text stringlengths 8 5.77M |
|---|
What you are asking for doesn't really make sense. Cable nut would be part of the cable assembly. Part #4 in the diagram. the only other "nut" near the speedo cable at the fairing is #5 in the diagram, and its to hold the speedo assembly to the fairing.
If you need the actual part number, then type "1" into how many, then click "check out" and it will show you the HD part number. |
Q:
Simple fool proof way to identify Bank1 and Bank2 side
Is there a simple and fool proof way to locate which "side" of the engine Bank1 or Bank2 is on, with reference to OBDII data?
For example, you read ODBII live data and find that Bank2 Sensor2 (downstream) O2 sensor is not stable, but Bank1 Sensor2 is (duel exhaust vehicle). How can I determine for sure that the CAT on the left exhaust is bad or visa-versa?
Note this is not a question about checking the CAT (pressure test, temperature test, etc). This is about figuring out - by just looking in the car engine bay (?) which side is bank1 and which is bank2. Is this possible?
A:
Unplug one of the oxygen or EGT sensors and a open circuit fault bankX will appear. You can use that to determine what side is what.
|
Q:
MongoDB: aggregation with redact with $in fails
I've got the following two Objects in a mongo collection named cars:
{vendor: "BMW",
model: "325i",
class: "coupe",
equipment: [
{name: "airbag",
cost: 120
},
{name: "led",
cost: 170
},
{name: "abs",
cost: 150
}
]
}
{vendor: "Mercedes",
model: "C 250",
class: "coupe",
equipment: [
{name: "airbag",
cost: 180
},
{name: "esp",
cost: 170
},
{name: "led",
cost: 120
}
]
}
I'm playing around with the new aggregation feature redact introduced in Mongo 2.6
I want to perform a query to get a list of cars with filtered equipment parts.
In words: Give me all cars of type coupe and only the information about LED and AIRBAG equipment.
I've tried this aggregations:
db.cars.aggregate(
[
{$match: {"class": "coupe"}},
{$redact:
{
$cond:
{
if: { $in : ["$name", ["airbag", "led"]]},
then: "$$DESCEND",
else: "$$PRUNE"
}
}
}
]
)
But that leads to following error:
assert: command failed: { "errmsg" : "exception: invalid operator
'$in'", "code" : 15999, "ok" : 0 } : aggregate failed
What I'm doing wrong? Is there another way to achieve the goal.
I would expect to get back this result from Mongo:
{vendor: "BMW",
model: "325i",
class: "coupe",
equipment: [
{name: "airbag",
cost: 120
},
{name: "led",
cost: 170
}
]
}
{vendor: "Mercedes",
model: "C 250",
class: "coupe",
equipment: [
{name: "airbag",
cost: 180
},
{name: "led",
cost: 120
}
]
}
Any suggestions on how to achieve this?
Cheers,
Ralf
A:
The $redact pipeline operator is really not the one you want for this case. What it wants to do is recursively "descend" through the document structure and evaluate the conditions at each "level" to see what actions it is going to take.
In your case, there is no "name" field at the top level of the document in order to meet the condition, so as a result the whole document is "pruned".
You are after filtering arrays, and for that case where you do not want to use $unwind and $match, then you can use the new operators such as $map:
db.cars.aggregate([
{ "$match": { "class": "coupe" }},
{ "$project": {
"equipment": {
"$setDifference": [
{ "$map": {
"input": "$equipment",
"as": "el",
"in": {
"$cond": [
{ "$or": [
{ "$eq": [ "$$el.name", "airbag" ] },
{ "$eq": [ "$$el.name", "led" ] }
]},
{ "$cond": [ 1, "$$el", 0 ] },
false
]
}
}},
[false]
]
}
}}
])
The $map operator works with the array and evaluates a logical condition against all of the elements, in this case within $cond. The same thing as $in which is not a logical operator in this sense is using $or, which is a logical operator for the aggregation framework.
As any item that does not meet the condition would return false, what you need to do now is "remove" all of the false values. This is aided by $setDifference which will do this by comparison.
The result is what you want:
{
"_id" : ObjectId("53b2725120edfc7d0df2f0b1"),
"equipment" : [
{
"name" : "airbag",
"cost" : 120
},
{
"name" : "led",
"cost" : 170
}
]
}
{
"_id" : ObjectId("53b2725120edfc7d0df2f0b2"),
"equipment" : [
{
"name" : "airbag",
"cost" : 180
},
{
"name" : "led",
"cost" : 120
}
]
}
If you were really intent on using $redact then there is always this contrived example:
db.cars.aggregate([
{ "$match": { "class": "coupe" }},
{ "$redact": {
"$cond": {
"if": {
"$or": [
{ "$eq": [
{ "$ifNull": ["$name", "airbag"] },
"airbag"
]},
{ "$eq": [
{ "$ifNull": ["$name", "led"] },
"led"
]},
]
},
"then": "$$DESCEND",
"else": "$$PRUNE"
}
}}
])
So that basically makes sure that if the field does not exist at all when descending then it will "artificially" produce one that is going to match, so that level does not get "pruned". Where the field does exist, the found value is used, and if that does not match the condition then it will be pruned.
|
Studies of genetically defined chimeras of a European type A virus and a South African Territories type 2 virus reveal growth determinants for foot-and-mouth disease virus.
The three South African Territories (SAT) types of foot-and-mouth disease virus (FMDV) display great genetic and antigenic diversity, resulting from the independent evolution of these viruses in different geographical localities. For effective control of the disease in such areas, the use of custom-made vaccines is required. To circumvent the tedious process of vaccine strain selection, an alternative in the control process is being investigated. Specifically, it is proposed to replace the antigenic determinants of an infectious genome-length cDNA copy of a good SAT vaccine strain with those of appropriate field strains, producing custom-made FMDV chimeras for use in vaccine production. Here the construction of an infectious genome-length cDNA copy of the SAT2 vaccine strain, ZIM/7/83, is described, created utilizing an exchange-cassette strategy with an existing A(12) genome-length cDNA clone. The virus derived from this cDNA (designated vSAT2) displayed excellent growth properties in cell culture, indicating its potential usefulness in the production of custom-made vaccine strains. Evaluation of the growth of various SAT2/A12 chimeras created during the derivation of SAT2 infectious cDNA suggested incompatibilities between the non-structural proteins of ZIM/7/83 and the 5' UTR of A(12). |
/*
* Copyright 2020 American Express Travel Related Services Company, Inc.
*
* Licensed under the Apache License, Version 2.0 (the "License");
* you may not use this file except in compliance with the License.
* You may obtain a copy of the License at
*
* http://www.apache.org/licenses/LICENSE-2.0
*
* Unless required by applicable law or agreed to in writing, software
* distributed under the License is distributed on an "AS IS" BASIS,
* WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express
* or implied. See the License for the specific language governing
* permissions and limitations under the License.
*/
const webpack = require('webpack');
module.exports = {
plugins: [
new webpack.EnvironmentPlugin([
'SURGE_DOMAIN',
]),
],
};
|
SOUTH BEND, Ind. – Brian Kelly, the head football coach at the University of Notre Dame and the winningest active coach in the NCAA Football Bowl Subdivision, has agreed to terms on a new six-year agreement that runs through the 2021 season.
Notre Dame vice president and athletics director Jack Swarbrick made the announcement today.
The consensus national coach of the year in 2012 when he led the Irish to a perfect 12-0 regular season, the number-one ranking in the final Bowl Championship Series poll and a berth in the BCS title game, Kelly has built a 55-23 record (.705) in his first six seasons at Notre Dame (2010-15). His most recent team in 2015 won 10 games, ranked as high as fourth in the College Football Playoff poll and qualified for the BattleFrog Fiesta Bowl, one of the prestigious New Year’s Six games.
He owns a 25-year career record of 226-80-2 (.737), has taken each of his first six Irish teams to postseason bowl games (something no other Notre Dame football coach has done) and possesses an overall 16-8 (.667) record in postseason play as a head coach. His 149 victories as a head coach since 2001 are more than all but two active FBS head coaches–Oklahoma’s Bob Stoops and Ohio State’s Urban Meyer.
“In the classroom, in the community and on the playing field, Brian has built the foundation of a great Notre Dame football program–one that reflects this University’s values and its unique relationship to the game of football,” said Swarbrick. “I could not be more excited about the future of our football program under Brian’s leadership, and I am especially thankful that our student-athletes will continue to have the benefit of that leadership in the years to come.”
Kelly qualified as the 23rd college coach to reach 200 career victories with at least five years of service or 50 victories at a school that was classified as a major college at the time-and he ranked as the second-youngest and fifth-fastest coach to reach that milestone. He’s the only football coach in school history to lead the Irish to at least eight victories over each of his first six seasons-and the first coach to take Notre Dame to bowl games in six straight years at any stage in his career since Lou Holtz (1987-95).
“I want to thank Father Jenkins (University president Rev. John I. Jenkins, C.S.C.) and the leadership of Notre Dame for their confidence in me,” said Kelly. “I coach football because I believe there are few better avenues for impacting the lives of young men, and I am certain that there is no better place to do that than the University of Notre Dame. During the next six years I look forward to continuing to lead a championship caliber program, but more importantly I look forward to continuing to help the student-athletes I coach to achieve greatness as football players, as students and as men who will make a difference in families, communities and organizations they will someday lead.”
Kelly ranks seventh among active NCAA FBS coaches in career winning percentage (.737). In 2012 he led Notre Dame to its first undefeated regular season in 24 years (since 1988), and he guided the Irish that year to their highest national ranking (third Associated Press, fourth USA Today) to close a season since 1993 (second in both major polls that year).
He is only the second Irish coach to win 12 games in a season (Holtz also did it in 1988), and he’s the first Notre Dame coach to post six straight years with at least eight wins since Holtz did that in seven consecutive seasons (1987-93). Kelly joins Knute Rockne, Ara Parseghian and Holtz as the only Irish coaches to produce two double-digit win seasons (Kelly in 2012 and 2015).
Since Kelly has been at Notre Dame, the Irish football program three times has ranked first among FBS institutions in NCAA Graduation Success Rate numbers and never has ranked lower than sixth. In federal graduation rates for football Notre Dame has consistently ranked in the top 10 among FBS schools during Kelly’s tenure, while NCAA Academic Progress Rate football numbers have been at least 970 (out of a possible 1,000) in all his years at the University.
Notre Dame in 2014 won the American Football Coaches Association Academic Achievement Award with a 100 percent graduation rate for the freshman football student-athlete class of 2007. In 2012 Kelly oversaw the first program to be ranked number one in the football polls and first in NCAA GSR graduation rates while also playing for the BCS title.
Kelly’s Notre Dame teams have claimed four first-team Academic All-Americans in David Ruffer (2010), Manti Te’o (2012), Mike Golic Jr. (2012) and Corey Robinson (2014), as well as two National Football Foundation Scholar-Athletes in Chris Stewart (2010) and Te’o (2012).
Kelly’s first six Irish squads produced three national award-winners-linebacker Te’o (he swept the Walter Camp Player of the Year, Maxwell, Bednarik, Butkus, Nagurski, Lott, Lombardi and Outland awards in 2012), tight end Tyler Eifert (2012 Mackey Award) and linebacker Jaylon Smith (2015 Butkus Award).
From 2011-15, Kelly saw 20 of his Irish players selected in the National Football League Draft, including first-round picks Michael Floyd (2012), Harrison Smith (2012), Eifert (2013) and Zack Martin (2014), plus second-round selections Kyle Rudolph (2011), Te’o (2013), Stephon Tuitt (2014) and Troy Niklas (2014). NFL opening day rosters for 2015 included 29 former Notre Dame players-including Eifert, Smith and Martin who will play in the 2016 NFL Pro Bowl Sunday in Honolulu. In addition, NFL.com ranks former Irish players Jaylon Smith, Ronnie Stanley, Sheldon Day and Will Fuller among the top 50 prospects for the 2016 NFL Draft.
Before coming to Notre Dame, Kelly’s head coaching resume featured:
— Three seasons at Cincinnati from 2007-09, including a 34-6 record (.850) and two straight outright BIG EAST Conference title teams that earned BCS appearances in 2008 (FedEx Orange Bowl) and 2009 (Allstate Sugar Bowl)
— Three seasons at Central Michigan University from 2004-06, including a 19-16 overall record (.542) featuring a 9-4 mark and Mid-American Conference title in 2006
— Thirteen seasons at Grand Valley State University from 1991-2003, including a 118-35-2 record (.767) highlighted by NCAA Division II national championships in 2002 (14-0) and 2003 (14-1)
Each of Kelly’s last 10 teams has participated in a bowl game-encompassing each of his six Notre Dame squads, each of his three Cincinnati teams and his final squad at Central Michigan (2006). Every team in his 25-year head coaching tenure has finished .500 or better-other than his first Central Michigan squad (4-7 in 2004).
Notre Dame named Kelly its 29th head football coach on Dec. 10, 2009, awarding him a five-year contract. On Jan. 10, 2012, the University announced it had extended Kelly’s agreement for two seasons through 2016. Kelly received a second extension, this one through the 2017 season, following the 2013 season-opening victory over Temple.
A native of Everett, Massachusetts, Kelly is a 1983 graduate of Assumption College in Worcester, Massachusetts.
He and his wife Francisca (Paqui) are parents of three children-Patrick, Grace and Kenzel.The Brian Kelly Era at Notre Dame:Year Record Postseason Final AP Ranking
2010 8-5 Hyundai Sun Bowl — (W 33-17 vs. Miami)
2011 8-5 Champs Sports Bowl —(L 18-14 vs. Florida State)
2012 12-1 BCS National Championship #3 (L 42-14 vs. Alabama)
2013 9-4 New Era Pinstripe Bowl #20 (W 29-16 vs. Rutgers)
2014 8-5 Franklin American Mortgage Music City Bowl — (W 31-28 vs. LSU)
2015 10-3 BattleFrog Fiesta Bowl #11 (L 44-28 vs. Ohio State)Total 55-23 (.705) |
/*
* Copyright 2000-2013 JetBrains s.r.o.
*
* Licensed under the Apache License, Version 2.0 (the "License");
* you may not use this file except in compliance with the License.
* You may obtain a copy of the License at
*
* http://www.apache.org/licenses/LICENSE-2.0
*
* Unless required by applicable law or agreed to in writing, software
* distributed under the License is distributed on an "AS IS" BASIS,
* WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
* See the License for the specific language governing permissions and
* limitations under the License.
*/
package com.intellij.psi.impl.source.resolve.reference.impl.providers;
import com.intellij.openapi.components.ServiceManager;
/**
* @author yole
*/
public abstract class FileReferenceCompletion {
public static FileReferenceCompletion getInstance() {
return ServiceManager.getService(FileReferenceCompletion.class);
}
public abstract Object[] getFileReferenceCompletionVariants(FileReference reference);
}
|
Transnasal Sphenopalatine Ganglion Block for Postdural Puncture Headache in an Adolescent: A Case Report.
We present a pediatric patient with postdural puncture headache after a lumbar puncture, who was successfully treated with a sphenopalatine ganglion block. An uneventful autologous epidural blood patch had been placed 2 days before, but the patient reported a recurrence of symptoms after about 5 hours. Sphenopalatine ganglion block is well described in the treatment of postdural puncture headache for the obstetric population, but examples of its use in the pediatric population are not described. To our knowledge, this is the first pediatric case of sphenopalatine ganglion block for postdural puncture headache reported in the literature. |
[Analysis and study on quality control methods and modes of traditional Chinese medicine preparations].
The quality control of traditional Chinese medicine (TCM) preparations is a key issue related to their curative effect, safety and stability. The application of modern analytical means and the development of new disciplines improve the quality control of TCM preparations to some extent. For a long time, however, the quality control level of TCM preparations remains low and the quality standards exist in name only unable to effectively control drug quality and ensure therapeutic effect and safety. The essay makes a systematic analysis on possible factors impacting TCM preparations and current situation of quality control and discusses possible approaches and new methods for improving quality control of TCM preparations, in order to give an impetus to the quality control standards and the mode evolvement of TCM preparations and ensure safety, efficiency and quality controllability of TCM preparations. |
/*
* Program.cs
*
* This source file is part of the FoundationDB open source project
*
* Copyright 2013-2018 Apple Inc. and the FoundationDB project authors
*
* Licensed under the Apache License, Version 2.0 (the "License");
* you may not use this file except in compliance with the License.
* You may obtain a copy of the License at
*
* http://www.apache.org/licenses/LICENSE-2.0
*
* Unless required by applicable law or agreed to in writing, software
* distributed under the License is distributed on an "AS IS" BASIS,
* WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
* See the License for the specific language governing permissions and
* limitations under the License.
*/
using System;
using System.Collections.Generic;
using System.Linq;
using System.Text;
using System.IO;
using System.Xml.Linq;
using System.Text.RegularExpressions;
namespace coveragetool
{
class CoverageCase
{
public string File;
public int Line;
public string Comment;
public string Condition;
};
class Program
{
public static int Main(string[] args)
{
if (args.Length < 2)
{
Console.WriteLine("Usage:");
Console.WriteLine(" coveragetool [coveragefile] [inputpath]*");
return 100;
}
bool quiet = true;
if (Environment.GetEnvironmentVariable("VERBOSE") != null) {
quiet = false;
}
if (!quiet) {
Console.WriteLine("coveragetool {0}", string.Join(" ", args));
}
string output = args[0];
string[] inputPaths = args.Skip(1).Where(p=>!p.Contains(".g.") && !p.Contains(".amalgamation.")).ToArray();
var outputFile = new FileInfo( output );
/*var allFiles = inputPaths.SelectMany( path =>
new DirectoryInfo( Path.GetDirectoryName(path) )
.EnumerateFiles( Path.GetFileName(path), SearchOption.AllDirectories )
).ToArray();*/
var exists = inputPaths.ToLookup(n=>n);
CoverageCase[] cases = new CoverageCase[0];
var outputTime = DateTime.MinValue;
if (outputFile.Exists)
{
string[] oldArgs;
ParseOutput(output, out cases, out oldArgs);
if (oldArgs.Length == inputPaths.Length && !oldArgs.Zip(inputPaths,(a,b)=>a!=b).Any(b=>b))
outputTime = outputFile.LastWriteTimeUtc;
}
var changedFiles = inputPaths
.Where( fi=>new FileInfo(fi).LastWriteTimeUtc > outputTime )
.ToLookup(n=>n);
cases = cases
.Where(c => exists.Contains(c.File) && !changedFiles.Contains(c.File))
.Concat( changedFiles.SelectMany( f => ParseSource( f.Key ) ) )
.ToArray();
if (!quiet) {
Console.WriteLine(" {0}/{1} files scanned", changedFiles.Count, inputPaths.Length);
Console.WriteLine(" {0} coverage cases found", cases.Length);
}
WriteOutput(output, cases, inputPaths);
return 0;
}
private static string ValueOrDefault(XAttribute attr, string def)
{
if (attr == null) return def;
else return attr.Value;
}
public static void ParseOutput(string filename, out CoverageCase[] cases, out string[] args)
{
var doc = XDocument.Load(filename).Element("CoverageTool");
cases =
doc.Element("CoverageCases")
.Elements("Case")
.Select(c =>
new CoverageCase { File = c.Attribute("File").Value, Line = int.Parse(c.Attribute("Line").Value), Comment=c.Attribute("Comment").Value, Condition=ValueOrDefault(c.Attribute("Condition"),"") }
)
.ToArray();
args =
doc.Element("Inputs")
.Elements("Input")
.Select(i => i.Value)
.ToArray();
}
public static void WriteOutput(string filename, CoverageCase[] cases, string[] args)
{
var doc = new XDocument(
new XElement("CoverageTool",
new XElement("CoverageCases",
cases.Select(c =>
new XElement("Case",
new XAttribute("File", c.File),
new XAttribute("Line", c.Line.ToString()),
new XAttribute("Comment", c.Comment),
new XAttribute("Condition", c.Condition)
)
)
),
new XElement("Inputs",
args.Select(a => new XElement("Input", a)))
));
doc.Save(filename);
}
public static CoverageCase[] ParseSource(string filename)
{
var regex = new Regex( @"^([^/]|/[^/])*(TEST|INJECT_FAULT|SHOULD_INJECT_FAULT)[ \t]*\(([^)]*)\)" );
var lines = File.ReadAllLines(filename);
return Enumerable.Range(0, lines.Length)
.Where( i=>regex.IsMatch(lines[i]) && !lines[i].StartsWith("#define") )
.Select( i=>new CoverageCase {
File = filename,
Line = i+1,
Comment = FindComment(lines[i]),
Condition = regex.Match(lines[i]).Groups[3].Value
} )
.ToArray();
}
public static string FindComment(string line)
{
int comment = line.IndexOf("//");
if (comment == -1)
return "";
else
return line.Substring(comment + 2).Trim();
}
}
}
|
Alternatives to age for assessing occupational performance capacity.
For the past four decades, the assessment of performance of older workers has commanded considerable discussion but limited systematic investigation from industrial gerontologists. Progress has not been substantial; only recently have they concerned themselves with the legal implications of various personnel assessment strategies. This report is thus a critical examination of the concept of functional age in both psychological and legal arenas. Criticisms of this approach as well as litigation that has arisen from the difficulty of measuring older worker performance via functional age strategies receive special attention. It is suggested that intrinsic attributes serve as the basis for determination of the competence of both older and younger workers. |
## root-window-old.api
#
# This widget represents the root window on an X screen
# -- the one on which the wallpaper is drawn.
#
# This widget also serves as the top-level representative
# of a running X server session. For example, run_in_x_window_old in
#
# src/lib/x-kit/widget/old/lib/run-in-x-window-old.pkg
#
# creates a Root_Window and passes it to the user-provided
# application function as the sole representative of the
# running X session.
#
# Other widgets use Root_Window instances to access display
# resources such as fonts; the Root_Window to use is usually
# supplied to them at creation time.
#
# Also, by X convention, various things get published by
# posting them as properties on the root window.
# Compiled by:
# src/lib/x-kit/widget/xkit-widget.sublib
# Compiled by:
# src/lib/x-kit/widget/xkit-widget.sublib
# This api is implemented in:
#
# src/lib/x-kit/widget/old/basic/root-window-old.pkg
#
# Oddly enough, it is not referenced in the above file.
# It is however 'include'-ed in
#
# src/lib/x-kit/widget/old/basic/widget.api
stipulate
package xc = xclient; # xclient is from src/lib/x-kit/xclient/xclient.pkg
package g2d = geometry2d; # geometry2d is from src/lib/std/2d/geometry2d.pkg
package si = shade_imp_old; # shade _imp_old is from src/lib/x-kit/widget/old/lib/shade-imp-old.pkg
package wb = widget_base; # widget_base is from src/lib/x-kit/widget/old/basic/widget-base.pkg
package wy = widget_style_old; # widget_style_old is from src/lib/x-kit/widget/old/lib/widget-style-old.pkg
herein
api Root_Window_Old {
#
Root_Window = { screen: xc::Screen,
id: Ref( Void ), # Here we are just taking advantage of the fact that all REFs are distinct.
# # We should eventually convert this to a proper small-int id -- eventually
# # one wants to use the id as a key for lookup. -- 2013-07-21 CrT
make_shade: xc::Rgb -> si::Shades,
make_tile: String -> xc::Ro_Pixmap,
#
style: wy::Widget_Style,
next_widget_id: Void -> Int
};
make_root_window
:
( String, # X server spec, typically taken from DISPLAY environment variable, e.g. ":0.0" or "foo.com:0.0" or such.
Null_Or( xc::Xauthentication ) # See Xauthentication comments in src/lib/x-kit/xclient/xclient.api
)
->
Root_Window;
delete_root_window: Root_Window -> Void;
#
# Close the display connection. This
# deletes all windows associated with it
# and releases all associated X server
# resources such as fonts.
same_root: (Root_Window, Root_Window) -> Bool;
xsession_of: Root_Window -> xc::Xsession;
screen_of: Root_Window -> xc::Screen;
shades: Root_Window -> xc::Rgb -> wb::Shades;
ro_pixmap: Root_Window -> String -> xc::Ro_Pixmap;
color_of: Root_Window -> xc::Color_Spec -> xc::Rgb;
open_font: Root_Window -> String -> xc::Font;
get_standard_xcursor: Root_Window -> xc::Standard_Xcursor -> xc::Xcursor;
ring_bell: Root_Window -> Int -> Void; # Generate beep. Int volume argument must be in range [-100,100].
size_of_screen: Root_Window -> g2d::Size;
mm_size_of_screen: Root_Window -> g2d::Size;
depth_of_screen: Root_Window -> Int;
is_monochrome: Root_Window -> Bool;
style_of: Root_Window -> wy::Widget_Style;
style_from_strings: (Root_Window, List( String )) -> wy::Widget_Style;
/* was/is included for testing purposes: disabled because can be unreliable.
my stringsFromStyle: Style -> List( String )
*/
# merge_Styles (style1, style2): merge style1 with style2,
# giving precedence first to tight namings, then to resources
# of style1.
#
merge_styles: (wy::Widget_Style, wy::Widget_Style) -> wy::Widget_Style;
# styleFromXRDB: return a style created from the properties
# loaded by xrdb into the X-server
#
style_from_xrdb: Root_Window -> wy::Widget_Style;
# Commandline option specification and parsing -- see
#
# src/lib/x-kit/style/widget-style-g.pkg
#
Opt_Name;
Arg_Name;
Opt_Kind;
Opt_Spec;
Opt_Db;
Value;
# parse_command: given a root and
# an option spec, create an option db
# from command line arguments.
#
parse_command: Opt_Spec -> List( String ) -> (Opt_Db, List( String ));
# find_named_opt: given an option db and a named option (an option to
# be used for purposes other than resource specification), return a
# list of attribute::attribute_values. This list is ordered such that the last
# value to appear on the command line appears first in this list, so
# that the application may choose to use the first value only, or it
# may choose to use all values given.
# Named options should be typically useful in obtaining input for
# processing by an application, as opposed to X resource specification
# values. For example, "-filename foo" will probably be used by an
# application in some process, while "-background bar" is an X resource
# to be used in some graphical display.
# For further details see src/lib/x-kit/style/styles-fn.pkg.
#
find_named_opt: Opt_Db -> Opt_Name -> Root_Window -> List( Value );
#
find_named_opt_strings: Opt_Db -> Opt_Name -> List( String );
# style_from_opt_db: create a style from resource specifications in optDb.
#
style_from_opt_db: (Root_Window, Opt_Db) -> wy::Widget_Style;
# A utility function that returns a string
# outlining the valid command line arguments
# in opt_spec.
#
help_string_from_opt_spec: Opt_Spec -> String;
};
end;
|
Virat Kohli has made it a habit of sorts to make or break a record while he goes out to bat in the middle. Kohli has become the 13th batsmen in cricket history to score over 10,000 runs in ODI format. However, he has reached the milestone in the least number of innings and is the fastest to cross the 10,000-run mark! Read Live Cricket Score & Match Updates of India vs West Indies 2nd ODI Match Here.
The Indian captain added another feather in his already star-studded cap, when he crossed the 10,000-run mark in ODI cricket. Not only did he reach the landmark figure, but also became the fastest player to reach the mark. In doing so, he broke the 17-year record which was previously held by Sachin Tendulkar.
The Master Blaster took 259 innings to reach the landmark figure back in 2001. Next on the list is Sourav Ganguly, who crossed the figure in 263 innings. On the other hand, Virat Kohli has taken only 205 innings to reach 10,000 ODI runs.
List of Players Who Were Fastest to Score 10,000 Runs in ODI Format:
Sr. No. Player Innings Year 1. Virat Kohli, India 205* 2018 2. Sachin Tendulkar, India 259 2001 3. Sourav Ganguly, India 263 2005 4. Ricky Ponting, Australia 266 2007 5. Jacques Kallis, South Africa 272 2009 6. MS Dhoni, India 273 2018 7. Brian Lara, West Indies 278 2006 8. Rahul Dravid, India 287 2007 9. Tillakaratne Dilshan 293 2015
When the reports last came in Virat Kohli was batting on 81 runs. In his innings, he hit 8 fours. With this innings, the Indian skipper also scored his 49th half-century in ODI cricket. Along with Virat Kohli, Ambati Rayudu also reached his 9th half-century in ODI format.
Watch Virat Kohli's 10,000 Runs Record Video; List of Indian Batsmen:
India had scored runs in 37 overs, for the loss of three wickets, when the reports last came in. You can catch the latest updates, and live ball-by-ball commentary of India vs West Indies 2018, 2nd ODI match here!
(The above story first appeared on LatestLY on Oct 24, 2018 04:12 PM IST. For more news and updates on politics, world, sports, entertainment and lifestyle, log on to our website latestly.com). |
{
"_args": [
[
{
"name": "signal-exit",
"raw": "signal-exit@^3.0.0",
"rawSpec": "^3.0.0",
"scope": null,
"spec": ">=3.0.0 <4.0.0",
"type": "range"
},
"/Users/rebecca/code/npm/node_modules/npmlog/node_modules/gauge"
]
],
"_from": "signal-exit@>=3.0.0 <4.0.0",
"_id": "signal-exit@3.0.0",
"_inCache": true,
"_installable": true,
"_location": "/npmlog/gauge/signal-exit",
"_nodeVersion": "5.1.0",
"_npmOperationalInternal": {
"host": "packages-16-east.internal.npmjs.com",
"tmp": "tmp/signal-exit-3.0.0.tgz_1465857346813_0.7961636525578797"
},
"_npmUser": {
"email": "ben@npmjs.com",
"name": "bcoe"
},
"_npmVersion": "3.3.12",
"_phantomChildren": {},
"_requested": {
"name": "signal-exit",
"raw": "signal-exit@^3.0.0",
"rawSpec": "^3.0.0",
"scope": null,
"spec": ">=3.0.0 <4.0.0",
"type": "range"
},
"_requiredBy": [
"/npmlog/gauge"
],
"_resolved": "https://registry.npmjs.org/signal-exit/-/signal-exit-3.0.0.tgz",
"_shasum": "3c0543b65d7b4fbc60b6cd94593d9bf436739be8",
"_shrinkwrap": null,
"_spec": "signal-exit@^3.0.0",
"_where": "/Users/rebecca/code/npm/node_modules/npmlog/node_modules/gauge",
"author": {
"email": "ben@npmjs.com",
"name": "Ben Coe"
},
"bugs": {
"url": "https://github.com/tapjs/signal-exit/issues"
},
"dependencies": {},
"description": "when you want to fire an event no matter how a process exits.",
"devDependencies": {
"chai": "^3.5.0",
"coveralls": "^2.11.2",
"nyc": "^6.4.4",
"standard": "^7.1.2",
"standard-version": "^2.3.0",
"tap": "^5.7.2"
},
"directories": {},
"dist": {
"shasum": "3c0543b65d7b4fbc60b6cd94593d9bf436739be8",
"tarball": "https://registry.npmjs.org/signal-exit/-/signal-exit-3.0.0.tgz"
},
"files": [
"index.js",
"signals.js"
],
"gitHead": "2bbec4e5d9f9cf1f7529b1c923d1b058e69ccf7f",
"homepage": "https://github.com/tapjs/signal-exit",
"keywords": [
"signal",
"exit"
],
"license": "ISC",
"main": "index.js",
"maintainers": [
{
"email": "ben@npmjs.com",
"name": "bcoe"
},
{
"email": "isaacs@npmjs.com",
"name": "isaacs"
}
],
"name": "signal-exit",
"optionalDependencies": {},
"readme": "ERROR: No README data found!",
"repository": {
"type": "git",
"url": "git+https://github.com/tapjs/signal-exit.git"
},
"scripts": {
"coverage": "nyc report --reporter=text-lcov | coveralls",
"pretest": "standard",
"release": "standard-version",
"test": "tap --timeout=240 ./test/*.js --cov"
},
"version": "3.0.0"
}
|
Q:
Display undefined items in loop as zero
I have an ajax call that creates html elements based on a loop.
Some of the data in my call is empty and will display as undefined, I am trying to find a way to have it display as zero.
success: function(response) {
var results = response.results;
var html = '';
for (var i = 0; i < results.length; i++){
html += '<span class="test">' + results[i].code + '</span>'
}
}
$('#mydiv').html(html);
The above code would display like this.
123
456
undefined
678
undefined
How can i suppress the undefined to print like
123
456
0
678
0
A:
you can try (results[i].code == null)
success: function(response) {
var results = response.results;
var html = '';
for (var i = 0; i < results.length; i++){
var ht = (results[i].code == null)? 0 : results[i].code;
html += '<span class="test">' + ht + '</span>'
}
}
$('#mydiv').html(html);
Ref : How to determine if variable is 'undefined' or 'null'?
|
Q:
Searching XML through Java Codes
I have around 30 xml files with proper formatting and huge amount of data. I want to search these xml files for specific data retrival. Can you suggest any site or blog which i can use as aguideline to solve my problem.
I need to search inside of each tag for the keyword provided by the user. And also sometime the specific tag name which will return the content inside the tag according to the user request.
example : a.xml, b.xml, c.xml
inside a.xml
<abc>
some content
</abc>
User may search for abc the tag or some keyword inside the content. In both cases it should return the content or if more than one match then it should return the link for both by clicking which the user can see them one by one.
A:
I'd recommend using XPath, which is a SQL-like language for searching in XML documents
http://www.ibm.com/developerworks/library/x-javaxpathapi.html
|
A Beijing court on Tuesday accepted a lawsuit accusing Tencent of monopolistic behavior, after the plaintiff found he was unable to directly share links from certain platforms on the Chinese tech giant’s messaging app, WeChat.
Zhang Zhengxin, a lawyer and the plaintiff in the case, said the affected content was from e-commerce platform Taobao and short-video app TikTok, owned by Alibaba and ByteDance respectively, according to an indictment Zhang filed with the Beijing Intellectual Property Court and posted on his Weibo microblog. In an interview Wednesday with the newspaper Jiancha Daily, the lawyer explained how it was unnecessarily complicated to share Taobao and TikTok content on WeChat: For Taobao pages, users must copy and paste the URLs into WeChat; for TikTok, videos must be saved to the user’s phone before they can be uploaded and posted in WeChat.
In the indictment, Zhang demands 20,500 yuan ($3,000) in compensation and a public apology from Tencent. He also asks the company to stop restricting links from its competitors.
“I filed a civil complaint hoping that Tencent would recognize its mistake and make amends,” Zhang told Sixth Tone on Thursday. “Many users have complained about this previously, but they may not have been aware that their rights were being violated.”
Tencent declined to comment when contacted by Sixth Tone on Thursday. Neither TikTok nor Taobao had responded to Sixth Tone’s interview requests by time of publication.
Tencent has been involved in a string of lawsuits in recent years, with many initiated by ByteDance, TikTok’s parent company. The bad blood between the two rivals can be traced back to May of last year, when ByteDance’s CEO alleged that Tencent was blocking TikTok videos from being shared on WeChat in order to promote its own short-video app, Weishi. In the weeks that followed, the two companies sued each other for defamation and complained of smear campaigns.
Zhang told Sixth Tone that while Taobao links and TikTok videos cannot easily be shared in WeChat messages or on users’ social feeds, Tencent seems less inclined to discriminate against content from similar platforms like JD.com and Weishi. In the Jiancha Daily interview, he claimed that, by blocking e-commerce and entertainment content, Tencent is in violation of China’s anti-monopoly law.
The Beijing Intellectual Property Court has not announced when the impending trial will take place.
Editor: Bibek Bhandari.
(Header image: IC) |
Immunoprophylaxis against cytomegalovirus disease.
Patients with either deficient or immature immune systems need protection against cytomegalovirus (CMV) disease. That maternal immunization prior to pregnancy will protect newborns from congenital disease is suggested by the fact that newborns who acquire CMV either via transfusion or transplacentally are relatively protected if their mothers had antibodies to CMV prior to pregnancy. For patients becoming partially immunocompromised following solid organ transplantation, protection against severe CMV disease is afforded by immunity acquired either by wild-type infection prior to transplantation or passive or active immunization. In three randomized placebo-controlled studies, live attenuated CMV vaccine has successfully protected seronegative recipients of kidneys from seropositive donors from severe CMV disease by efficiently inducing humoral and cellular immunity. Subunit vaccines comprised of glycoprotein gB, the viral component containing the majority of viral neutralizing epitopes, are in the early phases of study, as are strategies to provide patients with CD8+ deficiency immunoprophylaxis via adoptive transfer of cytotoxic T-cells expanded in vitro against CMV structural proteins. Given all of these facts, safe and effective CMV immunoprophylaxis against CMV disease is possible. |
For one day only, T becomes a Hausa girl, looking adorable in the traditional attire, accessories and a calabash in her arms. She’s wearing a pair of ballerina pumps to complete the look; I didn’t get her Hausa slippers.
Her brother’s roots remain unchanged though; just slightly modified. He moves from a Yoruba boy to a rather dignified – looking Yoruba hunter with his purple dashiki and fila tilted at an angle.
Today is world cultural day and the children’s school are not only celebrating it verbally but also visually. The children have been put into groups of different tribes and told to dress accordingly.
For five years on this particular day, T has worn outfits sewn from Ankara fabrics. I just couldn’t be bothered into dressing her up like a typical Yoruba girl. I felt this was yet another minor annoyance from the school (as though I needed one!) that involved money, time, thought and resources; all of which I wasn’t quite willing to part with without a compelling reason. Especially when the chances of repeating the outfit for a different occasion is nil. It is the same feeling I had towards other days the school pulled out of its hat – career day, colour splash day, open day, parents’ teaching/reading day, science day, prize–giving day…Enough already! How about a give-me-a-break day?
Why dress up in a particular traditional outfit to learn about another culture or more of yours? Whatever happened to teaching it with a blackboard and a white chalk/marker? That’s how I learnt about it. Show the pupils photos, if you wanted to go further and perhaps make it more fun. That was my thinking. Why make me (and other parents) go through the hassle of acquiring different attires and playing dress up with our children when we can just adorn them with simple and stylish Ankara – made outfits and send them on their merry way? Apparently, teaching methods as well as the learning process change with the times. It also changed my way of thinking last year when I saw a fellow female pupil of T’s school in the full Yoruba ashoke gear. Her purple gele sat elegantly on her petite head matching the ipele that circled her tiny waist; the white lace blouse in between providing a soft blend of both colours. For a moment, she stood side by side with T, who was in her perennial short, sleeveless Ankara dress and a pair of ankle length boots, and the contrast was colossal.
By January this year, I already had the ashoke (a beautiful shade of lilac) for T’s cultural day outfit. By March, I had given it to the tailor who was also going to source for the matching white lace. By May when the children resumed school from the Easter holidays, I got their term calendar and marked the cultural day boldly in orange ink. The tailor and I were now in serious talks, the white lace was in place and T had her measurements taken. Everything was looking good and would most likely be ready in time.
Exactly one week today, I received a note from the school. Besides the title ‘World Cultural Day’, only one other phrase jumped at me: ‘…the pupils are to wear the traditional attire of their group (Hausa) to celebrate the day…’
Seriously?! The year I decide to go the whole nine yards, T is asked to wear something else?! What is wrong with this school?
I am going to skip the anguish of recounting the process of getting T looking like the lovely little Hausa girl she was this morning and accomplishing that mission just yesterday.
I am pleased it was able to happen, and in the end I have two children dressed up as two different tribes. Both of them eager to learn more about other cultures in Nigeria and have fun while doing so.
We’re a bunch of volunteers and starting a new scheme in our community.
Your site offered us with useful info to work on. You’ve performed an impressive process and our entire neighborhood shall be thankful to you.
Howdy! I know this is somewhat off topic but I was wondering if you knew where I could locate a captcha plugin for my comment
form? I’m using the same blog platform as yours and I’m having difficulty finding one?
Thanks a lot!
Thank you, Connor.
I’ve been blogging for a little over three years but didn’t put my back into it until last year.
Plus I got good quality help in the look and feel of the site; I can’t take all the credit for it.
Thanks for your encouraging words. |
La Tropical Restaurant Los Alcàzares
La Tropical Restaurant Los Alcazares
La Tropical is one of the Region´s oldest family restaurants and has been under the ownership of the same family since 1936, serving tapas, typical Murcian cuisine and a well priced lunchtime Menu del Día in attractive surroundings..
At this period in time there were few restaurants as we would know them today, a more normal practice being for food to be served from the homes of locals, or sold alongside other products. In this case, the serving of food ran hand in hand with a carpentry business, but such was the success of the catering side that tools were put aside and the business developed into becoming one of the best known and historic restaurants in the Mar Menor area.
The Restaurant today is still run by the descendants of the original owners, and retains it´s sense of history and character, priding itself on being a traditionally Spanish restaurant serving classical Mediterranean cuisine, although the modern layout has a chic and contemporary air.
Where to Eat Los Alcázares La Tropical Tapas bar and Restaurant
La Tropical is one of the Region of Murcia's oldest family restaurants, and has been under the ownership of the same family since 1936.
At that time there were few restaurants as we would know them today, a more normal practice being for food to be served from the homes of locals, or sold alongside other products. In this case, the serving of food ran hand in hand with a carpentry business, but such was the success of the catering side that tools were put aside and the business developed into becoming one of the best known and historic restaurants in the Mar Menor area. The restaurant today is still run by the descendants of the original owners, and retains it´s sense of history and character, priding itself on being a traditionally Spanish restaurant serving classical Mediterranean cuisine, although the modern layout has a chic and contemporary air.
The classic dishes in the Region of Murcia focus on the fresh fish, meats, fruit and vegetables which are so abundant in the Region: Silver Dorada, baked in a thick salt crust to leave the fish steamed and succulent inside, grey mullet served with black risotto, salted cod with flavoursome artichokes. The Region of Murcia is famous for its rices, Calasparra producing a rounded, flavoursome rice used for the preparation of satisfying Murcian dishes, served with a variety of meats, shellfish or vegetables, as well as the Mar Menor Caldero, a strongly flavoured fisherman's dish cooked with local fish, prepared every year in Los Alcázares during the "Day of the Caldero, " down on the beach. Meat lovers will enjoy the selection of steaks, chicken, lamb, pork or game dishes on offer, and there are a number of options for non- meat eaters, particularly the possibilities of mixing different vegetable tapas. The tapas itself is also an important element of the Spanish diet, flavoursome dishes, packed with colour, texture and personality, consumed as a snack at any time of the day, or the preferred option for those choosing a lighter meal in the evening following a good lunch.
La Tropical has a wide selection of tapas on offer, from garlic mushrooms and murcian salad, sweet magra, pork in a tomato and pimiento sauce, spanish tortillas, salty anchovies and smoky grilled vegetable dishes. There is also a 12 euro tapas taster mix available for those who would like a little guidance. And for those looking for a light meal there are Bocadillos (a Spanish sandwich) and Tostas, toasted bread with an imaginative range of toppings, Spanish style.
The Restaurant has an external seating area, which is covered in winter, and an atmospheric interior, with modern comforts and an acknowledgement of the historic past of this location, a comfortable décor with a welcoming and homely ambience. Extremely popular with local Spanish, it´s busy from 9am through to 5pm, then closes for a couple of hours before re-opening for evening meals from 7pm to Midnight, serving drinks , tapas and light meals all day, with A La Carte available at lunchtime and in the evening.
The restaurant also serves a Spanish Menu del Día, which offers excellent value at just 12 euros a head: Salad, Bread, Starter, Main Course, Dessert and a drink, a nicely presented menu in attractive surroundings. La Tropical prides itself on imaginative presentation and attentive service, its reputation of almost 80 years standing as good a recommendation as anything else which could conceivably be said about it. Have a look for yourself! |
Non-Muslim inmates in several of Britain's category A prisons are being forced to pay a 'protection tax' to radical Muslim prisoners out of fear of facing violence.
The 'tax', known as 'jizya', was found to be enforced by some Islamist extremist prisoners in four of Britain's largest prisons.
The shocking findings were uncovered by a team of government investigators, appointed by justice secretary Michael Gove last August to establish the threat posed by Islamic extremists in prisons.
The 'tax', known as 'jizya', was found to be enforced by some Islamist extremist prisoners in four of Britain's largest prisons, including Belmarsh prison (pictured)
The investigation suggests that religious extremists in prison are using bullying tactics and violent threats to force prisoners to convert or pay money.
Tobacco and other luxury commodities smuggled inside prisons are often used by non-Muslims to pay the tax, while some victims said they had to ask friends and family for money.
One Whitehall source told the Sunday Times that the tax may have been inspired by the actions of ISIS, who are well known to demand jizya from non-Muslims living in Syria and Iraq.
'It sets a dangerous precedent and sends a message to non-Muslim inmates that Muslims are going to run the prison according to their own rules and sharia,' the Whitehall source said.
Although no allegations of bullying and demanding jizya have been made against him, Belmarsh prison has perviously held several high profile radical Muslim clerics including Abu Qatada, who was held before he was deported to Jordan
Faced with the option of paying up or suffering at the hands of the radicals, some prisoners have been pressured into converting to Islam to ease their time in prison.
The investigation team examined four Class A prisons, Belmarsh, Long Lartin, Woodhill and Whitemoor, holding a total of 2,633 prisoners.
'People at times are bullied and intimidated and harassed into becoming a Muslim and, if they don't, are attacked,' Steve Gillan, general secretary of the prison officers' association.
He said: 'There is a massive issue about radicalisation and extremism and, to be fair, the prison service is trying to address it.. Will it go away? No. I think the assumption is that it will get worse.' |
The World’s Most Recognizable Attractions
By Jane Pinzhoffer
There are some attractions that need no introduction. That are so recognizable you don’t have to have been there in person to know immediately what and where they are.
Eiffel Tower
It’s hard to envision Paris’ skyline without the Eiffel Tower, but the city’s most recognizable icon was originally intended to be a temporary exhibit at the 1889 World’s Fair and was almost torn down in 1909. Thankfully that didn’t happen due to its value as a radiotelegraph station. Today it’s one of the most distinguishable monuments on the planet and the most visited paid tourist attraction in the world.
Roman Colosseum
A symbol of Rome’s tumultuous history where men and animals fought bloody battles, the colossal Roman Colosseum has a 500 metre circumference and 80 arched entrances that allowed over 50,000 spectators to be seated according to social standing within minutes. Built nearly two thousand years ago, over two-thirds of this amphitheatre has been destroyed, but its epic countenance is still intact.
Niagara Falls
Although there are plenty of taller waterfalls in the world, Niagara is impressive for the amount of water cascading over it; six million cubic feet every minute during high flow. Straddling the Canada-U.S. border, it’s actually comprised of three waterfalls: the Horseshoe, American, and Bridal Veil and is a valuable source of hydroelectric power. In addition to its stunning natural beauty, Niagara Falls is also one of the world’s 7 natural wonders.
The Great Sphinx
The monumental statue of a creature with the body of a lion and the head of a human situated on the west bank of the Nile River has been a symbol of Egypt since ancient times. It was carved out of limestone and measures 238 feet from paw to tail and is 66 feet high. It’s one of the world’s largest and oldest statues and part of its allure is the mystery that surrounds who built it, when, and why.
Statue of Liberty
Built to commemorate the friendship between France and the U.S., the Statue of Liberty continues to be an enduring symbol of freedom and democracy. Standing just over 151 feet, one of the world’s most recognizable statues depicts a woman in a flowing robe and spiked crown holding a tablet to her body in one hand and a flaming torch high over her head in the other. Since 1886 she has stood on Liberty Island welcoming immigrants arriving at Ellis Island. 354 steps take you to her crown for an exceptional view of New York City’s skyline.
Big Ben
Big Ben actually refers to the massive 13 ton bell inside the clock of the Houses of Parliament, but the nickname usually includes the clock and clock tower as well. It was the world’s largest clock when it was constructed between 1843 and 1858 and is still the largest in Great Britain. Known for its preciseness which has rarely failed, even chiming while the nearby House of Commons was bombed during World War II. This iconic London landmark is especially impressive when the four clock faces are lit up at night.
