id int64 5 1.93M | title stringlengths 0 128 | description stringlengths 0 25.5k | collection_id int64 0 28.1k | published_timestamp timestamp[s] | canonical_url stringlengths 14 581 | tag_list stringlengths 0 120 | body_markdown stringlengths 0 716k | user_username stringlengths 2 30 |
|---|---|---|---|---|---|---|---|---|
1,921,203 | Document Your API With Swagger | by Gabriel Chinedu Not only can [Swagger](https://swagger.io/docs/) be used to document... | 0 | 2024-07-12T13:24:15 | https://blog.openreplay.com/document-your-api-with-swagger/ | by [Gabriel Chinedu](https://blog.openreplay.com/authors/gabriel-chinedu)
<blockquote><em>
Not only can [Swagger](https://swagger.io/docs/) be used to document [APIs](https://developer.mozilla.org/en-US/docs/Web/API), but it also makes integration easier by bringing them to life and producing smooth, interactive doc... | asayerio_techblog | |
1,921,204 | Explore how BitPower Loop works | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide... | 0 | 2024-07-12T13:26:37 | https://dev.to/wgac_0f8ada999859bdd2c0e5/explore-how-bitpower-loop-works-3ei3 | BitPower Loop is a decentralized lending platform based on blockchain technology that aims to provide secure, efficient and transparent lending services. Here is how it works in detail:
1️⃣ Smart Contract Guarantee
BitPower Loop uses smart contract technology to automatically execute all lending transactions. This aut... | wgac_0f8ada999859bdd2c0e5 | |
1,921,205 | Vue.JS 3.4.31: A Comprehensive Guide Towards the Modern Web Development | Introduction to Vue.js 3.4.31 Vue.js is known for its approachable design and versatility.... | 0 | 2024-07-12T13:27:15 | https://dev.to/samik_wgt_usa/vuejs-3431-a-comprehensive-guide-towards-the-modern-web-development-idf | vue, javascript | ## Introduction to Vue.js 3.4.31
Vue.js is known for its approachable design and versatility. The progressive JavaScript framework, Vue.js has launched its new update, Vue.js 3.4.31. It is designed to simplify web development and create reactive user interfaces with ease. Vue.js continues to evolve, offering developer... | samik_wgt_usa |
1,921,206 | Task 3 | Functional testing & Non functional testing are white & Black box testing, it will checked by... | 0 | 2024-07-12T13:30:09 | https://dev.to/tamizh/task-3-56j1 | Functional testing & Non functional testing are white & Black box testing, it will checked by developers of the programmer.
They are different types of testing techniques are used to checking the Functional & Non Functional testing.
The main difference between Functional and Non Functional testing are,
1. Functional te... | tamizh | |
1,921,207 | 具,TG商海客营销助手 | 电报(TG)吸粉软件,TG商海客营销工具,TG商海客营销助手 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T13:30:23 | https://dev.to/pwft_wjbr_7a92b79fb8e8451/ju-tgshang-hai-ke-ying-xiao-zhu-shou-eig |
电报(TG)吸粉软件,TG商海客营销工具,TG商海客营销助手
了解相关软件请登录 http://www.vst.tw
电报(TG)吸粉软件,双刃剑的社交营销
在数字营销日益激烈的今天,电报(TG)吸粉软件应运而生,成为众多企业和个人推广的利器。这类软件通过自动化手段,帮助用户快速增加电报群组或频道的订阅者数量,实现快速曝光和粉丝积累。
软件功能强大,支持多种加粉模式,如通过搜索特定关键词添加用户、自动发送邀请链接等,大大提高了吸粉效率。然而,使用此类软件也需谨慎。过度依赖可能导致粉丝质量参差不齐,甚至引发用户反感。同时,滥用软件功能还可能违反电报平台的规定,导致账号被封禁。
因此,在使用电报吸粉软件时,应注重策... | pwft_wjbr_7a92b79fb8e8451 | |
1,921,208 | BitPower: A New Era of Blockchain Investing | BitPower Loop smart contracts lead the new trend of investment, providing efficient and transparent... | 0 | 2024-07-12T13:30:29 | https://dev.to/_dcaa0119ee00d57596d05/bitpower-a-new-era-of-blockchain-investing-4ce3 |
BitPower Loop smart contracts lead the new trend of investment, providing efficient and transparent liquidity solutions through a distributed decentralized circulation model. Users participate anonymously, choose a circulation period of 1 to 28 days, and obtain different yields. For example, if you invest 10,000 USDT,... | _dcaa0119ee00d57596d05 | |
1,921,209 | Discover the Best Free Advertising Websites in the UK for Maximum Exposure | In today's digital age, where businesses of all sizes are vying for online visibility, the importance... | 0 | 2024-07-12T13:30:35 | https://dev.to/localseo_working_07fbb9fc/discover-the-best-free-advertising-websites-in-the-uk-for-maximum-exposure-24k4 | advertising, website | In today's digital age, where businesses of all sizes are vying for online visibility, the importance of leveraging free advertising websites cannot be overstated. These platforms provide a cost-effective way for businesses to reach a wider audience without breaking the bank. Among the plethora of options available, Wo... | localseo_working_07fbb9fc |
1,921,210 | Explore the power of innovative technology: BitPower Loop | In this era of digitalization and rapid development, power management and energy efficiency have... | 0 | 2024-07-12T13:31:26 | https://dev.to/_3576936cf5cca6b2ee1d4/explore-the-power-of-innovative-technology-bitpower-loop-45aj | In this era of digitalization and rapid development, power management and energy efficiency have become particularly important. As an industry leader, BitPower Loop is redefining how we think about and manage energy. Whether you are a home user or a business user, BitPower Loop provides you with efficient, reliable and... | _3576936cf5cca6b2ee1d4 | |
1,921,211 | ,获客群发助手,获客群发助手 | 全球获客吸粉软件,获客群发助手,获客群发助手 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T13:31:56 | https://dev.to/hlor_zssx_90ec3c40004ffdc/huo-ke-qun-fa-zhu-shou-huo-ke-qun-fa-zhu-shou-3o28 |
全球获客吸粉软件,获客群发助手,获客群发助手
了解相关软件请登录 http://www.vst.tw
全球范围内,随着数字化转型的深入,企业竞争的关键点逐渐从产品本身转向了市场营销和客户互动的能力。在这个背景下,获客吸粉软件(Customer Acquisition and Engagement Software)成为了企业不可或缺的重要工具。这类软件不仅帮助企业扩展客户群体,还能有效提升客户参与度,增强品牌影响力。
获客吸粉软件的功能与作用
获客吸粉软件涵盖了多种功能和工具,旨在全面支持企业的市场营销和客户关系管理,
营销自动化, 这是其中的核心功能之一,允许企业自动化营销流程,包括电子邮件营销、社交媒... | hlor_zssx_90ec3c40004ffdc | |
1,921,212 | CSS For Print: Designing Web Content For Physical Output | by Queendarlin Nnamani The demand for web-to-print functionality continues to grow across various... | 0 | 2024-07-12T13:35:26 | https://blog.openreplay.com/css-for-print--designing-web-content-for-physical-output/ | by [Queendarlin Nnamani](https://blog.openreplay.com/authors/queendarlin-nnamani)
<blockquote><em>
The demand for web-to-print functionality continues to grow across various industries, and users often require the ability to print web content for offline access or archival purposes. However, designing web content fo... | asayerio_techblog | |
1,921,213 | Django Admin: customize the auth system | Django admin is insanely good for an out-of-the-box lean and clean admin panel; it's not the most... | 0 | 2024-07-12T13:58:15 | https://dev.to/kwnaidoo/django-admin-customize-the-auth-system-58pd | webdev, programming, tutorial, python | Django admin is insanely good for an out-of-the-box lean and clean admin panel; it's not the most "sexy" looking dashboard around but it gets the job done for internal company tools.
If you don't like the look and feel of Django Admin but want to be lazy like me and re-use the auth system to get a basic login/logout s... | kwnaidoo |
1,921,214 | Importance of HTML Semantics in SEO Optimization and Accessibility Improvements | https://docs.google.com/document/d/1OU_l49xuFcxe7zdhglen5CRrtfu4HYBOVxrhV5H63Fs/edit?usp=drivesdk | 0 | 2024-07-12T13:37:14 | https://dev.to/sharon_wangui_/importance-of-html-semantics-in-seo-optimization-and-accessibility-improvements-jk9 | webdev, html, beginners, programming | https://docs.google.com/document/d/1OU_l49xuFcxe7zdhglen5CRrtfu4HYBOVxrhV5H63Fs/edit?usp=drivesdk | sharon_wangui_ |
1,921,215 | Create and Configure a Virtual Network with Four Subnets | Azure Virtual Network (VNet) is a fundamental building block for private network in Azure. VNet... | 0 | 2024-07-12T13:37:34 | https://dev.to/dera2024/how-to-create-and-configure-a-virtual-network-with-four-subnets-o40 | microsoft, azure, networking, beginners | Azure Virtual Network (VNet) is a fundamental building block for private network in Azure. VNet enables many types of Azure resources, such as Azure Virtual Machines (VMs), to securely communicate with each other, the internet, and on-premises networks.
Provided you were given an IP Address **192.148.30.0/26** to creat... | dera2024 |
1,921,216 | METAPhilosophy | Understanding MetaPhilosophy thoroughly in 1, 2 & 3 Philosophy ... Love of wisdom META ...... | 0 | 2024-07-12T13:39:10 | https://dev.to/seremonia/metaphilosophy-25i3 | metaphilosophy, philosophy | Understanding MetaPhilosophy thoroughly in 1, 2 & 3
Philosophy ... Love of wisdom
META ... Beyond
🔰 MetaPhilosophy is Beyond the Love of Wisdom. What is Beyond the Love of Wisdom❓
🧩 Wisdom is Truth Itself & Truth Represents the Right Boundaries
🎯 Loving Wisdom Means Loving the Right Boundaries
Right Boundaries ... | seremonia |
1,921,217 | Experience the powerful charm of BitPower Loop | In today's rapidly developing technological era, finding efficient, reliable and innovative solutions... | 0 | 2024-07-12T13:41:01 | https://dev.to/akjajaj_82d65819e4dfd5f9/experience-the-powerful-charm-of-bitpower-loop-4fj9 | In today's rapidly developing technological era, finding efficient, reliable and innovative solutions has become a common pursuit of enterprises and individuals. BitPower Loop came into being under this background and is committed to providing users with excellent services and unparalleled experience.
What is BitPower... | akjajaj_82d65819e4dfd5f9 | |
1,921,218 | Justified Cognitive | This the 1st, initial step is to ensure avoidance of cognitive biases. Don’t focus on logical... | 0 | 2024-07-12T13:41:39 | https://dev.to/seremonia/justified-cognitive-313m | metaphilosophy, cognitivebias | This the 1st, initial step is to ensure avoidance of cognitive biases. Don’t focus on logical rule-checking first. Instead, focus on avoiding cognitive biases.
It's like not trying to apply logic to something that is inherently beyond logic. Isn't it logical to detect whether something is beyond logic or not?
This is... | seremonia |
1,921,219 | 获客系统自动筛选,获客群发防封号工具,获客过滤软件 | 获客系统自动筛选,获客群发防封号工具,获客过滤软件 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T13:41:56 | https://dev.to/cswb_fvas_1c0a325c34ee02a/huo-ke-xi-tong-zi-dong-shai-xuan-huo-ke-qun-fa-fang-feng-hao-gong-ju-huo-ke-guo-lu-ruan-jian-28p |
获客系统自动筛选,获客群发防封号工具,获客过滤软件
了解相关软件请登录 http://www.vst.tw
自动化获客系统,优化您的客户筛选流程
在竞争激烈的市场环境中,企业需要高效地找到潜在客户并将其转化为实际的销售机会。传统的手动获客方法已经不能满足现代企业的需求,因此越来越多的公司转向自动化获客系统来优化他们的客户筛选过程。
1. 什么是自动化获客系统?
