Unnamed: 0 int64 0 832k | id float64 2.49B 32.1B | type stringclasses 1 value | created_at stringlengths 19 19 | repo stringlengths 5 112 | repo_url stringlengths 34 141 | action stringclasses 3 values | title stringlengths 1 855 | labels stringlengths 4 721 | body stringlengths 1 261k | index stringclasses 13 values | text_combine stringlengths 96 261k | label stringclasses 2 values | text stringlengths 96 240k | binary_label int64 0 1 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
266,066 | 23,220,847,923 | IssuesEvent | 2022-08-02 18:03:33 | pytorch/pytorch | https://api.github.com/repos/pytorch/pytorch | closed | test_functionalization.py flaky under torchdynamo | triaged module: flaky-tests module: functionalization | ### 🐛 Describe the bug
stub issue for disables like https://github.com/pytorch/pytorch/issues/81221
### Versions
master
cc @bdhirsh @ezyang | 1.0 | test_functionalization.py flaky under torchdynamo - ### 🐛 Describe the bug
stub issue for disables like https://github.com/pytorch/pytorch/issues/81221
### Versions
master
cc @bdhirsh @ezyang | non_priority | test functionalization py flaky under torchdynamo 🐛 describe the bug stub issue for disables like versions master cc bdhirsh ezyang | 0 |
65,656 | 8,825,150,347 | IssuesEvent | 2019-01-02 19:44:22 | certbot/certbot | https://api.github.com/repos/certbot/certbot | opened | Ensure readthedocs isn't relying on GitHub Services | area: documentation | GitHub Services are going away at the end of this month. See https://developer.github.com/v3/guides/replacing-github-services/. It looks like our readthedocs setup is relying on GitHub services. | 1.0 | Ensure readthedocs isn't relying on GitHub Services - GitHub Services are going away at the end of this month. See https://developer.github.com/v3/guides/replacing-github-services/. It looks like our readthedocs setup is relying on GitHub services. | non_priority | ensure readthedocs isn t relying on github services github services are going away at the end of this month see it looks like our readthedocs setup is relying on github services | 0 |
48,837 | 13,398,650,270 | IssuesEvent | 2020-09-03 13:27:34 | mixellent/demo-app | https://api.github.com/repos/mixellent/demo-app | opened | CVE-2016-4970 (High) detected in netty-all-4.0.33.Final.jar | security vulnerability | ## CVE-2016-4970 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-all-4.0.33.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /tmp/ws-scm/demo-app/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.33.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mixellent/demo-app/commit/e224ec4297971467bc3e91a705b785158ac67da0">e224ec4297971467bc3e91a705b785158ac67da0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handler/ssl/OpenSslEngine.java in Netty 4.0.x before 4.0.37.Final and 4.1.x before 4.1.1.Final allows remote attackers to cause a denial of service (infinite loop).
<p>Publish Date: 2017-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-4970>CVE-2016-4970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4970">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4970</a></p>
<p>Release Date: 2017-04-13</p>
<p>Fix Resolution: io.netty:netty-all:4.0.37.Final,4.1.1.Final,io.netty:netty-handler:4.0.37.Final,4.1.1.Final</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.33.Final","isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.33.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.0.37.Final,4.1.1.Final,io.netty:netty-handler:4.0.37.Final,4.1.1.Final"}],"vulnerabilityIdentifier":"CVE-2016-4970","vulnerabilityDetails":"handler/ssl/OpenSslEngine.java in Netty 4.0.x before 4.0.37.Final and 4.1.x before 4.1.1.Final allows remote attackers to cause a denial of service (infinite loop).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-4970","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-4970 (High) detected in netty-all-4.0.33.Final.jar - ## CVE-2016-4970 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-all-4.0.33.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Library home page: <a href="http://netty.io/">http://netty.io/</a></p>
<p>Path to dependency file: /tmp/ws-scm/demo-app/pom.xml</p>
<p>Path to vulnerable library: canner/.m2/repository/io/netty/netty-all/4.0.33.Final/netty-all-4.0.33.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-all-4.0.33.Final.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/mixellent/demo-app/commit/e224ec4297971467bc3e91a705b785158ac67da0">e224ec4297971467bc3e91a705b785158ac67da0</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
handler/ssl/OpenSslEngine.java in Netty 4.0.x before 4.0.37.Final and 4.1.x before 4.1.1.Final allows remote attackers to cause a denial of service (infinite loop).
<p>Publish Date: 2017-04-13
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-4970>CVE-2016-4970</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4970">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2016-4970</a></p>
<p>Release Date: 2017-04-13</p>
<p>Fix Resolution: io.netty:netty-all:4.0.37.Final,4.1.1.Final,io.netty:netty-handler:4.0.37.Final,4.1.1.Final</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-all","packageVersion":"4.0.33.Final","isTransitiveDependency":false,"dependencyTree":"io.netty:netty-all:4.0.33.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.0.37.Final,4.1.1.Final,io.netty:netty-handler:4.0.37.Final,4.1.1.Final"}],"vulnerabilityIdentifier":"CVE-2016-4970","vulnerabilityDetails":"handler/ssl/OpenSslEngine.java in Netty 4.0.x before 4.0.37.Final and 4.1.x before 4.1.1.Final allows remote attackers to cause a denial of service (infinite loop).","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-4970","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in netty all final jar cve high severity vulnerability vulnerable library netty all final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients library home page a href path to dependency file tmp ws scm demo app pom xml path to vulnerable library canner repository io netty netty all final netty all final jar dependency hierarchy x netty all final jar vulnerable library found in head commit a href vulnerability details handler ssl opensslengine java in netty x before final and x before final allows remote attackers to cause a denial of service infinite loop publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io netty netty all final final io netty netty handler final final rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails handler ssl opensslengine java in netty x before final and x before final allows remote attackers to cause a denial of service infinite loop vulnerabilityurl | 0 |
237,429 | 18,160,197,366 | IssuesEvent | 2021-09-27 08:45:06 | AY2122S1-CS2103-T14-4/tp | https://api.github.com/repos/AY2122S1-CS2103-T14-4/tp | opened | Update README.md | documentation | * Add a UI mockup, the image of the UI should be docs/images/Ui.png
* Update the contents
* Update the link of the GitHub Actions build status badge (Build Status) | 1.0 | Update README.md - * Add a UI mockup, the image of the UI should be docs/images/Ui.png
* Update the contents
* Update the link of the GitHub Actions build status badge (Build Status) | non_priority | update readme md add a ui mockup the image of the ui should be docs images ui png update the contents update the link of the github actions build status badge build status | 0 |
39,304 | 12,663,344,858 | IssuesEvent | 2020-06-18 01:02:55 | robertjfinn/hadoop | https://api.github.com/repos/robertjfinn/hadoop | opened | CVE-2020-7238 (High) detected in netty-codec-http-4.1.42.Final.jar | security vulnerability | ## CVE-2020-7238 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.42.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Path to vulnerable library: /hadoop/hadoop-yarn-project/hadoop-yarn/hadoop-yarn-csi/target/lib/netty-codec-http-4.1.42.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-codec-http-4.1.42.Final.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty 4.1.43.Final allows HTTP Request Smuggling because it mishandles Transfer-Encoding whitespace (such as a [space]Transfer-Encoding:chunked line) and a later Content-Length header. This issue exists because of an incomplete fix for CVE-2019-16869.
<p>Publish Date: 2020-01-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7238>CVE-2020-7238</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/netty/netty/issues/9861">https://github.com/netty/netty/issues/9861</a></p>
<p>Release Date: 2020-01-27</p>
<p>Fix Resolution: io.netty:netty-all:4.1.44.Final;io.netty:netty-codec-http:4.1.44.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-codec-http","packageVersion":"4.1.42.Final","isTransitiveDependency":false,"dependencyTree":"io.netty:netty-codec-http:4.1.42.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.1.44.Final;io.netty:netty-codec-http:4.1.44.Final"}],"vulnerabilityIdentifier":"CVE-2020-7238","vulnerabilityDetails":"Netty 4.1.43.Final allows HTTP Request Smuggling because it mishandles Transfer-Encoding whitespace (such as a [space]Transfer-Encoding:chunked line) and a later Content-Length header. This issue exists because of an incomplete fix for CVE-2019-16869.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7238","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2020-7238 (High) detected in netty-codec-http-4.1.42.Final.jar - ## CVE-2020-7238 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>netty-codec-http-4.1.42.Final.jar</b></p></summary>
<p>Netty is an asynchronous event-driven network application framework for
rapid development of maintainable high performance protocol servers and
clients.</p>
<p>Path to vulnerable library: /hadoop/hadoop-yarn-project/hadoop-yarn/hadoop-yarn-csi/target/lib/netty-codec-http-4.1.42.Final.jar</p>
<p>
Dependency Hierarchy:
- :x: **netty-codec-http-4.1.42.Final.jar** (Vulnerable Library)
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Netty 4.1.43.Final allows HTTP Request Smuggling because it mishandles Transfer-Encoding whitespace (such as a [space]Transfer-Encoding:chunked line) and a later Content-Length header. This issue exists because of an incomplete fix for CVE-2019-16869.
<p>Publish Date: 2020-01-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7238>CVE-2020-7238</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/netty/netty/issues/9861">https://github.com/netty/netty/issues/9861</a></p>
<p>Release Date: 2020-01-27</p>
<p>Fix Resolution: io.netty:netty-all:4.1.44.Final;io.netty:netty-codec-http:4.1.44.Final</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"io.netty","packageName":"netty-codec-http","packageVersion":"4.1.42.Final","isTransitiveDependency":false,"dependencyTree":"io.netty:netty-codec-http:4.1.42.Final","isMinimumFixVersionAvailable":true,"minimumFixVersion":"io.netty:netty-all:4.1.44.Final;io.netty:netty-codec-http:4.1.44.Final"}],"vulnerabilityIdentifier":"CVE-2020-7238","vulnerabilityDetails":"Netty 4.1.43.Final allows HTTP Request Smuggling because it mishandles Transfer-Encoding whitespace (such as a [space]Transfer-Encoding:chunked line) and a later Content-Length header. This issue exists because of an incomplete fix for CVE-2019-16869.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-7238","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in netty codec http final jar cve high severity vulnerability vulnerable library netty codec http final jar netty is an asynchronous event driven network application framework for rapid development of maintainable high performance protocol servers and clients path to vulnerable library hadoop hadoop yarn project hadoop yarn hadoop yarn csi target lib netty codec http final jar dependency hierarchy x netty codec http final jar vulnerable library vulnerability details netty final allows http request smuggling because it mishandles transfer encoding whitespace such as a transfer encoding chunked line and a later content length header this issue exists because of an incomplete fix for cve publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution io netty netty all final io netty netty codec http final isopenpronvulnerability false ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails netty final allows http request smuggling because it mishandles transfer encoding whitespace such as a transfer encoding chunked line and a later content length header this issue exists because of an incomplete fix for cve vulnerabilityurl | 0 |
42,730 | 22,793,192,259 | IssuesEvent | 2022-07-10 10:13:41 | NeunEinser/bingo | https://api.github.com/repos/NeunEinser/bingo | closed | Reduce sign placing in the lobby | High Prio Performance | Currently all lobby signs are replaced every tick.
It is necessary to place signs continuously for the following reasons:
- When joining, the player will by default not have the resource pack enabled, causing signs to render their translation keys instead of their actual translation. See also [MC-162441](https://bugs.mojang.com/browse/MC-162441)
- To prevent accidental permanent breaking of lobby functionality
While these are valid reasons, it is unnecessary to do this in every tick, and on servers can cause a high amount of network traffic, causing players to have bad ping in the lobby.
This could be improved by:
- Not running the function every tick, but every second or so
- Only replacing signs close to a player, skipping signs that are further away | True | Reduce sign placing in the lobby - Currently all lobby signs are replaced every tick.
It is necessary to place signs continuously for the following reasons:
- When joining, the player will by default not have the resource pack enabled, causing signs to render their translation keys instead of their actual translation. See also [MC-162441](https://bugs.mojang.com/browse/MC-162441)
- To prevent accidental permanent breaking of lobby functionality
While these are valid reasons, it is unnecessary to do this in every tick, and on servers can cause a high amount of network traffic, causing players to have bad ping in the lobby.
This could be improved by:
- Not running the function every tick, but every second or so
- Only replacing signs close to a player, skipping signs that are further away | non_priority | reduce sign placing in the lobby currently all lobby signs are replaced every tick it is necessary to place signs continuously for the following reasons when joining the player will by default not have the resource pack enabled causing signs to render their translation keys instead of their actual translation see also to prevent accidental permanent breaking of lobby functionality while these are valid reasons it is unnecessary to do this in every tick and on servers can cause a high amount of network traffic causing players to have bad ping in the lobby this could be improved by not running the function every tick but every second or so only replacing signs close to a player skipping signs that are further away | 0 |
97,448 | 20,262,528,904 | IssuesEvent | 2022-02-15 09:01:03 | jOOQ/jOOQ | https://api.github.com/repos/jOOQ/jOOQ | opened | Support implicit joins over many-to-one relationship tables | T: Enhancement C: Functionality C: Code Generation P: Medium E: All Editions | In principle, it's possible to design a many-to-one relationship using a relationship table like this:
```sql
CREATE TABLE author (
author_id INT PRIMARY KEY
);
CREATE TABLE book (
book_id INT PRIMARY KEY
);
CREATE TABLE authorship (
author_id INT REFERENCES author,
book_id INT UNIQUE REFERENCES book,
...
);
```
What looks like a many-to-many relationship table is really a many-to-one relationship where a book can have only one author.
In such a case, it would be convenient to still offer the usual code generation goodies on the relevant tables, including:
- [ ] Implicit join from `BOOK.author()`
- [ ] Row nesting convenience from `BOOK.authorRow()` (see https://github.com/jOOQ/jOOQ/issues/13069) | 1.0 | Support implicit joins over many-to-one relationship tables - In principle, it's possible to design a many-to-one relationship using a relationship table like this:
```sql
CREATE TABLE author (
author_id INT PRIMARY KEY
);
CREATE TABLE book (
book_id INT PRIMARY KEY
);
CREATE TABLE authorship (
author_id INT REFERENCES author,
book_id INT UNIQUE REFERENCES book,
...
);
```
What looks like a many-to-many relationship table is really a many-to-one relationship where a book can have only one author.
In such a case, it would be convenient to still offer the usual code generation goodies on the relevant tables, including:
- [ ] Implicit join from `BOOK.author()`
- [ ] Row nesting convenience from `BOOK.authorRow()` (see https://github.com/jOOQ/jOOQ/issues/13069) | non_priority | support implicit joins over many to one relationship tables in principle it s possible to design a many to one relationship using a relationship table like this sql create table author author id int primary key create table book book id int primary key create table authorship author id int references author book id int unique references book what looks like a many to many relationship table is really a many to one relationship where a book can have only one author in such a case it would be convenient to still offer the usual code generation goodies on the relevant tables including implicit join from book author row nesting convenience from book authorrow see | 0 |
67,170 | 27,746,660,814 | IssuesEvent | 2023-03-15 17:29:31 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | RRFBs Data Publication is Not Working | Workgroup: AMD Service: Geo Service: Dev Type: DevOps Product: AMD Data Tracker | <!-- Email -->
<!-- jen.duthie@austintexas.gov -->
> What application are you using?
ArcGIS
> Describe the problem.
The new RRFBs aren't showing up on the asset map. Should these be pulled in automatically when we add new RRFBs in Data Tracker? (They are currently in the layer "Hazard Flashers", but I submitted a separate request asking to change that to "Flashing Beacons" and to use the same types that are in Data Tracker.)
> How soon do you need this?
Flexible — An extended timeline is OK
> Requested By
Jen D.
Request ID: DTS20-101165
| 2.0 | RRFBs Data Publication is Not Working - <!-- Email -->
<!-- jen.duthie@austintexas.gov -->
> What application are you using?
ArcGIS
> Describe the problem.
The new RRFBs aren't showing up on the asset map. Should these be pulled in automatically when we add new RRFBs in Data Tracker? (They are currently in the layer "Hazard Flashers", but I submitted a separate request asking to change that to "Flashing Beacons" and to use the same types that are in Data Tracker.)
> How soon do you need this?
Flexible — An extended timeline is OK
> Requested By
Jen D.
Request ID: DTS20-101165
| non_priority | rrfbs data publication is not working what application are you using arcgis describe the problem the new rrfbs aren t showing up on the asset map should these be pulled in automatically when we add new rrfbs in data tracker they are currently in the layer hazard flashers but i submitted a separate request asking to change that to flashing beacons and to use the same types that are in data tracker how soon do you need this flexible — an extended timeline is ok requested by jen d request id | 0 |
68,109 | 14,901,214,633 | IssuesEvent | 2021-01-21 16:13:26 | AlexRogalskiy/gradle-java-sample | https://api.github.com/repos/AlexRogalskiy/gradle-java-sample | opened | WS-2017-3734 (Medium) detected in httpclient-4.2.1.jar | security vulnerability | ## WS-2017-3734 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>httpclient-4.2.1.jar</b></p></summary>
<p>HttpComponents Client (base module)</p>
<p>Path to dependency file: gradle-java-sample/buildSrc/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.httpcomponents/httpclient/4.2.1/b69bd03af60bf487b3ae1209a644ecac587bf6fc/httpclient-4.2.1.jar</p>
<p>
Dependency Hierarchy:
- gradle-nexus-staging-plugin-0.22.0.jar (Root Library)
- http-builder-0.7.1.jar
- :x: **httpclient-4.2.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/gradle-java-sample/commit/7c836cf738f498554b47fba8fe1cf0cd6f909c21">7c836cf738f498554b47fba8fe1cf0cd6f909c21</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache httpclient before 4.5.3 are vulnerable to Directory Traversal. The user-provided path was able to override the specified host, resulting in giving network access to a sensitive environment.
<p>Publish Date: 2017-01-21
<p>URL: <a href=https://github.com/apache/httpcomponents-client/commit/0554271750599756d4946c0d7ba43d04b1a7b220>WS-2017-3734</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/HTTPCLIENT-1803">https://issues.apache.org/jira/browse/HTTPCLIENT-1803</a></p>
<p>Release Date: 2017-01-21</p>
<p>Fix Resolution: org.apache.httpcomponents:httpclient:4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2017-3734 (Medium) detected in httpclient-4.2.1.jar - ## WS-2017-3734 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>httpclient-4.2.1.jar</b></p></summary>
<p>HttpComponents Client (base module)</p>
<p>Path to dependency file: gradle-java-sample/buildSrc/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.apache.httpcomponents/httpclient/4.2.1/b69bd03af60bf487b3ae1209a644ecac587bf6fc/httpclient-4.2.1.jar</p>
<p>
Dependency Hierarchy:
- gradle-nexus-staging-plugin-0.22.0.jar (Root Library)
- http-builder-0.7.1.jar
- :x: **httpclient-4.2.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/gradle-java-sample/commit/7c836cf738f498554b47fba8fe1cf0cd6f909c21">7c836cf738f498554b47fba8fe1cf0cd6f909c21</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Apache httpclient before 4.5.3 are vulnerable to Directory Traversal. The user-provided path was able to override the specified host, resulting in giving network access to a sensitive environment.
<p>Publish Date: 2017-01-21
<p>URL: <a href=https://github.com/apache/httpcomponents-client/commit/0554271750599756d4946c0d7ba43d04b1a7b220>WS-2017-3734</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://issues.apache.org/jira/browse/HTTPCLIENT-1803">https://issues.apache.org/jira/browse/HTTPCLIENT-1803</a></p>
<p>Release Date: 2017-01-21</p>
<p>Fix Resolution: org.apache.httpcomponents:httpclient:4.5.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in httpclient jar ws medium severity vulnerability vulnerable library httpclient jar httpcomponents client base module path to dependency file gradle java sample buildsrc build gradle path to vulnerable library home wss scanner gradle caches modules files org apache httpcomponents httpclient httpclient jar dependency hierarchy gradle nexus staging plugin jar root library http builder jar x httpclient jar vulnerable library found in head commit a href found in base branch master vulnerability details apache httpclient before are vulnerable to directory traversal the user provided path was able to override the specified host resulting in giving network access to a sensitive environment publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache httpcomponents httpclient step up your open source security game with whitesource | 0 |
170,040 | 13,171,411,699 | IssuesEvent | 2020-08-11 16:37:41 | istio/istio | https://api.github.com/repos/istio/istio | closed | Prepare Release-1.7 branches | area/test and release lifecycle/needs-triage | This issue aims to track all steps needed to prepare the release 1.7 branches/builds.
Please add all steps taken here so we can document for future releases
- [x] Set up release manager team (owner: JimmyCYJ) - Make sure the new team has write access to the repositories.
- [x] Update dependencies. This must be done **before branching** so that PRs can be easily backported later. (owner: JimmyCYJ https://github.com/istio/istio/pull/25707)
Run the following command in istio/istio `UPDATE_BRANCH=master ./bin/update_deps.sh; make gen`
- [x] Adjust istio/proxy to correct version of istio/envoy (https://github.com/istio/proxy/pull/2938)
- [x] Create a `release-1.7` branch in every Istio repo - run commands `export org=xyz ; export repo=xyz ; (git clone git@github.com:${org}/${repo}.git && cd $repo && git checkout -b release-1.7 && git push --set-upstream origin release-1.7)`.
- [x] istio/istio
- [x] istio/pkg
- [x] istio/api
- [x] istio/proxy
- [x] istio/envoy
- [x] istio/client-go
- [x] istio/tools
- [x] istio/common-files
- [x] istio/gogo-genproto
- [x] istio/release-builder
- [x] Explicitly skipped: istio-releases/pipeline, istio/tests, istio/istio.io, istio/test-infra
- [x] Set up prow on release branches (owner: howardjohn) `go run generate.go branch 1.7` https://github.com/istio/test-infra/pull/2821
- [x] Set up branch protection (owner: howardjohn). Modify prow/config.yaml in test-infra to add release manages as owners for branch. https://github.com/istio/test-infra/pull/2820
- [x] Update all repos that point to master branch of another repo to point to the release branch. `master-latest-daily` -> `1.7-dev` (see https://discuss.istio.io/t/deprecation-notice-daily-builds/3991), `latest` -> `1.7-dev`, `git clone master` to `git clone release-1.5`, etc. Commit a PR into every `release-1.7` branch to modify every `CODEOWNERS` to contain only the release managers for this release. Command: `export org=xyz ; export repo=xyz ; (git clone git@github.com:${org}/${repo}.git && cd $repo && git checkout release-1.7 && git checkout -b release-1.7-codeowners && echo '* @istio/release-managers-1-7' > CODEOWNERS && git add CODEOWNERS && git commit -m 'Set release managers as CODEOWNERS for release-1.7' && git push --set-upstream origin release-1.7-codeowners)`.
- [x] istio/istio (https://github.com/istio/istio/pull/25715)
- [x] istio/pkg (https://github.com/istio/pkg/pull/195)
- [x] istio/api (https://github.com/istio/api/pull/1544)
- [x] istio/envoy (https://github.com/istio/envoy/pull/239)
- [x] istio/proxy (https://github.com/istio/proxy/pull/2932)
- [x] istio/client-go (https://github.com/istio/client-go/pull/206)
- [x] istio/tools (https://github.com/istio/tools/pull/1097)
- [x] istio/common-files (https://github.com/istio/common-files/pull/285)
- [x] istio/gogo-genproto (https://github.com/istio/gogo-genproto/pull/112)
- [x] istio/release-builder (https://github.com/istio/release-builder/pull/324)
- [x] istio/release-builder branch change in build.sh too! (https://github.com/istio/release-builder/pull/325)
- [x] Update common-files in _new release_. You first have to manually update the _common/Makefile.common.mk_ *update-common* target to point to the _new release_ and then run 'make update-common'. It may be that this step could be combined in the prior step in the 'make update-common' was done before the branch.
- [x] istio/common-files should have the branch updated above. (https://github.com/istio/common-files/pull/286)
- [x] istio/istio (https://github.com/istio/istio/pull/25759)
- [x] istio/pkg (https://github.com/istio/pkg/pull/196)
- [x] istio/api (https://github.com/istio/api/pull/1547)
- [x] istio/envoy (not needed)
- [x] istio/client-go (https://github.com/istio/client-go/pull/208)
- [x] istio/gogo-genproto (https://github.com/istio/gogo-genproto/pull/113)
- [x] istio/proxy (https://github.com/istio/proxy/pull/2940)
- [x] istio/release-builder (https://github.com/istio/release-builder/pull/325)
- [x] istio/tools (https://github.com/istio/tools/pull/1098)
- [x] Bump master to version 1.8 (https://github.com/istio/istio/pull/25742)
- [x] Stop publishing `latest` tags (owner: JimmyCYJ https://github.com/istio/istio/pull/25764)
- [x] Add new label: cherrypick/release-1.8 (https://github.com/istio/bots/pull/237)
- [x] Run the long-running tests on the dev builds (owner: richardwxn)
- [x] Send an announcement on Discuss (https://discuss.istio.io/t/1-7-release-branch-cut/7610)
- [ ] Add release lock for release 1.7 in master branch of API repo. (https://github.com/istio/api/pull/1551)
- [x] Update build tools
- [x] Update istio/tools to build with release-1.7 build image (owner: JimmyCYJ https://github.com/istio/tools/pull/1098)
- [x] Update istio/common-files to set release-1.7 build image (owner: JimmyCYJ https://github.com/istio/common-files/pull/286, https://github.com/istio/common-files/pull/287)
- [x] Publish an alpha release
- [x] Trigger a 1.7 alpha build (JimmyCYJ: https://github.com/istio/release-builder/pull/328)
- [x] Publish a 1.7 alpha release (JimmyCYJ: https://github.com/istio/release-builder/pull/329, https://github.com/istio/release-builder/pull/330) | 1.0 | Prepare Release-1.7 branches - This issue aims to track all steps needed to prepare the release 1.7 branches/builds.
Please add all steps taken here so we can document for future releases
- [x] Set up release manager team (owner: JimmyCYJ) - Make sure the new team has write access to the repositories.
- [x] Update dependencies. This must be done **before branching** so that PRs can be easily backported later. (owner: JimmyCYJ https://github.com/istio/istio/pull/25707)
Run the following command in istio/istio `UPDATE_BRANCH=master ./bin/update_deps.sh; make gen`
- [x] Adjust istio/proxy to correct version of istio/envoy (https://github.com/istio/proxy/pull/2938)
- [x] Create a `release-1.7` branch in every Istio repo - run commands `export org=xyz ; export repo=xyz ; (git clone git@github.com:${org}/${repo}.git && cd $repo && git checkout -b release-1.7 && git push --set-upstream origin release-1.7)`.
- [x] istio/istio
- [x] istio/pkg
- [x] istio/api
- [x] istio/proxy
- [x] istio/envoy
- [x] istio/client-go
- [x] istio/tools
- [x] istio/common-files
- [x] istio/gogo-genproto
- [x] istio/release-builder
- [x] Explicitly skipped: istio-releases/pipeline, istio/tests, istio/istio.io, istio/test-infra
- [x] Set up prow on release branches (owner: howardjohn) `go run generate.go branch 1.7` https://github.com/istio/test-infra/pull/2821
- [x] Set up branch protection (owner: howardjohn). Modify prow/config.yaml in test-infra to add release manages as owners for branch. https://github.com/istio/test-infra/pull/2820
- [x] Update all repos that point to master branch of another repo to point to the release branch. `master-latest-daily` -> `1.7-dev` (see https://discuss.istio.io/t/deprecation-notice-daily-builds/3991), `latest` -> `1.7-dev`, `git clone master` to `git clone release-1.5`, etc. Commit a PR into every `release-1.7` branch to modify every `CODEOWNERS` to contain only the release managers for this release. Command: `export org=xyz ; export repo=xyz ; (git clone git@github.com:${org}/${repo}.git && cd $repo && git checkout release-1.7 && git checkout -b release-1.7-codeowners && echo '* @istio/release-managers-1-7' > CODEOWNERS && git add CODEOWNERS && git commit -m 'Set release managers as CODEOWNERS for release-1.7' && git push --set-upstream origin release-1.7-codeowners)`.
- [x] istio/istio (https://github.com/istio/istio/pull/25715)
- [x] istio/pkg (https://github.com/istio/pkg/pull/195)
- [x] istio/api (https://github.com/istio/api/pull/1544)
- [x] istio/envoy (https://github.com/istio/envoy/pull/239)
- [x] istio/proxy (https://github.com/istio/proxy/pull/2932)
- [x] istio/client-go (https://github.com/istio/client-go/pull/206)
- [x] istio/tools (https://github.com/istio/tools/pull/1097)
- [x] istio/common-files (https://github.com/istio/common-files/pull/285)
- [x] istio/gogo-genproto (https://github.com/istio/gogo-genproto/pull/112)
- [x] istio/release-builder (https://github.com/istio/release-builder/pull/324)
- [x] istio/release-builder branch change in build.sh too! (https://github.com/istio/release-builder/pull/325)
- [x] Update common-files in _new release_. You first have to manually update the _common/Makefile.common.mk_ *update-common* target to point to the _new release_ and then run 'make update-common'. It may be that this step could be combined in the prior step in the 'make update-common' was done before the branch.
- [x] istio/common-files should have the branch updated above. (https://github.com/istio/common-files/pull/286)
- [x] istio/istio (https://github.com/istio/istio/pull/25759)
- [x] istio/pkg (https://github.com/istio/pkg/pull/196)
- [x] istio/api (https://github.com/istio/api/pull/1547)
- [x] istio/envoy (not needed)
- [x] istio/client-go (https://github.com/istio/client-go/pull/208)
- [x] istio/gogo-genproto (https://github.com/istio/gogo-genproto/pull/113)
- [x] istio/proxy (https://github.com/istio/proxy/pull/2940)
- [x] istio/release-builder (https://github.com/istio/release-builder/pull/325)
- [x] istio/tools (https://github.com/istio/tools/pull/1098)
- [x] Bump master to version 1.8 (https://github.com/istio/istio/pull/25742)
- [x] Stop publishing `latest` tags (owner: JimmyCYJ https://github.com/istio/istio/pull/25764)
- [x] Add new label: cherrypick/release-1.8 (https://github.com/istio/bots/pull/237)
- [x] Run the long-running tests on the dev builds (owner: richardwxn)
- [x] Send an announcement on Discuss (https://discuss.istio.io/t/1-7-release-branch-cut/7610)
- [ ] Add release lock for release 1.7 in master branch of API repo. (https://github.com/istio/api/pull/1551)
- [x] Update build tools
- [x] Update istio/tools to build with release-1.7 build image (owner: JimmyCYJ https://github.com/istio/tools/pull/1098)
- [x] Update istio/common-files to set release-1.7 build image (owner: JimmyCYJ https://github.com/istio/common-files/pull/286, https://github.com/istio/common-files/pull/287)
- [x] Publish an alpha release
- [x] Trigger a 1.7 alpha build (JimmyCYJ: https://github.com/istio/release-builder/pull/328)
- [x] Publish a 1.7 alpha release (JimmyCYJ: https://github.com/istio/release-builder/pull/329, https://github.com/istio/release-builder/pull/330) | non_priority | prepare release branches this issue aims to track all steps needed to prepare the release branches builds please add all steps taken here so we can document for future releases set up release manager team owner jimmycyj make sure the new team has write access to the repositories update dependencies this must be done before branching so that prs can be easily backported later owner jimmycyj run the following command in istio istio update branch master bin update deps sh make gen adjust istio proxy to correct version of istio envoy create a release branch in every istio repo run commands export org xyz export repo xyz git clone git github com org repo git cd repo git checkout b release git push set upstream origin release istio istio istio pkg istio api istio proxy istio envoy istio client go istio tools istio common files istio gogo genproto istio release builder explicitly skipped istio releases pipeline istio tests istio istio io istio test infra set up prow on release branches owner howardjohn go run generate go branch set up branch protection owner howardjohn modify prow config yaml in test infra to add release manages as owners for branch update all repos that point to master branch of another repo to point to the release branch master latest daily dev see latest dev git clone master to git clone release etc commit a pr into every release branch to modify every codeowners to contain only the release managers for this release command export org xyz export repo xyz git clone git github com org repo git cd repo git checkout release git checkout b release codeowners echo istio release managers codeowners git add codeowners git commit m set release managers as codeowners for release git push set upstream origin release codeowners istio istio istio pkg istio api istio envoy istio proxy istio client go istio tools istio common files istio gogo genproto istio release builder istio release builder branch change in build sh too update common files in new release you first have to manually update the common makefile common mk update common target to point to the new release and then run make update common it may be that this step could be combined in the prior step in the make update common was done before the branch istio common files should have the branch updated above istio istio istio pkg istio api istio envoy not needed istio client go istio gogo genproto istio proxy istio release builder istio tools bump master to version stop publishing latest tags owner jimmycyj add new label cherrypick release run the long running tests on the dev builds owner richardwxn send an announcement on discuss add release lock for release in master branch of api repo update build tools update istio tools to build with release build image owner jimmycyj update istio common files to set release build image owner jimmycyj publish an alpha release trigger a alpha build jimmycyj publish a alpha release jimmycyj | 0 |
236,364 | 26,006,174,521 | IssuesEvent | 2022-12-20 19:36:26 | swagger-api/swagger-codegen | https://api.github.com/repos/swagger-api/swagger-codegen | closed | CVE-2022-45685 (High) detected in jettison-1.1.jar - autoclosed | security vulnerability | ## CVE-2022-45685 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.1.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /samples/client/petstore/scala/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar</p>
<p>
Dependency Hierarchy:
- jersey-ahc-client-1.0.5.jar (Root Library)
- jersey-json-1.14.jar
- :x: **jettison-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/swagger-api/swagger-codegen/commit/4b7a8d7d7384aa6a27d6309c35ade0916edae7ed">4b7a8d7d7384aa6a27d6309c35ade0916edae7ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A stack overflow in Jettison before v1.5.2 allows attackers to cause a Denial of Service (DoS) via crafted JSON data.
<p>Publish Date: 2022-12-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-45685>CVE-2022-45685</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-12-13</p>
<p>Fix Resolution: org.codehaus.jettison:jettison:1.5.2</p>
</p>
</details>
<p></p>
| True | CVE-2022-45685 (High) detected in jettison-1.1.jar - autoclosed - ## CVE-2022-45685 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jettison-1.1.jar</b></p></summary>
<p>A StAX implementation for JSON.</p>
<p>Path to dependency file: /samples/client/petstore/scala/build.gradle</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar,/home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.codehaus.jettison/jettison/1.1/1a01a2a1218fcf9faa2cc2a6ced025bdea687262/jettison-1.1.jar</p>
<p>
Dependency Hierarchy:
- jersey-ahc-client-1.0.5.jar (Root Library)
- jersey-json-1.14.jar
- :x: **jettison-1.1.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/swagger-api/swagger-codegen/commit/4b7a8d7d7384aa6a27d6309c35ade0916edae7ed">4b7a8d7d7384aa6a27d6309c35ade0916edae7ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A stack overflow in Jettison before v1.5.2 allows attackers to cause a Denial of Service (DoS) via crafted JSON data.
<p>Publish Date: 2022-12-13
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2022-45685>CVE-2022-45685</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Release Date: 2022-12-13</p>
<p>Fix Resolution: org.codehaus.jettison:jettison:1.5.2</p>
</p>
</details>
<p></p>
| non_priority | cve high detected in jettison jar autoclosed cve high severity vulnerability vulnerable library jettison jar a stax implementation for json path to dependency file samples client petstore scala build gradle path to vulnerable library home wss scanner gradle caches modules files org codehaus jettison jettison jettison jar home wss scanner gradle caches modules files org codehaus jettison jettison jettison jar dependency hierarchy jersey ahc client jar root library jersey json jar x jettison jar vulnerable library found in head commit a href found in base branch master vulnerability details a stack overflow in jettison before allows attackers to cause a denial of service dos via crafted json data publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version release date fix resolution org codehaus jettison jettison | 0 |
56,817 | 15,377,947,289 | IssuesEvent | 2021-03-02 17:41:55 | NREL/EnergyPlus | https://api.github.com/repos/NREL/EnergyPlus | closed | [pyenergyplus] system exit called when energyplus can't run | Defect | Issue overview
--------------
When invalid arguments prevent EnergyPlus binary from running, system exit (1) is called and api caller program is interrupted.
Example:
```python
from pyenergyplus.api import EnergyPlusAPI
if __name__ == "__main__":
api = EnergyPlusAPI()
exit_code = api.runtime.run_energyplus(api.state_manager.new_state(), "wrong")
print("exit:", exit_code)
```
Output is:
```
ERROR: Multiple input files specified:
Input file #1: w
Input file #2: r
Input file #3: o
Input file #4: n
Input file #5: g
Type 'energyplus --help' for usage.
```
then script exists with code 1. Last print statement isn't executed.
In library mode, the caller program should be responsible for calling system exit.
### Details
- Platform: Ubuntu 20.04 LTS
- Version of EnergyPlus: v9.4.0
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [ ] Defect file added (list location of defect file here)
- [x] Ticket added to Pivotal for defect (development team task)
- [ ] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect) | 1.0 | [pyenergyplus] system exit called when energyplus can't run - Issue overview
--------------
When invalid arguments prevent EnergyPlus binary from running, system exit (1) is called and api caller program is interrupted.
Example:
```python
from pyenergyplus.api import EnergyPlusAPI
if __name__ == "__main__":
api = EnergyPlusAPI()
exit_code = api.runtime.run_energyplus(api.state_manager.new_state(), "wrong")
print("exit:", exit_code)
```
Output is:
```
ERROR: Multiple input files specified:
Input file #1: w
Input file #2: r
Input file #3: o
Input file #4: n
Input file #5: g
Type 'energyplus --help' for usage.
```
then script exists with code 1. Last print statement isn't executed.
In library mode, the caller program should be responsible for calling system exit.
### Details
- Platform: Ubuntu 20.04 LTS
- Version of EnergyPlus: v9.4.0
### Checklist
Add to this list or remove from it as applicable. This is a simple templated set of guidelines.
