Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
153,318 | 24,110,702,141 | IssuesEvent | 2022-09-20 11:05:59 | gotogether-s/gotogether-s | https://api.github.com/repos/gotogether-s/gotogether-s | opened | Make a Category, Recommend product and more button | design | ## About
Make a Category, Recommend product and more button
## To do list
- [ ] Category
- [ ] Recommend-product
- [ ] Nation-Recommend-prodcut
- [ ] Group-Recommend-product
- [ ] Golf-Recommend-product
- [ ] Culture-Recommend-product
- [ ] more button
## Other
Attatch reference or link
| 1.0 | Make a Category, Recommend product and more button - ## About
Make a Category, Recommend product and more button
## To do list
- [ ] Category
- [ ] Recommend-product
- [ ] Nation-Recommend-prodcut
- [ ] Group-Recommend-product
- [ ] Golf-Recommend-product
- [ ] Culture-Recommend-product
- [ ] more button
## Other
Attatch reference or link
| non_priority | make a category recommend product and more button about make a category recommend product and more button to do list category recommend product nation recommend prodcut group recommend product golf recommend product culture recommend product more button other attatch reference or link | 0 |
280,972 | 21,315,305,186 | IssuesEvent | 2022-04-16 06:58:27 | snss231/pe | https://api.github.com/repos/snss231/pe | opened | The term "clientele" is used but not defined | severity.Low type.DocumentationBug | 
"Clientele" is not a word that most insurance agents necessarily understand
<!--session: 1650087234279-774db252-41b3-4132-9c1c-a4f3d303f427-->
<!--Version: Web v3.4.2--> | 1.0 | The term "clientele" is used but not defined - 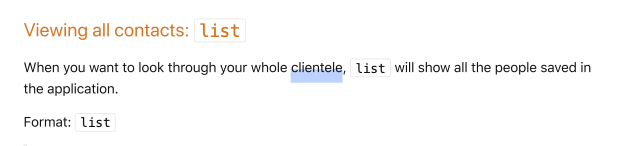
"Clientele" is not a word that most insurance agents necessarily understand
<!--session: 1650087234279-774db252-41b3-4132-9c1c-a4f3d303f427-->
<!--Version: Web v3.4.2--> | non_priority | the term clientele is used but not defined clientele is not a word that most insurance agents necessarily understand | 0 |
29,211 | 5,609,485,344 | IssuesEvent | 2017-04-02 01:29:24 | Cockatrice/Cockatrice | https://api.github.com/repos/Cockatrice/Cockatrice | closed | Cannot add/delete buddies | App - Cockatrice Defect - Regression | This issue was unfortunately caused by #2501.
This is a bad regression that causes the "Add/remove buddylist/ignorelist" buttons to not populate.
Build before merge:
<img width="227" alt="screenshot 2017-04-01 01 44 13" src="https://cloud.githubusercontent.com/assets/7460172/24575759/b782025c-167c-11e7-9c6d-68ed3acf47fd.png">
Build after merge:
<img width="233" alt="screenshot 2017-04-01 01 43 28" src="https://cloud.githubusercontent.com/assets/7460172/24575757/b06ab1bc-167c-11e7-9fb0-9b091cc1f59c.png">
| 1.0 | Cannot add/delete buddies - This issue was unfortunately caused by #2501.
This is a bad regression that causes the "Add/remove buddylist/ignorelist" buttons to not populate.
Build before merge:
<img width="227" alt="screenshot 2017-04-01 01 44 13" src="https://cloud.githubusercontent.com/assets/7460172/24575759/b782025c-167c-11e7-9c6d-68ed3acf47fd.png">
Build after merge:
<img width="233" alt="screenshot 2017-04-01 01 43 28" src="https://cloud.githubusercontent.com/assets/7460172/24575757/b06ab1bc-167c-11e7-9fb0-9b091cc1f59c.png">
| non_priority | cannot add delete buddies this issue was unfortunately caused by this is a bad regression that causes the add remove buddylist ignorelist buttons to not populate build before merge img width alt screenshot src build after merge img width alt screenshot src | 0 |
38,330 | 4,939,196,754 | IssuesEvent | 2016-11-29 13:42:30 | cockpit-project/cockpit | https://api.github.com/repos/cockpit-project/cockpit | closed | accounts: tooltip over "Create New Account" button slides under the main menu bar | needsdesign | Generally I log into Cockpit not as root user.
Therefore, if I go to the Accounts tool, I don't have privileges to create a new account. For this reason, the "Create New Account" button is inactive, which is good. But, if I hover over the button, a grey tooltip appears above it (probably telling me that user so-and-so is not permitted to create new accounts). However, I can only see the bottom edge of this tooltip, the rest disappears under the main menu bar, specifically it is obscured by the Dashboard and Cluster button in the menu bar.
| 1.0 | accounts: tooltip over "Create New Account" button slides under the main menu bar - Generally I log into Cockpit not as root user.
Therefore, if I go to the Accounts tool, I don't have privileges to create a new account. For this reason, the "Create New Account" button is inactive, which is good. But, if I hover over the button, a grey tooltip appears above it (probably telling me that user so-and-so is not permitted to create new accounts). However, I can only see the bottom edge of this tooltip, the rest disappears under the main menu bar, specifically it is obscured by the Dashboard and Cluster button in the menu bar.
| non_priority | accounts tooltip over create new account button slides under the main menu bar generally i log into cockpit not as root user therefore if i go to the accounts tool i don t have privileges to create a new account for this reason the create new account button is inactive which is good but if i hover over the button a grey tooltip appears above it probably telling me that user so and so is not permitted to create new accounts however i can only see the bottom edge of this tooltip the rest disappears under the main menu bar specifically it is obscured by the dashboard and cluster button in the menu bar | 0 |
18,300 | 25,304,015,718 | IssuesEvent | 2022-11-17 12:55:07 | woocommerce/woocommerce-blocks | https://api.github.com/repos/woocommerce/woocommerce-blocks | closed | Add a cart update button | needs feedback category: feedback plugin incompatibility | Hello !
Thanks a lot for your job !
## What do you like about the Cart & Checkout blocks?
## What do you think is missing from the Cart & Checkout blocks?
Maybe a cart update button would be great, or permit to refresh cart when there is an add by the cart cross-sells product. Currently, when somebody select a product to this area, the product is correctly added to the cart, but coupons about the cart aren't applied, because the cart is'nt reloaded.
| True | Add a cart update button - Hello !
Thanks a lot for your job !
## What do you like about the Cart & Checkout blocks?
## What do you think is missing from the Cart & Checkout blocks?
Maybe a cart update button would be great, or permit to refresh cart when there is an add by the cart cross-sells product. Currently, when somebody select a product to this area, the product is correctly added to the cart, but coupons about the cart aren't applied, because the cart is'nt reloaded.
| non_priority | add a cart update button hello thanks a lot for your job what do you like about the cart checkout blocks what do you think is missing from the cart checkout blocks maybe a cart update button would be great or permit to refresh cart when there is an add by the cart cross sells product currently when somebody select a product to this area the product is correctly added to the cart but coupons about the cart aren t applied because the cart is nt reloaded | 0 |
149,185 | 19,566,507,328 | IssuesEvent | 2022-01-04 01:43:36 | moqui/moqui-framework | https://api.github.com/repos/moqui/moqui-framework | closed | CVE-2021-44832 (Medium) detected in log4j-core-2.17.0.jar | security vulnerability | ## CVE-2021-44832 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.17.0.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /framework/build.gradle</p>
<p>Path to vulnerable library: /aches/modules-2/files-2.1/org.apache.logging.log4j/log4j-core/2.17.0/fe6e7a32c1228884b9691a744f953a55d0dd8ead/log4j-core-2.17.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.logging.log4j/log4j-core/2.17.0/fe6e7a32c1228884b9691a744f953a55d0dd8ead/log4j-core-2.17.0.jar</p>
<p>
Dependency Hierarchy:
- log4j-slf4j-impl-2.17.0.jar (Root Library)
- :x: **log4j-core-2.17.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/moqui/moqui-framework/commit/9b676d3e15ef41539b4dcc5a0fb533767bb2909a">9b676d3e15ef41539b4dcc5a0fb533767bb2909a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Log4j2 versions 2.0-beta7 through 2.17.0 (excluding security fix releases 2.3.2 and 2.12.4) are vulnerable to a remote code execution (RCE) attack when a configuration uses a JDBC Appender with a JNDI LDAP data source URI when an attacker has control of the target LDAP server. This issue is fixed by limiting JNDI data source names to the java protocol in Log4j2 versions 2.17.1, 2.12.4, and 2.3.2.
<p>Publish Date: 2021-12-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44832>CVE-2021-44832</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-28</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.3.2,2.12.4,2.17.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-44832 (Medium) detected in log4j-core-2.17.0.jar - ## CVE-2021-44832 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.17.0.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/">https://logging.apache.org/log4j/2.x/</a></p>
<p>Path to dependency file: /framework/build.gradle</p>
<p>Path to vulnerable library: /aches/modules-2/files-2.1/org.apache.logging.log4j/log4j-core/2.17.0/fe6e7a32c1228884b9691a744f953a55d0dd8ead/log4j-core-2.17.0.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.logging.log4j/log4j-core/2.17.0/fe6e7a32c1228884b9691a744f953a55d0dd8ead/log4j-core-2.17.0.jar</p>
<p>
Dependency Hierarchy:
- log4j-slf4j-impl-2.17.0.jar (Root Library)
- :x: **log4j-core-2.17.0.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/moqui/moqui-framework/commit/9b676d3e15ef41539b4dcc5a0fb533767bb2909a">9b676d3e15ef41539b4dcc5a0fb533767bb2909a</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache Log4j2 versions 2.0-beta7 through 2.17.0 (excluding security fix releases 2.3.2 and 2.12.4) are vulnerable to a remote code execution (RCE) attack when a configuration uses a JDBC Appender with a JNDI LDAP data source URI when an attacker has control of the target LDAP server. This issue is fixed by limiting JNDI data source names to the java protocol in Log4j2 versions 2.17.1, 2.12.4, and 2.3.2.
<p>Publish Date: 2021-12-28
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-44832>CVE-2021-44832</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-28</p>
<p>Fix Resolution: org.apache.logging.log4j:log4j-core:2.3.2,2.12.4,2.17.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in core jar cve medium severity vulnerability vulnerable library core jar the apache implementation library home page a href path to dependency file framework build gradle path to vulnerable library aches modules files org apache logging core core jar home wss scanner gradle caches modules files org apache logging core core jar dependency hierarchy impl jar root library x core jar vulnerable library found in head commit a href vulnerability details apache versions through excluding security fix releases and are vulnerable to a remote code execution rce attack when a configuration uses a jdbc appender with a jndi ldap data source uri when an attacker has control of the target ldap server this issue is fixed by limiting jndi data source names to the java protocol in versions and publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache logging core step up your open source security game with whitesource | 0 |
136,531 | 11,049,475,804 | IssuesEvent | 2019-12-09 23:51:38 | MangopearUK/European-Boating-Association--Theme | https://api.github.com/repos/MangopearUK/European-Boating-Association--Theme | closed | Test & audit BP view: Group > Manage > Delete | Testing: second round | ## Table of contents
- [x] **Task 1:** Perform automated audits _(10 tasks)_
- [x] **Task 2:** Manual standards & accessibility tests _(61 tasks)_
- [x] **Task 3:** Breakpoint testing _(15 tasks)_
- [x] **Task 4:** Re-run automated audits _(10 tasks)_
## 1: Perform automated audits _(10 tasks)_
### Lighthouse:
- [x] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [x] Run "Performance" audit in lighthouse _(using incognito tab)_
- [x] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [x] Run "SEO" audit in lighthouse _(using incognito tab)_
- [x] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [x] Run full audit of the the page's performance in Pingdom
### Browser's console
- [x] Check Chrome's console for errors
### Log results of audits
- [x] Screenshot snapshot of the lighthouse audits
- [x] Upload PDF of detailed lighthouse reports
- [x] Provide a screenshot of any console errors
## 2: Manual standards & accessibility tests _(61 tasks)_
### Forms
- [x] Give all form elements permanently visible labels
- [x] Place labels above form elements
- [x] Mark invalid fields clearly and provide associated error messages
- [x] Make forms as short as possible; offer shortcuts like autocompleting the address using the postcode
- [x] Ensure all form fields have the correct requried state
- [x] Provide status and error messages as WAI-ARIA live regions
### Readability of content
- [x] Ensure page has good grammar
- [x] Ensure page content has been spell-checked
- [x] Make sure headings are in logical order
- [x] Ensure the same content is available across different devices and platforms
- [x] Begin long, multi-section documents with a table of contents
### Presentation
- [x] Make sure all content is formatted correctly
- [x] Avoid all-caps text
- [x] Make sure data tables wider than their container can be scrolled horizontally
- [x] Use the same design patterns to solve the same problems
- [x] Do not mark up subheadings/straplines with separate heading elements
### Links & buttons
#### Links
- [x] Check all links to ensure they work
- [x] Check all links to third party websites use `rel="noopener"`
- [x] Make sure the purpose of a link is clearly described: "read more" vs. "read more about accessibility"
- [x] Provide a skip link if necessary
- [x] Underline links — at least in body copy
- [x] Warn users of links that have unusual behaviors, like linking off-site, or loading a new tab (i.e. aria-label)
#### Buttons
- [x] Ensure primary calls to action are easy to recognize and reach
- [x] Provide clear, unambiguous focus styles
- [x] Ensure states (pressed, expanded, invalid, etc) are communicated to assistive software
- [x] Ensure disabled controls are not focusable
- [x] Make sure controls within hidden content are not focusable
- [x] Provide large touch "targets" for interactive elements
- [x] Make controls look like controls; give them strong perceived affordance
- [x] Use well-established, therefore recognizable, icons and symbols
### Assistive technology
- [x] Ensure content is not obscured through zooming
- [x] Support Windows high contrast mode (use images, not background images)
- [x] Provide alternative text for salient images
- [x] Make scrollable elements focusable for keyboard users
- [x] Ensure keyboard focus order is logical regarding visual layout
- [x] Match semantics to behavior for assistive technology users
- [x] Provide a default language and use lang="[ISO code]" for subsections in different languages
- [x] Inform the user when there are important changes to the application state
- [x] Do not hijack standard scrolling behavior
- [x] Do not instate "infinite scroll" by default; provide buttons to load more items
### General accessibility
- [x] Make sure text and background colors contrast sufficiently
- [x] Do not rely on color for differentiation of visual elements
- [x] Avoid images of text — text that cannot be translated, selected, or understood by assistive tech
- [x] Provide a print stylesheet
- [x] Honour requests to remove animation via the prefers-reduced-motion media query
### SEO
- [x] Ensure all pages have appropriate title
- [x] Ensure all pages have meta descriptions
- [x] Make content easier to find and improve search results with structured data [Read more](https://developers.google.com/search/docs/guides/prototype)
- [x] Check whether page should be appearing in sitemap
- [x] Make sure page has Facebook and Twitter large image previews set correctly
- [x] Check canonical links for page
- [x] Mark as cornerstone content?
### Performance
- [x] Ensure all CSS assets are minified and concatenated
- [x] Ensure all JS assets are minified and concatenated
- [x] Ensure all images are compressed
- [x] Where possible, remove redundant code
- [x] Ensure all SVG assets have been optimised
- [x] Make sure styles and scripts are not render blocking
- [x] Ensure large image assets are lazy loaded
### Other
- [x] Make sure all content belongs to a landmark element
- [x] Provide a manifest.json file for identifiable homescreen entries
## 3: Breakpoint testing _(15 tasks)_
### Desktop
- [x] Provide a full screenshot of **1920px** wide page
- [x] Provide a full screenshot of **1500px** wide page
- [x] Provide a full screenshot of **1280px** wide page
- [x] Provide a full screenshot of **1024px** wide page
### Tablet
- [x] Provide a full screenshot of **960px** wide page
- [x] Provide a full screenshot of **800px** wide page
- [x] Provide a full screenshot of **760px** wide page
- [x] Provide a full screenshot of **650px** wide page
### Mobile
- [x] Provide a full screenshot of **600px** wide page
- [x] Provide a full screenshot of **500px** wide page
- [x] Provide a full screenshot of **450px** wide page
- [x] Provide a full screenshot of **380px** wide page
- [x] Provide a full screenshot of **320px** wide page
- [x] Provide a full screenshot of **280px** wide page
- [x] Provide a full screenshot of **250px** wide page
## 4: Re-run automated audits _(10 tasks)_
### Lighthouse:
- [x] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [x] Run "Performance" audit in lighthouse _(using incognito tab)_
- [x] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [x] Run "SEO" audit in lighthouse _(using incognito tab)_
- [x] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [x] Run full audit of the the page's performance in Pingdom
### Browser's console
- [x] Check Chrome's console for errors
### Log results of audits
- [x] Screenshot snapshot of the lighthouse audits
- [x] Upload PDF of detailed lighthouse reports
- [x] Provide a screenshot of any console errors | 1.0 | Test & audit BP view: Group > Manage > Delete - ## Table of contents
- [x] **Task 1:** Perform automated audits _(10 tasks)_
- [x] **Task 2:** Manual standards & accessibility tests _(61 tasks)_
- [x] **Task 3:** Breakpoint testing _(15 tasks)_
- [x] **Task 4:** Re-run automated audits _(10 tasks)_
## 1: Perform automated audits _(10 tasks)_
### Lighthouse:
- [x] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [x] Run "Performance" audit in lighthouse _(using incognito tab)_
- [x] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [x] Run "SEO" audit in lighthouse _(using incognito tab)_
- [x] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [x] Run full audit of the the page's performance in Pingdom
### Browser's console
- [x] Check Chrome's console for errors
### Log results of audits
- [x] Screenshot snapshot of the lighthouse audits
- [x] Upload PDF of detailed lighthouse reports
- [x] Provide a screenshot of any console errors
## 2: Manual standards & accessibility tests _(61 tasks)_
### Forms
- [x] Give all form elements permanently visible labels
- [x] Place labels above form elements
- [x] Mark invalid fields clearly and provide associated error messages
- [x] Make forms as short as possible; offer shortcuts like autocompleting the address using the postcode
- [x] Ensure all form fields have the correct requried state
- [x] Provide status and error messages as WAI-ARIA live regions
### Readability of content
- [x] Ensure page has good grammar
- [x] Ensure page content has been spell-checked
- [x] Make sure headings are in logical order
- [x] Ensure the same content is available across different devices and platforms
- [x] Begin long, multi-section documents with a table of contents
### Presentation
- [x] Make sure all content is formatted correctly
- [x] Avoid all-caps text
- [x] Make sure data tables wider than their container can be scrolled horizontally
- [x] Use the same design patterns to solve the same problems
- [x] Do not mark up subheadings/straplines with separate heading elements
### Links & buttons
#### Links
- [x] Check all links to ensure they work
- [x] Check all links to third party websites use `rel="noopener"`
- [x] Make sure the purpose of a link is clearly described: "read more" vs. "read more about accessibility"
- [x] Provide a skip link if necessary
- [x] Underline links — at least in body copy
- [x] Warn users of links that have unusual behaviors, like linking off-site, or loading a new tab (i.e. aria-label)
#### Buttons
- [x] Ensure primary calls to action are easy to recognize and reach
- [x] Provide clear, unambiguous focus styles
- [x] Ensure states (pressed, expanded, invalid, etc) are communicated to assistive software
- [x] Ensure disabled controls are not focusable
- [x] Make sure controls within hidden content are not focusable
- [x] Provide large touch "targets" for interactive elements
- [x] Make controls look like controls; give them strong perceived affordance
- [x] Use well-established, therefore recognizable, icons and symbols
### Assistive technology
- [x] Ensure content is not obscured through zooming
- [x] Support Windows high contrast mode (use images, not background images)
- [x] Provide alternative text for salient images
- [x] Make scrollable elements focusable for keyboard users
- [x] Ensure keyboard focus order is logical regarding visual layout
- [x] Match semantics to behavior for assistive technology users
- [x] Provide a default language and use lang="[ISO code]" for subsections in different languages
- [x] Inform the user when there are important changes to the application state
- [x] Do not hijack standard scrolling behavior
- [x] Do not instate "infinite scroll" by default; provide buttons to load more items
### General accessibility
- [x] Make sure text and background colors contrast sufficiently
- [x] Do not rely on color for differentiation of visual elements
- [x] Avoid images of text — text that cannot be translated, selected, or understood by assistive tech
- [x] Provide a print stylesheet
- [x] Honour requests to remove animation via the prefers-reduced-motion media query
### SEO
- [x] Ensure all pages have appropriate title
- [x] Ensure all pages have meta descriptions
- [x] Make content easier to find and improve search results with structured data [Read more](https://developers.google.com/search/docs/guides/prototype)
- [x] Check whether page should be appearing in sitemap
- [x] Make sure page has Facebook and Twitter large image previews set correctly
- [x] Check canonical links for page
- [x] Mark as cornerstone content?
### Performance
- [x] Ensure all CSS assets are minified and concatenated
- [x] Ensure all JS assets are minified and concatenated
- [x] Ensure all images are compressed
- [x] Where possible, remove redundant code
- [x] Ensure all SVG assets have been optimised
- [x] Make sure styles and scripts are not render blocking
- [x] Ensure large image assets are lazy loaded
### Other
- [x] Make sure all content belongs to a landmark element
- [x] Provide a manifest.json file for identifiable homescreen entries
## 3: Breakpoint testing _(15 tasks)_
### Desktop
- [x] Provide a full screenshot of **1920px** wide page
- [x] Provide a full screenshot of **1500px** wide page
- [x] Provide a full screenshot of **1280px** wide page
- [x] Provide a full screenshot of **1024px** wide page
### Tablet
- [x] Provide a full screenshot of **960px** wide page
- [x] Provide a full screenshot of **800px** wide page
- [x] Provide a full screenshot of **760px** wide page
- [x] Provide a full screenshot of **650px** wide page
### Mobile
- [x] Provide a full screenshot of **600px** wide page
- [x] Provide a full screenshot of **500px** wide page
- [x] Provide a full screenshot of **450px** wide page
- [x] Provide a full screenshot of **380px** wide page
- [x] Provide a full screenshot of **320px** wide page
- [x] Provide a full screenshot of **280px** wide page
- [x] Provide a full screenshot of **250px** wide page
## 4: Re-run automated audits _(10 tasks)_
### Lighthouse:
- [x] Run "Accessibility" audit in lighthouse _(using incognito tab)_
- [x] Run "Performance" audit in lighthouse _(using incognito tab)_
- [x] Run "Best practices" audit in lighthouse _(using incognito tab)_
- [x] Run "SEO" audit in lighthouse _(using incognito tab)_
- [x] Run "PWA" audit in lighthouse _(using incognito tab)_
### Pingdom
- [x] Run full audit of the the page's performance in Pingdom
### Browser's console
- [x] Check Chrome's console for errors
### Log results of audits
- [x] Screenshot snapshot of the lighthouse audits
- [x] Upload PDF of detailed lighthouse reports
- [x] Provide a screenshot of any console errors | non_priority | test audit bp view group manage delete table of contents task perform automated audits tasks task manual standards accessibility tests tasks task breakpoint testing tasks task re run automated audits tasks perform automated audits tasks lighthouse run accessibility audit in lighthouse using incognito tab run performance audit in lighthouse using incognito tab run best practices audit in lighthouse using incognito tab run seo audit in lighthouse using incognito tab run pwa audit in lighthouse using incognito tab pingdom run full audit of the the page s performance in pingdom browser s console check chrome s console for errors log results of audits screenshot snapshot of the lighthouse audits upload pdf of detailed lighthouse reports provide a screenshot of any console errors manual standards accessibility tests tasks forms give all form elements permanently visible labels place labels above form elements mark invalid fields clearly and provide associated error messages make forms as short as possible offer shortcuts like autocompleting the address using the postcode ensure all form fields have the correct requried state provide status and error messages as wai aria live regions readability of content ensure page has good grammar ensure page content has been spell checked make sure headings are in logical order ensure the same content is available across different devices and platforms begin long multi section documents with a table of contents presentation make sure all content is formatted correctly avoid all caps text make sure data tables wider than their container can be scrolled horizontally use the same design patterns to solve the same problems do not mark up subheadings straplines with separate heading elements links buttons links check all links to ensure they work check all links to third party websites use rel noopener make sure the purpose of a link is clearly described read more vs read more about accessibility provide a skip link if necessary underline links — at least in body copy warn users of links that have unusual behaviors like linking off site or loading a new tab i e aria label buttons ensure primary calls to action are easy to recognize and reach provide clear unambiguous focus styles ensure states pressed expanded invalid etc are communicated to assistive software ensure disabled controls are not focusable make sure controls within hidden content are not focusable provide large touch targets for interactive elements make controls look like controls give them strong perceived affordance use well established therefore recognizable icons and symbols assistive technology ensure content is not obscured through zooming support windows high contrast mode use images not background images provide alternative text for salient images make scrollable elements focusable for keyboard users ensure keyboard focus order is logical regarding visual layout match semantics to behavior for assistive technology users provide a default language and use lang for subsections in different languages inform the user when there are important changes to the application state do not hijack standard scrolling behavior do not instate infinite scroll by default provide buttons to load more items general accessibility make sure text and background colors contrast sufficiently do not rely on color for differentiation of visual elements avoid images of text — text that cannot be translated selected or understood by assistive tech provide a print stylesheet honour requests to remove animation via the prefers reduced motion media query seo ensure all pages have appropriate title ensure all pages have meta descriptions make content easier to find and improve search results with structured data check whether page should be appearing in sitemap make sure page has facebook and twitter large image previews set correctly check canonical links for page mark as cornerstone content performance ensure all css assets are minified and concatenated ensure all js assets are minified and concatenated ensure all images are compressed where possible remove redundant code ensure all svg assets have been optimised make sure styles and scripts are not render blocking ensure large image assets are lazy loaded other make sure all content belongs to a landmark element provide a manifest json file for identifiable homescreen entries breakpoint testing tasks desktop provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page tablet provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page mobile provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page provide a full screenshot of wide page re run automated audits tasks lighthouse run accessibility audit in lighthouse using incognito tab run performance audit in lighthouse using incognito tab run best practices audit in lighthouse using incognito tab run seo audit in lighthouse using incognito tab run pwa audit in lighthouse using incognito tab pingdom run full audit of the the page s performance in pingdom browser s console check chrome s console for errors log results of audits screenshot snapshot of the lighthouse audits upload pdf of detailed lighthouse reports provide a screenshot of any console errors | 0 |
27,541 | 12,627,371,529 | IssuesEvent | 2020-06-14 21:09:02 | Azure/azure-sdk-for-net | https://api.github.com/repos/Azure/azure-sdk-for-net | opened | Rename `Whitelist subscription` to `AllowList subscription` in DigitalTwins test prerequisites | Service Attention | See https://github.com/Azure/azure-sdk-for-net/blob/master/sdk/digitaltwins/Azure.DigitalTwins.Core/tests/prerequisites/prerequisite%20readme.md#3-whitelist-subscription | 1.0 | Rename `Whitelist subscription` to `AllowList subscription` in DigitalTwins test prerequisites - See https://github.com/Azure/azure-sdk-for-net/blob/master/sdk/digitaltwins/Azure.DigitalTwins.Core/tests/prerequisites/prerequisite%20readme.md#3-whitelist-subscription | non_priority | rename whitelist subscription to allowlist subscription in digitaltwins test prerequisites see | 0 |
52,503 | 13,752,932,925 | IssuesEvent | 2020-10-06 15:04:06 | NixOS/nixpkgs | https://api.github.com/repos/NixOS/nixpkgs | opened | Vulnerability roundup 93: geary-3.36.2: 1 advisory [5.9] | 1.severity: security | [search](https://search.nix.gsc.io/?q=geary&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=geary+in%3Apath&type=Code)
* [ ] [CVE-2020-24661](https://nvd.nist.gov/vuln/detail/CVE-2020-24661) CVSSv3=5.9 (nixos-20.09, nixos-unstable)
Scanned versions: nixos-20.09: ad3a5d5092e; nixos-unstable: 84d74ae9c9c.
Cc @dasj19
Cc @hedning
Cc @jtojnar
Cc @worldofpeace
| True | Vulnerability roundup 93: geary-3.36.2: 1 advisory [5.9] - [search](https://search.nix.gsc.io/?q=geary&i=fosho&repos=NixOS-nixpkgs), [files](https://github.com/NixOS/nixpkgs/search?utf8=%E2%9C%93&q=geary+in%3Apath&type=Code)
* [ ] [CVE-2020-24661](https://nvd.nist.gov/vuln/detail/CVE-2020-24661) CVSSv3=5.9 (nixos-20.09, nixos-unstable)
Scanned versions: nixos-20.09: ad3a5d5092e; nixos-unstable: 84d74ae9c9c.
Cc @dasj19
Cc @hedning
Cc @jtojnar
Cc @worldofpeace
| non_priority | vulnerability roundup geary advisory nixos nixos unstable scanned versions nixos nixos unstable cc cc hedning cc jtojnar cc worldofpeace | 0 |
211,090 | 16,168,236,536 | IssuesEvent | 2021-05-01 23:33:34 | mgba-emu/mgba | https://api.github.com/repos/mgba-emu/mgba | closed | mGBA 0.9.0 Introduces Lighting Offset in F-Zero: Maximum Velocity | blocked:needs hw testing platform:GBA | 
mGBA 0.9.0 introduced something very unusual. This does not apply to Falcon Densetsu (GP Legend) or Climax (from what I saw), so it is exclusive to Maximum Velocity. What I noticed is that the lighting on the track was shifted downward by one pixel. Again, while very minor, I spotted it most easily on Tenth Zone East: Snake Circuit. | 1.0 | mGBA 0.9.0 Introduces Lighting Offset in F-Zero: Maximum Velocity - 
mGBA 0.9.0 introduced something very unusual. This does not apply to Falcon Densetsu (GP Legend) or Climax (from what I saw), so it is exclusive to Maximum Velocity. What I noticed is that the lighting on the track was shifted downward by one pixel. Again, while very minor, I spotted it most easily on Tenth Zone East: Snake Circuit. | non_priority | mgba introduces lighting offset in f zero maximum velocity mgba introduced something very unusual this does not apply to falcon densetsu gp legend or climax from what i saw so it is exclusive to maximum velocity what i noticed is that the lighting on the track was shifted downward by one pixel again while very minor i spotted it most easily on tenth zone east snake circuit | 0 |
130,172 | 18,154,959,906 | IssuesEvent | 2021-09-26 22:38:24 | ghc-dev/Brittany-Stuart | https://api.github.com/repos/ghc-dev/Brittany-Stuart | opened | CVE-2020-8244 (Medium) detected in bl-1.1.2.tgz | security vulnerability | ## CVE-2020-8244 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bl-1.1.2.tgz</b></p></summary>
<p>Buffer List: collect buffers and access with a standard readable Buffer interface, streamable too!</p>
<p>Library home page: <a href="https://registry.npmjs.org/bl/-/bl-1.1.2.tgz">https://registry.npmjs.org/bl/-/bl-1.1.2.tgz</a></p>
<p>Path to dependency file: Brittany-Stuart/package.json</p>
<p>Path to vulnerable library: Brittany-Stuart/node_modules/bl/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-15.1.1.tgz (Root Library)
- jest-environment-jsdom-15.1.1.tgz
- jsdom-9.5.0.tgz
- request-2.75.0.tgz
- :x: **bl-1.1.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Brittany-Stuart/commit/bcaffdd09c362f72ce29afdaafeacfc08ccf2424">bcaffdd09c362f72ce29afdaafeacfc08ccf2424</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A buffer over-read vulnerability exists in bl <4.0.3, <3.0.1, <2.2.1, and <1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.
<p>Publish Date: 2020-08-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244>CVE-2020-8244</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8244">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8244</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.2.1,3.0.1,4.0.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"bl","packageVersion":"1.1.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"jest-cli:15.1.1;jest-environment-jsdom:15.1.1;jsdom:9.5.0;request:2.75.0;bl:1.1.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.2.1,3.0.1,4.0.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8244","vulnerabilityDetails":"A buffer over-read vulnerability exists in bl \u003c4.0.3, \u003c3.0.1, \u003c2.2.1, and \u003c1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-8244 (Medium) detected in bl-1.1.2.tgz - ## CVE-2020-8244 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bl-1.1.2.tgz</b></p></summary>
<p>Buffer List: collect buffers and access with a standard readable Buffer interface, streamable too!</p>
<p>Library home page: <a href="https://registry.npmjs.org/bl/-/bl-1.1.2.tgz">https://registry.npmjs.org/bl/-/bl-1.1.2.tgz</a></p>
<p>Path to dependency file: Brittany-Stuart/package.json</p>
<p>Path to vulnerable library: Brittany-Stuart/node_modules/bl/package.json</p>
<p>
Dependency Hierarchy:
- jest-cli-15.1.1.tgz (Root Library)
- jest-environment-jsdom-15.1.1.tgz
- jsdom-9.5.0.tgz
- request-2.75.0.tgz
- :x: **bl-1.1.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/ghc-dev/Brittany-Stuart/commit/bcaffdd09c362f72ce29afdaafeacfc08ccf2424">bcaffdd09c362f72ce29afdaafeacfc08ccf2424</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A buffer over-read vulnerability exists in bl <4.0.3, <3.0.1, <2.2.1, and <1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.
<p>Publish Date: 2020-08-30
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244>CVE-2020-8244</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8244">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-8244</a></p>
<p>Release Date: 2020-07-21</p>
<p>Fix Resolution: 2.2.1,3.0.1,4.0.3</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"bl","packageVersion":"1.1.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"jest-cli:15.1.1;jest-environment-jsdom:15.1.1;jsdom:9.5.0;request:2.75.0;bl:1.1.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.2.1,3.0.1,4.0.3"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-8244","vulnerabilityDetails":"A buffer over-read vulnerability exists in bl \u003c4.0.3, \u003c3.0.1, \u003c2.2.1, and \u003c1.2.3 which could allow an attacker to supply user input (even typed) that if it ends up in consume() argument and can become negative, the BufferList state can be corrupted, tricking it into exposing uninitialized memory via regular .slice() calls.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-8244","cvss3Severity":"medium","cvss3Score":"6.5","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in bl tgz cve medium severity vulnerability vulnerable library bl tgz buffer list collect buffers and access with a standard readable buffer interface streamable too library home page a href path to dependency file brittany stuart package json path to vulnerable library brittany stuart node modules bl package json dependency hierarchy jest cli tgz root library jest environment jsdom tgz jsdom tgz request tgz x bl tgz vulnerable library found in head commit a href found in base branch master vulnerability details a buffer over read vulnerability exists in bl and which could allow an attacker to supply user input even typed that if it ends up in consume argument and can become negative the bufferlist state can be corrupted tricking it into exposing uninitialized memory via regular slice calls publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree jest cli jest environment jsdom jsdom request bl isminimumfixversionavailable true minimumfixversion basebranches vulnerabilityidentifier cve vulnerabilitydetails a buffer over read vulnerability exists in bl and which could allow an attacker to supply user input even typed that if it ends up in consume argument and can become negative the bufferlist state can be corrupted tricking it into exposing uninitialized memory via regular slice calls vulnerabilityurl | 0 |
155,539 | 12,260,019,706 | IssuesEvent | 2020-05-06 17:34:19 | Azure-Samples/Cognitive-Services-Voice-Assistant | https://api.github.com/repos/Azure-Samples/Cognitive-Services-Voice-Assistant | opened | Use common naming convention for variable across samples | Devices Console Client (C++) UWP Voice Assistant (C# UWP) Voice Assistant Test Tool (C# .NET Core) Windows Voice Assistant Client (C# WPF) | We should use a common convention for variables across all samples. We could use Win32: https://docs.microsoft.com/en-us/windows/win32/stg/coding-style-conventions
or come up with our own, but we should be consistent
### This issue is for a: (mark with an `x`)
```
- [ ] bug report -> please search issues before submitting
- [x] feature request
- [ ] documentation issue or request
- [ ] regression (a behavior that used to work and stopped in a new release)
``` | 1.0 | Use common naming convention for variable across samples - We should use a common convention for variables across all samples. We could use Win32: https://docs.microsoft.com/en-us/windows/win32/stg/coding-style-conventions
or come up with our own, but we should be consistent
### This issue is for a: (mark with an `x`)
```
- [ ] bug report -> please search issues before submitting
- [x] feature request
- [ ] documentation issue or request
- [ ] regression (a behavior that used to work and stopped in a new release)
``` | non_priority | use common naming convention for variable across samples we should use a common convention for variables across all samples we could use or come up with our own but we should be consistent this issue is for a mark with an x bug report please search issues before submitting feature request documentation issue or request regression a behavior that used to work and stopped in a new release | 0 |
417,223 | 28,110,215,412 | IssuesEvent | 2023-03-31 06:27:16 | gwynethguo/ped | https://api.github.com/repos/gwynethguo/ped | opened | "Viewing help: `help`" section of the User Guide | severity.Medium type.DocumentationBug | The description of the viewing help section of the User Guide is:
"Shows a message explaining how to access the help page.", which is wrong, because viewing help should show a message explaining how to access the user guide, instead of the help page.
Moreover, the picture is incorrect because the link to the User Guide is wrong (linked to the previous bug report).
<!--session: 1680243335325-53dcaf51-bc82-44fc-9368-c2921950189e-->
<!--Version: Web v3.4.7--> | 1.0 | "Viewing help: `help`" section of the User Guide - The description of the viewing help section of the User Guide is:
"Shows a message explaining how to access the help page.", which is wrong, because viewing help should show a message explaining how to access the user guide, instead of the help page.
Moreover, the picture is incorrect because the link to the User Guide is wrong (linked to the previous bug report).
<!--session: 1680243335325-53dcaf51-bc82-44fc-9368-c2921950189e-->
<!--Version: Web v3.4.7--> | non_priority | viewing help help section of the user guide the description of the viewing help section of the user guide is shows a message explaining how to access the help page which is wrong because viewing help should show a message explaining how to access the user guide instead of the help page moreover the picture is incorrect because the link to the user guide is wrong linked to the previous bug report | 0 |
77,664 | 21,922,747,327 | IssuesEvent | 2022-05-22 20:26:00 | ClickHouse/ClickHouse | https://api.github.com/repos/ClickHouse/ClickHouse | closed | CMake: Target "common" links to ch_contrib::replxx but the target was not found | build | > Make sure that `git diff` result is empty and you've just pulled fresh master. Try cleaning up cmake cache. Just in case, official build instructions are published here: https://clickhouse.com/docs/en/development/build/
**Operating system**
Arch Linux:
```
5.17.9-arch1-1 #1 SMP PREEMPT Wed, 18 May 2022 17:30:11 +0000 x86_64 GNU/Linux
```
> OS kind or distribution, specific version/release, non-standard kernel if any. If you are trying to build inside virtual machine, please mention it too.
**Cmake version**
3.23.1
**Ninja version**
1.10.2
**Compiler name and version**
clang 13:
```
clang version 13.0.1
Target: x86_64-pc-linux-gnu
Thread model: posix
```
**Full cmake and/or ninja output**
```
cmake .. \
-DCMAKE_C_COMPILER=$(which clang) \
-DCMAKE_CXX_COMPILER=$(which clang++) \
-DCMAKE_BUILD_TYPE=Debug \
-DENABLE_CLICKHOUSE_ALL=OFF \
-DENABLE_CLICKHOUSE_SERVER=ON \
-DENABLE_CLICKHOUSE_CLIENT=ON \
-DENABLE_LIBRARIES=OFF \
-DUSE_UNWIND=ON \
-DENABLE_UTILS=OFF \
-DENABLE_TESTS=OFF \
-DENABLE_CCACHE=0
```
```
-- The C compiler identification is Clang 13.0.1
-- The CXX compiler identification is Clang 13.0.1
-- The ASM compiler identification is Clang with GNU-like command-line
-- Found assembler: /usr/bin/clang
-- Detecting C compiler ABI info
-- Detecting C compiler ABI info - done
-- Check for working C compiler: /usr/bin/clang - skipped
-- Detecting C compile features
-- Detecting C compile features - done
-- Detecting CXX compiler ABI info
-- Detecting CXX compiler ABI info - done
-- Check for working CXX compiler: /usr/bin/clang++ - skipped
-- Detecting CXX compile features
-- Detecting CXX compile features - done
-- Cross-compiling for target:
-- Using compiler:
clang version 13.0.1
Target: x86_64-pc-linux-gnu
Thread model: posix
InstalledDir: /usr/bin
-- Using linker: /usr/bin/ld.gold
-- Using archiver: /usr/bin/llvm-ar
-- Using ranlib: /usr/bin/llvm-ranlib
-- Using install-name-tool: /usr/bin/llvm-install-name-tool
-- Using objcopy: /usr/bin/llvm-objcopy
-- Using strip: /usr/bin/llvm-strip
-- Using ccache: no (disabled via configuration)
-- Found Git: /usr/bin/git (found version "2.36.1")
-- HEAD's commit hash 74f5301225b0870d7cd3f3bed93312962aece3cd
On branch master
Your branch is up to date with 'origin/master'.
