Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 4 112 | repo_url stringlengths 33 141 | action stringclasses 3 values | title stringlengths 1 1.02k | labels stringlengths 4 1.54k | body stringlengths 1 262k | index stringclasses 17 values | text_combine stringlengths 95 262k | label stringclasses 2 values | text stringlengths 96 252k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
256,788 | 8,129,058,143 | IssuesEvent | 2018-08-17 13:58:27 | vmware/vic | https://api.github.com/repos/vmware/vic | reopened | Docker pull on docker store fails | area/docker component/imagec priority/p1 source/customer | Docker pull on images on docker store fails. For instance,
```
docker pull store/ibmcorp/db2wh_ce:v2.9.0-db2wh_client-linux
```
Internal bug 2152747. | 1.0 | Docker pull on docker store fails - Docker pull on images on docker store fails. For instance,
```
docker pull store/ibmcorp/db2wh_ce:v2.9.0-db2wh_client-linux
```
Internal bug 2152747. | non_test | docker pull on docker store fails docker pull on images on docker store fails for instance docker pull store ibmcorp ce client linux internal bug | 0 |
43,620 | 13,025,132,069 | IssuesEvent | 2020-07-27 13:04:49 | elastic/elasticsearch | https://api.github.com/repos/elastic/elasticsearch | closed | [DOC] Improve clarity for dervied API key behaviour | :Security/Authentication >docs Team:Docs Team:Security | The [7.6.2 breaking changes](https://www.elastic.co/guide/en/elasticsearch/reference/current/breaking-changes-7.6.html#_elasticsearch_api_key_privileges) says:
>To create derived keys with no privileges, you must explicitly specify an empty role descriptor.
>
This could give users the impression that there are options other than "no privileges". But in fact, this is the only option, i.e. derived keys must be created with no privilege. We could improve the wording so the intention is more explicit. | True | [DOC] Improve clarity for dervied API key behaviour - The [7.6.2 breaking changes](https://www.elastic.co/guide/en/elasticsearch/reference/current/breaking-changes-7.6.html#_elasticsearch_api_key_privileges) says:
>To create derived keys with no privileges, you must explicitly specify an empty role descriptor.
>
This could give users the impression that there are options other than "no privileges". But in fact, this is the only option, i.e. derived keys must be created with no privilege. We could improve the wording so the intention is more explicit. | non_test | improve clarity for dervied api key behaviour the says to create derived keys with no privileges you must explicitly specify an empty role descriptor this could give users the impression that there are options other than no privileges but in fact this is the only option i e derived keys must be created with no privilege we could improve the wording so the intention is more explicit | 0 |
69,385 | 14,988,505,257 | IssuesEvent | 2021-01-29 01:25:03 | Omni3Tech/corda | https://api.github.com/repos/Omni3Tech/corda | opened | WS-2017-0268 (Medium) detected in angular-v1.5.8 | security vulnerability | ## WS-2017-0268 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-v1.5.8</b></p></summary>
<p>null</p>
<p>
Dependency Hierarchy:
- :x: **angular-v1.5.8** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Omni3Tech/corda/commit/29c33d3b0ae2ca5fdb1be95ae420943d69013d34">29c33d3b0ae2ca5fdb1be95ae420943d69013d34</a></p>
<p>Found in base branch: <b>release/os/4.8</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Both Firefox and Safari are vulnerable to XSS if we use an inert document created via `document.implementation.createHTMLDocument()`.
<p>Publish Date: 2017-05-25
<p>URL: <a href=https://github.com/angular/angular.js/commit/8f31f1ff43b673a24f84422d5c13d6312b2c4d94>WS-2017-0268</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/RetireJS/retire.js/commit/a47c5f939e8ed4f5148acb147923f31863cb73c8">https://github.com/RetireJS/retire.js/commit/a47c5f939e8ed4f5148acb147923f31863cb73c8</a></p>
<p>Release Date: 2017-07-06</p>
<p>Fix Resolution: Replace or update the following file: jsrepository.json</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2017-0268 (Medium) detected in angular-v1.5.8 - ## WS-2017-0268 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>angular-v1.5.8</b></p></summary>
<p>null</p>
<p>
Dependency Hierarchy:
- :x: **angular-v1.5.8** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Omni3Tech/corda/commit/29c33d3b0ae2ca5fdb1be95ae420943d69013d34">29c33d3b0ae2ca5fdb1be95ae420943d69013d34</a></p>
<p>Found in base branch: <b>release/os/4.8</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Both Firefox and Safari are vulnerable to XSS if we use an inert document created via `document.implementation.createHTMLDocument()`.
<p>Publish Date: 2017-05-25
<p>URL: <a href=https://github.com/angular/angular.js/commit/8f31f1ff43b673a24f84422d5c13d6312b2c4d94>WS-2017-0268</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/RetireJS/retire.js/commit/a47c5f939e8ed4f5148acb147923f31863cb73c8">https://github.com/RetireJS/retire.js/commit/a47c5f939e8ed4f5148acb147923f31863cb73c8</a></p>
<p>Release Date: 2017-07-06</p>
<p>Fix Resolution: Replace or update the following file: jsrepository.json</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | ws medium detected in angular ws medium severity vulnerability vulnerable library angular null dependency hierarchy x angular vulnerable library found in head commit a href found in base branch release os vulnerability details both firefox and safari are vulnerable to xss if we use an inert document created via document implementation createhtmldocument publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type change files origin a href release date fix resolution replace or update the following file jsrepository json step up your open source security game with whitesource | 0 |
400,468 | 27,286,932,226 | IssuesEvent | 2023-02-23 14:08:44 | woocommerce/woocommerce-blocks | https://api.github.com/repos/woocommerce/woocommerce-blocks | closed | Add a CI job that checks that all the links in docs folder are valid | type: documentation type: cooldown | We are working hard to create great documentation. Furthermore, we are adding a lot of links and resources. I think that it makes sense to create a CI job that checks that all the links in the `docs` folder are valid. I think that we could use [this project](https://github.com/tcort/markdown-link-check). | 1.0 | Add a CI job that checks that all the links in docs folder are valid - We are working hard to create great documentation. Furthermore, we are adding a lot of links and resources. I think that it makes sense to create a CI job that checks that all the links in the `docs` folder are valid. I think that we could use [this project](https://github.com/tcort/markdown-link-check). | non_test | add a ci job that checks that all the links in docs folder are valid we are working hard to create great documentation furthermore we are adding a lot of links and resources i think that it makes sense to create a ci job that checks that all the links in the docs folder are valid i think that we could use | 0 |
100,104 | 12,505,717,297 | IssuesEvent | 2020-06-02 11:15:25 | gitcoinco/web | https://api.github.com/repos/gitcoinco/web | closed | Onboarding web2 users to web3. | Check: Owocki Gitcoin FTUX design-help discussion onboarding strategic | I think that as evangelists of the ethereum and web3 ecosystem, we may be living in an echo chamber in some ways. If you've lived & breathed blockchain for months, it can be easy to forget that the average internet user (even the average github user), doesnt have Ether, metamask installed, or even know why they can care.
What is the most efficient and impactful way you've found for telling people why they should care about understanding this ecosystem?
| 1.0 | Onboarding web2 users to web3. - I think that as evangelists of the ethereum and web3 ecosystem, we may be living in an echo chamber in some ways. If you've lived & breathed blockchain for months, it can be easy to forget that the average internet user (even the average github user), doesnt have Ether, metamask installed, or even know why they can care.
What is the most efficient and impactful way you've found for telling people why they should care about understanding this ecosystem?
| non_test | onboarding users to i think that as evangelists of the ethereum and ecosystem we may be living in an echo chamber in some ways if you ve lived breathed blockchain for months it can be easy to forget that the average internet user even the average github user doesnt have ether metamask installed or even know why they can care what is the most efficient and impactful way you ve found for telling people why they should care about understanding this ecosystem | 0 |
334,323 | 29,830,998,166 | IssuesEvent | 2023-06-18 09:15:42 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix jax_numpy_math.test_jax_numpy_deg2rad | JAX Frontend Sub Task Failing Test | | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix jax_numpy_math.test_jax_numpy_deg2rad - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5302683745/jobs/9597784377"><img src=https://img.shields.io/badge/-success-success></a>
| test | fix jax numpy math test jax numpy tensorflow a href src numpy a href src torch a href src jax a href src paddle a href src | 1 |
73,422 | 7,333,942,602 | IssuesEvent | 2018-03-05 21:04:17 | litehelpers/Cordova-sqlite-help | https://api.github.com/repos/litehelpers/Cordova-sqlite-help | opened | How to develop with desktop browser platform | doc-clarity doc-general doc-pitfall doc-todo question testing user community help | Since cordova-sqlite-storage and related plugins do not support the browser platform, the recommended workaround is to use <https://github.com/brodybits/sql-promise-helper>. Open the database with `sql-promise-helper` as follows (not tested but I did follow a similar approach on a client project):
```js
var newPromiseHelper = require('sql-promise-helper').newPromiseHelper;
var isBrowser = (cordova.platformId === 'browser');
var sqlHelper = newPromiseHelper(isBrowser ?
window.openDatabase('my.db', '1.0', 'MyDatabase', 5*1024*1024) :
window.sqlitePlugin.openDatabase({name: 'my.db', location: 'default'}));
```
then access as follows:
```js
var tx = helper.newBatchTransaction();
tx.executeStatement('DROP TABLE IF EXISTS tt');
tx.executeStatement('CREATE TABLE tt(a,b)');
tx.executeStatement('INSERT INTO tt VALUES(?,?)', [101, 'Alice']);
tx.commit().then(function() {
return helper.executeStatement('SELECT * FROM tt', null);
}).then(function(rs) {
alert('GOT RESULT LENGTH: ' + rs.rows.length + ' FIRST: ' + JSON.stringify(rs.rows.item(0)));
}).then(null, function(error) {
alert('GOT ERROR: ' + error.message);
});
``` | 1.0 | How to develop with desktop browser platform - Since cordova-sqlite-storage and related plugins do not support the browser platform, the recommended workaround is to use <https://github.com/brodybits/sql-promise-helper>. Open the database with `sql-promise-helper` as follows (not tested but I did follow a similar approach on a client project):
```js
var newPromiseHelper = require('sql-promise-helper').newPromiseHelper;
var isBrowser = (cordova.platformId === 'browser');
var sqlHelper = newPromiseHelper(isBrowser ?
window.openDatabase('my.db', '1.0', 'MyDatabase', 5*1024*1024) :
window.sqlitePlugin.openDatabase({name: 'my.db', location: 'default'}));
```
then access as follows:
```js
var tx = helper.newBatchTransaction();
tx.executeStatement('DROP TABLE IF EXISTS tt');
tx.executeStatement('CREATE TABLE tt(a,b)');
tx.executeStatement('INSERT INTO tt VALUES(?,?)', [101, 'Alice']);
tx.commit().then(function() {
return helper.executeStatement('SELECT * FROM tt', null);
}).then(function(rs) {
alert('GOT RESULT LENGTH: ' + rs.rows.length + ' FIRST: ' + JSON.stringify(rs.rows.item(0)));
}).then(null, function(error) {
alert('GOT ERROR: ' + error.message);
});
``` | test | how to develop with desktop browser platform since cordova sqlite storage and related plugins do not support the browser platform the recommended workaround is to use open the database with sql promise helper as follows not tested but i did follow a similar approach on a client project js var newpromisehelper require sql promise helper newpromisehelper var isbrowser cordova platformid browser var sqlhelper newpromisehelper isbrowser window opendatabase my db mydatabase window sqliteplugin opendatabase name my db location default then access as follows js var tx helper newbatchtransaction tx executestatement drop table if exists tt tx executestatement create table tt a b tx executestatement insert into tt values tx commit then function return helper executestatement select from tt null then function rs alert got result length rs rows length first json stringify rs rows item then null function error alert got error error message | 1 |
229,150 | 7,571,919,144 | IssuesEvent | 2018-04-23 13:40:03 | strapi/strapi | https://api.github.com/repos/strapi/strapi | reopened | Import / export data | priority: low type: feature request 🙏 | **Node.js version**:
8.9.4
**npm version**:
5.6.0
**Strapi version**:
latest
**Operating system**:
Windows 10
**Do you want to request a *feature* or report a *bug*?**
request a feature
Is there a simple way to upload data from csv file? For example, I would like to create new API called "products" with couple of features (size, color and so on). I do not want to add entry by entry, but prefer to upload all the products from csv file.
Is that currently possible or I need to create a plugin/develop it by myself/etc? | 1.0 | Import / export data - **Node.js version**:
8.9.4
**npm version**:
5.6.0
**Strapi version**:
latest
**Operating system**:
Windows 10
**Do you want to request a *feature* or report a *bug*?**
request a feature
Is there a simple way to upload data from csv file? For example, I would like to create new API called "products" with couple of features (size, color and so on). I do not want to add entry by entry, but prefer to upload all the products from csv file.
Is that currently possible or I need to create a plugin/develop it by myself/etc? | non_test | import export data node js version npm version strapi version latest operating system windows do you want to request a feature or report a bug request a feature is there a simple way to upload data from csv file for example i would like to create new api called products with couple of features size color and so on i do not want to add entry by entry but prefer to upload all the products from csv file is that currently possible or i need to create a plugin develop it by myself etc | 0 |
14,096 | 3,798,376,215 | IssuesEvent | 2016-03-23 12:16:21 | vigetlabs/microcosm | https://api.github.com/repos/vigetlabs/microcosm | closed | Documentation - Add console.logs values | documentation | In our guides, we use console.log in a few places. We should add a little comment on the side of them that lets the reader know what they should see.
Thanks, @cwmanning | 1.0 | Documentation - Add console.logs values - In our guides, we use console.log in a few places. We should add a little comment on the side of them that lets the reader know what they should see.
Thanks, @cwmanning | non_test | documentation add console logs values in our guides we use console log in a few places we should add a little comment on the side of them that lets the reader know what they should see thanks cwmanning | 0 |
102,229 | 31,877,106,064 | IssuesEvent | 2023-09-16 00:56:23 | SethClydesdale/code-vein-builder | https://api.github.com/repos/SethClydesdale/code-vein-builder | closed | Build Submission [by Sentaired1] | build | Build Name: Church of Zwei
Build Category: Two Handed Weapons
Build Link/Code: https://sethclydesdale.github.io/code-vein-builder/?build=IIZgjAPgQpAMHEoi9kFFIGEwBYEE5p4AxEQ0vbeAEXjUsMwA4JMQBWIA / IIZgjAPgQpAMHEoi9kFFIGEwBYEE5p4AxEQ0vbeAEXjUsMwA4JMQBWIA
Build Description: Utilizes a Zwiehander to tear through everyone | 1.0 | Build Submission [by Sentaired1] - Build Name: Church of Zwei
Build Category: Two Handed Weapons
Build Link/Code: https://sethclydesdale.github.io/code-vein-builder/?build=IIZgjAPgQpAMHEoi9kFFIGEwBYEE5p4AxEQ0vbeAEXjUsMwA4JMQBWIA / IIZgjAPgQpAMHEoi9kFFIGEwBYEE5p4AxEQ0vbeAEXjUsMwA4JMQBWIA
Build Description: Utilizes a Zwiehander to tear through everyone | non_test | build submission build name church of zwei build category two handed weapons build link code build description utilizes a zwiehander to tear through everyone | 0 |
111,065 | 17,009,700,993 | IssuesEvent | 2021-07-02 01:08:59 | tamirdahan/keycloak | https://api.github.com/repos/tamirdahan/keycloak | opened | CVE-2017-7658 (High) detected in multiple libraries | security vulnerability | ## CVE-2017-7658 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jetty-http-9.4.3.v20170317.jar</b>, <b>jetty-http-9.4.5.v20170502.jar</b>, <b>jetty-server-9.4.6.v20170531.jar</b>, <b>jetty-http-9.4.6.v20170531.jar</b></p></summary>
<p>
<details><summary><b>jetty-http-9.4.3.v20170317.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: keycloak/testsuite/model/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.3.v20170317/jetty-http-9.4.3.v20170317.jar</p>
<p>
Dependency Hierarchy:
- integration-arquillian-tests-base-15.0.0-SNAPSHOT.jar (Root Library)
- graphene-webdriver-2.3.2.pom
- arquillian-drone-webdriver-depchain-2.4.3.pom
- htmlunit-driver-2.26.jar
- htmlunit-2.26.jar
- websocket-client-9.4.3.v20170317.jar
- jetty-client-9.4.3.v20170317.jar
- :x: **jetty-http-9.4.3.v20170317.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-http-9.4.5.v20170502.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.5.v20170502/jetty-http-9.4.5.v20170502.jar</p>
<p>
Dependency Hierarchy:
- graphene-webdriver-2.3.2.pom (Root Library)
- arquillian-drone-webdriver-depchain-2.5.2.pom
- htmlunit-driver-2.27.jar
- htmlunit-2.27.jar
- websocket-client-9.4.5.v20170502.jar
- jetty-client-9.4.5.v20170502.jar
- :x: **jetty-http-9.4.5.v20170502.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-server-9.4.6.v20170531.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: keycloak/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-server/9.4.6.v20170531/jetty-server-9.4.6.v20170531.jar</p>
<p>
Dependency Hierarchy:
- camel-jetty9-2.21.2.jar (Root Library)
- :x: **jetty-server-9.4.6.v20170531.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-http-9.4.6.v20170531.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: keycloak/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.6.v20170531/jetty-http-9.4.6.v20170531.jar</p>
<p>
Dependency Hierarchy:
- camel-jetty9-2.21.2.jar (Root Library)
- jetty-server-9.4.6.v20170531.jar
- :x: **jetty-http-9.4.6.v20170531.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Eclipse Jetty Server, versions 9.2.x and older, 9.3.x (all non HTTP/1.x configurations), and 9.4.x (all HTTP/1.x configurations), when presented with two content-lengths headers, Jetty ignored the second. When presented with a content-length and a chunked encoding header, the content-length was ignored (as per RFC 2616). If an intermediary decided on the shorter length, but still passed on the longer body, then body content could be interpreted by Jetty as a pipelined request. If the intermediary was imposing authorization, the fake pipelined request would bypass that authorization.
<p>Publish Date: 2018-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7658>CVE-2017-7658</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7658">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7658</a></p>
<p>Release Date: 2018-06-26</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.4.3.v20170317","packageFilePaths":["/testsuite/model/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.keycloak.testsuite:integration-arquillian-tests-base:15.0.0-SNAPSHOT;org.jboss.arquillian.graphene:graphene-webdriver:2.3.2;org.jboss.arquillian.extension:arquillian-drone-webdriver-depchain:2.4.3;org.seleniumhq.selenium:htmlunit-driver:2.26;net.sourceforge.htmlunit:htmlunit:2.26;org.eclipse.jetty.websocket:websocket-client:9.4.3.v20170317;org.eclipse.jetty:jetty-client:9.4.3.v20170317;org.eclipse.jetty:jetty-http:9.4.3.v20170317","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.4.5.v20170502","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.jboss.arquillian.graphene:graphene-webdriver:2.3.2;org.jboss.arquillian.extension:arquillian-drone-webdriver-depchain:2.5.2;org.seleniumhq.selenium:htmlunit-driver:2.27;net.sourceforge.htmlunit:htmlunit:2.27;org.eclipse.jetty.websocket:websocket-client:9.4.5.v20170502;org.eclipse.jetty:jetty-client:9.4.5.v20170502;org.eclipse.jetty:jetty-http:9.4.5.v20170502","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-server","packageVersion":"9.4.6.v20170531","packageFilePaths":["/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.camel:camel-jetty9:2.21.2;org.eclipse.jetty:jetty-server:9.4.6.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.4.6.v20170531","packageFilePaths":["/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.camel:camel-jetty9:2.21.2;org.eclipse.jetty:jetty-server:9.4.6.v20170531;org.eclipse.jetty:jetty-http:9.4.6.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-7658","vulnerabilityDetails":"In Eclipse Jetty Server, versions 9.2.x and older, 9.3.x (all non HTTP/1.x configurations), and 9.4.x (all HTTP/1.x configurations), when presented with two content-lengths headers, Jetty ignored the second. When presented with a content-length and a chunked encoding header, the content-length was ignored (as per RFC 2616). If an intermediary decided on the shorter length, but still passed on the longer body, then body content could be interpreted by Jetty as a pipelined request. If the intermediary was imposing authorization, the fake pipelined request would bypass that authorization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7658","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-7658 (High) detected in multiple libraries - ## CVE-2017-7658 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jetty-http-9.4.3.v20170317.jar</b>, <b>jetty-http-9.4.5.v20170502.jar</b>, <b>jetty-server-9.4.6.v20170531.jar</b>, <b>jetty-http-9.4.6.v20170531.jar</b></p></summary>
<p>
<details><summary><b>jetty-http-9.4.3.v20170317.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: keycloak/testsuite/model/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.3.v20170317/jetty-http-9.4.3.v20170317.jar</p>
<p>
Dependency Hierarchy:
- integration-arquillian-tests-base-15.0.0-SNAPSHOT.jar (Root Library)
- graphene-webdriver-2.3.2.pom
- arquillian-drone-webdriver-depchain-2.4.3.pom
- htmlunit-driver-2.26.jar
- htmlunit-2.26.jar
- websocket-client-9.4.3.v20170317.jar
- jetty-client-9.4.3.v20170317.jar
- :x: **jetty-http-9.4.3.v20170317.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-http-9.4.5.v20170502.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.5.v20170502/jetty-http-9.4.5.v20170502.jar</p>
<p>
Dependency Hierarchy:
- graphene-webdriver-2.3.2.pom (Root Library)
- arquillian-drone-webdriver-depchain-2.5.2.pom
- htmlunit-driver-2.27.jar
- htmlunit-2.27.jar
- websocket-client-9.4.5.v20170502.jar
- jetty-client-9.4.5.v20170502.jar
- :x: **jetty-http-9.4.5.v20170502.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-server-9.4.6.v20170531.jar</b></p></summary>
<p>The core jetty server artifact.</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: keycloak/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-server/9.4.6.v20170531/jetty-server-9.4.6.v20170531.jar</p>
<p>
Dependency Hierarchy:
- camel-jetty9-2.21.2.jar (Root Library)
- :x: **jetty-server-9.4.6.v20170531.jar** (Vulnerable Library)
</details>
<details><summary><b>jetty-http-9.4.6.v20170531.jar</b></p></summary>
<p>The Eclipse Jetty Project</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to dependency file: keycloak/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/eclipse/jetty/jetty-http/9.4.6.v20170531/jetty-http-9.4.6.v20170531.jar</p>
<p>
Dependency Hierarchy:
- camel-jetty9-2.21.2.jar (Root Library)
- jetty-server-9.4.6.v20170531.jar
- :x: **jetty-http-9.4.6.v20170531.jar** (Vulnerable Library)
</details>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Eclipse Jetty Server, versions 9.2.x and older, 9.3.x (all non HTTP/1.x configurations), and 9.4.x (all HTTP/1.x configurations), when presented with two content-lengths headers, Jetty ignored the second. When presented with a content-length and a chunked encoding header, the content-length was ignored (as per RFC 2616). If an intermediary decided on the shorter length, but still passed on the longer body, then body content could be interpreted by Jetty as a pipelined request. If the intermediary was imposing authorization, the fake pipelined request would bypass that authorization.
<p>Publish Date: 2018-06-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7658>CVE-2017-7658</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7658">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-7658</a></p>
<p>Release Date: 2018-06-26</p>
<p>Fix Resolution: org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.4.3.v20170317","packageFilePaths":["/testsuite/model/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.keycloak.testsuite:integration-arquillian-tests-base:15.0.0-SNAPSHOT;org.jboss.arquillian.graphene:graphene-webdriver:2.3.2;org.jboss.arquillian.extension:arquillian-drone-webdriver-depchain:2.4.3;org.seleniumhq.selenium:htmlunit-driver:2.26;net.sourceforge.htmlunit:htmlunit:2.26;org.eclipse.jetty.websocket:websocket-client:9.4.3.v20170317;org.eclipse.jetty:jetty-client:9.4.3.v20170317;org.eclipse.jetty:jetty-http:9.4.3.v20170317","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.4.5.v20170502","packageFilePaths":[],"isTransitiveDependency":true,"dependencyTree":"org.jboss.arquillian.graphene:graphene-webdriver:2.3.2;org.jboss.arquillian.extension:arquillian-drone-webdriver-depchain:2.5.2;org.seleniumhq.selenium:htmlunit-driver:2.27;net.sourceforge.htmlunit:htmlunit:2.27;org.eclipse.jetty.websocket:websocket-client:9.4.5.v20170502;org.eclipse.jetty:jetty-client:9.4.5.v20170502;org.eclipse.jetty:jetty-http:9.4.5.v20170502","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-server","packageVersion":"9.4.6.v20170531","packageFilePaths":["/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.camel:camel-jetty9:2.21.2;org.eclipse.jetty:jetty-server:9.4.6.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"},{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-http","packageVersion":"9.4.6.v20170531","packageFilePaths":["/testsuite/integration-arquillian/test-apps/fuse/camel/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.camel:camel-jetty9:2.21.2;org.eclipse.jetty:jetty-server:9.4.6.v20170531;org.eclipse.jetty:jetty-http:9.4.6.v20170531","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.eclipse.jetty:jetty-server:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty.aggregate:jetty-client:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606;org.eclipse.jetty:jetty-http:9.4.11.v20180605,9.3.24.v20180605,9.2.25.v20180606"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-7658","vulnerabilityDetails":"In Eclipse Jetty Server, versions 9.2.x and older, 9.3.x (all non HTTP/1.x configurations), and 9.4.x (all HTTP/1.x configurations), when presented with two content-lengths headers, Jetty ignored the second. When presented with a content-length and a chunked encoding header, the content-length was ignored (as per RFC 2616). If an intermediary decided on the shorter length, but still passed on the longer body, then body content could be interpreted by Jetty as a pipelined request. If the intermediary was imposing authorization, the fake pipelined request would bypass that authorization.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-7658","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries jetty http jar jetty http jar jetty server jar jetty http jar jetty http jar the eclipse jetty project library home page a href path to dependency file keycloak testsuite model pom xml path to vulnerable library home wss scanner repository org eclipse jetty jetty http jetty http jar dependency hierarchy integration arquillian tests base snapshot jar root library graphene webdriver pom arquillian drone webdriver depchain pom htmlunit driver jar htmlunit jar websocket client jar jetty client jar x jetty http jar vulnerable library jetty http jar the eclipse jetty project library home page a href path to vulnerable library home wss scanner repository org eclipse jetty jetty http jetty http jar dependency hierarchy graphene webdriver pom root library arquillian drone webdriver depchain pom htmlunit driver jar htmlunit jar websocket client jar jetty client jar x jetty http jar vulnerable library jetty server jar the core jetty server artifact library home page a href path to dependency file keycloak testsuite integration arquillian test apps fuse camel pom xml path to vulnerable library home wss scanner repository org eclipse jetty jetty server jetty server jar dependency hierarchy camel jar root library x jetty server jar vulnerable library jetty http jar the eclipse jetty project library home page a href path to dependency file keycloak testsuite integration arquillian test apps fuse camel pom xml path to vulnerable library home wss scanner repository org eclipse jetty jetty http jetty http jar dependency hierarchy camel jar root library jetty server jar x jetty http jar vulnerable library found in base branch master vulnerability details in eclipse jetty server versions x and older x all non http x configurations and x all http x configurations when presented with two content lengths headers jetty ignored the second when presented with a content length and a chunked encoding header the content length was ignored as per rfc if an intermediary decided on the shorter length but still passed on the longer body then body content could be interpreted by jetty as a pipelined request if the intermediary was imposing authorization the fake pipelined request would bypass that authorization publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org eclipse jetty jetty server org eclipse jetty aggregate jetty client org eclipse jetty jetty http isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org keycloak testsuite integration arquillian tests base snapshot org jboss arquillian graphene graphene webdriver org jboss arquillian extension arquillian drone webdriver depchain org seleniumhq selenium htmlunit driver net sourceforge htmlunit htmlunit org eclipse jetty websocket websocket client org eclipse jetty jetty client org eclipse jetty jetty http isminimumfixversionavailable true minimumfixversion org eclipse jetty jetty server org eclipse jetty aggregate jetty client org eclipse jetty jetty http packagetype java groupid org eclipse jetty packagename jetty http packageversion packagefilepaths istransitivedependency true dependencytree org jboss arquillian graphene graphene webdriver org jboss arquillian extension arquillian drone webdriver depchain org seleniumhq selenium htmlunit driver net sourceforge htmlunit htmlunit org eclipse jetty websocket websocket client org eclipse jetty jetty client org eclipse jetty jetty http isminimumfixversionavailable true minimumfixversion org eclipse jetty jetty server org eclipse jetty aggregate jetty client org eclipse jetty jetty http packagetype java groupid org eclipse jetty packagename jetty server packageversion packagefilepaths istransitivedependency true dependencytree org apache camel camel org eclipse jetty jetty server isminimumfixversionavailable true minimumfixversion org eclipse jetty jetty server org eclipse jetty aggregate jetty client org eclipse jetty jetty http packagetype java groupid org eclipse jetty packagename jetty http packageversion packagefilepaths istransitivedependency true dependencytree org apache camel camel org eclipse jetty jetty server org eclipse jetty jetty http isminimumfixversionavailable true minimumfixversion org eclipse jetty jetty server org eclipse jetty aggregate jetty client org eclipse jetty jetty http basebranches vulnerabilityidentifier cve vulnerabilitydetails in eclipse jetty server versions x and older x all non http x configurations and x all http x configurations when presented with two content lengths headers jetty ignored the second when presented with a content length and a chunked encoding header the content length was ignored as per rfc if an intermediary decided on the shorter length but still passed on the longer body then body content could be interpreted by jetty as a pipelined request if the intermediary was imposing authorization the fake pipelined request would bypass that authorization vulnerabilityurl | 0 |
415,279 | 12,127,291,507 | IssuesEvent | 2020-04-22 18:28:22 | Reese2596/CPW215-Spring2020-DataTracker | https://api.github.com/repos/Reese2596/CPW215-Spring2020-DataTracker | opened | Fill out Features paragraph | interface low priority | The "Features" paragraph on the home page was not filled out because we don't have/know all the features that will be implemented. Near the end of our project this quarter, I believe that we will be able to properly fill this out with what features we have implemented. | 1.0 | Fill out Features paragraph - The "Features" paragraph on the home page was not filled out because we don't have/know all the features that will be implemented. Near the end of our project this quarter, I believe that we will be able to properly fill this out with what features we have implemented. | non_test | fill out features paragraph the features paragraph on the home page was not filled out because we don t have know all the features that will be implemented near the end of our project this quarter i believe that we will be able to properly fill this out with what features we have implemented | 0 |
8,367 | 7,360,995,507 | IssuesEvent | 2018-03-11 00:53:53 | procxx/kepka | https://api.github.com/repos/procxx/kepka | closed | Appveyor Level Up | infrastructure | - [x] build only `RelWithDebInfo` on Appveyor
- [x] pack it without PDB
- [x] pack PDBs into a separate archive
- [x] run `ctest` (`ctest .`, see on Travis)
- [x] publish `Release` to GitHub releases (see [this](https://github.com/matwey/fips3/blob/60c1bfd5d6cee9bced17fe5b19347c5be9cffa8e/.appveyor.yml#L32-L43) as an example) | 1.0 | Appveyor Level Up - - [x] build only `RelWithDebInfo` on Appveyor
- [x] pack it without PDB
- [x] pack PDBs into a separate archive
- [x] run `ctest` (`ctest .`, see on Travis)
- [x] publish `Release` to GitHub releases (see [this](https://github.com/matwey/fips3/blob/60c1bfd5d6cee9bced17fe5b19347c5be9cffa8e/.appveyor.yml#L32-L43) as an example) | non_test | appveyor level up build only relwithdebinfo on appveyor pack it without pdb pack pdbs into a separate archive run ctest ctest see on travis publish release to github releases see as an example | 0 |
332,198 | 29,190,581,422 | IssuesEvent | 2023-05-19 19:33:26 | ValveSoftware/steam-for-linux | https://api.github.com/repos/ValveSoftware/steam-for-linux | closed | Stuck Update Install Loop / Rebuilding | Steam client Need Retest Distro Family: Ubuntu | Phenom II 1090T
12GB DDR3
nVIDIA RTX2060; Driver 435
Now unknown at this point
OS: Kubuntu 20.04
Beta? No
Regularly perform Updates
Persistently oscillating between "Pins potentially out-of-date Rebuilding" / "update eternally hanging at 0 progress", every attempt for running steam. Also have attempted, without any internet connection applied [hoping to perform a clear cache on layout]. Multiple wipe downs of steam / dependencies... Occasionally mentions about an "uninstalled manifest found"
"client-download.steampowered.com/client/steam_client_ubuntu_12"?
How to clear this mess?
Is their anyway, to STOP these client bricking updates!?
| 1.0 | Stuck Update Install Loop / Rebuilding - Phenom II 1090T
12GB DDR3
nVIDIA RTX2060; Driver 435
Now unknown at this point
OS: Kubuntu 20.04
Beta? No
Regularly perform Updates
Persistently oscillating between "Pins potentially out-of-date Rebuilding" / "update eternally hanging at 0 progress", every attempt for running steam. Also have attempted, without any internet connection applied [hoping to perform a clear cache on layout]. Multiple wipe downs of steam / dependencies... Occasionally mentions about an "uninstalled manifest found"
"client-download.steampowered.com/client/steam_client_ubuntu_12"?
How to clear this mess?
Is their anyway, to STOP these client bricking updates!?
| test | stuck update install loop rebuilding phenom ii nvidia driver now unknown at this point os kubuntu beta no regularly perform updates persistently oscillating between pins potentially out of date rebuilding update eternally hanging at progress every attempt for running steam also have attempted without any internet connection applied multiple wipe downs of steam dependencies occasionally mentions about an uninstalled manifest found client download steampowered com client steam client ubuntu how to clear this mess is their anyway to stop these client bricking updates | 1 |
379,835 | 26,389,684,439 | IssuesEvent | 2023-01-12 14:51:15 | linkall-labs/docs | https://api.github.com/repos/linkall-labs/docs | closed | [Good First Issues]: Update Transformer Concept "linkall-labs/docs/blob/main/content/introduction/concepts.md" worth 4 Points | documentation good first issue help wanted | Documentation
Motivation
The best way to learn about an open-source project starts with reading its documentation. In order to better know about Vanus and improve the quality of Vanus documentation, we're looking for OSS enthusiasts to review our docs.
