Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
186,532 | 14,396,548,408 | IssuesEvent | 2020-12-03 06:31:17 | apache/pulsar | https://api.github.com/repos/apache/pulsar | closed | [TEST] OverloadShedderTest fails on machines with non English locale | component/test flaky-tests help wanted triage/week-49 type/bug | **Describe the bug**
The test is failing due to unexpected formatting of decimal separators.
```
[ERROR] testPrintResourceUsage(org.apache.pulsar.broker.loadbalance.impl.OverloadShedderTest) Time elapsed: 0.04 s <<< FAILURE!
java.lang.AssertionError: expected [cpu: 10.00%, memory: 50.00%, directMemory: 90.00%, bandwidthIn: 30.00%, bandwidthOut: 20.00%] but found [cpu: 10,00%, memory: 50,00%, directMemory: 90,00%, bandwidthIn: 30,00%, bandwidthOut: 20,00%]
at org.testng.Assert.fail(Assert.java:99)
at org.testng.Assert.failNotEquals(Assert.java:1037)
at org.testng.Assert.assertEqualsImpl(Assert.java:140)
at org.testng.Assert.assertEquals(Assert.java:122)
at org.testng.Assert.assertEquals(Assert.java:629)
at org.testng.Assert.assertEquals(Assert.java:639)
at org.apache.pulsar.broker.loadbalance.impl.OverloadShedderTest.testPrintResourceUsage(OverloadShedderTest.java:202)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
at org.testng.internal.InvokeMethodRunnable.runOne(InvokeMethodRunnable.java:45)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:73)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:11)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:748)
```
**To Reproduce**
Run the tests on a machine with Italian locale
**Expected behavior**
The test should pass
| 2.0 | [TEST] OverloadShedderTest fails on machines with non English locale - **Describe the bug**
The test is failing due to unexpected formatting of decimal separators.
```
[ERROR] testPrintResourceUsage(org.apache.pulsar.broker.loadbalance.impl.OverloadShedderTest) Time elapsed: 0.04 s <<< FAILURE!
java.lang.AssertionError: expected [cpu: 10.00%, memory: 50.00%, directMemory: 90.00%, bandwidthIn: 30.00%, bandwidthOut: 20.00%] but found [cpu: 10,00%, memory: 50,00%, directMemory: 90,00%, bandwidthIn: 30,00%, bandwidthOut: 20,00%]
at org.testng.Assert.fail(Assert.java:99)
at org.testng.Assert.failNotEquals(Assert.java:1037)
at org.testng.Assert.assertEqualsImpl(Assert.java:140)
at org.testng.Assert.assertEquals(Assert.java:122)
at org.testng.Assert.assertEquals(Assert.java:629)
at org.testng.Assert.assertEquals(Assert.java:639)
at org.apache.pulsar.broker.loadbalance.impl.OverloadShedderTest.testPrintResourceUsage(OverloadShedderTest.java:202)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:132)
at org.testng.internal.InvokeMethodRunnable.runOne(InvokeMethodRunnable.java:45)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:73)
at org.testng.internal.InvokeMethodRunnable.call(InvokeMethodRunnable.java:11)
at java.util.concurrent.FutureTask.run(FutureTask.java:266)
at java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1149)
at java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:624)
at java.lang.Thread.run(Thread.java:748)
```
**To Reproduce**
Run the tests on a machine with Italian locale
**Expected behavior**
The test should pass
| test | overloadsheddertest fails on machines with non english locale describe the bug the test is failing due to unexpected formatting of decimal separators testprintresourceusage org apache pulsar broker loadbalance impl overloadsheddertest time elapsed s failure java lang assertionerror expected but found at org testng assert fail assert java at org testng assert failnotequals assert java at org testng assert assertequalsimpl assert java at org testng assert assertequals assert java at org testng assert assertequals assert java at org testng assert assertequals assert java at org apache pulsar broker loadbalance impl overloadsheddertest testprintresourceusage overloadsheddertest java at sun reflect nativemethodaccessorimpl native method at sun reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at sun reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal invokemethodrunnable runone invokemethodrunnable java at org testng internal invokemethodrunnable call invokemethodrunnable java at org testng internal invokemethodrunnable call invokemethodrunnable java at java util concurrent futuretask run futuretask java at java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java lang thread run thread java to reproduce run the tests on a machine with italian locale expected behavior the test should pass | 1 |
52,938 | 6,287,001,000 | IssuesEvent | 2017-07-19 14:09:50 | apache/couchdb | https://api.github.com/repos/apache/couchdb | closed | JS test: replication did not cancel correctly | replication testsuite | @nickva you might want to take a look at this one.
## Makefile output
```
test/javascript/tests/replication.js
Error: expected 'null', got '{"node":"node1@127.0.0.1","pid":"<0.13402.3>","changes_pending":null,"checkpoint_interval":30000,"checkpointed_source_seq":"5-g1AAAAIreJyV0FEKwiAYB3DbguqpI9QJYjrXp0_tJqVTWWPZU891k7pJ3aRuslwGK8ZgQ1DQ7_-DvyVCaJqHCs3tUWmcYgKryC1cuodAILmoqqrIQzE6uIsJz6Sbwu3xTkIu3S43XwV9FMhowphUaHaySpu91ao7n9b57V9eiLUCMP3yuzp__muRUGriiAxoYcduRxd3OOhaS4FvwjmhEA-Wbl66N50yI4jkvFcnbzy88WyMiLFEAx5gvLzx-zcEICPQThVvi7qNnQ","continuous":true,"database":null,"doc_id":null,"doc_write_failures":0,"docs_read":5,"docs_written":5,"missing_revisions_found":5,"replication_id":"cf3a9ef1437e08d66706fbf0d77e148b+continuous+create_target","revisions_checked":5,"source":"http://127.0.0.1:15984/test_suite_db_jqsznub_src/","source_seq":"5-g1AAAAIreJyV0FEKwiAYB3DbguqpI9QJYjrXp0_tJqVTWWPZU891k7pJ3aRuslwGK8ZgQ1DQ7_-DvyVCaJqHCs3tUWmcYgKryC1cuodAILmoqqrIQzE6uIsJz6Sbwu3xTkIu3S43XwV9FMhowphUaHaySpu91ao7n9b57V9eiLUCMP3yuzp__muRUGriiAxoYcduRxd3OOhaS4FvwjmhEA-Wbl66N50yI4jkvFcnbzy88WyMiLFEAx5gvLzx-zcEICPQThVvi7qNnQ","started_on":1498697053,"target":"http://127.0.0.1:15984/test_suite_db_iqkzcel_tgt/","through_seq":"5-g1AAAAIreJyV0FEKwiAYB3DbguqpI9QJYjrXp0_tJqVTWWPZU891k7pJ3aRuslwGK8ZgQ1DQ7_-DvyVCaJqHCs3tUWmcYgKryC1cuodAILmoqqrIQzE6uIsJz6Sbwu3xTkIu3S43XwV9FMhowphUaHaySpu91ao7n9b57V9eiLUCMP3yuzp__muRUGriiAxoYcduRxd3OOhaS4FvwjmhEA-Wbl66N50yI4jkvFcnbzy88WyMiLFEAx5gvLzx-zcEICPQThVvi7qNnQ","type":"replication","updated_on":1498697054,"user":null}'
321: test/javascript/couch_test_runner.js
TEquals(null,[object Object],"Replication was canceled")
1828: test/javascript/tests/replication.js
()
37: test/javascript/cli_runner.js
runTest()
48: test/javascript/cli_runner.js
```
## Instance(s)
* https://builds.apache.org/blue/organizations/jenkins/CouchDB/detail/master/43/pipeline/50
* https://couchdb-vm2.apache.org/ci_errorlogs/jenkins-couchdb-43-2017-06-29T00:44:15.560348/couchlog.tar.gz
| 1.0 | JS test: replication did not cancel correctly - @nickva you might want to take a look at this one.
## Makefile output
```
test/javascript/tests/replication.js
Error: expected 'null', got '{"node":"node1@127.0.0.1","pid":"<0.13402.3>","changes_pending":null,"checkpoint_interval":30000,"checkpointed_source_seq":"5-g1AAAAIreJyV0FEKwiAYB3DbguqpI9QJYjrXp0_tJqVTWWPZU891k7pJ3aRuslwGK8ZgQ1DQ7_-DvyVCaJqHCs3tUWmcYgKryC1cuodAILmoqqrIQzE6uIsJz6Sbwu3xTkIu3S43XwV9FMhowphUaHaySpu91ao7n9b57V9eiLUCMP3yuzp__muRUGriiAxoYcduRxd3OOhaS4FvwjmhEA-Wbl66N50yI4jkvFcnbzy88WyMiLFEAx5gvLzx-zcEICPQThVvi7qNnQ","continuous":true,"database":null,"doc_id":null,"doc_write_failures":0,"docs_read":5,"docs_written":5,"missing_revisions_found":5,"replication_id":"cf3a9ef1437e08d66706fbf0d77e148b+continuous+create_target","revisions_checked":5,"source":"http://127.0.0.1:15984/test_suite_db_jqsznub_src/","source_seq":"5-g1AAAAIreJyV0FEKwiAYB3DbguqpI9QJYjrXp0_tJqVTWWPZU891k7pJ3aRuslwGK8ZgQ1DQ7_-DvyVCaJqHCs3tUWmcYgKryC1cuodAILmoqqrIQzE6uIsJz6Sbwu3xTkIu3S43XwV9FMhowphUaHaySpu91ao7n9b57V9eiLUCMP3yuzp__muRUGriiAxoYcduRxd3OOhaS4FvwjmhEA-Wbl66N50yI4jkvFcnbzy88WyMiLFEAx5gvLzx-zcEICPQThVvi7qNnQ","started_on":1498697053,"target":"http://127.0.0.1:15984/test_suite_db_iqkzcel_tgt/","through_seq":"5-g1AAAAIreJyV0FEKwiAYB3DbguqpI9QJYjrXp0_tJqVTWWPZU891k7pJ3aRuslwGK8ZgQ1DQ7_-DvyVCaJqHCs3tUWmcYgKryC1cuodAILmoqqrIQzE6uIsJz6Sbwu3xTkIu3S43XwV9FMhowphUaHaySpu91ao7n9b57V9eiLUCMP3yuzp__muRUGriiAxoYcduRxd3OOhaS4FvwjmhEA-Wbl66N50yI4jkvFcnbzy88WyMiLFEAx5gvLzx-zcEICPQThVvi7qNnQ","type":"replication","updated_on":1498697054,"user":null}'
321: test/javascript/couch_test_runner.js
TEquals(null,[object Object],"Replication was canceled")
1828: test/javascript/tests/replication.js
()
37: test/javascript/cli_runner.js
runTest()
48: test/javascript/cli_runner.js
```
## Instance(s)
* https://builds.apache.org/blue/organizations/jenkins/CouchDB/detail/master/43/pipeline/50
* https://couchdb-vm2.apache.org/ci_errorlogs/jenkins-couchdb-43-2017-06-29T00:44:15.560348/couchlog.tar.gz
| test | js test replication did not cancel correctly nickva you might want to take a look at this one makefile output test javascript tests replication js error expected null got node pid changes pending null checkpoint interval checkpointed source seq continuous true database null doc id null doc write failures docs read docs written missing revisions found replication id continuous create target revisions checked source test javascript couch test runner js tequals null replication was canceled test javascript tests replication js test javascript cli runner js runtest test javascript cli runner js instance s | 1 |
191,570 | 14,594,787,215 | IssuesEvent | 2020-12-20 08:00:41 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | kubeup/kube-aliyun: vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go; 3 LoC | fresh test tiny vendored |
Found a possible issue in [kubeup/kube-aliyun](https://www.github.com/kubeup/kube-aliyun) at [vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go](https://github.com/kubeup/kube-aliyun/blob/54e3b167f343aff686bd9c979792c1e0434b0b08/vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go#L31-L33)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to subnet at line 32 may start a goroutine
[Click here to see the code in its original context.](https://github.com/kubeup/kube-aliyun/blob/54e3b167f343aff686bd9c979792c1e0434b0b08/vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go#L31-L33)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, subnet := range allSubnets {
PrintSubnet(t, &subnet)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 54e3b167f343aff686bd9c979792c1e0434b0b08
| 1.0 | kubeup/kube-aliyun: vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go; 3 LoC -
Found a possible issue in [kubeup/kube-aliyun](https://www.github.com/kubeup/kube-aliyun) at [vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go](https://github.com/kubeup/kube-aliyun/blob/54e3b167f343aff686bd9c979792c1e0434b0b08/vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go#L31-L33)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to subnet at line 32 may start a goroutine
[Click here to see the code in its original context.](https://github.com/kubeup/kube-aliyun/blob/54e3b167f343aff686bd9c979792c1e0434b0b08/vendor/github.com/gophercloud/gophercloud/acceptance/openstack/networking/v2/subnets_test.go#L31-L33)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, subnet := range allSubnets {
PrintSubnet(t, &subnet)
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 54e3b167f343aff686bd9c979792c1e0434b0b08
| test | kubeup kube aliyun vendor github com gophercloud gophercloud acceptance openstack networking subnets test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to subnet at line may start a goroutine click here to show the line s of go which triggered the analyzer go for subnet range allsubnets printsubnet t subnet leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
183,530 | 21,765,529,440 | IssuesEvent | 2022-05-13 01:05:10 | Nivaskumark/system_bt | https://api.github.com/repos/Nivaskumark/system_bt | opened | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0: 28 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p></summary>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-0103](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2021-0474](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2020-0225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2021-0316](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r26 | ❌ |
| [CVE-2021-0507](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2021-0968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-12.0.0_r16 | ❌ |
| [CVE-2020-0449](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r12 | ❌ |
| [CVE-2021-39674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2020-0129](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2021-0589](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r39 | ❌ |
| [CVE-2021-0431](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2021-0435](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2020-0463](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2020-0413](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2020-0377](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4 | ❌ |
| [CVE-2020-0176](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0176) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2021-0522](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0522) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2020-0196](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0196) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0379) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.7 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-8.0.0_r50 | ❌ |
| [CVE-2020-0185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0185) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2022-20010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20010) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-12.1.0_r5 | ❌ |
| [CVE-2019-2226](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2226) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2020-0149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0149) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0145) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0146) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0147) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0148) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0144) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
## Details
> Partial details (15 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0103</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_aac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_aac_decoder_cleanup of a2dp_aac_decoder.cc, there is a possible invalid free due to memory corruption. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-9Android ID: A-148107188
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103>CVE-2020-0103</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0474</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds write due to a heap buffer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-177611958
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474>CVE-2021-0474</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0225</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_vendor_ldac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_vendor_ldac_decoder_decode_packet of a2dp_vendor_ldac_decoder.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546668
<p>Publish Date: 2020-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225>CVE-2020-0225</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0316</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_pars_vendor_cmd of avrc_pars_tg.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-11, Android-8.0, Android-8.1, Android-9, Android-10; Android ID: A-168802990.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316>CVE-2021-0316</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r26</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0507</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In handle_rc_metamsg_cmd of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-181860042
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507>CVE-2021-0507</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-06-01">https://source.android.com/security/bulletin/2021-06-01</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution: android-11.0.0_r38</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0968</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/osi/src/allocator.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In osi_malloc and osi_calloc of allocator.cc, there is a possible out of bounds write due to an integer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-197868577
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968>CVE-2021-0968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r16</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0449</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_disconnected of btm_sec.cc, there is a possible memory corruption due to a use after free. This could lead to remote code execution in the Bluetooth server with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-162497143
<p>Publish Date: 2020-11-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449>CVE-2020-0449</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-11.0.0_r12</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-39674</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_connected and btm_sec_disconnected of btm_sec.cc file , there is a possible use after free. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12Android ID: A-201083442
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674>CVE-2021-39674</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0129</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_ble_multi_adv.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SetData of btm_ble_multi_adv.cc, there is a possible out-of-bound write due to an incorrect bounds check. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-123292010
<p>Publish Date: 2020-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129>CVE-2020-0129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37</a></p>
<p>Release Date: 2020-06-11</p>
<p>Fix Resolution: android-10.0.0_r37</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0589</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_acl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In BTM_TryAllocateSCN of btm_scn.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-180939982
<p>Publish Date: 2021-07-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589>CVE-2021-0589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-07-01">https://source.android.com/security/bulletin/2021-07-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r39</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0431</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure to a paired device with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174149901
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431>CVE-2021-0431</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0435</summary>
### Vulnerable Libraries - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_proc_vendor_command of avrc_api.cc, there is a possible leak of heap data due to uninitialized data. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174150451
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435>CVE-2021-0435</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0463</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/sdp/sdp_server.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In sdp_server_handle_client_req of sdp_server.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.0 Android-8.1 Android-9Android ID: A-169342531
<p>Publish Date: 2020-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463>CVE-2020-0463</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0413</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158778659
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413>CVE-2020-0413</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0377</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158833854
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377>CVE-2020-0377</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks">https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0103","vulnerabilityDetails":"In a2dp_aac_decoder_cleanup of a2dp_aac_decoder.cc, there is a possible invalid free due to memory corruption. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-9Android ID: A-148107188","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0474","vulnerabilityDetails":"In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds write due to a heap buffer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-177611958","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0225","vulnerabilityDetails":"In a2dp_vendor_ldac_decoder_decode_packet of a2dp_vendor_ldac_decoder.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546668","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0316","vulnerabilityDetails":"In avrc_pars_vendor_cmd of avrc_pars_tg.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-11, Android-8.0, Android-8.1, Android-9, Android-10; Android ID: A-168802990.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0507","vulnerabilityDetails":"In handle_rc_metamsg_cmd of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-181860042","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Adjacent","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0968","vulnerabilityDetails":"In osi_malloc and osi_calloc of allocator.cc, there is a possible out of bounds write due to an integer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-197868577","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0449","vulnerabilityDetails":"In btm_sec_disconnected of btm_sec.cc, there is a possible memory corruption due to a use after free. This could lead to remote code execution in the Bluetooth server with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-162497143","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-39674","vulnerabilityDetails":"In btm_sec_connected and btm_sec_disconnected of btm_sec.cc file , there is a possible use after free. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12Android ID: A-201083442","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0129","vulnerabilityDetails":"In SetData of btm_ble_multi_adv.cc, there is a possible out-of-bound write due to an incorrect bounds check. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-123292010","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0589","vulnerabilityDetails":"In BTM_TryAllocateSCN of btm_scn.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-180939982","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0431","vulnerabilityDetails":"In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure to a paired device with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174149901","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0435","vulnerabilityDetails":"In avrc_proc_vendor_command of avrc_api.cc, there is a possible leak of heap data due to uninitialized data. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174150451","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0463","vulnerabilityDetails":"In sdp_server_handle_client_req of sdp_server.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.0 Android-8.1 Android-9Android ID: A-169342531","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0413","vulnerabilityDetails":"In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158778659","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0377","vulnerabilityDetails":"In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158833854","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0176","vulnerabilityDetails":"In avdt_msg_prs_rej of avdt_msg.cc, there is a possible out-of-bounds read due to improper input validation. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-79702484","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0176","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0522","vulnerabilityDetails":"In ConnectionHandler::SdpCb of connection_handler.cc, there is a possible out of bounds read due to a use after free. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-9 Android-10Android ID: A-174182139","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0522","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0196","vulnerabilityDetails":"In RegisterNotificationResponse::GetEvent of register_notification_packet.cc, there is a possible abort due to improper input validation. This could lead to remote denial of service of the Bluetooth service, over Bluetooth, with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-144066833","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0196","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Adjacent","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0379","vulnerabilityDetails":"In the Bluetooth service, there is a possible spoofing attack due to a logic error. This could lead to remote information disclosure of sensitive information with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10 Android-11Android ID: A-150156492","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0379","cvss3Severity":"medium","cvss3Score":"5.7","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Adjacent","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0185","vulnerabilityDetails":"In avrc_pars_browsing_cmd of avrc_pars_tg.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-79945152","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0185","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-20010","vulnerabilityDetails":"In l2cble_process_sig_cmd of l2c_ble.cc, there is a possible out of bounds read due to an incorrect bounds check. This could lead to remote information disclosure through Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12LAndroid ID: A-213519176","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20010","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-2226","vulnerabilityDetails":"In device_class_to_int of device_class.cc, there is a possible out of bounds read due to improper casting. This could lead to local information disclosure in the Bluetooth server with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-140152619","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2226","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0149","vulnerabilityDetails":"In btu_hcif_mode_change_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142544089","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0149","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0145","vulnerabilityDetails":"In btm_simple_pair_complete of btm_sec.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142544079","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0145","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0146","vulnerabilityDetails":"In btu_hcif_hardware_error_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546561","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0146","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0147","vulnerabilityDetails":"In btu_hcif_esco_connection_chg_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142638392","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0147","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0148","vulnerabilityDetails":"In btu_hcif_pin_code_request_evt, btu_hcif_link_key_request_evt, and btu_hcif_link_key_notification_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142638492","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0148","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0144","vulnerabilityDetails":"In btm_proc_sp_req_evt of btm_sec.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142543497","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0144","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0: 28 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p></summary>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
</p>
</p></p>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2020-0103](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2021-0474](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r36 | ❌ |
| [CVE-2020-0225](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2021-0316](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r26 | ❌ |
| [CVE-2021-0507](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2021-0968](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-12.0.0_r16 | ❌ |
| [CVE-2020-0449](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r12 | ❌ |
| [CVE-2021-39674](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2020-0129](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2021-0589](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.8 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r39 | ❌ |
| [CVE-2021-0431](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2021-0435](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r34 | ❌ |
| [CVE-2020-0463](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2020-0413](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | N/A | ❌ |
| [CVE-2020-0377](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4 | ❌ |
| [CVE-2020-0176](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0176) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2021-0522](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0522) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 7.5 | multiple | Direct | android-11.0.0_r38 | ❌ |
| [CVE-2020-0196](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0196) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0379](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0379) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.7 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-8.0.0_r50 | ❌ |
| [CVE-2020-0185](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0185) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2022-20010](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20010) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-12.1.0_r5 | ❌ |
| [CVE-2019-2226](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2226) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-8.0.0_r41;android-8.1.0_r71;android-9.0.0_r51;android-10.0.0_r17 | ❌ |
| [CVE-2020-0149](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0149) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0145](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0145) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0146](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0146) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0147](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0147) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0148](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0148) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
| [CVE-2020-0144](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0144) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 4.4 | https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0 | Direct | android-10.0.0_r37 | ❌ |
## Details
> Partial details (15 vulnerabilities) are displayed below due to a content size limitation in GitHub. To view information on the remaining vulnerabilities, navigate to the WhiteSource Application.<br>
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0103</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_aac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_aac_decoder_cleanup of a2dp_aac_decoder.cc, there is a possible invalid free due to memory corruption. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-9Android ID: A-148107188
<p>Publish Date: 2020-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103>CVE-2020-0103</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0474</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds write due to a heap buffer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-177611958
<p>Publish Date: 2021-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474>CVE-2021-0474</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-05-01">https://source.android.com/security/bulletin/2021-05-01</a></p>
<p>Release Date: 2021-06-11</p>
<p>Fix Resolution: android-11.0.0_r36</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0225</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/a2dp/a2dp_vendor_ldac_decoder.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In a2dp_vendor_ldac_decoder_decode_packet of a2dp_vendor_ldac_decoder.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546668
<p>Publish Date: 2020-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225>CVE-2020-0225</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0316</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_pars_vendor_cmd of avrc_pars_tg.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-11, Android-8.0, Android-8.1, Android-9, Android-10; Android ID: A-168802990.
<p>Publish Date: 2021-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316>CVE-2021-0316</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r26</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r26</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0507</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_pars_tg.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In handle_rc_metamsg_cmd of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-181860042
<p>Publish Date: 2021-06-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507>CVE-2021-0507</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Adjacent
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-06-01">https://source.android.com/security/bulletin/2021-06-01</a></p>
<p>Release Date: 2021-06-21</p>
<p>Fix Resolution: android-11.0.0_r38</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0968</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/osi/src/allocator.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In osi_malloc and osi_calloc of allocator.cc, there is a possible out of bounds write due to an integer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-197868577
<p>Publish Date: 2021-12-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968>CVE-2021-0968</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-0968</a></p>
<p>Release Date: 2021-12-15</p>
<p>Fix Resolution: android-12.0.0_r16</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0449</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_disconnected of btm_sec.cc, there is a possible memory corruption due to a use after free. This could lead to remote code execution in the Bluetooth server with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-162497143
<p>Publish Date: 2020-11-10
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449>CVE-2020-0449</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-11.0.0_r12</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-11.0.0_r12</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-39674</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_sec.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In btm_sec_connected and btm_sec_disconnected of btm_sec.cc file , there is a possible use after free. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12Android ID: A-201083442
<p>Publish Date: 2022-02-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674>CVE-2021-39674</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0129</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_ble_multi_adv.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In SetData of btm_ble_multi_adv.cc, there is a possible out-of-bound write due to an incorrect bounds check. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-123292010
<p>Publish Date: 2020-06-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129>CVE-2020-0129</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37">https://android.googlesource.com/platform/system/bt/+/refs/tags/android-10.0.0_r37</a></p>
<p>Release Date: 2020-06-11</p>
<p>Fix Resolution: android-10.0.0_r37</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0589</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/btm/btm_acl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In BTM_TryAllocateSCN of btm_scn.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-180939982
<p>Publish Date: 2021-07-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589>CVE-2021-0589</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-07-01">https://source.android.com/security/bulletin/2021-07-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r39</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0431</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/avrc/avrc_api.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure to a paired device with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174149901
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431>CVE-2021-0431</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-0435</summary>
### Vulnerable Libraries - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b>, <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
</p>
<p></p>
### Vulnerability Details
<p>
In avrc_proc_vendor_command of avrc_api.cc, there is a possible leak of heap data due to uninitialized data. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174150451
<p>Publish Date: 2021-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435>CVE-2021-0435</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://source.android.com/security/bulletin/2021-04-01">https://source.android.com/security/bulletin/2021-04-01</a></p>
<p>Release Date: 2020-11-07</p>
<p>Fix Resolution: android-11.0.0_r34</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0463</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/sdp/sdp_server.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In sdp_server_handle_client_req of sdp_server.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.0 Android-8.1 Android-9Android ID: A-169342531
<p>Publish Date: 2020-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463>CVE-2020-0463</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0413</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158778659
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413>CVE-2020-0413</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2020-0377</summary>
### Vulnerable Library - <b>https://source.codeaurora.org/quic/la/platform/system/bt/LA.AU.0.1.1.r1-04800-gen3meta.0</b></p>
<p>
<p>Library home page: <a href=https://source.codeaurora.org/quic/la/platform/system/bt/>https://source.codeaurora.org/quic/la/platform/system/bt/</a></p>
<p>Found in base branch: <b>master</b></p></p>
</p></p>
### Vulnerable Source Files (1)
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/stack/gatt/gatt_cl.cc</b>
</p>
<p></p>
</p>
<p></p>
### Vulnerability Details
<p>
In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158833854
<p>Publish Date: 2020-10-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377>CVE-2020-0377</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>7.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks">https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-9.0.0_r61,https://android.googlesource.com/platform/frameworks/opt/net/wifi/+/refs/tags/android-10.0.0_r46,https://android.googlesource.com/platform/frameworks</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: android-9.0.0_r61,android-10.0.0_r46, android-11.0.0_r4</p>
</p>
<p></p>
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0103","vulnerabilityDetails":"In a2dp_aac_decoder_cleanup of a2dp_aac_decoder.cc, there is a possible invalid free due to memory corruption. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-9Android ID: A-148107188","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0103","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0474","vulnerabilityDetails":"In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds write due to a heap buffer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-177611958","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0474","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0225","vulnerabilityDetails":"In a2dp_vendor_ldac_decoder_decode_packet of a2dp_vendor_ldac_decoder.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546668","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0225","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0316","vulnerabilityDetails":"In avrc_pars_vendor_cmd of avrc_pars_tg.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation. Product: Android; Versions: Android-11, Android-8.0, Android-8.1, Android-9, Android-10; Android ID: A-168802990.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0316","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0507","vulnerabilityDetails":"In handle_rc_metamsg_cmd of btif_rc.cc, there is a possible out of bounds write due to a missing bounds check. This could lead to remote code execution over Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-181860042","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0507","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Adjacent","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0968","vulnerabilityDetails":"In osi_malloc and osi_calloc of allocator.cc, there is a possible out of bounds write due to an integer overflow. This could lead to remote code execution with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12 Android-9Android ID: A-197868577","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0968","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0449","vulnerabilityDetails":"In btm_sec_disconnected of btm_sec.cc, there is a possible memory corruption due to a use after free. This could lead to remote code execution in the Bluetooth server with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-9 Android-10 Android-11 Android-8.0 Android-8.1Android ID: A-162497143","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0449","cvss3Severity":"high","cvss3Score":"8.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Network","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-39674","vulnerabilityDetails":"In btm_sec_connected and btm_sec_disconnected of btm_sec.cc file , there is a possible use after free. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-12Android ID: A-201083442","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-39674","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0129","vulnerabilityDetails":"In SetData of btm_ble_multi_adv.cc, there is a possible out-of-bound write due to an incorrect bounds check. This could lead to local escalation of privilege with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-123292010","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0129","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0589","vulnerabilityDetails":"In BTM_TryAllocateSCN of btm_scn.cc, there is a possible out of bounds write due to an incorrect bounds check. This could lead to local escalation of privilege with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-180939982","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0589","cvss3Severity":"high","cvss3Score":"7.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"High"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0431","vulnerabilityDetails":"In avrc_msg_cback of avrc_api.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure to a paired device with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174149901","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0431","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0435","vulnerabilityDetails":"In avrc_proc_vendor_command of avrc_api.cc, there is a possible leak of heap data due to uninitialized data. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-8.1 Android-9 Android-10Android ID: A-174150451","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0435","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0463","vulnerabilityDetails":"In sdp_server_handle_client_req of sdp_server.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10 Android-11 Android-8.0 Android-8.1 Android-9Android ID: A-169342531","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0463","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0413","vulnerabilityDetails":"In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158778659","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0413","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0377","vulnerabilityDetails":"In gatt_process_read_by_type_rsp of gatt_cl.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to remote information disclosure in the Bluetooth server with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.1 Android-9 Android-10 Android-11 Android-8.0Android ID: A-158833854","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0377","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0176","vulnerabilityDetails":"In avdt_msg_prs_rej of avdt_msg.cc, there is a possible out-of-bounds read due to improper input validation. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-79702484","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0176","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-0522","vulnerabilityDetails":"In ConnectionHandler::SdpCb of connection_handler.cc, there is a possible out of bounds read due to a use after free. This could lead to remote information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-11 Android-9 Android-10Android ID: A-174182139","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-0522","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0196","vulnerabilityDetails":"In RegisterNotificationResponse::GetEvent of register_notification_packet.cc, there is a possible abort due to improper input validation. This could lead to remote denial of service of the Bluetooth service, over Bluetooth, with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-144066833","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0196","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Adjacent","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0379","vulnerabilityDetails":"In the Bluetooth service, there is a possible spoofing attack due to a logic error. This could lead to remote information disclosure of sensitive information with no additional execution privileges needed. User interaction is needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10 Android-11Android ID: A-150156492","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0379","cvss3Severity":"medium","cvss3Score":"5.7","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"Required","AV":"Adjacent","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0185","vulnerabilityDetails":"In avrc_pars_browsing_cmd of avrc_pars_tg.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-79945152","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0185","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-20010","vulnerabilityDetails":"In l2cble_process_sig_cmd of l2c_ble.cc, there is a possible out of bounds read due to an incorrect bounds check. This could lead to remote information disclosure through Bluetooth with no additional execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-12 Android-12LAndroid ID: A-213519176","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-20010","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"Required","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2019-2226","vulnerabilityDetails":"In device_class_to_int of device_class.cc, there is a possible out of bounds read due to improper casting. This could lead to local information disclosure in the Bluetooth server with User execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-8.0 Android-8.1 Android-9 Android-10Android ID: A-140152619","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-2226","cvss3Severity":"medium","cvss3Score":"5.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"Low","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0149","vulnerabilityDetails":"In btu_hcif_mode_change_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142544089","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0149","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0145","vulnerabilityDetails":"In btm_simple_pair_complete of btm_sec.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142544079","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0145","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0146","vulnerabilityDetails":"In btu_hcif_hardware_error_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142546561","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0146","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0147","vulnerabilityDetails":"In btu_hcif_esco_connection_chg_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142638392","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0147","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0148","vulnerabilityDetails":"In btu_hcif_pin_code_request_evt, btu_hcif_link_key_request_evt, and btu_hcif_link_key_notification_evt of btu_hcif.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142638492","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0148","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-0144","vulnerabilityDetails":"In btm_proc_sp_req_evt of btm_sec.cc, there is a possible out of bounds read due to a missing bounds check. This could lead to local information disclosure via compromised device firmware with System execution privileges needed. User interaction is not needed for exploitation.Product: AndroidVersions: Android-10Android ID: A-142543497","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-0144","cvss3Severity":"medium","cvss3Score":"4.4","cvss3Metrics":{"A":"None","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Local","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_test | vulnerabilities highest severity is vulnerable library library home page a href vulnerable source files stack avrc avrc pars tg cc vulnerabilities cve severity cvss dependency type fixed in remediation available high direct n a high direct android high direct n a high direct android high direct android high direct android high direct android high direct n a high direct android high direct android high direct android high multiple direct android high direct n a high direct n a high direct android android android high direct android high multiple direct android medium direct android medium direct android medium direct android medium direct android medium direct android android android android medium direct android medium direct android medium direct android medium direct android medium direct android medium direct android details partial details vulnerabilities are displayed below due to a content size limitation in github to view information on the remaining vulnerabilities navigate to the whitesource application cve vulnerable library library home page a href found in base branch master vulnerable source files stack aac decoder cc vulnerability details in aac decoder cleanup of aac decoder cc there is a possible invalid free due to memory corruption this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack avrc avrc api cc vulnerability details in avrc msg cback of avrc api cc there is a possible out of bounds write due to a heap buffer overflow this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack vendor ldac decoder cc vulnerability details in vendor ldac decoder decode packet of vendor ldac decoder cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack avrc avrc pars tg cc vulnerability details in avrc pars vendor cmd of avrc pars tg cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product android versions android android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack avrc avrc pars tg cc vulnerability details in handle rc metamsg cmd of btif rc cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector adjacent attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files osi src allocator cc vulnerability details in osi malloc and osi calloc of allocator cc there is a possible out of bounds write due to an integer overflow this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack btm btm sec cc vulnerability details in btm sec disconnected of btm sec cc there is a possible memory corruption due to a use after free this could lead to remote code execution in the bluetooth server with no additional execution privileges needed user interaction is needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack btm btm sec cc vulnerability details in btm sec connected and btm sec disconnected of btm sec cc file there is a possible use after free this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack btm btm ble multi adv cc vulnerability details in setdata of btm ble multi adv cc there is a possible out of bound write due to an incorrect bounds check this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack btm btm acl cc vulnerability details in btm tryallocatescn of btm scn cc there is a possible out of bounds write due to an incorrect bounds check this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack avrc avrc api cc vulnerability details in avrc msg cback of avrc api cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure to a paired device with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable libraries vulnerability details in avrc proc vendor command of avrc api cc there is a possible leak of heap data due to uninitialized data this could lead to remote information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack sdp sdp server cc vulnerability details in sdp server handle client req of sdp server cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack gatt gatt cl cc vulnerability details in gatt process read by type rsp of gatt cl cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure in the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href step up your open source security game with whitesource cve vulnerable library library home page a href found in base branch master vulnerable source files stack gatt gatt cl cc vulnerability details in gatt process read by type rsp of gatt cl cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure in the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution android android android step up your open source security game with whitesource basebranches vulnerabilityidentifier cve vulnerabilitydetails in aac decoder cleanup of aac decoder cc there is a possible invalid free due to memory corruption this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in avrc msg cback of avrc api cc there is a possible out of bounds write due to a heap buffer overflow this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in vendor ldac decoder decode packet of vendor ldac decoder cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in avrc pars vendor cmd of avrc pars tg cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product android versions android android android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in handle rc metamsg cmd of btif rc cc there is a possible out of bounds write due to a missing bounds check this could lead to remote code execution over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in osi malloc and osi calloc of allocator cc there is a possible out of bounds write due to an integer overflow this could lead to remote code execution with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btm sec disconnected of btm sec cc there is a possible memory corruption due to a use after free this could lead to remote code execution in the bluetooth server with no additional execution privileges needed user interaction is needed for exploitation product androidversions android android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btm sec connected and btm sec disconnected of btm sec cc file there is a possible use after free this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in setdata of btm ble multi adv cc there is a possible out of bound write due to an incorrect bounds check this could lead to local escalation of privilege with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btm tryallocatescn of btm scn cc there is a possible out of bounds write due to an incorrect bounds check this could lead to local escalation of privilege with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in avrc msg cback of avrc api cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure to a paired device with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in avrc proc vendor command of avrc api cc there is a possible leak of heap data due to uninitialized data this could lead to remote information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in sdp server handle client req of sdp server cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure from the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in gatt process read by type rsp of gatt cl cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure in the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in gatt process read by type rsp of gatt cl cc there is a possible out of bounds read due to a missing bounds check this could lead to remote information disclosure in the bluetooth server with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in avdt msg prs rej of avdt msg cc there is a possible out of bounds read due to improper input validation this could lead to remote information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in connectionhandler sdpcb of connection handler cc there is a possible out of bounds read due to a use after free this could lead to remote information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in registernotificationresponse getevent of register notification packet cc there is a possible abort due to improper input validation this could lead to remote denial of service of the bluetooth service over bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in the bluetooth service there is a possible spoofing attack due to a logic error this could lead to remote information disclosure of sensitive information with no additional execution privileges needed user interaction is needed for exploitation product androidversions android android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in avrc pars browsing cmd of avrc pars tg cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in process sig cmd of ble cc there is a possible out of bounds read due to an incorrect bounds check this could lead to remote information disclosure through bluetooth with no additional execution privileges needed user interaction is not needed for exploitation product androidversions android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in device class to int of device class cc there is a possible out of bounds read due to improper casting this could lead to local information disclosure in the bluetooth server with user execution privileges needed user interaction is not needed for exploitation product androidversions android android android android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btu hcif mode change evt of btu hcif cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure via compromised device firmware with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btm simple pair complete of btm sec cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure via compromised device firmware with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btu hcif hardware error evt of btu hcif cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure via compromised device firmware with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btu hcif esco connection chg evt of btu hcif cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure via compromised device firmware with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btu hcif pin code request evt btu hcif link key request evt and btu hcif link key notification evt of btu hcif cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure via compromised device firmware with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl basebranches vulnerabilityidentifier cve vulnerabilitydetails in btm proc sp req evt of btm sec cc there is a possible out of bounds read due to a missing bounds check this could lead to local information disclosure via compromised device firmware with system execution privileges needed user interaction is not needed for exploitation product androidversions android id a vulnerabilityurl | 0 |
94,859 | 11,935,976,793 | IssuesEvent | 2020-04-02 09:30:56 | the-tale/the-tale | https://api.github.com/repos/the-tale/the-tale | opened | Эмиссары: обновление эффектов мероприятий | comp_emissary cont_game_designe est_medium type_improvement | Обновление эффектов мероприятий сейчас работает несогласованно.
Сила мероприятия замораживается при его создании. Однако если включается бонус протектората и эффект пересоздаётся (например, эмиссар был лидером, перестал им быть и снова стал), то мероприятие получит бонус.
В целом замораживание мероприятий выглядит непонятно и необосновано.
Необходимо синхронизировать эффекты мероприятий во время их мониторинга. | 1.0 | Эмиссары: обновление эффектов мероприятий - Обновление эффектов мероприятий сейчас работает несогласованно.
Сила мероприятия замораживается при его создании. Однако если включается бонус протектората и эффект пересоздаётся (например, эмиссар был лидером, перестал им быть и снова стал), то мероприятие получит бонус.
В целом замораживание мероприятий выглядит непонятно и необосновано.
Необходимо синхронизировать эффекты мероприятий во время их мониторинга. | non_test | эмиссары обновление эффектов мероприятий обновление эффектов мероприятий сейчас работает несогласованно сила мероприятия замораживается при его создании однако если включается бонус протектората и эффект пересоздаётся например эмиссар был лидером перестал им быть и снова стал то мероприятие получит бонус в целом замораживание мероприятий выглядит непонятно и необосновано необходимо синхронизировать эффекты мероприятий во время их мониторинга | 0 |
458,253 | 13,171,807,447 | IssuesEvent | 2020-08-11 17:18:48 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | torch.orgqr aborts and core dump | high priority module: numpy module: operators topic: crash triaged | ## 🐛 Bug
`torch.orgqr` aborts and core dump when inputs are having some random dimensions. It seems there's a lack of input validity check and proper memory management.
<!-- A clear and concise description of what the bug is. -->
## To Reproduce
```python
import torch
import numpy as np
input = torch.tensor(np.random.rand(14,7))
input2 = torch.tensor(np.random.rand(12,6))
torch.orgqr(input, input2)
```
Run the above code snippet multiple times could get different errors.
> free(): invalid size
Aborted (core dumped)
> malloc(): memory corruption
Aborted (core dumped)
Changing the dimensions slightly could also get other errors:
```python
import torch
import numpy as np
input = torch.tensor(np.random.rand(14,7))
input2 = torch.tensor(np.random.rand(12,16)) # changed here
torch.orgqr(input, input2)
```
> corrupted size vs. prev_size
Aborted (core dumped)
Using different numbers as dimensions could cause other errors, such as:
> double free or corruption (out)
> malloc_consolidate(): invalid chunk size
> corrupted double-linked list
It seems the memory management is not done properly.
<!-- If you have a code sample, error messages, stack traces, please provide it here as well -->
## Expected behavior
Should not abort and core dump.
<!-- A clear and concise description of what you expected to happen. -->
## Environment
Please copy and paste the output from our
[environment collection script](https://raw.githubusercontent.com/pytorch/pytorch/master/torch/utils/collect_env.py)
(or fill out the checklist below manually).
You can get the script and run it with:
```
wget https://raw.githubusercontent.com/pytorch/pytorch/master/torch/utils/collect_env.py
# For security purposes, please check the contents of collect_env.py before running it.
python collect_env.py
```
PyTorch version: 1.5.0
Is debug build: No
CUDA used to build PyTorch: 10.1
OS: Ubuntu 18.04.4 LTS
GCC version: Could not collect
CMake version: version 3.14.0
Python version: 3.7
Is CUDA available: No
CUDA runtime version: No CUDA
GPU models and configuration: No CUDA
Nvidia driver version: No CUDA
cuDNN version: No CUDA
Versions of relevant libraries:
[pip] numpy==1.18.1
[pip] torch==1.5.0
[pip] torchvision==0.6.0a0+82fd1c8
[conda] blas 1.0 mkl
[conda] cudatoolkit 10.1.243 h6bb024c_0
[conda] mkl 2020.1 217
[conda] mkl-include 2020.1 217
[conda] mkl-service 2.3.0 py37he904b0f_0
[conda] mkl_fft 1.0.15 py37ha843d7b_0
[conda] mkl_random 1.1.0 py37hd6b4f25_0
[conda] numpy 1.18.1 py37h4f9e942_0
[conda] numpy-base 1.18.1 py37hde5b4d6_1
[conda] pytorch 1.5.0 py3.7_cuda10.1.243_cudnn7.6.3_0 pytorch
[conda] torchvision 0.6.0 py37_cu101 pytorch
## Additional context
<!-- Add any other context about the problem here. -->
cc @ezyang @gchanan @zou3519 @mruberry @rgommers | 1.0 | torch.orgqr aborts and core dump - ## 🐛 Bug
`torch.orgqr` aborts and core dump when inputs are having some random dimensions. It seems there's a lack of input validity check and proper memory management.
<!-- A clear and concise description of what the bug is. -->
## To Reproduce
```python
import torch
import numpy as np
input = torch.tensor(np.random.rand(14,7))
input2 = torch.tensor(np.random.rand(12,6))
torch.orgqr(input, input2)
```
Run the above code snippet multiple times could get different errors.
> free(): invalid size
Aborted (core dumped)
> malloc(): memory corruption
Aborted (core dumped)
Changing the dimensions slightly could also get other errors:
```python
import torch
import numpy as np
input = torch.tensor(np.random.rand(14,7))
input2 = torch.tensor(np.random.rand(12,16)) # changed here
torch.orgqr(input, input2)
```
> corrupted size vs. prev_size
Aborted (core dumped)
Using different numbers as dimensions could cause other errors, such as:
> double free or corruption (out)
> malloc_consolidate(): invalid chunk size
> corrupted double-linked list
It seems the memory management is not done properly.
<!-- If you have a code sample, error messages, stack traces, please provide it here as well -->
## Expected behavior
Should not abort and core dump.
<!-- A clear and concise description of what you expected to happen. -->
## Environment
Please copy and paste the output from our
[environment collection script](https://raw.githubusercontent.com/pytorch/pytorch/master/torch/utils/collect_env.py)
(or fill out the checklist below manually).
You can get the script and run it with:
```
wget https://raw.githubusercontent.com/pytorch/pytorch/master/torch/utils/collect_env.py
# For security purposes, please check the contents of collect_env.py before running it.
python collect_env.py
```
PyTorch version: 1.5.0
Is debug build: No
CUDA used to build PyTorch: 10.1
OS: Ubuntu 18.04.4 LTS
GCC version: Could not collect
CMake version: version 3.14.0
Python version: 3.7
Is CUDA available: No
CUDA runtime version: No CUDA
GPU models and configuration: No CUDA
Nvidia driver version: No CUDA
cuDNN version: No CUDA
Versions of relevant libraries:
[pip] numpy==1.18.1
[pip] torch==1.5.0
[pip] torchvision==0.6.0a0+82fd1c8
[conda] blas 1.0 mkl
[conda] cudatoolkit 10.1.243 h6bb024c_0
[conda] mkl 2020.1 217
[conda] mkl-include 2020.1 217
[conda] mkl-service 2.3.0 py37he904b0f_0
[conda] mkl_fft 1.0.15 py37ha843d7b_0
[conda] mkl_random 1.1.0 py37hd6b4f25_0
[conda] numpy 1.18.1 py37h4f9e942_0
[conda] numpy-base 1.18.1 py37hde5b4d6_1
[conda] pytorch 1.5.0 py3.7_cuda10.1.243_cudnn7.6.3_0 pytorch
[conda] torchvision 0.6.0 py37_cu101 pytorch
## Additional context
<!-- Add any other context about the problem here. -->
cc @ezyang @gchanan @zou3519 @mruberry @rgommers | non_test | torch orgqr aborts and core dump 🐛 bug torch orgqr aborts and core dump when inputs are having some random dimensions it seems there s a lack of input validity check and proper memory management to reproduce python import torch import numpy as np input torch tensor np random rand torch tensor np random rand torch orgqr input run the above code snippet multiple times could get different errors free invalid size aborted core dumped malloc memory corruption aborted core dumped changing the dimensions slightly could also get other errors python import torch import numpy as np input torch tensor np random rand torch tensor np random rand changed here torch orgqr input corrupted size vs prev size aborted core dumped using different numbers as dimensions could cause other errors such as double free or corruption out malloc consolidate invalid chunk size corrupted double linked list it seems the memory management is not done properly expected behavior should not abort and core dump environment please copy and paste the output from our or fill out the checklist below manually you can get the script and run it with wget for security purposes please check the contents of collect env py before running it python collect env py pytorch version is debug build no cuda used to build pytorch os ubuntu lts gcc version could not collect cmake version version python version is cuda available no cuda runtime version no cuda gpu models and configuration no cuda nvidia driver version no cuda cudnn version no cuda versions of relevant libraries numpy torch torchvision blas mkl cudatoolkit mkl mkl include mkl service mkl fft mkl random numpy numpy base pytorch pytorch torchvision pytorch additional context cc ezyang gchanan mruberry rgommers | 0 |
262,129 | 22,796,523,341 | IssuesEvent | 2022-07-10 20:02:24 | aws-observability/aws-otel-collector | https://api.github.com/repos/aws-observability/aws-otel-collector | closed | Support multiple regions for test in canary, CD, CI | stale testing-integ ADOT Test Framework | **Description**:
Currently, some of the tests are bounded to one region. However, we can separate these tests such as the integration test in two regions: us-west-2 and us-east-2. This will help us in increasing the capacities/ quota for each resource. My intention was to get all the ec2-test in region us-east-2 and other platform such as eks, ecs on region us-west-2.
**Progress**:
Able to code review and merge the PR successfully; however, it [cannot passed the integration test](https://github.com/aws-observability/aws-otel-collector/actions/runs/1729002494) with the CI even though I have tested it locally.
Things I have tried:
- Try different regions such as us-east-1 but still failed
- Try using apply twice since there [was an issue with data sources](https://github.com/hashicorp/terraform/issues/17034) which find resource during "refresh stage".
**Errors**:
VPC and Security Group not found | 2.0 | Support multiple regions for test in canary, CD, CI - **Description**:
Currently, some of the tests are bounded to one region. However, we can separate these tests such as the integration test in two regions: us-west-2 and us-east-2. This will help us in increasing the capacities/ quota for each resource. My intention was to get all the ec2-test in region us-east-2 and other platform such as eks, ecs on region us-west-2.
**Progress**:
Able to code review and merge the PR successfully; however, it [cannot passed the integration test](https://github.com/aws-observability/aws-otel-collector/actions/runs/1729002494) with the CI even though I have tested it locally.
Things I have tried:
- Try different regions such as us-east-1 but still failed
- Try using apply twice since there [was an issue with data sources](https://github.com/hashicorp/terraform/issues/17034) which find resource during "refresh stage".
**Errors**:
VPC and Security Group not found | test | support multiple regions for test in canary cd ci description currently some of the tests are bounded to one region however we can separate these tests such as the integration test in two regions us west and us east this will help us in increasing the capacities quota for each resource my intention was to get all the test in region us east and other platform such as eks ecs on region us west progress able to code review and merge the pr successfully however it with the ci even though i have tested it locally things i have tried try different regions such as us east but still failed try using apply twice since there which find resource during refresh stage errors vpc and security group not found | 1 |
449,236 | 12,965,580,735 | IssuesEvent | 2020-07-20 22:41:04 | SchulIT/idp | https://api.github.com/repos/SchulIT/idp | closed | Aktuelles Passwort prüfen bei Passwort-Änderung | Priority: High Type: Enhancement | Aktuell wird das aktuelle Passwort bei einer Passwortänderung nicht überprüft. Um die Sicherheit zu erhöhen, sollte auch das aktuelle Passwort überprüft werden. | 1.0 | Aktuelles Passwort prüfen bei Passwort-Änderung - Aktuell wird das aktuelle Passwort bei einer Passwortänderung nicht überprüft. Um die Sicherheit zu erhöhen, sollte auch das aktuelle Passwort überprüft werden. | non_test | aktuelles passwort prüfen bei passwort änderung aktuell wird das aktuelle passwort bei einer passwortänderung nicht überprüft um die sicherheit zu erhöhen sollte auch das aktuelle passwort überprüft werden | 0 |
284,813 | 24,624,140,010 | IssuesEvent | 2022-10-16 09:41:01 | dotnet/efcore | https://api.github.com/repos/dotnet/efcore | closed | Improve end-to-end experience of annotating model and flowing thru migrations to schema | area-test closed-out-of-scope | Spun off from https://github.com/aspnet/EntityFramework/issues/5297 (flowing `[Description]` into SQL Server extended properties).
| 1.0 | Improve end-to-end experience of annotating model and flowing thru migrations to schema - Spun off from https://github.com/aspnet/EntityFramework/issues/5297 (flowing `[Description]` into SQL Server extended properties).
| test | improve end to end experience of annotating model and flowing thru migrations to schema spun off from flowing into sql server extended properties | 1 |
103,080 | 16,601,975,476 | IssuesEvent | 2021-06-01 20:51:48 | samq-ghdemo/SEARCH-NCJIS-nibrs | https://api.github.com/repos/samq-ghdemo/SEARCH-NCJIS-nibrs | opened | CVE-2020-14060 (High) detected in multiple libraries | security vulnerability | ## CVE-2020-14060 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.10.jar</b>, <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.8.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: SEARCH-NCJIS-nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/jackson-databind-2.8.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.10/jackson-databind-2.8.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.10.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-validation/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,SEARCH-NCJIS-nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/jackson-databind-2.9.6.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-flatfile/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/SEARCH-NCJIS-nibrs/commit/2643373aa9a184ff4ea81e98caf4009bf2ee8e91">2643373aa9a184ff4ea81e98caf4009bf2ee8e91</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oadd.org.apache.xalan.lib.sql.JNDIConnectionPool (aka apache/drill).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060>CVE-2020-14060</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.10","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.8.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter-json:2.1.5.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","packageFilePaths":["/tools/nibrs-validation/pom.xml","/tools/nibrs-staging-data/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-summary-report/pom.xml","/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.5","packageFilePaths":["/tools/nibrs-flatfile/pom.xml","/tools/nibrs-validate-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;com.fasterxml.jackson.core:jackson-databind:2.9.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-14060","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oadd.org.apache.xalan.lib.sql.JNDIConnectionPool (aka apache/drill).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-14060 (High) detected in multiple libraries - ## CVE-2020-14060 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.8.10.jar</b>, <b>jackson-databind-2.9.8.jar</b>, <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.8.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-fbi-service/pom.xml</p>
<p>Path to vulnerable library: SEARCH-NCJIS-nibrs/tools/nibrs-fbi-service/target/nibrs-fbi-service-1.0.0/WEB-INF/lib/jackson-databind-2.8.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.10/jackson-databind-2.8.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.8.10.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.8.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-summary-report-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.8/jackson-databind-2.9.8.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.1.5.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.1.5.RELEASE.jar
- :x: **jackson-databind-2.9.8.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-validation/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,SEARCH-NCJIS-nibrs/web/nibrs-web/target/nibrs-web/WEB-INF/lib/jackson-databind-2.9.6.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.6/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: SEARCH-NCJIS-nibrs/tools/nibrs-flatfile/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- tika-parsers-1.18.jar (Root Library)
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/SEARCH-NCJIS-nibrs/commit/2643373aa9a184ff4ea81e98caf4009bf2ee8e91">2643373aa9a184ff4ea81e98caf4009bf2ee8e91</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oadd.org.apache.xalan.lib.sql.JNDIConnectionPool (aka apache/drill).
<p>Publish Date: 2020-06-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060>CVE-2020-14060</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14060</a></p>
<p>Release Date: 2020-06-14</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.10.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.10","packageFilePaths":["/tools/nibrs-fbi-service/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.8.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.8","packageFilePaths":["/tools/nibrs-summary-report-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.1.5.RELEASE;org.springframework.boot:spring-boot-starter-json:2.1.5.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.9.8","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.6","packageFilePaths":["/tools/nibrs-validation/pom.xml","/tools/nibrs-staging-data/pom.xml","/tools/nibrs-staging-data-common/pom.xml","/tools/nibrs-xmlfile/pom.xml","/tools/nibrs-route/pom.xml","/tools/nibrs-summary-report/pom.xml","/web/nibrs-web/pom.xml"],"isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"},{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.5","packageFilePaths":["/tools/nibrs-flatfile/pom.xml","/tools/nibrs-validate-common/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.tika:tika-parsers:1.18;com.fasterxml.jackson.core:jackson-databind:2.9.5","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.10.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-14060","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to oadd.org.apache.xalan.lib.sql.JNDIConnectionPool (aka apache/drill).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14060","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file search ncjis nibrs tools nibrs fbi service pom xml path to vulnerable library search ncjis nibrs tools nibrs fbi service target nibrs fbi service web inf lib jackson databind jar canner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file search ncjis nibrs tools nibrs summary report common pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file search ncjis nibrs tools nibrs validation pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar search ncjis nibrs web nibrs web target nibrs web web inf lib jackson databind jar canner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file search ncjis nibrs tools nibrs flatfile pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy tika parsers jar root library x jackson databind jar vulnerable library found in head commit a href found in base branch master vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to oadd org apache xalan lib sql jndiconnectionpool aka apache drill publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework boot spring boot starter json release com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency false dependencytree com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind packagetype java groupid com fasterxml jackson core packagename jackson databind packageversion packagefilepaths istransitivedependency true dependencytree org apache tika tika parsers com fasterxml jackson core jackson databind isminimumfixversionavailable true minimumfixversion com fasterxml jackson core jackson databind basebranches vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to oadd org apache xalan lib sql jndiconnectionpool aka apache drill vulnerabilityurl | 0 |
4,667 | 7,293,705,387 | IssuesEvent | 2018-02-25 16:50:13 | ErikMast3r/Exclusiv-Altis-Life-new | https://api.github.com/repos/ErikMast3r/Exclusiv-Altis-Life-new | opened | Weitere Kompatibilitätsarbeiten durchführen | area/compatibility mod area/missionfile kind/bug fix kind/optimization | - [ ] alle neuen Modfahrzeuge mit Blaulicht und Sirene ausstatten
- [ ] Defibrilator kaufbar machen | True | Weitere Kompatibilitätsarbeiten durchführen - - [ ] alle neuen Modfahrzeuge mit Blaulicht und Sirene ausstatten
- [ ] Defibrilator kaufbar machen | non_test | weitere kompatibilitätsarbeiten durchführen alle neuen modfahrzeuge mit blaulicht und sirene ausstatten defibrilator kaufbar machen | 0 |
770,784 | 27,056,503,954 | IssuesEvent | 2023-02-13 16:30:30 | matrixorigin/matrixone | https://api.github.com/repos/matrixorigin/matrixone | closed | [Feature Request]: Support more date and time function | priority/p0 kind/feature source/on-demand | ### Is there an existing issue for the same feature request?
- [X] I have checked the existing issues.
### Is your feature request related to a problem?
_No response_
### Describe the feature you'd like
YEAR(date/datetime/timestamp), return the year of the given date/datetime/timestamp.
MONTH(date/datetime/timestamp), return the month of the given date/datetime/timestamp.
DAY(date/datetime/timestamp), return the day of the given date/datetime/timestamp.
HOUR(date/datetime/timestamp), return the hour of the given date/datetime/timestamp.
MINUTE(date/datetime/timestamp), return the minute of the given date/datetime/timestamp.
SECOND(date/datetime/timestamp), return the second of the given date/datetime/timestamp.
Example
create table t1(a datetime);
insert into t1 values('2022-01-01 12:03:12');
select year(a) from t1;
+---------+
| year(a) |
+---------+
| 2022 |
+---------+
mysql> select month(a) from t1;
+----------+
| month(a) |
+----------+
| 1 |
+----------+
select day(a) from t1;
+--------+
| day(a) |
+--------+
| 1 |
+--------+
1 row in set (0.00 sec)
select hour(a) from t1;
+---------+
| hour(a) |
+---------+
| 12 |
+---------+
1 row in set (0.00 sec)
select minute(a) from t1;
+-----------+
| minute(a) |
+-----------+
| 3 |
+-----------+
select second(a) from t1;
+-----------+
| second(a) |
+-----------+
| 12 |
+-----------+
### Describe implementation you've considered
_No response_
### Documentation, Adoption, Use Case, Migration Strategy
_No response_
### Additional information
_No response_ | 1.0 | [Feature Request]: Support more date and time function - ### Is there an existing issue for the same feature request?
- [X] I have checked the existing issues.
### Is your feature request related to a problem?
_No response_
### Describe the feature you'd like
YEAR(date/datetime/timestamp), return the year of the given date/datetime/timestamp.
MONTH(date/datetime/timestamp), return the month of the given date/datetime/timestamp.
DAY(date/datetime/timestamp), return the day of the given date/datetime/timestamp.
HOUR(date/datetime/timestamp), return the hour of the given date/datetime/timestamp.
MINUTE(date/datetime/timestamp), return the minute of the given date/datetime/timestamp.
SECOND(date/datetime/timestamp), return the second of the given date/datetime/timestamp.
Example
create table t1(a datetime);
insert into t1 values('2022-01-01 12:03:12');
select year(a) from t1;
+---------+
| year(a) |
+---------+
| 2022 |
+---------+
mysql> select month(a) from t1;
+----------+
| month(a) |
+----------+
| 1 |
+----------+
select day(a) from t1;
+--------+
| day(a) |
+--------+
| 1 |
+--------+
1 row in set (0.00 sec)
select hour(a) from t1;
+---------+
| hour(a) |
+---------+
| 12 |
+---------+
1 row in set (0.00 sec)
select minute(a) from t1;
+-----------+
| minute(a) |
+-----------+
| 3 |
+-----------+
select second(a) from t1;
+-----------+
| second(a) |
+-----------+
| 12 |
+-----------+
### Describe implementation you've considered
_No response_
### Documentation, Adoption, Use Case, Migration Strategy
_No response_
### Additional information
_No response_ | non_test | support more date and time function is there an existing issue for the same feature request i have checked the existing issues is your feature request related to a problem no response describe the feature you d like year date datetime timestamp return the year of the given date datetime timestamp month date datetime timestamp return the month of the given date datetime timestamp day date datetime timestamp return the day of the given date datetime timestamp hour date datetime timestamp return the hour of the given date datetime timestamp minute date datetime timestamp return the minute of the given date datetime timestamp second date datetime timestamp return the second of the given date datetime timestamp example create table a datetime insert into values select year a from year a mysql select month a from month a select day a from day a row in set sec select hour a from hour a row in set sec select minute a from minute a select second a from second a describe implementation you ve considered no response documentation adoption use case migration strategy no response additional information no response | 0 |
136,223 | 19,724,725,999 | IssuesEvent | 2022-01-13 18:46:31 | backdrop/backdrop-issues | https://api.github.com/repos/backdrop/backdrop-issues | closed | [UX] "Add another item" buttons are hard to distinguish from the field label | type - bug report status - has pull request good first issue design pr - ready to be committed pr - works for me | This was reported by @bradbulger in #3516 along with other, related issues. Separating it to its own issue here:
> These started as comments from a client, I largely agree though. The overall point is that once the content types get to a certain level of complexity, the node forms begin to look awkward in the default Seven styles. Buttons and other elements that are there for the user to perform some kind of action aren't always easy to see and tell what they are.
>
>For instance, on a text field with unlimited values, the "ADD ANOTHER ITEM" button is the same size, shape, and color as the field title. ... If you have several of these fields in a form, it gets confusing visually.