自动化获客系统是一种利用软件和技术工具来自动化和优化客户获取过程的系统。这些系统利用数据分析、人工智能和机器学习等技术,帮助企业在庞大的潜在客户群中找到最有可能成为付费客户的个体。这种系统不仅仅限于简单的营销自动化,还包括更高级的客户分析和预测功能... | cswb_fvas_1c0a325c34ee02a | |
1,921,220 | 加粉软件,reddit筛选助手,reddit过滤助手 | Reddit加粉软件,reddit筛选助手,reddit过滤助手 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T13:43:14 | https://dev.to/itfd_plsf_5a713dbbb68e2a8/jia-fen-ruan-jian-redditshai-xuan-zhu-shou-redditguo-lu-zhu-shou-58kl |
Reddit加粉软件,reddit筛选助手,reddit过滤助手
了解相关软件请登录 http://www.vst.tw
在当前社交媒体充斥着各种内容的时代,Reddit作为一个知识分享和社区讨论的平台,吸引了无数用户的关注和参与。然而,随着Reddit的用户群体不断扩大,许多人开始寻求提升自己帖子的可见性和影响力的方法。这就导致了一些用户使用Reddit加粉软件来增加其粉丝数量和帖子的点赞数,以此来提高其在社区中的影响力和知名度。
Reddit加粉软件通常被设计为自动化工具,可以快速地增加用户的粉丝数和帖子的点赞数。这些软件可能通过机器人账号自动订阅其他用户、自动点赞帖子,甚至自动发布评论,以制造看似真实的... | itfd_plsf_5a713dbbb68e2a8 | |
1,921,221 | BitPower Loop - Helping you step into the door of future energy | As global energy demand continues to grow, people's demand for renewable energy and energy management... | 0 | 2024-07-12T13:44:27 | https://dev.to/_9abdd486c02b48be694ef8/bitpower-loop-helping-you-step-into-the-door-of-future-energy-n88 | As global energy demand continues to grow, people's demand for renewable energy and energy management is also increasing. In this era of pursuing sustainable development, BitPower Loop came into being. As a revolutionary energy solution, it is not only a product, but also a new paradigm of energy self-management.
What... | _9abdd486c02b48be694ef8 | |
1,921,222 | BitPower: A New Era of Blockchain Investing | BitPower Loop smart contracts lead the new trend of investment, providing efficient and transparent... | 0 | 2024-07-12T13:44:40 | https://dev.to/_d0d87a598f80abadc87b9/bitpower-a-new-era-of-blockchain-investing-ki4 | webdev, beginners | BitPower Loop smart contracts lead the new trend of investment, providing efficient and transparent liquidity solutions through a distributed decentralized circulation model. Users participate anonymously, choose a circulation period of 1 to 28 days, and obtain different yields. For example, if you invest 10,000 USDT, ... | _d0d87a598f80abadc87b9 |
1,921,223 | Unlocking the Power of 2-in-1: How to Thrive in Online Business and Network Marketing | In today's fast-paced digital landscape, entrepreneurs are constantly seeking innovative ways to... | 0 | 2024-07-12T13:44:42 | https://dev.to/drey_jordan_3b45300108e98/unlocking-the-power-of-2-in-1-how-to-thrive-in-online-business-and-network-marketing-24h9 |
In today's fast-paced [digital](https://legenddiamondgeneration.com/<u></u>) landscape, entrepreneurs are constantly seeking innovative ways to diversify their income streams and maximize their [earning](https://legenddiamondgeneration.com/<u></u>) potential. Two lucrative opportunities have emerged as frontrunners in... | drey_jordan_3b45300108e98 | |
1,921,224 | The value of API-First design on side-projects | Cover Photo by Douglas Lopes on Unsplash Intro Lately, I had a chance to try out the... | 0 | 2024-07-12T14:02:07 | https://devopsian.net/p/the-value-of-api-first-design-on-side-projects/ | api, go, typescript, fullstack | _Cover Photo by Douglas Lopes on Unsplash_
## Intro
Lately, I had a chance to try out the API-First design approach. I had never written an OpenAPI document before, so I had no real knowledge of its benefits. It always seemed like too much prep work.
As developers, we often prefer writing code to writing documentati... | chen |
1,921,225 | Elevate Your Business Aesthetics with Polished Concrete in Houston | In the vibrant city of Houston, businesses are always looking for innovative ways to stand out and... | 0 | 2024-07-12T13:46:20 | https://dev.to/ricospolishedconcrete/elevate-your-business-aesthetics-with-polished-concrete-in-houston-2ice | In the vibrant city of Houston, businesses are always looking for innovative ways to stand out and make a lasting impression. One of the most transformative yet often overlooked upgrades is polished concrete flooring. This modern solution not only enhances the visual appeal of your space but also offers durability and ... | ricospolishedconcrete | |
1,921,226 | plots for sale hyderbad | plots for sale... | 0 | 2024-07-12T13:49:05 | https://dev.to/plotsforsalehyderaba/plots-for-sale-hyderbad-5433 | productivity | plots for sale hyderbad
https://www.landwey.in/property/plot-for-sale-in-hyderabad/plot-for-sale-dukes-urban-village--i%2C-ii%2C-premium-villa-plots-in-kothur/66893005c9fec3ca118f2cef
https://www.landwey.in/property/plot-for-sale-in-pargi/plot-for-sale-tropic-%7C-premium-villa-plots-in-vikarabad/6689329da6a73d7857f177... | plotsforsalehyderaba |
1,921,227 | plots for sale Hyderabad | **https://www.landwey.in/property/apartment-for-sale-in-tellapur/3-bhk-flats-in-tellapur-hyderabad-fo... | 0 | 2024-07-12T13:50:27 | https://dev.to/plotsforsalehyderaba/plots-for-sale-2115 | website | **https://www.landwey.in/property/apartment-for-sale-in-tellapur/3-bhk-flats-in-tellapur-hyderabad-for-sale/6645dbdbbcd9ed1daa55c2f0
https://www.landwey.in/property/villa-for-sale-in-kollur/3-bhk-luxury-villas-in-kollur-for-sale/66795171c9fec3ca118e83b4
https://www.landwey.in/property/apartment-for-sale-in-bahadurpally... | plotsforsalehyderaba |
1,921,228 | How to Build A YouTube Clone in HTML CSS and JavaScript | Building a YouTube clone is a fun and educational project that can greatly boost your front-end... | 0 | 2024-07-12T13:51:14 | https://www.codingnepalweb.com/build-youtube-homepage-clone-html-css/ | webdev, html, css, javascript | 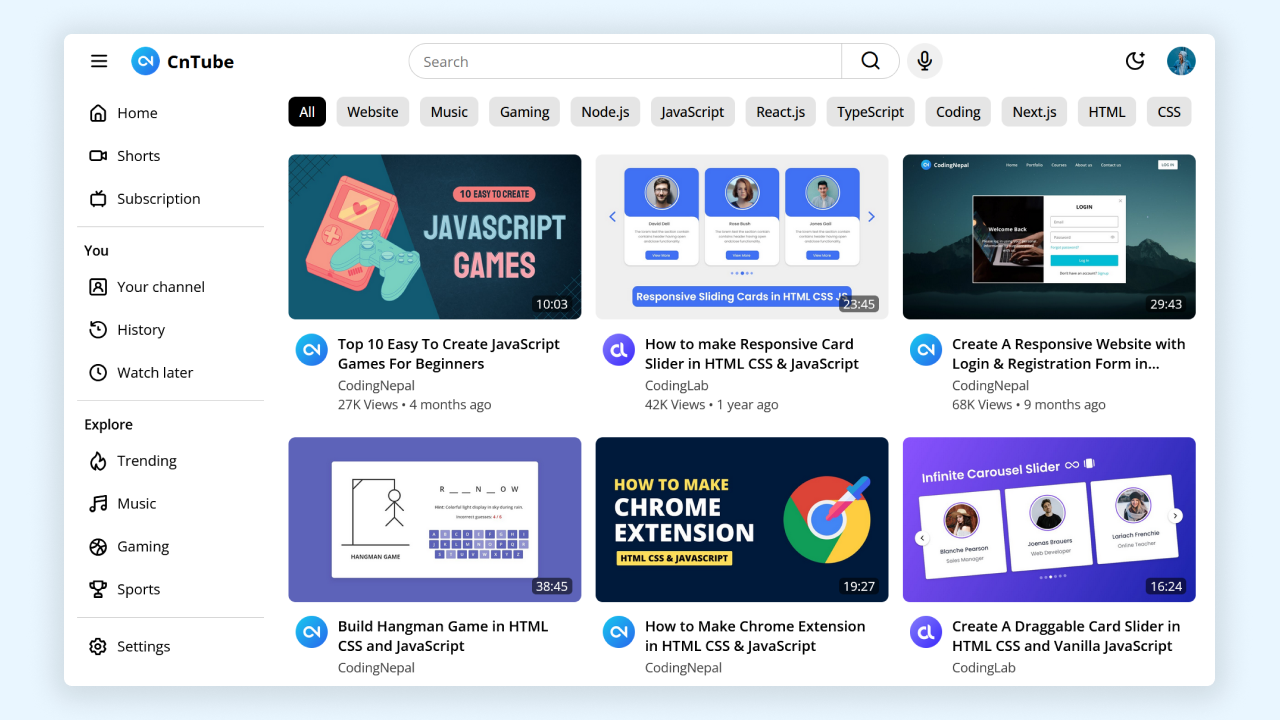
Building a [YouTube clone](https://www.codingnepalweb.com/create-youtube-homepage-tailwind-reactjs/) is a fun and educational project that can greatly boost your front-end devel... | codingnepal |
1,921,229 | BitPower: A New Era of Blockchain Investing | BitPower Loop smart contracts lead the new trend of investment, providing efficient and transparent... | 0 | 2024-07-12T13:52:07 | https://dev.to/_32d1554462535885b588b/bitpower-a-new-era-of-blockchain-investing-1aba | BitPower Loop smart contracts lead the new trend of investment, providing efficient and transparent liquidity solutions through a distributed decentralized circulation model. Users participate anonymously, choose a circulation period of 1 to 28 days, and obtain different yields. For example, if you invest 10,000 USDT, ... | _32d1554462535885b588b | |
1,921,533 | movedim() in PyTorch | *Memos: My post explains permute(). My post explains transpose() and t(). My post explains... | 0 | 2024-07-12T18:46:21 | https://dev.to/hyperkai/movedim-in-pytorch-5gla | pytorch, movedim, tensor, function | *Memos:
- [My post](https://dev.to/hyperkai/permute-in-pytorch-5d49) explains [permute()](https://pytorch.org/docs/stable/generated/torch.permute.html).
