectDirectories": ["src", "tests"],
"targetFrameworks": ["win_x64", "win_x86", "MSIL"],
"buildConfigurations": [ // anything set in here gets inherited by all projects in the src/tests directory
{
"name": "debug",
"compilationOptions": {
"applyOptimizations": false,
"compiledFiles": ["**/*.fli"], // default
"excludedFiles": ["**/*.dll"], // for example, default is empty
"copiedFiles": ["**/*.png"] // files to be copied to output directory, default is empty
}
}
]
}
## aeonproj.json
`aeonproj.json` is the project level file that has the following format:
{
"packageName": "fli.sample",
"version": "1.0.0", // semver
"authors": [{
"name": "Stuart Blackler", // required
"email": "not@areal.email", // optional
"website": "https://im5tu.io" // optional
}],
"licenseUrl": "https://im5tu.io", // required
"projectUrl": "https://im5tu.io", // required
}
## aeontool.json
`aeontool.json` is the tool definition file that has the following format:
{
toolName: "aeon-compile",
repository: "git@github.com:aeonlang/compiler.git"
configuration: [
{ key: "", value: "" }
]
}
Properties:
- `toolName`: The name of the executable (minus extensions) that is ran.
- `configuration`: Default key value pairs which are passed to the application when called from `aeon.exe` | non_test | file structures intro this document describes the initial document structures for projects and solutions pretext the key words must must not required shall shall should should not recommended may and optional in this document are to be interpreted as described in aeon json aeon json is the solution level file that has the following format projectdirectories targetframeworks buildconfigurations anything set in here gets inherited by all projects in the src tests directory name debug compilationoptions applyoptimizations false compiledfiles default excludedfiles for example default is empty copiedfiles files to be copied to output directory default is empty aeonproj json aeonproj json is the project level file that has the following format packagename fli sample version semver authors name stuart blackler required email not areal email optional website optional licenseurl required projecturl required aeontool json aeontool json is the tool definition file that has the following format toolname aeon compile repository git github com aeonlang compiler git configuration key value properties toolname the name of the executable minus extensions that is ran configuration default key value pairs which are passed to the application when called from aeon exe | 0 |
123,162 | 10,255,965,593 | IssuesEvent | 2019-08-21 16:31:29 | spack/spack | https://api.github.com/repos/spack/spack | closed | `spack pkg` command and tests fail for git < 1.8.5 | bug robustness tests | The implementation of the `spack pkg` command assumes one is working in an environment with a git >= 1.8.5, as the `-C` option is used for all invocations of the `git` command. Associated tests also fail, see `spack test cmd/pkg`:
```console
$ spack test cmd/pkg
...
E ProcessError: Command exited with status 129:
E '/usr/bin/git' '-C' '/tmp/pytest-of-greenc/pytest-52/mock_pkg_git_repo0/builtin.mock/packages' 'ls-tree' '--name-only' 'HEAD^^'
../util/executable.py:189: ProcessError
-------------------------------------------------------------------------- Captured stderr call ---------------------------------------------------------------------------
Unknown option: -C
usage: git [--version] [--help] [-c name=value]
[--exec-path[=<path>]] [--html-path] [--man-path] [--info-path]
[-p|--paginate|--no-pager] [--no-replace-objects] [--bare]
[--git-dir=<path>] [--work-tree=<path>] [--namespace=<name>]
<command> [<args>]
```
On a standard `Scientific7` (or `RHEL7`) system, the version of git available is `1.8.3.1`. On `RHEL6` (still in extensive use in HEP), it is `1.7.1`.
A reasonable solution might be to test for the version and fall back on a function wrapper to the git `Executable` that invokes it with the current directory corresponding to the desired `path`. | 1.0 | `spack pkg` command and tests fail for git < 1.8.5 - The implementation of the `spack pkg` command assumes one is working in an environment with a git >= 1.8.5, as the `-C` option is used for all invocations of the `git` command. Associated tests also fail, see `spack test cmd/pkg`:
```console
$ spack test cmd/pkg
...
E ProcessError: Command exited with status 129:
E '/usr/bin/git' '-C' '/tmp/pytest-of-greenc/pytest-52/mock_pkg_git_repo0/builtin.mock/packages' 'ls-tree' '--name-only' 'HEAD^^'
../util/executable.py:189: ProcessError
-------------------------------------------------------------------------- Captured stderr call ---------------------------------------------------------------------------
Unknown option: -C
usage: git [--version] [--help] [-c name=value]
[--exec-path[=<path>]] [--html-path] [--man-path] [--info-path]
[-p|--paginate|--no-pager] [--no-replace-objects] [--bare]
[--git-dir=<path>] [--work-tree=<path>] [--namespace=<name>]
<command> [<args>]
```
On a standard `Scientific7` (or `RHEL7`) system, the version of git available is `1.8.3.1`. On `RHEL6` (still in extensive use in HEP), it is `1.7.1`.
A reasonable solution might be to test for the version and fall back on a function wrapper to the git `Executable` that invokes it with the current directory corresponding to the desired `path`. | test | spack pkg command and tests fail for git as the c option is used for all invocations of the git command associated tests also fail see spack test cmd pkg console spack test cmd pkg e processerror command exited with status e usr bin git c tmp pytest of greenc pytest mock pkg git builtin mock packages ls tree name only head util executable py processerror captured stderr call unknown option c usage git on a standard or system the version of git available is on still in extensive use in hep it is a reasonable solution might be to test for the version and fall back on a function wrapper to the git executable that invokes it with the current directory corresponding to the desired path | 1 |
89,236 | 8,198,466,482 | IssuesEvent | 2018-08-31 16:29:31 | aspnet/Hosting | https://api.github.com/repos/aspnet/Hosting | closed | Test failure: ShutdownTestRun | Branch:2.2 Branch:master test-failure | This test [fails](http://aspnetci/viewLog.html?buildId=528440&buildTypeId=Releases_22xPublic_UbuntuUniverse) occasionally with the following error:
```
System.NullReferenceException : Object reference not set to an instance of an object.
at Microsoft.AspNetCore.Server.IntegrationTesting.ApplicationDeployer.CleanPublishedOutput() in /_/src/Microsoft.AspNetCore.Server.IntegrationTesting/Deployers/ApplicationDeployer.cs:line 100
at Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer.Dispose() in /_/src/Microsoft.AspNetCore.Server.IntegrationTesting/Deployers/SelfHostDeployer.cs:line 205
at Microsoft.AspNetCore.Hosting.FunctionalTests.ShutdownTests.ExecuteShutdownTest(String testName, String shutdownMechanic) in /_/test/Microsoft.AspNetCore.Hosting.FunctionalTests/ShutdownTests.cs:line 114
at Microsoft.AspNetCore.Hosting.FunctionalTests.ShutdownTests.ShutdownTestRun() in /_/test/Microsoft.AspNetCore.Hosting.FunctionalTests/ShutdownTests.cs:line 33
--- End of stack trace from previous location where exception was thrown ---
------- Stdout: -------
| [0.015s] TestLifetime Information: Starting test ShutdownTestRun at 2018-08-10T22:40:24
| [0.001s] TestLifetime Information: Starting test ExecuteShutdownTest at 2018-08-10T22:40:24
| [0.009s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: Deploying [Variation] :: ServerType=Kestrel, Runtime=CoreClr, Arch=x64, BaseUrlHint=, Publish=True
| [0.014s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: Executing command dotnet publish --output "/mnt/temp/buildTmp/27932f56ea2345cc9813f135d51da328" --framework netcoreapp2.2 --configuration Release --no-restore -p:VerifyMatchingImplicitPackageVersion=false
| [0.332s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: Microsoft (R) Build Engine version 15.7.179.6572 for .NET Core
| [0.333s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: Copyright (C) Microsoft Corporation. All rights reserved.
| [2.505s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/GenerateAssemblyInfo.targets(25,5): error MSB4062: The "Microsoft.AspNetCore.BuildTools.Sdk_GetAssemblyFileVersion" task could not be loaded from the assembly /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/../tools/netcoreapp2.1/Internal.AspNetCore.Sdk.dll. Assembly with same name is already loaded Confirm that the <UsingTask> declaration is correct, that the assembly and all its dependencies are available, and that the task contains a public class that implements Microsoft.Build.Framework.ITask. [/mnt/work/33bdfc1cae7b2a38/modules/Hosting/src/Microsoft.Extensions.Hosting.Abstractions/Microsoft.Extensions.Hosting.Abstractions.csproj]
| [2.515s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/GenerateAssemblyInfo.targets(25,5): error MSB4062: The "Microsoft.AspNetCore.BuildTools.Sdk_GetAssemblyFileVersion" task could not be loaded from the assembly /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/../tools/netcoreapp2.1/Internal.AspNetCore.Sdk.dll. Assembly with same name is already loaded Confirm that the <UsingTask> declaration is correct, that the assembly and all its dependencies are available, and that the task contains a public class that implements Microsoft.Build.Framework.ITask. [/mnt/work/33bdfc1cae7b2a38/modules/Hosting/src/Microsoft.AspNetCore.Hosting.Server.Abstractions/Microsoft.AspNetCore.Hosting.Server.Abstractions.csproj]
| [2.602s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Error: dotnet publish exited with exit code : 1
| [2.605s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Warning: Host process already exited or never started successfully.
| [2.607s] TestLifetime Information: Finished test ExecuteShutdownTest in 2.6064648s
| [2.664s] TestLifetime Information: Finished test ShutdownTestRun in 2.6582765s
```
Other tests within that build may have failed with a similar message, but they are not listed here. Check the link above for more info.
This test failed on 2.2.
CC @Eilon (because the bot doesn't know who else to pick)
This issue was made automatically. If there is a problem contact ryanbrandenburg. | 1.0 | Test failure: ShutdownTestRun - This test [fails](http://aspnetci/viewLog.html?buildId=528440&buildTypeId=Releases_22xPublic_UbuntuUniverse) occasionally with the following error:
```
System.NullReferenceException : Object reference not set to an instance of an object.
at Microsoft.AspNetCore.Server.IntegrationTesting.ApplicationDeployer.CleanPublishedOutput() in /_/src/Microsoft.AspNetCore.Server.IntegrationTesting/Deployers/ApplicationDeployer.cs:line 100
at Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer.Dispose() in /_/src/Microsoft.AspNetCore.Server.IntegrationTesting/Deployers/SelfHostDeployer.cs:line 205
at Microsoft.AspNetCore.Hosting.FunctionalTests.ShutdownTests.ExecuteShutdownTest(String testName, String shutdownMechanic) in /_/test/Microsoft.AspNetCore.Hosting.FunctionalTests/ShutdownTests.cs:line 114
at Microsoft.AspNetCore.Hosting.FunctionalTests.ShutdownTests.ShutdownTestRun() in /_/test/Microsoft.AspNetCore.Hosting.FunctionalTests/ShutdownTests.cs:line 33
--- End of stack trace from previous location where exception was thrown ---
------- Stdout: -------
| [0.015s] TestLifetime Information: Starting test ShutdownTestRun at 2018-08-10T22:40:24
| [0.001s] TestLifetime Information: Starting test ExecuteShutdownTest at 2018-08-10T22:40:24
| [0.009s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: Deploying [Variation] :: ServerType=Kestrel, Runtime=CoreClr, Arch=x64, BaseUrlHint=, Publish=True
| [0.014s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: Executing command dotnet publish --output "/mnt/temp/buildTmp/27932f56ea2345cc9813f135d51da328" --framework netcoreapp2.2 --configuration Release --no-restore -p:VerifyMatchingImplicitPackageVersion=false
| [0.332s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: Microsoft (R) Build Engine version 15.7.179.6572 for .NET Core
| [0.333s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: Copyright (C) Microsoft Corporation. All rights reserved.
| [2.505s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/GenerateAssemblyInfo.targets(25,5): error MSB4062: The "Microsoft.AspNetCore.BuildTools.Sdk_GetAssemblyFileVersion" task could not be loaded from the assembly /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/../tools/netcoreapp2.1/Internal.AspNetCore.Sdk.dll. Assembly with same name is already loaded Confirm that the <UsingTask> declaration is correct, that the assembly and all its dependencies are available, and that the task contains a public class that implements Microsoft.Build.Framework.ITask. [/mnt/work/33bdfc1cae7b2a38/modules/Hosting/src/Microsoft.Extensions.Hosting.Abstractions/Microsoft.Extensions.Hosting.Abstractions.csproj]
| [2.515s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Information: dotnet-publish stdout: /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/GenerateAssemblyInfo.targets(25,5): error MSB4062: The "Microsoft.AspNetCore.BuildTools.Sdk_GetAssemblyFileVersion" task could not be loaded from the assembly /mnt/work/33bdfc1cae7b2a38/.packages/internal.aspnetcore.sdk/2.2.0-preview1-20180807.2/build/../tools/netcoreapp2.1/Internal.AspNetCore.Sdk.dll. Assembly with same name is already loaded Confirm that the <UsingTask> declaration is correct, that the assembly and all its dependencies are available, and that the task contains a public class that implements Microsoft.Build.Framework.ITask. [/mnt/work/33bdfc1cae7b2a38/modules/Hosting/src/Microsoft.AspNetCore.Hosting.Server.Abstractions/Microsoft.AspNetCore.Hosting.Server.Abstractions.csproj]
| [2.602s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Error: dotnet publish exited with exit code : 1
| [2.605s] Microsoft.AspNetCore.Server.IntegrationTesting.SelfHostDeployer Warning: Host process already exited or never started successfully.
| [2.607s] TestLifetime Information: Finished test ExecuteShutdownTest in 2.6064648s
| [2.664s] TestLifetime Information: Finished test ShutdownTestRun in 2.6582765s
```
Other tests within that build may have failed with a similar message, but they are not listed here. Check the link above for more info.
This test failed on 2.2.
CC @Eilon (because the bot doesn't know who else to pick)
This issue was made automatically. If there is a problem contact ryanbrandenburg. | test | test failure shutdowntestrun this test occasionally with the following error system nullreferenceexception object reference not set to an instance of an object at microsoft aspnetcore server integrationtesting applicationdeployer cleanpublishedoutput in src microsoft aspnetcore server integrationtesting deployers applicationdeployer cs line at microsoft aspnetcore server integrationtesting selfhostdeployer dispose in src microsoft aspnetcore server integrationtesting deployers selfhostdeployer cs line at microsoft aspnetcore hosting functionaltests shutdowntests executeshutdowntest string testname string shutdownmechanic in test microsoft aspnetcore hosting functionaltests shutdowntests cs line at microsoft aspnetcore hosting functionaltests shutdowntests shutdowntestrun in test microsoft aspnetcore hosting functionaltests shutdowntests cs line end of stack trace from previous location where exception was thrown stdout testlifetime information starting test shutdowntestrun at testlifetime information starting test executeshutdowntest at microsoft aspnetcore server integrationtesting selfhostdeployer information deploying servertype kestrel runtime coreclr arch baseurlhint publish true microsoft aspnetcore server integrationtesting selfhostdeployer information executing command dotnet publish output mnt temp buildtmp framework configuration release no restore p verifymatchingimplicitpackageversion false microsoft aspnetcore server integrationtesting selfhostdeployer information dotnet publish stdout microsoft r build engine version for net core microsoft aspnetcore server integrationtesting selfhostdeployer information dotnet publish stdout copyright c microsoft corporation all rights reserved microsoft aspnetcore server integrationtesting selfhostdeployer information dotnet publish stdout mnt work packages internal aspnetcore sdk build generateassemblyinfo targets error the microsoft aspnetcore buildtools sdk getassemblyfileversion task could not be loaded from the assembly mnt work packages internal aspnetcore sdk build tools internal aspnetcore sdk dll assembly with same name is already loaded confirm that the declaration is correct that the assembly and all its dependencies are available and that the task contains a public class that implements microsoft build framework itask microsoft aspnetcore server integrationtesting selfhostdeployer information dotnet publish stdout mnt work packages internal aspnetcore sdk build generateassemblyinfo targets error the microsoft aspnetcore buildtools sdk getassemblyfileversion task could not be loaded from the assembly mnt work packages internal aspnetcore sdk build tools internal aspnetcore sdk dll assembly with same name is already loaded confirm that the declaration is correct that the assembly and all its dependencies are available and that the task contains a public class that implements microsoft build framework itask microsoft aspnetcore server integrationtesting selfhostdeployer error dotnet publish exited with exit code microsoft aspnetcore server integrationtesting selfhostdeployer warning host process already exited or never started successfully testlifetime information finished test executeshutdowntest in testlifetime information finished test shutdowntestrun in other tests within that build may have failed with a similar message but they are not listed here check the link above for more info this test failed on cc eilon because the bot doesn t know who else to pick this issue was made automatically if there is a problem contact ryanbrandenburg | 1 |
340,814 | 30,544,906,717 | IssuesEvent | 2023-07-20 02:26:56 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | roachtest: schemachange/mixed-versions-compat failed | C-test-failure O-robot O-roachtest T-sql-foundations branch-release-22.2 | roachtest.schemachange/mixed-versions-compat [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10830317?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10830317?buildTab=artifacts#/schemachange/mixed-versions-compat) on release-22.2 @ [f0bda42400b5bcd7a2ccad3611144793a00f18a8](https://github.com/cockroachdb/cockroach/commits/f0bda42400b5bcd7a2ccad3611144793a00f18a8):
```
test artifacts and logs in: /artifacts/schemachange/mixed-versions-compat/run_1
(mixed_version_decl_schemachange_compat.go:64).fetchCorpusToTmpDir: Missing validation corpus for release-22.1 (output in run_142406.749563148_n1_gsutil-cp-gscockroac: gsutil cp gs://cockroach-corpus/corpus-release-22.1/corpus /tmp/corpus2031648367/corpus returned: COMMAND_PROBLEM: ssh verbose log retained in ssh_142406.755148833_n1_gsutil-cp-gscockroac.log: exit status 1)
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-foundations
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*schemachange/mixed-versions-compat.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-29581 | 2.0 | roachtest: schemachange/mixed-versions-compat failed - roachtest.schemachange/mixed-versions-compat [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10830317?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/10830317?buildTab=artifacts#/schemachange/mixed-versions-compat) on release-22.2 @ [f0bda42400b5bcd7a2ccad3611144793a00f18a8](https://github.com/cockroachdb/cockroach/commits/f0bda42400b5bcd7a2ccad3611144793a00f18a8):
```
test artifacts and logs in: /artifacts/schemachange/mixed-versions-compat/run_1
(mixed_version_decl_schemachange_compat.go:64).fetchCorpusToTmpDir: Missing validation corpus for release-22.1 (output in run_142406.749563148_n1_gsutil-cp-gscockroac: gsutil cp gs://cockroach-corpus/corpus-release-22.1/corpus /tmp/corpus2031648367/corpus returned: COMMAND_PROBLEM: ssh verbose log retained in ssh_142406.755148833_n1_gsutil-cp-gscockroac.log: exit status 1)
```
<p>Parameters: <code>ROACHTEST_arch=amd64</code>
, <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-foundations
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*schemachange/mixed-versions-compat.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-29581 | test | roachtest schemachange mixed versions compat failed roachtest schemachange mixed versions compat with on release test artifacts and logs in artifacts schemachange mixed versions compat run mixed version decl schemachange compat go fetchcorpustotmpdir missing validation corpus for release output in run gsutil cp gscockroac gsutil cp gs cockroach corpus corpus release corpus tmp corpus returned command problem ssh verbose log retained in ssh gsutil cp gscockroac log exit status parameters roachtest arch roachtest cloud gce roachtest cpu roachtest encrypted false roachtest ssd help see see cc cockroachdb sql foundations jira issue crdb | 1 |
97,828 | 20,424,198,337 | IssuesEvent | 2022-02-24 00:50:13 | WordPress/openverse-catalog | https://api.github.com/repos/WordPress/openverse-catalog | opened | Enable XCom pickling | good first issue help wanted 🟩 priority: low ✨ goal: improvement 💻 aspect: code 🐳 tech: docker | ## Problem
<!-- Describe a problem solved by this feature; or delete the section entirely. -->
XComs by default are inserted into the database as strings. While this is more secure, it can make handling native Python types very difficult.
## Description
<!-- Describe the feature and how it solves the problem. -->
We should [enable XCom pickling](https://airflow.apache.org/docs/apache-airflow/stable/configurations-ref.html#enable-xcom-pickling) in the Airflow configuration. This will make operations which use upstream XComs easier since we will not have to do string/JSON conversions each time we pull the XCom (e.g. see [this comment](https://github.com/WordPress/openverse-catalog/pull/369#discussion_r813215801)).
This is something we can add to the [Docker Airflow configuration block in the Dockerfile](https://github.com/WordPress/openverse-catalog/blob/69b2eb7aaa2daf54029fac57b3b99405734da7de/docker/airflow/Dockerfile#L16).
## Alternatives
<!-- Describe any alternative solutions or features you have considered. How is this feature better? -->
## Additional context
<!-- Add any other context about the feature here; or delete the section entirely. -->
[Pickling](https://docs.python.org/3/library/pickle.html) serializes/deserializes native Python objects, which introduces an opportunity for remote code execution. Since our Airflow is behind authentication, I believe that the benefit we gain from pickling is worth this extra risk. In any case, **we should always be careful what data we're passing via XComs**. Those values go into the database, so we need to 1) make sure we trust them and 2) be careful not to try and store too much information in an XCom (e.g. passing Pandas DataFrames via XComs is generally considered a Bad Idea, unless one is certain they will be small).
## Implementation
<!-- Replace the [ ] with [x] to check the box. -->
- [ ] 🙋 I would be interested in implementing this feature.
| 1.0 | Enable XCom pickling - ## Problem
<!-- Describe a problem solved by this feature; or delete the section entirely. -->
XComs by default are inserted into the database as strings. While this is more secure, it can make handling native Python types very difficult.
## Description
<!-- Describe the feature and how it solves the problem. -->
We should [enable XCom pickling](https://airflow.apache.org/docs/apache-airflow/stable/configurations-ref.html#enable-xcom-pickling) in the Airflow configuration. This will make operations which use upstream XComs easier since we will not have to do string/JSON conversions each time we pull the XCom (e.g. see [this comment](https://github.com/WordPress/openverse-catalog/pull/369#discussion_r813215801)).
This is something we can add to the [Docker Airflow configuration block in the Dockerfile](https://github.com/WordPress/openverse-catalog/blob/69b2eb7aaa2daf54029fac57b3b99405734da7de/docker/airflow/Dockerfile#L16).
## Alternatives
<!-- Describe any alternative solutions or features you have considered. How is this feature better? -->
## Additional context
<!-- Add any other context about the feature here; or delete the section entirely. -->
[Pickling](https://docs.python.org/3/library/pickle.html) serializes/deserializes native Python objects, which introduces an opportunity for remote code execution. Since our Airflow is behind authentication, I believe that the benefit we gain from pickling is worth this extra risk. In any case, **we should always be careful what data we're passing via XComs**. Those values go into the database, so we need to 1) make sure we trust them and 2) be careful not to try and store too much information in an XCom (e.g. passing Pandas DataFrames via XComs is generally considered a Bad Idea, unless one is certain they will be small).
## Implementation
<!-- Replace the [ ] with [x] to check the box. -->
- [ ] 🙋 I would be interested in implementing this feature.
| non_test | enable xcom pickling problem xcoms by default are inserted into the database as strings while this is more secure it can make handling native python types very difficult description we should in the airflow configuration this will make operations which use upstream xcoms easier since we will not have to do string json conversions each time we pull the xcom e g see this is something we can add to the alternatives additional context serializes deserializes native python objects which introduces an opportunity for remote code execution since our airflow is behind authentication i believe that the benefit we gain from pickling is worth this extra risk in any case we should always be careful what data we re passing via xcoms those values go into the database so we need to make sure we trust them and be careful not to try and store too much information in an xcom e g passing pandas dataframes via xcoms is generally considered a bad idea unless one is certain they will be small implementation 🙋 i would be interested in implementing this feature | 0 |
245,665 | 20,792,425,615 | IssuesEvent | 2022-03-17 04:35:33 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | sql: TestDistSQLRunningInAbortedTxn failed | C-test-failure O-robot branch-master T-sql-queries | sql.TestDistSQLRunningInAbortedTxn [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4575824&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4575824&tab=artifacts#/) on master @ [f5fc84fb5707428ae9505c5e3e90cf3f63d465ad](https://github.com/cockroachdb/cockroach/commits/f5fc84fb5707428ae9505c5e3e90cf3f63d465ad):
```
=== RUN TestDistSQLRunningInAbortedTxn
test_log_scope.go:79: test logs captured to: /artifacts/tmp/_tmp/233e6aa31ff7ad29c896f0479cb5d0c4/logTestDistSQLRunningInAbortedTxn177929880
test_log_scope.go:80: use -show-logs to present logs inline
```
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
Parameters in this failure:
- TAGS=bazel,gss,deadlock
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestDistSQLRunningInAbortedTxn.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-13789 | 1.0 | sql: TestDistSQLRunningInAbortedTxn failed - sql.TestDistSQLRunningInAbortedTxn [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=4575824&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=4575824&tab=artifacts#/) on master @ [f5fc84fb5707428ae9505c5e3e90cf3f63d465ad](https://github.com/cockroachdb/cockroach/commits/f5fc84fb5707428ae9505c5e3e90cf3f63d465ad):
```
=== RUN TestDistSQLRunningInAbortedTxn
test_log_scope.go:79: test logs captured to: /artifacts/tmp/_tmp/233e6aa31ff7ad29c896f0479cb5d0c4/logTestDistSQLRunningInAbortedTxn177929880
test_log_scope.go:80: use -show-logs to present logs inline
```
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
Parameters in this failure:
- TAGS=bazel,gss,deadlock
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestDistSQLRunningInAbortedTxn.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-13789 | test | sql testdistsqlrunninginabortedtxn failed sql testdistsqlrunninginabortedtxn with on master run testdistsqlrunninginabortedtxn test log scope go test logs captured to artifacts tmp tmp test log scope go use show logs to present logs inline help see also parameters in this failure tags bazel gss deadlock cc cockroachdb sql queries jira issue crdb | 1 |
83,028 | 7,859,641,575 | IssuesEvent | 2018-06-21 17:15:37 | coreos/etcd | https://api.github.com/repos/coreos/etcd | closed | etcd integration_e2e test "TestV3CurlCipherSuitesMismatch" is failing | Testing | test log:
```
--- PASS: TestV3CurlCipherSuitesValid (1.12s)
=== RUN TestV3CurlCipherSuitesMismatch
--- FAIL: TestV3CurlCipherSuitesMismatch (1.11s)
v3_curl_test.go:391: failed get with curl (read /dev/ptmx: input/output error (expected "alert handshake failure", got ["# HELP etcd_debugging_lease_granted_total The total number of granted leases.
# TYPE etcd_debugging_lease_granted_total counter
etcd_debugging_lease_granted_total
# HELP etcd_debugging_lease_renewed_total The number of renewed leases seen by the leader.
# TYPE etcd_debugging_lease_renewed_total counter
etcd_debugging_lease_renewed_total
# HELP etcd_debugging_lease_revoked_total The total number of revoked leases.
# TYPE etcd_debugging_lease_revoked_total counter
etcd_debugging_lease_revoked_total
# HELP etcd_debugging_lease_ttl_total Bucketed histogram of lease TTLs.
# TYPE etcd_debugging_lease_ttl_total histogram
etcd_debugging_lease_ttl_total_bucket{le=\"1\"}
etcd_debugging_lease_ttl_total_bucket{le=\"2\"}
etcd_debugging_lease_ttl_total_bucket{le=\"4\"}
etcd_debugging_lease_ttl_total_bucket{le=\"8\"}
etcd_debugging_lease_ttl_total_bucket{le=\"16\"}
etcd_debugging_lease_ttl_total_bucket{le=\"32\"}
etcd_debugging_lease_ttl_total_bucket{le=\"64\"}
etcd_debugging_lease_ttl_total_bucket{le=\"128\"}
etcd_debugging_lease_ttl_total_bucket{le=\"256\"}
etcd_debugging_lease_ttl_total_bucket{le=\"512\"}
etcd_debugging_lease_ttl_total_bucket{le=\"1024\"}
etcd_debugging_lease_ttl_total_bucket{le=\"2048\"}
etcd_debugging_lease_ttl_total_bucket{le=\"4096\"}
etcd_debugging_lease_ttl_total_bucket{le=\"8192\"}
etcd_debugging_lease_ttl_total_bucket{le=\"16384\"}
etcd_debugging_lease_ttl_total_bucket{le=\"32768\"}
etcd_debugging_lease_ttl_total_bucket{le=\"65536\"}
etcd_debugging_lease_ttl_total_bucket{le=\"131072\"}
etcd_debugging_lease_ttl_total_bucket{le=\"262144\"}
etcd_debugging_lease_ttl_total_bucket{le=\"524288\"}
etcd_debugging_lease_ttl_total_bucket{le=\"1.048576e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"2.097152e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"4.194304e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"8.388608e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"+Inf\"}
etcd_debugging_lease_ttl_total_sum
etcd_debugging_lease_ttl_total_count
# HELP etcd_debugging_mvcc_db_compaction_keys_total Total number of db keys compacted.
# TYPE etcd_debugging_mvcc_db_compaction_keys_total counter
etcd_debugging_mvcc_db_compaction_keys_total
# HELP etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds Bucketed histogram of db compaction pause duration.
# TYPE etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds histogram
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"1\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"2\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"4\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"8\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"16\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"32\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"64\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"128\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"256\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"512\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"1024\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"2048\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"4096\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"+Inf\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_sum
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_count
# HELP etcd_debugging_mvcc_db_compaction_total_duration_milliseconds Bucketed histogram of db compaction total duration.
# TYPE etcd_debugging_mvcc_db_compaction_total_duration_milliseconds histogram
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"100\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"400\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"800\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"1600\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"3200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"6400\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"12800\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"25600\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"51200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"102400\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"204800\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"409600\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"819200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"+Inf\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_sum
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_count
# HELP etcd_debugging_mvcc_db_total_size_in_bytes Total size of the underlying database physically allocated in bytes.
# TYPE etcd_debugging_mvcc_db_total_size_in_bytes gauge
etcd_debugging_mvcc_db_total_size_in_bytes 32768
# HELP etcd_debugging_mvcc_delete_total Total number of deletes seen by this member.
# TYPE etcd_debugging_mvcc_delete_total counter
etcd_debugging_mvcc_delete_total
# HELP etcd_debugging_mvcc_events_total Total number of events sent by this member.
# TYPE etcd_debugging_mvcc_events_total counter
etcd_debugging_mvcc_events_total
# HELP etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds Bucketed histogram of index compaction pause duration.
# TYPE etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds histogram
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"0.5\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"1\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"2\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"4\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"8\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"16\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"32\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"64\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"128\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"256\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"512\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"1024\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"2048\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"4096\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"+Inf\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_sum
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_count
# HELP etcd_debugging_mvcc_keys_total Total number of keys.
# TYPE etcd_debugging_mvcc_keys_total gauge
etcd_debugging_mvcc_keys_total
# HELP etcd_debugging_mvcc_pending_events_total Total number of pending events to be sent.
# TYPE etcd_debugging_mvcc_pending_events_total gauge
etcd_debugging_mvcc_pending_events_total
# HELP etcd_debugging_mvcc_put_total Total number of puts seen by this member.
# TYPE etcd_debugging_mvcc_put_total counter
etcd_debugging_mvcc_put_total
# HELP etcd_debugging_mvcc_range_total Total number of ranges seen by this member.
# TYPE etcd_debugging_mvcc_range_total counter
etcd_debugging_mvcc_range_total
# HELP etcd_debugging_mvcc_slow_watcher_total Total number of unsynced slow watchers.
# TYPE etcd_debugging_mvcc_slow_watcher_total gauge
etcd_debugging_mvcc_slow_watcher_total
# HELP etcd_debugging_mvcc_txn_total Total number of txns seen by this member.
# TYPE etcd_debugging_mvcc_txn_total counter
etcd_debugging_mvcc_txn_total
# HELP etcd_debugging_mvcc_watch_stream_total Total number of watch streams.
# TYPE etcd_debugging_mvcc_watch_stream_total gauge
etcd_debugging_mvcc_watch_stream_total
# HELP etcd_debugging_mvcc_watcher_total Total number of watchers.
# TYPE etcd_debugging_mvcc_watcher_total gauge
etcd_debugging_mvcc_watcher_total
# HELP etcd_debugging_server_lease_expired_total The total number of expired leases.
# TYPE etcd_debugging_server_lease_expired_total counter
etcd_debugging_server_lease_expired_total
# HELP etcd_debugging_snap_save_marshalling_duration_seconds The marshalling cost distributions of save called by snapshot.
# TYPE etcd_debugging_snap_save_marshalling_duration_seconds histogram
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.001\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.002\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.004\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.008\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.016\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.032\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.064\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.128\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.256\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.512\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"1.024\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"2.048\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"4.096\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"8.192\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"+Inf\"}
etcd_debugging_snap_save_marshalling_duration_seconds_sum
etcd_debugging_snap_save_marshalling_duration_seconds_count
# HELP etcd_debugging_snap_save_total_duration_seconds The total latency distributions of save called by snapshot.
# TYPE etcd_debugging_snap_save_total_duration_seconds histogram
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.001\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.002\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.004\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.008\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.016\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.032\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.064\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.128\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.256\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.512\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"1.024\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"2.048\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"4.096\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"8.192\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"+Inf\"}
etcd_debugging_snap_save_total_duration_seconds_sum
etcd_debugging_snap_save_total_duration_seconds_count
# HELP etcd_debugging_store_expires_total Total number of expired keys.
# TYPE etcd_debugging_store_expires_total counter
etcd_debugging_store_expires_total
# HELP etcd_debugging_store_reads_total Total number of reads action by (get/getRecursive), local to this member.
# TYPE etcd_debugging_store_reads_total counter
etcd_debugging_store_reads_total{action=\"getRecursive\"} 1
# HELP etcd_debugging_store_watch_requests_total Total number of incoming watch requests (new or reestablished).
# TYPE etcd_debugging_store_watch_requests_total counter
etcd_debugging_store_watch_requests_total
# HELP etcd_debugging_store_watchers Count of currently active watchers.
# TYPE etcd_debugging_store_watchers gauge
etcd_debugging_store_watchers
# HELP etcd_debugging_store_writes_total Total number of writes (e.g. set/compareAndDelete) seen by this member.
# TYPE etcd_debugging_store_writes_total counter
etcd_debugging_store_writes_total{action=\"create\"} 1
etcd_debugging_store_writes_total{action=\"set\"} 2
# HELP etcd_disk_backend_commit_duration_seconds The latency distributions of commit called by backend.
# TYPE etcd_disk_backend_commit_duration_seconds histogram
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.001\"}
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.002\"}
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.004\"}
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.008\"} 4
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.016\"} 5
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.032\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.064\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.128\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.256\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.512\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"1.024\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"2.048\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"4.096\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"8.192\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"+Inf\"} 6
etcd_disk_backend_commit_duration_seconds_sum 0.061365869999999996
etcd_disk_backend_commit_duration_seconds_count 6
# HELP etcd_disk_backend_defrag_duration_seconds The latency distribution of backend defragmentation.
# TYPE etcd_disk_backend_defrag_duration_seconds histogram
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.1\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.2\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.4\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.8\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"1.6\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"3.2\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"6.4\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"12.8\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"25.6\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"51.2\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"102.4\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"204.8\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"409.6\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"+Inf\"}
etcd_disk_backend_defrag_duration_seconds_sum
etcd_disk_backend_defrag_duration_seconds_count
# HELP etcd_disk_backend_snapshot_duration_seconds The latency distribution of backend snapshots.
# TYPE etcd_disk_backend_snapshot_duration_seconds histogram
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.01\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.02\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.04\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.08\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.16\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.32\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.64\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"1.28\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"2.56\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"5.12\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"10.24\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"20.48\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"40.96\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"81.92\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"163.84\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"327.68\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"655.36\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"+Inf\"}
etcd_disk_backend_snapshot_duration_seconds_sum
etcd_disk_backend_snapshot_duration_seconds_count
# HELP etcd_disk_wal_fsync_duration_seconds The latency distributions of fsync called by WAL.
# TYPE etcd_disk_wal_fsync_duration_seconds histogram
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.001\"} 1
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.002\"} 2
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.004\"} 3
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.008\"} 3
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.016\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.032\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.064\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.128\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.256\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.512\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"1.024\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"2.048\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"4.096\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"8.192\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"+Inf\"} 4
etcd_disk_wal_fsync_duration_seconds_sum 0.012822563
etcd_disk_wal_fsync_duration_seconds_count 4
# HELP etcd_grpc_proxy_cache_hits_total Total number of cache hits
# TYPE etcd_grpc_proxy_cache_hits_total gauge
etcd_grpc_proxy_cache_hits_total
# HELP etcd_grpc_proxy_cache_keys_total Total number of keys/ranges cached
# TYPE etcd_grpc_proxy_cache_keys_total gauge
etcd_grpc_proxy_cache_keys_total
# HELP etcd_grpc_proxy_cache_misses_total Total number of cache misses
# TYPE etcd_grpc_proxy_cache_misses_total gauge
etcd_grpc_proxy_cache_misses_total
# HELP etcd_grpc_proxy_events_coalescing_total Total number of events coalescing
# TYPE etcd_grpc_proxy_events_coalescing_total counter
etcd_grpc_proxy_events_coalescing_total
# HELP etcd_grpc_proxy_watchers_coalescing_total Total number of current watchers coalescing
# TYPE etcd_grpc_proxy_watchers_coalescing_total gauge
etcd_grpc_proxy_watchers_coalescing_total
# HELP etcd_mvcc_db_total_size_in_bytes Total size of the underlying database physically allocated in bytes.
# TYPE etcd_mvcc_db_total_size_in_bytes gauge
etcd_mvcc_db_total_size_in_bytes 32768
# HELP etcd_mvcc_db_total_size_in_use_in_bytes Total size of the underlying database logically in use in bytes.
# TYPE etcd_mvcc_db_total_size_in_use_in_bytes gauge
etcd_mvcc_db_total_size_in_use_in_bytes 262144
# HELP etcd_mvcc_hash_duration_seconds The latency distribution of storage hash operation.
# TYPE etcd_mvcc_hash_duration_seconds histogram
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.01\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.02\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.04\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.08\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.16\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.32\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.64\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"1.28\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"2.56\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"5.12\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"10.24\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"20.48\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"40.96\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"81.92\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"163.84\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"+Inf\"}
etcd_mvcc_hash_duration_seconds_sum
etcd_mvcc_hash_duration_seconds_count
# HELP etcd_mvcc_hash_rev_duration_seconds The latency distribution of storage hash by revision operation.
# TYPE etcd_mvcc_hash_rev_duration_seconds histogram
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.01\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.02\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.04\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.08\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.16\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.32\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.64\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"1.28\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"2.56\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"5.12\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"10.24\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"20.48\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"40.96\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"81.92\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"163.84\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"+Inf\"}
etcd_mvcc_hash_rev_duration_seconds_sum
etcd_mvcc_hash_rev_duration_seconds_count
# HELP etcd_network_client_grpc_received_bytes_total The total number of bytes received from grpc clients.
# TYPE etcd_network_client_grpc_received_bytes_total counter
etcd_network_client_grpc_received_bytes_total
# HELP etcd_network_client_grpc_sent_bytes_total The total number of bytes sent to grpc clients.
# TYPE etcd_network_client_grpc_sent_bytes_total counter
etcd_network_client_grpc_sent_bytes_total
# HELP etcd_server_has_leader Whether or not a leader exists. 1 is existence, 0 is not.
# TYPE etcd_server_has_leader gauge
etcd_server_has_leader 1
# HELP etcd_server_heartbeat_send_failures_total The total number of leader heartbeat send failures (likely overloaded from slow disk).
# TYPE etcd_server_heartbeat_send_failures_total counter
etcd_server_heartbeat_send_failures_total
# HELP etcd_server_is_leader Whether or not this member is a leader. 1 if is, 0 otherwise.
# TYPE etcd_server_is_leader gauge
etcd_server_is_leader 1
# HELP etcd_server_leader_changes_seen_total The number of leader changes seen.
# TYPE etcd_server_leader_changes_seen_total counter
etcd_server_leader_changes_seen_total 1
# HELP etcd_server_proposals_applied_total The total number of consensus proposals applied.
# TYPE etcd_server_proposals_applied_total gauge
etcd_server_proposals_applied_total 4
# HELP etcd_server_proposals_committed_total The total number of consensus proposals committed.
# TYPE etcd_server_proposals_committed_total gauge
etcd_server_proposals_committed_total 4
# HELP etcd_server_proposals_failed_total The total number of failed proposals seen.
# TYPE etcd_server_proposals_failed_total counter
etcd_server_proposals_failed_total
# HELP etcd_server_proposals_pending The current number of pending proposals to commit.
# TYPE etcd_server_proposals_pending gauge
etcd_server_proposals_pending
# HELP etcd_server_quota_backend_bytes Current backend storage quota size in bytes.
# TYPE etcd_server_quota_backend_bytes gauge
etcd_server_quota_backend_bytes 2.147483648e+09
# HELP etcd_server_slow_apply_total The total number of slow apply requests (likely overloaded from slow disk).
# TYPE etcd_server_slow_apply_total counter
etcd_server_slow_apply_total
# HELP etcd_server_version Which version is running. 1 for 'server_version' label with current version.
# TYPE etcd_server_version gauge
etcd_server_version{server_version=\"3.3.0+git\"} 1
# HELP etcd_snap_fsync_duration_seconds The latency distributions of fsync called by snap.
# TYPE etcd_snap_fsync_duration_seconds histogram
etcd_snap_fsync_duration_seconds_bucket{le=\"0.001\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.002\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.004\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.008\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.016\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.032\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.064\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.128\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.256\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.512\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"1.024\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"2.048\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"4.096\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"8.192\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"+Inf\"}
etcd_snap_fsync_duration_seconds_sum
etcd_snap_fsync_duration_seconds_count
# HELP go_gc_duration_seconds A summary of the GC invocation durations.
# TYPE go_gc_duration_seconds summary
go_gc_duration_seconds{quantile=\"0\"} 0.00015764
go_gc_duration_seconds{quantile=\"0.25\"} 0.00015764
go_gc_duration_seconds{quantile=\"0.5\"} 0.000177495
go_gc_duration_seconds{quantile=\"0.75\"} 0.000184464
go_gc_duration_seconds{quantile=\"1\"} 0.000184464
go_gc_duration_seconds_sum 0.000519599
go_gc_duration_seconds_count 3
# HELP go_goroutines Number of goroutines that currently exist.
# TYPE go_goroutines gauge
go_goroutines 47
# HELP go_info Information about the Go environment.
# TYPE go_info gauge
go_info{version=\"devel +b74f732 Mon Jun 11 00:45:20 2018 +0000\"} 1
# HELP go_memstats_alloc_bytes Number of bytes allocated and still in use.
# TYPE go_memstats_alloc_bytes gauge
go_memstats_alloc_bytes 4.150712e+06
# HELP go_memstats_alloc_bytes_total Total number of bytes allocated, even if freed.
# TYPE go_memstats_alloc_bytes_total counter
go_memstats_alloc_bytes_total 8.208744e+06
# HELP go_memstats_buck_hash_sys_bytes Number of bytes used by the profiling bucket hash table.
# TYPE go_memstats_buck_hash_sys_bytes gauge
go_memstats_buck_hash_sys_bytes 1.446981e+06
# HELP go_memstats_frees_total Total number of frees.
# TYPE go_memstats_frees_total counter
go_memstats_frees_total 996
# HELP go_memstats_gc_cpu_fraction The fraction of this program's available CPU time used by the GC since the program started.
# TYPE go_memstats_gc_cpu_fraction gauge
go_memstats_gc_cpu_fraction 0.001566909347503071
# HELP go_memstats_gc_sys_bytes Number of bytes used for garbage collection system metadata.
# TYPE go_memstats_gc_sys_bytes gauge
go_memstats_gc_sys_bytes 2.371584e+06
# HELP go_memstats_heap_alloc_bytes Number of heap bytes allocated and still in use.
# TYPE go_memstats_heap_alloc_bytes gauge
go_memstats_heap_alloc_bytes 4.150712e+06
# HELP go_memstats_heap_idle_bytes Number of heap bytes waiting to be used.
# TYPE go_memstats_heap_idle_bytes gauge
go_memstats_heap_idle_bytes 5.9342848e+07
# HELP go_memstats_heap_inuse_bytes Number of heap bytes that are in use.
# TYPE go_memstats_heap_inuse_bytes gauge
go_memstats_heap_inuse_bytes 6.22592e+06
# HELP go_memstats_heap_objects Number of allocated objects.
# TYPE go_memstats_heap_objects gauge
go_memstats_heap_objects 2812
# HELP go_memstats_heap_released_bytes Number of heap bytes released to OS.
# TYPE go_memstats_heap_released_bytes gauge
go_memstats_heap_released_bytes
# HELP go_memstats_heap_sys_bytes Number of heap bytes obtained from system.
# TYPE go_memstats_heap_sys_bytes gauge
go_memstats_heap_sys_bytes 6.5568768e+07
# HELP go_memstats_last_gc_time_seconds Number of seconds since 1970 of last garbage collection.
# TYPE go_memstats_last_gc_time_seconds gauge
go_memstats_last_gc_time_seconds 1.5286935487193735e+09
# HELP go_memstats_lookups_total Total number of pointer lookups.
# TYPE go_memstats_lookups_total counter
go_memstats_lookups_total
# HELP go_memstats_mallocs_total Total number of mallocs.
# TYPE go_memstats_mallocs_total counter
go_memstats_mallocs_total 3808
# HELP go_memstats_mcache_inuse_bytes Number of bytes in use by mcache structures.
# TYPE go_memstats_mcache_inuse_bytes gauge
go_memstats_mcache_inuse_bytes 27648
# HELP go_memstats_mcache_sys_bytes Number of bytes used for mcache structures obtained from system.
# TYPE go_memstats_mcache_sys_bytes gauge
go_memstats_mcache_sys_bytes 32768
# HELP go_memstats_mspan_inuse_bytes Number of bytes in use by mspan structures.
# TYPE go_memstats_mspan_inuse_bytes gauge
go_memstats_mspan_inuse_bytes 74784
# HELP go_memstats_mspan_sys_bytes Number of bytes used for mspan structures obtained from system.
# TYPE go_memstats_mspan_sys_bytes gauge
go_memstats_mspan_sys_bytes 8192
# HELP go_memstats_next_gc_bytes Number of heap bytes when next garbage collection will take place.
# TYPE go_memstats_next_gc_bytes gauge
go_memstats_next_gc_bytes 6.983584e+06
# HELP go_memstats_other_sys_bytes Number of bytes used for other system allocations.
# TYPE go_memstats_other_sys_bytes gauge
go_memstats_other_sys_bytes 2.290867e+06
# HELP go_memstats_stack_inuse_bytes Number of bytes in use by the stack allocator.
# TYPE go_memstats_stack_inuse_bytes gauge
go_memstats_stack_inuse_bytes 1.540096e+06
# HELP go_memstats_stack_sys_bytes Number of bytes obtained from system for stack allocator.
# TYPE go_memstats_stack_sys_bytes gauge
go_memstats_stack_sys_bytes 1.540096e+06
# HELP go_memstats_sys_bytes Number of bytes obtained from system.
# TYPE go_memstats_sys_bytes gauge
go_memstats_sys_bytes 7.3332984e+07
# HELP go_threads Number of OS threads created.
# TYPE go_threads gauge
go_threads 23
# HELP grpc_server_handled_total Total number of RPCs completed on the server, regardless of success or failure.
# TYPE grpc_server_handled_total counter
grpc_server_handled_total{grpc_code=\"Aborted\",grpc_method=\"Alarm\",grpc_service=\"etcdserverpb.Maintenance\",grpc_type=\"unary\"}
grpc_server_handled_total{grpc_code=\"Aborted\",grpc_method=\"AuthDisable\",grpc_service=\"etcdserverpb.Auth\",grpc_type=\"unary\"}
<snip>
grpc_server_started_total{grpc_method=\"UserList\",grpc_service=\"etcdserverpb.Auth\",grpc_type=\"unary\"}
grpc_server_started_total{grpc_method=\"UserRevokeRole\",grpc_service=\"etcdserverpb.Auth\",grpc_type=\"unary\"}
grpc_server_started_total{grpc_method=\"Watch\",grpc_service=\"etcdserverpb.Watch\",grpc_type=\"bidi_stream\"}
# HELP process_cpu_seconds_total Total user and system CPU time spent in seconds.
# TYPE process_cpu_seconds_total counter
process_cpu_seconds_total 0.12
# HELP process_max_fds Maximum number of open file descriptors.
# TYPE process_max_fds gauge
process_max_fds 1.048576e+06
# HELP process_open_fds Number of open file descriptors.
# TYPE process_open_fds gauge
process_open_fds 14
# HELP process_resident_memory_bytes Resident memory size in bytes.
# TYPE process_resident_memory_bytes gauge
process_resident_memory_bytes 1.7301504e+07
# HELP process_start_time_seconds Start time of the process since unix epoch in seconds.
# TYPE process_start_time_seconds gauge
process_start_time_seconds 1.52869354775e+09
# HELP process_virtual_memory_bytes Virtual memory size in bytes.
# TYPE process_virtual_memory_bytes gauge
process_virtual_memory_bytes 1.08675072e+1
"]))
=== RUN TestCtlV2Set
sudeeshjohn:/tmp$
```
etcd version: 3.3.0+git | 1.0 | etcd integration_e2e test "TestV3CurlCipherSuitesMismatch" is failing - test log:
```
--- PASS: TestV3CurlCipherSuitesValid (1.12s)
=== RUN TestV3CurlCipherSuitesMismatch
--- FAIL: TestV3CurlCipherSuitesMismatch (1.11s)
v3_curl_test.go:391: failed get with curl (read /dev/ptmx: input/output error (expected "alert handshake failure", got ["# HELP etcd_debugging_lease_granted_total The total number of granted leases.
# TYPE etcd_debugging_lease_granted_total counter
etcd_debugging_lease_granted_total
# HELP etcd_debugging_lease_renewed_total The number of renewed leases seen by the leader.
# TYPE etcd_debugging_lease_renewed_total counter
etcd_debugging_lease_renewed_total
# HELP etcd_debugging_lease_revoked_total The total number of revoked leases.
# TYPE etcd_debugging_lease_revoked_total counter
etcd_debugging_lease_revoked_total
# HELP etcd_debugging_lease_ttl_total Bucketed histogram of lease TTLs.
# TYPE etcd_debugging_lease_ttl_total histogram
etcd_debugging_lease_ttl_total_bucket{le=\"1\"}
etcd_debugging_lease_ttl_total_bucket{le=\"2\"}
etcd_debugging_lease_ttl_total_bucket{le=\"4\"}
etcd_debugging_lease_ttl_total_bucket{le=\"8\"}
etcd_debugging_lease_ttl_total_bucket{le=\"16\"}
etcd_debugging_lease_ttl_total_bucket{le=\"32\"}
etcd_debugging_lease_ttl_total_bucket{le=\"64\"}
etcd_debugging_lease_ttl_total_bucket{le=\"128\"}
etcd_debugging_lease_ttl_total_bucket{le=\"256\"}
etcd_debugging_lease_ttl_total_bucket{le=\"512\"}
etcd_debugging_lease_ttl_total_bucket{le=\"1024\"}
etcd_debugging_lease_ttl_total_bucket{le=\"2048\"}
etcd_debugging_lease_ttl_total_bucket{le=\"4096\"}
etcd_debugging_lease_ttl_total_bucket{le=\"8192\"}
etcd_debugging_lease_ttl_total_bucket{le=\"16384\"}
etcd_debugging_lease_ttl_total_bucket{le=\"32768\"}
etcd_debugging_lease_ttl_total_bucket{le=\"65536\"}
etcd_debugging_lease_ttl_total_bucket{le=\"131072\"}
etcd_debugging_lease_ttl_total_bucket{le=\"262144\"}
etcd_debugging_lease_ttl_total_bucket{le=\"524288\"}
etcd_debugging_lease_ttl_total_bucket{le=\"1.048576e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"2.097152e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"4.194304e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"8.388608e+06\"}
etcd_debugging_lease_ttl_total_bucket{le=\"+Inf\"}
etcd_debugging_lease_ttl_total_sum
etcd_debugging_lease_ttl_total_count
# HELP etcd_debugging_mvcc_db_compaction_keys_total Total number of db keys compacted.
# TYPE etcd_debugging_mvcc_db_compaction_keys_total counter
etcd_debugging_mvcc_db_compaction_keys_total
# HELP etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds Bucketed histogram of db compaction pause duration.
# TYPE etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds histogram
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"1\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"2\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"4\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"8\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"16\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"32\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"64\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"128\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"256\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"512\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"1024\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"2048\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"4096\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_bucket{le=\"+Inf\"}
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_sum
etcd_debugging_mvcc_db_compaction_pause_duration_milliseconds_count
# HELP etcd_debugging_mvcc_db_compaction_total_duration_milliseconds Bucketed histogram of db compaction total duration.
# TYPE etcd_debugging_mvcc_db_compaction_total_duration_milliseconds histogram
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"100\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"400\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"800\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"1600\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"3200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"6400\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"12800\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"25600\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"51200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"102400\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"204800\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"409600\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"819200\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_bucket{le=\"+Inf\"}
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_sum
etcd_debugging_mvcc_db_compaction_total_duration_milliseconds_count
# HELP etcd_debugging_mvcc_db_total_size_in_bytes Total size of the underlying database physically allocated in bytes.
# TYPE etcd_debugging_mvcc_db_total_size_in_bytes gauge
etcd_debugging_mvcc_db_total_size_in_bytes 32768
# HELP etcd_debugging_mvcc_delete_total Total number of deletes seen by this member.
# TYPE etcd_debugging_mvcc_delete_total counter
etcd_debugging_mvcc_delete_total
# HELP etcd_debugging_mvcc_events_total Total number of events sent by this member.
# TYPE etcd_debugging_mvcc_events_total counter
etcd_debugging_mvcc_events_total
# HELP etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds Bucketed histogram of index compaction pause duration.
# TYPE etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds histogram
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"0.5\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"1\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"2\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"4\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"8\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"16\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"32\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"64\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"128\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"256\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"512\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"1024\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"2048\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"4096\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_bucket{le=\"+Inf\"}
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_sum
etcd_debugging_mvcc_index_compaction_pause_duration_milliseconds_count
# HELP etcd_debugging_mvcc_keys_total Total number of keys.
# TYPE etcd_debugging_mvcc_keys_total gauge
etcd_debugging_mvcc_keys_total
# HELP etcd_debugging_mvcc_pending_events_total Total number of pending events to be sent.
# TYPE etcd_debugging_mvcc_pending_events_total gauge
etcd_debugging_mvcc_pending_events_total
# HELP etcd_debugging_mvcc_put_total Total number of puts seen by this member.
# TYPE etcd_debugging_mvcc_put_total counter
etcd_debugging_mvcc_put_total
# HELP etcd_debugging_mvcc_range_total Total number of ranges seen by this member.
# TYPE etcd_debugging_mvcc_range_total counter
etcd_debugging_mvcc_range_total
# HELP etcd_debugging_mvcc_slow_watcher_total Total number of unsynced slow watchers.
# TYPE etcd_debugging_mvcc_slow_watcher_total gauge
etcd_debugging_mvcc_slow_watcher_total
# HELP etcd_debugging_mvcc_txn_total Total number of txns seen by this member.
# TYPE etcd_debugging_mvcc_txn_total counter
etcd_debugging_mvcc_txn_total
# HELP etcd_debugging_mvcc_watch_stream_total Total number of watch streams.
# TYPE etcd_debugging_mvcc_watch_stream_total gauge
etcd_debugging_mvcc_watch_stream_total
# HELP etcd_debugging_mvcc_watcher_total Total number of watchers.
# TYPE etcd_debugging_mvcc_watcher_total gauge
etcd_debugging_mvcc_watcher_total
# HELP etcd_debugging_server_lease_expired_total The total number of expired leases.
# TYPE etcd_debugging_server_lease_expired_total counter
etcd_debugging_server_lease_expired_total
# HELP etcd_debugging_snap_save_marshalling_duration_seconds The marshalling cost distributions of save called by snapshot.