D8 for comparison:
 | 1.0 | [UX] "Add another item" buttons are hard to distinguish from the field label - This was reported by @bradbulger in #3516 along with other, related issues. Separating it to its own issue here:
> These started as comments from a client, I largely agree though. The overall point is that once the content types get to a certain level of complexity, the node forms begin to look awkward in the default Seven styles. Buttons and other elements that are there for the user to perform some kind of action aren't always easy to see and tell what they are.
>
>For instance, on a text field with unlimited values, the "ADD ANOTHER ITEM" button is the same size, shape, and color as the field title. ... If you have several of these fields in a form, it gets confusing visually.

D8 for comparison:
 | non_test | add another item buttons are hard to distinguish from the field label this was reported by bradbulger in along with other related issues separating it to its own issue here these started as comments from a client i largely agree though the overall point is that once the content types get to a certain level of complexity the node forms begin to look awkward in the default seven styles buttons and other elements that are there for the user to perform some kind of action aren t always easy to see and tell what they are for instance on a text field with unlimited values the add another item button is the same size shape and color as the field title if you have several of these fields in a form it gets confusing visually for comparison | 0 |
184,677 | 14,289,809,775 | IssuesEvent | 2020-11-23 19:51:47 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | polaris1119/go_src_comment: src/pkg/net/timeout_test.go; 68 LoC | fresh medium test |
Found a possible issue in [polaris1119/go_src_comment](https://www.github.com/polaris1119/go_src_comment) at [src/pkg/net/timeout_test.go](https://github.com/polaris1119/go_src_comment/blob/db5552f6835cfd80e43a87236fa1639e88b1d982/src/pkg/net/timeout_test.go#L453-L520)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/polaris1119/go_src_comment/blob/db5552f6835cfd80e43a87236fa1639e88b1d982/src/pkg/net/timeout_test.go#L453-L520)
<details>
<summary>Click here to show the 68 line(s) of Go which triggered the analyzer.</summary>
```go
for _, timeout := range []time.Duration{
1 * time.Nanosecond,
2 * time.Nanosecond,
5 * time.Nanosecond,
50 * time.Nanosecond,
100 * time.Nanosecond,
200 * time.Nanosecond,
500 * time.Nanosecond,
750 * time.Nanosecond,
1 * time.Microsecond,
5 * time.Microsecond,
25 * time.Microsecond,
250 * time.Microsecond,
500 * time.Microsecond,
1 * time.Millisecond,
5 * time.Millisecond,
100 * time.Millisecond,
250 * time.Millisecond,
500 * time.Millisecond,
1 * time.Second,
} {
numRuns := 3
if testing.Short() {
numRuns = 1
if timeout > 500*time.Microsecond {
continue
}
}
for run := 0; run < numRuns; run++ {
name := fmt.Sprintf("%v run %d/%d", timeout, run+1, numRuns)
t.Log(name)
c, err := Dial("tcp", ln.Addr().String())
if err != nil {
t.Fatalf("Dial: %v", err)
}
clientc := make(chan copyRes)
go func() {
t0 := time.Now()
c.SetDeadline(t0.Add(timeout))
n, err := io.Copy(ioutil.Discard, c)
d := time.Since(t0)
c.Close()
clientc <- copyRes{n, err, d}
}()
const tooLong = 2000 * time.Millisecond
select {
case res := <-clientc:
if isTimeout(res.err) {
t.Logf("for %v, good client timeout after %v, reading %d bytes", name, res.d, res.n)
} else {
t.Fatalf("for %v: client Copy = %d, %v (want timeout)", name, res.n, res.err)
}
case <-time.After(tooLong):
t.Fatalf("for %v: timeout (%v) waiting for client to timeout (%v) reading", name, tooLong, timeout)
}
select {
case res := <-servec:
t.Logf("for %v: server in %v wrote %d, %v", name, res.d, res.n, res.err)
case err := <-acceptc:
t.Fatalf("for %v: server Accept = %v", name, err)
case <-time.After(tooLong):
t.Fatalf("for %v, timeout waiting for server to finish writing", name)
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: db5552f6835cfd80e43a87236fa1639e88b1d982
| 1.0 | polaris1119/go_src_comment: src/pkg/net/timeout_test.go; 68 LoC -
Found a possible issue in [polaris1119/go_src_comment](https://www.github.com/polaris1119/go_src_comment) at [src/pkg/net/timeout_test.go](https://github.com/polaris1119/go_src_comment/blob/db5552f6835cfd80e43a87236fa1639e88b1d982/src/pkg/net/timeout_test.go#L453-L520)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/polaris1119/go_src_comment/blob/db5552f6835cfd80e43a87236fa1639e88b1d982/src/pkg/net/timeout_test.go#L453-L520)
<details>
<summary>Click here to show the 68 line(s) of Go which triggered the analyzer.</summary>
```go
for _, timeout := range []time.Duration{
1 * time.Nanosecond,
2 * time.Nanosecond,
5 * time.Nanosecond,
50 * time.Nanosecond,
100 * time.Nanosecond,
200 * time.Nanosecond,
500 * time.Nanosecond,
750 * time.Nanosecond,
1 * time.Microsecond,
5 * time.Microsecond,
25 * time.Microsecond,
250 * time.Microsecond,
500 * time.Microsecond,
1 * time.Millisecond,
5 * time.Millisecond,
100 * time.Millisecond,
250 * time.Millisecond,
500 * time.Millisecond,
1 * time.Second,
} {
numRuns := 3
if testing.Short() {
numRuns = 1
if timeout > 500*time.Microsecond {
continue
}
}
for run := 0; run < numRuns; run++ {
name := fmt.Sprintf("%v run %d/%d", timeout, run+1, numRuns)
t.Log(name)
c, err := Dial("tcp", ln.Addr().String())
if err != nil {
t.Fatalf("Dial: %v", err)
}
clientc := make(chan copyRes)
go func() {
t0 := time.Now()
c.SetDeadline(t0.Add(timeout))
n, err := io.Copy(ioutil.Discard, c)
d := time.Since(t0)
c.Close()
clientc <- copyRes{n, err, d}
}()
const tooLong = 2000 * time.Millisecond
select {
case res := <-clientc:
if isTimeout(res.err) {
t.Logf("for %v, good client timeout after %v, reading %d bytes", name, res.d, res.n)
} else {
t.Fatalf("for %v: client Copy = %d, %v (want timeout)", name, res.n, res.err)
}
case <-time.After(tooLong):
t.Fatalf("for %v: timeout (%v) waiting for client to timeout (%v) reading", name, tooLong, timeout)
}
select {
case res := <-servec:
t.Logf("for %v: server in %v wrote %d, %v", name, res.d, res.n, res.err)
case err := <-acceptc:
t.Fatalf("for %v: server Accept = %v", name, err)
case <-time.After(tooLong):
t.Fatalf("for %v, timeout waiting for server to finish writing", name)
}
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: db5552f6835cfd80e43a87236fa1639e88b1d982
| test | go src comment src pkg net timeout test go loc found a possible issue in at the below snippet of go code triggered static analysis which searches for goroutines and or defer statements which capture loop variables click here to show the line s of go which triggered the analyzer go for timeout range time duration time nanosecond time nanosecond time nanosecond time nanosecond time nanosecond time nanosecond time nanosecond time nanosecond time microsecond time microsecond time microsecond time microsecond time microsecond time millisecond time millisecond time millisecond time millisecond time millisecond time second numruns if testing short numruns if timeout time microsecond continue for run run numruns run name fmt sprintf v run d d timeout run numruns t log name c err dial tcp ln addr string if err nil t fatalf dial v err clientc make chan copyres go func time now c setdeadline add timeout n err io copy ioutil discard c d time since c close clientc copyres n err d const toolong time millisecond select case res clientc if istimeout res err t logf for v good client timeout after v reading d bytes name res d res n else t fatalf for v client copy d v want timeout name res n res err case time after toolong t fatalf for v timeout v waiting for client to timeout v reading name toolong timeout select case res servec t logf for v server in v wrote d v name res d res n res err case err acceptc t fatalf for v server accept v name err case time after toolong t fatalf for v timeout waiting for server to finish writing name leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
180,475 | 13,933,161,066 | IssuesEvent | 2020-10-22 08:19:44 | uselagoon/lagoon-charts | https://api.github.com/repos/uselagoon/lagoon-charts | closed | Facilitate running helm test suite locally | lagoon-test | We currently have a lot of complex test logic in https://github.com/uselagoon/lagoon-charts/blob/main/.github/workflows/lint-test.yaml
It would be nice to move that out to a `Makefile` or similar so it's easy to run locally. | 1.0 | Facilitate running helm test suite locally - We currently have a lot of complex test logic in https://github.com/uselagoon/lagoon-charts/blob/main/.github/workflows/lint-test.yaml
It would be nice to move that out to a `Makefile` or similar so it's easy to run locally. | test | facilitate running helm test suite locally we currently have a lot of complex test logic in it would be nice to move that out to a makefile or similar so it s easy to run locally | 1 |
239,190 | 19,827,947,768 | IssuesEvent | 2022-01-20 08:59:23 | NLCR/SeznamDNNT | https://api.github.com/repos/NLCR/SeznamDNNT | closed | Změna konečného stavu NL | enhancement ToTests Done změna existující funkcionality | Dobrý den,
dnes jsme se domluvily s paní Lichtenbergovou, že bychom potřebovaly upravit konečné rozhodnutí stavu NL. Týká se výstupu, kdy dílo bylo vydáno. Stav nebude N, ale A s licencí DNNTT. Vzhledem k obsáhlé problematice je potřeba to upravit, protože nakladatelé nemohou vyřazovat díla jiných nakladatelů ze SDNNT.
NL → dílo bylo vydáno → A, licence DNNTT
Cypzirschová
@Lichtenbergova | 1.0 | Změna konečného stavu NL - Dobrý den,
dnes jsme se domluvily s paní Lichtenbergovou, že bychom potřebovaly upravit konečné rozhodnutí stavu NL. Týká se výstupu, kdy dílo bylo vydáno. Stav nebude N, ale A s licencí DNNTT. Vzhledem k obsáhlé problematice je potřeba to upravit, protože nakladatelé nemohou vyřazovat díla jiných nakladatelů ze SDNNT.
NL → dílo bylo vydáno → A, licence DNNTT
Cypzirschová
@Lichtenbergova | test | změna konečného stavu nl dobrý den dnes jsme se domluvily s paní lichtenbergovou že bychom potřebovaly upravit konečné rozhodnutí stavu nl týká se výstupu kdy dílo bylo vydáno stav nebude n ale a s licencí dnntt vzhledem k obsáhlé problematice je potřeba to upravit protože nakladatelé nemohou vyřazovat díla jiných nakladatelů ze sdnnt nl → dílo bylo vydáno → a licence dnntt cypzirschová lichtenbergova | 1 |
32,894 | 6,965,061,397 | IssuesEvent | 2017-12-09 01:23:31 | primefaces/primefaces | https://api.github.com/repos/primefaces/primefaces | closed | Ensure correct resources ordering | defect | Following this discussion https://github.com/primefaces/primefaces/commit/9c65354cce5e22545d702f879f5f50cfb40a7d93#commitcomment-25488348
Basically, some components have `jquery-plugins` _(I'll abbreviate this by JQP)_ has a dependency and other don't. If the first non JQP component is loaded first, `jquery-plugins` will be loaded in last then, after core.js/component.js by the JQP components. The result of the html becomes like this:
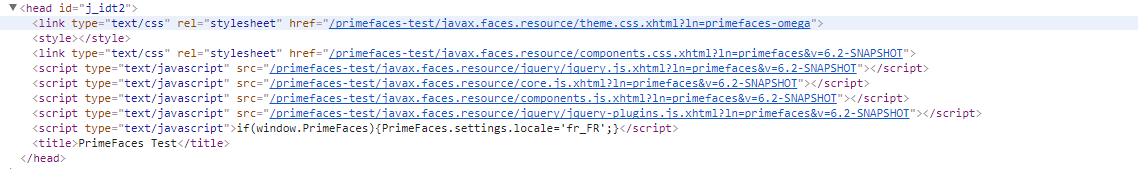
And as a consequence, javascript errors such as:
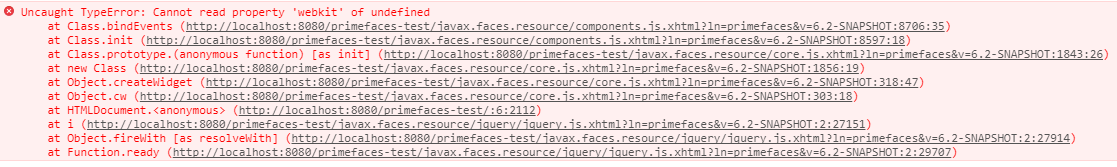
Several solutions have been mentionned:
- Should we add jquery-plugins to every components?
- Modifying xml component definition file?
- Tweaking maven-jsf-plugin to make sure JQP is loaded right after `jquery.js`?
IMO, none of these are good enough. It looks like BootsFaces have faced this issue, and they create a listener for that: [AddResourcesListener](https://github.com/TheCoder4eu/BootsFaces-OSP/blob/master/src/main/java/net/bootsfaces/listeners/AddResourcesListener.java)
I think we should do something similar, actually the idea is to make sure that `jquery-plugins` is loaded right after `jquery.js` and before `core/component.js`¨. Would it be a reasonable idea to sort resources in `HeadRenderer` right before they get encoded?
The problem can be easily reproduced:
```xml
<!DOCTYPE html>
<html xmlns="http://www.w3.org/1999/xhtml"
xmlns:ui="http://java.sun.com/jsf/facelets"
xmlns:f="http://java.sun.com/jsf/core"
xmlns:p="http://primefaces.org/ui"
xmlns:h="http://java.sun.com/jsf/html">
<h:head>
<title>PrimeFaces Test</title>
</h:head>
<h:body>
<p:inputText />
<p:selectOneMenu />
</h:body>
</html>
``` | 1.0 | Ensure correct resources ordering - Following this discussion https://github.com/primefaces/primefaces/commit/9c65354cce5e22545d702f879f5f50cfb40a7d93#commitcomment-25488348
Basically, some components have `jquery-plugins` _(I'll abbreviate this by JQP)_ has a dependency and other don't. If the first non JQP component is loaded first, `jquery-plugins` will be loaded in last then, after core.js/component.js by the JQP components. The result of the html becomes like this:
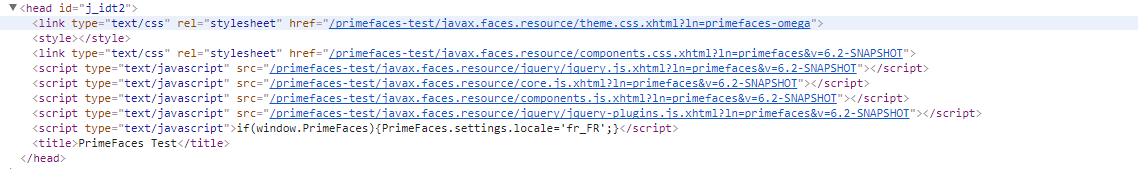
And as a consequence, javascript errors such as:
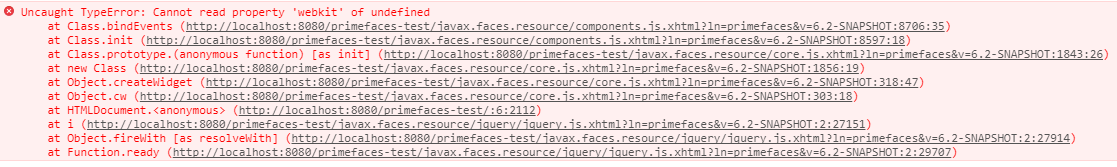
Several solutions have been mentionned:
- Should we add jquery-plugins to every components?
- Modifying xml component definition file?
- Tweaking maven-jsf-plugin to make sure JQP is loaded right after `jquery.js`?
IMO, none of these are good enough. It looks like BootsFaces have faced this issue, and they create a listener for that: [AddResourcesListener](https://github.com/TheCoder4eu/BootsFaces-OSP/blob/master/src/main/java/net/bootsfaces/listeners/AddResourcesListener.java)
I think we should do something similar, actually the idea is to make sure that `jquery-plugins` is loaded right after `jquery.js` and before `core/component.js`¨. Would it be a reasonable idea to sort resources in `HeadRenderer` right before they get encoded?
The problem can be easily reproduced:
```xml
<!DOCTYPE html>
<html xmlns="http://www.w3.org/1999/xhtml"
xmlns:ui="http://java.sun.com/jsf/facelets"
xmlns:f="http://java.sun.com/jsf/core"
xmlns:p="http://primefaces.org/ui"
xmlns:h="http://java.sun.com/jsf/html">
<h:head>
<title>PrimeFaces Test</title>
</h:head>
<h:body>
<p:inputText />
<p:selectOneMenu />
</h:body>
</html>
``` | non_test | ensure correct resources ordering following this discussion basically some components have jquery plugins i ll abbreviate this by jqp has a dependency and other don t if the first non jqp component is loaded first jquery plugins will be loaded in last then after core js component js by the jqp components the result of the html becomes like this and as a consequence javascript errors such as several solutions have been mentionned should we add jquery plugins to every components modifying xml component definition file tweaking maven jsf plugin to make sure jqp is loaded right after jquery js imo none of these are good enough it looks like bootsfaces have faced this issue and they create a listener for that i think we should do something similar actually the idea is to make sure that jquery plugins is loaded right after jquery js and before core component js ¨ would it be a reasonable idea to sort resources in headrenderer right before they get encoded the problem can be easily reproduced xml html xmlns xmlns ui xmlns f xmlns p xmlns h primefaces test | 0 |
703,596 | 24,167,497,486 | IssuesEvent | 2022-09-22 16:09:47 | akinsho/bufferline.nvim | https://api.github.com/repos/akinsho/bufferline.nvim | closed | [Feature Request]: Commands `BufferlineClose*` close modified buffers | enhancement low priority | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### What happened?
Commands `BuferlineCloseLeft`, `BuferlineCloseRight` and `BufferlinePickClose` close modified buffers.
### What did you expect to happen?
I would expect to have an error message like "Unable to close modified buffer, add ! to override". So it would be nice to have the current behavior with bang and the expected behavior without it.
### Config
```lua
require("bufferline").setup({})
```
### Additional Information
_No response_
### commit
_No response_ | 1.0 | [Feature Request]: Commands `BufferlineClose*` close modified buffers - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### What happened?
Commands `BuferlineCloseLeft`, `BuferlineCloseRight` and `BufferlinePickClose` close modified buffers.
### What did you expect to happen?
I would expect to have an error message like "Unable to close modified buffer, add ! to override". So it would be nice to have the current behavior with bang and the expected behavior without it.
### Config
```lua
require("bufferline").setup({})
```
### Additional Information
_No response_
### commit
_No response_ | non_test | commands bufferlineclose close modified buffers is there an existing issue for this i have searched the existing issues what happened commands buferlinecloseleft buferlinecloseright and bufferlinepickclose close modified buffers what did you expect to happen i would expect to have an error message like unable to close modified buffer add to override so it would be nice to have the current behavior with bang and the expected behavior without it config lua require bufferline setup additional information no response commit no response | 0 |
319,261 | 27,360,913,606 | IssuesEvent | 2023-02-27 15:48:50 | trinodb/trino | https://api.github.com/repos/trinodb/trino | closed | Flaky tests in trino-main & others: surefire sometimes fails: Cannot invoke "java.io.File.getAbsolutePath()" because the return value of "org.apache.maven.artifact.Artifact.getFile()" | bug test | eg https://github.com/trinodb/trino/actions/runs/3237106331/jobs/5306229110
```
[INFO] Results:
[INFO]
[INFO] Tests run: 682, Failures: 0, Errors: 0, Skipped: 0
[INFO]
[INFO] Downloading from central: https://repo.maven.apache.org/maven2/org/testng/testng/5.10/testng-5.10.pom
[INFO] Failure detected.
[INFO] ------------------------------------------------------------------------
[INFO] BUILD FAILURE
[INFO] ------------------------------------------------------------------------
[INFO] Total time: 05:44 min
[INFO] Finished at: 2022-10-12T23:08:40Z
[INFO] ------------------------------------------------------------------------
Error: Failed to execute goal org.apache.maven.plugins:maven-surefire-plugin:3.0.0-M5:test (default-test) on project trino-main: Execution default-test of goal org.apache.maven.plugins:maven-surefire-plugin:3.0.0-M5:test failed: Cannot invoke "java.io.File.getAbsolutePath()" because the return value of "org.apache.maven.artifact.Artifact.getFile()" is null -> [Help 1]
Error:
Error: To see the full stack trace of the errors, re-run Maven with the -e switch.
Error: Re-run Maven using the -X switch to enable full debug logging.
Error:
Error: For more information about the errors and possible solutions, please read the following articles:
Error: [Help 1] http://cwiki.apache.org/confluence/display/MAVEN/PluginExecutionException
Error: Process completed with exit code 1.
``` | 1.0 | Flaky tests in trino-main & others: surefire sometimes fails: Cannot invoke "java.io.File.getAbsolutePath()" because the return value of "org.apache.maven.artifact.Artifact.getFile()" - eg https://github.com/trinodb/trino/actions/runs/3237106331/jobs/5306229110
```
[INFO] Results:
[INFO]
[INFO] Tests run: 682, Failures: 0, Errors: 0, Skipped: 0
[INFO]
[INFO] Downloading from central: https://repo.maven.apache.org/maven2/org/testng/testng/5.10/testng-5.10.pom
[INFO] Failure detected.
[INFO] ------------------------------------------------------------------------
[INFO] BUILD FAILURE
[INFO] ------------------------------------------------------------------------
[INFO] Total time: 05:44 min
[INFO] Finished at: 2022-10-12T23:08:40Z
[INFO] ------------------------------------------------------------------------
Error: Failed to execute goal org.apache.maven.plugins:maven-surefire-plugin:3.0.0-M5:test (default-test) on project trino-main: Execution default-test of goal org.apache.maven.plugins:maven-surefire-plugin:3.0.0-M5:test failed: Cannot invoke "java.io.File.getAbsolutePath()" because the return value of "org.apache.maven.artifact.Artifact.getFile()" is null -> [Help 1]
Error:
Error: To see the full stack trace of the errors, re-run Maven with the -e switch.
Error: Re-run Maven using the -X switch to enable full debug logging.
Error:
Error: For more information about the errors and possible solutions, please read the following articles:
Error: [Help 1] http://cwiki.apache.org/confluence/display/MAVEN/PluginExecutionException
Error: Process completed with exit code 1.
``` | test | flaky tests in trino main others surefire sometimes fails cannot invoke java io file getabsolutepath because the return value of org apache maven artifact artifact getfile eg results tests run failures errors skipped downloading from central failure detected build failure total time min finished at error failed to execute goal org apache maven plugins maven surefire plugin test default test on project trino main execution default test of goal org apache maven plugins maven surefire plugin test failed cannot invoke java io file getabsolutepath because the return value of org apache maven artifact artifact getfile is null error error to see the full stack trace of the errors re run maven with the e switch error re run maven using the x switch to enable full debug logging error error for more information about the errors and possible solutions please read the following articles error error process completed with exit code | 1 |
312,536 | 26,870,940,105 | IssuesEvent | 2023-02-04 13:01:42 | dotnet/maui | https://api.github.com/repos/dotnet/maui | closed | ApplyQueryAttributes when go back to one tab and two views is invoked in the wrong view | t/bug area/shell 🐢 s/try-latest-version | ### Description
With Shell navigation and MVVM and NET6.0, if two pages exist in the same tab like:
```
<Tab Title="Search"
Icon="search">
<ShellContent Title="Page1"
ContentTemplate="{DataTemplate views:Page1View}" />
<ShellContent Title="Page2"
ContentTemplate="{DataTemplate views:Page2View}" />
</Tab>
```
Both viewmodels (Page1ViewModel and Page2ViewModel) implement IQueryAttributable
And both views can access to another view (i.e. `SecondLevelPageView`), and from this page we invoke:
`await Shell.Current.GoToAsync($"..?test=hello");`
If I access to SecondLevelPageView from Page2View and go back with the previous code, it goes back to Page2View, this is correct. However, it's always the `ApplyQueryAttributes` method from `Page1ViewModel` which is invoked, and if I go back to `Page2View` it should be the `ApplyQueryAttributes` method from `Page2ViewModel` which should be invoked.
### Steps to Reproduce
1. Start the app TestErrorApplyQueryAttributes on Android
2. Go to tab "Page2"
3. Click button "Go to second level"
4. Click button "Go back"
### Link to public reproduction project repository
https://github.com/Victorbp09/TestErrorApplyQueryAttributes
### Version with bug
Unknown/Other (please specify)
### Last version that worked well
Unknown/Other
### Affected platforms
Android, I was *not* able test on other platforms
### Affected platform versions
Android 12 - API 31
### Did you find any workaround?
No. Use await Shell.Current.GoToAsync(nameof(Page2View), true) will invoke the constructor again, and this doesn't match with my requirements
### Relevant log output
_No response_ | 1.0 | ApplyQueryAttributes when go back to one tab and two views is invoked in the wrong view - ### Description
With Shell navigation and MVVM and NET6.0, if two pages exist in the same tab like:
```
<Tab Title="Search"
Icon="search">
<ShellContent Title="Page1"
ContentTemplate="{DataTemplate views:Page1View}" />
<ShellContent Title="Page2"
ContentTemplate="{DataTemplate views:Page2View}" />
</Tab>
```
Both viewmodels (Page1ViewModel and Page2ViewModel) implement IQueryAttributable
And both views can access to another view (i.e. `SecondLevelPageView`), and from this page we invoke:
`await Shell.Current.GoToAsync($"..?test=hello");`
If I access to SecondLevelPageView from Page2View and go back with the previous code, it goes back to Page2View, this is correct. However, it's always the `ApplyQueryAttributes` method from `Page1ViewModel` which is invoked, and if I go back to `Page2View` it should be the `ApplyQueryAttributes` method from `Page2ViewModel` which should be invoked.
### Steps to Reproduce
1. Start the app TestErrorApplyQueryAttributes on Android
2. Go to tab "Page2"
3. Click button "Go to second level"
4. Click button "Go back"
### Link to public reproduction project repository
https://github.com/Victorbp09/TestErrorApplyQueryAttributes
### Version with bug
Unknown/Other (please specify)
### Last version that worked well
Unknown/Other
### Affected platforms
Android, I was *not* able test on other platforms
### Affected platform versions
Android 12 - API 31
### Did you find any workaround?
No. Use await Shell.Current.GoToAsync(nameof(Page2View), true) will invoke the constructor again, and this doesn't match with my requirements
### Relevant log output
_No response_ | test | applyqueryattributes when go back to one tab and two views is invoked in the wrong view description with shell navigation and mvvm and if two pages exist in the same tab like tab title search icon search shellcontent title contenttemplate datatemplate views shellcontent title contenttemplate datatemplate views both viewmodels and implement iqueryattributable and both views can access to another view i e secondlevelpageview and from this page we invoke await shell current gotoasync test hello if i access to secondlevelpageview from and go back with the previous code it goes back to this is correct however it s always the applyqueryattributes method from which is invoked and if i go back to it should be the applyqueryattributes method from which should be invoked steps to reproduce start the app testerrorapplyqueryattributes on android go to tab click button go to second level click button go back link to public reproduction project repository version with bug unknown other please specify last version that worked well unknown other affected platforms android i was not able test on other platforms affected platform versions android api did you find any workaround no use await shell current gotoasync nameof true will invoke the constructor again and this doesn t match with my requirements relevant log output no response | 1 |
126,771 | 12,299,352,782 | IssuesEvent | 2020-05-11 12:14:08 | paritytech/polkadot | https://api.github.com/repos/paritytech/polkadot | closed | Add cli documentation for --enable-authority-discovery | F5-documentation enhancement | Currently there isn't any documentation around this cli flag, so people probably don't know it exists. | 1.0 | Add cli documentation for --enable-authority-discovery - Currently there isn't any documentation around this cli flag, so people probably don't know it exists. | non_test | add cli documentation for enable authority discovery currently there isn t any documentation around this cli flag so people probably don t know it exists | 0 |
130,956 | 18,163,569,106 | IssuesEvent | 2021-09-27 12:27:26 | Kotlin/kotlinx.coroutines | https://api.github.com/repos/Kotlin/kotlinx.coroutines | closed | Impossible to use combine(Iterable<Flow>) with type params from non-inlined call site | design breaking change flow | It's not possible to use `combine<Iterable<Flow<T>>` with type parameters unless the call site is also inlined, supplying the `T` type param as reified.
Example:
```kotlin
// Does not compile
fun <N : Number> first(flows: Iterable<Flow<N>>) = combine(flows) { array -> array.first() }
```
This example is trivial for brevity, but in many cases it's not at all practical to make the calling function `inline`.
```
Cannot use 'N' as reified type parameter. Use a class instead.
```
This is a significant and unnecessary limitation. If `List` was used instead of `Array`, or an alternative `combine` function using `List` was available, this wouldn't be a problem.
It's not clear why `Array` is in use at all. I assume it's for performance.
Since `combineInternal` is `internal`, we have no choice but to copy its entire implementation in order to use it in the above scenario. | 1.0 | Impossible to use combine(Iterable<Flow>) with type params from non-inlined call site - It's not possible to use `combine<Iterable<Flow<T>>` with type parameters unless the call site is also inlined, supplying the `T` type param as reified.
Example:
```kotlin
// Does not compile
fun <N : Number> first(flows: Iterable<Flow<N>>) = combine(flows) { array -> array.first() }
```
This example is trivial for brevity, but in many cases it's not at all practical to make the calling function `inline`.
```
Cannot use 'N' as reified type parameter. Use a class instead.
```
This is a significant and unnecessary limitation. If `List` was used instead of `Array`, or an alternative `combine` function using `List` was available, this wouldn't be a problem.
It's not clear why `Array` is in use at all. I assume it's for performance.
Since `combineInternal` is `internal`, we have no choice but to copy its entire implementation in order to use it in the above scenario. | non_test | impossible to use combine iterable with type params from non inlined call site it s not possible to use combine with type parameters unless the call site is also inlined supplying the t type param as reified example kotlin does not compile fun first flows iterable combine flows array array first this example is trivial for brevity but in many cases it s not at all practical to make the calling function inline cannot use n as reified type parameter use a class instead this is a significant and unnecessary limitation if list was used instead of array or an alternative combine function using list was available this wouldn t be a problem it s not clear why array is in use at all i assume it s for performance since combineinternal is internal we have no choice but to copy its entire implementation in order to use it in the above scenario | 0 |
78,276 | 7,624,933,355 | IssuesEvent | 2018-05-03 19:41:51 | eth-cscs/reframe | https://api.github.com/repos/eth-cscs/reframe | closed | Investigate dynamic module creation by a ReFrame test | prio: important question regression test | Given the COSMO complexity, MCH wants to generate on-the-fly a module file (by running a shell script), which will take care of the environment setup of the test. The ReFrame test will load then this environment.
We need to investigate this scenario and if it can be supported from the current framework. What changes would be needed to make it feasible? Alternatives? | 1.0 | Investigate dynamic module creation by a ReFrame test - Given the COSMO complexity, MCH wants to generate on-the-fly a module file (by running a shell script), which will take care of the environment setup of the test. The ReFrame test will load then this environment.
We need to investigate this scenario and if it can be supported from the current framework. What changes would be needed to make it feasible? Alternatives? | test | investigate dynamic module creation by a reframe test given the cosmo complexity mch wants to generate on the fly a module file by running a shell script which will take care of the environment setup of the test the reframe test will load then this environment we need to investigate this scenario and if it can be supported from the current framework what changes would be needed to make it feasible alternatives | 1 |
691,890 | 23,715,496,354 | IssuesEvent | 2022-08-30 11:25:36 | AkjoStudios/AkjoNav | https://api.github.com/repos/AkjoStudios/AkjoNav | closed | [Feature Enhancement] Move DesktopMapper error system to JSON file | priority: high status: planned type: enhancement Official Issue | ### In which module is the feature you want to enhance?
AkjoNav-DesktopMapper
### Feature
Error system
### Description
Instead of using individual classes for creating errors, define all the errors beforehand in a JSON file and reference them by using their error code. Create a service which then can create the corresponding error with its error code.
### Additional Context
No additional context/screenshots. | 1.0 | [Feature Enhancement] Move DesktopMapper error system to JSON file - ### In which module is the feature you want to enhance?
AkjoNav-DesktopMapper
### Feature
Error system
### Description
Instead of using individual classes for creating errors, define all the errors beforehand in a JSON file and reference them by using their error code. Create a service which then can create the corresponding error with its error code.
### Additional Context
No additional context/screenshots. | non_test | move desktopmapper error system to json file in which module is the feature you want to enhance akjonav desktopmapper feature error system description instead of using individual classes for creating errors define all the errors beforehand in a json file and reference them by using their error code create a service which then can create the corresponding error with its error code additional context no additional context screenshots | 0 |
811,732 | 30,297,940,309 | IssuesEvent | 2023-07-10 01:48:30 | steedos/steedos-platform | https://api.github.com/repos/steedos/steedos-platform | closed | [Bug]: 导入数据,lookup字段的“关联失败时保存key”功能无效 | bug done priority: High | ### Description
底层代码问题,当关联失败时,判断数据条数的地方已经通过 .length 转换成数值了,后面的if里面又来了一次 .length 造成判断无效,全部进入最后的else

### Steps To Reproduce 重现步骤
1. 配置数据导入
2. 配置关联表字段的导入
3. 配置对应的 “关联失败时保存key” 为打勾状态
4. 保存
5. 到对应的对象上导入数据
### Version 版本
所有版本 | 1.0 | [Bug]: 导入数据,lookup字段的“关联失败时保存key”功能无效 - ### Description
底层代码问题,当关联失败时,判断数据条数的地方已经通过 .length 转换成数值了,后面的if里面又来了一次 .length 造成判断无效,全部进入最后的else