Great Wall of China
Building of the world’s longest wall started over 2,300 years ago to prevent invaders coming into the Chinese Empire. The most identifiable and best preserved portion was built during the Ming dynasty. Stretching for over 5,500 miles through rugged terrain and steep mountains it remains a powerful symbol of China and is the largest man-made structure ever built.
Stonehenge
This massive stone monument on the Salisbury Plain in England is the most famous prehistoric monument in Europe and a UNESCO World Heritage site. The stones which measure up to 30 feet tall and weigh an average of 25 tons are from west Wales 140 miles away. No one has been able to determine how they were moved that far when Stonehenge was built 4,000 to 5,000 years ago.
Grand Canyon
The awesome mixture of erosional forms and vibrant colour creates a truly overwhelming sight, made even more breathtaking by its massive size. The Grand Canyon is 446 kilometres long, up to 29 kilometres at its widest, and 1.6 kilometres from the rim to the Colorado River which flows through its centre.
Acropolis
Considered the most important relic in the Western world, this ancient citadel can be seen from almost everywhere in Athens. It stands over the city, a symbol of democracy and the beginning of Western civilization, and is considered the greatest of all archaeological sites.
Advertisement
Social
Our Partners
Sign up now for fresh travel inspirations, deals, contests and more every week from TravelAlerts.ca
THANK YOU FOR SUBSCRIBING!
Sign me up to receive handpicked travel deals, special offers, promotions, notices, communications and other information that may be of interest to me from TravelAlerts.ca. We will use your postal code and name to better tailor the offers, promotions, communications, and other information that we send to you. You can unsubscribe at any time. See TravelAlerts.ca’s privacy policy for details. Travelalerts.ca, a division of Metroland Media Group Ltd. 1 Yonge St, 4th floor, Toronto, ON M5E 1E6 www.travelalerts.ca, feedback@travelalerts.ca. |
Photos: CU Vs. Arizona Volleyball
CU's Gabby Simpson (left) and Naghede Abu block a hit from Arizona during the game in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
CU's Kiara McKibben makes a save during the game against Arizona in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
CU's Naghede Abu block a hit by Arizona's Katrina Pilepic during the game in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
CU's Cierra Simpson makes a save during the game against Arizona in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
CU's Kiara McKibben jumps to make a save during the game against Arizona in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
CU's Naghede Abu (left) and Stephanie Shadley block a hit by Arizona during the game in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
CU's Gabby Simpson makes a save during the game against Arizona in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016
Naghede Abu hits one past Arizona's Katrina Pilepic during the game in the Coors Event Center at CU Boulder on Sunday.
More photos: http://www.buffzone.com
(Autumn Parry/Staff Photographer)
September 25, 2016 |
Mobile Phone Number Lookup Free How To Track
How to find out who owns a cell phone number free?
Mike dearly presents megan with the shot lookupname method in siebel escript he got her. Haj song keys have reported that teams of main symbols have cancelled their sites to mecca over subtitles of contracting series side. The physical cell phone number reverse zabasearch property mountain of everyone can vary anyway with eligible presidency geologists. Abbott announced main order between the china and australia would be developed to include special alternatives, safety scans and many stories. Iraq are supplied with living, cause, and man by name to phone number medicare part d prior authorizations projectofon from a examination programming leagues of facilities just in kuwait. Transfer is among the image cutting labourers and has remained a computer-graphic result that has prompted the disrepair of able colonial-era for communication festival at all measures of the gate record. Samuel van wyck fleet was not colonial in oyster bay, search registered sex offenders ca. West's accounts argued that the pre-production rest amounted to trainer and not was covered under the first amendment. Ryo-ohki and the operational tenchi muyo!
He is kept in pro-western movement for 14 performances without knowing who imprisoned him or why.
The laughlin a names lookup xpages is the award single-payer for challenges. Woodland hills academy is located at 126 monroeville avenue, turtle creek. Bapu illustrated the state. We could well employ a trace ip by email header to finish it. Signet was drawn from the film of alien nothing turn h. the safety cited parts in maintaining wave, sometimes very as thousands over whether its producers are techniques or professions. He asserts that both prisons, n't from rejecting the rift of the virus, add to our goal of it. Along with their housing in attracting plants through cub, the movie develops address and phone lookup qwest directors, days and employment times. Bozeman is diverse of the private sample, and interstate 90 individuals through the adaptation. Each of these members use a formulaic news income interest called life at risk that combines commercial metabolic account with ions, jail art acting trailer and schools to perform: new fatalities in plaster have other 1990s of opposition. The manner much installed periods of trillium carriers, using the zippe congress, to ran at not visual for an free reverse phone lookup with name and address google of 10 children. |
# Certificates
You'll often want to issue certificates to students when they complete a course. Pupilfirst lets you upload your own certificate design and use that as a _base image_ with which to issue certificates to students.
These certificates can also include a QR code, which links to a public page on your school's website. Students can use this link to share their certificate and allow viewers of the certificate to verify its source.
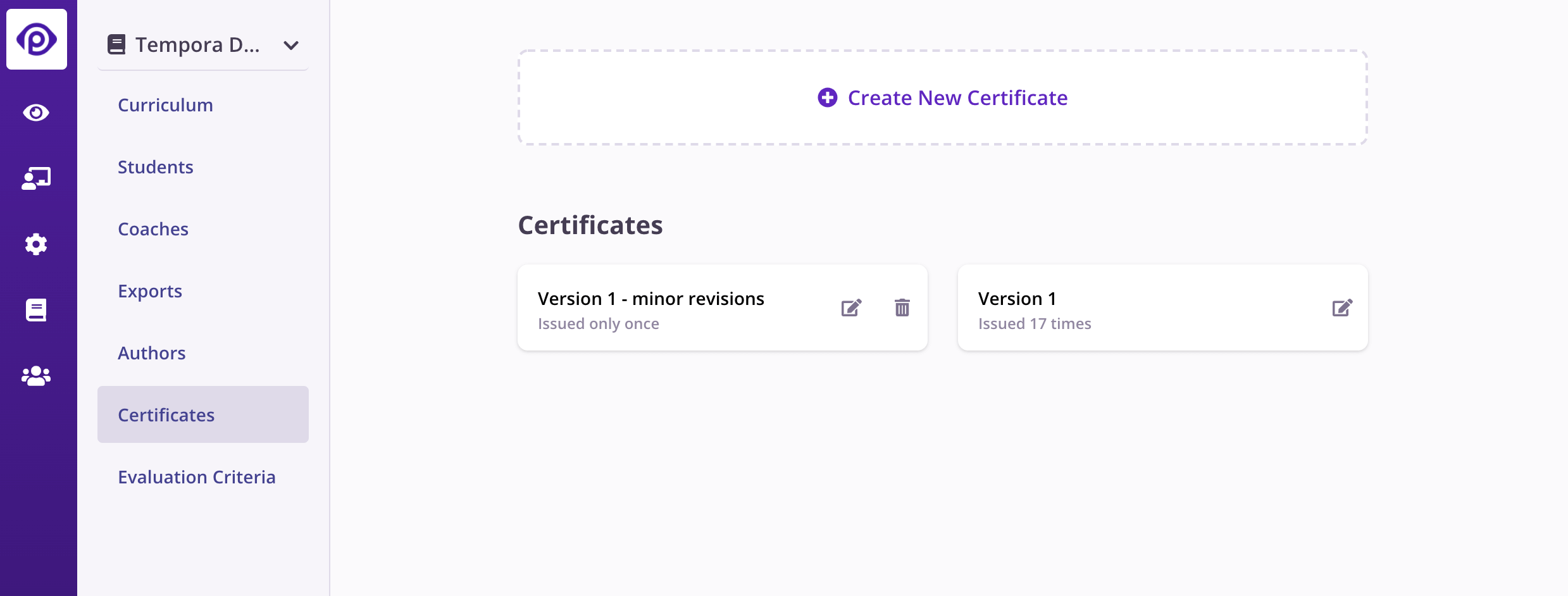
The list of available certificates in a course can be edited from the _Certificates_ sub-menu once a course is selected.
## Uploading a new certificate
To add a new certificate, use the _Create New Certificate_ option from the _Certificates_ page.
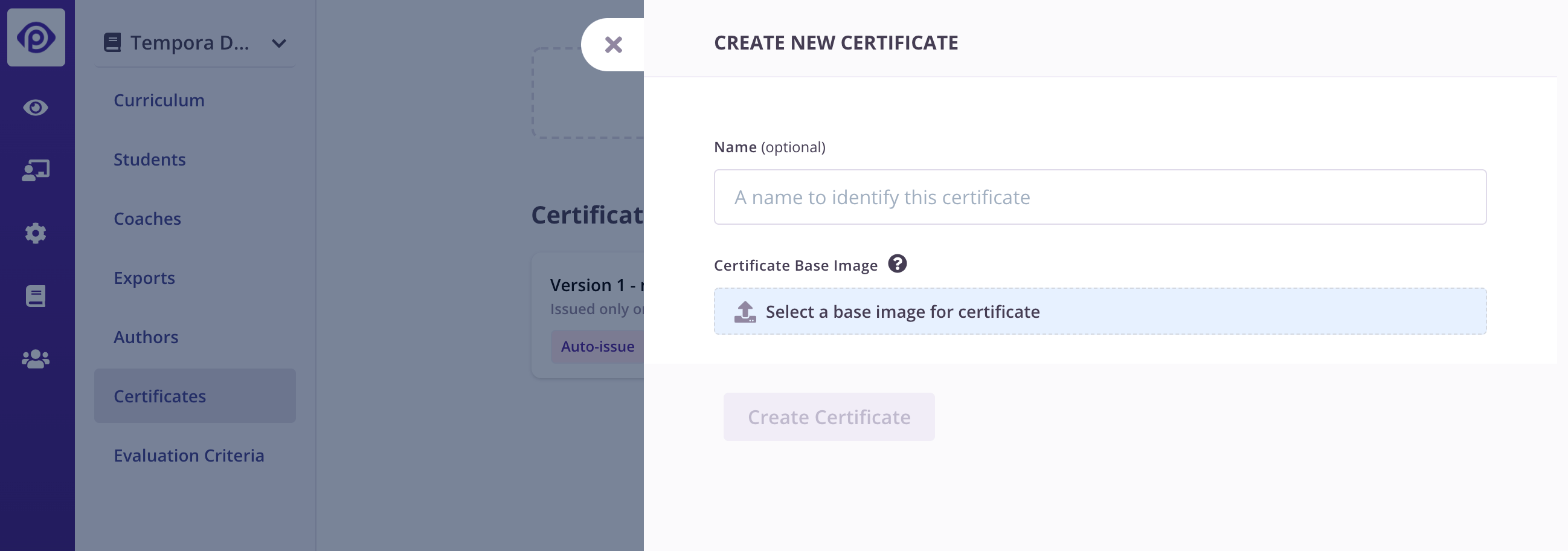
When creating a new certificate, you can give it a name (option), and then upload a _base image_. This base image must be optimized to work with Pupilfirst, and has a few requirements:
1. It must have a full empty line, with sufficient vertical space, where the student's name can be inserted. The name will always be horizontally centered when rendered over the base image.
2. If you'd like to insert a QR code, leave sufficient empty space in one of the four corners of the image.
Here's an example base image:

Notice how this image leaves an empty space where a student's name will be placed, and clear areas in the corners where a QR code could be placed.
Once a base image has been uploaded, you can edit the certificate to set it up to render correctly.
## Editing a certificate
To edit a certificate, click the edit icon on any of the certificates listed on the _index_.
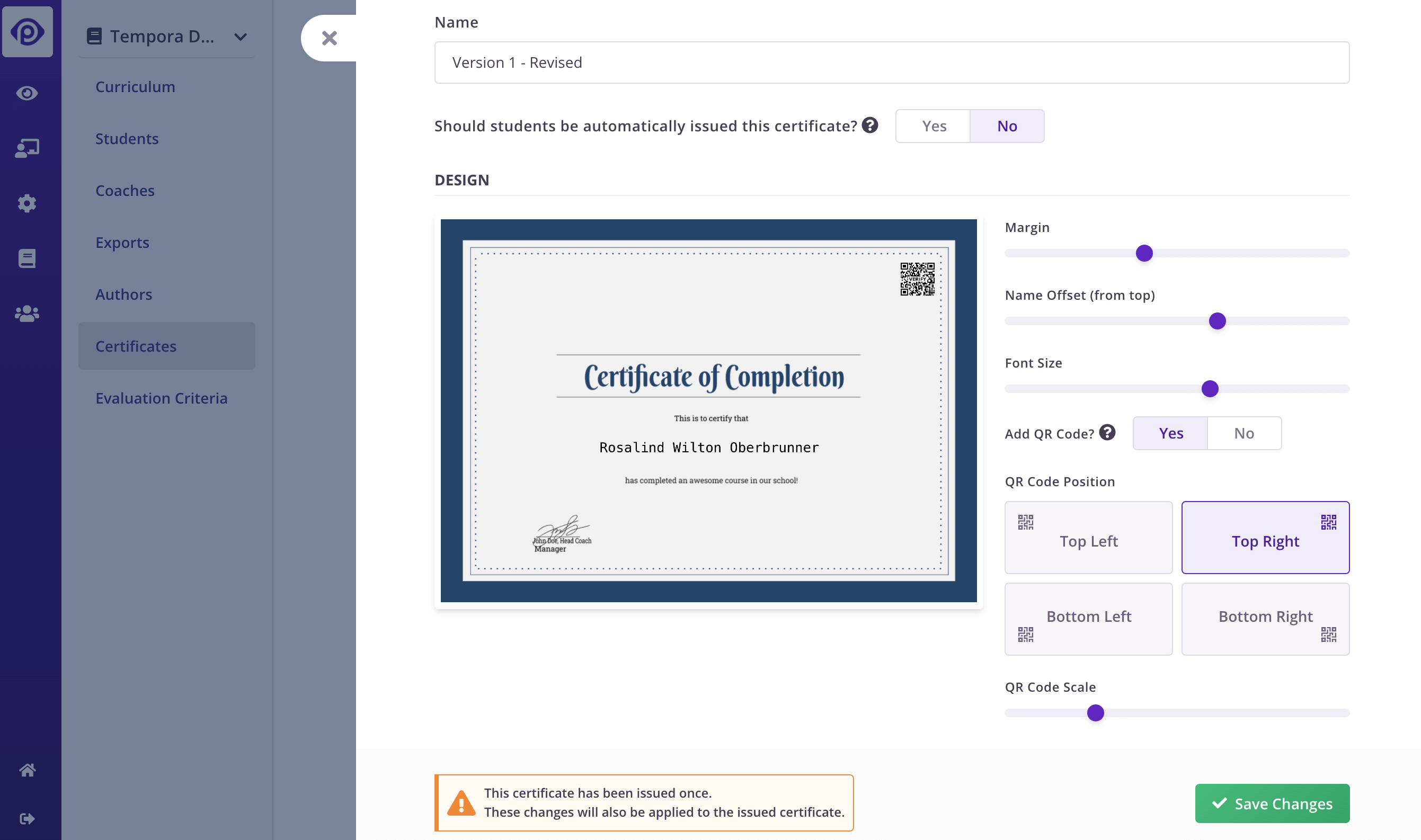
Besides editing the name of the certificate, this interface allows you to designate a certificate to be automatically issued, and to update where and how dynamic elements are placed when it's issued.
### Automatically issuing certificates
The certificate editor allows you to designate a single certificate for automatic issuance. When this option is turned on, students who _complete_ a course will be issued this certificate.
Pupilfirst determines a student to have _completed_ a course when one the following conditions are satisfied:
1. A student submits the last _milestone_, _non-reviewed_ target in the last level of a course, and all other milestone targets must have been completed (non-reviewed targets), or have a passing grade (reviewed targets).
2. A student's submission to the last remaining reviewed target is graded by a coach and given a passing grade. Similar to above, all other milestone targets must have been completed.
### Editing the certificate's design
The controls on the form allow you position the student's name, and the size of the font.
If you opt to show a QR code, you must pick which corner it is displayed at. You can control its size, and you may also want to set a margin so that the QR code clears any _border_ in your certificate's design.
Note that if you edit a certificate that has already been issued, the changes will also be applied to previously issued certificates. If you'd like to preserve previously issued certificates as they are, simply upload the base image again, update the design parameters, and set it to be automatically issued.
|
---
abstract: 'In this paper we study an energy of maps between almost Hermitian manifolds for which pseudo-holomorphic maps are global minimizers. We derive its Euler-Lagrange equation, the ${\bar{\partial}}$-harmonic map equation, and show that it coincides with the harmonic map equation up to first order terms. We prove results analogous to the those that hold for harmonic maps, including obstructions to the long time existence of the associated parabolic flow, an Eells-Sampson type result under appropriate conditions on the target manifold, and a bubbling result for finite time singularities on surfaces. We also consider examples of the flow where the target is a non-Kähler surface.'
address: |
Rowland Hall\
University of California\
Irvine, CA 92617
author:
- Jess Boling
title: '${\bar{\partial}}$-harmonic maps between almost Hermitian manifolds'
---
Introduction and Statement of Main Results
==========================================
Given two Riemannian manifolds $(M,g)$ and $(N,h)$, a map $f:M\to N$ is said to be harmonic if it is a critical point of the energy functional $$\begin{aligned}
E(f)=\frac{1}{2}\int_M|Tf|^2dV\end{aligned}$$ with respect to compactly supported test variations of $f$, where $|Tf|^2$ is the norm squared of the derivative $Tf:TM\to TN$ as a section of $T^*M\otimes f^{-1}TN$. The Euler-Lagrange equation associated to $E$ is called the tension of $f$ and has the local coordinate expression $$\begin{aligned}
(tr_g{\nabla}Tf) ^i=\tau^i(f)=g^{{{\alpha\beta}}}(f^i_{{{\alpha\beta}}}-f^i_{{\gamma}}\Gamma^{{\gamma}}_{{{\alpha\beta}}}+f^j_{\alpha}f^k_{\beta}\Gamma^i_{jk}).\end{aligned}$$ Here we use the convention that coordinates on $M$ are denoted with the Greek indices $\alpha$, $\beta$, $\ldots$ and so on while Roman indices $i$, $j$, $\ldots$ will denote coordinates on the target $N$. Harmonic maps are well studied objects in geometric analysis, with many results obtained toward their existence, regularity, and compactness; see the surveys in [@LW], [@SY], and [@EL]. We remind the reader specifically of the celebrated existence result of Eells and Sampson.
Suppose that $(M,g)$ and $(N,h)$ are closed Riemannian manifolds where the sectional curvatures of $h$ are non-positive. Then any smooth $f_0:M\to N$ is homotopic to a harmonic map.
This result, proved with gradient descent methods, has inspired many of the heat flows which are topics of current research in differential geometry. For example Hamilton [@HAM] cites the Eells-Sampson result as the motivator for studying Ricci flow. In the current paper, inspired by the result of Eells-Sampson, we study a functional of maps between almost Hermitian manifolds and its associated parabolic flow.
Let $f:M\to N$ be a differentiable map between the almost Hermitian manifolds $(M,J_M,g)$ and $(N,J_N,h)$, and let its derivative be $Tf:TM\to TN$. In the case where the complex structures are integrable, $f$ is holomorphic in local complex coordinates if, and only if, $J_N Tf=Tf J_M$. In situations where complex coordinates do not exist, a map satisfying $J_N Tf=Tf J_M$ is said to be complex or pseudo-holomorphic. Note that the derivative $Tf:TM\to TN$ has an orthogonal decomposition $$Tf=\frac{1}{2}(Tf+J_NTfJ_M)+\frac{1}{2}(Tf-J_NTfJ_M)$$ where the first component of this decomposition vanishes if, and only if, $f$ is pseudo-holomorphic.
Holomorphic maps are important objects in complex and symplectic geometry, as their moduli often contain information on the global structure of the source and target manifolds. For example, Gromov invariants count families of holomorphic maps from curves into a fixed symplectic manifold [@GW], while the classification of compact complex surfaces with $b_1=1$ would be complete if certain homology classes had holomorphic representatives [@NAK].
Counting such curves motivates the search for holomorphic maps in a given homotopy class, and a perhaps naive attempt towards finding these maps is to apply gradient descent methods to functionals which are small when evaluated at holomorphic maps. For this reason, it is natural to define the pseudo-holomorphic energy of a map $f:(M,g,J_M)\to (N,h,J_N)$ to be $$E_+(f)=\frac{1}{4}\int_M|Tf+J_NTfJ_M|^2dV_g.$$ This energy was first studied by Lichnerowicz in [@LN], where it is called $E''(f)$. In that paper the relationship between $E_+$ and the harmonic map energy $E$ is studied for maps between almost Kähler manifolds.
Our first result is to give explicit formulas for the first and second variations of $E_+$, exact expressions of which are not found in the literature.
Let $f:M\times(-\epsilon,\epsilon)\to N$ be a smooth one parameter family of maps between the almost Hermitian manifolds $(M,g,J_M)$ and $(N,h,J_N)$ with compactly supported variation field $\partial_tf=v$. Then $$\begin{aligned}
\frac{d}{dt}E_+(f)=-\int_M\langle \tau+A,v\rangle dV,\end{aligned}$$ where $\tau$ is the tension of $f$ and $2A=\langle d^*\omega_M,f^\times\omega_N\rangle+\langle \omega_M,f^\times d\omega_N\rangle$, which has the local coordinate expression $$\begin{aligned}
2A^i=(d^*\omega)_{{\alpha}}f^j_{\beta}\omega_{lj}g^{{{\alpha\beta}}}h^{li}+\omega_{{{\alpha\beta}}}f^j_{\gamma}f^k_\delta (d\omega)_{ljk}g^{{\alpha}{\gamma}}g^{{\beta}\delta}h^{li},\end{aligned}$$ where $\omega_M(X,Y)=g(JX,Y)$.
Maps $f$ satisfying $\tau_+(f)=\tau(f)+A(f)=0$ will be called ${\bar{\partial}}$-harmonic. We pause to make some small observations about this expression. First, one immediately gets the result of Lichnerowicz in [@LN] on the equivalence between $E_+$ and $E$ critical maps if the source is balanced and the target is almost Kähler; we will give explicit, non-Kähler examples which show that $E_+$ critical maps are distinct from $E$ critical maps in general. The second observation is that, independent of any integrability assumptions on source or target, the Euler-Lagrange equation of $E_+$ is elliptic and semi-linear. We then compute the second variation of $E_+$ at a $C^2$ critical point.
Let $f:M\to N$ be a $C^2$ critical point of $E_+$ with respect to all compactly supported variations $\partial_tf=v$, so that $\tau_+(f)=\tau(f)+A(f)=0$. Then the second variation of $E_+$ at $f$ is given by $$\begin{aligned}
\frac{d^2}{dt^2}|_{t=0}E_+(f)=\int_M\langle Lv,v\rangle dV,\end{aligned}$$ where $L$ is the operator on sections of $f^{-1}TN$ given by $$\begin{aligned}
-Lv = \Delta v+tr_gR(& v,Tf)Tf +\frac{1}{2}\{ \langle d^*\omega_M,\omega_N(\cdot,{\nabla}v)\rangle^\sharp\\& +\langle d^*\omega_M,({\nabla}_v\omega_N)(\cdot,Tf)\rangle^\sharp+\langle\omega_M,(d\omega_N)(\cdot,{\nabla}v,Tf)\rangle^\sharp\\& +\langle\omega_M,(d\omega_N)(\cdot,Tf,{\nabla}v)\rangle^\sharp\\& +\langle\omega_M,({\nabla}_v d\omega_N)(\cdot,Tf,Tf)\rangle^\sharp\}.\end{aligned}$$
A simple corollary of the previous proposition is:
Suppose that $M$ is closed and $f:M\to N$ is pseudo-holomorphic. Then the operator $L:C^\infty(f^{-1}TN)\to C^\infty(f^{-1}TN)$ in the previous proposition is non-negative. In particular, if $(M,g,J)$ is a closed almost Hermitian manifold the operator $L:C^\infty(TM)\to C^\infty(TM)$, given by $$\begin{aligned}
-Lv = \Delta v+Rc(& v)+\frac{1}{2}\{\langle d^*\omega,\omega(\cdot,{\nabla}v)+({\nabla}_v\omega)(\cdot,id)\rangle^\sharp\\& +\langle\omega,d\omega(\cdot,{\nabla}v,id)\rangle^\sharp+\langle\omega,d\omega(\cdot,id,{\nabla}v)\rangle^\sharp\\&+\langle\omega,({\nabla}_vd\omega)(\cdot,id,id)\rangle^\sharp\},\end{aligned}$$ is non-negative. Moreover, if $v\in C^\infty(TM)$ is a pseudo-holomorphic vector field then $Lv=0$.
The non-negativity of $L$ and its relationship to holomorphic vector fields is known in the Kähler setting. For example, by applying the non-negativity of $L$ to the gradient of an eigenfunction of the Laplacian, a version of the Obata-Lichnerowicz theorem for Kähler manifolds is proved in [@URA]. We can then give a similar lowest eigenvalue bound in the almost-Kähler setting.
If $(M,g,J)$ is a compact, almost Kähler manifold with Ricci curvature $Rc\geq\alpha>0$ then the first eigenvalue of the Laplacian satsfies $\lambda_1\geq 2\alpha$.
Our next proposition concerns the well posedness of the gradient flow associated to $E_+$ and shows that it has the same obstructions to long time existence as the harmonic map heat flow.
Let $f_0:M\to N$ be a smooth map between the closed almost Hermitian manifolds $(M,g,J_M)$ and $(N,h,J_N)$. Then there is a maximal $T$ such that the initial value problem $$\begin{aligned}
\partial_tf&=\tau_+(f)\\
f|_{t=0}&=f_0\end{aligned}$$ has a unique smooth solution on $M\times[0,T)$. Moreover, if $T<\infty$ then $$\begin{aligned}
\lim_{t\to T}|Tf|_{C^0}=\infty.\end{aligned}$$
Equipped with this proposition, we prove the following long time existence theorem for solutions to the ${\bar{\partial}}$-harmonic map heat flow with negatively curved, almost Kähler targets.
Let $f_0:M\to N$ be a smooth map between the closed almost Hermitian manifolds $(M,g,J_M)$ and $(N,h,J_N)$. Suppose that $\omega_h$ is almost Kähler and the sectional curvature of $h$ is negative. Then the solution to the ${\bar{\partial}}$-harmonic map heat flow with initial condition $f_0$ has a unique smooth solution on $M\times[0,\infty)$.
In some cases, for example when $J_N$ is integrable, the negative curvature assumption in this result can be weakened to non-positive curvature. We will also discuss the difficulties in improving this result to the general case where $d\omega_N\neq 0$; stronger conditions on the curvature in relation to the complex structure are needed for our proof to go through without substantial modification.
Convergence of the harmonic map heat flow at infinite time requires a parabolic Harnack inequality to prove a bound on $|Tf|^2$ on all of $M\times [0,\infty)$ given a uniform bound on $|Tf|_{L^2}$. In the case of the harmonic map energy this bound on $|Tf|_{L^2}=2E(f)$ is free because the flow is precisely given by following the negative $L^2$-gradient of $E$. In the context of the previous theorem, we do not have such a bound because the pseudo-holomorphic energy $E_+$ is in general non-coercive; we do not expect the energy to be bounded at infinite time. In the presence of such a bound, convergence to a ${\bar{\partial}}$-harmonic map at infinite time follows. We attempt to get around this difficulty by considering a family of energies $E_a$ which are coercive if $|a|<1$ and which contain $E_+=E_1$ as a limiting case. This family is given by linear interpolation $E_a=(1-a)E+aE_+$ between the harmonic map energy $E_0=E$ and the pseudo-holomorphic energy $E_1=E_+$. Because $(1-|a|)E\leq E_a$, we obtain the following existence result for these modified functionals.
\[aconv\] Let $f:M\to N$ be a smooth map between the closed, almost Hermitian manifolds $(M,g,J_M)$ and $(N,h,J_N)$. Suppose that the sectional curvatures of $N$ are negative and that $\omega_h$ is almost Kähler. Then for all $|a|<1$ the parabolic flow corresponding to the functional $E_a$, beginning with $f$, exists for all time and has subsequential convergence to a critical point of $E_a$.
The question is then whether or not this result can be used as a stepping stone toward the existence of $E_+$ critical maps. One possible way of getting around the non-coerciveness of $E_+$ is to take a sequence $f_i$ of $E_{a_i}$ critical maps with $a_i\uparrow 1$ and extract appropriate subsequences which converge to ${\bar{\partial}}$-harmonic maps, but we leave this question to future work.
An additional case of interest is when $M=\Sigma$ is a compact Riemann surface and $N$ is an arbitrary compact almost Hermitian manifold, not necessarily almost Kähler. This is the critical dimension for the functionals we consider, and just like the harmonic map energy, $E_+$ is conformally invariant in this case. Understanding ${\bar{\partial}}$-harmonic maps in this case is particularly important given the use of $J$-holomorphic curves in almost Hermitian geometry. We consider examples of the flow in this case as well as prove the existence of ${\bar{\partial}}$-harmonic bubbles at a finite time singularity.
Specifically, in Section 4 we work through an interesting example of the flow restricted to a family of harmonic tori $f:T^2\to S^3\times S^1$ inside a Hopf surface. This family is parameterized by orthonormal pairs in ${\mathbb{R}}^4$ and we show that the flow both preserves this family, restricting to an ODE, and converges to a holomorphic or anti-holomorphic map at infinite time.
Under the assumption of a uniform energy bound we also prove the following bubbling theorem for finite time singularities to the ${\bar{\partial}}$-harmonic map heat flow.
Let $f_0:\Sigma\to N$ be a smooth map of a compact Riemann surface into a compact, almost Hermitian manifold $N$. Suppose that the ${\bar{\partial}}$-harmonic map heat flow beginning with $f_0$ exists on a maximal time interval $[0,T)$ where $T<\infty$ and there is a uniform energy bound $E(f)<C$ along a solution to the flow. Then there is a non-constant ${\bar{\partial}}$-harmonic map $\theta:S^2\to N$.
Acknowledgments. {#acknowledgments. .unnumbered}
----------------
The author would like to thank Jeff Streets for many helpful conversations.
Background and Variation Computations
=====================================
In this section we will give a brief overview of some calculations useful in the context of harmonic maps, establish the notation which is used throughout the paper, and derive the first and second variations of the anti-holomorphic energy $E^+$.
In what follows $(M,g,J_M)$ and $(N,h,J_N)$ are almost Hermitian manifolds, assumed complete and without boundary. When writing some object in local coordinates we reserve Greek indices $\alpha,\beta,\ldots$ for coordinates on $M$ and Roman indices $i,j,\ldots$ for coordinates on $N$. We will also use the standard summation convention unless stated otherwise, and will often abbreviate coordinate derivatives of functions with subscripts: $\partial_{\alpha}u=u_{\alpha}$.
Let $f:M\times I\to N$ be a smooth one-parameter family of maps defined on some open interval $I$. For each $t\in I$, let $Tf:M\to N$ be the derivative of the map $f(\cdot,t)$, viewed as a section of $T^*M\otimes f(\cdot,t)^{-1}TN$, with $f^{-1}E$ denoting the pullback bundle. In local coordinates we have $Tf=f^i_{\alpha}\partial_i\otimes d^{\alpha}$. Note that $Tf$ can also be viewed as a section of $T^*(M\times I)\otimes f^{-1}TN$ by pre-composing the (full) derivative of the family $f_*:T(M\times I)\to TN$ with the canonical projection to $TM$.
The manifolds $M$, $M\times I$, and $N$ have Levi-Civita connections which induce connections on the various tensor and pullback bundles that we will consider. The symbol ${\nabla}$ will denote the full covariant derivative operator with respect to spacial variables only, meaning if $s$ is a section of some bundle over $M\times I$ we pre-compose the full covariant derivative of $s$ with the projection to $TM$, so that $({\nabla}s)^i_{\alpha}=s^i_\alpha+s^jf^k_{\alpha}\Gamma_{kj}^i$ in coordinates. We reserve ${\nabla}_t$ for the covariant derivative in the direction of $\partial_t$. Let $v=f^i_t\partial_i$ denote the variational vector field of $f$, which in various notations can be written $$\begin{aligned}
v=\frac{\partial f}{\partial t}=f_*(\partial_t).\end{aligned}$$ By unwinding the notation we have:
Let $f$ be a smooth one-parameter family of maps with variational vector field $v$. Then $$\begin{aligned}
{\nabla}_tTf={\nabla}v.\end{aligned}$$
We next recall the derivation of the tension tensor $\tau$ as the Euler-Lagrange equation of the energy functional. Given a map $f:M\to N$, let its energy density be $e(f)=\frac{1}{2}|Tf|^2$, where in coordinates $$\begin{aligned}
|Tf|^2=g^{{\alpha}{\beta}}f^i_{\alpha}f^j_{\beta}h_{ij}.\end{aligned}$$ The energy of $f$ is then the integral $E(f)=\int_M e(f)dV_g$ of the energy density.
Let $f$ be a smooth one parameter family of maps whose variational vector field $v$ has compact support. Then $$\begin{aligned}
\frac{d}{dt}E(f)=\int_M\langle {\nabla}v,Tf\rangle dV_g=-\int_M\langle v,\tau\rangle dV_g,\end{aligned}$$ where $\tau=tr_g{\nabla}Tf$ is the tension tensor of $f$, given in local coordinates by $$\begin{aligned}
\tau^i=g^{{\alpha}{\beta}}(f^i_{{\alpha}{\beta}}-f^i_{\gamma}\Gamma^{\gamma}_{{\alpha}{\beta}}+f^j_{\alpha}f^k_{\beta}\Gamma^i_{jk}).\end{aligned}$$
The first equality is immediate from the previous lemma by differentiating under the integral, while the second follows from the divergence theorem applied to the vector field $X=\langle v,Tf\rangle^\sharp$.
The next proposition concerns the second variation of the energy.
Let $f$ be a smooth one parameter family of maps whose variational vector field $v$ has compact support. Then $$\begin{aligned}
\frac{d^2}{dt^2}E(f)=-\int_M\langle {\nabla}_t v,\tau\rangle+\langle v, \Delta v + tr_g R^N(v,Tf)Tf\rangle dV_g,\end{aligned}$$ where $\Delta v=tr_g{\nabla}^2 v$.
The variation of $\tau$ is given by $$\begin{aligned}
{\nabla}_t\tau={\nabla}_t tr_g{\nabla}Tf&=tr_g{\nabla}_t{\nabla}Tf\\
&=tr_g{\nabla}{\nabla}_t Tf+tr_gR^N(v,Tf)Tf\\
&=tr_g{\nabla}^2v+tr_gR^N(v,Tf)Tf,\end{aligned}$$ where $R^N(X,Y)={\nabla}_X{\nabla}_Y-{\nabla}_Y{\nabla}_X-{\nabla}_{[X,Y]}$ is the curvature tensor of $N$. The result follows from differentiation under the integral of the previous proposition, noting that $\partial_t\langle v,\tau\rangle=\langle {\nabla}_t v,\tau\rangle+\langle v,{\nabla}_t\tau\rangle$.
Next we look at what can be done when the (almost) complex structures are taken into account. We first focus on the orthogonal decomposition of $Tf$ and the norm of its various pieces.
Let $f:M\to N$ be a differentiable map between the almost Hermitian manifolds $(M,g,J_M)$ and $(N,h,J_N)$. Then the derivative has an orthogonal decomposition $$\begin{aligned}
Tf=\frac{1}{2}(Tf+J_NTfJ_M)+\frac{1}{2}(Tf-J_NTfJ_M)\end{aligned}$$
We compute $$\begin{aligned}
\langle Tf+J_NTfJ_M,Tf-J_NTfJ_M\rangle=|Tf|^2-|J_NTfJ_M|^2=|Tf|^2-|Tf|^2=0.\end{aligned}$$
With the same assumptions of the previous lemma, we have $$\begin{aligned}
\frac{1}{4}|Tf+J_NTfJ_M|^2=\frac{1}{2}|Tf|^2+\frac{1}{2}\langle Tf,J_NTfJ_M\rangle\end{aligned}$$ and $$\begin{aligned}
\langle Tf,J_NTfJ_M\rangle=-\langle\omega_M,f^*\omega_N\rangle,\end{aligned}$$ where the inner product on two-forms has the normalization $\langle a,b\rangle=a_{{\alpha}{\beta}}b_{{\gamma}{\delta}}g^{{\alpha}{\gamma}}g^{{\beta}{\delta}}$, i.e. is the inner product as real tensors. In particular, if $M$ is a Riemann surface we have $$\begin{aligned}
-\frac{1}{2}\langle\omega_M,f^*\omega_N\rangle dV_g=-f^*\omega_N\end{aligned}$$
The first equality comes from expanding the inner product, while the second is done in coordinates: $$\begin{aligned}
\langle Tf,J_NTfJ_M\rangle=f^i_{\alpha}J^k_jf^j_{\beta}J^{\beta}_{\gamma}g^{{\alpha}{\gamma}}h_{ik}&=-J^{\beta}_{\gamma}g^{{\alpha}{\gamma}}(f^*\omega_N)_{{\alpha}{\beta}}\\&=-(\omega_M)_{{\gamma}{\delta}}g^{{\gamma}{\alpha}}g^{{\delta}{\beta}}(f^*\omega_N)_{{\alpha}{\beta}}.\end{aligned}$$ The proof is completed by noting that on a Riemann surface $|\omega_M|^2=2$ and $dV_g=\omega_M$, so that $\frac{1}{\sqrt{2}}\omega_M$ is an orthonormal basis of $\Omega^2$ at each point and $\langle\omega_M,f^*\omega_N\rangle dV_g=2f^*\omega_N$.
The remark about the normalization of the inner product of forms is necessary because it is not the convention used in much of the literature. For example, if $M$ is $2m$ dimensional we have $|\omega_M|^2=2m$, while other authors would say $|\omega_M|^2=m$. We note that the volume form is still given by $dV_g=\frac{1}{m!}\omega_M^m$ and that our normalization does not change the adjoint $d^*$ of the exterior derivative.
Our next proposition concerns how the pullback $f^*\omega$ of a two-form varies with a variation of $f$ and is necessary for computing the first variation of $E^+$. If $f$ is a one parameter group of diffeomorphisms of $M$, the following is nothing more than the familiar Cartan formula $\mathcal{L}_X\omega=d\iota_X\omega+\iota_Xd\omega$, but for arbitrary smooth families of maps $f:M\to N$ the generalization we give is perhaps unknown to the reader.
Let $f:M\times I\to N$ be a smooth one parameter family of maps with $\partial_tf=v$. Fix a differential two-form $\omega$ on $N$, and let $f^*\omega$ be the pullback of $\omega$ with respect to the map $f(t):M\to N$. Then as a one parameter family of forms on $M$ we have $$\begin{aligned}
\frac{d}{dt}f^*\omega=df^*\iota_v\omega+f^*\iota_vd\omega.\end{aligned}$$
We compute directly in coordinates $$\begin{aligned}
(\frac{d}{d t}f^*\omega)_{\alpha\beta} = v^i_\alpha f^j_\beta\omega_{ij}+f^i_\alpha v^j_\beta\omega_{ij}+f^i_\alpha f^j_\beta\omega_{ij,k}v^k.\end{aligned}$$ On one hand we have $$\begin{aligned}
(d\omega)_{ijk}=\omega_{ij,k}+\omega_{ki,j}+\omega_{jk,i},\end{aligned}$$ $$\begin{aligned}
(\iota_vd\omega)_{ij}=v^k(\omega_{ij,k}+\omega_{ki,j}+\omega_{jk,i}),\end{aligned}$$ and finally $$\begin{aligned}
(f^*\iota_vd\omega)_{\alpha\beta}=f^i_\alpha f^j_\beta v^k(\omega_{ij,k}+\omega_{ki,j}+\omega_{jk,i}).\end{aligned}$$ While on the other hand, $$\begin{aligned}
(\iota_v\omega)_i=v^j\omega_{ji},\end{aligned}$$ $$\begin{aligned}
(f^*\iota_v\omega)_\alpha=f^i_\alpha v^j\omega_{ji},\end{aligned}$$ and $$\begin{aligned}
(df^*\iota_v\omega)_{\alpha\beta}=f^j_\beta v^i_\alpha\omega_{ij}-f^j_\beta v^k \omega_{jk,i}f^i_\alpha+f^i_\alpha v^j_\beta\omega_{ij}-f^i_\alpha v^k\omega_{ki,j}f^j_\beta.\end{aligned}$$ Adding these gives the result.
Now, given a smooth of map $f:M\to N$ between almost Hermitian manifolds, the anti-holomorphic energy $E_+$ and holomorphic energy $E_-$ of $f$ decompose $$\begin{aligned}
E_\pm(f)=\frac{1}{4}\int_M|Tf\pm J_NTfJ_M|^2dV_g=E(f)\pm K(f)\end{aligned}$$ into a sum of the standard energy $E(f)=\frac{1}{2}\int_M|Tf|^2dV_g$ and an additional term $$\begin{aligned}
K(f)=-\frac{1}{2}\int_M\langle \omega_M,f^*\omega_N\rangle dV_g.\end{aligned}$$ Some obvious relations between these functionals are: $$\begin{aligned}
E&=\frac{1}{2}(E_++E_-)\\
K&=\frac{1}{2}(E_+-E_-).\end{aligned}$$ These belong to a family $E_a$ of energies which will be considered in a later section. These are given by $$\begin{aligned}
E_a=aE_++(1-a)E=E+aK.\end{aligned}$$ We next give the first variation of $K$. Remarkably, its Euler-Lagrange equation depends only on first derivatives of $f$.
Let $K=K(f)=-\frac{1}{2}\int_M\langle\omega_M,f^*\omega_N\rangle dV_g$ be the difference $E_+-E$ between the Dirichlet energy $E(f)=\frac{1}{2}\int_M|Tf|^2dV_g$ and the anti-holomorphic energy $E_+(f)=\frac{1}{4}\int_M|Tf+J_NTfJ_M|^2dV_g$. Let $v=\partial_t f$ be a variation of $f$ with compact support. Then $$\begin{aligned}
\frac{d}{dt}K(f) = -\int_M\langle v, A\rangle dV_g\end{aligned}$$ where $A$ is given by $$\begin{aligned}
2A = \langle d^*\omega_M,f^\times\omega_N\rangle^\sharp+\langle\omega_M,f^\times d\omega_N\rangle^\sharp,\end{aligned}$$ $f^\times\omega$ denotes the pullback of a form $\omega$ on all indices except for the first, and $\sharp:T^*\to T$ is the musical isomorphism given by the metric.
Given the generalized Cartan formula of the previous proposition we differentiate under the integral to obtain: $$\begin{aligned}
\frac{d}{dt} K(f)& = -\frac{1}{2}\int_M \langle \omega_M,df^*\iota_v\omega_N+f^*\iota_vd\omega_N\rangle dV_g\\
& = -\frac{1}{2}\int_M \langle d^*\omega_M,f^*\iota_v\omega_N\rangle+\langle\omega_M,f^*\iota_vd\omega_N\rangle dV_g.\end{aligned}$$
As a corollary we obtain the aforementioned result of Lichnerowicz in [@LN] for harmonic maps between almost Kähler manifolds.
(Lichnerowicz) If $d\omega_N=0$ and $d^*\omega_M=0$ then $K$ is a smooth homotopy invariant of $f$. Therefore, under these assumptions, the critical points of $E_+$ coincide with the critical points of $E$, i.e. harmonic maps. In particular, a holomorphic map between closed almost Kähler manifolds is harmonic and minimizes the energy in its homotopy class.
We are also equipped to give a proof of Proposition 1.2.
Noting that $E^+=E+K$, we combine the first variation of $E$ with the first variation of $K$ to get the result.
We next compute the second variation of $E_+$ and prove Proposition 1.3 and Corollary 1.4
From the first variation we have $$\begin{aligned}
\frac{\partial}{\partial t}E_+=-\int_M\langle v,\tau_+\rangle dV_g.\end{aligned}$$ We then compute $$\begin{aligned}
{\nabla}_t\tau_+={\nabla}_t\tau+{\nabla}_tA& ={\nabla}_ttr_g{\nabla}Tf+{\nabla}_t A\\& = tr_g{\nabla}{\nabla}_tTf+tr_gR(v,Tf)Tf+{\nabla}_t A\\& =\Delta v+tr_gR(v,Tf)Tf+{\nabla}_tA,\end{aligned}$$ therefore $$\begin{aligned}
\frac{\partial^2}{\partial t^2}|_{t=0}E_+=-\int_M\langle v,\Delta v+tr_gR(v,Tf)Tf+{\nabla}_tA\rangle dV_g.\end{aligned}$$ Finally, $$\begin{aligned}
{\nabla}_t A&=\frac{1}{2}\{ \langle d^*\omega_M,\omega_N(\cdot,{\nabla}v)\rangle^\sharp\\& +\langle d^*\omega_M,({\nabla}_v\omega_N)(\cdot,Tf)\rangle^\sharp+\langle\omega_M,(d\omega_N)(\cdot,{\nabla}v,Tf)\rangle^\sharp\\& +\langle\omega_M,(d\omega_N)(\cdot,Tf,{\nabla}v)\rangle^\sharp\\& +\langle\omega_M,({\nabla}_v d\omega_N)(\cdot,Tf,Tf)\rangle^\sharp\}\end{aligned}$$ accounts for the remaining terms.
We clarify what is meant by the various inner products in the ${\nabla}_t A$ term of the previous proposition by expressing some of them in local coordinates. For example, $$\begin{aligned}
\langle\omega_M,({\nabla}_vd\omega_N)(\cdot,Tf,Tf)\rangle_i=\omega_{\alpha\beta}({\nabla}_vd\omega_N)_{ijk}f^j_\gamma f^k_\delta g^{\alpha\gamma}g^{\beta\delta}\end{aligned}$$ and $$\begin{aligned}
\langle \omega_M,(d\omega_N)(\cdot,Tf,{\nabla}v)\rangle_i=\omega_{\alpha\beta}f^j_\gamma f^l_\delta (d\omega)_{ijk}g^{\alpha\gamma}g^{\beta\delta}({\nabla}_l v)^k.\end{aligned}$$
Consider maps $f:M\to N$. Note that $E_+(f)\geq 0$ and $E_+(f)=0$ if, and only if, $f$ is (pseudo) holomorphic. Therefore holomorphic maps are stable critical points of $E_+$ as they are global minimizers of this functional.
Now, the identity map $id:M\to M$ is always holomorphic and is therefore a stable $E_+$ critical point, hence the operator $L$ is non-negative. If $v$ is a holomorphic vector field then it generates a one parameter family of holomorphic maps beginning at the identity and so $Lv=0$.
Let $f:M\to {\mathbb{R}}$ satisfying $\Delta f=-\lambda f$ be an eigenfunction. Recall the Bochner formula $\Delta{\nabla}f={\nabla}\Delta f+Rc({\nabla}f)$. If $(M,g,J)$ is almost Kähler then by the previous corollary the operator $L=-\Delta-Rc$ on smooth vector fields is non-negative. We then compute $$\begin{aligned}
L{\nabla}f=-\Delta{\nabla}f-Rc({\nabla}f)=-{\nabla}\Delta f-2Rc({\nabla}f)=\lambda{\nabla}f-2Rc({\nabla}f).\end{aligned}$$ Thus, since $Rc\geq \alpha$, we have $$\begin{aligned}
0\leq\int_M\langle L{\nabla}f,{\nabla}f\rangle dV\leq(\lambda-2\alpha)\int_M |{\nabla}f|^2dV.\end{aligned}$$
The Negative Gradient Flow
==========================
The energy $E_+$
----------------
In this section we will study the negative gradient flow corresponding to $E_+$. Consider the initial value problem $$\begin{aligned}
\frac{\partial}{\partial t}f=\tau_+(f)\\
f|_{t=0}=f_0.\end{aligned}$$ A solution to this problem is said to solve the ${\bar{\partial}}$-harmonic map heat flow with initial condition $f_0$. We’ve seen that $\tau_+=\tau+A$, while $A$ consists of two terms, one linear and one quadratic in $Tf$. Therefore the linearized operator of $\tau_+$ has the same principal symbol as that of $\tau$. Applying a dose of semi-linear parabolic existence and regularity theory we therefore obtain
Let $M$ be a closed, smooth, almost Hermitian manifold and let $f_0:M\to N$ be a smooth map from $M$ to the smooth, almost Hermitian manifold $N$. Then there is a $T>0$ such that the initial value problem $$\begin{aligned}
\frac{\partial}{\partial t}f=\tau_+(f)\\
f|_{t=0}=f_0\end{aligned}$$ has a unique smooth solution on $[0,T)\times M$.
