id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,884,324 | 7-kaliber" refererer typisk til | Forskellige skydevåben er designet til at rumme specifikke kalibre, og brug af den forkerte kaliber... | 0 | 2024-06-11T11:24:01 | https://dev.to/cskeisari665/7-kaliber-refererer-typisk-til-mb0 | Forskellige skydevåben er designet til at rumme specifikke kalibre, og brug af den forkerte kaliber ammunition kan være farligt, hvilket kan føre til funktionsfejl, beskadigelse af skydevåbnet eller endda personskade. Derfor er det vigtigt for våbenejere at forstå og overholde de korrekte kaliberspecifikationer for der... | cskeisari665 | |
1,884,323 | Exploring Web Hosting: Types and Essential Details | Having a website requires a hosting service to store your website’s data and make it accessible... | 0 | 2024-06-11T11:23:48 | https://dev.to/wewphosting/exploring-web-hosting-types-and-essential-details-578c |

Having a website requires a hosting service to store your website’s data and make it accessible online. Here’s a breakdown of popular options:
- **Shared Hosting**: Affordable for low-traffic websites (blogs, smal... | wewphosting | |
1,884,300 | IOS captive portal | Hi all, I wonder if someone could help. I have 2 iPhones, one with 17.4.1 and another 14.7.1. I am... | 0 | 2024-06-11T11:17:54 | https://dev.to/mike_dodbiba_55a987925a78/ios-captive-portal-213f | help | Hi all,
I wonder if someone could help.
I have 2 iPhones, one with 17.4.1 and another 14.7.1.
I am connecting both of them on a hotspot.
In that hotspot i am blocking captive.apple.com for 5 sec after user authentication, so the done/ok button not to appear straight away.
The user ends up in a landing page that has a ... | mike_dodbiba_55a987925a78 |
1,884,299 | Web Hosting vs WordPress Hosting: Unraveling the Variances | Having a website requires it to be stored on a server, just like a store needs a physical location.... | 0 | 2024-06-11T11:16:21 | https://dev.to/wewphosting/web-hosting-vs-wordpress-hosting-unraveling-the-variances-2ncb |
Having a website requires it to be stored on a server, just like a store needs a physical location. This is where web hosting comes in. Web hosting providers rent out space on their servers to store your website’s ... | wewphosting | |
1,884,298 | Step-by-Step Guide To Install OpenCV For Python | OpenCV is an open-source computer vision library that provides a comprehensive set of tools for image... | 0 | 2024-06-11T11:16:12 | https://dev.to/codetradeindia/step-by-step-guide-to-install-opencv-for-python-91m | opencv, python, aiandml, computervision | OpenCV is an open-source **[computer vision](https://www.codetrade.io/blog/essential-value-of-computer-vision-in-a-digital-world/)** library that provides a comprehensive set of tools for image processing, video analysis, and machine learning.
It is written in C++ and Python, and available for a variety of platforms,... | codetradeindia |
1,884,296 | Free API Testing Tools: A Comprehensive Guide | API testing is a crucial aspect of modern software development, ensuring that applications... | 0 | 2024-06-11T11:15:10 | https://dev.to/keploy/free-api-testing-tools-a-comprehensive-guide-3fm0 | api, testing, webdev, devops |
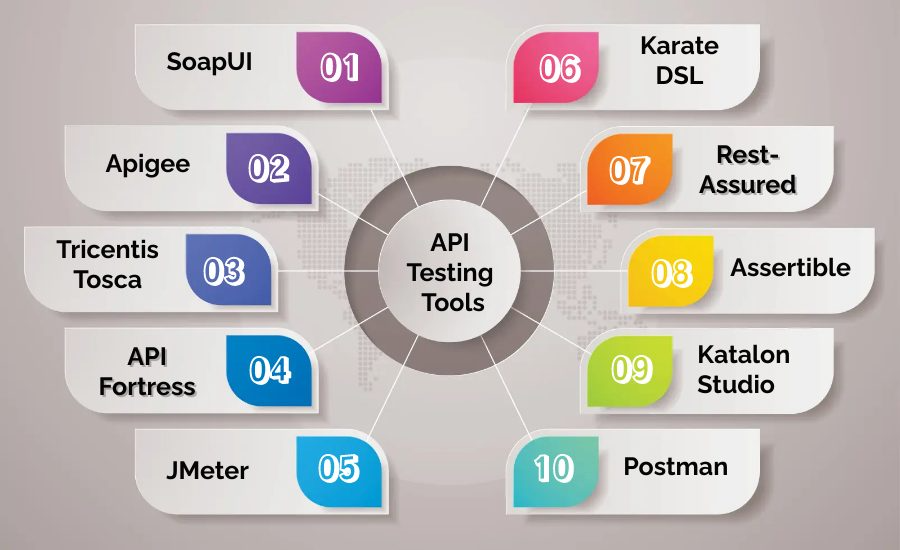
API testing is a crucial aspect of modern software development, ensuring that applications communicate correctly, securely, and efficiently. While there are many paid tools available, several high-quality free tools... | keploy |
1,884,295 | Inland Tek Inc: IT Services and IT Consulting San Dimas United States | InlandTek's Simple and Fast Workflow for Customer Onboarding InlandTek has the experience and... | 0 | 2024-06-11T11:14:00 | https://dev.to/digitalimple/inland-tek-inc-it-services-and-it-consulting-san-dimas-united-states-54ln | webdev, devops, design, mobile | **InlandTek's Simple and Fast Workflow for Customer Onboarding**
[InlandTek](https://inlandtek.com/) has the experience and versatility to take on any online project. We’ve been at the forefront of the internet and technology industries, successfully developing thousands of digital solutions for startups and medium si... | digitalimple |
1,884,294 | How much UB is in my compiler? | C and C++ developers have two bug-related headaches: memory leaks and undefined behavior. As you can... | 0 | 2024-06-11T11:13:33 | https://dev.to/anogneva/how-much-ub-is-in-my-compiler-4gkc | cpp, programming | C and C\+\+ developers have two bug\-related headaches: memory leaks and undefined behavior\. As you can guess, I'll talk about undefined behavior—and about "my" compiler\. To be more precise, I'll talk about the set of compilers and the tools to develop them, the one called LLVM\. Why did I say "my" compiler? Our team... | anogneva |
1,884,293 | #CodePenChallenge: Smooth Scrolling | Check out this Pen I made! | 0 | 2024-06-11T11:12:07 | https://dev.to/gafar27/codepenchallenge-smooth-scrolling-57f6 | codepen | Check out this Pen I made!
{% codepen https://codepen.io/vii120/pen/dyEWaNR %} | gafar27 |
1,884,291 | Brendon Pack | 1-800Accountant Announces Strategic Partnership With BizFilings | 1-800Accountant, one of the nation's largest virtual accounting firms servicing over 200,000 small... | 0 | 2024-06-11T11:12:05 | https://dev.to/brendonpack/brendon-pack-1-800accountant-announces-strategic-partnership-with-bizfilings-278h | 1-800Accountant, one of the nation's largest virtual accounting firms servicing over 200,000 small and medium-sized businesses, recently announced an innovative new partnership with BizFilings, the full-service legal and business partner for small businesses.
Clients can take advantage of 1-800Accountant’s expert tax... | brendonpack | |
1,884,289 | Brendon Pack | 1-800Accountant Announces Strategic Partnership With BetterLegal | 1-800Accountant, the nation's leading virtual accounting firm servicing over 200,000 small and... | 0 | 2024-06-11T11:11:24 | https://dev.to/brendonpack/brendon-pack-1-800accountant-announces-strategic-partnership-with-betterlegal-21h3 | 1-800Accountant, the nation's leading virtual accounting firm servicing over 200,000 small and medium-sized businesses, announced a new strategic partnership with BetterLegal.
This innovative partnership gives BetterLegal's clients access to 1-800Accountant's award-winning accounting services. Through this partnershi... | brendonpack | |
1,884,288 | Call for Authors: Paid Collaboration on Oracle Testing | Are you an expert in Oracle technologies with a talent for writing? We're seeking skilled authors to... | 0 | 2024-06-11T11:10:42 | https://dev.to/kateryna_gandzeichuk_3dcb/call-for-authors-paid-collaboration-on-oracle-testing-2n82 | Are you an expert in Oracle technologies with a talent for writing? We're seeking skilled authors to create high-quality content focused on Oracle testing.
This is a paid opportunity to share your expertise with a wider audience.
