Unnamed: 0
int64 0
832k
| id
float64 2.49B
32.1B
| type
stringclasses 1
value | created_at
stringlengths 19
19
| repo
stringlengths 4
112
| repo_url
stringlengths 33
141
| action
stringclasses 3
values | title
stringlengths 1
1.02k
| labels
stringlengths 4
1.54k
| body
stringlengths 1
262k
| index
stringclasses 17
values | text_combine
stringlengths 95
262k
| label
stringclasses 2
values | text
stringlengths 96
252k
| binary_label
int64 0
1
|
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
97,386
| 8,653,075,233
|
IssuesEvent
|
2018-11-27 09:53:40
|
humera987/FXLabs-Test-Automation
|
https://api.github.com/repos/humera987/FXLabs-Test-Automation
|
reopened
|
new tested 27 : ApiV1SystemSettingsGetQueryParamPageInvalidDatatype
|
new tested 27
|
Project : new tested 27
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=ZWE5OTMyNWEtMzFjOS00MjFlLTgwNTUtZDJiYmZjNjNiY2Qy; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 27 Nov 2018 09:50:59 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/system-settings?page=LSYtaJ
Request :
Response :
{
"timestamp" : "2018-11-27T09:50:59.929+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/system-settings"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot ---
|
1.0
|
new tested 27 : ApiV1SystemSettingsGetQueryParamPageInvalidDatatype - Project : new tested 27
Job : UAT
Env : UAT
Region : US_WEST
Result : fail
Status Code : 404
Headers : {X-Content-Type-Options=[nosniff], X-XSS-Protection=[1; mode=block], Cache-Control=[no-cache, no-store, max-age=0, must-revalidate], Pragma=[no-cache], Expires=[0], X-Frame-Options=[DENY], Set-Cookie=[SESSION=ZWE5OTMyNWEtMzFjOS00MjFlLTgwNTUtZDJiYmZjNjNiY2Qy; Path=/; HttpOnly], Content-Type=[application/json;charset=UTF-8], Transfer-Encoding=[chunked], Date=[Tue, 27 Nov 2018 09:50:59 GMT]}
Endpoint : http://13.56.210.25/api/v1/api/v1/system-settings?page=LSYtaJ
Request :
Response :
{
"timestamp" : "2018-11-27T09:50:59.929+0000",
"status" : 404,
"error" : "Not Found",
"message" : "No message available",
"path" : "/api/v1/api/v1/system-settings"
}
Logs :
Assertion [@StatusCode != 401] resolved-to [404 != 401] result [Passed]Assertion [@StatusCode != 404] resolved-to [404 != 404] result [Failed]
--- FX Bot ---
|
test
|
new tested project new tested job uat env uat region us west result fail status code headers x content type options x xss protection cache control pragma expires x frame options set cookie content type transfer encoding date endpoint request response timestamp status error not found message no message available path api api system settings logs assertion resolved to result assertion resolved to result fx bot
| 1
|
44,228
| 13,049,251,994
|
IssuesEvent
|
2020-07-29 13:49:11
|
jgeraigery/proctor
|
https://api.github.com/repos/jgeraigery/proctor
|
closed
|
CVE-2020-14195 (High) detected in jackson-databind-2.9.10.jar
|
security vulnerability
|
## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/proctor/proctor-ant-plugin/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/proctor/proctor-webapp/target/proctor-webapp-9999-SNAPSHOT/WEB-INF/lib/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/proctor/commit/d194b2983ab6244b61d261f69fea2853a11e56ce">d194b2983ab6244b61d261f69fea2853a11e56ce</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.10","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.5"}],"vulnerabilityIdentifier":"CVE-2020-14195","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2020-14195 (High) detected in jackson-databind-2.9.10.jar - ## CVE-2020-14195 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /tmp/ws-scm/proctor/proctor-ant-plugin/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/proctor/proctor-webapp/target/proctor-webapp-9999-SNAPSHOT/WEB-INF/lib/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,canner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.10/jackson-databind-2.9.10.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/proctor/commit/d194b2983ab6244b61d261f69fea2853a11e56ce">d194b2983ab6244b61d261f69fea2853a11e56ce</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).
<p>Publish Date: 2020-06-16
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195>CVE-2020-14195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-14195</a></p>
<p>Release Date: 2020-06-16</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.5</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.9.10","isTransitiveDependency":false,"dependencyTree":"com.fasterxml.jackson.core:jackson-databind:2.9.10","isMinimumFixVersionAvailable":true,"minimumFixVersion":"com.fasterxml.jackson.core:jackson-databind:2.9.10.5"}],"vulnerabilityIdentifier":"CVE-2020-14195","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.5 mishandles the interaction between serialization gadgets and typing, related to org.jsecurity.realm.jndi.JndiRealmFactory (aka org.jsecurity).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-14195","cvss3Severity":"high","cvss3Score":"8.1","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_test
|
cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file tmp ws scm proctor proctor ant plugin pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar canner repository com fasterxml jackson core jackson databind jackson databind jar proctor proctor webapp target proctor webapp snapshot web inf lib jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar canner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar canner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org jsecurity realm jndi jndirealmfactory aka org jsecurity vulnerabilityurl
| 0
|
205,997
| 15,704,203,030
|
IssuesEvent
|
2021-03-26 14:44:32
|
kyma-project/kyma
|
https://api.github.com/repos/kyma-project/kyma
|
closed
|
K3s integration tests are failing because istioctl cannot be found
|
area/ci test-failing
|
**Description**
The Prow jobs `kyma-integration-k3s-compass-dev` and `kyma-integration-k3s` is failing with the error message `istio-1.8.2/bin/istioctl: not found`.
**Expected result**
Compass integration test passes successfully.
**Actual result**
1) Kyma with Compass test
Install Kyma:
Error: Command failed with exit code 127: istio-1.8.2/bin/istioctl install -y --set profile=demo -f /home/sa_117798148653314453801/kyma/tests/fast-integration/installer/config-istio.yaml
/bin/sh: 1: istio-1.8.2/bin/istioctl: not found
at makeError (node_modules/execa/lib/error.js:59:11)
at handlePromise (node_modules/execa/index.js:114:26)
at processTicksAndRejections (internal/process/task_queues.js:93:5)
at async installIstio (installer/istioctl.js:37:22)
at async Object.installKyma (installer/index.js:399:7)
at async Context.<anonymous> (compass-test/compass-test.js:38:5)
2) Kyma with Compass test
Register Kyma instance in Compass:
Error: k8sApply error, cannot create: {"apiVersion":"v1","kind":"Secret","metadata":{"name":"compass-agent-configuration","namespace":"compass-system"},"data":{"CONNECTOR_URL":"aHR0cHM6Ly9jb21wYXNzLWdhdGV3YXkubXBzLmRldi5reW1hLmNsb3VkLnNhcC9jb25uZWN0b3IvZ3JhcGhxbA==","RUNTIME_ID":"ZTcyN2RkNzMtNTFkZS00MTI1LTgyMGQtYzU3NDYyYjkzMTdj","TENANT":"ZTQ0OWY4NzUtYjViMi00NDg1LWI3YzAtOTg3MjVjMDU3MWJm","TOKEN":"Szh0Tlg3YkNCaUNIcVlkYk9WS0hCSkFCQUxPcEtpSVhRTmlxOGRpN3FnNTdJcUxHbXdmb1Y5MklaTEkzamdnSDRpVXBMRDY5dmVuSndSM0VPdG4tMlE9PQ=="}}
at /home/sa_117798148653314453801/kyma/tests/fast-integration/utils/index.js:269:19
at processTicksAndRejections (internal/process/task_queues.js:93:5)
at async /home/sa_117798148653314453801/kyma/tests/fast-integration/utils/index.js:268:18
at async Promise.all (index 0)
at async registerKymaInCompass (compass/fixtures.js:35:5)
at async Context.<anonymous> (compass-test/compass-test.js:42:5)
**Steps to reproduce**
See
* https://status.build.kyma-project.io/view/gcs/kyma-prow-logs/logs/kyma-integration-k3s-compass-dev/1375101499817857024
* https://status.build.kyma-project.io/view/gcs/kyma-prow-logs/logs/kyma-integration-k3s/1375116598125268992
**Troubleshooting**
<!-- Describe the steps you have already taken to solve the issue. -->
|
1.0
|
K3s integration tests are failing because istioctl cannot be found - **Description**
The Prow jobs `kyma-integration-k3s-compass-dev` and `kyma-integration-k3s` is failing with the error message `istio-1.8.2/bin/istioctl: not found`.
**Expected result**
Compass integration test passes successfully.
**Actual result**
1) Kyma with Compass test
Install Kyma:
Error: Command failed with exit code 127: istio-1.8.2/bin/istioctl install -y --set profile=demo -f /home/sa_117798148653314453801/kyma/tests/fast-integration/installer/config-istio.yaml
/bin/sh: 1: istio-1.8.2/bin/istioctl: not found
at makeError (node_modules/execa/lib/error.js:59:11)
at handlePromise (node_modules/execa/index.js:114:26)
at processTicksAndRejections (internal/process/task_queues.js:93:5)
at async installIstio (installer/istioctl.js:37:22)
at async Object.installKyma (installer/index.js:399:7)
at async Context.<anonymous> (compass-test/compass-test.js:38:5)
2) Kyma with Compass test
Register Kyma instance in Compass:
Error: k8sApply error, cannot create: {"apiVersion":"v1","kind":"Secret","metadata":{"name":"compass-agent-configuration","namespace":"compass-system"},"data":{"CONNECTOR_URL":"aHR0cHM6Ly9jb21wYXNzLWdhdGV3YXkubXBzLmRldi5reW1hLmNsb3VkLnNhcC9jb25uZWN0b3IvZ3JhcGhxbA==","RUNTIME_ID":"ZTcyN2RkNzMtNTFkZS00MTI1LTgyMGQtYzU3NDYyYjkzMTdj","TENANT":"ZTQ0OWY4NzUtYjViMi00NDg1LWI3YzAtOTg3MjVjMDU3MWJm","TOKEN":"Szh0Tlg3YkNCaUNIcVlkYk9WS0hCSkFCQUxPcEtpSVhRTmlxOGRpN3FnNTdJcUxHbXdmb1Y5MklaTEkzamdnSDRpVXBMRDY5dmVuSndSM0VPdG4tMlE9PQ=="}}
at /home/sa_117798148653314453801/kyma/tests/fast-integration/utils/index.js:269:19
at processTicksAndRejections (internal/process/task_queues.js:93:5)
at async /home/sa_117798148653314453801/kyma/tests/fast-integration/utils/index.js:268:18
at async Promise.all (index 0)
at async registerKymaInCompass (compass/fixtures.js:35:5)
at async Context.<anonymous> (compass-test/compass-test.js:42:5)
**Steps to reproduce**
See
* https://status.build.kyma-project.io/view/gcs/kyma-prow-logs/logs/kyma-integration-k3s-compass-dev/1375101499817857024
* https://status.build.kyma-project.io/view/gcs/kyma-prow-logs/logs/kyma-integration-k3s/1375116598125268992
**Troubleshooting**
<!-- Describe the steps you have already taken to solve the issue. -->
|
test
|
integration tests are failing because istioctl cannot be found description the prow jobs kyma integration compass dev and kyma integration is failing with the error message istio bin istioctl not found expected result compass integration test passes successfully actual result kyma with compass test install kyma error command failed with exit code istio bin istioctl install y set profile demo f home sa kyma tests fast integration installer config istio yaml bin sh istio bin istioctl not found at makeerror node modules execa lib error js at handlepromise node modules execa index js at processticksandrejections internal process task queues js at async installistio installer istioctl js at async object installkyma installer index js at async context compass test compass test js kyma with compass test register kyma instance in compass error error cannot create apiversion kind secret metadata name compass agent configuration namespace compass system data connector url runtime id tenant token at home sa kyma tests fast integration utils index js at processticksandrejections internal process task queues js at async home sa kyma tests fast integration utils index js at async promise all index at async registerkymaincompass compass fixtures js at async context compass test compass test js steps to reproduce see troubleshooting
| 1
|
99,312
| 16,445,268,023
|
IssuesEvent
|
2021-05-20 18:47:31
|
MicrosoftDocs/azure-devops-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-devops-docs
|
closed
|
AzureDevOps tag not available in NSG service tags
|
devops-security/tech devops/prod doc-bug
|
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: dc5a4cfa-aa84-9f0f-55f4-71ec4861c070
* Version Independent ID: d621620a-c924-03b1-8b43-f99c33e58bb8
* Content: [Allowed address lists and network connections - Azure DevOps](https://docs.microsoft.com/en-us/azure/devops/organizations/security/allow-list-ip-url?view=azure-devops)
* Content Source: [docs/organizations/security/allow-list-ip-url.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/master/docs/organizations/security/allow-list-ip-url.md)
* Product: **devops**
* Technology: **devops-security**
* GitHub Login: @chcomley
* Microsoft Alias: **chcomley**
|
True
|
AzureDevOps tag not available in NSG service tags -
[Enter feedback here]
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: dc5a4cfa-aa84-9f0f-55f4-71ec4861c070
* Version Independent ID: d621620a-c924-03b1-8b43-f99c33e58bb8
* Content: [Allowed address lists and network connections - Azure DevOps](https://docs.microsoft.com/en-us/azure/devops/organizations/security/allow-list-ip-url?view=azure-devops)
* Content Source: [docs/organizations/security/allow-list-ip-url.md](https://github.com/MicrosoftDocs/azure-devops-docs/blob/master/docs/organizations/security/allow-list-ip-url.md)
* Product: **devops**
* Technology: **devops-security**
* GitHub Login: @chcomley
* Microsoft Alias: **chcomley**
|
non_test
|
azuredevops tag not available in nsg service tags document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source product devops technology devops security github login chcomley microsoft alias chcomley
| 0
|
143,655
| 19,210,923,928
|
IssuesEvent
|
2021-12-07 01:45:42
|
turkdevops/generator-firebase-angular-node
|
https://api.github.com/repos/turkdevops/generator-firebase-angular-node
|
opened
|
CVE-2019-10744 (High) detected in multiple libraries
|
security vulnerability
|
## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-2.4.2.tgz</b>, <b>lodash-1.0.2.tgz</b>, <b>lodash-3.10.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: generator-firebase-angular-node/package.json</p>
<p>Path to vulnerable library: generator-firebase-angular-node/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- yeoman-generator-0.18.10.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: generator-firebase-angular-node/package.json</p>
<p>Path to vulnerable library: generator-firebase-angular-node/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- yeoman-generator-0.18.10.tgz (Root Library)
- download-3.3.0.tgz
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: generator-firebase-angular-node/package.json</p>
<p>Path to vulnerable library: generator-firebase-angular-node/node_modules/inquirer/node_modules/lodash/package.json,generator-firebase-angular-node/node_modules/mem-fs-editor/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- yeoman-generator-0.18.10.tgz (Root Library)
- inquirer-0.8.5.tgz
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/generator-firebase-angular-node/commit/64054d7ffbe5ef99b3a9ceac0707c272ee7ac1a3">64054d7ffbe5ef99b3a9ceac0707c272ee7ac1a3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-10744 (High) detected in multiple libraries - ## CVE-2019-10744 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-2.4.2.tgz</b>, <b>lodash-1.0.2.tgz</b>, <b>lodash-3.10.1.tgz</b></p></summary>
<p>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: generator-firebase-angular-node/package.json</p>
<p>Path to vulnerable library: generator-firebase-angular-node/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- yeoman-generator-0.18.10.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-1.0.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, and extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz">https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz</a></p>
<p>Path to dependency file: generator-firebase-angular-node/package.json</p>
<p>Path to vulnerable library: generator-firebase-angular-node/node_modules/globule/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- yeoman-generator-0.18.10.tgz (Root Library)
- download-3.3.0.tgz
- vinyl-fs-0.3.14.tgz
- glob-watcher-0.0.6.tgz
- gaze-0.5.2.tgz
- globule-0.1.0.tgz
- :x: **lodash-1.0.2.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-3.10.1.tgz</b></p></summary>
<p>The modern build of lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz">https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz</a></p>
<p>Path to dependency file: generator-firebase-angular-node/package.json</p>
<p>Path to vulnerable library: generator-firebase-angular-node/node_modules/inquirer/node_modules/lodash/package.json,generator-firebase-angular-node/node_modules/mem-fs-editor/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- yeoman-generator-0.18.10.tgz (Root Library)
- inquirer-0.8.5.tgz
- :x: **lodash-3.10.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/generator-firebase-angular-node/commit/64054d7ffbe5ef99b3a9ceac0707c272ee7ac1a3">64054d7ffbe5ef99b3a9ceac0707c272ee7ac1a3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
<p>Publish Date: 2019-07-26
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10744>CVE-2019-10744</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-jf85-cpcp-j695">https://github.com/advisories/GHSA-jf85-cpcp-j695</a></p>
<p>Release Date: 2019-07-26</p>
<p>Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file generator firebase angular node package json path to vulnerable library generator firebase angular node node modules lodash package json dependency hierarchy yeoman generator tgz root library x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance and extras library home page a href path to dependency file generator firebase angular node package json path to vulnerable library generator firebase angular node node modules globule node modules lodash package json dependency hierarchy yeoman generator tgz root library download tgz vinyl fs tgz glob watcher tgz gaze tgz globule tgz x lodash tgz vulnerable library lodash tgz the modern build of lodash modular utilities library home page a href path to dependency file generator firebase angular node package json path to vulnerable library generator firebase angular node node modules inquirer node modules lodash package json generator firebase angular node node modules mem fs editor node modules lodash package json dependency hierarchy yeoman generator tgz root library inquirer tgz x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details versions of lodash lower than are vulnerable to prototype pollution the function defaultsdeep could be tricked into adding or modifying properties of object prototype using a constructor payload publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash lodash amd lodash es lodash defaultsdeep lodash merge lodash mergewith lodash template step up your open source security game with whitesource
| 0
|
321,329
| 27,520,932,772
|
IssuesEvent
|
2023-03-06 15:00:10
|
unifyai/ivy
|
https://api.github.com/repos/unifyai/ivy
|
reopened
|
Fix view_tensor.test_view_tensor_arcsin_
|
PyTorch Frontend Sub Task Failing Test
|
| | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4132051526/jobs/7140322020" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4132051526/jobs/7140317679" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4132051526/jobs/7140319257" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>Not found</summary>
Not found
</details>
|
1.0
|
Fix view_tensor.test_view_tensor_arcsin_ - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4132051526/jobs/7140322020" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4132051526/jobs/7140317679" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4132051526/jobs/7140319257" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-failure-red></a>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>Not found</summary>
Not found
</details>
<details>
<summary>Not found</summary>
Not found
</details>
|
test
|
fix view tensor test view tensor arcsin tensorflow img src torch img src numpy img src jax img src not found not found not found not found not found not found
| 1
|
63,675
| 6,877,837,647
|
IssuesEvent
|
2017-11-20 09:40:39
|
willjjacobs/dora
|
https://api.github.com/repos/willjjacobs/dora
|
opened
|
Re-add core functionality and add unit tests for them
|
enhancement testing
|
I deleted and removed a lot of stuff. Depending on how #17 goes we should re add all those functions and create unit tests for them as it will boost our LOC and code coverage. Threading shit needs to be figured out first/in tandem though.
|
1.0
|
Re-add core functionality and add unit tests for them - I deleted and removed a lot of stuff. Depending on how #17 goes we should re add all those functions and create unit tests for them as it will boost our LOC and code coverage. Threading shit needs to be figured out first/in tandem though.
|
test
|
re add core functionality and add unit tests for them i deleted and removed a lot of stuff depending on how goes we should re add all those functions and create unit tests for them as it will boost our loc and code coverage threading shit needs to be figured out first in tandem though
| 1
|
42,749
| 22,819,978,225
|
IssuesEvent
|
2022-07-12 00:32:40
|
samcf/ogre.tools
|
https://api.github.com/repos/samcf/ogre.tools
|
closed
|
Optimize uploaded token images
|
multiplayer performance
|
One of ogre.tools most important priorities is ease of use and low barrier to entry. Users can upload images directly from their computer and are not asked to crop and resize these images. It doesn't attempt to modify the image at all.
This works great when you are the only consumer of these images. However, sharing these images over the network to many different players on the session may introduce long loading times since these uncompressed images are sometimes very large; in both file size and dimensions.
The application should resize and compress token images via HTML Canvas before adding them to state and cache.
https://developer.mozilla.org/en-US/docs/Web/API/HTMLCanvasElement/toBlob
Some concerns
- Is the checksum of the compressed image deterministic? The app should prevent uploading the same image twice, resulting in duplicates.
|
True
|
Optimize uploaded token images - One of ogre.tools most important priorities is ease of use and low barrier to entry. Users can upload images directly from their computer and are not asked to crop and resize these images. It doesn't attempt to modify the image at all.
This works great when you are the only consumer of these images. However, sharing these images over the network to many different players on the session may introduce long loading times since these uncompressed images are sometimes very large; in both file size and dimensions.
The application should resize and compress token images via HTML Canvas before adding them to state and cache.
https://developer.mozilla.org/en-US/docs/Web/API/HTMLCanvasElement/toBlob
Some concerns
- Is the checksum of the compressed image deterministic? The app should prevent uploading the same image twice, resulting in duplicates.
|
non_test
|
optimize uploaded token images one of ogre tools most important priorities is ease of use and low barrier to entry users can upload images directly from their computer and are not asked to crop and resize these images it doesn t attempt to modify the image at all this works great when you are the only consumer of these images however sharing these images over the network to many different players on the session may introduce long loading times since these uncompressed images are sometimes very large in both file size and dimensions the application should resize and compress token images via html canvas before adding them to state and cache some concerns is the checksum of the compressed image deterministic the app should prevent uploading the same image twice resulting in duplicates
| 0
|
246,713
| 26,612,083,870
|
IssuesEvent
|
2023-01-24 01:33:15
|
Nidhi77777/linux-4.1.15
|
https://api.github.com/repos/Nidhi77777/linux-4.1.15
|
reopened
|
CVE-2021-43057 (High) detected in linux-stable-rtv4.1.33
|
security vulnerability
|
## CVE-2021-43057 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.14.8. A use-after-free in selinux_ptrace_traceme (aka the SELinux handler for PTRACE_TRACEME) could be used by local attackers to cause memory corruption and escalate privileges, aka CID-a3727a8bac0a. This occurs because of an attempt to access the subjective credentials of another task.
<p>Publish Date: 2021-10-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43057>CVE-2021-43057</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-43057">https://www.linuxkernelcves.com/cves/CVE-2021-43057</a></p>
<p>Release Date: 2021-10-28</p>
<p>Fix Resolution: v5.14.8,v5.15-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2021-43057 (High) detected in linux-stable-rtv4.1.33 - ## CVE-2021-43057 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linux-stable-rtv4.1.33</b>, <b>linuxlinux-4.6</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.14.8. A use-after-free in selinux_ptrace_traceme (aka the SELinux handler for PTRACE_TRACEME) could be used by local attackers to cause memory corruption and escalate privileges, aka CID-a3727a8bac0a. This occurs because of an attempt to access the subjective credentials of another task.
<p>Publish Date: 2021-10-28
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-43057>CVE-2021-43057</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-43057">https://www.linuxkernelcves.com/cves/CVE-2021-43057</a></p>
<p>Release Date: 2021-10-28</p>
<p>Fix Resolution: v5.14.8,v5.15-rc3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in linux stable cve high severity vulnerability vulnerable libraries linux stable linuxlinux vulnerability details an issue was discovered in the linux kernel before a use after free in selinux ptrace traceme aka the selinux handler for ptrace traceme could be used by local attackers to cause memory corruption and escalate privileges aka cid this occurs because of an attempt to access the subjective credentials of another task publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
142,132
| 21,673,097,131
|
IssuesEvent
|
2022-05-08 09:17:27
|
hats-finance/hats
|
https://api.github.com/repos/hats-finance/hats
|
opened
|
SEO optimizations
|
Needs design
|
**Is your feature request related to a problem? Please describe.**
A clear and concise description of what the problem is. Ex. I'm always frustrated when [...]
**Describe the solution you'd like**
A clear and concise description of what you want to happen.
|
1.0
|
SEO optimizations - **Is your feature request related to a problem? Please describe.**
A clear and concise description of what the problem is. Ex. I'm always frustrated when [...]
**Describe the solution you'd like**
A clear and concise description of what you want to happen.
|
non_test
|
seo optimizations is your feature request related to a problem please describe a clear and concise description of what the problem is ex i m always frustrated when describe the solution you d like a clear and concise description of what you want to happen
| 0
|
147,124
| 11,774,065,296
|
IssuesEvent
|
2020-03-16 08:44:51
|
zeebe-io/zeebe
|
https://api.github.com/repos/zeebe-io/zeebe
|
opened
|
SnapshotReplicationTest.shouldReceiveNewSnapshotsOnRejoin is flaky
|
Scope: broker Status: Ready Type: Unstable Test
|
**Description**
It sometimes happens that there are more snapshots than expected, even though the snapshot interval is 5 minutes, these snapshots (from the logged timestamp) seem to be taken with smaller intervals - it is a controlled clock however, so we should investigate.
<details>
<summary>Sample output</summary>
<pre>
Failures:
[ERROR] SnapshotReplicationTest.shouldReceiveNewSnapshotsOnRejoin:120
Expecting:
<{"2-1-1584316799462/000091.log"=2794790440L, "2-1-1584316799462/000092.sst"=3762184780L, "2-1-1584316799462/000093.sst"=2073560521L, "2-1-1584316799462/000095.sst"=2902222425L, "2-1-1584316799462/000096.sst"=3165565020L, "2-1-1584316799462/000097.sst"=3946582159L, "2-1-1584316799462/000098.sst"=400477988L, "2-1-1584316799462/000099.sst"=30820173L, "2-1-1584316799462/000100.sst"=1959921764L, "2-1-1584316799462/000101.sst"=3306696654L, "2-1-1584316799462/CURRENT"=2380087979L, "2-1-1584316799462/MANIFEST-000004"=4035880576L, "2-1-1584316799462/OPTIONS-000090"=3042895128L, "2-1-1584316808269/000092.sst"=3762184780L, "2-1-1584316808269/000093.sst"=2073560521L, "2-1-1584316808269/000095.sst"=2902222425L, "2-1-1584316808269/000096.sst"=3165565020L, "2-1-1584316808269/000097.sst"=3946582159L, "2-1-1584316808269/000098.sst"=400477988L, "2-1-1584316808269/000099.sst"=30820173L, "2-1-1584316808269/000100.sst"=1959921764L, "2-1-1584316808269/000101.sst"=3306696654L, "2-1-1584316808269/000103.sst"=1095198306L, "2-1-1584316808269/000108.log"=874173147L, "2-1-1584316808269/000109.sst"=35270537L, "2-1-1584316808269/000110.sst"=1968252910L, "2-1-1584316808269/000111.sst"=1199288592L, "2-1-1584316808269/000112.sst"=1337337557L, "2-1-1584316808269/000113.sst"=548214779L, "2-1-1584316808269/CURRENT"=1352198163L, "2-1-1584316808269/MANIFEST-000104"=1667902739L, "2-1-1584316808269/OPTIONS-000107"=2111876784L}>
to contain:
<[2-1-1584316808269/000096.sst=3165565020,
2-1-1584316808269/000103.sst=1095198306,
2-1-1584316808269/000112.sst=1337337557,
2-1-1584316799462/000091.log=2794790440,
2-1-1584316802297/000095.sst=2902222425,
2-1-1584316808269/000095.sst=2902222425,
2-1-1584316799462/000096.sst=3165565020,
2-1-1584316799462/000092.sst=3762184780,
2-1-1584316799462/000095.sst=2902222425,
2-1-1584316799462/OPTIONS-000090=3042895128,
2-1-1584316808269/000099.sst=30820173,
2-1-1584316808269/CURRENT=1352198163,
2-1-1584316808269/000110.sst=1968252910,
2-1-1584316808269/000100.sst=1959921764,
2-1-1584316802297/000099.sst=30820173,
2-1-1584316808269/000113.sst=548214779,
2-1-1584316802297/OPTIONS-000090=3042895128,
2-1-1584316808269/000109.sst=35270537,
2-1-1584316802297/CURRENT=2380087979,
2-1-1584316802297/000098.sst=400477988,
2-1-1584316808269/000098.sst=400477988,
2-1-1584316799462/MANIFEST-000004=4035880576,
2-1-1584316808269/000101.sst=3306696654,
2-1-1584316802297/000101.sst=3306696654,
2-1-1584316799462/000099.sst=30820173,
2-1-1584316802297/000100.sst=1959921764,
2-1-1584316799462/000101.sst=3306696654,
2-1-1584316799462/CURRENT=2380087979,
2-1-1584316808269/000093.sst=2073560521,
2-1-1584316802297/000093.sst=2073560521,
2-1-1584316808269/000097.sst=3946582159,
2-1-1584316802297/000102.sst=764452740,
2-1-1584316802297/000097.sst=3946582159,
2-1-1584316799462/000098.sst=400477988,
2-1-1584316799462/000100.sst=1959921764,
2-1-1584316808269/OPTIONS-000107=2111876784,
2-1-1584316808269/MANIFEST-000104=1667902739,
2-1-1584316808269/000111.sst=1199288592,
2-1-1584316799462/000097.sst=3946582159,
2-1-1584316802297/000096.sst=3165565020,
2-1-1584316799462/000093.sst=2073560521,
2-1-1584316808269/000108.log=874173147,
2-1-1584316802297/MANIFEST-000004=1466873043,
2-1-1584316808269/000092.sst=3762184780,
2-1-1584316802297/000092.sst=3762184780]>
but could not find:
<[2-1-1584316802297/000095.sst=2902222425,
2-1-1584316802297/000099.sst=30820173,
2-1-1584316802297/OPTIONS-000090=3042895128,
2-1-1584316802297/CURRENT=2380087979,
2-1-1584316802297/000098.sst=400477988,
2-1-1584316802297/000101.sst=3306696654,
2-1-1584316802297/000100.sst=1959921764,
2-1-1584316802297/000093.sst=2073560521,
2-1-1584316802297/000102.sst=764452740,
2-1-1584316802297/000097.sst=3946582159,
2-1-1584316802297/000096.sst=3165565020,
2-1-1584316802297/MANIFEST-000004=1466873043,
2-1-1584316802297/000092.sst=3762184780]>
</pre>
</details>
|
1.0
|
SnapshotReplicationTest.shouldReceiveNewSnapshotsOnRejoin is flaky - **Description**
It sometimes happens that there are more snapshots than expected, even though the snapshot interval is 5 minutes, these snapshots (from the logged timestamp) seem to be taken with smaller intervals - it is a controlled clock however, so we should investigate.
