Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
16,333 | 10,789,057,249 | IssuesEvent | 2019-11-05 11:02:58 | spacemeshos/go-spacemesh | https://api.github.com/repos/spacemeshos/go-spacemesh | closed | GetTotalReward api | API & Usability TN-1.0 | # Overview / Motivation
Return the total reward that the miner received
# The Task
This api isn't final, consider adding a layer checkpoint so that the wallet won't need to calc the result for the entire mesh. (Current design:)
rpc GetTotalAwards(google.protobuf.Empty) returns (SimpleMessage) {
option (google.api.http) = {
post: "/v1/gettotalawards"
body: "*"
};
}
# Implementation Notes
TODO: Add links to relevant resources, specs, related issues, etc...
# Contribution Guidelines
Important: Issue assignment to developers will be by the order of their application and proficiency level according to the tasks complexity. We will not assign tasks to developers who have'nt introduced themselves on our Gitter [dev channel](https://gitter.im/spacemesh-os/Lobby)
1. Introduce yourself on go-spacemesh [dev chat channel](https://gitter.im/spacemesh-os/Lobby) - ask our team any question you may have about this task
2. Fork branch `develop` to your own repo and work in your repo
3. You must document all methods, enums and types with [godoc comments](https://blog.golang.org/godoc-documenting-go-code)
4. You must write go unit tests for all types and methods when submitting a component, and integration tests if you submit a feature
5. When ready for code review, submit a PR from your repo back to branch `develop`
6. Attach relevant issue to PR
| True | GetTotalReward api - # Overview / Motivation
Return the total reward that the miner received
# The Task
This api isn't final, consider adding a layer checkpoint so that the wallet won't need to calc the result for the entire mesh. (Current design:)
rpc GetTotalAwards(google.protobuf.Empty) returns (SimpleMessage) {
option (google.api.http) = {
post: "/v1/gettotalawards"
body: "*"
};
}
# Implementation Notes
TODO: Add links to relevant resources, specs, related issues, etc...
# Contribution Guidelines
Important: Issue assignment to developers will be by the order of their application and proficiency level according to the tasks complexity. We will not assign tasks to developers who have'nt introduced themselves on our Gitter [dev channel](https://gitter.im/spacemesh-os/Lobby)
1. Introduce yourself on go-spacemesh [dev chat channel](https://gitter.im/spacemesh-os/Lobby) - ask our team any question you may have about this task
2. Fork branch `develop` to your own repo and work in your repo
3. You must document all methods, enums and types with [godoc comments](https://blog.golang.org/godoc-documenting-go-code)
4. You must write go unit tests for all types and methods when submitting a component, and integration tests if you submit a feature
5. When ready for code review, submit a PR from your repo back to branch `develop`
6. Attach relevant issue to PR
| non_priority | gettotalreward api overview motivation return the total reward that the miner received the task this api isn t final consider adding a layer checkpoint so that the wallet won t need to calc the result for the entire mesh current design rpc gettotalawards google protobuf empty returns simplemessage option google api http post gettotalawards body implementation notes todo add links to relevant resources specs related issues etc contribution guidelines important issue assignment to developers will be by the order of their application and proficiency level according to the tasks complexity we will not assign tasks to developers who have nt introduced themselves on our gitter introduce yourself on go spacemesh ask our team any question you may have about this task fork branch develop to your own repo and work in your repo you must document all methods enums and types with you must write go unit tests for all types and methods when submitting a component and integration tests if you submit a feature when ready for code review submit a pr from your repo back to branch develop attach relevant issue to pr | 0 |
3,585 | 3,489,464,450 | IssuesEvent | 2016-01-03 22:21:32 | godotengine/godot | https://api.github.com/repos/godotengine/godot | closed | Tooltips flashing in Editor UI on Windows | bug platform:windows topic:editor usability | There is an annoying bug in the Windows version that makes tooltips in the editor to not show correctly, but instead to constantly flash on and off:
https://youtu.be/oUM-cz9hKq8
Both the 64bit and 32bit versions seem to be affected.
System: Windows 8.1
Version tested: 1.1stable | True | Tooltips flashing in Editor UI on Windows - There is an annoying bug in the Windows version that makes tooltips in the editor to not show correctly, but instead to constantly flash on and off:
https://youtu.be/oUM-cz9hKq8
Both the 64bit and 32bit versions seem to be affected.
System: Windows 8.1
Version tested: 1.1stable | non_priority | tooltips flashing in editor ui on windows there is an annoying bug in the windows version that makes tooltips in the editor to not show correctly but instead to constantly flash on and off both the and versions seem to be affected system windows version tested | 0 |
44,194 | 12,035,660,265 | IssuesEvent | 2020-04-13 18:18:02 | carbon-design-system/ibm-security | https://api.github.com/repos/carbon-design-system/ibm-security | opened | Update product title font weights | Defect | The font weights should be: IBM (regular) **Security (bold)** Application (regular)
Applies to Shell (Security) & UIShell (Carbon)
Security currently appears to be semibold
| 1.0 | Update product title font weights - The font weights should be: IBM (regular) **Security (bold)** Application (regular)
Applies to Shell (Security) & UIShell (Carbon)
Security currently appears to be semibold
| non_priority | update product title font weights the font weights should be ibm regular security bold application regular applies to shell security uishell carbon security currently appears to be semibold | 0 |
228,204 | 17,438,839,137 | IssuesEvent | 2021-08-05 00:08:48 | cilium/cilium | https://api.github.com/repos/cilium/cilium | closed | kernel 5.7: could not insert 'ip6_tables' | area/documentation good-first-issue kind/community-report | ## Bug report
I enabled `enable-ipv6` options in cilium ConfigMap.
When agents is starting I get this error
```
level=error msg="Command execution failed" cmd="[ip6tables -w 5 -t filter -N CILIUM_INPUT]" error="exit status 3" subsys=iptables
level=warning msg="modprobe: ERROR: could not insert 'ip6_tables': Exec format error" subsys=iptables
level=warning msg="ip6tables v1.6.1: can't initialize ip6tables table `filter': Table does not exist (do you need to insmod?)" subsys=iptables
level=warning msg="Perhaps ip6tables or your kernel needs to be upgraded." subsys=iptables
level=error msg="Error while initializing daemon" error="cannot add custom chain CILIUM_INPUT: exit status 3" subsys=daemon
level=fatal msg="Error while creating daemon" error="cannot add custom chain CILIUM_INPUT: exit status 3" subsys=daemon
```
**General Information**
- Cilium version (run `cilium version`) - 1.7.2
- Kernel version (run `uname -a`)
```
Linux safarov-server.home 5.7.0-0.rc1.20200416git9786cab67457.1.el8.x86_64 #1 SMP Tue Apr 21 07:52:08 GMT 2020 x86_64 x86_64 x86_64 GNU/Linux
```
- Orchestration system version in use (e.g. `kubectl version`, Mesos, ...) - kubernetes
- Link to relevant artifacts (policies, deployments scripts, ...)
- Upload a system dump
[cilium-sysdump-20200427-042111.zip](https://github.com/cilium/cilium/files/4537433/cilium-sysdump-20200427-042111.zip)
**How to reproduce the issue**
1. required enable `enable-ipv6` options in cilium ConfigMap
2. restart cilium agent
3. check cilium logs
| 1.0 | kernel 5.7: could not insert 'ip6_tables' - ## Bug report
I enabled `enable-ipv6` options in cilium ConfigMap.
When agents is starting I get this error
```
level=error msg="Command execution failed" cmd="[ip6tables -w 5 -t filter -N CILIUM_INPUT]" error="exit status 3" subsys=iptables
level=warning msg="modprobe: ERROR: could not insert 'ip6_tables': Exec format error" subsys=iptables
level=warning msg="ip6tables v1.6.1: can't initialize ip6tables table `filter': Table does not exist (do you need to insmod?)" subsys=iptables
level=warning msg="Perhaps ip6tables or your kernel needs to be upgraded." subsys=iptables
level=error msg="Error while initializing daemon" error="cannot add custom chain CILIUM_INPUT: exit status 3" subsys=daemon
level=fatal msg="Error while creating daemon" error="cannot add custom chain CILIUM_INPUT: exit status 3" subsys=daemon
```
**General Information**
- Cilium version (run `cilium version`) - 1.7.2
- Kernel version (run `uname -a`)
```
Linux safarov-server.home 5.7.0-0.rc1.20200416git9786cab67457.1.el8.x86_64 #1 SMP Tue Apr 21 07:52:08 GMT 2020 x86_64 x86_64 x86_64 GNU/Linux
```
- Orchestration system version in use (e.g. `kubectl version`, Mesos, ...) - kubernetes
- Link to relevant artifacts (policies, deployments scripts, ...)
- Upload a system dump
[cilium-sysdump-20200427-042111.zip](https://github.com/cilium/cilium/files/4537433/cilium-sysdump-20200427-042111.zip)
**How to reproduce the issue**
1. required enable `enable-ipv6` options in cilium ConfigMap
2. restart cilium agent
3. check cilium logs
| non_priority | kernel could not insert tables bug report i enabled enable options in cilium configmap when agents is starting i get this error level error msg command execution failed cmd error exit status subsys iptables level warning msg modprobe error could not insert tables exec format error subsys iptables level warning msg can t initialize table filter table does not exist do you need to insmod subsys iptables level warning msg perhaps or your kernel needs to be upgraded subsys iptables level error msg error while initializing daemon error cannot add custom chain cilium input exit status subsys daemon level fatal msg error while creating daemon error cannot add custom chain cilium input exit status subsys daemon general information cilium version run cilium version kernel version run uname a linux safarov server home smp tue apr gmt gnu linux orchestration system version in use e g kubectl version mesos kubernetes link to relevant artifacts policies deployments scripts upload a system dump how to reproduce the issue required enable enable options in cilium configmap restart cilium agent check cilium logs | 0 |
4,840 | 2,879,469,831 | IssuesEvent | 2015-06-10 10:21:12 | pjuu/pjuu | https://api.github.com/repos/pjuu/pjuu | closed | Add link to license on about us page | Application Documentation Normal UX | In the **About Us** page, you mention the GNU AGPLv3 license. I think making the license text into a hyperlink is very important.
> Pjuu is an open-source social networking application released under a "free as in freedom" license, the > GNU AGPLv3.
The link.to the license is here: http://www.gnu.org/licenses/agpl-3.0.html | 1.0 | Add link to license on about us page - In the **About Us** page, you mention the GNU AGPLv3 license. I think making the license text into a hyperlink is very important.
> Pjuu is an open-source social networking application released under a "free as in freedom" license, the > GNU AGPLv3.
The link.to the license is here: http://www.gnu.org/licenses/agpl-3.0.html | non_priority | add link to license on about us page in the about us page you mention the gnu license i think making the license text into a hyperlink is very important pjuu is an open source social networking application released under a free as in freedom license the gnu the link to the license is here | 0 |
79,625 | 9,922,003,456 | IssuesEvent | 2019-06-30 23:32:27 | askmench/mench-web-app | https://api.github.com/repos/askmench/mench-web-app | closed | Expand "Other Intentions" Scope | Design/UI/UX | Currently, we only list featured intentions and parent intentions that are starting points.
We can expand the scope to also include:
- [x] Sibling intentions that are starting points
- [x] Child intentions that are starting points | 1.0 | Expand "Other Intentions" Scope - Currently, we only list featured intentions and parent intentions that are starting points.
We can expand the scope to also include:
- [x] Sibling intentions that are starting points
- [x] Child intentions that are starting points | non_priority | expand other intentions scope currently we only list featured intentions and parent intentions that are starting points we can expand the scope to also include sibling intentions that are starting points child intentions that are starting points | 0 |
13,222 | 8,374,181,190 | IssuesEvent | 2018-10-05 12:57:31 | th-koeln/open-product-evaluation-server-admin | https://api.github.com/repos/th-koeln/open-product-evaluation-server-admin | closed | Dashboard Visualisierung im Backend | bootstrap usability visualization vue | Für die Ersteller der Umfragen und die Administratoren soll es ein einheitliches Userinterface geben, welches die Ergebnisse auf eine geeignete Weise visualisiert. Aktuell gibt es dazu noch folgende Themen:
* Welche Ergebnisse sollen visualisiert werden?
* Mit welchen Methoden sollen diese visualisiert werden?
* Werden dazu neue GraphQL Queries oder Mutationen benötigt?
* Welche Frameworks sollen dafür genutzt werden?
* Welche Kriterien sollen bei der Implementierung berücksichtigt werden? | True | Dashboard Visualisierung im Backend - Für die Ersteller der Umfragen und die Administratoren soll es ein einheitliches Userinterface geben, welches die Ergebnisse auf eine geeignete Weise visualisiert. Aktuell gibt es dazu noch folgende Themen:
* Welche Ergebnisse sollen visualisiert werden?
* Mit welchen Methoden sollen diese visualisiert werden?
* Werden dazu neue GraphQL Queries oder Mutationen benötigt?
* Welche Frameworks sollen dafür genutzt werden?
* Welche Kriterien sollen bei der Implementierung berücksichtigt werden? | non_priority | dashboard visualisierung im backend für die ersteller der umfragen und die administratoren soll es ein einheitliches userinterface geben welches die ergebnisse auf eine geeignete weise visualisiert aktuell gibt es dazu noch folgende themen welche ergebnisse sollen visualisiert werden mit welchen methoden sollen diese visualisiert werden werden dazu neue graphql queries oder mutationen benötigt welche frameworks sollen dafür genutzt werden welche kriterien sollen bei der implementierung berücksichtigt werden | 0 |
72,067 | 31,151,532,193 | IssuesEvent | 2023-08-16 10:16:55 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Incorrect arguments shown in sample code | app-service/svc triaged assigned-to-author doc-bug Pri1 | I'm trying to follow the docs to deploy single file to azure web app service. Here is the deep [link](https://learn.microsoft.com/en-us/azure/app-service/deploy-zip?tabs=cli#deploy-a-static-file) showing sample command on how to do this.
However, when I run this command, it throws error about missing path argument. The sample command has `--src-path` argument instead of `path`. However, the following API reference table on this link doesn't have any reference of `--src-path` either.
Looks like there is a disconnect somewhere.
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: 4ce674e6-fcb7-a867-2a74-f28f6a1b0204
* Version Independent ID: 461fc0b5-ac32-54b8-cdb6-76a2c8e6052f
* Content: [Deploy files to App Service - Azure App Service](https://learn.microsoft.com/en-us/azure/app-service/deploy-zip?tabs=cli)
* Content Source: [articles/app-service/deploy-zip.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/app-service/deploy-zip.md)
* Service: **app-service**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | 1.0 | Incorrect arguments shown in sample code - I'm trying to follow the docs to deploy single file to azure web app service. Here is the deep [link](https://learn.microsoft.com/en-us/azure/app-service/deploy-zip?tabs=cli#deploy-a-static-file) showing sample command on how to do this.
However, when I run this command, it throws error about missing path argument. The sample command has `--src-path` argument instead of `path`. However, the following API reference table on this link doesn't have any reference of `--src-path` either.
Looks like there is a disconnect somewhere.
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: 4ce674e6-fcb7-a867-2a74-f28f6a1b0204
* Version Independent ID: 461fc0b5-ac32-54b8-cdb6-76a2c8e6052f
* Content: [Deploy files to App Service - Azure App Service](https://learn.microsoft.com/en-us/azure/app-service/deploy-zip?tabs=cli)
* Content Source: [articles/app-service/deploy-zip.md](https://github.com/MicrosoftDocs/azure-docs/blob/main/articles/app-service/deploy-zip.md)
* Service: **app-service**
* GitHub Login: @cephalin
* Microsoft Alias: **cephalin** | non_priority | incorrect arguments shown in sample code i m trying to follow the docs to deploy single file to azure web app service here is the deep showing sample command on how to do this however when i run this command it throws error about missing path argument the sample command has src path argument instead of path however the following api reference table on this link doesn t have any reference of src path either looks like there is a disconnect somewhere document details ⚠ do not edit this section it is required for learn microsoft com ➟ github issue linking id version independent id content content source service app service github login cephalin microsoft alias cephalin | 0 |
22,563 | 3,963,259,947 | IssuesEvent | 2016-05-02 19:48:04 | medic/medic-webapp | https://api.github.com/repos/medic/medic-webapp | closed | Modals : don't preload them | 4 - Acceptance testing Performance | We create and render modals at app startup, and then hide them.
Instead, instantiate them when you need them. | 1.0 | Modals : don't preload them - We create and render modals at app startup, and then hide them.
Instead, instantiate them when you need them. | non_priority | modals don t preload them we create and render modals at app startup and then hide them instead instantiate them when you need them | 0 |
15,143 | 11,372,782,467 | IssuesEvent | 2020-01-28 03:16:04 | battlecode/battlecode20 | https://api.github.com/repos/battlecode/battlecode20 | opened | More helpful error message on compilation failed | backend for-next-year infrastructure | I'm envisioning a `compile_logs` field in the `api_submission` table. | 1.0 | More helpful error message on compilation failed - I'm envisioning a `compile_logs` field in the `api_submission` table. | non_priority | more helpful error message on compilation failed i m envisioning a compile logs field in the api submission table | 0 |
38,966 | 10,271,626,007 | IssuesEvent | 2019-08-23 14:32:12 | google/shaderc | https://api.github.com/repos/google/shaderc | closed | Add DEPs file to Shaderc | buildbot | Add a DEPS file and a copy of git-sync-deps to shaderc and update the bots to use that script instead of ToT everywhere | 1.0 | Add DEPs file to Shaderc - Add a DEPS file and a copy of git-sync-deps to shaderc and update the bots to use that script instead of ToT everywhere | non_priority | add deps file to shaderc add a deps file and a copy of git sync deps to shaderc and update the bots to use that script instead of tot everywhere | 0 |
4,722 | 2,743,706,859 | IssuesEvent | 2015-04-21 23:38:49 | pydata/pandas | https://api.github.com/repos/pydata/pandas | closed | API/BUG: awkward syntax to add categories to a Categorical | API Design Categorical Difficulty Intermediate Effort Low | from [SO](http://stackoverflow.com/questions/29709918/pandas-and-category-replacement/29712287#29712287)
- the ``.add_categories`` should be able to take an ``Index``/ndarray, ATM it must be converted to a list
- should be a keyword for something like: add any additional categories that I am passing to you (even if the current ones are duplicates, just add these to the end). e.g.
```
In [147]: s = pd.Categorical(list('aabbcd'))
In [148]: s2 = list('aabbcdefg')
In [149]: s
Out[149]:
[a, a, b, b, c, d]
Categories (4, object): [a, b, c, d]
In [150]: s.add_categories(s.categories.sym_diff(Index(s2)).tolist())
Out[150]:
[a, a, b, b, c, d]
Categories (7, object): [a, b, c, d, e, f, g]
```
I would ideally just like to say:
```
s.add_categories(s2, take_new=True)
```
(maybe not the best keyword, but something like this) | 1.0 | API/BUG: awkward syntax to add categories to a Categorical - from [SO](http://stackoverflow.com/questions/29709918/pandas-and-category-replacement/29712287#29712287)
- the ``.add_categories`` should be able to take an ``Index``/ndarray, ATM it must be converted to a list
- should be a keyword for something like: add any additional categories that I am passing to you (even if the current ones are duplicates, just add these to the end). e.g.
```
In [147]: s = pd.Categorical(list('aabbcd'))
In [148]: s2 = list('aabbcdefg')
In [149]: s
Out[149]:
[a, a, b, b, c, d]
Categories (4, object): [a, b, c, d]
In [150]: s.add_categories(s.categories.sym_diff(Index(s2)).tolist())
Out[150]:
[a, a, b, b, c, d]
Categories (7, object): [a, b, c, d, e, f, g]
```
I would ideally just like to say:
```
s.add_categories(s2, take_new=True)
```
(maybe not the best keyword, but something like this) | non_priority | api bug awkward syntax to add categories to a categorical from the add categories should be able to take an index ndarray atm it must be converted to a list should be a keyword for something like add any additional categories that i am passing to you even if the current ones are duplicates just add these to the end e g in s pd categorical list aabbcd in list aabbcdefg in s out categories object in s add categories s categories sym diff index tolist out categories object i would ideally just like to say s add categories take new true maybe not the best keyword but something like this | 0 |
270,237 | 23,497,338,126 | IssuesEvent | 2022-08-18 03:55:45 | crypto-org-chain/cronos | https://api.github.com/repos/crypto-org-chain/cronos | closed | Problem: no integration test for base fee reset | tests | There's a way to reset base fee right now with following procedure:
- disable feemarket using gov proposal
- reenable it using gov proposal at least one block later
- the base fee should be reset to initial-base-fee. | 1.0 | Problem: no integration test for base fee reset - There's a way to reset base fee right now with following procedure:
- disable feemarket using gov proposal
- reenable it using gov proposal at least one block later
- the base fee should be reset to initial-base-fee. | non_priority | problem no integration test for base fee reset there s a way to reset base fee right now with following procedure disable feemarket using gov proposal reenable it using gov proposal at least one block later the base fee should be reset to initial base fee | 0 |
21,030 | 3,671,429,873 | IssuesEvent | 2016-02-22 07:20:36 | narendra-addweb/MyImmoPix | https://api.github.com/repos/narendra-addweb/MyImmoPix | closed | PDF Homepage T.A.3.c | Complete Design | Rework the design and alignments of the adjustments listed. See example. The icons
could also be a little bigger.

| 1.0 | PDF Homepage T.A.3.c - Rework the design and alignments of the adjustments listed. See example. The icons
could also be a little bigger.

| non_priority | pdf homepage t a c rework the design and alignments of the adjustments listed see example the icons could also be a little bigger | 0 |
283,172 | 21,316,055,089 | IssuesEvent | 2022-04-16 09:42:55 | sethlxk/pe | https://api.github.com/repos/sethlxk/pe | opened | Mode_number in start function in UG is not reflected accurately | severity.Medium type.DocumentationBug | For the mode number for the start function in UG, only numbers 0,1,2 and 3 are allowed. However the UG inaccurately states 0-4.
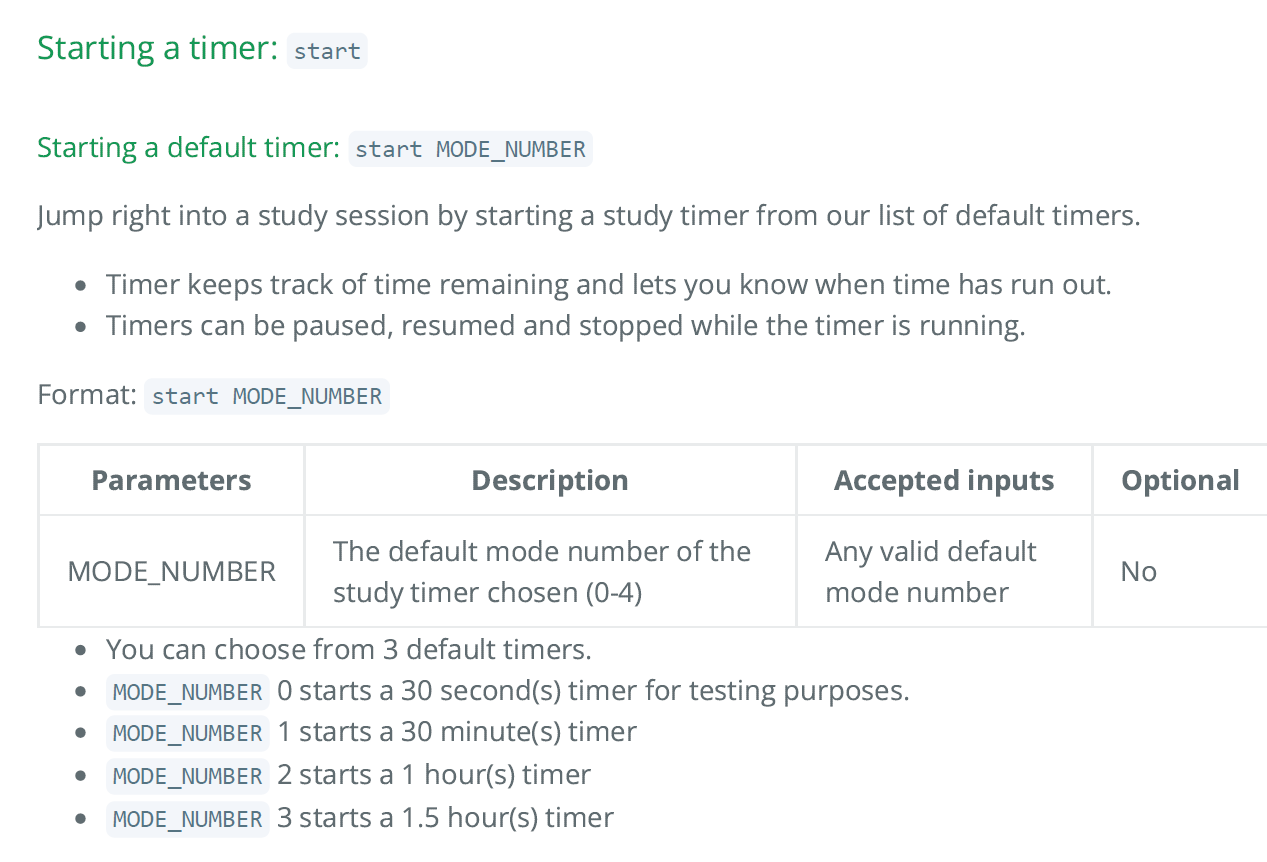
<!--session: 1650093659287-b3d57680-79a8-4862-8390-556fe098b676-->
<!--Version: Web v3.4.2--> | 1.0 | Mode_number in start function in UG is not reflected accurately - For the mode number for the start function in UG, only numbers 0,1,2 and 3 are allowed. However the UG inaccurately states 0-4.
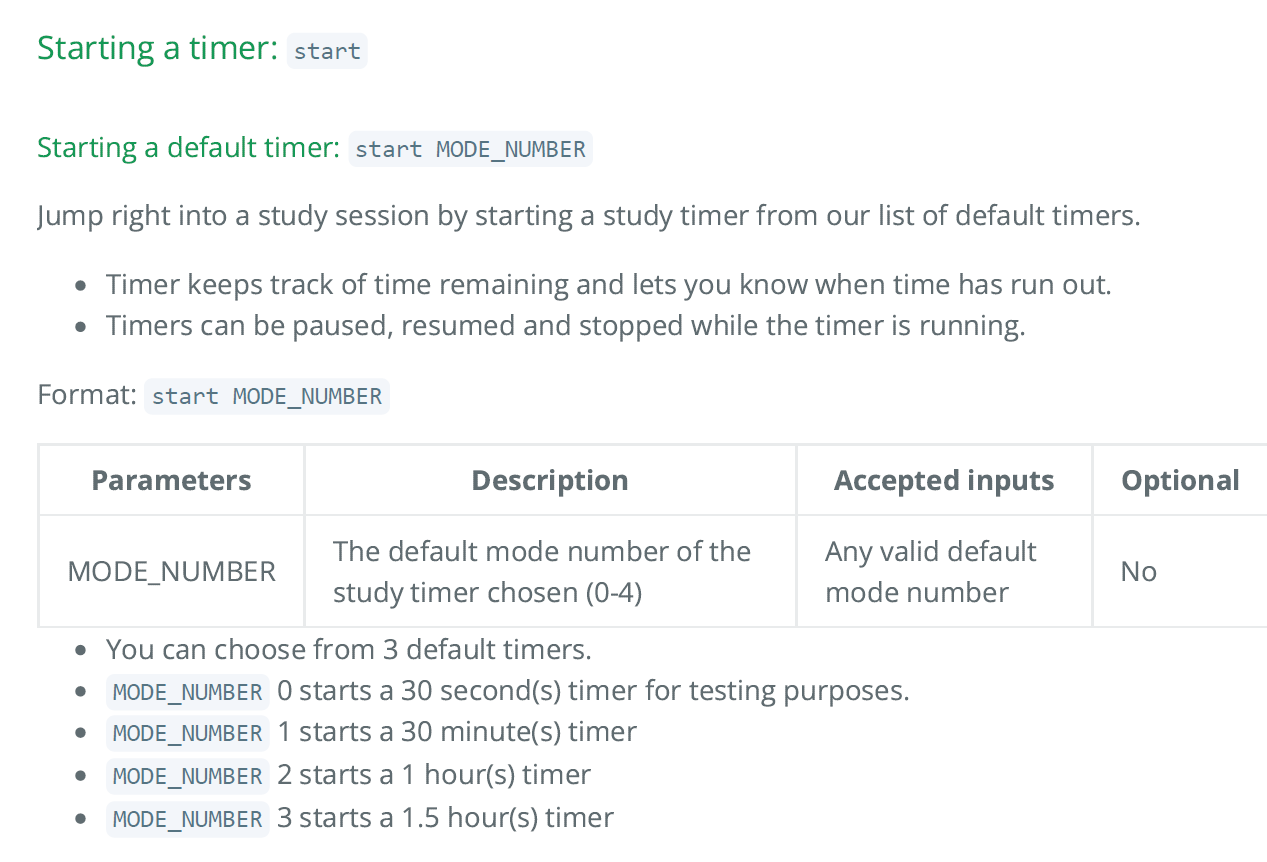
<!--session: 1650093659287-b3d57680-79a8-4862-8390-556fe098b676-->
<!--Version: Web v3.4.2--> | non_priority | mode number in start function in ug is not reflected accurately for the mode number for the start function in ug only numbers and are allowed however the ug inaccurately states | 0 |
110,015 | 16,964,173,152 | IssuesEvent | 2021-06-29 08:52:13 | HorizenOfficial/ginger-lib | https://api.github.com/repos/HorizenOfficial/ginger-lib | reopened | Re-check Poseidon Parameters | security issue | Generation scripts of Poseidon parameters at https://extgit.iaik.tugraz.at/krypto/hadeshash/-/tree/master have been recently updated.
We should re-execute the scripts for our curves and check if any of the parameters we currently have in the code has been affected by the changes. | True | Re-check Poseidon Parameters - Generation scripts of Poseidon parameters at https://extgit.iaik.tugraz.at/krypto/hadeshash/-/tree/master have been recently updated.
We should re-execute the scripts for our curves and check if any of the parameters we currently have in the code has been affected by the changes. | non_priority | re check poseidon parameters generation scripts of poseidon parameters at have been recently updated we should re execute the scripts for our curves and check if any of the parameters we currently have in the code has been affected by the changes | 0 |
161,372 | 12,542,010,700 | IssuesEvent | 2020-06-05 13:22:05 | OpenLiberty/open-liberty | https://api.github.com/repos/OpenLiberty/open-liberty | closed | WC - AsyncReadListenerHttpUnit changes client side to send fix length data | in:Web Components team:Sirius test bug | Data is sent by client in CHUNKED encoding (i.e there will be one 0 byte package to signal the end of the stream data). This 0 byte typically sent immediately along with the main data. In the failing case, it is somehow arrived to the server a bit later.