# TYPE etcd_debugging_snap_save_marshalling_duration_seconds histogram
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.001\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.002\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.004\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.008\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.016\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.032\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.064\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.128\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.256\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"0.512\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"1.024\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"2.048\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"4.096\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"8.192\"}
etcd_debugging_snap_save_marshalling_duration_seconds_bucket{le=\"+Inf\"}
etcd_debugging_snap_save_marshalling_duration_seconds_sum
etcd_debugging_snap_save_marshalling_duration_seconds_count
# HELP etcd_debugging_snap_save_total_duration_seconds The total latency distributions of save called by snapshot.
# TYPE etcd_debugging_snap_save_total_duration_seconds histogram
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.001\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.002\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.004\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.008\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.016\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.032\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.064\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.128\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.256\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"0.512\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"1.024\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"2.048\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"4.096\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"8.192\"}
etcd_debugging_snap_save_total_duration_seconds_bucket{le=\"+Inf\"}
etcd_debugging_snap_save_total_duration_seconds_sum
etcd_debugging_snap_save_total_duration_seconds_count
# HELP etcd_debugging_store_expires_total Total number of expired keys.
# TYPE etcd_debugging_store_expires_total counter
etcd_debugging_store_expires_total
# HELP etcd_debugging_store_reads_total Total number of reads action by (get/getRecursive), local to this member.
# TYPE etcd_debugging_store_reads_total counter
etcd_debugging_store_reads_total{action=\"getRecursive\"} 1
# HELP etcd_debugging_store_watch_requests_total Total number of incoming watch requests (new or reestablished).
# TYPE etcd_debugging_store_watch_requests_total counter
etcd_debugging_store_watch_requests_total
# HELP etcd_debugging_store_watchers Count of currently active watchers.
# TYPE etcd_debugging_store_watchers gauge
etcd_debugging_store_watchers
# HELP etcd_debugging_store_writes_total Total number of writes (e.g. set/compareAndDelete) seen by this member.
# TYPE etcd_debugging_store_writes_total counter
etcd_debugging_store_writes_total{action=\"create\"} 1
etcd_debugging_store_writes_total{action=\"set\"} 2
# HELP etcd_disk_backend_commit_duration_seconds The latency distributions of commit called by backend.
# TYPE etcd_disk_backend_commit_duration_seconds histogram
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.001\"}
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.002\"}
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.004\"}
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.008\"} 4
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.016\"} 5
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.032\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.064\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.128\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.256\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"0.512\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"1.024\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"2.048\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"4.096\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"8.192\"} 6
etcd_disk_backend_commit_duration_seconds_bucket{le=\"+Inf\"} 6
etcd_disk_backend_commit_duration_seconds_sum 0.061365869999999996
etcd_disk_backend_commit_duration_seconds_count 6
# HELP etcd_disk_backend_defrag_duration_seconds The latency distribution of backend defragmentation.
# TYPE etcd_disk_backend_defrag_duration_seconds histogram
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.1\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.2\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.4\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"0.8\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"1.6\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"3.2\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"6.4\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"12.8\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"25.6\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"51.2\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"102.4\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"204.8\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"409.6\"}
etcd_disk_backend_defrag_duration_seconds_bucket{le=\"+Inf\"}
etcd_disk_backend_defrag_duration_seconds_sum
etcd_disk_backend_defrag_duration_seconds_count
# HELP etcd_disk_backend_snapshot_duration_seconds The latency distribution of backend snapshots.
# TYPE etcd_disk_backend_snapshot_duration_seconds histogram
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.01\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.02\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.04\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.08\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.16\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.32\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"0.64\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"1.28\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"2.56\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"5.12\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"10.24\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"20.48\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"40.96\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"81.92\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"163.84\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"327.68\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"655.36\"}
etcd_disk_backend_snapshot_duration_seconds_bucket{le=\"+Inf\"}
etcd_disk_backend_snapshot_duration_seconds_sum
etcd_disk_backend_snapshot_duration_seconds_count
# HELP etcd_disk_wal_fsync_duration_seconds The latency distributions of fsync called by WAL.
# TYPE etcd_disk_wal_fsync_duration_seconds histogram
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.001\"} 1
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.002\"} 2
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.004\"} 3
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.008\"} 3
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.016\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.032\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.064\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.128\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.256\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"0.512\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"1.024\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"2.048\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"4.096\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"8.192\"} 4
etcd_disk_wal_fsync_duration_seconds_bucket{le=\"+Inf\"} 4
etcd_disk_wal_fsync_duration_seconds_sum 0.012822563
etcd_disk_wal_fsync_duration_seconds_count 4
# HELP etcd_grpc_proxy_cache_hits_total Total number of cache hits
# TYPE etcd_grpc_proxy_cache_hits_total gauge
etcd_grpc_proxy_cache_hits_total
# HELP etcd_grpc_proxy_cache_keys_total Total number of keys/ranges cached
# TYPE etcd_grpc_proxy_cache_keys_total gauge
etcd_grpc_proxy_cache_keys_total
# HELP etcd_grpc_proxy_cache_misses_total Total number of cache misses
# TYPE etcd_grpc_proxy_cache_misses_total gauge
etcd_grpc_proxy_cache_misses_total
# HELP etcd_grpc_proxy_events_coalescing_total Total number of events coalescing
# TYPE etcd_grpc_proxy_events_coalescing_total counter
etcd_grpc_proxy_events_coalescing_total
# HELP etcd_grpc_proxy_watchers_coalescing_total Total number of current watchers coalescing
# TYPE etcd_grpc_proxy_watchers_coalescing_total gauge
etcd_grpc_proxy_watchers_coalescing_total
# HELP etcd_mvcc_db_total_size_in_bytes Total size of the underlying database physically allocated in bytes.
# TYPE etcd_mvcc_db_total_size_in_bytes gauge
etcd_mvcc_db_total_size_in_bytes 32768
# HELP etcd_mvcc_db_total_size_in_use_in_bytes Total size of the underlying database logically in use in bytes.
# TYPE etcd_mvcc_db_total_size_in_use_in_bytes gauge
etcd_mvcc_db_total_size_in_use_in_bytes 262144
# HELP etcd_mvcc_hash_duration_seconds The latency distribution of storage hash operation.
# TYPE etcd_mvcc_hash_duration_seconds histogram
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.01\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.02\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.04\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.08\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.16\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.32\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"0.64\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"1.28\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"2.56\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"5.12\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"10.24\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"20.48\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"40.96\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"81.92\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"163.84\"}
etcd_mvcc_hash_duration_seconds_bucket{le=\"+Inf\"}
etcd_mvcc_hash_duration_seconds_sum
etcd_mvcc_hash_duration_seconds_count
# HELP etcd_mvcc_hash_rev_duration_seconds The latency distribution of storage hash by revision operation.
# TYPE etcd_mvcc_hash_rev_duration_seconds histogram
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.01\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.02\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.04\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.08\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.16\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.32\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"0.64\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"1.28\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"2.56\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"5.12\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"10.24\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"20.48\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"40.96\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"81.92\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"163.84\"}
etcd_mvcc_hash_rev_duration_seconds_bucket{le=\"+Inf\"}
etcd_mvcc_hash_rev_duration_seconds_sum
etcd_mvcc_hash_rev_duration_seconds_count
# HELP etcd_network_client_grpc_received_bytes_total The total number of bytes received from grpc clients.
# TYPE etcd_network_client_grpc_received_bytes_total counter
etcd_network_client_grpc_received_bytes_total
# HELP etcd_network_client_grpc_sent_bytes_total The total number of bytes sent to grpc clients.
# TYPE etcd_network_client_grpc_sent_bytes_total counter
etcd_network_client_grpc_sent_bytes_total
# HELP etcd_server_has_leader Whether or not a leader exists. 1 is existence, 0 is not.
# TYPE etcd_server_has_leader gauge
etcd_server_has_leader 1
# HELP etcd_server_heartbeat_send_failures_total The total number of leader heartbeat send failures (likely overloaded from slow disk).
# TYPE etcd_server_heartbeat_send_failures_total counter
etcd_server_heartbeat_send_failures_total
# HELP etcd_server_is_leader Whether or not this member is a leader. 1 if is, 0 otherwise.
# TYPE etcd_server_is_leader gauge
etcd_server_is_leader 1
# HELP etcd_server_leader_changes_seen_total The number of leader changes seen.
# TYPE etcd_server_leader_changes_seen_total counter
etcd_server_leader_changes_seen_total 1
# HELP etcd_server_proposals_applied_total The total number of consensus proposals applied.
# TYPE etcd_server_proposals_applied_total gauge
etcd_server_proposals_applied_total 4
# HELP etcd_server_proposals_committed_total The total number of consensus proposals committed.
# TYPE etcd_server_proposals_committed_total gauge
etcd_server_proposals_committed_total 4
# HELP etcd_server_proposals_failed_total The total number of failed proposals seen.
# TYPE etcd_server_proposals_failed_total counter
etcd_server_proposals_failed_total
# HELP etcd_server_proposals_pending The current number of pending proposals to commit.
# TYPE etcd_server_proposals_pending gauge
etcd_server_proposals_pending
# HELP etcd_server_quota_backend_bytes Current backend storage quota size in bytes.
# TYPE etcd_server_quota_backend_bytes gauge
etcd_server_quota_backend_bytes 2.147483648e+09
# HELP etcd_server_slow_apply_total The total number of slow apply requests (likely overloaded from slow disk).
# TYPE etcd_server_slow_apply_total counter
etcd_server_slow_apply_total
# HELP etcd_server_version Which version is running. 1 for 'server_version' label with current version.
# TYPE etcd_server_version gauge
etcd_server_version{server_version=\"3.3.0+git\"} 1
# HELP etcd_snap_fsync_duration_seconds The latency distributions of fsync called by snap.
# TYPE etcd_snap_fsync_duration_seconds histogram
etcd_snap_fsync_duration_seconds_bucket{le=\"0.001\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.002\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.004\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.008\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.016\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.032\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.064\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.128\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.256\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"0.512\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"1.024\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"2.048\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"4.096\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"8.192\"}
etcd_snap_fsync_duration_seconds_bucket{le=\"+Inf\"}
etcd_snap_fsync_duration_seconds_sum
etcd_snap_fsync_duration_seconds_count
# HELP go_gc_duration_seconds A summary of the GC invocation durations.
# TYPE go_gc_duration_seconds summary
go_gc_duration_seconds{quantile=\"0\"} 0.00015764
go_gc_duration_seconds{quantile=\"0.25\"} 0.00015764
go_gc_duration_seconds{quantile=\"0.5\"} 0.000177495
go_gc_duration_seconds{quantile=\"0.75\"} 0.000184464
go_gc_duration_seconds{quantile=\"1\"} 0.000184464
go_gc_duration_seconds_sum 0.000519599
go_gc_duration_seconds_count 3
# HELP go_goroutines Number of goroutines that currently exist.
# TYPE go_goroutines gauge
go_goroutines 47
# HELP go_info Information about the Go environment.
# TYPE go_info gauge
go_info{version=\"devel +b74f732 Mon Jun 11 00:45:20 2018 +0000\"} 1
# HELP go_memstats_alloc_bytes Number of bytes allocated and still in use.
# TYPE go_memstats_alloc_bytes gauge
go_memstats_alloc_bytes 4.150712e+06
# HELP go_memstats_alloc_bytes_total Total number of bytes allocated, even if freed.
# TYPE go_memstats_alloc_bytes_total counter
go_memstats_alloc_bytes_total 8.208744e+06
# HELP go_memstats_buck_hash_sys_bytes Number of bytes used by the profiling bucket hash table.
# TYPE go_memstats_buck_hash_sys_bytes gauge
go_memstats_buck_hash_sys_bytes 1.446981e+06
# HELP go_memstats_frees_total Total number of frees.
# TYPE go_memstats_frees_total counter
go_memstats_frees_total 996
# HELP go_memstats_gc_cpu_fraction The fraction of this program's available CPU time used by the GC since the program started.
# TYPE go_memstats_gc_cpu_fraction gauge
go_memstats_gc_cpu_fraction 0.001566909347503071
# HELP go_memstats_gc_sys_bytes Number of bytes used for garbage collection system metadata.
# TYPE go_memstats_gc_sys_bytes gauge
go_memstats_gc_sys_bytes 2.371584e+06
# HELP go_memstats_heap_alloc_bytes Number of heap bytes allocated and still in use.
# TYPE go_memstats_heap_alloc_bytes gauge
go_memstats_heap_alloc_bytes 4.150712e+06
# HELP go_memstats_heap_idle_bytes Number of heap bytes waiting to be used.
# TYPE go_memstats_heap_idle_bytes gauge
go_memstats_heap_idle_bytes 5.9342848e+07
# HELP go_memstats_heap_inuse_bytes Number of heap bytes that are in use.
# TYPE go_memstats_heap_inuse_bytes gauge
go_memstats_heap_inuse_bytes 6.22592e+06
# HELP go_memstats_heap_objects Number of allocated objects.
# TYPE go_memstats_heap_objects gauge
go_memstats_heap_objects 2812
# HELP go_memstats_heap_released_bytes Number of heap bytes released to OS.
# TYPE go_memstats_heap_released_bytes gauge
go_memstats_heap_released_bytes
# HELP go_memstats_heap_sys_bytes Number of heap bytes obtained from system.
# TYPE go_memstats_heap_sys_bytes gauge
go_memstats_heap_sys_bytes 6.5568768e+07
# HELP go_memstats_last_gc_time_seconds Number of seconds since 1970 of last garbage collection.
# TYPE go_memstats_last_gc_time_seconds gauge
go_memstats_last_gc_time_seconds 1.5286935487193735e+09
# HELP go_memstats_lookups_total Total number of pointer lookups.
# TYPE go_memstats_lookups_total counter
go_memstats_lookups_total
# HELP go_memstats_mallocs_total Total number of mallocs.
# TYPE go_memstats_mallocs_total counter
go_memstats_mallocs_total 3808
# HELP go_memstats_mcache_inuse_bytes Number of bytes in use by mcache structures.
# TYPE go_memstats_mcache_inuse_bytes gauge
go_memstats_mcache_inuse_bytes 27648
# HELP go_memstats_mcache_sys_bytes Number of bytes used for mcache structures obtained from system.
# TYPE go_memstats_mcache_sys_bytes gauge
go_memstats_mcache_sys_bytes 32768
# HELP go_memstats_mspan_inuse_bytes Number of bytes in use by mspan structures.
# TYPE go_memstats_mspan_inuse_bytes gauge
go_memstats_mspan_inuse_bytes 74784
# HELP go_memstats_mspan_sys_bytes Number of bytes used for mspan structures obtained from system.
# TYPE go_memstats_mspan_sys_bytes gauge
go_memstats_mspan_sys_bytes 8192
# HELP go_memstats_next_gc_bytes Number of heap bytes when next garbage collection will take place.
# TYPE go_memstats_next_gc_bytes gauge
go_memstats_next_gc_bytes 6.983584e+06
# HELP go_memstats_other_sys_bytes Number of bytes used for other system allocations.
# TYPE go_memstats_other_sys_bytes gauge
go_memstats_other_sys_bytes 2.290867e+06
# HELP go_memstats_stack_inuse_bytes Number of bytes in use by the stack allocator.
# TYPE go_memstats_stack_inuse_bytes gauge
go_memstats_stack_inuse_bytes 1.540096e+06
# HELP go_memstats_stack_sys_bytes Number of bytes obtained from system for stack allocator.
# TYPE go_memstats_stack_sys_bytes gauge
go_memstats_stack_sys_bytes 1.540096e+06
# HELP go_memstats_sys_bytes Number of bytes obtained from system.
# TYPE go_memstats_sys_bytes gauge
go_memstats_sys_bytes 7.3332984e+07
# HELP go_threads Number of OS threads created.
# TYPE go_threads gauge
go_threads 23
# HELP grpc_server_handled_total Total number of RPCs completed on the server, regardless of success or failure.
# TYPE grpc_server_handled_total counter
grpc_server_handled_total{grpc_code=\"Aborted\",grpc_method=\"Alarm\",grpc_service=\"etcdserverpb.Maintenance\",grpc_type=\"unary\"}
grpc_server_handled_total{grpc_code=\"Aborted\",grpc_method=\"AuthDisable\",grpc_service=\"etcdserverpb.Auth\",grpc_type=\"unary\"}
<snip>
grpc_server_started_total{grpc_method=\"UserList\",grpc_service=\"etcdserverpb.Auth\",grpc_type=\"unary\"}
grpc_server_started_total{grpc_method=\"UserRevokeRole\",grpc_service=\"etcdserverpb.Auth\",grpc_type=\"unary\"}
grpc_server_started_total{grpc_method=\"Watch\",grpc_service=\"etcdserverpb.Watch\",grpc_type=\"bidi_stream\"}
# HELP process_cpu_seconds_total Total user and system CPU time spent in seconds.
# TYPE process_cpu_seconds_total counter
process_cpu_seconds_total 0.12
# HELP process_max_fds Maximum number of open file descriptors.
# TYPE process_max_fds gauge
process_max_fds 1.048576e+06
# HELP process_open_fds Number of open file descriptors.
# TYPE process_open_fds gauge
process_open_fds 14
# HELP process_resident_memory_bytes Resident memory size in bytes.
# TYPE process_resident_memory_bytes gauge
process_resident_memory_bytes 1.7301504e+07
# HELP process_start_time_seconds Start time of the process since unix epoch in seconds.
# TYPE process_start_time_seconds gauge
process_start_time_seconds 1.52869354775e+09
# HELP process_virtual_memory_bytes Virtual memory size in bytes.
# TYPE process_virtual_memory_bytes gauge
process_virtual_memory_bytes 1.08675072e+1
"]))
=== RUN TestCtlV2Set
sudeeshjohn:/tmp$
```
etcd version: 3.3.0+git | test | etcd integration test is failing test log pass run fail curl test go failed get with curl read dev ptmx input output error expected alert handshake failure got help etcd debugging lease granted total the total number of granted leases type etcd debugging lease granted total counter etcd debugging lease granted total help etcd debugging lease renewed total the number of renewed leases seen by the leader type etcd debugging lease renewed total counter etcd debugging lease renewed total help etcd debugging lease revoked total the total number of revoked leases type etcd debugging lease revoked total counter etcd debugging lease revoked total help etcd debugging lease ttl total bucketed histogram of lease ttls type etcd debugging lease ttl total histogram etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le etcd debugging lease ttl total bucket le inf etcd debugging lease ttl total sum etcd debugging lease ttl total count help etcd debugging mvcc db compaction keys total total number of db keys compacted type etcd debugging mvcc db compaction keys total counter etcd debugging mvcc db compaction keys total help etcd debugging mvcc db compaction pause duration milliseconds bucketed histogram of db compaction pause duration type etcd debugging mvcc db compaction pause duration milliseconds histogram etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le etcd debugging mvcc db compaction pause duration milliseconds bucket le inf etcd debugging mvcc db compaction pause duration milliseconds sum etcd debugging mvcc db compaction pause duration milliseconds count help etcd debugging mvcc db compaction total duration milliseconds bucketed histogram of db compaction total duration type etcd debugging mvcc db compaction total duration milliseconds histogram etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le etcd debugging mvcc db compaction total duration milliseconds bucket le inf etcd debugging mvcc db compaction total duration milliseconds sum etcd debugging mvcc db compaction total duration milliseconds count help etcd debugging mvcc db total size in bytes total size of the underlying database physically allocated in bytes type etcd debugging mvcc db total size in bytes gauge etcd debugging mvcc db total size in bytes help etcd debugging mvcc delete total total number of deletes seen by this member type etcd debugging mvcc delete total counter etcd debugging mvcc delete total help etcd debugging mvcc events total total number of events sent by this member type etcd debugging mvcc events total counter etcd debugging mvcc events total help etcd debugging mvcc index compaction pause duration milliseconds bucketed histogram of index compaction pause duration type etcd debugging mvcc index compaction pause duration milliseconds histogram etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le etcd debugging mvcc index compaction pause duration milliseconds bucket le inf etcd debugging mvcc index compaction pause duration milliseconds sum etcd debugging mvcc index compaction pause duration milliseconds count help etcd debugging mvcc keys total total number of keys type etcd debugging mvcc keys total gauge etcd debugging mvcc keys total help etcd debugging mvcc pending events total total number of pending events to be sent type etcd debugging mvcc pending events total gauge etcd debugging mvcc pending events total help etcd debugging mvcc put total total number of puts seen by this member type etcd debugging mvcc put total counter etcd debugging mvcc put total help etcd debugging mvcc range total total number of ranges seen by this member type etcd debugging mvcc range total counter etcd debugging mvcc range total help etcd debugging mvcc slow watcher total total number of unsynced slow watchers type etcd debugging mvcc slow watcher total gauge etcd debugging mvcc slow watcher total help etcd debugging mvcc txn total total number of txns seen by this member type etcd debugging mvcc txn total counter etcd debugging mvcc txn total help etcd debugging mvcc watch stream total total number of watch streams type etcd debugging mvcc watch stream total gauge etcd debugging mvcc watch stream total help etcd debugging mvcc watcher total total number of watchers type etcd debugging mvcc watcher total gauge etcd debugging mvcc watcher total help etcd debugging server lease expired total the total number of expired leases type etcd debugging server lease expired total counter etcd debugging server lease expired total help etcd debugging snap save marshalling duration seconds the marshalling cost distributions of save called by snapshot type etcd debugging snap save marshalling duration seconds histogram etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le etcd debugging snap save marshalling duration seconds bucket le inf etcd debugging snap save marshalling duration seconds sum etcd debugging snap save marshalling duration seconds count help etcd debugging snap save total duration seconds the total latency distributions of save called by snapshot type etcd debugging snap save total duration seconds histogram etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le etcd debugging snap save total duration seconds bucket le inf etcd debugging snap save total duration seconds sum etcd debugging snap save total duration seconds count help etcd debugging store expires total total number of expired keys type etcd debugging store expires total counter etcd debugging store expires total help etcd debugging store reads total total number of reads action by get getrecursive local to this member type etcd debugging store reads total counter etcd debugging store reads total action getrecursive help etcd debugging store watch requests total total number of incoming watch requests new or reestablished type etcd debugging store watch requests total counter etcd debugging store watch requests total help etcd debugging store watchers count of currently active watchers type etcd debugging store watchers gauge etcd debugging store watchers help etcd debugging store writes total total number of writes e g set compareanddelete seen by this member type etcd debugging store writes total counter etcd debugging store writes total action create etcd debugging store writes total action set help etcd disk backend commit duration seconds the latency distributions of commit called by backend type etcd disk backend commit duration seconds histogram etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le etcd disk backend commit duration seconds bucket le inf etcd disk backend commit duration seconds sum etcd disk backend commit duration seconds count help etcd disk backend defrag duration seconds the latency distribution of backend defragmentation type etcd disk backend defrag duration seconds histogram etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le etcd disk backend defrag duration seconds bucket le inf etcd disk backend defrag duration seconds sum etcd disk backend defrag duration seconds count help etcd disk backend snapshot duration seconds the latency distribution of backend snapshots type etcd disk backend snapshot duration seconds histogram etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le etcd disk backend snapshot duration seconds bucket le inf etcd disk backend snapshot duration seconds sum etcd disk backend snapshot duration seconds count help etcd disk wal fsync duration seconds the latency distributions of fsync called by wal type etcd disk wal fsync duration seconds histogram etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le etcd disk wal fsync duration seconds bucket le inf etcd disk wal fsync duration seconds sum etcd disk wal fsync duration seconds count help etcd grpc proxy cache hits total total number of cache hits type etcd grpc proxy cache hits total gauge etcd grpc proxy cache hits total help etcd grpc proxy cache keys total total number of keys ranges cached type etcd grpc proxy cache keys total gauge etcd grpc proxy cache keys total help etcd grpc proxy cache misses total total number of cache misses type etcd grpc proxy cache misses total gauge etcd grpc proxy cache misses total help etcd grpc proxy events coalescing total total number of events coalescing type etcd grpc proxy events coalescing total counter etcd grpc proxy events coalescing total help etcd grpc proxy watchers coalescing total total number of current watchers coalescing type etcd grpc proxy watchers coalescing total gauge etcd grpc proxy watchers coalescing total help etcd mvcc db total size in bytes total size of the underlying database physically allocated in bytes type etcd mvcc db total size in bytes gauge etcd mvcc db total size in bytes help etcd mvcc db total size in use in bytes total size of the underlying database logically in use in bytes type etcd mvcc db total size in use in bytes gauge etcd mvcc db total size in use in bytes help etcd mvcc hash duration seconds the latency distribution of storage hash operation type etcd mvcc hash duration seconds histogram etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le etcd mvcc hash duration seconds bucket le inf etcd mvcc hash duration seconds sum etcd mvcc hash duration seconds count help etcd mvcc hash rev duration seconds the latency distribution of storage hash by revision operation type etcd mvcc hash rev duration seconds histogram etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le etcd mvcc hash rev duration seconds bucket le inf etcd mvcc hash rev duration seconds sum etcd mvcc hash rev duration seconds count help etcd network client grpc received bytes total the total number of bytes received from grpc clients type etcd network client grpc received bytes total counter etcd network client grpc received bytes total help etcd network client grpc sent bytes total the total number of bytes sent to grpc clients type etcd network client grpc sent bytes total counter etcd network client grpc sent bytes total help etcd server has leader whether or not a leader exists is existence is not type etcd server has leader gauge etcd server has leader help etcd server heartbeat send failures total the total number of leader heartbeat send failures likely overloaded from slow disk type etcd server heartbeat send failures total counter etcd server heartbeat send failures total help etcd server is leader whether or not this member is a leader if is otherwise type etcd server is leader gauge etcd server is leader help etcd server leader changes seen total the number of leader changes seen type etcd server leader changes seen total counter etcd server leader changes seen total help etcd server proposals applied total the total number of consensus proposals applied type etcd server proposals applied total gauge etcd server proposals applied total help etcd server proposals committed total the total number of consensus proposals committed type etcd server proposals committed total gauge etcd server proposals committed total help etcd server proposals failed total the total number of failed proposals seen type etcd server proposals failed total counter etcd server proposals failed total help etcd server proposals pending the current number of pending proposals to commit type etcd server proposals pending gauge etcd server proposals pending help etcd server quota backend bytes current backend storage quota size in bytes type etcd server quota backend bytes gauge etcd server quota backend bytes help etcd server slow apply total the total number of slow apply requests likely overloaded from slow disk type etcd server slow apply total counter etcd server slow apply total help etcd server version which version is running for server version label with current version type etcd server version gauge etcd server version server version git help etcd snap fsync duration seconds the latency distributions of fsync called by snap type etcd snap fsync duration seconds histogram etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le etcd snap fsync duration seconds bucket le inf etcd snap fsync duration seconds sum etcd snap fsync duration seconds count help go gc duration seconds a summary of the gc invocation durations type go gc duration seconds summary go gc duration seconds quantile go gc duration seconds quantile go gc duration seconds quantile go gc duration seconds quantile go gc duration seconds quantile go gc duration seconds sum go gc duration seconds count help go goroutines number of goroutines that currently exist type go goroutines gauge go goroutines help go info information about the go environment type go info gauge go info version devel mon jun help go memstats alloc bytes number of bytes allocated and still in use type go memstats alloc bytes gauge go memstats alloc bytes help go memstats alloc bytes total total number of bytes allocated even if freed type go memstats alloc bytes total counter go memstats alloc bytes total help go memstats buck hash sys bytes number of bytes used by the profiling bucket hash table type go memstats buck hash sys bytes gauge go memstats buck hash sys bytes help go memstats frees total total number of frees type go memstats frees total counter go memstats frees total help go memstats gc cpu fraction the fraction of this program s available cpu time used by the gc since the program started type go memstats gc cpu fraction gauge go memstats gc cpu fraction help go memstats gc sys bytes number of bytes used for garbage collection system metadata type go memstats gc sys bytes gauge go memstats gc sys bytes help go memstats heap alloc bytes number of heap bytes allocated and still in use type go memstats heap alloc bytes gauge go memstats heap alloc bytes help go memstats heap idle bytes number of heap bytes waiting to be used type go memstats heap idle bytes gauge go memstats heap idle bytes help go memstats heap inuse bytes number of heap bytes that are in use type go memstats heap inuse bytes gauge go memstats heap inuse bytes help go memstats heap objects number of allocated objects type go memstats heap objects gauge go memstats heap objects help go memstats heap released bytes number of heap bytes released to os type go memstats heap released bytes gauge go memstats heap released bytes help go memstats heap sys bytes number of heap bytes obtained from system type go memstats heap sys bytes gauge go memstats heap sys bytes help go memstats last gc time seconds number of seconds since of last garbage collection type go memstats last gc time seconds gauge go memstats last gc time seconds help go memstats lookups total total number of pointer lookups type go memstats lookups total counter go memstats lookups total help go memstats mallocs total total number of mallocs type go memstats mallocs total counter go memstats mallocs total help go memstats mcache inuse bytes number of bytes in use by mcache structures type go memstats mcache inuse bytes gauge go memstats mcache inuse bytes help go memstats mcache sys bytes number of bytes used for mcache structures obtained from system type go memstats mcache sys bytes gauge go memstats mcache sys bytes help go memstats mspan inuse bytes number of bytes in use by mspan structures type go memstats mspan inuse bytes gauge go memstats mspan inuse bytes help go memstats mspan sys bytes number of bytes used for mspan structures obtained from system type go memstats mspan sys bytes gauge go memstats mspan sys bytes help go memstats next gc bytes number of heap bytes when next garbage collection will take place type go memstats next gc bytes gauge go memstats next gc bytes help go memstats other sys bytes number of bytes used for other system allocations type go memstats other sys bytes gauge go memstats other sys bytes help go memstats stack inuse bytes number of bytes in use by the stack allocator type go memstats stack inuse bytes gauge go memstats stack inuse bytes help go memstats stack sys bytes number of bytes obtained from system for stack allocator type go memstats stack sys bytes gauge go memstats stack sys bytes help go memstats sys bytes number of bytes obtained from system type go memstats sys bytes gauge go memstats sys bytes help go threads number of os threads created type go threads gauge go threads help grpc server handled total total number of rpcs completed on the server regardless of success or failure type grpc server handled total counter grpc server handled total grpc code aborted grpc method alarm grpc service etcdserverpb maintenance grpc type unary grpc server handled total grpc code aborted grpc method authdisable grpc service etcdserverpb auth grpc type unary grpc server started total grpc method userlist grpc service etcdserverpb auth grpc type unary grpc server started total grpc method userrevokerole grpc service etcdserverpb auth grpc type unary grpc server started total grpc method watch grpc service etcdserverpb watch grpc type bidi stream help process cpu seconds total total user and system cpu time spent in seconds type process cpu seconds total counter process cpu seconds total help process max fds maximum number of open file descriptors type process max fds gauge process max fds help process open fds number of open file descriptors type process open fds gauge process open fds help process resident memory bytes resident memory size in bytes type process resident memory bytes gauge process resident memory bytes help process start time seconds start time of the process since unix epoch in seconds type process start time seconds gauge process start time seconds help process virtual memory bytes virtual memory size in bytes type process virtual memory bytes gauge process virtual memory bytes run sudeeshjohn tmp etcd version git | 1 |
159,176 | 20,036,683,502 | IssuesEvent | 2022-02-02 12:40:35 | kapseliboi/broker | https://api.github.com/repos/kapseliboi/broker | opened | CVE-2020-7788 (High) detected in ini-1.3.5.tgz | security vulnerability | ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.5.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.5.tgz">https://registry.npmjs.org/ini/-/ini-1.3.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-datachannel/node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- streamr-network-24.3.0.tgz (Root Library)
- node-datachannel-0.1.4.tgz
- prebuild-install-5.3.6.tgz
- rc-1.2.8.tgz
- :x: **ini-1.3.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/broker/commit/f1837aa3159e17151d81e973e4c79872a4bdf782">f1837aa3159e17151d81e973e4c79872a4bdf782</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: v1.3.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7788 (High) detected in ini-1.3.5.tgz - ## CVE-2020-7788 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ini-1.3.5.tgz</b></p></summary>
<p>An ini encoder/decoder for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/ini/-/ini-1.3.5.tgz">https://registry.npmjs.org/ini/-/ini-1.3.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/node-datachannel/node_modules/ini/package.json</p>
<p>
Dependency Hierarchy:
- streamr-network-24.3.0.tgz (Root Library)
- node-datachannel-0.1.4.tgz
- prebuild-install-5.3.6.tgz
- rc-1.2.8.tgz
- :x: **ini-1.3.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/kapseliboi/broker/commit/f1837aa3159e17151d81e973e4c79872a4bdf782">f1837aa3159e17151d81e973e4c79872a4bdf782</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788>CVE-2020-7788</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7788</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: v1.3.6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in ini tgz cve high severity vulnerability vulnerable library ini tgz an ini encoder decoder for node library home page a href path to dependency file package json path to vulnerable library node modules node datachannel node modules ini package json dependency hierarchy streamr network tgz root library node datachannel tgz prebuild install tgz rc tgz x ini tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
148,859 | 11,868,556,678 | IssuesEvent | 2020-03-26 09:24:42 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] createNodeKeyStore failed on Jenkins darwin worker due to DNS name | :Query Languages/SQL >test-failure | https://gradle-enterprise.elastic.co/s/r3hcjn6yivexe failed with the following error in a darwin build (https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+master+multijob-darwin-compatibility/595):
```
00:08:37 keytool error: java.lang.RuntimeException: java.io.IOException: DNSName components must begin with a letter
00:08:37
00:08:37 build complete, generating: /private/var/lib/jenkins/workspace/elastic+elasticsearch+master+multijob-darwin-compatibility/build/595.tar.bz2
00:09:40
00:09:40 FAILURE: Build failed with an exception.
00:09:40
00:09:40 * What went wrong:
00:09:40 Execution failed for task ':x-pack:plugin:sql:qa:security:with-ssl:createNodeKeyStore'.
00:09:40 > Process '/var/lib/jenkins/.java/openjdk11/bin/keytool [-genkey, -alias, test-node, -keystore, /private/var/lib/jenkins/workspace/elastic+elasticsearch+master+multijob-darwin-compatibility/x-pack/plugin/sql/qa/security/with-ssl/build/keystore/test-node.jks, -keyalg, RSA, -keysize, 2048, -validity, 712, -dname, CN=smoke-test-plugins-ssl, -keypass, keypass, -storepass, keypass, -ext, san=ip:fe80::1,dns:20049.local,ip:::1,dns:localhost,ip:127.0.0.1,dns:localhost]' finished with non-zero exit value 1
```
I am guessing the part of that that `keytool` took offence at is `dns:20049.local`.
I can run `./gradlew ':x-pack:plugin:sql:qa:security:with-ssl:createNodeKeyStore'` without problems on my Macbook. Presumably there is something different about the way the macOS Jenkins workers are configured that means they have a technically invalid DNS name. | 1.0 | [CI] createNodeKeyStore failed on Jenkins darwin worker due to DNS name - https://gradle-enterprise.elastic.co/s/r3hcjn6yivexe failed with the following error in a darwin build (https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+master+multijob-darwin-compatibility/595):
```
00:08:37 keytool error: java.lang.RuntimeException: java.io.IOException: DNSName components must begin with a letter
00:08:37
00:08:37 build complete, generating: /private/var/lib/jenkins/workspace/elastic+elasticsearch+master+multijob-darwin-compatibility/build/595.tar.bz2
00:09:40
00:09:40 FAILURE: Build failed with an exception.
00:09:40
00:09:40 * What went wrong:
00:09:40 Execution failed for task ':x-pack:plugin:sql:qa:security:with-ssl:createNodeKeyStore'.
00:09:40 > Process '/var/lib/jenkins/.java/openjdk11/bin/keytool [-genkey, -alias, test-node, -keystore, /private/var/lib/jenkins/workspace/elastic+elasticsearch+master+multijob-darwin-compatibility/x-pack/plugin/sql/qa/security/with-ssl/build/keystore/test-node.jks, -keyalg, RSA, -keysize, 2048, -validity, 712, -dname, CN=smoke-test-plugins-ssl, -keypass, keypass, -storepass, keypass, -ext, san=ip:fe80::1,dns:20049.local,ip:::1,dns:localhost,ip:127.0.0.1,dns:localhost]' finished with non-zero exit value 1
```
I am guessing the part of that that `keytool` took offence at is `dns:20049.local`.
I can run `./gradlew ':x-pack:plugin:sql:qa:security:with-ssl:createNodeKeyStore'` without problems on my Macbook. Presumably there is something different about the way the macOS Jenkins workers are configured that means they have a technically invalid DNS name. | test | createnodekeystore failed on jenkins darwin worker due to dns name failed with the following error in a darwin build keytool error java lang runtimeexception java io ioexception dnsname components must begin with a letter build complete generating private var lib jenkins workspace elastic elasticsearch master multijob darwin compatibility build tar failure build failed with an exception what went wrong execution failed for task x pack plugin sql qa security with ssl createnodekeystore process var lib jenkins java bin keytool finished with non zero exit value i am guessing the part of that that keytool took offence at is dns local i can run gradlew x pack plugin sql qa security with ssl createnodekeystore without problems on my macbook presumably there is something different about the way the macos jenkins workers are configured that means they have a technically invalid dns name | 1 |
55,434 | 6,475,980,459 | IssuesEvent | 2017-08-17 21:39:15 | RocketChat/Rocket.Chat.Electron | https://api.github.com/repos/RocketChat/Rocket.Chat.Electron | closed | Uncaught exception when opening "About Rocket.Chat+" | plat: linux stat: needs testing | ## My Setup
- Operating System: Ubuntu 17.04
- App Version: 2.7.0
- [x] I have tested with the latest version
- [x] I can simulate the issue easily
## Description
When opening the About Rocket.Chat+ menu option the "About" window opens, empty, and I also get an error window "A JavaScript error occurred in the main process" with the following content:
```Uncaught Exception:
TypeError: Error processing argument at index 0, conversion failure from undefined
at Event.set (/opt/Rocket.Chat+/resources/electron.asar/browser/api/web-contents.js:252:22)
at EventEmitter.electron.ipcMain.on (/opt/Rocket.Chat+/resources/app.asar/app/background.js:496:27)
at emitTwo (events.js:106:13)
at EventEmitter.emit (events.js:191:7)
at WebContents.<anonymous> (/opt/Rocket.Chat+/resources/electron.asar/browser/api/web-contents.js:256:37)
at emitTwo (events.js:106:13)
at WebContents.emit (events.js:191:7)
```
I believe this did not happen with previous versions, but started with 2.7.0. | 1.0 | Uncaught exception when opening "About Rocket.Chat+" - ## My Setup
- Operating System: Ubuntu 17.04
- App Version: 2.7.0
- [x] I have tested with the latest version
- [x] I can simulate the issue easily
## Description
When opening the About Rocket.Chat+ menu option the "About" window opens, empty, and I also get an error window "A JavaScript error occurred in the main process" with the following content:
```Uncaught Exception:
TypeError: Error processing argument at index 0, conversion failure from undefined
at Event.set (/opt/Rocket.Chat+/resources/electron.asar/browser/api/web-contents.js:252:22)
at EventEmitter.electron.ipcMain.on (/opt/Rocket.Chat+/resources/app.asar/app/background.js:496:27)
at emitTwo (events.js:106:13)
at EventEmitter.emit (events.js:191:7)
at WebContents.<anonymous> (/opt/Rocket.Chat+/resources/electron.asar/browser/api/web-contents.js:256:37)
at emitTwo (events.js:106:13)
at WebContents.emit (events.js:191:7)
```
I believe this did not happen with previous versions, but started with 2.7.0. | test | uncaught exception when opening about rocket chat my setup operating system ubuntu app version i have tested with the latest version i can simulate the issue easily description when opening the about rocket chat menu option the about window opens empty and i also get an error window a javascript error occurred in the main process with the following content uncaught exception typeerror error processing argument at index conversion failure from undefined at event set opt rocket chat resources electron asar browser api web contents js at eventemitter electron ipcmain on opt rocket chat resources app asar app background js at emittwo events js at eventemitter emit events js at webcontents opt rocket chat resources electron asar browser api web contents js at emittwo events js at webcontents emit events js i believe this did not happen with previous versions but started with | 1 |
304,440 | 26,276,529,389 | IssuesEvent | 2023-01-06 22:48:23 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | compose/compare/compare: TestCompare failed | C-test-failure O-robot T-sql-sessions branch-release-22.2.0 | compose/compare/compare.TestCompare [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800161?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800161?buildTab=artifacts#/) on release-22.2.0 @ [413dc596348780a8c81a450dc135135985ed70af](https://github.com/cockroachdb/cockroach/commits/413dc596348780a8c81a450dc135135985ed70af):
```
=== RUN TestCompare
compare_test.go:119: Checking connection to: cockroach1
I221202 07:29:31.305388 6644 testutils/soon.go:40 [-] 1 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:32.311448 6644 testutils/soon.go:40 [-] 2 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:33.318711 6644 testutils/soon.go:40 [-] 3 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:34.328892 6644 testutils/soon.go:40 [-] 4 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:35.340001 6644 testutils/soon.go:40 [-] 5 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:36.348195 6644 testutils/soon.go:40 [-] 6 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:37.355682 6644 testutils/soon.go:40 [-] 7 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:38.364528 6644 testutils/soon.go:40 [-] 8 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:39.372193 6644 testutils/soon.go:40 [-] 9 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:40.377310 6644 testutils/soon.go:40 [-] 10 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:41.389140 6644 testutils/soon.go:40 [-] 11 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:42.394586 6644 testutils/soon.go:40 [-] 12 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:43.401772 6644 testutils/soon.go:40 [-] 13 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:44.408743 6644 testutils/soon.go:40 [-] 14 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:45.417169 6644 testutils/soon.go:40 [-] 15 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:46.424574 6644 testutils/soon.go:40 [-] 16 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:47.430855 6644 testutils/soon.go:40 [-] 17 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:48.437342 6644 testutils/soon.go:40 [-] 18 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:49.444158 6644 testutils/soon.go:40 [-] 19 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:50.454701 6644 testutils/soon.go:40 [-] 20 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:51.461972 6644 testutils/soon.go:40 [-] 21 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:52.472098 6644 testutils/soon.go:40 [-] 22 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:53.479802 6644 testutils/soon.go:40 [-] 23 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:54.488111 6644 testutils/soon.go:40 [-] 24 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:55.494594 6644 testutils/soon.go:40 [-] 25 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:56.501172 6644 testutils/soon.go:40 [-] 26 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:57.506943 6644 testutils/soon.go:40 [-] 27 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:58.516928 6644 testutils/soon.go:40 [-] 28 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:59.522566 6644 testutils/soon.go:40 [-] 29 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:00.529021 6644 testutils/soon.go:40 [-] 30 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:01.535990 6644 testutils/soon.go:40 [-] 31 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:02.542401 6644 testutils/soon.go:40 [-] 32 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:03.549572 6644 testutils/soon.go:40 [-] 33 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:04.555510 6644 testutils/soon.go:40 [-] 34 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:05.565682 6644 testutils/soon.go:40 [-] 35 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:06.573276 6644 testutils/soon.go:40 [-] 36 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:07.586920 6644 testutils/soon.go:40 [-] 37 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:08.591984 6644 testutils/soon.go:40 [-] 38 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:09.600497 6644 testutils/soon.go:40 [-] 39 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:10.606837 6644 testutils/soon.go:40 [-] 40 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:11.613003 6644 testutils/soon.go:40 [-] 41 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:12.619454 6644 testutils/soon.go:40 [-] 42 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
compare_test.go:120: condition failed to evaluate within 45s: failed to connect to ``host=cockroach1 user=root database=postgres``: hostname resolving error (lookup cockroach1 on 169.254.169.254:53: no such host)
--- FAIL: TestCompare (45.60s)
```
<p>Parameters: <code>TAGS=bazel,gss,deadlock</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #92815 compose/compare/compare: TestCompare failed [C-test-failure O-robot T-sql-experience branch-release-22.2]
- #92044 compose/compare/compare: TestCompare failed [C-test-failure O-robot T-sql-experience branch-master]
</p>
</details>
/cc @cockroachdb/sql-experience
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestCompare.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-22028 | 1.0 | compose/compare/compare: TestCompare failed - compose/compare/compare.TestCompare [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800161?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_StressBazel/7800161?buildTab=artifacts#/) on release-22.2.0 @ [413dc596348780a8c81a450dc135135985ed70af](https://github.com/cockroachdb/cockroach/commits/413dc596348780a8c81a450dc135135985ed70af):
```
=== RUN TestCompare
compare_test.go:119: Checking connection to: cockroach1
I221202 07:29:31.305388 6644 testutils/soon.go:40 [-] 1 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:32.311448 6644 testutils/soon.go:40 [-] 2 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:33.318711 6644 testutils/soon.go:40 [-] 3 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:34.328892 6644 testutils/soon.go:40 [-] 4 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:35.340001 6644 testutils/soon.go:40 [-] 5 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:36.348195 6644 testutils/soon.go:40 [-] 6 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:37.355682 6644 testutils/soon.go:40 [-] 7 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:38.364528 6644 testutils/soon.go:40 [-] 8 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:39.372193 6644 testutils/soon.go:40 [-] 9 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:40.377310 6644 testutils/soon.go:40 [-] 10 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:41.389140 6644 testutils/soon.go:40 [-] 11 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:42.394586 6644 testutils/soon.go:40 [-] 12 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:43.401772 6644 testutils/soon.go:40 [-] 13 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:44.408743 6644 testutils/soon.go:40 [-] 14 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:45.417169 6644 testutils/soon.go:40 [-] 15 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:46.424574 6644 testutils/soon.go:40 [-] 16 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:47.430855 6644 testutils/soon.go:40 [-] 17 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:48.437342 6644 testutils/soon.go:40 [-] 18 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:49.444158 6644 testutils/soon.go:40 [-] 19 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:50.454701 6644 testutils/soon.go:40 [-] 20 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:51.461972 6644 testutils/soon.go:40 [-] 21 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:52.472098 6644 testutils/soon.go:40 [-] 22 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:53.479802 6644 testutils/soon.go:40 [-] 23 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:54.488111 6644 testutils/soon.go:40 [-] 24 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:55.494594 6644 testutils/soon.go:40 [-] 25 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:56.501172 6644 testutils/soon.go:40 [-] 26 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:57.506943 6644 testutils/soon.go:40 [-] 27 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:58.516928 6644 testutils/soon.go:40 [-] 28 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:29:59.522566 6644 testutils/soon.go:40 [-] 29 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:00.529021 6644 testutils/soon.go:40 [-] 30 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:01.535990 6644 testutils/soon.go:40 [-] 31 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:02.542401 6644 testutils/soon.go:40 [-] 32 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:03.549572 6644 testutils/soon.go:40 [-] 33 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:04.555510 6644 testutils/soon.go:40 [-] 34 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:05.565682 6644 testutils/soon.go:40 [-] 35 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:06.573276 6644 testutils/soon.go:40 [-] 36 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:07.586920 6644 testutils/soon.go:40 [-] 37 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:08.591984 6644 testutils/soon.go:40 [-] 38 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:09.600497 6644 testutils/soon.go:40 [-] 39 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:10.606837 6644 testutils/soon.go:40 [-] 40 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:11.613003 6644 testutils/soon.go:40 [-] 41 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
I221202 07:30:12.619454 6644 testutils/soon.go:40 [-] 42 SucceedsSoon: lookup cockroach1 on 169.254.169.254:53: no such host
compare_test.go:120: condition failed to evaluate within 45s: failed to connect to ``host=cockroach1 user=root database=postgres``: hostname resolving error (lookup cockroach1 on 169.254.169.254:53: no such host)
--- FAIL: TestCompare (45.60s)
```
<p>Parameters: <code>TAGS=bazel,gss,deadlock</code>
</p>
<details><summary>Help</summary>
<p>
See also: [How To Investigate a Go Test Failure \(internal\)](https://cockroachlabs.atlassian.net/l/c/HgfXfJgM)
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #92815 compose/compare/compare: TestCompare failed [C-test-failure O-robot T-sql-experience branch-release-22.2]
- #92044 compose/compare/compare: TestCompare failed [C-test-failure O-robot T-sql-experience branch-master]
</p>
</details>
/cc @cockroachdb/sql-experience
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*TestCompare.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
Jira issue: CRDB-22028 | test | compose compare compare testcompare failed compose compare compare testcompare with on release run testcompare compare test go checking connection to testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host testutils soon go succeedssoon lookup on no such host compare test go condition failed to evaluate within failed to connect to host user root database postgres hostname resolving error lookup on no such host fail testcompare parameters tags bazel gss deadlock help see also same failure on other branches compose compare compare testcompare failed compose compare compare testcompare failed cc cockroachdb sql experience jira issue crdb | 1 |
261,756 | 22,773,001,706 | IssuesEvent | 2022-07-08 11:54:54 | admiral-team/admiralui-android | https://api.github.com/repos/admiral-team/admiralui-android | closed | [FEATURE] - Badges screen clicker test | enhancement test | **Описание задачи:**
Сделать тест с прокликиванием экрана Badges
**Фреймворк**
XML
**Ресурсы:**
Ссылка на макеты или ресурсы...
| 1.0 | [FEATURE] - Badges screen clicker test - **Описание задачи:**
Сделать тест с прокликиванием экрана Badges
**Фреймворк**
XML
**Ресурсы:**
Ссылка на макеты или ресурсы...
| test | badges screen clicker test описание задачи сделать тест с прокликиванием экрана badges фреймворк xml ресурсы ссылка на макеты или ресурсы | 1 |
224,955 | 17,785,503,772 | IssuesEvent | 2021-08-31 10:31:24 | SAPDocuments/Issues | https://api.github.com/repos/SAPDocuments/Issues | closed | Req. Product Details - API portal provisioning issue - AP region | High-Prio SCPTest-trial3 SCPTest-cloudin SCPTest-2108A | Hello,
Tutorial Link: https://developers.sap.com/tutorials/cp-starter-isuite-onboard-subscribe.html
Step 5: Verify the activated capabilities
Issue: After both the capabilities are active and the boosters are executed, we should be able to access them both. But I can't access API Portal. It is running into the error and says there is a temporary problem provisioning your account. (In AP region)
Screenshot:

Please check the issue.
Thanks,
Shubham
Labels to be added:
Sprint Label: SCPTest-2108A
Scenario Label: SCPTest-cloudin
Landscape Label: AP
Prio: High-prio | 3.0 | Req. Product Details - API portal provisioning issue - AP region - Hello,
Tutorial Link: https://developers.sap.com/tutorials/cp-starter-isuite-onboard-subscribe.html
Step 5: Verify the activated capabilities
Issue: After both the capabilities are active and the boosters are executed, we should be able to access them both. But I can't access API Portal. It is running into the error and says there is a temporary problem provisioning your account. (In AP region)
Screenshot:

Please check the issue.
Thanks,
Shubham
Labels to be added:
Sprint Label: SCPTest-2108A
Scenario Label: SCPTest-cloudin
Landscape Label: AP
Prio: High-prio | test | req product details api portal provisioning issue ap region hello tutorial link step verify the activated capabilities issue after both the capabilities are active and the boosters are executed we should be able to access them both but i can t access api portal it is running into the error and says there is a temporary problem provisioning your account in ap region screenshot please check the issue thanks shubham labels to be added sprint label scptest scenario label scptest cloudin landscape label ap prio high prio | 1 |
195,574 | 15,531,014,131 | IssuesEvent | 2021-03-13 21:32:16 | Sustaingineering/Pump-Firmware | https://api.github.com/repos/Sustaingineering/Pump-Firmware | closed | Document a 'Getting Started' Page | common documentation | If someone joins our team, we need a self contained page that help that person get up to speed. | 1.0 | Document a 'Getting Started' Page - If someone joins our team, we need a self contained page that help that person get up to speed. | non_test | document a getting started page if someone joins our team we need a self contained page that help that person get up to speed | 0 |
106,467 | 11,489,438,244 | IssuesEvent | 2020-02-11 15:30:42 | 11ty/eleventy | https://api.github.com/repos/11ty/eleventy | closed | Document example of Next/Previous blog post links (without pagination) | documentation needs-votes | #211 solved the Pagination Next/Previous docs example but we still need one without pagination. | 1.0 | Document example of Next/Previous blog post links (without pagination) - #211 solved the Pagination Next/Previous docs example but we still need one without pagination. | non_test | document example of next previous blog post links without pagination solved the pagination next previous docs example but we still need one without pagination | 0 |
249,842 | 26,988,741,217 | IssuesEvent | 2023-02-09 18:04:31 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] Application Security Protection for the Masses | SecurityWeek Stale |
I’ve always found it entertaining that so many sales pitches are essentially a listing of features for the product or service being sold. The reason I find this entertaining is that for anyone who has worked on the customer side or has ever listened to customers, it is obvious that customers buy solutions, not products. Thus, the notion of showing off how proud you are of your product by rattling off a laundry list of features has always seemed a bit odd to me.
In other words, customers have a number of different problems, issues, and challenges that they are looking to solve. They are not necessarily interested in all of the different things your product or service can do. Rather, they are interested in learning how your solution can help them address their strategic priorities and move forward on the goals they have set for their security and fraud problems. It is incumbent upon vendors to understand that and to make it easy for potential customers to understand that mapping.
Along those lines, improving application security is a common goal customers have. As you might imagine, any solution geared towards improving the security of an application is going to be complex, consisting of many different moving parts. Thus, forcing customers to hunt for the components they need within your product data sheets and overviews is not going to be an effective way to convince those customers that you have a solution they might be in the market for.
So what can vendors do to convince customers that they have a solution worth that customer’s time to evaluate? For starters, they can bundle various features into use cases that can be easily demonstrated to, evaluated, and consumed by customers. Along those lines, what would a bundle around the popular application security protection use case look like?
While not an exhaustive list, here are some thoughts:
- **App Proxy:** Putting a proxy in front of applications is perhaps one of the most basic application security requirements, and for good reason. Having an intermediary allows us to inspect and monitor traffic going to and from the application, as well as to block or filter as necessary for security purposes.
- **Rate Limiting and Fast Access Control Lists (ACLs):** Flooding a site is an old standby of attackers. It is a primitive, yet effective tactic. Rate limiting is a relatively straightforward way to prevent this type of attack. Similarly, fast-performing Access Control Lists (ACLs) are another effective way to keep unwanted traffic at bay.
- **Path Discovery:** Applying machine learning (ML) to traffic transiting the environment allows us to track the rate of requests, the identity of clients accessing applications, the size of the payloads being sent, and other important telemetry elements. Using ML allows us to identify and block nefarious traffic before it becomes a more serious issue – often in minutes as opposed to hours.
- **Web Application Firewall:** WAF has become a required technology for application providers and should be included as a part of any application security bundle.
- **L3/L4/L7 DDoS:** DDoS protection has also become a requirement for application providers and should also be included as part of any application security bundle.
- **Bot Defense:** Advanced bots that know how to get around the defenses listed above can cause application providers monetary loss and reputation damage. As such, bot defense should also be included as part of an application security bundle.
- **Auto-Certificates:** Speed of deploying applications is essential for remaining competitive, as is speed of protecting those applications. The ability to auto-issue certificates and to auto-register DNS for resources saves time, allowing application providers to go from no protection to full protection in a matter of minutes.
- **Malicious User Detection:** Another great application for machine learning (ML) is quickly understanding which users and patterns appear to be behaving maliciously. This is something that often takes application providers hours or days to identify. With ML, this can be done in minutes, allowing those application providers to quickly take action and block/mitigate.
- **Client-Side Defense:** Visibility into the end-user environment is something many application providers lack. The ability to inspect how JavaScript is being called, where requests are going, and what third party scripts are being called gives important insight that is extremely helpful for application security purposes.
- **URI Routing:** The ability to quickly and easily control where certain requests are routing gives application providers the ability to block/control specific endpoints (URIs). No application security solution would be complete without this important feature.
- **Service Policies:** Quick and easy policy deployment is a must for application security. The ability to chain together service policies as needed based on requirements, along with the ability to generate custom rules for steering traffic or allowing/denying traffic beyond the capabilities of the other defensive capabilities is another essential part of the total application security package.
- **Synthetic Monitors:** How are applications performing externally? What are my customers experiencing? These are important questions that synthetic monitors allow a business to answer, which can quickly identify any issues that might affect the application.
- **TLS Fingerprinting and Device Identification:** While IP addresses change frequently, TLS fingerprints and device identifiers change much more rarely. Thus, basing policies and rules on them rather than IP address makes a lot of sense when it comes to application security.
- **Cross-Site Request Forgery Protection:** Scripts that operate cross-site can cause serious problems for application providers. Thus mitigating the risk they present should be part of any application security bundle as well.
Securing applications is a top priority for nearly all businesses. While there are many routes to application security, bundles that allow security teams to quickly and easily secure applications and affect security posture in a self-service manner are becoming increasingly popular. These bundles inform application providers and allow them to make better, more informed decisions to improve security posture without introducing unnecessary friction to the end-user.
The post [Application Security Protection for the Masses](https://www.securityweek.com/application-security-protection-for-the-masses/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/application-security-protection-for-the-masses/>
| True | [SecurityWeek] Application Security Protection for the Masses -
I’ve always found it entertaining that so many sales pitches are essentially a listing of features for the product or service being sold. The reason I find this entertaining is that for anyone who has worked on the customer side or has ever listened to customers, it is obvious that customers buy solutions, not products. Thus, the notion of showing off how proud you are of your product by rattling off a laundry list of features has always seemed a bit odd to me.