If you're interested, send an email to shiftsync@tricentis.com
| kateryna_gandzeichuk_3dcb | |
1,884,287 | Brendon Pack | Podcast – Sue Tse – Quick Cash – Pros & Cons in Using a Business Credit Card | Interview with Tax Expert Sue Tse It’s no secret that cash flow is what keeps a business running.... | 0 | 2024-06-11T11:10:22 | https://dev.to/brendonpack/brendon-pack-podcast-sue-tse-quick-cash-pros-cons-in-using-a-business-credit-card-5i9 | Interview with Tax Expert Sue Tse
It’s no secret that cash flow is what keeps a business running. Ideally, businesses will have enough money coming in to keep the wheels turning. But that doesn’t always happen. When revenues and expenses don’t quite line up, like economic difficulties or when a business opportunity ar... | brendonpack | |
1,884,286 | Buy Negative Google Reviews | https://dmhelpshop.com/product/buy-negative-google-reviews/ Buy Negative Google Reviews Negative... | 0 | 2024-06-11T11:08:38 | https://dev.to/jiyej67470/buy-negative-google-reviews-4p8 | machinelearning, node, aws, career | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-negative-google-reviews/\n\n\n\n\nBuy Negative Google Reviews\nNegative reviews on Google are detrimental critiques that expose customers’ unfavorable experiences with a business. These reviews can significantly damage a company’s reputation, presenting challenges in both attracting new customers and retaining current ones. If you are considering purchasing negative Google reviews from dmhelpshop.com, we encourage you to reconsider and instead focus on providing exceptional products and services to ensure positive feedback and sustainable success.\n\nWhy Buy Negative Google Reviews from dmhelpshop\nWe take pride in our fully qualified, hardworking, and experienced team, who are committed to providing quality and safe services that meet all your needs. Our professional team ensures that you can trust us completely, knowing that your satisfaction is our top priority. With us, you can rest assured that you’re in good hands.\n\nIs Buy Negative Google Reviews safe?\nAt dmhelpshop, we understand the concern many business persons have about the safety of purchasing Buy negative Google reviews. We are here to guide you through a process that sheds light on the importance of these reviews and how we ensure they appear realistic and safe for your business. Our team of qualified and experienced computer experts has successfully handled similar cases before, and we are committed to providing a solution tailored to your specific needs. Contact us today to learn more about how we can help your business thrive.\n\nBuy Google 5 Star Reviews\nReviews represent the opinions of experienced customers who have utilized services or purchased products from various online or offline markets. These reviews convey customer demands and opinions, and ratings are assigned based on the quality of the products or services and the overall user experience. Google serves as an excellent platform for customers to leave reviews since the majority of users engage with it organically. When you purchase Buy Google 5 Star Reviews, you have the potential to influence a large number of people either positively or negatively. Positive reviews can attract customers to purchase your products, while negative reviews can deter potential customers.\n\nIf you choose to Buy Google 5 Star Reviews, people will be more inclined to consider your products. However, it is important to recognize that reviews can have both positive and negative impacts on your business. Therefore, take the time to determine which type of reviews you wish to acquire. Our experience indicates that purchasing Buy Google 5 Star Reviews can engage and connect you with a wide audience. By purchasing positive reviews, you can enhance your business profile and attract online traffic. Additionally, it is advisable to seek reviews from reputable platforms, including social media, to maintain a positive flow. We are an experienced and reliable service provider, highly knowledgeable about the impacts of reviews. Hence, we recommend purchasing verified Google reviews and ensuring their stability and non-gropability.\n\nLet us now briefly examine the direct and indirect benefits of reviews:\nReviews have the power to enhance your business profile, influencing users at an affordable cost.\nTo attract customers, consider purchasing only positive reviews, while negative reviews can be acquired to undermine your competitors. Collect negative reports on your opponents and present them as evidence.\nIf you receive negative reviews, view them as an opportunity to understand user reactions, make improvements to your products and services, and keep up with current trends.\nBy earning the trust and loyalty of customers, you can control the market value of your products. Therefore, it is essential to buy online reviews, including Buy Google 5 Star Reviews.\nReviews serve as the captivating fragrance that entices previous customers to return repeatedly.\nPositive customer opinions expressed through reviews can help you expand your business globally and achieve profitability and credibility.\nWhen you purchase positive Buy Google 5 Star Reviews, they effectively communicate the history of your company or the quality of your individual products.\nReviews act as a collective voice representing potential customers, boosting your business to amazing heights.\nNow, let’s delve into a comprehensive understanding of reviews and how they function:\nGoogle, with its significant organic user base, stands out as the premier platform for customers to leave reviews. When you purchase Buy Google 5 Star Reviews , you have the power to positively influence a vast number of individuals. Reviews are essentially written submissions by users that provide detailed insights into a company, its products, services, and other relevant aspects based on their personal experiences. In today’s business landscape, it is crucial for every business owner to consider buying verified Buy Google 5 Star Reviews, both positive and negative, in order to reap various benefits.\n\nWhy are Google reviews considered the best tool to attract customers?\nGoogle, being the leading search engine and the largest source of potential and organic customers, is highly valued by business owners. Many business owners choose to purchase Google reviews to enhance their business profiles and also sell them to third parties. Without reviews, it is challenging to reach a large customer base globally or locally. Therefore, it is crucial to consider buying positive Buy Google 5 Star Reviews from reliable sources. When you invest in Buy Google 5 Star Reviews for your business, you can expect a significant influx of potential customers, as these reviews act as a pheromone, attracting audiences towards your products and services. Every business owner aims to maximize sales and attract a substantial customer base, and purchasing Buy Google 5 Star Reviews is a strategic move.\n\nAccording to online business analysts and economists, trust and affection are the essential factors that determine whether people will work with you or do business with you. However, there are additional crucial factors to consider, such as establishing effective communication systems, providing 24/7 customer support, and maintaining product quality to engage online audiences. If any of these rules are broken, it can lead to a negative impact on your business. Therefore, obtaining positive reviews is vital for the success of an online business\n\nWhat are the benefits of purchasing reviews online?\nIn today’s fast-paced world, the impact of new technologies and IT sectors is remarkable. Compared to the past, conducting business has become significantly easier, but it is also highly competitive. To reach a global customer base, businesses must increase their presence on social media platforms as they provide the easiest way to generate organic traffic. Numerous surveys have shown that the majority of online buyers carefully read customer opinions and reviews before making purchase decisions. In fact, the percentage of customers who rely on these reviews is close to 97%. Considering these statistics, it becomes evident why we recommend buying reviews online. In an increasingly rule-based world, it is essential to take effective steps to ensure a smooth online business journey.\n\nBuy Google 5 Star Reviews\nMany people purchase reviews online from various sources and witness unique progress. Reviews serve as powerful tools to instill customer trust, influence their decision-making, and bring positive vibes to your business. Making a single mistake in this regard can lead to a significant collapse of your business. Therefore, it is crucial to focus on improving product quality, quantity, communication networks, facilities, and providing the utmost support to your customers.\n\nReviews reflect customer demands, opinions, and ratings based on their experiences with your products or services. If you purchase Buy Google 5-star reviews, it will undoubtedly attract more people to consider your offerings. Google is the ideal platform for customers to leave reviews due to its extensive organic user involvement. Therefore, investing in Buy Google 5 Star Reviews can significantly influence a large number of people in a positive way.\n\nHow to generate google reviews on my business profile?\nFocus on delivering high-quality customer service in every interaction with your customers. By creating positive experiences for them, you increase the likelihood of receiving reviews. These reviews will not only help to build loyalty among your customers but also encourage them to spread the word about your exceptional service. It is crucial to strive to meet customer needs and exceed their expectations in order to elicit positive feedback. If you are interested in purchasing affordable Google reviews, we offer that service.\n\n\n\n\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | jiyej67470 |
1,884,285 | MY PROGRAMMING JOURNEY | Hello everyone,I’m James emeka and I’ll be sharing with you my experiences as a Tech student learning... | 0 | 2024-06-11T11:08:11 | https://dev.to/james_emeka/my-programming-journey-2619 | webdev, programming, css, html |
Hello everyone,I’m James emeka and I’ll be sharing with you my experiences as a Tech student learning programming.
First of,I never knew anything about programming not until 2021 when I gained admission into the university to study computer science but before then I always admire sci-fi movies,advanced artificial robo... | james_emeka |
1,890,195 | How to Create a Calculator Shortcut on the Windows 11? | The calculator is one of the most unique devices ever created by humans. We rely on calculators... | 0 | 2024-06-18T04:54:25 | https://winsides.com/create-calculator-shortcut-windows-11-desktop/ | desktopshortcuts, calculator, shortcuts, winsides | ---
title: How to Create a Calculator Shortcut on the Windows 11?
published: true
date: 2024-06-11 11:08:00 UTC
tags: DesktopShortcuts,Calculator,Shortcuts,winsides
canonical_url: https://winsides.com/create-calculator-shortcut-windows-11-desktop/
cover_image: https://winsides.com/wp-content/uploads/2024/06/Create-Calc... | vigneshwaran_vijayakumar |
1,884,405 | Performing SQL query on MySQL server | Hey everyone, In this blog we are going to see how you can create API Endpoints that perform SQL... | 0 | 2024-06-18T06:36:38 | https://blog.elest.io/n8n/ | elestio, sql, mysql | ---
title: Performing SQL query on MySQL server
published: true
date: 2024-06-11 11:00:42 UTC
tags: Elestio, SQL, MySQL
canonical_url: https://blog.elest.io/n8n/
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/np5mnseeeqlljxtctdr9.png
---
Hey everyone, In this blog we are going to see how you can... | kaiwalyakoparkar |
1,884,282 | Observability 101: A Beginner's Journey Free of Print Statements. | Abandon your Print statements and embark on a long journey to master Observability. 🚫 No More Print... | 0 | 2024-06-11T11:00:31 | https://dev.to/cloudnative_eng/observability-101-a-beginners-journey-free-of-print-statements-3lb2 | monitoring, programming, devops, beginners | Abandon your Print statements and embark on a long journey to master Observability.