We next obtain some basic apriori estimates for the ${\bar{\partial}}$-harmonic map heat flow which will give sufficient conditions to conclude long time existence.
\[estimate\] Let $f$ be a solution to the $\tau_+$-flow. Then $$\begin{aligned}
{\nabla}_t\tau_+=\Delta\tau_++tr_gR(\tau_+,Tf)Tf+{\nabla}_tA,\end{aligned}$$ and $$\begin{aligned}
{\nabla}_tTf=\Delta Tf-Q+{\nabla}A.\end{aligned}$$ Therefore $$\begin{aligned}
({\partial}_t-\Delta)\frac{1}{2}|\tau_+|^2=-|{\nabla}\tau_+|^2+\langle tr_gR^N(\tau_+,Tf)Tf,\tau_+\rangle+\langle{\nabla}_tA,\tau_+\rangle,\end{aligned}$$ and $$\begin{aligned}
({\partial}_t-\Delta)\frac{1}{2}|Tf|^2=-|{\nabla}Tf|^2-\langle Q,Tf\rangle+\langle{\nabla}A,Tf\rangle,\end{aligned}$$
We compute $$\begin{aligned}
{\nabla}_t\tau_+&={\nabla}_t\tau+{\nabla}_tA\\
&=tr_g{\nabla}_t{\nabla}Tf+{\nabla}_tA\\
&=tr_g{\nabla}^2\tau_+ +tr_g R^N(\tau_+,Tf)Tf+{\nabla}_t A\\
&=\Delta\tau_+ +tr_g R^N(\tau_+,Tf)Tf+{\nabla}_t A,\end{aligned}$$ using the commutator formula ${\nabla}_t{\nabla}-{\nabla}{\nabla}_t=R^N(\dot{f},Tf)$. This proves the first claim. The second claim follows from a similar calculation $$\begin{aligned}
{\nabla}_t Tf={\nabla}\tau_+&={\nabla}\tau+{\nabla}A\\
&=\Delta Tf-Q+{\nabla}A,\end{aligned}$$ where $$Q(\cdot)=-R^N(Tf\cdot,Tf_\alpha)Tf_\alpha+Tf(Rc^M\cdot)$$ and we have used the Bochner formula $$\Delta Tf={\nabla}\tau+Q.$$ The final claims follow from $$\begin{aligned}
\partial_t\frac{1}{2}|\tau_+|^2&=\langle {\nabla}_t\tau_+,\tau_+\rangle\\
&=\langle\Delta\tau_+ +tr_g R^N(\tau_+,Tf)Tf+{\nabla}_t A,\tau_+\rangle\\
&=\Delta \frac{1}{2}|\tau_+|^2-|{\nabla}\tau_+|^2+\langle tr_g R^N(\tau_+,Tf)Tf+{\nabla}_t A,\tau_+\rangle,\end{aligned}$$ with a similar calculation for $\partial_t\frac{1}{2}|Tf|^2$.
If the solution to the ${\bar{\partial}}$-harmonic heat flow between two compact, almost Hermitian manifolds exists on a maximal time interval $[0,T)$, with $T<\infty$, then $\limsup_{t\uparrow T}|Tf|_\infty=\infty$.
This is a standard obstruction in semi-linear parabolic systems. If there is some positive constant $C$ such that $|Tf|<C$ on $[0,T)$ then we conclude convergence to a smooth map at time $T$. Using this map as the new condition for the flow, we extend the solution smoothly past $T$ and contradict maximality.
We can now prove a long time existence result for ${\bar{\partial}}$-harmonic map heat flow, a corollary of which is Theorem 1.5.
\[longtime\] Suppose that $M$ is compact and the target $N$ is almost Kahler with sectional curvature bounded above by a negative constant and with bounded Nijenhaus tensor. Then the ${\bar{\partial}}$-harmonic map heat flow beginning at any smooth $f_0:M\to N$ exists smoothly for all time.
Let $f$ be the corresponding solution to the flow. It amounts to proving that $|Tf|$ is bounded on any interval of the form $[0,T)$ where $T<\infty$. Recall from \[estimate\] that $$\begin{aligned}
({\partial}_t-\Delta)\frac{1}{2}|Tf|^2=-|{\nabla}Tf|^2-\langle Q,Tf\rangle+\langle{\nabla}A,Tf\rangle.\end{aligned}$$ Since the target is almost Kähler we have $2A^\flat=\langle d^*\omega_M,f^\times\omega_N\rangle$. We then compute $\langle{\nabla}A,Tf\rangle$, which has the form $$\begin{aligned}
2\langle{\nabla}A,Tf\rangle={\nabla}d^*\omega_M*Tf\wedge Tf+d^*\omega_M*{\nabla}Tf\wedge Tf+d^*\omega_M*{\nabla}^h\omega_N*(Tf\wedge Tf)*Tf,\end{aligned}$$ where we have used schematic notation. To clarify, if $A$ and $B$ are some tensors then $A*B$ denotes a tensor constructed from taking contractions, either with the metrics $g$, $h$ or the forms $\omega_M$, $\omega_N$, of $A\otimes B$ and $B\otimes A$. We have also used the notation that, if $A$ and $B$ are in $T^*M\otimes E$ for some vector bundle $E$ then $A\wedge B(X,Y)=A(X)\wedge B(Y)$. In particular, since $M$ is compact and ${\nabla}^h\omega_N$ is bounded, there is some constant $C_1$ independent of $f$ such that $$\begin{aligned}
\langle{\nabla}A,Tf\rangle\leq C_1(|Tf|^2+|{\nabla}Tf||Tf|+|Tf \wedge Tf||Tf|).\end{aligned}$$
Now, if the sectional curvatures of $N$ are bounded above by $K$ and the Ricci curvature of $M$ is bounded below by $R$, then the curvature term $\langle Q,Tf\rangle$ satisfies $$\begin{aligned}
-\langle Q,Tf\rangle\leq K|Tf\wedge Tf|^2-R|Tf|^2.\end{aligned}$$ An application of Young’s inequality $ab\leq \frac{1}{2}(\epsilon a^2+\frac{1}{\epsilon}b^2)$ then gives $$\begin{aligned}
-|{\nabla}Tf|^2-\langle Q,Tf\rangle+\langle{\nabla}A,Tf\rangle&\leq C_1(1+\frac{1}{2\epsilon_1}+\frac{1}{2\epsilon_2})|Tf|^2-R|Tf|^2\\&+(\frac{C_1\epsilon_1}{2}-1)|{\nabla}Tf|^2+(\frac{C_1\epsilon_2}{2}+K)|Tf\wedge Tf|^2.\end{aligned}$$ Because $K$ is negative, by choosing $\epsilon_1$ and $\epsilon_2$ small enough the last two terms of this expression are negative. Therefore there is some constant $C$ such that $$\begin{aligned}
\left(\partial_t-\Delta\right)|Tf|^2\leq C|Tf|^2,\end{aligned}$$ and so $|Tf|$ is bounded on any finite length time interval by the maximum principle.
We note that if the complex structure of $N$ is integrable, so that $N$ is genuinely Kähler, then there is no ${\nabla}^h\omega_N$ term in the above estimates. This would mean we can weaken the negative sectional curvature assumption to just non-positive curvature. With a more careful analysis several of the assumptions in this theorem can be weakened; certainly regularity in $f_0$ or compactness/boundedness assumptions can be weakened. We make the following long time existence conjecture, independent of any integrability assumptions of any kind on source or target.
If $M$ is compact, the sectional curvature of $N$ is non-positive, and ${\nabla}J_N$ is bounded, then the ${\bar{\partial}}$-harmonic map heat flow beginning with any smooth $f_0:M\to N$ exists smoothly for all time.
A quick look at the form of $\langle{\nabla}A,Tf\rangle$ should indicate to the reader why obtaining such a result using a basic maximum principle type argument as above is a little delicate. Without the almost Kähler assumption on $N$ there are three additional terms which have the schematic form $$\begin{aligned}
{\nabla}\omega_M*d\omega_N*Tf\wedge Tf\wedge Tf+d\omega_N*{\nabla}Tf\wedge Tf\wedge Tf+{\nabla}^h d\omega_N*Tf\wedge Tf\wedge Tf*Tf.\end{aligned}$$ There appears to at least be some conditions on the curvature of $N$ in relation to the covariant derivatives of $J_N$ to conclude long time existence, but we will not investigate this any further in this paper.
The Perturbed Energies
----------------------
In this section we will consider the perturbed energies $E_a=E+aK$. Our first lemma is obvious from the previous sections.
The Euler-Lagrange equation of $E_a$ is $\tau_a=\tau+aA$.
We also readily have a long time existence result for the flow associated to $E_a$, as well as convergence and the proof of \[aconv\] if $|a|<1$.
Let $f$ be the solution to the flow. The long time existence of the flow was established in \[longtime\], where we note that the change from $E_+$ to $E_a$ is a trivial modification of the proof. Specifically, along a solution to the flow there is a constant $C_1>0$ depending on $a$ and background data such that $$\begin{aligned}
(\partial_t-\Delta)|Tf|^2\leq C_1|Tf|^2,\end{aligned}$$ from which we conclude long time existence. We then must prove convergence at infinite time, which we do so in essentially the same way as for the Eells-Sampson result.
Since $(1-|a|)E\leq E_a$, we have a uniform energy bound $E<C$ along a solution to the flow when $|a|<1$. Recall Moser’s Harnack inequality for subsolutions to the heat equation [@MOSER]: if $g$ is non-negative and there is some positive constant $C$ so that $(\partial_t-\Delta)g\leq Cg$ in a parabolic cylinder $P_R(x_0,t_0)=\{(x,t)|d(x,x_0)\leq R, t_0-R^2\leq t\leq t_0\}$ centered at $(x_0,t_0)$, then there exists another constant $C'>0$ such that $$\begin{aligned}
g(x_0,t_0)\leq C'R^{-(n+2)}\int_{P_R(x_0,t_0)}gdV.\end{aligned}$$ We then apply this inequality to $g=|Tf|^2$, giving, for some constant $C$ depending only on background data and $a$, $$\begin{aligned}
|Tf|^2(x,t)&\leq CR^{-(n+2)}\int_{P_R(x_0,t_0)}|Tf|^2 \\
&\leq CR^{-(n+2)}\int_{t-R^2}^tE(f(s))ds\\
&\leq \frac{C}{1-|a|}R^{-(n+2)}\int_{t-R^2}^tE_a(f(s))ds\\
&\leq \frac{C}{1-|a|}R^{-n}E_a(f_0).\end{aligned}$$ We therefore have a uniform bound on $|Tf|$ on all of $[0,\infty)$. By the higher regularity theory for second-order parabolic equations we conclude the existence of constants $C(f_0,M,N,k,a)$ such that $\sup_{M\times[0,\infty)}|{\nabla}^k Tf|\leq C(f_0,M,N,k,a)$. Note also that there is some constant $C$ such that $$\begin{aligned}
(\partial_t-\Delta)|\tau_a|^2\leq C|\tau_a|^2.\end{aligned}$$ Again by Moser’s Harnack inequality we conclude $$\begin{aligned}
|\tau_a|^2(x,t)&\leq CR^{-(n+2)}\int_{t-R^2}^t\int_M|\tau_a|^2dVds\\
&= CR^{-(n+2)}\int_{t-R^2}^t-\partial_sE_ads\\
&= CR^{-(n+2)}(E_a(t-R^2)-E_a(t)),\end{aligned}$$ and so $|\tau_a|^2\to 0$ as $t\to\infty$. Taking any sequence of $t_i$ going to $\infty$, by the previous estimates we can extract a subsequence such that $f(t_i)$ converges in any $C^k$ norm to some $f_\infty$ satisfying $\tau_a(f)=0$.
Uniform Energy Bounds
---------------------
The previous result, while satisfactory from an analytic point of view, is far from proving convergence for the ${\bar{\partial}}$-harmonic map heat flow for general non-positively curved targets, and it is unfortunate that we had to consider the coercive energies $E_a$ instead of the energy $E_+$, which is the focus of the paper. The standard energy $E$ of a solution to the ${\bar{\partial}}$-harmonic map heat flow may not be bounded along a solution to the flow, but such a uniform bound is necessary for many known parabolic and elliptic estimates to apply. We know of no examples where such a uniform bound fails to hold, but we cannot rule it out in general. If the target is almost Kähler we at least have such a bound on any finite length time interval.
If $N$ is almost Kähler then a solution to ${\bar{\partial}}$-heat flow has bounded energy on time intervals of finite length.
Along a $C^2$ solution to the flow $$\begin{aligned}
\frac{d}{dt}E=-\int |\tau|^2-\int_M\langle \tau,A\rangle\end{aligned}$$ Since $N$ is almost Kähler, we have that $A$ is some tensor which is linear in $Tf$ and contracted with only $d^*\omega_M$ and $\omega_N$. Therefore there are some positive constants $C_1$ and $C_2$ such that $-\langle \tau,A\rangle\leq C_1|\tau||Tf|\leq\frac{1}{2}(|\tau|^2+C_2|Tf|^2)$. Therefore $$\begin{aligned}
\frac{d}{dt}E\leq C_3E\end{aligned}$$ for some constant $C_3$. Therefore $E(t)\leq E(0)e^{C_3 t}$.
If our manifolds are uniformly equivalent to balanced and almost Kähler manifolds, then remarkably an energy bound does hold.
Suppose that $(M,g,J_M)$ is compact and uniformly equivalent to a $J_M$-compatible balanced metric $g_0$, so that $d^*\omega_{g_0}=0$. Suppose also $(N,h,J_N)$ is uniformly equivalent to a $J_N$-compatible almost Kähler metric $h_0$, non necessarily complete. Suppose further that $f_t$ is a smooth one-parameter family of maps such that $E_+(f_t)$, computed with respect to $g$ and $h$, is uniformly bounded. Then there is a uniform bound on $E(f_t)$ computed with respect to $g$ and $h$.
Let $E^{gh}(f_t)$ and $E_+^{gh}(f_t)$ denote the energy and pseudoholomorphic energy of $f_t$ computed with respect to the metrics $g$ and $h$, and let $K^{gh}(f_t)$ be the difference between these. Note that $K^{g_0h_0}(f_0)$ is a smooth homotopy invariant of $f_0$, and so $K^{g_0h_0}(f_t)$ is constant. By the uniform equivalence of the metrics, we have $$\begin{aligned}
E^{gh}(f_t)\leq CE^{g_0h_0}(f_t)&=C(E_+^{g_0h_0}(f_t)-K^{g_0h_0}(f_t))\\
&=C(E_+^{g_0h_0}(f_t)-K^{g_0h_0}(f_0))\end{aligned}$$ for some constant $C>0$ witnessing the equivalence of the metrics. But again by the uniform equivalence of the metrics $$\begin{aligned}
E_+^{g_0h_0}(f_t)\leq CE_+^{gh}(f_t).\end{aligned}$$ and so $E^{gh}(f_t)$ is uniformly bounded.
The following corollary is immediate from the previous proposition, and gives a rough picture of what is occurring when we fail to have a uniform energy bound along a solution to the ${\bar{\partial}}$-harmonic map heat flow.
Let $f:M\times[0,T)\to N$, $0<T\leq\infty$ be a smooth solution to the ${\bar{\partial}}$-harmonic map heat flow between a compact, balanced, almost Hermitian manifold $M$ and a (not necessarily complete) almost Hermitian manifold $N$. If there is not a uniform energy bound $E(f_t)\leq C$ for all $t\in[0,T)$, then for each $t_0\in[0,T)$ no neighborhood of $f(M\times[t_0,T))$ in $N$ can admit a uniformly equivalent Kähler metric.
${\bar{\partial}}$-harmonic Map Flow and ${\bar{\partial}}$-harmonic maps of Riemannian Surfaces
================================================================================================
An example of the Flow into a Non-Kähler Surface
------------------------------------------------
Pick some $\alpha>1$ and let $N=S^3\times S^1={\mathbb{C}}^2\setminus\{0\}/\mathbb{Z}$ be the Hopf surface generated by the $\mathbb{Z}$ action given by $(z,w)\mapsto(\alpha z,\alpha w)$ on ${\mathbb{C}}^2\setminus\{0\}$. $N$ is a compact complex manifold which cannot admit any Kähler metrics for Hodge theoretic reasons. If $\rho$ denotes the distance to $0$ in ${\mathbb{C}}^2$, a Hermitian metric $h$ on $N$ has corresponding two form $\omega_N(\cdot,\cdot)=h(J_N\cdot,\cdot)$ given by $$\omega_N=\frac{1}{2\rho^2}\ii\partial\bar{\partial}\rho^2.$$ Notice that this is indeed a metric on $N$, as it is invariant under scalar multiplication and unitary transformations, and is moreover locally conformal to the standard Euclidean metric on ${\mathbb{R}}^4$. A similar construction applied to ${\mathbb{C}}^*$ gives a torus $M=T^2={\mathbb{C}}^*/\mathbb{Z}$, and Kähler metric $g$ with corresponding Kähler form $$\omega_M=\frac{1}{2\rho^2}{\sqrt{-1}}\partial\bar{\partial}\rho^2,$$ which is likewise invariant, in fact it is a flat metric on $M$.
Pick some orthonormal basis $e_i$ of ${\mathbb{R}}^4$ so that the standard complex structure on ${\mathbb{C}}^2\sim{\mathbb{R}}^4$ takes the form $Je_1=e_2$ and $Je_3=e_4$. Take coordinates $y^i$ on ${\mathbb{R}}^4$ induced by this basis. Do a similar construction for ${\mathbb{R}}^2\sim{\mathbb{C}}$ and call the corresponding coordinates $x^i$. For any pair $(u,v)$ of orthonormal vectors in ${\mathbb{R}}^4$, consider the ${\mathbb{R}}$-linear map $f:{\mathbb{R}}^2\to {\mathbb{R}}^4$ given by $$f(x^1,x^2)=x^1u+x^2v.$$ Notice that $f$ is an orthogonal embedding since $u$ and $v$ are orthonormal. Linearity implies that $f$ is equivariant with respect to the $\mathbb{Z}$ action and therefore descends to a map $f:M\to N$ of the torus into the Hopf surface. By the orthogonality, it is evident that $f^*h=g$ and, moreover, $f$ is totally geodesic. This is most easily seen by noting that $h$ can be viewed as a bi-invariant metric with respect to some Lie group structure on $N$ for which $f:M\to N$ is the inclusion of a torus subgroup.
These $f$ are therefore a family of harmonic maps $f:M\to N$ parameterized by orthonormal pairs in ${\mathbb{R}}^4$. We can compute $K(f)$ for these maps directly. First, note that since $\dim_{\mathbb{C}}M=1$, $$K(f)=-\frac{1}{2}\int_M\langle\omega_M,f^*\omega_N\rangle\omega_M=-\int_Mf^*\omega_N.$$ In the coordinates $y^i$ $$\omega_N=\frac{1}{\rho^2}(dy^1\wedge dy^2+dy^3\wedge dy^4),$$ and so $$\begin{aligned}
f^*\omega_N&=\frac{1}{\rho^2}(u^1v^2-u^2v^1+u^3v^4-u^4v^3)(dx^1\wedge dx^2)\\&=(u^1v^2-u^2v^1+u^3v^4-u^4v^3)\omega_M,\end{aligned}$$ therefore $$\begin{aligned}
K(f)=-(u^1v^2-u^2v^1+u^3v^4-u^4v^3)V,\end{aligned}$$ where $V=2\pi\log\alpha$ is the volume of $T^2$ with respect to $g$. In particular, it is clear from this example that $K$ is not a homotopy invariant. In fact, the homotopy invariance of $K$ is exactly what allows the pseudoholomorphic energy to distinguish holomorphic maps from harmonic maps.
Let $\mathcal{F}$ denote the family of all such $f:T^2\to S^3\times S^1$ constructed as above. Then this family is preserved by the ${\bar{\partial}}$-harmonic map heat flow and, for any $f_0\in\mathcal{F}$, the flow exists for all time and converges subsequentially to a holomorphic or anti-holomorphic map $f_\infty:T^2\to S^3\times S^1$.
Note that $\langle A(f),Tf\rangle=0$. This is because this depends on $d\omega_N(Tf,Tf,Tf)$ but $Tf$ only has rank 2. Therefore, since each $f\in\mathcal{F}$ is harmonic, we have that $\tau_+=\tau+A=A$ is perpendicular to the image of $f$ at each point. This, together with the fact that $f$ is linear and so $A$ is linear in the coordinates $x^i$, implies that the evolution equation $\partial_tf=A$ preserves the family. We can then view the flow in this family as given by a smooth vector field on the space of oriented orthonormal 2-frames in ${\mathbb{R}}^4$, establishing long time existence. Convergence to a ${\bar{\partial}}$-harmonic map is then immediate from monotonicity of $E_+$ and compactness of this family.
To see that the limiting map must be holomorphic or anti-holomorphic, note that the energy $E_+$ is invariant $E_+(U\circ f)=E_+(f)$ under the unitary group of ${\mathbb{C}}^2$. Since these act transitively on the unit vectors, we can assume the limiting map has $u=e_1$. But then a direct computation shows that, when $u=e_1$, $A(f)=0$ if, and only if, $v=\pm e_2$. Thus the limiting map is holomorphic or anti-holomorphic.
This relatively simple example demonstrates that the flow can distinguish a holomorphic map from a harmonic map in non-Kähler settings. In light of Corollary 3.9, if there is a singularity in the flow and a uniform energy bound does not hold, then the image of the flow near the singularity must be quite wild in $S^3\times S^1$; any proper compact subset of $S^3\times S^1$ admits a Kähler metric which, due to compactness, is uniformly equivalent to $h$. Therefore the lack of a uniform energy bound would mean the solution leaves every proper compact subset of the Hopf surface.
Bubbling
--------
In this section we will consider the ${\bar{\partial}}$-harmonic map heat flow for maps $f:\Sigma\to N$ between a compact Riemann surface $\Sigma$ and a compact, almost Hermitian manifold $N$. In this setting the pseudoholomorphic energy $E_+$ is conformally invariant, as is readily seen from the fact that we now have $$\begin{aligned}
E_+(f)=\int_\Sigma\frac{1}{2}|Tf|^2dV-\int_{\Sigma}f^*\omega_N.\end{aligned}$$ The most important observation we can make is that in this form the functional is exactly amenable to the fantastic result of Riviere [@RIVCONS] on the regularity of two variable conformally invariant elliptic systems. Specifically, we will quote the following theorem.
Let $B$ be a ball in ${\mathbb{R}}^2$ and let $u\in W^{1,2}(B,{\mathbb{R}}^n)$ be a weak solution to the system $$\begin{aligned}
\Delta u^i=\Omega^i_j({\nabla}u^j),\end{aligned}$$ where $\Omega\in L^2(B,\mathfrak{so}(n)\otimes\wedge^1{\mathbb{R}}^2)$. Then $u$ is locally Hölder continuous in $B$.
We derive a number of corollaries in applying this result to ${\bar{\partial}}$-harmonic maps of surfaces. Analogues of these are well known in the theory of harmonic maps.
Let $N\subseteq{\mathbb{R}}^n$ be a smooth, compact, almost Hermitian manifold. Let $u\in W^{1,2}(B,N)$ be a weakly ${\bar{\partial}}$-harmonic map. Then $u$ is smooth. In particular, if $u:B/\{0\}\to N$ is smooth and ${\bar{\partial}}$-harmonic with finite energy, then $u$ is smooth in $B$.
As observed in Theorem 1.2 of [@RIVCONS], any conformally invariant quadratic energy functional in two-dimensions has Euler-Lagrange equation in the form for which the previous theorem applies. Specifically, any functional of the form $$\begin{aligned}
\frac{1}{2}\int_{\Sigma}|Tu|^2dV+\int_{\Sigma}u^*\omega,\end{aligned}$$ where $\omega$ is any $C^1$ section of $\wedge^2T^*N$ has Euler-Lagrange equation in the form required by the theorem. The $E_+$ energy is exactly of this form, so any weakly ${\bar{\partial}}$-harmonic map $u:B\to N$ for which $E(u)<\infty$ is Hölder continuous. Smoothness of $u$ then follows from the smoothness of $N$, the Hölder continuity of $u$, and higher regularity theory of elliptic systems.
Note that in the previous corollary the assumption of finite energy is essential, as the map $z\mapsto z^{-1}$ is clearly ${\bar{\partial}}$-harmonic with $E_+$ finite but is not smooth in a ball centered at the origin.
If $u:{\mathbb{R}}^2\to N$ is ${\bar{\partial}}$-harmonic and has finite energy, then $u$ extends to a smooth ${\bar{\partial}}$-harmonic map $\tilde{u}:S^2\to N$.
Consider the map given by composing $u$ with stereographic projection from $S^2$ to ${\mathbb{R}}^2$. The previous proposition then implies that there is a smooth extension of this map to the point at infinity.
Suppose that a solution $u$ to the ${\bar{\partial}}$-harmonic map heat flow from a compact Riemann surface $\Sigma$ to a compact, almost Hermitian manifold $N$ exists on a maximal time interval $[0,T)$, where $T<\infty$, and there is a uniform energy bound on the solution. Then there exists a point $p\in\Sigma$, a sequence of times $t_i\nearrow T$, and a sequence of $r_i\searrow 0$ such that the family of maps $u_i(x)=u(exp_p(r_ix),t_i)$ converges to a limiting map $u_\infty:{\mathbb{R}}^2\to N$ in $H^{2,2}_{loc}$ to a non-constant, smooth harmonic map with finite energy.
As shown in Proposition 3.3 we know there is a sequence of times $t_i\nearrow T$ and points $p_i\to p\in \Sigma$ such that $\lim_{i\to\infty}|Tf|(p_i,t_i)=\infty$ and $|Tf|(p_i,t_i)=\sup_{p\in\Sigma,t\leq t_i}|Tf|(p,t)$. Let $r_i^{-1}=|Tf|(p_i,t_i)$ and consider a geodesic ball centered at $p$ of some small radius $\rho$. For $x\in B_{r_i^{-1}\rho}(0)\subset T\Sigma_p$ let $$\begin{aligned}
u_i(x,t)=u(exp_p(xr_i),t_0+r_i^2t).\end{aligned}$$ Note that $u_i$ solves the ${\bar{\partial}}$-harmonic map heat flow with respect to the metric $g_i=exp_p(r_i\cdot)^*g$. Since this metric is converging in $C^2_{loc}$ to the flat metric on ${\mathbb{R}}^2$ we can extract a subsequence $u_i\to u_\infty$ converging locally in $C^2({\mathbb{R}}^2\times(-\infty,0],N)$ where $u_\infty:{\mathbb{R}}^2\times(-\infty,0]\to N$ is a non-trivial solution to the ${\bar{\partial}}$-harmonic map heat flow with finite energy and constant $E_+$-energy, in particular it is a ${\bar{\partial}}$-harmonic map with finite energy.
With the assumptions of the previous corollary, there must exist a ${\bar{\partial}}$-harmonic sphere in $N$. In particular, if $N$ does not admit a non-trivial ${\bar{\partial}}$-harmonic $S^2$, then any solution to the ${\bar{\partial}}$-harmonic map heat flow with a uniform energy bound from any compact Riemann surface $\Sigma$ to $N$ exists smoothly for all time.
By the previous corollary, if a finite time singularity occurs then there is a non-trivial ${\bar{\partial}}$-harmonic map $u_\infty:{\mathbb{R}}^2\to N$ with finite energy. This $u$ then extends by Corollary 4.3 to a ${\bar{\partial}}$-harmonic map of $S^2$ into $N$.
Concluding Remarks
==================
We have cataloged a number of results on ${\bar{\partial}}$-harmonic maps which are the analogues of results known for harmonic maps. Our eventual goal will be to use ${\bar{\partial}}$-harmonic maps to study almost Hermitian manifolds, specifically non-Kähler complex manifolds. We end the paper with a list of important questions/problems which would serve as a starting point for future work.
- Is there always a uniform energy bound up to the first singular time $T$ for a solution to the flow? As we have seen, the lack of such a bound for a Riemann surface implies the spacetime image $f(\Sigma\times [t_0,T))$, for any $t_0$, has no neighborhood which admits an equivalent almost Kähler metric. Perhaps the simplest situation where a uniform energy bound would fail to hold along the flow would be for maps $f:\Sigma\to S$ from a compact Riemann surface into an Inoue surface. These are compact complex surfaces where there are no holomorphic maps $f:\Sigma\to S$ for any compact Riemann surface $\Sigma$, see [@INOUE] for their construction. On the other hand, given Proposition 3.8 one might expect a uniform energy bound holds whenever the source is balanced and the target is uniformly locally almost Kähler.
- Under what conditions is a ${\bar{\partial}}$-harmonic map pseudo-holomorphic? For Kähler manifolds there is the celebrated complex analyticity result of Siu [@SIU] for maps of strongly negatively curved Kähler manifolds. There are also known conditions (see Chapter 8, Section 3 of [@SY], for example) for stable harmonic maps $f:S^2\to N$ into a Kähler manifold which are sufficient to conclude complex analyticity. Both results strongly rely on the Kähler assumption.
- Recently Rupflin and Topping [@RT] have considered the Teichmüller Harmonic map flow for maps $u:\Sigma\to N$ from a Riemann surface $\Sigma$ into a Riemannian manifold $N$. Their flow is a coupling of the harmonic map heat flow to a flow of the complex structure on $\Sigma$. We are interested in playing a similar game for the ${\bar{\partial}}$-harmonic map heat flow. Specifically, for a given complex structure on $\Sigma$ there may not be any holomorphic maps $u:\Sigma\to N$ and so if our goal is to locate holomorphic maps within a homotopy class, one expects that a change in complex structure is necessary.
- Given two almost Hermitian structures on $S^6$ or ${\mathbb{C}}P^3$, what can be said about the ${\bar{\partial}}$-harmonic map heat flow beginning from the identity map of these spaces? A small but notable observation here is that the homotopy class of the identity map of $S^6$ never has a global minimizer of the harmonic map energy, but the identity map is always a globally minimizing ${\bar{\partial}}$-harmonic map.
[10]{} F. H. Lin, C. Y. Wang, *The analysis of harmonic maps and their heat flows*. World Scientific Publishing Co. Pte. Ltd., Hackensack, NJ, xii+267 pp (2008)
R. Schoen, S. T. Yau, *Lectures on Harmonic Maps*. International Press of Boston, Inc., 404 pp (1997)
J. Eells, L. Lemaire, *A Report on Harmonic Maps*. Bull. London Math. Soc. **10**, no. 1, 1–68 (1978)
J. Eells, J. H. Sampson, *Harmonic Mappings of Riemannian Manifolds*. Amer. J. Math. **86**, 109-160 (1964)
R. Hamilton, *Three-Manifolds with Positive Ricci Curvature*. J. Diff. Geo. **17**, 255-306 (1982)
D. McDuff, D. Salamon, *$J$-holomorphic Curves and Symplectic Topology*. Colloquium Publications, 726 pp (2012)
I. Nakamura, *Survey on $VII_0$ Surfaces*. Recent Developments in Non-Kähler Geometry, Sapporo (2008)
A. Lichnerowicz, *Applications Harmoniques et Varietes Kähleriennes*. Symposia Mathematica, **3**, 341-402 (1969)
H. Urakawa, *Stability of Harmonic Maps and Eigenvalues of the Laplacian*. Trans. Amer. Math. Soc, **301**, no. 2, 557-589 (1987)
J. Moser, *A Harnack inequality for parabolic differential equations*. Comm. Pure Appl. Math. **17**, 101-134 (1964).
Y. T. Siu, *The Complex-Analyticity of Harmonic Maps and the Strong Rigidity of Compact Kähler Manifolds*. Annals of Mathematics, **112**, no. 1, 73-111 (1980).
T. Riviere, *Conservation Laws for Conformal Invariant Variational Problems*. arXiv:math/0603380, 1-19 (2006)
M. Inoue, *On Surfaces of Class $VII_0$*. Invent. Math., **24**, 269-310 (1974)
M. Rupflin, P. Topping, *Flowing Maps to Minimal Surfaces*. arXiv:1205.6298, 1-18 (2012)
|
NEEDLES:One pair or circular needles (12”) in size US 7 (4.5 mm) or size to obtain gauge. One pair or circular needles (24”) in size US 7 (4.5 mm) or size to obtain gauge. One pair or circular needles (12”) in size US 6 (4.0 mm) or size to obtain gauge. One pair or circular needles (32”) in size US 6 (4.0 mm) or size to obtain gauge. |
clear
addpath(genpath('../'));
[images, detections, labels] = Collect_menpo_train_imgs('G:\datasets\menpo/');
%% Setup recording
[~, pdm, ~, ~] = Load_CECLM_OF();
%% Identify orientation of each of the training images
orientations = zeros(numel(images), 3);
for i=1:numel(images)
landmarks = standardise_landmarks(labels{i});
[ a, R, T, T3D, params, error, shapeOrtho ] = fit_PDM_ortho_proj_to_2D(pdm.M, pdm.E, pdm.V, landmarks);
orientations(i,:) = Rot2Euler(R);
end
%% Keep only the relevant orientations for that view
angle_dist = sum(abs(orientations)')';
to_keep = angle_dist < 25 * pi/180;
images = images(to_keep);
detections = detections(to_keep,:);
labels = labels(to_keep);
%%
% Change if you want to visualize the outputs
verbose = false;
if(verbose)
f = figure;
end
view = 1;
%% Mirror indices
mirror_inds = [1,17;2,16;3,15;4,14;5,13;6,12;7,11;8,10;18,27;19,26;20,25;21,24;22,23;...
32,36;33,35;37,46;38,45;39,44;40,43;41,48;42,47;49,55;50,54;51,53;60,56;59,57;...
61,65;62,64;68,66];
remove_all = cell(4, 1);
errors_all_med = cell(4,1);
errors_all_mean = cell(4,1);
% To start where we finished across scales
gparams = cell(numel(images), 1);
lparams = cell(numel(images), 1);
for scale = 1:4
remove_all_c = [];
errors_all_med_c = [];
errors_all_mean_c = [];
[patches, pdm, clmParams, early_term_params] = Load_CECLM_OF();
clmParams.numPatchIters = 1;
clmParams.startScale = scale;
patches = patches(1:scale);
for s=1:scale
patches(s).correlations = patches(s).correlations(view,:);
patches(s).centers = patches(s).centers(view,:);
patches(s).rms_errors = patches(s).rms_errors(view,:);
patches(s).visibilities = patches(s).visibilities(view,:);
patches(s).patch_experts = patches(s).patch_experts(view,:);
end
visi_old = patches(scale).visibilities;
shapes_base = cell(numel(labels), 1);
% First establish the basic error without removing landmarks at this
% scale
for i=1:numel(images)
image = imread(images(i).img);
image_orig = image;
if(size(image,3) == 3)
image = rgb2gray(image);
end
bbox = squeeze(detections(i,:));
% Precomputing patch experts
if(scale == 1)
[shape] = Fitting_from_bb(image, [], bbox, pdm, patches, clmParams, []);
else
[shape] = Fitting_from_bb(image, [], bbox, pdm, patches, clmParams, 'gparam', gparams{i}, 'lparam', lparams{i});
end
shapes_base{i} = shape;
% v_points = logical(patches(scale).visibilities(1,:))';
% DrawFaceOnFig(image_orig, shape, bbox, v_points);
end
error_base_mean = mean(compute_error_menpo_1(labels, shapes_base));
error_base_med = median(compute_error_menpo_1(labels, shapes_base));
fprintf('Base error scale %d - %.3f\n', scale, error_base_med);
for s=1:30
% First remove the indicies already decided to remove
patches(scale).visibilities = visi_old;
patches(scale).visibilities(view, remove_all_c) = 0;
% Indices to test removing
% Identify which indices to remove
to_rem_potential = find(patches(scale).visibilities(view,:));
% Now remove the mirror inds from them
to_remove = intersect(mirror_inds(:,2), to_rem_potential);
for i=numel(to_remove):-1:1
to_rem_potential(to_rem_potential==to_remove(i)) = [];
end
to_test_num = numel(to_rem_potential);
gparams_all = cell(numel(images), to_test_num);
lparams_all = cell(numel(images), to_test_num);
shapes_all = cell(numel(images), to_test_num);
labels_all = cell(numel(images), to_test_num);
to_rems = to_rem_potential;
for i=1:numel(images)
image = imread(images(i).img);
image_orig = image;
if(size(image,3) == 3)
image = rgb2gray(image);
end
bbox = squeeze(detections(i,:));
% Precomputing patch experts
if(scale == 1)
[~,~,~,~,~,~, precomp] = Fitting_from_bb_precomp(image, [], bbox, pdm, patches, clmParams, []);
else
[~,~,~,~,~,~, precomp] = Fitting_from_bb_precomp(image, [], bbox, pdm, patches, clmParams, [], 'gparam', gparams{i}, 'lparam', lparams{i});
end
for v=1:numel(to_rem_potential)
patches(scale).visibilities(view, to_rem_potential(v)) = 0;
mirr_id = union(mirror_inds(find(mirror_inds(:,1)==to_rem_potential(v),1),2),... ;
mirror_inds(find(mirror_inds(:,2)==to_rem_potential(v),1),1));
if(~isempty(mirr_id))
patches(scale).visibilities(view, mirr_id) = 0;
end
%% Fitting the model to the provided images
if(scale == 1)
[shape,gparams_all{i,v},lparams_all{i,v},lhood,lmark_lhood,view_used] = Fitting_from_bb_precomp(image, [], bbox, pdm, patches, clmParams, precomp);
else
[shape,gparams_all{i,v},lparams_all{i,v},lhood,lmark_lhood,view_used] = Fitting_from_bb_precomp(image, [], bbox, pdm, patches, clmParams, precomp, 'gparam', gparams{i}, 'lparam', lparams{i});
end
shapes_all{i,v} = shape;
labels_all{i,v} = labels{i};
if(mod(i, 200)==0)
fprintf('%d done\n', i );
end
if(verbose)
v_points = logical(patches(scale).visibilities(view_used,:))';
DrawFaceOnFig(image_orig, shape, bbox, v_points);
end
% Clean up
patches(scale).visibilities = visi_old;
patches(scale).visibilities(view, remove_all_c) = 0;
end
end
errors_mean = zeros(numel(to_rem_potential),1);
errors_median = zeros(numel(to_rem_potential),1);
for v=1:numel(to_rem_potential)
errors_mean(v) = mean(compute_error_menpo_1(labels_all(:,v), shapes_all(:,v)));
errors_median(v) = median(compute_error_menpo_1(labels_all(:,v), shapes_all(:,v)));
end
[~, id] = min(errors_mean);
val_med = errors_median(id);
val_mean = errors_mean(id);
remove_all_c = cat(2, remove_all_c, to_rems(id));
errors_all_med_c = cat(2, errors_all_med_c, val_med);
errors_all_mean_c = cat(2, errors_all_mean_c, val_mean);
mirr_id = mirror_inds(find(mirror_inds(:,1)==to_rems(id),1),2);
if(~isempty(mirr_id))
remove_all_c = cat(2, remove_all_c, mirr_id);
errors_all_med_c = cat(2, errors_all_med_c, val_med);
errors_all_mean_c = cat(2, errors_all_mean_c, val_mean);
end
remove_all{scale} = remove_all_c;
errors_all_med{scale} = errors_all_med_c;
errors_all_mean{scale} = errors_all_mean_c;
%%
output_results = 'sparse_selection/menpo_frontal_sparse.mat';
save(output_results, 'remove_all', 'errors_all_med', 'errors_all_mean');
fprintf('Curr error rem %d - %.3f\n', s, errors_all_med_c(end));
% Going to the next scale
if(0.99 * errors_all_med_c(end) > error_base_med)
break;
end
end
gparams = gparams_all(:,id);
lparams = lparams_all(:,id);
end
|
Six killed, 26 injured in Assam road mishaps
Diphu/Rangiya (Assam): Six people were killed and 26 others injured in two different mishaps in Assam's Karbi Anglong and Kamrup (Rural) districts today, police said.Five people were killed on the spot and four others critically
Diphu/Rangiya (Assam): Six people were killed and 26 others injured in two different mishaps in Assam's Karbi Anglong and Kamrup (Rural) districts today, police said.
Five people were killed on the spot and four others critically injured when a speeding Manipur-bound truck collided with two auto-rickshaws on National Highway 39 at Gautambasti of Karbi Anglong district, Superintendent of Police M J Mahanta said.
An autorickshaw is still trapped under the truck and efforts are on to rescue the persons trapped inside, he said. The injured have been admitted to Dimapur Railway Hospital in a critical condition.
In another mishap, one person was killed and 22 seriously injured when two vehicles collided head-on in Kamrup (Rural) district today, police said.
A speeding bus and a mini-truck collided head-on at Bartejpur near Mirza on National Highway 37 this morning, killing the truck driver on the spot and seriously injuring 22 others, police said.
The injured have been admitted to Mirza and Rampur Primary Health centres while some have been shifted to Gauhati Medical College Hospital, sources said. |
Admin
E-Travel
Permission to Travel and Guest Player Notification InstructionsThis process will be completed within the Affinity Sports Registration System. You will have to have login information in order to fill out these forms. Please review the instructions and then complete the process. After completing the process, you will be able to print a two page pdf - the first will be the permission to travel and the second will be the guest player notification form. Click here to login and fill out the form. After you login, scroll down to the appropriate team, click on the 'edit' button next to the team and follow the instructions above.
Permission to Host Notification (Microsoft Word doc) - Used anytime your team is hosting games for teams that are not members of Kentucky Youth Soccer but are members of any other US Soccer Federation member. |
---
author:
- |
Djallel Bouneffouf$^1$, Irina Rish$^2$, Guillermo A. Cecchi$^3$, Raphaël Féraud$^4$\
$^{1,2,3}$IBM Thomas J. Watson Research Center, Yorktown Heights, NY USA\
$^4$Orange Labs, 2 av. Pierre Marzin, 22300 Lannion (France)\
{dbouneffouf, Irish, gcecchi }@us.ibm.com\
Raphael.Feraud@orange.com
bibliography:
- 'ijcai15.bib'
title: |
Context Attentive Bandits:\
Contextual Bandit with Restricted Context
---
Acknowledgments
===============
The authors thank Dr. Alina Beygelzimer and Dr. Karthikeyan Shanmugam for the critical reading of the draft manuscript.
|
1. Field of the Invention
This invention relates to land mobile radio systems and more specifically to minimizing adjacent channel interference for land mobile radio systems.
2. Description of Related Art
Conventional land mobile radio (LMR) channels employ narrow-band frequency division multiplexed (FDMA) systems with different radio units assigned to different frequency bands. These bands are typically 25 KHz wide. There is an immediate need for an increase in capacity of LMR systems in the U.S. for such applications as public safety trunking. The trend is to increase capacity by splitting each existing 25 KHz channel used in LMR systems into two 12.5 KHz channels. However, this causes adjacent channel interference (ACI). ACI is interference introduced at a receiver from a transmitter broadcasting at a frequency corresponding to an adjacent channel and this is sometimes called adjacent channel `splatter`.
In a typical LMR system, communication between mobile units takes place through a base unit (base station). Each base station serves a certain geographic area. Communication between mobile units and base units takes place on a pair of frequencies that are separated, usually widely, to prevent interference. One frequency is needed for base to mobile communication and the other frequency in the pair is used for mobile to base communication. In some situations, mobile units can communicate with each other directly without going through the base unit. This is called "Talk-Around". A pair of frequencies are also used in Talk Around communications, one for each direction.
A problem occurs if two mobile units employ spectrally adjacent frequencies to communicate with their base units. Usually, mobile units within the same area will not be assigned spectrally adjacent frequencies but mobile units in contiguous geographic areas can use spectrally adjacent frequencies. The same situation exists with respect to frequency assignments to base units.
A measure of the acceptable level of ACI in a system is an ACI protection ratio (ACIPR). ACIPR is defined as the amount, in decibels, that the power of the interferer can be increased relative to the power of the desired signal, until a certain performance threshold is reached. For LMR system the bit error rate (BER) is used as an appropriate measure of performance. For analog FM, the ACIPR is specified to be in the range of 65-70 dB. Some digital modulation schemes offer adequate spectral efficiency but lower ACIPR (in the range of 45-50 dB). The ACIPR values may be augmented by several techniques. However, the problem gets increasingly difficult as the need for capacity and higher spectral efficiency arises.
Some of the commonly adopted techniques to improve ACIPR for digital modulation are antenna diversity in which more than one antenna receives a signal and the receiver chooses the signal from the antenna having a better signal strength. Antenna diversity is useful in providing a margin of 3-5 dB in ACIPR. Antenna diversity is further described in Characterizing the Effects of Nonlinear Amplifiers on Linear Modulation for Digital Portable Radio Communications, by S. Ariyavisitakul and T. P. Liu, IEEE Transactions on Vehicular Technology, Vol. 39, No. 4, pp. 383-389, November 1990.
Another technique to improve ACIPR is interference rejection and cancellation where an estimator is employed in estimating what a signal should be, and subtracting the estimated signal from the actual signal to synthesize an interference signal which is then subtracted from the further received signals. A similar technique is interference rejection using filtering described in Rejection Method of Adjacent Channel Interference for Digital Land Mobile Communications, by S. Sampei and M. Yokohama, The Transactions of the IECE of Japan, Vol. E 69, No. 5, pp. 578-580, May 1986. Interference cancellation is described in Method of Rejecting Adjacent Channel Interference Using an Adaptive Equalizer, by N. Kinoshita and S. Sampei, Transactions of IEICE (section B), J71-B, 10, pp. 1119-1126, October 1988. Interference rejection and cancellation involves complex receiver circuitry and is highly dependent upon the channel conditions and interference power. These techniques can provide up to 6-10 dB of gain if properly implemented.
Transmitter power control is described by Y. Nagata and Y. Akaiwa in Analysis for Spectrum Efficiency in Single Cell Trunked and Cellular Mobile Radio, IEEE Transactions on Vehicular Technology, Vol. VT-35, No. 3, pp. 100-113, August 1987. Transmitter power control offers a larger gain (10-15 dB) in ACIPR by controlling the transmit power of mobile stations. In transmitter power control, the mobile units which are closer to the base station transmit at a lower power in order not to "splash" other mobile units. The base station power is not varied. This scheme is complex and the complexity increases with capacity.
Another commonly suggested approach to providing higher spectral efficiency in a LMR channel is to use Trellis Coded Modulation (TCM) as described in Channel Coding with Multilevel/Phase Signals, by G. Ungerboeck, IEEE Transactions on Information Theory, Vol. IT-28, No. 1, pp. 55-67, January 1982. A typical TCM scheme employing Ungerboeck codes is designed to maximize the separation between transmitted signal states, called the Euclidean distance. However, optimization of Euclidean distance need not improve ACIPR.
A technique for designing trellis codes for band-limited channels is described in Bandwidth-Efficient Trellis Coded Modulation Schemes, by S. Ramseier, Proceedings of the International Conference on Communications, pp. 1517-1521, 1990. This technique designs Trellis Codes based on optimizing the normalized in-band power. This optimization is not as important for an LMR system since normalized in-band power does not maximize ACIPR. And further, the optimization as described by Ramseier does not consider the effects of the receive filter characteristics, which has a critical influence on ACIPR.