4/6/20, 19:34:07:262 UTC] 0000003b HttpServiceCo 3 Read chunk size 100
[4/6/20, 19:34:07:266 UTC] 0000003b HttpServiceCo 3 Read chunk size 0
[4/6/20, 19:34:07:476 UTC] 0000003a HttpServiceCo 3 Read chunk size 1024
[4/6/20, 19:34:07:478 UTC] 00000031 HttpServiceCo 3 Read chunk size 0
All 1024 was received and processed OK. However, because the last 0 was received later and on a different thread, the ReadListener onDataAvailable() for that 0 bytes finishes early and commits the response (this is the same response object in both threads) before the 1024 thread. When onDataComplete() is called on 1024 to update the response header with the result, it can't due to response already committed; thus the client can't verify it
"expected:<1024> but was:<null>"
(i.e the test was designed to use the response's header to communicate the received data back to the client for verification. It should have used the body's response data instead).
Quickest change is to have the client side to send FIXED length data (i.e with Content-Length). | 1.0 | WC - AsyncReadListenerHttpUnit changes client side to send fix length data - Data is sent by client in CHUNKED encoding (i.e there will be one 0 byte package to signal the end of the stream data). This 0 byte typically sent immediately along with the main data. In the failing case, it is somehow arrived to the server a bit later.
4/6/20, 19:34:07:262 UTC] 0000003b HttpServiceCo 3 Read chunk size 100
[4/6/20, 19:34:07:266 UTC] 0000003b HttpServiceCo 3 Read chunk size 0
[4/6/20, 19:34:07:476 UTC] 0000003a HttpServiceCo 3 Read chunk size 1024
[4/6/20, 19:34:07:478 UTC] 00000031 HttpServiceCo 3 Read chunk size 0
All 1024 was received and processed OK. However, because the last 0 was received later and on a different thread, the ReadListener onDataAvailable() for that 0 bytes finishes early and commits the response (this is the same response object in both threads) before the 1024 thread. When onDataComplete() is called on 1024 to update the response header with the result, it can't due to response already committed; thus the client can't verify it
"expected:<1024> but was:<null>"
(i.e the test was designed to use the response's header to communicate the received data back to the client for verification. It should have used the body's response data instead).
Quickest change is to have the client side to send FIXED length data (i.e with Content-Length). | non_priority | wc asyncreadlistenerhttpunit changes client side to send fix length data data is sent by client in chunked encoding i e there will be one byte package to signal the end of the stream data this byte typically sent immediately along with the main data in the failing case it is somehow arrived to the server a bit later utc httpserviceco read chunk size httpserviceco read chunk size httpserviceco read chunk size httpserviceco read chunk size all was received and processed ok however because the last was received later and on a different thread the readlistener ondataavailable for that bytes finishes early and commits the response this is the same response object in both threads before the thread when ondatacomplete is called on to update the response header with the result it can t due to response already committed thus the client can t verify it expected but was i e the test was designed to use the response s header to communicate the received data back to the client for verification it should have used the body s response data instead quickest change is to have the client side to send fixed length data i e with content length | 0 |
119,445 | 10,053,798,310 | IssuesEvent | 2019-07-21 19:49:32 | Rocologo/BagOfGold | https://api.github.com/repos/Rocologo/BagOfGold | closed | Reserve Support | Fixed - To be tested | I am the developer of the plugin Reserve, a modern economy API with modern economy features in mind. As I am now ready to publicly push the API, I'm currently looking for developers to add support for it.
Link: https://github.com/TheNewEconomy/Reserve
Advantages over Vault:
- Multi-currency support
- Async support using Java's completeable futures
- Optional Extended API to allow third party plugins to add new currencies
Current Plugins that support Reserve:
- Towny
- ChestShop3
- MineBay
Current Providers/Planned Providers:
- The New Economy
- Towny Eco
- GemsEconomy
Thanks in advance,
creatorfromhell | 1.0 | Reserve Support - I am the developer of the plugin Reserve, a modern economy API with modern economy features in mind. As I am now ready to publicly push the API, I'm currently looking for developers to add support for it.
Link: https://github.com/TheNewEconomy/Reserve
Advantages over Vault:
- Multi-currency support
- Async support using Java's completeable futures
- Optional Extended API to allow third party plugins to add new currencies
Current Plugins that support Reserve:
- Towny
- ChestShop3
- MineBay
Current Providers/Planned Providers:
- The New Economy
- Towny Eco
- GemsEconomy
Thanks in advance,
creatorfromhell | non_priority | reserve support i am the developer of the plugin reserve a modern economy api with modern economy features in mind as i am now ready to publicly push the api i m currently looking for developers to add support for it link advantages over vault multi currency support async support using java s completeable futures optional extended api to allow third party plugins to add new currencies current plugins that support reserve towny minebay current providers planned providers the new economy towny eco gemseconomy thanks in advance creatorfromhell | 0 |
188,970 | 15,174,307,683 | IssuesEvent | 2021-02-13 17:51:42 | tezos-reward-distributor-organization/tezos-reward-distributor | https://api.github.com/repos/tezos-reward-distributor-organization/tezos-reward-distributor | closed | Overwritten successful payment items in case of retried failed payments | bug documentation & logging | **Describe the bug**
In case that some payment items are failed, these are retried by the TRD usually at the beginning of the script. However, when these items are paid successfully when retried, they overwrite the already existing successful payment items under the reports directory.
**To Reproduce**
Steps to reproduce the behavior:
1. Pay out cycle X and cause one payment item/batch to fail (KT1 account with high fees for example)
2. Change the parameters to make TRD able to payout that item/batch (gas limit/fee)
3. Restart TRD and trigger retry payments (usually automatically triggered if not run mode 3)
4. Check reports/payments/done/X.csv
| 1.0 | Overwritten successful payment items in case of retried failed payments - **Describe the bug**
In case that some payment items are failed, these are retried by the TRD usually at the beginning of the script. However, when these items are paid successfully when retried, they overwrite the already existing successful payment items under the reports directory.
**To Reproduce**
Steps to reproduce the behavior:
1. Pay out cycle X and cause one payment item/batch to fail (KT1 account with high fees for example)
2. Change the parameters to make TRD able to payout that item/batch (gas limit/fee)
3. Restart TRD and trigger retry payments (usually automatically triggered if not run mode 3)
4. Check reports/payments/done/X.csv
| non_priority | overwritten successful payment items in case of retried failed payments describe the bug in case that some payment items are failed these are retried by the trd usually at the beginning of the script however when these items are paid successfully when retried they overwrite the already existing successful payment items under the reports directory to reproduce steps to reproduce the behavior pay out cycle x and cause one payment item batch to fail account with high fees for example change the parameters to make trd able to payout that item batch gas limit fee restart trd and trigger retry payments usually automatically triggered if not run mode check reports payments done x csv | 0 |
68,189 | 9,134,544,193 | IssuesEvent | 2019-02-26 00:18:34 | iNavFlight/LuaTelemetry | https://api.github.com/repos/iNavFlight/LuaTelemetry | closed | Update Wiki to only give Horus widget install instructions | documentation merged to development | Since running Lua Telemetry as a widget on Horus is stable and full featured, only provide instructions on how to add Lua Telemetry as a widget on Horus transmitters. Users will still be able to run as a one-time script if they wish, just as they can on Taranis. It's just not the preferred way, so there's no reason to explain it in two different ways causing possible confusion and unneeded complexity. | 1.0 | Update Wiki to only give Horus widget install instructions - Since running Lua Telemetry as a widget on Horus is stable and full featured, only provide instructions on how to add Lua Telemetry as a widget on Horus transmitters. Users will still be able to run as a one-time script if they wish, just as they can on Taranis. It's just not the preferred way, so there's no reason to explain it in two different ways causing possible confusion and unneeded complexity. | non_priority | update wiki to only give horus widget install instructions since running lua telemetry as a widget on horus is stable and full featured only provide instructions on how to add lua telemetry as a widget on horus transmitters users will still be able to run as a one time script if they wish just as they can on taranis it s just not the preferred way so there s no reason to explain it in two different ways causing possible confusion and unneeded complexity | 0 |
282,203 | 21,315,471,420 | IssuesEvent | 2022-04-16 07:35:00 | howardwhw2/pe | https://api.github.com/repos/howardwhw2/pe | opened | Lack of instructions for manual testing | type.DocumentationBug severity.Medium | There is very little documentation in the developer guide for Manual Testing which prevents the reader from knowing what are the expected valid and invalid commands which makes testing and improvement of features difficult since it is hard to tell what is expected and unexpected behaviour.
<!--session: 1650088109928-f515cb12-49f5-49a8-9181-fd4f861f6847-->
<!--Version: Web v3.4.2--> | 1.0 | Lack of instructions for manual testing - There is very little documentation in the developer guide for Manual Testing which prevents the reader from knowing what are the expected valid and invalid commands which makes testing and improvement of features difficult since it is hard to tell what is expected and unexpected behaviour.
<!--session: 1650088109928-f515cb12-49f5-49a8-9181-fd4f861f6847-->
<!--Version: Web v3.4.2--> | non_priority | lack of instructions for manual testing there is very little documentation in the developer guide for manual testing which prevents the reader from knowing what are the expected valid and invalid commands which makes testing and improvement of features difficult since it is hard to tell what is expected and unexpected behaviour | 0 |
37,690 | 10,058,992,303 | IssuesEvent | 2019-07-22 14:59:15 | mono/mono | https://api.github.com/repos/mono/mono | closed | Why can we not use Mono 5.18 to build Mono 5.20 but need to bootstrap again? | area-Build | For Fedora, we are happy to have upgraded to Mono 5.18 successfully, with a bootstrap.
Now I tried to work on Mono 5.20, without doing another bootstrap.
But it seems, I get the error: runtime is not usable.
BUILDSTDERR: *** Downloading bootstrap required 'monolite-linux/B886E13F-6276-4BE5-85F8-C6BF5EDBD200'
BUILDSTDERR: *** The runtime 'mono' doesn't appear to be usable.
BUILDSTDERR: *** Check README for information on how to bootstrap a Mono installation.
see https://bugzilla.redhat.com/show_bug.cgi?id=1697526
I did some debugging, and tried to tweak the build process.
I have an installed MONO_CORLIB_VERSION = 179F7FD7-9CE8-424E-84AF-0DF5B0B8B469
But even if I change that value in mcs/build/config.make, and point the monolite directory to my installed mono:
cd /root/rpmbuild/BUILD/mono-5.20.1.27/mcs/class/lib/monolite-linux
ln -s /usr/lib/mono/4.5 179F7FD7-9CE8-424E-84AF-0DF5B0B8B469
I get these issues:
Corlib not in sync with this runtime: The runtime did not find the mscorlib.dll it expected. Expected interface version B886E13F-6276-4BE5-85F8-C6BF5EDBD200 but found 179F7FD7-9CE8-424E-84AF-0DF5B0B8B469. Check that your runtime and class libraries are matching.
Loaded from: /usr/lib/mono/4.5/mscorlib.dll
The question is: Is bootstrap required for each minor release?
If that is the case, then be it, but if there would be a way around that, I would appreciate any help! Thanks!
| 1.0 | Why can we not use Mono 5.18 to build Mono 5.20 but need to bootstrap again? - For Fedora, we are happy to have upgraded to Mono 5.18 successfully, with a bootstrap.
Now I tried to work on Mono 5.20, without doing another bootstrap.
But it seems, I get the error: runtime is not usable.
BUILDSTDERR: *** Downloading bootstrap required 'monolite-linux/B886E13F-6276-4BE5-85F8-C6BF5EDBD200'
BUILDSTDERR: *** The runtime 'mono' doesn't appear to be usable.
BUILDSTDERR: *** Check README for information on how to bootstrap a Mono installation.
see https://bugzilla.redhat.com/show_bug.cgi?id=1697526
I did some debugging, and tried to tweak the build process.
I have an installed MONO_CORLIB_VERSION = 179F7FD7-9CE8-424E-84AF-0DF5B0B8B469
But even if I change that value in mcs/build/config.make, and point the monolite directory to my installed mono:
cd /root/rpmbuild/BUILD/mono-5.20.1.27/mcs/class/lib/monolite-linux
ln -s /usr/lib/mono/4.5 179F7FD7-9CE8-424E-84AF-0DF5B0B8B469
I get these issues:
Corlib not in sync with this runtime: The runtime did not find the mscorlib.dll it expected. Expected interface version B886E13F-6276-4BE5-85F8-C6BF5EDBD200 but found 179F7FD7-9CE8-424E-84AF-0DF5B0B8B469. Check that your runtime and class libraries are matching.
Loaded from: /usr/lib/mono/4.5/mscorlib.dll
The question is: Is bootstrap required for each minor release?
If that is the case, then be it, but if there would be a way around that, I would appreciate any help! Thanks!
| non_priority | why can we not use mono to build mono but need to bootstrap again for fedora we are happy to have upgraded to mono successfully with a bootstrap now i tried to work on mono without doing another bootstrap but it seems i get the error runtime is not usable buildstderr downloading bootstrap required monolite linux buildstderr the runtime mono doesn t appear to be usable buildstderr check readme for information on how to bootstrap a mono installation see i did some debugging and tried to tweak the build process i have an installed mono corlib version but even if i change that value in mcs build config make and point the monolite directory to my installed mono cd root rpmbuild build mono mcs class lib monolite linux ln s usr lib mono i get these issues corlib not in sync with this runtime the runtime did not find the mscorlib dll it expected expected interface version but found check that your runtime and class libraries are matching loaded from usr lib mono mscorlib dll the question is is bootstrap required for each minor release if that is the case then be it but if there would be a way around that i would appreciate any help thanks | 0 |
55,861 | 8,032,757,106 | IssuesEvent | 2018-07-28 19:04:15 | spring-projects/spring-vault | https://api.github.com/repos/spring-projects/spring-vault | closed | Where's the doWithRestTemplate callback method? | status: waiting-for-feedback type: bug type: documentation | The docs mention in section 7.5 Execution Callbacks a method doWithRestTemplate(...), but a github search for it yields no results. Has it been implemented yet? | 1.0 | Where's the doWithRestTemplate callback method? - The docs mention in section 7.5 Execution Callbacks a method doWithRestTemplate(...), but a github search for it yields no results. Has it been implemented yet? | non_priority | where s the dowithresttemplate callback method the docs mention in section execution callbacks a method dowithresttemplate but a github search for it yields no results has it been implemented yet | 0 |
109,334 | 9,378,450,863 | IssuesEvent | 2019-04-04 12:56:10 | edenlabllc/ehealth.api | https://api.github.com/repos/edenlabllc/ehealth.api | closed | Bug on get conditions,observations by search params | [zube]: In Test kind/bug project/medical_events | Combination of search params "episode_id" and "encounter_id" does not work right- only first filter is applied
```
curl -X GET \
'https://api.dev.asclepius.com.ua/api/patients/7d60d862-6df2-4dd9-95b3-7496b189b906/conditions?episode_id=79f9f0d2-371a-4933-bb9a-6164a40af11b&encounter_id=8bca979d-2532-4cbd-a6fc-c93d9f290c34' \
-H 'Authorization: Bearer aTJLMmIyMjZrQnBmU2NOanNwZE83UT09' \
-H 'Content-Type: application/json' \
-H 'Postman-Token: cfc068e0-7ce4-48d4-978e-31f17a49c1bc' \
-H 'api-key: ejJ1VWFqZlNUUlpmMWNIMmc0YTB1UT09' \
-H 'cache-control: no-cache'
``` | 1.0 | Bug on get conditions,observations by search params - Combination of search params "episode_id" and "encounter_id" does not work right- only first filter is applied
```
curl -X GET \
'https://api.dev.asclepius.com.ua/api/patients/7d60d862-6df2-4dd9-95b3-7496b189b906/conditions?episode_id=79f9f0d2-371a-4933-bb9a-6164a40af11b&encounter_id=8bca979d-2532-4cbd-a6fc-c93d9f290c34' \
-H 'Authorization: Bearer aTJLMmIyMjZrQnBmU2NOanNwZE83UT09' \
-H 'Content-Type: application/json' \
-H 'Postman-Token: cfc068e0-7ce4-48d4-978e-31f17a49c1bc' \
-H 'api-key: ejJ1VWFqZlNUUlpmMWNIMmc0YTB1UT09' \
-H 'cache-control: no-cache'
``` | non_priority | bug on get conditions observations by search params combination of search params episode id and encounter id does not work right only first filter is applied curl x get h authorization bearer h content type application json h postman token h api key h cache control no cache | 0 |
224,433 | 17,187,674,697 | IssuesEvent | 2021-07-16 06:10:04 | Daimler/sechub | https://api.github.com/repos/Daimler/sechub | reopened | Mention plugins SecHub documentation | documentation | ## Problem
The SecHub team developed and published 3 plugins for different IDEs. The plugins allow users to navigate in SecHub reports much quicker. However, those plugins are not mentioned as part of our SecHub documentation.
## Solution
Create a new top level document in the SecHub documentation and link to all plugins in the document with a short description and screenshot. | 1.0 | Mention plugins SecHub documentation - ## Problem
The SecHub team developed and published 3 plugins for different IDEs. The plugins allow users to navigate in SecHub reports much quicker. However, those plugins are not mentioned as part of our SecHub documentation.
## Solution
Create a new top level document in the SecHub documentation and link to all plugins in the document with a short description and screenshot. | non_priority | mention plugins sechub documentation problem the sechub team developed and published plugins for different ides the plugins allow users to navigate in sechub reports much quicker however those plugins are not mentioned as part of our sechub documentation solution create a new top level document in the sechub documentation and link to all plugins in the document with a short description and screenshot | 0 |
38,770 | 6,699,782,719 | IssuesEvent | 2017-10-11 00:11:14 | LibreHealthIO/LibreEHR | https://api.github.com/repos/LibreHealthIO/LibreEHR | opened | Documentation Dir needs a top level index | Feature: Documentation | There is no way to provide a link to all the subdirs in the Documentation/ directory from Setup or the Main Menu.
```
1_Installing 3_Billing 5_Healthcare 9_doc_and_logo_sources README-phpgacl.md
2_Configuration 4_FeatureManuals 8_ForDevelopers FAQ.MD
``` | 1.0 | Documentation Dir needs a top level index - There is no way to provide a link to all the subdirs in the Documentation/ directory from Setup or the Main Menu.
```
1_Installing 3_Billing 5_Healthcare 9_doc_and_logo_sources README-phpgacl.md
2_Configuration 4_FeatureManuals 8_ForDevelopers FAQ.MD
``` | non_priority | documentation dir needs a top level index there is no way to provide a link to all the subdirs in the documentation directory from setup or the main menu installing billing healthcare doc and logo sources readme phpgacl md configuration featuremanuals fordevelopers faq md | 0 |
55,986 | 14,075,759,771 | IssuesEvent | 2020-11-04 09:30:40 | teena24/clumsy-bird | https://api.github.com/repos/teena24/clumsy-bird | closed | WS-2015-0017 Medium Severity Vulnerability detected by WhiteSource - autoclosed | security vulnerability | ## WS-2015-0017 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>uglify-js-2.4.24.tgz</b></p></summary>
<p>JavaScript parser, mangler/compressor and beautifier toolkit</p>
<p>path: /tmp/git/clumsy-bird/node_modules/uglify-js/package.json</p>
<p>
<p>Library home page: <a href=http://registry.npmjs.org/uglify-js/-/uglify-js-2.4.24.tgz>http://registry.npmjs.org/uglify-js/-/uglify-js-2.4.24.tgz</a></p>
Dependency Hierarchy:
- grunt-contrib-uglify-0.2.7.tgz (Root Library)
- :x: **uglify-js-2.4.24.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Uglify-js is vulnerable to regular expression denial of service (ReDoS) when certain types of input is passed into .parse().
<p>Publish Date: 2015-10-24
<p>URL: <a href=>WS-2015-0017</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/48">https://nodesecurity.io/advisories/48</a></p>
<p>Release Date: 2015-10-24</p>
<p>Fix Resolution: Update to version 2.6.0 or later</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2015-0017 Medium Severity Vulnerability detected by WhiteSource - autoclosed - ## WS-2015-0017 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>uglify-js-2.4.24.tgz</b></p></summary>
<p>JavaScript parser, mangler/compressor and beautifier toolkit</p>
<p>path: /tmp/git/clumsy-bird/node_modules/uglify-js/package.json</p>
<p>
<p>Library home page: <a href=http://registry.npmjs.org/uglify-js/-/uglify-js-2.4.24.tgz>http://registry.npmjs.org/uglify-js/-/uglify-js-2.4.24.tgz</a></p>
Dependency Hierarchy:
- grunt-contrib-uglify-0.2.7.tgz (Root Library)
- :x: **uglify-js-2.4.24.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Uglify-js is vulnerable to regular expression denial of service (ReDoS) when certain types of input is passed into .parse().
<p>Publish Date: 2015-10-24
<p>URL: <a href=>WS-2015-0017</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nodesecurity.io/advisories/48">https://nodesecurity.io/advisories/48</a></p>
<p>Release Date: 2015-10-24</p>
<p>Fix Resolution: Update to version 2.6.0 or later</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium severity vulnerability detected by whitesource autoclosed ws medium severity vulnerability vulnerable library uglify js tgz javascript parser mangler compressor and beautifier toolkit path tmp git clumsy bird node modules uglify js package json library home page a href dependency hierarchy grunt contrib uglify tgz root library x uglify js tgz vulnerable library vulnerability details uglify js is vulnerable to regular expression denial of service redos when certain types of input is passed into parse publish date url ws cvss score details base score metrics not available suggested fix type upgrade version origin a href release date fix resolution update to version or later step up your open source security game with whitesource | 0 |
7,653 | 7,042,602,138 | IssuesEvent | 2017-12-30 15:28:39 | gfx-rs/gfx | https://api.github.com/repos/gfx-rs/gfx | opened | Feature gated Debug implementations | api: ll difficulty: easy module: infrastructure status: ready for work type: discussion type: feature value: low | `Debug` slows down the compilation time, apparently. We could have a `debug` feature gating it, enabled by default. Since logging often prints our own structs, we can even make `log` a dependency of `debug` feature. | 1.0 | Feature gated Debug implementations - `Debug` slows down the compilation time, apparently. We could have a `debug` feature gating it, enabled by default. Since logging often prints our own structs, we can even make `log` a dependency of `debug` feature. | non_priority | feature gated debug implementations debug slows down the compilation time apparently we could have a debug feature gating it enabled by default since logging often prints our own structs we can even make log a dependency of debug feature | 0 |
312,209 | 26,848,759,267 | IssuesEvent | 2023-02-03 09:24:46 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | Failing test: X-Pack Saved Object Tagging Functional Tests.x-pack/test/saved_object_tagging/functional/tests/discover_integration·ts - saved objects tagging - functional tests discover integration creating allows to create a tag from the tag selector | failed-test | A test failed on a tracked branch
```
Error: retry.try timeout: Error: save modal still open
at common_page.ts:471:15
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.try (retry.ts:31:12)
at CommonPageObject.waitForSaveModalToClose (common_page.ts:469:5)
at Context.<anonymous> (discover_integration.ts:138:9)
at Object.apply (wrap_function.js:73:16)
at onFailure (retry_for_success.ts:17:9)
at retryForSuccess (retry_for_success.ts:59:13)
at RetryService.try (retry.ts:31:12)
at CommonPageObject.waitForSaveModalToClose (common_page.ts:469:5)
at Context.<anonymous> (discover_integration.ts:138:9)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/26433#01861662-762d-4e17-99d4-9c1c84efd994)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Saved Object Tagging Functional Tests.x-pack/test/saved_object_tagging/functional/tests/discover_integration·ts","test.name":"saved objects tagging - functional tests discover integration creating allows to create a tag from the tag selector","test.failCount":1}} --> | 1.0 | Failing test: X-Pack Saved Object Tagging Functional Tests.x-pack/test/saved_object_tagging/functional/tests/discover_integration·ts - saved objects tagging - functional tests discover integration creating allows to create a tag from the tag selector - A test failed on a tracked branch
```
Error: retry.try timeout: Error: save modal still open
at common_page.ts:471:15
at runMicrotasks (<anonymous>)
at processTicksAndRejections (node:internal/process/task_queues:96:5)
at runAttempt (retry_for_success.ts:29:15)
at retryForSuccess (retry_for_success.ts:68:21)
at RetryService.try (retry.ts:31:12)
at CommonPageObject.waitForSaveModalToClose (common_page.ts:469:5)
at Context.<anonymous> (discover_integration.ts:138:9)
at Object.apply (wrap_function.js:73:16)
at onFailure (retry_for_success.ts:17:9)
at retryForSuccess (retry_for_success.ts:59:13)
at RetryService.try (retry.ts:31:12)
at CommonPageObject.waitForSaveModalToClose (common_page.ts:469:5)
at Context.<anonymous> (discover_integration.ts:138:9)
at Object.apply (wrap_function.js:73:16)
```
First failure: [CI Build - main](https://buildkite.com/elastic/kibana-on-merge/builds/26433#01861662-762d-4e17-99d4-9c1c84efd994)
<!-- kibanaCiData = {"failed-test":{"test.class":"X-Pack Saved Object Tagging Functional Tests.x-pack/test/saved_object_tagging/functional/tests/discover_integration·ts","test.name":"saved objects tagging - functional tests discover integration creating allows to create a tag from the tag selector","test.failCount":1}} --> | non_priority | failing test x pack saved object tagging functional tests x pack test saved object tagging functional tests discover integration·ts saved objects tagging functional tests discover integration creating allows to create a tag from the tag selector a test failed on a tracked branch error retry try timeout error save modal still open at common page ts at runmicrotasks at processticksandrejections node internal process task queues at runattempt retry for success ts at retryforsuccess retry for success ts at retryservice try retry ts at commonpageobject waitforsavemodaltoclose common page ts at context discover integration ts at object apply wrap function js at onfailure retry for success ts at retryforsuccess retry for success ts at retryservice try retry ts at commonpageobject waitforsavemodaltoclose common page ts at context discover integration ts at object apply wrap function js first failure | 0 |
76,241 | 15,495,886,142 | IssuesEvent | 2021-03-11 01:40:26 | DODHI5/react-kanban | https://api.github.com/repos/DODHI5/react-kanban | opened | CVE-2018-19797 (Medium) detected in node-sass-4.7.2.tgz | security vulnerability | ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.7.2.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.7.2.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.7.2.tgz</a></p>
<p>Path to dependency file: /react-kanban/package.json</p>
<p>Path to vulnerable library: react-kanban/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-3.1.0.tgz (Root Library)
- :x: **node-sass-4.7.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19797>CVE-2018-19797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19797">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19797</a></p>
<p>Release Date: 2018-12-03</p>
<p>Fix Resolution: libsass-3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-19797 (Medium) detected in node-sass-4.7.2.tgz - ## CVE-2018-19797 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>node-sass-4.7.2.tgz</b></p></summary>
<p>Wrapper around libsass</p>
<p>Library home page: <a href="https://registry.npmjs.org/node-sass/-/node-sass-4.7.2.tgz">https://registry.npmjs.org/node-sass/-/node-sass-4.7.2.tgz</a></p>
<p>Path to dependency file: /react-kanban/package.json</p>
<p>Path to vulnerable library: react-kanban/node_modules/node-sass/package.json</p>
<p>
Dependency Hierarchy:
- gulp-sass-3.1.0.tgz (Root Library)
- :x: **node-sass-4.7.2.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In LibSass 3.5.5, a NULL Pointer Dereference in the function Sass::Selector_List::populate_extends in SharedPtr.hpp (used by ast.cpp and ast_selectors.cpp) may cause a Denial of Service (application crash) via a crafted sass input file.
<p>Publish Date: 2018-12-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-19797>CVE-2018-19797</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19797">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-19797</a></p>
<p>Release Date: 2018-12-03</p>
<p>Fix Resolution: libsass-3.6.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in node sass tgz cve medium severity vulnerability vulnerable library node sass tgz wrapper around libsass library home page a href path to dependency file react kanban package json path to vulnerable library react kanban node modules node sass package json dependency hierarchy gulp sass tgz root library x node sass tgz vulnerable library vulnerability details in libsass a null pointer dereference in the function sass selector list populate extends in sharedptr hpp used by ast cpp and ast selectors cpp may cause a denial of service application crash via a crafted sass input file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution libsass step up your open source security game with whitesource | 0 |
199,309 | 15,762,476,982 | IssuesEvent | 2021-03-31 11:07:42 | atc0005/go-teams-notify | https://api.github.com/repos/atc0005/go-teams-notify | opened | Review tests, add additional documentation to emphasize intentions | documentation tests | Currently I find the tests to be both to be brittle and not as clear as they could be. This is probably from a lack of an "ah ha!" moment.
I've made attempts to refactor with recent releases, but further work is needed to document exactly what is happening and why.
For example, one thing I spent an embarrassing amount of time on this AM was "remembering" the relationship between `resError` and `error` in the table test entries:
https://github.com/atc0005/go-teams-notify/blob/cea9269476396cad8c4860713d8d31a18960256c/send_test.go#L31-L39
If I recall correctly, you're specifying what client error is expected (e.g., connectivity issue) and what error is expected from invoking library functions/methods using provided table test data.
This table test entry is an example of where there is no client error, but there is an error returned from validating the target endpoint or request URL:
https://github.com/atc0005/go-teams-notify/blob/cea9269476396cad8c4860713d8d31a18960256c/send_test.go#L50-L59
| 1.0 | Review tests, add additional documentation to emphasize intentions - Currently I find the tests to be both to be brittle and not as clear as they could be. This is probably from a lack of an "ah ha!" moment.
I've made attempts to refactor with recent releases, but further work is needed to document exactly what is happening and why.
For example, one thing I spent an embarrassing amount of time on this AM was "remembering" the relationship between `resError` and `error` in the table test entries:
https://github.com/atc0005/go-teams-notify/blob/cea9269476396cad8c4860713d8d31a18960256c/send_test.go#L31-L39
If I recall correctly, you're specifying what client error is expected (e.g., connectivity issue) and what error is expected from invoking library functions/methods using provided table test data.
This table test entry is an example of where there is no client error, but there is an error returned from validating the target endpoint or request URL:
https://github.com/atc0005/go-teams-notify/blob/cea9269476396cad8c4860713d8d31a18960256c/send_test.go#L50-L59
| non_priority | review tests add additional documentation to emphasize intentions currently i find the tests to be both to be brittle and not as clear as they could be this is probably from a lack of an ah ha moment i ve made attempts to refactor with recent releases but further work is needed to document exactly what is happening and why for example one thing i spent an embarrassing amount of time on this am was remembering the relationship between reserror and error in the table test entries if i recall correctly you re specifying what client error is expected e g connectivity issue and what error is expected from invoking library functions methods using provided table test data this table test entry is an example of where there is no client error but there is an error returned from validating the target endpoint or request url | 0 |
2,701 | 3,812,851,915 | IssuesEvent | 2016-03-27 21:56:36 | amyrebecca/socialite | https://api.github.com/repos/amyrebecca/socialite | opened | investigate client-side streaming libraries | Infrastructure Major Research Task | eventually we'll want to connect to the twitter and facebook streaming apis and use those to push updates from the server to the connected clients. there are probably libraries out there to make this easier (rather than just twiddling parameters to fetch ourselves). this probably involves building a proof-of-concept | 1.0 | investigate client-side streaming libraries - eventually we'll want to connect to the twitter and facebook streaming apis and use those to push updates from the server to the connected clients. there are probably libraries out there to make this easier (rather than just twiddling parameters to fetch ourselves). this probably involves building a proof-of-concept | non_priority | investigate client side streaming libraries eventually we ll want to connect to the twitter and facebook streaming apis and use those to push updates from the server to the connected clients there are probably libraries out there to make this easier rather than just twiddling parameters to fetch ourselves this probably involves building a proof of concept | 0 |
26,033 | 12,341,943,153 | IssuesEvent | 2020-05-14 23:14:49 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | Please add a note to indicate `azureuser` expires | Pri1 assigned-to-author container-service/svc doc-enhancement triaged | Per https://github.com/Azure/AKS/issues/1170 and https://github.com/MicrosoftDocs/azure-docs/issues/47302, the `azureuser` account on VMs expires after 30 days. So, we tried following the steps here and were scratching our heads as to why our SSH key wasn't being accepted; turned out to be that the public and private keys were deployed correctly but the account was locked.