<details>
<summary>Sample output</summary>
<pre>
Failures:
[ERROR] SnapshotReplicationTest.shouldReceiveNewSnapshotsOnRejoin:120
Expecting:
<{"2-1-1584316799462/000091.log"=2794790440L, "2-1-1584316799462/000092.sst"=3762184780L, "2-1-1584316799462/000093.sst"=2073560521L, "2-1-1584316799462/000095.sst"=2902222425L, "2-1-1584316799462/000096.sst"=3165565020L, "2-1-1584316799462/000097.sst"=3946582159L, "2-1-1584316799462/000098.sst"=400477988L, "2-1-1584316799462/000099.sst"=30820173L, "2-1-1584316799462/000100.sst"=1959921764L, "2-1-1584316799462/000101.sst"=3306696654L, "2-1-1584316799462/CURRENT"=2380087979L, "2-1-1584316799462/MANIFEST-000004"=4035880576L, "2-1-1584316799462/OPTIONS-000090"=3042895128L, "2-1-1584316808269/000092.sst"=3762184780L, "2-1-1584316808269/000093.sst"=2073560521L, "2-1-1584316808269/000095.sst"=2902222425L, "2-1-1584316808269/000096.sst"=3165565020L, "2-1-1584316808269/000097.sst"=3946582159L, "2-1-1584316808269/000098.sst"=400477988L, "2-1-1584316808269/000099.sst"=30820173L, "2-1-1584316808269/000100.sst"=1959921764L, "2-1-1584316808269/000101.sst"=3306696654L, "2-1-1584316808269/000103.sst"=1095198306L, "2-1-1584316808269/000108.log"=874173147L, "2-1-1584316808269/000109.sst"=35270537L, "2-1-1584316808269/000110.sst"=1968252910L, "2-1-1584316808269/000111.sst"=1199288592L, "2-1-1584316808269/000112.sst"=1337337557L, "2-1-1584316808269/000113.sst"=548214779L, "2-1-1584316808269/CURRENT"=1352198163L, "2-1-1584316808269/MANIFEST-000104"=1667902739L, "2-1-1584316808269/OPTIONS-000107"=2111876784L}>
to contain:
<[2-1-1584316808269/000096.sst=3165565020,
2-1-1584316808269/000103.sst=1095198306,
2-1-1584316808269/000112.sst=1337337557,
2-1-1584316799462/000091.log=2794790440,
2-1-1584316802297/000095.sst=2902222425,
2-1-1584316808269/000095.sst=2902222425,
2-1-1584316799462/000096.sst=3165565020,
2-1-1584316799462/000092.sst=3762184780,
2-1-1584316799462/000095.sst=2902222425,
2-1-1584316799462/OPTIONS-000090=3042895128,
2-1-1584316808269/000099.sst=30820173,
2-1-1584316808269/CURRENT=1352198163,
2-1-1584316808269/000110.sst=1968252910,
2-1-1584316808269/000100.sst=1959921764,
2-1-1584316802297/000099.sst=30820173,
2-1-1584316808269/000113.sst=548214779,
2-1-1584316802297/OPTIONS-000090=3042895128,
2-1-1584316808269/000109.sst=35270537,
2-1-1584316802297/CURRENT=2380087979,
2-1-1584316802297/000098.sst=400477988,
2-1-1584316808269/000098.sst=400477988,
2-1-1584316799462/MANIFEST-000004=4035880576,
2-1-1584316808269/000101.sst=3306696654,
2-1-1584316802297/000101.sst=3306696654,
2-1-1584316799462/000099.sst=30820173,
2-1-1584316802297/000100.sst=1959921764,
2-1-1584316799462/000101.sst=3306696654,
2-1-1584316799462/CURRENT=2380087979,
2-1-1584316808269/000093.sst=2073560521,
2-1-1584316802297/000093.sst=2073560521,
2-1-1584316808269/000097.sst=3946582159,
2-1-1584316802297/000102.sst=764452740,
2-1-1584316802297/000097.sst=3946582159,
2-1-1584316799462/000098.sst=400477988,
2-1-1584316799462/000100.sst=1959921764,
2-1-1584316808269/OPTIONS-000107=2111876784,
2-1-1584316808269/MANIFEST-000104=1667902739,
2-1-1584316808269/000111.sst=1199288592,
2-1-1584316799462/000097.sst=3946582159,
2-1-1584316802297/000096.sst=3165565020,
2-1-1584316799462/000093.sst=2073560521,
2-1-1584316808269/000108.log=874173147,
2-1-1584316802297/MANIFEST-000004=1466873043,
2-1-1584316808269/000092.sst=3762184780,
2-1-1584316802297/000092.sst=3762184780]>
but could not find:
<[2-1-1584316802297/000095.sst=2902222425,
2-1-1584316802297/000099.sst=30820173,
2-1-1584316802297/OPTIONS-000090=3042895128,
2-1-1584316802297/CURRENT=2380087979,
2-1-1584316802297/000098.sst=400477988,
2-1-1584316802297/000101.sst=3306696654,
2-1-1584316802297/000100.sst=1959921764,
2-1-1584316802297/000093.sst=2073560521,
2-1-1584316802297/000102.sst=764452740,
2-1-1584316802297/000097.sst=3946582159,
2-1-1584316802297/000096.sst=3165565020,
2-1-1584316802297/MANIFEST-000004=1466873043,
2-1-1584316802297/000092.sst=3762184780]>
</pre>
</details>
|
test
|
snapshotreplicationtest shouldreceivenewsnapshotsonrejoin is flaky description it sometimes happens that there are more snapshots than expected even though the snapshot interval is minutes these snapshots from the logged timestamp seem to be taken with smaller intervals it is a controlled clock however so we should investigate sample output failures snapshotreplicationtest shouldreceivenewsnapshotsonrejoin expecting to contain sst sst sst log sst sst sst sst sst options sst current sst sst sst sst options sst current sst sst manifest sst sst sst sst sst current sst sst sst sst sst sst sst options manifest sst sst sst sst log manifest sst sst but could not find sst sst options current sst sst sst sst sst sst sst manifest sst
| 1
|
71,651
| 18,835,723,215
|
IssuesEvent
|
2021-11-11 00:29:06
|
RobotLocomotion/drake
|
https://api.github.com/repos/RobotLocomotion/drake
|
closed
|
Create test workspace inside of `drake` tree to immediately test external workspaces
|
priority: low team: kitware component: build system
|
Per f2f with @jamiesnape during meeting.
Modalities to test:
- [ ] Bazel - perhaps just touch analysis phase, `bazel analyze-profile`, or lint `libdrake.so`
- [ ] CMake - just run off of install
Relates https://github.com/RobotLocomotion/drake/pull/9207
|
1.0
|
Create test workspace inside of `drake` tree to immediately test external workspaces - Per f2f with @jamiesnape during meeting.
Modalities to test:
- [ ] Bazel - perhaps just touch analysis phase, `bazel analyze-profile`, or lint `libdrake.so`
- [ ] CMake - just run off of install
Relates https://github.com/RobotLocomotion/drake/pull/9207
|
non_test
|
create test workspace inside of drake tree to immediately test external workspaces per with jamiesnape during meeting modalities to test bazel perhaps just touch analysis phase bazel analyze profile or lint libdrake so cmake just run off of install relates
| 0
|
194,479
| 14,679,382,678
|
IssuesEvent
|
2020-12-31 06:51:37
|
github-vet/rangeloop-pointer-findings
|
https://api.github.com/repos/github-vet/rangeloop-pointer-findings
|
closed
|
elastic/cloud-on-k8s: test/e2e/es/auth_test.go; 3 LoC
|
fresh test tiny
|
Found a possible issue in [elastic/cloud-on-k8s](https://www.github.com/elastic/cloud-on-k8s) at [test/e2e/es/auth_test.go](https://github.com/elastic/cloud-on-k8s/blob/b998979b0004550281d619fe01a80458ecabc5ad/test/e2e/es/auth_test.go#L190-L192)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to s was used in a composite literal at line 191
[Click here to see the code in its original context.](https://github.com/elastic/cloud-on-k8s/blob/b998979b0004550281d619fe01a80458ecabc5ad/test/e2e/es/auth_test.go#L190-L192)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, s := range authSecrets {
require.NoError(t, k.Client.Delete(&s))
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: b998979b0004550281d619fe01a80458ecabc5ad
|
1.0
|
elastic/cloud-on-k8s: test/e2e/es/auth_test.go; 3 LoC -
Found a possible issue in [elastic/cloud-on-k8s](https://www.github.com/elastic/cloud-on-k8s) at [test/e2e/es/auth_test.go](https://github.com/elastic/cloud-on-k8s/blob/b998979b0004550281d619fe01a80458ecabc5ad/test/e2e/es/auth_test.go#L190-L192)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first issue it finds, so please do not limit your consideration to the contents of the below message.
> reference to s was used in a composite literal at line 191
[Click here to see the code in its original context.](https://github.com/elastic/cloud-on-k8s/blob/b998979b0004550281d619fe01a80458ecabc5ad/test/e2e/es/auth_test.go#L190-L192)
<details>
<summary>Click here to show the 3 line(s) of Go which triggered the analyzer.</summary>
```go
for _, s := range authSecrets {
require.NoError(t, k.Client.Delete(&s))
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: b998979b0004550281d619fe01a80458ecabc5ad
|
test
|
elastic cloud on test es auth test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message reference to s was used in a composite literal at line click here to show the line s of go which triggered the analyzer go for s range authsecrets require noerror t k client delete s leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id
| 1
|
267,629
| 23,310,878,674
|
IssuesEvent
|
2022-08-08 08:09:29
|
vaadin/flow
|
https://api.github.com/repos/vaadin/flow
|
closed
|
2.5: ComplexDialogShortcutIT.dialogOpenedWithShortcutNoListenOn_sameShortcutListeningOnUi_bothExecuted is flaky
|
internal improvement testing
|
```
Caused by: org.junit.ComparisonFailure: Invalid latest event with 0::UI-ID expected:<[3-UI-ID]> but was:<[1-ui-button]>
at org.junit.Assert.assertEquals(Assert.java:117)
at com.vaadin.flow.uitest.ui.DialogShortcutIT.validateShortcutEvent(DialogShortcutIT.java:205)
at com.vaadin.flow.uitest.ui.DialogShortcutIT.validateLatestShortcutEvent(DialogShortcutIT.java:198)
at com.vaadin.flow.uitest.ui.DialogShortcutIT.dialogOpenedWithShortcutNoListenOn_sameShortcutListeningOnUi_bothExecuted(DialogShortcutIT.java:70)
```
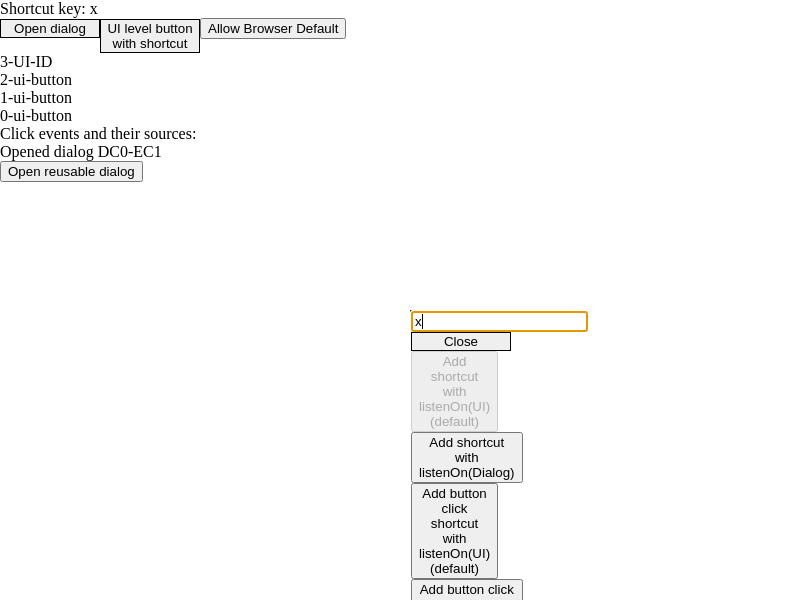
https://bender.vaadin.com/viewLog.html?buildId=223677&buildTypeId=Flow_Flow25_Flow25Snapshot&tab=buildResultsDiv
|
1.0
|
2.5: ComplexDialogShortcutIT.dialogOpenedWithShortcutNoListenOn_sameShortcutListeningOnUi_bothExecuted is flaky - ```
Caused by: org.junit.ComparisonFailure: Invalid latest event with 0::UI-ID expected:<[3-UI-ID]> but was:<[1-ui-button]>
at org.junit.Assert.assertEquals(Assert.java:117)
at com.vaadin.flow.uitest.ui.DialogShortcutIT.validateShortcutEvent(DialogShortcutIT.java:205)
at com.vaadin.flow.uitest.ui.DialogShortcutIT.validateLatestShortcutEvent(DialogShortcutIT.java:198)
at com.vaadin.flow.uitest.ui.DialogShortcutIT.dialogOpenedWithShortcutNoListenOn_sameShortcutListeningOnUi_bothExecuted(DialogShortcutIT.java:70)
```
https://bender.vaadin.com/viewLog.html?buildId=223677&buildTypeId=Flow_Flow25_Flow25Snapshot&tab=buildResultsDiv
|
test
|
complexdialogshortcutit dialogopenedwithshortcutnolistenon sameshortcutlisteningonui bothexecuted is flaky caused by org junit comparisonfailure invalid latest event with ui id expected but was at org junit assert assertequals assert java at com vaadin flow uitest ui dialogshortcutit validateshortcutevent dialogshortcutit java at com vaadin flow uitest ui dialogshortcutit validatelatestshortcutevent dialogshortcutit java at com vaadin flow uitest ui dialogshortcutit dialogopenedwithshortcutnolistenon sameshortcutlisteningonui bothexecuted dialogshortcutit java
| 1
|
330,963
| 28,498,211,928
|
IssuesEvent
|
2023-04-18 15:28:03
|
wazuh/wazuh-qa
|
https://api.github.com/repos/wazuh/wazuh-qa
|
closed
|
macOS Ventura SCA policy - check 3 to 5.2.8
|
team/qa feature/sca dev-testing subteam/qa-main level/task type/test
|
| Target version | Related issue | Related PR |
|---|---|---|
| 4.4.x | #3850 | https://github.com/wazuh/wazuh/pull/16027|
|Check Id and Name| Status| Extra|
|---|---|---|
|3 Logging and Auditing|||
|3.1 Ensure Security Auditing Is Enabled (Automated)|||
|3.2 Ensure Security Auditing Flags For User-Attributable Events Are Configured Per Local Organizational Requirements (Automated)|||
|3.3 Ensure install.log Is Retained for 365 or More Days and No Maximum Size (Automated)|||
|3.4 Ensure Security Auditing Retention Is Enabled (Automated)|||
|3.5 Ensure Access to Audit Records Is Controlled (Automated)|||
|3.6 Ensure Firewall Logging Is Enabled and Configured (Automated)|||
|3.7 Audit Software Inventory (Manual)|||
||||
|4 Network Configurations|||
|4.1 Ensure Bonjour Advertising Services Is Disabled (Automated)|||
|4.2 Ensure HTTP Server Is Disabled (Automated)|||
|4.3 Ensure NFS Server Is Disabled (Automated)|||
||||
|5 System Access, Authentication and Authorization|||
|5.1 File System Permissions and Access Controls|||
|5.1.1 Ensure Home Folders Are Secure (Automated)|||
|5.1.2 Ensure System Integrity Protection Status (SIP) Is Enabled (Automated)|||
|5.1.3 Ensure Apple Mobile File Integrity (AMFI) Is Enabled (Automated)|||
|5.1.4 Ensure Sealed System Volume (SSV) Is Enabled (Automated)|||
|5.1.5 Ensure Appropriate Permissions Are Enabled for System Wide Applications (Automated)|||
|5.1.6 Ensure No World Writable Files Exist in the System Folder (Automated)|||
|5.1.7 Ensure No World Writable Files Exist in the Library Folder (Automated)|||
||||
|5.2 Password Management|||
|5.2.1 Ensure Password Account Lockout Threshold Is Configured (Automated)|||
|5.2.2 Ensure Password Minimum Length Is Configured (Automated)|||
|5.2.3 Ensure Complex Password Must Contain Alphabetic Characters Is Configured (Manual)|||
|5.2.4 Ensure Complex Password Must Contain Numeric Character Is Configured (Manual)|||
|5.2.5 Ensure Complex Password Must Contain Special Character Is Configured (Manual)|||
|5.2.6 Ensure Complex Password Must Contain Uppercase and Lowercase Characters Is Configured (Manual)|||
|5.2.7 Ensure Password Age Is Configured (Automated)|||
|5.2.8 Ensure Password History Is Configured (Automated)|||
|
2.0
|
macOS Ventura SCA policy - check 3 to 5.2.8 -
| Target version | Related issue | Related PR |
|---|---|---|
| 4.4.x | #3850 | https://github.com/wazuh/wazuh/pull/16027|
|Check Id and Name| Status| Extra|
|---|---|---|
|3 Logging and Auditing|||
|3.1 Ensure Security Auditing Is Enabled (Automated)|||
|3.2 Ensure Security Auditing Flags For User-Attributable Events Are Configured Per Local Organizational Requirements (Automated)|||
|3.3 Ensure install.log Is Retained for 365 or More Days and No Maximum Size (Automated)|||
|3.4 Ensure Security Auditing Retention Is Enabled (Automated)|||
|3.5 Ensure Access to Audit Records Is Controlled (Automated)|||
|3.6 Ensure Firewall Logging Is Enabled and Configured (Automated)|||
|3.7 Audit Software Inventory (Manual)|||
||||
|4 Network Configurations|||
|4.1 Ensure Bonjour Advertising Services Is Disabled (Automated)|||
|4.2 Ensure HTTP Server Is Disabled (Automated)|||
|4.3 Ensure NFS Server Is Disabled (Automated)|||
||||
|5 System Access, Authentication and Authorization|||
|5.1 File System Permissions and Access Controls|||
|5.1.1 Ensure Home Folders Are Secure (Automated)|||
|5.1.2 Ensure System Integrity Protection Status (SIP) Is Enabled (Automated)|||
|5.1.3 Ensure Apple Mobile File Integrity (AMFI) Is Enabled (Automated)|||
|5.1.4 Ensure Sealed System Volume (SSV) Is Enabled (Automated)|||
|5.1.5 Ensure Appropriate Permissions Are Enabled for System Wide Applications (Automated)|||
|5.1.6 Ensure No World Writable Files Exist in the System Folder (Automated)|||
|5.1.7 Ensure No World Writable Files Exist in the Library Folder (Automated)|||
||||
|5.2 Password Management|||
|5.2.1 Ensure Password Account Lockout Threshold Is Configured (Automated)|||
|5.2.2 Ensure Password Minimum Length Is Configured (Automated)|||
|5.2.3 Ensure Complex Password Must Contain Alphabetic Characters Is Configured (Manual)|||
|5.2.4 Ensure Complex Password Must Contain Numeric Character Is Configured (Manual)|||
|5.2.5 Ensure Complex Password Must Contain Special Character Is Configured (Manual)|||
|5.2.6 Ensure Complex Password Must Contain Uppercase and Lowercase Characters Is Configured (Manual)|||
|5.2.7 Ensure Password Age Is Configured (Automated)|||
|5.2.8 Ensure Password History Is Configured (Automated)|||
|
test
|
macos ventura sca policy check to target version related issue related pr x check id and name status extra logging and auditing ensure security auditing is enabled automated ensure security auditing flags for user attributable events are configured per local organizational requirements automated ensure install log is retained for or more days and no maximum size automated ensure security auditing retention is enabled automated ensure access to audit records is controlled automated ensure firewall logging is enabled and configured automated audit software inventory manual network configurations ensure bonjour advertising services is disabled automated ensure http server is disabled automated ensure nfs server is disabled automated system access authentication and authorization file system permissions and access controls ensure home folders are secure automated ensure system integrity protection status sip is enabled automated ensure apple mobile file integrity amfi is enabled automated ensure sealed system volume ssv is enabled automated ensure appropriate permissions are enabled for system wide applications automated ensure no world writable files exist in the system folder automated ensure no world writable files exist in the library folder automated password management ensure password account lockout threshold is configured automated ensure password minimum length is configured automated ensure complex password must contain alphabetic characters is configured manual ensure complex password must contain numeric character is configured manual ensure complex password must contain special character is configured manual ensure complex password must contain uppercase and lowercase characters is configured manual ensure password age is configured automated ensure password history is configured automated
| 1
|
34,477
| 4,927,638,152
|
IssuesEvent
|
2016-11-26 21:22:17
|
rancher/rancher
|
https://api.github.com/repos/rancher/rancher
|
closed
|
Traffic is not directed when there is a port conflicts and stopping an old LB to allow a new LB use the same port
|
area/LBRefactor kind/bug status/blocker status/resolved status/to-test
|
**Rancher Version:**
v1.2.0-pre4-rc14
**Environment Type: (Cattle/Kubernetes/Swarm/Mesos)**
Cattle
**Steps to Reproduce:**
Note: I only have 3 hosts.
1. Create 1 service (nginx)
2. Start 3 Load balancers using the same source port pointing to the service
3. Start 4th load balancer using the same source port pointing to the service.
4. As expected, there is a scheduling conflict as there is no available port so the 4th LB doesn't start up.
5. Stop 1 of the 3 active load balancers.
6. 4th LB starts as expected as there is a port available.
7. Click on the link to the port.
**Results:**
I am not directed to the service. Not even 503.
**Expected:**
I should be directed to the target service.
Note: I checked haproxy.cfg and it looks like it was programmed correctly for the target service with the correct source port.
If I restart the service, traffic is now directed to the target service, but the initial container doesn't work.
|
1.0
|
Traffic is not directed when there is a port conflicts and stopping an old LB to allow a new LB use the same port - **Rancher Version:**
v1.2.0-pre4-rc14
**Environment Type: (Cattle/Kubernetes/Swarm/Mesos)**
Cattle
**Steps to Reproduce:**
Note: I only have 3 hosts.
1. Create 1 service (nginx)
2. Start 3 Load balancers using the same source port pointing to the service
3. Start 4th load balancer using the same source port pointing to the service.
4. As expected, there is a scheduling conflict as there is no available port so the 4th LB doesn't start up.
5. Stop 1 of the 3 active load balancers.
6. 4th LB starts as expected as there is a port available.
7. Click on the link to the port.
**Results:**
I am not directed to the service. Not even 503.
**Expected:**
I should be directed to the target service.
Note: I checked haproxy.cfg and it looks like it was programmed correctly for the target service with the correct source port.
If I restart the service, traffic is now directed to the target service, but the initial container doesn't work.
|
test
|
traffic is not directed when there is a port conflicts and stopping an old lb to allow a new lb use the same port rancher version environment type cattle kubernetes swarm mesos cattle steps to reproduce note i only have hosts create service nginx start load balancers using the same source port pointing to the service start load balancer using the same source port pointing to the service as expected there is a scheduling conflict as there is no available port so the lb doesn t start up stop of the active load balancers lb starts as expected as there is a port available click on the link to the port results i am not directed to the service not even expected i should be directed to the target service note i checked haproxy cfg and it looks like it was programmed correctly for the target service with the correct source port if i restart the service traffic is now directed to the target service but the initial container doesn t work
| 1
|
75,731
| 3,474,665,675
|
IssuesEvent
|
2015-12-25 01:34:21
|
HTTYMD-Team/HTTYMD-Mod
|
https://api.github.com/repos/HTTYMD-Team/HTTYMD-Mod
|
closed
|
New Animation System attempts to render animations for all entities
|
bug moderate priority verified
|
(Currently found with the Night Fury, only user of the new system)
2 or more existing entities will cause animations to attempt to render both entities at the same time, which will force animations to cycle between all available animations, even if they naturally conflict.
Suggestion: move animation system to render
|
1.0
|
New Animation System attempts to render animations for all entities - (Currently found with the Night Fury, only user of the new system)
2 or more existing entities will cause animations to attempt to render both entities at the same time, which will force animations to cycle between all available animations, even if they naturally conflict.
Suggestion: move animation system to render
|
non_test
|
new animation system attempts to render animations for all entities currently found with the night fury only user of the new system or more existing entities will cause animations to attempt to render both entities at the same time which will force animations to cycle between all available animations even if they naturally conflict suggestion move animation system to render
| 0
|
55,067
| 6,888,868,468
|
IssuesEvent
|
2017-11-22 08:16:39
|
moatwel/rosetta
|
https://api.github.com/repos/moatwel/rosetta
|
closed
|
Design of Unicoroid
|
Design
|
Design our app, "Unicoroid".
# Motivation
The reason I started to develop Unicoroid is that I have been irritated dealing with Labels when I use the existing android GitHub client.
# Core
## 1. GitHub is a SNS, so Unicoroid should be a SNS
Definition of SNS is below
> A social networking service (also social networking site, SNS or social media) is an online platform that people use to build social networks or social relations with other people who share similar personal or career interests, activities, backgrounds or real-life connections.
thus, GitHub is a SNS. Add some repository to your favorite, discussion on one issue etc...
## 2. Do Comment Without Any Stress
User can send comment to Issue or PullRequest so nicely without stress, like Slack or Messanger.
## 3. Intuitive Handling Label
User can deal with labels (edit, attach etc...)
# Important
## 1. Nice Design
## 2. Show code on this app
Many programmers want to check someone's code on their smartphone, so this app Unicoroid should have the function to display code. But this is not urgent. Because Unicoroid has developed for the purpose of sending comment seamlessly and putting Labels. Thanks.
# Nice to have
- see the whole code
|
1.0
|
Design of Unicoroid - Design our app, "Unicoroid".
# Motivation
The reason I started to develop Unicoroid is that I have been irritated dealing with Labels when I use the existing android GitHub client.
# Core
## 1. GitHub is a SNS, so Unicoroid should be a SNS
Definition of SNS is below
> A social networking service (also social networking site, SNS or social media) is an online platform that people use to build social networks or social relations with other people who share similar personal or career interests, activities, backgrounds or real-life connections.
thus, GitHub is a SNS. Add some repository to your favorite, discussion on one issue etc...
## 2. Do Comment Without Any Stress
User can send comment to Issue or PullRequest so nicely without stress, like Slack or Messanger.
## 3. Intuitive Handling Label
User can deal with labels (edit, attach etc...)
# Important
## 1. Nice Design
## 2. Show code on this app
Many programmers want to check someone's code on their smartphone, so this app Unicoroid should have the function to display code. But this is not urgent. Because Unicoroid has developed for the purpose of sending comment seamlessly and putting Labels. Thanks.
# Nice to have
- see the whole code
|
non_test
|
design of unicoroid design our app unicoroid motivation the reason i started to develop unicoroid is that i have been irritated dealing with labels when i use the existing android github client core github is a sns so unicoroid should be a sns definition of sns is below a social networking service also social networking site sns or social media is an online platform that people use to build social networks or social relations with other people who share similar personal or career interests activities backgrounds or real life connections thus github is a sns add some repository to your favorite discussion on one issue etc do comment without any stress user can send comment to issue or pullrequest so nicely without stress like slack or messanger intuitive handling label user can deal with labels edit attach etc important nice design show code on this app many programmers want to check someone s code on their smartphone so this app unicoroid should have the function to display code but this is not urgent because unicoroid has developed for the purpose of sending comment seamlessly and putting labels thanks nice to have see the whole code
| 0
|
96,180
| 19,911,044,384
|
IssuesEvent
|
2022-01-25 17:11:13
|
github/vscode-codeql
|
https://api.github.com/repos/github/vscode-codeql
|
closed
|
Migrate to new vscode testing APIs
|
enhancement VSCode
|
Currently, this extension uses the [UI test explorer](https://github.com/hbenl/vscode-test-explorer) as a ui for testing. However, this extension has recently become deprecated due to the release of [native APIs for testing](https://code.visualstudio.com/api/extension-guides/testing).
We should migrate to this new API. It will simplify our development since this extension would no longer have any dependencies on a third party extension.
Here is a [migration guide](https://code.visualstudio.com/api/extension-guides/testing).
Note that when we change this, we can also change the devcontainer files on the vscode-codeql starter repo to avoid installing the test UI extension by default.
|
1.0
|
Migrate to new vscode testing APIs - Currently, this extension uses the [UI test explorer](https://github.com/hbenl/vscode-test-explorer) as a ui for testing. However, this extension has recently become deprecated due to the release of [native APIs for testing](https://code.visualstudio.com/api/extension-guides/testing).
