id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,903,545 | Mastering Government Contract Negotiations Tips and Techniques for Success | Learn effective negotiation strategies to ensure favorable terms and conditions in government contracts, including preparation tips and common pitfalls to avoid. | 0 | 2024-06-28T03:25:38 | https://www.govcon.me/blog/mastering_government_contract_negotiations_tips_and_techniques_for_success | governmentcontracting, negotiationstrategies, contractmanagement, procurement | # Mastering Government Contract Negotiations: Tips and Techniques for Success
Negotiating government contracts can be a daunting task, but with the right strategies and preparation, you can secure favorable terms and conditions. This article provides valuable insights into effective negotiation tactics, preparation ti... | quantumcybersolution |
1,903,544 | How Construction Technology is Shaping the Future of Real Estate Development | Explore how cutting-edge construction technologies like AI, robotics, and sustainable materials are revolutionizing the real estate industry, making it more efficient, cost-effective, and sustainable. | 0 | 2024-06-28T03:25:10 | https://www.govcon.me/blog/how_construction_technology_is_shaping_the_future_of_real_estate_development | constructiontechnology, realestate, innovation | # How Construction Technology is Shaping the Future of Real Estate Development
The real estate industry has always been a cornerstone of economic growth and societal development. However, with traditional methods, real estate development has often been a slow and costly process. Enter construction technology - a burge... | quantumcybersolution |
1,903,543 | Delving into the World of 3D Math: Building Blocks for a Graphical Reality | The captivating visuals of video games, the immersive experiences of VR, and the intricate designs of... | 0 | 2024-06-28T03:24:55 | https://dev.to/epakconsultant/delving-into-the-world-of-3d-math-building-blocks-for-a-graphical-reality-4ef9 | 3d | The captivating visuals of video games, the immersive experiences of VR, and the intricate designs of 3D modeling software – all rely on the foundation of 3D math. This article embarks on a journey into the realm of 3D mathematics, exploring its core concepts and applications in the captivating world of computer graphi... | epakconsultant |
1,903,542 | Mastering Arrow Plotting with Matplotlib | Matplotlib is a powerful plotting library in Python. It provides a variety of customizable visualizations such as line plots, scatter plots, bar graphs, histograms, and more. One of the visualizations that Matplotlib provides is the Arrow Plot. Arrow plots are used to encode arrow 'strength' such as transition probabil... | 27,880 | 2024-06-28T03:24:27 | https://labex.io/tutorials/python-arrow-plotting-using-matplotlib-48552 | matplotlib, coding, programming, tutorial |
## Introduction
Matplotlib is a powerful plotting library in Python. It provides a variety of customizable visualizations such as line plots, scatter plots, bar graphs, histograms, and more. One of the visualizations that Matplotlib provides is the Arrow Plot. Arrow plots are used to encode arrow "strength" such as t... | labby |
1,903,541 | BPM的基本应用研究报告 | 一、引言 随着企业竞争的加剧和市场的不断变化,如何提高企业运营效率、降低成本、提升客户满意度成为了企业关注的焦点。BPM(业务流程管理)作为一种先进的管理方法,通过对企业业务流程进行规划、设计、执行、... | 0 | 2024-06-28T03:24:13 | https://dev.to/hotentbpm/bpmde-ji-ben-ying-yong-yan-jiu-bao-gao-4ji | webdev, beginners, ai, react | 一、引言
随着企业竞争的加剧和市场的不断变化,如何提高企业运营效率、降低成本、提升客户满意度成为了企业关注的焦点。BPM(业务流程管理)作为一种先进的管理方法,通过对企业业务流程进行规划、设计、执行、监控和优化,有助于企业实现这些目标。本报告旨在探讨BPM的基本应用及其在不同领域的实践效果。
二、BPM概述
BPM(Business Process Management)是指通过一系列的工具和方法,对企业业务流程进行规划、设计、执行、监控和优化的过程。BPM的目标是提高企业运营效率、降低成本、提升客户满意度和风险管理能力。BPM的实施需要跨部门、跨职能的协同工作,以确保业务流程的高效、稳定和可控。
三、BPM的基本应用
流... | hotentbpm |
1,903,467 | Github as Helm repository | Originally posted in my blog For my personal projects, I use Github as a Helm repository. This is a... | 0 | 2024-06-28T02:39:43 | https://dev.to/boris/github-as-helm-repository-1lcf | github, kubernetes, helm, deployment | ---
title: Github as Helm repository
published: true
description:
tags: github, kubernetes, helm, deployment
# cover_image: https://direct_url_to_image.jpg
# Use a ratio of 100:42 for best results.
# published_at: 2024-06-28 02:36 +0000
---
_Originally posted in [my blog](https://borisquiroz.dev/posts/github-as-helm-r... | boris |
1,903,539 | Kundalini Yoga The Path to Awakening and Self-Realization | Discover the transformative power of Kundalini Yoga, its origins, and how to practice it for a balanced and fulfilling life. | 0 | 2024-06-28T03:23:16 | https://www.rics-notebook.com/blog/Health/Kundalini | kundalini, yoga, meditation, spirituality | ## 🧘♂️ Kundalini Yoga: The Path to Awakening and Self-Realization 🌟
Kundalini Yoga, often referred to as the 'Yoga of Awareness,' is an ancient
practice that focuses on awakening the dormant Kundalini energy located at the
base of the spine. This form of yoga combines physical postures, breathwork,
medita... | eric_dequ |
1,903,504 | Mastering CDRLs Efficiently Managing Contract Data Requirements in Government Projects | Unlock the secrets to managing Contract Data Requirements Lists (CDRLs) in government projects with ease and efficiency. Learn the best practices, tools, and strategies to streamline your workflow and avoid common pitfalls. | 0 | 2024-06-28T03:20:31 | https://www.govcon.me/blog/mastering_cdrls_efficiently_managing_contract_data_requirements_in_government_projects | governmentprojects, datamanagement, cdrl | # Mastering CDRLs: Efficiently Managing Contract Data Requirements in Government Projects
If you've ever managed a government project, you're likely familiar with the elaborate labyrinth of paperwork, submissions, and compliance requirements. One crucial aspect of this bureaucracy is the Contract Data Requir... | quantumcybersolution |
1,903,500 | Ibogaine Pharmacological Profile Anti-Addiction Properties and Spiritual Impact | Explore the potential of ibogaine as a transformative treatment for addiction. Delve into its pharmacological makeup, therapeutic applications, and the profound spiritual impact it can have on individuals seeking recovery. 🌿💊🧠 | 0 | 2024-06-28T03:18:09 | https://www.rics-notebook.com/blog/Health/ibogaine | ibogaine, addictiontreatment, psychedelics, pharmacology | ## 🌿 Ibogaine: Pharmacological Profile, Anti-Addiction Properties, and Spiritual Impact
Ibogaine, a naturally occurring psychoactive substance derived from the root bark of the African shrub Tabernanthe iboga, has gained attention for its unique ability to combat addiction and its profound spiritual effects. This blo... | eric_dequ |
1,903,499 | Reverse engineering octet stream messages | hey, im trying to reverse engineer this app but it uses octet stream in http requests so im trying to... | 0 | 2024-06-28T03:17:17 | https://dev.to/kuba1703/reverse-engineering-octet-stream-messages-jj2 | reverse, engineering, programming, decoding | hey, im trying to reverse engineer this app but it uses octet stream in http requests so im trying to reverse it and understand what exactly the request is sending but its encoded, for last 2 days ive been trying to decode it with tools and stuff but idk, never done anything similar to this like decoding protobufs with... | kuba1703 |
1,903,497 | Market Research Methods for Identifying Government Contracting Opportunities | Unveil the secrets to discovering lucrative government contracts through advanced market research techniques. From data mining to leveraging technological tools, explore the methods that will put your business ahead of the competition. | 0 | 2024-06-28T03:15:23 | https://www.govcon.me/blog/market_research_methods_for_identifying_government_contracting_opportunities | governmentcontracting, marketresearch, businessstrategy | # Market Research Methods for Identifying Government Contracting Opportunities
With billions of dollars in government contracts awarded annually, uncovering these opportunities is crucial for businesses aiming to expand their revenue streams. Effective market research can transform your business strategy, propelling y... | quantumcybersolution |
1,903,496 | How Construction Technology is Helping to Achieve Zero Waste Goals | Explore how cutting-edge construction technology is paving the way towards achieving zero waste goals and revolutionizing the industry. | 0 | 2024-06-28T03:15:03 | https://www.govcon.me/blog/how_construction_technology_is_helping_to_achieve_zero_waste_goals | construction, technology, sustainability | # How Construction Technology is Helping to Achieve Zero Waste Goals
Construction is evolving, and with it, so are our ambitions for a sustainable future. Historically, the construction industry has been one of the largest contributors to waste globally. However, recent technological advancements are turning this narr... | quantumcybersolution |