Was able to get in by first resetting the password on `azureuser` to a long, random throwaway password (to unlock the account) and then by re-deploying the SSH public key. Others might not understand that's what's happening here.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 3b81a147-db1c-b92f-88d1-6dd0991a72fe
* Version Independent ID: f5a2c949-498f-5848-d89c-031d1a757120
* Content: [SSH into Azure Kubernetes Service (AKS) cluster nodes - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/ssh)
* Content Source: [articles/aks/ssh.md](https://github.com/Microsoft/azure-docs/blob/master/articles/aks/ssh.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **mlearned** | 1.0 | Please add a note to indicate `azureuser` expires - Per https://github.com/Azure/AKS/issues/1170 and https://github.com/MicrosoftDocs/azure-docs/issues/47302, the `azureuser` account on VMs expires after 30 days. So, we tried following the steps here and were scratching our heads as to why our SSH key wasn't being accepted; turned out to be that the public and private keys were deployed correctly but the account was locked.
Was able to get in by first resetting the password on `azureuser` to a long, random throwaway password (to unlock the account) and then by re-deploying the SSH public key. Others might not understand that's what's happening here.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 3b81a147-db1c-b92f-88d1-6dd0991a72fe
* Version Independent ID: f5a2c949-498f-5848-d89c-031d1a757120
* Content: [SSH into Azure Kubernetes Service (AKS) cluster nodes - Azure Kubernetes Service](https://docs.microsoft.com/en-us/azure/aks/ssh)
* Content Source: [articles/aks/ssh.md](https://github.com/Microsoft/azure-docs/blob/master/articles/aks/ssh.md)
* Service: **container-service**
* GitHub Login: @mlearned
* Microsoft Alias: **mlearned** | non_priority | please add a note to indicate azureuser expires per and the azureuser account on vms expires after days so we tried following the steps here and were scratching our heads as to why our ssh key wasn t being accepted turned out to be that the public and private keys were deployed correctly but the account was locked was able to get in by first resetting the password on azureuser to a long random throwaway password to unlock the account and then by re deploying the ssh public key others might not understand that s what s happening here document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service container service github login mlearned microsoft alias mlearned | 0 |
306,014 | 26,428,776,892 | IssuesEvent | 2023-01-14 14:45:27 | PalisadoesFoundation/talawa-api | https://api.github.com/repos/PalisadoesFoundation/talawa-api | closed | Resolver: Create tests for mailer.js | good first issue parent points 01 test | The Talawa-API code base needs to be 100% reliable. This means we need to have 100% test code coverage.
Tests need to be written for file `lib/helper_functions/mailer.js`
- We will need the API to be refactored for all methods, classes and/or functions found in this file for testing to be correctly executed.
- When complete, all methods, classes and/or functions in the refactored file will need to be tested. These tests must be placed in a
single file with the name `tests/helper_functions/mailer.sepc.js`. You may need to create the appropriate directory structure to do this.
### IMPORTANT:
Please refer to the parent issue on how to implement these tests correctly:
- https://github.com/PalisadoesFoundation/talawa-api/issues/490
### PR Acceptance Criteria
- When complete this file must show **100%** coverage when merged into the code base. This will be clearly visible when you submit your PR.
- [The current code coverage for the file can be found here](https://codecov.io/gh/PalisadoesFoundation/talawa-api/tree/develop/lib/resolvers/organization_query/). If the file isn't found in this directory, or there is a 404 error, then tests have not been created.
- The PR will show a report for the code coverage for the file you have added. You can use that as a guide. | 1.0 | Resolver: Create tests for mailer.js - The Talawa-API code base needs to be 100% reliable. This means we need to have 100% test code coverage.
Tests need to be written for file `lib/helper_functions/mailer.js`
- We will need the API to be refactored for all methods, classes and/or functions found in this file for testing to be correctly executed.
- When complete, all methods, classes and/or functions in the refactored file will need to be tested. These tests must be placed in a
single file with the name `tests/helper_functions/mailer.sepc.js`. You may need to create the appropriate directory structure to do this.
### IMPORTANT:
Please refer to the parent issue on how to implement these tests correctly:
- https://github.com/PalisadoesFoundation/talawa-api/issues/490
### PR Acceptance Criteria
- When complete this file must show **100%** coverage when merged into the code base. This will be clearly visible when you submit your PR.
- [The current code coverage for the file can be found here](https://codecov.io/gh/PalisadoesFoundation/talawa-api/tree/develop/lib/resolvers/organization_query/). If the file isn't found in this directory, or there is a 404 error, then tests have not been created.
- The PR will show a report for the code coverage for the file you have added. You can use that as a guide. | non_priority | resolver create tests for mailer js the talawa api code base needs to be reliable this means we need to have test code coverage tests need to be written for file lib helper functions mailer js we will need the api to be refactored for all methods classes and or functions found in this file for testing to be correctly executed when complete all methods classes and or functions in the refactored file will need to be tested these tests must be placed in a single file with the name tests helper functions mailer sepc js you may need to create the appropriate directory structure to do this important please refer to the parent issue on how to implement these tests correctly pr acceptance criteria when complete this file must show coverage when merged into the code base this will be clearly visible when you submit your pr if the file isn t found in this directory or there is a error then tests have not been created the pr will show a report for the code coverage for the file you have added you can use that as a guide | 0 |
16,676 | 4,075,979,829 | IssuesEvent | 2016-05-29 15:50:44 | tdwg/vocab | https://api.github.com/repos/tdwg/vocab | closed | Acknowledging contributors to documents and standards | documentation | The hierarchy model as currently constituted in the draft Documentation Specification is more complicated than what was envisioned in the original draft documentation spec. How, and at what level, do we acknowledge contributors? For a standard that contains multiple documents (such as Darwin Core), the contributors are acknowledged at the document level rather than at the standard level, and that seems right. However, on the level of a vocabulary, particularly an evolving vocabulary, how do we acknowledge the continuing contributions to the development of the vocabulary? There will ultimately be many contributors, so do we just not worry about that and list only the contributors to the original vocabulary? Since releases/versions of the vocabulary are tracked as time goes by, do we add names of new significant contributors? see section 4.2 of the draft
Also, I think that it's a serious omission to not acknowledge the review manager for a standard. Although the review manager isn't an author, it's a huge job and the review manager does make a significant contribution to the standard. I think it's somewhat of a parallel to acknowledging the subject/corresponding editors of journal articles. In this case, the contribution would need to be acknowledged at the standard level. The current draft of the specification is silent on this. | 1.0 | Acknowledging contributors to documents and standards - The hierarchy model as currently constituted in the draft Documentation Specification is more complicated than what was envisioned in the original draft documentation spec. How, and at what level, do we acknowledge contributors? For a standard that contains multiple documents (such as Darwin Core), the contributors are acknowledged at the document level rather than at the standard level, and that seems right. However, on the level of a vocabulary, particularly an evolving vocabulary, how do we acknowledge the continuing contributions to the development of the vocabulary? There will ultimately be many contributors, so do we just not worry about that and list only the contributors to the original vocabulary? Since releases/versions of the vocabulary are tracked as time goes by, do we add names of new significant contributors? see section 4.2 of the draft
Also, I think that it's a serious omission to not acknowledge the review manager for a standard. Although the review manager isn't an author, it's a huge job and the review manager does make a significant contribution to the standard. I think it's somewhat of a parallel to acknowledging the subject/corresponding editors of journal articles. In this case, the contribution would need to be acknowledged at the standard level. The current draft of the specification is silent on this. | non_priority | acknowledging contributors to documents and standards the hierarchy model as currently constituted in the draft documentation specification is more complicated than what was envisioned in the original draft documentation spec how and at what level do we acknowledge contributors for a standard that contains multiple documents such as darwin core the contributors are acknowledged at the document level rather than at the standard level and that seems right however on the level of a vocabulary particularly an evolving vocabulary how do we acknowledge the continuing contributions to the development of the vocabulary there will ultimately be many contributors so do we just not worry about that and list only the contributors to the original vocabulary since releases versions of the vocabulary are tracked as time goes by do we add names of new significant contributors see section of the draft also i think that it s a serious omission to not acknowledge the review manager for a standard although the review manager isn t an author it s a huge job and the review manager does make a significant contribution to the standard i think it s somewhat of a parallel to acknowledging the subject corresponding editors of journal articles in this case the contribution would need to be acknowledged at the standard level the current draft of the specification is silent on this | 0 |
259,084 | 22,390,433,334 | IssuesEvent | 2022-06-17 07:05:01 | mozilla-mobile/fenix | https://api.github.com/repos/mozilla-mobile/fenix | opened | Intermittent UI test failure - < SmokeTest. tabsSettingsMenuItemsTest > | b:crash eng:intermittent-test eng:ui-test | ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/7928883451320111681/executions/bs.3e691cc93ef03470/testcases/1/test-cases)
### Stacktrace:
java.lang.RuntimeException: Error while connecting UiAutomation@3dcced2[id=-1, flags=0]
at android.app.UiAutomation.connect(UiAutomation.java:259)
at android.app.Instrumentation.getUiAutomation(Instrumentation.java:2176)
at androidx.test.uiautomator.UiDevice.getUiAutomation(UiDevice.java:1129)
at androidx.test.uiautomator.QueryController.<init>(QueryController.java:95)
at androidx.test.uiautomator.UiDevice.<init>(UiDevice.java:109)
at androidx.test.uiautomator.UiDevice.getInstance(UiDevice.java:261)
at org.mozilla.fenix.ui.SmokeTest.<init>(SmokeTest.kt:64)
### Build: 6/16
### Notes: Similar with: #25416 #25414 #25342 #25341 #25453 #25468 #25579 #25578 #25624 #25625 #25628 #25630 #25642 #25655 #25656
| 2.0 | Intermittent UI test failure - < SmokeTest. tabsSettingsMenuItemsTest > - ### Firebase Test Run: [Firebase link](https://console.firebase.google.com/u/0/project/moz-fenix/testlab/histories/bh.66b7091e15d53d45/matrices/7928883451320111681/executions/bs.3e691cc93ef03470/testcases/1/test-cases)
### Stacktrace:
java.lang.RuntimeException: Error while connecting UiAutomation@3dcced2[id=-1, flags=0]
at android.app.UiAutomation.connect(UiAutomation.java:259)
at android.app.Instrumentation.getUiAutomation(Instrumentation.java:2176)
at androidx.test.uiautomator.UiDevice.getUiAutomation(UiDevice.java:1129)
at androidx.test.uiautomator.QueryController.<init>(QueryController.java:95)
at androidx.test.uiautomator.UiDevice.<init>(UiDevice.java:109)
at androidx.test.uiautomator.UiDevice.getInstance(UiDevice.java:261)
at org.mozilla.fenix.ui.SmokeTest.<init>(SmokeTest.kt:64)
### Build: 6/16
### Notes: Similar with: #25416 #25414 #25342 #25341 #25453 #25468 #25579 #25578 #25624 #25625 #25628 #25630 #25642 #25655 #25656
| non_priority | intermittent ui test failure firebase test run stacktrace java lang runtimeexception error while connecting uiautomation at android app uiautomation connect uiautomation java at android app instrumentation getuiautomation instrumentation java at androidx test uiautomator uidevice getuiautomation uidevice java at androidx test uiautomator querycontroller querycontroller java at androidx test uiautomator uidevice uidevice java at androidx test uiautomator uidevice getinstance uidevice java at org mozilla fenix ui smoketest smoketest kt build notes similar with | 0 |
78,253 | 15,569,949,965 | IssuesEvent | 2021-03-17 01:22:17 | jrrk/riscv-linux | https://api.github.com/repos/jrrk/riscv-linux | opened | CVE-2020-11609 (Medium) detected in aspeedaspeed-4.19-devicetree-no-fsi | security vulnerability | ## CVE-2020-11609 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>aspeedaspeed-4.19-devicetree-no-fsi</b></p></summary>
<p>
<p>ASPEED ARM SoC development</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git>https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (4)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx_pb0100.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx_pb0100.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the stv06xx subsystem in the Linux kernel before 5.6.1. drivers/media/usb/gspca/stv06xx/stv06xx.c and drivers/media/usb/gspca/stv06xx/stv06xx_pb0100.c mishandle invalid descriptors, as demonstrated by a NULL pointer dereference, aka CID-485b06aadb93.
<p>Publish Date: 2020-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11609>CVE-2020-11609</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-11609">https://nvd.nist.gov/vuln/detail/CVE-2020-11609</a></p>
<p>Release Date: 2020-04-07</p>
<p>Fix Resolution: linux - v5.7-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11609 (Medium) detected in aspeedaspeed-4.19-devicetree-no-fsi - ## CVE-2020-11609 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>aspeedaspeed-4.19-devicetree-no-fsi</b></p></summary>
<p>
<p>ASPEED ARM SoC development</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git>https://git.kernel.org/pub/scm/linux/kernel/git/joel/aspeed.git</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (4)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx_pb0100.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx_pb0100.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>riscv-linux/drivers/media/usb/gspca/stv06xx/stv06xx.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the stv06xx subsystem in the Linux kernel before 5.6.1. drivers/media/usb/gspca/stv06xx/stv06xx.c and drivers/media/usb/gspca/stv06xx/stv06xx_pb0100.c mishandle invalid descriptors, as demonstrated by a NULL pointer dereference, aka CID-485b06aadb93.
<p>Publish Date: 2020-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11609>CVE-2020-11609</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://nvd.nist.gov/vuln/detail/CVE-2020-11609">https://nvd.nist.gov/vuln/detail/CVE-2020-11609</a></p>
<p>Release Date: 2020-04-07</p>
<p>Fix Resolution: linux - v5.7-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in aspeedaspeed devicetree no fsi cve medium severity vulnerability vulnerable library aspeedaspeed devicetree no fsi aspeed arm soc development library home page a href vulnerable source files riscv linux drivers media usb gspca c riscv linux drivers media usb gspca c riscv linux drivers media usb gspca c riscv linux drivers media usb gspca c vulnerability details an issue was discovered in the subsystem in the linux kernel before drivers media usb gspca c and drivers media usb gspca c mishandle invalid descriptors as demonstrated by a null pointer dereference aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution linux step up your open source security game with whitesource | 0 |
72,869 | 31,769,572,684 | IssuesEvent | 2023-09-12 10:53:28 | gauravrs18/issue_onboarding | https://api.github.com/repos/gauravrs18/issue_onboarding | closed | dev-angular-style-account-services-new-connection-component-approve-component
-consumer-details-component
-activate-component
-approve-button-component | CX-account-services | dev-angular-style-account-services-new-connection-component-approve-component
-consumer-details-component
-activate-component
-approve-button-component | 1.0 | dev-angular-style-account-services-new-connection-component-approve-component
-consumer-details-component
-activate-component
-approve-button-component - dev-angular-style-account-services-new-connection-component-approve-component
-consumer-details-component
-activate-component
-approve-button-component | non_priority | dev angular style account services new connection component approve component consumer details component activate component approve button component dev angular style account services new connection component approve component consumer details component activate component approve button component | 0 |
48,905 | 25,893,179,309 | IssuesEvent | 2022-12-14 19:50:01 | elementor/elementor | https://api.github.com/repos/elementor/elementor | closed | 🐞 Bug Report: Improve video fallback timing | product/pro type/performance component/video | ## Prerequisites
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] I have searched for similar issues in both open and closed tickets and cannot find a duplicate.
- [x] The issue still exists against the latest stable version of Elementor.
## Description
Hello, I have a YouTube background in one of my sites, and the fallback is disappearing before the video loads, giving the user a black loading screen.
After searching for this issue,it was fixed in v1.5.1 but I'm in 2.7.4 (2.7.2 pro) and I have this issue.
I've run Elementor in safe mode, and it's the same.
[https://ultimateshadesandblinds.com/](https://ultimateshadesandblinds.com/)
Some related issues:
#1644
#1901
## Steps to reproduce
1. Add a background video and a background fallback.
2. Put a YouTube video.
3. Start time: 5 seconds
## Isolating the problem
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] This bug happens with only Elementor plugin active (and Elementor Pro).
- [x] This bug happens with a default WordPress theme active.
- [x] I can reproduce this bug consistently using the steps above.
## Environment
[https://pastebin.com/qExYSn9c](https://pastebin.com/qExYSn9c)
| True | 🐞 Bug Report: Improve video fallback timing - ## Prerequisites
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] I have searched for similar issues in both open and closed tickets and cannot find a duplicate.
- [x] The issue still exists against the latest stable version of Elementor.
## Description
Hello, I have a YouTube background in one of my sites, and the fallback is disappearing before the video loads, giving the user a black loading screen.
After searching for this issue,it was fixed in v1.5.1 but I'm in 2.7.4 (2.7.2 pro) and I have this issue.
I've run Elementor in safe mode, and it's the same.
[https://ultimateshadesandblinds.com/](https://ultimateshadesandblinds.com/)
Some related issues:
#1644
#1901
## Steps to reproduce
1. Add a background video and a background fallback.
2. Put a YouTube video.
3. Start time: 5 seconds
## Isolating the problem
<!-- MARK COMPLETED ITEMS WITH AN [x] -->
- [x] This bug happens with only Elementor plugin active (and Elementor Pro).
- [x] This bug happens with a default WordPress theme active.
- [x] I can reproduce this bug consistently using the steps above.
## Environment
[https://pastebin.com/qExYSn9c](https://pastebin.com/qExYSn9c)
| non_priority | 🐞 bug report improve video fallback timing prerequisites i have searched for similar issues in both open and closed tickets and cannot find a duplicate the issue still exists against the latest stable version of elementor description hello i have a youtube background in one of my sites and the fallback is disappearing before the video loads giving the user a black loading screen after searching for this issue it was fixed in but i m in pro and i have this issue i ve run elementor in safe mode and it s the same some related issues steps to reproduce add a background video and a background fallback put a youtube video start time seconds isolating the problem this bug happens with only elementor plugin active and elementor pro this bug happens with a default wordpress theme active i can reproduce this bug consistently using the steps above environment | 0 |
120,949 | 17,644,539,527 | IssuesEvent | 2021-08-20 02:42:53 | Killy85/game_ai_trainer | https://api.github.com/repos/Killy85/game_ai_trainer | opened | CVE-2021-29519 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2021-29519 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. The API of `tf.raw_ops.SparseCross` allows combinations which would result in a `CHECK`-failure and denial of service. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/3d782b7d47b1bf2ed32bd4a246d6d6cadc4c903d/tensorflow/core/kernels/sparse_cross_op.cc#L114-L116) is tricked to consider a tensor of type `tstring` which in fact contains integral elements. Fixing the type confusion by preventing mixing `DT_STRING` and `DT_INT64` types solves this issue. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29519>CVE-2021-29519</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-772j-h9xw-ffp5">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-772j-h9xw-ffp5</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-29519 (Medium) detected in tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2021-29519 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>TensorFlow is an open source machine learning framework for everyone.</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/d2/ea/ab2c8c0e81bd051cc1180b104c75a865ab0fc66c89be992c4b20bbf6d624/tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>
Dependency Hierarchy:
- :x: **tensorflow-1.13.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
TensorFlow is an end-to-end open source platform for machine learning. The API of `tf.raw_ops.SparseCross` allows combinations which would result in a `CHECK`-failure and denial of service. This is because the implementation(https://github.com/tensorflow/tensorflow/blob/3d782b7d47b1bf2ed32bd4a246d6d6cadc4c903d/tensorflow/core/kernels/sparse_cross_op.cc#L114-L116) is tricked to consider a tensor of type `tstring` which in fact contains integral elements. Fixing the type confusion by preventing mixing `DT_STRING` and `DT_INT64` types solves this issue. The fix will be included in TensorFlow 2.5.0. We will also cherrypick this commit on TensorFlow 2.4.2, TensorFlow 2.3.3, TensorFlow 2.2.3 and TensorFlow 2.1.4, as these are also affected and still in supported range.
<p>Publish Date: 2021-05-14
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29519>CVE-2021-29519</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/tensorflow/tensorflow/security/advisories/GHSA-772j-h9xw-ffp5">https://github.com/tensorflow/tensorflow/security/advisories/GHSA-772j-h9xw-ffp5</a></p>
<p>Release Date: 2021-05-14</p>
<p>Fix Resolution: tensorflow - 2.5.0, tensorflow-cpu - 2.5.0, tensorflow-gpu - 2.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tensorflow whl cve medium severity vulnerability vulnerable library tensorflow whl tensorflow is an open source machine learning framework for everyone library home page a href dependency hierarchy x tensorflow whl vulnerable library vulnerability details tensorflow is an end to end open source platform for machine learning the api of tf raw ops sparsecross allows combinations which would result in a check failure and denial of service this is because the implementation is tricked to consider a tensor of type tstring which in fact contains integral elements fixing the type confusion by preventing mixing dt string and dt types solves this issue the fix will be included in tensorflow we will also cherrypick this commit on tensorflow tensorflow tensorflow and tensorflow as these are also affected and still in supported range publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution tensorflow tensorflow cpu tensorflow gpu step up your open source security game with whitesource | 0 |
259,849 | 27,738,891,207 | IssuesEvent | 2023-03-15 13:08:06 | MatBenfield/news | https://api.github.com/repos/MatBenfield/news | closed | [SecurityWeek] Fortinet Finds Zero-Day Exploit in Government Attacks After Devices Detect Integrity Breach | SecurityWeek Stale |
Fortinet says recently patched FortiOS vulnerability was exploited in sophisticated attacks targeting government entities.
The post [Fortinet Finds Zero-Day Exploit in Government Attacks After Devices Detect Integrity Breach](https://www.securityweek.com/fortinet-finds-zero-day-exploit-in-government-attacks-after-devices-detect-integrity-breach/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/fortinet-finds-zero-day-exploit-in-government-attacks-after-devices-detect-integrity-breach/>
| True | [SecurityWeek] Fortinet Finds Zero-Day Exploit in Government Attacks After Devices Detect Integrity Breach -
Fortinet says recently patched FortiOS vulnerability was exploited in sophisticated attacks targeting government entities.
The post [Fortinet Finds Zero-Day Exploit in Government Attacks After Devices Detect Integrity Breach](https://www.securityweek.com/fortinet-finds-zero-day-exploit-in-government-attacks-after-devices-detect-integrity-breach/) appeared first on [SecurityWeek](https://www.securityweek.com).
<https://www.securityweek.com/fortinet-finds-zero-day-exploit-in-government-attacks-after-devices-detect-integrity-breach/>
| non_priority | fortinet finds zero day exploit in government attacks after devices detect integrity breach fortinet says recently patched fortios vulnerability was exploited in sophisticated attacks targeting government entities the post appeared first on | 0 |
3,815 | 2,702,742,006 | IssuesEvent | 2015-04-06 11:56:05 | jvalanen/diomber | https://api.github.com/repos/jvalanen/diomber | closed | Diory-information as a fixed sized table | 3 - Under testing / done Design |
<!---
@huboard:{"order":2.75,"milestone_order":13,"custom_state":""}
-->
| 1.0 | Diory-information as a fixed sized table -
<!---
@huboard:{"order":2.75,"milestone_order":13,"custom_state":""}
-->
| non_priority | diory information as a fixed sized table huboard order milestone order custom state | 0 |
147,137 | 11,774,752,118 | IssuesEvent | 2020-03-16 10:02:38 | proarc/proarc | https://api.github.com/repos/proarc/proarc | closed | Import dat z Krameria - prázdný formulář | 1 chyba 6 k testování Release-3.5.16 | Když naimportuji export z Krameria do ProArcu (číslo periodika), tak formulář se zobrazí prázdný a v xml je starý mods.
Prázdný formulář:
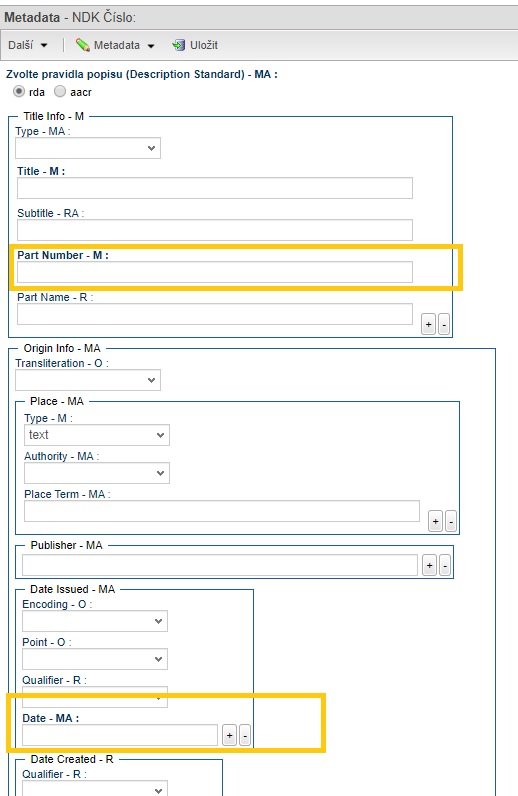
XML:
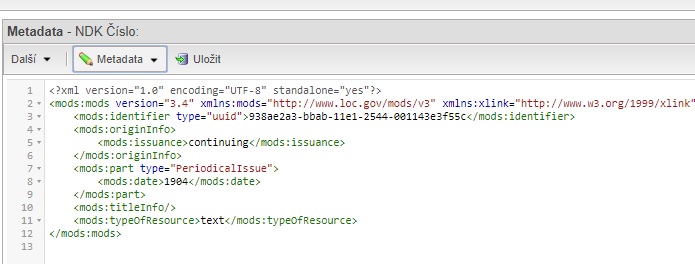
Když něco změním ve formuláři, tak se celé xml přepíše.
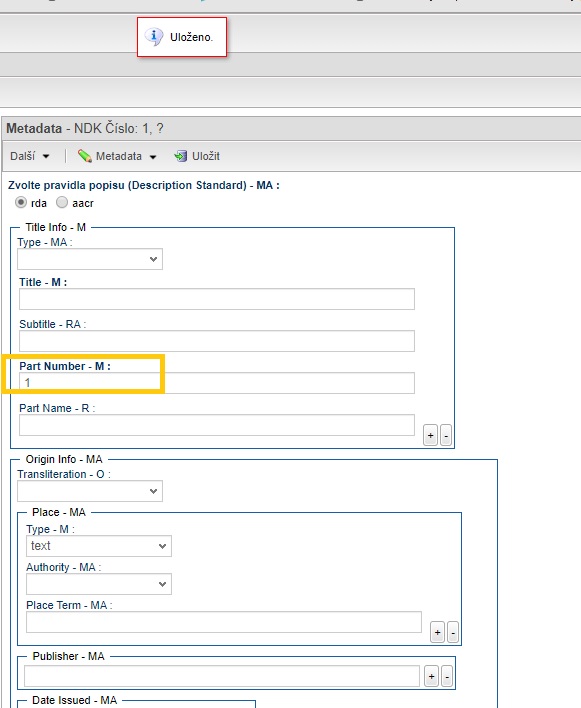
XML:
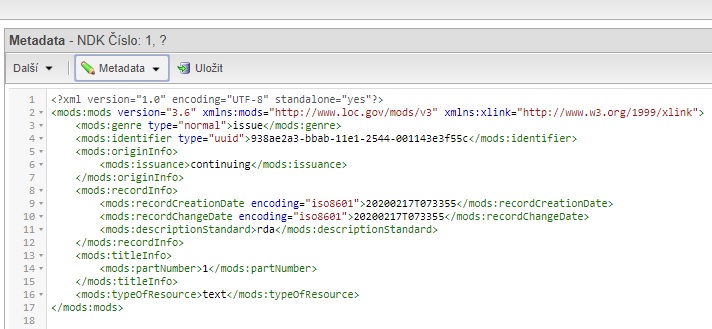
Bylo by spíš potřeba, aby to xml vypadalo správně už od začátku a aby se ta data propsala do formuláře. Předpokládám, že k tomu asi bude potřeba vyrobit mapování...?
| 1.0 | Import dat z Krameria - prázdný formulář - Když naimportuji export z Krameria do ProArcu (číslo periodika), tak formulář se zobrazí prázdný a v xml je starý mods.
Prázdný formulář:
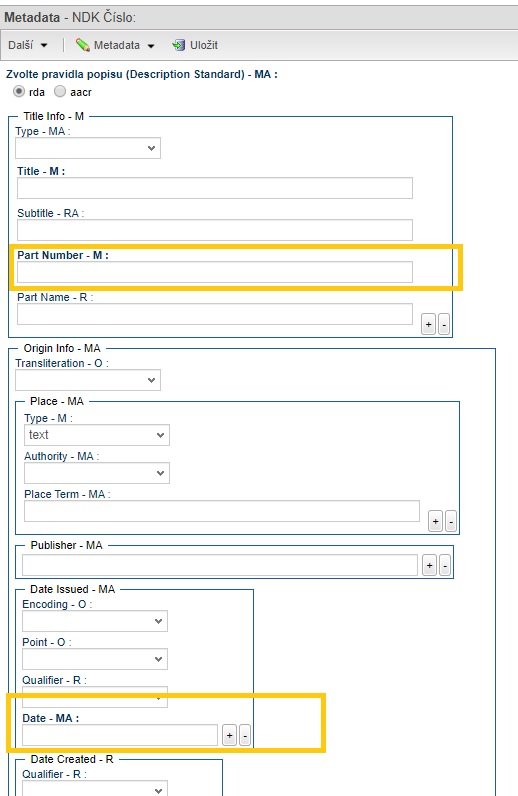
XML:
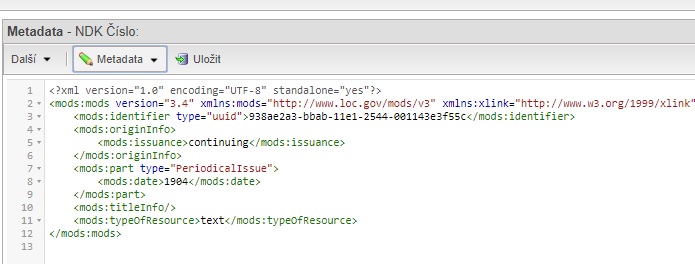
Když něco změním ve formuláři, tak se celé xml přepíše.