nothing to commit, working tree clean
-- CMAKE_BUILD_TYPE: Debug
-- Performing Test HAS_RESERVED_IDENTIFIER
-- Performing Test HAS_RESERVED_IDENTIFIER - Success
-- Performing Test HAS_SUGGEST_DESTRUCTOR_OVERRIDE
-- Performing Test HAS_SUGGEST_DESTRUCTOR_OVERRIDE - Success
-- Performing Test HAS_SUGGEST_OVERRIDE
-- Performing Test HAS_SUGGEST_OVERRIDE - Success
-- Performing Test HAS_USE_CTOR_HOMING
-- Performing Test HAS_USE_CTOR_HOMING - Success
-- Performing Test HAVE_SSSE3
-- Performing Test HAVE_SSSE3 - Success
-- Performing Test HAVE_SSE41
-- Performing Test HAVE_SSE41 - Success
-- Performing Test HAVE_SSE42
-- Performing Test HAVE_SSE42 - Success
-- Performing Test HAVE_PCLMULQDQ
-- Performing Test HAVE_PCLMULQDQ - Success
-- Performing Test HAVE_POPCNT
-- Performing Test HAVE_POPCNT - Success
-- Performing Test HAVE_AVX
-- Performing Test HAVE_AVX - Success
-- Performing Test HAVE_AVX2
-- Performing Test HAVE_AVX2 - Success
-- Performing Test HAVE_AVX512
-- Performing Test HAVE_AVX512 - Success
-- Performing Test HAVE_BMI
-- Performing Test HAVE_BMI - Success
-- Default libraries: -nodefaultlibs /usr/lib/clang/13.0.1/lib/linux/libclang_rt.builtins-x86_64.a -lc -lm -lrt -lpthread -ldl
-- Looking for pthread.h
-- Looking for pthread.h - found
-- Performing Test CMAKE_HAVE_LIBC_PTHREAD
-- Performing Test CMAKE_HAVE_LIBC_PTHREAD - Success
-- Found Threads: TRUE
-- Looking for sys/random.h
-- Looking for sys/random.h - found
-- Performing Test SUPPORTS_CXXFLAG_no_unused_command_line_argument
-- Performing Test SUPPORTS_CXXFLAG_no_unused_command_line_argument - Success
-- Performing Test SUPPORTS_CXXFLAG_no_unused_but_set_variable
-- Performing Test SUPPORTS_CXXFLAG_no_unused_but_set_variable - Success
-- Performing Test SUPPORTS_CXXFLAG_no_builtin_requires_header
-- Performing Test SUPPORTS_CXXFLAG_no_builtin_requires_header - Success
-- Some symbols from glibc will be replaced for compatibility
-- Performing Test HAVE_WARNING_UNUSED_BUT_SET_VARIABLE
-- Performing Test HAVE_WARNING_UNUSED_BUT_SET_VARIABLE - Success
-- Performing Test HAVE_WARNING_MISSING_ATTRIBUTES
-- Performing Test HAVE_WARNING_MISSING_ATTRIBUTES - Failed
-- Performing Test HAVE_WARNING_MAYBE_UNINITIALIZED
-- Performing Test HAVE_WARNING_MAYBE_UNINITIALIZED - Failed
-- Performing Test HAVE_WARNING_REGISTER
-- Performing Test HAVE_WARNING_REGISTER - Success
-- Using libunwind: unwind
-- Using exception handler: unwind
-- Unit tests are disabled
-- Building for: Linux x86_64 ;
USE_STATIC_LIBRARIES=ON
SPLIT_SHARED=
-- Adding contrib module miniselect (configuring with miniselect-cmake)
-- Adding contrib module pdqsort (configuring with pdqsort-cmake)
-- Adding contrib module sparsehash-c11 (configuring with sparsehash-c11-cmake)
-- Adding contrib module abseil-cpp (configuring with abseil-cpp-cmake)
-- Adding contrib module magic_enum (configuring with magic-enum-cmake)
-- Adding contrib module boost (configuring with boost-cmake)
-- Adding contrib module cctz (configuring with cctz-cmake)
-- Packaging with tzdata version: 2021c
-- Adding contrib module consistent-hashing (configuring with consistent-hashing)
-- Adding contrib module dragonbox (configuring with dragonbox-cmake)
-- Adding contrib module hyperscan (configuring with hyperscan-cmake)
-- Not using hyperscan
-- Adding contrib module jemalloc (configuring with jemalloc-cmake)
-- Not using jemalloc
-- Adding contrib module libcpuid (configuring with libcpuid-cmake)
Not using cpuid
-- Adding contrib module libdivide (configuring with libdivide)
-- Adding contrib module libmetrohash (configuring with libmetrohash)
-- Adding contrib module lz4 (configuring with lz4-cmake)
-- Adding contrib module murmurhash (configuring with murmurhash)
-- Adding contrib module replxx (configuring with replxx-cmake)
-- Not using replxx
-- Adding contrib module unixodbc (configuring with unixodbc-cmake)
-- Not using ODBC
-- Adding contrib module nanodbc (configuring with nanodbc-cmake)
-- Adding contrib module capnproto (configuring with capnproto-cmake)
-- Not using Cap'n Proto library
-- Adding contrib module yaml-cpp (configuring with yaml-cpp-cmake)
-- Not using yaml
-- Adding contrib module re2 (configuring with re2-cmake)
-- Adding contrib module xz (configuring with xz-cmake)
-- Adding contrib module brotli (configuring with brotli-cmake)
-- Not using brotli
-- Adding contrib module double-conversion (configuring with double-conversion-cmake)
-- Adding contrib module boringssl (configuring with boringssl-cmake)
-- Not using openssl
-- Adding contrib module poco (configuring with poco-cmake)
-- Not using Poco::Crypto
-- Not using Poco::Data::ODBC
-- Not using Poco::Net::SSL
-- Adding contrib module croaring (configuring with croaring-cmake)
-- Adding contrib module zstd (configuring with zstd-cmake)
-- ZSTD VERSION 1.5.0
-- Adding contrib module zlib-ng (configuring with zlib-ng-cmake)
-- Adding contrib module bzip2 (configuring with bzip2-cmake)
-- bzip2 compression disabled
-- Adding contrib module minizip-ng (configuring with minizip-ng-cmake)
-- minizip-ng disabled
-- Adding contrib module snappy (configuring with snappy-cmake)
-- Adding contrib module rocksdb (configuring with rocksdb-cmake)
-- Not using rocksdb
-- Adding contrib module thrift (configuring with thrift-cmake)
-- thrift disabled
-- Adding contrib module arrow (configuring with arrow-cmake)
-- Building without Parquet support
-- Adding contrib module avro (configuring with avro-cmake)
-- Not using avro
-- Adding contrib module protobuf (configuring with protobuf-cmake)
-- Not using protobuf
-- Adding contrib module openldap (configuring with openldap-cmake)
-- Not using ldap
-- Adding contrib module grpc (configuring with grpc-cmake)
-- Not using gRPC
-- Adding contrib module msgpack-c (configuring with msgpack-c-cmake)
-- Not using msgpack
-- Adding contrib module wyhash (configuring with wyhash-cmake)
-- Adding contrib module cityhash102 (configuring with cityhash102)
-- Adding contrib module libfarmhash (configuring with libfarmhash)
-- Adding contrib module icu (configuring with icu-cmake)
-- Not using icu
-- Adding contrib module h3 (configuring with h3-cmake)
-- Not using H3
-- Adding contrib module mariadb-connector-c (configuring with mariadb-connector-c-cmake)
-- Build without mysqlclient (support for MYSQL dictionary source will be disabled)
-- Adding contrib module llvm (configuring with llvm-cmake)
-- LLVM include Directory: /home/workspace/forks/ClickHouse/contrib/llvm/llvm/include;/home/workspace/forks/ClickHouse/build/contrib/llvm/llvm/include
-- LLVM library Directory: /home/workspace/forks/ClickHouse/build/contrib/llvm/llvm
-- LLVM C++ compiler flags:
-- Looking for dlfcn.h
-- Looking for dlfcn.h - found
-- Looking for errno.h
-- Looking for errno.h - found
-- Looking for fcntl.h
-- Looking for fcntl.h - found
-- Looking for link.h
-- Looking for link.h - found
-- Looking for malloc/malloc.h
-- Looking for malloc/malloc.h - not found
-- Looking for pthread.h
-- Looking for pthread.h - found
-- Looking for signal.h
-- Looking for signal.h - found
-- Looking for sys/ioctl.h
-- Looking for sys/ioctl.h - found
-- Looking for sys/mman.h
-- Looking for sys/mman.h - found
-- Looking for sys/param.h
-- Looking for sys/param.h - found
-- Looking for sys/resource.h
-- Looking for sys/resource.h - found
-- Looking for sys/stat.h
-- Looking for sys/stat.h - found
-- Looking for sys/time.h
-- Looking for sys/time.h - found
-- Looking for sys/types.h
-- Looking for sys/types.h - found
-- Looking for sysexits.h
-- Looking for sysexits.h - found
-- Looking for termios.h
-- Looking for termios.h - found
-- Looking for unistd.h
-- Looking for unistd.h - found
-- Looking for valgrind/valgrind.h
-- Looking for valgrind/valgrind.h - not found
-- Looking for fenv.h
-- Looking for fenv.h - found
-- Looking for FE_ALL_EXCEPT
-- Looking for FE_ALL_EXCEPT - found
-- Looking for FE_INEXACT
-- Looking for FE_INEXACT - found
-- Looking for mach/mach.h
-- Looking for mach/mach.h - not found
-- Looking for histedit.h
-- Looking for histedit.h - not found
-- Looking for CrashReporterClient.h
-- Looking for CrashReporterClient.h - not found
-- Looking for linux/magic.h
-- Looking for linux/magic.h - not found
-- Looking for linux/nfs_fs.h
-- Looking for linux/nfs_fs.h - not found
-- Looking for linux/smb.h
-- Looking for linux/smb.h - not found
-- Looking for pthread_create in pthread
-- Looking for pthread_create in pthread - found
-- Looking for pthread_getspecific in pthread
-- Looking for pthread_getspecific in pthread - found
-- Looking for pthread_rwlock_init in pthread
-- Looking for pthread_rwlock_init in pthread - found
-- Looking for pthread_mutex_lock in pthread
-- Looking for pthread_mutex_lock in pthread - found
-- Looking for dlopen in dl
-- Looking for dlopen in dl - found
-- Looking for clock_gettime in rt
-- Looking for clock_gettime in rt - found
-- Looking for xar_open in xar
-- Looking for xar_open in xar - found
-- Looking for arc4random
-- Looking for arc4random - not found
-- Looking for backtrace
-- Looking for backtrace - found
-- backtrace facility detected in default set of libraries
-- Found Backtrace: /home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64/x86_64-linux-gnu/libc/usr/include
-- Performing Test C_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW
-- Performing Test C_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW - Success
-- Looking for __register_frame
-- Looking for __register_frame - found
-- Looking for __deregister_frame
-- Looking for __deregister_frame - found
-- Looking for _Unwind_Backtrace
-- Looking for _Unwind_Backtrace - found
-- Looking for getpagesize
-- Looking for getpagesize - found
-- Looking for sysconf
-- Looking for sysconf - found
-- Looking for getrusage
-- Looking for getrusage - found
-- Looking for setrlimit
-- Looking for setrlimit - found
-- Looking for isatty
-- Looking for isatty - found
-- Looking for futimens
-- Looking for futimens - found
-- Looking for futimes
-- Looking for futimes - found
-- Looking for posix_fallocate
-- Looking for posix_fallocate - found
-- Looking for sigaltstack
-- Looking for sigaltstack - found
-- Looking for lseek64
-- Looking for lseek64 - found
-- Looking for mallctl
-- Looking for mallctl - not found
-- Looking for mallinfo
-- Looking for mallinfo - found
-- Looking for malloc_zone_statistics
-- Looking for malloc_zone_statistics - not found
-- Looking for getrlimit
-- Looking for getrlimit - found
-- Looking for posix_spawn
-- Looking for posix_spawn - found
-- Looking for pread
-- Looking for pread - found
-- Looking for sbrk
-- Looking for sbrk - found
-- Looking for strerror
-- Looking for strerror - found
-- Looking for strerror_r
-- Looking for strerror_r - found
-- Looking for strerror_s
-- Looking for strerror_s - not found
-- Looking for setenv
-- Looking for setenv - found
-- Looking for dlopen
-- Looking for dlopen - found
-- Looking for dladdr
-- Looking for dladdr - not found
-- Performing Test HAVE_STRUCT_STAT_ST_MTIMESPEC_TV_NSEC
-- Performing Test HAVE_STRUCT_STAT_ST_MTIMESPEC_TV_NSEC - Failed
-- Performing Test HAVE_STRUCT_STAT_ST_MTIM_TV_NSEC
-- Performing Test HAVE_STRUCT_STAT_ST_MTIM_TV_NSEC - Success
-- Looking for __GLIBC__
-- Looking for __GLIBC__ - found
-- Looking for pthread_getname_np
-- Looking for pthread_getname_np - found
-- Looking for pthread_setname_np
-- Looking for pthread_setname_np - found
-- Performing Test SUPPORTS_NO_PIE_FLAG
-- Performing Test SUPPORTS_NO_PIE_FLAG - Success
-- Performing Test SUPPORTS_VARIADIC_MACROS_FLAG
-- Performing Test SUPPORTS_VARIADIC_MACROS_FLAG - Success
-- Performing Test SUPPORTS_GNU_ZERO_VARIADIC_MACRO_ARGUMENTS_FLAG
-- Performing Test SUPPORTS_GNU_ZERO_VARIADIC_MACRO_ARGUMENTS_FLAG - Success
-- Native target architecture is X86
-- Threads enabled.
-- Doxygen disabled.
-- Go bindings disabled.
-- Ninja version: 1.10.2
-- Could NOT find OCaml (missing: OCAMLFIND OCAML_VERSION OCAML_STDLIB_PATH)
-- OCaml bindings disabled.
-- Could NOT find Python module pygments
-- Could NOT find Python module pygments.lexers.c_cpp
-- Could NOT find Python module yaml
-- LLVM host triple: x86_64-unknown-linux-gnu
-- LLVM default target triple: x86_64-unknown-linux-gnu
-- Performing Test SUPPORTS_FVISIBILITY_INLINES_HIDDEN_FLAG
-- Performing Test SUPPORTS_FVISIBILITY_INLINES_HIDDEN_FLAG - Success
-- Performing Test C_SUPPORTS_WERROR_DATE_TIME
-- Performing Test C_SUPPORTS_WERROR_DATE_TIME - Success
-- Performing Test CXX_SUPPORTS_WERROR_DATE_TIME
-- Performing Test CXX_SUPPORTS_WERROR_DATE_TIME - Success
-- Performing Test CXX_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW
-- Performing Test CXX_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW - Success
-- Performing Test CXX_SUPPORTS_MISSING_FIELD_INITIALIZERS_FLAG
-- Performing Test CXX_SUPPORTS_MISSING_FIELD_INITIALIZERS_FLAG - Success
-- Performing Test C_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG
-- Performing Test C_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG - Success
-- Performing Test CXX_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG
-- Performing Test CXX_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG - Success
-- Performing Test C_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG
-- Performing Test C_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG - Success
-- Performing Test CXX_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG
-- Performing Test CXX_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG - Success
-- Performing Test CXX_SUPPORTS_CLASS_MEMACCESS_FLAG
-- Performing Test CXX_SUPPORTS_CLASS_MEMACCESS_FLAG - Success
-- Performing Test CXX_SUPPORTS_NOEXCEPT_TYPE_FLAG
-- Performing Test CXX_SUPPORTS_NOEXCEPT_TYPE_FLAG - Success
-- Performing Test CXX_WONT_WARN_ON_FINAL_NONVIRTUALDTOR
-- Performing Test CXX_WONT_WARN_ON_FINAL_NONVIRTUALDTOR - Success
-- Performing Test C_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG
-- Performing Test C_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG - Success
-- Performing Test CXX_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG
-- Performing Test CXX_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG - Success
-- Performing Test CXX_SUPPORTS_SUGGEST_OVERRIDE_FLAG
-- Performing Test CXX_SUPPORTS_SUGGEST_OVERRIDE_FLAG - Success
-- Performing Test CXX_WSUGGEST_OVERRIDE_ALLOWS_ONLY_FINAL
-- Performing Test CXX_WSUGGEST_OVERRIDE_ALLOWS_ONLY_FINAL - Success
-- Performing Test C_WCOMMENT_ALLOWS_LINE_WRAP
-- Performing Test C_WCOMMENT_ALLOWS_LINE_WRAP - Success
-- Performing Test C_SUPPORTS_STRING_CONVERSION_FLAG
-- Performing Test C_SUPPORTS_STRING_CONVERSION_FLAG - Success
-- Performing Test CXX_SUPPORTS_STRING_CONVERSION_FLAG
-- Performing Test CXX_SUPPORTS_STRING_CONVERSION_FLAG - Success
-- Performing Test LINKER_SUPPORTS_COLOR_DIAGNOSTICS
-- Performing Test LINKER_SUPPORTS_COLOR_DIAGNOSTICS - Success
-- Looking for os_signpost_interval_begin
-- Looking for os_signpost_interval_begin - not found
-- Found Python3: /usr/bin/python3.10 (found version "3.10.4") found components: Interpreter
-- Linker detection: unknown
-- Setting native build dir to /home/workspace/forks/ClickHouse/build/contrib/llvm/llvm/NATIVE
-- LLVMHello ignored -- Loadable modules not supported on this platform.
-- Targeting X86
-- Targeting AArch64
-- Adding contrib module libxml2 (configuring with libxml2-cmake)
-- Adding contrib module aws;aws-c-common;aws-c-event-stream;aws-checksums (configuring with aws-s3-cmake)
-- Not using S3
-- Adding contrib module base64 (configuring with base64-cmake)
-- Not using base64
-- Adding contrib module simdjson (configuring with simdjson-cmake)
-- Not using simdjson
-- Adding contrib module rapidjson (configuring with rapidjson-cmake)
-- Not using rapidjson
-- Adding contrib module fastops (configuring with fastops-cmake)
-- Not using fast vectorized mathematical functions library by Mikhail Parakhin
-- Adding contrib module libuv (configuring with libuv-cmake)
-- Adding contrib module AMQP-CPP (configuring with amqpcpp-cmake)
-- Not using AMQP-CPP
-- Adding contrib module cassandra (configuring with cassandra-cmake)
-- Not using cassandra
-- Adding contrib module curl (configuring with curl-cmake)
-- Not using curl
-- Adding contrib module azure (configuring with azure-cmake)
-- Not using Azure blob storage
-- Adding contrib module sentry-native (configuring with sentry-native-cmake)
-- Not using sentry
-- Adding contrib module fmtlib (configuring with fmtlib-cmake)
-- Adding contrib module krb5 (configuring with krb5-cmake)
-- Not using krb5
-- Adding contrib module cyrus-sasl (configuring with cyrus-sasl-cmake)
-- Not using cyrus-sasl
-- Adding contrib module libgsasl (configuring with libgsasl-cmake)
-- Not using gsasl library
-- Adding contrib module librdkafka (configuring with librdkafka-cmake)
-- Not using librdkafka
-- Adding contrib module libhdfs3 (configuring with libhdfs3-cmake)
-- Not using hdfs
-- Adding contrib module hive-metastore (configuring with hive-metastore-cmake)
Hive disabled
-- Adding contrib module cppkafka (configuring with cppkafka-cmake)
-- Not using librdkafka (skip cppkafka)
-- Adding contrib module libpqxx (configuring with libpqxx-cmake)
-- Not using libpqxx
-- Adding contrib module libpq (configuring with libpq-cmake)
-- Adding contrib module NuRaft (configuring with nuraft-cmake)
-- Not using NuRaft
-- Adding contrib module fast_float (configuring with fast_float-cmake)
-- Adding contrib module datasketches-cpp (configuring with datasketches-cpp-cmake)
-- Not using DataSketches
-- Adding contrib module hashidsxx (configuring with hashidsxx-cmake)
-- Adding contrib module sqlite-amalgamation (configuring with sqlite-cmake)
-- Not using sqlite
-- Adding contrib module s2geometry (configuring with s2geometry-cmake)
-- Not using S2 geometry
-- Adding contrib module eigen (configuring with eigen-cmake)
CMake Warning at CMakeLists.txt:487 (message):
Non default allocator is disabled. This is not recommended for production
builds.
-- Performing Test SUPPORTS_CXXFLAG_everything
-- Performing Test SUPPORTS_CXXFLAG_everything - Success
-- Performing Test SUPPORTS_CFLAG_everything
-- Performing Test SUPPORTS_CFLAG_everything - Success
-- Performing Test SUPPORTS_CXXFLAG_pedantic
-- Performing Test SUPPORTS_CXXFLAG_pedantic - Success
-- Performing Test SUPPORTS_CFLAG_pedantic
-- Performing Test SUPPORTS_CFLAG_pedantic - Success
-- Performing Test SUPPORTS_CXXFLAG_no_vla_extension
-- Performing Test SUPPORTS_CXXFLAG_no_vla_extension - Success
-- Performing Test SUPPORTS_CFLAG_no_vla_extension
-- Performing Test SUPPORTS_CFLAG_no_vla_extension - Success
-- Performing Test SUPPORTS_CXXFLAG_no_zero_length_array
-- Performing Test SUPPORTS_CXXFLAG_no_zero_length_array - Success
-- Performing Test SUPPORTS_CFLAG_no_zero_length_array
-- Performing Test SUPPORTS_CFLAG_no_zero_length_array - Success
-- Performing Test SUPPORTS_CXXFLAG_no_c11_extensions
-- Performing Test SUPPORTS_CXXFLAG_no_c11_extensions - Success
-- Performing Test SUPPORTS_CFLAG_no_c11_extensions
-- Performing Test SUPPORTS_CFLAG_no_c11_extensions - Success
-- Performing Test SUPPORTS_CFLAG_no_unused_command_line_argument
-- Performing Test SUPPORTS_CFLAG_no_unused_command_line_argument - Success
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat_pedantic
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat_pedantic - Success
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat_pedantic
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat_pedantic - Success
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat - Success
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat - Success
-- Performing Test SUPPORTS_CXXFLAG_no_c99_extensions
-- Performing Test SUPPORTS_CXXFLAG_no_c99_extensions - Success
-- Performing Test SUPPORTS_CFLAG_no_c99_extensions
-- Performing Test SUPPORTS_CFLAG_no_c99_extensions - Success
-- Performing Test SUPPORTS_CXXFLAG_no_conversion
-- Performing Test SUPPORTS_CXXFLAG_no_conversion - Success
-- Performing Test SUPPORTS_CFLAG_no_conversion
-- Performing Test SUPPORTS_CFLAG_no_conversion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_ctad_maybe_unsupported
-- Performing Test SUPPORTS_CXXFLAG_no_ctad_maybe_unsupported - Success
-- Performing Test SUPPORTS_CFLAG_no_ctad_maybe_unsupported
-- Performing Test SUPPORTS_CFLAG_no_ctad_maybe_unsupported - Success
-- Performing Test SUPPORTS_CXXFLAG_no_deprecated_dynamic_exception_spec
-- Performing Test SUPPORTS_CXXFLAG_no_deprecated_dynamic_exception_spec - Success
-- Performing Test SUPPORTS_CFLAG_no_deprecated_dynamic_exception_spec
-- Performing Test SUPPORTS_CFLAG_no_deprecated_dynamic_exception_spec - Success
-- Performing Test SUPPORTS_CXXFLAG_no_disabled_macro_expansion
-- Performing Test SUPPORTS_CXXFLAG_no_disabled_macro_expansion - Success
-- Performing Test SUPPORTS_CFLAG_no_disabled_macro_expansion
-- Performing Test SUPPORTS_CFLAG_no_disabled_macro_expansion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_documentation_unknown_command
-- Performing Test SUPPORTS_CXXFLAG_no_documentation_unknown_command - Success
-- Performing Test SUPPORTS_CFLAG_no_documentation_unknown_command
-- Performing Test SUPPORTS_CFLAG_no_documentation_unknown_command - Success
-- Performing Test SUPPORTS_CXXFLAG_no_double_promotion
-- Performing Test SUPPORTS_CXXFLAG_no_double_promotion - Success
-- Performing Test SUPPORTS_CFLAG_no_double_promotion
-- Performing Test SUPPORTS_CFLAG_no_double_promotion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_exit_time_destructors
-- Performing Test SUPPORTS_CXXFLAG_no_exit_time_destructors - Success
-- Performing Test SUPPORTS_CFLAG_no_exit_time_destructors
-- Performing Test SUPPORTS_CFLAG_no_exit_time_destructors - Success
-- Performing Test SUPPORTS_CXXFLAG_no_float_equal
-- Performing Test SUPPORTS_CXXFLAG_no_float_equal - Success
-- Performing Test SUPPORTS_CFLAG_no_float_equal
-- Performing Test SUPPORTS_CFLAG_no_float_equal - Success
-- Performing Test SUPPORTS_CXXFLAG_no_global_constructors
-- Performing Test SUPPORTS_CXXFLAG_no_global_constructors - Success
-- Performing Test SUPPORTS_CFLAG_no_global_constructors
-- Performing Test SUPPORTS_CFLAG_no_global_constructors - Success
-- Performing Test SUPPORTS_CXXFLAG_no_missing_prototypes
-- Performing Test SUPPORTS_CXXFLAG_no_missing_prototypes - Success
-- Performing Test SUPPORTS_CFLAG_no_missing_prototypes
-- Performing Test SUPPORTS_CFLAG_no_missing_prototypes - Success
-- Performing Test SUPPORTS_CXXFLAG_no_missing_variable_declarations
-- Performing Test SUPPORTS_CXXFLAG_no_missing_variable_declarations - Success
-- Performing Test SUPPORTS_CFLAG_no_missing_variable_declarations
-- Performing Test SUPPORTS_CFLAG_no_missing_variable_declarations - Success
-- Performing Test SUPPORTS_CXXFLAG_no_nested_anon_types
-- Performing Test SUPPORTS_CXXFLAG_no_nested_anon_types - Success
-- Performing Test SUPPORTS_CFLAG_no_nested_anon_types
-- Performing Test SUPPORTS_CFLAG_no_nested_anon_types - Success
-- Performing Test SUPPORTS_CXXFLAG_no_packed
-- Performing Test SUPPORTS_CXXFLAG_no_packed - Success
-- Performing Test SUPPORTS_CFLAG_no_packed
-- Performing Test SUPPORTS_CFLAG_no_packed - Success
-- Performing Test SUPPORTS_CXXFLAG_no_padded
-- Performing Test SUPPORTS_CXXFLAG_no_padded - Success
-- Performing Test SUPPORTS_CFLAG_no_padded
-- Performing Test SUPPORTS_CFLAG_no_padded - Success
-- Performing Test SUPPORTS_CXXFLAG_no_return_std_move_in_cxx11
-- Performing Test SUPPORTS_CXXFLAG_no_return_std_move_in_cxx11 - Failed
-- Performing Test SUPPORTS_CFLAG_no_return_std_move_in_cxx11
-- Performing Test SUPPORTS_CFLAG_no_return_std_move_in_cxx11 - Failed
-- Flag -Wno-return-std-move-in-c++11 is unsupported
-- Flag -Wno-return-std-move-in-c++11 is unsupported
-- Performing Test SUPPORTS_CXXFLAG_no_shift_sign_overflow
-- Performing Test SUPPORTS_CXXFLAG_no_shift_sign_overflow - Success
-- Performing Test SUPPORTS_CFLAG_no_shift_sign_overflow
-- Performing Test SUPPORTS_CFLAG_no_shift_sign_overflow - Success
-- Performing Test SUPPORTS_CXXFLAG_no_sign_conversion
-- Performing Test SUPPORTS_CXXFLAG_no_sign_conversion - Success
-- Performing Test SUPPORTS_CFLAG_no_sign_conversion
-- Performing Test SUPPORTS_CFLAG_no_sign_conversion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_switch_enum
-- Performing Test SUPPORTS_CXXFLAG_no_switch_enum - Success
-- Performing Test SUPPORTS_CFLAG_no_switch_enum
-- Performing Test SUPPORTS_CFLAG_no_switch_enum - Success
-- Performing Test SUPPORTS_CXXFLAG_no_undefined_func_template
-- Performing Test SUPPORTS_CXXFLAG_no_undefined_func_template - Success
-- Performing Test SUPPORTS_CFLAG_no_undefined_func_template
-- Performing Test SUPPORTS_CFLAG_no_undefined_func_template - Success
-- Performing Test SUPPORTS_CXXFLAG_no_unused_template
-- Performing Test SUPPORTS_CXXFLAG_no_unused_template - Success
-- Performing Test SUPPORTS_CFLAG_no_unused_template
-- Performing Test SUPPORTS_CFLAG_no_unused_template - Success
-- Performing Test SUPPORTS_CXXFLAG_no_vla
-- Performing Test SUPPORTS_CXXFLAG_no_vla - Success
-- Performing Test SUPPORTS_CFLAG_no_vla
-- Performing Test SUPPORTS_CFLAG_no_vla - Success
-- Performing Test SUPPORTS_CXXFLAG_no_weak_template_vtables
-- Performing Test SUPPORTS_CXXFLAG_no_weak_template_vtables - Success
-- Performing Test SUPPORTS_CFLAG_no_weak_template_vtables
-- Performing Test SUPPORTS_CFLAG_no_weak_template_vtables - Success
-- Performing Test SUPPORTS_CXXFLAG_no_weak_vtables
-- Performing Test SUPPORTS_CXXFLAG_no_weak_vtables - Success
-- Performing Test SUPPORTS_CFLAG_no_weak_vtables
-- Performing Test SUPPORTS_CFLAG_no_weak_vtables - Success
-- compiler C = /usr/bin/clang --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 -fdiagnostics-color=always -Xclang -fuse-ctor-homing -gdwarf-aranges -pipe -mssse3 -msse4.1 -msse4.2 -mpclmul -mpopcnt -fasynchronous-unwind-tables -falign-functions=32 -fdiagnostics-absolute-paths -fexperimental-new-pass-manager -Weverything -Wpedantic -Wno-vla-extension -Wno-zero-length-array -Wno-c11-extensions -Wno-unused-command-line-argument -Wno-c++98-compat-pedantic -Wno-c++98-compat -Wno-c99-extensions -Wno-conversion -Wno-ctad-maybe-unsupported -Wno-deprecated-dynamic-exception-spec -Wno-disabled-macro-expansion -Wno-documentation-unknown-command -Wno-double-promotion -Wno-exit-time-destructors -Wno-float-equal -Wno-global-constructors -Wno-missing-prototypes -Wno-missing-variable-declarations -Wno-nested-anon-types -Wno-packed -Wno-padded -Wno-shift-sign-overflow -Wno-sign-conversion -Wno-switch-enum -Wno-undefined-func-template -Wno-unused-template -Wno-vla -Wno-weak-template-vtables -Wno-weak-vtables -g -O0 -g -gdwarf-4 -fno-inline
-- compiler CXX = /usr/bin/clang++ --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 -std=c++20 -fdiagnostics-color=always -Xclang -fuse-ctor-homing -fsized-deallocation -gdwarf-aranges -pipe -mssse3 -msse4.1 -msse4.2 -mpclmul -mpopcnt -fasynchronous-unwind-tables -falign-functions=32 -fdiagnostics-absolute-paths -fstrict-vtable-pointers -fexperimental-new-pass-manager -Wall -Wextra -Weverything -Wpedantic -Wno-vla-extension -Wno-zero-length-array -Wno-c11-extensions -Wno-unused-command-line-argument -Wno-c++98-compat-pedantic -Wno-c++98-compat -Wno-c99-extensions -Wno-conversion -Wno-ctad-maybe-unsupported -Wno-deprecated-dynamic-exception-spec -Wno-disabled-macro-expansion -Wno-documentation-unknown-command -Wno-double-promotion -Wno-exit-time-destructors -Wno-float-equal -Wno-global-constructors -Wno-missing-prototypes -Wno-missing-variable-declarations -Wno-nested-anon-types -Wno-packed -Wno-padded -Wno-shift-sign-overflow -Wno-sign-conversion -Wno-switch-enum -Wno-undefined-func-template -Wno-unused-template -Wno-vla -Wno-weak-template-vtables -Wno-weak-vtables -g -O0 -g -gdwarf-4 -fno-inline -D_LIBCPP_DEBUG=0
-- LINKER_FLAGS = --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --ld-path=/usr/bin/ld.gold -rdynamic -no-pie -Wl,-no-pie
-- /home/workspace/forks/ClickHouse/src: Have 27842 megabytes of memory.
Limiting concurrent linkers jobs to 7 and compiler jobs to 11 (system has 16 logical cores)
-- Will build ClickHouse 22.6.1.1 revision 54463
-- Generating debugger info for ClickHouse functions
-- clickhouse-keeper and clickhouse-keeper-converter will not be built (lack of NuRaft)
-- ClickHouse modes:
-- Server mode: ON
-- Client mode: ON
-- Local mode: OFF
-- Benchmark mode: OFF
-- Extract from config mode: OFF
-- Compressor mode: OFF
-- Copier mode: OFF
-- Format mode: OFF
-- Obfuscator mode: OFF
-- ODBC bridge mode: OFF
-- Library bridge mode: OFF
-- ClickHouse install: OFF
-- ClickHouse git-import: OFF
-- ClickHouse keeper mode: OFF
-- ClickHouse keeper-converter mode: OFF
-- bash_completion will be written to /usr/local/share/bash-completion/completions
-- Target check already exists
-- /home/workspace/forks/ClickHouse/utils: Have 27842 megabytes of memory.
Limiting concurrent linkers jobs to 7 and compiler jobs to OFF (system has 16 logical cores)
-- Configuring done
CMake Error at base/base/CMakeLists.txt:52 (target_link_libraries):
Target "common" links to:
ch_contrib::replxx
but the target was not found. Possible reasons include:
* There is a typo in the target name.
* A find_package call is missing for an IMPORTED target.
* An ALIAS target is missing.
-- Generating done
CMake Generate step failed. Build files cannot be regenerated correctly.
```
Of course, I've checked it:
```
ClickHouse/build [master] » cd ../contrib/replxx && git status
HEAD detached at 3fd0e3c
nothing to commit, working tree clean
``` | 1.0 | CMake: Target "common" links to ch_contrib::replxx but the target was not found - > Make sure that `git diff` result is empty and you've just pulled fresh master. Try cleaning up cmake cache. Just in case, official build instructions are published here: https://clickhouse.com/docs/en/development/build/
**Operating system**
Arch Linux:
```
5.17.9-arch1-1 #1 SMP PREEMPT Wed, 18 May 2022 17:30:11 +0000 x86_64 GNU/Linux
```
> OS kind or distribution, specific version/release, non-standard kernel if any. If you are trying to build inside virtual machine, please mention it too.
**Cmake version**
3.23.1
**Ninja version**
1.10.2
**Compiler name and version**
clang 13:
```
clang version 13.0.1
Target: x86_64-pc-linux-gnu
Thread model: posix
```
**Full cmake and/or ninja output**
```
cmake .. \
-DCMAKE_C_COMPILER=$(which clang) \
-DCMAKE_CXX_COMPILER=$(which clang++) \
-DCMAKE_BUILD_TYPE=Debug \
-DENABLE_CLICKHOUSE_ALL=OFF \
-DENABLE_CLICKHOUSE_SERVER=ON \
-DENABLE_CLICKHOUSE_CLIENT=ON \
-DENABLE_LIBRARIES=OFF \
-DUSE_UNWIND=ON \
-DENABLE_UTILS=OFF \
-DENABLE_TESTS=OFF \
-DENABLE_CCACHE=0
```
```
-- The C compiler identification is Clang 13.0.1
-- The CXX compiler identification is Clang 13.0.1
-- The ASM compiler identification is Clang with GNU-like command-line
-- Found assembler: /usr/bin/clang
-- Detecting C compiler ABI info
-- Detecting C compiler ABI info - done
-- Check for working C compiler: /usr/bin/clang - skipped
-- Detecting C compile features
-- Detecting C compile features - done
-- Detecting CXX compiler ABI info
-- Detecting CXX compiler ABI info - done
-- Check for working CXX compiler: /usr/bin/clang++ - skipped
-- Detecting CXX compile features
-- Detecting CXX compile features - done
-- Cross-compiling for target:
-- Using compiler:
clang version 13.0.1
Target: x86_64-pc-linux-gnu
Thread model: posix
InstalledDir: /usr/bin
-- Using linker: /usr/bin/ld.gold
-- Using archiver: /usr/bin/llvm-ar
-- Using ranlib: /usr/bin/llvm-ranlib
-- Using install-name-tool: /usr/bin/llvm-install-name-tool
-- Using objcopy: /usr/bin/llvm-objcopy
-- Using strip: /usr/bin/llvm-strip
-- Using ccache: no (disabled via configuration)
-- Found Git: /usr/bin/git (found version "2.36.1")
-- HEAD's commit hash 74f5301225b0870d7cd3f3bed93312962aece3cd
On branch master
Your branch is up to date with 'origin/master'.
nothing to commit, working tree clean
-- CMAKE_BUILD_TYPE: Debug
-- Performing Test HAS_RESERVED_IDENTIFIER
-- Performing Test HAS_RESERVED_IDENTIFIER - Success
-- Performing Test HAS_SUGGEST_DESTRUCTOR_OVERRIDE
-- Performing Test HAS_SUGGEST_DESTRUCTOR_OVERRIDE - Success
-- Performing Test HAS_SUGGEST_OVERRIDE
-- Performing Test HAS_SUGGEST_OVERRIDE - Success
-- Performing Test HAS_USE_CTOR_HOMING
-- Performing Test HAS_USE_CTOR_HOMING - Success
-- Performing Test HAVE_SSSE3
-- Performing Test HAVE_SSSE3 - Success
-- Performing Test HAVE_SSE41
-- Performing Test HAVE_SSE41 - Success
-- Performing Test HAVE_SSE42
-- Performing Test HAVE_SSE42 - Success
-- Performing Test HAVE_PCLMULQDQ
-- Performing Test HAVE_PCLMULQDQ - Success
-- Performing Test HAVE_POPCNT
-- Performing Test HAVE_POPCNT - Success
-- Performing Test HAVE_AVX
-- Performing Test HAVE_AVX - Success
-- Performing Test HAVE_AVX2
-- Performing Test HAVE_AVX2 - Success
-- Performing Test HAVE_AVX512
-- Performing Test HAVE_AVX512 - Success
-- Performing Test HAVE_BMI
-- Performing Test HAVE_BMI - Success
-- Default libraries: -nodefaultlibs /usr/lib/clang/13.0.1/lib/linux/libclang_rt.builtins-x86_64.a -lc -lm -lrt -lpthread -ldl
-- Looking for pthread.h
-- Looking for pthread.h - found
-- Performing Test CMAKE_HAVE_LIBC_PTHREAD
-- Performing Test CMAKE_HAVE_LIBC_PTHREAD - Success
-- Found Threads: TRUE
-- Looking for sys/random.h
-- Looking for sys/random.h - found
-- Performing Test SUPPORTS_CXXFLAG_no_unused_command_line_argument
-- Performing Test SUPPORTS_CXXFLAG_no_unused_command_line_argument - Success
-- Performing Test SUPPORTS_CXXFLAG_no_unused_but_set_variable
-- Performing Test SUPPORTS_CXXFLAG_no_unused_but_set_variable - Success
-- Performing Test SUPPORTS_CXXFLAG_no_builtin_requires_header
-- Performing Test SUPPORTS_CXXFLAG_no_builtin_requires_header - Success
-- Some symbols from glibc will be replaced for compatibility
-- Performing Test HAVE_WARNING_UNUSED_BUT_SET_VARIABLE
-- Performing Test HAVE_WARNING_UNUSED_BUT_SET_VARIABLE - Success
-- Performing Test HAVE_WARNING_MISSING_ATTRIBUTES
-- Performing Test HAVE_WARNING_MISSING_ATTRIBUTES - Failed
-- Performing Test HAVE_WARNING_MAYBE_UNINITIALIZED
-- Performing Test HAVE_WARNING_MAYBE_UNINITIALIZED - Failed
-- Performing Test HAVE_WARNING_REGISTER
-- Performing Test HAVE_WARNING_REGISTER - Success
-- Using libunwind: unwind
-- Using exception handler: unwind
-- Unit tests are disabled
-- Building for: Linux x86_64 ;
USE_STATIC_LIBRARIES=ON
SPLIT_SHARED=
-- Adding contrib module miniselect (configuring with miniselect-cmake)
-- Adding contrib module pdqsort (configuring with pdqsort-cmake)
-- Adding contrib module sparsehash-c11 (configuring with sparsehash-c11-cmake)
-- Adding contrib module abseil-cpp (configuring with abseil-cpp-cmake)
-- Adding contrib module magic_enum (configuring with magic-enum-cmake)
-- Adding contrib module boost (configuring with boost-cmake)
-- Adding contrib module cctz (configuring with cctz-cmake)
-- Packaging with tzdata version: 2021c
-- Adding contrib module consistent-hashing (configuring with consistent-hashing)
-- Adding contrib module dragonbox (configuring with dragonbox-cmake)
-- Adding contrib module hyperscan (configuring with hyperscan-cmake)
-- Not using hyperscan
-- Adding contrib module jemalloc (configuring with jemalloc-cmake)
-- Not using jemalloc
-- Adding contrib module libcpuid (configuring with libcpuid-cmake)
Not using cpuid
-- Adding contrib module libdivide (configuring with libdivide)
-- Adding contrib module libmetrohash (configuring with libmetrohash)
-- Adding contrib module lz4 (configuring with lz4-cmake)
-- Adding contrib module murmurhash (configuring with murmurhash)
-- Adding contrib module replxx (configuring with replxx-cmake)
-- Not using replxx
-- Adding contrib module unixodbc (configuring with unixodbc-cmake)
-- Not using ODBC
-- Adding contrib module nanodbc (configuring with nanodbc-cmake)
-- Adding contrib module capnproto (configuring with capnproto-cmake)
-- Not using Cap'n Proto library
-- Adding contrib module yaml-cpp (configuring with yaml-cpp-cmake)
-- Not using yaml
-- Adding contrib module re2 (configuring with re2-cmake)
-- Adding contrib module xz (configuring with xz-cmake)
-- Adding contrib module brotli (configuring with brotli-cmake)
-- Not using brotli
-- Adding contrib module double-conversion (configuring with double-conversion-cmake)
-- Adding contrib module boringssl (configuring with boringssl-cmake)
-- Not using openssl
-- Adding contrib module poco (configuring with poco-cmake)
-- Not using Poco::Crypto
-- Not using Poco::Data::ODBC
-- Not using Poco::Net::SSL
-- Adding contrib module croaring (configuring with croaring-cmake)
-- Adding contrib module zstd (configuring with zstd-cmake)
-- ZSTD VERSION 1.5.0
-- Adding contrib module zlib-ng (configuring with zlib-ng-cmake)
-- Adding contrib module bzip2 (configuring with bzip2-cmake)
-- bzip2 compression disabled
-- Adding contrib module minizip-ng (configuring with minizip-ng-cmake)
-- minizip-ng disabled
-- Adding contrib module snappy (configuring with snappy-cmake)
-- Adding contrib module rocksdb (configuring with rocksdb-cmake)
-- Not using rocksdb
-- Adding contrib module thrift (configuring with thrift-cmake)
-- thrift disabled
-- Adding contrib module arrow (configuring with arrow-cmake)
-- Building without Parquet support
-- Adding contrib module avro (configuring with avro-cmake)
-- Not using avro
-- Adding contrib module protobuf (configuring with protobuf-cmake)
-- Not using protobuf
-- Adding contrib module openldap (configuring with openldap-cmake)
-- Not using ldap
-- Adding contrib module grpc (configuring with grpc-cmake)
-- Not using gRPC
-- Adding contrib module msgpack-c (configuring with msgpack-c-cmake)
-- Not using msgpack
-- Adding contrib module wyhash (configuring with wyhash-cmake)
-- Adding contrib module cityhash102 (configuring with cityhash102)
-- Adding contrib module libfarmhash (configuring with libfarmhash)
-- Adding contrib module icu (configuring with icu-cmake)
-- Not using icu
-- Adding contrib module h3 (configuring with h3-cmake)
-- Not using H3
-- Adding contrib module mariadb-connector-c (configuring with mariadb-connector-c-cmake)
-- Build without mysqlclient (support for MYSQL dictionary source will be disabled)
-- Adding contrib module llvm (configuring with llvm-cmake)
-- LLVM include Directory: /home/workspace/forks/ClickHouse/contrib/llvm/llvm/include;/home/workspace/forks/ClickHouse/build/contrib/llvm/llvm/include
-- LLVM library Directory: /home/workspace/forks/ClickHouse/build/contrib/llvm/llvm
-- LLVM C++ compiler flags:
-- Looking for dlfcn.h
-- Looking for dlfcn.h - found
-- Looking for errno.h
-- Looking for errno.h - found
-- Looking for fcntl.h
-- Looking for fcntl.h - found
-- Looking for link.h
-- Looking for link.h - found
-- Looking for malloc/malloc.h
-- Looking for malloc/malloc.h - not found
-- Looking for pthread.h
-- Looking for pthread.h - found
-- Looking for signal.h
-- Looking for signal.h - found
-- Looking for sys/ioctl.h
-- Looking for sys/ioctl.h - found
-- Looking for sys/mman.h
-- Looking for sys/mman.h - found
-- Looking for sys/param.h
-- Looking for sys/param.h - found
-- Looking for sys/resource.h
-- Looking for sys/resource.h - found
-- Looking for sys/stat.h
-- Looking for sys/stat.h - found
-- Looking for sys/time.h
-- Looking for sys/time.h - found
-- Looking for sys/types.h
-- Looking for sys/types.h - found
-- Looking for sysexits.h
-- Looking for sysexits.h - found
-- Looking for termios.h
-- Looking for termios.h - found
-- Looking for unistd.h
-- Looking for unistd.h - found
-- Looking for valgrind/valgrind.h
-- Looking for valgrind/valgrind.h - not found
-- Looking for fenv.h
-- Looking for fenv.h - found
-- Looking for FE_ALL_EXCEPT
-- Looking for FE_ALL_EXCEPT - found
-- Looking for FE_INEXACT
-- Looking for FE_INEXACT - found
-- Looking for mach/mach.h
-- Looking for mach/mach.h - not found
-- Looking for histedit.h
-- Looking for histedit.h - not found
-- Looking for CrashReporterClient.h
-- Looking for CrashReporterClient.h - not found
-- Looking for linux/magic.h
-- Looking for linux/magic.h - not found
-- Looking for linux/nfs_fs.h
-- Looking for linux/nfs_fs.h - not found
-- Looking for linux/smb.h
-- Looking for linux/smb.h - not found
-- Looking for pthread_create in pthread
-- Looking for pthread_create in pthread - found
-- Looking for pthread_getspecific in pthread
-- Looking for pthread_getspecific in pthread - found
-- Looking for pthread_rwlock_init in pthread
-- Looking for pthread_rwlock_init in pthread - found
-- Looking for pthread_mutex_lock in pthread
-- Looking for pthread_mutex_lock in pthread - found
-- Looking for dlopen in dl
-- Looking for dlopen in dl - found
-- Looking for clock_gettime in rt
-- Looking for clock_gettime in rt - found
-- Looking for xar_open in xar
-- Looking for xar_open in xar - found
-- Looking for arc4random
-- Looking for arc4random - not found
-- Looking for backtrace
-- Looking for backtrace - found
-- backtrace facility detected in default set of libraries
-- Found Backtrace: /home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64/x86_64-linux-gnu/libc/usr/include
-- Performing Test C_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW
-- Performing Test C_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW - Success
-- Looking for __register_frame
-- Looking for __register_frame - found
-- Looking for __deregister_frame
-- Looking for __deregister_frame - found
-- Looking for _Unwind_Backtrace
-- Looking for _Unwind_Backtrace - found
-- Looking for getpagesize
-- Looking for getpagesize - found
-- Looking for sysconf
-- Looking for sysconf - found
-- Looking for getrusage
-- Looking for getrusage - found
-- Looking for setrlimit
-- Looking for setrlimit - found
-- Looking for isatty
-- Looking for isatty - found
-- Looking for futimens
-- Looking for futimens - found
-- Looking for futimes
-- Looking for futimes - found
-- Looking for posix_fallocate
-- Looking for posix_fallocate - found
-- Looking for sigaltstack
-- Looking for sigaltstack - found
-- Looking for lseek64
-- Looking for lseek64 - found
-- Looking for mallctl
-- Looking for mallctl - not found
-- Looking for mallinfo
-- Looking for mallinfo - found
-- Looking for malloc_zone_statistics
-- Looking for malloc_zone_statistics - not found
-- Looking for getrlimit
-- Looking for getrlimit - found
-- Looking for posix_spawn
-- Looking for posix_spawn - found
-- Looking for pread
-- Looking for pread - found
-- Looking for sbrk
-- Looking for sbrk - found
-- Looking for strerror
-- Looking for strerror - found
-- Looking for strerror_r
-- Looking for strerror_r - found
-- Looking for strerror_s
-- Looking for strerror_s - not found
-- Looking for setenv
-- Looking for setenv - found
-- Looking for dlopen
-- Looking for dlopen - found
-- Looking for dladdr
-- Looking for dladdr - not found
-- Performing Test HAVE_STRUCT_STAT_ST_MTIMESPEC_TV_NSEC
-- Performing Test HAVE_STRUCT_STAT_ST_MTIMESPEC_TV_NSEC - Failed
-- Performing Test HAVE_STRUCT_STAT_ST_MTIM_TV_NSEC
-- Performing Test HAVE_STRUCT_STAT_ST_MTIM_TV_NSEC - Success
-- Looking for __GLIBC__
-- Looking for __GLIBC__ - found
-- Looking for pthread_getname_np
-- Looking for pthread_getname_np - found
-- Looking for pthread_setname_np
-- Looking for pthread_setname_np - found
-- Performing Test SUPPORTS_NO_PIE_FLAG
-- Performing Test SUPPORTS_NO_PIE_FLAG - Success
-- Performing Test SUPPORTS_VARIADIC_MACROS_FLAG
-- Performing Test SUPPORTS_VARIADIC_MACROS_FLAG - Success
-- Performing Test SUPPORTS_GNU_ZERO_VARIADIC_MACRO_ARGUMENTS_FLAG
-- Performing Test SUPPORTS_GNU_ZERO_VARIADIC_MACRO_ARGUMENTS_FLAG - Success
-- Native target architecture is X86
-- Threads enabled.
-- Doxygen disabled.
-- Go bindings disabled.
-- Ninja version: 1.10.2
-- Could NOT find OCaml (missing: OCAMLFIND OCAML_VERSION OCAML_STDLIB_PATH)
-- OCaml bindings disabled.