### Steps To Reproduce 重现步骤
1. 配置数据导入
2. 配置关联表字段的导入
3. 配置对应的 “关联失败时保存key” 为打勾状态
4. 保存
5. 到对应的对象上导入数据
### Version 版本
所有版本 | non_test | 导入数据,lookup字段的“关联失败时保存key”功能无效 description 底层代码问题,当关联失败时,判断数据条数的地方已经通过 length 转换成数值了,后面的if里面又来了一次 length 造成判断无效,全部进入最后的else steps to reproduce 重现步骤 配置数据导入 配置关联表字段的导入 配置对应的 “关联失败时保存key” 为打勾状态 保存 到对应的对象上导入数据 version 版本 所有版本 | 0 |
318,187 | 27,293,072,554 | IssuesEvent | 2023-02-23 18:00:55 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | closed | Java Batch 2.1 FTS (EE 10) | Feature Test Summary | ## Test Strategy
**Describe the test strategy & approach for this feature, and describe how the approach verifies the functions delivered by this feature.**
There are two new pieces of function with this feature: new value types for BatchProperty CDI injection, and the ability to inject the default JobOperator via CDI.
The new test cases in the JBatch CDI FAT test:
1. That properly-defined BatchProperty injections of all new value types are processed correctly when defined in the JSL
2. That the same BatchProperty injections are processed correctly when values are submitted as job parameters
3. That the default JobOperator instance can be injected via CDI
4. That the expected failure condition occurs when a BatchProperty value is incorrectly defined
### List of FAT projects affected
* com.ibm.ws.jbatch.cdi_fat
### Test strategy
* What functionality is new or modified by this feature?
The @BatchProperty annotation can now handle additional types for injection, as opposed to just String. Additionally, the default JobOperator instance is now available as a CDI artifact.
* What are the positive and negative tests for that functionality? (Tell me the specific scenarios you tested. What kind of tests do you have for when everything ends up working (positive tests)? What about tests that verify we fail gracefully when things go wrong (negative tests)? See the [Positive and negative tests](https://github.ibm.com/websphere/WS-CD-Open/wiki/Feature-Review-(Feature-Test-Summary-Process)#positive-and-negative-tests) section of the Feature Test Summary Process wiki for more detail.)
Positive: The first new test verifies that the user can supply the new value types for BatchProperty injection, both as literals in the JSL or as job parameters at runtime, and that those injected values match the input. There is also verification that the default JobOperator is supplied if an injection point is provided.
Negative: Another new test verifies that when a BatchProperty value type is improperly defined (e.g., trying to inject a String value into an Integer field), the expected failure case occurs - the job fails, and FFDCs are created.
* What manual tests are there (if any)? (Note: Automated testing is expected for all features with manual testing considered an exception to the rule.)
None
## Confidence Level
**Collectively as a team you need to assess your confidence in the testing delivered based on the values below. This should be done as a team and not an individual to ensure more eyes are on it and that pressures to deliver quickly are absorbed by the team as a whole.**
Please indicate your confidence in the testing (up to and including FAT) delivered with this feature by selecting one of these values:
**4 -** We could potentially add dozens of additional tests checking the behavior of every improper value assignment combination (e.g. String to Integer, String to Double, String to Float, Float to Integer...), but we do not believe this would add any meaningful value.
| 1.0 | Java Batch 2.1 FTS (EE 10) - ## Test Strategy
**Describe the test strategy & approach for this feature, and describe how the approach verifies the functions delivered by this feature.**
There are two new pieces of function with this feature: new value types for BatchProperty CDI injection, and the ability to inject the default JobOperator via CDI.
The new test cases in the JBatch CDI FAT test:
1. That properly-defined BatchProperty injections of all new value types are processed correctly when defined in the JSL
2. That the same BatchProperty injections are processed correctly when values are submitted as job parameters
3. That the default JobOperator instance can be injected via CDI
4. That the expected failure condition occurs when a BatchProperty value is incorrectly defined
### List of FAT projects affected
* com.ibm.ws.jbatch.cdi_fat
### Test strategy
* What functionality is new or modified by this feature?
The @BatchProperty annotation can now handle additional types for injection, as opposed to just String. Additionally, the default JobOperator instance is now available as a CDI artifact.
* What are the positive and negative tests for that functionality? (Tell me the specific scenarios you tested. What kind of tests do you have for when everything ends up working (positive tests)? What about tests that verify we fail gracefully when things go wrong (negative tests)? See the [Positive and negative tests](https://github.ibm.com/websphere/WS-CD-Open/wiki/Feature-Review-(Feature-Test-Summary-Process)#positive-and-negative-tests) section of the Feature Test Summary Process wiki for more detail.)
Positive: The first new test verifies that the user can supply the new value types for BatchProperty injection, both as literals in the JSL or as job parameters at runtime, and that those injected values match the input. There is also verification that the default JobOperator is supplied if an injection point is provided.
Negative: Another new test verifies that when a BatchProperty value type is improperly defined (e.g., trying to inject a String value into an Integer field), the expected failure case occurs - the job fails, and FFDCs are created.
* What manual tests are there (if any)? (Note: Automated testing is expected for all features with manual testing considered an exception to the rule.)
None
## Confidence Level
**Collectively as a team you need to assess your confidence in the testing delivered based on the values below. This should be done as a team and not an individual to ensure more eyes are on it and that pressures to deliver quickly are absorbed by the team as a whole.**
Please indicate your confidence in the testing (up to and including FAT) delivered with this feature by selecting one of these values:
**4 -** We could potentially add dozens of additional tests checking the behavior of every improper value assignment combination (e.g. String to Integer, String to Double, String to Float, Float to Integer...), but we do not believe this would add any meaningful value.
| test | java batch fts ee test strategy describe the test strategy approach for this feature and describe how the approach verifies the functions delivered by this feature there are two new pieces of function with this feature new value types for batchproperty cdi injection and the ability to inject the default joboperator via cdi the new test cases in the jbatch cdi fat test that properly defined batchproperty injections of all new value types are processed correctly when defined in the jsl that the same batchproperty injections are processed correctly when values are submitted as job parameters that the default joboperator instance can be injected via cdi that the expected failure condition occurs when a batchproperty value is incorrectly defined list of fat projects affected com ibm ws jbatch cdi fat test strategy what functionality is new or modified by this feature the batchproperty annotation can now handle additional types for injection as opposed to just string additionally the default joboperator instance is now available as a cdi artifact what are the positive and negative tests for that functionality tell me the specific scenarios you tested what kind of tests do you have for when everything ends up working positive tests what about tests that verify we fail gracefully when things go wrong negative tests see the section of the feature test summary process wiki for more detail positive the first new test verifies that the user can supply the new value types for batchproperty injection both as literals in the jsl or as job parameters at runtime and that those injected values match the input there is also verification that the default joboperator is supplied if an injection point is provided negative another new test verifies that when a batchproperty value type is improperly defined e g trying to inject a string value into an integer field the expected failure case occurs the job fails and ffdcs are created what manual tests are there if any note automated testing is expected for all features with manual testing considered an exception to the rule none confidence level collectively as a team you need to assess your confidence in the testing delivered based on the values below this should be done as a team and not an individual to ensure more eyes are on it and that pressures to deliver quickly are absorbed by the team as a whole please indicate your confidence in the testing up to and including fat delivered with this feature by selecting one of these values we could potentially add dozens of additional tests checking the behavior of every improper value assignment combination e g string to integer string to double string to float float to integer but we do not believe this would add any meaningful value | 1 |
223,004 | 17,533,566,475 | IssuesEvent | 2021-08-12 02:21:47 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: jepsen/g2/strobe-skews failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.jepsen/g2/strobe-skews [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3286047&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3286047&tab=artifacts#/jepsen/g2/strobe-skews) on master @ [90809c048d05f923a67ce9b89597b2779fc73e32](https://github.com/cockroachdb/cockroach/commits/90809c048d05f923a67ce9b89597b2779fc73e32):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/jepsen/g2/strobe-skews/run_1
cluster.go:1887,jepsen.go:93,jepsen.go:147,jepsen.go:360,test_runner.go:777: output in run_201600.990083867_n1-6_sh: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3286047-1628662905-67-n6cpu4:1-6 -- sh -c "sudo apt-get -y upgrade -o Dpkg::Options::='--force-confold' > logs/apt-upgrade.log 2>&1" returned: context canceled
(1) attached stack trace
-- stack trace:
| main.(*clusterImpl).RunE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:1977
| main.(*clusterImpl).Run
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:1885
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.initJepsen
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:93
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:147
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.RegisterJepsen.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:360
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:777
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1371
Wraps: (2) output in run_201600.990083867_n1-6_sh
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3286047-1628662905-67-n6cpu4:1-6 -- sh -c "sudo apt-get -y upgrade -o Dpkg::Options::='--force-confold' > logs/apt-upgrade.log 2>&1" returned
| stderr:
|
| stdout:
| <... some data truncated by circular buffer; go to artifacts for details ...>
| ................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................
Wraps: (4) secondary error attachment
| signal: interrupt
| (1) signal: interrupt
| Error types: (1) *exec.ExitError
Wraps: (5) context canceled
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *secondary.withSecondaryError (5) *errors.errorString
```
<details><summary>Reproduce</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/roachtest)
See: [CI job to stress roachtests](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestStress)
<p>For the CI stress job, click the ellipsis (...) next to the Run button and fill in:
* Changes / Build branch: master
* Parameters / `env.TESTS`: `^jepsen/g2/strobe-skews$`
* Parameters / `env.COUNT`: <number of runs>
</p>
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #68759 roachtest: jepsen/g2/strobe-skews failed [C-test-failure O-roachtest O-robot branch-release-21.1 release-blocker]
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/g2/strobe-skews.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: jepsen/g2/strobe-skews failed - roachtest.jepsen/g2/strobe-skews [failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=3286047&tab=buildLog) with [artifacts](https://teamcity.cockroachdb.com/viewLog.html?buildId=3286047&tab=artifacts#/jepsen/g2/strobe-skews) on master @ [90809c048d05f923a67ce9b89597b2779fc73e32](https://github.com/cockroachdb/cockroach/commits/90809c048d05f923a67ce9b89597b2779fc73e32):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/jepsen/g2/strobe-skews/run_1
cluster.go:1887,jepsen.go:93,jepsen.go:147,jepsen.go:360,test_runner.go:777: output in run_201600.990083867_n1-6_sh: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3286047-1628662905-67-n6cpu4:1-6 -- sh -c "sudo apt-get -y upgrade -o Dpkg::Options::='--force-confold' > logs/apt-upgrade.log 2>&1" returned: context canceled
(1) attached stack trace
-- stack trace:
| main.(*clusterImpl).RunE
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:1977
| main.(*clusterImpl).Run
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:1885
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.initJepsen
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:93
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.runJepsen
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:147
| github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests.RegisterJepsen.func1
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tests/jepsen.go:360
| main.(*testRunner).runTest.func2
| /home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:777
| runtime.goexit
| /usr/local/go/src/runtime/asm_amd64.s:1371
Wraps: (2) output in run_201600.990083867_n1-6_sh
Wraps: (3) /home/agent/work/.go/src/github.com/cockroachdb/cockroach/bin/roachprod run teamcity-3286047-1628662905-67-n6cpu4:1-6 -- sh -c "sudo apt-get -y upgrade -o Dpkg::Options::='--force-confold' > logs/apt-upgrade.log 2>&1" returned
| stderr:
|
| stdout:
| <... some data truncated by circular buffer; go to artifacts for details ...>
| ................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................................
Wraps: (4) secondary error attachment
| signal: interrupt
| (1) signal: interrupt
| Error types: (1) *exec.ExitError
Wraps: (5) context canceled
Error types: (1) *withstack.withStack (2) *errutil.withPrefix (3) *cluster.WithCommandDetails (4) *secondary.withSecondaryError (5) *errors.errorString
```
<details><summary>Reproduce</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/roachtest)
See: [CI job to stress roachtests](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestStress)
<p>For the CI stress job, click the ellipsis (...) next to the Run button and fill in:
* Changes / Build branch: master
* Parameters / `env.TESTS`: `^jepsen/g2/strobe-skews$`
* Parameters / `env.COUNT`: <number of runs>
</p>
</p>
</details>
<details><summary>Same failure on other branches</summary>
<p>
- #68759 roachtest: jepsen/g2/strobe-skews failed [C-test-failure O-roachtest O-robot branch-release-21.1 release-blocker]
</p>
</details>
/cc @cockroachdb/kv-triage
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*jepsen/g2/strobe-skews.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | roachtest jepsen strobe skews failed roachtest jepsen strobe skews with on master the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts jepsen strobe skews run cluster go jepsen go jepsen go jepsen go test runner go output in run sh home agent work go src github com cockroachdb cockroach bin roachprod run teamcity sh c sudo apt get y upgrade o dpkg options force confold logs apt upgrade log returned context canceled attached stack trace stack trace main clusterimpl rune home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main clusterimpl run home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go github com cockroachdb cockroach pkg cmd roachtest tests initjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go github com cockroachdb cockroach pkg cmd roachtest tests runjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go github com cockroachdb cockroach pkg cmd roachtest tests registerjepsen home agent work go src github com cockroachdb cockroach pkg cmd roachtest tests jepsen go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go runtime goexit usr local go src runtime asm s wraps output in run sh wraps home agent work go src github com cockroachdb cockroach bin roachprod run teamcity sh c sudo apt get y upgrade o dpkg options force confold logs apt upgrade log returned stderr stdout wraps secondary error attachment signal interrupt signal interrupt error types exec exiterror wraps context canceled error types withstack withstack errutil withprefix cluster withcommanddetails secondary withsecondaryerror errors errorstring reproduce see see for the ci stress job click the ellipsis next to the run button and fill in changes build branch master parameters env tests jepsen strobe skews parameters env count lt number of runs gt same failure on other branches roachtest jepsen strobe skews failed cc cockroachdb kv triage | 1 |
132,930 | 10,773,753,900 | IssuesEvent | 2019-11-02 22:44:39 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] Timeouts in CcrRetentionLeaseIT#testRetentionLeaseIsAddedIfItDisappearsWhileFollowing | :Distributed/CCR >test-failure | https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+7.3+release-tests/132/consoleFull
https://scans.gradle.com/s/mepm4zqla2kiq
Doesn't reproduce:
```
./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT" \
-Dtests.seed=CC7F564515EB24C5 \
-Dtests.security.manager=true \
-Dbuild.snapshot=false \
-Dtests.jvm.argline="-Dbuild.snapshot=false" \
-Dtests.locale=en-US \
-Dtests.timezone=Etc/UTC \
-Dcompiler.java=12 \
-Druntime.java=8
./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT.testRetentionLeaseIsAddedIfItDisappearsWhileFollowing" \
-Dtests.seed=CC7F564515EB24C5 \
-Dtests.security.manager=true \
-Dbuild.snapshot=false \
-Dtests.jvm.argline="-Dbuild.snapshot=false" \
-Dtests.locale=en-SG \
-Dtests.timezone=America/Jamaica \
-Dcompiler.java=12 \
-Druntime.java=8
```
Stacktrace:
```
13:05:36 org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT > testRetentionLeaseIsAddedIfItDisappearsWhileFollowing FAILED
13:05:36 java.lang.Exception: Test abandoned because suite timeout was reached.
13:05:45 REPRODUCE WITH: ./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT.testRetentionLeaseIsAddedIfItDisappearsWhileFollowing" -Dtests.seed=CC7F564515EB24C5 -Dtests.security.manager=true -Dbuild.snapshot=false -Dtests.jvm.argline="-Dbuild.snapshot=false" -Dtests.locale=en-SG -Dtests.timezone=America/Jamaica -Dcompiler.java=12 -Druntime.java=8
13:05:45
13:05:45 org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT > classMethod FAILED
13:05:45 java.lang.Exception: Suite timeout exceeded (>= 1200000 msec).
13:05:45 REPRODUCE WITH: ./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT.testRetentionLeaseIsAddedIfItDisappearsWhileFollowing" -Dtests.seed=CC7F564515EB24C5 -Dtests.security.manager=true -Dbuild.snapshot=false -Dtests.jvm.argline="-Dbuild.snapshot=false" -Dtests.locale=en-SG -Dtests.timezone=America/Jamaica -Dcompiler.java=12 -Druntime.java=8
13:05:45
```
Full log can be found [here](https://github.com/elastic/elasticsearch/files/3467219/console.log.zip)
Seems similar to: #41737
| 1.0 | [CI] Timeouts in CcrRetentionLeaseIT#testRetentionLeaseIsAddedIfItDisappearsWhileFollowing - https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+7.3+release-tests/132/consoleFull
https://scans.gradle.com/s/mepm4zqla2kiq
Doesn't reproduce:
```
./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT" \
-Dtests.seed=CC7F564515EB24C5 \
-Dtests.security.manager=true \
-Dbuild.snapshot=false \
-Dtests.jvm.argline="-Dbuild.snapshot=false" \
-Dtests.locale=en-US \
-Dtests.timezone=Etc/UTC \
-Dcompiler.java=12 \
-Druntime.java=8
./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT.testRetentionLeaseIsAddedIfItDisappearsWhileFollowing" \
-Dtests.seed=CC7F564515EB24C5 \
-Dtests.security.manager=true \
-Dbuild.snapshot=false \
-Dtests.jvm.argline="-Dbuild.snapshot=false" \
-Dtests.locale=en-SG \
-Dtests.timezone=America/Jamaica \
-Dcompiler.java=12 \
-Druntime.java=8
```
Stacktrace:
```
13:05:36 org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT > testRetentionLeaseIsAddedIfItDisappearsWhileFollowing FAILED
13:05:36 java.lang.Exception: Test abandoned because suite timeout was reached.
13:05:45 REPRODUCE WITH: ./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT.testRetentionLeaseIsAddedIfItDisappearsWhileFollowing" -Dtests.seed=CC7F564515EB24C5 -Dtests.security.manager=true -Dbuild.snapshot=false -Dtests.jvm.argline="-Dbuild.snapshot=false" -Dtests.locale=en-SG -Dtests.timezone=America/Jamaica -Dcompiler.java=12 -Druntime.java=8
13:05:45
13:05:45 org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT > classMethod FAILED
13:05:45 java.lang.Exception: Suite timeout exceeded (>= 1200000 msec).
13:05:45 REPRODUCE WITH: ./gradlew :x-pack:plugin:ccr:internalClusterTest --tests "org.elasticsearch.xpack.ccr.CcrRetentionLeaseIT.testRetentionLeaseIsAddedIfItDisappearsWhileFollowing" -Dtests.seed=CC7F564515EB24C5 -Dtests.security.manager=true -Dbuild.snapshot=false -Dtests.jvm.argline="-Dbuild.snapshot=false" -Dtests.locale=en-SG -Dtests.timezone=America/Jamaica -Dcompiler.java=12 -Druntime.java=8
13:05:45
```
Full log can be found [here](https://github.com/elastic/elasticsearch/files/3467219/console.log.zip)
Seems similar to: #41737
| test | timeouts in ccrretentionleaseit testretentionleaseisaddedifitdisappearswhilefollowing doesn t reproduce gradlew x pack plugin ccr internalclustertest tests org elasticsearch xpack ccr ccrretentionleaseit dtests seed dtests security manager true dbuild snapshot false dtests jvm argline dbuild snapshot false dtests locale en us dtests timezone etc utc dcompiler java druntime java gradlew x pack plugin ccr internalclustertest tests org elasticsearch xpack ccr ccrretentionleaseit testretentionleaseisaddedifitdisappearswhilefollowing dtests seed dtests security manager true dbuild snapshot false dtests jvm argline dbuild snapshot false dtests locale en sg dtests timezone america jamaica dcompiler java druntime java stacktrace org elasticsearch xpack ccr ccrretentionleaseit testretentionleaseisaddedifitdisappearswhilefollowing failed java lang exception test abandoned because suite timeout was reached reproduce with gradlew x pack plugin ccr internalclustertest tests org elasticsearch xpack ccr ccrretentionleaseit testretentionleaseisaddedifitdisappearswhilefollowing dtests seed dtests security manager true dbuild snapshot false dtests jvm argline dbuild snapshot false dtests locale en sg dtests timezone america jamaica dcompiler java druntime java org elasticsearch xpack ccr ccrretentionleaseit classmethod failed java lang exception suite timeout exceeded msec reproduce with gradlew x pack plugin ccr internalclustertest tests org elasticsearch xpack ccr ccrretentionleaseit testretentionleaseisaddedifitdisappearswhilefollowing dtests seed dtests security manager true dbuild snapshot false dtests jvm argline dbuild snapshot false dtests locale en sg dtests timezone america jamaica dcompiler java druntime java full log can be found seems similar to | 1 |
117,980 | 9,967,167,092 | IssuesEvent | 2019-07-08 13:02:24 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [CI] failed to initialize a TrustManager | :Security/Security >test-failure | https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+7.3+matrix-java-periodic/ES_BUILD_JAVA=openjdk12,ES_RUNTIME_JAVA=java8fips,nodes=general-purpose/9/console
https://scans.gradle.com/s/3f7h7yv2hd7iq
The full cluster restart test task `:qa:full-cluster-restart:v7.2.1#oldClusterTestCluster#wait` failed because the node threw a fatal error
```
[2019-07-08T00:04:30,214][ERROR][o.e.b.Bootstrap ] [node-0] Exception
org.elasticsearch.common.ssl.SslConfigException: failed to initialize a TrustManager for the system keystore
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:70) ~[?:?]
at org.elasticsearch.common.ssl.SslConfiguration.createSslContext(SslConfiguration.java:136) ~[?:?]
at org.elasticsearch.index.reindex.ReindexSslConfig.reload(ReindexSslConfig.java:145) ~[?:?]
at org.elasticsearch.index.reindex.ReindexSslConfig.<init>(ReindexSslConfig.java:115) ~[?:?]
at org.elasticsearch.index.reindex.ReindexPlugin.createComponents(ReindexPlugin.java:88) ~[?:?]
at org.elasticsearch.node.Node.lambda$new$9(Node.java:438) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at java.util.stream.ReferencePipeline$7$1.accept(ReferencePipeline.java:271) ~[?:?]
at java.util.ArrayList$ArrayListSpliterator.forEachRemaining(ArrayList.java:1654) ~[?:?]
at java.util.stream.AbstractPipeline.copyInto(AbstractPipeline.java:484) ~[?:?]
at java.util.stream.AbstractPipeline.wrapAndCopyInto(AbstractPipeline.java:474) ~[?:?]
at java.util.stream.ReduceOps$ReduceOp.evaluateSequential(ReduceOps.java:913) ~[?:?]
at java.util.stream.AbstractPipeline.evaluate(AbstractPipeline.java:234) ~[?:?]
at java.util.stream.ReferencePipeline.collect(ReferencePipeline.java:578) ~[?:?]
at org.elasticsearch.node.Node.<init>(Node.java:441) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.node.Node.<init>(Node.java:251) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Bootstrap$5.<init>(Bootstrap.java:221) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Bootstrap.setup(Bootstrap.java:221) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Bootstrap.init(Bootstrap.java:349) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.init(Elasticsearch.java:159) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.execute(Elasticsearch.java:150) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.cli.EnvironmentAwareCommand.execute(EnvironmentAwareCommand.java:86) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.cli.Command.mainWithoutErrorHandling(Command.java:124) [elasticsearch-cli-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.cli.Command.main(Command.java:90) [elasticsearch-cli-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.main(Elasticsearch.java:115) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.main(Elasticsearch.java:92) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
Caused by: java.security.KeyStoreException: problem accessing trust store
at sun.security.ssl.TrustManagerFactoryImpl.engineInit(TrustManagerFactoryImpl.java:73) ~[?:?]
at javax.net.ssl.TrustManagerFactory.init(TrustManagerFactory.java:278) ~[?:?]
at org.elasticsearch.common.ssl.KeyStoreUtil.createTrustManager(KeyStoreUtil.java:151) ~[?:?]
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:68) ~[?:?]
... 24 more
Caused by: java.io.IOException: Keystore was tampered with, or password was incorrect
at sun.security.provider.JavaKeyStore.engineLoad(JavaKeyStore.java:785) ~[?:?]
at sun.security.util.KeyStoreDelegator.engineLoad(KeyStoreDelegator.java:243) ~[?:?]
at java.security.KeyStore.load(KeyStore.java:1472) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.loadKeyStore(TrustStoreManager.java:365) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.getTrustedCerts(TrustStoreManager.java:313) ~[?:?]
at sun.security.ssl.TrustStoreManager.getTrustedCerts(TrustStoreManager.java:55) ~[?:?]
at sun.security.ssl.TrustManagerFactoryImpl.engineInit(TrustManagerFactoryImpl.java:49) ~[?:?]
at javax.net.ssl.TrustManagerFactory.init(TrustManagerFactory.java:278) ~[?:?]
at org.elasticsearch.common.ssl.KeyStoreUtil.createTrustManager(KeyStoreUtil.java:151) ~[?:?]
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:68) ~[?:?]
... 24 more
Caused by: java.security.UnrecoverableKeyException: Password verification failed
at sun.security.provider.JavaKeyStore.engineLoad(JavaKeyStore.java:783) ~[?:?]
at sun.security.util.KeyStoreDelegator.engineLoad(KeyStoreDelegator.java:243) ~[?:?]
at java.security.KeyStore.load(KeyStore.java:1472) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.loadKeyStore(TrustStoreManager.java:365) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.getTrustedCerts(TrustStoreManager.java:313) ~[?:?]
at sun.security.ssl.TrustStoreManager.getTrustedCerts(TrustStoreManager.java:55) ~[?:?]
at sun.security.ssl.TrustManagerFactoryImpl.engineInit(TrustManagerFactoryImpl.java:49) ~[?:?]
at javax.net.ssl.TrustManagerFactory.init(TrustManagerFactory.java:278) ~[?:?]
at org.elasticsearch.common.ssl.KeyStoreUtil.createTrustManager(KeyStoreUtil.java:151) ~[?:?]
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:68) ~[?:?]
````
Both nodes failed with the same error here's the logs
[node0.log](https://github.com/elastic/elasticsearch/files/3368369/node0.log)
[node1.log](https://github.com/elastic/elasticsearch/files/3368370/node1.log)
| 1.0 | [CI] failed to initialize a TrustManager - https://elasticsearch-ci.elastic.co/job/elastic+elasticsearch+7.3+matrix-java-periodic/ES_BUILD_JAVA=openjdk12,ES_RUNTIME_JAVA=java8fips,nodes=general-purpose/9/console
https://scans.gradle.com/s/3f7h7yv2hd7iq
The full cluster restart test task `:qa:full-cluster-restart:v7.2.1#oldClusterTestCluster#wait` failed because the node threw a fatal error
```
[2019-07-08T00:04:30,214][ERROR][o.e.b.Bootstrap ] [node-0] Exception
org.elasticsearch.common.ssl.SslConfigException: failed to initialize a TrustManager for the system keystore
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:70) ~[?:?]
at org.elasticsearch.common.ssl.SslConfiguration.createSslContext(SslConfiguration.java:136) ~[?:?]
at org.elasticsearch.index.reindex.ReindexSslConfig.reload(ReindexSslConfig.java:145) ~[?:?]
at org.elasticsearch.index.reindex.ReindexSslConfig.<init>(ReindexSslConfig.java:115) ~[?:?]
at org.elasticsearch.index.reindex.ReindexPlugin.createComponents(ReindexPlugin.java:88) ~[?:?]
at org.elasticsearch.node.Node.lambda$new$9(Node.java:438) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at java.util.stream.ReferencePipeline$7$1.accept(ReferencePipeline.java:271) ~[?:?]
at java.util.ArrayList$ArrayListSpliterator.forEachRemaining(ArrayList.java:1654) ~[?:?]
at java.util.stream.AbstractPipeline.copyInto(AbstractPipeline.java:484) ~[?:?]
at java.util.stream.AbstractPipeline.wrapAndCopyInto(AbstractPipeline.java:474) ~[?:?]
at java.util.stream.ReduceOps$ReduceOp.evaluateSequential(ReduceOps.java:913) ~[?:?]
at java.util.stream.AbstractPipeline.evaluate(AbstractPipeline.java:234) ~[?:?]
at java.util.stream.ReferencePipeline.collect(ReferencePipeline.java:578) ~[?:?]
at org.elasticsearch.node.Node.<init>(Node.java:441) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.node.Node.<init>(Node.java:251) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Bootstrap$5.<init>(Bootstrap.java:221) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Bootstrap.setup(Bootstrap.java:221) ~[elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Bootstrap.init(Bootstrap.java:349) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.init(Elasticsearch.java:159) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.execute(Elasticsearch.java:150) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.cli.EnvironmentAwareCommand.execute(EnvironmentAwareCommand.java:86) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.cli.Command.mainWithoutErrorHandling(Command.java:124) [elasticsearch-cli-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.cli.Command.main(Command.java:90) [elasticsearch-cli-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.main(Elasticsearch.java:115) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
at org.elasticsearch.bootstrap.Elasticsearch.main(Elasticsearch.java:92) [elasticsearch-7.2.1-SNAPSHOT.jar:7.2.1-SNAPSHOT]
Caused by: java.security.KeyStoreException: problem accessing trust store
at sun.security.ssl.TrustManagerFactoryImpl.engineInit(TrustManagerFactoryImpl.java:73) ~[?:?]
at javax.net.ssl.TrustManagerFactory.init(TrustManagerFactory.java:278) ~[?:?]
at org.elasticsearch.common.ssl.KeyStoreUtil.createTrustManager(KeyStoreUtil.java:151) ~[?:?]
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:68) ~[?:?]
... 24 more
Caused by: java.io.IOException: Keystore was tampered with, or password was incorrect
at sun.security.provider.JavaKeyStore.engineLoad(JavaKeyStore.java:785) ~[?:?]
at sun.security.util.KeyStoreDelegator.engineLoad(KeyStoreDelegator.java:243) ~[?:?]
at java.security.KeyStore.load(KeyStore.java:1472) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.loadKeyStore(TrustStoreManager.java:365) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.getTrustedCerts(TrustStoreManager.java:313) ~[?:?]
at sun.security.ssl.TrustStoreManager.getTrustedCerts(TrustStoreManager.java:55) ~[?:?]
at sun.security.ssl.TrustManagerFactoryImpl.engineInit(TrustManagerFactoryImpl.java:49) ~[?:?]
at javax.net.ssl.TrustManagerFactory.init(TrustManagerFactory.java:278) ~[?:?]
at org.elasticsearch.common.ssl.KeyStoreUtil.createTrustManager(KeyStoreUtil.java:151) ~[?:?]
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:68) ~[?:?]
... 24 more
Caused by: java.security.UnrecoverableKeyException: Password verification failed
at sun.security.provider.JavaKeyStore.engineLoad(JavaKeyStore.java:783) ~[?:?]
at sun.security.util.KeyStoreDelegator.engineLoad(KeyStoreDelegator.java:243) ~[?:?]
at java.security.KeyStore.load(KeyStore.java:1472) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.loadKeyStore(TrustStoreManager.java:365) ~[?:?]
at sun.security.ssl.TrustStoreManager$TrustAnchorManager.getTrustedCerts(TrustStoreManager.java:313) ~[?:?]
at sun.security.ssl.TrustStoreManager.getTrustedCerts(TrustStoreManager.java:55) ~[?:?]
at sun.security.ssl.TrustManagerFactoryImpl.engineInit(TrustManagerFactoryImpl.java:49) ~[?:?]
at javax.net.ssl.TrustManagerFactory.init(TrustManagerFactory.java:278) ~[?:?]
at org.elasticsearch.common.ssl.KeyStoreUtil.createTrustManager(KeyStoreUtil.java:151) ~[?:?]
at org.elasticsearch.common.ssl.DefaultJdkTrustConfig.createTrustManager(DefaultJdkTrustConfig.java:68) ~[?:?]
````
Both nodes failed with the same error here's the logs
[node0.log](https://github.com/elastic/elasticsearch/files/3368369/node0.log)
[node1.log](https://github.com/elastic/elasticsearch/files/3368370/node1.log)
| test | failed to initialize a trustmanager the full cluster restart test task qa full cluster restart oldclustertestcluster wait failed because the node threw a fatal error exception org elasticsearch common ssl sslconfigexception failed to initialize a trustmanager for the system keystore at org elasticsearch common ssl defaultjdktrustconfig createtrustmanager defaultjdktrustconfig java at org elasticsearch common ssl sslconfiguration createsslcontext sslconfiguration java at org elasticsearch index reindex reindexsslconfig reload reindexsslconfig java at org elasticsearch index reindex reindexsslconfig reindexsslconfig java at org elasticsearch index reindex reindexplugin createcomponents reindexplugin java at org elasticsearch node node lambda new node java at java util stream referencepipeline accept referencepipeline java at java util arraylist arraylistspliterator foreachremaining arraylist java at java util stream abstractpipeline copyinto abstractpipeline java at java util stream abstractpipeline wrapandcopyinto abstractpipeline java at java util stream reduceops reduceop evaluatesequential reduceops java at java util stream abstractpipeline evaluate abstractpipeline java at java util stream referencepipeline collect referencepipeline java at org elasticsearch node node node java at org elasticsearch node node node java at org elasticsearch bootstrap bootstrap bootstrap java at org elasticsearch bootstrap bootstrap setup bootstrap java at org elasticsearch bootstrap bootstrap init bootstrap java at org elasticsearch bootstrap elasticsearch init elasticsearch java at org elasticsearch bootstrap elasticsearch execute elasticsearch java at org elasticsearch cli environmentawarecommand execute environmentawarecommand java at org elasticsearch cli command mainwithouterrorhandling command java at org elasticsearch cli command main command java at org elasticsearch bootstrap elasticsearch main elasticsearch java at org elasticsearch bootstrap elasticsearch main elasticsearch java caused by java security keystoreexception problem accessing trust store at sun security ssl trustmanagerfactoryimpl engineinit trustmanagerfactoryimpl java at javax net ssl trustmanagerfactory init trustmanagerfactory java at org elasticsearch common ssl keystoreutil createtrustmanager keystoreutil java at org elasticsearch common ssl defaultjdktrustconfig createtrustmanager defaultjdktrustconfig java more caused by java io ioexception keystore was tampered with or password was incorrect at sun security provider javakeystore engineload javakeystore java at sun security util keystoredelegator engineload keystoredelegator java at java security keystore load keystore java at sun security ssl truststoremanager trustanchormanager loadkeystore truststoremanager java at sun security ssl truststoremanager trustanchormanager gettrustedcerts truststoremanager java at sun security ssl truststoremanager gettrustedcerts truststoremanager java at sun security ssl trustmanagerfactoryimpl engineinit trustmanagerfactoryimpl java at javax net ssl trustmanagerfactory init trustmanagerfactory java at org elasticsearch common ssl keystoreutil createtrustmanager keystoreutil java at org elasticsearch common ssl defaultjdktrustconfig createtrustmanager defaultjdktrustconfig java more caused by java security unrecoverablekeyexception password verification failed at sun security provider javakeystore engineload javakeystore java at sun security util keystoredelegator engineload keystoredelegator java at java security keystore load keystore java at sun security ssl truststoremanager trustanchormanager loadkeystore truststoremanager java at sun security ssl truststoremanager trustanchormanager gettrustedcerts truststoremanager java at sun security ssl truststoremanager gettrustedcerts truststoremanager java at sun security ssl trustmanagerfactoryimpl engineinit trustmanagerfactoryimpl java at javax net ssl trustmanagerfactory init trustmanagerfactory java at org elasticsearch common ssl keystoreutil createtrustmanager keystoreutil java at org elasticsearch common ssl defaultjdktrustconfig createtrustmanager defaultjdktrustconfig java both nodes failed with the same error here s the logs | 1 |
200,705 | 15,145,154,949 | IssuesEvent | 2021-02-11 03:33:13 | projectcontour/contour | https://api.github.com/repos/projectcontour/contour | closed | CI doesn't fail when API reference docs haven't been updated | area/testing kind/bug | PR #3288 updated some API godoc but didn't run `make codegen` to update the API reference docs. However, this wasn't flagged as an error by CI that checks for uncommitted codegen.
It looks like the [script that checks for changes](https://github.com/projectcontour/contour/blob/main/hack/actions/check-uncommitted-codegen.sh#L10-L15) isn't looking at the API reference docs. We should be able to directly add the file to the list. | 1.0 | CI doesn't fail when API reference docs haven't been updated - PR #3288 updated some API godoc but didn't run `make codegen` to update the API reference docs. However, this wasn't flagged as an error by CI that checks for uncommitted codegen.
It looks like the [script that checks for changes](https://github.com/projectcontour/contour/blob/main/hack/actions/check-uncommitted-codegen.sh#L10-L15) isn't looking at the API reference docs. We should be able to directly add the file to the list. | test | ci doesn t fail when api reference docs haven t been updated pr updated some api godoc but didn t run make codegen to update the api reference docs however this wasn t flagged as an error by ci that checks for uncommitted codegen it looks like the isn t looking at the api reference docs we should be able to directly add the file to the list | 1 |
132,193 | 18,266,184,964 | IssuesEvent | 2021-10-04 08:43:52 | artsking/linux-3.0.35_CVE-2020-15436_withPatch | https://api.github.com/repos/artsking/linux-3.0.35_CVE-2020-15436_withPatch | closed | CVE-2013-2148 (Medium) detected in linux-stable-rtv3.8.6 - autoclosed | security vulnerability | ## CVE-2013-2148 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35_CVE-2020-15436_withPatch/commit/594a70cb9871ddd73cf61197bb1a2a1b1777a7ae">594a70cb9871ddd73cf61197bb1a2a1b1777a7ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/fanotify/fanotify_user.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/fanotify/fanotify_user.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/fanotify/fanotify_user.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fill_event_metadata function in fs/notify/fanotify/fanotify_user.c in the Linux kernel through 3.9.4 does not initialize a certain structure member, which allows local users to obtain sensitive information from kernel memory via a read operation on the fanotify descriptor.
<p>Publish Date: 2013-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-2148>CVE-2013-2148</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2148">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2148</a></p>
<p>Release Date: 2013-06-07</p>
<p>Fix Resolution: v3.11-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2013-2148 (Medium) detected in linux-stable-rtv3.8.6 - autoclosed - ## CVE-2013-2148 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35_CVE-2020-15436_withPatch/commit/594a70cb9871ddd73cf61197bb1a2a1b1777a7ae">594a70cb9871ddd73cf61197bb1a2a1b1777a7ae</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/fanotify/fanotify_user.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/fanotify/fanotify_user.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/fs/notify/fanotify/fanotify_user.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fill_event_metadata function in fs/notify/fanotify/fanotify_user.c in the Linux kernel through 3.9.4 does not initialize a certain structure member, which allows local users to obtain sensitive information from kernel memory via a read operation on the fanotify descriptor.
<p>Publish Date: 2013-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2013-2148>CVE-2013-2148</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: N/A
- Attack Complexity: N/A
- Privileges Required: N/A
- User Interaction: N/A
- Scope: N/A
- Impact Metrics:
- Confidentiality Impact: N/A
- Integrity Impact: N/A
- Availability Impact: N/A
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2148">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2013-2148</a></p>
<p>Release Date: 2013-06-07</p>
<p>Fix Resolution: v3.11-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linux stable autoclosed cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files fs notify fanotify fanotify user c fs notify fanotify fanotify user c fs notify fanotify fanotify user c vulnerability details the fill event metadata function in fs notify fanotify fanotify user c in the linux kernel through does not initialize a certain structure member which allows local users to obtain sensitive information from kernel memory via a read operation on the fanotify descriptor publish date url a href cvss score details base score metrics exploitability metrics attack vector n a attack complexity n a privileges required n a user interaction n a scope n a impact metrics confidentiality impact n a integrity impact n a availability impact n a for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
775,738 | 27,235,713,341 | IssuesEvent | 2023-02-21 16:10:36 | ascheid/itsg33-pbmm-issue-gen | https://api.github.com/repos/ascheid/itsg33-pbmm-issue-gen | closed | AC-7: Unsuccessful Login Attempts | Priority: P1 Class: Technical ITSG-33 Suggested Assignment: IT Projects Control: AC-7 | # Control Definition
(A) The information system enforces a limit of [Assignment: organization-defined number] consecutive invalid logon attempts by a user during a [Assignment: organization-defined time period].
(B) The information system automatically [Selection: locks the account/node for an [Assignment: organization-defined time period]; locks the account/node until released by an administrator; delays next logon prompt according to [Assignment: organization-defined delay algorithm]] when the maximum number of unsuccessful attempts is exceeded.
# Class
Technical
# Supplemental Guidance
Due to the potential for denial of service, automatic lockouts initiated by the information system are usually temporary and automatically release after a predetermined time period established by the organization. If a delay algorithm is selected, the organization may choose to employ different algorithms for different information system components based on the capabilities of those components. Response to unsuccessful login attempts may be implemented at both the operating system and the application levels. This control applies to all accesses other than those accesses explicitly identified and documented by the organization in AC-14
# General Guide
This security control/enhancement requires careful balance between usability and security. Care needs to be taken to ensure that the appropriate balance between the two seemingly conflicting requirements is achieved.
If possible, an increasing time-out period should be used to deter determined attackers. For example, an original time-out of 5 minutes can become 10 minutes after the next 3 unsuccessful attempts, then 20 minutes, then 40 minutes, etc.
# Suggested Placeholder Values
X
# Profile Specific Notes
(A) number [of a maximum of 5]
(A) time period [period of at least 5 minutes]
(B) automatic response [locks the account/node for an organization defined time period]
# Suggested Assignment
IT Projects
# Support Teams
IT Security Function, IT Operations Group
| 1.0 | AC-7: Unsuccessful Login Attempts - # Control Definition
(A) The information system enforces a limit of [Assignment: organization-defined number] consecutive invalid logon attempts by a user during a [Assignment: organization-defined time period].
(B) The information system automatically [Selection: locks the account/node for an [Assignment: organization-defined time period]; locks the account/node until released by an administrator; delays next logon prompt according to [Assignment: organization-defined delay algorithm]] when the maximum number of unsuccessful attempts is exceeded.
# Class
Technical
# Supplemental Guidance
Due to the potential for denial of service, automatic lockouts initiated by the information system are usually temporary and automatically release after a predetermined time period established by the organization. If a delay algorithm is selected, the organization may choose to employ different algorithms for different information system components based on the capabilities of those components. Response to unsuccessful login attempts may be implemented at both the operating system and the application levels. This control applies to all accesses other than those accesses explicitly identified and documented by the organization in AC-14
# General Guide
This security control/enhancement requires careful balance between usability and security. Care needs to be taken to ensure that the appropriate balance between the two seemingly conflicting requirements is achieved.
If possible, an increasing time-out period should be used to deter determined attackers. For example, an original time-out of 5 minutes can become 10 minutes after the next 3 unsuccessful attempts, then 20 minutes, then 40 minutes, etc.
# Suggested Placeholder Values
X
# Profile Specific Notes
(A) number [of a maximum of 5]
(A) time period [period of at least 5 minutes]
(B) automatic response [locks the account/node for an organization defined time period]
# Suggested Assignment
IT Projects
# Support Teams
IT Security Function, IT Operations Group
| non_test | ac unsuccessful login attempts control definition a the information system enforces a limit of consecutive invalid logon attempts by a user during a b the information system automatically locks the account node until released by an administrator delays next logon prompt according to when the maximum number of unsuccessful attempts is exceeded class technical supplemental guidance due to the potential for denial of service automatic lockouts initiated by the information system are usually temporary and automatically release after a predetermined time period established by the organization if a delay algorithm is selected the organization may choose to employ different algorithms for different information system components based on the capabilities of those components response to unsuccessful login attempts may be implemented at both the operating system and the application levels this control applies to all accesses other than those accesses explicitly identified and documented by the organization in ac general guide this security control enhancement requires careful balance between usability and security care needs to be taken to ensure that the appropriate balance between the two seemingly conflicting requirements is achieved if possible an increasing time out period should be used to deter determined attackers for example an original time out of minutes can become minutes after the next unsuccessful attempts then minutes then minutes etc suggested placeholder values x profile specific notes a number a time period b automatic response suggested assignment it projects support teams it security function it operations group | 0 |
178,216 | 13,768,924,221 | IssuesEvent | 2020-10-07 17:49:10 | quarkusio/quarkus | https://api.github.com/repos/quarkusio/quarkus | reopened | QuarkusTest fails with "Error while reading file as JAR: ...\target\classes" in test-only module | area/bootstrap area/testing kind/bug | **Describe the bug**
In a multi-module Maven project, you might want to have test-only modules (= nothing in `src/main/java`) with `@QuarkusTest` classes (in `src/test/java`).
As of 1.8.2 this does fails with:
```
java.lang.RuntimeException: java.io.UncheckedIOException: Error while reading file as JAR: C:\Develop\someproject\middleware\_develop-2\someproject-middleware\patient\test-integration\target\classes
at io.quarkus.test.junit.QuarkusTestExtension.throwBootFailureException(QuarkusTestExtension.java:526)
at io.quarkus.test.junit.QuarkusTestExtension.beforeEach(QuarkusTestExtension.java:376)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeBeforeEachCallbacks$1(TestMethodTestDescriptor.java:161)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeBeforeMethodsOrCallbacksUntilExceptionOccurs$5(TestMethodTestDescriptor.java:197)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeBeforeMethodsOrCallbacksUntilExceptionOccurs(TestMethodTestDescriptor.java:197)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeBeforeEachCallbacks(TestMethodTestDescriptor.java:160)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:131)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:71)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:135)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1540)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1540)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.submit(SameThreadHierarchicalTestExecutorService.java:32)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestExecutor.execute(HierarchicalTestExecutor.java:57)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestEngine.execute(HierarchicalTestEngine.java:51)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:248)
at org.junit.platform.launcher.core.DefaultLauncher.lambda$execute$5(DefaultLauncher.java:211)
at org.junit.platform.launcher.core.DefaultLauncher.withInterceptedStreams(DefaultLauncher.java:226)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:199)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:132)
at org.apache.maven.surefire.junitplatform.JUnitPlatformProvider.execute(JUnitPlatformProvider.java:188)
at org.apache.maven.surefire.junitplatform.JUnitPlatformProvider.invokeAllTests(JUnitPlatformProvider.java:154)
at org.apache.maven.surefire.junitplatform.JUnitPlatformProvider.invoke(JUnitPlatformProvider.java:128)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:428)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:162)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:562)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:548)
Caused by: java.io.UncheckedIOException: Error while reading file as JAR: C:\Develop\someproject\middleware\_develop-2\someproject-middleware\patient\test-integration\target\classes
at io.quarkus.bootstrap.classloading.JarClassPathElement.<init>(JarClassPathElement.java:46)
at io.quarkus.bootstrap.classloading.ClassPathElement.fromPath(ClassPathElement.java:51)
at io.quarkus.bootstrap.app.CuratedApplication.getBaseRuntimeClassLoader(CuratedApplication.java:210)
at io.quarkus.test.junit.QuarkusTestExtension.doJavaStart(QuarkusTestExtension.java:211)
at io.quarkus.test.junit.QuarkusTestExtension.ensureStarted(QuarkusTestExtension.java:504)
at io.quarkus.test.junit.QuarkusTestExtension.beforeAll(QuarkusTestExtension.java:537)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.lambda$invokeBeforeAllCallbacks$7(ClassBasedTestDescriptor.java:359)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.invokeBeforeAllCallbacks(ClassBasedTestDescriptor.java:359)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.before(ClassBasedTestDescriptor.java:189)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.before(ClassBasedTestDescriptor.java:78)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:132)
... 32 more
Caused by: java.nio.file.NoSuchFileException: C:\Develop\someproject\middleware\_develop-2\someproject-middleware\patient\test-integration\target\classes
at java.base/sun.nio.fs.WindowsException.translateToIOException(WindowsException.java:85)
at java.base/sun.nio.fs.WindowsException.rethrowAsIOException(WindowsException.java:103)
at java.base/sun.nio.fs.WindowsException.rethrowAsIOException(WindowsException.java:108)
at java.base/sun.nio.fs.WindowsFileAttributeViews$Basic.readAttributes(WindowsFileAttributeViews.java:53)
at java.base/sun.nio.fs.WindowsFileAttributeViews$Basic.readAttributes(WindowsFileAttributeViews.java:38)
at java.base/sun.nio.fs.WindowsFileSystemProvider.readAttributes(WindowsFileSystemProvider.java:198)
at java.base/java.nio.file.Files.readAttributes(Files.java:1763)
at java.base/java.util.zip.ZipFile$Source.get(ZipFile.java:1225)
at java.base/java.util.zip.ZipFile$CleanableResource.<init>(ZipFile.java:727)
at java.base/java.util.zip.ZipFile$CleanableResource.get(ZipFile.java:844)
at java.base/java.util.zip.ZipFile.<init>(ZipFile.java:247)
at java.base/java.util.zip.ZipFile.<init>(ZipFile.java:177)
at java.base/java.util.jar.JarFile.<init>(JarFile.java:348)
at io.smallrye.common.io.jar.JarFiles.create(JarFiles.java:33)
at io.quarkus.bootstrap.classloading.JarClassPathElement.<init>(JarClassPathElement.java:44)
... 43 more
```
Adding some dummy java file to `src/main/java` works around this problem.
**Expected behavior**
Executing tests in a test-only module should work.
**Actual behavior**
Executing tests in a test-only module fails.
**To Reproduce**
Steps to reproduce the behavior:
1. none yet, will try to reproduce ASAP
**Configuration**
Many. Should not be relevant.
**Environment (please complete the following information):**
- Output of `uname -a` or `ver`: `MINGW64_NT-10.0-18363 XXX 3.0.7-338.x86_64 2019-11-21 23:07 UTC x86_64 Msys`
- Output of `java -version`: `OpenJDK Runtime Environment AdoptOpenJDK (build 11.0.7+10)`
- GraalVM version (if different from Java): n/a
- Quarkus version or git rev: `1.8.2.Final`
- Build tool (ie. output of `mvnw --version` or `gradlew --version`): `Apache Maven 3.6.3`
**Additional context**
IIRC, there was once a limitation in the build mojo that also required some dummy java class in `main`. That bug/limitation was fixed a few releases ago.
Also happens with 1.8.0.Final and probably also in even older versions. | 1.0 | QuarkusTest fails with "Error while reading file as JAR: ...\target\classes" in test-only module - **Describe the bug**
In a multi-module Maven project, you might want to have test-only modules (= nothing in `src/main/java`) with `@QuarkusTest` classes (in `src/test/java`).
As of 1.8.2 this does fails with:
```
java.lang.RuntimeException: java.io.UncheckedIOException: Error while reading file as JAR: C:\Develop\someproject\middleware\_develop-2\someproject-middleware\patient\test-integration\target\classes
at io.quarkus.test.junit.QuarkusTestExtension.throwBootFailureException(QuarkusTestExtension.java:526)
at io.quarkus.test.junit.QuarkusTestExtension.beforeEach(QuarkusTestExtension.java:376)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeBeforeEachCallbacks$1(TestMethodTestDescriptor.java:161)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.lambda$invokeBeforeMethodsOrCallbacksUntilExceptionOccurs$5(TestMethodTestDescriptor.java:197)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeBeforeMethodsOrCallbacksUntilExceptionOccurs(TestMethodTestDescriptor.java:197)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.invokeBeforeEachCallbacks(TestMethodTestDescriptor.java:160)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:131)
at org.junit.jupiter.engine.descriptor.TestMethodTestDescriptor.execute(TestMethodTestDescriptor.java:71)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:135)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1540)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at java.base/java.util.ArrayList.forEach(ArrayList.java:1540)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.invokeAll(SameThreadHierarchicalTestExecutorService.java:38)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:139)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$7(NodeTestTask.java:125)
at org.junit.platform.engine.support.hierarchical.Node.around(Node.java:135)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$8(NodeTestTask.java:123)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.executeRecursively(NodeTestTask.java:122)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.execute(NodeTestTask.java:80)
at org.junit.platform.engine.support.hierarchical.SameThreadHierarchicalTestExecutorService.submit(SameThreadHierarchicalTestExecutorService.java:32)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestExecutor.execute(HierarchicalTestExecutor.java:57)
at org.junit.platform.engine.support.hierarchical.HierarchicalTestEngine.execute(HierarchicalTestEngine.java:51)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:248)
at org.junit.platform.launcher.core.DefaultLauncher.lambda$execute$5(DefaultLauncher.java:211)
at org.junit.platform.launcher.core.DefaultLauncher.withInterceptedStreams(DefaultLauncher.java:226)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:199)
at org.junit.platform.launcher.core.DefaultLauncher.execute(DefaultLauncher.java:132)
at org.apache.maven.surefire.junitplatform.JUnitPlatformProvider.execute(JUnitPlatformProvider.java:188)
at org.apache.maven.surefire.junitplatform.JUnitPlatformProvider.invokeAllTests(JUnitPlatformProvider.java:154)
at org.apache.maven.surefire.junitplatform.JUnitPlatformProvider.invoke(JUnitPlatformProvider.java:128)
at org.apache.maven.surefire.booter.ForkedBooter.runSuitesInProcess(ForkedBooter.java:428)
at org.apache.maven.surefire.booter.ForkedBooter.execute(ForkedBooter.java:162)
at org.apache.maven.surefire.booter.ForkedBooter.run(ForkedBooter.java:562)
at org.apache.maven.surefire.booter.ForkedBooter.main(ForkedBooter.java:548)
Caused by: java.io.UncheckedIOException: Error while reading file as JAR: C:\Develop\someproject\middleware\_develop-2\someproject-middleware\patient\test-integration\target\classes
at io.quarkus.bootstrap.classloading.JarClassPathElement.<init>(JarClassPathElement.java:46)
at io.quarkus.bootstrap.classloading.ClassPathElement.fromPath(ClassPathElement.java:51)
at io.quarkus.bootstrap.app.CuratedApplication.getBaseRuntimeClassLoader(CuratedApplication.java:210)
at io.quarkus.test.junit.QuarkusTestExtension.doJavaStart(QuarkusTestExtension.java:211)
at io.quarkus.test.junit.QuarkusTestExtension.ensureStarted(QuarkusTestExtension.java:504)
at io.quarkus.test.junit.QuarkusTestExtension.beforeAll(QuarkusTestExtension.java:537)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.lambda$invokeBeforeAllCallbacks$7(ClassBasedTestDescriptor.java:359)
at org.junit.platform.engine.support.hierarchical.ThrowableCollector.execute(ThrowableCollector.java:73)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.invokeBeforeAllCallbacks(ClassBasedTestDescriptor.java:359)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.before(ClassBasedTestDescriptor.java:189)
at org.junit.jupiter.engine.descriptor.ClassBasedTestDescriptor.before(ClassBasedTestDescriptor.java:78)
at org.junit.platform.engine.support.hierarchical.NodeTestTask.lambda$executeRecursively$5(NodeTestTask.java:132)
... 32 more
Caused by: java.nio.file.NoSuchFileException: C:\Develop\someproject\middleware\_develop-2\someproject-middleware\patient\test-integration\target\classes
at java.base/sun.nio.fs.WindowsException.translateToIOException(WindowsException.java:85)
at java.base/sun.nio.fs.WindowsException.rethrowAsIOException(WindowsException.java:103)
at java.base/sun.nio.fs.WindowsException.rethrowAsIOException(WindowsException.java:108)
at java.base/sun.nio.fs.WindowsFileAttributeViews$Basic.readAttributes(WindowsFileAttributeViews.java:53)
at java.base/sun.nio.fs.WindowsFileAttributeViews$Basic.readAttributes(WindowsFileAttributeViews.java:38)
at java.base/sun.nio.fs.WindowsFileSystemProvider.readAttributes(WindowsFileSystemProvider.java:198)
at java.base/java.nio.file.Files.readAttributes(Files.java:1763)
at java.base/java.util.zip.ZipFile$Source.get(ZipFile.java:1225)
at java.base/java.util.zip.ZipFile$CleanableResource.<init>(ZipFile.java:727)
at java.base/java.util.zip.ZipFile$CleanableResource.get(ZipFile.java:844)
at java.base/java.util.zip.ZipFile.<init>(ZipFile.java:247)
at java.base/java.util.zip.ZipFile.<init>(ZipFile.java:177)
at java.base/java.util.jar.JarFile.<init>(JarFile.java:348)
at io.smallrye.common.io.jar.JarFiles.create(JarFiles.java:33)
at io.quarkus.bootstrap.classloading.JarClassPathElement.<init>(JarClassPathElement.java:44)
... 43 more
```
Adding some dummy java file to `src/main/java` works around this problem.
**Expected behavior**
Executing tests in a test-only module should work.
**Actual behavior**
Executing tests in a test-only module fails.
**To Reproduce**
Steps to reproduce the behavior:
1. none yet, will try to reproduce ASAP
**Configuration**
Many. Should not be relevant.
**Environment (please complete the following information):**
- Output of `uname -a` or `ver`: `MINGW64_NT-10.0-18363 XXX 3.0.7-338.x86_64 2019-11-21 23:07 UTC x86_64 Msys`
- Output of `java -version`: `OpenJDK Runtime Environment AdoptOpenJDK (build 11.0.7+10)`
- GraalVM version (if different from Java): n/a
- Quarkus version or git rev: `1.8.2.Final`
- Build tool (ie. output of `mvnw --version` or `gradlew --version`): `Apache Maven 3.6.3`
**Additional context**
IIRC, there was once a limitation in the build mojo that also required some dummy java class in `main`. That bug/limitation was fixed a few releases ago.
Also happens with 1.8.0.Final and probably also in even older versions. | test | quarkustest fails with error while reading file as jar target classes in test only module describe the bug in a multi module maven project you might want to have test only modules nothing in src main java with quarkustest classes in src test java as of this does fails with java lang runtimeexception java io uncheckedioexception error while reading file as jar c develop someproject middleware develop someproject middleware patient test integration target classes at io quarkus test junit quarkustestextension throwbootfailureexception quarkustestextension java at io quarkus test junit quarkustestextension beforeeach quarkustestextension java at org junit jupiter engine descriptor testmethodtestdescriptor lambda invokebeforeeachcallbacks testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor lambda invokebeforemethodsorcallbacksuntilexceptionoccurs testmethodtestdescriptor java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit jupiter engine descriptor testmethodtestdescriptor invokebeforemethodsorcallbacksuntilexceptionoccurs testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor invokebeforeeachcallbacks testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor execute testmethodtestdescriptor java at org junit jupiter engine descriptor testmethodtestdescriptor execute testmethodtestdescriptor java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at java base java util arraylist foreach arraylist java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice invokeall samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at java base java util arraylist foreach arraylist java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice invokeall samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical node around node java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit platform engine support hierarchical nodetesttask executerecursively nodetesttask java at org junit platform engine support hierarchical nodetesttask execute nodetesttask java at org junit platform engine support hierarchical samethreadhierarchicaltestexecutorservice submit samethreadhierarchicaltestexecutorservice java at org junit platform engine support hierarchical hierarchicaltestexecutor execute hierarchicaltestexecutor java at org junit platform engine support hierarchical hierarchicaltestengine execute hierarchicaltestengine java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org junit platform launcher core defaultlauncher lambda execute defaultlauncher java at org junit platform launcher core defaultlauncher withinterceptedstreams defaultlauncher java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org junit platform launcher core defaultlauncher execute defaultlauncher java at org apache maven surefire junitplatform junitplatformprovider execute junitplatformprovider java at org apache maven surefire junitplatform junitplatformprovider invokealltests junitplatformprovider java at org apache maven surefire junitplatform junitplatformprovider invoke junitplatformprovider java at org apache maven surefire booter forkedbooter runsuitesinprocess forkedbooter java at org apache maven surefire booter forkedbooter execute forkedbooter java at org apache maven surefire booter forkedbooter run forkedbooter java at org apache maven surefire booter forkedbooter main forkedbooter java caused by java io uncheckedioexception error while reading file as jar c develop someproject middleware develop someproject middleware patient test integration target classes at io quarkus bootstrap classloading jarclasspathelement jarclasspathelement java at io quarkus bootstrap classloading classpathelement frompath classpathelement java at io quarkus bootstrap app curatedapplication getbaseruntimeclassloader curatedapplication java at io quarkus test junit quarkustestextension dojavastart quarkustestextension java at io quarkus test junit quarkustestextension ensurestarted quarkustestextension java at io quarkus test junit quarkustestextension beforeall quarkustestextension java at org junit jupiter engine descriptor classbasedtestdescriptor lambda invokebeforeallcallbacks classbasedtestdescriptor java at org junit platform engine support hierarchical throwablecollector execute throwablecollector java at org junit jupiter engine descriptor classbasedtestdescriptor invokebeforeallcallbacks classbasedtestdescriptor java at org junit jupiter engine descriptor classbasedtestdescriptor before classbasedtestdescriptor java at org junit jupiter engine descriptor classbasedtestdescriptor before classbasedtestdescriptor java at org junit platform engine support hierarchical nodetesttask lambda executerecursively nodetesttask java more caused by java nio file nosuchfileexception c develop someproject middleware develop someproject middleware patient test integration target classes at java base sun nio fs windowsexception translatetoioexception windowsexception java at java base sun nio fs windowsexception rethrowasioexception windowsexception java at java base sun nio fs windowsexception rethrowasioexception windowsexception java at java base sun nio fs windowsfileattributeviews basic readattributes windowsfileattributeviews java at java base sun nio fs windowsfileattributeviews basic readattributes windowsfileattributeviews java at java base sun nio fs windowsfilesystemprovider readattributes windowsfilesystemprovider java at java base java nio file files readattributes files java at java base java util zip zipfile source get zipfile java at java base java util zip zipfile cleanableresource zipfile java at java base java util zip zipfile cleanableresource get zipfile java at java base java util zip zipfile zipfile java at java base java util zip zipfile zipfile java at java base java util jar jarfile jarfile java at io smallrye common io jar jarfiles create jarfiles java at io quarkus bootstrap classloading jarclasspathelement jarclasspathelement java more adding some dummy java file to src main java works around this problem expected behavior executing tests in a test only module should work actual behavior executing tests in a test only module fails to reproduce steps to reproduce the behavior none yet will try to reproduce asap configuration many should not be relevant environment please complete the following information output of uname a or ver nt xxx utc msys output of java version openjdk runtime environment adoptopenjdk build graalvm version if different from java n a quarkus version or git rev final build tool ie output of mvnw version or gradlew version apache maven additional context iirc there was once a limitation in the build mojo that also required some dummy java class in main that bug limitation was fixed a few releases ago also happens with final and probably also in even older versions | 1 |
298,849 | 22,576,339,059 | IssuesEvent | 2022-06-28 07:42:22 | demisto/content-docs | https://api.github.com/repos/demisto/content-docs | closed | Issue with "Generic Export Indicators Service" in @site/docs/reference/integrations/edl.md | documentation | <!--
Thank you for taking the time to help us improve our documentation! Please describe the problem and a suggested fix below and we'll get back to you as soon as we can.
-->
## Describe the problem
* Page: [Generic Export Indicators Service](https://xsoar.pan.dev/docs/reference/integrations/edl)
* Source: https://github.com/demisto/content/blob/master//Packs/EDL/Integrations/EDL/README.md
Community notes missing from exportable fields
## Screenshots
<!-- If applicable, add screenshots to help explain your problem. -->
## Environment
- OS: [e.g. Windows] n/a
- Browser: [e.g. chrome, safari, firefox..] n/a
- Browser Version: n/a
## Suggested fix
Can you add community notes as a field that can be exported . I noticed that missing from the list.
| 1.0 | Issue with "Generic Export Indicators Service" in @site/docs/reference/integrations/edl.md - <!--
Thank you for taking the time to help us improve our documentation! Please describe the problem and a suggested fix below and we'll get back to you as soon as we can.
-->
## Describe the problem
* Page: [Generic Export Indicators Service](https://xsoar.pan.dev/docs/reference/integrations/edl)
* Source: https://github.com/demisto/content/blob/master//Packs/EDL/Integrations/EDL/README.md
Community notes missing from exportable fields
## Screenshots
<!-- If applicable, add screenshots to help explain your problem. -->
## Environment
- OS: [e.g. Windows] n/a
- Browser: [e.g. chrome, safari, firefox..] n/a
- Browser Version: n/a
## Suggested fix
Can you add community notes as a field that can be exported . I noticed that missing from the list.
| non_test | issue with generic export indicators service in site docs reference integrations edl md thank you for taking the time to help us improve our documentation please describe the problem and a suggested fix below and we ll get back to you as soon as we can describe the problem page source community notes missing from exportable fields screenshots environment os n a browser n a browser version n a suggested fix can you add community notes as a field that can be exported i noticed that missing from the list | 0 |
255,052 | 21,897,266,730 | IssuesEvent | 2022-05-20 09:50:16 | timescale/timescaledb | https://api.github.com/repos/timescale/timescaledb | closed | remote_connection test failure on postgres REL_14_STABLE | testing pg14 | This test is going to start failing on the next PG release. Noticed it on the prerelease tests that use a development snapshot as well.
Here is how it looks:
```
SELECT test.remote_async_tests();
- remote_async_tests
---------------------
-
-(1 row)
-
-\echo 'End Of Test'
-End Of Test
+ERROR: failed to panic @ line 230
```
Link: https://github.com/timescale/timescaledb/runs/5181345428?check_suite_focus=true#step:16:30
The reason seems to be [this commit](https://github.com/postgres/postgres/commit/ae27b1acc43d58badad356a4da8fc0c72d46d7fb) that subtly changed how the connection loss is handled, so now we don't get an exception where we used to. | 1.0 | remote_connection test failure on postgres REL_14_STABLE - This test is going to start failing on the next PG release. Noticed it on the prerelease tests that use a development snapshot as well.
Here is how it looks:
```
SELECT test.remote_async_tests();
- remote_async_tests
---------------------
-
-(1 row)
-
-\echo 'End Of Test'
-End Of Test
+ERROR: failed to panic @ line 230
```
Link: https://github.com/timescale/timescaledb/runs/5181345428?check_suite_focus=true#step:16:30
The reason seems to be [this commit](https://github.com/postgres/postgres/commit/ae27b1acc43d58badad356a4da8fc0c72d46d7fb) that subtly changed how the connection loss is handled, so now we don't get an exception where we used to. | test | remote connection test failure on postgres rel stable this test is going to start failing on the next pg release noticed it on the prerelease tests that use a development snapshot as well here is how it looks select test remote async tests remote async tests row echo end of test end of test error failed to panic line link the reason seems to be that subtly changed how the connection loss is handled so now we don t get an exception where we used to | 1 |
71,607 | 3,362,969,507 | IssuesEvent | 2015-11-20 09:46:50 | cloudify-cosmo/cloudify-azure-plugin | https://api.github.com/repos/cloudify-cosmo/cloudify-azure-plugin | opened | Support using more than one rule of security group | Priority-50 | Change _get_security_group_params (in securitygroup.py) to support specifying more than one rule. | 1.0 | Support using more than one rule of security group - Change _get_security_group_params (in securitygroup.py) to support specifying more than one rule. | non_test | support using more than one rule of security group change get security group params in securitygroup py to support specifying more than one rule | 0 |
249,238 | 21,134,262,696 | IssuesEvent | 2022-04-06 04:04:16 | ita-social-projects/EventsExpress | https://api.github.com/repos/ita-social-projects/EventsExpress | opened | Verify that an unregistered user is able to create an event | test case | **Date Time**
04/05/2022
**Priority**
High
**Description**
This test case verifies if an unregistered user is able to create an event.
**Pre-requisites**
Steps to be fulfilled before the test:
1. Follow https://eventsexpress-test.azurewebsites.net/.
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1. | Click on the button "Create event" on the landing page. | <br> | Window with information should appear: "Please Log in to the system or create an account" | <br> | <br> | <br> |
| 2. | Click on the button "Create new account" | <br> | The user is redirected to the "Registration form". | <br> | <br> | <br> |
| 3. | Enter valid data into 'Email' field. | User 10. | <br> | <br> | <br> | <br> |
| 4. | Enter valid data into 'Password' field. | User 10. | | <br> | <br> | <br> |
| 5. | Enter valid data into "Repeat password" field. | User 10. | <br> | <br> | <br> | <br> |
| 6. | Click on the button "Sign up" | <br> | The confirmation link is sent to the email. | <br> |
| 7. | Go to the email and click on the confirmation link. | <br> | Page "Step 2 (Complete profile)" is opened. |
| 8. | Enter valid data into Email field. | User 10. | <br> |
| 9. | Fill in the First and Last name fields. | First name: Test1; Last name:Test2 | <br> |
| 10. | Choose any gender from the dropdown list. | <br> | <br> |
| 11. | Choose birth date. | 01.01.2001 | <br> |
| 12. | Enter valid phone number. | +380961234567 | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
**Screenshots**
If applicable, add screenshots to help explain your test.
**Environment:**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the test here.
User story links E.g.: "User story #100 "
Labels to be added "Test case", Priority ("pri: "), Type ("UI, "Functional"), "API" .
| 1.0 | Verify that an unregistered user is able to create an event - **Date Time**
04/05/2022
**Priority**
High
**Description**
This test case verifies if an unregistered user is able to create an event.
**Pre-requisites**
Steps to be fulfilled before the test:
1. Follow https://eventsexpress-test.azurewebsites.net/.
**Test Cases**
| S# | Action | Test Data | Expected Result | Actual Result | P/F | Automated |
|:-----------:|:-----------:|:-----------:|:---------------:|:-------------:|:-----------:|:-----------:|
| 1. | Click on the button "Create event" on the landing page. | <br> | Window with information should appear: "Please Log in to the system or create an account" | <br> | <br> | <br> |
| 2. | Click on the button "Create new account" | <br> | The user is redirected to the "Registration form". | <br> | <br> | <br> |
| 3. | Enter valid data into 'Email' field. | User 10. | <br> | <br> | <br> | <br> |
| 4. | Enter valid data into 'Password' field. | User 10. | | <br> | <br> | <br> |
| 5. | Enter valid data into "Repeat password" field. | User 10. | <br> | <br> | <br> | <br> |
| 6. | Click on the button "Sign up" | <br> | The confirmation link is sent to the email. | <br> |
| 7. | Go to the email and click on the confirmation link. | <br> | Page "Step 2 (Complete profile)" is opened. |
| 8. | Enter valid data into Email field. | User 10. | <br> |
| 9. | Fill in the First and Last name fields. | First name: Test1; Last name:Test2 | <br> |
| 10. | Choose any gender from the dropdown list. | <br> | <br> |
| 11. | Choose birth date. | 01.01.2001 | <br> |
| 12. | Enter valid phone number. | +380961234567 | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
| <br> | <br> | <br> | <br> |
**Screenshots**
If applicable, add screenshots to help explain your test.
**Environment:**
- OS: [e.g. iOS]
- Browser [e.g. chrome, safari]
- Version [e.g. 22]
**Additional context**
Add any other context about the test here.
User story links E.g.: "User story #100 "
Labels to be added "Test case", Priority ("pri: "), Type ("UI, "Functional"), "API" .
| test | verify that an unregistered user is able to create an event date time priority high description this test case verifies if an unregistered user is able to create an event pre requisites steps to be fulfilled before the test follow test cases s action test data expected result actual result p f automated click on the button create event on the landing page window with information should appear please log in to the system or create an account click on the button create new account the user is redirected to the registration form enter valid data into email field user enter valid data into password field user enter valid data into repeat password field user click on the button sign up the confirmation link is sent to the email go to the email and click on the confirmation link page step complete profile is opened enter valid data into email field user fill in the first and last name fields first name last name choose any gender from the dropdown list choose birth date enter valid phone number screenshots if applicable add screenshots to help explain your test environment os browser version additional context add any other context about the test here user story links e g user story labels to be added test case priority pri type ui functional api | 1 |
18,124 | 3,669,921,195 | IssuesEvent | 2016-02-21 15:02:36 | coala-analyzer/coala | https://api.github.com/repos/coala-analyzer/coala | closed | bug: PHPLintBearTest.test_run fails on test | area/tests type/bug | All other tests pass. Only this one fails.
# Steps to reproduce
1. Run `py.test`.
# Actual results