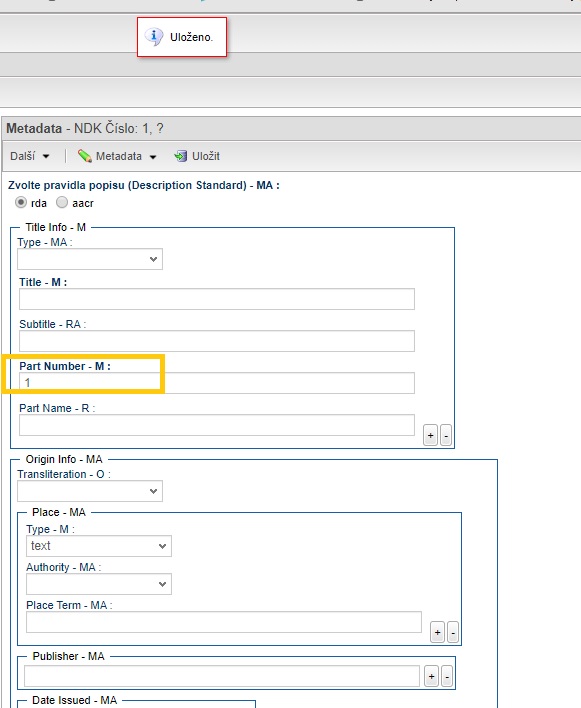
XML:
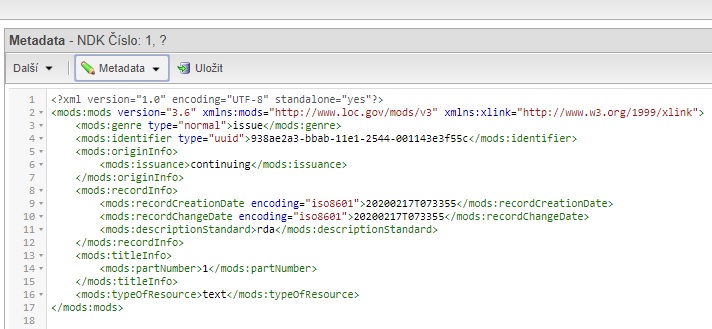
Bylo by spíš potřeba, aby to xml vypadalo správně už od začátku a aby se ta data propsala do formuláře. Předpokládám, že k tomu asi bude potřeba vyrobit mapování...?
| non_priority | import dat z krameria prázdný formulář když naimportuji export z krameria do proarcu číslo periodika tak formulář se zobrazí prázdný a v xml je starý mods prázdný formulář xml když něco změním ve formuláři tak se celé xml přepíše xml bylo by spíš potřeba aby to xml vypadalo správně už od začátku a aby se ta data propsala do formuláře předpokládám že k tomu asi bude potřeba vyrobit mapování | 0 |
21,212 | 3,689,901,396 | IssuesEvent | 2016-02-25 18:01:51 | RestComm/RestComm-Core | https://api.github.com/repos/RestComm/RestComm-Core | closed | Adapt RVD Project synchronisation to use project sid instead of project name | 2. Enhancement Peer Review Visual App Designer | Consider the Project SID for RVD operations as create, rename or delete projects.
Also review the creation of a new project (including import) to ensure that the directory name inside the workspace will use a SID. | 1.0 | Adapt RVD Project synchronisation to use project sid instead of project name - Consider the Project SID for RVD operations as create, rename or delete projects.
Also review the creation of a new project (including import) to ensure that the directory name inside the workspace will use a SID. | non_priority | adapt rvd project synchronisation to use project sid instead of project name consider the project sid for rvd operations as create rename or delete projects also review the creation of a new project including import to ensure that the directory name inside the workspace will use a sid | 0 |
285,685 | 31,155,095,008 | IssuesEvent | 2023-08-16 12:39:55 | Trinadh465/linux-4.1.15_CVE-2018-5873 | https://api.github.com/repos/Trinadh465/linux-4.1.15_CVE-2018-5873 | opened | CVE-2017-1000371 (High) detected in linuxlinux-4.1.52, linuxlinux-4.1.52 | Mend: dependency security vulnerability | ## CVE-2017-1000371 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.1.52</b>, <b>linuxlinux-4.1.52</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The offset2lib patch as used by the Linux Kernel contains a vulnerability, if RLIMIT_STACK is set to RLIM_INFINITY and 1 Gigabyte of memory is allocated (the maximum under the 1/4 restriction) then the stack will be grown down to 0x80000000, and as the PIE binary is mapped above 0x80000000 the minimum distance between the end of the PIE binary's read-write segment and the start of the stack becomes small enough that the stack guard page can be jumped over by an attacker. This affects Linux Kernel version 4.11.5. This is a different issue than CVE-2017-1000370 and CVE-2017-1000365. This issue appears to be limited to i386 based systems.
<p>Publish Date: 2017-06-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-1000371>CVE-2017-1000371</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000371">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000371</a></p>
<p>Release Date: 2017-06-19</p>
<p>Fix Resolution: v4.13-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2017-1000371 (High) detected in linuxlinux-4.1.52, linuxlinux-4.1.52 - ## CVE-2017-1000371 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>linuxlinux-4.1.52</b>, <b>linuxlinux-4.1.52</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The offset2lib patch as used by the Linux Kernel contains a vulnerability, if RLIMIT_STACK is set to RLIM_INFINITY and 1 Gigabyte of memory is allocated (the maximum under the 1/4 restriction) then the stack will be grown down to 0x80000000, and as the PIE binary is mapped above 0x80000000 the minimum distance between the end of the PIE binary's read-write segment and the start of the stack becomes small enough that the stack guard page can be jumped over by an attacker. This affects Linux Kernel version 4.11.5. This is a different issue than CVE-2017-1000370 and CVE-2017-1000365. This issue appears to be limited to i386 based systems.
<p>Publish Date: 2017-06-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2017-1000371>CVE-2017-1000371</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000371">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-1000371</a></p>
<p>Release Date: 2017-06-19</p>
<p>Fix Resolution: v4.13-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux linuxlinux cve high severity vulnerability vulnerable libraries linuxlinux linuxlinux vulnerability details the patch as used by the linux kernel contains a vulnerability if rlimit stack is set to rlim infinity and gigabyte of memory is allocated the maximum under the restriction then the stack will be grown down to and as the pie binary is mapped above the minimum distance between the end of the pie binary s read write segment and the start of the stack becomes small enough that the stack guard page can be jumped over by an attacker this affects linux kernel version this is a different issue than cve and cve this issue appears to be limited to based systems publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
137,348 | 18,752,691,258 | IssuesEvent | 2021-11-05 05:50:07 | madhans23/linux-4.15 | https://api.github.com/repos/madhans23/linux-4.15 | opened | CVE-2021-29650 (Medium) detected in minimal-linux78bd5fefcf303e772cdcdfe18b049fe97a1bf832, linux-stablev4.17.12 | security vulnerability | ## CVE-2021-29650 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimal-linux78bd5fefcf303e772cdcdfe18b049fe97a1bf832</b>, <b>linux-stablev4.17.12</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.11.11. The netfilter subsystem allows attackers to cause a denial of service (panic) because net/netfilter/x_tables.c and include/linux/netfilter/x_tables.h lack a full memory barrier upon the assignment of a new table value, aka CID-175e476b8cdf.
<p>Publish Date: 2021-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29650>CVE-2021-29650</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-29650">https://www.linuxkernelcves.com/cves/CVE-2021-29650</a></p>
<p>Release Date: 2021-03-30</p>
<p>Fix Resolution: v4.19.184, V5.4.109, V5.10.27, V5.11.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-29650 (Medium) detected in minimal-linux78bd5fefcf303e772cdcdfe18b049fe97a1bf832, linux-stablev4.17.12 - ## CVE-2021-29650 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>minimal-linux78bd5fefcf303e772cdcdfe18b049fe97a1bf832</b>, <b>linux-stablev4.17.12</b></p></summary>
<p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.11.11. The netfilter subsystem allows attackers to cause a denial of service (panic) because net/netfilter/x_tables.c and include/linux/netfilter/x_tables.h lack a full memory barrier upon the assignment of a new table value, aka CID-175e476b8cdf.
<p>Publish Date: 2021-03-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-29650>CVE-2021-29650</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.linuxkernelcves.com/cves/CVE-2021-29650">https://www.linuxkernelcves.com/cves/CVE-2021-29650</a></p>
<p>Release Date: 2021-03-30</p>
<p>Fix Resolution: v4.19.184, V5.4.109, V5.10.27, V5.11.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in minimal linux cve medium severity vulnerability vulnerable libraries minimal linux vulnerability details an issue was discovered in the linux kernel before the netfilter subsystem allows attackers to cause a denial of service panic because net netfilter x tables c and include linux netfilter x tables h lack a full memory barrier upon the assignment of a new table value aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
171,116 | 20,922,078,635 | IssuesEvent | 2022-03-24 18:23:02 | opensearch-project/sql | https://api.github.com/repos/opensearch-project/sql | opened | CVE-2021-3795 (High) detected in semver-regex-2.0.0.tgz | security vulnerability | ## CVE-2021-3795 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p></summary>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- husky-4.3.6.tgz (Root Library)
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/opensearch-project/sql/commit/677196811328749b619a19443cceeadfde74fbd3">677196811328749b619a19443cceeadfde74fbd3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
semver-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3795>CVE-2021-3795</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sindresorhus/semver-regex/releases/tag/v4.0.1">https://github.com/sindresorhus/semver-regex/releases/tag/v4.0.1</a></p>
<p>Release Date: 2021-09-15</p>
<p>Fix Resolution (semver-regex): 3.1.3</p>
<p>Direct dependency fix Resolution (husky): 4.3.7</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"husky","packageVersion":"4.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"husky:4.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.7","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-3795","vulnerabilityDetails":"semver-regex is vulnerable to Inefficient Regular Expression Complexity","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3795","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-3795 (High) detected in semver-regex-2.0.0.tgz - ## CVE-2021-3795 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p></summary>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>
Dependency Hierarchy:
- husky-4.3.6.tgz (Root Library)
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/opensearch-project/sql/commit/677196811328749b619a19443cceeadfde74fbd3">677196811328749b619a19443cceeadfde74fbd3</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
semver-regex is vulnerable to Inefficient Regular Expression Complexity
<p>Publish Date: 2021-09-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3795>CVE-2021-3795</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/sindresorhus/semver-regex/releases/tag/v4.0.1">https://github.com/sindresorhus/semver-regex/releases/tag/v4.0.1</a></p>
<p>Release Date: 2021-09-15</p>
<p>Fix Resolution (semver-regex): 3.1.3</p>
<p>Direct dependency fix Resolution (husky): 4.3.7</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"husky","packageVersion":"4.3.6","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"husky:4.3.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.3.7","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2021-3795","vulnerabilityDetails":"semver-regex is vulnerable to Inefficient Regular Expression Complexity","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-3795","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in semver regex tgz cve high severity vulnerability vulnerable library semver regex tgz regular expression for matching semver versions library home page a href dependency hierarchy husky tgz root library find versions tgz x semver regex tgz vulnerable library found in head commit a href found in base branch main vulnerability details semver regex is vulnerable to inefficient regular expression complexity publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution semver regex direct dependency fix resolution husky isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree husky isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails semver regex is vulnerable to inefficient regular expression complexity vulnerabilityurl | 0 |
119,447 | 10,053,889,036 | IssuesEvent | 2019-07-21 20:37:51 | uqbar-project/wollok | https://api.github.com/repos/uqbar-project/wollok | closed | Agregar tiempo de ejecución de tests en milisegundos | component: tests type: Nice to Have | En la UI sería interesante poder saber cuánto tardan los tests (y si figura en la solapa JUnit, hay lugar abajo ahora que se agrega el botón copiar el stacktrace). También lo dejo para que wollok-cli lo muestre.
Eso permite que cuando un alumno nos diga: "tardan mucho los tests" lo pueda reflejar objetivamente. | 1.0 | Agregar tiempo de ejecución de tests en milisegundos - En la UI sería interesante poder saber cuánto tardan los tests (y si figura en la solapa JUnit, hay lugar abajo ahora que se agrega el botón copiar el stacktrace). También lo dejo para que wollok-cli lo muestre.
Eso permite que cuando un alumno nos diga: "tardan mucho los tests" lo pueda reflejar objetivamente. | non_priority | agregar tiempo de ejecución de tests en milisegundos en la ui sería interesante poder saber cuánto tardan los tests y si figura en la solapa junit hay lugar abajo ahora que se agrega el botón copiar el stacktrace también lo dejo para que wollok cli lo muestre eso permite que cuando un alumno nos diga tardan mucho los tests lo pueda reflejar objetivamente | 0 |
247,698 | 26,728,760,518 | IssuesEvent | 2023-01-30 01:03:35 | ostest33/test1 | https://api.github.com/repos/ostest33/test1 | opened | CVE-2022-48285 (Medium) detected in jszip-3.7.1.tgz | security vulnerability | ## CVE-2022-48285 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jszip-3.7.1.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.7.1.tgz">https://registry.npmjs.org/jszip/-/jszip-3.7.1.tgz</a></p>
<p>Path to dependency file: /ClientApp/package.json</p>
<p>Path to vulnerable library: /ClientApp/node_modules/jszip/package.json</p>
<p>
Dependency Hierarchy:
- protractor-7.0.0.tgz (Root Library)
- selenium-webdriver-3.6.0.tgz
- :x: **jszip-3.7.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ostest33/test1/commit/275cfdd25e4a42e20932e2fb636dced652d9f111">275cfdd25e4a42e20932e2fb636dced652d9f111</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
loadAsync in JSZip before 3.8.0 allows Directory Traversal via a crafted ZIP archive.
<p>Publish Date: 2023-01-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-48285>CVE-2022-48285</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-48285">https://www.cve.org/CVERecord?id=CVE-2022-48285</a></p>
<p>Release Date: 2023-01-29</p>
<p>Fix Resolution: jszip - 3.8.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-48285 (Medium) detected in jszip-3.7.1.tgz - ## CVE-2022-48285 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jszip-3.7.1.tgz</b></p></summary>
<p>Create, read and edit .zip files with JavaScript http://stuartk.com/jszip</p>
<p>Library home page: <a href="https://registry.npmjs.org/jszip/-/jszip-3.7.1.tgz">https://registry.npmjs.org/jszip/-/jszip-3.7.1.tgz</a></p>
<p>Path to dependency file: /ClientApp/package.json</p>
<p>Path to vulnerable library: /ClientApp/node_modules/jszip/package.json</p>
<p>
Dependency Hierarchy:
- protractor-7.0.0.tgz (Root Library)
- selenium-webdriver-3.6.0.tgz
- :x: **jszip-3.7.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ostest33/test1/commit/275cfdd25e4a42e20932e2fb636dced652d9f111">275cfdd25e4a42e20932e2fb636dced652d9f111</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
loadAsync in JSZip before 3.8.0 allows Directory Traversal via a crafted ZIP archive.
<p>Publish Date: 2023-01-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-48285>CVE-2022-48285</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.cve.org/CVERecord?id=CVE-2022-48285">https://www.cve.org/CVERecord?id=CVE-2022-48285</a></p>
<p>Release Date: 2023-01-29</p>
<p>Fix Resolution: jszip - 3.8.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jszip tgz cve medium severity vulnerability vulnerable library jszip tgz create read and edit zip files with javascript library home page a href path to dependency file clientapp package json path to vulnerable library clientapp node modules jszip package json dependency hierarchy protractor tgz root library selenium webdriver tgz x jszip tgz vulnerable library found in head commit a href found in base branch master vulnerability details loadasync in jszip before allows directory traversal via a crafted zip archive publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jszip step up your open source security game with mend | 0 |
1,231 | 14,145,581,243 | IssuesEvent | 2020-11-10 17:56:40 | microsoft/calculator | https://api.github.com/repos/microsoft/calculator | closed | Copy pasting into Currency locks the editor | Area: Reliability Bug Pri: 2 investigate | <!--
Before filing a bug
- Ensure the bug reproduces on the latest version of the app.
- Search existing issues and make sure this issue is not already filed.
-->
**Describe the bug**
<!-- A clear and concise description of what the bug is. -->
Copy pasting from any source into the currency locks the editor and you cannot clear the editor.
**Steps To Reproduce**
<!--
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
-->
Open Notepad
Type text "20.83" and copy the text
Open the calculator app and paste the text with Ctrl+V
See that you removing or CE button doesn't clear anything.
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
I would expect the editor still continue to edit. Nothing happens after copy paste.
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->

**Device and Application Information**
- OS Build: 10.0.19041.0
- Architecture: X64
- Application Version: 10.2009.4.0
- Region: en-US
- Dev Version Installed: false
<!--
Run the following commands in Powershell and copy/paste the output.
" - OS Build: $([Environment]::OSVersion.Version)"
" - Architecture: $((Get-AppxPackage -Name Microsoft.WindowsCalculator).Architecture)"
" - Application Version: $((Get-AppxPackage -Name Microsoft.WindowsCalculator).Version)"
" - Region: $((Get-Culture).Name)"
" - Dev Version Installed: $($null -ne (Get-AppxPackage -Name Microsoft.WindowsCalculator.Dev))"
-->
**Additional context**
<!-- Add any other context about the problem here. -->
N/A
**Requested Assignment**
<!--
Some people just want to report a bug and let someone else fix it.
Other people want to not only submit the bug report, but fix it as well.
Both scenarios are completely ok. We just want to know which one it is.
Please indicate which bucket you fall into by keeping one and removing the other.
-->
If possible, I would like to fix this.
| True | Copy pasting into Currency locks the editor - <!--
Before filing a bug
- Ensure the bug reproduces on the latest version of the app.
- Search existing issues and make sure this issue is not already filed.
-->
**Describe the bug**
<!-- A clear and concise description of what the bug is. -->
Copy pasting from any source into the currency locks the editor and you cannot clear the editor.
**Steps To Reproduce**
<!--
Steps to reproduce the behavior:
1. Go to '...'
2. Click on '....'
3. Scroll down to '....'
4. See error
-->
Open Notepad
Type text "20.83" and copy the text
Open the calculator app and paste the text with Ctrl+V
See that you removing or CE button doesn't clear anything.
**Expected behavior**
<!-- A clear and concise description of what you expected to happen. -->
I would expect the editor still continue to edit. Nothing happens after copy paste.
**Screenshots**
<!-- If applicable, add screenshots to help explain your problem. -->

**Device and Application Information**
- OS Build: 10.0.19041.0
- Architecture: X64
- Application Version: 10.2009.4.0
- Region: en-US
- Dev Version Installed: false
<!--
Run the following commands in Powershell and copy/paste the output.
" - OS Build: $([Environment]::OSVersion.Version)"
" - Architecture: $((Get-AppxPackage -Name Microsoft.WindowsCalculator).Architecture)"
" - Application Version: $((Get-AppxPackage -Name Microsoft.WindowsCalculator).Version)"
" - Region: $((Get-Culture).Name)"
" - Dev Version Installed: $($null -ne (Get-AppxPackage -Name Microsoft.WindowsCalculator.Dev))"
-->
**Additional context**
<!-- Add any other context about the problem here. -->
N/A
**Requested Assignment**
<!--
Some people just want to report a bug and let someone else fix it.
Other people want to not only submit the bug report, but fix it as well.
Both scenarios are completely ok. We just want to know which one it is.
Please indicate which bucket you fall into by keeping one and removing the other.
-->
If possible, I would like to fix this.
| non_priority | copy pasting into currency locks the editor before filing a bug ensure the bug reproduces on the latest version of the app search existing issues and make sure this issue is not already filed describe the bug copy pasting from any source into the currency locks the editor and you cannot clear the editor steps to reproduce steps to reproduce the behavior go to click on scroll down to see error open notepad type text and copy the text open the calculator app and paste the text with ctrl v see that you removing or ce button doesn t clear anything expected behavior i would expect the editor still continue to edit nothing happens after copy paste screenshots device and application information os build architecture application version region en us dev version installed false run the following commands in powershell and copy paste the output os build osversion version architecture get appxpackage name microsoft windowscalculator architecture application version get appxpackage name microsoft windowscalculator version region get culture name dev version installed null ne get appxpackage name microsoft windowscalculator dev additional context n a requested assignment some people just want to report a bug and let someone else fix it other people want to not only submit the bug report but fix it as well both scenarios are completely ok we just want to know which one it is please indicate which bucket you fall into by keeping one and removing the other if possible i would like to fix this | 0 |
411,503 | 27,824,032,994 | IssuesEvent | 2023-03-19 15:05:35 | torrust/torrust-index | https://api.github.com/repos/torrust/torrust-index | opened | Overhall Readme File | documentation help wanted | The Torrust-Index Meta-Repository dose not have an appropriate readme file. The readme needs to be much more professional, concise, and more technically explain the rationale for the meta-repo. | 1.0 | Overhall Readme File - The Torrust-Index Meta-Repository dose not have an appropriate readme file. The readme needs to be much more professional, concise, and more technically explain the rationale for the meta-repo. | non_priority | overhall readme file the torrust index meta repository dose not have an appropriate readme file the readme needs to be much more professional concise and more technically explain the rationale for the meta repo | 0 |
183,285 | 14,937,076,043 | IssuesEvent | 2021-01-25 14:12:24 | project-leek/project-leek | https://api.github.com/repos/project-leek/project-leek | closed | Collect previous retro summarys for report | documentation report | Collect previous retro summarys for report so they dont get lost and can be collected in one place in the future | 1.0 | Collect previous retro summarys for report - Collect previous retro summarys for report so they dont get lost and can be collected in one place in the future | non_priority | collect previous retro summarys for report collect previous retro summarys for report so they dont get lost and can be collected in one place in the future | 0 |
230,198 | 25,443,051,904 | IssuesEvent | 2022-11-24 01:36:46 | nanopathi/linux-4.19.72_CVE-2021-3347 | https://api.github.com/repos/nanopathi/linux-4.19.72_CVE-2021-3347 | closed | CVE-2019-15505 (High) detected in linuxlinux-4.19.239 - autoclosed | security vulnerability | ## CVE-2019-15505 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.239</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nanopathi/linux-4.19.72_CVE-2021-3347/commit/8b7c061438f230c475fd8cd97a0917f6ebb9fbe0">8b7c061438f230c475fd8cd97a0917f6ebb9fbe0</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/media/usb/dvb-usb/technisat-usb2.c in the Linux kernel through 5.2.9 has an out-of-bounds read via crafted USB device traffic (which may be remote via usbip or usbredir).
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-15505>CVE-2019-15505</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505</a></p>
<p>Release Date: 2019-09-04</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-15505 (High) detected in linuxlinux-4.19.239 - autoclosed - ## CVE-2019-15505 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.239</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nanopathi/linux-4.19.72_CVE-2021-3347/commit/8b7c061438f230c475fd8cd97a0917f6ebb9fbe0">8b7c061438f230c475fd8cd97a0917f6ebb9fbe0</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/dvb-usb/technisat-usb2.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
drivers/media/usb/dvb-usb/technisat-usb2.c in the Linux kernel through 5.2.9 has an out-of-bounds read via crafted USB device traffic (which may be remote via usbip or usbredir).
<p>Publish Date: 2019-08-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-15505>CVE-2019-15505</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: Low
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505">http://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2019-15505</a></p>
<p>Release Date: 2019-09-04</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux autoclosed cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch master vulnerable source files drivers media usb dvb usb technisat c drivers media usb dvb usb technisat c vulnerability details drivers media usb dvb usb technisat c in the linux kernel through has an out of bounds read via crafted usb device traffic which may be remote via usbip or usbredir publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact low availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
145,372 | 22,678,248,247 | IssuesEvent | 2022-07-04 07:31:40 | microsoft/AdaptiveCards | https://api.github.com/repos/microsoft/AdaptiveCards | opened | [Designer] Bug Title Her[Bug 40020683](https://microsoft.visualstudio.com/OS/_workitems/edit/40020683): [ProductVideo.json-Video Slider.]: No shortcut key to exit the full screen mode is available for users.e | Bug Area-Designer | ### Problem Description
[Bug 40020683](https://microsoft.visualstudio.com/OS/_workitems/edit/40020683): [ProductVideo.json-Video Slider.]: No shortcut key to exit the full screen mode is available for users.
### Card JSON
```JSON
[Bug 40020683](https://microsoft.visualstudio.com/OS/_workitems/edit/40020683): [ProductVideo.json-Video Slider.]: No shortcut key to exit the full screen mode is available for users.
```
### Screenshot
_No response_ | 1.0 | [Designer] Bug Title Her[Bug 40020683](https://microsoft.visualstudio.com/OS/_workitems/edit/40020683): [ProductVideo.json-Video Slider.]: No shortcut key to exit the full screen mode is available for users.e - ### Problem Description
[Bug 40020683](https://microsoft.visualstudio.com/OS/_workitems/edit/40020683): [ProductVideo.json-Video Slider.]: No shortcut key to exit the full screen mode is available for users.
### Card JSON
```JSON
[Bug 40020683](https://microsoft.visualstudio.com/OS/_workitems/edit/40020683): [ProductVideo.json-Video Slider.]: No shortcut key to exit the full screen mode is available for users.
```
### Screenshot
_No response_ | non_priority | bug title her no shortcut key to exit the full screen mode is available for users e problem description no shortcut key to exit the full screen mode is available for users card json json no shortcut key to exit the full screen mode is available for users screenshot no response | 0 |
68,034 | 8,210,768,627 | IssuesEvent | 2018-09-04 11:52:51 | Ulm-IQO/qudi | https://api.github.com/repos/Ulm-IQO/qudi | closed | Make predefined methods more readable/more easy to customize | comp:pulsed design issue enhancement | ## *What* is affected by this bug?
Each "generate_"-method currently has a lot of additional parameters that are not directly linked to the measurement (like gate_channel, laser_length, etc.). Writing a new generate method includes a lot of code duplication which makes the code less readable. These "infrastructure"-parameters should be somehow handled globally for the sequence_generator_logic.
## *When* does this occur?
When writing custom predefined methods.
## *How* do we replicate the issue?
Just have a look at predefined methods.
## Expected behavior (i.e. solution)
New methods should only have important/physical parameters that are related to the actual measurement sequence.
| 1.0 | Make predefined methods more readable/more easy to customize - ## *What* is affected by this bug?
Each "generate_"-method currently has a lot of additional parameters that are not directly linked to the measurement (like gate_channel, laser_length, etc.). Writing a new generate method includes a lot of code duplication which makes the code less readable. These "infrastructure"-parameters should be somehow handled globally for the sequence_generator_logic.
## *When* does this occur?
When writing custom predefined methods.
## *How* do we replicate the issue?
Just have a look at predefined methods.
## Expected behavior (i.e. solution)
New methods should only have important/physical parameters that are related to the actual measurement sequence.
| non_priority | make predefined methods more readable more easy to customize what is affected by this bug each generate method currently has a lot of additional parameters that are not directly linked to the measurement like gate channel laser length etc writing a new generate method includes a lot of code duplication which makes the code less readable these infrastructure parameters should be somehow handled globally for the sequence generator logic when does this occur when writing custom predefined methods how do we replicate the issue just have a look at predefined methods expected behavior i e solution new methods should only have important physical parameters that are related to the actual measurement sequence | 0 |
90,308 | 10,678,162,300 | IssuesEvent | 2019-10-21 16:43:58 | cclagodna/goblins-stole-my-bike | https://api.github.com/repos/cclagodna/goblins-stole-my-bike | closed | game flow | documentation feature | 1. The player battles
2. The player wins the battle
Total_gold += (Creature_Base_gold + Base_gold*creature_multilper )*Level_multiplier
Total_experience = Total_expereince + (Base_win_expereince*creature_multiplier )*level_multipler
I wrote these two differently to show how It could be done using += or just
3. OR the player dies instead
This one should be an if statement instead because the later the game goes the more the player would lose, one lost battle in the late game if there is no if statement used could result in the player losing significant amounts of gold possibly discouraging players.
If(total_gold<1,000,000)
Total_gold = total_gold-(total_gold*x)
Where x is a random double going from 0.05 to 0.09 making the player lose a maxium of 90,000 gold and when they for example only have 2000 gold they can only lose a max of roughly 200 gold.
ELSE
Total_gold = total_gold-(100,000+player_level*10)
This should still cause the player to lose a decent amount of gold for losing without being discouraging
4. The player fights the boss and wins
Total_gold += (Creature_Base_gold + Base_gold*creature_multilper )*Level_multiplier + Boss_bouns_gold
5. The player fights the boss and loses
Use the normal “death” loss gold formula I put above in 3.
No experience or items are lost on death but we could add items for them winning battle or even with a chance just watch for the max size of the inventory array and how we add it to the array because it could overwrite or delete items inadvertently from the players inventory.
| 1.0 | game flow - 1. The player battles
2. The player wins the battle
Total_gold += (Creature_Base_gold + Base_gold*creature_multilper )*Level_multiplier
Total_experience = Total_expereince + (Base_win_expereince*creature_multiplier )*level_multipler
I wrote these two differently to show how It could be done using += or just
3. OR the player dies instead
This one should be an if statement instead because the later the game goes the more the player would lose, one lost battle in the late game if there is no if statement used could result in the player losing significant amounts of gold possibly discouraging players.
If(total_gold<1,000,000)
Total_gold = total_gold-(total_gold*x)
Where x is a random double going from 0.05 to 0.09 making the player lose a maxium of 90,000 gold and when they for example only have 2000 gold they can only lose a max of roughly 200 gold.
ELSE
Total_gold = total_gold-(100,000+player_level*10)
This should still cause the player to lose a decent amount of gold for losing without being discouraging
4. The player fights the boss and wins
Total_gold += (Creature_Base_gold + Base_gold*creature_multilper )*Level_multiplier + Boss_bouns_gold
5. The player fights the boss and loses
Use the normal “death” loss gold formula I put above in 3.
No experience or items are lost on death but we could add items for them winning battle or even with a chance just watch for the max size of the inventory array and how we add it to the array because it could overwrite or delete items inadvertently from the players inventory.
| non_priority | game flow the player battles the player wins the battle total gold creature base gold base gold creature multilper level multiplier total experience total expereince base win expereince creature multiplier level multipler i wrote these two differently to show how it could be done using or just or the player dies instead this one should be an if statement instead because the later the game goes the more the player would lose one lost battle in the late game if there is no if statement used could result in the player losing significant amounts of gold possibly discouraging players if total gold total gold total gold total gold x where x is a random double going from to making the player lose a maxium of gold and when they for example only have gold they can only lose a max of roughly gold else total gold total gold player level this should still cause the player to lose a decent amount of gold for losing without being discouraging the player fights the boss and wins total gold creature base gold base gold creature multilper level multiplier boss bouns gold the player fights the boss and loses use the normal “death” loss gold formula i put above in no experience or items are lost on death but we could add items for them winning battle or even with a chance just watch for the max size of the inventory array and how we add it to the array because it could overwrite or delete items inadvertently from the players inventory | 0 |
188,975 | 15,174,326,960 | IssuesEvent | 2021-02-13 17:56:35 | tezos-reward-distributor-organization/tezos-reward-distributor | https://api.github.com/repos/tezos-reward-distributor-organization/tezos-reward-distributor | closed | Feature Request: Self Bonded Delegator Payout | documentation & logging | Is it currently possible to calculate rewards for a delegator that deposited their full stake in the baker, and is charged 0% for baking? Their reward would be added to their initial stake and keep on baking at 0%. | 1.0 | Feature Request: Self Bonded Delegator Payout - Is it currently possible to calculate rewards for a delegator that deposited their full stake in the baker, and is charged 0% for baking? Their reward would be added to their initial stake and keep on baking at 0%. | non_priority | feature request self bonded delegator payout is it currently possible to calculate rewards for a delegator that deposited their full stake in the baker and is charged for baking their reward would be added to their initial stake and keep on baking at | 0 |
126,471 | 10,424,078,188 | IssuesEvent | 2019-09-16 12:56:09 | microsoft/appcenter | https://api.github.com/repos/microsoft/appcenter | closed | Xamarin.UITest unable to interact with Azure Login(web-view) | feature request response required test | **What App Center service does this affect?**
App Center Testing using Xamarin.UI.Test
**Describe the bug**
Creating UITests for a Xamarin MVVM cross platform app that uses Azure login through web-view.