-- Could NOT find Python module pygments
-- Could NOT find Python module pygments.lexers.c_cpp
-- Could NOT find Python module yaml
-- LLVM host triple: x86_64-unknown-linux-gnu
-- LLVM default target triple: x86_64-unknown-linux-gnu
-- Performing Test SUPPORTS_FVISIBILITY_INLINES_HIDDEN_FLAG
-- Performing Test SUPPORTS_FVISIBILITY_INLINES_HIDDEN_FLAG - Success
-- Performing Test C_SUPPORTS_WERROR_DATE_TIME
-- Performing Test C_SUPPORTS_WERROR_DATE_TIME - Success
-- Performing Test CXX_SUPPORTS_WERROR_DATE_TIME
-- Performing Test CXX_SUPPORTS_WERROR_DATE_TIME - Success
-- Performing Test CXX_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW
-- Performing Test CXX_SUPPORTS_WERROR_UNGUARDED_AVAILABILITY_NEW - Success
-- Performing Test CXX_SUPPORTS_MISSING_FIELD_INITIALIZERS_FLAG
-- Performing Test CXX_SUPPORTS_MISSING_FIELD_INITIALIZERS_FLAG - Success
-- Performing Test C_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG
-- Performing Test C_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG - Success
-- Performing Test CXX_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG
-- Performing Test CXX_SUPPORTS_IMPLICIT_FALLTHROUGH_FLAG - Success
-- Performing Test C_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG
-- Performing Test C_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG - Success
-- Performing Test CXX_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG
-- Performing Test CXX_SUPPORTS_COVERED_SWITCH_DEFAULT_FLAG - Success
-- Performing Test CXX_SUPPORTS_CLASS_MEMACCESS_FLAG
-- Performing Test CXX_SUPPORTS_CLASS_MEMACCESS_FLAG - Success
-- Performing Test CXX_SUPPORTS_NOEXCEPT_TYPE_FLAG
-- Performing Test CXX_SUPPORTS_NOEXCEPT_TYPE_FLAG - Success
-- Performing Test CXX_WONT_WARN_ON_FINAL_NONVIRTUALDTOR
-- Performing Test CXX_WONT_WARN_ON_FINAL_NONVIRTUALDTOR - Success
-- Performing Test C_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG
-- Performing Test C_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG - Success
-- Performing Test CXX_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG
-- Performing Test CXX_SUPPORTS_DELETE_NON_VIRTUAL_DTOR_FLAG - Success
-- Performing Test CXX_SUPPORTS_SUGGEST_OVERRIDE_FLAG
-- Performing Test CXX_SUPPORTS_SUGGEST_OVERRIDE_FLAG - Success
-- Performing Test CXX_WSUGGEST_OVERRIDE_ALLOWS_ONLY_FINAL
-- Performing Test CXX_WSUGGEST_OVERRIDE_ALLOWS_ONLY_FINAL - Success
-- Performing Test C_WCOMMENT_ALLOWS_LINE_WRAP
-- Performing Test C_WCOMMENT_ALLOWS_LINE_WRAP - Success
-- Performing Test C_SUPPORTS_STRING_CONVERSION_FLAG
-- Performing Test C_SUPPORTS_STRING_CONVERSION_FLAG - Success
-- Performing Test CXX_SUPPORTS_STRING_CONVERSION_FLAG
-- Performing Test CXX_SUPPORTS_STRING_CONVERSION_FLAG - Success
-- Performing Test LINKER_SUPPORTS_COLOR_DIAGNOSTICS
-- Performing Test LINKER_SUPPORTS_COLOR_DIAGNOSTICS - Success
-- Looking for os_signpost_interval_begin
-- Looking for os_signpost_interval_begin - not found
-- Found Python3: /usr/bin/python3.10 (found version "3.10.4") found components: Interpreter
-- Linker detection: unknown
-- Setting native build dir to /home/workspace/forks/ClickHouse/build/contrib/llvm/llvm/NATIVE
-- LLVMHello ignored -- Loadable modules not supported on this platform.
-- Targeting X86
-- Targeting AArch64
-- Adding contrib module libxml2 (configuring with libxml2-cmake)
-- Adding contrib module aws;aws-c-common;aws-c-event-stream;aws-checksums (configuring with aws-s3-cmake)
-- Not using S3
-- Adding contrib module base64 (configuring with base64-cmake)
-- Not using base64
-- Adding contrib module simdjson (configuring with simdjson-cmake)
-- Not using simdjson
-- Adding contrib module rapidjson (configuring with rapidjson-cmake)
-- Not using rapidjson
-- Adding contrib module fastops (configuring with fastops-cmake)
-- Not using fast vectorized mathematical functions library by Mikhail Parakhin
-- Adding contrib module libuv (configuring with libuv-cmake)
-- Adding contrib module AMQP-CPP (configuring with amqpcpp-cmake)
-- Not using AMQP-CPP
-- Adding contrib module cassandra (configuring with cassandra-cmake)
-- Not using cassandra
-- Adding contrib module curl (configuring with curl-cmake)
-- Not using curl
-- Adding contrib module azure (configuring with azure-cmake)
-- Not using Azure blob storage
-- Adding contrib module sentry-native (configuring with sentry-native-cmake)
-- Not using sentry
-- Adding contrib module fmtlib (configuring with fmtlib-cmake)
-- Adding contrib module krb5 (configuring with krb5-cmake)
-- Not using krb5
-- Adding contrib module cyrus-sasl (configuring with cyrus-sasl-cmake)
-- Not using cyrus-sasl
-- Adding contrib module libgsasl (configuring with libgsasl-cmake)
-- Not using gsasl library
-- Adding contrib module librdkafka (configuring with librdkafka-cmake)
-- Not using librdkafka
-- Adding contrib module libhdfs3 (configuring with libhdfs3-cmake)
-- Not using hdfs
-- Adding contrib module hive-metastore (configuring with hive-metastore-cmake)
Hive disabled
-- Adding contrib module cppkafka (configuring with cppkafka-cmake)
-- Not using librdkafka (skip cppkafka)
-- Adding contrib module libpqxx (configuring with libpqxx-cmake)
-- Not using libpqxx
-- Adding contrib module libpq (configuring with libpq-cmake)
-- Adding contrib module NuRaft (configuring with nuraft-cmake)
-- Not using NuRaft
-- Adding contrib module fast_float (configuring with fast_float-cmake)
-- Adding contrib module datasketches-cpp (configuring with datasketches-cpp-cmake)
-- Not using DataSketches
-- Adding contrib module hashidsxx (configuring with hashidsxx-cmake)
-- Adding contrib module sqlite-amalgamation (configuring with sqlite-cmake)
-- Not using sqlite
-- Adding contrib module s2geometry (configuring with s2geometry-cmake)
-- Not using S2 geometry
-- Adding contrib module eigen (configuring with eigen-cmake)
CMake Warning at CMakeLists.txt:487 (message):
Non default allocator is disabled. This is not recommended for production
builds.
-- Performing Test SUPPORTS_CXXFLAG_everything
-- Performing Test SUPPORTS_CXXFLAG_everything - Success
-- Performing Test SUPPORTS_CFLAG_everything
-- Performing Test SUPPORTS_CFLAG_everything - Success
-- Performing Test SUPPORTS_CXXFLAG_pedantic
-- Performing Test SUPPORTS_CXXFLAG_pedantic - Success
-- Performing Test SUPPORTS_CFLAG_pedantic
-- Performing Test SUPPORTS_CFLAG_pedantic - Success
-- Performing Test SUPPORTS_CXXFLAG_no_vla_extension
-- Performing Test SUPPORTS_CXXFLAG_no_vla_extension - Success
-- Performing Test SUPPORTS_CFLAG_no_vla_extension
-- Performing Test SUPPORTS_CFLAG_no_vla_extension - Success
-- Performing Test SUPPORTS_CXXFLAG_no_zero_length_array
-- Performing Test SUPPORTS_CXXFLAG_no_zero_length_array - Success
-- Performing Test SUPPORTS_CFLAG_no_zero_length_array
-- Performing Test SUPPORTS_CFLAG_no_zero_length_array - Success
-- Performing Test SUPPORTS_CXXFLAG_no_c11_extensions
-- Performing Test SUPPORTS_CXXFLAG_no_c11_extensions - Success
-- Performing Test SUPPORTS_CFLAG_no_c11_extensions
-- Performing Test SUPPORTS_CFLAG_no_c11_extensions - Success
-- Performing Test SUPPORTS_CFLAG_no_unused_command_line_argument
-- Performing Test SUPPORTS_CFLAG_no_unused_command_line_argument - Success
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat_pedantic
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat_pedantic - Success
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat_pedantic
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat_pedantic - Success
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat
-- Performing Test SUPPORTS_CXXFLAG_no_cxx98_compat - Success
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat
-- Performing Test SUPPORTS_CFLAG_no_cxx98_compat - Success
-- Performing Test SUPPORTS_CXXFLAG_no_c99_extensions
-- Performing Test SUPPORTS_CXXFLAG_no_c99_extensions - Success
-- Performing Test SUPPORTS_CFLAG_no_c99_extensions
-- Performing Test SUPPORTS_CFLAG_no_c99_extensions - Success
-- Performing Test SUPPORTS_CXXFLAG_no_conversion
-- Performing Test SUPPORTS_CXXFLAG_no_conversion - Success
-- Performing Test SUPPORTS_CFLAG_no_conversion
-- Performing Test SUPPORTS_CFLAG_no_conversion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_ctad_maybe_unsupported
-- Performing Test SUPPORTS_CXXFLAG_no_ctad_maybe_unsupported - Success
-- Performing Test SUPPORTS_CFLAG_no_ctad_maybe_unsupported
-- Performing Test SUPPORTS_CFLAG_no_ctad_maybe_unsupported - Success
-- Performing Test SUPPORTS_CXXFLAG_no_deprecated_dynamic_exception_spec
-- Performing Test SUPPORTS_CXXFLAG_no_deprecated_dynamic_exception_spec - Success
-- Performing Test SUPPORTS_CFLAG_no_deprecated_dynamic_exception_spec
-- Performing Test SUPPORTS_CFLAG_no_deprecated_dynamic_exception_spec - Success
-- Performing Test SUPPORTS_CXXFLAG_no_disabled_macro_expansion
-- Performing Test SUPPORTS_CXXFLAG_no_disabled_macro_expansion - Success
-- Performing Test SUPPORTS_CFLAG_no_disabled_macro_expansion
-- Performing Test SUPPORTS_CFLAG_no_disabled_macro_expansion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_documentation_unknown_command
-- Performing Test SUPPORTS_CXXFLAG_no_documentation_unknown_command - Success
-- Performing Test SUPPORTS_CFLAG_no_documentation_unknown_command
-- Performing Test SUPPORTS_CFLAG_no_documentation_unknown_command - Success
-- Performing Test SUPPORTS_CXXFLAG_no_double_promotion
-- Performing Test SUPPORTS_CXXFLAG_no_double_promotion - Success
-- Performing Test SUPPORTS_CFLAG_no_double_promotion
-- Performing Test SUPPORTS_CFLAG_no_double_promotion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_exit_time_destructors
-- Performing Test SUPPORTS_CXXFLAG_no_exit_time_destructors - Success
-- Performing Test SUPPORTS_CFLAG_no_exit_time_destructors
-- Performing Test SUPPORTS_CFLAG_no_exit_time_destructors - Success
-- Performing Test SUPPORTS_CXXFLAG_no_float_equal
-- Performing Test SUPPORTS_CXXFLAG_no_float_equal - Success
-- Performing Test SUPPORTS_CFLAG_no_float_equal
-- Performing Test SUPPORTS_CFLAG_no_float_equal - Success
-- Performing Test SUPPORTS_CXXFLAG_no_global_constructors
-- Performing Test SUPPORTS_CXXFLAG_no_global_constructors - Success
-- Performing Test SUPPORTS_CFLAG_no_global_constructors
-- Performing Test SUPPORTS_CFLAG_no_global_constructors - Success
-- Performing Test SUPPORTS_CXXFLAG_no_missing_prototypes
-- Performing Test SUPPORTS_CXXFLAG_no_missing_prototypes - Success
-- Performing Test SUPPORTS_CFLAG_no_missing_prototypes
-- Performing Test SUPPORTS_CFLAG_no_missing_prototypes - Success
-- Performing Test SUPPORTS_CXXFLAG_no_missing_variable_declarations
-- Performing Test SUPPORTS_CXXFLAG_no_missing_variable_declarations - Success
-- Performing Test SUPPORTS_CFLAG_no_missing_variable_declarations
-- Performing Test SUPPORTS_CFLAG_no_missing_variable_declarations - Success
-- Performing Test SUPPORTS_CXXFLAG_no_nested_anon_types
-- Performing Test SUPPORTS_CXXFLAG_no_nested_anon_types - Success
-- Performing Test SUPPORTS_CFLAG_no_nested_anon_types
-- Performing Test SUPPORTS_CFLAG_no_nested_anon_types - Success
-- Performing Test SUPPORTS_CXXFLAG_no_packed
-- Performing Test SUPPORTS_CXXFLAG_no_packed - Success
-- Performing Test SUPPORTS_CFLAG_no_packed
-- Performing Test SUPPORTS_CFLAG_no_packed - Success
-- Performing Test SUPPORTS_CXXFLAG_no_padded
-- Performing Test SUPPORTS_CXXFLAG_no_padded - Success
-- Performing Test SUPPORTS_CFLAG_no_padded
-- Performing Test SUPPORTS_CFLAG_no_padded - Success
-- Performing Test SUPPORTS_CXXFLAG_no_return_std_move_in_cxx11
-- Performing Test SUPPORTS_CXXFLAG_no_return_std_move_in_cxx11 - Failed
-- Performing Test SUPPORTS_CFLAG_no_return_std_move_in_cxx11
-- Performing Test SUPPORTS_CFLAG_no_return_std_move_in_cxx11 - Failed
-- Flag -Wno-return-std-move-in-c++11 is unsupported
-- Flag -Wno-return-std-move-in-c++11 is unsupported
-- Performing Test SUPPORTS_CXXFLAG_no_shift_sign_overflow
-- Performing Test SUPPORTS_CXXFLAG_no_shift_sign_overflow - Success
-- Performing Test SUPPORTS_CFLAG_no_shift_sign_overflow
-- Performing Test SUPPORTS_CFLAG_no_shift_sign_overflow - Success
-- Performing Test SUPPORTS_CXXFLAG_no_sign_conversion
-- Performing Test SUPPORTS_CXXFLAG_no_sign_conversion - Success
-- Performing Test SUPPORTS_CFLAG_no_sign_conversion
-- Performing Test SUPPORTS_CFLAG_no_sign_conversion - Success
-- Performing Test SUPPORTS_CXXFLAG_no_switch_enum
-- Performing Test SUPPORTS_CXXFLAG_no_switch_enum - Success
-- Performing Test SUPPORTS_CFLAG_no_switch_enum
-- Performing Test SUPPORTS_CFLAG_no_switch_enum - Success
-- Performing Test SUPPORTS_CXXFLAG_no_undefined_func_template
-- Performing Test SUPPORTS_CXXFLAG_no_undefined_func_template - Success
-- Performing Test SUPPORTS_CFLAG_no_undefined_func_template
-- Performing Test SUPPORTS_CFLAG_no_undefined_func_template - Success
-- Performing Test SUPPORTS_CXXFLAG_no_unused_template
-- Performing Test SUPPORTS_CXXFLAG_no_unused_template - Success
-- Performing Test SUPPORTS_CFLAG_no_unused_template
-- Performing Test SUPPORTS_CFLAG_no_unused_template - Success
-- Performing Test SUPPORTS_CXXFLAG_no_vla
-- Performing Test SUPPORTS_CXXFLAG_no_vla - Success
-- Performing Test SUPPORTS_CFLAG_no_vla
-- Performing Test SUPPORTS_CFLAG_no_vla - Success
-- Performing Test SUPPORTS_CXXFLAG_no_weak_template_vtables
-- Performing Test SUPPORTS_CXXFLAG_no_weak_template_vtables - Success
-- Performing Test SUPPORTS_CFLAG_no_weak_template_vtables
-- Performing Test SUPPORTS_CFLAG_no_weak_template_vtables - Success
-- Performing Test SUPPORTS_CXXFLAG_no_weak_vtables
-- Performing Test SUPPORTS_CXXFLAG_no_weak_vtables - Success
-- Performing Test SUPPORTS_CFLAG_no_weak_vtables
-- Performing Test SUPPORTS_CFLAG_no_weak_vtables - Success
-- compiler C = /usr/bin/clang --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 -fdiagnostics-color=always -Xclang -fuse-ctor-homing -gdwarf-aranges -pipe -mssse3 -msse4.1 -msse4.2 -mpclmul -mpopcnt -fasynchronous-unwind-tables -falign-functions=32 -fdiagnostics-absolute-paths -fexperimental-new-pass-manager -Weverything -Wpedantic -Wno-vla-extension -Wno-zero-length-array -Wno-c11-extensions -Wno-unused-command-line-argument -Wno-c++98-compat-pedantic -Wno-c++98-compat -Wno-c99-extensions -Wno-conversion -Wno-ctad-maybe-unsupported -Wno-deprecated-dynamic-exception-spec -Wno-disabled-macro-expansion -Wno-documentation-unknown-command -Wno-double-promotion -Wno-exit-time-destructors -Wno-float-equal -Wno-global-constructors -Wno-missing-prototypes -Wno-missing-variable-declarations -Wno-nested-anon-types -Wno-packed -Wno-padded -Wno-shift-sign-overflow -Wno-sign-conversion -Wno-switch-enum -Wno-undefined-func-template -Wno-unused-template -Wno-vla -Wno-weak-template-vtables -Wno-weak-vtables -g -O0 -g -gdwarf-4 -fno-inline
-- compiler CXX = /usr/bin/clang++ --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 -std=c++20 -fdiagnostics-color=always -Xclang -fuse-ctor-homing -fsized-deallocation -gdwarf-aranges -pipe -mssse3 -msse4.1 -msse4.2 -mpclmul -mpopcnt -fasynchronous-unwind-tables -falign-functions=32 -fdiagnostics-absolute-paths -fstrict-vtable-pointers -fexperimental-new-pass-manager -Wall -Wextra -Weverything -Wpedantic -Wno-vla-extension -Wno-zero-length-array -Wno-c11-extensions -Wno-unused-command-line-argument -Wno-c++98-compat-pedantic -Wno-c++98-compat -Wno-c99-extensions -Wno-conversion -Wno-ctad-maybe-unsupported -Wno-deprecated-dynamic-exception-spec -Wno-disabled-macro-expansion -Wno-documentation-unknown-command -Wno-double-promotion -Wno-exit-time-destructors -Wno-float-equal -Wno-global-constructors -Wno-missing-prototypes -Wno-missing-variable-declarations -Wno-nested-anon-types -Wno-packed -Wno-padded -Wno-shift-sign-overflow -Wno-sign-conversion -Wno-switch-enum -Wno-undefined-func-template -Wno-unused-template -Wno-vla -Wno-weak-template-vtables -Wno-weak-vtables -g -O0 -g -gdwarf-4 -fno-inline -D_LIBCPP_DEBUG=0
-- LINKER_FLAGS = --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --gcc-toolchain=/home/workspace/forks/ClickHouse/cmake/linux/../../contrib/sysroot/linux-x86_64 --ld-path=/usr/bin/ld.gold -rdynamic -no-pie -Wl,-no-pie
-- /home/workspace/forks/ClickHouse/src: Have 27842 megabytes of memory.
Limiting concurrent linkers jobs to 7 and compiler jobs to 11 (system has 16 logical cores)
-- Will build ClickHouse 22.6.1.1 revision 54463
-- Generating debugger info for ClickHouse functions
-- clickhouse-keeper and clickhouse-keeper-converter will not be built (lack of NuRaft)
-- ClickHouse modes:
-- Server mode: ON
-- Client mode: ON
-- Local mode: OFF
-- Benchmark mode: OFF
-- Extract from config mode: OFF
-- Compressor mode: OFF
-- Copier mode: OFF
-- Format mode: OFF
-- Obfuscator mode: OFF
-- ODBC bridge mode: OFF
-- Library bridge mode: OFF
-- ClickHouse install: OFF
-- ClickHouse git-import: OFF
-- ClickHouse keeper mode: OFF
-- ClickHouse keeper-converter mode: OFF
-- bash_completion will be written to /usr/local/share/bash-completion/completions
-- Target check already exists
-- /home/workspace/forks/ClickHouse/utils: Have 27842 megabytes of memory.
Limiting concurrent linkers jobs to 7 and compiler jobs to OFF (system has 16 logical cores)
-- Configuring done
CMake Error at base/base/CMakeLists.txt:52 (target_link_libraries):
Target "common" links to:
ch_contrib::replxx
but the target was not found. Possible reasons include:
* There is a typo in the target name.
* A find_package call is missing for an IMPORTED target.
* An ALIAS target is missing.
-- Generating done
CMake Generate step failed. Build files cannot be regenerated correctly.
```
Of course, I've checked it:
```
ClickHouse/build [master] » cd ../contrib/replxx && git status
HEAD detached at 3fd0e3c
nothing to commit, working tree clean
``` | non_priority | cmake target common links to ch contrib replxx but the target was not found make sure that git diff result is empty and you ve just pulled fresh master try cleaning up cmake cache just in case official build instructions are published here operating system arch linux smp preempt wed may gnu linux os kind or distribution specific version release non standard kernel if any if you are trying to build inside virtual machine please mention it too cmake version ninja version compiler name and version clang clang version target pc linux gnu thread model posix full cmake and or ninja output cmake dcmake c compiler which clang dcmake cxx compiler which clang dcmake build type debug denable clickhouse all off denable clickhouse server on denable clickhouse client on denable libraries off duse unwind on denable utils off denable tests off denable ccache the c compiler identification is clang the cxx compiler identification is clang the asm compiler identification is clang with gnu like command line found assembler usr bin clang detecting c compiler abi info detecting c compiler abi info done check for working c compiler usr bin clang skipped detecting c compile features detecting c compile features done detecting cxx compiler abi info detecting cxx compiler abi info done check for working cxx compiler usr bin clang skipped detecting cxx compile features detecting cxx compile features done cross compiling for target using compiler clang version target pc linux gnu thread model posix installeddir usr bin using linker usr bin ld gold using archiver usr bin llvm ar using ranlib usr bin llvm ranlib using install name tool usr bin llvm install name tool using objcopy usr bin llvm objcopy using strip usr bin llvm strip using ccache no disabled via configuration found git usr bin git found version head s commit hash on branch master your branch is up to date with origin master nothing to commit working tree clean cmake build type debug performing test has reserved identifier performing test has reserved identifier success performing test has suggest destructor override performing test has suggest destructor override success performing test has suggest override performing test has suggest override success performing test has use ctor homing performing test has use ctor homing success performing test have performing test have success performing test have performing test have success performing test have performing test have success performing test have pclmulqdq performing test have pclmulqdq success performing test have popcnt performing test have popcnt success performing test have avx performing test have avx success performing test have performing test have success performing test have performing test have success performing test have bmi performing test have bmi success default libraries nodefaultlibs usr lib clang lib linux libclang rt builtins a lc lm lrt lpthread ldl looking for pthread h looking for pthread h found performing test cmake have libc pthread performing test cmake have libc pthread success found threads true looking for sys random h looking for sys random h found performing test supports cxxflag no unused command line argument performing test supports cxxflag no unused command line argument success performing test supports cxxflag no unused but set variable performing test supports cxxflag no unused but set variable success performing test supports cxxflag no builtin requires header performing test supports cxxflag no builtin requires header success some symbols from glibc will be replaced for compatibility performing test have warning unused but set variable performing test have warning unused but set variable success performing test have warning missing attributes performing test have warning missing attributes failed performing test have warning maybe uninitialized performing test have warning maybe uninitialized failed performing test have warning register performing test have warning register success using libunwind unwind using exception handler unwind unit tests are disabled building for linux use static libraries on split shared adding contrib module miniselect configuring with miniselect cmake adding contrib module pdqsort configuring with pdqsort cmake adding contrib module sparsehash configuring with sparsehash cmake adding contrib module abseil cpp configuring with abseil cpp cmake adding contrib module magic enum configuring with magic enum cmake adding contrib module boost configuring with boost cmake adding contrib module cctz configuring with cctz cmake packaging with tzdata version adding contrib module consistent hashing configuring with consistent hashing adding contrib module dragonbox configuring with dragonbox cmake adding contrib module hyperscan configuring with hyperscan cmake not using hyperscan adding contrib module jemalloc configuring with jemalloc cmake not using jemalloc adding contrib module libcpuid configuring with libcpuid cmake not using cpuid adding contrib module libdivide configuring with libdivide adding contrib module libmetrohash configuring with libmetrohash adding contrib module configuring with cmake adding contrib module murmurhash configuring with murmurhash adding contrib module replxx configuring with replxx cmake not using replxx adding contrib module unixodbc configuring with unixodbc cmake not using odbc adding contrib module nanodbc configuring with nanodbc cmake adding contrib module capnproto configuring with capnproto cmake not using cap n proto library adding contrib module yaml cpp configuring with yaml cpp cmake not using yaml adding contrib module configuring with cmake adding contrib module xz configuring with xz cmake adding contrib module brotli configuring with brotli cmake not using brotli adding contrib module double conversion configuring with double conversion cmake adding contrib module boringssl configuring with boringssl cmake not using openssl adding contrib module poco configuring with poco cmake not using poco crypto not using poco data odbc not using poco net ssl adding contrib module croaring configuring with croaring cmake adding contrib module zstd configuring with zstd cmake zstd version adding contrib module zlib ng configuring with zlib ng cmake adding contrib module configuring with cmake compression disabled adding contrib module minizip ng configuring with minizip ng cmake minizip ng disabled adding contrib module snappy configuring with snappy cmake adding contrib module rocksdb configuring with rocksdb cmake not using rocksdb adding contrib module thrift configuring with thrift cmake thrift disabled adding contrib module arrow configuring with arrow cmake building without parquet support adding contrib module avro configuring with avro cmake not using avro adding contrib module protobuf configuring with protobuf cmake not using protobuf adding contrib module openldap configuring with openldap cmake not using ldap adding contrib module grpc configuring with grpc cmake not using grpc adding contrib module msgpack c configuring with msgpack c cmake not using msgpack adding contrib module wyhash configuring with wyhash cmake adding contrib module configuring with adding contrib module libfarmhash configuring with libfarmhash adding contrib module icu configuring with icu cmake not using icu adding contrib module configuring with cmake not using adding contrib module mariadb connector c configuring with mariadb connector c cmake build without mysqlclient support for mysql dictionary source will be disabled adding contrib module llvm configuring with llvm cmake llvm include directory home workspace forks clickhouse contrib llvm llvm include home workspace forks clickhouse build contrib llvm llvm include llvm library directory home workspace forks clickhouse build contrib llvm llvm llvm c compiler flags looking for dlfcn h looking for dlfcn h found looking for errno h looking for errno h found looking for fcntl h looking for fcntl h found looking for link h looking for link h found looking for malloc malloc h looking for malloc malloc h not found looking for pthread h looking for pthread h found looking for signal h looking for signal h found looking for sys ioctl h looking for sys ioctl h found looking for sys mman h looking for sys mman h found looking for sys param h looking for sys param h found looking for sys resource h looking for sys resource h found looking for sys stat h looking for sys stat h found looking for sys time h looking for sys time h found looking for sys types h looking for sys types h found looking for sysexits h looking for sysexits h found looking for termios h looking for termios h found looking for unistd h looking for unistd h found looking for valgrind valgrind h looking for valgrind valgrind h not found looking for fenv h looking for fenv h found looking for fe all except looking for fe all except found looking for fe inexact looking for fe inexact found looking for mach mach h looking for mach mach h not found looking for histedit h looking for histedit h not found looking for crashreporterclient h looking for crashreporterclient h not found looking for linux magic h looking for linux magic h not found looking for linux nfs fs h looking for linux nfs fs h not found looking for linux smb h looking for linux smb h not found looking for pthread create in pthread looking for pthread create in pthread found looking for pthread getspecific in pthread looking for pthread getspecific in pthread found looking for pthread rwlock init in pthread looking for pthread rwlock init in pthread found looking for pthread mutex lock in pthread looking for pthread mutex lock in pthread found looking for dlopen in dl looking for dlopen in dl found looking for clock gettime in rt looking for clock gettime in rt found looking for xar open in xar looking for xar open in xar found looking for looking for not found looking for backtrace looking for backtrace found backtrace facility detected in default set of libraries found backtrace home workspace forks clickhouse cmake linux contrib sysroot linux linux gnu libc usr include performing test c supports werror unguarded availability new performing test c supports werror unguarded availability new success looking for register frame looking for register frame found looking for deregister frame looking for deregister frame found looking for unwind backtrace looking for unwind backtrace found looking for getpagesize looking for getpagesize found looking for sysconf looking for sysconf found looking for getrusage looking for getrusage found looking for setrlimit looking for setrlimit found looking for isatty looking for isatty found looking for futimens looking for futimens found looking for futimes looking for futimes found looking for posix fallocate looking for posix fallocate found looking for sigaltstack looking for sigaltstack found looking for looking for found looking for mallctl looking for mallctl not found looking for mallinfo looking for mallinfo found looking for malloc zone statistics looking for malloc zone statistics not found looking for getrlimit looking for getrlimit found looking for posix spawn looking for posix spawn found looking for pread looking for pread found looking for sbrk looking for sbrk found looking for strerror looking for strerror found looking for strerror r looking for strerror r found looking for strerror s looking for strerror s not found looking for setenv looking for setenv found looking for dlopen looking for dlopen found looking for dladdr looking for dladdr not found performing test have struct stat st mtimespec tv nsec performing test have struct stat st mtimespec tv nsec failed performing test have struct stat st mtim tv nsec performing test have struct stat st mtim tv nsec success looking for glibc looking for glibc found looking for pthread getname np looking for pthread getname np found looking for pthread setname np looking for pthread setname np found performing test supports no pie flag performing test supports no pie flag success performing test supports variadic macros flag performing test supports variadic macros flag success performing test supports gnu zero variadic macro arguments flag performing test supports gnu zero variadic macro arguments flag success native target architecture is threads enabled doxygen disabled go bindings disabled ninja version could not find ocaml missing ocamlfind ocaml version ocaml stdlib path ocaml bindings disabled could not find python module pygments could not find python module pygments lexers c cpp could not find python module yaml llvm host triple unknown linux gnu llvm default target triple unknown linux gnu performing test supports fvisibility inlines hidden flag performing test supports fvisibility inlines hidden flag success performing test c supports werror date time performing test c supports werror date time success performing test cxx supports werror date time performing test cxx supports werror date time success performing test cxx supports werror unguarded availability new performing test cxx supports werror unguarded availability new success performing test cxx supports missing field initializers flag performing test cxx supports missing field initializers flag success performing test c supports implicit fallthrough flag performing test c supports implicit fallthrough flag success performing test cxx supports implicit fallthrough flag performing test cxx supports implicit fallthrough flag success performing test c supports covered switch default flag performing test c supports covered switch default flag success performing test cxx supports covered switch default flag performing test cxx supports covered switch default flag success performing test cxx supports class memaccess flag performing test cxx supports class memaccess flag success performing test cxx supports noexcept type flag performing test cxx supports noexcept type flag success performing test cxx wont warn on final nonvirtualdtor performing test cxx wont warn on final nonvirtualdtor success performing test c supports delete non virtual dtor flag performing test c supports delete non virtual dtor flag success performing test cxx supports delete non virtual dtor flag performing test cxx supports delete non virtual dtor flag success performing test cxx supports suggest override flag performing test cxx supports suggest override flag success performing test cxx wsuggest override allows only final performing test cxx wsuggest override allows only final success performing test c wcomment allows line wrap performing test c wcomment allows line wrap success performing test c supports string conversion flag performing test c supports string conversion flag success performing test cxx supports string conversion flag performing test cxx supports string conversion flag success performing test linker supports color diagnostics performing test linker supports color diagnostics success looking for os signpost interval begin looking for os signpost interval begin not found found usr bin found version found components interpreter linker detection unknown setting native build dir to home workspace forks clickhouse build contrib llvm llvm native llvmhello ignored loadable modules not supported on this platform targeting targeting adding contrib module configuring with cmake adding contrib module aws aws c common aws c event stream aws checksums configuring with aws cmake not using adding contrib module configuring with cmake not using adding contrib module simdjson configuring with simdjson cmake not using simdjson adding contrib module rapidjson configuring with rapidjson cmake not using rapidjson adding contrib module fastops configuring with fastops cmake not using fast vectorized mathematical functions library by mikhail parakhin adding contrib module libuv configuring with libuv cmake adding contrib module amqp cpp configuring with amqpcpp cmake not using amqp cpp adding contrib module cassandra configuring with cassandra cmake not using cassandra adding contrib module curl configuring with curl cmake not using curl adding contrib module azure configuring with azure cmake not using azure blob storage adding contrib module sentry native configuring with sentry native cmake not using sentry adding contrib module fmtlib configuring with fmtlib cmake adding contrib module configuring with cmake not using adding contrib module cyrus sasl configuring with cyrus sasl cmake not using cyrus sasl adding contrib module libgsasl configuring with libgsasl cmake not using gsasl library adding contrib module librdkafka configuring with librdkafka cmake not using librdkafka adding contrib module configuring with cmake not using hdfs adding contrib module hive metastore configuring with hive metastore cmake hive disabled adding contrib module cppkafka configuring with cppkafka cmake not using librdkafka skip cppkafka adding contrib module libpqxx configuring with libpqxx cmake not using libpqxx adding contrib module libpq configuring with libpq cmake adding contrib module nuraft configuring with nuraft cmake not using nuraft adding contrib module fast float configuring with fast float cmake adding contrib module datasketches cpp configuring with datasketches cpp cmake not using datasketches adding contrib module hashidsxx configuring with hashidsxx cmake adding contrib module sqlite amalgamation configuring with sqlite cmake not using sqlite adding contrib module configuring with cmake not using geometry adding contrib module eigen configuring with eigen cmake cmake warning at cmakelists txt message non default allocator is disabled this is not recommended for production builds performing test supports cxxflag everything performing test supports cxxflag everything success performing test supports cflag everything performing test supports cflag everything success performing test supports cxxflag pedantic performing test supports cxxflag pedantic success performing test supports cflag pedantic performing test supports cflag pedantic success performing test supports cxxflag no vla extension performing test supports cxxflag no vla extension success performing test supports cflag no vla extension performing test supports cflag no vla extension success performing test supports cxxflag no zero length array performing test supports cxxflag no zero length array success performing test supports cflag no zero length array performing test supports cflag no zero length array success performing test supports cxxflag no extensions performing test supports cxxflag no extensions success performing test supports cflag no extensions performing test supports cflag no extensions success performing test supports cflag no unused command line argument performing test supports cflag no unused command line argument success performing test supports cxxflag no compat pedantic performing test supports cxxflag no compat pedantic success performing test supports cflag no compat pedantic performing test supports cflag no compat pedantic success performing test supports cxxflag no compat performing test supports cxxflag no compat success performing test supports cflag no compat performing test supports cflag no compat success performing test supports cxxflag no extensions performing test supports cxxflag no extensions success performing test supports cflag no extensions performing test supports cflag no extensions success performing test supports cxxflag no conversion performing test supports cxxflag no conversion success performing test supports cflag no conversion performing test supports cflag no conversion success performing test supports cxxflag no ctad maybe unsupported performing test supports cxxflag no ctad maybe unsupported success performing test supports cflag no ctad maybe unsupported performing test supports cflag no ctad maybe unsupported success performing test supports cxxflag no deprecated dynamic exception spec performing test supports cxxflag no deprecated dynamic exception spec success performing test supports cflag no deprecated dynamic exception spec performing test supports cflag no deprecated dynamic exception spec success performing test supports cxxflag no disabled macro expansion performing test supports cxxflag no disabled macro expansion success performing test supports cflag no disabled macro expansion performing test supports cflag no disabled macro expansion success performing test supports cxxflag no documentation unknown command performing test supports cxxflag no documentation unknown command success performing test supports cflag no documentation unknown command performing test supports cflag no documentation unknown command success performing test supports cxxflag no double promotion performing test supports cxxflag no double promotion success performing test supports cflag no double promotion performing test supports cflag no double promotion success performing test supports cxxflag no exit time destructors performing test supports cxxflag no exit time destructors success performing test supports cflag no exit time destructors performing test supports cflag no exit time destructors success performing test supports cxxflag no float equal performing test supports cxxflag no float equal success performing test supports cflag no float equal performing test supports cflag no float equal success performing test supports cxxflag no global constructors performing test supports cxxflag no global constructors success performing test supports cflag no global constructors performing test supports cflag no global constructors success performing test supports cxxflag no missing prototypes performing test supports cxxflag no missing prototypes success performing test supports cflag no missing prototypes performing test supports cflag no missing prototypes success performing test supports cxxflag no missing variable declarations performing test supports cxxflag no missing variable declarations success performing test supports cflag no missing variable declarations performing test supports cflag no missing variable declarations success performing test supports cxxflag no nested anon types performing test supports cxxflag no nested anon types success performing test supports cflag no nested anon types performing test supports cflag no nested anon types success performing test supports cxxflag no packed performing test supports cxxflag no packed success performing test supports cflag no packed performing test supports cflag no packed success performing test supports cxxflag no padded performing test supports cxxflag no padded success performing test supports cflag no padded performing test supports cflag no padded success performing test supports cxxflag no return std move in performing test supports cxxflag no return std move in failed performing test supports cflag no return std move in performing test supports cflag no return std move in failed flag wno return std move in c is unsupported flag wno return std move in c is unsupported performing test supports cxxflag no shift sign overflow performing test supports cxxflag no shift sign overflow success performing test supports cflag no shift sign overflow performing test supports cflag no shift sign overflow success performing test supports cxxflag no sign conversion performing test supports cxxflag no sign conversion success performing test supports cflag no sign conversion performing test supports cflag no sign conversion success performing test supports cxxflag no switch enum performing test supports cxxflag no switch enum success performing test supports cflag no switch enum performing test supports cflag no switch enum success performing test supports cxxflag no undefined func template performing test supports cxxflag no undefined func template success performing test supports cflag no undefined func template performing test supports cflag no undefined func template success performing test supports cxxflag no unused template performing test supports cxxflag no unused template success performing test supports cflag no unused template performing test supports cflag no unused template success performing test supports cxxflag no vla performing test supports cxxflag no vla success performing test supports cflag no vla performing test supports cflag no vla success performing test supports cxxflag no weak template vtables performing test supports cxxflag no weak template vtables success performing test supports cflag no weak template vtables performing test supports cflag no weak template vtables success performing test supports cxxflag no weak vtables performing test supports cxxflag no weak vtables success performing test supports cflag no weak vtables performing test supports cflag no weak vtables success compiler c usr bin clang gcc toolchain home workspace forks clickhouse cmake linux contrib sysroot linux gcc toolchain home workspace forks clickhouse cmake linux contrib sysroot linux fdiagnostics color always xclang fuse ctor homing gdwarf aranges pipe mpclmul mpopcnt fasynchronous unwind tables falign functions fdiagnostics absolute paths fexperimental new pass manager weverything wpedantic wno vla extension wno zero length array wno extensions wno unused command line argument wno c compat pedantic wno c compat wno extensions wno conversion wno ctad maybe unsupported wno deprecated dynamic exception spec wno disabled macro expansion wno documentation unknown command wno double promotion wno exit time destructors wno float equal wno global constructors wno missing prototypes wno missing variable declarations wno nested anon types wno packed wno padded wno shift sign overflow wno sign conversion wno switch enum wno undefined func template wno unused template wno vla wno weak template vtables wno weak vtables g g gdwarf fno inline compiler cxx usr bin clang gcc toolchain home workspace forks clickhouse cmake linux contrib sysroot linux gcc toolchain home workspace forks clickhouse cmake linux contrib sysroot linux std c fdiagnostics color always xclang fuse ctor homing fsized deallocation gdwarf aranges pipe mpclmul mpopcnt fasynchronous unwind tables falign functions fdiagnostics absolute paths fstrict vtable pointers fexperimental new pass manager wall wextra weverything wpedantic wno vla extension wno zero length array wno extensions wno unused command line argument wno c compat pedantic wno c compat wno extensions wno conversion wno ctad maybe unsupported wno deprecated dynamic exception spec wno disabled macro expansion wno documentation unknown command wno double promotion wno exit time destructors wno float equal wno global constructors wno missing prototypes wno missing variable declarations wno nested anon types wno packed wno padded wno shift sign overflow wno sign conversion wno switch enum wno undefined func template wno unused template wno vla wno weak template vtables wno weak vtables g g gdwarf fno inline d libcpp debug linker flags gcc toolchain home workspace forks clickhouse cmake linux contrib sysroot linux gcc toolchain home workspace forks clickhouse cmake linux contrib sysroot linux ld path usr bin ld gold rdynamic no pie wl no pie home workspace forks clickhouse src have megabytes of memory limiting concurrent linkers jobs to and compiler jobs to system has logical cores will build clickhouse revision generating debugger info for clickhouse functions clickhouse keeper and clickhouse keeper converter will not be built lack of nuraft clickhouse modes server mode on client mode on local mode off benchmark mode off extract from config mode off compressor mode off copier mode off format mode off obfuscator mode off odbc bridge mode off library bridge mode off clickhouse install off clickhouse git import off clickhouse keeper mode off clickhouse keeper converter mode off bash completion will be written to usr local share bash completion completions target check already exists home workspace forks clickhouse utils have megabytes of memory limiting concurrent linkers jobs to and compiler jobs to off system has logical cores configuring done cmake error at base base cmakelists txt target link libraries target common links to ch contrib replxx but the target was not found possible reasons include there is a typo in the target name a find package call is missing for an imported target an alias target is missing generating done cmake generate step failed build files cannot be regenerated correctly of course i ve checked it clickhouse build » cd contrib replxx git status head detached at nothing to commit working tree clean | 0 |
116,336 | 14,943,790,077 | IssuesEvent | 2021-01-25 23:51:24 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | [EPIC] MyVA copy | content design vsa-authenticated-exp vsp-product-support | ## Background
This is a ticket to track copy for MyVA 2.0
## Tasks
- [ ] Matt creates tickets for each case below
- [ ] Tressa/Cassandra add info to tickets
- [ ] Peggy reviews each ticket
LOA1 user
LOA3 First-time user experience
LOA3 user who has everything
LOA3 user who has things but has no updates
| 1.0 | [EPIC] MyVA copy - ## Background
This is a ticket to track copy for MyVA 2.0
## Tasks
- [ ] Matt creates tickets for each case below
- [ ] Tressa/Cassandra add info to tickets
- [ ] Peggy reviews each ticket
LOA1 user
LOA3 First-time user experience
LOA3 user who has everything
LOA3 user who has things but has no updates
| non_priority | myva copy background this is a ticket to track copy for myva tasks matt creates tickets for each case below tressa cassandra add info to tickets peggy reviews each ticket user first time user experience user who has everything user who has things but has no updates | 0 |
255,272 | 19,297,399,162 | IssuesEvent | 2021-12-12 20:17:36 | celestiaorg/celestia-specs | https://api.github.com/repos/celestiaorg/celestia-specs | closed | Investigate canonical encoding scheme | documentation enhancement serialization investigation | Currently, [a canonical variant of protobuf3 is used to define data structures and do serialization/deserialization](https://github.com/lazyledger/lazyledger-specs/blob/e5df39c617db4a1af0590d505a9009ee311619de/specs/data_structures.md#serialization). This is great for portability, isn't ideal for blockchain applications. For example, there are no fixed-size byte arrays (32-bytes hashes used all over the place in blockchains), or optional fields. Robust protobuf implementations for embedded devices (e.g. hardware wallets) or blockchain smart contracts (e.g. Solidity) are non-existent and would be prohibitive to develop.
The crux is that protobuf was designed for client-server communication, with different versions (i.e. both forwards and backwards compatibility are key features). This is unneeded for core blockchain data structures (e.g. blocks, votes, or transactions), but may be good for node-to-node communication (e.g. messages that wrap around block data, vote data, or transaction data).
We should investigate the feasibility of using a simpler serialization scheme for core data structures.
Desiderata:
* fully deterministic (specifically, bijective)
* binary, not text
* native support for basic blockchain data types (esp. fixed-sized arrays)
* typedefs / type aliases (i.e. zero-cost abstractions)
* no requirements on backwards or forwards compatibility
# Comparison of Difference Schemes
## Protobuf
https://developers.google.com/protocol-buffers/docs/overview
https://github.com/lazyledger/protobuf3-solidity-lib
https://github.com/cosmos/cosmos-sdk/blob/master/docs/architecture/adr-027-deterministic-protobuf-serialization.md
https://github.com/cosmos/cosmos-sdk/issues/7488
https://github.com/protocolbuffers/protobuf/issues/3521
## XDR
https://tools.ietf.org/html/rfc4506
https://developers.stellar.org/docs/glossary/xdr
## Veriform
https://github.com/iqlusioninc/veriform
## SimpleSerialize (SSZ)
https://github.com/ethereum/eth2.0-specs/blob/dev/ssz/simple-serialize.md
┆Issue is synchronized with this [Asana task](https://app.asana.com/0/1200392411185755/1200392614340638) by [Unito](https://www.unito.io)
| 1.0 | Investigate canonical encoding scheme - Currently, [a canonical variant of protobuf3 is used to define data structures and do serialization/deserialization](https://github.com/lazyledger/lazyledger-specs/blob/e5df39c617db4a1af0590d505a9009ee311619de/specs/data_structures.md#serialization). This is great for portability, isn't ideal for blockchain applications. For example, there are no fixed-size byte arrays (32-bytes hashes used all over the place in blockchains), or optional fields. Robust protobuf implementations for embedded devices (e.g. hardware wallets) or blockchain smart contracts (e.g. Solidity) are non-existent and would be prohibitive to develop.
The crux is that protobuf was designed for client-server communication, with different versions (i.e. both forwards and backwards compatibility are key features). This is unneeded for core blockchain data structures (e.g. blocks, votes, or transactions), but may be good for node-to-node communication (e.g. messages that wrap around block data, vote data, or transaction data).
We should investigate the feasibility of using a simpler serialization scheme for core data structures.