# Expected results
Test should pass.
# Additional info
Output to some commands:


/cc @AbdealiJK | 1.0 | bug: PHPLintBearTest.test_run fails on test - All other tests pass. Only this one fails.
# Steps to reproduce
1. Run `py.test`.
# Actual results

# Expected results
Test should pass.
# Additional info
Output to some commands:


/cc @AbdealiJK | test | bug phplintbeartest test run fails on test all other tests pass only this one fails steps to reproduce run py test actual results expected results test should pass additional info output to some commands cc abdealijk | 1 |
21,762 | 4,745,296,743 | IssuesEvent | 2016-10-21 06:37:51 | facebook/react-native | https://api.github.com/repos/facebook/react-native | closed | [Docs] Make Platform/OS combinations linkable in "Getting started" | Documentation Ran Commands | I really love new concept of picking Platform/OS combination in "Getting started" docs section.
What I miss is ability to link to "active" combination. This is crucial and easier to share. | 1.0 | [Docs] Make Platform/OS combinations linkable in "Getting started" - I really love new concept of picking Platform/OS combination in "Getting started" docs section.
What I miss is ability to link to "active" combination. This is crucial and easier to share. | non_test | make platform os combinations linkable in getting started i really love new concept of picking platform os combination in getting started docs section what i miss is ability to link to active combination this is crucial and easier to share | 0 |
124,409 | 10,310,794,986 | IssuesEvent | 2019-08-29 15:51:43 | kcigeospatial/Fred_Co_Land-Management | https://api.github.com/repos/kcigeospatial/Fred_Co_Land-Management | closed | R4C - Plumbing Misc Trade License - License Category Options (Xtreme #13702540) | Ready for Test Env. Retest | When trying to create a Plumbing Misc Trade License in R4C, I think I'm getting too many options to choose from for the License Category. Some of the options are liquor board options.
In the back office the only options I see are Journeyman and Septic System Installer.
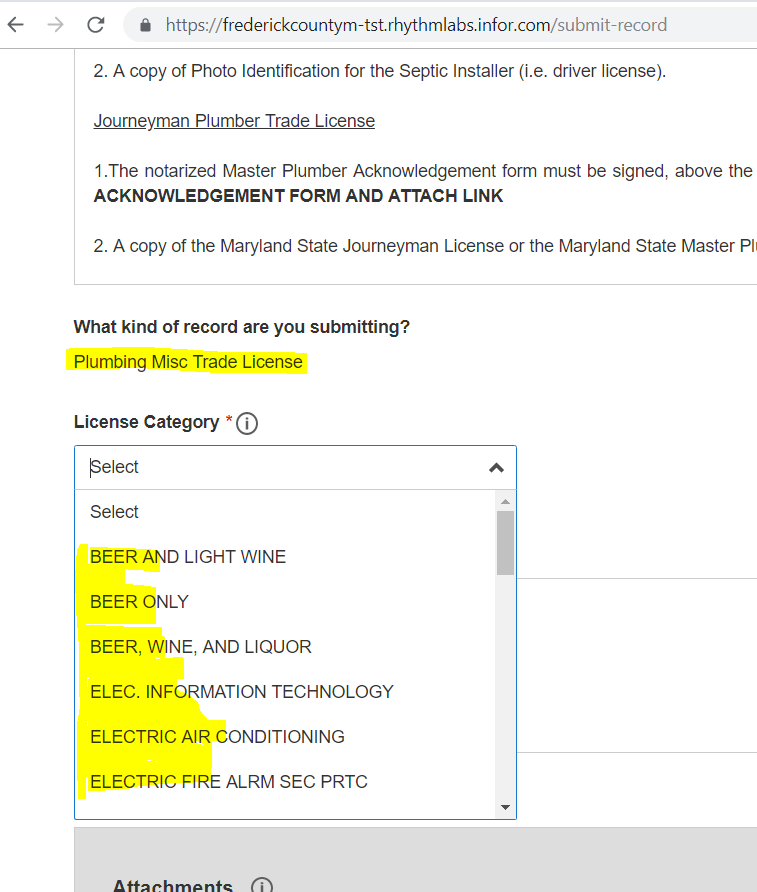

| 2.0 | R4C - Plumbing Misc Trade License - License Category Options (Xtreme #13702540) - When trying to create a Plumbing Misc Trade License in R4C, I think I'm getting too many options to choose from for the License Category. Some of the options are liquor board options.
In the back office the only options I see are Journeyman and Septic System Installer.
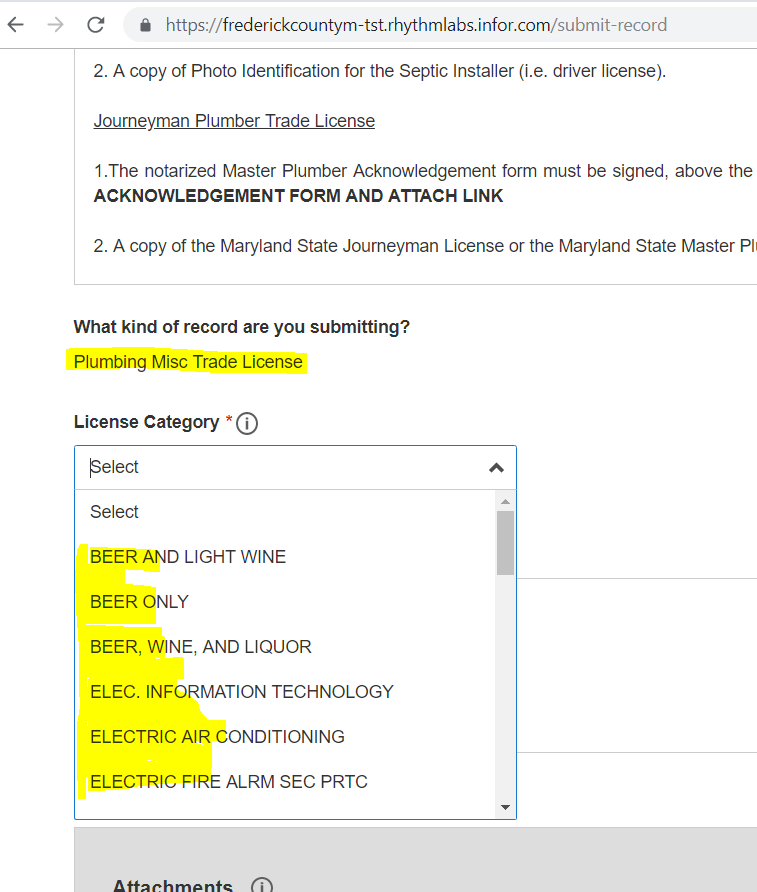

| test | plumbing misc trade license license category options xtreme when trying to create a plumbing misc trade license in i think i m getting too many options to choose from for the license category some of the options are liquor board options in the back office the only options i see are journeyman and septic system installer | 1 |
191,900 | 14,597,142,561 | IssuesEvent | 2020-12-20 18:49:07 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | swiftstack/ProxyFS: vendor/go.etcd.io/etcd/mvcc/kv_test.go; 20 LoC | fresh small test vendored |
Found a possible issue in [swiftstack/ProxyFS](https://www.github.com/swiftstack/ProxyFS) at [vendor/go.etcd.io/etcd/mvcc/kv_test.go](https://github.com/swiftstack/ProxyFS/blob/5d6fcf6d1cf1b6b87fc087b288eab7ff3e955e9b/vendor/go.etcd.io/etcd/mvcc/kv_test.go#L412-L431)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable tt used in defer or goroutine at line 416
[Click here to see the code in its original context.](https://github.com/swiftstack/ProxyFS/blob/5d6fcf6d1cf1b6b87fc087b288eab7ff3e955e9b/vendor/go.etcd.io/etcd/mvcc/kv_test.go#L412-L431)
<details>
<summary>Click here to show the 20 line(s) of Go which triggered the analyzer.</summary>
```go
for i, tt := range tests {
txn := s.Write(traceutil.TODO())
done := make(chan struct{}, 1)
go func() {
tt()
done <- struct{}{}
}()
select {
case <-done:
t.Fatalf("#%d: operation failed to be blocked", i)
case <-time.After(10 * time.Millisecond):
}
txn.End()
select {
case <-done:
case <-time.After(10 * time.Second):
testutil.FatalStack(t, fmt.Sprintf("#%d: operation failed to be unblocked", i))
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 5d6fcf6d1cf1b6b87fc087b288eab7ff3e955e9b
| 1.0 | swiftstack/ProxyFS: vendor/go.etcd.io/etcd/mvcc/kv_test.go; 20 LoC -
Found a possible issue in [swiftstack/ProxyFS](https://www.github.com/swiftstack/ProxyFS) at [vendor/go.etcd.io/etcd/mvcc/kv_test.go](https://github.com/swiftstack/ProxyFS/blob/5d6fcf6d1cf1b6b87fc087b288eab7ff3e955e9b/vendor/go.etcd.io/etcd/mvcc/kv_test.go#L412-L431)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> range-loop variable tt used in defer or goroutine at line 416
[Click here to see the code in its original context.](https://github.com/swiftstack/ProxyFS/blob/5d6fcf6d1cf1b6b87fc087b288eab7ff3e955e9b/vendor/go.etcd.io/etcd/mvcc/kv_test.go#L412-L431)
<details>
<summary>Click here to show the 20 line(s) of Go which triggered the analyzer.</summary>
```go
for i, tt := range tests {
txn := s.Write(traceutil.TODO())
done := make(chan struct{}, 1)
go func() {
tt()
done <- struct{}{}
}()
select {
case <-done:
t.Fatalf("#%d: operation failed to be blocked", i)
case <-time.After(10 * time.Millisecond):
}
txn.End()
select {
case <-done:
case <-time.After(10 * time.Second):
testutil.FatalStack(t, fmt.Sprintf("#%d: operation failed to be unblocked", i))
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 5d6fcf6d1cf1b6b87fc087b288eab7ff3e955e9b
| test | swiftstack proxyfs vendor go etcd io etcd mvcc kv test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message range loop variable tt used in defer or goroutine at line click here to show the line s of go which triggered the analyzer go for i tt range tests txn s write traceutil todo done make chan struct go func tt done struct select case done t fatalf d operation failed to be blocked i case time after time millisecond txn end select case done case time after time second testutil fatalstack t fmt sprintf d operation failed to be unblocked i leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
265,794 | 23,198,521,260 | IssuesEvent | 2022-08-01 18:54:19 | LibreCS/plcd | https://api.github.com/repos/LibreCS/plcd | closed | EOF Input Error during `pytest` and `run-dist.yml` | bug CI/Test | The gh action `test-lint.yml` errors out during `test-sniff.py` every time due to a problem with reading the initial host address input in the program. Verbose error as follows:
```bash
==================================== ERRORS ====================================
_____________________ ERROR collecting tests/test-sniff.py _____________________
tests/test-sniff.py:3: in <module>
from src.plcd.ping import portSniff
src/plcd/ping.py:[29](https://github.com/LibreCS/plcd/runs/7617169221?check_suite_focus=true#step:5:30)7: in <module>
main()
src/plcd/ping.py:210: in main
netLocationPLC = configure()
src/plcd/ping.py:58: in configure
hostUsrIn = process_input(addressInMsg)
src/plcd/ping.py:[33](https://github.com/LibreCS/plcd/runs/7617169221?check_suite_focus=true#step:5:34): in process_input
line = input(msg)
E EOFError: EOF when reading a line
=============================== warnings summary ===============================
src/plcd/ping.py:201
/home/runner/work/plcd/plcd/src/plcd/ping.py:201: DeprecationWarning: invalid escape sequence '\/'
print(bcolors.HEADER + " __ __\n ____ / /________/ /\n / __ \/ / ___/ __ / \n / /_/ / / /__/ /_/ / \n / .___/_/\___/\__,_/ \n/_/ \n" + bcolors.ENDC)
-- Docs: https://docs.pytest.org/en/stable/how-to/capture-warnings.html
=========================== short test summary info ============================
ERROR tests/test-sniff.py - EOFError: EOF when reading a line
!!!!!!!!!!!!!!!!!!!! Interrupted: 1 error during collection !!!!!!!!!!!!!!!!!!!!
========================= 1 warning, 1 error in 0.11s ==========================
```
I attempted to implement the solution found [in this thread](https://stackoverflow.com/questions/42891603/how-to-remove-eoferror-eof-when-reading-a-line) without any success. Will inform on changes and updates | 1.0 | EOF Input Error during `pytest` and `run-dist.yml` - The gh action `test-lint.yml` errors out during `test-sniff.py` every time due to a problem with reading the initial host address input in the program. Verbose error as follows:
```bash
==================================== ERRORS ====================================
_____________________ ERROR collecting tests/test-sniff.py _____________________
tests/test-sniff.py:3: in <module>
from src.plcd.ping import portSniff
src/plcd/ping.py:[29](https://github.com/LibreCS/plcd/runs/7617169221?check_suite_focus=true#step:5:30)7: in <module>
main()
src/plcd/ping.py:210: in main
netLocationPLC = configure()
src/plcd/ping.py:58: in configure
hostUsrIn = process_input(addressInMsg)
src/plcd/ping.py:[33](https://github.com/LibreCS/plcd/runs/7617169221?check_suite_focus=true#step:5:34): in process_input
line = input(msg)
E EOFError: EOF when reading a line
=============================== warnings summary ===============================
src/plcd/ping.py:201
/home/runner/work/plcd/plcd/src/plcd/ping.py:201: DeprecationWarning: invalid escape sequence '\/'
print(bcolors.HEADER + " __ __\n ____ / /________/ /\n / __ \/ / ___/ __ / \n / /_/ / / /__/ /_/ / \n / .___/_/\___/\__,_/ \n/_/ \n" + bcolors.ENDC)
-- Docs: https://docs.pytest.org/en/stable/how-to/capture-warnings.html
=========================== short test summary info ============================
ERROR tests/test-sniff.py - EOFError: EOF when reading a line
!!!!!!!!!!!!!!!!!!!! Interrupted: 1 error during collection !!!!!!!!!!!!!!!!!!!!
========================= 1 warning, 1 error in 0.11s ==========================
```
I attempted to implement the solution found [in this thread](https://stackoverflow.com/questions/42891603/how-to-remove-eoferror-eof-when-reading-a-line) without any success. Will inform on changes and updates | test | eof input error during pytest and run dist yml the gh action test lint yml errors out during test sniff py every time due to a problem with reading the initial host address input in the program verbose error as follows bash errors error collecting tests test sniff py tests test sniff py in from src plcd ping import portsniff src plcd ping py in main src plcd ping py in main netlocationplc configure src plcd ping py in configure hostusrin process input addressinmsg src plcd ping py in process input line input msg e eoferror eof when reading a line warnings summary src plcd ping py home runner work plcd plcd src plcd ping py deprecationwarning invalid escape sequence print bcolors header n n n n n n bcolors endc docs short test summary info error tests test sniff py eoferror eof when reading a line interrupted error during collection warning error in i attempted to implement the solution found without any success will inform on changes and updates | 1 |
349,143 | 24,935,230,081 | IssuesEvent | 2022-10-31 14:41:29 | apache/incubator-eventmesh | https://api.github.com/repos/apache/incubator-eventmesh | closed | [Doc] Document directory rectification [zh metrics-tracing] | documentation good first issue Hacktoberfest | ### Search before asking
- [X] I had searched in the [issues](https://github.com/apache/eventmesh/issues?q=is%3Aissue) and found no similar issues.
### Documentation Related
Move the documents under directory https://github.com/apache/incubator-eventmesh/tree/master/docs/zh/metrics-tracing
to directory https://github.com/apache/incubator-eventmesh/tree/master/docs/zh/desing-document ,and delete the metrics-tracing directory.
notice:The names of documents moved to design document should be sorted by number.
eg:
<img width="354" alt="image" src="https://user-images.githubusercontent.com/91315508/191908990-065d40dd-35f2-4acb-a456-f89b18cf7a53.png">
Because some Chinese documents have not been translated, please sort and name them according to the order of the last file. The next file starts with 11-.
### Are you willing to submit PR?
- [ ] Yes I am willing to submit a PR! | 1.0 | [Doc] Document directory rectification [zh metrics-tracing] - ### Search before asking
- [X] I had searched in the [issues](https://github.com/apache/eventmesh/issues?q=is%3Aissue) and found no similar issues.
### Documentation Related
Move the documents under directory https://github.com/apache/incubator-eventmesh/tree/master/docs/zh/metrics-tracing
to directory https://github.com/apache/incubator-eventmesh/tree/master/docs/zh/desing-document ,and delete the metrics-tracing directory.
notice:The names of documents moved to design document should be sorted by number.
eg:
<img width="354" alt="image" src="https://user-images.githubusercontent.com/91315508/191908990-065d40dd-35f2-4acb-a456-f89b18cf7a53.png">
Because some Chinese documents have not been translated, please sort and name them according to the order of the last file. The next file starts with 11-.
### Are you willing to submit PR?
- [ ] Yes I am willing to submit a PR! | non_test | document directory rectification search before asking i had searched in the and found no similar issues documentation related move the documents under directory to directory and delete the metrics tracing directory notice the names of documents moved to design document should be sorted by number eg img width alt image src because some chinese documents have not been translated please sort and name them according to the order of the last file the next file starts with are you willing to submit pr yes i am willing to submit a pr | 0 |
169,014 | 13,110,706,795 | IssuesEvent | 2020-08-04 21:12:57 | eclipse/openj9 | https://api.github.com/repos/eclipse/openj9 | opened | JDK8 Win32 : System configuration does not support option '-Xlp' | test failure | Failure link
------------
From an internal build `Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/39`:
```
03:10:12 openjdk version "1.8.0_265-internal"
03:10:12 OpenJDK Runtime Environment (build 1.8.0_265-internal-jenkins_2020_08_03_21_19-b00)
03:10:12 Eclipse OpenJ9 VM (build master-1c194db6e72, JRE 1.8.0 Windows Server 2016 x86-32-Bit 20200803_480 (JIT enabled, AOT enabled)
03:10:12 OpenJ9 - 1c194db6e72
03:10:12 OMR - 7b76a160bc7
03:10:12 JCL - bf6e4d1cc0b based on jdk8u265-b01)
```
Optional info
-------------
Failure output (captured from console output)
---------------------------------------------
```
===============================================
Running test J9vmTest_0 ...
===============================================
JVMJ9GC032E System configuration does not support option '-Xlp'
JVMJ9VM015W Initialization error for library j9gc29(2): Failed to initialize; unable to parse command line
Error: Could not create the Java Virtual Machine.
Error: A fatal exception has occurred. Program will exit.
no-zero exit value: 1
Xlp is not supported on this machine. Skipping Test.
command: C:/Users/jenkins/workspace/Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/openjdkbinary/j2sdk-image\\bin\\java -Xjit -Xgcpolicy:gencon -Xnocompressedrefs -Xdump -Xms64m -Xmx64m -verbose:sizes -Xlp4K -Xlp -Xbootclasspath:C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\bin\default\jclSC180\vm.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\se-service.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\rt.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\resources.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\jsse.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\charsets.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\jce.jar -classpath C:/Users/jenkins/workspace/Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/openjdk-tests///..//jvmtest\functional\VM_Test\VM_Test.jar;C:/Users/jenkins/workspace/Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/openjdk-tests/\TKG\lib\asm-all.jar j9vm.test.xlpcodecache.XlpCodeCacheOptionsTest
72 passed / 1 failed
J9vmTest_0_FAILED72 passed / 1 failed
J9vmTest_0_FAILED
```
For example, to rebuild the failed tests in <Jenkins URL>=https://hyc-runtimes-jenkins.swg-devops.com/job/Grinder, use the following links:
04:23:41 https://hyc-runtimes-jenkins.swg-devops.com/job/Grinder/parambuild/?JDK_VERSION=8&JDK_IMPL=openj9&BUILD_LIST=functional&PLATFORM=x86-32_windows&TARGET=J9vmTest_0 | 1.0 | JDK8 Win32 : System configuration does not support option '-Xlp' - Failure link
------------
From an internal build `Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/39`:
```
03:10:12 openjdk version "1.8.0_265-internal"
03:10:12 OpenJDK Runtime Environment (build 1.8.0_265-internal-jenkins_2020_08_03_21_19-b00)
03:10:12 Eclipse OpenJ9 VM (build master-1c194db6e72, JRE 1.8.0 Windows Server 2016 x86-32-Bit 20200803_480 (JIT enabled, AOT enabled)
03:10:12 OpenJ9 - 1c194db6e72
03:10:12 OMR - 7b76a160bc7
03:10:12 JCL - bf6e4d1cc0b based on jdk8u265-b01)
```
Optional info
-------------
Failure output (captured from console output)
---------------------------------------------
```
===============================================
Running test J9vmTest_0 ...
===============================================
JVMJ9GC032E System configuration does not support option '-Xlp'
JVMJ9VM015W Initialization error for library j9gc29(2): Failed to initialize; unable to parse command line
Error: Could not create the Java Virtual Machine.
Error: A fatal exception has occurred. Program will exit.
no-zero exit value: 1
Xlp is not supported on this machine. Skipping Test.
command: C:/Users/jenkins/workspace/Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/openjdkbinary/j2sdk-image\\bin\\java -Xjit -Xgcpolicy:gencon -Xnocompressedrefs -Xdump -Xms64m -Xmx64m -verbose:sizes -Xlp4K -Xlp -Xbootclasspath:C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\bin\default\jclSC180\vm.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\se-service.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\rt.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\resources.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\jsse.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\charsets.jar;C:\Users\jenkins\workspace\Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1\openjdkbinary\j2sdk-image\jre\lib\jce.jar -classpath C:/Users/jenkins/workspace/Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/openjdk-tests///..//jvmtest\functional\VM_Test\VM_Test.jar;C:/Users/jenkins/workspace/Test_openjdk8_j9_sanity.functional_x86-32_windows_Nightly_testList_1/openjdk-tests/\TKG\lib\asm-all.jar j9vm.test.xlpcodecache.XlpCodeCacheOptionsTest
72 passed / 1 failed
J9vmTest_0_FAILED72 passed / 1 failed
J9vmTest_0_FAILED
```
For example, to rebuild the failed tests in <Jenkins URL>=https://hyc-runtimes-jenkins.swg-devops.com/job/Grinder, use the following links:
04:23:41 https://hyc-runtimes-jenkins.swg-devops.com/job/Grinder/parambuild/?JDK_VERSION=8&JDK_IMPL=openj9&BUILD_LIST=functional&PLATFORM=x86-32_windows&TARGET=J9vmTest_0 | test | system configuration does not support option xlp failure link from an internal build test sanity functional windows nightly testlist openjdk version internal openjdk runtime environment build internal jenkins eclipse vm build master jre windows server bit jit enabled aot enabled omr jcl based on optional info failure output captured from console output running test system configuration does not support option xlp initialization error for library failed to initialize unable to parse command line error could not create the java virtual machine error a fatal exception has occurred program will exit no zero exit value xlp is not supported on this machine skipping test command c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image bin java xjit xgcpolicy gencon xnocompressedrefs xdump verbose sizes xlp xbootclasspath c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre bin default vm jar c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre lib se service jar c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre lib rt jar c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre lib resources jar c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre lib jsse jar c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre lib charsets jar c users jenkins workspace test sanity functional windows nightly testlist openjdkbinary image jre lib jce jar classpath c users jenkins workspace test sanity functional windows nightly testlist openjdk tests jvmtest functional vm test vm test jar c users jenkins workspace test sanity functional windows nightly testlist openjdk tests tkg lib asm all jar test xlpcodecache xlpcodecacheoptionstest passed failed passed failed failed for example to rebuild the failed tests in use the following links | 1 |
343,170 | 30,653,355,055 | IssuesEvent | 2023-07-25 10:22:29 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix linalg.test_slogdet | Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix linalg.test_slogdet - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5654975898/job/15319128355"><img src=https://img.shields.io/badge/-success-success></a>
| test | fix linalg test slogdet jax a href src numpy a href src tensorflow a href src torch a href src paddle a href src | 1 |
123,933 | 26,359,685,481 | IssuesEvent | 2023-01-11 12:28:00 | EddieHubCommunity/LinkFree | https://api.github.com/repos/EddieHubCommunity/LinkFree | closed | [BUG] When filtering events the profile picture is not correct | 💻 aspect: code 🏁 status: ready for dev 🛠 goal: fix 🔢 points: 3 | ### Description
When filtering events the profile picture is not correct
### Screenshots
Without filtering (all events)

-> profile picture of eddie
when filtering for cfp open

wrong user image
but it is linking to the right linkfree profile (eddies)
### Additional information
_No response_ | 1.0 | [BUG] When filtering events the profile picture is not correct - ### Description
When filtering events the profile picture is not correct
### Screenshots
Without filtering (all events)

-> profile picture of eddie
when filtering for cfp open

wrong user image
but it is linking to the right linkfree profile (eddies)
### Additional information
_No response_ | non_test | when filtering events the profile picture is not correct description when filtering events the profile picture is not correct screenshots without filtering all events profile picture of eddie when filtering for cfp open wrong user image but it is linking to the right linkfree profile eddies additional information no response | 0 |
528,986 | 15,378,473,780 | IssuesEvent | 2021-03-02 18:22:12 | pdybowski/booking-clone-Api | https://api.github.com/repos/pdybowski/booking-clone-Api | closed | add route for an admin | Routes priority HIGH | GET:
all users
POST:
delete users, body should be table with users ids.
We should check if some user has any reservation
if we cant delete user we should response with array of objectes:
[
{
userId: 2312312,
error: "cos tam sie nie powiodlo"
}
]
PUT:
change hotel owner status
DELETE:
remove hotel (check remove Hotel by owner diagram)
force flag
| 1.0 | add route for an admin - GET:
all users
POST:
delete users, body should be table with users ids.
We should check if some user has any reservation
if we cant delete user we should response with array of objectes:
[
{
userId: 2312312,
error: "cos tam sie nie powiodlo"
}
]
PUT:
change hotel owner status
DELETE:
remove hotel (check remove Hotel by owner diagram)
force flag
| non_test | add route for an admin get all users post delete users body should be table with users ids we should check if some user has any reservation if we cant delete user we should response with array of objectes userid error cos tam sie nie powiodlo put change hotel owner status delete remove hotel check remove hotel by owner diagram force flag | 0 |
270,332 | 23,501,401,197 | IssuesEvent | 2022-08-18 08:45:01 | wazuh/wazuh | https://api.github.com/repos/wazuh/wazuh | closed | Release 4.3.7 - Revision 1 - Release Candidate RC1 - Footprint Metrics - ALL-EXCEPT-SCA (4h) | release test/4.3.7 | ## Footprint metrics information
| | |
|---------------------------------|--------------------------------------------|
| **Main release candidate issue #** | # |
| **Main footprint metrics issue #** | #14554 |
| **Version** | 4.3.7 |
| **Release candidate #** | RC1 |
| **Tag** | https://github.com/wazuh/wazuh/tree/4.3.7-rc1 |
## Stress test documentation
### Packages used
- Repository: `packages-dev.wazuh.com`
- Package path: `pre-release`
- Package revision: `1`
- **Jenkins build**: https://ci.wazuh.info/job/Test_stress/3530/
---
<details><summary>Manager</summary>
+ <details><summary>Plots</summary>

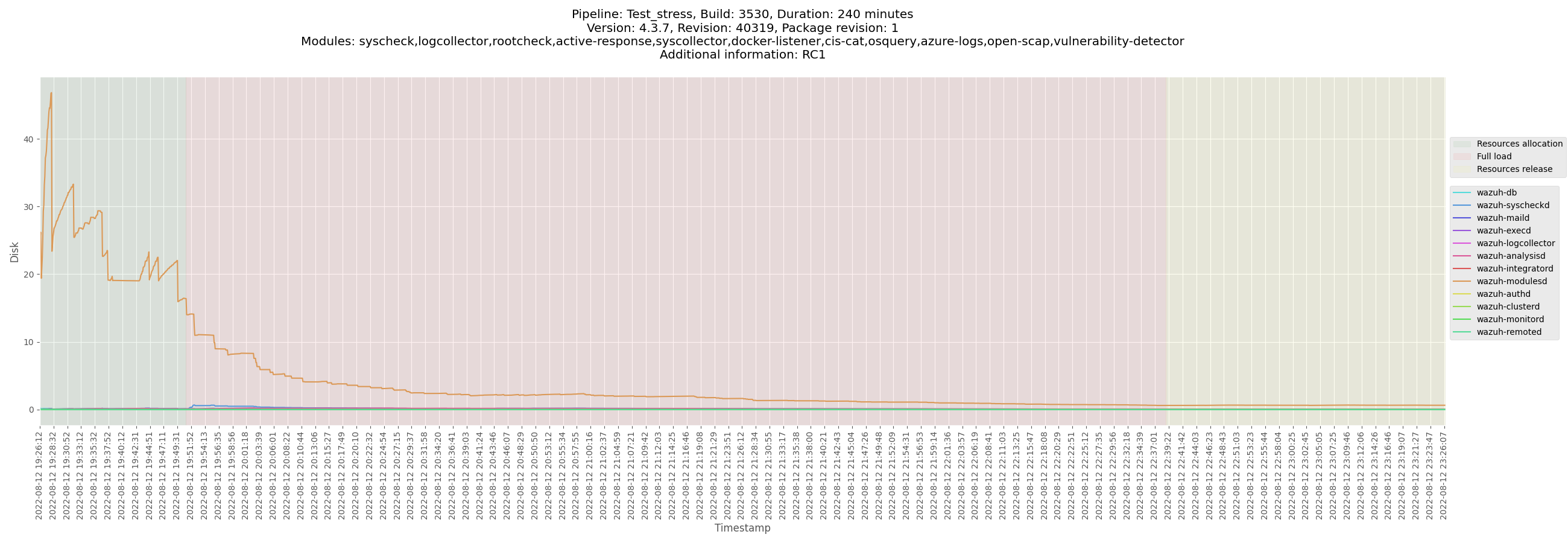

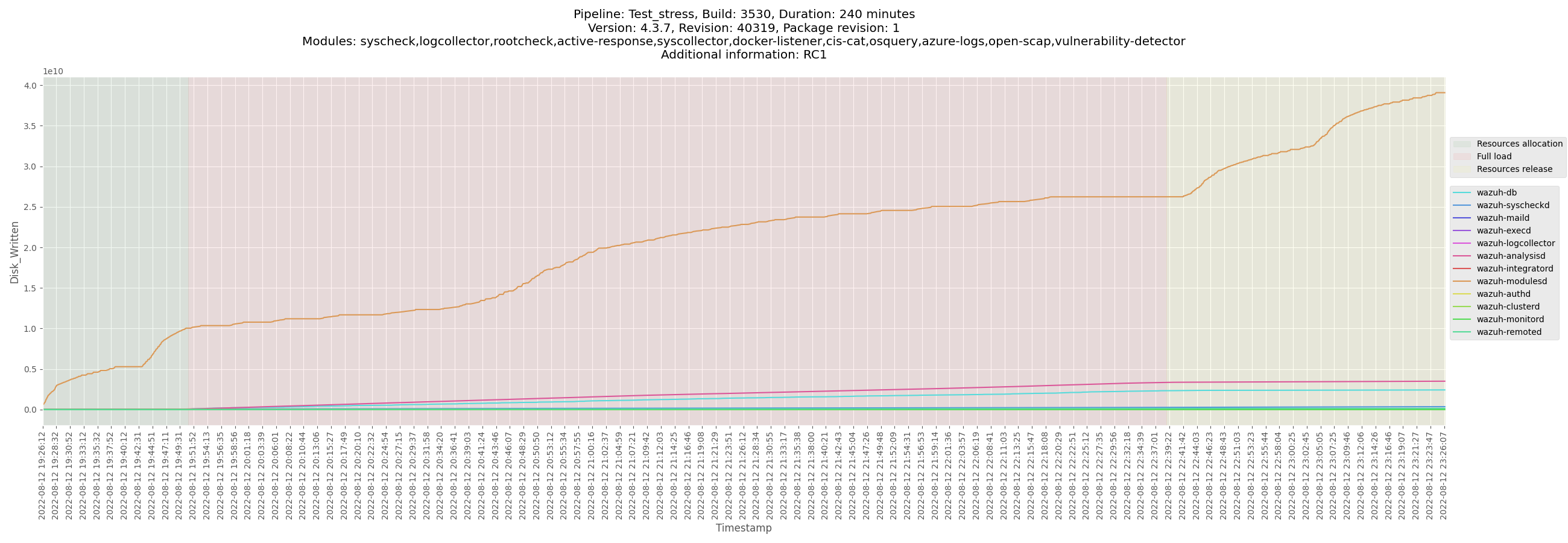
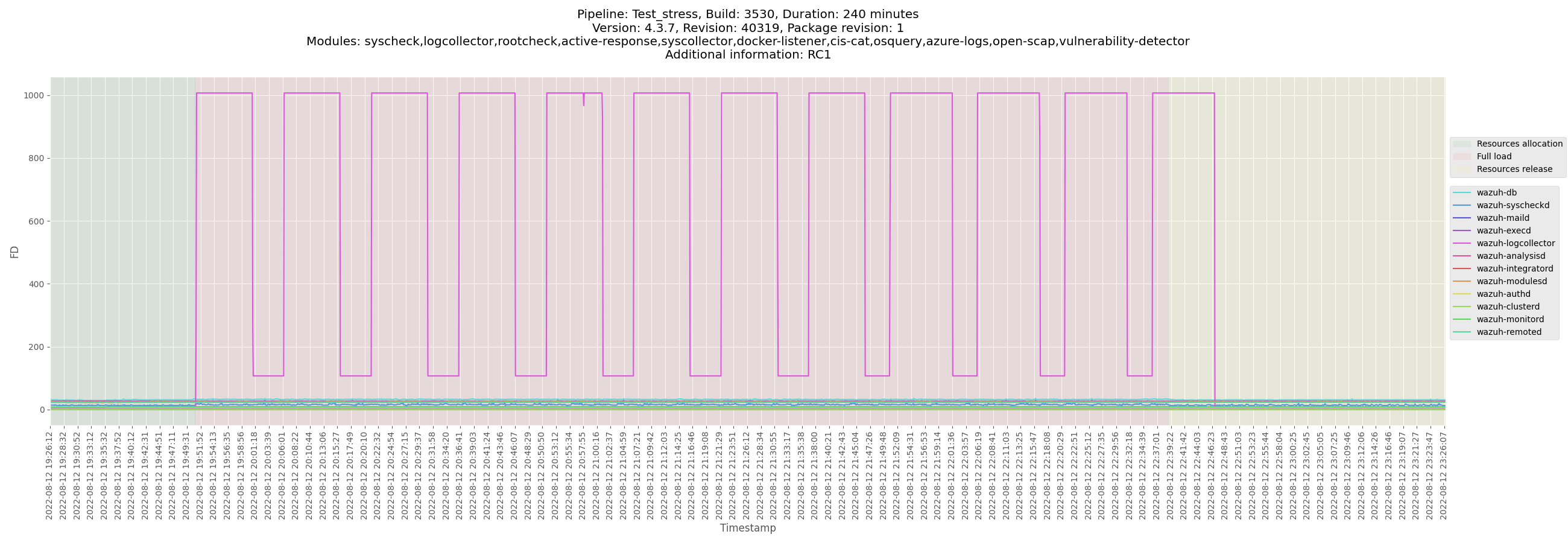


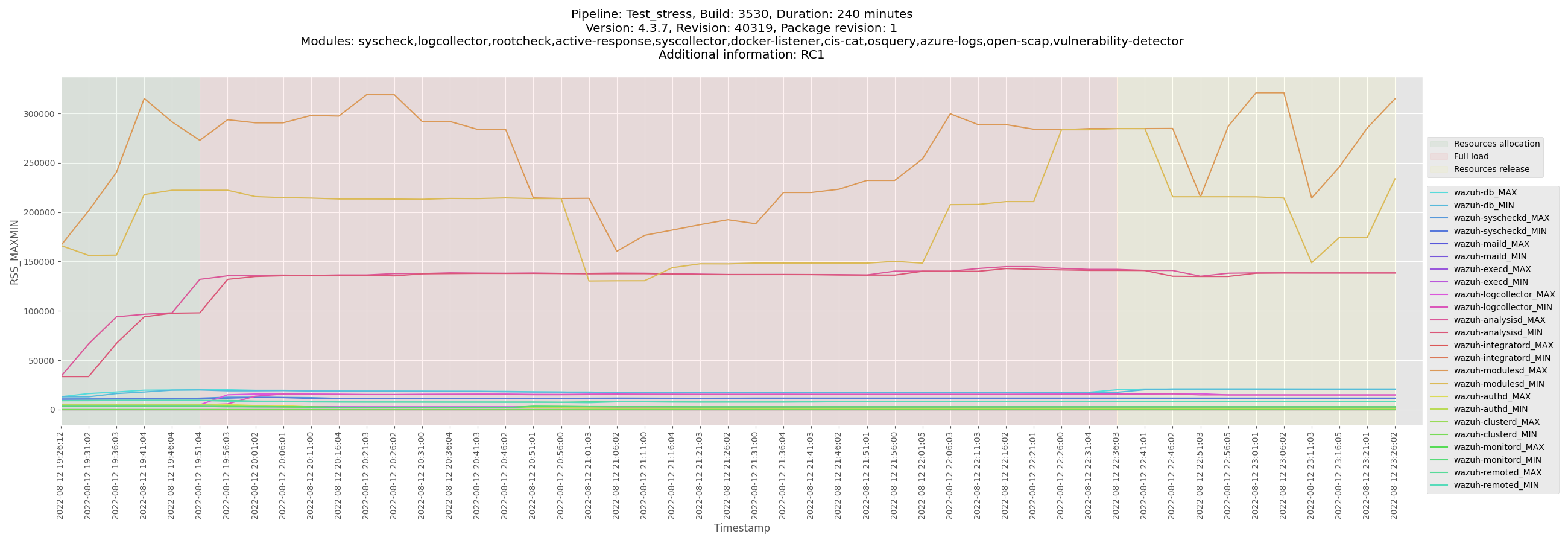
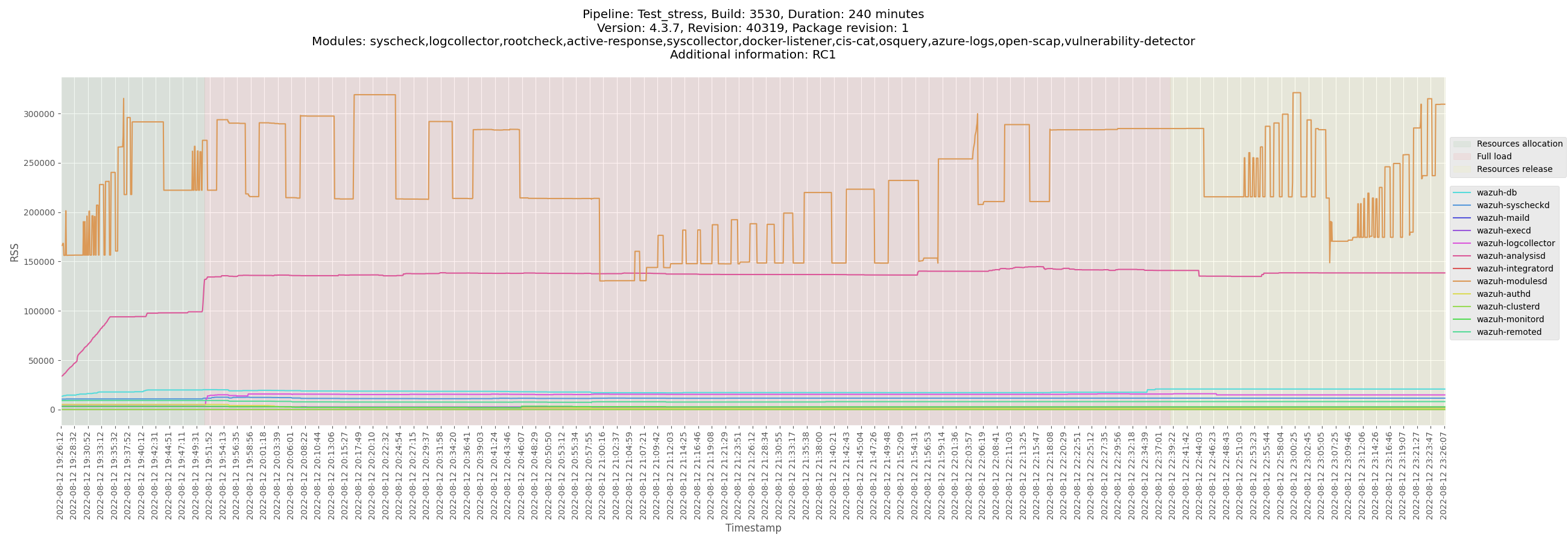







</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_manager_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/logs/ossec_Test_stress_B3530_manager_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-manager-Test_stress_B3530_manager-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/data/monitor-manager-Test_stress_B3530_manager-pre-release.csv)
[Test_stress_B3530_manager_analysisd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/data/Test_stress_B3530_manager_analysisd_state.csv)
[Test_stress_B3530_manager_remoted_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/data/Test_stress_B3530_manager_remoted_state.csv)
</details>
</details>
<details><summary>Centos agent</summary>
+ <details><summary>Plots</summary>