1,903,495 | 低代码的基本应用研究报告 | 一、引言 随着信息技术的快速发展和数字化转型的深入,企业对于软件应用的需求日益增长。然而,传统的软件开发方法面临着周期长、成本高、技术门槛高等问题,难以满足企业的快速响应和灵活调整需求。低代码开发平台... | 0 | 2024-06-28T03:12:45 | https://dev.to/hotentbpm/di-dai-ma-de-ji-ben-ying-yong-yan-jiu-bao-gao-25nm | webdev, javascript, beginners, tutorial | 一、引言
随着信息技术的快速发展和数字化转型的深入,企业对于软件应用的需求日益增长。然而,传统的软件开发方法面临着周期长、成本高、技术门槛高等问题,难以满足企业的快速响应和灵活调整需求。低代码开发平台作为一种新兴的软件开发方法,通过减少手动编码的需求,使开发人员能够更快速地构建和部署应用程序,为企业提供了一种新的解决方案。本报告旨在探讨低代码的基本应用及其在不同领域的实践效果。
二、低代码概述
低代码(Low-Code)是一种软件开发方法,旨在通过最小化手动编码的需求,使开发人员能够更快速地构建和部署应用程序。低代码平台提供了一套可视化的工具和组件,使开发人员可以通过拖放、配置和设置属性来创建应用程序,从而降低了开发难度和成本... | hotentbpm |
1,903,494 | GBase 8a Implementation Guide: Parameter Optimization | 1. Overview Optimizing the configuration of GBase 8a clusters varies across different... | 0 | 2024-06-28T03:11:07 | https://dev.to/congcong/gbase-8a-implementation-guide-parameter-optimization-5g9j | ## 1. Overview
Optimizing the configuration of GBase 8a clusters varies across different application scenarios. A single set of fixed parameters cannot meet all situations. This chapter provides general principles for parameter tuning based on accumulated optimization experiences in various projects and business scena... | congcong | |
1,903,466 | Difference between CommonJS and ESM modules | Intro CommonJS (CJS) and ECMAScript Modules (ESM) are two different module systems in... | 0 | 2024-06-28T02:37:18 | https://dev.to/vinay_madan/difference-between-commonjs-and-esm-modules-4pff | javascript, node | ### Intro
CommonJS (CJS) and ECMAScript Modules (ESM) are two different module systems in JavaScript used for organizing and structuring code. They have different syntax and behaviors, and they are often used in different contexts. Let's explore each format:
#### CommonJS (CJS):
1. Synchronous: CommonJS modules are lo... | vinay_madan |
1,903,492 | Marketing Your Products and Services to Government Agencies via GSA Advantage | Unlock the secrets to successfully marketing your products and services to government agencies through GSA Advantage! Learn how to navigate the platform, optimize your listings, and stand out in the competitive landscape. | 0 | 2024-06-28T03:10:16 | https://www.govcon.me/blog/marketing_your_products_and_services_to_government_agencies_via_gsa_advantage | gsaadvantage, governmentmarketing, technology | # Marketing Your Products and Services to Government Agencies via GSA Advantage!
Government contracts can be a treasure trove for businesses of all sizes. The General Services Administration (GSA) provides an excellent conduit for businesses to market their products and services to government agencies through its GSA ... | quantumcybersolution |
1,903,491 | The Science of Hangovers Understanding the Causes and Effective Supplements for Prevention | Discover the science behind hangovers and learn about effective supplements that can help minimize their impact. From the causes to prevention strategies, this blog post explores the complexities of alcohol's effects on the body and offers practical solutions for a more comfortable morning after. 🌅 | 0 | 2024-06-28T03:07:54 | https://www.rics-notebook.com/blog/Health/Hangover | hangovers, alcohol, supplements, prevention | ## 🌟 The Science of Hangovers: Understanding the Causes and Effective Supplements for Prevention
We've all been there – the morning after a night of indulgence, feeling the unpleasant effects of a hangover. The pounding headache, the nausea, the fatigue – it's a reminder that our bodies are not designed to ... | eric_dequ |
1,903,462 | Dockerize a Laravel 11 app | Dockerizing a Laravel application is not as simple as it seems, which is why today I will guide you... | 0 | 2024-06-28T03:06:28 | https://dev.to/frankalvarez/dockerize-a-laravel-11-app-4g4a | docker, laravel, php, nginx |
Dockerizing a Laravel application is not as simple as it seems, which is why today I will guide you through the process of creating a Docker image for Laravel 11 in 2024.
To do this, we will configure a complete environment using Docker Compose, ensuring that our Laravel application is ready for deployment in any env... | frankalvarez |
1,903,490 | Leveraging Technology for Efficient Government Contract Management | Explore how cutting-edge technology is revolutionizing government contract management, making processes more efficient, transparent, and reliable. | 0 | 2024-06-28T03:05:09 | https://www.govcon.me/blog/leveraging_technology_for_efficient_government_contract_management | technology, government, contractmanagement, innovation | # Leveraging Technology for Efficient Government Contract Management
In an era marked by rapid technological advancements, the realm of government contract management is no exception to the transformative power of innovation. The application of technology in this sector promises enhanced efficiency, increased transpar... | quantumcybersolution |
1,903,489 | How Construction Technology is Enhancing Disaster Resilience | Discover how cutting-edge construction technologies are transforming the way we build to withstand natural disasters and protect communities. | 0 | 2024-06-28T03:04:55 | https://www.govcon.me/blog/how_construction_technology_is_enhancing_disaster_resilience | constructiontechnology, disasterresilience, innovation | # How Construction Technology is Enhancing Disaster Resilience
When natural disasters strike, the physical and emotional toll can be devastating. Yet, in today's age of rapid technological advancement, innovative construction technologies are playing a pivotal role in enhancing disaster resilience. These next-gen... | quantumcybersolution |
1,903,488 | From the Eleusinian Mysteries to the Salem Witch Trials The Role of Ergot and LSA in History | Explore the fascinating connections between the ancient Eleusinian Mysteries, the psychoactive properties of ergot and LSA, and the infamous Salem Witch Trials. Delve into how these elements intersected to shape pivotal moments in history. 🌾🔮 | 0 | 2024-06-28T03:02:47 | https://www.rics-notebook.com/blog/Health/Ergot | eleusinianmysteries, ergot, lsa, salemwitchtrials | ## 🌾 From the Eleusinian Mysteries to the Salem Witch Trials: The Role of Ergot and LSA in History
The interplay between psychoactive substances and human culture has shaped significant historical events and spiritual practices. This blog post explores the ancient Eleusinian Mysteries, the properties of ergot and LSA... | eric_dequ |
1,903,487 | Leveraging Technology for Contract Performance Monitoring | Explore how groundbreaking technologies are revolutionizing contract performance monitoring and driving efficiency in business operations. | 0 | 2024-06-28T03:00:02 | https://www.govcon.me/blog/leveraging_technology_for_contract_performance_monitoring | contractmanagement, technology, innovation | # Leveraging Technology for Contract Performance Monitoring
In today's fast-paced business environment, contract performance monitoring (CPM) has evolved from a tedious manual process into a sophisticated, technology-driven operation. Delving into the world of automated contract monitoring offers businesses strat... | quantumcybersolution |
1,903,486 | Exploring Electromagnetic Field Therapy Healing with Energy Waves | Discover the potential of Electromagnetic Field Therapy for healing and wellness. This blog post explores the science behind EMF Therapy, its applications, benefits, and the current state of research in this emerging field. 🌟✨ | 0 | 2024-06-28T02:57:40 | https://www.rics-notebook.com/blog/Health/ElectromagneticFieldTherapy | electromagneticfieldtherapy, emftherapy, alternativemedicine, painmanagement | ## 🌟 Exploring Electromagnetic Field Therapy: Healing with Energy Waves
Electromagnetic Field Therapy (EMF Therapy) is an innovative approach to healing that uses electromagnetic fields to promote wellness and treat various medical conditions. This blog post delves into the science behind EMF Therapy, its application... | eric_dequ |
1,903,484 | The Future of IT Jobs: Skills You Need to Succeed | 👨💻 The IT industry is evolving rapidly, driven by technological advancements and changing business... | 0 | 2024-06-28T02:56:25 | https://dev.to/dipakahirav/the-future-of-it-jobs-skills-you-need-to-succeed-1952 | it, jobs, webdev, javascript | 👨💻 The IT industry is evolving rapidly, driven by technological advancements and changing business needs. To stay relevant and succeed in this dynamic field, IT professionals need to continuously update their skills. Here are some key skills that will be essential for future IT jobs:
please subscribe to my [YouTube... | dipakahirav |