We should migrate to this new API. It will simplify our development since this extension would no longer have any dependencies on a third party extension.
Here is a [migration guide](https://code.visualstudio.com/api/extension-guides/testing).
Note that when we change this, we can also change the devcontainer files on the vscode-codeql starter repo to avoid installing the test UI extension by default.
|
non_test
|
migrate to new vscode testing apis currently this extension uses the as a ui for testing however this extension has recently become deprecated due to the release of we should migrate to this new api it will simplify our development since this extension would no longer have any dependencies on a third party extension here is a note that when we change this we can also change the devcontainer files on the vscode codeql starter repo to avoid installing the test ui extension by default
| 0
|
299,037
| 25,875,546,310
|
IssuesEvent
|
2022-12-14 07:33:43
|
zephyrproject-rtos/test_results
|
https://api.github.com/repos/zephyrproject-rtos/test_results
|
closed
|
tests-ci : net: dns: resolve test No Console Output(Timeout)
|
bug area: Tests
|
**Describe the bug**
resolve test is No Console Output(Timeout) on zephyr-v3.2.0-2490-ga1b4896efe46 on mimxrt1170_evk_cm7
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p mimxrt1170_evk_cm7 --sub-test net.dns
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
E: ***** USAGE FAULT *****
E: Illegal use of the EPSR
E: r0/a1: 0x496fb751 r1/a2: 0xe000ed00 r2/a3: 0xffffffe8
E: r3/a4: 0x800038ec r12/ip: 0x40460000 r14/lr: 0x3000bdd5
E: xpsr: 0x60000000
E: Faulting instruction address (r15/pc): 0x00000000
E: >>> ZEPHYR FATAL ERROR 0: CPU exception on CPU 0
E: Current thread: 0x80000f10 (main)
E: Halting system
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v3.2.0-2490-ga1b4896efe46
|
1.0
|
tests-ci : net: dns: resolve test No Console Output(Timeout)
-
**Describe the bug**
resolve test is No Console Output(Timeout) on zephyr-v3.2.0-2490-ga1b4896efe46 on mimxrt1170_evk_cm7
see logs for details
**To Reproduce**
1.
```
scripts/twister --device-testing --device-serial /dev/ttyACM0 -p mimxrt1170_evk_cm7 --sub-test net.dns
```
2. See error
**Expected behavior**
test pass
**Impact**
**Logs and console output**
```
E: ***** USAGE FAULT *****
E: Illegal use of the EPSR
E: r0/a1: 0x496fb751 r1/a2: 0xe000ed00 r2/a3: 0xffffffe8
E: r3/a4: 0x800038ec r12/ip: 0x40460000 r14/lr: 0x3000bdd5
E: xpsr: 0x60000000
E: Faulting instruction address (r15/pc): 0x00000000
E: >>> ZEPHYR FATAL ERROR 0: CPU exception on CPU 0
E: Current thread: 0x80000f10 (main)
E: Halting system
```
**Environment (please complete the following information):**
- OS: (e.g. Linux )
- Toolchain (e.g Zephyr SDK)
- Commit SHA or Version used: zephyr-v3.2.0-2490-ga1b4896efe46
|
test
|
tests ci net dns resolve test no console output timeout describe the bug resolve test is no console output timeout on zephyr on evk see logs for details to reproduce scripts twister device testing device serial dev p evk sub test net dns see error expected behavior test pass impact logs and console output e usage fault e illegal use of the epsr e e ip lr e xpsr e faulting instruction address pc e zephyr fatal error cpu exception on cpu e current thread main e halting system environment please complete the following information os e g linux toolchain e g zephyr sdk commit sha or version used zephyr
| 1
|
165,502
| 14,003,905,575
|
IssuesEvent
|
2020-10-28 16:26:18
|
veracruz-project/veracruz
|
https://api.github.com/repos/veracruz-project/veracruz
|
closed
|
Create a Veracruz homepage/blog
|
documentation enhancement
|
Create a dedicated Veracruz homepage, distinct from the README.markdown file in the repository, as a proper landing page for the Veracruz project. A blog featuring the latest Veracruz news may also be a good idea, following feedback from @geky on how effective this was for mbed.
|
1.0
|
Create a Veracruz homepage/blog - Create a dedicated Veracruz homepage, distinct from the README.markdown file in the repository, as a proper landing page for the Veracruz project. A blog featuring the latest Veracruz news may also be a good idea, following feedback from @geky on how effective this was for mbed.
|
non_test
|
create a veracruz homepage blog create a dedicated veracruz homepage distinct from the readme markdown file in the repository as a proper landing page for the veracruz project a blog featuring the latest veracruz news may also be a good idea following feedback from geky on how effective this was for mbed
| 0
|
125,177
| 26,606,694,281
|
IssuesEvent
|
2023-01-23 19:59:19
|
sourcegraph/sourcegraph
|
https://api.github.com/repos/sourcegraph/sourcegraph
|
closed
|
insights: Backfiller Improvements (backfill by series) Tracking issue
|
tracking team/code-insights insights-backfiller-refactor
|
### Plan
The original backfill process for code insights backfills all insight series runs in two steps the first step determines all the queries that need to be run for any series that needs to be backfilled and puts them in to a queue. The 2nd step runs the queries and records the results. There are several challenges with this approach:
- Determining all the queries can be a long process and if it fails it needs to restart completely
- The worker that runs the backfill queries processes all series in parallel which delays the time until any series is complete
- It is difficult to determine the current status of a backfill and how much work it has remaining
To solve these issues we will make a new backfilling mechanism that backfills a series at a time and breaks the work into repo sized chunks. When backfilling it will plan, execute and record the data for 1 repo at a time. This will allow for smaller units of work that require retries if an error occurs and will enable a more accurate progress/status.
Backfilling a series at a time means that insights over a smaller set of repos could be delayed behind insights over a larger set of repos. To address this the backfill process will be made interruptible, so that if any work with a higher priority is created it can be processed before continuing on with lower priority work.
<!--
Summarize what the team wants to achieve this iteration.
- What are the problems we want to solve or what information do we want to gather?
- Why is solving those problems or gathering that information important?
- How do we plan to solve those problems or gather that information?
-->
### Tracked issues
<!-- BEGIN WORK -->
<!-- BEGIN ASSIGNEE: chwarwick -->
@chwarwick
- [ ] https://github.com/sourcegraph/sourcegraph/issues/43068
- [x] (🏁 86 days ago) https://github.com/sourcegraph/sourcegraph/issues/43516
Completed
- [x] (🏁 103 days ago) https://github.com/sourcegraph/sourcegraph/issues/42431 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42890
- [x] (🏁 94 days ago) https://github.com/sourcegraph/sourcegraph/issues/42888
- [x] (🏁 91 days ago) https://github.com/sourcegraph/sourcegraph/issues/42889
- [x] (🏁 88 days ago) https://github.com/sourcegraph/sourcegraph/issues/42887
- [x] (🏁 86 days ago) https://github.com/sourcegraph/sourcegraph/issues/43516
- [x] (🏁 83 days ago) https://github.com/sourcegraph/sourcegraph/issues/42959
- [x] (🏁 67 days ago) https://github.com/sourcegraph/sourcegraph/issues/42891
- [x] (🏁 47 days ago) https://github.com/sourcegraph/sourcegraph/issues/43565
<!-- END ASSIGNEE -->
<!-- BEGIN ASSIGNEE: coury-clark -->
@coury-clark
- [ ] https://github.com/sourcegraph/sourcegraph/issues/42328
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42429 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [ ] https://github.com/sourcegraph/sourcegraph/issues/43068
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42429 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
Completed
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42429 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [x] (🏁 87 days ago) https://github.com/sourcegraph/sourcegraph/issues/43495
- [x] (🏁 81 days ago) https://github.com/sourcegraph/sourcegraph/issues/42724 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [x] (🏁 77 days ago) https://github.com/sourcegraph/sourcegraph/issues/42958
- [x] (🏁 49 days ago) https://github.com/sourcegraph/sourcegraph/issues/43890
<!-- END ASSIGNEE -->
<!-- BEGIN ASSIGNEE: leonore -->
@leonore
Completed
- [x] (🏁 87 days ago) https://github.com/sourcegraph/sourcegraph/issues/43351
<!-- END ASSIGNEE -->
<!-- END WORK -->
#### Legend
- 👩 Customer issue
- 🐛 Bug
- 🧶 Technical debt
- 🎩 Quality of life
- 🛠️ [Roadmap](https://handbook.sourcegraph.com/departments/product-engineering/process/planning-process#roadmap)
- 🕵️ [Spike](https://en.wikipedia.org/wiki/Spike_(software_development))
- 🔒 Security issue
- 🙆 Stretch goal
/cc @joelkw @felixfbecker @vovakulikov
|
1.0
|
insights: Backfiller Improvements (backfill by series) Tracking issue - ### Plan
The original backfill process for code insights backfills all insight series runs in two steps the first step determines all the queries that need to be run for any series that needs to be backfilled and puts them in to a queue. The 2nd step runs the queries and records the results. There are several challenges with this approach:
- Determining all the queries can be a long process and if it fails it needs to restart completely
- The worker that runs the backfill queries processes all series in parallel which delays the time until any series is complete
- It is difficult to determine the current status of a backfill and how much work it has remaining
To solve these issues we will make a new backfilling mechanism that backfills a series at a time and breaks the work into repo sized chunks. When backfilling it will plan, execute and record the data for 1 repo at a time. This will allow for smaller units of work that require retries if an error occurs and will enable a more accurate progress/status.
Backfilling a series at a time means that insights over a smaller set of repos could be delayed behind insights over a larger set of repos. To address this the backfill process will be made interruptible, so that if any work with a higher priority is created it can be processed before continuing on with lower priority work.
<!--
Summarize what the team wants to achieve this iteration.
- What are the problems we want to solve or what information do we want to gather?
- Why is solving those problems or gathering that information important?
- How do we plan to solve those problems or gather that information?
-->
### Tracked issues
<!-- BEGIN WORK -->
<!-- BEGIN ASSIGNEE: chwarwick -->
@chwarwick
- [ ] https://github.com/sourcegraph/sourcegraph/issues/43068
- [x] (🏁 86 days ago) https://github.com/sourcegraph/sourcegraph/issues/43516
Completed
- [x] (🏁 103 days ago) https://github.com/sourcegraph/sourcegraph/issues/42431 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42890
- [x] (🏁 94 days ago) https://github.com/sourcegraph/sourcegraph/issues/42888
- [x] (🏁 91 days ago) https://github.com/sourcegraph/sourcegraph/issues/42889
- [x] (🏁 88 days ago) https://github.com/sourcegraph/sourcegraph/issues/42887
- [x] (🏁 86 days ago) https://github.com/sourcegraph/sourcegraph/issues/43516
- [x] (🏁 83 days ago) https://github.com/sourcegraph/sourcegraph/issues/42959
- [x] (🏁 67 days ago) https://github.com/sourcegraph/sourcegraph/issues/42891
- [x] (🏁 47 days ago) https://github.com/sourcegraph/sourcegraph/issues/43565
<!-- END ASSIGNEE -->
<!-- BEGIN ASSIGNEE: coury-clark -->
@coury-clark
- [ ] https://github.com/sourcegraph/sourcegraph/issues/42328
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42429 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [ ] https://github.com/sourcegraph/sourcegraph/issues/43068
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42429 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
Completed
- [x] (🏁 96 days ago) https://github.com/sourcegraph/sourcegraph/issues/42429 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [x] (🏁 87 days ago) https://github.com/sourcegraph/sourcegraph/issues/43495
- [x] (🏁 81 days ago) https://github.com/sourcegraph/sourcegraph/issues/42724 🏳️ [Insights iteration 28](https://github.com/sourcegraph/sourcegraph/milestone/170)
- [x] (🏁 77 days ago) https://github.com/sourcegraph/sourcegraph/issues/42958
- [x] (🏁 49 days ago) https://github.com/sourcegraph/sourcegraph/issues/43890
<!-- END ASSIGNEE -->
<!-- BEGIN ASSIGNEE: leonore -->
@leonore
Completed
- [x] (🏁 87 days ago) https://github.com/sourcegraph/sourcegraph/issues/43351
<!-- END ASSIGNEE -->
<!-- END WORK -->
#### Legend
- 👩 Customer issue
- 🐛 Bug
- 🧶 Technical debt
- 🎩 Quality of life
- 🛠️ [Roadmap](https://handbook.sourcegraph.com/departments/product-engineering/process/planning-process#roadmap)
- 🕵️ [Spike](https://en.wikipedia.org/wiki/Spike_(software_development))
- 🔒 Security issue
- 🙆 Stretch goal
/cc @joelkw @felixfbecker @vovakulikov
|
non_test
|
insights backfiller improvements backfill by series tracking issue plan the original backfill process for code insights backfills all insight series runs in two steps the first step determines all the queries that need to be run for any series that needs to be backfilled and puts them in to a queue the step runs the queries and records the results there are several challenges with this approach determining all the queries can be a long process and if it fails it needs to restart completely the worker that runs the backfill queries processes all series in parallel which delays the time until any series is complete it is difficult to determine the current status of a backfill and how much work it has remaining to solve these issues we will make a new backfilling mechanism that backfills a series at a time and breaks the work into repo sized chunks when backfilling it will plan execute and record the data for repo at a time this will allow for smaller units of work that require retries if an error occurs and will enable a more accurate progress status backfilling a series at a time means that insights over a smaller set of repos could be delayed behind insights over a larger set of repos to address this the backfill process will be made interruptible so that if any work with a higher priority is created it can be processed before continuing on with lower priority work summarize what the team wants to achieve this iteration what are the problems we want to solve or what information do we want to gather why is solving those problems or gathering that information important how do we plan to solve those problems or gather that information tracked issues chwarwick 🏁 days ago completed 🏁 days ago 🏳️ 🏁 days ago 🏁 days ago 🏁 days ago 🏁 days ago 🏁 days ago 🏁 days ago 🏁 days ago 🏁 days ago coury clark 🏁 days ago 🏳️ 🏁 days ago 🏳️ completed 🏁 days ago 🏳️ 🏁 days ago 🏁 days ago 🏳️ 🏁 days ago 🏁 days ago leonore completed 🏁 days ago legend 👩 customer issue 🐛 bug 🧶 technical debt 🎩 quality of life 🛠️ 🕵️ 🔒 security issue 🙆 stretch goal cc joelkw felixfbecker vovakulikov
| 0
|
188,646
| 14,449,161,933
|
IssuesEvent
|
2020-12-08 07:37:42
|
facebook/react-native
|
https://api.github.com/repos/facebook/react-native
|
reopened
|
App sometimes reloads the js bundle when switching from background to foreground.
|
Needs: Attention Needs: Repro Needs: Verify on Latest Version
|
## Description
App sometimes reloads the js bundle when switching from background to foreground.
## React Native version:
0.61
## Steps To Reproduce
Provide a detailed list of steps that reproduce the issue.
Create a new react-native application. Install react-navigation. Create a stack navigator. Open app, go trough several screens. Switch app to another one in the background. Open as many apps as you can so you have a lot of them in the memory. Switch back and the react-native app reloads the bundle.
## Expected Results
I should be able to manually disable this reaload. Since I don't kill the app I should go back to where I was. This is very annoying when you try to fill a form and you go to another application to copy and come back to paste.
|
1.0
|
App sometimes reloads the js bundle when switching from background to foreground. - ## Description
App sometimes reloads the js bundle when switching from background to foreground.
## React Native version:
0.61
## Steps To Reproduce
Provide a detailed list of steps that reproduce the issue.
Create a new react-native application. Install react-navigation. Create a stack navigator. Open app, go trough several screens. Switch app to another one in the background. Open as many apps as you can so you have a lot of them in the memory. Switch back and the react-native app reloads the bundle.
## Expected Results
I should be able to manually disable this reaload. Since I don't kill the app I should go back to where I was. This is very annoying when you try to fill a form and you go to another application to copy and come back to paste.
|
test
|
app sometimes reloads the js bundle when switching from background to foreground description app sometimes reloads the js bundle when switching from background to foreground react native version steps to reproduce provide a detailed list of steps that reproduce the issue create a new react native application install react navigation create a stack navigator open app go trough several screens switch app to another one in the background open as many apps as you can so you have a lot of them in the memory switch back and the react native app reloads the bundle expected results i should be able to manually disable this reaload since i don t kill the app i should go back to where i was this is very annoying when you try to fill a form and you go to another application to copy and come back to paste
| 1
|
17,552
| 3,620,935,205
|
IssuesEvent
|
2016-02-08 21:57:55
|
thomaschampagne/stravistix
|
https://api.github.com/repos/thomaschampagne/stravistix
|
closed
|
VAM Mismatch between strava and plugin on segment efforts
|
bug enhancement in test major
|
From Allan Ruyters <allan.ruyters@gmail.com>
VAM (Vm/hr) stats are totally different from Strava. Screenshot from a recent ride for the same segment. Strava VAM first, then Stravistix VAM. Why do they differ so much?
This is not isolated, VAM numbers are much higher on all segments, from Stravistix, vs Strava.
Id: https://www.strava.com/activities/473467654
----
Also reported by: Antti Rasinen <ars@iki.fi>
>I installed Stravistix and checked out my statistics on a long bike ride I did last summer. To my surprise, the plugin reported my average VAM as nearly 1600 m/h… which sounds way way way too high.
The activity is at https://www.strava.com/activities/328700911 if you want to see what goes wrong. I can also provide a GPX dump if necessary.
…
**Segment efforts test samples:**
Compare **Strava VAM value** with **avg ascent speed from plugin** -> Make them match :)
- [ ] https://www.strava.com/activities/473467654/segments/11367189001
- [ ] https://www.strava.com/activities/187311473/segments/4385440906
- [ ] https://www.strava.com/activities/187311473/segments/4385441236
- [ ] https://www.strava.com/activities/343080886/segments/8147784775
- [ ] https://www.strava.com/activities/208748758/segments/7153239651
- [ ] https://www.strava.com/activities/482167925/segments/11569886558
- [ ] https://www.strava.com/activities/482167925/segments/11569886558
- [ ] https://www.strava.com/activities/482830818/segments/11586493730
|
1.0
|
VAM Mismatch between strava and plugin on segment efforts - From Allan Ruyters <allan.ruyters@gmail.com>
VAM (Vm/hr) stats are totally different from Strava. Screenshot from a recent ride for the same segment. Strava VAM first, then Stravistix VAM. Why do they differ so much?
This is not isolated, VAM numbers are much higher on all segments, from Stravistix, vs Strava.
Id: https://www.strava.com/activities/473467654
----
Also reported by: Antti Rasinen <ars@iki.fi>
>I installed Stravistix and checked out my statistics on a long bike ride I did last summer. To my surprise, the plugin reported my average VAM as nearly 1600 m/h… which sounds way way way too high.
The activity is at https://www.strava.com/activities/328700911 if you want to see what goes wrong. I can also provide a GPX dump if necessary.
…
**Segment efforts test samples:**
Compare **Strava VAM value** with **avg ascent speed from plugin** -> Make them match :)
- [ ] https://www.strava.com/activities/473467654/segments/11367189001
- [ ] https://www.strava.com/activities/187311473/segments/4385440906
- [ ] https://www.strava.com/activities/187311473/segments/4385441236
- [ ] https://www.strava.com/activities/343080886/segments/8147784775
- [ ] https://www.strava.com/activities/208748758/segments/7153239651
- [ ] https://www.strava.com/activities/482167925/segments/11569886558
- [ ] https://www.strava.com/activities/482167925/segments/11569886558
- [ ] https://www.strava.com/activities/482830818/segments/11586493730
|
test
|
vam mismatch between strava and plugin on segment efforts from allan ruyters vam vm hr stats are totally different from strava screenshot from a recent ride for the same segment strava vam first then stravistix vam why do they differ so much this is not isolated vam numbers are much higher on all segments from stravistix vs strava id also reported by antti rasinen i installed stravistix and checked out my statistics on a long bike ride i did last summer to my surprise the plugin reported my average vam as nearly m h… which sounds way way way too high the activity is at if you want to see what goes wrong i can also provide a gpx dump if necessary … segment efforts test samples compare strava vam value with avg ascent speed from plugin make them match
| 1
|
293,918
| 25,333,369,156
|
IssuesEvent
|
2022-11-18 14:56:11
|
WPChill/download-monitor
|
https://api.github.com/repos/WPChill/download-monitor
|
closed
|
Redo Extensions page
|
enhancement needs testing
|
**Is your feature request related to a problem? Please describe.**
Should have a similar UI as the Welcome Banner
|
1.0
|
Redo Extensions page - **Is your feature request related to a problem? Please describe.**
Should have a similar UI as the Welcome Banner
|
test
|
redo extensions page is your feature request related to a problem please describe should have a similar ui as the welcome banner
| 1
|
21,565
| 11,270,354,913
|
IssuesEvent
|
2020-01-14 10:42:44
|
flutter/flutter
|
https://api.github.com/repos/flutter/flutter
|
closed
|
Displaying text like '🔥' causing significant memory growth
|
severe: performance
|
## Details
I find that when displaying text like '🔥' ,the memory grows significantly.
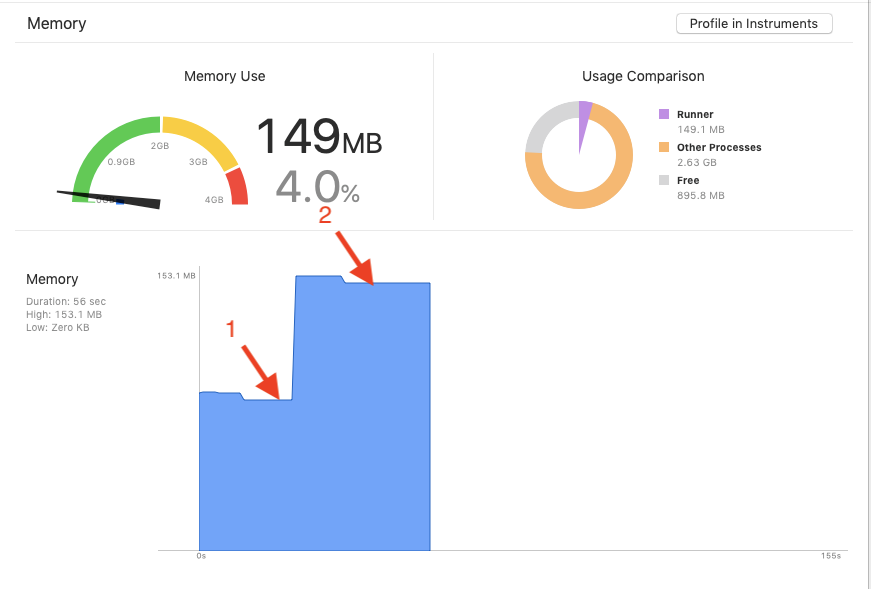
(Device: iPhone XS MAX)
As shown in the figure:
1. Before displaying the '🔥', the memory is 84MB
2. After displaying the '🔥', the memory is 149MB
How do we reduce memory usage in this scenario? Any suggestions?
Demo: https://github.com/Qxyat/flutter_demo/tree/master/emoji_memory_demo
Doctor summary (to see all details, run flutter doctor -v):
[✓] Flutter (Channel beta, v1.7.8+hotfix.3, on Mac OS X 10.14.5 18F203, locale
zh-Hans-CN)
[✓] Android toolchain - develop for Android devices (Android SDK version 28.0.3)
[!] Xcode - develop for iOS and macOS (Xcode 10.2)
! CocoaPods out of date (1.6.0 is recommended).
CocoaPods is used to retrieve the iOS and macOS platform side's plugin
code that responds to your plugin usage on the Dart side.
Without CocoaPods, plugins will not work on iOS or macOS.
For more info, see https://flutter.dev/platform-plugins
To upgrade:
brew upgrade cocoapods
pod setup
[✓] iOS tools - develop for iOS devices
[✓] Android Studio (version 3.2)
[✓] VS Code (version 1.34.0)
[✓] Connected device (1 available)
! Doctor found issues in 1 category.
|
True
|
Displaying text like '🔥' causing significant memory growth - ## Details
I find that when displaying text like '🔥' ,the memory grows significantly.
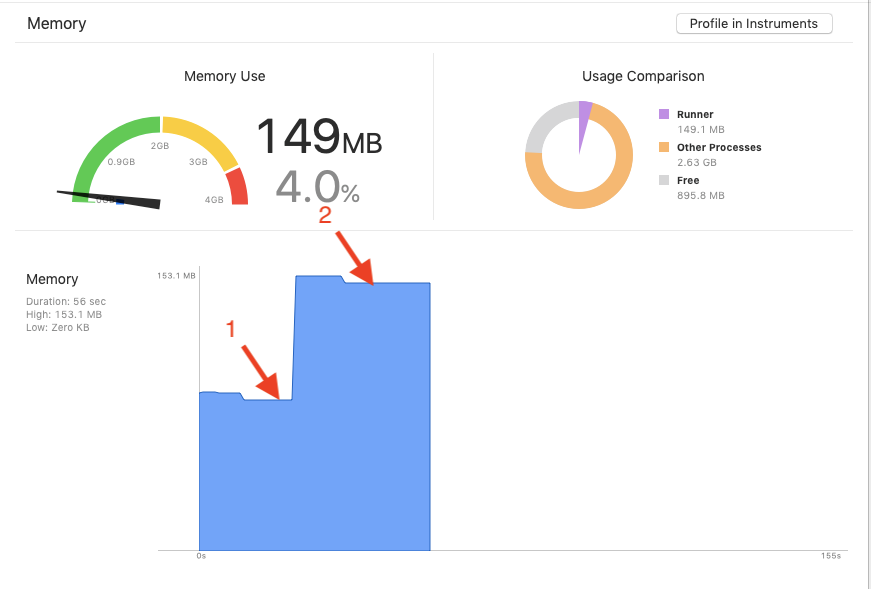
(Device: iPhone XS MAX)
As shown in the figure:
1. Before displaying the '🔥', the memory is 84MB
2. After displaying the '🔥', the memory is 149MB
How do we reduce memory usage in this scenario? Any suggestions?
Demo: https://github.com/Qxyat/flutter_demo/tree/master/emoji_memory_demo
Doctor summary (to see all details, run flutter doctor -v):
[✓] Flutter (Channel beta, v1.7.8+hotfix.3, on Mac OS X 10.14.5 18F203, locale
zh-Hans-CN)
[✓] Android toolchain - develop for Android devices (Android SDK version 28.0.3)
[!] Xcode - develop for iOS and macOS (Xcode 10.2)
! CocoaPods out of date (1.6.0 is recommended).
CocoaPods is used to retrieve the iOS and macOS platform side's plugin
code that responds to your plugin usage on the Dart side.
Without CocoaPods, plugins will not work on iOS or macOS.
For more info, see https://flutter.dev/platform-plugins
To upgrade:
brew upgrade cocoapods
pod setup
[✓] iOS tools - develop for iOS devices
[✓] Android Studio (version 3.2)
[✓] VS Code (version 1.34.0)
[✓] Connected device (1 available)
! Doctor found issues in 1 category.
|
non_test
|
displaying text like 🔥 causing significant memory growth details i find that when displaying text like 🔥 ,the memory grows significantly device iphone xs max as shown in the figure: before displaying the 🔥 the memory is after displaying the 🔥 the memory is how do we reduce memory usage in this scenario any suggestions demo doctor summary to see all details run flutter doctor v flutter channel beta hotfix on mac os x locale zh hans cn android toolchain develop for android devices android sdk version xcode develop for ios and macos xcode cocoapods out of date is recommended cocoapods is used to retrieve the ios and macos platform side s plugin code that responds to your plugin usage on the dart side without cocoapods plugins will not work on ios or macos for more info see to upgrade brew upgrade cocoapods pod setup ios tools develop for ios devices android studio version vs code version connected device available doctor found issues in category
| 0
|
175,572
| 13,564,075,353
|
IssuesEvent
|
2020-09-18 09:29:43
|
HOWISYUNI/Artreea
|
https://api.github.com/repos/HOWISYUNI/Artreea
|
opened
|
[Back] Windows 10 에서 Ubuntu 를 돌려보자(feat. Docker)
|
TEST
|
**오늘의 작업**
타 os를 동작시키는 수많은 방법 중(랩탑 구매, VirtualBox, Linux cloud instance 구매) 중 Docker를 활용한 가상화를 통해
로컬 windows 10 환경에서 nginx + uwsgi + django 연동 테스트 환경을 조성합니다.
**적용 환경:**
- OS: Windows 10 + Ubuntu 18.04
- Browser : chrome, edge
- Version : up to date version(nginx, uwsi, django)
|
1.0
|
[Back] Windows 10 에서 Ubuntu 를 돌려보자(feat. Docker) - **오늘의 작업**
타 os를 동작시키는 수많은 방법 중(랩탑 구매, VirtualBox, Linux cloud instance 구매) 중 Docker를 활용한 가상화를 통해
로컬 windows 10 환경에서 nginx + uwsgi + django 연동 테스트 환경을 조성합니다.