Desiderata:
* fully deterministic (specifically, bijective)
* binary, not text
* native support for basic blockchain data types (esp. fixed-sized arrays)
* typedefs / type aliases (i.e. zero-cost abstractions)
* no requirements on backwards or forwards compatibility
# Comparison of Difference Schemes
## Protobuf
https://developers.google.com/protocol-buffers/docs/overview
https://github.com/lazyledger/protobuf3-solidity-lib
https://github.com/cosmos/cosmos-sdk/blob/master/docs/architecture/adr-027-deterministic-protobuf-serialization.md
https://github.com/cosmos/cosmos-sdk/issues/7488
https://github.com/protocolbuffers/protobuf/issues/3521
## XDR
https://tools.ietf.org/html/rfc4506
https://developers.stellar.org/docs/glossary/xdr
## Veriform
https://github.com/iqlusioninc/veriform
## SimpleSerialize (SSZ)
https://github.com/ethereum/eth2.0-specs/blob/dev/ssz/simple-serialize.md
┆Issue is synchronized with this [Asana task](https://app.asana.com/0/1200392411185755/1200392614340638) by [Unito](https://www.unito.io)
| non_priority | investigate canonical encoding scheme currently this is great for portability isn t ideal for blockchain applications for example there are no fixed size byte arrays bytes hashes used all over the place in blockchains or optional fields robust protobuf implementations for embedded devices e g hardware wallets or blockchain smart contracts e g solidity are non existent and would be prohibitive to develop the crux is that protobuf was designed for client server communication with different versions i e both forwards and backwards compatibility are key features this is unneeded for core blockchain data structures e g blocks votes or transactions but may be good for node to node communication e g messages that wrap around block data vote data or transaction data we should investigate the feasibility of using a simpler serialization scheme for core data structures desiderata fully deterministic specifically bijective binary not text native support for basic blockchain data types esp fixed sized arrays typedefs type aliases i e zero cost abstractions no requirements on backwards or forwards compatibility comparison of difference schemes protobuf xdr veriform simpleserialize ssz ┆issue is synchronized with this by | 0 |
339,247 | 24,615,111,000 | IssuesEvent | 2022-10-15 07:47:50 | torsteingrindvik/bevy-vfx-bag | https://api.github.com/repos/torsteingrindvik/bevy-vfx-bag | closed | Add images | documentation enhancement | This repo/crate is about something graphical.
Not having images showing off things should be illegal. | 1.0 | Add images - This repo/crate is about something graphical.
Not having images showing off things should be illegal. | non_priority | add images this repo crate is about something graphical not having images showing off things should be illegal | 0 |
67,880 | 14,891,996,988 | IssuesEvent | 2021-01-21 01:46:48 | phytomichael/KSA | https://api.github.com/repos/phytomichael/KSA | opened | CVE-2020-36180 (Medium) detected in jackson-databind-2.8.1.jar | security vulnerability | ## CVE-2020-36180 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /KSA/ksa/ksa/ksa-service-root/ksa-finance-service/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,KSA/ksa/ksa/ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/jackson-databind-2.8.1.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.1.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180>CVE-2020-36180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.1","isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.4.0.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.8.1","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2020-36180","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.cpdsadapter.DriverAdapterCPDS.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | True | CVE-2020-36180 (Medium) detected in jackson-databind-2.8.1.jar - ## CVE-2020-36180 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jackson-databind-2.8.1.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: /KSA/ksa/ksa/ksa-service-root/ksa-finance-service/pom.xml</p>
<p>Path to vulnerable library: /root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,/root/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.8.1/jackson-databind-2.8.1.jar,KSA/ksa/ksa/ksa-web-root/ksa-web/target/ROOT/WEB-INF/lib/jackson-databind-2.8.1.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-1.4.0.RELEASE.jar (Root Library)
- :x: **jackson-databind-2.8.1.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.cpdsadapter.DriverAdapterCPDS.
<p>Publish Date: 2021-01-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180>CVE-2020-36180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>6.8</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"com.fasterxml.jackson.core","packageName":"jackson-databind","packageVersion":"2.8.1","isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:1.4.0.RELEASE;com.fasterxml.jackson.core:jackson-databind:2.8.1","isMinimumFixVersionAvailable":false}],"vulnerabilityIdentifier":"CVE-2020-36180","vulnerabilityDetails":"FasterXML jackson-databind 2.x before 2.9.10.8 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.dbcp2.cpdsadapter.DriverAdapterCPDS.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-36180","cvss2Severity":"medium","cvss2Score":"6.8","extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jackson databind jar cve medium severity vulnerability vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file ksa ksa ksa ksa service root ksa finance service pom xml path to vulnerable library root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar root repository com fasterxml jackson core jackson databind jackson databind jar ksa ksa ksa ksa web root ksa web target root web inf lib jackson databind jar dependency hierarchy spring boot starter web release jar root library x jackson databind jar vulnerable library vulnerability details fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons cpdsadapter driveradaptercpds publish date url a href cvss score details base score metrics not available isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails fasterxml jackson databind x before mishandles the interaction between serialization gadgets and typing related to org apache commons cpdsadapter driveradaptercpds vulnerabilityurl | 0 |
5,509 | 8,067,170,159 | IssuesEvent | 2018-08-05 02:47:39 | PrasadHonrao/GoToMan | https://api.github.com/repos/PrasadHonrao/GoToMan | closed | About Author section for post | requirement | Add about author abstract and display it under each post. This section should have minimal details about author and link to the detail page | 1.0 | About Author section for post - Add about author abstract and display it under each post. This section should have minimal details about author and link to the detail page | non_priority | about author section for post add about author abstract and display it under each post this section should have minimal details about author and link to the detail page | 0 |
184,065 | 14,268,892,949 | IssuesEvent | 2020-11-20 23:35:02 | thefrontside/bigtest | https://api.github.com/repos/thefrontside/bigtest | opened | Including declaration for a non-export (Cypress + Typescript) | @bigtest/interactor chore | Related to #672
## Goal
I would like for the `interactor` package to compile and include the declaration of the Cypress commands:
```js
// interactor/dist/types/integrations/cypress.d.ts
declare namespace Cypress {
interface Chainable<Subject> {
do(interaction: any): Chainable<Subject>;
expect(interaction: any): Chainable<Subject>;
}
}
```
Since we're importing the Cypress commands into `packages/interactor/src/index.ts`, they're being loaded up as a side effect when any of the interactors are imported. This allows Cypress-users to import interactors and use them right away without having to go through any other configuration process.
## Problems
1. Whenever the namespace is exported, the commands are no longer recognized in the tests (in one of my personal repositories that's consuming the preview package from the PR). Is it possible to compile the declaration exactly as shown above?
2. These namespaces can't be declared with ES imports and thus preventing me from importing `Interaction` and `ReadonlyInteraction` types so that I can type out the commands like so: `do(interaction: Interaction<void> | Interaction<void>[]): Chainable<Subject>;` which makes me wonder if declaring a namespace is the wrong approach. | 1.0 | Including declaration for a non-export (Cypress + Typescript) - Related to #672
## Goal
I would like for the `interactor` package to compile and include the declaration of the Cypress commands:
```js
// interactor/dist/types/integrations/cypress.d.ts
declare namespace Cypress {
interface Chainable<Subject> {
do(interaction: any): Chainable<Subject>;
expect(interaction: any): Chainable<Subject>;
}
}
```
Since we're importing the Cypress commands into `packages/interactor/src/index.ts`, they're being loaded up as a side effect when any of the interactors are imported. This allows Cypress-users to import interactors and use them right away without having to go through any other configuration process.
## Problems
1. Whenever the namespace is exported, the commands are no longer recognized in the tests (in one of my personal repositories that's consuming the preview package from the PR). Is it possible to compile the declaration exactly as shown above?
2. These namespaces can't be declared with ES imports and thus preventing me from importing `Interaction` and `ReadonlyInteraction` types so that I can type out the commands like so: `do(interaction: Interaction<void> | Interaction<void>[]): Chainable<Subject>;` which makes me wonder if declaring a namespace is the wrong approach. | non_priority | including declaration for a non export cypress typescript related to goal i would like for the interactor package to compile and include the declaration of the cypress commands js interactor dist types integrations cypress d ts declare namespace cypress interface chainable do interaction any chainable expect interaction any chainable since we re importing the cypress commands into packages interactor src index ts they re being loaded up as a side effect when any of the interactors are imported this allows cypress users to import interactors and use them right away without having to go through any other configuration process problems whenever the namespace is exported the commands are no longer recognized in the tests in one of my personal repositories that s consuming the preview package from the pr is it possible to compile the declaration exactly as shown above these namespaces can t be declared with es imports and thus preventing me from importing interaction and readonlyinteraction types so that i can type out the commands like so do interaction interaction interaction chainable which makes me wonder if declaring a namespace is the wrong approach | 0 |
121,496 | 17,658,428,128 | IssuesEvent | 2021-08-21 02:31:17 | elastic/kibana | https://api.github.com/repos/elastic/kibana | closed | [RAC] Workflow status button group on Security is showing different than on Observability | bug Team:Detections and Resp fixed Team: SecuritySolution v7.15.0 | The workflow status button group is different on Security compared to Observability. And should mimic the recent PR in Observability (https://github.com/elastic/kibana/pull/108215)
**Security**

**Observability:**

| True | [RAC] Workflow status button group on Security is showing different than on Observability - The workflow status button group is different on Security compared to Observability. And should mimic the recent PR in Observability (https://github.com/elastic/kibana/pull/108215)
**Security**

**Observability:**

| non_priority | workflow status button group on security is showing different than on observability the workflow status button group is different on security compared to observability and should mimic the recent pr in observability security observability | 0 |
274,975 | 20,886,012,575 | IssuesEvent | 2022-03-23 05:17:39 | dokc/dokc.github.io | https://api.github.com/repos/dokc/dokc.github.io | closed | [DOCS] | documentation | ### Description
Links not working in **Introduction to the How to DoK Project.**
### Additional information
_No response_ | 1.0 | [DOCS] - ### Description
Links not working in **Introduction to the How to DoK Project.**
### Additional information
_No response_ | non_priority | description links not working in introduction to the how to dok project additional information no response | 0 |
194,069 | 22,261,831,745 | IssuesEvent | 2022-06-10 01:43:23 | artsking/linux-4.19.72 | https://api.github.com/repos/artsking/linux-4.19.72 | reopened | CVE-2019-19081 (Medium) detected in linux-yoctov5.4.51 | security vulnerability | ## CVE-2019-19081 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.19.72/commit/8519fe4185f1a7567a708f01b476f195b0f1046c">8519fe4185f1a7567a708f01b476f195b0f1046c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the nfp_flower_spawn_vnic_reprs() function in drivers/net/ethernet/netronome/nfp/flower/main.c in the Linux kernel before 5.3.4 allows attackers to cause a denial of service (memory consumption), aka CID-8ce39eb5a67a.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19081>CVE-2019-19081</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-19081 (Medium) detected in linux-yoctov5.4.51 - ## CVE-2019-19081 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yoctov5.4.51</b></p></summary>
<p>
<p>Yocto Linux Embedded kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto>https://git.yoctoproject.org/git/linux-yocto</a></p>
<p>Found in HEAD commit: <a href="https://github.com/artsking/linux-4.19.72/commit/8519fe4185f1a7567a708f01b476f195b0f1046c">8519fe4185f1a7567a708f01b476f195b0f1046c</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A memory leak in the nfp_flower_spawn_vnic_reprs() function in drivers/net/ethernet/netronome/nfp/flower/main.c in the Linux kernel before 5.3.4 allows attackers to cause a denial of service (memory consumption), aka CID-8ce39eb5a67a.
<p>Publish Date: 2019-11-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-19081>CVE-2019-19081</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-19081</a></p>
<p>Release Date: 2019-11-18</p>
<p>Fix Resolution: v5.4-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux cve medium severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch master vulnerable source files vulnerability details a memory leak in the nfp flower spawn vnic reprs function in drivers net ethernet netronome nfp flower main c in the linux kernel before allows attackers to cause a denial of service memory consumption aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
244,080 | 20,607,448,366 | IssuesEvent | 2022-03-07 03:12:57 | trinodb/trino | https://api.github.com/repos/trinodb/trino | opened | Flaky TestBigQueryConnectorTest.testConcurrentScans | test | ```
Error: Tests run: 248, Failures: 1, Errors: 0, Skipped: 43, Time elapsed: 1,125.276 s <<< FAILURE! - in TestSuite
Error: io.trino.plugin.bigquery.TestBigQueryConnectorTest.testConcurrentScans Time elapsed: 317.586 s <<< FAILURE!
java.lang.AssertionError: Execution of 'actual' query failed: SELECT sum(if(rand() >= 0, orderkey)) FROM (SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders)
at org.testng.Assert.fail(Assert.java:83)
at io.trino.testing.QueryAssertions.assertQuery(QueryAssertions.java:150)
at io.trino.testing.QueryAssertions.assertQuery(QueryAssertions.java:106)
at io.trino.testing.AbstractTestQueryFramework.assertQuery(AbstractTestQueryFramework.java:210)
at io.trino.testing.BaseConnectorTest.testConcurrentScans(BaseConnectorTest.java:436)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:104)
at org.testng.internal.Invoker.invokeMethod(Invoker.java:645)
at org.testng.internal.Invoker.invokeTestMethod(Invoker.java:851)
at org.testng.internal.Invoker.invokeTestMethods(Invoker.java:1177)
at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:129)
at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:112)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:829)
Caused by: java.lang.RuntimeException: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED: deadline exceeded after 599.997227967s. [closed=[], open=[[buffered_nanos=21991761, remote_addr=bigquerystorage.googleapis.com/172.217.13.74:443]]]
at io.trino.testing.AbstractTestingTrinoClient.execute(AbstractTestingTrinoClient.java:122)
at io.trino.testing.DistributedQueryRunner.execute(DistributedQueryRunner.java:507)
at io.trino.testing.QueryAssertions.assertQuery(QueryAssertions.java:147)
... 16 more
Suppressed: java.lang.Exception: SQL: SELECT sum(if(rand() >= 0, orderkey)) FROM (SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders)
at io.trino.testing.DistributedQueryRunner.execute(DistributedQueryRunner.java:510)
... 17 more
Caused by: com.google.api.gax.rpc.DeadlineExceededException: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED: deadline exceeded after 599.997227967s. [closed=[], open=[[buffered_nanos=21991761, remote_addr=bigquerystorage.googleapis.com/172.217.13.74:443]]]
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:49)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:72)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:60)
at com.google.api.gax.grpc.GrpcExceptionCallable$ExceptionTransformingFuture.onFailure(GrpcExceptionCallable.java:97)
at com.google.api.core.ApiFutures$1.onFailure(ApiFutures.java:68)
at com.google.common.util.concurrent.Futures$CallbackListener.run(Futures.java:1133)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1277)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.setException(AbstractFuture.java:808)
at io.grpc.stub.ClientCalls$GrpcFuture.setException(ClientCalls.java:564)
at io.grpc.stub.ClientCalls$UnaryStreamToFuture.onClose(ClientCalls.java:534)
at io.grpc.internal.DelayedClientCall$DelayedListener$3.run(DelayedClientCall.java:463)
at io.grpc.internal.DelayedClientCall$DelayedListener.delayOrExecute(DelayedClientCall.java:427)
at io.grpc.internal.DelayedClientCall$DelayedListener.onClose(DelayedClientCall.java:460)
at io.grpc.internal.ClientCallImpl.closeObserver(ClientCallImpl.java:562)
at io.grpc.internal.ClientCallImpl.access$300(ClientCallImpl.java:70)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInternal(ClientCallImpl.java:743)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInContext(ClientCallImpl.java:722)
at io.grpc.internal.ContextRunnable.run(ContextRunnable.java:37)
at io.grpc.internal.SerializingExecutor.run(SerializingExecutor.java:133)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:829)
Suppressed: com.google.api.gax.rpc.AsyncTaskException: Asynchronous task failed
at com.google.api.gax.rpc.ApiExceptions.callAndTranslateApiException(ApiExceptions.java:57)
at com.google.api.gax.rpc.UnaryCallable.call(UnaryCallable.java:112)
at com.google.cloud.bigquery.storage.v1.BigQueryReadClient.createReadSession(BigQueryReadClient.java:232)
at io.trino.plugin.bigquery.ReadSessionCreator.create(ReadSessionCreator.java:73)
at io.trino.plugin.bigquery.BigQuerySplitManager.readFromBigQuery(BigQuerySplitManager.java:116)
at io.trino.plugin.bigquery.BigQuerySplitManager.getSplits(BigQuerySplitManager.java:98)
at io.trino.spi.connector.ConnectorSplitManager.getSplits(ConnectorSplitManager.java:37)
at io.trino.split.SplitManager.getSplits(SplitManager.java:75)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitScanAndFilter(SplitSourceFactory.java:183)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitTableScan(SplitSourceFactory.java:157)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitTableScan(SplitSourceFactory.java:128)
at io.trino.sql.planner.plan.TableScanNode.accept(TableScanNode.java:222)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitProject(SplitSourceFactory.java:324)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitProject(SplitSourceFactory.java:128)
at io.trino.sql.planner.plan.ProjectNode.accept(ProjectNode.java:82)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitAggregation(SplitSourceFactory.java:282)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitAggregation(SplitSourceFactory.java:128)
at io.trino.sql.planner.plan.AggregationNode.accept(AggregationNode.java:203)
at io.trino.sql.planner.SplitSourceFactory.createSplitSources(SplitSourceFactory.java:108)
at io.trino.execution.scheduler.SqlQueryScheduler$PipelinedDistributedStagesScheduler.createStageScheduler(SqlQueryScheduler.java:1321)
at io.trino.execution.scheduler.SqlQueryScheduler$PipelinedDistributedStagesScheduler.create(SqlQueryScheduler.java:1201)
at io.trino.execution.scheduler.SqlQueryScheduler.createDistributedStagesScheduler(SqlQueryScheduler.java:349)
at io.trino.execution.scheduler.SqlQueryScheduler.start(SqlQueryScheduler.java:314)
at io.trino.execution.SqlQueryExecution.start(SqlQueryExecution.java:413)
at io.trino.execution.SqlQueryManager.createQuery(SqlQueryManager.java:243)
at io.trino.dispatcher.LocalDispatchQuery.lambda$startExecution$7(LocalDispatchQuery.java:143)
at io.trino.$gen.Trino_testversion____20220305_093813_3.run(Unknown Source)
... 3 more
Caused by: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED: deadline exceeded after 599.997227967s. [closed=[], open=[[buffered_nanos=21991761, remote_addr=bigquerystorage.googleapis.com/172.217.13.74:443]]]
at io.grpc.Status.asRuntimeException(Status.java:535)
... 13 more
```
https://github.com/trinodb/trino/runs/5432178477 | 1.0 | Flaky TestBigQueryConnectorTest.testConcurrentScans - ```
Error: Tests run: 248, Failures: 1, Errors: 0, Skipped: 43, Time elapsed: 1,125.276 s <<< FAILURE! - in TestSuite
Error: io.trino.plugin.bigquery.TestBigQueryConnectorTest.testConcurrentScans Time elapsed: 317.586 s <<< FAILURE!
java.lang.AssertionError: Execution of 'actual' query failed: SELECT sum(if(rand() >= 0, orderkey)) FROM (SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders)
at org.testng.Assert.fail(Assert.java:83)
at io.trino.testing.QueryAssertions.assertQuery(QueryAssertions.java:150)
at io.trino.testing.QueryAssertions.assertQuery(QueryAssertions.java:106)
at io.trino.testing.AbstractTestQueryFramework.assertQuery(AbstractTestQueryFramework.java:210)
at io.trino.testing.BaseConnectorTest.testConcurrentScans(BaseConnectorTest.java:436)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at java.base/jdk.internal.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at java.base/jdk.internal.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.base/java.lang.reflect.Method.invoke(Method.java:566)
at org.testng.internal.MethodInvocationHelper.invokeMethod(MethodInvocationHelper.java:104)
at org.testng.internal.Invoker.invokeMethod(Invoker.java:645)
at org.testng.internal.Invoker.invokeTestMethod(Invoker.java:851)
at org.testng.internal.Invoker.invokeTestMethods(Invoker.java:1177)
at org.testng.internal.TestMethodWorker.invokeTestMethods(TestMethodWorker.java:129)
at org.testng.internal.TestMethodWorker.run(TestMethodWorker.java:112)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:829)
Caused by: java.lang.RuntimeException: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED: deadline exceeded after 599.997227967s. [closed=[], open=[[buffered_nanos=21991761, remote_addr=bigquerystorage.googleapis.com/172.217.13.74:443]]]
at io.trino.testing.AbstractTestingTrinoClient.execute(AbstractTestingTrinoClient.java:122)
at io.trino.testing.DistributedQueryRunner.execute(DistributedQueryRunner.java:507)
at io.trino.testing.QueryAssertions.assertQuery(QueryAssertions.java:147)
... 16 more
Suppressed: java.lang.Exception: SQL: SELECT sum(if(rand() >= 0, orderkey)) FROM (SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders UNION ALL SELECT * FROM orders)
at io.trino.testing.DistributedQueryRunner.execute(DistributedQueryRunner.java:510)
... 17 more
Caused by: com.google.api.gax.rpc.DeadlineExceededException: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED: deadline exceeded after 599.997227967s. [closed=[], open=[[buffered_nanos=21991761, remote_addr=bigquerystorage.googleapis.com/172.217.13.74:443]]]
at com.google.api.gax.rpc.ApiExceptionFactory.createException(ApiExceptionFactory.java:49)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:72)
at com.google.api.gax.grpc.GrpcApiExceptionFactory.create(GrpcApiExceptionFactory.java:60)
at com.google.api.gax.grpc.GrpcExceptionCallable$ExceptionTransformingFuture.onFailure(GrpcExceptionCallable.java:97)
at com.google.api.core.ApiFutures$1.onFailure(ApiFutures.java:68)
at com.google.common.util.concurrent.Futures$CallbackListener.run(Futures.java:1133)
at com.google.common.util.concurrent.DirectExecutor.execute(DirectExecutor.java:31)
at com.google.common.util.concurrent.AbstractFuture.executeListener(AbstractFuture.java:1277)
at com.google.common.util.concurrent.AbstractFuture.complete(AbstractFuture.java:1038)
at com.google.common.util.concurrent.AbstractFuture.setException(AbstractFuture.java:808)
at io.grpc.stub.ClientCalls$GrpcFuture.setException(ClientCalls.java:564)
at io.grpc.stub.ClientCalls$UnaryStreamToFuture.onClose(ClientCalls.java:534)
at io.grpc.internal.DelayedClientCall$DelayedListener$3.run(DelayedClientCall.java:463)
at io.grpc.internal.DelayedClientCall$DelayedListener.delayOrExecute(DelayedClientCall.java:427)
at io.grpc.internal.DelayedClientCall$DelayedListener.onClose(DelayedClientCall.java:460)
at io.grpc.internal.ClientCallImpl.closeObserver(ClientCallImpl.java:562)
at io.grpc.internal.ClientCallImpl.access$300(ClientCallImpl.java:70)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInternal(ClientCallImpl.java:743)
at io.grpc.internal.ClientCallImpl$ClientStreamListenerImpl$1StreamClosed.runInContext(ClientCallImpl.java:722)
at io.grpc.internal.ContextRunnable.run(ContextRunnable.java:37)
at io.grpc.internal.SerializingExecutor.run(SerializingExecutor.java:133)
at java.base/java.util.concurrent.ThreadPoolExecutor.runWorker(ThreadPoolExecutor.java:1128)
at java.base/java.util.concurrent.ThreadPoolExecutor$Worker.run(ThreadPoolExecutor.java:628)
at java.base/java.lang.Thread.run(Thread.java:829)
Suppressed: com.google.api.gax.rpc.AsyncTaskException: Asynchronous task failed
at com.google.api.gax.rpc.ApiExceptions.callAndTranslateApiException(ApiExceptions.java:57)
at com.google.api.gax.rpc.UnaryCallable.call(UnaryCallable.java:112)
at com.google.cloud.bigquery.storage.v1.BigQueryReadClient.createReadSession(BigQueryReadClient.java:232)
at io.trino.plugin.bigquery.ReadSessionCreator.create(ReadSessionCreator.java:73)
at io.trino.plugin.bigquery.BigQuerySplitManager.readFromBigQuery(BigQuerySplitManager.java:116)
at io.trino.plugin.bigquery.BigQuerySplitManager.getSplits(BigQuerySplitManager.java:98)
at io.trino.spi.connector.ConnectorSplitManager.getSplits(ConnectorSplitManager.java:37)
at io.trino.split.SplitManager.getSplits(SplitManager.java:75)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitScanAndFilter(SplitSourceFactory.java:183)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitTableScan(SplitSourceFactory.java:157)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitTableScan(SplitSourceFactory.java:128)
at io.trino.sql.planner.plan.TableScanNode.accept(TableScanNode.java:222)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitProject(SplitSourceFactory.java:324)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitProject(SplitSourceFactory.java:128)
at io.trino.sql.planner.plan.ProjectNode.accept(ProjectNode.java:82)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitAggregation(SplitSourceFactory.java:282)
at io.trino.sql.planner.SplitSourceFactory$Visitor.visitAggregation(SplitSourceFactory.java:128)
at io.trino.sql.planner.plan.AggregationNode.accept(AggregationNode.java:203)
at io.trino.sql.planner.SplitSourceFactory.createSplitSources(SplitSourceFactory.java:108)
at io.trino.execution.scheduler.SqlQueryScheduler$PipelinedDistributedStagesScheduler.createStageScheduler(SqlQueryScheduler.java:1321)
at io.trino.execution.scheduler.SqlQueryScheduler$PipelinedDistributedStagesScheduler.create(SqlQueryScheduler.java:1201)
at io.trino.execution.scheduler.SqlQueryScheduler.createDistributedStagesScheduler(SqlQueryScheduler.java:349)
at io.trino.execution.scheduler.SqlQueryScheduler.start(SqlQueryScheduler.java:314)
at io.trino.execution.SqlQueryExecution.start(SqlQueryExecution.java:413)
at io.trino.execution.SqlQueryManager.createQuery(SqlQueryManager.java:243)
at io.trino.dispatcher.LocalDispatchQuery.lambda$startExecution$7(LocalDispatchQuery.java:143)
at io.trino.$gen.Trino_testversion____20220305_093813_3.run(Unknown Source)
... 3 more
Caused by: io.grpc.StatusRuntimeException: DEADLINE_EXCEEDED: deadline exceeded after 599.997227967s. [closed=[], open=[[buffered_nanos=21991761, remote_addr=bigquerystorage.googleapis.com/172.217.13.74:443]]]
at io.grpc.Status.asRuntimeException(Status.java:535)
... 13 more
```
https://github.com/trinodb/trino/runs/5432178477 | non_priority | flaky testbigqueryconnectortest testconcurrentscans error tests run failures errors skipped time elapsed s failure in testsuite error io trino plugin bigquery testbigqueryconnectortest testconcurrentscans time elapsed s failure java lang assertionerror execution of actual query failed select sum if rand orderkey from select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders at org testng assert fail assert java at io trino testing queryassertions assertquery queryassertions java at io trino testing queryassertions assertquery queryassertions java at io trino testing abstracttestqueryframework assertquery abstracttestqueryframework java at io trino testing baseconnectortest testconcurrentscans baseconnectortest java at java base jdk internal reflect nativemethodaccessorimpl native method at java base jdk internal reflect nativemethodaccessorimpl invoke nativemethodaccessorimpl java at java base jdk internal reflect delegatingmethodaccessorimpl invoke delegatingmethodaccessorimpl java at java base java lang reflect method invoke method java at org testng internal methodinvocationhelper invokemethod methodinvocationhelper java at org testng internal invoker invokemethod invoker java at org testng internal invoker invoketestmethod invoker java at org testng internal invoker invoketestmethods invoker java at org testng internal testmethodworker invoketestmethods testmethodworker java at org testng internal testmethodworker run testmethodworker java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java caused by java lang runtimeexception io grpc statusruntimeexception deadline exceeded deadline exceeded after open at io trino testing abstracttestingtrinoclient execute abstracttestingtrinoclient java at io trino testing distributedqueryrunner execute distributedqueryrunner java at io trino testing queryassertions assertquery queryassertions java more suppressed java lang exception sql select sum if rand orderkey from select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders union all select from orders at io trino testing distributedqueryrunner execute distributedqueryrunner java more caused by com google api gax rpc deadlineexceededexception io grpc statusruntimeexception deadline exceeded deadline exceeded after open at com google api gax rpc apiexceptionfactory createexception apiexceptionfactory java at com google api gax grpc grpcapiexceptionfactory create grpcapiexceptionfactory java at com google api gax grpc grpcapiexceptionfactory create grpcapiexceptionfactory java at com google api gax grpc grpcexceptioncallable exceptiontransformingfuture onfailure grpcexceptioncallable java at com google api core apifutures onfailure apifutures java at com google common util concurrent futures callbacklistener run futures java at com google common util concurrent directexecutor execute directexecutor java at com google common util concurrent abstractfuture executelistener abstractfuture java at com google common util concurrent abstractfuture complete abstractfuture java at com google common util concurrent abstractfuture setexception abstractfuture java at io grpc stub clientcalls grpcfuture setexception clientcalls java at io grpc stub clientcalls unarystreamtofuture onclose clientcalls java at io grpc internal delayedclientcall delayedlistener run delayedclientcall java at io grpc internal delayedclientcall delayedlistener delayorexecute delayedclientcall java at io grpc internal delayedclientcall delayedlistener onclose delayedclientcall java at io grpc internal clientcallimpl closeobserver clientcallimpl java at io grpc internal clientcallimpl access clientcallimpl java at io grpc internal clientcallimpl clientstreamlistenerimpl runinternal clientcallimpl java at io grpc internal clientcallimpl clientstreamlistenerimpl runincontext clientcallimpl java at io grpc internal contextrunnable run contextrunnable java at io grpc internal serializingexecutor run serializingexecutor java at java base java util concurrent threadpoolexecutor runworker threadpoolexecutor java at java base java util concurrent threadpoolexecutor worker run threadpoolexecutor java at java base java lang thread run thread java suppressed com google api gax rpc asynctaskexception asynchronous task failed at com google api gax rpc apiexceptions callandtranslateapiexception apiexceptions java at com google api gax rpc unarycallable call unarycallable java at com google cloud bigquery storage bigqueryreadclient createreadsession bigqueryreadclient java at io trino plugin bigquery readsessioncreator create readsessioncreator java at io trino plugin bigquery bigquerysplitmanager readfrombigquery bigquerysplitmanager java at io trino plugin bigquery bigquerysplitmanager getsplits bigquerysplitmanager java at io trino spi connector connectorsplitmanager getsplits connectorsplitmanager java at io trino split splitmanager getsplits splitmanager java at io trino sql planner splitsourcefactory visitor visitscanandfilter splitsourcefactory java at io trino sql planner splitsourcefactory visitor visittablescan splitsourcefactory java at io trino sql planner splitsourcefactory visitor visittablescan splitsourcefactory java at io trino sql planner plan tablescannode accept tablescannode java at io trino sql planner splitsourcefactory visitor visitproject splitsourcefactory java at io trino sql planner splitsourcefactory visitor visitproject splitsourcefactory java at io trino sql planner plan projectnode accept projectnode java at io trino sql planner splitsourcefactory visitor visitaggregation splitsourcefactory java at io trino sql planner splitsourcefactory visitor visitaggregation splitsourcefactory java at io trino sql planner plan aggregationnode accept aggregationnode java at io trino sql planner splitsourcefactory createsplitsources splitsourcefactory java at io trino execution scheduler sqlqueryscheduler pipelineddistributedstagesscheduler createstagescheduler sqlqueryscheduler java at io trino execution scheduler sqlqueryscheduler pipelineddistributedstagesscheduler create sqlqueryscheduler java at io trino execution scheduler sqlqueryscheduler createdistributedstagesscheduler sqlqueryscheduler java at io trino execution scheduler sqlqueryscheduler start sqlqueryscheduler java at io trino execution sqlqueryexecution start sqlqueryexecution java at io trino execution sqlquerymanager createquery sqlquerymanager java at io trino dispatcher localdispatchquery lambda startexecution localdispatchquery java at io trino gen trino testversion run unknown source more caused by io grpc statusruntimeexception deadline exceeded deadline exceeded after open at io grpc status asruntimeexception status java more | 0 |
56,144 | 14,947,664,869 | IssuesEvent | 2021-01-26 08:59:49 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | Metamodel is missing length of array element type | T: Defect | ### Expected behavior
The metamodel of an array with an element type of defined length should contain the length on the element type.
### Actual behavior
The element type does not contain a length.
### Steps to reproduce the problem
This code illustrates to issue:
`@Test
public void testCreateTable() throws Exception {
Connection conn = getSourceDbConnection();
conn.createStatement().execute("create table test_table (col5 varchar(10)[] not null)");
DSLContext dsl = DSL.using(conn);
org.jooq.Table<?> testTable = dsl.meta().getSchemas("test-source").get(0).getTable("test_table");
Field field = testTable.field(0);
DataType dataType = field.getDataType(dsl.configuration());
DataType elementType = dataType.getArrayComponentDataType();
assertThat(elementType.length(), is(10));
}`
### Versions
- jOOQ: jOOQ-3.15.0-SNAPSHOT-20210126004003.zip
- Java: 11
- Database (include vendor): Postgresql 10.7
- OS: Linux
- JDBC Driver (include name if inofficial driver): org.postgresql (42.2.5)
| 1.0 | Metamodel is missing length of array element type - ### Expected behavior
The metamodel of an array with an element type of defined length should contain the length on the element type.
### Actual behavior
The element type does not contain a length.
### Steps to reproduce the problem
This code illustrates to issue:
`@Test
public void testCreateTable() throws Exception {
Connection conn = getSourceDbConnection();
conn.createStatement().execute("create table test_table (col5 varchar(10)[] not null)");
DSLContext dsl = DSL.using(conn);
org.jooq.Table<?> testTable = dsl.meta().getSchemas("test-source").get(0).getTable("test_table");
Field field = testTable.field(0);
DataType dataType = field.getDataType(dsl.configuration());
DataType elementType = dataType.getArrayComponentDataType();
assertThat(elementType.length(), is(10));
}`
### Versions
- jOOQ: jOOQ-3.15.0-SNAPSHOT-20210126004003.zip
- Java: 11
- Database (include vendor): Postgresql 10.7
- OS: Linux
- JDBC Driver (include name if inofficial driver): org.postgresql (42.2.5)
| non_priority | metamodel is missing length of array element type expected behavior the metamodel of an array with an element type of defined length should contain the length on the element type actual behavior the element type does not contain a length steps to reproduce the problem this code illustrates to issue test public void testcreatetable throws exception connection conn getsourcedbconnection conn createstatement execute create table test table varchar not null dslcontext dsl dsl using conn org jooq table testtable dsl meta getschemas test source get gettable test table field field testtable field datatype datatype field getdatatype dsl configuration datatype elementtype datatype getarraycomponentdatatype assertthat elementtype length is versions jooq jooq snapshot zip java database include vendor postgresql os linux jdbc driver include name if inofficial driver org postgresql | 0 |
9,893 | 3,078,195,764 | IssuesEvent | 2015-08-21 08:34:39 | devprovers/QA-Teamwork-Provers | https://api.github.com/repos/devprovers/QA-Teamwork-Provers | closed | Display Company | To Be Tested Use Case | Use Case №24: Display Company
Primary Actor: User
Pre Condition: User logged in
Scenario:
1. User selects a company from CRM/Companies (left pane, refer user screens in Appendix )
2. System displays the contact information
| 1.0 | Display Company - Use Case №24: Display Company
Primary Actor: User
Pre Condition: User logged in
Scenario:
1. User selects a company from CRM/Companies (left pane, refer user screens in Appendix )
2. System displays the contact information
| non_priority | display company use case № display company primary actor user pre condition user logged in scenario user selects a company from crm companies left pane refer user screens in appendix system displays the contact information | 0 |
43,066 | 5,567,172,767 | IssuesEvent | 2017-03-27 02:11:03 | dotnet/roslyn | https://api.github.com/repos/dotnet/roslyn | closed | Please extend the object-initialization syntax so that json literals could literally initialize json data | 4 - In Review Area-Language Design | Please extend the syntax for object initializers so that json literals would be valid, and would cause the construction of some representation isomorphic to the json data.
It would be nice if there were some way to indicate which json data structure should be constructed, but obviously that cannot be _within_ the data, as it would no longer be json.
| 1.0 | Please extend the object-initialization syntax so that json literals could literally initialize json data - Please extend the syntax for object initializers so that json literals would be valid, and would cause the construction of some representation isomorphic to the json data.
It would be nice if there were some way to indicate which json data structure should be constructed, but obviously that cannot be _within_ the data, as it would no longer be json.
| non_priority | please extend the object initialization syntax so that json literals could literally initialize json data please extend the syntax for object initializers so that json literals would be valid and would cause the construction of some representation isomorphic to the json data it would be nice if there were some way to indicate which json data structure should be constructed but obviously that cannot be within the data as it would no longer be json | 0 |
278,684 | 30,702,386,164 | IssuesEvent | 2023-07-27 01:25:42 | panasalap/linux-4.1.15 | https://api.github.com/repos/panasalap/linux-4.1.15 | closed | CVE-2019-15216 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 - autoclosed | Mend: dependency security vulnerability | ## CVE-2019-15216 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Library home page: <a href=https://github.com/gregkh/linux.git>https://github.com/gregkh/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/misc/yurex.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/misc/yurex.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.0.14. There is a NULL pointer dereference caused by a malicious USB device in the drivers/usb/misc/yurex.c driver.
<p>Publish Date: 2019-08-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-15216>CVE-2019-15216</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-15216">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-15216</a></p>
<p>Release Date: 2019-09-03</p>
<p>Fix Resolution: v5.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-15216 (Medium) detected in linux179e72b561d3d331c850e1a5779688d7a7de5246 - autoclosed - ## CVE-2019-15216 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux179e72b561d3d331c850e1a5779688d7a7de5246</b></p></summary>
<p>
<p>Linux kernel stable tree mirror</p>
<p>Library home page: <a href=https://github.com/gregkh/linux.git>https://github.com/gregkh/linux.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/misc/yurex.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/usb/misc/yurex.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
An issue was discovered in the Linux kernel before 5.0.14. There is a NULL pointer dereference caused by a malicious USB device in the drivers/usb/misc/yurex.c driver.
<p>Publish Date: 2019-08-19
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-15216>CVE-2019-15216</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.6</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Physical
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-15216">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-15216</a></p>
<p>Release Date: 2019-09-03</p>
<p>Fix Resolution: v5.1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in autoclosed cve medium severity vulnerability vulnerable library linux kernel stable tree mirror library home page a href found in base branch master vulnerable source files drivers usb misc yurex c drivers usb misc yurex c vulnerability details an issue was discovered in the linux kernel before there is a null pointer dereference caused by a malicious usb device in the drivers usb misc yurex c driver publish date url a href cvss score details base score metrics exploitability metrics attack vector physical attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
8,517 | 2,994,758,848 | IssuesEvent | 2015-07-22 13:41:44 | softlayer/sl-ember-components | https://api.github.com/repos/softlayer/sl-ember-components | closed | Reformat to follow style guide | 2 - Working sl-textarea tests | https://github.com/softlayer/sl-ember-components/blob/develop/tests/unit/components/sl-textarea-test.js#L45
Style Guide: https://github.com/softlayer/ember-style-guide#whitespace
<!---
@huboard:{"order":411.0,"milestone_order":364.9998779296875}
-->
| 1.0 | Reformat to follow style guide - https://github.com/softlayer/sl-ember-components/blob/develop/tests/unit/components/sl-textarea-test.js#L45
Style Guide: https://github.com/softlayer/ember-style-guide#whitespace
<!---
@huboard:{"order":411.0,"milestone_order":364.9998779296875}
-->
| non_priority | reformat to follow style guide style guide huboard order milestone order | 0 |
153,349 | 19,705,162,505 | IssuesEvent | 2022-01-12 21:02:47 | jacobfowlkes-p/sbt | https://api.github.com/repos/jacobfowlkes-p/sbt | opened | CVE-2020-11023 (Medium) detected in jquery-2.1.4.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jacobfowlkes-p/sbt/commit/11e9d6d5498f81fb31b937eec8b879bbf9622021">11e9d6d5498f81fb31b937eec8b879bbf9622021</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"2.1.4","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"jquery:2.1.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11023 (Medium) detected in jquery-2.1.4.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-2.1.4.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.4/jquery.min.js</a></p>
<p>
Dependency Hierarchy:
- :x: **jquery-2.1.4.min.js** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jacobfowlkes-p/sbt/commit/11e9d6d5498f81fb31b937eec8b879bbf9622021">11e9d6d5498f81fb31b937eec8b879bbf9622021</a></p>
<p>Found in base branch: <b>develop</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"2.1.4","packageFilePaths":[null],"isTransitiveDependency":false,"dependencyTree":"jquery:2.1.4","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0","isBinary":false}],"baseBranches":["develop"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href dependency hierarchy x jquery min js vulnerable library found in head commit a href found in base branch develop vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery jquery rails isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery jquery rails isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl | 0 |
111,941 | 14,173,645,831 | IssuesEvent | 2020-11-12 18:39:39 | dotnet/project-system | https://api.github.com/repos/dotnet/project-system | closed | Visual Studio new projects not adhering to Microsoft.CodeAnalysis.FxCopAnalyzers | Discussion/Question Feature-Templates Resolution-By-Design Triage-Won't-Fix | _This issue has been moved from [a ticket on Developer Community](https://developercommunity.visualstudio.com/content/idea/653066/visual-studio-new-projects-not-adhering-to-microso.html)._
---
When one creates a new Visual Studio project from one of the templates, and then analyze it using the FxCopAnalyzers (and probably other Microsoft.CodeAnalysis analyzers) then there are many warnings.
My suggestion is that Microsoft should update their templates to adhere to this, and ideally all other Roslyn analyzers.
---
### Original Comments
#### Jane Wu [MSFT] on 7/22/2019, 03:53 AM:
<p>Thank you for taking the time to provide your suggestion. We will do some preliminary checks to make sure we can proceed further. We’ll provide an update once the issue has been triaged by the product team.</p>
| 1.0 | Visual Studio new projects not adhering to Microsoft.CodeAnalysis.FxCopAnalyzers - _This issue has been moved from [a ticket on Developer Community](https://developercommunity.visualstudio.com/content/idea/653066/visual-studio-new-projects-not-adhering-to-microso.html)._
---
When one creates a new Visual Studio project from one of the templates, and then analyze it using the FxCopAnalyzers (and probably other Microsoft.CodeAnalysis analyzers) then there are many warnings.
My suggestion is that Microsoft should update their templates to adhere to this, and ideally all other Roslyn analyzers.
---
### Original Comments
#### Jane Wu [MSFT] on 7/22/2019, 03:53 AM:
<p>Thank you for taking the time to provide your suggestion. We will do some preliminary checks to make sure we can proceed further. We’ll provide an update once the issue has been triaged by the product team.</p>
| non_priority | visual studio new projects not adhering to microsoft codeanalysis fxcopanalyzers this issue has been moved from when one creates a new visual studio project from one of the templates and then analyze it using the fxcopanalyzers and probably other microsoft codeanalysis analyzers then there are many warnings my suggestion is that microsoft should update their templates to adhere to this and ideally all other roslyn analyzers original comments jane wu on am thank you for taking the time to provide your suggestion we will do some preliminary checks to make sure we can proceed further we’ll provide an update once the issue has been triaged by the product team | 0 |
259,638 | 27,702,891,474 | IssuesEvent | 2023-03-14 09:18:07 | harrinry/drupal | https://api.github.com/repos/harrinry/drupal | opened | webpack-5.63.0.tgz: 1 vulnerabilities (highest severity is: 5.5) | Mend: dependency security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>webpack-5.63.0.tgz</b></p></summary>
<p>Packs CommonJs/AMD modules for the browser. Allows to split your codebase into multiple bundles, which can be loaded on demand. Support loaders to preprocess files, i.e. json, jsx, es7, css, less, ... and your custom stuff.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz">https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz</a></p>
<p>Path to dependency file: /core/package.json</p>
<p>Path to vulnerable library: /core/node_modules/webpack/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/harrinry/drupal/commit/16626d58172731968ccace84d2e7487bf814dc11">16626d58172731968ccace84d2e7487bf814dc11</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (webpack version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-28154](https://www.mend.io/vulnerability-database/CVE-2023-28154) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | webpack-5.63.0.tgz | Direct | webpack - 5.76.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-28154</summary>
### Vulnerable Library - <b>webpack-5.63.0.tgz</b></p>
<p>Packs CommonJs/AMD modules for the browser. Allows to split your codebase into multiple bundles, which can be loaded on demand. Support loaders to preprocess files, i.e. json, jsx, es7, css, less, ... and your custom stuff.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz">https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz</a></p>
<p>Path to dependency file: /core/package.json</p>
<p>Path to vulnerable library: /core/node_modules/webpack/package.json</p>
<p>
Dependency Hierarchy:
- :x: **webpack-5.63.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/drupal/commit/16626d58172731968ccace84d2e7487bf814dc11">16626d58172731968ccace84d2e7487bf814dc11</a></p>
<p>Found in base branch: <b>9.4.x</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Webpack 5 before 5.76.0 does not avoid cross-realm object access. ImportParserPlugin.js mishandles the magic comment feature. An attacker who controls a property of an untrusted object can obtain access to the real global object.
<p>Publish Date: 2023-03-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28154>CVE-2023-28154</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-03-13</p>
<p>Fix Resolution: webpack - 5.76.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | True | webpack-5.63.0.tgz: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>webpack-5.63.0.tgz</b></p></summary>
<p>Packs CommonJs/AMD modules for the browser. Allows to split your codebase into multiple bundles, which can be loaded on demand. Support loaders to preprocess files, i.e. json, jsx, es7, css, less, ... and your custom stuff.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz">https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz</a></p>
<p>Path to dependency file: /core/package.json</p>
<p>Path to vulnerable library: /core/node_modules/webpack/package.json</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/harrinry/drupal/commit/16626d58172731968ccace84d2e7487bf814dc11">16626d58172731968ccace84d2e7487bf814dc11</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (webpack version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2023-28154](https://www.mend.io/vulnerability-database/CVE-2023-28154) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | webpack-5.63.0.tgz | Direct | webpack - 5.76.0 | ✅ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2023-28154</summary>
### Vulnerable Library - <b>webpack-5.63.0.tgz</b></p>
<p>Packs CommonJs/AMD modules for the browser. Allows to split your codebase into multiple bundles, which can be loaded on demand. Support loaders to preprocess files, i.e. json, jsx, es7, css, less, ... and your custom stuff.</p>
<p>Library home page: <a href="https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz">https://registry.npmjs.org/webpack/-/webpack-5.63.0.tgz</a></p>
<p>Path to dependency file: /core/package.json</p>
<p>Path to vulnerable library: /core/node_modules/webpack/package.json</p>
<p>
Dependency Hierarchy:
- :x: **webpack-5.63.0.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/harrinry/drupal/commit/16626d58172731968ccace84d2e7487bf814dc11">16626d58172731968ccace84d2e7487bf814dc11</a></p>
<p>Found in base branch: <b>9.4.x</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
Webpack 5 before 5.76.0 does not avoid cross-realm object access. ImportParserPlugin.js mishandles the magic comment feature. An attacker who controls a property of an untrusted object can obtain access to the real global object.