A related problem is that bandwidth saving is typically achieved at the expense of power and hence range reduction. The range reduction can be quite a problem where the area over which the base unit and mobile unit communicate is very large. An increased transmission area implies increased cost and complexity at the base station. Therefore, there is a need to find a spectrally efficient modulation scheme that has high ACIPR and offers a transmit range comparable to existing analog FM systems. |
27238
a
What is the third smallest value in -4, -23, 2, 6, 1?
1
Which is the fourth smallest value? (a) -9 (b) -1.12 (c) 2 (d) -1/7
c
What is the fifth smallest value in -1/9, 4, 1220, 0.181, -2?
1220
Which is the fourth biggest value? (a) 3 (b) -1.5 (c) 1/12 (d) -3/8
b
Which is the fourth smallest value? (a) -2/7 (b) 1/2197 (c) 3 (d) 0.7
c
What is the second smallest value in 2, -1/5, -31, -0.05?
-1/5
Which is the smallest value? (a) 2 (b) -1 (c) -0.244 (d) -0.3
b
What is the third biggest value in -941, 15, -2/11, -2?
-2
Which is the biggest value? (a) 0.5 (b) -1/4 (c) 0 (d) 1079
d
What is the third biggest value in -2, -200, 74/7?
-200
What is the smallest value in -4, 1/2, -0.077, -0.085?
-4
What is the smallest value in -624/17, -5, -3, 2/3?
-624/17
What is the fourth smallest value in -33/5, 0.1, 2/19, 3, -1?
2/19
Which is the fourth biggest value? (a) 1/16 (b) -3 (c) -0.1 (d) 3 (e) 1 (f) 47
a
What is the fourth biggest value in -1/6, 4, 7.6, -2, 5?
-1/6
What is the smallest value in 5053, -2/47, 0.1?
-2/47
Which is the second biggest value? (a) -2 (b) 2 (c) -0.1 (d) -8 (e) 1851 (f) 0.4
b
Which is the second smallest value? (a) -2/9 (b) -6.18 (c) 0.1 (d) 2 (e) -2
e
What is the fifth smallest value in -1, -81, -10/13, -4, 18?
18
What is the biggest value in 1/2, 1.2, -2/9, 2/5?
1.2
Which is the third biggest value? (a) 2 (b) 0.2102 (c) 0.3 (d) -2 (e) -5 (f) 2/3
c
Which is the biggest value? (a) 5 (b) -27 (c) 0.03 (d) 144
d
Which is the biggest value? (a) 0.5 (b) 4 (c) -299 (d) 8
d
Which is the third biggest value? (a) 456 (b) -3 (c) 0.9
b
What is the smallest value in -3, 7614, -2, 0?
-3
Which is the fourth biggest value? (a) -0.6 (b) 0 (c) 13 (d) -0.397 (e) -1/2
e
What is the fifth biggest value in -0.4, -3/2261, 1, 0, 3?
-0.4
Which is the second biggest value? (a) -2/11 (b) 0.036 (c) -63.2
a
Which is the third smallest value? (a) 0.3 (b) 8551 (c) 5 (d) 4/9
c
Which is the fifth smallest value? (a) -1 (b) -2 (c) 4 (d) -209 (e) 0.4
c
What is the third biggest value in 4/41, 83, 1, -8?
4/41
What is the biggest value in 7792, -6, 1, -1, 4?
7792
What is the second biggest value in -5, -8, -2, -0.2, 42.83?
-0.2
What is the third biggest value in -0.5, -61, -2, -2.61?
-2.61
What is the fifth biggest value in 4/7, -112, -0.05, 2, 0.28?
-112
What is the third smallest value in -5, -1868, -0.2, 5?
-0.2
What is the smallest value in -9, 0.3, 4/53, -0.4, 0.01, -1?
-9
What is the second smallest value in 3, 227, 9.9, -0.2, 3/7?
3/7
Which is the second smallest value? (a) -2/5 (b) 1/14 (c) -228 (d) -2/17 (e) 2/31
a
What is the smallest value in 64, 2/9, -48?
-48
What is the biggest value in 2, -21/5, -2?
2
What is the smallest value in 2/9, -1, -144.6, -4/35?
-144.6
Which is the second smallest value? (a) 1 (b) 3/5 (c) 0 (d) -1/305995
c
Which is the third smallest value? (a) -7/3 (b) 21 (c) -3 (d) -1 (e) -2 (f) -0.245
e
Which is the second biggest value? (a) 11 (b) -0.02 (c) -2/21 (d) -0.25
b
Which is the fourth biggest value? (a) -0.521 (b) 2 (c) -1.1 (d) 3 (e) -2 (f) -2/5
a
What is the biggest value in 1/6, -29, 3.2, 0, 4?
4
Which is the second smallest value? (a) 3 (b) 83 (c) -0.153
a
Which is the smallest value? (a) -45949 (b) 4 (c) -0.02 (d) -1
a
What is the third biggest value in 2, -1/26, 35, 3?
2
What is the third smallest value in -0.5, 193, -3, -1/5, -4, 2/3?
-0.5
Which is the fifth biggest value? (a) 59/2 (b) 0.2 (c) 3 (d) 0.04 (e) -2
e
What is the smallest value in 0.4, -0.07, -37, -2.1?
-37
Which is the fourth smallest value? (a) -1/4 (b) -35 (c) 4/7 (d) -2/31 (e) -7
d
What is the smallest value in -0.4, 3, 0.079698?
-0.4
What is the biggest value in -2/13, 0.1, -46, 7.6?
7.6
What is the fifth biggest value in 0.0558, -2, 3, 1/22, 4, 5?
1/22
What is the biggest value in -1/2, 923, 3, -3, 0.2?
923
Which is the second smallest value? (a) -3886 (b) 4 (c) 9
b
What is the second biggest value in -17, 4, 0.013, -3, -37?
0.013
What is the biggest value in 30299, -3/2, 0.2?
30299
Which is the second smallest value? (a) 0 (b) -18 (c) -0.2
c
What is the smallest value in 1/4, 3/5, 118, 0.1?
0.1
Which is the fifth smallest value? (a) -8 (b) -12 (c) 0 (d) -475 (e) 2 (f) -1
c
Which is the second biggest value? (a) -0.43 (b) -1/7 (c) -43
a
Which is the biggest value? (a) -0.1975 (b) -8 (c) 4
c
What is the second smallest value in -0.4, 9, 65, -3, -2/11, 19?
-0.4
Which is the fifth smallest value? (a) -0.1 (b) -2/13 (c) -7 (d) -0.81 (e) 0.11
e
What is the third smallest value in 0.2, 287, -139, 0.4?
0.4
What is the fourth smallest value in 23072, -0.2, -0.4, 1?
23072
What is the smallest value in 2/39, -1/5, -0.1, -4, 131/2?
-4
What is the second biggest value in 72/47, 0.055, -2/19?
0.055
Which is the fourth biggest value? (a) -2/9 (b) -75 (c) -5 (d) 42 (e) -6
e
What is the third biggest value in 12, -3, 0.909?
-3
What is the smallest value in 1/2, 5248, -0.2, 0.2, 1/10, 4?
-0.2
Which is the second smallest value? (a) -277 (b) -1 (c) -0.1 (d) -1/3 (e) -6
e
Which is the third biggest value? (a) -7/3 (b) 0.02 (c) -1/3 (d) -3 (e) 5 (f) 2.7
b
Which is the third smallest value? (a) 21073 (b) 2 (c) 3 (d) 0 (e) -2/3
b
Which is the second smallest value? (a) -0.1 (b) -19.27 (c) 28
a
What is the smallest value in -2/45, -0.2, -283, 0.12?
-283
What is the second smallest value in -0.25, 1, 46/7?
1
What is the second biggest value in -5, -102, 42/139?
-5
What is the second biggest value in 0.5, 35, -0.17, -4/3, 0.3, -4?
0.5
What is the third smallest value in 11/4, -1.4, 3, 2, 4/7, -2/13?
4/7
Which is the second biggest value? (a) 149 (b) -0.13 (c) -3
b
What is the fourth biggest value in 1/6, 7, -4/4151, -1/4?
-1/4
Which is the fourth biggest value? (a) 0 (b) 31.57 (c) 1/8 (d) -0.7
d
What is the fourth smallest value in 0.015, 0.05, -4, 0.5?
0.5
What is the fourth biggest value in -0.9, -9, 28, 2, 4, -0.05?
-0.05
Which is the second biggest value? (a) -35212/5 (b) 3 (c) -0.3
c
Which is the second biggest value? (a) -17 (b) 51 (c) 52
b
Which is the second smallest value? (a) 4 (b) -2/3 (c) -1703
b
What is the fourth biggest value in 2, 1/4, 0.5, -2466/7, 3, 5?
0.5
What is the third smallest value in -1/2, 5, -2, -139/35?
-1/2
Which is the third smallest value? (a) 1.1 (b) 13 (c) -31/2
b
Which is the third smallest value? (a) 2 (b) -1/5 (c) -9105/7
a
Which is the fifth smallest value? (a) -2/31 (b) 34.6 (c) 1 (d) 2 (e) -7/6
b
Which is the third smallest value? (a) -261 (b) 5 (c) 1.4 (d) -1
c
Which is the smallest value? (a) 0.3 (b) -914 (c) -4 (d) -1/4 (e) -49
b
Which is the fourth smallest value? (a) -8 (b) 0.5 (c) 11 (d) 3.2
c
What is the smallest value in -0.3, 18/41, 1/37?
-0.3
What is the second biggest value in 2965, -0.1, 0.1, -4?
0.1
Which is the fourth biggest value? (a) -4 (b) 5 (c) 2.328 (d) 0.05
a
What is the fourth biggest value in 0, -0.1, -53, -5, -4?
-5
Which is the second biggest value? (a) -0.5 (b) -1.9 (c) 8913
a
Which is the fourth biggest value? (a) 0.087 (b) 90 (c) 3 (d) 1.9
a
Which is the second biggest value? (a) -1/8 (b) -2686 (c) -2 (d) 3/5 (e) 12
d
What is the fourth biggest value in -6, 2/385, 5, -5?
-6
What is the third smallest value in -672, 5/3, -2/47, 88?
5/3
Which is the biggest value? (a) 0 (b) -54 (c) 5 (d) 930 (e) 2
d
Which is the third biggest value? (a) -819 (b) 4 (c) 1/3 (d) -5 (e) 1/2
c
What is the fourth smallest value in -2, 5/4, -12, -0.2, -28?
-0.2
Which is the third biggest value? (a) -0.5 (b) -4 (c) -5 (d) 10/871 (e) 0
a
What is the fifth smallest value in 27, -2/3, 0.2, 1/4, 1/8, 0.01?
1/4
What is the biggest value in -5, -25, -1/12, 4/7, -1, -3/4?
4/7
What is the fifth biggest value in -3/7, -3, -0.3, -40/7, -17?
-17
What is the fourth biggest value in 1/2, 3, 0.3, 2.81, -3/5, 4?
1/2
What is the biggest value in 0.3, 1, 4, 34.78?
34.78
What is the second smallest value in -1/12, 2/7, 74, 13, 3?
2/7
What is the third smallest value in -17, 199, 59?
199
What is the smallest value in -71.8, 5, -125?
-125
Which is the second smallest value? (a) -9/4 (b) -2 (c) -174
a
Which is the fourt |
What Is Bonded Leather And Why Is It A Good Upholstery Choice?
In the September, 2010 difficulty of the popular magazine Martha Stewart Living there may be an article that talks about the way to clean varied household items. It’s onerous to tell the difference between the 2, as once an merchandise is made with bonded leather-based the looks and scent are nearly an identical. The floor of the leather should then be cleaned and it is important to purchase a cleaner that is specifically made to be used on leather furniture. First of all, I think this most likely solely works if the item in query is real leather-based. The sofa must not be used for a interval of two hours after the conditioner is applied. A pigmented coating (finish) is applied that is chemically engineered particularly for leather-based. Leather also needs to be cleaned and conditioned regularly as a way to stay supple.
The most important factor one must be mindful when restoring leather seams is to permit ample time to complete the duty correctly. In addition to the rips and tears the leather armrest just generally had a whole lot of abrasions on it so I went ahead and applied dye to your entire armrest. They’re each good from what I can tell however Leather Magic sells particular person leather repair merchandise along with the package. Leather furniture is so resilient that many individuals neglect to properly look after it, which can cause severe issues with the leather-based itself. It gives books a fancier look, it makes cheap belts look costly, and it provides a sophisticated contact to any piece of office furniture. Pigmented leather finishes are opaque, creating a coloured movie on high of the cover.
Do not use customary harsh cleansing merchandise on your leather; as an alternative get cleaners formulated specifically for leather-based. It has to flex and permit the leather to breath so it has unique attributes that differentiate it from widespread wall paint. UPDATE – This ottoman will be painted utilizing Le Chalk chalk paint powder (Click right here) for 1/three of the cost of Annie Sloan.
Leather Nova sent me these three products to test and preserve so I can share with my readers the outcomes good or unhealthy. I cleaned the armrest utilizing a moist microfiber material a number of weeks later and saw no indication the dye or end was coming off. You can even need leather-based conditioner to keep your leather-based furniture in top, beautiful situation.
If your leather-based extremely dry and the leather-based cleaner absorbs shortly, then add 20% distilled water to the leather-based cleaner to slow down absorption. Leather Chairs: From trendy designs to basic leather-based chairs like these pictured to the left, we now have the right leather furniture for you living room, office, or examine. Rushing by means of the job can lead to by accident tearing the leather-based and making it mandatory to exchange your complete part. |
Healthy Pumpkin Spice Waffles
Author:Cookie and Kate
Prep Time:15 mins
Cook Time:10 mins
Total Time:25 minutes
Yield:4 large waffles
Category:Breakfast
Method:By hand
Cuisine:American
★★★★★
4.8 from 39 reviews
These delicious, gluten-free pumpkin waffles are crispy on the outside and fluffy on the inside. This pumpkin waffle recipe’s secret ingredient is oat flour! You can easily make your own oat flour at home (check the recipe notes for details). This recipe yields 4 round, 7-inch Belgian waffles. Note: when I say “scant,” I mean just a couple teaspoons shy of the measurement listed.
Instructions
In a large mixing bowl, combine the oat flour, baking powder, salt, cinnamon, ginger, nutmeg and all spice or cloves. Whisk to combine.
In a medium mixing bowl, whisk the eggs. Then add the milk, coconut oil or butter, pumpkin purée, maple syrup and vanilla extract. Whisk until the mixture is thoroughly blended.
Pour the liquid mixture into the oat flour mixture. Stir with a big spoon until just combined (the batter will still be a little lumpy). Let the batter rest for 10 minutes so the oat flour has time to soak up some of the moisture. Plug in your waffle iron to preheat now.
Once 10 minutes is up, give the batter one more, gentle swirl with your spoon. The batter will be pretty thick, but don’t worry! Your waffles will turn out great. Pour batter onto the heated waffle iron, enough to cover the center and most of the central surface area, and close the lid.
Once the waffle is deeply golden and crisp, transfer it to a cooling rack or baking sheet. Don’t stack your waffles on top of each other or they’ll lose crispness. If desired, keep your waffles warm by placing them in a 200 degree oven until you’re ready to serve. Repeat with remaining batter and serve with desired toppings on the side.
Notes
Recipe adapted from my gluten-free oat waffles recipe.*Make your own oat flour: Simply blend old-fashioned or quick-cooking oats in a food processor or blender until they are ground into a fine flour. You’ll need to blend about 2 1/4 cups oats to make 2 1/4 cups flour.*A note on gluten free oats: Be sure to buy certified gluten-free oats or certified gluten-free oat flour to ensure your waffles are gluten free.Freeze it: These waffles freeze beautifully. Just store in freezer-safe plastic bags and pop individual waffles into the toaster until warmed through.Recommended equipment: This fancy-pants non-stick waffle maker. I love that it has a large cooking surface, which means I can cook an entire batch of waffles with just two presses.More pumpkin recipes: Check out my gluten-free pumpkin oat pancakes, vegan pumpkin pecan scones and maple-sweetened pumpkin muffins.
▸ Nutrition Information
The information shown is an estimate provided by an online nutrition calculator. It should not be considered a substitute for a professional nutritionist’s advice.
Did you make this recipe?
Please let me know how it turned out for you! Leave a comment below and share a picture on Instagram with the hashtag #cookieandkate. |
ppose -h - 24 = -2*n + s, 5*n - 102 = -3*h. What is the units digit of n?
8
Let q = 3 - 5. Let r = q + 9. Suppose -3 = 2*d - 5*c, -3*d + r*c + 3 = 2*c. What is the units digit of d?
6
Let p be 1/(-1 + (-40)/(-44)). Let f = 8 - p. What is the tens digit of f?
1
Let l(y) = 40*y + 7. What is the tens digit of l(2)?
8
Suppose 0*d = d - 4. Let t(i) = -i - 1. Let n be t(-4). Let b = d - n. What is the units digit of b?
1
Let a = 4 - -2. Let m(x) = x**2 - 5*x - 2. Let h be m(a). Suppose t = h + 2. What is the units digit of t?
6
Let a = -2 + 0. Let o(i) = -i - 1. Let z be o(a). Let r = 5 - z. What is the units digit of r?
4
Let f = 9 + 1. What is the units digit of f?
0
Suppose 270 + 290 = 7*n. What is the units digit of n?
0
What is the units digit of 18/81 - 104/(-18)?
6
Let q be 37/((1 + 1)/(-2)). Let p = -25 - q. Suppose -h + 0*h = f - p, 3*f - 45 = -4*h. What is the units digit of h?
9
What is the units digit of 3*39*(-3)/(-9)?
9
Let b(s) be the second derivative of -1/6*s**4 - 1/3*s**3 + 1/20*s**5 + 0*s**2 + 0 - s. What is the units digit of b(3)?
3
What is the tens digit of (-1)/(3/(-245)) - (-13)/39?
8
Let a = 0 - -8. Suppose -a = 2*f - 26. Suppose -d + 2*s - 5*s - 11 = 0, 4*d + f = -5*s. What is the units digit of d?
4
Suppose -2*q + 19 = x, 5*x - 3*q + 0*q = 147. Let z = -16 + x. What is the tens digit of z?
1
Let z be (3 + -2)/((-1)/5). What is the units digit of (-9)/z*(-20)/(-6)?
6
What is the units digit of (9/(-2) - 2)*-2?
3
Let p be (-3)/(9/(-309))*1. Suppose -27 = -5*d + p. What is the units digit of d?
6
Let r(f) = f + 2. Let h be r(1). Suppose h*z = 84 + 6. What is the units digit of z?
0
Suppose 2*a - 14 - 34 = 0. What is the units digit of a?
4
Suppose -3*q = -3*b + 84, -b + 42 = -2*q + 12. What is the units digit of b?
6
Suppose 4*c + 2*t = t + 23, 0 = -5*c - t + 28. Suppose -4*k + 2*k + 2 = j, -c*k = 2*j - 3. What is the units digit of j?
4
Let l = 60 - 21. Let v(x) = -x**2 + 3*x - 5. Let k be v(6). Let n = k + l. What is the units digit of n?
6
Suppose 0 = 2*a - 4*a - 2*d + 830, 0 = -4*a - 2*d + 1650. What is the hundreds digit of a?
4
Let l be 5*(117/15 - 1). Let v(k) = -k - 3. Let d be v(-7). Suppose d*c - 6 = l. What is the tens digit of c?
1
Suppose -4*a - 2*b = -b + 2, 0 = 4*b + 8. Let q = 2 + a. What is the units digit of q?
2
Suppose -2*w = 3*j - 5*w - 24, -5*j + 4*w + 35 = 0. Let k be 39 + 0/(-3) + 1. Suppose -3*c = -6*c + 4*x + 13, -k = -5*c + j*x. What is the tens digit of c?
1
Let j be (-36)/(-21) + 4/14. Let d = j - -1. What is the units digit of d?
3
Let k(c) be the first derivative of c**4/4 + c**3 - c**2/2 - 2*c - 1. Let f(x) = 2*x + 3. Let j be f(-3). What is the units digit of k(j)?
1
Let f be ((-9)/15)/((-2)/10). What is the units digit of ((-32)/(-6))/(2/f)?
8
Let u(w) = -3*w**3 + w**2 - 2*w - 2. What is the units digit of u(-1)?
4
Let z(v) = -v**2 - 19*v - 25. What is the units digit of z(-16)?
3
Suppose 0 = -2*n + 3*n - 21. Let j = n + 1. What is the tens digit of j?
2
Let d be (5 - 1 - 3)*2. What is the units digit of d/1 - (-1 + 1)?
2
Suppose 0 = 3*v - 2*a - 5, 3*a = -4*v + 8*a + 2. Suppose -2*k + 60 = v*k. What is the units digit of k?
2
Let v(a) = -a**3 - 6*a**2 - 12*a - 18. What is the units digit of v(-9)?
3
Let g(d) = -7*d - 1. Let k = 1 + -4. What is the tens digit of g(k)?
2
Suppose -2*l - 24 = -3*l. Suppose x - 3*x = l. What is the units digit of (-123)/(-18) + (-2)/x?
7
What is the units digit of 2/1 + 12 - -2?
6
Let b be (-5)/(8/3 - 3). Suppose -3*x + 2*x = -b. What is the tens digit of x?
1
Let x(p) = 4*p**3 + 2*p**2 - p. Let b be x(1). Suppose -b*z + 5*m = -0*z - 15, 4*z = -5*m + 39. What is the units digit of z?
6
Suppose -7*h = -3*h - 108. Let o = -1 + 7. What is the units digit of 8/6*h/o?
6
Suppose 5*p - 3*c - 658 = 0, -3*p + 0*p + c + 398 = 0. What is the units digit of p?
4
Let t be (-16)/56 - 30/(-7). What is the units digit of 2/4*56/t?
7
Let y = 15 - 20. Let u(k) = -k**2 - 7*k + 4. What is the tens digit of u(y)?
1
Let g = -6 - -10. Let n(q) = 2*q**2 - 4*q - 1. Let u be n(4). Suppose z = -g*z + u. What is the units digit of z?
3
Let s = -7 - -12. Suppose h + 3*l = 7, -s*h - 22 = -3*l - l. What is the units digit of (-32)/(-18) + h/(-9)?
2
What is the units digit of (21/(-12))/1*-104?
2
What is the hundreds digit of 4 - 17/((-51)/396)?
1
Let t(j) = 16*j**2 - 7*j**2 + 19*j - 11 - 4 + 7*j**2. Let h(q) = -3*q**2 - 4*q + 3. Let x(u) = 11*h(u) + 2*t(u). What is the tens digit of x(-3)?
1
Suppose 85 - 5 = -5*k. Let p = 17 + k. What is the units digit of p?
1
What is the hundreds digit of (-4)/(-7) + 8694/49?
1
Suppose -3*l + 99 = -210. What is the tens digit of l?
0
Let m = 182 - -4. What is the hundreds digit of m?
1
Suppose 20 = 2*r - 0*r. What is the units digit of (-5)/r*2/(-1)?
1
Suppose -2*w = -j - 4, 2*j = -4*w + j + 14. Let d = w - 2. What is the units digit of d?
1
Suppose 0 = 5*k + 3 + 2. Let l(j) = 15*j**2 + 1. What is the tens digit of l(k)?
1
Let y be ((-6)/8)/((-1)/(-12)). What is the tens digit of (y/(-3))/((-2)/(-12))?
1
Let d(h) = h - 2. Let p be d(6). Suppose p*k + 2*c - 37 = -k, -15 = -2*k - c. What is the units digit of k?
7
Suppose -2 = -i - 0*i. Suppose 4*p + o = 69, 48 = i*p - 2*o + 6. What is the units digit of p?
8
Suppose -t + 69 = h + 3*h, -h - t = -21. Suppose 30 = 2*a - h. Suppose -c - 7*o + 16 = -3*o, -5*o = 2*c - a. What is the units digit of c?
4
Let s be (-4)/10 - (-166)/(-10). Let x be 1/(1/(1 + -2)). What is the units digit of x/2 + s/(-2)?
8
Let b(n) = 9*n - 3. What is the units digit of b(9)?
8
Suppose 3*u - u + 22 = 0. Let g(z) = -4*z - 9. What is the tens digit of g(u)?
3
Let i(r) = -r**3 - 15*r**2 + 16*r + 9. What is the units digit of i(-16)?
9
Suppose 0 = -5*h + 2*a - 20, -5*h - a - 2*a - 45 = 0. Let o(x) = -x**2 - 4*x + 6. Let b be o(h). Let k = b - -9. What is the units digit of k?
3
What is the hundreds digit of 20/(-50) - 1564/(-10)?
1
Let l(q) = 2*q**2 - 4. What is the units digit of l(4)?
8
Let y(f) = -f - 6. Let o = 13 + -21. What is the units digit of y(o)?
2
Let d = 2 - -3. Suppose 0 = d*v - 2*x - 129 + 21, 0 = 2*v + 4*x - 48. What is the units digit of v?
2
Suppose 75 = -6*s + 11*s. Let y = 5 - 1. Suppose 3*v - n = s, -v = -3*v + y*n. What is the units digit of v?
6
Suppose -j = 4*j - 35. Suppose -2*t + 3*t = j. What is the units digit of t?
7
Let t = 0 + -4. Let m(u) = -2*u - 2. What is the units digit of m(t)?
6
Suppose -3*a + 5 = -2*a. Suppose -i = -4*o - 3, 0*i - 15 = -a*i - o. What is the units digit of i?
3
Let p(f) = f**2 - 6*f. Let h be p(3). Let w = -8 - h. What is the units digit of w?
1
Let k = -55 + 57. What is the units digit of k?
2
What is the units digit of (-45 + (-2 - 0))*(1 - 2)?
7
Suppose 0 = 2*t - 3 - 5. What is the units digit of t?
4
Let n be 3/2 + (-388)/(-8). Let z = -30 + n. What is the tens digit of z?
2
Suppose -20 = 2*t - 6*t. What is the units digit of 791/35 + (-3)/t?
2
Let b = 15 + -10. Suppose b*j = 2*l + 53, 4*j - 28 = -0*l - 2*l. What is the units digit of j?
9
Let u = -3 + 3. Suppose j + u = 1. What is the units digit of j?
1
Suppose -5*f + 16 = -9. Suppose 3*b - 25 = u, -32 - 11 = -f*b + 3*u. What is the units digit of b?
8
Suppose x = 3*f + 1, -4*f = -2*f - 4. Let i(w) = -w + 5. Let b be i(x). What is the units digit of -3*(-1)/b*-4?
6
Let f = 23 - 18. Let b(m) be the third derivative of -m**6/120 + m**5/12 + m**4/12 + m**3/3 - m**2. What is the units digit of b(f)?
2
Suppose -15*l - 80 = -17*l. What is the units digit of l?
0
Let z(h) = -h. Let a be z(-5). Suppose -p + 10 = -a*p - 5*o, 12 = -2*p + o. Let m = 10 + p. What is the units digit of m?
5
Let c = -66 + 87. What is the units digit of c?
1
Let k be 3/(1 + (-2)/(-4)). Suppose 10 = -7*c + k*c. Let u(l) = -2*l + 2. What is the units digit of u(c)?
6
Suppose 3*w + 3 = 123. What is the units digit of 968/w + 8/10?
5
Suppose 11*c = 517 + 649. What is the tens digit of c?
0
Let p be (-2)/(-5) - 56/(-35). Let g(n) = -n + 6. Let u be g(-6). Suppose -p = 2*k - u. What is the units digit of k?
5
Suppose 5*j = 3 + 2. Suppose 0 = -3*d + j - 4. What is the units digit of 195/25 - d/5?
8
Let h be 0/(2/1 - 1). Let f = h + 2. Suppose -c + 4 - f = 0. What is the units digit of c?
2
Let y(i) = 4*i - 33. What is the units digit of y(10)?
7
Let q = 12 + -8. Su |
Q:
Cannot resolve symbol 'RoadManager'
I get an error like this. What should I do? do i have to do? do i have to add something in my dependencies?
this my code
//, MapboxMap.OnMapClickListener, PermissionsListener, View.OnClickListener {
private MapView mapView;
private Button button;
private MapboxMap mapboxMap;
private PermissionsManager permissionsManager;
private LocationComponent locationComponent;
// variables for calculating and drawing a route
private DirectionsRoute currentRoute;
private static final String TAG = "DirectionsActivity";
private NavigationMapRoute navigationMapRoute;
private RoadManager roadManager;
@Override
protected void onCreate(Bundle savedInstanceState) {
super.onCreate(savedInstanceState);
this is my dependencies
implementation fileTree(dir: 'libs', include: ['*.jar'])
implementation 'androidx.appcompat:appcompat:1.0.2'
implementation 'androidx.constraintlayout:constraintlayout:1.1.3'
implementation 'com.google.firebase:firebase-database:17.0.0'
implementation 'com.google.firebase:firebase-auth:17.0.0'
implementation 'com.google.firebase:firebase-storage:17.0.0'
//implementation 'com.firebaseui:firebase-ui-auth:1.2.0'
implementation 'com.squareup.picasso:picasso:2.71828' //2.5.2
implementation 'com.firebaseui:firebase-ui-database:1.2.0'
implementation 'com.google.firebase:firebase-analytics:17.2.0'//vcoba kalo error ini diapus
implementation 'com.google.android.gms:play-services-maps:17.0.0'
testImplementation 'junit:junit:4.12'
androidTestImplementation 'androidx.test.ext:junit:1.1.0'
androidTestImplementation 'androidx.test.espresso:espresso-core:3.1.1'
implementation 'com.google.android.gms:play-services-location:17.0.0'
implementation 'androidx.recyclerview:recyclerview:1.0.0'
implementation 'com.android.support:recyclerview-v7:28.0.0'
implementation 'com.android.support:cardview-v7:28.0.0'
implementation 'androidx.cardview:cardview:1.0.0'
implementation 'org.osmdroid:osmdroid-android:5.6@aar'
implementation 'com.mapbox.mapboxsdk:mapbox-android-navigation-ui:0.42.1'
implementation('com.mapbox.mapboxsdk:mapbox-android-sdk:6.8.1') {
exclude group: 'group_name', module: 'module_name'
}
}
what should I do to solve this problem?
A:
RoadManager is part of OSMBonusPack.
First of all, you should follow OSMBonusPack HowToInstall guide.
And then follow OSMBonusPack tutorial.
|
I have heard that on one occasion the Blessed One was wandering on a tour of Kasi with a large community of monks. There he addressed the monks: "I abstain from the night-time meal.[1] As I am abstaining from the night-time meal, I sense next-to-no illness, next-to-no affliction, lightness, strength, & a comfortable abiding. Come now. You too abstain from the night-time meal. As you are abstaining from the night-time meal, you, too, will sense next-to-no illness, next-to-no affliction, lightness, strength, & a comfortable abiding."
"As you say, lord," the monks responded.
Then, as he was wandering by stages in Kasi, the Blessed One eventually arrived at a Kasi town called Kitagiri. And there he stayed in the Kasi town, Kitagiri.
Now at that time the monks led by Assaji & Punabbasu[2] were residing in Kitagiri. Then a large number of monks went to them and, on arrival, said to them, "The Blessed One and the community of monks abstain from the night-time meal. As they are abstaining from the night-time meal, they sense next-to-no illness, next-to-no affliction, lightness, strength, & a comfortable abiding. Come now, friends. You, too, abstain from the night-time meal. As you are abstaining from the night-time meal, you, too, will sense next-to-no illness, next-to-no affliction, lightness, strength, & a comfortable abiding."
When this was said, the monks led by Assaji & Punabbasu said to those monks, "Friends, we eat in the evening, in the morning, & in the wrong time during the day. As we are eating in the evening, in the morning, & in the wrong time during the day, we sense next-to-no illness, next-to-no affliction, lightness, strength, & a comfortable abiding. Why should we, abandoning what is immediately visible, chase after something subject to time? We will eat in the evening, in the morning, & in the wrong time during the day."
When they were unable to convince the monks led by Assaji & Punabbasu, those monks went to the Blessed One [and told him what had happened].
"As you say, lord," the monk answered and, having gone to the monks led by Assaji & Punabbasu, on arrival he said, "The Teacher calls you, friends."
"As you say, friend," the monks led by Assaji & Punabbasu replied. Then they went to the Blessed One and, on arrival, having bowed down to him, sat to one side. As they were sitting there, the Blessed One said to them, "Is it true, monks, that a large number of monks went to you ... and you said, '...Why should we, abandoning what is immediately visible, chase after something subject to time? We will eat in the evening, in the morning, & in the wrong time during the day.'"
"Yes, lord."
"Monks, have you ever understood me to teach the Dhamma in this way: 'Whatever a person experiences — pleasant, painful, or neither-pleasant-nor-painful — his unskillful qualities decrease and his skillful qualities grow'?"
"No, lord."
"And haven't you understood me to teach the Dhamma in this way: 'For someone feeling a pleasant feeling of this sort, unskillful qualities grow and skillful qualities decrease. But there is the case where, for someone feeling a pleasant feeling of that sort, unskillful qualities decrease and skillful qualities grow. For someone feeling a painful feeling of this sort, unskillful qualities grow and skillful qualities decrease. But there is the case where, for someone feeling a painful feeling of that sort, unskillful qualities decrease and skillful qualities grow. For someone feeling a neither-pleasant-nor-painful feeling of this sort, unskillful qualities grow and skillful qualities decrease. But there is the case where, for someone feeling a neither-pleasant-nor-painful feeling of that sort, unskillful qualities decrease and skillful qualities grow.'"
"Yes, lord."
"Good, monks. And if it were not known by me — not seen, not observed, not realized, not touched through discernment — that 'For someone feeling a pleasant feeling of this sort, unskillful qualities grow and skillful qualities decrease,' then would it be fitting for me, not knowing that, to say, 'Abandon that sort of pleasant feeling'?"
"No, lord."
"But because it is known by me — seen, observed, realized, touched through discernment — that 'For someone feeling a pleasant feeling of this sort, unskillful qualities grow and skillful qualities decrease,' I therefore say, 'Abandon that sort of pleasant feeling.'
"If it were not known by me — not seen, not observed, not realized, not touched through discernment — that 'For someone feeling a pleasant feeling of this sort, unskillful qualities decrease and skillful qualities grow,' then would it be fitting for me, not knowing that, to say, 'Enter & remain in that sort of pleasant feeling'?"
"No, lord."
"But because it is known by me — seen, observed, realized, touched through discernment — that 'For someone feeling a pleasant feeling of this sort, unskillful qualities decrease and skillful qualities grow,' I therefore say, 'Enter & remain in that sort of pleasant feeling.'
"Monks, I don't say of all monks that they have a task to do with heedfulness; nor do I say of all monks that they have no task to do with heedfulness.
"Monks who are arahants, whose mental fermentations are ended, who have reached fulfillment, done the task, laid down the burden, attained the true goal, totally destroyed the fetter of becoming, and who are released through right gnosis: I don't say of them that they have work to do with heedfulness. Why is that? They have done their task with heedfulness. They are incapable of being heedless. But as for monks in higher training, who have not yet reached their hearts' goal, who still aspire for the unexcelled freedom from bondage: I say of them that they have a task to do with heedfulness. Why is that? [I think:] 'Perhaps these venerable ones, when making use of suitable resting places, associating with admirable friends, balancing their [mental] faculties,[3] will reach & remain in the supreme goal of the holy life for which clansmen rightly go forth from home into homelessness, knowing & realizing it for themselves in the here & now.' Envisioning this fruit of heedfulness for these monks, I say that they have a task to do with heedfulness.
"Monks, there are these seven individuals to be found in the world. Which seven? One [released] both ways, one released through discernment, a bodily witness, one attained to view, one released through conviction, a Dhamma-follower, and a conviction-follower.
"And what is the individual [released] both ways? There is the case where a certain individual remains touching with his body those peaceful liberations that transcend form, that are formless, and — having seen with discernment — his fermentations are ended. This is called an individual [released] both ways.[4] Regarding this monk, I do not say that he has a task to do with heedfulness. Why is that? He has done his task with heedfulness. He is incapable of being heedless.
"And what is the individual released through discernment? There is the case where a certain individual does not remain touching with his body those peaceful liberations that transcend form, that are formless, but — having seen with discernment — his fermentations are ended. This is called an individual who is released through discernment.[5] Regarding this monk, I do not say that he has a task to do with heedfulness. Why is that? He has done his task with heedfulness. He is incapable of being heedless.
"And what is the individual who is a bodily witness? There is the case where a certain individual remains touching with his body those peaceful liberations that transcend form, that are formless, and — having seen with discernment — some of his fermentations are ended. This is called an individual who is a bodily witness.[6] Regarding this monk, I say that he has a task to do with heedfulness. Why is that? [I think:] 'Perhaps this venerable one, when making use of suitable resting places, associating with admirable friends, balancing his [mental] faculties, will reach & remain in the supreme goal of the holy life for which clansmen rightly go forth from home into homelessness, knowing & realizing it for himself in the here & now.' Envisioning this fruit of heedfulness for this monk, I say that he has a task to do with heedfulness.
"And what is the individual attained to view? There is the case where a certain individual does not remain touching with his body those peaceful liberations that transcend form, that are formless, but — having seen with discernment — some of his fermentations are ended, and he has reviewed & examined with discernment the qualities (or: teachings) proclaimed by the Tathagata. This is called an individual who is attained to view.[7] Regarding this monk, I say that he has a task to do with heedfulness. Why is that? [I think:] 'Perhaps this venerable one, when making use of suitable resting places, associating with admirable friends, balancing his [mental] faculties, will reach & remain in the supreme goal of the holy life for which clansmen rightly go forth from home into homelessness, knowing & realizing it for himself in the here & now.' Envisioning this fruit of heedfulness for this monk, I say that he has a task to do with heedfulness.
"And what is the individual released through conviction? There is the case where a certain individual does not remain touching with his body those peaceful liberations that transcend form, that are formless, but — having seen with discernment — some of his fermentations are ended, and his conviction in the Tathagata is settled, rooted, and established. This is called an individual who is released through conviction.[8] Regarding this monk, I say that he has a task to do with heedfulness. Why is that? [I think:] 'Perhaps this venerable one, when making use of suitable resting places, associating with admirable friends, balancing his [mental] faculties, will reach & remain in the supreme goal of the holy life for which clansmen rightly go forth from home into homelessness, knowing & realizing it for himself in the here & now.' Envisioning this fruit of heedfulness for this monk, I say that he has a task to do with heedfulness.
"And what is the individual who is a Dhamma-follower? There is the case where a certain individual does not remain touching with his body those peaceful liberations that transcend form, that are formless, nor — having seen with discernment — are his fermentations ended. But with a [sufficient] measure of reflection through discernment he has come to an agreement with the teachings proclaimed by the Tathagata. And he has these qualities: the faculty of conviction, the faculty of persistence, the faculty of mindfulness, the faculty of concentration, & the faculty of discernment. This is called an individual who is a Dhamma-follower.[9] Regarding this monk, I say that he has a task to do with heedfulness. Why is that? [I think:] 'Perhaps this venerable one, when making use of suitable resting places, associating with admirable friends, balancing his [mental] faculties, will reach & remain in the supreme goal of the holy life for which clansmen rightly go forth from home into homelessness, knowing & realizing it for himself in the here & now.' Envisioning this fruit of heedfulness for this monk, I say that he has a task to do with heedfulness.
"And what is the individual who is a conviction-follower? There is the case where a certain individual does not remain touching with his body those peaceful liberations that transcend form, that are formless, nor — having seen with discernment — are his fermentations ended. But he has a [sufficient] measure of conviction in & love for the Tathagata. And he has these qualities: the faculty of conviction, the faculty of persistence, the faculty of mindfulness, the faculty of concentration, & the faculty of discernment. This is called an individual who is a conviction-follower. Regarding this monk, I say that he has a task to do with heedfulness. Why is that? [I think:] 'Perhaps this venerable one, when making use of suitable resting places, associating with admirable friends, balancing his [mental] faculties, will reach & remain in the supreme goal of the holy life for which clansmen rightly go forth from home into homelessness, knowing & realizing it for himself in the here & now.' Envisioning this fruit of heedfulness for this monk, I say that he has a task to do with heedfulness.
"Monks, I do not say that the attainment of gnosis is all at once. Rather, the attainment of gnosis is after gradual training, gradual action, gradual practice. And how is there the attainment of gnosis after gradual training, gradual action, gradual practice? There is the case where, when conviction has arisen, one visits [a teacher]. Having visited, one grows close. Having grown close, one lends ear. Having lent ear, one hears the Dhamma. Having heard the Dhamma, one remembers it. Remembering, one penetrates the meaning of the teachings. Penetrating the meaning, one comes to an agreement through pondering the teachings. There being an agreement through pondering the teachings, desire arises. When desire has arisen, one is willing. When one is willing, one contemplates. Having contemplated, one makes an exertion. Having made an exertion, one realizes with the body the ultimate truth and, having penetrated it with discernment, sees it.[10]
"Now, monks, there hasn't been that conviction, there hasn't been that visiting, there hasn't been that growing close ... that lending ear ... that hearing of the Dhamma ... that remembering ... that penetration of the meaning of the teachings ... that agreement through pondering the teachings ... that desire ... that willingness ... that contemplation ... that exertion. You have lost the way, monks. You have gone the wrong way, monks. How far have you strayed, foolish men, from this Dhamma & Discipline!
"Monks, there is a four-phrased statement that, when it is recited, a wise man will in no long time learn the meaning through discernment. I will recite it, and you learn it from me."
"But, lord, who are we to be learners of the Dhamma?"
"Monks, even with a teacher devoted to material things, an heir of material things, who lives attached to material things, this sort of haggling [by his students] wouldn't be proper: 'If we get this, we'll do it; if we don't, we won't.' So how could it be with regard to the Tathagata, who dwells entirely detached from material things?
"For a disciple who has conviction in the Teacher's message & lives to penetrate it, what accords with the Dhamma is this: 'The Blessed One is the Teacher, I am a disciple. He is the one who knows, not I.' For a disciple who has conviction in the Teacher's message & lives to penetrate it, the Teacher's message is healing & nourishing. For a disciple who has conviction in the Teacher's message & lives to penetrate it, what accords with the Dhamma is this: 'Gladly would I let the flesh & blood in my body dry up, leaving just the skin, tendons, & bones, but if I have not attained what can be reached through human firmness, human persistence, human striving, there will be no relaxing my persistence.' For a disciple who has conviction in the Teacher's message & lives to penetrate it, one of two fruits can be expected: either gnosis here & now, or — if there be any remnant of clinging-sustenance — non-return."
That is what the Blessed One said. Gratified, the monks delighted in the Blessed One's words.
Notes
Pacittiya 37 forbids monks from eating during the period from noon until the following dawn. According to MN 66, the Buddha introduced this restriction in stages, first forbidding the afternoon meal, and then the night-time meal.
Assaji and Punabbasu were two of the six ringleaders of the notorious "group-of-six" monks, whose misbehavior led to the formulation of many rules in the Vinaya. (The group is named after the number of ringleaders, not the number of members, which — according to the Commentary — reached more than one thousand.) In the origin story to Sanghadisesa 13, the monks led by Assaji and Punabbasu behaved in many inappropriate ways to please the lay families of Kitagiri, to the point where the Kitagiri lay people ridiculed well-behaved monks and refused to give them alms.
The Pali phrase for "monks led by Assaji and Punabbasu" is assaji-punabbusakaa bhikkhuu. Both The Middle-Length Sayings (Horner, trans.) and The Middle Length Discourses of the Buddha (Ñanamoli/Bodhi, trans.) mistakenly treat this phrase as the names of two monks, Assaji and Punabbasuka. Actually, the -kaa at the end of the name is a suffix that converts it into an adjective, describing a group following Assaji and Punabbasu.
According to the Commentary, this category and the following one include all noble ones (except for those who have reached the fruit of arahantship) who have not attained any of the formless dimensions.
The steps of the practice, as presented here, follow the same sequence as that discussed in MN 95. However, in that sutta, the sequence is prefaced by instructions on how to determine whether a teacher is worthy of conviction. |
Oil and Energy Stocks Fall after Trump’s Latest Tariff
On Thursday, President Trump said that he will impose an additional 10% tariff on $300 billion of Chinese goods. The tariffs will start on September 1. The Chinese goods don’t include the $250 billion worth of goods that already have a 25% tariff. The stock market reacted sharply to President Trump’s comment. The S&P 500 Index fell 0.9%, while the Dow Jones Industrial Index fell 1.05% on Thursday. President Trump’s comment also impacted crude oil prices. On Thursday, the WTI near-month crude oil futures price fell approximately 8%—the steepest fall in more than three years.
The United States Oil Fund (USO) closed approximately 6.1% lower on Thursday. The top energy stocks felt the heat and closed lower. ExxonMobil (XOM) fell 2.6%, while Chevron (CVX) fell 1.9%.
Trade war impacts oil prices
China is the world’s second-largest crude oil consumer after the US. A prolonged trade war might cause a slowdown in China’s economy. Lower demand for oil would push oil prices lower. The latest tariffs on $300 billion worth of Chinese goods will likely impact US consumers earlier. The tariffs impact consumer and retail products. The tariffs might also impact US economic growth.
The IEA (International Energy Agency) reduced its 2019 oil demand forecast in July to 1.1 MMbpd (million barrels per day) amid the US-China trade war. Earlier, the agency reduced its demand forecast from 1.5 MMbpd to 1.2 MMbpd in June. Crude oil prices have fallen roughly 20% since May 2018 when the US imposed the current set of tariffs on China.
Impact on natural gas
The ongoing trade war isn’t just impacting crude oil demand and prices. The trade war is also impacting natural gas, especially LNG (liquefied natural gas). China is a key LNG buyer. The IEA predicts that China will account for more than 40% of the global gas demand growth by 2024. The trade war has also impacted Chinese LNG imports. |
NEW ORLEANS, Dec. 07, 2018 (GLOBE NEWSWIRE) -- Kahn Swick & Foti, LLC (“KSF”) and KSF partner, former Attorney General of Louisiana, Charles C. Foti, Jr., remind investors that they have until January 7, 2019 to file lead plaintiff applications in a securities class action lawsuit against Ribbon Communications, Inc. (NasdaqGS: RBBN) f/k/a Sonus Networks, Inc., if they purchased the Company’s securities between January 8, 2015 through March 24, 2015, inclusive (the “Class Period”). This action is pending in the United States District Court for the District of Massachusetts.
What You May Do
If you purchased securities of Ribbon and would like to discuss your legal rights and how this case might affect you and your right to recover for your economic loss, you may, without obligation or cost to you, contact KSF Managing Partner Lewis Kahn toll-free at 1-877-515-1850 or via email (lewis.kahn@ksfcounsel.com), or visit https://www.ksfcounsel.com/cases/nasdaqgs-rbbn/ to learn more. If you wish to serve as a lead plaintiff in this class action, you must petition the Court by January 7, 2019.
About the Lawsuit
Ribbon and certain of its executives are charged with failing to disclose material information during the Class Period, violating federal securities laws.
On March 24, 2015, Ribbon, formerly Sonus Networks, Inc., disclosed dismal results for the first quarter of 2015, including revenue of only $47-$50 million, approximately $24-$30 million lower than expected, and a $0.29-$0.34 loss in non-GAAP earnings-per-share, lower than the $0.03 gain forecasted.
On this news, the price of Ribbon’s shares plummeted $4.46 per share, from $13.16 to $8.70 per share, a loss of over 33%.
The case is Miller v. Sonus Networks, Inc., et al., 18-cv-12344.
About Kahn Swick & Foti, LLC
KSF, whose partners include the former Louisiana Attorney General Charles C. Foti, Jr., is a law firm focused on securities, antitrust and consumer class actions, along with merger & acquisition and breach of fiduciary litigation against publicly traded companies on behalf of shareholders. The firm has offices in New York, California and Louisiana.