- [ ] Defect file added (list location of defect file here)
- [x] Ticket added to Pivotal for defect (development team task)
- [ ] Pull request created (the pull request will have additional tasks related to reviewing changes that fix this defect) | non_priority | system exit called when energyplus can t run issue overview when invalid arguments prevent energyplus binary from running system exit is called and api caller program is interrupted example python from pyenergyplus api import energyplusapi if name main api energyplusapi exit code api runtime run energyplus api state manager new state wrong print exit exit code output is error multiple input files specified input file w input file r input file o input file n input file g type energyplus help for usage then script exists with code last print statement isn t executed in library mode the caller program should be responsible for calling system exit details platform ubuntu lts version of energyplus checklist add to this list or remove from it as applicable this is a simple templated set of guidelines defect file added list location of defect file here ticket added to pivotal for defect development team task pull request created the pull request will have additional tasks related to reviewing changes that fix this defect | 0 |
16,552 | 3,537,726,683 | IssuesEvent | 2016-01-18 04:19:01 | TexnologiaLog/SnapChatApp | https://api.github.com/repos/TexnologiaLog/SnapChatApp | closed | Υλοποίηση Κλάσεων Test | Testing | Υλοποίηση των παρακάτω κλάσεων .
TestingCameraActivityTest
DetailsScreenActivityTest
UserProfileActivityTest
FriendsScreenActivityTest
WebServiceActivityTest | 1.0 | Υλοποίηση Κλάσεων Test - Υλοποίηση των παρακάτω κλάσεων .
TestingCameraActivityTest
DetailsScreenActivityTest
UserProfileActivityTest
FriendsScreenActivityTest
WebServiceActivityTest | non_priority | υλοποίηση κλάσεων test υλοποίηση των παρακάτω κλάσεων testingcameraactivitytest detailsscreenactivitytest userprofileactivitytest friendsscreenactivitytest webserviceactivitytest | 0 |
163,148 | 12,706,147,058 | IssuesEvent | 2020-06-23 06:35:10 | DrewScoggins/performance-2 | https://api.github.com/repos/DrewScoggins/performance-2 | closed | [Perf -10%] Inlining.InlineGCStruct.WithFormat | Baseline Outlier Bimodal Test Test Test Test Test Windows 10.0.18362 refs/heads/master x64 | ### Run Information
Architecture | x64
-- | --
OS | Windows 10.0.18362
Changes | [diff](https://github.com/dotnet/runtime/compare/518df4f20d20f233727cba2fcc42603a31f750df...8e3b55435b3ed75cffb6687916ae1edcf7253408)
### Regressions in Inlining.InlineGCStruct
Benchmark | Baseline | Test | Test/Base | Modality | Baseline Outlier
-- | -- | -- | -- | -- | --
WithFormat | 1.07 ns | 1.18 ns | 1.10 | Bimodal | True

[Historical Data in Reporting System](<https://pvscmdupload.blob.core.windows.net/autofilereport/autofilereports/06_12_2020/refs/heads/master_x64_Windows%2010.0.18362_Test%20Test%20Test%20Test%20Test/Inlining.InlineGCStruct.html>)
### Repro
```cmd
git clone https://github.com/dotnet/performance.git
py .\performance\scripts\benchmarks_ci.py -f netcoreapp5.0 --filter 'Inlining.InlineGCStruct*';
```
<details>
### Histogram
#### Inlining.InlineGCStruct.WithFormat
```log
[1.017 ; 1.094) | @@@@@@@@@@@@@@
[1.094 ; 1.132) |
[1.132 ; 1.209) | @@@@@@@@@
[1.209 ; 1.238) |
[1.238 ; 1.318) | @@@@@@
```
### Docs
[Profiling workflow for dotnet/runtime repository](https://github.com/dotnet/performance/blob/master/docs/profiling-workflow-dotnet-runtime.md)
[Benchmarking workflow for dotnet/runtime repository](https://github.com/dotnet/performance/blob/master/docs/benchmarking-workflow-dotnet-runtime.md)
</details> | 5.0 | [Perf -10%] Inlining.InlineGCStruct.WithFormat - ### Run Information
Architecture | x64
-- | --
OS | Windows 10.0.18362
Changes | [diff](https://github.com/dotnet/runtime/compare/518df4f20d20f233727cba2fcc42603a31f750df...8e3b55435b3ed75cffb6687916ae1edcf7253408)
### Regressions in Inlining.InlineGCStruct
Benchmark | Baseline | Test | Test/Base | Modality | Baseline Outlier
-- | -- | -- | -- | -- | --
WithFormat | 1.07 ns | 1.18 ns | 1.10 | Bimodal | True

[Historical Data in Reporting System](<https://pvscmdupload.blob.core.windows.net/autofilereport/autofilereports/06_12_2020/refs/heads/master_x64_Windows%2010.0.18362_Test%20Test%20Test%20Test%20Test/Inlining.InlineGCStruct.html>)
### Repro
```cmd
git clone https://github.com/dotnet/performance.git
py .\performance\scripts\benchmarks_ci.py -f netcoreapp5.0 --filter 'Inlining.InlineGCStruct*';
```
<details>
### Histogram
#### Inlining.InlineGCStruct.WithFormat
```log
[1.017 ; 1.094) | @@@@@@@@@@@@@@
[1.094 ; 1.132) |
[1.132 ; 1.209) | @@@@@@@@@
[1.209 ; 1.238) |
[1.238 ; 1.318) | @@@@@@
```
### Docs
[Profiling workflow for dotnet/runtime repository](https://github.com/dotnet/performance/blob/master/docs/profiling-workflow-dotnet-runtime.md)
[Benchmarking workflow for dotnet/runtime repository](https://github.com/dotnet/performance/blob/master/docs/benchmarking-workflow-dotnet-runtime.md)
</details> | non_priority | inlining inlinegcstruct withformat run information architecture os windows changes regressions in inlining inlinegcstruct benchmark baseline test test base modality baseline outlier withformat ns ns bimodal true repro cmd git clone py performance scripts benchmarks ci py f filter inlining inlinegcstruct histogram inlining inlinegcstruct withformat log docs | 0 |
263,796 | 23,083,153,859 | IssuesEvent | 2022-07-26 09:02:51 | netdjw/ddata-core | https://api.github.com/repos/netdjw/ddata-core | opened | Create test for SearchModelFunctions model | testing | Need to be tested:
1. The model needs to be created
2. The model should have all required properties
3. All properties should have correct type
4. The model should have the following functions:
- init
- setUrl
- setIcon
5. The above listed functions should provide correct output | 1.0 | Create test for SearchModelFunctions model - Need to be tested:
1. The model needs to be created
2. The model should have all required properties
3. All properties should have correct type
4. The model should have the following functions:
- init
- setUrl
- setIcon
5. The above listed functions should provide correct output | non_priority | create test for searchmodelfunctions model need to be tested the model needs to be created the model should have all required properties all properties should have correct type the model should have the following functions init seturl seticon the above listed functions should provide correct output | 0 |
50,526 | 6,100,509,111 | IssuesEvent | 2017-06-20 12:46:50 | hazelcast/hazelcast-cpp-client | https://api.github.com/repos/hazelcast/hazelcast-cpp-client | closed | ClusterTest.testListenersWhenClusterDown failed at nightly tests cpp-centos7-nightly-32-STATIC-Release | test-failure | Test ClusterTest.testListenersWhenClusterDown failed at nightly tests cpp-centos7-nightly-32-STATIC-Release for master branch at e5548cc2785a7c551925e475f8e56f4abb1de058 (failure started after https://github.com/hazelcast/hazelcast-cpp-client/pull/246 )
The test caused segmentation fault.
The core stack trace is:
04:51:22 Using host libthread_db library "/lib64/libthread_db.so.1".
04:51:22 Core was generated by `buildSTATIC32Release/hazelcast/test/src/clientTest_STATIC_32 --gtest_output=xml'.
04:51:22 Program terminated with signal 11, Segmentation fault.
04:51:22 #0 0x086dcd5d in hazelcast::client::connection::OwnerConnectionFuture::getOrWaitForCreation() ()
04:51:22
04:51:22 Thread 3 (Thread 0xf6fa0b40 (LWP 8412)):
04:51:22 #0 0xf775d430 in __kernel_vsyscall ()
04:51:22 No symbol table info available.
04:51:22 #1 0xf72c06d1 in select () from /lib/libc.so.6
04:51:22 No symbol table info available.
04:51:22 #2 0x0877c8d6 in hazelcast::client::connection::OutSelector::listenInternal() ()
04:51:22 No symbol table info available.
04:51:22 #3 0x0877ba08 in hazelcast::client::connection::IOSelector::listen() ()
04:51:22 No symbol table info available.
04:51:22 #4 0x087421a2 in hazelcast::util::Thread::controlledThread(void*) ()
04:51:22 No symbol table info available.
04:51:22 #5 0xf7720b2c in start_thread () from /lib/libpthread.so.0
04:51:22 No symbol table info available.
04:51:22 #6 0xf72ca08e in clone () from /lib/libc.so.6
04:51:22 No symbol table info available.
04:51:22
04:51:22 Thread 2 (Thread 0xf6fa27c0 (LWP 4151)):
04:51:22 #0 0xf775d430 in __kernel_vsyscall ()
04:51:22 No symbol table info available.
04:51:22 #1 0xf7721d15 in pthread_join () from /lib/libpthread.so.0
04:51:22 No symbol table info available.
04:51:22 #2 0x087420a3 in hazelcast::util::Thread::join() ()
04:51:22 No symbol table info available.
04:51:22 #3 0x086d574f in hazelcast::client::connection::ConnectionManager::shutdown() ()
04:51:22 No symbol table info available.
04:51:22 #4 0x08726034 in hazelcast::client::spi::LifecycleService::shutdown() ()
04:51:22 No symbol table info available.
04:51:22 #5 0x08737919 in hazelcast::client::HazelcastClient::~HazelcastClient() ()
04:51:22 No symbol table info available.
04:51:22 #6 0x084ba614 in hazelcast::client::test::ClusterTest_testListenersWhenClusterDown_Test::TestBody() ()
04:51:22 No symbol table info available.
04:51:22 #7 0x087aff6c in void testing::internal::HandleExceptionsInMethodIfSupported<testing::Test, void>(testing::Test*, void (testing::Test::*)(), char const*) ()
04:51:22 No symbol table info available.
04:51:22 #8 0x087a4b04 in testing::Test::Run() ()
04:51:22 No symbol table info available.
04:51:22 #9 0x087a4d24 in testing::TestInfo::Run() ()
04:51:22 No symbol table info available.
04:51:22 #10 0x087a4e6f in testing::TestCase::Run() ()
04:51:22 No symbol table info available.
04:51:22 #11 0x087a7ad6 in testing::internal::UnitTestImpl::RunAllTests() [clone .part.445] ()
04:51:22 No symbol table info available.
04:51:22 #12 0x087a7e9e in testing::UnitTest::Run() ()
04:51:22 No symbol table info available.
04:51:22 #13 0x083992a8 in main ()
04:51:22 No symbol table info available.
04:51:22
04:51:22 Thread 1 (Thread 0xf679fb40 (LWP 8411)):
04:51:22 #0 0x086dcd5d in hazelcast::client::connection::OwnerConnectionFuture::getOrWaitForCreation() ()
04:51:22 No symbol table info available.
04:51:22 #1 0x086d7d74 in hazelcast::client::connection::ConnectionManager::getOrConnectResolved(hazelcast::client::Address const&) ()
04:51:22 No symbol table info available.
04:51:22 #2 0x086d82c3 in hazelcast::client::connection::ConnectionManager::getOrConnect(hazelcast::client::Address const&) ()
04:51:22 No symbol table info available.
04:51:22 #3 0x086d84f3 in hazelcast::client::connection::ConnectionManager::getOrConnect(hazelcast::client::Address const&, int) ()
04:51:22 No symbol table info available.
04:51:22 #4 0x086d89ef in hazelcast::client::connection::ConnectionManager::getRandomConnection(int, std::string const&, int) ()
04:51:22 No symbol table info available.
04:51:22 #5 0x08722a09 in hazelcast::client::spi::InvocationService::resend(boost::shared_ptr<hazelcast::client::connection::CallPromise>, std::string const&) ()
04:51:22 No symbol table info available.
04:51:22 #6 0x08728dc6 in hazelcast::client::spi::ServerListenerService::retryFailedListener(boost::shared_ptr<hazelcast::client::connection::CallPromise>) ()
04:51:22 No symbol table info available.
04:51:22 #7 0x08721105 in hazelcast::client::spi::InvocationService::cleanEventHandlers(hazelcast::client::connection::Connection&) ()
04:51:22 No symbol table info available.
04:51:22 #8 0x08723310 in hazelcast::client::spi::InvocationService::cleanResources(hazelcast::client::connection::Connection&) ()
04:51:22 No symbol table info available.
04:51:22 #9 0x086d31fe in hazelcast::client::connection::Connection::close() ()
04:51:22 No symbol table info available.
04:51:22 #10 0x08776e1d in hazelcast::client::connection::IOHandler::handleSocketException(std::string const&) ()
04:51:22 No symbol table info available.
04:51:22 #11 0x08776fbd in hazelcast::client::connection::ReadHandler::handle() ()
04:51:22 No symbol table info available.
04:51:22 #12 0x0877c69e in hazelcast::client::connection::InSelector::listenInternal() ()
04:51:22 No symbol table info available.
04:51:22 #13 0x0877ba08 in hazelcast::client::connection::IOSelector::listen() ()
04:51:22 No symbol table info available.
04:51:22 #14 0x087421a2 in hazelcast::util::Thread::controlledThread(void*) ()
04:51:22 No symbol table info available.
04:51:22 #15 0xf7720b2c in start_thread () from /lib/libpthread.so.0
04:51:22 No symbol table info available.
04:51:22 #16 0xf72ca08e in clone () from /lib/libc.so.6
| 1.0 | ClusterTest.testListenersWhenClusterDown failed at nightly tests cpp-centos7-nightly-32-STATIC-Release - Test ClusterTest.testListenersWhenClusterDown failed at nightly tests cpp-centos7-nightly-32-STATIC-Release for master branch at e5548cc2785a7c551925e475f8e56f4abb1de058 (failure started after https://github.com/hazelcast/hazelcast-cpp-client/pull/246 )
The test caused segmentation fault.
The core stack trace is:
04:51:22 Using host libthread_db library "/lib64/libthread_db.so.1".
04:51:22 Core was generated by `buildSTATIC32Release/hazelcast/test/src/clientTest_STATIC_32 --gtest_output=xml'.
04:51:22 Program terminated with signal 11, Segmentation fault.
04:51:22 #0 0x086dcd5d in hazelcast::client::connection::OwnerConnectionFuture::getOrWaitForCreation() ()
04:51:22
04:51:22 Thread 3 (Thread 0xf6fa0b40 (LWP 8412)):
04:51:22 #0 0xf775d430 in __kernel_vsyscall ()
04:51:22 No symbol table info available.
04:51:22 #1 0xf72c06d1 in select () from /lib/libc.so.6
04:51:22 No symbol table info available.
04:51:22 #2 0x0877c8d6 in hazelcast::client::connection::OutSelector::listenInternal() ()
04:51:22 No symbol table info available.
04:51:22 #3 0x0877ba08 in hazelcast::client::connection::IOSelector::listen() ()
04:51:22 No symbol table info available.
04:51:22 #4 0x087421a2 in hazelcast::util::Thread::controlledThread(void*) ()
04:51:22 No symbol table info available.
04:51:22 #5 0xf7720b2c in start_thread () from /lib/libpthread.so.0
04:51:22 No symbol table info available.
04:51:22 #6 0xf72ca08e in clone () from /lib/libc.so.6
04:51:22 No symbol table info available.
04:51:22
04:51:22 Thread 2 (Thread 0xf6fa27c0 (LWP 4151)):
04:51:22 #0 0xf775d430 in __kernel_vsyscall ()
04:51:22 No symbol table info available.
04:51:22 #1 0xf7721d15 in pthread_join () from /lib/libpthread.so.0
04:51:22 No symbol table info available.
04:51:22 #2 0x087420a3 in hazelcast::util::Thread::join() ()
04:51:22 No symbol table info available.
04:51:22 #3 0x086d574f in hazelcast::client::connection::ConnectionManager::shutdown() ()
04:51:22 No symbol table info available.
04:51:22 #4 0x08726034 in hazelcast::client::spi::LifecycleService::shutdown() ()
04:51:22 No symbol table info available.
04:51:22 #5 0x08737919 in hazelcast::client::HazelcastClient::~HazelcastClient() ()
04:51:22 No symbol table info available.
04:51:22 #6 0x084ba614 in hazelcast::client::test::ClusterTest_testListenersWhenClusterDown_Test::TestBody() ()
04:51:22 No symbol table info available.
04:51:22 #7 0x087aff6c in void testing::internal::HandleExceptionsInMethodIfSupported<testing::Test, void>(testing::Test*, void (testing::Test::*)(), char const*) ()
04:51:22 No symbol table info available.
04:51:22 #8 0x087a4b04 in testing::Test::Run() ()
04:51:22 No symbol table info available.
04:51:22 #9 0x087a4d24 in testing::TestInfo::Run() ()
04:51:22 No symbol table info available.
04:51:22 #10 0x087a4e6f in testing::TestCase::Run() ()
04:51:22 No symbol table info available.
04:51:22 #11 0x087a7ad6 in testing::internal::UnitTestImpl::RunAllTests() [clone .part.445] ()
04:51:22 No symbol table info available.
04:51:22 #12 0x087a7e9e in testing::UnitTest::Run() ()
04:51:22 No symbol table info available.
04:51:22 #13 0x083992a8 in main ()
04:51:22 No symbol table info available.
04:51:22
04:51:22 Thread 1 (Thread 0xf679fb40 (LWP 8411)):
04:51:22 #0 0x086dcd5d in hazelcast::client::connection::OwnerConnectionFuture::getOrWaitForCreation() ()
04:51:22 No symbol table info available.
04:51:22 #1 0x086d7d74 in hazelcast::client::connection::ConnectionManager::getOrConnectResolved(hazelcast::client::Address const&) ()
04:51:22 No symbol table info available.
04:51:22 #2 0x086d82c3 in hazelcast::client::connection::ConnectionManager::getOrConnect(hazelcast::client::Address const&) ()
04:51:22 No symbol table info available.
04:51:22 #3 0x086d84f3 in hazelcast::client::connection::ConnectionManager::getOrConnect(hazelcast::client::Address const&, int) ()
04:51:22 No symbol table info available.
04:51:22 #4 0x086d89ef in hazelcast::client::connection::ConnectionManager::getRandomConnection(int, std::string const&, int) ()
04:51:22 No symbol table info available.
04:51:22 #5 0x08722a09 in hazelcast::client::spi::InvocationService::resend(boost::shared_ptr<hazelcast::client::connection::CallPromise>, std::string const&) ()
04:51:22 No symbol table info available.
04:51:22 #6 0x08728dc6 in hazelcast::client::spi::ServerListenerService::retryFailedListener(boost::shared_ptr<hazelcast::client::connection::CallPromise>) ()
04:51:22 No symbol table info available.
04:51:22 #7 0x08721105 in hazelcast::client::spi::InvocationService::cleanEventHandlers(hazelcast::client::connection::Connection&) ()
04:51:22 No symbol table info available.
04:51:22 #8 0x08723310 in hazelcast::client::spi::InvocationService::cleanResources(hazelcast::client::connection::Connection&) ()
04:51:22 No symbol table info available.
04:51:22 #9 0x086d31fe in hazelcast::client::connection::Connection::close() ()
04:51:22 No symbol table info available.
04:51:22 #10 0x08776e1d in hazelcast::client::connection::IOHandler::handleSocketException(std::string const&) ()
04:51:22 No symbol table info available.
04:51:22 #11 0x08776fbd in hazelcast::client::connection::ReadHandler::handle() ()
04:51:22 No symbol table info available.
04:51:22 #12 0x0877c69e in hazelcast::client::connection::InSelector::listenInternal() ()
04:51:22 No symbol table info available.
04:51:22 #13 0x0877ba08 in hazelcast::client::connection::IOSelector::listen() ()
04:51:22 No symbol table info available.
04:51:22 #14 0x087421a2 in hazelcast::util::Thread::controlledThread(void*) ()
04:51:22 No symbol table info available.
04:51:22 #15 0xf7720b2c in start_thread () from /lib/libpthread.so.0
04:51:22 No symbol table info available.
04:51:22 #16 0xf72ca08e in clone () from /lib/libc.so.6
| non_priority | clustertest testlistenerswhenclusterdown failed at nightly tests cpp nightly static release test clustertest testlistenerswhenclusterdown failed at nightly tests cpp nightly static release for master branch at failure started after the test caused segmentation fault the core stack trace is using host libthread db library libthread db so core was generated by hazelcast test src clienttest static gtest output xml program terminated with signal segmentation fault in hazelcast client connection ownerconnectionfuture getorwaitforcreation thread thread lwp in kernel vsyscall no symbol table info available in select from lib libc so no symbol table info available in hazelcast client connection outselector listeninternal no symbol table info available in hazelcast client connection ioselector listen no symbol table info available in hazelcast util thread controlledthread void no symbol table info available in start thread from lib libpthread so no symbol table info available in clone from lib libc so no symbol table info available thread thread lwp in kernel vsyscall no symbol table info available in pthread join from lib libpthread so no symbol table info available in hazelcast util thread join no symbol table info available in hazelcast client connection connectionmanager shutdown no symbol table info available in hazelcast client spi lifecycleservice shutdown no symbol table info available in hazelcast client hazelcastclient hazelcastclient no symbol table info available in hazelcast client test clustertest testlistenerswhenclusterdown test testbody no symbol table info available in void testing internal handleexceptionsinmethodifsupported testing test void testing test char const no symbol table info available in testing test run no symbol table info available in testing testinfo run no symbol table info available in testing testcase run no symbol table info available in testing internal unittestimpl runalltests no symbol table info available in testing unittest run no symbol table info available in main no symbol table info available thread thread lwp in hazelcast client connection ownerconnectionfuture getorwaitforcreation no symbol table info available in hazelcast client connection connectionmanager getorconnectresolved hazelcast client address const no symbol table info available in hazelcast client connection connectionmanager getorconnect hazelcast client address const no symbol table info available in hazelcast client connection connectionmanager getorconnect hazelcast client address const int no symbol table info available in hazelcast client connection connectionmanager getrandomconnection int std string const int no symbol table info available in hazelcast client spi invocationservice resend boost shared ptr std string const no symbol table info available in hazelcast client spi serverlistenerservice retryfailedlistener boost shared ptr no symbol table info available in hazelcast client spi invocationservice cleaneventhandlers hazelcast client connection connection no symbol table info available in hazelcast client spi invocationservice cleanresources hazelcast client connection connection no symbol table info available in hazelcast client connection connection close no symbol table info available in hazelcast client connection iohandler handlesocketexception std string const no symbol table info available in hazelcast client connection readhandler handle no symbol table info available in hazelcast client connection inselector listeninternal no symbol table info available in hazelcast client connection ioselector listen no symbol table info available in hazelcast util thread controlledthread void no symbol table info available in start thread from lib libpthread so no symbol table info available in clone from lib libc so | 0 |
40,988 | 12,809,636,548 | IssuesEvent | 2020-07-03 16:08:24 | tech256/jobs | https://api.github.com/repos/tech256/jobs | closed | Senior Information Assurance / Network Administrator (#1293002) | Active Clearance Required Cyber Security Hiring stale | PeopleTec is currently seeking a Senior Information Assurance / Network Administrator to support our Huntsville, AL location.
PeopleTec is seeking a Senior Information Assurance / Network Administrator to support multiple programs on Redstone Arsenal, AL. The successful candidate will perform Information Security System Manager (ISSM) and similar duties for multiple networks. The successful candidate will have significant and demonstrated knowledge of Military network architectures and processes at multiple classification levels. The successful candidate will also have demonstrated experience developing and staffing Risk Management Framework (RMF) packages for networks and enclaves.
Required Skills/Experience:
Demonstrated experience as an Information Assurance Manager
Required Certifications include: CISSP, Security + and at least one operating system-specific certification
Experience in network architecture, installation, and maintenance across multiple classification levels
Experience with software scanning and accreditation analysis
Travel: Up to 5%
Must be a U.S. Citizen
An active DoD Top Secret clearance with SCI eligibility is required to perform this work. Candidates are required to have an active Top Secret clearance upon hire, and the ability to maintain this level of clearance during their employment.
Education Requirements:
Required experience varies with education level. Candidates with a MS/MA or equivalent require 10+ years of demonstrated experience. Candidates with BS/BA or equivalent require 18 years of experience. Candidates without a degree require 22 years of experience.
Physical Job Requirements:
The ability to lift up to 20 lb is required. The physical ability to install, inspect and maintain computer systems, networks, and wiring in enclosed spaces is also required.
Desired Skills:
Software development experience
Certification as a Certified Ethical Hacker (CEH)
Network and/or communications experience in uniformed service
EOE/Minorities/Females/Veterans/Disabled
PeopleTec, Inc. is an Equal Employment Opportunity employer and provides reasonable accommodation for qualified individuals with disabilities and disabled veterans in its job application procedures. If you have any difficulty using our online system and you need an accommodation due to a disability, you may use the following email address, HR@peopletec.com and/or phone number (256.319.3800) to contact us about your interest in employment with PeopleTec, Inc.
All qualified applicants will receive consideration for employment without regard to race, color, religion, sex, sexual orientation, gender identity, national origin, age, genetic information, citizenship, ancestry, marital status, protected veteran status, disability status or any other status protected by federal, state, or local law. PeopleTec, Inc. participates in E-Verify.
For more information, or to apply now, you must go to the website below. Please DO NOT email your resume to us as we only accept applications through our website.
https://www.applicantpro.com/j/1293002-424912 | True | Senior Information Assurance / Network Administrator (#1293002) - PeopleTec is currently seeking a Senior Information Assurance / Network Administrator to support our Huntsville, AL location.
PeopleTec is seeking a Senior Information Assurance / Network Administrator to support multiple programs on Redstone Arsenal, AL. The successful candidate will perform Information Security System Manager (ISSM) and similar duties for multiple networks. The successful candidate will have significant and demonstrated knowledge of Military network architectures and processes at multiple classification levels. The successful candidate will also have demonstrated experience developing and staffing Risk Management Framework (RMF) packages for networks and enclaves.
Required Skills/Experience:
Demonstrated experience as an Information Assurance Manager
Required Certifications include: CISSP, Security + and at least one operating system-specific certification
Experience in network architecture, installation, and maintenance across multiple classification levels
Experience with software scanning and accreditation analysis
Travel: Up to 5%
Must be a U.S. Citizen
An active DoD Top Secret clearance with SCI eligibility is required to perform this work. Candidates are required to have an active Top Secret clearance upon hire, and the ability to maintain this level of clearance during their employment.
Education Requirements:
Required experience varies with education level. Candidates with a MS/MA or equivalent require 10+ years of demonstrated experience. Candidates with BS/BA or equivalent require 18 years of experience. Candidates without a degree require 22 years of experience.
Physical Job Requirements:
The ability to lift up to 20 lb is required. The physical ability to install, inspect and maintain computer systems, networks, and wiring in enclosed spaces is also required.
Desired Skills:
Software development experience
Certification as a Certified Ethical Hacker (CEH)
Network and/or communications experience in uniformed service
EOE/Minorities/Females/Veterans/Disabled
PeopleTec, Inc. is an Equal Employment Opportunity employer and provides reasonable accommodation for qualified individuals with disabilities and disabled veterans in its job application procedures. If you have any difficulty using our online system and you need an accommodation due to a disability, you may use the following email address, HR@peopletec.com and/or phone number (256.319.3800) to contact us about your interest in employment with PeopleTec, Inc.
All qualified applicants will receive consideration for employment without regard to race, color, religion, sex, sexual orientation, gender identity, national origin, age, genetic information, citizenship, ancestry, marital status, protected veteran status, disability status or any other status protected by federal, state, or local law. PeopleTec, Inc. participates in E-Verify.
For more information, or to apply now, you must go to the website below. Please DO NOT email your resume to us as we only accept applications through our website.
https://www.applicantpro.com/j/1293002-424912 | non_priority | senior information assurance network administrator peopletec is currently seeking a senior information assurance network administrator to support our huntsville al location peopletec is seeking a senior information assurance network administrator to support multiple programs on redstone arsenal al the successful candidate will perform information security system manager issm and similar duties for multiple networks the successful candidate will have significant and demonstrated knowledge of military network architectures and processes at multiple classification levels the successful candidate will also have demonstrated experience developing and staffing risk management framework rmf packages for networks and enclaves required skills experience demonstrated experience as an information assurance manager required certifications include cissp security and at least one operating system specific certification experience in network architecture installation and maintenance across multiple classification levels experience with software scanning and accreditation analysis travel up to must be a u s citizen an active dod top secret clearance with sci eligibility is required to perform this work candidates are required to have an active top secret clearance upon hire and the ability to maintain this level of clearance during their employment education requirements required experience varies with education level candidates with a ms ma or equivalent require years of demonstrated experience candidates with bs ba or equivalent require years of experience candidates without a degree require years of experience physical job requirements the ability to lift up to lb is required the physical ability to install inspect and maintain computer systems networks and wiring in enclosed spaces is also required desired skills software development experience certification as a certified ethical hacker ceh network and or communications experience in uniformed service eoe minorities females veterans disabled peopletec inc is an equal employment opportunity employer and provides reasonable accommodation for qualified individuals with disabilities and disabled veterans in its job application procedures if you have any difficulty using our online system and you need an accommodation due to a disability you may use the following email address hr peopletec com and or phone number to contact us about your interest in employment with peopletec inc all qualified applicants will receive consideration for employment without regard to race color religion sex sexual orientation gender identity national origin age genetic information citizenship ancestry marital status protected veteran status disability status or any other status protected by federal state or local law peopletec inc participates in e verify for more information or to apply now you must go to the website below please do not email your resume to us as we only accept applications through our website | 0 |
25,585 | 6,673,242,956 | IssuesEvent | 2017-10-04 14:30:26 | Automattic/jetpack | https://api.github.com/repos/Automattic/jetpack | closed | Google: Enqueue minified Javascript | Google+ Performance Sharing Shortcodes [Type] Enhancement [Type] Good First Bug [Type] Good For Community | Google has a minified Javascript file for the "plus one" script we're using in the Sharing buttons and Google shortcode embed. Thus, we can replace `https://apis.google.com/js/plusone.js` with `https://apis.google.com/js/plusone.min.js` instead.
This file is found in two places currently:
- https://github.com/Automattic/jetpack/blob/98c78e2cdd7ad6bb4461cb0c67417bdea5311d2e/modules/sharedaddy/sharing-sources.php#L1166
- https://github.com/Automattic/jetpack/blob/adcb1a221b8e4e528cba5fd18c221373535aebec/modules/shortcodes/googleplus.php#L14
Requested in the forums: https://wordpress.org/support/topic/please-use-minified-3rd-party-libraries/ | 1.0 | Google: Enqueue minified Javascript - Google has a minified Javascript file for the "plus one" script we're using in the Sharing buttons and Google shortcode embed. Thus, we can replace `https://apis.google.com/js/plusone.js` with `https://apis.google.com/js/plusone.min.js` instead.
This file is found in two places currently:
- https://github.com/Automattic/jetpack/blob/98c78e2cdd7ad6bb4461cb0c67417bdea5311d2e/modules/sharedaddy/sharing-sources.php#L1166
- https://github.com/Automattic/jetpack/blob/adcb1a221b8e4e528cba5fd18c221373535aebec/modules/shortcodes/googleplus.php#L14
Requested in the forums: https://wordpress.org/support/topic/please-use-minified-3rd-party-libraries/ | non_priority | google enqueue minified javascript google has a minified javascript file for the plus one script we re using in the sharing buttons and google shortcode embed thus we can replace with instead this file is found in two places currently requested in the forums | 0 |
157,281 | 12,368,916,966 | IssuesEvent | 2020-05-18 14:31:13 | ImisDevelopers/1_011_a_infektionsfall_uebermittellung | https://api.github.com/repos/ImisDevelopers/1_011_a_infektionsfall_uebermittellung | opened | zurück bei Detailview, vorherige Seite wird nicht gespeichert | netlight-testing | **Beschreibung**
wenn ich auf eine Patientin in der Detail Ansicht klicke und dann auf den Zurück pfeil komme ich nicht in die Ansicht die ich verlassen habe sondern wieder auf seite 1 der patienten
**Eingeloggt als**
DPH (Department of Health)
**Link**
https://staging.imis-prototyp.de/app/patient-list
**Browser**
Chrome
**Screenshot**
<img width="1050" alt="Screenshot 2020-05-18 at 16 29 23" src="https://user-images.githubusercontent.com/65396248/82225071-f6666700-9924-11ea-890d-abd222e92f50.png">
<img width="1065" alt="Screenshot 2020-05-18 at 16 29 30" src="https://user-images.githubusercontent.com/65396248/82225079-fa928480-9924-11ea-8f3c-71073d3f3d6d.png">
| 1.0 | zurück bei Detailview, vorherige Seite wird nicht gespeichert - **Beschreibung**
wenn ich auf eine Patientin in der Detail Ansicht klicke und dann auf den Zurück pfeil komme ich nicht in die Ansicht die ich verlassen habe sondern wieder auf seite 1 der patienten
**Eingeloggt als**
DPH (Department of Health)
**Link**
https://staging.imis-prototyp.de/app/patient-list
**Browser**
Chrome
**Screenshot**
<img width="1050" alt="Screenshot 2020-05-18 at 16 29 23" src="https://user-images.githubusercontent.com/65396248/82225071-f6666700-9924-11ea-890d-abd222e92f50.png">
<img width="1065" alt="Screenshot 2020-05-18 at 16 29 30" src="https://user-images.githubusercontent.com/65396248/82225079-fa928480-9924-11ea-8f3c-71073d3f3d6d.png">
| non_priority | zurück bei detailview vorherige seite wird nicht gespeichert beschreibung wenn ich auf eine patientin in der detail ansicht klicke und dann auf den zurück pfeil komme ich nicht in die ansicht die ich verlassen habe sondern wieder auf seite der patienten eingeloggt als dph department of health link browser chrome screenshot img width alt screenshot at src img width alt screenshot at src | 0 |
22,872 | 11,798,930,561 | IssuesEvent | 2020-03-18 15:08:13 | BeamMW/beam | https://api.github.com/repos/BeamMW/beam | closed | BBS Monitor - expires | Wallet service | Need to handle 'expires' in 'subscribe method'. Now params are the following:
{
"address": as before,
"privateKey": as before,
"expires": - new, unix timestamp
}
| 1.0 | BBS Monitor - expires - Need to handle 'expires' in 'subscribe method'. Now params are the following:
{
"address": as before,
"privateKey": as before,
"expires": - new, unix timestamp
}
| non_priority | bbs monitor expires need to handle expires in subscribe method now params are the following address as before privatekey as before expires new unix timestamp | 0 |
74,328 | 14,235,286,812 | IssuesEvent | 2020-11-18 14:39:09 | GIScience/ohsome-api | https://api.github.com/repos/GIScience/ohsome-api | opened | Change 'groupByObject" to 'groupByObjectId' in JSON response | code quality | The value of groupByObject in a JSON response represents the ID of the object, not the object itself.
groupByObject should be changed to groupByObjectId or something similar.
| 1.0 | Change 'groupByObject" to 'groupByObjectId' in JSON response - The value of groupByObject in a JSON response represents the ID of the object, not the object itself.
groupByObject should be changed to groupByObjectId or something similar.
| non_priority | change groupbyobject to groupbyobjectid in json response the value of groupbyobject in a json response represents the id of the object not the object itself groupbyobject should be changed to groupbyobjectid or something similar | 0 |
25,930 | 3,974,301,851 | IssuesEvent | 2016-05-04 21:39:43 | MarlinFirmware/MarlinDev | https://api.github.com/repos/MarlinFirmware/MarlinDev | closed | More parsable M115. More useful M115? | Discussion: Design Concept Needs: Feedback Status: Inactive Support: Hosts & Protocols | Currently the output of `M115` looks like this:
FIRMWARE_NAME:Marlin 1.1 abc-123-de4db33f SOURCE_CODE_URL:https://github.com/MarlinFirmware/Marlin/ PROTOCOL_VERSION:1.0 MACHINE_TYPE:Mendel RepRap EXTRUDER_COUNT:1 UUID:00000000-0000-0000-0000-000000000000
This is more difficult to parse than it needs to be. It would help to add a unique delimiter, such as a semicolon, between parts. This results in…
FIRMWARE_NAME:Marlin 1.1 abc-123-de4db33f; SOURCE_CODE_URL:https://github.com/MarlinFirmware/Marlin/; PROTOCOL_VERSION:1.0; MACHINE_TYPE:Mendel RepRap; EXTRUDER_COUNT:1; UUID:00000000-0000-0000-0000-000000000000;
Or, more concisely…
FIRMWARE_NAME:Marlin 1.1 abc-123-de4db33f;SOURCE_CODE_URL:https://github.com/MarlinFirmware/Marlin/;PROTOCOL_VERSION:1.0;MACHINE_TYPE:Mendel RepRap;EXTRUDER_COUNT:1;UUID:00000000-0000-0000-0000-000000000000;
But, is `M115` in any way useful to our various hosts? How can it be more useful? | 1.0 | More parsable M115. More useful M115? - Currently the output of `M115` looks like this:
FIRMWARE_NAME:Marlin 1.1 abc-123-de4db33f SOURCE_CODE_URL:https://github.com/MarlinFirmware/Marlin/ PROTOCOL_VERSION:1.0 MACHINE_TYPE:Mendel RepRap EXTRUDER_COUNT:1 UUID:00000000-0000-0000-0000-000000000000
This is more difficult to parse than it needs to be. It would help to add a unique delimiter, such as a semicolon, between parts. This results in…
FIRMWARE_NAME:Marlin 1.1 abc-123-de4db33f; SOURCE_CODE_URL:https://github.com/MarlinFirmware/Marlin/; PROTOCOL_VERSION:1.0; MACHINE_TYPE:Mendel RepRap; EXTRUDER_COUNT:1; UUID:00000000-0000-0000-0000-000000000000;
Or, more concisely…
FIRMWARE_NAME:Marlin 1.1 abc-123-de4db33f;SOURCE_CODE_URL:https://github.com/MarlinFirmware/Marlin/;PROTOCOL_VERSION:1.0;MACHINE_TYPE:Mendel RepRap;EXTRUDER_COUNT:1;UUID:00000000-0000-0000-0000-000000000000;
But, is `M115` in any way useful to our various hosts? How can it be more useful? | non_priority | more parsable more useful currently the output of looks like this firmware name marlin abc source code url protocol version machine type mendel reprap extruder count uuid this is more difficult to parse than it needs to be it would help to add a unique delimiter such as a semicolon between parts this results in… firmware name marlin abc source code url protocol version machine type mendel reprap extruder count uuid or more concisely… firmware name marlin abc source code url reprap extruder count uuid but is in any way useful to our various hosts how can it be more useful | 0 |
6,924 | 9,214,022,826 | IssuesEvent | 2019-03-10 16:40:38 | fimbullinter/wotan | https://api.github.com/repos/fimbullinter/wotan | closed | no-inferred-empty-object: test with higher order functions | upstream compatibility | https://github.com/Microsoft/TypeScript/pull/30215 adds inference for higher order function types.