In other words, customers have a number of different problems, issues, and challenges that they are looking to solve. They are not necessarily interested in all of the different things your product or service can do. Rather, they are interested in learning how your solution can help them address their strategic priorities and move forward on the goals they have set for their security and fraud problems. It is incumbent upon vendors to understand that and to make it easy for potential customers to understand that mapping.
Along those lines, improving application security is a common goal customers have. As you might imagine, any solution geared towards improving the security of an application is going to be complex, consisting of many different moving parts. Thus, forcing customers to hunt for the components they need within your product data sheets and overviews is not going to be an effective way to convince those customers that you have a solution they might be in the market for.
So what can vendors do to convince customers that they have a solution worth that customer’s time to evaluate? For starters, they can bundle various features into use cases that can be easily demonstrated to, evaluated, and consumed by customers. Along those lines, what would a bundle around the popular application security protection use case look like?
While not an exhaustive list, here are some thoughts:
- **App Proxy:** Putting a proxy in front of applications is perhaps one of the most basic application security requirements, and for good reason. Having an intermediary allows us to inspect and monitor traffic going to and from the application, as well as to block or filter as necessary for security purposes.
- **Rate Limiting and Fast Access Control Lists (ACLs):** Flooding a site is an old standby of attackers. It is a primitive, yet effective tactic. Rate limiting is a relatively straightforward way to prevent this type of attack. Similarly, fast-performing Access Control Lists (ACLs) are another effective way to keep unwanted traffic at bay.
- **Path Discovery:** Applying machine learning (ML) to traffic transiting the environment allows us to track the rate of requests, the identity of clients accessing applications, the size of the payloads being sent, and other important telemetry elements. Using ML allows us to identify and block nefarious traffic before it becomes a more serious issue – often in minutes as opposed to hours.
- **Web Application Firewall:** WAF has become a required technology for application providers and should be included as a part of any application security bundle.
- **L3/L4/L7 DDoS:** DDoS protection has also become a requirement for application providers and should also be included as part of any application security bundle.
- **Bot Defense:** Advanced bots that know how to get around the defenses listed above can cause application providers monetary loss and reputation damage. As such, bot defense should also be included as part of an application security bundle.
- **Auto-Certificates:** Speed of deploying applications is essential for remaining competitive, as is speed of protecting those applications. The ability to auto-issue certificates and to auto-register DNS for resources saves time, allowing application providers to go from no protection to full protection in a matter of minutes.
- **Malicious User Detection:** Another great application for machine learning (ML) is quickly understanding which users and patterns appear to be behaving maliciously. This is something that often takes application providers hours or days to identify. With ML, this can be done in minutes, allowing those application providers to quickly take action and block/mitigate.
- **Client-Side Defense:** Visibility into the end-user environment is something many application providers lack. The ability to inspect how JavaScript is being called, where requests are going, and what third party scripts are being called gives important insight that is extremely helpful for application security purposes.
- **URI Routing:** The ability to quickly and easily control where certain requests are routing gives application providers the ability to block/control specific endpoints (URIs). No application security solution would be complete without this important feature.
- **Service Policies:** Quick and easy policy deployment is a must for application security. The ability to chain together service policies as needed based on requirements, along with the ability to generate custom rules for steering traffic or allowing/denying traffic beyond the capabilities of the other defensive capabilities is another essential part of the total application security package.
- **Synthetic Monitors:** How are applications performing externally? What are my customers experiencing? These are important questions that synthetic monitors allow a business to answer, which can quickly identify any issues that might affect the application.
- **TLS Fingerprinting and Device Identification:** While IP addresses change frequently, TLS fingerprints and device identifiers change much more rarely. Thus, basing policies and rules on them rather than IP address makes a lot of sense when it comes to application security.
- **Cross-Site Request Forgery Protection:** Scripts that operate cross-site can cause serious problems for application providers. Thus mitigating the risk they present should be part of any application security bundle as well.
Securing applications is a top priority for nearly all businesses. While there are many routes to application security, bundles that allow security teams to quickly and easily secure applications and affect security posture in a self-service manner are becoming increasingly popular. These bundles inform application providers and allow them to make better, more informed decisions to improve security posture without introducing unnecessary friction to the end-user.
The post [Application Security Protection for the Masses](https://www.securityweek.com/application-security-protection-for-the-masses/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/application-security-protection-for-the-masses/>
| non_test | application security protection for the masses i’ve always found it entertaining that so many sales pitches are essentially a listing of features for the product or service being sold the reason i find this entertaining is that for anyone who has worked on the customer side or has ever listened to customers it is obvious that customers buy solutions not products thus the notion of showing off how proud you are of your product by rattling off a laundry list of features has always seemed a bit odd to me in other words customers have a number of different problems issues and challenges that they are looking to solve they are not necessarily interested in all of the different things your product or service can do rather they are interested in learning how your solution can help them address their strategic priorities and move forward on the goals they have set for their security and fraud problems it is incumbent upon vendors to understand that and to make it easy for potential customers to understand that mapping along those lines improving application security is a common goal customers have as you might imagine any solution geared towards improving the security of an application is going to be complex consisting of many different moving parts thus forcing customers to hunt for the components they need within your product data sheets and overviews is not going to be an effective way to convince those customers that you have a solution they might be in the market for so what can vendors do to convince customers that they have a solution worth that customer’s time to evaluate for starters they can bundle various features into use cases that can be easily demonstrated to evaluated and consumed by customers along those lines what would a bundle around the popular application security protection use case look like while not an exhaustive list here are some thoughts app proxy putting a proxy in front of applications is perhaps one of the most basic application security requirements and for good reason having an intermediary allows us to inspect and monitor traffic going to and from the application as well as to block or filter as necessary for security purposes rate limiting and fast access control lists acls flooding a site is an old standby of attackers it is a primitive yet effective tactic rate limiting is a relatively straightforward way to prevent this type of attack similarly fast performing access control lists acls are another effective way to keep unwanted traffic at bay path discovery applying machine learning ml to traffic transiting the environment allows us to track the rate of requests the identity of clients accessing applications the size of the payloads being sent and other important telemetry elements using ml allows us to identify and block nefarious traffic before it becomes a more serious issue – often in minutes as opposed to hours web application firewall waf has become a required technology for application providers and should be included as a part of any application security bundle ddos ddos protection has also become a requirement for application providers and should also be included as part of any application security bundle bot defense advanced bots that know how to get around the defenses listed above can cause application providers monetary loss and reputation damage as such bot defense should also be included as part of an application security bundle auto certificates speed of deploying applications is essential for remaining competitive as is speed of protecting those applications the ability to auto issue certificates and to auto register dns for resources saves time allowing application providers to go from no protection to full protection in a matter of minutes malicious user detection another great application for machine learning ml is quickly understanding which users and patterns appear to be behaving maliciously this is something that often takes application providers hours or days to identify with ml this can be done in minutes allowing those application providers to quickly take action and block mitigate client side defense visibility into the end user environment is something many application providers lack the ability to inspect how javascript is being called where requests are going and what third party scripts are being called gives important insight that is extremely helpful for application security purposes uri routing the ability to quickly and easily control where certain requests are routing gives application providers the ability to block control specific endpoints uris no application security solution would be complete without this important feature service policies quick and easy policy deployment is a must for application security the ability to chain together service policies as needed based on requirements along with the ability to generate custom rules for steering traffic or allowing denying traffic beyond the capabilities of the other defensive capabilities is another essential part of the total application security package synthetic monitors how are applications performing externally what are my customers experiencing these are important questions that synthetic monitors allow a business to answer which can quickly identify any issues that might affect the application tls fingerprinting and device identification while ip addresses change frequently tls fingerprints and device identifiers change much more rarely thus basing policies and rules on them rather than ip address makes a lot of sense when it comes to application security cross site request forgery protection scripts that operate cross site can cause serious problems for application providers thus mitigating the risk they present should be part of any application security bundle as well securing applications is a top priority for nearly all businesses while there are many routes to application security bundles that allow security teams to quickly and easily secure applications and affect security posture in a self service manner are becoming increasingly popular these bundles inform application providers and allow them to make better more informed decisions to improve security posture without introducing unnecessary friction to the end user the post appeared first on | 0 |
116,790 | 9,884,089,418 | IssuesEvent | 2019-06-24 21:06:26 | rancher/rio | https://api.github.com/repos/rancher/rio | closed | registry does not start due to cert-checker error | to-test | rio install against AKS 1.13.5
registry deployment stays at 0/2; error in the cert-checker init container is:
Can't open /etc/registry/tls.crt for reading, No such file or directory
140601283124072:error:02001002:system library:fopen:No such file or directory:crypto/bio/bss_file.c:72:fopen('/etc/registry/tls.crt','r')
140601283124072:error:2006D080:BIO routines:BIO_new_file:no such file:crypto/bio/bss_file.c:79:
unable to load certificate
| 1.0 | registry does not start due to cert-checker error - rio install against AKS 1.13.5
registry deployment stays at 0/2; error in the cert-checker init container is:
Can't open /etc/registry/tls.crt for reading, No such file or directory
140601283124072:error:02001002:system library:fopen:No such file or directory:crypto/bio/bss_file.c:72:fopen('/etc/registry/tls.crt','r')
140601283124072:error:2006D080:BIO routines:BIO_new_file:no such file:crypto/bio/bss_file.c:79:
unable to load certificate
| test | registry does not start due to cert checker error rio install against aks registry deployment stays at error in the cert checker init container is can t open etc registry tls crt for reading no such file or directory error system library fopen no such file or directory crypto bio bss file c fopen etc registry tls crt r error bio routines bio new file no such file crypto bio bss file c unable to load certificate | 1 |
561,754 | 16,623,252,492 | IssuesEvent | 2021-06-03 06:09:36 | rancher/rke2 | https://api.github.com/repos/rancher/rke2 | closed | Restoring from snapshot fails executable file not found in $PATH | kind/bug priority/critical-urgent | **Environmental Info:**
RKE2 Version:
* `v1.21.1-rc1+rke2r1`
Node(s) CPU architecture, OS, and Version:
Ubuntu 20.04
Cluster Configuration:
Single node cluster
**Describe the bug:**
Restoring from snapshot fails with Containerd Exited: exec: "containerd": executable file not found in $PATH, exiting kubelet
**Steps To Reproduce:**
Create a single node cluster
Take snapshot
Stop rke2 service
Run killall
Restore using the snapshot
```
rke2 server \
--cluster-reset \
--cluster-reset-restore-path=/var/lib/rancher/rke2/server/db/snapshots/on-demand-<unix-timestamp
```
**Expected behavior:**
Reset should be run and cluster-reset msg is expected to be seen on the console
**Actual behavior:**
Errors with Containerd Exited: exec: "containerd": executable file not found in $PATH, exiting kubelet and panic
**Additional context / logs:**
```
sudo rke2 server --cluster-reset --cluster-reset-restore-path=/var/lib/rancher/rke2/server/db/snapshots/on-demand-ip-172-31-39-67-1621896967
WARN[0000] not running in CIS mode
INFO[0000] starting kubelet to clean up old static pods
INFO[0005] Containerd Exited: exec: "containerd": executable file not found in $PATH, exiting kubelet
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x0 pc=0x4be89b]
goroutine 1 [running]:
os.(*Process).signal(0x0, 0x70cc4b8, 0x9be7958, 0x0, 0x0)
/usr/local/go/src/os/exec_unix.go:63 +0x3b
os.(*Process).Signal(...)
/usr/local/go/src/os/exec.go:135
os.(*Process).kill(...)
/usr/local/go/src/os/exec_posix.go:66
os.(*Process).Kill(...)
/usr/local/go/src/os/exec.go:120
github.com/rancher/rke2/pkg/rke2.removeOldPodManifests(0x66d7963, 0x15, 0xc001699a70, 0x1, 0x0, 0x0)
/source/pkg/rke2/rke2.go:229 +0x945
github.com/rancher/rke2/pkg/rke2.setup(0xc000a4b4a0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/source/pkg/rke2/rke2.go:164 +0x8a5
github.com/rancher/rke2/pkg/rke2.Server(0xc000a4b4a0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/source/pkg/rke2/rke2.go:48 +0x6b
github.com/rancher/rke2/pkg/cli/cmds.ServerRun(0xc000a4b4a0, 0x0, 0x0)
/source/pkg/cli/cmds/server.go:143 +0x98
github.com/urfave/cli.HandleAction(0x57f1f00, 0x68fece0, 0xc000a4b4a0, 0xc000a4b4a0, 0x0)
/go/pkg/mod/github.com/urfave/cli@v1.22.5/app.go:524 +0x105
github.com/urfave/cli.Command.Run(0x6693772, 0x6, 0x0, 0x0, 0x0, 0x0, 0x0, 0x66da585, 0x15, 0xc0017b8a50, ...)
/go/pkg/mod/github.com/urfave/cli@v1.22.5/command.go:173 +0x579
github.com/urfave/cli.(*App).Run(0xc0009afc00, 0xc000a52c00, 0x4, 0x4, 0x0, 0x0)
/go/pkg/mod/github.com/urfave/cli@v1.22.5/app.go:277 +0x808
main.main()
/source/main.go:20 +0x714
```
| 1.0 | Restoring from snapshot fails executable file not found in $PATH - **Environmental Info:**
RKE2 Version:
* `v1.21.1-rc1+rke2r1`
Node(s) CPU architecture, OS, and Version:
Ubuntu 20.04
Cluster Configuration:
Single node cluster
**Describe the bug:**
Restoring from snapshot fails with Containerd Exited: exec: "containerd": executable file not found in $PATH, exiting kubelet
**Steps To Reproduce:**
Create a single node cluster
Take snapshot
Stop rke2 service
Run killall
Restore using the snapshot
```
rke2 server \
--cluster-reset \
--cluster-reset-restore-path=/var/lib/rancher/rke2/server/db/snapshots/on-demand-<unix-timestamp
```
**Expected behavior:**
Reset should be run and cluster-reset msg is expected to be seen on the console
**Actual behavior:**
Errors with Containerd Exited: exec: "containerd": executable file not found in $PATH, exiting kubelet and panic
**Additional context / logs:**
```
sudo rke2 server --cluster-reset --cluster-reset-restore-path=/var/lib/rancher/rke2/server/db/snapshots/on-demand-ip-172-31-39-67-1621896967
WARN[0000] not running in CIS mode
INFO[0000] starting kubelet to clean up old static pods
INFO[0005] Containerd Exited: exec: "containerd": executable file not found in $PATH, exiting kubelet
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x0 pc=0x4be89b]
goroutine 1 [running]:
os.(*Process).signal(0x0, 0x70cc4b8, 0x9be7958, 0x0, 0x0)
/usr/local/go/src/os/exec_unix.go:63 +0x3b
os.(*Process).Signal(...)
/usr/local/go/src/os/exec.go:135
os.(*Process).kill(...)
/usr/local/go/src/os/exec_posix.go:66
os.(*Process).Kill(...)
/usr/local/go/src/os/exec.go:120
github.com/rancher/rke2/pkg/rke2.removeOldPodManifests(0x66d7963, 0x15, 0xc001699a70, 0x1, 0x0, 0x0)
/source/pkg/rke2/rke2.go:229 +0x945
github.com/rancher/rke2/pkg/rke2.setup(0xc000a4b4a0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/source/pkg/rke2/rke2.go:164 +0x8a5
github.com/rancher/rke2/pkg/rke2.Server(0xc000a4b4a0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/source/pkg/rke2/rke2.go:48 +0x6b
github.com/rancher/rke2/pkg/cli/cmds.ServerRun(0xc000a4b4a0, 0x0, 0x0)
/source/pkg/cli/cmds/server.go:143 +0x98
github.com/urfave/cli.HandleAction(0x57f1f00, 0x68fece0, 0xc000a4b4a0, 0xc000a4b4a0, 0x0)
/go/pkg/mod/github.com/urfave/cli@v1.22.5/app.go:524 +0x105
github.com/urfave/cli.Command.Run(0x6693772, 0x6, 0x0, 0x0, 0x0, 0x0, 0x0, 0x66da585, 0x15, 0xc0017b8a50, ...)
/go/pkg/mod/github.com/urfave/cli@v1.22.5/command.go:173 +0x579
github.com/urfave/cli.(*App).Run(0xc0009afc00, 0xc000a52c00, 0x4, 0x4, 0x0, 0x0)
/go/pkg/mod/github.com/urfave/cli@v1.22.5/app.go:277 +0x808
main.main()
/source/main.go:20 +0x714
```
| non_test | restoring from snapshot fails executable file not found in path environmental info version node s cpu architecture os and version ubuntu cluster configuration single node cluster describe the bug restoring from snapshot fails with containerd exited exec containerd executable file not found in path exiting kubelet steps to reproduce create a single node cluster take snapshot stop service run killall restore using the snapshot server cluster reset cluster reset restore path var lib rancher server db snapshots on demand unix timestamp expected behavior reset should be run and cluster reset msg is expected to be seen on the console actual behavior errors with containerd exited exec containerd executable file not found in path exiting kubelet and panic additional context logs sudo server cluster reset cluster reset restore path var lib rancher server db snapshots on demand ip warn not running in cis mode info starting kubelet to clean up old static pods info containerd exited exec containerd executable file not found in path exiting kubelet panic runtime error invalid memory address or nil pointer dereference goroutine os process signal usr local go src os exec unix go os process signal usr local go src os exec go os process kill usr local go src os exec posix go os process kill usr local go src os exec go github com rancher pkg removeoldpodmanifests source pkg go github com rancher pkg setup source pkg go github com rancher pkg server source pkg go github com rancher pkg cli cmds serverrun source pkg cli cmds server go github com urfave cli handleaction go pkg mod github com urfave cli app go github com urfave cli command run go pkg mod github com urfave cli command go github com urfave cli app run go pkg mod github com urfave cli app go main main source main go | 0 |
72,488 | 3,386,466,912 | IssuesEvent | 2015-11-27 17:48:42 | ccrama/Slide | https://api.github.com/repos/ccrama/Slide | opened | Slide reopens itself from background when leaved in landscape | bug high priority | Happens every minute or so, when it isn't killed through recents. Newest self compiled apk.
@ccrama Please fix this before pushing newest update | 1.0 | Slide reopens itself from background when leaved in landscape - Happens every minute or so, when it isn't killed through recents. Newest self compiled apk.
@ccrama Please fix this before pushing newest update | non_test | slide reopens itself from background when leaved in landscape happens every minute or so when it isn t killed through recents newest self compiled apk ccrama please fix this before pushing newest update | 0 |
252,765 | 8,041,562,805 | IssuesEvent | 2018-07-31 03:45:11 | Zicerite/Gavania-Project | https://api.github.com/repos/Zicerite/Gavania-Project | closed | Spiking skill for Swordsman | Medium Priority Skill Related | Swordsman should have a skill that spikes enemies downward. Deals decent damage, but not much else. | 1.0 | Spiking skill for Swordsman - Swordsman should have a skill that spikes enemies downward. Deals decent damage, but not much else. | non_test | spiking skill for swordsman swordsman should have a skill that spikes enemies downward deals decent damage but not much else | 0 |
352,332 | 32,060,099,919 | IssuesEvent | 2023-09-24 15:01:12 | tijlleenders/ZinZen | https://api.github.com/repos/tijlleenders/ZinZen | opened | Add Playwright Tests for sharing feature | UI devex test dev research more_than_a_day | Follow the steps: -
- On User 1 window
1. Open app, finish onboarding
2. Select a goal on my goals page
3. click on circle and select share action
4. select "share privately" from the popup
5. click on plus btn to add contact
6. write a name "User 2" and click on share invitation
- Open that link in new window that will be acting as User 2
1. Open app, finish onboarding
2. paste link and add the contact
- On user 1 window
8. click on the contact btn again to share the goal this time
- On user 2 window
4. refresh the window
5. switch to my time and switch back to my goals
6. check if inbox icon is visible
7. click on inbox and check whether goal is present or not | 1.0 | Add Playwright Tests for sharing feature - Follow the steps: -
- On User 1 window
1. Open app, finish onboarding
2. Select a goal on my goals page
3. click on circle and select share action
4. select "share privately" from the popup
5. click on plus btn to add contact
6. write a name "User 2" and click on share invitation
- Open that link in new window that will be acting as User 2
1. Open app, finish onboarding
2. paste link and add the contact
- On user 1 window
8. click on the contact btn again to share the goal this time
- On user 2 window
4. refresh the window
5. switch to my time and switch back to my goals
6. check if inbox icon is visible
7. click on inbox and check whether goal is present or not | test | add playwright tests for sharing feature follow the steps on user window open app finish onboarding select a goal on my goals page click on circle and select share action select share privately from the popup click on plus btn to add contact write a name user and click on share invitation open that link in new window that will be acting as user open app finish onboarding paste link and add the contact on user window click on the contact btn again to share the goal this time on user window refresh the window switch to my time and switch back to my goals check if inbox icon is visible click on inbox and check whether goal is present or not | 1 |
323,159 | 27,700,042,837 | IssuesEvent | 2023-03-14 07:10:56 | astronomer/astronomer-providers | https://api.github.com/repos/astronomer/astronomer-providers | closed | Test the timeout parameter for all the Triggers | testing | Test the timeout parameter for all the Triggers (see Trigger table in airflow ) | 1.0 | Test the timeout parameter for all the Triggers - Test the timeout parameter for all the Triggers (see Trigger table in airflow ) | test | test the timeout parameter for all the triggers test the timeout parameter for all the triggers see trigger table in airflow | 1 |
96,445 | 8,614,954,380 | IssuesEvent | 2018-11-19 19:03:20 | nebula-plugins/gradle-nebula-integration | https://api.github.com/repos/nebula-plugins/gradle-nebula-integration | closed | Dependencies which have transitive=false in ivy file are not included in alignment | priority testable | I have a dependency which has transitive dependencies defined in ivy file. All of them are members of the same group for alignment. However, one of them is defined with transitive=false.
`<dependency org="com.netflix.governator" name="governator-jetty" rev="1.14.4" conf="compile->default" transitive="false"/>`
This dependency is not added to a platform for alignment.
`./gradlew dI --dependency governator --configuration compile` gives the following output.
```
> Task :dependencyInsight
com.netflix.governator:governator-api:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
com.netflix.governator:governator-api:1.17.5
\--- com.netflix.governator:governator-core:1.17.5
+--- netflix:library:1.173
| \--- compile
+--- com.netflix.governator:governator-jersey:1.17.5
| +--- netflix:library:1.173 (*)
| \--- compile
+--- com.netflix.governator:governator-servlet:1.17.5
| +--- netflix:library:1.173 (*)
| \--- compile
\--- compile
com.netflix.governator:governator-core:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- Forced
- By constraint : belongs to platform aligned-platform:governator:1.17.5
com.netflix.governator:governator-core:1.17.5
+--- com.netflix.governator:governator-jersey:1.17.5
| +--- netflix:library:1.173
| | \--- compile
| \--- compile
\--- com.netflix.governator:governator-servlet:1.17.5
+--- netflix:library:1.173 (*)
\--- compile
com.netflix.governator:governator-core:1.14.4 -> 1.17.5
\--- netflix:library:1.173
\--- compile
com.netflix.governator:governator-jersey:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
- Forced
com.netflix.governator:governator-jersey:1.14.4 -> 1.17.5
\--- netflix:library:1.173
\--- compile
com.netflix.governator:governator-jetty:1.14.4
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
com.netflix.governator:governator-jetty:1.14.4
\--- netflix:library:1.173
\--- compile
com.netflix.governator:governator-providers:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
com.netflix.governator:governator-providers:1.17.5
\--- com.netflix.governator:governator-jersey:1.17.5
+--- netflix:library:1.173
| \--- compile
\--- compile
com.netflix.governator:governator-servlet:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
- Forced
com.netflix.governator:governator-servlet:1.14.4 -> 1.17.5
\--- netflix:library:1.173
\--- compile
```
See `com.netflix.governator:governator-jetty:1.14.4`
Here is the full example project https://github.com/nebula-plugins/gradle-nebula-integration/tree/master/transitive-false-not-aligned
| 1.0 | Dependencies which have transitive=false in ivy file are not included in alignment - I have a dependency which has transitive dependencies defined in ivy file. All of them are members of the same group for alignment. However, one of them is defined with transitive=false.
`<dependency org="com.netflix.governator" name="governator-jetty" rev="1.14.4" conf="compile->default" transitive="false"/>`
This dependency is not added to a platform for alignment.
`./gradlew dI --dependency governator --configuration compile` gives the following output.
```
> Task :dependencyInsight
com.netflix.governator:governator-api:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
com.netflix.governator:governator-api:1.17.5
\--- com.netflix.governator:governator-core:1.17.5
+--- netflix:library:1.173
| \--- compile
+--- com.netflix.governator:governator-jersey:1.17.5
| +--- netflix:library:1.173 (*)
| \--- compile
+--- com.netflix.governator:governator-servlet:1.17.5
| +--- netflix:library:1.173 (*)
| \--- compile
\--- compile
com.netflix.governator:governator-core:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- Forced
- By constraint : belongs to platform aligned-platform:governator:1.17.5
com.netflix.governator:governator-core:1.17.5
+--- com.netflix.governator:governator-jersey:1.17.5
| +--- netflix:library:1.173
| | \--- compile
| \--- compile
\--- com.netflix.governator:governator-servlet:1.17.5
+--- netflix:library:1.173 (*)
\--- compile
com.netflix.governator:governator-core:1.14.4 -> 1.17.5
\--- netflix:library:1.173
\--- compile
com.netflix.governator:governator-jersey:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
- Forced
com.netflix.governator:governator-jersey:1.14.4 -> 1.17.5
\--- netflix:library:1.173
\--- compile
com.netflix.governator:governator-jetty:1.14.4
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
com.netflix.governator:governator-jetty:1.14.4
\--- netflix:library:1.173
\--- compile
com.netflix.governator:governator-providers:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
com.netflix.governator:governator-providers:1.17.5
\--- com.netflix.governator:governator-jersey:1.17.5
+--- netflix:library:1.173
| \--- compile
\--- compile
com.netflix.governator:governator-servlet:1.17.5
variant "runtime" [
org.gradle.status = release (not requested)
org.gradle.usage = java-runtime (not requested)
org.gradle.component.category = library (not requested)
]
Selection reasons:
- By constraint : belongs to platform aligned-platform:governator:1.17.5
- Forced
com.netflix.governator:governator-servlet:1.14.4 -> 1.17.5
\--- netflix:library:1.173
\--- compile
```
See `com.netflix.governator:governator-jetty:1.14.4`
Here is the full example project https://github.com/nebula-plugins/gradle-nebula-integration/tree/master/transitive-false-not-aligned
| test | dependencies which have transitive false in ivy file are not included in alignment i have a dependency which has transitive dependencies defined in ivy file all of them are members of the same group for alignment however one of them is defined with transitive false this dependency is not added to a platform for alignment gradlew di dependency governator configuration compile gives the following output task dependencyinsight com netflix governator governator api variant runtime org gradle status release not requested org gradle usage java runtime not requested org gradle component category library not requested selection reasons by constraint belongs to platform aligned platform governator com netflix governator governator api com netflix governator governator core netflix library compile com netflix governator governator jersey netflix library compile com netflix governator governator servlet netflix library compile compile com netflix governator governator core variant runtime org gradle status release not requested org gradle usage java runtime not requested org gradle component category library not requested selection reasons forced by constraint belongs to platform aligned platform governator com netflix governator governator core com netflix governator governator jersey netflix library compile compile com netflix governator governator servlet netflix library compile com netflix governator governator core netflix library compile com netflix governator governator jersey variant runtime org gradle status release not requested org gradle usage java runtime not requested org gradle component category library not requested selection reasons by constraint belongs to platform aligned platform governator forced com netflix governator governator jersey netflix library compile com netflix governator governator jetty variant runtime org gradle status release not requested org gradle usage java runtime not requested org gradle component category library not requested com netflix governator governator jetty netflix library compile com netflix governator governator providers variant runtime org gradle status release not requested org gradle usage java runtime not requested org gradle component category library not requested selection reasons by constraint belongs to platform aligned platform governator com netflix governator governator providers com netflix governator governator jersey netflix library compile compile com netflix governator governator servlet variant runtime org gradle status release not requested org gradle usage java runtime not requested org gradle component category library not requested selection reasons by constraint belongs to platform aligned platform governator forced com netflix governator governator servlet netflix library compile see com netflix governator governator jetty here is the full example project | 1 |
297,585 | 9,178,830,844 | IssuesEvent | 2019-03-05 00:35:27 | minio/mc | https://api.github.com/repos/minio/mc | closed | Change --insecure flag to --skipcertcheck | priority: medium | *** Not using standard template ***
`mc` currently uses `--insecureflag` flag for the case where self signed certificates are used. The name is a little misleading. So, this needs to be changed to `--skipcertcheck`
| 1.0 | Change --insecure flag to --skipcertcheck - *** Not using standard template ***
`mc` currently uses `--insecureflag` flag for the case where self signed certificates are used. The name is a little misleading. So, this needs to be changed to `--skipcertcheck`
| non_test | change insecure flag to skipcertcheck not using standard template mc currently uses insecureflag flag for the case where self signed certificates are used the name is a little misleading so this needs to be changed to skipcertcheck | 0 |
245,623 | 20,789,934,698 | IssuesEvent | 2022-03-17 00:08:35 | Ale-Torres/BrowserQuest | https://api.github.com/repos/Ale-Torres/BrowserQuest | closed | Need to add unit tests for astar.js | no unit testing | We need to add unit tests to astar.js so that when we fix the code smell, we can ensure it is still working correctly | 1.0 | Need to add unit tests for astar.js - We need to add unit tests to astar.js so that when we fix the code smell, we can ensure it is still working correctly | test | need to add unit tests for astar js we need to add unit tests to astar js so that when we fix the code smell we can ensure it is still working correctly | 1 |
179,867 | 13,908,229,502 | IssuesEvent | 2020-10-20 13:34:42 | QubesOS/updates-status | https://api.github.com/repos/QubesOS/updates-status | closed | app-linux-pdf-converter v2.1.10 (r4.1) | r4.1-bullseye-cur-test r4.1-buster-cur-test r4.1-centos8-cur-test r4.1-dom0-cur-test r4.1-fc29-cur-test r4.1-fc30-cur-test r4.1-fc31-cur-test r4.1-fc32-cur-test | Update of app-linux-pdf-converter to v2.1.10 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-app-linux-pdf-converter/commit/0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8
[Changes since previous version](https://github.com/QubesOS/qubes-app-linux-pdf-converter/compare/v2.1.8...v2.1.10):
QubesOS/qubes-app-linux-pdf-converter@0c9d97e version 2.1.10
QubesOS/qubes-app-linux-pdf-converter@6b7f71f Python38 is now available for CentOS8
QubesOS/qubes-app-linux-pdf-converter@6d1ba08 version 2.1.9
QubesOS/qubes-app-linux-pdf-converter@b83e354 require python 3.7+, exclude stretch, jessie and centos
QubesOS/qubes-app-linux-pdf-converter@653c55f Use proper python package installation for the VM part too
QubesOS/qubes-app-linux-pdf-converter@229e68a Drop executable bit from nautilus extension
QubesOS/qubes-app-linux-pdf-converter@617c2a7 Add qubespdfconverter/__init__.py
QubesOS/qubes-app-linux-pdf-converter@6d457d6 Move tests back to qubespdfconverter.tests
QubesOS/qubes-app-linux-pdf-converter@f1559c9 Install only tests with older python
QubesOS/qubes-app-linux-pdf-converter@04991c3 travis: include R4.0 dom0 too
QubesOS/qubes-app-linux-pdf-converter@73a9012 Adjust dependencies after python rewrite
QubesOS/qubes-app-linux-pdf-converter@60b6b5c Merge remote-tracking branch 'origin/pr/7'
QubesOS/qubes-app-linux-pdf-converter@1ee08f7 makefile: Resolve makefile conflict
QubesOS/qubes-app-linux-pdf-converter@64cc14f pylint: Add expression-not-assigned
QubesOS/qubes-app-linux-pdf-converter@379659b client: Add support for older tqdm versions
QubesOS/qubes-app-linux-pdf-converter@f1d35f2 client: Handle out of space error
QubesOS/qubes-app-linux-pdf-converter@5eab363 client: Fix output spacing
QubesOS/qubes-app-linux-pdf-converter@c87e61b client: Simplify image appending
QubesOS/qubes-app-linux-pdf-converter@9b655af pylint: Add bad-continuation to .pylintrc
QubesOS/qubes-app-linux-pdf-converter@388278a debian: update control syntax for python nautilus
QubesOS/qubes-app-linux-pdf-converter@2abacda meta: Copyright info
QubesOS/qubes-app-linux-pdf-converter@ef41913 client: Exit with 1 on error
QubesOS/qubes-app-linux-pdf-converter@bcbaf9e client: Implement bulk saves and remove reps appropriately
QubesOS/qubes-app-linux-pdf-converter@8e32abb server: Rename batch entry variables
QubesOS/qubes-app-linux-pdf-converter@c00e7a1 server: Prevent CPU hogging by PNG tasks
QubesOS/qubes-app-linux-pdf-converter@5772fdf server: Handle non-ASCII output from pdfinfo(1)
QubesOS/qubes-app-linux-pdf-converter@61437ca client: Use python3 shebang
QubesOS/qubes-app-linux-pdf-converter@deb6c87 travis: Update imports and pylint exceptions
QubesOS/qubes-app-linux-pdf-converter@467a7c3 travis: remove --exit-code
QubesOS/qubes-app-linux-pdf-converter@0b1e80c travis: Attempt to fix pylint
QubesOS/qubes-app-linux-pdf-converter@cd08b7e debian: fix typo in rules
QubesOS/qubes-app-linux-pdf-converter@4e3fee3 travis: Re-add --exit-code because i was right the first time
QubesOS/qubes-app-linux-pdf-converter@2718653 travis: fix paths and try without --exit-code
QubesOS/qubes-app-linux-pdf-converter@32dd0d2 travis: Add pylint dependency
QubesOS/qubes-app-linux-pdf-converter@35524b7 client, server: Replace shellcheck with pylint
QubesOS/qubes-app-linux-pdf-converter@4cfb5e9 client: Update docstring
QubesOS/qubes-app-linux-pdf-converter@5ac1bf0 setup: Add tqdm dependency
QubesOS/qubes-app-linux-pdf-converter@21a6314 client: Update shebang to 3.7
QubesOS/qubes-app-linux-pdf-converter@f05f4d5 client: Fix lower bound for batch size
QubesOS/qubes-app-linux-pdf-converter@7243999 client, server: Update UI, design, and error handling
QubesOS/qubes-app-linux-pdf-converter@924824f client: Replace namedtuple with dataclass
QubesOS/qubes-app-linux-pdf-converter@2a5d8b9 client: Add initial version of tqdm output
QubesOS/qubes-app-linux-pdf-converter@9a61502 client: Implement --in-place
QubesOS/qubes-app-linux-pdf-converter@225780e client: Add --archive, --dry-run, and --in-place
QubesOS/qubes-app-linux-pdf-converter@24dc64f client, server: Rename unsanitized file class
QubesOS/qubes-app-linux-pdf-converter@4e6b286 client, server: Remove unused imports
QubesOS/qubes-app-linux-pdf-converter@3fd4636 server: Remove nonexistent PageError
QubesOS/qubes-app-linux-pdf-converter@4e5e87e client, server: Add Representation & *File objects
QubesOS/qubes-app-linux-pdf-converter@dc4742b client: Replace click.echo()
QubesOS/qubes-app-linux-pdf-converter@7c9a21f server: Update sending process
QubesOS/qubes-app-linux-pdf-converter@1fa078b server: Update error handling
QubesOS/qubes-app-linux-pdf-converter@06bafaf server: Remove recv_pdf()
QubesOS/qubes-app-linux-pdf-converter@89ebda3 client: Update error handling
QubesOS/qubes-app-linux-pdf-converter@8c0054c client: Add CLI parameter handling
QubesOS/qubes-app-linux-pdf-converter@8905550 client: Start batch processing code
QubesOS/qubes-app-linux-pdf-converter@11d610a Rename source directory
QubesOS/qubes-app-linux-pdf-converter@8dd8d6f server: Remove uneeded quoting in identify command
QubesOS/qubes-app-linux-pdf-converter@523aab8 client: Remove unused recv()
QubesOS/qubes-app-linux-pdf-converter@1c4f61d client: Remove unneeded PID prefix for tmpdir
QubesOS/qubes-app-linux-pdf-converter@e057643 client: Remove extra byte for send()
QubesOS/qubes-app-linux-pdf-converter@ee7420d client: Fix error handling for readexactly()
QubesOS/qubes-app-linux-pdf-converter@d7dade5 meta: Remove wrapper
QubesOS/qubes-app-linux-pdf-converter@a0cffae meta: Remove extra file
QubesOS/qubes-app-linux-pdf-converter@456ac9a tests: Moved to pdf-converter/tests
QubesOS/qubes-app-linux-pdf-converter@23a45e5 meta: Remove extra file
QubesOS/qubes-app-linux-pdf-converter@5979f9f client, server: Move to pdf-converter directory
QubesOS/qubes-app-linux-pdf-converter@f4291c3 client, server: Update to asyncio and new model
QubesOS/qubes-app-linux-pdf-converter@4d1ac9e client, server: Update initial phase
QubesOS/qubes-app-linux-pdf-converter@f66da6e client: Combine image dimension functions
QubesOS/qubes-app-linux-pdf-converter@8178f1d client, server: Update utility functions
QubesOS/qubes-app-linux-pdf-converter@c6f6be4 client, server: Add custom exceptions
QubesOS/qubes-app-linux-pdf-converter@7913920 client: Remove redundant check condition
QubesOS/qubes-app-linux-pdf-converter@672ad1a client, server: Replace recv() with recvline_b()
QubesOS/qubes-app-linux-pdf-converter@3fd5912 Update docs
QubesOS/qubes-app-linux-pdf-converter@54e25fe Add support for multiple files
QubesOS/qubes-app-linux-pdf-converter@574e63c readme: Update language
QubesOS/qubes-app-linux-pdf-converter@a4b70cb server, client: Remove unecessary documentation
QubesOS/qubes-app-linux-pdf-converter@7279415 wrapper, client, server: Qualify variable names
QubesOS/qubes-app-linux-pdf-converter@88acf01 wrapper: Add non-file check
QubesOS/qubes-app-linux-pdf-converter@098ef25 wrapper: Simplify argument parsing
QubesOS/qubes-app-linux-pdf-converter@e43c071 server: Fix location of STDOUT flush call
QubesOS/qubes-app-linux-pdf-converter@82b7e73 client: Use OG stdout file descriptor
QubesOS/qubes-app-linux-pdf-converter@dd4abde server, client: Grammar
QubesOS/qubes-app-linux-pdf-converter@f937480 server: Avoid errors if subprocess command fails
QubesOS/qubes-app-linux-pdf-converter@8d5bc16 client: Handle EOFErrors if server suddenly dies
QubesOS/qubes-app-linux-pdf-converter@2857aa4 client, server: Fix stream flushing
QubesOS/qubes-app-linux-pdf-converter@c6831f5 wrapper: Move logging config to global namespace
QubesOS/qubes-app-linux-pdf-converter@3d941e8 wrapper: Trim down argument parsing
QubesOS/qubes-app-linux-pdf-converter@21407f1 wrapper: Fix leftover debugging command
QubesOS/qubes-app-linux-pdf-converter@150793c readme: Update usage example
QubesOS/qubes-app-linux-pdf-converter@b8b41da Add .py extensions and update install commands
QubesOS/qubes-app-linux-pdf-converter@ec754fc wrapper: Add documentation
QubesOS/qubes-app-linux-pdf-converter@5cfaab7 server: Make check_output() return a String instead of a bytestring
QubesOS/qubes-app-linux-pdf-converter@8a8283d client, server: Add documentation
QubesOS/qubes-app-linux-pdf-converter@f6c90fb server: Refactor to Python 3
QubesOS/qubes-app-linux-pdf-converter@552d2f4 client: PEP 8
QubesOS/qubes-app-linux-pdf-converter@516cd21 client: Add qrexec wrapper functions
QubesOS/qubes-app-linux-pdf-converter@588a9e2 wrapper: PEP 8
QubesOS/qubes-app-linux-pdf-converter@4d88ecf wrapper, client: Re-add logging
QubesOS/qubes-app-linux-pdf-converter@0a7cfae client: Update to Python 3
QubesOS/qubes-app-linux-pdf-converter@fd9175f wrapper: Remove logging
QubesOS/qubes-app-linux-pdf-converter@a014fb3 wrapper: Remove unneeded main() try block
QubesOS/qubes-app-linux-pdf-converter@9668bfb wrapper: Prepare for multiple file support
QubesOS/qubes-app-linux-pdf-converter@7ef5b33 wrapper: Add logging and trim options
QubesOS/qubes-app-linux-pdf-converter@4e0d635 wrapper: Update qvm-convert-pdf into Python 3
QubesOS/qubes-app-linux-pdf-converter@a84a215 readme: Remove extra parenthesis
QubesOS/qubes-app-linux-pdf-converter@99629af Merge remote-tracking branch 'origin/pr/10'
QubesOS/qubes-app-linux-pdf-converter@f748f50 debian: conditional python version dependencies
Referenced issues:
QubesOS/qubes-issues#5868
If you're release manager, you can issue GPG-inline signed command:
* `Upload app-linux-pdf-converter 0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8 r4.1 current repo` (available 7 days from now)
* `Upload app-linux-pdf-converter 0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8 r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload app-linux-pdf-converter 0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8 r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| 8.0 | app-linux-pdf-converter v2.1.10 (r4.1) - Update of app-linux-pdf-converter to v2.1.10 for Qubes r4.1, see comments below for details.
Built from: https://github.com/QubesOS/qubes-app-linux-pdf-converter/commit/0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8
[Changes since previous version](https://github.com/QubesOS/qubes-app-linux-pdf-converter/compare/v2.1.8...v2.1.10):
QubesOS/qubes-app-linux-pdf-converter@0c9d97e version 2.1.10
QubesOS/qubes-app-linux-pdf-converter@6b7f71f Python38 is now available for CentOS8
QubesOS/qubes-app-linux-pdf-converter@6d1ba08 version 2.1.9
QubesOS/qubes-app-linux-pdf-converter@b83e354 require python 3.7+, exclude stretch, jessie and centos
QubesOS/qubes-app-linux-pdf-converter@653c55f Use proper python package installation for the VM part too
QubesOS/qubes-app-linux-pdf-converter@229e68a Drop executable bit from nautilus extension
QubesOS/qubes-app-linux-pdf-converter@617c2a7 Add qubespdfconverter/__init__.py
QubesOS/qubes-app-linux-pdf-converter@6d457d6 Move tests back to qubespdfconverter.tests
QubesOS/qubes-app-linux-pdf-converter@f1559c9 Install only tests with older python
QubesOS/qubes-app-linux-pdf-converter@04991c3 travis: include R4.0 dom0 too
QubesOS/qubes-app-linux-pdf-converter@73a9012 Adjust dependencies after python rewrite
QubesOS/qubes-app-linux-pdf-converter@60b6b5c Merge remote-tracking branch 'origin/pr/7'
QubesOS/qubes-app-linux-pdf-converter@1ee08f7 makefile: Resolve makefile conflict
QubesOS/qubes-app-linux-pdf-converter@64cc14f pylint: Add expression-not-assigned
QubesOS/qubes-app-linux-pdf-converter@379659b client: Add support for older tqdm versions
QubesOS/qubes-app-linux-pdf-converter@f1d35f2 client: Handle out of space error
QubesOS/qubes-app-linux-pdf-converter@5eab363 client: Fix output spacing
QubesOS/qubes-app-linux-pdf-converter@c87e61b client: Simplify image appending
QubesOS/qubes-app-linux-pdf-converter@9b655af pylint: Add bad-continuation to .pylintrc
QubesOS/qubes-app-linux-pdf-converter@388278a debian: update control syntax for python nautilus
QubesOS/qubes-app-linux-pdf-converter@2abacda meta: Copyright info
QubesOS/qubes-app-linux-pdf-converter@ef41913 client: Exit with 1 on error
QubesOS/qubes-app-linux-pdf-converter@bcbaf9e client: Implement bulk saves and remove reps appropriately
QubesOS/qubes-app-linux-pdf-converter@8e32abb server: Rename batch entry variables
QubesOS/qubes-app-linux-pdf-converter@c00e7a1 server: Prevent CPU hogging by PNG tasks
QubesOS/qubes-app-linux-pdf-converter@5772fdf server: Handle non-ASCII output from pdfinfo(1)
QubesOS/qubes-app-linux-pdf-converter@61437ca client: Use python3 shebang
QubesOS/qubes-app-linux-pdf-converter@deb6c87 travis: Update imports and pylint exceptions
QubesOS/qubes-app-linux-pdf-converter@467a7c3 travis: remove --exit-code
QubesOS/qubes-app-linux-pdf-converter@0b1e80c travis: Attempt to fix pylint
QubesOS/qubes-app-linux-pdf-converter@cd08b7e debian: fix typo in rules
QubesOS/qubes-app-linux-pdf-converter@4e3fee3 travis: Re-add --exit-code because i was right the first time
QubesOS/qubes-app-linux-pdf-converter@2718653 travis: fix paths and try without --exit-code
QubesOS/qubes-app-linux-pdf-converter@32dd0d2 travis: Add pylint dependency
QubesOS/qubes-app-linux-pdf-converter@35524b7 client, server: Replace shellcheck with pylint
QubesOS/qubes-app-linux-pdf-converter@4cfb5e9 client: Update docstring
QubesOS/qubes-app-linux-pdf-converter@5ac1bf0 setup: Add tqdm dependency
QubesOS/qubes-app-linux-pdf-converter@21a6314 client: Update shebang to 3.7
QubesOS/qubes-app-linux-pdf-converter@f05f4d5 client: Fix lower bound for batch size
QubesOS/qubes-app-linux-pdf-converter@7243999 client, server: Update UI, design, and error handling
QubesOS/qubes-app-linux-pdf-converter@924824f client: Replace namedtuple with dataclass
QubesOS/qubes-app-linux-pdf-converter@2a5d8b9 client: Add initial version of tqdm output
QubesOS/qubes-app-linux-pdf-converter@9a61502 client: Implement --in-place
QubesOS/qubes-app-linux-pdf-converter@225780e client: Add --archive, --dry-run, and --in-place
QubesOS/qubes-app-linux-pdf-converter@24dc64f client, server: Rename unsanitized file class
QubesOS/qubes-app-linux-pdf-converter@4e6b286 client, server: Remove unused imports
QubesOS/qubes-app-linux-pdf-converter@3fd4636 server: Remove nonexistent PageError
QubesOS/qubes-app-linux-pdf-converter@4e5e87e client, server: Add Representation & *File objects
QubesOS/qubes-app-linux-pdf-converter@dc4742b client: Replace click.echo()
QubesOS/qubes-app-linux-pdf-converter@7c9a21f server: Update sending process
QubesOS/qubes-app-linux-pdf-converter@1fa078b server: Update error handling
QubesOS/qubes-app-linux-pdf-converter@06bafaf server: Remove recv_pdf()
QubesOS/qubes-app-linux-pdf-converter@89ebda3 client: Update error handling
QubesOS/qubes-app-linux-pdf-converter@8c0054c client: Add CLI parameter handling
QubesOS/qubes-app-linux-pdf-converter@8905550 client: Start batch processing code
QubesOS/qubes-app-linux-pdf-converter@11d610a Rename source directory
QubesOS/qubes-app-linux-pdf-converter@8dd8d6f server: Remove uneeded quoting in identify command
QubesOS/qubes-app-linux-pdf-converter@523aab8 client: Remove unused recv()
QubesOS/qubes-app-linux-pdf-converter@1c4f61d client: Remove unneeded PID prefix for tmpdir
QubesOS/qubes-app-linux-pdf-converter@e057643 client: Remove extra byte for send()
QubesOS/qubes-app-linux-pdf-converter@ee7420d client: Fix error handling for readexactly()
QubesOS/qubes-app-linux-pdf-converter@d7dade5 meta: Remove wrapper
QubesOS/qubes-app-linux-pdf-converter@a0cffae meta: Remove extra file
QubesOS/qubes-app-linux-pdf-converter@456ac9a tests: Moved to pdf-converter/tests
QubesOS/qubes-app-linux-pdf-converter@23a45e5 meta: Remove extra file
QubesOS/qubes-app-linux-pdf-converter@5979f9f client, server: Move to pdf-converter directory
QubesOS/qubes-app-linux-pdf-converter@f4291c3 client, server: Update to asyncio and new model
QubesOS/qubes-app-linux-pdf-converter@4d1ac9e client, server: Update initial phase
QubesOS/qubes-app-linux-pdf-converter@f66da6e client: Combine image dimension functions
QubesOS/qubes-app-linux-pdf-converter@8178f1d client, server: Update utility functions
QubesOS/qubes-app-linux-pdf-converter@c6f6be4 client, server: Add custom exceptions
QubesOS/qubes-app-linux-pdf-converter@7913920 client: Remove redundant check condition
QubesOS/qubes-app-linux-pdf-converter@672ad1a client, server: Replace recv() with recvline_b()
QubesOS/qubes-app-linux-pdf-converter@3fd5912 Update docs
QubesOS/qubes-app-linux-pdf-converter@54e25fe Add support for multiple files
QubesOS/qubes-app-linux-pdf-converter@574e63c readme: Update language
QubesOS/qubes-app-linux-pdf-converter@a4b70cb server, client: Remove unecessary documentation
QubesOS/qubes-app-linux-pdf-converter@7279415 wrapper, client, server: Qualify variable names
QubesOS/qubes-app-linux-pdf-converter@88acf01 wrapper: Add non-file check
QubesOS/qubes-app-linux-pdf-converter@098ef25 wrapper: Simplify argument parsing
QubesOS/qubes-app-linux-pdf-converter@e43c071 server: Fix location of STDOUT flush call
QubesOS/qubes-app-linux-pdf-converter@82b7e73 client: Use OG stdout file descriptor
QubesOS/qubes-app-linux-pdf-converter@dd4abde server, client: Grammar
QubesOS/qubes-app-linux-pdf-converter@f937480 server: Avoid errors if subprocess command fails
QubesOS/qubes-app-linux-pdf-converter@8d5bc16 client: Handle EOFErrors if server suddenly dies
QubesOS/qubes-app-linux-pdf-converter@2857aa4 client, server: Fix stream flushing
QubesOS/qubes-app-linux-pdf-converter@c6831f5 wrapper: Move logging config to global namespace
QubesOS/qubes-app-linux-pdf-converter@3d941e8 wrapper: Trim down argument parsing
QubesOS/qubes-app-linux-pdf-converter@21407f1 wrapper: Fix leftover debugging command
QubesOS/qubes-app-linux-pdf-converter@150793c readme: Update usage example
QubesOS/qubes-app-linux-pdf-converter@b8b41da Add .py extensions and update install commands
QubesOS/qubes-app-linux-pdf-converter@ec754fc wrapper: Add documentation
QubesOS/qubes-app-linux-pdf-converter@5cfaab7 server: Make check_output() return a String instead of a bytestring
QubesOS/qubes-app-linux-pdf-converter@8a8283d client, server: Add documentation
QubesOS/qubes-app-linux-pdf-converter@f6c90fb server: Refactor to Python 3
QubesOS/qubes-app-linux-pdf-converter@552d2f4 client: PEP 8
QubesOS/qubes-app-linux-pdf-converter@516cd21 client: Add qrexec wrapper functions
QubesOS/qubes-app-linux-pdf-converter@588a9e2 wrapper: PEP 8
QubesOS/qubes-app-linux-pdf-converter@4d88ecf wrapper, client: Re-add logging
QubesOS/qubes-app-linux-pdf-converter@0a7cfae client: Update to Python 3
QubesOS/qubes-app-linux-pdf-converter@fd9175f wrapper: Remove logging
QubesOS/qubes-app-linux-pdf-converter@a014fb3 wrapper: Remove unneeded main() try block
QubesOS/qubes-app-linux-pdf-converter@9668bfb wrapper: Prepare for multiple file support
QubesOS/qubes-app-linux-pdf-converter@7ef5b33 wrapper: Add logging and trim options
QubesOS/qubes-app-linux-pdf-converter@4e0d635 wrapper: Update qvm-convert-pdf into Python 3
QubesOS/qubes-app-linux-pdf-converter@a84a215 readme: Remove extra parenthesis
QubesOS/qubes-app-linux-pdf-converter@99629af Merge remote-tracking branch 'origin/pr/10'
QubesOS/qubes-app-linux-pdf-converter@f748f50 debian: conditional python version dependencies
Referenced issues:
QubesOS/qubes-issues#5868
If you're release manager, you can issue GPG-inline signed command:
* `Upload app-linux-pdf-converter 0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8 r4.1 current repo` (available 7 days from now)
* `Upload app-linux-pdf-converter 0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8 r4.1 current (dists) repo`, you can choose subset of distributions, like `vm-fc24 vm-fc25` (available 7 days from now)
* `Upload app-linux-pdf-converter 0c9d97e0b8cef2d4ce2beed65e2c64d70e235de8 r4.1 security-testing repo`
Above commands will work only if packages in current-testing repository were built from given commit (i.e. no new version superseded it).
| test | app linux pdf converter update of app linux pdf converter to for qubes see comments below for details built from qubesos qubes app linux pdf converter version qubesos qubes app linux pdf converter is now available for qubesos qubes app linux pdf converter version qubesos qubes app linux pdf converter require python exclude stretch jessie and centos qubesos qubes app linux pdf converter use proper python package installation for the vm part too qubesos qubes app linux pdf converter drop executable bit from nautilus extension qubesos qubes app linux pdf converter add qubespdfconverter init py qubesos qubes app linux pdf converter move tests back to qubespdfconverter tests qubesos qubes app linux pdf converter install only tests with older python qubesos qubes app linux pdf converter travis include too qubesos qubes app linux pdf converter adjust dependencies after python rewrite qubesos qubes app linux pdf converter merge remote tracking branch origin pr qubesos qubes app linux pdf converter makefile resolve makefile conflict qubesos qubes app linux pdf converter pylint add expression not assigned qubesos qubes app linux pdf converter client add support for older tqdm versions qubesos qubes app linux pdf converter client handle out of space error qubesos qubes app linux pdf converter client fix output spacing qubesos qubes app linux pdf converter client simplify image appending qubesos qubes app linux pdf converter pylint add bad continuation to pylintrc qubesos qubes app linux pdf converter debian update control syntax for python nautilus qubesos qubes app linux pdf converter meta copyright info qubesos qubes app linux pdf converter client exit with on error qubesos qubes app linux pdf converter client implement bulk saves and remove reps appropriately qubesos qubes app linux pdf converter server rename batch entry variables qubesos qubes app linux pdf converter server prevent cpu hogging by png tasks qubesos qubes app linux pdf converter server handle non ascii output from pdfinfo qubesos qubes app linux pdf converter client use shebang qubesos qubes app linux pdf converter travis update imports and pylint exceptions qubesos qubes app linux pdf converter travis remove exit code qubesos qubes app linux pdf converter travis attempt to fix pylint qubesos qubes app linux pdf converter debian fix typo in rules qubesos qubes app linux pdf converter travis re add exit code because i was right the first time qubesos qubes app linux pdf converter travis fix paths and try without exit code qubesos qubes app linux pdf converter travis add pylint dependency qubesos qubes app linux pdf converter client server replace shellcheck with pylint qubesos qubes app linux pdf converter client update docstring qubesos qubes app linux pdf converter setup add tqdm dependency qubesos qubes app linux pdf converter client update shebang to qubesos qubes app linux pdf converter client fix lower bound for batch size qubesos qubes app linux pdf converter client server update ui design and error handling qubesos qubes app linux pdf converter client replace namedtuple with dataclass qubesos qubes app linux pdf converter client add initial version of tqdm output qubesos qubes app linux pdf converter client implement in place qubesos qubes app linux pdf converter client add archive dry run and in place qubesos qubes app linux pdf converter client server rename unsanitized file class qubesos qubes app linux pdf converter client server remove unused imports qubesos qubes app linux pdf converter server remove nonexistent pageerror qubesos qubes app linux pdf converter client server add representation file objects qubesos qubes app linux pdf converter client replace click echo qubesos qubes app linux pdf converter server update sending process qubesos qubes app linux pdf converter server update error handling qubesos qubes app linux pdf converter server remove recv pdf qubesos qubes app linux pdf converter client update error handling qubesos qubes app linux pdf converter client add cli parameter handling qubesos qubes app linux pdf converter client start batch processing code qubesos qubes app linux pdf converter rename source directory qubesos qubes app linux pdf converter server remove uneeded quoting in identify command qubesos qubes app linux pdf converter client remove unused recv qubesos qubes app linux pdf converter client remove unneeded pid prefix for tmpdir qubesos qubes app linux pdf converter client remove extra byte for send qubesos qubes app linux pdf converter client fix error handling for readexactly qubesos qubes app linux pdf converter meta remove wrapper qubesos qubes app linux pdf converter meta remove extra file qubesos qubes app linux pdf converter tests moved to pdf converter tests qubesos qubes app linux pdf converter meta remove extra file qubesos qubes app linux pdf converter client server move to pdf converter directory qubesos qubes app linux pdf converter client server update to asyncio and new model qubesos qubes app linux pdf converter client server update initial phase qubesos qubes app linux pdf converter client combine image dimension functions qubesos qubes app linux pdf converter client server update utility functions qubesos qubes app linux pdf converter client server add custom exceptions qubesos qubes app linux pdf converter client remove redundant check condition qubesos qubes app linux pdf converter client server replace recv with recvline b qubesos qubes app linux pdf converter update docs qubesos qubes app linux pdf converter add support for multiple files qubesos qubes app linux pdf converter readme update language qubesos qubes app linux pdf converter server client remove unecessary documentation qubesos qubes app linux pdf converter wrapper client server qualify variable names qubesos qubes app linux pdf converter wrapper add non file check qubesos qubes app linux pdf converter wrapper simplify argument parsing qubesos qubes app linux pdf converter server fix location of stdout flush call qubesos qubes app linux pdf converter client use og stdout file descriptor qubesos qubes app linux pdf converter server client grammar qubesos qubes app linux pdf converter server avoid errors if subprocess command fails qubesos qubes app linux pdf converter client handle eoferrors if server suddenly dies qubesos qubes app linux pdf converter client server fix stream flushing qubesos qubes app linux pdf converter wrapper move logging config to global namespace qubesos qubes app linux pdf converter wrapper trim down argument parsing qubesos qubes app linux pdf converter wrapper fix leftover debugging command qubesos qubes app linux pdf converter readme update usage example qubesos qubes app linux pdf converter add py extensions and update install commands qubesos qubes app linux pdf converter wrapper add documentation qubesos qubes app linux pdf converter server make check output return a string instead of a bytestring qubesos qubes app linux pdf converter client server add documentation qubesos qubes app linux pdf converter server refactor to python qubesos qubes app linux pdf converter client pep qubesos qubes app linux pdf converter client add qrexec wrapper functions qubesos qubes app linux pdf converter wrapper pep qubesos qubes app linux pdf converter wrapper client re add logging qubesos qubes app linux pdf converter client update to python qubesos qubes app linux pdf converter wrapper remove logging qubesos qubes app linux pdf converter wrapper remove unneeded main try block qubesos qubes app linux pdf converter wrapper prepare for multiple file support qubesos qubes app linux pdf converter wrapper add logging and trim options qubesos qubes app linux pdf converter wrapper update qvm convert pdf into python qubesos qubes app linux pdf converter readme remove extra parenthesis qubesos qubes app linux pdf converter merge remote tracking branch origin pr qubesos qubes app linux pdf converter debian conditional python version dependencies referenced issues qubesos qubes issues if you re release manager you can issue gpg inline signed command upload app linux pdf converter current repo available days from now upload app linux pdf converter current dists repo you can choose subset of distributions like vm vm available days from now upload app linux pdf converter security testing repo above commands will work only if packages in current testing repository were built from given commit i e no new version superseded it | 1 |
77,058 | 9,978,309,287 | IssuesEvent | 2019-07-09 19:32:12 | apollographql/apollo-server | https://api.github.com/repos/apollographql/apollo-server | closed | Error masking does not work | :memo: documentation :rose: has-reproduction 🚧👷♀️👷♂️🚧 in triage | <!--**Issue Labels**
While not necessary, you can help organize our issues by labeling this issue when you open it. To add a label automatically, simply [x] mark the appropriate box below:
- [x] has-reproduction
- [ ] feature
- [x] docs
- [ ] blocking
- [ ] good first issue
To add a label not listed above, simply place `/label another-label-name` on a line by itself.