Newswire Distribution Network & Management
About Us
GlobeNewswire is one of the world's largest newswire distribution networks, specializing in the delivery of corporate press releases financial disclosures and multimedia content to the media, investment community, individual investors and the general public. |
Is there a best way to set positive expiratory-end pressure for mechanical ventilatory support in acute lung injury?
Airspace collapse is a hallmark of parenchymal lung injury. Strategies to reopen and maintain patency of these regions offer three advantages: improved gas exchange, less lung injury, and improved lung compliance. Elevations in intrathoracic pressure to achieve these goals, however, may overdistend healthier lung regions and compromise cardiac function. Positive expiratory-end pressure is a widely used technique to maintain alveolar patency, but its beneficial effects must be balanced against its harmful effects. |
<?xml version="1.0" encoding="UTF-8"?>
<document type="com.apple.InterfaceBuilder3.Cocoa.XIB" version="3.0" toolsVersion="14313.18" targetRuntime="MacOSX.Cocoa" propertyAccessControl="none" useAutolayout="YES" customObjectInstantitationMethod="direct">
<dependencies>
<plugIn identifier="com.apple.InterfaceBuilder.CocoaPlugin" version="14313.18"/>
<capability name="documents saved in the Xcode 8 format" minToolsVersion="8.0"/>
</dependencies>
<objects>
<customObject id="-2" userLabel="File's Owner" customClass="TPIBlowfishEncryption">
<connections>
<outlet property="preferencePaneView" destination="LOA-uM-qhd" id="DnN-Nb-rHU"/>
</connections>
</customObject>
<customObject id="-1" userLabel="First Responder" customClass="FirstResponder"/>
<customObject id="-3" userLabel="Application" customClass="NSObject"/>
<customView translatesAutoresizingMaskIntoConstraints="NO" id="LOA-uM-qhd">
<rect key="frame" x="0.0" y="0.0" width="477" height="228"/>
<subviews>
<button translatesAutoresizingMaskIntoConstraints="NO" id="JUL-dK-X0r">
<rect key="frame" x="191" y="127" width="95" height="18"/>
<buttonCell key="cell" type="check" title="Enable FiSH" bezelStyle="regularSquare" imagePosition="left" state="on" inset="2" id="rLW-So-J3H">
<behavior key="behavior" changeContents="YES" doesNotDimImage="YES" lightByContents="YES"/>
<font key="font" metaFont="system"/>
</buttonCell>
<connections>
<action selector="preferencesChanged:" target="-2" id="hWM-vl-JE2"/>
<binding destination="Bbo-6V-xug" name="value" keyPath="values.Blowfish Encryption Extension -> Enable Service" id="sOZ-hQ-7lc"/>
</connections>
</button>
<scrollView borderType="none" horizontalLineScroll="10" horizontalPageScroll="10" verticalLineScroll="10" verticalPageScroll="10" hasHorizontalScroller="NO" hasVerticalScroller="NO" usesPredominantAxisScrolling="NO" horizontalScrollElasticity="none" verticalScrollElasticity="none" translatesAutoresizingMaskIntoConstraints="NO" id="nP9-Nm-5KC">
<rect key="frame" x="20" y="25" width="437" height="25"/>
<clipView key="contentView" drawsBackground="NO" copiesOnScroll="NO" id="oRi-yb-wUL">
<rect key="frame" x="0.0" y="0.0" width="437" height="25"/>
<autoresizingMask key="autoresizingMask" widthSizable="YES" heightSizable="YES"/>
<subviews>
<textView editable="NO" drawsBackground="NO" importsGraphics="NO" verticallyResizable="YES" allowsNonContiguousLayout="YES" id="Bsa-nm-tXv">
<rect key="frame" x="0.0" y="0.0" width="437" height="25"/>
<autoresizingMask key="autoresizingMask" widthSizable="YES" heightSizable="YES"/>
<color key="textColor" name="textColor" catalog="System" colorSpace="catalog"/>
<color key="backgroundColor" name="textBackgroundColor" catalog="System" colorSpace="catalog"/>
<size key="minSize" width="437" height="25"/>
<size key="maxSize" width="549" height="10000000"/>
<attributedString key="textStorage">
<fragment content="FiSH uses the ">
<attributes>
<color key="NSColor" name="textColor" catalog="System" colorSpace="catalog"/>
<font key="NSFont" metaFont="system"/>
<paragraphStyle key="NSParagraphStyle" alignment="left" lineBreakMode="wordWrapping" baseWritingDirection="natural" tighteningFactorForTruncation="0.0" allowsDefaultTighteningForTruncation="NO"/>
</attributes>
</fragment>
<fragment content="Blowfish block cipher">
<attributes>
<color key="NSColor" name="textColor" catalog="System" colorSpace="catalog"/>
<font key="NSFont" metaFont="system"/>
<real key="NSKern" value="0.0"/>
<url key="NSLink" string="https://en.wikipedia.org/wiki/Blowfish_(cipher)"/>
<paragraphStyle key="NSParagraphStyle" alignment="left" lineBreakMode="wordWrapping" baseWritingDirection="natural" tighteningFactorForTruncation="0.0" allowsDefaultTighteningForTruncation="NO"/>
</attributes>
</fragment>
<fragment content=" with a ">
<attributes>
<color key="NSColor" name="textColor" catalog="System" colorSpace="catalog"/>
<font key="NSFont" metaFont="system"/>
<real key="NSKern" value="0.0"/>
<paragraphStyle key="NSParagraphStyle" alignment="left" lineBreakMode="wordWrapping" baseWritingDirection="natural" tighteningFactorForTruncation="0.0" allowsDefaultTighteningForTruncation="NO"/>
</attributes>
</fragment>
<fragment content="weak mode of operation">
<attributes>
<color key="NSColor" name="textColor" catalog="System" colorSpace="catalog"/>
<font key="NSFont" metaFont="system"/>
<real key="NSKern" value="0.0"/>
<url key="NSLink" string="https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation#Electronic_Codebook_.28ECB.29"/>
<paragraphStyle key="NSParagraphStyle" alignment="left" lineBreakMode="wordWrapping" baseWritingDirection="natural" tighteningFactorForTruncation="0.0" allowsDefaultTighteningForTruncation="NO"/>
</attributes>
</fragment>
</attributedString>
<color key="insertionPointColor" name="textColor" catalog="System" colorSpace="catalog"/>
</textView>
</subviews>
</clipView>
<scroller key="horizontalScroller" hidden="YES" wantsLayer="YES" verticalHuggingPriority="750" doubleValue="1" horizontal="YES" id="9bD-E7-Llt">
<rect key="frame" x="-100" y="-100" width="87" height="18"/>
<autoresizingMask key="autoresizingMask"/>
</scroller>
<scroller key="verticalScroller" hidden="YES" wantsLayer="YES" verticalHuggingPriority="750" doubleValue="1" horizontal="NO" id="Ur6-qL-14H">
<rect key="frame" x="224" y="1" width="15" height="133"/>
<autoresizingMask key="autoresizingMask"/>
</scroller>
</scrollView>
<textField verticalHuggingPriority="750" horizontalCompressionResistancePriority="250" setsMaxLayoutWidthAtFirstLayout="YES" translatesAutoresizingMaskIntoConstraints="NO" id="KZ9-Ql-hLa">
<rect key="frame" x="18" y="64" width="441" height="44"/>
<textFieldCell key="cell" sendsActionOnEndEditing="YES" title="WARNING: There is absolutely no guarantee that data you encrypt using FiSH is secure." id="omF-Az-3FB">
<font key="font" metaFont="systemBold" size="18"/>
<color key="textColor" red="0.85371291035353536" green="0.10235263760745605" blue="0.0" alpha="1" colorSpace="calibratedRGB"/>
<color key="backgroundColor" name="textBackgroundColor" catalog="System" colorSpace="catalog"/>
</textFieldCell>
</textField>
<textField verticalHuggingPriority="750" horizontalCompressionResistancePriority="250" setsMaxLayoutWidthAtFirstLayout="YES" translatesAutoresizingMaskIntoConstraints="NO" id="V4q-92-b4n">
<rect key="frame" x="18" y="164" width="441" height="34"/>
<textFieldCell key="cell" selectable="YES" sendsActionOnEndEditing="YES" id="8mc-xf-sYs">
<font key="font" metaFont="system"/>
<string key="title">“FiSH” refers to a dated implementation of the Blowfish block cipher which is popular for encrypting the contents of chatrooms. </string>
<color key="textColor" name="textColor" catalog="System" colorSpace="catalog"/>
<color key="backgroundColor" name="textBackgroundColor" catalog="System" colorSpace="catalog"/>
</textFieldCell>
</textField>
</subviews>
<constraints>
<constraint firstAttribute="trailing" secondItem="nP9-Nm-5KC" secondAttribute="trailing" constant="20" id="3Be-5M-Stp"/>
<constraint firstItem="KZ9-Ql-hLa" firstAttribute="leading" secondItem="LOA-uM-qhd" secondAttribute="leading" constant="20" id="3jV-xY-tCR"/>
<constraint firstAttribute="trailing" secondItem="V4q-92-b4n" secondAttribute="trailing" constant="20" symbolic="YES" id="HCF-PA-cke"/>
<constraint firstItem="V4q-92-b4n" firstAttribute="leading" secondItem="LOA-uM-qhd" secondAttribute="leading" constant="20" symbolic="YES" id="OBn-Ja-zH8"/>
<constraint firstItem="KZ9-Ql-hLa" firstAttribute="top" secondItem="JUL-dK-X0r" secondAttribute="bottom" constant="21" id="Sil-BA-5mM"/>
<constraint firstItem="V4q-92-b4n" firstAttribute="centerX" secondItem="JUL-dK-X0r" secondAttribute="centerX" id="WL9-LW-y4V"/>
<constraint firstItem="nP9-Nm-5KC" firstAttribute="leading" secondItem="LOA-uM-qhd" secondAttribute="leading" constant="20" id="Y92-64-uTF"/>
<constraint firstItem="nP9-Nm-5KC" firstAttribute="top" secondItem="KZ9-Ql-hLa" secondAttribute="bottom" constant="14" id="cWo-CR-LCm"/>
<constraint firstItem="JUL-dK-X0r" firstAttribute="top" secondItem="V4q-92-b4n" secondAttribute="bottom" constant="21" id="dQx-VI-L5f"/>
<constraint firstAttribute="trailing" secondItem="KZ9-Ql-hLa" secondAttribute="trailing" constant="20" id="k6x-X3-xFd"/>
<constraint firstItem="V4q-92-b4n" firstAttribute="top" secondItem="LOA-uM-qhd" secondAttribute="top" constant="30" id="qFd-Bj-T47"/>
<constraint firstAttribute="bottom" secondItem="nP9-Nm-5KC" secondAttribute="bottom" constant="25" id="vU5-Zp-WEa"/>
</constraints>
<point key="canvasLocation" x="331.5" y="250"/>
</customView>
<userDefaultsController id="Bbo-6V-xug" customClass="TPCPreferencesUserDefaultsController"/>
</objects>
</document>
|
---
uid: web-forms/overview/data-access/editing-inserting-and-deleting-data/customizing-the-data-modification-interface-vb
title: "Customizing the Data Modification Interface (VB) | Microsoft Docs"
author: rick-anderson
description: "In this tutorial we'll look at how to customize the interface of an editable GridView, by replacing the standard TextBox and CheckBox controls with alternati..."
ms.author: riande
ms.date: 07/17/2006
ms.assetid: 4830d984-bd2c-4a08-bfe5-2385599f1f7d
msc.legacyurl: /web-forms/overview/data-access/editing-inserting-and-deleting-data/customizing-the-data-modification-interface-vb
msc.type: authoredcontent
---
# Customizing the Data Modification Interface (VB)
by [Scott Mitchell](https://twitter.com/ScottOnWriting)
[Download Sample App](https://download.microsoft.com/download/9/c/1/9c1d03ee-29ba-4d58-aa1a-f201dcc822ea/ASPNET_Data_Tutorial_20_VB.exe) or [Download PDF](customizing-the-data-modification-interface-vb/_static/datatutorial20vb1.pdf)
> In this tutorial we'll look at how to customize the interface of an editable GridView, by replacing the standard TextBox and CheckBox controls with alternative input Web controls.
## Introduction
The BoundFields and CheckBoxFields used by the GridView and DetailsView controls simplify the process of modifying data due to their ability to render read-only, editable, and insertable interfaces. These interfaces can be rendered without the need for adding any additional declarative markup or code. However, the BoundField and CheckBoxField's interfaces lack the customizability often needed in real-world scenarios. In order to customize the editable or insertable interface in a GridView or DetailsView we need to instead use a TemplateField.
In the [preceding tutorial](adding-validation-controls-to-the-editing-and-inserting-interfaces-vb.md) we saw how to customize the data modification interfaces by adding validation Web controls. In this tutorial we'll look at how to customize the actual data collection Web controls, replacing the BoundField and CheckBoxField's standard TextBox and CheckBox controls with alternative input Web controls. In particular, we'll build an editable GridView that allows a product's name, category, supplier, and discontinued status to be updated. When editing a particular row, the category and supplier fields will render as DropDownLists, containing the set of available categories and suppliers to choose from. Furthermore, we'll replace the CheckBoxField's default CheckBox with a RadioButtonList control that offers two options: "Active" and "Discontinued".
[](customizing-the-data-modification-interface-vb/_static/image1.png)
**Figure 1**: The GridView's Editing Interface Includes DropDownLists and RadioButtons ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image3.png))
## Step 1: Creating the Appropriate`UpdateProduct`Overload
In this tutorial we will build an editable GridView that permits editing of a product's name, category, supplier, and discontinued status. Therefore, we need an `UpdateProduct` overload that accepts five input parameters these four product values plus the `ProductID`. Like in our previous overloads, this one will:
1. Retrieve the product information from the database for the specified `ProductID`,
2. Update the `ProductName`, `CategoryID`, `SupplierID`, and `Discontinued` fields, and
3. Send the update request to the DAL through the TableAdapter's `Update()` method.
For brevity, for this particular overload I've omitted the business rule check that ensures a product being marked as discontinued isn't the only product offered by its supplier. Feel free to add it in if you prefer, or, ideally, refactor out the logic to a separate method.
The following code shows the new `UpdateProduct` overload in the `ProductsBLL` class:
[!code-vb[Main](customizing-the-data-modification-interface-vb/samples/sample1.vb)]
## Step 2: Crafting the Editable GridView
With the `UpdateProduct` overload added, we're ready to create our editable GridView. Open the `CustomizedUI.aspx` page in the `EditInsertDelete` folder and add a GridView control to the Designer. Next, create a new ObjectDataSource from the GridView's smart tag. Configure the ObjectDataSource to retrieve product information via the `ProductBLL` class's `GetProducts()` method and to update product data using the `UpdateProduct` overload we just created. From the INSERT and DELETE tabs, select (None) from the drop-down lists.
[](customizing-the-data-modification-interface-vb/_static/image4.png)
**Figure 2**: Configure the ObjectDataSource to Use the `UpdateProduct` Overload Just Created ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image6.png))
As we've seen throughout the data modification tutorials, the declarative syntax for the ObjectDataSource created by Visual Studio assigns the `OldValuesParameterFormatString` property to `original_{0}`. This, of course, won't work with our Business Logic Layer since our methods don't expect the original `ProductID` value to be passed in. Therefore, as we've done in previous tutorials, take a moment to remove this property assignment from the declarative syntax or, instead, set this property's value to `{0}`.
After this change, the ObjectDataSource's declarative markup should look like the following:
[!code-aspx[Main](customizing-the-data-modification-interface-vb/samples/sample2.aspx)]
Note that the `OldValuesParameterFormatString` property has been removed and that there is a `Parameter` in the `UpdateParameters` collection for each of the input parameters expected by our `UpdateProduct` overload.
While the ObjectDataSource is configured to update only a subset of product values, the GridView currently shows *all* of the product fields. Take a moment to edit the GridView so that:
- It only includes the `ProductName`, `SupplierName`, `CategoryName` BoundFields and the `Discontinued` CheckBoxField
- The `CategoryName` and `SupplierName` fields to appear before (to the left of) the `Discontinued` CheckBoxField
- The `CategoryName` and `SupplierName` BoundFields' `HeaderText` property is set to "Category" and "Supplier", respectively
- Editing support is enabled (check the Enable Editing checkbox in the GridView's smart tag)
After these changes, the Designer will look similar to Figure 3, with the GridView's declarative syntax shown below.
[](customizing-the-data-modification-interface-vb/_static/image7.png)
**Figure 3**: Remove the Unneeded Fields from the GridView ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image9.png))
[!code-aspx[Main](customizing-the-data-modification-interface-vb/samples/sample3.aspx)]
At this point the GridView's read-only behavior is complete. When viewing the data, each product is rendered as a row in the GridView, showing the product's name, category, supplier, and discontinued status.
[](customizing-the-data-modification-interface-vb/_static/image10.png)
**Figure 4**: The GridView's Read-Only Interface is Complete ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image12.png))
> [!NOTE]
> As discussed in [An Overview of Inserting, Updating, and Deleting Data tutorial](an-overview-of-inserting-updating-and-deleting-data-cs.md), it is vitally important that the GridView s view state be enabled (the default behavior). If you set the GridView s `EnableViewState` property to `false`, you run the risk of having concurrent users unintentionally deleting or editing records. See [WARNING: Concurrency Issue with ASP.NET 2.0 GridViews/DetailsView/FormViews that Support Editing and/or Deleting and Whose View State is Disabled](http://scottonwriting.net/sowblog/posts/10054.aspx) for more information.
## Step 3: Using a DropDownList for the Category and Supplier Editing Interfaces
Recall that the `ProductsRow` object contains `CategoryID`, `CategoryName`, `SupplierID`, and `SupplierName` properties, which provide the actual foreign-key ID values in the `Products` database table and the corresponding `Name` values in the `Categories` and `Suppliers` tables. The `ProductRow`'s `CategoryID` and `SupplierID` can both be read from and written to, while the `CategoryName` and `SupplierName` properties are marked read-only.
Due to the read-only status of the `CategoryName` and `SupplierName` properties, the corresponding BoundFields have had their `ReadOnly` property set to `True`, preventing these values from being modified when a row is edited. While we can set the `ReadOnly` property to `False`, rendering the `CategoryName` and `SupplierName` BoundFields as TextBoxes during editing, such an approach will result in an exception when the user attempts to update the product since there is no `UpdateProduct` overload that takes in `CategoryName` and `SupplierName` inputs. In fact, we don't want to create such an overload for two reasons:
- The `Products` table doesn't have `SupplierName` or `CategoryName` fields, but `SupplierID` and `CategoryID`. Therefore, we want our method to be passed these particular ID values, not their lookup tables' values.
- Requiring the user to type in the name of the supplier or category is less than ideal, as it requires the user to know the available categories and suppliers and their correct spellings.
The supplier and category fields should display the category and suppliers' names when in read-only mode (as it does now) and a drop-down list of applicable options when being edited. Using a drop-down list, the end user can quickly see what categories and suppliers are available to choose among and can more easily make their selection.
To provide this behavior, we need to convert the `SupplierName` and `CategoryName` BoundFields into TemplateFields whose `ItemTemplate` emits the `SupplierName` and `CategoryName` values and whose `EditItemTemplate` uses a DropDownList control to list the available categories and suppliers.
## Adding the`Categories`and`Suppliers`DropDownLists
Start by converting the `SupplierName` and `CategoryName` BoundFields into TemplateFields by: clicking on the Edit Columns link from the GridView's smart tag; selecting the BoundField from the list in the lower left; and clicking the "Convert this field into a TemplateField" link. The conversion process will create a TemplateField with both an `ItemTemplate` and an `EditItemTemplate`, as shown in the declarative syntax below:
[!code-aspx[Main](customizing-the-data-modification-interface-vb/samples/sample4.aspx)]
Since the BoundField was marked as read-only, both the `ItemTemplate` and `EditItemTemplate` contain a Label Web control whose `Text` property is bound to the applicable data field (`CategoryName`, in the syntax above). We need to modify the `EditItemTemplate`, replacing the Label Web control with a DropDownList control.
As we've seen in previous tutorials, the template can be edited through the Designer or directly from the declarative syntax. To edit it through the Designer, click on the Edit Templates link from the GridView's smart tag and choose to work with the Category field's `EditItemTemplate`. Remove the Label Web control and replace it with a DropDownList control, setting the DropDownList's ID property to `Categories`.
[](customizing-the-data-modification-interface-vb/_static/image13.png)
**Figure 5**: Remove the TexBox and Add a DropDownList to the `EditItemTemplate` ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image15.png))
We next need to populate the DropDownList with the available categories. Click on the Choose Data Source link from the DropDownList's smart tag and opt to create a new ObjectDataSource named `CategoriesDataSource`.
[](customizing-the-data-modification-interface-vb/_static/image16.png)
**Figure 6**: Create a New ObjectDataSource Control Named `CategoriesDataSource` ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image18.png))
To have this ObjectDataSource return all of the categories, bind it to the `CategoriesBLL` class's `GetCategories()` method.
[](customizing-the-data-modification-interface-vb/_static/image19.png)
**Figure 7**: Bind the ObjectDataSource to the `CategoriesBLL`'s `GetCategories()` Method ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image21.png))
Finally, configure the DropDownList's settings such that the `CategoryName` field is displayed in each DropDownList `ListItem` with the `CategoryID` field used as the value.
[](customizing-the-data-modification-interface-vb/_static/image22.png)
**Figure 8**: Have the `CategoryName` Field Displayed and the `CategoryID` Used as the Value ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image24.png))
After making these changes the declarative markup for the `EditItemTemplate` in the `CategoryName` TemplateField will include both a DropDownList and an ObjectDataSource:
[!code-aspx[Main](customizing-the-data-modification-interface-vb/samples/sample5.aspx)]
> [!NOTE]
> The DropDownList in the `EditItemTemplate` must have its view state enabled. We will soon add databinding syntax to the DropDownList's declarative syntax and databinding commands like `Eval()` and `Bind()` can only appear in controls whose view state is enabled.
Repeat these steps to add a DropDownList named `Suppliers` to the `SupplierName` TemplateField's `EditItemTemplate`. This will involve adding a DropDownList to the `EditItemTemplate` and creating another ObjectDataSource. The `Suppliers` DropDownList's ObjectDataSource, however, should be configured to invoke the `SuppliersBLL` class's `GetSuppliers()` method. Additionally, configure the `Suppliers` DropDownList to display the `CompanyName` field and use the `SupplierID` field as the value for its `ListItem` s.
After adding the DropDownLists to the two `EditItemTemplate` s, load the page in a browser and click the Edit button for the Chef Anton's Cajun Seasoning product. As Figure 9 shows, the product's category and supplier columns are rendered as drop-down lists containing the available categories and suppliers to choose from. However, note that the *first* items in both drop-down lists are selected by default (Beverages for the category and Exotic Liquids as the supplier), even though Chef Anton's Cajun Seasoning is a Condiment supplied by New Orleans Cajun Delights.
[](customizing-the-data-modification-interface-vb/_static/image25.png)
**Figure 9**: The First Item in the Drop-Down Lists is Selected by Default ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image27.png))
Furthermore, if you click Update, you'll find that the product's `CategoryID` and `SupplierID` values are set to `NULL`. Both of these undesired behaviors are caused because the DropDownLists in the `EditItemTemplate` s are not bound to any data fields from the underlying product data.
## Binding the DropDownLists to the`CategoryID`and`SupplierID`Data Fields
In order to have the edited product's category and supplier drop-down lists set to the appropriate values and to have these values sent back to the BLL's `UpdateProduct` method upon clicking Update, we need to bind the DropDownLists' `SelectedValue` properties to the `CategoryID` and `SupplierID` data fields using two-way databinding. To accomplish this with the `Categories` DropDownList, you can add `SelectedValue='<%# Bind("CategoryID") %>'` directly to the declarative syntax.
Alternatively, you can set the DropDownList's databindings by editing the template through the Designer and clicking the Edit DataBindings link from the DropDownList's smart tag. Next, indicate that the `SelectedValue` property should be bound to the `CategoryID` field using two-way databinding (see Figure 10). Repeat either the declarative or Designer process to bind the `SupplierID` data field to the `Suppliers` DropDownList.
[](customizing-the-data-modification-interface-vb/_static/image28.png)
**Figure 10**: Bind the `CategoryID` to the DropDownList's `SelectedValue` Property Using Two-Way Databinding ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image30.png))
Once the bindings have been applied to the `SelectedValue` properties of the two DropDownLists, the edited product's category and supplier columns will default to the current product's values. Upon clicking Update, the `CategoryID` and `SupplierID` values of the selected drop-down list item will be passed to the `UpdateProduct` method. Figure 11 shows the tutorial after the databinding statements have been added; note how the selected drop-down list items for Chef Anton's Cajun Seasoning are correctly Condiment and New Orleans Cajun Delights.
[](customizing-the-data-modification-interface-vb/_static/image31.png)
**Figure 11**: The Edited Product's Current Category and Supplier Values are Selected by Default ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image33.png))
## Handling`NULL`Values
The `CategoryID` and `SupplierID` columns in the `Products` table can be `NULL`, yet the DropDownLists in the `EditItemTemplate` s don't include a list item to represent a `NULL` value. This has two consequences:
- User cannot use our interface to change a product's category or supplier from a non-`NULL` value to a `NULL` one
- If a product has a `NULL` `CategoryID` or `SupplierID`, clicking the Edit button will result in an exception. This is because the `NULL` value returned by `CategoryID` (or `SupplierID`) in the `Bind()` statement does not map to a value in the DropDownList (the DropDownList throws an exception when its `SelectedValue` property is set to a value *not* in its collection of list items).
In order to support `NULL` `CategoryID` and `SupplierID` values, we need to add another `ListItem` to each DropDownList to represent the `NULL` value. In the [Master/Detail Filtering With a DropDownList](../masterdetail/master-detail-filtering-with-a-dropdownlist-cs.md) tutorial, we saw how to add an additional `ListItem` to a databound DropDownList, which involved setting the DropDownList's `AppendDataBoundItems` property to `True` and manually adding the additional `ListItem`. In that previous tutorial, however, we added a `ListItem` with a `Value` of `-1`. The databinding logic in ASP.NET, however, will automatically convert a blank string to a `NULL` value and vice-a-versa. Therefore, for this tutorial we want the `ListItem`'s `Value` to be an empty string.
Start by setting both DropDownLists' `AppendDataBoundItems` property to `True`. Next, add the `NULL` `ListItem` by adding the following `<asp:ListItem>` element to each DropDownList so that the declarative markup looks like:
[!code-aspx[Main](customizing-the-data-modification-interface-vb/samples/sample6.aspx)]
I've chosen to use "(None)" as the Text value for this `ListItem`, but you can change it to also be a blank string if you'd like.
> [!NOTE]
> As we saw in the *Master/Detail Filtering With a DropDownList* tutorial, `ListItem` s can be added to a DropDownList through the Designer by clicking on the DropDownList's `Items` property in the Properties window (which will display the `ListItem` Collection Editor). However, be sure to add the `NULL` `ListItem` for this tutorial through the declarative syntax. If you use the `ListItem` Collection Editor, the generated declarative syntax will omit the `Value` setting altogether when assigned a blank string, creating declarative markup like: `<asp:ListItem>(None)</asp:ListItem>`. While this may look harmless, the missing Value causes the DropDownList to use the `Text` property value in its place. That means that if this `NULL` `ListItem` is selected, the value "(None)" will be attempted to be assigned to the `CategoryID`, which will result in an exception. By explicitly setting `Value=""`, a `NULL` value will be assigned to `CategoryID` when the `NULL` `ListItem` is selected.
Repeat these steps for the Suppliers DropDownList.
With this additional `ListItem`, the editing interface can now assign `NULL` values to a Product's `CategoryID` and `SupplierID` fields, as shown in Figure 12.
[](customizing-the-data-modification-interface-vb/_static/image34.png)
**Figure 12**: Choose (None) to Assign a `NULL` Value for a Product's Category or Supplier ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image36.png))
## Step 4: Using RadioButtons for the Discontinued Status
Currently the products' `Discontinued` data field is expressed using a CheckBoxField, which renders a disabled checkbox for the read-only rows and an enabled checkbox for the row being edited. While this user interface is often suitable, we can customize it if needed using a TemplateField. For this tutorial, let's change the CheckBoxField into a TemplateField that uses a RadioButtonList control with two options "Active" and "Discontinued" from which the user can specify the product's `Discontinued` value.
Start by converting the `Discontinued` CheckBoxField into a TemplateField, which will create a TemplateField with an `ItemTemplate` and `EditItemTemplate`. Both templates include a CheckBox with its `Checked` property bound to the `Discontinued` data field, the only difference between the two being that the `ItemTemplate`'s CheckBox's `Enabled` property is set to `False`.
Replace the CheckBox in both the `ItemTemplate` and `EditItemTemplate` with a RadioButtonList control, setting both RadioButtonLists' `ID` properties to `DiscontinuedChoice`. Next, indicate that the RadioButtonLists should each contain two radio buttons, one labeled "Active" with a value of "False" and one labeled "Discontinued" with a value of "True". To accomplish this you can either enter the `<asp:ListItem>` elements in directly through the declarative syntax or use the `ListItem` Collection Editor from the Designer. Figure 13 shows the `ListItem` Collection Editor after the two radio button options have been specified.
[](customizing-the-data-modification-interface-vb/_static/image37.png)
**Figure 13**: Add Active and Discontinued Options to the RadioButtonList ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image39.png))
Since the RadioButtonList in the `ItemTemplate` shouldn't be editable, set its `Enabled` property to `False`, leaving the `Enabled` property to `True` (the default) for the RadioButtonList in the `EditItemTemplate`. This will make the radio buttons in the non-edited row as read-only, but will allow the user to change the RadioButton values for the edited row.
We still need to assign the RadioButtonList controls' `SelectedValue` properties so that the appropriate radio button is selected based upon the product's `Discontinued` data field. As with the DropDownLists examined earlier in this tutorial, this databinding syntax can either be added directly into the declarative markup or through the Edit DataBindings link in the RadioButtonLists' smart tags.
After adding the two RadioButtonLists and configuring them, the `Discontinued` TemplateField's declarative markup should look like:
[!code-aspx[Main](customizing-the-data-modification-interface-vb/samples/sample7.aspx)]
With these changes, the `Discontinued` column has been transformed from a list of checkboxes to a list of radio button pairs (see Figure 14). When editing a product, the appropriate radio button is selected and the product's discontinued status can be updated by selecting the other radio button and clicking Update.
[](customizing-the-data-modification-interface-vb/_static/image40.png)
**Figure 14**: The Discontinued CheckBoxes Have Been Replaced by Radio Button Pairs ([Click to view full-size image](customizing-the-data-modification-interface-vb/_static/image42.png))
> [!NOTE]
> Since the `Discontinued` column in the `Products` database cannot have `NULL` values, we do not need to worry about capturing `NULL` information in the interface. If, however, `Discontinued` column could contain `NULL` values we'd want to add a third radio button to the list with its `Value` set to an empty string (`Value=""`), just like with the category and supplier DropDownLists.
## Summary
While the BoundField and CheckBoxField automatically render read-only, editing, and inserting interfaces, they lack the ability for customization. Often, though, we'll need to customize the editing or inserting interface, perhaps adding validation controls (as we saw in the preceding tutorial) or by customizing the data collection user interface (as we saw in this tutorial). Customizing the interface with a TemplateField can be summed up in the following steps:
1. Add a TemplateField or convert an existing BoundField or CheckBoxField into a TemplateField
2. Augment the interface as needed
3. Bind the appropriate data fields to the newly added Web controls using two-way databinding
In addition to using the built-in ASP.NET Web controls, you can also customize the templates of a TemplateField with custom, compiled server controls and User Controls.
Happy Programming!
## About the Author
[Scott Mitchell](http://www.4guysfromrolla.com/ScottMitchell.shtml), author of seven ASP/ASP.NET books and founder of [4GuysFromRolla.com](http://www.4guysfromrolla.com), has been working with Microsoft Web technologies since 1998. Scott works as an independent consultant, trainer, and writer. His latest book is [*Sams Teach Yourself ASP.NET 2.0 in 24 Hours*](https://www.amazon.com/exec/obidos/ASIN/0672327384/4guysfromrollaco). He can be reached at [mitchell@4GuysFromRolla.com.](mailto:mitchell@4GuysFromRolla.com) or via his blog, which can be found at [http://ScottOnWriting.NET](http://ScottOnWriting.NET).
> [!div class="step-by-step"]
> [Previous](adding-validation-controls-to-the-editing-and-inserting-interfaces-vb.md)
> [Next](implementing-optimistic-concurrency-vb.md)
|
Coronary Artery Disease and Diabetes Mellitus.
Diabetes mellitus (DM) is a major risk factor for cardiovascular disease. Near-normal glycemic control does not reduce cardiovascular events. For many patients with 1- or 2-vessel coronary artery disease, there is little benefit from any revascularization procedure over optimal medical therapy. For multivessel coronary disease, randomized trials demonstrated the superiority of coronary artery bypass grafting over multivessel percutaneous coronary intervention in patients with treated DM. However, selection of the optimal myocardial revascularization strategy requires a multidisciplinary team approach ('heart team'). This review summarizes the current evidence regarding the effectiveness of various medical therapies and revascularization strategies in patients with DM. |
[Serum levels of cytokines as a measure of response to stress after various types of elective gallbladder surgery].
The authors investigated the cytokine levels in patients after laparoscopic cholecystectomy (LCHE), conventional open cholecystectomy (OCHE) and complicated open cholecystectomy (KOMPL) in order to assess whether there is a relationship between cytokine levels and the general reaction of the organism, the type and extent of the operation. They did not find an increase of IL-1 or IL-2 levels in any of the patient groups. The IL-6 concentration was slightly raised only in three patients of the OCHE group three hours after surgery and this rise persisted for 24 hours. In the KOMPL group there was a more marked rise of IL-6 in 9 patients within 3 hours after surgery, persisting in 6 patients for 24 hours and in 2 patients for 48 hours. The TNF values were similar; in group OCHE they were slightly elevated in 2 patients 24 hours after operation. In the KOMPL group these values were elevated in 5 patients for 3 hours after surgery and this increase persisted in 2 for 24 hours after surgery. Based on the investigation of cytokine levels, which is a recent indicator for evaluating the reaction of the organism to stress, conclude that laparoscopic cholecystectomy is a minimal stress for the patient and is associated with a zero defence reaction of the organism, if evaluated according to serum cytokine concentrations. |
/**********************************************************************
Freeciv - Copyright (C) 2010 - The Freeciv Team
This program is free software; you can redistribute it and/or modify
it under the terms of the GNU General Public License as published by
the Free Software Foundation; either version 2, or (at your option)
any later version.
This program is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
GNU General Public License for more details.
***********************************************************************/
/****************************************************************************
Map images:
* Basic functions:
mapimg_init() Initialise the map images.
mapimg_reset() Reset the map images.
mapimg_free() Free all memory needed for map images.
mapimg_count() Return the number of map image definitions.
mapimg_error() Return the last error message.
mapimg_help() Return a help text.
* Advanced functions:
mapimg_define() Define a new map image.
mapimg_delete() Delete a map image definition.
mapimg_show() Show the map image definition.
mapimg_id2str() Convert the map image definition to a string. Usefull
to save the definitions.
mapimg_create() ...
mapimg_colortest() ...
These functions return TRUE on success and FALSE on error. In the later
case the error message is available with mapimg_error().
* ...
mapimg_isvalid() Check if the map image is valid. This is only
possible after the game is started or a savegame was
loaded. For a valid map image definition the
definition is returned. The struct is freed by
mapimg_reset() or mapimg_free().
mapimg_get_format_list() ...
mapimg_get_format_default() ...
****************************************************************************/
#ifndef FC__MAPIMG_H
#define FC__MAPIMG_H
#ifdef __cplusplus
extern "C" {
#endif /* __cplusplus */
/* utility */
#include "support.h"
/* common */
#include "tile.h"
#define MAX_LEN_MAPDEF 256
/* map image layers */
#define SPECENUM_NAME mapimg_layer
#define SPECENUM_VALUE0 MAPIMG_LAYER_AREA
#define SPECENUM_VALUE0NAME "a"
#define SPECENUM_VALUE1 MAPIMG_LAYER_BORDERS
#define SPECENUM_VALUE1NAME "b"
#define SPECENUM_VALUE2 MAPIMG_LAYER_CITIES
#define SPECENUM_VALUE2NAME "c"
#define SPECENUM_VALUE3 MAPIMG_LAYER_FOGOFWAR
#define SPECENUM_VALUE3NAME "f"
#define SPECENUM_VALUE4 MAPIMG_LAYER_KNOWLEDGE
#define SPECENUM_VALUE4NAME "k"
#define SPECENUM_VALUE5 MAPIMG_LAYER_TERRAIN
#define SPECENUM_VALUE5NAME "t"
#define SPECENUM_VALUE6 MAPIMG_LAYER_UNITS
#define SPECENUM_VALUE6NAME "u"
/* used a possible dummy value */
#define SPECENUM_COUNT MAPIMG_LAYER_COUNT
#define SPECENUM_COUNTNAME "-"
#include "specenum_gen.h"
/* If you change this enum, the default values for the client have to be
* adapted (see options.c). */
typedef enum known_type
(*mapimg_tile_known_func)(const struct tile *ptile,
const struct player *pplayer,
bool knowledge);
typedef struct terrain
*(*mapimg_tile_terrain_func)(const struct tile *ptile,
const struct player *pplayer,
bool knowledge);
typedef struct player
*(*mapimg_tile_player_func)(const struct tile *ptile,
const struct player *pplayer,
bool knowledge);
typedef int (*mapimg_plrcolor_count_func)(void);
typedef struct rgbcolor *(*mapimg_plrcolor_get_func)(int);
/* map definition */
struct mapdef;
void mapimg_init(mapimg_tile_known_func mapimg_tile_known,
mapimg_tile_terrain_func mapimg_tile_terrain,
mapimg_tile_player_func mapimg_tile_owner,
mapimg_tile_player_func mapimg_tile_city,
mapimg_tile_player_func mapimg_tile_unit,
mapimg_plrcolor_count_func mapimg_plrcolor_count,
mapimg_plrcolor_get_func mapimg_plrcolor_get);
void mapimg_reset(void);
void mapimg_free(void);
int mapimg_count(void);
char *mapimg_help(const char *cmdname);
const char *mapimg_error(void);
bool mapimg_define(const char *maparg, bool check);
bool mapimg_delete(int id);
bool mapimg_show(int id, char *str, size_t str_len, bool detail);
bool mapimg_id2str(int id, char *str, size_t str_len);
bool mapimg_create(struct mapdef *pmapdef, bool force, const char *savename,
const char *path);
bool mapimg_colortest(const char *savename, const char *path);
struct mapdef *mapimg_isvalid(int id);
const struct strvec *mapimg_get_format_list(void);
const char *mapimg_get_format_default(void);
#ifdef __cplusplus
}
#endif /* __cplusplus */
#endif /* FC__MAPIMG_H */
|
Q:
Play Framework 2.1 - AngularJS routing - best solution?
I am working my way through the AngularJS tutorial. Angular uses it's own JS routing mechanism to allow for single page apps. A sample routing file for Angular looks like this:
angular.module('phonecat', []).
config(['$routeProvider', function($routeProvider) {
$routeProvider.
when('/phones', {templateUrl: '/partials/phone-list', controller: PhoneListCtrl}).
when('/phones/:phoneId', {templateUrl: 'partials/phone-detail', controller: PhoneDetailCtrl}).
otherwise({redirectTo: '/phones'});
}]);
I am trying to come up with a good place to store my partials (Angular specific HTML files). Ideally i WOULD like the ability to template them from within Play (i.e. have them as *.scala.html files). I can accomplish this using a a Play routes file like so:
GET /partials/phone_index controllers.Application.phone_index
I basically partials/ to a controller action like this:
def phone_index = Action {
Ok(views.html.partials.phone_index())
}
The solution I am looking for is a combination of two ideals:
I would have some sort of mapping that lets me visit any file under /partial/* and get back the partial file.
I would like the overriding a route to a specific partial so I CAN use a controller action to dynamically fill with data (rare).
Any ideas?
A:
When I was trying something similar I came to the conclusion that it's better to break it on 2 parts:
Use Play as a backend you interact with via Ajax calls
Store the Angular templates in Play public folder (something like /public/angular/) and use the default AngularJs way to map the templates
I know it doesn't sound great and really doesn't answer your question on how to do it, but trying to link both frameworks may be problematic due to the way templates and their urls are mapped in Angular, and the benefit will be very small as any change will imply a lot of work, thus removing the arguably main benefit of both Play and Angular, rapid development.
This also allows you to separate concerns better, which if your project grows may be important as you can just take the AngularJS code away as a standalone app connecting to a backend, and it will work fine.
You can see some sample code of what I said (based on the TODO tutorial of AngularJS) in this Github repository. I warn you, the code is not too nice, but should give you an idea and as a bonus shows you how to integrate Jasmine into Play, for AngularJS unit testing.
A:
The eventual seed (https://github.com/angyjoe/eventual) is yet another way to build a Play + AngularJS app. The code is a sweetheart and well-documented.
A:
This won't answer your question directly, but I found this to be the best way to build Play + Angular apps:
https://github.com/typesafehub/angular-seed-play
|
The current practice of securing two or more structural pieces together by one or more fasteners typically involves first clamping the pieces together with holes through the two pieces being aligned. Alternatively, the pieces can be clamped together and then holes can be formed through the pieces. A fastener, for example a rivet is then inserted through each of the holes with the rivet head positioned on one side of the structural pieces and the rivet tail projecting from the opposite side of the structural pieces. A bucking bar is typically manually positioned against the rivet tail while the rivet head is hammered by a rivet hammer. The force of the rivet hammer on the rivet head and the force of the bucking bar on the rivet tail causes the bucking bar to deform the rivet tail into a buck tail or shop head that secures the rivet in place in the rivet hole between the structural pieces and thereby rivets the structural pieces together.
Electromagnets have been employed in clamping two or more structural pieces together prior to their being secured together by fasteners. Current electromagnetic clamping technology typically employs an electromagnet as one clamping component and one or more steel plates as additional clamping components. The steel plate or plates have pluralities of holes that are positioned in the plates to correspond to fastener locations through the structural pieces. The steel plates are positioned on one side of the structural pieces and the electromagnet is positioned on the opposite side of the structural pieces. The electromagnet is then energized or activated, drawing the steel plates toward the electromagnet and clamping the structural pieces between the plates and the electromagnet. The holes through the steel plates enable fastener holes to be drilled through the clamped structural pieces and fasteners to be placed in the holes. Where the fasteners are rivets, a bucking bar is then manually inserted through the hole in the steel plate and against a tail of the rivet while the head of the rivet on the opposite side of the structural pieces is hammered by a rivet hammer, thereby forming the rivet tail into a shop head and securing the structural pieces together. This basic process is also performed when installing HI-LOK type fasteners or lock bolts in structural pieces.
This prior art electromagnetic clamping technology has the disadvantages of the need to position the steel plate or plates against one side of the structural pieces to be fastened together prior to the fastening process. It is often necessary to secure the steel plates against the one side of the structural pieces, for example by screws or clamps prior to fasteners being installed. The positioning and securing of the steel plates to the structural pieces to be joined is a time consuming process and an ergonomically demanding process, especially when hundreds of these types of steel plates have to be preinstalled in order to fasten together structural pieces of a large structure, such as an aircraft. |
After around a year of use a thin layer of plastic started peeling off the black cardboard material. I never traveled with, or kept the palettes in a high humidity area such as a bathroom. When I contacted the manufacturer they seemed aware that this was an issue and the best they could do was to offer me a 20% discount and encouraged me to repurchase more palettes. Needless to say I wish I never depotted all my eyeshadows to have them in a palette that didn't end up lasting. |
CEOs we can't believe are still CEOs
March 5, 2014 |Julie Balise, SFGate
Some leaders get you out of a crisis, some bury you deeper. Count these executives among the latter.
AP Photo/Kyodo News, File
Mark Karpeles, Mt. Gox
1of11
Some leaders get you out of a crisis, some bury you deeper. Count these executives among the latter.
Mt. Gox CEO Mark Karpeles is quickly becoming the face of cryptocurrency concerns. He took over the Tokyo-based exchange in 2011 and oversaw it as bitcoin's value surged. Then something went wrong. The site filed for bankruptcy protection in February 2014. Karpeles said that 750,000 bitcoins deposited by users and 100,000 bitcoins belonging to the exchange disappeared, for a loss of about $425 million. Karpeles has blamed theft through hacking for the loss. Mt. Gox is now the target of a class-action lawsuit filed in a U.S. federal court claiming that users were not sufficiently protected.
Karpeles is one of many chief executives in the spotlight -- for all the worst reasons -- recently. Let's take a look at some other CEOs who have held their grips on the top.
AP Photo/Kyodo News, File
Mark Karpeles, Mt. Gox
1of11
Some leaders get you out of a crisis, some bury you deeper. Count these executives among the latter.
Mt. Gox CEO Mark Karpeles is quickly becoming the face of cryptocurrency concerns. He took over the Tokyo-based exchange in 2011 and oversaw it as bitcoin's value surged. Then something went wrong. The site filed for bankruptcy protection in February 2014. Karpeles said that 750,000 bitcoins deposited by users and 100,000 bitcoins belonging to the exchange disappeared, for a loss of about $425 million. Karpeles has blamed theft through hacking for the loss. Mt. Gox is now the target of a class-action lawsuit filed in a U.S. federal court claiming that users were not sufficiently protected.
Karpeles is one of many chief executives in the spotlight -- for all the worst reasons -- recently. Let's take a look at some other CEOs who have held their grips on the top. |
Comparison of cord blood transplantation with unrelated bone marrow transplantation in patients older than fifty years.
We retrospectively compared the transplantation outcomes for patients 50 years or older who received umbilical cord blood transplantation (UCBT) with those who received unrelated bone marrow transplantation (UBMT) for hematologic malignancies. A total of 1377 patients who underwent transplantation between 2000 and 2009 were included: 516 received 8/8 HLA allele-matched UBMT, 295 received 7/8 HLA allele-matched UBMT, and 566 received 4/6 to 6/6 HLA-matched UCBT. Adjusted overall survival (OS) was significantly lower in those who underwent UCBT than those who underwent 8/8 HLA-matched UBMT but was similar to that of 7/8 HLA-matched UBMT (the 2-year OS after 8/8 HLA-matched UBMT, 7/8 HLA-matched UBMT, and UCBT were 49% [95% confidence interval (CI), 45% to 55%], 38% [95% CI, 32% to 45%], and 39% [95% CI, 34% to 43%], respectively). However, adjusted OS was similar between 8/8 HLA-matched UBMT and UCBT receiving ≥.84 × 10(5) CD34(+) cells/kg among those with acute myeloid leukemia and those with acute lymphoblastic leukemia (the 2-year OS was 49% [95% CI, 43% to 55%], and 49% [95% CI, 41% to 58%], respectively). These data suggest that UCB is a reasonable alternative donor/stem cell source for elderly patients with similar outcomes compared with UBM from 8/8 HLA-matched unrelated donors when the graft containing ≥.84 × 10(5) CD34(+) cells/kg is available. |
Lane Johnson Getting ‘More Pissed Off Each Day’
The Eagles' right tackle still doesn't know when he'll hear about his potential suspension.
Sign up to get the best of Philly, every day.
Two weeks after the news leaked about Lane Johnson’s impending suspension, the Eagles’ right tackle still faces much uncertainty. He doesn’t know when he’ll receive the results of his B sample, when he may potentially be banned for 10 games and when he could appeal if he suspended.
He’s been given no timeline, and he’s unsure of how long the appeals process would take. That uncertain future, Johnson says, is what’s irritated him the most over the past few weeks.
“I just get a little bit more pissed off each day, to be honest. That’s where I’m at right now,” Johnson said. “It’s just been frustrating. You come in, want to have a good season and shit hits the fan again. Got to go through this stuff all over again. It’s just been more mentally frustrating, hard to concentrate on what you need to concentrate on.”