- [My post](https://dev.to/hyperkai/transpose-and-t-in-pytorch-1pp2) explains [transpose()](https://pytorch.org/docs/stable/generated/torch.transpose.html) and [t()](h... | hyperkai |
1,921,230 | Create A Screen Recorder With JavaScript | by Andrew Ezeani Screen recording lets you capture your computer's visual and audio activity,... | 0 | 2024-07-12T13:52:14 | https://blog.openreplay.com/create-a-screen-recorder-with-javascript/ |
by [Andrew Ezeani](https://blog.openreplay.com/authors/andrew-ezeani)
<blockquote><em>
Screen recording lets you capture your computer's visual and audio activity, creating a video record of what is happening on your screen. It's useful for tutorials, presentations, gameplay sessions, and software demonstrations. ... | asayerio_techblog | |
1,921,231 | YouTube自动评论,Youtube筛号工具,Youtube筛号机器人 | YouTube自动评论,Youtube筛号工具,Youtube筛号机器人 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T13:52:15 | https://dev.to/lepv_lwfe_f04c5476a9b2afc/youtubezi-dong-ping-lun-youtubeshai-hao-gong-ju-youtubeshai-hao-ji-qi-ren-1h9c |
YouTube自动评论,Youtube筛号工具,Youtube筛号机器人
了解相关软件请登录 http://www.vst.tw
在数字化时代,YouTube自动评论工具成为了内容创作者与观众互动的新方式。自动评论,顾名思义,是指通过预设的脚本或算法,自动在视频下方发布评论内容。这一功能不仅提升了评论的生成效率,还能在视频发布初期迅速积累互动数据,增强视频的曝光率。
自动评论的优点显而易见,它能有效节省创作者的时间与精力,让他们更专注于内容创作本身;同时,通过精准定位目标观众群体,自动评论还能帮助创作者更好地与粉丝互动,增强用户粘性。然而,自动评论也面临着一系列挑战与问题,如评论内容的真实性与个性化不足,可能导... | lepv_lwfe_f04c5476a9b2afc | |
1,921,232 | Elevating Cloud Security: Highlights from CloudNativeSecurityCon 2024 | When you think of Seattle, you might immediately think of Starbucks, the Space Needle. or maybe... | 0 | 2024-07-12T13:53:01 | https://blog.gitguardian.com/cloudnativesecuritycon-2024/ | security, cybersecurity, opensource, techtalks | When you think of Seattle, you might immediately think of [Starbucks](https://stories.starbucks.com/stories/2015/store-tour-inside-1912-pike-place-seattle-usa/?ref=blog.gitguardian.com), the [Space Needle](https://en.wikipedia.org/wiki/Space_Needle?ref=blog.gitguardian.com). or maybe even [Fraiser](https://en.wikipedia... | dwayne_mcdaniel |
1,921,233 | plots for sale hyerabad | https://www.bigproperty.in/properties/residential-plot/yadadri-bhuvanagiri/new-sale/yadagiri-gutta/re... | 0 | 2024-07-12T13:54:06 | https://dev.to/plotsforsalehyderaba/plots-for-sale-hyerabad-2b8e | opensource | https://www.bigproperty.in/properties/residential-plot/yadadri-bhuvanagiri/new-sale/yadagiri-gutta/residential-plots-for-sale-in-peddakandukur-yadadri/
https://www.bigproperty.in/properties/villa/sangareddy/new-sale/kollur/premium-villas-for-sale-in-kollur-sangareddy/
https://www.bigproperty.in/properties/apartment-fla... | plotsforsalehyderaba |
1,921,235 | Task 4 | Manual testing is a process to test the application manually without using any software. Application... | 0 | 2024-07-12T13:55:36 | https://dev.to/tamizh/task-4-5b21 | 1. Manual testing is a process to test the application manually without using any software. Application tested manually by humans to ensure the performance.
2. Advantages
A. Identifying the bugs
B. Flexibility in testing process to changes the test cases.
C. Easier to learn new tester
Disadvantages
A. Manual testing... | tamizh | |
1,921,237 | App landing page | I created this app landing page. Features Responsive. Tailwind css, for rapid... | 0 | 2024-07-12T13:57:23 | https://dev.to/paul_freeman/app-landing-page-20k7 | showdev, frontend, webdev, html | I created this app landing page.
### Features
* Responsive.
* Tailwind css, for rapid development.
### Live site
You can view the live site here: [app landing page](https://chatorigin.netlify.app/)
### Screenshot
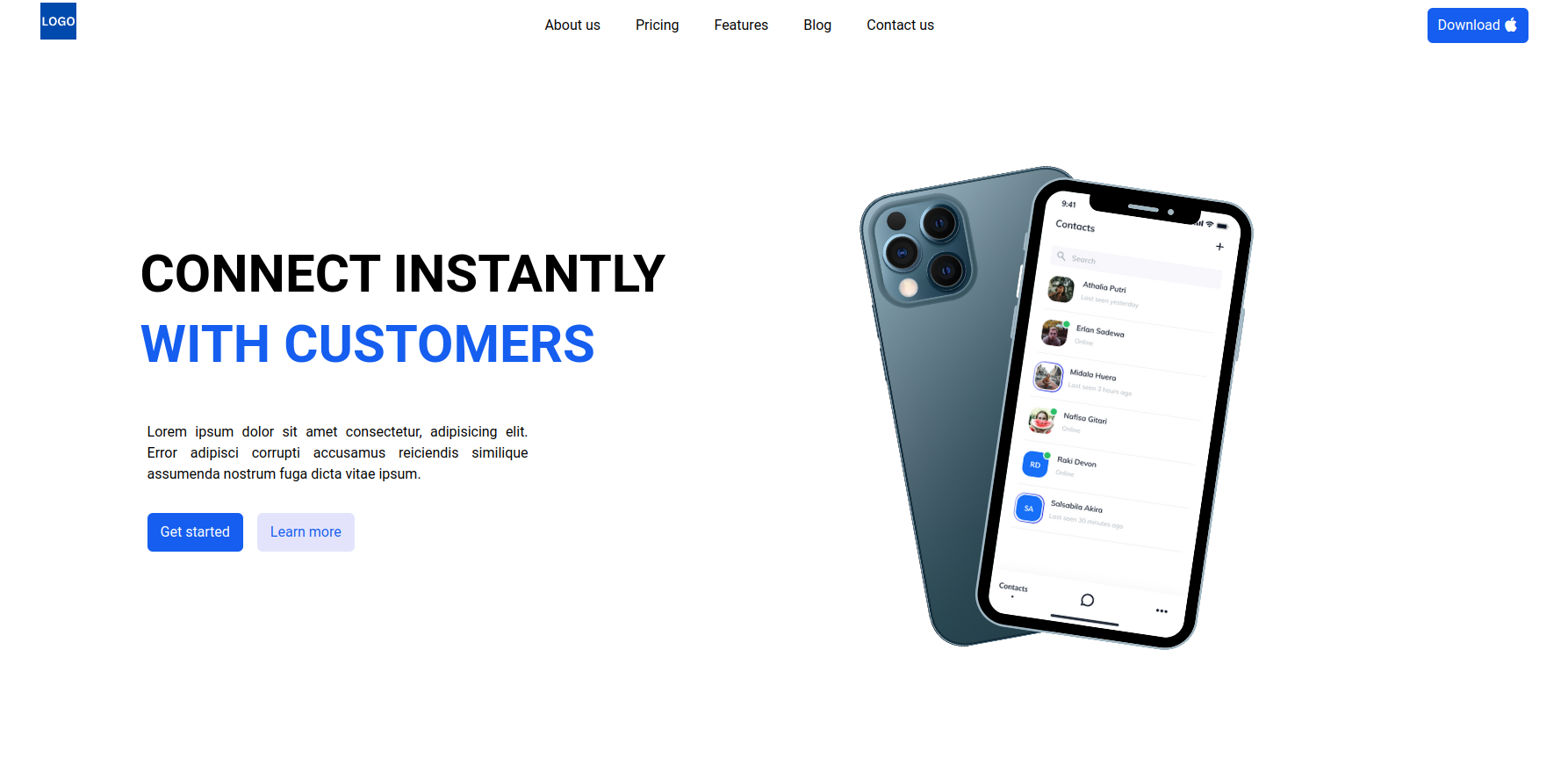
... | paul_freeman |
1,921,238 | Experience the powerful charm of BitPower Loop | In today's rapidly developing technological era, finding efficient, reliable and innovative solutions... | 0 | 2024-07-12T13:56:37 | https://dev.to/ssassaasa_c3ee63dd655a1b/experience-the-powerful-charm-of-bitpower-loop-3lm0 | In today's rapidly developing technological era, finding efficient, reliable and innovative solutions has become a common pursuit of enterprises and individuals. BitPower Loop came into being under this background and is committed to providing users with excellent services and unparalleled experience.
What is BitPower... | ssassaasa_c3ee63dd655a1b | |
1,921,239 | FB采集软件,FB精准引流,FB自动加好友机器人 | FB采集软件,FB精准引流,FB自动加好友机器人 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T13:57:31 | https://dev.to/gxeg_fxtp_e95999defc5ac08/fbcai-ji-ruan-jian-fbjing-zhun-yin-liu-fbzi-dong-jia-hao-you-ji-qi-ren-4l15 |
FB采集软件,FB精准引流,FB自动加好友机器人
了解相关软件请登录 http://www.vst.tw
FB采集软件是一款专为商家和营销人员设计的数据采集工具。它基于facebook网站,通过输入关键词,实时采集店铺数据,包括手机电话、邮箱、标题名称、网址等信息。这款软件不仅功能强大,还内置数据库保存采集到的数据,并支持库内去重,确保数据不会重复。
FB采集软件的价格实惠,半年订阅价为280元,一年订阅价为380元。它广泛应用于facebook营销领域,帮助企业快速准确地筛选和分析用户数据,提升营销效果。
随着facebook营销的不断发展,越来越多的企业选择使用FB采集软件来辅助其营销策略。它不仅提升了数据... | gxeg_fxtp_e95999defc5ac08 | |
1,921,242 | Flutter Fortified: Mastering Updates And Security | by Ukoko Alfred In this modern digital era, keeping users’ data safe and ensuring that apps are... | 0 | 2024-07-12T13:59:43 | https://blog.openreplay.com/flutter-fortified--mastering-updates-and-security/ | by [Ukoko Alfred](https://blog.openreplay.com/authors/ukoko-alfred)
<blockquote><em>
In this modern digital era, keeping users’ data safe and ensuring that apps are working as expected is essential. This article will show you how to handle security and updates in Flutter-written apps.
</em></blockquote>
<div styl... | asayerio_techblog | |
1,921,244 | The Ultimate Guide to Container Orchestration | Container orchestration is a critical component of modern software development and deployment,... | 0 | 2024-07-12T14:00:45 | https://dev.to/platform_engineers/the-ultimate-guide-to-container-orchestration-317c | Container orchestration is a critical component of modern software development and deployment, particularly in the context of [platform engineering](www.platformengineers.io). It involves the automated management of containers, ensuring efficient deployment, scaling, and lifecycle management. This comprehensive guide d... | shahangita | |
1,921,245 | Structured Content guide: Reusable blocks for scalable websites | Is your site too inconsistent? Is your content team ineffective? Are you spending too much time on... | 0 | 2024-07-12T14:01:24 | https://dev.to/momciloo/structured-content-guide-reusable-blocks-for-scalable-websites-4jon | Is your site too inconsistent? Is your content team ineffective? Are you spending too much time on technical SEO? Structured content is the solution. This guide explores the basics of structured content and how it can help solve common challenges in content management. Learn how to create reusable content blocks and bu... | momciloo | |
1,921,246 | Backend Performance Optimization | In today’s fast-paced digital landscape, optimizing the performance of backend code is crucial for... | 0 | 2024-07-12T14:01:39 | https://dev.to/sammi_mak_d80a57468774173/backend-performance-optimization-2nik | In today’s fast-paced digital landscape, optimizing the performance of backend code is crucial for delivering a seamless and efficient user experience. As the number of users/requests of an application increases, it becomes important that it maintains its performance.