-->
An example given here https://github.com/apollographql/apollo-server/blob/ae9da10e625cf283568ba6d29cea8c3e69a7a03f/docs/source/features/errors.md#masking-and-logging-errors does not work returning empty object. I've reproduced this issue here https://github.com/almostprogrammer/format-error
Also I'd like to know whether it's a good practice to handle errors in `formatError` avoiding duplicating code throughout the app? | 1.0 | Error masking does not work - <!--**Issue Labels**
While not necessary, you can help organize our issues by labeling this issue when you open it. To add a label automatically, simply [x] mark the appropriate box below:
- [x] has-reproduction
- [ ] feature
- [x] docs
- [ ] blocking
- [ ] good first issue
To add a label not listed above, simply place `/label another-label-name` on a line by itself.
-->
An example given here https://github.com/apollographql/apollo-server/blob/ae9da10e625cf283568ba6d29cea8c3e69a7a03f/docs/source/features/errors.md#masking-and-logging-errors does not work returning empty object. I've reproduced this issue here https://github.com/almostprogrammer/format-error
Also I'd like to know whether it's a good practice to handle errors in `formatError` avoiding duplicating code throughout the app? | non_test | error masking does not work issue labels while not necessary you can help organize our issues by labeling this issue when you open it to add a label automatically simply mark the appropriate box below has reproduction feature docs blocking good first issue to add a label not listed above simply place label another label name on a line by itself an example given here does not work returning empty object i ve reproduced this issue here also i d like to know whether it s a good practice to handle errors in formaterror avoiding duplicating code throughout the app | 0 |
227,059 | 7,526,461,868 | IssuesEvent | 2018-04-13 14:06:20 | webpack-contrib/sass-loader | https://api.github.com/repos/webpack-contrib/sass-loader | closed | Sass imports inside node_modules broken | priority: 1 (critical) semver: Patch severity: 2 (regression) type: Bug | It appears that 7.0 breaks sass modules we are using from npm. I guess it is related to https://github.com/webpack-contrib/sass-loader/pull/479
For example foundation-sites that we are using imports it's internal modules like this:
```
// Sass utilities
@import 'util/util';
```
Now, unfortunately 'util/util' is a valid file inside node_modules (from 'node-util' pkg), and the build fails with errror like this:
```
ERROR in ./src/style.scss (./node_modules/css-loader!./node_modules/sass-loader/lib/loader.js!./src/style.scss)
Module build failed:
// Copyright Joyent, Inc. and other Node contributors.
^
Invalid CSS after "...N THE SOFTWARE.": expected 1 selector or at-rule, was "var formatRegExp = "
in ###/webpack-sass-broken-imports/node_modules/util/util.js (line 1, column 1)
@ ./src/style.scss 2:14-117
@ ./src/index.js
```
repro repo: https://github.com/larpo/webpack-sass-broken-module-imports
Is there a way to revert to the old behaviour? I don't see any mentions on READMe about how to configure the aliasing behaviour. | 1.0 | Sass imports inside node_modules broken - It appears that 7.0 breaks sass modules we are using from npm. I guess it is related to https://github.com/webpack-contrib/sass-loader/pull/479
For example foundation-sites that we are using imports it's internal modules like this:
```
// Sass utilities
@import 'util/util';
```
Now, unfortunately 'util/util' is a valid file inside node_modules (from 'node-util' pkg), and the build fails with errror like this:
```
ERROR in ./src/style.scss (./node_modules/css-loader!./node_modules/sass-loader/lib/loader.js!./src/style.scss)
Module build failed:
// Copyright Joyent, Inc. and other Node contributors.
^
Invalid CSS after "...N THE SOFTWARE.": expected 1 selector or at-rule, was "var formatRegExp = "
in ###/webpack-sass-broken-imports/node_modules/util/util.js (line 1, column 1)
@ ./src/style.scss 2:14-117
@ ./src/index.js
```
repro repo: https://github.com/larpo/webpack-sass-broken-module-imports
Is there a way to revert to the old behaviour? I don't see any mentions on READMe about how to configure the aliasing behaviour. | non_test | sass imports inside node modules broken it appears that breaks sass modules we are using from npm i guess it is related to for example foundation sites that we are using imports it s internal modules like this sass utilities import util util now unfortunately util util is a valid file inside node modules from node util pkg and the build fails with errror like this error in src style scss node modules css loader node modules sass loader lib loader js src style scss module build failed copyright joyent inc and other node contributors invalid css after n the software expected selector or at rule was var formatregexp in webpack sass broken imports node modules util util js line column src style scss src index js repro repo is there a way to revert to the old behaviour i don t see any mentions on readme about how to configure the aliasing behaviour | 0 |
12,826 | 15,211,211,283 | IssuesEvent | 2021-02-17 08:45:46 | GoogleCloudPlatform/fda-mystudies | https://api.github.com/repos/GoogleCloudPlatform/fda-mystudies | closed | Work flows are failed for participant manager and Participant manager datastore | Bug Process: Fixed | Please go through this links for the errors
https://github.com/boston-tech/develop-fda-mystudies/actions/runs/558335875
https://github.com/boston-tech/develop-fda-mystudies/actions/runs/558335871
| 1.0 | Work flows are failed for participant manager and Participant manager datastore - Please go through this links for the errors
https://github.com/boston-tech/develop-fda-mystudies/actions/runs/558335875
https://github.com/boston-tech/develop-fda-mystudies/actions/runs/558335871
| non_test | work flows are failed for participant manager and participant manager datastore please go through this links for the errors | 0 |
534,040 | 15,608,018,495 | IssuesEvent | 2021-03-19 10:05:31 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | FileSystemAlreadyDefined Exception thrown when trying to load balos and projects from language server | Area/ProjectAPI Priority/Blocker SwanLakeDump Team/DevTools Type/Bug | **Description:**
getting FileSystemAlreadyDefined exception when try to load balos within language server, following are the use-cases,
1. We need to read the package names within the distribution (standard libs and langlibs), for that we use the getPackages API in PackageRepository as follows
```
Environment environment = EnvironmentBuilder.buildDefault();
BallerinaDistribution ballerinaDistribution = BallerinaDistribution.from(environment);
PackageRepository packageRepository = ballerinaDistribution.packageRepository();
Map<String, List<String>> pkgMap = packageRepository.getPackages();
```
Above works without any issue
2. We read the balos and get semantic models
```
ProjectEnvironmentBuilder defaultBuilder = ProjectEnvironmentBuilder.getBuilder(environment);
defaultBuilder.addCompilationCacheFactory(TempDirCompilationCache::from);
BaloProject baloProject = BaloProject.loadProject(defaultBuilder, pkg.project().sourceRoot());
```
the above also works fine and both environment instances are the same.
Both of the use-cases are independent of use-case 3
3. Building a project, given the project root,
```
BuildProject.load(projectRoot, options);
Use case three has the exception mentioned earlier.
```
Is there any way we can achieve the above three use-cases in the same process?
**Steps to reproduce:**
**Affected Versions:**
SLP8 at least
| 1.0 | FileSystemAlreadyDefined Exception thrown when trying to load balos and projects from language server - **Description:**
getting FileSystemAlreadyDefined exception when try to load balos within language server, following are the use-cases,
1. We need to read the package names within the distribution (standard libs and langlibs), for that we use the getPackages API in PackageRepository as follows
```
Environment environment = EnvironmentBuilder.buildDefault();
BallerinaDistribution ballerinaDistribution = BallerinaDistribution.from(environment);
PackageRepository packageRepository = ballerinaDistribution.packageRepository();
Map<String, List<String>> pkgMap = packageRepository.getPackages();
```
Above works without any issue
2. We read the balos and get semantic models
```
ProjectEnvironmentBuilder defaultBuilder = ProjectEnvironmentBuilder.getBuilder(environment);
defaultBuilder.addCompilationCacheFactory(TempDirCompilationCache::from);
BaloProject baloProject = BaloProject.loadProject(defaultBuilder, pkg.project().sourceRoot());
```
the above also works fine and both environment instances are the same.
Both of the use-cases are independent of use-case 3
3. Building a project, given the project root,
```
BuildProject.load(projectRoot, options);
Use case three has the exception mentioned earlier.
```
Is there any way we can achieve the above three use-cases in the same process?
**Steps to reproduce:**
**Affected Versions:**
SLP8 at least
| non_test | filesystemalreadydefined exception thrown when trying to load balos and projects from language server description getting filesystemalreadydefined exception when try to load balos within language server following are the use cases we need to read the package names within the distribution standard libs and langlibs for that we use the getpackages api in packagerepository as follows environment environment environmentbuilder builddefault ballerinadistribution ballerinadistribution ballerinadistribution from environment packagerepository packagerepository ballerinadistribution packagerepository map pkgmap packagerepository getpackages above works without any issue we read the balos and get semantic models projectenvironmentbuilder defaultbuilder projectenvironmentbuilder getbuilder environment defaultbuilder addcompilationcachefactory tempdircompilationcache from baloproject baloproject baloproject loadproject defaultbuilder pkg project sourceroot the above also works fine and both environment instances are the same both of the use cases are independent of use case building a project given the project root buildproject load projectroot options use case three has the exception mentioned earlier is there any way we can achieve the above three use cases in the same process steps to reproduce affected versions at least | 0 |
341,340 | 30,581,966,678 | IssuesEvent | 2023-07-21 10:22:09 | adoptium/infrastructure | https://api.github.com/repos/adoptium/infrastructure | closed | jdk11 java/beans/Beans/TypoInBeanDescription.java timeout on test-osuosl-aix715-ppc64-3 | os:aix provider:osuosl testFail | java/beans/Beans/TypoInBeanDescription.java timeout on [test-osuosl-aix715-ppc64-3](https://ci.adoptopenjdk.net/computer/test-osuosl-aix715-ppc64-3)
on passed machine https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder/5044
- test suite/name?
- Is there an existing issue elsewhere covering this?
- Which machine(s) does it work on? [build-osuosl-aix71-ppc64-2](https://ci.adoptopenjdk.net/computer/build-osuosl-aix71-ppc64-2)
- Which machine(s) does it fail on? [test-osuosl-aix715-ppc64-3](https://ci.adoptopenjdk.net/computer/test-osuosl-aix715-ppc64-3)
- Do you have a link to a Grinder re-run if the test with the failure?
rerun
on failed machine https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder/5042/
on passed machine https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder/5044
| 1.0 | jdk11 java/beans/Beans/TypoInBeanDescription.java timeout on test-osuosl-aix715-ppc64-3 - java/beans/Beans/TypoInBeanDescription.java timeout on [test-osuosl-aix715-ppc64-3](https://ci.adoptopenjdk.net/computer/test-osuosl-aix715-ppc64-3)
on passed machine https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder/5044
- test suite/name?
- Is there an existing issue elsewhere covering this?
- Which machine(s) does it work on? [build-osuosl-aix71-ppc64-2](https://ci.adoptopenjdk.net/computer/build-osuosl-aix71-ppc64-2)
- Which machine(s) does it fail on? [test-osuosl-aix715-ppc64-3](https://ci.adoptopenjdk.net/computer/test-osuosl-aix715-ppc64-3)
- Do you have a link to a Grinder re-run if the test with the failure?
rerun
on failed machine https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder/5042/
on passed machine https://ci.adoptopenjdk.net/view/Test_grinder/job/Grinder/5044
| test | java beans beans typoinbeandescription java timeout on test osuosl java beans beans typoinbeandescription java timeout on on passed machine test suite name is there an existing issue elsewhere covering this which machine s does it work on which machine s does it fail on do you have a link to a grinder re run if the test with the failure rerun on failed machine on passed machine | 1 |
38,325 | 19,100,326,141 | IssuesEvent | 2021-11-29 21:38:56 | golang/go | https://api.github.com/repos/golang/go | closed | cmd/compile: optimize comparisons to min/max (u)ints by checking for overflow | Performance help wanted NeedsFix | ```go
package p
import "math"
func f(x int64) bool {
return x == math.MinInt64
}
```
On amd64, the core of this compiles to:
```
0x0005 00005 (z.go:6) MOVQ $-9223372036854775808, CX
0x000f 00015 (z.go:6) CMPQ AX, CX
0x0012 00018 (z.go:6) SETEQ "".~r1+16(SP)
```
It would be cheaper and smaller instead to decrement CX and check the flags for underflow. A similar trick can be used for checking min and max ints and uints of all sizes. It might also be useful in the division fix-up code, where we must check for min int divisor.
cc @randall77 @dr2chase @martisch @mundaym
| True | cmd/compile: optimize comparisons to min/max (u)ints by checking for overflow - ```go
package p
import "math"
func f(x int64) bool {
return x == math.MinInt64
}
```
On amd64, the core of this compiles to:
```
0x0005 00005 (z.go:6) MOVQ $-9223372036854775808, CX
0x000f 00015 (z.go:6) CMPQ AX, CX
0x0012 00018 (z.go:6) SETEQ "".~r1+16(SP)
```
It would be cheaper and smaller instead to decrement CX and check the flags for underflow. A similar trick can be used for checking min and max ints and uints of all sizes. It might also be useful in the division fix-up code, where we must check for min int divisor.
cc @randall77 @dr2chase @martisch @mundaym
| non_test | cmd compile optimize comparisons to min max u ints by checking for overflow go package p import math func f x bool return x math on the core of this compiles to z go movq cx z go cmpq ax cx z go seteq sp it would be cheaper and smaller instead to decrement cx and check the flags for underflow a similar trick can be used for checking min and max ints and uints of all sizes it might also be useful in the division fix up code where we must check for min int divisor cc martisch mundaym | 0 |
313,986 | 26,967,856,076 | IssuesEvent | 2023-02-09 00:35:26 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | opened | pull-kubernetes-unit failing | kind/failing-test | ### Which jobs are failing?
https://kubernetes.slack.com/archives/C7J9RP96G/p1675902134074689
https://prow.k8s.io/?job=pull-kubernetes-unit
### Which tests are failing?
the entire job
### Since when has it been failing?
recently
### Testgrid link
_No response_
### Reason for failure (if possible)
prow issue, permission denied on /.gitconfig
### Anything else we need to know?
https://github.com/kubernetes/test-infra/pull/28688#issuecomment-1423427848
### Relevant SIG(s)
/sig testing
/assign | 1.0 | pull-kubernetes-unit failing - ### Which jobs are failing?
https://kubernetes.slack.com/archives/C7J9RP96G/p1675902134074689
https://prow.k8s.io/?job=pull-kubernetes-unit
### Which tests are failing?
the entire job
### Since when has it been failing?
recently
### Testgrid link
_No response_
### Reason for failure (if possible)
prow issue, permission denied on /.gitconfig
### Anything else we need to know?
https://github.com/kubernetes/test-infra/pull/28688#issuecomment-1423427848
### Relevant SIG(s)
/sig testing
/assign | test | pull kubernetes unit failing which jobs are failing which tests are failing the entire job since when has it been failing recently testgrid link no response reason for failure if possible prow issue permission denied on gitconfig anything else we need to know relevant sig s sig testing assign | 1 |
79,199 | 7,698,323,423 | IssuesEvent | 2018-05-18 22:35:09 | aspnet/SignalR | https://api.github.com/repos/aspnet/SignalR | closed | Flaky test: CanInvokeClientMethodFromServer | flaky test | This test [fails](http://aspnetci/viewLog.html?buildId=470227&buildTypeId=Lite_SignalR) occasionally with the following error:
```
System.AggregateException : One or more errors occurred. (Value cannot be null.
Parameter name: path3) (The following constructor parameters did not have matching fixture data: ServerFixture`1 serverFixture)
---- System.ArgumentNullException : Value cannot be null.
Parameter name: path3
---- The following constructor parameters did not have matching fixture data: ServerFixture`1 serverFixture
----- Inner Stack Trace #1 (System.ArgumentNullException) -----
at System.IO.Path.Combine(String path1, String path2, String path3)
at Microsoft.Extensions.Logging.Testing.AssemblyTestLog.Create(Assembly assembly, String baseDirectory)
at Microsoft.Extensions.Logging.Testing.AssemblyTestLog.ForAssembly(Assembly assembly)
at Microsoft.AspNetCore.SignalR.Tests.ServerFixture`1..ctor(ILoggerFactory loggerFactory) in /_/test/Microsoft.AspNetCore.SignalR.Tests.Utils/ServerFixture.cs:line 65
----- Inner Stack Trace #2 (Xunit.Sdk.TestClassException) -----
```
This happens on just regular builds of SignalR, so I assume it reproduces locally. | 1.0 | Flaky test: CanInvokeClientMethodFromServer - This test [fails](http://aspnetci/viewLog.html?buildId=470227&buildTypeId=Lite_SignalR) occasionally with the following error:
```
System.AggregateException : One or more errors occurred. (Value cannot be null.
Parameter name: path3) (The following constructor parameters did not have matching fixture data: ServerFixture`1 serverFixture)
---- System.ArgumentNullException : Value cannot be null.
Parameter name: path3
---- The following constructor parameters did not have matching fixture data: ServerFixture`1 serverFixture
----- Inner Stack Trace #1 (System.ArgumentNullException) -----
at System.IO.Path.Combine(String path1, String path2, String path3)
at Microsoft.Extensions.Logging.Testing.AssemblyTestLog.Create(Assembly assembly, String baseDirectory)
at Microsoft.Extensions.Logging.Testing.AssemblyTestLog.ForAssembly(Assembly assembly)
at Microsoft.AspNetCore.SignalR.Tests.ServerFixture`1..ctor(ILoggerFactory loggerFactory) in /_/test/Microsoft.AspNetCore.SignalR.Tests.Utils/ServerFixture.cs:line 65
----- Inner Stack Trace #2 (Xunit.Sdk.TestClassException) -----
```
This happens on just regular builds of SignalR, so I assume it reproduces locally. | test | flaky test caninvokeclientmethodfromserver this test occasionally with the following error system aggregateexception one or more errors occurred value cannot be null parameter name the following constructor parameters did not have matching fixture data serverfixture serverfixture system argumentnullexception value cannot be null parameter name the following constructor parameters did not have matching fixture data serverfixture serverfixture inner stack trace system argumentnullexception at system io path combine string string string at microsoft extensions logging testing assemblytestlog create assembly assembly string basedirectory at microsoft extensions logging testing assemblytestlog forassembly assembly assembly at microsoft aspnetcore signalr tests serverfixture ctor iloggerfactory loggerfactory in test microsoft aspnetcore signalr tests utils serverfixture cs line inner stack trace xunit sdk testclassexception this happens on just regular builds of signalr so i assume it reproduces locally | 1 |
131,982 | 10,726,642,252 | IssuesEvent | 2019-10-28 09:51:44 | wix/wix-style-react | https://api.github.com/repos/wix/wix-style-react | closed | Using enzyme as a dependency while it is served as a dev dependency | Priority:High Priority:Major testkit:bug | `wix-ui-test-utils`
[`create-driver-factory`](https://github.com/wix/wix-ui/blob/7ad19b46dc5e73e36da1e2d0ac230709f78f5c2a/packages/wix-ui-test-utils/src/driver-factory/createDriverFactory.tsx#L4) is importing `enzyme`:
We have drivers in wsr and in wix-ui-core which are importing this module from `wix-ui-test-utils`
for example this [one](https://github.com/wix/wix-style-react/blob/5a24230f868a19bd65b2b3afffeb4950c7a7b2c9/src/Tooltip/Tooltip.driver.d.ts#L1)
The outcome of it is - consumers which are using these kind of drivers without using installing `enzyme` themeselfs, their build will break.
Priority: Major
Solution:
Remove enzyme import and [usage](https://github.com/wix/wix-ui/blob/7ad19b46dc5e73e36da1e2d0ac230709f78f5c2a/packages/wix-ui-test-utils/src/driver-factory/createDriverFactory.tsx#L15) which is just the `ReactWrapper` type
**Update**
Problem is that consumers are using `wix-ui-test-utils` directly and use `createDriverFactory` so it can break them.
| 1.0 | Using enzyme as a dependency while it is served as a dev dependency - `wix-ui-test-utils`
[`create-driver-factory`](https://github.com/wix/wix-ui/blob/7ad19b46dc5e73e36da1e2d0ac230709f78f5c2a/packages/wix-ui-test-utils/src/driver-factory/createDriverFactory.tsx#L4) is importing `enzyme`:
We have drivers in wsr and in wix-ui-core which are importing this module from `wix-ui-test-utils`
for example this [one](https://github.com/wix/wix-style-react/blob/5a24230f868a19bd65b2b3afffeb4950c7a7b2c9/src/Tooltip/Tooltip.driver.d.ts#L1)
The outcome of it is - consumers which are using these kind of drivers without using installing `enzyme` themeselfs, their build will break.
Priority: Major
Solution:
Remove enzyme import and [usage](https://github.com/wix/wix-ui/blob/7ad19b46dc5e73e36da1e2d0ac230709f78f5c2a/packages/wix-ui-test-utils/src/driver-factory/createDriverFactory.tsx#L15) which is just the `ReactWrapper` type
**Update**
Problem is that consumers are using `wix-ui-test-utils` directly and use `createDriverFactory` so it can break them.
| test | using enzyme as a dependency while it is served as a dev dependency wix ui test utils is importing enzyme we have drivers in wsr and in wix ui core which are importing this module from wix ui test utils for example this the outcome of it is consumers which are using these kind of drivers without using installing enzyme themeselfs their build will break priority major solution remove enzyme import and which is just the reactwrapper type update problem is that consumers are using wix ui test utils directly and use createdriverfactory so it can break them | 1 |
333,173 | 29,513,185,261 | IssuesEvent | 2023-06-04 07:00:55 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix MaskedArray.test_numpy_maskedarray_property_fill_value | NumPy Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="null" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix MaskedArray.test_numpy_maskedarray_property_fill_value - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5033602665/jobs/9027925557" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="null" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
| test | fix maskedarray test numpy maskedarray property fill value tensorflow img src torch img src numpy img src jax img src paddle img src | 1 |
36,316 | 5,047,364,699 | IssuesEvent | 2016-12-20 09:10:29 | hazelcast/hazelcast | https://api.github.com/repos/hazelcast/hazelcast | closed | MapLoaderMultiNodeTest.testLoadAgain_whenLoadedAllCalledMultipleTimes | Team: Core Type: Test-Failure | ```
java.lang.AssertionError: expected:<20000> but was:<10000>
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at com.hazelcast.map.mapstore.MapLoaderMultiNodeTest.testLoadAgain_whenLoadedAllCalledMultipleTimes(MapLoaderMultiNodeTest.java:127)
```
https://hazelcast-l337.ci.cloudbees.com/view/Hazelcast/job/Hazelcast-3.x-OracleJDK1.7/com.hazelcast$hazelcast/303/testReport/junit/com.hazelcast.map.mapstore/MapLoaderMultiNodeTest/testLoadAgain_whenLoadedAllCalledMultipleTimes/
| 1.0 | MapLoaderMultiNodeTest.testLoadAgain_whenLoadedAllCalledMultipleTimes - ```
java.lang.AssertionError: expected:<20000> but was:<10000>
at org.junit.Assert.fail(Assert.java:88)
at org.junit.Assert.failNotEquals(Assert.java:834)
at org.junit.Assert.assertEquals(Assert.java:645)
at org.junit.Assert.assertEquals(Assert.java:631)
at com.hazelcast.map.mapstore.MapLoaderMultiNodeTest.testLoadAgain_whenLoadedAllCalledMultipleTimes(MapLoaderMultiNodeTest.java:127)
```
https://hazelcast-l337.ci.cloudbees.com/view/Hazelcast/job/Hazelcast-3.x-OracleJDK1.7/com.hazelcast$hazelcast/303/testReport/junit/com.hazelcast.map.mapstore/MapLoaderMultiNodeTest/testLoadAgain_whenLoadedAllCalledMultipleTimes/
| test | maploadermultinodetest testloadagain whenloadedallcalledmultipletimes java lang assertionerror expected but was at org junit assert fail assert java at org junit assert failnotequals assert java at org junit assert assertequals assert java at org junit assert assertequals assert java at com hazelcast map mapstore maploadermultinodetest testloadagain whenloadedallcalledmultipletimes maploadermultinodetest java | 1 |
41,646 | 12,836,314,066 | IssuesEvent | 2020-07-07 14:11:08 | GNS3/gns3-web-ui | https://api.github.com/repos/GNS3/gns3-web-ui | closed | CVE-2019-14863 (Medium) detected in angular-1.3.14.min.js | security vulnerability | ## CVE-2019-14863 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-1.3.14.min.js</b></p></summary>
<p>AngularJS is an MVC framework for building web applications. The core features include HTML enhanced with custom component and data-binding capabilities, dependency injection and strong focus on simplicity, testability, maintainability and boiler-plate reduction.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/angular.js/1.3.14/angular.min.js">https://cdnjs.cloudflare.com/ajax/libs/angular.js/1.3.14/angular.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/gns3-web-ui/node_modules/save-svg-as-png/viewboxtest.html</p>
<p>Path to vulnerable library: /gns3-web-ui/node_modules/save-svg-as-png/viewboxtest.html</p>
<p>
Dependency Hierarchy:
- :x: **angular-1.3.14.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GNS3/gns3-web-ui/commit/f0ec495ff41b611f048247d2919a7d1ebc5a2899">f0ec495ff41b611f048247d2919a7d1ebc5a2899</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a vulnerability in all angular versions before 1.5.0-beta.0, where after escaping the context of the web application, the web application delivers data to its users along with other trusted dynamic content, without validating it.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14863>CVE-2019-14863</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/angular/angular.js/pull/12524">https://github.com/angular/angular.js/pull/12524</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: angular - v1.5.0-beta.1;org.webjars:angularjs:1.5.0-rc.0 </p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"angular.js","packageVersion":"1.3.14","isTransitiveDependency":false,"dependencyTree":"angular.js:1.3.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"angular - v1.5.0-beta.1;org.webjars:angularjs:1.5.0-rc.0\t"}],"vulnerabilityIdentifier":"CVE-2019-14863","vulnerabilityDetails":"There is a vulnerability in all angular versions before 1.5.0-beta.0, where after escaping the context of the web application, the web application delivers data to its users along with other trusted dynamic content, without validating it.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14863","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2019-14863 (Medium) detected in angular-1.3.14.min.js - ## CVE-2019-14863 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-1.3.14.min.js</b></p></summary>
<p>AngularJS is an MVC framework for building web applications. The core features include HTML enhanced with custom component and data-binding capabilities, dependency injection and strong focus on simplicity, testability, maintainability and boiler-plate reduction.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/angular.js/1.3.14/angular.min.js">https://cdnjs.cloudflare.com/ajax/libs/angular.js/1.3.14/angular.min.js</a></p>
<p>Path to dependency file: /tmp/ws-scm/gns3-web-ui/node_modules/save-svg-as-png/viewboxtest.html</p>
<p>Path to vulnerable library: /gns3-web-ui/node_modules/save-svg-as-png/viewboxtest.html</p>
<p>
Dependency Hierarchy:
- :x: **angular-1.3.14.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GNS3/gns3-web-ui/commit/f0ec495ff41b611f048247d2919a7d1ebc5a2899">f0ec495ff41b611f048247d2919a7d1ebc5a2899</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
There is a vulnerability in all angular versions before 1.5.0-beta.0, where after escaping the context of the web application, the web application delivers data to its users along with other trusted dynamic content, without validating it.
<p>Publish Date: 2020-01-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14863>CVE-2019-14863</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/angular/angular.js/pull/12524">https://github.com/angular/angular.js/pull/12524</a></p>
<p>Release Date: 2020-01-02</p>
<p>Fix Resolution: angular - v1.5.0-beta.1;org.webjars:angularjs:1.5.0-rc.0 </p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"angular.js","packageVersion":"1.3.14","isTransitiveDependency":false,"dependencyTree":"angular.js:1.3.14","isMinimumFixVersionAvailable":true,"minimumFixVersion":"angular - v1.5.0-beta.1;org.webjars:angularjs:1.5.0-rc.0\t"}],"vulnerabilityIdentifier":"CVE-2019-14863","vulnerabilityDetails":"There is a vulnerability in all angular versions before 1.5.0-beta.0, where after escaping the context of the web application, the web application delivers data to its users along with other trusted dynamic content, without validating it.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-14863","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_test | cve medium detected in angular min js cve medium severity vulnerability vulnerable library angular min js angularjs is an mvc framework for building web applications the core features include html enhanced with custom component and data binding capabilities dependency injection and strong focus on simplicity testability maintainability and boiler plate reduction library home page a href path to dependency file tmp ws scm web ui node modules save svg as png viewboxtest html path to vulnerable library web ui node modules save svg as png viewboxtest html dependency hierarchy x angular min js vulnerable library found in head commit a href vulnerability details there is a vulnerability in all angular versions before beta where after escaping the context of the web application the web application delivers data to its users along with other trusted dynamic content without validating it publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution angular beta org webjars angularjs rc isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails there is a vulnerability in all angular versions before beta where after escaping the context of the web application the web application delivers data to its users along with other trusted dynamic content without validating it vulnerabilityurl | 0 |
40,811 | 12,799,740,718 | IssuesEvent | 2020-07-02 15:52:10 | mwilliams7197/zuul | https://api.github.com/repos/mwilliams7197/zuul | opened | WS-2019-0379 (Medium) detected in commons-codec-1.9.jar | security vulnerability | ## WS-2019-0379 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-codec-1.9.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Path to dependency file: /tmp/ws-scm/zuul/zuul-sample/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar</p>
<p>
Dependency Hierarchy:
- ribbon-httpclient-2.2.4.jar (Root Library)
- httpclient-4.5.3.jar
- :x: **commons-codec-1.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/mwilliams7197/zuul/commits/8588a970f404a14680bea9a4eda267023e612256">8588a970f404a14680bea9a4eda267023e612256</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.
<p>Publish Date: 2019-05-20
<p>URL: <a href=https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113>WS-2019-0379</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113">https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113</a></p>
<p>Release Date: 2019-05-12</p>
<p>Fix Resolution: 1.13-RC1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"commons-codec","packageName":"commons-codec","packageVersion":"1.9","isTransitiveDependency":true,"dependencyTree":"com.netflix.ribbon:ribbon-httpclient:2.2.4;org.apache.httpcomponents:httpclient:4.5.3;commons-codec:commons-codec:1.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.13-RC1"}],"vulnerabilityIdentifier":"WS-2019-0379","vulnerabilityDetails":"Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.","vulnerabilityUrl":"https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | WS-2019-0379 (Medium) detected in commons-codec-1.9.jar - ## WS-2019-0379 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>commons-codec-1.9.jar</b></p></summary>
<p>The Apache Commons Codec package contains simple encoder and decoders for
various formats such as Base64 and Hexadecimal. In addition to these
widely used encoders and decoders, the codec package also maintains a
collection of phonetic encoding utilities.</p>
<p>Path to dependency file: /tmp/ws-scm/zuul/zuul-sample/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/commons-codec/commons-codec/1.9/9ce04e34240f674bc72680f8b843b1457383161a/commons-codec-1.9.jar</p>
<p>
Dependency Hierarchy:
- ribbon-httpclient-2.2.4.jar (Root Library)
- httpclient-4.5.3.jar
- :x: **commons-codec-1.9.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/mwilliams7197/zuul/commits/8588a970f404a14680bea9a4eda267023e612256">8588a970f404a14680bea9a4eda267023e612256</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.
<p>Publish Date: 2019-05-20
<p>URL: <a href=https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113>WS-2019-0379</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113">https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113</a></p>
<p>Release Date: 2019-05-12</p>
<p>Fix Resolution: 1.13-RC1</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"commons-codec","packageName":"commons-codec","packageVersion":"1.9","isTransitiveDependency":true,"dependencyTree":"com.netflix.ribbon:ribbon-httpclient:2.2.4;org.apache.httpcomponents:httpclient:4.5.3;commons-codec:commons-codec:1.9","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.13-RC1"}],"vulnerabilityIdentifier":"WS-2019-0379","vulnerabilityDetails":"Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.","vulnerabilityUrl":"https://github.com/apache/commons-codec/commit/48b615756d1d770091ea3322eefc08011ee8b113","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_test | ws medium detected in commons codec jar ws medium severity vulnerability vulnerable library commons codec jar the apache commons codec package contains simple encoder and decoders for various formats such as and hexadecimal in addition to these widely used encoders and decoders the codec package also maintains a collection of phonetic encoding utilities path to dependency file tmp ws scm zuul zuul sample build gradle path to vulnerable library home wss scanner gradle caches modules files commons codec commons codec commons codec jar home wss scanner gradle caches modules files commons codec commons codec commons codec jar dependency hierarchy ribbon httpclient jar root library httpclient jar x commons codec jar vulnerable library found in head commit a href vulnerability details apache commons codec before version “commons codec ” is vulnerable to information disclosure due to improper input validation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier ws vulnerabilitydetails apache commons codec before version “commons codec ” is vulnerable to information disclosure due to improper input validation vulnerabilityurl | 0 |
52,157 | 6,221,642,827 | IssuesEvent | 2017-07-10 06:40:06 | arquillian/smart-testing | https://api.github.com/repos/arquillian/smart-testing | closed | Test Bed - functional tests improvement | Component: Test Bed Priority: High Status: In Progress Type: Feature | We need to have a better way for writing and running functional tests. Currently, we have modules `-ftest` which have little to no value. Ideally, we should provide an easy way to write tests which will illustrate real-world scenarios. So we would start with the clean project and then:
* add smart-testing to it
* define the priorities/strategies
* make necessary changes for the given scenario
* run the build and see what was the order of tests etc
### Suggested solution
We could create a separate project to be used as a source for all our tests. Then we could apply all the changes as described above, execute the build using embedded maven and collect the results (either through grepping the log or looking at surefire reports).
As for applying changes, for the moment I have two ideas in mind:
* using templates / forge way
* have already prepared changes as commits on some branch different than master (with tags) and just cherry-pick them.
Suggestions welcome.
| 1.0 | Test Bed - functional tests improvement - We need to have a better way for writing and running functional tests. Currently, we have modules `-ftest` which have little to no value. Ideally, we should provide an easy way to write tests which will illustrate real-world scenarios. So we would start with the clean project and then:
* add smart-testing to it
* define the priorities/strategies
* make necessary changes for the given scenario
* run the build and see what was the order of tests etc
### Suggested solution
We could create a separate project to be used as a source for all our tests. Then we could apply all the changes as described above, execute the build using embedded maven and collect the results (either through grepping the log or looking at surefire reports).
As for applying changes, for the moment I have two ideas in mind:
* using templates / forge way
* have already prepared changes as commits on some branch different than master (with tags) and just cherry-pick them.
Suggestions welcome.
| test | test bed functional tests improvement we need to have a better way for writing and running functional tests currently we have modules ftest which have little to no value ideally we should provide an easy way to write tests which will illustrate real world scenarios so we would start with the clean project and then add smart testing to it define the priorities strategies make necessary changes for the given scenario run the build and see what was the order of tests etc suggested solution we could create a separate project to be used as a source for all our tests then we could apply all the changes as described above execute the build using embedded maven and collect the results either through grepping the log or looking at surefire reports as for applying changes for the moment i have two ideas in mind using templates forge way have already prepared changes as commits on some branch different than master with tags and just cherry pick them suggestions welcome | 1 |
331,634 | 29,044,885,594 | IssuesEvent | 2023-05-13 12:32:25 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | Failing test: X-Pack Case API Integration Tests.x-pack/test/cases_api_integration/security_and_spaces/tests/trial/cases/push_case·ts - cases security and spaces enabled: trial push_case memoryless server should push to a connector without mapping | failed-test Team:ResponseOps | A test failed on a tracked branch
```
Error: expected 200 "OK", got 403 "Forbidden"
at Test._assertStatus (node_modules/supertest/lib/test.js:268:12)
at Test._assertFunction (node_modules/supertest/lib/test.js:283:11)
at Test.assert (node_modules/supertest/lib/test.js:173:18)
at localAssert (node_modules/supertest/lib/test.js:131:12)
at /home/buildkite-agent/builds/kb-n2-4-spot-0431e15284df11c1/elastic/kibana-on-merge/kibana/node_modules/supertest/lib/test.js:128:5
at Test.Request.callback (node_modules/superagent/lib/node/index.js:728:3)
at /home/buildkite-agent/builds/kb-n2-4-spot-0431e15284df11c1/elastic/kibana-on-merge/kibana/node_modules/superagent/lib/node/index.js:916:18
at IncomingMessage.<anonymous> (node_modules/superagent/lib/node/parsers/json.js:19:7)
at IncomingMessage.emit (node:events:525:35)
at endReadableNT (node:internal/streams/readable:1358:12)
at processTicksAndRejections (node:internal/process/task_queues:83:21)
```
First failure: [CI Build - 8.8](https://buildkite.com/elastic/kibana-on-merge/builds/30378#01881150-c3e6-4d3d-8eb0-32da324fbeb3)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Case API Integration Tests.x-pack/test/cases_api_integration/security_and_spaces/tests/trial/cases/push_case·ts","test.name":"cases security and spaces enabled: trial push_case memoryless server should push to a connector without mapping","test.failCount":2}} --> | 1.0 | Failing test: X-Pack Case API Integration Tests.x-pack/test/cases_api_integration/security_and_spaces/tests/trial/cases/push_case·ts - cases security and spaces enabled: trial push_case memoryless server should push to a connector without mapping - A test failed on a tracked branch
```
Error: expected 200 "OK", got 403 "Forbidden"
at Test._assertStatus (node_modules/supertest/lib/test.js:268:12)
at Test._assertFunction (node_modules/supertest/lib/test.js:283:11)
at Test.assert (node_modules/supertest/lib/test.js:173:18)
at localAssert (node_modules/supertest/lib/test.js:131:12)
at /home/buildkite-agent/builds/kb-n2-4-spot-0431e15284df11c1/elastic/kibana-on-merge/kibana/node_modules/supertest/lib/test.js:128:5
at Test.Request.callback (node_modules/superagent/lib/node/index.js:728:3)
at /home/buildkite-agent/builds/kb-n2-4-spot-0431e15284df11c1/elastic/kibana-on-merge/kibana/node_modules/superagent/lib/node/index.js:916:18
at IncomingMessage.<anonymous> (node_modules/superagent/lib/node/parsers/json.js:19:7)
at IncomingMessage.emit (node:events:525:35)
at endReadableNT (node:internal/streams/readable:1358:12)
at processTicksAndRejections (node:internal/process/task_queues:83:21)
```
First failure: [CI Build - 8.8](https://buildkite.com/elastic/kibana-on-merge/builds/30378#01881150-c3e6-4d3d-8eb0-32da324fbeb3)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Case API Integration Tests.x-pack/test/cases_api_integration/security_and_spaces/tests/trial/cases/push_case·ts","test.name":"cases security and spaces enabled: trial push_case memoryless server should push to a connector without mapping","test.failCount":2}} --> | test | failing test x pack case api integration tests x pack test cases api integration security and spaces tests trial cases push case·ts cases security and spaces enabled trial push case memoryless server should push to a connector without mapping a test failed on a tracked branch error expected ok got forbidden at test assertstatus node modules supertest lib test js at test assertfunction node modules supertest lib test js at test assert node modules supertest lib test js at localassert node modules supertest lib test js at home buildkite agent builds kb spot elastic kibana on merge kibana node modules supertest lib test js at test request callback node modules superagent lib node index js at home buildkite agent builds kb spot elastic kibana on merge kibana node modules superagent lib node index js at incomingmessage node modules superagent lib node parsers json js at incomingmessage emit node events at endreadablent node internal streams readable at processticksandrejections node internal process task queues first failure | 1 |
86,251 | 8,030,103,707 | IssuesEvent | 2018-07-27 18:22:30 | italia/spid-testenv2 | https://api.github.com/repos/italia/spid-testenv2 | closed | AuthnRequest: errore "KeyError: 'binding'" | bug needs regression test | Inviando questa AuthnRequest:
```xml
<saml2p:AuthnRequest ForceAuthn="false" IssueInstant="2018-07-24T17:15:47Z" Version="2.0" Destination="http://localhost:8088/sso" ID="_b09d06c33ba8649e14b34421d5a5d102" AttributeConsumingServiceIndex="1" AssertionConsumerServiceIndex="0" xmlns:saml2p="urn:oasis:names:tc:SAML:2.0:protocol" xmlns:saml2="urn:oasis:names:tc:SAML:2.0:assertion"><saml2:Issuer Format="urn:oasis:names:tc:SAML:2.0:nameid-format:entity" NameQualifier="https://www.prova.it/">https://www.prova.it/</saml2:Issuer><saml2p:NameIDPolicy Format="urn:oasis:names:tc:SAML:2.0:nameid-format:transient"></saml2p:NameIDPolicy><saml2p:RequestedAuthnContext Comparison="minimum"><saml2:AuthnContextClassRef>https://www.spid.gov.it/SpidL1</saml2:AuthnContextClassRef></saml2p:RequestedAuthnContext></saml2p:AuthnRequest>
```
ottengo il seguente errore:
```
Traceback (most recent call last):
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 2309, in __call__
return self.wsgi_app(environ, start_response)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 2295, in wsgi_app
response = self.handle_exception(e)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1741, in handle_exception
reraise(exc_type, exc_value, tb)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/_compat.py", line 35, in reraise
raise value
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 2292, in wsgi_app
response = self.full_dispatch_request()
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1815, in full_dispatch_request
rv = self.handle_user_exception(e)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1718, in handle_user_exception
reraise(exc_type, exc_value, tb)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/_compat.py", line 35, in reraise
raise value
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1813, in full_dispatch_request
rv = self.dispatch_request()
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1799, in dispatch_request
return self.view_functions[rule.endpoint](**req.view_args)
File "/Users/alranel/Documents/git/TD/spid-testenv2/spid-testenv.py", line 1020, in single_sign_on_service
atcss = self.server.metadata.attribute_consuming_service(sp_id)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/saml2/mdstore.py", line 1108, in attribute_consuming_service
"attribute_consuming_service", binding)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/saml2/mdstore.py", line 978, in service
srvs = _md.service(entity_id, typ, service, binding)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/saml2/mdstore.py", line 575, in service
if srv["binding"] == binding:
KeyError: 'binding'
``` | 1.0 | AuthnRequest: errore "KeyError: 'binding'" - Inviando questa AuthnRequest:
```xml
<saml2p:AuthnRequest ForceAuthn="false" IssueInstant="2018-07-24T17:15:47Z" Version="2.0" Destination="http://localhost:8088/sso" ID="_b09d06c33ba8649e14b34421d5a5d102" AttributeConsumingServiceIndex="1" AssertionConsumerServiceIndex="0" xmlns:saml2p="urn:oasis:names:tc:SAML:2.0:protocol" xmlns:saml2="urn:oasis:names:tc:SAML:2.0:assertion"><saml2:Issuer Format="urn:oasis:names:tc:SAML:2.0:nameid-format:entity" NameQualifier="https://www.prova.it/">https://www.prova.it/</saml2:Issuer><saml2p:NameIDPolicy Format="urn:oasis:names:tc:SAML:2.0:nameid-format:transient"></saml2p:NameIDPolicy><saml2p:RequestedAuthnContext Comparison="minimum"><saml2:AuthnContextClassRef>https://www.spid.gov.it/SpidL1</saml2:AuthnContextClassRef></saml2p:RequestedAuthnContext></saml2p:AuthnRequest>
```
ottengo il seguente errore:
```
Traceback (most recent call last):
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 2309, in __call__
return self.wsgi_app(environ, start_response)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 2295, in wsgi_app
response = self.handle_exception(e)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1741, in handle_exception
reraise(exc_type, exc_value, tb)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/_compat.py", line 35, in reraise
raise value
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 2292, in wsgi_app
response = self.full_dispatch_request()
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1815, in full_dispatch_request
rv = self.handle_user_exception(e)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1718, in handle_user_exception
reraise(exc_type, exc_value, tb)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/_compat.py", line 35, in reraise
raise value
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1813, in full_dispatch_request
rv = self.dispatch_request()
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/flask/app.py", line 1799, in dispatch_request
return self.view_functions[rule.endpoint](**req.view_args)
File "/Users/alranel/Documents/git/TD/spid-testenv2/spid-testenv.py", line 1020, in single_sign_on_service
atcss = self.server.metadata.attribute_consuming_service(sp_id)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/saml2/mdstore.py", line 1108, in attribute_consuming_service
"attribute_consuming_service", binding)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/saml2/mdstore.py", line 978, in service
srvs = _md.service(entity_id, typ, service, binding)
File "/Users/alranel/Documents/git/TD/spid-testenv2/env/lib/python3.7/site-packages/saml2/mdstore.py", line 575, in service
if srv["binding"] == binding:
KeyError: 'binding'
``` | test | authnrequest errore keyerror binding inviando questa authnrequest xml ottengo il seguente errore traceback most recent call last file users alranel documents git td spid env lib site packages flask app py line in call return self wsgi app environ start response file users alranel documents git td spid env lib site packages flask app py line in wsgi app response self handle exception e file users alranel documents git td spid env lib site packages flask app py line in handle exception reraise exc type exc value tb file users alranel documents git td spid env lib site packages flask compat py line in reraise raise value file users alranel documents git td spid env lib site packages flask app py line in wsgi app response self full dispatch request file users alranel documents git td spid env lib site packages flask app py line in full dispatch request rv self handle user exception e file users alranel documents git td spid env lib site packages flask app py line in handle user exception reraise exc type exc value tb file users alranel documents git td spid env lib site packages flask compat py line in reraise raise value file users alranel documents git td spid env lib site packages flask app py line in full dispatch request rv self dispatch request file users alranel documents git td spid env lib site packages flask app py line in dispatch request return self view functions req view args file users alranel documents git td spid spid testenv py line in single sign on service atcss self server metadata attribute consuming service sp id file users alranel documents git td spid env lib site packages mdstore py line in attribute consuming service attribute consuming service binding file users alranel documents git td spid env lib site packages mdstore py line in service srvs md service entity id typ service binding file users alranel documents git td spid env lib site packages mdstore py line in service if srv binding keyerror binding | 1 |
144,824 | 22,573,395,088 | IssuesEvent | 2022-06-28 04:02:31 | szwathub/LeetCode.swift | https://api.github.com/repos/szwathub/LeetCode.swift | closed | 715. Range 模块 | question: hard design ordered set segment tree | # [715. Range 模块](https://leetcode.cn/problems/range-module/)
Range模块是跟踪数字范围的模块。设计一个数据结构来跟踪表示为 **半开区间** 的范围并查询它们。
**半开区间** `[left, right)` 表示所有 `left <= x < right` 的实数 `x` 。
实现 **RangeModule** 类:
- `RangeModule()` 初始化数据结构的对象。
- `void addRange(int left, int right)` 添加 **半开区间** `[left, right)`,跟踪该区间中的每个实数。添加与当前跟踪的数字部分重叠的区间时,应当添加在区间 `[left, right)` 中尚未跟踪的任何数字到该区间中。
- `boolean queryRange(int left, int right)` 只有在当前正在跟踪区间 **[left, right)** 中的每一个实数时,才返回 `true` ,否则返回 `false` 。
- `void removeRange(int left, int right)` 停止跟踪 **半开区间** `[left, right)` 中当前正在跟踪的每个实数。
**示例 1:**
```
输入
["RangeModule", "addRange", "removeRange", "queryRange", "queryRange", "queryRange"]
[[], [10, 20], [14, 16], [10, 14], [13, 15], [16, 17]]
输出
[null, null, null, true, false, true]
解释
RangeModule rangeModule = new RangeModule();
rangeModule.addRange(10, 20);
rangeModule.removeRange(14, 16);
rangeModule.queryRange(10, 14); 返回 true (区间 [10, 14) 中的每个数都正在被跟踪)
rangeModule.queryRange(13, 15); 返回 false(未跟踪区间 [13, 15) 中像 14, 14.03, 14.17 这样的数字)
rangeModule.queryRange(16, 17); 返回 true (尽管执行了删除操作,区间 [16, 17) 中的数字 16 仍然会被跟踪)
```
**提示:**
- 1 <= left < right <= 10<sup>9</sup>
- 在单个测试用例中,对 `addRange` 、 `queryRange` 和 `removeRange` 的调用总数不超过 10<sup>4</sup> 次
----
来源:力扣(LeetCode)
链接:https://leetcode.cn/problems/range-module | 1.0 | 715. Range 模块 - # [715. Range 模块](https://leetcode.cn/problems/range-module/)
Range模块是跟踪数字范围的模块。设计一个数据结构来跟踪表示为 **半开区间** 的范围并查询它们。
**半开区间** `[left, right)` 表示所有 `left <= x < right` 的实数 `x` 。
实现 **RangeModule** 类:
- `RangeModule()` 初始化数据结构的对象。
- `void addRange(int left, int right)` 添加 **半开区间** `[left, right)`,跟踪该区间中的每个实数。添加与当前跟踪的数字部分重叠的区间时,应当添加在区间 `[left, right)` 中尚未跟踪的任何数字到该区间中。
- `boolean queryRange(int left, int right)` 只有在当前正在跟踪区间 **[left, right)** 中的每一个实数时,才返回 `true` ,否则返回 `false` 。
- `void removeRange(int left, int right)` 停止跟踪 **半开区间** `[left, right)` 中当前正在跟踪的每个实数。
**示例 1:**
```
输入
["RangeModule", "addRange", "removeRange", "queryRange", "queryRange", "queryRange"]
[[], [10, 20], [14, 16], [10, 14], [13, 15], [16, 17]]
输出
[null, null, null, true, false, true]
解释
RangeModule rangeModule = new RangeModule();
rangeModule.addRange(10, 20);
rangeModule.removeRange(14, 16);
rangeModule.queryRange(10, 14); 返回 true (区间 [10, 14) 中的每个数都正在被跟踪)
rangeModule.queryRange(13, 15); 返回 false(未跟踪区间 [13, 15) 中像 14, 14.03, 14.17 这样的数字)
rangeModule.queryRange(16, 17); 返回 true (尽管执行了删除操作,区间 [16, 17) 中的数字 16 仍然会被跟踪)
```
**提示:**
- 1 <= left < right <= 10<sup>9</sup>
- 在单个测试用例中,对 `addRange` 、 `queryRange` 和 `removeRange` 的调用总数不超过 10<sup>4</sup> 次
----
来源:力扣(LeetCode)
链接:https://leetcode.cn/problems/range-module | non_test | range 模块 range模块是跟踪数字范围的模块。设计一个数据结构来跟踪表示为 半开区间 的范围并查询它们。 半开区间 left right 表示所有 left x right 的实数 x 。 实现 rangemodule 类 rangemodule 初始化数据结构的对象。 void addrange int left int right 添加 半开区间 left right ,跟踪该区间中的每个实数。添加与当前跟踪的数字部分重叠的区间时,应当添加在区间 left right 中尚未跟踪的任何数字到该区间中。 boolean queryrange int left int right 只有在当前正在跟踪区间 left right 中的每一个实数时,才返回 true ,否则返回 false 。 void removerange int left int right 停止跟踪 半开区间 left right 中当前正在跟踪的每个实数。 示例 : 输入 输出 解释 rangemodule rangemodule new rangemodule rangemodule addrange rangemodule removerange rangemodule queryrange 返回 true (区间 中的每个数都正在被跟踪) rangemodule queryrange 返回 false(未跟踪区间 中像 这样的数字) rangemodule queryrange 返回 true (尽管执行了删除操作,区间 中的数字 仍然会被跟踪) 提示: 在单个测试用例中,对 addrange 、 queryrange 和 removerange 的调用总数不超过 次 来源:力扣(leetcode) 链接: | 0 |
292,431 | 25,213,728,158 | IssuesEvent | 2022-11-14 07:19:12 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | opened | Release 4.3.10 | release test/4.3.10 | Main issue gathering all the tasks regarding the preparation and validation of Wazuh version 4.3.10 release.
Close the issue only after the GA release.
## Release info
| | |
|---------------------------------------|------------------------------------------------------|
| Release name| Wazuh v4.3.10|
| Tag | https://github.com/wazuh/wazuh/tree/v4.3.10 |
| Branch | https://github.com/wazuh/wazuh/tree/4.3 |
| Changelog | https://github.com/wazuh/wazuh/blob/4.3/CHANGELOG.md |
| Latest release candidate (GA version) | N/A | |
## Release candidates
As usual, in order to publish, one or more release candidate versions are generated and fully tested, in the links below you can check the status and evolution of each version.
| Version | Issue | Tag | Status |
|---------|-------|-------------------------------------------------|-----------|
| RC1 | - | [v4.3.10-rc1](https://github.com/wazuh/wazuh/tree/v4.3.10-rc1) | In progress |
- _In progress: Fixes are being implemented._
- _In review: All the fixes have been implemented. The RC is now tagged and the QA process kicks off._
- _Closed: Fixes and QA process has finished._
## Tests
All the test results for this release can be found in the [v4.3.10 project](https://github.com/orgs/wazuh/projects/23/views/2).
## Fixes/Known issues
All the fixes and the issues detected in the testing phase that won't be solved in this version can be found in the [v4.3.10 project](https://github.com/orgs/wazuh/projects/23/views/1).
| 1.0 | Release 4.3.10 - Main issue gathering all the tasks regarding the preparation and validation of Wazuh version 4.3.10 release.
Close the issue only after the GA release.