<p>Publish Date: 2023-03-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2023-28154>CVE-2023-28154</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2023-03-13</p>
<p>Fix Resolution: webpack - 5.76.0</p>
</p>
<p></p>
:rescue_worker_helmet: Automatic Remediation is available for this issue
</details>
***
<p>:rescue_worker_helmet: Automatic Remediation is available for this issue.</p> | non_priority | webpack tgz vulnerabilities highest severity is vulnerable library webpack tgz packs commonjs amd modules for the browser allows to split your codebase into multiple bundles which can be loaded on demand support loaders to preprocess files i e json jsx css less and your custom stuff library home page a href path to dependency file core package json path to vulnerable library core node modules webpack package json found in head commit a href vulnerabilities cve severity cvss dependency type fixed in webpack version remediation available medium webpack tgz direct webpack details cve vulnerable library webpack tgz packs commonjs amd modules for the browser allows to split your codebase into multiple bundles which can be loaded on demand support loaders to preprocess files i e json jsx css less and your custom stuff library home page a href path to dependency file core package json path to vulnerable library core node modules webpack package json dependency hierarchy x webpack tgz vulnerable library found in head commit a href found in base branch x vulnerability details webpack before does not avoid cross realm object access importparserplugin js mishandles the magic comment feature an attacker who controls a property of an untrusted object can obtain access to the real global object publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution webpack rescue worker helmet automatic remediation is available for this issue rescue worker helmet automatic remediation is available for this issue | 0 |
51,723 | 13,211,297,164 | IssuesEvent | 2020-08-15 22:07:39 | icecube-trac/tix4 | https://api.github.com/repos/icecube-trac/tix4 | opened | PROPOSAL - tries to generate tables into $I3_TESTDATA (Trac #927) | Incomplete Migration Migrated from Trac combo simulation defect | <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/927">https://code.icecube.wisc.edu/projects/icecube/ticket/927</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-04-13T20:38:32",
"_ts": "1428957512789301",
"description": "In response to #923:\n\nThe underlying issue is that PROPOSAL is trying to generate tables (correctly) into $I3_TESTDATA (incorrectly). It should generate them into a local directory instead.",
"reporter": "nega",
"cc": "munser",
"resolution": "fixed",
"time": "2015-04-13T16:23:19",
"component": "combo simulation",
"summary": "PROPOSAL - tries to generate tables into $I3_TESTDATA",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | PROPOSAL - tries to generate tables into $I3_TESTDATA (Trac #927) - <details>
<summary><em>Migrated from <a href="https://code.icecube.wisc.edu/projects/icecube/ticket/927">https://code.icecube.wisc.edu/projects/icecube/ticket/927</a>, reported by negaand owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2015-04-13T20:38:32",
"_ts": "1428957512789301",
"description": "In response to #923:\n\nThe underlying issue is that PROPOSAL is trying to generate tables (correctly) into $I3_TESTDATA (incorrectly). It should generate them into a local directory instead.",
"reporter": "nega",
"cc": "munser",
"resolution": "fixed",
"time": "2015-04-13T16:23:19",
"component": "combo simulation",
"summary": "PROPOSAL - tries to generate tables into $I3_TESTDATA",
"priority": "normal",
"keywords": "",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| non_priority | proposal tries to generate tables into testdata trac migrated from json status closed changetime ts description in response to n nthe underlying issue is that proposal is trying to generate tables correctly into testdata incorrectly it should generate them into a local directory instead reporter nega cc munser resolution fixed time component combo simulation summary proposal tries to generate tables into testdata priority normal keywords milestone owner nega type defect | 0 |
130,052 | 27,615,405,050 | IssuesEvent | 2023-03-09 18:56:58 | ArctosDB/arctos | https://api.github.com/repos/ArctosDB/arctos | opened | Code Table Request - LFL: CSU Larval Fish Lab | Function-CodeTables | ## Instructions
This is a template to facilitate communication with the Arctos Code Table Committee. Submit a separate request for each relevant value. This form is appropriate for exploring how data may best be stored, for adding vocabulary, or for updating existing definitions.
Reviewing documentation before proceeding will result in a more enjoyable experience.
* [Issue Documentation](http://handbook.arctosdb.org/how_to/How-to-Use-Issues-in-Arctos.html)
* [Code Table Documentation](https://handbook.arctosdb.org/how_to/How-To-Manage-Code-Table-Requests.html)
* [Video Tutorial - Submit a Code Table Request](https://youtu.be/t2jHbsRA3lk)
------------------------------
## Initial Request
**Goal**: Describe what you're trying to accomplish. This is the only necessary step to start this process. The Committee is available to assist with all other steps. Please clearly indicate any uncertainty or desired guidance if you proceed beyond this step.
All [LFL: CSU Larval Fish Lab](https://arctos.database.museum/info/ctDocumentation.cfm?table=ctcoll_other_id_type#lfl__csu_larval_fish_lab) should be replaced with other ID type = other identifier and issued by agent [Colorado State University Larval Fish Laboratory](https://arctos.database.museum/agent/21347717)
**Proposed Value**: Proposed new value. This should be clear and compatible with similar values in the relevant table and across Arctos.
**Proposed Definition**: Clear, complete, non-collection-type-specific **functional** definition of the value. Avoid discipline-specific terminology if possible, include parenthetically if unavoidable.
**Context**: Describe why this new value is necessary and existing values are not.
**Table**: Code Tables are http://arctos.database.museum/info/ctDocumentation.cfm. Link to the specific table or value. This may involve multiple tables and will control datatype for Attributes. OtherID requests require BaseURL (and example) or explanation. Please ask for assistance if unsure.
**Collection type**: Some code tables contain collection-type-specific values. ``collection_cde`` may be found from https://arctos.database.museum/home.cfm
**Priority**: Please describe the urgency and/or choose a priority-label to the right. You should expect a response within two working days, and may utilize [Arctos Contacts](https://arctosdb.org/contacts/) if you feel response is lacking.
**Available for Public View**: Most data are by default publicly available. Describe any necessary access restrictions.
**Project**: Add the issue to the [Code Table Management Project](https://github.com/ArctosDB/arctos/projects/13#card-31628184).
**Discussion**: Please reach out to anyone who might be affected by this change. Leave a comment or add this to the Committee agenda if you believe more focused conversation is necessary.
## Approval
All of the following must be checked before this may proceed.
The [How-To Document](https://handbook.arctosdb.org/how_to/How-To-Manage-Code-Table-Requests.html) should be followed. Pay particular attention to terminology (with emphasis on consistency) and documentation (with emphasis on functionality).
- [ ] Code Table Administrator[1] - check and initial, comment, or thumbs-up to indicate that the request complies with the how-to documentation and has your approval
- [ ] Code Table Administrator[2] - check and initial, comment, or thumbs-up to indicate that the request complies with the how-to documentation and has your approval
- [ ] DBA - The request is functionally acceptable. The term is not a functional duplicate, and is compatible with existing data and code.
- [ ] DBA - Appropriate code or handlers are in place as necessary. (ID_References, Media Relationships, Encumbrances, etc. require particular attention)
## Rejection
If you believe this request should not proceed, explain why here. Suggest any changes that would make the change acceptable, alternate (usually existing) paths to the same goals, etc.
1. Can a suitable solution be found here? If not, proceed to (2)
2. Can a suitable solution be found by Code Table Committee discussion? If not, proceed to (3)
3. Take the discussion to a monthly Arctos Working Group meeting for final resolution.
## Implementation
Once all of the Approval Checklist is appropriately checked and there are no Rejection comments, or in special circumstances by decree of the Arctos Working Group, the change may be made.
Review everything one last time. Ensure the How-To has been followed. Ensure all checks have been made by appropriate personnel.
Make changes as described above. Ensure the URL of this Issue is included in the definition.
Close this Issue.
**DO NOT** modify Arctos Authorities in any way before all points in this Issue have been fully addressed; data loss may result.
## Special Exemptions
In very specific cases and by prior approval of The Committee, the approval process may be skipped, and implementation requirements may be slightly altered. Please note here if you are proceeding under one of these use cases.
1. Adding an existing term to additional collection types may proceed immediately and without discussion, but doing so may also subject users to future cleanup efforts. If time allows, please review the term and definition as part of this step.
2. The Committee may grant special access on particular tables to particular users. This should be exercised with great caution only after several smooth test cases, and generally limited to "taxonomy-like" data such as International Commission on Stratigraphy terminology.
| 1.0 | Code Table Request - LFL: CSU Larval Fish Lab - ## Instructions
This is a template to facilitate communication with the Arctos Code Table Committee. Submit a separate request for each relevant value. This form is appropriate for exploring how data may best be stored, for adding vocabulary, or for updating existing definitions.
Reviewing documentation before proceeding will result in a more enjoyable experience.
* [Issue Documentation](http://handbook.arctosdb.org/how_to/How-to-Use-Issues-in-Arctos.html)
* [Code Table Documentation](https://handbook.arctosdb.org/how_to/How-To-Manage-Code-Table-Requests.html)
* [Video Tutorial - Submit a Code Table Request](https://youtu.be/t2jHbsRA3lk)
------------------------------
## Initial Request
**Goal**: Describe what you're trying to accomplish. This is the only necessary step to start this process. The Committee is available to assist with all other steps. Please clearly indicate any uncertainty or desired guidance if you proceed beyond this step.
All [LFL: CSU Larval Fish Lab](https://arctos.database.museum/info/ctDocumentation.cfm?table=ctcoll_other_id_type#lfl__csu_larval_fish_lab) should be replaced with other ID type = other identifier and issued by agent [Colorado State University Larval Fish Laboratory](https://arctos.database.museum/agent/21347717)
**Proposed Value**: Proposed new value. This should be clear and compatible with similar values in the relevant table and across Arctos.
**Proposed Definition**: Clear, complete, non-collection-type-specific **functional** definition of the value. Avoid discipline-specific terminology if possible, include parenthetically if unavoidable.
**Context**: Describe why this new value is necessary and existing values are not.
**Table**: Code Tables are http://arctos.database.museum/info/ctDocumentation.cfm. Link to the specific table or value. This may involve multiple tables and will control datatype for Attributes. OtherID requests require BaseURL (and example) or explanation. Please ask for assistance if unsure.
**Collection type**: Some code tables contain collection-type-specific values. ``collection_cde`` may be found from https://arctos.database.museum/home.cfm
**Priority**: Please describe the urgency and/or choose a priority-label to the right. You should expect a response within two working days, and may utilize [Arctos Contacts](https://arctosdb.org/contacts/) if you feel response is lacking.
**Available for Public View**: Most data are by default publicly available. Describe any necessary access restrictions.
**Project**: Add the issue to the [Code Table Management Project](https://github.com/ArctosDB/arctos/projects/13#card-31628184).
**Discussion**: Please reach out to anyone who might be affected by this change. Leave a comment or add this to the Committee agenda if you believe more focused conversation is necessary.
## Approval
All of the following must be checked before this may proceed.
The [How-To Document](https://handbook.arctosdb.org/how_to/How-To-Manage-Code-Table-Requests.html) should be followed. Pay particular attention to terminology (with emphasis on consistency) and documentation (with emphasis on functionality).
- [ ] Code Table Administrator[1] - check and initial, comment, or thumbs-up to indicate that the request complies with the how-to documentation and has your approval
- [ ] Code Table Administrator[2] - check and initial, comment, or thumbs-up to indicate that the request complies with the how-to documentation and has your approval
- [ ] DBA - The request is functionally acceptable. The term is not a functional duplicate, and is compatible with existing data and code.
- [ ] DBA - Appropriate code or handlers are in place as necessary. (ID_References, Media Relationships, Encumbrances, etc. require particular attention)
## Rejection
If you believe this request should not proceed, explain why here. Suggest any changes that would make the change acceptable, alternate (usually existing) paths to the same goals, etc.
1. Can a suitable solution be found here? If not, proceed to (2)
2. Can a suitable solution be found by Code Table Committee discussion? If not, proceed to (3)
3. Take the discussion to a monthly Arctos Working Group meeting for final resolution.
## Implementation
Once all of the Approval Checklist is appropriately checked and there are no Rejection comments, or in special circumstances by decree of the Arctos Working Group, the change may be made.
Review everything one last time. Ensure the How-To has been followed. Ensure all checks have been made by appropriate personnel.
Make changes as described above. Ensure the URL of this Issue is included in the definition.
Close this Issue.
**DO NOT** modify Arctos Authorities in any way before all points in this Issue have been fully addressed; data loss may result.
## Special Exemptions
In very specific cases and by prior approval of The Committee, the approval process may be skipped, and implementation requirements may be slightly altered. Please note here if you are proceeding under one of these use cases.
1. Adding an existing term to additional collection types may proceed immediately and without discussion, but doing so may also subject users to future cleanup efforts. If time allows, please review the term and definition as part of this step.
2. The Committee may grant special access on particular tables to particular users. This should be exercised with great caution only after several smooth test cases, and generally limited to "taxonomy-like" data such as International Commission on Stratigraphy terminology.
| non_priority | code table request lfl csu larval fish lab instructions this is a template to facilitate communication with the arctos code table committee submit a separate request for each relevant value this form is appropriate for exploring how data may best be stored for adding vocabulary or for updating existing definitions reviewing documentation before proceeding will result in a more enjoyable experience initial request goal describe what you re trying to accomplish this is the only necessary step to start this process the committee is available to assist with all other steps please clearly indicate any uncertainty or desired guidance if you proceed beyond this step all should be replaced with other id type other identifier and issued by agent proposed value proposed new value this should be clear and compatible with similar values in the relevant table and across arctos proposed definition clear complete non collection type specific functional definition of the value avoid discipline specific terminology if possible include parenthetically if unavoidable context describe why this new value is necessary and existing values are not table code tables are link to the specific table or value this may involve multiple tables and will control datatype for attributes otherid requests require baseurl and example or explanation please ask for assistance if unsure collection type some code tables contain collection type specific values collection cde may be found from priority please describe the urgency and or choose a priority label to the right you should expect a response within two working days and may utilize if you feel response is lacking available for public view most data are by default publicly available describe any necessary access restrictions project add the issue to the discussion please reach out to anyone who might be affected by this change leave a comment or add this to the committee agenda if you believe more focused conversation is necessary approval all of the following must be checked before this may proceed the should be followed pay particular attention to terminology with emphasis on consistency and documentation with emphasis on functionality code table administrator check and initial comment or thumbs up to indicate that the request complies with the how to documentation and has your approval code table administrator check and initial comment or thumbs up to indicate that the request complies with the how to documentation and has your approval dba the request is functionally acceptable the term is not a functional duplicate and is compatible with existing data and code dba appropriate code or handlers are in place as necessary id references media relationships encumbrances etc require particular attention rejection if you believe this request should not proceed explain why here suggest any changes that would make the change acceptable alternate usually existing paths to the same goals etc can a suitable solution be found here if not proceed to can a suitable solution be found by code table committee discussion if not proceed to take the discussion to a monthly arctos working group meeting for final resolution implementation once all of the approval checklist is appropriately checked and there are no rejection comments or in special circumstances by decree of the arctos working group the change may be made review everything one last time ensure the how to has been followed ensure all checks have been made by appropriate personnel make changes as described above ensure the url of this issue is included in the definition close this issue do not modify arctos authorities in any way before all points in this issue have been fully addressed data loss may result special exemptions in very specific cases and by prior approval of the committee the approval process may be skipped and implementation requirements may be slightly altered please note here if you are proceeding under one of these use cases adding an existing term to additional collection types may proceed immediately and without discussion but doing so may also subject users to future cleanup efforts if time allows please review the term and definition as part of this step the committee may grant special access on particular tables to particular users this should be exercised with great caution only after several smooth test cases and generally limited to taxonomy like data such as international commission on stratigraphy terminology | 0 |
120,362 | 15,732,996,971 | IssuesEvent | 2021-03-29 18:59:42 | CDCgov/prime-simplereport | https://api.github.com/repos/CDCgov/prime-simplereport | opened | Content: Create one pager on School Testing | Design | Talk to Sparkle for more details. This came out of a conversation with CSTE. | 1.0 | Content: Create one pager on School Testing - Talk to Sparkle for more details. This came out of a conversation with CSTE. | non_priority | content create one pager on school testing talk to sparkle for more details this came out of a conversation with cste | 0 |
207,973 | 15,864,682,746 | IssuesEvent | 2021-04-08 14:01:24 | eclipse/che | https://api.github.com/repos/eclipse/che | closed | Error launching task in IDE: Error starting process (ENOENT) | area/editor/che-theia e2e-test/failure kind/bug severity/blocker status/need-triage | ### Describe the bug
Happy path tests failed on launching task 'build-file-output' in IDE https://codeready-workspaces-jenkins.rhev-ci-vms.eng.rdu2.redhat.com/job/Multiuser-Che-PR-check-E2E-Happy-path-tests-against-k8s/4803/console:
```
‣ DriverHelper.waitVisibility By(css selector, li[title='build-file-output'] div.p-TabBar-tabIcon)
‣ DriverHelper.waitVisibility - Element is located and is visible.
[ERROR] Task "build-file-output" failed.
1) Build application
[ERROR] CheReporter runner.on.fail: Validation of workspace build and run Build application failed after 2301ms
8 passing (9m)
1 pending
1 failing
1) Validation of workspace build and run
Build application:
Error: Task "build-file-output" failed.
at driverHelper.getDriver.wait (/tmp/e2e/pageobjects/ide/Terminal.ts:179:23)
at process._tickCallback (internal/process/next_tick.js:68:7)
From: Task: <anonymous>
at pollCondition (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2195:19)
at /tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2191:7
at new ManagedPromise (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:1077:7)
at ControlFlow.promise (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2505:12)
at /tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2190:22
at TaskQueue.execute_ (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:3084:14)
at TaskQueue.executeNext_ (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:3067:27)
at asyncRun (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2974:25)
at /tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:668:7
at process._tickCallback (internal/process/next_tick.js:68:7)
From: Task: Timed out waiting for task build-file-output to succeed.
at scheduleWait (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2188:20)
at ControlFlow.wait (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2517:12)
at thenableWebDriverProxy.wait (/tmp/e2e/node_modules/selenium-webdriver/lib/webdriver.js:934:29)
at Terminal.waitIconSuccess (/tmp/e2e/pageobjects/ide/Terminal.ts:172:45)
at process._tickCallback (internal/process/next_tick.js:68:7)
```
[Che-theia container logs](https://codeready-workspaces-jenkins.rhev-ci-vms.eng.rdu2.redhat.com/job/Multiuser-Che-PR-check-E2E-Happy-path-tests-against-k8s/4806/artifact/logs-and-configs/workspace-logs/theia-ide3qp.container.log/*view*/):
```
2021-04-08 08:35:27.525 process ERROR Error: ENOENT
at EventEmitter.<anonymous> (/home/theia/node_modules/@theia/process/lib/node/terminal-process.js:88:33)
at EventEmitter.emit (events.js:314:20)
at UnixTerminal.Terminal.emit (/home/theia/node_modules/@theia/node-pty/lib/terminal.js:132:42)
at /home/theia/node_modules/@theia/node-pty/lib/unixTerminal.js:117:23
at processTicksAndRejections (internal/process/task_queues.js:79:11)
2021-04-08 08:35:27.525 task ERROR Error occurred while creating task: Error: Error starting process (ENOENT)
2021-04-08 08:35:27.531 process WARN This process was not registered or was already unregistered. [ID: 0]
2021-04-08 08:35:27.693 root ERROR Error launching task 'build-file-output': Error starting process (ENOENT) Params: Error: Request 'run' failed
at Proxy.<anonymous> (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:1633372)
at t.<anonymous> (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:942820)
at https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:942002
at Object.next (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:942107)
at a (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:940821)
Caused by: Error: Error starting process (ENOENT)
at /home/theia/node_modules/@theia/task/lib/node/process/process-task-runner.js:137:77
at /home/theia/node_modules/@theia/core/lib/common/event.js:176:33
at CallbackList.invoke (/home/theia/node_modules/@theia/core/lib/common/event.js:191:39)
at Emitter.fire (/home/theia/node_modules/@theia/core/lib/common/event.js:318:29)
at TerminalProcess.Process.emitOnError (/home/theia/node_modules/@theia/process/lib/node/process.js:161:27)
at EventEmitter.<anonymous> (/home/theia/node_modules/@theia/process/lib/node/terminal-process.js:90:27)
at EventEmitter.emit (events.js:314:20)
at UnixTerminal.Terminal.emit (/home/theia/node_modules/@theia/node-pty/lib/terminal.js:132:42)
at /home/theia/node_modules/@theia/node-pty/lib/unixTerminal.js:117:23
at processTicksAndRejections (internal/process/task_queues.js:79:11)
```
### Che version
<!-- (if workspace is running, version can be obtained with help/about menu) -->
- [ ] latest
- [x] nightly
- [ ] other: please specify
### Steps to reproduce
1. Deploy nightly Eclipse Che 7.29.0.
2. Create and start java maven workspace
3. Run build task.
### Expected behavior
Build task has been executed with logs inside terminal window.
### Runtime
- [ ] kubernetes (include output of `kubectl version`)
- [x] Openshift (include output of `oc version`)
- [x] minikube (include output of `minikube version` and `kubectl version`)
- [ ] minishift (include output of `minishift version` and `oc version`)
- [ ] docker-desktop + K8S (include output of `docker version` and `kubectl version`)
- [ ] other: (please specify)
### Screenshots
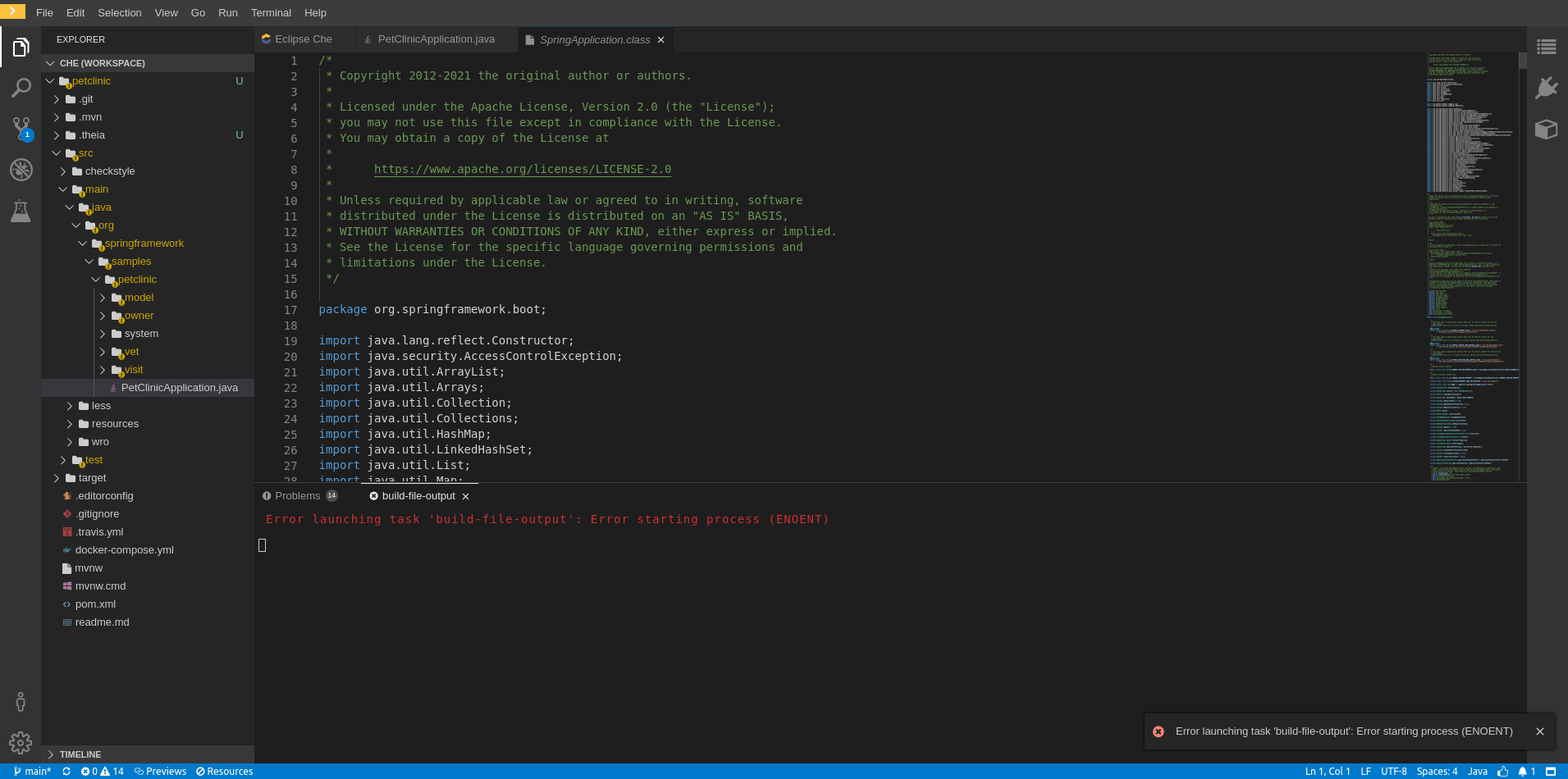
### Installation method
- [x] chectl
* provide a full command that was used to deploy Eclipse Che (including the output)
* provide an output of `chectl version` command
- [ ] OperatorHub
- [ ] I don't know
### Environment
- [ ] my computer
- [ ] Windows
- [x] Linux
- [ ] macOS
- [ ] Cloud
- [ ] Amazon
- [ ] Azure
- [ ] GCE
- [ ] other (please specify)
- [ ] Dev Sandbox (workspaces.openshift.com)
- [ ] other: please specify
### Eclipse Che Logs
<!-- https://www.eclipse.org/che/docs/che-7/collecting-logs-using-chectl -->
### Additional context
Related changes: https://github.com/eclipse-che/che-theia/pull/1071
| 1.0 | Error launching task in IDE: Error starting process (ENOENT) - ### Describe the bug
Happy path tests failed on launching task 'build-file-output' in IDE https://codeready-workspaces-jenkins.rhev-ci-vms.eng.rdu2.redhat.com/job/Multiuser-Che-PR-check-E2E-Happy-path-tests-against-k8s/4803/console:
```
‣ DriverHelper.waitVisibility By(css selector, li[title='build-file-output'] div.p-TabBar-tabIcon)
‣ DriverHelper.waitVisibility - Element is located and is visible.
[ERROR] Task "build-file-output" failed.
1) Build application
[ERROR] CheReporter runner.on.fail: Validation of workspace build and run Build application failed after 2301ms
8 passing (9m)
1 pending
1 failing
1) Validation of workspace build and run
Build application:
Error: Task "build-file-output" failed.
at driverHelper.getDriver.wait (/tmp/e2e/pageobjects/ide/Terminal.ts:179:23)
at process._tickCallback (internal/process/next_tick.js:68:7)
From: Task: <anonymous>
at pollCondition (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2195:19)
at /tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2191:7
at new ManagedPromise (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:1077:7)
at ControlFlow.promise (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2505:12)
at /tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2190:22
at TaskQueue.execute_ (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:3084:14)
at TaskQueue.executeNext_ (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:3067:27)
at asyncRun (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2974:25)
at /tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:668:7
at process._tickCallback (internal/process/next_tick.js:68:7)
From: Task: Timed out waiting for task build-file-output to succeed.
at scheduleWait (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2188:20)
at ControlFlow.wait (/tmp/e2e/node_modules/selenium-webdriver/lib/promise.js:2517:12)
at thenableWebDriverProxy.wait (/tmp/e2e/node_modules/selenium-webdriver/lib/webdriver.js:934:29)
at Terminal.waitIconSuccess (/tmp/e2e/pageobjects/ide/Terminal.ts:172:45)
at process._tickCallback (internal/process/next_tick.js:68:7)
```
[Che-theia container logs](https://codeready-workspaces-jenkins.rhev-ci-vms.eng.rdu2.redhat.com/job/Multiuser-Che-PR-check-E2E-Happy-path-tests-against-k8s/4806/artifact/logs-and-configs/workspace-logs/theia-ide3qp.container.log/*view*/):
```
2021-04-08 08:35:27.525 process ERROR Error: ENOENT
at EventEmitter.<anonymous> (/home/theia/node_modules/@theia/process/lib/node/terminal-process.js:88:33)
at EventEmitter.emit (events.js:314:20)
at UnixTerminal.Terminal.emit (/home/theia/node_modules/@theia/node-pty/lib/terminal.js:132:42)
at /home/theia/node_modules/@theia/node-pty/lib/unixTerminal.js:117:23
at processTicksAndRejections (internal/process/task_queues.js:79:11)
2021-04-08 08:35:27.525 task ERROR Error occurred while creating task: Error: Error starting process (ENOENT)
2021-04-08 08:35:27.531 process WARN This process was not registered or was already unregistered. [ID: 0]
2021-04-08 08:35:27.693 root ERROR Error launching task 'build-file-output': Error starting process (ENOENT) Params: Error: Request 'run' failed
at Proxy.<anonymous> (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:1633372)
at t.<anonymous> (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:942820)
at https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:942002
at Object.next (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:942107)
at a (https://serverjxq69wfj-jwtproxy-server-4402.10.0.206.194.nip.io/theia.43ea6a7bbfd07c6aab07.js:1:940821)
Caused by: Error: Error starting process (ENOENT)
at /home/theia/node_modules/@theia/task/lib/node/process/process-task-runner.js:137:77
at /home/theia/node_modules/@theia/core/lib/common/event.js:176:33
at CallbackList.invoke (/home/theia/node_modules/@theia/core/lib/common/event.js:191:39)
at Emitter.fire (/home/theia/node_modules/@theia/core/lib/common/event.js:318:29)
at TerminalProcess.Process.emitOnError (/home/theia/node_modules/@theia/process/lib/node/process.js:161:27)
at EventEmitter.<anonymous> (/home/theia/node_modules/@theia/process/lib/node/terminal-process.js:90:27)
at EventEmitter.emit (events.js:314:20)
at UnixTerminal.Terminal.emit (/home/theia/node_modules/@theia/node-pty/lib/terminal.js:132:42)
at /home/theia/node_modules/@theia/node-pty/lib/unixTerminal.js:117:23
at processTicksAndRejections (internal/process/task_queues.js:79:11)
```
### Che version
<!-- (if workspace is running, version can be obtained with help/about menu) -->
- [ ] latest
- [x] nightly
- [ ] other: please specify
### Steps to reproduce
1. Deploy nightly Eclipse Che 7.29.0.
2. Create and start java maven workspace
3. Run build task.
### Expected behavior
Build task has been executed with logs inside terminal window.
### Runtime
- [ ] kubernetes (include output of `kubectl version`)
- [x] Openshift (include output of `oc version`)
- [x] minikube (include output of `minikube version` and `kubectl version`)
- [ ] minishift (include output of `minishift version` and `oc version`)
- [ ] docker-desktop + K8S (include output of `docker version` and `kubectl version`)
- [ ] other: (please specify)
### Screenshots
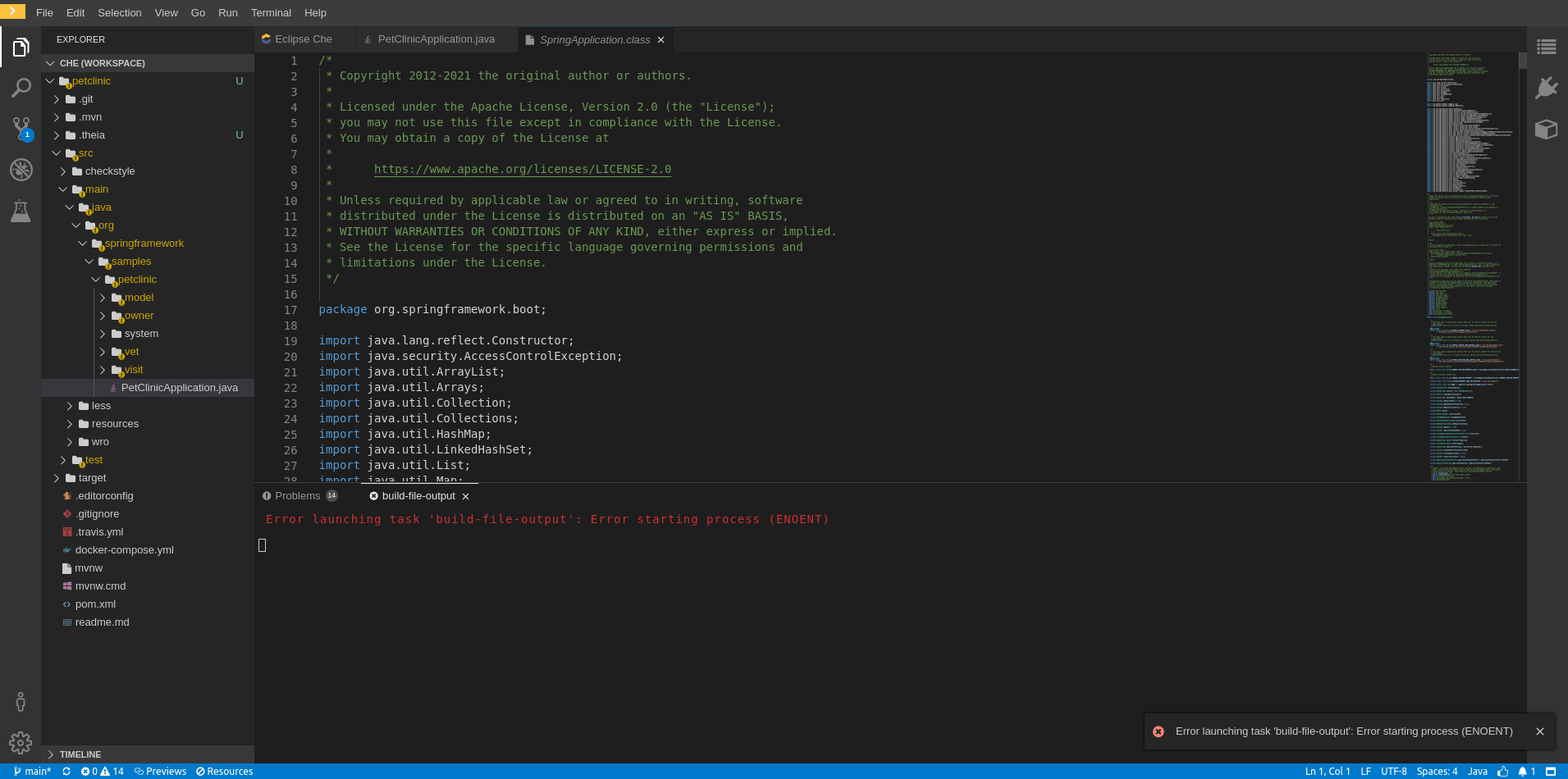
### Installation method
- [x] chectl
* provide a full command that was used to deploy Eclipse Che (including the output)
* provide an output of `chectl version` command
- [ ] OperatorHub
- [ ] I don't know
### Environment
- [ ] my computer
- [ ] Windows
- [x] Linux
- [ ] macOS
- [ ] Cloud
- [ ] Amazon
- [ ] Azure
- [ ] GCE
- [ ] other (please specify)
- [ ] Dev Sandbox (workspaces.openshift.com)
- [ ] other: please specify
### Eclipse Che Logs
<!-- https://www.eclipse.org/che/docs/che-7/collecting-logs-using-chectl -->
### Additional context
Related changes: https://github.com/eclipse-che/che-theia/pull/1071
| non_priority | error launching task in ide error starting process enoent describe the bug happy path tests failed on launching task build file output in ide ‣ driverhelper waitvisibility by css selector li div p tabbar tabicon ‣ driverhelper waitvisibility element is located and is visible task build file output failed build application chereporter runner on fail validation of workspace build and run build application failed after passing pending failing validation of workspace build and run build application error task build file output failed at driverhelper getdriver wait tmp pageobjects ide terminal ts at process tickcallback internal process next tick js from task at pollcondition tmp node modules selenium webdriver lib promise js at tmp node modules selenium webdriver lib promise js at new managedpromise tmp node modules selenium webdriver lib promise js at controlflow promise tmp node modules selenium webdriver lib promise js at tmp node modules selenium webdriver lib promise js at taskqueue execute tmp node modules selenium webdriver lib promise js at taskqueue executenext tmp node modules selenium webdriver lib promise js at asyncrun tmp node modules selenium webdriver lib promise js at tmp node modules selenium webdriver lib promise js at process tickcallback internal process next tick js from task timed out waiting for task build file output to succeed at schedulewait tmp node modules selenium webdriver lib promise js at controlflow wait tmp node modules selenium webdriver lib promise js at thenablewebdriverproxy wait tmp node modules selenium webdriver lib webdriver js at terminal waiticonsuccess tmp pageobjects ide terminal ts at process tickcallback internal process next tick js process error error enoent at eventemitter home theia node modules theia process lib node terminal process js at eventemitter emit events js at unixterminal terminal emit home theia node modules theia node pty lib terminal js at home theia node modules theia node pty lib unixterminal js at processticksandrejections internal process task queues js task error error occurred while creating task error error starting process enoent process warn this process was not registered or was already unregistered root error error launching task build file output error starting process enoent params error request run failed at proxy at t at at object next at a caused by error error starting process enoent at home theia node modules theia task lib node process process task runner js at home theia node modules theia core lib common event js at callbacklist invoke home theia node modules theia core lib common event js at emitter fire home theia node modules theia core lib common event js at terminalprocess process emitonerror home theia node modules theia process lib node process js at eventemitter home theia node modules theia process lib node terminal process js at eventemitter emit events js at unixterminal terminal emit home theia node modules theia node pty lib terminal js at home theia node modules theia node pty lib unixterminal js at processticksandrejections internal process task queues js che version latest nightly other please specify steps to reproduce deploy nightly eclipse che create and start java maven workspace run build task expected behavior build task has been executed with logs inside terminal window runtime kubernetes include output of kubectl version openshift include output of oc version minikube include output of minikube version and kubectl version minishift include output of minishift version and oc version docker desktop include output of docker version and kubectl version other please specify screenshots installation method chectl provide a full command that was used to deploy eclipse che including the output provide an output of chectl version command operatorhub i don t know environment my computer windows linux macos cloud amazon azure gce other please specify dev sandbox workspaces openshift com other please specify eclipse che logs additional context related changes | 0 |
15,253 | 10,269,947,922 | IssuesEvent | 2019-08-23 10:15:55 | terraform-providers/terraform-provider-aws | https://api.github.com/repos/terraform-providers/terraform-provider-aws | closed | Error: Provider produced inconsistent final plan | needs-triage service/autoscaling | ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
### Terraform Version
v0.12.6
### Affected Resource(s)
* aws_autoscaling_group
### Terraform Configuration Files
https://github.com/Magicloud/ifp-example/blob/master/alb-test/tester.tf
All modules it uses is in the repo.
### Debug Output
https://github.com/Magicloud/ifp-example/blob/master/alb-test/tf-debug.log
### Panic Output
N/A
### Expected Behavior
A VPC, an ASG, an ELB setup.
### Actual Behavior
```
Error: Provider produced inconsistent final plan
When expanding the plan for module.asg.aws_autoscaling_group.cluster to
include new values learned so far during apply, provider "aws" produced an
invalid new value for .availability_zones: was known, but now unknown.
This is a bug in the provider, which should be reported in the provider's own
issue tracker.
```
### Steps to Reproduce
1. `terraform apply`
Get error.
2. `terraform apply` again
Works.
### Important Factoids
Nothing special I guess.
### References
I have read some other issues here about "inconsistent final plan". None are similar. | 1.0 | Error: Provider produced inconsistent final plan - ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or "me too" comments, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
### Terraform Version
v0.12.6
### Affected Resource(s)
* aws_autoscaling_group
### Terraform Configuration Files
https://github.com/Magicloud/ifp-example/blob/master/alb-test/tester.tf
All modules it uses is in the repo.
### Debug Output
https://github.com/Magicloud/ifp-example/blob/master/alb-test/tf-debug.log
### Panic Output
N/A
### Expected Behavior
A VPC, an ASG, an ELB setup.
### Actual Behavior
```
Error: Provider produced inconsistent final plan
When expanding the plan for module.asg.aws_autoscaling_group.cluster to
include new values learned so far during apply, provider "aws" produced an
invalid new value for .availability_zones: was known, but now unknown.
This is a bug in the provider, which should be reported in the provider's own
issue tracker.
```
### Steps to Reproduce
1. `terraform apply`
Get error.
2. `terraform apply` again
Works.
### Important Factoids
Nothing special I guess.
### References
I have read some other issues here about "inconsistent final plan". None are similar. | non_priority | error provider produced inconsistent final plan community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or me too comments they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment terraform version affected resource s aws autoscaling group terraform configuration files all modules it uses is in the repo debug output panic output n a expected behavior a vpc an asg an elb setup actual behavior error provider produced inconsistent final plan when expanding the plan for module asg aws autoscaling group cluster to include new values learned so far during apply provider aws produced an invalid new value for availability zones was known but now unknown this is a bug in the provider which should be reported in the provider s own issue tracker steps to reproduce terraform apply get error terraform apply again works important factoids nothing special i guess references i have read some other issues here about inconsistent final plan none are similar | 0 |
982 | 4,763,093,892 | IssuesEvent | 2016-10-25 13:34:51 | Terasology/LightAndShadow | https://api.github.com/repos/Terasology/LightAndShadow | opened | Pathing for mobs | Architecture Content | @synopia has been previously working on a pathfinding module. Hoping to make that part of round one when we have creatures to move around :-) | 1.0 | Pathing for mobs - @synopia has been previously working on a pathfinding module. Hoping to make that part of round one when we have creatures to move around :-) | non_priority | pathing for mobs synopia has been previously working on a pathfinding module hoping to make that part of round one when we have creatures to move around | 0 |
32,165 | 4,755,284,417 | IssuesEvent | 2016-10-24 10:16:03 | d3athrow/vgstation13 | https://api.github.com/repos/d3athrow/vgstation13 | closed | Hivehand infinite ammo bug | Bug / Fix Exploitable Needs Moar Testing | Get hivehand, switch to empty hand, click on hivehand. Repeat a dozen times.
Marvel as your hivehand now has infinite ammo. | 1.0 | Hivehand infinite ammo bug - Get hivehand, switch to empty hand, click on hivehand. Repeat a dozen times.
Marvel as your hivehand now has infinite ammo. | non_priority | hivehand infinite ammo bug get hivehand switch to empty hand click on hivehand repeat a dozen times marvel as your hivehand now has infinite ammo | 0 |
152,390 | 13,453,295,066 | IssuesEvent | 2020-09-09 00:31:02 | pradeepkoneti/Softwareassurance | https://api.github.com/repos/pradeepkoneti/Softwareassurance | closed | Individual Project Selection and Presentation to team | documentation | @pradeepkoneti @LucasAsato @bgopisetty @stankasala @ReshmaBabuChethan | 1.0 | Individual Project Selection and Presentation to team - @pradeepkoneti @LucasAsato @bgopisetty @stankasala @ReshmaBabuChethan | non_priority | individual project selection and presentation to team pradeepkoneti lucasasato bgopisetty stankasala reshmababuchethan | 0 |
33,675 | 27,709,932,669 | IssuesEvent | 2023-03-14 13:40:54 | CDCgov/data-exchange-hl7 | https://api.github.com/repos/CDCgov/data-exchange-hl7 | opened | Need to install the Fortify software | infrastructure | Before deploying code into dev server need to Run Security Scan and remediate bugs in code using Fortify Static Code Analysis tool. | 1.0 | Need to install the Fortify software - Before deploying code into dev server need to Run Security Scan and remediate bugs in code using Fortify Static Code Analysis tool. | non_priority | need to install the fortify software before deploying code into dev server need to run security scan and remediate bugs in code using fortify static code analysis tool | 0 |
26,753 | 5,284,775,901 | IssuesEvent | 2017-02-08 01:39:29 | facebook/react-native | https://api.github.com/repos/facebook/react-native | closed | android getting started documentation improvements | Android Documentation | Issue #9024 has a lot of comments, including by me, and in release 0.35.0 the installation documentation for Android was improved. It's however not perfect yet, so here are a few suggestions that can hopefully be implemented with less effort:
- Step 2 has you install Android 7 with API 24. But `react-native init` hardcodes API version 23. When you do `react-native run-android` it actually fails:
```
* What went wrong:
A problem occurred configuring project ':app'.
> failed to find target with hash string 'android-23' in: /mnt/tb/faassen/Android/Sdk
```
I had to adjust various values in `android/build/app.gradle` to 24 instead of the default 23 to make that work:
- `compileSdkVersion 24`
- `buildToolsVersion "24.0.3"`
- `targetSdkVersion 24`
- `compile "com.android.support:appcompat-v7:24.0.0"`
Unless this hardcoding can be lifted somehow, instructions to this effect need to be in the documentation, otherwise people will get stuck straight away and have to look up issues like this one. Alternatively you change the instructions to install a fixed Android version.
- Step 2 has the Android SDK manager. Then at step 4 there's a small print note saying that if you click on "Show Package Details" you can install missing images such as the actual Android emulator image. This seems to be a required step and it should just be presented in step 2, otherwise people have to backtrack to the Android SDK manager. Okay, I read in step 4 that this is only needed if the Android SDK manager _fails_ to install an AVD, which it always seems to do for me. So it should at least have people check for this image data here, right? If it's missing there can't be an AVD.