That means there are signatures without a real declaration, that can have type parameters.
We need to make sure that the rule doesn't crash on such types.
In addition, it should work as expected on those signatures. | True | no-inferred-empty-object: test with higher order functions - https://github.com/Microsoft/TypeScript/pull/30215 adds inference for higher order function types.
That means there are signatures without a real declaration, that can have type parameters.
We need to make sure that the rule doesn't crash on such types.
In addition, it should work as expected on those signatures. | non_priority | no inferred empty object test with higher order functions adds inference for higher order function types that means there are signatures without a real declaration that can have type parameters we need to make sure that the rule doesn t crash on such types in addition it should work as expected on those signatures | 0 |
379,078 | 26,352,122,533 | IssuesEvent | 2023-01-11 06:20:03 | TanmoySG/wunderDB | https://api.github.com/repos/TanmoySG/wunderDB | opened | [💻 Development] Setup Access Control with RBAC and Authentication on each Route | documentation enhancement v2 | Create the Permission based access control for different operations on the different methods of WDB.
See,
- https://github.com/TanmoySG/wunderDB/blob/9ac6910986ed533ced3b09981cf8c8ee8054f94d/internal/server/handlers/users.go#L70
- Simplify existing authN and authZ usage | 1.0 | [💻 Development] Setup Access Control with RBAC and Authentication on each Route - Create the Permission based access control for different operations on the different methods of WDB.
See,
- https://github.com/TanmoySG/wunderDB/blob/9ac6910986ed533ced3b09981cf8c8ee8054f94d/internal/server/handlers/users.go#L70
- Simplify existing authN and authZ usage | non_priority | setup access control with rbac and authentication on each route create the permission based access control for different operations on the different methods of wdb see simplify existing authn and authz usage | 0 |
45,127 | 7,162,509,560 | IssuesEvent | 2018-01-29 00:36:47 | OrienteerBAP/Orienteer | https://api.github.com/repos/OrienteerBAP/Orienteer | closed | Create docs for 'orienteer-architect' | documentation | 1) Create user guide for 'orienteer-architect'
2) Create description of code executing 'orienteer-archtiect' | 1.0 | Create docs for 'orienteer-architect' - 1) Create user guide for 'orienteer-architect'
2) Create description of code executing 'orienteer-archtiect' | non_priority | create docs for orienteer architect create user guide for orienteer architect create description of code executing orienteer archtiect | 0 |
3,753 | 2,910,397,450 | IssuesEvent | 2015-06-21 18:22:49 | joomla/joomla-cms | https://api.github.com/repos/joomla/joomla-cms | closed | Template Bug | No Code Attached Yet | Hi there. Check this [http://www.joomla.org/?template=](http://www.joomla.org/?template= "http://www.joomla.org/?template= ")
It looking not good in main Joomla site.
I have checked this at my projects - yea, looks like bad bug, when you add ?template after joomlasiteurl/ | 1.0 | Template Bug - Hi there. Check this [http://www.joomla.org/?template=](http://www.joomla.org/?template= "http://www.joomla.org/?template= ")
It looking not good in main Joomla site.
I have checked this at my projects - yea, looks like bad bug, when you add ?template after joomlasiteurl/ | non_priority | template bug hi there check this it looking not good in main joomla site i have checked this at my projects yea looks like bad bug when you add template after joomlasiteurl | 0 |
185,740 | 21,843,735,147 | IssuesEvent | 2022-05-18 01:04:53 | AlexRogalskiy/gradle-kotlin-sample | https://api.github.com/repos/AlexRogalskiy/gradle-kotlin-sample | closed | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.56.jar - autoclosed | security vulnerability | ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: gradle-kotlin-sample/buildSrc/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- oss-licenses-plugin-0.10.2.jar (Root Library)
- gradle-3.5.1.jar
- builder-3.5.1.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/gradle-kotlin-sample/commit/e348400d001bd34078a32dcbcd6b8e0747255083">e348400d001bd34078a32dcbcd6b8e0747255083</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2018-1000180 (High) detected in bcprov-jdk15on-1.56.jar - autoclosed - ## CVE-2018-1000180 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>bcprov-jdk15on-1.56.jar</b></p></summary>
<p>The Bouncy Castle Crypto package is a Java implementation of cryptographic algorithms. This jar contains JCE provider and lightweight API for the Bouncy Castle Cryptography APIs for JDK 1.5 to JDK 1.8.</p>
<p>Library home page: <a href="http://www.bouncycastle.org/java.html">http://www.bouncycastle.org/java.html</a></p>
<p>Path to dependency file: gradle-kotlin-sample/buildSrc/build.gradle.kts</p>
<p>Path to vulnerable library: /home/wss-scanner/.gradle/caches/modules-2/files-2.1/org.bouncycastle/bcprov-jdk15on/1.56/a153c6f9744a3e9dd6feab5e210e1c9861362ec7/bcprov-jdk15on-1.56.jar</p>
<p>
Dependency Hierarchy:
- oss-licenses-plugin-0.10.2.jar (Root Library)
- gradle-3.5.1.jar
- builder-3.5.1.jar
- :x: **bcprov-jdk15on-1.56.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/AlexRogalskiy/gradle-kotlin-sample/commit/e348400d001bd34078a32dcbcd6b8e0747255083">e348400d001bd34078a32dcbcd6b8e0747255083</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Bouncy Castle BC 1.54 - 1.59, BC-FJA 1.0.0, BC-FJA 1.0.1 and earlier have a flaw in the Low-level interface to RSA key pair generator, specifically RSA Key Pairs generated in low-level API with added certainty may have less M-R tests than expected. This appears to be fixed in versions BC 1.60 beta 4 and later, BC-FJA 1.0.2 and later.
<p>Publish Date: 2018-06-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-1000180>CVE-2018-1000180</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-1000180</a></p>
<p>Release Date: 2018-06-05</p>
<p>Fix Resolution: org.bouncycastle:bcprov-jdk15on:1.60,org.bouncycastle:bcprov-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk14:1.60,org.bouncycastle:bcprov-ext-jdk15on:1.60</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in bcprov jar autoclosed cve high severity vulnerability vulnerable library bcprov jar the bouncy castle crypto package is a java implementation of cryptographic algorithms this jar contains jce provider and lightweight api for the bouncy castle cryptography apis for jdk to jdk library home page a href path to dependency file gradle kotlin sample buildsrc build gradle kts path to vulnerable library home wss scanner gradle caches modules files org bouncycastle bcprov bcprov jar dependency hierarchy oss licenses plugin jar root library gradle jar builder jar x bcprov jar vulnerable library found in head commit a href found in base branch master vulnerability details bouncy castle bc bc fja bc fja and earlier have a flaw in the low level interface to rsa key pair generator specifically rsa key pairs generated in low level api with added certainty may have less m r tests than expected this appears to be fixed in versions bc beta and later bc fja and later publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org bouncycastle bcprov org bouncycastle bcprov org bouncycastle bcprov ext org bouncycastle bcprov ext step up your open source security game with whitesource | 0 |
1,539 | 10,316,684,224 | IssuesEvent | 2019-08-30 10:37:40 | MicrosoftDocs/azure-docs | https://api.github.com/repos/MicrosoftDocs/azure-docs | closed | More Detail for using the automatic cert renewal script | Pri1 assigned-to-author automation/svc product-issue shared-capabilities/subsvc triaged | These scripts would be so useful. I am not Global Admin on our corporate AAD. So I cannot use the setup script. I would like to install the cert update script manually, but the instructions contained seem to be out of date, or I'm just confused. But I can't follow step 3 of Update-AutomationRunAsCredential.ps1 which says "
3. Select the application and click Settings button -> Required Permissions -> Add button
Add the "Manage apps that this app creates or owns" permission from Windows Azure Active Directory." I can't find the settings button.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 56e2500f-e1f5-bc87-6e5c-f41b59265049
* Version Independent ID: d212be48-7d05-847d-3045-cea82e6ba603
* Content: [Manage Azure Automation Run As accounts](https://docs.microsoft.com/en-us/azure/automation/manage-runas-account#feedback)
* Content Source: [articles/automation/manage-runas-account.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/manage-runas-account.md)
* Service: **automation**
* Sub-service: **shared-capabilities**
* GitHub Login: @bobbytreed
* Microsoft Alias: **robreed** | 1.0 | More Detail for using the automatic cert renewal script - These scripts would be so useful. I am not Global Admin on our corporate AAD. So I cannot use the setup script. I would like to install the cert update script manually, but the instructions contained seem to be out of date, or I'm just confused. But I can't follow step 3 of Update-AutomationRunAsCredential.ps1 which says "
3. Select the application and click Settings button -> Required Permissions -> Add button
Add the "Manage apps that this app creates or owns" permission from Windows Azure Active Directory." I can't find the settings button.
---
#### Document Details
⚠ *Do not edit this section. It is required for docs.microsoft.com ➟ GitHub issue linking.*
* ID: 56e2500f-e1f5-bc87-6e5c-f41b59265049
* Version Independent ID: d212be48-7d05-847d-3045-cea82e6ba603
* Content: [Manage Azure Automation Run As accounts](https://docs.microsoft.com/en-us/azure/automation/manage-runas-account#feedback)
* Content Source: [articles/automation/manage-runas-account.md](https://github.com/Microsoft/azure-docs/blob/master/articles/automation/manage-runas-account.md)
* Service: **automation**
* Sub-service: **shared-capabilities**
* GitHub Login: @bobbytreed
* Microsoft Alias: **robreed** | non_priority | more detail for using the automatic cert renewal script these scripts would be so useful i am not global admin on our corporate aad so i cannot use the setup script i would like to install the cert update script manually but the instructions contained seem to be out of date or i m just confused but i can t follow step of update automationrunascredential which says select the application and click settings button gt required permissions gt add button add the manage apps that this app creates or owns permission from windows azure active directory i can t find the settings button document details ⚠ do not edit this section it is required for docs microsoft com ➟ github issue linking id version independent id content content source service automation sub service shared capabilities github login bobbytreed microsoft alias robreed | 0 |
1,433 | 3,955,376,146 | IssuesEvent | 2016-04-29 20:40:43 | facebook/hhvm | https://api.github.com/repos/facebook/hhvm | closed | Saving localized floats to database cuts off decimal numbers | framework parity no isolated repro php5 incompatibility | I noticed that a Laravel DB insert with floating numbers using HHVM is cutting off the decimal part. In the example below, the value actually stored in the MySQL database is 7.00. The MySQL field is a decimal field.
DB::table('test')->insert([
[
'name' => 'Some name',
'description' => 'Some description',
'price' => 7.99
]);
When using PHP instead of HHVM, the value is stored correctly. Also, when replacing 7.99 with '7.99' (as a string) using HHVM, the value is also stored correctly.
Is this an incompatibility between Laravel's insert() function and HHVM, or am I overlooking something here? | True | Saving localized floats to database cuts off decimal numbers - I noticed that a Laravel DB insert with floating numbers using HHVM is cutting off the decimal part. In the example below, the value actually stored in the MySQL database is 7.00. The MySQL field is a decimal field.
DB::table('test')->insert([
[
'name' => 'Some name',
'description' => 'Some description',
'price' => 7.99
]);
When using PHP instead of HHVM, the value is stored correctly. Also, when replacing 7.99 with '7.99' (as a string) using HHVM, the value is also stored correctly.
Is this an incompatibility between Laravel's insert() function and HHVM, or am I overlooking something here? | non_priority | saving localized floats to database cuts off decimal numbers i noticed that a laravel db insert with floating numbers using hhvm is cutting off the decimal part in the example below the value actually stored in the mysql database is the mysql field is a decimal field db table test insert name some name description some description price when using php instead of hhvm the value is stored correctly also when replacing with as a string using hhvm the value is also stored correctly is this an incompatibility between laravel s insert function and hhvm or am i overlooking something here | 0 |
13,107 | 4,634,945,313 | IssuesEvent | 2016-09-29 04:10:39 | ionous/sushi | https://api.github.com/repos/ionous/sushi | opened | cleanup files ending in "state.js" and files ending in "control.js" | code cleanup | some controls were renamed "state" to help with ui refactoring before the preview edition. these should be renamed back to "control" | 1.0 | cleanup files ending in "state.js" and files ending in "control.js" - some controls were renamed "state" to help with ui refactoring before the preview edition. these should be renamed back to "control" | non_priority | cleanup files ending in state js and files ending in control js some controls were renamed state to help with ui refactoring before the preview edition these should be renamed back to control | 0 |
56,397 | 14,078,427,565 | IssuesEvent | 2020-11-04 13:33:32 | themagicalmammal/android_kernel_samsung_a5xelte | https://api.github.com/repos/themagicalmammal/android_kernel_samsung_a5xelte | opened | CVE-2020-25212 (High) detected in linux-yocto-4.12v3.10.107 | security vulnerability | ## CVE-2020-25212 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.10.107</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/themagicalmammal/android_kernel_samsung_a5xelte/commit/738375813823cb33918102af385bdd5d82225e17">738375813823cb33918102af385bdd5d82225e17</a></p>
<p>Found in base branch: <b>cosmic-1.6-experimental</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_a5xelte/fs/nfs/nfs4xdr.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A TOCTOU mismatch in the NFS client code in the Linux kernel before 5.8.3 could be used by local attackers to corrupt memory or possibly have unspecified other impact because a size check is in fs/nfs/nfs4proc.c instead of fs/nfs/nfs4xdr.c, aka CID-b4487b935452.
<p>Publish Date: 2020-09-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25212>CVE-2020-25212</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212</a></p>
<p>Release Date: 2020-09-09</p>
<p>Fix Resolution: 5.8.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-25212 (High) detected in linux-yocto-4.12v3.10.107 - ## CVE-2020-25212 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linux-yocto-4.12v3.10.107</b></p></summary>
<p>
<p>Linux 4.12 Embedded Kernel</p>
<p>Library home page: <a href=https://git.yoctoproject.org/git/linux-yocto-4.12>https://git.yoctoproject.org/git/linux-yocto-4.12</a></p>
<p>Found in HEAD commit: <a href="https://github.com/themagicalmammal/android_kernel_samsung_a5xelte/commit/738375813823cb33918102af385bdd5d82225e17">738375813823cb33918102af385bdd5d82225e17</a></p>
<p>Found in base branch: <b>cosmic-1.6-experimental</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (1)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>android_kernel_samsung_a5xelte/fs/nfs/nfs4xdr.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
A TOCTOU mismatch in the NFS client code in the Linux kernel before 5.8.3 could be used by local attackers to corrupt memory or possibly have unspecified other impact because a size check is in fs/nfs/nfs4proc.c instead of fs/nfs/nfs4xdr.c, aka CID-b4487b935452.
<p>Publish Date: 2020-09-09
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-25212>CVE-2020-25212</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-25212</a></p>
<p>Release Date: 2020-09-09</p>
<p>Fix Resolution: 5.8.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linux yocto cve high severity vulnerability vulnerable library linux yocto linux embedded kernel library home page a href found in head commit a href found in base branch cosmic experimental vulnerable source files android kernel samsung fs nfs c vulnerability details a toctou mismatch in the nfs client code in the linux kernel before could be used by local attackers to corrupt memory or possibly have unspecified other impact because a size check is in fs nfs c instead of fs nfs c aka cid publish date url a href cvss score details base score metrics exploitability metrics attack vector local attack complexity high privileges required low user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
4,153 | 6,955,445,166 | IssuesEvent | 2017-12-07 07:40:49 | PrinceOfAmber/Cyclic | https://api.github.com/repos/PrinceOfAmber/Cyclic | closed | Harvester/Scythe Not correctly reaping ResourcefulCrops plants | bug: gameplay mod compatibility | Minecraft version & Mod Version:
1.12.1
Cyclic-1.12-1.7.9.jar
Single player or Server:
Both
Describe problem (what you were doing / what happened):
Harvester and Scythe do not properly reap crops whose drops contain NBT
This example: **resourceful crops**. The crops drop a shard that is defined by it's nbt tag. When harvested by cyclic harvester or scythe the shard is "invalid" and doesn't match the nbt/meta of the shard that's supposed to drop.
Crash log (if any):
none
Normal Crop drops:
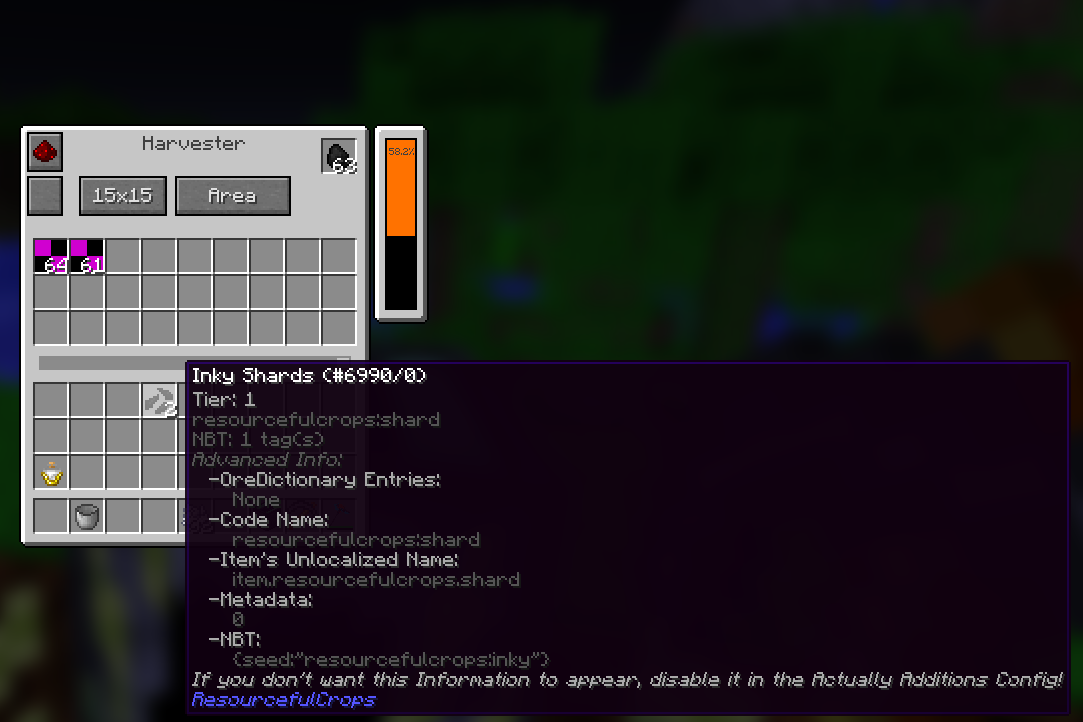
Cyclic reaped:
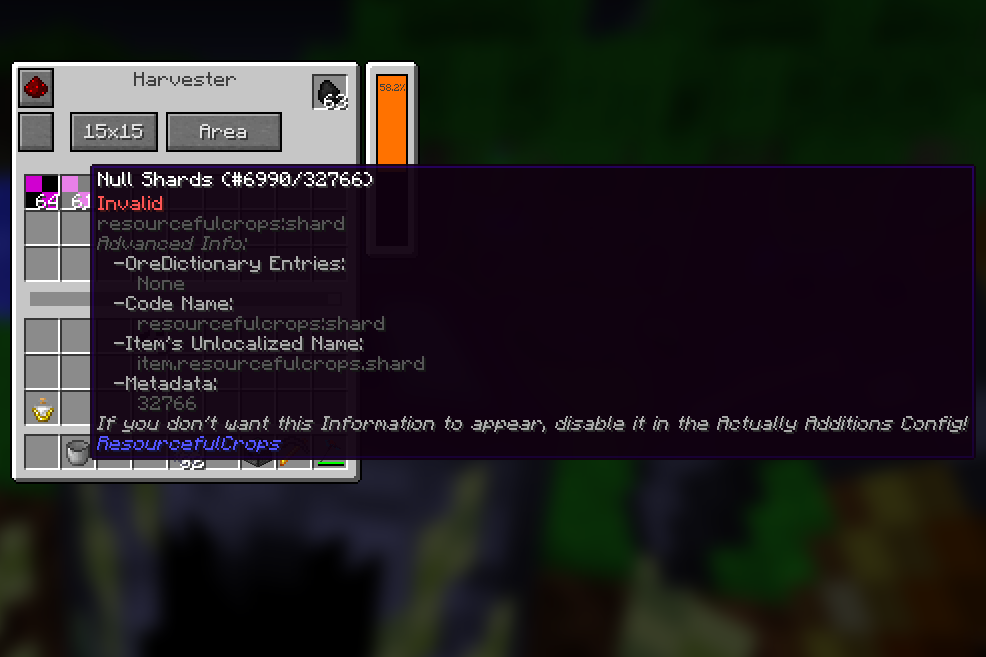
| True | Harvester/Scythe Not correctly reaping ResourcefulCrops plants - Minecraft version & Mod Version:
1.12.1
Cyclic-1.12-1.7.9.jar
Single player or Server:
Both
Describe problem (what you were doing / what happened):
Harvester and Scythe do not properly reap crops whose drops contain NBT
This example: **resourceful crops**. The crops drop a shard that is defined by it's nbt tag. When harvested by cyclic harvester or scythe the shard is "invalid" and doesn't match the nbt/meta of the shard that's supposed to drop.
Crash log (if any):
none
Normal Crop drops:
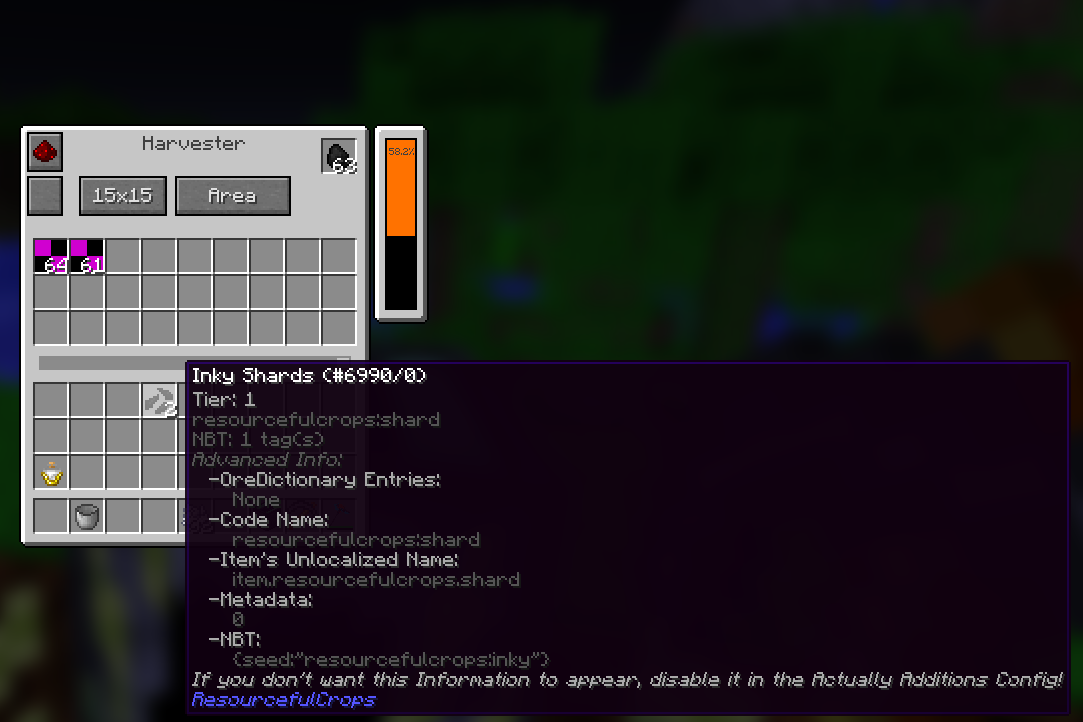
Cyclic reaped:
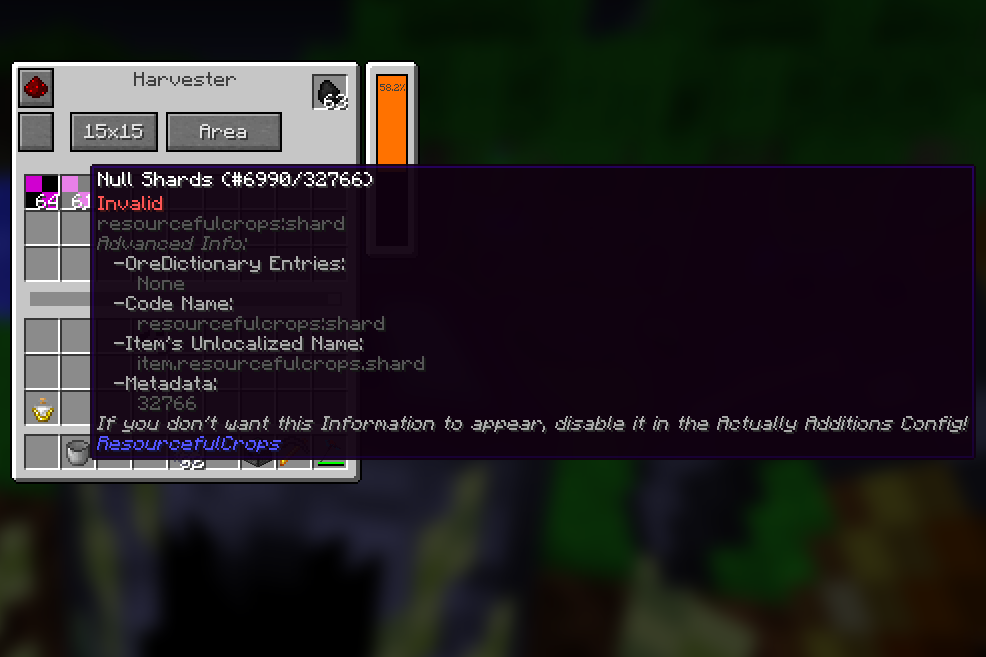
| non_priority | harvester scythe not correctly reaping resourcefulcrops plants minecraft version mod version cyclic jar single player or server both describe problem what you were doing what happened harvester and scythe do not properly reap crops whose drops contain nbt this example resourceful crops the crops drop a shard that is defined by it s nbt tag when harvested by cyclic harvester or scythe the shard is invalid and doesn t match the nbt meta of the shard that s supposed to drop crash log if any none normal crop drops cyclic reaped | 0 |
95,178 | 16,074,078,183 | IssuesEvent | 2021-04-25 02:16:54 | samq-ghdemo/JS-Demo | https://api.github.com/repos/samq-ghdemo/JS-Demo | opened | CVE-2021-23337 (High) detected in multiple libraries | security vulnerability | ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.13.1.tgz</b>, <b>lodash-4.17.11.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.13.1.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.13.1.tgz">https://registry.npmjs.org/lodash/-/lodash-4.13.1.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/nyc/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-if-0.2.0.tgz (Root Library)
- grunt-contrib-nodeunit-1.0.0.tgz
- nodeunit-0.9.5.tgz
- tap-7.1.2.tgz
- nyc-7.1.0.tgz
- istanbul-lib-instrument-1.1.0-alpha.4.tgz
- babel-generator-6.11.4.tgz
- :x: **lodash-4.13.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- async-2.6.1.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/zaproxy/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- zaproxy-0.2.0.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/46781df511f58c350408cb5158290290709b373c">46781df511f58c350408cb5158290290709b373c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.13.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-if:0.2.0;grunt-contrib-nodeunit:1.0.0;nodeunit:0.9.5;tap:7.1.2;nyc:7.1.0;istanbul-lib-instrument:1.1.0-alpha.4;babel-generator:6.11.4;lodash:4.13.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21"},{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.11","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"async:2.6.1;lodash:4.17.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21"},{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"2.4.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"zaproxy:0.2.0;lodash:2.4.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-23337 (High) detected in multiple libraries - ## CVE-2021-23337 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>lodash-4.13.1.tgz</b>, <b>lodash-4.17.11.tgz</b>, <b>lodash-2.4.2.tgz</b></p></summary>
<p>
<details><summary><b>lodash-4.13.1.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.13.1.tgz">https://registry.npmjs.org/lodash/-/lodash-4.13.1.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/nyc/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- grunt-if-0.2.0.tgz (Root Library)
- grunt-contrib-nodeunit-1.0.0.tgz
- nodeunit-0.9.5.tgz
- tap-7.1.2.tgz
- nyc-7.1.0.tgz
- istanbul-lib-instrument-1.1.0-alpha.4.tgz
- babel-generator-6.11.4.tgz
- :x: **lodash-4.13.1.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-4.17.11.tgz</b></p></summary>
<p>Lodash modular utilities.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz">https://registry.npmjs.org/lodash/-/lodash-4.17.11.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- async-2.6.1.tgz (Root Library)
- :x: **lodash-4.17.11.tgz** (Vulnerable Library)
</details>
<details><summary><b>lodash-2.4.2.tgz</b></p></summary>
<p>A utility library delivering consistency, customization, performance, & extras.</p>
<p>Library home page: <a href="https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz">https://registry.npmjs.org/lodash/-/lodash-2.4.2.tgz</a></p>
<p>Path to dependency file: JS-Demo/package.json</p>
<p>Path to vulnerable library: JS-Demo/node_modules/zaproxy/node_modules/lodash/package.json</p>
<p>
Dependency Hierarchy:
- zaproxy-0.2.0.tgz (Root Library)
- :x: **lodash-2.4.2.tgz** (Vulnerable Library)
</details>
<p>Found in HEAD commit: <a href="https://github.com/samq-ghdemo/JS-Demo/commit/46781df511f58c350408cb5158290290709b373c">46781df511f58c350408cb5158290290709b373c</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.
<p>Publish Date: 2021-02-15
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337>CVE-2021-23337</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.2</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: High
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c">https://github.com/lodash/lodash/commit/3469357cff396a26c363f8c1b5a91dde28ba4b1c</a></p>
<p>Release Date: 2021-02-15</p>
<p>Fix Resolution: lodash - 4.17.21</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.13.1","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"grunt-if:0.2.0;grunt-contrib-nodeunit:1.0.0;nodeunit:0.9.5;tap:7.1.2;nyc:7.1.0;istanbul-lib-instrument:1.1.0-alpha.4;babel-generator:6.11.4;lodash:4.13.1","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21"},{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"4.17.11","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"async:2.6.1;lodash:4.17.11","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21"},{"packageType":"javascript/Node.js","packageName":"lodash","packageVersion":"2.4.2","packageFilePaths":["/package.json"],"isTransitiveDependency":true,"dependencyTree":"zaproxy:0.2.0;lodash:2.4.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"lodash - 4.17.21"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-23337","vulnerabilityDetails":"Lodash versions prior to 4.17.21 are vulnerable to Command Injection via the template function.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-23337","cvss3Severity":"high","cvss3Score":"7.2","cvss3Metrics":{"A":"High","AC":"Low","PR":"High","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in multiple libraries cve high severity vulnerability vulnerable libraries lodash tgz lodash tgz lodash tgz lodash tgz lodash modular utilities library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules nyc node modules lodash package json dependency hierarchy grunt if tgz root library grunt contrib nodeunit tgz nodeunit tgz tap tgz nyc tgz istanbul lib instrument alpha tgz babel generator tgz x lodash tgz vulnerable library lodash tgz lodash modular utilities library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules lodash package json dependency hierarchy async tgz root library x lodash tgz vulnerable library lodash tgz a utility library delivering consistency customization performance extras library home page a href path to dependency file js demo package json path to vulnerable library js demo node modules zaproxy node modules lodash package json dependency hierarchy zaproxy tgz root library x lodash tgz vulnerable library found in head commit a href found in base branch master vulnerability details lodash versions prior to are vulnerable to command injection via the template function publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required high user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution lodash isopenpronvulnerability false ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree grunt if grunt contrib nodeunit nodeunit tap nyc istanbul lib instrument alpha babel generator lodash isminimumfixversionavailable true minimumfixversion lodash packagetype javascript node js packagename lodash packageversion packagefilepaths istransitivedependency true dependencytree async lodash isminimumfixversionavailable true minimumfixversion lodash packagetype javascript node js packagename lodash packageversion packagefilepaths istransitivedependency true dependencytree zaproxy lodash isminimumfixversionavailable true minimumfixversion lodash basebranches vulnerabilityidentifier cve vulnerabilitydetails lodash versions prior to are vulnerable to command injection via the template function vulnerabilityurl | 0 |
84,188 | 24,255,541,402 | IssuesEvent | 2022-09-27 17:26:33 | merive-inc/Parzibot | https://api.github.com/repos/merive-inc/Parzibot | closed | [Build] Update runtime.txt | build | ### Build Changes
Needs update python version to `python-3.10.7`
### Any extra info
_No response_ | 1.0 | [Build] Update runtime.txt - ### Build Changes
Needs update python version to `python-3.10.7`
### Any extra info
_No response_ | non_priority | update runtime txt build changes needs update python version to python any extra info no response | 0 |
19,165 | 11,162,275,219 | IssuesEvent | 2019-12-26 17:12:21 | azure-deprecation/dashboard | https://api.github.com/repos/azure-deprecation/dashboard | closed | Kubernetes v1.11 on Azure Kubernetes Service will be end-of-life on Dec 9th, 2019 | area:service-runtime impact:limited impact:migration-required services:kubernetes-service verified | Kubernetes v1.11 on Azure Kubernetes Service will be end-of-life on Dec 9th, 2019
**Deadline:** Dec 9th, 2019
**Impacted Services:** Azure Kubernetes Service
**More information:**
- https://github.com/Azure/AKS/releases/tag/2019-09-09
- https://github.com/Azure/AKS/issues/1235
- https://azure.microsoft.com/en-au/updates/azure-kubernetes-service-will-be-retiring-support-for-kubernetes-versions-1-11-and-1-12/
### Notice
> AKS Kubernetes 1.11 & 1.12 support will be end-of-lifed on Dec 9th, 2019
> - Kubernetes 1.15 support on AKS will go GA in Oct 2019
### Impact
No clear statement yet but if it's similar to #18 then you will no longer be able to open support tickets without upgrading the Kubernetes version.
### Required Action
Upgrade Kubernetes to v1.13 or above given v1.12 (#19) is end-of-life as well.
For more information about the supported Kubernetes version policy, [read the documentation](https://docs.microsoft.com/en-us/azure/aks/supported-kubernetes-versions).
| 3.0 | Kubernetes v1.11 on Azure Kubernetes Service will be end-of-life on Dec 9th, 2019 - Kubernetes v1.11 on Azure Kubernetes Service will be end-of-life on Dec 9th, 2019
**Deadline:** Dec 9th, 2019
**Impacted Services:** Azure Kubernetes Service
**More information:**
- https://github.com/Azure/AKS/releases/tag/2019-09-09
- https://github.com/Azure/AKS/issues/1235
- https://azure.microsoft.com/en-au/updates/azure-kubernetes-service-will-be-retiring-support-for-kubernetes-versions-1-11-and-1-12/
### Notice
> AKS Kubernetes 1.11 & 1.12 support will be end-of-lifed on Dec 9th, 2019
> - Kubernetes 1.15 support on AKS will go GA in Oct 2019
### Impact
No clear statement yet but if it's similar to #18 then you will no longer be able to open support tickets without upgrading the Kubernetes version.
### Required Action
Upgrade Kubernetes to v1.13 or above given v1.12 (#19) is end-of-life as well.
For more information about the supported Kubernetes version policy, [read the documentation](https://docs.microsoft.com/en-us/azure/aks/supported-kubernetes-versions).
| non_priority | kubernetes on azure kubernetes service will be end of life on dec kubernetes on azure kubernetes service will be end of life on dec deadline dec impacted services azure kubernetes service more information notice aks kubernetes support will be end of lifed on dec kubernetes support on aks will go ga in oct impact no clear statement yet but if it s similar to then you will no longer be able to open support tickets without upgrading the kubernetes version required action upgrade kubernetes to or above given is end of life as well for more information about the supported kubernetes version policy | 0 |
61,654 | 25,587,670,505 | IssuesEvent | 2022-12-01 10:32:46 | ndsev/zserio | https://api.github.com/repos/ndsev/zserio | closed | Allow using raw bytes as request/response in services | enhancement python java core c++ doc service xml | Currently, there is no possibility how to send/receive raw bytes in Zserio Services. Zserio services accept only Zserio structures. Consider the following structure:
```
struct Request
{
uint8 image[];
}
```
If the structure `Request` is serialized and used in Zserio service, it will contain the number of elements before array `image`. This could be makes a problem, e.g. for the REST API.
Therefore, it would be good to allow pure raw bytes in services. Possible solution could be to enable parameterized types and introduce new keyword `@size` (meaning would be the size of all received/sent data):
```
struct Image(varsize length)
{
uint8 data[length];
}
service ImageConverterService
{
Image(@size) convertImage(Image(@size));
};
```
| 1.0 | Allow using raw bytes as request/response in services - Currently, there is no possibility how to send/receive raw bytes in Zserio Services. Zserio services accept only Zserio structures. Consider the following structure:
```
struct Request
{
uint8 image[];
}
```
If the structure `Request` is serialized and used in Zserio service, it will contain the number of elements before array `image`. This could be makes a problem, e.g. for the REST API.