## Release info
| | |
|---------------------------------------|------------------------------------------------------|
| Release name| Wazuh v4.3.10|
| Tag | https://github.com/wazuh/wazuh/tree/v4.3.10 |
| Branch | https://github.com/wazuh/wazuh/tree/4.3 |
| Changelog | https://github.com/wazuh/wazuh/blob/4.3/CHANGELOG.md |
| Latest release candidate (GA version) | N/A | |
## Release candidates
As usual, in order to publish, one or more release candidate versions are generated and fully tested, in the links below you can check the status and evolution of each version.
| Version | Issue | Tag | Status |
|---------|-------|-------------------------------------------------|-----------|
| RC1 | - | [v4.3.10-rc1](https://github.com/wazuh/wazuh/tree/v4.3.10-rc1) | In progress |
- _In progress: Fixes are being implemented._
- _In review: All the fixes have been implemented. The RC is now tagged and the QA process kicks off._
- _Closed: Fixes and QA process has finished._
## Tests
All the test results for this release can be found in the [v4.3.10 project](https://github.com/orgs/wazuh/projects/23/views/2).
## Fixes/Known issues
All the fixes and the issues detected in the testing phase that won't be solved in this version can be found in the [v4.3.10 project](https://github.com/orgs/wazuh/projects/23/views/1).
| test | release main issue gathering all the tasks regarding the preparation and validation of wazuh version release close the issue only after the ga release release info release name wazuh tag branch changelog latest release candidate ga version n a release candidates as usual in order to publish one or more release candidate versions are generated and fully tested in the links below you can check the status and evolution of each version version issue tag status in progress in progress fixes are being implemented in review all the fixes have been implemented the rc is now tagged and the qa process kicks off closed fixes and qa process has finished tests all the test results for this release can be found in the fixes known issues all the fixes and the issues detected in the testing phase that won t be solved in this version can be found in the | 1 |
320,723 | 27,454,617,429 | IssuesEvent | 2023-03-02 20:13:13 | MPMG-DCC-UFMG/F01 | https://api.github.com/repos/MPMG-DCC-UFMG/F01 | closed | Teste de generalizacao para a tag Orçamento - Todas - Brumadinho | generalization test development tag - Orçamento subtag - Todas | DoD: Realizar o teste de Generalização do validador da tag Orçamento - Todas para o Município de Brumadinho. | 1.0 | Teste de generalizacao para a tag Orçamento - Todas - Brumadinho - DoD: Realizar o teste de Generalização do validador da tag Orçamento - Todas para o Município de Brumadinho. | test | teste de generalizacao para a tag orçamento todas brumadinho dod realizar o teste de generalização do validador da tag orçamento todas para o município de brumadinho | 1 |
434,918 | 30,476,248,543 | IssuesEvent | 2023-07-17 16:43:36 | labring/sealos | https://api.github.com/repos/labring/sealos | closed | doc: sealos load and sealos save doc for new release | kind/documentation | When this version is released, the corresponding save and load documents need to be updated
_Originally posted by @cuisongliu in https://github.com/labring/sealos/issues/3442#issuecomment-1614194081_
| 1.0 | doc: sealos load and sealos save doc for new release - When this version is released, the corresponding save and load documents need to be updated
_Originally posted by @cuisongliu in https://github.com/labring/sealos/issues/3442#issuecomment-1614194081_
| non_test | doc sealos load and sealos save doc for new release when this version is released the corresponding save and load documents need to be updated originally posted by cuisongliu in | 0 |
231,371 | 18,763,056,518 | IssuesEvent | 2021-11-05 18:59:32 | astropy/astropy | https://api.github.com/repos/astropy/astropy | closed | [5.0RC1] exact double comparison in test_spline.py, exposed by Debian/ppc64el | testing Bug modeling | ### Description
Some tests in `astropy/modeling/tests/test_spline.py` compare doubles by equal, which not always works. Specifically on the PowerPC 64 Little Endian architecture on Debian, this gives failures
### Expected behavior
Tests should pass :-)
### Actual behavior
```
_________________ TestSpline1D.test_interpolate_fitter[2-None] _________________
self = <astropy.modeling.tests.test_spline.TestSpline1D object at 0x7ffeb53a7a90>
w = None, k = 2
@pytest.mark.parametrize('w', wieght_tests)
@pytest.mark.parametrize('k', degree_tests)
def test_interpolate_fitter(self, w, k):
[...]
assert (fit_spl.t == spline._eval_args[0]).all()
assert (fit_spl.c == spline._eval_args[1]).all()
assert (fitter.fit_info['spline']._eval_args[0] == spline._eval_args[0]).all()
assert (fitter.fit_info['spline']._eval_args[1] == spline._eval_args[1]).all()
assert spline.get_residual() == fitter.fit_info['resid'] == 0
> assert (fit_spl(self.x) == spline(self.x)).all()
E assert False
E + where False = <built-in method all of numpy.ndarray object at 0x7ffeb52a9030>()
E + where <built-in method all of numpy.ndarray object at 0x7ffeb52a9030> = array([ 0.073... 0.05145015]) == array([ 0.073... 0.05145015])
E Use -v to get the full diff.all
```
The same happens on `test_smoothing_fitter` (line 1207) and `test_exact_knots_fitter` (line 1267), all fails several times for different parameters.
[Full build log](https://buildd.debian.org/status/fetch.php?pkg=astropy&arch=ppc64el&ver=5.0%7Erc1-1&stamp=1636027474&raw=0)
### Steps to Reproduce
This happens when running on PowerPC 64 bit little endian.
### System Details
platform linux -- Python 3.9.7, pytest-6.2.5, py-1.10.0, pluggy-0.13.0
Matplotlib: 3.3.4
Freetype: 2.11.0
Running tests with Astropy version 5.0-rc1.
Running tests in .pybuild/cpython3_3.9/build.
Date: 2021-11-04T11:57:20
Platform: Linux-5.10.0-9-powerpc64le-ppc64le-with-glibc2.32
Executable: /usr/bin/python3.9
Full Python Version:
3.9.7 (default, Sep 24 2021, 09:43:00)
[GCC 10.3.0]
encodings: sys: utf-8, locale: UTF-8, filesystem: utf-8
byteorder: little
float info: dig: 15, mant_dig: 15
Package versions:
Numpy: 1.19.5
Scipy: 1.7.1
Matplotlib: 3.3.4
h5py: 3.3.0
Pandas: not available
PyERFA: 2.0.0
Cython: 0.29.24
Scikit-image: not available
asdf: not available
pyarrow: not available
Using Astropy options: remote_data: none.
ARCH_ON_CI: undefined
IS_CRON: undefined
rootdir: /<<PKGBUILDDIR>>, configfile: setup.cfg
plugins: mpl-0.11, remotedata-0.3.2, openfiles-0.5.0, mock-3.6.1, filter-subpackage-0.1.1, doctestplus-0.11.0, cov-3.0.0, astropy-header-0.1.2, arraydiff-0.3, hypothesis-5.43.3
| 1.0 | [5.0RC1] exact double comparison in test_spline.py, exposed by Debian/ppc64el - ### Description
Some tests in `astropy/modeling/tests/test_spline.py` compare doubles by equal, which not always works. Specifically on the PowerPC 64 Little Endian architecture on Debian, this gives failures
### Expected behavior
Tests should pass :-)
### Actual behavior
```
_________________ TestSpline1D.test_interpolate_fitter[2-None] _________________
self = <astropy.modeling.tests.test_spline.TestSpline1D object at 0x7ffeb53a7a90>
w = None, k = 2
@pytest.mark.parametrize('w', wieght_tests)
@pytest.mark.parametrize('k', degree_tests)
def test_interpolate_fitter(self, w, k):
[...]
assert (fit_spl.t == spline._eval_args[0]).all()
assert (fit_spl.c == spline._eval_args[1]).all()
assert (fitter.fit_info['spline']._eval_args[0] == spline._eval_args[0]).all()
assert (fitter.fit_info['spline']._eval_args[1] == spline._eval_args[1]).all()
assert spline.get_residual() == fitter.fit_info['resid'] == 0
> assert (fit_spl(self.x) == spline(self.x)).all()
E assert False
E + where False = <built-in method all of numpy.ndarray object at 0x7ffeb52a9030>()
E + where <built-in method all of numpy.ndarray object at 0x7ffeb52a9030> = array([ 0.073... 0.05145015]) == array([ 0.073... 0.05145015])
E Use -v to get the full diff.all
```
The same happens on `test_smoothing_fitter` (line 1207) and `test_exact_knots_fitter` (line 1267), all fails several times for different parameters.
[Full build log](https://buildd.debian.org/status/fetch.php?pkg=astropy&arch=ppc64el&ver=5.0%7Erc1-1&stamp=1636027474&raw=0)
### Steps to Reproduce
This happens when running on PowerPC 64 bit little endian.
### System Details
platform linux -- Python 3.9.7, pytest-6.2.5, py-1.10.0, pluggy-0.13.0
Matplotlib: 3.3.4
Freetype: 2.11.0
Running tests with Astropy version 5.0-rc1.
Running tests in .pybuild/cpython3_3.9/build.
Date: 2021-11-04T11:57:20
Platform: Linux-5.10.0-9-powerpc64le-ppc64le-with-glibc2.32
Executable: /usr/bin/python3.9
Full Python Version:
3.9.7 (default, Sep 24 2021, 09:43:00)
[GCC 10.3.0]
encodings: sys: utf-8, locale: UTF-8, filesystem: utf-8
byteorder: little
float info: dig: 15, mant_dig: 15
Package versions:
Numpy: 1.19.5
Scipy: 1.7.1
Matplotlib: 3.3.4
h5py: 3.3.0
Pandas: not available
PyERFA: 2.0.0
Cython: 0.29.24
Scikit-image: not available
asdf: not available
pyarrow: not available
Using Astropy options: remote_data: none.
ARCH_ON_CI: undefined
IS_CRON: undefined
rootdir: /<<PKGBUILDDIR>>, configfile: setup.cfg
plugins: mpl-0.11, remotedata-0.3.2, openfiles-0.5.0, mock-3.6.1, filter-subpackage-0.1.1, doctestplus-0.11.0, cov-3.0.0, astropy-header-0.1.2, arraydiff-0.3, hypothesis-5.43.3
| test | exact double comparison in test spline py exposed by debian description some tests in astropy modeling tests test spline py compare doubles by equal which not always works specifically on the powerpc little endian architecture on debian this gives failures expected behavior tests should pass actual behavior test interpolate fitter self w none k pytest mark parametrize w wieght tests pytest mark parametrize k degree tests def test interpolate fitter self w k assert fit spl t spline eval args all assert fit spl c spline eval args all assert fitter fit info eval args spline eval args all assert fitter fit info eval args spline eval args all assert spline get residual fitter fit info assert fit spl self x spline self x all e assert false e where false e where array array e use v to get the full diff all the same happens on test smoothing fitter line and test exact knots fitter line all fails several times for different parameters steps to reproduce this happens when running on powerpc bit little endian system details platform linux python pytest py pluggy matplotlib freetype running tests with astropy version running tests in pybuild build date platform linux with executable usr bin full python version default sep encodings sys utf locale utf filesystem utf byteorder little float info dig mant dig package versions numpy scipy matplotlib pandas not available pyerfa cython scikit image not available asdf not available pyarrow not available using astropy options remote data none arch on ci undefined is cron undefined rootdir configfile setup cfg plugins mpl remotedata openfiles mock filter subpackage doctestplus cov astropy header arraydiff hypothesis | 1 |
344,992 | 30,779,821,130 | IssuesEvent | 2023-07-31 09:14:46 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | closed | Release 4.5.0 - Alpha 1 - Workload benchmarks metrics | type/test level/subtask | The following issue aims to run all `workload benchmarks` for the current release candidate, report the results, and open new issues for any encountered errors.
## Workload benchmarks metrics information
| | |
|-----------------------------------------------|--------------------------------------------|
| **Main release candidate issue** |https://github.com/wazuh/wazuh/issues/18058|
| **Version** |4.5.0|
| **Release candidate #** |Alpha 1|
| **Tag** |[v4.5.0-alpha1](https://github.com/wazuh/wazuh/tree/v4.5.0-alpha1)|
| **Previous Workload benchmarks metrics issue**|https://github.com/wazuh/wazuh/issues/16975|
## Test configuration
All tests will be run and workload performance metrics will be obtained for the following clustered environment configurations:
| | |
|-------------------|--------------------|
| **# Agents** | **# Worker nodes** |
|50000|25|
## Test report procedure
All individual test checks must be marked as:
| | |
|---------------------------------|--------------------------------------------|
| Pass | The test ran successfully. |
| Xfail | The test was expected to fail and it failed. It must be properly justified and reported in an issue. |
| Skip | The test was not run. It must be properly justified and reported in an issue. |
| Fail | The test failed. A new issue must be opened to evaluate and address the problem. |
All test results must have one the following statuses:
| | |
|---------------------------------|--------------------------------------------|
| :green_circle: | All checks passed. |
| :red_circle: | There is at least one failed check. |
| :yellow_circle: | There is at least one expected fail or skipped test and no failures. |
Any failing test must be properly addressed with a new issue, detailing the error and the possible cause. It must be included in the `Fixes` section of the current release candidate main issue.
Any expected fail or skipped test must have an issue justifying the reason. All auditors must validate the justification for an expected fail or skipped test.
An extended report of the test results must be attached as a zip or txt. This report can be used by the auditors to dig deeper into any possible failures and details.
## Conclusions
All tests have been executed and the results can be found [here](https://github.com/wazuh/wazuh/issues/18113#issuecomment-1657894781).
All tests have passed and the fails have been reported or justified. I therefore conclude that this issue is finished and OK for this release candidate.
## Auditors validation
The definition of done for this one is the validation of the conclusions and the test results from all auditors.
All checks from below must be accepted in order to close this issue.
- [x] @Selutario
| 1.0 | Release 4.5.0 - Alpha 1 - Workload benchmarks metrics - The following issue aims to run all `workload benchmarks` for the current release candidate, report the results, and open new issues for any encountered errors.
## Workload benchmarks metrics information
| | |
|-----------------------------------------------|--------------------------------------------|
| **Main release candidate issue** |https://github.com/wazuh/wazuh/issues/18058|
| **Version** |4.5.0|
| **Release candidate #** |Alpha 1|
| **Tag** |[v4.5.0-alpha1](https://github.com/wazuh/wazuh/tree/v4.5.0-alpha1)|
| **Previous Workload benchmarks metrics issue**|https://github.com/wazuh/wazuh/issues/16975|
## Test configuration
All tests will be run and workload performance metrics will be obtained for the following clustered environment configurations:
| | |
|-------------------|--------------------|
| **# Agents** | **# Worker nodes** |
|50000|25|
## Test report procedure
All individual test checks must be marked as:
| | |
|---------------------------------|--------------------------------------------|
| Pass | The test ran successfully. |
| Xfail | The test was expected to fail and it failed. It must be properly justified and reported in an issue. |
| Skip | The test was not run. It must be properly justified and reported in an issue. |
| Fail | The test failed. A new issue must be opened to evaluate and address the problem. |
All test results must have one the following statuses:
| | |
|---------------------------------|--------------------------------------------|
| :green_circle: | All checks passed. |
| :red_circle: | There is at least one failed check. |
| :yellow_circle: | There is at least one expected fail or skipped test and no failures. |
Any failing test must be properly addressed with a new issue, detailing the error and the possible cause. It must be included in the `Fixes` section of the current release candidate main issue.
Any expected fail or skipped test must have an issue justifying the reason. All auditors must validate the justification for an expected fail or skipped test.
An extended report of the test results must be attached as a zip or txt. This report can be used by the auditors to dig deeper into any possible failures and details.
## Conclusions
All tests have been executed and the results can be found [here](https://github.com/wazuh/wazuh/issues/18113#issuecomment-1657894781).
All tests have passed and the fails have been reported or justified. I therefore conclude that this issue is finished and OK for this release candidate.
## Auditors validation
The definition of done for this one is the validation of the conclusions and the test results from all auditors.
All checks from below must be accepted in order to close this issue.
- [x] @Selutario
| test | release alpha workload benchmarks metrics the following issue aims to run all workload benchmarks for the current release candidate report the results and open new issues for any encountered errors workload benchmarks metrics information main release candidate issue version release candidate alpha tag previous workload benchmarks metrics issue test configuration all tests will be run and workload performance metrics will be obtained for the following clustered environment configurations agents worker nodes test report procedure all individual test checks must be marked as pass the test ran successfully xfail the test was expected to fail and it failed it must be properly justified and reported in an issue skip the test was not run it must be properly justified and reported in an issue fail the test failed a new issue must be opened to evaluate and address the problem all test results must have one the following statuses green circle all checks passed red circle there is at least one failed check yellow circle there is at least one expected fail or skipped test and no failures any failing test must be properly addressed with a new issue detailing the error and the possible cause it must be included in the fixes section of the current release candidate main issue any expected fail or skipped test must have an issue justifying the reason all auditors must validate the justification for an expected fail or skipped test an extended report of the test results must be attached as a zip or txt this report can be used by the auditors to dig deeper into any possible failures and details conclusions all tests have been executed and the results can be found all tests have passed and the fails have been reported or justified i therefore conclude that this issue is finished and ok for this release candidate auditors validation the definition of done for this one is the validation of the conclusions and the test results from all auditors all checks from below must be accepted in order to close this issue selutario | 1 |
268,472 | 8,407,193,573 | IssuesEvent | 2018-10-11 20:11:54 | clearlinux/swupd-client | https://api.github.com/repos/clearlinux/swupd-client | opened | Testlib: Consolidate Minversion Implementation | low priority | The update_minversion and bump_format testlib functions both perform a minversion update, but with separate implementations. These implementations should be consolidated. | 1.0 | Testlib: Consolidate Minversion Implementation - The update_minversion and bump_format testlib functions both perform a minversion update, but with separate implementations. These implementations should be consolidated. | non_test | testlib consolidate minversion implementation the update minversion and bump format testlib functions both perform a minversion update but with separate implementations these implementations should be consolidated | 0 |
88,709 | 17,647,679,761 | IssuesEvent | 2021-08-20 08:43:27 | WordPress/gutenberg | https://api.github.com/repos/WordPress/gutenberg | closed | Code editor not accepting block element (<h3>) inside anchor tag (<a>) | [Type] Bug [Feature] Code Editor [Package] Autop | **Describe the bug**
Whenever editing a page/post through the code editor instead of the visual one and adding a block element inside an anchor tag, whenever focusing out or saving the page, the editor automatically changes the code creating an orphan anchor tag.
**To reproduce**
Steps to reproduce the behaviour:
1. Go to 'edit post or page'
2. Click on '3-dotted menu > code editor`
3. Paste the mark up below
4. Click outside the editor (focusing out)
5. The markup changes automatically
6. Publish it
7. The mark up on front end changes even further
```html
<ul>
<li>
<a href='#'>
<h3>Title</h3>
</a>
</li>
</ul>
```
**Expected behaviour**
Since the markup added is valid HTML I would expect it to be kept as is. But instead, on focusing out the editor, it is changed to (adjusted indentation for readability)
```html
<ul>
<li>
<a href="#">
<h3>Title</h3>
</a>
<a href="#"></a>
</li>
</ul>
```
However, when publishing, it changes the markup even further to:
```html
<ul>
<li>
<a href="#">
</p>
<h3>Title</h3>
<p>
</a>
<a href="#"></a>
</li>
</ul>
```
**Additional context**
- WordPress 5.3 | 1.0 | Code editor not accepting block element (<h3>) inside anchor tag (<a>) - **Describe the bug**
Whenever editing a page/post through the code editor instead of the visual one and adding a block element inside an anchor tag, whenever focusing out or saving the page, the editor automatically changes the code creating an orphan anchor tag.
**To reproduce**
Steps to reproduce the behaviour:
1. Go to 'edit post or page'
2. Click on '3-dotted menu > code editor`
3. Paste the mark up below
4. Click outside the editor (focusing out)
5. The markup changes automatically
6. Publish it
7. The mark up on front end changes even further
```html
<ul>
<li>
<a href='#'>
<h3>Title</h3>
</a>
</li>
</ul>
```
**Expected behaviour**
Since the markup added is valid HTML I would expect it to be kept as is. But instead, on focusing out the editor, it is changed to (adjusted indentation for readability)
```html
<ul>
<li>
<a href="#">
<h3>Title</h3>
</a>
<a href="#"></a>
</li>
</ul>
```
However, when publishing, it changes the markup even further to:
```html
<ul>
<li>
<a href="#">
</p>
<h3>Title</h3>
<p>
</a>
<a href="#"></a>
</li>
</ul>
```
**Additional context**
- WordPress 5.3 | non_test | code editor not accepting block element inside anchor tag describe the bug whenever editing a page post through the code editor instead of the visual one and adding a block element inside an anchor tag whenever focusing out or saving the page the editor automatically changes the code creating an orphan anchor tag to reproduce steps to reproduce the behaviour go to edit post or page click on dotted menu code editor paste the mark up below click outside the editor focusing out the markup changes automatically publish it the mark up on front end changes even further html title expected behaviour since the markup added is valid html i would expect it to be kept as is but instead on focusing out the editor it is changed to adjusted indentation for readability html title however when publishing it changes the markup even further to html title additional context wordpress | 0 |
216,958 | 16,825,618,970 | IssuesEvent | 2021-06-17 18:08:34 | ansible/awx | https://api.github.com/repos/ansible/awx | closed | Expose the output of the EE resolver in the job template detail API endpoints | component:api priority:medium state:needs_test | ##### ISSUE TYPE
- Feature Idea
##### SUMMARY
It seems like it would be useful and would mitigate some confusion to expose which EE would be used when executing a template that doesn't have an EE explicitly assigned.
**Clarification**: template detail endpoints. | 1.0 | Expose the output of the EE resolver in the job template detail API endpoints - ##### ISSUE TYPE
- Feature Idea
##### SUMMARY
It seems like it would be useful and would mitigate some confusion to expose which EE would be used when executing a template that doesn't have an EE explicitly assigned.
**Clarification**: template detail endpoints. | test | expose the output of the ee resolver in the job template detail api endpoints issue type feature idea summary it seems like it would be useful and would mitigate some confusion to expose which ee would be used when executing a template that doesn t have an ee explicitly assigned clarification template detail endpoints | 1 |
462,674 | 13,251,419,707 | IssuesEvent | 2020-08-20 02:06:33 | department-of-veterans-affairs/caseflow | https://api.github.com/repos/department-of-veterans-affairs/caseflow | closed | Get stats on time spent on tasks during Case Decision Review | Priority: Low Product: caseflow-queue Stakeholder: BVA Team: Echo 🐬 Type: Metrics or Reporting | ## Description
Get statistics on how much time users' spend on [tasks associated with Case Decision Review](https://github.com/department-of-veterans-affairs/appeals-team/blob/master/Project%20Folders/Tasks/tasktrees/descr/tasks-overview.md#decision-phase).
Getting actual time spent working on task will be challenging, so get as close an estimate as possible using `AppealViews`, `Task.assigned_at`, `updated_at`, `closed_at` and fields in other associated models (e.g., timestamps in `RequestIssue`, `DecisionIssue`, `AttorneyCaseReview`, `JudgeCaseReview`, but ignore `DocumentViews` and other Document-related models as this will be addressed in a different ticket). See #12455. For other ideas, see [Caseflow Metrics](https://docs.google.com/spreadsheets/d/1Q3GYUu5WGwOZErZqGIwwS4OtWIxqOWKTWxBQVcnQ9mo/edit#gid=0).
Consider using Google Analytics or other user activity logs.
## Acceptance criteria
- [ ] Report containing stats on time spent on tasks associated with Case Decision Review
- [ ] If appropriate, identify more accurate measurements or logging that can be implemented
## Background/context/resources
To understand where we can improve timeliness of appeals processing, we need to track how users are spending their time in Caseflow. This ticket is a first dip into measuring this and identifying shortcomings, scoped only to the Case Decision Review process.
## Technical notes
| 1.0 | Get stats on time spent on tasks during Case Decision Review - ## Description
Get statistics on how much time users' spend on [tasks associated with Case Decision Review](https://github.com/department-of-veterans-affairs/appeals-team/blob/master/Project%20Folders/Tasks/tasktrees/descr/tasks-overview.md#decision-phase).
Getting actual time spent working on task will be challenging, so get as close an estimate as possible using `AppealViews`, `Task.assigned_at`, `updated_at`, `closed_at` and fields in other associated models (e.g., timestamps in `RequestIssue`, `DecisionIssue`, `AttorneyCaseReview`, `JudgeCaseReview`, but ignore `DocumentViews` and other Document-related models as this will be addressed in a different ticket). See #12455. For other ideas, see [Caseflow Metrics](https://docs.google.com/spreadsheets/d/1Q3GYUu5WGwOZErZqGIwwS4OtWIxqOWKTWxBQVcnQ9mo/edit#gid=0).
Consider using Google Analytics or other user activity logs.
## Acceptance criteria
- [ ] Report containing stats on time spent on tasks associated with Case Decision Review
- [ ] If appropriate, identify more accurate measurements or logging that can be implemented
## Background/context/resources
To understand where we can improve timeliness of appeals processing, we need to track how users are spending their time in Caseflow. This ticket is a first dip into measuring this and identifying shortcomings, scoped only to the Case Decision Review process.
## Technical notes
| non_test | get stats on time spent on tasks during case decision review description get statistics on how much time users spend on getting actual time spent working on task will be challenging so get as close an estimate as possible using appealviews task assigned at updated at closed at and fields in other associated models e g timestamps in requestissue decisionissue attorneycasereview judgecasereview but ignore documentviews and other document related models as this will be addressed in a different ticket see for other ideas see consider using google analytics or other user activity logs acceptance criteria report containing stats on time spent on tasks associated with case decision review if appropriate identify more accurate measurements or logging that can be implemented background context resources to understand where we can improve timeliness of appeals processing we need to track how users are spending their time in caseflow this ticket is a first dip into measuring this and identifying shortcomings scoped only to the case decision review process technical notes | 0 |
230,723 | 18,685,462,744 | IssuesEvent | 2021-11-01 11:52:15 | Tencent/bk-ci | https://api.github.com/repos/Tencent/bk-ci | closed | 研发商店插件的YAML展示 兼容插件配置错误展示 | kind/bug stage/uat stage/test area/ci/frontend area/ci/backend test/passed uat/passed | 用户在配置task.json 时,若出现如图
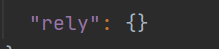
情况配置成了
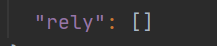
则会出现插件市场页面显示错误如图
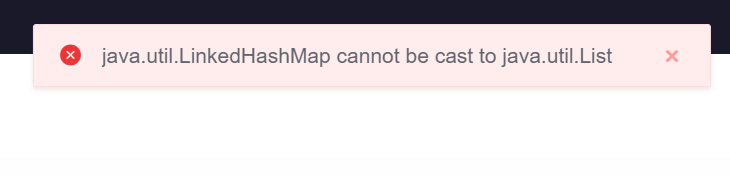
目前期望在

如图指定区域提醒用户task.json 配置格式有误,并且用户进入查看页面时,页面不要弹框报错。
| 2.0 | 研发商店插件的YAML展示 兼容插件配置错误展示 - 用户在配置task.json 时,若出现如图
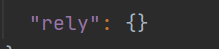
情况配置成了
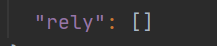
则会出现插件市场页面显示错误如图
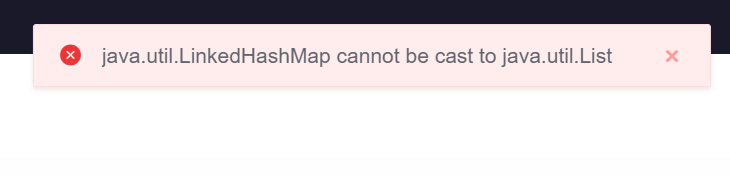
目前期望在

如图指定区域提醒用户task.json 配置格式有误,并且用户进入查看页面时,页面不要弹框报错。
| test | 研发商店插件的yaml展示 兼容插件配置错误展示 用户在配置task json 时,若出现如图 情况配置成了 则会出现插件市场页面显示错误如图 目前期望在 如图指定区域提醒用户task json 配置格式有误,并且用户进入查看页面时,页面不要弹框报错。 | 1 |
165,901 | 12,883,125,492 | IssuesEvent | 2020-07-12 20:22:10 | PyTorchLightning/pytorch-lightning | https://api.github.com/repos/PyTorchLightning/pytorch-lightning | closed | Enable Deepsource checks in CI/CD | enhancement help wanted tests / CI wontfix | In addition to flake8, mypy and other checks, I use https://deepsource.io/ for my projects.
It is free and from time to time it finds non-trivial bugs.
When I use it for projects with Pytorch-lightning and several validation loaders it throws me an error in python style and syntax. To overcome this I need to add things like:
`# skipcq: PYL-W0201` to my code. I would prefer to avoid it.
Is it possible that Deepsource checks would be allowed in Pytorch Lightning repo? I believe it will lead to better code quality.
| 1.0 | Enable Deepsource checks in CI/CD - In addition to flake8, mypy and other checks, I use https://deepsource.io/ for my projects.
It is free and from time to time it finds non-trivial bugs.
When I use it for projects with Pytorch-lightning and several validation loaders it throws me an error in python style and syntax. To overcome this I need to add things like:
`# skipcq: PYL-W0201` to my code. I would prefer to avoid it.
Is it possible that Deepsource checks would be allowed in Pytorch Lightning repo? I believe it will lead to better code quality.
| test | enable deepsource checks in ci cd in addition to mypy and other checks i use for my projects it is free and from time to time it finds non trivial bugs when i use it for projects with pytorch lightning and several validation loaders it throws me an error in python style and syntax to overcome this i need to add things like skipcq pyl to my code i would prefer to avoid it is it possible that deepsource checks would be allowed in pytorch lightning repo i believe it will lead to better code quality | 1 |
206,945 | 15,784,749,271 | IssuesEvent | 2021-04-01 15:29:52 | qauser21/backup3 | https://api.github.com/repos/qauser21/backup3 | opened | ABAC_Level3 on PUT:/api/v1/primary-transaction | CVSS_3.1 8.1 GitBack Test 3 High apisec |
Title: ABAC_Level3 Vulnerability on PUT:/api/v1/primary-transaction
Project: GitBack Test 3
Description: The ABAC exploit allows an attacker to read, modify, delete, add and perform actions on customer/un-authorized data.
<style>strong { color: #ef5350!important;}</style><strong>Assertion </strong>
<b><font color="#ef5350">Name: </font></b> Attribute Based Access Control 3 (ABAC 3) <b><font color="#ef5350"><sup>(
1 )</sup></font></b><br> <br> <b><font color="#ef5350">Overview: </font></b> Access Control (or Authorization) is
the process of granting or denying specific requests from a user, program, or process. Access control also involves the
act of granting and revoking those privileges. Attribute Based Access Control (ABAC) will grant or deny user requests
based on arbitrary attributes of the user and arbitrary attributes of the object, and environment conditions that may be
globally recognized and more relevant to the policies at hand. <br> <br>'Attribute-based-access-control 3' identifies
dependent and nested resource/data/record vulnerabilities. e.g. vulnerabilities in tasks which is nested within a
project and the access-controls may only be applied at the project level. ABAC scanning identifies data/resource
leak/attack vulnerabilities. Looks for private user/account data being illegally read, written, updated, deleted or
operated by other users or tenants or accounts.<br> <br>This scanner requires a private-account/user to create private
data/resources e.g. UserA. And it also requires other users who shouldn't have any access to UserA's data like UserB,
UserC, & UserD based on your App multi-tenancy model. e.g. UserA can be a user from tenant/org-a and UserB can be a user
in tenant-b and UserC can be a user in tenant-c with admin privileges.<br /> <br />APIs tend to expose endpoints that
handle object identifiers, creating a wide attack surface Level Access Control issue. Object-level authorization checks
should be considered in every function that accesses a data source using input from the user.<br> <br> <b><font color="#ef5350">Severity: </font></b> OWASP 2019 API Top 10 ranks ABAC vulnerabilities at Top 1 position and is
named Broken Object Level Authorization. <b><font color="#ef5350"><sup>( 2 )</sup></font></b> <br> <br> <b><font color="#ef5350">Vulnerability Impact: </font></b> With flawed or broken ABAC security control policy in place, The
following are some of the consequences. <br> <br>
<ul>
<li>Unauthorized access can result in data disclosure to unauthorized parties, data loss, or data manipulation.</li>
<li>Unauthorized access to objects can also lead to full account takeover.</li>
</ul> <b><font color="#ef5350">Exploitation: </font></b> Attackers can exploit API endpoints that are vulnerable to
broken object level authorization by manipulating the ID of an object that is sent within the request. This may lead to
unauthorized access to sensitive data. This issue is extremely common in API-based applications because the server
component usually does not fully track the client’s state, and instead, relies more on parameters like object IDs, that
are sent from the client to decide which objects to access. <br> <br> <b><font color="#ef5350">Remediation: </font></b>
The following techniques may be checked for ensuring RBAC is in place <b><font color="#ef5350"><sup>( 2 ) ( 3 ) ( 4
)</sup></font></b>. <br> <br>
<ul>
<li>Implement a proper authorization mechanism that relies on the user policies and hierarchy.</li>
<li>Prefer not to use an ID that has been sent from the client, but instead use an ID that is stored in the session
object when accessing a database record by the record ID.</li>
<li>Use an authorization mechanism to check if the logged-in user has access to perform the requested action on the
record in every function that uses an client input to access a record in the database.</li>
<li>Prefer to use random and unpredictable values as GUIDs for records’ IDs.</li>
<li>Write tests to evaluate the authorization mechanism. Do not deploy vulnerable changes that break the tests.</li>
</ul> <b><font color="#ef5350">References: </font></b><br>
<ol>
<li>Enforce Access Controls -
https://owasp-top-10-proactive-controls-2018.readthedocs.io/en/latest/c7-enforce-access-controls.html</li>
<li>OWASP 2019 API Top 10 -
https://github.com/OWASP/API-Security/raw/master/2019/en/dist/owasp-api-security-top-10.pdf</li>
<li>OWASP Access Control Cheat Sheet -
https://cheatsheetseries.owasp.org/cheatsheets/Access_Control_Cheat_Sheet.html</li>
<li>OWASP REST Security Cheat Sheet - https://cheatsheetseries.owasp.org/cheatsheets/REST_Security_Cheat_Sheet.html
</li>
</ol> <br>Risk: ABAC_Level3
Severity: High
API Endpoint: http://95.217.118.53:8080/api/v1/primary-transaction
Environment: Master
Playbook: ApiV1PrimaryTransactionPutPrimarytransactionuserbDisallowAbact3
Researcher: [apisec Bot]
QUICK TIPS
Suggestion: Add access-control checks on incoming requests against all data calls.
Effort Estimate: 2.0
Wire Logs:
IMPORTANT LINKS
Vulnerability Details:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/recommendations/8a8083b8788dc46901788e0df69f32d4/details
Project:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/jobs
Environment:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/environments/8a8083b8788dc46901788e09055921c9/edit
Scan Dashboard:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/jobs/8a8083b8788dc46901788e090fe32356/runs/8a8083b8788dc46901788e0dcfa532aa
Playbook:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/template/ApiV1PrimaryTransactionPutPrimarytransactionuserbDisallowAbact3
Coverage:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/configuration
Code Sample:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/recommendations/8a8083b8788dc46901788e0df69f32d4/codesamples
PS: Please contact support@apisec.ai for apisec access and login issues.
--- apisec Bot --- | 1.0 | ABAC_Level3 on PUT:/api/v1/primary-transaction -
Title: ABAC_Level3 Vulnerability on PUT:/api/v1/primary-transaction
Project: GitBack Test 3
Description: The ABAC exploit allows an attacker to read, modify, delete, add and perform actions on customer/un-authorized data.
<style>strong { color: #ef5350!important;}</style><strong>Assertion </strong>
<b><font color="#ef5350">Name: </font></b> Attribute Based Access Control 3 (ABAC 3) <b><font color="#ef5350"><sup>(
1 )</sup></font></b><br> <br> <b><font color="#ef5350">Overview: </font></b> Access Control (or Authorization) is
the process of granting or denying specific requests from a user, program, or process. Access control also involves the
act of granting and revoking those privileges. Attribute Based Access Control (ABAC) will grant or deny user requests
based on arbitrary attributes of the user and arbitrary attributes of the object, and environment conditions that may be
globally recognized and more relevant to the policies at hand. <br> <br>'Attribute-based-access-control 3' identifies
dependent and nested resource/data/record vulnerabilities. e.g. vulnerabilities in tasks which is nested within a
project and the access-controls may only be applied at the project level. ABAC scanning identifies data/resource
leak/attack vulnerabilities. Looks for private user/account data being illegally read, written, updated, deleted or
operated by other users or tenants or accounts.<br> <br>This scanner requires a private-account/user to create private
data/resources e.g. UserA. And it also requires other users who shouldn't have any access to UserA's data like UserB,
UserC, & UserD based on your App multi-tenancy model. e.g. UserA can be a user from tenant/org-a and UserB can be a user
in tenant-b and UserC can be a user in tenant-c with admin privileges.<br /> <br />APIs tend to expose endpoints that
handle object identifiers, creating a wide attack surface Level Access Control issue. Object-level authorization checks
should be considered in every function that accesses a data source using input from the user.<br> <br> <b><font color="#ef5350">Severity: </font></b> OWASP 2019 API Top 10 ranks ABAC vulnerabilities at Top 1 position and is
named Broken Object Level Authorization. <b><font color="#ef5350"><sup>( 2 )</sup></font></b> <br> <br> <b><font color="#ef5350">Vulnerability Impact: </font></b> With flawed or broken ABAC security control policy in place, The
following are some of the consequences. <br> <br>
<ul>
<li>Unauthorized access can result in data disclosure to unauthorized parties, data loss, or data manipulation.</li>
<li>Unauthorized access to objects can also lead to full account takeover.</li>
</ul> <b><font color="#ef5350">Exploitation: </font></b> Attackers can exploit API endpoints that are vulnerable to
broken object level authorization by manipulating the ID of an object that is sent within the request. This may lead to
unauthorized access to sensitive data. This issue is extremely common in API-based applications because the server
component usually does not fully track the client’s state, and instead, relies more on parameters like object IDs, that
are sent from the client to decide which objects to access. <br> <br> <b><font color="#ef5350">Remediation: </font></b>
The following techniques may be checked for ensuring RBAC is in place <b><font color="#ef5350"><sup>( 2 ) ( 3 ) ( 4
)</sup></font></b>. <br> <br>
<ul>
<li>Implement a proper authorization mechanism that relies on the user policies and hierarchy.</li>
<li>Prefer not to use an ID that has been sent from the client, but instead use an ID that is stored in the session
object when accessing a database record by the record ID.</li>
<li>Use an authorization mechanism to check if the logged-in user has access to perform the requested action on the
record in every function that uses an client input to access a record in the database.</li>
<li>Prefer to use random and unpredictable values as GUIDs for records’ IDs.</li>
<li>Write tests to evaluate the authorization mechanism. Do not deploy vulnerable changes that break the tests.</li>
</ul> <b><font color="#ef5350">References: </font></b><br>
<ol>
<li>Enforce Access Controls -
https://owasp-top-10-proactive-controls-2018.readthedocs.io/en/latest/c7-enforce-access-controls.html</li>
<li>OWASP 2019 API Top 10 -
https://github.com/OWASP/API-Security/raw/master/2019/en/dist/owasp-api-security-top-10.pdf</li>
<li>OWASP Access Control Cheat Sheet -
https://cheatsheetseries.owasp.org/cheatsheets/Access_Control_Cheat_Sheet.html</li>
<li>OWASP REST Security Cheat Sheet - https://cheatsheetseries.owasp.org/cheatsheets/REST_Security_Cheat_Sheet.html
</li>
</ol> <br>Risk: ABAC_Level3
Severity: High
API Endpoint: http://95.217.118.53:8080/api/v1/primary-transaction
Environment: Master
Playbook: ApiV1PrimaryTransactionPutPrimarytransactionuserbDisallowAbact3
Researcher: [apisec Bot]
QUICK TIPS
Suggestion: Add access-control checks on incoming requests against all data calls.
Effort Estimate: 2.0
Wire Logs:
IMPORTANT LINKS
Vulnerability Details:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/recommendations/8a8083b8788dc46901788e0df69f32d4/details
Project:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/jobs
Environment:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/environments/8a8083b8788dc46901788e09055921c9/edit
Scan Dashboard:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/jobs/8a8083b8788dc46901788e090fe32356/runs/8a8083b8788dc46901788e0dcfa532aa
Playbook:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/template/ApiV1PrimaryTransactionPutPrimarytransactionuserbDisallowAbact3
Coverage:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/configuration
Code Sample:
https://95.217.198.167/#/app/projects/8a8083b8788dc46901788e09054221c6/recommendations/8a8083b8788dc46901788e0df69f32d4/codesamples
PS: Please contact support@apisec.ai for apisec access and login issues.
--- apisec Bot --- | test | abac on put api primary transaction title abac vulnerability on put api primary transaction project gitback test description the abac exploit allows an attacker to read modify delete add and perform actions on customer un authorized data strong color important assertion name attribute based access control abac overview access control or authorization is the process of granting or denying specific requests from a user program or process access control also involves the act of granting and revoking those privileges attribute based access control abac will grant or deny user requests based on arbitrary attributes of the user and arbitrary attributes of the object and environment conditions that may be globally recognized and more relevant to the policies at hand attribute based access control identifies dependent and nested resource data record vulnerabilities e g vulnerabilities in tasks which is nested within a project and the access controls may only be applied at the project level abac scanning identifies data resource leak attack vulnerabilities looks for private user account data being illegally read written updated deleted or operated by other users or tenants or accounts this scanner requires a private account user to create private data resources e g usera and it also requires other users who shouldn t have any access to usera s data like userb userc userd based on your app multi tenancy model e g usera can be a user from tenant org a and userb can be a user in tenant b and userc can be a user in tenant c with admin privileges apis tend to expose endpoints that handle object identifiers creating a wide attack surface level access control issue object level authorization checks should be considered in every function that accesses a data source using input from the user severity owasp api top ranks abac vulnerabilities at top position and is named broken object level authorization vulnerability impact with flawed or broken abac security control policy in place the following are some of the consequences unauthorized access can result in data disclosure to unauthorized parties data loss or data manipulation unauthorized access to objects can also lead to full account takeover exploitation attackers can exploit api endpoints that are vulnerable to broken object level authorization by manipulating the id of an object that is sent within the request this may lead to unauthorized access to sensitive data this issue is extremely common in api based applications because the server component usually does not fully track the client’s state and instead relies more on parameters like object ids that are sent from the client to decide which objects to access remediation the following techniques may be checked for ensuring rbac is in place implement a proper authorization mechanism that relies on the user policies and hierarchy prefer not to use an id that has been sent from the client but instead use an id that is stored in the session object when accessing a database record by the record id use an authorization mechanism to check if the logged in user has access to perform the requested action on the record in every function that uses an client input to access a record in the database prefer to use random and unpredictable values as guids for records’ ids write tests to evaluate the authorization mechanism do not deploy vulnerable changes that break the tests references enforce access controls owasp api top owasp access control cheat sheet owasp rest security cheat sheet risk abac severity high api endpoint environment master playbook researcher quick tips suggestion add access control checks on incoming requests against all data calls effort estimate wire logs important links vulnerability details project environment scan dashboard playbook coverage code sample ps please contact support apisec ai for apisec access and login issues apisec bot | 1 |
271,407 | 23,602,627,581 | IssuesEvent | 2022-08-24 04:36:53 | woocommerce/woocommerce-ios | https://api.github.com/repos/woocommerce/woocommerce-ios | closed | [UI Testing] - Re-enable skipped login test cases | type: task feature: login category: ui tests | When the gear icon was moved from My Store to the Settings screen, some of the login-related test cases were skipped because of the screen change: https://github.com/woocommerce/woocommerce-ios/blob/65eed594fb215341616722158b4973335ad6a69f/WooCommerce/WooCommerceUITests/Tests/LoginTests.swift#L15-L54
This is to track the work to re-enable the tests. | 1.0 | [UI Testing] - Re-enable skipped login test cases - When the gear icon was moved from My Store to the Settings screen, some of the login-related test cases were skipped because of the screen change: https://github.com/woocommerce/woocommerce-ios/blob/65eed594fb215341616722158b4973335ad6a69f/WooCommerce/WooCommerceUITests/Tests/LoginTests.swift#L15-L54
This is to track the work to re-enable the tests. | test | re enable skipped login test cases when the gear icon was moved from my store to the settings screen some of the login related test cases were skipped because of the screen change this is to track the work to re enable the tests | 1 |
114,792 | 24,664,748,615 | IssuesEvent | 2022-10-18 09:26:40 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | JIT: GDV reorders null checks of 'this' with arguments | area-CodeGen-coreclr in-pr | The following example throws NRE without printing any output when tiered PGO is enabled. It should print "Should be printed" before throwing NRE.
```csharp
using System;
using System.Runtime.CompilerServices;
using System.Threading;
public class Program
{
public static void Main()
{
for (int i = 0; i < 100; i++)
{
long sum = Foo(i => i * 42, true);
if (i > 30 && i < 40)
Thread.Sleep(100);
}
Foo(null, false);
}
[MethodImpl(MethodImplOptions.NoInlining)]
private static long Foo(Func<long, long> f, bool silent)
{
long result = 0;
for (long i = 0; i < 100000; i++)
result += f(Test(i, silent));
return result;
}
[MethodImpl(MethodImplOptions.NoInlining)]
private static long Test(long i, bool silent)
{
if (i == 0 && !silent)
Console.WriteLine("Should be printed");
return i;
}
}
```
The evaluation order is meant to be:
1. Evaluate this
2. Evaluate arguments
3. Null check this
4. Do call
With GDV, since the guard involves dereferencing 'this', step 3 happens too early. This happens for both vtable, interface and delegate GDV.
Tricky to solve unfortunately. We need to evaluate the guard after the arguments (hard to represent without lots of additional spilling) or add a null check to the guard (expensive). cc @AndyAyersMS @EgorBo | 1.0 | JIT: GDV reorders null checks of 'this' with arguments - The following example throws NRE without printing any output when tiered PGO is enabled. It should print "Should be printed" before throwing NRE.
```csharp
using System;
using System.Runtime.CompilerServices;
using System.Threading;
public class Program
{
public static void Main()
{
for (int i = 0; i < 100; i++)
{
long sum = Foo(i => i * 42, true);
if (i > 30 && i < 40)
Thread.Sleep(100);
}
Foo(null, false);
}
[MethodImpl(MethodImplOptions.NoInlining)]
private static long Foo(Func<long, long> f, bool silent)
{
long result = 0;
for (long i = 0; i < 100000; i++)
result += f(Test(i, silent));
return result;
}
[MethodImpl(MethodImplOptions.NoInlining)]
private static long Test(long i, bool silent)
{
if (i == 0 && !silent)
Console.WriteLine("Should be printed");
return i;
}
}
```
The evaluation order is meant to be:
1. Evaluate this
2. Evaluate arguments
3. Null check this
4. Do call
With GDV, since the guard involves dereferencing 'this', step 3 happens too early. This happens for both vtable, interface and delegate GDV.
Tricky to solve unfortunately. We need to evaluate the guard after the arguments (hard to represent without lots of additional spilling) or add a null check to the guard (expensive). cc @AndyAyersMS @EgorBo | non_test | jit gdv reorders null checks of this with arguments the following example throws nre without printing any output when tiered pgo is enabled it should print should be printed before throwing nre csharp using system using system runtime compilerservices using system threading public class program public static void main for int i i i long sum foo i i true if i i thread sleep foo null false private static long foo func f bool silent long result for long i i i result f test i silent return result private static long test long i bool silent if i silent console writeline should be printed return i the evaluation order is meant to be evaluate this evaluate arguments null check this do call with gdv since the guard involves dereferencing this step happens too early this happens for both vtable interface and delegate gdv tricky to solve unfortunately we need to evaluate the guard after the arguments hard to represent without lots of additional spilling or add a null check to the guard expensive cc andyayersms egorbo | 0 |
53,331 | 11,037,677,655 | IssuesEvent | 2019-12-08 08:17:05 | pywbem/pywbem | https://api.github.com/repos/pywbem/pywbem | closed | MOF compiler: Does not raise errors from ModifyClass when compiling an existing class | area: code resolution: fixed roll back/forward done type: bug | When the MOF compiler compiles a class, it invokes `p_mp_createClass()` which invokes `handle.CreateClass()` and falls back to `handle.ModifyClass()` if the `handle.CreateClass()` method returns that the class already exists.
The issue is that if the `handle.ModifyClass()` call raises a CIMError, that error is logged but not re-raised.
I verified the code back to branch stable_0.8 and it never raised such an error.
The situation is complicated by the fact that `MOFWBEMConnection.CreateClass()` already replaces the class if it already exists, so that method never returns that the class already exists. Issue #991 describes that behavior. So if the MOFCompiler handle is a `MOFWBEMConnection` object, the issue described above does not have any bad consequences. However, the MOFCompiler handle does not have to be a `MOFWBEMConnection` object, so in the general case (e.g. with a real WBEM server), the issue does have bad consequences.
Proposal:
* Change `MOFWBEMConnection.CreateClass()` to no longer replace an existing class, but to return that it exists. This fixes issue #991.
* Change `p_mp_createClass()` to raise an error if `handle.ModifyClass()` returns an error.
* Add according testcases. | 1.0 | MOF compiler: Does not raise errors from ModifyClass when compiling an existing class - When the MOF compiler compiles a class, it invokes `p_mp_createClass()` which invokes `handle.CreateClass()` and falls back to `handle.ModifyClass()` if the `handle.CreateClass()` method returns that the class already exists.
The issue is that if the `handle.ModifyClass()` call raises a CIMError, that error is logged but not re-raised.
I verified the code back to branch stable_0.8 and it never raised such an error.
The situation is complicated by the fact that `MOFWBEMConnection.CreateClass()` already replaces the class if it already exists, so that method never returns that the class already exists. Issue #991 describes that behavior. So if the MOFCompiler handle is a `MOFWBEMConnection` object, the issue described above does not have any bad consequences. However, the MOFCompiler handle does not have to be a `MOFWBEMConnection` object, so in the general case (e.g. with a real WBEM server), the issue does have bad consequences.
Proposal:
* Change `MOFWBEMConnection.CreateClass()` to no longer replace an existing class, but to return that it exists. This fixes issue #991.
* Change `p_mp_createClass()` to raise an error if `handle.ModifyClass()` returns an error.
* Add according testcases. | non_test | mof compiler does not raise errors from modifyclass when compiling an existing class when the mof compiler compiles a class it invokes p mp createclass which invokes handle createclass and falls back to handle modifyclass if the handle createclass method returns that the class already exists the issue is that if the handle modifyclass call raises a cimerror that error is logged but not re raised i verified the code back to branch stable and it never raised such an error the situation is complicated by the fact that mofwbemconnection createclass already replaces the class if it already exists so that method never returns that the class already exists issue describes that behavior so if the mofcompiler handle is a mofwbemconnection object the issue described above does not have any bad consequences however the mofcompiler handle does not have to be a mofwbemconnection object so in the general case e g with a real wbem server the issue does have bad consequences proposal change mofwbemconnection createclass to no longer replace an existing class but to return that it exists this fixes issue change p mp createclass to raise an error if handle modifyclass returns an error add according testcases | 0 |
57,472 | 14,163,296,086 | IssuesEvent | 2020-11-12 02:00:59 | dotnet/aspnetcore | https://api.github.com/repos/dotnet/aspnetcore | closed | GetExternalLoginInfoAsync is null when called from ExternalLoginModel.OnGetCallbackAsync - IFrames involved. | area-security | Goal: Perform a silent login using a hidden iframe to google.
Result: I can achieve this by passing prompt=none to google which then doesn't x-frame-options=deny me.
All Good when I run the app normally and I route to ``` https://localhost:5001/Plugin ``` and ``` https://127.0.0.1.xip.io:5001/Plugin ```
My Plugin Page has my hidden iFrame.
```
<button id='signin'>signin</button>
<p id="received-message">I've heard nothing yet</p>
<form style="display: none;" id="loginform" target="guestFrame"
action="/Identity/Account/ExternalLogin?returnUrl=%2FOIDCIFrameResult&errorUrl=%2FOIDCIFrameResult&prompt=none&provider=google"
method="post">
<div>
<p>
<input type="submit">
</p>
</div>
</form>
<iframe style="display: none;" id="guestFrame" name="guestFrame" src="/Blank">
Your browser does not support inline frames.
</iframe>
```
Ok, now put the entire app in an iFrame and try to do a silent login under that context.
```
<iframe id="guestFrame" name="guestFrame" src="https://127.0.0.1.xip.io:5001/Plugin">
</iframe>
```
The above ```iFrame``` is hosted in ```https://localhost:5001/IFrameHost```
I am using [xip.io](https://xip.io) as my wildcard DNS. ```https://127.0.0.1.xip.io:5001```
My ```signin-google``` gets hit and it looks like there is a good code in there.