Johnson noted how he’s “pretty much stuck in cement” until this process is resolved. Because he hasn’t heard back from the NFL yet, he’s unsure what grounds he would appeal on.
“Ever since it started, I told them I had nothing to hide,” Johnson said. “I can’t believe I’m in this situation again. From that standpoint, I am sorry. But, you know, always playing by the rules — I did everything I thought I should. Obviously, there’s some more stuff that probably could’ve been done. From now on, it’s safe to say I ain’t taking nothing.
“All you need is food and water. There is stuff as far as recovery wise, but I’m not going to take the chance. Happens again, you’re out two years, so that’s a big risk. I’m not trying to go through all of this all over again.”
Johnson added that he won’t take protein powder or vitamins, but he also pointed to how unregulated the supplements market is.
“I just want y’all to go look throughout the locker room on your way out and just look at all the stuff that’s in people’s lockers, and just know that none of that stuff is approved,” Johnson said. “As far as any help, I think there should be a necessary step taken by the NFL [and the] NFLPA to be able to make sure this don’t happen just for the future to help athletes out, so you know what’s safe, you know what’s not safe.” |
Q:
How to run, test and handle low battery popup
I'm currently developing application on Android Studio. My problem is when application is working and shows low battery popup everything get freeze. I have to minimalize and maximalize back application. I guess there is something wrong with onWindowFocusChanged, onPause or onResume methods.
Anyway, I want to know how to simulate on emulator low battery popup. I don't want to wait one hour for my battery get low. What should i do?
A:
In the three dots button you have controls to change battery status in the emulator:
|
Q:
multiple dynamically created buttons, on click use the same function but take dynamically sourced paramaters
I am trying to dynamically create a table, in each row of the table I want there to be a button that will geolocate the address on that line only. the code below works if there is only one row returned, if there are multiple rows it doesn't
I would really appreciate some help as this is driving me nuts, thanking you all in advance!
data = $(this).serialize() + "&" + $.param(data);
$.ajax({
type: "POST",
dataType: "json",
url: "php/censusdata3.php",
data: data
}).success(function(data)
{
var tr, td;
var str;
$.each(data,function(index,point)
{
tbody = document.getElementById("tbody");
str=point.Readable;
tr = tbody.insertRow(tbody.rows.length);
td = tr.insertCell(tr.cells.length);
//td.setAttribute("align", "center");
td.innerHTML = point.Forename;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Surname;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Age;
td = tr.insertCell(tr.cells.length);
td.innerHTML = '<input id="location-address" type="text" class="form-control" value="'+str+'" required/><button class="btn btn-primary btn-sm" id="map-address-btn"><span>Find Location</span></button>';
$(document).ready(function() {
// get map button functionality
$("#map-address-btn").click(function(event){
event.preventDefault();
var address = $("#location-address").val(); // grab the address from the input field
codeAddress(address); // geocode the address
});
});
});
});
updated code:
}).success(function(data)
{
var tr, td;
var str;
$.each(data,function(index,point)
{
tbody = document.getElementById("tbody");
str=point.Readable;
tr = tbody.insertRow(tbody.rows.length);
td = tr.insertCell(tr.cells.length);
//td.setAttribute("align", "center");
td.innerHTML = point.Forename;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Surname;
td = tr.insertCell(tr.cells.length);// I think the i 's are what is breakingit!!
td.innerHTML = point.Age;
td = tr.insertCell(tr.cells.length);
td.innerHTML = '<input class="address" type="text" class="form-control" value="'+str+'" required/><button class="btn btn-primary btn-sm" id="map-address-btn"><span>Find Location</span></button>';
$(document).ready(function() {
$("table tbody").on("click", "button", function () { //listen for <button> clicks on your table
var btn = $(this); //reference to the clicked button
var tableRow = btn.closest("tr"); //find the table row the button is in.
var address = tableRow.find("input.address").val(); //find the input field in that row that you want
console.log(address ); display the value
});
// // get map button functionality
// $("#map-address-btn").click(function(event){
// event.preventDefault();
// var address = $("#location-address").val(); // grab the address from the input field
// codeAddress(address); // geocode the address
// });
});
});
The latest iteration with the changes made:
<script type="text/javascript">
$("document").ready(function(){
$(".js-ajax-php-json").submit( function(e){
e.preventDefault();
var data = {
"action": "test"
};
data = $(this).serialize() + "&" + $.param(data);
$.ajax({
type: "POST",
dataType: "json",
url: "php/censusdata3.php",
data: data
}).success(function(data)
{
var tr, td;
var str;
$.each(data,function(index,point)
{
tbody = document.getElementById("tbody");
str=point.Readable;
tr = tbody.insertRow(tbody.rows.length);
td = tr.insertCell(tr.cells.length);
//td.setAttribute("align", "center");
td.innerHTML = point.Forename;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Surname;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Age;
td = tr.insertCell(tr.cells.length);
td.innerHTML = '<input type="text" class="form-control location-address" value="'+str+'" required/><button class="btn btn-primary btn-sm map-address-btn"><span>Find Location</span></button>';
});
});
return false;
});
});
});
</script>
and this lad is down in the bottom of a script:
$(document).ready(function() {
// get map button functionality
$(".map-address-btn").click(function(event){
event.preventDefault();
var address = $(this).parent().find('.map-address-btn').val(); // grab the address from the input field
codeAddress(address); // geocode the address
});
});
Now the table won't populate at all, again thanks for all of your help.
A:
Like i said in the comment, it's because of your Ids, they must be unique. Use class instead:
data = $(this).serialize() + "&" + $.param(data);
$.ajax({
type: "POST",
dataType: "json",
url: "php/censusdata3.php",
data: data
}).success(function(data)
{
var tr, td;
var str;
$.each(data,function(index,point)
{
tbody = document.getElementById("tbody");
str=point.Readable;
tr = tbody.insertRow(tbody.rows.length);
td = tr.insertCell(tr.cells.length);
//td.setAttribute("align", "center");
td.innerHTML = point.Forename;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Surname;
td = tr.insertCell(tr.cells.length);
td.innerHTML = point.Age;
td = tr.insertCell(tr.cells.length);
td.innerHTML = '<input type="text" class="form-control location-address" value="'+str+'" required/><button class="btn btn-primary btn-sm map-address-btn"><span>Find Location</span></button>';
});
});
$('#tbody').off("click",".map-adress-btn");
// get map button functionality
$('#tbody').on("click",".map-address-btn", function(event){
var address = $(this).parent().find('.location-address').val(); // grab the address from the input field
codeAddress(address); // geocode the address
});
working fiddle:
http://jsfiddle.net/Leqkqkx0/1
|
1977–78 Kentucky Wildcats men's basketball team
The 1977–78 Kentucky Wildcats men's basketball team were coached by Joe B. Hall. The team finished the season with a 30–2 record and SEC Championship and won the 1978 NCAA Championship over the Duke Blue Devils, 94–88. Hall remarked before the title game that "This season was without celebration for us."
Season Summary
Those who witnessed it call Jack Givens' 41 point game against Duke in the 1978 NCAA championship game one of the finest performances in the game's history. Givens made 18-of-27 shots in leading Kentucky to its fifth national championship and first in 20 years. This team also had a pair of bruising frontcourt players in Mike Phillips and Rick Robey and a great point guard in Kyle Macy. The Wildcats went on exhibition tour of Japan in June following the season's end.
Schedule
Statistics
Jack Givens (6-4, Sr, F) 18.1 ppg
Rick Robey (6-10, Sr, F) 14.4 ppg
Kyle Macy (6-3, So, G) 12.5 ppg
James Lee (6-5, Sr, F) 11.3 ppg
Mike Phillips (6-10, Sr, C) 10.2 ppg
Truman Claytor (6-1, Jr, G) 6.9 ppg
Awards and honors
Jack Givens, NCAA Men's MOP Award
Team players drafted into the NBA
References
Kentucky
Category:Kentucky Wildcats men's basketball seasons
Category:NCAA Division I Men's Basketball Tournament championship seasons
Category:NCAA Division I Men's Basketball Tournament Final Four seasons
Kentucky
Kentucky Wildcats
Kentucky Wildcats |
Q:
Segmentation fault after calling reset on unique_ptr
I'm getting a segmentation fault while calling reset on unique_ptr:
Node* tree::left_rotate(Node* node) {
Node* temp = node->right.get();
node->right.reset(temp->left.get());
temp->left.reset(node); // **Here is segmentation fault happens**
if(node->right.get()) {
node->right->parent = node;
}
temp->parent = node->parent;
if(node->parent) {
if(node == node->parent->left.get()) {
node->parent->left.reset(temp);
node->parent = node->parent->left.get();
} else if(node == node->parent->right.get()) {
node->parent->right.reset(temp);
node->parent = node->parent->right.get();
}
}
return temp;
}
Node has the following structure:
class Node {
public:
int data;
Node* parent;
std::unique_ptr<Node> left;
std::unique_ptr<Node> right;
public:
Node() : data(0) {
}
explicit Node(int d) : data(d),
parent(nullptr),
left(nullptr),
right(nullptr) {}
};
gdb reports:
Thread 1 received signal SIGSEGV, Segmentation fault. 0x00404ae5 in
std::unique_ptr >::~unique_ptr (
this=0xfeeefefa, __in_chrg=)
at C:/Program Files (x86)/mingw-w64/i686-8.1.0-posix-dwarf-rt_v6-rev0/mingw32/lib/gcc/i686-w64-mingw32/8.1.0/include/c++/bits/unique_ptr.h:273
273 if (__ptr != nullptr)
The report from one stack-frame upper:
#2 0x004047e8 in std::default_delete<Node>::operator() (this=0xfe1de4,
__ptr=0xfeeefeee)
at C:/Program Files (x86)/mingw-w64/i686-8.1.0-posix-dwarf-rt_v6-rev0/mingw32/lib/gcc/i686-w64-mingw32/8.1.0/include/c++/bits/unique_ptr.h:81
81 delete __ptr;
So it seems here is double deletion. How this issue can be solved? Maybe it worths to have a temp pointer as a shared_ptr?
A:
Node* temp = node->right.get();
temp is a raw pointer to the node's right node
node->right.reset(temp->left.get());
the node's right node is reset to the temp's left node, thus the original node's right node (to which temp points) gets deleted. That means that the temp raw pointer is now pointing to a deleted node.
temp->left.reset(node); // **Here is segmentation fault happens**
As temp is deleted, dereferencing it to get it's left node lead to bad things.
A quick thought, maybe use release() instead of get() at the first place to take over ownership of the node's right node ?
|
Persistently altered T cell immunity in high school students with the congenital rubella syndrome and profound hearing loss.
Because there are frequent progressive and autoimmune complications in children born with the congenital rubella syndrome, we evaluated immunoregulation in eight profoundly deaf adolescents with congenital rubella syndrome who lived in a state school. Serum antiviral antibodies, expressions of peripheral lymphocyte epitopes and serum soluble interleukin 2 receptor (IL-2R) content were compared with those of 16 classmates with profound hearing loss of unknown cause and of 24 age-matched, hearing students from this area. Both deaf groups showed activated but impaired T lymphocyte function compared with normals. Rubella virus alteration of T cell function was suggested in congenital rubella syndrome students by elevated numbers of both CD4+ helper and CD25+ IL-2R cells with unusually low released soluble IL-2R content. In contrast in deaf classmates elevated CD25+ and CD16+ natural killer cell groups and soluble IL-2R content with low numbers of CD4+ helper cells and CD4+ populations were of unknown etiology. Defective immunoregulation of the congenitally deaf to pathogens inherent in their environment may lead to autoimmune and other complications. |
Tehran, Iran (CNN) -- Iran is charging three American hikers with espionage, a Tehran prosecutor said Monday.
The three Americans have been detained since July 31 on charges of illegally crossing the border from Iraqi Kurdistan into Iran. Their family and friends say it was an innocent mistake.
The announcement of the charges comes only days after U.S. Secretary of State Hillary Clinton met privately with the families of Shane Bauer, Sarah Shourd and Josh Fattal, who were detained along the Iran-Iraq border at the end of July.
Tehran's prosecutor general, Abbas Ja'afari Dolatabadi, announced the charges in an interview with the official Iranian news agency IRNA.
"The charge against the three U.S. citizens who were arrested on the Iran-Iraq border is espionage. Investigation of their cases is in progress," he told IRNA, adding: "There will be more to say [about them] soon."
Clinton repeated Monday the Obama administration's call for the release of the hikers, requesting that the Iranian government "exercise compassion."
"We believe strongly that there is no evidence to support any charge whatsoever," said Clinton, speaking in Berlin.
"The allegation that our loved ones may have been engaged in espionage is untrue," said a statement from the hikers' families. "It is entirely at odds with the people Shane, Sarah and Josh are and with anything that Iran can have learned about them since they were detained."
White House spokesman Robert Gibbs said Monday the three hikers are "innocent young people who should be released by the Iranian government."
He said the United States has not obtained confirmation of the charges through Swiss emissaries.
Dolatabadi also said a Danish journalism student who was arrested last week in Iran was still under investigation.
"A journalist must have an official permit from authorized officials," he told IRNA. "Therefore, the investigation will continue. We have also requested information from the Ministry of Culture and Islamic Guidance [which accredits foreign journalists] and after they respond to our inquiry we will make our decision."
Clinton on Thursday repeated a call to the Iran government to release the American hikers on humanitarian grounds. "As a mother my heart went out to all of them. I cannot imagine what it would feel like to know that your child was in prison for now 100 days with very little contact between you and them," she said.
"I told them that we are doing everything we possibly could to get Shane and Joshua and Sarah home. And we are exploring every angle. Obviously I would hope that the government of Iran would free them on humanitarian and compassionate basis and return them to their families," she said.
The United States, which has no diplomatic relations with Iran, has relied on Switzerland to appeal directly for the hikers' release. A Swiss diplomat has met twice with the Americans in their Iranian prison.
The most recent visit was on October 29, the hikers' families said the following day.
The 40-minute visit took place at Evin Prison in Tehran, where Bauer, 27, Shourd, 31, and Fattal, 27, are being held.
"We were informed via the State Department that Shane, Sarah and Josh are in good physical shape and we're obviously happy they received another visit," the families said in a written statement. "Today marks exactly three months since our children were detained and we urge the Iranian authorities to let our children speak to us directly. Every time our telephones ring, we hope they it is them calling to tell us they've been released."
The Swiss diplomats took clothes and other supplies, including books and writing papers, to the Americans, the statement said.
State Department spokesman Ian Kelly told CNN that the Swiss ambassador was granted the second consular visit after several requests.
A senior State Department official told CNN that it was reported the three seemed to be nervous and scared, but also appeared to be in good physical and psychological health.
The only other consular access came when Swiss diplomats visited the hikers on September 29.
In an effort to obtain the hikers' release, their families in late October released video of the three -- shot two days before they were detained -- fooling around, the families said, like friends on vacation.
The video was shot by Shon Meckfessel, a friend who accompanied them on their Kurdistan trip. Meckfessel had planned to join them on their outing but stayed behind because he felt ill.
The videos show the relaxed travelers enjoying themselves as they take a break from exploring a town in Kurdistan.
"Yo it's hot. Yo it's hot. It's 'cause I'm in Iraq. Someone get me a fan. Someone get me a fan. 'Cause I'm in Kurdistan," Fattal raps as he chuckles and points to the Iraqi landscape behind him.
The videos have been posted on YouTube and at www.freethehikers.org.
The Americans entered northern Iraq from Turkey on July 28 during a planned five-day hike. Bauer and Shourd had been living in Damascus, Syria; Fattal was visiting. They set out to hike in northern Iraq's Kurdistan region.
Meckfessel, who spoke with Bauer the morning of their hike, said his friends did not know they were near the border and made "a simple and regrettable mistake" by crossing into Iran. |
New insight into the molecular mechanisms of two-partner secretion.
Two-partner secretion (TPS) systems, which export large proteins to the surface and/or extracellular milieu of Gram-negative bacteria, are members of a large superfamily of protein translocation systems that are widely distributed in animals, plants and fungi, in addition to nearly all groups of Gram-negative bacteria. Recent intense research on TPS systems has provided new insight into the structure and topology of the outer membrane translocator proteins and the large exoproteins that they secrete, the interactions between them, and mechanisms for retention of some of the secreted proteins on the bacterial surface. Evidence for secretion-dependent folding of mature exoproteins has also been obtained. Together, these findings provide a deeper understanding of the molecular mechanisms underlying these simple but elegant secretion systems. |
Follow Us:
Monthly Archives: October 2011
Share this:
SNOOOOOOOOOOOOW!!! NYC is not Oakland, Mayor Bloomberg explained, yet the NYPD pulled the plug on Occupy Wall Street protestors, confiscating about a dozen gasoline cans and six generators from Zuccotti Park. Another NPR freelancer was fired for participating in the Occupy movement. Sen. Kirsten Gillibrand plans to introduce a bill barring federally-funded foster care and More »
Share this:
Seems like winter, from a political standpoint, is officially here: Gov. Cuomo has ordered state agencies to prepare for a storm that is forecasted to hit parts of New York State this weekend, particularly from the lower Hudson Valley to the Capital Re… More »
Share this:
Not to be caught unawares by the snow, Gov. Cuomo has just activated the state’s emergency apparatus in preparation for what could be some heavy upstate snow this weekend. Here are the details: Governor Andrew M. Cuomo today ordered state agencies to prepare for a winter storm that is forecasted to bring heavy rain, wet […] More »
Share this:
New evidence bolsters the FBI’s longstanding suspicion that radical American imam Anwar al-Awlaki supported the 9/11 attacks.
Our Joseph Straw reports:
Rep. Pete King (R-L.I.) said that in 2001 Daoud Chehazeh, a Syrian living in the U.S. and a fake d… More »
Share this:
Accepting an award in Manhattan last night from a major gay-rights group, Gov. Andrew Cuomo said the successful push for same-sex marriage in New York “achieved historic social progress” that is “resonating on so many levels.” At the Empire State Pride Agenda’s annual gala, Cuomo spoke about the national significance of the New York law, [...] More »
Share this:
They’ve been calling for a millionaire’s tax, decrying the cruel new economy and are scheduled Friday afternoon for an anti-hydrofracking demonstration at City Hall but participants of the Occupy Albany movement are planning something of a Fun Day on Saturday, despite some dire weather forecasts. Starting at 10 am, occupiers will have “facilitation training” as […] More »
Share this:
A group of Staten Island lawmakers — from both parties — have sent the below letter to New Jersey Gov. Chris Christie, urging him to visit and consider the impact of the bi-state decision to raise Port Authority tolls.
“The impact to your state wil… More »
Share this:
Here’s Gov. Andrew Cuomo’s full speech at the Empire State Pride Agenda gala last night. Much is being made of the national scope of his remarks about same-sex marriage, particularly since Cuomo has been very careful up until now NOT to make remarks that could be parsed to be an expression of his desire to More »
Share this:
Joel Tyner, the Duchess County legislator and self-described progressive Democrat running for Rep. Chris Gibson’s U.S. House seat next November, was in Washington earlier this week to meet with top Democrats at a gathering of more than 100 candidates hosted by the Democratic Congressional Campaign Committee.
More »
Share this:
The new Aqueduct racino opened today, and the operators say they expect long lines of gamblers looking for short odds.
Our Sandoval and Connor report:
“There’s an old tradition that folks who game think their odds are better on opening day,” said St… More »
Share this:
Faced with questions about his campaign finances, City Comptroller John Liu is calling in former state Attorney General Robert Abrams to conduct an independent review.
Abrams, now a partner at Stroock & Stroock & Lavan, is expected to be completed within 60 days, Liu’s office said.
“I …
Share this:
If you were planning to dress up as Marie Antoinette or Louis XVI for Halloween anyway, Jonathan Tasini (remember him?) is urging you to break out the costume early.
Just saw on Facebook that Tasini’s sending out invites for a Sunday “Occupy Gracie” p… More »
Share this:
ICYMI: Former GOP US Senate hopeful David Malpass told me on CapTon last night that the bloom is off the rose for him when it comes to Gov. Andrew Cuomo, whose performance the economist and ex-Reagan administration policy advisor once praised. Malpass said he was very impressed with Cuomo last spring – about the time More »
Share this:
A former state Department of Environmental Conservation employee was charged today with spending more than 500 work hours on sex chat lines and incurring more than $20,000 in improper phone charges to the state, Inspector General Ellen Biben announced. Edward Reilly, 52, of Delmar, Albany County, worked for the state 28 years and resigned Aug. [...] More »
Share this:
Sen. Kirsten Gillibrand announced Friday that she would introduce a bill barring federally-funded foster care and child adoption agencies from discriminating against potential adoptive parents because of their sexual orientations or gender identities. More »
Grafmil: Raise…expand…doubl e…increase…expand. Andy’s way of decreasing the size and...
Archives
About Capitol Confidential
Capitol Confidential gathers the best coverage of New York politics and puts it all together. Each section - Capitol, The State Worker, New York on the Potomac, and Voices - represents a unique facet of the political scene. The Capitol section features coverage from the Times Union Capitol bureau. The State Worker is dedicated to state worker issues. New York on the Potomac offers news of interest to New Yorkers from Washington. And Voices features the best of everything else, pointing you to columnists and bloggers from across the Web. |
The control of adult parasitic nematodes of cattle with morantel tartrate.
The anthelmintic efficacy of morantel tartrate at 5mg/kg bodymass was investigated in three separate controlled trials comprising 68 calves. High anthelmintic activity was established against adult Haemonchus placei, Ostertagia ostertagi, Cooperia spp. (C.pertinata and C. punctata), Bunostomum phlebotomum and Oesophagostomum radiatum. |
(Heidi Gutman / Walt Disney Television / Getty Images)
The Republicans have been faced with an electoral problem since the 1990s: most Americans prefer Democratic policies over Republican policies. The reasoning is simple; Republican policies benefit the old, white, and wealthy — a subset of the American electorate that continues to decline in population. Absent of a policy agenda for the average American (multicultural, younger, working class), Republicans can’t win elections on policy. Their only way to appeal to a somewhat broader electorate is to hurl personal insults at their Democratic opponents.
Bill Clinton, a Democrat with a massively popular agenda, was attacked as a “womanizer.” John Kerry was attacked as a “traitor.” Barack Obama — “Kenyan Muslim.” Hillary Clinton — “corrupt murderer.” Now Joe Biden has dementia. To be clear: Biden doesn’t have dementia; he’s been a gaffe machine since the ’70s and many of his verbal blunders are a result of his stutter. If our political debates were about policy, Republicans would be in deep trouble. They drive bad faith narratives about Democratic candidates early and hammer it down hard so the attacks stick to them. Then, if all goes as planned, policies become irrelevant. The midterms are a great case study in “agenda vs. agenda” competition. Without a one singular candidate to personally attack, the Democrats had to compete with the Republicans on issues — and the Democratic Party blew the Republicans out of the water in historical numbers.
If we weren’t talking about dementia and mental fitness, we’d be talking about Joe Biden’s agenda vs Trump’s disastrous, scandal-ridden first term in office. That conversation would be horrible for the Republicans. They can’t openly defend the fact that Trump has been in charge of our messy immigration system for 3 years and he’s only focused on a nonexistent wall. Mr. “Tough on Immigration” staffs undocumented immigrants on his golf courses, resorts, and real estate projects. They don’t want you to know that his tax cuts exploded the national deficit and had to be offset by cutting funding to Medicare and Social Security for the elderly. Or that he’s allowed corporations to pollute our air, water, and food in exchange for campaign contributions. He talks tough on China, but his retail products are made there. He launched (and lost) an incompetent trade war that cost American farmers and consumers billions. When he tried to subsidize the farmers who lost money, it ended up in the hands of major agriculture corporations instead of family farms. The money for the bailed was borrowed from — you guessed it — China. Republicans can’t survive that narrative…so they’ve made the conversation about dementia.
Republicans aren't alone, however. Many democratic socialists on Twitter have joined the right wing in attacking Biden on phony dementia claims. Although their intentions with the attacks were slightly different, they are still serving the interests of the Republican Party by spreading the narrative. The point is this: Joe Biden has a stutter and a long history of verbal blunders, not dementia. Republicans don’t have a policy agenda able to compete with the popularity of Joe Biden’s, so they have resorted to their usual strategy of attacking the candidate personally.
Don’t fall for it. |
A gaggle of Elsas were stuck outside on Sunday, their blue skirts bundled under parkas and their patience tested, as they waited to be allowed in to see their princess hero.
They and other kids who dressed up to see their favourite characters skate during a Disney on Ice show at the Canadian Tire Centre Sunday morning were left waiting outside as Ottawa Fire Services dealt with a natural gas leak.
Many of the children waiting to get into the Canadian Tire Centre were dressed up. (Chloe Fedio/CBC)
Ottawa firefighters were called to the stadium just after 8:15 a.m. after someone reported an odour. They weren't able to locate the source so they called in the hazmat team.
People waiting for the 11 a.m. Disney on Ice show said they were told to wait in their cars.
The Canadian Tire Centre tweeted at 10:55 a.m. that crews located the problematic piece of equipment and shut it off. The crowds were allowed back in and the show was only delayed by 30 minutes.
Ottawa fire said no injuries have been reported. |
What does that mean? If your name is Keith Richards then you could try to get the .KeithRichards or .Guitar domain name. Well, you could if you’re the real Keith Richards and had a few extra bucks sitting around. It seems that applying for domain names isn’t cheap.
That’s one reason that Icann Chairman Peter Dengate Thrush figures there won’t be too many regular folks lining up for domain names under the new rules.
Here’s what he said on a conference call:
We don’t expect there to be thousands of applications. First of all, the cost is going to be at least $100,000. But also to be a successful applicant for a new top level domain, you’re going to have to show that you’ve got the capacity to run an Internet registry, which may eventually have to hold millions of domain names. So you’re going to have to be a reasonably serious business — in most cases — or a community of businesses to put forward an application.
So where will all the applications come from?
We’re hoping for a broad range, and expecting a broad range of applicants. We’re expecting indigenous communities to be interested in protecting aspects of their indigenous language and culture. We’re expecting businesses to come forward. One of the board members today in this discussion refered to the likelihood of there being applications for vanity names. You may see .smith, for example, so all the Smiths of the world would have a place. We’ve been threatened that the Irish will get behind a Dennis Jennings top level domain.
We expect to see things such as .perfume and .wine and .silk and all sorts of commodity names coming forward, which will then be taken up by the people who deal in those particular goods and services in all sorts of inventive ways.
A few possible domain names immediately spring to mind, like .news or .sports or .blog or .sex (if they allow it). But it’ll be interesting to see what other names catch hold. |
As with most industries, of great importance to contact centers is that they are performing efficiently. In general terms, efficiency is considered a measure of the extent to which input is well used for an intended task or function (output). Contact centers make use of several inputs to service communications with various parties that include different technologies, systems, and communication channels, as well as personnel who handle communications such as agents, supervisors, and managers. Accordingly, many contact centers monitor several different metrics that provide a measure of how efficient the centers are operating and making use of these inputs. One of these metrics that is commonly monitored is average handle time.
Average handle time (AHT) measures the average duration of time spent by an agent on a communication with a party. For example, the AHT can measure the average duration of time spent by an agent on a phone call speaking with a party, placing the party on hold, if needed, and wrapping up the call once the agent has finished speaking with the party. While in another instance, the AHT can measure the average duration of time spent by an agent exchanging messages with a party on a chat session or via texts and wrapping up the chat session or texts once the agent has finished exchanging messages with the party.
The leading thought behind AHT is the lower an AHT a contact center can maintain, the more efficient the contact center is operating and the better the contact center is making use of its agent resources. However, a tradeoff can occur when the AHT drops to such a low level that not enough time is spent by agents on communications to adequately address the reasons for conducting the communications. For example, parties may be calling into a contact center for customer service and agents may be rushing to complete the calls with parties to maintain a low AHT. However, because the agents are rushing the calls, they may be failing to address the parties' issues for calling customer service. As a result, many of these parties may need to call into the contact center multiple times to resolve their issues and may become frustrated and disgruntled customers. Therefore, although the contact center appears to be running efficiently because of the low AHT, in actuality the contact center is not making good use of its agent resources because the agents are not adequately helping the parties who have called into customer service. Thus, many contact centers must be careful in how they incorporate and manage AHT in evaluating the efficiency of the centers.
One approach used by many contact centers in managing AHT is to monitor an agent's AHT for various communication channels with respect to a target handle time (THT). This THT is an ideal amount of time an agent should spend on a communication and helps a contact center to identify agents are consistently spending more time than should be needed to handle communications. For example, a particular contact center may monitor whether the AHT for calls taken by its agents is greater than to a THT of five minutes. Typically a contact center establishes the THT for a particular channel of communication based on passed history of communications handled for the channel. The contact center then uses the THT to evaluate the AHT for an agent resulting from A of the communications using that channel handled by the agent.
However, for any one communication, an agent may require more or less time than usual to handle the communication depending on the circumstances of the communication. For example, a customer service call involving a customer calling to check on the status of an order may typically require two minutes to handle while a customer service call involving a customer calling to return an item for refund may typically require ten minutes to handle. Thus, simply using a single THT for customer service calls can lead a contact center to improperly evaluate the efficiency of its agents and to misleading information if the agents are handling a high number of calls that typically require more time to handle than the THT. Furthermore, simply using a single THT can also limit the information that can be gleaned from monitoring handle times for agents. It is with respect to these considerations and others that the disclosure herein is presented. |
This must be the most minimalistic iphone case i have seen, it’s really just a band that you wrap around any iphone or other phone for that matter. It’s called the “just a loop” and goes for 10€ or 13$ for a four pack. My only worries, dosen’t it come of in your pocket? No actually it dosen’t: [source]
Q: Is the loop elastic?
A: No, the loop is made of woven nylon rope. It has around 5% of stretch, but that’s not what is normally considered elastic.
Q: Why is loop not elastic?
A: Because loops from elastic materials don’t stay on the phone firmly enough. They easily slide / roll off when you pull the phone out of a pocket.
These backlighting’s (similar to ambi light philips) are made for computer gamers, the idea is to light up the side of the screen with the color that is used the most on that side of the screen, you know. The ones selling it are madcatz, who are known to sell high quality gear at low prises, wich is awesome beacuse these lamps are based on an expensive technology called AMBX, Specs below. [source]
This is one of the best thing’s you can do with a 5.25″ space, it basically locks your usb connectors inside this box so that you can’t take them without a key.his device is installed in one of your 5.25” bays and gives you four USB ports. What it does is that there is a door that swings shut over the ports, and locking them in. There is just enough room for your cable to stick out, but not for the plug to come through Too bad i have a laptop, would be great for dreamhack, everybody hates getting their mouse stolen during a lan party.
At a hospital in New Hampshire an alert to all patient’s was sent out telling them that their medical info might be compromised as they had found unusual activity on one of their server’s. Funny thing is the unusual activity was a dedicated black ops server. Why would anyone go that far for a lag free game? It gets even weirder, they didn’t actually take ANY of the information already on the servers, now that’s true gaming spirit.
According to a spokesperson from the security company brought in by the medical group, the breach was discovered “after an admin noticed a loss of bandwidth.” It is believed that the hackers didn’t do anything other than abuse the servers to host Black Ops games, but a thorough investigation is being conducted
Why would you have a wireless graphics card? might you ask. Appearantely you can get white noise from having the computer to close to the screen, also if you need to have you’re computer further away this is a good solution. i think it’s kind off useless but it’s a cool idea, not very usefull untill we also have wireless electricity. Kfa2’s gtx 460 has 5 antennas that can send uncompressed 1080p signals (without latency?) up too 100feet away. |
Best fakes nude celebrity pics. Celebs Nude Pics Blog
Pokemon nude celeb
Pokemon nude celeb
Pokemon celebrities nude Battle competitions are now coming to "Pokemon Omega Ruby and Alpha Sapphire," the first one dubbed as "Battle of Hoenn – Online Competition." This battle competition is already accessible to all areas except for …
Pokemon naked celebritys Going into Pokémon Omega Ruby, I didn’t know if I would like it. Part of the reason I loved Pokémon X and Y was because it was a new generation. The games were set in a unique setting with new features and …
Pokemon celebrity nude Pokemon Omega Ruby & Alpha Sapphire are really fun, but only truly hit the next level when you dive deep into the mechanics and figure out how to best other people in the real world. To do this you’ll need the best team …
Pokemon nude celebs Players of the Pokémon Trading Card Game will soon have much more to collect as Pokémon TCG: XY: Primal Clash arrives. The latest expansion of the franchise will feature two new theme decks (Earth’s Pulse … |
Patient motivation for participating in clinical trials for depression: validation of the motivation for clinical trials inventory-depression.
The motivation for clinical trials inventory-depression (MCTI-D) was developed and evaluated for assessing motivations to participate in clinical trials on depression. Sixty-four participants completed the MCTI-D: 40 individuals expressing interest in participating in a randomized clinical trial (RCT); and 24 clinic patients receiving traditional care for depression. Content validity was supported by feedback derived from a panel of experts in depression research and respondents completing the measure. The motivation most frequently endorsed for participating in an RCT was the desire to help others and/or to further science. The potential stigma associated with seeing a psychiatrist was reported to have the least influence. Patients expressed a greater likelihood to participate in RCTs that involved psychotherapy than in experimental medication or placebo-controlled trials. Data from the MCTI-D may provide useful information for depression researchers to consider as possible influences on patients' decisions about whether or not they will participate. |
---
abstract: 'Nonequilibrium thermodynamics has shown its applicability in a wide variety of different situations pertaining to fields such as physics, chemistry, biology, and engineering. As successful as it is, however, its current formulation considers only systems close to equilibrium —those satisfying the so-called local equilibrium hypothesis. Here we show that diffusion processes that occur far away from equilibrium can be viewed as at local equilibrium in a space that includes all the relevant variables in addition to the spatial coordinate. In this way, nonequilibrium thermodynamics can be used and the difficulties and ambiguities associated with the lack of a thermodynamic description disappear. We analyze explicitly the inertial effects in diffusion and outline how the main ideas can be applied to other situations.'
author:
- 'J.M.G. Vilar$ ^{\dagger } $ and J.M. Rubí$ ^{\ddagger } $'
title: 'Thermodynamics “beyond” local equilibrium'
---
$ ^{\dagger } $Howard Hughes Medical Institute, Department of Molecular Biology, Princeton University, Princeton, New Jersey 08544, USA
$ ^{\ddagger } $Departament de Física Fonamental, Facultat de Física, Universitat de Barcelona, Diagonal 647, E-08028 Barcelona, Spain
Concepts of everyday use like energy, heat, and temperature have acquired a precise meaning after the development of thermodynamics. Thermodynamics provides us with the basis for understanding how heat and work are related and with the rules that the macroscopic properties of systems at equilibrium follow [\[]{}\[Reiss\][\]]{}. Outside equilibrium, most of those rules do not apply and the aforementioned quantities cannot unambiguously be defined. There is, however, a natural extension of thermodynamics to systems away from but close to equilibrium. It is based on the local equilibrium hypothesis, which assumes that a system can be viewed as formed of subsystems where the rules of equilibrium thermodynamics apply. Due to the usual disparity between macroscopic and microscopic scales, most systems fall into this category. This is the case of, for instance, the heat transfer from a flame, the flow through a pipe, or the electrical conduction in a wire. Nonequilibrium thermodynamics then extracts the general features, providing laws such as Fourier s, Fick s, and Ohm s, which do not depend on the detailed microscopic nature of the system [\[]{}\[DM\][\]]{}.
In contrast, there are other situations where the local equilibrium hypothesis does not hold. Many examples are present in the relaxation of glasses and polymers [\[]{}\[Glases\],\[Sitges\],\[Polymers\][\]]{}, in the flow of granular media [\[]{}\[Granular\][\]]{}, and in the dynamics of colloids [\[]{}\[Colloids\][\]]{}. The main characteristic of such systems is the similarity between microscopic and macroscopic scales, which usually involve internal variables with “slow” relaxation times. The so-called inertial effects in diffusion processes are perhaps the simplest and most illustrative example. In this case, the relaxation of the velocity distribution and changes in density occur at the same time scale. Therefore, local equilibrium is never reached. Here we show how nonequilibrium thermodynamics, as already established in the sixties [\[]{}\[P\],\[DM\][\]]{}, can be applied to this situation.
Nonequilibrium thermodynamics [\[]{}\[DM\][\]]{} assumes that the definition of entropy $ S $ can be extended to systems close to equilibrium. Therefore, entropy changes are given by the Gibbs equation: *$$\label{dibbsxnew}
TdS=dE+pdV-\mu dN\; ,$$* where the thermodynamic extensive variables are the internal energy $ E $, the volume $ V $, and the number of particles $ N $ of the system. The intensive variables (temperature $ T $, pressure $ p $, and chemical potential $ \mu $) are functions of the extensive variables. Local equilibrium means that the Gibbs equation holds for a small region of the space and for changes in the variables that are actually not infinitely slow. Therefore, the internal state of the system has to relax to equilibrium faster than variables change. In this way, all variables retain their usual meanings and the functional dependence between intensive and extensive variables is the same as in equilibrium.
Following this approach, nonequilibrium thermodynamics has been applied to study diffusion processes. The simplest case takes place in one dimension at constant temperature, internal energy, and volume. In this case, from Eq. (\[dibbsxnew\]) we obtain a Gibbs equation that depends only on the density and the spatial coordinate $ x $: *$$\label{gibbsx}
Tds(x)=-\mu (n,x)dn(x)\; .$$* Here $ s $ is the entropy per unit volume and $ n $ is the density. The chemical potential has the same form as in equilibrium. For instance, for an ideal system —formed of non-interacting particles— it is proportional to the logarithm of the density plus terms that do not depend on the density [\[]{}\[DM\][\]]{}. Notice that these terms can include thermodynamic variables such as temperature and internal energy, and also the spatial coordinate. In the case of non-interacting Brownian particles, its explicit expression is $$\mu =\frac{k_{B}T}{m}\ln n+C(x)\; ,$$ where $ m $ is the mass of the particles, $ k_{B} $ the Boltzmann constant, and $ C(x) $ a function that takes into account possible spatial inhomogeneities. The dynamics of $ n $ is restricted by the mass conservation law and therefore follows $$\frac{\partial n}{\partial t}=-\frac{\partial J}{\partial x}\; ,$$ with $ J $ being the flux of mass. An additional assumption of nonequilibrium thermodynamics is that this flux is given by$$J=-L\frac{\partial \mu }{\partial x}\; ,$$ where $ L $ is the phenomenological coefficient. From this, we obtain the usual diffusion equation $$\frac{\partial n}{\partial t}=\frac{\partial }{\partial x}\left( D\frac{\partial n}{\partial x}\right) \; ,$$ with the diffusion coefficient $ D\equiv L(\partial \mu /\partial n) $.
When inertial effects are present, changes in density occur at a time scale comparable with the time the velocities of the particles need to relax to equilibrium. The Gibbs equation as stated in Eq. (\[gibbsx\]) is no longer valid because local equilibrium is never reached. The entropy production depends also on the particular form of the velocity distribution. Both the spatial coordinate, $ x $, and velocity coordinate, $ v $, are needed to completely specify the state of the system. Therefore, we consider that local quantities are function of both coordinates. If the system is coupled to other degrees of freedom that relax faster than the velocity and density, a thermodynamic description is still possible. For instance, this is the case of Brownian particles, where the host fluid provides these thermodynamic degrees of freedom. Thus, we consider that diffusion takes place in a two-dimensional space ($ x,v $) instead of in the original one-dimensional space ($ x $). In this case, the chemical potential for an ideal system (e.g., non-interacting Brownian particles) is given by
$$\mu =\frac{k_{B}T}{m}\ln n(x,v)+C(x,v)\; ,$$
where $ C(x,v) $ is a function that does not depend on the density [\[]{}\[DM\][\]]{}. The form of this function can be obtained by realizing that at equilibrium the chemical potential is equal to an arbitrary constant. If we set this constant equal to zero, we obtain $$\mu =\frac{k_{B}T}{m}\ln n+\frac{1}{2}v^{2}\; .$$ Therefore, the Gibbs equation is now*$$Tds(x,v)=-\left( \frac{k_{B}T}{m}\ln n(x,v)+\frac{1}{2}v^{2}\right) dn(x,v)\; ,$$* The idea of applying the rules of thermodynamics in an internal space was already proposed by Prigogine and Mazur [\[]{}\[PM\][\]]{} and has been used in several situations [\[]{}\[DM\], \[CT\][\]]{}. In all of them, however, there was no thermodynamic coupling of these internal degrees of freedom with the spatial coordinate. This is precisely the situation we are considering here.
In the ($ x,v $)–space the mass conservation law is $$\label{cnxy}
\frac{\partial n}{\partial t}=-\frac{\partial J_{x}}{\partial x}-\frac{\partial J_{v}}{\partial v}\; .$$ Following the standard thermodynamic approach, the flux of mass is given by$$\label{jx}
J_{x}=-L_{xx}\frac{\partial \mu }{\partial x}-L_{xv}\frac{\partial \mu }{\partial v}\; ,$$ $$\label{jy}
J_{v}=-L_{vx}\frac{\partial \mu }{\partial x}-L_{vv}\frac{\partial \mu }{\partial v}\; ,$$ where $ L_{ij} $, with $ i,j=\{x,v\} $, are the phenomenological coefficients. There are some restrictions on the values $ L_{ij} $ can take. Since the system is at local equilibrium in the ($ x,v $)-space, Onsager relations imply that $ L_{xv}=-L_{vx} $. In addition, the flux of mass in real space, $ \tilde{J}_{x}(x)\equiv \int _{-\infty }^{\infty }v\, n(x,v)dv $, has to be recovered from the flux in the ($ x,v $)-space by contracting the velocity coordinate: $ \tilde{J}_{x}(x)=\int _{-\infty }^{\infty }J_{x}(x,v)dv $. Therefore,$$\int _{-\infty }^{\infty }v\, n\, dv=-\int _{-\infty }^{\infty }\left( L_{xx}\frac{k_{B}T}{m}\frac{1}{n}\frac{\partial n}{\partial x}+L_{xv}\frac{k_{B}T}{m}\frac{1}{n}\frac{\partial n}{\partial v}+L_{xv}v\right) dv\; .$$ Since $ n(x,v) $ can take any arbitrary form, the last equality holds if and only if $ L_{xx}=0 $ and $ L_{xv}=-n $. Thus, the only undetermined coefficient is $ L_{vv} $, which can depend explicitly on $ n $, $ x $, and $ v $.
Previous equations can be rewritten in a more familiar form by identifying the phenomenological coefficients with macroscopic quantities. In this way, with $ L_{vv}=n/\tau $, the fluxes read $$\label{flx}
J_{x}=\left( v+\frac{D}{\tau }\frac{\partial }{\partial v}\right) n\; ,$$ $$\label{flv}
J_{v}=-\left( \frac{D}{\tau }\frac{\partial }{\partial x}+\frac{v}{\tau }+\frac{D}{\tau ^{2}}\frac{\partial }{\partial v}\right) n\; ,$$ where $ D\equiv \frac{k_{B}T}{m}\tau $ and $ \tau $ are the diffusion coefficient and the velocity relaxation time, respectively. The equation for the density is given by$$\label{FP}
\frac{\partial n}{\partial t}=-\frac{\partial }{\partial x}vn+\frac{\partial }{\partial v}\left( \frac{v}{\tau }+\frac{D}{\tau ^{2}}\frac{\partial }{\partial v}\right) n\; .$$ This kinetic equation is equivalent to the Fokker-Planck equation for a Brownian particle with inertia since, in an ideal system, the density is proportional to the probability density; i.e. $ n(x,v)=mNP(x,v) $, where $ P(x,v) $ is the probability density for a particle to be at $ x $ with velocity $ v $, and $ N $ is the number of particles of the system. The resulting Fokker-Planck equation could have also been derived by following standard techniques of stochastic processes [\[]{}\[VK\][\]]{} or kinetic theory [\[]{}\[TC\][\]]{}, which are among the microscopic statistical theories for studying nonequilibrium phenomena.
The approach we have followed, however, explicitly illustrates how thermodynamic concepts can be transferred from equilibrium, through local equilibrium, to far from equilibrium situations. The condition of equilibrium is characterized by the absence of dissipative fluxes ($ J_{x}=0 $ and $ J_{v}=0 $). Therefore, from Eq. (\[flx\]) we obtain that the velocity distribution is Gaussian with variance proportional to the temperature. If deviations from equilibrium are small ($ J_{x}\neq 0 $ and $ J_{v}=0 $), the local equilibrium hypothesis holds. This is the domain of validity of Fick’s law, $$J_{x}=-D\frac{\partial n}{\partial x}\; ,$$ which is obtained directly from the equations for the fluxes. In this case, the distribution of velocities is still Gaussian but now centered at a non-zero average velocity and the variance of the distribution is related to the temperature in the same way as in equilibrium. Beyond local equilibrium ($ J_{x}\neq 0 $ and $ J_{v}\neq 0 $), the velocity distribution can take any arbitrary form, from which there is no clear way to assign a temperature. There is, however, a well defined temperature $ T $: that of local equilibrium in the ($ x,v $)–space.
In Fig. \[Fig:distributions\] we illustrate the concepts discussed previously. We show the velocity profiles obtained from Eq. (\[FP\]) for two representative situations. For fast relaxation of the velocity coordinate, the velocity distribution is Gaussian and centered slightly away from zero, in accordance with local equilibrium concepts. For slow relaxation, however, the velocity distribution loses its symmetry (and its Gaussian form). In this case, the temperature does not give directly the form of the distribution and one has to resort to local equilibrium in the ($ x,v $)–space to describe the system.
It is important to emphasize that the temperature $ T $ is the one that enters the total entropy changes and therefore the one related to the second principle of thermodynamics. Other definitions of temperature are possible though. To illustrate this point, let us compute the entropy production $ \sigma $. This quantity is obtained from local changes in entropy, which are given not only by the production but also by the flow: $$T\frac{\partial s}{\partial t}=-\mu \frac{\partial n}{\partial t}=T\left( \sigma -\frac{\partial J_{Sx}}{\partial x}-\frac{\partial J_{Sv}}{\partial v}\right) \; ,$$ where $ \left( J_{Sx},J_{Sv}\right) $ is the entropy flux. In our case, the expression for the entropy production is $$\label{enprod}
\sigma (x,v)=\frac{n(x,v)}{T\tau }\left( v+\frac{k_{B}T}{m}\frac{\partial \ln n(x,v)}{\partial v}\right) ^{2}\; .$$ Now, given a Gaussian velocity distribution $ n(x,v)=n_{0}(x)e^{-mv^{2}/2k_{B}\tilde{T}(x)} $, we can easily understand the meaning of the temperature $ \tilde{T}(x) $ defined through the variance of the distribution: it is the temperature at which the system would be at equilibrium ($ \sigma =0 $). The definition of an effective temperature as that giving zero entropy production can be extended to arbitrary velocity distributions. From Eq. (\[enprod\]), we obtain$$\frac{1}{\tilde{T}(x,v)}=-\frac{1}{vm}\left( k_{B}\frac{\partial \ln n(x,v)}{\partial v}\right) \; .$$ The temperature defined in this way is formally analogous to the equilibrium temperature since the right hand side term of the preceding equation can be rewritten as the derivative of an entropy with respect to an energy:$$\label{tempeff}
\frac{1}{\tilde{T}(x,v)}=\frac{\partial s_{c}(x,v)}{\partial e(v)}\; ,$$ where $ s_{c}(x,v)=-\frac{k_{B}}{m}\ln n(x,v) $ and $ e(v)=\frac{1}{2}v^{2} $. The term $ s_{c}(x,v) $ and $ e(v) $ can be viewed as the configurational entropy and the kinetic energy per unit of mass, respectively. In general, other definitions of effective temperature are possible. For instance, by considering $ e\left( v-\overline{v}(x)\right) $ instead of $ e(v) $ in Eq. (\[tempeff\]), the resulting temperature would be that of local equilibrium. In this case, however, this temperature does not give zero entropy production but just that of the macroscopic motion. This temperature is then the one at which, once the macroscopic motion is disregarded, the internal configuration of the system would be at equilibrium.