Therefore, it would be good to allow pure raw bytes in services. Possible solution could be to enable parameterized types and introduce new keyword `@size` (meaning would be the size of all received/sent data):
```
struct Image(varsize length)
{
uint8 data[length];
}
service ImageConverterService
{
Image(@size) convertImage(Image(@size));
};
```
| non_priority | allow using raw bytes as request response in services currently there is no possibility how to send receive raw bytes in zserio services zserio services accept only zserio structures consider the following structure struct request image if the structure request is serialized and used in zserio service it will contain the number of elements before array image this could be makes a problem e g for the rest api therefore it would be good to allow pure raw bytes in services possible solution could be to enable parameterized types and introduce new keyword size meaning would be the size of all received sent data struct image varsize length data service imageconverterservice image size convertimage image size | 0 |
282,176 | 21,315,469,626 | IssuesEvent | 2022-04-16 07:34:36 | KwanHW/pe | https://api.github.com/repos/KwanHW/pe | opened | Incomplete use cases | severity.Medium type.DocumentationBug | Under `Use cases`, there are many essential use cases that are missing in this section (such as `grab`, `filter`, `list`). Currently, this section only contains use cases for attach and editing an existing person.
<!--session: 1650087749445-834633ed-53c5-43c3-ab6c-84624835c2b3-->
<!--Version: Web v3.4.2--> | 1.0 | Incomplete use cases - Under `Use cases`, there are many essential use cases that are missing in this section (such as `grab`, `filter`, `list`). Currently, this section only contains use cases for attach and editing an existing person.
<!--session: 1650087749445-834633ed-53c5-43c3-ab6c-84624835c2b3-->
<!--Version: Web v3.4.2--> | non_priority | incomplete use cases under use cases there are many essential use cases that are missing in this section such as grab filter list currently this section only contains use cases for attach and editing an existing person | 0 |
319,764 | 27,399,871,313 | IssuesEvent | 2023-02-28 23:13:50 | facebookexperimental/object-introspection | https://api.github.com/repos/facebookexperimental/object-introspection | closed | Test cases with a `config` section may fail with a relative config | bug good first issue testing | The config section causes a new config to be created in a different temporary location (https://github.com/facebookexperimental/object-introspection/blob/5c5bfd315c4095c0cfbb869576040a0a9719bca7/test/integration/runner_common.cpp#L155-L163). Now that the config file can contain relative paths this may break it.
Possibly the easiest solution to this is to canonicalise the paths in the base config first, allowing it to be moved anywhere after. | 1.0 | Test cases with a `config` section may fail with a relative config - The config section causes a new config to be created in a different temporary location (https://github.com/facebookexperimental/object-introspection/blob/5c5bfd315c4095c0cfbb869576040a0a9719bca7/test/integration/runner_common.cpp#L155-L163). Now that the config file can contain relative paths this may break it.
Possibly the easiest solution to this is to canonicalise the paths in the base config first, allowing it to be moved anywhere after. | non_priority | test cases with a config section may fail with a relative config the config section causes a new config to be created in a different temporary location now that the config file can contain relative paths this may break it possibly the easiest solution to this is to canonicalise the paths in the base config first allowing it to be moved anywhere after | 0 |
15,555 | 11,583,501,270 | IssuesEvent | 2020-02-22 11:28:27 | davids91/rafko | https://api.github.com/repos/davids91/rafko | opened | Implement Learning rate hook / Schedule | infrastructure unclear | A bit more advanced possibility to do in the world of deep learning is to attach the change of the learning rate to a schedule. This could be made possible with a hook, or trigger in the training system. | 1.0 | Implement Learning rate hook / Schedule - A bit more advanced possibility to do in the world of deep learning is to attach the change of the learning rate to a schedule. This could be made possible with a hook, or trigger in the training system. | non_priority | implement learning rate hook schedule a bit more advanced possibility to do in the world of deep learning is to attach the change of the learning rate to a schedule this could be made possible with a hook or trigger in the training system | 0 |
50,387 | 13,527,733,001 | IssuesEvent | 2020-09-15 15:46:54 | jgeraigery/datasite | https://api.github.com/repos/jgeraigery/datasite | opened | CVE-2016-1000232 (Medium) detected in tough-cookie-2.2.2.tgz | security vulnerability | ## CVE-2016-1000232 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tough-cookie-2.2.2.tgz</b></p></summary>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz</a></p>
<p>Path to dependency file: datasite/package.json</p>
<p>Path to vulnerable library: datasite/node_modules/bower/lib/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- phantomjs-2.1.7.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tough-cookie-2.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/datasite/commit/3c660385be55c990e4e78aa43a6488b91fcf043e">3c660385be55c990e4e78aa43a6488b91fcf043e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.
<p>Publish Date: 2018-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232>CVE-2016-1000232</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/130">https://www.npmjs.com/advisories/130</a></p>
<p>Release Date: 2018-09-05</p>
<p>Fix Resolution: 2.3.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tough-cookie","packageVersion":"2.2.2","isTransitiveDependency":true,"dependencyTree":"phantomjs:2.1.7;request:2.67.0;tough-cookie:2.2.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.3.0"}],"vulnerabilityIdentifier":"CVE-2016-1000232","vulnerabilityDetails":"NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2016-1000232 (Medium) detected in tough-cookie-2.2.2.tgz - ## CVE-2016-1000232 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tough-cookie-2.2.2.tgz</b></p></summary>
<p>RFC6265 Cookies and Cookie Jar for node.js</p>
<p>Library home page: <a href="https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz">https://registry.npmjs.org/tough-cookie/-/tough-cookie-2.2.2.tgz</a></p>
<p>Path to dependency file: datasite/package.json</p>
<p>Path to vulnerable library: datasite/node_modules/bower/lib/node_modules/tough-cookie/package.json</p>
<p>
Dependency Hierarchy:
- phantomjs-2.1.7.tgz (Root Library)
- request-2.67.0.tgz
- :x: **tough-cookie-2.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/jgeraigery/datasite/commit/3c660385be55c990e4e78aa43a6488b91fcf043e">3c660385be55c990e4e78aa43a6488b91fcf043e</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.
<p>Publish Date: 2018-09-05
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232>CVE-2016-1000232</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: Low
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/130">https://www.npmjs.com/advisories/130</a></p>
<p>Release Date: 2018-09-05</p>
<p>Fix Resolution: 2.3.0</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"tough-cookie","packageVersion":"2.2.2","isTransitiveDependency":true,"dependencyTree":"phantomjs:2.1.7;request:2.67.0;tough-cookie:2.2.2","isMinimumFixVersionAvailable":true,"minimumFixVersion":"2.3.0"}],"vulnerabilityIdentifier":"CVE-2016-1000232","vulnerabilityDetails":"NodeJS Tough-Cookie version 2.2.2 contains a Regular Expression Parsing vulnerability in HTTP request Cookie Header parsing that can result in Denial of Service. This attack appear to be exploitable via Custom HTTP header passed by client. This vulnerability appears to have been fixed in 2.3.0.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2016-1000232","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"Low","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in tough cookie tgz cve medium severity vulnerability vulnerable library tough cookie tgz cookies and cookie jar for node js library home page a href path to dependency file datasite package json path to vulnerable library datasite node modules bower lib node modules tough cookie package json dependency hierarchy phantomjs tgz root library request tgz x tough cookie tgz vulnerable library found in head commit a href found in base branch master vulnerability details nodejs tough cookie version contains a regular expression parsing vulnerability in http request cookie header parsing that can result in denial of service this attack appear to be exploitable via custom http header passed by client this vulnerability appears to have been fixed in publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact low for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution isopenpronvulnerability true ispackagebased true isdefaultbranch true packages vulnerabilityidentifier cve vulnerabilitydetails nodejs tough cookie version contains a regular expression parsing vulnerability in http request cookie header parsing that can result in denial of service this attack appear to be exploitable via custom http header passed by client this vulnerability appears to have been fixed in vulnerabilityurl | 0 |
201,565 | 15,803,215,064 | IssuesEvent | 2021-04-03 13:23:05 | anitab-org/documentation | https://api.github.com/repos/anitab-org/documentation | closed | Create document that tracks the state of tooling adoption | Category: Documentation/Training | ## Description
We need to be more transparent in some of our goals, in particular, tools that we decided to adopt along the way, but did not write this in a such a public and common place like GitHub.
We want a document that tracks the adoption of such tools. Tools include GitHub Actions for our CI/CD pipeline (instead of Travis CI), use of Docusaurus for our documentation (instead of Google Docs - when possible, and GitHub Wiki)
## Acceptance Criteria
- [ ] Set goals for the tooling we use
- [ ] Add a table with the projects and the tooling adoption | 1.0 | Create document that tracks the state of tooling adoption - ## Description
We need to be more transparent in some of our goals, in particular, tools that we decided to adopt along the way, but did not write this in a such a public and common place like GitHub.
We want a document that tracks the adoption of such tools. Tools include GitHub Actions for our CI/CD pipeline (instead of Travis CI), use of Docusaurus for our documentation (instead of Google Docs - when possible, and GitHub Wiki)
## Acceptance Criteria
- [ ] Set goals for the tooling we use
- [ ] Add a table with the projects and the tooling adoption | non_priority | create document that tracks the state of tooling adoption description we need to be more transparent in some of our goals in particular tools that we decided to adopt along the way but did not write this in a such a public and common place like github we want a document that tracks the adoption of such tools tools include github actions for our ci cd pipeline instead of travis ci use of docusaurus for our documentation instead of google docs when possible and github wiki acceptance criteria set goals for the tooling we use add a table with the projects and the tooling adoption | 0 |
927 | 2,520,606,096 | IssuesEvent | 2015-01-19 06:04:27 | rbsl-gaurav/rbframework | https://api.github.com/repos/rbsl-gaurav/rbframework | opened | [CLOSED] Should not call boolen and save function of table. | Test | <a href="https://github.com/rbsl-gaurav"><img src="https://avatars.githubusercontent.com/u/2246860?v=3" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [rbsl-gaurav](https://github.com/rbsl-gaurav)**
_Friday Oct 11, 2013 at 07:29 GMT_
_Originally opened as https://github.com/readybytes/rbframework/issues/15_
----
Tag are getting deleted when we do any boolean operation from grid screen, because we call tables' save fucntion.
And Joomla runs a query to make boolean operation.
| 1.0 | [CLOSED] Should not call boolen and save function of table. - <a href="https://github.com/rbsl-gaurav"><img src="https://avatars.githubusercontent.com/u/2246860?v=3" align="left" width="96" height="96" hspace="10"></img></a> **Issue by [rbsl-gaurav](https://github.com/rbsl-gaurav)**
_Friday Oct 11, 2013 at 07:29 GMT_
_Originally opened as https://github.com/readybytes/rbframework/issues/15_
----
Tag are getting deleted when we do any boolean operation from grid screen, because we call tables' save fucntion.
And Joomla runs a query to make boolean operation.
| non_priority | should not call boolen and save function of table issue by friday oct at gmt originally opened as tag are getting deleted when we do any boolean operation from grid screen because we call tables save fucntion and joomla runs a query to make boolean operation | 0 |
247,626 | 26,724,911,553 | IssuesEvent | 2023-01-29 15:45:30 | Mend-developer-platform-load/8667642_2263_rerun | https://api.github.com/repos/Mend-developer-platform-load/8667642_2263_rerun | closed | CVE-2021-45046 (Critical) detected in log4j-core-2.8.2.jar - autoclosed | security vulnerability | ## CVE-2021-45046 - Critical Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/8667642_2263_rerun/commit/35614250ae57ce27108fe19fc9f05724cda050e7">35614250ae57ce27108fe19fc9f05724cda050e7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45046>CVE-2021-45046</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-14</p>
<p>Fix Resolution: 2.16.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | True | CVE-2021-45046 (Critical) detected in log4j-core-2.8.2.jar - autoclosed - ## CVE-2021-45046 - Critical Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>log4j-core-2.8.2.jar</b></p></summary>
<p>The Apache Log4j Implementation</p>
<p>Library home page: <a href="https://logging.apache.org/log4j/2.x/log4j-core/">https://logging.apache.org/log4j/2.x/log4j-core/</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/logging/log4j/log4j-core/2.8.2/log4j-core-2.8.2.jar</p>
<p>
Dependency Hierarchy:
- :x: **log4j-core-2.8.2.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Mend-developer-platform-load/8667642_2263_rerun/commit/35614250ae57ce27108fe19fc9f05724cda050e7">35614250ae57ce27108fe19fc9f05724cda050e7</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/critical_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
It was found that the fix to address CVE-2021-44228 in Apache Log4j 2.15.0 was incomplete in certain non-default configurations. This could allows attackers with control over Thread Context Map (MDC) input data when the logging configuration uses a non-default Pattern Layout with either a Context Lookup (for example, $${ctx:loginId}) or a Thread Context Map pattern (%X, %mdc, or %MDC) to craft malicious input data using a JNDI Lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments. Log4j 2.16.0 (Java 8) and 2.12.2 (Java 7) fix this issue by removing support for message lookup patterns and disabling JNDI functionality by default.
<p>Publish Date: 2021-12-14
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2021-45046>CVE-2021-45046</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.0</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://logging.apache.org/log4j/2.x/security.html">https://logging.apache.org/log4j/2.x/security.html</a></p>
<p>Release Date: 2021-12-14</p>
<p>Fix Resolution: 2.16.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue | non_priority | cve critical detected in core jar autoclosed cve critical severity vulnerability vulnerable library core jar the apache implementation library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org apache logging core core jar dependency hierarchy x core jar vulnerable library found in head commit a href found in base branch main vulnerability details it was found that the fix to address cve in apache was incomplete in certain non default configurations this could allows attackers with control over thread context map mdc input data when the logging configuration uses a non default pattern layout with either a context lookup for example ctx loginid or a thread context map pattern x mdc or mdc to craft malicious input data using a jndi lookup pattern resulting in an information leak and remote code execution in some environments and local code execution in all environments java and java fix this issue by removing support for message lookup patterns and disabling jndi functionality by default publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope changed impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution rescue worker helmet automatic remediation is available for this issue | 0 |
24,182 | 7,463,374,985 | IssuesEvent | 2018-04-01 04:10:34 | mattrubin/OneTimePassword | https://api.github.com/repos/mattrubin/OneTimePassword | closed | error: 'deallocate(capacity:)' is deprecated | Carthage build issue | I'm using Xcode version 9.3 (9E145) to build from Carthage.
```
Checkouts/OneTimePassword/Sources/Crypto.swift:33:20: error: 'deallocate(capacity:)' is deprecated: Swift currently only supports freeing entire heap blocks, use deallocate() instead
defer { macOut.deallocate(capacity: hashLength) }
^
** ARCHIVE FAILED **
The following build commands failed:
CompileSwiftSources normal arm64 com.apple.xcode.tools.swift.compiler
CompileSwift normal arm64
(2 failures)
``` | 1.0 | error: 'deallocate(capacity:)' is deprecated - I'm using Xcode version 9.3 (9E145) to build from Carthage.
```
Checkouts/OneTimePassword/Sources/Crypto.swift:33:20: error: 'deallocate(capacity:)' is deprecated: Swift currently only supports freeing entire heap blocks, use deallocate() instead
defer { macOut.deallocate(capacity: hashLength) }
^
** ARCHIVE FAILED **
The following build commands failed:
CompileSwiftSources normal arm64 com.apple.xcode.tools.swift.compiler
CompileSwift normal arm64
(2 failures)
``` | non_priority | error deallocate capacity is deprecated i m using xcode version to build from carthage checkouts onetimepassword sources crypto swift error deallocate capacity is deprecated swift currently only supports freeing entire heap blocks use deallocate instead defer macout deallocate capacity hashlength archive failed the following build commands failed compileswiftsources normal com apple xcode tools swift compiler compileswift normal failures | 0 |
451 | 2,718,426,637 | IssuesEvent | 2015-04-12 09:13:26 | lidel/ipfs-firefox-addon | https://api.github.com/repos/lidel/ipfs-firefox-addon | closed | Signing XPI package | question security |
> The cheapest universally supported (Mozilla, Java, Microsoft) certificate seems to be the Comodo Instant-SSL offering. You can get a free certificate for open-source developers from Unizeto Certum, in 2010 it is a Certum Level III CA.
Refs:
- [So you want to sign your XPI package?](https://www.mozdevgroup.com/docs/pete/Signing-an-XPI.html)
- [Obtaining a valid software developer code-signing certificate](https://developer.mozilla.org/en-US/docs/Signing_a_XPI#Obtaining_a_valid_software_developer_code-signing_certificate)
- [Incorporating signing into your build process](https://developer.mozilla.org/en-US/docs/Signing_a_XPI#Incorporating_signing_into_your_build_process) | True | Signing XPI package -
> The cheapest universally supported (Mozilla, Java, Microsoft) certificate seems to be the Comodo Instant-SSL offering. You can get a free certificate for open-source developers from Unizeto Certum, in 2010 it is a Certum Level III CA.
Refs:
- [So you want to sign your XPI package?](https://www.mozdevgroup.com/docs/pete/Signing-an-XPI.html)
- [Obtaining a valid software developer code-signing certificate](https://developer.mozilla.org/en-US/docs/Signing_a_XPI#Obtaining_a_valid_software_developer_code-signing_certificate)
- [Incorporating signing into your build process](https://developer.mozilla.org/en-US/docs/Signing_a_XPI#Incorporating_signing_into_your_build_process) | non_priority | signing xpi package the cheapest universally supported mozilla java microsoft certificate seems to be the comodo instant ssl offering you can get a free certificate for open source developers from unizeto certum in it is a certum level iii ca refs | 0 |
302,169 | 26,129,825,641 | IssuesEvent | 2022-12-29 02:07:08 | axellang/axel | https://api.github.com/repos/axellang/axel | opened | Add tests for prelude macros | stdlib testing | The macros defined in the Axel prelude do not have any associated tests. | 1.0 | Add tests for prelude macros - The macros defined in the Axel prelude do not have any associated tests. | non_priority | add tests for prelude macros the macros defined in the axel prelude do not have any associated tests | 0 |
21,413 | 6,150,408,436 | IssuesEvent | 2017-06-27 22:29:41 | mozilla/addons-frontend | https://api.github.com/repos/mozilla/addons-frontend | opened | Unwrap HOC components to make shallow render tests more effective | component: code quality | Since we use shallow Enzyme rendering now we no longer have to test the base (i.e. unwrapped) components. We should be able to introduce a helper that unwraps them automatically.
Example: https://github.com/mozilla/addons-frontend/pull/2618#discussion_r123585638 | 1.0 | Unwrap HOC components to make shallow render tests more effective - Since we use shallow Enzyme rendering now we no longer have to test the base (i.e. unwrapped) components. We should be able to introduce a helper that unwraps them automatically.
Example: https://github.com/mozilla/addons-frontend/pull/2618#discussion_r123585638 | non_priority | unwrap hoc components to make shallow render tests more effective since we use shallow enzyme rendering now we no longer have to test the base i e unwrapped components we should be able to introduce a helper that unwraps them automatically example | 0 |
249,814 | 18,858,239,714 | IssuesEvent | 2021-11-12 09:32:28 | WangGLJoseph/pe | https://api.github.com/repos/WangGLJoseph/pe | opened | Formatting in the UG is hard to follow | severity.Medium type.DocumentationBug | On pages 5-11, 15-17, 20-23 of the UG, the screenshots accompanying the featured command are not on the same page as the explanations. This makes it difficult for the reader to follow and understand the explanation using the examples, as they may confuse the screenshots as screenshots for the following command, instead of the previous one.
There also seems to be an empty line highlighted in yellow at the start of page 23 that does not serve the purpose of highlighting
<!--session: 1636703138116-7b95fda7-844b-4fbb-9bfb-08bc8fe736b7-->
<!--Version: Web v3.4.1--> | 1.0 | Formatting in the UG is hard to follow - On pages 5-11, 15-17, 20-23 of the UG, the screenshots accompanying the featured command are not on the same page as the explanations. This makes it difficult for the reader to follow and understand the explanation using the examples, as they may confuse the screenshots as screenshots for the following command, instead of the previous one.
There also seems to be an empty line highlighted in yellow at the start of page 23 that does not serve the purpose of highlighting
<!--session: 1636703138116-7b95fda7-844b-4fbb-9bfb-08bc8fe736b7-->
<!--Version: Web v3.4.1--> | non_priority | formatting in the ug is hard to follow on pages of the ug the screenshots accompanying the featured command are not on the same page as the explanations this makes it difficult for the reader to follow and understand the explanation using the examples as they may confuse the screenshots as screenshots for the following command instead of the previous one there also seems to be an empty line highlighted in yellow at the start of page that does not serve the purpose of highlighting | 0 |
190,860 | 22,171,419,862 | IssuesEvent | 2022-06-06 01:24:53 | kaidisn/docs.hackerone.com | https://api.github.com/repos/kaidisn/docs.hackerone.com | opened | CVE-2021-43307 (Medium) detected in semver-regex-2.0.0.tgz | security vulnerability | ## CVE-2021-43307 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p></summary>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/semver-regex</p>
<p>
Dependency Hierarchy:
- gatsby-plugin-sharp-3.11.0.tgz (Root Library)
- imagemin-pngquant-9.0.2.tgz
- pngquant-bin-6.0.0.tgz
- bin-wrapper-4.1.0.tgz
- bin-version-check-4.0.0.tgz
- bin-version-3.1.0.tgz
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An exponential ReDoS (Regular Expression Denial of Service) can be triggered in the semver-regex npm package, when an attacker is able to supply arbitrary input to the test() method
<p>Publish Date: 2022-06-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43307>CVE-2021-43307</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/">https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution (semver-regex): 3.1.4</p>
<p>Direct dependency fix Resolution (gatsby-plugin-sharp): 4.12.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"gatsby-plugin-sharp","packageVersion":"3.11.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"gatsby-plugin-sharp:3.11.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.12.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-43307","vulnerabilityDetails":"An exponential ReDoS (Regular Expression Denial of Service) can be triggered in the semver-regex npm package, when an attacker is able to supply arbitrary input to the test() method","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43307","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | True | CVE-2021-43307 (Medium) detected in semver-regex-2.0.0.tgz - ## CVE-2021-43307 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>semver-regex-2.0.0.tgz</b></p></summary>
<p>Regular expression for matching semver versions</p>
<p>Library home page: <a href="https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz">https://registry.npmjs.org/semver-regex/-/semver-regex-2.0.0.tgz</a></p>
<p>Path to dependency file: /package.json</p>
<p>Path to vulnerable library: /node_modules/semver-regex</p>
<p>
Dependency Hierarchy:
- gatsby-plugin-sharp-3.11.0.tgz (Root Library)
- imagemin-pngquant-9.0.2.tgz
- pngquant-bin-6.0.0.tgz
- bin-wrapper-4.1.0.tgz
- bin-version-check-4.0.0.tgz
- bin-version-3.1.0.tgz
- find-versions-3.2.0.tgz
- :x: **semver-regex-2.0.0.tgz** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
An exponential ReDoS (Regular Expression Denial of Service) can be triggered in the semver-regex npm package, when an attacker is able to supply arbitrary input to the test() method
<p>Publish Date: 2022-06-02
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43307>CVE-2021-43307</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.9</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/">https://research.jfrog.com/vulnerabilities/semver-regex-redos-xray-211349/</a></p>
<p>Release Date: 2021-11-03</p>
<p>Fix Resolution (semver-regex): 3.1.4</p>
<p>Direct dependency fix Resolution (gatsby-plugin-sharp): 4.12.0</p>
</p>
</details>
<p></p>
***
:rescue_worker_helmet: Automatic Remediation is available for this issue
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"javascript/Node.js","packageName":"gatsby-plugin-sharp","packageVersion":"3.11.0","packageFilePaths":["/package.json"],"isTransitiveDependency":false,"dependencyTree":"gatsby-plugin-sharp:3.11.0","isMinimumFixVersionAvailable":true,"minimumFixVersion":"4.12.0","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2021-43307","vulnerabilityDetails":"An exponential ReDoS (Regular Expression Denial of Service) can be triggered in the semver-regex npm package, when an attacker is able to supply arbitrary input to the test() method","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2021-43307","cvss3Severity":"medium","cvss3Score":"5.9","cvss3Metrics":{"A":"High","AC":"High","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"None"},"extraData":{}}</REMEDIATE> --> | non_priority | cve medium detected in semver regex tgz cve medium severity vulnerability vulnerable library semver regex tgz regular expression for matching semver versions library home page a href path to dependency file package json path to vulnerable library node modules semver regex dependency hierarchy gatsby plugin sharp tgz root library imagemin pngquant tgz pngquant bin tgz bin wrapper tgz bin version check tgz bin version tgz find versions tgz x semver regex tgz vulnerable library found in base branch master vulnerability details an exponential redos regular expression denial of service can be triggered in the semver regex npm package when an attacker is able to supply arbitrary input to the test method publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution semver regex direct dependency fix resolution gatsby plugin sharp rescue worker helmet automatic remediation is available for this issue isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency false dependencytree gatsby plugin sharp isminimumfixversionavailable true minimumfixversion isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails an exponential redos regular expression denial of service can be triggered in the semver regex npm package when an attacker is able to supply arbitrary input to the test method vulnerabilityurl | 0 |
16,800 | 4,097,300,362 | IssuesEvent | 2016-06-03 00:41:44 | golang/go | https://api.github.com/repos/golang/go | closed | encoding/json: doc on valid key names is outdated | Documentation NeedsFix | On master, the [documentation for json.Marshal](https://github.com/golang/go/blob/7f52b43954d75aa0c444d57b9d0eb7ff36eb3dd0/src/encoding/json/encode.go#L91-L93) says:
```
// The key name will be used if it's a non-empty string consisting of
// only Unicode letters, digits, dollar signs, percent signs, hyphens,
// underscores and slashes.
```
However, this is [quite outdated](https://github.com/golang/go/commit/52f122d72ee3fab46603ccd76259d1f9db50be7b). The [current list of allowed characters](https://github.com/golang/go/blob/7f52b43954d75aa0c444d57b9d0eb7ff36eb3dd0/src/encoding/json/encode.go#L754) consists of letters, digits, space, and these punctuation characters: `!#$%&()*+-./:<=>?@[]^_{|}~`
I'm happy to send a Gerrit CL to fix this but am curious about what people think would be better: literally listing this set of characters, or saying something like "most punctuation characters, excluding backslash, quotes, and comma"? | 1.0 | encoding/json: doc on valid key names is outdated - On master, the [documentation for json.Marshal](https://github.com/golang/go/blob/7f52b43954d75aa0c444d57b9d0eb7ff36eb3dd0/src/encoding/json/encode.go#L91-L93) says:
```
// The key name will be used if it's a non-empty string consisting of
// only Unicode letters, digits, dollar signs, percent signs, hyphens,
// underscores and slashes.
```
However, this is [quite outdated](https://github.com/golang/go/commit/52f122d72ee3fab46603ccd76259d1f9db50be7b). The [current list of allowed characters](https://github.com/golang/go/blob/7f52b43954d75aa0c444d57b9d0eb7ff36eb3dd0/src/encoding/json/encode.go#L754) consists of letters, digits, space, and these punctuation characters: `!#$%&()*+-./:<=>?@[]^_{|}~`
I'm happy to send a Gerrit CL to fix this but am curious about what people think would be better: literally listing this set of characters, or saying something like "most punctuation characters, excluding backslash, quotes, and comma"? | non_priority | encoding json doc on valid key names is outdated on master the says the key name will be used if it s a non empty string consisting of only unicode letters digits dollar signs percent signs hyphens underscores and slashes however this is the consists of letters digits space and these punctuation characters i m happy to send a gerrit cl to fix this but am curious about what people think would be better literally listing this set of characters or saying something like most punctuation characters excluding backslash quotes and comma | 0 |
186,869 | 14,426,868,119 | IssuesEvent | 2020-12-06 00:28:34 | kalexmills/github-vet-tests-dec2020 | https://api.github.com/repos/kalexmills/github-vet-tests-dec2020 | closed | KablamoOSS/kombustion-plugin-network: vendor/golang.org/x/net/dns/dnsmessage/message_test.go; 14 LoC | fresh small test vendored |
Found a possible issue in [KablamoOSS/kombustion-plugin-network](https://www.github.com/KablamoOSS/kombustion-plugin-network) at [vendor/golang.org/x/net/dns/dnsmessage/message_test.go](https://github.com/KablamoOSS/kombustion-plugin-network/blob/fba7b5b3ad7910717ea1e568f9cfecbc0579c6a8/vendor/golang.org/x/net/dns/dnsmessage/message_test.go#L351-L364)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to want at line 362 may start a goroutine
[Click here to see the code in its original context.](https://github.com/KablamoOSS/kombustion-plugin-network/blob/fba7b5b3ad7910717ea1e568f9cfecbc0579c6a8/vendor/golang.org/x/net/dns/dnsmessage/message_test.go#L351-L364)
<details>
<summary>Click here to show the 14 line(s) of Go which triggered the analyzer.</summary>
```go
for i, want := range wants {
b, err := want.Pack()
if err != nil {
t.Fatalf("%d: Message.Pack() = %v", i, err)
}
var got Message
err = got.Unpack(b)
if err != nil {
t.Fatalf("%d: Message.Unapck() = %v", i, err)
}
if !reflect.DeepEqual(got, want) {
t.Errorf("%d: Message.Pack/Unpack() roundtrip: got = %+v, want = %+v", i, &got, &want)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: fba7b5b3ad7910717ea1e568f9cfecbc0579c6a8
| 1.0 | KablamoOSS/kombustion-plugin-network: vendor/golang.org/x/net/dns/dnsmessage/message_test.go; 14 LoC -
Found a possible issue in [KablamoOSS/kombustion-plugin-network](https://www.github.com/KablamoOSS/kombustion-plugin-network) at [vendor/golang.org/x/net/dns/dnsmessage/message_test.go](https://github.com/KablamoOSS/kombustion-plugin-network/blob/fba7b5b3ad7910717ea1e568f9cfecbc0579c6a8/vendor/golang.org/x/net/dns/dnsmessage/message_test.go#L351-L364)
Below is the message reported by the analyzer for this snippet of code. Beware that the analyzer only reports the first
issue it finds, so please do not limit your consideration to the contents of the below message.
> function call which takes a reference to want at line 362 may start a goroutine
[Click here to see the code in its original context.](https://github.com/KablamoOSS/kombustion-plugin-network/blob/fba7b5b3ad7910717ea1e568f9cfecbc0579c6a8/vendor/golang.org/x/net/dns/dnsmessage/message_test.go#L351-L364)
<details>
<summary>Click here to show the 14 line(s) of Go which triggered the analyzer.</summary>
```go
for i, want := range wants {
b, err := want.Pack()
if err != nil {
t.Fatalf("%d: Message.Pack() = %v", i, err)
}
var got Message
err = got.Unpack(b)
if err != nil {
t.Fatalf("%d: Message.Unapck() = %v", i, err)
}
if !reflect.DeepEqual(got, want) {
t.Errorf("%d: Message.Pack/Unpack() roundtrip: got = %+v, want = %+v", i, &got, &want)
}
}
```
</details>
Leave a reaction on this issue to contribute to the project by classifying this instance as a **Bug** :-1:, **Mitigated** :+1:, or **Desirable Behavior** :rocket:
See the descriptions of the classifications [here](https://github.com/github-vet/rangeclosure-findings#how-can-i-help) for more information.
commit ID: fba7b5b3ad7910717ea1e568f9cfecbc0579c6a8
| non_priority | kablamooss kombustion plugin network vendor golang org x net dns dnsmessage message test go loc found a possible issue in at below is the message reported by the analyzer for this snippet of code beware that the analyzer only reports the first issue it finds so please do not limit your consideration to the contents of the below message function call which takes a reference to want at line may start a goroutine click here to show the line s of go which triggered the analyzer go for i want range wants b err want pack if err nil t fatalf d message pack v i err var got message err got unpack b if err nil t fatalf d message unapck v i err if reflect deepequal got want t errorf d message pack unpack roundtrip got v want v i got want leave a reaction on this issue to contribute to the project by classifying this instance as a bug mitigated or desirable behavior rocket see the descriptions of the classifications for more information commit id | 0 |
167,704 | 13,039,470,765 | IssuesEvent | 2020-07-28 16:48:26 | envoyproxy/envoy | https://api.github.com/repos/envoyproxy/envoy | closed | cx_limit_integration_test flakes | area/test flakes help wanted | 2020-07-01T13:04:39.4991615Z [ RUN ] IpVersions/ConnectionLimitIntegrationTest.TestBothLimits/IPv4
2020-07-01T13:04:39.4992248Z test/integration/cx_limit_integration_test.cc:74: Failure
2020-07-01T13:04:39.4993196Z Value of: fake_upstreams_[0]->waitForRawConnection(raw_conns.back())
2020-07-01T13:04:39.4994095Z Actual: false (Timed out waiting for raw connection)
2020-07-01T13:04:39.4994618Z Expected: true
2020-07-01T13:04:39.4995531Z Stack trace:
2020-07-01T13:04:39.4996224Z 0x1d3caf5: __llvm_coverage_mapping
2020-07-01T13:04:39.4999246Z 0x1d43958: __llvm_coverage_mapping
2020-07-01T13:04:39.4999853Z 0x59ff1b6: testing::internal::HandleSehExceptionsInMethodIfSupported<>()
2020-07-01T13:04:39.5000495Z 0x59ea751: testing::internal::HandleExceptionsInMethodIfSupported<>()
2020-07-01T13:04:39.5001236Z 0x59d4d82: testing::Test::Run()
2020-07-01T13:04:39.5001716Z 0x59d5888: testing::TestInfo::Run()
2020-07-01T13:04:39.5002321Z ... Google Test internal frames ...
2020-07-01T13:04:39.5002653Z
2020-07-01T13:04:39.5003721Z [ FAILED ] IpVersions/ConnectionLimitIntegrationTest.TestBothLimits/IPv4, where GetParam() = 4-byte object <00-00 00-00> (16148 ms)
| 1.0 | cx_limit_integration_test flakes - 2020-07-01T13:04:39.4991615Z [ RUN ] IpVersions/ConnectionLimitIntegrationTest.TestBothLimits/IPv4
2020-07-01T13:04:39.4992248Z test/integration/cx_limit_integration_test.cc:74: Failure
2020-07-01T13:04:39.4993196Z Value of: fake_upstreams_[0]->waitForRawConnection(raw_conns.back())
2020-07-01T13:04:39.4994095Z Actual: false (Timed out waiting for raw connection)
2020-07-01T13:04:39.4994618Z Expected: true
2020-07-01T13:04:39.4995531Z Stack trace:
2020-07-01T13:04:39.4996224Z 0x1d3caf5: __llvm_coverage_mapping
2020-07-01T13:04:39.4999246Z 0x1d43958: __llvm_coverage_mapping
2020-07-01T13:04:39.4999853Z 0x59ff1b6: testing::internal::HandleSehExceptionsInMethodIfSupported<>()
2020-07-01T13:04:39.5000495Z 0x59ea751: testing::internal::HandleExceptionsInMethodIfSupported<>()
2020-07-01T13:04:39.5001236Z 0x59d4d82: testing::Test::Run()
2020-07-01T13:04:39.5001716Z 0x59d5888: testing::TestInfo::Run()
2020-07-01T13:04:39.5002321Z ... Google Test internal frames ...