Details
Rewrite the concept of transformer in the documentation. The Concept should introduce the idea of the transformer tool and briefly the idea of Define, Function, and template. You can look at the "How to Transformer Document" to help you better. Also the concept should be simple and a concept, not how to.
How to change it:
<img width="512" alt="Screen Shot 2023-01-10 at 16 37 42" src="https://user-images.githubusercontent.com/62085623/211504728-26a8e37f-e81a-437f-8594-7ee11892a359.png">
1. Fork the docs repository.
2. Create a branch update-Concept-Transformer
3. Update file linkall-labs/docs/blob/main/content/introduction/concepts.md
4. In the section Transformer.
5. Replace the content.
To understand transform read the following page > https://www.linkall.com/how-to/manage-subscription/transformer
| 1.0 | [Good First Issues]: Update Transformer Concept "linkall-labs/docs/blob/main/content/introduction/concepts.md" worth 4 Points - Documentation
Motivation
The best way to learn about an open-source project starts with reading its documentation. In order to better know about Vanus and improve the quality of Vanus documentation, we're looking for OSS enthusiasts to review our docs.
Details
Rewrite the concept of transformer in the documentation. The Concept should introduce the idea of the transformer tool and briefly the idea of Define, Function, and template. You can look at the "How to Transformer Document" to help you better. Also the concept should be simple and a concept, not how to.
How to change it:
<img width="512" alt="Screen Shot 2023-01-10 at 16 37 42" src="https://user-images.githubusercontent.com/62085623/211504728-26a8e37f-e81a-437f-8594-7ee11892a359.png">
1. Fork the docs repository.
2. Create a branch update-Concept-Transformer
3. Update file linkall-labs/docs/blob/main/content/introduction/concepts.md
4. In the section Transformer.
5. Replace the content.
To understand transform read the following page > https://www.linkall.com/how-to/manage-subscription/transformer
| non_test | update transformer concept linkall labs docs blob main content introduction concepts md worth points documentation motivation the best way to learn about an open source project starts with reading its documentation in order to better know about vanus and improve the quality of vanus documentation we re looking for oss enthusiasts to review our docs details rewrite the concept of transformer in the documentation the concept should introduce the idea of the transformer tool and briefly the idea of define function and template you can look at the how to transformer document to help you better also the concept should be simple and a concept not how to how to change it img width alt screen shot at src fork the docs repository create a branch update concept transformer update file linkall labs docs blob main content introduction concepts md in the section transformer replace the content to understand transform read the following page | 0 |
3,042 | 2,652,792,007 | IssuesEvent | 2015-03-16 19:17:52 | softlayer/sl-ember-components | https://api.github.com/repos/softlayer/sl-ember-components | closed | Add tests for sl-calendar-month component | 0 - Backlog sl-calendar tests |
<!---
@huboard:{"order":4.263256414560601e-14,"milestone_order":204,"custom_state":""}
-->
| 1.0 | Add tests for sl-calendar-month component -
<!---
@huboard:{"order":4.263256414560601e-14,"milestone_order":204,"custom_state":""}
-->
| test | add tests for sl calendar month component huboard order milestone order custom state | 1 |
182,941 | 14,171,223,167 | IssuesEvent | 2020-11-12 15:27:41 | appirio-tech/connect-app | https://api.github.com/repos/appirio-tech/connect-app | closed | New Intake Form: Beacon | Feature: Intake P2 QA Pass in Prod QA Pass in Test intake_form_update | ### Context
A new project solution intake form needs to be created for Data Science.
### Catalog: Pathway, Copy Content, Visibility
**Display Pathway:** + New Project > + Solution > Data Science Section
**Title:** Beacon
**Catalog Description:** Get your problem unstuck, de-risked, and solved to exacting standards with this wayfinding solution. First, we bring your early-stage, thorny problems and tap into direct feedback from Topcoder crowd experts to define your problem statement, identify performance metrics, and estimate solution performance. Then, a bounty-driven, pay-for-performance competition is launched to produce the results you need without unnecessary risks.
**Catalog Expected Deliverables:**
- Report of crowd-generated recommendations
- Tested algorithm/model or application that meets performance criteria
- Analysis and documentation for winning solution
**Form Visibility:** Catalog/form can be viewed by all registered users.
### Intake Form
**Objective Flags:** No changes.
**Intro**
- Name your project: [Free Text Field]
- What are the objectives of your data science project?: [Free Text Response]
- Reference Code: [Free Text Response]
**Main Body**
- **Question 1:** Describe the problem’s background. What ambiguities or sticking points do you need resolved?
- **Question 1, Answer 1 Format:** [Free Text Response]
- **Question 2:** Are there academic papers or other sources that should be considered as inputs for your project?
- **Question 2, Answer 1 Format:** [Yes/No Toggle Button], defaulted to No.
- **Question 2, Answer 2 Format:** If “Yes” is selected, display a [Free Text Response] field with this text displayed over the field: “Please list source URLs”
- **Question 3:** Describe the relevant data (format/structure) you can share with crowd participants.
- **Question 3, Answer 1 Format:** [Free Text Response]
- **Question 4:** What is the approximate best fit for your data set size?
- **Question 4, Answer 1 Format:** [Radio Buttons]
-Less than 100MB
-100MB - 10GB
-10GB - 50GB
-More than 50GB
-More than 1TB
- **Question 5:** Where is your data located?
- **Question 5, Sub-Text:** Please provide URLs, if possible.
- **Question 5, Answer 1 Format:** [Free Text Response]
- **Question 6:** Is your data licensed, subject to any patent, export or treaty restrictions, or are there other roadblocks of which Topcoder should be aware?
- **Question 6, Answer 1 Format:** [Yes/No Toggle Button], defaulted to No.
- **Question 6, Answer 2 Format:** If Yes is selected, display [Free Text Entry] field.
- **Question 7.A:** Approximately what percent of your data is labeled?
- **Question 7.A, Answer 1 Format:** [Radio Buttons]
-0%
-10%
-20%
-30%
-40%
-50%
-60%
-70%
-80%
-90%
-100%
_Note: Only display Question 7.B if the user selected any answer option other than “100%” in Question 7.A._
- **Question 7.B:** Can Topcoder help label your data?
- **Question 7.B, Answer 1 Format:** [Yes/No Toggle Button], defaulted to Yes.
- **Question 8.A:** Solutions are delivered as command line programs. Will you need your output to be further prepared for production use?
- **Question 8.A, Answer 1 Format:** [Radio Buttons]
-Yes, I will need results fitted with a GUI, deployed as an API, etc.
-No, I will work with the command line results.
_Note: Only display Question 8.B if the user selected “Yes, I will need results fitted with a GUI, deployed as an API, etc.” in Question 8.A._
- **Question 8.B:** Describe how you will interact with and deploy your results.
- **Question 8.B, Answer 1 Format:** [Free Text Entry]
- **Question 9:** Please provide any additional notes/context you believe is important for us to know.
- **Question 9, Answer 1 Format:** [Free Text Entry]
| 1.0 | New Intake Form: Beacon - ### Context
A new project solution intake form needs to be created for Data Science.
### Catalog: Pathway, Copy Content, Visibility
**Display Pathway:** + New Project > + Solution > Data Science Section
**Title:** Beacon
**Catalog Description:** Get your problem unstuck, de-risked, and solved to exacting standards with this wayfinding solution. First, we bring your early-stage, thorny problems and tap into direct feedback from Topcoder crowd experts to define your problem statement, identify performance metrics, and estimate solution performance. Then, a bounty-driven, pay-for-performance competition is launched to produce the results you need without unnecessary risks.
**Catalog Expected Deliverables:**
- Report of crowd-generated recommendations
- Tested algorithm/model or application that meets performance criteria
- Analysis and documentation for winning solution
**Form Visibility:** Catalog/form can be viewed by all registered users.
### Intake Form
**Objective Flags:** No changes.
**Intro**
- Name your project: [Free Text Field]
- What are the objectives of your data science project?: [Free Text Response]
- Reference Code: [Free Text Response]
**Main Body**
- **Question 1:** Describe the problem’s background. What ambiguities or sticking points do you need resolved?
- **Question 1, Answer 1 Format:** [Free Text Response]
- **Question 2:** Are there academic papers or other sources that should be considered as inputs for your project?
- **Question 2, Answer 1 Format:** [Yes/No Toggle Button], defaulted to No.
- **Question 2, Answer 2 Format:** If “Yes” is selected, display a [Free Text Response] field with this text displayed over the field: “Please list source URLs”
- **Question 3:** Describe the relevant data (format/structure) you can share with crowd participants.
- **Question 3, Answer 1 Format:** [Free Text Response]
- **Question 4:** What is the approximate best fit for your data set size?
- **Question 4, Answer 1 Format:** [Radio Buttons]
-Less than 100MB
-100MB - 10GB
-10GB - 50GB
-More than 50GB
-More than 1TB
- **Question 5:** Where is your data located?
- **Question 5, Sub-Text:** Please provide URLs, if possible.
- **Question 5, Answer 1 Format:** [Free Text Response]
- **Question 6:** Is your data licensed, subject to any patent, export or treaty restrictions, or are there other roadblocks of which Topcoder should be aware?
- **Question 6, Answer 1 Format:** [Yes/No Toggle Button], defaulted to No.
- **Question 6, Answer 2 Format:** If Yes is selected, display [Free Text Entry] field.
- **Question 7.A:** Approximately what percent of your data is labeled?
- **Question 7.A, Answer 1 Format:** [Radio Buttons]
-0%
-10%
-20%
-30%
-40%
-50%
-60%
-70%
-80%
-90%
-100%
_Note: Only display Question 7.B if the user selected any answer option other than “100%” in Question 7.A._
- **Question 7.B:** Can Topcoder help label your data?
- **Question 7.B, Answer 1 Format:** [Yes/No Toggle Button], defaulted to Yes.
- **Question 8.A:** Solutions are delivered as command line programs. Will you need your output to be further prepared for production use?
- **Question 8.A, Answer 1 Format:** [Radio Buttons]
-Yes, I will need results fitted with a GUI, deployed as an API, etc.
-No, I will work with the command line results.
_Note: Only display Question 8.B if the user selected “Yes, I will need results fitted with a GUI, deployed as an API, etc.” in Question 8.A._
- **Question 8.B:** Describe how you will interact with and deploy your results.
- **Question 8.B, Answer 1 Format:** [Free Text Entry]
- **Question 9:** Please provide any additional notes/context you believe is important for us to know.
- **Question 9, Answer 1 Format:** [Free Text Entry]
| test | new intake form beacon context a new project solution intake form needs to be created for data science catalog pathway copy content visibility display pathway new project solution data science section title beacon catalog description get your problem unstuck de risked and solved to exacting standards with this wayfinding solution first we bring your early stage thorny problems and tap into direct feedback from topcoder crowd experts to define your problem statement identify performance metrics and estimate solution performance then a bounty driven pay for performance competition is launched to produce the results you need without unnecessary risks catalog expected deliverables report of crowd generated recommendations tested algorithm model or application that meets performance criteria analysis and documentation for winning solution form visibility catalog form can be viewed by all registered users intake form objective flags no changes intro name your project what are the objectives of your data science project reference code main body question describe the problem’s background what ambiguities or sticking points do you need resolved question answer format question are there academic papers or other sources that should be considered as inputs for your project question answer format defaulted to no question answer format if “yes” is selected display a field with this text displayed over the field “please list source urls” question describe the relevant data format structure you can share with crowd participants question answer format question what is the approximate best fit for your data set size question answer format less than more than more than question where is your data located question sub text please provide urls if possible question answer format question is your data licensed subject to any patent export or treaty restrictions or are there other roadblocks of which topcoder should be aware question answer format defaulted to no question answer format if yes is selected display field question a approximately what percent of your data is labeled question a answer format note only display question b if the user selected any answer option other than “ ” in question a question b can topcoder help label your data question b answer format defaulted to yes question a solutions are delivered as command line programs will you need your output to be further prepared for production use question a answer format yes i will need results fitted with a gui deployed as an api etc no i will work with the command line results note only display question b if the user selected “yes i will need results fitted with a gui deployed as an api etc ” in question a question b describe how you will interact with and deploy your results question b answer format question please provide any additional notes context you believe is important for us to know question answer format | 1 |
233,875 | 19,074,617,973 | IssuesEvent | 2021-11-27 14:46:14 | ericcornelissen/shescape | https://api.github.com/repos/ericcornelissen/shescape | opened | Fuzzing for Windows | help wanted test | # Task
- **Shescape version**: `1.2.1`
- **Operating system**: Windows (10 or higher)
## Description
[The existing fuzz test suite](https://github.com/ericcornelissen/shescape/blob/c880abe6c68349dbcab192cb38da73618bd45bd7/test/index.fuzz.cjs) is build for unix system. As escaping arguments on Windows is fundamentally different it would ideally be fuzz tested as well.
This ticket exists as a reminder of sorts to, ideally, build a fuzz target for Windows. There's no real requirement other than that it should be relatively straightforward to get working on any Windows system. I.e. the fuzz target may require an additional [dependencies](https://github.com/ericcornelissen/shescape/blob/c880abe6c68349dbcab192cb38da73618bd45bd7/package.json#L48) or [prerequisites](https://github.com/ericcornelissen/shescape/blob/main/CONTRIBUTING.md#project-setup), but not something that requires extensive expertise to get working. | 1.0 | Fuzzing for Windows - # Task
- **Shescape version**: `1.2.1`
- **Operating system**: Windows (10 or higher)
## Description
[The existing fuzz test suite](https://github.com/ericcornelissen/shescape/blob/c880abe6c68349dbcab192cb38da73618bd45bd7/test/index.fuzz.cjs) is build for unix system. As escaping arguments on Windows is fundamentally different it would ideally be fuzz tested as well.
This ticket exists as a reminder of sorts to, ideally, build a fuzz target for Windows. There's no real requirement other than that it should be relatively straightforward to get working on any Windows system. I.e. the fuzz target may require an additional [dependencies](https://github.com/ericcornelissen/shescape/blob/c880abe6c68349dbcab192cb38da73618bd45bd7/package.json#L48) or [prerequisites](https://github.com/ericcornelissen/shescape/blob/main/CONTRIBUTING.md#project-setup), but not something that requires extensive expertise to get working. | test | fuzzing for windows task shescape version operating system windows or higher description is build for unix system as escaping arguments on windows is fundamentally different it would ideally be fuzz tested as well this ticket exists as a reminder of sorts to ideally build a fuzz target for windows there s no real requirement other than that it should be relatively straightforward to get working on any windows system i e the fuzz target may require an additional or but not something that requires extensive expertise to get working | 1 |
95,210 | 16,074,200,470 | IssuesEvent | 2021-04-25 02:56:41 | samq-ghdemo/JS-Demo | https://api.github.com/repos/samq-ghdemo/JS-Demo | closed | CVE-2017-16042 (High) detected in growl-1.9.2.tgz - autoclosed | security vulnerability | ## CVE-2017-16042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>growl-1.9.2.tgz</b></p></summary>
<p>Growl unobtrusive notifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/growl/-/growl-1.9.2.tgz">https://registry.npmjs.org/growl/-/growl-1.9.2.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/growl/package.json</p>
<p>
Dependency Hierarchy:
- mocha-2.5.3.tgz (Root Library)
- :x: **growl-1.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/46781df511f58c350408cb5158290290709b373c">46781df511f58c350408cb5158290290709b373c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042>CVE-2017-16042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16042">https://nvd.nist.gov/vuln/detail/CVE-2017-16042</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: 1.10.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"growl","packageVersion":"1.9.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"mocha:2.5.3;growl:1.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.10.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-16042","vulnerabilityDetails":"Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2017-16042 (High) detected in growl-1.9.2.tgz - autoclosed - ## CVE-2017-16042 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>growl-1.9.2.tgz</b></p></summary>
<p>Growl unobtrusive notifications</p>
<p>Library home page: <a href="https://registry.npmjs.org/growl/-/growl-1.9.2.tgz">https://registry.npmjs.org/growl/-/growl-1.9.2.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/growl/package.json</p>
<p>
Dependency Hierarchy:
- mocha-2.5.3.tgz (Root Library)
- :x: **growl-1.9.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/46781df511f58c350408cb5158290290709b373c">46781df511f58c350408cb5158290290709b373c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.
<p>Publish Date: 2018-06-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042>CVE-2017-16042</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2017-16042">https://nvd.nist.gov/vuln/detail/CVE-2017-16042</a></p>
<p>Release Date: 2018-06-04</p>
<p>Fix Resolution: 1.10.2</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"growl","packageVersion":"1.9.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"mocha:2.5.3;growl:1.9.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"1.10.2"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2017-16042","vulnerabilityDetails":"Growl adds growl notification support to nodejs. Growl before 1.10.2 does not properly sanitize input before passing it to exec, allowing for arbitrary command execution.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2017-16042","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in growl tgz autoclosed cve high severity vulnerability vulnerable library growl tgz growl unobtrusive notifications library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules growl package json dependency hierarchy mocha tgz root library x growl tgz vulnerable library found in head commit a href found in base branch master vulnerability details growl adds growl notification support to nodejs growl before does not properly sanitize input before passing it to exec allowing for arbitrary command execution publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree mocha growl isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails growl adds growl notification support to nodejs growl before does not properly sanitize input before passing it to exec allowing for arbitrary command execution vulnerabilityurl | 0 |
266,591 | 23,247,614,501 | IssuesEvent | 2022-08-03 22:03:34 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | closed | acceptance: `TestComposeGSS` broken with Go 1.17 | C-test-failure A-testing skipped-test T-sql-experience T-server-and-security | `TestComposeGSS` fails with:
```
Step 5/10 : RUN GO111MODULE=off go test -v -c -tags gss_compose -o gss.test
---> Running in e80775fb9678
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:698:14: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:703:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:705:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:707:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:710:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:712:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:1092:30: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:1115:40: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/marshal.go:738:18: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/marshal.go:744:28: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:712:17: too many errors
```
This is because it depends on `github.com/jcmturner/gofork` without pinning the version, and it now requires Go 1.18. A simple Go version bump to 1.18 causes the test to fail differently.
Jira issue: CRDB-17984 | 3.0 | acceptance: `TestComposeGSS` broken with Go 1.17 - `TestComposeGSS` fails with:
```
Step 5/10 : RUN GO111MODULE=off go test -v -c -tags gss_compose -o gss.test
---> Running in e80775fb9678
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:698:14: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:703:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:705:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:707:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:710:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:712:17: cannot assign string to result in multiple assignment
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:1092:30: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:1115:40: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/marshal.go:738:18: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/marshal.go:744:28: undefined: any
/go/src/github.com/jcmturner/gofork/encoding/asn1/asn1.go:712:17: too many errors
```
This is because it depends on `github.com/jcmturner/gofork` without pinning the version, and it now requires Go 1.18. A simple Go version bump to 1.18 causes the test to fail differently.
Jira issue: CRDB-17984 | test | acceptance testcomposegss broken with go testcomposegss fails with step run off go test v c tags gss compose o gss test running in go src github com jcmturner gofork encoding go undefined any go src github com jcmturner gofork encoding go cannot assign string to result in multiple assignment go src github com jcmturner gofork encoding go cannot assign string to result in multiple assignment go src github com jcmturner gofork encoding go cannot assign string to result in multiple assignment go src github com jcmturner gofork encoding go cannot assign string to result in multiple assignment go src github com jcmturner gofork encoding go cannot assign string to result in multiple assignment go src github com jcmturner gofork encoding go undefined any go src github com jcmturner gofork encoding go undefined any go src github com jcmturner gofork encoding marshal go undefined any go src github com jcmturner gofork encoding marshal go undefined any go src github com jcmturner gofork encoding go too many errors this is because it depends on github com jcmturner gofork without pinning the version and it now requires go a simple go version bump to causes the test to fail differently jira issue crdb | 1 |
167,311 | 26,484,211,201 | IssuesEvent | 2023-01-17 16:44:18 | laurareimann/Finanztracker | https://api.github.com/repos/laurareimann/Finanztracker | closed | Dimens.xml: Dimensionen-Variablen festlegen | concept & design | wie auch bei String und colors, kann man in der dimens.xml unter Values Sachen wie font size etc festlegen.
Das können wir standardisieren, damit das Design der Seiten einheitlich ist und man sich nicht selber überlegen muss, welche Zahlen man da eingeben soll | 1.0 | Dimens.xml: Dimensionen-Variablen festlegen - wie auch bei String und colors, kann man in der dimens.xml unter Values Sachen wie font size etc festlegen.
Das können wir standardisieren, damit das Design der Seiten einheitlich ist und man sich nicht selber überlegen muss, welche Zahlen man da eingeben soll | non_test | dimens xml dimensionen variablen festlegen wie auch bei string und colors kann man in der dimens xml unter values sachen wie font size etc festlegen das können wir standardisieren damit das design der seiten einheitlich ist und man sich nicht selber überlegen muss welche zahlen man da eingeben soll | 0 |
106,212 | 9,121,998,111 | IssuesEvent | 2019-02-23 03:14:22 | knative/build | https://api.github.com/repos/knative/build | closed | v0.4.0 build.yaml file is missing config-logging configmap, controller and webhook deployments | area/test-and-release kind/bug | <!--
Pro-tip: You can leave this block commented, and it still works!
Select the appropriate areas for your issue and remove the leading >
> /area API
> /area monitoring
/area test-and-release
Classify what kind of issue this is:
> /kind question
/kind bug
> /kind cleanup
> /kind doc
> /kind feature
> /kind good-first-issue
> /kind process
> /kind spec
-->
## Expected Behavior
The v0.4.0 build.yaml should presumably include the config-logging configmap and the controller and webhook deployments. Not sure if it's by design, but relative to the v0.3.0 release, definitions of kind image are also missing.
## Actual Behavior
## Steps to Reproduce the Problem
1.
2.
3.
## Additional Info
| 1.0 | v0.4.0 build.yaml file is missing config-logging configmap, controller and webhook deployments - <!--
Pro-tip: You can leave this block commented, and it still works!
Select the appropriate areas for your issue and remove the leading >
> /area API
> /area monitoring
/area test-and-release
Classify what kind of issue this is:
> /kind question
/kind bug
> /kind cleanup
> /kind doc
> /kind feature
> /kind good-first-issue
> /kind process
> /kind spec
-->
## Expected Behavior
The v0.4.0 build.yaml should presumably include the config-logging configmap and the controller and webhook deployments. Not sure if it's by design, but relative to the v0.3.0 release, definitions of kind image are also missing.
## Actual Behavior
## Steps to Reproduce the Problem
1.
2.
3.
## Additional Info
| test | build yaml file is missing config logging configmap controller and webhook deployments pro tip you can leave this block commented and it still works select the appropriate areas for your issue and remove the leading area api area monitoring area test and release classify what kind of issue this is kind question kind bug kind cleanup kind doc kind feature kind good first issue kind process kind spec expected behavior the build yaml should presumably include the config logging configmap and the controller and webhook deployments not sure if it s by design but relative to the release definitions of kind image are also missing actual behavior steps to reproduce the problem additional info | 1 |
146,506 | 19,406,105,000 | IssuesEvent | 2021-12-20 01:03:37 | samqws-marketing/amzn-ion-hive-serde | https://api.github.com/repos/samqws-marketing/amzn-ion-hive-serde | opened | CVE-2021-4104 (High) detected in log4j-1.2.17.jar | security vulnerability | ## CVE-2021-4104 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: amzn-ion-hive-serde/serde/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/log4j/log4j/1.2.17/5af35056b4d257e4b64b9e8069c0746e8b08629f/log4j-1.2.17.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/log4j/log4j/1.2.17/5af35056b4d257e4b64b9e8069c0746e8b08629f/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- hadoop-common-2.7.1.jar (Root Library)
- slf4j-log4j12-1.7.10.jar
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
<p>Found in base branch: <b>0.3.0</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JMSAppender in Log4j 1.2 is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration. The attacker can provide TopicBindingName and TopicConnectionFactoryBindingName configurations causing JMSAppender to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-44228. Note this issue only affects Log4j 1.2 when specifically configured to use JMSAppender, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-4104>CVE-2021-4104</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.17","packageFilePaths":["/serde/build.gradle","/integration-test/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hadoop:hadoop-common:2.7.1;org.slf4j:slf4j-log4j12:1.7.10;log4j:log4j:1.2.17","isMinimumFixVersionAvailable":false,"isBinary":false}],"baseBranches":["0.3.0"],"vulnerabilityIdentifier":"CVE-2021-4104","vulnerabilityDetails":"JMSAppender in Log4j 1.2 is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration. The attacker can provide TopicBindingName and TopicConnectionFactoryBindingName configurations causing JMSAppender to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-44228. Note this issue only affects Log4j 1.2 when specifically configured to use JMSAppender, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-4104","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-4104 (High) detected in log4j-1.2.17.jar - ## CVE-2021-4104 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-1.2.17.jar</b></p></summary>
<p>Apache Log4j 1.2</p>
<p>Path to dependency file: amzn-ion-hive-serde/serde/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/log4j/log4j/1.2.17/5af35056b4d257e4b64b9e8069c0746e8b08629f/log4j-1.2.17.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/log4j/log4j/1.2.17/5af35056b4d257e4b64b9e8069c0746e8b08629f/log4j-1.2.17.jar</p>
<p>
Dependency Hierarchy:
- hadoop-common-2.7.1.jar (Root Library)
- slf4j-log4j12-1.7.10.jar
- :x: **log4j-1.2.17.jar** (Vulnerable Library)
<p>Found in base branch: <b>0.3.0</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
JMSAppender in Log4j 1.2 is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration. The attacker can provide TopicBindingName and TopicConnectionFactoryBindingName configurations causing JMSAppender to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-44228. Note this issue only affects Log4j 1.2 when specifically configured to use JMSAppender, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-4104>CVE-2021-4104</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"log4j","packageName":"log4j","packageVersion":"1.2.17","packageFilePaths":["/serde/build.gradle","/integration-test/build.gradle"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hadoop:hadoop-common:2.7.1;org.slf4j:slf4j-log4j12:1.7.10;log4j:log4j:1.2.17","isMinimumFixVersionAvailable":false,"isBinary":false}],"baseBranches":["0.3.0"],"vulnerabilityIdentifier":"CVE-2021-4104","vulnerabilityDetails":"JMSAppender in Log4j 1.2 is vulnerable to deserialization of untrusted data when the attacker has write access to the Log4j configuration. The attacker can provide TopicBindingName and TopicConnectionFactoryBindingName configurations causing JMSAppender to perform JNDI requests that result in remote code execution in a similar fashion to CVE-2021-44228. Note this issue only affects Log4j 1.2 when specifically configured to use JMSAppender, which is not the default. Apache Log4j 1.2 reached end of life in August 2015. Users should upgrade to Log4j 2 as it addresses numerous other issues from the previous versions.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-4104","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_test | cve high detected in jar cve high severity vulnerability vulnerable library jar apache path to dependency file amzn ion hive serde serde build gradle path to vulnerable library home wss scanner gradle caches modules files jar home wss scanner gradle caches modules files jar dependency hierarchy hadoop common jar root library jar x jar vulnerable library found in base branch vulnerability details jmsappender in is vulnerable to deserialization of untrusted data when the attacker has write access to the configuration the attacker can provide topicbindingname and topicconnectionfactorybindingname configurations causing jmsappender to perform jndi requests that result in remote code execution in a similar fashion to cve note this issue only affects when specifically configured to use jmsappender which is not the default apache reached end of life in august users should upgrade to as it addresses numerous other issues from the previous versions publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache hadoop hadoop common org isminimumfixversionavailable false isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails jmsappender in is vulnerable to deserialization of untrusted data when the attacker has write access to the configuration the attacker can provide topicbindingname and topicconnectionfactorybindingname configurations causing jmsappender to perform jndi requests that result in remote code execution in a similar fashion to cve note this issue only affects when specifically configured to use jmsappender which is not the default apache reached end of life in august users should upgrade to as it addresses numerous other issues from the previous versions vulnerabilityurl | 0 |
272,534 | 23,679,733,955 | IssuesEvent | 2022-08-28 16:11:50 | nodejs/node | https://api.github.com/repos/nodejs/node | opened | DNS channel cancel tests do not work as intended | dns test | See https://github.com/nodejs/node/pull/44022#discussion_r932056817.
`test/parallel/test-dns-channel-cancel-promise.js` and `test/parallel/test-dns-channel-cancel.js` do not work as intended.
Both tests use `mustNotCall()` incorrectly, passing `mustNotCall` (i.e., a utility function that returns a function) when they should likely be passing `mustNotCall()` (i.e., the function returned by `mustNotCall`). However, properly using `mustNotCall()` (as in https://github.com/nodejs/node/pull/44022) leads to failures because the function is indeed being called when the tests say that it should not be.
https://github.com/nodejs/node/blob/3370e7c53a41c70a1e16ff8acb0e23817775d812/test/parallel/test-dns-channel-cancel-promise.js#L10-L18
https://github.com/nodejs/node/blob/3370e7c53a41c70a1e16ff8acb0e23817775d812/test/parallel/test-dns-channel-cancel.js#L13-L21
Example output in https://github.com/nodejs/node/pull/44022:
```
16:49:21 not ok 575 parallel/test-dns-channel-cancel
16:49:21 ---
16:49:21 duration_ms: 0.116
16:49:21 severity: fail
16:49:21 exitcode: 1
16:49:21 stack: |-
16:49:21 node:assert:171
16:49:21 throw err;
16:49:21 ^
16:49:21
16:49:21 AssertionError [ERR_ASSERTION]: function should not have been called at /home/iojs/build/workspace/node-test-commit-linuxone/test/parallel/test-dns-channel-cancel.js:17
16:49:21 called with arguments: <Buffer b0 9b 01 00 00 01 00 00 00 00 00 00 08 65 78 61 6d 70 6c 65 32 03 6f 72 67 00 00 01 00 01>, { address: '127.0.0.1', family: 'IPv4', port: 60918, size: 30 }
16:49:21 at Socket.mustNotCall (/home/iojs/build/workspace/node-test-commit-linuxone/test/common/index.js:522:12)
16:49:21 at Object.onceWrapper (node:events:628:26)
16:49:21 at Socket.emit (node:events:513:28)
16:49:21 at UDP.onMessage [as onmessage] (node:dgram:930:8) {
16:49:21 generatedMessage: false,
16:49:21 code: 'ERR_ASSERTION',
16:49:21 actual: undefined,
16:49:21 expected: undefined,
16:49:21 operator: 'fail'
16:49:21 }
16:49:21
16:49:21 Node.js v19.0.0-pre
16:49:21 ...
```
```
16:49:21 not ok 576 parallel/test-dns-channel-cancel-promise
16:49:21 ---
16:49:21 duration_ms: 0.59
16:49:21 severity: fail
16:49:21 exitcode: 1
16:49:21 stack: |-
16:49:21 node:assert:171
16:49:21 throw err;
16:49:21 ^
16:49:21
16:49:21 AssertionError [ERR_ASSERTION]: function should not have been called at /home/iojs/build/workspace/node-test-commit-linuxone/test/parallel/test-dns-channel-cancel-promise.js:14
16:49:21 called with arguments: <Buffer b0 9b 01 00 00 01 00 00 00 00 00 00 08 65 78 61 6d 70 6c 65 32 03 6f 72 67 00 00 01 00 01>, { address: '127.0.0.1', family: 'IPv4', port: 33976, size: 30 }
16:49:21 at Socket.mustNotCall (/home/iojs/build/workspace/node-test-commit-linuxone/test/common/index.js:522:12)
16:49:21 at Object.onceWrapper (node:events:628:26)
16:49:21 at Socket.emit (node:events:513:28)
16:49:21 at UDP.onMessage [as onmessage] (node:dgram:930:8) {
16:49:21 generatedMessage: false,
16:49:21 code: 'ERR_ASSERTION',
16:49:21 actual: undefined,
16:49:21 expected: undefined,
16:49:21 operator: 'fail'
16:49:21 }
16:49:21
16:49:21 Node.js v19.0.0-pre
16:49:21 ...
``` | 1.0 | DNS channel cancel tests do not work as intended - See https://github.com/nodejs/node/pull/44022#discussion_r932056817.
`test/parallel/test-dns-channel-cancel-promise.js` and `test/parallel/test-dns-channel-cancel.js` do not work as intended.
Both tests use `mustNotCall()` incorrectly, passing `mustNotCall` (i.e., a utility function that returns a function) when they should likely be passing `mustNotCall()` (i.e., the function returned by `mustNotCall`). However, properly using `mustNotCall()` (as in https://github.com/nodejs/node/pull/44022) leads to failures because the function is indeed being called when the tests say that it should not be.
https://github.com/nodejs/node/blob/3370e7c53a41c70a1e16ff8acb0e23817775d812/test/parallel/test-dns-channel-cancel-promise.js#L10-L18
https://github.com/nodejs/node/blob/3370e7c53a41c70a1e16ff8acb0e23817775d812/test/parallel/test-dns-channel-cancel.js#L13-L21
Example output in https://github.com/nodejs/node/pull/44022:
```
16:49:21 not ok 575 parallel/test-dns-channel-cancel
16:49:21 ---
16:49:21 duration_ms: 0.116
16:49:21 severity: fail
16:49:21 exitcode: 1
16:49:21 stack: |-
16:49:21 node:assert:171
16:49:21 throw err;
16:49:21 ^
16:49:21
16:49:21 AssertionError [ERR_ASSERTION]: function should not have been called at /home/iojs/build/workspace/node-test-commit-linuxone/test/parallel/test-dns-channel-cancel.js:17
16:49:21 called with arguments: <Buffer b0 9b 01 00 00 01 00 00 00 00 00 00 08 65 78 61 6d 70 6c 65 32 03 6f 72 67 00 00 01 00 01>, { address: '127.0.0.1', family: 'IPv4', port: 60918, size: 30 }
16:49:21 at Socket.mustNotCall (/home/iojs/build/workspace/node-test-commit-linuxone/test/common/index.js:522:12)
16:49:21 at Object.onceWrapper (node:events:628:26)
16:49:21 at Socket.emit (node:events:513:28)
16:49:21 at UDP.onMessage [as onmessage] (node:dgram:930:8) {
16:49:21 generatedMessage: false,
16:49:21 code: 'ERR_ASSERTION',
16:49:21 actual: undefined,
16:49:21 expected: undefined,
16:49:21 operator: 'fail'
16:49:21 }
16:49:21
16:49:21 Node.js v19.0.0-pre
16:49:21 ...