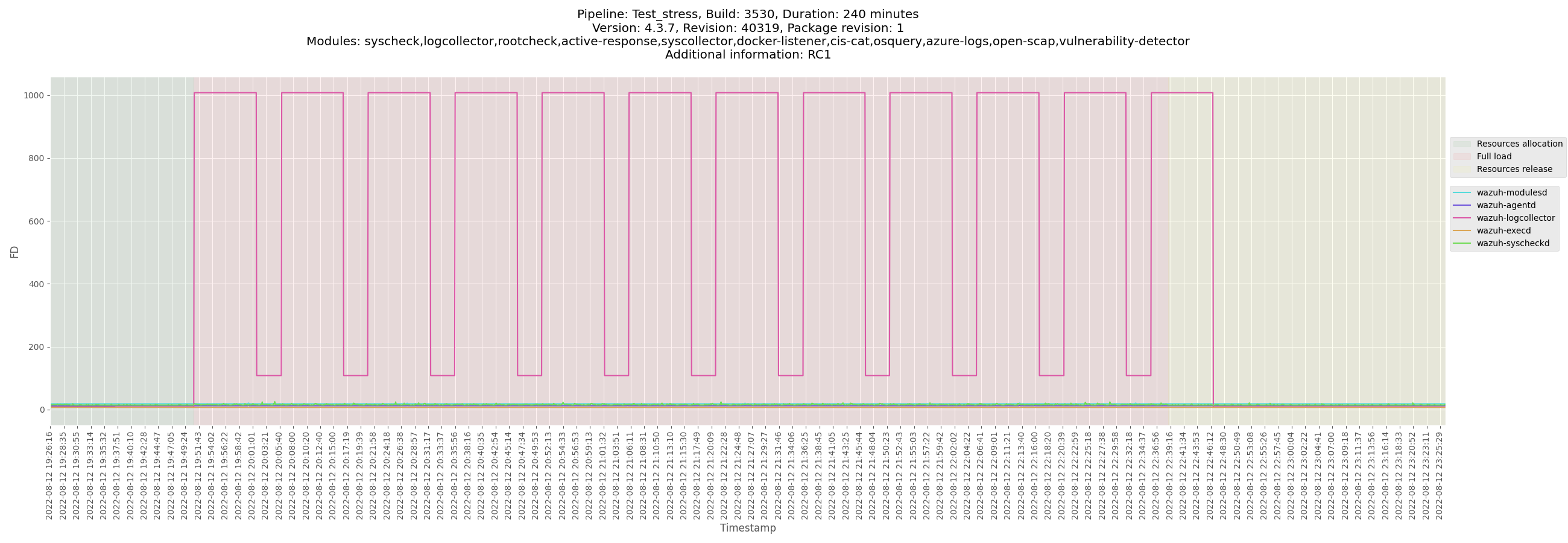

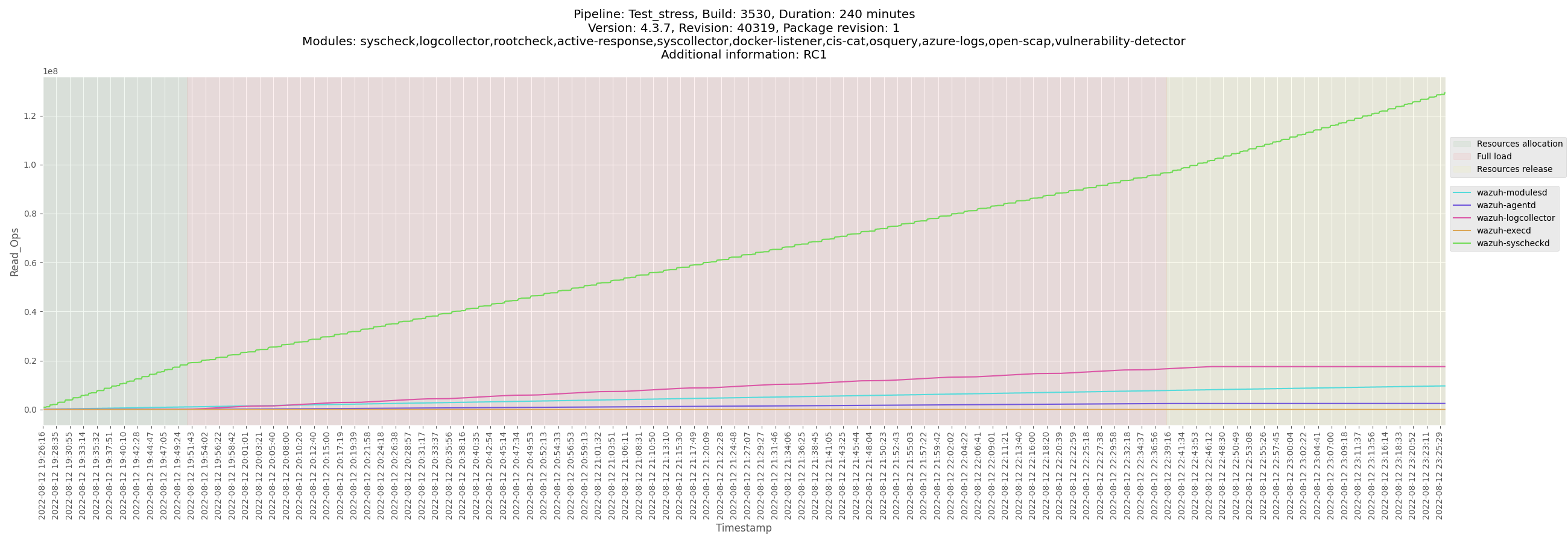







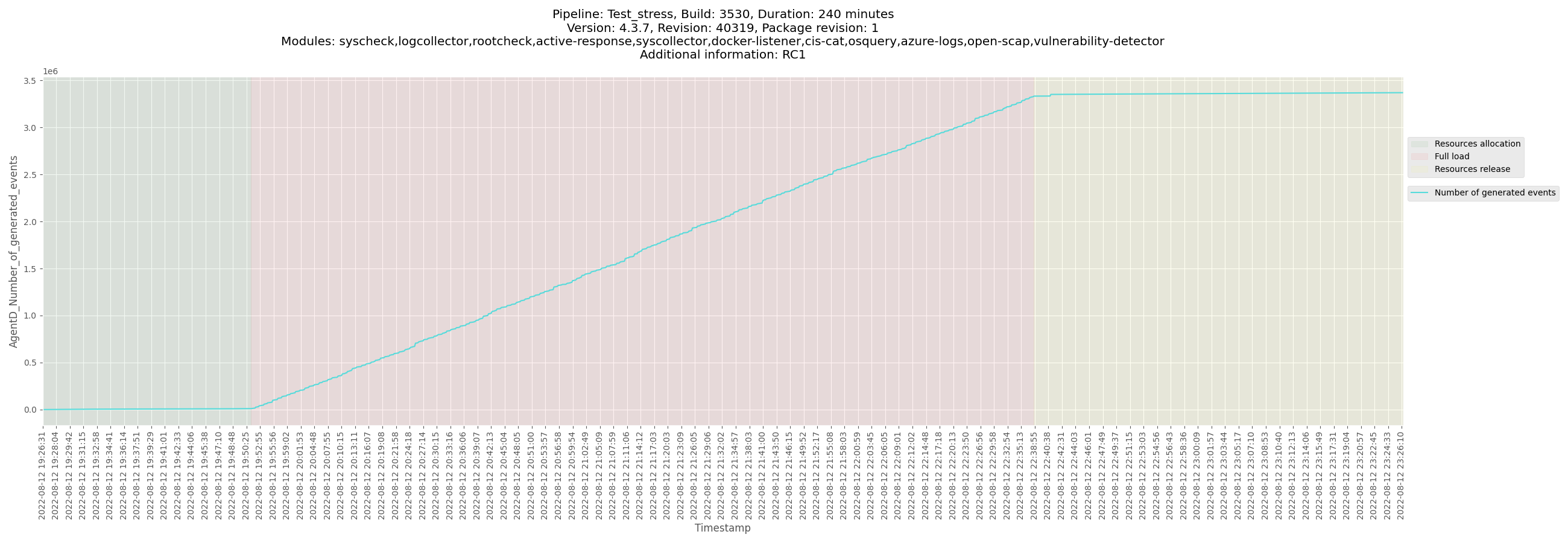

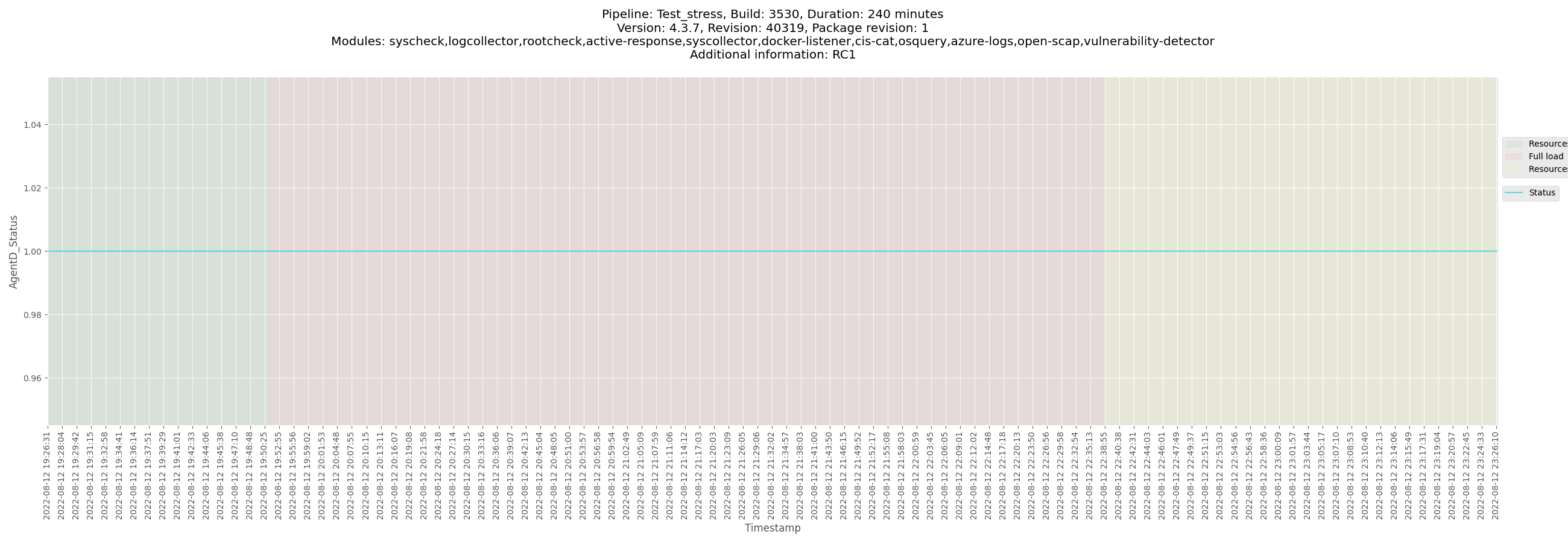
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_centos_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_centos/logs/ossec_Test_stress_B3530_centos_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3530_centos-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_centos/data/monitor-agent-Test_stress_B3530_centos-pre-release.csv)
[Test_stress_B3530_centos_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_centos/data/Test_stress_B3530_centos_agentd_state.csv)
</details>
</details>
<details><summary>Ubuntu agent</summary>
+ <details><summary>Plots</summary>









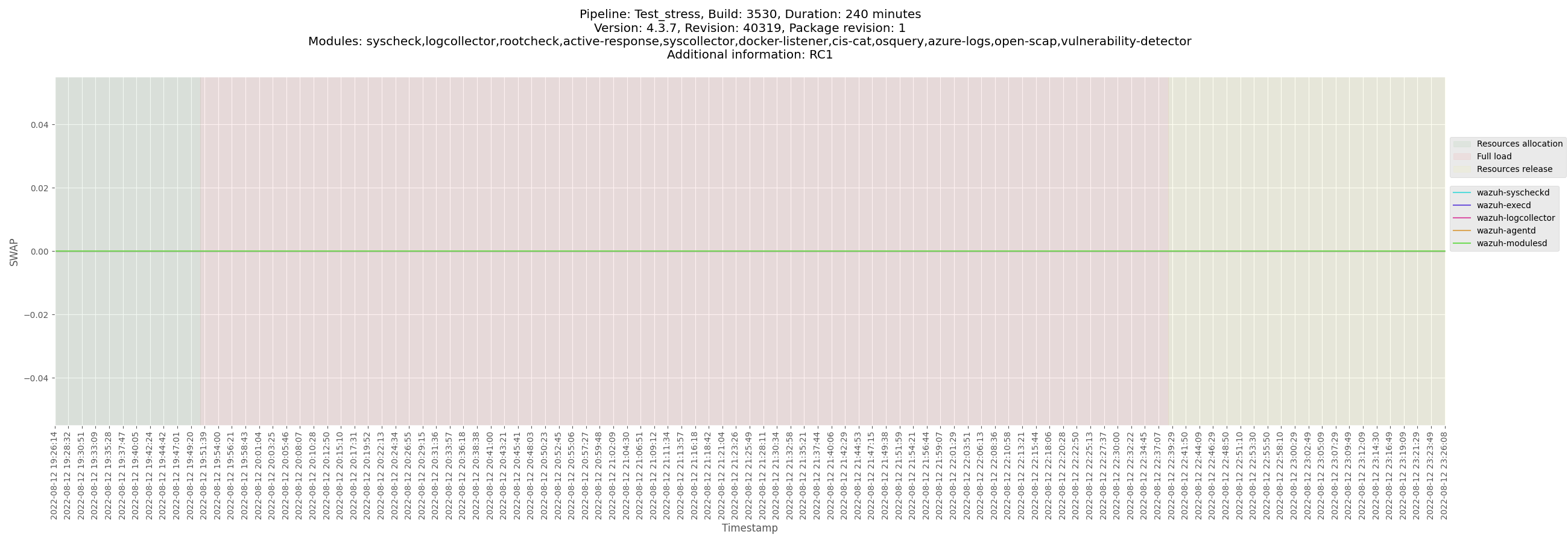







</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_ubuntu_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_ubuntu/logs/ossec_Test_stress_B3530_ubuntu_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3530_ubuntu-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_ubuntu/data/monitor-agent-Test_stress_B3530_ubuntu-pre-release.csv)
[Test_stress_B3530_ubuntu_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_ubuntu/data/Test_stress_B3530_ubuntu_agentd_state.csv)
</details>
</details>
<details><summary>Windows agent</summary>
+ <details><summary>Plots</summary>















</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_windows_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_windows/logs/ossec_Test_stress_B3530_windows_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-winagent-Test_stress_B3530_windows-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_windows/data/monitor-winagent-Test_stress_B3530_windows-pre-release.csv)
[Test_stress_B3530_windows_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_windows/data/Test_stress_B3530_windows_agentd_state.csv)
</details>
</details>
<details><summary>macOS agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details>
<details><summary>Solaris agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details> | 1.0 | Release 4.3.7 - Revision 1 - Release Candidate RC1 - Footprint Metrics - ALL-EXCEPT-SCA (4h) - ## Footprint metrics information
| | |
|---------------------------------|--------------------------------------------|
| **Main release candidate issue #** | # |
| **Main footprint metrics issue #** | #14554 |
| **Version** | 4.3.7 |
| **Release candidate #** | RC1 |
| **Tag** | https://github.com/wazuh/wazuh/tree/4.3.7-rc1 |
## Stress test documentation
### Packages used
- Repository: `packages-dev.wazuh.com`
- Package path: `pre-release`
- Package revision: `1`
- **Jenkins build**: https://ci.wazuh.info/job/Test_stress/3530/
---
<details><summary>Manager</summary>
+ <details><summary>Plots</summary>

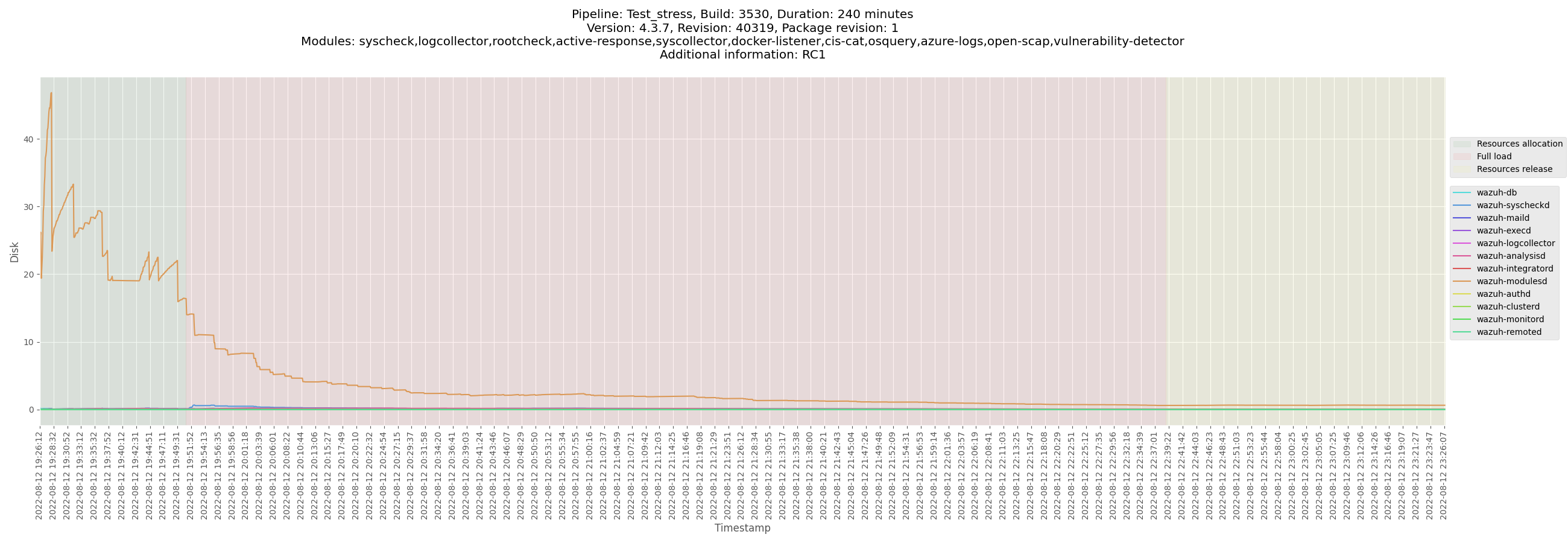

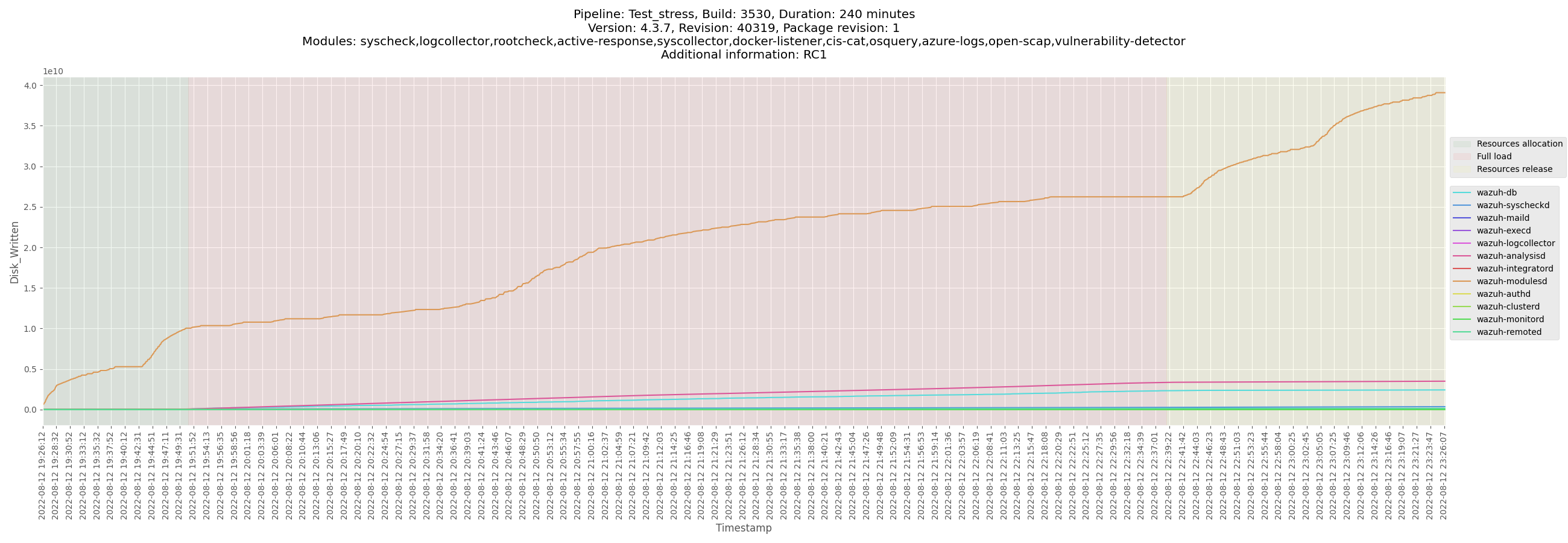
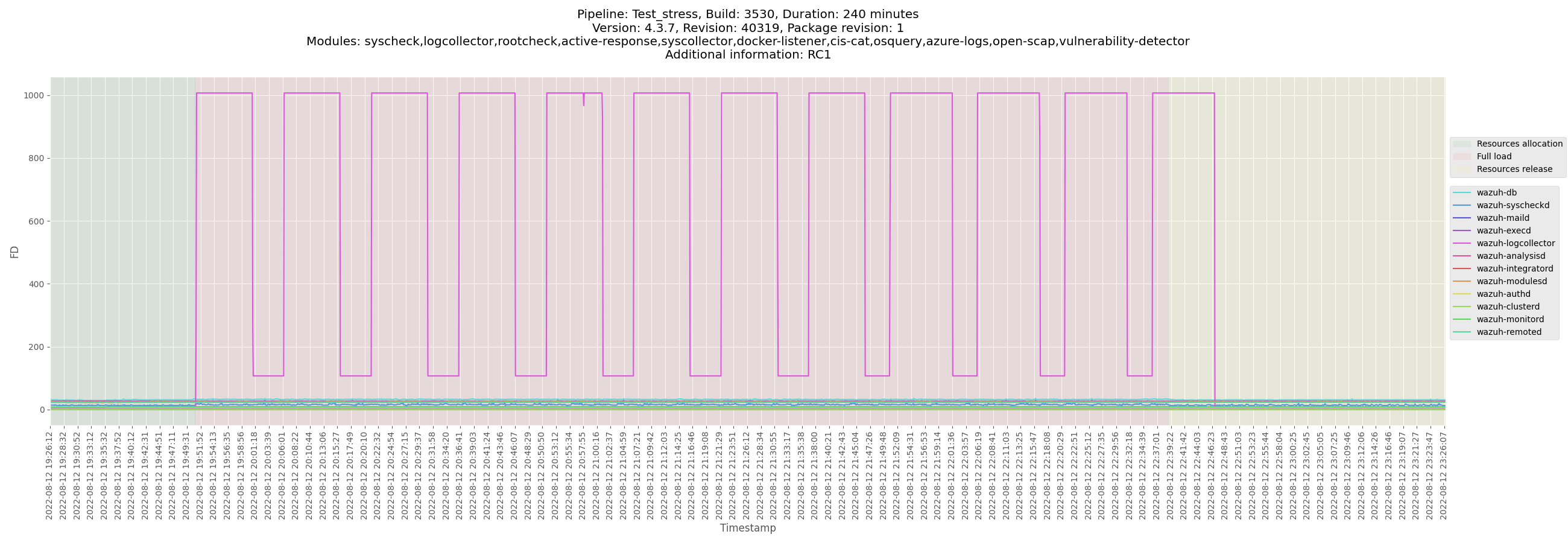


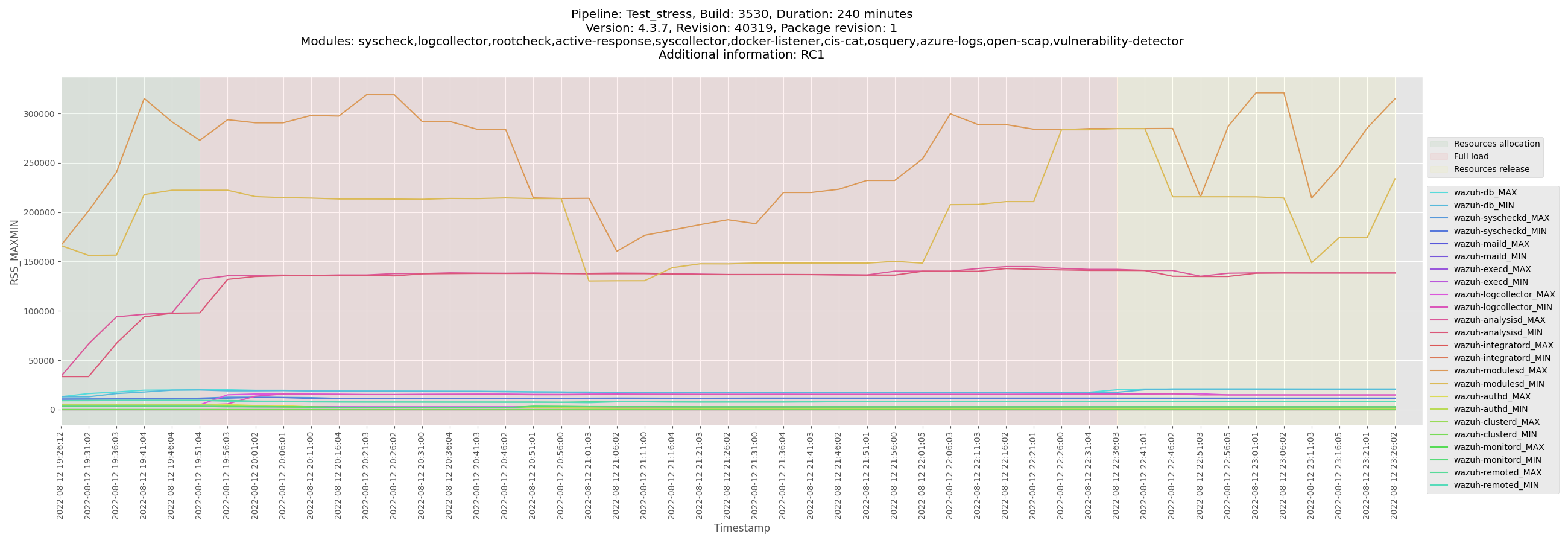
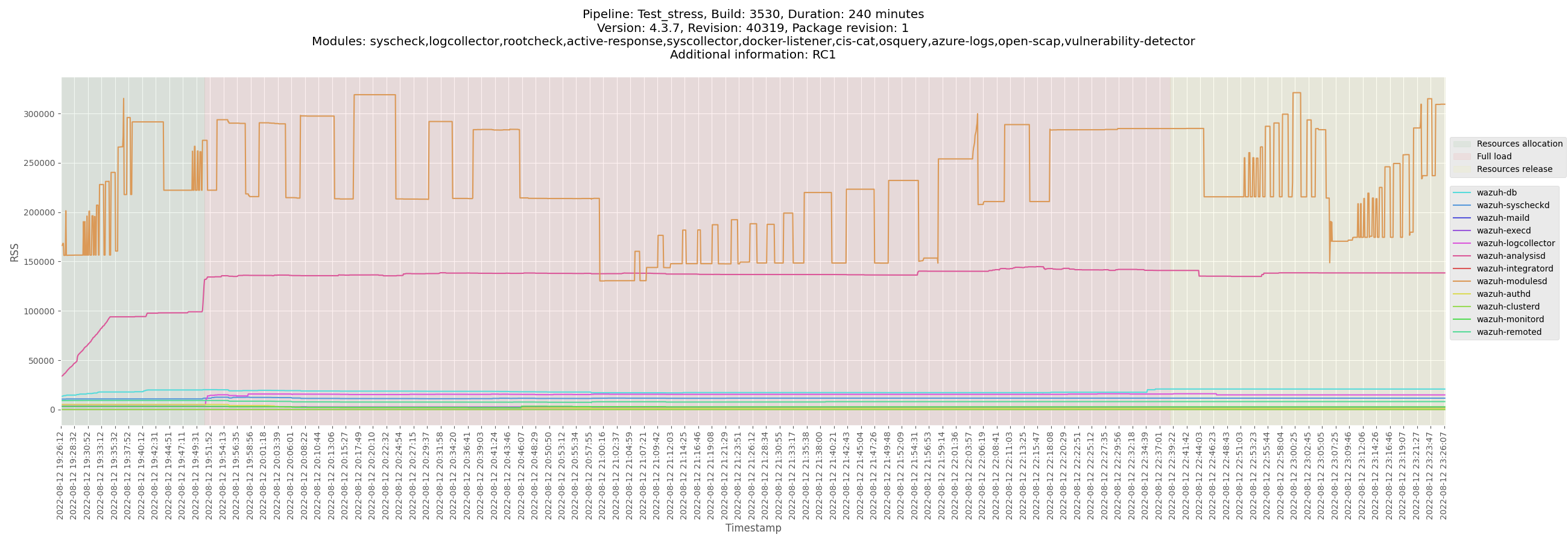







</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_manager_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/logs/ossec_Test_stress_B3530_manager_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-manager-Test_stress_B3530_manager-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/data/monitor-manager-Test_stress_B3530_manager-pre-release.csv)
[Test_stress_B3530_manager_analysisd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/data/Test_stress_B3530_manager_analysisd_state.csv)
[Test_stress_B3530_manager_remoted_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_manager_centos/data/Test_stress_B3530_manager_remoted_state.csv)
</details>
</details>
<details><summary>Centos agent</summary>
+ <details><summary>Plots</summary>




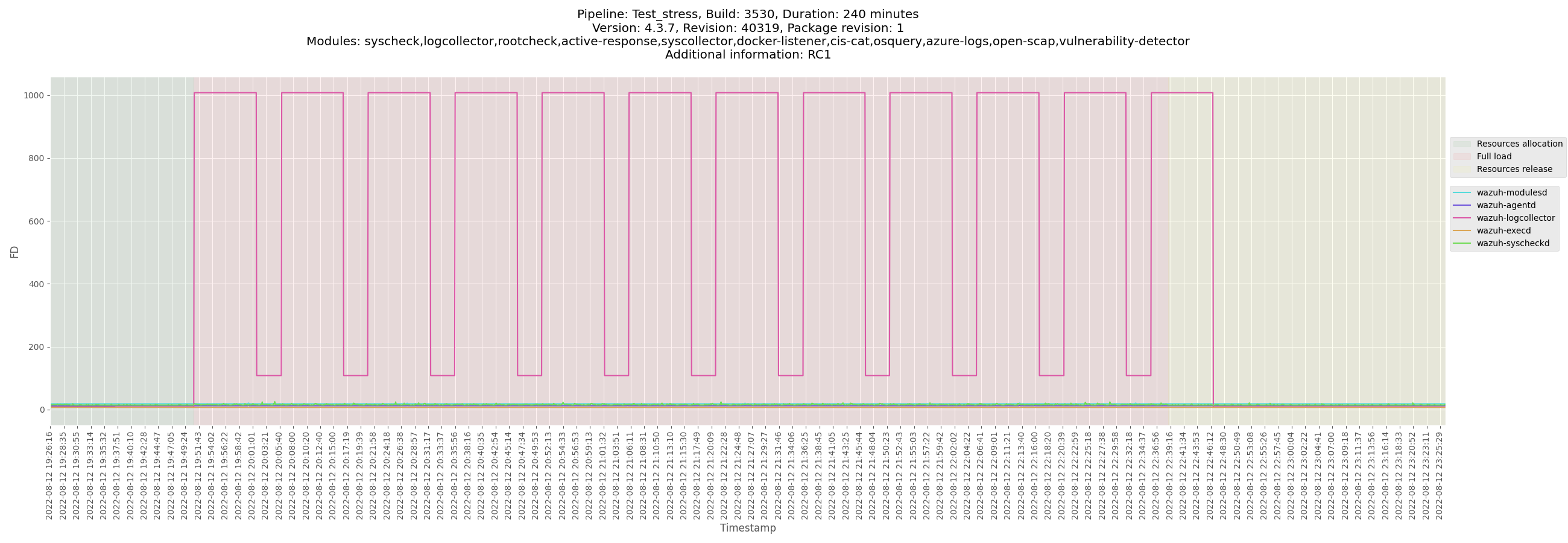

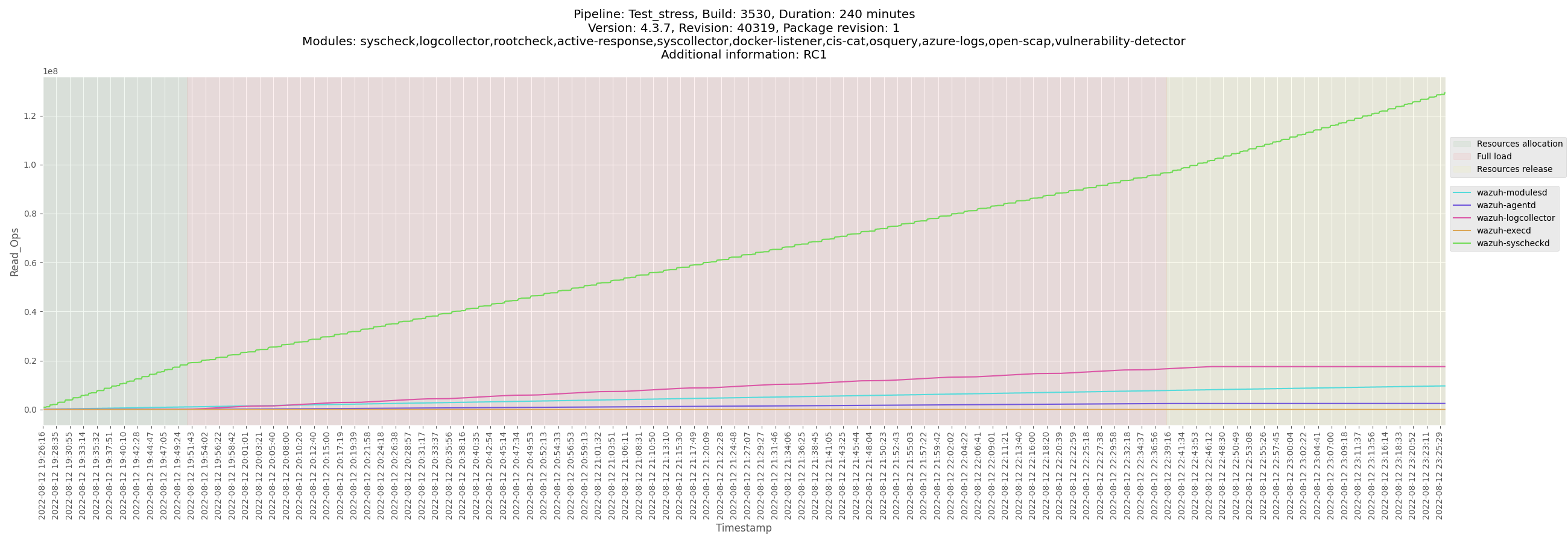







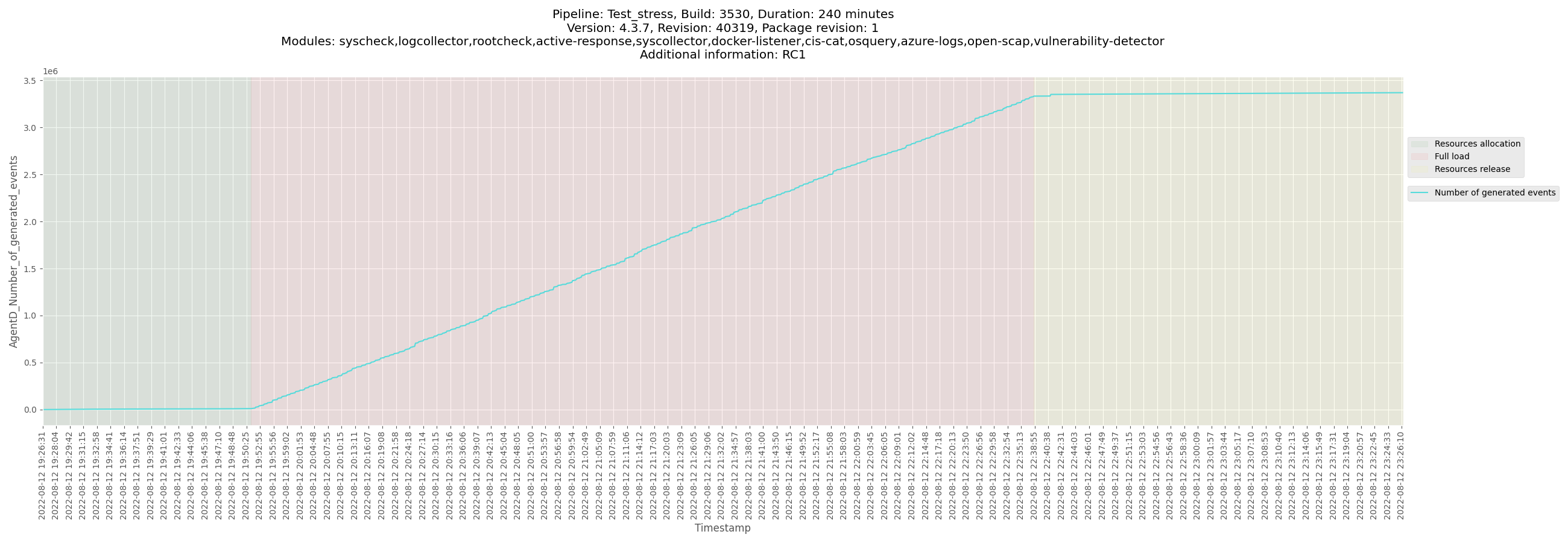

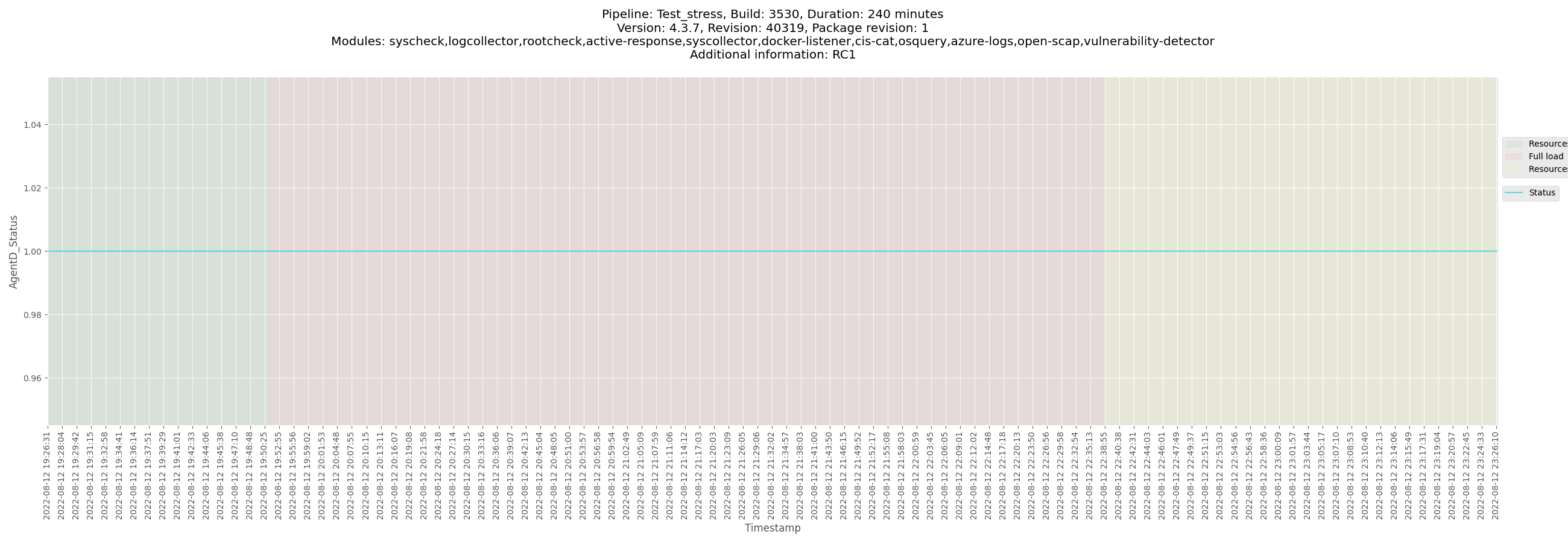
</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_centos_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_centos/logs/ossec_Test_stress_B3530_centos_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3530_centos-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_centos/data/monitor-agent-Test_stress_B3530_centos-pre-release.csv)
[Test_stress_B3530_centos_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_centos/data/Test_stress_B3530_centos_agentd_state.csv)
</details>
</details>
<details><summary>Ubuntu agent</summary>
+ <details><summary>Plots</summary>









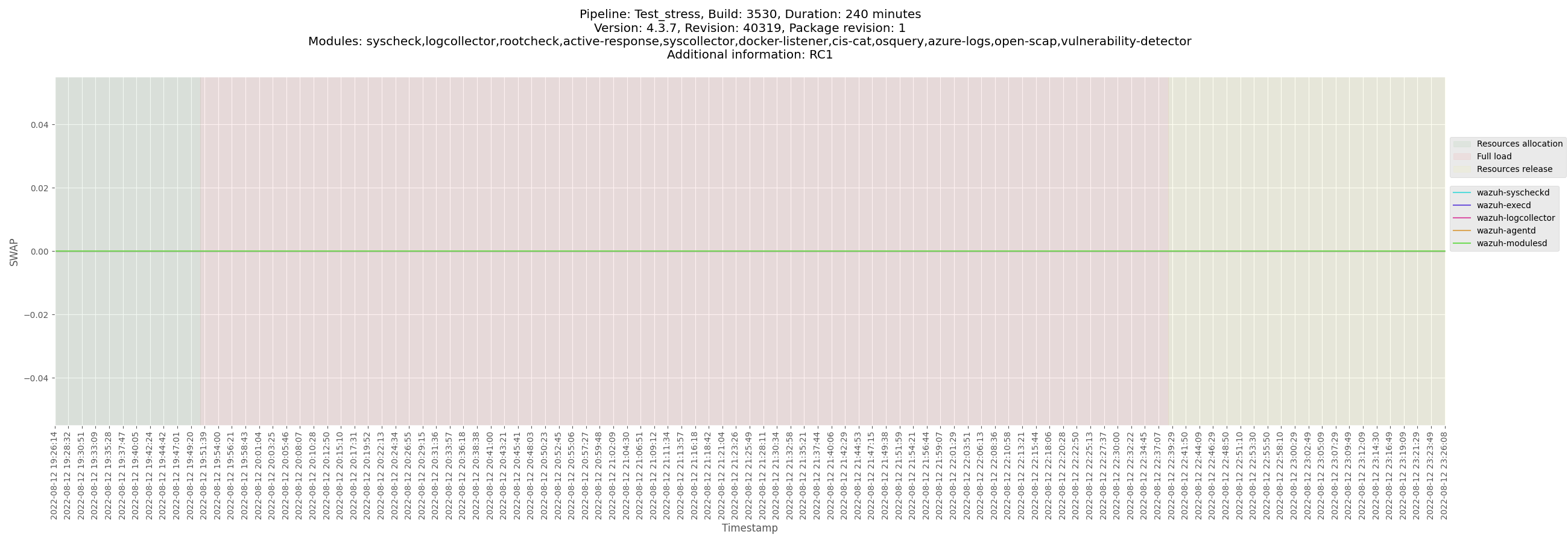







</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_ubuntu_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_ubuntu/logs/ossec_Test_stress_B3530_ubuntu_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-agent-Test_stress_B3530_ubuntu-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_ubuntu/data/monitor-agent-Test_stress_B3530_ubuntu-pre-release.csv)
[Test_stress_B3530_ubuntu_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_ubuntu/data/Test_stress_B3530_ubuntu_agentd_state.csv)
</details>
</details>
<details><summary>Windows agent</summary>
+ <details><summary>Plots</summary>