- Step 3 has you set up paths, but doesn't actually set up an essential path to `platform-tools` in the SDK, otherwise the `adb` tool cannot be found and you can't run `react-native run-android`:
``export PATH=${PATH}:${ANDROID_HOME}/platform-tools`
- Step 4 Talks about a common issue where Android Studio doesn't install an AVD. I seem to hit this issue then. It hasn't installed AVDs on two separate linux boxes already. It doesn't say it failed to install an AVD. Weird.
- Testing your Android installation should, I think, just step 5, as it has you actually create a project in the first place. A few steps are missing:
- It immediately throws you into a screen where you need to give screen overlay permissions for the application. If you don't, it doesn't seem to work.
- if you don't close all apps after that, I believe there is some difficulty in getting it started too, but more testing is needed.
- It often fails the first time with a scary red screen saying it can't connect telling people to look into network settings. This falsely leads people into thinking they need to fix network settings, but actually trying it again makes it work. So a note to that effect would be helpful.
- I thought you needed to become developer by pressing build a lot of times, but apparently that's not required. I did this before thinking it fixed an issue, but I just tested with a new Android image and it's not required.
A useful command-line way to start the emulator:
```
$ emulator -avd Nexus_5X_API_24_x86
```
### Additional Information
- React Native version: 0.35.0
- Platform(s) (iOS, Android, or both?): Android
- Operating System (macOS, Linux, or Windows?): Linux
| 1.0 | android getting started documentation improvements - Issue #9024 has a lot of comments, including by me, and in release 0.35.0 the installation documentation for Android was improved. It's however not perfect yet, so here are a few suggestions that can hopefully be implemented with less effort:
- Step 2 has you install Android 7 with API 24. But `react-native init` hardcodes API version 23. When you do `react-native run-android` it actually fails:
```
* What went wrong:
A problem occurred configuring project ':app'.
> failed to find target with hash string 'android-23' in: /mnt/tb/faassen/Android/Sdk
```
I had to adjust various values in `android/build/app.gradle` to 24 instead of the default 23 to make that work:
- `compileSdkVersion 24`
- `buildToolsVersion "24.0.3"`
- `targetSdkVersion 24`
- `compile "com.android.support:appcompat-v7:24.0.0"`
Unless this hardcoding can be lifted somehow, instructions to this effect need to be in the documentation, otherwise people will get stuck straight away and have to look up issues like this one. Alternatively you change the instructions to install a fixed Android version.
- Step 2 has the Android SDK manager. Then at step 4 there's a small print note saying that if you click on "Show Package Details" you can install missing images such as the actual Android emulator image. This seems to be a required step and it should just be presented in step 2, otherwise people have to backtrack to the Android SDK manager. Okay, I read in step 4 that this is only needed if the Android SDK manager _fails_ to install an AVD, which it always seems to do for me. So it should at least have people check for this image data here, right? If it's missing there can't be an AVD.
- Step 3 has you set up paths, but doesn't actually set up an essential path to `platform-tools` in the SDK, otherwise the `adb` tool cannot be found and you can't run `react-native run-android`:
``export PATH=${PATH}:${ANDROID_HOME}/platform-tools`
- Step 4 Talks about a common issue where Android Studio doesn't install an AVD. I seem to hit this issue then. It hasn't installed AVDs on two separate linux boxes already. It doesn't say it failed to install an AVD. Weird.
- Testing your Android installation should, I think, just step 5, as it has you actually create a project in the first place. A few steps are missing:
- It immediately throws you into a screen where you need to give screen overlay permissions for the application. If you don't, it doesn't seem to work.
- if you don't close all apps after that, I believe there is some difficulty in getting it started too, but more testing is needed.
- It often fails the first time with a scary red screen saying it can't connect telling people to look into network settings. This falsely leads people into thinking they need to fix network settings, but actually trying it again makes it work. So a note to that effect would be helpful.
- I thought you needed to become developer by pressing build a lot of times, but apparently that's not required. I did this before thinking it fixed an issue, but I just tested with a new Android image and it's not required.
A useful command-line way to start the emulator:
```
$ emulator -avd Nexus_5X_API_24_x86
```
### Additional Information
- React Native version: 0.35.0
- Platform(s) (iOS, Android, or both?): Android
- Operating System (macOS, Linux, or Windows?): Linux
| non_priority | android getting started documentation improvements issue has a lot of comments including by me and in release the installation documentation for android was improved it s however not perfect yet so here are a few suggestions that can hopefully be implemented with less effort step has you install android with api but react native init hardcodes api version when you do react native run android it actually fails what went wrong a problem occurred configuring project app failed to find target with hash string android in mnt tb faassen android sdk i had to adjust various values in android build app gradle to instead of the default to make that work compilesdkversion buildtoolsversion targetsdkversion compile com android support appcompat unless this hardcoding can be lifted somehow instructions to this effect need to be in the documentation otherwise people will get stuck straight away and have to look up issues like this one alternatively you change the instructions to install a fixed android version step has the android sdk manager then at step there s a small print note saying that if you click on show package details you can install missing images such as the actual android emulator image this seems to be a required step and it should just be presented in step otherwise people have to backtrack to the android sdk manager okay i read in step that this is only needed if the android sdk manager fails to install an avd which it always seems to do for me so it should at least have people check for this image data here right if it s missing there can t be an avd step has you set up paths but doesn t actually set up an essential path to platform tools in the sdk otherwise the adb tool cannot be found and you can t run react native run android export path path android home platform tools step talks about a common issue where android studio doesn t install an avd i seem to hit this issue then it hasn t installed avds on two separate linux boxes already it doesn t say it failed to install an avd weird testing your android installation should i think just step as it has you actually create a project in the first place a few steps are missing it immediately throws you into a screen where you need to give screen overlay permissions for the application if you don t it doesn t seem to work if you don t close all apps after that i believe there is some difficulty in getting it started too but more testing is needed it often fails the first time with a scary red screen saying it can t connect telling people to look into network settings this falsely leads people into thinking they need to fix network settings but actually trying it again makes it work so a note to that effect would be helpful i thought you needed to become developer by pressing build a lot of times but apparently that s not required i did this before thinking it fixed an issue but i just tested with a new android image and it s not required a useful command line way to start the emulator emulator avd nexus api additional information react native version platform s ios android or both android operating system macos linux or windows linux | 0 |
298,671 | 25,845,592,368 | IssuesEvent | 2022-12-13 06:06:41 | boostcampwm-2022/Web04-Fitory | https://api.github.com/repos/boostcampwm-2022/Web04-Fitory | closed | [BE] 테스팅 - USER API - 버그 수정 | 🐛 bug 🚀 backend 🧪 test | ## 기능 설명
- 테스트 완료시 자동 종료 수정
- 오타 수정
## 완료 조건
- [x] 테스트 완료시 자동 종료 수정
- [x] 오타 수정
| 1.0 | [BE] 테스팅 - USER API - 버그 수정 - ## 기능 설명
- 테스트 완료시 자동 종료 수정
- 오타 수정
## 완료 조건
- [x] 테스트 완료시 자동 종료 수정
- [x] 오타 수정
| non_priority | 테스팅 user api 버그 수정 기능 설명 테스트 완료시 자동 종료 수정 오타 수정 완료 조건 테스트 완료시 자동 종료 수정 오타 수정 | 0 |
9,479 | 6,900,187,537 | IssuesEvent | 2017-11-24 17:03:24 | devtools-html/debugger.html | https://api.github.com/repos/devtools-html/debugger.html | closed | Batch update new sources | not-available performance | We currently add sources one at a time. We have a batch update reducer called addSources but it is not being used. We should use it, as it will reduce repaints
a good place to start is at `newSources`. it calls `newSource` for each source, but we could just as easily add all the sources at once.
there are a couple of other parts to this. ask me if you want to take a look at this! | True | Batch update new sources - We currently add sources one at a time. We have a batch update reducer called addSources but it is not being used. We should use it, as it will reduce repaints
a good place to start is at `newSources`. it calls `newSource` for each source, but we could just as easily add all the sources at once.
there are a couple of other parts to this. ask me if you want to take a look at this! | non_priority | batch update new sources we currently add sources one at a time we have a batch update reducer called addsources but it is not being used we should use it as it will reduce repaints a good place to start is at newsources it calls newsource for each source but we could just as easily add all the sources at once there are a couple of other parts to this ask me if you want to take a look at this | 0 |
337,268 | 24,532,832,457 | IssuesEvent | 2022-10-11 17:57:40 | SigNoz/signoz.io | https://api.github.com/repos/SigNoz/signoz.io | opened | Add annotation docs for java instrumentation | documentation | Java otel agent supports adding custom spans without too much change: https://opentelemetry.io/docs/instrumentation/java/automatic/annotations/
It is different from manual instrumentation which is tedious and requires too much code changes. | 1.0 | Add annotation docs for java instrumentation - Java otel agent supports adding custom spans without too much change: https://opentelemetry.io/docs/instrumentation/java/automatic/annotations/
It is different from manual instrumentation which is tedious and requires too much code changes. | non_priority | add annotation docs for java instrumentation java otel agent supports adding custom spans without too much change it is different from manual instrumentation which is tedious and requires too much code changes | 0 |
171,843 | 27,188,033,743 | IssuesEvent | 2023-02-19 13:09:13 | PoliNetworkOrg/PoliFemo | https://api.github.com/repos/PoliNetworkOrg/PoliFemo | closed | [Design] Scritta in alto a SX al posto del vuoto | target: Design | 
Io qui scriverei "aule libere"
O comunque il titolo in cui siamo
Però questa mi sa che è una cosa generica, non riguarda solo questa pagina | 1.0 | [Design] Scritta in alto a SX al posto del vuoto - 
Io qui scriverei "aule libere"
O comunque il titolo in cui siamo
Però questa mi sa che è una cosa generica, non riguarda solo questa pagina | non_priority | scritta in alto a sx al posto del vuoto io qui scriverei aule libere o comunque il titolo in cui siamo però questa mi sa che è una cosa generica non riguarda solo questa pagina | 0 |
84,700 | 15,728,251,235 | IssuesEvent | 2021-03-29 13:37:08 | ssobue/neo4j-domain-name-system | https://api.github.com/repos/ssobue/neo4j-domain-name-system | closed | CVE-2021-25329 (High) detected in tomcat-embed-core-9.0.35.jar | security vulnerability | ## CVE-2021-25329 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.35.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: neo4j-domain-name-system/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.35/8a99064fce4b152a7dc9bea1798ba828a2cecf0f/tomcat-embed-core-9.0.35.jar,/root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.35/8a99064fce4b152a7dc9bea1798ba828a2cecf0f/tomcat-embed-core-9.0.35.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-actuator-2.3.0.RELEASE.jar (Root Library)
- spring-boot-dependencies-2.3.0.RELEASE
- :x: **tomcat-embed-core-9.0.35.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329>CVE-2021-25329</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-25329 (High) detected in tomcat-embed-core-9.0.35.jar - ## CVE-2021-25329 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.35.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: neo4j-domain-name-system/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.35/8a99064fce4b152a7dc9bea1798ba828a2cecf0f/tomcat-embed-core-9.0.35.jar,/root/.gradle/caches/modules-2/files-2.1/org.apache.tomcat.embed/tomcat-embed-core/9.0.35/8a99064fce4b152a7dc9bea1798ba828a2cecf0f/tomcat-embed-core-9.0.35.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-actuator-2.3.0.RELEASE.jar (Root Library)
- spring-boot-dependencies-2.3.0.RELEASE
- :x: **tomcat-embed-core-9.0.35.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The fix for CVE-2020-9484 was incomplete. When using Apache Tomcat 10.0.0-M1 to 10.0.0, 9.0.0.M1 to 9.0.41, 8.5.0 to 8.5.61 or 7.0.0. to 7.0.107 with a configuration edge case that was highly unlikely to be used, the Tomcat instance was still vulnerable to CVE-2020-9494. Note that both the previously published prerequisites for CVE-2020-9484 and the previously published mitigations for CVE-2020-9484 also apply to this issue.
<p>Publish Date: 2021-03-01
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-25329>CVE-2021-25329</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/rfe62fbf9d4c314f166fe8c668e50e5d9dd882a99447f26f0367474bf%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2021-03-01</p>
<p>Fix Resolution: org.apache.tomcat:tomcat:7.0.108, org.apache.tomcat:tomcat:8.5.63, org.apache.tomcat:tomcat:9.0.43,org.apache.tomcat:tomcat:10.0.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in tomcat embed core jar cve high severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file domain name system build gradle path to vulnerable library root gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar root gradle caches modules files org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy spring boot starter actuator release jar root library spring boot dependencies release x tomcat embed core jar vulnerable library vulnerability details the fix for cve was incomplete when using apache tomcat to to to or to with a configuration edge case that was highly unlikely to be used the tomcat instance was still vulnerable to cve note that both the previously published prerequisites for cve and the previously published mitigations for cve also apply to this issue publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat org apache tomcat tomcat step up your open source security game with whitesource | 0 |
101,301 | 11,222,947,773 | IssuesEvent | 2020-01-07 21:24:53 | department-of-veterans-affairs/va.gov-team | https://api.github.com/repos/department-of-veterans-affairs/va.gov-team | closed | Documentation Mapping (Table of Contents) | documentation sprint objective tools-be | ## User Story or Problem Statement
As a _____, I need _____ so I can _____.
As a new member of the Backend Tools team, I need a one pager (table of contents) that links me to all the relevant documents that I need so I can be be more productive in finding information across the different repos.
## Goal
To create a one page document that is broken out into sections that assists us as a new team in finding important information that is dispersed across different repos.
## Acceptance Criteria
- [ ] Anna Reviewed Doc
- [ ] Bill Reviewed Doc
- [ ] Johnny Reviewed Doc
- [ ] Keifer Reviewed Doc
- [ ] Travis Reviewed Doc
- [x] Lindsey Reviewed Doc
- [ ]A table of contents is created and stored is a centralized location that links to any and all of the relevant documents or practice areas. | 1.0 | Documentation Mapping (Table of Contents) - ## User Story or Problem Statement
As a _____, I need _____ so I can _____.
As a new member of the Backend Tools team, I need a one pager (table of contents) that links me to all the relevant documents that I need so I can be be more productive in finding information across the different repos.
## Goal
To create a one page document that is broken out into sections that assists us as a new team in finding important information that is dispersed across different repos.
## Acceptance Criteria
- [ ] Anna Reviewed Doc
- [ ] Bill Reviewed Doc
- [ ] Johnny Reviewed Doc
- [ ] Keifer Reviewed Doc
- [ ] Travis Reviewed Doc
- [x] Lindsey Reviewed Doc
- [ ]A table of contents is created and stored is a centralized location that links to any and all of the relevant documents or practice areas. | non_priority | documentation mapping table of contents user story or problem statement as a i need so i can as a new member of the backend tools team i need a one pager table of contents that links me to all the relevant documents that i need so i can be be more productive in finding information across the different repos goal to create a one page document that is broken out into sections that assists us as a new team in finding important information that is dispersed across different repos acceptance criteria anna reviewed doc bill reviewed doc johnny reviewed doc keifer reviewed doc travis reviewed doc lindsey reviewed doc a table of contents is created and stored is a centralized location that links to any and all of the relevant documents or practice areas | 0 |
79,891 | 15,586,245,300 | IssuesEvent | 2021-03-18 01:30:13 | jyothsna/votingapplication | https://api.github.com/repos/jyothsna/votingapplication | opened | CVE-2021-20190 (High) detected in jackson-databind-2.9.6.jar, jackson-databind-2.9.0.jar | security vulnerability | ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.9.0.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: votingapplication/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.3.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.3.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: votingapplication/pom.xml</p>
<p>Path to vulnerable library: epository/com/fasterxml/jackson/core/jackson-databind/2.9.0/jackson-databind-2.9.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.0.jar** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190>CVE-2021-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2854">https://github.com/FasterXML/jackson-databind/issues/2854</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind-2.9.10.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2021-20190 (High) detected in jackson-databind-2.9.6.jar, jackson-databind-2.9.0.jar - ## CVE-2021-20190 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jackson-databind-2.9.6.jar</b>, <b>jackson-databind-2.9.0.jar</b></p></summary>
<p>
<details><summary><b>jackson-databind-2.9.6.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: votingapplication/build.gradle</p>
<p>Path to vulnerable library: /root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar,/root/.gradle/caches/modules-2/files-2.1/com.fasterxml.jackson.core/jackson-databind/2.9.6/cfa4f316351a91bfd95cb0644c6a2c95f52db1fc/jackson-databind-2.9.6.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.0.3.RELEASE.jar (Root Library)
- spring-boot-starter-json-2.0.3.RELEASE.jar
- :x: **jackson-databind-2.9.6.jar** (Vulnerable Library)
</details>
<details><summary><b>jackson-databind-2.9.0.jar</b></p></summary>
<p>General data-binding functionality for Jackson: works on core streaming API</p>
<p>Library home page: <a href="http://github.com/FasterXML/jackson">http://github.com/FasterXML/jackson</a></p>
<p>Path to dependency file: votingapplication/pom.xml</p>
<p>Path to vulnerable library: epository/com/fasterxml/jackson/core/jackson-databind/2.9.0/jackson-databind-2.9.0.jar</p>
<p>
Dependency Hierarchy:
- :x: **jackson-databind-2.9.0.jar** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A flaw was found in jackson-databind before 2.9.10.7. FasterXML mishandles the interaction between serialization gadgets and typing. The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.
<p>Publish Date: 2021-01-19
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-20190>CVE-2021-20190</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/FasterXML/jackson-databind/issues/2854">https://github.com/FasterXML/jackson-databind/issues/2854</a></p>
<p>Release Date: 2021-01-19</p>
<p>Fix Resolution: com.fasterxml.jackson.core:jackson-databind-2.9.10.7</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in jackson databind jar jackson databind jar cve high severity vulnerability vulnerable libraries jackson databind jar jackson databind jar jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file votingapplication build gradle path to vulnerable library root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar root gradle caches modules files com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy spring boot starter web release jar root library spring boot starter json release jar x jackson databind jar vulnerable library jackson databind jar general data binding functionality for jackson works on core streaming api library home page a href path to dependency file votingapplication pom xml path to vulnerable library epository com fasterxml jackson core jackson databind jackson databind jar dependency hierarchy x jackson databind jar vulnerable library vulnerability details a flaw was found in jackson databind before fasterxml mishandles the interaction between serialization gadgets and typing the highest threat from this vulnerability is to data confidentiality and integrity as well as system availability publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution com fasterxml jackson core jackson databind step up your open source security game with whitesource | 0 |
184,839 | 14,289,966,158 | IssuesEvent | 2020-11-23 20:06:50 | github-vet/rangeclosure-findings | https://api.github.com/repos/github-vet/rangeclosure-findings | closed | kubernetes/kubectl: pkg/util/i18n/i18n_test.go; 7 LoC | experts: :-1: test tiny | Found a possible issue in [kubernetes/kubectl](https://www.github.com/kubernetes/kubectl) at [pkg/util/i18n/i18n_test.go](https://github.com/kubernetes/kubectl/blob/b155278f1f4a21a0be2d4f6f0037258dee4d1a22/pkg/util/i18n/i18n_test.go#L136-L142)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/kubernetes/kubectl/blob/b155278f1f4a21a0be2d4f6f0037258dee4d1a22/pkg/util/i18n/i18n_test.go#L136-L142)
<details>
<summary>Click here to show the 7 line(s) of Go which triggered the analyzer.</summary>
```go
for _, envVar := range envVarsToBackup {
if envVarValue := os.Getenv(envVar); envVarValue != "" {
os.Unsetenv(envVar)
// Restore env var at the end
defer func() { os.Setenv(envVar, envVarValue) }()
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: b155278f1f4a21a0be2d4f6f0037258dee4d1a22
| 1.0 | kubernetes/kubectl: pkg/util/i18n/i18n_test.go; 7 LoC - Found a possible issue in [kubernetes/kubectl](https://www.github.com/kubernetes/kubectl) at [pkg/util/i18n/i18n_test.go](https://github.com/kubernetes/kubectl/blob/b155278f1f4a21a0be2d4f6f0037258dee4d1a22/pkg/util/i18n/i18n_test.go#L136-L142)
The below snippet of Go code triggered static analysis which searches for goroutines and/or defer statements
which capture loop variables.
[Click here to see the code in its original context.](https://github.com/kubernetes/kubectl/blob/b155278f1f4a21a0be2d4f6f0037258dee4d1a22/pkg/util/i18n/i18n_test.go#L136-L142)
<details>
<summary>Click here to show the 7 line(s) of Go which triggered the analyzer.</summary>
```go
for _, envVar := range envVarsToBackup {
if envVarValue := os.Getenv(envVar); envVarValue != "" {
os.Unsetenv(envVar)
// Restore env var at the end
defer func() { os.Setenv(envVar, envVarValue) }()
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: b155278f1f4a21a0be2d4f6f0037258dee4d1a22
| non_priority | kubernetes kubectl pkg util test go loc found a possible issue in at the below snippet of go code triggered static analysis which searches for goroutines and or defer statements which capture loop variables click here to show the line s of go which triggered the analyzer go for envvar range envvarstobackup if envvarvalue os getenv envvar envvarvalue os unsetenv envvar restore env var at the end defer func os setenv envvar envvarvalue leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
145,186 | 13,145,706,446 | IssuesEvent | 2020-08-08 05:14:11 | SforAiDl/genrl | https://api.github.com/repos/SforAiDl/genrl | closed | Restructuring + Expanding docs | documentation | 1. Exposing the docs for the `common` modules.
2. Exposing the docs for `environments`
3. Restructuring docs for `bandits` | 1.0 | Restructuring + Expanding docs - 1. Exposing the docs for the `common` modules.
2. Exposing the docs for `environments`
3. Restructuring docs for `bandits` | non_priority | restructuring expanding docs exposing the docs for the common modules exposing the docs for environments restructuring docs for bandits | 0 |
226,604 | 18,041,914,138 | IssuesEvent | 2021-09-18 07:15:42 | Tencent/bk-job | https://api.github.com/repos/Tencent/bk-job | closed | bug: 下发给gse的脚本任务路径不一致 | kind/bug stage/test layer/backend stage/dev | 现象:
1. 脚本执行时 有带上 user name ,脚本会存储在 对应的user 目录下 如:/tmp/bkjob/username
2. 执行python 时没有带上 user name,脚本会存储在 根目录下 如:/tmp/bkjob
需求:
需要将 所有脚本类型的存储目录同一为 /tmp/bkjob/{user name} | 1.0 | bug: 下发给gse的脚本任务路径不一致 - 现象:
1. 脚本执行时 有带上 user name ,脚本会存储在 对应的user 目录下 如:/tmp/bkjob/username
2. 执行python 时没有带上 user name,脚本会存储在 根目录下 如:/tmp/bkjob
需求:
需要将 所有脚本类型的存储目录同一为 /tmp/bkjob/{user name} | non_priority | bug 下发给gse的脚本任务路径不一致 现象: 脚本执行时 有带上 user name ,脚本会存储在 对应的user 目录下 如: tmp bkjob username 执行python 时没有带上 user name,脚本会存储在 根目录下 如: tmp bkjob 需求: 需要将 所有脚本类型的存储目录同一为 tmp bkjob user name | 0 |
55,857 | 23,618,075,222 | IssuesEvent | 2022-08-24 17:42:53 | hashicorp/terraform-provider-awscc | https://api.github.com/repos/hashicorp/terraform-provider-awscc | closed | awscc_mediapackage_channel: | service/mediapackage | ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
* The resources and data sources in this provider are generated from the CloudFormation schema, so they can only support the actions that the underlying schema supports. For this reason submitted bugs should be limited to defects in the generation and runtime code of the provider. Customizing behavior of the resource, or noting a gap in behavior are not valid bugs and should be submitted as enhancements to AWS via the Cloudformation Open Coverage Roadmap.
### Terraform CLI and Terraform AWS Cloud Control Provider Version
Terraform v1.0.10
AWSCC v0.4.0
### Affected Resource(s)
* awscc_mediapackage_channel
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
resource "awscc_mediapackage_channel" "this" {
id = "some-id"
description = "Managed by Terraform."
}
```
### Expected Behavior
To apply successfully with no error.
### Actual Behavior
Channel resource created fine, but errored out.
Plan:
```
# awscc_mediapackage_channel.this will be created
+ resource "awscc_mediapackage_channel" "this" {
+ arn = (known after apply)
+ description = "Managed by Terraform."
+ hls_ingest = {
+ ingest_endpoints = [
+ { },
] -> (known after apply)
}
+ id = "some-id"
}
```
Apply:
```
│ Error: Provider returned invalid result object after apply
│
│ After the apply operation, the provider still indicated an unknown value for module.us_west_2[0].awscc_mediapackage_channel.this["channel-us-west-2-0"].arn. All values must be known after apply, so this is always a bug in the provider and should be reported in the provider's own repository. Terraform will still save the other known object values in the state.
|
|
│ Error: Provider returned invalid result object after apply
│
│ After the apply operation, the provider still indicated an unknown value for module.us_west_2[0].awscc_mediapackage_channel.this["channel-us-west-2-0"].hls_ingest. All values must be known after apply, so this is always a bug in the provider and should be reported in the provider's own repository. Terraform will still save the other known object values in the state.
|
|
| Error: Creation Of Terraform State Unsuccessful
│
│ with awscc_mediapackage_channel.this,
│ on pipeline.tf line 22, in resource "awscc_mediapackage_channel" "this":
│ 22: resource "awscc_mediapackage_channel" "this" {
│
│ Unable to set Terraform State Unknown values from Cloud Control API Properties. This is typically an error with the Terraform provider implementation. Original Error: error setting value at AttributeName("hls_ingest"): 1 error occurred:
│ * An unexpected error was encountered trying to convert from value. This is always an error in the provider. Please report the following to the provider developer:
│
│ cannot use type map[string]interface {} as schema type types.ObjectType; types.ObjectType must be an attr.TypeWithElementType to hold map[string]interface {}
```
### Steps to Reproduce
1. `terraform apply` | 1.0 | awscc_mediapackage_channel: - ### Community Note
* Please vote on this issue by adding a 👍 [reaction](https://blog.github.com/2016-03-10-add-reactions-to-pull-requests-issues-and-comments/) to the original issue to help the community and maintainers prioritize this request
* Please do not leave "+1" or other comments that do not add relevant new information or questions, they generate extra noise for issue followers and do not help prioritize the request
* If you are interested in working on this issue or have submitted a pull request, please leave a comment
* The resources and data sources in this provider are generated from the CloudFormation schema, so they can only support the actions that the underlying schema supports. For this reason submitted bugs should be limited to defects in the generation and runtime code of the provider. Customizing behavior of the resource, or noting a gap in behavior are not valid bugs and should be submitted as enhancements to AWS via the Cloudformation Open Coverage Roadmap.
### Terraform CLI and Terraform AWS Cloud Control Provider Version
Terraform v1.0.10
AWSCC v0.4.0
### Affected Resource(s)
* awscc_mediapackage_channel
### Terraform Configuration Files
<!--- Information about code formatting: https://help.github.com/articles/basic-writing-and-formatting-syntax/#quoting-code --->
Please include all Terraform configurations required to reproduce the bug. Bug reports without a functional reproduction may be closed without investigation.
```hcl
resource "awscc_mediapackage_channel" "this" {
id = "some-id"
description = "Managed by Terraform."
}
```
### Expected Behavior
To apply successfully with no error.
### Actual Behavior
Channel resource created fine, but errored out.
Plan:
```
# awscc_mediapackage_channel.this will be created
+ resource "awscc_mediapackage_channel" "this" {
+ arn = (known after apply)
+ description = "Managed by Terraform."
+ hls_ingest = {
+ ingest_endpoints = [
+ { },
] -> (known after apply)
}
+ id = "some-id"
}
```
Apply:
```
│ Error: Provider returned invalid result object after apply
│
│ After the apply operation, the provider still indicated an unknown value for module.us_west_2[0].awscc_mediapackage_channel.this["channel-us-west-2-0"].arn. All values must be known after apply, so this is always a bug in the provider and should be reported in the provider's own repository. Terraform will still save the other known object values in the state.
|
|
│ Error: Provider returned invalid result object after apply
│
│ After the apply operation, the provider still indicated an unknown value for module.us_west_2[0].awscc_mediapackage_channel.this["channel-us-west-2-0"].hls_ingest. All values must be known after apply, so this is always a bug in the provider and should be reported in the provider's own repository. Terraform will still save the other known object values in the state.
|
|
| Error: Creation Of Terraform State Unsuccessful
│
│ with awscc_mediapackage_channel.this,
│ on pipeline.tf line 22, in resource "awscc_mediapackage_channel" "this":
│ 22: resource "awscc_mediapackage_channel" "this" {
│
│ Unable to set Terraform State Unknown values from Cloud Control API Properties. This is typically an error with the Terraform provider implementation. Original Error: error setting value at AttributeName("hls_ingest"): 1 error occurred:
│ * An unexpected error was encountered trying to convert from value. This is always an error in the provider. Please report the following to the provider developer:
│
│ cannot use type map[string]interface {} as schema type types.ObjectType; types.ObjectType must be an attr.TypeWithElementType to hold map[string]interface {}
```
### Steps to Reproduce
1. `terraform apply` | non_priority | awscc mediapackage channel community note please vote on this issue by adding a 👍 to the original issue to help the community and maintainers prioritize this request please do not leave or other comments that do not add relevant new information or questions they generate extra noise for issue followers and do not help prioritize the request if you are interested in working on this issue or have submitted a pull request please leave a comment the resources and data sources in this provider are generated from the cloudformation schema so they can only support the actions that the underlying schema supports for this reason submitted bugs should be limited to defects in the generation and runtime code of the provider customizing behavior of the resource or noting a gap in behavior are not valid bugs and should be submitted as enhancements to aws via the cloudformation open coverage roadmap terraform cli and terraform aws cloud control provider version terraform awscc affected resource s awscc mediapackage channel terraform configuration files please include all terraform configurations required to reproduce the bug bug reports without a functional reproduction may be closed without investigation hcl resource awscc mediapackage channel this id some id description managed by terraform expected behavior to apply successfully with no error actual behavior channel resource created fine but errored out plan awscc mediapackage channel this will be created resource awscc mediapackage channel this arn known after apply description managed by terraform hls ingest ingest endpoints known after apply id some id apply │ error provider returned invalid result object after apply │ │ after the apply operation the provider still indicated an unknown value for module us west awscc mediapackage channel this arn all values must be known after apply so this is always a bug in the provider and should be reported in the provider s own repository terraform will still save the other known object values in the state │ error provider returned invalid result object after apply │ │ after the apply operation the provider still indicated an unknown value for module us west awscc mediapackage channel this hls ingest all values must be known after apply so this is always a bug in the provider and should be reported in the provider s own repository terraform will still save the other known object values in the state error creation of terraform state unsuccessful │ │ with awscc mediapackage channel this │ on pipeline tf line in resource awscc mediapackage channel this │ resource awscc mediapackage channel this │ │ unable to set terraform state unknown values from cloud control api properties this is typically an error with the terraform provider implementation original error error setting value at attributename hls ingest error occurred │ an unexpected error was encountered trying to convert from value this is always an error in the provider please report the following to the provider developer │ │ cannot use type map interface as schema type types objecttype types objecttype must be an attr typewithelementtype to hold map interface steps to reproduce terraform apply | 0 |
46,122 | 7,238,245,643 | IssuesEvent | 2018-02-13 14:01:48 | saraervik/zulip | https://api.github.com/repos/saraervik/zulip | opened | Write Patch file | documentation | The patch file should be oriented on the change logs written in the Zulip repo | 1.0 | Write Patch file - The patch file should be oriented on the change logs written in the Zulip repo | non_priority | write patch file the patch file should be oriented on the change logs written in the zulip repo | 0 |
105,615 | 13,200,536,613 | IssuesEvent | 2020-08-14 08:25:50 | raiden-network/light-client | https://api.github.com/repos/raiden-network/light-client | closed | I don't see the same capacity on the transfer screen that I see on the channel screen while closing a channel | 3 Design 🎨 bug 💣 dApp 📱 | ## Thanks for filing a bug report :-)
## Steps to Reproduce
1. Close the last channel in a token network
## Expected Result
- Is see a message `No open channel` instead of the token amount
## Actual Result
- I see a capacity of 0
## Additional Infos (Optional)
```
- Browser & version
- Browser console errors
- Device / OS
```
| 1.0 | I don't see the same capacity on the transfer screen that I see on the channel screen while closing a channel - ## Thanks for filing a bug report :-)
## Steps to Reproduce
1. Close the last channel in a token network
## Expected Result
- Is see a message `No open channel` instead of the token amount
## Actual Result
- I see a capacity of 0
## Additional Infos (Optional)
```
- Browser & version
- Browser console errors
- Device / OS
```
| non_priority | i don t see the same capacity on the transfer screen that i see on the channel screen while closing a channel thanks for filing a bug report steps to reproduce close the last channel in a token network expected result is see a message no open channel instead of the token amount actual result i see a capacity of additional infos optional browser version browser console errors device os | 0 |
105,609 | 23,081,114,222 | IssuesEvent | 2022-07-26 07:18:15 | FerretDB/FerretDB | https://api.github.com/repos/FerretDB/FerretDB | opened | `tjson`: Add more schema-related test cases | code/enhancement | This task is a part of 683 epic.
Currently, in `tjson` tests we cover the simplest cases of dealing with schemas (valid schemas that correspond to the given types).
Let's add some invalid schemas and fuzzing.
To Do:
- [ ] Test data types with valid schemas that don't represent the given type
- [ ] Test data types with invalid schemas
- [ ] Add schema fuzzing to the `fuzzJSON` function with something like:
```
f.Add(tc.canonJ, schemaAsString)
// ...
f.Fuzz(func(t *testing.T, j, schema string) {
``` | 1.0 | `tjson`: Add more schema-related test cases - This task is a part of 683 epic.
Currently, in `tjson` tests we cover the simplest cases of dealing with schemas (valid schemas that correspond to the given types).
Let's add some invalid schemas and fuzzing.
To Do:
- [ ] Test data types with valid schemas that don't represent the given type
- [ ] Test data types with invalid schemas
- [ ] Add schema fuzzing to the `fuzzJSON` function with something like:
```
f.Add(tc.canonJ, schemaAsString)
// ...
f.Fuzz(func(t *testing.T, j, schema string) {
``` | non_priority | tjson add more schema related test cases this task is a part of epic currently in tjson tests we cover the simplest cases of dealing with schemas valid schemas that correspond to the given types let s add some invalid schemas and fuzzing to do test data types with valid schemas that don t represent the given type test data types with invalid schemas add schema fuzzing to the fuzzjson function with something like f add tc canonj schemaasstring f fuzz func t testing t j schema string | 0 |
288,234 | 31,861,202,983 | IssuesEvent | 2023-09-15 11:03:04 | nidhi7598/linux-v4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564 | opened | CVE-2019-20810 (Medium) detected in linuxlinux-4.19.294 | Mend: dependency security vulnerability | ## CVE-2019-20810 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/go7007/snd-go7007.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/go7007/snd-go7007.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
go7007_snd_init in drivers/media/usb/go7007/snd-go7007.c in the Linux kernel before 5.6 does not call snd_card_free for a failure path, which causes a memory leak, aka CID-9453264ef586.
<p>Publish Date: 2020-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20810>CVE-2019-20810</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20810">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20810</a></p>
<p>Release Date: 2020-06-03</p>
<p>Fix Resolution: v5.6-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-20810 (Medium) detected in linuxlinux-4.19.294 - ## CVE-2019-20810 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/go7007/snd-go7007.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/media/usb/go7007/snd-go7007.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
go7007_snd_init in drivers/media/usb/go7007/snd-go7007.c in the Linux kernel before 5.6 does not call snd_card_free for a failure path, which causes a memory leak, aka CID-9453264ef586.
<p>Publish Date: 2020-06-03
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-20810>CVE-2019-20810</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20810">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-20810</a></p>
<p>Release Date: 2020-06-03</p>
<p>Fix Resolution: v5.6-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linuxlinux cve medium severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files drivers media usb snd c drivers media usb snd c vulnerability details snd init in drivers media usb snd c in the linux kernel before does not call snd card free for a failure path which causes a memory leak aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
16,332 | 10,475,950,343 | IssuesEvent | 2019-09-23 17:28:53 | microsoft/MixedRealityToolkit-Unity | https://api.github.com/repos/microsoft/MixedRealityToolkit-Unity | opened | Changing ActiveProfile duplicates DefaultCursor object in hierarchy | Bug Profile and Inspectors Services | ## Describe the bug
When switching the MixedRealityToolkit.ActiveProfle value, the DefaultCursor object may get duplicated in the hierarchy. This appears to be most common when switching from the DefaultHoloLens2ConfigurationProfile to the DefaultMixedRealityToolkitConfigurationProfile.
## To reproduce
1. Create a new scene and configure for the MixedRealityToolkit
2. Add a button to the scene and apply / configure the included script
3. Enter play mode and expand the MixedRealityPlayspace object in the hierarchy
4. Click the button to toggle between profiles
5. Note the additional DefaultCursor(clone) objects
## Expected behavior
The number of DefaultCursor objects to be consistent
## Your Setup (please complete the following information)
- Unity Version 2018.4.9f1
- MRTK Version 2.0.0 + fixes that will be in 2.1.0
## SwapActiveProfile.cs
using Microsoft.MixedReality.Toolkit;
using UnityEngine;
public class SwapActiveProfile : MonoBehaviour
{
public MixedRealityToolkitConfigurationProfile profile1;
public MixedRealityToolkitConfigurationProfile profile2;
void Start()
{ }
public void Swap()
{
MixedRealityToolkit.Instance.ActiveProfile = (MixedRealityToolkit.Instance.ActiveProfile == profile1) ? profile2 : profile1;
}
}
| 1.0 | Changing ActiveProfile duplicates DefaultCursor object in hierarchy - ## Describe the bug
When switching the MixedRealityToolkit.ActiveProfle value, the DefaultCursor object may get duplicated in the hierarchy. This appears to be most common when switching from the DefaultHoloLens2ConfigurationProfile to the DefaultMixedRealityToolkitConfigurationProfile.
## To reproduce
1. Create a new scene and configure for the MixedRealityToolkit
2. Add a button to the scene and apply / configure the included script
3. Enter play mode and expand the MixedRealityPlayspace object in the hierarchy
4. Click the button to toggle between profiles
5. Note the additional DefaultCursor(clone) objects
## Expected behavior
The number of DefaultCursor objects to be consistent
## Your Setup (please complete the following information)
- Unity Version 2018.4.9f1
- MRTK Version 2.0.0 + fixes that will be in 2.1.0
## SwapActiveProfile.cs
using Microsoft.MixedReality.Toolkit;
using UnityEngine;
public class SwapActiveProfile : MonoBehaviour
{
public MixedRealityToolkitConfigurationProfile profile1;
public MixedRealityToolkitConfigurationProfile profile2;
void Start()
{ }
public void Swap()
{
MixedRealityToolkit.Instance.ActiveProfile = (MixedRealityToolkit.Instance.ActiveProfile == profile1) ? profile2 : profile1;
}
}
| non_priority | changing activeprofile duplicates defaultcursor object in hierarchy describe the bug when switching the mixedrealitytoolkit activeprofle value the defaultcursor object may get duplicated in the hierarchy this appears to be most common when switching from the to the defaultmixedrealitytoolkitconfigurationprofile to reproduce create a new scene and configure for the mixedrealitytoolkit add a button to the scene and apply configure the included script enter play mode and expand the mixedrealityplayspace object in the hierarchy click the button to toggle between profiles note the additional defaultcursor clone objects expected behavior the number of defaultcursor objects to be consistent your setup please complete the following information unity version mrtk version fixes that will be in swapactiveprofile cs using microsoft mixedreality toolkit using unityengine public class swapactiveprofile monobehaviour public mixedrealitytoolkitconfigurationprofile public mixedrealitytoolkitconfigurationprofile void start public void swap mixedrealitytoolkit instance activeprofile mixedrealitytoolkit instance activeprofile | 0 |
394,452 | 27,029,558,153 | IssuesEvent | 2023-02-12 02:09:37 | Zaba505/breakout-boards | https://api.github.com/repos/Zaba505/breakout-boards | opened | story(coral_ai): design breakout board | documentation | ### Description
As an end user, I want a breakout board for the Coral AI accelerator module, so that I can build projects with it as well as test it out before designing more complex boards.
### Acceptance Criteria
- [ ] All pins are mapped to hole passthroughs
### Related Issues
_No response_ | 1.0 | story(coral_ai): design breakout board - ### Description
As an end user, I want a breakout board for the Coral AI accelerator module, so that I can build projects with it as well as test it out before designing more complex boards.
### Acceptance Criteria
- [ ] All pins are mapped to hole passthroughs
### Related Issues
_No response_ | non_priority | story coral ai design breakout board description as an end user i want a breakout board for the coral ai accelerator module so that i can build projects with it as well as test it out before designing more complex boards acceptance criteria all pins are mapped to hole passthroughs related issues no response | 0 |
351,140 | 31,935,076,764 | IssuesEvent | 2023-09-19 09:55:17 | unifyai/ivy | https://api.github.com/repos/unifyai/ivy | opened | Fix stat.test_paddle_numel | Sub Task Failing Test | | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
| 1.0 | Fix stat.test_paddle_numel - | | |
|---|---|
|numpy|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
|jax|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
|tensorflow|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
|torch|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-success-success></a>
|paddle|<a href="https://github.com/unifyai/ivy/actions/runs/6206066513/job/16849904352"><img src=https://img.shields.io/badge/-failure-red></a>
| non_priority | fix stat test paddle numel numpy a href src jax a href src tensorflow a href src torch a href src paddle a href src | 0 |
9,320 | 4,479,367,736 | IssuesEvent | 2016-08-27 15:22:18 | thibmaek/worker | https://api.github.com/repos/thibmaek/worker | closed | Build fails | Can not find test directory | breaks-build | ```console
$ for TEST in tests/*; do chmod +x $TEST; done
chmod: tests/*: No such file or directory
The command "for TEST in tests/*; do chmod +x $TEST; done" failed and exited with 1 during .
``` | 1.0 | Build fails | Can not find test directory - ```console
$ for TEST in tests/*; do chmod +x $TEST; done
chmod: tests/*: No such file or directory
The command "for TEST in tests/*; do chmod +x $TEST; done" failed and exited with 1 during .
``` | non_priority | build fails can not find test directory console for test in tests do chmod x test done chmod tests no such file or directory the command for test in tests do chmod x test done failed and exited with during | 0 |
63,765 | 12,374,101,610 | IssuesEvent | 2020-05-19 00:30:14 | Regalis11/Barotrauma | https://api.github.com/repos/Regalis11/Barotrauma | closed | [Unstable] [Modding] Overriding default signalitems.xml file with mod breaks signal items | Bug Code Modding | [A different mod.zip](https://github.com/Regalis11/Barotrauma/files/4241411/A.different.mod.zip)
**Description**
Overriding this file, for example in order to change item prices, breakes the game in a weird way. Everything that the file relates to gets turned to it's default state, so signal components stop working as intended when you load a sub (you cannot undock on vanilla subs, thats the most noticable one). Same with pump.xml and electricity.xml.
**Steps To Reproduce**
-Create a new mod folder in /Mods the usual way, non-core package
-Get signalitems.xml and all it's relevant files in there and refer to it in filelist.xml
-Override signalitems.xml with classic override start and override end tags
-Start the game, enable the mod and start any match
-Open Nav terminal and press Undock
-The submarine will not undock
**Version**
Unstable
**Additional information**
Just the act of overriding the, in other ways completely vanilla item, sets everything else to default.
| 1.0 | [Unstable] [Modding] Overriding default signalitems.xml file with mod breaks signal items - [A different mod.zip](https://github.com/Regalis11/Barotrauma/files/4241411/A.different.mod.zip)
**Description**
Overriding this file, for example in order to change item prices, breakes the game in a weird way. Everything that the file relates to gets turned to it's default state, so signal components stop working as intended when you load a sub (you cannot undock on vanilla subs, thats the most noticable one). Same with pump.xml and electricity.xml.
**Steps To Reproduce**
-Create a new mod folder in /Mods the usual way, non-core package
-Get signalitems.xml and all it's relevant files in there and refer to it in filelist.xml
-Override signalitems.xml with classic override start and override end tags
-Start the game, enable the mod and start any match
-Open Nav terminal and press Undock
-The submarine will not undock
**Version**
Unstable
**Additional information**
Just the act of overriding the, in other ways completely vanilla item, sets everything else to default.
| non_priority | overriding default signalitems xml file with mod breaks signal items description overriding this file for example in order to change item prices breakes the game in a weird way everything that the file relates to gets turned to it s default state so signal components stop working as intended when you load a sub you cannot undock on vanilla subs thats the most noticable one same with pump xml and electricity xml steps to reproduce create a new mod folder in mods the usual way non core package get signalitems xml and all it s relevant files in there and refer to it in filelist xml override signalitems xml with classic override start and override end tags start the game enable the mod and start any match open nav terminal and press undock the submarine will not undock version unstable additional information just the act of overriding the in other ways completely vanilla item sets everything else to default | 0 |
80,173 | 10,155,098,682 | IssuesEvent | 2019-08-06 09:32:14 | scikit-learn/scikit-learn | https://api.github.com/repos/scikit-learn/scikit-learn | closed | add recommendation system libraries to the FAQ | Documentation Easy | People often ask about libraries for recommendation engines.
There is a good summary here: https://www.quora.com/What-is-the-best-open-source-package-to-build-a-recommender-system-in-Python/answer/Xavier-Amatriain?srid=cgo
I think we might want to add this to the FAQ, either by linking to it, or by putting this listing in the "related packages" page and then linking to that from the FAQ. | 1.0 | add recommendation system libraries to the FAQ - People often ask about libraries for recommendation engines.