Whether you’re developing a web application, an API... | sammi_mak_d80a57468774173 | |
1,921,247 | Docker Compose Develop Watch and Syncing Files from the Host Container to a Service | This thread has helped me better understand the "develop" behavior with Docker Compose The Docker... | 0 | 2024-07-12T14:02:19 | https://dev.to/rudolfolah/docker-compose-develop-watch-and-syncing-files-from-the-host-container-to-a-service-18hh | docker, containers, development, productivity | [This thread has helped me better understand the "develop" behavior with Docker Compose](https://github.com/docker/compose/issues/11102)
[The Docker Compose documentation of "Example 1" in "Use Compose Watch"](https://docs.docker.com/compose/file-watch/#example-1) does a pretty good job explaining things. Perhaps part... | rudolfolah |
1,921,248 | BitPower Loop - Helping you step into the door of future energy | As global energy demand continues to grow, people's demand for renewable energy and energy management... | 0 | 2024-07-12T14:03:11 | https://dev.to/_27d27a660816b4b00a62d/bitpower-loop-helping-you-step-into-the-door-of-future-energy-4kno | As global energy demand continues to grow, people's demand for renewable energy and energy management is also increasing. In this era of pursuing sustainable development, BitPower Loop came into being. As a revolutionary energy solution, it is not only a product, but also a new paradigm of energy self-management.
What... | _27d27a660816b4b00a62d | |
1,921,249 | Centralized Crypto Exchange Security | Introduction The realm of cryptocurrency has expanded exponentially over the past... | 27,673 | 2024-07-12T14:05:33 | https://dev.to/rapidinnovation/centralized-crypto-exchange-security-37kk | ## Introduction
The realm of cryptocurrency has expanded exponentially over the past decade,
introducing a new paradigm of financial transactions and investment
opportunities. At the heart of this digital financial revolution are
cryptocurrency exchanges—platforms where users can buy, sell, or trade
cryptocurrencies. ... | rapidinnovation | |
1,921,251 | Experience the powerful charm of BitPower Loop | In today's rapidly developing technological era, finding efficient, reliable and innovative solutions... | 0 | 2024-07-12T14:07:34 | https://dev.to/asdasda_6f1402a25f086fd1/experience-the-powerful-charm-of-bitpower-loop-5759 | In today's rapidly developing technological era, finding efficient, reliable and innovative solutions has become a common pursuit of enterprises and individuals. BitPower Loop came into being under this background and is committed to providing users with excellent services and unparalleled experience.
What is BitPower... | asdasda_6f1402a25f086fd1 | |
1,921,252 | The Sunshine Vitamin: A Comprehensive Guide to Vitamin D | Vitamin D, often referred to as the "sunshine vitamin," plays a crucial role in maintaining overall... | 0 | 2024-07-12T14:08:05 | https://dev.to/ethan_reynolds_3418d1416d/the-sunshine-vitamin-a-comprehensive-guide-to-vitamin-d-j72 | <p><a href="https://www.healthline.com/health/food-nutrition/benefits-vitamin-d">Vitamin D</a>, often referred to as the "sunshine vitamin," plays a crucial role in maintaining overall health. This fat-soluble vitamin is essential for bone health, immune function, and overall well-being. In this article, we will delve ... | ethan_reynolds_3418d1416d | |
1,921,253 | Entendendo Ponteiros | Em graduações da área de tecnologia, existem conceitos e matérias que geralmente assustam os alunos,... | 0 | 2024-07-12T14:08:50 | https://dev.to/adrielh024/entendendo-ponteiros-1n8e | c, cpp, tutorial | Em graduações da área de tecnologia, existem conceitos e matérias que geralmente assustam os alunos, alguns dos principais exemplos são matérias relacionadas a Programação Orientada a Objetos e Cálculo, outro exemplo são algumas noções mais abstratas tal como ponteiros, principalmente em C, tema deste artigo.
Diferente... | adrielh024 |
1,921,255 | 🚀Welcome to BitPower Loop, a new era of blockchain technology! 🎉 | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions... | 0 | 2024-07-12T14:12:44 | https://dev.to/fg_da_e946e3e52399df4c6b1/welcome-to-bitpower-loop-a-new-era-of-blockchain-technology-2i4m |
BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions and low gas fees. We are committed to building a strong and flexible economic ecosystem through decentralized sma... | fg_da_e946e3e52399df4c6b1 | |
1,921,256 | Singly Linked List using C++ | In this C++ program, I will show you a basic singly linked list. It begins by defining a node... | 0 | 2024-07-12T14:32:23 | https://dev.to/praneshchow/singly-linked-list-using-c-5008 | cpp, linked, datastructures, algorithms | In this C++ program, I will show you a basic singly linked list. It begins by defining a `node` structure to store an integer (`data`) and a pointer to the next node (`next`).
### Node Structure Definition:
```cpp
struct node {
int data;
node* next;
};
```
data to store the integer value.
next to store the... | praneshchow |
1,921,257 | Explore the power of innovative technology: BitPower Loop | In this era of digitalization and rapid development, power management and energy efficiency have... | 0 | 2024-07-12T14:15:24 | https://dev.to/_1a641b3285c96c4d7d76d/explore-the-power-of-innovative-technology-bitpower-loop-5c5d | In this era of digitalization and rapid development, power management and energy efficiency have become particularly important. As an industry leader, BitPower Loop is redefining how we think about and manage energy. Whether you are a home user or a business user, BitPower Loop provides you with efficient, reliable and... | _1a641b3285c96c4d7d76d | |
1,921,258 | 🌐 Discover BitPower Loop! | A revolutionary digital currency mining solution that brings new possibilities to your crypto mining... | 0 | 2024-07-12T14:15:34 | https://dev.to/dasfca_dfa_a62e0847a566b/discover-bitpower-loop-418b | bitpower, btc | A revolutionary digital currency mining solution that brings new possibilities to your crypto mining experience. Using advanced energy recovery technology, BitPower Loop not only improves efficiency but also reduces environmental impact. Join us now to explore the future of innovation!
💡 Innovative Energy Recovery: T... | dasfca_dfa_a62e0847a566b |
1,921,259 | BitPower Loop - Helping you step into the door of future energy | As global energy demand continues to grow, people's demand for renewable energy and energy management... | 0 | 2024-07-12T14:16:04 | https://dev.to/_e216fa31c2c2e936f4bae8/bitpower-loop-helping-you-step-into-the-door-of-future-energy-57ll | As global energy demand continues to grow, people's demand for renewable energy and energy management is also increasing. In this era of pursuing sustainable development, BitPower Loop came into being. As a revolutionary energy solution, it is not only a product, but also a new paradigm of energy self-management.
What... | _e216fa31c2c2e936f4bae8 | |
1,921,260 | Mathematics for Machine Learning - Day 5 | Disclaimer Today's topic will still be split between today and tomorrow. Since you might... | 27,993 | 2024-07-12T14:27:26 | https://pourterra.com/blogs/5 | learning, machinelearning, tutorial, beginners | 
## Disclaimer
Today's topic will still be split between today and tomorrow. Since you might tell from the meme, I don't know if I'm a genius, an idiot, or that's just how math maths. Usually it's the secon... | pourlehommes |
1,921,261 | Telegram采集附近人,Telegram拉群助手,Telegram行销助手 | Telegram采集附近人,Telegram拉群助手,Telegram行销助手 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T14:19:21 | https://dev.to/exzf_rwwg_508af768adcaaa2/telegramcai-ji-fu-jin-ren-telegramla-qun-zhu-shou-telegramxing-xiao-zhu-shou-3ige |
Telegram采集附近人,Telegram拉群助手,Telegram行销助手
了解相关软件请登录 http://www.vst.tw
在Telegram这款广受欢迎的即时通讯应用中,用户不仅可以与全球各地的朋友保持联系,还能利用其独特的“附近的人”功能,发现周围的Telegram用户。通过开启该功能,用户可以浏览到与自己地理位置相近的其他Telegram用户,从而扩大社交圈,结识新朋友。
然而,在使用“附近的人”功能时,用户需要注意保护个人隐私和安全。首先,避免在公共场合透露过多个人信息,如家庭住址、工作单位等敏感信息。其次,谨慎与陌生人交流,避免陷入网络诈骗或其他不良行为。最后,定期检查和更新账户安全设置,... | exzf_rwwg_508af768adcaaa2 | |
1,921,262 | React Native QR Code Reader / QR Code Scanner July 2024 | I tired a different way to implement qr code reading functionality and I want to share it with you.... | 0 | 2024-07-12T14:30:24 | https://dev.to/raguram90/react-native-qr-code-reader-qr-code-scanner-july-2024-2i7h | react, reactnative, android, ios | I tired a different way to implement qr code reading functionality and I want to share it with you. Since the general approach of using `react-native-qrcode-scanner` package not updated recently or not maintained I went to try out this **react-native-vision-camera** package.
## Package
```
yarn add react-native-vect... | raguram90 |
1,921,263 | Telegram商海客营销,Telegram改资料软件,Telegram营销机器人 | Telegram商海客营销,Telegram改资料软件,Telegram营销机器人 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T14:22:03 | https://dev.to/otid_alve_e5bd34391bb3fee/telegramshang-hai-ke-ying-xiao-telegramgai-zi-liao-ruan-jian-telegramying-xiao-ji-qi-ren-1f0b |
Telegram商海客营销,Telegram改资料软件,Telegram营销机器人
了解相关软件请登录 http://www.vst.tw
在当今数字化时代,社交媒体平台的崛起改变了商业营销的面貌,其中Telegram作为一个全球性的即时通讯应用,不仅仅是个人交流的工具,也逐渐成为了企业营销的重要平台之一。本文将探讨Telegram在商业营销中的应用以及其优势。
Telegram在商业营销中的应用
1. 直接沟通和客户服务
Telegram提供了即时通讯的功能,企业可以通过创建公共频道或私密聊天与客户直接互动。这种直接的沟通方式不仅有助于建立客户关系,还可以快速响应客户的问题和需求,提升客户满意度和忠诚度。... | otid_alve_e5bd34391bb3fee | |
1,921,264 | 5 VS CODE EXTENSIONS I USE DAILY ! | Guys, I think this is my 5th VS code extension post if I am right. Ok, basically one of my highest... | 0 | 2024-07-12T14:22:16 | https://dev.to/mince/5-vs-code-extensions-i-use-daily--53on | webdev, javascript, beginners, programming | Guys, I think this is my 5th VS code extension post if I am right. Ok, basically one of my highest viewership posts are all about vs code extensions. So, I wanted to make a really big awesome list about vs code extensions. So, let us get straight into this.
## BETTER COMMENTS ❗
Better comments formats the comments yo... | mince |
1,921,265 | Snowflake: Revolutionizing Data Warehousing | Snowflake is a cloud-based data warehousing solution that has garnered significant attention for its... | 0 | 2024-07-12T14:26:50 | https://dev.to/dbdeveloper/snowflake-revolutionizing-data-warehousing-b2c | snowflake, database, odbc | Snowflake is a cloud-based data warehousing solution that has garnered significant attention for its innovative approach to data management and analytics. Unlike traditional data warehouses, Snowflake is designed to leverage the full potential of cloud computing, offering a scalable, flexible, and efficient platform fo... | dbdeveloper |
1,921,267 | What IS HTML ? | Hope everyone is well. From today we will discuss all the topics of our web programming. Today's... | 0 | 2024-07-12T14:28:12 | https://dev.to/sagor_cnits_73eb557b53820/what-is-html--2k16 | webdev, javascript, beginners, programming | Hope everyone is well.
From today we will discuss all the topics of our web programming.
**Today's topic is: What is HTML?**
The full name of HTML is (Hyper Text Markup Language).It is a good language for creating web pages.