Unable to interact with any of the elements and therefore unable login with credentials then navigated back to the native app. This leaves us unable to create an automated test suite to run in app center.
REPL: example
>>> tree
[[object CalabashRootView]]
**Smartphone (please complete the following information):**
- Device: Any
- OS: Android and iOS
--iOS: Has a springboardalert that is also unable to interact as described in the issue reported below. Once this issue is corrected this issue will be the next issue that will prevent devs from creating a full automation test suite.
https://github.com/Microsoft/appcenter/issues/213
- Browser [e.g. stock browser, safari] All
Visual Studio Enterprise 2019 for Mac
Version 8.0 (build 3001)
Xamarin.iOS
Version: 12.6.0.25 (Visual Studio Enterprise)
Operating System
Mac OS X 10.14.4
Xcode
Version 10.2 (10E125)
| 1.0 | Xamarin.UITest unable to interact with Azure Login(web-view) - **What App Center service does this affect?**
App Center Testing using Xamarin.UI.Test
**Describe the bug**
Creating UITests for a Xamarin MVVM cross platform app that uses Azure login through web-view.
Unable to interact with any of the elements and therefore unable login with credentials then navigated back to the native app. This leaves us unable to create an automated test suite to run in app center.
REPL: example
>>> tree
[[object CalabashRootView]]
**Smartphone (please complete the following information):**
- Device: Any
- OS: Android and iOS
--iOS: Has a springboardalert that is also unable to interact as described in the issue reported below. Once this issue is corrected this issue will be the next issue that will prevent devs from creating a full automation test suite.
https://github.com/Microsoft/appcenter/issues/213
- Browser [e.g. stock browser, safari] All
Visual Studio Enterprise 2019 for Mac
Version 8.0 (build 3001)
Xamarin.iOS
Version: 12.6.0.25 (Visual Studio Enterprise)
Operating System
Mac OS X 10.14.4
Xcode
Version 10.2 (10E125)
| non_priority | xamarin uitest unable to interact with azure login web view what app center service does this affect app center testing using xamarin ui test describe the bug creating uitests for a xamarin mvvm cross platform app that uses azure login through web view unable to interact with any of the elements and therefore unable login with credentials then navigated back to the native app this leaves us unable to create an automated test suite to run in app center repl example tree smartphone please complete the following information device any os android and ios ios has a springboardalert that is also unable to interact as described in the issue reported below once this issue is corrected this issue will be the next issue that will prevent devs from creating a full automation test suite browser all visual studio enterprise for mac version build xamarin ios version visual studio enterprise operating system mac os x xcode version | 0 |
97,073 | 8,643,509,117 | IssuesEvent | 2018-11-25 18:37:28 | ollo-ride-nico/P8-Todo | https://api.github.com/repos/ollo-ride-nico/P8-Todo | opened | Coverage Report | Test | Fournir un rapport de couverture de code au terme du projet. Il doit être supérieur à 70%. | 1.0 | Coverage Report - Fournir un rapport de couverture de code au terme du projet. Il doit être supérieur à 70%. | non_priority | coverage report fournir un rapport de couverture de code au terme du projet il doit être supérieur à | 0 |
405,877 | 27,538,914,494 | IssuesEvent | 2023-03-07 06:53:52 | aptos-labs/aptos-core | https://api.github.com/repos/aptos-labs/aptos-core | closed | [Docs] Create Contribute section and highlight internal and external contributions | bug documentation P0 | # Aptos Documentation Issue
We need to create a *Contribute* section with Josh to include pages on:
* Highlights for external contributions
* Research papers
* Examples summarizing:
https://github.com/aptos-labs/aptos-core/tree/main/aptos-move/move-examples
* Specifications in our `documentation/` subdirectory
* Help for contributors to update docs and code (see: https://github.com/aptos-labs/aptos-core/issues/6310)
## Location
What are the existing URLs containing the issue, if any?
N/A
Where should this information land if new? (Start Aptos, Build Apps, Run Nodes, Reference, etc.)
This will be an entirely new section, which may reside under Reference until we have the pages to justify a distinct tab.
## Description
How would you describe the issue?
We need to highlight more of our existing materials while creating a clear path for more, from both internal and external contributors.
## Audience
Who is the audience for that information? (App developers, investors, creators, validators, someone else?)
Internal and external contributors.
What precisely must they do with it? (Configure a new service? Process some output?
Learn from our deeper docs and contribute new tutorials. | 1.0 | [Docs] Create Contribute section and highlight internal and external contributions - # Aptos Documentation Issue
We need to create a *Contribute* section with Josh to include pages on:
* Highlights for external contributions
* Research papers
* Examples summarizing:
https://github.com/aptos-labs/aptos-core/tree/main/aptos-move/move-examples
* Specifications in our `documentation/` subdirectory
* Help for contributors to update docs and code (see: https://github.com/aptos-labs/aptos-core/issues/6310)
## Location
What are the existing URLs containing the issue, if any?
N/A
Where should this information land if new? (Start Aptos, Build Apps, Run Nodes, Reference, etc.)
This will be an entirely new section, which may reside under Reference until we have the pages to justify a distinct tab.
## Description
How would you describe the issue?
We need to highlight more of our existing materials while creating a clear path for more, from both internal and external contributors.
## Audience
Who is the audience for that information? (App developers, investors, creators, validators, someone else?)
Internal and external contributors.
What precisely must they do with it? (Configure a new service? Process some output?
Learn from our deeper docs and contribute new tutorials. | non_priority | create contribute section and highlight internal and external contributions aptos documentation issue we need to create a contribute section with josh to include pages on highlights for external contributions research papers examples summarizing specifications in our documentation subdirectory help for contributors to update docs and code see location what are the existing urls containing the issue if any n a where should this information land if new start aptos build apps run nodes reference etc this will be an entirely new section which may reside under reference until we have the pages to justify a distinct tab description how would you describe the issue we need to highlight more of our existing materials while creating a clear path for more from both internal and external contributors audience who is the audience for that information app developers investors creators validators someone else internal and external contributors what precisely must they do with it configure a new service process some output learn from our deeper docs and contribute new tutorials | 0 |
275,388 | 23,912,263,641 | IssuesEvent | 2022-09-09 09:18:56 | Plant-for-the-Planet-org/treemapper | https://api.github.com/repos/Plant-for-the-Planet-org/treemapper | opened | t in __cxa_throw | bug bugsnag testflight 1.0.9 | ## Error in Tree Mapper
**t** in **__cxa_throw**
Network Error
[View on Bugsnag](https://app.bugsnag.com/plant-for-the-planet/tree-mapper/errors/631b04fdb99f4f0008f2cedd?event_id=631b04fd00965ee836220000&i=gh&m=ci)
## Stacktrace
TreeMapper:0 - __cxa_throw
TreeMapper:0 - __cxa_throw
TreeMapper:0 - __cxa_throw
TreeMapper:0 - facebook::react::JSIExecutor::defaultTimeoutInvoker(std::__1::function<void ()> const&, std::__1::function<std::__1::basic_string<char, std::__1::char_traits<char>, std::__1::allocator<char> > ()>)
TreeMapper:0 - facebook::react::JSIExecutor::defaultTimeoutInvoker(std::__1::function<void ()> const&, std::__1::function<std::__1::basic_string<char, std::__1::char_traits<char>, std::__1::allocator<char> > ()>)
TreeMapper:0 - facebook::react::JSIExecutor::defaultTimeoutInvoker(std::__1::function<void ()> const&, std::__1::function<std::__1::basic_string<char, std::__1::char_traits<char>, std::__1::allocator<char> > ()>)
[View full stacktrace](https://app.bugsnag.com/plant-for-the-planet/tree-mapper/errors/631b04fdb99f4f0008f2cedd?event_id=631b04fd00965ee836220000&i=gh&m=ci)
*Created automatically via Bugsnag* | 1.0 | t in __cxa_throw - ## Error in Tree Mapper
**t** in **__cxa_throw**
Network Error
[View on Bugsnag](https://app.bugsnag.com/plant-for-the-planet/tree-mapper/errors/631b04fdb99f4f0008f2cedd?event_id=631b04fd00965ee836220000&i=gh&m=ci)
## Stacktrace
TreeMapper:0 - __cxa_throw
TreeMapper:0 - __cxa_throw
TreeMapper:0 - __cxa_throw
TreeMapper:0 - facebook::react::JSIExecutor::defaultTimeoutInvoker(std::__1::function<void ()> const&, std::__1::function<std::__1::basic_string<char, std::__1::char_traits<char>, std::__1::allocator<char> > ()>)
TreeMapper:0 - facebook::react::JSIExecutor::defaultTimeoutInvoker(std::__1::function<void ()> const&, std::__1::function<std::__1::basic_string<char, std::__1::char_traits<char>, std::__1::allocator<char> > ()>)
TreeMapper:0 - facebook::react::JSIExecutor::defaultTimeoutInvoker(std::__1::function<void ()> const&, std::__1::function<std::__1::basic_string<char, std::__1::char_traits<char>, std::__1::allocator<char> > ()>)
[View full stacktrace](https://app.bugsnag.com/plant-for-the-planet/tree-mapper/errors/631b04fdb99f4f0008f2cedd?event_id=631b04fd00965ee836220000&i=gh&m=ci)
*Created automatically via Bugsnag* | non_priority | t in cxa throw error in tree mapper t in cxa throw network error stacktrace treemapper cxa throw treemapper cxa throw treemapper cxa throw treemapper facebook react jsiexecutor defaulttimeoutinvoker std function const std function std allocator treemapper facebook react jsiexecutor defaulttimeoutinvoker std function const std function std allocator treemapper facebook react jsiexecutor defaulttimeoutinvoker std function const std function std allocator created automatically via bugsnag | 0 |
277,121 | 24,050,455,435 | IssuesEvent | 2022-09-16 12:20:46 | tianzhongs/ObPublish | https://api.github.com/repos/tianzhongs/ObPublish | opened | 链接测试test2 | Gitalk https://ob.tianzhongs.ml/test2/ | https://ob.tianzhongs.ml/test2/
图片测试 图片测试
标准markdwon !【】() 相对路径 基于仓库目录 直接使用文件名称 图片测试2‘ wiki语法 ![[asset/Pasted image 20220916174257.png]]
连接其他页面 标准语法 【】()
» 本库常用的dataview工作流 显示其他页面!【】() wiki语法 [[]] [[test]] | 1.0 | 链接测试test2 - https://ob.tianzhongs.ml/test2/
图片测试 图片测试
标准markdwon !【】() 相对路径 基于仓库目录 直接使用文件名称 图片测试2‘ wiki语法 ![[asset/Pasted image 20220916174257.png]]
连接其他页面 标准语法 【】()
» 本库常用的dataview工作流 显示其他页面!【】() wiki语法 [[]] [[test]] | non_priority | 图片测试 图片测试 标准markdwon !【】() 相对路径 基于仓库目录 直接使用文件名称 ‘ wiki语法 连接其他页面 标准语法 【】() » 本库常用的dataview工作流 显示其他页面!【】() wiki语法 | 0 |
196,885 | 22,571,829,114 | IssuesEvent | 2022-06-28 01:27:20 | tz924/cs116-lab10 | https://api.github.com/repos/tz924/cs116-lab10 | opened | npm-run-all-4.1.5.tgz: 1 vulnerabilities (highest severity is: 9.8) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-run-all-4.1.5.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /ctf-spring2022/www/wp-content/themes/twentynineteen/package.json</p>
<p>Path to vulnerable library: /ctf-spring2022/www/wp-content/themes/twentynineteen/node_modules/shell-quote/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/tz924/cs116-lab10/commit/7f949f4f48089e4e1ea7eb0b2482120d3327d7c4">7f949f4f48089e4e1ea7eb0b2482120d3327d7c4</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-42740](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42740) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | shell-quote-1.6.1.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-42740</summary>
### Vulnerable Library - <b>shell-quote-1.6.1.tgz</b></p>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz</a></p>
<p>Path to dependency file: /ctf-spring2022/www/wp-content/themes/twentynineteen/package.json</p>
<p>Path to vulnerable library: /ctf-spring2022/www/wp-content/themes/twentynineteen/node_modules/shell-quote/package.json</p>
<p>
Dependency Hierarchy:
- npm-run-all-4.1.5.tgz (Root Library)
- :x: **shell-quote-1.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tz924/cs116-lab10/commit/7f949f4f48089e4e1ea7eb0b2482120d3327d7c4">7f949f4f48089e4e1ea7eb0b2482120d3327d7c4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution: shell-quote - 1.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | npm-run-all-4.1.5.tgz: 1 vulnerabilities (highest severity is: 9.8) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-run-all-4.1.5.tgz</b></p></summary>
<p></p>
<p>Path to dependency file: /ctf-spring2022/www/wp-content/themes/twentynineteen/package.json</p>
<p>Path to vulnerable library: /ctf-spring2022/www/wp-content/themes/twentynineteen/node_modules/shell-quote/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/tz924/cs116-lab10/commit/7f949f4f48089e4e1ea7eb0b2482120d3327d7c4">7f949f4f48089e4e1ea7eb0b2482120d3327d7c4</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2021-42740](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42740) | <img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> High | 9.8 | shell-quote-1.6.1.tgz | Transitive | N/A | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> CVE-2021-42740</summary>
### Vulnerable Library - <b>shell-quote-1.6.1.tgz</b></p>
<p>quote and parse shell commands</p>
<p>Library home page: <a href="https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz">https://registry.npmjs.org/shell-quote/-/shell-quote-1.6.1.tgz</a></p>
<p>Path to dependency file: /ctf-spring2022/www/wp-content/themes/twentynineteen/package.json</p>
<p>Path to vulnerable library: /ctf-spring2022/www/wp-content/themes/twentynineteen/node_modules/shell-quote/package.json</p>
<p>
Dependency Hierarchy:
- npm-run-all-4.1.5.tgz (Root Library)
- :x: **shell-quote-1.6.1.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/tz924/cs116-lab10/commit/7f949f4f48089e4e1ea7eb0b2482120d3327d7c4">7f949f4f48089e4e1ea7eb0b2482120d3327d7c4</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
The shell-quote package before 1.7.3 for Node.js allows command injection. An attacker can inject unescaped shell metacharacters through a regex designed to support Windows drive letters. If the output of this package is passed to a real shell as a quoted argument to a command with exec(), an attacker can inject arbitrary commands. This is because the Windows drive letter regex character class is {A-z] instead of the correct {A-Za-z]. Several shell metacharacters exist in the space between capital letter Z and lower case letter a, such as the backtick character.
<p>Publish Date: 2021-10-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-42740>CVE-2021-42740</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>9.8</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-42740</a></p>
<p>Release Date: 2021-10-21</p>
<p>Fix Resolution: shell-quote - 1.7.3</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | npm run all tgz vulnerabilities highest severity is vulnerable library npm run all tgz path to dependency file ctf www wp content themes twentynineteen package json path to vulnerable library ctf www wp content themes twentynineteen node modules shell quote package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available high shell quote tgz transitive n a details cve vulnerable library shell quote tgz quote and parse shell commands library home page a href path to dependency file ctf www wp content themes twentynineteen package json path to vulnerable library ctf www wp content themes twentynineteen node modules shell quote package json dependency hierarchy npm run all tgz root library x shell quote tgz vulnerable library found in head commit a href found in base branch master vulnerability details the shell quote package before for node js allows command injection an attacker can inject unescaped shell metacharacters through a regex designed to support windows drive letters if the output of this package is passed to a real shell as a quoted argument to a command with exec an attacker can inject arbitrary commands this is because the windows drive letter regex character class is a z instead of the correct a za z several shell metacharacters exist in the space between capital letter z and lower case letter a such as the backtick character publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution shell quote step up your open source security game with mend | 0 |
4,045 | 6,889,851,282 | IssuesEvent | 2017-11-22 11:52:24 | skuschel/postpic | https://api.github.com/repos/skuschel/postpic | closed | savecsv option for plotField() broken | bug not downwards compatible question/support | If I set the option `savecsv=True` when calling `plotField()`, either of this happens:
- If it is a 2d plot, nothing happens.
- If it is a 1d plot, I get the following error:
``` python
postpic/postpic/plotting/plotter_matplotlib.py in plotFields1d(self, *fields, **kwargs)
325 ax = fig.add_subplot(1, 1, 1)
326 name = kwargs.pop('name', fields[0].name)
--> 327 MatplotlibPlotter.addFields1d(ax, *fields, **kwargs)
328 self._plotfinalize(fig)
329 self.annotate(fig, project=self.project)
/home_4TB/stietze/postpic/postpic/plotting/plotter_matplotlib.py in addFields1d(ax, *fields, **kwargs)
234 if clearinfos:
235 field.infos = []
--> 236 MatplotlibPlotter.addField1d(ax, field, **kwargs)
237 MatplotlibPlotter.annotate_fromfield(ax, field)
238 MatplotlibPlotter.annotate(ax, infostring=str(infostrings))
TypeError: addField1d() got an unexpected keyword argument 'savecsv'
```
In either case, no csv file is written.
| True | savecsv option for plotField() broken - If I set the option `savecsv=True` when calling `plotField()`, either of this happens:
- If it is a 2d plot, nothing happens.
- If it is a 1d plot, I get the following error:
``` python
postpic/postpic/plotting/plotter_matplotlib.py in plotFields1d(self, *fields, **kwargs)
325 ax = fig.add_subplot(1, 1, 1)
326 name = kwargs.pop('name', fields[0].name)
--> 327 MatplotlibPlotter.addFields1d(ax, *fields, **kwargs)
328 self._plotfinalize(fig)
329 self.annotate(fig, project=self.project)
/home_4TB/stietze/postpic/postpic/plotting/plotter_matplotlib.py in addFields1d(ax, *fields, **kwargs)
234 if clearinfos:
235 field.infos = []
--> 236 MatplotlibPlotter.addField1d(ax, field, **kwargs)
237 MatplotlibPlotter.annotate_fromfield(ax, field)
238 MatplotlibPlotter.annotate(ax, infostring=str(infostrings))
TypeError: addField1d() got an unexpected keyword argument 'savecsv'
```
In either case, no csv file is written.
| non_priority | savecsv option for plotfield broken if i set the option savecsv true when calling plotfield either of this happens if it is a plot nothing happens if it is a plot i get the following error python postpic postpic plotting plotter matplotlib py in self fields kwargs ax fig add subplot name kwargs pop name fields name matplotlibplotter ax fields kwargs self plotfinalize fig self annotate fig project self project home stietze postpic postpic plotting plotter matplotlib py in ax fields kwargs if clearinfos field infos matplotlibplotter ax field kwargs matplotlibplotter annotate fromfield ax field matplotlibplotter annotate ax infostring str infostrings typeerror got an unexpected keyword argument savecsv in either case no csv file is written | 0 |
295,114 | 25,455,988,605 | IssuesEvent | 2022-11-24 14:14:02 | ContinualAI/avalanche | https://api.github.com/repos/ContinualAI/avalanche | closed | Creation of a new envirnment failed for python 3.7 | test Continuous integration | Here are the differences between the last working environment and the new one that I tried to run:
```
57c57
< - google-auth=2.14.0=pyh1a96a4e_0
---
> - google-auth=2.14.1=pyh1a96a4e_0
84,85c84,85
< - libclang=15.0.4=default_h2e3cab8_0
< - libclang13=15.0.4=default_h3a83d3e_0
---
> - libclang=15.0.5=default_h2e3cab8_0
> - libclang13=15.0.5=default_h3a83d3e_0
101c101
< - libllvm15=15.0.4=h63197d8_1
---
> - libllvm15=15.0.5=h63197d8_0
109c109
< - libsqlite=3.39.4=h753d276_0
---
> - libsqlite=3.40.0=h753d276_0
121c121
< - llvm-openmp=15.0.4=he0ac6c6_0
---
> - llvm-openmp=15.0.5=he0ac6c6_0
180c180
< - sentry-sdk=1.10.1=pyhd8ed1ab_0
---
> - sentry-sdk=1.11.0=pyhd8ed1ab_0
183c183
< - shortuuid=1.0.10=pyha770c72_0
---
> - shortuuid=1.0.11=pyhd8ed1ab_0
187,188c187,188
< - sqlite=3.39.4=h4ff8645_0
< - tbb=2021.6.0=h924138e_1
---
> - sqlite=3.40.0=h4ff8645_0
> - tbb=2021.7.0=h924138e_0
195c195
< - torchmetrics=0.10.2=pyhd8ed1ab_0
---
> - torchmetrics=0.10.3=pyhd8ed1ab_0
``` | 1.0 | Creation of a new envirnment failed for python 3.7 - Here are the differences between the last working environment and the new one that I tried to run:
```
57c57
< - google-auth=2.14.0=pyh1a96a4e_0
---
> - google-auth=2.14.1=pyh1a96a4e_0
84,85c84,85
< - libclang=15.0.4=default_h2e3cab8_0
< - libclang13=15.0.4=default_h3a83d3e_0
---
> - libclang=15.0.5=default_h2e3cab8_0
> - libclang13=15.0.5=default_h3a83d3e_0
101c101
< - libllvm15=15.0.4=h63197d8_1
---
> - libllvm15=15.0.5=h63197d8_0
109c109
< - libsqlite=3.39.4=h753d276_0
---
> - libsqlite=3.40.0=h753d276_0
121c121
< - llvm-openmp=15.0.4=he0ac6c6_0
---
> - llvm-openmp=15.0.5=he0ac6c6_0
180c180
< - sentry-sdk=1.10.1=pyhd8ed1ab_0
---
> - sentry-sdk=1.11.0=pyhd8ed1ab_0
183c183
< - shortuuid=1.0.10=pyha770c72_0
---
> - shortuuid=1.0.11=pyhd8ed1ab_0
187,188c187,188
< - sqlite=3.39.4=h4ff8645_0
< - tbb=2021.6.0=h924138e_1
---
> - sqlite=3.40.0=h4ff8645_0
> - tbb=2021.7.0=h924138e_0
195c195
< - torchmetrics=0.10.2=pyhd8ed1ab_0
---
> - torchmetrics=0.10.3=pyhd8ed1ab_0
``` | non_priority | creation of a new envirnment failed for python here are the differences between the last working environment and the new one that i tried to run google auth google auth libclang default default libclang default default libsqlite libsqlite llvm openmp llvm openmp sentry sdk sentry sdk shortuuid shortuuid sqlite tbb sqlite tbb torchmetrics torchmetrics | 0 |
48,604 | 25,709,040,582 | IssuesEvent | 2022-12-07 04:24:06 | cockroachdb/cockroach | https://api.github.com/repos/cockroachdb/cockroach | opened | sql: leasing of virtual table privileges adds to latency on first use | C-enhancement C-performance A-sql-privileges A-multiregion | **Describe the problem**
In 22.2 we added synthetic privileges which are used for things like external connections, and, critically, virtual tables. These privileges need to be checked when iterating through various system catalog schemas (`pg_catalog`, `information schema`, `SHOW TABLES`, ...).
We populate these caches lazily.
**Describe the solution you'd like**
We could eagerly launch routines to populate these caches for the different virtual tables concurrently rather than serially.
**Describe alternatives you've considered**
We could do some sort of special initialization to preload data. These tables are almost always empty and are small when populated. We could scan it all and avoid the cost of all the parallel work.
Epic: CRDB-18596 | True | sql: leasing of virtual table privileges adds to latency on first use - **Describe the problem**
In 22.2 we added synthetic privileges which are used for things like external connections, and, critically, virtual tables. These privileges need to be checked when iterating through various system catalog schemas (`pg_catalog`, `information schema`, `SHOW TABLES`, ...).
We populate these caches lazily.
**Describe the solution you'd like**
We could eagerly launch routines to populate these caches for the different virtual tables concurrently rather than serially.
**Describe alternatives you've considered**
We could do some sort of special initialization to preload data. These tables are almost always empty and are small when populated. We could scan it all and avoid the cost of all the parallel work.
Epic: CRDB-18596 | non_priority | sql leasing of virtual table privileges adds to latency on first use describe the problem in we added synthetic privileges which are used for things like external connections and critically virtual tables these privileges need to be checked when iterating through various system catalog schemas pg catalog information schema show tables we populate these caches lazily describe the solution you d like we could eagerly launch routines to populate these caches for the different virtual tables concurrently rather than serially describe alternatives you ve considered we could do some sort of special initialization to preload data these tables are almost always empty and are small when populated we could scan it all and avoid the cost of all the parallel work epic crdb | 0 |
96,651 | 8,628,171,805 | IssuesEvent | 2018-11-21 16:41:53 | SME-Issues/issues | https://api.github.com/repos/SME-Issues/issues | closed | Test Summary - 21/11/2018 - 5004 | NLP Api pulse_tests | ### Intent
- **Intent Errors: 3** (#739)
### Canonical
- Query Payment Tests Canonical (182): **86%** pass (145), 24 failed understood (#738)
| 1.0 | Test Summary - 21/11/2018 - 5004 - ### Intent
- **Intent Errors: 3** (#739)
### Canonical
- Query Payment Tests Canonical (182): **86%** pass (145), 24 failed understood (#738)
| non_priority | test summary intent intent errors canonical query payment tests canonical pass failed understood | 0 |
381,150 | 26,440,237,990 | IssuesEvent | 2023-01-15 21:55:46 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | It's hard to tell what udev rules are in force and why | 9.needs: documentation | ## Problem
Figuring out what udev rules are in effect is nontrivial, and I still don't understand the exact mechanism.
Obviously all rules that end up being installed into `/etc/udev/rules.d` are in effect. The unexpected thing is that it seems that rules from the systemd package also take effect, even though they are not there (e.g. [50-udev-defaults.rules](https://cgit.freedesktop.org/systemd/systemd/tree/rules/50-udev-default.rules)). I don't really know what mechanism causes them to take effect (I'm guessing they are found by some search relative to systemd-udevd's location).
I think we should make it clear (maybe somewhere in https://github.com/NixOS/nixpkgs/blob/master/nixos/modules/services/hardware/udev.nix) what is the total set of rules that will be considered (incl. their priorities), and should consider making it possible to override all of them.
## Checklist
<!-- make sure this issue is not redundant or obsolete -->
- [x] checked [latest Nixpkgs manual] \([source][nixpkgs-source]) and [latest NixOS manual] \([source][nixos-source])
- [x] checked [open documentation issues] for possible duplicates
- [x] checked [open documentation pull requests] for possible solutions
[latest Nixpkgs manual]: https://nixos.org/manual/nixpkgs/unstable/
[latest NixOS manual]: https://nixos.org/manual/nixos/unstable/
[nixpkgs-source]: https://github.com/NixOS/nixpkgs/tree/master/doc
[nixos-source]: https://github.com/NixOS/nixpkgs/tree/master/nixos/doc/manual
[open documentation issues]: https://github.com/NixOS/nixpkgs/issues?q=is%3Aissue+is%3Aopen+label%3A%229.needs%3A+documentation%22
[open documentation pull requests]: https://github.com/NixOS/nixpkgs/pulls?q=is%3Aopen+is%3Apr+label%3A%228.has%3A+documentation%22%2C%226.topic%3A+documentation%22
## Proposal
Consider whether we want those default rules to be overridable.
If so, make them and document their existence next to the configuration that allows one to override them.
If not, document their existence probably somewhere close to documentation of ways to add more rules.
| 1.0 | It's hard to tell what udev rules are in force and why - ## Problem
Figuring out what udev rules are in effect is nontrivial, and I still don't understand the exact mechanism.
Obviously all rules that end up being installed into `/etc/udev/rules.d` are in effect. The unexpected thing is that it seems that rules from the systemd package also take effect, even though they are not there (e.g. [50-udev-defaults.rules](https://cgit.freedesktop.org/systemd/systemd/tree/rules/50-udev-default.rules)). I don't really know what mechanism causes them to take effect (I'm guessing they are found by some search relative to systemd-udevd's location).
I think we should make it clear (maybe somewhere in https://github.com/NixOS/nixpkgs/blob/master/nixos/modules/services/hardware/udev.nix) what is the total set of rules that will be considered (incl. their priorities), and should consider making it possible to override all of them.
## Checklist
<!-- make sure this issue is not redundant or obsolete -->
- [x] checked [latest Nixpkgs manual] \([source][nixpkgs-source]) and [latest NixOS manual] \([source][nixos-source])
- [x] checked [open documentation issues] for possible duplicates
- [x] checked [open documentation pull requests] for possible solutions
[latest Nixpkgs manual]: https://nixos.org/manual/nixpkgs/unstable/
[latest NixOS manual]: https://nixos.org/manual/nixos/unstable/
[nixpkgs-source]: https://github.com/NixOS/nixpkgs/tree/master/doc
[nixos-source]: https://github.com/NixOS/nixpkgs/tree/master/nixos/doc/manual
[open documentation issues]: https://github.com/NixOS/nixpkgs/issues?q=is%3Aissue+is%3Aopen+label%3A%229.needs%3A+documentation%22
[open documentation pull requests]: https://github.com/NixOS/nixpkgs/pulls?q=is%3Aopen+is%3Apr+label%3A%228.has%3A+documentation%22%2C%226.topic%3A+documentation%22
## Proposal
Consider whether we want those default rules to be overridable.
If so, make them and document their existence next to the configuration that allows one to override them.
If not, document their existence probably somewhere close to documentation of ways to add more rules.
| non_priority | it s hard to tell what udev rules are in force and why problem figuring out what udev rules are in effect is nontrivial and i still don t understand the exact mechanism obviously all rules that end up being installed into etc udev rules d are in effect the unexpected thing is that it seems that rules from the systemd package also take effect even though they are not there e g i don t really know what mechanism causes them to take effect i m guessing they are found by some search relative to systemd udevd s location i think we should make it clear maybe somewhere in what is the total set of rules that will be considered incl their priorities and should consider making it possible to override all of them checklist checked and checked for possible duplicates checked for possible solutions proposal consider whether we want those default rules to be overridable if so make them and document their existence next to the configuration that allows one to override them if not document their existence probably somewhere close to documentation of ways to add more rules | 0 |
198,240 | 22,620,970,311 | IssuesEvent | 2022-06-30 06:16:38 | ioana-nicolae/renovate2 | https://api.github.com/repos/ioana-nicolae/renovate2 | opened | CVE-2022-29078 (High) detected in ejs-2.7.4.tgz | security vulnerability | ## CVE-2022-29078 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ioana-nicolae/renovate2/commit/9d0f2692d355dfff0d0ba18825cd40f2074a31f9">9d0f2692d355dfff0d0ba18825cd40f2074a31f9</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The ejs (aka Embedded JavaScript templates) package 3.1.6 for Node.js allows server-side template injection in settings[view options][outputFunctionName]. This is parsed as an internal option, and overwrites the outputFunctionName option with an arbitrary OS command (which is executed upon template compilation).