There is a good summary here: https://www.quora.com/What-is-the-best-open-source-package-to-build-a-recommender-system-in-Python/answer/Xavier-Amatriain?srid=cgo
I think we might want to add this to the FAQ, either by linking to it, or by putting this listing in the "related packages" page and then linking to that from the FAQ. | non_priority | add recommendation system libraries to the faq people often ask about libraries for recommendation engines there is a good summary here i think we might want to add this to the faq either by linking to it or by putting this listing in the related packages page and then linking to that from the faq | 0 |
3,827 | 14,664,388,951 | IssuesEvent | 2020-12-29 11:53:27 | SAP/fundamental-ngx | https://api.github.com/repos/SAP/fundamental-ngx | closed | File uploader - user is able to upload the incorrect file via automation tests | E2E automation Medium bug core | **Description:** user is able to upload the incorrect file via automation tests
**Expected result:** user should be able to upload the incorrect file via automation tests | 1.0 | File uploader - user is able to upload the incorrect file via automation tests - **Description:** user is able to upload the incorrect file via automation tests
**Expected result:** user should be able to upload the incorrect file via automation tests | non_priority | file uploader user is able to upload the incorrect file via automation tests description user is able to upload the incorrect file via automation tests expected result user should be able to upload the incorrect file via automation tests | 0 |
21,264 | 6,132,559,238 | IssuesEvent | 2017-06-25 03:48:31 | ganeti/ganeti | https://api.github.com/repos/ganeti/ganeti | closed | gnt-backup import fails | imported_from_google_code Status:Obsolete | Originally reported of Google Code with ID 276.
```
What software version are you running? Please provide the output of "gnt-
cluster --version" and "gnt-cluster version".
gnt-cluster (ganeti v2.5.2) 2.5.2
Software version: 2.5.2
Internode protocol: 2050000
Configuration format: 2050000
OS api version: 20
Export interface: 0
<b>What distribution are you using?</b>
Centos 6.3
<b>What steps will reproduce the problem?</b>
1. gnt-backup export -n msgnt1.milestoneip.com inst1
2. gnt-backup import -n msgnt1.milestoneip.com --src-node=msgnt1.milestoneip.com --src-dir=/srv/ganeti/export/inst1 inst2
What is the expected output?
it should import the backup to a new instance
What do you see instead ?
Failure: prerequisites not met for this operation:
error type: wrong_input, error details:
Parameter 'OP_INSTANCE_CREATE.disk_template' fails validation
```
Originally added on 2012-10-15 15:34:30 +0000 UTC. | 1.0 | gnt-backup import fails - Originally reported of Google Code with ID 276.
```
What software version are you running? Please provide the output of "gnt-
cluster --version" and "gnt-cluster version".
gnt-cluster (ganeti v2.5.2) 2.5.2
Software version: 2.5.2
Internode protocol: 2050000
Configuration format: 2050000
OS api version: 20
Export interface: 0
<b>What distribution are you using?</b>
Centos 6.3
<b>What steps will reproduce the problem?</b>
1. gnt-backup export -n msgnt1.milestoneip.com inst1
2. gnt-backup import -n msgnt1.milestoneip.com --src-node=msgnt1.milestoneip.com --src-dir=/srv/ganeti/export/inst1 inst2
What is the expected output?
it should import the backup to a new instance
What do you see instead ?
Failure: prerequisites not met for this operation:
error type: wrong_input, error details:
Parameter 'OP_INSTANCE_CREATE.disk_template' fails validation
```
Originally added on 2012-10-15 15:34:30 +0000 UTC. | non_priority | gnt backup import fails originally reported of google code with id what software version are you running please provide the output of gnt cluster version and gnt cluster version gnt cluster ganeti software version internode protocol configuration format os api version export interface what distribution are you using centos what steps will reproduce the problem gnt backup export n milestoneip com gnt backup import n milestoneip com src node milestoneip com src dir srv ganeti export what is the expected output it should import the backup to a new instance what do you see instead failure prerequisites not met for this operation error type wrong input error details parameter op instance create disk template fails validation originally added on utc | 0 |
282,086 | 30,889,157,131 | IssuesEvent | 2023-08-04 02:19:22 | madhans23/linux-4.1.15 | https://api.github.com/repos/madhans23/linux-4.1.15 | reopened | CVE-2019-5489 (Medium) detected in linux-stable-rtv4.1.33 | Mend: dependency security vulnerability | ## CVE-2019-5489 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mincore.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mincore.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The mincore() implementation in mm/mincore.c in the Linux kernel through 4.19.13 allowed local attackers to observe page cache access patterns of other processes on the same system, potentially allowing sniffing of secret information. (Fixing this affects the output of the fincore program.) Limited remote exploitation may be possible, as demonstrated by latency differences in accessing public files from an Apache HTTP Server.
<p>Publish Date: 2019-01-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-5489>CVE-2019-5489</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-5489">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-5489</a></p>
<p>Release Date: 2019-01-07</p>
<p>Fix Resolution: v5.0-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-5489 (Medium) detected in linux-stable-rtv4.1.33 - ## CVE-2019-5489 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-stable-rtv4.1.33</b></p></summary>
<p>
<p>Julia Cartwright's fork of linux-stable-rt.git</p>
<p>Library home page: <a href=https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git>https://git.kernel.org/pub/scm/linux/kernel/git/julia/linux-stable-rt.git</a></p>
<p>Found in base branch: <b>master</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mincore.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/mm/mincore.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
The mincore() implementation in mm/mincore.c in the Linux kernel through 4.19.13 allowed local attackers to observe page cache access patterns of other processes on the same system, potentially allowing sniffing of secret information. (Fixing this affects the output of the fincore program.) Limited remote exploitation may be possible, as demonstrated by latency differences in accessing public files from an Apache HTTP Server.
<p>Publish Date: 2019-01-07
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-5489>CVE-2019-5489</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-5489">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-5489</a></p>
<p>Release Date: 2019-01-07</p>
<p>Fix Resolution: v5.0-rc1</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in linux stable cve medium severity vulnerability vulnerable library linux stable julia cartwright s fork of linux stable rt git library home page a href found in base branch master vulnerable source files mm mincore c mm mincore c vulnerability details the mincore implementation in mm mincore c in the linux kernel through allowed local attackers to observe page cache access patterns of other processes on the same system potentially allowing sniffing of secret information fixing this affects the output of the fincore program limited remote exploitation may be possible as demonstrated by latency differences in accessing public files from an apache http server publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
207,844 | 23,498,624,571 | IssuesEvent | 2022-08-18 06:03:18 | RG4421/featuretools | https://api.github.com/repos/RG4421/featuretools | opened | CVE-2022-33891 (High) detected in pyspark-3.0.2.tar.gz | security vulnerability | ## CVE-2022-33891 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pyspark-3.0.2.tar.gz</b></p></summary>
<p>Apache Spark Python API</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/27/67/5158f846202d7f012d1c9ca21c3549a58fd3c6707ae8ee823adcaca6473c/pyspark-3.0.2.tar.gz">https://files.pythonhosted.org/packages/27/67/5158f846202d7f012d1c9ca21c3549a58fd3c6707ae8ee823adcaca6473c/pyspark-3.0.2.tar.gz</a></p>
<p>Path to dependency file: /koalas-requirements.txt</p>
<p>Path to vulnerable library: /koalas-requirements.txt,/docs/source</p>
<p>
Dependency Hierarchy:
- :x: **pyspark-3.0.2.tar.gz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Apache Spark UI offers the possibility to enable ACLs via the configuration option spark.acls.enable. With an authentication filter, this checks whether a user has access permissions to view or modify the application. If ACLs are enabled, a code path in HttpSecurityFilter can allow someone to perform impersonation by providing an arbitrary user name. A malicious user might then be able to reach a permission check function that will ultimately build a Unix shell command based on their input, and execute it. This will result in arbitrary shell command execution as the user Spark is currently running as. This affects Apache Spark versions 3.0.3 and earlier, versions 3.1.1 to 3.1.2, and versions 3.2.0 to 3.2.1.
<p>Publish Date: 2022-07-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33891>CVE-2022-33891</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-4x9r-j582-cgr8">https://github.com/advisories/GHSA-4x9r-j582-cgr8</a></p>
<p>Release Date: 2022-07-18</p>
<p>Fix Resolution: org.apache.spark:spark-core:3.1.3,3.2.2,3.3.0, pyspark - 3.1.3,3.2.2</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2022-33891 (High) detected in pyspark-3.0.2.tar.gz - ## CVE-2022-33891 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>pyspark-3.0.2.tar.gz</b></p></summary>
<p>Apache Spark Python API</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/27/67/5158f846202d7f012d1c9ca21c3549a58fd3c6707ae8ee823adcaca6473c/pyspark-3.0.2.tar.gz">https://files.pythonhosted.org/packages/27/67/5158f846202d7f012d1c9ca21c3549a58fd3c6707ae8ee823adcaca6473c/pyspark-3.0.2.tar.gz</a></p>
<p>Path to dependency file: /koalas-requirements.txt</p>
<p>Path to vulnerable library: /koalas-requirements.txt,/docs/source</p>
<p>
Dependency Hierarchy:
- :x: **pyspark-3.0.2.tar.gz** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The Apache Spark UI offers the possibility to enable ACLs via the configuration option spark.acls.enable. With an authentication filter, this checks whether a user has access permissions to view or modify the application. If ACLs are enabled, a code path in HttpSecurityFilter can allow someone to perform impersonation by providing an arbitrary user name. A malicious user might then be able to reach a permission check function that will ultimately build a Unix shell command based on their input, and execute it. This will result in arbitrary shell command execution as the user Spark is currently running as. This affects Apache Spark versions 3.0.3 and earlier, versions 3.1.1 to 3.1.2, and versions 3.2.0 to 3.2.1.
<p>Publish Date: 2022-07-18
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-33891>CVE-2022-33891</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-4x9r-j582-cgr8">https://github.com/advisories/GHSA-4x9r-j582-cgr8</a></p>
<p>Release Date: 2022-07-18</p>
<p>Fix Resolution: org.apache.spark:spark-core:3.1.3,3.2.2,3.3.0, pyspark - 3.1.3,3.2.2</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve high detected in pyspark tar gz cve high severity vulnerability vulnerable library pyspark tar gz apache spark python api library home page a href path to dependency file koalas requirements txt path to vulnerable library koalas requirements txt docs source dependency hierarchy x pyspark tar gz vulnerable library found in base branch main vulnerability details the apache spark ui offers the possibility to enable acls via the configuration option spark acls enable with an authentication filter this checks whether a user has access permissions to view or modify the application if acls are enabled a code path in httpsecurityfilter can allow someone to perform impersonation by providing an arbitrary user name a malicious user might then be able to reach a permission check function that will ultimately build a unix shell command based on their input and execute it this will result in arbitrary shell command execution as the user spark is currently running as this affects apache spark versions and earlier versions to and versions to publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache spark spark core pyspark rescue worker helmet automatic remediation is available for this issue | 0 |
249,577 | 18,858,212,477 | IssuesEvent | 2021-11-12 09:30:38 | Zenlzb/pe | https://api.github.com/repos/Zenlzb/pe | opened | [DG] Common classes section still references seedu.addressbook.commons | severity.VeryLow type.DocumentationBug | Common classes section still references seedu.addressbook.commons
<!--session: 1636696497012-67e92c92-f1de-4aff-9d61-c6a8e85d2444-->
<!--Version: Web v3.4.1--> | 1.0 | [DG] Common classes section still references seedu.addressbook.commons - Common classes section still references seedu.addressbook.commons
<!--session: 1636696497012-67e92c92-f1de-4aff-9d61-c6a8e85d2444-->
<!--Version: Web v3.4.1--> | non_priority | common classes section still references seedu addressbook commons common classes section still references seedu addressbook commons | 0 |
76,390 | 21,393,822,296 | IssuesEvent | 2022-04-21 09:39:49 | yatinappsmith/TestCaseRepo | https://api.github.com/repos/yatinappsmith/TestCaseRepo | opened | [TestCase] To verify the functionality of Required toggle | Automated App Viewers Pod UI Building Pod Switch Group Widget | ### Steps
**Step1.** Drag and drop Switch group widget to the canvas
**Expected** Ensure the switch group widget is plaved on canvas
**Step2.** Click on the widget to open property pane
**Expected** Ensure switch group widget property pane is opened
**Step3.** Check the default Required toggle status
**Expected** By default the required toggle status will be disabled
**Step4.** Disable all the switch button option from the switch group
**Expected** All the switch button option are disabled
**Step5.** Drag and drop a form widget
**Expected** Form widget is placed on the canvas
**Step6.** Place the Switch group widget inside button
**Expected** Ensure the submit button of the form will be disabled and the Switch group widget will be highlighted in red colour
**Step7.** Enable any of thr switch butotn option
**Expected** Ensure the submit button of the form will be enabled
### Expected behaviour
| 1.0 | [TestCase] To verify the functionality of Required toggle - ### Steps
**Step1.** Drag and drop Switch group widget to the canvas
**Expected** Ensure the switch group widget is plaved on canvas
**Step2.** Click on the widget to open property pane
**Expected** Ensure switch group widget property pane is opened
**Step3.** Check the default Required toggle status
**Expected** By default the required toggle status will be disabled
**Step4.** Disable all the switch button option from the switch group
**Expected** All the switch button option are disabled
**Step5.** Drag and drop a form widget
**Expected** Form widget is placed on the canvas
**Step6.** Place the Switch group widget inside button
**Expected** Ensure the submit button of the form will be disabled and the Switch group widget will be highlighted in red colour
**Step7.** Enable any of thr switch butotn option
**Expected** Ensure the submit button of the form will be enabled
### Expected behaviour
| non_priority | to verify the functionality of required toggle steps drag and drop switch group widget to the canvas expected ensure the switch group widget is plaved on canvas click on the widget to open property pane expected ensure switch group widget property pane is opened check the default required toggle status expected by default the required toggle status will be disabled disable all the switch button option from the switch group expected all the switch button option are disabled drag and drop a form widget expected form widget is placed on the canvas place the switch group widget inside button expected ensure the submit button of the form will be disabled and the switch group widget will be highlighted in red colour enable any of thr switch butotn option expected ensure the submit button of the form will be enabled expected behaviour | 0 |
129,766 | 18,109,738,165 | IssuesEvent | 2021-09-23 01:01:52 | maorkuriel/ksa | https://api.github.com/repos/maorkuriel/ksa | opened | CVE-2020-11023 (Medium) detected in jquery-1.7.2.min.js | security vulnerability | ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to vulnerable library: ksa-web-root/ksa-web/src/main/webapp/rs/jquery/jquery-1.7.2.min.js,ksa-web-root/ksa-web/target/ROOT/rs/jquery/jquery-1.7.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.7.2","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jquery:1.7.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-11023 (Medium) detected in jquery-1.7.2.min.js - ## CVE-2020-11023 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js">https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
<p>Path to vulnerable library: ksa-web-root/ksa-web/src/main/webapp/rs/jquery/jquery-1.7.2.min.js,ksa-web-root/ksa-web/target/ROOT/rs/jquery/jquery-1.7.2.min.js</p>
<p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing <option> elements from untrusted sources - even after sanitizing it - to one of jQuery's DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.
<p>Publish Date: 2020-04-29
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023>CVE-2020-11023</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440">https://github.com/jquery/jquery/security/advisories/GHSA-jpcq-cgw6-v4j6,https://github.com/rails/jquery-rails/blob/master/CHANGELOG.md#440</a></p>
<p>Release Date: 2020-04-29</p>
<p>Fix Resolution: jquery - 3.5.0;jquery-rails - 4.4.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"JavaScript","packageName":"jquery","packageVersion":"1.7.2","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"jquery:1.7.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"jquery - 3.5.0;jquery-rails - 4.4.0"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2020-11023","vulnerabilityDetails":"In jQuery versions greater than or equal to 1.0.3 and before 3.5.0, passing HTML containing \u003coption\u003e elements from untrusted sources - even after sanitizing it - to one of jQuery\u0027s DOM manipulation methods (i.e. .html(), .append(), and others) may execute untrusted code. This problem is patched in jQuery 3.5.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-11023","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in jquery min js cve medium severity vulnerability vulnerable library jquery min js javascript library for dom operations library home page a href path to vulnerable library ksa web root ksa web src main webapp rs jquery jquery min js ksa web root ksa web target root rs jquery jquery min js dependency hierarchy x jquery min js vulnerable library found in base branch master vulnerability details in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery s dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution jquery jquery rails isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree jquery isminimumfixversionavailable true minimumfixversion jquery jquery rails basebranches vulnerabilityidentifier cve vulnerabilitydetails in jquery versions greater than or equal to and before passing html containing elements from untrusted sources even after sanitizing it to one of jquery dom manipulation methods i e html append and others may execute untrusted code this problem is patched in jquery vulnerabilityurl | 0 |
397,267 | 27,157,545,439 | IssuesEvent | 2023-02-17 09:11:31 | humanprotocol/human-protocol | https://api.github.com/repos/humanprotocol/human-protocol | closed | Fortune - Development of a specification for a decentralized solution | documentation Fortune | ### Description
Develop a new specification for Fortune's successful decentralization.
This specification will be based on [the diagrams described in miro](https://miro.com/app/board/uXjVPG1mXJc=/). The new update will affect changes in the statuses and events of the [Escrow Contract](https://github.com/humanprotocol/human-protocol/blob/feat/staking-slashing/packages/core/contracts/Escrow.sol), as well as changes in the [current implementation of Fortune services](https://github.com/humanprotocol/human-protocol/tree/feat/staking-slashing/packages/examples/fortune).
### Motivation
Get rid of the Web2 dependency between the oracle services and the launcher inside the Fortune, as well as exchange data and updates through the blockchain (contract storage) and s3 storage.
All specs will be described in [notion](https://www.notion.so/human-protocol/Fortune-V2-637eced86e71442594dd7c2eda801816). | 1.0 | Fortune - Development of a specification for a decentralized solution - ### Description
Develop a new specification for Fortune's successful decentralization.
This specification will be based on [the diagrams described in miro](https://miro.com/app/board/uXjVPG1mXJc=/). The new update will affect changes in the statuses and events of the [Escrow Contract](https://github.com/humanprotocol/human-protocol/blob/feat/staking-slashing/packages/core/contracts/Escrow.sol), as well as changes in the [current implementation of Fortune services](https://github.com/humanprotocol/human-protocol/tree/feat/staking-slashing/packages/examples/fortune).
### Motivation
Get rid of the Web2 dependency between the oracle services and the launcher inside the Fortune, as well as exchange data and updates through the blockchain (contract storage) and s3 storage.
All specs will be described in [notion](https://www.notion.so/human-protocol/Fortune-V2-637eced86e71442594dd7c2eda801816). | non_priority | fortune development of a specification for a decentralized solution description develop a new specification for fortune s successful decentralization this specification will be based on the new update will affect changes in the statuses and events of the as well as changes in the motivation get rid of the dependency between the oracle services and the launcher inside the fortune as well as exchange data and updates through the blockchain contract storage and storage all specs will be described in | 0 |
71,845 | 15,209,860,174 | IssuesEvent | 2021-02-17 06:18:05 | YJSoft/xe-core-old | https://api.github.com/repos/YJSoft/xe-core-old | opened | CVE-2019-1010266 (Medium) detected in lodash-2.4.2.js, lodash-0.9.2.js | security vulnerability | ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-2.4.2.js</b>, <b>lodash-0.9.2.js</b></p></summary>
<p>
<details><summary><b>lodash-2.4.2.js</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/lodash.js/2.4.2/lodash.js">https://cdnjs.cloudflare.com/ajax/libs/lodash.js/2.4.2/lodash.js</a></p>
<p>Path to vulnerable library: xe-core-old/node_modules/grunt-legacy-log-utils/node_modules/lodash/lodash.js,xe-core-old/node_modules/findup-sync/node_modules/lodash/lodash.js,xe-core-old/node_modules/grunt-contrib-csslint/node_modules/lodash/lodash.js,xe-core-old/node_modules/grunt-legacy-log/node_modules/lodash/lodash.js</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.4.2.js** (Vulnerable Library)
</details>
<details><summary><b>lodash-0.9.2.js</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/lodash.js/0.9.2/lodash.js">https://cdnjs.cloudflare.com/ajax/libs/lodash.js/0.9.2/lodash.js</a></p>
<p>Path to vulnerable library: xe-core-old/node_modules/lodash/lodash.js</p>
<p>
Dependency Hierarchy:
- :x: **lodash-0.9.2.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/YJSoft/xe-core-old/commit/721f00c7479af73f0a73be46c2bc6853e1da863b">721f00c7479af73f0a73be46c2bc6853e1da863b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-1010266 (Medium) detected in lodash-2.4.2.js, lodash-0.9.2.js - ## CVE-2019-1010266 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-2.4.2.js</b>, <b>lodash-0.9.2.js</b></p></summary>
<p>
<details><summary><b>lodash-2.4.2.js</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/lodash.js/2.4.2/lodash.js">https://cdnjs.cloudflare.com/ajax/libs/lodash.js/2.4.2/lodash.js</a></p>
<p>Path to vulnerable library: xe-core-old/node_modules/grunt-legacy-log-utils/node_modules/lodash/lodash.js,xe-core-old/node_modules/findup-sync/node_modules/lodash/lodash.js,xe-core-old/node_modules/grunt-contrib-csslint/node_modules/lodash/lodash.js,xe-core-old/node_modules/grunt-legacy-log/node_modules/lodash/lodash.js</p>
<p>
Dependency Hierarchy:
- :x: **lodash-2.4.2.js** (Vulnerable Library)
</details>
<details><summary><b>lodash-0.9.2.js</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://cdnjs.cloudflare.com/ajax/libs/lodash.js/0.9.2/lodash.js">https://cdnjs.cloudflare.com/ajax/libs/lodash.js/0.9.2/lodash.js</a></p>
<p>Path to vulnerable library: xe-core-old/node_modules/lodash/lodash.js</p>
<p>
Dependency Hierarchy:
- :x: **lodash-0.9.2.js** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/YJSoft/xe-core-old/commit/721f00c7479af73f0a73be46c2bc6853e1da863b">721f00c7479af73f0a73be46c2bc6853e1da863b</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lodash prior to 4.17.11 is affected by: CWE-400: Uncontrolled Resource Consumption. The impact is: Denial of service. The component is: Date handler. The attack vector is: Attacker provides very long strings, which the library attempts to match using a regular expression. The fixed version is: 4.17.11.
<p>Publish Date: 2019-07-17
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-1010266>CVE-2019-1010266</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>6.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1010266</a></p>
<p>Release Date: 2019-07-17</p>
<p>Fix Resolution: 4.17.11</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in lodash js lodash js cve medium severity vulnerability vulnerable libraries lodash js lodash js lodash js a utility library delivering consistency customization performance extras library home page a href path to vulnerable library xe core old node modules grunt legacy log utils node modules lodash lodash js xe core old node modules findup sync node modules lodash lodash js xe core old node modules grunt contrib csslint node modules lodash lodash js xe core old node modules grunt legacy log node modules lodash lodash js dependency hierarchy x lodash js vulnerable library lodash js a utility library delivering consistency customization performance extras library home page a href path to vulnerable library xe core old node modules lodash lodash js dependency hierarchy x lodash js vulnerable library found in head commit a href found in base branch master vulnerability details lodash prior to is affected by cwe uncontrolled resource consumption the impact is denial of service the component is date handler the attack vector is attacker provides very long strings which the library attempts to match using a regular expression the fixed version is publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
50,389 | 13,187,473,450 | IssuesEvent | 2020-08-13 03:31:36 | icecube-trac/tix3 | https://api.github.com/repos/icecube-trac/tix3 | closed | can't find python libs > python 2.6.x (Trac #627) | Migrated from Trac cmake defect | cmake 2.6.x only has support for python < 2.6.x in its PythonFindX.cmake modules. (hard coded values). this seems to have been fixed in cmake 2.8.x, but is currently untested by !IceCube. (i personally use cmake 2.8.x but not python 2.7.x)
currently i solve this on the build bots by hard coding python paths in a I3_CITE_CMAKE_DIR file on akuma (rhel4 + external python 2.7) and beastie (freebsd 9RC + freebsd port install of python 2.7.1 in /usr/local).
this '''can not''' be solved by including the cmake 2.8 FindPythonX modules, as we'd get into dependency hell w/ the cmake modules.
probably be able to solve this w/ i3-tools-v4 (#278)
<details>
<summary><em>Migrated from https://code.icecube.wisc.edu/ticket/627
, reported by nega and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2011-05-11T19:50:31",
"description": "cmake 2.6.x only has support for python < 2.6.x in its PythonFindX.cmake modules. (hard coded values). this seems to have been fixed in cmake 2.8.x, but is currently untested by !IceCube. (i personally use cmake 2.8.x but not python 2.7.x)\n\ncurrently i solve this on the build bots by hard coding python paths in a I3_CITE_CMAKE_DIR file on akuma (rhel4 + external python 2.7) and beastie (freebsd 9RC + freebsd port install of python 2.7.1 in /usr/local).\n\nthis '''can not''' be solved by including the cmake 2.8 FindPythonX modules, as we'd get into dependency hell w/ the cmake modules.\n\nprobably be able to solve this w/ i3-tools-v4 (#278)",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1305143431000000",
"component": "cmake",
"summary": "can't find python libs > python 2.6.x",
"priority": "major",
"keywords": "cmake python freebsd rhel",
"time": "2011-04-30T16:22:01",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| 1.0 | can't find python libs > python 2.6.x (Trac #627) - cmake 2.6.x only has support for python < 2.6.x in its PythonFindX.cmake modules. (hard coded values). this seems to have been fixed in cmake 2.8.x, but is currently untested by !IceCube. (i personally use cmake 2.8.x but not python 2.7.x)
currently i solve this on the build bots by hard coding python paths in a I3_CITE_CMAKE_DIR file on akuma (rhel4 + external python 2.7) and beastie (freebsd 9RC + freebsd port install of python 2.7.1 in /usr/local).
this '''can not''' be solved by including the cmake 2.8 FindPythonX modules, as we'd get into dependency hell w/ the cmake modules.
probably be able to solve this w/ i3-tools-v4 (#278)
<details>
<summary><em>Migrated from https://code.icecube.wisc.edu/ticket/627
, reported by nega and owned by nega</em></summary>
<p>
```json
{
"status": "closed",
"changetime": "2011-05-11T19:50:31",
"description": "cmake 2.6.x only has support for python < 2.6.x in its PythonFindX.cmake modules. (hard coded values). this seems to have been fixed in cmake 2.8.x, but is currently untested by !IceCube. (i personally use cmake 2.8.x but not python 2.7.x)\n\ncurrently i solve this on the build bots by hard coding python paths in a I3_CITE_CMAKE_DIR file on akuma (rhel4 + external python 2.7) and beastie (freebsd 9RC + freebsd port install of python 2.7.1 in /usr/local).\n\nthis '''can not''' be solved by including the cmake 2.8 FindPythonX modules, as we'd get into dependency hell w/ the cmake modules.\n\nprobably be able to solve this w/ i3-tools-v4 (#278)",
"reporter": "nega",
"cc": "",
"resolution": "fixed",
"_ts": "1305143431000000",
"component": "cmake",
"summary": "can't find python libs > python 2.6.x",
"priority": "major",
"keywords": "cmake python freebsd rhel",
"time": "2011-04-30T16:22:01",
"milestone": "",
"owner": "nega",
"type": "defect"
}
```
</p>
</details>
| non_priority | can t find python libs python x trac cmake x only has support for python x in its pythonfindx cmake modules hard coded values this seems to have been fixed in cmake x but is currently untested by icecube i personally use cmake x but not python x currently i solve this on the build bots by hard coding python paths in a cite cmake dir file on akuma external python and beastie freebsd freebsd port install of python in usr local this can not be solved by including the cmake findpythonx modules as we d get into dependency hell w the cmake modules probably be able to solve this w tools migrated from reported by nega and owned by nega json status closed changetime description cmake x only has support for python x in its pythonfindx cmake modules hard coded values this seems to have been fixed in cmake x but is currently untested by icecube i personally use cmake x but not python x n ncurrently i solve this on the build bots by hard coding python paths in a cite cmake dir file on akuma external python and beastie freebsd freebsd port install of python in usr local n nthis can not be solved by including the cmake findpythonx modules as we d get into dependency hell w the cmake modules n nprobably be able to solve this w tools reporter nega cc resolution fixed ts component cmake summary can t find python libs python x priority major keywords cmake python freebsd rhel time milestone owner nega type defect | 0 |
34,254 | 14,344,808,397 | IssuesEvent | 2020-11-28 16:09:10 | datorama/akita | https://api.github.com/repos/datorama/akita | closed | [Question] Concatenate extra URL segments to the base URL in the NgEntityService | comp: NgEntityService question | ## I'm submitting a...
<!-- Check one of the following options with "x" -->
<pre><code>
[ ] Regression (a behavior that used to work and stopped working in a new release)
[ ] Bug report <!-- Please search GitHub for a similar issue or PR before submitting -->
[ ] Performance issue
[ ] Feature request
[ ] Documentation issue or request
[x] Support request
[ ] Other... Please describe:
</code></pre>
## Problem
I'm currently using the NgEntityService and I need to consume an API that have endpoints like this:
**PUT** `example.com/api/v1/usuarios/1/detalles`
**PATCH** `example.com/api/v1/usuarios/1/status`
**GET** `example.com/api/v1/municipios/departamento/1`
## Example
1. Set the base URL
app.module
```ts
providers: [
...
{
provide: NG_ENTITY_SERVICE_CONFIG,
useValue: {
baseUrl: environment.apiUrl,
},
}
]
```
2. Add resource name
users.service
```ts
@NgEntityServiceConfig({
resourceName: 'usuarios',
})
@Injectable({ providedIn: 'root' })
export class UsersService extends NgEntityService<UsersState> {
constructor(protected store: UsersStore) {
super(store);
}
}
```
3. Call service
account.page.ts
```ts
updateUserDetails(): void {
this.usersService
.put<User>({
extras: ['detalles'], // <--- Is there a way to do this?
mapResponseFn: (res) => res.data as User,
})
.subscribe();
}
```
#### WORKAROUND
```ts
updateUserDetails(): void {
this.usersService
.put<User>({
url: `${environment.apiUrl}/usuarios/detalles`,
mapResponseFn: (res) => res.data as User,
})
.subscribe();
}
```
## Question
How can I concatenate extra endpoints to the API resource?
## Environment
```
Angular 11.0.0
```
P.D. I know I could use query parameters for some of the examples but I don't have control over the API.
Thanks in advance!
| 1.0 | [Question] Concatenate extra URL segments to the base URL in the NgEntityService - ## I'm submitting a...
<!-- Check one of the following options with "x" -->
<pre><code>
[ ] Regression (a behavior that used to work and stopped working in a new release)
[ ] Bug report <!-- Please search GitHub for a similar issue or PR before submitting -->
[ ] Performance issue
[ ] Feature request
[ ] Documentation issue or request
[x] Support request
[ ] Other... Please describe:
</code></pre>
## Problem
I'm currently using the NgEntityService and I need to consume an API that have endpoints like this:
**PUT** `example.com/api/v1/usuarios/1/detalles`
**PATCH** `example.com/api/v1/usuarios/1/status`
**GET** `example.com/api/v1/municipios/departamento/1`
## Example
1. Set the base URL
app.module
```ts
providers: [
...
{
provide: NG_ENTITY_SERVICE_CONFIG,
useValue: {
baseUrl: environment.apiUrl,
},
}
]
```
2. Add resource name
users.service
```ts
@NgEntityServiceConfig({
resourceName: 'usuarios',
})
@Injectable({ providedIn: 'root' })
export class UsersService extends NgEntityService<UsersState> {
constructor(protected store: UsersStore) {
super(store);
}
}
```
3. Call service
account.page.ts
```ts
updateUserDetails(): void {
this.usersService
.put<User>({
extras: ['detalles'], // <--- Is there a way to do this?
mapResponseFn: (res) => res.data as User,
})
.subscribe();
}
```
#### WORKAROUND
```ts
updateUserDetails(): void {
this.usersService
.put<User>({
url: `${environment.apiUrl}/usuarios/detalles`,
mapResponseFn: (res) => res.data as User,
})
.subscribe();
}
```
## Question
How can I concatenate extra endpoints to the API resource?
## Environment
```
Angular 11.0.0
```
P.D. I know I could use query parameters for some of the examples but I don't have control over the API.
Thanks in advance!
| non_priority | concatenate extra url segments to the base url in the ngentityservice i m submitting a regression a behavior that used to work and stopped working in a new release bug report performance issue feature request documentation issue or request support request other please describe problem i m currently using the ngentityservice and i need to consume an api that have endpoints like this put example com api usuarios detalles patch example com api usuarios status get example com api municipios departamento example set the base url app module ts providers provide ng entity service config usevalue baseurl environment apiurl add resource name users service ts ngentityserviceconfig resourcename usuarios injectable providedin root export class usersservice extends ngentityservice constructor protected store usersstore super store call service account page ts ts updateuserdetails void this usersservice put extras is there a way to do this mapresponsefn res res data as user subscribe workaround ts updateuserdetails void this usersservice put url environment apiurl usuarios detalles mapresponsefn res res data as user subscribe question how can i concatenate extra endpoints to the api resource environment angular p d i know i could use query parameters for some of the examples but i don t have control over the api thanks in advance | 0 |
172,470 | 21,046,972,487 | IssuesEvent | 2022-03-31 16:55:32 | tuanducdesign/email-sending-verification | https://api.github.com/repos/tuanducdesign/email-sending-verification | closed | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz, glob-parent-5.1.1.tgz | security vulnerability | ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/client/node_modules/webpack-dev-server/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- eslint-7.13.0.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/tuanducdesign/email-sending-verification/commit/6c0c478a4770af860b9a85980a5919a9f37493b7">6c0c478a4770af860b9a85980a5919a9f37493b7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0-next.31</p><p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0-next.31</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-28469 (High) detected in glob-parent-3.1.0.tgz, glob-parent-5.1.1.tgz - ## CVE-2020-28469 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>glob-parent-3.1.0.tgz</b>, <b>glob-parent-5.1.1.tgz</b></p></summary>
<p>
<details><summary><b>glob-parent-3.1.0.tgz</b></p></summary>
<p>Strips glob magic from a string to provide the parent directory path</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-3.1.0.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/watchpack-chokidar2/node_modules/glob-parent/package.json,/client/node_modules/webpack-dev-server/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- webpack-dev-server-3.11.0.tgz
- chokidar-2.1.8.tgz
- :x: **glob-parent-3.1.0.tgz** (Vulnerable Library)
</details>
<details><summary><b>glob-parent-5.1.1.tgz</b></p></summary>
<p>Extract the non-magic parent path from a glob string.</p>
<p>Library home page: <a href="https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz">https://registry.npmjs.org/glob-parent/-/glob-parent-5.1.1.tgz</a></p>
<p>Path to dependency file: /client/package.json</p>
<p>Path to vulnerable library: /client/node_modules/glob-parent/package.json</p>
<p>
Dependency Hierarchy:
- react-scripts-4.0.0.tgz (Root Library)
- eslint-7.13.0.tgz
- :x: **glob-parent-5.1.1.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/tuanducdesign/email-sending-verification/commit/6c0c478a4770af860b9a85980a5919a9f37493b7">6c0c478a4770af860b9a85980a5919a9f37493b7</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
This affects the package glob-parent before 5.1.2. The enclosure regex used to check for strings ending in enclosure containing path separator.
<p>Publish Date: 2021-06-03
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-28469>CVE-2020-28469</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-28469</a></p>
<p>Release Date: 2021-06-03</p>
<p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0-next.31</p><p>Fix Resolution (glob-parent): 5.1.2</p>
<p>Direct dependency fix Resolution (react-scripts): 5.0.0-next.31</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in glob parent tgz glob parent tgz cve high severity vulnerability vulnerable libraries glob parent tgz glob parent tgz glob parent tgz strips glob magic from a string to provide the parent directory path library home page a href path to dependency file client package json path to vulnerable library client node modules watchpack node modules glob parent package json client node modules webpack dev server node modules glob parent package json dependency hierarchy react scripts tgz root library webpack dev server tgz chokidar tgz x glob parent tgz vulnerable library glob parent tgz extract the non magic parent path from a glob string library home page a href path to dependency file client package json path to vulnerable library client node modules glob parent package json dependency hierarchy react scripts tgz root library eslint tgz x glob parent tgz vulnerable library found in head commit a href found in base branch master vulnerability details this affects the package glob parent before the enclosure regex used to check for strings ending in enclosure containing path separator publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution glob parent direct dependency fix resolution react scripts next fix resolution glob parent direct dependency fix resolution react scripts next step up your open source security game with whitesource | 0 |
12,818 | 7,998,022,918 | IssuesEvent | 2018-07-21 04:39:17 | shssoichiro/oxipng | https://api.github.com/repos/shssoichiro/oxipng | closed | OOM when passing files via xargs | I-Critical T-Bug T-Performance | I tried compressing pngs of wesnoth https://github.com/wesnoth/wesnoth
```` find . | grep "\.png$" | xargs oxipng -o6```` does reliably eat all my memory until oxipng is OOM-killed
a for loop that passes images one by one seems to work though
````
for i in `find . | grep "\.png$"` ; do ;
oxipng $i -o6
done
````
oxipng 2.0.0 | True | OOM when passing files via xargs - I tried compressing pngs of wesnoth https://github.com/wesnoth/wesnoth
```` find . | grep "\.png$" | xargs oxipng -o6```` does reliably eat all my memory until oxipng is OOM-killed
a for loop that passes images one by one seems to work though
````
for i in `find . | grep "\.png$"` ; do ;
oxipng $i -o6
done
````
oxipng 2.0.0 | non_priority | oom when passing files via xargs i tried compressing pngs of wesnoth find grep png xargs oxipng does reliably eat all my memory until oxipng is oom killed a for loop that passes images one by one seems to work though for i in find grep png do oxipng i done oxipng | 0 |
74,791 | 20,371,825,877 | IssuesEvent | 2022-02-21 12:00:32 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | opened | [Bug]: Icon widget's appearance changes when added whitespace in Button variant | Bug App Viewers Pod Low UI Building Pod Needs Triaging UI Builders Pod Icon Button Widget | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
After enabling JS for icon widget button variant, if we add a space after button variant options, the outer layer of the icon widget gets disappear. Observe in the video
https://www.loom.com/share/37ac2c819c614051a3826c7a14ad2eab
### Steps To Reproduce
1. Add icon widget to canvas
2. Enable JS for button-variant from property pane
3. Type "PRIMARY " and add space after text and observe the icon widget appearance
### Environment
Production
### Version
Cloud | 2.0 | [Bug]: Icon widget's appearance changes when added whitespace in Button variant - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### Current Behavior
After enabling JS for icon widget button variant, if we add a space after button variant options, the outer layer of the icon widget gets disappear. Observe in the video
https://www.loom.com/share/37ac2c819c614051a3826c7a14ad2eab
### Steps To Reproduce
1. Add icon widget to canvas
2. Enable JS for button-variant from property pane
3. Type "PRIMARY " and add space after text and observe the icon widget appearance
### Environment
Production
### Version
Cloud | non_priority | icon widget s appearance changes when added whitespace in button variant is there an existing issue for this i have searched the existing issues current behavior after enabling js for icon widget button variant if we add a space after button variant options the outer layer of the icon widget gets disappear observe in the video steps to reproduce add icon widget to canvas enable js for button variant from property pane type primary and add space after text and observe the icon widget appearance environment production version cloud | 0 |
344,672 | 30,752,132,165 | IssuesEvent | 2023-07-28 20:21:59 | saltstack/salt | https://api.github.com/repos/saltstack/salt | opened | [Increase Test Coverage] Batch 93 | Tests | Increase the code coverage percent on the following files to at least 80%.
Please be aware that currently the percentage might be inaccurate if the module uses salt due to #64696
File | Percent
salt/modules/win_auditpol.py 78
salt/modules/win_event.py 64
salt/modules/win_psget.py 48
salt/modules/win_smtp_server.py 10
salt/modules/winrepo.py 42
| 1.0 | [Increase Test Coverage] Batch 93 - Increase the code coverage percent on the following files to at least 80%.
Please be aware that currently the percentage might be inaccurate if the module uses salt due to #64696
File | Percent
salt/modules/win_auditpol.py 78
salt/modules/win_event.py 64
salt/modules/win_psget.py 48
salt/modules/win_smtp_server.py 10
salt/modules/winrepo.py 42
| non_priority | batch increase the code coverage percent on the following files to at least please be aware that currently the percentage might be inaccurate if the module uses salt due to file percent salt modules win auditpol py salt modules win event py salt modules win psget py salt modules win smtp server py salt modules winrepo py | 0 |
181,226 | 21,657,807,188 | IssuesEvent | 2022-05-06 15:45:22 | elastic/integrations | https://api.github.com/repos/elastic/integrations | closed | Elastic Agent CrowdStrike FDR Integration Javascript emulator SQS Processing Delay | Team:Security-External Integrations Integration:Crowdstrike | We have been running the CrowdStrike FDR integration for about 3-4 months with no data arriving via the Elastic Agent integration. We recently started receiving 20-50 million events per day over several days (no changes our side - data suddenly started arriving), but this has gone down to 500,000 to 1 million per day. We expect normal ingestion to stay at 20-50 million events per day.
I looked at the "crowdstrike.fdr" data stream dataset in logs-* and found 75,000 ProcessRollup2 events over the last 48 hours. This came through in a single burst over a 30 minute period.
Since 8am today we have seen 12 million ProcessRollup2 events in CrowdStrike. This doesn't correlate with the number of ProcessRollup2 events we are getting through FDR and Elastic Agent.
Over the last 24 hours we have see 28 million process created events in winlogbeat. This correlates with the number of ProcessRollup2 processes seen in CrowdStrike.
We've asked CrowdStrike to confirm if this is intended behaviour, and if not there might be a bug in Elastic Agent or the FDR integration.
| True | Elastic Agent CrowdStrike FDR Integration Javascript emulator SQS Processing Delay - We have been running the CrowdStrike FDR integration for about 3-4 months with no data arriving via the Elastic Agent integration. We recently started receiving 20-50 million events per day over several days (no changes our side - data suddenly started arriving), but this has gone down to 500,000 to 1 million per day. We expect normal ingestion to stay at 20-50 million events per day.
I looked at the "crowdstrike.fdr" data stream dataset in logs-* and found 75,000 ProcessRollup2 events over the last 48 hours. This came through in a single burst over a 30 minute period.
Since 8am today we have seen 12 million ProcessRollup2 events in CrowdStrike. This doesn't correlate with the number of ProcessRollup2 events we are getting through FDR and Elastic Agent.
Over the last 24 hours we have see 28 million process created events in winlogbeat. This correlates with the number of ProcessRollup2 processes seen in CrowdStrike.
We've asked CrowdStrike to confirm if this is intended behaviour, and if not there might be a bug in Elastic Agent or the FDR integration.
| non_priority | elastic agent crowdstrike fdr integration javascript emulator sqs processing delay we have been running the crowdstrike fdr integration for about months with no data arriving via the elastic agent integration we recently started receiving million events per day over several days no changes our side data suddenly started arriving but this has gone down to to million per day we expect normal ingestion to stay at million events per day i looked at the crowdstrike fdr data stream dataset in logs and found events over the last hours this came through in a single burst over a minute period since today we have seen million events in crowdstrike this doesn t correlate with the number of events we are getting through fdr and elastic agent over the last hours we have see million process created events in winlogbeat this correlates with the number of processes seen in crowdstrike we ve asked crowdstrike to confirm if this is intended behaviour and if not there might be a bug in elastic agent or the fdr integration | 0 |
127,835 | 12,340,672,367 | IssuesEvent | 2020-05-14 20:22:27 | thephpleague/commonmark | https://api.github.com/repos/thephpleague/commonmark | opened | [1.5] Release Goals | documentation pinned | Creating this issue to track a few odds and ends
- Minimize BC breaks between 1.5 API and 2.0 API (#475)
- Modify 2.0 docs to show migration path from 1.5 -> 2.0 instead of 1.4 -> 2.0 | 1.0 | [1.5] Release Goals - Creating this issue to track a few odds and ends
- Minimize BC breaks between 1.5 API and 2.0 API (#475)
- Modify 2.0 docs to show migration path from 1.5 -> 2.0 instead of 1.4 -> 2.0 | non_priority | release goals creating this issue to track a few odds and ends minimize bc breaks between api and api modify docs to show migration path from instead of | 0 |
35,331 | 4,647,637,470 | IssuesEvent | 2016-10-01 16:20:14 | angular-ui/ui-router | https://api.github.com/repos/angular-ui/ui-router | closed | Bug in duplicate state name checking when using 'parent' definitions | design | Currently there are [3 ways](https://github.com/angular-ui/ui-router/wiki/Nested-States-%26-Nested-Views) of defining states:
1. Using 'dot notation'. For example `name: 'contacts.list'`
2. Using the parent property with the parent name as string. For example: `parent: 'contacts'`
3. Using the parent property with the parent object. For example `parent: contacts` (where 'contacts' is an stateObject)
What you would expect is that method 2 and 3 would resolve the name to the 'dot notation'. However, currently this doesn't seem to happen. Because of this the code which checks for duplicate stateNames wrongfully throws errors when 2 children of different parents have the same name.
For example:
``` js
$stateProvider
.state({
name: 'contacts',
templateUrl: 'contacts.html'
})
.state({
name: 'list',
parent: 'contacts',
templateUrl: 'contacts.list.html'
})
.state({
name: 'products',
templateUrl: 'products.html'
})
.state({
name: 'list',
parent: 'products',
templateUrl: 'products.list.html'
});
```
Or object notation:
``` js
var contacts = {
name: 'contacts',
templateUrl: 'contacts.html'
};
var contactsList = {
name: 'list',
parent: contacts,
templateUrl: 'contacts.list.html'
};
var products = {
name: 'products',
templateUrl: 'products.html'
};
var productsList = {
name: 'list',
parent: products,
templateUrl: 'products.list.html'
};
$stateProvider
.state(contacts)
.state(contactsList)
.state(products)
.state(productsList)
```
Both throw an error:
```
Error: [$injector:modulerr] Failed to instantiate module `APP_MODULE` due to: State 'list'' is already defined
```
While defining this example using method 1 does work:
```js
$stateProvider
.state({
name: 'contacts',
templateUrl: 'contacts.html'
})
.state({
name: 'contacts.list',
templateUrl: 'contacts.list.html'
})
.state({
name: 'products',
templateUrl: 'products.html'
})
.state({
name: 'products.list',
templateUrl: 'products.list.html'
});
```
| 1.0 | Bug in duplicate state name checking when using 'parent' definitions - Currently there are [3 ways](https://github.com/angular-ui/ui-router/wiki/Nested-States-%26-Nested-Views) of defining states:
1. Using 'dot notation'. For example `name: 'contacts.list'`
2. Using the parent property with the parent name as string. For example: `parent: 'contacts'`
3. Using the parent property with the parent object. For example `parent: contacts` (where 'contacts' is an stateObject)
What you would expect is that method 2 and 3 would resolve the name to the 'dot notation'. However, currently this doesn't seem to happen. Because of this the code which checks for duplicate stateNames wrongfully throws errors when 2 children of different parents have the same name.