```
GENERAL
Request URL: https://127.0.0.1.xip.io:5001/signin-google
Request Method: POST
Status Code: 302
Remote Address: 127.0.0.1:5001
Referrer Policy: no-referrer-when-downgrade
Response Headers
cache-control: no-cache
content-length: 0
date: Fri, 28 Aug 2020 20:51:15 GMT
expires: Thu, 01 Jan 1970 00:00:00 GMT
location: /Identity/Account/ExternalLogin?returnUrl=%2FOIDCIFrameResult&handler=Callback
pragma: no-cache
server: Kestrel
set-cookie: .AspNetCore.Correlation.google.gxGuRZ5ZVbOr4SmC3zd6CLQpHZ_j-ZTc-jyvSnAF-IQ=; expires=Thu, 01 Jan 1970 00:00:00 GMT; path=/signin-google; secure; samesite=none; httponly
set-cookie: .AspNetCore.OpenIdConnect.Nonce.CfDJ8L16rcoVAjJMt5TusKivrFcSEujxcxPIbAwED3uPgd2mk-J_fEJKkogtr3NaSVolWh5Rv5DcehuReLphIyvY7VG-iypvHqGc7knVZXv2FWJaFed1bQaA2jkGFbmEmQs4DydnmwOdlA4Df_o8SjCPEW8Bq54SWJz6uNI8L9p0_e8ZllW1gaF0zCOuoQn_XdEm8jUW6o1h2N1o9YLFAbj3-w0rj5BWqOfl6ysEkeY0DXe7xm8Ycmd7PpC98edYtnkUgs5Kfs7H_4bn0E4TSP_1XS8=; expires=Thu, 01 Jan 1970 00:00:00 GMT; path=/signin-google; secure; samesite=none; httponly
set-cookie: Identity.External=CfDJ8L16rcoVAjJMt5TusKivrFecjgIwf31r3SrfRXOwnrnUe9wLJ38mJtd8HAzKOc_2rsgrFsLc6lAnKcHa5pYmafjUFaKJcmBZt2ys2JSUl3qFKVqSTZaSpS4E21Tt70yaz2T9AzSzDOhBv2hIBrtj1Y9c1Ximra9zPlTXLI1PuUNPl7ZQSTzQfep7-hhr7Fj0aCz4Qq14UvjHBaU8QjGd_XACdODJc4aX1PlT8_JgXDl5ob9RtDxmta1egpT6EkFOFwBC1Ngb0UiY5Ilz-c1R3255SDIxa6PVVNjy55ccFo0Hpfik9JWj6oTgGApt6koNrxbFOTK5sLAt5S7lR1FbL8Jkq_DOpmTzfSgEPVV7PIfW6AK4zZav6qawqgTn01mYRM-NO8f_gcrhTBfQpEbrYAFqVTu-Svo6ZkKTI-iRMe57arPz8e8nUvRnqplAvR8MbRKvXNAHGdRcN-JDvzxZQHxm7I0u-gX0MUm1CezYDhbaENhosyZrcxZhNZ9u7XdVgEtAlPe_KX1Vdn0zHmgHadcW_q8l1yvVzMTigryWr8-6wvGyeCPVhGGfRH6vIqkF9hGgTNXLpIso3xESmRJveCXbYWZfZ9Tm2w51T4ToCwOc5ymNmYkUBvQYX0HCpKkwOIlCn1JLGWy7q6WcN1VRcZHImvX-TA3R9aiIqRwbuAe3Ju4Qop8oAGoXW1FxFPAGIQRytj_m7uPBdngitb5bZgcFKhXr5vgxngWrE2Ns55ItXu85aGHi8DymfUmuH-Wtsd6haLpq39E08D_zudyY11hbt2_raO9OPNkWV8R_QCYR4eij7sp1OTG_Jq1tkdsQRTe0DfmxE9-reYYw8hK_sF4Hb8GU8QO0Zrn0Ia9UrF6tqW-LNhO5Id02Jmxl2Yn6yOipNwO9FbRDmLy9O4LumZWZw1miLS-XJ9KxPRPcR3x_wCONtKrxfWZzEqYs7T34CSQB71okiKFwfMu_vUNJl44TUsmgZ9QEtgIxlHcSeIHPc7Y2FYU3ZEM3gBmekbGGywzQ48TxNedsHo9PJ_We5BHbyBQK5XvVJ8r22VBOYlZHaNbcOt3WS7KxJp-uHmlfCY7NuC5d27IqVN0Ir5sLDbnr6KSblI2y82faQXoXUQz-HQlTly4O6lEJc1YbEAcfgHWieye-3A9wbjEt6N7HISTjcWWNgJIk_IfJcQC2lP95wP5VHZgwKQrIitkRCYaUxwfTEqUzVZq34chEd9Y8eF1A-LAJjHpT4nsovrRuD1qof63XmJ-dqwdAEeC41CLRDgWRZRdAsFj2xEZkTIDu8IQZugOfxucgYBH8TxWIssU7YLtR4CVQoDOCmT-EIodwEPAY0Bi_mMHh6O0EhrGyXsvEFFm_M-A-6uLZgrL8jjU2DNUG9ZhFSIUncDZ1_9iEvuZfv8OMUCWayEmmml8-SXeElPvZTDk4O2Els11JRP7q1jTHZ-5vakdbRDql68HiHryY8xEsDN_4LW_blaHCwKV32npzrB_vnETmj0Ii7M1QytZV3Nfdr8R-bfYg6wF46z5bm-9TwWkX4_pwJ5dp116kvE5LkADo-NIrNo33EJCsp-iYYhmUWRVL5Rh7nszVHr-1fj2TramHcKRn7_oi4djcFIHl0w-i4dF3kRPy-dgE2nKHsSM9Rpyjn-whNSQfPM7AOxIYTbllejAmGVJxUU83TIrQiOeNxml6e5mlp3GrVmC5qtBmnUA4hdrpyGgWFzXx5uBCtLN2z39HrrKvIKD25naRPqu6mRHI5QRqSFL9mpmv4Cseqk975MnuUPtjI-8BhpGoavN_4PALb_VeM-JTh3TW0W40S6BOi3c97ZojY_J34EEO-WSk5zNw1WHS233etkQ5qCsjtae2f3_dC9Gi_SI9CgFgEnz6LjqqaXOisgVGJTGC-D4V-Ms0teHoEklFYrvhUMZiCmxGdW8FwrZF6bG9uAKX1iRvg_557SIczHx24v9zXZL33dN0m11THnnD_0yVAc6ac9uiXBWmI0eZ-0jxk0Rg2dZsZ75RS-Mj8CNQZPfPfvfQj9LpZh8uyS3c3IPJVLzLyVpmEC0co-8gty45-qFU-cjoyiPI3v9hH9HWcO6bcdp7w1dgj-nQxPCj0Sb8MkPbW2cvl2y9Hwr5MmAjEp8gnCtLlfvm7hbbzwntkQURVP2V7ir83ZjNfObKcXN7SPbcsf88yTNfnilrLyF-GfaufOiqz5PEEy33k2geQMRbjbjdzpEarQjLZnQGLZ5hupMmbr7UdME2e1PCZPBp-KWZP4qA8uW3gCsmSqhBQgo4fcmjFocPPyt1IEnhmJqfI8c32_CvCK8Df98f183xwuBBVJr23MN1rVYf4avXEnrTfrs6I6CJfy8ZN5upxcUqpMxTQiMcO1lVycx8WYvcZTl1VXc9CipLiE7t92rqLeoyUQENWSvryTIL5JDtEexJTZ5fGDyLc1NCq5JidkG-oH32aPtSwm1hEQa8MsWfK64N_8f5YA5KVQuen-d-IQil_u7LVNS5BfIjEuhydZqRdoEi-8IKoraDCFzs6prdaXzqB3rQJwa2cOnuCjQNT8xz2kvRBCq75rt7I-srPSYNA57W9SwP5dn8GR2AxUI8CcO7zCfuBwO4FbcEgBtxCWaDmhAVnZd91MH0sslMo4hqNI8PQnNNvtGDXuHsM68tETZflcEW1EEH6Ylr2LWCDGlEZEK6PI1QyYI8TteMw0Rv6dxHbJqhYtvmb3Mx9FIf48NCEWNOnHK6DLt4R6gf-DjZp8pe8z1yMQ8sUccE_4R53irREwFrwij8BUHm1ncDzAVBK8uaGoHskM4oeLjKn8xCEW5pOuOBzXryrt9d0-3ymmLXUsI8du2WB0LmsMOJ3IM4f7zi9P-TjWTt4bdJ7YAmF5lp_zU0ltvMexKB9aTj-b7gfoEd2nBL3rd4E_VCqh_WosaI_t27CulyuuWCsGEFChO1vC0ONeyKHcjJSBv7E3kUYoYvo664SGC8OBZe69VCxFSPOhersp8XS74F6VtTzj7B8xvht8IsuOmZ7Ce5dj6ZuacUarAVppJBzeFfE2HrDOKLQGZ9Irq9berzA9zmQlHFDGNbj3GkZ5x8RmAc-pn1w_GAHeIVzULfNZ8Gxc-3AkqwlqkbDVZEuUL10zgtjh9vezwhiAvllcKS86AunCdb6UKegoSKPHmAWHQBLNwVYBjs5lDBOlxpzN41UhHAAlKmBfBS4QDoejTZN8yZGWS7irf-9VmBDiI1oSh6UbajAXLVmKJ6cE2zqXBjrl_YEpqyPVIIENYDuaa2v4f_t-ErgUQb3QN7jOKVF_QhOru3NQyWcZcBPEUlStTnayT1V0LK_2yjApvG9tLGgpZVGdsza9sbMexUQjRu3phFS1maVP3nV3Ee5D2mWWCzOwqjRvgOObzR4XxY8-9hIDI7iho3mNhpoiNubvH4s2ocmfImHmZqRBuLB-pNZ4dSAAnPIBDLpVWLmLLnxp5zIs2phfI7_GrHAz3LUj1ODVT2lyBjQYI_bNgpBHzfKhNfMBnHm4HpC_d7v7tD4X1cD_dOCBu3VQIs77u60sjOemot7g_F__P9GdrJQC60jZyWnW7IOE8V1Kg1ZtRISRBGavq3kj37H1qLHqEE6_R4tIgUvQiWb-9BoegnTKaX6_Cpq4L_OFGiegOr7EalAf2KcDm1AL15FEcHuYlHe5YeW-XGaHQdG7Ovt2owKAO1Kg; path=/; secure; samesite=lax; httponly
status: 302
x-correlation-id: d5a7b7fe-c5e9-4ab0-b6ae-0cb3ba891827
FORM-DATA
state=CfDJ8L16rcoVAjJMt5TusKivrFf2GEKRNyWN6Am9QMgqgxz17T9ThyCs-KUxjv1eUpwqojsNxikmLmsC5QXNBURb4gj8IzcQ1lYVPx4iP20oEk3bO2ZQgibTGRDlkBOAp6S7fSCUOPi1lwI1a5H9JjmewSY_4lpEftzbPKn9PCIbHuIkEcbh1UIDkptbanBb-ALt40tmtX8_UzgR7ZQJLLzzNp7POLvKSSXR8qugXU8CefSHCJGGNFM4GnNEVkRVW4oIhm2afXjlLJ13D90yaa8XzVPz_gHAiCgrCM4LVaDqTBfjHWZDiDAyDl66H_XGTaYjyNosKGStsZR3pF-23O0BQrmaXriT6hPTxKQnimMytT3DREAG0G6otxk_mBBMbQziepTeIqNWAMePCEOXZ5Ha367R343Kzyill8D_YNt82uTcFmf9xe-pAT7Mn9Q6P-p0Vsvs5WWN8dQyXposYpUThN-Ub6IoK4WtnNI2gYKBMR_S&code=REDACTED&scope=profile+openid+https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fuserinfo.profile&authuser=0&prompt=none
```
```ExternalLoginModel.OnGetCallbackAsync``` gets called but then I get a ```null``` when calling ```GetExternalLoginInfoAsync ```
I recall that some cookies get cleared during this exchange, but why would simply hosting my app in an iFrame result in different behavior?
| True | GetExternalLoginInfoAsync is null when called from ExternalLoginModel.OnGetCallbackAsync - IFrames involved. - Goal: Perform a silent login using a hidden iframe to google.
Result: I can achieve this by passing prompt=none to google which then doesn't x-frame-options=deny me.
All Good when I run the app normally and I route to ``` https://localhost:5001/Plugin ``` and ``` https://127.0.0.1.xip.io:5001/Plugin ```
My Plugin Page has my hidden iFrame.
```
<button id='signin'>signin</button>
<p id="received-message">I've heard nothing yet</p>
<form style="display: none;" id="loginform" target="guestFrame"
action="/Identity/Account/ExternalLogin?returnUrl=%2FOIDCIFrameResult&errorUrl=%2FOIDCIFrameResult&prompt=none&provider=google"
method="post">
<div>
<p>
<input type="submit">
</p>
</div>
</form>
<iframe style="display: none;" id="guestFrame" name="guestFrame" src="/Blank">
Your browser does not support inline frames.
</iframe>
```
Ok, now put the entire app in an iFrame and try to do a silent login under that context.
```
<iframe id="guestFrame" name="guestFrame" src="https://127.0.0.1.xip.io:5001/Plugin">
</iframe>
```
The above ```iFrame``` is hosted in ```https://localhost:5001/IFrameHost```
I am using [xip.io](https://xip.io) as my wildcard DNS. ```https://127.0.0.1.xip.io:5001```
My ```signin-google``` gets hit and it looks like there is a good code in there.
```
GENERAL
Request URL: https://127.0.0.1.xip.io:5001/signin-google
Request Method: POST
Status Code: 302
Remote Address: 127.0.0.1:5001
Referrer Policy: no-referrer-when-downgrade
Response Headers
cache-control: no-cache
content-length: 0
date: Fri, 28 Aug 2020 20:51:15 GMT
expires: Thu, 01 Jan 1970 00:00:00 GMT
location: /Identity/Account/ExternalLogin?returnUrl=%2FOIDCIFrameResult&handler=Callback
pragma: no-cache
server: Kestrel
set-cookie: .AspNetCore.Correlation.google.gxGuRZ5ZVbOr4SmC3zd6CLQpHZ_j-ZTc-jyvSnAF-IQ=; expires=Thu, 01 Jan 1970 00:00:00 GMT; path=/signin-google; secure; samesite=none; httponly
set-cookie: .AspNetCore.OpenIdConnect.Nonce.CfDJ8L16rcoVAjJMt5TusKivrFcSEujxcxPIbAwED3uPgd2mk-J_fEJKkogtr3NaSVolWh5Rv5DcehuReLphIyvY7VG-iypvHqGc7knVZXv2FWJaFed1bQaA2jkGFbmEmQs4DydnmwOdlA4Df_o8SjCPEW8Bq54SWJz6uNI8L9p0_e8ZllW1gaF0zCOuoQn_XdEm8jUW6o1h2N1o9YLFAbj3-w0rj5BWqOfl6ysEkeY0DXe7xm8Ycmd7PpC98edYtnkUgs5Kfs7H_4bn0E4TSP_1XS8=; expires=Thu, 01 Jan 1970 00:00:00 GMT; path=/signin-google; secure; samesite=none; httponly
set-cookie: Identity.External=CfDJ8L16rcoVAjJMt5TusKivrFecjgIwf31r3SrfRXOwnrnUe9wLJ38mJtd8HAzKOc_2rsgrFsLc6lAnKcHa5pYmafjUFaKJcmBZt2ys2JSUl3qFKVqSTZaSpS4E21Tt70yaz2T9AzSzDOhBv2hIBrtj1Y9c1Ximra9zPlTXLI1PuUNPl7ZQSTzQfep7-hhr7Fj0aCz4Qq14UvjHBaU8QjGd_XACdODJc4aX1PlT8_JgXDl5ob9RtDxmta1egpT6EkFOFwBC1Ngb0UiY5Ilz-c1R3255SDIxa6PVVNjy55ccFo0Hpfik9JWj6oTgGApt6koNrxbFOTK5sLAt5S7lR1FbL8Jkq_DOpmTzfSgEPVV7PIfW6AK4zZav6qawqgTn01mYRM-NO8f_gcrhTBfQpEbrYAFqVTu-Svo6ZkKTI-iRMe57arPz8e8nUvRnqplAvR8MbRKvXNAHGdRcN-JDvzxZQHxm7I0u-gX0MUm1CezYDhbaENhosyZrcxZhNZ9u7XdVgEtAlPe_KX1Vdn0zHmgHadcW_q8l1yvVzMTigryWr8-6wvGyeCPVhGGfRH6vIqkF9hGgTNXLpIso3xESmRJveCXbYWZfZ9Tm2w51T4ToCwOc5ymNmYkUBvQYX0HCpKkwOIlCn1JLGWy7q6WcN1VRcZHImvX-TA3R9aiIqRwbuAe3Ju4Qop8oAGoXW1FxFPAGIQRytj_m7uPBdngitb5bZgcFKhXr5vgxngWrE2Ns55ItXu85aGHi8DymfUmuH-Wtsd6haLpq39E08D_zudyY11hbt2_raO9OPNkWV8R_QCYR4eij7sp1OTG_Jq1tkdsQRTe0DfmxE9-reYYw8hK_sF4Hb8GU8QO0Zrn0Ia9UrF6tqW-LNhO5Id02Jmxl2Yn6yOipNwO9FbRDmLy9O4LumZWZw1miLS-XJ9KxPRPcR3x_wCONtKrxfWZzEqYs7T34CSQB71okiKFwfMu_vUNJl44TUsmgZ9QEtgIxlHcSeIHPc7Y2FYU3ZEM3gBmekbGGywzQ48TxNedsHo9PJ_We5BHbyBQK5XvVJ8r22VBOYlZHaNbcOt3WS7KxJp-uHmlfCY7NuC5d27IqVN0Ir5sLDbnr6KSblI2y82faQXoXUQz-HQlTly4O6lEJc1YbEAcfgHWieye-3A9wbjEt6N7HISTjcWWNgJIk_IfJcQC2lP95wP5VHZgwKQrIitkRCYaUxwfTEqUzVZq34chEd9Y8eF1A-LAJjHpT4nsovrRuD1qof63XmJ-dqwdAEeC41CLRDgWRZRdAsFj2xEZkTIDu8IQZugOfxucgYBH8TxWIssU7YLtR4CVQoDOCmT-EIodwEPAY0Bi_mMHh6O0EhrGyXsvEFFm_M-A-6uLZgrL8jjU2DNUG9ZhFSIUncDZ1_9iEvuZfv8OMUCWayEmmml8-SXeElPvZTDk4O2Els11JRP7q1jTHZ-5vakdbRDql68HiHryY8xEsDN_4LW_blaHCwKV32npzrB_vnETmj0Ii7M1QytZV3Nfdr8R-bfYg6wF46z5bm-9TwWkX4_pwJ5dp116kvE5LkADo-NIrNo33EJCsp-iYYhmUWRVL5Rh7nszVHr-1fj2TramHcKRn7_oi4djcFIHl0w-i4dF3kRPy-dgE2nKHsSM9Rpyjn-whNSQfPM7AOxIYTbllejAmGVJxUU83TIrQiOeNxml6e5mlp3GrVmC5qtBmnUA4hdrpyGgWFzXx5uBCtLN2z39HrrKvIKD25naRPqu6mRHI5QRqSFL9mpmv4Cseqk975MnuUPtjI-8BhpGoavN_4PALb_VeM-JTh3TW0W40S6BOi3c97ZojY_J34EEO-WSk5zNw1WHS233etkQ5qCsjtae2f3_dC9Gi_SI9CgFgEnz6LjqqaXOisgVGJTGC-D4V-Ms0teHoEklFYrvhUMZiCmxGdW8FwrZF6bG9uAKX1iRvg_557SIczHx24v9zXZL33dN0m11THnnD_0yVAc6ac9uiXBWmI0eZ-0jxk0Rg2dZsZ75RS-Mj8CNQZPfPfvfQj9LpZh8uyS3c3IPJVLzLyVpmEC0co-8gty45-qFU-cjoyiPI3v9hH9HWcO6bcdp7w1dgj-nQxPCj0Sb8MkPbW2cvl2y9Hwr5MmAjEp8gnCtLlfvm7hbbzwntkQURVP2V7ir83ZjNfObKcXN7SPbcsf88yTNfnilrLyF-GfaufOiqz5PEEy33k2geQMRbjbjdzpEarQjLZnQGLZ5hupMmbr7UdME2e1PCZPBp-KWZP4qA8uW3gCsmSqhBQgo4fcmjFocPPyt1IEnhmJqfI8c32_CvCK8Df98f183xwuBBVJr23MN1rVYf4avXEnrTfrs6I6CJfy8ZN5upxcUqpMxTQiMcO1lVycx8WYvcZTl1VXc9CipLiE7t92rqLeoyUQENWSvryTIL5JDtEexJTZ5fGDyLc1NCq5JidkG-oH32aPtSwm1hEQa8MsWfK64N_8f5YA5KVQuen-d-IQil_u7LVNS5BfIjEuhydZqRdoEi-8IKoraDCFzs6prdaXzqB3rQJwa2cOnuCjQNT8xz2kvRBCq75rt7I-srPSYNA57W9SwP5dn8GR2AxUI8CcO7zCfuBwO4FbcEgBtxCWaDmhAVnZd91MH0sslMo4hqNI8PQnNNvtGDXuHsM68tETZflcEW1EEH6Ylr2LWCDGlEZEK6PI1QyYI8TteMw0Rv6dxHbJqhYtvmb3Mx9FIf48NCEWNOnHK6DLt4R6gf-DjZp8pe8z1yMQ8sUccE_4R53irREwFrwij8BUHm1ncDzAVBK8uaGoHskM4oeLjKn8xCEW5pOuOBzXryrt9d0-3ymmLXUsI8du2WB0LmsMOJ3IM4f7zi9P-TjWTt4bdJ7YAmF5lp_zU0ltvMexKB9aTj-b7gfoEd2nBL3rd4E_VCqh_WosaI_t27CulyuuWCsGEFChO1vC0ONeyKHcjJSBv7E3kUYoYvo664SGC8OBZe69VCxFSPOhersp8XS74F6VtTzj7B8xvht8IsuOmZ7Ce5dj6ZuacUarAVppJBzeFfE2HrDOKLQGZ9Irq9berzA9zmQlHFDGNbj3GkZ5x8RmAc-pn1w_GAHeIVzULfNZ8Gxc-3AkqwlqkbDVZEuUL10zgtjh9vezwhiAvllcKS86AunCdb6UKegoSKPHmAWHQBLNwVYBjs5lDBOlxpzN41UhHAAlKmBfBS4QDoejTZN8yZGWS7irf-9VmBDiI1oSh6UbajAXLVmKJ6cE2zqXBjrl_YEpqyPVIIENYDuaa2v4f_t-ErgUQb3QN7jOKVF_QhOru3NQyWcZcBPEUlStTnayT1V0LK_2yjApvG9tLGgpZVGdsza9sbMexUQjRu3phFS1maVP3nV3Ee5D2mWWCzOwqjRvgOObzR4XxY8-9hIDI7iho3mNhpoiNubvH4s2ocmfImHmZqRBuLB-pNZ4dSAAnPIBDLpVWLmLLnxp5zIs2phfI7_GrHAz3LUj1ODVT2lyBjQYI_bNgpBHzfKhNfMBnHm4HpC_d7v7tD4X1cD_dOCBu3VQIs77u60sjOemot7g_F__P9GdrJQC60jZyWnW7IOE8V1Kg1ZtRISRBGavq3kj37H1qLHqEE6_R4tIgUvQiWb-9BoegnTKaX6_Cpq4L_OFGiegOr7EalAf2KcDm1AL15FEcHuYlHe5YeW-XGaHQdG7Ovt2owKAO1Kg; path=/; secure; samesite=lax; httponly
status: 302
x-correlation-id: d5a7b7fe-c5e9-4ab0-b6ae-0cb3ba891827
FORM-DATA
state=CfDJ8L16rcoVAjJMt5TusKivrFf2GEKRNyWN6Am9QMgqgxz17T9ThyCs-KUxjv1eUpwqojsNxikmLmsC5QXNBURb4gj8IzcQ1lYVPx4iP20oEk3bO2ZQgibTGRDlkBOAp6S7fSCUOPi1lwI1a5H9JjmewSY_4lpEftzbPKn9PCIbHuIkEcbh1UIDkptbanBb-ALt40tmtX8_UzgR7ZQJLLzzNp7POLvKSSXR8qugXU8CefSHCJGGNFM4GnNEVkRVW4oIhm2afXjlLJ13D90yaa8XzVPz_gHAiCgrCM4LVaDqTBfjHWZDiDAyDl66H_XGTaYjyNosKGStsZR3pF-23O0BQrmaXriT6hPTxKQnimMytT3DREAG0G6otxk_mBBMbQziepTeIqNWAMePCEOXZ5Ha367R343Kzyill8D_YNt82uTcFmf9xe-pAT7Mn9Q6P-p0Vsvs5WWN8dQyXposYpUThN-Ub6IoK4WtnNI2gYKBMR_S&code=REDACTED&scope=profile+openid+https%3A%2F%2Fwww.googleapis.com%2Fauth%2Fuserinfo.profile&authuser=0&prompt=none
```
```ExternalLoginModel.OnGetCallbackAsync``` gets called but then I get a ```null``` when calling ```GetExternalLoginInfoAsync ```
I recall that some cookies get cleared during this exchange, but why would simply hosting my app in an iFrame result in different behavior?
| non_test | getexternallogininfoasync is null when called from externalloginmodel ongetcallbackasync iframes involved goal perform a silent login using a hidden iframe to google result i can achieve this by passing prompt none to google which then doesn t x frame options deny me all good when i run the app normally and i route to and my plugin page has my hidden iframe signin i ve heard nothing yet form style display none id loginform target guestframe action identity account externallogin returnurl amp errorurl amp prompt none amp provider google method post your browser does not support inline frames ok now put the entire app in an iframe and try to do a silent login under that context iframe id guestframe name guestframe src the above iframe is hosted in i am using as my wildcard dns my signin google gets hit and it looks like there is a good code in there general request url request method post status code remote address referrer policy no referrer when downgrade response headers cache control no cache content length date fri aug gmt expires thu jan gmt location identity account externallogin returnurl handler callback pragma no cache server kestrel set cookie aspnetcore correlation google j ztc jyvsnaf iq expires thu jan gmt path signin google secure samesite none httponly set cookie aspnetcore openidconnect nonce j expires thu jan gmt path signin google secure samesite none httponly set cookie identity external gcrhtbfqpebryafqvtu m a vem qfu d iqil vcqh wosai t f path secure samesite lax httponly status x correlation id form data state s code redacted scope profile openid https externalloginmodel ongetcallbackasync gets called but then i get a null when calling getexternallogininfoasync i recall that some cookies get cleared during this exchange but why would simply hosting my app in an iframe result in different behavior | 0 |
117,183 | 4,712,108,175 | IssuesEvent | 2016-10-14 15:44:44 | geosolutions-it/MapStore2 | https://api.github.com/repos/geosolutions-it/MapStore2 | closed | Move the visibility icon (the eye) to the side of the tools for the layer in the layer tree | enhancement Priority: High task | Right now the eye icon that allows users to change the visibility of the layer is in a position which is strange, see below:

I would rather have something like this:

which can be taken from the SIRA product we are doing.
| 1.0 | Move the visibility icon (the eye) to the side of the tools for the layer in the layer tree - Right now the eye icon that allows users to change the visibility of the layer is in a position which is strange, see below:

I would rather have something like this:

which can be taken from the SIRA product we are doing.
| non_test | move the visibility icon the eye to the side of the tools for the layer in the layer tree right now the eye icon that allows users to change the visibility of the layer is in a position which is strange see below i would rather have something like this which can be taken from the sira product we are doing | 0 |
160,424 | 20,100,272,398 | IssuesEvent | 2022-02-07 02:35:53 | dwanprac/django.nv | https://api.github.com/repos/dwanprac/django.nv | opened | grunt-npm-install-0.3.1.tgz: 28 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-npm-install-0.3.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-3918](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | json-schema-0.2.3.tgz | Transitive | N/A | ❌ |
| [CVE-2018-16492](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | extend-3.0.0.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23807](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jsonpointer-4.0.0.tgz | Transitive | N/A | ❌ |
| [WS-2020-0344](https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [WS-2020-0345](https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.2 | jsonpointer-4.0.0.tgz | Transitive | N/A | ❌ |
| [CVE-2019-16776](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16776) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2021-32804](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tar-2.2.1.tgz | Transitive | N/A | ❌ |
| [CVE-2018-20834](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20834) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | tar-2.2.1.tgz | Transitive | N/A | ❌ |
| [CVE-2017-15010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | tough-cookie-2.3.1.tgz | Transitive | N/A | ❌ |
| [WS-2020-0180](https://github.com/npm/npm-user-validate/commit/c8a87dac1a4cc6988b5418f30411a8669bef204e) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | npm-user-validate-0.1.5.tgz | Transitive | N/A | ❌ |
| [WS-2018-0069](https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [CVE-2017-1000048](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-6.2.1.tgz | Transitive | N/A | ❌ |
| [CVE-2020-7754](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7754) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | npm-user-validate-0.1.5.tgz | Transitive | N/A | ❌ |
| [CVE-2018-3737](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3737) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | sshpk-1.10.1.tgz | Transitive | N/A | ❌ |
| [CVE-2017-18077](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18077) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | brace-expansion-1.1.6.tgz | Transitive | N/A | ❌ |
| [WS-2020-0342](https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [CVE-2019-13173](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-13173) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | fstream-1.0.10.tgz | Transitive | N/A | ❌ |
| [CVE-2020-7788](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.4.tgz | Transitive | N/A | ❌ |
| [CVE-2018-21270](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-21270) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | stringstream-0.0.5.tgz | Transitive | N/A | ❌ |
| [CVE-2020-8244](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | bl-1.1.2.tgz | Transitive | N/A | ❌ |
| [CVE-2019-16775](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16775) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2019-16777](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16777) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2017-16032](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16032) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | brace-expansion-1.1.6.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23362](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | hosted-git-info-2.1.5.tgz | Transitive | N/A | ❌ |
| [CVE-2018-1107](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1107) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [WS-2018-0103](https://hackerone.com/reports/321670) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | stringstream-0.0.5.tgz | Transitive | N/A | ❌ |
| [CVE-2020-15095](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15095) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2017-18869](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18869) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.5 | chownr-1.0.1.tgz | Transitive | N/A | ❌ |
## Details
> Partial details (11 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3918</summary>
### Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/http-signature/node_modules/jsprim/node_modules/json-schema/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- http-signature-1.1.1.tgz
- jsprim-1.3.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution: json-schema - 0.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-16492</summary>
### Vulnerable Library - <b>extend-3.0.0.tgz</b></p>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-3.0.0.tgz">https://registry.npmjs.org/extend/-/extend-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- :x: **extend-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in module extend <2.0.2, ~<3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492>CVE-2018-16492</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/381185">https://hackerone.com/reports/381185</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: extend - v3.0.2,v2.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23807</summary>
### Vulnerable Library - <b>jsonpointer-4.0.0.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.15.0.tgz
- :x: **jsonpointer-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.
<p>Publish Date: 2021-11-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807>CVE-2021-23807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution: jsonpointer - 5.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0344</summary>
### Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.
<p>Publish Date: 2020-06-09
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d>WS-2020-0344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-09</p>
<p>Fix Resolution: is-my-json-valid - 2.20.3</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0345</summary>
### Vulnerable Library - <b>jsonpointer-4.0.0.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.15.0.tgz
- :x: **jsonpointer-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.
<p>Publish Date: 2020-07-03
<p>URL: <a href=https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34>WS-2020-0345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0">https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0</a></p>
<p>Release Date: 2020-07-03</p>
<p>Fix Resolution: jsonpointer - 4.1.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16776</summary>
### Vulnerable Library - <b>npm-3.10.10.tgz</b></p>
<p>a package manager for JavaScript</p>
<p>Library home page: <a href="https://registry.npmjs.org/npm/-/npm-3.10.10.tgz">https://registry.npmjs.org/npm/-/npm-3.10.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- :x: **npm-3.10.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the npm CLI prior to 6.13.3 are vulnerable to an Arbitrary File Write. It fails to prevent access to folders outside of the intended node_modules folder through the bin field. A properly constructed entry in the package.json bin field would allow a package publisher to modify and/or gain access to arbitrary files on a user's system when the package is installed. This behavior is still possible through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.
<p>Publish Date: 2019-12-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16776>CVE-2019-16776</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.npmjs.org/post/189618601100/binary-planting-with-the-npm-cli">https://blog.npmjs.org/post/189618601100/binary-planting-with-the-npm-cli</a></p>
<p>Release Date: 2020-10-07</p>
<p>Fix Resolution: npm - 6.13.3;yarn - 1.21.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-32804</summary>
### Vulnerable Library - <b>tar-2.2.1.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution: tar - 3.2.2, 4.4.14, 5.0.6, 6.1.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-20834</summary>
### Vulnerable Library - <b>tar-2.2.1.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in node-tar before version 4.4.2 (excluding version 2.2.2). An Arbitrary File Overwrite issue exists when extracting a tarball containing a hardlink to a file that already exists on the system, in conjunction with a later plain file with the same name as the hardlink. This plain file content replaces the existing file content. A patch has been applied to node-tar v2.2.2).
<p>Publish Date: 2019-04-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20834>CVE-2018-20834</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082</a></p>
<p>Release Date: 2019-04-30</p>
<p>Fix Resolution: 2.2.2,4.4.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-15010</summary>
### Vulnerable Library - <b>tough-cookie-2.3.1.tgz</b></p>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.3.1.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- :x: **tough-cookie-2.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.
<p>Publish Date: 2017-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010>CVE-2017-15010</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15010">https://nvd.nist.gov/vuln/detail/CVE-2017-15010</a></p>
<p>Release Date: 2017-10-04</p>
<p>Fix Resolution: 2.3.3</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0180</summary>
### Vulnerable Library - <b>npm-user-validate-0.1.5.tgz</b></p>
<p>User validations for npm</p>
<p>Library home page: <a href="https://registry.npmjs.org/npm-user-validate/-/npm-user-validate-0.1.5.tgz">https://registry.npmjs.org/npm-user-validate/-/npm-user-validate-0.1.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/npm-user-validate/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- :x: **npm-user-validate-0.1.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package npm-user-validate prior to version 1.0.1 is vulnerable to REDoS. The regex that validates a user's email took exponentially longer to process input strings that begin with the '@' character.
<p>Publish Date: 2020-10-16
<p>URL: <a href=https://github.com/npm/npm-user-validate/commit/c8a87dac1a4cc6988b5418f30411a8669bef204e>WS-2020-0180</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-xgh6-85xh-479p">https://github.com/advisories/GHSA-xgh6-85xh-479p</a></p>
<p>Release Date: 2020-10-16</p>
<p>Fix Resolution: 1.0.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0069</summary>
### Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Version of is-my-json-valid before 1.4.1 or 2.17.2 are vulnerable to regular expression denial of service (ReDoS) via the email validation function.
<p>Publish Date: 2018-02-14
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976>WS-2018-0069</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/572">https://nodesecurity.io/advisories/572</a></p>
<p>Release Date: 2018-02-14</p>
<p>Fix Resolution: 1.4.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"json-schema","packageVersion":"0.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;http-signature:1.1.1;jsprim:1.3.1;json-schema:0.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"json-schema - 0.4.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-3918","vulnerabilityDetails":"json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (\u0027Prototype Pollution\u0027)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"extend","packageVersion":"3.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;extend:3.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"extend - v3.0.2,v2.0.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-16492","vulnerabilityDetails":"A prototype pollution vulnerability was found in module extend \u003c2.0.2, ~\u003c3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"jsonpointer","packageVersion":"4.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0;jsonpointer:4.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jsonpointer - 5.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23807","vulnerabilityDetails":"This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"is-my-json-valid - 2.20.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0344","vulnerabilityDetails":"Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"jsonpointer","packageVersion":"4.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0;jsonpointer:4.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jsonpointer - 4.1.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0345","vulnerabilityDetails":"Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.","vulnerabilityUrl":"https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34","cvss3Severity":"high","cvss3Score":"8.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.13.3;yarn - 1.21.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-16776","vulnerabilityDetails":"Versions of the npm CLI prior to 6.13.3 are vulnerable to an Arbitrary File Write. It fails to prevent access to folders outside of the intended node_modules folder through the bin field. A properly constructed entry in the package.json bin field would allow a package publisher to modify and/or gain access to arbitrary files on a user\u0027s system when the package is installed. This behavior is still possible through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16776","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tar","packageVersion":"2.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;tar:2.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tar - 3.2.2, 4.4.14, 5.0.6, 6.1.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-32804","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tar","packageVersion":"2.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;tar:2.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.2.2,4.4.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20834","vulnerabilityDetails":"A vulnerability was found in node-tar before version 4.4.2 (excluding version 2.2.2). An Arbitrary File Overwrite issue exists when extracting a tarball containing a hardlink to a file that already exists on the system, in conjunction with a later plain file with the same name as the hardlink. This plain file content replaces the existing file content. A patch has been applied to node-tar v2.2.2).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20834","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tough-cookie","packageVersion":"2.3.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;tough-cookie:2.3.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.3.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-15010","vulnerabilityDetails":"A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm-user-validate","packageVersion":"0.1.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;npm-user-validate:0.1.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0180","vulnerabilityDetails":"The package npm-user-validate prior to version 1.0.1 is vulnerable to REDoS. The regex that validates a user\u0027s email took exponentially longer to process input strings that begin with the \u0027@\u0027 character.","vulnerabilityUrl":"https://github.com/npm/npm-user-validate/commit/c8a87dac1a4cc6988b5418f30411a8669bef204e","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0069","vulnerabilityDetails":"Version of is-my-json-valid before 1.4.1 or 2.17.2 are vulnerable to regular expression denial of service (ReDoS) via the email validation function.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"6.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;qs:6.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-1000048","vulnerabilityDetails":"the web framework using ljharb\u0027s qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm-user-validate","packageVersion":"0.1.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;npm-user-validate:0.1.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7754","vulnerabilityDetails":"This affects the package npm-user-validate before 1.0.1. The regex that validates user emails took exponentially longer to process long input strings beginning with @ characters.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7754","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"sshpk","packageVersion":"1.10.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;http-signature:1.1.1;sshpk:1.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.13.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-3737","vulnerabilityDetails":"sshpk is vulnerable to ReDoS when parsing crafted invalid public keys.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3737","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"brace-expansion","packageVersion":"1.1.6","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;init-package-json:1.9.4;glob:6.0.4;minimatch:3.0.3;brace-expansion:1.1.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.1.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-18077","vulnerabilityDetails":"index.js in brace-expansion before 1.1.7 is vulnerable to Regular Expression Denial of Service (ReDoS) attacks, as demonstrated by an expand argument containing many comma characters.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18077","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"is-my-json-valid - 2.20.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0342","vulnerabilityDetails":"Regular Expression Denial of Service (ReDoS) vulnerability was found in is-my-json-valid before 2.20.2 via the style format.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"fstream","packageVersion":"1.0.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;fstream:1.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.12","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-13173","vulnerabilityDetails":"fstream before 1.0.12 is vulnerable to Arbitrary File Overwrite. Extracting tarballs containing a hardlink to a file that already exists in the system, and a file that matches the hardlink, will overwrite the system\u0027s file with the contents of the extracted file. The fstream.DirWriter() function is vulnerable.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-13173","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ini","packageVersion":"1.3.4","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;ini:1.3.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v1.3.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7788","vulnerabilityDetails":"This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"stringstream","packageVersion":"0.0.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;stringstream:0.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.0.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-21270","vulnerabilityDetails":"Versions less than 0.0.6 of the Node.js stringstream module are vulnerable to an out-of-bounds read because of allocation of uninitialized buffers when a number is passed in the input stream (when using Node.js 4.x).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-21270","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"bl","packageVersion":"1.1.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;bl:1.1.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bl - 1.2.3,2.2.1,3.0.1,4.0.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-8244","vulnerabilityDetails":"A buffer over-read vulnerability exists in bl \u003c4.0.3, \u003c3.0.1, \u003c2.2.1, and \u003c1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.13.3;yarn - 1.21.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-16775","vulnerabilityDetails":"Versions of the npm CLI prior to 6.13.3 are vulnerable to an Arbitrary File Write. It is possible for packages to create symlinks to files outside of thenode_modules folder through the bin field upon installation. A properly constructed entry in the package.json bin field would allow a package publisher to create a symlink pointing to arbitrary files on a user\u0027s system when the package is installed. This behavior is still possible through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16775","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.13.4","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-16777","vulnerabilityDetails":"Versions of the npm CLI prior to 6.13.4 are vulnerable to an Arbitrary File Overwrite. It fails to prevent existing globally-installed binaries to be overwritten by other package installations. For example, if a package was installed globally and created a serve binary, any subsequent installs of packages that also create a serve binary would overwrite the previous serve binary. This behavior is still allowed in local installations and also through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16777","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"brace-expansion","packageVersion":"1.1.6","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;init-package-json:1.9.4;glob:6.0.4;minimatch:3.0.3;brace-expansion:1.1.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v1.1.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16032","vulnerabilityDetails":"brace-expansion before 1.1.7 are vulnerable to a regular expression denial of service.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16032","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Unchanged","C":"Low","UI":"Required","AV":"Local","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hosted-git-info","packageVersion":"2.1.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;hosted-git-info:2.1.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hosted-git-info - 2.8.9,3.0.8","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23362","vulnerabilityDetails":"The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"is-my-json-valid - 1.4.1, 2.17.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-1107","vulnerabilityDetails":"It was discovered that the is-my-json-valid JavaScript library used an inefficient regular expression to validate JSON fields defined to have email format. A specially crafted JSON file could cause it to consume an excessive amount of CPU time when validated.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1107","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"stringstream","packageVersion":"0.0.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;stringstream:0.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.0.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0103","vulnerabilityDetails":"All versions of stringstream are vulnerable to out-of-bounds read as it allocates uninitialized Buffers when number is passed in input stream on Node.js 4.x and below.","vulnerabilityUrl":"https://hackerone.com/reports/321670","cvss3Severity":"medium","cvss3Score":"4.8","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.14.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-15095","vulnerabilityDetails":"Versions of the npm CLI prior to 6.14.6 are vulnerable to an information exposure vulnerability through log files. The CLI supports URLs like \"\u003cprotocol\u003e://[\u003cuser\u003e[:\u003cpassword\u003e]@]\u003chostname\u003e[:\u003cport\u003e][:][/]\u003cpath\u003e\". The password value is not redacted and is printed to stdout and also to any generated log files.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15095","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"High","PR":"Low","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"chownr","packageVersion":"1.0.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;chownr:1.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.1.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-18869","vulnerabilityDetails":"A TOCTOU issue in the chownr package before 1.1.0 for Node.js 10.10 could allow a local attacker to trick it into descending into unintended directories via symlink attacks.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18869","cvss3Severity":"low","cvss3Score":"2.5","cvss3Metrics":{"A":"None","AC":"High","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"Low"},"extraData":{}}]</REMEDIATE> --> | True | grunt-npm-install-0.3.1.tgz: 28 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>grunt-npm-install-0.3.1.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-3918](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | json-schema-0.2.3.tgz | Transitive | N/A | ❌ |
| [CVE-2018-16492](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | extend-3.0.0.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23807](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | jsonpointer-4.0.0.tgz | Transitive | N/A | ❌ |
| [WS-2020-0344](https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [WS-2020-0345](https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.2 | jsonpointer-4.0.0.tgz | Transitive | N/A | ❌ |
| [CVE-2019-16776](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16776) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2021-32804](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | tar-2.2.1.tgz | Transitive | N/A | ❌ |
| [CVE-2018-20834](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20834) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | tar-2.2.1.tgz | Transitive | N/A | ❌ |
| [CVE-2017-15010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | tough-cookie-2.3.1.tgz | Transitive | N/A | ❌ |
| [WS-2020-0180](https://github.com/npm/npm-user-validate/commit/c8a87dac1a4cc6988b5418f30411a8669bef204e) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | npm-user-validate-0.1.5.tgz | Transitive | N/A | ❌ |
| [WS-2018-0069](https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [CVE-2017-1000048](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | qs-6.2.1.tgz | Transitive | N/A | ❌ |
| [CVE-2020-7754](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7754) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | npm-user-validate-0.1.5.tgz | Transitive | N/A | ❌ |
| [CVE-2018-3737](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3737) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | sshpk-1.10.1.tgz | Transitive | N/A | ❌ |
| [CVE-2017-18077](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18077) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | brace-expansion-1.1.6.tgz | Transitive | N/A | ❌ |
| [WS-2020-0342](https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [CVE-2019-13173](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-13173) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | fstream-1.0.10.tgz | Transitive | N/A | ❌ |
| [CVE-2020-7788](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.3 | ini-1.3.4.tgz | Transitive | N/A | ❌ |
| [CVE-2018-21270](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-21270) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | stringstream-0.0.5.tgz | Transitive | N/A | ❌ |
| [CVE-2020-8244](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | bl-1.1.2.tgz | Transitive | N/A | ❌ |
| [CVE-2019-16775](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16775) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2019-16777](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16777) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2017-16032](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16032) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | brace-expansion-1.1.6.tgz | Transitive | N/A | ❌ |
| [CVE-2021-23362](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | hosted-git-info-2.1.5.tgz | Transitive | N/A | ❌ |
| [CVE-2018-1107](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1107) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | is-my-json-valid-2.15.0.tgz | Transitive | N/A | ❌ |
| [WS-2018-0103](https://hackerone.com/reports/321670) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.8 | stringstream-0.0.5.tgz | Transitive | N/A | ❌ |
| [CVE-2020-15095](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15095) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | npm-3.10.10.tgz | Transitive | N/A | ❌ |
| [CVE-2017-18869](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18869) | <img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Low | 2.5 | chownr-1.0.1.tgz | Transitive | N/A | ❌ |
## Details
> Partial details (11 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-3918</summary>
### Vulnerable Library - <b>json-schema-0.2.3.tgz</b></p>
<p>JSON Schema validation and specifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz">https://registry.npmjs.org/json-schema/-/json-schema-0.2.3.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/http-signature/node_modules/jsprim/node_modules/json-schema/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- http-signature-1.1.1.tgz
- jsprim-1.3.1.tgz
- :x: **json-schema-0.2.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes ('Prototype Pollution')
<p>Publish Date: 2021-11-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918>CVE-2021-3918</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2021-3918">https://nvd.nist.gov/vuln/detail/CVE-2021-3918</a></p>
<p>Release Date: 2021-11-13</p>
<p>Fix Resolution: json-schema - 0.4.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-16492</summary>
### Vulnerable Library - <b>extend-3.0.0.tgz</b></p>
<p>Port of jQuery.extend for node.js and the browser</p>
<p>Library home page: <a href="https://registry.npmjs.org/extend/-/extend-3.0.0.tgz">https://registry.npmjs.org/extend/-/extend-3.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/extend/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- :x: **extend-3.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A prototype pollution vulnerability was found in module extend <2.0.2, ~<3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.
<p>Publish Date: 2019-02-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492>CVE-2018-16492</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://hackerone.com/reports/381185">https://hackerone.com/reports/381185</a></p>
<p>Release Date: 2019-02-01</p>
<p>Fix Resolution: extend - v3.0.2,v2.0.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-23807</summary>
### Vulnerable Library - <b>jsonpointer-4.0.0.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.15.0.tgz
- :x: **jsonpointer-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.
<p>Publish Date: 2021-11-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807>CVE-2021-23807</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-23807</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution: jsonpointer - 5.0.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0344</summary>
### Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.
<p>Publish Date: 2020-06-09
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d>WS-2020-0344</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb">https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb</a></p>
<p>Release Date: 2020-06-09</p>
<p>Fix Resolution: is-my-json-valid - 2.20.3</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0345</summary>
### Vulnerable Library - <b>jsonpointer-4.0.0.tgz</b></p>
<p>Simple JSON Addressing.</p>
<p>Library home page: <a href="https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz">https://registry.npmjs.org/jsonpointer/-/jsonpointer-4.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/node_modules/jsonpointer/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- is-my-json-valid-2.15.0.tgz
- :x: **jsonpointer-4.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.
<p>Publish Date: 2020-07-03
<p>URL: <a href=https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34>WS-2020-0345</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.2</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0">https://github.com/janl/node-jsonpointer/releases/tag/v4.1.0</a></p>
<p>Release Date: 2020-07-03</p>
<p>Fix Resolution: jsonpointer - 4.1.0</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2019-16776</summary>
### Vulnerable Library - <b>npm-3.10.10.tgz</b></p>
<p>a package manager for JavaScript</p>
<p>Library home page: <a href="https://registry.npmjs.org/npm/-/npm-3.10.10.tgz">https://registry.npmjs.org/npm/-/npm-3.10.10.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- :x: **npm-3.10.10.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Versions of the npm CLI prior to 6.13.3 are vulnerable to an Arbitrary File Write. It fails to prevent access to folders outside of the intended node_modules folder through the bin field. A properly constructed entry in the package.json bin field would allow a package publisher to modify and/or gain access to arbitrary files on a user's system when the package is installed. This behavior is still possible through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.
<p>Publish Date: 2019-12-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16776>CVE-2019-16776</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.npmjs.org/post/189618601100/binary-planting-with-the-npm-cli">https://blog.npmjs.org/post/189618601100/binary-planting-with-the-npm-cli</a></p>
<p>Release Date: 2020-10-07</p>
<p>Fix Resolution: npm - 6.13.3;yarn - 1.21.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-32804</summary>
### Vulnerable Library - <b>tar-2.2.1.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The npm package "tar" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.
<p>Publish Date: 2021-08-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804>CVE-2021-32804</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9">https://github.com/npm/node-tar/security/advisories/GHSA-3jfq-g458-7qm9</a></p>
<p>Release Date: 2021-08-03</p>
<p>Fix Resolution: tar - 3.2.2, 4.4.14, 5.0.6, 6.1.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2018-20834</summary>
### Vulnerable Library - <b>tar-2.2.1.tgz</b></p>
<p>tar for node</p>
<p>Library home page: <a href="https://registry.npmjs.org/tar/-/tar-2.2.1.tgz">https://registry.npmjs.org/tar/-/tar-2.2.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/tar/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- :x: **tar-2.2.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A vulnerability was found in node-tar before version 4.4.2 (excluding version 2.2.2). An Arbitrary File Overwrite issue exists when extracting a tarball containing a hardlink to a file that already exists on the system, in conjunction with a later plain file with the same name as the hardlink. This plain file content replaces the existing file content. A patch has been applied to node-tar v2.2.2).
<p>Publish Date: 2019-04-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20834>CVE-2018-20834</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-16082</a></p>
<p>Release Date: 2019-04-30</p>
<p>Fix Resolution: 2.2.2,4.4.2</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2017-15010</summary>
### Vulnerable Library - <b>tough-cookie-2.3.1.tgz</b></p>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.3.1.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.3.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- :x: **tough-cookie-2.3.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.
<p>Publish Date: 2017-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010>CVE-2017-15010</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-15010">https://nvd.nist.gov/vuln/detail/CVE-2017-15010</a></p>
<p>Release Date: 2017-10-04</p>
<p>Fix Resolution: 2.3.3</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2020-0180</summary>
### Vulnerable Library - <b>npm-user-validate-0.1.5.tgz</b></p>
<p>User validations for npm</p>
<p>Library home page: <a href="https://registry.npmjs.org/npm-user-validate/-/npm-user-validate-0.1.5.tgz">https://registry.npmjs.org/npm-user-validate/-/npm-user-validate-0.1.5.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/npm-user-validate/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- :x: **npm-user-validate-0.1.5.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The package npm-user-validate prior to version 1.0.1 is vulnerable to REDoS. The regex that validates a user's email took exponentially longer to process input strings that begin with the '@' character.
<p>Publish Date: 2020-10-16
<p>URL: <a href=https://github.com/npm/npm-user-validate/commit/c8a87dac1a4cc6988b5418f30411a8669bef204e>WS-2020-0180</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-xgh6-85xh-479p">https://github.com/advisories/GHSA-xgh6-85xh-479p</a></p>
<p>Release Date: 2020-10-16</p>
<p>Fix Resolution: 1.0.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> WS-2018-0069</summary>
### Vulnerable Library - <b>is-my-json-valid-2.15.0.tgz</b></p>
<p>A JSONSchema validator that uses code generation to be extremely fast</p>
<p>Library home page: <a href="https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz">https://registry.npmjs.org/is-my-json-valid/-/is-my-json-valid-2.15.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/npm/node_modules/request/node_modules/har-validator/node_modules/is-my-json-valid/package.json</p>
<p>
Dependency Hierarchy:
- grunt-npm-install-0.3.1.tgz (Root Library)
- npm-3.10.10.tgz
- request-2.75.0.tgz
- har-validator-2.0.6.tgz
- :x: **is-my-json-valid-2.15.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/dwanprac/django.nv/commit/b5ec9bd74b4b27b2af49cf824e527f391e9437b0">b5ec9bd74b4b27b2af49cf824e527f391e9437b0</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Version of is-my-json-valid before 1.4.1 or 2.17.2 are vulnerable to regular expression denial of service (ReDoS) via the email validation function.