2020-07-01T13:04:39.5002653Z
2020-07-01T13:04:39.5003721Z [ FAILED ] IpVersions/ConnectionLimitIntegrationTest.TestBothLimits/IPv4, where GetParam() = 4-byte object <00-00 00-00> (16148 ms)
| non_priority | cx limit integration test flakes ipversions connectionlimitintegrationtest testbothlimits test integration cx limit integration test cc failure value of fake upstreams waitforrawconnection raw conns back actual false timed out waiting for raw connection expected true stack trace llvm coverage mapping llvm coverage mapping testing internal handlesehexceptionsinmethodifsupported testing internal handleexceptionsinmethodifsupported testing test run testing testinfo run google test internal frames ipversions connectionlimitintegrationtest testbothlimits where getparam byte object ms | 0 |
102,520 | 32,034,658,338 | IssuesEvent | 2023-09-22 14:32:56 | olive-editor/olive | https://api.github.com/repos/olive-editor/olive | opened | [BUILD] OpenColorIO 3.2.0 demands new argument at GetColorContext | Building/Packaging Triage | <!-- ⚠ Do not delete this issue template! ⚠ -->
**Commit Hash** <!-- 8 character string of letters/numbers in title bar or Help > About dialog (e.g. 3ea173c9) -->
8ce00fd97589d53f3e0d2ce1fda60374db381a04
**Platform** <!-- e.g. Windows 10, Ubuntu 20.04 or macOS 10.15 -->
ArchLinux
**Summary**
Sorry for being in German:
```
./olive/app/render/renderer.cpp: In Elementfunktion »bool olive::Renderer::GetColorContext(const olive::ColorTransformJob&, ColorContext*)«:
./olive/app/render/renderer.cpp:245:30: Fehler: keine passende Funktion für Aufruf von »OpenColorIO_v2_3dev::GpuShaderDesc::getTexture(unsigned int&, const char*&, const char*&, unsigned int&, unsigned int&, OpenColorIO_v2_3dev::GpuShaderCreator::TextureType&, OpenColorIO_v2_3dev::Interpolation&)«
245 | shader_desc->getTexture(i, tex_name, sampler_name, width, height, channel, interpolation);
| ~~~~~~~~~~~~~~~~~~~~~~~^~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
In Datei, eingebunden von ./olive/app/common/ocioutils.h:24,
von ./olive/app/render/colorprocessor.h:25,
von ./olive/app/render/renderer.h:30,
von ./olive/app/render/renderer.cpp:21:
/usr/include/OpenColorIO/OpenColorIO.h:3534:18: Anmerkung: Kandidat: »virtual void OpenColorIO_v2_3dev::GpuShaderDesc::getTexture(unsigned int, const char*&, const char*&, unsigned int&, unsigned int&, OpenColorIO_v2_3dev::GpuShaderCreator::TextureType&, OpenColorIO_v2_3dev::GpuShaderCreator::TextureDimensions&, OpenColorIO_v2_3dev::Interpolation&) const«
3534 | virtual void getTexture(unsigned index,
| ^~~~~~~~~~
/usr/include/OpenColorIO/OpenColorIO.h:3534:18: Anmerkung: Kandidat erwartet 8 Argumente, 7 angegeben
```
OpenColorIO 3.2.0 introduced **TextureDimensions & dimensions** between channel and interpolation:
```
virtual void getTexture(unsigned index,
const char *& textureName,
const char *& samplerName,
unsigned & width,
unsigned & height,
TextureType & channel,
TextureDimensions & dimensions,
Interpolation & interpolation) const = 0;
``` | 1.0 | [BUILD] OpenColorIO 3.2.0 demands new argument at GetColorContext - <!-- ⚠ Do not delete this issue template! ⚠ -->
**Commit Hash** <!-- 8 character string of letters/numbers in title bar or Help > About dialog (e.g. 3ea173c9) -->
8ce00fd97589d53f3e0d2ce1fda60374db381a04
**Platform** <!-- e.g. Windows 10, Ubuntu 20.04 or macOS 10.15 -->
ArchLinux
**Summary**
Sorry for being in German:
```
./olive/app/render/renderer.cpp: In Elementfunktion »bool olive::Renderer::GetColorContext(const olive::ColorTransformJob&, ColorContext*)«:
./olive/app/render/renderer.cpp:245:30: Fehler: keine passende Funktion für Aufruf von »OpenColorIO_v2_3dev::GpuShaderDesc::getTexture(unsigned int&, const char*&, const char*&, unsigned int&, unsigned int&, OpenColorIO_v2_3dev::GpuShaderCreator::TextureType&, OpenColorIO_v2_3dev::Interpolation&)«
245 | shader_desc->getTexture(i, tex_name, sampler_name, width, height, channel, interpolation);
| ~~~~~~~~~~~~~~~~~~~~~~~^~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
In Datei, eingebunden von ./olive/app/common/ocioutils.h:24,
von ./olive/app/render/colorprocessor.h:25,
von ./olive/app/render/renderer.h:30,
von ./olive/app/render/renderer.cpp:21:
/usr/include/OpenColorIO/OpenColorIO.h:3534:18: Anmerkung: Kandidat: »virtual void OpenColorIO_v2_3dev::GpuShaderDesc::getTexture(unsigned int, const char*&, const char*&, unsigned int&, unsigned int&, OpenColorIO_v2_3dev::GpuShaderCreator::TextureType&, OpenColorIO_v2_3dev::GpuShaderCreator::TextureDimensions&, OpenColorIO_v2_3dev::Interpolation&) const«
3534 | virtual void getTexture(unsigned index,
| ^~~~~~~~~~
/usr/include/OpenColorIO/OpenColorIO.h:3534:18: Anmerkung: Kandidat erwartet 8 Argumente, 7 angegeben
```
OpenColorIO 3.2.0 introduced **TextureDimensions & dimensions** between channel and interpolation:
```
virtual void getTexture(unsigned index,
const char *& textureName,
const char *& samplerName,
unsigned & width,
unsigned & height,
TextureType & channel,
TextureDimensions & dimensions,
Interpolation & interpolation) const = 0;
``` | non_priority | opencolorio demands new argument at getcolorcontext commit hash about dialog e g platform archlinux summary sorry for being in german olive app render renderer cpp in elementfunktion »bool olive renderer getcolorcontext const olive colortransformjob colorcontext « olive app render renderer cpp fehler keine passende funktion für aufruf von »opencolorio gpushaderdesc gettexture unsigned int const char const char unsigned int unsigned int opencolorio gpushadercreator texturetype opencolorio interpolation « shader desc gettexture i tex name sampler name width height channel interpolation in datei eingebunden von olive app common ocioutils h von olive app render colorprocessor h von olive app render renderer h von olive app render renderer cpp usr include opencolorio opencolorio h anmerkung kandidat »virtual void opencolorio gpushaderdesc gettexture unsigned int const char const char unsigned int unsigned int opencolorio gpushadercreator texturetype opencolorio gpushadercreator texturedimensions opencolorio interpolation const« virtual void gettexture unsigned index usr include opencolorio opencolorio h anmerkung kandidat erwartet argumente angegeben opencolorio introduced texturedimensions dimensions between channel and interpolation virtual void gettexture unsigned index const char texturename const char samplername unsigned width unsigned height texturetype channel texturedimensions dimensions interpolation interpolation const | 0 |
430,857 | 30,203,798,560 | IssuesEvent | 2023-07-05 08:03:59 | KasperskyLab/uif | https://api.github.com/repos/KasperskyLab/uif | closed | Typo in kl-components-v6/README | bug documentation | > Tests **is** running with Jest & Puppeteer. Tests **is** placed in [./screenshots](https://github.com/KasperskyLab/uif/blob/master/packages/kl-components-v6/screenshots). Tests **are** run via docker-compose.
Typo in [kl-components-v6/README.](https://github.com/KasperskyLab/uif/blob/master/packages/kl-components-v6/README.md) | 1.0 | Typo in kl-components-v6/README - > Tests **is** running with Jest & Puppeteer. Tests **is** placed in [./screenshots](https://github.com/KasperskyLab/uif/blob/master/packages/kl-components-v6/screenshots). Tests **are** run via docker-compose.
Typo in [kl-components-v6/README.](https://github.com/KasperskyLab/uif/blob/master/packages/kl-components-v6/README.md) | non_priority | typo in kl components readme tests is running with jest puppeteer tests is placed in tests are run via docker compose typo in | 0 |
361 | 2,660,528,757 | IssuesEvent | 2015-03-19 08:14:35 | openSUSE/daps | https://api.github.com/repos/openSUSE/daps | closed | Update DAPS homepage [sf#182] | infrastructure | **Reported by sknorr on 2013-10-02 12:46 UTC**
It might be good to update the daps.sf.net homepage (and the documentation linked from there) to the new layout.
The documentation should be simple to regenerate, I would volunteer to re-do the homepage in a matching style. | 1.0 | Update DAPS homepage [sf#182] - **Reported by sknorr on 2013-10-02 12:46 UTC**
It might be good to update the daps.sf.net homepage (and the documentation linked from there) to the new layout.
The documentation should be simple to regenerate, I would volunteer to re-do the homepage in a matching style. | non_priority | update daps homepage reported by sknorr on utc it might be good to update the daps sf net homepage and the documentation linked from there to the new layout the documentation should be simple to regenerate i would volunteer to re do the homepage in a matching style | 0 |
39,625 | 9,582,690,516 | IssuesEvent | 2019-05-08 01:52:12 | jccastillo0007/eFacturaT | https://api.github.com/repos/jccastillo0007/eFacturaT | opened | No cancela facturas timbradas por finkok | bug defect | Es uno de los clientes que está alambrado para que se vaya por finkok.
Es del conector.
El rfc es EPN010312GC0
Y la factura es la num 28600
intentamos cancelarla ayer, y marcó error | 1.0 | No cancela facturas timbradas por finkok - Es uno de los clientes que está alambrado para que se vaya por finkok.
Es del conector.
El rfc es EPN010312GC0
Y la factura es la num 28600
intentamos cancelarla ayer, y marcó error | non_priority | no cancela facturas timbradas por finkok es uno de los clientes que está alambrado para que se vaya por finkok es del conector el rfc es y la factura es la num intentamos cancelarla ayer y marcó error | 0 |
12,652 | 7,934,608,199 | IssuesEvent | 2018-07-08 21:14:19 | jkomoros/boardgame | https://api.github.com/repos/jkomoros/boardgame | opened | Improve performance of moveProgressionChecks | performance | As of fixing #633 they're pretty expensive because we redo each one per move, which mainly duplicates the logic.
Will get worse after fixing #627 | True | Improve performance of moveProgressionChecks - As of fixing #633 they're pretty expensive because we redo each one per move, which mainly duplicates the logic.
Will get worse after fixing #627 | non_priority | improve performance of moveprogressionchecks as of fixing they re pretty expensive because we redo each one per move which mainly duplicates the logic will get worse after fixing | 0 |
100,550 | 30,723,566,239 | IssuesEvent | 2023-07-27 17:45:51 | MicrosoftDocs/visualstudio-docs | https://api.github.com/repos/MicrosoftDocs/visualstudio-docs | closed | Still Unclear How to Install MSBuild without Visual Studio | doc-bug visual-studio-windows/prod msbuild/tech Pri1 | The article mentions that MSBuild can be installed through .Net SDK, which is false. After .Net SDK installation my hard drive does not have MSBuild. Download page for Visual Studio says Build Tools require a Visual Studio license. Since MSBuild is licensed as MIT it is unclear what the right way of installing the tool is.
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: 911666fa-55ac-cbc1-ce79-66c058859ad9
* Version Independent ID: 571eec5d-8fb9-2401-fc4c-8a7896723eb7
* Content: [MSBuild - MSBuild](https://learn.microsoft.com/en-us/visualstudio/msbuild/msbuild?view=vs-2022)
* Content Source: [docs/msbuild/msbuild.md](https://github.com/MicrosoftDocs/visualstudio-docs/blob/main/docs/msbuild/msbuild.md)
* Product: **visual-studio-windows**
* Technology: **msbuild**
* GitHub Login: @ghogen
* Microsoft Alias: **ghogen** | 1.0 | Still Unclear How to Install MSBuild without Visual Studio - The article mentions that MSBuild can be installed through .Net SDK, which is false. After .Net SDK installation my hard drive does not have MSBuild. Download page for Visual Studio says Build Tools require a Visual Studio license. Since MSBuild is licensed as MIT it is unclear what the right way of installing the tool is.
---
#### Document Details
⚠ *Do not edit this section. It is required for learn.microsoft.com ➟ GitHub issue linking.*
* ID: 911666fa-55ac-cbc1-ce79-66c058859ad9
* Version Independent ID: 571eec5d-8fb9-2401-fc4c-8a7896723eb7
* Content: [MSBuild - MSBuild](https://learn.microsoft.com/en-us/visualstudio/msbuild/msbuild?view=vs-2022)
* Content Source: [docs/msbuild/msbuild.md](https://github.com/MicrosoftDocs/visualstudio-docs/blob/main/docs/msbuild/msbuild.md)
* Product: **visual-studio-windows**
* Technology: **msbuild**
* GitHub Login: @ghogen
* Microsoft Alias: **ghogen** | non_priority | still unclear how to install msbuild without visual studio the article mentions that msbuild can be installed through net sdk which is false after net sdk installation my hard drive does not have msbuild download page for visual studio says build tools require a visual studio license since msbuild is licensed as mit it is unclear what the right way of installing the tool is document details ⚠ do not edit this section it is required for learn microsoft com ➟ github issue linking id version independent id content content source product visual studio windows technology msbuild github login ghogen microsoft alias ghogen | 0 |
51,958 | 27,317,273,351 | IssuesEvent | 2023-02-24 16:39:33 | GSM-MSG/GCMS-FrontEnd-V2 | https://api.github.com/repos/GSM-MSG/GCMS-FrontEnd-V2 | opened | 신청자 합격/불합격, 동아리 멤버 추방/위임, 유저 로그아웃/탈퇴 시 모달 구현 | ⚡️performance | ### Describe
현재 alert로 사용하고 있으나 최근 모달 디자인이 추가 되어 6개의 상황에 모달을 구현해야 합니다.
- 동아리 신청자 합격
- 동아리 신청자 불합격
- 동아리 멤버 추방
- 동아리 멤버 부장 권한 위임
- 로그아웃
- 회원 탈퇴
### Additional
_No response_ | True | 신청자 합격/불합격, 동아리 멤버 추방/위임, 유저 로그아웃/탈퇴 시 모달 구현 - ### Describe
현재 alert로 사용하고 있으나 최근 모달 디자인이 추가 되어 6개의 상황에 모달을 구현해야 합니다.
- 동아리 신청자 합격
- 동아리 신청자 불합격
- 동아리 멤버 추방
- 동아리 멤버 부장 권한 위임
- 로그아웃
- 회원 탈퇴
### Additional
_No response_ | non_priority | 신청자 합격 불합격 동아리 멤버 추방 위임 유저 로그아웃 탈퇴 시 모달 구현 describe 현재 alert로 사용하고 있으나 최근 모달 디자인이 추가 되어 상황에 모달을 구현해야 합니다 동아리 신청자 합격 동아리 신청자 불합격 동아리 멤버 추방 동아리 멤버 부장 권한 위임 로그아웃 회원 탈퇴 additional no response | 0 |
198,859 | 15,726,293,747 | IssuesEvent | 2021-03-29 11:06:25 | didi/Hummer | https://api.github.com/repos/didi/Hummer | closed | 可滚动视图布局适配 | Platform: iOS documentation | ## 背景
可滚动视图一般由 UIView 实现,通过修改 bounds.origin 做到视口的上下左右滑动,但是布局引擎判断一个视图是否为重新布局的视图,是通过
```
struct HMLayoutMetrics {
CGRect frame;
CGRect contentFrame;
UIEdgeInsets borderWidth;
HMDisplayType displayType;
UIUserInterfaceLayoutDirection layoutDirection;
};
```
该结构体作为指标来判断的,如果一个滚动视图被限定了高度和宽度,那么这个视图永远不需要重新布局,但是实际上 contentSize 和 contentOffset 是需要被重新设置的,因此需要有个时机更新这些属性
## 解决方案
ScrollView 添加一个 contentView 作为唯一子视图,其他视图都被添加到 contentView,当高度发生变化的时候,contentView 会强制 ScrollView 更新属性
### 视图管理处理
1. addSubview:
2. insertSubview:atIndex:
3. insertSubview:aboveSubview:
4. insertSubview:belowSubview:
需要重定向到 contentView
### contentSize 发生变化处理
1. contentView 的 hummerSetFrame 可以得知自身大小发生变化
2. 应当通知 ScrollView
3. ScrollView 需要根据 contentView.frame.size 的变化计算 offset 变化
4. 更新 offset 和 contentSize
### 视口本身发生变化
比如 ScrollView 本身的 height width 约束发生变化,而 contentView 没有任何变化,建议使用 setFrame 方法来感知,因为 hummerSetFrame: -> self.bounds = bounds; 会触发 setFrame | 1.0 | 可滚动视图布局适配 - ## 背景
可滚动视图一般由 UIView 实现,通过修改 bounds.origin 做到视口的上下左右滑动,但是布局引擎判断一个视图是否为重新布局的视图,是通过
```
struct HMLayoutMetrics {
CGRect frame;
CGRect contentFrame;
UIEdgeInsets borderWidth;
HMDisplayType displayType;
UIUserInterfaceLayoutDirection layoutDirection;
};
```
该结构体作为指标来判断的,如果一个滚动视图被限定了高度和宽度,那么这个视图永远不需要重新布局,但是实际上 contentSize 和 contentOffset 是需要被重新设置的,因此需要有个时机更新这些属性
## 解决方案
ScrollView 添加一个 contentView 作为唯一子视图,其他视图都被添加到 contentView,当高度发生变化的时候,contentView 会强制 ScrollView 更新属性
### 视图管理处理
1. addSubview:
2. insertSubview:atIndex:
3. insertSubview:aboveSubview:
4. insertSubview:belowSubview:
需要重定向到 contentView
### contentSize 发生变化处理
1. contentView 的 hummerSetFrame 可以得知自身大小发生变化
2. 应当通知 ScrollView
3. ScrollView 需要根据 contentView.frame.size 的变化计算 offset 变化
4. 更新 offset 和 contentSize
### 视口本身发生变化
比如 ScrollView 本身的 height width 约束发生变化,而 contentView 没有任何变化,建议使用 setFrame 方法来感知,因为 hummerSetFrame: -> self.bounds = bounds; 会触发 setFrame | non_priority | 可滚动视图布局适配 背景 可滚动视图一般由 uiview 实现,通过修改 bounds origin 做到视口的上下左右滑动,但是布局引擎判断一个视图是否为重新布局的视图,是通过 struct hmlayoutmetrics cgrect frame cgrect contentframe uiedgeinsets borderwidth hmdisplaytype displaytype uiuserinterfacelayoutdirection layoutdirection 该结构体作为指标来判断的,如果一个滚动视图被限定了高度和宽度,那么这个视图永远不需要重新布局,但是实际上 contentsize 和 contentoffset 是需要被重新设置的,因此需要有个时机更新这些属性 解决方案 scrollview 添加一个 contentview 作为唯一子视图,其他视图都被添加到 contentview,当高度发生变化的时候,contentview 会强制 scrollview 更新属性 视图管理处理 addsubview insertsubview atindex insertsubview abovesubview insertsubview belowsubview 需要重定向到 contentview contentsize 发生变化处理 contentview 的 hummersetframe 可以得知自身大小发生变化 应当通知 scrollview scrollview 需要根据 contentview frame size 的变化计算 offset 变化 更新 offset 和 contentsize 视口本身发生变化 比如 scrollview 本身的 height width 约束发生变化,而 contentview 没有任何变化,建议使用 setframe 方法来感知,因为 hummersetframe self bounds bounds 会触发 setframe | 0 |
65,205 | 7,861,490,024 | IssuesEvent | 2018-06-22 00:49:56 | quicwg/base-drafts | https://api.github.com/repos/quicwg/base-drafts | opened | Prevent connection ID exhaustion | -transport design | In #1452, we realized that we need connection ID sequence numbers back, and it seems like the design in #1465 depends on symmetry: if you see connection ID X, then you have to use at least connection ID X (and not X-1).
In that case, there will never be a case where an endpoint is going to want to provide significantly more connection IDs than its peer. If any of those are used, it won't be able to send anything in response. So that suggests a simple solution to exhaustion: if you receive NEW_CONNECTION_ID, you are required to provide NEW_CONNECTION_ID frames up to the sequence number you have received.
Then, an endpoint that wants to maintain N spare connection IDs can simply issue NEW_CONNECTION_ID frames until it has made that many connection IDs available to its peer. It's peer is then obligated to provide the same number in return. | 1.0 | Prevent connection ID exhaustion - In #1452, we realized that we need connection ID sequence numbers back, and it seems like the design in #1465 depends on symmetry: if you see connection ID X, then you have to use at least connection ID X (and not X-1).
In that case, there will never be a case where an endpoint is going to want to provide significantly more connection IDs than its peer. If any of those are used, it won't be able to send anything in response. So that suggests a simple solution to exhaustion: if you receive NEW_CONNECTION_ID, you are required to provide NEW_CONNECTION_ID frames up to the sequence number you have received.
Then, an endpoint that wants to maintain N spare connection IDs can simply issue NEW_CONNECTION_ID frames until it has made that many connection IDs available to its peer. It's peer is then obligated to provide the same number in return. | non_priority | prevent connection id exhaustion in we realized that we need connection id sequence numbers back and it seems like the design in depends on symmetry if you see connection id x then you have to use at least connection id x and not x in that case there will never be a case where an endpoint is going to want to provide significantly more connection ids than its peer if any of those are used it won t be able to send anything in response so that suggests a simple solution to exhaustion if you receive new connection id you are required to provide new connection id frames up to the sequence number you have received then an endpoint that wants to maintain n spare connection ids can simply issue new connection id frames until it has made that many connection ids available to its peer it s peer is then obligated to provide the same number in return | 0 |
106,657 | 13,339,895,248 | IssuesEvent | 2020-08-28 13:37:37 | nextcloud/nextcloud-vue | https://api.github.com/repos/nextcloud/nextcloud-vue | opened | emoji picker focus missing | design enhancement feature: emoji picker | * When clicking the emoji picker, it would be nice if the search field would be immediately focused;
* and when hitting enter, the top emoji should be pasted...
* I guess it would also be nice if the arrow keys would navigate between the emoji's so `enter` pastes the right one. | 1.0 | emoji picker focus missing - * When clicking the emoji picker, it would be nice if the search field would be immediately focused;
* and when hitting enter, the top emoji should be pasted...
* I guess it would also be nice if the arrow keys would navigate between the emoji's so `enter` pastes the right one. | non_priority | emoji picker focus missing when clicking the emoji picker it would be nice if the search field would be immediately focused and when hitting enter the top emoji should be pasted i guess it would also be nice if the arrow keys would navigate between the emoji s so enter pastes the right one | 0 |
172,615 | 21,051,723,320 | IssuesEvent | 2022-03-31 21:10:10 | MValle21/demo-java-telnyx | https://api.github.com/repos/MValle21/demo-java-telnyx | opened | CVE-2022-22965 (High) detected in spring-beans-5.2.10.RELEASE.jar | security vulnerability | ## CVE-2022-22965 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-beans-5.2.10.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /spring-masked-calling/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.10.RELEASE/spring-beans-5.2.10.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.10.RELEASE/spring-beans-5.2.10.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.10.RELEASE/spring-beans-5.2.10.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.5.RELEASE.jar (Root Library)
- spring-web-5.2.10.RELEASE.jar
- :x: **spring-beans-5.2.10.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״. The current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution). Please note that the ease of exploitation may diverge by the code implementation.Currently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux. Spring Framework 5.3.18 and 5.2.20 have already been released. WhiteSource's research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.
<p>Publish Date: 2022-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22965>CVE-2022-22965</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-01-11</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.20.RELEASE,5.3.18</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-beans","packageVersion":"5.2.10.RELEASE","packageFilePaths":["/spring-masked-calling/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.3.5.RELEASE;org.springframework:spring-web:5.2.10.RELEASE;org.springframework:spring-beans:5.2.10.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.20.RELEASE,5.3.18","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-22965","vulnerabilityDetails":"Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״. The current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution). Please note that the ease of exploitation may diverge by the code implementation.Currently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux. Spring Framework 5.3.18 and 5.2.20 have already been released. WhiteSource\u0027s research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22965","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2022-22965 (High) detected in spring-beans-5.2.10.RELEASE.jar - ## CVE-2022-22965 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-beans-5.2.10.RELEASE.jar</b></p></summary>
<p>Spring Beans</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /spring-masked-calling/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.10.RELEASE/spring-beans-5.2.10.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.10.RELEASE/spring-beans-5.2.10.RELEASE.jar,/home/wss-scanner/.m2/repository/org/springframework/spring-beans/5.2.10.RELEASE/spring-beans-5.2.10.RELEASE.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-web-2.3.5.RELEASE.jar (Root Library)
- spring-web-5.2.10.RELEASE.jar
- :x: **spring-beans-5.2.10.RELEASE.jar** (Vulnerable Library)
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״. The current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution). Please note that the ease of exploitation may diverge by the code implementation.Currently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux. Spring Framework 5.3.18 and 5.2.20 have already been released. WhiteSource's research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.
<p>Publish Date: 2022-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22965>CVE-2022-22965</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>9.8</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: High
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement">https://spring.io/blog/2022/03/31/spring-framework-rce-early-announcement</a></p>
<p>Release Date: 2022-01-11</p>
<p>Fix Resolution: org.springframework:spring-beans:5.2.20.RELEASE,5.3.18</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.springframework","packageName":"spring-beans","packageVersion":"5.2.10.RELEASE","packageFilePaths":["/spring-masked-calling/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.springframework.boot:spring-boot-starter-web:2.3.5.RELEASE;org.springframework:spring-web:5.2.10.RELEASE;org.springframework:spring-beans:5.2.10.RELEASE","isMinimumFixVersionAvailable":true,"minimumFixVersion":"org.springframework:spring-beans:5.2.20.RELEASE,5.3.18","isBinary":false}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2022-22965","vulnerabilityDetails":"Spring Framework before 5.2.20 and 5.3.x before 5.3.18 are vulnerable due to a vulnerability in Spring-beans which allows attackers under certain circumstances to achieve remote code execution, this vulnerability is also known as ״Spring4Shell״ or ״SpringShell״. The current POC related to the attack is done by creating a specially crafted request which manipulates ClassLoader to successfully achieve RCE (Remote Code Execution). Please note that the ease of exploitation may diverge by the code implementation.Currently, the exploit requires JDK 9 or higher, Apache Tomcat as the Servlet container, the application Packaged as WAR, and dependency on spring-webmvc or spring-webflux. Spring Framework 5.3.18 and 5.2.20 have already been released. WhiteSource\u0027s research team is carefully observing developments and researching the case. We will keep updating this page and our WhiteSource resources with updates.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22965","cvss3Severity":"high","cvss3Score":"9.8","cvss3Metrics":{"A":"High","AC":"Low","PR":"None","S":"Unchanged","C":"High","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in spring beans release jar cve high severity vulnerability vulnerable library spring beans release jar spring beans library home page a href path to dependency file spring masked calling pom xml path to vulnerable library home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar home wss scanner repository org springframework spring beans release spring beans release jar dependency hierarchy spring boot starter web release jar root library spring web release jar x spring beans release jar vulnerable library found in base branch master vulnerability details spring framework before and x before are vulnerable due to a vulnerability in spring beans which allows attackers under certain circumstances to achieve remote code execution this vulnerability is also known as ״ ״ or ״springshell״ the current poc related to the attack is done by creating a specially crafted request which manipulates classloader to successfully achieve rce remote code execution please note that the ease of exploitation may diverge by the code implementation currently the exploit requires jdk or higher apache tomcat as the servlet container the application packaged as war and dependency on spring webmvc or spring webflux spring framework and have already been released whitesource s research team is carefully observing developments and researching the case we will keep updating this page and our whitesource resources with updates publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact high integrity impact high availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring beans release isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org springframework boot spring boot starter web release org springframework spring web release org springframework spring beans release isminimumfixversionavailable true minimumfixversion org springframework spring beans release isbinary false basebranches vulnerabilityidentifier cve vulnerabilitydetails spring framework before and x before are vulnerable due to a vulnerability in spring beans which allows attackers under certain circumstances to achieve remote code execution this vulnerability is also known as ״ ״ or ״springshell״ the current poc related to the attack is done by creating a specially crafted request which manipulates classloader to successfully achieve rce remote code execution please note that the ease of exploitation may diverge by the code implementation currently the exploit requires jdk or higher apache tomcat as the servlet container the application packaged as war and dependency on spring webmvc or spring webflux spring framework and have already been released whitesource research team is carefully observing developments and researching the case we will keep updating this page and our whitesource resources with updates vulnerabilityurl | 0 |
112,609 | 24,302,952,473 | IssuesEvent | 2022-09-29 15:06:46 | sourcegraph/sourcegraph | https://api.github.com/repos/sourcegraph/sourcegraph | opened | Codemirror blob: Evaluate text selection behavior via keyboard | team/code-intelligence team/code-navigation codemirror | Currently when pressing arrow down/up/left/right, a text selection starts at a seemingly random location (it's not random but CodeMirror's internal cursor state is not visible to the user so it seems random).
The old blob view only allows extending existing text selections via keyboard (I assume that's the normal browser behavior).
We should probably do the same for the CodeMirror version. | 3.0 | Codemirror blob: Evaluate text selection behavior via keyboard - Currently when pressing arrow down/up/left/right, a text selection starts at a seemingly random location (it's not random but CodeMirror's internal cursor state is not visible to the user so it seems random).
The old blob view only allows extending existing text selections via keyboard (I assume that's the normal browser behavior).
We should probably do the same for the CodeMirror version. | non_priority | codemirror blob evaluate text selection behavior via keyboard currently when pressing arrow down up left right a text selection starts at a seemingly random location it s not random but codemirror s internal cursor state is not visible to the user so it seems random the old blob view only allows extending existing text selections via keyboard i assume that s the normal browser behavior we should probably do the same for the codemirror version | 0 |
174,716 | 21,300,390,854 | IssuesEvent | 2022-04-15 01:46:10 | MikeGratsas/currency-converter | https://api.github.com/repos/MikeGratsas/currency-converter | opened | CVE-2022-22968 (Low) detected in spring-context-5.3.12.jar | security vulnerability | ## CVE-2022-22968 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-context-5.3.12.jar</b></p></summary>
<p>Spring Context</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/5.3.12/spring-context-5.3.12.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-data-jpa-2.5.6.jar (Root Library)
- spring-data-jpa-2.5.6.jar
- :x: **spring-context-5.3.12.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework versions 5.3.0 - 5.3.18, 5.2.0 - 5.2.20, and older unsupported versions, the patterns for disallowedFields on a DataBinder are case sensitive which means a field is not effectively protected unless it is listed with both upper and lower case for the first character of the field, including upper and lower case for the first character of all nested fields within the property path
<p>Publish Date: 2022-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22968>CVE-2022-22968</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22968">https://tanzu.vmware.com/security/cve-2022-22968</a></p>
<p>Release Date: 2022-01-11</p>
<p>Fix Resolution: org.springframework:spring-context:5.2.21,5.3.19</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2022-22968 (Low) detected in spring-context-5.3.12.jar - ## CVE-2022-22968 - Low Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>spring-context-5.3.12.jar</b></p></summary>
<p>Spring Context</p>
<p>Library home page: <a href="https://github.com/spring-projects/spring-framework">https://github.com/spring-projects/spring-framework</a></p>
<p>Path to dependency file: /pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/springframework/spring-context/5.3.12/spring-context-5.3.12.jar</p>
<p>
Dependency Hierarchy:
- spring-boot-starter-data-jpa-2.5.6.jar (Root Library)
- spring-data-jpa-2.5.6.jar
- :x: **spring-context-5.3.12.jar** (Vulnerable Library)
<p>Found in base branch: <b>main</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/low_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In Spring Framework versions 5.3.0 - 5.3.18, 5.2.0 - 5.2.20, and older unsupported versions, the patterns for disallowedFields on a DataBinder are case sensitive which means a field is not effectively protected unless it is listed with both upper and lower case for the first character of the field, including upper and lower case for the first character of all nested fields within the property path
<p>Publish Date: 2022-01-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2022-22968>CVE-2022-22968</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>3.7</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: High
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://tanzu.vmware.com/security/cve-2022-22968">https://tanzu.vmware.com/security/cve-2022-22968</a></p>
<p>Release Date: 2022-01-11</p>
<p>Fix Resolution: org.springframework:spring-context:5.2.21,5.3.19</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve low detected in spring context jar cve low severity vulnerability vulnerable library spring context jar spring context library home page a href path to dependency file pom xml path to vulnerable library home wss scanner repository org springframework spring context spring context jar dependency hierarchy spring boot starter data jpa jar root library spring data jpa jar x spring context jar vulnerable library found in base branch main vulnerability details in spring framework versions and older unsupported versions the patterns for disallowedfields on a databinder are case sensitive which means a field is not effectively protected unless it is listed with both upper and lower case for the first character of the field including upper and lower case for the first character of all nested fields within the property path publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity high privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org springframework spring context step up your open source security game with whitesource | 0 |
64,795 | 26,871,484,409 | IssuesEvent | 2023-02-04 14:20:26 | mastodon-dart/mastodon-api | https://api.github.com/repos/mastodon-dart/mastodon-api | closed | Feature Request: Add endpoints in `statuses API methods` | enhancement help wanted service/statuses feat | <!-- When reporting a feature, please read this complete template and fill all the questions in order to get a better response -->
# 1. Problem to solve
<!-- Which problem would be solved with this feature? -->
- https://docs.joinmastodon.org/methods/statuses/#history
- https://docs.joinmastodon.org/methods/statuses/#source
# 2. Proposal
<!-- What do you propose as a solution? Add as much information as you can! -->
# 3. More information
<!-- Do you have any other useful information about this feature report? Please write it down here -->
<!-- Possible helpful information: references to other sites/repositories -->
<!-- Are you interested in working on a PR for this? -->
| 1.0 | Feature Request: Add endpoints in `statuses API methods` - <!-- When reporting a feature, please read this complete template and fill all the questions in order to get a better response -->
# 1. Problem to solve
<!-- Which problem would be solved with this feature? -->
- https://docs.joinmastodon.org/methods/statuses/#history
- https://docs.joinmastodon.org/methods/statuses/#source
# 2. Proposal
<!-- What do you propose as a solution? Add as much information as you can! -->
# 3. More information
<!-- Do you have any other useful information about this feature report? Please write it down here -->
<!-- Possible helpful information: references to other sites/repositories -->
<!-- Are you interested in working on a PR for this? -->
| non_priority | feature request add endpoints in statuses api methods problem to solve proposal more information | 0 |
106,693 | 13,349,495,152 | IssuesEvent | 2020-08-30 01:15:21 | LetsUpgrade/Algorithmic-Treasure | https://api.github.com/repos/LetsUpgrade/Algorithmic-Treasure | closed | Website Task - 1 | Website Designing documentation enhancement | Bring some templates of the documentation websites which used bootstrap and no backend.
Two things to notice while bringing the template,
**1 - It must be inside MIT license, I mean no copyright issues.
2 - It must not have any backend programming involved.**
Submission Deadline - **25th Aug 2020** | 1.0 | Website Task - 1 - Bring some templates of the documentation websites which used bootstrap and no backend.
Two things to notice while bringing the template,
**1 - It must be inside MIT license, I mean no copyright issues.
2 - It must not have any backend programming involved.**
Submission Deadline - **25th Aug 2020** | non_priority | website task bring some templates of the documentation websites which used bootstrap and no backend two things to notice while bringing the template it must be inside mit license i mean no copyright issues it must not have any backend programming involved submission deadline aug | 0 |
5,052 | 3,899,699,014 | IssuesEvent | 2016-04-17 22:01:51 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 13124776: Back button jumps to top of previous page | classification:ui/usability reproducible:always status:open | #### Description
Summary: the Back button in Xcode's documentation browser jumps to the top of the previous page.
Steps to Reproduce:
1. View some documentation in the Xcode documentation browser. For this example, we will use UIView from the iOS 6 documentation.
2. Scroll down until you see a link that you know goes to a different page. For example, "OpenGL ES Programming Guide for iOS," which is in a box two paragraphs after the heading, "The View Drawing Cycle."
3. Click the link.
4. Click the Back button, or, depending on how you have your trackpad set up, swipe with two fingers to the right or three to the left.
Expected Results:
The documentation browser will go back a page, and show the point where you left off, scrolled to the same place you were when you left.
Actual Results:
The documentation browser jumps back a page, but is always scrolled to the top, no matter where you were scrolled to when you clicked the link.
Regression:
It was definitely like this in Xcode 4.5, possibly in 4.4. I don't remember how it worked in previous versions.
Notes:
Safari also has this problem when viewing iOS documentation pages, but not when viewing most normal Web pages.
-
Product Version: Xcode Version 4.6 (4H127)
Created: 2013-01-31T16:42:46.912134
Originated: 2013-01-31T11:42:00
Open Radar Link: http://www.openradar.me/13124776 | True | 13124776: Back button jumps to top of previous page - #### Description
Summary: the Back button in Xcode's documentation browser jumps to the top of the previous page.
Steps to Reproduce:
1. View some documentation in the Xcode documentation browser. For this example, we will use UIView from the iOS 6 documentation.
2. Scroll down until you see a link that you know goes to a different page. For example, "OpenGL ES Programming Guide for iOS," which is in a box two paragraphs after the heading, "The View Drawing Cycle."
3. Click the link.
4. Click the Back button, or, depending on how you have your trackpad set up, swipe with two fingers to the right or three to the left.
Expected Results:
The documentation browser will go back a page, and show the point where you left off, scrolled to the same place you were when you left.
Actual Results:
The documentation browser jumps back a page, but is always scrolled to the top, no matter where you were scrolled to when you clicked the link.
Regression:
It was definitely like this in Xcode 4.5, possibly in 4.4. I don't remember how it worked in previous versions.
Notes:
Safari also has this problem when viewing iOS documentation pages, but not when viewing most normal Web pages.
-
Product Version: Xcode Version 4.6 (4H127)
Created: 2013-01-31T16:42:46.912134
Originated: 2013-01-31T11:42:00
Open Radar Link: http://www.openradar.me/13124776 | non_priority | back button jumps to top of previous page description summary the back button in xcode s documentation browser jumps to the top of the previous page steps to reproduce view some documentation in the xcode documentation browser for this example we will use uiview from the ios documentation scroll down until you see a link that you know goes to a different page for example opengl es programming guide for ios which is in a box two paragraphs after the heading the view drawing cycle click the link click the back button or depending on how you have your trackpad set up swipe with two fingers to the right or three to the left expected results the documentation browser will go back a page and show the point where you left off scrolled to the same place you were when you left actual results the documentation browser jumps back a page but is always scrolled to the top no matter where you were scrolled to when you clicked the link regression it was definitely like this in xcode possibly in i don t remember how it worked in previous versions notes safari also has this problem when viewing ios documentation pages but not when viewing most normal web pages product version xcode version created originated open radar link | 0 |
95,040 | 11,950,263,445 | IssuesEvent | 2020-04-03 14:56:03 | algebraicdb/algebraicdb | https://api.github.com/repos/algebraicdb/algebraicdb | closed | Write Ahead Log | design | This is a thing, that would be nice if it existed.
After this is implemented we can make pretty accurate benchmarks to compare with other databases.
Right now the idea is to have a single file that we first write modification queries to, and after that handle the dbms state.
1. Write query to logfile.
2. Write commit transaction to dbms state.
3. Increment dbms tracker.
At a later point the dbms state can be written as a whole onto disk, locking all tables for a short time.
We need to probably refactor `resource_manager` in local and create a new function that handles the overarching transaction handling. | 1.0 | Write Ahead Log - This is a thing, that would be nice if it existed.
After this is implemented we can make pretty accurate benchmarks to compare with other databases.
Right now the idea is to have a single file that we first write modification queries to, and after that handle the dbms state.
1. Write query to logfile.
2. Write commit transaction to dbms state.
3. Increment dbms tracker.
At a later point the dbms state can be written as a whole onto disk, locking all tables for a short time.
We need to probably refactor `resource_manager` in local and create a new function that handles the overarching transaction handling. | non_priority | write ahead log this is a thing that would be nice if it existed after this is implemented we can make pretty accurate benchmarks to compare with other databases right now the idea is to have a single file that we first write modification queries to and after that handle the dbms state write query to logfile write commit transaction to dbms state increment dbms tracker at a later point the dbms state can be written as a whole onto disk locking all tables for a short time we need to probably refactor resource manager in local and create a new function that handles the overarching transaction handling | 0 |
69,264 | 8,389,930,333 | IssuesEvent | 2018-10-09 11:03:38 | gitcoinco/web | https://api.github.com/repos/gitcoinco/web | opened | Experiment Ways to Highlight Features on the Issue Explorer | design-help revenue | <!--
Hello Gitcoiner!
Please use the template below for feature requests for Gitcoin.
If it is general support you need, reach out to us at
gitcoin.co/slack
-->
### User Story
As a funder with a new bounty, I'd like a way to callout the issue that I've just posted so I can turn the project around using the best talent on Gitcoin.
Funders expect some interest on their github pages within the first 12-24 hrs and tasks to be picked up soon after that.
### Definition of Done
- [ ] Mockup 3 different ways to solve for the above.
- [ ] Create a high level flow to illustrate the strongest idea - consider the end-end-experience for a funder (should tweets/sharing be part of this experience).?
- [ ] Consider how to solve for responsiveness of the page.
| 1.0 | Experiment Ways to Highlight Features on the Issue Explorer - <!--
Hello Gitcoiner!