For example:
``` js
$stateProvider
.state({
name: 'contacts',
templateUrl: 'contacts.html'
})
.state({
name: 'list',
parent: 'contacts',
templateUrl: 'contacts.list.html'
})
.state({
name: 'products',
templateUrl: 'products.html'
})
.state({
name: 'list',
parent: 'products',
templateUrl: 'products.list.html'
});
```
Or object notation:
``` js
var contacts = {
name: 'contacts',
templateUrl: 'contacts.html'
};
var contactsList = {
name: 'list',
parent: contacts,
templateUrl: 'contacts.list.html'
};
var products = {
name: 'products',
templateUrl: 'products.html'
};
var productsList = {
name: 'list',
parent: products,
templateUrl: 'products.list.html'
};
$stateProvider
.state(contacts)
.state(contactsList)
.state(products)
.state(productsList)
```
Both throw an error:
```
Error: [$injector:modulerr] Failed to instantiate module `APP_MODULE` due to: State 'list'' is already defined
```
While defining this example using method 1 does work:
```js
$stateProvider
.state({
name: 'contacts',
templateUrl: 'contacts.html'
})
.state({
name: 'contacts.list',
templateUrl: 'contacts.list.html'
})
.state({
name: 'products',
templateUrl: 'products.html'
})
.state({
name: 'products.list',
templateUrl: 'products.list.html'
});
```
| non_priority | bug in duplicate state name checking when using parent definitions currently there are of defining states using dot notation for example name contacts list using the parent property with the parent name as string for example parent contacts using the parent property with the parent object for example parent contacts where contacts is an stateobject what you would expect is that method and would resolve the name to the dot notation however currently this doesn t seem to happen because of this the code which checks for duplicate statenames wrongfully throws errors when children of different parents have the same name for example js stateprovider state name contacts templateurl contacts html state name list parent contacts templateurl contacts list html state name products templateurl products html state name list parent products templateurl products list html or object notation js var contacts name contacts templateurl contacts html var contactslist name list parent contacts templateurl contacts list html var products name products templateurl products html var productslist name list parent products templateurl products list html stateprovider state contacts state contactslist state products state productslist both throw an error error failed to instantiate module app module due to state list is already defined while defining this example using method does work js stateprovider state name contacts templateurl contacts html state name contacts list templateurl contacts list html state name products templateurl products html state name products list templateurl products list html | 0 |
121,539 | 15,963,285,119 | IssuesEvent | 2021-04-16 03:30:01 | Mafia-Hands/Mafia | https://api.github.com/repos/Mafia-Hands/Mafia | closed | Redesign of voting to kill or abstain system | design frontend ready to implement | ### What are you proposing?
- Replace the 'click on the user to vote to kill them, or click abstain' system with a thumbs up (kill) or thumbs down (no confidence) two-button system below the newly created platform in the middle of the screen.
- After timer runs out/everyone has voted, people's votes are now revealed by showing a thumbs up or thumbs down icon below each player.
- The system to be replaced can be seen here:
<img width="180" alt="Screen Shot 2021-04-06 at 12 11 39 PM" src="https://user-images.githubusercontent.com/54383847/113987129-25215f00-98a2-11eb-9e52-5075909e412c.png">
### Is this ready to implement?
Yes.
Hi-fi prototype: https://www.figma.com/file/zoB3yUb1s6WonkGmRZcRYR/MAFIA-Assignment-2?node-id=309%3A259
Screenshots of new design:
<img width="562" alt="Screen Shot 2021-04-08 at 8 56 21 PM" src="https://user-images.githubusercontent.com/54383847/113998148-e47b1300-98ac-11eb-9873-5ab1cfbcd6d4.png">
<img width="289" alt="Screen Shot 2021-04-08 at 7 40 56 PM" src="https://user-images.githubusercontent.com/54383847/113987289-59951b00-98a2-11eb-9c35-b8ce94776417.png">
Assets:
Material UI thumbs up and down icons can be used
### Redesign approval:
- [X] Redesign approved by: @Benjamin-Piper
| 1.0 | Redesign of voting to kill or abstain system - ### What are you proposing?
- Replace the 'click on the user to vote to kill them, or click abstain' system with a thumbs up (kill) or thumbs down (no confidence) two-button system below the newly created platform in the middle of the screen.
- After timer runs out/everyone has voted, people's votes are now revealed by showing a thumbs up or thumbs down icon below each player.
- The system to be replaced can be seen here:
<img width="180" alt="Screen Shot 2021-04-06 at 12 11 39 PM" src="https://user-images.githubusercontent.com/54383847/113987129-25215f00-98a2-11eb-9e52-5075909e412c.png">
### Is this ready to implement?
Yes.
Hi-fi prototype: https://www.figma.com/file/zoB3yUb1s6WonkGmRZcRYR/MAFIA-Assignment-2?node-id=309%3A259
Screenshots of new design:
<img width="562" alt="Screen Shot 2021-04-08 at 8 56 21 PM" src="https://user-images.githubusercontent.com/54383847/113998148-e47b1300-98ac-11eb-9873-5ab1cfbcd6d4.png">
<img width="289" alt="Screen Shot 2021-04-08 at 7 40 56 PM" src="https://user-images.githubusercontent.com/54383847/113987289-59951b00-98a2-11eb-9c35-b8ce94776417.png">
Assets:
Material UI thumbs up and down icons can be used
### Redesign approval:
- [X] Redesign approved by: @Benjamin-Piper
| non_priority | redesign of voting to kill or abstain system what are you proposing replace the click on the user to vote to kill them or click abstain system with a thumbs up kill or thumbs down no confidence two button system below the newly created platform in the middle of the screen after timer runs out everyone has voted people s votes are now revealed by showing a thumbs up or thumbs down icon below each player the system to be replaced can be seen here img width alt screen shot at pm src is this ready to implement yes hi fi prototype screenshots of new design img width alt screen shot at pm src img width alt screen shot at pm src assets material ui thumbs up and down icons can be used redesign approval redesign approved by benjamin piper | 0 |
64,831 | 14,685,827,691 | IssuesEvent | 2021-01-01 11:34:52 | punesemu/puNES | https://api.github.com/repos/punesemu/puNES | opened | CVE-2016-2335 (High) detected in sevenzip7z922 | security vulnerability | ## CVE-2016-2335 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sevenzip7z922</b></p></summary>
<p>
<p>A free file archiver for extremely high compression</p>
<p>Library home page: <a href=https://sourceforge.net/projects/sevenzip/>https://sourceforge.net/projects/sevenzip/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/punesemu/puNES/commit/c8c9741762d6b86452cf0f4e959b8ab9dd78e7d9">c8c9741762d6b86452cf0f4e959b8ab9dd78e7d9</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>puNES/src/extra/p7zip_9.20.1/CPP/7zip/Archive/Udf/UdfIn.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The CInArchive::ReadFileItem method in Archive/Udf/UdfIn.cpp in 7zip 9.20 and 15.05 beta and p7zip allows remote attackers to cause a denial of service (out-of-bounds read) or execute arbitrary code via the PartitionRef field in the Long Allocation Descriptor in a UDF file.
<p>Publish Date: 2016-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2335>CVE-2016-2335</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2335">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2335</a></p>
<p>Release Date: 2016-06-07</p>
<p>Fix Resolution: 16.02</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2016-2335 (High) detected in sevenzip7z922 - ## CVE-2016-2335 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>sevenzip7z922</b></p></summary>
<p>
<p>A free file archiver for extremely high compression</p>
<p>Library home page: <a href=https://sourceforge.net/projects/sevenzip/>https://sourceforge.net/projects/sevenzip/</a></p>
<p>Found in HEAD commit: <a href="https://github.com/punesemu/puNES/commit/c8c9741762d6b86452cf0f4e959b8ab9dd78e7d9">c8c9741762d6b86452cf0f4e959b8ab9dd78e7d9</a></p>
</p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>puNES/src/extra/p7zip_9.20.1/CPP/7zip/Archive/Udf/UdfIn.cpp</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
The CInArchive::ReadFileItem method in Archive/Udf/UdfIn.cpp in 7zip 9.20 and 15.05 beta and p7zip allows remote attackers to cause a denial of service (out-of-bounds read) or execute arbitrary code via the PartitionRef field in the Long Allocation Descriptor in a UDF file.
<p>Publish Date: 2016-06-07
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-2335>CVE-2016-2335</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2335">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-2335</a></p>
<p>Release Date: 2016-06-07</p>
<p>Fix Resolution: 16.02</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in cve high severity vulnerability vulnerable library a free file archiver for extremely high compression library home page a href found in head commit a href vulnerable source files punes src extra cpp archive udf udfin cpp vulnerability details the cinarchive readfileitem method in archive udf udfin cpp in and beta and allows remote attackers to cause a denial of service out of bounds read or execute arbitrary code via the partitionref field in the long allocation descriptor in a udf file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
128,362 | 27,247,549,012 | IssuesEvent | 2023-02-22 04:13:34 | TravelMapping/EduTools | https://api.github.com/repos/TravelMapping/EduTools | closed | HDX/AV: use visualSettings objects in RCB | existing algorithm visualization code organization | It looks like some parts of this implementation are creating objects to play the role of the `visualSettings` inline as actual parameters, such as:
https://github.com/TravelMapping/EduTools/blob/3a71d1b6a26fcb9a6e14b9ce031d8e49aa61abd0/HighwayDataExaminer/hdxpartitionerrecursive.js#L113
These should probably be given nice names in an AV-specific `visualSettings` array, and used appropriately throughout. | 1.0 | HDX/AV: use visualSettings objects in RCB - It looks like some parts of this implementation are creating objects to play the role of the `visualSettings` inline as actual parameters, such as:
https://github.com/TravelMapping/EduTools/blob/3a71d1b6a26fcb9a6e14b9ce031d8e49aa61abd0/HighwayDataExaminer/hdxpartitionerrecursive.js#L113
These should probably be given nice names in an AV-specific `visualSettings` array, and used appropriately throughout. | non_priority | hdx av use visualsettings objects in rcb it looks like some parts of this implementation are creating objects to play the role of the visualsettings inline as actual parameters such as these should probably be given nice names in an av specific visualsettings array and used appropriately throughout | 0 |
154,665 | 12,223,865,649 | IssuesEvent | 2020-05-02 19:35:46 | gbroques/ose-3d-printer-workbench | https://api.github.com/repos/gbroques/ose-3d-printer-workbench | closed | Add Unit Tests for Attaching Axes to Frame With Corners | test | We have unit tests for attaching axes to a "CNC Cut Frame".
See https://github.com/gbroques/ose-3d-printer-workbench/blob/master/test/get_axis_frame_attachment_kwargs_for_cnc_cut_frame_test.py.
However, we also want tests for attaching axes to the frame when it has corners, or when `HasCorners` equals `True`. | 1.0 | Add Unit Tests for Attaching Axes to Frame With Corners - We have unit tests for attaching axes to a "CNC Cut Frame".
See https://github.com/gbroques/ose-3d-printer-workbench/blob/master/test/get_axis_frame_attachment_kwargs_for_cnc_cut_frame_test.py.
However, we also want tests for attaching axes to the frame when it has corners, or when `HasCorners` equals `True`. | non_priority | add unit tests for attaching axes to frame with corners we have unit tests for attaching axes to a cnc cut frame see however we also want tests for attaching axes to the frame when it has corners or when hascorners equals true | 0 |
6,854 | 6,641,395,667 | IssuesEvent | 2017-09-27 01:00:34 | missimer/canine-railroad | https://api.github.com/repos/missimer/canine-railroad | opened | Contact Google about map API | infrastructure | So the site is going to require an invite-only account to access it. This violates the free use terms of the google map API. This ticket is to contact Google in the hopes for an exception to this rule. Hopefully, they will give one to a 501(c)(3) which NBRAN is. If not hopefully a discounted rate. | 1.0 | Contact Google about map API - So the site is going to require an invite-only account to access it. This violates the free use terms of the google map API. This ticket is to contact Google in the hopes for an exception to this rule. Hopefully, they will give one to a 501(c)(3) which NBRAN is. If not hopefully a discounted rate. | non_priority | contact google about map api so the site is going to require an invite only account to access it this violates the free use terms of the google map api this ticket is to contact google in the hopes for an exception to this rule hopefully they will give one to a c which nbran is if not hopefully a discounted rate | 0 |
212,178 | 23,868,449,357 | IssuesEvent | 2022-09-07 13:05:15 | CharesFang/WeiboSpider | https://api.github.com/repos/CharesFang/WeiboSpider | closed | WS-2022-0181 (Medium) detected in Scrapy-2.6.0-py2.py3-none-any.whl - autoclosed | security vulnerability | ## WS-2022-0181 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Scrapy-2.6.0-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Web Crawling and Web Scraping framework</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/89/47/10c1197316233761afb5522d48a8e27f65389044ddda58d91d0eaeaecd20/Scrapy-2.6.0-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/89/47/10c1197316233761afb5522d48a8e27f65389044ddda58d91d0eaeaecd20/Scrapy-2.6.0-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Scrapy-2.6.0-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Scrapy before v2.6.2 and v1.8.3 vulnerable to one proxy sending credentials to another
<p>Publish Date: 2022-07-29
<p>URL: <a href=https://github.com/scrapy/scrapy/commit/af7dd16d8ded3e6cb2946603688f4f4a5212e80f>WS-2022-0181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9x8m-2xpf-crp3">https://github.com/advisories/GHSA-9x8m-2xpf-crp3</a></p>
<p>Release Date: 2022-07-29</p>
<p>Fix Resolution: Scrapy - 1.8.3,2.6.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2022-0181 (Medium) detected in Scrapy-2.6.0-py2.py3-none-any.whl - autoclosed - ## WS-2022-0181 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>Scrapy-2.6.0-py2.py3-none-any.whl</b></p></summary>
<p>A high-level Web Crawling and Web Scraping framework</p>
<p>Library home page: <a href="https://files.pythonhosted.org/packages/89/47/10c1197316233761afb5522d48a8e27f65389044ddda58d91d0eaeaecd20/Scrapy-2.6.0-py2.py3-none-any.whl">https://files.pythonhosted.org/packages/89/47/10c1197316233761afb5522d48a8e27f65389044ddda58d91d0eaeaecd20/Scrapy-2.6.0-py2.py3-none-any.whl</a></p>
<p>Path to dependency file: /requirements.txt</p>
<p>Path to vulnerable library: /requirements.txt</p>
<p>
Dependency Hierarchy:
- :x: **Scrapy-2.6.0-py2.py3-none-any.whl** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Scrapy before v2.6.2 and v1.8.3 vulnerable to one proxy sending credentials to another
<p>Publish Date: 2022-07-29
<p>URL: <a href=https://github.com/scrapy/scrapy/commit/af7dd16d8ded3e6cb2946603688f4f4a5212e80f>WS-2022-0181</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/advisories/GHSA-9x8m-2xpf-crp3">https://github.com/advisories/GHSA-9x8m-2xpf-crp3</a></p>
<p>Release Date: 2022-07-29</p>
<p>Fix Resolution: Scrapy - 1.8.3,2.6.2</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in scrapy none any whl autoclosed ws medium severity vulnerability vulnerable library scrapy none any whl a high level web crawling and web scraping framework library home page a href path to dependency file requirements txt path to vulnerable library requirements txt dependency hierarchy x scrapy none any whl vulnerable library found in base branch master vulnerability details scrapy before and vulnerable to one proxy sending credentials to another publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution scrapy step up your open source security game with mend | 0 |
21,445 | 10,608,457,945 | IssuesEvent | 2019-10-11 07:35:36 | sjtug/mirror-requests | https://api.github.com/repos/sjtug/mirror-requests | closed | 疑似数据泄露 | security | <!-- 新增镜像还是Bug反馈? -->
**类别**:Bug 反馈
https://twitter.com/isukkaw/status/1181989528069795841
> 某高校镜像站将 Log 全部交给第三方 Log 处理平台处理,页面甚至没有任何鉴权。。
通过日志可以发现,该高校镜像站的 PyPi 甚至使用了 V2Ray 反代。
dig 一下甚至能发现这所高校的 LUG 架设的另外两台 V2Ray 服务器。。。 | True | 疑似数据泄露 - <!-- 新增镜像还是Bug反馈? -->
**类别**:Bug 反馈
https://twitter.com/isukkaw/status/1181989528069795841
> 某高校镜像站将 Log 全部交给第三方 Log 处理平台处理,页面甚至没有任何鉴权。。
通过日志可以发现,该高校镜像站的 PyPi 甚至使用了 V2Ray 反代。
dig 一下甚至能发现这所高校的 LUG 架设的另外两台 V2Ray 服务器。。。 | non_priority | 疑似数据泄露 类别 :bug 反馈 某高校镜像站将 log 全部交给第三方 log 处理平台处理,页面甚至没有任何鉴权。。 通过日志可以发现,该高校镜像站的 pypi 甚至使用了 反代。 dig 一下甚至能发现这所高校的 lug 架设的另外两台 服务器。。。 | 0 |
74,020 | 9,743,938,174 | IssuesEvent | 2019-06-03 04:40:46 | OrBin/gramhopper | https://api.github.com/repos/OrBin/gramhopper | closed | Document filter triggers | documentation good first issue | This issue was split up from #26.
Filter triggers should be documented just like other triggers (for a reference, look at the documentation for match triggers).
Work on this issue should begin **only after #39 is done**. | 1.0 | Document filter triggers - This issue was split up from #26.
Filter triggers should be documented just like other triggers (for a reference, look at the documentation for match triggers).
Work on this issue should begin **only after #39 is done**. | non_priority | document filter triggers this issue was split up from filter triggers should be documented just like other triggers for a reference look at the documentation for match triggers work on this issue should begin only after is done | 0 |
94,429 | 10,822,127,154 | IssuesEvent | 2019-11-08 20:25:01 | ObiWanLansi/SIGENCE-Scenario-Tool | https://api.github.com/repos/ObiWanLansi/SIGENCE-Scenario-Tool | closed | Cheatsheet - Link To Downloadable Scenariotool-Zip File Does Not Work | documentation test | In the Cheat Sheet (section: Installation), the link to https://github.com/ObiWanLansi/SIGENCE-Scenario-Tool/archive/master.zip does not work.
Cause:
1. This link is not activated
2. The sub-directory /archive is non-existent
Viele Grüße
Andre | 1.0 | Cheatsheet - Link To Downloadable Scenariotool-Zip File Does Not Work - In the Cheat Sheet (section: Installation), the link to https://github.com/ObiWanLansi/SIGENCE-Scenario-Tool/archive/master.zip does not work.
Cause:
1. This link is not activated
2. The sub-directory /archive is non-existent
Viele Grüße
Andre | non_priority | cheatsheet link to downloadable scenariotool zip file does not work in the cheat sheet section installation the link to does not work cause this link is not activated the sub directory archive is non existent viele grüße andre | 0 |
45,651 | 24,151,813,967 | IssuesEvent | 2022-09-22 02:08:22 | brooksryba/Alpha | https://api.github.com/repos/brooksryba/Alpha | closed | Create assembly definition for plugins folder | performance | By creating a unity assembly definition for the plugins folder we can tell unity not to rebuild that folder for compile unless it changes. This should speed up load and compile times. | True | Create assembly definition for plugins folder - By creating a unity assembly definition for the plugins folder we can tell unity not to rebuild that folder for compile unless it changes. This should speed up load and compile times. | non_priority | create assembly definition for plugins folder by creating a unity assembly definition for the plugins folder we can tell unity not to rebuild that folder for compile unless it changes this should speed up load and compile times | 0 |
249,128 | 26,887,012,872 | IssuesEvent | 2023-02-06 04:46:10 | MendDemo/PoiMakia | https://api.github.com/repos/MendDemo/PoiMakia | opened | poi-ooxml-3.17.jar: 1 vulnerabilities (highest severity is: 5.5) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>poi-ooxml-3.17.jar</b></p></summary>
<p>Apache POI - Java API To Access Microsoft Format Files</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar,/lib/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/MendDemo/PoiMakia/commit/47d070b80133c8fe80f3796674688596a612e8dd">47d070b80133c8fe80f3796674688596a612e8dd</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (poi-ooxml version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-12415](https://www.mend.io/vulnerability-database/CVE-2019-12415) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | poi-ooxml-3.17.jar | Direct | 4.1.1 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-12415</summary>
### Vulnerable Library - <b>poi-ooxml-3.17.jar</b></p>
<p>Apache POI - Java API To Access Microsoft Format Files</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar,/lib/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **poi-ooxml-3.17.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/MendDemo/PoiMakia/commit/47d070b80133c8fe80f3796674688596a612e8dd">47d070b80133c8fe80f3796674688596a612e8dd</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache POI up to 4.1.0, when using the tool XSSFExportToXml to convert user-provided Microsoft Excel documents, a specially crafted document can allow an attacker to read files from the local filesystem or from internal network resources via XML External Entity (XXE) Processing.
<p>Publish Date: 2019-10-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-12415>CVE-2019-12415</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12415">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12415</a></p>
<p>Release Date: 2019-10-23</p>
<p>Fix Resolution: 4.1.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | True | poi-ooxml-3.17.jar: 1 vulnerabilities (highest severity is: 5.5) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>poi-ooxml-3.17.jar</b></p></summary>
<p>Apache POI - Java API To Access Microsoft Format Files</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar,/lib/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/MendDemo/PoiMakia/commit/47d070b80133c8fe80f3796674688596a612e8dd">47d070b80133c8fe80f3796674688596a612e8dd</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in (poi-ooxml version) | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | ------------- | --- |
| [CVE-2019-12415](https://www.mend.io/vulnerability-database/CVE-2019-12415) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.5 | poi-ooxml-3.17.jar | Direct | 4.1.1 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-12415</summary>
### Vulnerable Library - <b>poi-ooxml-3.17.jar</b></p>
<p>Apache POI - Java API To Access Microsoft Format Files</p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar,/lib/org/apache/poi/poi-ooxml/3.17/poi-ooxml-3.17.jar</p>
<p>
Dependency Hierarchy:
- :x: **poi-ooxml-3.17.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/MendDemo/PoiMakia/commit/47d070b80133c8fe80f3796674688596a612e8dd">47d070b80133c8fe80f3796674688596a612e8dd</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Apache POI up to 4.1.0, when using the tool XSSFExportToXml to convert user-provided Microsoft Excel documents, a specially crafted document can allow an attacker to read files from the local filesystem or from internal network resources via XML External Entity (XXE) Processing.
<p>Publish Date: 2019-10-23
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-12415>CVE-2019-12415</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.5</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12415">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12415</a></p>
<p>Release Date: 2019-10-23</p>
<p>Fix Resolution: 4.1.1</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details> | non_priority | poi ooxml jar vulnerabilities highest severity is vulnerable library poi ooxml jar apache poi java api to access microsoft format files path to dependency file pom xml path to vulnerable library home wss scanner repository org apache poi poi ooxml poi ooxml jar lib org apache poi poi ooxml poi ooxml jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in poi ooxml version remediation available medium poi ooxml jar direct details cve vulnerable library poi ooxml jar apache poi java api to access microsoft format files path to dependency file pom xml path to vulnerable library home wss scanner repository org apache poi poi ooxml poi ooxml jar lib org apache poi poi ooxml poi ooxml jar dependency hierarchy x poi ooxml jar vulnerable library found in head commit a href found in base branch master vulnerability details in apache poi up to when using the tool xssfexporttoxml to convert user provided microsoft excel documents a specially crafted document can allow an attacker to read files from the local filesystem or from internal network resources via xml external entity xxe processing publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
416,996 | 28,108,697,150 | IssuesEvent | 2023-03-31 04:36:23 | GUESS-ME-GDSC/Server | https://api.github.com/repos/GUESS-ME-GDSC/Server | closed | 인물 정보 삭제 response status code 변경 | documentation | # HTTP Response Status Code 변경
요청을 성공적으로 수행했다고 알리는 응답이므로
201이 아닌 200이 적절하다고 판단되어 수정 작업을 진행 | 1.0 | 인물 정보 삭제 response status code 변경 - # HTTP Response Status Code 변경
요청을 성공적으로 수행했다고 알리는 응답이므로
201이 아닌 200이 적절하다고 판단되어 수정 작업을 진행 | non_priority | 인물 정보 삭제 response status code 변경 http response status code 변경 요청을 성공적으로 수행했다고 알리는 응답이므로 아닌 적절하다고 판단되어 수정 작업을 진행 | 0 |
323,121 | 23,934,904,366 | IssuesEvent | 2022-09-11 04:22:55 | cs-utulsa/Hackaton-Team-5 | https://api.github.com/repos/cs-utulsa/Hackaton-Team-5 | closed | Documentation: Create Architecture Document | documentation | Need fully detailed architecture document to detail what we are going to implement for each class.
- [x] Design for students class
- [x] Design for events class
- [x] Design for testing class | 1.0 | Documentation: Create Architecture Document - Need fully detailed architecture document to detail what we are going to implement for each class.
- [x] Design for students class
- [x] Design for events class
- [x] Design for testing class | non_priority | documentation create architecture document need fully detailed architecture document to detail what we are going to implement for each class design for students class design for events class design for testing class | 0 |
68,755 | 9,213,655,527 | IssuesEvent | 2019-03-10 13:55:21 | PX4/Firmware | https://api.github.com/repos/PX4/Firmware | closed | Build PX4 on Windows using Eclipse/MSVS2017 IDE | documentation wontfix | Hi,
@MaEtUgR, @hamishwillee,
@dagar
I am very interested to setup a PX4 build environment on Windows using Eclipse or MS VS 2017 IDE.
I tried to use last PX4 toolchain 0.4 for building on Eclipse but there is no preconfigured Eclipse as it was in previous versions of pixhawk_toolchain and with new versions I run into problems.
I am looking for some help/suggestions with this.
Thanks
| 1.0 | Build PX4 on Windows using Eclipse/MSVS2017 IDE - Hi,
@MaEtUgR, @hamishwillee,
@dagar
I am very interested to setup a PX4 build environment on Windows using Eclipse or MS VS 2017 IDE.
I tried to use last PX4 toolchain 0.4 for building on Eclipse but there is no preconfigured Eclipse as it was in previous versions of pixhawk_toolchain and with new versions I run into problems.
I am looking for some help/suggestions with this.
Thanks
| non_priority | build on windows using eclipse ide hi maetugr hamishwillee dagar i am very interested to setup a build environment on windows using eclipse or ms vs ide i tried to use last toolchain for building on eclipse but there is no preconfigured eclipse as it was in previous versions of pixhawk toolchain and with new versions i run into problems i am looking for some help suggestions with this thanks | 0 |
14,933 | 18,359,893,387 | IssuesEvent | 2021-10-09 03:13:23 | edmobe/android-video-magnification | https://api.github.com/repos/edmobe/android-video-magnification | closed | OB-1002 El procesamiento de vídeo consume mucha memoria RAM | video-processing obstacle | El vídeo [`face.mp4`](http://people.csail.mit.edu/mrub/evm/video/face.mp4) disponible en la [página web del proyecto](http://people.csail.mit.edu/mrub/evm/#:~:text=%C2%A0-,Data,-All%20videos%20are) consumió más de 8GB de RAM. | 1.0 | OB-1002 El procesamiento de vídeo consume mucha memoria RAM - El vídeo [`face.mp4`](http://people.csail.mit.edu/mrub/evm/video/face.mp4) disponible en la [página web del proyecto](http://people.csail.mit.edu/mrub/evm/#:~:text=%C2%A0-,Data,-All%20videos%20are) consumió más de 8GB de RAM. | non_priority | ob el procesamiento de vídeo consume mucha memoria ram el vídeo disponible en la consumió más de de ram | 0 |
137,555 | 30,713,012,908 | IssuesEvent | 2023-07-27 11:07:59 | appsmithorg/appsmith | https://api.github.com/repos/appsmithorg/appsmith | closed | [Task]: Better instrumentation for JS execution | Task JS Objects FE Coders Pod | ### Is there an existing issue for this?
- [X] I have searched the existing issues
### SubTasks
1. Modify the payload for EXECUTE_ACTION event on JSObject function execution
```
{
"type": "JS",
"name": "myFun1", // to be changed. only send the function name.
"JSObjectName": "JSObject1", // to be added
"pageId": "62f0b9e9b2f8027edfbf9008", // to be added
"appId": "62f0b9e9b2f8027edfbf9005", // to be added
"appMode": "EDIT", // to be added
"appName": "Testbed1123", // to be added
"isExampleApp": false, // to be added
"actionId": "62f4a31274d6e95d0a544da8", // to be added
"userData": {
"userId": "",
"email": "",
"appId": "",
"source": "cloud"
},
"instanceId": "" // to be added
}
```
2. Track JS Expression execution on event handlers
```
{
"type": "JS_EXPRESSION",
"unevalValue": "{{console.log("hello")}}"
"pageId": "62f0b9e9b2f8027edfbf9008",
"appId": "62f0b9e9b2f8027edfbf9005",
"appMode": "EDIT",
"appName": "Testbed1123",
"isExampleApp": false,
"actionId": "62f4a31274d6e95d0a544da8",
"userData": {
"userId": "",
"email": "",
"appId": "",
"source": "cloud"
},
"instanceId": ""
}
```
3. Track execution success and failures for JSObject functions and JS Expressions
`EXECUTE_ACTION_SUCCESS` or `EXECUTE_ACTION_FAILURE`
```
{
"type": "JS",
"name": "myFun1",
"JSObjectName": "JSObject1",
"pageId": "62f0b9e9b2f8027edfbf9008",
"appId": "62f0b9e9b2f8027edfbf9005",
"appMode": "EDIT",
"appName": "Testbed1123",
"isExampleApp": false,
"actionId": "62f4a31274d6e95d0a544da8",
"userData": {
"userId": "",
"email": "",
"appId": "",
"source": "cloud"
},
"instanceId": ""
}
```
| 1.0 | [Task]: Better instrumentation for JS execution - ### Is there an existing issue for this?
- [X] I have searched the existing issues
### SubTasks
1. Modify the payload for EXECUTE_ACTION event on JSObject function execution
```
{
"type": "JS",
"name": "myFun1", // to be changed. only send the function name.
"JSObjectName": "JSObject1", // to be added
"pageId": "62f0b9e9b2f8027edfbf9008", // to be added
"appId": "62f0b9e9b2f8027edfbf9005", // to be added
"appMode": "EDIT", // to be added
"appName": "Testbed1123", // to be added
"isExampleApp": false, // to be added
"actionId": "62f4a31274d6e95d0a544da8", // to be added
"userData": {
"userId": "",
"email": "",
"appId": "",
"source": "cloud"
},
"instanceId": "" // to be added
}
```
2. Track JS Expression execution on event handlers
```
{
"type": "JS_EXPRESSION",
"unevalValue": "{{console.log("hello")}}"
"pageId": "62f0b9e9b2f8027edfbf9008",
"appId": "62f0b9e9b2f8027edfbf9005",
"appMode": "EDIT",
"appName": "Testbed1123",
"isExampleApp": false,
"actionId": "62f4a31274d6e95d0a544da8",
"userData": {
"userId": "",
"email": "",
"appId": "",
"source": "cloud"
},
"instanceId": ""
}
```
3. Track execution success and failures for JSObject functions and JS Expressions
`EXECUTE_ACTION_SUCCESS` or `EXECUTE_ACTION_FAILURE`
```
{
"type": "JS",
"name": "myFun1",
"JSObjectName": "JSObject1",
"pageId": "62f0b9e9b2f8027edfbf9008",
"appId": "62f0b9e9b2f8027edfbf9005",
"appMode": "EDIT",
"appName": "Testbed1123",
"isExampleApp": false,
"actionId": "62f4a31274d6e95d0a544da8",
"userData": {
"userId": "",
"email": "",
"appId": "",
"source": "cloud"
},
"instanceId": ""
}
```
| non_priority | better instrumentation for js execution is there an existing issue for this i have searched the existing issues subtasks modify the payload for execute action event on jsobject function execution type js name to be changed only send the function name jsobjectname to be added pageid to be added appid to be added appmode edit to be added appname to be added isexampleapp false to be added actionid to be added userdata userid email appid source cloud instanceid to be added track js expression execution on event handlers type js expression unevalvalue console log hello pageid appid appmode edit appname isexampleapp false actionid userdata userid email appid source cloud instanceid track execution success and failures for jsobject functions and js expressions execute action success or execute action failure type js name jsobjectname pageid appid appmode edit appname isexampleapp false actionid userdata userid email appid source cloud instanceid | 0 |
206,124 | 16,020,245,576 | IssuesEvent | 2021-04-20 21:45:00 | AzureAD/microsoft-authentication-library-for-js | https://api.github.com/repos/AzureAD/microsoft-authentication-library-for-js | closed | Trying to understand dynamic scopes and incremental consent | answered documentation msal-browser msal-react question | ### Core Library
@azure/msal-browser
### Core Library Version
2.12.0
### Wrapper Library
@azure/msal-react
### Wrapper Library Version
1.0.0-beta.1
### Description
I am reading about [`Dynamic Scopes and Incremental Consent`](https://github.com/AzureAD/microsoft-authentication-library-for-js/blob/dev/lib/msal-browser/docs/resources-and-scopes.md#dynamic-scopes-and-incremental-consent) and following example caught my attention:
```
const loginRequest = {
scopes: [ "openid", "profile", "User.Read", "api://<myCustomApiClientId>/My.Scope" ]
};
const tokenRequest = {
scopes: [ "Mail.Read" ]
};
const anotherTokenRequest = {
scopes: [ "api://<myCustomApiClientId>/My.Scope" ]
}
// will return an ID Token and an Access Token with scopes: "openid", "profile" and "User.Read"
msalInstance.loginPopup(loginRequest);
// will fail and fallback to an interactive method prompting a consent screen
msalInstance.acquireTokenSilent(tokenRequest);
// will succeed and return an Access Token with scopes "openid", "profile", "User.Read" and "api://<myCustomApiClientId>/My.Scope"
msalInstance.acquireTokenSilent(anotherTokenRequest);
```
Based on the documentation, it is my understanding that when I make a request to acquire token for `"api://<myCustomApiClientId>/My.Scope"` scope, the resultant access token will have scopes for which the token has already been acquired + the my custom API scope.
However, when I see the token in the browser and check its scopes it only has `api://<myCustomApiClientId>/My.Scope` scope. All previous scopes are not there.
### Error Message
_No response_
### Msal Logs
_No response_
### MSAL Configuration
```javascript
export const msalConfig = {
auth: {
clientId: "application-client-id",
authority: "https://login.microsoftonline.com/tenant-id",
redirectUri: "http://localhost:3000/"
},
cache: {
cacheLocation: "sessionStorage", // This configures where your cache will be stored
storeAuthStateInCookie: false, // Set this to "true" if you are having issues on IE11 or Edge
},
system: {
loggerOptions: {
loggerCallback: (level, message, containsPii) => {
if (containsPii) {
return;
}
switch (level) {
case LogLevel.Error:
console.error(message);
return;
case LogLevel.Info:
console.info(message);
return;
case LogLevel.Verbose:
console.debug(message);
return;
case LogLevel.Warning:
console.warn(message);
return;
}
}
}
}
};
```
### Relevant Code Snippets
```javascript
export const loginRequest = {
scopes: ["User.Read"]
};
export const customApiRequest = {
scopes: ["api://5fbbd10d-39c2-fac2-901b-38e58523badf/access_as_user"]
}
```
```
instance.acquireTokenSilent({
...loginRequest,
account: accounts[0]
}).then((response) => {
instance.acquireTokenSilent({
... customApiRequest,
account: accounts[0]
}).then((response) => {
setAccessToken(response.accessToken);
callMsGraph(response.accessToken).then(response => setGraphData(response));
})
});
```
When I inspect the response of token request after 1st one (`...loginRequest`), I see the following:
```
{
"token_type": "Bearer",
"scope": "openid profile User.Read email",
"expires_in": 3599,
"ext_expires_in": 3599,
"access_token": "eyJ0eXAiOiJKV1QiLCJub25jZSI6Inhybjg4QktJSG93UFRYLUNWU002OUtCRGt5aVgwTEMwM05GdFYwNGxsaFUiLCJhbGciOi...
}
```
which is correct. However the response of the token request after the 2nd one (`... customApiRequest`), I see the following:
```
{
"token_type": "Bearer",
"scope": "api://5fbbd10d-39c2-fac2-901b-38e58523badf/access_as_user",
"expires_in": 3599,
"ext_expires_in": 3599,
"access_token": "eyJ0eXAiOiJKV1QiLCJhbGciOiJSUzI1NiIsIng1dCI6Im5PbzNaRHJPRFhFSzFqS1doWHNsSFJfS1hFZyIsImtpZCI6Im5Pb...
}
```
Shouldn't I be seeing scopes like `openid profile User.Read email api://5fbbd10d-39c2-fac2-901b-38e58523badf/access_as_user`?
```
### Reproduction Steps
1. Get the token for one scope (e.g. "User.Read").
2. Get the token for another scope (e.g. a custom API or may be Azure Service Management API).
### Expected Behavior
Based on the documentation, scopes should be added however scopes are being overwritten.
### Identity Provider
Azure AD / MSA
### Browsers Affected (Select all that apply)
Safari
### Regression
_No response_
### Source
External (Customer) | 1.0 | Trying to understand dynamic scopes and incremental consent - ### Core Library
@azure/msal-browser
### Core Library Version
2.12.0
### Wrapper Library
@azure/msal-react
### Wrapper Library Version
1.0.0-beta.1
### Description
I am reading about [`Dynamic Scopes and Incremental Consent`](https://github.com/AzureAD/microsoft-authentication-library-for-js/blob/dev/lib/msal-browser/docs/resources-and-scopes.md#dynamic-scopes-and-incremental-consent) and following example caught my attention:
```
const loginRequest = {
scopes: [ "openid", "profile", "User.Read", "api://<myCustomApiClientId>/My.Scope" ]
};
const tokenRequest = {
scopes: [ "Mail.Read" ]
};
const anotherTokenRequest = {
scopes: [ "api://<myCustomApiClientId>/My.Scope" ]
}
// will return an ID Token and an Access Token with scopes: "openid", "profile" and "User.Read"
msalInstance.loginPopup(loginRequest);
// will fail and fallback to an interactive method prompting a consent screen
msalInstance.acquireTokenSilent(tokenRequest);
// will succeed and return an Access Token with scopes "openid", "profile", "User.Read" and "api://<myCustomApiClientId>/My.Scope"
msalInstance.acquireTokenSilent(anotherTokenRequest);
```
Based on the documentation, it is my understanding that when I make a request to acquire token for `"api://<myCustomApiClientId>/My.Scope"` scope, the resultant access token will have scopes for which the token has already been acquired + the my custom API scope.
However, when I see the token in the browser and check its scopes it only has `api://<myCustomApiClientId>/My.Scope` scope. All previous scopes are not there.
### Error Message
_No response_
### Msal Logs
_No response_
### MSAL Configuration
```javascript
export const msalConfig = {
auth: {
clientId: "application-client-id",
authority: "https://login.microsoftonline.com/tenant-id",
redirectUri: "http://localhost:3000/"
},
cache: {
cacheLocation: "sessionStorage", // This configures where your cache will be stored
storeAuthStateInCookie: false, // Set this to "true" if you are having issues on IE11 or Edge
},
system: {
loggerOptions: {
loggerCallback: (level, message, containsPii) => {
if (containsPii) {
return;
}
switch (level) {
case LogLevel.Error:
console.error(message);
return;
case LogLevel.Info:
console.info(message);
return;
case LogLevel.Verbose:
console.debug(message);
return;
case LogLevel.Warning:
console.warn(message);
return;
}
}
}
}
};
```
### Relevant Code Snippets
```javascript
export const loginRequest = {
scopes: ["User.Read"]
};
export const customApiRequest = {
scopes: ["api://5fbbd10d-39c2-fac2-901b-38e58523badf/access_as_user"]
}
```
```
instance.acquireTokenSilent({
...loginRequest,
account: accounts[0]
}).then((response) => {
instance.acquireTokenSilent({
... customApiRequest,
account: accounts[0]
}).then((response) => {
setAccessToken(response.accessToken);
callMsGraph(response.accessToken).then(response => setGraphData(response));
})
});
```
When I inspect the response of token request after 1st one (`...loginRequest`), I see the following:
```
{
"token_type": "Bearer",
"scope": "openid profile User.Read email",
"expires_in": 3599,
"ext_expires_in": 3599,
"access_token": "eyJ0eXAiOiJKV1QiLCJub25jZSI6Inhybjg4QktJSG93UFRYLUNWU002OUtCRGt5aVgwTEMwM05GdFYwNGxsaFUiLCJhbGciOi...
}
```
which is correct. However the response of the token request after the 2nd one (`... customApiRequest`), I see the following:
```
{
"token_type": "Bearer",
"scope": "api://5fbbd10d-39c2-fac2-901b-38e58523badf/access_as_user",
"expires_in": 3599,
"ext_expires_in": 3599,
"access_token": "eyJ0eXAiOiJKV1QiLCJhbGciOiJSUzI1NiIsIng1dCI6Im5PbzNaRHJPRFhFSzFqS1doWHNsSFJfS1hFZyIsImtpZCI6Im5Pb...
}
```
Shouldn't I be seeing scopes like `openid profile User.Read email api://5fbbd10d-39c2-fac2-901b-38e58523badf/access_as_user`?
```
### Reproduction Steps
1. Get the token for one scope (e.g. "User.Read").
2. Get the token for another scope (e.g. a custom API or may be Azure Service Management API).
### Expected Behavior
Based on the documentation, scopes should be added however scopes are being overwritten.
### Identity Provider
Azure AD / MSA
### Browsers Affected (Select all that apply)
Safari
### Regression
_No response_
### Source
External (Customer) | non_priority | trying to understand dynamic scopes and incremental consent core library azure msal browser core library version wrapper library azure msal react wrapper library version beta description i am reading about and following example caught my attention const loginrequest scopes const tokenrequest scopes const anothertokenrequest scopes will return an id token and an access token with scopes openid profile and user read msalinstance loginpopup loginrequest will fail and fallback to an interactive method prompting a consent screen msalinstance acquiretokensilent tokenrequest will succeed and return an access token with scopes openid profile user read and api my scope msalinstance acquiretokensilent anothertokenrequest based on the documentation it is my understanding that when i make a request to acquire token for api my scope scope the resultant access token will have scopes for which the token has already been acquired the my custom api scope however when i see the token in the browser and check its scopes it only has api my scope scope all previous scopes are not there error message no response msal logs no response msal configuration javascript export const msalconfig auth clientid application client id authority redirecturi cache cachelocation sessionstorage this configures where your cache will be stored storeauthstateincookie false set this to true if you are having issues on or edge system loggeroptions loggercallback level message containspii if containspii return switch level case loglevel error console error message return case loglevel info console info message return case loglevel verbose console debug message return case loglevel warning console warn message return relevant code snippets javascript export const loginrequest scopes export const customapirequest scopes instance acquiretokensilent loginrequest account accounts then response instance acquiretokensilent customapirequest account accounts then response setaccesstoken response accesstoken callmsgraph response accesstoken then response setgraphdata response when i inspect the response of token request after one loginrequest i see the following token type bearer scope openid profile user read email expires in ext expires in access token which is correct however the response of the token request after the one customapirequest i see the following token type bearer scope api access as user expires in ext expires in access token shouldn t i be seeing scopes like openid profile user read email api access as user reproduction steps get the token for one scope e g user read get the token for another scope e g a custom api or may be azure service management api expected behavior based on the documentation scopes should be added however scopes are being overwritten identity provider azure ad msa browsers affected select all that apply safari regression no response source external customer | 0 |
223,504 | 17,603,752,334 | IssuesEvent | 2021-08-17 14:42:12 | UCBerkeleySETI/blimpy | https://api.github.com/repos/UCBerkeleySETI/blimpy | opened | Inadvertently, testing is using the previous release | bug testing | Blimpy testing needs setigen for regression testing.
Setigen needs blimpy to save data in Filterbank or HDF5 files.
So, when the blimpy dependency of setigen is installed and blimpy is not yet installed, testing proceeds with the previous release level from pypi.
Solution: Take setigen out of requirements.txt and install it after ```python setup.py install```.
Impacted files:
* .github/workflows/python_tests.yml
* Dockerfile | 1.0 | Inadvertently, testing is using the previous release - Blimpy testing needs setigen for regression testing.
Setigen needs blimpy to save data in Filterbank or HDF5 files.
So, when the blimpy dependency of setigen is installed and blimpy is not yet installed, testing proceeds with the previous release level from pypi.
Solution: Take setigen out of requirements.txt and install it after ```python setup.py install```.
Impacted files:
* .github/workflows/python_tests.yml
* Dockerfile | non_priority | inadvertently testing is using the previous release blimpy testing needs setigen for regression testing setigen needs blimpy to save data in filterbank or files so when the blimpy dependency of setigen is installed and blimpy is not yet installed testing proceeds with the previous release level from pypi solution take setigen out of requirements txt and install it after python setup py install impacted files github workflows python tests yml dockerfile | 0 |
3,108 | 8,924,066,998 | IssuesEvent | 2019-01-21 17:22:40 | aa-software2112/SOEN390_SimpleCamera | https://api.github.com/repos/aa-software2112/SOEN390_SimpleCamera | closed | Make a layer diagram | Architecture task | Represent the layers of the app, highest level on top. It is the development view of the 4 +1 architectural views. Example: the main activity that includes all modules should be on top
Source Story: #6
[Ideal hours: 1] | 1.0 | Make a layer diagram - Represent the layers of the app, highest level on top. It is the development view of the 4 +1 architectural views. Example: the main activity that includes all modules should be on top
Source Story: #6
[Ideal hours: 1] | non_priority | make a layer diagram represent the layers of the app highest level on top it is the development view of the architectural views example the main activity that includes all modules should be on top source story | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.