</details>
+ <details><summary>Logs and configuration</summary>
[ossec_Test_stress_B3530_windows_2022-08-16.zip](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_windows/logs/ossec_Test_stress_B3530_windows_2022-08-16.zip)
</details>
+ <details><summary>CSV</summary>
[monitor-winagent-Test_stress_B3530_windows-pre-release.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_windows/data/monitor-winagent-Test_stress_B3530_windows-pre-release.csv)
[Test_stress_B3530_windows_agentd_state.csv](https://ci.wazuh.com/data/Test_stress/pre-release/4.3.7/B3530-240m/B3530_agent_windows/data/Test_stress_B3530_windows_agentd_state.csv)
</details>
</details>
<details><summary>macOS agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details>
<details><summary>Solaris agent</summary>
+ <details><summary>Plots</summary>
</details>
+ <details><summary>Logs and configuration</summary>
</details>
+ <details><summary>CSV</summary>
</details>
</details> | test | release revision release candidate footprint metrics all except sca footprint metrics information main release candidate issue main footprint metrics issue version release candidate tag stress test documentation packages used repository packages dev wazuh com package path pre release package revision jenkins build manager plots logs and configuration csv centos agent plots logs and configuration csv ubuntu agent plots logs and configuration csv windows agent plots logs and configuration csv macos agent plots logs and configuration csv solaris agent plots logs and configuration csv | 1 |
48,946 | 13,429,026,816 | IssuesEvent | 2020-09-07 00:25:55 | tt9133github/libraryiotest | https://api.github.com/repos/tt9133github/libraryiotest | opened | CVE-2017-9804 (High) detected in struts2-core-2.5.jar | security vulnerability | ## CVE-2017-9804 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>struts2-core-2.5.jar</b></p></summary>
<p>Apache Struts 2</p>
<p>Path to dependency file: /tmp/ws-scm/libraryiotest/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/org/apache/struts/struts2-core/2.5/struts2-core-2.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tt9133github/libraryiotest/commit/2267c2a6bfeaa7bfa3e2402035c45501cd8f7360">2267c2a6bfeaa7bfa3e2402035c45501cd8f7360</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Apache Struts 2.3.7 through 2.3.33 and 2.5 through 2.5.12, if an application allows entering a URL in a form field and built-in URLValidator is used, it is possible to prepare a special URL which will be used to overload server process when performing validation of the URL. NOTE: this vulnerability exists because of an incomplete fix for S2-047 / CVE-2017-7672.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-9804>CVE-2017-9804</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-9804">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-9804</a></p>
<p>Release Date: 2017-09-20</p>
<p>Fix Resolution: org.apache.struts:struts2-core:2.5.13</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-9804 (High) detected in struts2-core-2.5.jar - ## CVE-2017-9804 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>struts2-core-2.5.jar</b></p></summary>
<p>Apache Struts 2</p>
<p>Path to dependency file: /tmp/ws-scm/libraryiotest/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/org/apache/struts/struts2-core/2.5/struts2-core-2.5.jar</p>
<p>
Dependency Hierarchy:
- :x: **struts2-core-2.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tt9133github/libraryiotest/commit/2267c2a6bfeaa7bfa3e2402035c45501cd8f7360">2267c2a6bfeaa7bfa3e2402035c45501cd8f7360</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Apache Struts 2.3.7 through 2.3.33 and 2.5 through 2.5.12, if an application allows entering a URL in a form field and built-in URLValidator is used, it is possible to prepare a special URL which will be used to overload server process when performing validation of the URL. NOTE: this vulnerability exists because of an incomplete fix for S2-047 / CVE-2017-7672.
<p>Publish Date: 2017-09-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-9804>CVE-2017-9804</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-9804">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-9804</a></p>
<p>Release Date: 2017-09-20</p>
<p>Fix Resolution: org.apache.struts:struts2-core:2.5.13</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve high detected in core jar cve high severity vulnerability vulnerable library core jar apache struts path to dependency file tmp ws scm libraryiotest pom xml path to vulnerable library canner repository org apache struts core core jar dependency hierarchy x core jar vulnerable library found in head commit a href vulnerability details in apache struts through and through if an application allows entering a url in a form field and built in urlvalidator is used it is possible to prepare a special url which will be used to overload server process when performing validation of the url note this vulnerability exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache struts core step up your open source security game with whitesource | 0 |
170,417 | 13,186,697,840 | IssuesEvent | 2020-08-13 01:01:36 | near/rainbow-bridge | https://api.github.com/repos/near/rainbow-bridge | closed | e2e test for eth-relay catchup | P1 testing | We need to have a test that checks that the fast catchup of eth-relay works. We can achieve it by copying our existing e2e.sh test and placing a large delay before the eth-relay starts (additionally we might want to increase ganache block production speed to 1 block each 3 sec to exercise our eth-relay speed). | 1.0 | e2e test for eth-relay catchup - We need to have a test that checks that the fast catchup of eth-relay works. We can achieve it by copying our existing e2e.sh test and placing a large delay before the eth-relay starts (additionally we might want to increase ganache block production speed to 1 block each 3 sec to exercise our eth-relay speed). | test | test for eth relay catchup we need to have a test that checks that the fast catchup of eth relay works we can achieve it by copying our existing sh test and placing a large delay before the eth relay starts additionally we might want to increase ganache block production speed to block each sec to exercise our eth relay speed | 1 |
140,561 | 11,351,232,808 | IssuesEvent | 2020-01-24 10:43:39 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed | C-test-failure O-roachtest O-robot branch-master release-blocker | [(roachtest).tpccbench/nodes=9/cpu=4/chaos/partition failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1708438&tab=buildLog) on [master@3c408a47707a15d4b5c92031c4eafcfa643d307c](https://github.com/cockroachdb/cockroach/commits/3c408a47707a15d4b5c92031c4eafcfa643d307c):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/20200124-1708438/tpccbench/nodes=9/cpu=4/chaos/partition/run_1
cluster.go:2315,tpcc.go:720,tpcc.go:561,test_runner.go:719: error with attached stack trace:
main.(*monitor).WaitE
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2306
main.(*monitor).Wait
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2314
main.runTPCCBench
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:720
main.registerTPCCBenchSpec.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:561
main.(*testRunner).runTest.func2
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:719
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1357
- monitor failure:
- unexpected node event: 9: dead
```
<details><summary>More</summary><p>
Artifacts: [/tpccbench/nodes=9/cpu=4/chaos/partition](https://teamcity.cockroachdb.com/viewLog.html?buildId=1708438&tab=artifacts#/tpccbench/nodes=9/cpu=4/chaos/partition)
Related:
- #44293 roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-2.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-2.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44287 roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-19.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-19.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44259 roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202001221958_v2.1.11](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202001221958_v2.1.11) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Atpccbench%2Fnodes%3D9%2Fcpu%3D4%2Fchaos%2Fpartition.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| 2.0 | roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed - [(roachtest).tpccbench/nodes=9/cpu=4/chaos/partition failed](https://teamcity.cockroachdb.com/viewLog.html?buildId=1708438&tab=buildLog) on [master@3c408a47707a15d4b5c92031c4eafcfa643d307c](https://github.com/cockroachdb/cockroach/commits/3c408a47707a15d4b5c92031c4eafcfa643d307c):
```
The test failed on branch=master, cloud=gce:
test artifacts and logs in: /home/agent/work/.go/src/github.com/cockroachdb/cockroach/artifacts/20200124-1708438/tpccbench/nodes=9/cpu=4/chaos/partition/run_1
cluster.go:2315,tpcc.go:720,tpcc.go:561,test_runner.go:719: error with attached stack trace:
main.(*monitor).WaitE
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2306
main.(*monitor).Wait
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/cluster.go:2314
main.runTPCCBench
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:720
main.registerTPCCBenchSpec.func1
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/tpcc.go:561
main.(*testRunner).runTest.func2
/home/agent/work/.go/src/github.com/cockroachdb/cockroach/pkg/cmd/roachtest/test_runner.go:719
runtime.goexit
/usr/local/go/src/runtime/asm_amd64.s:1357
- monitor failure:
- unexpected node event: 9: dead
```
<details><summary>More</summary><p>
Artifacts: [/tpccbench/nodes=9/cpu=4/chaos/partition](https://teamcity.cockroachdb.com/viewLog.html?buildId=1708438&tab=artifacts#/tpccbench/nodes=9/cpu=4/chaos/partition)
Related:
- #44293 roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-2.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-2.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44287 roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-release-19.1](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-release-19.1) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
- #44259 roachtest: tpccbench/nodes=9/cpu=4/chaos/partition failed [C-test-failure](https://api.github.com/repos/cockroachdb/cockroach/labels/C-test-failure) [O-roachtest](https://api.github.com/repos/cockroachdb/cockroach/labels/O-roachtest) [O-robot](https://api.github.com/repos/cockroachdb/cockroach/labels/O-robot) [branch-provisional_202001221958_v2.1.11](https://api.github.com/repos/cockroachdb/cockroach/labels/branch-provisional_202001221958_v2.1.11) [release-blocker](https://api.github.com/repos/cockroachdb/cockroach/labels/release-blocker)
[See this test on roachdash](https://roachdash.crdb.dev/?filter=status%3Aopen+t%3A.%2Atpccbench%2Fnodes%3D9%2Fcpu%3D4%2Fchaos%2Fpartition.%2A&sort=title&restgroup=false&display=lastcommented+project)
<sub>powered by [pkg/cmd/internal/issues](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)</sub></p></details>
| test | roachtest tpccbench nodes cpu chaos partition failed on the test failed on branch master cloud gce test artifacts and logs in home agent work go src github com cockroachdb cockroach artifacts tpccbench nodes cpu chaos partition run cluster go tpcc go tpcc go test runner go error with attached stack trace main monitor waite home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main monitor wait home agent work go src github com cockroachdb cockroach pkg cmd roachtest cluster go main runtpccbench home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main registertpccbenchspec home agent work go src github com cockroachdb cockroach pkg cmd roachtest tpcc go main testrunner runtest home agent work go src github com cockroachdb cockroach pkg cmd roachtest test runner go runtime goexit usr local go src runtime asm s monitor failure unexpected node event dead more artifacts related roachtest tpccbench nodes cpu chaos partition failed roachtest tpccbench nodes cpu chaos partition failed roachtest tpccbench nodes cpu chaos partition failed powered by | 1 |
278,881 | 24,182,828,869 | IssuesEvent | 2022-09-23 10:30:55 | icon-project/icon-bridge | https://api.github.com/repos/icon-project/icon-bridge | opened | feat(test): Add setter getter tests for javascore BMC | type: test :test_tube: status: in progress :running_man: team: ibriz | ## Feature
Add unit test for all setter and getter methods in javascore BMC | 2.0 | feat(test): Add setter getter tests for javascore BMC - ## Feature
Add unit test for all setter and getter methods in javascore BMC | test | feat test add setter getter tests for javascore bmc feature add unit test for all setter and getter methods in javascore bmc | 1 |
2,278 | 2,674,003,588 | IssuesEvent | 2015-03-24 22:30:46 | OctopusDeploy/Issues | https://api.github.com/repos/OctopusDeploy/Issues | opened | Update TC documentation to include create release | documentation | Just to let you know your documentation against TeamCity is out of date as the plugin now has 3 options and not the 2 on the current documentation. the 3 are : -
1. create release
2. deploy release
3. promote release | 1.0 | Update TC documentation to include create release - Just to let you know your documentation against TeamCity is out of date as the plugin now has 3 options and not the 2 on the current documentation. the 3 are : -
1. create release
2. deploy release
3. promote release | non_test | update tc documentation to include create release just to let you know your documentation against teamcity is out of date as the plugin now has options and not the on the current documentation the are create release deploy release promote release | 0 |
167,140 | 12,992,620,347 | IssuesEvent | 2020-07-23 07:16:58 | ballerina-platform/ballerina-lang | https://api.github.com/repos/ballerina-platform/ballerina-lang | closed | Intermittent test failure in Failover Client testcase | Area/StandardLibs Type/TestFailure | **Description:**
The following tests are failing intermittently. need to fix asap.
```
jBallerina-Test-Suite > ballerina-websocket-tests > org.ballerinalang.test.service.websocket.FailoverClientTest > testTextFrameWithSecondServer FAILED org.ballerinalang.test.context.BallerinaTestException: Unable to start ballerina server on port 15200 : Port already in use at org.ballerinalang.test.context.Utils.checkPortAvailability(Utils.java:127) at org.ballerinalang.test.util.websocket.server.WebSocketRemoteServer.run(WebSocketRemoteServer.java:55) at org.ballerinalang.test.service.websocket.FailoverClientTest.initiateServer(FailoverClientTest.java:142) at org.ballerinalang.test.service.websocket.FailoverClientTest.testTextFrameWithSecondServer(FailoverClientTest.java:51)
--
```
```
jBallerina-Test-Suite > ballerina-websocket-tests > org.ballerinalang.test.service.websocket.FailoverClientTest > testHandshakeTimeout FAILED org.ballerinalang.test.context.BallerinaTestException: Unable to start ballerina server on port 15300 : Port already in use at org.ballerinalang.test.context.Utils.checkPortAvailability(Utils.java:127) at org.ballerinalang.test.util.websocket.server.WebSocketRemoteServer.run(WebSocketRemoteServer.java:55) at org.ballerinalang.test.service.websocket.FailoverClientTest.initiateServer(FailoverClientTest.java:142) at org.ballerinalang.test.service.websocket.FailoverClientTest.testHandshakeTimeout(FailoverClientTest.java:90)
```
```
jBallerina-Test-Suite > ballerina-websocket-tests > org.ballerinalang.test.service.websocket.FailoverClientTest > testFailoverWithBothServerFirstStartSecondServer FAILED org.ballerinalang.test.context.BallerinaTestException: Unable to start ballerina server on port 15200 : Port already in use at org.ballerinalang.test.context.Utils.checkPortAvailability(Utils.java:127) at org.ballerinalang.test.util.websocket.server.WebSocketRemoteServer.run(WebSocketRemoteServer.java:55) at org.ballerinalang.test.service.websocket.FailoverClientTest.initiateServer(FailoverClientTest.java:142)
```
**Steps to reproduce:**
**Affected Versions:**
**OS, DB, other environment details and versions:**
**Related Issues (optional):**
<!-- Any related issues such as sub tasks, issues reported in other repositories (e.g component repositories), similar problems, etc. -->
**Suggested Labels (optional):**
<!-- Optional comma separated list of suggested labels. Non committers can’t assign labels to issues, so this will help issue creators who are not a committer to suggest possible labels-->
**Suggested Assignees (optional):**
<!--Optional comma separated list of suggested team members who should attend the issue. Non committers can’t assign issues to assignees, so this will help issue creators who are not a committer to suggest possible assignees-->
| 1.0 | Intermittent test failure in Failover Client testcase - **Description:**
The following tests are failing intermittently. need to fix asap.
```
jBallerina-Test-Suite > ballerina-websocket-tests > org.ballerinalang.test.service.websocket.FailoverClientTest > testTextFrameWithSecondServer FAILED org.ballerinalang.test.context.BallerinaTestException: Unable to start ballerina server on port 15200 : Port already in use at org.ballerinalang.test.context.Utils.checkPortAvailability(Utils.java:127) at org.ballerinalang.test.util.websocket.server.WebSocketRemoteServer.run(WebSocketRemoteServer.java:55) at org.ballerinalang.test.service.websocket.FailoverClientTest.initiateServer(FailoverClientTest.java:142) at org.ballerinalang.test.service.websocket.FailoverClientTest.testTextFrameWithSecondServer(FailoverClientTest.java:51)
--
```
```
jBallerina-Test-Suite > ballerina-websocket-tests > org.ballerinalang.test.service.websocket.FailoverClientTest > testHandshakeTimeout FAILED org.ballerinalang.test.context.BallerinaTestException: Unable to start ballerina server on port 15300 : Port already in use at org.ballerinalang.test.context.Utils.checkPortAvailability(Utils.java:127) at org.ballerinalang.test.util.websocket.server.WebSocketRemoteServer.run(WebSocketRemoteServer.java:55) at org.ballerinalang.test.service.websocket.FailoverClientTest.initiateServer(FailoverClientTest.java:142) at org.ballerinalang.test.service.websocket.FailoverClientTest.testHandshakeTimeout(FailoverClientTest.java:90)
```
```
jBallerina-Test-Suite > ballerina-websocket-tests > org.ballerinalang.test.service.websocket.FailoverClientTest > testFailoverWithBothServerFirstStartSecondServer FAILED org.ballerinalang.test.context.BallerinaTestException: Unable to start ballerina server on port 15200 : Port already in use at org.ballerinalang.test.context.Utils.checkPortAvailability(Utils.java:127) at org.ballerinalang.test.util.websocket.server.WebSocketRemoteServer.run(WebSocketRemoteServer.java:55) at org.ballerinalang.test.service.websocket.FailoverClientTest.initiateServer(FailoverClientTest.java:142)
```
**Steps to reproduce:**
**Affected Versions:**
**OS, DB, other environment details and versions:**
**Related Issues (optional):**
<!-- Any related issues such as sub tasks, issues reported in other repositories (e.g component repositories), similar problems, etc. -->
**Suggested Labels (optional):**
<!-- Optional comma separated list of suggested labels. Non committers can’t assign labels to issues, so this will help issue creators who are not a committer to suggest possible labels-->
**Suggested Assignees (optional):**
<!--Optional comma separated list of suggested team members who should attend the issue. Non committers can’t assign issues to assignees, so this will help issue creators who are not a committer to suggest possible assignees-->
| test | intermittent test failure in failover client testcase description the following tests are failing intermittently need to fix asap jballerina test suite ballerina websocket tests org ballerinalang test service websocket failoverclienttest testtextframewithsecondserver failed org ballerinalang test context ballerinatestexception unable to start ballerina server on port port already in use at org ballerinalang test context utils checkportavailability utils java at org ballerinalang test util websocket server websocketremoteserver run websocketremoteserver java at org ballerinalang test service websocket failoverclienttest initiateserver failoverclienttest java at org ballerinalang test service websocket failoverclienttest testtextframewithsecondserver failoverclienttest java jballerina test suite ballerina websocket tests org ballerinalang test service websocket failoverclienttest testhandshaketimeout failed org ballerinalang test context ballerinatestexception unable to start ballerina server on port port already in use at org ballerinalang test context utils checkportavailability utils java at org ballerinalang test util websocket server websocketremoteserver run websocketremoteserver java at org ballerinalang test service websocket failoverclienttest initiateserver failoverclienttest java at org ballerinalang test service websocket failoverclienttest testhandshaketimeout failoverclienttest java jballerina test suite ballerina websocket tests org ballerinalang test service websocket failoverclienttest testfailoverwithbothserverfirststartsecondserver failed org ballerinalang test context ballerinatestexception unable to start ballerina server on port port already in use at org ballerinalang test context utils checkportavailability utils java at org ballerinalang test util websocket server websocketremoteserver run websocketremoteserver java at org ballerinalang test service websocket failoverclienttest initiateserver failoverclienttest java steps to reproduce affected versions os db other environment details and versions related issues optional suggested labels optional suggested assignees optional | 1 |
9,589 | 3,059,293,979 | IssuesEvent | 2015-08-14 14:16:44 | webrtc/adapter | https://api.github.com/repos/webrtc/adapter | closed | Add console.log test case for when not loaded as a module | test | Current test case only validates the case when added as a module. | 1.0 | Add console.log test case for when not loaded as a module - Current test case only validates the case when added as a module. | test | add console log test case for when not loaded as a module current test case only validates the case when added as a module | 1 |
482,272 | 13,903,876,955 | IssuesEvent | 2020-10-20 07:52:01 | aau-giraf/weekplanner | https://api.github.com/repos/aau-giraf/weekplanner | closed | Refactor the code so we don't use the Observable class | group 6 point: 5 priority: high type: refactor | **Is your feature request related to a problem? Please describe.**
In the Weekplanner application, we are using the Observable class from the rxdart library but it is not a part of the newest version.
The task is to refractor the code and upgrade the dependencies in order to block further use of deprecated classes.
**Describe the solution you'd like**
A solution is described at the following link:
https://pub.dev/packages/rxdart#-changelog-tab-
**Describe alternatives you've considered**
Change the code manually?
**Additional context**
<img width="553" alt="Skærmbillede 2020-05-06 kl 08 42 43" src="https://user-images.githubusercontent.com/13853315/81144981-927f8e00-8f75-11ea-898f-1d65c82c9874.png">
The same problem happens in web api: https://github.com/aau-giraf/api_client/issues/56 | 1.0 | Refactor the code so we don't use the Observable class - **Is your feature request related to a problem? Please describe.**
In the Weekplanner application, we are using the Observable class from the rxdart library but it is not a part of the newest version.
The task is to refractor the code and upgrade the dependencies in order to block further use of deprecated classes.
**Describe the solution you'd like**
A solution is described at the following link:
https://pub.dev/packages/rxdart#-changelog-tab-
**Describe alternatives you've considered**
Change the code manually?
**Additional context**
<img width="553" alt="Skærmbillede 2020-05-06 kl 08 42 43" src="https://user-images.githubusercontent.com/13853315/81144981-927f8e00-8f75-11ea-898f-1d65c82c9874.png">
The same problem happens in web api: https://github.com/aau-giraf/api_client/issues/56 | non_test | refactor the code so we don t use the observable class is your feature request related to a problem please describe in the weekplanner application we are using the observable class from the rxdart library but it is not a part of the newest version the task is to refractor the code and upgrade the dependencies in order to block further use of deprecated classes describe the solution you d like a solution is described at the following link describe alternatives you ve considered change the code manually additional context img width alt skærmbillede kl src the same problem happens in web api | 0 |
780,568 | 27,400,203,199 | IssuesEvent | 2023-02-28 23:38:19 | testifysec/witness | https://api.github.com/repos/testifysec/witness | closed | Add flag to exclude files from subjector | priority high | Currently, the product attestor creates thousands of subjects when witnessing an `npm ci` command. We should limit the total number of subjects for an envelope and give the user a flag to ignore glob patterns from the subjector. | 1.0 | Add flag to exclude files from subjector - Currently, the product attestor creates thousands of subjects when witnessing an `npm ci` command. We should limit the total number of subjects for an envelope and give the user a flag to ignore glob patterns from the subjector. | non_test | add flag to exclude files from subjector currently the product attestor creates thousands of subjects when witnessing an npm ci command we should limit the total number of subjects for an envelope and give the user a flag to ignore glob patterns from the subjector | 0 |
148,963 | 11,872,969,944 | IssuesEvent | 2020-03-26 16:35:22 | laradg/copra-todo | https://api.github.com/repos/laradg/copra-todo | closed | Add sort functionality to columns in CMT | ready-to-test | In COPRA Management Tool, can the sort functionality also be added to columns Project Code and End date (already available on Professional and Start date).

| 1.0 | Add sort functionality to columns in CMT - In COPRA Management Tool, can the sort functionality also be added to columns Project Code and End date (already available on Professional and Start date).

| test | add sort functionality to columns in cmt in copra management tool can the sort functionality also be added to columns project code and end date already available on professional and start date | 1 |
27,807 | 22,351,436,621 | IssuesEvent | 2022-06-15 12:25:41 | microsoftgraph/microsoft-graph-explorer-v4 | https://api.github.com/repos/microsoftgraph/microsoft-graph-explorer-v4 | closed | Speed up tests | Type: Eng Infrastructure Epic | **Describe the bug**
We are currently not running tests for .tsx files because they are slow. The .tsx files recursively render components.
For instance, let's say component A has inner components B and C.
- When testing component A, it will render component B and C. To fix this, we can mock component B and C so as to test component A in isolation.
However, we do not need to test all the tsx components individually. We can just test the root App component that renders all other components. From this single test, we can make all necessary assertions to ensure all components are rendered as expected.
This will be an extension of this effort: https://github.com/microsoftgraph/microsoft-graph-explorer-v4/issues/1513
- [ ] Remove .spec.tsx files and add assertions on App.spec.tsx
- [ ] Add config changes for speeding up tests | 1.0 | Speed up tests - **Describe the bug**
We are currently not running tests for .tsx files because they are slow. The .tsx files recursively render components.
For instance, let's say component A has inner components B and C.
- When testing component A, it will render component B and C. To fix this, we can mock component B and C so as to test component A in isolation.
However, we do not need to test all the tsx components individually. We can just test the root App component that renders all other components. From this single test, we can make all necessary assertions to ensure all components are rendered as expected.
This will be an extension of this effort: https://github.com/microsoftgraph/microsoft-graph-explorer-v4/issues/1513
- [ ] Remove .spec.tsx files and add assertions on App.spec.tsx
- [ ] Add config changes for speeding up tests | non_test | speed up tests describe the bug we are currently not running tests for tsx files because they are slow the tsx files recursively render components for instance let s say component a has inner components b and c when testing component a it will render component b and c to fix this we can mock component b and c so as to test component a in isolation however we do not need to test all the tsx components individually we can just test the root app component that renders all other components from this single test we can make all necessary assertions to ensure all components are rendered as expected this will be an extension of this effort remove spec tsx files and add assertions on app spec tsx add config changes for speeding up tests | 0 |
118,048 | 15,217,393,623 | IssuesEvent | 2021-02-17 16:33:43 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | [Design] MyVA 2.0: Recruit for research | design vsa-authenticated-exp | ## Background
We need to recruit participants for usability testing for MyVA dashboard 2.0.
# Tasks
- [x] Tressa kicks off recruiting with Lauren Alexanderson. | 1.0 | [Design] MyVA 2.0: Recruit for research - ## Background
We need to recruit participants for usability testing for MyVA dashboard 2.0.
# Tasks
- [x] Tressa kicks off recruiting with Lauren Alexanderson. | non_test | myva recruit for research background we need to recruit participants for usability testing for myva dashboard tasks tressa kicks off recruiting with lauren alexanderson | 0 |
155,982 | 12,289,317,639 | IssuesEvent | 2020-05-09 20:53:52 | openshift/openshift-azure | https://api.github.com/repos/openshift/openshift-azure | closed | readiness failed on DeploymentConfig | kind/test-flake lifecycle/rotten | /kind test-flake
During scale up/down readiness failed during sanity check
`time="2019-12-10T13:48:45Z" level=error msg="templateinstance e2e-test-h3dty/e2e-test-h3dty failed: Failed (readiness failed on DeploymentConfig e2e-test-h3dty/django-psql-persistent)" func="github.com/openshift/openshift-azure/test/e2e/standard.(*SanityChecker).CreateTestApp" file="/home/prow/go/src/github.com/openshift/openshift-azure/test/e2e/standard/sanitychecker.go:85"` | 1.0 | readiness failed on DeploymentConfig - /kind test-flake
During scale up/down readiness failed during sanity check
`time="2019-12-10T13:48:45Z" level=error msg="templateinstance e2e-test-h3dty/e2e-test-h3dty failed: Failed (readiness failed on DeploymentConfig e2e-test-h3dty/django-psql-persistent)" func="github.com/openshift/openshift-azure/test/e2e/standard.(*SanityChecker).CreateTestApp" file="/home/prow/go/src/github.com/openshift/openshift-azure/test/e2e/standard/sanitychecker.go:85"` | test | readiness failed on deploymentconfig kind test flake during scale up down readiness failed during sanity check time level error msg templateinstance test test failed failed readiness failed on deploymentconfig test django psql persistent func github com openshift openshift azure test standard sanitychecker createtestapp file home prow go src github com openshift openshift azure test standard sanitychecker go | 1 |
162,235 | 25,507,170,893 | IssuesEvent | 2022-11-28 10:18:52 | microsoft/fluentui | https://api.github.com/repos/microsoft/fluentui | closed | [Feature]: Ability to close triggered dialogs programmatically | Type: Feature Resolution: By Design Component: Dialog Fluent UI react-components (v9) | ### Library
React Components / v9 (@fluentui/react-components)
### Describe the feature that you would like added
Export `useDialogContext_unstable` to allow closing dialog box programmatically. As per documentation it is recomended to use state and open property to close dialog boxes in async submission scenarios. It is cumbersome and makes `<DialogTrigger />` mechanism useless in many scenarios.
[DialogWithForm](https://github.com/microsoft/fluentui/blob/master/packages/react-components/react-dialog/stories/Dialog/DialogWithForm.md)
### Have you discussed this feature with our team
_No response_
### Additional context
Right now I am using the following hook to close dialog box by calling the close method after form submission.
```tsx
export const useDialogCloser = () => {
const ref = useRef<HTMLButtonElement>(null);
const close = () => ref.current?.click();
return {
closer: (
<DialogTrigger action="close">
<button style={{ display: 'none' }} ref={ref} />
</DialogTrigger>
),
close
};
};
```
```tsx
export const SampleDialog = () => {
const styles = useStyles();
return (
<Dialog modalType="alert">
<DialogTrigger>
<Button appearance="primary" size="small">Open</Button>
</DialogTrigger>
<DialogSurface>
<SampleDialogBody />
</DialogSurface>
</Dialog>
);
};
```
```tsx
const SampleDialogBody = (props: StatementProps) => {
const { mutateAsync } = useMutation();
const { closer, close } = useDialogCloser();
const onSubmit: SubmitHandler = async () => {
await mutateAsync();
close();
};
return (
<form onSubmit={handleSubmit(onSubmit)}>
<DialogBody>
{closer}
<DialogContent>{/* form inputs */}</DialogContent>
<DialogActions>
<Button appearance="primary" type="submit">
Save
</Button>
<DialogTrigger>
<Button>Close</Button>
</DialogTrigger>
</DialogActions>
</DialogBody>
</form>
);
};
```
### Validations
- [X] Check that there isn't already an issue that request the same feature to avoid creating a duplicate. | 1.0 | [Feature]: Ability to close triggered dialogs programmatically - ### Library
React Components / v9 (@fluentui/react-components)
### Describe the feature that you would like added
Export `useDialogContext_unstable` to allow closing dialog box programmatically. As per documentation it is recomended to use state and open property to close dialog boxes in async submission scenarios. It is cumbersome and makes `<DialogTrigger />` mechanism useless in many scenarios.
[DialogWithForm](https://github.com/microsoft/fluentui/blob/master/packages/react-components/react-dialog/stories/Dialog/DialogWithForm.md)
### Have you discussed this feature with our team
_No response_
### Additional context
Right now I am using the following hook to close dialog box by calling the close method after form submission.
```tsx
export const useDialogCloser = () => {
const ref = useRef<HTMLButtonElement>(null);
const close = () => ref.current?.click();
return {
closer: (
<DialogTrigger action="close">
<button style={{ display: 'none' }} ref={ref} />
</DialogTrigger>
),
close
};
};
```
```tsx
export const SampleDialog = () => {
const styles = useStyles();
return (
<Dialog modalType="alert">
<DialogTrigger>
<Button appearance="primary" size="small">Open</Button>
</DialogTrigger>
<DialogSurface>
<SampleDialogBody />
</DialogSurface>
</Dialog>
);
};
```
```tsx
const SampleDialogBody = (props: StatementProps) => {
const { mutateAsync } = useMutation();
const { closer, close } = useDialogCloser();
const onSubmit: SubmitHandler = async () => {
await mutateAsync();
close();
};
return (
<form onSubmit={handleSubmit(onSubmit)}>
<DialogBody>
{closer}
<DialogContent>{/* form inputs */}</DialogContent>
<DialogActions>
<Button appearance="primary" type="submit">
Save
</Button>
<DialogTrigger>
<Button>Close</Button>
</DialogTrigger>
</DialogActions>
</DialogBody>
</form>
);
};
```
### Validations
- [X] Check that there isn't already an issue that request the same feature to avoid creating a duplicate. | non_test | ability to close triggered dialogs programmatically library react components fluentui react components describe the feature that you would like added export usedialogcontext unstable to allow closing dialog box programmatically as per documentation it is recomended to use state and open property to close dialog boxes in async submission scenarios it is cumbersome and makes mechanism useless in many scenarios have you discussed this feature with our team no response additional context right now i am using the following hook to close dialog box by calling the close method after form submission tsx export const usedialogcloser const ref useref null const close ref current click return closer close tsx export const sampledialog const styles usestyles return open tsx const sampledialogbody props statementprops const mutateasync usemutation const closer close usedialogcloser const onsubmit submithandler async await mutateasync close return closer form inputs save close validations check that there isn t already an issue that request the same feature to avoid creating a duplicate | 0 |
313,909 | 26,961,820,728 | IssuesEvent | 2023-02-08 18:49:19 | brave/qa-resources | https://api.github.com/repos/brave/qa-resources | closed | remove citeseerx PDF test from manual passes | testsheet | Remove the below from manual passes as page does not exist anymore:
```
Test that https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.105.6357&rep=rep1&type=pdf opens without issues
```
cc @kjozwiak | 1.0 | remove citeseerx PDF test from manual passes - Remove the below from manual passes as page does not exist anymore:
```
Test that https://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.105.6357&rep=rep1&type=pdf opens without issues
```
cc @kjozwiak | test | remove citeseerx pdf test from manual passes remove the below from manual passes as page does not exist anymore test that opens without issues cc kjozwiak | 1 |
7,909 | 8,109,135,360 | IssuesEvent | 2018-08-14 06:13:31 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Please elaborate on the use of scopes | app-service/svc cxp in-progress product-question triaged | Can you please elaborate on the usage of the scopes?
Are the given scopes somehow automagically required, even if the authentication call was made using less (or even different) scopes?
Or are those scopes only used when the authentication-redirect takes place?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 47770286-78c2-00ac-b923-e03041d2c059
* Version Independent ID: a0835218-8f50-4cfc-d927-c3d61b6202e0
* Content: [How to configure Microsoft Account authentication for your App Services application](https://docs.microsoft.com/en-us/azure/app-service/app-service-mobile-how-to-configure-microsoft-authentication)
* Content Source: [articles/app-service/app-service-mobile-how-to-configure-microsoft-authentication.md](https://github.com/Microsoft/azure-docs/blob/master/articles/app-service/app-service-mobile-how-to-configure-microsoft-authentication.md)
* Service: **app-service**
* GitHub Login: @mattchenderson
* Microsoft Alias: **mahender** | 1.0 | Please elaborate on the use of scopes - Can you please elaborate on the usage of the scopes?
Are the given scopes somehow automagically required, even if the authentication call was made using less (or even different) scopes?
Or are those scopes only used when the authentication-redirect takes place?
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 47770286-78c2-00ac-b923-e03041d2c059
* Version Independent ID: a0835218-8f50-4cfc-d927-c3d61b6202e0
* Content: [How to configure Microsoft Account authentication for your App Services application](https://docs.microsoft.com/en-us/azure/app-service/app-service-mobile-how-to-configure-microsoft-authentication)
* Content Source: [articles/app-service/app-service-mobile-how-to-configure-microsoft-authentication.md](https://github.com/Microsoft/azure-docs/blob/master/articles/app-service/app-service-mobile-how-to-configure-microsoft-authentication.md)
* Service: **app-service**
* GitHub Login: @mattchenderson
* Microsoft Alias: **mahender** | non_test | please elaborate on the use of scopes can you please elaborate on the usage of the scopes are the given scopes somehow automagically required even if the authentication call was made using less or even different scopes or are those scopes only used when the authentication redirect takes place document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service app service github login mattchenderson microsoft alias mahender | 0 |
290,921 | 25,106,136,978 | IssuesEvent | 2022-11-08 16:45:33 | ibm-openbmc/dev | https://api.github.com/repos/ibm-openbmc/dev | closed | eBMC GUI : Server Overview | Epic GUI Test on WSP-TAC | ## SMEs
**BMC**:
## Overview
This section already exists and only new features will be associated with this Epic. The new features include:
1.0.8: Realtime Progress Indicators (Unclear if they belong in this section)
1.0.9: Pending Serviceable tasks (Logs)
1.0.10: Singular Collect Service Data Button
View the section in the eBMC Content inventory spreadsheet for more information.
## Use Case
TBD
## References/Resources
- eBMC Feature Item: 1.0
- feature discovery folder:
- user research notes*:
- user research synthesis:
* This folder is restricted in accordance with GDPR guidelines.
| 1.0 | eBMC GUI : Server Overview - ## SMEs
**BMC**:
## Overview
This section already exists and only new features will be associated with this Epic. The new features include:
1.0.8: Realtime Progress Indicators (Unclear if they belong in this section)
1.0.9: Pending Serviceable tasks (Logs)
1.0.10: Singular Collect Service Data Button
View the section in the eBMC Content inventory spreadsheet for more information.
## Use Case
TBD
## References/Resources
- eBMC Feature Item: 1.0
- feature discovery folder:
- user research notes*:
- user research synthesis:
* This folder is restricted in accordance with GDPR guidelines.
| test | ebmc gui server overview smes bmc overview this section already exists and only new features will be associated with this epic the new features include realtime progress indicators unclear if they belong in this section pending serviceable tasks logs singular collect service data button view the section in the ebmc content inventory spreadsheet for more information use case tbd references resources ebmc feature item feature discovery folder user research notes user research synthesis this folder is restricted in accordance with gdpr guidelines | 1 |
39,250 | 5,225,005,246 | IssuesEvent | 2017-01-27 16:57:42 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | github.com/cockroachdb/cockroach/pkg/storage: TestStoreRangeUpReplicate failed under stress | Robot test-failure | SHA: https://github.com/cockroachdb/cockroach/commits/45a6db355ffacca06f19e52eb4c293656d798f85
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=false
TAGS=
GOFLAGS=-race
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=130482&tab=buildLog
```
I170127 09:47:25.413303 14298 storage/store.go:1261 [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170127 09:47:25.413492 14298 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:33495" > attrs:<> locality:<>
W170127 09:47:25.440023 14298 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170127 09:47:25.464044 14374 gossip/client.go:131 [n2] started gossip client to 127.0.0.1:33495
I170127 09:47:25.468377 14298 storage/store.go:1261 [n2,s2]: failed initial metrics computation: [n2,s2]: system config not yet available
I170127 09:47:25.468562 14298 gossip/gossip.go:293 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:44476" > attrs:<> locality:<>
W170127 09:47:25.514767 14298 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170127 09:47:25.521767 14298 storage/store.go:1261 [n3,s3]: failed initial metrics computation: [n3,s3]: system config not yet available
I170127 09:47:25.521954 14298 gossip/gossip.go:293 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:38668" > attrs:<> locality:<>
I170127 09:47:25.524001 14551 gossip/client.go:131 [n3] started gossip client to 127.0.0.1:33495
I170127 09:47:25.597140 14298 storage/client_test.go:403 gossip network initialized
I170127 09:47:25.598170 14298 storage/replica_raftstorage.go:411 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] generated preemptive snapshot ba08c09a at index 15
I170127 09:47:25.600047 14298 storage/store.go:3296 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] streamed snapshot: kv pairs: 34, log entries: 5, 1ms
I170127 09:47:25.600984 14554 storage/replica_raftstorage.go:570 [s2,r1/?:{-},@c420dc8300] applying preemptive snapshot at index 15 (id=ba08c09a, encoded size=5155, 1 rocksdb batches, 5 log entries)
I170127 09:47:25.602025 14554 storage/replica_raftstorage.go:578 [s2,r1/?:/M{in-ax},@c420dc8300] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170127 09:47:25.604771 14298 storage/replica_command.go:3210 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] change replicas (remove {2 2 2}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I170127 09:47:25.608823 14559 storage/replica.go:2435 [s1,r1/1:/M{in-ax},@c4209f6000] proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I170127 09:47:25.616542 14362 storage/replica_raftstorage.go:411 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] generated preemptive snapshot a32ae079 at index 17
I170127 09:47:25.620387 14452 storage/replica_raftstorage.go:570 [s3,r1/?:{-},@c4205ea000] applying preemptive snapshot at index 17 (id=a32ae079, encoded size=6091, 1 rocksdb batches, 7 log entries)
I170127 09:47:25.621623 14452 storage/replica_raftstorage.go:578 [s3,r1/?:/M{in-ax},@c4205ea000] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170127 09:47:25.624072 14362 storage/store.go:3296 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] streamed snapshot: kv pairs: 37, log entries: 7, 7ms
I170127 09:47:25.624225 14444 util/stop/stopper.go:472 quiescing; tasks left:
1 storage/queue.go:507
E170127 09:47:25.625016 14362 storage/queue.go:599 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] change replicas of range 1 failed: node unavailable; try another peer
I170127 09:47:25.636309 14357 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:33495->127.0.0.1:56811: use of closed network connection
I170127 09:47:25.637014 14506 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:38668->127.0.0.1:57903: use of closed network connection
I170127 09:47:25.637328 14417 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:44476->127.0.0.1:55791: use of closed network connection
client_raft_test.go:1032: expected 1 preemptive snapshots, but found 2
``` | 1.0 | github.com/cockroachdb/cockroach/pkg/storage: TestStoreRangeUpReplicate failed under stress - SHA: https://github.com/cockroachdb/cockroach/commits/45a6db355ffacca06f19e52eb4c293656d798f85
Parameters:
```
COCKROACH_PROPOSER_EVALUATED_KV=false
TAGS=
GOFLAGS=-race
```
Stress build found a failed test: https://teamcity.cockroachdb.com/viewLog.html?buildId=130482&tab=buildLog
```
I170127 09:47:25.413303 14298 storage/store.go:1261 [n1,s1]: failed initial metrics computation: [n1,s1]: system config not yet available
I170127 09:47:25.413492 14298 gossip/gossip.go:293 [n1] NodeDescriptor set to node_id:1 address:<network_field:"tcp" address_field:"127.0.0.1:33495" > attrs:<> locality:<>
W170127 09:47:25.440023 14298 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170127 09:47:25.464044 14374 gossip/client.go:131 [n2] started gossip client to 127.0.0.1:33495
I170127 09:47:25.468377 14298 storage/store.go:1261 [n2,s2]: failed initial metrics computation: [n2,s2]: system config not yet available
I170127 09:47:25.468562 14298 gossip/gossip.go:293 [n2] NodeDescriptor set to node_id:2 address:<network_field:"tcp" address_field:"127.0.0.1:44476" > attrs:<> locality:<>
W170127 09:47:25.514767 14298 gossip/gossip.go:1178 [n?] no incoming or outgoing connections
I170127 09:47:25.521767 14298 storage/store.go:1261 [n3,s3]: failed initial metrics computation: [n3,s3]: system config not yet available
I170127 09:47:25.521954 14298 gossip/gossip.go:293 [n3] NodeDescriptor set to node_id:3 address:<network_field:"tcp" address_field:"127.0.0.1:38668" > attrs:<> locality:<>
I170127 09:47:25.524001 14551 gossip/client.go:131 [n3] started gossip client to 127.0.0.1:33495
I170127 09:47:25.597140 14298 storage/client_test.go:403 gossip network initialized
I170127 09:47:25.598170 14298 storage/replica_raftstorage.go:411 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] generated preemptive snapshot ba08c09a at index 15
I170127 09:47:25.600047 14298 storage/store.go:3296 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] streamed snapshot: kv pairs: 34, log entries: 5, 1ms
I170127 09:47:25.600984 14554 storage/replica_raftstorage.go:570 [s2,r1/?:{-},@c420dc8300] applying preemptive snapshot at index 15 (id=ba08c09a, encoded size=5155, 1 rocksdb batches, 5 log entries)
I170127 09:47:25.602025 14554 storage/replica_raftstorage.go:578 [s2,r1/?:/M{in-ax},@c420dc8300] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170127 09:47:25.604771 14298 storage/replica_command.go:3210 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] change replicas (remove {2 2 2}): read existing descriptor range_id:1 start_key:"" end_key:"\377\377" replicas:<node_id:1 store_id:1 replica_id:1 > next_replica_id:2
I170127 09:47:25.608823 14559 storage/replica.go:2435 [s1,r1/1:/M{in-ax},@c4209f6000] proposing ADD_REPLICA {NodeID:2 StoreID:2 ReplicaID:2}: [{NodeID:1 StoreID:1 ReplicaID:1} {NodeID:2 StoreID:2 ReplicaID:2}]
I170127 09:47:25.616542 14362 storage/replica_raftstorage.go:411 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] generated preemptive snapshot a32ae079 at index 17
I170127 09:47:25.620387 14452 storage/replica_raftstorage.go:570 [s3,r1/?:{-},@c4205ea000] applying preemptive snapshot at index 17 (id=a32ae079, encoded size=6091, 1 rocksdb batches, 7 log entries)
I170127 09:47:25.621623 14452 storage/replica_raftstorage.go:578 [s3,r1/?:/M{in-ax},@c4205ea000] applied preemptive snapshot in 1ms [clear=0ms batch=0ms entries=0ms commit=0ms]
I170127 09:47:25.624072 14362 storage/store.go:3296 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] streamed snapshot: kv pairs: 37, log entries: 7, 7ms
I170127 09:47:25.624225 14444 util/stop/stopper.go:472 quiescing; tasks left:
1 storage/queue.go:507
E170127 09:47:25.625016 14362 storage/queue.go:599 [replicate,s1,r1/1:/M{in-ax},@c4209f6000] change replicas of range 1 failed: node unavailable; try another peer
I170127 09:47:25.636309 14357 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:33495->127.0.0.1:56811: use of closed network connection
I170127 09:47:25.637014 14506 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:38668->127.0.0.1:57903: use of closed network connection
I170127 09:47:25.637328 14417 vendor/google.golang.org/grpc/transport/http2_server.go:320 transport: http2Server.HandleStreams failed to read frame: read tcp 127.0.0.1:44476->127.0.0.1:55791: use of closed network connection
client_raft_test.go:1032: expected 1 preemptive snapshots, but found 2
``` | test | github com cockroachdb cockroach pkg storage teststorerangeupreplicate failed under stress sha parameters cockroach proposer evaluated kv false tags goflags race stress build found a failed test storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality gossip gossip go no incoming or outgoing connections gossip client go started gossip client to storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality gossip gossip go no incoming or outgoing connections storage store go failed initial metrics computation system config not yet available gossip gossip go nodedescriptor set to node id address attrs locality gossip client go started gossip client to storage client test go gossip network initialized storage replica raftstorage go generated preemptive snapshot at index storage store go streamed snapshot kv pairs log entries storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage replica command go change replicas remove read existing descriptor range id start key end key replicas next replica id storage replica go proposing add replica nodeid storeid replicaid storage replica raftstorage go generated preemptive snapshot at index storage replica raftstorage go applying preemptive snapshot at index id encoded size rocksdb batches log entries storage replica raftstorage go applied preemptive snapshot in storage store go streamed snapshot kv pairs log entries util stop stopper go quiescing tasks left storage queue go storage queue go change replicas of range failed node unavailable try another peer vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection vendor google golang org grpc transport server go transport handlestreams failed to read frame read tcp use of closed network connection client raft test go expected preemptive snapshots but found | 1 |
5,786 | 5,167,624,733 | IssuesEvent | 2017-01-17 19:19:01 | tensorflow/tensorflow | https://api.github.com/repos/tensorflow/tensorflow | closed | Nvidia GTX 960: Abnormal Memory Usage | awaiting response type:bug/performance type:support | ### Environment info
Operating System: Ubuntu 16.04
Installed version of CUDA and cuDNN:
(please attach the output of `ls -l /path/to/cuda/lib/libcud*`):
-rw-r--r-- 1 root root 558720 Dec 17 21:39 libcudadevrt.a
lrwxrwxrwx 1 root root 16 Dec 17 21:39 libcudart.so -> libcudart.so.8.0
lrwxrwxrwx 1 root root 19 Dec 17 21:39 libcudart.so.8.0 -> libcudart.so.8.0.44
-rwxr-xr-x 1 root root 415432 Dec 17 21:39 libcudart.so.8.0.44
-rw-r--r-- 1 root root 775162 Dec 17 21:39 libcudart_static.a
lrwxrwxrwx 1 root root 13 Dec 18 16:34 libcudnn.so -> libcudnn.so.5
lrwxrwxrwx 1 root root 17 Dec 18 16:34 libcudnn.so.5 -> libcudnn.so.5.1.5
-rwxr-xr-x 1 root root 78065952 Dec 18 16:34 libcudnn.so.5.0.5
-rwxr-xr-x 1 root root 79337624 Dec 18 16:34 libcudnn.so.5.1.5
-rw-r--r-- 1 root root 69756172 Dec 18 16:34 libcudnn_static.a
### If possible, provide a minimal reproducible example (We usually don't have time to read hundreds of lines of your code)
Just any neural network model. Strangely enough CIFAR functioned fine.
I used images of size 1750 * 1750.
### What other attempted solutions have you tried?
I ran it on CPU and there was no issue at all other than the slow training speed.
### Logs or other output that would be helpful
(If logs are large, please upload as attachment or provide link).
Unfortunately because the memory leak crashes my computer within seconds, I can only give a rough example. It roughly says" GPU has failed to allocate ~~ around 8 GB of ram. The GTX 960 on my machine only has 4 GB of ram. I'm not sure why 8 GB was suddenly gobbled up at once.
| True | Nvidia GTX 960: Abnormal Memory Usage - ### Environment info
Operating System: Ubuntu 16.04
Installed version of CUDA and cuDNN:
(please attach the output of `ls -l /path/to/cuda/lib/libcud*`):
-rw-r--r-- 1 root root 558720 Dec 17 21:39 libcudadevrt.a
lrwxrwxrwx 1 root root 16 Dec 17 21:39 libcudart.so -> libcudart.so.8.0
lrwxrwxrwx 1 root root 19 Dec 17 21:39 libcudart.so.8.0 -> libcudart.so.8.0.44
-rwxr-xr-x 1 root root 415432 Dec 17 21:39 libcudart.so.8.0.44
-rw-r--r-- 1 root root 775162 Dec 17 21:39 libcudart_static.a
lrwxrwxrwx 1 root root 13 Dec 18 16:34 libcudnn.so -> libcudnn.so.5
lrwxrwxrwx 1 root root 17 Dec 18 16:34 libcudnn.so.5 -> libcudnn.so.5.1.5
-rwxr-xr-x 1 root root 78065952 Dec 18 16:34 libcudnn.so.5.0.5
-rwxr-xr-x 1 root root 79337624 Dec 18 16:34 libcudnn.so.5.1.5
-rw-r--r-- 1 root root 69756172 Dec 18 16:34 libcudnn_static.a
### If possible, provide a minimal reproducible example (We usually don't have time to read hundreds of lines of your code)
Just any neural network model. Strangely enough CIFAR functioned fine.
I used images of size 1750 * 1750.
### What other attempted solutions have you tried?
I ran it on CPU and there was no issue at all other than the slow training speed.
### Logs or other output that would be helpful
(If logs are large, please upload as attachment or provide link).
Unfortunately because the memory leak crashes my computer within seconds, I can only give a rough example. It roughly says" GPU has failed to allocate ~~ around 8 GB of ram. The GTX 960 on my machine only has 4 GB of ram. I'm not sure why 8 GB was suddenly gobbled up at once.
| non_test | nvidia gtx abnormal memory usage environment info operating system ubuntu installed version of cuda and cudnn please attach the output of ls l path to cuda lib libcud rw r r root root dec libcudadevrt a lrwxrwxrwx root root dec libcudart so libcudart so lrwxrwxrwx root root dec libcudart so libcudart so rwxr xr x root root dec libcudart so rw r r root root dec libcudart static a lrwxrwxrwx root root dec libcudnn so libcudnn so lrwxrwxrwx root root dec libcudnn so libcudnn so rwxr xr x root root dec libcudnn so rwxr xr x root root dec libcudnn so rw r r root root dec libcudnn static a if possible provide a minimal reproducible example we usually don t have time to read hundreds of lines of your code just any neural network model strangely enough cifar functioned fine i used images of size what other attempted solutions have you tried i ran it on cpu and there was no issue at all other than the slow training speed logs or other output that would be helpful if logs are large please upload as attachment or provide link unfortunately because the memory leak crashes my computer within seconds i can only give a rough example it roughly says gpu has failed to allocate around gb of ram the gtx on my machine only has gb of ram i m not sure why gb was suddenly gobbled up at once | 0 |
290,448 | 25,068,772,148 | IssuesEvent | 2022-11-07 10:25:45 | MJZwart/motivation-app | https://api.github.com/repos/MJZwart/motivation-app | closed | Create E2E tests for admin | test | - Admin can see the admin dashboard
- Admin can send a notification to all users
- Admin can see balancing
- Admin can update the village balancing
- Admin can update the character balancing
- Admin can see achievements
- Admin can add a new achievement
- Admin can edit an achievement
- Admin can see bug reports
- Admin can edit a bug report
- Admin can send an email to bug report author
- Admin can see the reported users
- Admin can suspend a reported user
- Admin can email a reported user
- Admin can suspend a user through their profile
- Admin can edit a ban
- Admin can unban a user
- Admin can see feedback
- Admin can archive feedback
- Admin can see archived feedback | 1.0 | Create E2E tests for admin - - Admin can see the admin dashboard
- Admin can send a notification to all users
- Admin can see balancing
- Admin can update the village balancing
- Admin can update the character balancing
- Admin can see achievements
- Admin can add a new achievement
- Admin can edit an achievement
- Admin can see bug reports
- Admin can edit a bug report
- Admin can send an email to bug report author
- Admin can see the reported users
- Admin can suspend a reported user
- Admin can email a reported user
- Admin can suspend a user through their profile
- Admin can edit a ban
- Admin can unban a user
- Admin can see feedback
- Admin can archive feedback
- Admin can see archived feedback | test | create tests for admin admin can see the admin dashboard admin can send a notification to all users admin can see balancing admin can update the village balancing admin can update the character balancing admin can see achievements admin can add a new achievement admin can edit an achievement admin can see bug reports admin can edit a bug report admin can send an email to bug report author admin can see the reported users admin can suspend a reported user admin can email a reported user admin can suspend a user through their profile admin can edit a ban admin can unban a user admin can see feedback admin can archive feedback admin can see archived feedback | 1 |
212,070 | 7,228,111,789 | IssuesEvent | 2018-02-11 05:04:11 | openshift/origin | https://api.github.com/repos/openshift/origin | closed | Inconsistent oc rollout command structure | component/apps component/cli kind/question lifecycle/stale priority/P3 | `oc rollout` subcommands are not consistent in their argument structure. Some require only the name of the deploymentconfig, some type/deploymentconfig:
```
$ oc rollout latest myapp
$ oc rollout statue dc/myapp
```
The command should be consistent and all rollout commands either require type/name or just name.
##### Version
oc v3.5.5.5
kubernetes v1.5.2+43a9be4
features: Basic-Auth
Server https://api.ded-stage-aws.openshift.com:443
openshift v3.5.5.10
kubernetes v1.5.2+43a9be4
| 1.0 | Inconsistent oc rollout command structure - `oc rollout` subcommands are not consistent in their argument structure. Some require only the name of the deploymentconfig, some type/deploymentconfig:
```
$ oc rollout latest myapp
$ oc rollout statue dc/myapp
```
The command should be consistent and all rollout commands either require type/name or just name.
##### Version
oc v3.5.5.5
kubernetes v1.5.2+43a9be4
features: Basic-Auth
Server https://api.ded-stage-aws.openshift.com:443
openshift v3.5.5.10
kubernetes v1.5.2+43a9be4
| non_test | inconsistent oc rollout command structure oc rollout subcommands are not consistent in their argument structure some require only the name of the deploymentconfig some type deploymentconfig oc rollout latest myapp oc rollout statue dc myapp the command should be consistent and all rollout commands either require type name or just name version oc kubernetes features basic auth server openshift kubernetes | 0 |
249,936 | 21,218,186,383 | IssuesEvent | 2022-04-11 09:22:20 | stores-cedcommerce/Internal-Diat-Food-Due-15th-March | https://api.github.com/repos/stores-cedcommerce/Internal-Diat-Food-Due-15th-March | closed | The page of refund policy need to be Returns and Refund Policy it will be much better and the url have to be also change for it. | Footer section Desktop Issue Ready to test Fixed | The url : https://107soyodhyqw1pzu-59207385288.shopifypreview.com/pages/refund-policy
**Actual result:**
1: The url is coming of refund policy only.
2: The title of the policy is only of Refund poilicy.

**Expected result:**
1: The url have to be returns and refund policy.
2: The title of policy should be Returns and Refund Policy.
--------------------------------------------------------------------------------------------------------------------------------------
**RETESTING:**
Actual result:
The title is coming Refund and Refund policy.

Expected result: Return & Refund Policy. it will be much better.
-----------------------------------------------------------------------------------------------------------------------------------
**Again retesting:**
**Actual result:**
The title on return & refund policy the word return is in singular.
The url: https://sugarlessbliss.com/pages/return-and-refund-policy
**Expected result:**
1: The url have to be change i should be like returns and refund policy.
2: The work inside the form have to be Returns and Refund Policy it is coming , like Return and Refund Policy
| 1.0 | The page of refund policy need to be Returns and Refund Policy it will be much better and the url have to be also change for it. - The url : https://107soyodhyqw1pzu-59207385288.shopifypreview.com/pages/refund-policy
**Actual result:**
1: The url is coming of refund policy only.
2: The title of the policy is only of Refund poilicy.

**Expected result:**
1: The url have to be returns and refund policy.
2: The title of policy should be Returns and Refund Policy.
--------------------------------------------------------------------------------------------------------------------------------------
**RETESTING:**
Actual result:
The title is coming Refund and Refund policy.

Expected result: Return & Refund Policy. it will be much better.
-----------------------------------------------------------------------------------------------------------------------------------
**Again retesting:**
**Actual result:**
The title on return & refund policy the word return is in singular.
The url: https://sugarlessbliss.com/pages/return-and-refund-policy
**Expected result:**
1: The url have to be change i should be like returns and refund policy.
2: The work inside the form have to be Returns and Refund Policy it is coming , like Return and Refund Policy
| test | the page of refund policy need to be returns and refund policy it will be much better and the url have to be also change for it the url actual result the url is coming of refund policy only the title of the policy is only of refund poilicy expected result the url have to be returns and refund policy the title of policy should be returns and refund policy retesting actual result the title is coming refund and refund policy expected result return refund policy it will be much better again retesting actual result the title on return refund policy the word return is in singular the url expected result the url have to be change i should be like returns and refund policy the work inside the form have to be returns and refund policy it is coming like return and refund policy | 1 |
317,491 | 27,241,111,441 | IssuesEvent | 2023-02-21 20:32:27 | Azure/azure-sdk-for-js | https://api.github.com/repos/Azure/azure-sdk-for-js | closed | [Event Hubs] Authentication via (service version live) AzureNamedKeyCredential supports key rotation EventHubConsumerClient receive calls failing in nightly runs | Client Event Hubs test-reliability | Event Hubs nightly test runs are failing with:
> Error message:
>Step 2 failed. Expected to see a list of events.
>
> Stack trace:
>Error: Step 2 failed. Expected to see a list of events.
at /Users/runner/work/1/s/sdk/eventhub/event-hubs/test/public/auth.spec.ts:135:26
at Object.processError (/Users/runner/work/1/s/sdk/eventhub/event-hubs/test/public/auth.spec.ts:164:29)
at PartitionProcessor.processError (/Users/runner/work/1/s/sdk/eventhub/event-hubs/dist-esm/src/partitionProcessor.js:53:228)
at PartitionPump._receiveEvents (/Users/runner/work/1/s/sdk/eventhub/event-hubs/src/partitionPump.ts:44:14)
at processTicksAndRejections (node:internal/process/task_queues:95:5)
For more details check here:
- https://dev.azure.com/azure-sdk/internal/_build/results?buildId=2196950&view=results | 1.0 | [Event Hubs] Authentication via (service version live) AzureNamedKeyCredential supports key rotation EventHubConsumerClient receive calls failing in nightly runs - Event Hubs nightly test runs are failing with:
> Error message:
>Step 2 failed. Expected to see a list of events.
>
> Stack trace:
>Error: Step 2 failed. Expected to see a list of events.
at /Users/runner/work/1/s/sdk/eventhub/event-hubs/test/public/auth.spec.ts:135:26
at Object.processError (/Users/runner/work/1/s/sdk/eventhub/event-hubs/test/public/auth.spec.ts:164:29)
at PartitionProcessor.processError (/Users/runner/work/1/s/sdk/eventhub/event-hubs/dist-esm/src/partitionProcessor.js:53:228)
at PartitionPump._receiveEvents (/Users/runner/work/1/s/sdk/eventhub/event-hubs/src/partitionPump.ts:44:14)
at processTicksAndRejections (node:internal/process/task_queues:95:5)
For more details check here:
- https://dev.azure.com/azure-sdk/internal/_build/results?buildId=2196950&view=results | test | authentication via service version live azurenamedkeycredential supports key rotation eventhubconsumerclient receive calls failing in nightly runs event hubs nightly test runs are failing with error message step failed expected to see a list of events stack trace error step failed expected to see a list of events at users runner work s sdk eventhub event hubs test public auth spec ts at object processerror users runner work s sdk eventhub event hubs test public auth spec ts at partitionprocessor processerror users runner work s sdk eventhub event hubs dist esm src partitionprocessor js at partitionpump receiveevents users runner work s sdk eventhub event hubs src partitionpump ts at processticksandrejections node internal process task queues for more details check here | 1 |
283,260 | 24,535,890,820 | IssuesEvent | 2022-10-11 20:42:41 | cse-labs/ratify | https://api.github.com/repos/cse-labs/ratify | closed | binary Verifier plugin: unit tests | plugins verifier tests | Unit tests for the revamped verify function with coverage equivalent to current state
related to #4 | 1.0 | binary Verifier plugin: unit tests - Unit tests for the revamped verify function with coverage equivalent to current state
related to #4 | test | binary verifier plugin unit tests unit tests for the revamped verify function with coverage equivalent to current state related to | 1 |