- 🚫 No More Print Statements: Avoid using print statements (a poor's man tool); instead, use structured logs, metrics, and traces.
- 🔍 Key Tools: Use logs for events, metrics for counts, traces for durations, and debuggers for state ... | cloudnative_eng |
1,884,281 | DevOps Fundamentals : Harnessing the Power of Collaboration and Automation | Introduction 📍 In today's fast-paced tech world, organizations aim to deliver software... | 0 | 2024-06-11T10:59:05 | https://dev.to/pateldeep34/devops-fundamentals-harnessing-the-power-of-collaboration-and-automation-4888 | devops, sdlc, agile | ## **Introduction** 📍
In today's fast-paced tech world, organizations aim to deliver software quickly, with better quality, and reliability. DevOps bridges the gap between development and operations, transforming the software development and deployment process.
In this blog post, we'll cover the basics of DevOps, i... | pateldeep34 |
1,884,273 | Scifi Scroll UI | Just a concept for a scroll to top option. The JS is just for the numbers and the fading. You could... | 0 | 2024-06-11T10:54:03 | https://dev.to/gafar27/scifi-scroll-ui-4k17 | codepen | Just a concept for a scroll to top option. The JS is just for the numbers and the fading. You could keep it pure CSS too.
{% codepen https://codepen.io/Juxtopposed/pen/yLWbKya %} | gafar27 |
1,884,272 | The Guide To Parallel Testing | Automation entails boosting testability, but there is a roadblock in the path. The frequency of the... | 0 | 2024-06-11T10:51:40 | https://dev.to/jamescantor38/the-guide-to-parallel-testing-5a4h | paralleltesting, testgrid | Automation entails boosting testability, but there is a roadblock in the path. The frequency of the massive amount of tests and the lack of time to test the features make traditional sequential automated testing insufficient.
As a result, the need for parallel testing arises. Yet, some people are reluctant to adopt par... | jamescantor38 |
1,884,271 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-06-11T10:51:14 | https://dev.to/jiyej67470/buy-verified-cash-app-account-3ab9 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com" | jiyej67470 |
1,884,269 | Apple iOS 18 Unveiled: Discover the Latest Game-Changing Features from Apple #WWDC24 | Apple has just released the highly anticipated iOS 18, and the latest update is packed with... | 0 | 2024-06-11T10:50:45 | https://dev.to/asharfdevv/apple-ios-18-unveiled-discover-the-latest-game-changing-features-from-apple-wwdc24-d7i | discuss, techtalks, tutorial, productivity | Apple has just released the highly anticipated iOS 18, and the latest update is packed with groundbreaking features that are set to revolutionize your iPhone experience. Unveiled at the #WWDC24, iOS 18 introduces a range of functionalities designed to enhance connectivity, customization, and user control. Here’s a rund... | asharfdevv |
1,884,268 | internship for cse students | Kaashiv Infotech, a renowned IT solutions provider, offers specialized internships tailored for... | 0 | 2024-06-11T10:46:34 | https://dev.to/cse-students/internship-for-cse-students-5epe | Kaashiv Infotech, a renowned IT solutions provider, offers specialized internships tailored for [internship for cse students](https://www.kaashivinfotech.com/internship-for-cse-students/). Renowned for its excellence, Kaashiv provides hands-on experience in cutting-edge technologies like AI, machine learning, cybersecu... | cse-students | |
1,884,265 | Is there any option for Mock EncryptAsync() in Azure.Security.KeyVault.Keys.Cryptography | I am trying to mock the functionality of the EncryptAsync method in... | 0 | 2024-06-11T10:45:40 | https://dev.to/manu_vr/how-to-mock-encryptasync-in-azuresecuritykeyvaultkeyscryptography-16kg | azure, keyvault, dotnetcore, mock | I am trying to mock the functionality of the EncryptAsync method in Azure.Security.KeyVault.Keys.Cryptography.CryptographyClient.
This is the method I am trying to cover in my unit test.
```
public KeyVaultClientWrapper(KeyClient keyClient, SecretClient secretClient, CryptographyClient cryptographyClient)
... | manu_vr |
1,884,264 | Teen Patti Master Download- Why it is called the best card game | Welcome to the world of Teen Patti, the Indian edition of the famous rummy card game. Teen Patti... | 0 | 2024-06-11T10:45:40 | https://dev.to/monu_singh_9485c943e09eb7/teen-patti-master-download-why-it-is-called-the-best-card-game-2jep | tutorial, programming, opensource, node | Welcome to the world of Teen Patti, the Indian edition of the famous rummy card game. [Teen Patti Master](https://masterteenpattidownload.com.in/) is the ultimate app that gives players a platform to play Teen Patti and different types of card games like Andar Bahar, rummy slots, Dragon vs. Tiger, Up and Down, blackjac... | monu_singh_9485c943e09eb7 |
1,884,263 | CAS No.: 52-51-7 in Pharmaceutical Applications | CAS No: 52-51-7 – A Wonder Molecule for Safe and Effective Pharmaceutical Applications Regarding... | 0 | 2024-06-11T10:43:32 | https://dev.to/fjsmwe_mdjene_9db878e6b49/cas-no-52-51-7-in-pharmaceutical-applications-5pb | design | CAS No: 52-51-7 – A Wonder Molecule for Safe and Effective Pharmaceutical Applications
Regarding applications that are pharmaceutical there is one molecule that stands out from the crowd – CAS NO.:52-51-7. This wonder molecule has become the favorite of medical professionals and patients alike, because of its numerous... | fjsmwe_mdjene_9db878e6b49 |
1,884,260 | Responsive Dashboard with Sliders and Music Player | This pen has a responsive dashboard with sliders and a built-in music player. With the music player,... | 0 | 2024-06-11T10:42:23 | https://dev.to/gafar27/responsive-dashboard-with-sliders-and-music-player-1m59 | codepen | This pen has a responsive dashboard with sliders and a built-in music player. With the music player, you can easily skip songs or play them on a loop. Plus, each song comes with its album cover, and there's a record player effect with a rotating animation. And when you explore the artists, albums, and songs sections, e... | gafar27 |
1,884,259 | Why Become a Full-Stack Developer? | The role of a full-stack developer has gained significant prominence in the tech industry over recent... | 0 | 2024-06-11T10:41:53 | https://dev.to/klimd1389/why-become-a-full-stack-developer-20kp | webdev, programming, fullstack, productivity | The role of a full-stack developer has gained significant prominence in the tech industry over recent years. This multifaceted position involves working on both the front-end and back-end of web applications, offering a comprehensive skill set highly valued in today's digital landscape. But why is becoming a full-stack... | klimd1389 |
1,884,257 | ASE Technologies | At ASE Technologies, we're more than just a digital marketing agency; we're your dedicated partner in... | 0 | 2024-06-11T10:40:54 | https://dev.to/ase_tech_d5dd82beb016c854/ase-technologies-1f15 | At ASE Technologies, we're more than just a digital marketing agency; we're your dedicated partner in achieving online excellence.
With a team of seasoned professionals, cutting-edge technologies, and a passion for innovation, we're here to propel your brand to new heights in the digital realm
Do follow [](https://... | ase_tech_d5dd82beb016c854 | |
1,884,256 | Effortless Global Trade: Unleashing the Power of Customs Clearance Software | In the intricate realm of global commerce, navigating customs regulations can be a daunting task.... | 0 | 2024-06-11T10:39:49 | https://dev.to/john_hall/effortless-global-trade-unleashing-the-power-of-customs-clearance-software-4ga4 | ai, learning, blockchain, logistics | In the intricate realm of global commerce, navigating customs regulations can be a daunting task. Enter customs clearance software: the ultimate solution to streamline operations and ensure seamless compliance.
Who Benefits from Customs Clearance Software?
**Businesses:**
- Retailers, Manufacturers, and Wholesalers: ... | john_hall |
1,884,255 | Project of deploying simple cloud infrastructure as code with Aws Cloudformation. | Project objective: To deploy a basic cloud infrastructure as a code on Aws based on specification... | 0 | 2024-06-11T10:39:08 | https://dev.to/mantizo_dedon_c5190cdc65/project-of-deploying-simple-cloud-infrastructure-as-code-with-aws-cloudformation-18ob | aws, development, cloud, coding | **Project objective:**
- To deploy a basic cloud infrastructure as a code on Aws based on specification defined in the Cloudformation template.