Please use the template below for feature requests for Gitcoin.
If it is general support you need, reach out to us at
gitcoin.co/slack
-->
### User Story
As a funder with a new bounty, I'd like a way to callout the issue that I've just posted so I can turn the project around using the best talent on Gitcoin.
Funders expect some interest on their github pages within the first 12-24 hrs and tasks to be picked up soon after that.
### Definition of Done
- [ ] Mockup 3 different ways to solve for the above.
- [ ] Create a high level flow to illustrate the strongest idea - consider the end-end-experience for a funder (should tweets/sharing be part of this experience).?
- [ ] Consider how to solve for responsiveness of the page.
| non_priority | experiment ways to highlight features on the issue explorer hello gitcoiner please use the template below for feature requests for gitcoin if it is general support you need reach out to us at gitcoin co slack user story as a funder with a new bounty i d like a way to callout the issue that i ve just posted so i can turn the project around using the best talent on gitcoin funders expect some interest on their github pages within the first hrs and tasks to be picked up soon after that definition of done mockup different ways to solve for the above create a high level flow to illustrate the strongest idea consider the end end experience for a funder should tweets sharing be part of this experience consider how to solve for responsiveness of the page | 0 |
43,069 | 17,397,654,555 | IssuesEvent | 2021-08-02 15:15:22 | pulumi/pulumi-azure-native | https://api.github.com/repos/pulumi/pulumi-azure-native | closed | Azure Functions `kind` not being set properly | kind/question upstream/service | I have a script to create a Azure Functions app and specify the `kind` to be `functionapp,linux,container` but it is stripping the `container` part and creating it wrong.
## Steps to reproduce
Here is my code showing use of WebApp API, setting the `kind`. You can see in the detail of `pulumi up` the value for `kind`
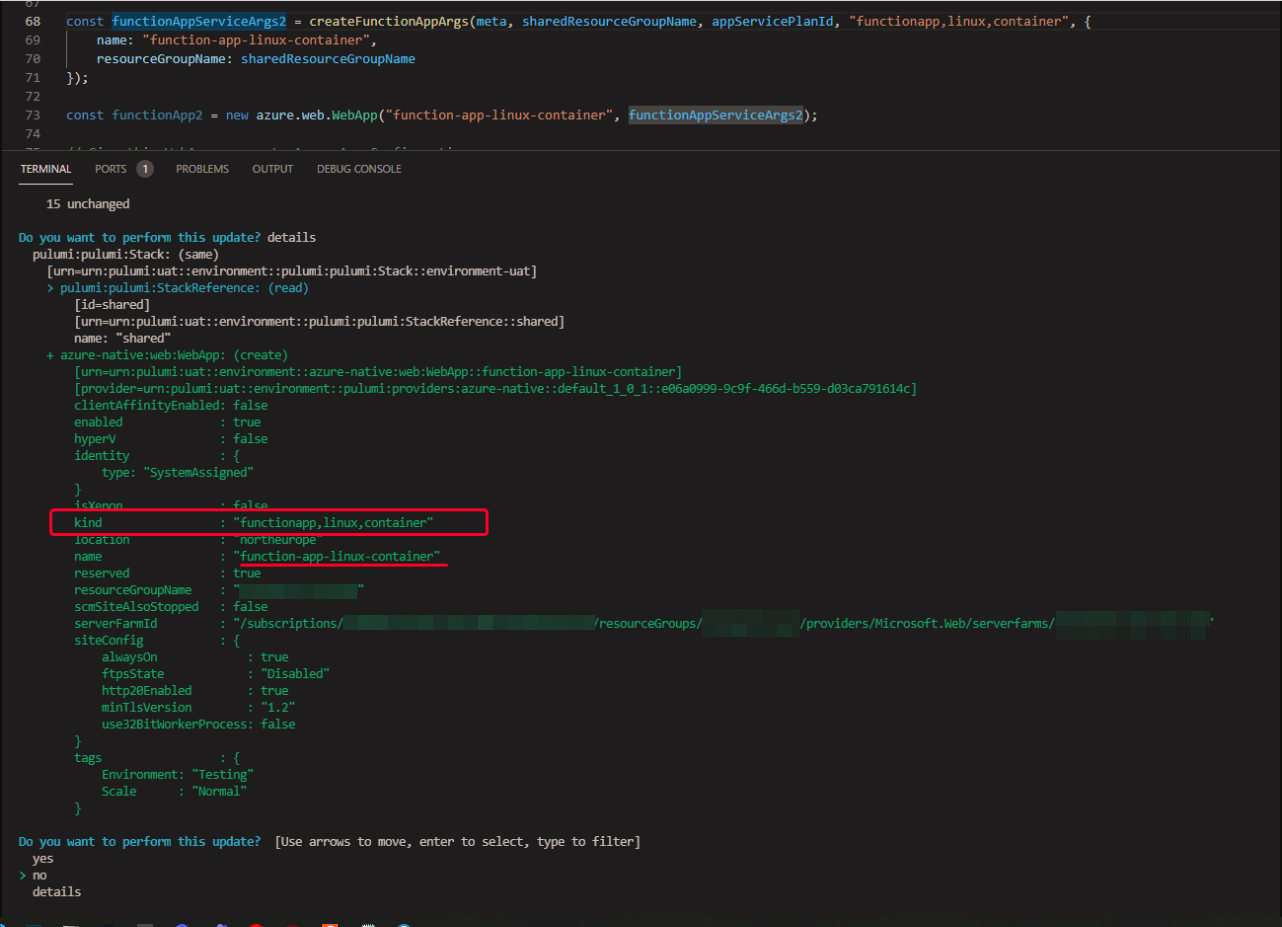
Here is the little function I use to create my `args`:
```js
export const createFunctionAppArgs = (
meta: Meta,
groupName: Output<string>,
appServicePlanId: Output<string>,
kind: string,
args?: azure.web.WebAppArgs): azure.web.WebAppArgs => {
const functionAppName = generateResourceName(meta, "fa", false);
// TODO: Ask for optional application insights and wire it up?
const defaultArgs: azure.web.WebAppArgs = {
name: functionAppName,
location: meta.locationName as string,
resourceGroupName: groupName,
serverFarmId: appServicePlanId,
siteConfig: {
alwaysOn: true,
ftpsState: "Disabled",
http20Enabled: true,
minTlsVersion: azure.web.SupportedTlsVersions.SupportedTlsVersions_1_2,
use32BitWorkerProcess: false,
},
clientAffinityEnabled: false,
kind,
enabled: true,
reserved: true,
identity: {
type: "SystemAssigned"
}
};
return defaultArgs;
};
```
Expected: To set the `kind` correctly as specified
Actual:
The `container` part has been removed
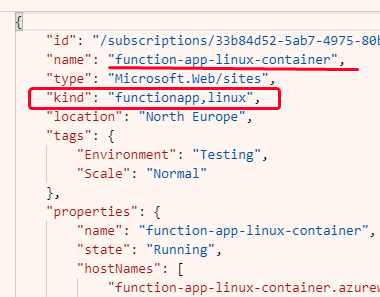
| 1.0 | Azure Functions `kind` not being set properly - I have a script to create a Azure Functions app and specify the `kind` to be `functionapp,linux,container` but it is stripping the `container` part and creating it wrong.
## Steps to reproduce
Here is my code showing use of WebApp API, setting the `kind`. You can see in the detail of `pulumi up` the value for `kind`
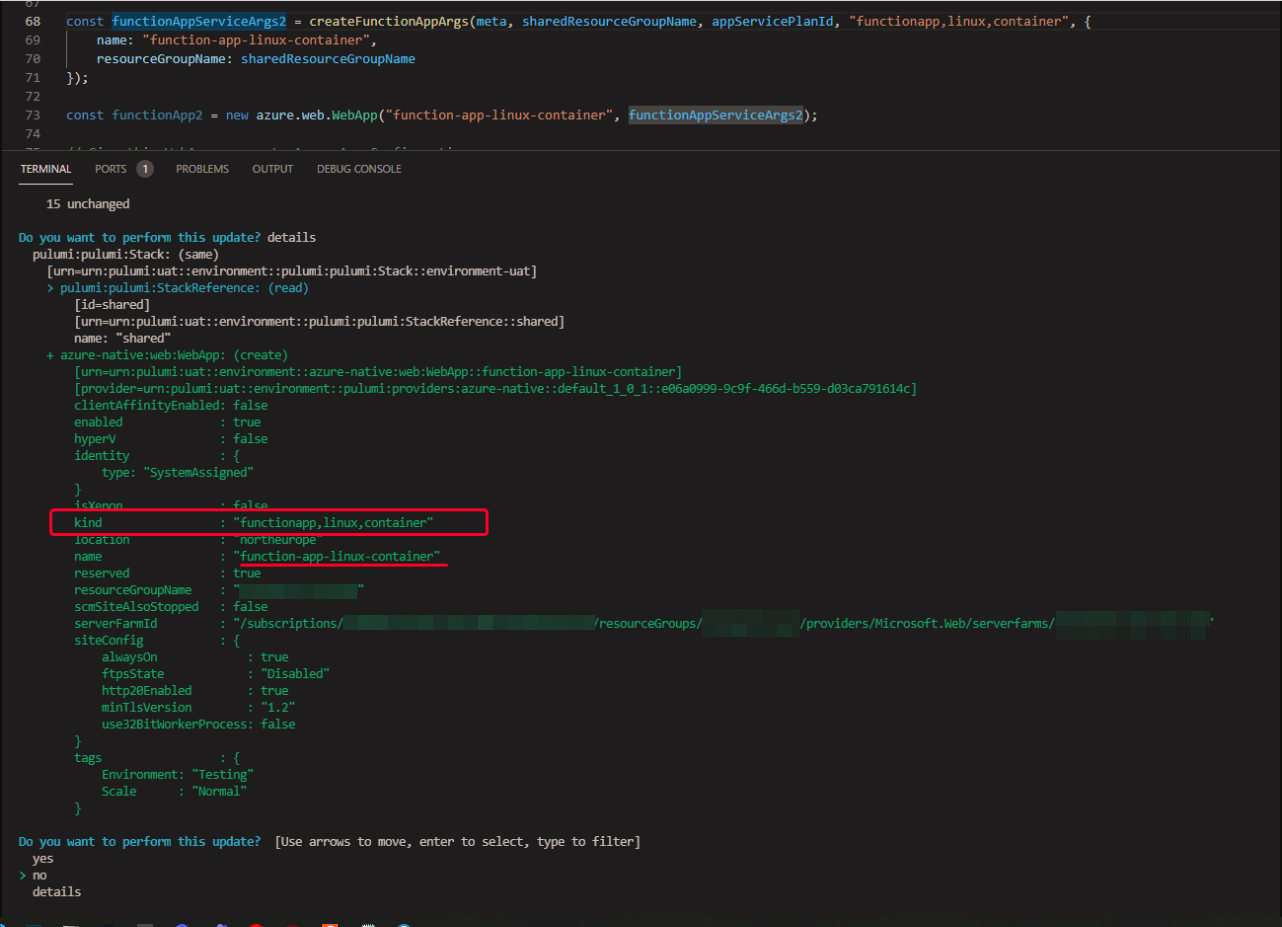
Here is the little function I use to create my `args`:
```js
export const createFunctionAppArgs = (
meta: Meta,
groupName: Output<string>,
appServicePlanId: Output<string>,
kind: string,
args?: azure.web.WebAppArgs): azure.web.WebAppArgs => {
const functionAppName = generateResourceName(meta, "fa", false);
// TODO: Ask for optional application insights and wire it up?
const defaultArgs: azure.web.WebAppArgs = {
name: functionAppName,
location: meta.locationName as string,
resourceGroupName: groupName,
serverFarmId: appServicePlanId,
siteConfig: {
alwaysOn: true,
ftpsState: "Disabled",
http20Enabled: true,
minTlsVersion: azure.web.SupportedTlsVersions.SupportedTlsVersions_1_2,
use32BitWorkerProcess: false,
},
clientAffinityEnabled: false,
kind,
enabled: true,
reserved: true,
identity: {
type: "SystemAssigned"
}
};
return defaultArgs;
};
```
Expected: To set the `kind` correctly as specified
Actual:
The `container` part has been removed
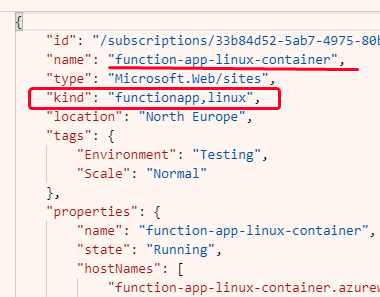
| non_priority | azure functions kind not being set properly i have a script to create a azure functions app and specify the kind to be functionapp linux container but it is stripping the container part and creating it wrong steps to reproduce here is my code showing use of webapp api setting the kind you can see in the detail of pulumi up the value for kind here is the little function i use to create my args js export const createfunctionappargs meta meta groupname output appserviceplanid output kind string args azure web webappargs azure web webappargs const functionappname generateresourcename meta fa false todo ask for optional application insights and wire it up const defaultargs azure web webappargs name functionappname location meta locationname as string resourcegroupname groupname serverfarmid appserviceplanid siteconfig alwayson true ftpsstate disabled true mintlsversion azure web supportedtlsversions supportedtlsversions false clientaffinityenabled false kind enabled true reserved true identity type systemassigned return defaultargs expected to set the kind correctly as specified actual the container part has been removed | 0 |
21,553 | 3,519,553,021 | IssuesEvent | 2016-01-12 17:15:14 | idaholab/moose | https://api.github.com/repos/idaholab/moose | closed | Fix strain rate in tensor mechanics | C: Modules T: defect T: task | In all incremental strain calculation classes in the TensorMechanics module, the strain_rate tensor is calculated according to:
```
_strain_rate[_qp] = _strain_increment[_qp] / _t_step;
```
`_t_step` is actually an integer, the number of the time step.
It should rather be
```
_strain_rate[_qp] = _strain_increment[_qp] / _dt;
``` | 1.0 | Fix strain rate in tensor mechanics - In all incremental strain calculation classes in the TensorMechanics module, the strain_rate tensor is calculated according to:
```
_strain_rate[_qp] = _strain_increment[_qp] / _t_step;
```
`_t_step` is actually an integer, the number of the time step.
It should rather be
```
_strain_rate[_qp] = _strain_increment[_qp] / _dt;
``` | non_priority | fix strain rate in tensor mechanics in all incremental strain calculation classes in the tensormechanics module the strain rate tensor is calculated according to strain rate strain increment t step t step is actually an integer the number of the time step it should rather be strain rate strain increment dt | 0 |
23,675 | 11,941,238,192 | IssuesEvent | 2020-04-02 18:05:19 | cityofaustin/atd-data-tech | https://api.github.com/repos/cityofaustin/atd-data-tech | closed | 2020 Esri UC Cancellation | Service: Geo Type: Training Workgroup: DTS | Denise notified me that our travel to the Esri UC in July has been cancelled. | 1.0 | 2020 Esri UC Cancellation - Denise notified me that our travel to the Esri UC in July has been cancelled. | non_priority | esri uc cancellation denise notified me that our travel to the esri uc in july has been cancelled | 0 |
412,337 | 27,854,348,192 | IssuesEvent | 2023-03-20 21:22:35 | strictdoc-project/strictdoc | https://api.github.com/repos/strictdoc-project/strictdoc | closed | docs: document the existing capability of UI v0 | Documentation UI/UX | Also:
- New requirement style options
- Project config file and its options | 1.0 | docs: document the existing capability of UI v0 - Also:
- New requirement style options
- Project config file and its options | non_priority | docs document the existing capability of ui also new requirement style options project config file and its options | 0 |
195,665 | 22,350,077,709 | IssuesEvent | 2022-06-15 11:14:49 | turkdevops/angular-cli | https://api.github.com/repos/turkdevops/angular-cli | closed | WS-2020-0127 (Medium) detected in npm-registry-fetch-4.0.3.tgz - autoclosed | security vulnerability | ## WS-2020-0127 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-registry-fetch-4.0.3.tgz</b></p></summary>
<p>Fetch-based http client for use with npm registry APIs</p>
<p>Library home page: <a href="https://registry.npmjs.org/npm-registry-fetch/-/npm-registry-fetch-4.0.3.tgz">https://registry.npmjs.org/npm-registry-fetch/-/npm-registry-fetch-4.0.3.tgz</a></p>
<p>Path to dependency file: /integration/angular_cli/package.json</p>
<p>Path to vulnerable library: /integration/angular_cli/node_modules/npm-registry-fetch/package.json</p>
<p>
Dependency Hierarchy:
- cli-9.1.15.tgz (Root Library)
- pacote-9.5.12.tgz
- :x: **npm-registry-fetch-4.0.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/angular-cli/commit/df8abeb8e49f7a19502084e835c603107b21e7a3">df8abeb8e49f7a19502084e835c603107b21e7a3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
npm-registry-fetch before 4.0.5 and 8.1.1 is vulnerable to an information exposure vulnerability through log files.
<p>Publish Date: 2020-07-07
<p>URL: <a href=https://github.com/npm/npm-registry-fetch/commit/18bf9b97fb1deecdba01ffb05580370846255c88>WS-2020-0127</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1544">https://www.npmjs.com/advisories/1544</a></p>
<p>Release Date: 2020-07-07</p>
<p>Fix Resolution (npm-registry-fetch): 4.0.5</p>
<p>Direct dependency fix Resolution (@angular/cli): 13.3.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2020-0127 (Medium) detected in npm-registry-fetch-4.0.3.tgz - autoclosed - ## WS-2020-0127 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>npm-registry-fetch-4.0.3.tgz</b></p></summary>
<p>Fetch-based http client for use with npm registry APIs</p>
<p>Library home page: <a href="https://registry.npmjs.org/npm-registry-fetch/-/npm-registry-fetch-4.0.3.tgz">https://registry.npmjs.org/npm-registry-fetch/-/npm-registry-fetch-4.0.3.tgz</a></p>
<p>Path to dependency file: /integration/angular_cli/package.json</p>
<p>Path to vulnerable library: /integration/angular_cli/node_modules/npm-registry-fetch/package.json</p>
<p>
Dependency Hierarchy:
- cli-9.1.15.tgz (Root Library)
- pacote-9.5.12.tgz
- :x: **npm-registry-fetch-4.0.3.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/turkdevops/angular-cli/commit/df8abeb8e49f7a19502084e835c603107b21e7a3">df8abeb8e49f7a19502084e835c603107b21e7a3</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
npm-registry-fetch before 4.0.5 and 8.1.1 is vulnerable to an information exposure vulnerability through log files.
<p>Publish Date: 2020-07-07
<p>URL: <a href=https://github.com/npm/npm-registry-fetch/commit/18bf9b97fb1deecdba01ffb05580370846255c88>WS-2020-0127</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://www.npmjs.com/advisories/1544">https://www.npmjs.com/advisories/1544</a></p>
<p>Release Date: 2020-07-07</p>
<p>Fix Resolution (npm-registry-fetch): 4.0.5</p>
<p>Direct dependency fix Resolution (@angular/cli): 13.3.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium detected in npm registry fetch tgz autoclosed ws medium severity vulnerability vulnerable library npm registry fetch tgz fetch based http client for use with npm registry apis library home page a href path to dependency file integration angular cli package json path to vulnerable library integration angular cli node modules npm registry fetch package json dependency hierarchy cli tgz root library pacote tgz x npm registry fetch tgz vulnerable library found in head commit a href found in base branch master vulnerability details npm registry fetch before and is vulnerable to an information exposure vulnerability through log files publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution npm registry fetch direct dependency fix resolution angular cli step up your open source security game with mend | 0 |
9,628 | 24,927,786,059 | IssuesEvent | 2022-10-31 09:03:31 | MRC-CSO-SPHSU/LoneParentsModel.jl | https://api.github.com/repos/MRC-CSO-SPHSU/LoneParentsModel.jl | closed | Demography Data | model architecture | As mentioned in a comment within mainHelpers.jl, demographydata.jl needs to be placed within a module.
I see two options:
- as it is related to ParamTypes, it fits there
- or another module for Data
Although currently not that significant amount of code within demographydata.jl, it makes sense to have a module for Data | 1.0 | Demography Data - As mentioned in a comment within mainHelpers.jl, demographydata.jl needs to be placed within a module.
I see two options:
- as it is related to ParamTypes, it fits there
- or another module for Data
Although currently not that significant amount of code within demographydata.jl, it makes sense to have a module for Data | non_priority | demography data as mentioned in a comment within mainhelpers jl demographydata jl needs to be placed within a module i see two options as it is related to paramtypes it fits there or another module for data although currently not that significant amount of code within demographydata jl it makes sense to have a module for data | 0 |
15,300 | 9,936,423,175 | IssuesEvent | 2019-07-02 19:05:15 | PuzzleServer/mainpuzzleserver | https://api.github.com/repos/PuzzleServer/mainpuzzleserver | closed | When you have answer submission soft-locked and serve out the time, you shouldn't see a message that makes you think you submitted twice | enhancement good first issue usability | When the timer disappears, it is replaced by a string that says "You already submitted X!"
But no, I only submitted X once -- it merely caused the time lock
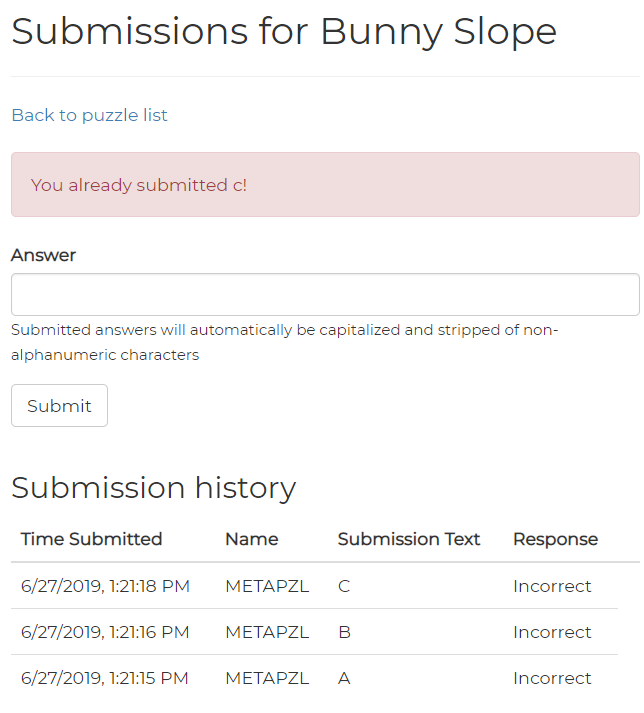
| True | When you have answer submission soft-locked and serve out the time, you shouldn't see a message that makes you think you submitted twice - When the timer disappears, it is replaced by a string that says "You already submitted X!"
But no, I only submitted X once -- it merely caused the time lock
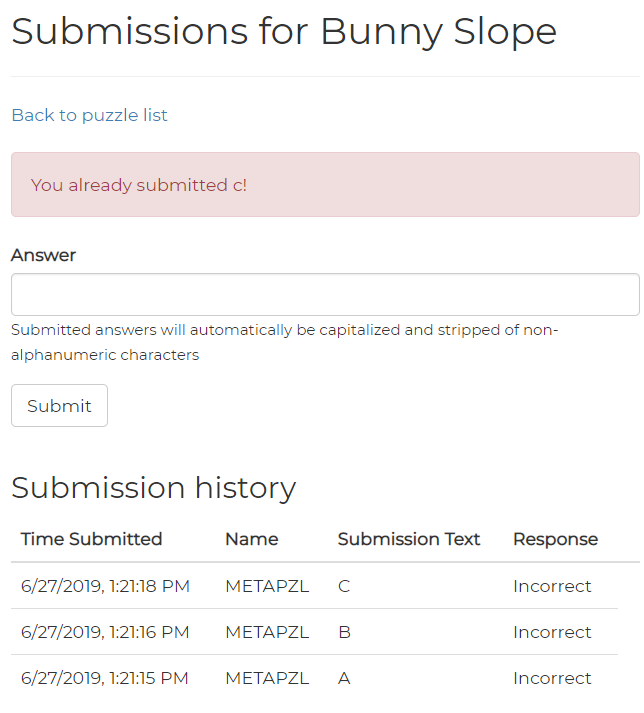
| non_priority | when you have answer submission soft locked and serve out the time you shouldn t see a message that makes you think you submitted twice when the timer disappears it is replaced by a string that says you already submitted x but no i only submitted x once it merely caused the time lock | 0 |
285,225 | 21,508,936,504 | IssuesEvent | 2022-04-28 00:45:29 | objectos/objectos | https://api.github.com/repos/objectos/objectos | closed | Logging Docs 0.1.0: Getting started section | c:documentation t:work a:logging g:incubator | Contents:
- [x] About logging
- [x] Objectos Logging
- [x] Installation
- [x] Quick tutorial | 1.0 | Logging Docs 0.1.0: Getting started section - Contents:
- [x] About logging
- [x] Objectos Logging
- [x] Installation
- [x] Quick tutorial | non_priority | logging docs getting started section contents about logging objectos logging installation quick tutorial | 0 |
97,444 | 28,297,625,440 | IssuesEvent | 2023-04-10 00:44:25 | joncampbell123/dosbox-x | https://api.github.com/repos/joncampbell123/dosbox-x | closed | 2023.03.31 - SDL2 build fails on macOS Ventura | bug build issues platform: Mac | ### Describe the bug
macOS Ventura, Apple Silicon Mac:. `build-macos-sdl2` fails with these errors:
```
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:269:21: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
IOHIDElementRef elem = IOHIDValueGetElement(value);
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:326:21: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
CFDictionaryRef keyboard = NULL, keypad = NULL;
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:586:15: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
CFDataRef uchrDataRef = TISGetInputSourceProperty(key_layout, kTISPropertyUnicodeKeyLayoutData);
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:666:13: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
NSView *parentView = [nswindow contentView];
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:720:20: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
unsigned short scancode = [event keyCode];
^
3 warnings and 7 errors generated.
make: *** [build/SDL_cocoakeyboard.lo] Error 1
```
### Steps to reproduce the behaviour
Open a terminal in macOS Ventura; enter `build-macos-sdl2`.
### Expected behavior
Build completes without errors
### What operating system(s) this bug have occurred on?
macOS Ventura 13.3, M1 Mac
### What version(s) of DOSBox-X have this bug?
source code of latest release, 2023.03.31
### Used configuration
_No response_
### Output log
_No response_
### Additional information
_No response_
### Have you checked that no similar bug report(s) exist?
- [X] I have searched and didn't find any similar bug report.
### Code of Conduct & Contributing Guidelines
- [X] I agree to follow the code of conduct and the contributing guidelines. | 1.0 | 2023.03.31 - SDL2 build fails on macOS Ventura - ### Describe the bug
macOS Ventura, Apple Silicon Mac:. `build-macos-sdl2` fails with these errors:
```
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:269:21: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
IOHIDElementRef elem = IOHIDValueGetElement(value);
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:326:21: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
CFDictionaryRef keyboard = NULL, keypad = NULL;
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:586:15: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
CFDataRef uchrDataRef = TISGetInputSourceProperty(key_layout, kTISPropertyUnicodeKeyLayoutData);
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:666:13: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
NSView *parentView = [nswindow contentView];
^
/Users/edward/Development/dosbox-x-dosbox-x-v2023.03.31/vs/sdl2/src/video/cocoa/SDL_cocoakeyboard.m:720:20: error: mixing declarations and code is incompatible with standards before C99 [-Werror,-Wdeclaration-after-statement]
unsigned short scancode = [event keyCode];
^
3 warnings and 7 errors generated.
make: *** [build/SDL_cocoakeyboard.lo] Error 1
```
### Steps to reproduce the behaviour
Open a terminal in macOS Ventura; enter `build-macos-sdl2`.
### Expected behavior
Build completes without errors
### What operating system(s) this bug have occurred on?
macOS Ventura 13.3, M1 Mac
### What version(s) of DOSBox-X have this bug?
source code of latest release, 2023.03.31
### Used configuration
_No response_
### Output log
_No response_
### Additional information
_No response_
### Have you checked that no similar bug report(s) exist?
- [X] I have searched and didn't find any similar bug report.
### Code of Conduct & Contributing Guidelines
- [X] I agree to follow the code of conduct and the contributing guidelines. | non_priority | build fails on macos ventura describe the bug macos ventura apple silicon mac build macos fails with these errors users edward development dosbox x dosbox x vs src video cocoa sdl cocoakeyboard m error mixing declarations and code is incompatible with standards before iohidelementref elem iohidvaluegetelement value users edward development dosbox x dosbox x vs src video cocoa sdl cocoakeyboard m error mixing declarations and code is incompatible with standards before cfdictionaryref keyboard null keypad null users edward development dosbox x dosbox x vs src video cocoa sdl cocoakeyboard m error mixing declarations and code is incompatible with standards before cfdataref uchrdataref tisgetinputsourceproperty key layout ktispropertyunicodekeylayoutdata users edward development dosbox x dosbox x vs src video cocoa sdl cocoakeyboard m error mixing declarations and code is incompatible with standards before nsview parentview users edward development dosbox x dosbox x vs src video cocoa sdl cocoakeyboard m error mixing declarations and code is incompatible with standards before unsigned short scancode warnings and errors generated make error steps to reproduce the behaviour open a terminal in macos ventura enter build macos expected behavior build completes without errors what operating system s this bug have occurred on macos ventura mac what version s of dosbox x have this bug source code of latest release used configuration no response output log no response additional information no response have you checked that no similar bug report s exist i have searched and didn t find any similar bug report code of conduct contributing guidelines i agree to follow the code of conduct and the contributing guidelines | 0 |
246,786 | 26,621,873,359 | IssuesEvent | 2023-01-24 11:52:30 | st4sd/st4sd-registry-ui | https://api.github.com/repos/st4sd/st4sd-registry-ui | opened | Fix misalignment in Experiment View for ExperimentHistory and AddPackage | security | Issue: when browsing the website, the content in the "History" and "Get this package" sections isn't aligned with the rest of the content, see screenshot:
<img width="707" alt="image" src="https://user-images.githubusercontent.com/10339005/214284464-f8ff01f0-1adb-4198-9851-8b17df385005.png">
We should fix this so the UI feels more consistent
Done when:
- [ ] Content in the "History" and "Get this package" section is aligned correctly | True | Fix misalignment in Experiment View for ExperimentHistory and AddPackage - Issue: when browsing the website, the content in the "History" and "Get this package" sections isn't aligned with the rest of the content, see screenshot:
<img width="707" alt="image" src="https://user-images.githubusercontent.com/10339005/214284464-f8ff01f0-1adb-4198-9851-8b17df385005.png">
We should fix this so the UI feels more consistent
Done when:
- [ ] Content in the "History" and "Get this package" section is aligned correctly | non_priority | fix misalignment in experiment view for experimenthistory and addpackage issue when browsing the website the content in the history and get this package sections isn t aligned with the rest of the content see screenshot img width alt image src we should fix this so the ui feels more consistent done when content in the history and get this package section is aligned correctly | 0 |
106,527 | 16,682,352,841 | IssuesEvent | 2021-06-08 02:32:02 | vipinsun/TrustID | https://api.github.com/repos/vipinsun/TrustID | opened | CVE-2020-35149 (Medium) detected in mquery-3.2.2.tgz | security vulnerability | ## CVE-2020-35149 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mquery-3.2.2.tgz</b></p></summary>
<p>Expressive query building for MongoDB</p>
<p>Library home page: <a href="https://registry.npmjs.org/mquery/-/mquery-3.2.2.tgz">https://registry.npmjs.org/mquery/-/mquery-3.2.2.tgz</a></p>
<p>Path to dependency file: TrustID/trustid-sdk/package.json</p>
<p>Path to vulnerable library: TrustID/trustid-sdk/node_modules/mquery/package.json</p>
<p>
Dependency Hierarchy:
- mongoose-5.9.15.tgz (Root Library)
- :x: **mquery-3.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vipinsun/TrustID/commit/1c9178c5a1b42520307da1fa7f9b1899276178ed">1c9178c5a1b42520307da1fa7f9b1899276178ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lib/utils.js in mquery before 3.2.3 allows a pollution attack because a special property (e.g., __proto__) can be copied during a merge or clone operation.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35149>CVE-2020-35149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/aheckmann/mquery/releases/tag/3.2.3">https://github.com/aheckmann/mquery/releases/tag/3.2.3</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 3.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-35149 (Medium) detected in mquery-3.2.2.tgz - ## CVE-2020-35149 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>mquery-3.2.2.tgz</b></p></summary>
<p>Expressive query building for MongoDB</p>
<p>Library home page: <a href="https://registry.npmjs.org/mquery/-/mquery-3.2.2.tgz">https://registry.npmjs.org/mquery/-/mquery-3.2.2.tgz</a></p>
<p>Path to dependency file: TrustID/trustid-sdk/package.json</p>
<p>Path to vulnerable library: TrustID/trustid-sdk/node_modules/mquery/package.json</p>
<p>
Dependency Hierarchy:
- mongoose-5.9.15.tgz (Root Library)
- :x: **mquery-3.2.2.tgz** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/vipinsun/TrustID/commit/1c9178c5a1b42520307da1fa7f9b1899276178ed">1c9178c5a1b42520307da1fa7f9b1899276178ed</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
lib/utils.js in mquery before 3.2.3 allows a pollution attack because a special property (e.g., __proto__) can be copied during a merge or clone operation.
<p>Publish Date: 2020-12-11
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-35149>CVE-2020-35149</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/aheckmann/mquery/releases/tag/3.2.3">https://github.com/aheckmann/mquery/releases/tag/3.2.3</a></p>
<p>Release Date: 2020-12-11</p>
<p>Fix Resolution: 3.2.3</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in mquery tgz cve medium severity vulnerability vulnerable library mquery tgz expressive query building for mongodb library home page a href path to dependency file trustid trustid sdk package json path to vulnerable library trustid trustid sdk node modules mquery package json dependency hierarchy mongoose tgz root library x mquery tgz vulnerable library found in head commit a href found in base branch master vulnerability details lib utils js in mquery before allows a pollution attack because a special property e g proto can be copied during a merge or clone operation publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with whitesource | 0 |
89,399 | 8,202,634,318 | IssuesEvent | 2018-09-02 12:02:19 | humera987/HumTestData | https://api.github.com/repos/humera987/HumTestData | opened | Humera_Test_Proj : team_user_signup_invalid | Humera_Test_Proj | Project : Humera_Test_Proj
Job : Stg
Env : Stg
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.57.51.56/users/team-sign-up
Request :
{
"name" : "fn1 ln",
"email" : "test@",
"password" : "12345678",
"company" : "123"
}
Response :
I/O error on POST request for "http://13.57.51.56/users/team-sign-up": Timeout waiting for connection from pool; nested exception is org.apache.http.conn.ConnectionPoolTimeoutException: Timeout waiting for connection from pool
Logs :
Assertion [@Response.errors == true] failed, expected value [true] but found []
--- FX Bot --- | 1.0 | Humera_Test_Proj : team_user_signup_invalid - Project : Humera_Test_Proj
Job : Stg
Env : Stg
Region : FXLabs/US_WEST_1
Result : fail
Status Code : 500
Headers : {}
Endpoint : http://13.57.51.56/users/team-sign-up
Request :
{
"name" : "fn1 ln",
"email" : "test@",
"password" : "12345678",
"company" : "123"
}
Response :
I/O error on POST request for "http://13.57.51.56/users/team-sign-up": Timeout waiting for connection from pool; nested exception is org.apache.http.conn.ConnectionPoolTimeoutException: Timeout waiting for connection from pool
Logs :
Assertion [@Response.errors == true] failed, expected value [true] but found []
--- FX Bot --- | non_priority | humera test proj team user signup invalid project humera test proj job stg env stg region fxlabs us west result fail status code headers endpoint request name ln email test password company response i o error on post request for timeout waiting for connection from pool nested exception is org apache http conn connectionpooltimeoutexception timeout waiting for connection from pool logs assertion failed expected value but found fx bot | 0 |
128,224 | 12,367,566,168 | IssuesEvent | 2020-05-18 12:30:00 | MonkeyStation13/MonkeyStation | https://api.github.com/repos/MonkeyStation13/MonkeyStation | opened | Tutorials! | Documentation Question | > As someone who is learning the game, I rely heavily on the tgstation wiki to function, while most of the time it serves me fine, monkeystation uses modified beestation code, which is different. Some better information about the mechanics inside or outside of the game would be very nice.
**--Issue ported over from [old repository](https://github.com/TheRealUnabomber/Monkey-Station/issues/12)--**
Original Creator: @Darkpixel797 | 1.0 | Tutorials! - > As someone who is learning the game, I rely heavily on the tgstation wiki to function, while most of the time it serves me fine, monkeystation uses modified beestation code, which is different. Some better information about the mechanics inside or outside of the game would be very nice.
**--Issue ported over from [old repository](https://github.com/TheRealUnabomber/Monkey-Station/issues/12)--**
Original Creator: @Darkpixel797 | non_priority | tutorials as someone who is learning the game i rely heavily on the tgstation wiki to function while most of the time it serves me fine monkeystation uses modified beestation code which is different some better information about the mechanics inside or outside of the game would be very nice issue ported over from original creator | 0 |
288,491 | 31,861,409,828 | IssuesEvent | 2023-09-15 11:12:02 | nidhi7598/linux-v4.19.72_CVE-2022-3564 | https://api.github.com/repos/nidhi7598/linux-v4.19.72_CVE-2022-3564 | opened | CVE-2019-11597 (High) detected in linuxlinux-4.19.294 | Mend: dependency security vulnerability | ## CVE-2019-11597 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/infiniband/core/uverbs_main.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/infiniband/core/uverbs_main.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In ImageMagick 7.0.8-43 Q16, there is a heap-based buffer over-read in the function WriteTIFFImage of coders/tiff.c, which allows an attacker to cause a denial of service or possibly information disclosure via a crafted image file.