216,942 | 16,824,849,761 | IssuesEvent | 2021-06-17 17:07:17 | cybersemics/em | https://api.github.com/repos/cybersemics/em | closed | "Browserstack is not connected" warnings | test | I tried to get rid of these warnings to no avail.
We are setting `'browserstack.local': 'true'` exactly as specified here:
https://www.browserstack.com/question/779
The tests still pass.
```sh
Setup Test Environment for webdriverio.
Setup done
Using the currently running app on http://localhost:3000
BrowserstackLocal: Starting
wdio.remote
2021-06-12T14:14:08.660Z WARN webdriver: Request failed with status 200 due to [browserstack.local] is set to true but local testing through BrowserStack is not connected.
2021-06-12T14:14:10.239Z WARN webdriver: Request failed with status 200 due to [browserstack.local] is set to true but local testing through BrowserStack is not connected.
BrowserStackLocal: Running
2021-06-12T14:14:11.994Z WARN webdriver: Request failed with status 200 due to [browserstack.local] is set to true but local testing through BrowserStack is not connected.
Teardown Test Environment for webdriverio.
PASS src/e2e/__tests__/iOS/caret.ts (24.737 s)
Caret & Cursor Test
✓ Enter edit mode (11213 ms)
A worker process has failed to exit gracefully and has been force exited. This is likely caused by tests leaking due to improper teardown. Try running with --detectOpenHandles to find leaks.
Test Suites: 1 passed, 1 total
Tests: 1 passed, 1 total
Snapshots: 0 total
Time: 28.007 s
Ran all test suites matching /src\/e2e\/__tests__\/iOS\/caret\.ts/i.
Watch Usage: Press w to show more.
``` | 1.0 | "Browserstack is not connected" warnings - I tried to get rid of these warnings to no avail.
We are setting `'browserstack.local': 'true'` exactly as specified here:
https://www.browserstack.com/question/779
The tests still pass.
```sh
Setup Test Environment for webdriverio.
Setup done
Using the currently running app on http://localhost:3000
BrowserstackLocal: Starting
wdio.remote
2021-06-12T14:14:08.660Z WARN webdriver: Request failed with status 200 due to [browserstack.local] is set to true but local testing through BrowserStack is not connected.
2021-06-12T14:14:10.239Z WARN webdriver: Request failed with status 200 due to [browserstack.local] is set to true but local testing through BrowserStack is not connected.
BrowserStackLocal: Running
2021-06-12T14:14:11.994Z WARN webdriver: Request failed with status 200 due to [browserstack.local] is set to true but local testing through BrowserStack is not connected.
Teardown Test Environment for webdriverio.
PASS src/e2e/__tests__/iOS/caret.ts (24.737 s)
Caret & Cursor Test
✓ Enter edit mode (11213 ms)
A worker process has failed to exit gracefully and has been force exited. This is likely caused by tests leaking due to improper teardown. Try running with --detectOpenHandles to find leaks.
Test Suites: 1 passed, 1 total
Tests: 1 passed, 1 total
Snapshots: 0 total
Time: 28.007 s
Ran all test suites matching /src\/e2e\/__tests__\/iOS\/caret\.ts/i.
Watch Usage: Press w to show more.
``` | test | browserstack is not connected warnings i tried to get rid of these warnings to no avail we are setting browserstack local true exactly as specified here the tests still pass sh setup test environment for webdriverio setup done using the currently running app on browserstacklocal starting wdio remote warn webdriver request failed with status due to is set to true but local testing through browserstack is not connected warn webdriver request failed with status due to is set to true but local testing through browserstack is not connected browserstacklocal running warn webdriver request failed with status due to is set to true but local testing through browserstack is not connected teardown test environment for webdriverio pass src tests ios caret ts s caret cursor test ✓ enter edit mode ms a worker process has failed to exit gracefully and has been force exited this is likely caused by tests leaking due to improper teardown try running with detectopenhandles to find leaks test suites passed total tests passed total snapshots total time s ran all test suites matching src tests ios caret ts i watch usage press w to show more | 1 |
56,216 | 6,506,938,737 | IssuesEvent | 2017-08-24 11:07:24 | pandas-dev/pandas | https://api.github.com/repos/pandas-dev/pandas | opened | TST/CI: Use moto to mock S3 calls | CI Difficulty Novice Effort Medium Testing | https://github.com/spulec/moto
I think most of our tests hitting s3 can be mocked now that we're using s3fs and boto3. We don't have any code doing network requests, auth, etc. As an example:
```
import pytest
import pandas as pd
from moto import mock_s3
import boto3
f = open("pandas/tests/io/data/tips.csv", 'rb')
@mock_s3
def test_foo():
conn = boto3.resource("s3", region_name="us-east-1")
conn.create_bucket(Bucket="pandas-test")
conn.Bucket("pandas-test").put_object(Key="not-a-real-key.csv", Body=f)
result = pd.read_csv("s3://pandas-test/not-a-real-key.csv")
assert isinstance(result, pd.DataFrame)
with pytest.raises(Exception):
result = pd.read_csv("s3://pandas-test/for-real-not-a-real-key.csv")
```
It'd probably be good to have a few integration tests that actually hit S3, but I think most can be replaced with mocked calls. | 1.0 | TST/CI: Use moto to mock S3 calls - https://github.com/spulec/moto
I think most of our tests hitting s3 can be mocked now that we're using s3fs and boto3. We don't have any code doing network requests, auth, etc. As an example:
```
import pytest
import pandas as pd
from moto import mock_s3
import boto3
f = open("pandas/tests/io/data/tips.csv", 'rb')
@mock_s3
def test_foo():
conn = boto3.resource("s3", region_name="us-east-1")
conn.create_bucket(Bucket="pandas-test")
conn.Bucket("pandas-test").put_object(Key="not-a-real-key.csv", Body=f)
result = pd.read_csv("s3://pandas-test/not-a-real-key.csv")
assert isinstance(result, pd.DataFrame)
with pytest.raises(Exception):
result = pd.read_csv("s3://pandas-test/for-real-not-a-real-key.csv")
```
It'd probably be good to have a few integration tests that actually hit S3, but I think most can be replaced with mocked calls. | test | tst ci use moto to mock calls i think most of our tests hitting can be mocked now that we re using and we don t have any code doing network requests auth etc as an example import pytest import pandas as pd from moto import mock import f open pandas tests io data tips csv rb mock def test foo conn resource region name us east conn create bucket bucket pandas test conn bucket pandas test put object key not a real key csv body f result pd read csv pandas test not a real key csv assert isinstance result pd dataframe with pytest raises exception result pd read csv pandas test for real not a real key csv it d probably be good to have a few integration tests that actually hit but i think most can be replaced with mocked calls | 1 |
203,042 | 15,865,564,419 | IssuesEvent | 2021-04-08 14:51:22 | rovergulf/ngx-slice-kit | https://api.github.com/repos/rovergulf/ngx-slice-kit | opened | change home page badges | documentation | ```html
<img alt="npm peer dependency version" src="https://img.shields.io/npm/dependency-version/ngx-slice-kit/peer/@angular/core">
<img alt="npm peer dependency version" src="https://img.shields.io/npm/dependency-version/ngx-slice-kit/peer/@angular/cdk">
```
change to
```html
<img alt="GitHub package.json dependency version (prod)" src="https://img.shields.io/github/package-json/dependency-version/rovergulf/ngx-slice-kit/@angular/core">
<img alt="GitHub package.json dependency version (prod)" src="https://img.shields.io/github/package-json/dependency-version/rovergulf/ngx-slice-kit/@angular/cdk">
``` | 1.0 | change home page badges - ```html
<img alt="npm peer dependency version" src="https://img.shields.io/npm/dependency-version/ngx-slice-kit/peer/@angular/core">
<img alt="npm peer dependency version" src="https://img.shields.io/npm/dependency-version/ngx-slice-kit/peer/@angular/cdk">
```
change to
```html
<img alt="GitHub package.json dependency version (prod)" src="https://img.shields.io/github/package-json/dependency-version/rovergulf/ngx-slice-kit/@angular/core">
<img alt="GitHub package.json dependency version (prod)" src="https://img.shields.io/github/package-json/dependency-version/rovergulf/ngx-slice-kit/@angular/cdk">
``` | non_test | change home page badges html img alt npm peer dependency version src img alt npm peer dependency version src change to html img alt github package json dependency version prod src img alt github package json dependency version prod src | 0 |
232,779 | 25,706,319,164 | IssuesEvent | 2022-12-07 01:04:05 | detain/watchable | https://api.github.com/repos/detain/watchable | reopened | fabpot/goutte-v3.2.3: 1 vulnerabilities (highest severity is: 8.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fabpot/goutte-v3.2.3</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/detain/watchable/commit/aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3">aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (fabpot/goutte-v3.2.3 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-29248](https://www.mend.io/vulnerability-database/CVE-2022-29248) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | guzzlehttp/guzzle-6.5.x-dev | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-29248</summary>
### Vulnerable Library - <b>guzzlehttp/guzzle-6.5.x-dev</b></p>
<p>Guzzle is a PHP HTTP client library</p>
<p>Library home page: <a href="https://api.github.com/repos/guzzle/guzzle/zipball/a52f0440530b54fa079ce76e8c5d196a42cad981">https://api.github.com/repos/guzzle/guzzle/zipball/a52f0440530b54fa079ce76e8c5d196a42cad981</a></p>
<p>
Dependency Hierarchy:
- fabpot/goutte-v3.2.3 (Root Library)
- :x: **guzzlehttp/guzzle-6.5.x-dev** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/detain/watchable/commit/aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3">aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Guzzle is a PHP HTTP client. Guzzle prior to versions 6.5.6 and 7.4.3 contains a vulnerability with the cookie middleware. The vulnerability is that it is not checked if the cookie domain equals the domain of the server which sets the cookie via the Set-Cookie header, allowing a malicious server to set cookies for unrelated domains. The cookie middleware is disabled by default, so most library consumers will not be affected by this issue. Only those who manually add the cookie middleware to the handler stack or construct the client with ['cookies' => true] are affected. Moreover, those who do not use the same Guzzle client to call multiple domains and have disabled redirect forwarding are not affected by this vulnerability. Guzzle versions 6.5.6 and 7.4.3 contain a patch for this issue. As a workaround, turn off the cookie middleware.
<p>Publish Date: 2022-05-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29248>CVE-2022-29248</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29248">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29248</a></p>
<p>Release Date: 2022-05-25</p>
<p>Fix Resolution: guzzlehttp/guzzle - 6.5.6,guzzlehttp/guzzle - 7.4.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | fabpot/goutte-v3.2.3: 1 vulnerabilities (highest severity is: 8.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>fabpot/goutte-v3.2.3</b></p></summary>
<p></p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/detain/watchable/commit/aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3">aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (fabpot/goutte-v3.2.3 version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-29248](https://www.mend.io/vulnerability-database/CVE-2022-29248) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 8.1 | guzzlehttp/guzzle-6.5.x-dev | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-29248</summary>
### Vulnerable Library - <b>guzzlehttp/guzzle-6.5.x-dev</b></p>
<p>Guzzle is a PHP HTTP client library</p>
<p>Library home page: <a href="https://api.github.com/repos/guzzle/guzzle/zipball/a52f0440530b54fa079ce76e8c5d196a42cad981">https://api.github.com/repos/guzzle/guzzle/zipball/a52f0440530b54fa079ce76e8c5d196a42cad981</a></p>
<p>
Dependency Hierarchy:
- fabpot/goutte-v3.2.3 (Root Library)
- :x: **guzzlehttp/guzzle-6.5.x-dev** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/detain/watchable/commit/aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3">aa67e5c8feb26ac6176ddfd4899d3ecd6eb82bb3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Guzzle is a PHP HTTP client. Guzzle prior to versions 6.5.6 and 7.4.3 contains a vulnerability with the cookie middleware. The vulnerability is that it is not checked if the cookie domain equals the domain of the server which sets the cookie via the Set-Cookie header, allowing a malicious server to set cookies for unrelated domains. The cookie middleware is disabled by default, so most library consumers will not be affected by this issue. Only those who manually add the cookie middleware to the handler stack or construct the client with ['cookies' => true] are affected. Moreover, those who do not use the same Guzzle client to call multiple domains and have disabled redirect forwarding are not affected by this vulnerability. Guzzle versions 6.5.6 and 7.4.3 contain a patch for this issue. As a workaround, turn off the cookie middleware.
<p>Publish Date: 2022-05-25
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-29248>CVE-2022-29248</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>8.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29248">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29248</a></p>
<p>Release Date: 2022-05-25</p>
<p>Fix Resolution: guzzlehttp/guzzle - 6.5.6,guzzlehttp/guzzle - 7.4.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_test | fabpot goutte vulnerabilities highest severity is vulnerable library fabpot goutte found in head commit a href vulnerabilities cve severity cvss dependency type fixed in fabpot goutte version remediation available high guzzlehttp guzzle x dev transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library guzzlehttp guzzle x dev guzzle is a php http client library library home page a href dependency hierarchy fabpot goutte root library x guzzlehttp guzzle x dev vulnerable library found in head commit a href found in base branch main vulnerability details guzzle is a php http client guzzle prior to versions and contains a vulnerability with the cookie middleware the vulnerability is that it is not checked if the cookie domain equals the domain of the server which sets the cookie via the set cookie header allowing a malicious server to set cookies for unrelated domains the cookie middleware is disabled by default so most library consumers will not be affected by this issue only those who manually add the cookie middleware to the handler stack or construct the client with are affected moreover those who do not use the same guzzle client to call multiple domains and have disabled redirect forwarding are not affected by this vulnerability guzzle versions and contain a patch for this issue as a workaround turn off the cookie middleware publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution guzzlehttp guzzle guzzlehttp guzzle step up your open source security game with mend | 0 |
188,874 | 14,477,633,016 | IssuesEvent | 2020-12-10 06:57:31 | qrsforever/web_clipper_data | https://api.github.com/repos/qrsforever/web_clipper_data | opened | SIFT | How To Use SIFT For Image Matching In Python | test | ## Overview
- A beginner-friendly introduction to the powerful SIFT (Scale Invariant Feature Transform) technique
- Learn how to perform Feature Matching using SIFT
- We also showcase SIFT in Python through hands-on coding
## Introduction
Take a look at the below collection of images and think of the common element between them:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-20-17-49-55.png)
The resplendent Eiffel Tower, of course! The keen-eyed among you will also have noticed that each image has a different background, is captured from different angles, and also has different objects in the foreground (in some cases).
I’m sure all of this took you a fraction of a second to figure out. It doesn’t matter if the image is rotated at a weird angle or zoomed in to show only half of the Tower. This is primarily because you have seen the images of the Eiffel Tower multiple times and your memory easily recalls its features. We naturally understand that the scale or angle of the image may change but the object remains the same.
But machines have an almighty struggle with the same idea. It’s a challenge for them to identify the object in an image if we change certain things (like the angle or the scale). Here’s the good news – machines are super flexible and we can teach them to identify images at an almost human-level.
This is one of the most exciting aspects of working in [computer vision](https://courses.analyticsvidhya.com/courses/computer-vision-using-deep-learning-version2?utm_source=blog&utm_medium=detailed-guide-powerful-sift-technique-image-matching-python)!
So, in this article, we will talk about an image matching algorithm that identifies the key features from the images and is able to match these features to a new image of the same object. Let’s get rolling!
## Table of Contents
1. Introduction to SIFT
2. Constructing a Scale Space
1. Gaussian Blur
2. Difference of Gaussian
3. Keypoint Localization
1. Local Maxima/Minima
2. Keypoint Selection
4. Orientation Assignment
1. Calculate Magnitude & Orientation
2. Create Histogram of Magnitude & Orientation
5. Keypoint Descriptor
6. Feature Matching
## Introduction to SIFT
> SIFT, or Scale Invariant Feature Transform, is a feature detection algorithm in Computer Vision.
SIFT helps locate the local features in an image, commonly known as the ‘_keypoints_‘ of the image. These keypoints are scale & rotation invariant that can be used for various computer vision applications, like image matching, object detection, scene detection, etc.
We can also use the keypoints generated using SIFT as features for the image during model training. **The major advantage of SIFT features, over edge features or hog features, is that they are not affected by the size or orientation of the image.**
For example, here is another image of the Eiffel Tower along with its smaller version. The keypoints of the object in the first image are matched with the keypoints found in the second image. The same goes for two images when the object in the other image is slightly rotated. Amazing, right?
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/10/Screenshot-from-2019-10-01-16-08-16.png)
Let’s understand how these keypoints are identified and what are the techniques used to ensure the scale and rotation invariance. Broadly speaking, the entire process can be divided into 4 parts:
- **Constructing a Scale Space:** To make sure that features are scale-independent
- **Keypoint Localisation:** Identifying the suitable features or keypoints
- **Orientation Assignment:** Ensure the keypoints are rotation invariant
- **Keypoint Descriptor:** Assign a unique fingerprint to each keypoint
Finally, we can use these keypoints for feature matching!
_This article is based on the original paper by David G. Lowe. Here is the link: [Distinctive Image Features from Scale-Invariant Keypoints](https://people.eecs.berkeley.edu/~malik/cs294/lowe-ijcv04.pdf).
_
## Constructing the Scale Space
We need to identify the most distinct features in a given image while ignoring any noise. Additionally, we need to ensure that the features are not scale-dependent. These are critical concepts so let’s talk about them one-by-one.
> We use the **Gaussian Blurring technique** to reduce the noise in an image.
So, for every pixel in an image, the Gaussian Blur calculates a value based on its neighboring pixels. Below is an example of image before and after applying the Gaussian Blur. As you can see, the texture and minor details are removed from the image and only the relevant information like the shape and edges remain:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_110.png)
Gaussian Blur successfully removed the noise from the images and we have highlighted the important features of the image. Now, _we need to ensure that these features must not be scale-dependent._ This means we will be searching for these features on multiple scales, by creating a ‘scale space’.
> Scale space is a collection of images having different scales, generated from a single image.
Hence, these blur images are created for multiple scales. To create a new set of images of different scales, we will take the original image and reduce the scale by half. For each new image, we will create blur versions as we saw above.
Here is an example to understand it in a better manner. We have the original image of size (275, 183) and a scaled image of dimension (138, 92). For both the images, two blur images are created:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_21.png)
You might be thinking – how many times do we need to scale the image and how many subsequent blur images need to be created for each scaled image? **The ideal number of octaves should be four**, and for each octave, the number of blur images should be five.
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-24-18-27-46.png)
### Difference of Gaussian
So far we have created images of multiple scales (often represented by σ) and used Gaussian blur for each of them to reduce the noise in the image. Next, we will try to enhance the features using a technique called Difference of Gaussians or DoG.
> Difference of Gaussian is a feature enhancement algorithm that involves the subtraction of one blurred version of an original image from another, less blurred version of the original.
DoG creates another set of images, for each octave, by subtracting every image from the previous image in the same scale. Here is a visual explanation of how DoG is implemented:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-12-48-03.png)
_Note: The image is taken from the original paper. The octaves are now represented in a vertical form for a clearer view. _
Let us create the DoG for the images in scale space. Take a look at the below diagram. On the left, we have 5 images, all from the first octave (thus having the same scale). Each subsequent image is created by applying the Gaussian blur over the previous image.
On the right, we have four images generated by subtracting the consecutive Gaussians. The results are jaw-dropping!
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-14-18-26.png)
We have enhanced features for each of these images. Note that here I am implementing it only for the first octave but the same process happens for all the octaves.
Now that we have a new set of images, we are going to use this to find the important keypoints.
## Keypoint Localization
Once the images have been created, the next step is to find the important keypoints from the image that can be used for feature matching. **The idea is to find the local maxima and minima for the images.** This part is divided into two steps:
1. Find the local maxima and minima
2. Remove low contrast keypoints (keypoint selection)
### Local Maxima and Local Minima
> To locate the local maxima and minima, we go through every pixel in the image and compare it with its neighboring pixels.
When I say ‘neighboring’, this not only includes the surrounding pixels of that image (in which the pixel lies), but also the nine pixels for the previous and next image in the octave.
This means that every pixel value is compared with 26 other pixel values to find whether it is the local maxima/minima. For example, in the below diagram, we have three images from the first octave. The pixel marked _x_ is compared with the neighboring pixels (in green) and is selected as a keypoint if it is the highest or lowest among the neighbors:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-16-50-01.png)
We now have potential keypoints that represent the images and are scale-invariant. We will apply the last check over the selected keypoints to ensure that these are the most accurate keypoints to represent the image.
### Keypoint Selection
Kudos! So far we have successfully generated scale-invariant keypoints. But some of these keypoints may not be robust to noise. This is why we need to perform a final check to make sure that we have the most accurate keypoints to represent the image features.
**Hence, we will eliminate the keypoints that have low contrast, or lie very close to the edge.**
To deal with the low contrast keypoints, a second-order Taylor expansion is computed for each keypoint. If the resulting value is less than 0.03 (in magnitude), we reject the keypoint.
So what do we do about the remaining keypoints? Well, we perform a check to identify the poorly located keypoints. These are the keypoints that are close to the edge and have a high edge response but may not be robust to a small amount of noise. A second-order Hessian matrix is used to identify such keypoints. You can go through the math behind this here.
Now that we have performed both the contrast test and the edge test to reject the unstable keypoints, we will now assign an orientation value for each keypoint to make the rotation invariant.
## Orientation Assignment
At this stage, we have a set of stable keypoints for the images. We will now assign an orientation to each of these keypoints so that they are invariant to rotation. We can again divide this step into two smaller steps:
1. Calculate the magnitude and orientation
2. Create a histogram for magnitude and orientation
### Calculate Magnitude and Orientation
Consider the sample image shown below:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-19-22-24.png)
Let’s say we want to find the magnitude and orientation for the pixel value in red. For this, we will calculate the gradients in x and y directions by taking the difference between 55 & 46 and 56 & 42. This comes out to be Gx = 9 and Gy = 14 respectively.
Once we have the gradients, we can find the magnitude and orientation using the following formulas:
Magnitude = √\[(Gx)2+(Gy)2] = 16.64
Φ = atan(Gy / Gx) = atan(1.55) = 57.17
> The magnitude represents the intensity of the pixel and the orientation gives the direction for the same.
We can now create a histogram given that we have these magnitude and orientation values for the pixels.
### Creating a Histogram for Magnitude and Orientation
On the x-axis, we will have bins for angle values, like 0-9, 10 – 19, 20-29, up to 360. Since our angle value is 57, it will fall in the 6th bin. The 6th bin value will be in proportion to the magnitude of the pixel, i.e. 16.64. We will do this for all the pixels around the keypoint.
This is how we get the below histogram:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-26-18-53-12.png)
_You can refer to this article for a much detailed explanation for calculating the gradient, magnitude, orientation and plotting histogram –_ _[A Valuable Introduction to the Histogram of Oriented Gradients](https://www.analyticsvidhya.com/blog/2019/09/feature-engineering-images-introduction-hog-feature-descriptor/)._
This histogram would peak at some point. **The bin at which we see the peak will be the orientation for the keypoint.** Additionally, if there is another significant peak (seen between 80 – 100%), then another keypoint is generated with the magnitude and scale the same as the keypoint used to generate the histogram. And the angle or orientation will be equal to the new bin that has the peak.
Effectively at this point, we can say that there can be a small increase in the number of keypoints.
## Keypoint Descriptor
This is the final step for SIFT. So far, we have stable keypoints that are scale-invariant and rotation invariant. In this section, we will use the neighboring pixels, their orientations, and magnitude, to generate a unique fingerprint for this keypoint called a ‘descriptor’.
Additionally, since we use the surrounding pixels, the descriptors will be partially invariant to illumination or brightness of the images.
We will first take a 16×16 neighborhood around the keypoint. This 16×16 block is further divided into 4×4 sub-blocks and for each of these sub-blocks, we generate the histogram using magnitude and orientation.
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-26-20-10-52.png)
At this stage, the bin size is increased and we take only 8 bins (not 36). Each of these arrows represents the 8 bins and the length of the arrows define the magnitude. So, we will have a total of 128 bin values for every keypoint.
Here is an example:
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
| | #reading image |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | gray1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | #keypoints |
| | sift = cv2.xfeatures2d.SIFT_create() |
| | keypoints_1, descriptors_1 = sift.detectAndCompute(img1,None) |
| | img_1 = cv2.drawKeypoints(gray1,keypoints_1,img1) |
| | plt.imshow(img_1) |
[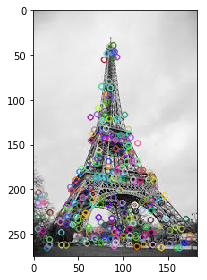
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_41.png)
## Feature Matching
We will now use the SIFT features for feature matching. For this purpose, I have downloaded two images of the Eiffel Tower, taken from different positions. You can try it with any two images that you want.
Here are the two images that I have used:
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
\| \| # read images |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | img2 = cv2.imread('eiffel_1.jpg') |
| | img1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | img2 = cv2.cvtColor(img2, cv2.COLOR_BGR2GRAY) |
| | figure, ax = plt.subplots(1, 2, figsize=(16, 8)) |
| | ax\[0].imshow(img1, cmap='gray') |
| | ax\[1].imshow(img2, cmap='gray') |
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_71.png)
Now, for both these images, we are going to generate the SIFT features. First, we have to construct a SIFT object and then use the function _detectAndCompute_ to get the keypoints. It will return two values – the keypoints and the descriptors.
Let’s determine the keypoints and print the total number of keypoints found in each image:
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
\| \| # read images |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | img2 = cv2.imread('eiffel_1.jpg') |
| | img1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | img2 = cv2.cvtColor(img2, cv2.COLOR_BGR2GRAY) |
| | #sift |
| | sift = cv2.xfeatures2d.SIFT_create() |
| | keypoints_1, descriptors_1 = sift.detectAndCompute(img1,None) |
| | keypoints_2, descriptors_2 = sift.detectAndCompute(img2,None) |
| | len(keypoints_1), len(keypoints_2) |
283, 540
Next, let’s try and match the features from image 1 with features from image 2. We will be using the function _match()_ from the _BFmatcher_ (brute force match) module. Also, we will draw lines between the features that match in both the images. This can be done using the _drawMatches_ function in OpenCV.
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
\| \| # read images |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | img2 = cv2.imread('eiffel_1.jpg') |
| | img1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | img2 = cv2.cvtColor(img2, cv2.COLOR_BGR2GRAY) |
| | #sift |
| | sift = cv2.xfeatures2d.SIFT_create() |
| | keypoints_1, descriptors_1 = sift.detectAndCompute(img1,None) |
| | keypoints_2, descriptors_2 = sift.detectAndCompute(img2,None) |
| | #feature matching |
| | bf = cv2.BFMatcher(cv2.NORM_L1, crossCheck=True) |
| | matches = bf.match(descriptors_1,descriptors_2) |
| | matches = sorted(matches, key = lambda x:x.distance) |
| | img3 = cv2.drawMatches(img1, keypoints_1, img2, keypoints_2, matches\[:50], img2, flags=2) |
| | plt.imshow(img3),plt.show() |
[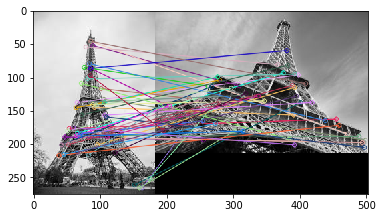
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_61.png)I have plotted only 50 matches here for clarity’s sake. You can increase the number according to what you prefer. To find out how many keypoints are matched, we can print the length of the variable _matches_. In this case, the answer would be 190.
## End Notes
In this article, we discussed the SIFT feature matching algorithm in detail. Here is a site that provides excellent visualization for each step of SIFT. You can add your own image and it will create the keypoints for that image as well. Check it out [here](http://weitz.de/sift/).
Another popular feature matching algorithm is SURF (Speeded Up Robust Feature), which is simply a faster version of SIFT. I would encourage you to go ahead and explore it as well.
And if you’re new to the world of computer vision and image data, I recommend checking out the below course:
- [Computer Vision using Deep Learning 2.0](https://courses.analyticsvidhya.com/courses/computer-vision-using-deep-learning-version2?utm_source=blog&utm_medium=detailed-guide-powerful-sift-technique-image-matching-python)
You can also read this article on our Mobile APP [
](https://play.google.com/store/apps/details?id=com.analyticsvidhya.android&utm_source=blog_article&utm_campaign=blog&pcampaignid=MKT-Other-global-all-co-prtnr-py-PartBadge-Mar2515-1)[
](https://apps.apple.com/us/app/analytics-vidhya/id1470025572)
### Related Articles
[https://www.analyticsvidhya.com/blog/2019/10/detailed-guide-powerful-sift-technique-image-matching-python/](https://www.analyticsvidhya.com/blog/2019/10/detailed-guide-powerful-sift-technique-image-matching-python/)
| 1.0 | SIFT | How To Use SIFT For Image Matching In Python - ## Overview
- A beginner-friendly introduction to the powerful SIFT (Scale Invariant Feature Transform) technique
- Learn how to perform Feature Matching using SIFT
- We also showcase SIFT in Python through hands-on coding
## Introduction
Take a look at the below collection of images and think of the common element between them:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-20-17-49-55.png)
The resplendent Eiffel Tower, of course! The keen-eyed among you will also have noticed that each image has a different background, is captured from different angles, and also has different objects in the foreground (in some cases).
I’m sure all of this took you a fraction of a second to figure out. It doesn’t matter if the image is rotated at a weird angle or zoomed in to show only half of the Tower. This is primarily because you have seen the images of the Eiffel Tower multiple times and your memory easily recalls its features. We naturally understand that the scale or angle of the image may change but the object remains the same.
But machines have an almighty struggle with the same idea. It’s a challenge for them to identify the object in an image if we change certain things (like the angle or the scale). Here’s the good news – machines are super flexible and we can teach them to identify images at an almost human-level.
This is one of the most exciting aspects of working in [computer vision](https://courses.analyticsvidhya.com/courses/computer-vision-using-deep-learning-version2?utm_source=blog&utm_medium=detailed-guide-powerful-sift-technique-image-matching-python)!
So, in this article, we will talk about an image matching algorithm that identifies the key features from the images and is able to match these features to a new image of the same object. Let’s get rolling!
## Table of Contents
1. Introduction to SIFT
2. Constructing a Scale Space
1. Gaussian Blur
2. Difference of Gaussian
3. Keypoint Localization
1. Local Maxima/Minima
2. Keypoint Selection
4. Orientation Assignment
1. Calculate Magnitude & Orientation
2. Create Histogram of Magnitude & Orientation
5. Keypoint Descriptor
6. Feature Matching
## Introduction to SIFT
> SIFT, or Scale Invariant Feature Transform, is a feature detection algorithm in Computer Vision.
SIFT helps locate the local features in an image, commonly known as the ‘_keypoints_‘ of the image. These keypoints are scale & rotation invariant that can be used for various computer vision applications, like image matching, object detection, scene detection, etc.
We can also use the keypoints generated using SIFT as features for the image during model training. **The major advantage of SIFT features, over edge features or hog features, is that they are not affected by the size or orientation of the image.**
For example, here is another image of the Eiffel Tower along with its smaller version. The keypoints of the object in the first image are matched with the keypoints found in the second image. The same goes for two images when the object in the other image is slightly rotated. Amazing, right?
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/10/Screenshot-from-2019-10-01-16-08-16.png)
Let’s understand how these keypoints are identified and what are the techniques used to ensure the scale and rotation invariance. Broadly speaking, the entire process can be divided into 4 parts:
- **Constructing a Scale Space:** To make sure that features are scale-independent
- **Keypoint Localisation:** Identifying the suitable features or keypoints
- **Orientation Assignment:** Ensure the keypoints are rotation invariant
- **Keypoint Descriptor:** Assign a unique fingerprint to each keypoint
Finally, we can use these keypoints for feature matching!
_This article is based on the original paper by David G. Lowe. Here is the link: [Distinctive Image Features from Scale-Invariant Keypoints](https://people.eecs.berkeley.edu/~malik/cs294/lowe-ijcv04.pdf).
_
## Constructing the Scale Space
We need to identify the most distinct features in a given image while ignoring any noise. Additionally, we need to ensure that the features are not scale-dependent. These are critical concepts so let’s talk about them one-by-one.
> We use the **Gaussian Blurring technique** to reduce the noise in an image.
So, for every pixel in an image, the Gaussian Blur calculates a value based on its neighboring pixels. Below is an example of image before and after applying the Gaussian Blur. As you can see, the texture and minor details are removed from the image and only the relevant information like the shape and edges remain:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_110.png)
Gaussian Blur successfully removed the noise from the images and we have highlighted the important features of the image. Now, _we need to ensure that these features must not be scale-dependent._ This means we will be searching for these features on multiple scales, by creating a ‘scale space’.
> Scale space is a collection of images having different scales, generated from a single image.
Hence, these blur images are created for multiple scales. To create a new set of images of different scales, we will take the original image and reduce the scale by half. For each new image, we will create blur versions as we saw above.
Here is an example to understand it in a better manner. We have the original image of size (275, 183) and a scaled image of dimension (138, 92). For both the images, two blur images are created:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_21.png)
You might be thinking – how many times do we need to scale the image and how many subsequent blur images need to be created for each scaled image? **The ideal number of octaves should be four**, and for each octave, the number of blur images should be five.
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-24-18-27-46.png)
### Difference of Gaussian
So far we have created images of multiple scales (often represented by σ) and used Gaussian blur for each of them to reduce the noise in the image. Next, we will try to enhance the features using a technique called Difference of Gaussians or DoG.
> Difference of Gaussian is a feature enhancement algorithm that involves the subtraction of one blurred version of an original image from another, less blurred version of the original.
DoG creates another set of images, for each octave, by subtracting every image from the previous image in the same scale. Here is a visual explanation of how DoG is implemented:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-12-48-03.png)
_Note: The image is taken from the original paper. The octaves are now represented in a vertical form for a clearer view. _
Let us create the DoG for the images in scale space. Take a look at the below diagram. On the left, we have 5 images, all from the first octave (thus having the same scale). Each subsequent image is created by applying the Gaussian blur over the previous image.
On the right, we have four images generated by subtracting the consecutive Gaussians. The results are jaw-dropping!
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-14-18-26.png)
We have enhanced features for each of these images. Note that here I am implementing it only for the first octave but the same process happens for all the octaves.
Now that we have a new set of images, we are going to use this to find the important keypoints.
## Keypoint Localization
Once the images have been created, the next step is to find the important keypoints from the image that can be used for feature matching. **The idea is to find the local maxima and minima for the images.** This part is divided into two steps:
1. Find the local maxima and minima
2. Remove low contrast keypoints (keypoint selection)
### Local Maxima and Local Minima
> To locate the local maxima and minima, we go through every pixel in the image and compare it with its neighboring pixels.
When I say ‘neighboring’, this not only includes the surrounding pixels of that image (in which the pixel lies), but also the nine pixels for the previous and next image in the octave.
This means that every pixel value is compared with 26 other pixel values to find whether it is the local maxima/minima. For example, in the below diagram, we have three images from the first octave. The pixel marked _x_ is compared with the neighboring pixels (in green) and is selected as a keypoint if it is the highest or lowest among the neighbors:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-16-50-01.png)
We now have potential keypoints that represent the images and are scale-invariant. We will apply the last check over the selected keypoints to ensure that these are the most accurate keypoints to represent the image.
### Keypoint Selection
Kudos! So far we have successfully generated scale-invariant keypoints. But some of these keypoints may not be robust to noise. This is why we need to perform a final check to make sure that we have the most accurate keypoints to represent the image features.
**Hence, we will eliminate the keypoints that have low contrast, or lie very close to the edge.**
To deal with the low contrast keypoints, a second-order Taylor expansion is computed for each keypoint. If the resulting value is less than 0.03 (in magnitude), we reject the keypoint.
So what do we do about the remaining keypoints? Well, we perform a check to identify the poorly located keypoints. These are the keypoints that are close to the edge and have a high edge response but may not be robust to a small amount of noise. A second-order Hessian matrix is used to identify such keypoints. You can go through the math behind this here.
Now that we have performed both the contrast test and the edge test to reject the unstable keypoints, we will now assign an orientation value for each keypoint to make the rotation invariant.
## Orientation Assignment
At this stage, we have a set of stable keypoints for the images. We will now assign an orientation to each of these keypoints so that they are invariant to rotation. We can again divide this step into two smaller steps:
1. Calculate the magnitude and orientation
2. Create a histogram for magnitude and orientation
### Calculate Magnitude and Orientation
Consider the sample image shown below:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-25-19-22-24.png)
Let’s say we want to find the magnitude and orientation for the pixel value in red. For this, we will calculate the gradients in x and y directions by taking the difference between 55 & 46 and 56 & 42. This comes out to be Gx = 9 and Gy = 14 respectively.
Once we have the gradients, we can find the magnitude and orientation using the following formulas:
Magnitude = √\[(Gx)2+(Gy)2] = 16.64
Φ = atan(Gy / Gx) = atan(1.55) = 57.17
> The magnitude represents the intensity of the pixel and the orientation gives the direction for the same.
We can now create a histogram given that we have these magnitude and orientation values for the pixels.
### Creating a Histogram for Magnitude and Orientation
On the x-axis, we will have bins for angle values, like 0-9, 10 – 19, 20-29, up to 360. Since our angle value is 57, it will fall in the 6th bin. The 6th bin value will be in proportion to the magnitude of the pixel, i.e. 16.64. We will do this for all the pixels around the keypoint.
This is how we get the below histogram:
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-26-18-53-12.png)
_You can refer to this article for a much detailed explanation for calculating the gradient, magnitude, orientation and plotting histogram –_ _[A Valuable Introduction to the Histogram of Oriented Gradients](https://www.analyticsvidhya.com/blog/2019/09/feature-engineering-images-introduction-hog-feature-descriptor/)._
This histogram would peak at some point. **The bin at which we see the peak will be the orientation for the keypoint.** Additionally, if there is another significant peak (seen between 80 – 100%), then another keypoint is generated with the magnitude and scale the same as the keypoint used to generate the histogram. And the angle or orientation will be equal to the new bin that has the peak.
Effectively at this point, we can say that there can be a small increase in the number of keypoints.
## Keypoint Descriptor
This is the final step for SIFT. So far, we have stable keypoints that are scale-invariant and rotation invariant. In this section, we will use the neighboring pixels, their orientations, and magnitude, to generate a unique fingerprint for this keypoint called a ‘descriptor’.
Additionally, since we use the surrounding pixels, the descriptors will be partially invariant to illumination or brightness of the images.
We will first take a 16×16 neighborhood around the keypoint. This 16×16 block is further divided into 4×4 sub-blocks and for each of these sub-blocks, we generate the histogram using magnitude and orientation.
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/Screenshot-from-2019-09-26-20-10-52.png)
At this stage, the bin size is increased and we take only 8 bins (not 36). Each of these arrows represents the 8 bins and the length of the arrows define the magnitude. So, we will have a total of 128 bin values for every keypoint.
Here is an example:
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
| | #reading image |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | gray1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | #keypoints |
| | sift = cv2.xfeatures2d.SIFT_create() |
| | keypoints_1, descriptors_1 = sift.detectAndCompute(img1,None) |
| | img_1 = cv2.drawKeypoints(gray1,keypoints_1,img1) |
| | plt.imshow(img_1) |
[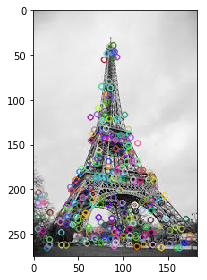
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_41.png)
## Feature Matching
We will now use the SIFT features for feature matching. For this purpose, I have downloaded two images of the Eiffel Tower, taken from different positions. You can try it with any two images that you want.
Here are the two images that I have used:
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
\| \| # read images |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | img2 = cv2.imread('eiffel_1.jpg') |
| | img1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | img2 = cv2.cvtColor(img2, cv2.COLOR_BGR2GRAY) |
| | figure, ax = plt.subplots(1, 2, figsize=(16, 8)) |
| | ax\[0].imshow(img1, cmap='gray') |
| | ax\[1].imshow(img2, cmap='gray') |
[
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_71.png)
Now, for both these images, we are going to generate the SIFT features. First, we have to construct a SIFT object and then use the function _detectAndCompute_ to get the keypoints. It will return two values – the keypoints and the descriptors.
Let’s determine the keypoints and print the total number of keypoints found in each image:
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
\| \| # read images |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | img2 = cv2.imread('eiffel_1.jpg') |
| | img1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | img2 = cv2.cvtColor(img2, cv2.COLOR_BGR2GRAY) |
| | #sift |
| | sift = cv2.xfeatures2d.SIFT_create() |
| | keypoints_1, descriptors_1 = sift.detectAndCompute(img1,None) |
| | keypoints_2, descriptors_2 = sift.detectAndCompute(img2,None) |
| | len(keypoints_1), len(keypoints_2) |
283, 540
Next, let’s try and match the features from image 1 with features from image 2. We will be using the function _match()_ from the _BFmatcher_ (brute force match) module. Also, we will draw lines between the features that match in both the images. This can be done using the _drawMatches_ function in OpenCV.
| | import cv2 |
| | import matplotlib.pyplot as plt |
| | %matplotlib inline |
\| \| # read images |
| | img1 = cv2.imread('eiffel_2.jpeg') |
| | img2 = cv2.imread('eiffel_1.jpg') |
| | img1 = cv2.cvtColor(img1, cv2.COLOR_BGR2GRAY) |
| | img2 = cv2.cvtColor(img2, cv2.COLOR_BGR2GRAY) |
| | #sift |
| | sift = cv2.xfeatures2d.SIFT_create() |
| | keypoints_1, descriptors_1 = sift.detectAndCompute(img1,None) |
| | keypoints_2, descriptors_2 = sift.detectAndCompute(img2,None) |
| | #feature matching |
| | bf = cv2.BFMatcher(cv2.NORM_L1, crossCheck=True) |
| | matches = bf.match(descriptors_1,descriptors_2) |
| | matches = sorted(matches, key = lambda x:x.distance) |
| | img3 = cv2.drawMatches(img1, keypoints_1, img2, keypoints_2, matches\[:50], img2, flags=2) |
| | plt.imshow(img3),plt.show() |
[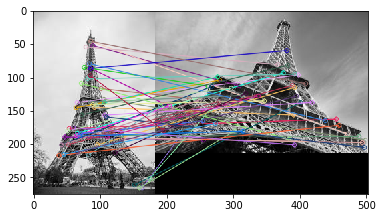
](https://cdn.analyticsvidhya.com/wp-content/uploads/2019/09/index_61.png)I have plotted only 50 matches here for clarity’s sake. You can increase the number according to what you prefer. To find out how many keypoints are matched, we can print the length of the variable _matches_. In this case, the answer would be 190.
## End Notes
In this article, we discussed the SIFT feature matching algorithm in detail. Here is a site that provides excellent visualization for each step of SIFT. You can add your own image and it will create the keypoints for that image as well. Check it out [here](http://weitz.de/sift/).
Another popular feature matching algorithm is SURF (Speeded Up Robust Feature), which is simply a faster version of SIFT. I would encourage you to go ahead and explore it as well.
And if you’re new to the world of computer vision and image data, I recommend checking out the below course:
- [Computer Vision using Deep Learning 2.0](https://courses.analyticsvidhya.com/courses/computer-vision-using-deep-learning-version2?utm_source=blog&utm_medium=detailed-guide-powerful-sift-technique-image-matching-python)
You can also read this article on our Mobile APP [
](https://play.google.com/store/apps/details?id=com.analyticsvidhya.android&utm_source=blog_article&utm_campaign=blog&pcampaignid=MKT-Other-global-all-co-prtnr-py-PartBadge-Mar2515-1)[
](https://apps.apple.com/us/app/analytics-vidhya/id1470025572)
### Related Articles
[https://www.analyticsvidhya.com/blog/2019/10/detailed-guide-powerful-sift-technique-image-matching-python/](https://www.analyticsvidhya.com/blog/2019/10/detailed-guide-powerful-sift-technique-image-matching-python/)
| test | sift how to use sift for image matching in python overview a beginner friendly introduction to the powerful sift scale invariant feature transform technique learn how to perform feature matching using sift we also showcase sift in python through hands on coding introduction take a look at the below collection of images and think of the common element between them the resplendent eiffel tower of course the keen eyed among you will also have noticed that each image has a different background is captured from different angles and also has different objects in the foreground in some cases i’m sure all of this took you a fraction of a second to figure out it doesn’t matter if the image is rotated at a weird angle or zoomed in to show only half of the tower this is primarily because you have seen the images of the eiffel tower multiple times and your memory easily recalls its features we naturally understand that the scale or angle of the image may change but the object remains the same but machines have an almighty struggle with the same idea it’s a challenge for them to identify the object in an image if we change certain things like the angle or the scale here’s the good news – machines are super flexible and we can teach them to identify images at an almost human level this is one of the most exciting aspects of working in so in this article we will talk about an image matching algorithm that identifies the key features from the images and is able to match these features to a new image of the same object let’s get rolling table of contents introduction to sift constructing a scale space gaussian blur difference of gaussian keypoint localization local maxima minima keypoint selection orientation assignment calculate magnitude orientation create histogram of magnitude orientation keypoint descriptor feature matching introduction to sift sift or scale invariant feature transform is a feature detection algorithm in computer vision sift helps locate the local features in an image commonly known as the ‘ keypoints ‘ of the image these keypoints are scale rotation invariant that can be used for various computer vision applications like image matching object detection scene detection etc we can also use the keypoints generated using sift as features for the image during model training the major advantage of sift features over edge features or hog features is that they are not affected by the size or orientation of the image for example here is another image of the eiffel tower along with its smaller version the keypoints of the object in the first image are matched with the keypoints found in the second image the same goes for two images when the object in the other image is slightly rotated amazing right let’s understand how these keypoints are identified and what are the techniques used to ensure the scale and rotation invariance broadly speaking the entire process can be divided into parts constructing a scale space to make sure that features are scale independent keypoint localisation identifying the suitable features or keypoints orientation assignment ensure the keypoints are rotation invariant keypoint descriptor assign a unique fingerprint to each keypoint finally we can use these keypoints for feature matching this article is based on the original paper by david g lowe here is the link constructing the scale space we need to identify the most distinct features in a given image while ignoring any noise additionally we need to ensure that the features are not scale dependent these are critical concepts so let’s talk about them one by one we use the gaussian blurring technique to reduce the noise in an image so for every pixel in an image the gaussian blur calculates a value based on its neighboring pixels below is an example of image before and after applying the gaussian blur as you can see the texture and minor details are removed from the image and only the relevant information like the shape and edges remain gaussian blur successfully removed the noise from the images and we have highlighted the important features of the image now we need to ensure that these features must not be scale dependent this means we will be searching for these features on multiple scales by creating a ‘scale space’ scale space is a collection of images having different scales generated from a single image hence these blur images are created for multiple scales to create a new set of images of different scales we will take the original image and reduce the scale by half for each new image we will create blur versions as we saw above here is an example to understand it in a better manner we have the original image of size and a scaled image of dimension for both the images two blur images are created you might be thinking – how many times do we need to scale the image and how many subsequent blur images need to be created for each scaled image the ideal number of octaves should be four and for each octave the number of blur images should be five difference of gaussian so far we have created images of multiple scales often represented by σ and used gaussian blur for each of them to reduce the noise in the image next we will try to enhance the features using a technique called difference of gaussians or dog difference of gaussian is a feature enhancement algorithm that involves the subtraction of one blurred version of an original image from another less blurred version of the original dog creates another set of images for each octave by subtracting every image from the previous image in the same scale here is a visual explanation of how dog is implemented note the image is taken from the original paper the octaves are now represented in a vertical form for a clearer view let us create the dog for the images in scale space take a look at the below diagram on the left we have images all from the first octave thus having the same scale each subsequent image is created by applying the gaussian blur over the previous image on the right we have four images generated by subtracting the consecutive gaussians the results are jaw dropping we have enhanced features for each of these images note that here i am implementing it only for the first octave but the same process happens for all the octaves now that we have a new set of images we are going to use this to find the important keypoints keypoint localization once the images have been created the next step is to find the important keypoints from the image that can be used for feature matching the idea is to find the local maxima and minima for the images this part is divided into two steps find the local maxima and minima remove low contrast keypoints keypoint selection local maxima and local minima to locate the local maxima and minima we go through every pixel in the image and compare it with its neighboring pixels when i say ‘neighboring’ this not only includes the surrounding pixels of that image in which the pixel lies but also the nine pixels for the previous and next image in the octave this means that every pixel value is compared with other pixel values to find whether it is the local maxima minima for example in the below diagram we have three images from the first octave the pixel marked x is compared with the neighboring pixels in green and is selected as a keypoint if it is the highest or lowest among the neighbors we now have potential keypoints that represent the images and are scale invariant we will apply the last check over the selected keypoints to ensure that these are the most accurate keypoints to represent the image keypoint selection kudos so far we have successfully generated scale invariant keypoints but some of these keypoints may not be robust to noise this is why we need to perform a final check to make sure that we have the most accurate keypoints to represent the image features hence we will eliminate the keypoints that have low contrast or lie very close to the edge to deal with the low contrast keypoints a second order taylor expansion is computed for each keypoint if the resulting value is less than in magnitude we reject the keypoint so what do we do about the remaining keypoints well we perform a check to identify the poorly located keypoints these are the keypoints that are close to the edge and have a high edge response but may not be robust to a small amount of noise a second order hessian matrix is used to identify such keypoints you can go through the math behind this here now that we have performed both the contrast test and the edge test to reject the unstable keypoints we will now assign an orientation value for each keypoint to make the rotation invariant orientation assignment at this stage we have a set of stable keypoints for the images we will now assign an orientation to each of these keypoints so that they are invariant to rotation we can again divide this step into two smaller steps calculate the magnitude and orientation create a histogram for magnitude and orientation calculate magnitude and orientation consider the sample image shown below let’s say we want to find the magnitude and orientation for the pixel value in red for this we will calculate the gradients in x and y directions by taking the difference between and this comes out to be gx and gy respectively once we have the gradients we can find the magnitude and orientation using the following formulas magnitude √ φ atan gy gx atan the magnitude represents the intensity of the pixel and the orientation gives the direction for the same we can now create a histogram given that we have these magnitude and orientation values for the pixels creating a histogram for magnitude and orientation on the x axis we will have bins for angle values like – up to since our angle value is it will fall in the bin the bin value will be in proportion to the magnitude of the pixel i e we will do this for all the pixels around the keypoint this is how we get the below histogram you can refer to this article for a much detailed explanation for calculating the gradient magnitude orientation and plotting histogram – this histogram would peak at some point the bin at which we see the peak will be the orientation for the keypoint additionally if there is another significant peak seen between – then another keypoint is generated with the magnitude and scale the same as the keypoint used to generate the histogram and the angle or orientation will be equal to the new bin that has the peak effectively at this point we can say that there can be a small increase in the number of keypoints keypoint descriptor this is the final step for sift so far we have stable keypoints that are scale invariant and rotation invariant in this section we will use the neighboring pixels their orientations and magnitude to generate a unique fingerprint for this keypoint called a ‘descriptor’ additionally since we use the surrounding pixels the descriptors will be partially invariant to illumination or brightness of the images we will first take a × neighborhood around the keypoint this × block is further divided into × sub blocks and for each of these sub blocks we generate the histogram using magnitude and orientation at this stage the bin size is increased and we take only bins not each of these arrows represents the bins and the length of the arrows define the magnitude so we will have a total of bin values for every keypoint here is an example import import matplotlib pyplot as plt matplotlib inline reading image imread eiffel jpeg cvtcolor color keypoints sift sift create keypoints descriptors sift detectandcompute none img drawkeypoints keypoints plt imshow img feature matching we will now use the sift features for feature matching for this purpose i have downloaded two images of the eiffel tower taken from different positions you can try it with any two images that you want here are the two images that i have used import import matplotlib pyplot as plt matplotlib inline read images imread eiffel jpeg imread eiffel jpg cvtcolor color cvtcolor color figure ax plt subplots figsize ax imshow cmap gray ax imshow cmap gray now for both these images we are going to generate the sift features first we have to construct a sift object and then use the function detectandcompute to get the keypoints it will return two values – the keypoints and the descriptors let’s determine the keypoints and print the total number of keypoints found in each image import import matplotlib pyplot as plt matplotlib inline read images imread eiffel jpeg imread eiffel jpg cvtcolor color cvtcolor color sift sift sift create keypoints descriptors sift detectandcompute none keypoints descriptors sift detectandcompute none len keypoints len keypoints next let’s try and match the features from image with features from image we will be using the function match from the bfmatcher brute force match module also we will draw lines between the features that match in both the images this can be done using the drawmatches function in opencv import import matplotlib pyplot as plt matplotlib inline read images imread eiffel jpeg imread eiffel jpg cvtcolor color cvtcolor color sift sift sift create keypoints descriptors sift detectandcompute none keypoints descriptors sift detectandcompute none feature matching bf bfmatcher norm crosscheck true matches bf match descriptors descriptors matches sorted matches key lambda x x distance drawmatches keypoints keypoints matches flags plt imshow plt show have plotted only matches here for clarity’s sake you can increase the number according to what you prefer to find out how many keypoints are matched we can print the length of the variable matches in this case the answer would be end notes in this article we discussed the sift feature matching algorithm in detail here is a site that provides excellent visualization for each step of sift you can add your own image and it will create the keypoints for that image as well check it out another popular feature matching algorithm is surf speeded up robust feature which is simply a faster version of sift i would encourage you to go ahead and explore it as well and if you’re new to the world of computer vision and image data i recommend checking out the below course you can also read this article on our mobile app related articles | 1 |
158,021 | 12,398,409,043 | IssuesEvent | 2020-05-21 01:46:42 | kubernetes/kubernetes | https://api.github.com/repos/kubernetes/kubernetes | reopened | Add Conformance kubectl test for cluster urls not in the form of <ip>:<port> | area/conformance kind/feature sig/testing | **What would you like to be added**:
kubectl supports a "server" argument where the value could be a base URL/IP address (<ip_addr>:443) or an URL with a path attached (<ip_addr>:443/clusterA). Our e2e tests rely on the former scheme, and we have no e2e tests testing the latter.
kubectl already has a unit test for the "<ip_addr>:443/clusterA" format (https://github.com/kubernetes/kubernetes/blob/master/staging/src/k8s.io/kubectl/pkg/cmd/config/config_test.go#L165)
It'd be beneficial to have this as a Conformance test.
**Why is this needed**:
This is useful in scenarios where the master is behind a load balancer, and cannot be represented via a base URL/IP address. Even though this currently works out of the box, it'd be useful having a Conformance test to validate this.
/sig testing
/area conformance
/cc @johnbelamaric
/cc @ianchakeres | 1.0 | Add Conformance kubectl test for cluster urls not in the form of <ip>:<port> - **What would you like to be added**:
kubectl supports a "server" argument where the value could be a base URL/IP address (<ip_addr>:443) or an URL with a path attached (<ip_addr>:443/clusterA). Our e2e tests rely on the former scheme, and we have no e2e tests testing the latter.
kubectl already has a unit test for the "<ip_addr>:443/clusterA" format (https://github.com/kubernetes/kubernetes/blob/master/staging/src/k8s.io/kubectl/pkg/cmd/config/config_test.go#L165)
It'd be beneficial to have this as a Conformance test.
**Why is this needed**:
This is useful in scenarios where the master is behind a load balancer, and cannot be represented via a base URL/IP address. Even though this currently works out of the box, it'd be useful having a Conformance test to validate this.
/sig testing
/area conformance
/cc @johnbelamaric
/cc @ianchakeres | test | add conformance kubectl test for cluster urls not in the form of what would you like to be added kubectl supports a server argument where the value could be a base url ip address or an url with a path attached clustera our tests rely on the former scheme and we have no tests testing the latter kubectl already has a unit test for the clustera format it d be beneficial to have this as a conformance test why is this needed this is useful in scenarios where the master is behind a load balancer and cannot be represented via a base url ip address even though this currently works out of the box it d be useful having a conformance test to validate this sig testing area conformance cc johnbelamaric cc ianchakeres | 1 |