1,903,483 | Technical Breakdown: How Huawei EG8143A5 Manages ONT CATV and CATV ONU Tasks | The Huawei EG8143A5 is an advanced Optical Network Terminal (ONT) renowned for its capability to... | 0 | 2024-06-28T02:55:01 | https://dev.to/jack_heryson_90d856aa50ff/technical-breakdown-how-huawei-eg8143a5-manages-ont-catv-and-catv-onu-tasks-2l4m | The [Huawei EG8143A5](http://www.ontolt.com) is an advanced Optical Network Terminal (ONT) renowned for its capability to seamlessly integrate Cable Television (CATV) services through its [ONT CATV](http://www.ontolt.com) and CATV ONU features. In this technical breakdown, we delve into the inner workings of the EG8143... | jack_heryson_90d856aa50ff | |
1,903,482 | Leveraging Small Business Set-Asides for Government Contracting Growth | Discover how leveraging small business set-asides can propel your company to new heights in the lucrative world of government contracting. | 0 | 2024-06-28T02:54:54 | https://www.govcon.me/blog/leveraging_small_business_set_asides_for_government_contracting_growth | governmentcontracting, smallbusiness, growthstrategies | # Leveraging Small Business Set-Asides for Government Contracting Growth
In the dynamic landscape of business, small enterprises are constantly seeking opportunities to scale and grow. One of the lesser-tapped yet highly lucrative avenues for small businesses is government contracting. The U.S. government earmarks bil... | quantumcybersolution |
1,903,481 | How Construction Technology is Enhancing Collaboration Among Teams | Explore how cutting-edge construction technologies are revolutionizing team collaboration, optimizing workflows, and driving the industry forward. | 0 | 2024-06-28T02:54:48 | https://www.govcon.me/blog/how_construction_technology_is_enhancing_collaboration_among_teams | constructiontechnology, collaboration, innovation | # How Construction Technology is Enhancing Collaboration Among Teams
The construction industry, often perceived as traditional and slow to change, is experiencing a remarkable transformation thanks to innovative technologies. These advancements are not just improving the efficiency and safety of construction projects,... | quantumcybersolution |
1,903,480 | DVD Rippers for Mac in 2024 | For Mac users, converting DVDs to digital formats is becoming increasingly essential. DVD ripping... | 0 | 2024-06-28T02:54:44 | https://dev.to/nancychiu_/dvd-rippers-for-mac-in-2024-1eik | software | For Mac users, converting DVDs to digital formats is becoming increasingly essential. DVD ripping software provides a practical solution, enabling the enjoyment of movies and shows on any device without relying on physical discs. With numerous options available in 2024, identifying the most suitable DVD ripper can be a... | nancychiu_ |
1,903,479 | Democratizing Drug Discovery The Case for Open Source Pharma Platforms | Explore the potential of open source pharma discovery platforms in democratizing drug discovery and empowering people. Learn how decentralizing the pharmaceutical industry, inspired by the success of AI communities like Hugging Face, can lead to more accessible and affordable medicines while still benefiting all stakeh... | 0 | 2024-06-28T02:52:32 | https://www.rics-notebook.com/blog/Health/DDD | opensource, pharma, drugdiscovery, decentralization | # Democratizing Drug Discovery: The Case for Open Source Pharma Platforms 💊🌍
The world of technology and artificial intelligence (AI) has witnessed the tremendous success of open source communities like Hugging Face, which have democratized access to cutting-edge AI tools and research. It's time for the pharmac... | eric_dequ |
1,903,478 | How to Enhance Content Marketing Effectiveness with Data and Analytics? | Hello, everyone! In today's digital market, content marketing is no longer just about creating... | 0 | 2024-06-28T02:51:54 | https://dev.to/juddiy/how-to-enhance-content-marketing-effectiveness-with-data-and-analytics-3cpj | learning, beginners | Hello, everyone!
In today's digital market, content marketing is no longer just about creating engaging articles or videos. It has evolved into a science that requires integrating data and deep analysis to achieve optimal results. With the right data and analytics tools, you can precisely understand audience needs, be... | juddiy |
1,903,477 | Javascript Ls/ss/cookies | Browser Memory: localStorage Session... | 0 | 2024-06-28T02:50:53 | https://dev.to/bekmuhammaddev/javascript-lssscookies-55f1 | engweb, aripovdev, javascript, localstorage | **Browser Memory:**
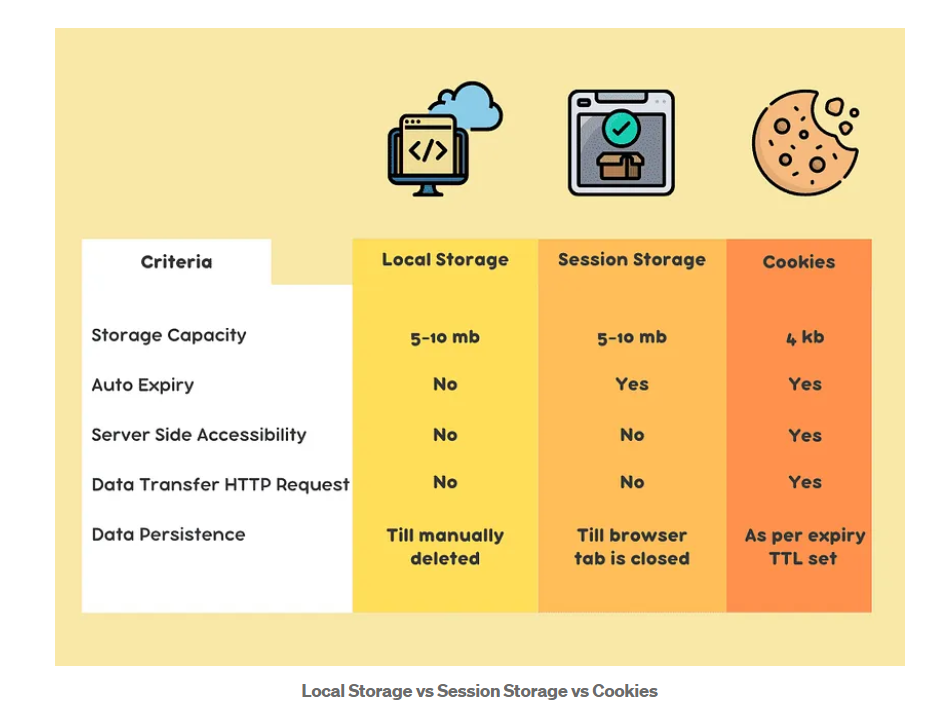
- localStorage
- Session Storage
- Cookies
**Method**
SetItem();
GetItem();
RemoveItem();
Clear();
**Local Storage**
localStorage for long-term storage of data in the browser. 5-10 MB of memo... | bekmuhammaddev |
1,903,475 | Leveraging Small Business Administration SBA Resources for Contracting Success | Discover how the Small Business Administration (SBA) can be a game-changer for small businesses seeking to break into government contracting. Learn about the myriad resources and programs SBA offers to help your business soar. | 0 | 2024-06-28T02:49:47 | https://www.govcon.me/blog/leveraging_small_business_administration_sba_resources_for_contracting_success | smallbusiness, sba, contracting, success | # Leveraging Small Business Administration (SBA) Resources for Contracting Success
Government contracts are a significant avenue for small businesses looking to expand their market reach and grow their customer base. However, navigating the complex world of government contracting can be daunting. Enter the **Small Bus... | quantumcybersolution |
1,903,331 | Angular and ReactJS : Which Front-End Technology to Choose ? | Hi everyone! My name is Dominique NLANDU, and I'm currently an intern at HNG. Passionate about web... | 0 | 2024-06-28T02:48:36 | https://dev.to/dom-nlk/angular-and-reactjs-which-front-end-technology-to-choose--158n | Hi everyone! My name is Dominique NLANDU, and I'm currently an intern at HNG. Passionate about web development, I've recently started exploring front-end technologies to create interactive and dynamic user interfaces. As part of my internship at HNG, I have the opportunity to work with ReactJS, one of the most popular ... | dom-nlk | |
1,903,472 | Datura The Enigmatic Plant and Its Spiritual Journey Through Time | Explore the mystical world of Datura, a plant shrouded in mystery and spiritual significance. From ancient shamanic rituals to modern-day spiritual exploration, discover the history, uses, and profound experiences associated with this enigmatic botanical ally. | 0 | 2024-06-28T02:47:25 | https://www.rics-notebook.com/blog/Health/Datura | entheogens, shamanism, spirituality, herbalism | # Datura: The Enigmatic Plant and Its Spiritual Journey Through Time 🌿🔮
Datura, a genus of plants known for their striking appearance and potent psychoactive properties, has captivated the minds of spiritual seekers and shamanic practitioners throughout history. This enigmatic botanical ally has been revered for its... | eric_dequ |
1,903,471 | How Construction Drones are Revolutionizing Project Surveys and Inspections | Unveil the transformative potential of drones in construction, boosting efficiency, cost-effectiveness, and safety through innovative project surveys and inspections. | 0 | 2024-06-28T02:44:40 | https://www.govcon.me/blog/how_construction_drones_are_revolutionizing_project_surveys_and_inspections | construction, drones, technology | # How Construction Drones are Revolutionizing Project Surveys and Inspections
In the ever-evolving landscape of construction technology, one advancement is soaring above the rest—drones. These unassuming airborne marvels are rewriting the rulebook on how project surveys and inspections are conducted. Once relegated to... | quantumcybersolution |
1,903,470 | Leveraging Procurement Technical Assistance Centers PTACs for Contracting Success | Discover how Procurement Technical Assistance Centers (PTACs) can boost your business contracting efforts. From expert guidance to invaluable resources, learn how PTACs can be a game-changer for your contracting success. | 0 | 2024-06-28T02:44:39 | https://www.govcon.me/blog/leveraging_procurement_technical_assistance_centers_ptacs_for_contracting_success | procurement, businessgrowth, contracting | # Leveraging Procurement Technical Assistance Centers (PTACs) for Contracting Success
In the competitive world of government and corporate contracting, having the right resources and support can significantly enhance your chances of success. Enter Procurement Technical Assistance Centers (PTACs), an often underutilize... | quantumcybersolution |
1,903,468 | Declaração e Inicialização de Variáveis em Java | Declaração de Variáveis Todas as variáveis devem ser declaradas antes de seu uso. Necessário para... | 0 | 2024-06-28T02:43:21 | https://dev.to/devsjavagirls/declaracao-e-inicializacao-de-variaveis-em-java-2h6o | java | **Declaração de Variáveis**
- Todas as variáveis devem ser declaradas antes de seu uso.