```
```
16:49:21 not ok 576 parallel/test-dns-channel-cancel-promise
16:49:21 ---
16:49:21 duration_ms: 0.59
16:49:21 severity: fail
16:49:21 exitcode: 1
16:49:21 stack: |-
16:49:21 node:assert:171
16:49:21 throw err;
16:49:21 ^
16:49:21
16:49:21 AssertionError [ERR_ASSERTION]: function should not have been called at /home/iojs/build/workspace/node-test-commit-linuxone/test/parallel/test-dns-channel-cancel-promise.js:14
16:49:21 called with arguments: <Buffer b0 9b 01 00 00 01 00 00 00 00 00 00 08 65 78 61 6d 70 6c 65 32 03 6f 72 67 00 00 01 00 01>, { address: '127.0.0.1', family: 'IPv4', port: 33976, size: 30 }
16:49:21 at Socket.mustNotCall (/home/iojs/build/workspace/node-test-commit-linuxone/test/common/index.js:522:12)
16:49:21 at Object.onceWrapper (node:events:628:26)
16:49:21 at Socket.emit (node:events:513:28)
16:49:21 at UDP.onMessage [as onmessage] (node:dgram:930:8) {
16:49:21 generatedMessage: false,
16:49:21 code: 'ERR_ASSERTION',
16:49:21 actual: undefined,
16:49:21 expected: undefined,
16:49:21 operator: 'fail'
16:49:21 }
16:49:21
16:49:21 Node.js v19.0.0-pre
16:49:21 ...
``` | test | dns channel cancel tests do not work as intended see test parallel test dns channel cancel promise js and test parallel test dns channel cancel js do not work as intended both tests use mustnotcall incorrectly passing mustnotcall i e a utility function that returns a function when they should likely be passing mustnotcall i e the function returned by mustnotcall however properly using mustnotcall as in leads to failures because the function is indeed being called when the tests say that it should not be example output in not ok parallel test dns channel cancel duration ms severity fail exitcode stack node assert throw err assertionerror function should not have been called at home iojs build workspace node test commit linuxone test parallel test dns channel cancel js called with arguments address family port size at socket mustnotcall home iojs build workspace node test commit linuxone test common index js at object oncewrapper node events at socket emit node events at udp onmessage node dgram generatedmessage false code err assertion actual undefined expected undefined operator fail node js pre not ok parallel test dns channel cancel promise duration ms severity fail exitcode stack node assert throw err assertionerror function should not have been called at home iojs build workspace node test commit linuxone test parallel test dns channel cancel promise js called with arguments address family port size at socket mustnotcall home iojs build workspace node test commit linuxone test common index js at object oncewrapper node events at socket emit node events at udp onmessage node dgram generatedmessage false code err assertion actual undefined expected undefined operator fail node js pre | 1 |
244,110 | 20,610,658,481 | IssuesEvent | 2022-03-07 08:15:25 | ckeditor/ckeditor4 | https://api.github.com/repos/ckeditor/ckeditor4 | closed | Failing test: tests/plugins/emoji/dropdown [Opera] | status:confirmed browser:opera type:failingtest | ## Type of report
Bug
## Provide detailed reproduction steps (if any)
Failing test: `test navigation highlights proper section when scrolls`
Full test path: `tests/plugins/emoji/dropdown#tests%2Fplugins%2Femoji%2Fdropdown%20test%20navigation%20highlights%20proper%20section%20when%20scrolls`
### Actual result
```
Travel item in navigation should be highlighted
Expected: true (boolean)
Actual: false (boolean)
```
## Other details
* Browser: Opera 78.0.4093.112 (arm64)
* OS: BigSur 11.4
* CKEditor version: 4.16.2
* Dev unit tests
This test is failing only when running with other tests in `tests/plugins/emoji/dropdown`. If I open a single test `test navigation highlights proper section when scrolls` then it's passing.
Seems like an issue with arm64 (macbooks with M1)? This test is passing when I'm running it on Mac with Intel CPU.
| 1.0 | Failing test: tests/plugins/emoji/dropdown [Opera] - ## Type of report
Bug
## Provide detailed reproduction steps (if any)
Failing test: `test navigation highlights proper section when scrolls`
Full test path: `tests/plugins/emoji/dropdown#tests%2Fplugins%2Femoji%2Fdropdown%20test%20navigation%20highlights%20proper%20section%20when%20scrolls`
### Actual result
```
Travel item in navigation should be highlighted
Expected: true (boolean)
Actual: false (boolean)
```
## Other details
* Browser: Opera 78.0.4093.112 (arm64)
* OS: BigSur 11.4
* CKEditor version: 4.16.2
* Dev unit tests
This test is failing only when running with other tests in `tests/plugins/emoji/dropdown`. If I open a single test `test navigation highlights proper section when scrolls` then it's passing.
Seems like an issue with arm64 (macbooks with M1)? This test is passing when I'm running it on Mac with Intel CPU.
| test | failing test tests plugins emoji dropdown type of report bug provide detailed reproduction steps if any failing test test navigation highlights proper section when scrolls full test path tests plugins emoji dropdown tests actual result travel item in navigation should be highlighted expected true boolean actual false boolean other details browser opera os bigsur ckeditor version dev unit tests this test is failing only when running with other tests in tests plugins emoji dropdown if i open a single test test navigation highlights proper section when scrolls then it s passing seems like an issue with macbooks with this test is passing when i m running it on mac with intel cpu | 1 |
226,479 | 18,021,193,189 | IssuesEvent | 2021-09-16 19:40:30 | eclipse-iceoryx/iceoryx-rs | https://api.github.com/repos/eclipse-iceoryx/iceoryx-rs | opened | Setup CI | test tooling | PR should only be merged when the tests pass
This is should most probably done after #5 | 1.0 | Setup CI - PR should only be merged when the tests pass
This is should most probably done after #5 | test | setup ci pr should only be merged when the tests pass this is should most probably done after | 1 |
204,583 | 15,936,576,271 | IssuesEvent | 2021-04-14 11:20:20 | kabouzeid/nvim-lspinstall | https://api.github.com/repos/kabouzeid/nvim-lspinstall | closed | wget dependacy errors on mac | documentation good first issue | Some `LspInstall <arg>` commands result in a call to `wget`. If this isn't installed (as it wasn't on my Mac) the process exits with the error
```
command not found: wget
```
I was able to install the typescript server just fine, but others (such as html) errored.
If this is a necessary dependacy I guess that should be documented? A simple `brew install wget` fixed the issue. | 1.0 | wget dependacy errors on mac - Some `LspInstall <arg>` commands result in a call to `wget`. If this isn't installed (as it wasn't on my Mac) the process exits with the error
```
command not found: wget
```
I was able to install the typescript server just fine, but others (such as html) errored.
If this is a necessary dependacy I guess that should be documented? A simple `brew install wget` fixed the issue. | non_test | wget dependacy errors on mac some lspinstall commands result in a call to wget if this isn t installed as it wasn t on my mac the process exits with the error command not found wget i was able to install the typescript server just fine but others such as html errored if this is a necessary dependacy i guess that should be documented a simple brew install wget fixed the issue | 0 |
174,726 | 13,507,882,832 | IssuesEvent | 2020-09-14 06:49:00 | home-assistant/core | https://api.github.com/repos/home-assistant/core | closed | test_clear_logs is flaky | flapping-test | <!-- READ THIS FIRST:
- If you need additional help with this template, please refer to https://www.home-assistant.io/help/reporting_issues/
- Make sure you are running the latest version of Home Assistant before reporting an issue: https://github.com/home-assistant/core/releases
- Do not report issues for integrations if you are using custom components or integrations.
- Provide as many details as possible. Paste logs, configuration samples and code into the backticks.
DO NOT DELETE ANY TEXT from this template! Otherwise, your issue may be closed without comment.
-->
## The problem
<!--
Describe the issue you are experiencing here to communicate to the
maintainers. Tell us what you were trying to do and what happened.
-->
The `test_clear_logs` test is flaky. Failed once, didn't fail on the second try.
## Environment
<!--
Provide details about the versions you are using, which helps us to reproduce
and find the issue quicker. Version information is found in the
Home Assistant frontend: Configuration -> Info.
-->
- Home Assistant Core release with the issue: 0.114.4
- Last working Home Assistant Core release (if known): no idea
- Operating environment (OS/Container/Supervised/Core): NixOS 20.09
- Integration causing this issue: n/a
- Link to integration documentation on our website: n/a
## Traceback/Error logs
<!--
If you come across any trace or error logs, please provide them.
-->
```txt
=================================== FAILURES ===================================
___________________________ test_clear_logs[pyloop] ____________________________
hass = <homeassistant.core.HomeAssistant object at 0x7ffff3c1b220>
simple_queue = <_queue.SimpleQueue object at 0x7ffff0651630>
hass_client = <function hass_client.<locals>.auth_client at 0x7ffff17261f0>
async def test_clear_logs(hass, simple_queue, hass_client):
"""Test that the log can be cleared via a service call."""
await async_setup_component(hass, system_log.DOMAIN, BASIC_CONFIG)
_LOGGER.error("error message")
await _async_block_until_queue_empty(hass, simple_queue)
hass.async_add_job(
hass.services.async_call(system_log.DOMAIN, system_log.SERVICE_CLEAR, {})
)
await _async_block_until_queue_empty(hass, simple_queue)
# Assert done by get_error_log
> await get_error_log(hass, hass_client, 0)
tests/components/system_log/test_init.py:237:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
hass = <homeassistant.core.HomeAssistant object at 0x7ffff3c1b220>
hass_client = <function hass_client.<locals>.auth_client at 0x7ffff17261f0>
expected_count = 0
async def get_error_log(hass, hass_client, expected_count):
"""Fetch all entries from system_log via the API."""
client = await hass_client()
resp = await client.get("/api/error/all")
assert resp.status == 200
data = await resp.json()
> assert len(data) == expected_count
E AssertionError: assert 1 == 0
E + where 1 = len([{'count': 1, 'exception': '', 'first_occurred': 1599952993.326157, 'level': 'ERROR', ...}])
tests/components/system_log/test_init.py:46: AssertionError
---------------------------- Captured stderr setup -----------------------------
DEBUG:asyncio:Using selector: EpollSelector
------------------------------ Captured log setup ------------------------------
DEBUG asyncio:selector_events.py:59 Using selector: EpollSelector
----------------------------- Captured stderr call -----------------------------
INFO:homeassistant.loader:Loaded test from custom_components.test
INFO:homeassistant.loader:Loaded test_package from custom_components.test_package
INFO:homeassistant.loader:Loaded system_log from homeassistant.components.system_log
INFO:homeassistant.loader:Loaded http from homeassistant.components.http
DEBUG:homeassistant.setup:Dependency system_log will wait for ['http']
INFO:homeassistant.setup:Setting up http
INFO:homeassistant.setup:Setup of domain http took 0.0 seconds
DEBUG:homeassistant.core:Bus:Handling <Event component_loaded[L]: component=http>
INFO:homeassistant.setup:Setting up system_log
DEBUG:homeassistant.core:Bus:Handling <Event service_registered[L]: domain=system_log, service=clear>
DEBUG:homeassistant.core:Bus:Handling <Event service_registered[L]: domain=system_log, service=write>
INFO:homeassistant.setup:Setup of domain system_log took 0.0 seconds
DEBUG:homeassistant.core:Bus:Handling <Event component_loaded[L]: component=system_log>
ERROR:test_logger:error message
DEBUG:homeassistant.core:Bus:Handling <Event call_service[L]: domain=system_log, service=clear, service_data=>
DEBUG:homeassistant.components.http.auth:Authenticated 127.0.0.1 for /api/error/all using bearer token
DEBUG:homeassistant.components.http.view:Serving /api/error/all to 127.0.0.1 (auth: True)
INFO:aiohttp.access:127.0.0.1 [12/Sep/2020:23:23:13 +0000] "GET /api/error/all HTTP/1.1" 200 339 "-" "Python/3.8 aiohttp/3.6.2"
------------------------------ Captured log call -------------------------------
INFO homeassistant.loader:loader.py:267 Loaded test from custom_components.test
INFO homeassistant.loader:loader.py:267 Loaded test_package from custom_components.test_package
INFO homeassistant.loader:loader.py:267 Loaded system_log from homeassistant.components.system_log
INFO homeassistant.loader:loader.py:267 Loaded http from homeassistant.components.http
DEBUG homeassistant.setup:setup.py:87 Dependency system_log will wait for ['http']
INFO homeassistant.setup:setup.py:159 Setting up http
INFO homeassistant.setup:setup.py:210 Setup of domain http took 0.0 seconds
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event component_loaded[L]: component=http>
INFO homeassistant.setup:setup.py:159 Setting up system_log
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event service_registered[L]: domain=system_log, service=clear>
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event service_registered[L]: domain=system_log, service=write>
INFO homeassistant.setup:setup.py:210 Setup of domain system_log took 0.0 seconds
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event component_loaded[L]: component=system_log>
ERROR test_logger:test_init.py:228 error message
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event call_service[L]: domain=system_log, service=clear, service_data=>
DEBUG homeassistant.components.http.auth:auth.py:119 Authenticated 127.0.0.1 for /api/error/all using bearer token
DEBUG homeassistant.components.http.view:view.py:118 Serving /api/error/all to 127.0.0.1 (auth: True)
INFO aiohttp.access:web_log.py:233 127.0.0.1 [12/Sep/2020:23:23:13 +0000] "GET /api/error/all HTTP/1.1" 200 339 "-" "Python/3.8 aiohttp/3.6.2"
--------------------------- Captured stderr teardown ---------------------------
DEBUG:homeassistant.core:Bus:Handling <Event homeassistant_stop[L]>
DEBUG:homeassistant.core:Bus:Handling <Event homeassistant_final_write[L]>
INFO:tests.common:Writing data to auth: {'version': 1, 'key': 'auth', 'data': {'users': [{'id': '9eb4b0411d02499da2e0f7395e8eba12', 'group_ids': ['system-admin'], 'is_owner': False, 'is_active': True, 'name': 'Mock User', 'system_generated': False}], 'groups': [{'id': 'system-admin', 'name': 'Administrators'}, {'id': 'system-users', 'name': 'Users'}, {'id': 'system-read-only', 'name': 'Read Only'}], 'credentials': [], 'refresh_tokens': [{'id': 'bed5072c9158470ea7caaeb2dbd4d699', 'user_id': '9eb4b0411d02499da2e0f7395e8eba12', 'client_id': 'https://example.com/app', 'client_name': None, 'client_icon': None, 'token_type': 'normal', 'created_at': '2020-09-12T23:23:13.315148+00:00', 'access_token_expiration': 1800.0, 'token': '1bbea525fb267f3b8af85654bda4034e14e24d99dc42df230510a9a51b5cc2483868dee45249e84a770a680cde59c1ed580d0c478e6ccc7501cbed48824444ef', 'jwt_key': '7ac93173388c2ea39274bb2ab39095f46aaabecb9e32366ce9d78f4ab19ffe6b0e5fccae216909aaeea19de8b32ee2a99ee4fa471ef82c786ce526426e89714d', 'last_used_at': '2020-09-12T23:23:13.315275+00:00', 'last_used_ip': None}]}}
DEBUG:homeassistant.core:Bus:Handling <Event homeassistant_close[L]>
---------------------------- Captured log teardown -----------------------------
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event homeassistant_stop[L]>
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event homeassistant_final_write[L]>
INFO tests.common:common.py:935 Writing data to auth: {'version': 1, 'key': 'auth', 'data': {'users': [{'id': '9eb4b0411d02499da2e0f7395e8eba12', 'group_ids': ['system-admin'], 'is_owner': False, 'is_active': True, 'name': 'Mock User', 'system_generated': False}], 'groups': [{'id': 'system-admin', 'name': 'Administrators'}, {'id': 'system-users', 'name': 'Users'}, {'id': 'system-read-only', 'name': 'Read Only'}], 'credentials': [], 'refresh_tokens': [{'id': 'bed5072c9158470ea7caaeb2dbd4d699', 'user_id': '9eb4b0411d02499da2e0f7395e8eba12', 'client_id': 'https://example.com/app', 'client_name': None, 'client_icon': None, 'token_type': 'normal', 'created_at': '2020-09-12T23:23:13.315148+00:00', 'access_token_expiration': 1800.0, 'token': '1bbea525fb267f3b8af85654bda4034e14e24d99dc42df230510a9a51b5cc2483868dee45249e84a770a680cde59c1ed580d0c478e6ccc7501cbed48824444ef', 'jwt_key': '7ac93173388c2ea39274bb2ab39095f46aaabecb9e32366ce9d78f4ab19ffe6b0e5fccae216909aaeea19de8b32ee2a99ee4fa471ef82c786ce526426e89714d', 'last_used_at': '2020-09-12T23:23:13.315275+00:00', 'last_used_ip': None}]}}
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event homeassistant_close[L]>
```
## Additional information
| 1.0 | test_clear_logs is flaky - <!-- READ THIS FIRST:
- If you need additional help with this template, please refer to https://www.home-assistant.io/help/reporting_issues/
- Make sure you are running the latest version of Home Assistant before reporting an issue: https://github.com/home-assistant/core/releases
- Do not report issues for integrations if you are using custom components or integrations.
- Provide as many details as possible. Paste logs, configuration samples and code into the backticks.
DO NOT DELETE ANY TEXT from this template! Otherwise, your issue may be closed without comment.
-->
## The problem
<!--
Describe the issue you are experiencing here to communicate to the
maintainers. Tell us what you were trying to do and what happened.
-->
The `test_clear_logs` test is flaky. Failed once, didn't fail on the second try.
## Environment
<!--
Provide details about the versions you are using, which helps us to reproduce
and find the issue quicker. Version information is found in the
Home Assistant frontend: Configuration -> Info.
-->
- Home Assistant Core release with the issue: 0.114.4
- Last working Home Assistant Core release (if known): no idea
- Operating environment (OS/Container/Supervised/Core): NixOS 20.09
- Integration causing this issue: n/a
- Link to integration documentation on our website: n/a
## Traceback/Error logs
<!--
If you come across any trace or error logs, please provide them.
-->
```txt
=================================== FAILURES ===================================
___________________________ test_clear_logs[pyloop] ____________________________
hass = <homeassistant.core.HomeAssistant object at 0x7ffff3c1b220>
simple_queue = <_queue.SimpleQueue object at 0x7ffff0651630>
hass_client = <function hass_client.<locals>.auth_client at 0x7ffff17261f0>
async def test_clear_logs(hass, simple_queue, hass_client):
"""Test that the log can be cleared via a service call."""
await async_setup_component(hass, system_log.DOMAIN, BASIC_CONFIG)
_LOGGER.error("error message")
await _async_block_until_queue_empty(hass, simple_queue)
hass.async_add_job(
hass.services.async_call(system_log.DOMAIN, system_log.SERVICE_CLEAR, {})
)
await _async_block_until_queue_empty(hass, simple_queue)
# Assert done by get_error_log
> await get_error_log(hass, hass_client, 0)
tests/components/system_log/test_init.py:237:
_ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _ _
hass = <homeassistant.core.HomeAssistant object at 0x7ffff3c1b220>
hass_client = <function hass_client.<locals>.auth_client at 0x7ffff17261f0>
expected_count = 0
async def get_error_log(hass, hass_client, expected_count):
"""Fetch all entries from system_log via the API."""
client = await hass_client()
resp = await client.get("/api/error/all")
assert resp.status == 200
data = await resp.json()
> assert len(data) == expected_count
E AssertionError: assert 1 == 0
E + where 1 = len([{'count': 1, 'exception': '', 'first_occurred': 1599952993.326157, 'level': 'ERROR', ...}])
tests/components/system_log/test_init.py:46: AssertionError
---------------------------- Captured stderr setup -----------------------------
DEBUG:asyncio:Using selector: EpollSelector
------------------------------ Captured log setup ------------------------------
DEBUG asyncio:selector_events.py:59 Using selector: EpollSelector
----------------------------- Captured stderr call -----------------------------
INFO:homeassistant.loader:Loaded test from custom_components.test
INFO:homeassistant.loader:Loaded test_package from custom_components.test_package
INFO:homeassistant.loader:Loaded system_log from homeassistant.components.system_log
INFO:homeassistant.loader:Loaded http from homeassistant.components.http
DEBUG:homeassistant.setup:Dependency system_log will wait for ['http']
INFO:homeassistant.setup:Setting up http
INFO:homeassistant.setup:Setup of domain http took 0.0 seconds
DEBUG:homeassistant.core:Bus:Handling <Event component_loaded[L]: component=http>
INFO:homeassistant.setup:Setting up system_log
DEBUG:homeassistant.core:Bus:Handling <Event service_registered[L]: domain=system_log, service=clear>
DEBUG:homeassistant.core:Bus:Handling <Event service_registered[L]: domain=system_log, service=write>
INFO:homeassistant.setup:Setup of domain system_log took 0.0 seconds
DEBUG:homeassistant.core:Bus:Handling <Event component_loaded[L]: component=system_log>
ERROR:test_logger:error message
DEBUG:homeassistant.core:Bus:Handling <Event call_service[L]: domain=system_log, service=clear, service_data=>
DEBUG:homeassistant.components.http.auth:Authenticated 127.0.0.1 for /api/error/all using bearer token
DEBUG:homeassistant.components.http.view:Serving /api/error/all to 127.0.0.1 (auth: True)
INFO:aiohttp.access:127.0.0.1 [12/Sep/2020:23:23:13 +0000] "GET /api/error/all HTTP/1.1" 200 339 "-" "Python/3.8 aiohttp/3.6.2"
------------------------------ Captured log call -------------------------------
INFO homeassistant.loader:loader.py:267 Loaded test from custom_components.test
INFO homeassistant.loader:loader.py:267 Loaded test_package from custom_components.test_package
INFO homeassistant.loader:loader.py:267 Loaded system_log from homeassistant.components.system_log
INFO homeassistant.loader:loader.py:267 Loaded http from homeassistant.components.http
DEBUG homeassistant.setup:setup.py:87 Dependency system_log will wait for ['http']
INFO homeassistant.setup:setup.py:159 Setting up http
INFO homeassistant.setup:setup.py:210 Setup of domain http took 0.0 seconds
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event component_loaded[L]: component=http>
INFO homeassistant.setup:setup.py:159 Setting up system_log
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event service_registered[L]: domain=system_log, service=clear>
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event service_registered[L]: domain=system_log, service=write>
INFO homeassistant.setup:setup.py:210 Setup of domain system_log took 0.0 seconds
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event component_loaded[L]: component=system_log>
ERROR test_logger:test_init.py:228 error message
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event call_service[L]: domain=system_log, service=clear, service_data=>
DEBUG homeassistant.components.http.auth:auth.py:119 Authenticated 127.0.0.1 for /api/error/all using bearer token
DEBUG homeassistant.components.http.view:view.py:118 Serving /api/error/all to 127.0.0.1 (auth: True)
INFO aiohttp.access:web_log.py:233 127.0.0.1 [12/Sep/2020:23:23:13 +0000] "GET /api/error/all HTTP/1.1" 200 339 "-" "Python/3.8 aiohttp/3.6.2"
--------------------------- Captured stderr teardown ---------------------------
DEBUG:homeassistant.core:Bus:Handling <Event homeassistant_stop[L]>
DEBUG:homeassistant.core:Bus:Handling <Event homeassistant_final_write[L]>
INFO:tests.common:Writing data to auth: {'version': 1, 'key': 'auth', 'data': {'users': [{'id': '9eb4b0411d02499da2e0f7395e8eba12', 'group_ids': ['system-admin'], 'is_owner': False, 'is_active': True, 'name': 'Mock User', 'system_generated': False}], 'groups': [{'id': 'system-admin', 'name': 'Administrators'}, {'id': 'system-users', 'name': 'Users'}, {'id': 'system-read-only', 'name': 'Read Only'}], 'credentials': [], 'refresh_tokens': [{'id': 'bed5072c9158470ea7caaeb2dbd4d699', 'user_id': '9eb4b0411d02499da2e0f7395e8eba12', 'client_id': 'https://example.com/app', 'client_name': None, 'client_icon': None, 'token_type': 'normal', 'created_at': '2020-09-12T23:23:13.315148+00:00', 'access_token_expiration': 1800.0, 'token': '1bbea525fb267f3b8af85654bda4034e14e24d99dc42df230510a9a51b5cc2483868dee45249e84a770a680cde59c1ed580d0c478e6ccc7501cbed48824444ef', 'jwt_key': '7ac93173388c2ea39274bb2ab39095f46aaabecb9e32366ce9d78f4ab19ffe6b0e5fccae216909aaeea19de8b32ee2a99ee4fa471ef82c786ce526426e89714d', 'last_used_at': '2020-09-12T23:23:13.315275+00:00', 'last_used_ip': None}]}}
DEBUG:homeassistant.core:Bus:Handling <Event homeassistant_close[L]>
---------------------------- Captured log teardown -----------------------------
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event homeassistant_stop[L]>
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event homeassistant_final_write[L]>
INFO tests.common:common.py:935 Writing data to auth: {'version': 1, 'key': 'auth', 'data': {'users': [{'id': '9eb4b0411d02499da2e0f7395e8eba12', 'group_ids': ['system-admin'], 'is_owner': False, 'is_active': True, 'name': 'Mock User', 'system_generated': False}], 'groups': [{'id': 'system-admin', 'name': 'Administrators'}, {'id': 'system-users', 'name': 'Users'}, {'id': 'system-read-only', 'name': 'Read Only'}], 'credentials': [], 'refresh_tokens': [{'id': 'bed5072c9158470ea7caaeb2dbd4d699', 'user_id': '9eb4b0411d02499da2e0f7395e8eba12', 'client_id': 'https://example.com/app', 'client_name': None, 'client_icon': None, 'token_type': 'normal', 'created_at': '2020-09-12T23:23:13.315148+00:00', 'access_token_expiration': 1800.0, 'token': '1bbea525fb267f3b8af85654bda4034e14e24d99dc42df230510a9a51b5cc2483868dee45249e84a770a680cde59c1ed580d0c478e6ccc7501cbed48824444ef', 'jwt_key': '7ac93173388c2ea39274bb2ab39095f46aaabecb9e32366ce9d78f4ab19ffe6b0e5fccae216909aaeea19de8b32ee2a99ee4fa471ef82c786ce526426e89714d', 'last_used_at': '2020-09-12T23:23:13.315275+00:00', 'last_used_ip': None}]}}
DEBUG homeassistant.core:core.py:645 Bus:Handling <Event homeassistant_close[L]>
```
## Additional information
| test | test clear logs is flaky read this first if you need additional help with this template please refer to make sure you are running the latest version of home assistant before reporting an issue do not report issues for integrations if you are using custom components or integrations provide as many details as possible paste logs configuration samples and code into the backticks do not delete any text from this template otherwise your issue may be closed without comment the problem describe the issue you are experiencing here to communicate to the maintainers tell us what you were trying to do and what happened the test clear logs test is flaky failed once didn t fail on the second try environment provide details about the versions you are using which helps us to reproduce and find the issue quicker version information is found in the home assistant frontend configuration info home assistant core release with the issue last working home assistant core release if known no idea operating environment os container supervised core nixos integration causing this issue n a link to integration documentation on our website n a traceback error logs if you come across any trace or error logs please provide them txt failures test clear logs hass simple queue hass client auth client at async def test clear logs hass simple queue hass client test that the log can be cleared via a service call await async setup component hass system log domain basic config logger error error message await async block until queue empty hass simple queue hass async add job hass services async call system log domain system log service clear await async block until queue empty hass simple queue assert done by get error log await get error log hass hass client tests components system log test init py hass hass client auth client at expected count async def get error log hass hass client expected count fetch all entries from system log via the api client await hass client resp await client get api error all assert resp status data await resp json assert len data expected count e assertionerror assert e where len tests components system log test init py assertionerror captured stderr setup debug asyncio using selector epollselector captured log setup debug asyncio selector events py using selector epollselector captured stderr call info homeassistant loader loaded test from custom components test info homeassistant loader loaded test package from custom components test package info homeassistant loader loaded system log from homeassistant components system log info homeassistant loader loaded http from homeassistant components http debug homeassistant setup dependency system log will wait for info homeassistant setup setting up http info homeassistant setup setup of domain http took seconds debug homeassistant core bus handling info homeassistant setup setting up system log debug homeassistant core bus handling debug homeassistant core bus handling info homeassistant setup setup of domain system log took seconds debug homeassistant core bus handling error test logger error message debug homeassistant core bus handling debug homeassistant components http auth authenticated for api error all using bearer token debug homeassistant components http view serving api error all to auth true info aiohttp access get api error all http python aiohttp captured log call info homeassistant loader loader py loaded test from custom components test info homeassistant loader loader py loaded test package from custom components test package info homeassistant loader loader py loaded system log from homeassistant components system log info homeassistant loader loader py loaded http from homeassistant components http debug homeassistant setup setup py dependency system log will wait for info homeassistant setup setup py setting up http info homeassistant setup setup py setup of domain http took seconds debug homeassistant core core py bus handling info homeassistant setup setup py setting up system log debug homeassistant core core py bus handling debug homeassistant core core py bus handling info homeassistant setup setup py setup of domain system log took seconds debug homeassistant core core py bus handling error test logger test init py error message debug homeassistant core core py bus handling debug homeassistant components http auth auth py authenticated for api error all using bearer token debug homeassistant components http view view py serving api error all to auth true info aiohttp access web log py get api error all http python aiohttp captured stderr teardown debug homeassistant core bus handling debug homeassistant core bus handling info tests common writing data to auth version key auth data users is owner false is active true name mock user system generated false groups credentials refresh tokens debug homeassistant core bus handling captured log teardown debug homeassistant core core py bus handling debug homeassistant core core py bus handling info tests common common py writing data to auth version key auth data users is owner false is active true name mock user system generated false groups credentials refresh tokens debug homeassistant core core py bus handling additional information | 1 |
432,040 | 30,264,980,070 | IssuesEvent | 2023-07-07 11:06:15 | Ashish-72Dragons/Time-Tracking-Tool | https://api.github.com/repos/Ashish-72Dragons/Time-Tracking-Tool | closed | Add a new change in the "service-1" of time tracking tool | documentation | As a developer i want to see the content in the table with 60vh height and 30vh width. | 1.0 | Add a new change in the "service-1" of time tracking tool - As a developer i want to see the content in the table with 60vh height and 30vh width. | non_test | add a new change in the service of time tracking tool as a developer i want to see the content in the table with height and width | 0 |
252,810 | 19,072,973,455 | IssuesEvent | 2021-11-27 08:18:15 | aws/karpenter | https://api.github.com/repos/aws/karpenter | closed | document topology spread; | documentation | since the topology spread PR (#619) has merged, we need to document it's impact. | 1.0 | document topology spread; - since the topology spread PR (#619) has merged, we need to document it's impact. | non_test | document topology spread since the topology spread pr has merged we need to document it s impact | 0 |
19,779 | 2,622,168,214 | IssuesEvent | 2015-03-04 00:13:21 | byzhang/rapidjson | https://api.github.com/repos/byzhang/rapidjson | closed | Serializing to a string | auto-migrated Priority-Medium Type-Enhancement | ```
Hello,
I am trying to serialize a JSON document to a string and I am not able to do
it. I have been reading the examples but I don´t find nothing similar. In all
the examples the serializing text is redirected to the standard output throught
the FileStream, but I need to redirect it to a string variable. How can I do
it? There is another class like String Stream or I have to implement it?
Thank you for your help.
```
Original issue reported on code.google.com by `unai.d...@gmail.com` on 27 Aug 2012 at 12:32 | 1.0 | Serializing to a string - ```
Hello,
I am trying to serialize a JSON document to a string and I am not able to do
it. I have been reading the examples but I don´t find nothing similar. In all
the examples the serializing text is redirected to the standard output throught
the FileStream, but I need to redirect it to a string variable. How can I do
it? There is another class like String Stream or I have to implement it?
Thank you for your help.
```
Original issue reported on code.google.com by `unai.d...@gmail.com` on 27 Aug 2012 at 12:32 | non_test | serializing to a string hello i am trying to serialize a json document to a string and i am not able to do it i have been reading the examples but i don´t find nothing similar in all the examples the serializing text is redirected to the standard output throught the filestream but i need to redirect it to a string variable how can i do it there is another class like string stream or i have to implement it thank you for your help original issue reported on code google com by unai d gmail com on aug at | 0 |
101,203 | 4,109,048,649 | IssuesEvent | 2016-06-06 18:10:39 | ProjectSidewalk/SidewalkWebpage | https://api.github.com/repos/ProjectSidewalk/SidewalkWebpage | opened | Moving with Arrow Keys in Street View | Priority: Low | This is a feature I noticed we do not have that seems pretty simple to implement. It does not come by default in Google Street View but I have seen it in GeoGuesser. | 1.0 | Moving with Arrow Keys in Street View - This is a feature I noticed we do not have that seems pretty simple to implement. It does not come by default in Google Street View but I have seen it in GeoGuesser. | non_test | moving with arrow keys in street view this is a feature i noticed we do not have that seems pretty simple to implement it does not come by default in google street view but i have seen it in geoguesser | 0 |
10,124 | 3,357,623,238 | IssuesEvent | 2015-11-19 02:52:03 | aroberge/reeborg | https://api.github.com/repos/aroberge/reeborg | closed | Special GvR menu | documentation | Create a world suite that reproduce those of Guido van Robot; include a special gvr.py module which reproduces all the builtin as closely as possible. Include information about this in an appendix of the tut/doc. | 1.0 | Special GvR menu - Create a world suite that reproduce those of Guido van Robot; include a special gvr.py module which reproduces all the builtin as closely as possible. Include information about this in an appendix of the tut/doc. | non_test | special gvr menu create a world suite that reproduce those of guido van robot include a special gvr py module which reproduces all the builtin as closely as possible include information about this in an appendix of the tut doc | 0 |
99,993 | 8,721,256,845 | IssuesEvent | 2018-12-08 21:06:38 | BradleyA/Linux-admin | https://api.github.com/repos/BradleyA/Linux-admin | closed | cluster-command.sh test environment variables and CLI options | additional testing needs investigation | cluster-command.sh test environment variables and CLI options | 1.0 | cluster-command.sh test environment variables and CLI options - cluster-command.sh test environment variables and CLI options | test | cluster command sh test environment variables and cli options cluster command sh test environment variables and cli options | 1 |
342,187 | 30,611,785,671 | IssuesEvent | 2023-07-23 17:51:48 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | closed | Fix general.test_container_types | Sub Task Failing Test | | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
| 1.0 | Fix general.test_container_types - | | |
|---|---|
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5637759637/job/15271192541"><img src=https://img.shields.io/badge/-success-success></a>
| test | fix general test container types jax a href src numpy a href src torch a href src tensorflow a href src paddle a href src | 1 |
184 | 2,559,659,125 | IssuesEvent | 2015-02-05 03:11:42 | DIOS-Tech/BlueHarvest | https://api.github.com/repos/DIOS-Tech/BlueHarvest | closed | Fix .gitignore to not allow committing of Nuget packages | Infrastructure | Because there is a feature in Visual Studio to restore Nuget packages they should not be committed to the repository.