- This infrastructure will be provisioned automatically, hence reduced manual intervention and ensuring consistency across deployment process.
**What is AWS CloudFormation?... | mantizo_dedon_c5190cdc65 |
1,884,254 | LeetCode Problem 217: Contains Duplicate | Checking for Duplicate Elements in an Array Let's solve the problem step-by-step,... | 0 | 2024-06-11T10:38:53 | https://dev.to/aditya210399/leetcode-problem-217-contains-duplicate-491b |
### Checking for Duplicate Elements in an Array
Let's solve the problem step-by-step, providing a detailed explanation, code implementation, and complexity analysis.
---
### Problem Statement
Given an integer array `nums`, return `true` if any value appears at least twice in the array, and return `false` if every ... | aditya210399 | |
1,884,253 | How to Develop and Monetize a Health Tech Startup | The health tech industry has been experiencing a tremendous surge in growth, driven by technological... | 0 | 2024-06-11T10:37:49 | https://dev.to/sofiamurphy/how-to-develop-and-monetize-a-health-tech-startup-36ca | healthcare, healthtech, startup | The health tech industry has been experiencing a tremendous surge in growth, driven by technological advancements and an increasing demand for better healthcare solutions. Health tech startups play a crucial role in this evolution, offering innovative products and services that can revolutionize patient care, improve m... | sofiamurphy |
1,884,251 | How drawing a chess board became my greatest coding lesson | his blog was originally published on Substack. Subscribe to ‘Letters to New Coders’ to receive free... | 0 | 2024-06-11T10:35:16 | https://dev.to/fahimulhaq/how-drawing-a-chess-board-became-my-greatest-coding-lesson-48c8 | webdev, programming, productivity, opensource | his blog was originally published on Substack. Subscribe to ‘Letters to New Coders’ to receive free weekly posts.
Within a few weeks of starting my university computer science program, I hit a pretty demoralizing “coder’s block.”
This hiccup was agonizing at the time — but ended up giving me one of the biggest lesson... | fahimulhaq |
1,884,250 | interview qs | JSON Questions - https://www.geeksforgeeks.org/json-interview-questions/ | 0 | 2024-06-11T10:34:30 | https://dev.to/shivam_sahu_704d021337aec/interview-qs-3h0j | JSON Questions - https://www.geeksforgeeks.org/json-interview-questions/ | shivam_sahu_704d021337aec | |
1,884,248 | Safety Measures for Handling CAS No.: 225708-80-6 | screenshot-1717828461843.png Safe Handling Measures for CAS No.: 225708-80-6 Introductory CAS No.:... | 0 | 2024-06-11T10:30:49 | https://dev.to/fjsmwe_mdjene_9db878e6b49/safety-measures-for-handling-cas-no-225708-80-6-39e5 | design |
screenshot-1717828461843.png
Safe Handling Measures for CAS No.: 225708-80-6
Introductory
CAS No.: 225708-80-6 is a chemical compound that is widely used in various industries, including pharmaceuticals, agrochemicals, and specialty chemicals. It is an innovative compound that offers numerous advantages over oth... | fjsmwe_mdjene_9db878e6b49 |
1,884,247 | 50 Powerful Personal Development Affirmations to Transform Your Life | Image description Embarking on a journey of personal development is a profound way to enhance every... | 0 | 2024-06-11T10:30:34 | https://dev.to/michel_johnson_dcedd0e144/50-powerful-personal-development-affirmations-to-transform-your-life-pnf | [Image description](https://dev-to-uploads.s3.amazonaws.com/uploads/articles/kkkuuw9imx6z914itq2v.jpg)
Embarking on a journey of personal development is a profound way to enhance every aspect of your life. Affirmations are a simple, yet powerful tool to help rewire our brains, encouraging positive thinking and self-emp... | michel_johnson_dcedd0e144 | |
1,884,246 | What is the best solution in face liveness detection SDK?? | The answer is simple: That is MiniAiLive!!! This solution got almost 500 stars for face liveness... | 0 | 2024-06-11T10:30:30 | https://dev.to/miniailive/what-is-the-best-solution-in-face-liveness-detection-sdk-a3i | webdev, androiddev, ai, android | - The answer is simple: That is **MiniAiLive**!!!
- This solution got almost 500 stars for face liveness detection androidSDK in GitHub.
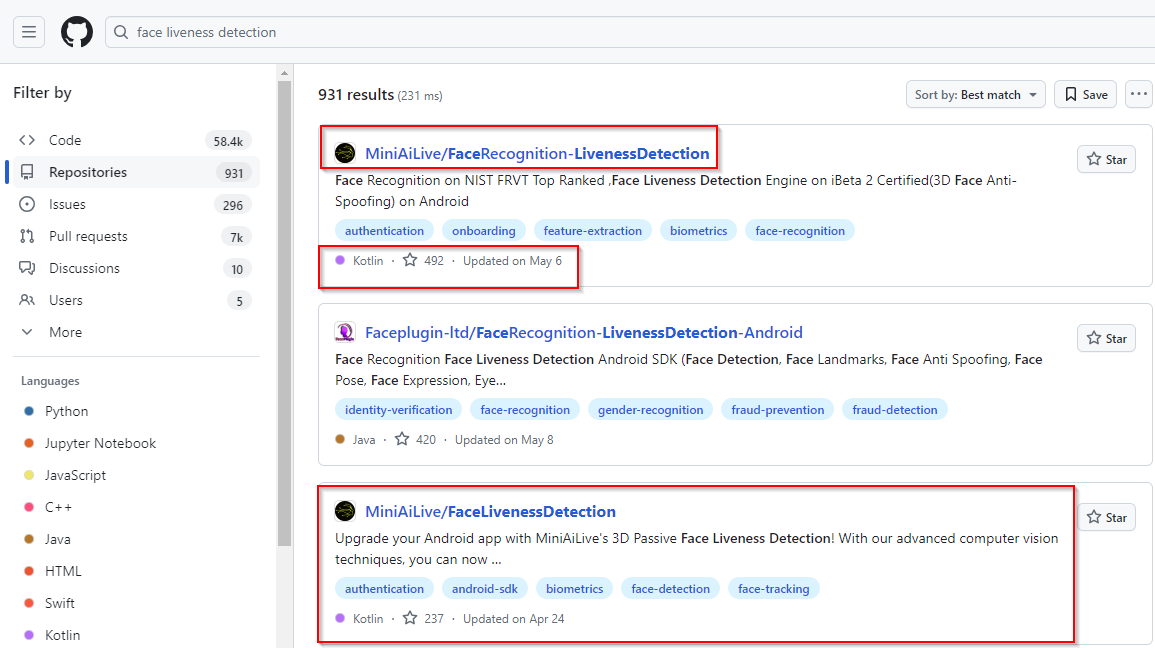
Please test this wonderful solution and give us stars!!
Thank you in advance. | miniailive |
1,884,245 | Cheese Cubism | Voronoi diagrams create the pattern on the cheese cube, which sits on a reflective presentation plate... | 0 | 2024-06-11T10:29:41 | https://dev.to/gafar27/cheese-cubism-4lc4 | codepen | Voronoi diagrams create the pattern on the cheese cube, which sits on a reflective presentation plate under a glass bell. Two octahedrons rotated against each other with their tips cut off by a plane form the handle of the glass bell.
{% codepen https://codepen.io/atzedent/pen/rNgLMaW %} | gafar27 |
1,884,234 | Advanced Time-Series & Python Libraries | Advanced Time-Series: Types, Methods, Applications and Top 20 Python Libraries 📈 Advanced time... | 0 | 2024-06-11T10:19:02 | https://dev.to/mursalfk/advanced-time-series-python-libraries-cd8 | python, programming, datascience, machinelearning | Advanced Time-Series: Types, Methods, Applications and Top 20 Python Libraries 📈
Advanced time series forecasting involves using machine learning, and deep learning techniques to predict future values of time-dependent data, accounting for complex patterns and seasonality, trends.
——————————
📈 Time series Types:
... | mursalfk |
1,884,244 | How to publish a Python package with GitHub Actions using Poetry | by John Franey | John Franey added steps to his previous article because things got changed the time he published... | 0 | 2024-06-11T10:29:00 | https://dev.to/tankala/how-to-publish-a-python-package-with-github-actions-using-poetry-by-john-franey-1g6n | python, packaging, programming, beginners | John Franey added steps to his previous article because things got changed the time he published previous article like trusted publishing at PyPI. If you are interested to know how to publish your package using poetry check out this article. It's easy compared to the conventional way.