<p>Publish Date: 2018-02-14
<p>URL: <a href=https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976>WS-2018-0069</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/572">https://nodesecurity.io/advisories/572</a></p>
<p>Release Date: 2018-02-14</p>
<p>Fix Resolution: 1.4.1</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"json-schema","packageVersion":"0.2.3","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;http-signature:1.1.1;jsprim:1.3.1;json-schema:0.2.3","isMinimumFixVersionAvailable":true,"minimumFixVersion":"json-schema - 0.4.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-3918","vulnerabilityDetails":"json-schema is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (\u0027Prototype Pollution\u0027)","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3918","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"extend","packageVersion":"3.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;extend:3.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"extend - v3.0.2,v2.0.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-16492","vulnerabilityDetails":"A prototype pollution vulnerability was found in module extend \u003c2.0.2, ~\u003c3.0.2 that allows an attacker to inject arbitrary properties onto Object.prototype.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-16492","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"jsonpointer","packageVersion":"4.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0;jsonpointer:4.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jsonpointer - 5.0.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23807","vulnerabilityDetails":"This affects the package jsonpointer before 5.0.0. A type confusion vulnerability can lead to a bypass of a previous Prototype Pollution fix when the pointer components are arrays.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23807","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"is-my-json-valid - 2.20.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0344","vulnerabilityDetails":"Arbitrary Code Execution vulnerability was found in is-my-json-valid before 2.20.3 via the fromatName function.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/3419563687df463b4ca709a2b46be8e15d6a2b3d","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"jsonpointer","packageVersion":"4.0.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0;jsonpointer:4.0.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jsonpointer - 4.1.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0345","vulnerabilityDetails":"Prototype Pollution vulnerability was found in jsonpointer before 4.1.0 via the set function.","vulnerabilityUrl":"https://github.com/janl/node-jsonpointer/commit/234e3437019c6c07537ed2ad1e03b3e132b85e34","cvss3Severity":"high","cvss3Score":"8.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.13.3;yarn - 1.21.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-16776","vulnerabilityDetails":"Versions of the npm CLI prior to 6.13.3 are vulnerable to an Arbitrary File Write. It fails to prevent access to folders outside of the intended node_modules folder through the bin field. A properly constructed entry in the package.json bin field would allow a package publisher to modify and/or gain access to arbitrary files on a user\u0027s system when the package is installed. This behavior is still possible through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16776","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tar","packageVersion":"2.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;tar:2.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"tar - 3.2.2, 4.4.14, 5.0.6, 6.1.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-32804","vulnerabilityDetails":"The npm package \"tar\" (aka node-tar) before versions 6.1.1, 5.0.6, 4.4.14, and 3.3.2 has a arbitrary File Creation/Overwrite vulnerability due to insufficient absolute path sanitization. node-tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the `preservePaths` flag is not set to `true`. This is achieved by stripping the absolute path root from any absolute file paths contained in a tar file. For example `/home/user/.bashrc` would turn into `home/user/.bashrc`. This logic was insufficient when file paths contained repeated path roots such as `////home/user/.bashrc`. `node-tar` would only strip a single path root from such paths. When given an absolute file path with repeating path roots, the resulting path (e.g. `///home/user/.bashrc`) would still resolve to an absolute path, thus allowing arbitrary file creation and overwrite. This issue was addressed in releases 3.2.2, 4.4.14, 5.0.6 and 6.1.1. Users may work around this vulnerability without upgrading by creating a custom `onentry` method which sanitizes the `entry.path` or a `filter` method which removes entries with absolute paths. See referenced GitHub Advisory for details. Be aware of CVE-2021-32803 which fixes a similar bug in later versions of tar.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-32804","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tar","packageVersion":"2.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;tar:2.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.2.2,4.4.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-20834","vulnerabilityDetails":"A vulnerability was found in node-tar before version 4.4.2 (excluding version 2.2.2). An Arbitrary File Overwrite issue exists when extracting a tarball containing a hardlink to a file that already exists on the system, in conjunction with a later plain file with the same name as the hardlink. This plain file content replaces the existing file content. A patch has been applied to node-tar v2.2.2).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-20834","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tough-cookie","packageVersion":"2.3.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;tough-cookie:2.3.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.3.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-15010","vulnerabilityDetails":"A ReDoS (regular expression denial of service) flaw was found in the tough-cookie module before 2.3.3 for Node.js. An attacker that is able to make an HTTP request using a specially crafted cookie may cause the application to consume an excessive amount of CPU.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-15010","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm-user-validate","packageVersion":"0.1.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;npm-user-validate:0.1.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0180","vulnerabilityDetails":"The package npm-user-validate prior to version 1.0.1 is vulnerable to REDoS. The regex that validates a user\u0027s email took exponentially longer to process input strings that begin with the \u0027@\u0027 character.","vulnerabilityUrl":"https://github.com/npm/npm-user-validate/commit/c8a87dac1a4cc6988b5418f30411a8669bef204e","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.4.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0069","vulnerabilityDetails":"Version of is-my-json-valid before 1.4.1 or 2.17.2 are vulnerable to regular expression denial of service (ReDoS) via the email validation function.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/b3051b277f7caa08cd2edc6f74f50aeda65d2976","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"qs","packageVersion":"6.2.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;qs:6.2.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"qs - 6.0.4,6.1.2,6.2.3,6.3.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-1000048","vulnerabilityDetails":"the web framework using ljharb\u0027s qs module older than v6.3.2, v6.2.3, v6.1.2, and v6.0.4 is vulnerable to a DoS. A malicious user can send a evil request to cause the web framework crash.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-1000048","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm-user-validate","packageVersion":"0.1.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;npm-user-validate:0.1.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7754","vulnerabilityDetails":"This affects the package npm-user-validate before 1.0.1. The regex that validates user emails took exponentially longer to process long input strings beginning with @ characters.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7754","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"sshpk","packageVersion":"1.10.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;http-signature:1.1.1;sshpk:1.10.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.13.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-3737","vulnerabilityDetails":"sshpk is vulnerable to ReDoS when parsing crafted invalid public keys.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-3737","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"brace-expansion","packageVersion":"1.1.6","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;init-package-json:1.9.4;glob:6.0.4;minimatch:3.0.3;brace-expansion:1.1.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.1.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-18077","vulnerabilityDetails":"index.js in brace-expansion before 1.1.7 is vulnerable to Regular Expression Denial of Service (ReDoS) attacks, as demonstrated by an expand argument containing many comma characters.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18077","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"is-my-json-valid - 2.20.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2020-0342","vulnerabilityDetails":"Regular Expression Denial of Service (ReDoS) vulnerability was found in is-my-json-valid before 2.20.2 via the style format.","vulnerabilityUrl":"https://github.com/mafintosh/is-my-json-valid/commit/c3fc04fc455d40e9b29537f8e2c73a28ce106edb","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"fstream","packageVersion":"1.0.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;fstream:1.0.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.0.12","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-13173","vulnerabilityDetails":"fstream before 1.0.12 is vulnerable to Arbitrary File Overwrite. Extracting tarballs containing a hardlink to a file that already exists in the system, and a file that matches the hardlink, will overwrite the system\u0027s file with the contents of the extracted file. The fstream.DirWriter() function is vulnerable.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-13173","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"ini","packageVersion":"1.3.4","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;ini:1.3.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v1.3.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-7788","vulnerabilityDetails":"This affects the package ini before 1.3.6. If an attacker submits a malicious INI file to an application that parses it with ini.parse, they will pollute the prototype on the application. This can be exploited further depending on the context.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7788","cvss3Severity":"high","cvss3Score":"7.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"stringstream","packageVersion":"0.0.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;stringstream:0.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.0.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-21270","vulnerabilityDetails":"Versions less than 0.0.6 of the Node.js stringstream module are vulnerable to an out-of-bounds read because of allocation of uninitialized buffers when a number is passed in the input stream (when using Node.js 4.x).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-21270","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"bl","packageVersion":"1.1.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;bl:1.1.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"bl - 1.2.3,2.2.1,3.0.1,4.0.3","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-8244","vulnerabilityDetails":"A buffer over-read vulnerability exists in bl \u003c4.0.3, \u003c3.0.1, \u003c2.2.1, and \u003c1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.13.3;yarn - 1.21.1","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-16775","vulnerabilityDetails":"Versions of the npm CLI prior to 6.13.3 are vulnerable to an Arbitrary File Write. It is possible for packages to create symlinks to files outside of thenode_modules folder through the bin field upon installation. A properly constructed entry in the package.json bin field would allow a package publisher to create a symlink pointing to arbitrary files on a user\u0027s system when the package is installed. This behavior is still possible through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16775","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.13.4","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-16777","vulnerabilityDetails":"Versions of the npm CLI prior to 6.13.4 are vulnerable to an Arbitrary File Overwrite. It fails to prevent existing globally-installed binaries to be overwritten by other package installations. For example, if a package was installed globally and created a serve binary, any subsequent installs of packages that also create a serve binary would overwrite the previous serve binary. This behavior is still allowed in local installations and also through install scripts. This vulnerability bypasses a user using the --ignore-scripts install option.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16777","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"brace-expansion","packageVersion":"1.1.6","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;init-package-json:1.9.4;glob:6.0.4;minimatch:3.0.3;brace-expansion:1.1.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"v1.1.7","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-16032","vulnerabilityDetails":"brace-expansion before 1.1.7 are vulnerable to a regular expression denial of service.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16032","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"High","PR":"Low","S":"Unchanged","C":"Low","UI":"Required","AV":"Local","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"hosted-git-info","packageVersion":"2.1.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;hosted-git-info:2.1.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"hosted-git-info - 2.8.9,3.0.8","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-23362","vulnerabilityDetails":"The package hosted-git-info before 3.0.8 are vulnerable to Regular Expression Denial of Service (ReDoS) via regular expression shortcutMatch in the fromUrl function in index.js. The affected regular expression exhibits polynomial worst-case time complexity.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23362","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"is-my-json-valid","packageVersion":"2.15.0","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;har-validator:2.0.6;is-my-json-valid:2.15.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"is-my-json-valid - 1.4.1, 2.17.2","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-1107","vulnerabilityDetails":"It was discovered that the is-my-json-valid JavaScript library used an inefficient regular expression to validate JSON fields defined to have email format. A specially crafted JSON file could cause it to consume an excessive amount of CPU time when validated.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1107","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"stringstream","packageVersion":"0.0.5","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;request:2.75.0;stringstream:0.0.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"0.0.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"WS-2018-0103","vulnerabilityDetails":"All versions of stringstream are vulnerable to out-of-bounds read as it allocates uninitialized Buffers when number is passed in input stream on Node.js 4.x and below.","vulnerabilityUrl":"https://hackerone.com/reports/321670","cvss3Severity":"medium","cvss3Score":"4.8","cvss3Metrics":{"A":"Low","AC":"High","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"npm","packageVersion":"3.10.10","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"npm - 6.14.6","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2020-15095","vulnerabilityDetails":"Versions of the npm CLI prior to 6.14.6 are vulnerable to an information exposure vulnerability through log files. The CLI supports URLs like \"\u003cprotocol\u003e://[\u003cuser\u003e[:\u003cpassword\u003e]@]\u003chostname\u003e[:\u003cport\u003e][:][/]\u003cpath\u003e\". The password value is not redacted and is printed to stdout and also to any generated log files.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-15095","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"High","PR":"Low","S":"Unchanged","C":"High","UI":"Required","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"chownr","packageVersion":"1.0.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-npm-install:0.3.1;npm:3.10.10;chownr:1.0.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.1.0","isBinary":false}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2017-18869","vulnerabilityDetails":"A TOCTOU issue in the chownr package before 1.1.0 for Node.js 10.10 could allow a local attacker to trick it into descending into unintended directories via symlink attacks.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-18869","cvss3Severity":"low","cvss3Score":"2.5","cvss3Metrics":{"A":"None","AC":"High","PR":"Low","S":"Unchanged","C":"None","UI":"None","AV":"Local","I":"Low"},"extraData":{}}]</REMEDIATE> --> | non_test | grunt npm install tgz vulnerabilities highest severity is vulnerable library grunt npm install tgz path to dependency file package json path to vulnerable library node modules npm node modules request node modules har validator node modules is my json valid package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high json schema tgz transitive n a ❌ high extend tgz transitive n a ❌ high jsonpointer tgz transitive n a ❌ high is my json valid tgz transitive n a ❌ high jsonpointer tgz transitive n a ❌ high npm tgz transitive n a ❌ high tar tgz transitive n a ❌ high tar tgz transitive n a ❌ high tough cookie tgz transitive n a ❌ high npm user validate tgz transitive n a ❌ high is my json valid tgz transitive n a ❌ high qs tgz transitive n a ❌ high npm user validate tgz transitive n a ❌ high sshpk tgz transitive n a ❌ high brace expansion tgz transitive n a ❌ high is my json valid tgz transitive n a ❌ high fstream tgz transitive n a ❌ high ini tgz transitive n a ❌ medium stringstream tgz transitive n a ❌ medium bl tgz transitive n a ❌ medium npm tgz transitive n a ❌ medium npm tgz transitive n a ❌ medium brace expansion tgz transitive n a ❌ medium hosted git info tgz transitive n a ❌ medium is my json valid tgz transitive n a ❌ medium stringstream tgz transitive n a ❌ medium npm tgz transitive n a ❌ low chownr tgz transitive n a ❌ details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library json schema tgz json schema validation and specifications library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules http signature node modules jsprim node modules json schema package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz http signature tgz jsprim tgz x json schema tgz vulnerable library found in head commit a href found in base branch main vulnerability details json schema is vulnerable to improperly controlled modification of object prototype attributes prototype pollution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution json schema step up your open source security game with whitesource cve vulnerable library extend tgz port of jquery extend for node js and the browser library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules extend package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz x extend tgz vulnerable library found in head commit a href found in base branch main vulnerability details a prototype pollution vulnerability was found in module extend that allows an attacker to inject arbitrary properties onto object prototype publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution extend step up your open source security game with whitesource cve vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules har validator node modules is my json valid node modules jsonpointer package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz har validator tgz is my json valid tgz x jsonpointer tgz vulnerable library found in head commit a href found in base branch main vulnerability details this affects the package jsonpointer before a type confusion vulnerability can lead to a bypass of a previous prototype pollution fix when the pointer components are arrays publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jsonpointer step up your open source security game with whitesource ws vulnerable library is my json valid tgz a jsonschema validator that uses code generation to be extremely fast library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules har validator node modules is my json valid package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz har validator tgz x is my json valid tgz vulnerable library found in head commit a href found in base branch main vulnerability details arbitrary code execution vulnerability was found in is my json valid before via the fromatname function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution is my json valid step up your open source security game with whitesource ws vulnerable library jsonpointer tgz simple json addressing library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules har validator node modules is my json valid node modules jsonpointer package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz har validator tgz is my json valid tgz x jsonpointer tgz vulnerable library found in head commit a href found in base branch main vulnerability details prototype pollution vulnerability was found in jsonpointer before via the set function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jsonpointer step up your open source security game with whitesource cve vulnerable library npm tgz a package manager for javascript library home page a href path to dependency file package json path to vulnerable library node modules npm package json dependency hierarchy grunt npm install tgz root library x npm tgz vulnerable library found in head commit a href found in base branch main vulnerability details versions of the npm cli prior to are vulnerable to an arbitrary file write it fails to prevent access to folders outside of the intended node modules folder through the bin field a properly constructed entry in the package json bin field would allow a package publisher to modify and or gain access to arbitrary files on a user s system when the package is installed this behavior is still possible through install scripts this vulnerability bypasses a user using the ignore scripts install option publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution npm yarn step up your open source security game with whitesource cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules npm node modules tar package json dependency hierarchy grunt npm install tgz root library npm tgz x tar tgz vulnerable library found in head commit a href found in base branch main vulnerability details the npm package tar aka node tar before versions and has a arbitrary file creation overwrite vulnerability due to insufficient absolute path sanitization node tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the preservepaths flag is not set to true this is achieved by stripping the absolute path root from any absolute file paths contained in a tar file for example home user bashrc would turn into home user bashrc this logic was insufficient when file paths contained repeated path roots such as home user bashrc node tar would only strip a single path root from such paths when given an absolute file path with repeating path roots the resulting path e g home user bashrc would still resolve to an absolute path thus allowing arbitrary file creation and overwrite this issue was addressed in releases and users may work around this vulnerability without upgrading by creating a custom onentry method which sanitizes the entry path or a filter method which removes entries with absolute paths see referenced github advisory for details be aware of cve which fixes a similar bug in later versions of tar publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tar step up your open source security game with whitesource cve vulnerable library tar tgz tar for node library home page a href path to dependency file package json path to vulnerable library node modules npm node modules tar package json dependency hierarchy grunt npm install tgz root library npm tgz x tar tgz vulnerable library found in head commit a href found in base branch main vulnerability details a vulnerability was found in node tar before version excluding version an arbitrary file overwrite issue exists when extracting a tarball containing a hardlink to a file that already exists on the system in conjunction with a later plain file with the same name as the hardlink this plain file content replaces the existing file content a patch has been applied to node tar publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource cve vulnerable library tough cookie tgz cookies and cookie jar for node js library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules tough cookie package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz x tough cookie tgz vulnerable library found in head commit a href found in base branch main vulnerability details a redos regular expression denial of service flaw was found in the tough cookie module before for node js an attacker that is able to make an http request using a specially crafted cookie may cause the application to consume an excessive amount of cpu publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource ws vulnerable library npm user validate tgz user validations for npm library home page a href path to dependency file package json path to vulnerable library node modules npm node modules npm user validate package json dependency hierarchy grunt npm install tgz root library npm tgz x npm user validate tgz vulnerable library found in head commit a href found in base branch main vulnerability details the package npm user validate prior to version is vulnerable to redos the regex that validates a user s email took exponentially longer to process input strings that begin with the character publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource ws vulnerable library is my json valid tgz a jsonschema validator that uses code generation to be extremely fast library home page a href path to dependency file package json path to vulnerable library node modules npm node modules request node modules har validator node modules is my json valid package json dependency hierarchy grunt npm install tgz root library npm tgz request tgz har validator tgz x is my json valid tgz vulnerable library found in head commit a href found in base branch main vulnerability details version of is my json valid before or are vulnerable to regular expression denial of service redos via the email validation function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource istransitivedependency true dependencytree grunt npm install npm request http signature jsprim json schema isminimumfixversionavailable true minimumfixversion json schema isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails json schema is vulnerable to improperly controlled modification of object prototype attributes pollution vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request extend isminimumfixversionavailable true minimumfixversion extend isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a prototype pollution vulnerability was found in module extend that allows an attacker to inject arbitrary properties onto object prototype vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request har validator is my json valid jsonpointer isminimumfixversionavailable true minimumfixversion jsonpointer isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package jsonpointer before a type confusion vulnerability can lead to a bypass of a previous prototype pollution fix when the pointer components are arrays vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request har validator is my json valid isminimumfixversionavailable true minimumfixversion is my json valid isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails arbitrary code execution vulnerability was found in is my json valid before via the fromatname function vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request har validator is my json valid jsonpointer isminimumfixversionavailable true minimumfixversion jsonpointer isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails prototype pollution vulnerability was found in jsonpointer before via the set function vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm isminimumfixversionavailable true minimumfixversion npm yarn isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of the npm cli prior to are vulnerable to an arbitrary file write it fails to prevent access to folders outside of the intended node modules folder through the bin field a properly constructed entry in the package json bin field would allow a package publisher to modify and or gain access to arbitrary files on a user system when the package is installed this behavior is still possible through install scripts this vulnerability bypasses a user using the ignore scripts install option vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm tar isminimumfixversionavailable true minimumfixversion tar isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the npm package tar aka node tar before versions and has a arbitrary file creation overwrite vulnerability due to insufficient absolute path sanitization node tar aims to prevent extraction of absolute file paths by turning absolute paths into relative paths when the preservepaths flag is not set to true this is achieved by stripping the absolute path root from any absolute file paths contained in a tar file for example home user bashrc would turn into home user bashrc this logic was insufficient when file paths contained repeated path roots such as home user bashrc node tar would only strip a single path root from such paths when given an absolute file path with repeating path roots the resulting path e g home user bashrc would still resolve to an absolute path thus allowing arbitrary file creation and overwrite this issue was addressed in releases and users may work around this vulnerability without upgrading by creating a custom onentry method which sanitizes the entry path or a filter method which removes entries with absolute paths see referenced github advisory for details be aware of cve which fixes a similar bug in later versions of tar vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm tar isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a vulnerability was found in node tar before version excluding version an arbitrary file overwrite issue exists when extracting a tarball containing a hardlink to a file that already exists on the system in conjunction with a later plain file with the same name as the hardlink this plain file content replaces the existing file content a patch has been applied to node tar vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request tough cookie isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a redos regular expression denial of service flaw was found in the tough cookie module before for node js an attacker that is able to make an http request using a specially crafted cookie may cause the application to consume an excessive amount of cpu vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm npm user validate isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails the package npm user validate prior to version is vulnerable to redos the regex that validates a user email took exponentially longer to process input strings that begin with the character vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request har validator is my json valid isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails version of is my json valid before or are vulnerable to regular expression denial of service redos via the email validation function vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request qs isminimumfixversionavailable true minimumfixversion qs isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the web framework using ljharb qs module older than and is vulnerable to a dos a malicious user can send a evil request to cause the web framework crash vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm npm user validate isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package npm user validate before the regex that validates user emails took exponentially longer to process long input strings beginning with characters vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request http signature sshpk isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails sshpk is vulnerable to redos when parsing crafted invalid public keys vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm init package json glob minimatch brace expansion isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails index js in brace expansion before is vulnerable to regular expression denial of service redos attacks as demonstrated by an expand argument containing many comma characters vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request har validator is my json valid isminimumfixversionavailable true minimumfixversion is my json valid isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails regular expression denial of service redos vulnerability was found in is my json valid before via the style format vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm fstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails fstream before is vulnerable to arbitrary file overwrite extracting tarballs containing a hardlink to a file that already exists in the system and a file that matches the hardlink will overwrite the system file with the contents of the extracted file the fstream dirwriter function is vulnerable vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm ini isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails this affects the package ini before if an attacker submits a malicious ini file to an application that parses it with ini parse they will pollute the prototype on the application this can be exploited further depending on the context vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request stringstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions less than of the node js stringstream module are vulnerable to an out of bounds read because of allocation of uninitialized buffers when a number is passed in the input stream when using node js x vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request bl isminimumfixversionavailable true minimumfixversion bl isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a buffer over read vulnerability exists in bl and which could allow an attacker to supply user input even typed that if it ends up in consume argument and can become negative the bufferlist state can be corrupted tricking it into exposing uninitialized memory via regular slice calls vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm isminimumfixversionavailable true minimumfixversion npm yarn isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of the npm cli prior to are vulnerable to an arbitrary file write it is possible for packages to create symlinks to files outside of thenode modules folder through the bin field upon installation a properly constructed entry in the package json bin field would allow a package publisher to create a symlink pointing to arbitrary files on a user system when the package is installed this behavior is still possible through install scripts this vulnerability bypasses a user using the ignore scripts install option vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm isminimumfixversionavailable true minimumfixversion npm isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of the npm cli prior to are vulnerable to an arbitrary file overwrite it fails to prevent existing globally installed binaries to be overwritten by other package installations for example if a package was installed globally and created a serve binary any subsequent installs of packages that also create a serve binary would overwrite the previous serve binary this behavior is still allowed in local installations and also through install scripts this vulnerability bypasses a user using the ignore scripts install option vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm init package json glob minimatch brace expansion isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails brace expansion before are vulnerable to a regular expression denial of service vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm hosted git info isminimumfixversionavailable true minimumfixversion hosted git info isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails the package hosted git info before are vulnerable to regular expression denial of service redos via regular expression shortcutmatch in the fromurl function in index js the affected regular expression exhibits polynomial worst case time complexity vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request har validator is my json valid isminimumfixversionavailable true minimumfixversion is my json valid isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails it was discovered that the is my json valid javascript library used an inefficient regular expression to validate json fields defined to have email format a specially crafted json file could cause it to consume an excessive amount of cpu time when validated vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm request stringstream isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier ws vulnerabilitydetails all versions of stringstream are vulnerable to out of bounds read as it allocates uninitialized buffers when number is passed in input stream on node js x and below vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm isminimumfixversionavailable true minimumfixversion npm isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of the npm cli prior to are vulnerable to an information exposure vulnerability through log files the cli supports urls like the password value is not redacted and is printed to stdout and also to any generated log files vulnerabilityurl istransitivedependency true dependencytree grunt npm install npm chownr isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails a toctou issue in the chownr package before for node js could allow a local attacker to trick it into descending into unintended directories via symlink attacks vulnerabilityurl | 0 |
202,185 | 15,265,649,195 | IssuesEvent | 2021-02-22 07:40:24 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | kv/kvserver: TestStrictGCEnforcement failed | C-test-failure O-robot branch-master | [(kv/kvserver).TestStrictGCEnforcement failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2697767&tab=buildLog) on [master@8b6f3c84cc256debeeb4d4055c5f0d5c9a481213](https://github.com/cockroachdb/cockroach/commits/8b6f3c84cc256debeeb4d4055c5f0d5c9a481213):
```
=== RUN TestStrictGCEnforcement
test_log_scope.go:73: test logs captured to: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStrictGCEnforcement865385043
test_log_scope.go:74: use -show-logs to present logs inline
=== CONT TestStrictGCEnforcement
client_replica_test.go:3277: -- test log scope end --
test logs left over in: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStrictGCEnforcement865385043
--- FAIL: TestStrictGCEnforcement (0.58s)
=== RUN TestStrictGCEnforcement/protected_timestamps_are_respected
client_replica_test.go:3275:
Error Trace: client_replica_test.go:3148
client_replica_test.go:3275
Error: Received unexpected error:
batch timestamp 1613803810.475835111,0 must be after replica GC threshold 1613803819.542992787,0
Test: TestStrictGCEnforcement/protected_timestamps_are_respected
E210220 06:50:20.549634 490766 kv/kvclient/kvcoord/txn_interceptor_committer.go:449 [-] 1 making txn commit explicit failed for "sql txn" meta={id=e4613806 pri=0.00440269 epo=0 ts=1613803820.543560449,0 min=1613803820.543560449,0 seq=6} lock=true stat=STAGING rts=1613803820.543560449,0 wto=false gul=1613803821.043560449,0 ifw=5: result is ambiguous (server shutdown)
--- FAIL: TestStrictGCEnforcement/protected_timestamps_are_respected (0.02s)
```
<details><summary>More</summary><p>
Parameters:
- TAGS=
- GOFLAGS=-parallel=4
```
make stressrace TESTS=TestStrictGCEnforcement PKG=./pkg/kv/kvserver TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestStrictGCEnforcement.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 1.0 | kv/kvserver: TestStrictGCEnforcement failed - [(kv/kvserver).TestStrictGCEnforcement failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=2697767&tab=buildLog) on [master@8b6f3c84cc256debeeb4d4055c5f0d5c9a481213](https://github.com/cockroachdb/cockroach/commits/8b6f3c84cc256debeeb4d4055c5f0d5c9a481213):
```
=== RUN TestStrictGCEnforcement
test_log_scope.go:73: test logs captured to: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStrictGCEnforcement865385043
test_log_scope.go:74: use -show-logs to present logs inline
=== CONT TestStrictGCEnforcement
client_replica_test.go:3277: -- test log scope end --
test logs left over in: /go/src/github.com/cockroachdb/cockroach/artifacts/logTestStrictGCEnforcement865385043
--- FAIL: TestStrictGCEnforcement (0.58s)
=== RUN TestStrictGCEnforcement/protected_timestamps_are_respected
client_replica_test.go:3275:
Error Trace: client_replica_test.go:3148
client_replica_test.go:3275
Error: Received unexpected error:
batch timestamp 1613803810.475835111,0 must be after replica GC threshold 1613803819.542992787,0
Test: TestStrictGCEnforcement/protected_timestamps_are_respected
E210220 06:50:20.549634 490766 kv/kvclient/kvcoord/txn_interceptor_committer.go:449 [-] 1 making txn commit explicit failed for "sql txn" meta={id=e4613806 pri=0.00440269 epo=0 ts=1613803820.543560449,0 min=1613803820.543560449,0 seq=6} lock=true stat=STAGING rts=1613803820.543560449,0 wto=false gul=1613803821.043560449,0 ifw=5: result is ambiguous (server shutdown)
--- FAIL: TestStrictGCEnforcement/protected_timestamps_are_respected (0.02s)
```
<details><summary>More</summary><p>
Parameters:
- TAGS=
- GOFLAGS=-parallel=4
```
make stressrace TESTS=TestStrictGCEnforcement PKG=./pkg/kv/kvserver TESTTIMEOUT=5m STRESSFLAGS='-timeout 5m' 2>&1
```
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2ATestStrictGCEnforcement.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| test | kv kvserver teststrictgcenforcement failed on run teststrictgcenforcement test log scope go test logs captured to go src github com cockroachdb cockroach artifacts test log scope go use show logs to present logs inline cont teststrictgcenforcement client replica test go test log scope end test logs left over in go src github com cockroachdb cockroach artifacts fail teststrictgcenforcement run teststrictgcenforcement protected timestamps are respected client replica test go error trace client replica test go client replica test go error received unexpected error batch timestamp must be after replica gc threshold test teststrictgcenforcement protected timestamps are respected kv kvclient kvcoord txn interceptor committer go making txn commit explicit failed for sql txn meta id pri epo ts min seq lock true stat staging rts wto false gul ifw result is ambiguous server shutdown fail teststrictgcenforcement protected timestamps are respected more parameters tags goflags parallel make stressrace tests teststrictgcenforcement pkg pkg kv kvserver testtimeout stressflags timeout powered by | 1 |
769,091 | 26,993,203,731 | IssuesEvent | 2023-02-09 21:48:38 | jbx-protocol/juice-interface | https://api.github.com/repos/jbx-protocol/juice-interface | closed | Downloading payments CSV sometimes fails | type:bug priority:2 | ## Summary
Getting this error intermittently:
https://user-images.githubusercontent.com/96150256/186579263-e7e045ae-bd65-4c97-9111-348b7e642940.mp4
<img width="1137" alt="Screen Shot 2022-08-25 at 3 02 35 pm" src="https://user-images.githubusercontent.com/96150256/186579240-f095be5b-1162-4e03-bdd9-7671f8f9f468.png">
(I see subgraph I click @peripheralist 😅)
## Steps to reproduce
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
## What is the _current_ bug behavior?
## What is the expected _correct_ behavior?
## Relevant logs and/or screenshots
## Environment
- **Device/OS**: [e.g. iOS]
- **Browser:** [e.g. chrome, safari]
- **Hardware wallet**: [e.g. Ledger w/ Metamask]
| 1.0 | Downloading payments CSV sometimes fails - ## Summary
Getting this error intermittently:
https://user-images.githubusercontent.com/96150256/186579263-e7e045ae-bd65-4c97-9111-348b7e642940.mp4
<img width="1137" alt="Screen Shot 2022-08-25 at 3 02 35 pm" src="https://user-images.githubusercontent.com/96150256/186579240-f095be5b-1162-4e03-bdd9-7671f8f9f468.png">
(I see subgraph I click @peripheralist 😅)
## Steps to reproduce
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
## What is the _current_ bug behavior?
## What is the expected _correct_ behavior?
## Relevant logs and/or screenshots
## Environment
- **Device/OS**: [e.g. iOS]
- **Browser:** [e.g. chrome, safari]
- **Hardware wallet**: [e.g. Ledger w/ Metamask]
| non_test | downloading payments csv sometimes fails summary getting this error intermittently img width alt screen shot at pm src i see subgraph i click peripheralist 😅 steps to reproduce go to click on scroll down to see error what is the current bug behavior what is the expected correct behavior relevant logs and or screenshots environment device os browser hardware wallet | 0 |
102,989 | 12,836,146,044 | IssuesEvent | 2020-07-07 13:57:06 | trezor/trezor-suite | https://api.github.com/repos/trezor/trezor-suite | closed | Accounts: Jumpy content | Design | It's a nitpick and I kind of understand why it's happening (rollup disappears when selecting Segwit account because we don't allow "non-selected" account). Let's discuss options if there is no obvious solution. (E.g. disable the rollup instead of removing it?)
| 1.0 | Accounts: Jumpy content - It's a nitpick and I kind of understand why it's happening (rollup disappears when selecting Segwit account because we don't allow "non-selected" account). Let's discuss options if there is no obvious solution. (E.g. disable the rollup instead of removing it?)
| non_test | accounts jumpy content it s a nitpick and i kind of understand why it s happening rollup disappears when selecting segwit account because we don t allow non selected account let s discuss options if there is no obvious solution e g disable the rollup instead of removing it | 0 |
416,776 | 12,151,541,998 | IssuesEvent | 2020-04-24 20:10:45 | jetstack/cert-manager | https://api.github.com/repos/jetstack/cert-manager | closed | Ingress-shim fails to use class of Ingress when creating http01 solver | area/acme/http01 area/ingress-shim kind/bug priority/backlog | **Describe the bug**:
Using `cert-manager` v0.11.0.
Certificates created by the `ingressShim` in response to the `kubernetes.io/tls-acme: "true"` annotation on an Ingress fail to be issued when the default solver is `http01` and the Ingress has a `kubernetes.io/ingress.class` annotation specifying a class _other than the default_.
Instead of using the `ingress.class` of the Ingress requesting the certificate, the Solver uses the default ingress class.
**Expected behavior**:
According to [the documentation](https://docs.cert-manager.io/en/release-0.11/tasks/issuing-certificates/ingress-shim.html#supported-annotations):
> `acme.cert-manager.io/http01-ingress-class` - this annotation allows you to configure ingress class that will be used to solve challenges for this ingress. Customising this is useful when you are trying to secure internal services, and need to solve challenges using different ingress class to that of the ingress. **If not specified and the ‘acme-http01-edit-in-place’ annotation is not set, this defaults to the ingress class of the ingress resource**. _(emphasis added)_
So I expect an Ingress like this:
```
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
annotations:
kubernetes.io/ingress.class: secondary
kubernetes.io/tls-acme: "true"
spec:
rules:
- host: cert-test-secondary.example.com
http:
paths:
- backend:
serviceName: cert-test-demo
servicePort: http
path: /
tls:
- hosts:
- cert-test-secondary.example.com
secretName: cert-test-tls
```
to generate an `http01` solver using `kubernetes.io/ingress.class: secondary`. Instead (because we have not specified a default `ingress.class` for the default solver), it generates an Ingress solver that has no `kubernetes.io/ingress.class` annotation at all.
**Steps to reproduce the bug**:
Install `cert-manager` v0.11.0 on Kubernetes 1.12.10 using `helm` chart v0.11.0 with
```
--set ingressShim.defaultIssuerName=letsencrypt-production \
--set ingressShim.defaultIssuerKind=ClusterIssuer
```
See above for Ingress spec.
ClusterIssuer:
```
apiVersion: cert-manager.io/v1alpha2
kind: ClusterIssuer
metadata:
name: letsencrypt-production
spec:
acme:
email: tls@example.com
privateKeySecretRef:
name: letsencrypt-production-private-key
server: https://acme-v02.api.letsencrypt.org/directory
solvers:
- http01:
ingress: {}
- dns01:
route53:
region: us-west-2
selector:
matchLabels:
cert-manager-solver: dns01
```
Note that if we specify an Ingress class in the Solver, like
```
- http01:
ingress:
class: none
```
Then the challenge solver ingress gets created with that `ingress.class`, not the one of the target ingress.
**Anything else we need to know?**:
We do not have a default ingress installed, nor do we have an easy mapping of domain names to ingresses to allow the ClusterIssuer to pick the right ingress based on the domain names of the certificate. We expect the Challenge Solver to use the Ingress class of the Ingress where it will be deployed, as described in the documentation.
The workaround is to add the `acme.cert-manager.io/http01-ingress-class` annotation to the Ingress, but that requires us to update all of our Ingresses and all of the `helm` charts/values that install them, which is highly undesirable.
**Environment details:**:
- Kubernetes version: v1.12.10
- Cloud-provider/provisioner: AWS
- cert-manager version : v0.11.0
- Install method: helm
/kind bug
| 1.0 | Ingress-shim fails to use class of Ingress when creating http01 solver - **Describe the bug**:
Using `cert-manager` v0.11.0.
Certificates created by the `ingressShim` in response to the `kubernetes.io/tls-acme: "true"` annotation on an Ingress fail to be issued when the default solver is `http01` and the Ingress has a `kubernetes.io/ingress.class` annotation specifying a class _other than the default_.
Instead of using the `ingress.class` of the Ingress requesting the certificate, the Solver uses the default ingress class.
**Expected behavior**:
According to [the documentation](https://docs.cert-manager.io/en/release-0.11/tasks/issuing-certificates/ingress-shim.html#supported-annotations):
> `acme.cert-manager.io/http01-ingress-class` - this annotation allows you to configure ingress class that will be used to solve challenges for this ingress. Customising this is useful when you are trying to secure internal services, and need to solve challenges using different ingress class to that of the ingress. **If not specified and the ‘acme-http01-edit-in-place’ annotation is not set, this defaults to the ingress class of the ingress resource**. _(emphasis added)_
So I expect an Ingress like this:
```
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
annotations:
kubernetes.io/ingress.class: secondary
kubernetes.io/tls-acme: "true"
spec:
rules:
- host: cert-test-secondary.example.com
http:
paths:
- backend:
serviceName: cert-test-demo
servicePort: http
path: /
tls:
- hosts:
- cert-test-secondary.example.com
secretName: cert-test-tls
```
to generate an `http01` solver using `kubernetes.io/ingress.class: secondary`. Instead (because we have not specified a default `ingress.class` for the default solver), it generates an Ingress solver that has no `kubernetes.io/ingress.class` annotation at all.
**Steps to reproduce the bug**:
Install `cert-manager` v0.11.0 on Kubernetes 1.12.10 using `helm` chart v0.11.0 with
```
--set ingressShim.defaultIssuerName=letsencrypt-production \
--set ingressShim.defaultIssuerKind=ClusterIssuer
```
See above for Ingress spec.
ClusterIssuer:
```
apiVersion: cert-manager.io/v1alpha2
kind: ClusterIssuer
metadata:
name: letsencrypt-production
spec:
acme:
email: tls@example.com
privateKeySecretRef:
name: letsencrypt-production-private-key
server: https://acme-v02.api.letsencrypt.org/directory
solvers:
- http01:
ingress: {}
- dns01:
route53:
region: us-west-2
selector:
matchLabels:
cert-manager-solver: dns01
```
Note that if we specify an Ingress class in the Solver, like
```
- http01:
ingress:
class: none
```
Then the challenge solver ingress gets created with that `ingress.class`, not the one of the target ingress.
**Anything else we need to know?**:
We do not have a default ingress installed, nor do we have an easy mapping of domain names to ingresses to allow the ClusterIssuer to pick the right ingress based on the domain names of the certificate. We expect the Challenge Solver to use the Ingress class of the Ingress where it will be deployed, as described in the documentation.
The workaround is to add the `acme.cert-manager.io/http01-ingress-class` annotation to the Ingress, but that requires us to update all of our Ingresses and all of the `helm` charts/values that install them, which is highly undesirable.
**Environment details:**:
- Kubernetes version: v1.12.10
- Cloud-provider/provisioner: AWS
- cert-manager version : v0.11.0
- Install method: helm
/kind bug
| non_test | ingress shim fails to use class of ingress when creating solver describe the bug using cert manager certificates created by the ingressshim in response to the kubernetes io tls acme true annotation on an ingress fail to be issued when the default solver is and the ingress has a kubernetes io ingress class annotation specifying a class other than the default instead of using the ingress class of the ingress requesting the certificate the solver uses the default ingress class expected behavior according to acme cert manager io ingress class this annotation allows you to configure ingress class that will be used to solve challenges for this ingress customising this is useful when you are trying to secure internal services and need to solve challenges using different ingress class to that of the ingress if not specified and the ‘acme edit in place’ annotation is not set this defaults to the ingress class of the ingress resource emphasis added so i expect an ingress like this apiversion extensions kind ingress metadata annotations kubernetes io ingress class secondary kubernetes io tls acme true spec rules host cert test secondary example com http paths backend servicename cert test demo serviceport http path tls hosts cert test secondary example com secretname cert test tls to generate an solver using kubernetes io ingress class secondary instead because we have not specified a default ingress class for the default solver it generates an ingress solver that has no kubernetes io ingress class annotation at all steps to reproduce the bug install cert manager on kubernetes using helm chart with set ingressshim defaultissuername letsencrypt production set ingressshim defaultissuerkind clusterissuer see above for ingress spec clusterissuer apiversion cert manager io kind clusterissuer metadata name letsencrypt production spec acme email tls example com privatekeysecretref name letsencrypt production private key server solvers ingress region us west selector matchlabels cert manager solver note that if we specify an ingress class in the solver like ingress class none then the challenge solver ingress gets created with that ingress class not the one of the target ingress anything else we need to know we do not have a default ingress installed nor do we have an easy mapping of domain names to ingresses to allow the clusterissuer to pick the right ingress based on the domain names of the certificate we expect the challenge solver to use the ingress class of the ingress where it will be deployed as described in the documentation the workaround is to add the acme cert manager io ingress class annotation to the ingress but that requires us to update all of our ingresses and all of the helm charts values that install them which is highly undesirable environment details kubernetes version cloud provider provisioner aws cert manager version install method helm kind bug | 0 |
82,283 | 7,836,299,014 | IssuesEvent | 2018-06-17 17:44:52 | vmware/vic | https://api.github.com/repos/vmware/vic | opened | Infra: parallelism: TLS certificates deleted mid test | area/infra component/test | This was found in the following CI build with parallelism of 6.
CI build: https://ci-vic.vmware.com/vmware/vic/19383/7
```
KEYWORD ${rc}, ${output} = OperatingSystem . Run And Return Rc And Output docker %{VCH-PARAMS} start ${container}
${rc} = 0
${output} = 6c79317fccbd061f6669c5d1abb6fc1919cbaf0ecaa36c56c74ff7e3af250b24
<snip logging step>
KEYWORD ${rc}, ${output} = OperatingSystem . Run And Return Rc And Output docker %{VCH-PARAMS} ps
${rc} = 1
${output} = could not read CA certificate "/go/src/github.com/vmware/vic/foo-bar-certs/ca.pem": open /go/src/github.com/vmware/vic/foo-bar-certs/ca.pem: no such file or directory
```
The following tests use `foo-bar-certs`:
* `6-13-TLS.Create VCH - defaults custom cert path` - test uses that path
* `6-17-Configure-TLS` - suite setup uses the path and tests explicitly delete it. | 1.0 | Infra: parallelism: TLS certificates deleted mid test - This was found in the following CI build with parallelism of 6.
CI build: https://ci-vic.vmware.com/vmware/vic/19383/7
```
KEYWORD ${rc}, ${output} = OperatingSystem . Run And Return Rc And Output docker %{VCH-PARAMS} start ${container}
${rc} = 0
${output} = 6c79317fccbd061f6669c5d1abb6fc1919cbaf0ecaa36c56c74ff7e3af250b24
<snip logging step>
KEYWORD ${rc}, ${output} = OperatingSystem . Run And Return Rc And Output docker %{VCH-PARAMS} ps
${rc} = 1
${output} = could not read CA certificate "/go/src/github.com/vmware/vic/foo-bar-certs/ca.pem": open /go/src/github.com/vmware/vic/foo-bar-certs/ca.pem: no such file or directory
```
The following tests use `foo-bar-certs`:
* `6-13-TLS.Create VCH - defaults custom cert path` - test uses that path
* `6-17-Configure-TLS` - suite setup uses the path and tests explicitly delete it. | test | infra parallelism tls certificates deleted mid test this was found in the following ci build with parallelism of ci build keyword rc output operatingsystem run and return rc and output docker vch params start container rc output keyword rc output operatingsystem run and return rc and output docker vch params ps rc output could not read ca certificate go src github com vmware vic foo bar certs ca pem open go src github com vmware vic foo bar certs ca pem no such file or directory the following tests use foo bar certs tls create vch defaults custom cert path test uses that path configure tls suite setup uses the path and tests explicitly delete it | 1 |
245,307 | 20,760,499,728 | IssuesEvent | 2022-03-15 15:46:10 | hzi-braunschweig/SORMAS-Project | https://api.github.com/repos/hzi-braunschweig/SORMAS-Project | closed | Investigate and fix failure of selected buttons from automated tests | testing task e2e-tests | Discovered failures in steps checking if a button from a group of options was selected.
Example:
https://jenkins.sormas.netzlink.com/view/SORMAS-Project/job/sormas-RunE2eTests/562/allure/#suites/ba64af4344a5d1b16948f67eae90e934/8a35195df3e9b1f2/
Checked and the locator is correct in debug/manual check, the problem is only from automated test execution.
Investigation starting point:
`private String getTaskContext() {
return webDriverHelpers.getCheckedOptionFromHorizontalOptionGroup(SELECTED_TASK_CONTEXT);
}`
Suggestions:
Try to update selenium version
Try to update browse's version
Try to discuss with UI developers if a checked tag can be added to component
Refactor all code to get all options from a group of buttons and look after selected one | 2.0 | Investigate and fix failure of selected buttons from automated tests - Discovered failures in steps checking if a button from a group of options was selected.
Example:
https://jenkins.sormas.netzlink.com/view/SORMAS-Project/job/sormas-RunE2eTests/562/allure/#suites/ba64af4344a5d1b16948f67eae90e934/8a35195df3e9b1f2/
Checked and the locator is correct in debug/manual check, the problem is only from automated test execution.
Investigation starting point:
`private String getTaskContext() {
return webDriverHelpers.getCheckedOptionFromHorizontalOptionGroup(SELECTED_TASK_CONTEXT);
}`
Suggestions:
Try to update selenium version
Try to update browse's version
Try to discuss with UI developers if a checked tag can be added to component
Refactor all code to get all options from a group of buttons and look after selected one | test | investigate and fix failure of selected buttons from automated tests discovered failures in steps checking if a button from a group of options was selected example checked and the locator is correct in debug manual check the problem is only from automated test execution investigation starting point private string gettaskcontext return webdriverhelpers getcheckedoptionfromhorizontaloptiongroup selected task context suggestions try to update selenium version try to update browse s version try to discuss with ui developers if a checked tag can be added to component refactor all code to get all options from a group of buttons and look after selected one | 1 |
107,902 | 9,247,884,773 | IssuesEvent | 2019-03-15 02:59:57 | open-apparel-registry/open-apparel-registry | https://api.github.com/repos/open-apparel-registry/open-apparel-registry | closed | Update fixture generator and committed fixtures to be more realistic | tested/verified | ## Overview
We will soon be taking screen captures for promotional videos and asking for design feedback from some trusted contributors. Attempt to avoid questions and confusion by making the fixture data more closely resemble actual data.
### Describe the solution you'd like
- Geocode the facility address so that they show up at real locations rather than randomized points around Philladelpha.
- Generate contributor names that match the type of the contributor, rather than random names i.e. Brand A, Brand B, Manufacturer Group A, Service Provider B
- Create a roughly equal distribution of contributors in each type.
| 1.0 | Update fixture generator and committed fixtures to be more realistic - ## Overview
We will soon be taking screen captures for promotional videos and asking for design feedback from some trusted contributors. Attempt to avoid questions and confusion by making the fixture data more closely resemble actual data.
### Describe the solution you'd like
- Geocode the facility address so that they show up at real locations rather than randomized points around Philladelpha.
- Generate contributor names that match the type of the contributor, rather than random names i.e. Brand A, Brand B, Manufacturer Group A, Service Provider B
- Create a roughly equal distribution of contributors in each type.
| test | update fixture generator and committed fixtures to be more realistic overview we will soon be taking screen captures for promotional videos and asking for design feedback from some trusted contributors attempt to avoid questions and confusion by making the fixture data more closely resemble actual data describe the solution you d like geocode the facility address so that they show up at real locations rather than randomized points around philladelpha generate contributor names that match the type of the contributor rather than random names i e brand a brand b manufacturer group a service provider b create a roughly equal distribution of contributors in each type | 1 |
96,092 | 8,586,089,280 | IssuesEvent | 2018-11-14 06:51:46 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | closed | Failing test: [sig-autoscaling] [HPA] Horizontal pod autoscaling (scale resource: CPU) [sig-autoscaling] [Serial] [Slow] ReplicationController Should scale from 1 pod to 3 pods and from 3 to 5 and verify decision stabilityChanges | kind/failing-test sig/autoscaling | <!-- Please only use this template for submitting reports about failing tests in Kubernetes CI jobs -->
**Which jobs are failing**:
[sig-release-master-upgrade/gce-new-master-upgrade-master](https://k8s-testgrid.appspot.com/sig-release-master-upgrade#gce-new-master-upgrade-master)
**Which test(s) are failing**:
[[HPA] Horizontal pod autoscaling (scale resource: CPU) [sig-autoscaling] [Serial] [Slow] ReplicationController Should scale from 1 pod to 3 pods and from 3 to 5 and verify decision stability](https://gubernator.k8s.io/build/kubernetes-jenkins/logs/ci-kubernetes-e2e-gce-new-master-upgrade-master/1862#sig-autoscaling-hpa-horizontal-pod-autoscaling-scale-resource-cpu-sig-autoscaling-serial-slow-replicationcontroller-should-scale-from-1-pod-to-3-pods-and-from-3-to-5-and-verify-decision-stability)
**Since when has it been failing**:
November 3rd, 2018
**Testgrid link**:
https://k8s-testgrid.appspot.com/sig-release-master-upgrade#gce-new-master-upgrade-master
https://gubernator.k8s.io/build/kubernetes-jenkins/logs/ci-kubernetes-e2e-gce-new-master-upgrade-master/1862#sig-autoscaling-hpa-horizontal-pod-autoscaling-scale-resource-cpu-sig-autoscaling-serial-slow-replicationcontroller-should-scale-from-1-pod-to-3-pods-and-from-3-to-5-and-verify-decision-stability
**Anything else we need to know**:
[diff towards last passing commit](https://github.com/kubernetes/kubernetes/compare/3293f02d0...46d173232?) hints at #69698 .
<!-- DO NOT EDIT BELOW THIS LINE -->
/kind failing-test | 1.0 | Failing test: [sig-autoscaling] [HPA] Horizontal pod autoscaling (scale resource: CPU) [sig-autoscaling] [Serial] [Slow] ReplicationController Should scale from 1 pod to 3 pods and from 3 to 5 and verify decision stabilityChanges - <!-- Please only use this template for submitting reports about failing tests in Kubernetes CI jobs -->
**Which jobs are failing**:
[sig-release-master-upgrade/gce-new-master-upgrade-master](https://k8s-testgrid.appspot.com/sig-release-master-upgrade#gce-new-master-upgrade-master)
**Which test(s) are failing**:
[[HPA] Horizontal pod autoscaling (scale resource: CPU) [sig-autoscaling] [Serial] [Slow] ReplicationController Should scale from 1 pod to 3 pods and from 3 to 5 and verify decision stability](https://gubernator.k8s.io/build/kubernetes-jenkins/logs/ci-kubernetes-e2e-gce-new-master-upgrade-master/1862#sig-autoscaling-hpa-horizontal-pod-autoscaling-scale-resource-cpu-sig-autoscaling-serial-slow-replicationcontroller-should-scale-from-1-pod-to-3-pods-and-from-3-to-5-and-verify-decision-stability)
**Since when has it been failing**:
November 3rd, 2018
**Testgrid link**:
https://k8s-testgrid.appspot.com/sig-release-master-upgrade#gce-new-master-upgrade-master
https://gubernator.k8s.io/build/kubernetes-jenkins/logs/ci-kubernetes-e2e-gce-new-master-upgrade-master/1862#sig-autoscaling-hpa-horizontal-pod-autoscaling-scale-resource-cpu-sig-autoscaling-serial-slow-replicationcontroller-should-scale-from-1-pod-to-3-pods-and-from-3-to-5-and-verify-decision-stability
**Anything else we need to know**:
[diff towards last passing commit](https://github.com/kubernetes/kubernetes/compare/3293f02d0...46d173232?) hints at #69698 .
<!-- DO NOT EDIT BELOW THIS LINE -->
/kind failing-test | test | failing test horizontal pod autoscaling scale resource cpu replicationcontroller should scale from pod to pods and from to and verify decision stabilitychanges which jobs are failing which test s are failing horizontal pod autoscaling scale resource cpu replicationcontroller should scale from pod to pods and from to and verify decision stability since when has it been failing november testgrid link anything else we need to know hints at kind failing test | 1 |
139,319 | 5,366,935,598 | IssuesEvent | 2017-02-22 01:55:16 | chrisblakley/Nebula | https://api.github.com/repos/chrisblakley/Nebula | closed | Consider better organizing of theme file structure. | Backend (Server) Feature Request Frontend (Script) Frontend (Style) Low Priority Parent / Child Theme | I see a lot of pro themes has their client side resources located in assets directory and each one in their respectives folders and one called lib to store all external resources
We could keep this folder structure too (also on nebula integrations)
Of course we need to update sass compiler too | 1.0 | Consider better organizing of theme file structure. - I see a lot of pro themes has their client side resources located in assets directory and each one in their respectives folders and one called lib to store all external resources
We could keep this folder structure too (also on nebula integrations)
Of course we need to update sass compiler too | non_test | consider better organizing of theme file structure i see a lot of pro themes has their client side resources located in assets directory and each one in their respectives folders and one called lib to store all external resources we could keep this folder structure too also on nebula integrations of course we need to update sass compiler too | 0 |
40,597 | 8,815,302,383 | IssuesEvent | 2018-12-29 16:51:11 | JWWeatherman/math_bot | https://api.github.com/repos/JWWeatherman/math_bot | opened | Implement Sounds | front end code | ### Robot animation sounds
- [x] Wall Bump Sound
- [x] Walk Sound
- [ ] Turn Sound
- [ ] Pickup Sound
- [ ] Drop Sound
### Star-system background sounds
- [x] Same Sound For All
- [ ] Get Different Sound For Each | 1.0 | Implement Sounds - ### Robot animation sounds
- [x] Wall Bump Sound
- [x] Walk Sound
- [ ] Turn Sound
- [ ] Pickup Sound
- [ ] Drop Sound
### Star-system background sounds
- [x] Same Sound For All
- [ ] Get Different Sound For Each | non_test | implement sounds robot animation sounds wall bump sound walk sound turn sound pickup sound drop sound star system background sounds same sound for all get different sound for each | 0 |
14,556 | 9,336,607,154 | IssuesEvent | 2019-03-28 21:44:27 | codevirtuel/osu-replayViewer-web | https://api.github.com/repos/codevirtuel/osu-replayViewer-web | closed | CVE-2018-19838 Medium Severity Vulnerability detected by WhiteSource | security vulnerability | ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (125)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/expand.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8/unchecked.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/output.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/util.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/emitter.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/lexer.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_node.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/plugins.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/base.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/position.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/operation.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/custom_importer_bridge.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/functions.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/eval.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_context_wrapper.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/node.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/parser.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/emitter.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/listize.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/output.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/functions.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/cssize.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/paths.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/inspect.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/color.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/values.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/source_map.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/list.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/json.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/units.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/units.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/context.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8/checked.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/listize.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/string.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/context.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/boolean.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass2scss.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/eval.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/expand.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/factory.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/operators.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/boolean.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/source_map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/value.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/callback_bridge.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/file.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/node.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/environment.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/extend.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/operators.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/constants.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/parser.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/constants.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/list.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/cssize.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/functions.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/util.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/custom_function_bridge.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/custom_importer_bridge.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/bind.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/inspect.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/backtrace.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/extend.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/debugger.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/cencode.c
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/number.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/color.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/c99func.c
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/position.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/values.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/null.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/context.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_c.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_value.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_context_wrapper.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/lexer.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_c.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_value.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/b64/encode.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/file.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/environment.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/plugins.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/binding.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/debug.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, functions inside ast.cpp for IMPLEMENT_AST_OPERATORS expansion allow attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, as demonstrated by recursive calls involving clone(), cloneChildren(), and copy().
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19838>CVE-2018-19838</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19838">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19838</a></p>
<p>Fix Resolution: 3.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19838 Medium Severity Vulnerability detected by WhiteSource - ## CVE-2018-19838 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sassv4.11.0</b></p></summary>
<p>
<p>:rainbow: Node.js bindings to libsass</p>
<p>Library home page: <a href=https://github.com/sass/node-sass.git>https://github.com/sass/node-sass.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Library Source Files (125)</summary>
<p></p>
<p> * The source files were matched to this source library based on a best effort match. Source libraries are selected from a list of probable public libraries.</p>
<p>
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/expand.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/color_maps.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_util.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8/unchecked.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/output.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_values.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/util.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/emitter.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/lexer.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_node.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/plugins.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/base.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/position.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/subset_map.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/operation.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/remove_placeholders.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/error_handling.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/custom_importer_bridge.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/contrib/plugin.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/functions.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_superselector.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/eval.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8_string.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_context_wrapper.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/error_handling.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/node.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/parser.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/subset_map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/emitter.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/listize.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_functions.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/memory/SharedPtr.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/output.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/check_nesting.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast_def_macros.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/functions.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/cssize.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/prelexer.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/paths.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast_fwd_decl.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/inspect.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/color.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_unification.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/values.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_util.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/source_map.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/list.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/check_nesting.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/json.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/units.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/units.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/context.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8/checked.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/listize.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/string.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/prelexer.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/context.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/boolean.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass2scss.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/eval.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/expand.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/factory.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/operators.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/boolean.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/source_map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/value.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/utf8_string.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/callback_bridge.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/file.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/node.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/environment.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/extend.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_context.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/operators.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/constants.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast_fwd_decl.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/parser.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/constants.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/list.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/cssize.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/functions.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/util.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/custom_function_bridge.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/custom_importer_bridge.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/bind.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/inspect.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_functions.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/backtrace.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/extend.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/sass_value_wrapper.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/debugger.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/cencode.c
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/base64vlq.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/number.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/color.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/c99func.c
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/position.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/remove_placeholders.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_values.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/values.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/test/test_subset_map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass2scss.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/null.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/ast.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/include/sass/context.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_c.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_value.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/color_maps.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_context_wrapper.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/script/test-leaks.pl
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/lexer.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/memory/SharedPtr.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_c.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/sass_types/map.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/to_value.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/b64/encode.h
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/file.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/environment.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/plugins.hpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/binding.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/sass_context.cpp
- /osu-replayViewer-web/bulma/node_modules/node-sass/src/libsass/src/debug.hpp
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass prior to 3.5.5, functions inside ast.cpp for IMPLEMENT_AST_OPERATORS expansion allow attackers to cause a denial-of-service resulting from stack consumption via a crafted sass file, as demonstrated by recursive calls involving clone(), cloneChildren(), and copy().
<p>Publish Date: 2018-12-04
<p>URL: <a href=https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19838>CVE-2018-19838</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19838">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19838</a></p>
<p>Fix Resolution: 3.5.5</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium severity vulnerability detected by whitesource cve medium severity vulnerability vulnerable library node rainbow node js bindings to libsass library home page a href library source files the source files were matched to this source library based on a best effort match source libraries are selected from a list of probable public libraries osu replayviewer web bulma node modules node sass src libsass src expand hpp osu replayviewer web bulma node modules node sass src libsass src color maps cpp osu replayviewer web bulma node modules node sass src libsass src sass util hpp osu replayviewer web bulma node modules node sass src libsass src unchecked h osu replayviewer web bulma node modules node sass src libsass src output hpp osu replayviewer web bulma node modules node sass src libsass src sass values hpp osu replayviewer web bulma node modules node sass src libsass src util hpp osu replayviewer web bulma node modules node sass src libsass src emitter hpp osu replayviewer web bulma node modules node sass src libsass src lexer cpp osu replayviewer web bulma node modules node sass src libsass test test node cpp osu replayviewer web bulma node modules node sass src libsass src plugins cpp osu replayviewer web bulma node modules node sass src libsass include sass base h osu replayviewer web bulma node modules node sass src libsass src position hpp osu replayviewer web bulma node modules node sass src libsass src subset map hpp osu replayviewer web bulma node modules node sass src libsass src operation hpp osu replayviewer web bulma node modules node sass src libsass src remove placeholders cpp osu replayviewer web bulma node modules node sass src libsass src error handling hpp osu replayviewer web bulma node modules node sass src custom importer bridge cpp osu replayviewer web bulma node modules node sass src libsass contrib plugin cpp osu replayviewer web bulma node modules node sass src libsass src functions hpp osu replayviewer web bulma node modules node sass src libsass test test superselector cpp osu replayviewer web bulma node modules node sass src libsass src eval hpp osu replayviewer web bulma node modules node sass src libsass src string hpp osu replayviewer web bulma node modules node sass src sass context wrapper h osu replayviewer web bulma node modules node sass src libsass src error handling cpp osu replayviewer web bulma node modules node sass src libsass src node cpp osu replayviewer web bulma node modules node sass src libsass src parser cpp osu replayviewer web bulma node modules node sass src libsass src subset map cpp osu replayviewer web bulma node modules node sass src libsass src emitter cpp osu replayviewer web bulma node modules node sass src libsass src listize cpp osu replayviewer web bulma node modules node sass src libsass src ast hpp osu replayviewer web bulma node modules node sass src libsass src sass functions hpp osu replayviewer web bulma node modules node sass src libsass src memory sharedptr cpp osu replayviewer web bulma node modules node sass src libsass src output cpp osu replayviewer web bulma node modules node sass src libsass src check nesting cpp osu replayviewer web bulma node modules node sass src libsass src ast def macros hpp osu replayviewer web bulma node modules node sass src libsass src functions cpp osu replayviewer web bulma node modules node sass src libsass src cssize hpp osu replayviewer web bulma node modules node sass src libsass src prelexer cpp osu replayviewer web bulma node modules node sass src libsass src paths hpp osu replayviewer web bulma node modules node sass src libsass src ast fwd decl hpp osu replayviewer web bulma node modules node sass src libsass src inspect hpp osu replayviewer web bulma node modules node sass src sass types color cpp osu replayviewer web bulma node modules node sass src libsass test test unification cpp osu replayviewer web bulma node modules node sass src libsass src values cpp osu replayviewer web bulma node modules node sass src libsass src sass util cpp osu replayviewer web bulma node modules node sass src libsass src source map hpp osu replayviewer web bulma node modules node sass src sass types list h osu replayviewer web bulma node modules node sass src libsass src check nesting hpp osu replayviewer web bulma node modules node sass src libsass src json cpp osu replayviewer web bulma node modules node sass src libsass src units cpp osu replayviewer web bulma node modules node sass src libsass src units hpp osu replayviewer web bulma node modules node sass src libsass src context cpp osu replayviewer web bulma node modules node sass src libsass src checked h osu replayviewer web bulma node modules node sass src libsass src listize hpp osu replayviewer web bulma node modules node sass src sass types string cpp osu replayviewer web bulma node modules node sass src libsass src prelexer hpp osu replayviewer web bulma node modules node sass src libsass src context hpp osu replayviewer web bulma node modules node sass src sass types boolean h osu replayviewer web bulma node modules node sass src libsass include h osu replayviewer web bulma node modules node sass src libsass src eval cpp osu replayviewer web bulma node modules node sass src libsass src expand cpp osu replayviewer web bulma node modules node sass src sass types factory cpp osu replayviewer web bulma node modules node sass src libsass src operators cpp osu replayviewer web bulma node modules node sass src sass types boolean cpp osu replayviewer web bulma node modules node sass src libsass src source map cpp osu replayviewer web bulma node modules node sass src sass types value h osu replayviewer web bulma node modules node sass src libsass src string cpp osu replayviewer web bulma node modules node sass src callback bridge h osu replayviewer web bulma node modules node sass src libsass src file cpp osu replayviewer web bulma node modules node sass src libsass src sass cpp osu replayviewer web bulma node modules node sass src libsass src node hpp osu replayviewer web bulma node modules node sass src libsass src environment cpp osu replayviewer web bulma node modules node sass src libsass src extend hpp osu replayviewer web bulma node modules node sass src libsass src sass context hpp osu replayviewer web bulma node modules node sass src libsass src operators hpp osu replayviewer web bulma node modules node sass src libsass src constants hpp osu replayviewer web bulma node modules node sass src libsass src sass hpp osu replayviewer web bulma node modules node sass src libsass src ast fwd decl cpp osu replayviewer web bulma node modules node sass src libsass src parser hpp osu replayviewer web bulma node modules node sass src libsass src constants cpp osu replayviewer web bulma node modules node sass src sass types list cpp osu replayviewer web bulma node modules node sass src libsass src cssize cpp osu replayviewer web bulma node modules node sass src libsass include sass functions h osu replayviewer web bulma node modules node sass src libsass src util cpp osu replayviewer web bulma node modules node sass src custom function bridge cpp osu replayviewer web bulma node modules node sass src custom importer bridge h osu replayviewer web bulma node modules node sass src libsass src bind cpp osu replayviewer web bulma node modules node sass src libsass src inspect cpp osu replayviewer web bulma node modules node sass src libsass src sass functions cpp osu replayviewer web bulma node modules node sass src libsass src backtrace cpp osu replayviewer web bulma node modules node sass src libsass src extend cpp osu replayviewer web bulma node modules node sass src sass types sass value wrapper h osu replayviewer web bulma node modules node sass src libsass src debugger hpp osu replayviewer web bulma node modules node sass src libsass src cencode c osu replayviewer web bulma node modules node sass src libsass src cpp osu replayviewer web bulma node modules node sass src sass types number cpp osu replayviewer web bulma node modules node sass src sass types color h osu replayviewer web bulma node modules node sass src libsass src c osu replayviewer web bulma node modules node sass src libsass src position cpp osu replayviewer web bulma node modules node sass src libsass src remove placeholders hpp osu replayviewer web bulma node modules node sass src libsass src sass values cpp osu replayviewer web bulma node modules node sass src libsass include sass values h osu replayviewer web bulma node modules node sass src libsass test test subset map cpp osu replayviewer web bulma node modules node sass src libsass src cpp osu replayviewer web bulma node modules node sass src sass types null cpp osu replayviewer web bulma node modules node sass src libsass src ast cpp osu replayviewer web bulma node modules node sass src libsass include sass context h osu replayviewer web bulma node modules node sass src libsass src to c cpp osu replayviewer web bulma node modules node sass src libsass src to value hpp osu replayviewer web bulma node modules node sass src libsass src color maps hpp osu replayviewer web bulma node modules node sass src sass context wrapper cpp osu replayviewer web bulma node modules node sass src libsass script test leaks pl osu replayviewer web bulma node modules node sass src libsass src lexer hpp osu replayviewer web bulma node modules node sass src libsass src memory sharedptr hpp osu replayviewer web bulma node modules node sass src libsass src to c hpp osu replayviewer web bulma node modules node sass src sass types map cpp osu replayviewer web bulma node modules node sass src libsass src to value cpp osu replayviewer web bulma node modules node sass src libsass src encode h osu replayviewer web bulma node modules node sass src libsass src file hpp osu replayviewer web bulma node modules node sass src libsass src environment hpp osu replayviewer web bulma node modules node sass src libsass src plugins hpp osu replayviewer web bulma node modules node sass src binding cpp osu replayviewer web bulma node modules node sass src libsass src sass context cpp osu replayviewer web bulma node modules node sass src libsass src debug hpp vulnerability details in libsass prior to functions inside ast cpp for implement ast operators expansion allow attackers to cause a denial of service resulting from stack consumption via a crafted sass file as demonstrated by recursive calls involving clone clonechildren and copy publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href fix resolution step up your open source security game with whitesource | 0 |
101,455 | 16,511,654,137 | IssuesEvent | 2021-05-26 05:25:17 | kijunb33/test | https://api.github.com/repos/kijunb33/test | opened | CVE-2021-25329 (High) detected in tomcat-embed-core-7.0.90.jar | security vulnerability | ## CVE-2021-25329 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-7.0.90.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to vulnerable library: test/tomcat-embed-core-7.0.90.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-7.0.90.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/kijunb33/test/commits/8df5c209ab0589b3f881b1e4a6c004c81ae3d659">8df5c209ab0589b3f881b1e4a6c004c81ae3d659</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329>CVE-2021-25329</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-25329 (High) detected in tomcat-embed-core-7.0.90.jar - ## CVE-2021-25329 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-7.0.90.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to vulnerable library: test/tomcat-embed-core-7.0.90.jar</p>
<p>
Dependency Hierarchy:
- :x: **tomcat-embed-core-7.0.90.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://api.github.com/repos/kijunb33/test/commits/8df5c209ab0589b3f881b1e4a6c004c81ae3d659">8df5c209ab0589b3f881b1e4a6c004c81ae3d659</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329>CVE-2021-25329</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to vulnerable library test tomcat embed core jar dependency hierarchy x tomcat embed core jar vulnerable library found in head commit a href found in base branch master vulnerability details the fix for cve was incomplete when using apache tomcat to to to or to with a configuration edge case that was highly unlikely to be used the tomcat instance was still vulnerable to cve note that both the previously published prerequisites for cve and the previously published mitigations for cve also apply to this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat step up your open source security game with whitesource | 0 |
71,641 | 3,366,122,828 | IssuesEvent | 2015-11-21 03:21:26 | hackthesystemATX/doctrinr | https://api.github.com/repos/hackthesystemATX/doctrinr | reopened | User Flow Diagram | high priority | Someone needs to creat a low-fidelity diagram of the userflow.