The .gitignore file is designed to ignore certain files from being commited. The current .gitignore contains the relevant bits but unfortunately the packages folder is commented out.
```
# NuGet Packages Directory
## TODO: If you have NuGet Package Restore enabled, uncomment the next line
#packages/
```
Turn on Nuget package restore and then uncomment this line. | 1.0 | Fix .gitignore to not allow committing of Nuget packages - Because there is a feature in Visual Studio to restore Nuget packages they should not be committed to the repository.
The .gitignore file is designed to ignore certain files from being commited. The current .gitignore contains the relevant bits but unfortunately the packages folder is commented out.
```
# NuGet Packages Directory
## TODO: If you have NuGet Package Restore enabled, uncomment the next line
#packages/
```
Turn on Nuget package restore and then uncomment this line. | non_test | fix gitignore to not allow committing of nuget packages because there is a feature in visual studio to restore nuget packages they should not be committed to the repository the gitignore file is designed to ignore certain files from being commited the current gitignore contains the relevant bits but unfortunately the packages folder is commented out nuget packages directory todo if you have nuget package restore enabled uncomment the next line packages turn on nuget package restore and then uncomment this line | 0 |
242,074 | 20,194,537,844 | IssuesEvent | 2022-02-11 09:26:50 | NOAA-EMC/WW3 | https://api.github.com/repos/NOAA-EMC/WW3 | opened | namelist for ww3_bounc | enhancement new feature Regression Test | **Describe the solution you'd like**
namelist feature for program ww3_bound
**Additional context**
can be tested with existing regtest ww3_tr1
| 1.0 | namelist for ww3_bounc - **Describe the solution you'd like**
namelist feature for program ww3_bound
**Additional context**
can be tested with existing regtest ww3_tr1
| test | namelist for bounc describe the solution you d like namelist feature for program bound additional context can be tested with existing regtest | 1 |
141,493 | 11,422,937,812 | IssuesEvent | 2020-02-03 15:03:45 | helmholtz-analytics/heat | https://api.github.com/repos/helmholtz-analytics/heat | closed | test_io getting stuck on multiple nodes | bug :bug: testing | **Description**
The unit test run gets stuck at test_io.py
**To Reproduce**
Steps to reproduce the behavior:
1. Which module/class/function is affected?
test_io.py
2. What are the circumstances under which the bug appears?
- Running on 2 nodes
3. What is the exact error-message/errorous behavious?
- no error message printed
- unit tests don't finish
**Expected behavior**
test ends successfully
**Version Info**
master / 0.2.1 | 1.0 | test_io getting stuck on multiple nodes - **Description**
The unit test run gets stuck at test_io.py
**To Reproduce**
Steps to reproduce the behavior:
1. Which module/class/function is affected?
test_io.py
2. What are the circumstances under which the bug appears?
- Running on 2 nodes
3. What is the exact error-message/errorous behavious?
- no error message printed
- unit tests don't finish
**Expected behavior**
test ends successfully
**Version Info**
master / 0.2.1 | test | test io getting stuck on multiple nodes description the unit test run gets stuck at test io py to reproduce steps to reproduce the behavior which module class function is affected test io py what are the circumstances under which the bug appears running on nodes what is the exact error message errorous behavious no error message printed unit tests don t finish expected behavior test ends successfully version info master | 1 |
790,711 | 27,833,977,347 | IssuesEvent | 2023-03-20 08:05:17 | HaDuve/TravelCostNative | https://api.github.com/repos/HaDuve/TravelCostNative | closed | adjust deep link invite to production | Bug 1 - High Priority Backend AAA - Complex | - [x] erklär text (überschrift) zu invite button
- [x] hyperlink invite link ist nicht anklickbar
- [x] bei expo schauen wie man in der production links verwendet | 1.0 | adjust deep link invite to production - - [x] erklär text (überschrift) zu invite button
- [x] hyperlink invite link ist nicht anklickbar
- [x] bei expo schauen wie man in der production links verwendet | non_test | adjust deep link invite to production erklär text überschrift zu invite button hyperlink invite link ist nicht anklickbar bei expo schauen wie man in der production links verwendet | 0 |
64,113 | 6,893,404,783 | IssuesEvent | 2017-11-23 03:29:39 | rancher/rke | https://api.github.com/repos/rancher/rke | closed | Panic-runtime error when upgrading Kubernetes cluster using an invalid cluster file | bug resolved to-test | rke version v0.0.2-dev
Steps:
1. Create a cluster(v1.7.5_coreos.0) with one master [controlplane, etcd] node and the other worker node using cluster.yml file. Use the command ./rke_darwin-amd64 cluster up --cluster-file cluster.yml
Cluster.yml file example:
```
auth:
strategy: x509
network:
plugin: flannel
hosts:
- advertised_hostname: server1
ip: 1.1.1.1
user: ubuntu
role: [controlplane, etcd]
docker_socket: /var/run/docker.sock
advertise_address: 10.1.1.1
- advertised_hostname: server2
ip: 2.2.2.2
user: ubuntu
role: [worker]
advertise_address: 10.2.2.2
services:
etcd:
image: quay.io/coreos/etcd:latest
kube-api:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
service_cluster_ip_range: 10.233.0.0/18
extra_args:
v: 4
kube-controller:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
cluster_cidr: 10.233.64.0/18
service_cluster_ip_range: 10.233.0.0/18
scheduler:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
kubelet:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
cluster_domain: cluster.local
cluster_dns_server: 10.233.0.3
infra_container_image: gcr.io/google_containers/pause-amd64:3.0
kubeproxy:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
```
2. Upgrade the cluster using a cluster file with version v1.7.6_coreos.0 but with different hosts/ip addresses not relevant to the existing cluster. It fails with the error below:
```
soumyas-MBP:rke soumya$ ./rke_darwin-amd64 cluster upgrade --cluster-file cluster1.yml
INFO[0000] Upgrading Kubernetes cluster
WARN[0000] Failed to initiate new Kubernetes Client: stat ./.kube_config_cluster1.yml: no such file or directory
panic: runtime error: invalid memory address or nil pointer dereference [recovered]
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x1d0 pc=0x1b41fbc]
goroutine 1 [running]:
github.com/rancher/rke/vendor/github.com/urfave/cli.HandleAction.func1(0xc420596900)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:472 +0x28d
panic(0x1c499e0, 0x24b77c0)
/usr/local/go/src/runtime/panic.go:489 +0x2cf
github.com/rancher/rke/cmd.ClusterUpgrade(0xc4203f2480, 0x440, 0x440, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/rancher/rke/cmd/cluster.go:202 +0x14c
github.com/rancher/rke/cmd.clusterUpgradeFromCli(0xc42049a000, 0x0, 0x0)
/go/src/github.com/rancher/rke/cmd/cluster.go:179 +0xdd
reflect.Value.call(0x1c07de0, 0x1dee648, 0x13, 0x1d78844, 0x4, 0xc4205968a0, 0x1, 0x1, 0xc420596828, 0x1d53f40, ...)
/usr/local/go/src/reflect/value.go:434 +0x91f
reflect.Value.Call(0x1c07de0, 0x1dee648, 0x13, 0xc4205968a0, 0x1, 0x1, 0x140, 0xc42049a000, 0x0)
/usr/local/go/src/reflect/value.go:302 +0xa4
github.com/rancher/rke/vendor/github.com/urfave/cli.HandleAction(0x1c07de0, 0x1dee648, 0xc42049a000, 0x0, 0x0)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:481 +0x198
github.com/rancher/rke/vendor/github.com/urfave/cli.Command.Run(0x1d7ab87, 0x7, 0x0, 0x0, 0x0, 0x0, 0x0, 0x1d92e4a, 0x22, 0x0, ...)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/command.go:186 +0xab8
github.com/rancher/rke/vendor/github.com/urfave/cli.(*App).RunAsSubcommand(0xc420498180, 0xc4201e5cc0, 0x0, 0x0)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:355 +0xa1f
github.com/rancher/rke/vendor/github.com/urfave/cli.Command.startApp(0x1d7a704, 0x7, 0x1d7a704, 0x7, 0x0, 0x0, 0x0, 0x1d8a255, 0x19, 0x0, ...)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/command.go:273 +0x81b
github.com/rancher/rke/vendor/github.com/urfave/cli.Command.Run(0x1d7a704, 0x7, 0x1d7a704, 0x7, 0x0, 0x0, 0x0, 0x1d8a255, 0x19, 0x0, ...)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/command.go:74 +0x142c
github.com/rancher/rke/vendor/github.com/urfave/cli.(*App).Run(0xc420498000, 0xc42000e140, 0x5, 0x5, 0x0, 0x0)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:235 +0x5d6
main.mainErr(0xc42025f3d0, 0xc420597f68)
/go/src/github.com/rancher/rke/main.go:41 +0x2f8
main.main()
/go/src/github.com/rancher/rke/main.go:14 +0x22
```
| 1.0 | Panic-runtime error when upgrading Kubernetes cluster using an invalid cluster file - rke version v0.0.2-dev
Steps:
1. Create a cluster(v1.7.5_coreos.0) with one master [controlplane, etcd] node and the other worker node using cluster.yml file. Use the command ./rke_darwin-amd64 cluster up --cluster-file cluster.yml
Cluster.yml file example:
```
auth:
strategy: x509
network:
plugin: flannel
hosts:
- advertised_hostname: server1
ip: 1.1.1.1
user: ubuntu
role: [controlplane, etcd]
docker_socket: /var/run/docker.sock
advertise_address: 10.1.1.1
- advertised_hostname: server2
ip: 2.2.2.2
user: ubuntu
role: [worker]
advertise_address: 10.2.2.2
services:
etcd:
image: quay.io/coreos/etcd:latest
kube-api:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
service_cluster_ip_range: 10.233.0.0/18
extra_args:
v: 4
kube-controller:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
cluster_cidr: 10.233.64.0/18
service_cluster_ip_range: 10.233.0.0/18
scheduler:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
kubelet:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
cluster_domain: cluster.local
cluster_dns_server: 10.233.0.3
infra_container_image: gcr.io/google_containers/pause-amd64:3.0
kubeproxy:
image: quay.io/coreos/hyperkube:v1.7.5_coreos.0
```
2. Upgrade the cluster using a cluster file with version v1.7.6_coreos.0 but with different hosts/ip addresses not relevant to the existing cluster. It fails with the error below:
```
soumyas-MBP:rke soumya$ ./rke_darwin-amd64 cluster upgrade --cluster-file cluster1.yml
INFO[0000] Upgrading Kubernetes cluster
WARN[0000] Failed to initiate new Kubernetes Client: stat ./.kube_config_cluster1.yml: no such file or directory
panic: runtime error: invalid memory address or nil pointer dereference [recovered]
panic: runtime error: invalid memory address or nil pointer dereference
[signal SIGSEGV: segmentation violation code=0x1 addr=0x1d0 pc=0x1b41fbc]
goroutine 1 [running]:
github.com/rancher/rke/vendor/github.com/urfave/cli.HandleAction.func1(0xc420596900)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:472 +0x28d
panic(0x1c499e0, 0x24b77c0)
/usr/local/go/src/runtime/panic.go:489 +0x2cf
github.com/rancher/rke/cmd.ClusterUpgrade(0xc4203f2480, 0x440, 0x440, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, 0x0, ...)
/go/src/github.com/rancher/rke/cmd/cluster.go:202 +0x14c
github.com/rancher/rke/cmd.clusterUpgradeFromCli(0xc42049a000, 0x0, 0x0)
/go/src/github.com/rancher/rke/cmd/cluster.go:179 +0xdd
reflect.Value.call(0x1c07de0, 0x1dee648, 0x13, 0x1d78844, 0x4, 0xc4205968a0, 0x1, 0x1, 0xc420596828, 0x1d53f40, ...)
/usr/local/go/src/reflect/value.go:434 +0x91f
reflect.Value.Call(0x1c07de0, 0x1dee648, 0x13, 0xc4205968a0, 0x1, 0x1, 0x140, 0xc42049a000, 0x0)
/usr/local/go/src/reflect/value.go:302 +0xa4
github.com/rancher/rke/vendor/github.com/urfave/cli.HandleAction(0x1c07de0, 0x1dee648, 0xc42049a000, 0x0, 0x0)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:481 +0x198
github.com/rancher/rke/vendor/github.com/urfave/cli.Command.Run(0x1d7ab87, 0x7, 0x0, 0x0, 0x0, 0x0, 0x0, 0x1d92e4a, 0x22, 0x0, ...)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/command.go:186 +0xab8
github.com/rancher/rke/vendor/github.com/urfave/cli.(*App).RunAsSubcommand(0xc420498180, 0xc4201e5cc0, 0x0, 0x0)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:355 +0xa1f
github.com/rancher/rke/vendor/github.com/urfave/cli.Command.startApp(0x1d7a704, 0x7, 0x1d7a704, 0x7, 0x0, 0x0, 0x0, 0x1d8a255, 0x19, 0x0, ...)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/command.go:273 +0x81b
github.com/rancher/rke/vendor/github.com/urfave/cli.Command.Run(0x1d7a704, 0x7, 0x1d7a704, 0x7, 0x0, 0x0, 0x0, 0x1d8a255, 0x19, 0x0, ...)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/command.go:74 +0x142c
github.com/rancher/rke/vendor/github.com/urfave/cli.(*App).Run(0xc420498000, 0xc42000e140, 0x5, 0x5, 0x0, 0x0)
/go/src/github.com/rancher/rke/vendor/github.com/urfave/cli/app.go:235 +0x5d6
main.mainErr(0xc42025f3d0, 0xc420597f68)
/go/src/github.com/rancher/rke/main.go:41 +0x2f8
main.main()
/go/src/github.com/rancher/rke/main.go:14 +0x22
```
| test | panic runtime error when upgrading kubernetes cluster using an invalid cluster file rke version dev steps create a cluster coreos with one master node and the other worker node using cluster yml file use the command rke darwin cluster up cluster file cluster yml cluster yml file example auth strategy network plugin flannel hosts advertised hostname ip user ubuntu role docker socket var run docker sock advertise address advertised hostname ip user ubuntu role advertise address services etcd image quay io coreos etcd latest kube api image quay io coreos hyperkube coreos service cluster ip range extra args v kube controller image quay io coreos hyperkube coreos cluster cidr service cluster ip range scheduler image quay io coreos hyperkube coreos kubelet image quay io coreos hyperkube coreos cluster domain cluster local cluster dns server infra container image gcr io google containers pause kubeproxy image quay io coreos hyperkube coreos upgrade the cluster using a cluster file with version coreos but with different hosts ip addresses not relevant to the existing cluster it fails with the error below soumyas mbp rke soumya rke darwin cluster upgrade cluster file yml info upgrading kubernetes cluster warn failed to initiate new kubernetes client stat kube config yml no such file or directory panic runtime error invalid memory address or nil pointer dereference panic runtime error invalid memory address or nil pointer dereference goroutine github com rancher rke vendor github com urfave cli handleaction go src github com rancher rke vendor github com urfave cli app go panic usr local go src runtime panic go github com rancher rke cmd clusterupgrade go src github com rancher rke cmd cluster go github com rancher rke cmd clusterupgradefromcli go src github com rancher rke cmd cluster go reflect value call usr local go src reflect value go reflect value call usr local go src reflect value go github com rancher rke vendor github com urfave cli handleaction go src github com rancher rke vendor github com urfave cli app go github com rancher rke vendor github com urfave cli command run go src github com rancher rke vendor github com urfave cli command go github com rancher rke vendor github com urfave cli app runassubcommand go src github com rancher rke vendor github com urfave cli app go github com rancher rke vendor github com urfave cli command startapp go src github com rancher rke vendor github com urfave cli command go github com rancher rke vendor github com urfave cli command run go src github com rancher rke vendor github com urfave cli command go github com rancher rke vendor github com urfave cli app run go src github com rancher rke vendor github com urfave cli app go main mainerr go src github com rancher rke main go main main go src github com rancher rke main go | 1 |
121,328 | 10,165,747,918 | IssuesEvent | 2019-08-07 14:29:25 | SAP/cloud-commerce-spartacus-storefront | https://api.github.com/repos/SAP/cloud-commerce-spartacus-storefront | opened | Failing E2E: payment-methods.e2e-spec.ts | e2e-tests | Failed on Jenkins with error:
``` 1) 576p resolution - Payment Methods should go to payment details page for login user should see payment method card:
CypressError: Timed out retrying: Expected to find element: 'cx-address-form', but never found it.```
https://jkmaster.test.c3po.b2c.ydev.hybris.com/job/spartacus-regression-tests/304/console | 1.0 | Failing E2E: payment-methods.e2e-spec.ts - Failed on Jenkins with error:
``` 1) 576p resolution - Payment Methods should go to payment details page for login user should see payment method card:
CypressError: Timed out retrying: Expected to find element: 'cx-address-form', but never found it.```
https://jkmaster.test.c3po.b2c.ydev.hybris.com/job/spartacus-regression-tests/304/console | test | failing payment methods spec ts failed on jenkins with error resolution payment methods should go to payment details page for login user should see payment method card cypresserror timed out retrying expected to find element cx address form but never found it | 1 |
313,080 | 9,556,782,393 | IssuesEvent | 2019-05-03 09:26:42 | OpenSourceEconomics/soepy | https://api.github.com/repos/OpenSourceEconomics/soepy | closed | overlapping tasks | pb package priority medium size medium | https://github.com/OpenSourceEconomics/soepy/blob/8f32fa2573ae1b17a39651d01021845a561bebc6/soepy/python/simulate/simulate_auxiliary.py#L140
it seems this is quite similar to the inner `construct_covariates` functionality. Can we refactor and align the treatment? | 1.0 | overlapping tasks - https://github.com/OpenSourceEconomics/soepy/blob/8f32fa2573ae1b17a39651d01021845a561bebc6/soepy/python/simulate/simulate_auxiliary.py#L140
it seems this is quite similar to the inner `construct_covariates` functionality. Can we refactor and align the treatment? | non_test | overlapping tasks it seems this is quite similar to the inner construct covariates functionality can we refactor and align the treatment | 0 |
255,725 | 21,949,322,054 | IssuesEvent | 2022-05-24 06:14:47 | keycloak/keycloak | https://api.github.com/repos/keycloak/keycloak | opened | WebAuthn test failures in admin console | area/testsuite kind/bug area/authentication/webauthn | ### Describe the bug
ssia
https://keycloak-jenkins.com/job/universal-test-pipeline-server/1522/testReport/org.keycloak.testsuite.webauthn.admin/
### Version
999
### Expected behavior
_No response_
### Actual behavior
_No response_
### How to Reproduce?
_No response_
### Anything else?
_No response_ | 1.0 | WebAuthn test failures in admin console - ### Describe the bug
ssia
https://keycloak-jenkins.com/job/universal-test-pipeline-server/1522/testReport/org.keycloak.testsuite.webauthn.admin/
### Version
999
### Expected behavior
_No response_
### Actual behavior
_No response_
### How to Reproduce?
_No response_
### Anything else?
_No response_ | test | webauthn test failures in admin console describe the bug ssia version expected behavior no response actual behavior no response how to reproduce no response anything else no response | 1 |
161,976 | 12,602,552,645 | IssuesEvent | 2020-06-11 11:56:45 | MachoThemes/modula-lite | https://api.github.com/repos/MachoThemes/modula-lite | closed | CTRL/CMD + S to save galleries | enhancement need testing | Maybe look into adding some keyboard shortcuts as well ¯\_(ツ)_/¯ | 1.0 | CTRL/CMD + S to save galleries - Maybe look into adding some keyboard shortcuts as well ¯\_(ツ)_/¯ | test | ctrl cmd s to save galleries maybe look into adding some keyboard shortcuts as well ¯ ツ ¯ | 1 |
69,381 | 7,132,894,283 | IssuesEvent | 2018-01-22 15:54:39 | textlint/textlint | https://api.github.com/repos/textlint/textlint | opened | textlint-tester: implement integration test | Type: Testing | From https://github.com/textlint/textlint/issues/488#issuecomment-359426241, we need integration test for maintain backward compatibility. | 1.0 | textlint-tester: implement integration test - From https://github.com/textlint/textlint/issues/488#issuecomment-359426241, we need integration test for maintain backward compatibility. | test | textlint tester implement integration test from we need integration test for maintain backward compatibility | 1 |
35,182 | 4,965,157,427 | IssuesEvent | 2016-12-04 04:59:58 | CS450-ECE461/fall2016-group2-apiserver | https://api.github.com/repos/CS450-ECE461/fall2016-group2-apiserver | closed | Refactor User related Tests to account for org_id | enhancement testing | We must now incorporate the users organization id when creating and working with users. Most of the tests do not account for org_id and will need to be refactored. I would recommend adding a before hook, or updating a before hook to create an organization, then create the user with the org_id. You won't be able to add the org_id to the fixtures because it is dynamic. So you will need to read the user fixture, add the org_id field to it then create the user. | 1.0 | Refactor User related Tests to account for org_id - We must now incorporate the users organization id when creating and working with users. Most of the tests do not account for org_id and will need to be refactored. I would recommend adding a before hook, or updating a before hook to create an organization, then create the user with the org_id. You won't be able to add the org_id to the fixtures because it is dynamic. So you will need to read the user fixture, add the org_id field to it then create the user. | test | refactor user related tests to account for org id we must now incorporate the users organization id when creating and working with users most of the tests do not account for org id and will need to be refactored i would recommend adding a before hook or updating a before hook to create an organization then create the user with the org id you won t be able to add the org id to the fixtures because it is dynamic so you will need to read the user fixture add the org id field to it then create the user | 1 |
386,123 | 26,668,239,643 | IssuesEvent | 2023-01-26 07:40:47 | IBM/ibm-spectrum-scale-bridge-for-grafana | https://api.github.com/repos/IBM/ibm-spectrum-scale-bridge-for-grafana | closed | openshift-marketplace doesn't available on KVM based installation | bug documentation cloud_native | **Describe the bug**
Trying to use Grafana/Grafana Bridge on a baremetal / KVM based OCP environment. But openshift-marketplace is not available to install grafana-operator
**Expected behavior**
openshift-marketplace available or grafana-operator installed
**Screenshots**
[root@helper ~]# oc get packagemanifests -n openshift-marketplace |grep grafana
No resources found in openshift-marketplace namespace.
[root@helper ~]# oc get packagemanifests -n openshift-marketplace
No resources found in openshift-marketplace namespace.
**Desktop (please complete the following information):**
- IBM Spectrum Scale system type:
- [ ] IBM Spectrum Scale classic cluster.
- [x] IBM Spectrum Scale Container Native Storage Access (CNSA).
- [ ] IBM Elastic Storage Server (ESS).
- IBM Spectrum Scale cluster version: 5.1.6
- IBM Spectrum Scale bridge for Grafana version:
- Grafana version:
- OS Grafana is installed on:
**Additional context**
Add any other context about the problem here.
| 1.0 | openshift-marketplace doesn't available on KVM based installation - **Describe the bug**
Trying to use Grafana/Grafana Bridge on a baremetal / KVM based OCP environment. But openshift-marketplace is not available to install grafana-operator
**Expected behavior**
openshift-marketplace available or grafana-operator installed
**Screenshots**
[root@helper ~]# oc get packagemanifests -n openshift-marketplace |grep grafana
No resources found in openshift-marketplace namespace.
[root@helper ~]# oc get packagemanifests -n openshift-marketplace
No resources found in openshift-marketplace namespace.
**Desktop (please complete the following information):**
- IBM Spectrum Scale system type:
- [ ] IBM Spectrum Scale classic cluster.
- [x] IBM Spectrum Scale Container Native Storage Access (CNSA).
- [ ] IBM Elastic Storage Server (ESS).
- IBM Spectrum Scale cluster version: 5.1.6
- IBM Spectrum Scale bridge for Grafana version:
- Grafana version:
- OS Grafana is installed on:
**Additional context**
Add any other context about the problem here.
| non_test | openshift marketplace doesn t available on kvm based installation describe the bug trying to use grafana grafana bridge on a baremetal kvm based ocp environment but openshift marketplace is not available to install grafana operator expected behavior openshift marketplace available or grafana operator installed screenshots oc get packagemanifests n openshift marketplace grep grafana no resources found in openshift marketplace namespace oc get packagemanifests n openshift marketplace no resources found in openshift marketplace namespace desktop please complete the following information ibm spectrum scale system type ibm spectrum scale classic cluster ibm spectrum scale container native storage access cnsa ibm elastic storage server ess ibm spectrum scale cluster version ibm spectrum scale bridge for grafana version grafana version os grafana is installed on additional context add any other context about the problem here | 0 |
77,680 | 7,595,310,236 | IssuesEvent | 2018-04-27 04:34:47 | intesar/Fx-Test-Data | https://api.github.com/repos/intesar/Fx-Test-Data | closed | Fx-Test-Data : vault_create_valid_desc | Fx-Test-Data Fx-Test-Data | Project : Fx-Test-Data
Job : Stg
Env : Stg
Region : FxLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MzBhZDk0YjItY2MxZS00NTZmLWE3ODQtMGY3YjdlZWRjZmY2; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Fri, 27 Apr 2018 02:34:47 GMT]}
Endpoint : http://stg1.fxlabs.io/api/v1/vault
Request :
{
"key" : "cBA0dq",
"val" : "oEUUoeYn"
}
Response :
{
"requestId" : "None",
"requestTime" : "2018-04-27T02:34:47.702+0000",
"errors" : false,
"messages" : [ ],
"data" : {
"id" : "8a8082a062f91bad016304f3f7ee7003",
"createdBy" : "8a80829061c17be10161c18999480002",
"createdDate" : "2018-04-27T02:34:47.662+0000",
"modifiedBy" : "8a80829061c17be10161c18999480002",
"modifiedDate" : "2018-04-27T02:34:47.662+0000",
"version" : null,
"inactive" : false,
"org" : {
"id" : "8a80829061c17be10161c189993d0001",
"createdBy" : null,
"createdDate" : null,
"modifiedBy" : null,
"modifiedDate" : null,
"version" : null,
"inactive" : false,
"name" : null
},
"key" : "cBA0dq",
"val" : "oEUUoeYn",
"description" : null,
"visibility" : "PRIVATE"
},
"totalPages" : 1,
"totalElements" : 1
}
Logs :
Assertion [@Response.data.key == @Request.key] passed, expected [cBA0dq] and found [cBA0dq]Assertion [@Response.data.val == @Request.val] passed, expected [oEUUoeYn] and found [oEUUoeYn]Assertion [@Response.errors == false] passed, expected [false] and found [false]Assertion [@StatusCode == 200] passed, expected [200] and found [200]
| 2.0 | Fx-Test-Data : vault_create_valid_desc - Project : Fx-Test-Data
Job : Stg
Env : Stg
Region : FxLabs/US_WEST_1
Result : fail
Status Code : 200
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=MzBhZDk0YjItY2MxZS00NTZmLWE3ODQtMGY3YjdlZWRjZmY2; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Fri, 27 Apr 2018 02:34:47 GMT]}
Endpoint : http://stg1.fxlabs.io/api/v1/vault
Request :
{
"key" : "cBA0dq",
"val" : "oEUUoeYn"
}
Response :
{
"requestId" : "None",
"requestTime" : "2018-04-27T02:34:47.702+0000",
"errors" : false,
"messages" : [ ],
"data" : {
"id" : "8a8082a062f91bad016304f3f7ee7003",
"createdBy" : "8a80829061c17be10161c18999480002",
"createdDate" : "2018-04-27T02:34:47.662+0000",
"modifiedBy" : "8a80829061c17be10161c18999480002",
"modifiedDate" : "2018-04-27T02:34:47.662+0000",
"version" : null,
"inactive" : false,
"org" : {
"id" : "8a80829061c17be10161c189993d0001",
"createdBy" : null,
"createdDate" : null,
"modifiedBy" : null,
"modifiedDate" : null,
"version" : null,
"inactive" : false,
"name" : null
},
"key" : "cBA0dq",
"val" : "oEUUoeYn",
"description" : null,
"visibility" : "PRIVATE"
},
"totalPages" : 1,
"totalElements" : 1
}
Logs :
Assertion [@Response.data.key == @Request.key] passed, expected [cBA0dq] and found [cBA0dq]Assertion [@Response.data.val == @Request.val] passed, expected [oEUUoeYn] and found [oEUUoeYn]Assertion [@Response.errors == false] passed, expected [false] and found [false]Assertion [@StatusCode == 200] passed, expected [200] and found [200]
| test | fx test data vault create valid desc project fx test data job stg env stg region fxlabs us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request key val oeuuoeyn response requestid none requesttime errors false messages data id createdby createddate modifiedby modifieddate version null inactive false org id createdby null createddate null modifiedby null modifieddate null version null inactive false name null key val oeuuoeyn description null visibility private totalpages totalelements logs assertion passed expected and found assertion passed expected and found assertion passed expected and found assertion passed expected and found | 1 |
345,972 | 30,857,165,859 | IssuesEvent | 2023-08-02 21:44:20 | gear-tech/gear | https://api.github.com/repos/gear-tech/gear | opened | Fix `test_gen_reproduction` slowness | P1-asap C0-bug D4-test | ### Problem
`gear_wasm_gen::tests::test_gen_reproduction` is too slow and makes CI unstable - sometimes it finishes fast, sometimes it kills CI with overtime run.
### Steps
-
### Possible Solution
_No response_
### Notes
_No response_
### Relevant Log Output
_No response_ | 1.0 | Fix `test_gen_reproduction` slowness - ### Problem
`gear_wasm_gen::tests::test_gen_reproduction` is too slow and makes CI unstable - sometimes it finishes fast, sometimes it kills CI with overtime run.
### Steps
-
### Possible Solution
_No response_
### Notes
_No response_
### Relevant Log Output
_No response_ | test | fix test gen reproduction slowness problem gear wasm gen tests test gen reproduction is too slow and makes ci unstable sometimes it finishes fast sometimes it kills ci with overtime run steps possible solution no response notes no response relevant log output no response | 1 |
128,721 | 5,074,341,619 | IssuesEvent | 2016-12-27 13:52:09 | JetBoom/noxiousnet-issues | https://api.github.com/repos/JetBoom/noxiousnet-issues | closed | [ZS] Shade takes damage from func_physbox and prop_physics | enhancement priority low | since rework (10/24/16 16:37:04+01:00) shade can take damage from func_physbox or prop_physics when manipulating physics objects | 1.0 | [ZS] Shade takes damage from func_physbox and prop_physics - since rework (10/24/16 16:37:04+01:00) shade can take damage from func_physbox or prop_physics when manipulating physics objects | non_test | shade takes damage from func physbox and prop physics since rework shade can take damage from func physbox or prop physics when manipulating physics objects | 0 |
2,434 | 2,688,754,827 | IssuesEvent | 2015-03-31 03:38:04 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Docs for ISymbol and its derived interfaces should say that they are not to be extended outside Roslyn | 2 - Ready Area-Compilers Bug Compatibility Documentation | The interface ISymbol and its derived interfaces should contain documentation that they are not intended to be extensible in client code. We intend to evolve these interfaces by the addition of members in future revisions (e.g. the addition of ILocalSymbol.IsReadonly), and we need to avoid having clients inherit or implement the interfaces to avoid breaking compatibility.
I recommend something like the following paragraph.
```cs
/// <remarks>
/// This interface is reserved for implementation by its associated APIs. We reserve the right to
/// change it in the future.
/// </remarks>
```
<!---
@huboard:{"order":326.99999821186066,"milestone_order":632,"custom_state":""}
-->
| 1.0 | Docs for ISymbol and its derived interfaces should say that they are not to be extended outside Roslyn - The interface ISymbol and its derived interfaces should contain documentation that they are not intended to be extensible in client code. We intend to evolve these interfaces by the addition of members in future revisions (e.g. the addition of ILocalSymbol.IsReadonly), and we need to avoid having clients inherit or implement the interfaces to avoid breaking compatibility.
I recommend something like the following paragraph.
```cs
/// <remarks>
/// This interface is reserved for implementation by its associated APIs. We reserve the right to
/// change it in the future.
/// </remarks>
```
<!---
@huboard:{"order":326.99999821186066,"milestone_order":632,"custom_state":""}
-->
| non_test | docs for isymbol and its derived interfaces should say that they are not to be extended outside roslyn the interface isymbol and its derived interfaces should contain documentation that they are not intended to be extensible in client code we intend to evolve these interfaces by the addition of members in future revisions e g the addition of ilocalsymbol isreadonly and we need to avoid having clients inherit or implement the interfaces to avoid breaking compatibility i recommend something like the following paragraph cs this interface is reserved for implementation by its associated apis we reserve the right to change it in the future huboard order milestone order custom state | 0 |
137,817 | 11,164,483,844 | IssuesEvent | 2019-12-27 05:11:47 | pingcap/tidb | https://api.github.com/repos/pingcap/tidb | opened | testSuite8.TestShardRowIDBits failed | component/test type/bug | ## Bug Report
Please answer these questions before submitting your issue. Thanks!