{% embed https://johnfraney.ca/bl... | tankala |
1,884,243 | Mobile App vs Mobile Website: What’s Best for Business? | The decision to choose between a mobile app vs mobile website is a tough one. With more than 5.1... | 0 | 2024-06-11T10:28:46 | https://www.peppersquare.com/blog/mobile-app-vs-mobile-website/ | mobile, development, webdev, website | The decision to choose between a mobile app vs mobile website is a tough one. With more than 5.1 billion mobile users in the world, it all comes down to how they should navigate around your business on their smartphones.
What are some of the major factors that affect this decision? We can help you make a conscious cho... | pepper_square |
1,884,242 | How Opkey Helps Streamline Oracle Redwood Migration with Continuous Testing? | As technology rapidly evolves, companies must constantly adapt to remain competitive. Oracle, a... | 0 | 2024-06-11T10:27:51 | https://dutable.com/2024/04/15/how-opkey-helps-streamline-oracle-redwood-migration-with-continuous-testing/ | oracle, redwood, migration | 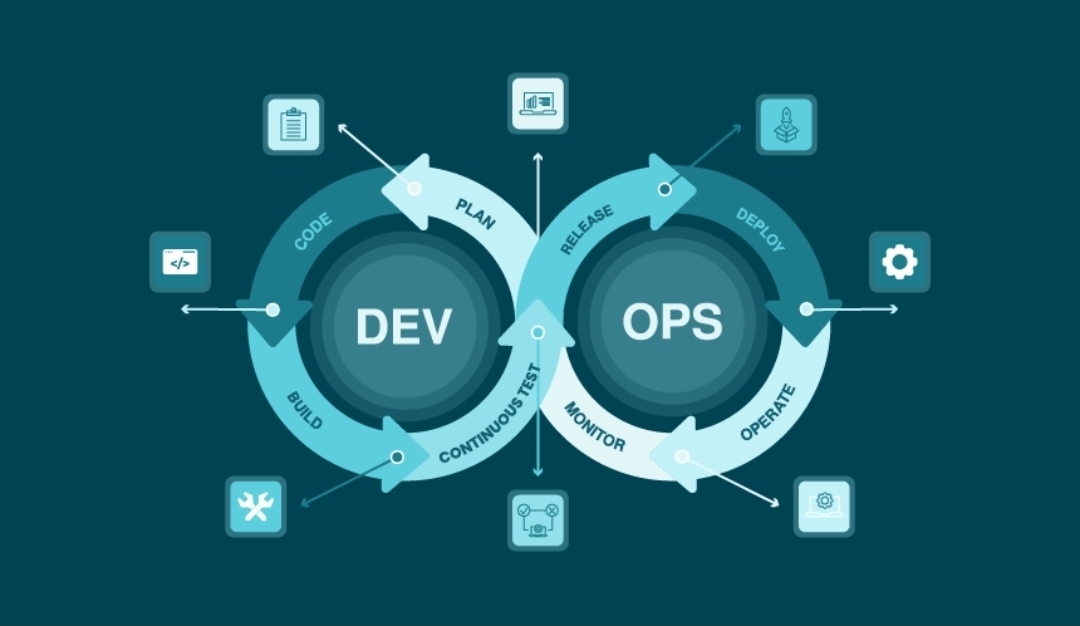
As technology rapidly evolves, companies must constantly adapt to remain competitive. Oracle, a leading enterprise solution provider, has launched Oracle Redwood—a groundbreaking framework designed to improve use... | rohitbhandari102 |
1,884,236 | How to Unlock the Power of Text-to-Speech AI for Developers | Discover how integrating a robust text-to-speech tool can enhance your application's user experience,... | 0 | 2024-06-11T10:26:23 | https://dev.to/novita_ai/how-to-unlock-the-power-of-text-to-speech-ai-for-developers-3ad |
Discover how integrating a robust text-to-speech tool can enhance your application's user experience, drive conversions, and ensure accessibility for all. This comprehensive guide provides developers with key insights and practical strategies to leverage the benefits of text-to-speech technology.
##Key Highlights
- ... | novita_ai | |
1,884,223 | 5 Ways a Web Development Consultant Can Boost Your ROI | Did you know? Businesses with a strong online presence will likely experience a 36% increase in... | 0 | 2024-06-11T10:04:55 | https://dev.to/himadripatelace/5-ways-a-web-development-consultant-can-boost-your-roi-572h | Did you know? Businesses with a strong online presence will likely experience a 36% increase in customer engagement! Imagine the impact on your bottom line if you could achieve such growth.
Discover how harnessing the expertise of a web development consultant can unlock unparalleled growth and maximize ROI for your bu... | himadripatelace | |
1,884,241 | Software Engineer career levels, a playbook for tech recruiters and aspiring software engineers | Navigating the Software Engineer Career Ladder: A Comprehensive Guide | 0 | 2024-06-11T10:25:54 | https://dev.to/pvgomes/software-engineer-career-levels-a-playbook-for-tech-recruiters-and-aspiring-software-engineers-1ofo | career, softwareengineer | ---
title: Software Engineer career levels, a playbook for tech recruiters and aspiring software engineers
published: true
description: Navigating the Software Engineer Career Ladder: A Comprehensive Guide
tags: career, softwareengineer
cover_image: https://dev-to-uploads.s3.amazonaws.com/uploads/articles/a9i1dywi47d4... | pvgomes |
1,884,240 | Zeeve Expands RaaS Platform to Support Tezos Smart Rollups | Zeeve, the leading provider of Rollups-as-a-Service (RaaS), is thrilled to announce the expansion of... | 0 | 2024-06-11T10:25:34 | https://www.zeeve.io/blog/zeeve-expands-raas-platform-to-support-tezos-smart-rollups/ | tezosrollups, announcement, zeeve | <p><a href="https://www.zeeve.io/">Zeeve</a>, the leading provider of Rollups-as-a-Service (RaaS), is thrilled to announce the expansion of its RaaS stack to support <a href="https://tezos.com/developers/smart-rollups/">Tezos Smart Rollups</a>. This strategic enhancement will empower businesses to swiftly launch and ma... | zeeve |
1,884,239 | Liv Pure: ⚠️Exploring Ingredients and Benefits — colibrip.com | LivPure is the only thing out there with a special mix that cleans your liver and helps burn fat. Its... | 0 | 2024-06-11T10:22:29 | https://dev.to/pushpender_kumar_a96c99dd/liv-pure-exploring-ingredients-and-benefits-colibripcom-2711 | livpure, benefitsoflivpure, colibrip | LivPure is the only thing out there with a special mix that cleans your liver and helps burn fat. Its special recipe can quickly clean up your liver, help you lose fat, and make your liver healthier overall.