**적용 환경:**
- OS: Windows 10 + Ubuntu 18.04
- Browser : chrome, edge
- Version : up to date version(nginx, uwsi, django)
|
test
|
windows 에서 ubuntu 를 돌려보자 feat docker 오늘의 작업 타 os를 동작시키는 수많은 방법 중 랩탑 구매 virtualbox linux cloud instance 구매 중 docker를 활용한 가상화를 통해 로컬 windows 환경에서 nginx uwsgi django 연동 테스트 환경을 조성합니다 적용 환경 os windows ubuntu browser chrome edge version up to date version nginx uwsi django
| 1
|
163,595
| 12,736,749,564
|
IssuesEvent
|
2020-06-25 17:28:34
|
Azure/aks-engine
|
https://api.github.com/repos/Azure/aks-engine
|
opened
|
azure-cni-networkmonitor pod can't be scheduled
|
bug e2e test signal
|
**Describe the bug**
```
07:24:22 Events:
07:24:22 Type Reason Age From Message
07:24:22 ---- ------ ---- ---- -------
07:24:22 Warning FailedScheduling 4m34s (x65 over 39m) default-scheduler 0/6 nodes are available: 5 node(s) didn't match node selector.
```
Might be related to #3531
**Steps To Reproduce**
<!-- Please include the API model used to deploy the cluster if applicable (make sure to redact any secrets) -->
**Expected behavior**
**AKS Engine version**
**Kubernetes version**
**Additional context**
|
1.0
|
azure-cni-networkmonitor pod can't be scheduled - **Describe the bug**
```
07:24:22 Events:
07:24:22 Type Reason Age From Message
07:24:22 ---- ------ ---- ---- -------
07:24:22 Warning FailedScheduling 4m34s (x65 over 39m) default-scheduler 0/6 nodes are available: 5 node(s) didn't match node selector.
```
Might be related to #3531
**Steps To Reproduce**
<!-- Please include the API model used to deploy the cluster if applicable (make sure to redact any secrets) -->
**Expected behavior**
**AKS Engine version**
**Kubernetes version**
**Additional context**
|
test
|
azure cni networkmonitor pod can t be scheduled describe the bug events type reason age from message warning failedscheduling over default scheduler nodes are available node s didn t match node selector might be related to steps to reproduce expected behavior aks engine version kubernetes version additional context
| 1
|
318,207
| 27,294,793,458
|
IssuesEvent
|
2023-02-23 19:22:36
|
matplotlib/matplotlib
|
https://api.github.com/repos/matplotlib/matplotlib
|
closed
|
CI: isort should check plot_types?
|
CI: testing
|
### Summary
https://github.com/matplotlib/matplotlib/blob/17db60b4de127347b319e60a7ae24224efbea09e/.pre-commit-config.yaml#L50 doesn't include `plot_types`. Not sure if that was on purpose or not. ping @dstansby, https://github.com/matplotlib/matplotlib/pull/25099
### Proposed fix
_No response_
|
1.0
|
CI: isort should check plot_types? - ### Summary
https://github.com/matplotlib/matplotlib/blob/17db60b4de127347b319e60a7ae24224efbea09e/.pre-commit-config.yaml#L50 doesn't include `plot_types`. Not sure if that was on purpose or not. ping @dstansby, https://github.com/matplotlib/matplotlib/pull/25099
### Proposed fix
_No response_
|
test
|
ci isort should check plot types summary doesn t include plot types not sure if that was on purpose or not ping dstansby proposed fix no response
| 1
|
121,762
| 10,195,048,889
|
IssuesEvent
|
2019-08-12 17:08:35
|
brave/brave-browser
|
https://api.github.com/repos/brave/brave-browser
|
closed
|
Manual test run on Linux for 0.67.x Hotfix 2 (Release Channel)
|
OS/Linux QA/Yes release-notes/exclude tests
|
### Per release specialty tests
- [x] Issue with Ads Payments (August 5) #5548
### Brave Ads
- [x] Verify when you enable Rewards from panel or brave://rewards, Ads are enabled by default
- [x] Verify Ads UI (panel, settings, etc) shows when in a region with Ads support
- [x] Verify Ads UI (panel, settings, etc) does not show when in a region without Ads support. Verify the Ads panel does show the 'Sorry! Ads are not yet available in your region.' message.
- [x] Verify when the system language is English, the Browser language is French, and you are in one of the supported regions, Ad notifications are still served to you.
- [x] Verify you are served Ad notifications when Ads are enabled
- [x] Windows only: Verify when `Focus Assist` is set to alarms only, Ads are not served to the user but are available in the `Notification Center`
- [x] Verify when Ads are toggled off, there are no Ad messages in the logs
- [x] Verify when Rewards are toggled off (but Ads were not explicitly toggled off), there are no Ads logs recorded
- [x] Verify view/click/dismiss/landed ad notifications show in confirmations.json
- [x] Verify pages you browse to are being classified in the logs
- [x] Verify tokens are redeemed by viewing the logs (you can use --rewards=debug=true to shorten redemption time)
- [x] Verify Ad is not shown if a tab is playing media and is only shown after it stops playing
- [x] Upgrade Cases
- [x] Verify when updating from the previous version Ads info in the panel is not lost
- [x] Update to latest version from 0.62.51 (or a version without Ads available). Verify you are notified to try ads via a BAT logo notification but Ads are not automatically turned on for you.
- [x] Update to latest version from some Ads enabled version (such as 0.66.x). Verify Ads status (on/off) is the same as it was prior to update.
- [x] Update to latest version from some Ads enabled version (such as 0.67.x). Verify Ads status (on/off) is the same as it was prior to update.
### Data(Upgrade from previous release)
- [x] Make sure that data from the last version appears in the new version OK
- [x] With data from the last version, verify that
- [x] bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] cookies are preserved
- [x] installed extensions are retained and work correctly
- [x] opened tabs can be reloaded
- [x] stored passwords are preserved
- [x] unpinned tabs can be pinned
|
1.0
|
Manual test run on Linux for 0.67.x Hotfix 2 (Release Channel) - ### Per release specialty tests
- [x] Issue with Ads Payments (August 5) #5548
### Brave Ads
- [x] Verify when you enable Rewards from panel or brave://rewards, Ads are enabled by default
- [x] Verify Ads UI (panel, settings, etc) shows when in a region with Ads support
- [x] Verify Ads UI (panel, settings, etc) does not show when in a region without Ads support. Verify the Ads panel does show the 'Sorry! Ads are not yet available in your region.' message.
- [x] Verify when the system language is English, the Browser language is French, and you are in one of the supported regions, Ad notifications are still served to you.
- [x] Verify you are served Ad notifications when Ads are enabled
- [x] Windows only: Verify when `Focus Assist` is set to alarms only, Ads are not served to the user but are available in the `Notification Center`
- [x] Verify when Ads are toggled off, there are no Ad messages in the logs
- [x] Verify when Rewards are toggled off (but Ads were not explicitly toggled off), there are no Ads logs recorded
- [x] Verify view/click/dismiss/landed ad notifications show in confirmations.json
- [x] Verify pages you browse to are being classified in the logs
- [x] Verify tokens are redeemed by viewing the logs (you can use --rewards=debug=true to shorten redemption time)
- [x] Verify Ad is not shown if a tab is playing media and is only shown after it stops playing
- [x] Upgrade Cases
- [x] Verify when updating from the previous version Ads info in the panel is not lost
- [x] Update to latest version from 0.62.51 (or a version without Ads available). Verify you are notified to try ads via a BAT logo notification but Ads are not automatically turned on for you.
- [x] Update to latest version from some Ads enabled version (such as 0.66.x). Verify Ads status (on/off) is the same as it was prior to update.
- [x] Update to latest version from some Ads enabled version (such as 0.67.x). Verify Ads status (on/off) is the same as it was prior to update.
### Data(Upgrade from previous release)
- [x] Make sure that data from the last version appears in the new version OK
- [x] With data from the last version, verify that
- [x] bookmarks on the bookmark toolbar and bookmark folders can be opened
- [x] cookies are preserved
- [x] installed extensions are retained and work correctly
- [x] opened tabs can be reloaded
- [x] stored passwords are preserved
- [x] unpinned tabs can be pinned
|
test
|
manual test run on linux for x hotfix release channel per release specialty tests issue with ads payments august brave ads verify when you enable rewards from panel or brave rewards ads are enabled by default verify ads ui panel settings etc shows when in a region with ads support verify ads ui panel settings etc does not show when in a region without ads support verify the ads panel does show the sorry ads are not yet available in your region message verify when the system language is english the browser language is french and you are in one of the supported regions ad notifications are still served to you verify you are served ad notifications when ads are enabled windows only verify when focus assist is set to alarms only ads are not served to the user but are available in the notification center verify when ads are toggled off there are no ad messages in the logs verify when rewards are toggled off but ads were not explicitly toggled off there are no ads logs recorded verify view click dismiss landed ad notifications show in confirmations json verify pages you browse to are being classified in the logs verify tokens are redeemed by viewing the logs you can use rewards debug true to shorten redemption time verify ad is not shown if a tab is playing media and is only shown after it stops playing upgrade cases verify when updating from the previous version ads info in the panel is not lost update to latest version from or a version without ads available verify you are notified to try ads via a bat logo notification but ads are not automatically turned on for you update to latest version from some ads enabled version such as x verify ads status on off is the same as it was prior to update update to latest version from some ads enabled version such as x verify ads status on off is the same as it was prior to update data upgrade from previous release make sure that data from the last version appears in the new version ok with data from the last version verify that bookmarks on the bookmark toolbar and bookmark folders can be opened cookies are preserved installed extensions are retained and work correctly opened tabs can be reloaded stored passwords are preserved unpinned tabs can be pinned
| 1
|
333,177
| 29,513,207,795
|
IssuesEvent
|
2023-06-04 07:04:57
|
unifyai/ivy
|
https://api.github.com/repos/unifyai/ivy
|
closed
|
Fix elementwise.test_lerp
|
Sub Task Ivy API Experimental Failing Test
|
| | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|
1.0
|
Fix elementwise.test_lerp - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/5166151729/jobs/9306067758" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|
test
|
fix elementwise test lerp tensorflow img src torch img src numpy img src jax img src paddle img src
| 1
|
648,021
| 21,163,015,197
|
IssuesEvent
|
2022-04-07 11:07:27
|
Holo-Host/bugs-n-issues
|
https://api.github.com/repos/Holo-Host/bugs-n-issues
|
closed
|
Configure log aggregation
|
priority
|
- [x] Recommend a third party log aggregation service
- [x] Prototype the implementation on Hydra
- [ ] Roll out the log aggregation to all of the devnet machines, by merging to develop
The log messages should be tagged by "main" net or "dev" net.
In support of #11.
|
1.0
|
Configure log aggregation - - [x] Recommend a third party log aggregation service
- [x] Prototype the implementation on Hydra
- [ ] Roll out the log aggregation to all of the devnet machines, by merging to develop
The log messages should be tagged by "main" net or "dev" net.
In support of #11.
|
non_test
|
configure log aggregation recommend a third party log aggregation service prototype the implementation on hydra roll out the log aggregation to all of the devnet machines by merging to develop the log messages should be tagged by main net or dev net in support of
| 0
|
263,867
| 23,086,009,208
|
IssuesEvent
|
2022-07-26 11:28:30
|
dontpanicdao/caigo
|
https://api.github.com/repos/dontpanicdao/caigo
|
opened
|
Implement tests for the whole Gateway API on testnet
|
test and ci golang easy hours
|
## Objectives
The Gateway API is fully implemented. However, not all the routes have their dedicated tests. Make sure we implement those tests with on testnet and it is added to the CI
## Acceptance criteria
- [ ] every API call from the `gateway` directory should be implemented on testnet
## Additional Notes
|
1.0
|
Implement tests for the whole Gateway API on testnet - ## Objectives
The Gateway API is fully implemented. However, not all the routes have their dedicated tests. Make sure we implement those tests with on testnet and it is added to the CI
## Acceptance criteria
- [ ] every API call from the `gateway` directory should be implemented on testnet
## Additional Notes
|
test
|
implement tests for the whole gateway api on testnet objectives the gateway api is fully implemented however not all the routes have their dedicated tests make sure we implement those tests with on testnet and it is added to the ci acceptance criteria every api call from the gateway directory should be implemented on testnet additional notes
| 1
|
98,946
| 11,101,600,220
|
IssuesEvent
|
2019-12-16 21:48:06
|
ChildMindInstitute/mindlogger-app-backend
|
https://api.github.com/repos/ChildMindInstitute/mindlogger-app-backend
|
closed
|
🍪 Cache is not refreshing for applets on dev
|
MongoDB Python backend bug documentation reproschema server
|
I tried posting [this applet](https://raw.githubusercontent.com/hotavocado/HBN_EMA_NIMH/master/protocols/EMA_HBN_NIMH/EMA_HBN_NIMH_schema) on my dev account this morning, but the applet that shows up is a cached version that is more than two days old.
I tried get/user/applets and get/applet/{id} with refresh=true, but that didn't work. I published the applet under a different branch and tried to post that, but ended up getting the same cached applet.
I don't think this is a problem with the user cache, since it was my first time posting this applet on my dev account.
Any ideas?
|
1.0
|
🍪 Cache is not refreshing for applets on dev - I tried posting [this applet](https://raw.githubusercontent.com/hotavocado/HBN_EMA_NIMH/master/protocols/EMA_HBN_NIMH/EMA_HBN_NIMH_schema) on my dev account this morning, but the applet that shows up is a cached version that is more than two days old.
I tried get/user/applets and get/applet/{id} with refresh=true, but that didn't work. I published the applet under a different branch and tried to post that, but ended up getting the same cached applet.
I don't think this is a problem with the user cache, since it was my first time posting this applet on my dev account.
Any ideas?
|
non_test
|
🍪 cache is not refreshing for applets on dev i tried posting on my dev account this morning but the applet that shows up is a cached version that is more than two days old i tried get user applets and get applet id with refresh true but that didn t work i published the applet under a different branch and tried to post that but ended up getting the same cached applet i don t think this is a problem with the user cache since it was my first time posting this applet on my dev account any ideas
| 0
|
70,082
| 7,176,748,048
|
IssuesEvent
|
2018-01-31 11:05:29
|
ntop/ntopng
|
https://api.github.com/repos/ntop/ntopng
|
closed
|
ntopng may hang on shutdown
|
bug testing needed
|
In case ntopng is listening on an interface with no traffic, after receiving a SIGTERM ntopng will hang forever in `pthread_join(pollLoop, &res)`.
The problem is that ntopng tries to interrupt the sniffer thread with `pcap_breakloop(pcap_handle)`.
However this will not interrupt `pcap_next_ex()`, on which the sniffer thread is blocked on. Interruption will happen only of there is traffic on the interface.
I tried to do some research and it looks like there is a way to get `pcap_next_ex()` interrupted. The solution may be to use select/epoll of the pcap file descriptor, so that the blocking call is now select/epoll, and it can be interrupted by writing onto a pipe or more easily via a periodic timeout.
Verified on Debian stretch on both 2.4 and latest dev branch.
|
1.0
|
ntopng may hang on shutdown - In case ntopng is listening on an interface with no traffic, after receiving a SIGTERM ntopng will hang forever in `pthread_join(pollLoop, &res)`.
The problem is that ntopng tries to interrupt the sniffer thread with `pcap_breakloop(pcap_handle)`.
However this will not interrupt `pcap_next_ex()`, on which the sniffer thread is blocked on. Interruption will happen only of there is traffic on the interface.
I tried to do some research and it looks like there is a way to get `pcap_next_ex()` interrupted. The solution may be to use select/epoll of the pcap file descriptor, so that the blocking call is now select/epoll, and it can be interrupted by writing onto a pipe or more easily via a periodic timeout.
Verified on Debian stretch on both 2.4 and latest dev branch.
|
test
|
ntopng may hang on shutdown in case ntopng is listening on an interface with no traffic after receiving a sigterm ntopng will hang forever in pthread join pollloop res the problem is that ntopng tries to interrupt the sniffer thread with pcap breakloop pcap handle however this will not interrupt pcap next ex on which the sniffer thread is blocked on interruption will happen only of there is traffic on the interface i tried to do some research and it looks like there is a way to get pcap next ex interrupted the solution may be to use select epoll of the pcap file descriptor so that the blocking call is now select epoll and it can be interrupted by writing onto a pipe or more easily via a periodic timeout verified on debian stretch on both and latest dev branch
| 1
|
1,136
| 2,507,996,799
|
IssuesEvent
|
2015-01-12 22:14:32
|
nprapps/app-template
|
https://api.github.com/repos/nprapps/app-template
|
opened
|
App config var for selecting Fontello icons, generating custom build
|
Priority: Low
|
Var would be the icons you want, script would get fontello build
|
1.0
|
App config var for selecting Fontello icons, generating custom build - Var would be the icons you want, script would get fontello build
|
non_test
|
app config var for selecting fontello icons generating custom build var would be the icons you want script would get fontello build
| 0
|
96,868
| 8,635,150,971
|
IssuesEvent
|
2018-11-22 20:39:07
|
chartjs/chartjs-plugin-datalabels
|
https://api.github.com/repos/chartjs/chartjs-plugin-datalabels
|
closed
|
Overlapping labels with scatter chart
|
duplicate needs test case
|
Hi,
I'm using the plugin with scatter charts and it's doing a great job. However, if there are two scatter points very close together the labels often overlap. Is there any way to avoid this?
Thanks a lot
|
1.0
|
Overlapping labels with scatter chart - Hi,
I'm using the plugin with scatter charts and it's doing a great job. However, if there are two scatter points very close together the labels often overlap. Is there any way to avoid this?
Thanks a lot
|
test
|
overlapping labels with scatter chart hi i m using the plugin with scatter charts and it s doing a great job however if there are two scatter points very close together the labels often overlap is there any way to avoid this thanks a lot
| 1
|
215,356
| 16,600,859,350
|
IssuesEvent
|
2021-06-01 19:14:35
|
anitab-org/documentation
|
https://api.github.com/repos/anitab-org/documentation
|
closed
|
Duplicate word on README
|
Category: Documentation/Training First Timers Only
|
## Description
There is a typo in the README, the duplicate word in the design guidelines bullet point.
## Acceptance Criteria
### Update [Required]
- [ ] Remove duplicate `Contributing` word from Design guidelines on README
## Definition of Done
- [ ] All of the required items are completed.
- [x] Approval by 1 mentor.
## Estimation
<!--[INSERT NUMBER HERE] hours-->
0.5 hours
|
1.0
|
Duplicate word on README - ## Description
There is a typo in the README, the duplicate word in the design guidelines bullet point.
## Acceptance Criteria
### Update [Required]
- [ ] Remove duplicate `Contributing` word from Design guidelines on README
## Definition of Done
- [ ] All of the required items are completed.
- [x] Approval by 1 mentor.
## Estimation
<!--[INSERT NUMBER HERE] hours-->
0.5 hours
|
non_test
|
duplicate word on readme description there is a typo in the readme the duplicate word in the design guidelines bullet point acceptance criteria update remove duplicate contributing word from design guidelines on readme definition of done all of the required items are completed approval by mentor estimation hours
| 0
|
114,705
| 11,854,556,640
|
IssuesEvent
|
2020-03-25 01:13:20
|
aws/sagemaker-experiments
|
https://api.github.com/repos/aws/sagemaker-experiments
|
closed
|
Log metrics in any environment
|
bug documentation
|
**Is your feature request related to a problem? Please describe.**
I create a Tracker via Tracker.create but I can not use such tracker to log metric.
It throws this log instead.
"Cannot write metrics in this environment."
**Describe the solution you'd like**
The tracker can be created should able to log metrics as well.
**Describe alternatives you've considered**
N/A
**Additional context**
I noticed that the create method creating Tracker with no metrics_writer which required to log metric and there is no way to opt that in. I can not find the intended way to use log_metric API from documentation either, maybe I missed something?
|
1.0
|
Log metrics in any environment - **Is your feature request related to a problem? Please describe.**
I create a Tracker via Tracker.create but I can not use such tracker to log metric.
It throws this log instead.
"Cannot write metrics in this environment."
**Describe the solution you'd like**
The tracker can be created should able to log metrics as well.
**Describe alternatives you've considered**
N/A
**Additional context**
I noticed that the create method creating Tracker with no metrics_writer which required to log metric and there is no way to opt that in. I can not find the intended way to use log_metric API from documentation either, maybe I missed something?
|
non_test
|
log metrics in any environment is your feature request related to a problem please describe i create a tracker via tracker create but i can not use such tracker to log metric it throws this log instead cannot write metrics in this environment describe the solution you d like the tracker can be created should able to log metrics as well describe alternatives you ve considered n a additional context i noticed that the create method creating tracker with no metrics writer which required to log metric and there is no way to opt that in i can not find the intended way to use log metric api from documentation either maybe i missed something
| 0
|
52,651
| 7,778,467,493
|
IssuesEvent
|
2018-06-05 14:15:49
|
spring-cloud/spring-cloud-commons
|
https://api.github.com/repos/spring-cloud/spring-cloud-commons
|
closed
|
[Enhancement] Need extra knowledge to be able to refresh immutable beans
|
documentation
|
Hello,
We have recently upgrade to spring boot 2.0.1 along with spring clould Finchley.RC1. During the migrations, we noticed a pretty implicit issue while using customized data source configuration with spring cloud context refreshing. The application could fail with such exceptions: "Caused by: java.lang.IllegalStateException: The configuration of the pool is sealed once started. Use HikariConfigMXBean for runtime changes."
Steps to reproduce:
1. Use spring boot 2.x with spring cloud Finchley.RC1, and spring-boot-starter-actuator to refresh the context
2. Define a customized data source like what's suggested in spring boot reference:
```java
@Configuration
public class DataSourceConfig {
@Bean
@ConfigurationProperties(prefix = "datasource.main", ignoreUnknownFields = false)
DataSource dataSource() {
return DataSourceBuilder.create().build();
}
}
```
Plus the yml config:
```yaml
datasource:
main:
jdbc-url: jdbc:h2:mem:main # jdbc-url is required by Hikari which is the default CP now
username: user
password: pass
```
3. Activate the refresh endpoint:
```yaml
management:
endpoints:
web:
exposure:
include: refresh
```
4. Start the application and hit POST /actuator/refresh, and you will see the error above.
Potential solutions:
Since the Hikari data source is immutable and can be only changed via jmx, it will always fail if we rebind the new properties using the same object. The solution would be using "@RefreshScope" in org.springframework.cloud.context.config.annotation on the declared data source or any other immutable beans. However, this knowledge is hard to find at least from your documentation. It would be great to have it stated explicitly which could potentially save a lot of time.
|
1.0
|
[Enhancement] Need extra knowledge to be able to refresh immutable beans - Hello,
We have recently upgrade to spring boot 2.0.1 along with spring clould Finchley.RC1. During the migrations, we noticed a pretty implicit issue while using customized data source configuration with spring cloud context refreshing. The application could fail with such exceptions: "Caused by: java.lang.IllegalStateException: The configuration of the pool is sealed once started. Use HikariConfigMXBean for runtime changes."
Steps to reproduce:
1. Use spring boot 2.x with spring cloud Finchley.RC1, and spring-boot-starter-actuator to refresh the context
2. Define a customized data source like what's suggested in spring boot reference:
```java
@Configuration
public class DataSourceConfig {
@Bean
@ConfigurationProperties(prefix = "datasource.main", ignoreUnknownFields = false)
DataSource dataSource() {
return DataSourceBuilder.create().build();
}
}
```
Plus the yml config:
```yaml
datasource:
main:
jdbc-url: jdbc:h2:mem:main # jdbc-url is required by Hikari which is the default CP now
username: user
password: pass
```
3. Activate the refresh endpoint:
```yaml
management:
endpoints:
web:
exposure:
include: refresh
```
4. Start the application and hit POST /actuator/refresh, and you will see the error above.
Potential solutions:
Since the Hikari data source is immutable and can be only changed via jmx, it will always fail if we rebind the new properties using the same object. The solution would be using "@RefreshScope" in org.springframework.cloud.context.config.annotation on the declared data source or any other immutable beans. However, this knowledge is hard to find at least from your documentation. It would be great to have it stated explicitly which could potentially save a lot of time.
|
non_test
|
need extra knowledge to be able to refresh immutable beans hello we have recently upgrade to spring boot along with spring clould finchley during the migrations we noticed a pretty implicit issue while using customized data source configuration with spring cloud context refreshing the application could fail with such exceptions caused by java lang illegalstateexception the configuration of the pool is sealed once started use hikariconfigmxbean for runtime changes steps to reproduce use spring boot x with spring cloud finchley and spring boot starter actuator to refresh the context define a customized data source like what s suggested in spring boot reference java configuration public class datasourceconfig bean configurationproperties prefix datasource main ignoreunknownfields false datasource datasource return datasourcebuilder create build plus the yml config yaml datasource main jdbc url jdbc mem main jdbc url is required by hikari which is the default cp now username user password pass activate the refresh endpoint yaml management endpoints web exposure include refresh start the application and hit post actuator refresh and you will see the error above potential solutions since the hikari data source is immutable and can be only changed via jmx it will always fail if we rebind the new properties using the same object the solution would be using refreshscope in org springframework cloud context config annotation on the declared data source or any other immutable beans however this knowledge is hard to find at least from your documentation it would be great to have it stated explicitly which could potentially save a lot of time
| 0
|
261,318
| 27,809,732,676
|
IssuesEvent
|
2023-03-18 01:34:42
|
madhans23/linux-4.1.15
|
https://api.github.com/repos/madhans23/linux-4.1.15
|
closed
|
CVE-2022-1972 (High) detected in linux-stable-rtv4.1.33 - autoclosed
|
Mend: dependency security vulnerability
|
## CVE-2022-1972 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/nf_tables_api.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/nf_tables_api.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
CVE-2022-1972 is duplicate of CVE-2022-2078, so please consider CVE-2022-2078 instead.
https://access.redhat.com/security/cve/CVE-2022-2078
<p>Publish Date: 2022-09-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1972>CVE-2022-1972</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-09-14</p>
<p>Fix Resolution: v5.10.120,v5.15.45,v5.17.13,v5.18.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2022-1972 (High) detected in linux-stable-rtv4.1.33 - autoclosed - ## CVE-2022-1972 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in HEAD commit: <a href="https://github.com/madhans23/linux-4.1.15/commit/f9d19044b0eef1965f9bc412d7d9e579b74ec968">f9d19044b0eef1965f9bc412d7d9e579b74ec968</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/nf_tables_api.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/net/netfilter/nf_tables_api.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
CVE-2022-1972 is duplicate of CVE-2022-2078, so please consider CVE-2022-2078 instead.
https://access.redhat.com/security/cve/CVE-2022-2078
<p>Publish Date: 2022-09-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-1972>CVE-2022-1972</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-09-14</p>
<p>Fix Resolution: v5.10.120,v5.15.45,v5.17.13,v5.18.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in linux stable autoclosed cve high severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in head commit a href found in base branch master vulnerable source files net netfilter nf tables api c net netfilter nf tables api c vulnerability details cve is duplicate of cve so please consider cve instead publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution step up your open source security game with mend
| 0
|
267,986
| 23,337,307,391
|
IssuesEvent
|
2022-08-09 11:07:56
|
LE2HE/coding
|
https://api.github.com/repos/LE2HE/coding
|
closed
|
수 정렬
|
coding test
|
BACKJOON
==========
10989번
---------
> 1번째 줄에 수의 개수 N이 주어진다.
> 2번째 줄부터 N개의 숫자가 주어진다.
> N개의 줄에 오름차순 정렬한 결과를 1줄에 1개씩 출력한다.
>
>
> 링크 : [10989](https://www.acmicpc.net/problem/10989)
|
1.0
|
수 정렬 - BACKJOON
==========
10989번
---------
> 1번째 줄에 수의 개수 N이 주어진다.
> 2번째 줄부터 N개의 숫자가 주어진다.
> N개의 줄에 오름차순 정렬한 결과를 1줄에 1개씩 출력한다.
>
>
> 링크 : [10989](https://www.acmicpc.net/problem/10989)
|
test
|
수 정렬 backjoon 줄에 수의 개수 n이 주어진다 줄부터 n개의 숫자가 주어진다 n개의 줄에 오름차순 정렬한 결과를 출력한다 링크
| 1
|
576,726
| 17,093,443,487
|
IssuesEvent
|
2021-07-08 20:56:26
|
brave/brave-browser
|
https://api.github.com/repos/brave/brave-browser
|
closed
|
Speedreader button not as accessible in private windows
|
OS/Desktop QA/No accessibility feature/speedreader priority/P3
|
<!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description
<!--Provide a brief description of the issue-->
The Speedreader button should use the dark theme colors instead of light theme in Private Window and Private Window with Tor for greater accessibility.
## Steps to Reproduce
<!--Please add a series of steps to reproduce the issue-->
1. Open a Private Window or Private Window with Tor
2. Go to a Speedreadable page
3. See the Speedreader button
## Actual result:
<!--Please add screenshots if needed-->
## Expected result:
Use dark theme colors:
<img width="159" alt="Screen Shot 2021-07-07 at 2 39 56 PM" src="https://user-images.githubusercontent.com/2388823/124832240-345f8980-df31-11eb-8406-1f3658075b5b.png">
## Reproduces how often:
<!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
easily
## Brave version (brave://version info)
<!--For installed build, please copy Brave, Revision and OS from brave://version and paste here. If building from source please mention it along with brave://version details-->
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current release? n/a
- Can you reproduce this issue with the beta channel? n/a
- Can you reproduce this issue with the nightly channel? yes
## Other Additional Information:
- Does the issue resolve itself when disabling Brave Shields? n/a
- Does the issue resolve itself when disabling Brave Rewards? n/a
- Is the issue reproducible on the latest version of Chrome? n/a
## Assets
Figma: https://www.figma.com/file/YHMNRL2XpZDOUe6n1Dw6K1/Desktop-Speedreader?node-id=571%3A23480
|
1.0
|
Speedreader button not as accessible in private windows - <!-- Have you searched for similar issues? Before submitting this issue, please check the open issues and add a note before logging a new issue.