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29078>CVE-2022-29078</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29078~">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29078~</a></p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: 3.1.7</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2022-29078 (High) detected in ejs-2.7.4.tgz - ## CVE-2022-29078 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>ejs-2.7.4.tgz</b></p></summary>
<p>Embedded JavaScript templates</p>
<p>Library home page: <a href="https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz">https://registry.npmjs.org/ejs/-/ejs-2.7.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/ejs/package.json</p>
<p>
Dependency Hierarchy:
- :x: **ejs-2.7.4.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ioana-nicolae/renovate2/commit/9d0f2692d355dfff0d0ba18825cd40f2074a31f9">9d0f2692d355dfff0d0ba18825cd40f2074a31f9</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The ejs (aka Embedded JavaScript templates) package 3.1.6 for Node.js allows server-side template injection in settings[view options][outputFunctionName]. This is parsed as an internal option, and overwrites the outputFunctionName option with an arbitrary OS command (which is executed upon template compilation).
<p>Publish Date: 2022-04-25
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-29078>CVE-2022-29078</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29078~">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29078~</a></p>
<p>Release Date: 2022-04-25</p>
<p>Fix Resolution: 3.1.7</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in ejs tgz cve high severity vulnerability vulnerable library ejs tgz embedded javascript templates library home page a href path to dependency file package json path to vulnerable library node modules ejs package json dependency hierarchy x ejs tgz vulnerable library found in head commit a href found in base branch main vulnerability details the ejs aka embedded javascript templates package for node js allows server side template injection in settings this is parsed as an internal option and overwrites the outputfunctionname option with an arbitrary os command which is executed upon template compilation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
171,389 | 14,289,174,663 | IssuesEvent | 2020-11-23 18:50:04 | HHS/Head-Start-TTADP | https://api.github.com/repos/HHS/Head-Start-TTADP | closed | Figure out workaround for CircleCI access issues | In epic 8 V1.0 MVP documentation | TRB partners are having difficulty accessing CircleCI. How can we communicate that information to them reliably? | 1.0 | Figure out workaround for CircleCI access issues - TRB partners are having difficulty accessing CircleCI. How can we communicate that information to them reliably? | non_priority | figure out workaround for circleci access issues trb partners are having difficulty accessing circleci how can we communicate that information to them reliably | 0 |
346,107 | 24,886,556,022 | IssuesEvent | 2022-10-28 08:17:23 | jia-han/ped | https://api.github.com/repos/jia-han/ped | opened | Example command in user guide does not work | severity.VeryLow type.DocumentationBug | The example `add` command given in the user guide returns and invalid command format error in the application.
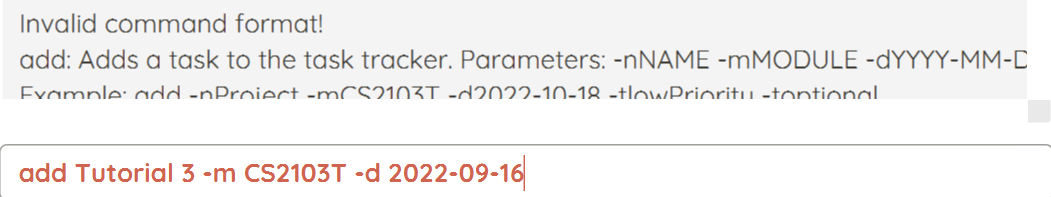
<!--session: 1666944893058-b30f3d5d-e04e-4e10-8dd4-0af5ceac9f02-->
<!--Version: Web v3.4.4--> | 1.0 | Example command in user guide does not work - The example `add` command given in the user guide returns and invalid command format error in the application.
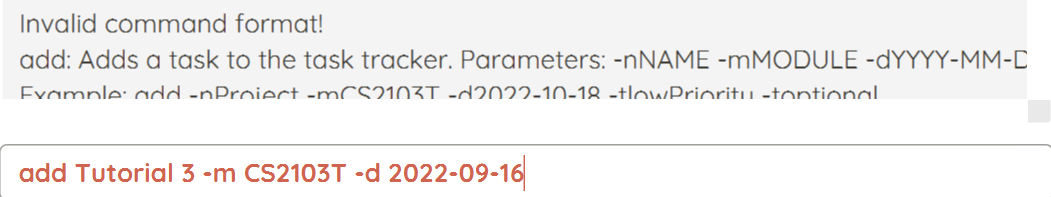
<!--session: 1666944893058-b30f3d5d-e04e-4e10-8dd4-0af5ceac9f02-->
<!--Version: Web v3.4.4--> | non_priority | example command in user guide does not work the example add command given in the user guide returns and invalid command format error in the application | 0 |
49,391 | 13,453,388,717 | IssuesEvent | 2020-09-09 00:48:18 | nasifimtiazohi/openmrs-module-fhir-1.20.0 | https://api.github.com/repos/nasifimtiazohi/openmrs-module-fhir-1.20.0 | opened | CVE-2020-11620 (High) detected in jackson-databind-2.9.10.1.jar | security vulnerability | ## CVE-2020-11620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /openmrs-module-fhir-1.20.0/omod/target/fhir-1.20.0/lib/jackson-databind-2.9.10.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-fhir-1.20.0/commit/af058c71e43795da6378a96dc75d1d9e6147f1a6">af058c71e43795da6378a96dc75d1d9e6147f1a6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.jelly.impl.Embedded (aka commons-jelly).
<p>Publish Date: 2020-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11620>CVE-2020-11620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11620">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11620</a></p>
<p>Release Date: 2020-04-07</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11620 (High) detected in jackson-databind-2.9.10.1.jar - ## CVE-2020-11620 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.10.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to vulnerable library: /openmrs-module-fhir-1.20.0/omod/target/fhir-1.20.0/lib/jackson-databind-2.9.10.1.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.10.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/nasifimtiazohi/openmrs-module-fhir-1.20.0/commit/af058c71e43795da6378a96dc75d1d9e6147f1a6">af058c71e43795da6378a96dc75d1d9e6147f1a6</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.jelly.impl.Embedded (aka commons-jelly).
<p>Publish Date: 2020-04-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11620>CVE-2020-11620</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11620">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11620</a></p>
<p>Release Date: 2020-04-07</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to vulnerable library openmrs module fhir omod target fhir lib jackson databind jar dependency hierarchy x jackson databind jar vulnerable library found in head commit a href vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons jelly impl embedded aka commons jelly publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
71,567 | 15,207,789,974 | IssuesEvent | 2021-02-17 01:01:34 | billmcchesney1/foxtrot | https://api.github.com/repos/billmcchesney1/foxtrot | opened | CVE-2016-10735 (Medium) detected in bootstrap-3.1.1.min.js | security vulnerability | ## CVE-2016-10735 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to dependency file: foxtrot/foxtrot-server/target/classes/console/echo/cluster/index.htm</p>
<p>Path to vulnerable library: foxtrot/foxtrot-server/target/classes/console/echo/cluster/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/echo/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/cluster/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/cluster/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/cluster/../js/bootstrap/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/foxtrot/commit/ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc">ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.1.1","packageFilePaths":["/foxtrot-server/target/classes/console/echo/cluster/index.htm","/foxtrot-server/src/main/resources/console/echo/fql/index.htm","/foxtrot-server/src/main/resources/console/fql/index.htm","/foxtrot-server/target/classes/console/echo/index.htm","/foxtrot-server/src/main/resources/console/echo/browse-events.htm","/foxtrot-server/target/classes/console/fql/index.htm","/foxtrot-server/target/classes/console/index.html","/foxtrot-server/src/main/resources/console/index.html","/foxtrot-server/target/classes/console/echo/fql/index.htm","/foxtrot-server/src/main/resources/console/cluster/index.htm","/foxtrot-server/src/main/resources/console/echo/cluster/index.htm","/foxtrot-server/target/classes/console/cluster/index.htm"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-10735 (Medium) detected in bootstrap-3.1.1.min.js - ## CVE-2016-10735 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bootstrap-3.1.1.min.js</b></p></summary>
<p>The most popular front-end framework for developing responsive, mobile first projects on the web.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js">https://cdnjs.cloudflare.com/ajax/libs/twitter-bootstrap/3.1.1/js/bootstrap.min.js</a></p>
<p>Path to dependency file: foxtrot/foxtrot-server/target/classes/console/echo/cluster/index.htm</p>
<p>Path to vulnerable library: foxtrot/foxtrot-server/target/classes/console/echo/cluster/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/echo/fql/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/cluster/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/src/main/resources/console/echo/cluster/../js/bootstrap/bootstrap.min.js,foxtrot/foxtrot-server/target/classes/console/cluster/../js/bootstrap/bootstrap.min.js</p>
<p>
Dependency Hierarchy:
- :x: **bootstrap-3.1.1.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/foxtrot/commit/ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc">ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.
<p>Publish Date: 2019-01-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735>CVE-2016-10735</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/twbs/bootstrap/issues/20184">https://github.com/twbs/bootstrap/issues/20184</a></p>
<p>Release Date: 2019-01-09</p>
<p>Fix Resolution: 3.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"twitter-bootstrap","packageVersion":"3.1.1","packageFilePaths":["/foxtrot-server/target/classes/console/echo/cluster/index.htm","/foxtrot-server/src/main/resources/console/echo/fql/index.htm","/foxtrot-server/src/main/resources/console/fql/index.htm","/foxtrot-server/target/classes/console/echo/index.htm","/foxtrot-server/src/main/resources/console/echo/browse-events.htm","/foxtrot-server/target/classes/console/fql/index.htm","/foxtrot-server/target/classes/console/index.html","/foxtrot-server/src/main/resources/console/index.html","/foxtrot-server/target/classes/console/echo/fql/index.htm","/foxtrot-server/src/main/resources/console/cluster/index.htm","/foxtrot-server/src/main/resources/console/echo/cluster/index.htm","/foxtrot-server/target/classes/console/cluster/index.htm"],"isTransitiveDependency":false,"dependencyTree":"twitter-bootstrap:3.1.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2016-10735","vulnerabilityDetails":"In Bootstrap 3.x before 3.4.0 and 4.x-beta before 4.0.0-beta.2, XSS is possible in the data-target attribute, a different vulnerability than CVE-2018-14041.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-10735","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in bootstrap min js cve medium severity vulnerability vulnerable library bootstrap min js the most popular front end framework for developing responsive mobile first projects on the web library home page a href path to dependency file foxtrot foxtrot server target classes console echo cluster index htm path to vulnerable library foxtrot foxtrot server target classes console echo cluster js bootstrap bootstrap min js foxtrot foxtrot server target classes console js bootstrap bootstrap min js foxtrot foxtrot server src main resources console echo fql js bootstrap bootstrap min js foxtrot foxtrot server src main resources console fql js bootstrap bootstrap min js foxtrot foxtrot server target classes console echo js bootstrap bootstrap min js foxtrot foxtrot server src main resources console echo js bootstrap bootstrap min js foxtrot foxtrot server target classes console fql js bootstrap bootstrap min js foxtrot foxtrot server src main resources console js bootstrap bootstrap min js foxtrot foxtrot server target classes console echo js bootstrap bootstrap min js foxtrot foxtrot server target classes console js bootstrap bootstrap min js foxtrot foxtrot server src main resources console js bootstrap bootstrap min js foxtrot foxtrot server target classes console echo fql js bootstrap bootstrap min js foxtrot foxtrot server src main resources console cluster js bootstrap bootstrap min js foxtrot foxtrot server src main resources console echo js bootstrap bootstrap min js foxtrot foxtrot server src main resources console echo cluster js bootstrap bootstrap min js foxtrot foxtrot server target classes console cluster js bootstrap bootstrap min js dependency hierarchy x bootstrap min js vulnerable library found in head commit a href found in base branch master vulnerability details in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree twitter bootstrap isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails in bootstrap x before and x beta before beta xss is possible in the data target attribute a different vulnerability than cve vulnerabilityurl | 0 |
36,695 | 6,545,979,370 | IssuesEvent | 2017-09-04 08:22:48 | saltstack/salt | https://api.github.com/repos/saltstack/salt | closed | Document passing **kwargs through states.module.run | Documentation stale | To pass kwargs through `states.module.run` (and `states.module.wait`) one must pass them in a very specific way. They must be a dict in the options to `run`, passed under the variable corresponding to the underlying module you wish to run's kwargs name.
For example, `mysql.query` is defined as `query(database, query, **connection_args)`, so you must put in the jinja:
```
your_name:
module.wait:
- name: mysql.query
- watch:
- something
- database: dbname
- query: SQL STATEMENT;
- connection_args:
query_kw_arg: value
connection_host: 'localhost'
```
The `connection_host` gives away why this is important - I am trying to override the mysql connection parameters in salt master (which are set up for a returner).
This is highly uninituitive as usually kwargs are siblings of the other args.
| 1.0 | Document passing **kwargs through states.module.run - To pass kwargs through `states.module.run` (and `states.module.wait`) one must pass them in a very specific way. They must be a dict in the options to `run`, passed under the variable corresponding to the underlying module you wish to run's kwargs name.
For example, `mysql.query` is defined as `query(database, query, **connection_args)`, so you must put in the jinja:
```
your_name:
module.wait:
- name: mysql.query
- watch:
- something
- database: dbname
- query: SQL STATEMENT;
- connection_args:
query_kw_arg: value
connection_host: 'localhost'
```
The `connection_host` gives away why this is important - I am trying to override the mysql connection parameters in salt master (which are set up for a returner).
This is highly uninituitive as usually kwargs are siblings of the other args.
| non_priority | document passing kwargs through states module run to pass kwargs through states module run and states module wait one must pass them in a very specific way they must be a dict in the options to run passed under the variable corresponding to the underlying module you wish to run s kwargs name for example mysql query is defined as query database query connection args so you must put in the jinja your name module wait name mysql query watch something database dbname query sql statement connection args query kw arg value connection host localhost the connection host gives away why this is important i am trying to override the mysql connection parameters in salt master which are set up for a returner this is highly uninituitive as usually kwargs are siblings of the other args | 0 |
202,476 | 23,077,325,640 | IssuesEvent | 2022-07-26 01:48:28 | victorlmneves/vue3-vite-boilerplate | https://api.github.com/repos/victorlmneves/vue3-vite-boilerplate | closed | CVE-2022-1214 (High) detected in axios-0.21.4.tgz, axios-0.24.0.tgz - autoclosed | security vulnerability | ## CVE-2022-1214 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>axios-0.21.4.tgz</b>, <b>axios-0.24.0.tgz</b></p></summary>
<p>
<details><summary><b>axios-0.21.4.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.4.tgz">https://registry.npmjs.org/axios/-/axios-0.21.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- start-server-and-test-1.14.0.tgz (Root Library)
- wait-on-6.0.0.tgz
- :x: **axios-0.21.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>axios-0.24.0.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.24.0.tgz">https://registry.npmjs.org/axios/-/axios-0.24.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- :x: **axios-0.24.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/victorlmneves/vue3-vite-boilerplate/commit/90b293f01b461af975128fb6af7a18d85a899dbb">90b293f01b461af975128fb6af7a18d85a899dbb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Exposure of Sensitive Information to an Unauthorized Actor in GitHub repository axios/axios prior to 0.26.
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1214>CVE-2022-1214</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/">https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution: 0.26.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-1214 (High) detected in axios-0.21.4.tgz, axios-0.24.0.tgz - autoclosed - ## CVE-2022-1214 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>axios-0.21.4.tgz</b>, <b>axios-0.24.0.tgz</b></p></summary>
<p>
<details><summary><b>axios-0.21.4.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.21.4.tgz">https://registry.npmjs.org/axios/-/axios-0.21.4.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- start-server-and-test-1.14.0.tgz (Root Library)
- wait-on-6.0.0.tgz
- :x: **axios-0.21.4.tgz** (Vulnerable Library)
</details>
<details><summary><b>axios-0.24.0.tgz</b></p></summary>
<p>Promise based HTTP client for the browser and node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/axios/-/axios-0.24.0.tgz">https://registry.npmjs.org/axios/-/axios-0.24.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/axios/package.json</p>
<p>
Dependency Hierarchy:
- :x: **axios-0.24.0.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/victorlmneves/vue3-vite-boilerplate/commit/90b293f01b461af975128fb6af7a18d85a899dbb">90b293f01b461af975128fb6af7a18d85a899dbb</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Exposure of Sensitive Information to an Unauthorized Actor in GitHub repository axios/axios prior to 0.26.
<p>Publish Date: 2022-05-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-1214>CVE-2022-1214</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/">https://huntr.dev/bounties/ef7b4ab6-a3f6-4268-a21a-e7104d344607/</a></p>
<p>Release Date: 2022-05-03</p>
<p>Fix Resolution: 0.26.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in axios tgz axios tgz autoclosed cve high severity vulnerability vulnerable libraries axios tgz axios tgz axios tgz promise based http client for the browser and node js library home page a href path to dependency file package json path to vulnerable library node modules axios package json dependency hierarchy start server and test tgz root library wait on tgz x axios tgz vulnerable library axios tgz promise based http client for the browser and node js library home page a href path to dependency file package json path to vulnerable library node modules axios package json dependency hierarchy x axios tgz vulnerable library found in head commit a href found in base branch main vulnerability details exposure of sensitive information to an unauthorized actor in github repository axios axios prior to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
50,568 | 13,540,116,363 | IssuesEvent | 2020-09-16 14:17:15 | cniweb/cniweb-demo | https://api.github.com/repos/cniweb/cniweb-demo | opened | CVE-2020-11022 (Medium) detected in jquery-1.12.4.min.js | security vulnerability | ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.12.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.12.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.12.4/jquery.min.js</a></p>
<p>Path to dependency file: cniweb-demo/src/main/resources/static/index.html</p>
<p>Path to vulnerable library: cniweb-demo/src/main/resources/static/index.html,cniweb-demo/target/classes/static/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.12.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/cniweb/cniweb-demo/commit/5b67285cc4e217cbdc85813b6705fb49ac7e91ab">5b67285cc4e217cbdc85813b6705fb49ac7e91ab</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-11022 (Medium) detected in jquery-1.12.4.min.js - ## CVE-2020-11022 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.12.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.12.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.12.4/jquery.min.js</a></p>
<p>Path to dependency file: cniweb-demo/src/main/resources/static/index.html</p>
<p>Path to vulnerable library: cniweb-demo/src/main/resources/static/index.html,cniweb-demo/target/classes/static/index.html</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.12.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/cniweb/cniweb-demo/commit/5b67285cc4e217cbdc85813b6705fb49ac7e91ab">5b67285cc4e217cbdc85813b6705fb49ac7e91ab</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.2 and before 3.5.0, passing HTML from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11022>CVE-2020-11022</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/">https://blog.jquery.com/2020/04/10/jquery-3-5-0-released/</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jQuery - 3.5.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to dependency file cniweb demo src main resources static index html path to vulnerable library cniweb demo src main resources static index html cniweb demo target classes static index html dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery step up your open source security game with whitesource | 0 |
71,240 | 8,637,004,830 | IssuesEvent | 2018-11-23 09:48:20 | CityOfZion/neon-wallet | https://api.github.com/repos/CityOfZion/neon-wallet | closed | Disable "Add" buttons on transaction confirmation page next to addresses which are added to contacts list | design-v2 enhancement | Also instead of wallet addresses, we should show their names from contact list?
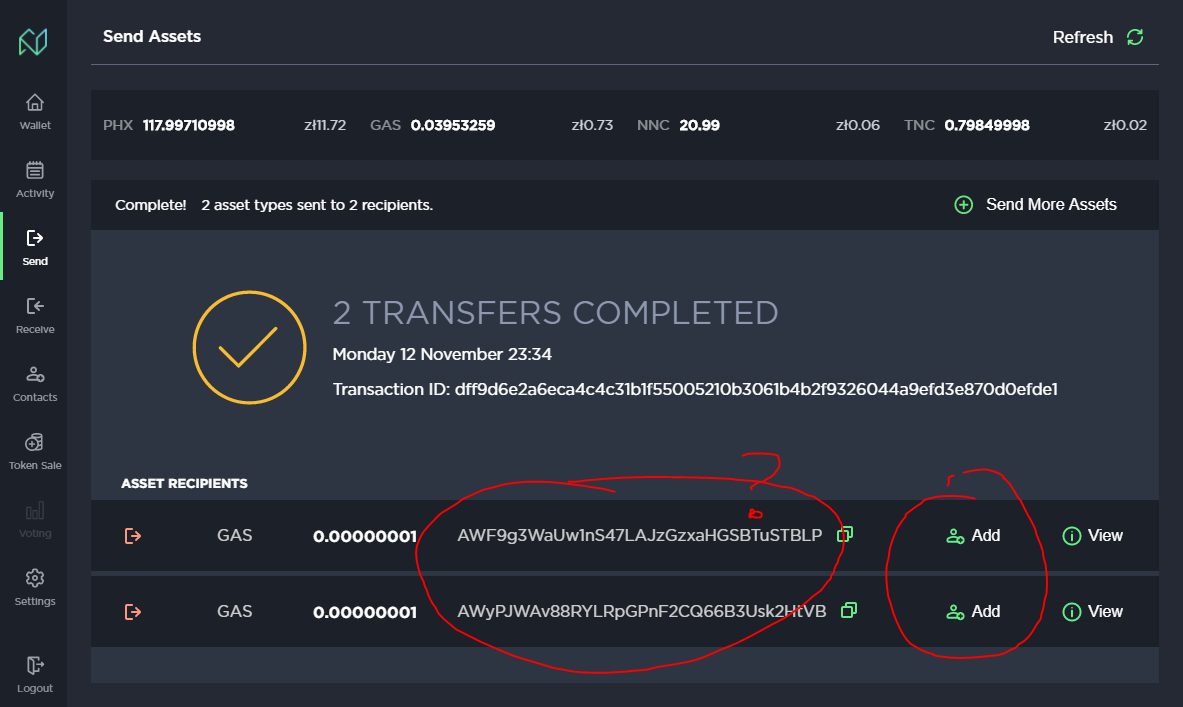
Correct example from "Activity" page:
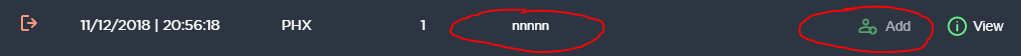
| 1.0 | Disable "Add" buttons on transaction confirmation page next to addresses which are added to contacts list - Also instead of wallet addresses, we should show their names from contact list?
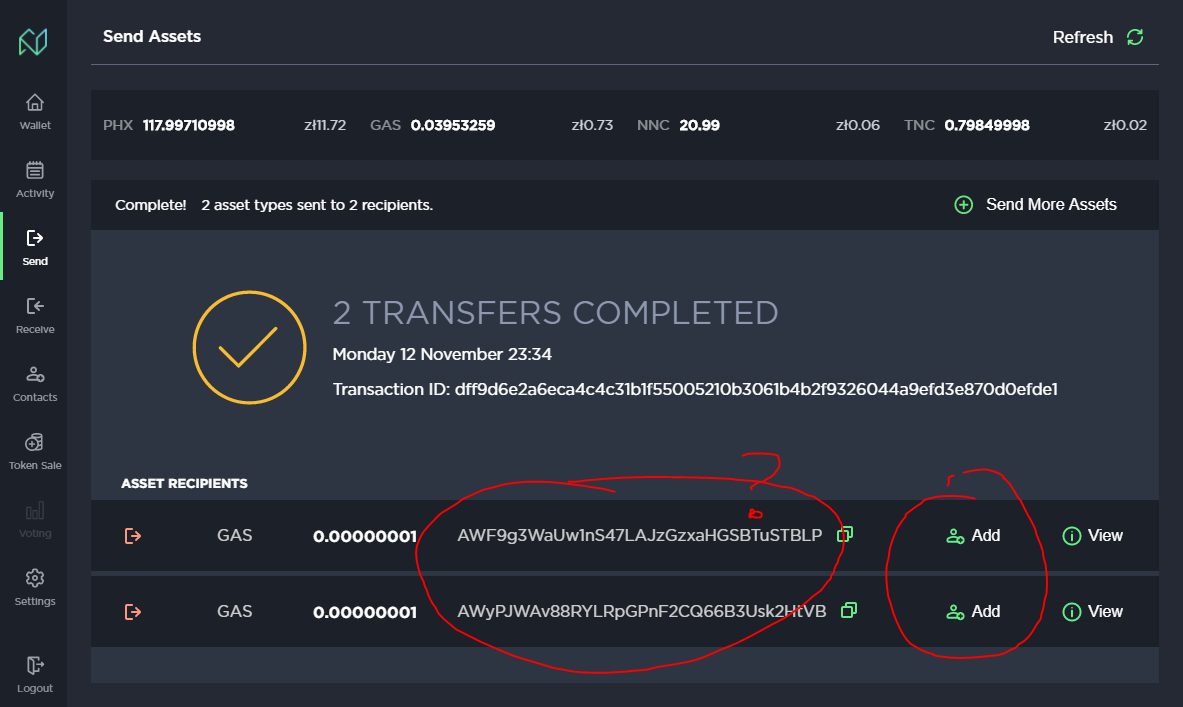
Correct example from "Activity" page:
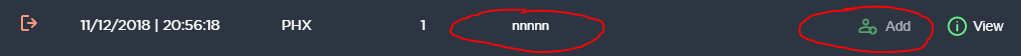
| non_priority | disable add buttons on transaction confirmation page next to addresses which are added to contacts list also instead of wallet addresses we should show their names from contact list correct example from activity page | 0 |
241,102 | 26,256,638,889 | IssuesEvent | 2023-01-06 01:43:59 | isubasinghe/COMP30022-reversegeo-micro | https://api.github.com/repos/isubasinghe/COMP30022-reversegeo-micro | closed | CVE-2021-33502 (High) detected in normalize-url-2.0.1.tgz - autoclosed | security vulnerability | ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-2.0.1.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-2.0.1.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-2.0.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/normalize-url/package.json</p>
<p>
Dependency Hierarchy:
- mapbox-sdk-0.7.0.tgz (Root Library)
- got-8.3.2.tgz
- cacheable-request-2.1.4.tgz
- :x: **normalize-url-2.0.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution: normalize-url - 4.5.1,5.3.1,6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-33502 (High) detected in normalize-url-2.0.1.tgz - autoclosed - ## CVE-2021-33502 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>normalize-url-2.0.1.tgz</b></p></summary>
<p>Normalize a URL</p>
<p>Library home page: <a href="https://registry.npmjs.org/normalize-url/-/normalize-url-2.0.1.tgz">https://registry.npmjs.org/normalize-url/-/normalize-url-2.0.1.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/normalize-url/package.json</p>
<p>
Dependency Hierarchy:
- mapbox-sdk-0.7.0.tgz (Root Library)
- got-8.3.2.tgz
- cacheable-request-2.1.4.tgz
- :x: **normalize-url-2.0.1.tgz** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The normalize-url package before 4.5.1, 5.x before 5.3.1, and 6.x before 6.0.1 for Node.js has a ReDoS (regular expression denial of service) issue because it has exponential performance for data: URLs.
<p>Publish Date: 2021-05-24
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-33502>CVE-2021-33502</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-33502</a></p>
<p>Release Date: 2021-05-24</p>
<p>Fix Resolution: normalize-url - 4.5.1,5.3.1,6.0.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in normalize url tgz autoclosed cve high severity vulnerability vulnerable library normalize url tgz normalize a url library home page a href path to dependency file package json path to vulnerable library node modules normalize url package json dependency hierarchy mapbox sdk tgz root library got tgz cacheable request tgz x normalize url tgz vulnerable library vulnerability details the normalize url package before x before and x before for node js has a redos regular expression denial of service issue because it has exponential performance for data urls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution normalize url step up your open source security game with mend | 0 |
21,186 | 3,688,364,923 | IssuesEvent | 2016-02-25 12:34:04 | redaxo/redaxo | https://api.github.com/repos/redaxo/redaxo | reopened | "Block hinzufügen" - lange Seite | Bug Design / CSS | Hi,
wenn der Contentbereich länger ist als der Navigationsbereich und ich einen "Block hinzufügen" möchte wird leicht das Design geschossen... (und das DropDown klebt sehr am unteren Rand bzw. ich muss scrollen...)
LG
Oliver

| 1.0 | "Block hinzufügen" - lange Seite - Hi,
wenn der Contentbereich länger ist als der Navigationsbereich und ich einen "Block hinzufügen" möchte wird leicht das Design geschossen... (und das DropDown klebt sehr am unteren Rand bzw. ich muss scrollen...)
LG
Oliver

| non_priority | block hinzufügen lange seite hi wenn der contentbereich länger ist als der navigationsbereich und ich einen block hinzufügen möchte wird leicht das design geschossen und das dropdown klebt sehr am unteren rand bzw ich muss scrollen lg oliver | 0 |
94,158 | 11,852,782,459 | IssuesEvent | 2020-03-24 20:37:28 | Princeton-CDH/startwords | https://api.github.com/repos/Princeton-CDH/startwords | closed | Design a homepage for mobile + tablet | awaiting review design | includes:
- featured content + metadata
- a short "about" + link to about
- nav
| 1.0 | Design a homepage for mobile + tablet - includes:
- featured content + metadata
- a short "about" + link to about
- nav
| non_priority | design a homepage for mobile tablet includes featured content metadata a short about link to about nav | 0 |
230,174 | 18,510,902,472 | IssuesEvent | 2021-10-20 02:48:15 | mattermost/mattermost-server | https://api.github.com/repos/mattermost/mattermost-server | closed | Write Webapp E2E with Cypress: "MM-T2373 Removing a file attachment" | Difficulty/1:Easy Hacktoberfest Area/E2E Tests Help Wanted Tech/Automation |
See our [documentation for Webapp end-to-end testing with Cypress](https://developers.mattermost.com/contribute/webapp/end-to-end-tests/) for reference.
<article>
<h1>MM-T2373 Removing a file attachment</h1>
<div>
<div>
<h3>Steps </h3>Removing a file attachment<br>————————————————————————————<ol><li>As Another user delete posts that contain image attachment</li><li>As the test user watch the vertical position of the thread while the off-screen post is deleted</li></ol><h3>Expected</h3><ul><li>The thread does not move when the offscreen attachment is deleted</li></ul><hr>
</div>
</div>
</article>
**Test Folder:** ``/cypress/integration/scroll``
**Test code arrangement:**
```
describe('Scroll', () => {
it('MM-T2373 Removing a file attachment', () => {
// code
});
});
```
Notes:
1. Do not add ``@prod`` label in a spec file
- If you're writing script into a newly created test file, ``@prod`` label should not be included.
- If you're adding script into an existing test file, ``@prod`` label should removed.