[Example] (https://www.google.com/search?q=userflow&source=lnms&tbm=isch&sa=X&ved=0ahUKEwjg9KfPxaDJAhWCUogKHTYzC0cQ_AUICCgC&biw=1036&bih=805)
Something simple so we can easily communicate it to a desiger/developer. | 1.0 | User Flow Diagram - Someone needs to creat a low-fidelity diagram of the userflow.
[Example] (https://www.google.com/search?q=userflow&source=lnms&tbm=isch&sa=X&ved=0ahUKEwjg9KfPxaDJAhWCUogKHTYzC0cQ_AUICCgC&biw=1036&bih=805)
Something simple so we can easily communicate it to a desiger/developer. | non_test | user flow diagram someone needs to creat a low fidelity diagram of the userflow something simple so we can easily communicate it to a desiger developer | 0 |
1,320 | 3,593,205,104 | IssuesEvent | 2016-02-01 18:50:36 | Azure/azure-powershell | https://api.github.com/repos/Azure/azure-powershell | closed | AzureRmBackupContainer V1VM/V2VM confusion | RecoveryServices | According to the documentation, and the source, there is a Parameter set for v2VMs
However when you run the command -
Register-AzureRmBackupContainer -Vault $vault -Name $vm.Name `
-ResourceGroupName $vm.ResourceGroupName
The error message `The specified Azure Virtual Machine Not Found.` suggests that a possible cause is `VM is Azure IaaS v2 VM`
Obviously this goes against what the command line options suggest.
Is it possible to backup an IaaS v2 VM with AzureRM.Backup? (considering that it is a RM cmdlet, it would hint towards it being possible!)
<!---@tfsbridge:{"tfsId":5629458}--> | 1.0 | AzureRmBackupContainer V1VM/V2VM confusion - According to the documentation, and the source, there is a Parameter set for v2VMs
However when you run the command -
Register-AzureRmBackupContainer -Vault $vault -Name $vm.Name `
-ResourceGroupName $vm.ResourceGroupName
The error message `The specified Azure Virtual Machine Not Found.` suggests that a possible cause is `VM is Azure IaaS v2 VM`
Obviously this goes against what the command line options suggest.
Is it possible to backup an IaaS v2 VM with AzureRM.Backup? (considering that it is a RM cmdlet, it would hint towards it being possible!)
<!---@tfsbridge:{"tfsId":5629458}--> | non_test | azurermbackupcontainer confusion according to the documentation and the source there is a parameter set for however when you run the command register azurermbackupcontainer vault vault name vm name resourcegroupname vm resourcegroupname the error message the specified azure virtual machine not found suggests that a possible cause is vm is azure iaas vm obviously this goes against what the command line options suggest is it possible to backup an iaas vm with azurerm backup considering that it is a rm cmdlet it would hint towards it being possible | 0 |
154,739 | 12,226,983,221 | IssuesEvent | 2020-05-03 13:25:05 | RomanKondratev90/Test-project | https://api.github.com/repos/RomanKondratev90/Test-project | opened | Тест - кейс №6 (ручка). Проверка ручки на внешние механические повреждения | test case (Pass) | Приоритет - средний
Шаги
1 Взять ручку руку.
2 Провести осмотр ручки
Ожидаемы результат
Длина - отсутствие повреждений ручки.
Статус
Положительный результат | 1.0 | Тест - кейс №6 (ручка). Проверка ручки на внешние механические повреждения - Приоритет - средний
Шаги
1 Взять ручку руку.
2 Провести осмотр ручки
Ожидаемы результат
Длина - отсутствие повреждений ручки.
Статус
Положительный результат | test | тест кейс № ручка проверка ручки на внешние механические повреждения приоритет средний шаги взять ручку руку провести осмотр ручки ожидаемы результат длина отсутствие повреждений ручки статус положительный результат | 1 |
45,051 | 5,682,977,852 | IssuesEvent | 2017-04-13 11:19:03 | carbontwelve/tapestry | https://api.github.com/repos/carbontwelve/tapestry | opened | Check that two files of the same permalink don't conflict | bug needs-tests | If you have two files with the same permalink, Tapestry should highlight to the user the error and fail-back to one of two configured modes:
1. Rename the file with an increment number e.g. `filename-1.html`
2. Throw an error and output to console the issue | 1.0 | Check that two files of the same permalink don't conflict - If you have two files with the same permalink, Tapestry should highlight to the user the error and fail-back to one of two configured modes:
1. Rename the file with an increment number e.g. `filename-1.html`
2. Throw an error and output to console the issue | test | check that two files of the same permalink don t conflict if you have two files with the same permalink tapestry should highlight to the user the error and fail back to one of two configured modes rename the file with an increment number e g filename html throw an error and output to console the issue | 1 |
298,147 | 25,793,338,747 | IssuesEvent | 2022-12-10 09:29:28 | red-hat-storage/ocs-ci | https://api.github.com/repos/red-hat-storage/ocs-ci | opened | test_unidirectional_bucket_replication failed with ubprocess.TimeoutExpired: Command '['yes | /home/jenkins/workspace/qe-deploy-ocs-cluster-prod/ocs-ci/data/mcg-cli backingstore create azure-blob azure-backingstore-8f648f21765242bd99c78 --account-key ZoIEOXRWuTrGpRMHC0AOybbMEzycDjO35H8mWo0MmGJXcLZQOZmJWLSHvcbYs5PlnQb3iQO6BrebY/m7r1iYfQ== --account-name mcgtestingstorage --target-blob-container azure-uls-42da9b353ccb4fe6b87c27692a880e -n openshift-storage']' timed out after 600 second | TestCase failing Squad/Red | Run details:
URL: https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#OCS/launches/362/7364/320363/320416/320422/log
Run ID: 1670509372
Test Case: test_unidirectional_bucket_replication
ODF Build: 4.12.0-130
OCP Version: 4.12
Job name: IBM Cloud IPI 3AZ RHCOS 3M 3W tier1
Jenkins job: https://ocs4-jenkins-csb-odf-qe.apps.ocp-c1.prod.psi.redhat.com/job/qe-deploy-ocs-cluster-prod/6343/
Logs URL: http://magna002.ceph.redhat.com/ocsci-jenkins/openshift-clusters/j-005ici3c33-t1/j-005ici3c33-t1_20221208T130227/logs/
Failure Details:
```
Message: subprocess.TimeoutExpired: Command '['yes | /home/jenkins/workspace/qe-deploy-ocs-cluster-prod/ocs-ci/data/mcg-cli backingstore create azure-blob azure-backingstore-8f648f21765242bd99c78 --account-key ZoIEOXRWuTrGpRMHC0AOybbMEzycDjO35H8mWo0MmGJXcLZQOZmJWLSHvcbYs5PlnQb3iQO6BrebY/m7r1iYfQ== --account-name mcgtestingstorage --target-blob-container azure-uls-42da9b353ccb4fe6b87c27692a880e -n openshift-storage']' timed out after 600 seconds
Type: None
Text:
self = <tests.manage.mcg.test_bucket_replication.TestReplication object at 0x7f91e590bb50>
awscli_pod_session = <ocs_ci.ocs.resources.pod.Pod object at 0x7f91e61dca30>
mcg_obj_session = <ocs_ci.ocs.resources.mcg.MCG object at 0x7f91e0e37910>
bucket_factory = <function bucket_factory_fixture.<locals>._create_buckets at 0x7f91e42178b0>
source_bucketclass = {'backingstore_dict': {'aws': [(1, 'eu-central-1')]}, 'interface': 'CLI'}
target_bucketclass = {'backingstore_dict': {'azure': [(1, None)]}, 'interface': 'CLI'}
@pytest.mark.parametrize(
argnames=["source_bucketclass", "target_bucketclass"],
argvalues=[
pytest.param(
{
"interface": "OC",
"backingstore_dict": {"aws": [(1, "eu-central-1")]},
},
{"interface": "OC", "backingstore_dict": {"azure": [(1, None)]}},
marks=[tier1, pytest.mark.polarion_id("OCS-2678")],
),
pytest.param(
{
"interface": "OC",
"backingstore_dict": {"gcp": [(1, None)]},
},
{
"interface": "OC",
"backingstore_dict": {"aws": [(1, "eu-central-1")]},
},
marks=[tier2],
),
pytest.param(
{
"interface": "CLI",
"backingstore_dict": {"azure": [(1, None)]},
},
{"interface": "CLI", "backingstore_dict": {"gcp": [(1, None)]}},
marks=[tier2],
),
pytest.param(
{
"interface": "CLI",
"backingstore_dict": {"aws": [(1, "eu-central-1")]},
},
{"interface": "CLI", "backingstore_dict": {"azure": [(1, None)]}},
marks=[tier1, pytest.mark.polarion_id("OCS-2679")],
),
pytest.param(
{
"interface": "OC",
"namespace_policy_dict": {
"type": "Single",
"namespacestore_dict": {"aws": [(1, "eu-central-1")]},
},
},
{
"interface": "OC",
"namespace_policy_dict": {
"type": "Single",
"namespacestore_dict": {"azure": [(1, None)]},
},
},
marks=[tier2],
),
pytest.param(
{
"interface": "OC",
"namespace_policy_dict": {
"type": "Single",
"namespacestore_dict": {"azure": [(1, None)]},
},
},
{
"interface": "CLI",
"backingstore_dict": {"gcp": [(1, None)]},
},
marks=[tier1],
),
],
ids=[
"AWStoAZURE-BS-OC",
"GCPtoAWS-BS-OC",
"AZUREtoCGP-BS-CLI",
"AWStoAZURE-BS-CLI",
"AWStoAZURE-NS-OC",
"AZUREtoGCP-NS-Hybrid",
],
)
def test_unidirectional_bucket_replication(
self,
awscli_pod_session,
mcg_obj_session,
bucket_factory,
source_bucketclass,
target_bucketclass,
):
"""
Test unidirectional bucket replication using CLI and YAML by adding objects
to a backingstore- and namespacestore-backed buckets
"""
> target_bucket_name = bucket_factory(bucketclass=target_bucketclass)[0].name
tests/manage/mcg/test_bucket_replication.py:121:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
tests/conftest.py:2557: in _create_buckets
bucketclass if bucketclass is None else bucket_class_factory(bucketclass)
ocs_ci/ocs/resources/bucketclass.py:169: in _create_bucket_class
for backingstore in backingstore_factory(
ocs_ci/ocs/resources/backingstore.py:349: in _create_backingstore
cmdMap[method.lower()][cloud.lower()](
ocs_ci/ocs/bucket_utils.py:602: in cli_create_azure_backingstore
mcg_obj.exec_mcg_cmd(
ocs_ci/ocs/resources/mcg.py:869: in exec_mcg_cmd
result = exec_cmd(
ocs_ci/utility/utils.py:607: in exec_cmd
completed_process = subprocess.run(
/usr/lib64/python3.8/subprocess.py:495: in run
stdout, stderr = process.communicate(input, timeout=timeout)
/usr/lib64/python3.8/subprocess.py:1028: in communicate
stdout, stderr = self._communicate(input, endtime, timeout)
/usr/lib64/python3.8/subprocess.py:1869: in _communicate
self._check_timeout(endtime, orig_timeout, stdout, stderr)
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
self = <subprocess.Popen object at 0x7f920d985df0>, endtime = 10075.34677407
orig_timeout = 600, stdout_seq = []
stderr_seq = [b'time="2022-12-08T15:39:44Z" level=info msg="\xe2\x9c\x85 Exists: NooBaa \\"noobaa\\"\\n"\n', b'time="2022-12-08T15:...re-backingstore-8f648f21765242bd99c78\\" Phase is \\"Creating\\": TemporaryError Target bucket doesn\'t exist"\n', ...]
skip_check_and_raise = False
def _check_timeout(self, endtime, orig_timeout, stdout_seq, stderr_seq,
skip_check_and_raise=False):
"""Convenience for checking if a timeout has expired."""
if endtime is None:
return
if skip_check_and_raise or _time() > endtime:
> raise TimeoutExpired(
self.args, orig_timeout,
output=b''.join(stdout_seq) if stdout_seq else None,
stderr=b''.join(stderr_seq) if stderr_seq else None)
E subprocess.TimeoutExpired: Command '['yes | /home/jenkins/workspace/qe-deploy-ocs-cluster-prod/ocs-ci/data/mcg-cli backingstore create azure-blob azure-backingstore-8f648f21765242bd99c78 --account-key ZoIEOXRWuTrGpRMHC0AOybbMEzycDjO35H8mWo0MmGJXcLZQOZmJWLSHvcbYs5PlnQb3iQO6BrebY/m7r1iYfQ== --account-name mcgtestingstorage --target-blob-container azure-uls-42da9b353ccb4fe6b87c27692a880e -n openshift-storage']' timed out after 600 seconds
/usr/lib64/python3.8/subprocess.py:1072: TimeoutExpired
``` | 1.0 | test_unidirectional_bucket_replication failed with ubprocess.TimeoutExpired: Command '['yes | /home/jenkins/workspace/qe-deploy-ocs-cluster-prod/ocs-ci/data/mcg-cli backingstore create azure-blob azure-backingstore-8f648f21765242bd99c78 --account-key ZoIEOXRWuTrGpRMHC0AOybbMEzycDjO35H8mWo0MmGJXcLZQOZmJWLSHvcbYs5PlnQb3iQO6BrebY/m7r1iYfQ== --account-name mcgtestingstorage --target-blob-container azure-uls-42da9b353ccb4fe6b87c27692a880e -n openshift-storage']' timed out after 600 second - Run details:
URL: https://reportportal-ocs4.apps.ocp-c1.prod.psi.redhat.com/ui/#OCS/launches/362/7364/320363/320416/320422/log
Run ID: 1670509372
Test Case: test_unidirectional_bucket_replication
ODF Build: 4.12.0-130
OCP Version: 4.12
Job name: IBM Cloud IPI 3AZ RHCOS 3M 3W tier1
Jenkins job: https://ocs4-jenkins-csb-odf-qe.apps.ocp-c1.prod.psi.redhat.com/job/qe-deploy-ocs-cluster-prod/6343/
Logs URL: http://magna002.ceph.redhat.com/ocsci-jenkins/openshift-clusters/j-005ici3c33-t1/j-005ici3c33-t1_20221208T130227/logs/
Failure Details:
```
Message: subprocess.TimeoutExpired: Command '['yes | /home/jenkins/workspace/qe-deploy-ocs-cluster-prod/ocs-ci/data/mcg-cli backingstore create azure-blob azure-backingstore-8f648f21765242bd99c78 --account-key ZoIEOXRWuTrGpRMHC0AOybbMEzycDjO35H8mWo0MmGJXcLZQOZmJWLSHvcbYs5PlnQb3iQO6BrebY/m7r1iYfQ== --account-name mcgtestingstorage --target-blob-container azure-uls-42da9b353ccb4fe6b87c27692a880e -n openshift-storage']' timed out after 600 seconds
Type: None
Text:
self = <tests.manage.mcg.test_bucket_replication.TestReplication object at 0x7f91e590bb50>
awscli_pod_session = <ocs_ci.ocs.resources.pod.Pod object at 0x7f91e61dca30>
mcg_obj_session = <ocs_ci.ocs.resources.mcg.MCG object at 0x7f91e0e37910>
bucket_factory = <function bucket_factory_fixture.<locals>._create_buckets at 0x7f91e42178b0>
source_bucketclass = {'backingstore_dict': {'aws': [(1, 'eu-central-1')]}, 'interface': 'CLI'}
target_bucketclass = {'backingstore_dict': {'azure': [(1, None)]}, 'interface': 'CLI'}
@pytest.mark.parametrize(
argnames=["source_bucketclass", "target_bucketclass"],
argvalues=[
pytest.param(
{
"interface": "OC",
"backingstore_dict": {"aws": [(1, "eu-central-1")]},
},
{"interface": "OC", "backingstore_dict": {"azure": [(1, None)]}},
marks=[tier1, pytest.mark.polarion_id("OCS-2678")],
),
pytest.param(
{
"interface": "OC",
"backingstore_dict": {"gcp": [(1, None)]},
},
{
"interface": "OC",
"backingstore_dict": {"aws": [(1, "eu-central-1")]},
},
marks=[tier2],
),
pytest.param(
{
"interface": "CLI",
"backingstore_dict": {"azure": [(1, None)]},
},
{"interface": "CLI", "backingstore_dict": {"gcp": [(1, None)]}},
marks=[tier2],
),
pytest.param(
{
"interface": "CLI",
"backingstore_dict": {"aws": [(1, "eu-central-1")]},
},
{"interface": "CLI", "backingstore_dict": {"azure": [(1, None)]}},
marks=[tier1, pytest.mark.polarion_id("OCS-2679")],
),
pytest.param(
{
"interface": "OC",
"namespace_policy_dict": {
"type": "Single",
"namespacestore_dict": {"aws": [(1, "eu-central-1")]},
},
},
{
"interface": "OC",
"namespace_policy_dict": {
"type": "Single",
"namespacestore_dict": {"azure": [(1, None)]},
},
},
marks=[tier2],
),
pytest.param(
{
"interface": "OC",
"namespace_policy_dict": {
"type": "Single",
"namespacestore_dict": {"azure": [(1, None)]},
},
},
{
"interface": "CLI",
"backingstore_dict": {"gcp": [(1, None)]},
},
marks=[tier1],
),
],
ids=[
"AWStoAZURE-BS-OC",
"GCPtoAWS-BS-OC",
"AZUREtoCGP-BS-CLI",
"AWStoAZURE-BS-CLI",
"AWStoAZURE-NS-OC",
"AZUREtoGCP-NS-Hybrid",
],
)
def test_unidirectional_bucket_replication(
self,
awscli_pod_session,
mcg_obj_session,
bucket_factory,
source_bucketclass,
target_bucketclass,
):
"""
Test unidirectional bucket replication using CLI and YAML by adding objects
to a backingstore- and namespacestore-backed buckets
"""
> target_bucket_name = bucket_factory(bucketclass=target_bucketclass)[0].name
tests/manage/mcg/test_bucket_replication.py:121:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
tests/conftest.py:2557: in _create_buckets
bucketclass if bucketclass is None else bucket_class_factory(bucketclass)
ocs_ci/ocs/resources/bucketclass.py:169: in _create_bucket_class
for backingstore in backingstore_factory(
ocs_ci/ocs/resources/backingstore.py:349: in _create_backingstore
cmdMap[method.lower()][cloud.lower()](
ocs_ci/ocs/bucket_utils.py:602: in cli_create_azure_backingstore
mcg_obj.exec_mcg_cmd(
ocs_ci/ocs/resources/mcg.py:869: in exec_mcg_cmd
result = exec_cmd(
ocs_ci/utility/utils.py:607: in exec_cmd
completed_process = subprocess.run(
/usr/lib64/python3.8/subprocess.py:495: in run
stdout, stderr = process.communicate(input, timeout=timeout)
/usr/lib64/python3.8/subprocess.py:1028: in communicate
stdout, stderr = self._communicate(input, endtime, timeout)
/usr/lib64/python3.8/subprocess.py:1869: in _communicate
self._check_timeout(endtime, orig_timeout, stdout, stderr)
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
self = <subprocess.Popen object at 0x7f920d985df0>, endtime = 10075.34677407
orig_timeout = 600, stdout_seq = []
stderr_seq = [b'time="2022-12-08T15:39:44Z" level=info msg="\xe2\x9c\x85 Exists: NooBaa \\"noobaa\\"\\n"\n', b'time="2022-12-08T15:...re-backingstore-8f648f21765242bd99c78\\" Phase is \\"Creating\\": TemporaryError Target bucket doesn\'t exist"\n', ...]
skip_check_and_raise = False
def _check_timeout(self, endtime, orig_timeout, stdout_seq, stderr_seq,
skip_check_and_raise=False):
"""Convenience for checking if a timeout has expired."""
if endtime is None:
return
if skip_check_and_raise or _time() > endtime:
> raise TimeoutExpired(
self.args, orig_timeout,
output=b''.join(stdout_seq) if stdout_seq else None,
stderr=b''.join(stderr_seq) if stderr_seq else None)
E subprocess.TimeoutExpired: Command '['yes | /home/jenkins/workspace/qe-deploy-ocs-cluster-prod/ocs-ci/data/mcg-cli backingstore create azure-blob azure-backingstore-8f648f21765242bd99c78 --account-key ZoIEOXRWuTrGpRMHC0AOybbMEzycDjO35H8mWo0MmGJXcLZQOZmJWLSHvcbYs5PlnQb3iQO6BrebY/m7r1iYfQ== --account-name mcgtestingstorage --target-blob-container azure-uls-42da9b353ccb4fe6b87c27692a880e -n openshift-storage']' timed out after 600 seconds
/usr/lib64/python3.8/subprocess.py:1072: TimeoutExpired
``` | test | test unidirectional bucket replication failed with ubprocess timeoutexpired command timed out after second run details url run id test case test unidirectional bucket replication odf build ocp version job name ibm cloud ipi rhcos jenkins job logs url failure details message subprocess timeoutexpired command timed out after seconds type none text self awscli pod session mcg obj session bucket factory create buckets at source bucketclass backingstore dict aws interface cli target bucketclass backingstore dict azure interface cli pytest mark parametrize argnames argvalues pytest param interface oc backingstore dict aws interface oc backingstore dict azure marks pytest param interface oc backingstore dict gcp interface oc backingstore dict aws marks pytest param interface cli backingstore dict azure interface cli backingstore dict gcp marks pytest param interface cli backingstore dict aws interface cli backingstore dict azure marks pytest param interface oc namespace policy dict type single namespacestore dict aws interface oc namespace policy dict type single namespacestore dict azure marks pytest param interface oc namespace policy dict type single namespacestore dict azure interface cli backingstore dict gcp marks ids awstoazure bs oc gcptoaws bs oc azuretocgp bs cli awstoazure bs cli awstoazure ns oc azuretogcp ns hybrid def test unidirectional bucket replication self awscli pod session mcg obj session bucket factory source bucketclass target bucketclass test unidirectional bucket replication using cli and yaml by adding objects to a backingstore and namespacestore backed buckets target bucket name bucket factory bucketclass target bucketclass name tests manage mcg test bucket replication py tests conftest py in create buckets bucketclass if bucketclass is none else bucket class factory bucketclass ocs ci ocs resources bucketclass py in create bucket class for backingstore in backingstore factory ocs ci ocs resources backingstore py in create backingstore cmdmap ocs ci ocs bucket utils py in cli create azure backingstore mcg obj exec mcg cmd ocs ci ocs resources mcg py in exec mcg cmd result exec cmd ocs ci utility utils py in exec cmd completed process subprocess run usr subprocess py in run stdout stderr process communicate input timeout timeout usr subprocess py in communicate stdout stderr self communicate input endtime timeout usr subprocess py in communicate self check timeout endtime orig timeout stdout stderr self endtime orig timeout stdout seq stderr seq skip check and raise false def check timeout self endtime orig timeout stdout seq stderr seq skip check and raise false convenience for checking if a timeout has expired if endtime is none return if skip check and raise or time endtime raise timeoutexpired self args orig timeout output b join stdout seq if stdout seq else none stderr b join stderr seq if stderr seq else none e subprocess timeoutexpired command timed out after seconds usr subprocess py timeoutexpired | 1 |
130,820 | 10,660,942,945 | IssuesEvent | 2019-10-18 11:06:53 | elastic/logstash | https://api.github.com/repos/elastic/logstash | opened | Test failure: "Test Dead Letter Queue using pipelines.yml with multiple pipelines behaves like it can send 1000 documents to and index from the dlq should index all documents" | test failure |
```
11:51:00 Failures:
11:51:00
11:51:00 1) Test Dead Letter Queue using pipelines.yml with multiple pipelines behaves like it can send 1000 documents to and index from the dlq should index all documents
11:51:00 Failure/Error: Unable to find matching line from backtrace
11:51:00
11:51:00 expected: 1000
11:51:00 got: 962
11:51:00
11:51:00 (compared using ==)
11:51:00 Shared Example Group: "it can send 1000 documents to and index from the dlq" called from ./specs/dlq_spec.rb:93
11:51:00
11:51:00 Finished in 20 minutes 33 seconds (files took 7.85 seconds to load)
11:51:00 25 examples, 1 failure, 1 pending
11:51:00
11:51:00 Failed examples:
11:51:00
11:51:00 rspec './specs/dlq_spec.rb[1:1:1:1:1]' # Test Dead Letter Queue using pipelines.yml with multiple pipelines behaves like it can send 1000 documents to and index from the dlq should index all documents
11:51:00
11:51:00 Randomized with seed 46841
``` | 1.0 | Test failure: "Test Dead Letter Queue using pipelines.yml with multiple pipelines behaves like it can send 1000 documents to and index from the dlq should index all documents" -
```
11:51:00 Failures:
11:51:00
11:51:00 1) Test Dead Letter Queue using pipelines.yml with multiple pipelines behaves like it can send 1000 documents to and index from the dlq should index all documents
11:51:00 Failure/Error: Unable to find matching line from backtrace
11:51:00
11:51:00 expected: 1000
11:51:00 got: 962
11:51:00
11:51:00 (compared using ==)
11:51:00 Shared Example Group: "it can send 1000 documents to and index from the dlq" called from ./specs/dlq_spec.rb:93
11:51:00
11:51:00 Finished in 20 minutes 33 seconds (files took 7.85 seconds to load)
11:51:00 25 examples, 1 failure, 1 pending
11:51:00
11:51:00 Failed examples:
11:51:00
11:51:00 rspec './specs/dlq_spec.rb[1:1:1:1:1]' # Test Dead Letter Queue using pipelines.yml with multiple pipelines behaves like it can send 1000 documents to and index from the dlq should index all documents
11:51:00
11:51:00 Randomized with seed 46841
``` | test | test failure test dead letter queue using pipelines yml with multiple pipelines behaves like it can send documents to and index from the dlq should index all documents failures test dead letter queue using pipelines yml with multiple pipelines behaves like it can send documents to and index from the dlq should index all documents failure error unable to find matching line from backtrace expected got compared using shared example group it can send documents to and index from the dlq called from specs dlq spec rb finished in minutes seconds files took seconds to load examples failure pending failed examples rspec specs dlq spec rb test dead letter queue using pipelines yml with multiple pipelines behaves like it can send documents to and index from the dlq should index all documents randomized with seed | 1 |
511,215 | 14,856,338,847 | IssuesEvent | 2021-01-18 14:01:41 | renovatebot/renovate | https://api.github.com/repos/renovatebot/renovate | closed | Gradle dependency Version using variable and set() | manager:gradle manager:gradle-lite priority-3-normal type:feature | **What Renovate type, platform and version are you using?**
we are using https://gitlab.com/renovate-bot/renovate-runner/-/blob/master/templates/renovate.gitlab-ci.yml as an include in gitlab-ci
**Describe the bug**
When generating a sample project at start.pring.io for gradle im getting this (I already changed BOM as found in #4614 to platform()):
```
plugins {
id 'org.springframework.boot' version '2.4.1'
id 'io.spring.dependency-management' version '1.0.10.RELEASE'
id 'java'
}
group = 'com.example'
version = '0.0.1-SNAPSHOT'
sourceCompatibility = '11'
repositories {
mavenCentral()
}
ext {
set('springCloudVersion', "Hoxton.SR8")
}
dependencies {
implementation platform("org.springframework.cloud:spring-cloud-dependencies:${springCloudVersion}")
implementation 'org.springframework.cloud:spring-cloud-starter-sleuth'
testImplementation 'org.springframework.boot:spring-boot-starter-test'
}
test {
useJUnitPlatform()
}
```
Renovate fails to upgrade ` set('springCloudVersion', "Hoxton.SR8")`, using `springCloudVersion = "Hoxton.SR8"` it does work.
regex to match this : `set\(\s*['"](.+)['"]\s*,\s*['"](.+)['"]\s*\)` and replacement: `$1 = "$2"`
Is there any chance to get this gradle syntax supported?
**Relevant debug logs**
```
DEBUG: gradle.updateDependency(): packageFile:settings.gradle depName:org.springframework.cloud:spring-cloud-dependencies, version:Hoxton.SR8 ==> 2020.0.0 (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: gradle.updateDependency(): packageFile:build.gradle depName:org.springframework.cloud:spring-cloud-dependencies, version:Hoxton.SR8 ==> 2020.0.0 (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: No package files need updating (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: No updated lock files in branch (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: No files to commit (repository=23671976, branch=renovate/major-spring-cloud)
```
**Have you created a minimal reproduction repository?**
https://gitlab.com/vgropp/renovate-spring-gradle-sample
| 1.0 | Gradle dependency Version using variable and set() - **What Renovate type, platform and version are you using?**
we are using https://gitlab.com/renovate-bot/renovate-runner/-/blob/master/templates/renovate.gitlab-ci.yml as an include in gitlab-ci
**Describe the bug**
When generating a sample project at start.pring.io for gradle im getting this (I already changed BOM as found in #4614 to platform()):
```
plugins {
id 'org.springframework.boot' version '2.4.1'
id 'io.spring.dependency-management' version '1.0.10.RELEASE'
id 'java'
}
group = 'com.example'
version = '0.0.1-SNAPSHOT'
sourceCompatibility = '11'
repositories {
mavenCentral()
}
ext {
set('springCloudVersion', "Hoxton.SR8")
}
dependencies {
implementation platform("org.springframework.cloud:spring-cloud-dependencies:${springCloudVersion}")
implementation 'org.springframework.cloud:spring-cloud-starter-sleuth'
testImplementation 'org.springframework.boot:spring-boot-starter-test'
}
test {
useJUnitPlatform()
}
```
Renovate fails to upgrade ` set('springCloudVersion', "Hoxton.SR8")`, using `springCloudVersion = "Hoxton.SR8"` it does work.
regex to match this : `set\(\s*['"](.+)['"]\s*,\s*['"](.+)['"]\s*\)` and replacement: `$1 = "$2"`
Is there any chance to get this gradle syntax supported?
**Relevant debug logs**
```
DEBUG: gradle.updateDependency(): packageFile:settings.gradle depName:org.springframework.cloud:spring-cloud-dependencies, version:Hoxton.SR8 ==> 2020.0.0 (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: gradle.updateDependency(): packageFile:build.gradle depName:org.springframework.cloud:spring-cloud-dependencies, version:Hoxton.SR8 ==> 2020.0.0 (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: No package files need updating (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: No updated lock files in branch (repository=23671976, branch=renovate/major-spring-cloud)
DEBUG: No files to commit (repository=23671976, branch=renovate/major-spring-cloud)
```
**Have you created a minimal reproduction repository?**
https://gitlab.com/vgropp/renovate-spring-gradle-sample
| non_test | gradle dependency version using variable and set what renovate type platform and version are you using we are using as an include in gitlab ci describe the bug when generating a sample project at start pring io for gradle im getting this i already changed bom as found in to platform plugins id org springframework boot version id io spring dependency management version release id java group com example version snapshot sourcecompatibility repositories mavencentral ext set springcloudversion hoxton dependencies implementation platform org springframework cloud spring cloud dependencies springcloudversion implementation org springframework cloud spring cloud starter sleuth testimplementation org springframework boot spring boot starter test test usejunitplatform renovate fails to upgrade set springcloudversion hoxton using springcloudversion hoxton it does work regex to match this set s s s s and replacement is there any chance to get this gradle syntax supported relevant debug logs debug gradle updatedependency packagefile settings gradle depname org springframework cloud spring cloud dependencies version hoxton repository branch renovate major spring cloud debug gradle updatedependency packagefile build gradle depname org springframework cloud spring cloud dependencies version hoxton repository branch renovate major spring cloud debug no package files need updating repository branch renovate major spring cloud debug no updated lock files in branch repository branch renovate major spring cloud debug no files to commit repository branch renovate major spring cloud have you created a minimal reproduction repository | 0 |
230,374 | 18,546,606,571 | IssuesEvent | 2021-10-21 23:28:10 | dotnet/machinelearning-modelbuilder | https://api.github.com/repos/dotnet/machinelearning-modelbuilder | closed | Squiggles are not displayed for the code in errors in Notebook file. | Priority:1 Test Team Notebook | **System Information (please complete the following information):**
- Microsoft Visual Studio Enterprise 2022 Preview: 17.0.0 Preview 5.0
- ML.Net Model Builder: 16.8.3.2151403 (Main Branch)
- Notebook Editor [Preview]: 0.2.1.2151402
**Describe the bug**
- On which step of the process did you run into an issue: The problematic code in the cell.
**To Reproduce**
Steps to reproduce the behavior:
1. Select Create a new project from the Visual Studio 2022 start window;
2. Choose the C# Console App (.NET Core) project template with .Net 5.0;
3. Right click the ConsoleApp project>Add>New Item...>Notebook;
4. Write invalid code in the code cell, see that Squiggles are not displayed under the code.
**Expected behavior**
Display squiggles for the code in errors in Notebook file.
**Screenshots**
If applicable, add screenshots to help explain your problem.

**Additional context**
Work in VS Code.
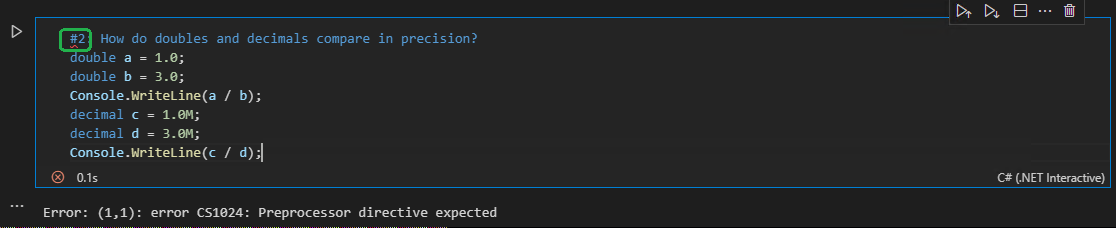
| 1.0 | Squiggles are not displayed for the code in errors in Notebook file. - **System Information (please complete the following information):**
- Microsoft Visual Studio Enterprise 2022 Preview: 17.0.0 Preview 5.0
- ML.Net Model Builder: 16.8.3.2151403 (Main Branch)
- Notebook Editor [Preview]: 0.2.1.2151402
**Describe the bug**
- On which step of the process did you run into an issue: The problematic code in the cell.
**To Reproduce**
Steps to reproduce the behavior:
1. Select Create a new project from the Visual Studio 2022 start window;
2. Choose the C# Console App (.NET Core) project template with .Net 5.0;
3. Right click the ConsoleApp project>Add>New Item...>Notebook;
4. Write invalid code in the code cell, see that Squiggles are not displayed under the code.
**Expected behavior**
Display squiggles for the code in errors in Notebook file.
**Screenshots**
If applicable, add screenshots to help explain your problem.

**Additional context**
Work in VS Code.
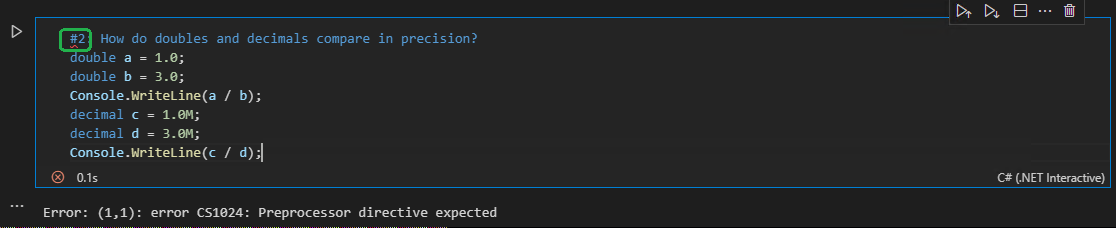
| test | squiggles are not displayed for the code in errors in notebook file system information please complete the following information microsoft visual studio enterprise preview preview ml net model builder main branch notebook editor describe the bug on which step of the process did you run into an issue the problematic code in the cell to reproduce steps to reproduce the behavior select create a new project from the visual studio start window choose the c console app net core project template with net right click the consoleapp project add new item notebook write invalid code in the code cell see that squiggles are not displayed under the code expected behavior display squiggles for the code in errors in notebook file screenshots if applicable add screenshots to help explain your problem additional context work in vs code | 1 |
49,974 | 6,288,950,632 | IssuesEvent | 2017-07-19 18:07:28 | roschaefer/story.board | https://api.github.com/repos/roschaefer/story.board | closed | tc Channel select: Sensorstory as a default | design Priority: medium User Story | As a reporter
I want sensorstory as the default channel
in order to save one click. | 1.0 | tc Channel select: Sensorstory as a default - As a reporter
I want sensorstory as the default channel
in order to save one click. | non_test | tc channel select sensorstory as a default as a reporter i want sensorstory as the default channel in order to save one click | 0 |
135,114 | 10,962,867,554 | IssuesEvent | 2019-11-27 18:15:26 | brave/brave-browser | https://api.github.com/repos/brave/brave-browser | opened | Chromium links are shown on toptiles on clean launch | QA/Test-Plan-Specified QA/Yes android-core-release | <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description
<!--Provide a brief description of the issue-->
Chromium links are shown on top tiles on clean launch
## Steps to Reproduce
<!--Please add a series of steps to reproduce the issue-->
1. Clean profile 2.0.0
2. Skip onboarding flow
3. Chromium links are shown on top tiles
## Actual result:
<!--Please add screenshots if needed-->
Chromium links are shown on top tiles on clean launch
## Expected result:
Chromium links shouldn't be shown on top tiles on clean launch
## Reproduces how often:
<!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
Always
## Brave version (brave://version info)
<!--For installed build, please copy Brave, Revision and OS from brave://version and paste here. If building from source please mention it along with brave://version details-->
Brave 2.0.0 Chromium 78.1.3.15
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current release? No
- Can you reproduce this issue with the beta channel? No
- Can you reproduce this issue with the dev channel? No
- Can you reproduce this issue with the nightly channel? No
## Other Additional Information:
- Does the issue resolve itself when disabling Brave Shields? NA
- Does the issue resolve itself when disabling Brave Rewards? NA
- Is the issue reproducible on the latest version of Chrome? NA
## Miscellaneous Information:
<!--Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue-->
cc: @brave/legacy_qa @emerick @yrliou @SergeyZhukovsky | 1.0 | Chromium links are shown on toptiles on clean launch - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description
<!--Provide a brief description of the issue-->
Chromium links are shown on top tiles on clean launch
## Steps to Reproduce
<!--Please add a series of steps to reproduce the issue-->
1. Clean profile 2.0.0
2. Skip onboarding flow
3. Chromium links are shown on top tiles
## Actual result:
<!--Please add screenshots if needed-->
Chromium links are shown on top tiles on clean launch
## Expected result:
Chromium links shouldn't be shown on top tiles on clean launch
## Reproduces how often:
<!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
Always
## Brave version (brave://version info)
<!--For installed build, please copy Brave, Revision and OS from brave://version and paste here. If building from source please mention it along with brave://version details-->
Brave 2.0.0 Chromium 78.1.3.15
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current release? No
- Can you reproduce this issue with the beta channel? No
- Can you reproduce this issue with the dev channel? No
- Can you reproduce this issue with the nightly channel? No
## Other Additional Information:
- Does the issue resolve itself when disabling Brave Shields? NA
- Does the issue resolve itself when disabling Brave Rewards? NA
- Is the issue reproducible on the latest version of Chrome? NA
## Miscellaneous Information:
<!--Any additional information, related issues, extra QA steps, configuration or data that might be necessary to reproduce the issue-->
cc: @brave/legacy_qa @emerick @yrliou @SergeyZhukovsky | test | chromium links are shown on toptiles on clean launch have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will only be reopened after sufficient info is provided description chromium links are shown on top tiles on clean launch steps to reproduce clean profile skip onboarding flow chromium links are shown on top tiles actual result chromium links are shown on top tiles on clean launch expected result chromium links shouldn t be shown on top tiles on clean launch reproduces how often always brave version brave version info brave chromium version channel information can you reproduce this issue with the current release no can you reproduce this issue with the beta channel no can you reproduce this issue with the dev channel no can you reproduce this issue with the nightly channel no other additional information does the issue resolve itself when disabling brave shields na does the issue resolve itself when disabling brave rewards na is the issue reproducible on the latest version of chrome na miscellaneous information cc brave legacy qa emerick yrliou sergeyzhukovsky | 1 |
48,328 | 5,954,082,896 | IssuesEvent | 2017-05-27 14:30:11 | lolmos/statictestting | https://api.github.com/repos/lolmos/statictestting | closed | Make all activities content and nav live | Activities section (1) Test | - [ ] Global nav changes (both languages)
- [ ] Ensure tabs are live (both languages)
- [ ] Ensure three sections and content pages are live (both languages)
- [ ] Test PDF links
- [ ] Check nothing else has broken in the process | 1.0 | Make all activities content and nav live - - [ ] Global nav changes (both languages)
- [ ] Ensure tabs are live (both languages)
- [ ] Ensure three sections and content pages are live (both languages)
- [ ] Test PDF links
- [ ] Check nothing else has broken in the process | test | make all activities content and nav live global nav changes both languages ensure tabs are live both languages ensure three sections and content pages are live both languages test pdf links check nothing else has broken in the process | 1 |
771,649 | 27,088,150,364 | IssuesEvent | 2023-02-14 18:37:41 | googleapis/google-cloud-ruby | https://api.github.com/repos/googleapis/google-cloud-ruby | closed | [Nightly CI Failures] Failures detected for google-cloud-spanner-v1 | type: bug priority: p1 nightly failure | At 2023-02-09 08:59:47 UTC, detected failures in google-cloud-spanner-v1 for: rubocop
report_key_ffba2d5871481bc08dc1434eb0d067c2 | 1.0 | [Nightly CI Failures] Failures detected for google-cloud-spanner-v1 - At 2023-02-09 08:59:47 UTC, detected failures in google-cloud-spanner-v1 for: rubocop
report_key_ffba2d5871481bc08dc1434eb0d067c2 | non_test | failures detected for google cloud spanner at utc detected failures in google cloud spanner for rubocop report key | 0 |
2,134 | 3,520,718,463 | IssuesEvent | 2016-01-12 22:02:10 | twosigma/beaker-notebook | https://api.github.com/repos/twosigma/beaker-notebook | closed | add option for location of prefs and temp files | Enhancement Infrastructure Priority High | this is especially important on windows in order to make a portable version of beaker that you can run from a thumb drive and does not modify any other volume.
this would be a cmd line, like --plugin-option and --public-server | 1.0 | add option for location of prefs and temp files - this is especially important on windows in order to make a portable version of beaker that you can run from a thumb drive and does not modify any other volume.
this would be a cmd line, like --plugin-option and --public-server | non_test | add option for location of prefs and temp files this is especially important on windows in order to make a portable version of beaker that you can run from a thumb drive and does not modify any other volume this would be a cmd line like plugin option and public server | 0 |
135,325 | 10,974,771,631 | IssuesEvent | 2019-11-29 09:54:16 | microsoft/vscode | https://api.github.com/repos/microsoft/vscode | closed | Smoke test failure: Debug stepOver, stepIn, stepOut | bug debug smoke-test | Insider version:
Version: 1.40.0-insider
Commit: c8846de84ab2f0a9279a41d80414465124c52a7a
Date: 2019-11-01T05:35:06.002Z
Electron: 6.1.2
Chrome: 76.0.3809.146
Node.js: 12.4.0
V8: 7.6.303.31-electron.0
OS: Linux x64 5.3.0-19-generic
Running Code
Debug
stepOver, stepIn, stepOut:
Error: Timeout: get elements 'div[id="workbench.view.debug"] .monaco-list-row .stack-frame' after 20 seconds.
at /home/dirkb/Projects/mseng/VSCode/vscode/test/automation/out/code.js:175:23
at Generator.next (<anonymous>)
at fulfilled (/home/dirkb/Projects/mseng/VSCode/vscode/test/automation/out/code.js:8:58)
| 1.0 | Smoke test failure: Debug stepOver, stepIn, stepOut - Insider version:
Version: 1.40.0-insider
Commit: c8846de84ab2f0a9279a41d80414465124c52a7a
Date: 2019-11-01T05:35:06.002Z
Electron: 6.1.2
Chrome: 76.0.3809.146
Node.js: 12.4.0
V8: 7.6.303.31-electron.0
OS: Linux x64 5.3.0-19-generic
Running Code
Debug
stepOver, stepIn, stepOut:
Error: Timeout: get elements 'div[id="workbench.view.debug"] .monaco-list-row .stack-frame' after 20 seconds.
at /home/dirkb/Projects/mseng/VSCode/vscode/test/automation/out/code.js:175:23
at Generator.next (<anonymous>)
at fulfilled (/home/dirkb/Projects/mseng/VSCode/vscode/test/automation/out/code.js:8:58)
| test | smoke test failure debug stepover stepin stepout insider version version insider commit date electron chrome node js electron os linux generic running code debug stepover stepin stepout error timeout get elements div monaco list row stack frame after seconds at home dirkb projects mseng vscode vscode test automation out code js at generator next at fulfilled home dirkb projects mseng vscode vscode test automation out code js | 1 |
506,399 | 14,664,253,821 | IssuesEvent | 2020-12-29 11:33:33 | bryntum/support | https://api.github.com/repos/bryntum/support | closed | Zooming in configuration demo breaks time axis | bug forum high-priority resolved | [Forum post](https://www.bryntum.com/forum/viewtopic.php?f=44&t=16217&p=80755)
https://www.bryntum.com/examples/scheduler/configuration/
If we run the above example(configuration), i found the time axis has left-over values
Steps
Click Zoom In
Check the time axis

If we scroll ahead it's seen that, it continues elsewhere too
 | 1.0 | Zooming in configuration demo breaks time axis - [Forum post](https://www.bryntum.com/forum/viewtopic.php?f=44&t=16217&p=80755)
https://www.bryntum.com/examples/scheduler/configuration/
If we run the above example(configuration), i found the time axis has left-over values
Steps
Click Zoom In
Check the time axis

If we scroll ahead it's seen that, it continues elsewhere too
 | non_test | zooming in configuration demo breaks time axis if we run the above example configuration i found the time axis has left over values steps click zoom in check the time axis if we scroll ahead it s seen that it continues elsewhere too | 0 |
133,190 | 10,799,399,573 | IssuesEvent | 2019-11-06 12:06:24 | bbc/simorgh | https://api.github.com/repos/bbc/simorgh | closed | Use more reliable selectors in AV e2e tests | Refinement Needed articles-av-epic articles-features-stream integration-testing ws-media-stream | **Is your feature request related to a problem? Please describe.**
We need a more robust way of selecting DOM nodes in our AV e2e tests. Using class selectors, when we don't control the the classes (Styled Components does), is fragile and sets us up for breakage.
**Describe the solution you'd like**
Explore the use of data attributes - there is already a precedence for `data-e2e=""` - and apply these to the relevant AV components. This will need a child Psammead issue.
**Describe alternatives you've considered**
N/A
**Testing notes**
[Tester to complete]
Dev insight: Will Cypress tests be required or are unit tests sufficient? Will there be any potential regression? etc
- [ ] This feature is expected to need manual testing.
**Additional context**
Add any other context or screenshots about the feature request here.
| 1.0 | Use more reliable selectors in AV e2e tests - **Is your feature request related to a problem? Please describe.**
We need a more robust way of selecting DOM nodes in our AV e2e tests. Using class selectors, when we don't control the the classes (Styled Components does), is fragile and sets us up for breakage.
**Describe the solution you'd like**
Explore the use of data attributes - there is already a precedence for `data-e2e=""` - and apply these to the relevant AV components. This will need a child Psammead issue.
**Describe alternatives you've considered**
N/A
**Testing notes**
[Tester to complete]
Dev insight: Will Cypress tests be required or are unit tests sufficient? Will there be any potential regression? etc
- [ ] This feature is expected to need manual testing.
**Additional context**
Add any other context or screenshots about the feature request here.
| test | use more reliable selectors in av tests is your feature request related to a problem please describe we need a more robust way of selecting dom nodes in our av tests using class selectors when we don t control the the classes styled components does is fragile and sets us up for breakage describe the solution you d like explore the use of data attributes there is already a precedence for data and apply these to the relevant av components this will need a child psammead issue describe alternatives you ve considered n a testing notes dev insight will cypress tests be required or are unit tests sufficient will there be any potential regression etc this feature is expected to need manual testing additional context add any other context or screenshots about the feature request here | 1 |
222,293 | 24,697,508,856 | IssuesEvent | 2022-10-19 13:11:10 | TreyM-WSS/ol-kit | https://api.github.com/repos/TreyM-WSS/ol-kit | opened | CVE-2022-37601 (High) detected in loader-utils-1.4.0.tgz | security vulnerability | ## CVE-2022-37601 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>loader-utils-1.4.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/loader-utils/package.json</p>
<p>
Dependency Hierarchy:
- babel-loader-8.0.6.tgz (Root Library)
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in function parseQuery in parseQuery.js in webpack loader-utils 2.0.0 via the name variable in parseQuery.js.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-37601>CVE-2022-37601</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution (loader-utils): 2.0.0</p>
<p>Direct dependency fix Resolution (babel-loader): 8.2.4</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2022-37601 (High) detected in loader-utils-1.4.0.tgz - ## CVE-2022-37601 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>loader-utils-1.4.0.tgz</b></p></summary>
<p>utils for webpack loaders</p>
<p>Library home page: <a href="https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz">https://registry.npmjs.org/loader-utils/-/loader-utils-1.4.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/loader-utils/package.json</p>
<p>
Dependency Hierarchy:
- babel-loader-8.0.6.tgz (Root Library)
- :x: **loader-utils-1.4.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Prototype pollution vulnerability in function parseQuery in parseQuery.js in webpack loader-utils 2.0.0 via the name variable in parseQuery.js.
<p>Publish Date: 2022-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-37601>CVE-2022-37601</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-10-12</p>
<p>Fix Resolution (loader-utils): 2.0.0</p>
<p>Direct dependency fix Resolution (babel-loader): 8.2.4</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_test | cve high detected in loader utils tgz cve high severity vulnerability vulnerable library loader utils tgz utils for webpack loaders library home page a href path to dependency file package json path to vulnerable library node modules loader utils package json dependency hierarchy babel loader tgz root library x loader utils tgz vulnerable library found in base branch master vulnerability details prototype pollution vulnerability in function parsequery in parsequery js in webpack loader utils via the name variable in parsequery js publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution loader utils direct dependency fix resolution babel loader rescue worker helmet automatic remediation is available for this issue | 0 |
307,770 | 26,561,698,992 | IssuesEvent | 2023-01-20 16:22:51 | nion-software/nionswift | https://api.github.com/repos/nion-software/nionswift | closed | Project items window | type - enhancement f - computations f - API f - inspector feature f - testing | This is a debugging/information tool for listing all internal objects in a minimal UI fashion.
This is almost required to move forward on more complex computations and data structures used in upcoming applications (such as elemental analysis).
- [x] nion-software/nionui#66
- [x] Implement default component handler registration in base Declarative.Handler
- [ ] List all referrers/containers of each component type
- [x] Register all component types and allow browsing
- [x] Allow component types to register a "best representation" handler
- [ ] Implement list/map/set property handlers
- [ ] Implement back/forward buttons in browser
- [ ] Implement tabs in project inspector for multiple paths in browser | 1.0 | Project items window - This is a debugging/information tool for listing all internal objects in a minimal UI fashion.
This is almost required to move forward on more complex computations and data structures used in upcoming applications (such as elemental analysis).
- [x] nion-software/nionui#66
- [x] Implement default component handler registration in base Declarative.Handler
- [ ] List all referrers/containers of each component type
- [x] Register all component types and allow browsing
- [x] Allow component types to register a "best representation" handler
- [ ] Implement list/map/set property handlers
- [ ] Implement back/forward buttons in browser
- [ ] Implement tabs in project inspector for multiple paths in browser | test | project items window this is a debugging information tool for listing all internal objects in a minimal ui fashion this is almost required to move forward on more complex computations and data structures used in upcoming applications such as elemental analysis nion software nionui implement default component handler registration in base declarative handler list all referrers containers of each component type register all component types and allow browsing allow component types to register a best representation handler implement list map set property handlers implement back forward buttons in browser implement tabs in project inspector for multiple paths in browser | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.