The concept of HTML was first developed by Tim Berners-Lee. He proposed the basic idea of ... | sagor_cnits_73eb557b53820 |
1,921,268 | #Bitpower#BTC | 🔥 Explore the energy revolution of the future! Bitpower is leading a new era of decentralized energy... | 0 | 2024-07-12T14:29:24 | https://dev.to/na_li_512c52d1c96d81e60b9/bitpowerbtc-432o | 🔥 Explore the energy revolution of the future! Bitpower is leading a new era of decentralized energy management 🌍⚡️ Our technology combines blockchain and artificial intelligence to achieve efficient distribution and use of energy, reduce costs, and improve sustainability. Join us to create a green future! Learn more... | na_li_512c52d1c96d81e60b9 | |
1,921,269 | 跨境电商吸粉软件,跨境营销机器人,跨境推广机器人 | 跨境电商吸粉软件,跨境营销机器人,跨境推广机器人 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T14:29:32 | https://dev.to/sbxs_zetj_cd63da61deb85e9/kua-jing-dian-shang-xi-fen-ruan-jian-kua-jing-ying-xiao-ji-qi-ren-kua-jing-tui-yan-ji-qi-ren-48mn |
跨境电商吸粉软件,跨境营销机器人,跨境推广机器人
了解相关软件请登录 http://www.vst.tw
跨境电商吸粉软件,助力商家拓展全球市场的利器
跨境电商吸粉软件,作为现代电商营销的重要工具,专为跨境商家设计,旨在通过精准营销和高效互动,吸引并留住全球消费者。这类软件集成了多种功能,如社交媒体管理、内容营销、数据分析等,帮助商家轻松打造个性化品牌形象,提升用户粘性。
其核心优势在于能够跨越地域限制,实现全球范围内的目标客户精准定位与触达。通过智能算法分析用户行为数据,软件能自动推送符合消费者兴趣的产品信息和优惠活动,有效促进销售转化。此外,其便捷的社交媒体集成功能,也让商家能够轻松管理多平台账号,实现信息... | sbxs_zetj_cd63da61deb85e9 | |
1,921,270 | Data Types | Every value in Rust is of a certain data type, which tells Rust what kind of data is being specified... | 28,032 | 2024-07-12T14:29:48 | https://dev.to/danielmwandiki/data-types-1dp3 | learning, rust, devops | Every value in Rust is of a certain data type, which tells Rust what kind of data is being specified so it knows how to work with it.
*Scalar data type*: Types that store only a single value.
*Compound data type*: Types that store multiple values, even values of different types.
###Scalar Types
Rust has four primary s... | danielmwandiki |
1,921,271 | Dive into Vector Search for Amazon MemoryDB: A Game-Changer for Enterprise Customers | Amazon has recently announced the general availability of Vector Search for Amazon MemoryDB, an... | 0 | 2024-07-12T14:30:27 | https://dev.to/stevewoodard/dive-into-vector-search-for-amazon-memorydb-a-game-changer-for-enterprise-customers-5gl3 | aws, redis, memorydb, vectordatabase | Amazon has recently announced the general availability of Vector Search for Amazon MemoryDB, an exciting development that promises to revolutionize how enterprises handle data. But what exactly is Vector Search, and how can it benefit your business? Let’s unpack this innovation and explore its potential.
What is Vecto... | stevewoodard |
1,921,272 | Talk to Strangers: Exploring the World of Online Conversations | Most Well-liked Chat Rooms for Strangers Numerous websites have become well-liked meeting... | 0 | 2024-07-12T14:32:20 | https://dev.to/tejcam/talk-to-strangers-exploring-the-world-of-online-conversations-18c | chat, talktostranger, chatrooms | ## Most Well-liked Chat Rooms for Strangers
Numerous websites have become well-liked meeting spots for online conversations with strangers. These are a handful of the most noteworthy ones:
### Speak With Stranger
A free online chat service called TalkWithStranger provides a number of chat rooms and random chat featu... | tejcam |
1,921,273 | Reddit群控软件,reddit群控助手,reddit群成员群发 | Reddit群控软件,reddit群控助手,reddit群成员群发 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T14:32:24 | https://dev.to/naps_jwjj_5a3706c59d1328c/redditqun-kong-ruan-jian-redditqun-kong-zhu-shou-redditqun-cheng-yuan-qun-fa-33e8 |
Reddit群控软件,reddit群控助手,reddit群成员群发
了解相关软件请登录 http://www.vst.tw
Reddit群控软件,作为网络社区管理和运营的工具,近年来在社交媒体管理中扮演着越来越重要的角色。这类软件能够帮助管理员和版主更有效地管理大规模的讨论和互动,尤其是在用户增长迅速、内容复杂多样的情况下,显得尤为重要。
Reddit群控软件的功能
Reddit群控软件通常提供以下核心功能,
内容管理与审查, 这些软件能够帮助管理员监控和审查发布到社区的内容。通过关键词过滤、自动审核等功能,能够快速识别和处理违规内容,如低质量的回复、广告垃圾或违反社区规范的言论。
用户管理与监控, 管... | naps_jwjj_5a3706c59d1328c | |
1,921,274 | Databases Deconstructed: The Value of Data Lakehouses and Table Formats | Checkout out my Apache Iceberg Crash Course Get a free copy of Apache Iceberg the Definitive... | 0 | 2024-07-12T14:36:49 | https://dev.to/alexmercedcoder/databases-deconstructed-the-value-of-data-lakhoues-and-table-formats-32en | database, dataengineering, datascience, data | - [Checkout out my Apache Iceberg Crash Course](https://bit.ly/am-2024-iceberg-live-crash-course-1)
- [Get a free copy of Apache Iceberg the Definitive Guide](https://bit.ly/am-iceberg-book)
Databases and data warehouses are powerful systems that simplify working with data by abstracting many of the inherent challeng... | alexmercedcoder |
1,921,275 | 🚀Welcome to BitPower Loop, a new era of blockchain technology! 🎉 | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions... | 0 | 2024-07-12T14:37:25 | https://dev.to/sa_li_c606ba7efa7a8c56c1c/welcome-to-bitpower-loop-a-new-era-of-blockchain-technology-21c4 | bitpower, btc | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions and low gas fees. We are committed to building a strong and flexible economic ecosystem through decentralized smart contract technology and a unique alliance structure. 💡
At BitPower Loop, you can enjoy unlimited inc... | sa_li_c606ba7efa7a8c56c1c |
1,921,276 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-07-12T14:38:25 | https://dev.to/gt3170542/buy-verified-cash-app-account-1le7 | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoinenablement, and an unmatched level of security.\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n• Genuine and activated email verified\n• Registered phone number (USA)\n• Selfie verified\n• SSN (social security number) verified\n• Driving license\n• BTC enable or not enable (BTC enable best)\n• 100% replacement guaranteed\n• 100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n \nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n \nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n \nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number.\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, Cash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n|||\\\\\\\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account. As part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly.\nHow cash used for international transaction?\n\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom. No matter if you're a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain.\nUnderstanding the currency capabilities of your selected payment application is essential in today's digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial. As we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available.\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform. We deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Trustbizs.com stands by the Cash App's superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management. Explore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs.\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller's pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Equally important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\nThe Importance Of Verified Cash App Accounts\nIn today's digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions. By acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller's pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Equally important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n" | gt3170542 |
1,921,277 | My Journey into Mobile and Web Development | Introduction Hello, dev.to community! I'm Jihed Ben Othmen, a Computer Science Engineer... | 0 | 2024-07-12T14:39:23 | https://dev.to/jihed_benothmen/my-journey-into-mobile-and-web-development-2bhc | ## Introduction
Hello, dev.to community! I'm Jihed Ben Othmen, a Computer Science Engineer from Mahdia, Tunisia. With 1.5 years of professional experience in web development and an additional year specializing in ReactJS, I've developed a strong passion for both mobile and web technologies. Today, I want to share my j... | jihed_benothmen | |
1,921,278 | 谷歌引流自动注册,谷歌推广工具,谷歌推广工具 | 谷歌引流自动注册,谷歌推广工具,谷歌推广工具 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T14:41:52 | https://dev.to/ibig_ybfc_268cc9a117544fb/gu-ge-yin-liu-zi-dong-zhu-ce-gu-ge-tui-yan-gong-ju-gu-ge-tui-yan-gong-ju-4dc5 |
谷歌引流自动注册,谷歌推广工具,谷歌推广工具
了解相关软件请登录 http://www.vst.tw
谷歌引流自动注册,技术的双刃剑
在当今信息化社会,谷歌引流自动注册技术日益引起关注。这项技术利用自动化程序,大量注册谷歌账号,并通过这些账号执行各种操作,从而实现特定目的。尽管这种技术在某些领域具有潜在的实用性,但其背后也存在着伦理、法律和安全等多重挑战。
技术原理与应用
谷歌引流自动注册依赖于自动化软件或脚本,通过模拟人工操作,快速生成大量的谷歌账号。这些账号可以用于自动化执行搜索、评论、点赞等操作,以此来提高特定内容的曝光度或影响力。在数字营销领域,这种技术被用来增加网站的流量,提升搜索引擎排名,或者... | ibig_ybfc_268cc9a117544fb | |
1,921,279 | Create hub and spoke virtual networks and subnets | Open a browser and navigate to the Azure portal and login. To create a Virtual Network, in the... | 0 | 2024-07-12T18:00:02 | https://dev.to/stephen_anosike_d6027f55f/create-hub-and-spoke-virtual-networks-and-subnets-2llp | 1. Open a browser and navigate to the Azure portal and login.
2. To create a Virtual Network, in the search bar at the top of the
portal type “Virtual Networks” and select “Virtual Networks” from
the results.
 and t() in PyTorch | *Memos: My post explains adjoint(), mH and mT. My post explains reshape() and view(). My post... | 0 | 2024-07-12T14:47:35 | https://dev.to/hyperkai/transpose-and-t-in-pytorch-1pp2 | pytorch, transpose, t, function | *Memos:
- [My post](https://dev.to/hyperkai/adjoint-mh-and-mt-in-pytorch-5c04) explains [adjoint()](https://pytorch.org/docs/stable/generated/torch.adjoint.html), [mH](https://pytorch.org/docs/stable/tensors.html#torch.Tensor.mH) and [mT](https://pytorch.org/docs/stable/tensors.html#torch.Tensor.mT).
- [My post](https:... | hyperkai |
1,921,282 | adjoint(), mH and mT in PyTorch | *Memos: My post explains transpose() and t(). My post explains reshape() and view(). My post... | 0 | 2024-07-12T14:49:03 | https://dev.to/hyperkai/adjoint-mh-and-mt-in-pytorch-5c04 | pytorch, adjoint, mh, mt | *Memos:
- [My post](https://dev.to/hyperkai/transpose-and-t-in-pytorch-1pp2) explains [transpose()](https://pytorch.org/docs/stable/generated/torch.transpose.html) and [t()](https://pytorch.org/docs/stable/generated/torch.t.html).