143,904 | 11,583,316,842 | IssuesEvent | 2020-02-22 10:07:51 | IntellectualSites/FastAsyncWorldEdit | https://api.github.com/repos/IntellectualSites/FastAsyncWorldEdit | opened | Exception on startup | Requires Testing | # Bug report for FastAsyncWorldEdit 1.14.4
<!--- If you are using 1.13 or 1.13.1 consider updating to 1.14.4 before raising an issue -->
<!--- The priority lays on 1.14 right now, so issues reported for 1.13 will be fixed for the 1.14 versions -->
<!--- In order to create a valid issue report you have to follow this template. -->
<!--- Remove this template if making a suggestion or asking a question. -->
<!--- Incomplete reports will most likely be marked as invalid, and closed, with few exceptions.-->
**[REQUIRED] FastAsyncWorldEdit Configuration Files:**
<!--- Issue /fawe debugpaste in game or in your console and copy the supplied URL here -->
<!--- If you cannot perform the above, we require logs/latest.log; config.yml and config-legacy.yml -->
<!--- If you are unwilling to supply the information we need, we reserve the right to not assist you. Redact IP addresses if you need to. -->
Not needed
**[REQUIRED] FastAsyncWorldEdit Version Number:**
<!--- Enter /fawe version in game or in your console and copy the full output here -->
Build #91 (currently latest)
**[REQUIRED] Spigot/Paper Version Number:**
<!--- Enter /version ingame or in your console and paste the full output here -->
Paper git-paper-243 (1.14.4)
**[REQUIRED] Description of the problem:**
<!--- Check your console for errors while testing -->
<!--- Include relevant information like errors or a picture of the problem -->
<!--- Be as specific as possible. Don't lie, redact information, or use false names/situations. -->
<!--- Who, What, When, Where, Why, How, Expected behavior, Resultant behavior, etc -->
Once the plugin is loaded, an exception is peintes in the logs. Nothing important, It's just missing a try-catch around the setupPlotSquared() call. If the plugin isn't present, an exception is thrown. Doesn't break anything but still logs.
**How to replicate**:
<!--- If you can reproduce the issue please tell us as detailed as possible step by step how to do that -->
Start a server with FAWE and without PlotSquared and wait for it to be fully loaded.
**Plugins being used on the server:**
<!--- Optional but recommended - issue "/plugins" in-game or in console and copy/paste the list -->
Confidential, but only using FAWE / FAVS and not PlotSquared.
**Checklist**:
<!--- Make sure you've completed the following steps (put an "X" between of brackets): -->
- [X] I included all information required in the sections above
- [X] I made sure there are no duplicates of this report [(Use Search)](https://github.com/IntellectualSites/FastAsyncWorldEdit-1.13/issues?utf8=%E2%9C%93&q=is%3Aissue)
- [X] I made sure I am using an up-to-date version of [FastAsyncWorldEdit for 1.14.4](https://ci.athion.net/job/FastAsyncWorldEdit-pipeline/)
- [X] I made sure the bug/error is not caused by any other plugin
| 1.0 | Exception on startup - # Bug report for FastAsyncWorldEdit 1.14.4
<!--- If you are using 1.13 or 1.13.1 consider updating to 1.14.4 before raising an issue -->
<!--- The priority lays on 1.14 right now, so issues reported for 1.13 will be fixed for the 1.14 versions -->
<!--- In order to create a valid issue report you have to follow this template. -->
<!--- Remove this template if making a suggestion or asking a question. -->
<!--- Incomplete reports will most likely be marked as invalid, and closed, with few exceptions.-->
**[REQUIRED] FastAsyncWorldEdit Configuration Files:**
<!--- Issue /fawe debugpaste in game or in your console and copy the supplied URL here -->
<!--- If you cannot perform the above, we require logs/latest.log; config.yml and config-legacy.yml -->
<!--- If you are unwilling to supply the information we need, we reserve the right to not assist you. Redact IP addresses if you need to. -->
Not needed
**[REQUIRED] FastAsyncWorldEdit Version Number:**
<!--- Enter /fawe version in game or in your console and copy the full output here -->
Build #91 (currently latest)
**[REQUIRED] Spigot/Paper Version Number:**
<!--- Enter /version ingame or in your console and paste the full output here -->
Paper git-paper-243 (1.14.4)
**[REQUIRED] Description of the problem:**
<!--- Check your console for errors while testing -->
<!--- Include relevant information like errors or a picture of the problem -->
<!--- Be as specific as possible. Don't lie, redact information, or use false names/situations. -->
<!--- Who, What, When, Where, Why, How, Expected behavior, Resultant behavior, etc -->
Once the plugin is loaded, an exception is peintes in the logs. Nothing important, It's just missing a try-catch around the setupPlotSquared() call. If the plugin isn't present, an exception is thrown. Doesn't break anything but still logs.
**How to replicate**:
<!--- If you can reproduce the issue please tell us as detailed as possible step by step how to do that -->
Start a server with FAWE and without PlotSquared and wait for it to be fully loaded.
**Plugins being used on the server:**
<!--- Optional but recommended - issue "/plugins" in-game or in console and copy/paste the list -->
Confidential, but only using FAWE / FAVS and not PlotSquared.
**Checklist**:
<!--- Make sure you've completed the following steps (put an "X" between of brackets): -->
- [X] I included all information required in the sections above
- [X] I made sure there are no duplicates of this report [(Use Search)](https://github.com/IntellectualSites/FastAsyncWorldEdit-1.13/issues?utf8=%E2%9C%93&q=is%3Aissue)
- [X] I made sure I am using an up-to-date version of [FastAsyncWorldEdit for 1.14.4](https://ci.athion.net/job/FastAsyncWorldEdit-pipeline/)
- [X] I made sure the bug/error is not caused by any other plugin
| test | exception on startup bug report for fastasyncworldedit fastasyncworldedit configuration files not needed fastasyncworldedit version number build currently latest spigot paper version number paper git paper description of the problem once the plugin is loaded an exception is peintes in the logs nothing important it s just missing a try catch around the setupplotsquared call if the plugin isn t present an exception is thrown doesn t break anything but still logs how to replicate start a server with fawe and without plotsquared and wait for it to be fully loaded plugins being used on the server confidential but only using fawe favs and not plotsquared checklist i included all information required in the sections above i made sure there are no duplicates of this report i made sure i am using an up to date version of i made sure the bug error is not caused by any other plugin | 1 |
275,561 | 30,263,069,196 | IssuesEvent | 2023-07-07 09:40:17 | amaybaum-dev/BenchmarkJava | https://api.github.com/repos/amaybaum-dev/BenchmarkJava | opened | bootstrap-3.3.4.js: 6 vulnerabilities (highest severity is: 6.1) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.4.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | True | bootstrap-3.3.4.js: 6 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.3.4.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (bootstrap version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-8331](https://www.mend.io/vulnerability-database/CVE-2019-8331) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1 | ❌ |
| [CVE-2018-14040](https://www.mend.io/vulnerability-database/CVE-2018-14040) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2018-20677](https://www.mend.io/vulnerability-database/CVE-2018-20677) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0 | ❌ |
| [CVE-2018-20676](https://www.mend.io/vulnerability-database/CVE-2018-20676) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | bootstrap - 3.4.0 | ❌ |
| [CVE-2018-14042](https://www.mend.io/vulnerability-database/CVE-2018-14042) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0 | ❌ |
| [CVE-2016-10735](https://www.mend.io/vulnerability-database/CVE-2016-10735) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium | 6.1 | bootstrap-3.3.4.js | Direct | 3.4.0 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2019-8331</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.1 and 4.3.x before 4.3.1, XSS is possible in the tooltip or popover data-template attribute.
<p>Publish Date: 2019-02-20
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-8331>CVE-2019-8331</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-02-20</p>
<p>Fix Resolution: bootstrap - 3.4.1,4.3.1;bootstrap-sass - 3.4.1,4.3.1</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-14040</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the collapse data-parent attribute.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14040>CVE-2018-14040</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2,org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-20677</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the affix configuration target property.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20677>CVE-2018-20677</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20677</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: Bootstrap - v3.4.0;NorDroN.AngularTemplate - 0.1.6;Dynamic.NET.Express.ProjectTemplates - 0.8.0;dotnetng.template - 1.0.0.4;ZNxtApp.Core.Module.Theme - 1.0.9-Beta;JMeter - 5.0.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-20676</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 3.4.0, XSS is possible in the tooltip data-viewport attribute.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-20676>CVE-2018-20676</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-20676</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: bootstrap - 3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2018-14042</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap before 4.1.2, XSS is possible in the data-container property of tooltip.
<p>Publish Date: 2018-07-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2018-14042>CVE-2018-14042</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2018-07-13</p>
<p>Fix Resolution: org.webjars.npm:bootstrap:4.1.2.org.webjars:bootstrap:3.4.0</p>
</p>
<p></p>
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> CVE-2016-10735</summary>
### Vulnerable Library - <b>bootstrap-3.3.4.js</b></p>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.3.4/js/bootstrap.js</a></p>
<p>Path to vulnerable library: /scorecard/content/js/bootstrap.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.3.4.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/amaybaum-dev/BenchmarkJava/commit/3fb13535ce3a5993f2bc2b02a3ece468e691a942">3fb13535ce3a5993f2bc2b02a3ece468e691a942</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
<p></p>
</details> | non_test | bootstrap js vulnerabilities highest severity is vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js found in head commit a href vulnerabilities cve severity cvss dependency type fixed in bootstrap version remediation available medium bootstrap js direct bootstrap bootstrap sass medium bootstrap js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap js direct bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter medium bootstrap js direct bootstrap medium bootstrap js direct org webjars npm bootstrap org webjars bootstrap medium bootstrap js direct details cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before and x before xss is possible in the tooltip or popover data template attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution bootstrap bootstrap sass cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the collapse data parent attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the affix configuration target property publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap nordron angulartemplate dynamic net express projecttemplates dotnetng template znxtapp core module theme beta jmeter cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the tooltip data viewport attribute publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap before xss is possible in the data container property of tooltip publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution org webjars npm bootstrap org webjars bootstrap cve vulnerable library bootstrap js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to vulnerable library scorecard content js bootstrap js dependency hierarchy x bootstrap js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version release date fix resolution | 0 |
406,727 | 27,580,256,704 | IssuesEvent | 2023-03-08 15:45:28 | kedro-org/kedro | https://api.github.com/repos/kedro-org/kedro | closed | Add documentation for Datasets stored on Databricks DBFS | Component: Documentation 📄 | ## Description
As part of the milestone to improve the Databricks user experience, we should add documentation regarding how to use datasets stored via DBFS.
## Context
Currently, there is no documentation informing users how they should handle Datasets stored and accessed via DBFS. Incorrectly specifying file paths for these datasets causes Kedro to fail to load them (as in https://github.com/kedro-org/kedro/issues/1801 and https://github.com/kedro-org/kedro/issues/2272). | 1.0 | Add documentation for Datasets stored on Databricks DBFS - ## Description
As part of the milestone to improve the Databricks user experience, we should add documentation regarding how to use datasets stored via DBFS.
## Context
Currently, there is no documentation informing users how they should handle Datasets stored and accessed via DBFS. Incorrectly specifying file paths for these datasets causes Kedro to fail to load them (as in https://github.com/kedro-org/kedro/issues/1801 and https://github.com/kedro-org/kedro/issues/2272). | non_test | add documentation for datasets stored on databricks dbfs description as part of the milestone to improve the databricks user experience we should add documentation regarding how to use datasets stored via dbfs context currently there is no documentation informing users how they should handle datasets stored and accessed via dbfs incorrectly specifying file paths for these datasets causes kedro to fail to load them as in and | 0 |
670,580 | 22,694,898,443 | IssuesEvent | 2022-07-05 04:16:33 | matrixorigin/matrixone | https://api.github.com/repos/matrixorigin/matrixone | closed | [Feature Request]: Support SELECT statements for TPCH | priority/critical kind/feature source/benchmark | ### Is there an existing issue for the same feature request?
- [X] I have checked the existing issues.
### Is your feature request related to a problem?
_No response_
### Describe the feature you'd like
According to the details of all the 22 queries in TPCH official document, SELECT statement is a must for it. We need support SELECT statement as following:
_SELECT
[DISTINCT]
select_expr [, select_expr] ...
FROM table_references
[WHERE where_condition]
[GROUP BY {col_name | expr | position}]
[HAVING where_condition]
[ORDER BY {col_name | expr | position}
[ASC | DESC]
[LIMIT {[offset,] row_count | row_count OFFSET offset}]
[into_option]_
_into_option: {
INTO OUTFILE 'file_name'
[CHARACTER SET charset_name]
export_options
}_
select_expr and table_references have to support alias.
### Describe implementation you've considered
_No response_
### Documentation, Adoption, Use Case, Migration Strategy
_No response_
### Additional information
_No response_ | 1.0 | [Feature Request]: Support SELECT statements for TPCH - ### Is there an existing issue for the same feature request?
- [X] I have checked the existing issues.
### Is your feature request related to a problem?
_No response_
### Describe the feature you'd like
According to the details of all the 22 queries in TPCH official document, SELECT statement is a must for it. We need support SELECT statement as following:
_SELECT
[DISTINCT]
select_expr [, select_expr] ...
FROM table_references
[WHERE where_condition]
[GROUP BY {col_name | expr | position}]
[HAVING where_condition]
[ORDER BY {col_name | expr | position}
[ASC | DESC]
[LIMIT {[offset,] row_count | row_count OFFSET offset}]
[into_option]_
_into_option: {
INTO OUTFILE 'file_name'
[CHARACTER SET charset_name]
export_options
}_
select_expr and table_references have to support alias.
### Describe implementation you've considered
_No response_
### Documentation, Adoption, Use Case, Migration Strategy
_No response_
### Additional information
_No response_ | non_test | support select statements for tpch is there an existing issue for the same feature request i have checked the existing issues is your feature request related to a problem no response describe the feature you d like according to the details of all the queries in tpch official document select statement is a must for it we need support select statement as following select select expr from table references order by col name expr position row count row count offset offset into option into outfile file name export options select expr and table references have to support alias describe implementation you ve considered no response documentation adoption use case migration strategy no response additional information no response | 0 |
128,854 | 10,553,855,849 | IssuesEvent | 2019-10-03 18:09:16 | pyro-ppl/pyro | https://api.github.com/repos/pyro-ppl/pyro | opened | Make pyro.generic.testing usable as a todo list | testing | Ideally I'd like to implement a very narrow testing interface with two methods that do not mention pytest and do not require testing code to mention pyro.generic. Their use is equivalent to the following:
```py
# in my_pyro_implementation/test/test_generic.py
import pytest
from pyro.generic.testing import get_test_cases, check_test_case
# n.b. do not import any pyro stuff, including pyro.generic
@pytest.mark.parametrize('test_case', get_test_cases())
def test_generic(test_case):
try:
check_test_case(test_case)
except NotImplementedError as e:
pytest.xfail(f"Not implemented:\n{e}")
```
I don't care what these are named or whether they are lists or functions or whatever, but I do think we should separate concerns such that:
1. all pyro.generic interface is hidden inside these test helpers, and
2. all testing infra (pytest) is applied outside these test helpers.
I see these helpers as kind of an autoconf mechanism for pyro implementations: running them automatically shows what features are available in a given backend.
(see original discussion in https://github.com/pyro-ppl/pyro/pull/2049#discussion_r331176695)
## Tasks
- [ ] refactor pyro.generic.testing to free users from mentioning pyro
- [ ] raise `NotImplementedError` in pyro.generic if a backend module is missing an attribute | 1.0 | Make pyro.generic.testing usable as a todo list - Ideally I'd like to implement a very narrow testing interface with two methods that do not mention pytest and do not require testing code to mention pyro.generic. Their use is equivalent to the following:
```py
# in my_pyro_implementation/test/test_generic.py
import pytest
from pyro.generic.testing import get_test_cases, check_test_case
# n.b. do not import any pyro stuff, including pyro.generic
@pytest.mark.parametrize('test_case', get_test_cases())
def test_generic(test_case):
try:
check_test_case(test_case)
except NotImplementedError as e:
pytest.xfail(f"Not implemented:\n{e}")
```
I don't care what these are named or whether they are lists or functions or whatever, but I do think we should separate concerns such that:
1. all pyro.generic interface is hidden inside these test helpers, and
2. all testing infra (pytest) is applied outside these test helpers.
I see these helpers as kind of an autoconf mechanism for pyro implementations: running them automatically shows what features are available in a given backend.
(see original discussion in https://github.com/pyro-ppl/pyro/pull/2049#discussion_r331176695)
## Tasks
- [ ] refactor pyro.generic.testing to free users from mentioning pyro
- [ ] raise `NotImplementedError` in pyro.generic if a backend module is missing an attribute | test | make pyro generic testing usable as a todo list ideally i d like to implement a very narrow testing interface with two methods that do not mention pytest and do not require testing code to mention pyro generic their use is equivalent to the following py in my pyro implementation test test generic py import pytest from pyro generic testing import get test cases check test case n b do not import any pyro stuff including pyro generic pytest mark parametrize test case get test cases def test generic test case try check test case test case except notimplementederror as e pytest xfail f not implemented n e i don t care what these are named or whether they are lists or functions or whatever but i do think we should separate concerns such that all pyro generic interface is hidden inside these test helpers and all testing infra pytest is applied outside these test helpers i see these helpers as kind of an autoconf mechanism for pyro implementations running them automatically shows what features are available in a given backend see original discussion in tasks refactor pyro generic testing to free users from mentioning pyro raise notimplementederror in pyro generic if a backend module is missing an attribute | 1 |
29,860 | 4,538,704,039 | IssuesEvent | 2016-09-09 08:07:17 | onyx-platform/onyx | https://api.github.com/repos/onyx-platform/onyx | opened | Add test for trigger/fire-all-extents? | state/windowing testing | We had a bug that triggers were always firing on all extents (#460). I think we need a target non-integration unit test for the triggers to ensure this doesn't happen any more. | 1.0 | Add test for trigger/fire-all-extents? - We had a bug that triggers were always firing on all extents (#460). I think we need a target non-integration unit test for the triggers to ensure this doesn't happen any more. | test | add test for trigger fire all extents we had a bug that triggers were always firing on all extents i think we need a target non integration unit test for the triggers to ensure this doesn t happen any more | 1 |
55,444 | 6,476,313,609 | IssuesEvent | 2017-08-17 22:33:06 | linchpin/mesh | https://api.github.com/repos/linchpin/mesh | closed | Cannot toggle collapse on section if closed after adding a new section | Bug In Progress Test Me | 1. Add a section to a page
2. Collapse section using the toggle arrow.
3. Add new section.
After that the previously closed section(s) will not be able to be opened. This is due to the click events being applied to the toggle arrow twice.
| 1.0 | Cannot toggle collapse on section if closed after adding a new section - 1. Add a section to a page
2. Collapse section using the toggle arrow.
3. Add new section.
After that the previously closed section(s) will not be able to be opened. This is due to the click events being applied to the toggle arrow twice.
| test | cannot toggle collapse on section if closed after adding a new section add a section to a page collapse section using the toggle arrow add new section after that the previously closed section s will not be able to be opened this is due to the click events being applied to the toggle arrow twice | 1 |
83,040 | 23,949,328,274 | IssuesEvent | 2022-09-12 10:05:38 | micrometer-metrics/micrometer | https://api.github.com/repos/micrometer-metrics/micrometer | opened | Project version is not correct during release tag build | build | See for instance this CI build: https://app.circleci.com/pipelines/github/micrometer-metrics/micrometer/3319/workflows/fa0296a1-7e7b-468c-b491-19dd3efc0ee0/jobs/17823
Or this Gradle build scan: https://ge.micrometer.io/s/g7zutvuq7su3e
This was a build of the `v1.9.4` tag, but the version during the build job is determined as `1.10.0-SNAPSHOT`. During the actual deploy, it would end up as `1.9.4` due to the following having `-Prelease.useLastTag=true`.
https://github.com/micrometer-metrics/micrometer/blob/3b6b2a7b482f9d285185831791541c196d26ed8d/gradle/deploy.sh#L24 | 1.0 | Project version is not correct during release tag build - See for instance this CI build: https://app.circleci.com/pipelines/github/micrometer-metrics/micrometer/3319/workflows/fa0296a1-7e7b-468c-b491-19dd3efc0ee0/jobs/17823
Or this Gradle build scan: https://ge.micrometer.io/s/g7zutvuq7su3e
This was a build of the `v1.9.4` tag, but the version during the build job is determined as `1.10.0-SNAPSHOT`. During the actual deploy, it would end up as `1.9.4` due to the following having `-Prelease.useLastTag=true`.
https://github.com/micrometer-metrics/micrometer/blob/3b6b2a7b482f9d285185831791541c196d26ed8d/gradle/deploy.sh#L24 | non_test | project version is not correct during release tag build see for instance this ci build or this gradle build scan this was a build of the tag but the version during the build job is determined as snapshot during the actual deploy it would end up as due to the following having prelease uselasttag true | 0 |
278,318 | 21,074,257,601 | IssuesEvent | 2022-04-02 00:14:46 | mansenfranzen/autodoc_pydantic | https://api.github.com/repos/mansenfranzen/autodoc_pydantic | closed | Show fields from parent model | documentation | In the following case
```python
class Foo(pydantic.BaseModel):
'''Foo class'''
x: str = pydantic.Field(description='The x.')
class Bar(Foo):
'''Bar class'''
y: int = pydantic.Field(description='The y.')
```
is there a way to have the documentation for `Bar` show both `x` and `y` as the fields? | 1.0 | Show fields from parent model - In the following case
```python
class Foo(pydantic.BaseModel):
'''Foo class'''
x: str = pydantic.Field(description='The x.')
class Bar(Foo):
'''Bar class'''
y: int = pydantic.Field(description='The y.')
```
is there a way to have the documentation for `Bar` show both `x` and `y` as the fields? | non_test | show fields from parent model in the following case python class foo pydantic basemodel foo class x str pydantic field description the x class bar foo bar class y int pydantic field description the y is there a way to have the documentation for bar show both x and y as the fields | 0 |
179,423 | 13,880,449,542 | IssuesEvent | 2020-10-17 18:49:49 | WarcraftPriests/sl-shadow-priest | https://api.github.com/repos/WarcraftPriests/sl-shadow-priest | closed | Verify Shadowy Apparitions damage | needs-testing | This looks to have been nerfed, make sure we caught that properly | 1.0 | Verify Shadowy Apparitions damage - This looks to have been nerfed, make sure we caught that properly | test | verify shadowy apparitions damage this looks to have been nerfed make sure we caught that properly | 1 |
96,317 | 16,129,615,237 | IssuesEvent | 2021-04-29 01:03:58 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | opened | CVE-2021-3411 (Medium) detected in linux-yocto-devv5.3 | security vulnerability | ## CVE-2021-3411 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv5.3</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/arch/x86/kernel/kprobes/opt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/arch/x86/kernel/kprobes/opt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/arch/x86/kernel/kprobes/opt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux kernel in versions prior to 5.10. A violation of memory access was found while detecting a padding of int3 in the linking state. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3411>CVE-2021-3411</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-3411">https://www.linuxkernelcves.com/cves/CVE-2021-3411</a></p>
<p>Release Date: 2021-02-13</p>
<p>Fix Resolution: v5.9.15, v5.10</p>
</p>
</details>
<p></p>
| True | CVE-2021-3411 (Medium) detected in linux-yocto-devv5.3 - ## CVE-2021-3411 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv5.3</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/arch/x86/kernel/kprobes/opt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/arch/x86/kernel/kprobes/opt.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>ampere-centos-kernel/arch/x86/kernel/kprobes/opt.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in the Linux kernel in versions prior to 5.10. A violation of memory access was found while detecting a padding of int3 in the linking state. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-03-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3411>CVE-2021-3411</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-3411">https://www.linuxkernelcves.com/cves/CVE-2021-3411</a></p>
<p>Release Date: 2021-02-13</p>
<p>Fix Resolution: v5.9.15, v5.10</p>
</p>
</details>
<p></p>
| non_test | cve medium detected in linux yocto cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel tracks the next mainline release library home page a href found in base branch amp centos kernel vulnerable source files ampere centos kernel arch kernel kprobes opt c ampere centos kernel arch kernel kprobes opt c ampere centos kernel arch kernel kprobes opt c vulnerability details a flaw was found in the linux kernel in versions prior to a violation of memory access was found while detecting a padding of in the linking state the highest threat from this vulnerability is to data confidentiality and integrity as well as system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
178,686 | 29,954,618,017 | IssuesEvent | 2023-06-23 06:19:43 | marigold-ui/marigold | https://api.github.com/repos/marigold-ui/marigold | closed | Creating Accordion for the B2B Theme | type:design status:rfc | ## Overview
| Component Name | Type | Theme |
Accordion
## Description
ACM Requires the created Accordion for the "Core" Theme, but with the B2B Style. This in order to update their already used
Additionaly they would like to have an Optional Subtitle next to the Title (see Example in Figma)
## Appearance Update <!-- If the appearance should change use this section -->
It should follow the B2B Style (see figma File)
**Figma Link:** [Accordion](https://www.figma.com/file/DFKyTGHAoDxOsUBPszLLxP/%F0%9F%8F%B5%EF%B8%8FMarigold?type=design&node-id=8551%3A14673&t=KvtWfzukUKwSYD49-1)
<!-- List all the required change -->
- ...
### Current
<!-- Upload an image or video of the current appearance -->
### New
<!-- Upload an image or video of the updated appearance -->
## Behavior Update <!-- If the behavior should change use this section -->
- Attached are 2 images, that show how did I create the structure for the elements that can be shown or hidden.
- It sould be possible to insert other objects inside a container under the tittle, when the accordion is expanded, for instance a box, a table, or anything in between.
- Responsiveness: it should be possible to be used with a grid, so that the developer can fill the whole space inside the container, and this one should be flexible.
- ...
### Current
<!-- Upload an image or video of the current behavior -->
### New
<!-- Upload an image or video of the updated behavior -->
<img width="686" alt="Screenshot 2023-05-04 at 11 49 14" src="https://user-images.githubusercontent.com/34473133/236172017-c50f5c61-e711-43af-8d73-d3a39c7fea3a.png">
<img width="701" alt="Screenshot 2023-05-04 at 11 49 27" src="https://user-images.githubusercontent.com/34473133/236172021-eaf4de3b-6ed7-48bd-8a97-a50778afed65.png">
| 1.0 | Creating Accordion for the B2B Theme - ## Overview
| Component Name | Type | Theme |
Accordion
## Description
ACM Requires the created Accordion for the "Core" Theme, but with the B2B Style. This in order to update their already used
Additionaly they would like to have an Optional Subtitle next to the Title (see Example in Figma)
## Appearance Update <!-- If the appearance should change use this section -->
It should follow the B2B Style (see figma File)
**Figma Link:** [Accordion](https://www.figma.com/file/DFKyTGHAoDxOsUBPszLLxP/%F0%9F%8F%B5%EF%B8%8FMarigold?type=design&node-id=8551%3A14673&t=KvtWfzukUKwSYD49-1)
<!-- List all the required change -->
- ...
### Current
<!-- Upload an image or video of the current appearance -->
### New
<!-- Upload an image or video of the updated appearance -->
## Behavior Update <!-- If the behavior should change use this section -->
- Attached are 2 images, that show how did I create the structure for the elements that can be shown or hidden.
- It sould be possible to insert other objects inside a container under the tittle, when the accordion is expanded, for instance a box, a table, or anything in between.
- Responsiveness: it should be possible to be used with a grid, so that the developer can fill the whole space inside the container, and this one should be flexible.
- ...
### Current
<!-- Upload an image or video of the current behavior -->
### New
<!-- Upload an image or video of the updated behavior -->
<img width="686" alt="Screenshot 2023-05-04 at 11 49 14" src="https://user-images.githubusercontent.com/34473133/236172017-c50f5c61-e711-43af-8d73-d3a39c7fea3a.png">
<img width="701" alt="Screenshot 2023-05-04 at 11 49 27" src="https://user-images.githubusercontent.com/34473133/236172021-eaf4de3b-6ed7-48bd-8a97-a50778afed65.png">
| non_test | creating accordion for the theme overview component name type theme accordion description acm requires the created accordion for the core theme but with the style this in order to update their already used additionaly they would like to have an optional subtitle next to the title see example in figma appearance update it should follow the style see figma file figma link current new behavior update attached are images that show how did i create the structure for the elements that can be shown or hidden it sould be possible to insert other objects inside a container under the tittle when the accordion is expanded for instance a box a table or anything in between responsiveness it should be possible to be used with a grid so that the developer can fill the whole space inside the container and this one should be flexible current new img width alt screenshot at src img width alt screenshot at src | 0 |
55,198 | 6,445,349,730 | IssuesEvent | 2017-08-13 03:01:59 | AddstarMC/Minigames | https://api.github.com/repos/AddstarMC/Minigames | closed | Play Sound Region Action Bug | More Information Needed Needs Testing | When trying to change the sound that plays if i double click like trying to type one in instead of scrolling through the list i get kicked and this shows up in console.
`ERROR io.netty.handler.codec.EncoderException: String too big (was 38456 bytes encoded, max 32767)` | 1.0 | Play Sound Region Action Bug - When trying to change the sound that plays if i double click like trying to type one in instead of scrolling through the list i get kicked and this shows up in console.
`ERROR io.netty.handler.codec.EncoderException: String too big (was 38456 bytes encoded, max 32767)` | test | play sound region action bug when trying to change the sound that plays if i double click like trying to type one in instead of scrolling through the list i get kicked and this shows up in console error io netty handler codec encoderexception string too big was bytes encoded max | 1 |
179,703 | 13,895,832,100 | IssuesEvent | 2020-10-19 16:20:40 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | closed | Port EJB 1.x XMI Custom Bindings Tests to Open Liberty | in:EJB Container team:Blizzard test delivery | Port EJB 1.x XMI Custom Bindings Tests to Open Liberty : suite.r40.base.spec
Should go into legacy_fat
Statefull and Stateless apps resulting in 20 test classes | 1.0 | Port EJB 1.x XMI Custom Bindings Tests to Open Liberty - Port EJB 1.x XMI Custom Bindings Tests to Open Liberty : suite.r40.base.spec
Should go into legacy_fat
Statefull and Stateless apps resulting in 20 test classes | test | port ejb x xmi custom bindings tests to open liberty port ejb x xmi custom bindings tests to open liberty suite base spec should go into legacy fat statefull and stateless apps resulting in test classes | 1 |
124,344 | 10,309,536,785 | IssuesEvent | 2019-08-29 13:29:30 | kcigeospatial/Fred_Co_Land-Management | https://api.github.com/repos/kcigeospatial/Fred_Co_Land-Management | closed | Plumbing Trade License Misc=Journeyman License skipped fees. | Ready for Test Env. Retest | PJ244456-license automatically jumped to active status after I resulted the completeness check review. -aw
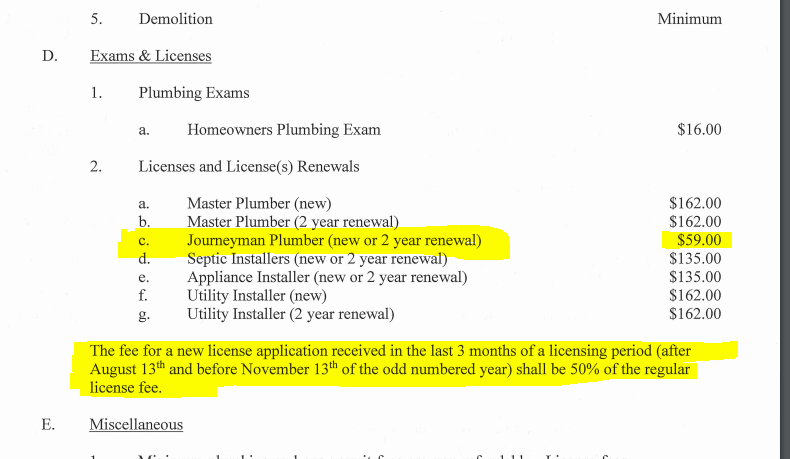


| 2.0 | Plumbing Trade License Misc=Journeyman License skipped fees. - PJ244456-license automatically jumped to active status after I resulted the completeness check review. -aw
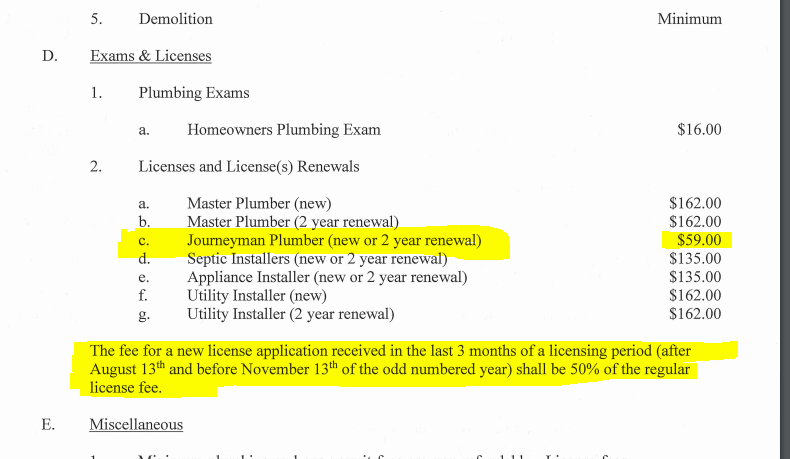


| test | plumbing trade license misc journeyman license skipped fees license automatically jumped to active status after i resulted the completeness check review aw | 1 |
2,954 | 2,607,967,457 | IssuesEvent | 2015-02-26 00:43:02 | chrsmithdemos/leveldb | https://api.github.com/repos/chrsmithdemos/leveldb | opened | Add a Get API which allows for caller-allocated result buffer storage ( e.g. on stack ) | auto-migrated Priority-Medium Type-Defect | ```
The current API provides:
virtual Status Get(const ReadOptions& options,
const Slice& key, std::string* value) = 0;
A downside of this API is that it uses dynamic memory allocation in std::string
It would be nice to have an additional API call:
virtual Status Get(const ReadOptions& options,
const Slice& key, char* buf, size_t* bufsize ) = 0;
This would allow a stack-based buffer. It would require a new status code
"buffer too small", the bufsize parameter is a pointer to receive the size of
the data copied / required
```
-----
Original issue reported on code.google.com by `jvb...@gmail.com` on 3 Jan 2013 at 5:35 | 1.0 | Add a Get API which allows for caller-allocated result buffer storage ( e.g. on stack ) - ```
The current API provides:
virtual Status Get(const ReadOptions& options,
const Slice& key, std::string* value) = 0;
A downside of this API is that it uses dynamic memory allocation in std::string
It would be nice to have an additional API call:
virtual Status Get(const ReadOptions& options,
const Slice& key, char* buf, size_t* bufsize ) = 0;
This would allow a stack-based buffer. It would require a new status code
"buffer too small", the bufsize parameter is a pointer to receive the size of
the data copied / required
```
-----
Original issue reported on code.google.com by `jvb...@gmail.com` on 3 Jan 2013 at 5:35 | non_test | add a get api which allows for caller allocated result buffer storage e g on stack the current api provides virtual status get const readoptions options const slice key std string value a downside of this api is that it uses dynamic memory allocation in std string it would be nice to have an additional api call virtual status get const readoptions options const slice key char buf size t bufsize this would allow a stack based buffer it would require a new status code buffer too small the bufsize parameter is a pointer to receive the size of the data copied required original issue reported on code google com by jvb gmail com on jan at | 0 |
69,029 | 7,122,338,977 | IssuesEvent | 2018-01-19 11:22:56 | weaveworks/cortex | https://api.github.com/repos/weaveworks/cortex | closed | TestIngesterTransfer fails intermittenly | flaky-test | Test that relies on system clock in intermittent failing shocker. News at 9pm.
c.f. https://circleci.com/gh/weaveworks/cortex/910
```
--- FAIL: TestIngesterTransfer (6.01s)
Error Trace: ingester_lifecycle_test.go:155
Error: Not equal: &cortex.QueryResponse{Timeseries: []cortex.TimeSeries{cortex.TimeSeries{Labels:[]cortex.LabelPair{cortex.LabelPair{Name:wire.Bytes{0x5f, 0x5f, 0x6e, 0x61, 0x6d, 0x65, 0x5f, 0x5f}, Value:wire.Bytes{0x66, 0x6f, 0x6f}}}, Samples:[]cortex.Sample{cortex.Sample{Value:456, TimestampMs:123000}}}},
} (expected)
!= &cortex.QueryResponse{} (actual)
Diff:
--- Expected
+++ Actual
@@ -1,2 +1,2 @@
-(*cortex.QueryResponse)(0xc4202a21a0)(&QueryResponse{Timeseries:[{[{[95 95 110 97 109 101 95 95] [102 111 111]}] [{456 123000}]}],})
+(*cortex.QueryResponse)(0xc4202a2180)(&QueryResponse{Timeseries:[],})
``` | 1.0 | TestIngesterTransfer fails intermittenly - Test that relies on system clock in intermittent failing shocker. News at 9pm.
c.f. https://circleci.com/gh/weaveworks/cortex/910
```
--- FAIL: TestIngesterTransfer (6.01s)
Error Trace: ingester_lifecycle_test.go:155
Error: Not equal: &cortex.QueryResponse{Timeseries: []cortex.TimeSeries{cortex.TimeSeries{Labels:[]cortex.LabelPair{cortex.LabelPair{Name:wire.Bytes{0x5f, 0x5f, 0x6e, 0x61, 0x6d, 0x65, 0x5f, 0x5f}, Value:wire.Bytes{0x66, 0x6f, 0x6f}}}, Samples:[]cortex.Sample{cortex.Sample{Value:456, TimestampMs:123000}}}},
} (expected)
!= &cortex.QueryResponse{} (actual)
Diff:
--- Expected
+++ Actual
@@ -1,2 +1,2 @@
-(*cortex.QueryResponse)(0xc4202a21a0)(&QueryResponse{Timeseries:[{[{[95 95 110 97 109 101 95 95] [102 111 111]}] [{456 123000}]}],})
+(*cortex.QueryResponse)(0xc4202a2180)(&QueryResponse{Timeseries:[],})
``` | test | testingestertransfer fails intermittenly test that relies on system clock in intermittent failing shocker news at c f fail testingestertransfer error trace ingester lifecycle test go error not equal cortex queryresponse timeseries cortex timeseries cortex timeseries labels cortex labelpair cortex labelpair name wire bytes value wire bytes samples cortex sample cortex sample value timestampms expected cortex queryresponse actual diff expected actual cortex queryresponse queryresponse timeseries cortex queryresponse queryresponse timeseries | 1 |
4,227 | 20,915,298,264 | IssuesEvent | 2022-03-24 12:56:58 | precice/precice | https://api.github.com/repos/precice/precice | closed | Dead code in Edge.hpp? | maintainability | In `mesh/Edge.hpp`, some types are forward declared, but I found no reference nor implementation to these.
They seem to be designed for iterating over an edge, but there is actually no iterator implementation.
https://github.com/precice/precice/blob/00e12ff66dc2b5337167761c0741aa718f441c63/src/mesh/Edge.hpp#L15-L18
For Triangle, the `IndexRangeIterator` class is used to implement iterators over vertices. It would be consistent to implement the same for an edge and remove the types declared above.
https://github.com/precice/precice/blob/00e12ff66dc2b5337167761c0741aa718f441c63/src/mesh/Triangle.hpp#L34 | True | Dead code in Edge.hpp? - In `mesh/Edge.hpp`, some types are forward declared, but I found no reference nor implementation to these.
They seem to be designed for iterating over an edge, but there is actually no iterator implementation.
https://github.com/precice/precice/blob/00e12ff66dc2b5337167761c0741aa718f441c63/src/mesh/Edge.hpp#L15-L18
For Triangle, the `IndexRangeIterator` class is used to implement iterators over vertices. It would be consistent to implement the same for an edge and remove the types declared above.
https://github.com/precice/precice/blob/00e12ff66dc2b5337167761c0741aa718f441c63/src/mesh/Triangle.hpp#L34 | non_test | dead code in edge hpp in mesh edge hpp some types are forward declared but i found no reference nor implementation to these they seem to be designed for iterating over an edge but there is actually no iterator implementation for triangle the indexrangeiterator class is used to implement iterators over vertices it would be consistent to implement the same for an edge and remove the types declared above | 0 |
823,658 | 31,028,870,767 | IssuesEvent | 2023-08-10 11:02:59 | owid/etl | https://api.github.com/repos/owid/etl | opened | Population dataset has multiple origins which take much space in per capita charts | data priority 2 - important | # Description
Many of our etl steps depend on our population dataset, which is used, for example, when creating per capita indicators. Since we are moving into a workflow where origins are propagated automatically, all these per capita indicators end up having many origins. Then, all charts that use these indicators end up having too many origins shown (mostly irrelevant).
Additionally, our population dataset is used in 513 charts, of which only a few (e.g. [Population](https://owid.cloud/admin/charts/4546/edit)) are actually about population. The rest use population "indirectly", e.g. in scatter charts.
In all those cases where population origins have little importance, it would be good to either hide those origins, or collapse them into a generic one, e.g. "Population is based on various sources".
# Proposed solutions
To achieve this, we [discussed](https://www.notion.so/owid/2023-Data-architecture-8b5492227e6d4911b913ac29de44a263?pvs=4#42769dcda3c249d39153051ebf53f117) various options:
1. Flagging all population origins as "auxiliary". This implies adding at least a new metadata field to origins (and possibly other to grapher configs and presentation or display). This way, in data pages or charts, we could decide to hide or show auxiliary origins. But we may want to cite those origins somehow, with a "Population is based on various sources", which we would need to do manually.
2. Adding a special kind of replacement origin to the population dataset. Then in data pages or charts we could choose whether to show all origins, or only the replacement ones. This implies adding possibly a few new metadata fields. It also needs some further logic. For example, if you have an indicator that uses population, then you have multiple origins including the replacement one. But then it's unclear how to identify the origins that need to be hidden.
3. Creating a new population dataset that has only one origin, combination of all others. This dataset would depend on the original population dataset. All other steps would depend on the new combined population dataset. This implies having more steps with duplicated data, and refactoring all charts so that they depend on the new dataset. This dataset could be hosted within the same namespace `demography` or in a new namespace for combined origins, e.g. `owid`.
4. Creating a new table in the current population garden step, with the same data as the existing one, but with one combined origin. We could call this new table `population_combined_origins`. However, for simplicity, we can call the new table `population`, and rename the existing table to, e.g. `population_original`. This way, all steps that currently depend on `population` would not need to be edited. And, for those steps that have automatic metadata propagation, all unnecessary origins (e.g. Gapminder, Hyde, UN) will be hidden from charts (and shown in the sources tab). This seems to be the better option.
# Chosen solution
Option 4 above seems to be the best option (and easiest to implement). It involves the following work:
* [ ] In the latest population garden step, rename the current table to, e.g. "population_original".
* [ ] In the latest population garden step, create a new table called "population", with only one origin. The`citation_producer` should combine all origins, but then, e.g. `producer='Various sources'`, `attribution='Population data is based on various sources'` (we would need to decide how exactly to fill out these fields).
* [ ] Ensure that metadata is properly stored at the indicator level of both `population` and `population_original` tables (I'm not sure if that's currently the case).
* [ ] Edit the latest population grapher step, so that it loads both tables, "population_original" and "population". Charts that show population as the main indicator should use `population_original` with all its origins, but charts that use population indirectly (e.g. for scatter plots) should use `population`.
# Caveats
* It is unclear whether the dataset `population_density` should use `population_original` or `population`. If it uses `population_original`, any step using `population_density` would then have all origins of `population_original`. This could be fixed, again, by creating a `population_density_original`, but this may be an overkill. So I think `population_density` should simply use `population`, like all other steps.
* We could create a new version of the population dataset, and then transfer all steps little by little to use the latest version. However, given that the actual data has not changed, it is safe to simply edit the current latest version. This will trigger a big ETL build (**so the resulting PR should be merged by the end of the day to avoid blocking others**). But it will not trigger any chart revisions. For this reason, it would be good to build ETL locally or in staging, and visually inspect some of the affected charts, to check that the result looks good.
* It is still unclear whether we want to always show a "Population is based on various sources" message on every chart where population is indirectly used (e.g. per capita indicators or scatter plots). To begin with, this will be the case (maybe we can figure out a very brief `attribution_short`). If we decide to hide these origins, it is still possibly by editing the `attribution` of per capita indicators. But if we want a more automatic solution, we may need to revisit again the idea of having auxiliary origins. | 1.0 | Population dataset has multiple origins which take much space in per capita charts - # Description
Many of our etl steps depend on our population dataset, which is used, for example, when creating per capita indicators. Since we are moving into a workflow where origins are propagated automatically, all these per capita indicators end up having many origins. Then, all charts that use these indicators end up having too many origins shown (mostly irrelevant).
Additionally, our population dataset is used in 513 charts, of which only a few (e.g. [Population](https://owid.cloud/admin/charts/4546/edit)) are actually about population. The rest use population "indirectly", e.g. in scatter charts.
In all those cases where population origins have little importance, it would be good to either hide those origins, or collapse them into a generic one, e.g. "Population is based on various sources".
# Proposed solutions
To achieve this, we [discussed](https://www.notion.so/owid/2023-Data-architecture-8b5492227e6d4911b913ac29de44a263?pvs=4#42769dcda3c249d39153051ebf53f117) various options:
1. Flagging all population origins as "auxiliary". This implies adding at least a new metadata field to origins (and possibly other to grapher configs and presentation or display). This way, in data pages or charts, we could decide to hide or show auxiliary origins. But we may want to cite those origins somehow, with a "Population is based on various sources", which we would need to do manually.
2. Adding a special kind of replacement origin to the population dataset. Then in data pages or charts we could choose whether to show all origins, or only the replacement ones. This implies adding possibly a few new metadata fields. It also needs some further logic. For example, if you have an indicator that uses population, then you have multiple origins including the replacement one. But then it's unclear how to identify the origins that need to be hidden.
3. Creating a new population dataset that has only one origin, combination of all others. This dataset would depend on the original population dataset. All other steps would depend on the new combined population dataset. This implies having more steps with duplicated data, and refactoring all charts so that they depend on the new dataset. This dataset could be hosted within the same namespace `demography` or in a new namespace for combined origins, e.g. `owid`.
4. Creating a new table in the current population garden step, with the same data as the existing one, but with one combined origin. We could call this new table `population_combined_origins`. However, for simplicity, we can call the new table `population`, and rename the existing table to, e.g. `population_original`. This way, all steps that currently depend on `population` would not need to be edited. And, for those steps that have automatic metadata propagation, all unnecessary origins (e.g. Gapminder, Hyde, UN) will be hidden from charts (and shown in the sources tab). This seems to be the better option.
# Chosen solution
Option 4 above seems to be the best option (and easiest to implement). It involves the following work:
* [ ] In the latest population garden step, rename the current table to, e.g. "population_original".
* [ ] In the latest population garden step, create a new table called "population", with only one origin. The`citation_producer` should combine all origins, but then, e.g. `producer='Various sources'`, `attribution='Population data is based on various sources'` (we would need to decide how exactly to fill out these fields).
* [ ] Ensure that metadata is properly stored at the indicator level of both `population` and `population_original` tables (I'm not sure if that's currently the case).
* [ ] Edit the latest population grapher step, so that it loads both tables, "population_original" and "population". Charts that show population as the main indicator should use `population_original` with all its origins, but charts that use population indirectly (e.g. for scatter plots) should use `population`.
# Caveats
* It is unclear whether the dataset `population_density` should use `population_original` or `population`. If it uses `population_original`, any step using `population_density` would then have all origins of `population_original`. This could be fixed, again, by creating a `population_density_original`, but this may be an overkill. So I think `population_density` should simply use `population`, like all other steps.
* We could create a new version of the population dataset, and then transfer all steps little by little to use the latest version. However, given that the actual data has not changed, it is safe to simply edit the current latest version. This will trigger a big ETL build (**so the resulting PR should be merged by the end of the day to avoid blocking others**). But it will not trigger any chart revisions. For this reason, it would be good to build ETL locally or in staging, and visually inspect some of the affected charts, to check that the result looks good.
* It is still unclear whether we want to always show a "Population is based on various sources" message on every chart where population is indirectly used (e.g. per capita indicators or scatter plots). To begin with, this will be the case (maybe we can figure out a very brief `attribution_short`). If we decide to hide these origins, it is still possibly by editing the `attribution` of per capita indicators. But if we want a more automatic solution, we may need to revisit again the idea of having auxiliary origins. | non_test | population dataset has multiple origins which take much space in per capita charts description many of our etl steps depend on our population dataset which is used for example when creating per capita indicators since we are moving into a workflow where origins are propagated automatically all these per capita indicators end up having many origins then all charts that use these indicators end up having too many origins shown mostly irrelevant additionally our population dataset is used in charts of which only a few e g are actually about population the rest use population indirectly e g in scatter charts in all those cases where population origins have little importance it would be good to either hide those origins or collapse them into a generic one e g population is based on various sources proposed solutions to achieve this we various options flagging all population origins as auxiliary this implies adding at least a new metadata field to origins and possibly other to grapher configs and presentation or display this way in data pages or charts we could decide to hide or show auxiliary origins but we may want to cite those origins somehow with a population is based on various sources which we would need to do manually adding a special kind of replacement origin to the population dataset then in data pages or charts we could choose whether to show all origins or only the replacement ones this implies adding possibly a few new metadata fields it also needs some further logic for example if you have an indicator that uses population then you have multiple origins including the replacement one but then it s unclear how to identify the origins that need to be hidden creating a new population dataset that has only one origin combination of all others this dataset would depend on the original population dataset all other steps would depend on the new combined population dataset this implies having more steps with duplicated data and refactoring all charts so that they depend on the new dataset this dataset could be hosted within the same namespace demography or in a new namespace for combined origins e g owid creating a new table in the current population garden step with the same data as the existing one but with one combined origin we could call this new table population combined origins however for simplicity we can call the new table population and rename the existing table to e g population original this way all steps that currently depend on population would not need to be edited and for those steps that have automatic metadata propagation all unnecessary origins e g gapminder hyde un will be hidden from charts and shown in the sources tab this seems to be the better option chosen solution option above seems to be the best option and easiest to implement it involves the following work in the latest population garden step rename the current table to e g population original in the latest population garden step create a new table called population with only one origin the citation producer should combine all origins but then e g producer various sources attribution population data is based on various sources we would need to decide how exactly to fill out these fields ensure that metadata is properly stored at the indicator level of both population and population original tables i m not sure if that s currently the case edit the latest population grapher step so that it loads both tables population original and population charts that show population as the main indicator should use population original with all its origins but charts that use population indirectly e g for scatter plots should use population caveats it is unclear whether the dataset population density should use population original or population if it uses population original any step using population density would then have all origins of population original this could be fixed again by creating a population density original but this may be an overkill so i think population density should simply use population like all other steps we could create a new version of the population dataset and then transfer all steps little by little to use the latest version however given that the actual data has not changed it is safe to simply edit the current latest version this will trigger a big etl build so the resulting pr should be merged by the end of the day to avoid blocking others but it will not trigger any chart revisions for this reason it would be good to build etl locally or in staging and visually inspect some of the affected charts to check that the result looks good it is still unclear whether we want to always show a population is based on various sources message on every chart where population is indirectly used e g per capita indicators or scatter plots to begin with this will be the case maybe we can figure out a very brief attribution short if we decide to hide these origins it is still possibly by editing the attribution of per capita indicators but if we want a more automatic solution we may need to revisit again the idea of having auxiliary origins | 0 |
196,110 | 15,575,529,384 | IssuesEvent | 2021-03-17 11:10:48 | DeepRank/deeprank | https://api.github.com/repos/DeepRank/deeprank | closed | NaivePSSM is still available in deeprank.features | documentation enhancement | NaivePSSM should be is an old test feature that should be removed.
I have removed it from the documentation in commit 1b087cf in doc_DM branch. Not sure yet I should remove the deeprank/features/NaivePSSM.py script as well. | 1.0 | NaivePSSM is still available in deeprank.features - NaivePSSM should be is an old test feature that should be removed.
I have removed it from the documentation in commit 1b087cf in doc_DM branch. Not sure yet I should remove the deeprank/features/NaivePSSM.py script as well. | non_test | naivepssm is still available in deeprank features naivepssm should be is an old test feature that should be removed i have removed it from the documentation in commit in doc dm branch not sure yet i should remove the deeprank features naivepssm py script as well | 0 |
64,112 | 6,893,396,292 | IssuesEvent | 2017-11-23 03:25:20 | SatelliteQE/robottelo | https://api.github.com/repos/SatelliteQE/robottelo | closed | Test's failing on upgrade boxes tests.foreman.ui.test_organization.OrganizationTestCase /LocationTestCase | 6.2 High test-failure UI | Test's which require tab locators are failing in saucelabs
Also ,failing for location
`
TimeoutException: Waiting for element '//a[@data-toggle='tab' and contains(@href,'environments')]' to display. Message: element //a[@data-toggle='tab' and contains(@href,'environments')] is not visible`
Needs more investigation

| 1.0 | Test's failing on upgrade boxes tests.foreman.ui.test_organization.OrganizationTestCase /LocationTestCase - Test's which require tab locators are failing in saucelabs
Also ,failing for location
`
TimeoutException: Waiting for element '//a[@data-toggle='tab' and contains(@href,'environments')]' to display. Message: element //a[@data-toggle='tab' and contains(@href,'environments')] is not visible`
Needs more investigation

| test | test s failing on upgrade boxes tests foreman ui test organization organizationtestcase locationtestcase test s which require tab locators are failing in saucelabs also failing for location timeoutexception waiting for element a to display message element a is not visible needs more investigation | 1 |
231,319 | 25,499,111,187 | IssuesEvent | 2022-11-28 01:07:46 | Gal-Doron/IaC_check | https://api.github.com/repos/Gal-Doron/IaC_check | opened | body-parser-1.19.0.tgz: 1 vulnerabilities (highest severity is: 5.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>body-parser-1.19.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/package.json</p>
<p>Path to vulnerable library: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/node_modules/qs/package.json</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (body-parser version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-24999](https://www.mend.io/vulnerability-database/CVE-2022-24999) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | qs-6.7.0.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24999</summary>
### Vulnerable Library - <b>qs-6.7.0.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.7.0.tgz">https://registry.npmjs.org/qs/-/qs-6.7.0.tgz</a></p>
<p>Path to dependency file: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/package.json</p>
<p>Path to vulnerable library: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- body-parser-1.19.0.tgz (Root Library)
- :x: **qs-6.7.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
qs before 6.10.3, as used in Express before 4.17.3 and other products, allows attackers to cause a Node process hang for an Express application because an __ proto__ key can be used. In many typical Express use cases, an unauthenticated remote attacker can place the attack payload in the query string of the URL that is used to visit the application, such as a[__proto__]=b&a[__proto__]&a[length]=100000000. The fix was backported to qs 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4 (and therefore Express 4.17.3, which has "deps: qs@6.9.7" in its release description, is not vulnerable).
<p>Publish Date: 2022-11-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24999>CVE-2022-24999</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-24999">https://www.cve.org/CVERecord?id=CVE-2022-24999</a></p>
<p>Release Date: 2022-11-26</p>
<p>Fix Resolution: qs - 6.2.4,6.3.3,6.4.1,6.5.3,6.6.1,6.7.3,6.8.3,6.9.7,6.10.3</p>
</p>
<p></p>
</details> | True | body-parser-1.19.0.tgz: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>body-parser-1.19.0.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/package.json</p>
<p>Path to vulnerable library: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/node_modules/qs/package.json</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (body-parser version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-24999](https://www.mend.io/vulnerability-database/CVE-2022-24999) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | qs-6.7.0.tgz | Transitive | N/A* | ❌ |
<p>*For some transitive vulnerabilities, there is no version of direct dependency with a fix. Check the section "Details" below to see if there is a version of transitive dependency where vulnerability is fixed.</p>
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2022-24999</summary>
### Vulnerable Library - <b>qs-6.7.0.tgz</b></p>
<p>A querystring parser that supports nesting and arrays, with a depth limit</p>
<p>Library home page: <a href="https://registry.npmjs.org/qs/-/qs-6.7.0.tgz">https://registry.npmjs.org/qs/-/qs-6.7.0.tgz</a></p>
<p>Path to dependency file: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/package.json</p>
<p>Path to vulnerable library: /kubernetes-goat-1.1.0/infrastructure/internal-api/code/node_modules/qs/package.json</p>
<p>
Dependency Hierarchy:
- body-parser-1.19.0.tgz (Root Library)
- :x: **qs-6.7.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
qs before 6.10.3, as used in Express before 4.17.3 and other products, allows attackers to cause a Node process hang for an Express application because an __ proto__ key can be used. In many typical Express use cases, an unauthenticated remote attacker can place the attack payload in the query string of the URL that is used to visit the application, such as a[__proto__]=b&a[__proto__]&a[length]=100000000. The fix was backported to qs 6.9.7, 6.8.3, 6.7.3, 6.6.1, 6.5.3, 6.4.1, 6.3.3, and 6.2.4 (and therefore Express 4.17.3, which has "deps: qs@6.9.7" in its release description, is not vulnerable).
<p>Publish Date: 2022-11-26
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24999>CVE-2022-24999</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-24999">https://www.cve.org/CVERecord?id=CVE-2022-24999</a></p>
<p>Release Date: 2022-11-26</p>
<p>Fix Resolution: qs - 6.2.4,6.3.3,6.4.1,6.5.3,6.6.1,6.7.3,6.8.3,6.9.7,6.10.3</p>
</p>
<p></p>
</details> | non_test | body parser tgz vulnerabilities highest severity is vulnerable library body parser tgz path to dependency file kubernetes goat infrastructure internal api code package json path to vulnerable library kubernetes goat infrastructure internal api code node modules qs package json vulnerabilities cve severity cvss dependency type fixed in body parser version remediation available medium qs tgz transitive n a for some transitive vulnerabilities there is no version of direct dependency with a fix check the section details below to see if there is a version of transitive dependency where vulnerability is fixed details cve vulnerable library qs tgz a querystring parser that supports nesting and arrays with a depth limit library home page a href path to dependency file kubernetes goat infrastructure internal api code package json path to vulnerable library kubernetes goat infrastructure internal api code node modules qs package json dependency hierarchy body parser tgz root library x qs tgz vulnerable library found in base branch main vulnerability details qs before as used in express before and other products allows attackers to cause a node process hang for an express application because an proto key can be used in many typical express use cases an unauthenticated remote attacker can place the attack payload in the query string of the url that is used to visit the application such as a b a a the fix was backported to qs and and therefore express which has deps qs in its release description is not vulnerable publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution qs | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.