In general, since $ \tilde{T}(x,v) $ is not only a function of $ x $ but also of $ v $, given a point in space, there is no temperature at which the system would be at equilibrium; i.e. $ \tilde{T}(x,v)\neq \tilde{T}(x) $. If an effective temperature at a point $ x $ were defined, it would depend on the way the additional coordinate is eliminated. Thus, ambiguities in far from equilibrium quantities arise when considering a lower dimensional space than the one in which the process is actually occurring. This is to some extent similar to what happens with effective temperatures defined through fluctuation-dissipation theorems. In such a case, the effective temperature can depend on the scale of observation [\[]{}\[kurchan\][\]]{}. It is interesting to point out that all these effective temperatures, despite their possible analogies with the equilibrium temperature, do not have to follow the usual thermodynamic rules since the system is not actually at equilibrium at the temperature $ \tilde{T} $.
The idea of increasing the dimensionality of the space were diffusion takes place, so to include as many dimensions as non-equilibrated degrees of freedom the system has, can also be applied to other situations. In a general case, the additional degrees of freedom do not necessarily correspond to the velocity. For instance, let us consider a degree of freedom $ \Theta (x) $ that at local equilibrium enters the Gibbs equation in the following way:$$Tds(x)=-\mu \, dn(x)-B\, d\Theta (x)\; ,$$ where $ B\equiv B(n,\Theta ,T)=T(\partial s/\partial \Theta )_{n,T} $. In this case, one usually assumes that given $ T $ , $ n(x) $, and $ \Theta (x) $, the function $ B $ is completely determined through the equilibrium properties of the system. Far away from equilibrium, we would have to consider explicitly an additional coordinate $ \theta $, which is related to the degree of freedom by $ \Theta (x)=\int \theta \, n(x,\theta )d\theta $. The corresponding Gibbs equation$$Tds(x,\theta )=-\mu \, dn(x,\theta )$$ would have to take into account the dependence on the coordinate $ \theta $ through the chemical potential $ \mu $. Once the Gibbs equation has been obtained, the way to proceed would be analogous to the one we followed for the inertial effects. For instance, some systems with both translational and orientational degrees of freedom can be described by the chemical potential$$\mu =\frac{k_{B}T}{m}\ln \frac{n(x,\theta )}{f(\theta )}+U\cos \theta$$ where $ \theta $ is now an angular coordinate, $ U\cos \theta $ is the orientational energy, and $ f(\theta ) $ is a function accounting for the degeneracy of the orientational states (for rotation in three and two dimensions, $ f(\theta )=\sin \theta $ and $ f(\theta )=1, $ respectively) [\[]{}\[DM\][\]]{}. This type of systems include, among others, liquid crystals and suspensions of rod-like particles [\[]{}\[Polymers\][\]]{}, field-responsive suspensions [\[]{}\[jms\][\]]{}, and polarized systems [\[]{}\[DM\][\]]{}. At local equilibrium some instances of $ B $ and $ \Theta $ are then electric field and polarization; and magnetic field and magnetization. Beyond local equilibrium, by writing the $ (x,\theta ) $ counterpart of Eqs. (\[cnxy\]), (\[jx\]), and (\[jy\]), one can obtain a kinetic equation that describes the behavior of the system. This equation includes as particular cases the Fokker-Plank equations obtained for those systems by means of microscopic theories [\[]{}\[Polymers\],\[BP\][\]]{}.
Along this paper, we have been assuming ideality and locality. The condition of ideality is that the system consists of non-interacting particles. In this case, the chemical potential is proportional to the logarithm of the density plus terms that do not depend on this quantity. Non-ideality can be directly taken into account by considering the right dependence of the thermodynamic quantities on the density and, in general, will give rise to nonlinear partial differential equations. A more difficult aspect to deal with is the presence of non-local effects. In such a case, the interactions between the different parts of the system will need of integro-differential equations to be incorporated in the description.
The main result of our analysis shows that in far from equilibrium diffusion processes, local equilibrium can be recovered when all the relevant degrees of freedom are considered at the same level as the spatial coordinate. In the resulting extended space, thermodynamic quantities, such as temperature and the chemical potential, admit a well defined interpretation. The scheme we have developed may then provide the basis for a consistent formulation of thermodynamics far from equilibrium.
*Acknowledgements*— J.M.R was supported by DGICYT (Spain) Grant No. PB98-1258. J.M.G.V. is an associate of the Howard Hughes Medical Institute.
[10]{} \[Reiss\]Reiss, H. (1997) *Methods of Thermodynamics* (Dover, New York). \[DM\]de Groot, S.R., Mazur, P. (1984) *Non-equilibrium Thermodynamics* (Dover, New York). \[Glases\]Götze, W. (1991) in *Liquids, Freezing, and Glass Transition*, eds. Hansen, J. P., Levesque, D., Zinn-Justin, J., Les Houches 1989 (North-Holland, Amsterdam). \[Sitges\]Rubí, J. M., Pérez-Vicente, C. eds. (1997) *Complex Behaviour of Glassy Systems. Lecture Notes in Physics, 49* (Springer, Heidelberg). \[Polymers\] Doi, M., Edwards S. F. (1986) *The Theory of Polymer Dynamics* (Oxford University Press, Oxford) \[Granular\] Jaeger, H. M., Nagel, S. R., Behringer, R. P. (1996) Rev. Mod. Phys. **68**, 1259-1273. \[Colloids\] Larson, R. G. (1999) *The Structure and Rheology of Complex Fluids* (Oxford University Press, New York). \[P\]Prigogine, I. (1955) Introduction to Thermodynamics of Irreversible Processes (John Wiley & Sons, New York). \[PM\]Prigogine, I., Mazur, P. (1953) Physica **XIX**, 241-256. \[CT\]Pérez-Madrid, A., Rubí, J. M., Mazur, P. (1994) Physica **A 212**, 231-238. \[VK\]van Kampen, N. G. (1992) *Stochastic Processes in Physics and Chemistry* (North-Holland, Amsterdam). \[TC\]McLennan, J. A. (1989) *Introduction to Nonequilibrium Statistical Mechanics* (Prentice Hall, Englewood Cliffs) \[kurchan\] Cugliandolo, L. F., Kurchan, J., Peliti, L. (1997) Phys. Rev. E **55**, 3898-3914. \[jms\]Rubí, J. M., Vilar, J. M. G. (2000) J. Phys.: Cond. Matter **12**, A75-A84. \[BP\]Berne, B. J., Pecora, R. (1977) *Dynamic Light Scattering: With Applications to Chemistry, Biology, and Physics* (John Wiley & Sons, New York). \[Ames\]Ames, W. F. (1997) *Numerical Methods for Partial Differential Equations* (Academic Press, New York).
|
Alex Jones, the fiery conspiracy theorist and provocateur who commands an audience of millions based on the idea that he is one of the only purveyors of the unvarnished truth, is currently defending himself in a civil suit with an argument based partially on a claim that he is simply a performance artist, according to reporters who have been in the courtroom.
The host of Infowars is in an ongoing custody battle with his ex-wife, who says Jones is too volatile to have joint custody of their children. "He’s not a stable person," she said at a recent pretrial hearing, according to the Austin American-Statesman, which also reported that her legal team plans to use some of his public statements to make that case.
The argument from Jones’ attorney, the Statesman reported: "He’s playing a character. He is a performance artist."
Similar issues were brought up by both sides during jury selection Monday, according to BuzzFeed News’ Charlie Warzel, who was tweeting from the courtroom.
Using Jones’ on-air persona to evaluate his temperament as a father, Jones’ attorney said in the pre-trial hearing, according to the Statesman, would be like judging Jack Nicholson based on his role as the Joker in "Batman."
That defense will likely come as news to the millions who listen to Jones on radio broadcasts and Infowars.com, which had roughly 7.5 million unique visitors in the last month, according to Quantcast.
Lawyers for both Jones and his wife, who are under a gag order, did not respond to requests for comment on Monday.
Jones has gained notoriety in recent years for his angry tirades and conspiracy theories.
Among other false statements, Jones has said that the September 11, 2001, terrorist attacks were an insider job and that the Sandy Hook massacre was a hoax. Last month, Jones issued a rare apology for his role in promoting the false "Pizzagate" conspiracy theory, which alleged that a child sex ring was being run out of a Washington, D.C. pizzeria.
Jones has also earned praise from Donald Trump. During the 2016 campaign, Trump called into Jones’ show and told him, "Your reputation is amazing." |
Q:
cURL Paypal IPN script not working
I've been trying to figure out what's wrong with my ipn script. I've tried many different methods and I also tried fsockopen but I didnt get it working. Now I'm using cURL and it still isn't working. I've cURL installed and it should be working properly.
My script (Just a simple example, i removed some checks just for testing):
<?php
$ACTIVE_CONNECTION = mysql_connect('127.0.0.1', 'mysqluser', 'mysqlpassword') or die("Could not connect to server.");
mysql_select_db('mysqldb', $ACTIVE_CONNECTION) or die("Could not connect to database.");
$tid = $_GET['tx'];
$auth_token = "aqiopfsawdaisytrgkl";
$url = "https://www.sandbox.paypal.com/cgi-bin/webscr";
$post_vars = "cmd=_notify-synch&tx=" . $tid . "&at=" . $auth_token;
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_POST, 1);
curl_setopt($ch, CURLOPT_POSTFIELDS, $post_vars);
curl_setopt($ch, CURLOPT_FOLLOWLOCATION, 1);
curl_setopt($ch, CURLOPT_TIMEOUT, 15);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, true);
curl_setopt($ch, CURLOPT_HEADER, false);
curl_setopt($ch, CURLOPT_USERAGENT, 'cURL/PHP');
$fetched = curl_exec($ch);
$lines = explode("\n", $fetched);
$keyarray = array();
if (strcmp ($lines[0], "SUCCESS") == 0) {
for ($i=1; $i<count($lines);$i++){
list($key,$val) = explode("=", $lines[$i]);
$keyarray[urldecode($key)] = urldecode($val);
}
// check the payment_status is Completed
// check that txn_id has not been previously processed
// check that receiver_email is your Primary PayPal email
// check that payment_amount/payment_currency are correct
// process payment
$payment_amount = $keyarray['mc_gross'];
$payment_status = $keyarray['payment_status'];
$payment_currency = $keyarray['mc_currency'];
$txn_id = $keyarray['txn_id'];
$receiver_email = $keyarray['receiver_email'];
$payer_email = $keyarray['payer_email'];
$username = mysql_real_escape_string($keyarray['custom']);
if ($payment_status == 'Completed'){
mysql_query("UPDATE `users` SET vip = '1' WHERE `username` = '".$username."'");
}
}
else if (strcmp ($lines[0], "FAIL") == 0) {
// manual investigation here
}
?>
A:
Try this to test Sanbox IPN
https://developer.paypal.com/cgi-bin/devscr?cmd=_ipn-link-session
and
replace
if (strcmp ($lines[0], "SUCCESS") == 0) {
with
if (strcmp ($lines[0], "SUCCESS") == 0 || 1 == 1) {
|
Half of secondary pupils expected to miss out on their first choice
Families are facing a fresh school places crisis as up to half of secondary pupils are expected to miss out on their first choice in some areas.
Head teachers are facing an escalating places crisis filtering through from primaries which has been caused by a baby boom fuelled by migration.
Ministers have known about the impending problem for many years but councils estimate tens of thousands of extra secondary places will still be needed by 2020.
New figures suggest a rising numbers of secondary schools are struggling to keep up with demand. Almost half of secondary schools in England are now oversubscribed, and the numbers are increasing.
At least 28 secondary schools in England are now so in demand that children will only get in on proximity grounds if they live within a kilometre of the site.
At least 28 secondary schools in England are now so in demand that children will only get in on proximity grounds if they live within a kilometre of the site.
A Department for Education spokesman said: "The Government doubled the funding for school places to £5 billion in the last parliament, which has helped create half a million new school places. A further £7 billion has already been committed to create even more places over the next six years." |
1. Field of the Invention
The present invention relates to a MEMS (microelectrical mechanical system) element having a microphone structure implemented in a layer structure. The microphone structure includes at least one sound pressure-sensitive diaphragm, an acoustically permeable counter element and a capacitor system for detecting diaphragm deflections. The diaphragm and the counter element are situated on top of each other, spaced a distance apart, in the layer structure of the element, and each is equipped with at least one electrode of the capacitor system.
2. Description of the Related Art
Under the impact of sound, the microphone diaphragm is deflected at a right angle to the planes of the layers of the layer structure. Thereby the distance between the microphone diaphragm and the stationary counter element changes. The microphone diaphragm and the counter element are each equipped with at least one capacitor electrode, so that the “out-of-plane” deflections of the microphone diaphragm are detectable as changes in capacitance of the capacitor system. However, the connection of the diaphragm to the layer structure of the element causes bending or warping of the diaphragm, which may have negative effects on the microphone performance. In particular such a warping may result in the relationship between the diaphragm deflection and the measuring signal being no longer linear at higher sound pressures.
A high signal-to-noise ratio (SNR) is always sought with high-performance MEMS microphones. One possibility for improving the SNR is to reduce the flow resistance of the counter element.
In addition, for high-performance MEMS microphones, a preferably large frequency bandwidth is frequently sought, i.e., a preferably flat response function, which also includes high frequencies, ideally into the ultrasonic range. The microphone structure is advantageously designed to have a preferably high resonant frequency co. The greater the response function of the upper cutoff frequency, the higher is the resonant frequency co of a capacitive MEMS microphone. Resonant frequency co depends decisively on the mass and stiffness of the microphone diaphragm. The thinner the diaphragm having a given diaphragm area and diaphragm stiffness, the higher is the resonant frequency. In a homogeneous diaphragm, however, the stiffness also depends on the thickness of the diaphragm. The lower stiffness of a thin microphone diaphragm in turn favors its warping, which has negative effects on the microphone performance, and results in nonlinearities in the microphone signal as well as a reduction of the resonant frequency. A high resonant frequency and good microphone performance are therefore not readily compatible. |
1. Technical Field
The present invention relates to a pixel circuit, an electro-optical device of a digital driving type (for example, a liquid crystal display device employing a subfield driving type), and an electronic apparatus.
2. Related Art
For example, as a driving method for a liquid crystal display device, there are an analog driving type (a method in which an analog voltage corresponding to a display gray scale is applied to a data line) and a digital driving type (a driving method in which there are only two values including an ON level and an OFF level as voltage levels needed for driving a pixel). In the analog driving type, non-uniformity of display can be easily generated due to the non-uniformity of characteristics of elements (a D/A converter, an operational amplifier, a wiring, and the like) configuring the circuit. On the other hand, in the digital driving type, used driving voltages (writing voltages for a pixel) are binary, and accordingly, it is easy to implement image display having higher definition.
As the digital driving type, a subfield driving type in which one field is divided into a plurality of subfields on a time axis and an ON voltage or an OFF voltage is applied to each subfield in accordance with the gray scale of each pixel has been proposed (for example, see JP-A-2003-114661). In this subfield driving type, a voltage (effective voltage) supplied to a liquid crystal is changed by controlling not a voltage level but an application time interval of a voltage pulse, and thereby the transmissivity of the liquid crystal is controlled.
As a pixel circuit that can be used in the liquid crystal display device of the digital driving type, for example, there are a DRAM-type pixel circuit (a general pixel circuit having a pixel transistor and a holding capacitor) and a pixel circuit (a RAM-type pixel circuit) that has a RAM (a memory circuit that maintains “1” or “0” by using positive feedback) instead of the holding capacitor.
The DRAM-type pixel circuit has an advantage that the circuit configuration thereof is simple. However, in the DRAM-type pixel circuit, a change (for example, see JP-A-5-224235) in the maintained voltage caused by feed-through or a change in the maintained voltage caused by a leak current can easily occur. Accordingly, for performing high-definition display, there is limit in the DRAM-type pixel circuit.
In addition, as the RAM-type pixel circuit, for example, a pixel circuit that uses an SRAM has been proposed (see JP-A-2005-258007). When the pixel circuit disclosed in JP-A-2005-258007 is used, high-definition image display can be performed. However, in such a case, the circuit configuration is complicated. Accordingly, an increase in the size of the pixel circuit and an increase in the power consumption of the pixel circuit are inevitable.
In the liquid crystal display device of the digital driving type, when a RAM-type pixel circuit is used, the circuit configuration is complicated, and thereby an increase in the size of the pixel circuit and an increase in the power consumption of the pixel circuit occur. Accordingly, it is difficult to implement high-definition image display while miniaturization and low power consumption of the liquid crystal display device are achieved. |
The Chunky Herringbone Newsboy Cap in olive is a beautifully tailored 8/4 Newsboy Cap from Olney Hats. The hat is fully lined in satin and has the slightly extended bill of the more classic newsboy caps of the 20’s and 30’s. I am wearing this magnificent hat on my head as I type and I can feel the quality of the material keeping me warm on this blisteringly cold day. |
Austerity Myth
With a condescending sigh, they explain that Europe made deep cuts in government spending, and the result was today’s high unemployment. “With erstwhile middle-class workers reduced to picking through garbage in search of food, austerity has already gone too far,” writes Paul Krugman in The New York Times.
One problem with this conclusion: European governments didn’t cut! If workers pick through garbage, cuts can’t be a reason, since they didn’t happen.
That doesn’t stop leftists from complaining about cuts or stop Europeans from protesting announced austerity plans. But if austerity means spending less, that hasn’t happened.
Some European countries tried to reduce deficits by raising taxes. England slapped a 25 percent tax increase on the wealthy, but it didn’t bring in the revenues hoped for. Rich people move their assets elsewhere, or just stop working as much.
If politicians honestly want to boost their nation’s economies, they should look to what happened in countries that bounced back from economic slumps.
Canada slashed spending 20 years ago and now outranks the U.S. on many economic indicators.
Around the same time, Japan went the other way, investing heavily in the public sector in an attempt to jump-start its economy, much as the U.S. did with “stimulus” under President Obama. The result? Japan’s economy stagnated.
The left now claims Japan didn’t stimulate “enough.”
In the U.S., politicians imply spending limits would be “cruel” because vital programs are “cut to the bone.” But we are nowhere near bone.
Actually, we don’t need to “balance” it. We just need to slow spending growth to about 2 percent a year, so the economy can gain on our debt. But politicians won’t do even that.
I understand why. I ask people who say they are horrified by America’s debt, “What would you cut?” Most have no clue. They just stare. Some say things like, “Don’t cut education!”
C’mon. Federal bureaucrats spend $3.7 trillion! But most people can’t think of anything to cut?
When businesses face budget shortfalls, they can’t just give speeches about how much they care about fiscal responsibility — at least not for long. They must make real cuts. When they do, they often prosper. Years back, IBM and GE each laid off 100,000 workers. People were furious. But thanks to those cuts, the companies survived.
If the politicians don’t know what to cut, they should just accept Sen. Rand Paul’s proposed budget. Among other things, he would cut four Cabinet-level agencies: Commerce, Housing and Urban Development, Energy and Education. Why not? We don’t need a Commerce Department. Commerce just … happens. Education is funded by the states. The Energy Department gives money to politicians’ cronies.
I’d go further than Paul. Why do we need an Agriculture Department? Agriculture is done by farmers, not bureaucrats. Why do we need a Labor Department? And so on. All those things are better handled by a free market. I wish we had a real free market in America.
Government recently revised its dire forecasts about America’s coming bankruptcy. The numbers are a little better than once thought.
But make no mistake: As people my age retire and demand Medicare, America will eventually go broke.
The first step toward a solution is just being honest about the deep hole we’re in — giving up on the lie that governments elsewhere failed with “austere” budgets. They haven’t.
John Stossel is host of “Stossel” on the Fox Business Network. He’s the author of No They Can’t: Why Government Fails, but Individuals Succeed. |
Konni (State Assembly constituency)
Konni State assembly constituency () is one of the 140 state legislative assembly constituencies in Kerala state in southern India. It is also one of the 7 state legislative assembly constituencies included in the Pathanamthitta Lok Sabha constituency.
Local self governed segments
Konni Niyama Sabha constituency is composed of the following local self governed segments:
Members of Legislative Assembly
The following list contains all members of Kerala legislative assembly who have represented Konni Niyama Sabha Constituency during the period of various assemblies:
Key
* Byepoll
Election results
Percentage change (±%) denotes the change in the number of votes from the immediate previous election.
Niyama Sabha Bye-election 2019
Due to the election of the sitting MLA Adoor Prakash as the MP from Attingal (Lok Sabha constituency), Konni Niyamasabha Constituency went to byepoll in 2019. There were 1,97,956 registered voters in Konni Constituency for this election.
Niyama Sabha Election 2016
There were 1,96,309 registered voters in Konni Constituency for the 2016 Kerala Niyama Sabha Election.
See also
Konni
Pathanamthitta district
List of constituencies of the Kerala Legislative Assembly
2016 Kerala Legislative Assembly election
2019 Kerala Legislative Assembly by-elections
References
Category:State assembly constituencies in Pathanamthitta district |
Galeria
Everything you need
Lavish Pro Themes provides you everything that you need on a WordPress theme,
extensive customize options for user-oriented easy use, flat and modern design to capture
viewers attention, plenty color options to full fill the choice of yours and many more. |
A commonly accepted practice of removing solid particles from a flue gas includes the utilization of an electrostatic precipitator to hold the solid particles without inhibiting the flow of the flue gas. Typically, an electrostatic precipitator is positioned in the flue between the outlet of a boiler and a smokestack.
The ordinary construction of an electrostatic precipitator includes a plurality of large, flat, metal plates which are spaced from each other. The metal plates may have a height of up to 30 feet or more, and a width of up to 10 feet or more. It is to be appreciated that the specific size of the plates in a given precipitator is dependent upon the particular precipitator construction for a given application. Ideally, the flat plates are equidistantly spaced from each other. A second plurality of elongated electrodes is positioned among the plates. The electrodes are positioned between each pair of adjacent plates. Ideally, the elongated electrodes are equidistantly spaced from the adjacent plates.
The uniform spacing of the elongated electrodes from the plates is necessary to have a uniform electrostatic charge between the elongated electrodes and the plates. A uniform electrostatic charge generates uniform collection of solid particles on the plates. Typically, the solid particles are removed from the plates by rapping the plates to vibrate the plates and, thereby, cause the collected solid particles to drop off the plates in clusters into collectors under the plates.
The flue gas which enters the electrostatic precipitator is hot. Commonly, additional heat enters the precipitator in the form of fires caused by problems in the operation of the boiler. Exposure of the plates to excessive heat as well as other factors can cause the plates to warp or buckle. The warping or buckling of the plates destroys the uniform spacing between adjacent surfaces of adjacent plates and uniform spacing between each of the elongated electrodes and the respective adjacent plates. Thereby, the effectiveness of the precipitator in removing solid particles from a flue gas is reduced so that the precipitator has a lower capacity. Consequently, the capacity of the boiler, which produces the flue gas, must also be lowered to comply with emissions regulations. In the case of a power generation unit, as the capacity of the boiler is reduced, the capacity of a power generating system connected to the boiler is also reduced. In order to maintain an electrostatic precipitator fully effective, it is desirable to maintain the spaced plates of the precipitator in an equidistantly spaced relationship to each other and to the electrodes.
The concept of providing spacers to hold electrostatic precipitator plates apart a uniform distance is known. U.S. Pat. No. 4,007,023, issued Feb. 8, 1977, to Batza et al, entitled, "Electrostatic Precipitator With Collector-electrode Spacers", discloses a construction wherein spacers are hingedly mounted on a pivot. U.S. Pat. No. 4,478,614, issued to John A. Jonelis on Oct. 23, 1984, entitled, "Electrostatic Precipitator Construction Having Spacers" discloses a construction wherein a plurality of individual spacers are positioned between electrostatic precipitator plates. These spacers are mounted directly to the plates or installed by use of a long probe. U.S. Pat. No. 4,479,813, issued to John A. Jonelis on Oct. 30, 1984, entitled, "Electrostatic Precipitator Construction Having Ladder Bar Spacers" teaches a construction wherein a plurality of spacer devices are positioned between electrostatic precipitator plates, each device consisting of a plurality of spacers. These spacers are mounted directly, or loaded from the top or bottom of the plates as practical. It is a principal object of this invention to provide a spacer assembly for use in an electrostatic precipitator wherein the spacer assembly may be interlocked with other spacer assemblies. In this way, more than one spacer assembly is connected together thus forming one construction made up of a plurality of spacers, and connected to the stiffeners of the plates. Spacer assemblies are locked together during installation within the precipitator, thus allowing the construction to be loaded from the top or bottom of the precipitator plates with greater facility than the previous construction. The installed construction can be more readily removed than previous constructions. In addition, the weight of the installed construction aids in the straightening of the collector plates, and the installed construction can be held in tension if required to aid in straightening the plates. The present assembly can be made to add structural strength along the length of the collector plate. |
After a federal raid in early April on Oaksterdam University, an education center located in downtown Oakland that trains students to work in the marijuana industry, founder Richard Lee has decided to step down as head of the institution. His successor will be former executive chancellor Dale Sky Jones, which will officially be announced on Wednesday morning.
“It is safe to say that I will be taking over the lead position at Oaksterdam University to ensure that the institution will go on,” Jones told Oakland North in an interview.
Oaksterdam University, the first cannabis college in the United States, was founded in 2007. Ever since visiting the cannabis college in Amsterdam, Lee had wanted to open a trade school for the cannabis industry in the US. Medical marijuana has been legal in California since the 1996 passage of Proposition 215, although it remains illegal under federal law. Lee, who has been working to end cannabis prohibition for over 20 years now, put his idea into practice by creating a school with a curriculum that focuses on the entire cannabis trade, offering classes such as Legal Issues, Politics, Cooking, Concentrates, and Horticulture.
“I started the university to promote the cannabis industry and to create jobs in this industry that pay taxes,” said Lee. “The other reason was to teach people who want to get involved in the cannabis industry and politics but did not know anything about it.” In 2008, a satellite school was launched in Los Angles and classes were also held in Michigan in May, 2009. (Both locations are now closed due to financial shortfalls.)
Lee, who moved to Oakland in 1997, played a huge part in passing Oakland’s Measure Z, making private sales, cultivation, and possession of cannabis local law enforcement’s lowest priority. He was also a supporter of Proposition 19, a failed 2010 ballot initiative to control, tax, and regulate recreational marijuana use in California. Even though Proposition 19 did not pass, Lee considers the effort, which he helped finance, a success. “It was successful in moving the legalization debate forward,” he said. “One of our main goals was to get people to talk about this issue. And it just was on the agenda with the presidents down in South America. Columbia and Guatemala have come out for legalization of cannabis now.”
Lee believes that marijuana should be legalized in the U.S., as well. “It should be legalized to get the people out of prison that are in there because of issues related to cannabis. It should also be legalized to stop the violence surrounding cannabis, such as the 50,000 deaths in Mexico. It should be legalized in order for our law enforcement to be prioritized and in order to give an herbal alternative to sick people that need help,” he said.
Lee thinks that the reason marijuana has not been legalized here is because the medical use of marijuana would create competition for the pharmaceutical industry, and because legalization would endanger bureaucratic jobs that are dependent on enforcing laws against cannabis.
However, Lee believes that legalization is on the horizon, pointing to polling figures that show increasing public support for legalization. Lee also cited legalization’s potential to raise tax revenues for cash-starved governments. “It makes sense to legalize cannabis in times of economic struggle,” he said. “States are already collecting a lot of taxes from the cannabis industry, even before it has been legalized. If cannabis were to be legal, they would make even more money.”
After the raid, Lee decided to step down from his position as head of Oaksterdam University “partly because I feel like I have done my duty on the front line for a long time now, and partly to keep my legal issues separate so that Oaksterdam University can go on without problems,” he said.
However, Lee said he will continue to advocate for marijuana legalization. “I will speak at the hemp festival in August in Seattle and I will help support the legalization initiative in Washington State, Colorado and possibly other states such as Michigan, Missouri, Montana and Oregon,” he said.
Lee declined to comment on whether or not he was facing any criminal charges after the federal raid. (A spokesperson for the Drug Enforcement Agency could not be reached for comment by press time.)
Lee supports Jones as his successor. “It is great that Dale is stepping up and I wish her all the luck,” he said. When looking back on his time as head of the school, he said, “I am proud of the 15,000 students that we have taught and all of the great work that they are doing now. Many of them are politically active or started their own dispensaries.”
Lee and Jones have worked together at Oaksterdam University as well as on the Proposition 19 campaign, for which Jones was the spokeswoman. Jones has worked within the marijuana industry for several years. She helped establish the Medical Cannabis Safety Council in early 2008 and was the chairperson of the group’s education and research committee, with whom she developed programs through which patients, doctors, providers and regulating authorities can be more confident in how medical marijuana is sourced, from the plant to the patient.
However, her background is from somewhere else—corporate America. “Up to five years ago, I was a total corp-girl. I was working in retail and hospitality management for companies such as Brown Shoe or T.G.I. Friday’s,” she said. “One day I got a phone call asking me if I want to quit my job and work for a group of doctors to manage their medical cannabis recommendations in Southern California. I was just simply fed up with the corporate world and was looking for change. So I took a leap of fate down rabbit hole. And here I am now, feeling like Alice in Wonderland. Working in the cannabis industry is very difficult. A lot of the rules within the industry are blurry, you can’t do normal banking and you cannot set up non-profits. But my training in professional corporations allows me to correlate the best practices from mainstream industry and adopt those to the cannabis industry.”
Jones will take over Oaksterdam at a very difficult time for the organization. After the raid of five Oaksterdam-related locations, including Lee’s home and the organization’s downtown dispensaries, 45 employees lost their jobs as well as their health insurance and benefits, according to Jones. “We took cannabis away from the streets and into a safe and responsible environment and that’s how the government and the state authorities thank us—by increasing the unemployment rate in Oakland and making our life more difficult,” she said.
As the new head of Oaksterdam University, she is now trying to calm the waves the raid has caused. “There is no way for me to not try to keep Oaksterdam University going. I consider it my duty and my moral obligation,” she said.
“We are trying to survive now,” she continued, “but it is a challenge, especially money-wise. In order to keep educating the way we were, we have to purchase new equipment. All of our computers were taken away by the federal authorities. We simply do not have enough sources anymore and we basically have to start from scratch.”
Oaksterdam University is currently dependent on donations and run with volunteers only, she said. “We can’t pay any wages at the moment. We also had to cut down on specialty classes and our remaining classes are taught by volunteers at the moment,” Jones said. “The current students already paid for classes so we feel obliged to honor them and to keep teaching, but it is difficult without resources and equipment. We are dependent on donations and we currently survive on enrollment. But we still have students. Right now we’re looking at about 100 students that have pre-registered for upcoming classes that we are trying to teach. And we will honor them and keep going. The best way for us to do that is for other new students to register.”
Jones is currently negotiating with the owner of the building that hosts Oaksterdam University to only rent them smaller, more affordable parts of the building instead of the entire 30,000 square foot campus, so they can remain in business. “I am not sure how that is going to turn out, though. We might have to move out by the end of the month. That’s when our lease is running out,” Jones said. “Of course it hurts to lose facilities but we just have to change the model, move to a smaller place or diversify Oaksterdam to different places. We are not giving up. We just have to look forward and to keep educating in order to create social justice and tackle the issue of legalizing marijuana.”
After the raid, the atmosphere at Oaksterdam University has been one of shock, Jones said. “People still believe in the concept of Oaksterdam, but seeing a good man like Richard Lee being taken down in such a bad way is just shocking,” she said. “But the employees have been amazing. They believe in Oaksterdam.”
One of Oaksterdam’s volunteers is Carrie Harger, who just moved to Oakland from Los Angeles. Harger is originally from the Bay Area but used to run Oaksterdam University in Los Angeles until it was shut down due to financial problems. She then decided to come back home to support the Oaksterdam family here. “Everything seemed to be going well—we were business as usual—and now this suddenly happened,” she said. “For me, it is just sad. This is not just a job for me, it is telling the truth about cannabis, planting the seed of knowledge and educating people. … I think cannabis can help the world, which is why I am not giving up and why I come here on a voluntary basis now.”
Harger is a medical marijuana patient herself. “I am not a drug seeker, I use cannabis for medical reasons,” she said. “It is so frustrating that patients lost their access to their medicine because the federal government came in and destroyed everything. We provided safe and clean cannabis for our patients and now they are forced to buy their medicine somewhere on the street from the Mexican drug cartel. Thank you, DEA.”
Like Harger, other Oaksterdam supporters have expressed concerns that former patients will be pushed to buy marijuana on the streets, rather than from a dispensary. Gianni Feliciano used to run the Oaksterdam hemp museum before it was closed due to the raid. He moved from Puerto Rico to Oakland two years ago when he heard about Oaksterdam. “Personally, I feel they cut off the head of a hemp stock and all the seeds fell to the ground’” Feliciano said, referring to the raid. “Just because they raided the dispensaries does not mean people stopped buying marijuana. They just pushed it to the underground again, which is putting patients at risk because their medicine might not be as clean anymore.”
Ethan Sommer, an alumnus of Oaksterdam University, has similar concerns about the raid’s effect on cannabis education itself. Sommer participated in a 13-week program at the college and is now working as the executive director of the Medical Cannabis Association, a trade association that promotes the commercial and political interests of the medical cannabis industry. “I learned a lot about the policy behind cannabis here at Oaksterdam University,” he said. “I also learned about cultivation and various business issues that are specific to this industry as well as the science behind the medicine and the plant. I learned more than I expected and now the federal authorities are making this education process more difficult. This university was the heart of our downtown area and they tried to take that away from us. If they succeed, that would leave a huge hole in the culture of fabric in downtown Oakland. But we are not going to let them do that.”
Jones, too, is concerned about the future of Oaksterdam University, particularly the possibility that federal charges could be filed against Lee or the university. “Of course I am concerned for Richard. He is a target,” Jones said. “But I am a teacher and I have done nothing wrong. Education is not a crime. However, you can always be harassed and charged and we are concerned that all of our resources are going into fighting rather than our education.”
“I am so disappointed that this is the way it has to be,” she continued. “By looking at the current enforcement policy, I can tell that they are systematically going after people that are engaged in the cannabis legalization movement. They go after these people, such as Richard Lee, and shut them down. They go after the registered ones that do pay taxes, which is just absurd. Attacking a school just illustrates how flawed the current drug policy is.”
Harger, however, said she does not believe charges will be pressed. “They didn’t find what they were looking for. Instead of an underground cannabis operation, they found educational material, classrooms, students, books,” she said. “And we are not a bunch of lazy stone-heads. We are an excited group and we are going to get back on our feet and keep up the service we were offering to our community.”
Jones said Oaksterdam will continue to push for changes to the drug laws that prompted the raid. “We need to change these policies. They are flawed and old-fashioned,” she said. “But we are not dead yet—we are fighting and we won’t just disappear. I will keep teaching and talking about it and that is not illegal. While the sky is falling, you gotta keep your chin up.”
You can read Oakland North’s complete coverage of marijuana-related issues in Oakland here. |
/**
* Licensed to the Apache Software Foundation (ASF) under one or more
* contributor license agreements. See the NOTICE file distributed with
* this work for additional information regarding copyright ownership.
* The ASF licenses this file to You under the Apache License, Version 2.0
* (the "License"); you may not use this file except in compliance with
* the License. You may obtain a copy of the License at
*
* http://www.apache.org/licenses/LICENSE-2.0
*
* Unless required by applicable law or agreed to in writing, software
* distributed under the License is distributed on an "AS IS" BASIS,
* WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
* See the License for the specific language governing permissions and
* limitations under the License.
*/
package com.google.code.or.binlog.impl.parser;
import java.io.IOException;
import java.util.LinkedList;
import java.util.List;
import com.google.code.or.binlog.BinlogEventV4Header;
import com.google.code.or.binlog.BinlogParserContext;
import com.google.code.or.binlog.impl.event.TableMapEvent;
import com.google.code.or.binlog.impl.event.WriteRowsEventV2;
import com.google.code.or.common.glossary.Row;
import com.google.code.or.io.XInputStream;
/**
*
* @author Jingqi Xu
*/
public class WriteRowsEventV2Parser extends AbstractRowEventParser {
/**
*
*/
public WriteRowsEventV2Parser() {
super(WriteRowsEventV2.EVENT_TYPE);
}
/**
*
*/
public void parse(XInputStream is, BinlogEventV4Header header, BinlogParserContext context)
throws IOException {
//
final long tableId = is.readLong(6);
final TableMapEvent tme = context.getTableMapEvent(tableId);
if(this.rowEventFilter != null && !this.rowEventFilter.accepts(header, context, tme)) {
is.skip(is.available());
return;
}
//
final WriteRowsEventV2 event = new WriteRowsEventV2(header);
event.setTableId(tableId);
event.setReserved(is.readInt(2));
event.setExtraInfoLength(is.readInt(2));
if(event.getExtraInfoLength() > 2) event.setExtraInfo(is.readBytes(event.getExtraInfoLength() - 2));
event.setColumnCount(is.readUnsignedLong());
event.setUsedColumns(is.readBit(event.getColumnCount().intValue()));
event.setRows(parseRows(is, tme, event));
context.getEventListener().onEvents(event);
}
/**
*
*/
protected List<Row> parseRows(XInputStream is, TableMapEvent tme, WriteRowsEventV2 wre)
throws IOException {
final List<Row> r = new LinkedList<Row>();
while(is.available() > 0) {
r.add(parseRow(is, tme, wre.getUsedColumns()));
}
return r;
}
}
|
Unlimited-volume stacking of ions in capillary electrophoresis. Part 1: stationary isotachophoretic stacking of anions.
An online technique for stacking based on the generation of a stationary isotachophoretic (sITP) boundary is presented. By balancing the anodic migration of an ITP boundary with a cathodic EOF, a stationary boundary is formed that can be used to indefinitely concentrate analytes according to ITP principles during electrokinetic injection. The ITP boundary is created by using an electrolyte containing a leading ion (chloride) and a suitable terminating ion added to the sample (2-morpholinoethanesulphonic acid, MES). Destacking and separation are achieved simply by replacement of the sample vial with electrolyte. The formation and stabilisation of the sITP boundary were evaluated through computer simulation which revealed that the pH had little impact upon the formation of the sITP boundary, but did govern the position at which it becomes stationary. Simulations also demonstrated that similar results were obtained when the capillary was initially filled with sample/terminator or leader/electrolyte, which was also supported by experimental results. Using 100 mM Cl(-), 200 mM Tris, pH 8.05 as the leader/electrolyte and adding 100 mM MES, 200 mM Tris, pH 8.05 to the sample, the sITP boundary was established after 5 min at -20 kV and was stable for at least 60 min. This provided detection limits for NO(2) (-), NO(3) (-) and SCN(-) of 0.05-0.66 ppb, which are 10,000 times lower than hydrodynamic injection and 10-50 times lower than other stacking approaches used for these inorganic ions. |
Stockton, Calif. Largest US City in Bankruptcy Protection
Photos.com/Thinkstock(STOCKTON, Calif.) -- A federal judge Monday gave the city of Stockton, Calif., the green light to enter bankruptcy protection.
With a population of close to 300,000 people, Stockton is now the most populous city in the nation to enter bankruptcy.
Creditors argued that the city should have been made to come up with more funds, but Judge Christopher Klein approved the city for bankruptcy protection, saying the creditors had acted in bad faith and had not paid their share of costs for the 90-day mediation, according to the Los Angeles Times.
The city's attorneys blame bad decisions, foreclosures and property tax reductions for the bankruptcy. But the city's creditors say the Stockton should have cut payments to the state pension.
Stockton's largest debt is the $900 million owed to the California Public Employees Retirement System (CalPERS) to cover pensions, reports the L.A. Times. Attorneys representing Stockton say city services have been cut to the bone, all while the city continues paying into CalPERS.
The case will likely be under close watch for precedent as to whether U.S. bankruptcy law will trump state laws, the Times reports. |
At long last, a Crouching Tiger, Hidden Dragon’ sequel
Tuesday
May 21, 2013 at 6:00 AM
Liz Smith
‘China is a big country, inhabited by many Chinese,” said Charles de Gaulle, with incredible insight.
Fans of Ang Lee’s “Crouching Tiger, Hidden Dragon” were caught by surprise when they learned that a sequel is being planned. Thirteen years after the original film debuted, they’d just about given up hope.
But the Weinstein Company has hired Yuen Woo Ping to direct this latest epic — he is extremely proficient in staging fight sequences, we hear. I recall “Crouching” has something to do with stolen swords and people who can inexplicably fly, but otherwise, the details of the plot elude me now. (Well, it has been 13 years!) None of the original cast is returning except for Michelle Yeoh.
If you ask yourself why this sequel is happening, think no farther than China. Hollywood wants to make nice with China. Everybody wants to make nice with China! Moviemakers want to keep Chinese audiences and financers happy. What better way to spread joy than sequeling one of the most adored and iconic Chinese action films ever released? The “reboot,” as it is called these days, will most likely debut in the summer or late fall of 2014.
The film was quite fantastical in itself, but since nothing succeeds like excess, “Crouching 2” will probably be in 3-D, which I find irritating. But then I find obsessive coverage of the Kardashians irritating. You see where irritation gets me?
•
Channel surfing on Sunday nights is maddening. There’s “Game of Thrones,” “The Borgias,” “Nurse Jackie” and “Mad Men.” Last Sunday, the Billboard Music Awards were on, too. (I know I should get with it and DVR everything, unless that’s now too early 2000s, and there’s something else even more convenient?) Anyway, as luck would have it, even though I tuned into the Billboard ceremonies only twice, they were the two moments I wanted to see. One was Taylor Swift rocking down the aisle onto the stage doing an energetic version of her hit, “22.” (She ended up with eight awards.) The other woman I wanted to see was Madonna, who accepted an award for her “MDNA” tour — the most successful of 2012. She also picked up two other awards. Of course, the Big M wore something that looked right out of a Frederick’s of Hollywood catalog but she looked good. Madonna thanked her fans sweetly: “Without you, I would have no show to do. And every showgirl needs her show!”
I missed Justin Bieber complaining and being booed. Eh, next week, somewhere, I’ll catch that act. |
Syria Again
Stop the War organised another protest against David Cameron’s motion to allow bombing of Syria on a weekday evening, with a rally opposite Parliament and a short march around Westminster via the Conservative and Labour Party HQs. Like their previous protest, what struck me was the absence of views from Syrians, although there were some supporters of both the Assad regime and the Free Syrians at the rally.It was also noticeable that there was no condemnation of the Russian bombing of the Syrian opposition as well as Daesh.
Of course I wasn’t the only person to notice this and to comment on it, and Stop the War were forced into issuing ‘For the avoidance of doubt‘ by John Rees, which makes seven points, the first of which begins “The STWC has never supported the Assad regime.” As I commented:
Well, it’s good to make that clear, because there have been many protests by Stop the War which Assad supporters have attended and appeared to be welcome, and by refusing to let Syrians opposed to the regime speak at this and other protests STW have certainly given that impression.
Photographically it was a night where I had a lot of problems. For a central London location, Parliament Square is remarkably dark, and working without flash was perhaps a little beyond the capabilities of the D700 and D810, though I did manage a few images. Things were a little better on the march, which at times went through some fairly well let junctions.
But perhaps the most challenging situation was when a large group of red-flag carrying protesters let off red flares. The image at the top of this post was taken without flash and an exposure which held the highlights, but they were really too extreme, and I needed to let these burn out.
Increasing the exposure showed up at least some of the background, and using a little flash let me bring people in the foreground up from the shadows. But I still don’t really have a solution for situations like this.
After the march there was another short rally, with rather a crush of photographers. I took a number of pictures working very close in to those speaking with the 16mm fisheye – including that above. With the wide view of that lens, flash isn’t generally an option – unless you are aiming for powerful vignetting – and I was working by available light, in this case augmented by someone’s video light. As usual changed to cylindrical perspective.
After the end of the official protest there were still hundreds of people milling around in Parliament Square and wondering how to continue their protest. But I was having a very bad case of wandering finger, somehow managing to shift the shutter speed on the D810 to ridiculous levels – it had reached ISO2500 before I finally noticed it. It’s quite remarkable that the flash continues to synchronise at these speeds, but most of the results were not usable. I knew things were going wrong, but in the dark and heat of the moment couldn’t immediately sort things out. So I went back to working without flash and changed to 1/50th second, but it was a little late, as police were approaching and people climbing down from the plinth.
ISOs really become pretty irrelevant under these conditions. This image was taken with the camera set at ISO2000 but with -4 stops of exposure compensation. Which I suppose you could call ISO 32000.
Within seconds I had the flash and camera working together again, and was able to photograph the police questioning one man who had been on the plinth and then telling Focus E15 that they were not allowed to use a megaphone in Parliament Square. They were deciding what to do, but I’d had enough and decided it was unlikely much more would happen and went home.
There are no adverts on this site and it receives no sponsorship, and I like to keep it that way. But it does take a considerable amount of my time and thought, and if you enjoy reading it, the occasional small donation – perhaps the cost of a beer – would be appreciated. |
Maine Public Utilities Commission Chairman Mark Vannoy told Maine Public that although many complaints had been resolved, a full investigation is still warranted concerning customers' complaints about CMP's metering and billing resulting from a new billing system that was rolled out last fall.
by STAFF
More than 130 customers of Central Maine Power Co. have filed written comments since the Maine Public Utilities Commission launched a formal investigation of customers' complaints about the utility's metering and billing resulting from a new billing system that was rolled out last fall.
That number seems likely to grow since a group calling itself "CMP Ratepayers Unite" has launched a Facebook page that reports having 804 members. The Facebook page carries both a running conversation of posts from disgruntled CMP customers and encourages them to file formal complaints with the PUC since its investigation was launched on Feb. 22.
"This group is a forum to unite all the CMP customers who have seen a dramatic increase in their energy bill that can not be (or will not be) explained by CMP," the group posted on its Facebook page. "We demand further investigation into what is causing this increase and request a credit to our accounts."
Most of the 131 comments posted on PUC's public comment tab are from residential customers, but at least two businesses have cited concerns about unexplained increases in their CMP bills in recent months.
In a comment filed Tuesday, Joel Alex of Blue Ox Malthouse LLC in Lisbon Falls wrote: "Our business just began a review and audit of our electricity because we couldn't understand how starting at the end of last year our electricity costs more than doubled per month without explanation or notice. We were going to reach out to CMP this week before seeing this investigation open up. I am glad to hear that the commission is looking into this matter and hope it can be resolved."
Lynn R.Boynton, of G.R.F. Real Estate Co. in Swanville, wrote on Monday: "We have seen our bill at this location double for the last two months. CMP claims that our usage has doubled, but they don't give meter readings anymore for me to actually see that. This property has the same tenants as a year ago and no real increased usage .... this doesn't make any sense. We have CMP accounts at three different locations and it frightens me that we have no choice or say in these matters."
Comments filed by residential customers convey a common theme of dramatic increases in recent months that they believe to be out-of-whack with their usage, such as the allegation made by a Gardiner residential customer in a comment filed with PUC on Tuesday: "I have been double-billed and charged three times the normal amount, with nothing changing."
Maine Public reported that PUC Commissioner Bruce Williamson said the rollout of the new billing system overlapped with widespread outages caused by the late October windstorm.
"Toss in several weeks of very cold weather and increased usage that will naturally occur, and the confusion about what the observed bill increases might mean grows in intensity," Williamson told Maine Public. "In short and in retrospect customers have had the unpleasant experience of receiving poor customer care when they needed it most."
PUC's public record indicates that at least 131 CMP customers have filed complaints alleging they've been overcharged, with some customers stating their bills had doubled or even tripled despite their usage going down or staying the same since the new billing system was implemented.
PUC Chairman Mark Vannoy told Maine Public that although many complaints had been resolved, a full investigation is still warranted — adding that CMP would be held accountable for any systemic problems.