## **W... | pushpender_kumar_a96c99dd |
1,884,238 | How safe are TRON tokens? | Introduction: TRON tokens, also known as TRX, are a form of cryptocurrency used on the TRON... | 0 | 2024-06-11T10:21:07 | https://dev.to/elena_marie_dad5c9d5d5706/how-safe-are-tron-tokens-3dkp | Introduction:
TRON tokens, also known as TRX, are a form of cryptocurrency used on the TRON blockchain. Launched by Justin Sun in 2017, TRON aims to decentralize the internet, allowing people to create, share, and enjoy digital content without the control of large corporations. TRON token development companies and *... | elena_marie_dad5c9d5d5706 | |
1,884,237 | Van Escorts: Your Personalized Travel Concierge on Wheels | Traveling can be one of the maximum worthwhile stories in existence. The freedom to discover new... | 0 | 2024-06-11T10:20:12 | https://dev.to/curren/van-escorts-your-personalized-travel-concierge-on-wheels-23c1 | Traveling can be one of the maximum worthwhile stories in existence. The freedom to discover new locations, meet new humans, and immerse yourself in unique cultures is unprecedented. However, the logistics of journey can frequently be disturbing and challenging. This is in which van escorts come into play, offering an ... | curren | |
1,882,417 | A primer on open-source intelligence for bug bounty hunting in Grafana | ℹ️ ANNOUNCEMENT Before getting to the main topic of this blog post, I’d like to take a moment to... | 25,060 | 2024-06-11T10:18:20 | https://secutils.dev/docs/blog/open-source-intelligence-grafana | opensource, buildinpublic, security, osint | > **ℹ️ ANNOUNCEMENT**
Before getting to the main topic of this blog post, I’d like to take a moment to share some exciting news (at least for me): [**Secutils.dev**](https://secutils.dev), the product for software engineers and security researchers that I’ve been working on lately, is **now generally available!**
> P... | azasypkin |
1,884,233 | Lei de Conway | Conhecendo a Lei de Conway | 0 | 2024-06-11T10:16:56 | https://dev.to/programadriano/lei-de-conway-bkk | conway | ---
title: Lei de Conway
published: true
description: Conhecendo a Lei de Conway
tags: conway
# cover_image: https://direct_url_to_image.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-06-11 10:10 +0000
---
A Lei de Conway, formulada por Melvin Conway em 1967, é uma observação empírica que sugere q... | programadriano |
1,884,231 | Transform Your Business with Microsoft Dynamics 365 | In the fast-paced world of modern business, staying ahead of the competition requires a blend of... | 0 | 2024-06-11T10:13:28 | https://dev.to/mylearnnest/transform-your-business-with-microsoft-dynamics-365-34ej | In the fast-paced world of modern business, staying ahead of the competition requires a blend of innovative technology and strategic foresight. Microsoft Dynamics 365 emerges as a game-changer, offering an integrated suite of [enterprise resource planning (ERP)](https://www.mylearnnest.com/microsoft-dynamics-365-traini... | mylearnnest | |
1,884,226 | Delving into Replika MOD APK: A Balanced Assessment of Its Features and Implications | Introduction Why are people talking about Replika MOD APK? What is it? What can I do with... | 0 | 2024-06-11T10:13:24 | https://dev.to/novita_ai/delving-into-replika-mod-apk-a-balanced-assessment-of-its-features-and-implications-1f4c | llm, chatbot, replika | ## Introduction
Why are people talking about Replika MOD APK? What is it? What can I do with it? What are the potential risks to consider when using it? What are the alternatives to Replika MOD APK? In this article, we will discuss these questions one by one. Importantly, considering the ethical and legal risks, it is ... | novita_ai |
1,884,230 | Custom Software Development Companies: Tailoring Technology to Meet Unique Business Needs | In today’s world, where technology is the backbone of nearly every business operation, the need for... | 0 | 2024-06-11T10:12:34 | https://dev.to/stevemax237/custom-software-development-companies-tailoring-technology-to-meet-unique-business-needs-jd7 | softwaredevelopment, technology | In today’s world, where technology is the backbone of nearly every business operation, the need for specialized software solutions is greater than ever. [**Software developing companies**](https://www.mobileappdaily.com/directory/software-development-companies?utm_source=dev&utm_medium=hc&utm_campaign=mad) are rising t... | stevemax237 |
1,884,228 | Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -ft | Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -Cash Assist.... | 0 | 2024-06-11T10:11:07 | https://dev.to/jeetendr_kumar_7db74de0bd/cash-assist-loan-app-customer-care-helpline-number-8653889187-896294o3o3-call-me-ft-iig | webdev, javascript, programming, react | Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -f | jeetendr_kumar_7db74de0bd |
1,884,227 | Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me - | Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -Cash Assist.... | 0 | 2024-06-11T10:09:27 | https://dev.to/jeetendr_kumar_7db74de0bd/cash-assist-loan-app-customer-care-helpline-number-8653889187-896294o3o3-call-me--4oma | Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -Cash Assist. Loan App Customer Care Helpline Number _8653889187 // 896294O3O3 call me -g | jeetendr_kumar_7db74de0bd | |
1,884,225 | How to Distribute Your Press Release for the Best Results | Publishing your press release on high-authority sites can amplify your message, enhance your brand’s... | 0 | 2024-06-11T10:06:59 | https://dev.to/emse1935/how-to-distribute-your-press-release-for-the-best-results-eoo | Publishing your press release on high-authority sites can amplify your message, enhance your brand’s credibility, and improve your SEO rankings. However, getting your press release picked up by these prestigious platforms requires a strategic approach. Here’s how you can effectively publish your press release on high-a... | emse1935 | |
1,884,224 | Enhancing Flavor with the Right Pizza Oven | screenshot-1717821713705.png Enhance the Flavor of Your Pizza with the Right Oven Do you love pizza... | 0 | 2024-06-11T10:05:08 | https://dev.to/fjsmwe_mdjene_9db878e6b49/enhancing-flavor-with-the-right-pizza-oven-5912 | design | screenshot-1717821713705.png
Enhance the Flavor of Your Pizza with the Right Oven
Do you love pizza as much as we do? If you want to make your pizza taste even better, then you need the right pizza oven. We'll explain how the right oven can enhance the flavor of your pizza and make it even more delicious.
Feat... | fjsmwe_mdjene_9db878e6b49 |
1,884,222 | Securing Weapons: The Role of a Weapon Tracking System | A weapon tracking system is essential for the secure and efficient management of firearms and other... | 0 | 2024-06-11T10:03:22 | https://dev.to/weapon_tracker/securing-weapons-the-role-of-a-weapon-tracking-system-1aeg | rfid, technology, trackingtechnology, trackingsystem | A weapon tracking system is essential for the secure and efficient management of firearms and other weapons. These systems are used in various sectors, including military, law enforcement, and private security, to ensure that weapons are properly tracked and accounted for. This article will discuss the key features of ... | weapon_tracker |
1,884,221 | A Deep Dive into "My Pods" - Creation, Management, and Best Practices | Introduction to Pod In the intricate world of modern server infrastructure and application... | 0 | 2024-06-11T10:03:22 | https://dev.to/novita_ai/a-deep-dive-into-my-pods-creation-management-and-best-practices-281k |
### Introduction to Pod
In the intricate world of modern server infrastructure and application deployment, the concept of Pods emerges as a cornerstone of efficiency and scalability. Pods, the fundamental building blocks of computing within Kubernetes, are the smallest deployable units that encapsulate the essence of ... | novita_ai | |
1,884,220 | What is HashiCorp Vault? | Protecting sensitive data like passwords, API keys, and database credentials is a top priority for... | 0 | 2024-06-11T10:02:46 | https://www.techielass.com/what-is-hashicorp-vault/ | hashicorp, security, devsecops, devops | 
Protecting sensitive data like passwords, API keys, and database credentials is a top priority for businesses. This is where HashiCorp Vault can help.
### What is HashiCorp Vault?
[HashiCorp Vault](https://www... | techielass |
1,884,219 | Klotski puzzle solver | I want to build this klotski puzzle solver app using javaFx any body help me to make it from... | 0 | 2024-06-11T10:01:19 | https://dev.to/prashant_sharma_6835a29dd/klotski-puzzle-solver-2ie6 | discuss, klotski, puzzle, solver | I want to build this klotski puzzle solver app using javaFx
, we've gained extensive experience from developing over 30 applications using technologies like Next.js and Firebase. One common feature that enhances user experience in web applications is infinite scrolling. This article dives into how you can implement this feature using... | antoineit |
1,881,308 | Converging project boilerplates with copier | Why? Technically when you start a new project the best way to approach it is by using the... | 0 | 2024-06-11T10:00:00 | https://artur.wtf/blog/multi-project-boilerplates/ | boilerplate, architecture | ## Why?
Technically when you start a new project the best way to approach it is by using the `CLI` tool of the realm, such as `svelte-kit`, `astro`, `django-cli` etc..., you get the idea. The huge bonus to doing this is that you get the best practices baked in and as new standards are created the `CLI` gets updated.
... | adaschevici |
1,882,076 | Cómo desarrollar habilidades de resolución de problemas en programación | La resolución de problemas es una habilidad fundamental para cualquier programador,... | 0 | 2024-06-11T10:00:00 | https://dev.to/rodri-oliveira-dev/como-desarrollar-habilidades-de-resolucion-de-problemas-en-programacion-3i83 | La resolución de problemas es una habilidad fundamental para cualquier programador, independientemente del nivel de experiencia o del lenguaje de programación utilizado. En este post, exploraremos algunos consejos y técnicas para ayudarte a desarrollar habilidades de resolución de problemas eficientes y mejorar tu capa... | rodri-oliveira-dev | |
1,880,501 | How To Write Elegant Code with C# Switch Expressions | Read originally blog post on my website https://antondevtips.com. Introduced in C# 8.0 switch... | 0 | 2024-06-11T09:59:22 | https://antondevtips.com/blog/how-to-write-elegant-code-with-csharp-switch-expressions | dotnet, csharp, programming, backend | ---
canonical_url: https://antondevtips.com/blog/how-to-write-elegant-code-with-csharp-switch-expressions
---
_Read originally blog post on my website_ [_https://antondevtips.com_](https://antondevtips.com/blog/how-to-write-elegant-code-with-csharp-switch-expressions/?utm_source=newsletter&utm_medium=email&utm_campaig... | antonmartyniuk |
1,884,217 | Released my first python package 🥳🙌🏻 | I am thrilled to announce the release of my first Python package, fillplace! 🪄🧑🏻💻 fillplace is a... | 0 | 2024-06-11T09:58:28 | https://dev.to/kunalkhairnar/released-my-first-python-package-24gh | python, fillplace, firstrelease | I am thrilled to announce the release of my first **Python package, `fillplace`! 🪄🧑🏻💻**
`fillplace` is a **placeholder** package designed to help developers seamlessly insert meaningful placeholders into their code. Whether you are building complex applications or just starting with Python, fillplace makes it eas... | kunalkhairnar |
1,884,216 | In Excel, Generate a List of All Days of the Month Where a Specified Data Belongs | Problem description & analysis: In the following Excel table, the value of cell A2 is the... | 0 | 2024-06-11T09:58:15 | https://dev.to/judith677/in-excel-generate-a-list-of-all-days-of-the-month-where-a-specified-data-belongs-2ehn | beginners, tutorial, productivity, database |
**Problem description & analysis**:
In the following Excel table, the value of cell A2 is the date.