- [My post](https://dev.to/hyperkai/reshape-and-view-in-pytorch-40n5) explains [reshape()... | hyperkai |
1,921,542 | Sähköpyörä – uutta virtaa ja hyvinvointia elämääsi | Sähköpyörät ovat uusin tulokas polkupyörien laajassa valikoimassa ja monipuolistavat... | 0 | 2024-07-12T19:00:06 | https://dev.to/frankstive/sahkopyora-uutta-virtaa-ja-hyvinvointia-elamaasi-j01 | Sähköpyörät ovat uusin tulokas polkupyörien laajassa valikoimassa ja monipuolistavat mahdollisuuksiasi liikkua helposti ja ympäristöystävällisesti. Ne ovat helppokäyttöinen ja mukautuva kulkuneuvo kaikenikäisille – niin nuorille kuin vanhemmillekin. Parhaimmillaan sähköpyörä auttaa sinua kohti aktiivisempaa ja terveell... | frankstive | |
1,921,283 | Reddit自动群组群发,reddit拉群软件,reddit获客机器人 | Reddit自动群组群发,reddit拉群软件,reddit获客机器人 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T14:51:32 | https://dev.to/wgqf_peuz_a81ea536cf5d42e/redditzi-dong-qun-zu-qun-fa-redditla-qun-ruan-jian-reddithuo-ke-ji-qi-ren-1pho |
Reddit自动群组群发,reddit拉群软件,reddit获客机器人
了解相关软件请登录 http://www.vst.tw
Reddit自动群组群发的现象与影响
Reddit作为全球最大的社交新闻平台之一,其独特的社区结构和内容分享机制,吸引了数以百万计的用户参与讨论、分享和互动。然而,近年来,Reddit上出现了一种新的现象,即自动群组群发。
自动群组群发是什么?
自动群组群发是指通过编写脚本或使用自动化工具,在Reddit上自动发布内容到多个群组(Subreddit)的行为。这些工具可以让用户在几秒钟内将同一篇内容或链接同时发布到数十个甚至上百个群组,从而迅速扩大内容的曝光和影响力。
现象背后的... | wgqf_peuz_a81ea536cf5d42e | |
1,921,284 | Buy verified cash app account | https://dmhelpshop.com/product/buy-verified-cash-app-account/ Buy verified cash app account Cash... | 0 | 2024-07-12T14:52:05 | https://dev.to/stoneddevid/buy-verified-cash-app-account-3ddk | webdev, javascript, beginners, programming | ERROR: type should be string, got "https://dmhelpshop.com/product/buy-verified-cash-app-account/\n\n\n\nBuy verified cash app account\nCash app has emerged as a dominant force in the realm of mobile banking within the USA, offering unparalleled convenience for digital money transfers, deposits, and trading. As the foremost provider of fully verified cash app accounts, we take pride in our ability to deliver accounts with substantial limits. Bitcoin enablement, and an unmatched level of security.\n\nOur commitment to facilitating seamless transactions and enabling digital currency trades has garnered significant acclaim, as evidenced by the overwhelming response from our satisfied clientele. Those seeking buy verified cash app account with 100% legitimate documentation and unrestricted access need look no further. Get in touch with us promptly to acquire your verified cash app account and take advantage of all the benefits it has to offer.\n\nWhy dmhelpshop is the best place to buy USA cash app accounts?\nIt’s crucial to stay informed about any updates to the platform you’re using. If an update has been released, it’s important to explore alternative options. Contact the platform’s support team to inquire about the status of the cash app service.\n\nClearly communicate your requirements and inquire whether they can meet your needs and provide the buy verified cash app account promptly. If they assure you that they can fulfill your requirements within the specified timeframe, proceed with the verification process using the required documents.\n\nOur account verification process includes the submission of the following documents: [List of specific documents required for verification].\n\nGenuine and activated email verified\nRegistered phone number (USA)\nSelfie verified\nSSN (social security number) verified\nDriving license\nBTC enable or not enable (BTC enable best)\n100% replacement guaranteed\n100% customer satisfaction\nWhen it comes to staying on top of the latest platform updates, it’s crucial to act fast and ensure you’re positioned in the best possible place. If you’re considering a switch, reaching out to the right contacts and inquiring about the status of the buy verified cash app account service update is essential.\n\nClearly communicate your requirements and gauge their commitment to fulfilling them promptly. Once you’ve confirmed their capability, proceed with the verification process using genuine and activated email verification, a registered USA phone number, selfie verification, social security number (SSN) verification, and a valid driving license.\n\nAdditionally, assessing whether BTC enablement is available is advisable, buy verified cash app account, with a preference for this feature. It’s important to note that a 100% replacement guarantee and ensuring 100% customer satisfaction are essential benchmarks in this process.\n\nHow to use the Cash Card to make purchases?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card. Alternatively, you can manually enter the CVV and expiration date. How To Buy Verified Cash App Accounts.\n\nAfter submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a buy verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account.\n\nWhy we suggest to unchanged the Cash App account username?\nTo activate your Cash Card, open the Cash App on your compatible device, locate the Cash Card icon at the bottom of the screen, and tap on it. Then select “Activate Cash Card” and proceed to scan the QR code on your card.\n\nAlternatively, you can manually enter the CVV and expiration date. After submitting your information, including your registered number, expiration date, and CVV code, you can start making payments by conveniently tapping your card on a contactless-enabled payment terminal. Consider obtaining a verified Cash App account for seamless transactions, especially for business purposes. Buy verified cash app account. Purchase Verified Cash App Accounts.\n\nSelecting a username in an app usually comes with the understanding that it cannot be easily changed within the app’s settings or options. This deliberate control is in place to uphold consistency and minimize potential user confusion, especially for those who have added you as a contact using your username. In addition, purchasing a Cash App account with verified genuine documents already linked to the account ensures a reliable and secure transaction experience.\n\n \n\nBuy verified cash app accounts quickly and easily for all your financial needs.\nAs the user base of our platform continues to grow, the significance of verified accounts cannot be overstated for both businesses and individuals seeking to leverage its full range of features. How To Buy Verified Cash App Accounts.\n\nFor entrepreneurs, freelancers, and investors alike, a verified cash app account opens the door to sending, receiving, and withdrawing substantial amounts of money, offering unparalleled convenience and flexibility. Whether you’re conducting business or managing personal finances, the benefits of a verified account are clear, providing a secure and efficient means to transact and manage funds at scale.\n\nWhen it comes to the rising trend of purchasing buy verified cash app account, it’s crucial to tread carefully and opt for reputable providers to steer clear of potential scams and fraudulent activities. How To Buy Verified Cash App Accounts. With numerous providers offering this service at competitive prices, it is paramount to be diligent in selecting a trusted source.\n\nThis article serves as a comprehensive guide, equipping you with the essential knowledge to navigate the process of procuring buy verified cash app account, ensuring that you are well-informed before making any purchasing decisions. Understanding the fundamentals is key, and by following this guide, you’ll be empowered to make informed choices with confidence.\n\n \n\nIs it safe to buy Cash App Verified Accounts?\nCash App, being a prominent peer-to-peer mobile payment application, is widely utilized by numerous individuals for their transactions. However, concerns regarding its safety have arisen, particularly pertaining to the purchase of “verified” accounts through Cash App. This raises questions about the security of Cash App’s verification process.\n\nUnfortunately, the answer is negative, as buying such verified accounts entails risks and is deemed unsafe. Therefore, it is crucial for everyone to exercise caution and be aware of potential vulnerabilities when using Cash App. How To Buy Verified Cash App Accounts.\n\nCash App has emerged as a widely embraced platform for purchasing Instagram Followers using PayPal, catering to a diverse range of users. This convenient application permits individuals possessing a PayPal account to procure authenticated Instagram Followers.\n\nLeveraging the Cash App, users can either opt to procure followers for a predetermined quantity or exercise patience until their account accrues a substantial follower count, subsequently making a bulk purchase. Although the Cash App provides this service, it is crucial to discern between genuine and counterfeit items. If you find yourself in search of counterfeit products such as a Rolex, a Louis Vuitton item, or a Louis Vuitton bag, there are two viable approaches to consider.\n\n \n\nWhy you need to buy verified Cash App accounts personal or business?\nThe Cash App is a versatile digital wallet enabling seamless money transfers among its users. However, it presents a concern as it facilitates transfer to both verified and unverified individuals.\n\nTo address this, the Cash App offers the option to become a verified user, which unlocks a range of advantages. Verified users can enjoy perks such as express payment, immediate issue resolution, and a generous interest-free period of up to two weeks. With its user-friendly interface and enhanced capabilities, the Cash App caters to the needs of a wide audience, ensuring convenient and secure digital transactions for all.\n\nIf you’re a business person seeking additional funds to expand your business, we have a solution for you. Payroll management can often be a challenging task, regardless of whether you’re a small family-run business or a large corporation. How To Buy Verified Cash App Accounts.\n\nImproper payment practices can lead to potential issues with your employees, as they could report you to the government. However, worry not, as we offer a reliable and efficient way to ensure proper payroll management, avoiding any potential complications. Our services provide you with the funds you need without compromising your reputation or legal standing. With our assistance, you can focus on growing your business while maintaining a professional and compliant relationship with your employees. Purchase Verified Cash App Accounts.\n\nA Cash App has emerged as a leading peer-to-peer payment method, catering to a wide range of users. With its seamless functionality, individuals can effortlessly send and receive cash in a matter of seconds, bypassing the need for a traditional bank account or social security number. Buy verified cash app account.