PLEASE USE THE TEMPLATE BELOW TO PROVIDE INFORMATION ABOUT THE ISSUE.
INSUFFICIENT INFO WILL GET THE ISSUE CLOSED. IT WILL ONLY BE REOPENED AFTER SUFFICIENT INFO IS PROVIDED-->
## Description
<!--Provide a brief description of the issue-->
The Speedreader button should use the dark theme colors instead of light theme in Private Window and Private Window with Tor for greater accessibility.
## Steps to Reproduce
<!--Please add a series of steps to reproduce the issue-->
1. Open a Private Window or Private Window with Tor
2. Go to a Speedreadable page
3. See the Speedreader button
## Actual result:
<!--Please add screenshots if needed-->
## Expected result:
Use dark theme colors:
<img width="159" alt="Screen Shot 2021-07-07 at 2 39 56 PM" src="https://user-images.githubusercontent.com/2388823/124832240-345f8980-df31-11eb-8406-1f3658075b5b.png">
## Reproduces how often:
<!--[Easily reproduced/Intermittent issue/No steps to reproduce]-->
easily
## Brave version (brave://version info)
<!--For installed build, please copy Brave, Revision and OS from brave://version and paste here. If building from source please mention it along with brave://version details-->
## Version/Channel Information:
<!--Does this issue happen on any other channels? Or is it specific to a certain channel?-->
- Can you reproduce this issue with the current release? n/a
- Can you reproduce this issue with the beta channel? n/a
- Can you reproduce this issue with the nightly channel? yes
## Other Additional Information:
- Does the issue resolve itself when disabling Brave Shields? n/a
- Does the issue resolve itself when disabling Brave Rewards? n/a
- Is the issue reproducible on the latest version of Chrome? n/a
## Assets
Figma: https://www.figma.com/file/YHMNRL2XpZDOUe6n1Dw6K1/Desktop-Speedreader?node-id=571%3A23480
|
non_test
|
speedreader button not as accessible in private windows have you searched for similar issues before submitting this issue please check the open issues and add a note before logging a new issue please use the template below to provide information about the issue insufficient info will get the issue closed it will only be reopened after sufficient info is provided description the speedreader button should use the dark theme colors instead of light theme in private window and private window with tor for greater accessibility steps to reproduce open a private window or private window with tor go to a speedreadable page see the speedreader button actual result expected result use dark theme colors img width alt screen shot at pm src reproduces how often easily brave version brave version info version channel information can you reproduce this issue with the current release n a can you reproduce this issue with the beta channel n a can you reproduce this issue with the nightly channel yes other additional information does the issue resolve itself when disabling brave shields n a does the issue resolve itself when disabling brave rewards n a is the issue reproducible on the latest version of chrome n a assets figma
| 0
|
263,378
| 23,052,947,386
|
IssuesEvent
|
2022-07-24 22:27:52
|
wfau/aglais
|
https://api.github.com/repos/wfau/aglais
|
opened
|
Tool to query list the Shiro accounts.
|
integration test gardening
|
Shell script callable from the client that returns a JSON list of accounts in the Shiro database.
Something we can use to create validation tests for the user accounts.
|
1.0
|
Tool to query list the Shiro accounts. - Shell script callable from the client that returns a JSON list of accounts in the Shiro database.
Something we can use to create validation tests for the user accounts.
|
test
|
tool to query list the shiro accounts shell script callable from the client that returns a json list of accounts in the shiro database something we can use to create validation tests for the user accounts
| 1
|
307,564
| 26,541,429,206
|
IssuesEvent
|
2023-01-19 19:36:36
|
tnc-ca-geo/animl-ingest
|
https://api.github.com/repos/tnc-ca-geo/animl-ingest
|
closed
|
Unify or seperate Python and Node parts
|
testing project structure
|
The presence of Python and Node in the same repo makes the creation of two test suites somewhat challenging. There are several possible solutions.
- [ ] migrate ingest_zip to Python (would be my preference)
- [ ] create two seperate repos
- [ ] create a deeper directory structure where Python parts and Node parts are separated out on the repo top level.
|
1.0
|
Unify or seperate Python and Node parts - The presence of Python and Node in the same repo makes the creation of two test suites somewhat challenging. There are several possible solutions.
- [ ] migrate ingest_zip to Python (would be my preference)
- [ ] create two seperate repos
- [ ] create a deeper directory structure where Python parts and Node parts are separated out on the repo top level.
|
test
|
unify or seperate python and node parts the presence of python and node in the same repo makes the creation of two test suites somewhat challenging there are several possible solutions migrate ingest zip to python would be my preference create two seperate repos create a deeper directory structure where python parts and node parts are separated out on the repo top level
| 1
|
180,620
| 13,940,167,279
|
IssuesEvent
|
2020-10-22 17:30:26
|
hashgraph/hedera-mirror-node
|
https://api.github.com/repos/hashgraph/hedera-mirror-node
|
closed
|
Postgresql deadlock in importer integration test
|
P3 bug java test
|
<!-- Thanks for submitting a bug report! Before submitting:
1. Try searching the existing issues to see if your issue has already been reported
2. Try asking on our Discord group (https://discordapp.com/invite/FFb9YFX)
3. If you're reporting a security vulnerability, please email security@hedera.com instead of opening an issue
-->
**Detailed Description**
Postgresql deadlock on rows in table `t_application_status` happens sporadically during importer integration tests. There is a race condition in the cleanup.sql script and `MirrorDateRangePropertiesProcessor`, both update `t_application_status` but in different order so deadlock happens.
**Actual Behavior**
Steps to reproduce the behavior:
1. ./mvnw package -pl hedera-mirror-importer
```
[ERROR] com.hedera.mirror.importer.reader.balance.BalanceFileReaderImplV1Test.readInvalidWhenFileDoesNotExist Time elapsed: 1.245 s <<< ERROR!
org.springframework.jdbc.datasource.init.ScriptStatementFailedException:
Failed to execute SQL script statement #12 of class path resource [db/scripts/cleanup.sql]: UPDATE t_application_status SET status_value = NULL; nested exception is org.postgresql.util.PSQLException: ERROR: deadlock detected
Detail: Process 53 waits for ShareLock on transaction 609; blocked by process 52.
Process 52 waits for ShareLock on transaction 608; blocked by process 53.
Hint: See server log for query details.
Where: while updating tuple (0,3) in relation "t_application_status"
Caused by: org.postgresql.util.PSQLException:
ERROR: deadlock detected
Detail: Process 53 waits for ShareLock on transaction 609; blocked by process 52.
Process 52 waits for ShareLock on transaction 608; blocked by process 53.
Hint: See server log for query details.
Where: while updating tuple (0,3) in relation "t_application_status"
```
**Expected Behavior**
Postgresql deadlock should not happen and integration tests run successfully
**Environment:**
- Java: [e.g. OpenJDK 11.0.4]
- Node: [e.g. v12.9.1-x86]
- OS: [e.g. Ubuntu 18.04]
- Version: [e.g. 1.0.1]
**Additional Context**
|
1.0
|
Postgresql deadlock in importer integration test - <!-- Thanks for submitting a bug report! Before submitting:
1. Try searching the existing issues to see if your issue has already been reported
2. Try asking on our Discord group (https://discordapp.com/invite/FFb9YFX)
3. If you're reporting a security vulnerability, please email security@hedera.com instead of opening an issue
-->
**Detailed Description**
Postgresql deadlock on rows in table `t_application_status` happens sporadically during importer integration tests. There is a race condition in the cleanup.sql script and `MirrorDateRangePropertiesProcessor`, both update `t_application_status` but in different order so deadlock happens.
**Actual Behavior**
Steps to reproduce the behavior:
1. ./mvnw package -pl hedera-mirror-importer
```
[ERROR] com.hedera.mirror.importer.reader.balance.BalanceFileReaderImplV1Test.readInvalidWhenFileDoesNotExist Time elapsed: 1.245 s <<< ERROR!
org.springframework.jdbc.datasource.init.ScriptStatementFailedException:
Failed to execute SQL script statement #12 of class path resource [db/scripts/cleanup.sql]: UPDATE t_application_status SET status_value = NULL; nested exception is org.postgresql.util.PSQLException: ERROR: deadlock detected
Detail: Process 53 waits for ShareLock on transaction 609; blocked by process 52.
Process 52 waits for ShareLock on transaction 608; blocked by process 53.
Hint: See server log for query details.
Where: while updating tuple (0,3) in relation "t_application_status"
Caused by: org.postgresql.util.PSQLException:
ERROR: deadlock detected
Detail: Process 53 waits for ShareLock on transaction 609; blocked by process 52.
Process 52 waits for ShareLock on transaction 608; blocked by process 53.
Hint: See server log for query details.
Where: while updating tuple (0,3) in relation "t_application_status"
```
**Expected Behavior**
Postgresql deadlock should not happen and integration tests run successfully
**Environment:**
- Java: [e.g. OpenJDK 11.0.4]
- Node: [e.g. v12.9.1-x86]
- OS: [e.g. Ubuntu 18.04]
- Version: [e.g. 1.0.1]
**Additional Context**
|
test
|
postgresql deadlock in importer integration test thanks for submitting a bug report before submitting try searching the existing issues to see if your issue has already been reported try asking on our discord group if you re reporting a security vulnerability please email security hedera com instead of opening an issue detailed description postgresql deadlock on rows in table t application status happens sporadically during importer integration tests there is a race condition in the cleanup sql script and mirrordaterangepropertiesprocessor both update t application status but in different order so deadlock happens actual behavior steps to reproduce the behavior mvnw package pl hedera mirror importer com hedera mirror importer reader balance readinvalidwhenfiledoesnotexist time elapsed s error org springframework jdbc datasource init scriptstatementfailedexception failed to execute sql script statement of class path resource update t application status set status value null nested exception is org postgresql util psqlexception error deadlock detected detail process waits for sharelock on transaction blocked by process process waits for sharelock on transaction blocked by process hint see server log for query details where while updating tuple in relation t application status caused by org postgresql util psqlexception error deadlock detected detail process waits for sharelock on transaction blocked by process process waits for sharelock on transaction blocked by process hint see server log for query details where while updating tuple in relation t application status expected behavior postgresql deadlock should not happen and integration tests run successfully environment java node os version additional context
| 1
|
789,019
| 27,776,231,849
|
IssuesEvent
|
2023-03-16 17:24:33
|
BIDMCDigitalPsychiatry/LAMP-platform
|
https://api.github.com/repos/BIDMCDigitalPsychiatry/LAMP-platform
|
opened
|
Toggle Feed
|
feature frontend priority LOW
|
We are interested in a toggle that allows a researcher to disable or enable the feed for a participant on the frontend of the app. When participants log-in to the app, they can see their upcoming surveys, if any:
<img width="1013" alt="Screen Shot 2023-03-16 at 1 22 16 PM" src="https://user-images.githubusercontent.com/103652751/225701319-2a3f264d-b3d4-4276-9f48-1b7aa040a8bb.png">
We would like to find a way to disable this feature from the researcher's perspective. We are open to the end product, but a possibility could be to replace the text under the "Feed" tab with a dialog that says "The managing researcher has disabled the user feed."
|
1.0
|
Toggle Feed - We are interested in a toggle that allows a researcher to disable or enable the feed for a participant on the frontend of the app. When participants log-in to the app, they can see their upcoming surveys, if any:
<img width="1013" alt="Screen Shot 2023-03-16 at 1 22 16 PM" src="https://user-images.githubusercontent.com/103652751/225701319-2a3f264d-b3d4-4276-9f48-1b7aa040a8bb.png">
We would like to find a way to disable this feature from the researcher's perspective. We are open to the end product, but a possibility could be to replace the text under the "Feed" tab with a dialog that says "The managing researcher has disabled the user feed."
|
non_test
|
toggle feed we are interested in a toggle that allows a researcher to disable or enable the feed for a participant on the frontend of the app when participants log in to the app they can see their upcoming surveys if any img width alt screen shot at pm src we would like to find a way to disable this feature from the researcher s perspective we are open to the end product but a possibility could be to replace the text under the feed tab with a dialog that says the managing researcher has disabled the user feed
| 0
|
140,732
| 11,357,737,845
|
IssuesEvent
|
2020-01-25 08:15:45
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
opened
|
Failing test: Firefox XPack UI Functional Tests.x-pack/test/functional/apps/infra/logs_source_configuration·ts - InfraOps app Logs Source Configuration Allows indices configuration can change the log columns
|
failed-test
|
A test failed on a tracked branch
```
{ TimeoutError: Waiting for element to be located By(css selector, [data-test-subj~="sourceConfigurationContent"])
Wait timed out after 17215ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:841:17
at process._tickCallback (internal/process/next_tick.js:68:7) name: 'TimeoutError', remoteStacktrace: '' }
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.6/97/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Firefox XPack UI Functional Tests.x-pack/test/functional/apps/infra/logs_source_configuration·ts","test.name":"InfraOps app Logs Source Configuration Allows indices configuration can change the log columns","test.failCount":1}} -->
|
1.0
|
Failing test: Firefox XPack UI Functional Tests.x-pack/test/functional/apps/infra/logs_source_configuration·ts - InfraOps app Logs Source Configuration Allows indices configuration can change the log columns - A test failed on a tracked branch
```
{ TimeoutError: Waiting for element to be located By(css selector, [data-test-subj~="sourceConfigurationContent"])
Wait timed out after 17215ms
at /dev/shm/workspace/kibana/node_modules/selenium-webdriver/lib/webdriver.js:841:17
at process._tickCallback (internal/process/next_tick.js:68:7) name: 'TimeoutError', remoteStacktrace: '' }
```
First failure: [Jenkins Build](https://kibana-ci.elastic.co/job/elastic+kibana+7.6/97/)
<!-- kibanaCiData = {"failed-test":{"test.class":"Firefox XPack UI Functional Tests.x-pack/test/functional/apps/infra/logs_source_configuration·ts","test.name":"InfraOps app Logs Source Configuration Allows indices configuration can change the log columns","test.failCount":1}} -->
|
test
|
failing test firefox xpack ui functional tests x pack test functional apps infra logs source configuration·ts infraops app logs source configuration allows indices configuration can change the log columns a test failed on a tracked branch timeouterror waiting for element to be located by css selector wait timed out after at dev shm workspace kibana node modules selenium webdriver lib webdriver js at process tickcallback internal process next tick js name timeouterror remotestacktrace first failure
| 1
|
239,180
| 26,212,344,484
|
IssuesEvent
|
2023-01-04 07:58:02
|
rapydo/do
|
https://api.github.com/repos/rapydo/do
|
closed
|
GitPython-3.1.29-py3-none-any.whl: 1 vulnerabilities (highest severity is: 9.8) - autoclosed
|
security vulnerability
|
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>GitPython-3.1.29-py3-none-any.whl</b></p></summary>
<p>GitPython is a python library used to interact with Git repositories</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl">https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (GitPython version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-24439](https://www.mend.io/vulnerability-database/CVE-2022-24439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | GitPython-3.1.29-py3-none-any.whl | Direct | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24439</summary>
### Vulnerable Library - <b>GitPython-3.1.29-py3-none-any.whl</b></p>
<p>GitPython is a python library used to interact with Git repositories</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl">https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **GitPython-3.1.29-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>3.0</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
All versions of package gitpython are vulnerable to Remote Code Execution (RCE) due to improper user input validation, which makes it possible to inject a maliciously crafted remote URL into the clone command. Exploiting this vulnerability is possible because the library makes external calls to git without sufficient sanitization of input arguments.
<p>Publish Date: 2022-12-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24439>CVE-2022-24439</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
True
|
GitPython-3.1.29-py3-none-any.whl: 1 vulnerabilities (highest severity is: 9.8) - autoclosed - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>GitPython-3.1.29-py3-none-any.whl</b></p></summary>
<p>GitPython is a python library used to interact with Git repositories</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl">https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
</details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (GitPython version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2022-24439](https://www.mend.io/vulnerability-database/CVE-2022-24439) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | GitPython-3.1.29-py3-none-any.whl | Direct | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2022-24439</summary>
### Vulnerable Library - <b>GitPython-3.1.29-py3-none-any.whl</b></p>
<p>GitPython is a python library used to interact with Git repositories</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl">https://files.pythonhosted.org/packages/1f/d3/020efb312a7d25fa00e144497a33378d415552e5581be080a99017af6d39/GitPython-3.1.29-py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **GitPython-3.1.29-py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>3.0</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
All versions of package gitpython are vulnerable to Remote Code Execution (RCE) due to improper user input validation, which makes it possible to inject a maliciously crafted remote URL into the clone command. Exploiting this vulnerability is possible because the library makes external calls to git without sufficient sanitization of input arguments.
<p>Publish Date: 2022-12-06
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-24439>CVE-2022-24439</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
|
non_test
|
gitpython none any whl vulnerabilities highest severity is autoclosed vulnerable library gitpython none any whl gitpython is a python library used to interact with git repositories library home page a href path to dependency file requirements txt path to vulnerable library requirements txt vulnerabilities cve severity cvss dependency type fixed in gitpython version remediation available high gitpython none any whl direct n a details cve vulnerable library gitpython none any whl gitpython is a python library used to interact with git repositories library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x gitpython none any whl vulnerable library found in base branch vulnerability details all versions of package gitpython are vulnerable to remote code execution rce due to improper user input validation which makes it possible to inject a maliciously crafted remote url into the clone command exploiting this vulnerability is possible because the library makes external calls to git without sufficient sanitization of input arguments publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href step up your open source security game with mend
| 0
|
284,112
| 24,579,624,386
|
IssuesEvent
|
2022-10-13 14:43:46
|
MPMG-DCC-UFMG/F01
|
https://api.github.com/repos/MPMG-DCC-UFMG/F01
|
closed
|
Teste de generalizacao para a tag Informações institucionais - Estrutura Organizacional - Memory - Prudente de Morais
|
generalization test development template - Memory (66) tag - Informações Institucionais subtag - Estrutura Organizacional
|
DoD: Realizar o teste de Generalização do validador da tag Informações institucionais - Estrutura Organizacional - Memory para o Município de Prudente de Morais.
|
1.0
|
Teste de generalizacao para a tag Informações institucionais - Estrutura Organizacional - Memory - Prudente de Morais - DoD: Realizar o teste de Generalização do validador da tag Informações institucionais - Estrutura Organizacional - Memory para o Município de Prudente de Morais.
|
test
|
teste de generalizacao para a tag informações institucionais estrutura organizacional memory prudente de morais dod realizar o teste de generalização do validador da tag informações institucionais estrutura organizacional memory para o município de prudente de morais
| 1
|
9,941
| 11,946,608,578
|
IssuesEvent
|
2020-04-03 08:26:39
|
pingcap/tidb
|
https://api.github.com/repos/pingcap/tidb
|
closed
|
Support explain on replace/insert statement
|
type/compatibility type/new-feature
|
## Feature Request
**Is your feature request related to a problem? Please describe:**
`explain` for `insert` or `replace` statement returns `ERROR 1105 (HY000): Unsupported type *core.Insert` now
**Describe the feature you'd like:**
we can get right `execute plan` for `insert` and `replace` statement.
**Describe alternatives you've considered:**
I don't know whether run explain on `insert` or `replace` is a little weird, it seems `insert` has no query plan?
|
True
|
Support explain on replace/insert statement - ## Feature Request
**Is your feature request related to a problem? Please describe:**
`explain` for `insert` or `replace` statement returns `ERROR 1105 (HY000): Unsupported type *core.Insert` now
**Describe the feature you'd like:**
we can get right `execute plan` for `insert` and `replace` statement.
**Describe alternatives you've considered:**
I don't know whether run explain on `insert` or `replace` is a little weird, it seems `insert` has no query plan?
|
non_test
|
support explain on replace insert statement feature request is your feature request related to a problem please describe explain for insert or replace statement returns error unsupported type core insert now describe the feature you d like we can get right execute plan for insert and replace statement describe alternatives you ve considered i don t know whether run explain on insert or replace is a little weird it seems insert has no query plan
| 0
|
306,920
| 26,506,232,992
|
IssuesEvent
|
2023-01-18 14:03:06
|
CarSnoop-Inc/carsnoop-issues
|
https://api.github.com/repos/CarSnoop-Inc/carsnoop-issues
|
closed
|
Refactor updateDocument and rename it to updateDocumentNotes
|
Andersen ready for testing
|
This endpoint should update document notes
|
1.0
|
Refactor updateDocument and rename it to updateDocumentNotes - This endpoint should update document notes
|
test
|
refactor updatedocument and rename it to updatedocumentnotes this endpoint should update document notes
| 1
|
329,926
| 24,238,741,385
|
IssuesEvent
|
2022-09-27 03:36:47
|
robert-altom/test
|
https://api.github.com/repos/robert-altom/test
|
closed
|
[License] Commands typos
|
bug documentation 1.7.1 gitlab
|
## Actual result
### AR
In [License section](https://staging-altomdotcom.kinsta.cloud/altunity/docs/altunitytester/pages/license.html#how-to-apply-these-terms-to-your-new-programs) there are two typos for the commands `show w` and `show c` (see screenshot)
### Additional info

---
<sub>You can find the original issue from GitLab [here](https://gitlab.com/altom/altunity/altunitytester/-/issues/847).</sub>
|
1.0
|
[License] Commands typos - ## Actual result
### AR
In [License section](https://staging-altomdotcom.kinsta.cloud/altunity/docs/altunitytester/pages/license.html#how-to-apply-these-terms-to-your-new-programs) there are two typos for the commands `show w` and `show c` (see screenshot)
### Additional info

---
<sub>You can find the original issue from GitLab [here](https://gitlab.com/altom/altunity/altunitytester/-/issues/847).</sub>
|
non_test
|
commands typos actual result ar in there are two typos for the commands show w and show c see screenshot additional info you can find the original issue from gitlab
| 0
|
129,901
| 5,105,767,017
|
IssuesEvent
|
2017-01-05 09:02:37
|
fossasia/susi_server
|
https://api.github.com/repos/fossasia/susi_server
|
closed
|
Arithmetic of numbers are not correct in http://api.asksusi.com but in localhost all working fine
|
bug Priority: High
|
**Actual Behavior**
Ask: 5+3
Response: Love you guys <3 that stream was awesome lol
**Expected Behavior**
Ask: 5+3
Response: 8
**API Console**
{
"query": "5+3",
"client_id": "aG9zdF8xMDEuNjMuMjUzLjkx",
"query_date": "2016-12-28T20:22:56.720Z",
"answer_date": "2016-12-28T20:22:59.394Z",
"answer_time": 2674,
"count": 1,
"answers": [{
"data": [
{
"text": "Love you guys <3 that stream was awesome lol",
"0": "5+3",
"1": "5+3",
"timezoneOffset": "-330"
},
{"text": "3 mins and you will see the fire"},
{"text": "I love you! <3"},
{"text": "1K!!! THE BIG 1K!! :O thank you all <3"},
{"text": "Day 5 of avoiding Passengers spoilers 🚀: UNSUCCESSFUL 😡 thank you twitter"},
{"text": "Niggas really want you to believe Drakengard 3 is not a broken game"},
{"text": "atla[5] i love you <3"},
{"text": "|| <3 Love you too, Anna Banana"},
{"text": "did you know there are at least 3 fics of \"dio/bread\"? well, now you do"},
{"text": "\"Congratulations Team Fortress 3 on best debut\" I love you, Jeff Gerstmann"},
{"text": "【時報】おはようございます☀5:00になりました。YOU ARE MY HEROにログインしましょう!"},
{"text": "\"so what did you do in the 3 weeks off?\" oh you know, absolutely nothing"},
{"text": "When your toddler headbutts you.. 5 times.. in 2 hours 🙃"},
{"text": "My SFV boycott continues. No Sagat, no Jerz. See you season 3."},
{"text": "2k17 😀😀😀 3 hari lagi. 2k16 thank you for all sweet sour memories ."},
{"text": "Rest in peace Carrie Fisher, you will be missed greatly <3"},
{"text": "3. lame jokes & puns i mean DADS. that's what they do best i tell you 😂"},
{"text": "JIA// 3 MONTHS NALAMG KULITAN NA ULE SA BAKASYON 😂HAHAHAHAHA MISS YOU💖"},
{"text": "you know you're out of shape when your mile drops from 4:58 to 5:45"}
],
"metadata": {"count": 19},
"actions": [{
"type": "answer",
"expression": "Love you guys <3 that stream was awesome lol"
}]
}],
"session": {"identity": {
"type": "host",
"name": "",
"anonymous": true
}}
}
|
1.0
|
Arithmetic of numbers are not correct in http://api.asksusi.com but in localhost all working fine - **Actual Behavior**
Ask: 5+3
Response: Love you guys <3 that stream was awesome lol
**Expected Behavior**
Ask: 5+3
Response: 8
**API Console**
{
"query": "5+3",
"client_id": "aG9zdF8xMDEuNjMuMjUzLjkx",
"query_date": "2016-12-28T20:22:56.720Z",
"answer_date": "2016-12-28T20:22:59.394Z",
"answer_time": 2674,
"count": 1,
"answers": [{
"data": [
{
"text": "Love you guys <3 that stream was awesome lol",
"0": "5+3",
"1": "5+3",
"timezoneOffset": "-330"
},
{"text": "3 mins and you will see the fire"},
{"text": "I love you! <3"},
{"text": "1K!!! THE BIG 1K!! :O thank you all <3"},
{"text": "Day 5 of avoiding Passengers spoilers 🚀: UNSUCCESSFUL 😡 thank you twitter"},
{"text": "Niggas really want you to believe Drakengard 3 is not a broken game"},
{"text": "atla[5] i love you <3"},
{"text": "|| <3 Love you too, Anna Banana"},
{"text": "did you know there are at least 3 fics of \"dio/bread\"? well, now you do"},
{"text": "\"Congratulations Team Fortress 3 on best debut\" I love you, Jeff Gerstmann"},
{"text": "【時報】おはようございます☀5:00になりました。YOU ARE MY HEROにログインしましょう!"},
{"text": "\"so what did you do in the 3 weeks off?\" oh you know, absolutely nothing"},
{"text": "When your toddler headbutts you.. 5 times.. in 2 hours 🙃"},
{"text": "My SFV boycott continues. No Sagat, no Jerz. See you season 3."},
{"text": "2k17 😀😀😀 3 hari lagi. 2k16 thank you for all sweet sour memories ."},
{"text": "Rest in peace Carrie Fisher, you will be missed greatly <3"},
{"text": "3. lame jokes & puns i mean DADS. that's what they do best i tell you 😂"},
{"text": "JIA// 3 MONTHS NALAMG KULITAN NA ULE SA BAKASYON 😂HAHAHAHAHA MISS YOU💖"},
{"text": "you know you're out of shape when your mile drops from 4:58 to 5:45"}
],
"metadata": {"count": 19},
"actions": [{
"type": "answer",
"expression": "Love you guys <3 that stream was awesome lol"
}]
}],
"session": {"identity": {
"type": "host",
"name": "",
"anonymous": true
}}
}
|
non_test
|
arithmetic of numbers are not correct in but in localhost all working fine actual behavior ask response love you guys lt that stream was awesome lol expected behavior ask response api console query client id query date answer date answer time count answers data text love you guys lt that stream was awesome lol timezoneoffset text mins and you will see the fire text i love you lt text the big o thank you all lt text day of avoiding passengers spoilers 🚀 unsuccessful 😡 thank you twitter text niggas really want you to believe drakengard is not a broken game text atla i love you lt text lt love you too anna banana text did you know there are at least fics of dio bread well now you do text congratulations team fortress on best debut i love you jeff gerstmann text 【時報】おはようございます☀ : 。you are my heroにログインしましょう! text so what did you do in the weeks off oh you know absolutely nothing text when your toddler headbutts you times in hours 🙃 text my sfv boycott continues no sagat no jerz see you season text 😀😀😀 hari lagi thank you for all sweet sour memories text rest in peace carrie fisher you will be missed greatly lt text lame jokes puns i mean dads that s what they do best i tell you 😂 text jia months nalamg kulitan na ule sa bakasyon 😂hahahahaha miss you💖 text you know you re out of shape when your mile drops from to metadata count actions type answer expression love you guys lt that stream was awesome lol session identity type host name anonymous true
| 0
|
271,829
| 23,634,023,422
|
IssuesEvent
|
2022-08-25 11:51:25
|
cjkrolak/ThermostatSupervisor
|
https://api.github.com/repos/cjkrolak/ThermostatSupervisor
|
closed
|
unit testing is not setting exit code for CI
|
bug test issue Priority-0 CI
|
failing unit test won't trigger a CI failure in Azure because exit code is not set. This issue was introduced some time ago when we switched from unittest discover to TestRunner in order to override runtime options for testing.
|
1.0
|
unit testing is not setting exit code for CI - failing unit test won't trigger a CI failure in Azure because exit code is not set. This issue was introduced some time ago when we switched from unittest discover to TestRunner in order to override runtime options for testing.
|
test
|
unit testing is not setting exit code for ci failing unit test won t trigger a ci failure in azure because exit code is not set this issue was introduced some time ago when we switched from unittest discover to testrunner in order to override runtime options for testing
| 1
|
195,297
| 14,713,417,263
|
IssuesEvent
|
2021-01-05 10:20:57
|
aeternity/aeternity
|
https://api.github.com/repos/aeternity/aeternity
|
closed
|
Missing local_lima_testnet setting
|
area/tests
|
There is a missing `local_lima_testnet` [here](https://github.com/aeternity/aeternity/blob/master/apps/aecore/src/aec_hard_forks.erl#L108-L135)
kudos to Marcolo for finding it.
|
1.0
|
Missing local_lima_testnet setting - There is a missing `local_lima_testnet` [here](https://github.com/aeternity/aeternity/blob/master/apps/aecore/src/aec_hard_forks.erl#L108-L135)
kudos to Marcolo for finding it.
|
test
|
missing local lima testnet setting there is a missing local lima testnet kudos to marcolo for finding it
| 1
|
267,242
| 23,287,710,578
|
IssuesEvent
|
2022-08-05 18:27:09
|
woocommerce/woocommerce
|
https://api.github.com/repos/woocommerce/woocommerce
|
closed
|
Fix E2E Package Linting Errors
|
package: @woocommerce/e2e-environment package: @woocommerce/e2e-core-tests package: @woocommerce/e2e-utils status: prioritization
|
### Prerequisites
- [X] I have carried out troubleshooting steps and I believe I have found a bug.