- Necessário para que o compilador saiba o tipo de dado da variável.
- Permite verificação rigorosa de tipos.
**Inicialização de Variáveis**
- É recomendável dar um valor à variável antes de usá-la.
**Pode ser feita por:**
- Instr... | devsjavagirls |
1,881,915 | State and Props In React | What is The State In React ? 👉 State is a way to Keep Track of Data that can Change in your... | 0 | 2024-06-09T09:15:07 | https://dev.to/pervez/state-and-props-in-react-4eib | **What is The State In React ?**
👉 State is a way to Keep Track of Data that can Change in your Application. State is a Plain JavaScript Object that holds information that may change during the components life cycle. this data directly Affects the Components behavior and appearance . When The state changes , React Re... | pervez | |
1,903,465 | Probiotics and Prebiotics Unleashing the Power of Gut Health for Mental Well-being | Explore the fascinating connection between gut health and mental well-being, and discover how probiotics and prebiotics can revolutionize the way we approach depression treatment. Could a new strain of alcohol-resistant probiotics be the key to unlocking a happier, healthier mind? 🔑 | 0 | 2024-06-28T02:37:10 | https://www.rics-notebook.com/blog/Health/Biotic | probiotics, prebiotics, guthealth, mentalhealth | ## 🌟 Probiotics and Prebiotics: Unleashing the Power of Gut Health for Mental Well-being
In recent years, the intricate connection between gut health and mental well-being has become increasingly evident. The complex ecosystem of bacteria residing in our gut, known as the gut microbiome, plays a crucial role not only... | eric_dequ |
1,903,463 | Diferença entre Strings e Literais de Caracteres | Um string composto por um único caractere é o mesmo que um literal de caractere? Por exemplo, "k" é o... | 0 | 2024-06-28T02:36:48 | https://dev.to/devsjavagirls/diferenca-entre-strings-e-literais-de-caracteres-414n | java | **Um string composto por um único caractere é o mesmo que um literal de caractere? Por exemplo, "k" é o mesmo que 'k'?**
**Literal de Caractere:**
- Representa uma única letra.
- Tipo char.
- Exemplo: 'k'.
**String de um Único Caractere:**
- Contém apenas uma letra, mas ainda é uma string.
- Tipo String.
**Exemplo: ... | devsjavagirls |
1,903,461 | How Big Data is Driving Decision-Making in Construction Projects | Discover how the revolutionary power of Big Data is transforming decision-making processes in the construction industry, leading to smarter, more efficient, and safer projects. | 0 | 2024-06-28T02:34:33 | https://www.govcon.me/blog/how_big_data_is_driving_decision_making_in_construction_projects | bigdata, construction, innovation | # How Big Data is Driving Decision-Making in Construction Projects
In the realm of marvels and skyscraping wonders, construction has always been a domain of grit, sweat, and an indefatigable spirit to build the impossible. But hold onto your hard hats, because the industry is evolving at breakneck speed. Big Data is h... | quantumcybersolution |
1,903,460 | Leveraging Certifications for Government Contracting Advantages 8a HUBZone and More | Discover how small businesses can gain a competitive edge in government contracting through certifications like 8(a), HUBZone, and others, unlocking opportunities and enhancing capabilities. | 0 | 2024-06-28T02:34:25 | https://www.govcon.me/blog/leveraging_certifications_for_government_contracting_advantages_8a_hubzone_and_more | governmentcontracting, certifications, smallbusiness | # Leveraging Certifications for Government Contracting Advantages: 8(a), HUBZone, and More
The world of government contracting can seem daunting, but it also offers a wealth of opportunities for small businesses. What if we told you that certifications could be your secret weapon? In this post, we’ll delve into the es... | quantumcybersolution |
1,903,459 | Overcoming a Challenging Backend Problem with TypeScript: My Journey and Aspiration | Introduction As a backend developer, you must solve complex challenges on a regular basis,... | 0 | 2024-06-28T02:32:25 | https://dev.to/greegman/overcoming-a-challenging-backend-problem-with-typescript-my-journey-and-aspiration-5gda | ## Introduction
As a backend developer, you must solve complex challenges on a regular basis, but every now and then, a particularly difficult problem emerges that tests your expertise and inventiveness. I recently experienced such a situation while working on a project, and I'd want to share my experience with it, pa... | greegman | |
1,903,458 | Ayahuasca Exploring the Spiritual Realm and the Science of MAOIs | Embark on a journey into the heart of the ayahuasca experience, where ancient shamanic wisdom intertwines with modern scientific understanding. Explore the spiritual significance of this sacred brew and uncover the pharmacological mechanisms that make it a potent tool for inner exploration and healing. 🌈 | 0 | 2024-06-28T02:32:03 | https://www.rics-notebook.com/blog/Health/Ayahuasca | ayahuasca, shamanism, spirituality, maois | ## 🌟 Ayahuasca: Exploring the Spiritual Realm and the Science of MAOIs
Deep within the lush Amazon rainforest, a sacred brew has been used for centuries by indigenous shamans to facilitate profound spiritual experiences and healing. This brew, known as ayahuasca, has garnered global attention for its ability to induc... | eric_dequ |
1,903,457 | MyFirstApp - React Native with Expo (P3) - Code Layout Detail Screen | MyFirstApp - React Native with Expo (P3) - Code Layout Detail Screen | 27,894 | 2024-06-28T02:31:55 | https://dev.to/skipperhoa/myfirstapp-react-native-with-expo-p3-code-layout-detail-screen-2264 | react, reactnative, webdev, tutorial | MyFirstApp - React Native with Expo (P3) - Code Layout Detail Screen
{% youtube 3BTwffSS8BA %} | skipperhoa |
1,903,456 | Literais em Java | Literais em Java 1. Definição de Literais: Valores fixos representados em forma legível por... | 0 | 2024-06-28T02:29:39 | https://dev.to/devsjavagirls/literais-em-java-d34 | java | **Literais em Java**
**1. Definição de Literais:**
- Valores fixos representados em forma legível por humanos (e.g., número 100).