\n\nThis accessibility makes it particularly appealing to millennials, addressing a common challenge they face in accessing physical currency. As a result, ACash App has established itself as a preferred choice among diverse audiences, enabling swift and hassle-free transactions for everyone. Purchase Verified Cash App Accounts.\n\n \n\nHow to verify Cash App accounts\nTo ensure the verification of your Cash App account, it is essential to securely store all your required documents in your account. This process includes accurately supplying your date of birth and verifying the US or UK phone number linked to your Cash App account.\n\nAs part of the verification process, you will be asked to submit accurate personal details such as your date of birth, the last four digits of your SSN, and your email address. If additional information is requested by the Cash App community to validate your account, be prepared to provide it promptly. Upon successful verification, you will gain full access to managing your account balance, as well as sending and receiving funds seamlessly. Buy verified cash app account.\n\n \n\nHow cash used for international transaction?\nExperience the seamless convenience of this innovative platform that simplifies money transfers to the level of sending a text message. It effortlessly connects users within the familiar confines of their respective currency regions, primarily in the United States and the United Kingdom.\n\nNo matter if you’re a freelancer seeking to diversify your clientele or a small business eager to enhance market presence, this solution caters to your financial needs efficiently and securely. Embrace a world of unlimited possibilities while staying connected to your currency domain. Buy verified cash app account.\n\nUnderstanding the currency capabilities of your selected payment application is essential in today’s digital landscape, where versatile financial tools are increasingly sought after. In this era of rapid technological advancements, being well-informed about platforms such as Cash App is crucial.\n\nAs we progress into the digital age, the significance of keeping abreast of such services becomes more pronounced, emphasizing the necessity of staying updated with the evolving financial trends and options available. Buy verified cash app account.\n\nOffers and advantage to buy cash app accounts cheap?\nWith Cash App, the possibilities are endless, offering numerous advantages in online marketing, cryptocurrency trading, and mobile banking while ensuring high security. As a top creator of Cash App accounts, our team possesses unparalleled expertise in navigating the platform.\n\nWe deliver accounts with maximum security and unwavering loyalty at competitive prices unmatched by other agencies. Rest assured, you can trust our services without hesitation, as we prioritize your peace of mind and satisfaction above all else.\n\nEnhance your business operations effortlessly by utilizing the Cash App e-wallet for seamless payment processing, money transfers, and various other essential tasks. Amidst a myriad of transaction platforms in existence today, the Cash App e-wallet stands out as a premier choice, offering users a multitude of functions to streamline their financial activities effectively. Buy verified cash app account.\n\nTrustbizs.com stands by the Cash App’s superiority and recommends acquiring your Cash App accounts from this trusted source to optimize your business potential.\n\nHow Customizable are the Payment Options on Cash App for Businesses?\nDiscover the flexible payment options available to businesses on Cash App, enabling a range of customization features to streamline transactions. Business users have the ability to adjust transaction amounts, incorporate tipping options, and leverage robust reporting tools for enhanced financial management.\n\nExplore trustbizs.com to acquire verified Cash App accounts with LD backup at a competitive price, ensuring a secure and efficient payment solution for your business needs. Buy verified cash app account.\n\nDiscover Cash App, an innovative platform ideal for small business owners and entrepreneurs aiming to simplify their financial operations. With its intuitive interface, Cash App empowers businesses to seamlessly receive payments and effectively oversee their finances. Emphasizing customization, this app accommodates a variety of business requirements and preferences, making it a versatile tool for all.\n\nWhere To Buy Verified Cash App Accounts\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nThe Importance Of Verified Cash App Accounts\nIn today’s digital age, the significance of verified Cash App accounts cannot be overstated, as they serve as a cornerstone for secure and trustworthy online transactions.\n\nBy acquiring verified Cash App accounts, users not only establish credibility but also instill the confidence required to participate in financial endeavors with peace of mind, thus solidifying its status as an indispensable asset for individuals navigating the digital marketplace.\n\nWhen considering purchasing a verified Cash App account, it is imperative to carefully scrutinize the seller’s pricing and payment methods. Look for pricing that aligns with the market value, ensuring transparency and legitimacy. Buy verified cash app account.\n\nEqually important is the need to opt for sellers who provide secure payment channels to safeguard your financial data. Trust your intuition; skepticism towards deals that appear overly advantageous or sellers who raise red flags is warranted. It is always wise to prioritize caution and explore alternative avenues if uncertainties arise.\n\nConclusion\nEnhance your online financial transactions with verified Cash App accounts, a secure and convenient option for all individuals. By purchasing these accounts, you can access exclusive features, benefit from higher transaction limits, and enjoy enhanced protection against fraudulent activities. Streamline your financial interactions and experience peace of mind knowing your transactions are secure and efficient with verified Cash App accounts.\n\nChoose a trusted provider when acquiring accounts to guarantee legitimacy and reliability. In an era where Cash App is increasingly favored for financial transactions, possessing a verified account offers users peace of mind and ease in managing their finances. Make informed decisions to safeguard your financial assets and streamline your personal transactions effectively.\n\nContact Us / 24 Hours Reply\nTelegram:dmhelpshop\nWhatsApp: +1 (980) 277-2786\nSkype:dmhelpshop\nEmail:dmhelpshop@gmail.com\n\n" | stoneddevid |
1,921,285 | Explore the power of innovative technology: BitPower Loop | In this era of digitalization and rapid development, power management and energy efficiency have... | 0 | 2024-07-12T14:52:13 | https://dev.to/_fe843d8789b5cf8701213/explore-the-power-of-innovative-technology-bitpower-loop-5a70 | In this era of digitalization and rapid development, power management and energy efficiency have become particularly important. As an industry leader, BitPower Loop is redefining how we think about and manage energy. Whether you are a home user or a business user, BitPower Loop provides you with efficient, reliable and... | _fe843d8789b5cf8701213 | |
1,921,286 | HOW TO CREATE AN AZURE VITUAL MACHINE SCALE SET. | In this blog we will be exploring how to create a virtual machine scales set VMSS on Azure. The steps... | 0 | 2024-07-12T14:52:40 | https://dev.to/phillip_ajifowobaje_68724/how-to-create-an-azure-vitual-machine-scale-set-lnm |
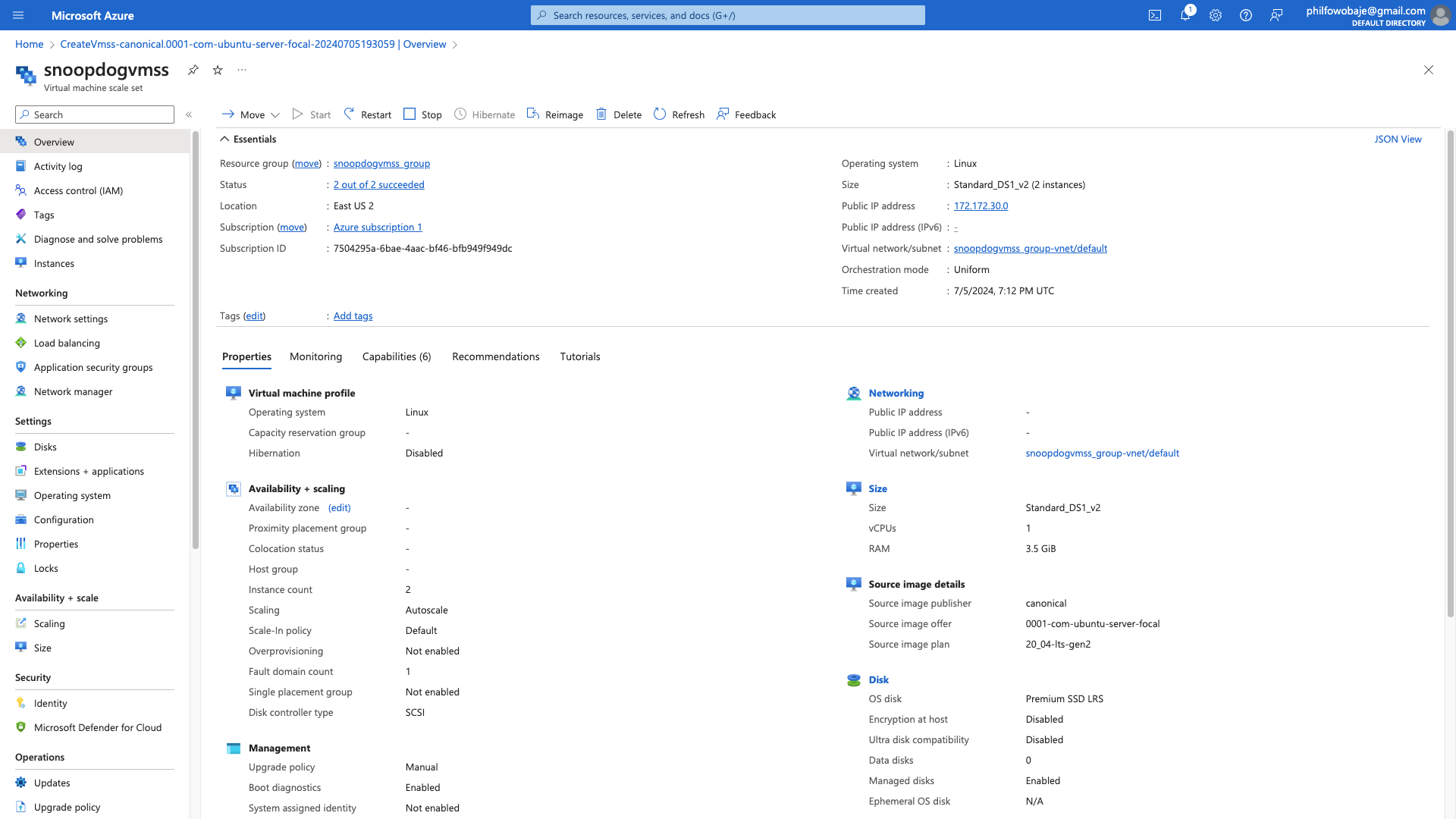In this blog we will be exploring how to create a virtual machine scales set VMSS on Azure. The steps are highlighted below:
Step 1. Log into the Azure Portal
From the Azure portal you search for virtual machine sc... | phillip_ajifowobaje_68724 | |
1,921,287 | Hut ham cau Binh Duong | Hút hầm cầu Bình Dương với kinh nghiệm 15 năm có tới 30 chi nhánh phục vụ nhanh có mặt ngay sau 15-... | 0 | 2024-07-12T14:54:34 | https://dev.to/huthamcaubdah/hut-ham-cau-binh-duong-an4 | Hút hầm cầu Bình Dương với kinh nghiệm 15 năm có tới 30 chi nhánh phục vụ nhanh có mặt ngay sau 15- 30 phút, luôn cam kết bảo hành dịch vụ từ 6 tháng – 2 năm tùy vào từng dịch vụ.
Website: https://huthamcauchuyennghiep.com/hut-ham-cau-binh-duong/
Phone: 0963422486
Address: 176 Nguyễn Văn Linh, Xã Tân Hiệp, Tân Uyên, Bì... | huthamcaubdah | |
1,921,289 | 🚀Welcome to BitPower Loop, a new era of blockchain technology! 🎉 | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions... | 0 | 2024-07-12T14:57:43 | https://dev.to/sa_la_bd0609f1691507edf03/welcome-to-bitpower-loop-a-new-era-of-blockchain-technology-560a | bitpower, btc | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions and low gas fees. We are committed to building a strong and flexible economic ecosystem through decentralized smart contract technology and a unique alliance structure. 💡
At BitPower Loop, you can enjoy unlimited inc... | sa_la_bd0609f1691507edf03 |
1,921,290 | Mastering Database Merging: Comparing Different Approaches | In today’s world, managing data efficiently is crucial for businesses. One key task in data... | 0 | 2024-07-12T14:58:40 | https://dev.to/andreaslennartz/mastering-database-merging-comparing-different-approaches-3ggf | csharp, etl, database, sql | In today’s world, managing data efficiently is crucial for businesses. One key task in data management is merging new data into existing database tables. Whether you’re adding new information or updating existing records, knowing how to do this properly can make a big difference. However, this task can be complex, and ... | andreaslennartz |
1,921,291 | Transforming Simplicity: Adapting Linear Regression to Capture Complex Non-Linear Phenomena with NumPy | In the field of Machine Learning, non-linear phenomena are ubiquitous. Often, people think that... | 0 | 2024-07-12T14:59:16 | https://dev.to/moubarakmohame4/transforming-simplicity-adapting-linear-regression-to-capture-complex-non-linear-phenomena-with-numpy-5efn | machinelearning, python, numpy, learning | In the field of Machine Learning, non-linear phenomena are ubiquitous. Often, people think that linear regression models cannot capture these complexities. However, with a few adjustments, linear regressions can be surprisingly effective in modeling non-linear relationships. In this article, we will explore how to adap... | moubarakmohame4 |
1,921,292 | 飞机筛选软件,纸飞机引流拓客,纸飞机好友群发 | 纸飞机筛选软件,纸飞机引流拓客,纸飞机好友群发 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T15:00:38 | https://dev.to/ngoe_qyny_aed4d6e8c23e182/fei-ji-shai-xuan-ruan-jian-zhi-fei-ji-yin-liu-tuo-ke-zhi-fei-ji-hao-you-qun-fa-1bpb |
纸飞机筛选软件,纸飞机引流拓客,纸飞机好友群发
了解相关软件请登录 http://www.vst.tw
纸飞机筛选软件,提升创意与效率的利器
在现代科技高度发达的时代,创意和技术结合的产物时常为人们带来惊喜。纸飞机筛选软件便是其中之一,它以其独特的方式帮助用户在设计和测试纸飞机时提升效率和精确度。本文将探讨纸飞机筛选软件的功能、应用场景及其对用户的益处。
功能与特点
纸飞机筛选软件的主要功能在于模拟和评估纸飞机的设计。它通常包括以下几个核心特点,
虚拟设计和模拟,用户可以通过软件设计纸飞机的各个方面,如翼展、机身长度、重心位置等。软件能够根据物理原理和算法模拟飞行过程,预测飞行轨迹和性能。