- [X] I have searched for similar bugs in both open and closed issues and cannot find a duplicate.
### Describe the bug
There are currently listing issues in one (or more?) of the E2E packages.
### Expected behavior
There should be no linting errors.
### Actual behavior
There are linting errors.
### Steps to reproduce
1. `pnpm -- turbo run lint --filter="@woocommerce/e2e*"`
### WordPress Environment
N/A
### Isolating the problem
- [X] I have deactivated other plugins and confirmed this bug occurs when only WooCommerce plugin is active.
- [X] This bug happens with a default WordPress theme active, or [Storefront](https://woocommerce.com/storefront/).
- [X] I can reproduce this bug consistently using the steps above.
|
1.0
|
Fix E2E Package Linting Errors - ### Prerequisites
- [X] I have carried out troubleshooting steps and I believe I have found a bug.
- [X] I have searched for similar bugs in both open and closed issues and cannot find a duplicate.
### Describe the bug
There are currently listing issues in one (or more?) of the E2E packages.
### Expected behavior
There should be no linting errors.
### Actual behavior
There are linting errors.
### Steps to reproduce
1. `pnpm -- turbo run lint --filter="@woocommerce/e2e*"`
### WordPress Environment
N/A
### Isolating the problem
- [X] I have deactivated other plugins and confirmed this bug occurs when only WooCommerce plugin is active.
- [X] This bug happens with a default WordPress theme active, or [Storefront](https://woocommerce.com/storefront/).
- [X] I can reproduce this bug consistently using the steps above.
|
test
|
fix package linting errors prerequisites i have carried out troubleshooting steps and i believe i have found a bug i have searched for similar bugs in both open and closed issues and cannot find a duplicate describe the bug there are currently listing issues in one or more of the packages expected behavior there should be no linting errors actual behavior there are linting errors steps to reproduce pnpm turbo run lint filter woocommerce wordpress environment n a isolating the problem i have deactivated other plugins and confirmed this bug occurs when only woocommerce plugin is active this bug happens with a default wordpress theme active or i can reproduce this bug consistently using the steps above
| 1
|
194,128
| 14,670,301,646
|
IssuesEvent
|
2020-12-30 04:18:59
|
felangel/bloc
|
https://api.github.com/repos/felangel/bloc
|
closed
|
[bloc_test] verify event dispached
|
pkg:bloc_test question
|
Is there a way to verify that the bloc in testing has dispached an event?
Example bloc:
```dart
if (event is MyEvent) {
...
add(MyOtherEvent());
...
}
```
Example test:
```dart
blocTest(
'should dispatch MyOtherEvent',
build: () {
return myBloc;
},
act: (bloc) => bloc.add(MyEvent()),
expect: [
...
],
verify: (bloc) async {
// ERROR: Used on a non-mockito object
verify(bloc.add(MyOtherEvent())).called(1);
},
);
```
|
1.0
|
[bloc_test] verify event dispached - Is there a way to verify that the bloc in testing has dispached an event?
Example bloc:
```dart
if (event is MyEvent) {
...
add(MyOtherEvent());
...
}
```
Example test:
```dart
blocTest(
'should dispatch MyOtherEvent',
build: () {
return myBloc;
},
act: (bloc) => bloc.add(MyEvent()),
expect: [
...
],
verify: (bloc) async {
// ERROR: Used on a non-mockito object
verify(bloc.add(MyOtherEvent())).called(1);
},
);
```
|
test
|
verify event dispached is there a way to verify that the bloc in testing has dispached an event example bloc dart if event is myevent add myotherevent example test dart bloctest should dispatch myotherevent build return mybloc act bloc bloc add myevent expect verify bloc async error used on a non mockito object verify bloc add myotherevent called
| 1
|
167,830
| 13,044,329,698
|
IssuesEvent
|
2020-07-29 04:20:24
|
OllisGit/OctoPrint-SpoolManager
|
https://api.github.com/repos/OllisGit/OctoPrint-SpoolManager
|
closed
|
Feature request: Sort-Options "Remaining Weight"
|
status: waitingForTestFeedback type: enhancement
|
I'd like to sort the spool list by "Remaining Weight" to be able to see which spools are running low.
|
1.0
|
Feature request: Sort-Options "Remaining Weight" - I'd like to sort the spool list by "Remaining Weight" to be able to see which spools are running low.
|
test
|
feature request sort options remaining weight i d like to sort the spool list by remaining weight to be able to see which spools are running low
| 1
|
38,480
| 5,188,831,040
|
IssuesEvent
|
2017-01-20 21:12:23
|
ngageoint/geowave
|
https://api.github.com/repos/ngageoint/geowave
|
opened
|
Add Unit tests to the package mil.nga.giat.geowave.adapter.raster.adapter
|
new contributor test coverage
|
There are currently no unit tests of any of the public methods in the java classes inside the mil.nga.giat.geowave.adapter.raster.adapter package. SourceThresholdMosaicDescriptor and SourceFixThresholdMosaicDescriptor can be ignored in this package as they are very specific to fixing a bug in a third-party library and other classes can be lightly touched, but primarily, RasterDataAdapter does a lot of important work for GeoWave’s ability to read and write rasters to and from key-value stores.
|
1.0
|
Add Unit tests to the package mil.nga.giat.geowave.adapter.raster.adapter - There are currently no unit tests of any of the public methods in the java classes inside the mil.nga.giat.geowave.adapter.raster.adapter package. SourceThresholdMosaicDescriptor and SourceFixThresholdMosaicDescriptor can be ignored in this package as they are very specific to fixing a bug in a third-party library and other classes can be lightly touched, but primarily, RasterDataAdapter does a lot of important work for GeoWave’s ability to read and write rasters to and from key-value stores.
|
test
|
add unit tests to the package mil nga giat geowave adapter raster adapter there are currently no unit tests of any of the public methods in the java classes inside the mil nga giat geowave adapter raster adapter package sourcethresholdmosaicdescriptor and sourcefixthresholdmosaicdescriptor can be ignored in this package as they are very specific to fixing a bug in a third party library and other classes can be lightly touched but primarily rasterdataadapter does a lot of important work for geowave’s ability to read and write rasters to and from key value stores
| 1
|
39,871
| 5,254,228,213
|
IssuesEvent
|
2017-02-02 12:12:41
|
QualiSystems/Azure-Shell
|
https://api.github.com/repos/QualiSystems/Azure-Shell
|
closed
|
OOTB Teardown will disconnect a "failed to connect" CVC
|
bug P3 ready to test Version 8.0
|
STR:
1)Deploy a blueprint that have an OpenStack app in it
2)When the sandbox is Active, connect the app to a manual VLAN with VLAN ID “3200000”
3)Connect the route à you should get error about the VLAN range, the connection will be changed to “connection failed”
4)End the Sandbox
Actual result:
The route will be disconnected during the teardown.
See gif:
\\qsnas1\shared\Tomer Admon\Disconnecting.gif
|
1.0
|
OOTB Teardown will disconnect a "failed to connect" CVC - STR:
1)Deploy a blueprint that have an OpenStack app in it
2)When the sandbox is Active, connect the app to a manual VLAN with VLAN ID “3200000”
3)Connect the route à you should get error about the VLAN range, the connection will be changed to “connection failed”
4)End the Sandbox
Actual result:
The route will be disconnected during the teardown.
See gif:
\\qsnas1\shared\Tomer Admon\Disconnecting.gif
|
test
|
ootb teardown will disconnect a failed to connect cvc str deploy a blueprint that have an openstack app in it when the sandbox is active connect the app to a manual vlan with vlan id “ ” connect the route à you should get error about the vlan range the connection will be changed to “connection failed” end the sandbox actual result the route will be disconnected during the teardown see gif shared tomer admon disconnecting gif
| 1
|
232,303
| 18,856,717,404
|
IssuesEvent
|
2021-11-12 07:36:51
|
ceph/ceph-csi
|
https://api.github.com/repos/ceph/ceph-csi
|
closed
|
Provisioner and Nodeplugin pods fails to come up
|
component/testing
|
# Describe the bug #
On creating the rook-ceph cluster using the deploy script, the provisioner and nodeplugin pods don't come up.
Steps to reproduce the behavior:
1. Run `./scripts/minikube.sh deploy-rook`
2. check if all the pods are up `kubectl get pods -nrook-ceph`
# Actual results #
```
[yatipadia@192 ceph-csi]$ kubectl get pods -nrook-ceph
NAME READY STATUS RESTARTS AGE
rook-ceph-mds-myfs-a-586646fdb9-tbjfl 1/1 Running 0 3m52s
rook-ceph-mds-myfs-b-58c86776c5-k5c8g 1/1 Running 0 3m51s
rook-ceph-mgr-a-7bd4584945-s2tsg 1/1 Running 0 4m27s
rook-ceph-mon-a-669488fd67-hvmpp 1/1 Running 0 4m37s
rook-ceph-operator-6459f5dc4b-vggbf 1/1 Running 0 12m
rook-ceph-osd-0-7b8d6c47c4-v97n4 1/1 Running 0 4m18s
rook-ceph-osd-prepare-minikube--1-js885 0/1 Completed 0 4m2s
rook-ceph-tools-7467d8bf8-nqc2v 1/1 Running 0 12m
```
The provisioner and Nodeplugin pods don't come up.
# Expected behavior #
All the pods including the provisioner and nodeplugin pods should come up
|
1.0
|
Provisioner and Nodeplugin pods fails to come up - # Describe the bug #
On creating the rook-ceph cluster using the deploy script, the provisioner and nodeplugin pods don't come up.
Steps to reproduce the behavior:
1. Run `./scripts/minikube.sh deploy-rook`
2. check if all the pods are up `kubectl get pods -nrook-ceph`
# Actual results #
```
[yatipadia@192 ceph-csi]$ kubectl get pods -nrook-ceph
NAME READY STATUS RESTARTS AGE
rook-ceph-mds-myfs-a-586646fdb9-tbjfl 1/1 Running 0 3m52s
rook-ceph-mds-myfs-b-58c86776c5-k5c8g 1/1 Running 0 3m51s
rook-ceph-mgr-a-7bd4584945-s2tsg 1/1 Running 0 4m27s
rook-ceph-mon-a-669488fd67-hvmpp 1/1 Running 0 4m37s
rook-ceph-operator-6459f5dc4b-vggbf 1/1 Running 0 12m
rook-ceph-osd-0-7b8d6c47c4-v97n4 1/1 Running 0 4m18s
rook-ceph-osd-prepare-minikube--1-js885 0/1 Completed 0 4m2s
rook-ceph-tools-7467d8bf8-nqc2v 1/1 Running 0 12m
```
The provisioner and Nodeplugin pods don't come up.
# Expected behavior #
All the pods including the provisioner and nodeplugin pods should come up
|
test
|
provisioner and nodeplugin pods fails to come up describe the bug on creating the rook ceph cluster using the deploy script the provisioner and nodeplugin pods don t come up steps to reproduce the behavior run scripts minikube sh deploy rook check if all the pods are up kubectl get pods nrook ceph actual results kubectl get pods nrook ceph name ready status restarts age rook ceph mds myfs a tbjfl running rook ceph mds myfs b running rook ceph mgr a running rook ceph mon a hvmpp running rook ceph operator vggbf running rook ceph osd running rook ceph osd prepare minikube completed rook ceph tools running the provisioner and nodeplugin pods don t come up expected behavior all the pods including the provisioner and nodeplugin pods should come up
| 1
|
224,985
| 7,476,290,632
|
IssuesEvent
|
2018-04-04 02:13:36
|
opencollective/opencollective
|
https://api.github.com/repos/opencollective/opencollective
|
closed
|
API response stream fails affecting webpack documentation build step
|
bug priority
|
> When requesting the API for backers of the webpack project, the response stream is cut of mid-response, leading to invalid json.
>
> This currently affects Webpacks documentation build step: https://travis-ci.org/webpack/webpack.js.org/builds/360812190?utm_source=github_status&utm_medium=notification
>
see https://github.com/opencollective/opencollective-api/issues/1205
|
1.0
|
API response stream fails affecting webpack documentation build step - > When requesting the API for backers of the webpack project, the response stream is cut of mid-response, leading to invalid json.
>
> This currently affects Webpacks documentation build step: https://travis-ci.org/webpack/webpack.js.org/builds/360812190?utm_source=github_status&utm_medium=notification
>
see https://github.com/opencollective/opencollective-api/issues/1205
|
non_test
|
api response stream fails affecting webpack documentation build step when requesting the api for backers of the webpack project the response stream is cut of mid response leading to invalid json this currently affects webpacks documentation build step see
| 0
|
28,825
| 13,837,732,323
|
IssuesEvent
|
2020-10-14 04:29:08
|
oceanomics/ecotaxa_dev
|
https://api.github.com/repos/oceanomics/ecotaxa_dev
|
closed
|
DB view 'objects' contains a useless outer join
|
performance
|
In manage.py:
```
database.ExecSQL("""create view objects as select oh.*,ofi.*
from obj_head oh left join obj_field ofi on oh.objid=ofi.objfid""")
```
The "left" keyword means OJ.
As the view is selected during filters, it makes unnecessary complicated execution plans.
Data state:
```
ecotaxa=# select objfid from obj_field ofl except select objid from obj_head;
objfid
--------
(0 ligne)
ecotaxa=# select objid from obj_head except select objfid as o2 from obj_field;
objid
-----------
109368670
(1 ligne)
```
So, a single object has no field, nor `orig_id` which "should not" be. To fix manually in production DB.
|
True
|
DB view 'objects' contains a useless outer join - In manage.py:
```
database.ExecSQL("""create view objects as select oh.*,ofi.*
from obj_head oh left join obj_field ofi on oh.objid=ofi.objfid""")
```
The "left" keyword means OJ.
As the view is selected during filters, it makes unnecessary complicated execution plans.
Data state:
```
ecotaxa=# select objfid from obj_field ofl except select objid from obj_head;
objfid
--------
(0 ligne)
ecotaxa=# select objid from obj_head except select objfid as o2 from obj_field;
objid
-----------
109368670
(1 ligne)
```
So, a single object has no field, nor `orig_id` which "should not" be. To fix manually in production DB.
|
non_test
|
db view objects contains a useless outer join in manage py database execsql create view objects as select oh ofi from obj head oh left join obj field ofi on oh objid ofi objfid the left keyword means oj as the view is selected during filters it makes unnecessary complicated execution plans data state ecotaxa select objfid from obj field ofl except select objid from obj head objfid ligne ecotaxa select objid from obj head except select objfid as from obj field objid ligne so a single object has no field nor orig id which should not be to fix manually in production db
| 0
|
305,286
| 26,375,857,903
|
IssuesEvent
|
2023-01-12 02:20:18
|
NHN-YesAladin/yesaladin_shop
|
https://api.github.com/repos/NHN-YesAladin/yesaladin_shop
|
closed
|
[Test] : BDDMockito에서 Mockito로 변경
|
Test[테스트]
|
<aside>
## 테스트 상세 내용
- [x] BDDMockito를 사용한 모든 테스트 코드를 Mockito로 통일합니다. (`given()` 사용하는 부분)
- CommandMemberControllerTest
## 참고사항
</aside>
|
1.0
|
[Test] : BDDMockito에서 Mockito로 변경 - <aside>
## 테스트 상세 내용
- [x] BDDMockito를 사용한 모든 테스트 코드를 Mockito로 통일합니다. (`given()` 사용하는 부분)
- CommandMemberControllerTest
## 참고사항
</aside>
|
test
|
bddmockito에서 mockito로 변경 테스트 상세 내용 bddmockito를 사용한 모든 테스트 코드를 mockito로 통일합니다 given 사용하는 부분 commandmembercontrollertest 참고사항
| 1
|
94,336
| 15,962,363,463
|
IssuesEvent
|
2021-04-16 01:09:03
|
xinYG/bootstrap-timepicker
|
https://api.github.com/repos/xinYG/bootstrap-timepicker
|
reopened
|
CVE-2019-19919 (High) detected in multiple libraries
|
security vulnerability
|
## CVE-2019-19919 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.10.min.js</b>, <b>handlebars-4.0.10.js</b>, <b>opennmsopennms-source-24.1.2-1</b>, <b>opennmsopennms-source-24.1.2-1</b>, <b>nodev4.3.2</b>, <b>nodev4.3.2</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.10.min.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js</a></p>
<p>
Dependency Hierarchy:
</details>
<details><summary><b>handlebars-4.0.10.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js</a></p>
<p>
Dependency Hierarchy:
</details>
<p>Found in HEAD commit: <a href="https://github.com/xinYG/bootstrap-timepicker/commit/b011a55ee3bfce5d2fedf4fd780e4196d446c504">b011a55ee3bfce5d2fedf4fd780e4196d446c504</a></p>
<p>Found in base branch: <b>gh-pages</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object's __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19919>CVE-2019-19919</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1164">https://www.npmjs.com/advisories/1164</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: 4.3.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","packageFilePaths":[],"isTransitiveDependency":false,"isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0"},{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","packageFilePaths":[],"isTransitiveDependency":false,"isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0"}],"baseBranches":["gh-pages"],"vulnerabilityIdentifier":"CVE-2019-19919","vulnerabilityDetails":"Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object\u0027s __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19919","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
True
|
CVE-2019-19919 (High) detected in multiple libraries - ## CVE-2019-19919 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>handlebars-4.0.10.min.js</b>, <b>handlebars-4.0.10.js</b>, <b>opennmsopennms-source-24.1.2-1</b>, <b>opennmsopennms-source-24.1.2-1</b>, <b>nodev4.3.2</b>, <b>nodev4.3.2</b></p></summary>
<p>
<details><summary><b>handlebars-4.0.10.min.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.min.js</a></p>
<p>
Dependency Hierarchy:
</details>
<details><summary><b>handlebars-4.0.10.js</b></p></summary>
<p>Handlebars provides the power necessary to let you build semantic templates effectively with no frustration</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js">https://cdnjs.cloudflare.com/ajax/libs/handlebars.js/4.0.10/handlebars.js</a></p>
<p>
Dependency Hierarchy:
</details>
<p>Found in HEAD commit: <a href="https://github.com/xinYG/bootstrap-timepicker/commit/b011a55ee3bfce5d2fedf4fd780e4196d446c504">b011a55ee3bfce5d2fedf4fd780e4196d446c504</a></p>
<p>Found in base branch: <b>gh-pages</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object's __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.
<p>Publish Date: 2019-12-20
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19919>CVE-2019-19919</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1164">https://www.npmjs.com/advisories/1164</a></p>
<p>Release Date: 2019-12-20</p>
<p>Fix Resolution: 4.3.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","packageFilePaths":[],"isTransitiveDependency":false,"isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0"},{"packageType":"JavaScript","packageName":"handlebars.js","packageVersion":"4.0.10","packageFilePaths":[],"isTransitiveDependency":false,"isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.0"}],"baseBranches":["gh-pages"],"vulnerabilityIdentifier":"CVE-2019-19919","vulnerabilityDetails":"Versions of handlebars prior to 4.3.0 are vulnerable to Prototype Pollution leading to Remote Code Execution. Templates may alter an Object\u0027s __proto__ and __defineGetter__ properties, which may allow an attacker to execute arbitrary code through crafted payloads.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19919","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> -->
|
non_test
|
cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries handlebars min js handlebars js opennmsopennms source opennmsopennms source handlebars min js handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href dependency hierarchy handlebars js handlebars provides the power necessary to let you build semantic templates effectively with no frustration library home page a href dependency hierarchy found in head commit a href found in base branch gh pages vulnerability details versions of handlebars prior to are vulnerable to prototype pollution leading to remote code execution templates may alter an object s proto and definegetter properties which may allow an attacker to execute arbitrary code through crafted payloads publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false isminimumfixversionavailable true minimumfixversion packagetype javascript packagename handlebars js packageversion packagefilepaths istransitivedependency false isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails versions of handlebars prior to are vulnerable to prototype pollution leading to remote code execution templates may alter an object proto and definegetter properties which may allow an attacker to execute arbitrary code through crafted payloads vulnerabilityurl
| 0
|
12,915
| 9,811,516,386
|
IssuesEvent
|
2019-06-13 00:06:30
|
MicrosoftDocs/azure-docs
|
https://api.github.com/repos/MicrosoftDocs/azure-docs
|
closed
|
Typo on 'hostHeader' attribute on 'Defining ports for role instances' XML sample
|
cloud-services/svc cxp doc-bug triaged
|
It should read 'hostHeader', not 'hostheader'.
<Site name="MailSite" packageDir="MailSite">
<Bindings>
<Binding name="mail" endpointName="HttpIn" hostheader="mail.mysite.cloudapp.net" />
</Bindings>
<VirtualDirectory name="artifacts" />
<VirtualApplication name="storageproxy">
<VirtualDirectory name="packages" packageDir="Sites\storageProxy\packages"/>
</VirtualApplication>
</Site>
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 9ab3a72c-f408-2bdc-55f6-c12c220cace2
* Version Independent ID: f9d36f07-723c-6354-383b-6b227a9648e9
* Content: [What is a Cloud Service model and package](https://docs.microsoft.com/en-us/azure/cloud-services/cloud-services-model-and-package#defining-ports-for-role-instances)
* Content Source: [articles/cloud-services/cloud-services-model-and-package.md](https://github.com/Microsoft/azure-docs/blob/master/articles/cloud-services/cloud-services-model-and-package.md)
* Service: **cloud-services**
* GitHub Login: @jpconnock
* Microsoft Alias: **jeconnoc**
|
1.0
|
Typo on 'hostHeader' attribute on 'Defining ports for role instances' XML sample - It should read 'hostHeader', not 'hostheader'.
<Site name="MailSite" packageDir="MailSite">
<Bindings>
<Binding name="mail" endpointName="HttpIn" hostheader="mail.mysite.cloudapp.net" />
</Bindings>
<VirtualDirectory name="artifacts" />
<VirtualApplication name="storageproxy">
<VirtualDirectory name="packages" packageDir="Sites\storageProxy\packages"/>
</VirtualApplication>
</Site>
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 9ab3a72c-f408-2bdc-55f6-c12c220cace2
* Version Independent ID: f9d36f07-723c-6354-383b-6b227a9648e9
* Content: [What is a Cloud Service model and package](https://docs.microsoft.com/en-us/azure/cloud-services/cloud-services-model-and-package#defining-ports-for-role-instances)
* Content Source: [articles/cloud-services/cloud-services-model-and-package.md](https://github.com/Microsoft/azure-docs/blob/master/articles/cloud-services/cloud-services-model-and-package.md)
* Service: **cloud-services**
* GitHub Login: @jpconnock
* Microsoft Alias: **jeconnoc**
|
non_test
|
typo on hostheader attribute on defining ports for role instances xml sample it should read hostheader not hostheader lt site name mailsite packagedir mailsite gt lt bindings gt lt binding name mail endpointname httpin hostheader mail mysite cloudapp net gt lt bindings gt lt virtualdirectory name artifacts gt lt virtualapplication name storageproxy gt lt virtualdirectory name packages packagedir sites storageproxy packages gt lt virtualapplication gt lt site gt document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service cloud services github login jpconnock microsoft alias jeconnoc
| 0
|
91,111
| 8,289,812,462
|
IssuesEvent
|
2018-09-19 15:35:25
|
phetsims/graphing-quadratics
|
https://api.github.com/repos/phetsims/graphing-quadratics
|
closed
|
CT: Cannot read property 'x' of undefined
|
type:automated-testing type:bug
|
Probably related to the massive refactoring I did yesterday.
graphing-quadratics : xss-fuzz : run
Uncaught TypeError: Cannot read property 'x' of undefined
TypeError: Cannot read property 'x' of undefined
at Array.VertexManipulator.vertexProperty.link.vertex (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/graphing-quadratics/js/common/view/VertexManipulator.js?bust=1537274144503:85:44)
at Emitter.emit2 (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Emitter.js?bust=1537274144503:182:52)
at Property._notifyListeners (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:304:29)
at Property.setValueAndNotifyListeners (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:287:14)
at Property.set (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:230:16)
at Property.set value [as value] (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:334:36)
at drag (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/graphing-quadratics/js/common/view/VertexManipulator.js?bust=1537274144503:136:32)
at Object.move (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/scenery/js/input/SimpleDragHandler.js?bust=1537274144503:199:29)
at Input.dispatchToListeners (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/scenery/js/input/Input.js?bust=1537274144503:1353:27)
at Input.dispatchEvent (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/scenery/js/input/Input.js?bust=1537274144503:1309:12)
Approximately 9/18/2018, 5:57:22 AM
|
1.0
|
CT: Cannot read property 'x' of undefined - Probably related to the massive refactoring I did yesterday.
graphing-quadratics : xss-fuzz : run
Uncaught TypeError: Cannot read property 'x' of undefined
TypeError: Cannot read property 'x' of undefined
at Array.VertexManipulator.vertexProperty.link.vertex (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/graphing-quadratics/js/common/view/VertexManipulator.js?bust=1537274144503:85:44)
at Emitter.emit2 (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Emitter.js?bust=1537274144503:182:52)
at Property._notifyListeners (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:304:29)
at Property.setValueAndNotifyListeners (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:287:14)
at Property.set (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:230:16)
at Property.set value [as value] (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/axon/js/Property.js?bust=1537274144503:334:36)
at drag (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/graphing-quadratics/js/common/view/VertexManipulator.js?bust=1537274144503:136:32)
at Object.move (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/scenery/js/input/SimpleDragHandler.js?bust=1537274144503:199:29)
at Input.dispatchToListeners (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/scenery/js/input/Input.js?bust=1537274144503:1353:27)
at Input.dispatchEvent (https://bayes.colorado.edu/continuous-testing/snapshot-1537271842828/scenery/js/input/Input.js?bust=1537274144503:1309:12)
Approximately 9/18/2018, 5:57:22 AM
|
test
|
ct cannot read property x of undefined probably related to the massive refactoring i did yesterday graphing quadratics xss fuzz run uncaught typeerror cannot read property x of undefined typeerror cannot read property x of undefined at array vertexmanipulator vertexproperty link vertex at emitter at property notifylisteners at property setvalueandnotifylisteners at property set at property set value at drag at object move at input dispatchtolisteners at input dispatchevent approximately am
| 1
|
15,400
| 11,497,050,750
|
IssuesEvent
|
2020-02-12 09:19:03
|
eclipse/antenna
|
https://api.github.com/repos/eclipse/antenna
|
opened
|
Provide a container that supports the ORT/Antenna compliance toolchain with necessary configuration possibilities
|
infrastructure
|
### Summary of the Improvement
A common container that contains the ORT/Antenna toolchain as a commonly usable Dockerfile. It should be easy to configure to add e.g., SW360 credentials or a branded template for document generation.
### Acceptance Criteria
- [ ] A Dockerfile exists that combines the whole toolchain with the needed configuration possibilities
- [ ] An example Jenkinsfile that allows to execute the container in a Jenkins environment
- [ ] Potentially support for other build environments (Azure, Travis, GH actions)
### Definition of Done
- Acceptance criteria fulfilled
- The ticket describes what has been done and describes how the results can be verified (e.g. new Jenkins step is inserted, the report can be viewed at X)
- All known limitations are listed and it is described how they will be addressed (e.g., a ticket for the remaining stuff)
- Documentation is updated
- The result has been reviewed: Everything works as described and can be verified reading only the documentation
|
1.0
|
Provide a container that supports the ORT/Antenna compliance toolchain with necessary configuration possibilities - ### Summary of the Improvement
A common container that contains the ORT/Antenna toolchain as a commonly usable Dockerfile. It should be easy to configure to add e.g., SW360 credentials or a branded template for document generation.
### Acceptance Criteria
- [ ] A Dockerfile exists that combines the whole toolchain with the needed configuration possibilities
- [ ] An example Jenkinsfile that allows to execute the container in a Jenkins environment
- [ ] Potentially support for other build environments (Azure, Travis, GH actions)
### Definition of Done
- Acceptance criteria fulfilled
- The ticket describes what has been done and describes how the results can be verified (e.g. new Jenkins step is inserted, the report can be viewed at X)
- All known limitations are listed and it is described how they will be addressed (e.g., a ticket for the remaining stuff)
- Documentation is updated
- The result has been reviewed: Everything works as described and can be verified reading only the documentation
|
non_test
|
provide a container that supports the ort antenna compliance toolchain with necessary configuration possibilities summary of the improvement a common container that contains the ort antenna toolchain as a commonly usable dockerfile it should be easy to configure to add e g credentials or a branded template for document generation acceptance criteria a dockerfile exists that combines the whole toolchain with the needed configuration possibilities an example jenkinsfile that allows to execute the container in a jenkins environment potentially support for other build environments azure travis gh actions definition of done acceptance criteria fulfilled the ticket describes what has been done and describes how the results can be verified e g new jenkins step is inserted the report can be viewed at x all known limitations are listed and it is described how they will be addressed e g a ticket for the remaining stuff documentation is updated the result has been reviewed everything works as described and can be verified reading only the documentation
| 0
|
111,960
| 9,548,483,632
|
IssuesEvent
|
2019-05-02 05:36:06
|
ESCOMP/ctsm
|
https://api.github.com/repos/ESCOMP/ctsm
|
opened
|
Add a cmip6_nociso_deck user-mods directory for 2-degree
|
branch tag: release priority: high type: enhance - software type: tests
|
For 2-degree CMIP6 deck experiments we need a cmip6_nociso_deck user-mods directory that is the same as cmip6_deck, but the Carbon isotopes are turned off.