```
A
1 Fecha
2 01/03/24
```
We need to generate a list of dates of the month where that date belongs.
```
A
1 WholeMonth
2 01/03/24
3 02/03/24
4 03/03/24
5 04/03/24
6 05/03/24
7 06/03/24
8 07/03/24
9 08/03/... | judith677 |
1,884,210 | Seeing the Unseen: How VR and AR are Revolutionizing Real Estate Marketing | The real estate industry is undergoing a technological transformation, with Virtual Reality (VR)... | 0 | 2024-06-11T09:52:24 | https://dev.to/intellimedianetworks/seeing-the-unseen-how-vr-and-ar-are-revolutionizing-real-estate-marketing-3j34 |

The real estate industry is undergoing a technological transformation, with Virtual Reality (VR) and Augmented Reality (AR) leading the charge. These innovative technologies are not just enhancing property marketi... | intellimedianetworks | |
1,884,215 | The Advantages of Using Conveyor Ovens for Pizzas | Conveyor Ovens for Pizzas: The Best Way to Bake You know that nothing beats a freshly-baked, piping... | 0 | 2024-06-11T09:55:36 | https://dev.to/fjsmwe_mdjene_9db878e6b49/the-advantages-of-using-conveyor-ovens-for-pizzas-58b7 | design | Conveyor Ovens for Pizzas: The Best Way to Bake
You know that nothing beats a freshly-baked, piping hot pizza if you’re a pizza lover. But have you ever wondered how your favorite pizza joint manages to churn out so many pizzas such a time short? The answer lies in their trusty conveyor ovens. We’ll explore the advanta... | fjsmwe_mdjene_9db878e6b49 |
1,884,214 | Top AI Strategies for Algorithmic Trading | Artificial Intelligence (AI) is reshaping the landscape of algorithmic trading, offering advanced... | 0 | 2024-06-11T09:54:31 | https://dev.to/georgewilliam4425/top-ai-strategies-for-algorithmic-trading-3kem | Artificial Intelligence (AI) is reshaping the landscape of algorithmic trading, offering advanced strategies that enhance decision-making and trade execution. In the realms of forex, CFD [markets](https://bit.ly/forex-markets-t4t-seo), and broker platforms, AI-driven techniques are proving to be invaluable. This articl... | georgewilliam4425 | |
1,884,213 | CodeHuntsPK: Leading the Way in AI, ML, and DL Innovation | Welcome to CodeHuntsPK.com, your ultimate destination for cutting-edge technology solutions. As a... | 0 | 2024-06-11T09:54:23 | https://dev.to/hmzi67/codehuntspk-leading-the-way-in-ai-ml-and-dl-innovation-12j5 | webdev, javascript, beginners, programming | Welcome to CodeHuntsPK.com, your ultimate destination for cutting-edge technology solutions. As a premier startup based in Islamabad, Pakistan, we specialize in Artificial Intelligence (AI), Machine Learning (ML), and Deep Learning (DL). Our mission is to transform businesses by leveraging the power of advanced technol... | hmzi67 |
1,884,212 | Curtains and blinds furnishing Dubai | We are based in Dubai specialize in Curtains & blind covers for cover up the window and doors. We... | 0 | 2024-06-11T09:53:54 | https://dev.to/four_square_0147bee28e45b/curtains-and-blinds-furnishing-dubai-2e19 | We are based in Dubai specialize in Curtains & blind covers for cover up the window and doors. We sell the curtains for apartmens and houses and offices. Just fill your space from premium quality of curtains.Contact us now
Visit: https://foursquarecurtains.com/
| four_square_0147bee28e45b | |
1,884,211 | Best Internship in Chennai | Best Internship in Chennai Kaashiv Infotech stands out as a leading destination for the best... | 0 | 2024-06-11T09:52:50 | https://dev.to/nanthamwari/best-internship-in-chennai-5116 | Best Internship in Chennai
Kaashiv Infotech stands out as a leading destination for the best internships in chennai, renowned for its innovative approach and industry-focused training programs. Specializing in IT solutions and training, Kaashiv Infotech offers interns a dynamic environment to refine their skills and ga... | nanthamwari | |
1,884,208 | Writing Better Javascript Classes and modules | Classes are something that took me a minute to understand why I needed them compared to simply using... | 0 | 2024-06-11T09:50:37 | https://dev.to/mtendekuyokwa19/writing-better-javascript-classes-and-modules-1ee1 | Classes are something that took me a minute to understand why I needed them compared to simply using object literals.
```javascript
let person={
name:"kwame";
age:45
}
```
Object literals were easy to create and less ambiguous to write.
It was all rainbows and chocolate until I wanted the objects I created t... | mtendekuyokwa19 | |
1,884,207 | Explore Cloud Security Management: Everything You Need to Know | Cloud software is being used by more and more businesses. However, while the cloud is convenient, it... | 0 | 2024-06-11T09:47:31 | https://dev.to/nicholajones075/explore-cloud-security-management-everything-you-need-to-know-faj | cloudsecurity, cloudmanagement, itsecurity, cloudstrategy | Cloud software is being used by more and more businesses. However, while the cloud is convenient, it is also very important to have strong cloud security authority. It is essential to comprehend the significance of cloud security, and it is necessary to take appropriate steps to protect your company's data, reputation,... | nicholajones075 |
1,884,206 | Need for volunteers!! | Hey, I'm Mazen. I'm starting a game-making group, and I'm looking for people to join. If you're... | 0 | 2024-06-11T09:45:56 | https://dev.to/mzez17_bb_cdfedde1d7ce0ad/need-for-volunteers-3o7n | Hey, I'm Mazen.
I'm starting a game-making group, and I'm looking for people to join. If you're interested, hit me up and I'll give you the details. You can then let me know if you want to help out.
I'll set up a space where we can share our progress and ideas.
Looking forward to meeting some fellow game devs!
Cheers,
... | mzez17_bb_cdfedde1d7ce0ad | |
1,884,205 | How to Choose the Right POS Machine for Your Business | Exactly just what is actually a POS Device You have most likely become aware of a POS device prior... | 0 | 2024-06-11T09:44:07 | https://dev.to/fjsmwe_mdjene_9db878e6b49/how-to-choose-the-right-pos-machine-for-your-business-1ip2 | design | Exactly just what is actually a POS Device
You have most likely become aware of a POS device prior to if you are an entrepreneur. However exactly what is actually it? POS means factor of purchase, as well towards procedure deals at your company as it is a body that enables you. Basically, it is exactly just what... | fjsmwe_mdjene_9db878e6b49 |
1,884,188 | Crypto News | Future Trends and Developments in Cryptocurrency: Innovation and Integration The landscape of... | 0 | 2024-06-11T09:22:47 | https://dev.to/landercesca24/crypto-news-4he6 | web3, blockchain, cryptocurrency, news | **_Future Trends and Developments in Cryptocurrency: Innovation and Integration_**
The landscape of cryptocurrencies and crypto cards is rapidly evolving, driven by a surge in innovation and technological advancements. This article explores the emerging trends in decentralized finance (DeFi), non-fungible tokens (NFTs)... | landercesca24 |
1,884,204 | In Laravel Blade components, should you pass content as slots or as attributes? | In Laravel Blade components, you can pass content as slots or as attributes. For HTML content, it's... | 0 | 2024-06-11T09:43:59 | https://dev.to/edriso/in-laravel-blade-components-should-you-pass-content-as-slots-or-as-attributes-47ng | laravel, blade | In Laravel Blade components, you can pass content as slots or as attributes.
For HTML content, it's clearer to pass it as slots because it indicates that the content is HTML and allows you to include HTML tags directly.
And, in the example below, if you pass the title as an attribute, it will also be used as the titl... | edriso |
1,884,203 | Create a fantastic GitHub developer portfolio with next js.🚀🚀 | Introduction Struggling to create a professional-looking portfolio website? Look no... | 0 | 2024-06-11T09:40:38 | https://dev.to/dharamgfx/create-a-fantastic-github-developer-portfolio-with-next-js-50c4 | webdev, javascript, react, nextjs | ## Introduction
Struggling to create a professional-looking portfolio website? Look no further! With this GitHub Portfolio template, you can easily create a personalized portfolio using just your GitHub username. Whether you're a developer or a freelancer, this user-friendly and customizable solution is perfect for sho... | dharamgfx |
1,884,202 | peviitor.ro pe Jitsi | Platforma Jitsi este folosita pentru a avea un mediu prielnic unde fiecare voluntar isi prezinta... | 0 | 2024-06-11T09:39:11 | https://dev.to/ale23yfm/peviitorto-pe-jitsi-mpe | peviitor, jitsi, meeting, community | Platforma [Jitsi](https://meet.jit.si/PEVIITOR.RO) este folosita pentru a avea un mediu prielnic unde fiecare voluntar isi prezinta munca depusa echipei din care face parte. Fiecare zi a saptamanii este prestabilita pentru echipele proiectului [peviitor.ro](https://peviitor.ro/).