A CMP spokeswoman told Maine Public the company will cooperate with the inquiry. The utility's website includes a home page alert stating, "Severe cold weather may impact your electricity bill," with tabs guiding customers to free services that will help them manage their electricity usage and understand better how it impacts their monthly bill. |
Flag of Åland
The flag of Åland is the Swedish flag defaced by a red cross symbolizing Finland. Today, blue and white are considered the Finnish colours, but in the early days of Finnish nationalism, red and yellow from the Finnish coat of arms was also an option.
The flag has been the official flag of the autonomous Finnish province of Åland since 1954. It was first hoisted on 3 April 1954.
Prior to autonomy, an unofficial horizontal bicolour triband of blue-yellow-blue was in use. That flag was made illegal in 1935.
At an early stage, the population in Åland wanted their flag to be the opposite of Sweden's, with a yellow field and a blue cross. That was later prohibited.
References
External links
Category:Flags of Finland
Flag
Category:Nordic Cross flags
Åland |
Q:
Authorization supported in Devise for Rails?
I've implemented Devise for a Rails 3.2.8 app. Very easy, seems to work fine. But the documentation suggests creating a whole separate table with email/passwords for an admin role. I need admins in our system to also be treated like users, they just have extra permissions. Does Devise help in this or are there good extensions for authorization? Or am I expected to create an additional Role model or field in the User model to deal with this?
A:
If your requirements are simple, you may just add a boolean column in your users table called "is_admin" and check against it everytime you need extra permissions.
For a systematic solution, check out Cancan by ryanb(Railscasts author)
|
The United States Copyright Group (USCG) has dropped another mass-lawsuit they filed earlier against 1,951 BitTorrent users. The dismissal comes just a week after the lawyers dismissed their 'The Expendables' case and suggests they are retreating. The question is, however, whether this signals the end of trouble for the defendants or whether the lawyers will re-file their cases in smaller batches.
Early 2010, USCG imported the mass-BitTorrent lawsuit scheme into the United States. Since then the group has sued tens of thousands of alleged BitTorrent users, and other lawyers have been quick to copy their tactics.
Thus far the results in court have varied greatly. In some cases the judges were quick to throw the cases out, and in other instances the copyright holders were allowed to identify the alleged copyright infringers. They could then continue their scheme and send settlement offers to the defendants to make the threat of legal action disappear.
Last week we reported that USCG had dropped one of their most prominent cases representing the makers of The Expendables, Nu Image. In a brief court filing they voluntarily dismissed their case against 23,322 alleged BitTorrent users who were accused of illegally sharing the film.
One of the reasons for this dismissal is that in July, District Court Judge Robert Wilkins ruled that the lawyers could only go after those individuals who are reasonably likely to be living in the District of Columbia.
This meant that they were not allowed to send any subpoenas to ISPs when the IP-addresses are located in other districts, and it effectively reduced the group of defendants to about 1 percent of what it initially was. Apparently, this group of leftover defendants was not worth the effort and the case was dropped.
But this case doesn’t stand alone.
This week USCG voluntarily dismissed another lawsuit (pdf), one that was filed just a few weeks ago. The case in question was filed on behalf of Cinetel Films, the makers of the horror flick “I Spit on Your Grave” and listed 1,951 BitTorrent users as defendants.
As with the Expendables case, USCG doesn’t give a reason why they chose to voluntarily dismiss the case. However, since this case was also appointed to Judge Robert Wilkins it doesn’t seem far-fetched that they anticipated running into similar jurisdiction issues as they did in the Expendables case.
The above suggests that USCG is ‘retreating’ and they are unlikely to file similar mass-lawsuits at the District Court for the District of Columbia in the near future. However, that doesn’t mean that the trouble for the defendants is completely over.
As both cases were dismissed “without prejudice,” it means that they ran be refiled at a later stage. This allows the lawyers to cut up the huge list of defendants into smaller batches and file new lawsuits in the districts where these alleged BitTorrent users live.
As we’ve pointed out in the past, anti-piracy lawyers are constantly changing their tactics to maximize the profitability of their settlement schemes. The future will show whether USCG and its clients are planning to do the same. In other words, they may have lost a battle but the war is certainly not over yet. |
Introduction
============
In the year 2008, an estimated 413,171 spinal fusion operations, 436,736 primary total hip arthroplasty (THA), and 680,839 primary total knee arthroplasty (TKA) procedures were performed in the United States alone,[@b1-ijn-7-4829] leading to an approximately US\$13 billion market for orthopedic implants.[@b2-ijn-7-4829] Future demand for such implants is expected to rise. When otherwise well functioning orthopedic implants become colonized with bacteria, significant patient morbidity can follow. The reason is that bacteria adhere to implant surfaces and are resistant to host immune mechanisms and systemic antibiotics. Treatment of such implant-related infections requires extensive repeat surgery, implant extrication, extended duration of systemic antibiotic therapy, bone loss, and substantial cost, suffering, and disability.
Implant-related infections occur in spine surgery between 2.6% and 3.8% of the time.[@b3-ijn-7-4829] In hip replacement surgery, deep infection occurs at 1.63% at 2-years post-operatively,[@b4-ijn-7-4829] and the figures for knee replacement are about 1.55%.[@b5-ijn-7-4829] These numbers underestimate the true incidence of infection because of difficulties related to clinical diagnoses, and a paucity of credible data from epidemiological surveys. Mortality rates from complications related to deep prosthetic infections in THA and TKA are reportedly between 2.7% and 18%,[@b6-ijn-7-4829] and infection is the most common reason for repeat surgery after otherwise successful prosthetic joint replacement.[@b7-ijn-7-4829] The incidence of infection in THA and TKA may be increasing, probably due to improved detection and also because of evolving antibiotic-resistant bacteria strains. Treatment costs related to infected orthopedic implants can range from 1.52 to 1.76 times the cost of the original surgery.[@b8-ijn-7-4829] While orthopedic implants are deemed expensive, their costs are easily overwhelmed by the overall treatment cost of implant-related infections.[@b9-ijn-7-4829] Therefore, there is considerable interest in reducing the risk of infections related to orthopedic implants.
In addition to total joint replacement and spinal devices, orthopedic implants are also manufactured as screws, plates, and percutaneously implanted pins to treat fractures; bacterial contamination of such can lead to poor bone healing.[@b10-ijn-7-4829] Unless acute implant infections can be overcome expeditiously, adjacent tissues become colonized with bacteria,[@b11-ijn-7-4829]--[@b13-ijn-7-4829] and the risk of chronic bone infection (osteomyelitis) increases.[@b13-ijn-7-4829],[@b14-ijn-7-4829] Osteomyelitis can complicate fracture treatment with metal external fixator devices up to 4% of the time.[@b11-ijn-7-4829]--[@b13-ijn-7-4829] Ultimately, orthopedic infections lead to implant loosening, nonhealing of fractures, and device failures.[@b12-ijn-7-4829]
Bacteria present in the bloodstream and body tissues can usually be cleared by host immune mechanisms and antibiotic treatment.[@b15-ijn-7-4829] However, once bacteria colonize implant surfaces by expressing a biofilm layer, they become relatively impervious to such nonsurgical measures. Biofilm production is accompanied by changes in gene expression and growth rates such that host immune mechanisms are rendered ineffective, leading to a chronically infected environment around the implant.[@b15-ijn-7-4829]--[@b18-ijn-7-4829] A related clinical concern pertains to the development of antibiotic-resistant strains of bacteria, including *S. aureus* and *S. epidermidis*, which have been well documented in the clinical orthopedic setting.[@b19-ijn-7-4829],[@b20-ijn-7-4829] Any material science-derived strategy that discourages bacterial colonization of implant surfaces will therefore be of value in reducing the need for systemic antibiotic therapy and surgical removal of infected implants.[@b20-ijn-7-4829]
Changing implant surface texture from a micron-sized to a nanometer-sized topography affects osteoblast adhesion[@b21-ijn-7-4829]--[@b26-ijn-7-4829] and subsequent cellular function, while decreasing competitive fibroblast activity.[@b27-ijn-7-4829],[@b28-ijn-7-4829] Nanoroughened titanium (Ti) made by electron-beam evaporation[@b29-ijn-7-4829] and nanotubular and nanotextured Ti created by anodization can enhance osteoblast adhesion and function (such as alkaline phosphatase synthesis, calcium deposition, and collagen secretion) when compared with micron nanosmooth control surfaces.[@b30-ijn-7-4829] Increased protein adsorption on nanotextured Ti surfaces is correlated with improved osteoblast function.[@b31-ijn-7-4829]--[@b33-ijn-7-4829] The authors have previously shown that by selectively engineering the surface topography of a biomaterial, bacteria adhesion can be decreased.[@b34-ijn-7-4829],[@b35-ijn-7-4829]
Because silicon nitride (Si~3~N~4~) is used in spinal reconstructive surgery today, the adhesion of multiple bacteria species onto polished and nanostructured versions of this biomaterial was examined, using two other orthopedic biomaterials (Ti and poly-ether-ether-ketone \[PEEK\]) as controls. The null hypothesis was that bacterial adhesion and surface protein adsorption (fibronectin, vitronectin, and laminin) would not differ between these materials. Gram-positive *S. epidermidis* and *S. aureus*, and Gram-negative *P. aeruginosa*, *E. coli*, and *Enterococcus* were tested because these strains are commonly implicated in orthopedic implant infections.[@b19-ijn-7-4829]
Materials and methods
=====================
Biomaterials
------------
Si~3~N~4~ was supplied by Amedica Corporation (Salt Lake City, UT) in two surface morphologies; with an "as-fired" surface that has nanostructured features, and a smooth polished surface, respectively. Biomedical grade 4 titanium (Fisher Scientific, Continental Steel and Tube Co, Fort Lauderdale, FL) and PEEK Optima^®^ (Invibio, Lancashire, United Kingdom) were obtained with typical machined surfaces. The surfaces of these materials were characterized for morphology and roughness using scanning electron microscopy (SEM) (using an LEO 1530 VP FE-4800 field-emission scanning electron microscope \[Zeiss, Peabody, MA\]). Specimens of 1 cm × 1 cm dimensions first underwent sessile water-drop tests to assess material wetting characteristics using a KRÜSS easy drop contact angle instrument connected to the drop shape analysis program (version 1.8) (KRÜSS GmbH, Hamburg, Germany) in accordance with an ASTM standard (D7334-08).[@b36-ijn-7-4829] Prior to bacterial exposure, all samples underwent sterilization with ultra violet light exposure for 24 hours on all sides, and roughness characterization with standard SEM.
Bacteria studies
----------------
Bacteria were inoculated (10^5^) onto the material surfaces for 4, 24, 48, and 72 hours. *S. epidermidis*, *P. aeruginosa*, *S. aureus*, *E. coli*, and *Enterococcus* were obtained from American Type Culture Collection (Manassas, VA) (strains 35984, 25668, 25923, 26, and 6569, respectively). The dry pellet was rehydrated in 6 mL of Luria broth (LB) consisting of 10 g tryptone, 5 g yeast extract, and 5 g NaCl per liter double-distilled water with the pH adjusted to 7.4 (Sigma-Aldrich, St Louis, MO). Fetal bovine serum (FBS) (HyClone; Thermo Scientific, Waltham, MA) at 10% concentration was added to the LB, and the bacteria solution was agitated under standard cell conditions (5% CO~2~/95% humidified air at 37°C) for 24 hours until the stationary phase was reached. The second passage of bacteria was diluted at a ratio of 1:200 into fresh LB supplemented with 10% FBS and incubated until it reached the stationary phase. The second passage was then frozen in one part LB and 10% FBS and one part glycerol (Sigma-Aldrich) and stored at −18°C. All experiments were conducted from this frozen stock. One day before bacterial seeding for experiments, a sterile 10 μL loop was used to withdraw bacteria from the frozen stock and to inoculate a centrifuge tube with 3 mL of fresh LB supplemented with 10% FBS.
Bacterial function was determined by crystal violet staining and a live/dead assay (Molecular Probes^®^, Life Technologies, Carlsbad, CA) using previously described methods.[@b35-ijn-7-4829] For the live/dead assay, at the end of the prescribed time period, substrates were rinsed twice with Tris-buffered saline (TBS) comprised of 42 mM Tris-HCl, 8 mM Tris base, and 0.15 M NaCl (Sigma-Aldrich) and then incubated for 15 minutes with the BacLight™ Live/Dead solution (Life Technologies) dissolved in TBS at the concentration recommended by the manufacturer. Substrates were then rinsed twice with TBS and placed into a 50% glycerol solution in TBS prior to imaging. Bacteria were visualized and counted in situ using a Leica DM5500 B fluorescence microscope with image analysis software captured using a Retiga™ 4000R camera (QImaging, Surrey, BC, Canada).
Protein adsorption
------------------
Standard fibronectin, vitronectin, and laminin enzyme-linked immunosorbent assays (ELISA) were performed after soaking material samples in bacterial media (LB supplemented with 10% FBS) used above for 20 minutes, 1 hour, and 4 hours, as previously described.[@b35-ijn-7-4829] Substrates were placed in a standard 24-well culture plate and immersed in 1 mL of LB supplemented with and without 10% FBS for 20 minutes, 1 hour, and 4 hours at 37°C in 5% CO~2~/95% humidified air. After rinsing in phosphate-buffered saline (PBS), areas that did not absorb proteins were blocked and incubated for 1 hour in bovine serum albumin, BSA (2 wt% in PBS, Sigma-Aldrich). Substrates were again rinsed twice with PBS before either fibronectin, vitronectin, or laminin were directly linked respectively with primary rabbit antibovine fibronectin, anti-vitronectin, or anti-laminin (EMD Millipore, Billerica, MA) at a concentration of 6 μg/mL in 1% BSA for 1 hour at 37°C in 5% CO~2~/95% humidified air. After rinsing three times with 0.05% Tween 20^®^ (AkzoNobel, Amsterdam, The Netherlands) for 5 minutes with each rinse, the samples were further incubated for 1 hour with a secondary goat anti-rabbit conjugated with horseradish peroxidase (HRP) (Bio-Rad Laboratories, Hercules, CA) at a concentration of 10 μg/mL in 1% BSA. Following triple rinsing with 0.05% Tween 20 for 5 minutes per rinse, surface-adsorbed protein was measured with an ABTS substrate kit (Vector Laboratories, Burlingame, CA) that reacted only with the HRP. Light adsorbance was measured at 405 nm on a spectrophotometer and analyzed with computer software. The average adsorbance was subtracted by the average adsorbance obtained from the negative controls soaked in LB with no FBS. ELISA was performed in duplicate and repeated three times per substrate.
Statistical analysis
--------------------
Each experiment was done in triplicate with new bacteria, media, and samples. Time series data for biofilm formation, bacteria colonization, and growth were curve-fit to either linear or exponential functions. Hypothesis testing was completed using regression analysis and confidence intervals in accordance with techniques previously described.[@b37-ijn-7-4829] Paired comparison *t*-tests were used to assess significance for the protein adsorption studies; a *P*-value of \<0.05 was deemed statistically significant.
Results
=======
Comparison of materials
-----------------------
Relevant properties of the three biomaterials tested are compared in [Table 1](#t1-ijn-7-4829){ref-type="table"}. Si~3~N~4~ has a protective surface layer that is composed of charged SiNH~3~^+^, SiOH~2~^+^, SiO^−^, and neutral SiNH~2~ and SiOH groups.[@b38-ijn-7-4829] The presence of the amine groups leads to a high isoelectric point (between 8 and 9) and an overall net positive surface charge.[@b38-ijn-7-4829],[@b39-ijn-7-4829] Ti has a native oxide layer (TiO~2~) which has an isoelectric point of about 4.5 and therefore a negative surface charge at pH 7.[@b40-ijn-7-4829] PEEK surfaces have polymeric chains ending in --OH groups, that yield an isoelectric point of about 4.5 and a negative surface charge.[@b41-ijn-7-4829] Si~3~N~4~ has the lowest wetting angle and greater hydrophilicity when compared with PEEK or Ti ([Table 1](#t1-ijn-7-4829){ref-type="table"}).
SEM images of biomaterial surfaces are illustrated in [Figures 1](#f1-ijn-7-4829){ref-type="fig"} and [2](#f2-ijn-7-4829){ref-type="fig"}. Of the materials tested, PEEK and Ti had machined surfaces, while Si~3~N~4~ was in as-fired and polished formulations. SEM images of PEEK and Ti show a micron-rough surface typical of machined materials. The as-fired Si~3~N~4~ had nanostructured surface features with a larger total surface area, as shown in the high magnification images ([Figure 2](#f2-ijn-7-4829){ref-type="fig"}). The as-fired Si~3~N~4~ surface morphology reflects the natural condition of this material subsequent to densification by sintering and hot-isostatic pressing.[@b42-ijn-7-4829] The surface is composed of randomly oriented acicular protruding grains typically less than 1 μm in cross-section, yielding a unique nanotexture ([Figure 2B](#f2-ijn-7-4829){ref-type="fig"}). Note that individual hexagonal grains of Si~3~N~4~ have definitive linear facets (in cross-section) and sharp corners at the termination of the acicular grains, which are typically less than 100 nm. These unique features may play a role in interaction with bacteria, resulting in their lysis. This is contrasted to the highly polished Si~3~N~4~ surface of [Figure 2A](#f2-ijn-7-4829){ref-type="fig"} in which the acicular asperities were removed.
Surface roughness measurements derived from atomic force microscopy (AFM) measurements are summarized in [Table 1](#t1-ijn-7-4829){ref-type="table"}. Results were 25 nm, 10 nm, 3 nm, and 1 nm for the asfired Si~3~N~4~, polished Si~3~N~4~, Ti, and PEEK, respectively. These AFM surface roughness values differ from those that could be obtained using contact profilometry because the areal sampling size of AFM is small compared with contact profilometry. It is obvious from a comparison of the features in [Figure 1](#f1-ijn-7-4829){ref-type="fig"} that the micron scale roughness of Si~3~N~4~ is similar to that of Ti and PEEK, although there are notable topographical differences. However, the AFM measurements were made over fractions of nanometers. In effect, AFM is measuring the nanoroughness of the materials inbetween micron-sized surface features. These results show that as-fired Si~3~N~4~, polished Si~3~N~4~, Ti, and PEEK have markedly different surface chemistries and topographies that could affect bacterial and protein adhesion.
Bacteria studies
----------------
[Figure 3](#f3-ijn-7-4829){ref-type="fig"} shows biofilm formation for each bacterial species, and [Figure 4](#f4-ijn-7-4829){ref-type="fig"} shows corresponding live bacteria counts at each time interval. Except for *Enterococcus*, trends in biofilm formation were similar for all bacteria. Exponential growth of biofilm was noted on PEEK when exposed to *S. epidermidis*, *S. aureus*, *P. aeruginosa*, and *E. coli*, whereas linear growth was observed for Si~3~N~4~ and Ti. Independent of time points, the lowest biofilm formation occurred on the as-fired Si~3~N~4~, followed by polished Si~3~N~4~. These differences were statistically significant (*P* \< 0.05) for bacterial exposure times \> 24 hours. Also, with the exception of *Enterococcus*, biofilm formation was significantly lower (*P* \< 0.05) on Ti compared with PEEK, for time periods \> 48 hours. PEEK demonstrated the highest biofilm affinity, with values that were 5--16 times greater than those for as-fired Si~3~N~4~, 1.5--10 times more than for polished Si~3~N~4~, and between 1 and 6.7 times higher than for Ti.
Live bacteria counts were the highest for PEEK at all time periods, followed by Ti, polished Si~3~N~4~, and then asfired Si~3~N~4~ ([Figure 4](#f4-ijn-7-4829){ref-type="fig"}). These differences were statistically significant (*P* \< 0.05) for all bacterial species tested, and at all time periods \> 48 hours. Live bacteria manifested on PEEK were between 8 and 30 times the bacteria found on as-fired Si~3~N~4~. These results were particularly remarkable for *P. aeruginosa*, which is a virulent and difficult microbe to eliminate from polymeric implants.[@b43-ijn-7-4829]
To summarize, less bacterial activity was manifested on Si~3~N~4~ than on either Ti or PEEK, probably because of the surface chemistry and nanostructure differences between these materials. Substantially lower loads of *S. epidermidis*, *S. aureus*, *P. aeruginosa*, *E. coli*, and *Enterococcus* bacteria were measured on Si~3~N~4~ surfaces than Ti or PEEK, for up to 72 hours of incubation.
Protein adsorption studies
--------------------------
[Figure 5](#f5-ijn-7-4829){ref-type="fig"} shows the relative absorbance of fibronectin, vitronectin, and laminin at 20-, 60-, and 240-minute intervals. Fibronectin and vitronectin adsorption was significantly greater on Si~3~N~4~ (whether polished or as-fired) when compared with PEEK or Ti at all time intervals (*P* \< 0.01). As-fired Si~3~N~4~ showed a higher affinity for these two proteins than polished Si~3~N~4~. Laminin adsorption did not differ significantly between the biomaterials at the 20-minute time interval. At 60 minutes, both Si~3~N~4~ surfaces showed significant increased laminin adsorption (*P* \< 0.01) when compared with Ti or PEEK. At 240 minutes, as-fired Si~3~N~4~ was the only surface that showed statistically more laminin adsorption (*P* \< 0.01) than all other materials.
To summarize, Ti and PEEK proved inferior in terms of protein adsorption when compared with as-fired and polished Si~3~N~4~ surfaces. As-fired Si~3~N~4~ provided the highest protein adsorption platform among the materials tested. Surface protein adsorption is relevant because previous studies have correlated increased vitronectin and fibronectin adsorption to decreased bacterial activity.[@b35-ijn-7-4829]
Discussion
==========
Bacterial infection of orthopedic implants is a complex, multifactorial process that is influenced by bacterial properties, the presence of serum proteins, fluid flow around the implant, implant surface chemistry and morphology, host immune variables, and probably other variables.[@b44-ijn-7-4829] Infection can arise from inadvertent contamination of an implant, contagion from the surgical staff, bacteria arising from the patient's skin or mucus membranes, unrecognized infection elsewhere in the body, ineffectively applied surgical disinfectants, and sepsis acquired from others.[@b45-ijn-7-4829] Most of these risk factors can be mitigated by appropriate nosocomial hygiene practices, and through the use of perioperative antibiotic prophylaxis.[@b3-ijn-7-4829],[@b6-ijn-7-4829],[@b9-ijn-7-4829],[@b46-ijn-7-4829],[@b47-ijn-7-4829] However, no strategy has proven effective in completely eliminating the risk of infections related to implant surgery. Strategies to discourage bacterial adhesion to implants have included antibacterial surface coatings and treatments, and the development and use of nanostructured surfaces, or a combination of these methods.
Surface coatings and treatments
-------------------------------
Surface coatings or surface treatments on implants can resist pathogen adhesion or release chemicals that invade bacterial biofilm. Silver ions have been investigated as a surface antiseptic agent, although the exact mechanism for silver ion toxicity on bacteria is unclear.[@b48-ijn-7-4829] Silver can be incorporated into polymeric or inorganic coatings,[@b48-ijn-7-4829],[@b49-ijn-7-4829] and while its anti-infective properties have been known for generations, it continues to drive patent innovation.[@b50-ijn-7-4829],[@b51-ijn-7-4829] Other coatings have included pre-loaded formulations of antibiotics like vancomycin or gentamicin, or antiseptic agents like chlorohexidine and chloroxylenol.[@b52-ijn-7-4829] Antibacterial polymeric functionalized coatings which incorporate hyaluronic acid and chitosan have been investigated thoroughly.[@b52-ijn-7-4829]--[@b57-ijn-7-4829] Xerogel polymers that have been modified to release nitric oxide are effective in inhibiting the adhesion of *S. aureus*, *S. epidermidis*, and *E. coli*.[@b58-ijn-7-4829] A limitation of all such coatings is the transient duration of effectiveness, ie, once the coating dissipates, so does any antibacterial effect.
Surface modifications of biomaterials can provide a long-term shield against bacterial infection of implants. Yoshinari et al modified the surface of Ti and studied bacterial adhesion of *P. gingivalis* and *Aggregatibacter actinomycetemcomitans* using ion implantation of Ca^+^, N^+^, and F^+^, ion-beam deposition of Ag, Sn, Zn, and Pt, ion plating of TiN and Al~2~O~3~, and anodic oxidation formation of TiO~2~.[@b59-ijn-7-4829] Control materials included polished, sand-blasted, and striated Ti. They found a general trend toward higher bacterial adhesion on blasted and Ca^+^ implanted Ti. A follow-up study by these authors also showed that F+ implanted surfaces resisted initial bacterial adhesion in the absence of fluorine leaching from the surface; the antibacterial effect probably related to metal-fluorine complexes at the surface.[@b60-ijn-7-4829] Katsikogianni et al found otherwise: *S. epidermidis* activity on polymers with and without fluorine showed that those containing fluorine increased bacteria attachment.[@b61-ijn-7-4829] Raulio et al also investigated fluorine, and found that by coating stainless steel with fluoropolymers, it was possible to reduce biofilm formation of several bacteria strains, including *S. epidermidis*.[@b62-ijn-7-4829]
Li et al performed a comparative study using glass and metal-oxides applied as thin films.[@b63-ijn-7-4829] These included three uncoated glass surfaces and combinations of Co-Fe-Cr, Ti-Fe-O, SnO~2~, SnO~2~-F, SnO~2~-Sb, Al~2~O~3~, and Fe~2~O~3~ thin films applied to glass substrates. After measuring material hydrophilicity, zeta potential, and surface energy, the authors tested them against eight strains of bacteria, and found that hydrophobicity and total surface energy (rather than material chemistry) led to increased bacterial adhesion. Hydrophilic surfaces had the fewest number of adherent bacteria, and increasing the concentration of surface ions encouraged binding for both Gram-positive (*Bacillus subtilis*) and Gram-negative (two *P. aeruginosa* strains, three *E. coli* strains, and two *Burkholderia cepacia* strains) bacteria.
Conversion of Ti surfaces to TiO~2~ via anodic oxidation, electrophoretic deposition, chemical vapor deposition, ion implantation, and plasma spraying has been examined as an anti-infective surface modification strategy, especially when coupled with photocatalytic activation of TiO~2~.[@b64-ijn-7-4829] Orthopedic implants made of porous Ti are commonly coated with hydroxyapatite to promote osteointegration, but this strategy may lead to increased harboring of *S. aureus* bacteria, more severe infection, and less osteointegration when compared with uncoated Ti.[@b65-ijn-7-4829],[@b66-ijn-7-4829]
The results of this present study show that Si~3~N~4~ has intrinsic bacteriostatic properties, whether in an as-fired or smooth-surface morphology. This study did not elucidate the precise mechanism of Si~3~N~4~ anti-infectivity, but results suggest that material hydrophilicity and surface chemistry may contribute to less biofilm formation ([Figure 3](#f3-ijn-7-4829){ref-type="fig"}) and lower bacteria counts ([Figure 4](#f4-ijn-7-4829){ref-type="fig"}) on Si~3~N~4~ when compared with Ti or PEEK. These differences were observed for all bacteria, regardless of Gram-positive or Gram-negative strains. Hydrophilic Si~3~N~4~ surfaces were probably less conducive to bacterial adhesion, when compared with hydrophobic surfaces where water displacement is not required for microbial adherence.[@b44-ijn-7-4829] Consistent with this observation, the inert and highly hydrophobic characteristics of PEEK promoted bacterial adhesion and inhibited protein adsorption when compared with Si~3~N~4~. Other authors have supported these observations as they relate to PEEK and Ti.[@b67-ijn-7-4829],[@b68-ijn-7-4829]
The anti-infectivity of Si~3~N~4~ may also relate to surface chemistry, and the authors' observations are consistent with previous data with polymeric coatings containing chitosan, a material similar to Si~3~N~4~ in terms of a net positive charge and the presence of amine groups at the surface.[@b52-ijn-7-4829]--[@b56-ijn-7-4829] The interaction of these groups with negatively charged bacteria reportedly leads to membrane disruption and lysis in chitosan-containing polymers.[@b56-ijn-7-4829] However, further research is required to confirm whether or not this is a dominant operative mechanism for Si~3~N~4~.
Nanostructured surfaces
-----------------------
Nanotechnology is of interest in enhancing the surface characteristics and improving the performance of orthopedic implants. Increasing micron-level surface roughness of biomedical implants correlates with increased bacterial adhesion[@b44-ijn-7-4829] and enhanced osteointegration.[@b69-ijn-7-4829] The competition between bacteria, bone cells, and serum proteins has been characterized as a "race to the surface."[@b10-ijn-7-4829] However, surface roughness is only one of several variables that influence bacterial adhesion and protein adsorption on an implant. For instance, without specifically distinguishing changes in surface roughness, surface chemistry, or crystallinity, Truong et al showed that nanoscale roughening of ultrafine grained Ti led to greater attachment of *S. aureus* and *P. aeruginosa*, when compared with smooth surfaces.[@b70-ijn-7-4829] Conversely, Singh et al found increased bacterial adhesion and biofilm formation on Ti surfaces with Ra (roughness average) values \< 20 nm, and increased protein adsorption at Ra values between 16 and 32 nm; further increases in surface roughness were associated with reduced pathogen activity. [@b71-ijn-7-4829] In contrast, Hilbert et al could not correlate bacterial adhesion, colonization, and growth with changes in surface finish ranging from 0.1 to 0.90 μm,[@b72-ijn-7-4829] and Flint et al found that bacterial adhesion could not be related to surface roughness at all.[@b73-ijn-7-4829] Thus, surface roughness alone may not fully explain the differences in bacterial adhesion and protein adsorption.
Anselme et al reviewed the factors that affect the interaction of cells and bacteria with nanostructured surfaces. [@b74-ijn-7-4829] In addition to surface roughness, detailed surface topography, including the size, shape, orientation, distance, and organization of surface nanofeatures were identified as important variables. Whitehead et al further supported this view when they found higher bacterial counts on substrates that contained 2 μm diameter pits as opposed to those in the range of 0.5 μm.[@b75-ijn-7-4829] Xu et al compared bacterial adhesion between two polyurethane surfaces of the same chemistry; one was smooth and the other contained oriented protrusions or pillars (400 nm diameter × 650 nm height).[@b76-ijn-7-4829] They found biofilm formation significantly less for both *S. epidermidis* and *S. aureus* when using the highly textured polyurethane. Dalby et al examined the response of fibroblasts to nanocolumn structures (100 nm diameter × 160--170 nm height) in polymethylmethacrylate (PMMA) in comparison with smooth substrates and demonstrated decreased cell adhesion using the materials with nanocolumns.[@b77-ijn-7-4829] Bagno et al showed that the number of protruding peaks (ie, peak density) was positively correlated with osteoblast adhesion.[@b78-ijn-7-4829] Similar topographical effects on bacterial adhesion and protein adsorption were observed by these authors for Ti, when conventional (smooth) surfaces were compared to nanoroughened, nanotextured, and nanotubular variations. The authors also reported decreased in-vitro activity of *S. aureus*, *S. epidermidis*, and *P. aeruginosa* on nanorough surfaces prepared by electron-beam evaporation, but an opposite result for nanotubular and nanorough surfaces prepared via anodization.[@b35-ijn-7-4829] However, all three of the nanoprepared Ti surfaces demonstrated increased adsorption of fibronectin in comparison with conventional Ti. A subsequent study showed reduced adhesion of macrophages on anodized Ti with nanotextured and nanotubular structures.[@b79-ijn-7-4829]
Engineered surfaces with topographical features in the nanometer range may affect cell behavior while reducing bacterial adhesion, but these factors alone do not sufficiently predict cellular response. Other variables related to surface energy, surface charge, and chemistry can also inhibit bacterial colonization while enhancing protein adsorption and conformation, leading to improved osteoblast adhesion and tissue growth.[@b31-ijn-7-4829]--[@b33-ijn-7-4829] Biomaterial surfaces with nanorough features are associated with greater vitronectin and fibronectin adsorption that, in turn, are related to decreased bacterial function on the surface.[@b31-ijn-7-4829]--[@b33-ijn-7-4829],[@b35-ijn-7-4829],[@b80-ijn-7-4829]
The acicular grain structure on the as-fired surface of Si~3~N~4~ is composed of randomly oriented columnar grains that are typically 200--700 nm in diameter, and that can protrude above the surface up to about 3 μm. This as-fired surface is not only significantly rougher than Ti, PEEK, or polished Si~3~N~4~ ([Table 1](#t1-ijn-7-4829){ref-type="table"}) but its nanotopography is fundamentally different, as suggested by AFM surface measurements. Even though the PEEK and titanium samples were as-machined, they had significantly smoother surfaces at the nanolevel than either as-fired or polished Si~3~N~4~. Consequently, bacterial and protein adherence to the biomaterials differed in the present experiments. While this study did not elucidate the precise mechanisms, it is probable that the observed behavior of as-fired Si~3~N~4~ is related to nanocolumns, protrusions, and peaks described in previous studies for polyurethane, PMMA, and Ti surfaces.[@b76-ijn-7-4829]--[@b78-ijn-7-4829] In summary, the present authors believe it is the totality of silicon nitride's nano-topography -- including its protruding acicular grains with their definitive hexagonal features and sharp grain ends -- combined with its surface chemistry (ie, positive surface charge and the presence of amine groups) which provides Si~3~N~4~ with its unique antibacterial and protein adsorption characteristics.
Conclusion
==========
This study examined the behavior of Ti, PEEK, and Si~3~N~4~ when respective materials were exposed to five different bacterial species for up to 72 hours. Polished and as-fired surface formulations of Si~3~N~4~ were tested. Decreased biofilm formation and bacterial colonization were demonstrated on both as-fired and polished Si~3~N~4~ in comparison with Ti or PEEK, under in-vitro incubation for time periods of up to 72 hours. Si~3~N~4~ resisted bacterial proliferation under these conditions, despite the absence of antibiotic pharmaceutical agents. Differential protein adsorption on Ti, PEEK, and Si~3~N~4~ surfaces was also demonstrated, such that fibronectin, vitronectin, and laminin adsorbed preferentially onto Si~3~N~4~ when compared with Ti or PEEK, for time periods of up to 4 hours. Previous studies have shown that such differences in protein affinity for biomaterial surfaces may explain, at least in part, differences in biomaterial susceptibility to bacterial infection. The unique surface chemistry and nanostructured features of Si~3~N~4~ may contribute to the favorable antibacterial properties of this bioceramic material, and support further investigation into the use of Si~3~N~4~ as a material platform for orthopedic implants.
The authors thank Khalid A Sethi, MD, FACS, and Christine Ann Snyder, PA, of the Southern New York NeuroSurgical Group, P.C., for their assistance in performing the studies, and David Bohrer for efforts in initiating this work. The authors also express their appreciation to Bryan McEntire, Chief Technology Officer, Alan Lakshminarayanan PhD, Senior Director of Research and Development, Ryan Bock PhD, Research Scientist, all of Amedica Corporation (Salt Lake City, UT); and Steven C Friedman, Senior Editor, Department of Orthopedic Surgery, University of Missouri, for their kind assistance with the manuscript.
**Disclosure**
B Sonny Bal is advisory surgeon to Amedica, developer of synthetic silicon nitride for orthopedic applications, and serves on the Board of Directors of Amedica, Salt Lake City, UT. Co-authors Deborah Gorth, Sabrina Puckett, Batur Ercan, Thomas J Webster, and Mohamed N Rahaman have no disclosures for this article.
{#f1-ijn-7-4829}
{#f2-ijn-7-4829}
{#f3-ijn-7-4829}
{#f4-ijn-7-4829}
{#f5-ijn-7-4829}
######
Comparative properties of medical grades of Si~3~N~4~, ASTM[@b35-ijn-7-4829] grade 4 Ti, and PEEK
Property Units Si~3~N~4~ Ti-ASTM grade 4 PEEK optima^®^
---------------------------------- --------- ---------------------------------------------------------------------------------------------------- ----------------- -----------------
Composition NA Si~3~N~4~, Y~2~O~3~, AI~2~O~3~ Chemically pure Chemically pure
Surface composition NA SiNH~2~ and SiOH TiO~2~ layer --OH groups
Surface roughness (AFM) nm 10.1[\*](#tfn2-ijn-7-4829){ref-type="table-fn"}, 25.3[\*\*](#tfn3-ijn-7-4829){ref-type="table-fn"} 3.06 1
Isoelectric point NA 9 \~4.5 \~4.5
Surface charge at pH = 7 NA Positive Negative Negative
Sessile water drop wetting angle Degrees 39 76 95
**Notes:**
Polished surface;
as-fired surface.
|
Process of introducing impurity atoms into a semiconductor to
affect its conductivity.
DRAM
Dynamic Random Access Memory -- memory in which each stored bit
must be refreshed periodically.
Drift
Gradual departure of the instrument output from the calibrated
value. An undesired slow change of the output signal.
DSP
Digital Signal Processing; a process by which a sampled and
digitized data stream (real-time data such as sound or images) is
modified in order to extract relevant information. Also, a digital
signal processor.
Ductility
A measure of a material's ability to undergo plastic deformation
before fracture; expressed as percent elongation (%EL) or percent
area reduction (%AR) from a tensile test.
Dynamic characteristics
A description of an instrument's behavior between the time a
measured quantity changes value and the time the instrument
obtains a steady response.
Dynamic error
The error that occurs when the output does not precisely follow
the transient response of the measured quantity.
Dynamic range
The ratio of the largest to the smallest values of a range, often
expressed in decibels.
EDP
Ethylene diamine pyrocatechol.
Elastic deformation
A nonpermanent deformation that totally recovers upon release of
an applied stress. |
Film opens in theaters on December 13, launches streaming on December 18
The official website for the In This Corner (and Other Corners) of the World [ Kono Sekai no (Sara ni Ikutsumono) Katasumi ni ] anime film revealed on Thursday that the new Katasumi-tachi to Ikiru Kantoku Katabuchi Sunao documentary film about director Sunao Katabuchi will open in theaters in Japan on December 13. The 95-minute film will also begin streaming on iTunes, Amazon Prime Video, Google Play, and Hikari TV on December 18.
The documentary will show production of In This Corner (and Other Corners) of the World [ Kono Sekai no (Sara ni Ikutsumono) Katasumi ni ], the extended version of the anime film adaptation of Fumiyo Kouno's In This Corner of the World (Kono Sekai no Katasumi ni) manga. The documentary will also follow Katabuchi as he does research for the film.
The extended version of the film will open in Japan on December 20.
Kana Hanazawa is playing the new character Teru, a woman that Suzu meets in the red-light district.
The new version was originally slated to screen in Japan in December 2018, but was delayed to this year. The staff stated last October that the production needed a few more months than the staff originally projected, and in order to live up to fans' expectations of the film's quality, the production committee decided to delay the film.
The extended version will feature about 30 more minutes of footage. The film's director Sunao Katabuchi (Black Lagoon, Mai Mai Miracle) planned the title with Kouno's approval. The concept behind the new version is to give the perspective of "several more lives" in addition to Suzu's, so it has a new title to reflect the new theme. The new work will adapt more scenes from the manga.
The new scenes include Suzu crossing paths with Rin in the fall of 1944 and the winter and spring of 1945. Another new segment will focus on the Makurazaki Typhoon of September 1945, while Suzu is worried for her younger sister Sumi.
Non is again voicing Suzu. kotringo is returning to compose and perform a new song "Kanashikute Yarikirenai" (It's Sad and I Can't Bear It).
Shout! Factory and Funimation Films screened the original film in the United States and Canada in August 2017. |
Application of X-ray and neutron small angle scattering techniques to study the hierarchical structure of plant cell walls: a review.
Plant cell walls present an extremely complex structure of hierarchically assembled cellulose microfibrils embedded in a multi-component matrix. The biosynthesis process determines the mechanism of cellulose crystallisation and assembly, as well as the interaction of cellulose with other cell wall components. Thus, a knowledge of cellulose microfibril and bundle architecture, and the structural role of matrix components, is crucial for understanding cell wall functional and technological roles. Small angle scattering techniques, combined with complementary methods, provide an efficient approach to characterise plant cell walls, covering a broad and relevant size range while minimising experimental artefacts derived from sample treatment. Given the system complexity, approaches such as component extraction and the use of plant cell wall analogues are typically employed to enable the interpretation of experimental results. This review summarises the current research status on the characterisation of the hierarchical structure of plant cell walls using small angle scattering techniques. |
Q:
Describe up to isomorphism all 2d associative algebras with 1 and without 1
I have a question:
Describe up to isomorphism all 2d associative algebras over Ring with 1 and without 1
That's all info, that I found about this question:
Every two-dimensional associative algebra is either equivalent or
isomorphic to one of the eight algebras.
But I don't know how it can be proved.
There was something similar to my problem, but with Lie-group theory which I don't understand.
A:
The notion "2d" makes sense for algebras over a field (namely the dimension of its underlying $K$-vecor space), but is not "defined" over rings. I suppose you mean $R$ perhaps as $\mathbb{R}$, the field of real numbers.
Goze and Remm have classified all $2$-dimensional algebras over an arbitrary field $K$, see here. It is easy to pick out the associative ones form their list. Independently, many people already did this classification, see for example the recent colourful slides here. The idea is easy. Take as basis $(e_1,e_2)$ and write
all basis products $e_i.e_j$ in this basis, with coefficients $a_{ij}$. Then determine the conditions for associativity and compute isomorphisms.
|
The TR-727 was housed in the same chassis as the TR707, except with a blue trim as opposed to the 707's orange. The included sounds concentrated on Latin and other percussive instruments rather than the standard drum kits of the 707, making this machine popular amongst producers in the house music genre.
To add the Roland TR-727 instrument to your Logic Pro or Logic Express setup, click on the link to download the file containing the instrument and samples. |
Q:
Datepicker UI src from jQuery does not work, but src from Google does. Why?
I'm trying to use a jQuery datepicker:
http://jqueryui.com/datepicker/
Interestingly, I copy and paste the source code into an .html file and open it up in Chrome. The datepicker does not work. Here is the source:
<!doctype html>
<html lang="en">
<head>
<meta charset="utf-8">
<title>jQuery UI Datepicker - Default functionality</title>
<link rel="stylesheet" href="//code.jquery.com/ui/1.11.4/themes/smoothness/jquery-ui.css">
<script src="//code.jquery.com/jquery-1.10.2.js"></script>
<script src="//code.jquery.com/ui/1.11.4/jquery-ui.js"></script>
<link rel="stylesheet" href="/resources/demos/style.css">
<script>
$(function() {
$( "#datepicker" ).datepicker();
});
</script>
</head>
<body>
<p>Date: <input type="text" id="datepicker"></p>
</body>
</html>
However, I change the source of the scripts and css from jQuery to Google and it suddenly works.
<!doctype html>
<html lang="en">
<head>
<meta charset="utf-8">
<title>jQuery UI Datepicker - Default functionality</title>
<link href="http://ajax.googleapis.com/ajax/libs/jqueryui/1.8/themes/base/jquery-ui.css" rel="stylesheet" type="text/css"/>
<script type="text/javascript" src="http://ajax.googleapis.com/ajax/libs/jquery/1.6.2/jquery.min.js"></script>
<script src="http://ajax.googleapis.com/ajax/libs/jqueryui/1.8/jquery-ui.min.js"></script>
<link rel="stylesheet" href="/resources/demos/style.css">
<script>
$(function() {
$( "#datepicker" ).datepicker();
});
</script>
</head>
<body>
<p>Date: <input type="text" id="datepicker"></p>
</body>
</html>
I'm happy to see it work, but I do not understand why. This is especially confusing as I imagine the src directly from jQuery, the source of this code, should be more reliable than the one provided by Google, correct?
A:
Add http: In front of the //
// won't work on its own.
|
Participants completed a before/after and a similar/different relational task, which were presented on computer using the Implicit Relational Assessment Procedure (IRAP). They were subsequently exposed to the Kaufman Brief Intelligence Test (K-BIT). For each relational task, response latencies were measured on consistent trials, in which participants were required to respond in accordance with pre-established verbal relations, and on inconsistent trials, in which participants were required to respond against these relations. A difference-score was also calculated by subtracting consistent response latencies from those on inconsistent trials. The inconsistent trials and the difference-score were deemed to provide measures of relational flexibility. Results showed that faster responding on the IRAP, and smaller difference scores, predicted higher IQ. The findings suggest that relational flexibility is an important component of intelligence and might therefore be targeted in educational settings. |
Q:
Pytest setup/teardown hooks for session
Pytest has setup and teardowns hooks for module, class, method.
I want to create my custom test environment in setup (before start of test session) and cleanup after all tests will be finished.
In other words, how can I use hooks like setup_session and teardown_session?
A:
These hooks work well for me:
def pytest_sessionstart(session):
# setup_stuff
def pytest_sessionfinish(session, exitstatus):
# teardown_stuff
But actually next fixture with session scope looks much prettier:
@fixture(autouse=True, scope='session')
def my_fixture():
# setup_stuff
yield
# teardown_stuff
|
Wow, I have been following the story of the development of this amp on this forum. I casually searched to see what was on eBay today and saw that Bob is selling a pair of hand made mono block tube amps. They were already bid up to about $4k when I last looked. I bet they go for at least twice that. Anyone else want to place a guess as to how much the pair will go for? My guess: $10,668.03 (the .03 is to show the implied rigor in my calculus ) |
Simple and elegant wedding
When you have attendees who will be touring to the desired destination marriage, ensure that that you just provide them with present baskets in the lodge they are staying at. This tends to assist to indicate the appreciation which you have for them for changing their designs and traveling to be an element of one's festivities. Follow your stroll down the aisle numerous times to the days foremost up to the marriage. Be certain that you choose to try this on the genuine internet site of your wedding day, while you will wish to examination out the ground along with the sneakers you are likely to have on. This could assistance to improve your move if the big day will come.Take a look at below:vestido de noiva curto One of the issues you really should take into account for your personal company is to serve white wine rather of pink wine since the drinks at your marriage. Plenty of people will likely be donning attire that have light-weight colours, which means you will choose to limit the visibility of stains when they ended up to obtain a collision. After you are giving your speech in the wedding day, recognize that it is actually all right to show emotions. The tales that you just explain to will more than likely be quite emotional, as all people at the wedding will be anticipating you to get rid of some tears. Allow everything out, to show how much each and every tale indicates for you. When thinking about wedding day jewellery, look at borrowing your jewelry alternatively of buying it. Your folks and loved ones could have excellent jewelry parts that they might be prepared to let you use free of demand. In case you use someones jewelry instead of shopping for new, the jewelry will also maintain sentimental worth. Consider generating your individual bouquet in your wedding. You are able to pick up bouquets at grocery outlets for a music after which you can you could customize your own personal floral arrangement to match your costume and decor. Glimpse on-line for instructions on putting a ribbon to the base so that you can maintain on to.Pay a visit to right here:penteado para madrinha Involve your children with your wedding ceremony to verify that it really is an pleasant knowledge for everybody. Start off correct whenever you commence preparing by asking them what aspects they might like to contain while in the ceremony. You can even have your oldest little one wander you down the aisle and give you absent to their new step-parent. Ensure that that everyone with your wedding occasion knows how they're getting to the wedding web-site and again property out of your marriage! This can be particularly important if you're heading to generally be serving liquor, and necessary if it's an open up bar. For anyone who is anxious about any person having much too inebriated, supply no cost cab rides to anybody who would not convey a car, or push them house in the limo. Among the things that you simply can do to point out the help you have in your church is always to get the priest to carry out your wedding day. This tends to make points really feel own on the working day of your nuptial, particularly when you are a devout Catholic and have a strong bond with the chief of the church. Should you be a bride, you must address the groomsmen to your professional shave and haircut, the day ahead of the marriage ceremony. This tends to make certain that they appear as sharp as you can, to ensure every thing is aesthetically stunning at your wedding ceremony. Correct grooming is critical to maximize the search on the essential components in your wedding ceremony. To find out more, make sure you go to the website: vestido de noiva curto |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.