@fvitt
|
1.0
|
Add a cmip6_nociso_deck user-mods directory for 2-degree - For 2-degree CMIP6 deck experiments we need a cmip6_nociso_deck user-mods directory that is the same as cmip6_deck, but the Carbon isotopes are turned off.
@fvitt
|
test
|
add a nociso deck user mods directory for degree for degree deck experiments we need a nociso deck user mods directory that is the same as deck but the carbon isotopes are turned off fvitt
| 1
|
121,897
| 17,670,908,585
|
IssuesEvent
|
2021-08-23 05:55:45
|
AlexRogalskiy/proverbs
|
https://api.github.com/repos/AlexRogalskiy/proverbs
|
closed
|
CVE-2019-1010266 (Medium) detected in lodash-2.4.2.tgz - autoclosed
|
security vulnerability
|
## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: proverbs/package.json</p>
<p>Path to vulnerable library: proverbs/node_modules/dockerfile_lint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- dockerfile_lint-0.3.4.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/proverbs/commit/e2e6d89dfb09a97540ede0daa46c8024ab9217cd">e2e6d89dfb09a97540ede0daa46c8024ab9217cd</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2019-1010266 (Medium) detected in lodash-2.4.2.tgz - autoclosed - ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: proverbs/package.json</p>
<p>Path to vulnerable library: proverbs/node_modules/dockerfile_lint/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- dockerfile_lint-0.3.4.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/proverbs/commit/e2e6d89dfb09a97540ede0daa46c8024ab9217cd">e2e6d89dfb09a97540ede0daa46c8024ab9217cd</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve medium detected in lodash tgz autoclosed cve medium severity vulnerability vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file proverbs package json path to vulnerable library proverbs node modules dockerfile lint node modules lodash package json dependency hierarchy dockerfile lint tgz root library x lodash tgz vulnerable library found in head commit a href vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource
| 0
|
146,366
| 11,734,931,010
|
IssuesEvent
|
2020-03-11 10:13:21
|
chameleon-system/chameleon-system
|
https://api.github.com/repos/chameleon-system/chameleon-system
|
closed
|
Highlight current entry in sidebar
|
Status: Test
|
**Describe the solution you'd like**
The sidebar entry matching the page shown on the right (table list or table entry) should be highlighted.
|
1.0
|
Highlight current entry in sidebar - **Describe the solution you'd like**
The sidebar entry matching the page shown on the right (table list or table entry) should be highlighted.
|
test
|
highlight current entry in sidebar describe the solution you d like the sidebar entry matching the page shown on the right table list or table entry should be highlighted
| 1
|
62,118
| 6,776,605,014
|
IssuesEvent
|
2017-10-27 18:31:42
|
babel/babel
|
https://api.github.com/repos/babel/babel
|
opened
|
Remove extraneous console output when running preset-env tests
|
area: tests
|
We're getting this from the @babel/preset-env test output, and it shouldn't be there (if there is a way to mock/remove from console output we should do it
```
@babel/preset-env: `DEBUG` option
Using targets:
{
"chrome": "55"
}
```
|
1.0
|
Remove extraneous console output when running preset-env tests - We're getting this from the @babel/preset-env test output, and it shouldn't be there (if there is a way to mock/remove from console output we should do it
```
@babel/preset-env: `DEBUG` option
Using targets:
{
"chrome": "55"
}
```
|
test
|
remove extraneous console output when running preset env tests we re getting this from the babel preset env test output and it shouldn t be there if there is a way to mock remove from console output we should do it babel preset env debug option using targets chrome
| 1
|
75,158
| 7,460,984,995
|
IssuesEvent
|
2018-03-30 22:29:48
|
runtimeverification/solidity
|
https://api.github.com/repos/runtimeverification/solidity
|
closed
|
Solidity feature: payable
|
bug tests: std
|
functions and accessors without the payable modifier should throw an exception if they are passed funds.
|
1.0
|
Solidity feature: payable - functions and accessors without the payable modifier should throw an exception if they are passed funds.
|
test
|
solidity feature payable functions and accessors without the payable modifier should throw an exception if they are passed funds
| 1
|
253,073
| 27,300,392,871
|
IssuesEvent
|
2023-02-24 01:05:23
|
phildav06/Groupomania
|
https://api.github.com/repos/phildav06/Groupomania
|
opened
|
CVE-2023-25813 (High) detected in sequelize-6.6.2.tgz
|
security vulnerability
|
## CVE-2023-25813 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sequelize-6.6.2.tgz</b></p></summary>
<p>Multi dialect ORM for Node.JS</p>
<p>Library home page: <a href="https://registry.npmjs.org/sequelize/-/sequelize-6.6.2.tgz">https://registry.npmjs.org/sequelize/-/sequelize-6.6.2.tgz</a></p>
<p>Path to dependency file: /backend/package.json</p>
<p>Path to vulnerable library: /backend/node_modules/sequelize/package.json</p>
<p>
Dependency Hierarchy:
- :x: **sequelize-6.6.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/phildav06/Groupomania/commit/b5dfa4dbb08d39b625f69bed42db0a7dad1bd26e">b5dfa4dbb08d39b625f69bed42db0a7dad1bd26e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Sequelize is a Node.js ORM tool. In versions prior to 6.19.1 a SQL injection exploit exists related to replacements. Parameters which are passed through replacements are not properly escaped which can lead to arbitrary SQL injection depending on the specific queries in use. The issue has been fixed in Sequelize 6.19.1. Users are advised to upgrade. Users unable to upgrade should not use the `replacements` and the `where` option in the same query.
<p>Publish Date: 2023-02-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-25813>CVE-2023-25813</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-25813">https://www.cve.org/CVERecord?id=CVE-2023-25813</a></p>
<p>Release Date: 2023-02-22</p>
<p>Fix Resolution: 6.19.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
CVE-2023-25813 (High) detected in sequelize-6.6.2.tgz - ## CVE-2023-25813 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sequelize-6.6.2.tgz</b></p></summary>
<p>Multi dialect ORM for Node.JS</p>
<p>Library home page: <a href="https://registry.npmjs.org/sequelize/-/sequelize-6.6.2.tgz">https://registry.npmjs.org/sequelize/-/sequelize-6.6.2.tgz</a></p>
<p>Path to dependency file: /backend/package.json</p>
<p>Path to vulnerable library: /backend/node_modules/sequelize/package.json</p>
<p>
Dependency Hierarchy:
- :x: **sequelize-6.6.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/phildav06/Groupomania/commit/b5dfa4dbb08d39b625f69bed42db0a7dad1bd26e">b5dfa4dbb08d39b625f69bed42db0a7dad1bd26e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Sequelize is a Node.js ORM tool. In versions prior to 6.19.1 a SQL injection exploit exists related to replacements. Parameters which are passed through replacements are not properly escaped which can lead to arbitrary SQL injection depending on the specific queries in use. The issue has been fixed in Sequelize 6.19.1. Users are advised to upgrade. Users unable to upgrade should not use the `replacements` and the `where` option in the same query.
<p>Publish Date: 2023-02-22
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-25813>CVE-2023-25813</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>10.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2023-25813">https://www.cve.org/CVERecord?id=CVE-2023-25813</a></p>
<p>Release Date: 2023-02-22</p>
<p>Fix Resolution: 6.19.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
cve high detected in sequelize tgz cve high severity vulnerability vulnerable library sequelize tgz multi dialect orm for node js library home page a href path to dependency file backend package json path to vulnerable library backend node modules sequelize package json dependency hierarchy x sequelize tgz vulnerable library found in head commit a href found in base branch master vulnerability details sequelize is a node js orm tool in versions prior to a sql injection exploit exists related to replacements parameters which are passed through replacements are not properly escaped which can lead to arbitrary sql injection depending on the specific queries in use the issue has been fixed in sequelize users are advised to upgrade users unable to upgrade should not use the replacements and the where option in the same query publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend
| 0
|
41,548
| 16,778,732,582
|
IssuesEvent
|
2021-06-15 03:18:55
|
Kenshin/simpread
|
https://api.github.com/repos/Kenshin/simpread
|
closed
|
建议:增加对Microsoft OneNote团队账号的支持
|
done service
|
OneNote的绑定现仅支持个人live账号,能否加入对microsoftonline.com的API支持从而能够从团队邮箱登录?谢谢!
|
1.0
|
建议:增加对Microsoft OneNote团队账号的支持 - OneNote的绑定现仅支持个人live账号,能否加入对microsoftonline.com的API支持从而能够从团队邮箱登录?谢谢!
|
non_test
|
建议:增加对microsoft onenote团队账号的支持 onenote的绑定现仅支持个人live账号,能否加入对microsoftonline com的api支持从而能够从团队邮箱登录?谢谢!
| 0
|
294,297
| 25,360,731,286
|
IssuesEvent
|
2022-11-20 21:23:24
|
fjarri/nucypher-async
|
https://api.github.com/repos/fjarri/nucypher-async
|
opened
|
Make `Logger` in tests use `MockClock` for timestamps
|
enhancement testing
|
This way it will be easier to debug its output in tests that use `autojump_clock` fixture and fast-forward through a significant amount of time.
|
1.0
|
Make `Logger` in tests use `MockClock` for timestamps - This way it will be easier to debug its output in tests that use `autojump_clock` fixture and fast-forward through a significant amount of time.
|
test
|
make logger in tests use mockclock for timestamps this way it will be easier to debug its output in tests that use autojump clock fixture and fast forward through a significant amount of time
| 1
|
116,852
| 9,885,705,818
|
IssuesEvent
|
2019-06-25 03:41:22
|
projectunic0rn/warmr
|
https://api.github.com/repos/projectunic0rn/warmr
|
opened
|
Set up automated unit & e2e tests for auth / user / events routes
|
api testing
|
I blew through nestjs guide without writing tests and would like to ensure these are covered. First attempt at this was a struggle given nest required modules to be mocked that depended on each other. This requires some investigation.
Todos:
- Set up unit tests for each service method for user, auth, and event modules.
- Set up an e2e test that goes through basic user flow: signup, login, create event, update event, delete event, etc.
- Look into automating these on each PR :)
|
1.0
|
Set up automated unit & e2e tests for auth / user / events routes - I blew through nestjs guide without writing tests and would like to ensure these are covered. First attempt at this was a struggle given nest required modules to be mocked that depended on each other. This requires some investigation.
Todos:
- Set up unit tests for each service method for user, auth, and event modules.
- Set up an e2e test that goes through basic user flow: signup, login, create event, update event, delete event, etc.
- Look into automating these on each PR :)
|
test
|
set up automated unit tests for auth user events routes i blew through nestjs guide without writing tests and would like to ensure these are covered first attempt at this was a struggle given nest required modules to be mocked that depended on each other this requires some investigation todos set up unit tests for each service method for user auth and event modules set up an test that goes through basic user flow signup login create event update event delete event etc look into automating these on each pr
| 1
|
239,246
| 7,787,792,834
|
IssuesEvent
|
2018-06-07 00:28:46
|
LessWrong2/Lesswrong2
|
https://api.github.com/repos/LessWrong2/Lesswrong2
|
closed
|
lesserwrong.com domain doesn't work on chrome/linux, or Safari on iPhone SE
|
2. Medium Priority (Hard)
|
From intercom:
The lesserwrong.com domain doesn't work in Chrome on Linux or Safari on iPhone SE. I would assume it should simply redirect to the equivalent lesswrong.com site, but it doesn't and a ton of links are broken due to that.
|
1.0
|
lesserwrong.com domain doesn't work on chrome/linux, or Safari on iPhone SE - From intercom:
The lesserwrong.com domain doesn't work in Chrome on Linux or Safari on iPhone SE. I would assume it should simply redirect to the equivalent lesswrong.com site, but it doesn't and a ton of links are broken due to that.
|
non_test
|
lesserwrong com domain doesn t work on chrome linux or safari on iphone se from intercom the lesserwrong com domain doesn t work in chrome on linux or safari on iphone se i would assume it should simply redirect to the equivalent lesswrong com site but it doesn t and a ton of links are broken due to that
| 0
|
199,341
| 22,693,306,306
|
IssuesEvent
|
2022-07-05 01:10:44
|
TechnoConserve/personal_website
|
https://api.github.com/repos/TechnoConserve/personal_website
|
closed
|
WS-2021-0369 (High) detected in sqlparse-0.3.0-py2.py3-none-any.whl - autoclosed
|
security vulnerability
|
## WS-2021-0369 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sqlparse-0.3.0-py2.py3-none-any.whl</b></p></summary>
<p>Non-validating SQL parser</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/ef/53/900f7d2a54557c6a37886585a91336520e5539e3ae2423ff1102daf4f3a7/sqlparse-0.3.0-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/ef/53/900f7d2a54557c6a37886585a91336520e5539e3ae2423ff1102daf4f3a7/sqlparse-0.3.0-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **sqlparse-0.3.0-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
StripComments filter contains a regular expression that is vulnerable to ReDOS (Regular Expression Denial of Service)
The formatter function that strips comments from a SQL contains a regular expression that is vulnerable to ReDoS (Regular Expression Denial of Service). The regular expression may cause exponential backtracking on strings containing many repetitions of '\r\n' in SQL comments.
<p>Publish Date: 2021-09-10
<p>URL: <a href=https://github.com/andialbrecht/sqlparse/commit/8238a9e450ed1524e40cb3a8b0b3c00606903aeb>WS-2021-0369</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-p5w8-wqhj-9hhf">https://github.com/advisories/GHSA-p5w8-wqhj-9hhf</a></p>
<p>Release Date: 2021-09-10</p>
<p>Fix Resolution: sqlparse - 0.4.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
True
|
WS-2021-0369 (High) detected in sqlparse-0.3.0-py2.py3-none-any.whl - autoclosed - ## WS-2021-0369 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sqlparse-0.3.0-py2.py3-none-any.whl</b></p></summary>
<p>Non-validating SQL parser</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/ef/53/900f7d2a54557c6a37886585a91336520e5539e3ae2423ff1102daf4f3a7/sqlparse-0.3.0-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/ef/53/900f7d2a54557c6a37886585a91336520e5539e3ae2423ff1102daf4f3a7/sqlparse-0.3.0-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **sqlparse-0.3.0-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
StripComments filter contains a regular expression that is vulnerable to ReDOS (Regular Expression Denial of Service)
The formatter function that strips comments from a SQL contains a regular expression that is vulnerable to ReDoS (Regular Expression Denial of Service). The regular expression may cause exponential backtracking on strings containing many repetitions of '\r\n' in SQL comments.
<p>Publish Date: 2021-09-10
<p>URL: <a href=https://github.com/andialbrecht/sqlparse/commit/8238a9e450ed1524e40cb3a8b0b3c00606903aeb>WS-2021-0369</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-p5w8-wqhj-9hhf">https://github.com/advisories/GHSA-p5w8-wqhj-9hhf</a></p>
<p>Release Date: 2021-09-10</p>
<p>Fix Resolution: sqlparse - 0.4.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
|
non_test
|
ws high detected in sqlparse none any whl autoclosed ws high severity vulnerability vulnerable library sqlparse none any whl non validating sql parser library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x sqlparse none any whl vulnerable library found in base branch main vulnerability details stripcomments filter contains a regular expression that is vulnerable to redos regular expression denial of service the formatter function that strips comments from a sql contains a regular expression that is vulnerable to redos regular expression denial of service the regular expression may cause exponential backtracking on strings containing many repetitions of r n in sql comments publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution sqlparse step up your open source security game with whitesource
| 0
|
218,049
| 16,920,557,551
|
IssuesEvent
|
2021-06-25 04:35:00
|
AtlasOfLivingAustralia/la-pipelines
|
https://api.github.com/repos/AtlasOfLivingAustralia/la-pipelines
|
closed
|
Spatial portal - single scatterplot issues
|
spatial-portal testing-findings
|
Issues:
- When Scatterplot single is selected and the parameters selection screen opens, only 6 environmental layers are available. There are 165 in production
- if you try to run the scatterplot with a custom area (bounding box defined) scatterplot hangs
- if you run the single scatterplot, then **Download** the scatterplot data and try to open in excel - you first get a message that excel will try to repair the file, then you get a message the file is corrupted. Sample data used for scatterplot - https://nectar-spatial-test.ala.org.au?ss=1619757132490
No background species selected. Layers used: **Endemism** and **Precipitation - annual (Bio12)**
|
1.0
|
Spatial portal - single scatterplot issues - Issues:
- When Scatterplot single is selected and the parameters selection screen opens, only 6 environmental layers are available. There are 165 in production
- if you try to run the scatterplot with a custom area (bounding box defined) scatterplot hangs
- if you run the single scatterplot, then **Download** the scatterplot data and try to open in excel - you first get a message that excel will try to repair the file, then you get a message the file is corrupted. Sample data used for scatterplot - https://nectar-spatial-test.ala.org.au?ss=1619757132490
No background species selected. Layers used: **Endemism** and **Precipitation - annual (Bio12)**
|
test
|
spatial portal single scatterplot issues issues when scatterplot single is selected and the parameters selection screen opens only environmental layers are available there are in production if you try to run the scatterplot with a custom area bounding box defined scatterplot hangs if you run the single scatterplot then download the scatterplot data and try to open in excel you first get a message that excel will try to repair the file then you get a message the file is corrupted sample data used for scatterplot no background species selected layers used endemism and precipitation annual
| 1
|
125,513
| 10,345,212,173
|
IssuesEvent
|
2019-09-04 13:01:49
|
ballerina-platform/ballerina-lang
|
https://api.github.com/repos/ballerina-platform/ballerina-lang
|
closed
|
[Tooling] Invalid/inaccurate suggestions for annotation access
|
Area/Tooling BetaTesting Type/Improvement
|
**Description:**
$title.
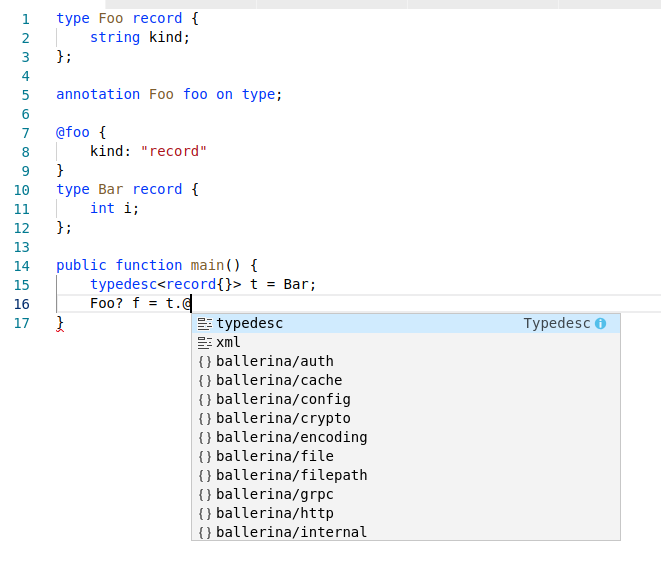
**Steps to reproduce:**
```ballerina
type Foo record {
string kind;
};
annotation Foo foo on type;
@foo {
kind: "record"
}
type Bar record {
int i;
};
public function main() {
typedesc<record{}> t = Bar;
// or even `Bar.@`
Foo? f = t.@
}
```
It would be better to suggest annotation tags here.
**Affected Versions:**
1.0.0-beta-SNAPSHOT - 15th August build
**Related Issues:**
https://github.com/ballerina-platform/ballerina-lang/issues/15947
|
1.0
|
[Tooling] Invalid/inaccurate suggestions for annotation access - **Description:**
$title.
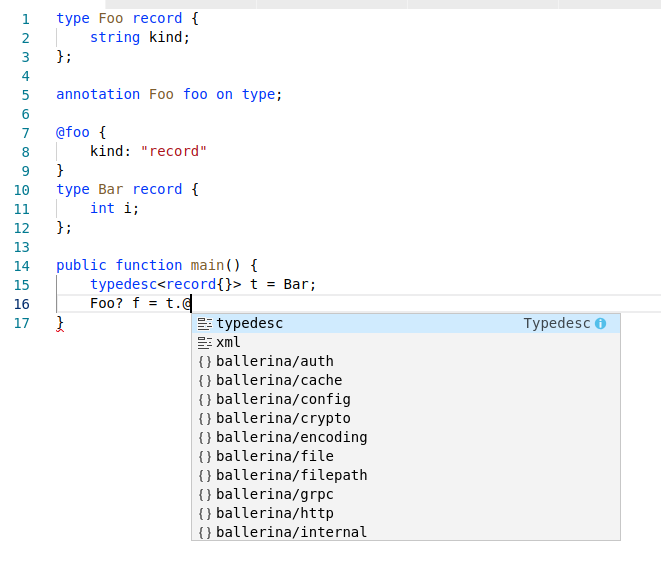
**Steps to reproduce:**
```ballerina
type Foo record {
string kind;
};
annotation Foo foo on type;
@foo {
kind: "record"
}
type Bar record {
int i;
};
public function main() {
typedesc<record{}> t = Bar;
// or even `Bar.@`
Foo? f = t.@
}
```
It would be better to suggest annotation tags here.
**Affected Versions:**
1.0.0-beta-SNAPSHOT - 15th August build
**Related Issues:**
https://github.com/ballerina-platform/ballerina-lang/issues/15947
|
test
|
invalid inaccurate suggestions for annotation access description title steps to reproduce ballerina type foo record string kind annotation foo foo on type foo kind record type bar record int i public function main typedesc t bar or even bar foo f t it would be better to suggest annotation tags here affected versions beta snapshot august build related issues
| 1
|
457
| 2,540,862,176
|
IssuesEvent
|
2015-01-28 01:11:38
|
Cockatrice/Cockatrice
|
https://api.github.com/repos/Cockatrice/Cockatrice
|
closed
|
[RELEASE REGRESSIONS] - Library Access, Hand Reveal, Sideboard Access.
|
Cockatrice Defect OSX
|
Using the F3 function, or menu selection to view entire library causes client to crash.
Example using menu option and then shortcut.http://screencast.com/t/8pVfXDYXZO
Platform: OSX
Version: Jan,23rd, 2015.
Update: Regression appears to also effect accessing the sideboard. Behaviour is same when selecting view sideboard, or using keyboard shortcuts to access it.
Update: When revealing your entire hand it also causes a full client crash. http://screencast.com/t/ohelseUXX1a
|
1.0
|
[RELEASE REGRESSIONS] - Library Access, Hand Reveal, Sideboard Access. - Using the F3 function, or menu selection to view entire library causes client to crash.
Example using menu option and then shortcut.http://screencast.com/t/8pVfXDYXZO
Platform: OSX
Version: Jan,23rd, 2015.
Update: Regression appears to also effect accessing the sideboard. Behaviour is same when selecting view sideboard, or using keyboard shortcuts to access it.
Update: When revealing your entire hand it also causes a full client crash. http://screencast.com/t/ohelseUXX1a
|
non_test
|
library access hand reveal sideboard access using the function or menu selection to view entire library causes client to crash example using menu option and then shortcut platform osx version jan update regression appears to also effect accessing the sideboard behaviour is same when selecting view sideboard or using keyboard shortcuts to access it update when revealing your entire hand it also causes a full client crash
| 0
|
331,981
| 29,175,074,481
|
IssuesEvent
|
2023-05-19 07:11:40
|
unifyai/ivy
|
https://api.github.com/repos/unifyai/ivy
|
reopened
|
Fix elementwise.test_trunc
|
Sub Task Failing Test
|
| | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|
1.0
|
Fix elementwise.test_trunc - | | |
|---|---|
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/4709674574/jobs/8352877382" rel="noopener noreferrer" target="_blank"><img src=https://img.shields.io/badge/-success-success></a>
|
test
|
fix elementwise test trunc tensorflow img src torch img src numpy img src jax img src
| 1
|
256,503
| 22,057,372,319
|
IssuesEvent
|
2022-05-30 14:02:55
|
IBM/operator-sample-go
|
https://api.github.com/repos/IBM/operator-sample-go
|
opened
|
Test Case-01- misleading pre-requisite
|
test_manual
|
**Issue:**
Deploying without OLM contains installation of OLM as a prerequisite
**Link to the documentation:**
https://github.com/IBM/operator-sample-go/blob/main/documentation/Prerequisites.md
|
1.0
|
Test Case-01- misleading pre-requisite - **Issue:**
Deploying without OLM contains installation of OLM as a prerequisite
**Link to the documentation:**
https://github.com/IBM/operator-sample-go/blob/main/documentation/Prerequisites.md
|
test
|
test case misleading pre requisite issue deploying without olm contains installation of olm as a prerequisite link to the documentation
| 1
|
331,409
| 28,962,031,785
|
IssuesEvent
|
2023-05-10 03:58:10
|
vmware-tanzu/tanzu-framework
|
https://api.github.com/repos/vmware-tanzu/tanzu-framework
|
closed
|
`make package-vendir-sync` does not work in Github Actions
|
area/testing kind/bug
|
**Bug description**
`make verify` fails in Github `verify` action. It calls `make package-vendir-sync` which seems to have trouble with mounted volumes on Github runners (probably because it's doing docker-in-docker stuff).
Logs from one of the failed jobs: https://github.com/vmware-tanzu/tanzu-framework/actions/runs/4833779855/jobs/8614195531
This failure must be fixed and the `verify` action needs to be restored.
**Affected product area (please put an X in all that apply)**
- ( ) APIs
- ( ) Addons
- ( ) CLI
- ( ) Docs
- ( ) IAM
- ( ) Installation
- ( ) Plugin
- ( ) Security
- (x) Test and Release
- ( ) User Experience
- ( ) Developer Experience
**Expected behavior**
No failures and verification of uncommitted files is done in actions.
**Steps to reproduce the bug**
**Version** (include the SHA if the version is not obvious)
**Environment where the bug was observed (cloud, OS, etc)**
**Relevant Debug Output (Logs, manifests, etc)**
|
1.0
|
`make package-vendir-sync` does not work in Github Actions - **Bug description**
`make verify` fails in Github `verify` action. It calls `make package-vendir-sync` which seems to have trouble with mounted volumes on Github runners (probably because it's doing docker-in-docker stuff).
Logs from one of the failed jobs: https://github.com/vmware-tanzu/tanzu-framework/actions/runs/4833779855/jobs/8614195531
This failure must be fixed and the `verify` action needs to be restored.
**Affected product area (please put an X in all that apply)**
- ( ) APIs
- ( ) Addons
- ( ) CLI
- ( ) Docs
- ( ) IAM
- ( ) Installation
- ( ) Plugin
- ( ) Security
- (x) Test and Release
- ( ) User Experience
- ( ) Developer Experience
**Expected behavior**
No failures and verification of uncommitted files is done in actions.