---
## Programul pentru fiecare zi
*... | ale23yfm |
1,884,307 | Developers’ reality check, according to Gergely Orosz: More work, ‘boring’ tech, and less promotions | Photo: Craft Conf For more content like this subscribe to the ShiftMag newsletter. Where there... | 0 | 2024-06-12T11:50:18 | https://shiftmag.dev/developer-careers-gergely-orosz-3512/ | career, craftconf, gergelyorosz, layoffs | ---
title: Developers’ reality check, according to Gergely Orosz: More work, ‘boring’ tech, and less promotions
published: true
date: 2024-06-11 09:37:06 UTC
tags: Career,CraftConf,GergelyOrosz,layoffs
canonical_url: https://shiftmag.dev/developer-careers-gergely-orosz-3512/
---
 là nền tảng bất động sản tiên phong tại Việt Nam, cung cấp công cụ tra cứu bản đồ quy hoạch BĐS chính xác và minh bạch. Sử dụng công nghệ AI và Big Data, Vnland.info tái định hình thị trường bằng cách kết nối người mua và người bán một cách thuận tiện, dễ dàng và nhanh chóng.
Trang ... | vnlandinfo |
1,884,197 | Navigating the Path to Java Proficiency: A Comprehensive Guide for Aspiring Developers | Introduction: Embark on a transformative journey into the world of Java programming with our... | 0 | 2024-06-11T09:32:06 | https://dev.to/roselie_jack_27cdbed045bd/navigating-the-path-to-java-proficiency-a-comprehensive-guide-for-aspiring-developers-2kjn | javascript |
Introduction:
Embark on a transformative journey into the world of Java programming with our comprehensive guide tailored for aspiring developers. This roadmap is designed to equip you with the essential skills, knowledge, and strategies needed to master Java development. Whether you're a beginner taking your first s... | roselie_jack_27cdbed045bd |
1,884,196 | A Novel Review Fallen by Lauren Kate | About the Author: Lauren Kate Lauren Kate is a celebrated American author known for her... | 0 | 2024-06-11T09:31:13 | https://dev.to/markhfd/a-novel-review-fallen-by-lauren-kate-4ppi | paranormal, novel | ## About the Author: Lauren Kate
Lauren Kate is a celebrated American author known for her contributions to young adult fiction, particularly in the paranormal romance genre. With a background in creative writing, Lauren Kate brings a unique blend of emotional depth and fantastical elements to her stories. Her Fallen s... | markhfd |
1,884,195 | Comparing Traditional and Modern Pizza Ovens | Comparing Conventional and Modern Pizza Ovens Pizza is unquestionably an all-time meals is favorite... | 0 | 2024-06-11T09:27:49 | https://dev.to/fjsmwe_mdjene_9db878e6b49/comparing-traditional-and-modern-pizza-ovens-21oh | design | Comparing Conventional and Modern Pizza Ovens
Pizza is unquestionably an all-time meals is favorite and there is not surprising why it's really a flavorful mixture of cheese, tomato sauce, and crust always strikes the location Making the perfect pizza involves more than simply the ingredients; it will require the pr... | fjsmwe_mdjene_9db878e6b49 |
1,884,194 | Workflow Orchestration on AWS: The Ultimate Guide to AWS Step Functions | Visit my blog Practical Cloud to read more Devops/Cloud topics. In the dynamic world of cloud... | 0 | 2024-06-11T09:27:08 | https://practicalcloud.net/workflow-orchestration-on-aws-the-ultimate-guide-to-aws-step-functions/ | aws, cloud, devops | Visit my blog [Practical Cloud](https://practicalcloud.net) to read more Devops/Cloud topics.
In the dynamic world of cloud computing, orchestrating complex workflows across multiple AWS services is crucial for creating scalable and maintainable applications. AWS Step Functions, a serverless orchestration service, is d... | kelvinskell |
1,884,193 | Looking for the Best Software Development Company in Gurgaon? | In today's digital age, having a strong online presence is essential for businesses of all sizes. A... | 0 | 2024-06-11T09:26:14 | https://dev.to/techmetronix_beb99eda8290/looking-for-the-best-software-development-company-in-gurgaon-4con | techmetronix | In today's digital age, having a strong online presence is essential for businesses of all sizes. A well-designed website and robust software can help you attract new customers, improve brand awareness, and boost your bottom line. But where do you start? If you're looking for a reliable and [best software development c... | techmetronix_beb99eda8290 |
1,884,177 | How to create your own AI chatbot with LangFlow | Today I’d like to start my series of articles on using the LangChain open source tool-set. LangChain... | 27,676 | 2024-06-11T09:26:14 | https://rolfstreefkerk.com/article/how-to-create-your-own-rag-ai-with-langflow | beginners, ai, rag, tutorial |
Today I’d like to start my series of articles on using the LangChain open source tool-set.
[LangChain](https://github.com/langchain-ai/langchain) is one of the most used frameworks to create AI agents with, if not THE most used. With nearly 90.000 stars and almost 14000 forks on GitHub at the time of this article, we... | rolfstreefkerk |
1,884,192 | Exploring the Best Korean Spas in Los Angeles | Beverly Hot Springs offers a more tranquil and intimate spa experience compared to the larger... | 0 | 2024-06-11T09:26:04 | https://dev.to/cskeisari665/exploring-the-best-korean-spas-in-los-angeles-m46 | Beverly Hot Springs offers a more tranquil and intimate spa experience compared to the larger jjimjilbangs. This unique spa is the only one in Los Angeles with natural hot springs, sourced from a well beneath the facility. The mineral-rich water is said to have numerous health benefits, including improved skin conditio... | cskeisari665 | |
1,884,180 | Wallet Digitalz App | Help Test the New App Wallet Digital on Google Play! Are you a tech enthusiast who loves... | 0 | 2024-06-11T09:22:00 | https://dev.to/lucasferreiralimax/wallet-digitalz-app-212m | playstore, react, reactnative, android | ---
title: Wallet Digitalz App
published: true
description:
tags: PlayStore, React, ReactNative, Android
# cover_image: 
# Use a ratio of 100:42 for best results.
# published_at: 2024-06-11 09:08 +0000
---
## Help... | lucasferreiralimax |
1,884,182 | ALB vs NLB | AWS offers multiple load-balancing solutions tailored to different use cases within the Elastic Load... | 0 | 2024-06-11T09:19:22 | https://dev.to/saumya27/alb-vs-nlb-22hc | aws, alb, nlb | AWS offers multiple load-balancing solutions tailored to different use cases within the Elastic Load Balancing (ELB) service. The two primary types are the Application Load Balancer (ALB) and the Network Load Balancer (NLB). Below is a detailed comparison of ALB and NLB, highlighting their features, use cases, and diff... | saumya27 |
1,884,181 | 10 must known JS/TS open-source packages | Under the Hood The story began when I was writing my newsletter. While reading a bunch of... | 0 | 2024-06-11T09:17:29 | https://dev.to/shreyvijayvargiya/10-must-known-jsts-open-source-packages-3i6o | news, programming, beginners, javascript | Under the Hood
==============
The story began when I was writing my [newsletter](http://ihatereading.in/newsletter).
While reading a bunch of javascript weekly articles online I’ve found an extensive list of open-source packages one-by-one.
We often need or rely on such packages but never discuss them as a tech stac... | shreyvijayvargiya |
1,850,871 | Handling RabbitMQ Reconnections With Go and amqp091-go | In a distributed system, maintaining a stable connection between components is crucial for ensuring... | 0 | 2024-06-11T09:15:42 | https://dev.to/tentanganak/handling-rabbitmq-reconnections-with-go-and-amqp091-go-1mce | In a distributed system, maintaining a stable connection between components is crucial for ensuring reliable communication. This article explores strategies for reconnecting to RabbitMQ, ensuring that your applications can recover from network disruptions or broker restarts without losing valuable data.
# Setting Up
... | dikac | |
1,884,179 | How Does Medical Coding Affect The Revenue Cycle? | The quote translates that revenue is vanity, definitely an achievement, but it’s not a complete... | 0 | 2024-06-11T09:15:07 | https://dev.to/aksharmedisolutions/how-does-medical-coding-affect-the-revenue-cycle-7c0 | medicalbilling, healthcare | The quote translates that revenue is vanity, definitely an achievement, but it’s not a complete picture of the company’s success. If the cash is not pouring into your business, there are high chances the cycle could be disrupted and the overall pipeline would be broken or distressed. A [Medical Billing Company in New J... | aksharmedisolutions |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.