<p>Publish Date: 2019-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11597>CVE-2019-11597</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11599">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11599</a></p>
<p>Release Date: 2019-04-29</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2019-11597 (High) detected in linuxlinux-4.19.294 - ## CVE-2019-11597 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>linuxlinux-4.19.294</b></p></summary>
<p>
<p>The Linux Kernel</p>
<p>Library home page: <a href=https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux>https://mirrors.edge.kernel.org/pub/linux/kernel/v4.x/?wsslib=linux</a></p>
<p>Found in HEAD commit: <a href="https://github.com/nidhi7598/linux-v4.19.72_CVE-2022-3564/commit/9ffee08efa44c7887e2babb8f304df0fa1094efb">9ffee08efa44c7887e2babb8f304df0fa1094efb</a></p>
<p>Found in base branch: <b>main</b></p></p>
</details>
</p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Source Files (2)</summary>
<p></p>
<p>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/infiniband/core/uverbs_main.c</b>
<img src='https://s3.amazonaws.com/wss-public/bitbucketImages/xRedImage.png' width=19 height=20> <b>/drivers/infiniband/core/uverbs_main.c</b>
</p>
</details>
<p></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png?' width=19 height=20> Vulnerability Details</summary>
<p>
In ImageMagick 7.0.8-43 Q16, there is a heap-based buffer over-read in the function WriteTIFFImage of coders/tiff.c, which allows an attacker to cause a denial of service or possibly information disclosure via a crafted image file.
<p>Publish Date: 2019-04-29
<p>URL: <a href=https://www.mend.io/vulnerability-database/CVE-2019-11597>CVE-2019-11597</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>8.1</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: High
- Integrity Impact: None
- Availability Impact: High
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11599">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-11599</a></p>
<p>Release Date: 2019-04-29</p>
<p>Fix Resolution: v5.1-rc6</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve high detected in linuxlinux cve high severity vulnerability vulnerable library linuxlinux the linux kernel library home page a href found in head commit a href found in base branch main vulnerable source files drivers infiniband core uverbs main c drivers infiniband core uverbs main c vulnerability details in imagemagick there is a heap based buffer over read in the function writetiffimage of coders tiff c which allows an attacker to cause a denial of service or possibly information disclosure via a crafted image file publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope unchanged impact metrics confidentiality impact high integrity impact none availability impact high for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend | 0 |
74,017 | 24,906,030,619 | IssuesEvent | 2022-10-29 08:54:39 | openzfs/zfs | https://api.github.com/repos/openzfs/zfs | closed | panic on zfs receive | Type: Defect Status: Stale | <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name |Ubuntu
Distribution Version |20.04
Linux Kernel |5.4.0-42-generic \#46-Ubuntu
Architecture |x86_64
ZFS Version |0.8.4-1~20.04.york0
SPL Version |0.8.4-1~20.04.york0
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
I am encountering a PANIC of ZFS upon a zfs recv that hangs the pool until the system is restarted.
I initially encountered this problem with Ubuntu 20.04's official version of ZFS (0.8.3) and then tried upgrading to 0.8.4 to see if the problem still exists. The PANIC occurs in both versions. I used the pre-built version from this PPA:
https://launchpad.net/~jonathonf/+archive/ubuntu/zfs
### Describe how to reproduce the problem
The zfs send command NOOP output:
```
# /sbin/zfs send -P -R -v -n rpool/scratch@2020-07-23-03-39-10
full rpool/scratch@2020-07-23-03-39-10 27955560808
size 27955560808
tosnap: '2020-07-23-03-39-10'
fss:
0x56f7d2ee5ca60cf0:
name: 'rpool/scratch'
parentfromsnap: 0
props:
snapshot_limit: 18446744073709551614
mountpoint: 'legacy'
snaps:
2020-07-23-03-39-10: 14988460586390450179
snapprops:
2020-07-23-03-39-10:
```
I can issue a zfs send to /dev/null that is successful:
```
# /sbin/zfs send -P -R rpool/scratch@2020-07-23-03-39-10 | pv -s 27955560808 -p -r -t -a >/dev/null
full rpool/scratch@2020-07-23-03-39-10 27955560808
size 27955560808
0:01:02 [ 430MiB/s] [ 430MiB/s] [==========================] 101%
```
The exact zfs send command used when the destination crashes:
```
# /sbin/zfs send -P -R -v rpool/scratch@2020-07-23-03-39-10
```
The zfs recv command that crashes:
```
# /sbin/zfs recv -svuF dpool/backups/xyz/jbsnet/latitude/CURRENT/rpool/scratch
```
Properties of the source dataset:
```
# zfs get all rpool/scratch@2020-07-23-03-39-10
NAME PROPERTY VALUE SOURCE
rpool/scratch@2020-07-23-03-39-10 type snapshot -
rpool/scratch@2020-07-23-03-39-10 creation Thu Jul 23 3:39 2020 -
rpool/scratch@2020-07-23-03-39-10 used 152M -
rpool/scratch@2020-07-23-03-39-10 referenced 22.1G -
rpool/scratch@2020-07-23-03-39-10 compressratio 1.21x -
rpool/scratch@2020-07-23-03-39-10 devices on default
rpool/scratch@2020-07-23-03-39-10 exec on default
rpool/scratch@2020-07-23-03-39-10 setuid on default
rpool/scratch@2020-07-23-03-39-10 createtxg 9180312 -
rpool/scratch@2020-07-23-03-39-10 xattr sa inherited from rpool
rpool/scratch@2020-07-23-03-39-10 version 5 -
rpool/scratch@2020-07-23-03-39-10 utf8only on -
rpool/scratch@2020-07-23-03-39-10 normalization formD -
rpool/scratch@2020-07-23-03-39-10 casesensitivity sensitive -
rpool/scratch@2020-07-23-03-39-10 nbmand off default
rpool/scratch@2020-07-23-03-39-10 guid 14988460586390450179 -
rpool/scratch@2020-07-23-03-39-10 primarycache all default
rpool/scratch@2020-07-23-03-39-10 secondarycache all default
rpool/scratch@2020-07-23-03-39-10 defer_destroy off -
rpool/scratch@2020-07-23-03-39-10 userrefs 1 -
rpool/scratch@2020-07-23-03-39-10 objsetid 49456 -
rpool/scratch@2020-07-23-03-39-10 mlslabel none default
rpool/scratch@2020-07-23-03-39-10 refcompressratio 1.21x -
rpool/scratch@2020-07-23-03-39-10 written 22.1G -
rpool/scratch@2020-07-23-03-39-10 clones -
rpool/scratch@2020-07-23-03-39-10 logicalreferenced 26.0G -
rpool/scratch@2020-07-23-03-39-10 acltype posixacl inherited from rpool
rpool/scratch@2020-07-23-03-39-10 context none default
rpool/scratch@2020-07-23-03-39-10 fscontext none default
rpool/scratch@2020-07-23-03-39-10 defcontext none default
rpool/scratch@2020-07-23-03-39-10 rootcontext none default
rpool/scratch@2020-07-23-03-39-10 encryption off default
```
### Include any warning/errors/backtraces from the system logs
Relevant dmesg:
```
[Mon Aug 10 09:30:15 2020] VERIFY3(count >= 0) failed (-1 >= 0)
[Mon Aug 10 09:30:15 2020] PANIC at dsl_dir.c:925:dsl_fs_ss_count_adjust()
[Mon Aug 10 09:30:15 2020] Showing stack for process 10815
[Mon Aug 10 09:30:15 2020] CPU: 0 PID: 10815 Comm: txg_sync Tainted: P OE 5.4.0-42-generic #46-Ubuntu
[Mon Aug 10 09:30:15 2020] Hardware name: HPE ProLiant MicroServer Gen10/ProLiant MicroServer Gen10, BIOS 5.12 06/26/2018
[Mon Aug 10 09:30:15 2020] Call Trace:
[Mon Aug 10 09:30:15 2020] dump_stack+0x6d/0x9a
[Mon Aug 10 09:30:15 2020] spl_dumpstack+0x29/0x2b [spl]
[Mon Aug 10 09:30:15 2020] spl_panic+0xd4/0xfc [spl]
[Mon Aug 10 09:30:15 2020] ? avl_find+0x5f/0x90 [zavl]
[Mon Aug 10 09:30:15 2020] ? dbuf_rele+0x3a/0x40 [zfs]
[Mon Aug 10 09:30:15 2020] ? dmu_buf_rele+0xe/0x10 [zfs]
[Mon Aug 10 09:30:15 2020] ? zap_unlockdir+0x3f/0x60 [zfs]
[Mon Aug 10 09:30:15 2020] ? zap_lookup_norm+0x95/0xc0 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_fs_ss_count_adjust+0x1ad/0x1c0 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_destroy_head_sync_impl+0x35c/0x980 [zfs]
[Mon Aug 10 09:30:15 2020] ? dbuf_rele+0x3a/0x40 [zfs]
[Mon Aug 10 09:30:15 2020] dmu_recv_end_sync+0x1ec/0x5a0 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_sync_task_sync+0xb6/0x100 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_pool_sync+0x3d6/0x4c0 [zfs]
[Mon Aug 10 09:30:15 2020] spa_sync+0x59b/0xf90 [zfs]
[Mon Aug 10 09:30:15 2020] ? spa_txg_history_init_io+0x106/0x110 [zfs]
[Mon Aug 10 09:30:15 2020] txg_sync_thread+0x2be/0x450 [zfs]
[Mon Aug 10 09:30:15 2020] ? txg_thread_exit.isra.0+0x60/0x60 [zfs]
[Mon Aug 10 09:30:15 2020] thread_generic_wrapper+0x79/0x90 [spl]
[Mon Aug 10 09:30:15 2020] kthread+0x104/0x140
[Mon Aug 10 09:30:15 2020] ? __thread_exit+0x20/0x20 [spl]
[Mon Aug 10 09:30:15 2020] ? kthread_park+0x90/0x90
[Mon Aug 10 09:30:15 2020] ret_from_fork+0x22/0x40
```
I've done plenty of sends and receives between these 2 systems but this only particular dataset is causing this problem, so reproducing it elsewhere may be difficult.
Is this certainly a problem with the destination side, or could it be a problem with the ZFS stream?
What other information can I provide that would help narrow the problem down?
Should the version of ZFS on the source machine matter even though its the receive that is crashing?
The source machine is running kernel 5.4.0-40-generic with the official Ubuntu zfs/spl 0.8.3-1ubuntu12.2.
| 1.0 | panic on zfs receive - <!-- Please fill out the following template, which will help other contributors address your issue. -->
<!--
Thank you for reporting an issue.
*IMPORTANT* - Please check our issue tracker before opening a new issue.
Additional valuable information can be found in the OpenZFS documentation
and mailing list archives.
Please fill in as much of the template as possible.
-->
### System information
<!-- add version after "|" character -->
Type | Version/Name
--- | ---
Distribution Name |Ubuntu
Distribution Version |20.04
Linux Kernel |5.4.0-42-generic \#46-Ubuntu
Architecture |x86_64
ZFS Version |0.8.4-1~20.04.york0
SPL Version |0.8.4-1~20.04.york0
<!--
Commands to find ZFS/SPL versions:
modinfo zfs | grep -iw version
modinfo spl | grep -iw version
-->
### Describe the problem you're observing
I am encountering a PANIC of ZFS upon a zfs recv that hangs the pool until the system is restarted.
I initially encountered this problem with Ubuntu 20.04's official version of ZFS (0.8.3) and then tried upgrading to 0.8.4 to see if the problem still exists. The PANIC occurs in both versions. I used the pre-built version from this PPA:
https://launchpad.net/~jonathonf/+archive/ubuntu/zfs
### Describe how to reproduce the problem
The zfs send command NOOP output:
```
# /sbin/zfs send -P -R -v -n rpool/scratch@2020-07-23-03-39-10
full rpool/scratch@2020-07-23-03-39-10 27955560808
size 27955560808
tosnap: '2020-07-23-03-39-10'
fss:
0x56f7d2ee5ca60cf0:
name: 'rpool/scratch'
parentfromsnap: 0
props:
snapshot_limit: 18446744073709551614
mountpoint: 'legacy'
snaps:
2020-07-23-03-39-10: 14988460586390450179
snapprops:
2020-07-23-03-39-10:
```
I can issue a zfs send to /dev/null that is successful:
```
# /sbin/zfs send -P -R rpool/scratch@2020-07-23-03-39-10 | pv -s 27955560808 -p -r -t -a >/dev/null
full rpool/scratch@2020-07-23-03-39-10 27955560808
size 27955560808
0:01:02 [ 430MiB/s] [ 430MiB/s] [==========================] 101%
```
The exact zfs send command used when the destination crashes:
```
# /sbin/zfs send -P -R -v rpool/scratch@2020-07-23-03-39-10
```
The zfs recv command that crashes:
```
# /sbin/zfs recv -svuF dpool/backups/xyz/jbsnet/latitude/CURRENT/rpool/scratch
```
Properties of the source dataset:
```
# zfs get all rpool/scratch@2020-07-23-03-39-10
NAME PROPERTY VALUE SOURCE
rpool/scratch@2020-07-23-03-39-10 type snapshot -
rpool/scratch@2020-07-23-03-39-10 creation Thu Jul 23 3:39 2020 -
rpool/scratch@2020-07-23-03-39-10 used 152M -
rpool/scratch@2020-07-23-03-39-10 referenced 22.1G -
rpool/scratch@2020-07-23-03-39-10 compressratio 1.21x -
rpool/scratch@2020-07-23-03-39-10 devices on default
rpool/scratch@2020-07-23-03-39-10 exec on default
rpool/scratch@2020-07-23-03-39-10 setuid on default
rpool/scratch@2020-07-23-03-39-10 createtxg 9180312 -
rpool/scratch@2020-07-23-03-39-10 xattr sa inherited from rpool
rpool/scratch@2020-07-23-03-39-10 version 5 -
rpool/scratch@2020-07-23-03-39-10 utf8only on -
rpool/scratch@2020-07-23-03-39-10 normalization formD -
rpool/scratch@2020-07-23-03-39-10 casesensitivity sensitive -
rpool/scratch@2020-07-23-03-39-10 nbmand off default
rpool/scratch@2020-07-23-03-39-10 guid 14988460586390450179 -
rpool/scratch@2020-07-23-03-39-10 primarycache all default
rpool/scratch@2020-07-23-03-39-10 secondarycache all default
rpool/scratch@2020-07-23-03-39-10 defer_destroy off -
rpool/scratch@2020-07-23-03-39-10 userrefs 1 -
rpool/scratch@2020-07-23-03-39-10 objsetid 49456 -
rpool/scratch@2020-07-23-03-39-10 mlslabel none default
rpool/scratch@2020-07-23-03-39-10 refcompressratio 1.21x -
rpool/scratch@2020-07-23-03-39-10 written 22.1G -
rpool/scratch@2020-07-23-03-39-10 clones -
rpool/scratch@2020-07-23-03-39-10 logicalreferenced 26.0G -
rpool/scratch@2020-07-23-03-39-10 acltype posixacl inherited from rpool
rpool/scratch@2020-07-23-03-39-10 context none default
rpool/scratch@2020-07-23-03-39-10 fscontext none default
rpool/scratch@2020-07-23-03-39-10 defcontext none default
rpool/scratch@2020-07-23-03-39-10 rootcontext none default
rpool/scratch@2020-07-23-03-39-10 encryption off default
```
### Include any warning/errors/backtraces from the system logs
Relevant dmesg:
```
[Mon Aug 10 09:30:15 2020] VERIFY3(count >= 0) failed (-1 >= 0)
[Mon Aug 10 09:30:15 2020] PANIC at dsl_dir.c:925:dsl_fs_ss_count_adjust()
[Mon Aug 10 09:30:15 2020] Showing stack for process 10815
[Mon Aug 10 09:30:15 2020] CPU: 0 PID: 10815 Comm: txg_sync Tainted: P OE 5.4.0-42-generic #46-Ubuntu
[Mon Aug 10 09:30:15 2020] Hardware name: HPE ProLiant MicroServer Gen10/ProLiant MicroServer Gen10, BIOS 5.12 06/26/2018
[Mon Aug 10 09:30:15 2020] Call Trace:
[Mon Aug 10 09:30:15 2020] dump_stack+0x6d/0x9a
[Mon Aug 10 09:30:15 2020] spl_dumpstack+0x29/0x2b [spl]
[Mon Aug 10 09:30:15 2020] spl_panic+0xd4/0xfc [spl]
[Mon Aug 10 09:30:15 2020] ? avl_find+0x5f/0x90 [zavl]
[Mon Aug 10 09:30:15 2020] ? dbuf_rele+0x3a/0x40 [zfs]
[Mon Aug 10 09:30:15 2020] ? dmu_buf_rele+0xe/0x10 [zfs]
[Mon Aug 10 09:30:15 2020] ? zap_unlockdir+0x3f/0x60 [zfs]
[Mon Aug 10 09:30:15 2020] ? zap_lookup_norm+0x95/0xc0 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_fs_ss_count_adjust+0x1ad/0x1c0 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_destroy_head_sync_impl+0x35c/0x980 [zfs]
[Mon Aug 10 09:30:15 2020] ? dbuf_rele+0x3a/0x40 [zfs]
[Mon Aug 10 09:30:15 2020] dmu_recv_end_sync+0x1ec/0x5a0 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_sync_task_sync+0xb6/0x100 [zfs]
[Mon Aug 10 09:30:15 2020] dsl_pool_sync+0x3d6/0x4c0 [zfs]
[Mon Aug 10 09:30:15 2020] spa_sync+0x59b/0xf90 [zfs]
[Mon Aug 10 09:30:15 2020] ? spa_txg_history_init_io+0x106/0x110 [zfs]
[Mon Aug 10 09:30:15 2020] txg_sync_thread+0x2be/0x450 [zfs]
[Mon Aug 10 09:30:15 2020] ? txg_thread_exit.isra.0+0x60/0x60 [zfs]
[Mon Aug 10 09:30:15 2020] thread_generic_wrapper+0x79/0x90 [spl]
[Mon Aug 10 09:30:15 2020] kthread+0x104/0x140
[Mon Aug 10 09:30:15 2020] ? __thread_exit+0x20/0x20 [spl]
[Mon Aug 10 09:30:15 2020] ? kthread_park+0x90/0x90
[Mon Aug 10 09:30:15 2020] ret_from_fork+0x22/0x40
```
I've done plenty of sends and receives between these 2 systems but this only particular dataset is causing this problem, so reproducing it elsewhere may be difficult.
Is this certainly a problem with the destination side, or could it be a problem with the ZFS stream?
What other information can I provide that would help narrow the problem down?
Should the version of ZFS on the source machine matter even though its the receive that is crashing?
The source machine is running kernel 5.4.0-40-generic with the official Ubuntu zfs/spl 0.8.3-1ubuntu12.2.
| non_priority | panic on zfs receive thank you for reporting an issue important please check our issue tracker before opening a new issue additional valuable information can be found in the openzfs documentation and mailing list archives please fill in as much of the template as possible system information type version name distribution name ubuntu distribution version linux kernel generic ubuntu architecture zfs version spl version commands to find zfs spl versions modinfo zfs grep iw version modinfo spl grep iw version describe the problem you re observing i am encountering a panic of zfs upon a zfs recv that hangs the pool until the system is restarted i initially encountered this problem with ubuntu s official version of zfs and then tried upgrading to to see if the problem still exists the panic occurs in both versions i used the pre built version from this ppa describe how to reproduce the problem the zfs send command noop output sbin zfs send p r v n rpool scratch full rpool scratch size tosnap fss name rpool scratch parentfromsnap props snapshot limit mountpoint legacy snaps snapprops i can issue a zfs send to dev null that is successful sbin zfs send p r rpool scratch pv s p r t a dev null full rpool scratch size the exact zfs send command used when the destination crashes sbin zfs send p r v rpool scratch the zfs recv command that crashes sbin zfs recv svuf dpool backups xyz jbsnet latitude current rpool scratch properties of the source dataset zfs get all rpool scratch name property value source rpool scratch type snapshot rpool scratch creation thu jul rpool scratch used rpool scratch referenced rpool scratch compressratio rpool scratch devices on default rpool scratch exec on default rpool scratch setuid on default rpool scratch createtxg rpool scratch xattr sa inherited from rpool rpool scratch version rpool scratch on rpool scratch normalization formd rpool scratch casesensitivity sensitive rpool scratch nbmand off default rpool scratch guid rpool scratch primarycache all default rpool scratch secondarycache all default rpool scratch defer destroy off rpool scratch userrefs rpool scratch objsetid rpool scratch mlslabel none default rpool scratch refcompressratio rpool scratch written rpool scratch clones rpool scratch logicalreferenced rpool scratch acltype posixacl inherited from rpool rpool scratch context none default rpool scratch fscontext none default rpool scratch defcontext none default rpool scratch rootcontext none default rpool scratch encryption off default include any warning errors backtraces from the system logs relevant dmesg count failed panic at dsl dir c dsl fs ss count adjust showing stack for process cpu pid comm txg sync tainted p oe generic ubuntu hardware name hpe proliant microserver proliant microserver bios call trace dump stack spl dumpstack spl panic avl find dbuf rele dmu buf rele zap unlockdir zap lookup norm dsl fs ss count adjust dsl destroy head sync impl dbuf rele dmu recv end sync dsl sync task sync dsl pool sync spa sync spa txg history init io txg sync thread txg thread exit isra thread generic wrapper kthread thread exit kthread park ret from fork i ve done plenty of sends and receives between these systems but this only particular dataset is causing this problem so reproducing it elsewhere may be difficult is this certainly a problem with the destination side or could it be a problem with the zfs stream what other information can i provide that would help narrow the problem down should the version of zfs on the source machine matter even though its the receive that is crashing the source machine is running kernel generic with the official ubuntu zfs spl | 0 |
154,392 | 19,716,547,855 | IssuesEvent | 2022-01-13 11:33:55 | elastic/kibana | https://api.github.com/repos/elastic/kibana | opened | [Security Solution] The message on the `Activity log` gets removed when the user refresh the page and shows `'Nothing more to show'`. | bug impact:medium Team: SecuritySolution Team:Onboarding and Lifecycle Mgt v7.17.0 | **Describe the bug:**
The message on the Activity log gets removed when the user refresh the page and shows 'Nothing more to show'.
**Build Details:**
VERSION: 7.17.0-BC1
BUILD: 46386
COMMIT: c9b31753ccda9d79ad1f6f7b106674a7ba430000
ARTIFACT: https://staging.elastic.co/7.17.0-2a228a35/summary-7.17.0.html
**Preconditions:**
Elastic 7.17.0-BC1 environment should be deployed.
**Steps to Reproduce:**
1. Navigate to the Endpoints tab under security app.
2. Click on the Hostname.
3. Navigate to the Activity Log.
4. Observe that the message on the `Activity log` gets removed when the user refresh the page and shows `'Nothing more to show'`.
**Test data:**
N/A
**Impacted Test case(s):**
N/A
**Actual Result:**
The message on the Activity log gets removed when the user refresh the page and shows 'Nothing more to show'.
**Expected Result:**
The message on the Activity log should not get remove when the user refresh the page.
**What's Working:**
N/A
**What's Not Working:**
N/A
**Screen-Recording:**
https://user-images.githubusercontent.com/84007952/149313013-73eb6aa1-79ab-4d36-a9aa-94a04346377c.mp4
**Logs:**
N/A
| True | [Security Solution] The message on the `Activity log` gets removed when the user refresh the page and shows `'Nothing more to show'`. - **Describe the bug:**
The message on the Activity log gets removed when the user refresh the page and shows 'Nothing more to show'.
**Build Details:**
VERSION: 7.17.0-BC1
BUILD: 46386
COMMIT: c9b31753ccda9d79ad1f6f7b106674a7ba430000
ARTIFACT: https://staging.elastic.co/7.17.0-2a228a35/summary-7.17.0.html
**Preconditions:**
Elastic 7.17.0-BC1 environment should be deployed.
**Steps to Reproduce:**
1. Navigate to the Endpoints tab under security app.
2. Click on the Hostname.
3. Navigate to the Activity Log.
4. Observe that the message on the `Activity log` gets removed when the user refresh the page and shows `'Nothing more to show'`.
**Test data:**
N/A
**Impacted Test case(s):**
N/A
**Actual Result:**
The message on the Activity log gets removed when the user refresh the page and shows 'Nothing more to show'.
**Expected Result:**
The message on the Activity log should not get remove when the user refresh the page.
**What's Working:**
N/A
**What's Not Working:**
N/A
**Screen-Recording:**
https://user-images.githubusercontent.com/84007952/149313013-73eb6aa1-79ab-4d36-a9aa-94a04346377c.mp4
**Logs:**
N/A
| non_priority | the message on the activity log gets removed when the user refresh the page and shows nothing more to show describe the bug the message on the activity log gets removed when the user refresh the page and shows nothing more to show build details version build commit artifact preconditions elastic environment should be deployed steps to reproduce navigate to the endpoints tab under security app click on the hostname navigate to the activity log observe that the message on the activity log gets removed when the user refresh the page and shows nothing more to show test data n a impacted test case s n a actual result the message on the activity log gets removed when the user refresh the page and shows nothing more to show expected result the message on the activity log should not get remove when the user refresh the page what s working n a what s not working n a screen recording logs n a | 0 |
26,178 | 6,755,461,707 | IssuesEvent | 2017-10-24 00:40:44 | jascam/CodePlexFoo | https://api.github.com/repos/jascam/CodePlexFoo | closed | ASP.NET GridView CRUD Demo | ASP.NET CodePlexMigrationInitiated impact: Medium Task | This example use GridView control to demonstrate all the common database operations in ASP.NET webform page, including data query, update, insert, delete.
#### Migrated CodePlex Work Item Details
CodePlex Work Item ID: '3552'
Vote count: '1'
| 1.0 | ASP.NET GridView CRUD Demo - This example use GridView control to demonstrate all the common database operations in ASP.NET webform page, including data query, update, insert, delete.
#### Migrated CodePlex Work Item Details
CodePlex Work Item ID: '3552'
Vote count: '1'
| non_priority | asp net gridview crud demo this example use gridview control to demonstrate all the common database operations in asp net webform page including data query update insert delete migrated codeplex work item details codeplex work item id vote count | 0 |
64,515 | 8,742,907,502 | IssuesEvent | 2018-12-12 17:36:52 | terraform-providers/terraform-provider-google | https://api.github.com/repos/terraform-providers/terraform-provider-google | closed | GCE instances being created with automatic_restart set to OFF | bug documentation upstream-terraform | ### Terraform Version
Terraform v0.11.8
+ provider.google v1.16.2
### Affected Resource(s)
- google_compute_instance
Affects multiple resources.
### Terraform Configuration Files
```hcl
data "google_compute_image" "memcache_image" {
project = "terraform-sandbox"
family = "${ var.base_disk_image }"
}
data "google_compute_subnetwork" "primary" {
name = "primary"
project = "sharedvpc-prod"
}
resource "google_compute_instance" "memcache-deploy" {
count = "${ var.size }"
name = "${ var.keyspace }${ format("%03d", count.index + 1) }"
machine_type = "${ var.machine_type }"
min_cpu_platform = "${ var.min_cpu_platform }"
zone = "${ count.index % 2 == 0 ? lookup(var.region_zone, 0) : lookup(var.region_zone, 1) }"
tags = "${ var.tags }"
boot_disk {
initialize_params {
size = "${ var.disk_size }"
type = "pd-standard"
image = "${ data.google_compute_image.memcache_image.self_link }"
}
}
allow_stopping_for_update = "true"
lifecycle {
ignore_changes = ["boot_disk"]
}
network_interface {
subnetwork = "${ data.google_compute_subnetwork.primary.self_link }"
access_config = []
}
}
```
### Debug Output
Not sure how to do this
### Expected Behavior
Newly created instances are instantiated with "Automatic Restart: On (true)"
### Actual Behavior
Newly created instances are coming up with "Automatic Restart: Off (false)"
### Steps to Reproduce
1. `terraform apply`
### Important Factoids
Nothing to mention, mostly vanilla Terraform
### References
None
| 1.0 | GCE instances being created with automatic_restart set to OFF - ### Terraform Version
Terraform v0.11.8
+ provider.google v1.16.2
### Affected Resource(s)
- google_compute_instance
Affects multiple resources.
### Terraform Configuration Files
```hcl
data "google_compute_image" "memcache_image" {
project = "terraform-sandbox"
family = "${ var.base_disk_image }"
}
data "google_compute_subnetwork" "primary" {
name = "primary"
project = "sharedvpc-prod"
}
resource "google_compute_instance" "memcache-deploy" {
count = "${ var.size }"
name = "${ var.keyspace }${ format("%03d", count.index + 1) }"
machine_type = "${ var.machine_type }"
min_cpu_platform = "${ var.min_cpu_platform }"
zone = "${ count.index % 2 == 0 ? lookup(var.region_zone, 0) : lookup(var.region_zone, 1) }"
tags = "${ var.tags }"
boot_disk {
initialize_params {
size = "${ var.disk_size }"
type = "pd-standard"
image = "${ data.google_compute_image.memcache_image.self_link }"
}
}
allow_stopping_for_update = "true"
lifecycle {
ignore_changes = ["boot_disk"]
}
network_interface {
subnetwork = "${ data.google_compute_subnetwork.primary.self_link }"
access_config = []
}
}
```
### Debug Output
Not sure how to do this
### Expected Behavior
Newly created instances are instantiated with "Automatic Restart: On (true)"
### Actual Behavior
Newly created instances are coming up with "Automatic Restart: Off (false)"
### Steps to Reproduce
1. `terraform apply`
### Important Factoids
Nothing to mention, mostly vanilla Terraform
### References
None
| non_priority | gce instances being created with automatic restart set to off terraform version terraform provider google affected resource s google compute instance affects multiple resources terraform configuration files hcl data google compute image memcache image project terraform sandbox family var base disk image data google compute subnetwork primary name primary project sharedvpc prod resource google compute instance memcache deploy count var size name var keyspace format count index machine type var machine type min cpu platform var min cpu platform zone count index lookup var region zone lookup var region zone tags var tags boot disk initialize params size var disk size type pd standard image data google compute image memcache image self link allow stopping for update true lifecycle ignore changes network interface subnetwork data google compute subnetwork primary self link access config debug output not sure how to do this expected behavior newly created instances are instantiated with automatic restart on true actual behavior newly created instances are coming up with automatic restart off false steps to reproduce terraform apply important factoids nothing to mention mostly vanilla terraform references none | 0 |
52,790 | 13,771,526,306 | IssuesEvent | 2020-10-07 22:12:24 | shaundmorris/ddf | https://api.github.com/repos/shaundmorris/ddf | closed | WS-2017-0195 Medium Severity Vulnerability detected by WhiteSource | security vulnerability wontfix | ## WS-2017-0195 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.2.min.js</b>, <b>jquery-2.1.3.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>path: /ddf/distribution/solr-distro/target/solr-7.4.0/server/solr-webapp/webapp/libs/jquery-1.7.2.min.js,/ddf/distribution/kernel/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-1.7.2.min.js,/ddf/distribution/ddf/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-1.7.2.min.js</p>
<p>
<p>Library home page: <a href=https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js>https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.1.3.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>path: /ddf/distribution/ddf/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-2.1.3.min.js,/ddf/distribution/solr-distro/target/solr-7.4.0/server/solr-webapp/webapp/libs/jquery-2.1.3.min.js,/ddf/distribution/kernel/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-2.1.3.min.js</p>
<p>
<p>Library home page: <a href=https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.3/jquery.min.js>https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.3/jquery.min.js</a></p>
Dependency Hierarchy:
- :x: **jquery-2.1.3.min.js** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In v2.2.4 and previous, a lowercasing logic was used on the attribute names and was removed in v3.0.0.
Because of this, boolean attributes whose names were not all lowercase cause infinite recursion, and will exceed the stack call limit.
<p>Publish Date: 2017-04-15
<p>URL: <a href=https://nodesecurity.io/advisories/330>WS-2017-0195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/jquery/jquery/commit/d12e13de19303b497cc99ddceb280d9d4d53ee5c">https://github.com/jquery/jquery/commit/d12e13de19303b497cc99ddceb280d9d4d53ee5c</a></p>
<p>Release Date: 2016-05-29</p>
<p>Fix Resolution: Replace or update the following files: attr.js, attributes.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | WS-2017-0195 Medium Severity Vulnerability detected by WhiteSource - ## WS-2017-0195 - Medium Severity Vulnerability
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/vulnerability_details.png' width=19 height=20> Vulnerable Libraries - <b>jquery-1.7.2.min.js</b>, <b>jquery-2.1.3.min.js</b></p></summary>
<p>
<details><summary><b>jquery-1.7.2.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>path: /ddf/distribution/solr-distro/target/solr-7.4.0/server/solr-webapp/webapp/libs/jquery-1.7.2.min.js,/ddf/distribution/kernel/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-1.7.2.min.js,/ddf/distribution/ddf/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-1.7.2.min.js</p>
<p>
<p>Library home page: <a href=https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js>https://cdnjs.cloudflare.com/ajax/libs/jquery/1.7.2/jquery.min.js</a></p>
Dependency Hierarchy:
- :x: **jquery-1.7.2.min.js** (Vulnerable Library)
</details>
<details><summary><b>jquery-2.1.3.min.js</b></p></summary>
<p>JavaScript library for DOM operations</p>
<p>path: /ddf/distribution/ddf/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-2.1.3.min.js,/ddf/distribution/solr-distro/target/solr-7.4.0/server/solr-webapp/webapp/libs/jquery-2.1.3.min.js,/ddf/distribution/kernel/target/dependencies/solr/server/solr-webapp/webapp/libs/jquery-2.1.3.min.js</p>
<p>
<p>Library home page: <a href=https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.3/jquery.min.js>https://cdnjs.cloudflare.com/ajax/libs/jquery/2.1.3/jquery.min.js</a></p>
Dependency Hierarchy:
- :x: **jquery-2.1.3.min.js** (Vulnerable Library)
</details>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
In v2.2.4 and previous, a lowercasing logic was used on the attribute names and was removed in v3.0.0.
Because of this, boolean attributes whose names were not all lowercase cause infinite recursion, and will exceed the stack call limit.
<p>Publish Date: 2017-04-15
<p>URL: <a href=https://nodesecurity.io/advisories/330>WS-2017-0195</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/cvss3.png' width=19 height=20> CVSS 2 Score Details (<b>5.3</b>)</summary>
<p>
Base Score Metrics not available</p>
</p>
</details>
<p></p>
<details><summary><img src='https://www.whitesourcesoftware.com/wp-content/uploads/2018/10/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Change files</p>
<p>Origin: <a href="https://github.com/jquery/jquery/commit/d12e13de19303b497cc99ddceb280d9d4d53ee5c">https://github.com/jquery/jquery/commit/d12e13de19303b497cc99ddceb280d9d4d53ee5c</a></p>
<p>Release Date: 2016-05-29</p>
<p>Fix Resolution: Replace or update the following files: attr.js, attributes.js</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | ws medium severity vulnerability detected by whitesource ws medium severity vulnerability vulnerable libraries jquery min js jquery min js jquery min js javascript library for dom operations path ddf distribution solr distro target solr server solr webapp webapp libs jquery min js ddf distribution kernel target dependencies solr server solr webapp webapp libs jquery min js ddf distribution ddf target dependencies solr server solr webapp webapp libs jquery min js library home page a href dependency hierarchy x jquery min js vulnerable library jquery min js javascript library for dom operations path ddf distribution ddf target dependencies solr server solr webapp webapp libs jquery min js ddf distribution solr distro target solr server solr webapp webapp libs jquery min js ddf distribution kernel target dependencies solr server solr webapp webapp libs jquery min js library home page a href dependency hierarchy x jquery min js vulnerable library vulnerability details in and previous a lowercasing logic was used on the attribute names and was removed in because of this boolean attributes whose names were not all lowercase cause infinite recursion and will exceed the stack call limit publish date url a href cvss score details base score metrics not available suggested fix type change files origin a href release date fix resolution replace or update the following files attr js attributes js step up your open source security game with whitesource | 0 |
71,550 | 15,207,776,905 | IssuesEvent | 2021-02-17 00:59:50 | billmcchesney1/foxtrot | https://api.github.com/repos/billmcchesney1/foxtrot | opened | CVE-2018-8012 (High) detected in zookeeper-3.4.6.jar | security vulnerability | ## CVE-2018-8012 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>zookeeper-3.4.6.jar</b></p></summary>
<p>null</p>
<p>Path to dependency file: foxtrot/foxtrot-translator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/zookeeper/zookeeper/3.4.6/zookeeper-3.4.6.jar</p>
<p>
Dependency Hierarchy:
- hbase-server-1.2.1.jar (Root Library)
- :x: **zookeeper-3.4.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/foxtrot/commit/ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc">ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
No authentication/authorization is enforced when a server attempts to join a quorum in Apache ZooKeeper before 3.4.10, and 3.5.0-alpha through 3.5.3-beta. As a result an arbitrary end point could join the cluster and begin propagating counterfeit changes to the leader.
<p>Publish Date: 2018-05-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8012>CVE-2018-8012</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-8012">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-8012</a></p>
<p>Release Date: 2018-05-21</p>
<p>Fix Resolution: 3.4.10,3.5.4-beta</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.zookeeper","packageName":"zookeeper","packageVersion":"3.4.6","packageFilePaths":["/foxtrot-translator/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hbase:hbase-server:1.2.1;org.apache.zookeeper:zookeeper:3.4.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.10,3.5.4-beta"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-8012","vulnerabilityDetails":"No authentication/authorization is enforced when a server attempts to join a quorum in Apache ZooKeeper before 3.4.10, and 3.5.0-alpha through 3.5.3-beta. As a result an arbitrary end point could join the cluster and begin propagating counterfeit changes to the leader.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8012","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | True | CVE-2018-8012 (High) detected in zookeeper-3.4.6.jar - ## CVE-2018-8012 - High Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>zookeeper-3.4.6.jar</b></p></summary>
<p>null</p>
<p>Path to dependency file: foxtrot/foxtrot-translator/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/zookeeper/zookeeper/3.4.6/zookeeper-3.4.6.jar</p>
<p>
Dependency Hierarchy:
- hbase-server-1.2.1.jar (Root Library)
- :x: **zookeeper-3.4.6.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/billmcchesney1/foxtrot/commit/ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc">ffb8a6014463ce8aac1bf6e7dc9a23fc4a2a8adc</a></p>
<p>Found in base branch: <b>master</b></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/high_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
No authentication/authorization is enforced when a server attempts to join a quorum in Apache ZooKeeper before 3.4.10, and 3.5.0-alpha through 3.5.3-beta. As a result an arbitrary end point could join the cluster and begin propagating counterfeit changes to the leader.