1. What did you do?
unit test failed in https://internal.pingcap.net/idc-jenkins/blue/organizations/jenkins/tidb_ghpr_unit_test/detail/tidb_ghpr_unit_test/20849/pipeline
2. What did you expect to see?
3. What did you see instead?
```
[2019-12-27T05:07:31.538Z] FAIL: ddl_test.go:571: testSuite8.TestShardRowIDBits
[2019-12-27T05:07:31.538Z]
[2019-12-27T05:07:31.538Z] ddl_test.go:660:
[2019-12-27T05:07:31.538Z] assertCountAndShard(tbl, 100)
[2019-12-27T05:07:31.538Z] ddl_test.go:601:
[2019-12-27T05:07:31.538Z] c.Assert(hasShardedID, IsTrue)
[2019-12-27T05:07:31.538Z] ... obtained bool = false
```
4. What version of TiDB are you using (`tidb-server -V` or run `select tidb_version();` on TiDB)?
4.0.0-alpha
| 1.0 | testSuite8.TestShardRowIDBits failed - ## Bug Report
Please answer these questions before submitting your issue. Thanks!
1. What did you do?
unit test failed in https://internal.pingcap.net/idc-jenkins/blue/organizations/jenkins/tidb_ghpr_unit_test/detail/tidb_ghpr_unit_test/20849/pipeline
2. What did you expect to see?
3. What did you see instead?
```
[2019-12-27T05:07:31.538Z] FAIL: ddl_test.go:571: testSuite8.TestShardRowIDBits
[2019-12-27T05:07:31.538Z]
[2019-12-27T05:07:31.538Z] ddl_test.go:660:
[2019-12-27T05:07:31.538Z] assertCountAndShard(tbl, 100)
[2019-12-27T05:07:31.538Z] ddl_test.go:601:
[2019-12-27T05:07:31.538Z] c.Assert(hasShardedID, IsTrue)
[2019-12-27T05:07:31.538Z] ... obtained bool = false
```
4. What version of TiDB are you using (`tidb-server -V` or run `select tidb_version();` on TiDB)?
4.0.0-alpha
| test | testshardrowidbits failed bug report please answer these questions before submitting your issue thanks what did you do unit test failed in what did you expect to see what did you see instead fail ddl test go testshardrowidbits ddl test go assertcountandshard tbl ddl test go c assert hasshardedid istrue obtained bool false what version of tidb are you using tidb server v or run select tidb version on tidb alpha | 1 |
265,540 | 23,175,840,809 | IssuesEvent | 2022-07-31 12:06:13 | QubesOS/qubes-issues | https://api.github.com/repos/QubesOS/qubes-issues | closed | Problems accessing SMB shares from Fedora-36 | T: bug C: Fedora P: default needs diagnosis updates testing | ### Qubes OS release
R4.1 with Fedora-36 installed from testing repos
### Brief summary
When trying to access an SMB share (in my case, on a machine running Windows 7), the prompt for workgroup, username and password is displayed, but then access is denied with an error message stating a parameter fault.
### Steps to reproduce
Start an AppVM based on a Fedora-36 template, open the Files utility (Nautilus), position to `Other places`, select `Connect to server` and enter a valid address like `smb://<Servername>/<Sharename>/`.
### Expected behavior
The share should be opened and usable from Nautilus.
### Actual behavior
Access is rejected due to parameter error.
### Additional information
This seems to be an upstream error from Fedora which already appeared some 2 months ago in Fedora-35 and then disappeared after an update some days after. For Fedora-36, it has now reappeared.
Currently, there is a rather simple workaround:
- In the template, execute the command `sudo dnf downgrade libsmbclient` .
- Then update again with `sudo dnf upgrade`.
After this, everything works again. Perhaps some library in the template has to be updated?
| 1.0 | Problems accessing SMB shares from Fedora-36 - ### Qubes OS release
R4.1 with Fedora-36 installed from testing repos
### Brief summary
When trying to access an SMB share (in my case, on a machine running Windows 7), the prompt for workgroup, username and password is displayed, but then access is denied with an error message stating a parameter fault.
### Steps to reproduce
Start an AppVM based on a Fedora-36 template, open the Files utility (Nautilus), position to `Other places`, select `Connect to server` and enter a valid address like `smb://<Servername>/<Sharename>/`.
### Expected behavior
The share should be opened and usable from Nautilus.
### Actual behavior
Access is rejected due to parameter error.
### Additional information
This seems to be an upstream error from Fedora which already appeared some 2 months ago in Fedora-35 and then disappeared after an update some days after. For Fedora-36, it has now reappeared.
Currently, there is a rather simple workaround:
- In the template, execute the command `sudo dnf downgrade libsmbclient` .
- Then update again with `sudo dnf upgrade`.
After this, everything works again. Perhaps some library in the template has to be updated?
| test | problems accessing smb shares from fedora qubes os release with fedora installed from testing repos brief summary when trying to access an smb share in my case on a machine running windows the prompt for workgroup username and password is displayed but then access is denied with an error message stating a parameter fault steps to reproduce start an appvm based on a fedora template open the files utility nautilus position to other places select connect to server and enter a valid address like smb expected behavior the share should be opened and usable from nautilus actual behavior access is rejected due to parameter error additional information this seems to be an upstream error from fedora which already appeared some months ago in fedora and then disappeared after an update some days after for fedora it has now reappeared currently there is a rather simple workaround in the template execute the command sudo dnf downgrade libsmbclient then update again with sudo dnf upgrade after this everything works again perhaps some library in the template has to be updated | 1 |
498,991 | 14,437,014,827 | IssuesEvent | 2020-12-07 10:55:44 | grpc/grpc | https://api.github.com/repos/grpc/grpc | opened | Look forward to publish grpcio wheel for Big Sur (macos 11.0.*) | kind/question priority/P3 |
RT
python3.6|3.7|3.8|3.9 etc...
Thank you. | 1.0 | Look forward to publish grpcio wheel for Big Sur (macos 11.0.*) -
RT
python3.6|3.7|3.8|3.9 etc...
Thank you. | non_test | look forward to publish grpcio wheel for big sur macos rt etc thank you | 0 |
248,246 | 21,004,866,607 | IssuesEvent | 2022-03-29 21:22:57 | commaai/panda | https://api.github.com/repos/commaai/panda | opened | HITL tests improvement | tests | Reliability
- [ ] latency test
- [ ] general USB stability
- [ ] DFU recovery
Quality
- [ ] faster
- [ ] run tests in parallel
- [ ] nicer failure output
- [ ] cleanup code | 1.0 | HITL tests improvement - Reliability
- [ ] latency test
- [ ] general USB stability
- [ ] DFU recovery
Quality
- [ ] faster
- [ ] run tests in parallel
- [ ] nicer failure output
- [ ] cleanup code | test | hitl tests improvement reliability latency test general usb stability dfu recovery quality faster run tests in parallel nicer failure output cleanup code | 1 |
131,823 | 28,035,769,757 | IssuesEvent | 2023-03-28 14:59:40 | OpenModelica/OpenModelica | https://api.github.com/repos/OpenModelica/OpenModelica | closed | The value of a parameter is not passed to submodel (regression) | COMP/OMC/SimCode regression COMP/OMC/Runtime | ### Description
I have a model in which the value of a parameter is not passed to a submodel: it stays to zero. This model works well with Dymola, and OM up to 1.18.0.
It shows the issue with 1.20.0.beta4 and 1.19.2.
<!--- A clear and concise description of what the bug is. -->
### Steps to Reproduce
1. Load Test.mo:
[Test.mo.txt](https://github.com/OpenModelica/OpenModelica/files/10130875/Test.mo.txt)
2. run M and look at the result. As you can see in the first screenshot below, the value of wMax, which in drive is 1200, inside tauLim stays to zero. In the second screenshot below you see the expected behaviour.
<!--- This could either be a list of actions or a script file. -->
### Expected Behavior
wMax inside limTau should be 1200 rad/s (second screenshot below)
<!--- A clear and concise description of what you expected to happen. -->
### Screenshots
With 1.20.0:

With 1.18:
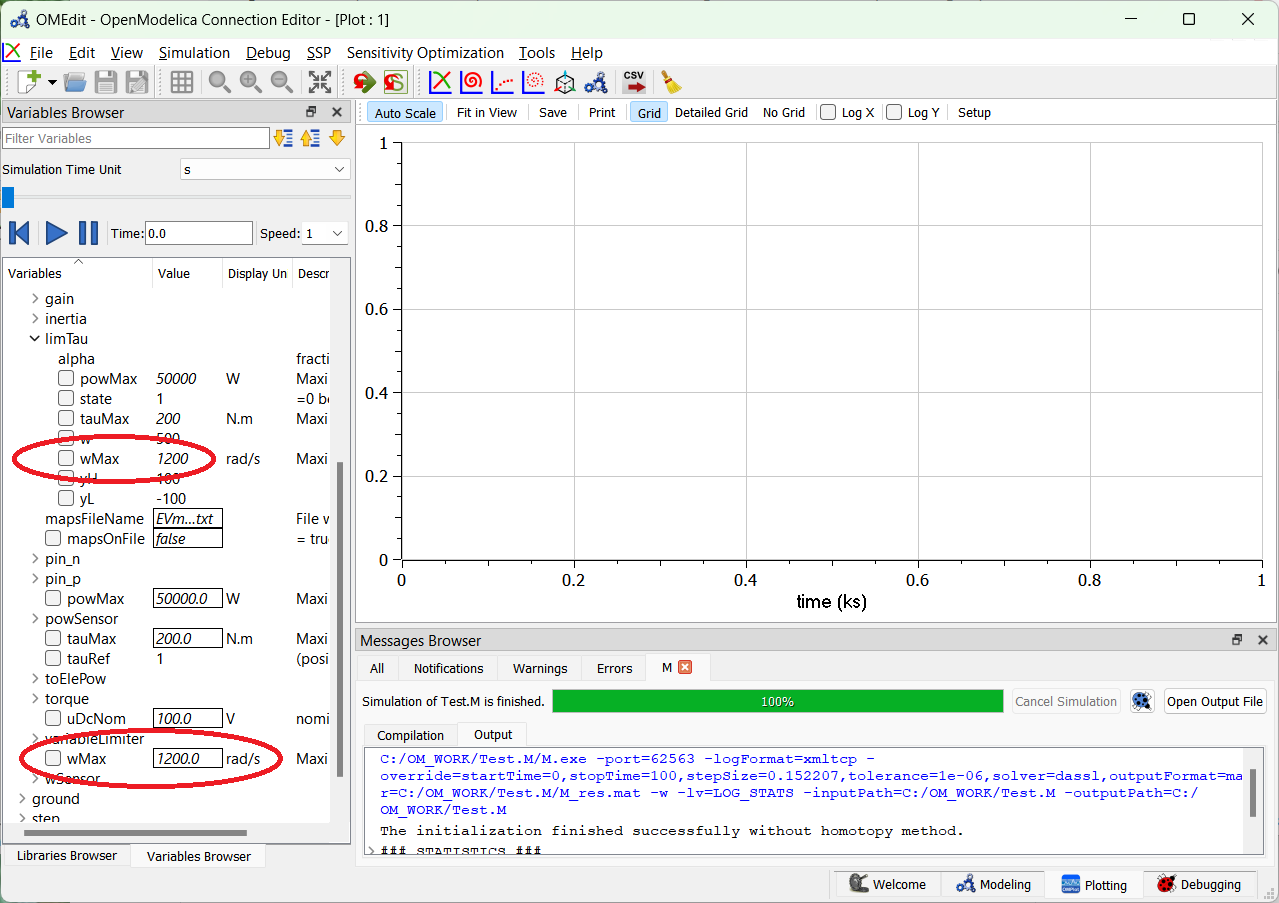
<!--- If applicable, add screenshots to help explain your problem. -->
| 1.0 | The value of a parameter is not passed to submodel (regression) - ### Description
I have a model in which the value of a parameter is not passed to a submodel: it stays to zero. This model works well with Dymola, and OM up to 1.18.0.
It shows the issue with 1.20.0.beta4 and 1.19.2.
<!--- A clear and concise description of what the bug is. -->
### Steps to Reproduce
1. Load Test.mo:
[Test.mo.txt](https://github.com/OpenModelica/OpenModelica/files/10130875/Test.mo.txt)
2. run M and look at the result. As you can see in the first screenshot below, the value of wMax, which in drive is 1200, inside tauLim stays to zero. In the second screenshot below you see the expected behaviour.
<!--- This could either be a list of actions or a script file. -->
### Expected Behavior
wMax inside limTau should be 1200 rad/s (second screenshot below)
<!--- A clear and concise description of what you expected to happen. -->
### Screenshots
With 1.20.0:

With 1.18:
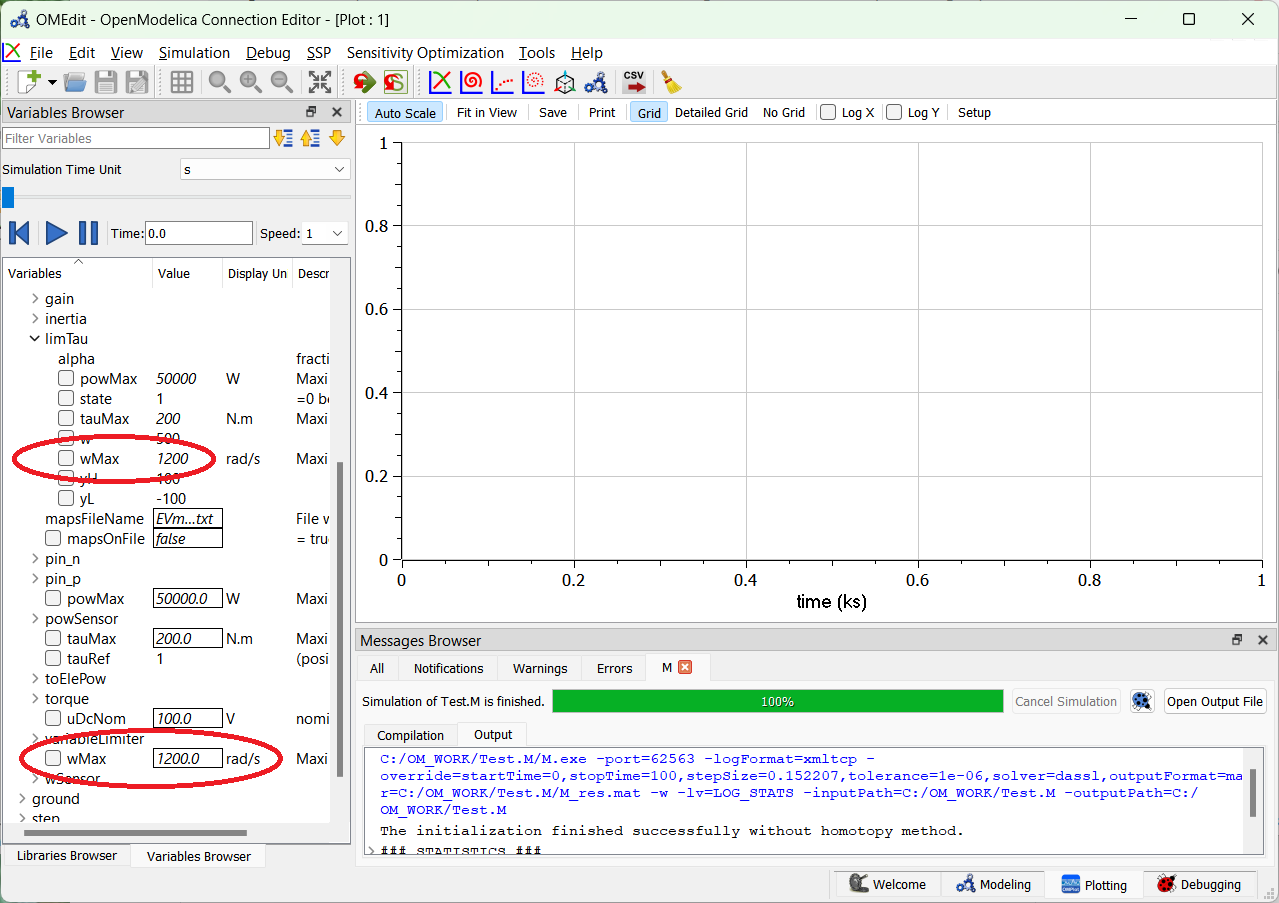
<!--- If applicable, add screenshots to help explain your problem. -->
| non_test | the value of a parameter is not passed to submodel regression description i have a model in which the value of a parameter is not passed to a submodel it stays to zero this model works well with dymola and om up to it shows the issue with and steps to reproduce load test mo run m and look at the result as you can see in the first screenshot below the value of wmax which in drive is inside taulim stays to zero in the second screenshot below you see the expected behaviour expected behavior wmax inside limtau should be rad s second screenshot below screenshots with with | 0 |
269,232 | 23,430,887,398 | IssuesEvent | 2022-08-15 02:10:03 | thesofproject/linux | https://api.github.com/repos/thesofproject/linux | closed | [BUG] check-kmod-load-unload.sh triggers hard kernel lockups | bug P1 Intel Daily tests | **Describe the bug**
`~/sof-test/test-case/check-kmod-load-unload.sh -l 25` causes hard kernel lockups
This is a very recent regression in daily tests.
**To Reproduce**
```
TPLG=/lib/firmware/intel/sof-tplg/sof-tgl-nocodec-ci.tplg \
MODEL=ADLP_RVP_NOCODEC_CI \
~/sof-test/test-case/check-kmod-load-unload.sh -l 25
```
or
```
TPLG=/lib/firmware/intel/sof-tplg/sof-tgl-rt715-rt711-rt1308-mono.tplg \
MODEL=TGLU_SKU0A3E_SDW \
~/sof-test/test-case/check-kmod-load-unload-after-playback.sh -l 5
```
**Reproduction Rate**
~Too early to tell.~ Seems very low.
**Environment**
First bad daily test: 12140
Start Time: 2022-04-27 22:29:55 UTC
End Time: 2022-04-28 02:49:19 UTC
< >>
Kernel Branch: topic/sof-dev
Kernel Commit: 95ec8d32e6b6
SOF Branch: main
SOF Commit: 94e6c9969730
Last good daily test: 12106
Start Time: 2022-04-26 22:29:40 UTC
End Time: 2022-04-27 05:52:13 UTC
< > >>
Kernel Branch: topic/sof-dev
Kernel Commit: 95ec8d32e6b6
SOF Branch: main
SOF Commit: 3334bede2a79
Only these commits are different between last good and first bad daily tests:
94e6c9969730 eddyhsu@chromium.org // (origin/main, origin/HEAD) kpb: Clean up params on component reset
99eac8de991d rander.wang@intel.com // ipc4: add format conversion support of s32le to s24le
f4f9e6541ee7 chao.song@linux.intel.com // sof: replace log calls with zephyr logging api
d67e2ea8a4bc eddyhsu@chromium.org // dcblock: Clean up processing function on reset.
426542d17f18 daniel.baluta@nxp.com // codec_adapter: cadence: Resolve api_id at runtime
02dd7a6dfb74 daniel.baluta@nxp.com // codec_adapter: cadence: Remove api_id parameter
05969a0e34da marc.herbert@intel.com // .github: IPC4: build supported TGL platforms first
dccf9c0798d5 marc.herbert@intel.com // .github/zephyr: download docker image from ghcr.io instead of docker.io
75dea11da97d chunxu.li@mediatek.com // topology1: add mt8186 related pipelines and components
Last good commit 3334bede2a79 seppo.ingalsuo@linux.intel.com // Tools: Testbench: Add components to testbench load
| 1.0 | [BUG] check-kmod-load-unload.sh triggers hard kernel lockups - **Describe the bug**
`~/sof-test/test-case/check-kmod-load-unload.sh -l 25` causes hard kernel lockups
This is a very recent regression in daily tests.
**To Reproduce**
```
TPLG=/lib/firmware/intel/sof-tplg/sof-tgl-nocodec-ci.tplg \
MODEL=ADLP_RVP_NOCODEC_CI \
~/sof-test/test-case/check-kmod-load-unload.sh -l 25
```
or
```
TPLG=/lib/firmware/intel/sof-tplg/sof-tgl-rt715-rt711-rt1308-mono.tplg \
MODEL=TGLU_SKU0A3E_SDW \
~/sof-test/test-case/check-kmod-load-unload-after-playback.sh -l 5
```
**Reproduction Rate**
~Too early to tell.~ Seems very low.
**Environment**
First bad daily test: 12140
Start Time: 2022-04-27 22:29:55 UTC
End Time: 2022-04-28 02:49:19 UTC
< >>
Kernel Branch: topic/sof-dev
Kernel Commit: 95ec8d32e6b6
SOF Branch: main
SOF Commit: 94e6c9969730
Last good daily test: 12106
Start Time: 2022-04-26 22:29:40 UTC
End Time: 2022-04-27 05:52:13 UTC
< > >>
Kernel Branch: topic/sof-dev
Kernel Commit: 95ec8d32e6b6
SOF Branch: main
SOF Commit: 3334bede2a79
Only these commits are different between last good and first bad daily tests:
94e6c9969730 eddyhsu@chromium.org // (origin/main, origin/HEAD) kpb: Clean up params on component reset
99eac8de991d rander.wang@intel.com // ipc4: add format conversion support of s32le to s24le
f4f9e6541ee7 chao.song@linux.intel.com // sof: replace log calls with zephyr logging api
d67e2ea8a4bc eddyhsu@chromium.org // dcblock: Clean up processing function on reset.
426542d17f18 daniel.baluta@nxp.com // codec_adapter: cadence: Resolve api_id at runtime
02dd7a6dfb74 daniel.baluta@nxp.com // codec_adapter: cadence: Remove api_id parameter
05969a0e34da marc.herbert@intel.com // .github: IPC4: build supported TGL platforms first
dccf9c0798d5 marc.herbert@intel.com // .github/zephyr: download docker image from ghcr.io instead of docker.io
75dea11da97d chunxu.li@mediatek.com // topology1: add mt8186 related pipelines and components
Last good commit 3334bede2a79 seppo.ingalsuo@linux.intel.com // Tools: Testbench: Add components to testbench load
| test | check kmod load unload sh triggers hard kernel lockups describe the bug sof test test case check kmod load unload sh l causes hard kernel lockups this is a very recent regression in daily tests to reproduce tplg lib firmware intel sof tplg sof tgl nocodec ci tplg model adlp rvp nocodec ci sof test test case check kmod load unload sh l or tplg lib firmware intel sof tplg sof tgl mono tplg model tglu sdw sof test test case check kmod load unload after playback sh l reproduction rate too early to tell seems very low environment first bad daily test start time utc end time utc kernel branch topic sof dev kernel commit sof branch main sof commit last good daily test start time utc end time utc kernel branch topic sof dev kernel commit sof branch main sof commit only these commits are different between last good and first bad daily tests eddyhsu chromium org origin main origin head kpb clean up params on component reset rander wang intel com add format conversion support of to chao song linux intel com sof replace log calls with zephyr logging api eddyhsu chromium org dcblock clean up processing function on reset daniel baluta nxp com codec adapter cadence resolve api id at runtime daniel baluta nxp com codec adapter cadence remove api id parameter marc herbert intel com github build supported tgl platforms first marc herbert intel com github zephyr download docker image from ghcr io instead of docker io chunxu li mediatek com add related pipelines and components last good commit seppo ingalsuo linux intel com tools testbench add components to testbench load | 1 |
96,954 | 16,174,570,356 | IssuesEvent | 2021-05-03 03:01:33 | andrewguest/cookiecutter-fullstack-fastapi-postgresql | https://api.github.com/repos/andrewguest/cookiecutter-fullstack-fastapi-postgresql | closed | CVE-2020-7789 (Medium) detected in node-notifier-5.4.3.tgz - autoclosed | security vulnerability | ## CVE-2020-7789 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-notifier-5.4.3.tgz</b></p></summary>
<p>A Node.js module for sending notifications on native Mac, Windows (post and pre 8) and Linux (or Growl as fallback)</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.3.tgz">https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.3.tgz</a></p>
<p>Path to dependency file: cookiecutter-fullstack-fastapi-postgresql/{{cookiecutter.project_slug}}/frontend/package.json</p>
<p>Path to vulnerable library: cookiecutter-fullstack-fastapi-postgresql/{{cookiecutter.project_slug}}/frontend/node_modules/node-notifier/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-unit-jest-4.5.9.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- core-24.9.0.tgz
- reporters-24.9.0.tgz
- :x: **node-notifier-5.4.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/andrewguest/cookiecutter-fullstack-fastapi-postgresql/commit/df96ffe2003ca437744ef3d2b21ed94a8a16f2f8">df96ffe2003ca437744ef3d2b21ed94a8a16f2f8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package node-notifier before 9.0.0. It allows an attacker to run arbitrary commands on Linux machines due to the options params not being sanitised when being passed an array.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7789>CVE-2020-7789</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 9.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-7789 (Medium) detected in node-notifier-5.4.3.tgz - autoclosed - ## CVE-2020-7789 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-notifier-5.4.3.tgz</b></p></summary>
<p>A Node.js module for sending notifications on native Mac, Windows (post and pre 8) and Linux (or Growl as fallback)</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.3.tgz">https://registry.npmjs.org/node-notifier/-/node-notifier-5.4.3.tgz</a></p>
<p>Path to dependency file: cookiecutter-fullstack-fastapi-postgresql/{{cookiecutter.project_slug}}/frontend/package.json</p>
<p>Path to vulnerable library: cookiecutter-fullstack-fastapi-postgresql/{{cookiecutter.project_slug}}/frontend/node_modules/node-notifier/package.json</p>
<p>
Dependency Hierarchy:
- cli-plugin-unit-jest-4.5.9.tgz (Root Library)
- jest-24.9.0.tgz
- jest-cli-24.9.0.tgz
- core-24.9.0.tgz
- reporters-24.9.0.tgz
- :x: **node-notifier-5.4.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/andrewguest/cookiecutter-fullstack-fastapi-postgresql/commit/df96ffe2003ca437744ef3d2b21ed94a8a16f2f8">df96ffe2003ca437744ef3d2b21ed94a8a16f2f8</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package node-notifier before 9.0.0. It allows an attacker to run arbitrary commands on Linux machines due to the options params not being sanitised when being passed an array.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7789>CVE-2020-7789</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7789</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 9.0.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in node notifier tgz autoclosed cve medium severity vulnerability vulnerable library node notifier tgz a node js module for sending notifications on native mac windows post and pre and linux or growl as fallback library home page a href path to dependency file cookiecutter fullstack fastapi postgresql cookiecutter project slug frontend package json path to vulnerable library cookiecutter fullstack fastapi postgresql cookiecutter project slug frontend node modules node notifier package json dependency hierarchy cli plugin unit jest tgz root library jest tgz jest cli tgz core tgz reporters tgz x node notifier tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package node notifier before it allows an attacker to run arbitrary commands on linux machines due to the options params not being sanitised when being passed an array publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact low availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
5,558 | 27,808,343,083 | IssuesEvent | 2023-03-17 22:47:15 | microsoft/UVAtlas | https://api.github.com/repos/microsoft/UVAtlas | closed | Retire legacy Xbox One XDK support | maintainence | The only scenario that still uses VS 2017 is for the legacy Xbox One XDK. This task is drop support for this older Xbox development model and remove the following projects:
```
UVAtlas_XboxOneXDK_2017.sln
``` | True | Retire legacy Xbox One XDK support - The only scenario that still uses VS 2017 is for the legacy Xbox One XDK. This task is drop support for this older Xbox development model and remove the following projects:
```
UVAtlas_XboxOneXDK_2017.sln
``` | non_test | retire legacy xbox one xdk support the only scenario that still uses vs is for the legacy xbox one xdk this task is drop support for this older xbox development model and remove the following projects uvatlas xboxonexdk sln | 0 |
308,376 | 9,438,496,508 | IssuesEvent | 2019-04-14 00:26:54 | x13pixels/remedybg-issues | https://api.github.com/repos/x13pixels/remedybg-issues | opened | Type expression into memory window | Component: Watch Window Priority: 6 (Medium) Status: Accepted Type: Enhancement | [casey, simon] Need to be able to type an expression into the watch window | 1.0 | Type expression into memory window - [casey, simon] Need to be able to type an expression into the watch window | non_test | type expression into memory window need to be able to type an expression into the watch window | 0 |
181,259 | 30,651,288,311 | IssuesEvent | 2023-07-25 09:04:58 | readthedocs/readthedocs.org | https://api.github.com/repos/readthedocs/readthedocs.org | closed | Build: `--upgrade-strategy eager` upgrade packages that were already pinned | Needed: design decision Support | ## Details
* Read the Docs project URL: https://readthedocs.org/projects/qdax/
* Build URL (if applicable): https://readthedocs.org/projects/qdax/builds/18693487/
* Read the Docs username (if applicable): https://readthedocs.org/profiles/felixchalumeau/
A recent PR from the project QDax has it's readthedocs's stage of CI [broken](https://github.com/adaptive-intelligent-robotics/QDax/pull/108) although there has been no core change in this PR. More generally speeking, all our recents PRs have a broken documentation, although they branch from develop that had a working CI.
Interestingly, I cannot reproduce the error when I try to serve the documentation on my local computer with `mkdocs serve` (everything is fine locally).
## Expected Result
I would expect the docs to build.
## Actual Result
Cf. to details section of this issue, the doc does not build on readthedocs while no breaking change happened in the code and while it seems to work locally. | 1.0 | Build: `--upgrade-strategy eager` upgrade packages that were already pinned - ## Details
* Read the Docs project URL: https://readthedocs.org/projects/qdax/
* Build URL (if applicable): https://readthedocs.org/projects/qdax/builds/18693487/
* Read the Docs username (if applicable): https://readthedocs.org/profiles/felixchalumeau/
A recent PR from the project QDax has it's readthedocs's stage of CI [broken](https://github.com/adaptive-intelligent-robotics/QDax/pull/108) although there has been no core change in this PR. More generally speeking, all our recents PRs have a broken documentation, although they branch from develop that had a working CI.
Interestingly, I cannot reproduce the error when I try to serve the documentation on my local computer with `mkdocs serve` (everything is fine locally).
## Expected Result
I would expect the docs to build.