2. Use [queries from testing-library](https://testing-library.com/docs/dom-testing-library/api-queries) whenever possible. We share the same philosophy as the [testing-library](https://testing-library.com/) when doing UI automation like "Interact with your app the same way as your users" and so, please follow their guidelines especially when querying an element.
If you're interested, please comment here and come [join our "Contributors" community channel](https://community.mattermost.com/core/channels/tickets) on our daily build server, where you can discuss questions with community members and the Mattermost core team. For technical advice or questions, please [join our "Developers" community channel](https://community.mattermost.com/core/channels/developers).
New contributors please see our [Developer's Guide](https://developers.mattermost.com/contribute/getting-started/).
| 1.0 | Write Webapp E2E with Cypress: "MM-T2373 Removing a file attachment" -
See our [documentation for Webapp end-to-end testing with Cypress](https://developers.mattermost.com/contribute/webapp/end-to-end-tests/) for reference.
<article>
<h1>MM-T2373 Removing a file attachment</h1>
<div>
<div>
<h3>Steps </h3>Removing a file attachment<br>————————————————————————————<ol><li>As Another user delete posts that contain image attachment</li><li>As the test user watch the vertical position of the thread while the off-screen post is deleted</li></ol><h3>Expected</h3><ul><li>The thread does not move when the offscreen attachment is deleted</li></ul><hr>
</div>
</div>
</article>
**Test Folder:** ``/cypress/integration/scroll``
**Test code arrangement:**
```
describe('Scroll', () => {
it('MM-T2373 Removing a file attachment', () => {
// code
});
});
```
Notes:
1. Do not add ``@prod`` label in a spec file
- If you're writing script into a newly created test file, ``@prod`` label should not be included.
- If you're adding script into an existing test file, ``@prod`` label should removed.
2. Use [queries from testing-library](https://testing-library.com/docs/dom-testing-library/api-queries) whenever possible. We share the same philosophy as the [testing-library](https://testing-library.com/) when doing UI automation like "Interact with your app the same way as your users" and so, please follow their guidelines especially when querying an element.
If you're interested, please comment here and come [join our "Contributors" community channel](https://community.mattermost.com/core/channels/tickets) on our daily build server, where you can discuss questions with community members and the Mattermost core team. For technical advice or questions, please [join our "Developers" community channel](https://community.mattermost.com/core/channels/developers).
New contributors please see our [Developer's Guide](https://developers.mattermost.com/contribute/getting-started/).
| non_priority | write webapp with cypress mm removing a file attachment see our for reference mm removing a file attachment steps removing a file attachment ———————————————————————————— as another user delete posts that contain image attachment as the test user watch the vertical position of the thread while the off screen post is deleted expected the thread does not move when the offscreen attachment is deleted test folder cypress integration scroll test code arrangement describe scroll it mm removing a file attachment code notes do not add prod label in a spec file if you re writing script into a newly created test file prod label should not be included if you re adding script into an existing test file prod label should removed use whenever possible we share the same philosophy as the when doing ui automation like interact with your app the same way as your users and so please follow their guidelines especially when querying an element if you re interested please comment here and come on our daily build server where you can discuss questions with community members and the mattermost core team for technical advice or questions please new contributors please see our | 0 |
342,718 | 24,754,769,526 | IssuesEvent | 2022-10-21 16:36:56 | cilium/cilium | https://api.github.com/repos/cilium/cilium | opened | Add date of last page edit to Cilium's documentation | area/documentation kind/feature | The documentation at https://docs.cilium.io/ have a commit reference in its footer, which tells from what Cilium commit the documentation was generated. However, it is global to the whole documentation, and does not really speak for the date of the last change on the document.
It would be nice to find a way to add this date, to reflect whether the page has been updated recently or whether it has remained untouched for a long time. Although this is not a perfect indicator on the freshness of the information, it can tell if a page has a high risk of being outdated.
Technically, I suppose it shouldn't be too hard to retrieve the commit id of the last change for a document, and to pass it for printing to the theme that we use for the docs. However, there are two things to keep in mind:
- It should be easy to retrieve the commit for the last update of a documentation source file, but it will likely be harder to reflect all changes for the resulting HTML page when this RST file includes another file as a fragment. I don't know if Sphinx provides an API to easily iterate on included files.
- Many pages would likely be dated from the recent reorganisation of the documentation files, given that source files were moved around, even though the actual text contents was unmodified. But there's probably not much to do here. | 1.0 | Add date of last page edit to Cilium's documentation - The documentation at https://docs.cilium.io/ have a commit reference in its footer, which tells from what Cilium commit the documentation was generated. However, it is global to the whole documentation, and does not really speak for the date of the last change on the document.
It would be nice to find a way to add this date, to reflect whether the page has been updated recently or whether it has remained untouched for a long time. Although this is not a perfect indicator on the freshness of the information, it can tell if a page has a high risk of being outdated.
Technically, I suppose it shouldn't be too hard to retrieve the commit id of the last change for a document, and to pass it for printing to the theme that we use for the docs. However, there are two things to keep in mind:
- It should be easy to retrieve the commit for the last update of a documentation source file, but it will likely be harder to reflect all changes for the resulting HTML page when this RST file includes another file as a fragment. I don't know if Sphinx provides an API to easily iterate on included files.
- Many pages would likely be dated from the recent reorganisation of the documentation files, given that source files were moved around, even though the actual text contents was unmodified. But there's probably not much to do here. | non_priority | add date of last page edit to cilium s documentation the documentation at have a commit reference in its footer which tells from what cilium commit the documentation was generated however it is global to the whole documentation and does not really speak for the date of the last change on the document it would be nice to find a way to add this date to reflect whether the page has been updated recently or whether it has remained untouched for a long time although this is not a perfect indicator on the freshness of the information it can tell if a page has a high risk of being outdated technically i suppose it shouldn t be too hard to retrieve the commit id of the last change for a document and to pass it for printing to the theme that we use for the docs however there are two things to keep in mind it should be easy to retrieve the commit for the last update of a documentation source file but it will likely be harder to reflect all changes for the resulting html page when this rst file includes another file as a fragment i don t know if sphinx provides an api to easily iterate on included files many pages would likely be dated from the recent reorganisation of the documentation files given that source files were moved around even though the actual text contents was unmodified but there s probably not much to do here | 0 |
416,767 | 28,099,347,356 | IssuesEvent | 2023-03-30 18:11:30 | matplotlib/matplotlib | https://api.github.com/repos/matplotlib/matplotlib | opened | [Doc]: Incorrect formatting for examples in user examples for user_explain | Documentation | ### Documentation Link
https://matplotlib.org/stable/tutorials/toolkits/index.html
### Problem
All the code is commented out in all three downloadable python examples from toolkits. When you download the files, either the .py or the .ipynb, built from each separate .py file, all the code is commented out in each example.
https://matplotlib.org/stable/tutorials/toolkits/axes_grid.html#sphx-glr-tutorials-toolkits-axes-grid-py
https://matplotlib.org/stable/tutorials/toolkits/axisartist.html
https://matplotlib.org/stable/tutorials/toolkits/mplot3d.html
### Suggested improvement
The solution would be to go through these files and format them correctly so that the code in the files is runnable without having to reformat the files yourself. The paths of the downloadable files referenced on the website are listed below.
./matplotlib/galleries/users_explain/toolkits/axes_grid.py
./matplotlib/galleries/users_explain/toolkits/axisartist.py
./matplotlib/galleries/users_explain/toolkits/axisartist.py
| 1.0 | [Doc]: Incorrect formatting for examples in user examples for user_explain - ### Documentation Link
https://matplotlib.org/stable/tutorials/toolkits/index.html
### Problem
All the code is commented out in all three downloadable python examples from toolkits. When you download the files, either the .py or the .ipynb, built from each separate .py file, all the code is commented out in each example.
https://matplotlib.org/stable/tutorials/toolkits/axes_grid.html#sphx-glr-tutorials-toolkits-axes-grid-py
https://matplotlib.org/stable/tutorials/toolkits/axisartist.html
https://matplotlib.org/stable/tutorials/toolkits/mplot3d.html
### Suggested improvement
The solution would be to go through these files and format them correctly so that the code in the files is runnable without having to reformat the files yourself. The paths of the downloadable files referenced on the website are listed below.
./matplotlib/galleries/users_explain/toolkits/axes_grid.py
./matplotlib/galleries/users_explain/toolkits/axisartist.py
./matplotlib/galleries/users_explain/toolkits/axisartist.py
| non_priority | incorrect formatting for examples in user examples for user explain documentation link problem all the code is commented out in all three downloadable python examples from toolkits when you download the files either the py or the ipynb built from each separate py file all the code is commented out in each example suggested improvement the solution would be to go through these files and format them correctly so that the code in the files is runnable without having to reformat the files yourself the paths of the downloadable files referenced on the website are listed below matplotlib galleries users explain toolkits axes grid py matplotlib galleries users explain toolkits axisartist py matplotlib galleries users explain toolkits axisartist py | 0 |
21,032 | 4,662,461,207 | IssuesEvent | 2016-10-05 04:01:54 | Microsoft/vsts-agent | https://api.github.com/repos/Microsoft/vsts-agent | closed | Windows 7 dependencies | documentation | When running on Windows 7, it appears the following are prerequisites for the agent (although the System Requirements document says there are none)
* A version of Windows PowerShell which supports the [Unblock-File](https://technet.microsoft.com/en-us/library/hh849924(v=wps.620).aspx) command - so 3.0 or higher, Windows 7 ships with 2.0
* The [Universal C Runtime](https://support.microsoft.com/en-us/kb/2999226)
It would be good if the Requirements document could list this. | 1.0 | Windows 7 dependencies - When running on Windows 7, it appears the following are prerequisites for the agent (although the System Requirements document says there are none)
* A version of Windows PowerShell which supports the [Unblock-File](https://technet.microsoft.com/en-us/library/hh849924(v=wps.620).aspx) command - so 3.0 or higher, Windows 7 ships with 2.0
* The [Universal C Runtime](https://support.microsoft.com/en-us/kb/2999226)
It would be good if the Requirements document could list this. | non_priority | windows dependencies when running on windows it appears the following are prerequisites for the agent although the system requirements document says there are none a version of windows powershell which supports the command so or higher windows ships with the it would be good if the requirements document could list this | 0 |
221,241 | 17,315,931,750 | IssuesEvent | 2021-07-27 06:04:24 | thesofproject/sof | https://api.github.com/repos/thesofproject/sof | opened | [BUG] timeout on STREAM_SD_OFFSET read when suspend-resume on CML | CML Intel Linux Daily tests bug | **Describe the bug**
timeout on STREAM_SD_OFFSET read when suspend-resume on CML
inner daily /5515?model=CML_HEL_RT5682&testcase=check-suspend-resume-with-capture-5
**To Reproduce**
TPLG=/lib/firmware/intel/sof-tplg/sof-cml-rt1011-rt5682.tplg ~/sof-test/test-case/check-suspend-resume-with-audio.sh -l 5 -m capture
**Environment**
Start Time: 2021-07-26 21:24:47 UTC
End Time: 2021-07-27 04:58:29 UTC
Kernel Branch: topic/sof-dev
Kernel Commit: 2113dc7f
SOF Branch: main
SOF Commit: 57ee04f2d931
Topology:sof-cml-rt1011-rt5682.tplg
Platform:CML_HEL_RT5682
**Screenshots or console output**
[console]
```
2021-07-26 23:04:00 UTC Sub-Test: [REMOTE_INFO] ===== Round(2/5) =====
2021-07-26 23:04:00 UTC Sub-Test: [REMOTE_COMMAND] Run the command: rtcwake -m mem -s 5
rtcwake: assuming RTC uses UTC ...
rtcwake: wakeup from "mem" using /dev/rtc0 at Mon Jul 26 23:04:07 2021
2021-07-26 23:04:10 UTC Sub-Test: [REMOTE_COMMAND] sleep for 5
arecord: suspend:1691: suspend: prepare error: Connection timed out
2021-07-26 23:04:15 UTC Sub-Test: [REMOTE_INFO] Check for the kernel log status
declare -- cmd="journalctl_cmd --since=@1627340635"
2021-07-26 23:04:15 UTC [ERROR] Caught kernel log error
===========================>>
[ 5378.823476] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: hda_dsp_stream_trigger: cmd 5: timeout on STREAM_SD_OFFSET read
[ 5382.615214] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: cl_copy_fw: timeout HDA_DSP_SRAM_REG_ROM_STATUS read
[ 5382.616259] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: hda_dsp_stream_trigger: cmd 0: timeout on STREAM_SD_OFFSET read
[ 5382.616266] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: DMA trigger stop failed
[ 5382.616272] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ DSP dump start ]------------
[ 5382.616305] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: extended rom status: 0x5000001 0x0 0x0 0x0 0x0 0x0 0x1811102 0x0
[ 5382.616311] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ DSP dump end ]------------
[ 5382.616315] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: load fw failed ret: -110
[ 5382.616373] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed to start DSP
[ 5382.616378] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed to boot DSP firmware after resume -110
[ 5382.616382] kernel: PM: dpm_run_callback(): pci_pm_resume+0x0/0x80 returns -110
[ 5382.616513] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: PM: failed to resume async: error -110
[ 5383.132839] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: ipc timed out for 0x30100000 size 48
[ 5383.132909] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ IPC dump start ]------------
[ 5383.132967] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: hda irq intsts 0x00000000 intlctl 0x00001388 rirb 00
[ 5383.133019] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: dsp irq ppsts 0x00000000 adspis 0x00000003
[ 5383.133077] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: host status 0x00000000 dsp status 0x00040000 mask 0x00000000
[ 5383.133131] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ IPC dump end ]------------
[ 5383.133175] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: load pipeline ipc failure
[ 5383.133216] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed to load widget PIPELINE.11.DMIC1.IN
[ 5383.133264] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed widget list set up for pcm 7 dir 1
[ 5383.133313] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: set pcm hw_params after resume
[ 5383.133356] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ASoC: error at snd_soc_pcm_component_prepare on 0000:00:1f.3: -110
[ 5383.133496] kernel: DMIC16kHz: ASoC: soc_pcm_prepare() failed (-110)
[ 5383.133535] kernel: DMIC16kHz: ASoC: dpcm_fe_dai_prepare() failed (-110)
<<===========================
``` | 1.0 | [BUG] timeout on STREAM_SD_OFFSET read when suspend-resume on CML - **Describe the bug**
timeout on STREAM_SD_OFFSET read when suspend-resume on CML
inner daily /5515?model=CML_HEL_RT5682&testcase=check-suspend-resume-with-capture-5
**To Reproduce**
TPLG=/lib/firmware/intel/sof-tplg/sof-cml-rt1011-rt5682.tplg ~/sof-test/test-case/check-suspend-resume-with-audio.sh -l 5 -m capture
**Environment**
Start Time: 2021-07-26 21:24:47 UTC
End Time: 2021-07-27 04:58:29 UTC
Kernel Branch: topic/sof-dev
Kernel Commit: 2113dc7f
SOF Branch: main
SOF Commit: 57ee04f2d931
Topology:sof-cml-rt1011-rt5682.tplg
Platform:CML_HEL_RT5682
**Screenshots or console output**
[console]
```
2021-07-26 23:04:00 UTC Sub-Test: [REMOTE_INFO] ===== Round(2/5) =====
2021-07-26 23:04:00 UTC Sub-Test: [REMOTE_COMMAND] Run the command: rtcwake -m mem -s 5
rtcwake: assuming RTC uses UTC ...
rtcwake: wakeup from "mem" using /dev/rtc0 at Mon Jul 26 23:04:07 2021
2021-07-26 23:04:10 UTC Sub-Test: [REMOTE_COMMAND] sleep for 5
arecord: suspend:1691: suspend: prepare error: Connection timed out
2021-07-26 23:04:15 UTC Sub-Test: [REMOTE_INFO] Check for the kernel log status
declare -- cmd="journalctl_cmd --since=@1627340635"
2021-07-26 23:04:15 UTC [ERROR] Caught kernel log error
===========================>>
[ 5378.823476] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: hda_dsp_stream_trigger: cmd 5: timeout on STREAM_SD_OFFSET read
[ 5382.615214] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: cl_copy_fw: timeout HDA_DSP_SRAM_REG_ROM_STATUS read
[ 5382.616259] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: hda_dsp_stream_trigger: cmd 0: timeout on STREAM_SD_OFFSET read
[ 5382.616266] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: DMA trigger stop failed
[ 5382.616272] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ DSP dump start ]------------
[ 5382.616305] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: extended rom status: 0x5000001 0x0 0x0 0x0 0x0 0x0 0x1811102 0x0
[ 5382.616311] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ DSP dump end ]------------
[ 5382.616315] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: load fw failed ret: -110
[ 5382.616373] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed to start DSP
[ 5382.616378] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed to boot DSP firmware after resume -110
[ 5382.616382] kernel: PM: dpm_run_callback(): pci_pm_resume+0x0/0x80 returns -110
[ 5382.616513] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: PM: failed to resume async: error -110
[ 5383.132839] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: ipc timed out for 0x30100000 size 48
[ 5383.132909] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ IPC dump start ]------------
[ 5383.132967] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: hda irq intsts 0x00000000 intlctl 0x00001388 rirb 00
[ 5383.133019] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: dsp irq ppsts 0x00000000 adspis 0x00000003
[ 5383.133077] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: host status 0x00000000 dsp status 0x00040000 mask 0x00000000
[ 5383.133131] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ------------[ IPC dump end ]------------
[ 5383.133175] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: load pipeline ipc failure
[ 5383.133216] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed to load widget PIPELINE.11.DMIC1.IN
[ 5383.133264] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: failed widget list set up for pcm 7 dir 1
[ 5383.133313] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: error: set pcm hw_params after resume
[ 5383.133356] kernel: sof-audio-pci-intel-cnl 0000:00:1f.3: ASoC: error at snd_soc_pcm_component_prepare on 0000:00:1f.3: -110
[ 5383.133496] kernel: DMIC16kHz: ASoC: soc_pcm_prepare() failed (-110)
[ 5383.133535] kernel: DMIC16kHz: ASoC: dpcm_fe_dai_prepare() failed (-110)
<<===========================
``` | non_priority | timeout on stream sd offset read when suspend resume on cml describe the bug timeout on stream sd offset read when suspend resume on cml inner daily model cml hel testcase check suspend resume with capture to reproduce tplg lib firmware intel sof tplg sof cml tplg sof test test case check suspend resume with audio sh l m capture environment start time utc end time utc kernel branch topic sof dev kernel commit sof branch main sof commit topology sof cml tplg platform cml hel screenshots or console output utc sub test round utc sub test run the command rtcwake m mem s rtcwake assuming rtc uses utc rtcwake wakeup from mem using dev at mon jul utc sub test sleep for arecord suspend suspend prepare error connection timed out utc sub test check for the kernel log status declare cmd journalctl cmd since utc caught kernel log error kernel sof audio pci intel cnl error hda dsp stream trigger cmd timeout on stream sd offset read kernel sof audio pci intel cnl error cl copy fw timeout hda dsp sram reg rom status read kernel sof audio pci intel cnl error hda dsp stream trigger cmd timeout on stream sd offset read kernel sof audio pci intel cnl error dma trigger stop failed kernel sof audio pci intel cnl kernel sof audio pci intel cnl error extended rom status kernel sof audio pci intel cnl kernel sof audio pci intel cnl error load fw failed ret kernel sof audio pci intel cnl error failed to start dsp kernel sof audio pci intel cnl error failed to boot dsp firmware after resume kernel pm dpm run callback pci pm resume returns kernel sof audio pci intel cnl pm failed to resume async error kernel sof audio pci intel cnl error ipc timed out for size kernel sof audio pci intel cnl kernel sof audio pci intel cnl error hda irq intsts intlctl rirb kernel sof audio pci intel cnl error dsp irq ppsts adspis kernel sof audio pci intel cnl error host status dsp status mask kernel sof audio pci intel cnl kernel sof audio pci intel cnl error load pipeline ipc failure kernel sof audio pci intel cnl error failed to load widget pipeline in kernel sof audio pci intel cnl error failed widget list set up for pcm dir kernel sof audio pci intel cnl error set pcm hw params after resume kernel sof audio pci intel cnl asoc error at snd soc pcm component prepare on kernel asoc soc pcm prepare failed kernel asoc dpcm fe dai prepare failed | 0 |
22,462 | 4,806,130,579 | IssuesEvent | 2016-11-02 17:44:16 | palantir/atlasdb | https://api.github.com/repos/palantir/atlasdb | closed | We should have schema mutation lock documentation | component: documentation | Many internal products have hit this issue. Knowledge and RUMINT about how it works are spreading organically. Let's have a source of truth.
| 1.0 | We should have schema mutation lock documentation - Many internal products have hit this issue. Knowledge and RUMINT about how it works are spreading organically. Let's have a source of truth.
| non_priority | we should have schema mutation lock documentation many internal products have hit this issue knowledge and rumint about how it works are spreading organically let s have a source of truth | 0 |
205,883 | 16,012,803,191 | IssuesEvent | 2021-04-20 12:48:42 | kirbydesign/designsystem | https://api.github.com/repos/kirbydesign/designsystem | closed | [Documentation] Write "Glossary"-section for contribution guidelines | documentation | **This is part of a larger issue - please read: https://github.com/kirbydesign/designsystem/issues/1393#issuecomment-802766408 before continuing!**
**Short description**
<!-- Replace the paragraph below with your own description -->
A "glossary" section should be added to the contribution guidelines. An outline already exists on the branch [`documentation/contribution-guidelines`](https://github.com/kirbydesign/designsystem/tree/documentation/contribution-guidelines) which should be expanded upon.
**Edit )** Might be made redundant by #1464
| 1.0 | [Documentation] Write "Glossary"-section for contribution guidelines - **This is part of a larger issue - please read: https://github.com/kirbydesign/designsystem/issues/1393#issuecomment-802766408 before continuing!**
**Short description**
<!-- Replace the paragraph below with your own description -->
A "glossary" section should be added to the contribution guidelines. An outline already exists on the branch [`documentation/contribution-guidelines`](https://github.com/kirbydesign/designsystem/tree/documentation/contribution-guidelines) which should be expanded upon.
**Edit )** Might be made redundant by #1464
| non_priority | write glossary section for contribution guidelines this is part of a larger issue please read before continuing short description a glossary section should be added to the contribution guidelines an outline already exists on the branch which should be expanded upon edit might be made redundant by | 0 |
2,062 | 3,633,961,028 | IssuesEvent | 2016-02-11 16:22:32 | owncloud/core | https://api.github.com/repos/owncloud/core | closed | Code signing for applications | 1 - To develop enhancement - approved security | With ownCloud 8 we’re aiming to move most of the shipped apps to the AppStore. However, this makes the ownCloud AppStore a high level target for cyber attacks. Currently, the applications served by the AppStore are not signed and thus an attacker might potentially alter or corrupt apps.
For ownCloud 8.1 we’re thus adding an optional Code signing process for applications. The aim of the code-signing process is not to prevent malicious applications per se, but to protect against a potentially hacked AppStore. However, we will introduce some trust levels such as “personal signed” which make it more unlikely for application authors to willingly deploy malicious code.
Especially, the aimed process is as following:
1. The ownCloud project will create a X.509 certificate authority suitable for the certificate generation (“ownCloud Code Signing Authority”)
2. The public key of this certificate authority is added to the ownCloud core.
3. The certificate authority is signing certificates for apps based on the application identifier (CN = application identifier).
4. Developers have the choice to sign their app with a certificate, ownCloud will implement an automatic code-signing procedure in the ocdev tool.
5. When installing an app there are different messages and warnings shown depending on the signature’s trust level. If an application was signed at one point of time further updates require always a signature of the same trust level.
This requires that apps need a unique application identifier, a good thing would be to demand the domain name in the application name. That’s what other vendors such as Google or Apple with their AppStores do. (for example “org.owncloud.files”)
The following trust levels are proposed (will be stored in the certificate in one of the extension fields or so):
1. Not signed - Untrusted
- App is shown unsupported by the ownCloud project
- Security warning about potential malicious and untrusted or insecure code that might get executed in a big red box - requires double confirmation when installing apps
- Can never be a “recommended” app.
2. Domain Identity verified - Somewhat trusted, given to everyone who has access to a webmaster@ mail address of a domain and is also in the WHOIS entry or can otherwise prove ownership.
- App is shown unsupported by the ownCloud project
- Security warning about potential malicious and untrusted or insecure code that might get executed in a big red box - requires double confirmation when installing apps
- Name of domain is shown to the user
3. Personal Identity verified - More trusted, given people that showed up at a developer conference and verified their identity to a representative of the CA.
- App is shown unsupported by the ownCloud project
- Security warning about potential malicious and untrusted or insecure code that might get executed in a smaller disclaimer, however it is noted that the application author has verified his identity
- Full Name of author is shown to the user
4. Core application - Perfectly trusted
- App is shown supported by the ownCloud project
- “Official ownCloud application” (or so) is displayed to the user
Certificates might be revoked via a CRL at any-time. In this case future updates signed from the same certificate are not permitted anymore. - The ownCloud project might create a new certificate for that application in that point then.
Please notice that this is only a work-in progress proposal and the final implementation might differ in some parts. Especially procedural questions (“Who maintains the CA?”, “How are certificate revocation and replacement certificate requests handled?”, “Which legal document needs to get signed to receive a certificate?”, “What is sufficient to verify an identitiy?”, “What is exactly displayed”?, etc…) are not covered by this public issue and needs to be further discussed.
Next steps:
- [ ] Implement a proof of concept implementation which only supports one trust-level (signed / unsigned)
- [ ] Discuss the different trust levels
- [ ] Discuss how certificates are issued
- [ ] Create guidelines and adjust documentation explaining the code signing
- [ ] Documentation about code-signing
- [ ] Guideline: "Handling of the certificate authority certificate".
- [ ] Guideline: "Signing of certificates and different trust-levels".
- [ ] Guideline: "Revocation of certificates"
- [ ] Guideline: "Handling of lost certificates"
- [ ] Add implementation to ocdev
- [ ] Add different trust levels
- [ ] Blog post abut code-signing
@bantu For further input as our very own PHPSecLib guru.
@Raydiation For ocdev.
@DeepDiver1975 For your information.
@karlitschek As discussed. | True | Code signing for applications - With ownCloud 8 we’re aiming to move most of the shipped apps to the AppStore. However, this makes the ownCloud AppStore a high level target for cyber attacks. Currently, the applications served by the AppStore are not signed and thus an attacker might potentially alter or corrupt apps.
For ownCloud 8.1 we’re thus adding an optional Code signing process for applications. The aim of the code-signing process is not to prevent malicious applications per se, but to protect against a potentially hacked AppStore. However, we will introduce some trust levels such as “personal signed” which make it more unlikely for application authors to willingly deploy malicious code.
Especially, the aimed process is as following:
1. The ownCloud project will create a X.509 certificate authority suitable for the certificate generation (“ownCloud Code Signing Authority”)
2. The public key of this certificate authority is added to the ownCloud core.
3. The certificate authority is signing certificates for apps based on the application identifier (CN = application identifier).
4. Developers have the choice to sign their app with a certificate, ownCloud will implement an automatic code-signing procedure in the ocdev tool.
5. When installing an app there are different messages and warnings shown depending on the signature’s trust level. If an application was signed at one point of time further updates require always a signature of the same trust level.
This requires that apps need a unique application identifier, a good thing would be to demand the domain name in the application name. That’s what other vendors such as Google or Apple with their AppStores do. (for example “org.owncloud.files”)
The following trust levels are proposed (will be stored in the certificate in one of the extension fields or so):
1. Not signed - Untrusted
- App is shown unsupported by the ownCloud project
- Security warning about potential malicious and untrusted or insecure code that might get executed in a big red box - requires double confirmation when installing apps
- Can never be a “recommended” app.
2. Domain Identity verified - Somewhat trusted, given to everyone who has access to a webmaster@ mail address of a domain and is also in the WHOIS entry or can otherwise prove ownership.
- App is shown unsupported by the ownCloud project
- Security warning about potential malicious and untrusted or insecure code that might get executed in a big red box - requires double confirmation when installing apps
- Name of domain is shown to the user
3. Personal Identity verified - More trusted, given people that showed up at a developer conference and verified their identity to a representative of the CA.
- App is shown unsupported by the ownCloud project
- Security warning about potential malicious and untrusted or insecure code that might get executed in a smaller disclaimer, however it is noted that the application author has verified his identity
- Full Name of author is shown to the user
4. Core application - Perfectly trusted
- App is shown supported by the ownCloud project
- “Official ownCloud application” (or so) is displayed to the user
Certificates might be revoked via a CRL at any-time. In this case future updates signed from the same certificate are not permitted anymore. - The ownCloud project might create a new certificate for that application in that point then.
Please notice that this is only a work-in progress proposal and the final implementation might differ in some parts. Especially procedural questions (“Who maintains the CA?”, “How are certificate revocation and replacement certificate requests handled?”, “Which legal document needs to get signed to receive a certificate?”, “What is sufficient to verify an identitiy?”, “What is exactly displayed”?, etc…) are not covered by this public issue and needs to be further discussed.
Next steps:
- [ ] Implement a proof of concept implementation which only supports one trust-level (signed / unsigned)
- [ ] Discuss the different trust levels
- [ ] Discuss how certificates are issued
- [ ] Create guidelines and adjust documentation explaining the code signing
- [ ] Documentation about code-signing
- [ ] Guideline: "Handling of the certificate authority certificate".
- [ ] Guideline: "Signing of certificates and different trust-levels".
- [ ] Guideline: "Revocation of certificates"
- [ ] Guideline: "Handling of lost certificates"
- [ ] Add implementation to ocdev
- [ ] Add different trust levels
- [ ] Blog post abut code-signing
@bantu For further input as our very own PHPSecLib guru.
@Raydiation For ocdev.
@DeepDiver1975 For your information.