- Também chamados de constantes.
- Intuitivos e usados frequentemente.
**2. Tipos de Literais:**
- Tipos Primitivos: Podem ser de qualquer tipo de dado primitivo.
- Caracteres: Delimitados... | devsjavagirls |
1,903,450 | MyFirstApp - React Native with Expo (P1) | ⚡ MyFirstApp - React Native with Expo (P1) | 27,894 | 2024-06-28T02:24:47 | https://dev.to/skipperhoa/myfirstapp-react-native-with-expo-p1-2of3 | react, reactnative, appmobi, webdev | **⚡ MyFirstApp - React Native with Expo (P1)**
{% youtube MeA5rSvGCa0 %}
| skipperhoa |
1,903,455 | Leveraging Artificial Intelligence for Contract Management | Examine how AI-powered tools are transforming contract management in government contracting, helping businesses automate processes, ensure compliance, and manage large volumes of contracts more effectively. | 0 | 2024-06-28T02:29:18 | https://www.govcon.me/blog/leveraging_artificial_intelligence_for_contract_management | ai, contractmanagement, governmentcontracting, automation | ## Leveraging Artificial Intelligence for Contract Management
### Introduction
In the ever-evolving landscape of government contracting, effective contract management is crucial for ensuring compliance, transparency, and efficiency. Artificial Intelligence (AI) has emerged as a transformative force, revolutionizing ho... | quantumcybersolution |
1,875,732 | Host Your Website With Only $0.50 A Month | How to Host Your Website for Just $0.50! Do you want to host your website for just $0.50?... | 0 | 2024-06-28T02:28:16 | https://dev.to/rishabh_verma_1fdfa7f9c0d/host-your-website-with-only-050-a-month-4hki | aws, devops | ## How to Host Your Website for Just $0.50!
Do you want to host your website for just $0.50? You heard me right! It’s not clickbait—just keep reading.
I’m in my final year, and I have a dream of building my own portfolio website. However, there’s a significant hurdle: hosting a website is expensive. If you check out ... | rishabh_verma_1fdfa7f9c0d |
1,903,453 | MyFirstApp - React Native with Expo (P2) - Code Layout Menu Screen | MyFirstApp - React Native with Expo (P2) - Code Layout Menu Screen | 27,894 | 2024-06-28T02:27:04 | https://dev.to/skipperhoa/myfirstapp-react-native-with-expo-p2-code-layout-menu-screen-300m | webdev, react, reactnative, appmobile | MyFirstApp - React Native with Expo (P2) - Code Layout Menu Screen
{% youtube abVcKdTwmfg %} | skipperhoa |
1,903,452 | Building an Auto Grow Mushroom Box A Comprehensive Guide | Interested in growing your own mushrooms effortlessly? Learn how to build an Auto Grow Mushroom Box with this detailed guide. From microcontrollers to sensors, we cover everything you need to get started. 🌱 | 0 | 2024-06-28T02:26:56 | https://www.rics-notebook.com/blog/Health/AGMB | mushroomgrowing, diyprojects, homegardening, technology | ## 🌟 Building an Auto Grow Mushroom Box: A Comprehensive Guide
Growing mushrooms at home can be both rewarding and fascinating. To make the process even easier, you can build an Auto Grow Mushroom Box that automates the key conditions required for mushroom cultivation. This guide will walk you through the parts neede... | eric_dequ |
1,903,451 | SOLID | SOLID é um acrônimo que representa cinco princípios fundamentais da programação orientada a objetos e... | 0 | 2024-06-28T02:26:01 | https://dev.to/edsonrodsilva/solid-4p86 | javascript, webdev | **SOLID** é um acrônimo que representa cinco princípios fundamentais da programação orientada a objetos e design de software. Esses princípios ajudam os desenvolvedores a criar sistemas mais compreensíveis, flexíveis e manuteníveis. Aqui está um breve resumo de cada princípio:
**S - Princípio da Responsabilidade Única... | edsonrodsilva |
1,903,449 | How Augmented Reality is Enhancing Construction Planning and Execution | Exploring how augmented reality (AR) is revolutionizing the construction industry, from meticulous planning to efficient execution. | 0 | 2024-06-28T02:24:26 | https://www.govcon.me/blog/how_augmented_reality_is_enhancing_construction_planning_and_execution | augmentedreality, construction, innovation | # How Augmented Reality is Enhancing Construction Planning and Execution
From blueprints to breathtaking skyscrapers, the construction industry has always been at the forefront of innovation. But in recent years, one technology is set to transform the game: Augmented Reality (AR). Imagine walking through a completed b... | quantumcybersolution |
1,903,447 | Labor Compliance Essentials for Government Contractors | Dive into the essentials of labor compliance for government contractors, exploring key regulations, innovative strategies, and best practices to ensure your business stays compliant and competitive. | 0 | 2024-06-28T02:24:11 | https://www.govcon.me/blog/labor_compliance_essentials_for_government_contractors | governmentcontracts, laborcompliance, regulations | # Labor Compliance Essentials for Government Contractors
Welcome, tech enthusiasts and innovators! Today, we're diving into a critical, yet often overlooked, aspect of government contracting: **Labor Compliance**.
## Why Labor Compliance Matters
Being a government contractor opens the door to numerous opportuni... | quantumcybersolution |
1,903,446 | ## How to Set Up ESLint and Prettier in a TypeScript Project | Setting up ESLint and Prettier in a TypeScript project can greatly enhance your development... | 0 | 2024-06-28T02:21:50 | https://dev.to/forhad96/-how-to-set-up-eslint-and-prettier-in-a-typescript-project-3pi2 | webdev, typescript, eslint, prettier | Setting up ESLint and Prettier in a TypeScript project can greatly enhance your development experience by automatically detecting and fixing various types of errors, ensuring a consistent code style, and reducing the likelihood of bugs. Here's a step-by-step guide to help you get started.
### Step 1: Initialize Your P... | forhad96 |
1,903,445 | Absinthe A Storied Elixir Poised for a Modern Revival | Dive into the rich history of absinthe, the legendary spirit that has captivated artists and writers for centuries. Discover why it’s time for absinthe to make a comeback in modern mixology and cultural appreciation. 🍸 | 0 | 2024-06-28T02:21:48 | https://www.rics-notebook.com/blog/Health/Absinthe | absinthe, history, spirits, revival | ## 🌟 Absinthe: A Storied Elixir Poised for a Modern Revival
Absinthe, often referred to as the "Green Fairy," is a spirit steeped in mystique and history. Known for its distinct flavor and association with artistic bohemian culture, absinthe has experienced both adulation and controversy. This blog post del... | eric_dequ |
1,895,188 | I made a Course | I’ve created a course with Newline called “Fullstack Typescript with TailwindCSS and tRPC Using... | 0 | 2024-06-21T07:21:25 | https://dev.to/kristiandupont/i-made-a-course-25ki | ---
title: I made a Course
published: true
date: 2024-06-20 19:08:36 UTC
tags:
canonical_url:
---
I’ve created a course with Newline called “Fullstack Typescript with TailwindCSS and tRPC Using Modern Features of PostgreSQL”. It basically teaches what is currently my favourite stack, from top to bottom. I am honestl... | kristiandupont | |
1,903,444 | Understanding Recurring Neural Networks (RNNs) | In the dynamic field of artificial intelligence and machine learning, Recurring Neural Networks... | 27,893 | 2024-06-28T02:21:48 | https://dev.to/monish3004/understanding-recurring-neural-networks-rnns-478f | deeplearning, computerscience, nlp, beginners | In the dynamic field of artificial intelligence and machine learning, Recurring Neural Networks (RNNs) hold a unique place. Unlike traditional neural networks, RNNs are designed to recognize patterns in sequences of data, such as time series, speech, text, financial data, and even DNA sequences. This ability to conside... | monish3004 |
1,903,418 | Implementing Earned Value Management EVM in Government Projects | Explore how Earned Value Management (EVM) can transform government projects, boost efficiency, transparency, and deliver value on time and within budget. | 0 | 2024-06-28T02:19:03 | https://www.govcon.me/blog/implementing_earned_value_management_evm_in_government_projects | evm, projectmanagement, government | # Implementing Earned Value Management (EVM) in Government Projects
When it comes to managing government projects, efficiency, transparency, and accountability are critical. As public funds fuel these projects, stakeholders demand a meticulous approach to ensure that every dollar is well-spent. Enter **Earned Value Ma... | quantumcybersolution |
1,903,417 | Protect Your Website from XSS Attacks | Cross-site scripting (XSS) is a type of security vulnerability that allows attackers to inject malicious code into a web page. Learn about the two main types of XSS attacks, best practices for preventing XSS attacks, and additional tips for protecting your website from XSS attacks. | 0 | 2024-06-28T02:16:41 | https://www.rics-notebook.com/blog/hacking/Xss | xss, attacks, cybersecurity | ## What are XSS Attacks?