## Actual Result
Cf. to details section of this issue, the doc does not build on readthedocs while no breaking change happened in the code and while it seems to work locally. | non_test | build upgrade strategy eager upgrade packages that were already pinned details read the docs project url build url if applicable read the docs username if applicable a recent pr from the project qdax has it s readthedocs s stage of ci although there has been no core change in this pr more generally speeking all our recents prs have a broken documentation although they branch from develop that had a working ci interestingly i cannot reproduce the error when i try to serve the documentation on my local computer with mkdocs serve everything is fine locally expected result i would expect the docs to build actual result cf to details section of this issue the doc does not build on readthedocs while no breaking change happened in the code and while it seems to work locally | 0 |
321,001 | 27,498,096,222 | IssuesEvent | 2023-03-05 11:35:48 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | roachtest: costfuzz/seed-multi-region failed | C-test-failure O-robot O-roachtest branch-master release-blocker | roachtest.costfuzz/seed-multi-region [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8926291?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8926291?buildTab=artifacts#/costfuzz/seed-multi-region) on master @ [cf14ad694ee562676f53e36fa8495206c3aed61f](https://github.com/cockroachdb/cockroach/commits/cf14ad694ee562676f53e36fa8495206c3aed61f):
```
test artifacts and logs in: /artifacts/costfuzz/seed-multi-region/run_1
(query_comparison_util.go:251).runOneRoundQueryComparison: . 1341 statements run: expected unperturbed and perturbed results to be equal
[]string{
... // 20 identical elements
"0",
"0",
- "0",
"NULL",
"NULL",
... // 38 identical elements
"NULL",
"NULL",
+ "NaN",
"NaN",
"NaN",
"NaN",
}
sql: SELECT
stddev_samp(tab447._float8::FLOAT8)::FLOAT8 AS col1448
FROM
defaultdb.public.seed_mr_table@[0] AS tab447
WHERE
EXISTS(
SELECT
ARRAY['[true, {"AHU": 0.0019103012458153434, "b": "T3bFtQ"}, false]':::JSONB,'{"cars": [{"make": "Volkswagen", "model": "Rabbit", "trim": "S", "year": "2009"}, {"make": "Toyota", "model": "Camry", "trim": "LE", "year": "2002"}, {"make": "Ford", "model": "Focus", "trim": "SE", "year": "2011"}, {"make": "Buick", "model": "Grand National", "trim": "T-Type", "year": "1987"}, {"make": "Buick", "model": "Skylark", "trim": "Gran Sport", "year": "1966"}, {"make": "Porsche", "model": "911", "trim": "Turbo S", "year": "2022"}, {"make": "Chevrolet", "model": "Corvette", "trim": "C8", "year": "2022"}]}':::JSONB,'1':::JSONB,'[[["bar", false], false, null], null, false, false]':::JSONB,'[1, 2]':::JSONB]
AS 😁col1446,
ARRAY[(-7800):::INT8,(-27556):::INT8,9:::INT8] AS col1447
)
GROUP BY
tab447._float8
HAVING
bool_or(tab447._bool::BOOL)::BOOL
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=true</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*costfuzz/seed-multi-region.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| 2.0 | roachtest: costfuzz/seed-multi-region failed - roachtest.costfuzz/seed-multi-region [failed](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8926291?buildTab=log) with [artifacts](https://teamcity.cockroachdb.com/buildConfiguration/Cockroach_Nightlies_RoachtestNightlyGceBazel/8926291?buildTab=artifacts#/costfuzz/seed-multi-region) on master @ [cf14ad694ee562676f53e36fa8495206c3aed61f](https://github.com/cockroachdb/cockroach/commits/cf14ad694ee562676f53e36fa8495206c3aed61f):
```
test artifacts and logs in: /artifacts/costfuzz/seed-multi-region/run_1
(query_comparison_util.go:251).runOneRoundQueryComparison: . 1341 statements run: expected unperturbed and perturbed results to be equal
[]string{
... // 20 identical elements
"0",
"0",
- "0",
"NULL",
"NULL",
... // 38 identical elements
"NULL",
"NULL",
+ "NaN",
"NaN",
"NaN",
"NaN",
}
sql: SELECT
stddev_samp(tab447._float8::FLOAT8)::FLOAT8 AS col1448
FROM
defaultdb.public.seed_mr_table@[0] AS tab447
WHERE
EXISTS(
SELECT
ARRAY['[true, {"AHU": 0.0019103012458153434, "b": "T3bFtQ"}, false]':::JSONB,'{"cars": [{"make": "Volkswagen", "model": "Rabbit", "trim": "S", "year": "2009"}, {"make": "Toyota", "model": "Camry", "trim": "LE", "year": "2002"}, {"make": "Ford", "model": "Focus", "trim": "SE", "year": "2011"}, {"make": "Buick", "model": "Grand National", "trim": "T-Type", "year": "1987"}, {"make": "Buick", "model": "Skylark", "trim": "Gran Sport", "year": "1966"}, {"make": "Porsche", "model": "911", "trim": "Turbo S", "year": "2022"}, {"make": "Chevrolet", "model": "Corvette", "trim": "C8", "year": "2022"}]}':::JSONB,'1':::JSONB,'[[["bar", false], false, null], null, false, false]':::JSONB,'[1, 2]':::JSONB]
AS 😁col1446,
ARRAY[(-7800):::INT8,(-27556):::INT8,9:::INT8] AS col1447
)
GROUP BY
tab447._float8
HAVING
bool_or(tab447._bool::BOOL)::BOOL
```
<p>Parameters: <code>ROACHTEST_cloud=gce</code>
, <code>ROACHTEST_cpu=4</code>
, <code>ROACHTEST_encrypted=false</code>
, <code>ROACHTEST_fs=ext4</code>
, <code>ROACHTEST_localSSD=true</code>
, <code>ROACHTEST_ssd=0</code>
</p>
<details><summary>Help</summary>
<p>
See: [roachtest README](https://github.com/cockroachdb/cockroach/blob/master/pkg/cmd/roachtest/README.md)
See: [How To Investigate \(internal\)](https://cockroachlabs.atlassian.net/l/c/SSSBr8c7)
</p>
</details>
/cc @cockroachdb/sql-queries
<sub>
[This test on roachdash](https://roachdash.crdb.dev/?filter=status:open%20t:.*costfuzz/seed-multi-region.*&sort=title+created&display=lastcommented+project) | [Improve this report!](https://github.com/cockroachdb/cockroach/tree/master/pkg/cmd/internal/issues)
</sub>
| test | roachtest costfuzz seed multi region failed roachtest costfuzz seed multi region with on master test artifacts and logs in artifacts costfuzz seed multi region run query comparison util go runoneroundquerycomparison statements run expected unperturbed and perturbed results to be equal string identical elements null null identical elements null null nan nan nan nan sql select stddev samp as from defaultdb public seed mr table as where exists select array jsonb cars jsonb jsonb false null null false false jsonb jsonb as 😁 array as group by having bool or bool bool bool parameters roachtest cloud gce roachtest cpu roachtest encrypted false roachtest fs roachtest localssd true roachtest ssd help see see cc cockroachdb sql queries | 1 |
262,059 | 19,760,084,936 | IssuesEvent | 2022-01-16 09:05:37 | team-moeller/better-access-charts | https://api.github.com/repos/team-moeller/better-access-charts | closed | Blogpost: Introduce property "AspectRatio" | documentation | Publish a blogpost and explain the new property "AspectRatio" | 1.0 | Blogpost: Introduce property "AspectRatio" - Publish a blogpost and explain the new property "AspectRatio" | non_test | blogpost introduce property aspectratio publish a blogpost and explain the new property aspectratio | 0 |
334,020 | 29,820,334,826 | IssuesEvent | 2023-06-17 01:29:43 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | reopened | Fix elementwise.test_log1p | Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5235978711/jobs/9453190700"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5235978711/jobs/9453190700"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="null"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5235978711/jobs/9453190700"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="null"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix elementwise.test_log1p - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5235978711/jobs/9453190700"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5235978711/jobs/9453190700"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="null"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5235978711/jobs/9453190700"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="null"><img src=https://img.shields.io/badge/-failure-red></a>
| test | fix elementwise test numpy a href src torch a href src jax img src tensorflow a href src paddle img src | 1 |
390,642 | 26,867,039,035 | IssuesEvent | 2023-02-04 02:00:33 | yugabyte/yugabyte-db | https://api.github.com/repos/yugabyte/yugabyte-db | closed | [Docs] Overview of compactions in YB | area/documentation priority/low | Need to create a doc that goes over how compactions work within YB. I have the start of the doc [here](https://docs.google.com/document/d/1eVxys6U9bH8YfvTSavGP3J6e5PFLRRaZPhtjUkF5nSU/edit#heading=h.ago7hn87mcou)
| 1.0 | [Docs] Overview of compactions in YB - Need to create a doc that goes over how compactions work within YB. I have the start of the doc [here](https://docs.google.com/document/d/1eVxys6U9bH8YfvTSavGP3J6e5PFLRRaZPhtjUkF5nSU/edit#heading=h.ago7hn87mcou)
| non_test | overview of compactions in yb need to create a doc that goes over how compactions work within yb i have the start of the doc | 0 |
132,605 | 18,268,791,487 | IssuesEvent | 2021-10-04 11:38:21 | artsking/linux-3.0.35 | https://api.github.com/repos/artsking/linux-3.0.35 | opened | CVE-2014-8989 (Medium) detected in linux-stable-rtv3.8.6 | security vulnerability | ## CVE-2014-8989 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35/commit/5992fa81c6ac1b4e9db13f5408d914525c5b7875">5992fa81c6ac1b4e9db13f5408d914525c5b7875</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/groups.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/groups.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/groups.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel through 3.17.4 does not properly restrict dropping of supplemental group memberships in certain namespace scenarios, which allows local users to bypass intended file permissions by leveraging a POSIX ACL containing an entry for the group category that is more restrictive than the entry for the other category, aka a "negative groups" issue, related to kernel/groups.c, kernel/uid16.c, and kernel/user_namespace.c.
<p>Publish Date: 2014-11-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-8989>CVE-2014-8989</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-8989">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-8989</a></p>
<p>Release Date: 2014-11-30</p>
<p>Fix Resolution: v3.19-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2014-8989 (Medium) detected in linux-stable-rtv3.8.6 - ## CVE-2014-8989 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv3.8.6</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-3.0.35/commit/5992fa81c6ac1b4e9db13f5408d914525c5b7875">5992fa81c6ac1b4e9db13f5408d914525c5b7875</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (3)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/groups.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/groups.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/kernel/groups.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Linux kernel through 3.17.4 does not properly restrict dropping of supplemental group memberships in certain namespace scenarios, which allows local users to bypass intended file permissions by leveraging a POSIX ACL containing an entry for the group category that is more restrictive than the entry for the other category, aka a "negative groups" issue, related to kernel/groups.c, kernel/uid16.c, and kernel/user_namespace.c.
<p>Publish Date: 2014-11-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2014-8989>CVE-2014-8989</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-8989">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2014-8989</a></p>
<p>Release Date: 2014-11-30</p>
<p>Fix Resolution: v3.19-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_test | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files kernel groups c kernel groups c kernel groups c vulnerability details the linux kernel through does not properly restrict dropping of supplemental group memberships in certain namespace scenarios which allows local users to bypass intended file permissions by leveraging a posix acl containing an entry for the group category that is more restrictive than the entry for the other category aka a negative groups issue related to kernel groups c kernel c and kernel user namespace c publish date url a href cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
185,422 | 14,352,338,544 | IssuesEvent | 2020-11-30 04:04:54 | maiertech/design-system | https://api.github.com/repos/maiertech/design-system | closed | Test PostList with fewer posts | test | Currently uses 10 posts, which results in very big screenshot files. | 1.0 | Test PostList with fewer posts - Currently uses 10 posts, which results in very big screenshot files. | test | test postlist with fewer posts currently uses posts which results in very big screenshot files | 1 |
25,370 | 4,155,836,892 | IssuesEvent | 2016-06-16 16:02:02 | dart-lang/sdk | https://api.github.com/repos/dart-lang/sdk | opened | socket_bind_test still fails sometimes | area-test area-vm | It seems this test still fails sometimes - possibly another error condition that is not properly handled by the test itself? @mkustermann
https://build.chromium.org/p/client.dart/builders/vm-linux-debug-simarm-be/builds/852/steps/vm%20tests/logs/stdio
```
FAILED: none-vm debug_simarm standalone/io/socket_bind_test
Expected: Pass
Actual: RuntimeError
CommandOutput[vm]:
stdout:
unittest-suite-wait-for-done
stderr:
Unhandled exception:
SocketException: Failed to create server socket (OS Error: Address already in use, errno = 98), address = 127.0.0.1, port = 57270
#0 _NativeSocket.bind.<anonymous closure> (dart:io-patch/socket_patch.dart:505)
#1 _RootZone.runUnary (dart:async/zone.dart:1204)
#2 _FutureListener.handleValue (dart:async/future_impl.dart:131)
#3 _Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:637)
#4 _Future._propagateToListeners (dart:async/future_impl.dart:667)
#5 _Future._completeWithValue (dart:async/future_impl.dart:477)
#6 _Future._asyncComplete.<anonymous closure> (dart:async/future_impl.dart:528)
#7 _microtaskLoop (dart:async/schedule_microtask.dart:41)
#8 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50)
#9 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:96)
#10 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:149)
Command[vm]: DART_CONFIGURATION=DebugSIMARM out/DebugSIMARM/dart --ignore-unrecognized-flags --package-root=out/DebugSIMARM/packages/ /mnt/data/b/build/slave/vm-linux-debug-simarm-be/build/sdk/tests/standalone/io/socket_bind_test.dart
Took 0:00:00.730646
Short reproduction command (experimental):
python tools/test.py -asimarm --write-debug-log --write-test-outcome-log --copy-coredumps --exclude-suite pkg -t480 standalone/io/socket_bind_test
```
| 1.0 | socket_bind_test still fails sometimes - It seems this test still fails sometimes - possibly another error condition that is not properly handled by the test itself? @mkustermann
https://build.chromium.org/p/client.dart/builders/vm-linux-debug-simarm-be/builds/852/steps/vm%20tests/logs/stdio
```
FAILED: none-vm debug_simarm standalone/io/socket_bind_test
Expected: Pass
Actual: RuntimeError
CommandOutput[vm]:
stdout:
unittest-suite-wait-for-done
stderr:
Unhandled exception:
SocketException: Failed to create server socket (OS Error: Address already in use, errno = 98), address = 127.0.0.1, port = 57270
#0 _NativeSocket.bind.<anonymous closure> (dart:io-patch/socket_patch.dart:505)
#1 _RootZone.runUnary (dart:async/zone.dart:1204)
#2 _FutureListener.handleValue (dart:async/future_impl.dart:131)
#3 _Future._propagateToListeners.handleValueCallback (dart:async/future_impl.dart:637)
#4 _Future._propagateToListeners (dart:async/future_impl.dart:667)
#5 _Future._completeWithValue (dart:async/future_impl.dart:477)
#6 _Future._asyncComplete.<anonymous closure> (dart:async/future_impl.dart:528)
#7 _microtaskLoop (dart:async/schedule_microtask.dart:41)
#8 _startMicrotaskLoop (dart:async/schedule_microtask.dart:50)
#9 _runPendingImmediateCallback (dart:isolate-patch/isolate_patch.dart:96)
#10 _RawReceivePortImpl._handleMessage (dart:isolate-patch/isolate_patch.dart:149)
Command[vm]: DART_CONFIGURATION=DebugSIMARM out/DebugSIMARM/dart --ignore-unrecognized-flags --package-root=out/DebugSIMARM/packages/ /mnt/data/b/build/slave/vm-linux-debug-simarm-be/build/sdk/tests/standalone/io/socket_bind_test.dart
Took 0:00:00.730646
Short reproduction command (experimental):
python tools/test.py -asimarm --write-debug-log --write-test-outcome-log --copy-coredumps --exclude-suite pkg -t480 standalone/io/socket_bind_test
```
| test | socket bind test still fails sometimes it seems this test still fails sometimes possibly another error condition that is not properly handled by the test itself mkustermann failed none vm debug simarm standalone io socket bind test expected pass actual runtimeerror commandoutput stdout unittest suite wait for done stderr unhandled exception socketexception failed to create server socket os error address already in use errno address port nativesocket bind dart io patch socket patch dart rootzone rununary dart async zone dart futurelistener handlevalue dart async future impl dart future propagatetolisteners handlevaluecallback dart async future impl dart future propagatetolisteners dart async future impl dart future completewithvalue dart async future impl dart future asynccomplete dart async future impl dart microtaskloop dart async schedule microtask dart startmicrotaskloop dart async schedule microtask dart runpendingimmediatecallback dart isolate patch isolate patch dart rawreceiveportimpl handlemessage dart isolate patch isolate patch dart command dart configuration debugsimarm out debugsimarm dart ignore unrecognized flags package root out debugsimarm packages mnt data b build slave vm linux debug simarm be build sdk tests standalone io socket bind test dart took short reproduction command experimental python tools test py asimarm write debug log write test outcome log copy coredumps exclude suite pkg standalone io socket bind test | 1 |
235,833 | 7,743,201,862 | IssuesEvent | 2018-05-29 12:05:48 | architecture-building-systems/CityEnergyAnalyst | https://api.github.com/repos/architecture-building-systems/CityEnergyAnalyst | closed | Thermal networks plots didn't work during test run | Priority 1 bug enhancement | 1-The choice of heating or cooling network should not be hidden under "Advanced" options since it is necessary in order to run the thermal networks plots.
2-The following error occurred when running the plots for DC for the CBD_medium_density case study:
```
Executing: PlotsTool SIN C:\temp\reference-case-WTP\reference-case-WTP\01_CBD_medium_density 01_CBD_medium_density # thermal_network 1;2;3 ind1 DC #
Start Time: Fri May 25 13:39:17 2018
Running script PlotsTool...
Executing: C:\ProgramData\CityEnergyAnalyst\python.exe -u -m cea.interfaces.cli.cli plots --buildings --network-names --scenario C:\temp\reference-case-WTP\reference-case-WTP\01_CBD_medium_density --region SIN --network-type DC --scenarios 01_CBD_medium_density --individual ind1 --generations 1, 2, 3 --categories thermal_network
Running `cea plots` with the following parameters:
- general:region = SIN
- general:scenario = C:\temp\reference-case-WTP\reference-case-WTP\01_CBD_medium_density
- plots:scenarios = ['01_CBD_medium_density']
- plots:buildings = []
- plots:categories = ['thermal_network']
- plots:generations = ['1', '2', '3']
- plots:individual = ind1
- plots:network-type = DC
- plots:network-names = []
Running plots for the next categories = ['thermal_network']
Creating plots for network:
C:\ProgramData\CityEnergyAnalyst\lib\site-packages\numpy\core\fromnumeric.py:57: RuntimeWarning:
invalid value encountered in rint
This application failed to start because it could not find or load the Qt platform plugin "windows"
in "".
Reinstalling the application may fix this problem.
Traceback (most recent call last):
File "C:\Users\TEMP\AppData\Roaming\ESRI\Desktop10.5\ArcToolbox\My Toolboxes\cea\interfaces\arcgis\arcgishelper.py", line 90, in execute
run_cli(self.cea_tool, **kwargs)
File "C:\Users\TEMP\AppData\Roaming\ESRI\Desktop10.5\ArcToolbox\My Toolboxes\cea\interfaces\arcgis\arcgishelper.py", line 177, in run_cli
raise Exception('Tool did not run successfully')
Exception: Tool did not run successfully
Failed to execute (PlotsTool).
Failed at Fri May 25 13:39:29 2018 (Elapsed Time: 11.67 seconds)
``` | 1.0 | Thermal networks plots didn't work during test run - 1-The choice of heating or cooling network should not be hidden under "Advanced" options since it is necessary in order to run the thermal networks plots.
2-The following error occurred when running the plots for DC for the CBD_medium_density case study:
```
Executing: PlotsTool SIN C:\temp\reference-case-WTP\reference-case-WTP\01_CBD_medium_density 01_CBD_medium_density # thermal_network 1;2;3 ind1 DC #
Start Time: Fri May 25 13:39:17 2018
Running script PlotsTool...
Executing: C:\ProgramData\CityEnergyAnalyst\python.exe -u -m cea.interfaces.cli.cli plots --buildings --network-names --scenario C:\temp\reference-case-WTP\reference-case-WTP\01_CBD_medium_density --region SIN --network-type DC --scenarios 01_CBD_medium_density --individual ind1 --generations 1, 2, 3 --categories thermal_network
Running `cea plots` with the following parameters:
- general:region = SIN
- general:scenario = C:\temp\reference-case-WTP\reference-case-WTP\01_CBD_medium_density
- plots:scenarios = ['01_CBD_medium_density']
- plots:buildings = []
- plots:categories = ['thermal_network']
- plots:generations = ['1', '2', '3']
- plots:individual = ind1
- plots:network-type = DC
- plots:network-names = []
Running plots for the next categories = ['thermal_network']
Creating plots for network:
C:\ProgramData\CityEnergyAnalyst\lib\site-packages\numpy\core\fromnumeric.py:57: RuntimeWarning:
invalid value encountered in rint
This application failed to start because it could not find or load the Qt platform plugin "windows"
in "".
Reinstalling the application may fix this problem.
Traceback (most recent call last):
File "C:\Users\TEMP\AppData\Roaming\ESRI\Desktop10.5\ArcToolbox\My Toolboxes\cea\interfaces\arcgis\arcgishelper.py", line 90, in execute
run_cli(self.cea_tool, **kwargs)
File "C:\Users\TEMP\AppData\Roaming\ESRI\Desktop10.5\ArcToolbox\My Toolboxes\cea\interfaces\arcgis\arcgishelper.py", line 177, in run_cli
raise Exception('Tool did not run successfully')
Exception: Tool did not run successfully
Failed to execute (PlotsTool).
Failed at Fri May 25 13:39:29 2018 (Elapsed Time: 11.67 seconds)
``` | non_test | thermal networks plots didn t work during test run the choice of heating or cooling network should not be hidden under advanced options since it is necessary in order to run the thermal networks plots the following error occurred when running the plots for dc for the cbd medium density case study executing plotstool sin c temp reference case wtp reference case wtp cbd medium density cbd medium density thermal network dc start time fri may running script plotstool executing c programdata cityenergyanalyst python exe u m cea interfaces cli cli plots buildings network names scenario c temp reference case wtp reference case wtp cbd medium density region sin network type dc scenarios cbd medium density individual generations categories thermal network running cea plots with the following parameters general region sin general scenario c temp reference case wtp reference case wtp cbd medium density plots scenarios plots buildings plots categories plots generations plots individual plots network type dc plots network names running plots for the next categories creating plots for network c programdata cityenergyanalyst lib site packages numpy core fromnumeric py runtimewarning invalid value encountered in rint this application failed to start because it could not find or load the qt platform plugin windows in reinstalling the application may fix this problem traceback most recent call last file c users temp appdata roaming esri arctoolbox my toolboxes cea interfaces arcgis arcgishelper py line in execute run cli self cea tool kwargs file c users temp appdata roaming esri arctoolbox my toolboxes cea interfaces arcgis arcgishelper py line in run cli raise exception tool did not run successfully exception tool did not run successfully failed to execute plotstool failed at fri may elapsed time seconds | 0 |
34,437 | 4,923,614,992 | IssuesEvent | 2016-11-25 10:58:54 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | Upgrading does not remove translations from app_settings | 4 - Acceptance Testing Bug | Going from `2.8.2` to `2.9.0-beta.3` the translations were updated, but not removed from app_settings. | 1.0 | Upgrading does not remove translations from app_settings - Going from `2.8.2` to `2.9.0-beta.3` the translations were updated, but not removed from app_settings. | test | upgrading does not remove translations from app settings going from to beta the translations were updated but not removed from app settings | 1 |
92,331 | 8,360,292,628 | IssuesEvent | 2018-10-03 11:02:17 | Microsoft/vsts-tasks | https://api.github.com/repos/Microsoft/vsts-tasks | closed | How to deploy test agent in TFS 2018 to run CodedUI tests? | Area: Test | ## Troubleshooting
Checkout how to troubleshoot failures and collect debug logs: https://docs.microsoft.com/en-us/vsts/build-release/actions/troubleshooting
## Environment
- Server -TFS on-premises
- 2018 Update 3
- Agent - Private:
-OS version : Windows Server 2016 (10.0.14393) and Agent Version : 2.136.1
## Issue Description
Since "Deploy test agent" task got deprecated in TFS 2018, there is no way to run the test agent in interactive mode automatically (like it did in TFS 2015 using Deploy Test agent task) to execute the CodedUI tests.
Please let me know if there is any alternative way to run TFS 2018 test agent in interactive mode.
Thanks
Selvaraj C | 1.0 | How to deploy test agent in TFS 2018 to run CodedUI tests? - ## Troubleshooting
Checkout how to troubleshoot failures and collect debug logs: https://docs.microsoft.com/en-us/vsts/build-release/actions/troubleshooting
## Environment
- Server -TFS on-premises
- 2018 Update 3
- Agent - Private:
-OS version : Windows Server 2016 (10.0.14393) and Agent Version : 2.136.1
## Issue Description
Since "Deploy test agent" task got deprecated in TFS 2018, there is no way to run the test agent in interactive mode automatically (like it did in TFS 2015 using Deploy Test agent task) to execute the CodedUI tests.
Please let me know if there is any alternative way to run TFS 2018 test agent in interactive mode.
Thanks
Selvaraj C | test | how to deploy test agent in tfs to run codedui tests troubleshooting checkout how to troubleshoot failures and collect debug logs environment server tfs on premises update agent private os version windows server and agent version issue description since deploy test agent task got deprecated in tfs there is no way to run the test agent in interactive mode automatically like it did in tfs using deploy test agent task to execute the codedui tests please let me know if there is any alternative way to run tfs test agent in interactive mode thanks selvaraj c | 1 |
155,540 | 5,956,814,332 | IssuesEvent | 2017-05-28 20:18:27 | TrinityCore/TrinityCore | https://api.github.com/repos/TrinityCore/TrinityCore | closed | [General] Evade/Movement Issues | Priority-High Sub-Miscellaneous | Hey
I didnt really know how to classify these problems im having
It started with the issue in ToC where some mobs got stuck in evade - this was fixed by applying this #4877 by @Vincent-Michael
The problem persist with other, more general mobs like world mobs etc
Players attack a mob, he keeps evading and when they try to run away he keeps following them to the end of time (or till server crashes/they die)
I have no idea how to reproduce this but im sure many of you have seen this problem or heard of it at least 1 time
Please confirm.
Hash: 8776158
## <bountysource-plugin>
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/65437-general-evade-movement-issues?utm_campaign=plugin&utm_content=tracker%2F1310&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F1310&utm_medium=issues&utm_source=github).
</bountysource-plugin>
| 1.0 | [General] Evade/Movement Issues - Hey
I didnt really know how to classify these problems im having
It started with the issue in ToC where some mobs got stuck in evade - this was fixed by applying this #4877 by @Vincent-Michael
The problem persist with other, more general mobs like world mobs etc
Players attack a mob, he keeps evading and when they try to run away he keeps following them to the end of time (or till server crashes/they die)
I have no idea how to reproduce this but im sure many of you have seen this problem or heard of it at least 1 time
Please confirm.
Hash: 8776158
## <bountysource-plugin>
Want to back this issue? **[Post a bounty on it!](https://www.bountysource.com/issues/65437-general-evade-movement-issues?utm_campaign=plugin&utm_content=tracker%2F1310&utm_medium=issues&utm_source=github)** We accept bounties via [Bountysource](https://www.bountysource.com/?utm_campaign=plugin&utm_content=tracker%2F1310&utm_medium=issues&utm_source=github).
</bountysource-plugin>
| non_test | evade movement issues hey i didnt really know how to classify these problems im having it started with the issue in toc where some mobs got stuck in evade this was fixed by applying this by vincent michael the problem persist with other more general mobs like world mobs etc players attack a mob he keeps evading and when they try to run away he keeps following them to the end of time or till server crashes they die i have no idea how to reproduce this but im sure many of you have seen this problem or heard of it at least time please confirm hash want to back this issue we accept bounties via | 0 |
1,603 | 17,455,588,681 | IssuesEvent | 2021-08-06 00:20:20 | ewxrjk/rsbackup | https://api.github.com/repos/ewxrjk/rsbackup | closed | constrain issue43 test output | reliability maintenance | Part of the point of issue #43 was to quieten certain harmless failure cases, but the tests don't constrain stdout:
```
[...]
absent ${WORKSPACE}/store1/host1/volume3
absent ${WORKSPACE}/store2/host1/volume2
absent ${WORKSPACE}/store2/host1/volume3
compare ${srcdir:-.}/expect/issue43/failhook.txt ${WORKSPACE}/got/overridden-stderr.txt
# TODO output
rm -f ${WORKSPACE}/hookdata
``` | True | constrain issue43 test output - Part of the point of issue #43 was to quieten certain harmless failure cases, but the tests don't constrain stdout:
```
[...]
absent ${WORKSPACE}/store1/host1/volume3
absent ${WORKSPACE}/store2/host1/volume2
absent ${WORKSPACE}/store2/host1/volume3
compare ${srcdir:-.}/expect/issue43/failhook.txt ${WORKSPACE}/got/overridden-stderr.txt
# TODO output
rm -f ${WORKSPACE}/hookdata
``` | non_test | constrain test output part of the point of issue was to quieten certain harmless failure cases but the tests don t constrain stdout absent workspace absent workspace absent workspace compare srcdir expect failhook txt workspace got overridden stderr txt todo output rm f workspace hookdata | 0 |
563,521 | 16,700,132,613 | IssuesEvent | 2021-06-09 00:14:55 | celo-org/wallet | https://api.github.com/repos/celo-org/wallet | closed | Inappropriate blue banner displayed when user taps on “Resend last message” button on Confirm page. | Component: Verification Priority: P2 bug ios qa-report regression wallet | **Frequency:** 100%
**Repro on build version:** Test Flight 1.15.1
**Does not repro version** Android internal build V1.15.1, Test Flight 1.15.0, Android internal build V1.15.0
**Repro on devices:** iPhone SE (14.2), iPhone 6+(12.4.5)
**Does not repro devices** Redmi Note 8 (9.0), One plus 6T (10)
**Pre-condition:** Make sure that user have pasted/entered 2 received codes on “Confirm” page
**Repro Steps:**
1. Launch the application & complete onboarding flow
2. Now user should on “Phone Number” page
3. Complete Captcha flow & make sure that 2 codes should be pasted
4. Now tap on “Resend Last Message”button & Observed that,
**Current Behavior:** “Sending 3 messages” displayed even user has requested for one message.
**Expected Behavior:** “Sending 1 message” banner should be displayed.
**Investigation:** Also it is observed that, user not able to receive last code after tapping on “Resend last message”
**Impact:** Users may be confused in exactly how many messages are required to complete the verification flow.
**Attachment:** [InappropriateBlueBannerDisplayed&LastCodeNotReceived](https://drive.google.com/file/d/1aMtxGaO-CmGYT-5DzG975Kf56ag0arLm/view?usp=sharing)
| 1.0 | Inappropriate blue banner displayed when user taps on “Resend last message” button on Confirm page. - **Frequency:** 100%
**Repro on build version:** Test Flight 1.15.1
**Does not repro version** Android internal build V1.15.1, Test Flight 1.15.0, Android internal build V1.15.0
**Repro on devices:** iPhone SE (14.2), iPhone 6+(12.4.5)
**Does not repro devices** Redmi Note 8 (9.0), One plus 6T (10)
**Pre-condition:** Make sure that user have pasted/entered 2 received codes on “Confirm” page
**Repro Steps:**
1. Launch the application & complete onboarding flow
2. Now user should on “Phone Number” page
3. Complete Captcha flow & make sure that 2 codes should be pasted
4. Now tap on “Resend Last Message”button & Observed that,
**Current Behavior:** “Sending 3 messages” displayed even user has requested for one message.
**Expected Behavior:** “Sending 1 message” banner should be displayed.
**Investigation:** Also it is observed that, user not able to receive last code after tapping on “Resend last message”
**Impact:** Users may be confused in exactly how many messages are required to complete the verification flow.
**Attachment:** [InappropriateBlueBannerDisplayed&LastCodeNotReceived](https://drive.google.com/file/d/1aMtxGaO-CmGYT-5DzG975Kf56ag0arLm/view?usp=sharing)
| non_test | inappropriate blue banner displayed when user taps on “resend last message” button on confirm page frequency repro on build version test flight does not repro version android internal build test flight android internal build repro on devices iphone se iphone does not repro devices redmi note one plus pre condition make sure that user have pasted entered received codes on “confirm” page repro steps launch the application complete onboarding flow now user should on “phone number” page complete captcha flow make sure that codes should be pasted now tap on “resend last message”button observed that current behavior “sending messages” displayed even user has requested for one message expected behavior “sending message” banner should be displayed investigation also it is observed that user not able to receive last code after tapping on “resend last message” impact users may be confused in exactly how many messages are required to complete the verification flow attachment | 0 |
140,413 | 31,990,505,918 | IssuesEvent | 2023-09-21 05:17:39 | SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670 | https://api.github.com/repos/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670 | opened | Code Security Report: 17 high severity findings, 29 total findings | Mend: code security findings | # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-09-21 05:16am
**Total Findings:** 29 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 1
**Detected Programming Languages:** 1 (Java*)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend Application](https://dev.whitesourcesoftware.com/app/orgs/UP-QA-ORG/scans/3d16d106-5d48-4520-ba84-fa52706e1221/sast?project=68d17758-5b54-40c4-8ef1-95b755aa464b).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:30](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25-L30
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:29](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L24-L29
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:123](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L118-L123
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L117
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:150](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L145-L150
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L139
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[LotOfFindings.java:30](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25-L30
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior SQL Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/sql/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior SQL Injection Video](https://media.securecodewarrior.com/v2/module_01_sql_injection.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP SQL Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP SQL Injection](https://owasp.org/www-community/attacks/SQL_Injection)</li>
<li>
[OWASP Query Parameterization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Query_Parameterization_Cheat_Sheet.html)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[LotOfFindings.java:29](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L24-L29
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior SQL Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/sql/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior SQL Injection Video](https://media.securecodewarrior.com/v2/module_01_sql_injection.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP SQL Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP SQL Injection](https://owasp.org/www-community/attacks/SQL_Injection)</li>
<li>
[OWASP Query Parameterization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Query_Parameterization_Cheat_Sheet.html)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[LotOfFindings.java:252](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L252)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L247-L252
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L239
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L240
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L243
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L245
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L252
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior SQL Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/sql/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior SQL Injection Video](https://media.securecodewarrior.com/v2/module_01_sql_injection.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP SQL Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP SQL Injection](https://owasp.org/www-community/attacks/SQL_Injection)</li>
<li>
[OWASP Query Parameterization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Query_Parameterization_Cheat_Sheet.html)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Expression Language Injection</td><td>
[CWE-917](https://cwe.mitre.org/data/definitions/917.html)
</td><td>
[LotOfFindings.java:89](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L89)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84-L89
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L88
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L89
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Videos<ul></ul></li>
<li>Further Reading<ul><li>
[OWASP Top Ten Proactive Controls 2018 C5: Validate All Inputs](https://owasp.org/www-project-proactive-controls/v3/en/c5-validate-inputs)</li>
<li>
[OWASP Injection Prevention Cheat Sheet in Java](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_in_Java_Cheat_Sheet.html)</li>
<li>
[OWASP Input Validation Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Input_Validation_Cheat_Sheet.html)</li>
<li>
[OWASP Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP Top Ten 2021 A03: Injection](https://owasp.org/Top10/A03_2021-Injection/)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Expression Language Injection</td><td>
[CWE-917](https://cwe.mitre.org/data/definitions/917.html)
</td><td>
[LotOfFindings.java:88](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L88)
</td><td>2</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L83-L88
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Videos<ul></ul></li>
<li>Further Reading<ul><li>
[OWASP Top Ten Proactive Controls 2018 C5: Validate All Inputs](https://owasp.org/www-project-proactive-controls/v3/en/c5-validate-inputs)</li>
<li>
[OWASP Injection Prevention Cheat Sheet in Java](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_in_Java_Cheat_Sheet.html)</li>
<li>
[OWASP Input Validation Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Input_Validation_Cheat_Sheet.html)</li>
<li>
[OWASP Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP Top Ten 2021 A03: Injection](https://owasp.org/Top10/A03_2021-Injection/)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Expression Language Injection</td><td>
[CWE-917](https://cwe.mitre.org/data/definitions/917.html)
</td><td>
[LotOfFindings.java:155](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L155)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150-L155
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L139
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Videos<ul></ul></li>
<li>Further Reading<ul><li>
[OWASP Top Ten Proactive Controls 2018 C5: Validate All Inputs](https://owasp.org/www-project-proactive-controls/v3/en/c5-validate-inputs)</li>
<li>
[OWASP Injection Prevention Cheat Sheet in Java](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_in_Java_Cheat_Sheet.html)</li>
<li>
[OWASP Input Validation Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Input_Validation_Cheat_Sheet.html)</li>
<li>
[OWASP Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP Top Ten 2021 A03: Injection](https://owasp.org/Top10/A03_2021-Injection/)</li>
</ul></li>
</ul>
</details>
</td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Command Injection|[CWE-78](https://cwe.mitre.org/data/definitions/78.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Expression Language Injection|[CWE-917](https://cwe.mitre.org/data/definitions/917.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Insecure Cryptographic Algorithm|[CWE-327](https://cwe.mitre.org/data/definitions/327.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Improper Verification of JWT Signature|[CWE-347](https://cwe.mitre.org/data/definitions/347.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Missing Cryptographic Step|[CWE-325](https://cwe.mitre.org/data/definitions/325.html)|Java*|5|
| 1.0 | Code Security Report: 17 high severity findings, 29 total findings - # Code Security Report
### Scan Metadata
**Latest Scan:** 2023-09-21 05:16am
**Total Findings:** 29 | **New Findings:** 0 | **Resolved Findings:** 0
**Tested Project Files:** 1
**Detected Programming Languages:** 1 (Java*)
<!-- SAST-MANUAL-SCAN-START -->
- [ ] Check this box to manually trigger a scan
<!-- SAST-MANUAL-SCAN-END -->
### Most Relevant Findings
> The below list presents the 10 most relevant findings that need your attention. To view information on the remaining findings, navigate to the [Mend Application](https://dev.whitesourcesoftware.com/app/orgs/UP-QA-ORG/scans/3d16d106-5d48-4520-ba84-fa52706e1221/sast?project=68d17758-5b54-40c4-8ef1-95b755aa464b).