@karlitschek As discussed. | non_priority | code signing for applications with owncloud we’re aiming to move most of the shipped apps to the appstore however this makes the owncloud appstore a high level target for cyber attacks currently the applications served by the appstore are not signed and thus an attacker might potentially alter or corrupt apps for owncloud we’re thus adding an optional code signing process for applications the aim of the code signing process is not to prevent malicious applications per se but to protect against a potentially hacked appstore however we will introduce some trust levels such as “personal signed” which make it more unlikely for application authors to willingly deploy malicious code especially the aimed process is as following the owncloud project will create a x certificate authority suitable for the certificate generation “owncloud code signing authority” the public key of this certificate authority is added to the owncloud core the certificate authority is signing certificates for apps based on the application identifier cn application identifier developers have the choice to sign their app with a certificate owncloud will implement an automatic code signing procedure in the ocdev tool when installing an app there are different messages and warnings shown depending on the signature’s trust level if an application was signed at one point of time further updates require always a signature of the same trust level this requires that apps need a unique application identifier a good thing would be to demand the domain name in the application name that’s what other vendors such as google or apple with their appstores do for example “org owncloud files” the following trust levels are proposed will be stored in the certificate in one of the extension fields or so not signed untrusted app is shown unsupported by the owncloud project security warning about potential malicious and untrusted or insecure code that might get executed in a big red box requires double confirmation when installing apps can never be a “recommended” app domain identity verified somewhat trusted given to everyone who has access to a webmaster mail address of a domain and is also in the whois entry or can otherwise prove ownership app is shown unsupported by the owncloud project security warning about potential malicious and untrusted or insecure code that might get executed in a big red box requires double confirmation when installing apps name of domain is shown to the user personal identity verified more trusted given people that showed up at a developer conference and verified their identity to a representative of the ca app is shown unsupported by the owncloud project security warning about potential malicious and untrusted or insecure code that might get executed in a smaller disclaimer however it is noted that the application author has verified his identity full name of author is shown to the user core application perfectly trusted app is shown supported by the owncloud project “official owncloud application” or so is displayed to the user certificates might be revoked via a crl at any time in this case future updates signed from the same certificate are not permitted anymore the owncloud project might create a new certificate for that application in that point then please notice that this is only a work in progress proposal and the final implementation might differ in some parts especially procedural questions “who maintains the ca ” “how are certificate revocation and replacement certificate requests handled ” “which legal document needs to get signed to receive a certificate ” “what is sufficient to verify an identitiy ” “what is exactly displayed” etc… are not covered by this public issue and needs to be further discussed next steps implement a proof of concept implementation which only supports one trust level signed unsigned discuss the different trust levels discuss how certificates are issued create guidelines and adjust documentation explaining the code signing documentation about code signing guideline handling of the certificate authority certificate guideline signing of certificates and different trust levels guideline revocation of certificates guideline handling of lost certificates add implementation to ocdev add different trust levels blog post abut code signing bantu for further input as our very own phpseclib guru raydiation for ocdev for your information karlitschek as discussed | 0 |
29,796 | 5,894,570,155 | IssuesEvent | 2017-05-18 02:38:17 | cakephp/cakephp | https://api.github.com/repos/cakephp/cakephp | closed | Inconsistent default behaviour between form::control and form::checkbox | Defect helpers | This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.4.6 (Possibly since 3.3.13, see below comment with attached blame)
* Platform and Target: Apache, Mysql 5.7, PHP 7.1
### What you did
Create a checkbox via the form helper.
`$this->Form->control('my_field'); // broken`
`$this->Form->checkbox('my_field'); // works`
### What happened
Using the control method, the hidden input field is _not_ generated. When using the checkbox method, the hidden field _is_ generated.
### What you expected to happen
The `control` method should by default behave in the same way as `checkbox` for generating checkbox fields. | 1.0 | Inconsistent default behaviour between form::control and form::checkbox - This is a (multiple allowed):
* [x] bug
* [ ] enhancement
* [ ] feature-discussion (RFC)
* CakePHP Version: 3.4.6 (Possibly since 3.3.13, see below comment with attached blame)
* Platform and Target: Apache, Mysql 5.7, PHP 7.1
### What you did
Create a checkbox via the form helper.
`$this->Form->control('my_field'); // broken`
`$this->Form->checkbox('my_field'); // works`
### What happened
Using the control method, the hidden input field is _not_ generated. When using the checkbox method, the hidden field _is_ generated.
### What you expected to happen
The `control` method should by default behave in the same way as `checkbox` for generating checkbox fields. | non_priority | inconsistent default behaviour between form control and form checkbox this is a multiple allowed bug enhancement feature discussion rfc cakephp version possibly since see below comment with attached blame platform and target apache mysql php what you did create a checkbox via the form helper this form control my field broken this form checkbox my field works what happened using the control method the hidden input field is not generated when using the checkbox method the hidden field is generated what you expected to happen the control method should by default behave in the same way as checkbox for generating checkbox fields | 0 |
178,161 | 21,509,331,244 | IssuesEvent | 2022-04-28 01:29:26 | bsbtd/Teste | https://api.github.com/repos/bsbtd/Teste | closed | CVE-2019-12086 (High) detected in jackson-databind-2.9.5.jar - autoclosed | security vulnerability | ## CVE-2019-12086 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Teste/liferay-portal/modules/etl/talend/talend-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- components-api-0.25.3.jar (Root Library)
- daikon-0.27.0.jar
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/bsbtd/Teste/commit/64dde89c50c07496423c4d4a865f2e16b92399ad">64dde89c50c07496423c4d4a865f2e16b92399ad</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint, the service has the mysql-connector-java jar (8.0.14 or earlier) in the classpath, and an attacker can host a crafted MySQL server reachable by the victim, an attacker can send a crafted JSON message that allows them to read arbitrary local files on the server. This occurs because of missing com.mysql.cj.jdbc.admin.MiniAdmin validation.
<p>Publish Date: 2019-05-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12086>CVE-2019-12086</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086</a></p>
<p>Release Date: 2019-05-17</p>
<p>Fix Resolution: 2.9.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-12086 (High) detected in jackson-databind-2.9.5.jar - autoclosed - ## CVE-2019-12086 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.9.5.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: Teste/liferay-portal/modules/etl/talend/talend-common/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar,/home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.9.5/jackson-databind-2.9.5.jar</p>
<p>
Dependency Hierarchy:
- components-api-0.25.3.jar (Root Library)
- daikon-0.27.0.jar
- :x: **jackson-databind-2.9.5.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/bsbtd/Teste/commit/64dde89c50c07496423c4d4a865f2e16b92399ad">64dde89c50c07496423c4d4a865f2e16b92399ad</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint, the service has the mysql-connector-java jar (8.0.14 or earlier) in the classpath, and an attacker can host a crafted MySQL server reachable by the victim, an attacker can send a crafted JSON message that allows them to read arbitrary local files on the server. This occurs because of missing com.mysql.cj.jdbc.admin.MiniAdmin validation.
<p>Publish Date: 2019-05-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-12086>CVE-2019-12086</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086</a></p>
<p>Release Date: 2019-05-17</p>
<p>Fix Resolution: 2.9.9</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar autoclosed cve high severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file teste liferay portal modules etl talend talend common pom xml path to vulnerable library home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar home wss scanner repository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy components api jar root library daikon jar x jackson databind jar vulnerable library found in head commit a href vulnerability details a polymorphic typing issue was discovered in fasterxml jackson databind x before when default typing is enabled either globally or for a specific property for an externally exposed json endpoint the service has the mysql connector java jar or earlier in the classpath and an attacker can host a crafted mysql server reachable by the victim an attacker can send a crafted json message that allows them to read arbitrary local files on the server this occurs because of missing com mysql cj jdbc admin miniadmin validation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
133,338 | 18,295,468,605 | IssuesEvent | 2021-10-05 20:01:09 | dotnet/runtime | https://api.github.com/repos/dotnet/runtime | closed | Interop+AppleCrypto+AppleCFErrorCryptographicException: The operation couldn’t be completed. (Internal CSSM error error -2147416032 - Internal error #80010820 at SignTransform_block_invoke... | area-System.Security | <!--This is just a template - feel free to delete any and all of it and replace as appropriate.-->
### Configuration
.Net Core SDK: 5.0.401
.Net Core Runtime: 5.0.10
System Version: macOS 11.6 (20G165)
Kernel Version: Darwin 20.6.0
### Description
I am encountering a Interop+AppleCrypto+AppleCFErrorCryptographicException while running an ASP.NET Core on my Mac. I found a duplicate of this issue [here](https://github.com/dotnet/runtime/issues/37522), but their solution was to simply update the dotnet version. There was also another similar problem [here](https://github.com/dotnet/runtime/issues/52766), but their CSSM error was different and reinstalling dotnet did not solve my problem.
I have noticed that the first time I encounter the error after running my application, these show up in the Mac Console:
<img width="978" alt="image" src="https://user-images.githubusercontent.com/24985544/135118129-603f2545-0ba2-4f8d-9c05-69b4db593bbb.png">
<!--
* Please share a clear and concise description of the problem.
* Include minimal steps to reproduce the problem if possible. E.g.: the smallest possible code snippet; or a small repo to clone, with steps to run it.
* What behavior are you seeing, and what behavior would you expect?
-->
### Stack Trace
`crit: IdentityServer4.Hosting.IdentityServerMiddleware[0]
Unhandled exception: The operation couldn’t be completed. (Internal CSSM error error -2147416032 - Internal error #80010820 at SignTransform_block_invoke /System/Volumes/Data/SWE/macOS/BuildRoots/38cf1d983f/Library/Caches/com.apple.xbs/Sources/Security/Security-59754.140.13/OSX/libsecurity_transform/lib/SecSignVerifyTransform.c:326)
Interop+AppleCrypto+AppleCFErrorCryptographicException: The operation couldn’t be completed. (Internal CSSM error error -2147416032 - Internal error #80010820 at SignTransform_block_invoke /System/Volumes/Data/SWE/macOS/BuildRoots/38cf1d983f/Library/Caches/com.apple.xbs/Sources/Security/Security-59754.140.13/OSX/libsecurity_transform/lib/SecSignVerifyTransform.c:326)
at Interop.AppleCrypto.ExecuteTransform(ReadOnlySpan`1 source, SecKeyTransform transform)
at Interop.AppleCrypto.GenerateSignature(SafeSecKeyRefHandle privateKey, ReadOnlySpan`1 dataHash, PAL_HashAlgorithm hashAlgorithm)
at System.Security.Cryptography.RSAImplementation.RSASecurityTransforms.SignHash(Byte[] hash, HashAlgorithmName hashAlgorithm, RSASignaturePadding padding)
at Microsoft.IdentityModel.Tokens.AsymmetricAdapter.SignWithRsa(Byte[] bytes)
at Microsoft.IdentityModel.Tokens.AsymmetricAdapter.Sign(Byte[] bytes)
at Microsoft.IdentityModel.Tokens.AsymmetricSignatureProvider.Sign(Byte[] input)
at Microsoft.IdentityModel.JsonWebTokens.JwtTokenUtilities.CreateEncodedSignature(String input, SigningCredentials signingCredentials)
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.WriteToken(SecurityToken token)
at IdentityServer4.Services.DefaultTokenCreationService.CreateJwtAsync(JwtSecurityToken jwt)
at IdentityServer4.Services.DefaultTokenCreationService.CreateTokenAsync(Token token)
at IdentityServer4.Services.DefaultTokenService.CreateSecurityTokenAsync(Token token)
at IdentityServer4.ResponseHandling.TokenResponseGenerator.CreateAccessTokenAsync(ValidatedTokenRequest request)
at IdentityServer4.ResponseHandling.TokenResponseGenerator.ProcessTokenRequestAsync(TokenRequestValidationResult validationResult)
at IdentityServer4.ResponseHandling.TokenResponseGenerator.ProcessAsync(TokenRequestValidationResult request)
at IdentityServer4.Endpoints.TokenEndpoint.ProcessTokenRequestAsync(HttpContext context)
at IdentityServer4.Endpoints.TokenEndpoint.ProcessAsync(HttpContext context)
at IdentityServer4.Hosting.IdentityServerMiddleware.Invoke(HttpContext context, IEndpointRouter router, IUserSession session, IEventService events, IBackChannelLogoutService backChannelLogoutService)`
<!--
* Please include any relevant stack traces or error messages. If possible please include text as text rather than images (so it shows up in searches).
* If you have an idea where the problem might lie, let us know that here. Please include any pointers to code, relevant changes, or related issues you know of.
* Do you know of any workarounds?
-->
| True | Interop+AppleCrypto+AppleCFErrorCryptographicException: The operation couldn’t be completed. (Internal CSSM error error -2147416032 - Internal error #80010820 at SignTransform_block_invoke... - <!--This is just a template - feel free to delete any and all of it and replace as appropriate.-->
### Configuration
.Net Core SDK: 5.0.401
.Net Core Runtime: 5.0.10
System Version: macOS 11.6 (20G165)
Kernel Version: Darwin 20.6.0
### Description
I am encountering a Interop+AppleCrypto+AppleCFErrorCryptographicException while running an ASP.NET Core on my Mac. I found a duplicate of this issue [here](https://github.com/dotnet/runtime/issues/37522), but their solution was to simply update the dotnet version. There was also another similar problem [here](https://github.com/dotnet/runtime/issues/52766), but their CSSM error was different and reinstalling dotnet did not solve my problem.
I have noticed that the first time I encounter the error after running my application, these show up in the Mac Console:
<img width="978" alt="image" src="https://user-images.githubusercontent.com/24985544/135118129-603f2545-0ba2-4f8d-9c05-69b4db593bbb.png">
<!--
* Please share a clear and concise description of the problem.
* Include minimal steps to reproduce the problem if possible. E.g.: the smallest possible code snippet; or a small repo to clone, with steps to run it.
* What behavior are you seeing, and what behavior would you expect?
-->
### Stack Trace
`crit: IdentityServer4.Hosting.IdentityServerMiddleware[0]
Unhandled exception: The operation couldn’t be completed. (Internal CSSM error error -2147416032 - Internal error #80010820 at SignTransform_block_invoke /System/Volumes/Data/SWE/macOS/BuildRoots/38cf1d983f/Library/Caches/com.apple.xbs/Sources/Security/Security-59754.140.13/OSX/libsecurity_transform/lib/SecSignVerifyTransform.c:326)
Interop+AppleCrypto+AppleCFErrorCryptographicException: The operation couldn’t be completed. (Internal CSSM error error -2147416032 - Internal error #80010820 at SignTransform_block_invoke /System/Volumes/Data/SWE/macOS/BuildRoots/38cf1d983f/Library/Caches/com.apple.xbs/Sources/Security/Security-59754.140.13/OSX/libsecurity_transform/lib/SecSignVerifyTransform.c:326)
at Interop.AppleCrypto.ExecuteTransform(ReadOnlySpan`1 source, SecKeyTransform transform)
at Interop.AppleCrypto.GenerateSignature(SafeSecKeyRefHandle privateKey, ReadOnlySpan`1 dataHash, PAL_HashAlgorithm hashAlgorithm)
at System.Security.Cryptography.RSAImplementation.RSASecurityTransforms.SignHash(Byte[] hash, HashAlgorithmName hashAlgorithm, RSASignaturePadding padding)
at Microsoft.IdentityModel.Tokens.AsymmetricAdapter.SignWithRsa(Byte[] bytes)
at Microsoft.IdentityModel.Tokens.AsymmetricAdapter.Sign(Byte[] bytes)
at Microsoft.IdentityModel.Tokens.AsymmetricSignatureProvider.Sign(Byte[] input)
at Microsoft.IdentityModel.JsonWebTokens.JwtTokenUtilities.CreateEncodedSignature(String input, SigningCredentials signingCredentials)
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.WriteToken(SecurityToken token)
at IdentityServer4.Services.DefaultTokenCreationService.CreateJwtAsync(JwtSecurityToken jwt)
at IdentityServer4.Services.DefaultTokenCreationService.CreateTokenAsync(Token token)
at IdentityServer4.Services.DefaultTokenService.CreateSecurityTokenAsync(Token token)
at IdentityServer4.ResponseHandling.TokenResponseGenerator.CreateAccessTokenAsync(ValidatedTokenRequest request)
at IdentityServer4.ResponseHandling.TokenResponseGenerator.ProcessTokenRequestAsync(TokenRequestValidationResult validationResult)
at IdentityServer4.ResponseHandling.TokenResponseGenerator.ProcessAsync(TokenRequestValidationResult request)
at IdentityServer4.Endpoints.TokenEndpoint.ProcessTokenRequestAsync(HttpContext context)
at IdentityServer4.Endpoints.TokenEndpoint.ProcessAsync(HttpContext context)
at IdentityServer4.Hosting.IdentityServerMiddleware.Invoke(HttpContext context, IEndpointRouter router, IUserSession session, IEventService events, IBackChannelLogoutService backChannelLogoutService)`
<!--
* Please include any relevant stack traces or error messages. If possible please include text as text rather than images (so it shows up in searches).
* If you have an idea where the problem might lie, let us know that here. Please include any pointers to code, relevant changes, or related issues you know of.
* Do you know of any workarounds?
-->
| non_priority | interop applecrypto applecferrorcryptographicexception the operation couldn’t be completed internal cssm error error internal error at signtransform block invoke configuration net core sdk net core runtime system version macos kernel version darwin description i am encountering a interop applecrypto applecferrorcryptographicexception while running an asp net core on my mac i found a duplicate of this issue but their solution was to simply update the dotnet version there was also another similar problem but their cssm error was different and reinstalling dotnet did not solve my problem i have noticed that the first time i encounter the error after running my application these show up in the mac console img width alt image src please share a clear and concise description of the problem include minimal steps to reproduce the problem if possible e g the smallest possible code snippet or a small repo to clone with steps to run it what behavior are you seeing and what behavior would you expect stack trace crit hosting identityservermiddleware unhandled exception the operation couldn’t be completed internal cssm error error internal error at signtransform block invoke system volumes data swe macos buildroots library caches com apple xbs sources security security osx libsecurity transform lib secsignverifytransform c interop applecrypto applecferrorcryptographicexception the operation couldn’t be completed internal cssm error error internal error at signtransform block invoke system volumes data swe macos buildroots library caches com apple xbs sources security security osx libsecurity transform lib secsignverifytransform c at interop applecrypto executetransform readonlyspan source seckeytransform transform at interop applecrypto generatesignature safeseckeyrefhandle privatekey readonlyspan datahash pal hashalgorithm hashalgorithm at system security cryptography rsaimplementation rsasecuritytransforms signhash byte hash hashalgorithmname hashalgorithm rsasignaturepadding padding at microsoft identitymodel tokens asymmetricadapter signwithrsa byte bytes at microsoft identitymodel tokens asymmetricadapter sign byte bytes at microsoft identitymodel tokens asymmetricsignatureprovider sign byte input at microsoft identitymodel jsonwebtokens jwttokenutilities createencodedsignature string input signingcredentials signingcredentials at system identitymodel tokens jwt jwtsecuritytokenhandler writetoken securitytoken token at services defaulttokencreationservice createjwtasync jwtsecuritytoken jwt at services defaulttokencreationservice createtokenasync token token at services defaulttokenservice createsecuritytokenasync token token at responsehandling tokenresponsegenerator createaccesstokenasync validatedtokenrequest request at responsehandling tokenresponsegenerator processtokenrequestasync tokenrequestvalidationresult validationresult at responsehandling tokenresponsegenerator processasync tokenrequestvalidationresult request at endpoints tokenendpoint processtokenrequestasync httpcontext context at endpoints tokenendpoint processasync httpcontext context at hosting identityservermiddleware invoke httpcontext context iendpointrouter router iusersession session ieventservice events ibackchannellogoutservice backchannellogoutservice please include any relevant stack traces or error messages if possible please include text as text rather than images so it shows up in searches if you have an idea where the problem might lie let us know that here please include any pointers to code relevant changes or related issues you know of do you know of any workarounds | 0 |
273,901 | 29,831,115,051 | IssuesEvent | 2023-06-18 09:34:16 | RG4421/ampere-centos-kernel | https://api.github.com/repos/RG4421/ampere-centos-kernel | closed | CVE-2022-25258 (Medium) detected in linux-yocto-devv5.3 - autoclosed | Mend: dependency security vulnerability | ## CVE-2022-25258 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv5.3</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in drivers/usb/gadget/composite.c in the Linux kernel before 5.16.10. The USB Gadget subsystem lacks certain validation of interface OS descriptor requests (ones with a large array index and ones associated with NULL function pointer retrieval). Memory corruption might occur.
<p>Publish Date: 2022-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25258>CVE-2022-25258</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25258">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25258</a></p>
<p>Release Date: 2022-02-16</p>
<p>Fix Resolution: v5.17-rc4</p>
</p>
</details>
<p></p>
| True | CVE-2022-25258 (Medium) detected in linux-yocto-devv5.3 - autoclosed - ## CVE-2022-25258 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-devv5.3</b></p></summary>
<p>
<p>Linux Embedded Kernel - tracks the next mainline release</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-dev>https://git.yoctoproject.org/git/linux-yocto-dev</a></p>
<p>Found in base branch: <b>amp-centos-8.0-kernel</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in drivers/usb/gadget/composite.c in the Linux kernel before 5.16.10. The USB Gadget subsystem lacks certain validation of interface OS descriptor requests (ones with a large array index and ones associated with NULL function pointer retrieval). Memory corruption might occur.
<p>Publish Date: 2022-02-16
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-25258>CVE-2022-25258</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25258">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-25258</a></p>
<p>Release Date: 2022-02-16</p>
<p>Fix Resolution: v5.17-rc4</p>
</p>
</details>
<p></p>
| non_priority | cve medium detected in linux yocto autoclosed cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel tracks the next mainline release library home page a href found in base branch amp centos kernel vulnerable source files vulnerability details an issue was discovered in drivers usb gadget composite c in the linux kernel before the usb gadget subsystem lacks certain validation of interface os descriptor requests ones with a large array index and ones associated with null function pointer retrieval memory corruption might occur publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution | 0 |
190,790 | 15,256,189,994 | IssuesEvent | 2021-02-20 19:07:47 | theBurgerSquad/theBurgerSquad.github.io | https://api.github.com/repos/theBurgerSquad/theBurgerSquad.github.io | opened | Visual Design | documentation | - [ ] Layout Grids
- [ ] Design Sketches
- [ ] Page Mock-ups
- [ ] Web-based Prototype (not required, but screenshots of this could be included) | 1.0 | Visual Design - - [ ] Layout Grids
- [ ] Design Sketches
- [ ] Page Mock-ups
- [ ] Web-based Prototype (not required, but screenshots of this could be included) | non_priority | visual design layout grids design sketches page mock ups web based prototype not required but screenshots of this could be included | 0 |
276,402 | 23,991,262,396 | IssuesEvent | 2022-09-14 01:30:09 | EscherLabs/Graphene | https://api.github.com/repos/EscherLabs/Graphene | closed | Versioning bug in micro app | bug awaiting test | **Description**
When I have tried to switch version in the past the template is unable to be opened.
**Feature / Subsystem**
Microapp
**To Reproduce**
Open below micro app
switch version to 1.0
try to select the template tab
- can't
**Console Errors**
no errors display
**Link(s)**
https://my.binghamton.edu/admin/apps/351)
| 1.0 | Versioning bug in micro app - **Description**
When I have tried to switch version in the past the template is unable to be opened.
**Feature / Subsystem**
Microapp
**To Reproduce**
Open below micro app
switch version to 1.0
try to select the template tab
- can't
**Console Errors**
no errors display
**Link(s)**
https://my.binghamton.edu/admin/apps/351)
| non_priority | versioning bug in micro app description when i have tried to switch version in the past the template is unable to be opened feature subsystem microapp to reproduce open below micro app switch version to try to select the template tab can t console errors no errors display link s | 0 |
275,847 | 23,945,696,793 | IssuesEvent | 2022-09-12 07:05:05 | AntaresSimulatorTeam/Antares_Simulator | https://api.github.com/repos/AntaresSimulatorTeam/Antares_Simulator | closed | UnicodeDecodeError: 'utf-8' codec can't decode byte 0xf0 in position 40159: invalid continuation byte | bug tests | **Description**
All `pytest` fail.
**How to Reproduce**
Run pytest like this
```bash
pytest output_compare_test.py --solver-path ~/Antares_Simulator/build/solver/antares-8.2-solver -k test_ntc_sc_builder
```
**Expected behavior**
The test should succed.
**Screenshots and additional files**
If applicable, add screenshots to help explain your problem. You may also include a .zip file containing your study.
**OS and version**
- OS: Ubuntu 20.04
- Antares Simulator version: 8.x | 1.0 | UnicodeDecodeError: 'utf-8' codec can't decode byte 0xf0 in position 40159: invalid continuation byte - **Description**
All `pytest` fail.
**How to Reproduce**
Run pytest like this
```bash
pytest output_compare_test.py --solver-path ~/Antares_Simulator/build/solver/antares-8.2-solver -k test_ntc_sc_builder
```
**Expected behavior**
The test should succed.
**Screenshots and additional files**
If applicable, add screenshots to help explain your problem. You may also include a .zip file containing your study.
**OS and version**
- OS: Ubuntu 20.04
- Antares Simulator version: 8.x | non_priority | unicodedecodeerror utf codec can t decode byte in position invalid continuation byte description all pytest fail how to reproduce run pytest like this bash pytest output compare test py solver path antares simulator build solver antares solver k test ntc sc builder expected behavior the test should succed screenshots and additional files if applicable add screenshots to help explain your problem you may also include a zip file containing your study os and version os ubuntu antares simulator version x | 0 |
98,537 | 20,751,908,187 | IssuesEvent | 2022-03-15 08:31:19 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | Can't join servers in unstable 0.16.1.0 | Bug Need more info Code Networking | *Sent by WordPress (issue@barotraumagame.com). Created by [fire](https://fire.fundersclub.com/).*
---
From: Fuoco1306
**Description**
I don't know if this was intentional, but the multiplayer doesnt' work for 8.1, Maybe it's just because the game is "unstable" i just want to make you know this.
**Steps To Reproduce**
I Justr tried to join the official multiplayer server
**Version**
1.61 (beta)
**Operating System**
Windows
| 1.0 | Can't join servers in unstable 0.16.1.0 - *Sent by WordPress (issue@barotraumagame.com). Created by [fire](https://fire.fundersclub.com/).*
---
From: Fuoco1306
**Description**
I don't know if this was intentional, but the multiplayer doesnt' work for 8.1, Maybe it's just because the game is "unstable" i just want to make you know this.
**Steps To Reproduce**
I Justr tried to join the official multiplayer server
**Version**
1.61 (beta)
**Operating System**
Windows
| non_priority | can t join servers in unstable sent by wordpress issue barotraumagame com created by from description i don t know if this was intentional but the multiplayer doesnt work for maybe it s just because the game is unstable i just want to make you know this steps to reproduce i justr tried to join the official multiplayer server version beta operating system windows | 0 |
388,134 | 26,752,488,919 | IssuesEvent | 2023-01-30 20:49:52 | fga-eps-mds/2022-2-CAPJu-Doc | https://api.github.com/repos/fga-eps-mds/2022-2-CAPJu-Doc | closed | Propagar alteração nos modelos | documentation EPS Tarefa DOCS | # Propagar alteração no tamanho das anotações
## Descrição
Alterar DE-R e DLD com os nomes das entidades configuradas nas migrações e as alterações no limite de caracteres das anotações.
## Critérios de aceitação
- [x] atualizar DE-R
- [x] renomear entidades
- [x] renomear atributos
- [x] atualizar DLD
- [x] renomear entidades
- [x] renomear atributos
- [x] alterar limite no atributo de conteúdo das anotações
- [x] configurar CASCADEs para RESTRICT
- [x] gerar novas imagens
- [x] DE-R
- [x] DLD
- [x] atualizar documentação com novas imagens | 1.0 | Propagar alteração nos modelos - # Propagar alteração no tamanho das anotações
## Descrição
Alterar DE-R e DLD com os nomes das entidades configuradas nas migrações e as alterações no limite de caracteres das anotações.
## Critérios de aceitação
- [x] atualizar DE-R
- [x] renomear entidades
- [x] renomear atributos
- [x] atualizar DLD
- [x] renomear entidades
- [x] renomear atributos
- [x] alterar limite no atributo de conteúdo das anotações
- [x] configurar CASCADEs para RESTRICT
- [x] gerar novas imagens
- [x] DE-R
- [x] DLD
- [x] atualizar documentação com novas imagens | non_priority | propagar alteração nos modelos propagar alteração no tamanho das anotações descrição alterar de r e dld com os nomes das entidades configuradas nas migrações e as alterações no limite de caracteres das anotações critérios de aceitação atualizar de r renomear entidades renomear atributos atualizar dld renomear entidades renomear atributos alterar limite no atributo de conteúdo das anotações configurar cascades para restrict gerar novas imagens de r dld atualizar documentação com novas imagens | 0 |
77,617 | 15,569,819,034 | IssuesEvent | 2021-03-17 01:03:52 | veshitala/flask-blogger | https://api.github.com/repos/veshitala/flask-blogger | opened | CVE-2019-16865 (High) detected in Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl | security vulnerability | ## CVE-2019-16865 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/0d/f3/421598450cb9503f4565d936860763b5af413a61009d87a5ab1e34139672/Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/0d/f3/421598450cb9503f4565d936860763b5af413a61009d87a5ab1e34139672/Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to vulnerable library: flask-blogger/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in Pillow before 6.2.0. When reading specially crafted invalid image files, the library can either allocate very large amounts of memory or take an extremely long period of time to process the image.
<p>Publish Date: 2019-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16865>CVE-2019-16865</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16865">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16865</a></p>
<p>Release Date: 2019-10-04</p>
<p>Fix Resolution: 6.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-16865 (High) detected in Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl - ## CVE-2019-16865 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl</b></p></summary>
<p>Python Imaging Library (Fork)</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/0d/f3/421598450cb9503f4565d936860763b5af413a61009d87a5ab1e34139672/Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl">https://files.pythonhosted.org/packages/0d/f3/421598450cb9503f4565d936860763b5af413a61009d87a5ab1e34139672/Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl</a></p>
<p>Path to vulnerable library: flask-blogger/requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Pillow-5.4.1-cp27-cp27mu-manylinux1_x86_64.whl** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in Pillow before 6.2.0. When reading specially crafted invalid image files, the library can either allocate very large amounts of memory or take an extremely long period of time to process the image.
<p>Publish Date: 2019-10-04
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-16865>CVE-2019-16865</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16865">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16865</a></p>
<p>Release Date: 2019-10-04</p>
<p>Fix Resolution: 6.2.0</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in pillow whl cve high severity vulnerability vulnerable library pillow whl python imaging library fork library home page a href path to vulnerable library flask blogger requirements txt dependency hierarchy x pillow whl vulnerable library vulnerability details an issue was discovered in pillow before when reading specially crafted invalid image files the library can either allocate very large amounts of memory or take an extremely long period of time to process the image publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
411,483 | 27,823,605,695 | IssuesEvent | 2023-03-19 14:15:04 | PhamNguyenNhutTruong/Nhom2_CCPTPM | https://api.github.com/repos/PhamNguyenNhutTruong/Nhom2_CCPTPM | closed | Tìm hiểu về React. | documentation | - Tìm hiểu về luồng đi của project của nhóm.
- Cố gắng lấy được data hiện lên giao diện sử dụng. | 1.0 | Tìm hiểu về React. - - Tìm hiểu về luồng đi của project của nhóm.
- Cố gắng lấy được data hiện lên giao diện sử dụng. | non_priority | tìm hiểu về react tìm hiểu về luồng đi của project của nhóm cố gắng lấy được data hiện lên giao diện sử dụng | 0 |
9,983 | 7,049,941,194 | IssuesEvent | 2018-01-03 01:41:13 | hyperapp/hyperapp | https://api.github.com/repos/hyperapp/hyperapp | closed | Preformance benchmarking | PERFORMANCE | As with dot-dom (another project I helped out with). What is the preformance like against react/preact proper?
A comparison chart would be helpful and potentially up your adoption. | True | Preformance benchmarking - As with dot-dom (another project I helped out with). What is the preformance like against react/preact proper?
A comparison chart would be helpful and potentially up your adoption. | non_priority | preformance benchmarking as with dot dom another project i helped out with what is the preformance like against react preact proper a comparison chart would be helpful and potentially up your adoption | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.