💻 Cross-site scripting (XSS) is a type of security vulnerability that allows an
attacker to inject malicious code into a web page. This malicious code can then
steal cookies, session tokens, or other sensitive information, hijack accounts,
deface websites, or redirect users to malicious websi... | eric_dequ |
1,903,416 | Teach you how to choose LED transparent screen correctly | When choosing LED transparent screen, many customers often only focus on price and ignore the... | 0 | 2024-06-28T02:16:01 | https://dev.to/sostrondylan/teach-you-how-to-choose-led-transparent-screen-correctly-107k | led, transparent, screen | When choosing [LED transparent screen](https://sostron.com/products/crystal-transparent-led-screen/), many customers often only focus on price and ignore the importance of technology, skills and equipment. This is mainly because customers lack understanding of transparent LED display screens and easily mistakenly belie... | sostrondylan |
1,879,445 | The case against comments | Most developers starting out assume comments are like sprinkles. They're something everyone likes and... | 0 | 2024-06-28T00:54:54 | https://dev.to/stackoverfloweth/the-case-against-comments-4kne | beginners | Most developers starting out assume comments are like sprinkles. They're something everyone likes and the more you use it, the prettier your donut. One of my favorite authors Robert C. Martin, author of "Clean Code", has this to say about comments.
> "Usually they are crutches or excuses for poor code or justification... | stackoverfloweth |
1,903,415 | How Artificial Intelligence is Improving Construction Site Security | Explore how cutting-edge AI technologies are revolutionizing construction site security by enhancing monitoring, predicting risks, and ensuring a safer work environment. | 0 | 2024-06-28T02:14:18 | https://www.govcon.me/blog/how_artificial_intelligence_is_improving_construction_site_security | ai, construction, security, innovation | # How Artificial Intelligence is Improving Construction Site Security
Construction sites are bustling hubs of activity. Bulldozers roar, cranes soar high, and hundreds of skilled workers work tirelessly to bring blueprints to life. Amidst this controlled chaos, ensuring the security of both personnel and equipment is ... | quantumcybersolution |
1,903,414 | Implementing Continuous Improvement Practices in Government Contracting | Exploring how continuous improvement practices can revolutionize government contracting by making it more efficient, transparent, and responsive to change. | 0 | 2024-06-28T02:13:56 | https://www.govcon.me/blog/implementing_continuous_improvement_practices_in_government_contracting | government, continuousimprovement, contracting | # Implementing Continuous Improvement Practices in Government Contracting
Government contracting is often seen as a complex and rigid field with numerous regulations and cumbersome processes. However, incorporating continuous improvement practices can revolutionize how these contracts are managed, making them more eff... | quantumcybersolution |
1,903,413 | Comparing ONT CATV and CATV ONU Devices: Why Huawei EG8143A5 Stands Out | In today's digitally connected world, the demand for high-speed internet and reliable cable... | 0 | 2024-06-28T02:12:18 | https://dev.to/mian_mudassariqbal_439eb/comparing-ont-catv-and-catv-onu-devices-why-huawei-eg8143a5-stands-out-2c7b | In today's digitally connected world, the demand for high-speed internet and reliable cable television services is ever-increasing. To meet this demand, devices like [ONT CATV](http://www.ontolt.com) (Optical Network Terminal Cable Television) and [CATV ONU](http://www.ontolt.com) (Cable Television Optical Network Unit... | mian_mudassariqbal_439eb | |
1,903,412 | TypeScript Node.js Boilerplate | When developing a Node.js application, integrating TypeScript can significantly enhance your coding... | 0 | 2024-06-28T02:11:56 | https://dev.to/rohanyh101/typescript-nodejs-boilerplate-1fpm | webdev, node, typescript, api |
When developing a Node.js application, integrating TypeScript can significantly enhance your coding experience Combining these benefits with tools like nodemon and ts-node can streamline your development workflow. Here's a ... | rohanyh101 |
1,903,411 | Getting Started with Kali Linux A Beginners Guide | This blog post introduces Kali Linux, a powerful Debian-based distribution designed for penetration testing and security auditing. We will cover the installation process, basic usage, setting up Kali Linux, and available resources to help you get started. 🚀 | 0 | 2024-06-28T02:11:34 | https://www.rics-notebook.com/blog/hacking/Kali | kalilinux, security, penetrationtesting | ## What is Kali Linux? 🐉
Kali Linux is a Debian-based Linux distribution designed for penetration testing and security auditing. It is a powerful tool that can be used to find and exploit vulnerabilities in computer systems. Kali Linux comes with a wide range of tools and utilities that can be used for a variety of s... | eric_dequ |
1,903,410 | Implementing an Earned Value Management System EVMS for Government Projects | Dive deep into the world of Earned Value Management Systems (EVMS) and discover the key benefits, challenges, and implementation strategies for managing government projects efficiently and effectively. | 0 | 2024-06-28T02:08:49 | https://www.govcon.me/blog/implementing_an_earned_value_management_system_evms_for_government_projects | evms, governmentprojects, projectmanagement | # Implementing an Earned Value Management System (EVMS) for Government Projects
Implementing an Earned Value Management System (EVMS) in government projects is not just a visionary approach—it's a game changer! Imagine tracking a project's performance in real-time, forecasting future trends, and diagnosing p... | quantumcybersolution |
1,903,409 | Protect Your Website from DDoS Attacks | Distributed denial-of-service (DDoS) attacks are becoming increasingly common and can result in significant damage to businesses and organizations. Learn about the causes of DDoS attacks, how to prevent them, and tips for protecting your website or server from this devastating cyber attack. | 0 | 2024-06-28T02:06:27 | https://www.rics-notebook.com/blog/hacking/DDos | ddos, cybersecurity | ## What is a DDoS Attack?
💻 A distributed denial-of-service (DDoS) attack is a cyber attack in which a
large number of computers are used to flood a website or server with so much
traffic that it becomes unavailable to its intended users. DDoS attacks can be
used to disrupt businesses, governments, and other organiza... | eric_dequ |
1,903,408 | How 5G Connectivity is Enhancing Construction Site Communication | Exploring how next-generation 5G technology is revolutionizing communication and operational efficiency on construction sites. | 0 | 2024-06-28T02:04:11 | https://www.govcon.me/blog/how_5g_connectivity_is_enhancing_construction_site_communication | 5g, construction, innovation | # How 5G Connectivity is Enhancing Construction Site Communication
Construction sites are inherently complex environments, bustling with activity, materials, machinery, and personnel. Effective communication is the backbone of a well-functioning construction site, directly influencing productivity, safety, and project... | quantumcybersolution |
1,903,407 | Harnessing the Power of PIEE for Seamless Contract Management | Explore how the Procurement Integrated Enterprise Environment (PIEE) transforms contract management with advanced features and seamless integration. | 0 | 2024-06-28T02:03:41 | https://www.govcon.me/blog/harnessing_the_power_of_piee_for_seamless_contract_management | contractmanagement, piee, technology | # Harnessing the Power of PIEE for Seamless Contract Management
In the fast-paced world of contract management, staying ahead of the curve is essential. Enter the **Procurement Integrated Enterprise Environment (PIEE)**, a game-changer that is revolutionizing the way organizations handle contracts. Whether you're... | quantumcybersolution |
1,903,406 | Be Safe and Secure with Credit Card Scanners | Credit card scanners are devices that can read magnetic stripes or chips on credit or debit cards. Learn about the two main types of credit card scanners, where they can be found, and tips for protecting yourself from credit card scanner fraud. | 0 | 2024-06-28T02:01:19 | https://www.rics-notebook.com/blog/hacking/CardScanner | creditcard, scanners, cybersecurity, fraudprevention | ## What are Credit Card Scanners?
💳 Credit card scanners are devices that can read the magnetic stripe or chip on
a credit or debit card. They are often used by merchants to process payments,
but they can also be used by criminals to steal card information.