<table role='table'><thead><tr><th>Severity</th><th>Vulnerability Type</th><th>CWE</th><th>File</th><th>Data Flows</th><th>Date</th></tr></thead><tbody><tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:30](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25-L30
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:29](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L24-L29
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:123](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L118-L123
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L117
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L123
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Command Injection</td><td>
[CWE-78](https://cwe.mitre.org/data/definitions/78.html)
</td><td>
[LotOfFindings.java:150](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L145-L150
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L139
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior Command Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/oscmd/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior Command Injection Video](https://media.securecodewarrior.com/OS+Command+Injections_v2.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP testing for Command Injection](https://wiki.owasp.org/index.php/Testing_for_Command_Injection_(OTG-INPVAL-013))</li>
<li>
[OWASP Command Injection](https://owasp.org/www-community/attacks/Command_Injection)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[LotOfFindings.java:30](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25-L30
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L30
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior SQL Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/sql/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior SQL Injection Video](https://media.securecodewarrior.com/v2/module_01_sql_injection.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP SQL Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP SQL Injection](https://owasp.org/www-community/attacks/SQL_Injection)</li>
<li>
[OWASP Query Parameterization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Query_Parameterization_Cheat_Sheet.html)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[LotOfFindings.java:29](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L24-L29
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L25
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L29
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior SQL Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/sql/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior SQL Injection Video](https://media.securecodewarrior.com/v2/module_01_sql_injection.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP SQL Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP SQL Injection](https://owasp.org/www-community/attacks/SQL_Injection)</li>
<li>
[OWASP Query Parameterization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Query_Parameterization_Cheat_Sheet.html)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>SQL Injection</td><td>
[CWE-89](https://cwe.mitre.org/data/definitions/89.html)
</td><td>
[LotOfFindings.java:252](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L252)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L247-L252
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L239
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L240
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L243
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L245
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L252
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Training<ul><li>
[Secure Code Warrior SQL Injection Training](https://portal.securecodewarrior.com/?utm_source=partner-integration:mend&partner_id=mend#/contextual-microlearning/web/injection/sql/java/vanilla)</li>
</ul></li>
<li>Videos<ul><li>
[Secure Code Warrior SQL Injection Video](https://media.securecodewarrior.com/v2/module_01_sql_injection.mp4)</li>
</ul></li>
<li>Further Reading<ul><li>
[OWASP SQL Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/SQL_Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP SQL Injection](https://owasp.org/www-community/attacks/SQL_Injection)</li>
<li>
[OWASP Query Parameterization Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Query_Parameterization_Cheat_Sheet.html)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Expression Language Injection</td><td>
[CWE-917](https://cwe.mitre.org/data/definitions/917.html)
</td><td>
[LotOfFindings.java:89](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L89)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84-L89
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L88
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L89
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Videos<ul></ul></li>
<li>Further Reading<ul><li>
[OWASP Top Ten Proactive Controls 2018 C5: Validate All Inputs](https://owasp.org/www-project-proactive-controls/v3/en/c5-validate-inputs)</li>
<li>
[OWASP Injection Prevention Cheat Sheet in Java](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_in_Java_Cheat_Sheet.html)</li>
<li>
[OWASP Input Validation Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Input_Validation_Cheat_Sheet.html)</li>
<li>
[OWASP Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP Top Ten 2021 A03: Injection](https://owasp.org/Top10/A03_2021-Injection/)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Expression Language Injection</td><td>
[CWE-917](https://cwe.mitre.org/data/definitions/917.html)
</td><td>
[LotOfFindings.java:88](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L88)
</td><td>2</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L83-L88
<details>
<summary>2 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84
</details>
<details>
<summary>View Data Flow 2</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L84
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Videos<ul></ul></li>
<li>Further Reading<ul><li>
[OWASP Top Ten Proactive Controls 2018 C5: Validate All Inputs](https://owasp.org/www-project-proactive-controls/v3/en/c5-validate-inputs)</li>
<li>
[OWASP Injection Prevention Cheat Sheet in Java](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_in_Java_Cheat_Sheet.html)</li>
<li>
[OWASP Input Validation Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Input_Validation_Cheat_Sheet.html)</li>
<li>
[OWASP Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP Top Ten 2021 A03: Injection](https://owasp.org/Top10/A03_2021-Injection/)</li>
</ul></li>
</ul>
</details>
</td></tr><tr><td colspan='6'> </td></tr>
<tr><td><a href='#'><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20></a> High</td><td>Expression Language Injection</td><td>
[CWE-917](https://cwe.mitre.org/data/definitions/917.html)
</td><td>
[LotOfFindings.java:155](https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L155)
</td><td>1</td><td>2023-09-21 05:17am</td></tr><tr><td colspan='6'><details><summary><a href='#'><img src='https://saas.mend.io/sast/favicon.png' width=15 height=15></a> Vulnerable Code</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L150-L155
<details>
<summary>1 Data Flow/s detected</summary></br>
<details>
<summary>View Data Flow 1</summary>
https://github.com/SAST-UP-DEV/SAST-Test-Repo-e09d628c-ffc2-46ba-b220-15c96a2d9670/blob/251b94f10330523aeb6c24c547acfc604209e931/LotOfFindings.java#L139
</details>
</details>
</details>
<details>
<summary><a href='#'><img src='https://integration-api.securecodewarrior.com/explorer/favicon-32x32.png' width=15 height=15></a> Secure Code Warrior Training Material</summary>
<ul><li>Videos<ul></ul></li>
<li>Further Reading<ul><li>
[OWASP Top Ten Proactive Controls 2018 C5: Validate All Inputs](https://owasp.org/www-project-proactive-controls/v3/en/c5-validate-inputs)</li>
<li>
[OWASP Injection Prevention Cheat Sheet in Java](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_in_Java_Cheat_Sheet.html)</li>
<li>
[OWASP Input Validation Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Input_Validation_Cheat_Sheet.html)</li>
<li>
[OWASP Injection Prevention Cheat Sheet](https://cheatsheetseries.owasp.org/cheatsheets/Injection_Prevention_Cheat_Sheet.html)</li>
<li>
[OWASP Top Ten 2021 A03: Injection](https://owasp.org/Top10/A03_2021-Injection/)</li>
</ul></li>
</ul>
</details>
</td></tr></tbody></table>
### Findings Overview
| Severity | Vulnerability Type | CWE | Language | Count |
|-|-|-|-|-|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Command Injection|[CWE-78](https://cwe.mitre.org/data/definitions/78.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Path/Directory Traversal|[CWE-22](https://cwe.mitre.org/data/definitions/22.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|SQL Injection|[CWE-89](https://cwe.mitre.org/data/definitions/89.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Expression Language Injection|[CWE-917](https://cwe.mitre.org/data/definitions/917.html)|Java*|4|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Deserialization of Untrusted Data|[CWE-502](https://cwe.mitre.org/data/definitions/502.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> High|Server Side Request Forgery|[CWE-918](https://cwe.mitre.org/data/definitions/918.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Insecure Cryptographic Algorithm|[CWE-327](https://cwe.mitre.org/data/definitions/327.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Hardcoded Password/Credentials|[CWE-798](https://cwe.mitre.org/data/definitions/798.html)|Java*|3|
|<img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Medium|Improper Verification of JWT Signature|[CWE-347](https://cwe.mitre.org/data/definitions/347.html)|Java*|2|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Weak Hash Strength|[CWE-328](https://cwe.mitre.org/data/definitions/328.html)|Java*|1|
|<img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png?' width=19 height=20> Low|Missing Cryptographic Step|[CWE-325](https://cwe.mitre.org/data/definitions/325.html)|Java*|5|
| non_test | code security report high severity findings total findings code security report scan metadata latest scan total findings new findings resolved findings tested project files detected programming languages java check this box to manually trigger a scan most relevant findings the below list presents the most relevant findings that need your attention to view information on the remaining findings navigate to the severity vulnerability type cwe file data flows date high command injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high command injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high command injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high command injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high sql injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high sql injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high sql injection vulnerable code data flow s detected view data flow secure code warrior training material training videos further reading nbsp high expression language injection vulnerable code data flow s detected view data flow secure code warrior training material videos further reading nbsp high expression language injection vulnerable code data flow s detected view data flow view data flow secure code warrior training material videos further reading nbsp high expression language injection vulnerable code data flow s detected view data flow secure code warrior training material videos further reading findings overview severity vulnerability type cwe language count high command injection high path directory traversal high sql injection high expression language injection high deserialization of untrusted data high server side request forgery medium insecure cryptographic algorithm medium hardcoded password credentials medium improper verification of jwt signature low weak hash strength low missing cryptographic step | 0 |
55,266 | 6,461,158,068 | IssuesEvent | 2017-08-16 07:18:01 | universam1/iSpindel | https://api.github.com/repos/universam1/iSpindel | closed | Deep sleep unreliable with resistor | enhancement tests required | Hi there,
Firstly wanted to say that you are doing an awesome job here. :+1:
My iSpindle is setup with the **Wemos D1 Mini PRO** which works fine except, the iSpindle wouldn't wake up from deep sleep with the config as described in your Wiki. A quick google told me that this is a known issue with the Wemos in general (all models) and that replacing the 470 ohms resistor with a diode solves this issue.
Credits go to **schufti** in this forum post: http://www.esp8266.com/viewtopic.php?f=13&t=7918&start=24#sthash.9AUQQ49G.dpuf
> " instead of experimenting with resistors and relying on the "it worked for me" value, it would be more technically correct to use a schottky diode (e.g. BAT43) to cleanly pull rst low without side effects when gpio16 is high.
>
> p.s.: the cathode (ring) towards gpio16 ..."
>
It worked for me so thought id share and hopefully it works for others as well.
Cheers | 1.0 | Deep sleep unreliable with resistor - Hi there,
Firstly wanted to say that you are doing an awesome job here. :+1:
My iSpindle is setup with the **Wemos D1 Mini PRO** which works fine except, the iSpindle wouldn't wake up from deep sleep with the config as described in your Wiki. A quick google told me that this is a known issue with the Wemos in general (all models) and that replacing the 470 ohms resistor with a diode solves this issue.
Credits go to **schufti** in this forum post: http://www.esp8266.com/viewtopic.php?f=13&t=7918&start=24#sthash.9AUQQ49G.dpuf
> " instead of experimenting with resistors and relying on the "it worked for me" value, it would be more technically correct to use a schottky diode (e.g. BAT43) to cleanly pull rst low without side effects when gpio16 is high.
>
> p.s.: the cathode (ring) towards gpio16 ..."
>
It worked for me so thought id share and hopefully it works for others as well.
Cheers | test | deep sleep unreliable with resistor hi there firstly wanted to say that you are doing an awesome job here my ispindle is setup with the wemos mini pro which works fine except the ispindle wouldn t wake up from deep sleep with the config as described in your wiki a quick google told me that this is a known issue with the wemos in general all models and that replacing the ohms resistor with a diode solves this issue credits go to schufti in this forum post instead of experimenting with resistors and relying on the it worked for me value it would be more technically correct to use a schottky diode e g to cleanly pull rst low without side effects when is high p s the cathode ring towards it worked for me so thought id share and hopefully it works for others as well cheers | 1 |
226,118 | 7,504,108,811 | IssuesEvent | 2018-04-10 01:42:25 | lidarr/Lidarr | https://api.github.com/repos/lidarr/Lidarr | closed | Add (feat. XXXX) to Track title cleaning | Area: Parsing Priority: Low Status: Accepted Type: Enhancement | Many tracks have the feat artist in the Track Tag. This would clean that before comparing the track name to the db to find a match. Ex. `The Monster (feat. Rihanna)` | 1.0 | Add (feat. XXXX) to Track title cleaning - Many tracks have the feat artist in the Track Tag. This would clean that before comparing the track name to the db to find a match. Ex. `The Monster (feat. Rihanna)` | non_test | add feat xxxx to track title cleaning many tracks have the feat artist in the track tag this would clean that before comparing the track name to the db to find a match ex the monster feat rihanna | 0 |
81,192 | 7,775,259,935 | IssuesEvent | 2018-06-05 01:44:18 | WebliniaERP/webliniaerp-web | https://api.github.com/repos/WebliniaERP/webliniaerp-web | closed | Redesenhar Rel. Posição de Estoque | 1-melhoria 2-prioridade alta 3- DONA ANA test | - O relatório na verdade não é um apontamento em si, mas o resultado de apontamentos.
- Dessa forma, ele deve deixar de existir como atualmente e deve ser gerado conforme filtros, e os produtos são carregados automaticamente.
(conversar comigo quando for implementar)
- Incluir coluna de indicação de Quebra Total (Col. Desperdícios + Col. Diferença):
- Verde: <= 0,30 %
- Amarelo: > 0,30 % e <= 0,49%
- Vermelho: > 0,50% | 1.0 | Redesenhar Rel. Posição de Estoque - - O relatório na verdade não é um apontamento em si, mas o resultado de apontamentos.
- Dessa forma, ele deve deixar de existir como atualmente e deve ser gerado conforme filtros, e os produtos são carregados automaticamente.
(conversar comigo quando for implementar)
- Incluir coluna de indicação de Quebra Total (Col. Desperdícios + Col. Diferença):
- Verde: <= 0,30 %
- Amarelo: > 0,30 % e <= 0,49%
- Vermelho: > 0,50% | test | redesenhar rel posição de estoque o relatório na verdade não é um apontamento em si mas o resultado de apontamentos dessa forma ele deve deixar de existir como atualmente e deve ser gerado conforme filtros e os produtos são carregados automaticamente conversar comigo quando for implementar incluir coluna de indicação de quebra total col desperdícios col diferença verde amarelo e vermelho | 1 |
325,792 | 27,962,881,820 | IssuesEvent | 2023-03-24 16:57:46 | kubernetes-sigs/cluster-api | https://api.github.com/repos/kubernetes-sigs/cluster-api | closed | Improve conversion fuzz-testing | kind/feature lifecycle/frozen area/testing triage/accepted | It looks like we have a gap in our fuzz testing. We had an issue today which should have been covered by the test: #6142
Our current theory is that this happened because there are a lot of fields in InitConfiguration/JoinConfiguration and we just never hit the case were only Patches were set.
Goal of this issue is to improve our fuzz testing so it would catch that issue the next time.
To do this we can use the current main branch and revert the fix PR(https://github.com/kubernetes-sigs/cluster-api/pull/6144). Then we can play around with fuzzing and see if we can adjust the test to detect the case.
One idea from Fabrizio is to configure the nil frequency for fields in the fuzzer (xref: https://github.com/kubernetes-sigs/cluster-api/pull/6144#issuecomment-1041380425)
/area testing
/kind feature
| 1.0 | Improve conversion fuzz-testing - It looks like we have a gap in our fuzz testing. We had an issue today which should have been covered by the test: #6142
Our current theory is that this happened because there are a lot of fields in InitConfiguration/JoinConfiguration and we just never hit the case were only Patches were set.
Goal of this issue is to improve our fuzz testing so it would catch that issue the next time.
To do this we can use the current main branch and revert the fix PR(https://github.com/kubernetes-sigs/cluster-api/pull/6144). Then we can play around with fuzzing and see if we can adjust the test to detect the case.
One idea from Fabrizio is to configure the nil frequency for fields in the fuzzer (xref: https://github.com/kubernetes-sigs/cluster-api/pull/6144#issuecomment-1041380425)
/area testing
/kind feature
| test | improve conversion fuzz testing it looks like we have a gap in our fuzz testing we had an issue today which should have been covered by the test our current theory is that this happened because there are a lot of fields in initconfiguration joinconfiguration and we just never hit the case were only patches were set goal of this issue is to improve our fuzz testing so it would catch that issue the next time to do this we can use the current main branch and revert the fix pr then we can play around with fuzzing and see if we can adjust the test to detect the case one idea from fabrizio is to configure the nil frequency for fields in the fuzzer xref area testing kind feature | 1 |
317,767 | 9,669,113,118 | IssuesEvent | 2019-05-21 16:33:18 | roboticslab-uc3m/questions-and-answers | https://api.github.com/repos/roboticslab-uc3m/questions-and-answers | closed | YARP 3.0 upgrade path | announcement help wanted horizontal priority: critical | Following https://github.com/roboticslab-uc3m/questions-and-answers/issues/65 (forward compat with YARP 3.x), https://github.com/roboticslab-uc3m/questions-and-answers/issues/78/https://github.com/roboticslab-uc3m/questions-and-answers/issues/82 (upgrade and require YCM v0.10+) and https://github.com/roboticslab-uc3m/questions-and-answers/issues/73 (migrating to Xenial builds in Travis), minimum required YARP version is going to be bumped from v2.3.70 to v3.0 soon enough. This issue will track code cleanup (remove pre-3.0 stuff), blockers and announcements.
**TODOs**
- Drop `find_package(YARP 2.3.70 REQUIRED)` fallbacks ([ref](https://github.com/roboticslab-uc3m/kinematics-dynamics/blob/95f65ff0b144ce4f2907fe4f4a6999d9ddf15258/CMakeLists.txt#L44-L46)).
- List optional and required components ([ref](https://github.com/roboticslab-uc3m/speech/blob/43801e151b9fdf20fc08d082fa10f116a97c7323/CMakeLists.txt#L41-L42), see also https://github.com/roboticslab-uc3m/questions-and-answers/issues/65#issuecomment-405119846 and https://github.com/roboticslab-uc3m/speech/issues/27).
- Update required YARP version in `doc/<repo>-install.md`.
- Remove version checks such as `#if YARP_VERSION_MAJOR != 3` in C++ and CMake code (e.g. https://github.com/roboticslab-uc3m/yarp-devices/commit/2af42cd5538f6be2d72b377efe1cc87c80e2a34f, https://github.com/roboticslab-uc3m/yarp-devices/issues/180).
- Fix C++/CMake deprecation warnings (check Travis builds).
- Rename local C++ implementation files regarding motor interfaces (e.g. *IControlMode2Impl.cpp* would become *IControlModeImpl.cpp*).
- Delete pre-v3.0 jobs in *.travis.yml* (delete the cache).
- Explore YARP [v3.0.0](https://github.com/robotology/yarp/releases/tag/v3.0.0) and [v3.0.1](https://github.com/robotology/yarp/releases/tag/v3.0.1) release notes, adopt new features (conditionally enable [v3.1.0](https://github.com/robotology/yarp/releases/tag/v3.1.0) and [v3.1.1](https://github.com/robotology/yarp/releases/tag/v3.1.1)).
- Tag the last pre-v3.0 commit.
- Upgrade robot on-board PCs.
- Review install guides, e.g. some CMake options have been renamed, removed, made optional or changed defaults ([ref](https://github.com/roboticslab-uc3m/installation-guides/blob/23ee6bd052ceb405f443726973bdd7a73d58fa98/install-yarp.md)).
**Blockers** (mostly related to a recent OpenNI2->RGBDSensor device migration, https://github.com/roboticslab-uc3m/vision/issues/83)
- [x] https://github.com/roboticslab-uc3m/teo-configuration-files/issues/16: update TEO's depth camera-related .xml files
- [x] https://github.com/roboticslab-uc3m/vision/issues/85: frame resolution mismatch bug
- [x] https://github.com/roboticslab-uc3m/openrave-yarp-plugins/issues/92: YARP v2.3.72.1-v3.1.0 bug, missing interface implementation | 1.0 | YARP 3.0 upgrade path - Following https://github.com/roboticslab-uc3m/questions-and-answers/issues/65 (forward compat with YARP 3.x), https://github.com/roboticslab-uc3m/questions-and-answers/issues/78/https://github.com/roboticslab-uc3m/questions-and-answers/issues/82 (upgrade and require YCM v0.10+) and https://github.com/roboticslab-uc3m/questions-and-answers/issues/73 (migrating to Xenial builds in Travis), minimum required YARP version is going to be bumped from v2.3.70 to v3.0 soon enough. This issue will track code cleanup (remove pre-3.0 stuff), blockers and announcements.
**TODOs**
- Drop `find_package(YARP 2.3.70 REQUIRED)` fallbacks ([ref](https://github.com/roboticslab-uc3m/kinematics-dynamics/blob/95f65ff0b144ce4f2907fe4f4a6999d9ddf15258/CMakeLists.txt#L44-L46)).
- List optional and required components ([ref](https://github.com/roboticslab-uc3m/speech/blob/43801e151b9fdf20fc08d082fa10f116a97c7323/CMakeLists.txt#L41-L42), see also https://github.com/roboticslab-uc3m/questions-and-answers/issues/65#issuecomment-405119846 and https://github.com/roboticslab-uc3m/speech/issues/27).
- Update required YARP version in `doc/<repo>-install.md`.
- Remove version checks such as `#if YARP_VERSION_MAJOR != 3` in C++ and CMake code (e.g. https://github.com/roboticslab-uc3m/yarp-devices/commit/2af42cd5538f6be2d72b377efe1cc87c80e2a34f, https://github.com/roboticslab-uc3m/yarp-devices/issues/180).
- Fix C++/CMake deprecation warnings (check Travis builds).
- Rename local C++ implementation files regarding motor interfaces (e.g. *IControlMode2Impl.cpp* would become *IControlModeImpl.cpp*).
- Delete pre-v3.0 jobs in *.travis.yml* (delete the cache).
- Explore YARP [v3.0.0](https://github.com/robotology/yarp/releases/tag/v3.0.0) and [v3.0.1](https://github.com/robotology/yarp/releases/tag/v3.0.1) release notes, adopt new features (conditionally enable [v3.1.0](https://github.com/robotology/yarp/releases/tag/v3.1.0) and [v3.1.1](https://github.com/robotology/yarp/releases/tag/v3.1.1)).
- Tag the last pre-v3.0 commit.
- Upgrade robot on-board PCs.
- Review install guides, e.g. some CMake options have been renamed, removed, made optional or changed defaults ([ref](https://github.com/roboticslab-uc3m/installation-guides/blob/23ee6bd052ceb405f443726973bdd7a73d58fa98/install-yarp.md)).
**Blockers** (mostly related to a recent OpenNI2->RGBDSensor device migration, https://github.com/roboticslab-uc3m/vision/issues/83)
- [x] https://github.com/roboticslab-uc3m/teo-configuration-files/issues/16: update TEO's depth camera-related .xml files
- [x] https://github.com/roboticslab-uc3m/vision/issues/85: frame resolution mismatch bug
- [x] https://github.com/roboticslab-uc3m/openrave-yarp-plugins/issues/92: YARP v2.3.72.1-v3.1.0 bug, missing interface implementation | non_test | yarp upgrade path following forward compat with yarp x upgrade and require ycm and migrating to xenial builds in travis minimum required yarp version is going to be bumped from to soon enough this issue will track code cleanup remove pre stuff blockers and announcements todos drop find package yarp required fallbacks list optional and required components see also and update required yarp version in doc install md remove version checks such as if yarp version major in c and cmake code e g fix c cmake deprecation warnings check travis builds rename local c implementation files regarding motor interfaces e g cpp would become icontrolmodeimpl cpp delete pre jobs in travis yml delete the cache explore yarp and release notes adopt new features conditionally enable and tag the last pre commit upgrade robot on board pcs review install guides e g some cmake options have been renamed removed made optional or changed defaults blockers mostly related to a recent rgbdsensor device migration update teo s depth camera related xml files frame resolution mismatch bug yarp bug missing interface implementation | 0 |
195,249 | 14,710,070,854 | IssuesEvent | 2021-01-05 04:07:42 | github-vet/rangeloop-pointer-findings | https://api.github.com/repos/github-vet/rangeloop-pointer-findings | closed | relax-space/rtc-api: models/project_test.go; 9 LoC | fresh test tiny |
Found a possible issue in [relax-space/rtc-api](https://www.github.com/relax-space/rtc-api) at [models/project_test.go](https://github.com/relax-space/rtc-api/blob/30f7dc9b95712ada8a5dc0b07324a47301237784/models/project_test.go#L50-L58)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to project is reassigned at line 52
[Click here to see the code in its original context.](https://github.com/relax-space/rtc-api/blob/30f7dc9b95712ada8a5dc0b07324a47301237784/models/project_test.go#L50-L58)
<details>
<summary>Click here to show the 9 line(s) of Go which triggered the analyzer.</summary>
```go
for i, project := range projects {
t.Run(fmt.Sprint("Create#", i+1), func(t *testing.T) {
f := &project
affectedRow, err := f.Create(ctx)
test.Ok(t, err)
test.Equals(t, int64(1), affectedRow)
test.Assert(t, f.Id == i+1, "create failure")
})
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 30f7dc9b95712ada8a5dc0b07324a47301237784
| 1.0 | relax-space/rtc-api: models/project_test.go; 9 LoC -
Found a possible issue in [relax-space/rtc-api](https://www.github.com/relax-space/rtc-api) at [models/project_test.go](https://github.com/relax-space/rtc-api/blob/30f7dc9b95712ada8a5dc0b07324a47301237784/models/project_test.go#L50-L58)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to project is reassigned at line 52
[Click here to see the code in its original context.](https://github.com/relax-space/rtc-api/blob/30f7dc9b95712ada8a5dc0b07324a47301237784/models/project_test.go#L50-L58)
<details>
<summary>Click here to show the 9 line(s) of Go which triggered the analyzer.</summary>
```go
for i, project := range projects {
t.Run(fmt.Sprint("Create#", i+1), func(t *testing.T) {
f := &project
affectedRow, err := f.Create(ctx)
test.Ok(t, err)
test.Equals(t, int64(1), affectedRow)
test.Assert(t, f.Id == i+1, "create failure")
})
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: 30f7dc9b95712ada8a5dc0b07324a47301237784
| test | relax space rtc api models project test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to project is reassigned at line click here to show the line s of go which triggered the analyzer go for i project range projects t run fmt sprint create i func t testing t f project affectedrow err f create ctx test ok t err test equals t affectedrow test assert t f id i create failure leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 1 |
170,532 | 26,977,874,863 | IssuesEvent | 2023-02-09 10:52:23 | gitpod-io/website | https://api.github.com/repos/gitpod-io/website | opened | Minor Improvements on Homepage | type: suggestion type: design polish | ### Description
> followup #3382, #3387
Tasks List:
- [ ] the animated quotes should start a bit earlier now that we don't have the contact pop-up anymore
- [ ] align icon size. The JetBrains IDE icons are a lot bigger than the other icons. Let's align them to the smaller style. Because of the spacing inside the cards is also not even
<img width="569" alt="Bildschirmfoto 2023-02-08 um 14 46 38" src="https://user-images.githubusercontent.com/46345125/217551435-2b48e7b9-be3d-41e2-97a3-a136c9e50911.png">
- [ ] dark theme: change design to this
<img width="637" alt="Bildschirmfoto 2023-02-08 um 15 00 16" src="https://user-images.githubusercontent.com/46345125/217550970-5a8f45b7-92f8-4986-a7e4-99bef2e309fa.png">
- [ ] mobile layout still needs some improvements. @chrifro will create mockups for them
| 1.0 | Minor Improvements on Homepage - ### Description
> followup #3382, #3387
Tasks List:
- [ ] the animated quotes should start a bit earlier now that we don't have the contact pop-up anymore
- [ ] align icon size. The JetBrains IDE icons are a lot bigger than the other icons. Let's align them to the smaller style. Because of the spacing inside the cards is also not even
<img width="569" alt="Bildschirmfoto 2023-02-08 um 14 46 38" src="https://user-images.githubusercontent.com/46345125/217551435-2b48e7b9-be3d-41e2-97a3-a136c9e50911.png">
- [ ] dark theme: change design to this
<img width="637" alt="Bildschirmfoto 2023-02-08 um 15 00 16" src="https://user-images.githubusercontent.com/46345125/217550970-5a8f45b7-92f8-4986-a7e4-99bef2e309fa.png">
- [ ] mobile layout still needs some improvements. @chrifro will create mockups for them
| non_test | minor improvements on homepage description followup tasks list the animated quotes should start a bit earlier now that we don t have the contact pop up anymore align icon size the jetbrains ide icons are a lot bigger than the other icons let s align them to the smaller style because of the spacing inside the cards is also not even img width alt bildschirmfoto um src dark theme change design to this img width alt bildschirmfoto um src mobile layout still needs some improvements chrifro will create mockups for them | 0 |
49,425 | 13,186,704,507 | IssuesEvent | 2020-08-13 01:02:52 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | opened | Missing Factor 2 in python implementation of paraboloid (Trac #1364) | Incomplete Migration Migrated from Trac combo reconstruction defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1364">https://code.icecube.wisc.edu/ticket/1364</a>, reported by reimann and owned by kjmeagher</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "In paraboloid/releases/V01-07-00/python/fit_paraboloid.py\n\nNice docu in code. I followed the calculation of the formulars. \nThere is an coefficient comparison between L. 30 and L. 38 which results in \nrelation between coefficients in L. 41-43.\nHere line 41 & 43 are missing a factor of 2.\nL. 41 should be \na = 2(A cosfi**2 + B sinfi**2)\nand L 43 should be\nc = 2(A sinfi**2 + B cosfi**2)\n\nthese factors are missing in all following calculations. \n\nI have done the exercise. The result should be:\ncase b=0 and a=c:\n A=B=a/2=c/2\ncase b=0 and a!=c:\n a=2A\n c=2B\ncase b!=0:\n tanfi_1/2 = 1/(2b) * [c-a +- sqrt( (a-c)**2 +4b**2)] ",
"reporter": "reimann",
"cc": "kmeagher@ulb.ac.be",
"resolution": "fixed",
"_ts": "1550067117911749",
"component": "combo reconstruction",
"summary": "Missing Factor 2 in python implementation of paraboloid",
"priority": "normal",
"keywords": "paraboloid",
"time": "2015-09-22T15:19:30",
"milestone": "",
"owner": "kjmeagher",
"type": "defect"
}
```
</p>
</details>
| 1.0 | Missing Factor 2 in python implementation of paraboloid (Trac #1364) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/ticket/1364">https://code.icecube.wisc.edu/ticket/1364</a>, reported by reimann and owned by kjmeagher</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2019-02-13T14:11:57",
"description": "In paraboloid/releases/V01-07-00/python/fit_paraboloid.py\n\nNice docu in code. I followed the calculation of the formulars. \nThere is an coefficient comparison between L. 30 and L. 38 which results in \nrelation between coefficients in L. 41-43.\nHere line 41 & 43 are missing a factor of 2.\nL. 41 should be \na = 2(A cosfi**2 + B sinfi**2)\nand L 43 should be\nc = 2(A sinfi**2 + B cosfi**2)\n\nthese factors are missing in all following calculations. \n\nI have done the exercise. The result should be:\ncase b=0 and a=c:\n A=B=a/2=c/2\ncase b=0 and a!=c:\n a=2A\n c=2B\ncase b!=0:\n tanfi_1/2 = 1/(2b) * [c-a +- sqrt( (a-c)**2 +4b**2)] ",
"reporter": "reimann",
"cc": "kmeagher@ulb.ac.be",
"resolution": "fixed",
"_ts": "1550067117911749",
"component": "combo reconstruction",
"summary": "Missing Factor 2 in python implementation of paraboloid",
"priority": "normal",
"keywords": "paraboloid",
"time": "2015-09-22T15:19:30",
"milestone": "",
"owner": "kjmeagher",
"type": "defect"
}
```
</p>
</details>
| non_test | missing factor in python implementation of paraboloid trac migrated from json status closed changetime description in paraboloid releases python fit paraboloid py n nnice docu in code i followed the calculation of the formulars nthere is an coefficient comparison between l and l which results in nrelation between coefficients in l nhere line are missing a factor of nl should be na a cosfi b sinfi nand l should be nc a sinfi b cosfi n nthese factors are missing in all following calculations n ni have done the exercise the result should be ncase b and a c n a b a c ncase b and a c n a n c ncase b n tanfi reporter reimann cc kmeagher ulb ac be resolution fixed ts component combo reconstruction summary missing factor in python implementation of paraboloid priority normal keywords paraboloid time milestone owner kjmeagher type defect | 0 |
98,918 | 30,220,926,508 | IssuesEvent | 2023-07-05 19:19:52 | teaxyz/pantry | https://api.github.com/repos/teaxyz/pantry | closed | ❌ build issues: capstone-engine.org=5.0 | build-failure | Running log of build failures for capstone-engine.org=5.0 | 1.0 | ❌ build issues: capstone-engine.org=5.0 - Running log of build failures for capstone-engine.org=5.0 | non_test | ❌ build issues capstone engine org running log of build failures for capstone engine org | 0 |
331,793 | 29,087,726,440 | IssuesEvent | 2023-05-16 02:21:20 | alibaba/nacos | https://api.github.com/repos/alibaba/nacos | closed | 建议优化 | area/Test |
1. com.alibaba.nacos.config.server.service.repository.ConfigInfoPersistService#createPaginationHelper 代码实现每次调用都会创建一个新对象
2. com.alibaba.nacos.config.server.utils.ResponseUtilTest java: 程序包sun.security.action不存在 。跑test代码的时候报错的。 jdk版本 graalvm17
| 1.0 | 建议优化 -
1. com.alibaba.nacos.config.server.service.repository.ConfigInfoPersistService#createPaginationHelper 代码实现每次调用都会创建一个新对象
2. com.alibaba.nacos.config.server.utils.ResponseUtilTest java: 程序包sun.security.action不存在 。跑test代码的时候报错的。 jdk版本 graalvm17
| test | 建议优化 com alibaba nacos config server service repository configinfopersistservice createpaginationhelper 代码实现每次调用都会创建一个新对象 com alibaba nacos config server utils responseutiltest java 程序包sun security action不存在 。跑test代码的时候报错的。 jdk版本 | 1 |
117,486 | 9,937,013,244 | IssuesEvent | 2019-07-02 20:41:21 | microsoft/vscode-python | https://api.github.com/repos/microsoft/vscode-python | closed | Please create a way to turn off test adornments. | feature-testing needs decision type-enhancement | <!--
Do you have a question instead of a bug report or enhancement request? Please ask it on https://stackoverflow.com/questions/tagged/visual-studio-code+python.