<p>Publish Date: 2018-05-21
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8012>CVE-2018-8012</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>7.5</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: None
- Integrity Impact: High
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-8012">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-8012</a></p>
<p>Release Date: 2018-05-21</p>
<p>Fix Resolution: 3.4.10,3.5.4-beta</p>
</p>
</details>
<p></p>
<!-- <REMEDIATE>{"isOpenPROnVulnerability":true,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.apache.zookeeper","packageName":"zookeeper","packageVersion":"3.4.6","packageFilePaths":["/foxtrot-translator/pom.xml"],"isTransitiveDependency":true,"dependencyTree":"org.apache.hbase:hbase-server:1.2.1;org.apache.zookeeper:zookeeper:3.4.6","isMinimumFixVersionAvailable":true,"minimumFixVersion":"3.4.10,3.5.4-beta"}],"baseBranches":["master"],"vulnerabilityIdentifier":"CVE-2018-8012","vulnerabilityDetails":"No authentication/authorization is enforced when a server attempts to join a quorum in Apache ZooKeeper before 3.4.10, and 3.5.0-alpha through 3.5.3-beta. As a result an arbitrary end point could join the cluster and begin propagating counterfeit changes to the leader.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-8012","cvss3Severity":"high","cvss3Score":"7.5","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"None","UI":"None","AV":"Network","I":"High"},"extraData":{}}</REMEDIATE> --> | non_priority | cve high detected in zookeeper jar cve high severity vulnerability vulnerable library zookeeper jar null path to dependency file foxtrot foxtrot translator pom xml path to vulnerable library home wss scanner repository org apache zookeeper zookeeper zookeeper jar dependency hierarchy hbase server jar root library x zookeeper jar vulnerable library found in head commit a href found in base branch master vulnerability details no authentication authorization is enforced when a server attempts to join a quorum in apache zookeeper before and alpha through beta as a result an arbitrary end point could join the cluster and begin propagating counterfeit changes to the leader publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact none integrity impact high availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution beta isopenpronvulnerability true ispackagebased true isdefaultbranch true packages istransitivedependency true dependencytree org apache hbase hbase server org apache zookeeper zookeeper isminimumfixversionavailable true minimumfixversion beta basebranches vulnerabilityidentifier cve vulnerabilitydetails no authentication authorization is enforced when a server attempts to join a quorum in apache zookeeper before and alpha through beta as a result an arbitrary end point could join the cluster and begin propagating counterfeit changes to the leader vulnerabilityurl | 0 |
108,643 | 16,796,211,161 | IssuesEvent | 2021-06-16 04:11:14 | Techini/WebGoat | https://api.github.com/repos/Techini/WebGoat | opened | CVE-2020-13943 (Medium) detected in tomcat-embed-core-9.0.27.jar | security vulnerability | ## CVE-2020-13943 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.27.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: WebGoat/webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.27/tomcat-embed-core-9.0.27.jar</p>
<p>
Dependency Hierarchy:
- webwolf-v8.0.0-SNAPSHOT.jar (Root Library)
- spring-boot-starter-web-2.2.0.RELEASE.jar
- spring-boot-starter-tomcat-2.2.0.RELEASE.jar
- :x: **tomcat-embed-core-9.0.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Techini/WebGoat/commit/d33cc0e32a0d1b949ff1b85af16890cd452276f8">d33cc0e32a0d1b949ff1b85af16890cd452276f8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
If an HTTP/2 client connecting to Apache Tomcat 10.0.0-M1 to 10.0.0-M7, 9.0.0.M1 to 9.0.37 or 8.5.0 to 8.5.57 exceeded the agreed maximum number of concurrent streams for a connection (in violation of the HTTP/2 protocol), it was possible that a subsequent request made on that connection could contain HTTP headers - including HTTP/2 pseudo headers - from a previous request rather than the intended headers. This could lead to users seeing responses for unexpected resources.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13943>CVE-2020-13943</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2020-10-12</p>
<p>Fix Resolution: org.apache.tomcat:tomcat-coyote:8.5.58,9.0.38,10.0.0-M8;org.apache.tomcat.embed:tomcat-embed-core:8.5.58,9.0.38,10.0.0-M8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | True | CVE-2020-13943 (Medium) detected in tomcat-embed-core-9.0.27.jar - ## CVE-2020-13943 - Medium Severity Vulnerability
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>tomcat-embed-core-9.0.27.jar</b></p></summary>
<p>Core Tomcat implementation</p>
<p>Library home page: <a href="https://tomcat.apache.org/">https://tomcat.apache.org/</a></p>
<p>Path to dependency file: WebGoat/webgoat-integration-tests/pom.xml</p>
<p>Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/tomcat/embed/tomcat-embed-core/9.0.27/tomcat-embed-core-9.0.27.jar</p>
<p>
Dependency Hierarchy:
- webwolf-v8.0.0-SNAPSHOT.jar (Root Library)
- spring-boot-starter-web-2.2.0.RELEASE.jar
- spring-boot-starter-tomcat-2.2.0.RELEASE.jar
- :x: **tomcat-embed-core-9.0.27.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/Techini/WebGoat/commit/d33cc0e32a0d1b949ff1b85af16890cd452276f8">d33cc0e32a0d1b949ff1b85af16890cd452276f8</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Vulnerability Details</summary>
<p>
If an HTTP/2 client connecting to Apache Tomcat 10.0.0-M1 to 10.0.0-M7, 9.0.0.M1 to 9.0.37 or 8.5.0 to 8.5.57 exceeded the agreed maximum number of concurrent streams for a connection (in violation of the HTTP/2 protocol), it was possible that a subsequent request made on that connection could contain HTTP headers - including HTTP/2 pseudo headers - from a previous request rather than the intended headers. This could lead to users seeing responses for unexpected resources.
<p>Publish Date: 2020-10-12
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2020-13943>CVE-2020-13943</a></p>
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS 3 Score Details (<b>4.3</b>)</summary>
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: Low
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
</details>
<p></p>
<details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/suggested_fix.png' width=19 height=20> Suggested Fix</summary>
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E">https://lists.apache.org/thread.html/r4a390027eb27e4550142fac6c8317cc684b157ae314d31514747f307%40%3Cannounce.tomcat.apache.org%3E</a></p>
<p>Release Date: 2020-10-12</p>
<p>Fix Resolution: org.apache.tomcat:tomcat-coyote:8.5.58,9.0.38,10.0.0-M8;org.apache.tomcat.embed:tomcat-embed-core:8.5.58,9.0.38,10.0.0-M8</p>
</p>
</details>
<p></p>
***
Step up your Open Source Security Game with WhiteSource [here](https://www.whitesourcesoftware.com/full_solution_bolt_github) | non_priority | cve medium detected in tomcat embed core jar cve medium severity vulnerability vulnerable library tomcat embed core jar core tomcat implementation library home page a href path to dependency file webgoat webgoat integration tests pom xml path to vulnerable library home wss scanner repository org apache tomcat embed tomcat embed core tomcat embed core jar dependency hierarchy webwolf snapshot jar root library spring boot starter web release jar spring boot starter tomcat release jar x tomcat embed core jar vulnerable library found in head commit a href vulnerability details if an http client connecting to apache tomcat to to or to exceeded the agreed maximum number of concurrent streams for a connection in violation of the http protocol it was possible that a subsequent request made on that connection could contain http headers including http pseudo headers from a previous request rather than the intended headers this could lead to users seeing responses for unexpected resources publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required low user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution org apache tomcat tomcat coyote org apache tomcat embed tomcat embed core step up your open source security game with whitesource | 0 |
2,766 | 3,851,781,129 | IssuesEvent | 2016-04-06 04:45:05 | deis/deis | https://api.github.com/repos/deis/deis | closed | Need long-running cluster test | test-infrastructure | To assess platform stability, we need to stand up a Deis cluster and hand it off for multi-day testing, interactive or automated. Most testing currently centers on provisioning and accomplishing the basic workflow without incident, but there could be issues that are missed that only appear after prolonged activity or heavy load. | 1.0 | Need long-running cluster test - To assess platform stability, we need to stand up a Deis cluster and hand it off for multi-day testing, interactive or automated. Most testing currently centers on provisioning and accomplishing the basic workflow without incident, but there could be issues that are missed that only appear after prolonged activity or heavy load. | non_priority | need long running cluster test to assess platform stability we need to stand up a deis cluster and hand it off for multi day testing interactive or automated most testing currently centers on provisioning and accomplishing the basic workflow without incident but there could be issues that are missed that only appear after prolonged activity or heavy load | 0 |
20,076 | 5,971,514,783 | IssuesEvent | 2017-05-31 02:52:39 | foodoasisla/site | https://api.github.com/repos/foodoasisla/site | opened | Possible code refactor: remove "uri" property from data files | code idea | Could instead get the URL of an individual item in a collection using collectionname.url in Jekyll, instead of using hard-coded "uri" property on each location. | 1.0 | Possible code refactor: remove "uri" property from data files - Could instead get the URL of an individual item in a collection using collectionname.url in Jekyll, instead of using hard-coded "uri" property on each location. | non_priority | possible code refactor remove uri property from data files could instead get the url of an individual item in a collection using collectionname url in jekyll instead of using hard coded uri property on each location | 0 |
80,244 | 30,183,640,914 | IssuesEvent | 2023-07-04 10:31:16 | vector-im/element-x-ios | https://api.github.com/repos/vector-im/element-x-ios | opened | Timeline flashes stale messages on entering a room (especially after SS expiration) | T-Defect | ### Steps to reproduce
1. Enter a room that you haven't viewed before in the current session (you may potentially need to wait for SS expiration)
2. As the room history syncs, watch the timeline flicker / spasm for a few frames (showing stale messages from ~20 messages ago), and recover again.
This video shows what the flashing looks like (in this instance it's triggered by a proxy misconfiguration bug causing SS to expires every few seconds):
https://github.com/vector-im/element-x-ios/assets/1294269/36164c6f-977a-41c4-86fd-790d1882c773
### Outcome
#### What did you expect?
Timeline that doesn't flicker horribly
#### What happened instead?
Flickering spasming timeline
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
271
### Homeserver
_No response_
### Will you send logs?
No | 1.0 | Timeline flashes stale messages on entering a room (especially after SS expiration) - ### Steps to reproduce
1. Enter a room that you haven't viewed before in the current session (you may potentially need to wait for SS expiration)
2. As the room history syncs, watch the timeline flicker / spasm for a few frames (showing stale messages from ~20 messages ago), and recover again.
This video shows what the flashing looks like (in this instance it's triggered by a proxy misconfiguration bug causing SS to expires every few seconds):
https://github.com/vector-im/element-x-ios/assets/1294269/36164c6f-977a-41c4-86fd-790d1882c773
### Outcome
#### What did you expect?
Timeline that doesn't flicker horribly
#### What happened instead?
Flickering spasming timeline
### Your phone model
_No response_
### Operating system version
_No response_
### Application version
271
### Homeserver
_No response_
### Will you send logs?
No | non_priority | timeline flashes stale messages on entering a room especially after ss expiration steps to reproduce enter a room that you haven t viewed before in the current session you may potentially need to wait for ss expiration as the room history syncs watch the timeline flicker spasm for a few frames showing stale messages from messages ago and recover again this video shows what the flashing looks like in this instance it s triggered by a proxy misconfiguration bug causing ss to expires every few seconds outcome what did you expect timeline that doesn t flicker horribly what happened instead flickering spasming timeline your phone model no response operating system version no response application version homeserver no response will you send logs no | 0 |
52,873 | 10,949,035,671 | IssuesEvent | 2019-11-26 10:03:48 | reflectoring/coderadar | https://api.github.com/repos/reflectoring/coderadar | closed | Cut dependencies between ResourceAssemblers and RestControllers | component:coderadar-core type:enhancement | Currently, the ResourceAssemblers access the Controllers they link to to create URIs for Hypermedia links. This leads to circular dependencies between all rest api packages.
The URIs should be all put in a simple URIRegistry or so to cut these circular dependencies.
| 1.0 | Cut dependencies between ResourceAssemblers and RestControllers - Currently, the ResourceAssemblers access the Controllers they link to to create URIs for Hypermedia links. This leads to circular dependencies between all rest api packages.
The URIs should be all put in a simple URIRegistry or so to cut these circular dependencies.
| non_priority | cut dependencies between resourceassemblers and restcontrollers currently the resourceassemblers access the controllers they link to to create uris for hypermedia links this leads to circular dependencies between all rest api packages the uris should be all put in a simple uriregistry or so to cut these circular dependencies | 0 |
3,993 | 18,495,026,731 | IssuesEvent | 2021-10-19 07:43:50 | camunda-cloud/zeebe | https://api.github.com/repos/camunda-cloud/zeebe | closed | Define a way to manage the state access | Type: Maintenance Impact: Performance Impact: Maintainability | **Description**
Define a way how to
* avoid multiple reads/writes of one state entity within one BPMN step.
* check invariants
* track state changes for debugging
Related to #4227 | True | Define a way to manage the state access - **Description**
Define a way how to
* avoid multiple reads/writes of one state entity within one BPMN step.
* check invariants
* track state changes for debugging
Related to #4227 | non_priority | define a way to manage the state access description define a way how to avoid multiple reads writes of one state entity within one bpmn step check invariants track state changes for debugging related to | 0 |
190,424 | 22,065,273,830 | IssuesEvent | 2022-05-31 01:54:54 | GerardSanR/Wisclick | https://api.github.com/repos/GerardSanR/Wisclick | opened | jetty-util-9.4.9.v20180320.jar: 2 vulnerabilities (highest severity is: 6.1) | security vulnerability | <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-util-9.4.9.v20180320.jar</b></p></summary>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /lib/jetty-util-9.4.9.v20180320.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/GerardSanR/Wisclick/commit/1ca95f3b6954fe38d52a6c73d6e4511aeec4912a">1ca95f3b6954fe38d52a6c73d6e4511aeec4912a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-10241](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10241) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jetty-util-9.4.9.v20180320.jar | Direct | 9.4.16.v20190411 | ❌ |
| [CVE-2018-12536](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jetty-util-9.4.9.v20180320.jar | Direct | 9.4.11.v20180605 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-10241</summary>
### Vulnerable Library - <b>jetty-util-9.4.9.v20180320.jar</b></p>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /lib/jetty-util-9.4.9.v20180320.jar</p>
<p>
Dependency Hierarchy:
- :x: **jetty-util-9.4.9.v20180320.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GerardSanR/Wisclick/commit/1ca95f3b6954fe38d52a6c73d6e4511aeec4912a">1ca95f3b6954fe38d52a6c73d6e4511aeec4912a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Eclipse Jetty version 9.2.26 and older, 9.3.25 and older, and 9.4.15 and older, the server is vulnerable to XSS conditions if a remote client USES a specially formatted URL against the DefaultServlet or ResourceHandler that is configured for showing a Listing of directory contents.
<p>Publish Date: 2019-04-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10241>CVE-2019-10241</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10241">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10241</a></p>
<p>Release Date: 2019-04-22</p>
<p>Fix Resolution: 9.4.16.v20190411</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-12536</summary>
### Vulnerable Library - <b>jetty-util-9.4.9.v20180320.jar</b></p>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /lib/jetty-util-9.4.9.v20180320.jar</p>
<p>
Dependency Hierarchy:
- :x: **jetty-util-9.4.9.v20180320.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GerardSanR/Wisclick/commit/1ca95f3b6954fe38d52a6c73d6e4511aeec4912a">1ca95f3b6954fe38d52a6c73d6e4511aeec4912a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Eclipse Jetty Server, all 9.x versions, on webapps deployed using default Error Handling, when an intentionally bad query arrives that doesn't match a dynamic url-pattern, and is eventually handled by the DefaultServlet's static file serving, the bad characters can trigger a java.nio.file.InvalidPathException which includes the full path to the base resource directory that the DefaultServlet and/or webapp is using. If this InvalidPathException is then handled by the default Error Handler, the InvalidPathException message is included in the error response, revealing the full server path to the requesting system.
<p>Publish Date: 2018-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12536>CVE-2018-12536</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eclipse/jetty.project/commit/ad4dceb1c08679baa2a6a64356fcde5309e13fd8">https://github.com/eclipse/jetty.project/commit/ad4dceb1c08679baa2a6a64356fcde5309e13fd8</a></p>
<p>Release Date: 2018-06-27</p>
<p>Fix Resolution: 9.4.11.v20180605</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-util","packageVersion":"9.4.9.v20180320","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"org.eclipse.jetty:jetty-util:9.4.9.v20180320","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.4.16.v20190411","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-10241","vulnerabilityDetails":"In Eclipse Jetty version 9.2.26 and older, 9.3.25 and older, and 9.4.15 and older, the server is vulnerable to XSS conditions if a remote client USES a specially formatted URL against the DefaultServlet or ResourceHandler that is configured for showing a Listing of directory contents.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10241","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-util","packageVersion":"9.4.9.v20180320","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"org.eclipse.jetty:jetty-util:9.4.9.v20180320","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.4.11.v20180605","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-12536","vulnerabilityDetails":"In Eclipse Jetty Server, all 9.x versions, on webapps deployed using default Error Handling, when an intentionally bad query arrives that doesn\u0027t match a dynamic url-pattern, and is eventually handled by the DefaultServlet\u0027s static file serving, the bad characters can trigger a java.nio.file.InvalidPathException which includes the full path to the base resource directory that the DefaultServlet and/or webapp is using. If this InvalidPathException is then handled by the default Error Handler, the InvalidPathException message is included in the error response, revealing the full server path to the requesting system.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12536","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | True | jetty-util-9.4.9.v20180320.jar: 2 vulnerabilities (highest severity is: 6.1) - <details><summary><img src='https://whitesource-resources.whitesourcesoftware.com/vulnerability_details.png' width=19 height=20> Vulnerable Library - <b>jetty-util-9.4.9.v20180320.jar</b></p></summary>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /lib/jetty-util-9.4.9.v20180320.jar</p>
<p>
<p>Found in HEAD commit: <a href="https://github.com/GerardSanR/Wisclick/commit/1ca95f3b6954fe38d52a6c73d6e4511aeec4912a">1ca95f3b6954fe38d52a6c73d6e4511aeec4912a</a></p></details>
## Vulnerabilities
| CVE | Severity | <img src='https://whitesource-resources.whitesourcesoftware.com/cvss3.png' width=19 height=20> CVSS | Dependency | Type | Fixed in | Remediation Available |
| ------------- | ------------- | ----- | ----- | ----- | --- | --- |
| [CVE-2019-10241](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10241) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 6.1 | jetty-util-9.4.9.v20180320.jar | Direct | 9.4.16.v20190411 | ❌ |
| [CVE-2018-12536](https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12536) | <img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> Medium | 5.3 | jetty-util-9.4.9.v20180320.jar | Direct | 9.4.11.v20180605 | ❌ |
## Details
<details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2019-10241</summary>
### Vulnerable Library - <b>jetty-util-9.4.9.v20180320.jar</b></p>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /lib/jetty-util-9.4.9.v20180320.jar</p>
<p>
Dependency Hierarchy:
- :x: **jetty-util-9.4.9.v20180320.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GerardSanR/Wisclick/commit/1ca95f3b6954fe38d52a6c73d6e4511aeec4912a">1ca95f3b6954fe38d52a6c73d6e4511aeec4912a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Eclipse Jetty version 9.2.26 and older, 9.3.25 and older, and 9.4.15 and older, the server is vulnerable to XSS conditions if a remote client USES a specially formatted URL against the DefaultServlet or ResourceHandler that is configured for showing a Listing of directory contents.
<p>Publish Date: 2019-04-22
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10241>CVE-2019-10241</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>6.1</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: Required
- Scope: Changed
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: Low
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10241">https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-10241</a></p>
<p>Release Date: 2019-04-22</p>
<p>Fix Resolution: 9.4.16.v20190411</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details><details>
<summary><img src='https://whitesource-resources.whitesourcesoftware.com/medium_vul.png' width=19 height=20> CVE-2018-12536</summary>
### Vulnerable Library - <b>jetty-util-9.4.9.v20180320.jar</b></p>
<p>Utility classes for Jetty</p>
<p>Library home page: <a href="http://www.eclipse.org/jetty">http://www.eclipse.org/jetty</a></p>
<p>Path to vulnerable library: /lib/jetty-util-9.4.9.v20180320.jar</p>
<p>
Dependency Hierarchy:
- :x: **jetty-util-9.4.9.v20180320.jar** (Vulnerable Library)
<p>Found in HEAD commit: <a href="https://github.com/GerardSanR/Wisclick/commit/1ca95f3b6954fe38d52a6c73d6e4511aeec4912a">1ca95f3b6954fe38d52a6c73d6e4511aeec4912a</a></p>
<p>Found in base branch: <b>main</b></p>
</p>
<p></p>
### Vulnerability Details
<p>
In Eclipse Jetty Server, all 9.x versions, on webapps deployed using default Error Handling, when an intentionally bad query arrives that doesn't match a dynamic url-pattern, and is eventually handled by the DefaultServlet's static file serving, the bad characters can trigger a java.nio.file.InvalidPathException which includes the full path to the base resource directory that the DefaultServlet and/or webapp is using. If this InvalidPathException is then handled by the default Error Handler, the InvalidPathException message is included in the error response, revealing the full server path to the requesting system.
<p>Publish Date: 2018-06-27
<p>URL: <a href=https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12536>CVE-2018-12536</a></p>
</p>
<p></p>
### CVSS 3 Score Details (<b>5.3</b>)
<p>
Base Score Metrics:
- Exploitability Metrics:
- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Scope: Unchanged
- Impact Metrics:
- Confidentiality Impact: Low
- Integrity Impact: None
- Availability Impact: None
</p>
For more information on CVSS3 Scores, click <a href="https://www.first.org/cvss/calculator/3.0">here</a>.
</p>
<p></p>
### Suggested Fix
<p>
<p>Type: Upgrade version</p>
<p>Origin: <a href="https://github.com/eclipse/jetty.project/commit/ad4dceb1c08679baa2a6a64356fcde5309e13fd8">https://github.com/eclipse/jetty.project/commit/ad4dceb1c08679baa2a6a64356fcde5309e13fd8</a></p>
<p>Release Date: 2018-06-27</p>
<p>Fix Resolution: 9.4.11.v20180605</p>
</p>
<p></p>
Step up your Open Source Security Game with Mend [here](https://www.whitesourcesoftware.com/full_solution_bolt_github)
</details>
<!-- <REMEDIATE>[{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-util","packageVersion":"9.4.9.v20180320","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"org.eclipse.jetty:jetty-util:9.4.9.v20180320","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.4.16.v20190411","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2019-10241","vulnerabilityDetails":"In Eclipse Jetty version 9.2.26 and older, 9.3.25 and older, and 9.4.15 and older, the server is vulnerable to XSS conditions if a remote client USES a specially formatted URL against the DefaultServlet or ResourceHandler that is configured for showing a Listing of directory contents.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2019-10241","cvss3Severity":"medium","cvss3Score":"6.1","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Changed","C":"Low","UI":"Required","AV":"Network","I":"Low"},"extraData":{}},{"isOpenPROnVulnerability":false,"isPackageBased":true,"isDefaultBranch":true,"packages":[{"packageType":"Java","groupId":"org.eclipse.jetty","packageName":"jetty-util","packageVersion":"9.4.9.v20180320","packageFilePaths":[],"isTransitiveDependency":false,"dependencyTree":"org.eclipse.jetty:jetty-util:9.4.9.v20180320","isMinimumFixVersionAvailable":true,"minimumFixVersion":"9.4.11.v20180605","isBinary":true}],"baseBranches":["main"],"vulnerabilityIdentifier":"CVE-2018-12536","vulnerabilityDetails":"In Eclipse Jetty Server, all 9.x versions, on webapps deployed using default Error Handling, when an intentionally bad query arrives that doesn\u0027t match a dynamic url-pattern, and is eventually handled by the DefaultServlet\u0027s static file serving, the bad characters can trigger a java.nio.file.InvalidPathException which includes the full path to the base resource directory that the DefaultServlet and/or webapp is using. If this InvalidPathException is then handled by the default Error Handler, the InvalidPathException message is included in the error response, revealing the full server path to the requesting system.","vulnerabilityUrl":"https://vuln.whitesourcesoftware.com/vulnerability/CVE-2018-12536","cvss3Severity":"medium","cvss3Score":"5.3","cvss3Metrics":{"A":"None","AC":"Low","PR":"None","S":"Unchanged","C":"Low","UI":"None","AV":"Network","I":"None"},"extraData":{}}]</REMEDIATE> --> | non_priority | jetty util jar vulnerabilities highest severity is vulnerable library jetty util jar utility classes for jetty library home page a href path to vulnerable library lib jetty util jar found in head commit a href vulnerabilities cve severity cvss dependency type fixed in remediation available medium jetty util jar direct medium jetty util jar direct details cve vulnerable library jetty util jar utility classes for jetty library home page a href path to vulnerable library lib jetty util jar dependency hierarchy x jetty util jar vulnerable library found in head commit a href found in base branch main vulnerability details in eclipse jetty version and older and older and and older the server is vulnerable to xss conditions if a remote client uses a specially formatted url against the defaultservlet or resourcehandler that is configured for showing a listing of directory contents publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction required scope changed impact metrics confidentiality impact low integrity impact low availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend cve vulnerable library jetty util jar utility classes for jetty library home page a href path to vulnerable library lib jetty util jar dependency hierarchy x jetty util jar vulnerable library found in head commit a href found in base branch main vulnerability details in eclipse jetty server all x versions on webapps deployed using default error handling when an intentionally bad query arrives that doesn t match a dynamic url pattern and is eventually handled by the defaultservlet s static file serving the bad characters can trigger a java nio file invalidpathexception which includes the full path to the base resource directory that the defaultservlet and or webapp is using if this invalidpathexception is then handled by the default error handler the invalidpathexception message is included in the error response revealing the full server path to the requesting system publish date url a href cvss score details base score metrics exploitability metrics attack vector network attack complexity low privileges required none user interaction none scope unchanged impact metrics confidentiality impact low integrity impact none availability impact none for more information on scores click a href suggested fix type upgrade version origin a href release date fix resolution step up your open source security game with mend istransitivedependency false dependencytree org eclipse jetty jetty util isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in eclipse jetty version and older and older and and older the server is vulnerable to xss conditions if a remote client uses a specially formatted url against the defaultservlet or resourcehandler that is configured for showing a listing of directory contents vulnerabilityurl istransitivedependency false dependencytree org eclipse jetty jetty util isminimumfixversionavailable true minimumfixversion isbinary true basebranches vulnerabilityidentifier cve vulnerabilitydetails in eclipse jetty server all x versions on webapps deployed using default error handling when an intentionally bad query arrives that doesn match a dynamic url pattern and is eventually handled by the defaultservlet static file serving the bad characters can trigger a java nio file invalidpathexception which includes the full path to the base resource directory that the defaultservlet and or webapp is using if this invalidpathexception is then handled by the default error handler the invalidpathexception message is included in the error response revealing the full server path to the requesting system vulnerabilityurl | 0 |
17,100 | 9,966,380,034 | IssuesEvent | 2019-07-08 11:02:00 | wojtpl2/ExtendedXmlSerializer | https://api.github.com/repos/wojtpl2/ExtendedXmlSerializer | closed | Introduce UsingKnownTypesFrom for Better Security | discussion security v3 | Something to consider for v3:
https://www.alphabot.com/security/blog/2017/net/How-to-configure-Json.NET-to-create-a-vulnerable-web-API.html
Essentially, we want to constrict allowable types by default. The problem with the approach taken by `DataContractSerializer` and `XmlSerializer` with their "known type" approaches is that they are cumbersome to use.
v2 uses an `InspectingTypes` approach for some of the classic type functionality. Perhaps this should be used as a reference point to traverse the given type to look for all known/expected types. We could also use this at deserialization-time, however, this is an expensive operation and should be opt-in.
So, essentially, if you have a type such as this:
```
sealed class Subject {
public object Property {get; set;}
}
```
It should throw with a message saying that property of type `object` are not allowed (by default). It could then recommend using `UsingKnownTypesFrom` to derive a list of supported/known types. It could further recommend visiting this (or another URL with documentation 😊) for more information.
The resulting container would look something like:
```
new ConfigurationContainer().UsingKnownTypesFrom<TRoot>().Create();
```
This would then traverse the graph starting from `TRoot` and yield supported types.
Also further consider a `UsingKnownTypesFrom<T>(ITraverseStrategy strategy)` which further defines how a type graph is traversed to yield the necessary known types. | True | Introduce UsingKnownTypesFrom for Better Security - Something to consider for v3:
https://www.alphabot.com/security/blog/2017/net/How-to-configure-Json.NET-to-create-a-vulnerable-web-API.html
Essentially, we want to constrict allowable types by default. The problem with the approach taken by `DataContractSerializer` and `XmlSerializer` with their "known type" approaches is that they are cumbersome to use.
v2 uses an `InspectingTypes` approach for some of the classic type functionality. Perhaps this should be used as a reference point to traverse the given type to look for all known/expected types. We could also use this at deserialization-time, however, this is an expensive operation and should be opt-in.
So, essentially, if you have a type such as this:
```
sealed class Subject {
public object Property {get; set;}
}
```
It should throw with a message saying that property of type `object` are not allowed (by default). It could then recommend using `UsingKnownTypesFrom` to derive a list of supported/known types. It could further recommend visiting this (or another URL with documentation 😊) for more information.
The resulting container would look something like:
```
new ConfigurationContainer().UsingKnownTypesFrom<TRoot>().Create();
```
This would then traverse the graph starting from `TRoot` and yield supported types.
Also further consider a `UsingKnownTypesFrom<T>(ITraverseStrategy strategy)` which further defines how a type graph is traversed to yield the necessary known types. | non_priority | introduce usingknowntypesfrom for better security something to consider for essentially we want to constrict allowable types by default the problem with the approach taken by datacontractserializer and xmlserializer with their known type approaches is that they are cumbersome to use uses an inspectingtypes approach for some of the classic type functionality perhaps this should be used as a reference point to traverse the given type to look for all known expected types we could also use this at deserialization time however this is an expensive operation and should be opt in so essentially if you have a type such as this sealed class subject public object property get set it should throw with a message saying that property of type object are not allowed by default it could then recommend using usingknowntypesfrom to derive a list of supported known types it could further recommend visiting this or another url with documentation 😊 for more information the resulting container would look something like new configurationcontainer usingknowntypesfrom create this would then traverse the graph starting from troot and yield supported types also further consider a usingknowntypesfrom itraversestrategy strategy which further defines how a type graph is traversed to yield the necessary known types | 0 |
3,518 | 4,479,865,108 | IssuesEvent | 2016-08-27 22:02:10 | lionheart/openradar-mirror | https://api.github.com/repos/lionheart/openradar-mirror | opened | 28045946: Filevault individual recovery key creation/regeneration timestamp not reflected permanently on filesystem | classification:security reproducible:always status:open | #### Description
Summary:
In addition to the issue reported in radar 28034006, being able to correlate the last time a FV2 recovery key was used with the timestamp of when it was last generated (as it could be regenerated/rotated after initiating encryption) allows admins to know that an individual recovery key would need to be escrowed. Currently there is no known/documented way to tell the last time a recovery key was generated for a volume, nor does it seem to persist anywhere on the filesystem.
Steps to Reproduce:
1. Initiate filevault encryption on a computer running 10.12 in system preferences, which generates a personal/individual recovery key.
2. run sudo log show --debug --info --predicate 'process == "fdesetup"'
Expected Results:
Somewhere in the logs or on the filesystem, a key to the effect of 'personal recovery key last generated date' would be set to a timestamp, or a subcommand of 'fdesetup' would report last time a distinct key became associated with a particular volume.
Actual Results:
There is no documented place on the filesystem or in the log that reflects the time a key became associated with the boot volume and allows FV2 unlock.
Regression:
All OSes that support filevault, including macOS 10.12, Sierra developer preview 7
Notes:
Affected install count: hundreds at Montefiore Medical Group, thousands at Einstein College of Medicine
-
Product Version: All 10.7+
Created: 2016-08-27T21:43:34.799450
Originated: 2016-08-27T17:43:00
Open Radar Link: http://www.openradar.me/28045946 | True | 28045946: Filevault individual recovery key creation/regeneration timestamp not reflected permanently on filesystem - #### Description
Summary:
In addition to the issue reported in radar 28034006, being able to correlate the last time a FV2 recovery key was used with the timestamp of when it was last generated (as it could be regenerated/rotated after initiating encryption) allows admins to know that an individual recovery key would need to be escrowed. Currently there is no known/documented way to tell the last time a recovery key was generated for a volume, nor does it seem to persist anywhere on the filesystem.
Steps to Reproduce:
1. Initiate filevault encryption on a computer running 10.12 in system preferences, which generates a personal/individual recovery key.
2. run sudo log show --debug --info --predicate 'process == "fdesetup"'
Expected Results:
Somewhere in the logs or on the filesystem, a key to the effect of 'personal recovery key last generated date' would be set to a timestamp, or a subcommand of 'fdesetup' would report last time a distinct key became associated with a particular volume.
Actual Results:
There is no documented place on the filesystem or in the log that reflects the time a key became associated with the boot volume and allows FV2 unlock.
Regression:
All OSes that support filevault, including macOS 10.12, Sierra developer preview 7
Notes:
Affected install count: hundreds at Montefiore Medical Group, thousands at Einstein College of Medicine
-
Product Version: All 10.7+
Created: 2016-08-27T21:43:34.799450
Originated: 2016-08-27T17:43:00
Open Radar Link: http://www.openradar.me/28045946 | non_priority | filevault individual recovery key creation regeneration timestamp not reflected permanently on filesystem description summary in addition to the issue reported in radar being able to correlate the last time a recovery key was used with the timestamp of when it was last generated as it could be regenerated rotated after initiating encryption allows admins to know that an individual recovery key would need to be escrowed currently there is no known documented way to tell the last time a recovery key was generated for a volume nor does it seem to persist anywhere on the filesystem steps to reproduce initiate filevault encryption on a computer running in system preferences which generates a personal individual recovery key run sudo log show debug info predicate process fdesetup expected results somewhere in the logs or on the filesystem a key to the effect of personal recovery key last generated date would be set to a timestamp or a subcommand of fdesetup would report last time a distinct key became associated with a particular volume actual results there is no documented place on the filesystem or in the log that reflects the time a key became associated with the boot volume and allows unlock regression all oses that support filevault including macos sierra developer preview notes affected install count hundreds at montefiore medical group thousands at einstein college of medicine product version all created originated open radar link | 0 |
71,341 | 8,648,921,654 | IssuesEvent | 2018-11-26 17:51:53 | 18F/cms-hitech-apd | https://api.github.com/repos/18F/cms-hitech-apd | closed | Replace the yes/no button styles with more appropriate interaction | P1 design | Carried forward from #1082
Problems with the current style and implementation:
- With only two options, it's hard to distinguish if white or black is the selected state
- In most instances where these are implemented, a two-choice option is better represented as a radio button set, with a conditional text area for people to input additional information when needed. In some instances where this is implemented, a single checkbox would be more appropriate.
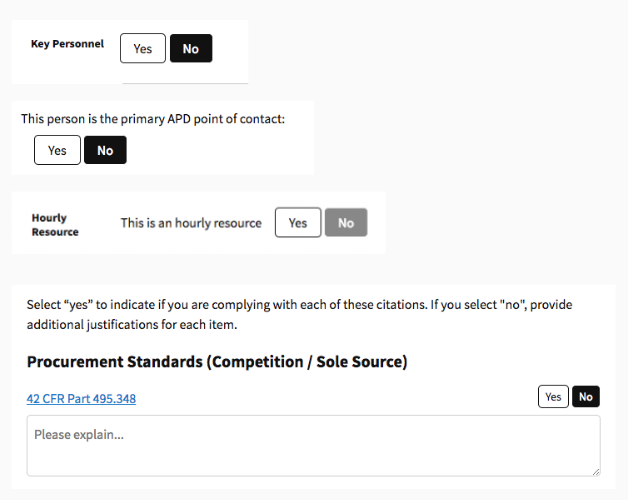
### This task is done when...
- [x] Each instance has been identified.
- [x] The more appropriate interaction has been assessed and mocked up by design
- [ ] An implementation issue has been created for the development team (that includes adding the pattern to storybook as a criteria for "done")
| 1.0 | Replace the yes/no button styles with more appropriate interaction - Carried forward from #1082
Problems with the current style and implementation:
- With only two options, it's hard to distinguish if white or black is the selected state
- In most instances where these are implemented, a two-choice option is better represented as a radio button set, with a conditional text area for people to input additional information when needed. In some instances where this is implemented, a single checkbox would be more appropriate.
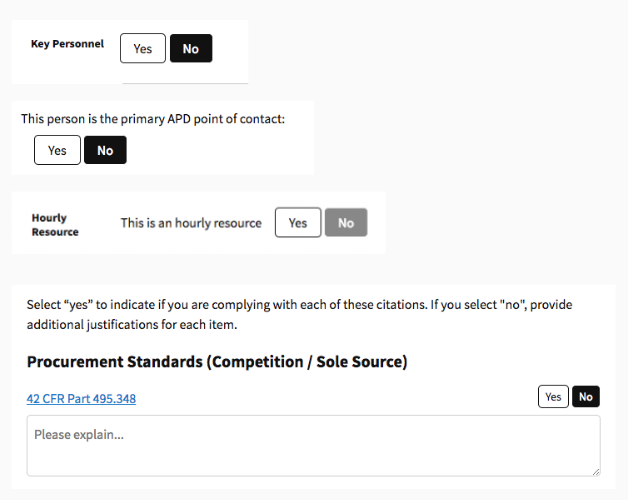
### This task is done when...
- [x] Each instance has been identified.
- [x] The more appropriate interaction has been assessed and mocked up by design
- [ ] An implementation issue has been created for the development team (that includes adding the pattern to storybook as a criteria for "done")
| non_priority | replace the yes no button styles with more appropriate interaction carried forward from problems with the current style and implementation with only two options it s hard to distinguish if white or black is the selected state in most instances where these are implemented a two choice option is better represented as a radio button set with a conditional text area for people to input additional information when needed in some instances where this is implemented a single checkbox would be more appropriate this task is done when each instance has been identified the more appropriate interaction has been assessed and mocked up by design an implementation issue has been created for the development team that includes adding the pattern to storybook as a criteria for done | 0 |
Subsets and Splits
No community queries yet
The top public SQL queries from the community will appear here once available.