## Types of Credit Card Scanners
There are two main types ... | eric_dequ |
1,903,405 | How to secure a REST API? | In this post, we'll discuss what REST APIs are and how to secure them. | 0 | 2024-06-28T02:00:28 | https://snyk.io/blog/how-to-secure-rest-api/ | applicationsecurity, codesecurity, opensourcesecurity | As developers, we often have to work with REST APIs when we integrate with third-party systems or connect between frontend and backend systems at work. APIs, and REST APIs in particular, are a fundamental part of modern web applications, allowing us to create, read, update, and delete data over HTTP. However, as with a... | snyk_sec |
1,903,404 | Harnessing GovWin IQ for Superior Government Contracting Market Intelligence | Discover how GovWin IQ can transform your approach to government contracting by providing unparalleled market intelligence and contract opportunities. | 0 | 2024-06-28T01:58:34 | https://www.govcon.me/blog/harnessing_govwin_iq_for_superior_government_contracting_market_intelligence | governmentcontracting, marketintelligence, govwiniq | ## Introduction
In the fast-paced world of government contracting, having up-to-date and accurate market intelligence is the key to success. Enter **GovWin IQ**, the premier market intelligence platform that acts as your gateway to unlocking government contract opportunities. Whether you're a seasoned contractor ... | quantumcybersolution |
1,903,403 | Building Trust The Importance of Past Performance in Government Sales | In the government contracting world, your track record speaks volumes. Understand why past performance is crucial and how to leverage it effectively in securing government contracts. | 0 | 2024-06-28T01:56:11 | https://www.rics-notebook.com/blog/Government/Trust | government, sales, trust, contracting | ## Why Past Performance Matters 🎖️🏛️
When it comes to government contracts, agencies want assurance. They seek vendors with a proven track record of delivering quality products or services on time and within budget.
## Benefits of a Strong Track Record
💥 A stellar past performance can be your business's stro... | eric_dequ |
1,893,298 | Chapter 1 | Introduction Hello, fellow developers and enthusiasts! I'm thrilled to share with you the... | 27,772 | 2024-06-19T08:25:19 | https://dev.to/mewdev/zusflix-chapter-1-3n2c | nextjs, junior, react, learning | ## Introduction
Hello, fellow developers and enthusiasts! I'm thrilled to share with you the journey of my most ambitious portfolio project to date – Zušflix. As a junior developer, I wanted to push myself beyond my comfort zone and create something that would not only challenge my existing skills but also help me gro... | mewdev |
1,903,402 | How 3D Scanning is Enhancing Construction Project Documentation | Explore how cutting-edge 3D scanning technology is revolutionizing the way construction projects are documented, making the building process more accurate, efficient, and safe. | 0 | 2024-06-28T01:54:04 | https://www.govcon.me/blog/how_3d_scanning_is_enhancing_construction_project_documentation | construction, 3dscanning, technology, innovation | # How 3D Scanning is Enhancing Construction Project Documentation
In an industry where precision is paramount, the construction field has always been an arena ripe for technological disruption. One innovation making waves is 3D scanning technology, which is rapidly transforming how construction projects are documented... | quantumcybersolution |
1,903,401 | Handling Contract Modifications What to Do When Scope Cost or Timeline Changes | Navigating contract modifications can be challenging. Learn effective strategies to handle changes in scope, cost, or timeline without disrupting your project flow. | 0 | 2024-06-28T01:53:26 | https://www.govcon.me/blog/handling_contract_modifications_what_to_do_when_scope_cost_or_timeline_changes | projectmanagement, contracts, businessstrategy | # Handling Contract Modifications: What to Do When Scope, Cost, or Timeline Changes
Contracts are the bedrock of any project initiative, setting the stage for deliverables, timelines, and costs. However, as projects evolve, so do realities. More often than not, we encounter changes in scope, cost, or timeline that nec... | quantumcybersolution |
1,903,135 | “Good Commit” vs “Your Commit”: How to Write a Perfect Git Commit Message | "A good commit shows whether a developer is a good collaborator." — Peter Hutterer, Linux. Years... | 0 | 2024-06-28T01:51:00 | https://dev.to/safdarali/good-commit-vs-your-commit-how-to-write-a-perfect-git-commit-message-59ol | git, commitmessages, versioncontrol, codequality | `"A good commit shows whether a developer is a good collaborator." — Peter Hutterer, Linux.`
Years ago, I never realized there were specific rules for writing commit messages until my curiosity got the best of me. I used to think that straightforward messages like “added feature 2,” “fixed the bug on the Main Navigati... | safdarali |
1,903,400 | GSA Schedules 101 What They Are and How to Get on Them | Unlock the secrets of GSA Schedules, the gateway to lucrative government contracts for your business. Learn what they are, their benefits, and how to get listed! | 0 | 2024-06-28T01:48:19 | https://www.govcon.me/blog/gsa_schedules_101_what_they_are_and_how_to_get_on_them | government, procurement, business | # GSA Schedules 101: What They Are and How to Get on Them
Welcome to the exciting world of GSA Schedules! If you’re a business owner looking to secure lucrative government contracts, you’ve come to the right place. Getting on a GSA Schedule is like having a golden ticket, allowing you to sell goods and services direct... | quantumcybersolution |
1,903,399 | Government RFPs Deciphering and Responding Effectively | Responding to a government Request for Proposal (RFP) can be daunting. Dive into the intricacies of RFPs and gather insights on crafting compelling responses that stand out. | 0 | 2024-06-28T01:45:57 | https://www.rics-notebook.com/blog/Government/RFP | rfps, government, sales, proposal | ## What is a Government RFP? 📜🔍
A Request for Proposal (RFP) is a formal document issued by government agencies when they seek to procure services or products. It provides detailed information about the project, requirements, and criteria for vendor selection.
## Why RFPs are Challenging
💥 Navigating a government... | eric_dequ |
1,903,398 | Creating an EC2 Instance and Connecting via SSH with IAM User | Introduction Creating and managing cloud infrastructure can be streamlined with AWS and Terraform.... | 0 | 2024-06-28T01:45:41 | https://dev.to/kaviya_kathirvelu_0505/creating-an-ec2-instance-and-connecting-via-ssh-with-iam-user-5c5e | aws, cloud, terraform | **Introduction**
Creating and managing cloud infrastructure can be streamlined with AWS and Terraform. This blog post will guide you through the process of creating an EC2 instance and an IAM user using the AWS Management Console, and then connecting to the instance via SSH.
**Prerequisites**
Before we begin, ensure... | kaviya_kathirvelu_0505 |
1,903,396 | Harnessing Technology for Effective Construction Waste Management | Discover how innovative technologies are transforming construction waste management, making it more efficient, sustainable, and cost-effective. | 0 | 2024-06-28T01:43:56 | https://www.govcon.me/blog/harnessing_technology_for_effective_construction_waste_management | technology, construction, wastemanagement | # Harnessing Technology for Effective Construction Waste Management
Construction projects, while spectacular achievements of human engineering and creativity, often generate significant amounts of waste. Managing this waste responsibly is crucial—not just for compliance and cost-saving, but for the environment. Enter ... | quantumcybersolution |
1,903,395 | GSA Contract Vehicle | The government is a major purchaser of goods and services, but selling to them is no walk in the park. Understand the intricacies of government procurement and how your business can effectively navigate them. | 0 | 2024-06-28T01:43:12 | https://www.govcon.me/blog/GSA | government, procurement, sales, business | ## Understanding Government Procurement 🏛️🔄
Government procurement, the process by which government agencies purchase goods and services from the private sector, operates under a unique set of regulations, standards, and procedures. While the potential for lucrative contracts is high, so is the complexity.
## Why S... | quantumcybersolution |
1,903,384 | Comprehensive React.js Cheatsheet for Developers | React.js has become a cornerstone in modern web development for building dynamic and high-performance... | 0 | 2024-06-28T01:26:54 | https://raajaryan.tech/comprehensive-reactjs-cheatsheet-for-developers | react, javascript, beginners, tutorial | React.js has become a cornerstone in modern web development for building dynamic and high-performance web applications. This comprehensive cheatsheet will cover everything you need to know to master React.js, including practical examples, code snippets, and detailed explanations of all features. The goal is to provide ... | raajaryan |
1,903,394 | Building Relationships The Key to Long-Term Government Sales Success | While bids and proposals play a role, nurturing relationships is often the secret sauce to long-term success in government sales. Understand the power of connections and how to cultivate them effectively. | 0 | 2024-06-28T01:40:50 | https://www.rics-notebook.com/blog/Government/Relationships | government, sales, relationship, networking | ## The Power of Relationships in Government Sales 🤝🏛️
In the world of government sales, it's not just about what you offer, but also who you know. Building and nurturing relationships with key stakeholders can be a game-changer.