Unable to install a linter or formatter? 'No installers available'?
Windows - https://stackoverflow.com/questions/4750806/how-do-i-install-pip-on-windows
Linux - https://www.cyberciti.biz/faq/debian-ubuntu-centos-rhel-linux-install-pipclient/ , https://www.tecmint.com/install-pip-in-linux/
Python configuration issues? Please check https://code.visualstudio.com/docs/python/python-tutorial#_prerequisites
Otherwise **please** fill in the requested details below. "XXX" markers should not be present in the final bug report.
If you think a GIF of what is happening would be helpful, consider tools like https://www.cockos.com/licecap/, https://github.com/phw/peek or https://www.screentogif.com/ .
-->
## Environment data
- VS Code version: Version 1.34.0 (1.34.0)
- Extension version (available under the Extensions sidebar): Python 2019.4.12954
- OS and version: maxOS High Sierra 10.13.6
- Python version (& distribution if applicable, e.g. Anaconda): Python 3.7.3
- Type of virtual environment used (N/A | venv | virtualenv | conda | ...): venv
- Relevant/affected Python packages and their versions: Python 2019.4.12954
## Expected behaviour
There is a way to turn off the very annoying code lens in test code.
## Actual behaviour
Code constantly jumps around when editing.
| 1.0 | Please create a way to turn off test adornments. - <!--
Do you have a question instead of a bug report or enhancement request? Please ask it on https://stackoverflow.com/questions/tagged/visual-studio-code+python.
Unable to install a linter or formatter? 'No installers available'?
Windows - https://stackoverflow.com/questions/4750806/how-do-i-install-pip-on-windows
Linux - https://www.cyberciti.biz/faq/debian-ubuntu-centos-rhel-linux-install-pipclient/ , https://www.tecmint.com/install-pip-in-linux/
Python configuration issues? Please check https://code.visualstudio.com/docs/python/python-tutorial#_prerequisites
Otherwise **please** fill in the requested details below. "XXX" markers should not be present in the final bug report.
If you think a GIF of what is happening would be helpful, consider tools like https://www.cockos.com/licecap/, https://github.com/phw/peek or https://www.screentogif.com/ .
-->
## Environment data
- VS Code version: Version 1.34.0 (1.34.0)
- Extension version (available under the Extensions sidebar): Python 2019.4.12954
- OS and version: maxOS High Sierra 10.13.6
- Python version (& distribution if applicable, e.g. Anaconda): Python 3.7.3
- Type of virtual environment used (N/A | venv | virtualenv | conda | ...): venv
- Relevant/affected Python packages and their versions: Python 2019.4.12954
## Expected behaviour
There is a way to turn off the very annoying code lens in test code.
## Actual behaviour
Code constantly jumps around when editing.
| test | please create a way to turn off test adornments do you have a question instead of a bug report or enhancement request please ask it on unable to install a linter or formatter no installers available windows linux python configuration issues please check otherwise please fill in the requested details below xxx markers should not be present in the final bug report if you think a gif of what is happening would be helpful consider tools like or environment data vs code version version extension version available under the extensions sidebar python os and version maxos high sierra python version distribution if applicable e g anaconda python type of virtual environment used n a venv virtualenv conda venv relevant affected python packages and their versions python expected behaviour there is a way to turn off the very annoying code lens in test code actual behaviour code constantly jumps around when editing | 1 |
288,733 | 8,850,933,599 | IssuesEvent | 2019-01-08 14:34:34 | xwikisas/application-diagram | https://api.github.com/repos/xwikisas/application-diagram | closed | If you install XWebIDE Application you can't use "W" letter in the diagram text | Priority: Major Type: Bug | Steps:
* install Diagram and XWebIDE Application
* then create a diagram page
* edit the diagram and write some text, then try to type W
Result:
* the W letter is not typed, you can't save changes
* you get redirected to a XWebIDE DefaultProject page
<img width="848" alt="screen shot 2018-11-30 at 9 29 40 am" src="https://user-images.githubusercontent.com/17314276/49275548-42e58a80-f484-11e8-87a4-31ec71c9930a.png">
<img width="798" alt="screen shot 2018-11-30 at 9 49 27 am" src="https://user-images.githubusercontent.com/17314276/49276935-98bc3180-f488-11e8-92e5-eefb175e61cf.png">
<img width="1162" alt="screen shot 2018-11-30 at 9 29 56 am" src="https://user-images.githubusercontent.com/17314276/49276958-ae315b80-f488-11e8-9b9a-b5940066f3f4.png">
**Notes:**
* tested with Firefox 63.0.3 and Chrome 70.0.3538.102
* the conflict comes from the XWebIDE App installed, for which W is a shortcut from XWiki (see https://extensions.xwiki.org/xwiki/bin/view/Extension/XWebIDE%20Application#HShortcuts)
** the issue is reproducing only when XWebIDE app is installed
** after uninstalling XWebIDE app the issue no longer reproduces | 1.0 | If you install XWebIDE Application you can't use "W" letter in the diagram text - Steps:
* install Diagram and XWebIDE Application
* then create a diagram page
* edit the diagram and write some text, then try to type W
Result:
* the W letter is not typed, you can't save changes
* you get redirected to a XWebIDE DefaultProject page
<img width="848" alt="screen shot 2018-11-30 at 9 29 40 am" src="https://user-images.githubusercontent.com/17314276/49275548-42e58a80-f484-11e8-87a4-31ec71c9930a.png">
<img width="798" alt="screen shot 2018-11-30 at 9 49 27 am" src="https://user-images.githubusercontent.com/17314276/49276935-98bc3180-f488-11e8-92e5-eefb175e61cf.png">
<img width="1162" alt="screen shot 2018-11-30 at 9 29 56 am" src="https://user-images.githubusercontent.com/17314276/49276958-ae315b80-f488-11e8-9b9a-b5940066f3f4.png">
**Notes:**
* tested with Firefox 63.0.3 and Chrome 70.0.3538.102
* the conflict comes from the XWebIDE App installed, for which W is a shortcut from XWiki (see https://extensions.xwiki.org/xwiki/bin/view/Extension/XWebIDE%20Application#HShortcuts)
** the issue is reproducing only when XWebIDE app is installed
** after uninstalling XWebIDE app the issue no longer reproduces | non_test | if you install xwebide application you can t use w letter in the diagram text steps install diagram and xwebide application then create a diagram page edit the diagram and write some text then try to type w result the w letter is not typed you can t save changes you get redirected to a xwebide defaultproject page img width alt screen shot at am src img width alt screen shot at am src img width alt screen shot at am src notes tested with firefox and chrome the conflict comes from the xwebide app installed for which w is a shortcut from xwiki see the issue is reproducing only when xwebide app is installed after uninstalling xwebide app the issue no longer reproduces | 0 |
29,788 | 13,171,522,671 | IssuesEvent | 2020-08-11 16:48:56 | microsoft/botbuilder-js | https://api.github.com/repos/microsoft/botbuilder-js | closed | Support for using TeamsInfo without a TurnContext | Bot Services customer-replied-to customer-reported enhancement | **Is your feature request related to a problem? Please describe.**
I'm in the process of porting Polly over from v3 to v4 botbuilder for Teams, and this is a bit of a stumbling block. We do mostly out of band communication and api calls for our application into Teams where we do not have a TurnContext to supply to the TeamsInfo static methods for api calls.
**Describe the solution you'd like**
Overload method for all the api calls that just takes the params required to make the call. Looking into TeamsInfo it mostly uses the TurnContext for the service url, conversation id, and the adapter for credentials which can be easily supplied directly to the method calls.
**Describe alternatives you've considered**
I'm currently going to just extract all the internals of TeamsInfo out into our own helper class to do these calls as described above for our application as needed.
[enhancement]
| 1.0 | Support for using TeamsInfo without a TurnContext - **Is your feature request related to a problem? Please describe.**
I'm in the process of porting Polly over from v3 to v4 botbuilder for Teams, and this is a bit of a stumbling block. We do mostly out of band communication and api calls for our application into Teams where we do not have a TurnContext to supply to the TeamsInfo static methods for api calls.
**Describe the solution you'd like**
Overload method for all the api calls that just takes the params required to make the call. Looking into TeamsInfo it mostly uses the TurnContext for the service url, conversation id, and the adapter for credentials which can be easily supplied directly to the method calls.
**Describe alternatives you've considered**
I'm currently going to just extract all the internals of TeamsInfo out into our own helper class to do these calls as described above for our application as needed.
[enhancement]
| non_test | support for using teamsinfo without a turncontext is your feature request related to a problem please describe i m in the process of porting polly over from to botbuilder for teams and this is a bit of a stumbling block we do mostly out of band communication and api calls for our application into teams where we do not have a turncontext to supply to the teamsinfo static methods for api calls describe the solution you d like overload method for all the api calls that just takes the params required to make the call looking into teamsinfo it mostly uses the turncontext for the service url conversation id and the adapter for credentials which can be easily supplied directly to the method calls describe alternatives you ve considered i m currently going to just extract all the internals of teamsinfo out into our own helper class to do these calls as described above for our application as needed | 0 |
204,795 | 15,553,501,711 | IssuesEvent | 2021-03-16 01:35:58 | xamarin/XamarinCommunityToolkit | https://api.github.com/repos/xamarin/XamarinCommunityToolkit | opened | [Enhancement] Migrate Xamarin.CommunityToolkit.UnitTests to NUnit | a/tests :test_tube: enhancement feature-request housekeeping proposal | ## Summary
This enhancement will migrate `Xamarin.CommunityToolkit.UnitTests` from xUnit (which it currently uses) to NUnit.
The reason for migrating to NUnit is two fold:
1. `Xamarin.CommunityToolkit.Markup.UnitTests` currently uses NUnit
- Keeping the unit testing framework consistent will allow for a consistent experience for contributors and maintainers
2. [xUnit doesn't support the command line command dotnet test for .NET Framework ](https://xunit.net/docs/getting-started/netcore/cmdline):

- Long story short, this is the bash script that is required for us to run .NET Framework tests for xUnit on macOS (that is now included in `azure-pipelines.yml`:
```bash
mono "`find ~/.nuget/packages | grep net461 | grep xunit.console.exe | grep -v config`" "`find . -name Xamarin.CommunityToolkit.UnitTests.dll | grep bin | grep 461`"
```
## Who Will Do The Work?
- [x] I am willing to take this on myself
| 2.0 | [Enhancement] Migrate Xamarin.CommunityToolkit.UnitTests to NUnit - ## Summary
This enhancement will migrate `Xamarin.CommunityToolkit.UnitTests` from xUnit (which it currently uses) to NUnit.
The reason for migrating to NUnit is two fold:
1. `Xamarin.CommunityToolkit.Markup.UnitTests` currently uses NUnit
- Keeping the unit testing framework consistent will allow for a consistent experience for contributors and maintainers
2. [xUnit doesn't support the command line command dotnet test for .NET Framework ](https://xunit.net/docs/getting-started/netcore/cmdline):

- Long story short, this is the bash script that is required for us to run .NET Framework tests for xUnit on macOS (that is now included in `azure-pipelines.yml`:
```bash
mono "`find ~/.nuget/packages | grep net461 | grep xunit.console.exe | grep -v config`" "`find . -name Xamarin.CommunityToolkit.UnitTests.dll | grep bin | grep 461`"
```
## Who Will Do The Work?
- [x] I am willing to take this on myself
| test | migrate xamarin communitytoolkit unittests to nunit summary this enhancement will migrate xamarin communitytoolkit unittests from xunit which it currently uses to nunit the reason for migrating to nunit is two fold xamarin communitytoolkit markup unittests currently uses nunit keeping the unit testing framework consistent will allow for a consistent experience for contributors and maintainers long story short this is the bash script that is required for us to run net framework tests for xunit on macos that is now included in azure pipelines yml bash mono find nuget packages grep grep xunit console exe grep v config find name xamarin communitytoolkit unittests dll grep bin grep who will do the work i am willing to take this on myself | 1 |
181,261 | 14,012,570,977 | IssuesEvent | 2020-10-29 09:13:55 | jetstack/cert-manager | https://api.github.com/repos/jetstack/cert-manager | closed | OpenShift testing in CI | Epic area/testing kind/feature priority/important-soon | We should let our CI run against OpenShift as well as Kubernetes
- Run e2e tests against OpenShift 3 #2698
- Run e2e tests against OpenShift 4 #2699 | 1.0 | OpenShift testing in CI - We should let our CI run against OpenShift as well as Kubernetes
- Run e2e tests against OpenShift 3 #2698
- Run e2e tests against OpenShift 4 #2699 | test | openshift testing in ci we should let our ci run against openshift as well as kubernetes run tests against openshift run tests against openshift | 1 |
31,384 | 6,510,847,795 | IssuesEvent | 2017-08-25 06:49:22 | contao/core | https://api.github.com/repos/contao/core | closed | Suchindex erst nach "Unveröffentlichen" | defect unconfirmed | Hallo,
setze gerade mein erstes Contao-Projekt auf. Beim erstellen des Suchindex habe ich nie bestimmte Seiten über die Suche finden können. Hab alles mögliche versucht und dann durch Zufall entdeckt, was die Seiten, die gefunden wurden, von den anderen, die nicht gefunden wurden, unterscheidet: die Hauptseiten sind "unveröffentlicht". Hab also dann die anderen Hauptseiten mal unveröffentlicht und siehe da, sie konnten nun gefunden werden. Danach hab ich sie wieder veröffentlicht und sie blieben in der Suche drin!?!?!?!?!?
Einerseits ärgerlich, daß die Seite zu Anfang nicht über die Suche gefunden werden kann. Andererseits, was eigentlich ja ein no-go sein sollte, daß eine Seite, die unveröffentlicht ist, über die Suche gefunden wird!
Hab Conta 3.5.28 installiert.
Danke im Voraus. | 1.0 | Suchindex erst nach "Unveröffentlichen" - Hallo,
setze gerade mein erstes Contao-Projekt auf. Beim erstellen des Suchindex habe ich nie bestimmte Seiten über die Suche finden können. Hab alles mögliche versucht und dann durch Zufall entdeckt, was die Seiten, die gefunden wurden, von den anderen, die nicht gefunden wurden, unterscheidet: die Hauptseiten sind "unveröffentlicht". Hab also dann die anderen Hauptseiten mal unveröffentlicht und siehe da, sie konnten nun gefunden werden. Danach hab ich sie wieder veröffentlicht und sie blieben in der Suche drin!?!?!?!?!?
Einerseits ärgerlich, daß die Seite zu Anfang nicht über die Suche gefunden werden kann. Andererseits, was eigentlich ja ein no-go sein sollte, daß eine Seite, die unveröffentlicht ist, über die Suche gefunden wird!
Hab Conta 3.5.28 installiert.
Danke im Voraus. | non_test | suchindex erst nach unveröffentlichen hallo setze gerade mein erstes contao projekt auf beim erstellen des suchindex habe ich nie bestimmte seiten über die suche finden können hab alles mögliche versucht und dann durch zufall entdeckt was die seiten die gefunden wurden von den anderen die nicht gefunden wurden unterscheidet die hauptseiten sind unveröffentlicht hab also dann die anderen hauptseiten mal unveröffentlicht und siehe da sie konnten nun gefunden werden danach hab ich sie wieder veröffentlicht und sie blieben in der suche drin einerseits ärgerlich daß die seite zu anfang nicht über die suche gefunden werden kann andererseits was eigentlich ja ein no go sein sollte daß eine seite die unveröffentlicht ist über die suche gefunden wird hab conta installiert danke im voraus | 0 |
171,071 | 13,216,486,566 | IssuesEvent | 2020-08-17 03:53:21 | railgun-rs/actix-raft | https://api.github.com/repos/railgun-rs/actix-raft | opened | Add dedicated integration test for lagging->line-rate recovery under load | enhancement good first issue tests | Here is a rough idea of what this test should do:
- It should be quite similar to the other tests which are currently in place.
- It should isolate a follower node, write a data to the cluster which will cause that node to fall behind into lagging state, but not into snapshotting state.
- It should then spawn a task which will continue to write data to the cluster.
- Just after it is spawned, the test should remove the isolated node from isolation should that it can begin the lagging state recovery process.
- The spawned client should be instructed to stop after a few seconds, and then the test should assert that the lagging node has caught up and has the expected state. | 1.0 | Add dedicated integration test for lagging->line-rate recovery under load - Here is a rough idea of what this test should do:
- It should be quite similar to the other tests which are currently in place.
- It should isolate a follower node, write a data to the cluster which will cause that node to fall behind into lagging state, but not into snapshotting state.
- It should then spawn a task which will continue to write data to the cluster.
- Just after it is spawned, the test should remove the isolated node from isolation should that it can begin the lagging state recovery process.
- The spawned client should be instructed to stop after a few seconds, and then the test should assert that the lagging node has caught up and has the expected state. | test | add dedicated integration test for lagging line rate recovery under load here is a rough idea of what this test should do it should be quite similar to the other tests which are currently in place it should isolate a follower node write a data to the cluster which will cause that node to fall behind into lagging state but not into snapshotting state it should then spawn a task which will continue to write data to the cluster just after it is spawned the test should remove the isolated node from isolation should that it can begin the lagging state recovery process the spawned client should be instructed to stop after a few seconds and then the test should assert that the lagging node has caught up and has the expected state | 1 |
126,265 | 4,981,942,366 | IssuesEvent | 2016-12-07 09:46:07 | odalic/odalic-ui | https://api.github.com/repos/odalic/odalic-ui | opened | File upload does not show uploaded files | bug priority: High | When using a different base URL, i.e. instead of http://localhost:8080/odalic/ I use http://localhost:8080/ (this is due to a use of a different IDE - IntelliJ IDEA), the REST requests seem to be OK. However, I get an exception when uploading a file. | 1.0 | File upload does not show uploaded files - When using a different base URL, i.e. instead of http://localhost:8080/odalic/ I use http://localhost:8080/ (this is due to a use of a different IDE - IntelliJ IDEA), the REST requests seem to be OK. However, I get an exception when uploading a file. | non_test | file upload does not show uploaded files when using a different base url i e instead of i use this is due to a use of a different ide intellij idea the rest requests seem to be ok however i get an exception when uploading a file | 0 |
395,457 | 27,070,183,540 | IssuesEvent | 2023-02-14 05:57:02 | cloudflare/cloudflare-docs | https://api.github.com/repos/cloudflare/cloudflare-docs | opened | Advanced Caching boilerplate using fetch API | documentation content:new | ### Which Cloudflare product(s) does this pertain to?
Workers
### Subject Matter
A worker script
### Content Location
https://developers.cloudflare.com/workers/examples/
### Additional information
```
addEventListener('fetch', event => {
return event.respondWith(handleRequest(event.request));
})
async function handleRequest(request) {
// Instantiate new URL to make it mutable
const newRequest = new URL(request.url)
// Set const to be used in the array later on
const customCacheKey = `${newRequest.hostname}${newRequest.pathname}`
const queryCacheKey = `${newRequest.hostname}${newRequest.pathname}${newRequest.search}`
// Here we set all variables needed to manipulate Cloudflare's cache using the fetch API in the cf object, we'll be passing these variables in the objects down
const cacheAssets = [
{asset: 'video', key: customCacheKey, regex: /(.*\/Video)|(.*\.(m4s|mp4|ts|avi|mpeg|mpg|mkv|bin|webm|vob|flv|m2ts|mts|3gp|m4v|wmv|qt))/, info: 0, ok: 31556952, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'image', key: queryCacheKey, regex: /(.*\/Images)|(.*\.(jpg|jpeg|png|bmp|pict|tif|tiff|webp|gif|heif|exif|bat|bpg|ppm|pgn|pbm|pnm))/, info: 0, ok: 3600, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'frontEnd', key: queryCacheKey, regex: /^.*\.(css|js)/, info: 0, ok: 3600, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'audio', key: customCacheKey, regex: /(.*\/Audio)|(.*\.(flac|aac|mp3|alac|aiff|wav|ogg|aiff|opus|ape|wma|3gp))/, info: 0, ok: 31556952, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'directPlay', key: customCacheKey, regex: /.*(\/Download)/, info: 0, ok: 31556952, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'manifest', key: customCacheKey, regex: /^.*\.(m3u8|mpd)/, info: 0, ok: 3, redirects: 2, clientError: 1, serverError: 0 }
]
// https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Global_Objects/Array/find we'll be using the regex to match on file extensions for caching
const { asset, regex, ...cache } = cacheAssets.find( ({regex}) => newRequest.pathname.match(regex)) ?? {}
const newResponse = await fetch(request,
{ cf:
{
cacheKey: cache.key,
polish: false,
cacheEverything: true,
cacheTtlByStatus: {
'100-199': cache.info,
'200-299': cache.ok,
'300-399': cache.redirects,
'400-499': cache.clientError,
'500-599': cache.serverError
},
cacheTags: [
'static'
]
},
})
const response = new Response(newResponse.body, newResponse)
// For debugging purposes
response.headers.set('debug', JSON.stringify(cache))
return response
}
``` | 1.0 | Advanced Caching boilerplate using fetch API - ### Which Cloudflare product(s) does this pertain to?
Workers
### Subject Matter
A worker script
### Content Location
https://developers.cloudflare.com/workers/examples/
### Additional information
```
addEventListener('fetch', event => {
return event.respondWith(handleRequest(event.request));
})
async function handleRequest(request) {
// Instantiate new URL to make it mutable
const newRequest = new URL(request.url)
// Set const to be used in the array later on
const customCacheKey = `${newRequest.hostname}${newRequest.pathname}`
const queryCacheKey = `${newRequest.hostname}${newRequest.pathname}${newRequest.search}`
// Here we set all variables needed to manipulate Cloudflare's cache using the fetch API in the cf object, we'll be passing these variables in the objects down
const cacheAssets = [
{asset: 'video', key: customCacheKey, regex: /(.*\/Video)|(.*\.(m4s|mp4|ts|avi|mpeg|mpg|mkv|bin|webm|vob|flv|m2ts|mts|3gp|m4v|wmv|qt))/, info: 0, ok: 31556952, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'image', key: queryCacheKey, regex: /(.*\/Images)|(.*\.(jpg|jpeg|png|bmp|pict|tif|tiff|webp|gif|heif|exif|bat|bpg|ppm|pgn|pbm|pnm))/, info: 0, ok: 3600, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'frontEnd', key: queryCacheKey, regex: /^.*\.(css|js)/, info: 0, ok: 3600, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'audio', key: customCacheKey, regex: /(.*\/Audio)|(.*\.(flac|aac|mp3|alac|aiff|wav|ogg|aiff|opus|ape|wma|3gp))/, info: 0, ok: 31556952, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'directPlay', key: customCacheKey, regex: /.*(\/Download)/, info: 0, ok: 31556952, redirects: 30, clientError: 10, serverError: 0 },
{asset: 'manifest', key: customCacheKey, regex: /^.*\.(m3u8|mpd)/, info: 0, ok: 3, redirects: 2, clientError: 1, serverError: 0 }
]
// https://developer.mozilla.org/en-US/docs/Web/JavaScript/Reference/Global_Objects/Array/find we'll be using the regex to match on file extensions for caching
const { asset, regex, ...cache } = cacheAssets.find( ({regex}) => newRequest.pathname.match(regex)) ?? {}
const newResponse = await fetch(request,
{ cf:
{
cacheKey: cache.key,
polish: false,
cacheEverything: true,
cacheTtlByStatus: {
'100-199': cache.info,
'200-299': cache.ok,
'300-399': cache.redirects,
'400-499': cache.clientError,
'500-599': cache.serverError
},
cacheTags: [
'static'
]
},
})
const response = new Response(newResponse.body, newResponse)
// For debugging purposes
response.headers.set('debug', JSON.stringify(cache))
return response
}
``` | non_test | advanced caching boilerplate using fetch api which cloudflare product s does this pertain to workers subject matter a worker script content location additional information addeventlistener fetch event return event respondwith handlerequest event request async function handlerequest request instantiate new url to make it mutable const newrequest new url request url set const to be used in the array later on const customcachekey newrequest hostname newrequest pathname const querycachekey newrequest hostname newrequest pathname newrequest search here we set all variables needed to manipulate cloudflare s cache using the fetch api in the cf object we ll be passing these variables in the objects down const cacheassets asset video key customcachekey regex video ts avi mpeg mpg mkv bin webm vob flv mts wmv qt info ok redirects clienterror servererror asset image key querycachekey regex images jpg jpeg png bmp pict tif tiff webp gif heif exif bat bpg ppm pgn pbm pnm info ok redirects clienterror servererror asset frontend key querycachekey regex css js info ok redirects clienterror servererror asset audio key customcachekey regex audio flac aac alac aiff wav ogg aiff opus ape wma info ok redirects clienterror servererror asset directplay key customcachekey regex download info ok redirects clienterror servererror asset manifest key customcachekey regex mpd info ok redirects clienterror servererror we ll be using the regex to match on file extensions for caching const asset regex cache cacheassets find regex newrequest pathname match regex const newresponse await fetch request cf cachekey cache key polish false cacheeverything true cachettlbystatus cache info cache ok cache redirects cache clienterror cache servererror cachetags static const response new response newresponse body newresponse for debugging purposes response headers set debug json stringify cache return response | 0 |
14,684 | 5,731,486,199 | IssuesEvent | 2017-04-21 12:33:53 | tarantool/tarantool | https://api.github.com/repos/tarantool/tarantool | closed | C7: Restart seems not to work after kill. Centos 7 unit file contains unknown option. | build prio1 systemd | 1.6.9-80
After killing tarantool with kill we got no restart by systemd
Unit file from rpm contains option, unknown by systemd:
RestartUSec
| 1.0 | C7: Restart seems not to work after kill. Centos 7 unit file contains unknown option. - 1.6.9-80
After killing tarantool with kill we got no restart by systemd
Unit file from rpm contains option, unknown by systemd:
RestartUSec
| non_test | restart seems not to work after kill centos unit file contains unknown option after killing tarantool with kill we got no restart by systemd unit file from rpm contains option unknown by systemd restartusec | 0 |
224,674 | 17,768,394,011 | IssuesEvent | 2021-08-30 10:30:41 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | opened | Intermittent debug(T) - org.mozilla.fenix.settings.quicksettings.DefaultQuickSettingsControllerTest - `WHEN forward nav menu item is pressed THEN the session navigates forward to active session` | eng:ui-test | ### Firebase Test Run:
https://treeherder.mozilla.org/logviewer?job_id=349907193&repo=fenix
### Stacktrace:
```
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:86)
at org.junit.Assert.assertTrue(Assert.java:41)
at org.junit.Assert.assertTrue(Assert.java:52)
at org.mozilla.samples.glean.MainActivityTest.checkGleanClickData(MainActivityTest.kt:48)
at java.lang.reflect.Method.invoke(Native Method)
at java.lang.reflect.Method.invoke(Method.java:372)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:48)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:55)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at androidx.test.ext.junit.runners.AndroidJUnit4.run(AndroidJUnit4.java:154)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at androidx.test.internal.runner.TestExecutor.execute(TestExecutor.java:56)
at androidx.test.runner.AndroidJUnitRunner.onStart(AndroidJUnitRunner.java:395)
at android.app.Instrumentation$InstrumentationThread.run(Instrumentation.java:1837)
```
### Build:
https://github.com/mozilla-mobile/fenix/commit/91819626b42b55232fff4fcf4b9f232e49e7b465 | 1.0 | Intermittent debug(T) - org.mozilla.fenix.settings.quicksettings.DefaultQuickSettingsControllerTest - `WHEN forward nav menu item is pressed THEN the session navigates forward to active session` - ### Firebase Test Run:
https://treeherder.mozilla.org/logviewer?job_id=349907193&repo=fenix
### Stacktrace:
```
java.lang.AssertionError
at org.junit.Assert.fail(Assert.java:86)
at org.junit.Assert.assertTrue(Assert.java:41)
at org.junit.Assert.assertTrue(Assert.java:52)
at org.mozilla.samples.glean.MainActivityTest.checkGleanClickData(MainActivityTest.kt:48)
at java.lang.reflect.Method.invoke(Native Method)
at java.lang.reflect.Method.invoke(Method.java:372)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.rules.ExternalResource$1.evaluate(ExternalResource.java:48)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:55)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at androidx.test.ext.junit.runners.AndroidJUnit4.run(AndroidJUnit4.java:154)
at org.junit.runners.Suite.runChild(Suite.java:128)
at org.junit.runners.Suite.runChild(Suite.java:27)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at org.junit.runner.JUnitCore.run(JUnitCore.java:115)
at androidx.test.internal.runner.TestExecutor.execute(TestExecutor.java:56)
at androidx.test.runner.AndroidJUnitRunner.onStart(AndroidJUnitRunner.java:395)
at android.app.Instrumentation$InstrumentationThread.run(Instrumentation.java:1837)
```
### Build:
https://github.com/mozilla-mobile/fenix/commit/91819626b42b55232fff4fcf4b9f232e49e7b465 | test | intermittent debug t org mozilla fenix settings quicksettings defaultquicksettingscontrollertest when forward nav menu item is pressed then the session navigates forward to active session firebase test run stacktrace java lang assertionerror at org junit assert fail assert java at org junit assert asserttrue assert java at org junit assert asserttrue assert java at org mozilla samples glean mainactivitytest checkgleanclickdata mainactivitytest kt at java lang reflect method invoke native method at java lang reflect method invoke method java at org junit runners model frameworkmethod runreflectivecall frameworkmethod java at org junit internal runners model reflectivecallable run reflectivecallable java at org junit runners model frameworkmethod invokeexplosively frameworkmethod java at org junit internal runners statements invokemethod evaluate invokemethod java at org junit rules externalresource evaluate externalresource java at org junit rules testwatcher evaluate testwatcher java at org junit rules runrules evaluate runrules java at org junit runners parentrunner runleaf parentrunner java at org junit runners runchild java at org junit runners runchild java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at androidx test ext junit runners run java at org junit runners suite runchild suite java at org junit runners suite runchild suite java at org junit runners parentrunner run parentrunner java at org junit runners parentrunner schedule parentrunner java at org junit runners parentrunner runchildren parentrunner java at org junit runners parentrunner access parentrunner java at org junit runners parentrunner evaluate parentrunner java at org junit runners parentrunner run parentrunner java at org junit runner junitcore run junitcore java at org junit runner junitcore run junitcore java at androidx test internal runner testexecutor execute testexecutor java at androidx test runner androidjunitrunner onstart androidjunitrunner java at android app instrumentation instrumentationthread run instrumentation java build | 1 |
724,368 | 24,927,545,856 | IssuesEvent | 2022-10-31 08:51:34 | open-mmlab/mmediting | https://api.github.com/repos/open-mmlab/mmediting | closed | [Feature Request] Add namespace when registering VisualizationHook | priority/P1 kind/feature | mmedit and mmgen both have VisualizationHook. It would be better to register this hook in a namespace to avoid key-value conflict.
related issue https://github.com/open-mmlab/mmgeneration/issues/32 | 1.0 | [Feature Request] Add namespace when registering VisualizationHook - mmedit and mmgen both have VisualizationHook. It would be better to register this hook in a namespace to avoid key-value conflict.
related issue https://github.com/open-mmlab/mmgeneration/issues/32 | non_test | add namespace when registering visualizationhook mmedit and mmgen both have visualizationhook it would be better to register this hook in a namespace to avoid key value conflict related issue | 0 |
12,337 | 3,266,659,495 | IssuesEvent | 2015-10-22 21:41:46 | WolfkillArcadia/ExileArcas | https://api.github.com/repos/WolfkillArcadia/ExileArcas | opened | Loot Table Configuration | needs testing todo | For the most part, it is done. The addons have been added so you can get them from the loot table.
They just need tested to make sure everything is working correctly and loot is spawning at the correct frequencies. | 1.0 | Loot Table Configuration - For the most part, it is done. The addons have been added so you can get them from the loot table.
They just need tested to make sure everything is working correctly and loot is spawning at the correct frequencies. | test | loot table configuration for the most part it is done the addons have been added so you can get them from the loot table they just need tested to make sure everything is working correctly and loot is spawning at the correct frequencies | 1 |
2,741 | 3,006,458,418 | IssuesEvent | 2015-07-27 10:31:35 | adminion/friends-of-friends | https://api.github.com/repos/adminion/friends-of-friends | closed | Update CONTRIBUTING.md | build meta | Contribution policy is changing to be more sane. Development and PRs should be pointed at master, and minor/patch changes will be cherry-picked from master into appropriate target branches (v3.x, v2.x, etc.)
Need to update [CONTRIBUTING.md](CONTRIBUTING.md) to reflect these changes. | 1.0 | Update CONTRIBUTING.md - Contribution policy is changing to be more sane. Development and PRs should be pointed at master, and minor/patch changes will be cherry-picked from master into appropriate target branches (v3.x, v2.x, etc.)
Need to update [CONTRIBUTING.md](CONTRIBUTING.md) to reflect these changes. | non_test | update contributing md contribution policy is changing to be more sane development and prs should be pointed at master and minor patch changes will be cherry picked from master into appropriate target branches x x etc need to update contributing md to reflect these changes | 0 |
112,139 | 9,554,663,206 | IssuesEvent | 2019-05-02 22:56:57 | material-components/material-components-ios | https://api.github.com/repos/material-components/material-components-ios | closed | [ActionSheet] Add snapshot tests for ActionSheet in Landscape Mode | [ActionSheet] type:Test | To have better coverage of our landscape mode for Action Sheet, we should add snapshot tests for it. Also, it would be nice to have snapshot tests also for phones with safe areas (not iphone 7)
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/131849003](http://b/131849003) | 1.0 | [ActionSheet] Add snapshot tests for ActionSheet in Landscape Mode - To have better coverage of our landscape mode for Action Sheet, we should add snapshot tests for it. Also, it would be nice to have snapshot tests also for phones with safe areas (not iphone 7)
<!-- Auto-generated content below, do not modify -->
---
#### Internal data
- Associated internal bug: [b/131849003](http://b/131849003) | test | add snapshot tests for actionsheet in landscape mode to have better coverage of our landscape mode for action sheet we should add snapshot tests for it also it would be nice to have snapshot tests also for phones with safe areas not iphone internal data associated internal bug | 1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.