**Steps to reproduce the bug**
**Version** (include the SHA if the version is not obvious)
**Environment where the bug was observed (cloud, OS, etc)**
**Relevant Debug Output (Logs, manifests, etc)**
|
test
|
make package vendir sync does not work in github actions bug description make verify fails in github verify action it calls make package vendir sync which seems to have trouble with mounted volumes on github runners probably because it s doing docker in docker stuff logs from one of the failed jobs this failure must be fixed and the verify action needs to be restored affected product area please put an x in all that apply apis addons cli docs iam installation plugin security x test and release user experience developer experience expected behavior no failures and verification of uncommitted files is done in actions steps to reproduce the bug version include the sha if the version is not obvious environment where the bug was observed cloud os etc relevant debug output logs manifests etc
| 1
|
40,153
| 9,866,720,869
|
IssuesEvent
|
2019-06-21 08:21:48
|
primefaces/primefaces
|
https://api.github.com/repos/primefaces/primefaces
|
closed
|
Listener not being called for the drop down, but the listener works for the date functionality
|
defect invalid
|
Listener not being called for the drop down, but the listener works for the date functionality
## 1) Environment
- PrimeFaces version: 5.2
- Does it work on the newest released PrimeFaces version? Version? No
- Does it work on the newest sources in GitHub? (Build by source -> https://github.com/primefaces/primefaces/wiki/Building-From-Source) No
- Application server + version: Websphere 10.3
- Affected browsers: All
## 2) Expected behavior
The ajax method listener should be called for the district drop down listener="#{dataMB.districtSelect}"
The ajax method listener should be called for the date select
## 3) Actual behavior
The ajax method listener is not called for the district drop down
The ajax method listener is called for the date select
## 4) Steps to reproduce
Declare a bean
Declare a <p:selectOneMenu and a p:ajax inside it
## 5) Sample XHTML
<div class="ui">
<p:panelGrid columns="9" layout="grid" id="dateFilterPanel" >
<h:panelGroup>
<p:outputLabel value="District">
<p:selectOneMenu id="district" value="#{dataMB.selectedDistrict}" >
<p:ajax event="select" listener="#{dataMB.districtSelect}" update=":dataForm" />
<f:selectItem itemLabel="Select District" itemValue="" />
<f:selectItems value="#{dataMB.districtList}" />
</p:selectOneMenu>
<h:outputLabel value="dateFrom" for="dateFrom">
<p:calendar id="dateFrom" mode="popup" readonlyInput="true" value="#{dataMB.dateFrom}" pattern="MM/dd/yyyy" navigator="true">
<p:ajax event="dateSelect" listener="#{dataMB.dateSelectFrom}" update=":dataForm" />
</p:calendar>
</p:panelGrid>
</div>
<div class="ui">
<p:dataTable styleClass="fixed-size" value="#{dataMB.searchResultsList}"
var="searchResultsRow" rows="10" paginator="true" widgetVar="searchResults"
emptyMessage="No results found for search." id="searchResults"
rowKey="#{searchResultsRow.dateFrom}" selection="#{dataMB.selectedData}"
draggableColumns="true" selectionMode="single" >
<p:column
headerText="Date From"
sortBy="#{searchResultsRow.dateFrom}"
filterBy="#{searchResultsRow.dateFrom}"
filterMatchMode="contains" id="dateFromId">
<h:outputText id="dateFrom" value="#{searchResultsRow.dateFrom}">
<f:convertDateTime pattern="MM-dd-yyyy" />
</h:outputText>
</p:column>
</p:dataTable>
</div>
</h:form>
</h:body>
6) Sample bean
public void dateSelectFrom(SelectEvent event) {
}
public void districtSelect(SelectEvent event) {
}
--------------
<p:ajax event="select"
<p:ajax event="itemSelect"
<p:ajax event="valueChange"
<p:ajax event="change"
I have tried these in the xhtml page, But none of them works. No errors in the console
|
1.0
|
Listener not being called for the drop down, but the listener works for the date functionality - Listener not being called for the drop down, but the listener works for the date functionality
## 1) Environment
- PrimeFaces version: 5.2
- Does it work on the newest released PrimeFaces version? Version? No
- Does it work on the newest sources in GitHub? (Build by source -> https://github.com/primefaces/primefaces/wiki/Building-From-Source) No
- Application server + version: Websphere 10.3
- Affected browsers: All
## 2) Expected behavior
The ajax method listener should be called for the district drop down listener="#{dataMB.districtSelect}"
The ajax method listener should be called for the date select
## 3) Actual behavior
The ajax method listener is not called for the district drop down
The ajax method listener is called for the date select
## 4) Steps to reproduce
Declare a bean
Declare a <p:selectOneMenu and a p:ajax inside it
## 5) Sample XHTML
<div class="ui">
<p:panelGrid columns="9" layout="grid" id="dateFilterPanel" >
<h:panelGroup>
<p:outputLabel value="District">
<p:selectOneMenu id="district" value="#{dataMB.selectedDistrict}" >
<p:ajax event="select" listener="#{dataMB.districtSelect}" update=":dataForm" />
<f:selectItem itemLabel="Select District" itemValue="" />
<f:selectItems value="#{dataMB.districtList}" />
</p:selectOneMenu>
<h:outputLabel value="dateFrom" for="dateFrom">
<p:calendar id="dateFrom" mode="popup" readonlyInput="true" value="#{dataMB.dateFrom}" pattern="MM/dd/yyyy" navigator="true">
<p:ajax event="dateSelect" listener="#{dataMB.dateSelectFrom}" update=":dataForm" />
</p:calendar>
</p:panelGrid>
</div>
<div class="ui">
<p:dataTable styleClass="fixed-size" value="#{dataMB.searchResultsList}"
var="searchResultsRow" rows="10" paginator="true" widgetVar="searchResults"
emptyMessage="No results found for search." id="searchResults"
rowKey="#{searchResultsRow.dateFrom}" selection="#{dataMB.selectedData}"
draggableColumns="true" selectionMode="single" >
<p:column
headerText="Date From"
sortBy="#{searchResultsRow.dateFrom}"
filterBy="#{searchResultsRow.dateFrom}"
filterMatchMode="contains" id="dateFromId">
<h:outputText id="dateFrom" value="#{searchResultsRow.dateFrom}">
<f:convertDateTime pattern="MM-dd-yyyy" />
</h:outputText>
</p:column>
</p:dataTable>
</div>
</h:form>
</h:body>
6) Sample bean
public void dateSelectFrom(SelectEvent event) {
}
public void districtSelect(SelectEvent event) {
}
--------------
<p:ajax event="select"
<p:ajax event="itemSelect"
<p:ajax event="valueChange"
<p:ajax event="change"
I have tried these in the xhtml page, But none of them works. No errors in the console
|
non_test
|
listener not being called for the drop down but the listener works for the date functionality listener not being called for the drop down but the listener works for the date functionality environment primefaces version does it work on the newest released primefaces version version no does it work on the newest sources in github build by source no application server version websphere affected browsers all expected behavior the ajax method listener should be called for the district drop down listener datamb districtselect the ajax method listener should be called for the date select actual behavior the ajax method listener is not called for the district drop down the ajax method listener is called for the date select steps to reproduce declare a bean declare a p selectonemenu and a p ajax inside it sample xhtml p datatable styleclass fixed size value datamb searchresultslist var searchresultsrow rows paginator true widgetvar searchresults emptymessage no results found for search id searchresults rowkey searchresultsrow datefrom selection datamb selecteddata draggablecolumns true selectionmode single p column headertext date from sortby searchresultsrow datefrom filterby searchresultsrow datefrom filtermatchmode contains id datefromid sample bean public void dateselectfrom selectevent event public void districtselect selectevent event p ajax event select p ajax event itemselect p ajax event valuechange p ajax event change i have tried these in the xhtml page but none of them works no errors in the console
| 0
|
55,037
| 11,362,582,787
|
IssuesEvent
|
2020-01-26 22:15:11
|
nmrih/source-game
|
https://api.github.com/repos/nmrih/source-game
|
closed
|
[public-1.10.0] MapHack: Can't find certain datadesc fields
|
Priority: Minimal Status: Assigned Type: Code
|
The following snippet fails to run:
```cpp
$edit_field
{
"id" "a" // func_brush
"fieldname" "m_vecMins"
"value" "10 -100 30"
}
```
with warning:
> MapHack WARNING: Couldn't find an entity datadesc field named "m_vecMins" (a)
but the data exists and Sourcemod finds it just fine:
```cpp
int ent = -1;
while ((ent = FindEntityByClassname(ent, "func_brush")) != -1)
{
float min[3];
GetEntPropVector(ent, Prop_Send, "m_vecMins", min);
PrintToServer("m_vecMins: %.1f, %.1f, %.1f" , min[0], min[1], min[2]);
}
```
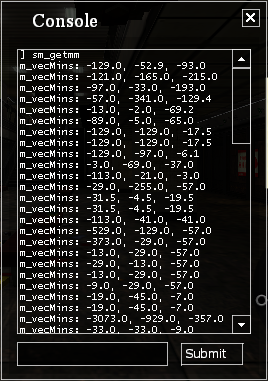
It can also set it successfully.
I don't know if this is a bug, limitation or a user error, to be honest.
|
1.0
|
[public-1.10.0] MapHack: Can't find certain datadesc fields - The following snippet fails to run:
```cpp
$edit_field
{
"id" "a" // func_brush
"fieldname" "m_vecMins"
"value" "10 -100 30"
}
```
with warning:
> MapHack WARNING: Couldn't find an entity datadesc field named "m_vecMins" (a)
but the data exists and Sourcemod finds it just fine:
```cpp
int ent = -1;
while ((ent = FindEntityByClassname(ent, "func_brush")) != -1)
{
float min[3];
GetEntPropVector(ent, Prop_Send, "m_vecMins", min);
PrintToServer("m_vecMins: %.1f, %.1f, %.1f" , min[0], min[1], min[2]);
}
```
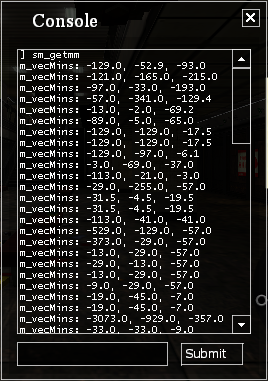
It can also set it successfully.
I don't know if this is a bug, limitation or a user error, to be honest.
|
non_test
|
maphack can t find certain datadesc fields the following snippet fails to run cpp edit field id a func brush fieldname m vecmins value with warning maphack warning couldn t find an entity datadesc field named m vecmins a but the data exists and sourcemod finds it just fine cpp int ent while ent findentitybyclassname ent func brush float min getentpropvector ent prop send m vecmins min printtoserver m vecmins min min min it can also set it successfully i don t know if this is a bug limitation or a user error to be honest
| 0
|
103,547
| 4,175,165,168
|
IssuesEvent
|
2016-06-21 16:01:51
|
rethinkdb/horizon
|
https://api.github.com/repos/rethinkdb/horizon
|
closed
|
Watch regression in Horizon 1.3
|
bug client High priority
|
I have been able to use the `watch()` functionality in Horizon with prior releases but having upgraded yesterday to **1.3** I now am unable to leverage **any** of the "real time" features of Horizon's "watches".
Specifically I have a very simple two table model: "person" and "todo". If I use the web console in either Safari or Chrome and type:
```js
hz = window.Horizon();
hz('person').watch().subscribe(changes => console.log(changes))
```
I would expect to get back the list of changes as they happen in real time. However, while I get back a returned collection object:

followed by two errors:

and immediately following that error is ...

While I understand there is movement-afoot to move away from `engine.io` (it was suggested that this issue might be related to that) ... I would point out the prior releases of Horizon worked just fine with this functionality so I suspect it isn't entirely an `engine.io` issue but rather some sort of introduced regression.
> **Note:** not only did I upgrade to Horizon 1.3 yesterday but I also upgraded the DB to latest ReThink DB
|
1.0
|
Watch regression in Horizon 1.3 - I have been able to use the `watch()` functionality in Horizon with prior releases but having upgraded yesterday to **1.3** I now am unable to leverage **any** of the "real time" features of Horizon's "watches".
Specifically I have a very simple two table model: "person" and "todo". If I use the web console in either Safari or Chrome and type:
```js
hz = window.Horizon();
hz('person').watch().subscribe(changes => console.log(changes))
```
I would expect to get back the list of changes as they happen in real time. However, while I get back a returned collection object:

followed by two errors:

and immediately following that error is ...

While I understand there is movement-afoot to move away from `engine.io` (it was suggested that this issue might be related to that) ... I would point out the prior releases of Horizon worked just fine with this functionality so I suspect it isn't entirely an `engine.io` issue but rather some sort of introduced regression.
> **Note:** not only did I upgrade to Horizon 1.3 yesterday but I also upgraded the DB to latest ReThink DB
|
non_test
|
watch regression in horizon i have been able to use the watch functionality in horizon with prior releases but having upgraded yesterday to i now am unable to leverage any of the real time features of horizon s watches specifically i have a very simple two table model person and todo if i use the web console in either safari or chrome and type js hz window horizon hz person watch subscribe changes console log changes i would expect to get back the list of changes as they happen in real time however while i get back a returned collection object followed by two errors and immediately following that error is while i understand there is movement afoot to move away from engine io it was suggested that this issue might be related to that i would point out the prior releases of horizon worked just fine with this functionality so i suspect it isn t entirely an engine io issue but rather some sort of introduced regression note not only did i upgrade to horizon yesterday but i also upgraded the db to latest rethink db
| 0
|
195,577
| 14,740,807,538
|
IssuesEvent
|
2021-01-07 09:39:35
|
Tencent/bk-ci
|
https://api.github.com/repos/Tencent/bk-ci
|
closed
|
bug:模板勾选推荐版本号后再不勾选保存一个新版本,用这个新版本实例化流水线时还显示推荐版本信息
|
area/ci/backend kind/bug stage/test stage/uat test/passed uat/passed
|
bug:模板勾选推荐版本号后再不勾选保存一个新版本,用这个新版本实例化流水线时还显示推荐版本信息
|
2.0
|
bug:模板勾选推荐版本号后再不勾选保存一个新版本,用这个新版本实例化流水线时还显示推荐版本信息 - bug:模板勾选推荐版本号后再不勾选保存一个新版本,用这个新版本实例化流水线时还显示推荐版本信息
|
test
|
bug 模板勾选推荐版本号后再不勾选保存一个新版本,用这个新版本实例化流水线时还显示推荐版本信息 bug 模板勾选推荐版本号后再不勾选保存一个新版本,用这个新版本实例化流水线时还显示推荐版本信息
| 1
|
312,648
| 26,873,457,843
|
IssuesEvent
|
2023-02-04 19:03:31
|
MPMG-DCC-UFMG/F01
|
https://api.github.com/repos/MPMG-DCC-UFMG/F01
|
closed
|
Teste de generalizacao para a tag Informações Institucionais - Leis Municipais - União de Minas
|
generalization test development template - GRP (27) tag - Informações Institucionais subtag - Leis Municipais
|
DoD: Realizar o teste de Generalização do validador da tag Informações Institucionais - Leis Municipais para o Município de União de Minas.
|
1.0
|
Teste de generalizacao para a tag Informações Institucionais - Leis Municipais - União de Minas - DoD: Realizar o teste de Generalização do validador da tag Informações Institucionais - Leis Municipais para o Município de União de Minas.
|
test
|
teste de generalizacao para a tag informações institucionais leis municipais união de minas dod realizar o teste de generalização do validador da tag informações institucionais leis municipais para o município de união de minas
| 1
|
699,451
| 24,017,411,703
|
IssuesEvent
|
2022-09-15 03:04:07
|
AngelUMICH/Long-Time-Dynamics
|
https://api.github.com/repos/AngelUMICH/Long-Time-Dynamics
|
closed
|
Calculate Energy with Lammps
|
refactoring priority lammps
|
### Details
The lammps total system energy is not always the current system energy. Therefore, a lammps command to compute the system energy must be done everytime OPLD asks for it.
### Definition of Done
- [ ] System energy is done through a lammps compute command
- [ ] System energy calculation is same before and after lammps compute
|
1.0
|
Calculate Energy with Lammps - ### Details
The lammps total system energy is not always the current system energy. Therefore, a lammps command to compute the system energy must be done everytime OPLD asks for it.
### Definition of Done
- [ ] System energy is done through a lammps compute command
- [ ] System energy calculation is same before and after lammps compute
|
non_test
|
calculate energy with lammps details the lammps total system energy is not always the current system energy therefore a lammps command to compute the system energy must be done everytime opld asks for it definition of done system energy is done through a lammps compute command system energy calculation is same before and after lammps compute
| 0
|
749,850
| 26,181,335,520
|
IssuesEvent
|
2023-01-02 16:00:39
|
bounswe/bounswe2022group4
|
https://api.github.com/repos/bounswe/bounswe2022group4
|
closed
|
Backend: Implementation of the Search Functionality for Posts
|
Category - To Do Priority - Medium Status: In Progress Difficulty - Medium Language - Python Team - Backend
|
Description:
In the application, the necessary service will be developed to be able to search posts. "1.2.1.3. The system shall enable users to make an advanced search based on a keyword and/or date and/or location" element in the requirements will be performed. The endpoint I will develop is as follows:
GET /api/search/post?query={input}&count={input}
query parameter will be used to get input from the user and generate a search results according to given query. count parameter will be developed to limit the number of posts in the response returned from the API.
Deadline: 25.12.2022 23.59
|
1.0
|
Backend: Implementation of the Search Functionality for Posts - Description:
In the application, the necessary service will be developed to be able to search posts. "1.2.1.3. The system shall enable users to make an advanced search based on a keyword and/or date and/or location" element in the requirements will be performed. The endpoint I will develop is as follows:
GET /api/search/post?query={input}&count={input}
query parameter will be used to get input from the user and generate a search results according to given query. count parameter will be developed to limit the number of posts in the response returned from the API.
Deadline: 25.12.2022 23.59
|
non_test
|
backend implementation of the search functionality for posts description in the application the necessary service will be developed to be able to search posts the system shall enable users to make an advanced search based on a keyword and or date and or location element in the requirements will be performed the endpoint i will develop is as follows get api search post query input count input query parameter will be used to get input from the user and generate a search results according to given query count parameter will be developed to limit the number of posts in the response returned from the api deadline
| 0
|
320,127
| 23,802,645,307
|
IssuesEvent
|
2022-09-03 14:43:34
|
neovide/neovide
|
https://api.github.com/repos/neovide/neovide
|
closed
|
`g:neovide_cursor_trail_length` option not working with MacOS
|
bug documentation
|
I like Neovide's soft cursor animation. But the way the cursor is stretched is too fancy.
I used the `g:neovide_cursor_trail_length` option, but it doesn't seem to work.
[video capture](https://streamable.com/e/d5471g?autoplay=1)
|
1.0
|
`g:neovide_cursor_trail_length` option not working with MacOS - I like Neovide's soft cursor animation. But the way the cursor is stretched is too fancy.
I used the `g:neovide_cursor_trail_length` option, but it doesn't seem to work.
[video capture](https://streamable.com/e/d5471g?autoplay=1)
|
non_test
|
g neovide cursor trail length option not working with macos i like neovide s soft cursor animation but the way the cursor is stretched is too fancy i used the g neovide cursor trail length option but it doesn t seem to work
| 0
|
65,894
| 6,977,857,493
|
IssuesEvent
|
2017-12-12 15:49:43
|
OpenLiberty/open-liberty
|
https://api.github.com/repos/OpenLiberty/open-liberty
|
opened
|
Test Failure (20171204-1120): junit.framework.TestSuite.com.ibm.ws.jca.fat.derbyra.DerbyResourceAdapterSecurityTest
|
team:Zombie Apocalypse test bug
|
The derbyra bucket is failing in the java 2 security builds with the following:
```[12/4/17 20:36:52:718 UTC] 00000025 com.ibm.ws.webcontainer.webapp E SRVE0315E: An exception occurred: java.lang.Throwable: java.lang.Exception: java.lang.ExceptionInInitializerError
at componenttest.topology.impl.LibertyServer.checkLogsForErrorsAndWarnings(LibertyServer.java:2170)
at componenttest.topology.impl.LibertyServer.stopServer(LibertyServer.java:2058)
at componenttest.topology.impl.LibertyServer.stopServer(LibertyServer.java:1952)
at componenttest.topology.impl.LibertyServer.stopServer(LibertyServer.java:1921)
at com.ibm.ws.jca.fat.derbyra.DerbyResourceAdapterSecurityTest.tearDown(DerbyResourceAdapterSecurityTest.java:76)
at componenttest.custom.junit.runner.FATRunner$2.evaluate(FATRunner.java:316)
at componenttest.custom.junit.runner.FATRunner.run(FATRunner.java:152)
The root cause is: `Caused by: java.security.AccessControlException: Access denied ("javax.management.MBeanServerPermission" "createMBeanServer")`
The Java permissions need to be corrected for this test bucket.
|
1.0
|
Test Failure (20171204-1120): junit.framework.TestSuite.com.ibm.ws.jca.fat.derbyra.DerbyResourceAdapterSecurityTest - The derbyra bucket is failing in the java 2 security builds with the following:
```[12/4/17 20:36:52:718 UTC] 00000025 com.ibm.ws.webcontainer.webapp E SRVE0315E: An exception occurred: java.lang.Throwable: java.lang.Exception: java.lang.ExceptionInInitializerError
at componenttest.topology.impl.LibertyServer.checkLogsForErrorsAndWarnings(LibertyServer.java:2170)
at componenttest.topology.impl.LibertyServer.stopServer(LibertyServer.java:2058)
at componenttest.topology.impl.LibertyServer.stopServer(LibertyServer.java:1952)
at componenttest.topology.impl.LibertyServer.stopServer(LibertyServer.java:1921)
at com.ibm.ws.jca.fat.derbyra.DerbyResourceAdapterSecurityTest.tearDown(DerbyResourceAdapterSecurityTest.java:76)
at componenttest.custom.junit.runner.FATRunner$2.evaluate(FATRunner.java:316)
at componenttest.custom.junit.runner.FATRunner.run(FATRunner.java:152)
The root cause is: `Caused by: java.security.AccessControlException: Access denied ("javax.management.MBeanServerPermission" "createMBeanServer")`
The Java permissions need to be corrected for this test bucket.
|
test
|
test failure junit framework testsuite com ibm ws jca fat derbyra derbyresourceadaptersecuritytest the derbyra bucket is failing in the java security builds with the following com ibm ws webcontainer webapp e an exception occurred java lang throwable java lang exception java lang exceptionininitializererror at componenttest topology impl libertyserver checklogsforerrorsandwarnings libertyserver java at componenttest topology impl libertyserver stopserver libertyserver java at componenttest topology impl libertyserver stopserver libertyserver java at componenttest topology impl libertyserver stopserver libertyserver java at com ibm ws jca fat derbyra derbyresourceadaptersecuritytest teardown derbyresourceadaptersecuritytest java at componenttest custom junit runner fatrunner evaluate fatrunner java at componenttest custom junit runner fatrunner run fatrunner java the root cause is caused by java security accesscontrolexception access denied javax management mbeanserverpermission creatembeanserver the java permissions need to be corrected for this test bucket
| 1
|
326,089
| 27,975,378,969
|
IssuesEvent
|
2023-03-25 14:16:24
|
dudykr/stc
|
https://api.github.com/repos/dudykr/stc
|
opened
|
Fix unit test: `tests/tsc/conformance/types/union/unionTypeConstructSignatures/.1.ts`
|
tsc-unit-test
|
---
Related test: https://github.com/dudykr/stc/blob/main/crates/stc_ts_file_analyzer/tests/tsc/conformance/types/union/unionTypeConstructSignatures/.1.ts
Test file name: `tests/tsc/conformance/types/union/unionTypeConstructSignatures/.1.ts`
---
This issue is created by sync script.
|
1.0
|
Fix unit test: `tests/tsc/conformance/types/union/unionTypeConstructSignatures/.1.ts` -
---
Related test: https://github.com/dudykr/stc/blob/main/crates/stc_ts_file_analyzer/tests/tsc/conformance/types/union/unionTypeConstructSignatures/.1.ts
Test file name: `tests/tsc/conformance/types/union/unionTypeConstructSignatures/.1.ts`
---
This issue is created by sync script.
|
test
|
fix unit test tests tsc conformance types union uniontypeconstructsignatures ts related test test file name tests tsc conformance types union uniontypeconstructsignatures ts this issue is created by sync script
| 1
|
166,877
| 12,974,974,467
|
IssuesEvent
|
2020-07-21 16:14:03
|
elastic/kibana
|
https://api.github.com/repos/elastic/kibana
|
closed
|
[test-failed]: X-Pack API Integration Tests1.x-pack/test/api_integration/apis/fleet/agents/enroll·ts - apis Fleet Endpoints fleet_agents_enroll "before all" hook for "should not allow to enroll an agent with a invalid enrollment"
|
Team:Ingest Management failed-test test-cloud
|
**Version: 7.9.0**
**Class: X-Pack API Integration Tests1.x-pack/test/api_integration/apis/fleet/agents/enroll·ts**
**Stack Trace:**
```
{ ConnectionError: self signed certificate in certificate chain
at ClientRequest.request.on.err (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackExt/TASK/saas_run_kibana_tests/node/linux-immutable/ci/cloud/common/build/kibana/node_modules/@elastic/elasticsearch/lib/Connection.js:107:18)
at TLSSocket.socketErrorListener (_http_client.js:401:9)
at emitErrorNT (internal/streams/destroy.js:91:8)
at emitErrorAndCloseNT (internal/streams/destroy.js:59:3)
at process._tickCallback (internal/process/next_tick.js:63:19)
name: 'ConnectionError',
meta:
{ body: null,
statusCode: null,
headers: null,
warnings: null,
meta:
{ context: null,
request: [Object],
name: 'elasticsearch-js',
connection: [Object],
attempts: 3,
aborted: false } } }
```
_Test Report: https://internal-ci.elastic.co/view/Stack%20Tests/job/elastic+estf-cloud-kibana-tests/495/testReport/_
|
2.0
|
[test-failed]: X-Pack API Integration Tests1.x-pack/test/api_integration/apis/fleet/agents/enroll·ts - apis Fleet Endpoints fleet_agents_enroll "before all" hook for "should not allow to enroll an agent with a invalid enrollment" - **Version: 7.9.0**
**Class: X-Pack API Integration Tests1.x-pack/test/api_integration/apis/fleet/agents/enroll·ts**
**Stack Trace:**
```
{ ConnectionError: self signed certificate in certificate chain
at ClientRequest.request.on.err (/var/lib/jenkins/workspace/elastic+estf-cloud-kibana-tests/JOB/xpackExt/TASK/saas_run_kibana_tests/node/linux-immutable/ci/cloud/common/build/kibana/node_modules/@elastic/elasticsearch/lib/Connection.js:107:18)
at TLSSocket.socketErrorListener (_http_client.js:401:9)
at emitErrorNT (internal/streams/destroy.js:91:8)
at emitErrorAndCloseNT (internal/streams/destroy.js:59:3)
at process._tickCallback (internal/process/next_tick.js:63:19)
name: 'ConnectionError',
meta:
{ body: null,
statusCode: null,
headers: null,
warnings: null,
meta:
{ context: null,
request: [Object],
name: 'elasticsearch-js',
connection: [Object],
attempts: 3,
aborted: false } } }
```
_Test Report: https://internal-ci.elastic.co/view/Stack%20Tests/job/elastic+estf-cloud-kibana-tests/495/testReport/_
|
test
|
x pack api integration x pack test api integration apis fleet agents enroll·ts apis fleet endpoints fleet agents enroll before all hook for should not allow to enroll an agent with a invalid enrollment version class x pack api integration x pack test api integration apis fleet agents enroll·ts stack trace connectionerror self signed certificate in certificate chain at clientrequest request on err var lib jenkins workspace elastic estf cloud kibana tests job xpackext task saas run kibana tests node linux immutable ci cloud common build kibana node modules elastic elasticsearch lib connection js at tlssocket socketerrorlistener http client js at emiterrornt internal streams destroy js at emiterrorandclosent internal streams destroy js at process tickcallback internal process next tick js name connectionerror meta body null statuscode null headers null warnings null meta context null request name elasticsearch js connection attempts aborted false test report
| 1
|
269,153
| 23,424,245,893
|
IssuesEvent
|
2022-08-14 06:19:46
|
Instagram-Clone-Coding/Spring_instagram-clone
|
https://api.github.com/repos/Instagram-Clone-Coding/Spring_instagram-clone
|
closed
|
story 도메인 테스트 코드 작성
|
🔍test
|
<!--
✅ 어떤 기능인지 구체적으로 설명해주세요.
-->
## Feature Description
- MemberStoryRedisRepository 테스트 코드 작성
- 현재 story 도메인 개발이 제대로 되지 않은 상태. 완성된 부분만 테스트 코드를 작성할 예정
<!--
✅ 개발이 필요한 기능을 요약해주세요.
-->
## Todo list
- [x] `List<MemberStory> findAllByMemberId(Long memberId)`
<!--
✅ Label을 설정하였는지 확인해주세요.
✅ Assignee를 지정하였는지 확인해주세요.
-->
|
1.0
|
story 도메인 테스트 코드 작성 - <!--
✅ 어떤 기능인지 구체적으로 설명해주세요.
-->
## Feature Description
- MemberStoryRedisRepository 테스트 코드 작성
- 현재 story 도메인 개발이 제대로 되지 않은 상태. 완성된 부분만 테스트 코드를 작성할 예정
<!--
✅ 개발이 필요한 기능을 요약해주세요.
-->
## Todo list
- [x] `List<MemberStory> findAllByMemberId(Long memberId)`
<!--
✅ Label을 설정하였는지 확인해주세요.
✅ Assignee를 지정하였는지 확인해주세요.
-->
|
test
|
story 도메인 테스트 코드 작성 ✅ 어떤 기능인지 구체적으로 설명해주세요 feature description memberstoryredisrepository 테스트 코드 작성 현재 story 도메인 개발이 제대로 되지 않은 상태 완성된 부분만 테스트 코드를 작성할 예정 ✅ 개발이 필요한 기능을 요약해주세요 todo list list findallbymemberid long memberid ✅ label을 설정하였는지 확인해주세요 ✅ assignee를 지정하였는지 확인해주세요
| 1
|
572,112
| 17,023,418,810
|
IssuesEvent
|
2021-07-03 01:55:54
|
tomhughes/trac-tickets
|
https://api.github.com/repos/tomhughes/trac-tickets
|
closed
|
unclassified with ref
|
Component: mapnik Priority: major Resolution: fixed Type: enhancement
|
**[Submitted to the original trac issue database at 12.40pm, Saturday, 6th June 2009]**
In Germany, some district roads are narrower than 4 metres, but they have an official reference number. So it would be a nice idea to show unclassified roads together with their official ref number, if they have one.
|
1.0
|
unclassified with ref - **[Submitted to the original trac issue database at 12.40pm, Saturday, 6th June 2009]**
In Germany, some district roads are narrower than 4 metres, but they have an official reference number. So it would be a nice idea to show unclassified roads together with their official ref number, if they have one.
|
non_test
|
unclassified with ref in germany some district roads are narrower than metres but they have an official reference number so it would be a nice idea to show unclassified roads together with their official ref number if they have one
| 0
|
34,308
| 2,776,945,504
|
IssuesEvent
|
2015-05-05 02:09:10
|
reminisceme/app
|
https://api.github.com/repos/reminisceme/app
|
closed
|
Refactor PlayGame
|
client priority-low refactoring
|
_From @romac on December 4, 2014 15:21_
_Copied from original issue: reminisceme/webapp#20_
|
1.0
|
Refactor PlayGame - _From @romac on December 4, 2014 15:21_
_Copied from original issue: reminisceme/webapp#20_
|
non_test
|
refactor playgame from romac on december copied from original issue reminisceme webapp
| 0
|
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.