## Why Relationships Matter
💥 In the government sector, relationships can:
- 🔥... | eric_dequ |
1,903,393 | Finding Your Niche Identifying the Right Government Contract Opportunities | Discover the keys to pinpointing the perfect government contract opportunities for your business, ensuring a competitive edge and a prosperous venture into the world of federal procurement. | 0 | 2024-06-28T01:38:05 | https://www.govcon.me/blog/finding_your_niche_identifying_the_right_government_contract_opportunities | governmentcontracts, businessdevelopment, entrepreneurship | # Finding Your Niche: Identifying the Right Government Contract Opportunities
If you're an entrepreneur, a business owner, or a startup founder, you've likely heard whispers about the lucrative world of government contracts. These federally funded opportunities can be a goldmine for businesses, but the key t... | quantumcybersolution |
1,903,392 | Get Free Image Hosting with Gur IMG | Get Free Image Hosting with Gur IMG In the digital age, having a reliable and free image... | 0 | 2024-06-28T01:36:09 | https://dev.to/sh20raj/get-free-image-hosting-with-gur-img-4p8i | javascript, hosting | # Get Free Image Hosting with Gur IMG
In the digital age, having a reliable and free image hosting service is crucial for bloggers, web developers, and anyone who needs to share images online. Gur IMG offers an excellent solution with its free and unlimited image hosting service, complete with CDN support for fast and... | sh20raj |
1,903,391 | How to Write a Winning Government Proposal | Learn how to write a winning government proposal and secure federal contracts for your small business. 💼🏛️ | 0 | 2024-06-28T01:35:43 | https://www.rics-notebook.com/blog/Government/Proposals | government, contracting, proposalwriting, businessgrowth | ## How to Write a Winning Government Proposal 💼🏛️
If you're a small business owner looking to secure federal contracts, writing a
winning government proposal is a critical step. Here are some tips to help you
craft a proposal that will stand out:
1. **Read the Request for Proposal (RFP) carefully**: This is th... | eric_dequ |
1,903,383 | GSA Contract Vehicle | The government is a major purchaser of goods and services, but selling to them is no walk in the park. Understand the intricacies of government procurement and how your business can effectively navigate them. | 0 | 2024-06-28T01:25:28 | https://www.rics-notebook.com/blog/Government/GSA | government, procurement, sales, business | ## Understanding Government Procurement 🏛️🔄
Government procurement, the process by which government agencies purchase goods and services from the private sector, operates under a unique set of regulations, standards, and procedures. While the potential for lucrative contracts is high, so is the complexity.
## Why S... | eric_dequ |
1,903,390 | Harnessing Technology for Effective Construction Stakeholder Management | Dive into how technology transforms stakeholder management in the construction industry, ensuring seamless collaboration, transparency, and efficiency. | 0 | 2024-06-28T01:33:49 | https://www.govcon.me/blog/harnessing_technology_for_effective_construction_stakeholder_management | construction, technology, stakeholdermanagement | # Harnessing Technology for Effective Construction Stakeholder Management
Stakeholder management in the construction industry can often feel like juggling a dozen flaming torches. With numerous stakeholders ranging from contractors, subcontractors, developers, local authorities, and even the end-users, ensuring everyo... | quantumcybersolution |
1,903,389 | Exploring Government Contract Financing Options | A deep dive into the diverse financing options available for businesses tackling government contracts and how to leverage them for growth and sustainability. | 0 | 2024-06-28T01:32:57 | https://www.govcon.me/blog/exploring_government_contract_financing_options | finance, governmentcontracts, business | # Exploring Government Contract Financing Options
If you're a business looking to secure a government contract, congratulations! You're stepping into a realm of stability and substantial opportunities. However, winning the contract is just the beginning. One core aspect that often gets overlooked is financin... | quantumcybersolution |
1,903,388 | Navigating the Complexities of Government Procurement | The government is a major purchaser of goods and services, but selling to them is no walk in the park. Understand the intricacies of government procurement and how your business can effectively navigate them. | 0 | 2024-06-28T01:30:35 | https://www.rics-notebook.com/blog/Government/NavigatingGovernment | government, procurement, sales, business | ## Understanding Government Procurement 🏛️🔄
Government procurement, the process by which government agencies purchase goods and services from the private sector, operates under a unique set of regulations, standards, and procedures. While the potential for lucrative contracts is high, so is the complexity.
## Why S... | eric_dequ |
1,903,385 | Ethics and Integrity in Government Contracting Maintaining High Standards | Exploring the crucial role of ethics and integrity in government contracting and how maintaining high standards ensures transparent, fair, and effective procurement processes. This post delves into the key aspects and benefits while uncovering best practices in the field. | 0 | 2024-06-28T01:27:50 | https://www.govcon.me/blog/ethics_and_integrity_in_government_contracting_maintaining_high_standards | ethics, government, integrity, contracting | # Ethics and Integrity in Government Contracting: Maintaining High Standards
In the intricate world of government contracting, where vast sums of taxpayer money are at play, ethics and integrity form the cornerstone of trust and efficacy. The complex interplay of policies, bids, and execution in this domain demands ri... | quantumcybersolution |
1,903,381 | Harnessing Predictive Analytics for Proactive Construction Risk Management | Discover the transformative power of predictive analytics in managing risks within the construction industry. Learn practical applications, benefits, and how this technology is revolutionizing the way construction projects are delivered. | 0 | 2024-06-28T01:23:41 | https://www.govcon.me/blog/harnessing_predictive_analytics_for_proactive_construction_risk_management | predictiveanalytics, construction, riskmanagement | # Harnessing Predictive Analytics for Proactive Construction Risk Management
In the dynamic, high-stakes world of construction, risk management is paramount. From safety concerns to project delays and cost overruns, the industry faces a myriad of challenges that can derail projects. Enter predictive analytics — a powe... | quantumcybersolution |
1,903,380 | Ensuring Compliance with Government Contract Reporting Requirements | In this deep dive, we explore how businesses can ensure compliance with stringent government contract reporting requirements using innovative technology solutions! | 0 | 2024-06-28T01:22:43 | https://www.govcon.me/blog/ensuring_compliance_with_government_contract_reporting_requirements | compliance, governmentcontracts, reporting | # Ensuring Compliance with Government Contract Reporting Requirements
As businesses expand into the domain of government contracting, they often face a maze of regulatory requirements. Ensuring compliance with government contract reporting is not just a bureaucratic necessity—it’s a vital component of operational inte... | quantumcybersolution |
1,903,370 | Top 20 Must-Have Tools for Modern Developers in 2024 | As we step into 2024, the landscape of software development continues to evolve rapidly. New tools... | 0 | 2024-06-28T01:21:17 | https://devtoys.io/2024/06/27/top-20-must-have-tools-for-modern-developers-in-2024/ | productivity, webdev, devtoys | ---
canonical_url: https://devtoys.io/2024/06/27/top-20-must-have-tools-for-modern-developers-in-2024/
---
As we step into 2024, the landscape of software development continues to evolve rapidly. New tools emerge, promising to enhance productivity, streamline workflows, and make coding a more enjoyable experience. Whe... | 3a5abi |
1,903,377 | Just drop a question..... | Any question you want to ask about Javascript? I am here to assist you. Just ask me | 0 | 2024-06-28T01:19:53 | https://dev.to/erasmuskotoka/just-drop-a-question-2ofm | Any question you want to ask about Javascript?
I am here to assist you. Just ask me | erasmuskotoka | |
1,903,150 | Tailwind vs CSS | It can be so tiring to write multiple lines of CSS styling in our web apps. One of the challenges I... | 0 | 2024-06-27T22:40:00 | https://dev.to/idighekere/tailwind-vs-css-hpk | webdev, css, tailwindcss, bootstrap |
It can be so tiring to write multiple lines of CSS styling in our web apps. One of the challenges I always face in using HTML and CSS is usually coming up with generic class names for my elements, but Tailwind CSS or Bootstrap comes in as an aid. The debate between which is best always springs up amongst developers an... | idighekere |
1,903,376 | Ensuring Compliance with Export Control Regulations in Government Contracts | Discover how to navigate the complex landscape of export control regulations in government contracts, ensuring your projects remain compliant and successful. | 0 | 2024-06-28T01:17:36 | https://www.govcon.me/blog/ensuring_compliance_with_export_control_regulations_in_government_contracts | exportcontrol, governmentcontracts, compliance | # Ensuring Compliance with Export Control Regulations in Government Contracts
In today's global economy, export control regulations are crucial for maintaining national security and foreign policy. These laws govern the export of sensitive technology, data, and services to foreign entities. For businesses involve... | quantumcybersolution |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.