性能分析,... | ngoe_qyny_aed4d6e8c23e182 | |
1,921,294 | 群控助手,Facebook好友群发 | Facebook群发助手,Facebook群控助手,Facebook好友群发 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T15:03:48 | https://dev.to/ydfs_ucst_efeee316eb50311/qun-kong-zhu-shou-facebookhao-you-qun-fa-4njo |
Facebook群发助手,Facebook群控助手,Facebook好友群发
了解相关软件请登录 http://www.vst.tw
Facebook群发助手,社交营销新利器
在社交媒体时代,Facebook群发助手成为了许多企业和个人用户提升沟通效率的重要工具。这款助手能够一键向多个群组或好友发送消息,极大地节省了手动发送的时间和精力。
群发助手的主要功能包括消息编辑、群组选择、定时发送等,用户可以根据需要灵活设置。通过群发助手,企业可以快速推广产品、发布活动信息,而个人用户则可以方便地通知好友聚会、分享重要资讯。
然而,群发助手也存在一定的局限性。过度使用可能导致消息被系统判定为垃圾信息,甚至被封号。因此,... | ydfs_ucst_efeee316eb50311 | |
1,921,295 | I Made ChatGPT Take the Myers–Briggs Personality Test (then I made him write an article about it) | In a quest to understand how artificial intelligence interacts with human personality frameworks, I... | 0 | 2024-07-12T15:06:14 | https://dev.to/nikolab/i-made-chatgpt-take-the-myers-briggs-personality-test-than-i-made-him-write-an-article-about-it-3gk1 | ai, psychology, webdev, fun | In a quest to understand how artificial intelligence interacts with human personality frameworks, I conducted an intriguing experiment: I asked ChatGPT, an advanced AI developed by OpenAI, to take the Myers–Briggs Type Indicator (MBTI) test. Using the popular online platform [16Personalities](https://www.16personalitie... | nikolab |
1,921,297 | 🚀Welcome to BitPower Loop, a new era of blockchain technology! 🎉 | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions... | 0 | 2024-07-12T15:08:16 | https://dev.to/05_li_4228ac4a70be60459b2/welcome-to-bitpower-loop-a-new-era-of-blockchain-technology-4kaa | bitpower, btc | BitPower Loop is an innovative platform based on the Tron blockchain, known for its fast transactions and low gas fees. We are committed to building a strong and flexible economic ecosystem through decentralized smart contract technology and a unique alliance structure. 💡
At BitPower Loop, you can enjoy unlimited inc... | 05_li_4228ac4a70be60459b2 |
1,921,298 | Explore the power of innovative technology: BitPower Loop | In this era of digitalization and rapid development, power management and energy efficiency have... | 0 | 2024-07-12T15:09:23 | https://dev.to/_b0632f7b521969d18faa4/explore-the-power-of-innovative-technology-bitpower-loop-432p | In this era of digitalization and rapid development, power management and energy efficiency have become particularly important. As an industry leader, BitPower Loop is redefining how we think about and manage energy. Whether you are a home user or a business user, BitPower Loop provides you with efficient, reliable and... | _b0632f7b521969d18faa4 | |
1,921,299 | Explore the power of innovative technology: BitPower Loop | In this era of digitalization and rapid development, power management and energy efficiency have... | 0 | 2024-07-12T15:09:27 | https://dev.to/_b0632f7b521969d18faa4/explore-the-power-of-innovative-technology-bitpower-loop-5ef2 | In this era of digitalization and rapid development, power management and energy efficiency have become particularly important. As an industry leader, BitPower Loop is redefining how we think about and manage energy. Whether you are a home user or a business user, BitPower Loop provides you with efficient, reliable and... | _b0632f7b521969d18faa4 | |
1,921,300 | How to Build an API with Laravel Breeze in Laravel 11 | A step-by-step guide on building a simple API with authentication using Laravel Breeze in Laravel 11. | 0 | 2024-07-12T15:10:22 | https://dev.to/johnmaths9/how-to-build-an-api-with-laravel-breeze-in-laravel-11-9k | laravel, php, api, tutorial | ---
title: "How to Build an API with Laravel Breeze in Laravel 11"
published: true
description: "A step-by-step guide on building a simple API with authentication using Laravel Breeze in Laravel 11."
tags: [laravel, php, api, tutorial]
---
## How to Build an API with Laravel Breeze in Laravel 11
A step-by-step guide ... | johnmaths9 |
1,921,301 | LeetCode Meditations: Longest Palindromic Substring | Let's start with the description for Longest Palindromic Substring: Given a string s, return the... | 26,418 | 2024-07-12T15:10:54 | https://rivea0.github.io/blog/leetcode-meditations-longest-palindromic-substring | computerscience, algorithms, typescript, javascript | Let's start with the description for [Longest Palindromic Substring](https://leetcode.com/problems/longest-palindromic-substring):
> Given a string `s`, return _the longest palindromic substring_ in `s`.
For example:
```
Input: s = "babad"
Output: "bab"
Explanation: "aba" is also a valid answer.
```
Or:
```
Input:... | rivea0 |
1,921,302 | My Facebook account has been hacked. | My Facebook account has been hacked. how do i get my account back. plase help... | 0 | 2024-07-12T15:10:54 | https://dev.to/mdrimonhossen549/my-facebook-account-has-been-hacked-240j | facebook, hack, recovary | My Facebook account has been hacked. how do i get my account back. plase help... | mdrimonhossen549 |
1,921,303 | Find the Closest Min-Max using Javascript | The Min Max algorithm efficiently finds the minimum (min) and maximum (max) values in an array of... | 0 | 2024-07-12T15:11:24 | https://techalgospotlight.com/find-the-closest-min-max-using-javascript/ | javascript, datastructures, competativeprogramming, tutorial | The Min Max algorithm efficiently finds the minimum (min) and maximum (max) values in an array of numbers. This approach involves traversing the array while keeping track of the current minimum and maximum values encountered.
## Problem Description
Given an array A, find the size of the smallest subarray such that it... | imkrunalkanojiya |
1,921,305 | Leveraging Zod for Form Validation in React: Unleashing the Power of superRefine | Introduction: The Quest for Perfect Form Validation Meet Lisa, a seasoned developer at... | 0 | 2024-07-12T15:12:29 | https://dev.to/gleidsonleite/leveraging-zod-for-form-validation-in-react-unleashing-the-power-of-superrefine-170j | react, typescript, frontend, node | ## Introduction: The Quest for Perfect Form Validation
Meet Lisa, a seasoned developer at EventPro, a company that creates software for managing events. One day, her manager approaches her with a new challenge: to build a sophisticated user registration form for their latest event management application. This form isn’... | gleidsonleite |
1,921,306 | 1.Role of semantic HTML in enhancing SEO and web accessibility | Semantic HTML elements are essential for creating accessible, SEO-friendly, and well-structured web... | 0 | 2024-07-12T15:14:12 | https://dev.to/gabriel_stanley_7c911d51b/1role-of-semantic-html-in-enhancing-seo-and-web-accessibility-355b | - Semantic HTML elements are essential for creating accessible, SEO-friendly, and well-structured web pages, by improving the readability and maintainability of your HTML code and also enhance the user experience.
-Semantic HTML tags are tags define the meaning of the content they contain. For example, tags like <head... | gabriel_stanley_7c911d51b | |
1,921,307 | YouTube行销工具,Youtube采集机器人,Youtube行销工具 | YouTube行销工具,Youtube采集机器人,Youtube行销工具 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T15:14:30 | https://dev.to/dcss_uwtl_ad9c9d697baba8b/youtubexing-xiao-gong-ju-youtubecai-ji-ji-qi-ren-youtubexing-xiao-gong-ju-3p9b |
YouTube行销工具,Youtube采集机器人,Youtube行销工具
了解相关软件请登录 http://www.vst.tw
YouTube行销工具,利用视频力量扩展品牌影响力
在当今数字化时代,视频内容已经成为品牌营销中不可或缺的一部分。而YouTube作为全球最大的视频分享平台,为企业提供了无限的行销机会。本文将探讨如何有效利用YouTube作为行销工具,扩展品牌的影响力和用户基础。
1. 视频内容的吸引力
YouTube的独特之处在于其视频内容的多样性和吸引力。企业可以通过发布各类视频来展示产品特点、解答常见问题、分享客户见证等。例如,教程和演示视频能够帮助潜在客户了解产品功能和使用方法,提升购... | dcss_uwtl_ad9c9d697baba8b | |
1,921,308 | 筛号软件,BAND筛号软件,BAND过滤机器人 | BAND筛号软件,BAND筛号软件,BAND过滤机器人 了解相关软件请登录 http://www.vst.tw... | 0 | 2024-07-12T15:16:41 | https://dev.to/wibu_notc_39238482cd66f0b/shai-hao-ruan-jian-bandshai-hao-ruan-jian-bandguo-lu-ji-qi-ren-1l64 |
BAND筛号软件,BAND筛号软件,BAND过滤机器人
了解相关软件请登录 http://www.vst.tw
探索BAND筛号软件,革新投资者的选择
在金融科技快速发展的今天,投资市场的参与者们越来越依赖于先进的工具和技术来辅助他们做出明智的投资决策。BAND筛号软件便是其中一款备受欢迎的工具,它以其独特的功能和强大的分析能力,吸引了众多投资者的注意。
什么是BAND筛号软件?
BAND筛号软件是一款专为投资者设计的工具,旨在通过大数据分析和智能算法来帮助用户找到潜在的投资机会。它结合了技术分析、基本面分析和市场情绪分析,为用户提供全面的市场洞察和个性化的投资建议。
主要特点和功能
多维度分析,BA... | wibu_notc_39238482cd66f0b | |
1,921,309 | Deciphering the Inner Workings of Spookyswap | Understanding the Mechanics of Spookyswap The Fundamentals of the Spookyswap Platform Spookyswap is a... | 0 | 2024-07-12T15:16:45 | https://dev.to/cryptokid/deciphering-the-inner-workings-of-spookyswap-2opn | cryptocurrency, ethereum | Understanding the Mechanics of Spookyswap
The Fundamentals of the Spookyswap Platform
[Spookyswap](https://spookyswap.net/) is a decentralized exchange platform that operates on the Ethereum blockchain. In this section, we will delve into the core principles that form the foundation of the Spookyswap platform.
By unde... | cryptokid |
1,921,338 | 🌐 Discover BitPower Loop! | A revolutionary digital currency mining solution that brings new possibilities to your crypto mining... | 0 | 2024-07-12T15:21:16 | https://dev.to/258_258_e84a621f5b0922943/discover-bitpower-loop-3aeb | bitpower, btc |
A revolutionary digital currency mining solution that brings new possibilities to your crypto mining experience. Using advanced energy recovery technology, BitPower Loop not only improves efficiency but also reduces ... | 258_258_e84a621f5b0922943 |
1,921,339 | The fear of making mistakes can be a significant barrier to learning complex technical skills like software engineering | Embrace the Power of Practice and Reflection As aspiring software engineers, you're embarking on a... | 0 | 2024-07-12T15:21:43 | https://dev.to/muhammad_salem/the-fear-of-making-mistakes-can-be-a-significant-barrier-to-learning-complex-technical-skills-like-software-engineering-13aj | **Embrace the Power of Practice and Reflection**
As aspiring software engineers, you're embarking on a journey to master complex technical skills. However, the path to true expertise might surprise you. While books, courses, and tutorials provide valuable knowledge, they're just the beginning. To truly excel, you must... | muhammad_salem | |
1,921,340 | 🌐 How SpookySwap is Bridging Blockchain Ecosystems with Cross-Chain Solutions | Exciting Partnership Announcement by SpookySwap SpookySwap is thrilled to announce a new and exciting... | 0 | 2024-07-12T15:22:02 | https://dev.to/satoshiseeker1/how-spookyswap-is-bridging-blockchain-ecosystems-with-cross-chain-solutions-1acb | cryptocurrency, ethereum, blockchain, web3 | Exciting Partnership Announcement by SpookySwap
SpookySwap is thrilled to announce a new and exciting partnership with Axelar! This collaboration is set to revolutionize the world of decentralized finance by bringing together two innovative platforms in the blockchain space.
Through this partnership, users of SpookySw... | satoshiseeker1 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.